Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
115,427 | 17,313,967,786 | IssuesEvent | 2021-07-27 01:37:49 | jinuem/React-Type-Script-Starter | https://api.github.com/repos/jinuem/React-Type-Script-Starter | opened | WS-2020-0344 (High) detected in is-my-json-valid-2.15.0.tgz | security vulnerability | ## WS-2020-0344 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p></summary>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-ts-2.5.0.tgz (Root Library)
- fsevents-1.0.17.tgz
- node-pre-gyp-0.6.32.tgz
- request-2.79.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.
<p>Publish Date: 2020-06-09
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d>WS-2020-0344</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-09</p>
<p>Fix Resolution: is-my-json-valid - 2.20.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0344 (High) detected in is-my-json-valid-2.15.0.tgz - ## WS-2020-0344 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p></summary>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>
Dependency Hierarchy:
- react-scripts-ts-2.5.0.tgz (Root Library)
- fsevents-1.0.17.tgz
- node-pre-gyp-0.6.32.tgz
- request-2.79.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.
<p>Publish Date: 2020-06-09
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d>WS-2020-0344</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-09</p>
<p>Fix Resolution: is-my-json-valid - 2.20.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in is my json valid tgz ws high severity vulnerability vulnerable library is my json valid tgz a jsonschema validator that uses code generation to be extremely fast library home page a href dependency hierarchy react scripts ts tgz root library fsevents tgz node pre gyp tgz request tgz har validator tgz x is my json valid tgz vulnerable library vulnerability details arbitrary code execution vulnerability was found in is my json valid before via the fromatname function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution is my json valid step up your open source security game with whitesource | 0 |
155,906 | 13,636,654,684 | IssuesEvent | 2020-09-25 06:21:34 | fuchicorp/terraform-helm-chart | https://api.github.com/repos/fuchicorp/terraform-helm-chart | closed | Please Update README file in Terraform-Helm-Chart | DevOps Documentation Helm Terraform | Please Update README file in terraform-helm-chart for remote chart deployment. so users can follow the steps and deploy the remote charts.
Thanks
Sprint Points:
link for the file, that needs to be updated:
https://github.com/fuchicorp/terraform-helm-chart/blob/master/README.md
| 1.0 | Please Update README file in Terraform-Helm-Chart - Please Update README file in terraform-helm-chart for remote chart deployment. so users can follow the steps and deploy the remote charts.
Thanks
Sprint Points:
link for the file, that needs to be updated:
https://github.com/fuchicorp/terraform-helm-chart/blob/master/README.md
| non_priority | please update readme file in terraform helm chart please update readme file in terraform helm chart for remote chart deployment so users can follow the steps and deploy the remote charts thanks sprint points link for the file that needs to be updated | 0 |
82,732 | 7,851,162,391 | IssuesEvent | 2018-06-20 10:47:19 | raiden-network/raiden | https://api.github.com/repos/raiden-network/raiden | closed | Create unit tests for new proxies | testing | Integration of new smart contracts: test basic contracts proxy functionality.
- [x] secret registry
- [x] token network registry
- [x] token
- [ ] token network
- [x] new_netting_channel
- [ ] channel_exists
- [ ] detail_participant
- [ ] detail_channel
- [x] deposit
- [ ] update transfer
- [x] close
- [ ] unlock
- [ ] settle
- [ ] events filter | 1.0 | Create unit tests for new proxies - Integration of new smart contracts: test basic contracts proxy functionality.
- [x] secret registry
- [x] token network registry
- [x] token
- [ ] token network
- [x] new_netting_channel
- [ ] channel_exists
- [ ] detail_participant
- [ ] detail_channel
- [x] deposit
- [ ] update transfer
- [x] close
- [ ] unlock
- [ ] settle
- [ ] events filter | non_priority | create unit tests for new proxies integration of new smart contracts test basic contracts proxy functionality secret registry token network registry token token network new netting channel channel exists detail participant detail channel deposit update transfer close unlock settle events filter | 0 |
53,217 | 13,261,190,888 | IssuesEvent | 2020-08-20 19:26:53 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | Coordinate services documentation is Unhelpful (Trac #977) | Migrated from Trac combo reconstruction defect | Most Astronomers use a coordinate system called J2000 to locate the position of astronomical objects which where the pole is the celestial pole at January 1st 2000. However sometimes a coordinate system called current is used where the pole is wherever the hell the celestial pole it is at the time of observation. Both of these cooridinate systems are refered to as equatorial cooridinates. as the difference is at most 18 arcseconds for time scales on the order of icecubes's lifetime.
coordinate-services handles these two cooridinate systems in a rather confusing way: to get from equatoraial to local cooridinates it provides two sets of functions:
Local2RA(), Local2Dec() and Local2RA_no(), Local2Dec_no()
as well as two sets of functions for the reverse transforms:
Equa2LocalAzimuth, Equa2LocalZenith() and Equa2LocalAzimuth_inv(), Equal2LocalZenith_inv()
It is completly unclear weather one should use the _no() functions or not and the _inv() functions or not, the function's doc strings only seem to add to the confusion
In addition there are the totally confusing Equa2LocalRA and Equal2LocalDec which claim to take an RA and Dec and convert them to another RA and Dec, such a function should not have local in its name.
furthermore all of these functions have epoch variables which is even more confusing, why would current coordinates need a local function. as well you need to be reading a pretty old paper to find anything in non J2000 coordinates. so epoch should never be anything but 2000 ( it looks like that is the default from the code, but you can't tell from the documentation)
What is needed is to figure out which functions are are for J2000 and which ones are for current. and properly document them. Then depreciate the old functions and replace them with functions with the string "J2000" and "Current". none of which should have an epoch variable. ( If a new epoch becomes popular J2050 for example then new functions can be added )
Python examples should also be provided
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/977">https://code.icecube.wisc.edu/projects/icecube/ticket/977</a>, reported by icecube</summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-06-26T21:13:56",
"_ts": "1435353236861155",
"description": "Most Astronomers use a coordinate system called J2000 to locate the position of astronomical objects which where the pole is the celestial pole at January 1st 2000. However sometimes a coordinate system called current is used where the pole is wherever the hell the celestial pole it is at the time of observation. Both of these cooridinate systems are refered to as equatorial cooridinates. as the difference is at most 18 arcseconds for time scales on the order of icecubes's lifetime. \n\ncoordinate-services handles these two cooridinate systems in a rather confusing way: to get from equatoraial to local cooridinates it provides two sets of functions:\nLocal2RA(), Local2Dec() and Local2RA_no(), Local2Dec_no()\n\nas well as two sets of functions for the reverse transforms:\nEqua2LocalAzimuth, Equa2LocalZenith() and Equa2LocalAzimuth_inv(), Equal2LocalZenith_inv()\n\nIt is completly unclear weather one should use the _no() functions or not and the _inv() functions or not, the function's doc strings only seem to add to the confusion\n\nIn addition there are the totally confusing Equa2LocalRA and Equal2LocalDec which claim to take an RA and Dec and convert them to another RA and Dec, such a function should not have local in its name.\n\nfurthermore all of these functions have epoch variables which is even more confusing, why would current coordinates need a local function. as well you need to be reading a pretty old paper to find anything in non J2000 coordinates. so epoch should never be anything but 2000 ( it looks like that is the default from the code, but you can't tell from the documentation)\n\nWhat is needed is to figure out which functions are are for J2000 and which ones are for current. and properly document them. Then depreciate the old functions and replace them with functions with the string \"J2000\" and \"Current\". none of which should have an epoch variable. ( If a new epoch becomes popular J2050 for example then new functions can be added )\n\nPython examples should also be provided\n",
"reporter": "icecube",
"cc": "",
"resolution": "wontfix",
"time": "2015-05-13T16:30:51",
"component": "combo reconstruction",
"summary": "Coordinate services documentation is Unhelpful",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| 1.0 | Coordinate services documentation is Unhelpful (Trac #977) - Most Astronomers use a coordinate system called J2000 to locate the position of astronomical objects which where the pole is the celestial pole at January 1st 2000. However sometimes a coordinate system called current is used where the pole is wherever the hell the celestial pole it is at the time of observation. Both of these cooridinate systems are refered to as equatorial cooridinates. as the difference is at most 18 arcseconds for time scales on the order of icecubes's lifetime.
coordinate-services handles these two cooridinate systems in a rather confusing way: to get from equatoraial to local cooridinates it provides two sets of functions:
Local2RA(), Local2Dec() and Local2RA_no(), Local2Dec_no()
as well as two sets of functions for the reverse transforms:
Equa2LocalAzimuth, Equa2LocalZenith() and Equa2LocalAzimuth_inv(), Equal2LocalZenith_inv()
It is completly unclear weather one should use the _no() functions or not and the _inv() functions or not, the function's doc strings only seem to add to the confusion
In addition there are the totally confusing Equa2LocalRA and Equal2LocalDec which claim to take an RA and Dec and convert them to another RA and Dec, such a function should not have local in its name.
furthermore all of these functions have epoch variables which is even more confusing, why would current coordinates need a local function. as well you need to be reading a pretty old paper to find anything in non J2000 coordinates. so epoch should never be anything but 2000 ( it looks like that is the default from the code, but you can't tell from the documentation)
What is needed is to figure out which functions are are for J2000 and which ones are for current. and properly document them. Then depreciate the old functions and replace them with functions with the string "J2000" and "Current". none of which should have an epoch variable. ( If a new epoch becomes popular J2050 for example then new functions can be added )
Python examples should also be provided
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/977">https://code.icecube.wisc.edu/projects/icecube/ticket/977</a>, reported by icecube</summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-06-26T21:13:56",
"_ts": "1435353236861155",
"description": "Most Astronomers use a coordinate system called J2000 to locate the position of astronomical objects which where the pole is the celestial pole at January 1st 2000. However sometimes a coordinate system called current is used where the pole is wherever the hell the celestial pole it is at the time of observation. Both of these cooridinate systems are refered to as equatorial cooridinates. as the difference is at most 18 arcseconds for time scales on the order of icecubes's lifetime. \n\ncoordinate-services handles these two cooridinate systems in a rather confusing way: to get from equatoraial to local cooridinates it provides two sets of functions:\nLocal2RA(), Local2Dec() and Local2RA_no(), Local2Dec_no()\n\nas well as two sets of functions for the reverse transforms:\nEqua2LocalAzimuth, Equa2LocalZenith() and Equa2LocalAzimuth_inv(), Equal2LocalZenith_inv()\n\nIt is completly unclear weather one should use the _no() functions or not and the _inv() functions or not, the function's doc strings only seem to add to the confusion\n\nIn addition there are the totally confusing Equa2LocalRA and Equal2LocalDec which claim to take an RA and Dec and convert them to another RA and Dec, such a function should not have local in its name.\n\nfurthermore all of these functions have epoch variables which is even more confusing, why would current coordinates need a local function. as well you need to be reading a pretty old paper to find anything in non J2000 coordinates. so epoch should never be anything but 2000 ( it looks like that is the default from the code, but you can't tell from the documentation)\n\nWhat is needed is to figure out which functions are are for J2000 and which ones are for current. and properly document them. Then depreciate the old functions and replace them with functions with the string \"J2000\" and \"Current\". none of which should have an epoch variable. ( If a new epoch becomes popular J2050 for example then new functions can be added )\n\nPython examples should also be provided\n",
"reporter": "icecube",
"cc": "",
"resolution": "wontfix",
"time": "2015-05-13T16:30:51",
"component": "combo reconstruction",
"summary": "Coordinate services documentation is Unhelpful",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "",
"type": "defect"
}
```
</p>
</details>
| non_priority | coordinate services documentation is unhelpful trac most astronomers use a coordinate system called to locate the position of astronomical objects which where the pole is the celestial pole at january however sometimes a coordinate system called current is used where the pole is wherever the hell the celestial pole it is at the time of observation both of these cooridinate systems are refered to as equatorial cooridinates as the difference is at most arcseconds for time scales on the order of icecubes s lifetime coordinate services handles these two cooridinate systems in a rather confusing way to get from equatoraial to local cooridinates it provides two sets of functions and no no as well as two sets of functions for the reverse transforms and inv inv it is completly unclear weather one should use the no functions or not and the inv functions or not the function s doc strings only seem to add to the confusion in addition there are the totally confusing and which claim to take an ra and dec and convert them to another ra and dec such a function should not have local in its name furthermore all of these functions have epoch variables which is even more confusing why would current coordinates need a local function as well you need to be reading a pretty old paper to find anything in non coordinates so epoch should never be anything but it looks like that is the default from the code but you can t tell from the documentation what is needed is to figure out which functions are are for and which ones are for current and properly document them then depreciate the old functions and replace them with functions with the string and current none of which should have an epoch variable if a new epoch becomes popular for example then new functions can be added python examples should also be provided migrated from json status closed changetime ts description most astronomers use a coordinate system called to locate the position of astronomical objects which where the pole is the celestial pole at january however sometimes a coordinate system called current is used where the pole is wherever the hell the celestial pole it is at the time of observation both of these cooridinate systems are refered to as equatorial cooridinates as the difference is at most arcseconds for time scales on the order of icecubes s lifetime n ncoordinate services handles these two cooridinate systems in a rather confusing way to get from equatoraial to local cooridinates it provides two sets of functions and no no n nas well as two sets of functions for the reverse transforms and inv inv n nit is completly unclear weather one should use the no functions or not and the inv functions or not the function s doc strings only seem to add to the confusion n nin addition there are the totally confusing and which claim to take an ra and dec and convert them to another ra and dec such a function should not have local in its name n nfurthermore all of these functions have epoch variables which is even more confusing why would current coordinates need a local function as well you need to be reading a pretty old paper to find anything in non coordinates so epoch should never be anything but it looks like that is the default from the code but you can t tell from the documentation n nwhat is needed is to figure out which functions are are for and which ones are for current and properly document them then depreciate the old functions and replace them with functions with the string and current none of which should have an epoch variable if a new epoch becomes popular for example then new functions can be added n npython examples should also be provided n reporter icecube cc resolution wontfix time component combo reconstruction summary coordinate services documentation is unhelpful priority normal keywords milestone owner type defect | 0 |
227,828 | 18,103,060,952 | IssuesEvent | 2021-09-22 16:03:38 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | closed | [Text Analytics] [AAD] TextAnalyticsClient LROs #health cancelled failing in nightly runs | Client Cognitive - Text Analytics test-reliability | Text Analytics nightly test runs are failing with:
> Stack trace:
> AssertionError: expected undefined to be truthy
at Context.<anonymous> (test/public/textAnalyticsClient.spec.ts:2675:19)
For more details check here:
- https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1107532&view=results | 1.0 | [Text Analytics] [AAD] TextAnalyticsClient LROs #health cancelled failing in nightly runs - Text Analytics nightly test runs are failing with:
> Stack trace:
> AssertionError: expected undefined to be truthy
at Context.<anonymous> (test/public/textAnalyticsClient.spec.ts:2675:19)
For more details check here:
- https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1107532&view=results | non_priority | textanalyticsclient lros health cancelled failing in nightly runs text analytics nightly test runs are failing with stack trace assertionerror expected undefined to be truthy at context test public textanalyticsclient spec ts for more details check here | 0 |
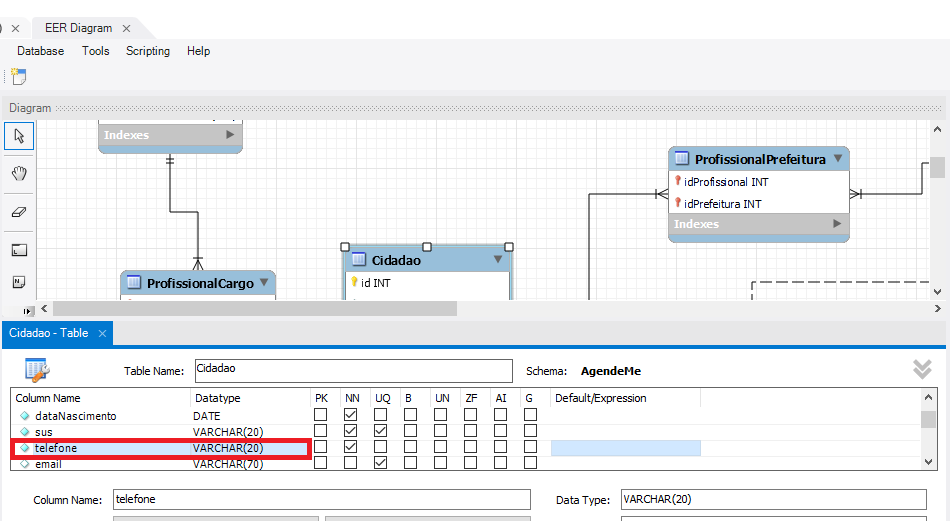
329,164 | 24,210,210,630 | IssuesEvent | 2022-09-25 19:38:40 | marcosdosea/AgendeMe | https://api.github.com/repos/marcosdosea/AgendeMe | closed | Alterar o tipo do atributo telefone da tabela cidadão | documentation 3.0 | Alterar do tipo **INT** para o tipo **VARCHAR(20)**
## Antes
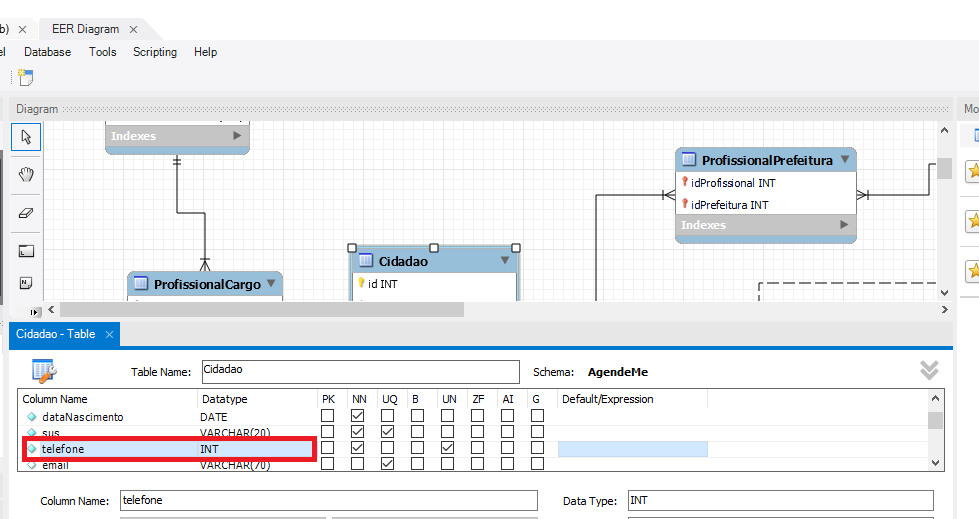
## Depois
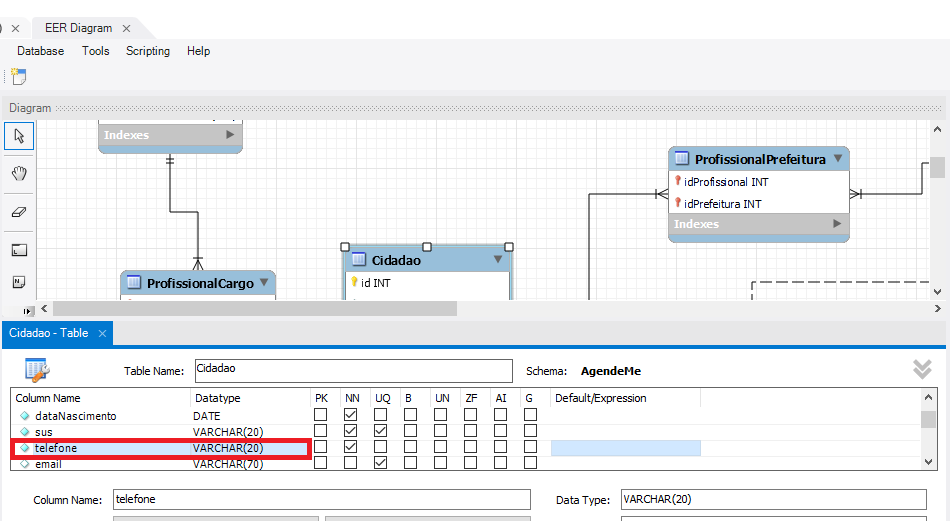
| 1.0 | Alterar o tipo do atributo telefone da tabela cidadão - Alterar do tipo **INT** para o tipo **VARCHAR(20)**
## Antes
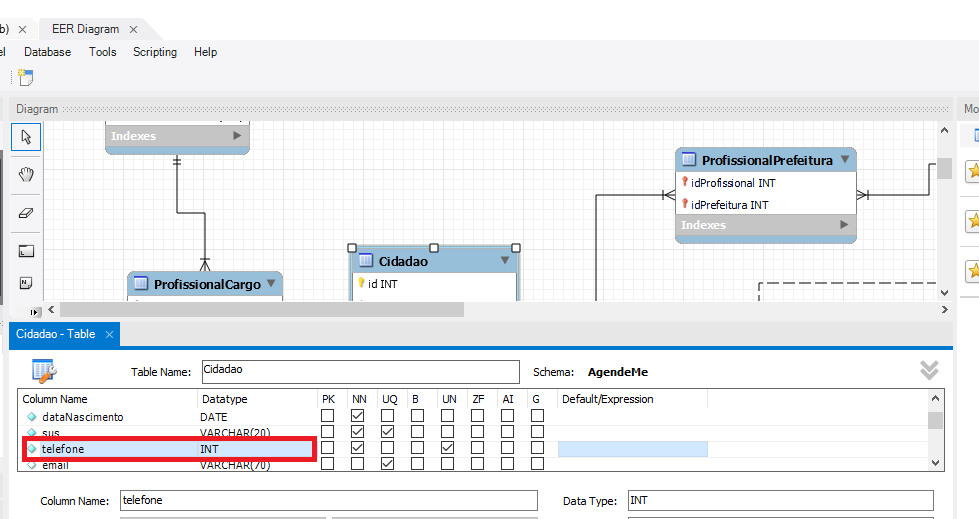
## Depois
| non_priority | alterar o tipo do atributo telefone da tabela cidadão alterar do tipo int para o tipo varchar antes depois | 0 |
410,866 | 27,805,819,187 | IssuesEvent | 2023-03-17 19:47:44 | liveview-native/liveview-client-swiftui | https://api.github.com/repos/liveview-native/liveview-client-swiftui | closed | Documentation: SwiftUI -> User Interface Element -> Controls and indicator -> Links: ShareLink | documentation | As a PO I'd like to have documentation for the [ShareLink](https://github.com/liveviewnative/liveview-client-swiftui/issues/65) | 1.0 | Documentation: SwiftUI -> User Interface Element -> Controls and indicator -> Links: ShareLink - As a PO I'd like to have documentation for the [ShareLink](https://github.com/liveviewnative/liveview-client-swiftui/issues/65) | non_priority | documentation swiftui user interface element controls and indicator links sharelink as a po i d like to have documentation for the | 0 |
187,118 | 22,031,535,395 | IssuesEvent | 2022-05-28 00:39:48 | vincenzodistasio97/Slack-Clone | https://api.github.com/repos/vincenzodistasio97/Slack-Clone | closed | CVE-2021-29060 (Medium) detected in color-string-1.5.3.tgz - autoclosed | security vulnerability | ## CVE-2021-29060 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>color-string-1.5.3.tgz</b></p></summary>
<p>Parser and generator for CSS color strings</p>
<p>Library home page: <a href="https://registry.npmjs.org/color-string/-/color-string-1.5.3.tgz">https://registry.npmjs.org/color-string/-/color-string-1.5.3.tgz</a></p>
<p>Path to dependency file: /server/package.json</p>
<p>Path to vulnerable library: /server/node_modules/color-string/package.json</p>
<p>
Dependency Hierarchy:
- winston-3.1.0.tgz (Root Library)
- diagnostics-1.1.1.tgz
- colorspace-1.1.1.tgz
- color-3.0.0.tgz
- :x: **color-string-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/Slack-Clone/commit/125be6381c29e8f8e1d4b2fed216db288fad9798">125be6381c29e8f8e1d4b2fed216db288fad9798</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Regular Expression Denial of Service (ReDOS) vulnerability was discovered in Color-String version 1.5.5 and below which occurs when the application is provided and checks a crafted invalid HWB string.
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29060>CVE-2021-29060</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-257v-vj4p-3w2h">https://github.com/advisories/GHSA-257v-vj4p-3w2h</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution (color-string): 1.5.5</p>
<p>Direct dependency fix Resolution (winston): 3.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-29060 (Medium) detected in color-string-1.5.3.tgz - autoclosed - ## CVE-2021-29060 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>color-string-1.5.3.tgz</b></p></summary>
<p>Parser and generator for CSS color strings</p>
<p>Library home page: <a href="https://registry.npmjs.org/color-string/-/color-string-1.5.3.tgz">https://registry.npmjs.org/color-string/-/color-string-1.5.3.tgz</a></p>
<p>Path to dependency file: /server/package.json</p>
<p>Path to vulnerable library: /server/node_modules/color-string/package.json</p>
<p>
Dependency Hierarchy:
- winston-3.1.0.tgz (Root Library)
- diagnostics-1.1.1.tgz
- colorspace-1.1.1.tgz
- color-3.0.0.tgz
- :x: **color-string-1.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vincenzodistasio97/Slack-Clone/commit/125be6381c29e8f8e1d4b2fed216db288fad9798">125be6381c29e8f8e1d4b2fed216db288fad9798</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Regular Expression Denial of Service (ReDOS) vulnerability was discovered in Color-String version 1.5.5 and below which occurs when the application is provided and checks a crafted invalid HWB string.
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29060>CVE-2021-29060</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-257v-vj4p-3w2h">https://github.com/advisories/GHSA-257v-vj4p-3w2h</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution (color-string): 1.5.5</p>
<p>Direct dependency fix Resolution (winston): 3.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in color string tgz autoclosed cve medium severity vulnerability vulnerable library color string tgz parser and generator for css color strings library home page a href path to dependency file server package json path to vulnerable library server node modules color string package json dependency hierarchy winston tgz root library diagnostics tgz colorspace tgz color tgz x color string tgz vulnerable library found in head commit a href found in base branch master vulnerability details a regular expression denial of service redos vulnerability was discovered in color string version and below which occurs when the application is provided and checks a crafted invalid hwb string publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution color string direct dependency fix resolution winston step up your open source security game with whitesource | 0 |
96,199 | 19,913,572,569 | IssuesEvent | 2022-01-25 19:49:31 | HumanCellAtlas/dcp2 | https://api.github.com/repos/HumanCellAtlas/dcp2 | closed | TDR's enumerateSnapshots response lacks name of Google project | orange enh no demo code | The response to a request to the `enumerateSnapshots` endpoint does not include the name of the Google project that hosts the BQ tables:
```
$ curl -X GET "https://jade-terra.datarepo-prod.broadinstitute.org/api/repository/v1/snapshots?limit=1" -H "accept: application/json" -H "authorization: Bearer REDACTED" | jq
{
"total": 22,
"filteredTotal": 22,
"items": [
{
"id": "ec40aa9f-43aa-4839-98e3-6362c96a0bee",
"name": "hca_prod_20201120_dcp2___20201124",
"description": "Create snapshot hca_prod_20201120_dcp2___20201124",
"createdDate": "2020-11-24T19:41:37.611318Z",
"profileId": "db61c343-6dfe-4d14-84e9-60ddf97ea73f",
"storage": [
{
"region": "us",
"cloudResource": "bigquery",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "bucket",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "firestore",
"cloudPlatform": "gcp"
}
]
}
]
}
```
The `retrieveSnapshot` response does (note the `dataProject` property):
```
$ curl -X GET "https://jade-terra.datarepo-prod.broadinstitute.org/api/repository/v1/snapshots/ec40aa9f-43aa-4839-98e3-6362c96a0bee?include=SOURCES&include=DATA_PROJECT" -H "accept: application/json" -H "authorization: Bearer REDACTED" | jq
{
"id": "ec40aa9f-43aa-4839-98e3-6362c96a0bee",
"name": "hca_prod_20201120_dcp2___20201124",
"description": "Create snapshot hca_prod_20201120_dcp2___20201124",
"createdDate": "2020-11-24T19:41:37.611318Z",
"source": [
{
"dataset": {
"id": "d30e68f8-c826-4639-88f3-ae35f00d4185",
"name": "hca_prod_20201120_dcp2",
"description": "Human Cell Atlas",
"defaultProfileId": "db61c343-6dfe-4d14-84e9-60ddf97ea73f",
"createdDate": "2020-11-20T19:46:28.951142Z",
"storage": [
{
"region": "us",
"cloudResource": "bigquery",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "bucket",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "firestore",
"cloudPlatform": "gcp"
}
]
},
"asset": null
}
],
"tables": null,
"relationships": null,
"profileId": null,
"dataProject": "broad-datarepo-terra-prod-hca2",
"accessInformation": null
}
```
Azul needs the Google Project name to compose BQ queries against the tables in a snapshot. We also prefer to use the `enumerateSnapshot` endpoint to efficiently get information about multiple snapshots at once but the lack of the Google Project lack in the `enumerateSnapshot` response forces us also hit the `retrieveSnapshot` endpoint for each snapshot individually. So we currently need to make N + 1 requests instead of N. This is aggravated by the fact that N is now large (>100) since we intend to create one snapshot per HCA project.
It seems that it should be relatively easy to add the `dataProject` property to the `enumerateSnapshot` response. Doing so would greatly reduce the latency of certain Azul requests, enhancing the overall user experience and reducing complexity in the Azul code base. | 1.0 | TDR's enumerateSnapshots response lacks name of Google project - The response to a request to the `enumerateSnapshots` endpoint does not include the name of the Google project that hosts the BQ tables:
```
$ curl -X GET "https://jade-terra.datarepo-prod.broadinstitute.org/api/repository/v1/snapshots?limit=1" -H "accept: application/json" -H "authorization: Bearer REDACTED" | jq
{
"total": 22,
"filteredTotal": 22,
"items": [
{
"id": "ec40aa9f-43aa-4839-98e3-6362c96a0bee",
"name": "hca_prod_20201120_dcp2___20201124",
"description": "Create snapshot hca_prod_20201120_dcp2___20201124",
"createdDate": "2020-11-24T19:41:37.611318Z",
"profileId": "db61c343-6dfe-4d14-84e9-60ddf97ea73f",
"storage": [
{
"region": "us",
"cloudResource": "bigquery",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "bucket",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "firestore",
"cloudPlatform": "gcp"
}
]
}
]
}
```
The `retrieveSnapshot` response does (note the `dataProject` property):
```
$ curl -X GET "https://jade-terra.datarepo-prod.broadinstitute.org/api/repository/v1/snapshots/ec40aa9f-43aa-4839-98e3-6362c96a0bee?include=SOURCES&include=DATA_PROJECT" -H "accept: application/json" -H "authorization: Bearer REDACTED" | jq
{
"id": "ec40aa9f-43aa-4839-98e3-6362c96a0bee",
"name": "hca_prod_20201120_dcp2___20201124",
"description": "Create snapshot hca_prod_20201120_dcp2___20201124",
"createdDate": "2020-11-24T19:41:37.611318Z",
"source": [
{
"dataset": {
"id": "d30e68f8-c826-4639-88f3-ae35f00d4185",
"name": "hca_prod_20201120_dcp2",
"description": "Human Cell Atlas",
"defaultProfileId": "db61c343-6dfe-4d14-84e9-60ddf97ea73f",
"createdDate": "2020-11-20T19:46:28.951142Z",
"storage": [
{
"region": "us",
"cloudResource": "bigquery",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "bucket",
"cloudPlatform": "gcp"
},
{
"region": "us-central1",
"cloudResource": "firestore",
"cloudPlatform": "gcp"
}
]
},
"asset": null
}
],
"tables": null,
"relationships": null,
"profileId": null,
"dataProject": "broad-datarepo-terra-prod-hca2",
"accessInformation": null
}
```
Azul needs the Google Project name to compose BQ queries against the tables in a snapshot. We also prefer to use the `enumerateSnapshot` endpoint to efficiently get information about multiple snapshots at once but the lack of the Google Project lack in the `enumerateSnapshot` response forces us also hit the `retrieveSnapshot` endpoint for each snapshot individually. So we currently need to make N + 1 requests instead of N. This is aggravated by the fact that N is now large (>100) since we intend to create one snapshot per HCA project.
It seems that it should be relatively easy to add the `dataProject` property to the `enumerateSnapshot` response. Doing so would greatly reduce the latency of certain Azul requests, enhancing the overall user experience and reducing complexity in the Azul code base. | non_priority | tdr s enumeratesnapshots response lacks name of google project the response to a request to the enumeratesnapshots endpoint does not include the name of the google project that hosts the bq tables curl x get h accept application json h authorization bearer redacted jq total filteredtotal items id name hca prod description create snapshot hca prod createddate profileid storage region us cloudresource bigquery cloudplatform gcp region us cloudresource bucket cloudplatform gcp region us cloudresource firestore cloudplatform gcp the retrievesnapshot response does note the dataproject property curl x get h accept application json h authorization bearer redacted jq id name hca prod description create snapshot hca prod createddate source dataset id name hca prod description human cell atlas defaultprofileid createddate storage region us cloudresource bigquery cloudplatform gcp region us cloudresource bucket cloudplatform gcp region us cloudresource firestore cloudplatform gcp asset null tables null relationships null profileid null dataproject broad datarepo terra prod accessinformation null azul needs the google project name to compose bq queries against the tables in a snapshot we also prefer to use the enumeratesnapshot endpoint to efficiently get information about multiple snapshots at once but the lack of the google project lack in the enumeratesnapshot response forces us also hit the retrievesnapshot endpoint for each snapshot individually so we currently need to make n requests instead of n this is aggravated by the fact that n is now large since we intend to create one snapshot per hca project it seems that it should be relatively easy to add the dataproject property to the enumeratesnapshot response doing so would greatly reduce the latency of certain azul requests enhancing the overall user experience and reducing complexity in the azul code base | 0 |
16,891 | 9,545,302,684 | IssuesEvent | 2019-05-01 16:39:04 | refinery-platform/refinery-platform | https://api.github.com/repos/refinery-platform/refinery-platform | opened | Impossible to delete certain data sets | HSCI requested bug dataset import important metadata performance server solr | * Specific code commit: v1.6.8
* Version of the web browser and OS: any
* Environment where the error occurred: any
### Steps to reproduce
1. Set up a dev/test instance of SCC using a recent RDS snapshot
1. Open `/admin/core/dataset/319` (all.gene.FPKM) in a web browser
1. Delete the data set
### Observed behavior
* After a few minutes web browser shows HTTP error 504
* Data set deleted after about 1 hour 20 minutes
* CPU utilization stayed at ~50% (on a t2.medium instance)
* Memory utilization went up to ~3GB:
* Django: ~1.5GB of RAM (~40% of total system memory)
* Solr: ~0.5GB

### Expected behavior
Data set should be deleted in seconds without excessive CPU or memory utilization
### Notes
See also: #463, #713, #2394, #2645
| True | Impossible to delete certain data sets - * Specific code commit: v1.6.8
* Version of the web browser and OS: any
* Environment where the error occurred: any
### Steps to reproduce
1. Set up a dev/test instance of SCC using a recent RDS snapshot
1. Open `/admin/core/dataset/319` (all.gene.FPKM) in a web browser
1. Delete the data set
### Observed behavior
* After a few minutes web browser shows HTTP error 504
* Data set deleted after about 1 hour 20 minutes
* CPU utilization stayed at ~50% (on a t2.medium instance)
* Memory utilization went up to ~3GB:
* Django: ~1.5GB of RAM (~40% of total system memory)
* Solr: ~0.5GB

### Expected behavior
Data set should be deleted in seconds without excessive CPU or memory utilization
### Notes
See also: #463, #713, #2394, #2645
| non_priority | impossible to delete certain data sets specific code commit version of the web browser and os any environment where the error occurred any steps to reproduce set up a dev test instance of scc using a recent rds snapshot open admin core dataset all gene fpkm in a web browser delete the data set observed behavior after a few minutes web browser shows http error data set deleted after about hour minutes cpu utilization stayed at on a medium instance memory utilization went up to django of ram of total system memory solr expected behavior data set should be deleted in seconds without excessive cpu or memory utilization notes see also | 0 |
124,991 | 12,244,456,057 | IssuesEvent | 2020-05-05 11:10:13 | pounard/goat-query | https://api.github.com/repos/pounard/goat-query | closed | Documentation : QueryBuilder - insertValues VS insertQuery | documentation | It's not clear the difference between insertValues and insertQuery in QueryuBuilder class. They have the same description, maybe it could be nice to have an example in function annotations.
```
/**
* Create an insert query builder
*
* @param string|ExpressionRelation $relation
* SQL from statement relation name
*/
public function insertValues($relation): InsertValuesQuery;
/**
* Create an insert with query builder
*
* @param string|ExpressionRelation $relation
* SQL from statement relation name
*/
public function insertQuery($relation): InsertQueryQuery;
``` | 1.0 | Documentation : QueryBuilder - insertValues VS insertQuery - It's not clear the difference between insertValues and insertQuery in QueryuBuilder class. They have the same description, maybe it could be nice to have an example in function annotations.
```
/**
* Create an insert query builder
*
* @param string|ExpressionRelation $relation
* SQL from statement relation name
*/
public function insertValues($relation): InsertValuesQuery;
/**
* Create an insert with query builder
*
* @param string|ExpressionRelation $relation
* SQL from statement relation name
*/
public function insertQuery($relation): InsertQueryQuery;
``` | non_priority | documentation querybuilder insertvalues vs insertquery it s not clear the difference between insertvalues and insertquery in queryubuilder class they have the same description maybe it could be nice to have an example in function annotations create an insert query builder param string expressionrelation relation sql from statement relation name public function insertvalues relation insertvaluesquery create an insert with query builder param string expressionrelation relation sql from statement relation name public function insertquery relation insertqueryquery | 0 |
249,269 | 18,858,177,527 | IssuesEvent | 2021-11-12 09:28:18 | JinxinZhao315/pe | https://api.github.com/repos/JinxinZhao315/pe | opened | Multiple DG use cases missing some extensions | severity.Medium type.DocumentationBug | In the "add student" use case in DG, the only two extensions written are "module not found" and "student ID already exists". However, things can go wrong in other ways when adding a student:
1) The command may be in invalid format:

Missing compulsory fields such as tele handle and email
2) The student details provided may be in invalid format:

Student ID is in invalid format, or name, tele handle, and email are in invalid format
These possible extensions are not included.
This problem is also present for `edit student`, `add module`, `edit module`, `add task`, and `edit task` use cases. The "invalid command" and "invalid detail" extensions are not in these use cases either.
<!--session: 1636704077350-5d00af5a-5d13-4ca5-ab0a-4089d2c81805-->
<!--Version: Web v3.4.1--> | 1.0 | Multiple DG use cases missing some extensions - In the "add student" use case in DG, the only two extensions written are "module not found" and "student ID already exists". However, things can go wrong in other ways when adding a student:
1) The command may be in invalid format:

Missing compulsory fields such as tele handle and email
2) The student details provided may be in invalid format:

Student ID is in invalid format, or name, tele handle, and email are in invalid format
These possible extensions are not included.
This problem is also present for `edit student`, `add module`, `edit module`, `add task`, and `edit task` use cases. The "invalid command" and "invalid detail" extensions are not in these use cases either.
<!--session: 1636704077350-5d00af5a-5d13-4ca5-ab0a-4089d2c81805-->
<!--Version: Web v3.4.1--> | non_priority | multiple dg use cases missing some extensions in the add student use case in dg the only two extensions written are module not found and student id already exists however things can go wrong in other ways when adding a student the command may be in invalid format missing compulsory fields such as tele handle and email the student details provided may be in invalid format student id is in invalid format or name tele handle and email are in invalid format these possible extensions are not included this problem is also present for edit student add module edit module add task and edit task use cases the invalid command and invalid detail extensions are not in these use cases either | 0 |
72,352 | 8,723,533,540 | IssuesEvent | 2018-12-09 22:39:36 | hypnospinner/Project-Focus | https://api.github.com/repos/hypnospinner/Project-Focus | closed | Создать back-end решение и настроить инфраструктуру | design groundwork important | Back-end приложение будет использовать .NET Core 2.1 микросервисы. В качестве языка наиболее выгодно использовать F# (алгебраические типы данных для команд и событий улучшат восприятие кода и ускорят разработку). В качестве СУБД предлагается использовать Mongo DB (структура хранимых типов данных будет сильно изменяться в ходе развития проекта) Возможность интеграции с реляционными СУБД на поздних стадиях развития проекта должна быть сохранена. В качестве шины событий предлагается использовать Rabbit MQ. | 1.0 | Создать back-end решение и настроить инфраструктуру - Back-end приложение будет использовать .NET Core 2.1 микросервисы. В качестве языка наиболее выгодно использовать F# (алгебраические типы данных для команд и событий улучшат восприятие кода и ускорят разработку). В качестве СУБД предлагается использовать Mongo DB (структура хранимых типов данных будет сильно изменяться в ходе развития проекта) Возможность интеграции с реляционными СУБД на поздних стадиях развития проекта должна быть сохранена. В качестве шины событий предлагается использовать Rabbit MQ. | non_priority | создать back end решение и настроить инфраструктуру back end приложение будет использовать net core микросервисы в качестве языка наиболее выгодно использовать f алгебраические типы данных для команд и событий улучшат восприятие кода и ускорят разработку в качестве субд предлагается использовать mongo db структура хранимых типов данных будет сильно изменяться в ходе развития проекта возможность интеграции с реляционными субд на поздних стадиях развития проекта должна быть сохранена в качестве шины событий предлагается использовать rabbit mq | 0 |
34,803 | 4,955,847,377 | IssuesEvent | 2016-12-01 21:37:42 | TransNexus/NexOSS | https://api.github.com/repos/TransNexus/NexOSS | closed | View Row Button does not work for Subnets | bug needs testing | #### Page Path
/ui/Accounts_Subnets
#### Description of Issue
View Row button does not work for Subnets.
Selected a row in the Subnets table, then click View Row. Nothing happens.
| 1.0 | View Row Button does not work for Subnets - #### Page Path
/ui/Accounts_Subnets
#### Description of Issue
View Row button does not work for Subnets.
Selected a row in the Subnets table, then click View Row. Nothing happens.
| non_priority | view row button does not work for subnets page path ui accounts subnets description of issue view row button does not work for subnets selected a row in the subnets table then click view row nothing happens | 0 |
39,795 | 10,375,142,233 | IssuesEvent | 2019-09-09 11:18:13 | widelands/widelands-issue-migration2 | https://api.github.com/repos/widelands/widelands-issue-migration2 | closed | CMake should offer a switch to disable GGZ support even if GGZ is found | Fix Released Low buildsystem cmake ggz | CMake should offer a switch to disable GGZ support even if GGZ is found
This will reduce dependencies for people who want a standalone application, and don't even think about something called GGZ. | 1.0 | CMake should offer a switch to disable GGZ support even if GGZ is found - CMake should offer a switch to disable GGZ support even if GGZ is found
This will reduce dependencies for people who want a standalone application, and don't even think about something called GGZ. | non_priority | cmake should offer a switch to disable ggz support even if ggz is found cmake should offer a switch to disable ggz support even if ggz is found this will reduce dependencies for people who want a standalone application and don t even think about something called ggz | 0 |
205,017 | 15,586,226,009 | IssuesEvent | 2021-03-18 01:27:42 | serum-390/soen390-team16-godzilla | https://api.github.com/repos/serum-390/soen390-team16-godzilla | closed | Add Docker container REST api tests | testing | Recently, there was a PR (#34) that broke some of the Spring APIs and it wasn't noticed until the CD pipeline failed to deploy to the AWS ECS cluster.
It would be great if the Docker build had failed instead and the PR was blocked from merging. It would be very easy to implement a health check test in the Docker build phase of the CI and CD pipelines.
The test should ping: `GET /` and see if it gets 200 (the error code from #28 was 404).
Related work items: #17 | 1.0 | Add Docker container REST api tests - Recently, there was a PR (#34) that broke some of the Spring APIs and it wasn't noticed until the CD pipeline failed to deploy to the AWS ECS cluster.
It would be great if the Docker build had failed instead and the PR was blocked from merging. It would be very easy to implement a health check test in the Docker build phase of the CI and CD pipelines.
The test should ping: `GET /` and see if it gets 200 (the error code from #28 was 404).
Related work items: #17 | non_priority | add docker container rest api tests recently there was a pr that broke some of the spring apis and it wasn t noticed until the cd pipeline failed to deploy to the aws ecs cluster it would be great if the docker build had failed instead and the pr was blocked from merging it would be very easy to implement a health check test in the docker build phase of the ci and cd pipelines the test should ping get and see if it gets the error code from was related work items | 0 |
379,551 | 26,375,183,301 | IssuesEvent | 2023-01-12 01:25:15 | plannigan/hyper-bump-it | https://api.github.com/repos/plannigan/hyper-bump-it | opened | Better terminal examples presentation | documentation enhancement | **Describe the solution you'd like**
The current documentation shows the output from a number of terminal prompts to demonstrate the functionality of `hyper-bump-it`. However, these example do not do the best job of demonstrating the what using the application is like.
Look into ways to show this output in a more visually appealing way. This could be an animated image or preferably a way to demonstrate the content in a text form that looks like a terminal prompt.
| 1.0 | Better terminal examples presentation - **Describe the solution you'd like**
The current documentation shows the output from a number of terminal prompts to demonstrate the functionality of `hyper-bump-it`. However, these example do not do the best job of demonstrating the what using the application is like.
Look into ways to show this output in a more visually appealing way. This could be an animated image or preferably a way to demonstrate the content in a text form that looks like a terminal prompt.
| non_priority | better terminal examples presentation describe the solution you d like the current documentation shows the output from a number of terminal prompts to demonstrate the functionality of hyper bump it however these example do not do the best job of demonstrating the what using the application is like look into ways to show this output in a more visually appealing way this could be an animated image or preferably a way to demonstrate the content in a text form that looks like a terminal prompt | 0 |
434,147 | 30,444,589,539 | IssuesEvent | 2023-07-15 13:54:40 | pypa/setuptools_scm | https://api.github.com/repos/pypa/setuptools_scm | closed | document a get_version pattern for editable installs staying as correct as sensible | enhancement help wanted deferred documentation | Is the following reasonable, e.g. for output of `--version`?
I am using this to get the current version with editable installs, useful
during development:
```python
def get_version():
try:
from setuptools_scm import get_version
return get_version(root='..', relative_to=__file__)
except (ImportError, LookupError):
from pkg_resources import get_distribution
return get_distribution(__package__).version
```
setup.py uses the basic:
```python
use_scm_version=True,
setup_requires=['setuptools_scm'],
```
btw: what is a use case for `write_to`? The file itself says that the file
should not be tracked in the SCM itself.
Ref: https://github.com/Vimjas/covimerage/pull/43
| 1.0 | document a get_version pattern for editable installs staying as correct as sensible - Is the following reasonable, e.g. for output of `--version`?
I am using this to get the current version with editable installs, useful
during development:
```python
def get_version():
try:
from setuptools_scm import get_version
return get_version(root='..', relative_to=__file__)
except (ImportError, LookupError):
from pkg_resources import get_distribution
return get_distribution(__package__).version
```
setup.py uses the basic:
```python
use_scm_version=True,
setup_requires=['setuptools_scm'],
```
btw: what is a use case for `write_to`? The file itself says that the file
should not be tracked in the SCM itself.
Ref: https://github.com/Vimjas/covimerage/pull/43
| non_priority | document a get version pattern for editable installs staying as correct as sensible is the following reasonable e g for output of version i am using this to get the current version with editable installs useful during development python def get version try from setuptools scm import get version return get version root relative to file except importerror lookuperror from pkg resources import get distribution return get distribution package version setup py uses the basic python use scm version true setup requires btw what is a use case for write to the file itself says that the file should not be tracked in the scm itself ref | 0 |
25,689 | 18,984,505,175 | IssuesEvent | 2021-11-21 13:38:22 | wordslab-org/wordslab | https://api.github.com/repos/wordslab-org/wordslab | opened | Port the command line installer to Linux (no GPU) | enhancement module-infrastructure | Create a Linux release
Document the install procedure in the wordslab.org website | 1.0 | Port the command line installer to Linux (no GPU) - Create a Linux release
Document the install procedure in the wordslab.org website | non_priority | port the command line installer to linux no gpu create a linux release document the install procedure in the wordslab org website | 0 |
188,953 | 22,046,955,824 | IssuesEvent | 2022-05-30 03:36:27 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | closed | CVE-2021-4090 (High) detected in linuxv4.19 - autoclosed | security vulnerability | ## CVE-2021-4090 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4xdr.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4xdr.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An out-of-bounds (OOB) memory write flaw was found in the NFSD in the Linux kernel. Missing sanity may lead to a write beyond bmval[bmlen-1] in nfsd4_decode_bitmap4 in fs/nfsd/nfs4xdr.c. In this flaw, a local attacker with user privilege may gain access to out-of-bounds memory, leading to a system integrity and confidentiality threat.
<p>Publish Date: 2022-02-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-4090>CVE-2021-4090</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/c0019b7db1d7ac62c711cda6b357a659d46428fe">https://github.com/torvalds/linux/commit/c0019b7db1d7ac62c711cda6b357a659d46428fe</a></p>
<p>Release Date: 2022-02-18</p>
<p>Fix Resolution: v5.16-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-4090 (High) detected in linuxv4.19 - autoclosed - ## CVE-2021-4090 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4xdr.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/nfs4xdr.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An out-of-bounds (OOB) memory write flaw was found in the NFSD in the Linux kernel. Missing sanity may lead to a write beyond bmval[bmlen-1] in nfsd4_decode_bitmap4 in fs/nfsd/nfs4xdr.c. In this flaw, a local attacker with user privilege may gain access to out-of-bounds memory, leading to a system integrity and confidentiality threat.
<p>Publish Date: 2022-02-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-4090>CVE-2021-4090</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/c0019b7db1d7ac62c711cda6b357a659d46428fe">https://github.com/torvalds/linux/commit/c0019b7db1d7ac62c711cda6b357a659d46428fe</a></p>
<p>Release Date: 2022-02-18</p>
<p>Fix Resolution: v5.16-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in autoclosed cve high severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files fs nfsd c fs nfsd c vulnerability details an out of bounds oob memory write flaw was found in the nfsd in the linux kernel missing sanity may lead to a write beyond bmval in decode in fs nfsd c in this flaw a local attacker with user privilege may gain access to out of bounds memory leading to a system integrity and confidentiality threat publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
162,553 | 12,680,489,276 | IssuesEvent | 2020-06-19 13:48:05 | Oldes/Rebol-issues | https://api.github.com/repos/Oldes/Rebol-issues | closed | TO-VALUE function to convert unset to none | Test.written Type.wish | _Submitted by:_ **BrianH**
I want a function that can take one normal parameter of any type, which returns that parameter unevaluated, except for an #[unset!] value. When it is passed an #[unset!](or end! I suppose if one of those escape) then it should return #[none] instead.
This function will need to be native, since it would be used in core control flow to defang unsets. And I have no idea what to call it, so I'm looking for suggestions.
``` rebol
; Rebol code equivalent
func [value [any-type!]] [unless unset? :value [:value]]
```
---
<sup>**Imported from:** **[CureCode](https://www.curecode.org/rebol3/ticket.rsp?id=2003)** [ Version: r3 master Type: Wish Platform: All Category: Native Reproduce: Always Fixed-in:none ]</sup>
<sup>**Imported from**: https://github.com/rebol/rebol-issues/issues/2003</sup>
Comments:
---
> **Rebolbot** commented on Mar 22, 2013:
_Submitted by:_ **BrianH**
Fork suggested DEVOID for this in SO chat, which is metaphorically accurate and less whimsical than DEFANG. The downside is that it makes reference to the "void" type in C-like languages that serves a similar purpose to returning unset in Rebol, but Rebol isn't a C-like language.
Another option would be TO-VALUE since it converts non-values like #[unset!] to values like #[none]. It's a little long, but it fits in with the other TO-\* functions, though without the copying that those do. I don't want to call it VALUE because that is a common variable name.
Other suggestions would be welcome.
---
> **Rebolbot** commented on Mar 22, 2013:
_Submitted by:_ **Ladislav**
I prefer the TO-VALUE alternative.
---
> **Rebolbot** commented on Mar 22, 2013:
_Submitted by:_ **abolka**
I prefer TO-VALUE as well.
---
> **Rebolbot** commented on Mar 6, 2014:
_Submitted by:_ **BrianH**
Implemented as TO-VALUE in https://github.com/rebol/rebol/pull/205
---
> **Rebolbot** mentioned this issue on Jan 12, 2016:
> [Make NONE! values no-op in slots processing results of a conditional expression](https://github.com/Oldes/Rebol-issues/issues/2078)
---
> **Rebolbot** mentioned this issue on Jan 22, 2016:
> [[Epic] Holes in our evaluation model](https://github.com/Oldes/Rebol-issues/issues/2127)
---
> **Hostilefork** mentioned this issue on May 1, 2018:
> [Allow INDEX? to take none as an argument, return none](https://github.com/Oldes/Rebol-issues/issues/1611)
---
> **Rebolbot** added the **Type.wish** on Jan 12, 2016
---
> **Hostilefork** added a commit to **[metaeducation/ren-c](https://github.com/metaeducation/ren-c/)** that referenced this issue on May 1, 2018:
> [Retake TRY for TO-VALUE, make NULL void's API representation](https://github.com/metaeducation/ren-c/commit/04f236d3bf5eac62565d1cb9fe2186e98293c6eb)
---
> **Hostilefork** added a commit to **[hostilefork/rebol](https://github.com/hostilefork/rebol/)** that referenced this issue on May 1, 2018:
> [Retake TRY for TO-VALUE, make NULL void's API representation](https://github.com/hostilefork/rebol/commit/4e44fe58da5417d381e83f3dc779fdc59fd16942)
---
> **Hostilefork** added a commit to **[hostilefork/rebol](https://github.com/hostilefork/rebol/)** that referenced this issue on May 1, 2018:
> [Retake TRY for TO-VALUE, make NULL void's API representation](https://github.com/hostilefork/rebol/commit/20f64be4519e9e6a852329088ec115546abba828)
--- | 1.0 | TO-VALUE function to convert unset to none - _Submitted by:_ **BrianH**
I want a function that can take one normal parameter of any type, which returns that parameter unevaluated, except for an #[unset!] value. When it is passed an #[unset!](or end! I suppose if one of those escape) then it should return #[none] instead.
This function will need to be native, since it would be used in core control flow to defang unsets. And I have no idea what to call it, so I'm looking for suggestions.
``` rebol
; Rebol code equivalent
func [value [any-type!]] [unless unset? :value [:value]]
```
---
<sup>**Imported from:** **[CureCode](https://www.curecode.org/rebol3/ticket.rsp?id=2003)** [ Version: r3 master Type: Wish Platform: All Category: Native Reproduce: Always Fixed-in:none ]</sup>
<sup>**Imported from**: https://github.com/rebol/rebol-issues/issues/2003</sup>
Comments:
---
> **Rebolbot** commented on Mar 22, 2013:
_Submitted by:_ **BrianH**
Fork suggested DEVOID for this in SO chat, which is metaphorically accurate and less whimsical than DEFANG. The downside is that it makes reference to the "void" type in C-like languages that serves a similar purpose to returning unset in Rebol, but Rebol isn't a C-like language.
Another option would be TO-VALUE since it converts non-values like #[unset!] to values like #[none]. It's a little long, but it fits in with the other TO-\* functions, though without the copying that those do. I don't want to call it VALUE because that is a common variable name.
Other suggestions would be welcome.
---
> **Rebolbot** commented on Mar 22, 2013:
_Submitted by:_ **Ladislav**
I prefer the TO-VALUE alternative.
---
> **Rebolbot** commented on Mar 22, 2013:
_Submitted by:_ **abolka**
I prefer TO-VALUE as well.
---
> **Rebolbot** commented on Mar 6, 2014:
_Submitted by:_ **BrianH**
Implemented as TO-VALUE in https://github.com/rebol/rebol/pull/205
---
> **Rebolbot** mentioned this issue on Jan 12, 2016:
> [Make NONE! values no-op in slots processing results of a conditional expression](https://github.com/Oldes/Rebol-issues/issues/2078)
---
> **Rebolbot** mentioned this issue on Jan 22, 2016:
> [[Epic] Holes in our evaluation model](https://github.com/Oldes/Rebol-issues/issues/2127)
---
> **Hostilefork** mentioned this issue on May 1, 2018:
> [Allow INDEX? to take none as an argument, return none](https://github.com/Oldes/Rebol-issues/issues/1611)
---
> **Rebolbot** added the **Type.wish** on Jan 12, 2016
---
> **Hostilefork** added a commit to **[metaeducation/ren-c](https://github.com/metaeducation/ren-c/)** that referenced this issue on May 1, 2018:
> [Retake TRY for TO-VALUE, make NULL void's API representation](https://github.com/metaeducation/ren-c/commit/04f236d3bf5eac62565d1cb9fe2186e98293c6eb)
---
> **Hostilefork** added a commit to **[hostilefork/rebol](https://github.com/hostilefork/rebol/)** that referenced this issue on May 1, 2018:
> [Retake TRY for TO-VALUE, make NULL void's API representation](https://github.com/hostilefork/rebol/commit/4e44fe58da5417d381e83f3dc779fdc59fd16942)
---
> **Hostilefork** added a commit to **[hostilefork/rebol](https://github.com/hostilefork/rebol/)** that referenced this issue on May 1, 2018:
> [Retake TRY for TO-VALUE, make NULL void's API representation](https://github.com/hostilefork/rebol/commit/20f64be4519e9e6a852329088ec115546abba828)
--- | non_priority | to value function to convert unset to none submitted by brianh i want a function that can take one normal parameter of any type which returns that parameter unevaluated except for an value when it is passed an or end i suppose if one of those escape then it should return instead this function will need to be native since it would be used in core control flow to defang unsets and i have no idea what to call it so i m looking for suggestions rebol rebol code equivalent func imported from imported from comments rebolbot commented on mar submitted by brianh fork suggested devoid for this in so chat which is metaphorically accurate and less whimsical than defang the downside is that it makes reference to the void type in c like languages that serves a similar purpose to returning unset in rebol but rebol isn t a c like language another option would be to value since it converts non values like to values like it s a little long but it fits in with the other to functions though without the copying that those do i don t want to call it value because that is a common variable name other suggestions would be welcome rebolbot commented on mar submitted by ladislav i prefer the to value alternative rebolbot commented on mar submitted by abolka i prefer to value as well rebolbot commented on mar submitted by brianh implemented as to value in rebolbot mentioned this issue on jan rebolbot mentioned this issue on jan holes in our evaluation model hostilefork mentioned this issue on may rebolbot added the type wish on jan hostilefork added a commit to that referenced this issue on may hostilefork added a commit to that referenced this issue on may hostilefork added a commit to that referenced this issue on may | 0 |
336,842 | 24,515,475,326 | IssuesEvent | 2022-10-11 04:21:35 | TechWiz-3/who-unfollowed-me | https://api.github.com/repos/TechWiz-3/who-unfollowed-me | closed | Make `README.md` compatible with Pypi | documentation good first issue hacktoberfest | Make the README.md link to image links rather than file locations to allow Pypi to render the README properly.
https://packaging.python.org/en/latest/guides/making-a-pypi-friendly-readme/
In `setup.py` add the repos README as the `long_description` as required by Pypi | 1.0 | Make `README.md` compatible with Pypi - Make the README.md link to image links rather than file locations to allow Pypi to render the README properly.
https://packaging.python.org/en/latest/guides/making-a-pypi-friendly-readme/
In `setup.py` add the repos README as the `long_description` as required by Pypi | non_priority | make readme md compatible with pypi make the readme md link to image links rather than file locations to allow pypi to render the readme properly in setup py add the repos readme as the long description as required by pypi | 0 |
129,067 | 18,070,758,728 | IssuesEvent | 2021-09-21 02:25:34 | Kalskiman/gentelella | https://api.github.com/repos/Kalskiman/gentelella | opened | CVE-2021-32804 (High) detected in tar-2.2.1.tgz, tar-0.1.20.tgz | security vulnerability | ## CVE-2021-32804 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tar-2.2.1.tgz</b>, <b>tar-0.1.20.tgz</b></p></summary>
<p>
<details><summary><b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: gentelella/vendors/bootstrap/package.json</p>
<p>Path to vulnerable library: gentelella/vendors/bootstrap/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.11.0.tgz (Root Library)
- node-gyp-3.8.0.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>tar-0.1.20.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-0.1.20.tgz">https://registry.npmjs.org/tar/-/tar-0.1.20.tgz</a></p>
<p>Path to dependency file: gentelella/vendors/switchery/package.json</p>
<p>Path to vulnerable library: gentelella/vendors/switchery/node_modules/tar/package.json,gentelella/vendors/switchery/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- bower-1.2.8.tgz (Root Library)
- :x: **tar-0.1.20.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution: tar - 3.2.2, 4.4.14, 5.0.6, 6.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-32804 (High) detected in tar-2.2.1.tgz, tar-0.1.20.tgz - ## CVE-2021-32804 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tar-2.2.1.tgz</b>, <b>tar-0.1.20.tgz</b></p></summary>
<p>
<details><summary><b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: gentelella/vendors/bootstrap/package.json</p>
<p>Path to vulnerable library: gentelella/vendors/bootstrap/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.11.0.tgz (Root Library)
- node-gyp-3.8.0.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>tar-0.1.20.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-0.1.20.tgz">https://registry.npmjs.org/tar/-/tar-0.1.20.tgz</a></p>
<p>Path to dependency file: gentelella/vendors/switchery/package.json</p>
<p>Path to vulnerable library: gentelella/vendors/switchery/node_modules/tar/package.json,gentelella/vendors/switchery/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- bower-1.2.8.tgz (Root Library)
- :x: **tar-0.1.20.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution: tar - 3.2.2, 4.4.14, 5.0.6, 6.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tar tgz tar tgz cve high severity vulnerability vulnerable libraries tar tgz tar tgz tar tgz tar for node library home page a href path to dependency file gentelella vendors bootstrap package json path to vulnerable library gentelella vendors bootstrap node modules tar package json dependency hierarchy node sass tgz root library node gyp tgz x tar tgz vulnerable library tar tgz tar for node library home page a href path to dependency file gentelella vendors switchery package json path to vulnerable library gentelella vendors switchery node modules tar package json gentelella vendors switchery node modules tar package json dependency hierarchy bower tgz root library x tar tgz vulnerable library vulnerability details the npm package tar aka node tar before versions and has a arbitrary file creation overwrite vulnerability due to insufficient absolute path sanitization node tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the preservepaths flag is not set to true this is achieved by stripping the absolute path root from any absolute file paths contained in a tar file for example home user bashrc would turn into home user bashrc this logic was insufficient when file paths contained repeated path roots such as home user bashrc node tar would only strip a single path root from such paths when given an absolute file path with repeating path roots the resulting path e g home user bashrc would still resolve to an absolute path thus allowing arbitrary file creation and overwrite this issue was addressed in releases and users may work around this vulnerability without upgrading by creating a custom onentry method which sanitizes the entry path or a filter method which removes entries with absolute paths see referenced github advisory for details be aware of cve which fixes a similar bug in later versions of tar publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar step up your open source security game with whitesource | 0 |
174,642 | 13,502,058,626 | IssuesEvent | 2020-09-13 06:16:13 | AdaptableTools/adaptable | https://api.github.com/repos/AdaptableTools/adaptable | closed | Cannot enter a new Date into Bulk Update Toolbar | Function: Bulk Update Sigal Test Type: Bug | Even though it knows the column is a date it shows a textbox - needs to be a Date Picker
The Bulk Update popup does allow new date creation but not the Toolbar control | 1.0 | Cannot enter a new Date into Bulk Update Toolbar - Even though it knows the column is a date it shows a textbox - needs to be a Date Picker
The Bulk Update popup does allow new date creation but not the Toolbar control | non_priority | cannot enter a new date into bulk update toolbar even though it knows the column is a date it shows a textbox needs to be a date picker the bulk update popup does allow new date creation but not the toolbar control | 0 |
243,244 | 26,277,982,710 | IssuesEvent | 2023-01-07 01:39:43 | kapseliboi/coronavirus-dashboard | https://api.github.com/repos/kapseliboi/coronavirus-dashboard | opened | CVE-2021-4279 (High) detected in fast-json-patch-3.1.0.tgz | security vulnerability | ## CVE-2021-4279 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fast-json-patch-3.1.0.tgz</b></p></summary>
<p>Fast implementation of JSON-Patch (RFC-6902) with duplex (observe changes) capabilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/fast-json-patch/-/fast-json-patch-3.1.0.tgz">https://registry.npmjs.org/fast-json-patch/-/fast-json-patch-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/fast-json-patch/package.json</p>
<p>
Dependency Hierarchy:
- swagger-ui-react-4.1.3.tgz (Root Library)
- swagger-client-3.17.0.tgz
- :x: **fast-json-patch-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/coronavirus-dashboard/commit/978d257a5c0738711e941b81eca0b20c284ec902">978d257a5c0738711e941b81eca0b20c284ec902</a></p>
<p>Found in base branch: <b>v3-development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability has been found in Starcounter-Jack JSON-Patch up to 3.1.0 and classified as problematic. This vulnerability affects unknown code. The manipulation leads to improperly controlled modification of object prototype attributes ('prototype pollution'). The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. Upgrading to version 3.1.1 is able to address this issue. The name of the patch is 7ad6af41eabb2d799f698740a91284d762c955c9. It is recommended to upgrade the affected component. VDB-216778 is the identifier assigned to this vulnerability.
<p>Publish Date: 2022-12-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-4279>CVE-2021-4279</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-4279">https://www.cve.org/CVERecord?id=CVE-2021-4279</a></p>
<p>Release Date: 2022-12-25</p>
<p>Fix Resolution (fast-json-patch): 3.1.1</p>
<p>Direct dependency fix Resolution (swagger-ui-react): 4.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-4279 (High) detected in fast-json-patch-3.1.0.tgz - ## CVE-2021-4279 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fast-json-patch-3.1.0.tgz</b></p></summary>
<p>Fast implementation of JSON-Patch (RFC-6902) with duplex (observe changes) capabilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/fast-json-patch/-/fast-json-patch-3.1.0.tgz">https://registry.npmjs.org/fast-json-patch/-/fast-json-patch-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/fast-json-patch/package.json</p>
<p>
Dependency Hierarchy:
- swagger-ui-react-4.1.3.tgz (Root Library)
- swagger-client-3.17.0.tgz
- :x: **fast-json-patch-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/coronavirus-dashboard/commit/978d257a5c0738711e941b81eca0b20c284ec902">978d257a5c0738711e941b81eca0b20c284ec902</a></p>
<p>Found in base branch: <b>v3-development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability has been found in Starcounter-Jack JSON-Patch up to 3.1.0 and classified as problematic. This vulnerability affects unknown code. The manipulation leads to improperly controlled modification of object prototype attributes ('prototype pollution'). The attack can be initiated remotely. The exploit has been disclosed to the public and may be used. Upgrading to version 3.1.1 is able to address this issue. The name of the patch is 7ad6af41eabb2d799f698740a91284d762c955c9. It is recommended to upgrade the affected component. VDB-216778 is the identifier assigned to this vulnerability.
<p>Publish Date: 2022-12-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-4279>CVE-2021-4279</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-4279">https://www.cve.org/CVERecord?id=CVE-2021-4279</a></p>
<p>Release Date: 2022-12-25</p>
<p>Fix Resolution (fast-json-patch): 3.1.1</p>
<p>Direct dependency fix Resolution (swagger-ui-react): 4.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in fast json patch tgz cve high severity vulnerability vulnerable library fast json patch tgz fast implementation of json patch rfc with duplex observe changes capabilities library home page a href path to dependency file package json path to vulnerable library node modules fast json patch package json dependency hierarchy swagger ui react tgz root library swagger client tgz x fast json patch tgz vulnerable library found in head commit a href found in base branch development vulnerability details a vulnerability has been found in starcounter jack json patch up to and classified as problematic this vulnerability affects unknown code the manipulation leads to improperly controlled modification of object prototype attributes prototype pollution the attack can be initiated remotely the exploit has been disclosed to the public and may be used upgrading to version is able to address this issue the name of the patch is it is recommended to upgrade the affected component vdb is the identifier assigned to this vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution fast json patch direct dependency fix resolution swagger ui react step up your open source security game with mend | 0 |
144,883 | 22,582,929,170 | IssuesEvent | 2022-06-28 13:10:58 | LanguageDev/Fresh-Language-suggestions | https://api.github.com/repos/LanguageDev/Fresh-Language-suggestions | opened | [WIP] Exceptions, try-catch-finally | Design document Syntax | <!-- Exceptions -->
## Introduction
Since there is not a lot of variation or redesign-choices here, I'll just propose the constructs for throwing and try-catch-finally.
## Throwing construct
There is not a lot of variation here, throwing itself is an expression with the syntax:
`throw expr`
The returned expression type (even though the expression does not evaluate to anything, it needs a type) could be converted to any type implicitly, so type-inference does not trip up in cases like this:
```swift
func div(a: int, b: int): int =
if (b == 0) throw DivByZeroExcepton()
else a / b;
```
## Try-catch-finally
This is the point where there is a bit more variation, I'll go through all I've come across. Since all other of our control structures are expressions, it would make sense for try-catch-finally as well.
### C#
Since the C# variant does not evaluate to values like expressions, it's not that interesting for us. In the most general form, try is mandatory, after that either a catch or finally block has to follow. If there is a finally block, there can be any number of catch blocks. Catch blocks try to match the exception type to the thrown exception, even allowing for a filter expression with the keyword `when`, implementing a limited pattern matching system. [Full docs can be found here.](https://docs.microsoft.com/en-us/dotnet/csharp/fundamentals/exceptions/)
Personally, I think it's a bit overengineered, and became a bit inconsistent after pattern matching hit the scene. It's a decision from the past, so there's really no one to blame for it.
### F#
F# decided to introduce two different constructs, [try-with](https://docs.microsoft.com/en-us/dotnet/fsharp/language-reference/exception-handling/the-try-with-expression) and [try-finally](https://docs.microsoft.com/en-us/dotnet/fsharp/language-reference/exception-handling/the-try-finally-expression). This means, if you need all 3 blocks, you'd have to nest them (example taken from the docs):
```fs
let function1 x y =
try
try
if x = y then raise (InnerError("inner"))
else raise (OuterError("outer"))
with
| InnerError(str) -> printfn "Error1 %s" str
finally
printfn "Always print this."
```
An interesting note is that `with` (which is the equivalent of `catch` in C#) is actually a regular pattern-matching construct, which actually makes a lot of sense. Instead of implementing specialized systems with multiple catch blocks and filters, F# simply utilizes the fact that it already has pattern matching.
In `try-with`, if there are no exceptions, the `try` body is evaluated as a result, otherwise, an exception is matched in `with`, and the corresponding value is returned. In `try-finally`, only the `try` contributes to the result.
Personally, I think this nesting can be really annoying, and it was a quite inelegant design.
### Kotlin
In Kotlin, `try-catch-finally` is also an expression:
```kt
val a: Int? = try { input.toInt() } catch (e: NumberFormatException) { null }
```
The semantics is very simple: if there are no exceptions, the body of `try` is returned, otherwise the body of the corresponding `catch` block is returned. The `finally` block does not contribute to the expression result.
Personally, I find this the best semantics out of all. What I found odd, is that Kotlin also does multiple catch blocks instead of utilizing its pattern-matching.
### Proposed for Fresh
I'd like to propose a mixture of Kotlin and F# for our construct. More precisely, the evaluation semantics of Kotlin, and the pattern matching of F#. This way we get multi-catch free, get the filters of C# free and are able to utilize everything that will be present in the language for pattern matching.
Syntax proposal:
```kt
val a = try {
int.Parse(line) / b
}
catch {
DivByZeroException -> int.MaxValue;
_ -> 0;
};
```
We could even have a one-liner versions, or a version of catch that simply matches everything and returns the specified value ("swallow-all" catch):
```kt
// Catch that simply ignores
val a = try { int.Parse(line) } catch { 0 };
// One-liner version
val a = try int.Parse(line) catch 0;
```
The `finally` block does not contribute to the evaluated expression, it is simply executed after the evaluation of try-catch. Example:
```kt
val a = try {
int.Parse(line) / b
}
catch {
DivByZeroException -> int.MaxValue;
_ -> 0;
}
finally {
WriteLine("This is always printed");
};
```
There can only be a single catch and a single finally block and at least one has to be present (there can't be a `try` block by itself). If there is a `catch` block, it has to evaluate to a compatible type with `try`.
| 1.0 | [WIP] Exceptions, try-catch-finally - <!-- Exceptions -->
## Introduction
Since there is not a lot of variation or redesign-choices here, I'll just propose the constructs for throwing and try-catch-finally.
## Throwing construct
There is not a lot of variation here, throwing itself is an expression with the syntax:
`throw expr`
The returned expression type (even though the expression does not evaluate to anything, it needs a type) could be converted to any type implicitly, so type-inference does not trip up in cases like this:
```swift
func div(a: int, b: int): int =
if (b == 0) throw DivByZeroExcepton()
else a / b;
```
## Try-catch-finally
This is the point where there is a bit more variation, I'll go through all I've come across. Since all other of our control structures are expressions, it would make sense for try-catch-finally as well.
### C#
Since the C# variant does not evaluate to values like expressions, it's not that interesting for us. In the most general form, try is mandatory, after that either a catch or finally block has to follow. If there is a finally block, there can be any number of catch blocks. Catch blocks try to match the exception type to the thrown exception, even allowing for a filter expression with the keyword `when`, implementing a limited pattern matching system. [Full docs can be found here.](https://docs.microsoft.com/en-us/dotnet/csharp/fundamentals/exceptions/)
Personally, I think it's a bit overengineered, and became a bit inconsistent after pattern matching hit the scene. It's a decision from the past, so there's really no one to blame for it.
### F#
F# decided to introduce two different constructs, [try-with](https://docs.microsoft.com/en-us/dotnet/fsharp/language-reference/exception-handling/the-try-with-expression) and [try-finally](https://docs.microsoft.com/en-us/dotnet/fsharp/language-reference/exception-handling/the-try-finally-expression). This means, if you need all 3 blocks, you'd have to nest them (example taken from the docs):
```fs
let function1 x y =
try
try
if x = y then raise (InnerError("inner"))
else raise (OuterError("outer"))
with
| InnerError(str) -> printfn "Error1 %s" str
finally
printfn "Always print this."
```
An interesting note is that `with` (which is the equivalent of `catch` in C#) is actually a regular pattern-matching construct, which actually makes a lot of sense. Instead of implementing specialized systems with multiple catch blocks and filters, F# simply utilizes the fact that it already has pattern matching.
In `try-with`, if there are no exceptions, the `try` body is evaluated as a result, otherwise, an exception is matched in `with`, and the corresponding value is returned. In `try-finally`, only the `try` contributes to the result.
Personally, I think this nesting can be really annoying, and it was a quite inelegant design.
### Kotlin
In Kotlin, `try-catch-finally` is also an expression:
```kt
val a: Int? = try { input.toInt() } catch (e: NumberFormatException) { null }
```
The semantics is very simple: if there are no exceptions, the body of `try` is returned, otherwise the body of the corresponding `catch` block is returned. The `finally` block does not contribute to the expression result.
Personally, I find this the best semantics out of all. What I found odd, is that Kotlin also does multiple catch blocks instead of utilizing its pattern-matching.
### Proposed for Fresh
I'd like to propose a mixture of Kotlin and F# for our construct. More precisely, the evaluation semantics of Kotlin, and the pattern matching of F#. This way we get multi-catch free, get the filters of C# free and are able to utilize everything that will be present in the language for pattern matching.
Syntax proposal:
```kt
val a = try {
int.Parse(line) / b
}
catch {
DivByZeroException -> int.MaxValue;
_ -> 0;
};
```
We could even have a one-liner versions, or a version of catch that simply matches everything and returns the specified value ("swallow-all" catch):
```kt
// Catch that simply ignores
val a = try { int.Parse(line) } catch { 0 };
// One-liner version
val a = try int.Parse(line) catch 0;
```
The `finally` block does not contribute to the evaluated expression, it is simply executed after the evaluation of try-catch. Example:
```kt
val a = try {
int.Parse(line) / b
}
catch {
DivByZeroException -> int.MaxValue;
_ -> 0;
}
finally {
WriteLine("This is always printed");
};
```
There can only be a single catch and a single finally block and at least one has to be present (there can't be a `try` block by itself). If there is a `catch` block, it has to evaluate to a compatible type with `try`.
| non_priority | exceptions try catch finally introduction since there is not a lot of variation or redesign choices here i ll just propose the constructs for throwing and try catch finally throwing construct there is not a lot of variation here throwing itself is an expression with the syntax throw expr the returned expression type even though the expression does not evaluate to anything it needs a type could be converted to any type implicitly so type inference does not trip up in cases like this swift func div a int b int int if b throw divbyzeroexcepton else a b try catch finally this is the point where there is a bit more variation i ll go through all i ve come across since all other of our control structures are expressions it would make sense for try catch finally as well c since the c variant does not evaluate to values like expressions it s not that interesting for us in the most general form try is mandatory after that either a catch or finally block has to follow if there is a finally block there can be any number of catch blocks catch blocks try to match the exception type to the thrown exception even allowing for a filter expression with the keyword when implementing a limited pattern matching system personally i think it s a bit overengineered and became a bit inconsistent after pattern matching hit the scene it s a decision from the past so there s really no one to blame for it f f decided to introduce two different constructs and this means if you need all blocks you d have to nest them example taken from the docs fs let x y try try if x y then raise innererror inner else raise outererror outer with innererror str printfn s str finally printfn always print this an interesting note is that with which is the equivalent of catch in c is actually a regular pattern matching construct which actually makes a lot of sense instead of implementing specialized systems with multiple catch blocks and filters f simply utilizes the fact that it already has pattern matching in try with if there are no exceptions the try body is evaluated as a result otherwise an exception is matched in with and the corresponding value is returned in try finally only the try contributes to the result personally i think this nesting can be really annoying and it was a quite inelegant design kotlin in kotlin try catch finally is also an expression kt val a int try input toint catch e numberformatexception null the semantics is very simple if there are no exceptions the body of try is returned otherwise the body of the corresponding catch block is returned the finally block does not contribute to the expression result personally i find this the best semantics out of all what i found odd is that kotlin also does multiple catch blocks instead of utilizing its pattern matching proposed for fresh i d like to propose a mixture of kotlin and f for our construct more precisely the evaluation semantics of kotlin and the pattern matching of f this way we get multi catch free get the filters of c free and are able to utilize everything that will be present in the language for pattern matching syntax proposal kt val a try int parse line b catch divbyzeroexception int maxvalue we could even have a one liner versions or a version of catch that simply matches everything and returns the specified value swallow all catch kt catch that simply ignores val a try int parse line catch one liner version val a try int parse line catch the finally block does not contribute to the evaluated expression it is simply executed after the evaluation of try catch example kt val a try int parse line b catch divbyzeroexception int maxvalue finally writeline this is always printed there can only be a single catch and a single finally block and at least one has to be present there can t be a try block by itself if there is a catch block it has to evaluate to a compatible type with try | 0 |
132,704 | 18,268,849,561 | IssuesEvent | 2021-10-04 11:42:32 | artsking/linux-3.0.35 | https://api.github.com/repos/artsking/linux-3.0.35 | opened | CVE-2016-2143 (High) detected in linux-stable-rtv3.8.6 | security vulnerability | ## CVE-2016-2143 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35/commit/5992fa81c6ac1b4e9db13f5408d914525c5b7875">5992fa81c6ac1b4e9db13f5408d914525c5b7875</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fork implementation in the Linux kernel before 4.5 on s390 platforms mishandles the case of four page-table levels, which allows local users to cause a denial of service (system crash) or possibly have unspecified other impact via a crafted application, related to arch/s390/include/asm/mmu_context.h and arch/s390/include/asm/pgalloc.h.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2143>CVE-2016-2143</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2143">https://nvd.nist.gov/vuln/detail/CVE-2016-2143</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: 4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-2143 (High) detected in linux-stable-rtv3.8.6 - ## CVE-2016-2143 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35/commit/5992fa81c6ac1b4e9db13f5408d914525c5b7875">5992fa81c6ac1b4e9db13f5408d914525c5b7875</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fork implementation in the Linux kernel before 4.5 on s390 platforms mishandles the case of four page-table levels, which allows local users to cause a denial of service (system crash) or possibly have unspecified other impact via a crafted application, related to arch/s390/include/asm/mmu_context.h and arch/s390/include/asm/pgalloc.h.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2143>CVE-2016-2143</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2143">https://nvd.nist.gov/vuln/detail/CVE-2016-2143</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: 4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details the fork implementation in the linux kernel before on platforms mishandles the case of four page table levels which allows local users to cause a denial of service system crash or possibly have unspecified other impact via a crafted application related to arch include asm mmu context h and arch include asm pgalloc h publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
112,606 | 17,092,588,914 | IssuesEvent | 2021-07-08 19:40:31 | Tim-sandbox/WebGoat | https://api.github.com/repos/Tim-sandbox/WebGoat | opened | CVE-2020-11023 (Medium) detected in jquery-2.1.4.min.js, jquery-3.4.1.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-3.4.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-2.1.4.min.js,WebGoat/webgoat-container/target/classes/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.4.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery.min.js,WebGoat/webgoat-container/target/classes/static/js/libs/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.4.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Tim-sandbox/WebGoat/commit/349164cb2ad66ba492c478574891b87f1c69d350">349164cb2ad66ba492c478574891b87f1c69d350</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"2.1.4","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jquery:2.1.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"3.4.1","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jquery:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11023 (Medium) detected in jquery-2.1.4.min.js, jquery-3.4.1.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-3.4.1.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-2.1.4.min.js,WebGoat/webgoat-container/target/classes/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.4.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery.min.js,WebGoat/webgoat-container/target/classes/static/js/libs/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.4.1.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Tim-sandbox/WebGoat/commit/349164cb2ad66ba492c478574891b87f1c69d350">349164cb2ad66ba492c478574891b87f1c69d350</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"2.1.4","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jquery:2.1.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"3.4.1","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jquery:3.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js jquery min js cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to vulnerable library webgoat webgoat container src main resources static js libs jquery min js webgoat webgoat container target classes static js libs jquery min js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library webgoat webgoat container src main resources static js libs jquery min js webgoat webgoat container target classes static js libs jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch develop vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery packagetype javascript packagename jquery packageversion packagefilepaths istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery basebranches vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl | 0 |
379,479 | 26,372,847,741 | IssuesEvent | 2023-01-11 22:22:04 | Bench-ai/Jula | https://api.github.com/repos/Bench-ai/Jula | opened | Send zip | documentation enhancement API-DB | Downloads layer files Model representation, entire throne app reqs.text, and many more. Zips it and sends it to the user | 1.0 | Send zip - Downloads layer files Model representation, entire throne app reqs.text, and many more. Zips it and sends it to the user | non_priority | send zip downloads layer files model representation entire throne app reqs text and many more zips it and sends it to the user | 0 |
55,246 | 7,966,773,186 | IssuesEvent | 2018-07-15 04:13:12 | errbit/errbit | https://api.github.com/repos/errbit/errbit | closed | Document ERRBIT_ADMIN_USER, ERRBIT_ADMIN_EMAIL and ERRBIT_ADMIN_PASSWORD | documentation help-wanted | https://github.com/errbit/errbit/blob/master/db/seeds.rb
ERRBIT_ADMIN_USER, ERRBIT_ADMIN_EMAIL and ERRBIT_ADMIN_PASSWORD can be set to help define the admin user
They are missing at https://github.com/errbit/errbit/blob/master/docs/configuration.md
This is related to Pull Request #1221 | 1.0 | Document ERRBIT_ADMIN_USER, ERRBIT_ADMIN_EMAIL and ERRBIT_ADMIN_PASSWORD - https://github.com/errbit/errbit/blob/master/db/seeds.rb
ERRBIT_ADMIN_USER, ERRBIT_ADMIN_EMAIL and ERRBIT_ADMIN_PASSWORD can be set to help define the admin user
They are missing at https://github.com/errbit/errbit/blob/master/docs/configuration.md
This is related to Pull Request #1221 | non_priority | document errbit admin user errbit admin email and errbit admin password errbit admin user errbit admin email and errbit admin password can be set to help define the admin user they are missing at this is related to pull request | 0 |
142,787 | 21,884,497,377 | IssuesEvent | 2022-05-19 17:11:33 | bcgov/cas-cif | https://api.github.com/repos/bcgov/cas-cif | closed | Prepare for wireframe testing session | Task UX Design UX Research | #### Describe the task
Prepare for testing session with the Ops team (ideally at 3rd week of May)
#### Acceptance Criteria
- [x] Create research goals
- [x] Create script
- [x] Finalize script after reviewing with team
- [x] Create observation notes file
- [x] Set up meeting sessions with Ops team
| 1.0 | Prepare for wireframe testing session - #### Describe the task
Prepare for testing session with the Ops team (ideally at 3rd week of May)
#### Acceptance Criteria
- [x] Create research goals
- [x] Create script
- [x] Finalize script after reviewing with team
- [x] Create observation notes file
- [x] Set up meeting sessions with Ops team
| non_priority | prepare for wireframe testing session describe the task prepare for testing session with the ops team ideally at week of may acceptance criteria create research goals create script finalize script after reviewing with team create observation notes file set up meeting sessions with ops team | 0 |
31,498 | 8,705,609,116 | IssuesEvent | 2018-12-05 23:01:14 | Microsoft/openenclave | https://api.github.com/repos/Microsoft/openenclave | opened | Set libcxx headers as SYSTEM headers | build | Like we did for the musl headers, we may want to set libcxx as SYSTEM headers so that CMake uses `-isystem`. However, we may run into a header ordering problem. | 1.0 | Set libcxx headers as SYSTEM headers - Like we did for the musl headers, we may want to set libcxx as SYSTEM headers so that CMake uses `-isystem`. However, we may run into a header ordering problem. | non_priority | set libcxx headers as system headers like we did for the musl headers we may want to set libcxx as system headers so that cmake uses isystem however we may run into a header ordering problem | 0 |
360,137 | 25,275,565,297 | IssuesEvent | 2022-11-16 12:23:12 | apache/apisix-docker | https://api.github.com/repos/apache/apisix-docker | opened | Remove separate section for APISIX Docker docs | documentation | Currently, the APISIX website has an Apache APISIX Docker subsection of documentation. This is unnecessary as all the documentation mentioned on the page could be moved to APISIX documentation.
This could make it easier to discover docs as they will be within the APISIX docs. | 1.0 | Remove separate section for APISIX Docker docs - Currently, the APISIX website has an Apache APISIX Docker subsection of documentation. This is unnecessary as all the documentation mentioned on the page could be moved to APISIX documentation.
This could make it easier to discover docs as they will be within the APISIX docs. | non_priority | remove separate section for apisix docker docs currently the apisix website has an apache apisix docker subsection of documentation this is unnecessary as all the documentation mentioned on the page could be moved to apisix documentation this could make it easier to discover docs as they will be within the apisix docs | 0 |
76,172 | 14,581,310,733 | IssuesEvent | 2020-12-18 10:31:26 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] Feature request: Make 'save as copy' available in front end | New Feature No Code Attached Yet | ### Is your feature request related to a problem? Please describe.
For non-techy editors who don't know much html or css, it is difficult to start some articles from scratch, especially if they'd like to keep it more or less the same format as existing articles.
At the moment, the only way to do this is to:
1. open an existing article,
2. copy the code,
3. close the article,
4. start a new one,
5. paste in the code and then
6. Edit
### Describe the solution you'd like
Add the 'Save as Copy' option to the front editor so,
1. Open article
2. Click 'save as copy'
3. Edit
### Additional context
| 1.0 | [4.0] Feature request: Make 'save as copy' available in front end - ### Is your feature request related to a problem? Please describe.
For non-techy editors who don't know much html or css, it is difficult to start some articles from scratch, especially if they'd like to keep it more or less the same format as existing articles.
At the moment, the only way to do this is to:
1. open an existing article,
2. copy the code,
3. close the article,
4. start a new one,
5. paste in the code and then
6. Edit
### Describe the solution you'd like
Add the 'Save as Copy' option to the front editor so,
1. Open article
2. Click 'save as copy'
3. Edit
### Additional context
| non_priority | feature request make save as copy available in front end is your feature request related to a problem please describe for non techy editors who don t know much html or css it is difficult to start some articles from scratch especially if they d like to keep it more or less the same format as existing articles at the moment the only way to do this is to open an existing article copy the code close the article start a new one paste in the code and then edit describe the solution you d like add the save as copy option to the front editor so open article click save as copy edit additional context | 0 |
384,888 | 26,606,636,516 | IssuesEvent | 2023-01-23 19:56:15 | cisagov/ScubaGear | https://api.github.com/repos/cisagov/ScubaGear | opened | Update the README to provide details on the tool file unblocking based on end-user environment's PowerShell execution policy. | documentation | # 💡 Summary #
The ScubaGear is implemented with code signing through #120. While testing the code-signing with different end-user environments, found a few oddities when the execution policy is set to 'unrestricted'. The recommendation from #120 is to document expected behavior based on end-user's PowerShell ExecutionPolicy and/or note the discrepancy for the 'unrestricted policy'. The README updates are recommended to be done close to Dolphin v0.3.0 release.
## Motivation and context ##
This would be useful to ScubaGear users to check their PowerShell execution policy and understand/debug the unblocking behavior of the tool.
## Implementation notes ##
Update the README
## Acceptance criteria ##
README lists the expected behavior for 'Unrestricted' policy along with a best practice recommendation.
| 1.0 | Update the README to provide details on the tool file unblocking based on end-user environment's PowerShell execution policy. - # 💡 Summary #
The ScubaGear is implemented with code signing through #120. While testing the code-signing with different end-user environments, found a few oddities when the execution policy is set to 'unrestricted'. The recommendation from #120 is to document expected behavior based on end-user's PowerShell ExecutionPolicy and/or note the discrepancy for the 'unrestricted policy'. The README updates are recommended to be done close to Dolphin v0.3.0 release.
## Motivation and context ##
This would be useful to ScubaGear users to check their PowerShell execution policy and understand/debug the unblocking behavior of the tool.
## Implementation notes ##
Update the README
## Acceptance criteria ##
README lists the expected behavior for 'Unrestricted' policy along with a best practice recommendation.
| non_priority | update the readme to provide details on the tool file unblocking based on end user environment s powershell execution policy 💡 summary the scubagear is implemented with code signing through while testing the code signing with different end user environments found a few oddities when the execution policy is set to unrestricted the recommendation from is to document expected behavior based on end user s powershell executionpolicy and or note the discrepancy for the unrestricted policy the readme updates are recommended to be done close to dolphin release motivation and context this would be useful to scubagear users to check their powershell execution policy and understand debug the unblocking behavior of the tool implementation notes update the readme acceptance criteria readme lists the expected behavior for unrestricted policy along with a best practice recommendation | 0 |
148,011 | 23,298,515,392 | IssuesEvent | 2022-08-07 00:36:41 | zuri-training/Proj-T_C_Gen-Team-74 | https://api.github.com/repos/zuri-training/Proj-T_C_Gen-Team-74 | closed | Conceive and Implement the designs for the login page | Design | ## Design the login modal.
# The Login should appear as a modal with a backdrop | 1.0 | Conceive and Implement the designs for the login page - ## Design the login modal.
# The Login should appear as a modal with a backdrop | non_priority | conceive and implement the designs for the login page design the login modal the login should appear as a modal with a backdrop | 0 |
14,415 | 8,580,156,245 | IssuesEvent | 2018-11-13 11:08:13 | Yoast/wordpress-seo | https://api.github.com/repos/Yoast/wordpress-seo | opened | Functional goal: Markings | UX backlog component: performance | # UX
As a user I want to:
- have markings always show the relevant parts for the selected analysis
- be able to modify the content or SEO attributes (keyphrase, synonyms) and have updated markings
- have (near) instant feedback/results when I modify the content
- have a "notification" whenever I resolved all marked problems
# Technical
- When a marker is active, only update the annotations when the list of what we need to annotate changes (annotations API should take care of this). _We should always be able to just provide a list, caching and performance should not be our concern._ | True | Functional goal: Markings - # UX
As a user I want to:
- have markings always show the relevant parts for the selected analysis
- be able to modify the content or SEO attributes (keyphrase, synonyms) and have updated markings
- have (near) instant feedback/results when I modify the content
- have a "notification" whenever I resolved all marked problems
# Technical
- When a marker is active, only update the annotations when the list of what we need to annotate changes (annotations API should take care of this). _We should always be able to just provide a list, caching and performance should not be our concern._ | non_priority | functional goal markings ux as a user i want to have markings always show the relevant parts for the selected analysis be able to modify the content or seo attributes keyphrase synonyms and have updated markings have near instant feedback results when i modify the content have a notification whenever i resolved all marked problems technical when a marker is active only update the annotations when the list of what we need to annotate changes annotations api should take care of this we should always be able to just provide a list caching and performance should not be our concern | 0 |
100,689 | 11,202,247,180 | IssuesEvent | 2020-01-04 10:55:13 | KaTeX/KaTeX | https://api.github.com/repos/KaTeX/KaTeX | closed | mhchem for server-side Katex | documentation | **Is your feature request related to a problem? Please describe.**
As far as I'm aware, there's no way to enable Katex's mhchem implementation when rendering server-side (in NodeJS). Some of us want to use this extension outside of the browser.
**Describe the solution you'd like:**
I'm not sure what the appropriate solution is. It sounds like what needs to happen is...
1. skip __defineMacro() invocations if running outside of a browser.
2. provide a streamlined way of injecting the relevant macros into KatexOptions when invoking renderToString().
```js
const out = katex.renderToString('...', {
macros: {
"\\ce": function(context) {
return chemParse(context.consumeArgs(1)[0], "ce")
},
"\\pu": function(context) {
return chemParse(context.consumeArgs(1)[0], "pu");
},
"\\tripledash": "{\\vphantom{-}\\raisebox{2.56mu}{$\\mkern2mu"
+ "\\tiny\\text{-}\\mkern1mu\\text{-}\\mkern1mu\\text{-}\\mkern2mu$}}"
}
})
```
**Link to or name of a (La)TeX package that provides the same feature:**
N/A
**Describe alternatives you've considered:**
So far all I've tried is forking mhchem.js.
**Additional context:**
N/A | 1.0 | mhchem for server-side Katex - **Is your feature request related to a problem? Please describe.**
As far as I'm aware, there's no way to enable Katex's mhchem implementation when rendering server-side (in NodeJS). Some of us want to use this extension outside of the browser.
**Describe the solution you'd like:**
I'm not sure what the appropriate solution is. It sounds like what needs to happen is...
1. skip __defineMacro() invocations if running outside of a browser.
2. provide a streamlined way of injecting the relevant macros into KatexOptions when invoking renderToString().
```js
const out = katex.renderToString('...', {
macros: {
"\\ce": function(context) {
return chemParse(context.consumeArgs(1)[0], "ce")
},
"\\pu": function(context) {
return chemParse(context.consumeArgs(1)[0], "pu");
},
"\\tripledash": "{\\vphantom{-}\\raisebox{2.56mu}{$\\mkern2mu"
+ "\\tiny\\text{-}\\mkern1mu\\text{-}\\mkern1mu\\text{-}\\mkern2mu$}}"
}
})
```
**Link to or name of a (La)TeX package that provides the same feature:**
N/A
**Describe alternatives you've considered:**
So far all I've tried is forking mhchem.js.
**Additional context:**
N/A | non_priority | mhchem for server side katex is your feature request related to a problem please describe as far as i m aware there s no way to enable katex s mhchem implementation when rendering server side in nodejs some of us want to use this extension outside of the browser describe the solution you d like i m not sure what the appropriate solution is it sounds like what needs to happen is skip definemacro invocations if running outside of a browser provide a streamlined way of injecting the relevant macros into katexoptions when invoking rendertostring js const out katex rendertostring macros ce function context return chemparse context consumeargs ce pu function context return chemparse context consumeargs pu tripledash vphantom raisebox tiny text text text link to or name of a la tex package that provides the same feature n a describe alternatives you ve considered so far all i ve tried is forking mhchem js additional context n a | 0 |
7,384 | 7,918,725,692 | IssuesEvent | 2018-07-04 14:13:02 | Drakkar-Software/OctoBot | https://api.github.com/repos/Drakkar-Software/OctoBot | opened | [Profitability] Add market average change when displaying profitability | enhancement services & interfaces trading & exchanges | When asking for profitability, also display the overall market (all crypto watched) average move from t0 (bot init) to tx (profitability ask time) | 1.0 | [Profitability] Add market average change when displaying profitability - When asking for profitability, also display the overall market (all crypto watched) average move from t0 (bot init) to tx (profitability ask time) | non_priority | add market average change when displaying profitability when asking for profitability also display the overall market all crypto watched average move from bot init to tx profitability ask time | 0 |
29,682 | 24,171,400,532 | IssuesEvent | 2022-09-22 19:35:07 | dotnet/arcade | https://api.github.com/repos/dotnet/arcade | opened | [AsmDiff] Types whose attributes are changed, but its child APIs don't have changes, do not get empty braces added | area-Infrastructure-libraries | Example: https://github.com/dotnet/core/pull/7808/files#r972460989
The empty "{}" should've been added afterwards. | 1.0 | [AsmDiff] Types whose attributes are changed, but its child APIs don't have changes, do not get empty braces added - Example: https://github.com/dotnet/core/pull/7808/files#r972460989
The empty "{}" should've been added afterwards. | non_priority | types whose attributes are changed but its child apis don t have changes do not get empty braces added example the empty should ve been added afterwards | 0 |
99,364 | 30,356,752,180 | IssuesEvent | 2023-07-12 00:50:51 | ziglang/zig | https://api.github.com/repos/ziglang/zig | closed | build: memory corruption on linux kernel 6.4.0 | bug os-linux downstream arch-x86_64 zig build system regression | Known bad kernel versions:
* 6.4.0
* 6.4.1
* 6.4.2
Mitigation: 6.4.3 :tada:
This causes a surprisingly large variety of fun crashes of which here are just a very small sampling that were encountered while trying to run the behavior tests:
```
error: unknown CPU feature: 'fp64'
thread 90061 panic: integer overflow
zig test Debug native: error: OutOfMemory
lib/std/Build/Step/Compile.zig:1933:21: 0x3c2a69 in make (build)
args_length += arg.len + 1; // +1 to account for null terminator
lib/std/heap/arena_allocator.zig:165:36: 0x36122e in createNode (build)
const len = big_enough_len + big_enough_len / 2;
lib/std/heap/arena_allocator.zig:190:74: 0x360e51 in alloc (build)
const adjusted_index = self.state.end_index + (adjusted_addr - addr);
zig test Debug aarch64-linux-none: error: error: UnknownArchitecture
zig test Debug aarch64-linux-gnu: error: error: unable to open zig lib directory '': FileNotFound
Segmentation fault at address 0x0
lib/std/Thread/Pool.zig:133:18: 0x3eecc3 in worker (build)
runFn(&run_node.data);
lib/std/Thread.zig:412:13: 0x39fcfd in callFn__anon_27109 (build)
@call(.auto, f, args);
lib/std/Build/Step/Compile.zig:1941:23: 0x3c2cde in make (build)
for (arg, 0..) |c, arg_idx| {
thread 80960 panic: start index 16 is larger than end index 0
zig test Debug aarch64-windows-gnu: error: error: unrecognized file extension of parameter ''
thread 84528 panic: reached unreachable code
lib/std/Thread/Mutex.zig:91:15: 0x2fdb65 in unlock (build)
assert(self.locking_thread.load(.Unordered) == Thread.getCurrentId());
thread 91966 panic: Deadlock detected
lib/std/Thread/Mutex.zig:84:13: 0x2fd9d3 in lock (build)
@panic("Deadlock detected");
error: the following build command crashed:
<infinite loop>
```
[upstream bug](https://bugzilla.kernel.org/show_bug.cgi?id=217624) | 1.0 | build: memory corruption on linux kernel 6.4.0 - Known bad kernel versions:
* 6.4.0
* 6.4.1
* 6.4.2
Mitigation: 6.4.3 :tada:
This causes a surprisingly large variety of fun crashes of which here are just a very small sampling that were encountered while trying to run the behavior tests:
```
error: unknown CPU feature: 'fp64'
thread 90061 panic: integer overflow
zig test Debug native: error: OutOfMemory
lib/std/Build/Step/Compile.zig:1933:21: 0x3c2a69 in make (build)
args_length += arg.len + 1; // +1 to account for null terminator
lib/std/heap/arena_allocator.zig:165:36: 0x36122e in createNode (build)
const len = big_enough_len + big_enough_len / 2;
lib/std/heap/arena_allocator.zig:190:74: 0x360e51 in alloc (build)
const adjusted_index = self.state.end_index + (adjusted_addr - addr);
zig test Debug aarch64-linux-none: error: error: UnknownArchitecture
zig test Debug aarch64-linux-gnu: error: error: unable to open zig lib directory '': FileNotFound
Segmentation fault at address 0x0
lib/std/Thread/Pool.zig:133:18: 0x3eecc3 in worker (build)
runFn(&run_node.data);
lib/std/Thread.zig:412:13: 0x39fcfd in callFn__anon_27109 (build)
@call(.auto, f, args);
lib/std/Build/Step/Compile.zig:1941:23: 0x3c2cde in make (build)
for (arg, 0..) |c, arg_idx| {
thread 80960 panic: start index 16 is larger than end index 0
zig test Debug aarch64-windows-gnu: error: error: unrecognized file extension of parameter ''
thread 84528 panic: reached unreachable code
lib/std/Thread/Mutex.zig:91:15: 0x2fdb65 in unlock (build)
assert(self.locking_thread.load(.Unordered) == Thread.getCurrentId());
thread 91966 panic: Deadlock detected
lib/std/Thread/Mutex.zig:84:13: 0x2fd9d3 in lock (build)
@panic("Deadlock detected");
error: the following build command crashed:
<infinite loop>
```
[upstream bug](https://bugzilla.kernel.org/show_bug.cgi?id=217624) | non_priority | build memory corruption on linux kernel known bad kernel versions mitigation tada this causes a surprisingly large variety of fun crashes of which here are just a very small sampling that were encountered while trying to run the behavior tests error unknown cpu feature thread panic integer overflow zig test debug native error outofmemory lib std build step compile zig in make build args length arg len to account for null terminator lib std heap arena allocator zig in createnode build const len big enough len big enough len lib std heap arena allocator zig in alloc build const adjusted index self state end index adjusted addr addr zig test debug linux none error error unknownarchitecture zig test debug linux gnu error error unable to open zig lib directory filenotfound segmentation fault at address lib std thread pool zig in worker build runfn run node data lib std thread zig in callfn anon build call auto f args lib std build step compile zig in make build for arg c arg idx thread panic start index is larger than end index zig test debug windows gnu error error unrecognized file extension of parameter thread panic reached unreachable code lib std thread mutex zig in unlock build assert self locking thread load unordered thread getcurrentid thread panic deadlock detected lib std thread mutex zig in lock build panic deadlock detected error the following build command crashed | 0 |
62,871 | 15,375,829,964 | IssuesEvent | 2021-03-02 15:20:33 | ZogopZ/to-do | https://api.github.com/repos/ZogopZ/to-do | closed | Add clock instance animation. | [clock] -> animations build-up | - [x] Add a nudge-like animation to the clock instance when the user tries to press IME_ACTION_DONE before completely filling in all the clock views. | 1.0 | Add clock instance animation. - - [x] Add a nudge-like animation to the clock instance when the user tries to press IME_ACTION_DONE before completely filling in all the clock views. | non_priority | add clock instance animation add a nudge like animation to the clock instance when the user tries to press ime action done before completely filling in all the clock views | 0 |
48,574 | 10,262,258,125 | IssuesEvent | 2019-08-22 11:54:20 | atomist-blogs/org-visualizer | https://api.github.com/repos/atomist-blogs/org-visualizer | closed | Code Inspection: Tslint on org-visualizer | bug code-inspection | ### no-implicit-dependencies
- [`lib/aspect/k8s/spec.ts:32`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/k8s/spec.ts#L32): _(error)_ Module 'js-yaml' is not listed as dependency in package.json
- [`lib/aspect/k8s/spec.ts:33`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/k8s/spec.ts#L33): _(error)_ Module 'json-stable-stringify' is not listed as dependency in package.json
- [`lib/aspect/node/npmDependencies.ts:39`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/node/npmDependencies.ts#L39): _(error)_ Module 'lodash' is not listed as dependency in package.json
- [`lib/aspect/node/TsLint.ts:23`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/node/TsLint.ts#L23): _(error)_ Module 'lodash' is not listed as dependency in package.json
- [`lib/aspect/node/TypeScriptVersion.ts:33`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/node/TypeScriptVersion.ts#L33): _(error)_ Module 'lodash' is not listed as dependency in package.json
- [`lib/aspect/travis/travisAspects.ts:25`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/travis/travisAspects.ts#L25): _(error)_ Module 'yamljs' is not listed as dependency in package.json
- [`lib/scorer/commonScorers.ts:31`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/scorer/commonScorers.ts#L31): _(error)_ Module 'lodash' is not listed as dependency in package.json
[atomist:code-inspection:org-visualizer=@atomist/atomist-sdm] | 1.0 | Code Inspection: Tslint on org-visualizer - ### no-implicit-dependencies
- [`lib/aspect/k8s/spec.ts:32`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/k8s/spec.ts#L32): _(error)_ Module 'js-yaml' is not listed as dependency in package.json
- [`lib/aspect/k8s/spec.ts:33`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/k8s/spec.ts#L33): _(error)_ Module 'json-stable-stringify' is not listed as dependency in package.json
- [`lib/aspect/node/npmDependencies.ts:39`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/node/npmDependencies.ts#L39): _(error)_ Module 'lodash' is not listed as dependency in package.json
- [`lib/aspect/node/TsLint.ts:23`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/node/TsLint.ts#L23): _(error)_ Module 'lodash' is not listed as dependency in package.json
- [`lib/aspect/node/TypeScriptVersion.ts:33`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/node/TypeScriptVersion.ts#L33): _(error)_ Module 'lodash' is not listed as dependency in package.json
- [`lib/aspect/travis/travisAspects.ts:25`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/aspect/travis/travisAspects.ts#L25): _(error)_ Module 'yamljs' is not listed as dependency in package.json
- [`lib/scorer/commonScorers.ts:31`](https://github.com/atomist-blogs/org-visualizer/blob/13e2721ded51ea2a95fe3f6afe95cf95352eacd6/lib/scorer/commonScorers.ts#L31): _(error)_ Module 'lodash' is not listed as dependency in package.json
[atomist:code-inspection:org-visualizer=@atomist/atomist-sdm] | non_priority | code inspection tslint on org visualizer no implicit dependencies error module js yaml is not listed as dependency in package json error module json stable stringify is not listed as dependency in package json error module lodash is not listed as dependency in package json error module lodash is not listed as dependency in package json error module lodash is not listed as dependency in package json error module yamljs is not listed as dependency in package json error module lodash is not listed as dependency in package json | 0 |
83,850 | 16,380,793,316 | IssuesEvent | 2021-05-17 01:56:06 | alibaba/nacos | https://api.github.com/repos/alibaba/nacos | reopened | [Code Quality] [nacos-config] [sub issue] improve the code quality of module nacos-config. | kind/code quality | <!-- Here is for bug reports and feature requests ONLY!
If you're looking for help, please check our mail list、WeChat group and the Gitter room.
Please try to use English to describe your issue, or at least provide a snippet of English translation.
我们鼓励使用英文,如果不能直接使用,可以使用翻译软件,您仍旧可以保留中文原文。
-->
**Description**
Module: `nacos-config`
This issue is the sub issue of #5726 , it will improve the code quality of module nacos-config. we improve the code quality by directory.
**the PR list**
| dirctory | PR | status |
| ---- | ---- | ---- |
| aspect | #5730 | open |
| auth | #5729 | open |
| controller | #5731 | open |
| remote | #5732 | open |
| service | #5744 #5752| open |
| utils | waiting | | | 1.0 | [Code Quality] [nacos-config] [sub issue] improve the code quality of module nacos-config. - <!-- Here is for bug reports and feature requests ONLY!
If you're looking for help, please check our mail list、WeChat group and the Gitter room.
Please try to use English to describe your issue, or at least provide a snippet of English translation.
我们鼓励使用英文,如果不能直接使用,可以使用翻译软件,您仍旧可以保留中文原文。
-->
**Description**
Module: `nacos-config`
This issue is the sub issue of #5726 , it will improve the code quality of module nacos-config. we improve the code quality by directory.
**the PR list**
| dirctory | PR | status |
| ---- | ---- | ---- |
| aspect | #5730 | open |
| auth | #5729 | open |
| controller | #5731 | open |
| remote | #5732 | open |
| service | #5744 #5752| open |
| utils | waiting | | | non_priority | improve the code quality of module nacos config here is for bug reports and feature requests only if you re looking for help please check our mail list、wechat group and the gitter room please try to use english to describe your issue or at least provide a snippet of english translation 我们鼓励使用英文,如果不能直接使用,可以使用翻译软件,您仍旧可以保留中文原文。 description module nacos config this issue is the sub issue of it will improve the code quality of module nacos config we improve the code quality by directory the pr list dirctory pr status aspect open auth open controller open remote open service open utils waiting | 0 |
216,224 | 16,653,313,555 | IssuesEvent | 2021-06-05 03:48:35 | AshokKumarChoppadandi/dev-environments | https://api.github.com/repos/AshokKumarChoppadandi/dev-environments | opened | Setting up Static IP | documentation | Prepare a document with all the steps to set the Static IP on Virtual / Physical Machine with screenshots for reference. | 1.0 | Setting up Static IP - Prepare a document with all the steps to set the Static IP on Virtual / Physical Machine with screenshots for reference. | non_priority | setting up static ip prepare a document with all the steps to set the static ip on virtual physical machine with screenshots for reference | 0 |
306,706 | 26,491,971,050 | IssuesEvent | 2023-01-17 23:53:44 | Xyaneon/Xyaneon.Games.Cards | https://api.github.com/repos/Xyaneon/Xyaneon.Games.Cards | closed | DefaultShuffleAlgorithm is missing unit test coverage | testing | Coveralls is reporting that the `DefaultShuffleAlgorithm` class has no unit test coverage as of the [first build on `main`](https://coveralls.io/builds/55964559) with it enabled. | 1.0 | DefaultShuffleAlgorithm is missing unit test coverage - Coveralls is reporting that the `DefaultShuffleAlgorithm` class has no unit test coverage as of the [first build on `main`](https://coveralls.io/builds/55964559) with it enabled. | non_priority | defaultshufflealgorithm is missing unit test coverage coveralls is reporting that the defaultshufflealgorithm class has no unit test coverage as of the with it enabled | 0 |
227,247 | 18,054,216,376 | IssuesEvent | 2021-09-20 05:15:31 | logicmoo/logicmoo_workspace | https://api.github.com/repos/logicmoo/logicmoo_workspace | opened | logicmoo.pfc.test.sanity_base.VERBATUMS_05 JUnit | Test_9999 logicmoo.pfc.test.sanity_base unit_test VERBATUMS_05 Failing | (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s swipl -x /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-clif verbatums_05.pfc)
% ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
% EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/pfc/t/sanity_base/verbatums_05.pfc
% JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/VERBATUMS_05/logicmoo_pfc_test_sanity_base_VERBATUMS_05_JUnit/
% ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AVERBATUMS_05
```
%~ init_phase(after_load)
%~ init_phase(restore_state)
%
running('/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/verbatums_05.pfc'),
%~ /var/lib/jenkins/.local/share/swi-prolog/pack/logicmoo_utils/prolog/logicmoo_test_header.pl:93
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
:- dynamic(total_income/3).
% RULES
% RULES
income(Person,_Source,Year,Dollars) ==> {increment_income(Person,Year,Dollars)}.
==> do_and_undo(increment_income(P,Y,D),decrement_income(P,Y,D)).
increment_income(P,Y,D) :-
(retract(total_income(P,Y,Old)) -> New is Old+D ; New = D),
assert(total_income(P,Y,New)).
decrement_income(P,Y,D) :-
retract(total_income(P,Y,Old)),
New is Old-D,
assert(total_income(P,Y,New)).
% FACTS
% FACTS
income(person,sourceOne,2035,6666).
income(person,sourceTwo,2035,1111).
income(person,sourceTwo,2036,2222).
% RESULTS PT 1
% RESULTS PT 1
:- listing(total_income/3).
%~ skipped( listing( total_income/3))
/*
total_income(person, 2035, 7777).
total_income(person, 2036, 2222).
*/
% UPDATE Remove some income
\+ income(person,_,2035,1111).
% RESULTS PT 2
%~ debugm( baseKB,
%~ show_success( baseKB,
%~ baseKB : mpred_withdraw( income(person,sourceTwo,2035,1111),
%~ ( mfl4(BaseKB,baseKB,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/edit/master/packs_sys/pfc/t/sanity_base/verbatums_05.pfc ',50) ,
%~ ax))))
% RESULTS PT 2
:- listing(total_income/3).
%~ skipped( listing( total_income/3))
%~ unused(no_junit_results)
%~ test_completed_exit(0)
```
totalTime=1.000
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k verbatums_05.pfc (returned 0) Add_LABELS='' Rem_LABELS='Skipped,Skipped,Errors,Warnings,Overtime,Skipped,Skipped'
| 3.0 | logicmoo.pfc.test.sanity_base.VERBATUMS_05 JUnit - (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s swipl -x /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-clif verbatums_05.pfc)
% ISSUE: https://github.com/logicmoo/logicmoo_workspace/issues/
% EDIT: https://github.com/logicmoo/logicmoo_workspace/edit/master/packs_sys/pfc/t/sanity_base/verbatums_05.pfc
% JENKINS: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/VERBATUMS_05/logicmoo_pfc_test_sanity_base_VERBATUMS_05_JUnit/
% ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3AVERBATUMS_05
```
%~ init_phase(after_load)
%~ init_phase(restore_state)
%
running('/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/verbatums_05.pfc'),
%~ /var/lib/jenkins/.local/share/swi-prolog/pack/logicmoo_utils/prolog/logicmoo_test_header.pl:93
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
:- dynamic(total_income/3).
% RULES
% RULES
income(Person,_Source,Year,Dollars) ==> {increment_income(Person,Year,Dollars)}.
==> do_and_undo(increment_income(P,Y,D),decrement_income(P,Y,D)).
increment_income(P,Y,D) :-
(retract(total_income(P,Y,Old)) -> New is Old+D ; New = D),
assert(total_income(P,Y,New)).
decrement_income(P,Y,D) :-
retract(total_income(P,Y,Old)),
New is Old-D,
assert(total_income(P,Y,New)).
% FACTS
% FACTS
income(person,sourceOne,2035,6666).
income(person,sourceTwo,2035,1111).
income(person,sourceTwo,2036,2222).
% RESULTS PT 1
% RESULTS PT 1
:- listing(total_income/3).
%~ skipped( listing( total_income/3))
/*
total_income(person, 2035, 7777).
total_income(person, 2036, 2222).
*/
% UPDATE Remove some income
\+ income(person,_,2035,1111).
% RESULTS PT 2
%~ debugm( baseKB,
%~ show_success( baseKB,
%~ baseKB : mpred_withdraw( income(person,sourceTwo,2035,1111),
%~ ( mfl4(BaseKB,baseKB,'* https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/edit/master/packs_sys/pfc/t/sanity_base/verbatums_05.pfc ',50) ,
%~ ax))))
% RESULTS PT 2
:- listing(total_income/3).
%~ skipped( listing( total_income/3))
%~ unused(no_junit_results)
%~ test_completed_exit(0)
```
totalTime=1.000
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k verbatums_05.pfc (returned 0) Add_LABELS='' Rem_LABELS='Skipped,Skipped,Errors,Warnings,Overtime,Skipped,Skipped'
| non_priority | logicmoo pfc test sanity base verbatums junit cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k swipl x var lib jenkins workspace logicmoo workspace bin lmoo clif verbatums pfc issue edit jenkins issue search init phase after load init phase restore state running var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base verbatums pfc var lib jenkins local share swi prolog pack logicmoo utils prolog logicmoo test header pl this test might need use module library logicmoo plarkc dynamic total income rules rules income person source year dollars increment income person year dollars do and undo increment income p y d decrement income p y d increment income p y d retract total income p y old new is old d new d assert total income p y new decrement income p y d retract total income p y old new is old d assert total income p y new facts facts income person sourceone income person sourcetwo income person sourcetwo results pt results pt listing total income skipped listing total income total income person total income person update remove some income income person results pt debugm basekb show success basekb basekb mpred withdraw income person sourcetwo basekb basekb ax results pt listing total income skipped listing total income unused no junit results test completed exit totaltime failed var lib jenkins workspace logicmoo workspace bin lmoo junit minor k verbatums pfc returned add labels rem labels skipped skipped errors warnings overtime skipped skipped | 0 |
196,694 | 22,497,941,781 | IssuesEvent | 2022-06-23 09:13:06 | padloc/padloc | https://api.github.com/repos/padloc/padloc | closed | Reproducible builds | security maintenance | Provide reproducible builds for all targets along with clear instructions on how to verify that published binaries match with what is published on Github. Not sure to what degree that is even possible for iOS and Android but at the very least it should be possible for the PWA, desktop apps and web extension. | True | Reproducible builds - Provide reproducible builds for all targets along with clear instructions on how to verify that published binaries match with what is published on Github. Not sure to what degree that is even possible for iOS and Android but at the very least it should be possible for the PWA, desktop apps and web extension. | non_priority | reproducible builds provide reproducible builds for all targets along with clear instructions on how to verify that published binaries match with what is published on github not sure to what degree that is even possible for ios and android but at the very least it should be possible for the pwa desktop apps and web extension | 0 |
140,373 | 21,089,959,149 | IssuesEvent | 2022-04-04 03:03:16 | Lakhankumawat/smart-home-app | https://api.github.com/repos/Lakhankumawat/smart-home-app | closed | Implement Set Event Screen | enhancement good first issue design develop GSSoC22 Assigned | ### Description
I'd like to work upon building the Set Event Screen as per the below shown UI Design
### Domain
UI/UX
### Type of Contribution
Addition
### Code of Conduct
- [X] I follow [Contributing Guidelines](https://github.com/Lakhankumawat/smart-home-app/blob/master/Contributing.md) & [Code of conduct](https://github.com/Lakhankumawat/smart-home-app/blob/master/.github/CODE_OF_CONDUCT.md) of Smart Home App. | 1.0 | Implement Set Event Screen - ### Description
I'd like to work upon building the Set Event Screen as per the below shown UI Design
### Domain
UI/UX
### Type of Contribution
Addition
### Code of Conduct
- [X] I follow [Contributing Guidelines](https://github.com/Lakhankumawat/smart-home-app/blob/master/Contributing.md) & [Code of conduct](https://github.com/Lakhankumawat/smart-home-app/blob/master/.github/CODE_OF_CONDUCT.md) of Smart Home App. | non_priority | implement set event screen description i d like to work upon building the set event screen as per the below shown ui design domain ui ux type of contribution addition code of conduct i follow of smart home app | 0 |
25,217 | 24,903,264,673 | IssuesEvent | 2022-10-29 00:42:32 | bevyengine/bevy | https://api.github.com/repos/bevyengine/bevy | closed | Implement Reflect traits for `NonZero` numeric types | D-Good-First-Issue C-Usability A-Reflection | ## What problem does this solve or what need does it fill?
I want to use these types in my code, but cannot impl `Reflect` due to orphan rules.
## What solution would you like?
Use the macro to impl this for all the numeric types in https://doc.rust-lang.org/stable/std/num/index.html.
## What alternative(s) have you considered?
Write my own NonZeroU32 type :(
| True | Implement Reflect traits for `NonZero` numeric types - ## What problem does this solve or what need does it fill?
I want to use these types in my code, but cannot impl `Reflect` due to orphan rules.
## What solution would you like?
Use the macro to impl this for all the numeric types in https://doc.rust-lang.org/stable/std/num/index.html.
## What alternative(s) have you considered?
Write my own NonZeroU32 type :(
| non_priority | implement reflect traits for nonzero numeric types what problem does this solve or what need does it fill i want to use these types in my code but cannot impl reflect due to orphan rules what solution would you like use the macro to impl this for all the numeric types in what alternative s have you considered write my own type | 0 |
269,822 | 28,960,304,233 | IssuesEvent | 2023-05-10 01:31:11 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | reopened | CVE-2022-0264 (Medium) detected in linuxlinux-4.19.6 | Mend: dependency security vulnerability | ## CVE-2022-0264 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/bpf/verifier.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the Linux kernel's eBPF verifier when handling internal data structures. Internal memory locations could be returned to userspace. A local attacker with the permissions to insert eBPF code to the kernel can use this to leak internal kernel memory details defeating some of the exploit mitigations in place for the kernel. This flaws affects kernel versions < v5.16-rc6
<p>Publish Date: 2022-02-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0264>CVE-2022-0264</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-0264">https://www.linuxkernelcves.com/cves/CVE-2022-0264</a></p>
<p>Release Date: 2022-02-04</p>
<p>Fix Resolution: v5.15.11,v5.16-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0264 (Medium) detected in linuxlinux-4.19.6 - ## CVE-2022-0264 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/bpf/verifier.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the Linux kernel's eBPF verifier when handling internal data structures. Internal memory locations could be returned to userspace. A local attacker with the permissions to insert eBPF code to the kernel can use this to leak internal kernel memory details defeating some of the exploit mitigations in place for the kernel. This flaws affects kernel versions < v5.16-rc6
<p>Publish Date: 2022-02-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-0264>CVE-2022-0264</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2022-0264">https://www.linuxkernelcves.com/cves/CVE-2022-0264</a></p>
<p>Release Date: 2022-02-04</p>
<p>Fix Resolution: v5.15.11,v5.16-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files kernel bpf verifier c vulnerability details a vulnerability was found in the linux kernel s ebpf verifier when handling internal data structures internal memory locations could be returned to userspace a local attacker with the permissions to insert ebpf code to the kernel can use this to leak internal kernel memory details defeating some of the exploit mitigations in place for the kernel this flaws affects kernel versions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
6,426 | 8,721,484,757 | IssuesEvent | 2018-12-08 23:42:15 | metarhia/impress | https://api.github.com/repos/metarhia/impress | closed | Compare host name without RegExp | compatibility optimization performance | In `lib/core.js/impress.dispatcher` we need no hostsRx (RegExp precompiled from `/applications/appName/confog/hosts.js`). We may add another restriction: only one `*` in host name. So we can use `startsWith` and `endsWith` instead of multiple regular expressions combined together.
Also remove `lib/config.js/Config.preprocessConfig` | True | Compare host name without RegExp - In `lib/core.js/impress.dispatcher` we need no hostsRx (RegExp precompiled from `/applications/appName/confog/hosts.js`). We may add another restriction: only one `*` in host name. So we can use `startsWith` and `endsWith` instead of multiple regular expressions combined together.
Also remove `lib/config.js/Config.preprocessConfig` | non_priority | compare host name without regexp in lib core js impress dispatcher we need no hostsrx regexp precompiled from applications appname confog hosts js we may add another restriction only one in host name so we can use startswith and endswith instead of multiple regular expressions combined together also remove lib config js config preprocessconfig | 0 |
64,339 | 7,786,911,212 | IssuesEvent | 2018-06-06 20:32:46 | quicwg/base-drafts | https://api.github.com/repos/quicwg/base-drafts | closed | Flags in HTTP/QUIC frames are wasted space | -http design has-proposal | Of the frame types defined in the draft, only one frame type actually defines any flags. Otherwise, the flags byte is a wasted byte per frame, every frame.
For the frames which don't use flags, the byte can simply be dropped from the generic frame definition without ill effect. For the one which does (PRIORITY), there are a few reasonable choices:
- Define a flags byte as the first byte of PRIORITY's payload; PRIORITY effectively remains unchanged
- Follow QUIC's lead: embed the flags in the type byte; PRIORITY consumes eight values in the frame type space
- Consider putting priority changes on a separate unidirectional stream (as in #1359) and not using control stream frames for them at all. They only need order with respect to each other, not anything else. | 1.0 | Flags in HTTP/QUIC frames are wasted space - Of the frame types defined in the draft, only one frame type actually defines any flags. Otherwise, the flags byte is a wasted byte per frame, every frame.
For the frames which don't use flags, the byte can simply be dropped from the generic frame definition without ill effect. For the one which does (PRIORITY), there are a few reasonable choices:
- Define a flags byte as the first byte of PRIORITY's payload; PRIORITY effectively remains unchanged
- Follow QUIC's lead: embed the flags in the type byte; PRIORITY consumes eight values in the frame type space
- Consider putting priority changes on a separate unidirectional stream (as in #1359) and not using control stream frames for them at all. They only need order with respect to each other, not anything else. | non_priority | flags in http quic frames are wasted space of the frame types defined in the draft only one frame type actually defines any flags otherwise the flags byte is a wasted byte per frame every frame for the frames which don t use flags the byte can simply be dropped from the generic frame definition without ill effect for the one which does priority there are a few reasonable choices define a flags byte as the first byte of priority s payload priority effectively remains unchanged follow quic s lead embed the flags in the type byte priority consumes eight values in the frame type space consider putting priority changes on a separate unidirectional stream as in and not using control stream frames for them at all they only need order with respect to each other not anything else | 0 |
106,293 | 23,206,181,805 | IssuesEvent | 2022-08-02 05:40:15 | microsoft/vsmarketplace | https://api.github.com/repos/microsoft/vsmarketplace | closed | i cant install live server | need-information vscode | Issue Type: <b>Feature Request</b>
cant install live server extension
VS Code version: Code 1.69.2 (3b889b090b5ad5793f524b5d1d39fda662b96a2a, 2022-07-18T16:12:52.460Z)
OS version: Windows_NT x64 10.0.19044
Restricted Mode: No
<!-- generated by issue reporter --> | 1.0 | i cant install live server - Issue Type: <b>Feature Request</b>
cant install live server extension
VS Code version: Code 1.69.2 (3b889b090b5ad5793f524b5d1d39fda662b96a2a, 2022-07-18T16:12:52.460Z)
OS version: Windows_NT x64 10.0.19044
Restricted Mode: No
<!-- generated by issue reporter --> | non_priority | i cant install live server issue type feature request cant install live server extension vs code version code os version windows nt restricted mode no | 0 |
177,222 | 21,468,763,664 | IssuesEvent | 2022-04-26 07:34:58 | Satheesh575555/external_tcpdump_AOSP10_r33 | https://api.github.com/repos/Satheesh575555/external_tcpdump_AOSP10_r33 | opened | CVE-2018-10105 (High) detected in tcpdumptcpdump-4.9.2 | security vulnerability | ## CVE-2018-10105 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tcpdumptcpdump-4.9.2</b></p></summary>
<p>
<p>the TCPdump network dissector</p>
<p>Library home page: <a href=https://github.com/the-tcpdump-group/tcpdump.git>https://github.com/the-tcpdump-group/tcpdump.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/external_tcpdump_AOSP10_r33/commit/2dfdd1ca649c09239da90330faa390fd66d5fc18">2dfdd1ca649c09239da90330faa390fd66d5fc18</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/print-smb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
tcpdump before 4.9.3 mishandles the printing of SMB data (issue 2 of 2).
<p>Publish Date: 2019-10-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10105>CVE-2018-10105</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/the-tcpdump-group/tcpdump/commit/428c37e02aa0d286da52185ecc365b22175ffcb8">https://github.com/the-tcpdump-group/tcpdump/commit/428c37e02aa0d286da52185ecc365b22175ffcb8</a></p>
<p>Release Date: 2019-10-03</p>
<p>Fix Resolution: 4.9.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-10105 (High) detected in tcpdumptcpdump-4.9.2 - ## CVE-2018-10105 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tcpdumptcpdump-4.9.2</b></p></summary>
<p>
<p>the TCPdump network dissector</p>
<p>Library home page: <a href=https://github.com/the-tcpdump-group/tcpdump.git>https://github.com/the-tcpdump-group/tcpdump.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/external_tcpdump_AOSP10_r33/commit/2dfdd1ca649c09239da90330faa390fd66d5fc18">2dfdd1ca649c09239da90330faa390fd66d5fc18</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/print-smb.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
tcpdump before 4.9.3 mishandles the printing of SMB data (issue 2 of 2).
<p>Publish Date: 2019-10-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10105>CVE-2018-10105</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/the-tcpdump-group/tcpdump/commit/428c37e02aa0d286da52185ecc365b22175ffcb8">https://github.com/the-tcpdump-group/tcpdump/commit/428c37e02aa0d286da52185ecc365b22175ffcb8</a></p>
<p>Release Date: 2019-10-03</p>
<p>Fix Resolution: 4.9.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tcpdumptcpdump cve high severity vulnerability vulnerable library tcpdumptcpdump the tcpdump network dissector library home page a href found in head commit a href found in base branch master vulnerable source files print smb c vulnerability details tcpdump before mishandles the printing of smb data issue of publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
200,768 | 15,148,400,478 | IssuesEvent | 2021-02-11 10:33:30 | hrwakeford/ExoTiC-ISM | https://api.github.com/repos/hrwakeford/ExoTiC-ISM | closed | Increase CI test coverage | Testing | We have set up CI with GitHub Actions which runs on every open PR, however our code coverage is extremely low and should be increased in the future to ensure robustness with new code and updates. | 1.0 | Increase CI test coverage - We have set up CI with GitHub Actions which runs on every open PR, however our code coverage is extremely low and should be increased in the future to ensure robustness with new code and updates. | non_priority | increase ci test coverage we have set up ci with github actions which runs on every open pr however our code coverage is extremely low and should be increased in the future to ensure robustness with new code and updates | 0 |
10,468 | 8,575,850,226 | IssuesEvent | 2018-11-12 18:30:46 | coddingtonbear/inthe.am | https://api.github.com/repos/coddingtonbear/inthe.am | closed | `update_statistics` and `gc_large_repos` overnight tasks are not executing currently. | bug infrastructure | When investigating a problem this morning, I found this notice in the logs for the above:
```
System check identified some issues:
WARNINGS:
taskmanager.UserMetadata.user: (fields.W342) Setting unique=True on a ForeignKey has the same effect as using a OneToOneField.
HINT: ForeignKey(unique=True) is usually better served by a OneToOneField.
Traceback (most recent call last):
File "/var/www/twweb/manage.py", line 15, in <module>
execute_from_command_line(sys.argv)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/__init__.py", line 354, in execute_from_command_line
utility.execute()
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/__init__.py", line 346, in execute
self.fetch_command(subcommand).run_from_argv(self.argv)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/base.py", line 394, in run_from_argv
self.execute(*args, **cmd_options)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/base.py", line 445, in execute
output = self.handle(*args, **options)
File "/var/www/twweb/inthe_am/taskmanager/management/commands/taskstore.py", line 107, in handle
for store in TaskStore.objects.order_by('-last_synced'):
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/query.py", line 162, in __iter__
self._fetch_all()
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/query.py", line 965, in _fetch_all
self._result_cache = list(self.iterator())
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/query.py", line 238, in iterator
results = compiler.execute_sql()
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/sql/compiler.py", line 840, in execute_sql
cursor.execute(sql, params)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/backends/utils.py", line 64, in execute
return self.cursor.execute(sql, params)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/utils.py", line 98, in __exit__
six.reraise(dj_exc_type, dj_exc_value, traceback)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/backends/utils.py", line 64, in execute
return self.cursor.execute(sql, params)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/backends/sqlite3/base.py", line 318, in execute
return Database.Cursor.execute(self, query, params)
django.db.utils.OperationalError: no such column: taskmanager_taskstore.secret_id
```
_Clearly_ it's connecting to sqlite (like it would for a dev environment) for some reason rather than the proper database backend. This is...a problem. | 1.0 | `update_statistics` and `gc_large_repos` overnight tasks are not executing currently. - When investigating a problem this morning, I found this notice in the logs for the above:
```
System check identified some issues:
WARNINGS:
taskmanager.UserMetadata.user: (fields.W342) Setting unique=True on a ForeignKey has the same effect as using a OneToOneField.
HINT: ForeignKey(unique=True) is usually better served by a OneToOneField.
Traceback (most recent call last):
File "/var/www/twweb/manage.py", line 15, in <module>
execute_from_command_line(sys.argv)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/__init__.py", line 354, in execute_from_command_line
utility.execute()
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/__init__.py", line 346, in execute
self.fetch_command(subcommand).run_from_argv(self.argv)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/base.py", line 394, in run_from_argv
self.execute(*args, **cmd_options)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/core/management/base.py", line 445, in execute
output = self.handle(*args, **options)
File "/var/www/twweb/inthe_am/taskmanager/management/commands/taskstore.py", line 107, in handle
for store in TaskStore.objects.order_by('-last_synced'):
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/query.py", line 162, in __iter__
self._fetch_all()
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/query.py", line 965, in _fetch_all
self._result_cache = list(self.iterator())
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/query.py", line 238, in iterator
results = compiler.execute_sql()
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/models/sql/compiler.py", line 840, in execute_sql
cursor.execute(sql, params)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/backends/utils.py", line 64, in execute
return self.cursor.execute(sql, params)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/utils.py", line 98, in __exit__
six.reraise(dj_exc_type, dj_exc_value, traceback)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/backends/utils.py", line 64, in execute
return self.cursor.execute(sql, params)
File "/var/www/envs/twweb/local/lib/python2.7/site-packages/django/db/backends/sqlite3/base.py", line 318, in execute
return Database.Cursor.execute(self, query, params)
django.db.utils.OperationalError: no such column: taskmanager_taskstore.secret_id
```
_Clearly_ it's connecting to sqlite (like it would for a dev environment) for some reason rather than the proper database backend. This is...a problem. | non_priority | update statistics and gc large repos overnight tasks are not executing currently when investigating a problem this morning i found this notice in the logs for the above system check identified some issues warnings taskmanager usermetadata user fields setting unique true on a foreignkey has the same effect as using a onetoonefield hint foreignkey unique true is usually better served by a onetoonefield traceback most recent call last file var www twweb manage py line in execute from command line sys argv file var www envs twweb local lib site packages django core management init py line in execute from command line utility execute file var www envs twweb local lib site packages django core management init py line in execute self fetch command subcommand run from argv self argv file var www envs twweb local lib site packages django core management base py line in run from argv self execute args cmd options file var www envs twweb local lib site packages django core management base py line in execute output self handle args options file var www twweb inthe am taskmanager management commands taskstore py line in handle for store in taskstore objects order by last synced file var www envs twweb local lib site packages django db models query py line in iter self fetch all file var www envs twweb local lib site packages django db models query py line in fetch all self result cache list self iterator file var www envs twweb local lib site packages django db models query py line in iterator results compiler execute sql file var www envs twweb local lib site packages django db models sql compiler py line in execute sql cursor execute sql params file var www envs twweb local lib site packages django db backends utils py line in execute return self cursor execute sql params file var www envs twweb local lib site packages django db utils py line in exit six reraise dj exc type dj exc value traceback file var www envs twweb local lib site packages django db backends utils py line in execute return self cursor execute sql params file var www envs twweb local lib site packages django db backends base py line in execute return database cursor execute self query params django db utils operationalerror no such column taskmanager taskstore secret id clearly it s connecting to sqlite like it would for a dev environment for some reason rather than the proper database backend this is a problem | 0 |
20,514 | 11,457,112,861 | IssuesEvent | 2020-02-06 22:48:39 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | User snippets suggestions on variable declaration | Feature: Auto-complete Language Service duplicate | **Type: LanguageService**
<!----- Input information below ----->
**Describe the bug**
- OS and Version: Linux (Arch and Ubuntu)
- VS Code Version: 1.40.0
- C/C++ Extension Version: 0.26.2-insiders
- Other extensions you installed (and if the issue persists after disabling them): Still happens when disabled
* CMake
- Docker
- Devicetree
- Indent to bracket
- Markdown
**To Reproduce**
<!-- Steps to reproduce the behavior: -->
<!-- *The most actionable issue reports include a code sample including configuration files such as c_cpp_properties.json* -->
1. Define a user snippet
2. Define a variable with the same prefix as the snippet
**Expected behavior**
No snippet suggestion on variable declaration
After defining my user snippets I'm receiving suggestion for it on variable declarations that start with the same letter of the snippet prefix which can be annoying. This also makes unusable the `ctrl + space` binding for manually sugestions (which is useful for `structs`). I can say that this does not happen with the official extension snippets so it can be a problem with my definitions. Here they are:
```
"For": {
"prefix": ["for"],
"body": ["for (int ${idx} = 0; ${idx} < ${size}; ${idx}++) {",
"\t$0",
"}"
],
"description": "For loop template"
},
"If": {
"prefix": ["if"],
"body": ["if (${expr}) {",
"\t$0",
"}"
],
"description": "if clause template"
},
"Else": {
"prefix": ["else"],
"body": ["else {",
"\t$0",
"}"
],
"description": "else clause template"
},
"ElseIf": {
"prefix": ["else if"],
"body": ["else if (${expr}) {",
"\t$0",
"}"
],
"description": "else if clause template"
},
"while": {
"prefix": ["while"],
"body": ["while (${expr}) {",
"\t$0",
"}"
],
"description": "while loop template"
},
"do": {
"prefix": ["do"],
"body": ["do {",
"\t$0",
"} while (${expr});"
],
"description": "do while loop template"
},
"switch": {
"prefix": ["switch"],
"body": ["switch (${expr}) {",
"case ${case_1}:",
"\t",
"default:",
"\t$0return ${error};",
"}"
],
"description": "switch case template"
},
```
I can also say that I tried some other extensions defining their own snippets and the problem still occurred. As a workaround, I just disabled my snippets for now
Honestly I'm not sure if this the right place to submit the issue (and not directly on code) so I apologize if it's not. Any help would be appreciated!
Thanks!
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
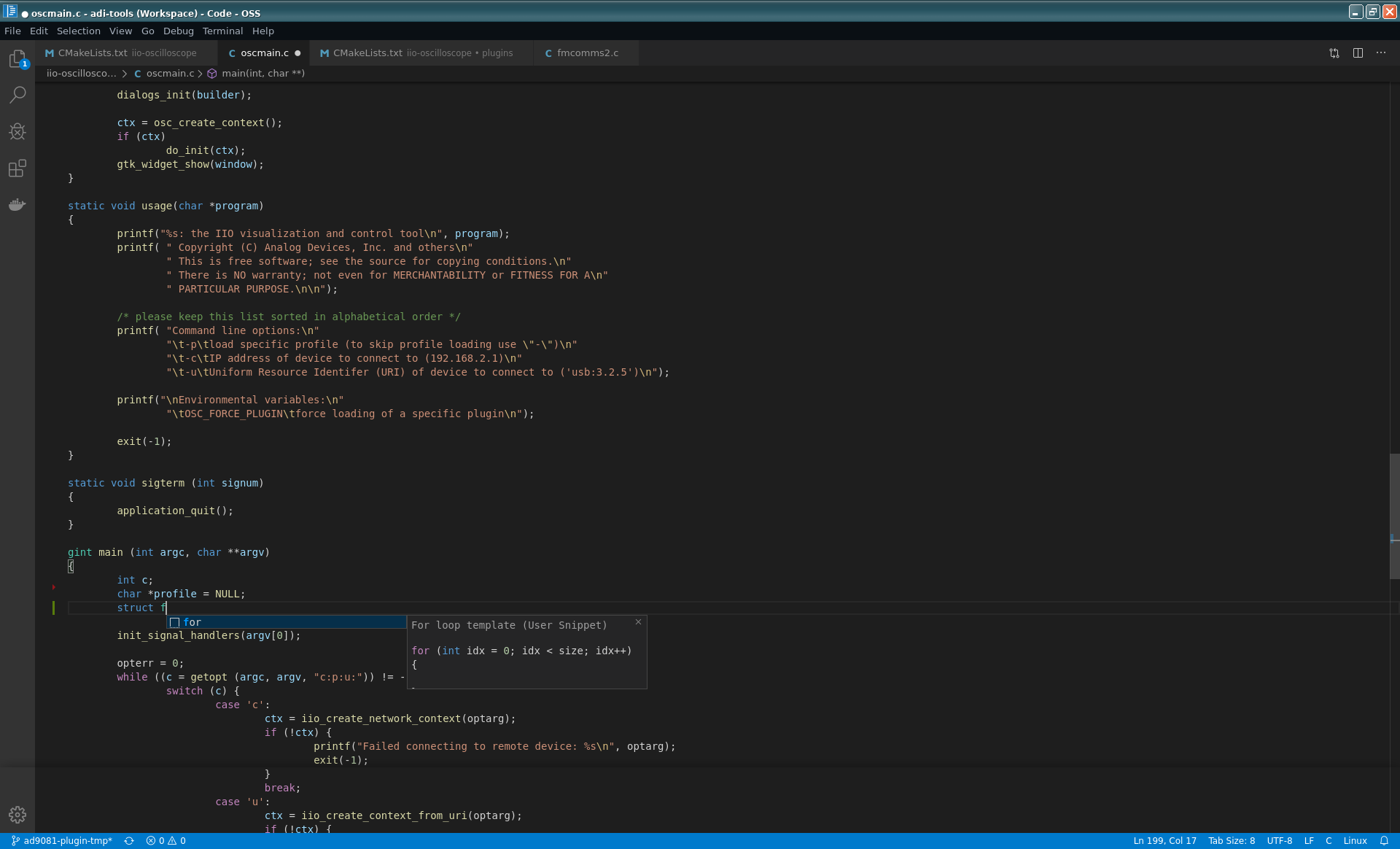
| 1.0 | User snippets suggestions on variable declaration - **Type: LanguageService**
<!----- Input information below ----->
**Describe the bug**
- OS and Version: Linux (Arch and Ubuntu)
- VS Code Version: 1.40.0
- C/C++ Extension Version: 0.26.2-insiders
- Other extensions you installed (and if the issue persists after disabling them): Still happens when disabled
* CMake
- Docker
- Devicetree
- Indent to bracket
- Markdown
**To Reproduce**
<!-- Steps to reproduce the behavior: -->
<!-- *The most actionable issue reports include a code sample including configuration files such as c_cpp_properties.json* -->
1. Define a user snippet
2. Define a variable with the same prefix as the snippet
**Expected behavior**
No snippet suggestion on variable declaration
After defining my user snippets I'm receiving suggestion for it on variable declarations that start with the same letter of the snippet prefix which can be annoying. This also makes unusable the `ctrl + space` binding for manually sugestions (which is useful for `structs`). I can say that this does not happen with the official extension snippets so it can be a problem with my definitions. Here they are:
```
"For": {
"prefix": ["for"],
"body": ["for (int ${idx} = 0; ${idx} < ${size}; ${idx}++) {",
"\t$0",
"}"
],
"description": "For loop template"
},
"If": {
"prefix": ["if"],
"body": ["if (${expr}) {",
"\t$0",
"}"
],
"description": "if clause template"
},
"Else": {
"prefix": ["else"],
"body": ["else {",
"\t$0",
"}"
],
"description": "else clause template"
},
"ElseIf": {
"prefix": ["else if"],
"body": ["else if (${expr}) {",
"\t$0",
"}"
],
"description": "else if clause template"
},
"while": {
"prefix": ["while"],
"body": ["while (${expr}) {",
"\t$0",
"}"
],
"description": "while loop template"
},
"do": {
"prefix": ["do"],
"body": ["do {",
"\t$0",
"} while (${expr});"
],
"description": "do while loop template"
},
"switch": {
"prefix": ["switch"],
"body": ["switch (${expr}) {",
"case ${case_1}:",
"\t",
"default:",
"\t$0return ${error};",
"}"
],
"description": "switch case template"
},
```
I can also say that I tried some other extensions defining their own snippets and the problem still occurred. As a workaround, I just disabled my snippets for now
Honestly I'm not sure if this the right place to submit the issue (and not directly on code) so I apologize if it's not. Any help would be appreciated!
Thanks!
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
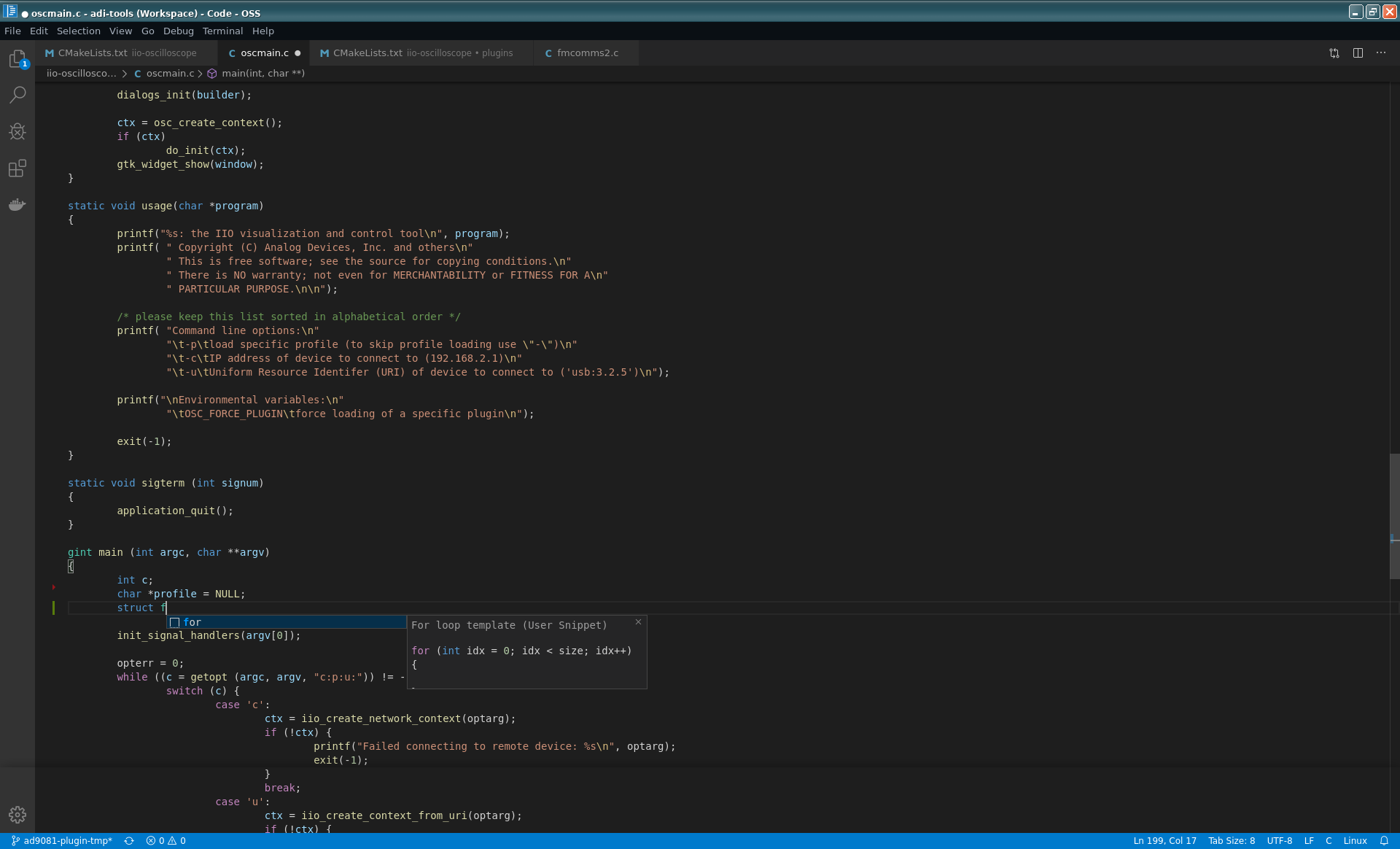
| non_priority | user snippets suggestions on variable declaration type languageservice describe the bug os and version linux arch and ubuntu vs code version c c extension version insiders other extensions you installed and if the issue persists after disabling them still happens when disabled cmake docker devicetree indent to bracket markdown to reproduce define a user snippet define a variable with the same prefix as the snippet expected behavior no snippet suggestion on variable declaration after defining my user snippets i m receiving suggestion for it on variable declarations that start with the same letter of the snippet prefix which can be annoying this also makes unusable the ctrl space binding for manually sugestions which is useful for structs i can say that this does not happen with the official extension snippets so it can be a problem with my definitions here they are for prefix body for int idx idx size idx t description for loop template if prefix body if expr t description if clause template else prefix body else t description else clause template elseif prefix body else if expr t description else if clause template while prefix body while expr t description while loop template do prefix body do t while expr description do while loop template switch prefix body switch expr case case t default t error description switch case template i can also say that i tried some other extensions defining their own snippets and the problem still occurred as a workaround i just disabled my snippets for now honestly i m not sure if this the right place to submit the issue and not directly on code so i apologize if it s not any help would be appreciated thanks screenshots | 0 |
33,196 | 6,177,485,526 | IssuesEvent | 2017-07-02 00:51:10 | bavc/signalserver | https://api.github.com/repos/bavc/signalserver | closed | add comments in frontend.sh | documentation | some commenting in frontend.sh would help re-assert the modifications that should be made to this file. | 1.0 | add comments in frontend.sh - some commenting in frontend.sh would help re-assert the modifications that should be made to this file. | non_priority | add comments in frontend sh some commenting in frontend sh would help re assert the modifications that should be made to this file | 0 |
324,234 | 27,790,444,123 | IssuesEvent | 2023-03-17 08:29:53 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | closed | The entities disappear when navigating to more than the 10th page then manually refreshing | :heavy_check_mark: merged 🧪 testing :gear: tables :beetle: regression | **Storage Explorer Version:** 1.29.0-dev
**Build Number:** 20230224.3
**Branch:** feature/table-explorer-react
**Platform/OS:** Windows 10/Linux Ubuntu 22.04/MacOS Ventura 13.2.1 (Apple M1 Pro)
**Architecture:** ia32/x64
**How Found:** From running test cases
**Regression From:** Previous release (1.28.0)
## Steps to Reproduce ##
1. Expand one storage account -> Tables.
2. Right click one table -> Click '[2] Open'.
3. Import more than 1000 entities.
4. Click 'Load more' -> Switch to the 11th page -> Click 'Refresh'.
5. Check whether the entities still display.
## Expected Experience ##
The entities still display.
## Actual Experience ##
The entities disappear.
## Additional Context ##
The page number changes to 1.
| 1.0 | The entities disappear when navigating to more than the 10th page then manually refreshing - **Storage Explorer Version:** 1.29.0-dev
**Build Number:** 20230224.3
**Branch:** feature/table-explorer-react
**Platform/OS:** Windows 10/Linux Ubuntu 22.04/MacOS Ventura 13.2.1 (Apple M1 Pro)
**Architecture:** ia32/x64
**How Found:** From running test cases
**Regression From:** Previous release (1.28.0)
## Steps to Reproduce ##
1. Expand one storage account -> Tables.
2. Right click one table -> Click '[2] Open'.
3. Import more than 1000 entities.
4. Click 'Load more' -> Switch to the 11th page -> Click 'Refresh'.
5. Check whether the entities still display.
## Expected Experience ##
The entities still display.
## Actual Experience ##
The entities disappear.
## Additional Context ##
The page number changes to 1.
| non_priority | the entities disappear when navigating to more than the page then manually refreshing storage explorer version dev build number branch feature table explorer react platform os windows linux ubuntu macos ventura apple pro architecture how found from running test cases regression from previous release steps to reproduce expand one storage account tables right click one table click open import more than entities click load more switch to the page click refresh check whether the entities still display expected experience the entities still display actual experience the entities disappear additional context the page number changes to | 0 |
11,428 | 14,248,189,867 | IssuesEvent | 2020-11-19 12:35:01 | tikv/tikv | https://api.github.com/repos/tikv/tikv | closed | AskTUG: Coprocessor support `bson` and `protocobuffers` | feature/review again sig/coprocessor status/help-wanted type/req-from-ask-tug | ## Feature Request
Could we support to push down functions for `bson` and `protocobuffers`?
With the above feature, tikv will be more friendly to users from No-SQL such as MongoDB. Then the No-SQL users can use tikv's computation source as `TiDB` did.
This is from [ask-tug](https://asktug.com/t/topic/34614/49?u=shirly-pingcap) | 1.0 | AskTUG: Coprocessor support `bson` and `protocobuffers` - ## Feature Request
Could we support to push down functions for `bson` and `protocobuffers`?
With the above feature, tikv will be more friendly to users from No-SQL such as MongoDB. Then the No-SQL users can use tikv's computation source as `TiDB` did.
This is from [ask-tug](https://asktug.com/t/topic/34614/49?u=shirly-pingcap) | non_priority | asktug coprocessor support bson and protocobuffers feature request could we support to push down functions for bson and protocobuffers with the above feature tikv will be more friendly to users from no sql such as mongodb then the no sql users can use tikv s computation source as tidb did this is from | 0 |
11,678 | 4,274,338,293 | IssuesEvent | 2016-07-13 20:11:59 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Article voting in core joomla | No Code Attached Yet | I understand Joomla already have voting system where any article can be display with this voting also people can vote for the best article.
but what happen next?
there is no way we can find out which article received the highest vote also a report/identify list of articles which has any vote.
There should be a component or mechanism to display this or a module to display with highest votes. | 1.0 | Article voting in core joomla - I understand Joomla already have voting system where any article can be display with this voting also people can vote for the best article.
but what happen next?
there is no way we can find out which article received the highest vote also a report/identify list of articles which has any vote.
There should be a component or mechanism to display this or a module to display with highest votes. | non_priority | article voting in core joomla i understand joomla already have voting system where any article can be display with this voting also people can vote for the best article but what happen next there is no way we can find out which article received the highest vote also a report identify list of articles which has any vote there should be a component or mechanism to display this or a module to display with highest votes | 0 |
409,690 | 27,748,614,823 | IssuesEvent | 2023-03-15 18:52:36 | hpcng/warewulf | https://api.github.com/repos/hpcng/warewulf | opened | Update documentation for node images to point to GHCR | documentation stake:ciq | Given the inability to automatically build Warewulf node images from GitHub CI/CD with our existing account, and the success in doing so in ghcr
* update the documentation to point to ghcr rather than DockerHub
* update the node images directory here to point to the warewulf-node-images repository
* update the DockerHub images to indicate that they are deprecated / no longer maintained | 1.0 | Update documentation for node images to point to GHCR - Given the inability to automatically build Warewulf node images from GitHub CI/CD with our existing account, and the success in doing so in ghcr
* update the documentation to point to ghcr rather than DockerHub
* update the node images directory here to point to the warewulf-node-images repository
* update the DockerHub images to indicate that they are deprecated / no longer maintained | non_priority | update documentation for node images to point to ghcr given the inability to automatically build warewulf node images from github ci cd with our existing account and the success in doing so in ghcr update the documentation to point to ghcr rather than dockerhub update the node images directory here to point to the warewulf node images repository update the dockerhub images to indicate that they are deprecated no longer maintained | 0 |
184,150 | 21,784,807,056 | IssuesEvent | 2022-05-14 01:23:27 | AlexRogalskiy/customiere | https://api.github.com/repos/AlexRogalskiy/customiere | opened | CVE-2022-22970 (Medium) detected in spring-beans-5.2.9.RELEASE.jar | security vulnerability | ## CVE-2022-22970 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-beans-5.2.9.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Path to dependency file: /modules/customiere-metrics/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-aop-2.3.4.RELEASE.jar (Root Library)
- spring-aop-5.2.9.RELEASE.jar
- :x: **spring-beans-5.2.9.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/customiere/commit/3f6027b95560e5bd6d2350b9d9f405245557f734">3f6027b95560e5bd6d2350b9d9f405245557f734</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22970>CVE-2022-22970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22970">https://tanzu.vmware.com/security/cve-2022-22970</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-22970 (Medium) detected in spring-beans-5.2.9.RELEASE.jar - ## CVE-2022-22970 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-beans-5.2.9.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Path to dependency file: /modules/customiere-metrics/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.9.RELEASE/spring-beans-5.2.9.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-aop-2.3.4.RELEASE.jar (Root Library)
- spring-aop-5.2.9.RELEASE.jar
- :x: **spring-beans-5.2.9.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/customiere/commit/3f6027b95560e5bd6d2350b9d9f405245557f734">3f6027b95560e5bd6d2350b9d9f405245557f734</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22970>CVE-2022-22970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22970">https://tanzu.vmware.com/security/cve-2022-22970</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in spring beans release jar cve medium severity vulnerability vulnerable library spring beans release jar spring beans path to dependency file modules customiere metrics pom xml path to vulnerable library home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar dependency hierarchy spring boot starter aop release jar root library spring aop release jar x spring beans release jar vulnerable library found in head commit a href found in base branch master vulnerability details in spring framework versions prior to and old unsupported versions applications that handle file uploads are vulnerable to dos attack if they rely on data binding to set a multipartfile or javax servlet part to a field in a model object publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans org springframework spring core step up your open source security game with whitesource | 0 |
115,992 | 24,838,361,561 | IssuesEvent | 2022-10-26 10:40:47 | SocialGouv/code-du-travail-numerique | https://api.github.com/repos/SocialGouv/code-du-travail-numerique | closed | Amélioration simulateurs (reduce) étape 1 | o: indemnité licenciement :hammer_and_wrench: tech publicodes | - [ ] Remplacer l'attribut component sur le State par une fonction prenant le form en paramètre et retournant le Composant ([exemple](https://github.com/SocialGouv/code-du-travail-numerique/commit/2dfb3bfc47def8c4bb85d08ff95431e970f2759e#diff-b1a70da7c25b162efa18d75780820e6115bc3267ba710a256c77ae996820168dR35))
- [ ] Eviter de passer le form sur les composants n'ayant pas besoin (props drilling) | 1.0 | Amélioration simulateurs (reduce) étape 1 - - [ ] Remplacer l'attribut component sur le State par une fonction prenant le form en paramètre et retournant le Composant ([exemple](https://github.com/SocialGouv/code-du-travail-numerique/commit/2dfb3bfc47def8c4bb85d08ff95431e970f2759e#diff-b1a70da7c25b162efa18d75780820e6115bc3267ba710a256c77ae996820168dR35))
- [ ] Eviter de passer le form sur les composants n'ayant pas besoin (props drilling) | non_priority | amélioration simulateurs reduce étape remplacer l attribut component sur le state par une fonction prenant le form en paramètre et retournant le composant eviter de passer le form sur les composants n ayant pas besoin props drilling | 0 |
180,541 | 14,786,011,884 | IssuesEvent | 2021-01-12 04:19:56 | alia-peterson/whats-cooking | https://api.github.com/repos/alia-peterson/whats-cooking | opened | Fix images in README | documentation | **Description of what needs refactoring**
A brief description of the code that needs refactoring and the reason for refactoring
- readme currently has so me rather lewd kitchen behavior displayed
**Additional Context**
File/function name or additional reasoning for the changes
- `readme.md`
**Screenshot of Issue**
Include a screenshot if it would help describe the issue
| 1.0 | Fix images in README - **Description of what needs refactoring**
A brief description of the code that needs refactoring and the reason for refactoring
- readme currently has so me rather lewd kitchen behavior displayed
**Additional Context**
File/function name or additional reasoning for the changes
- `readme.md`
**Screenshot of Issue**
Include a screenshot if it would help describe the issue
| non_priority | fix images in readme description of what needs refactoring a brief description of the code that needs refactoring and the reason for refactoring readme currently has so me rather lewd kitchen behavior displayed additional context file function name or additional reasoning for the changes readme md screenshot of issue include a screenshot if it would help describe the issue | 0 |
171,187 | 27,081,069,159 | IssuesEvent | 2023-02-14 14:04:23 | Olian04/simply-reactive | https://api.github.com/repos/Olian04/simply-reactive | closed | Add createStateProxy | further design needed | ```ts
const S = createStateProxy({
foo: 42,
bar: 'biz',
}});
S.foo // get 42
S.foo = 3 // set 3
S.foo // get 3
```
__Mock implementation:__
```ts
const createStateProxy = <T extends object>(defaultState: T, atomConstructor = createAtom) => {
const key = getNextAutoKey();
const Grp = createGroup({
key,
getDefault: propertyKey => atomConstructor({
key: `${key}_${propertyKey}`,
default: defaultState[key],
})
});
return new Proxy({} as T, {
get: (__, key) => Grp.find(key).get(),
set: (__, key, value) => Grp.find(key).set(value),
});
}
``` | 1.0 | Add createStateProxy - ```ts
const S = createStateProxy({
foo: 42,
bar: 'biz',
}});
S.foo // get 42
S.foo = 3 // set 3
S.foo // get 3
```
__Mock implementation:__
```ts
const createStateProxy = <T extends object>(defaultState: T, atomConstructor = createAtom) => {
const key = getNextAutoKey();
const Grp = createGroup({
key,
getDefault: propertyKey => atomConstructor({
key: `${key}_${propertyKey}`,
default: defaultState[key],
})
});
return new Proxy({} as T, {
get: (__, key) => Grp.find(key).get(),
set: (__, key, value) => Grp.find(key).set(value),
});
}
``` | non_priority | add createstateproxy ts const s createstateproxy foo bar biz s foo get s foo set s foo get mock implementation ts const createstateproxy defaultstate t atomconstructor createatom const key getnextautokey const grp creategroup key getdefault propertykey atomconstructor key key propertykey default defaultstate return new proxy as t get key grp find key get set key value grp find key set value | 0 |
24,521 | 7,522,540,126 | IssuesEvent | 2018-04-12 20:46:35 | golang/go | https://api.github.com/repos/golang/go | closed | x/build/cmd/pushback: fold into gopherbot | Builders | If maintner tracked PRs too (which it needs to for other reasons), then gopherbot can take over the x/build/cmd/pushback job and we could down that service and further unify our various bot functionality.
/cc @kevinburke @andybons | 1.0 | x/build/cmd/pushback: fold into gopherbot - If maintner tracked PRs too (which it needs to for other reasons), then gopherbot can take over the x/build/cmd/pushback job and we could down that service and further unify our various bot functionality.
/cc @kevinburke @andybons | non_priority | x build cmd pushback fold into gopherbot if maintner tracked prs too which it needs to for other reasons then gopherbot can take over the x build cmd pushback job and we could down that service and further unify our various bot functionality cc kevinburke andybons | 0 |
266,880 | 28,480,230,999 | IssuesEvent | 2023-04-18 01:36:22 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | opened | CVE-2023-30772 (Medium) detected in linuxlinux-4.19.6 | Mend: dependency security vulnerability | ## CVE-2023-30772 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/power/supply/da9150-charger.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/power/supply/da9150-charger.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/power/supply/da9150-charger.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel before 6.2.9 has a race condition and resultant use-after-free in drivers/power/supply/da9150-charger.c if a physically proximate attacker unplugs a device.
<p>Publish Date: 2023-04-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-30772>CVE-2023-30772</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-30772">https://www.linuxkernelcves.com/cves/CVE-2023-30772</a></p>
<p>Release Date: 2023-04-16</p>
<p>Fix Resolution: v4.14.312,v4.19.280,v5.4.240,v5.10.177,v5.15.105,v6.1.22,v6.2.9,v6.3-rc4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-30772 (Medium) detected in linuxlinux-4.19.6 - ## CVE-2023-30772 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/power/supply/da9150-charger.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/power/supply/da9150-charger.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/power/supply/da9150-charger.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel before 6.2.9 has a race condition and resultant use-after-free in drivers/power/supply/da9150-charger.c if a physically proximate attacker unplugs a device.
<p>Publish Date: 2023-04-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-30772>CVE-2023-30772</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-30772">https://www.linuxkernelcves.com/cves/CVE-2023-30772</a></p>
<p>Release Date: 2023-04-16</p>
<p>Fix Resolution: v4.14.312,v4.19.280,v5.4.240,v5.10.177,v5.15.105,v6.1.22,v6.2.9,v6.3-rc4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files drivers power supply charger c drivers power supply charger c drivers power supply charger c vulnerability details the linux kernel before has a race condition and resultant use after free in drivers power supply charger c if a physically proximate attacker unplugs a device publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
42,440 | 12,891,413,912 | IssuesEvent | 2020-07-13 17:41:23 | jtimberlake/jazz | https://api.github.com/repos/jtimberlake/jazz | opened | CVE-2018-14732 (High) detected in webpack-dev-server-2.3.0.tgz, webpack-dev-server-2.11.5.tgz | security vulnerability | ## CVE-2018-14732 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>webpack-dev-server-2.3.0.tgz</b>, <b>webpack-dev-server-2.11.5.tgz</b></p></summary>
<p>
<details><summary><b>webpack-dev-server-2.3.0.tgz</b></p></summary>
<p>Serves a webpack app. Updates the browser on changes.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.3.0.tgz">https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.3.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/jazz/core/jazz_ui/src/app/primary-components/daterange-picker/ng2-datepicker/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/jazz/core/jazz_ui/src/app/primary-components/daterange-picker/ng2-datepicker/node_modules/webpack-dev-server/package.json</p>
<p>
Dependency Hierarchy:
- cli-1.0.0-rc.0.tgz (Root Library)
- :x: **webpack-dev-server-2.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>webpack-dev-server-2.11.5.tgz</b></p></summary>
<p>Serves a webpack app. Updates the browser on changes.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.11.5.tgz">https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.11.5.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/jazz/core/jazz_ui/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/jazz/core/jazz_ui/node_modules/webpack-dev-server/package.json</p>
<p>
Dependency Hierarchy:
- cli-1.7.4.tgz (Root Library)
- :x: **webpack-dev-server-2.11.5.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/jazz/commit/f31a850168fa59ceb2dfbdfb70a04c1bbe9b9fec">f31a850168fa59ceb2dfbdfb70a04c1bbe9b9fec</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in lib/Server.js in webpack-dev-server before 3.1.6. Attackers are able to steal developer's code because the origin of requests is not checked by the WebSocket server, which is used for HMR (Hot Module Replacement). Anyone can receive the HMR message sent by the WebSocket server via a ws://127.0.0.1:8080/ connection from any origin.
<p>Publish Date: 2018-09-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14732>CVE-2018-14732</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14732">https://nvd.nist.gov/vuln/detail/CVE-2018-14732</a></p>
<p>Release Date: 2018-09-21</p>
<p>Fix Resolution: 3.1.6</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"webpack-dev-server","packageVersion":"2.3.0","isTransitiveDependency":true,"dependencyTree":"@angular/cli:1.0.0-rc.0;webpack-dev-server:2.3.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.1.6"},{"packageType":"javascript/Node.js","packageName":"webpack-dev-server","packageVersion":"2.11.5","isTransitiveDependency":true,"dependencyTree":"@angular/cli:1.7.4;webpack-dev-server:2.11.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.1.6"}],"vulnerabilityIdentifier":"CVE-2018-14732","vulnerabilityDetails":"An issue was discovered in lib/Server.js in webpack-dev-server before 3.1.6. Attackers are able to steal developer\u0027s code because the origin of requests is not checked by the WebSocket server, which is used for HMR (Hot Module Replacement). Anyone can receive the HMR message sent by the WebSocket server via a ws://127.0.0.1:8080/ connection from any origin.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14732","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-14732 (High) detected in webpack-dev-server-2.3.0.tgz, webpack-dev-server-2.11.5.tgz - ## CVE-2018-14732 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>webpack-dev-server-2.3.0.tgz</b>, <b>webpack-dev-server-2.11.5.tgz</b></p></summary>
<p>
<details><summary><b>webpack-dev-server-2.3.0.tgz</b></p></summary>
<p>Serves a webpack app. Updates the browser on changes.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.3.0.tgz">https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.3.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/jazz/core/jazz_ui/src/app/primary-components/daterange-picker/ng2-datepicker/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/jazz/core/jazz_ui/src/app/primary-components/daterange-picker/ng2-datepicker/node_modules/webpack-dev-server/package.json</p>
<p>
Dependency Hierarchy:
- cli-1.0.0-rc.0.tgz (Root Library)
- :x: **webpack-dev-server-2.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>webpack-dev-server-2.11.5.tgz</b></p></summary>
<p>Serves a webpack app. Updates the browser on changes.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.11.5.tgz">https://registry.npmjs.org/webpack-dev-server/-/webpack-dev-server-2.11.5.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/jazz/core/jazz_ui/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/jazz/core/jazz_ui/node_modules/webpack-dev-server/package.json</p>
<p>
Dependency Hierarchy:
- cli-1.7.4.tgz (Root Library)
- :x: **webpack-dev-server-2.11.5.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/jazz/commit/f31a850168fa59ceb2dfbdfb70a04c1bbe9b9fec">f31a850168fa59ceb2dfbdfb70a04c1bbe9b9fec</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in lib/Server.js in webpack-dev-server before 3.1.6. Attackers are able to steal developer's code because the origin of requests is not checked by the WebSocket server, which is used for HMR (Hot Module Replacement). Anyone can receive the HMR message sent by the WebSocket server via a ws://127.0.0.1:8080/ connection from any origin.
<p>Publish Date: 2018-09-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14732>CVE-2018-14732</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14732">https://nvd.nist.gov/vuln/detail/CVE-2018-14732</a></p>
<p>Release Date: 2018-09-21</p>
<p>Fix Resolution: 3.1.6</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"webpack-dev-server","packageVersion":"2.3.0","isTransitiveDependency":true,"dependencyTree":"@angular/cli:1.0.0-rc.0;webpack-dev-server:2.3.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.1.6"},{"packageType":"javascript/Node.js","packageName":"webpack-dev-server","packageVersion":"2.11.5","isTransitiveDependency":true,"dependencyTree":"@angular/cli:1.7.4;webpack-dev-server:2.11.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.1.6"}],"vulnerabilityIdentifier":"CVE-2018-14732","vulnerabilityDetails":"An issue was discovered in lib/Server.js in webpack-dev-server before 3.1.6. Attackers are able to steal developer\u0027s code because the origin of requests is not checked by the WebSocket server, which is used for HMR (Hot Module Replacement). Anyone can receive the HMR message sent by the WebSocket server via a ws://127.0.0.1:8080/ connection from any origin.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14732","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in webpack dev server tgz webpack dev server tgz cve high severity vulnerability vulnerable libraries webpack dev server tgz webpack dev server tgz webpack dev server tgz serves a webpack app updates the browser on changes library home page a href path to dependency file tmp ws scm jazz core jazz ui src app primary components daterange picker datepicker package json path to vulnerable library tmp ws scm jazz core jazz ui src app primary components daterange picker datepicker node modules webpack dev server package json dependency hierarchy cli rc tgz root library x webpack dev server tgz vulnerable library webpack dev server tgz serves a webpack app updates the browser on changes library home page a href path to dependency file tmp ws scm jazz core jazz ui package json path to vulnerable library tmp ws scm jazz core jazz ui node modules webpack dev server package json dependency hierarchy cli tgz root library x webpack dev server tgz vulnerable library found in head commit a href vulnerability details an issue was discovered in lib server js in webpack dev server before attackers are able to steal developer s code because the origin of requests is not checked by the websocket server which is used for hmr hot module replacement anyone can receive the hmr message sent by the websocket server via a ws connection from any origin publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails an issue was discovered in lib server js in webpack dev server before attackers are able to steal developer code because the origin of requests is not checked by the websocket server which is used for hmr hot module replacement anyone can receive the hmr message sent by the websocket server via a ws connection from any origin vulnerabilityurl | 0 |
253,893 | 21,712,543,502 | IssuesEvent | 2022-05-10 14:57:42 | aldrichtr/infraspective | https://api.github.com/repos/aldrichtr/infraspective | opened | Refactor unit tests so they do not rely on the module being loaded | >refactor @tests | The Pester unit tests should load the file that we want to test, and mock any supporting functions so that they are truly _unit_ tests. If the module is loaded first, then most of the functions will be coupled with their supporting functions. Those types of tests should be in **integration** not **unit** tests. | 1.0 | Refactor unit tests so they do not rely on the module being loaded - The Pester unit tests should load the file that we want to test, and mock any supporting functions so that they are truly _unit_ tests. If the module is loaded first, then most of the functions will be coupled with their supporting functions. Those types of tests should be in **integration** not **unit** tests. | non_priority | refactor unit tests so they do not rely on the module being loaded the pester unit tests should load the file that we want to test and mock any supporting functions so that they are truly unit tests if the module is loaded first then most of the functions will be coupled with their supporting functions those types of tests should be in integration not unit tests | 0 |
146,243 | 13,174,586,467 | IssuesEvent | 2020-08-11 22:54:04 | up-banking/api | https://api.github.com/repos/up-banking/api | closed | Suggestion: Community provided examples | documentation feature request | I think it would be cool if there was a folder in this repo, let's call it `/examples` where there are community submitted examples of how the API is being leveraged.
e.g
```
/examples
/JS-android-widget-shortcut
/RUBY-google-assistant-announcement
```
Thoughts?
Happy to start it off by providing a PR. | 1.0 | Suggestion: Community provided examples - I think it would be cool if there was a folder in this repo, let's call it `/examples` where there are community submitted examples of how the API is being leveraged.
e.g
```
/examples
/JS-android-widget-shortcut
/RUBY-google-assistant-announcement
```
Thoughts?
Happy to start it off by providing a PR. | non_priority | suggestion community provided examples i think it would be cool if there was a folder in this repo let s call it examples where there are community submitted examples of how the api is being leveraged e g examples js android widget shortcut ruby google assistant announcement thoughts happy to start it off by providing a pr | 0 |
45,766 | 24,202,468,090 | IssuesEvent | 2022-09-24 19:14:35 | havochvatten/MSP-Symphony | https://api.github.com/repos/havochvatten/MSP-Symphony | opened | Add a GPU calculation backend | enhancement performance | Cumulative impact calculations are highly suitable for parallell processing since calculations in a pixel is independent of adjacent pixels (which is why the current implementation is a PointOp in the JAI API).
The best calculation backend will thus be GPU-based since the massive amounts of cores could be expected to be utilized very well. Estimated performance increase is several orders of magnitude, and probably become largely IO-bound. Ideally all raster data would fit in GPU memory, which should enable extremely fast calculations.
OpenCL or some API that would abstract away different GPU vendors differences would be best, but straight CUDA would also be very good (and perhaps fastest), and most server-based GPUs tend to come from Nvidia at the time of writing.
A CUDA-based backend was developed has been developed in another Symphony implementation which has shown very good performance characteristics. | True | Add a GPU calculation backend - Cumulative impact calculations are highly suitable for parallell processing since calculations in a pixel is independent of adjacent pixels (which is why the current implementation is a PointOp in the JAI API).
The best calculation backend will thus be GPU-based since the massive amounts of cores could be expected to be utilized very well. Estimated performance increase is several orders of magnitude, and probably become largely IO-bound. Ideally all raster data would fit in GPU memory, which should enable extremely fast calculations.
OpenCL or some API that would abstract away different GPU vendors differences would be best, but straight CUDA would also be very good (and perhaps fastest), and most server-based GPUs tend to come from Nvidia at the time of writing.
A CUDA-based backend was developed has been developed in another Symphony implementation which has shown very good performance characteristics. | non_priority | add a gpu calculation backend cumulative impact calculations are highly suitable for parallell processing since calculations in a pixel is independent of adjacent pixels which is why the current implementation is a pointop in the jai api the best calculation backend will thus be gpu based since the massive amounts of cores could be expected to be utilized very well estimated performance increase is several orders of magnitude and probably become largely io bound ideally all raster data would fit in gpu memory which should enable extremely fast calculations opencl or some api that would abstract away different gpu vendors differences would be best but straight cuda would also be very good and perhaps fastest and most server based gpus tend to come from nvidia at the time of writing a cuda based backend was developed has been developed in another symphony implementation which has shown very good performance characteristics | 0 |
30,745 | 7,252,830,472 | IssuesEvent | 2018-02-16 00:59:39 | Microsoft/vscode-python | https://api.github.com/repos/Microsoft/vscode-python | closed | Enable unit testing of experimental debugger other than just launching | awaiting 2-PR feature-debugging type-code health | The current debugger test works just for launching:
To enable those tests:
* set pythonPath to environment containing necessary python packages (PTVSD depedencies)
* set `"env":{PYTHONPATH: "<fully qualified path to PTVSD repo>"` | 1.0 | Enable unit testing of experimental debugger other than just launching - The current debugger test works just for launching:
To enable those tests:
* set pythonPath to environment containing necessary python packages (PTVSD depedencies)
* set `"env":{PYTHONPATH: "<fully qualified path to PTVSD repo>"` | non_priority | enable unit testing of experimental debugger other than just launching the current debugger test works just for launching to enable those tests set pythonpath to environment containing necessary python packages ptvsd depedencies set env pythonpath | 0 |
338,570 | 24,590,910,613 | IssuesEvent | 2022-10-14 02:03:54 | PMEAL/OpenPNM | https://api.github.com/repos/PMEAL/OpenPNM | closed | Refactor callouts in example notebooks | documentation | It [seems](https://github.com/orgs/executablebooks/discussions/834#discussioncomment-3806602) that we can't add a custom title to the predefined callouts (note, warning, etc.). But, we can define custom callouts with custom titles. Here's how:
<div>```{admonition} Custom title<div/>
Custom content.<div>```<div/>
Personally, I'd say let's stick to the default callouts whenever possible (and consequently no title), and only use custom ones if we really care about the title. | 1.0 | Refactor callouts in example notebooks - It [seems](https://github.com/orgs/executablebooks/discussions/834#discussioncomment-3806602) that we can't add a custom title to the predefined callouts (note, warning, etc.). But, we can define custom callouts with custom titles. Here's how:
<div>```{admonition} Custom title<div/>
Custom content.<div>```<div/>
Personally, I'd say let's stick to the default callouts whenever possible (and consequently no title), and only use custom ones if we really care about the title. | non_priority | refactor callouts in example notebooks it that we can t add a custom title to the predefined callouts note warning etc but we can define custom callouts with custom titles here s how admonition custom title custom content personally i d say let s stick to the default callouts whenever possible and consequently no title and only use custom ones if we really care about the title | 0 |
56,803 | 8,125,890,469 | IssuesEvent | 2018-08-16 22:50:10 | jmcnamara/XlsxWriter | https://api.github.com/repos/jmcnamara/XlsxWriter | closed | Feature request: Example creating and sending workbooks on-the-fly with Python 3 & Django | django documentation short term | ```python
import xlsxwriter
from io import BytesIO
from django.http import StreamingHttpResponse
from django.views.generic import View
def get_foo_table_data():
"""
Some table data
"""
return [
[1, 2, 3],
[4, 5, 6],
[7, 8, 9],
]
class MyView(View):
def get(self, request):
data = get_foo_table_data()
# create workbook with worksheet
output = BytesIO()
book = xlsxwriter.Workbook(output)
sheet = book.add_worksheet()
# fill worksheet with foo data
for row, columns in enumerate(data):
for column, cell_data in enumerate(columns):
sheet.write(row, column, cell_data)
book.close() # close book and save it in "output"
output.seek(0) # seek stream on begin to retrieve all data from it
# send "output" object to stream with mimetype and filename
response = StreamingHttpResponse(
output, content_type='application/vnd.openxmlformats-officedocument.spreadsheetml.sheet'
)
response['Content-Disposition'] = 'attachment; filename=foo.xlsx'
return response
``` | 1.0 | Feature request: Example creating and sending workbooks on-the-fly with Python 3 & Django - ```python
import xlsxwriter
from io import BytesIO
from django.http import StreamingHttpResponse
from django.views.generic import View
def get_foo_table_data():
"""
Some table data
"""
return [
[1, 2, 3],
[4, 5, 6],
[7, 8, 9],
]
class MyView(View):
def get(self, request):
data = get_foo_table_data()
# create workbook with worksheet
output = BytesIO()
book = xlsxwriter.Workbook(output)
sheet = book.add_worksheet()
# fill worksheet with foo data
for row, columns in enumerate(data):
for column, cell_data in enumerate(columns):
sheet.write(row, column, cell_data)
book.close() # close book and save it in "output"
output.seek(0) # seek stream on begin to retrieve all data from it
# send "output" object to stream with mimetype and filename
response = StreamingHttpResponse(
output, content_type='application/vnd.openxmlformats-officedocument.spreadsheetml.sheet'
)
response['Content-Disposition'] = 'attachment; filename=foo.xlsx'
return response
``` | non_priority | feature request example creating and sending workbooks on the fly with python django python import xlsxwriter from io import bytesio from django http import streaminghttpresponse from django views generic import view def get foo table data some table data return class myview view def get self request data get foo table data create workbook with worksheet output bytesio book xlsxwriter workbook output sheet book add worksheet fill worksheet with foo data for row columns in enumerate data for column cell data in enumerate columns sheet write row column cell data book close close book and save it in output output seek seek stream on begin to retrieve all data from it send output object to stream with mimetype and filename response streaminghttpresponse output content type application vnd openxmlformats officedocument spreadsheetml sheet response attachment filename foo xlsx return response | 0 |
177,185 | 13,686,054,447 | IssuesEvent | 2020-09-30 08:08:04 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: scrub/index-only/tpcc/w=100 failed | C-test-failure O-roachtest O-robot branch-release-19.2 release-blocker | [(roachtest).scrub/index-only/tpcc/w=100 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2332325&tab=buildLog) on [release-19.2@3da44c56c8353afc179eea905a058aeeeebeb7c5](https://github.com/cockroachdb/cockroach/commits/3da44c56c8353afc179eea905a058aeeeebeb7c5):
```
The test failed on branch=release-19.2, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/scrub/index-only/tpcc/w=100/run_1
cluster.go:2209,tpcc.go:126,tpcc.go:138,tpcc.go:149,scrub.go:54,test_runner.go:755: output in run_080748.213_n5_workload_fixtures_import_tpcc: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2332325-1601445095-62-n5cpu4:5 -- ./workload fixtures import tpcc --warehouses=100 --deprecated-fk-indexes {pgurl:1} returned: exit status 20
(1) attached stack trace
-- stack trace:
| main.(*cluster).RunE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2287
| main.(*cluster).Run
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2207
| main.setupTPCC.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:126
| main.setupTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:138
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:149
| main.makeScrubTPCCTest.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/scrub.go:54
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:755
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (2) output in run_080748.213_n5_workload_fixtures_import_tpcc
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2332325-1601445095-62-n5cpu4:5 -- ./workload fixtures import tpcc --warehouses=100 --deprecated-fk-indexes {pgurl:1} returned
| stderr:
| I200930 08:07:49.689400 1 ccl/workloadccl/fixture.go:342 starting import of 9 tables
| Error: importing fixture: importing table warehouse: pq: expected tpcc version "2.2.0" but got "2.1.0"
| Error: COMMAND_PROBLEM: exit status 1
| (1) COMMAND_PROBLEM
| Wraps: (2) Node 5. Command with error:
| | ```
| | ./workload fixtures import tpcc --warehouses=100 --deprecated-fk-indexes {pgurl:1}
| | ```
| Wraps: (3) exit status 1
| Error types: (1) errors.Cmd (2) *hintdetail.withDetail (3) *exec.ExitError
|
| stdout:
Wraps: (4) exit status 20
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *main.withCommandDetails (4) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/scrub/index-only/tpcc/w=100](https://teamcity.cockroachdb.com/viewLog.html?buildId=2332325&tab=artifacts#/scrub/index-only/tpcc/w=100)
Related:
- #44069 roachtest: scrub/index-only/tpcc/w=100 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Ascrub%2Findex-only%2Ftpcc%2Fw%3D100.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: scrub/index-only/tpcc/w=100 failed - [(roachtest).scrub/index-only/tpcc/w=100 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2332325&tab=buildLog) on [release-19.2@3da44c56c8353afc179eea905a058aeeeebeb7c5](https://github.com/cockroachdb/cockroach/commits/3da44c56c8353afc179eea905a058aeeeebeb7c5):
```
The test failed on branch=release-19.2, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/scrub/index-only/tpcc/w=100/run_1
cluster.go:2209,tpcc.go:126,tpcc.go:138,tpcc.go:149,scrub.go:54,test_runner.go:755: output in run_080748.213_n5_workload_fixtures_import_tpcc: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2332325-1601445095-62-n5cpu4:5 -- ./workload fixtures import tpcc --warehouses=100 --deprecated-fk-indexes {pgurl:1} returned: exit status 20
(1) attached stack trace
-- stack trace:
| main.(*cluster).RunE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2287
| main.(*cluster).Run
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2207
| main.setupTPCC.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:126
| main.setupTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:138
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:149
| main.makeScrubTPCCTest.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/scrub.go:54
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:755
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (2) output in run_080748.213_n5_workload_fixtures_import_tpcc
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-2332325-1601445095-62-n5cpu4:5 -- ./workload fixtures import tpcc --warehouses=100 --deprecated-fk-indexes {pgurl:1} returned
| stderr:
| I200930 08:07:49.689400 1 ccl/workloadccl/fixture.go:342 starting import of 9 tables
| Error: importing fixture: importing table warehouse: pq: expected tpcc version "2.2.0" but got "2.1.0"
| Error: COMMAND_PROBLEM: exit status 1
| (1) COMMAND_PROBLEM
| Wraps: (2) Node 5. Command with error:
| | ```
| | ./workload fixtures import tpcc --warehouses=100 --deprecated-fk-indexes {pgurl:1}
| | ```
| Wraps: (3) exit status 1
| Error types: (1) errors.Cmd (2) *hintdetail.withDetail (3) *exec.ExitError
|
| stdout:
Wraps: (4) exit status 20
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *main.withCommandDetails (4) *exec.ExitError
```
<details><summary>More</summary><p>
Artifacts: [/scrub/index-only/tpcc/w=100](https://teamcity.cockroachdb.com/viewLog.html?buildId=2332325&tab=artifacts#/scrub/index-only/tpcc/w=100)
Related:
- #44069 roachtest: scrub/index-only/tpcc/w=100 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Ascrub%2Findex-only%2Ftpcc%2Fw%3D100.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | roachtest scrub index only tpcc w failed on the test failed on branch release cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts scrub index only tpcc w run cluster go tpcc go tpcc go tpcc go scrub go test runner go output in run workload fixtures import tpcc home agent work go src github com cockroachdb cockroach bin roachprod run teamcity workload fixtures import tpcc warehouses deprecated fk indexes pgurl returned exit status attached stack trace stack trace main cluster rune home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main cluster run home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main setuptpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main setuptpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main runtpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main makescrubtpcctest home agent work go src github com cockroachdb cockroach pkg cmd roachtest scrub go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go runtime goexit usr local go src runtime asm s wraps output in run workload fixtures import tpcc wraps home agent work go src github com cockroachdb cockroach bin roachprod run teamcity workload fixtures import tpcc warehouses deprecated fk indexes pgurl returned stderr ccl workloadccl fixture go starting import of tables error importing fixture importing table warehouse pq expected tpcc version but got error command problem exit status command problem wraps node command with error workload fixtures import tpcc warehouses deprecated fk indexes pgurl wraps exit status error types errors cmd hintdetail withdetail exec exiterror stdout wraps exit status error types withstack withstack errutil withprefix main withcommanddetails exec exiterror more artifacts related roachtest scrub index only tpcc w failed powered by | 0 |
87,183 | 15,756,116,434 | IssuesEvent | 2021-03-31 02:57:22 | OSWeekends/eventpoints-backend | https://api.github.com/repos/OSWeekends/eventpoints-backend | opened | CVE-2021-28957 (Medium) detected in lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-28957 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Powerful and Pythonic XML processing library combining libxml2/libxslt with the ElementTree API.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/e5/14/f4343239f955442da9da1919a99f7311bc5627522741bada61b2349c8def/lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/e5/14/f4343239f955442da9da1919a99f7311bc5627522741bada61b2349c8def/lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: eventpoints-backend/scrapers/requirements.txt</p>
<p>Path to vulnerable library: eventpoints-backend/scrapers/requirements.txt</p>
<p>
Dependency Hierarchy:
- Scrapy-1.5.1-py2.py3-none-any.whl (Root Library)
- :x: **lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/OSWeekends/eventpoints-backend/commit/51c25ecb67a2ad16fcee689d0e1dd491f1ccda8b">51c25ecb67a2ad16fcee689d0e1dd491f1ccda8b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lxml 4.6.2 allows XSS. It places the HTML action attribute into defs.link_attrs (in html/defs.py) for later use in input sanitization, but does not do the same for the HTML5 formaction attribute.
<p>Publish Date: 2021-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28957>CVE-2021-28957</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jq4v-f5q6-mjqq">https://github.com/advisories/GHSA-jq4v-f5q6-mjqq</a></p>
<p>Release Date: 2021-03-21</p>
<p>Fix Resolution: 4.6.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-28957 (Medium) detected in lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2021-28957 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Powerful and Pythonic XML processing library combining libxml2/libxslt with the ElementTree API.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/e5/14/f4343239f955442da9da1919a99f7311bc5627522741bada61b2349c8def/lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/e5/14/f4343239f955442da9da1919a99f7311bc5627522741bada61b2349c8def/lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: eventpoints-backend/scrapers/requirements.txt</p>
<p>Path to vulnerable library: eventpoints-backend/scrapers/requirements.txt</p>
<p>
Dependency Hierarchy:
- Scrapy-1.5.1-py2.py3-none-any.whl (Root Library)
- :x: **lxml-4.2.5-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/OSWeekends/eventpoints-backend/commit/51c25ecb67a2ad16fcee689d0e1dd491f1ccda8b">51c25ecb67a2ad16fcee689d0e1dd491f1ccda8b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lxml 4.6.2 allows XSS. It places the HTML action attribute into defs.link_attrs (in html/defs.py) for later use in input sanitization, but does not do the same for the HTML5 formaction attribute.
<p>Publish Date: 2021-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28957>CVE-2021-28957</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jq4v-f5q6-mjqq">https://github.com/advisories/GHSA-jq4v-f5q6-mjqq</a></p>
<p>Release Date: 2021-03-21</p>
<p>Fix Resolution: 4.6.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in lxml whl cve medium severity vulnerability vulnerable library lxml whl powerful and pythonic xml processing library combining libxslt with the elementtree api library home page a href path to dependency file eventpoints backend scrapers requirements txt path to vulnerable library eventpoints backend scrapers requirements txt dependency hierarchy scrapy none any whl root library x lxml whl vulnerable library found in head commit a href vulnerability details lxml allows xss it places the html action attribute into defs link attrs in html defs py for later use in input sanitization but does not do the same for the formaction attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
390 | 2,517,856,538 | IssuesEvent | 2015-01-16 17:40:35 | alimanfoo/petl | https://api.github.com/repos/alimanfoo/petl | closed | table mapping case study | Documentation | Proposed to write a case study illustrating row mapping based on clinical data mapping in malariagen. | 1.0 | table mapping case study - Proposed to write a case study illustrating row mapping based on clinical data mapping in malariagen. | non_priority | table mapping case study proposed to write a case study illustrating row mapping based on clinical data mapping in malariagen | 0 |
194,903 | 14,692,156,266 | IssuesEvent | 2021-01-03 00:09:16 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | cosmos/cosmos-sdk: x/staking/keeper/historical_info_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [cosmos/cosmos-sdk](https://www.github.com/cosmos/cosmos-sdk) at [x/staking/keeper/historical_info_test.go](https://github.com/cosmos/cosmos-sdk/blob/6a9b0caa57810b6e11332a0edfada28e10d38930/x/staking/keeper/historical_info_test.go#L138-L140)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
>
[Click here to see the code in its original context.](https://github.com/cosmos/cosmos-sdk/blob/6a9b0caa57810b6e11332a0edfada28e10d38930/x/staking/keeper/historical_info_test.go#L138-L140)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for i, hi := range expHistInfos {
app.StakingKeeper.SetHistoricalInfo(ctx, int64(10+i), &hi)
}
```
</details>
<details>
<summary>Click here to show extra information the analyzer produced.</summary>
```
No path was found through the callgraph that could lead to a function which writes a pointer argument.
No path was found through the callgraph that could lead to a function which passes a pointer to third-party code.
root signature {SetHistoricalInfo 3} was not found in the callgraph; reference was passed directly to third-party code
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 6a9b0caa57810b6e11332a0edfada28e10d38930
| 1.0 | cosmos/cosmos-sdk: x/staking/keeper/historical_info_test.go; 3 LoC -
Found a possible issue in [cosmos/cosmos-sdk](https://www.github.com/cosmos/cosmos-sdk) at [x/staking/keeper/historical_info_test.go](https://github.com/cosmos/cosmos-sdk/blob/6a9b0caa57810b6e11332a0edfada28e10d38930/x/staking/keeper/historical_info_test.go#L138-L140)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
>
[Click here to see the code in its original context.](https://github.com/cosmos/cosmos-sdk/blob/6a9b0caa57810b6e11332a0edfada28e10d38930/x/staking/keeper/historical_info_test.go#L138-L140)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for i, hi := range expHistInfos {
app.StakingKeeper.SetHistoricalInfo(ctx, int64(10+i), &hi)
}
```
</details>
<details>
<summary>Click here to show extra information the analyzer produced.</summary>
```
No path was found through the callgraph that could lead to a function which writes a pointer argument.
No path was found through the callgraph that could lead to a function which passes a pointer to third-party code.
root signature {SetHistoricalInfo 3} was not found in the callgraph; reference was passed directly to third-party code
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 6a9b0caa57810b6e11332a0edfada28e10d38930
| non_priority | cosmos cosmos sdk x staking keeper historical info test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message click here to show the line s of go which triggered the analyzer go for i hi range exphistinfos app stakingkeeper sethistoricalinfo ctx i hi click here to show extra information the analyzer produced no path was found through the callgraph that could lead to a function which writes a pointer argument no path was found through the callgraph that could lead to a function which passes a pointer to third party code root signature sethistoricalinfo was not found in the callgraph reference was passed directly to third party code leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
229,608 | 25,362,290,551 | IssuesEvent | 2022-11-21 01:04:03 | AkshayMukkavilli/Analyzing-the-Significance-of-Structure-in-Amazon-Review-Data-Using-Machine-Learning-Approaches | https://api.github.com/repos/AkshayMukkavilli/Analyzing-the-Significance-of-Structure-in-Amazon-Review-Data-Using-Machine-Learning-Approaches | opened | CVE-2022-41896 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2022-41896 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /FinalProject/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_8b9e071c-3b11-4aa9-ba60-cdeb60d053b7/20190525011350_65403/20190525011256_depth_0/9/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. If `ThreadUnsafeUnigramCandidateSampler` is given input `filterbank_channel_count` greater than the allowed max size, TensorFlow will crash. We have patched the issue in GitHub commit 39ec7eaf1428e90c37787e5b3fbd68ebd3c48860. The fix will be included in TensorFlow 2.11. We will also cherrypick this commit on TensorFlow 2.10.1, 2.9.3, and TensorFlow 2.8.4, as these are also affected and still in supported range.
<p>Publish Date: 2022-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41896>CVE-2022-41896</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-41896">https://www.cve.org/CVERecord?id=CVE-2022-41896</a></p>
<p>Release Date: 2022-11-18</p>
<p>Fix Resolution: tensorflow - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-cpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-gpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-41896 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2022-41896 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /FinalProject/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_8b9e071c-3b11-4aa9-ba60-cdeb60d053b7/20190525011350_65403/20190525011256_depth_0/9/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. If `ThreadUnsafeUnigramCandidateSampler` is given input `filterbank_channel_count` greater than the allowed max size, TensorFlow will crash. We have patched the issue in GitHub commit 39ec7eaf1428e90c37787e5b3fbd68ebd3c48860. The fix will be included in TensorFlow 2.11. We will also cherrypick this commit on TensorFlow 2.10.1, 2.9.3, and TensorFlow 2.8.4, as these are also affected and still in supported range.
<p>Publish Date: 2022-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41896>CVE-2022-41896</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-41896">https://www.cve.org/CVERecord?id=CVE-2022-41896</a></p>
<p>Release Date: 2022-11-18</p>
<p>Fix Resolution: tensorflow - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-cpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-gpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file finalproject requirements txt path to vulnerable library tesource archiveextractor depth tensorflow tensorflow data purelib tensorflow dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an open source platform for machine learning if threadunsafeunigramcandidatesampler is given input filterbank channel count greater than the allowed max size tensorflow will crash we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
54,869 | 6,877,856,752 | IssuesEvent | 2017-11-20 09:44:41 | syndesisio/syndesis | https://api.github.com/repos/syndesisio/syndesis | opened | Integrations list: add export action to kebab menu | cat/enhancement module/ui notif/ux-design | We should consider adding `Export` as one of the the available action. Now it's only hidden in detail view page.
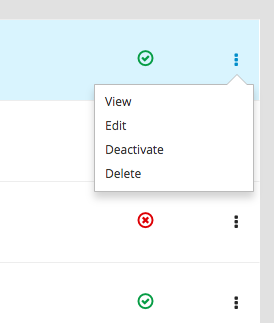
| 1.0 | Integrations list: add export action to kebab menu - We should consider adding `Export` as one of the the available action. Now it's only hidden in detail view page.
| non_priority | integrations list add export action to kebab menu we should consider adding export as one of the the available action now it s only hidden in detail view page | 0 |
76,709 | 15,496,174,986 | IssuesEvent | 2021-03-11 02:11:55 | mwilliams7197/zendo | https://api.github.com/repos/mwilliams7197/zendo | opened | CVE-2020-28498 (Medium) detected in elliptic-6.5.2.tgz | security vulnerability | ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: zendo/package.json</p>
<p>Path to vulnerable library: zendo/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-1.0.7.tgz (Root Library)
- webpack-2.6.1.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.1.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution: v6.5.4</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.5.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:1.0.7;webpack:2.6.1;node-libs-browser:2.2.1;crypto-browserify:3.12.0;browserify-sign:4.1.0;elliptic:6.5.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.4"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28498","vulnerabilityDetails":"The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498","cvss3Severity":"medium","cvss3Score":"6.8","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-28498 (Medium) detected in elliptic-6.5.2.tgz - ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: zendo/package.json</p>
<p>Path to vulnerable library: zendo/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-1.0.7.tgz (Root Library)
- webpack-2.6.1.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.1.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution: v6.5.4</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.5.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-scripts:1.0.7;webpack:2.6.1;node-libs-browser:2.2.1;crypto-browserify:3.12.0;browserify-sign:4.1.0;elliptic:6.5.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.4"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28498","vulnerabilityDetails":"The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498","cvss3Severity":"medium","cvss3Score":"6.8","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in elliptic tgz cve medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file zendo package json path to vulnerable library zendo node modules elliptic package json dependency hierarchy react scripts tgz root library webpack tgz node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in base branch master vulnerability details the package elliptic before are vulnerable to cryptographic issues via the implementation in elliptic ec key js there is no check to confirm that the public key point passed into the derive function actually exists on the curve this results in the potential for the private key used in this implementation to be revealed after a number of ecdh operations are performed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree react scripts webpack node libs browser crypto browserify browserify sign elliptic isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails the package elliptic before are vulnerable to cryptographic issues via the implementation in elliptic ec key js there is no check to confirm that the public key point passed into the derive function actually exists on the curve this results in the potential for the private key used in this implementation to be revealed after a number of ecdh operations are performed vulnerabilityurl | 0 |
68,471 | 7,097,662,429 | IssuesEvent | 2018-01-14 21:40:36 | null511/PiServerLite | https://api.github.com/repos/null511/PiServerLite | closed | Route Intercepter | Testing enhancement | Create toggle-able option for intercepting all incoming HTTP requests. As an example, this allows you to temporarily redirect all incoming requests to a 'loading' page while the server is performing long-running operations.
- Register `RouteOverride` object with `HttpReceiver` and unregister on `.Dispose()`. | 1.0 | Route Intercepter - Create toggle-able option for intercepting all incoming HTTP requests. As an example, this allows you to temporarily redirect all incoming requests to a 'loading' page while the server is performing long-running operations.
- Register `RouteOverride` object with `HttpReceiver` and unregister on `.Dispose()`. | non_priority | route intercepter create toggle able option for intercepting all incoming http requests as an example this allows you to temporarily redirect all incoming requests to a loading page while the server is performing long running operations register routeoverride object with httpreceiver and unregister on dispose | 0 |
366,766 | 25,600,657,082 | IssuesEvent | 2022-12-01 19:53:38 | abenteuerzeit/viva-la-carte | https://api.github.com/repos/abenteuerzeit/viva-la-carte | closed | A free tool to allow the average health-conscience consumer a way to make positive food choices tailored to a set of nutritional goals | documentation good first issue | # User experience
## Story time!
Characters
— Victoria works at Viva La Carte,
— James is a customer
James wants to simplify his meal planning. In fact, he wishes he had his own personal nutritionist who would help him plan well-balanced meals for the week. At the same time, the nutritionist should know which foods James likes to eat and which foods he is allergic to or just doesn't like, or which foods he doesn't feel like eating at any particular moment.
Here, the nutritionist shows James a meal plan for the week. Now, James can substitute meals to suit his tastes, or he just accepts whatever the nutritionist actually recommends. In addition, he can tell the nutritionist which brands he prefers over others.
So James goes to Victoria's Shopping Service with the shopping list he needs to get the foods set from his meal plan. When he gives Victoria his list, she gets all the products he needs. Victoria shows James how many calories each item has and how the items compare to each other based on a standard metric, such as kcal per 100g. The prices in Victoria's store are displayed last and are viewed as the least important. Victoria makes it a priority to be familiar with her customers personally. That's why when she sees James for the first time, she first asks him his name. Chatting helps Victoria figure out exactly the type of food James likes and dislikes, and beyond that, she indulges in gossip. For example, she tells James about what her other customers have bought recently, what his friends got, and she can provide James with his entire grocery shopping history for easy reference. She suggests that James might want to replace items or add and remove specific items to or from his shopping cart.
James has all the items he wants. He purchases them. Victoria takes note and thanks James. She asks him if he would like to set up his order for repeated delivery. James says yes, but he would need to modify some things. Victoria notes that and tells James about how they could arrange regular deliveries.
## Outline of Functionality
1. Register an account, login and logout
2. Enter personal data needed by the nutritionist.
3. Enter health goals and food and brand preferences
4. Generate a meal plan for a week. The customer can change the period.
5. Edit meal plan. Substitute parts by regenerating sections of the plan. E.g., for just one day, or just one meal.
## Flows
> Key:
> 1. Action
> 1. Success.
> 2. Failure
### Actions (CRUD or REST)
#### Identity
- ***Register a new account***
- ? View **Home page**
- : Return *register page with error message*
- ***Login to account***
- ? View **Home page**
- : Return *Login page with error message*
#### Profile Settings
- ***Food preferences***
- USer interacts with **ProductPreferenceManager** to set preferences
- Only 10 items can be favorite
- Collect: Procuct.Id
- Save for later viewing and editing (to change ratings)
```csharp
public enum Ratings
{
reject, dislike, like, love, favorite
}
```
- ***Meal preferences***
- Displayed on home page. You don't need an account to generate meals
- User interacts with Meal Planner to view generated meals
- Edit items
- Add new item; change quantities/portion sizes, substitute products, delete items
- **MealPlanManager** properties:
-
```csharp
public enum Diets
{
Whatever, Paleo, Vegetarian, Vegan, Keto, Mediterranean
}
public class MealPlanManager : IMealPlanManager
{
private double TotalCalories { get; set; }
private int MealCount { get; set; }
private Diets diet { get; set; }
private List<Recipe> Meals { get; set; }
...
}
```
### Flows
- Home Page displays Meal Plan Maker ⇒ User enters meal nutrition requirements and frequency ⇒ Accept / Modify / Reject meal plan.
- each meal is composed of recipes (like: how to make a hamburger, how to make french fries, how to make lemonade).
- User can see the nutritional data for the complete cart, an entire meal as well as for individual items
- Accept Meal Plan ⇒ Map as shopping list ⇒ Get, display, modify products ⇒ Checkout (Create Order) ⇒ Process Payment ⇒ Delivery Service
| 1.0 | A free tool to allow the average health-conscience consumer a way to make positive food choices tailored to a set of nutritional goals - # User experience
## Story time!
Characters
— Victoria works at Viva La Carte,
— James is a customer
James wants to simplify his meal planning. In fact, he wishes he had his own personal nutritionist who would help him plan well-balanced meals for the week. At the same time, the nutritionist should know which foods James likes to eat and which foods he is allergic to or just doesn't like, or which foods he doesn't feel like eating at any particular moment.
Here, the nutritionist shows James a meal plan for the week. Now, James can substitute meals to suit his tastes, or he just accepts whatever the nutritionist actually recommends. In addition, he can tell the nutritionist which brands he prefers over others.
So James goes to Victoria's Shopping Service with the shopping list he needs to get the foods set from his meal plan. When he gives Victoria his list, she gets all the products he needs. Victoria shows James how many calories each item has and how the items compare to each other based on a standard metric, such as kcal per 100g. The prices in Victoria's store are displayed last and are viewed as the least important. Victoria makes it a priority to be familiar with her customers personally. That's why when she sees James for the first time, she first asks him his name. Chatting helps Victoria figure out exactly the type of food James likes and dislikes, and beyond that, she indulges in gossip. For example, she tells James about what her other customers have bought recently, what his friends got, and she can provide James with his entire grocery shopping history for easy reference. She suggests that James might want to replace items or add and remove specific items to or from his shopping cart.
James has all the items he wants. He purchases them. Victoria takes note and thanks James. She asks him if he would like to set up his order for repeated delivery. James says yes, but he would need to modify some things. Victoria notes that and tells James about how they could arrange regular deliveries.
## Outline of Functionality
1. Register an account, login and logout
2. Enter personal data needed by the nutritionist.
3. Enter health goals and food and brand preferences
4. Generate a meal plan for a week. The customer can change the period.
5. Edit meal plan. Substitute parts by regenerating sections of the plan. E.g., for just one day, or just one meal.
## Flows
> Key:
> 1. Action
> 1. Success.
> 2. Failure
### Actions (CRUD or REST)
#### Identity
- ***Register a new account***
- ? View **Home page**
- : Return *register page with error message*
- ***Login to account***
- ? View **Home page**
- : Return *Login page with error message*
#### Profile Settings
- ***Food preferences***
- USer interacts with **ProductPreferenceManager** to set preferences
- Only 10 items can be favorite
- Collect: Procuct.Id
- Save for later viewing and editing (to change ratings)
```csharp
public enum Ratings
{
reject, dislike, like, love, favorite
}
```
- ***Meal preferences***
- Displayed on home page. You don't need an account to generate meals
- User interacts with Meal Planner to view generated meals
- Edit items
- Add new item; change quantities/portion sizes, substitute products, delete items
- **MealPlanManager** properties:
-
```csharp
public enum Diets
{
Whatever, Paleo, Vegetarian, Vegan, Keto, Mediterranean
}
public class MealPlanManager : IMealPlanManager
{
private double TotalCalories { get; set; }
private int MealCount { get; set; }
private Diets diet { get; set; }
private List<Recipe> Meals { get; set; }
...
}
```
### Flows
- Home Page displays Meal Plan Maker ⇒ User enters meal nutrition requirements and frequency ⇒ Accept / Modify / Reject meal plan.
- each meal is composed of recipes (like: how to make a hamburger, how to make french fries, how to make lemonade).
- User can see the nutritional data for the complete cart, an entire meal as well as for individual items
- Accept Meal Plan ⇒ Map as shopping list ⇒ Get, display, modify products ⇒ Checkout (Create Order) ⇒ Process Payment ⇒ Delivery Service
| non_priority | a free tool to allow the average health conscience consumer a way to make positive food choices tailored to a set of nutritional goals user experience story time characters — victoria works at viva la carte — james is a customer james wants to simplify his meal planning in fact he wishes he had his own personal nutritionist who would help him plan well balanced meals for the week at the same time the nutritionist should know which foods james likes to eat and which foods he is allergic to or just doesn t like or which foods he doesn t feel like eating at any particular moment here the nutritionist shows james a meal plan for the week now james can substitute meals to suit his tastes or he just accepts whatever the nutritionist actually recommends in addition he can tell the nutritionist which brands he prefers over others so james goes to victoria s shopping service with the shopping list he needs to get the foods set from his meal plan when he gives victoria his list she gets all the products he needs victoria shows james how many calories each item has and how the items compare to each other based on a standard metric such as kcal per the prices in victoria s store are displayed last and are viewed as the least important victoria makes it a priority to be familiar with her customers personally that s why when she sees james for the first time she first asks him his name chatting helps victoria figure out exactly the type of food james likes and dislikes and beyond that she indulges in gossip for example she tells james about what her other customers have bought recently what his friends got and she can provide james with his entire grocery shopping history for easy reference she suggests that james might want to replace items or add and remove specific items to or from his shopping cart james has all the items he wants he purchases them victoria takes note and thanks james she asks him if he would like to set up his order for repeated delivery james says yes but he would need to modify some things victoria notes that and tells james about how they could arrange regular deliveries outline of functionality register an account login and logout enter personal data needed by the nutritionist enter health goals and food and brand preferences generate a meal plan for a week the customer can change the period edit meal plan substitute parts by regenerating sections of the plan e g for just one day or just one meal flows key action success failure actions crud or rest identity register a new account view home page return register page with error message login to account view home page return login page with error message profile settings food preferences user interacts with productpreferencemanager to set preferences only items can be favorite collect procuct id save for later viewing and editing to change ratings csharp public enum ratings reject dislike like love favorite meal preferences displayed on home page you don t need an account to generate meals user interacts with meal planner to view generated meals edit items add new item change quantities portion sizes substitute products delete items mealplanmanager properties csharp public enum diets whatever paleo vegetarian vegan keto mediterranean public class mealplanmanager imealplanmanager private double totalcalories get set private int mealcount get set private diets diet get set private list meals get set flows home page displays meal plan maker ⇒ user enters meal nutrition requirements and frequency ⇒ accept modify reject meal plan each meal is composed of recipes like how to make a hamburger how to make french fries how to make lemonade user can see the nutritional data for the complete cart an entire meal as well as for individual items accept meal plan ⇒ map as shopping list ⇒ get display modify products ⇒ checkout create order ⇒ process payment ⇒ delivery service | 0 |
344,731 | 30,756,232,506 | IssuesEvent | 2023-07-29 04:43:10 | stockOneQ/back | https://api.github.com/repos/stockOneQ/back | closed | File 관련 테스트코드를 작성한다 | 🔨 Refactor ✅ Test | ## Description 🖊️
File 관련 테스트코드를 작성한다
## To-do 🧑💻
- [ ] File Test 작성
- [ ] File Controller, Service 리팩토링 | 1.0 | File 관련 테스트코드를 작성한다 - ## Description 🖊️
File 관련 테스트코드를 작성한다
## To-do 🧑💻
- [ ] File Test 작성
- [ ] File Controller, Service 리팩토링 | non_priority | file 관련 테스트코드를 작성한다 description 🖊️ file 관련 테스트코드를 작성한다 to do 🧑💻 file test 작성 file controller service 리팩토링 | 0 |
44,953 | 13,097,423,812 | IssuesEvent | 2020-08-03 17:26:16 | jtimberlake/COSMOS | https://api.github.com/repos/jtimberlake/COSMOS | opened | CVE-2020-7598 (Medium) detected in minimist-0.0.8.tgz | security vulnerability | ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/COSMOS/extensions/vscode/client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/COSMOS/extensions/vscode/client/node_modules/minimist/package.json,/tmp/ws-scm/COSMOS/extensions/vscode/client/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- mocha-2.5.3.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/COSMOS/commit/e967c77766e1b731bec2bab4f5fafb6af874c2c1">e967c77766e1b731bec2bab4f5fafb6af874c2c1</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","isTransitiveDependency":true,"dependencyTree":"mocha:2.5.3;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3"}],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7598 (Medium) detected in minimist-0.0.8.tgz - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/COSMOS/extensions/vscode/client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/COSMOS/extensions/vscode/client/node_modules/minimist/package.json,/tmp/ws-scm/COSMOS/extensions/vscode/client/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- mocha-2.5.3.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/COSMOS/commit/e967c77766e1b731bec2bab4f5fafb6af874c2c1">e967c77766e1b731bec2bab4f5fafb6af874c2c1</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","isTransitiveDependency":true,"dependencyTree":"mocha:2.5.3;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3"}],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in minimist tgz cve medium severity vulnerability vulnerable library minimist tgz parse argument options library home page a href path to dependency file tmp ws scm cosmos extensions vscode client package json path to vulnerable library tmp ws scm cosmos extensions vscode client node modules minimist package json tmp ws scm cosmos extensions vscode client node modules minimist package json dependency hierarchy mocha tgz root library mkdirp tgz x minimist tgz vulnerable library found in head commit a href vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl | 0 |
39,865 | 16,107,155,586 | IssuesEvent | 2021-04-27 16:12:14 | graphprotocol/indexer | https://api.github.com/repos/graphprotocol/indexer | closed | Failed to query indexer allocations, keeping existing | bug indexer-agent indexer-service | From service:
3|start_indexer_service | {"level":20,"time":1608416975921,"pid":1874424,"hostname":"suntzu-server","name":"IndexerService","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","component":"AllocationMonitor","msg":"Refresh active allocations"}
3|start_indexer_service | {"level":40,"time":1608416976209,"pid":1874424,"hostname":"suntzu-server","name":"IndexerService","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","component":"AllocationMonitor","allocations":[],"err":{"type":"IndexerError","message":"Failed to query indexer allocations","stack":"IndexerError: Failed to query indexer allocations\n at Object.indexerError (/usr/local/lib/node_modules/@graphprotocol/indexer-service/node_modules/@graphprotocol/indexer-common/dist/errors.js:97:12)\n at /usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:67:39\n at Generator.next (<anonymous>)\n at fulfilled (/usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:5:58)\n at processTicksAndRejections (internal/process/task_queues.js:93:5)","code":"IE010","explanation":"https://github.com/graphprotocol/indexer/blob/master/docs/errors.md#ie010","cause":{"type":"Error","message":"Indexer not found on chain","stack":"Error: Indexer not found on chain\n at /usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:59:23\n at Generator.next (<anonymous>)\n at fulfilled (/usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:5:58)\n at processTicksAndRejections (internal/process/task_queues.js:93:5)"}},"msg":"Failed to query indexer allocations, keeping existing"}
| 1.0 | Failed to query indexer allocations, keeping existing - From service:
3|start_indexer_service | {"level":20,"time":1608416975921,"pid":1874424,"hostname":"suntzu-server","name":"IndexerService","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","component":"AllocationMonitor","msg":"Refresh active allocations"}
3|start_indexer_service | {"level":40,"time":1608416976209,"pid":1874424,"hostname":"suntzu-server","name":"IndexerService","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","indexer":"0x4167EB613d784C910f5dc0F3f0515D61Ec6EC8DF","operator":"0xD96d4B52CAb35cF3DF1d58765bD2eA7cb1Fb6016","component":"AllocationMonitor","allocations":[],"err":{"type":"IndexerError","message":"Failed to query indexer allocations","stack":"IndexerError: Failed to query indexer allocations\n at Object.indexerError (/usr/local/lib/node_modules/@graphprotocol/indexer-service/node_modules/@graphprotocol/indexer-common/dist/errors.js:97:12)\n at /usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:67:39\n at Generator.next (<anonymous>)\n at fulfilled (/usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:5:58)\n at processTicksAndRejections (internal/process/task_queues.js:93:5)","code":"IE010","explanation":"https://github.com/graphprotocol/indexer/blob/master/docs/errors.md#ie010","cause":{"type":"Error","message":"Indexer not found on chain","stack":"Error: Indexer not found on chain\n at /usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:59:23\n at Generator.next (<anonymous>)\n at fulfilled (/usr/local/lib/node_modules/@graphprotocol/indexer-service/dist/allocations.js:5:58)\n at processTicksAndRejections (internal/process/task_queues.js:93:5)"}},"msg":"Failed to query indexer allocations, keeping existing"}
| non_priority | failed to query indexer allocations keeping existing from service start indexer service level time pid hostname suntzu server name indexerservice indexer operator indexer operator component allocationmonitor msg refresh active allocations start indexer service level time pid hostname suntzu server name indexerservice indexer operator indexer operator component allocationmonitor allocations err type indexererror message failed to query indexer allocations stack indexererror failed to query indexer allocations n at object indexererror usr local lib node modules graphprotocol indexer service node modules graphprotocol indexer common dist errors js n at usr local lib node modules graphprotocol indexer service dist allocations js n at generator next n at fulfilled usr local lib node modules graphprotocol indexer service dist allocations js n at processticksandrejections internal process task queues js code explanation not found on chain stack error indexer not found on chain n at usr local lib node modules graphprotocol indexer service dist allocations js n at generator next n at fulfilled usr local lib node modules graphprotocol indexer service dist allocations js n at processticksandrejections internal process task queues js msg failed to query indexer allocations keeping existing | 0 |
236,588 | 18,102,755,797 | IssuesEvent | 2021-09-22 15:46:00 | BlueBrain/nexus | https://api.github.com/repos/BlueBrain/nexus | closed | All links from W3 are broken | bug documentation | W3 has changed their website and their links are now broken. They didn't bother having a proper HTTP redirect, so we'll have to go one to one trying to find out what's their new Url.
For example:
- https://www.w3.org/TR/eventsource/ -> https://html.spec.whatwg.org/multipage/server-sent-events.html | 1.0 | All links from W3 are broken - W3 has changed their website and their links are now broken. They didn't bother having a proper HTTP redirect, so we'll have to go one to one trying to find out what's their new Url.
For example:
- https://www.w3.org/TR/eventsource/ -> https://html.spec.whatwg.org/multipage/server-sent-events.html | non_priority | all links from are broken has changed their website and their links are now broken they didn t bother having a proper http redirect so we ll have to go one to one trying to find out what s their new url for example | 0 |
284,646 | 24,612,392,171 | IssuesEvent | 2022-10-14 23:45:55 | harvester/harvester | https://api.github.com/repos/harvester/harvester | closed | [BUG] Cannot edit storage class when adding volume on edit VM page | kind/bug area/ui severity/2 reproduce/always not-require/test-plan | **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
Cannot edit storage class when adding volume on edit VM page
**To Reproduce**
Steps to reproduce the behavior:
1. Go to edit VM page
2. Go volume tab
3. Click the "Add Volume" button
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
"Storage class" should be editable
**Support bundle**
<!--
You can generate a support bundle in the bottom of Harvester UI (https://docs.harvesterhci.io/v1.0/troubleshooting/harvester/#generate-a-support-bundle). It includes logs and configurations that help diagnose the issue.
Tokens, passwords, and secrets are automatically removed from support bundles. If you feel it's not appropriate to share the bundle files publicly, please consider:
- Wait for a developer to reach you and provide the bundle file by any secure methods.
- Join our Slack community (https://rancher-users.slack.com/archives/C01GKHKAG0K) to provide the bundle.
- Send the bundle to harvester-support-bundle@suse.com with the correct issue ID. -->
**Environment**
- Harvester ISO version:
- Underlying Infrastructure (e.g. Baremetal with Dell PowerEdge R630):
**Additional context**
Add any other context about the problem here.
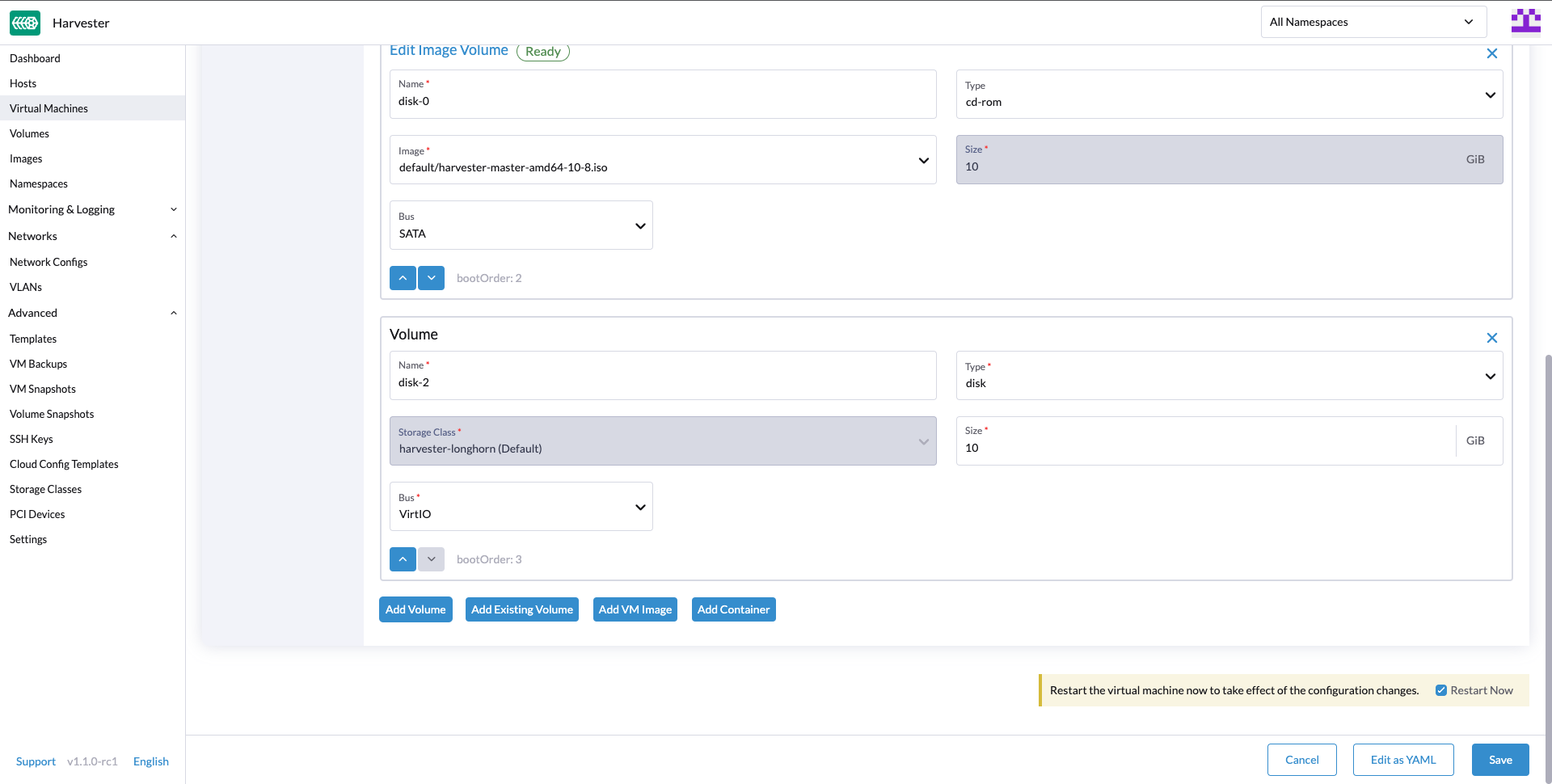
| 1.0 | [BUG] Cannot edit storage class when adding volume on edit VM page - **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
Cannot edit storage class when adding volume on edit VM page
**To Reproduce**
Steps to reproduce the behavior:
1. Go to edit VM page
2. Go volume tab
3. Click the "Add Volume" button
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
"Storage class" should be editable
**Support bundle**
<!--
You can generate a support bundle in the bottom of Harvester UI (https://docs.harvesterhci.io/v1.0/troubleshooting/harvester/#generate-a-support-bundle). It includes logs and configurations that help diagnose the issue.
Tokens, passwords, and secrets are automatically removed from support bundles. If you feel it's not appropriate to share the bundle files publicly, please consider:
- Wait for a developer to reach you and provide the bundle file by any secure methods.
- Join our Slack community (https://rancher-users.slack.com/archives/C01GKHKAG0K) to provide the bundle.
- Send the bundle to harvester-support-bundle@suse.com with the correct issue ID. -->
**Environment**
- Harvester ISO version:
- Underlying Infrastructure (e.g. Baremetal with Dell PowerEdge R630):
**Additional context**
Add any other context about the problem here.
| non_priority | cannot edit storage class when adding volume on edit vm page describe the bug cannot edit storage class when adding volume on edit vm page to reproduce steps to reproduce the behavior go to edit vm page go volume tab click the add volume button expected behavior storage class should be editable support bundle you can generate a support bundle in the bottom of harvester ui it includes logs and configurations that help diagnose the issue tokens passwords and secrets are automatically removed from support bundles if you feel it s not appropriate to share the bundle files publicly please consider wait for a developer to reach you and provide the bundle file by any secure methods join our slack community to provide the bundle send the bundle to harvester support bundle suse com with the correct issue id environment harvester iso version underlying infrastructure e g baremetal with dell poweredge additional context add any other context about the problem here | 0 |
92,835 | 11,714,794,893 | IssuesEvent | 2020-03-09 13:03:46 | EightShapes/esds-library | https://api.github.com/repos/EightShapes/esds-library | closed | Select [Design Asset] | Component [Design Asset] | ### Design Starting Point

### Must Have
* Follows input very closely
* Settings: white, light, dark, black
* States: default, selected/panel open, hover, focus, error, placeholder text, with value
Note: we favor native controls, so by default this should use the browser default panel. When we have a custom select list, it uses the List and Popover components.
### Nice to Have
* Sizes: `medium` and `small` | 1.0 | Select [Design Asset] - ### Design Starting Point

### Must Have
* Follows input very closely
* Settings: white, light, dark, black
* States: default, selected/panel open, hover, focus, error, placeholder text, with value
Note: we favor native controls, so by default this should use the browser default panel. When we have a custom select list, it uses the List and Popover components.
### Nice to Have
* Sizes: `medium` and `small` | non_priority | select design starting point must have follows input very closely settings white light dark black states default selected panel open hover focus error placeholder text with value note we favor native controls so by default this should use the browser default panel when we have a custom select list it uses the list and popover components nice to have sizes medium and small | 0 |
14,958 | 10,236,160,715 | IssuesEvent | 2019-08-19 10:53:45 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Terraform Azure vm custom_data bash script | question service/virtual-machine | I'm deploying an Azure VM and trying to run a script to partition a data disk and mount it upon provisioning. I've been using _"custom_data"_, but for some reason it's not working. When I login into the VM, the script is nowhere to be found and nothing is executed. Terraform apply succeeds without errors. Any clues ? or perhaps I have the wrong setup here.
As per Terraform docs: custom_data - (Optional) Specifies custom data to supply to the machine. On Linux-based systems, this can be used as a cloud-init script. On other systems, this will be copied as a file on disk. Internally, Terraform will base64 encode this value before sending it to the API. The maximum length of the binary array is 65535 bytes.
```
resource "azurerm_virtual_machine" "middleware_vm" {
name = "${var.middleware_vm}"
location = "${var.location}"
resource_group_name = "${azurerm_resource_group.middleware.name}"
network_interface_ids = ["${azurerm_network_interface.middleware.id}"]
vm_size = "Standard_DS4_v2"
storage_os_disk {
name = "centos_os_disk"
caching = "ReadWrite"
create_option = "FromImage"
managed_disk_type = "Premium_LRS"
}
storage_data_disk {
name = "managed_backup_disk"
create_option = "Empty"
caching = "ReadWrite"
disk_size_gb = "256"
managed_disk_type = "Premium_LRS"
lun = 0
}
storage_image_reference {
publisher = "OpenLogic"
offer = "CentOS"
sku = "7.5"
version = "latest"
}
os_profile {
computer_name = "${var.middleware_vm}"
admin_username = "middlewareadmin"
custom_data = "${file("scripts/middleware_disk.sh")}"
#custom_data = "${path.root}/scripts/middleware_disk.sh"
}
``` | 1.0 | Terraform Azure vm custom_data bash script - I'm deploying an Azure VM and trying to run a script to partition a data disk and mount it upon provisioning. I've been using _"custom_data"_, but for some reason it's not working. When I login into the VM, the script is nowhere to be found and nothing is executed. Terraform apply succeeds without errors. Any clues ? or perhaps I have the wrong setup here.
As per Terraform docs: custom_data - (Optional) Specifies custom data to supply to the machine. On Linux-based systems, this can be used as a cloud-init script. On other systems, this will be copied as a file on disk. Internally, Terraform will base64 encode this value before sending it to the API. The maximum length of the binary array is 65535 bytes.
```
resource "azurerm_virtual_machine" "middleware_vm" {
name = "${var.middleware_vm}"
location = "${var.location}"
resource_group_name = "${azurerm_resource_group.middleware.name}"
network_interface_ids = ["${azurerm_network_interface.middleware.id}"]
vm_size = "Standard_DS4_v2"
storage_os_disk {
name = "centos_os_disk"
caching = "ReadWrite"
create_option = "FromImage"
managed_disk_type = "Premium_LRS"
}
storage_data_disk {
name = "managed_backup_disk"
create_option = "Empty"
caching = "ReadWrite"
disk_size_gb = "256"
managed_disk_type = "Premium_LRS"
lun = 0
}
storage_image_reference {
publisher = "OpenLogic"
offer = "CentOS"
sku = "7.5"
version = "latest"
}
os_profile {
computer_name = "${var.middleware_vm}"
admin_username = "middlewareadmin"
custom_data = "${file("scripts/middleware_disk.sh")}"
#custom_data = "${path.root}/scripts/middleware_disk.sh"
}
``` | non_priority | terraform azure vm custom data bash script i m deploying an azure vm and trying to run a script to partition a data disk and mount it upon provisioning i ve been using custom data but for some reason it s not working when i login into the vm the script is nowhere to be found and nothing is executed terraform apply succeeds without errors any clues or perhaps i have the wrong setup here as per terraform docs custom data optional specifies custom data to supply to the machine on linux based systems this can be used as a cloud init script on other systems this will be copied as a file on disk internally terraform will encode this value before sending it to the api the maximum length of the binary array is bytes resource azurerm virtual machine middleware vm name var middleware vm location var location resource group name azurerm resource group middleware name network interface ids vm size standard storage os disk name centos os disk caching readwrite create option fromimage managed disk type premium lrs storage data disk name managed backup disk create option empty caching readwrite disk size gb managed disk type premium lrs lun storage image reference publisher openlogic offer centos sku version latest os profile computer name var middleware vm admin username middlewareadmin custom data file scripts middleware disk sh custom data path root scripts middleware disk sh | 0 |
91,060 | 8,288,423,599 | IssuesEvent | 2018-09-19 11:58:33 | humera987/HumTestData | https://api.github.com/repos/humera987/HumTestData | opened | tested : account_create_invalid_Microsoft_VSTS_Git | tested | Project : tested
Job : UAT 1&2
Env : UAT 1
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Wed, 19 Sep 2018 11:58:30 GMT]}
Endpoint : http://13.56.210.25/accounts
Request :
{
"name" : "Test-ldP4TESKiYG1WD6RQGO43CFs",
"accountType" : "Microsoft_VSTS_Git",
"accessKey" : " ",
"secretKey" : "testing secretKey"
}
Response :
{
"timestamp" : "2018-09-19T11:58:30.282+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/accounts"
}
Logs :
Assertion [@Response.errors == true] resolved-to [ == true] result [Failed]Assertion [@StatusCode == 200] resolved-to [404 == 200] result [Failed]
--- FX Bot --- | 1.0 | tested : account_create_invalid_Microsoft_VSTS_Git - Project : tested
Job : UAT 1&2
Env : UAT 1
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Wed, 19 Sep 2018 11:58:30 GMT]}
Endpoint : http://13.56.210.25/accounts
Request :
{
"name" : "Test-ldP4TESKiYG1WD6RQGO43CFs",
"accountType" : "Microsoft_VSTS_Git",
"accessKey" : " ",
"secretKey" : "testing secretKey"
}
Response :
{
"timestamp" : "2018-09-19T11:58:30.282+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/accounts"
}
Logs :
Assertion [@Response.errors == true] resolved-to [ == true] result [Failed]Assertion [@StatusCode == 200] resolved-to [404 == 200] result [Failed]
--- FX Bot --- | non_priority | tested account create invalid microsoft vsts git project tested job uat env uat region fxlabs us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options content type transfer encoding date endpoint request name test accounttype microsoft vsts git accesskey secretkey testing secretkey response timestamp status error not found message no message available path accounts logs assertion resolved to result assertion resolved to result fx bot | 0 |
11,450 | 4,227,128,798 | IssuesEvent | 2016-07-02 23:48:51 | rubberduck-vba/Rubberduck | https://api.github.com/repos/rubberduck-vba/Rubberduck | closed | Return value of function 'iReturnSomething' is never used | bug code-inspections code-parsing status-norepro | Inspection results have numerous examples of false positives, for example I have a function called OffSet like this:
```
Function OffSet(someTable As Table) As Integer
OffSet = someTable.Rows.Count -1
End Function
Sub UsesOffSet()
Dim iOffSet as Integer
iOffSet = modT.OffSet(Selection.Range.Tables(1)) <-- Result Used, but not detected
End Sub
```
Build: 2.0.1.33906 | 2.0 | Return value of function 'iReturnSomething' is never used - Inspection results have numerous examples of false positives, for example I have a function called OffSet like this:
```
Function OffSet(someTable As Table) As Integer
OffSet = someTable.Rows.Count -1
End Function
Sub UsesOffSet()
Dim iOffSet as Integer
iOffSet = modT.OffSet(Selection.Range.Tables(1)) <-- Result Used, but not detected
End Sub
```
Build: 2.0.1.33906 | non_priority | return value of function ireturnsomething is never used inspection results have numerous examples of false positives for example i have a function called offset like this function offset sometable as table as integer offset sometable rows count end function sub usesoffset dim ioffset as integer ioffset modt offset selection range tables result used but not detected end sub build | 0 |
39,918 | 12,727,980,753 | IssuesEvent | 2020-06-25 01:00:52 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Google Authentication Not working. | :heavy_check_mark: Resolution: Answered Needs: Attention :wave: Status: Resolved area-security | <!--
More information on our issue management policies can be found here: https://aka.ms/aspnet/issue-policies
Please keep in mind that the GitHub issue tracker is not intended as a general support forum, but for reporting **non-security** bugs and feature requests.
If you believe you have an issue that affects the SECURITY of the platform, please do NOT create an issue and instead email your issue details to secure@microsoft.com. Your report may be eligible for our [bug bounty](https://www.microsoft.com/en-us/msrc/bounty-dot-net-core) but ONLY if it is reported through email.
For other types of questions, consider using [StackOverflow](https://stackoverflow.com).
-->
I get a 404 page can't be found error after trying to authenticate with google in my .NET Core web app.
I get this error after choosing the account I want to you to login.
Error: No webpage was found for the web address: https://unifiedcamp.com/signin-google?state=CfDJ8FgDy3E-NgdMteo6azrxmI9HCCgEc3Zf0hcoqjg-8PtEj8bkME4BFV8Agh-xacojlFk4qupR0tQNriHi7_ycCUEZmWhVjiFsESdYyTFKsgq_zXTPmvHvxRDZM7gdnUj6eqSm5MrJiKGmnmiqbSCvZH90vMzjaITx99KttXlVDQFrbSS4woI-LHa-1wcobKTaq4mExvs2bULAre4mzyoois1R9E51vRrHOdo529hlIVObVs1zX_7e7HWE61ye4mLJ-sdzHz8N9qGzoSUVnF-uzYM&code=4%2F1AGa7kFi2spNbE90nS9DyawYAN4FVUfmcpEabn69VeNA2ZUUIxOgHXq-x_Ng8FdClfUDYFoOZ_uVfVVR4ZYsyBs&scope=email+profile+openid+https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fuserinfo.email+https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fuserinfo.profile&authuser=1&prompt=none#
I have temporarily removed the google auth because it is in production and do not want users to experience the issue at hand.
### To Reproduce
<!--
We ❤ code! Point us to a minimalistic repro project hosted in a GitHub repo.
For a repro project, create a new ASP.NET Core project using the template of your your choice, apply the minimum required code to result in the issue you're observing.
We will close this issue if:
- the repro project you share with us is complex. We can't investigate custom projects, so don't point us to such, please.
- if we will not be able to repro the behavior you're reporting
-->
### Exceptions (if any)
<!--
Include the exception you get when facing this issue
-->
### Further technical details
- ASP.NET Core version
- Include the output of `dotnet --info`
- The IDE (VS / VS Code/ VS4Mac) you're running on, and it's version
| True | Google Authentication Not working. - <!--
More information on our issue management policies can be found here: https://aka.ms/aspnet/issue-policies
Please keep in mind that the GitHub issue tracker is not intended as a general support forum, but for reporting **non-security** bugs and feature requests.
If you believe you have an issue that affects the SECURITY of the platform, please do NOT create an issue and instead email your issue details to secure@microsoft.com. Your report may be eligible for our [bug bounty](https://www.microsoft.com/en-us/msrc/bounty-dot-net-core) but ONLY if it is reported through email.
For other types of questions, consider using [StackOverflow](https://stackoverflow.com).
-->
I get a 404 page can't be found error after trying to authenticate with google in my .NET Core web app.
I get this error after choosing the account I want to you to login.
Error: No webpage was found for the web address: https://unifiedcamp.com/signin-google?state=CfDJ8FgDy3E-NgdMteo6azrxmI9HCCgEc3Zf0hcoqjg-8PtEj8bkME4BFV8Agh-xacojlFk4qupR0tQNriHi7_ycCUEZmWhVjiFsESdYyTFKsgq_zXTPmvHvxRDZM7gdnUj6eqSm5MrJiKGmnmiqbSCvZH90vMzjaITx99KttXlVDQFrbSS4woI-LHa-1wcobKTaq4mExvs2bULAre4mzyoois1R9E51vRrHOdo529hlIVObVs1zX_7e7HWE61ye4mLJ-sdzHz8N9qGzoSUVnF-uzYM&code=4%2F1AGa7kFi2spNbE90nS9DyawYAN4FVUfmcpEabn69VeNA2ZUUIxOgHXq-x_Ng8FdClfUDYFoOZ_uVfVVR4ZYsyBs&scope=email+profile+openid+https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fuserinfo.email+https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fuserinfo.profile&authuser=1&prompt=none#
I have temporarily removed the google auth because it is in production and do not want users to experience the issue at hand.
### To Reproduce
<!--
We ❤ code! Point us to a minimalistic repro project hosted in a GitHub repo.
For a repro project, create a new ASP.NET Core project using the template of your your choice, apply the minimum required code to result in the issue you're observing.
We will close this issue if:
- the repro project you share with us is complex. We can't investigate custom projects, so don't point us to such, please.
- if we will not be able to repro the behavior you're reporting
-->
### Exceptions (if any)
<!--
Include the exception you get when facing this issue
-->
### Further technical details
- ASP.NET Core version
- Include the output of `dotnet --info`
- The IDE (VS / VS Code/ VS4Mac) you're running on, and it's version
| non_priority | google authentication not working more information on our issue management policies can be found here please keep in mind that the github issue tracker is not intended as a general support forum but for reporting non security bugs and feature requests if you believe you have an issue that affects the security of the platform please do not create an issue and instead email your issue details to secure microsoft com your report may be eligible for our but only if it is reported through email for other types of questions consider using i get a page can t be found error after trying to authenticate with google in my net core web app i get this error after choosing the account i want to you to login error no webpage was found for the web address i have temporarily removed the google auth because it is in production and do not want users to experience the issue at hand to reproduce we ❤ code point us to a minimalistic repro project hosted in a github repo for a repro project create a new asp net core project using the template of your your choice apply the minimum required code to result in the issue you re observing we will close this issue if the repro project you share with us is complex we can t investigate custom projects so don t point us to such please if we will not be able to repro the behavior you re reporting exceptions if any include the exception you get when facing this issue further technical details asp net core version include the output of dotnet info the ide vs vs code you re running on and it s version | 0 |
316,120 | 23,616,034,984 | IssuesEvent | 2022-08-24 15:56:49 | PacktPublishing/Data-Engineering-with-Alteryx | https://api.github.com/repos/PacktPublishing/Data-Engineering-with-Alteryx | closed | Can't open workflows. | documentation | Every time I try to open one of your workflows, I get an error saying, ">" is an unexpected token. The expected token is "=", Line 16, position 76.
Any ideas? I have tried with multiple workflows and multiple versions of Alteryx.
| 1.0 | Can't open workflows. - Every time I try to open one of your workflows, I get an error saying, ">" is an unexpected token. The expected token is "=", Line 16, position 76.
Any ideas? I have tried with multiple workflows and multiple versions of Alteryx.
| non_priority | can t open workflows every time i try to open one of your workflows i get an error saying is an unexpected token the expected token is line position any ideas i have tried with multiple workflows and multiple versions of alteryx | 0 |
336,644 | 30,212,138,803 | IssuesEvent | 2023-07-05 13:26:47 | gameserverapp/Platform | https://api.github.com/repos/gameserverapp/Platform | closed | Patreon - Upgrades to Higher Tiers Only Being Partially Completed | status: to be tested | So - situation is that I had a player increase their patronage to a higher tier, but the actual actions that are supposed to take place when the system recognizes the upgrade did not take place.
When the system recognizes the user as this tier, this is what actions are supposed to execute.
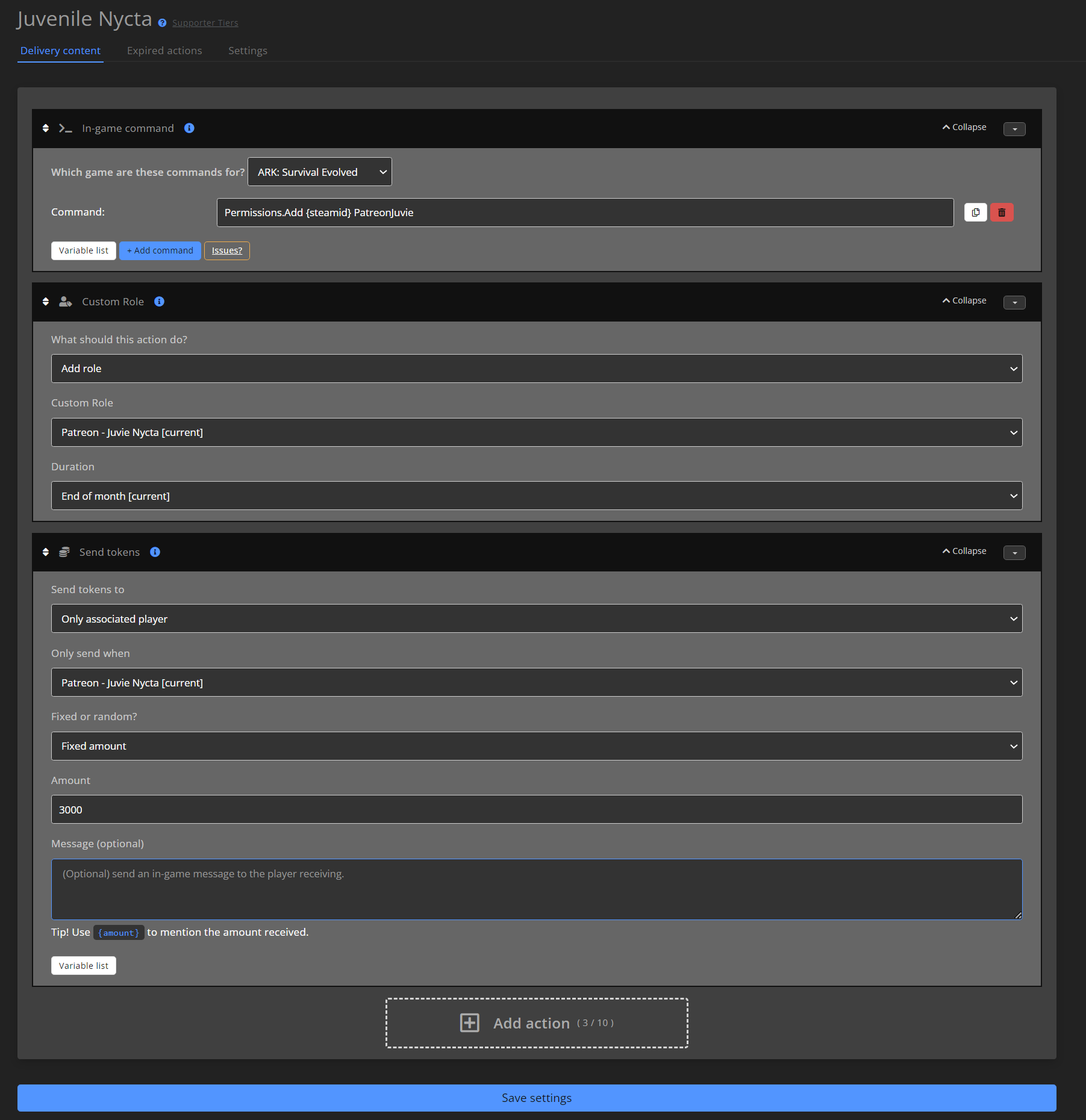
This is the character in question - unfortunately, while my list of subscribers is starting to grow, this is the only example I have, as they are the only one that has increased their Patronage during the month. Here is a list of their roles they have - they still have the Supporter and Hatchling roles, when those should have been removed when they had "stopped" those Patreon tiers.
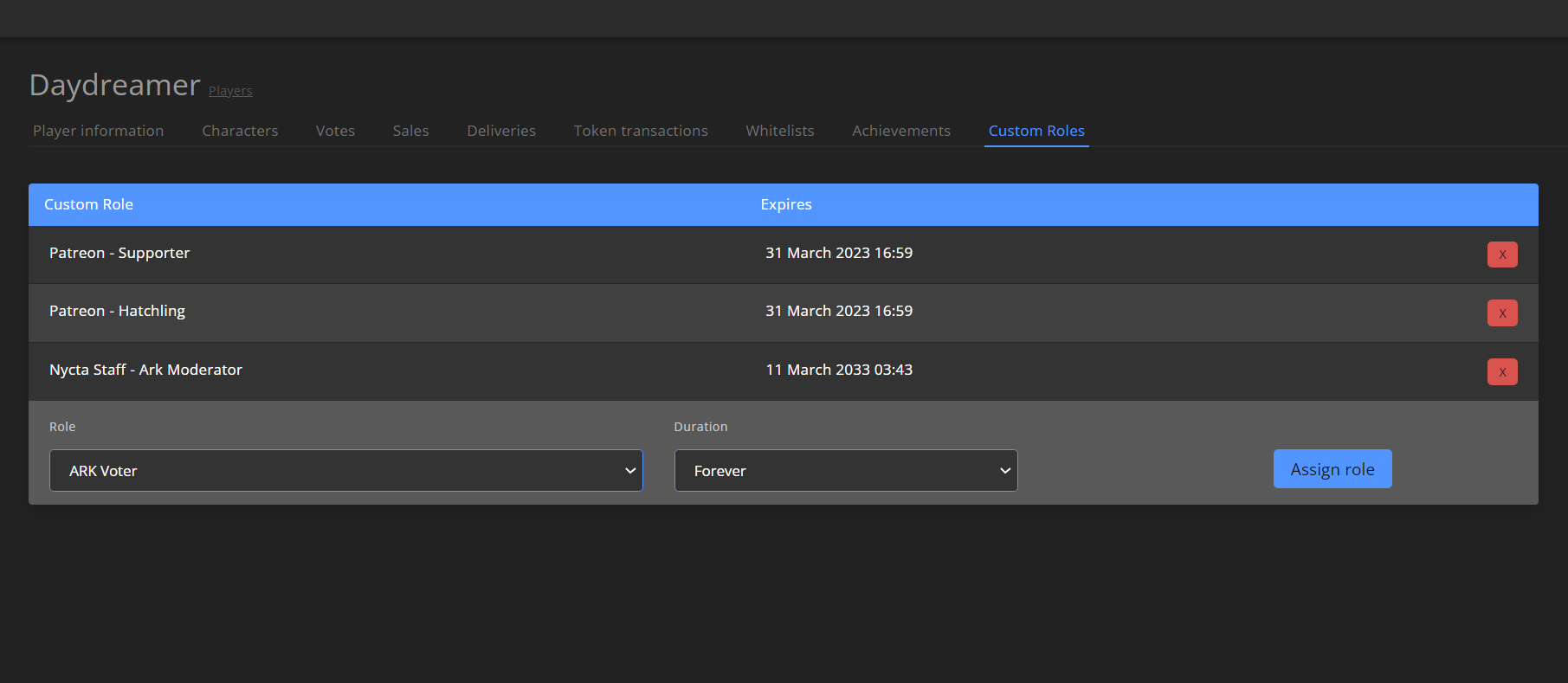
They still have the Supporter and Hatchling roles, when those should have been removed when they had "stopped" those Patreon tiers.
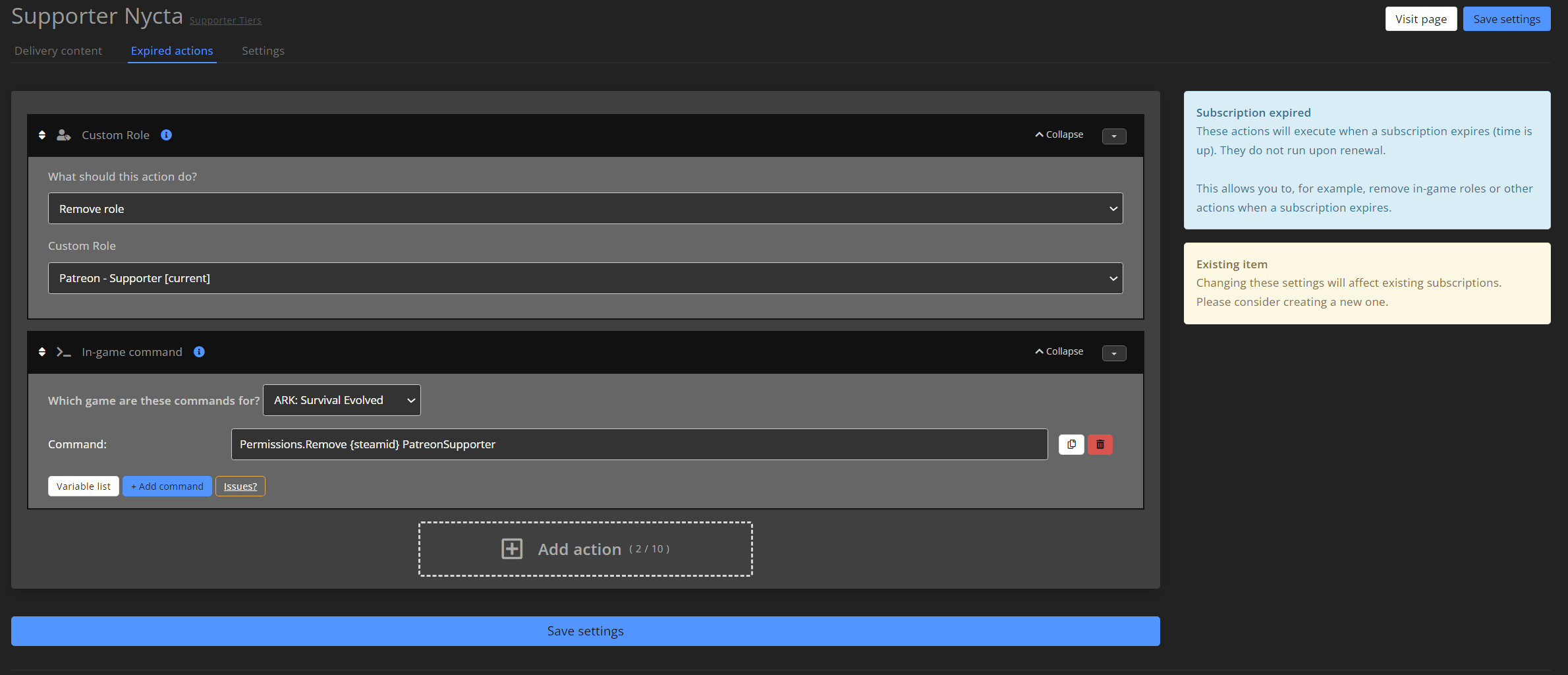
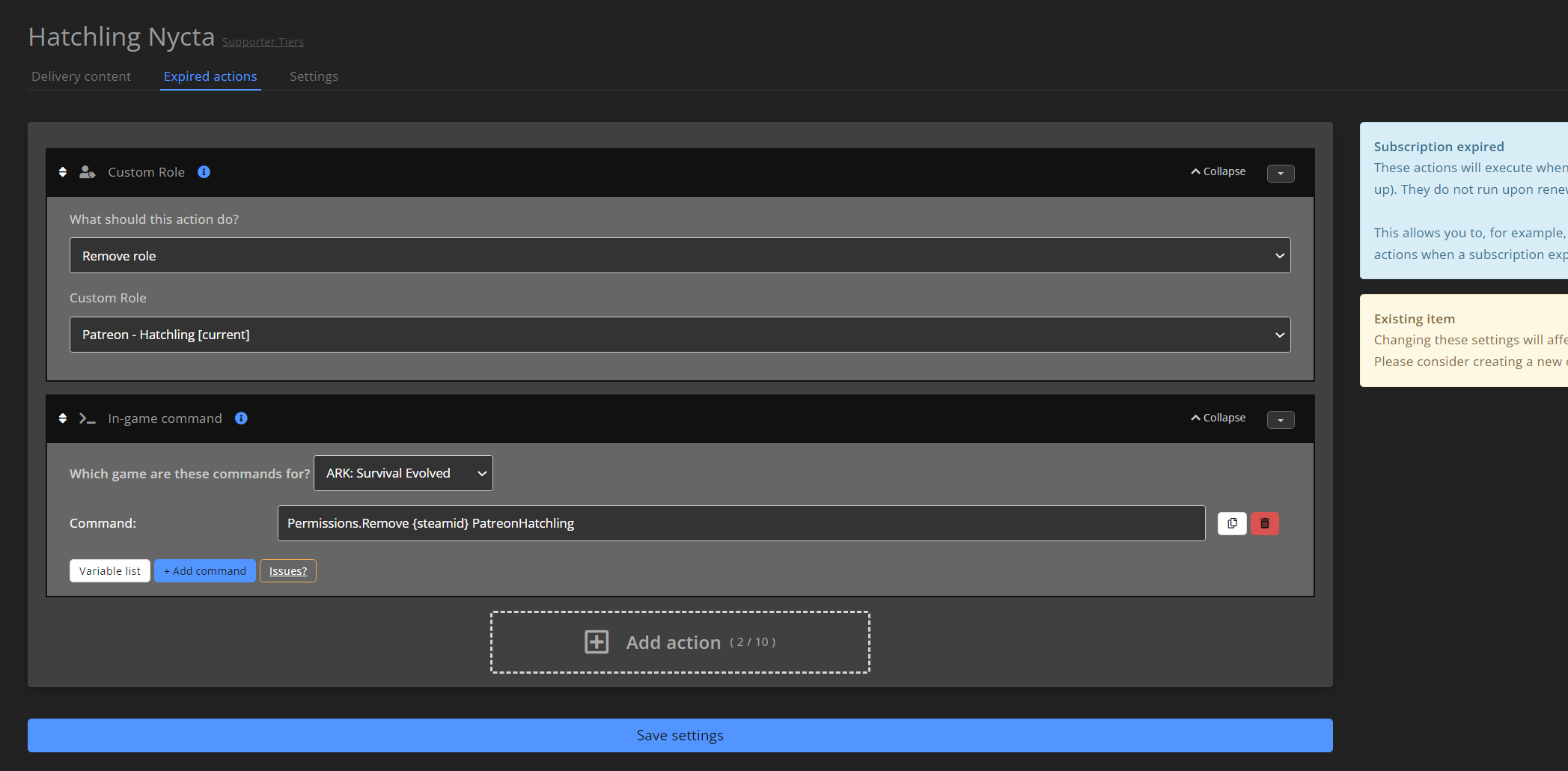
And here is the list of their transactions. Note the increase in Patreon tiers:
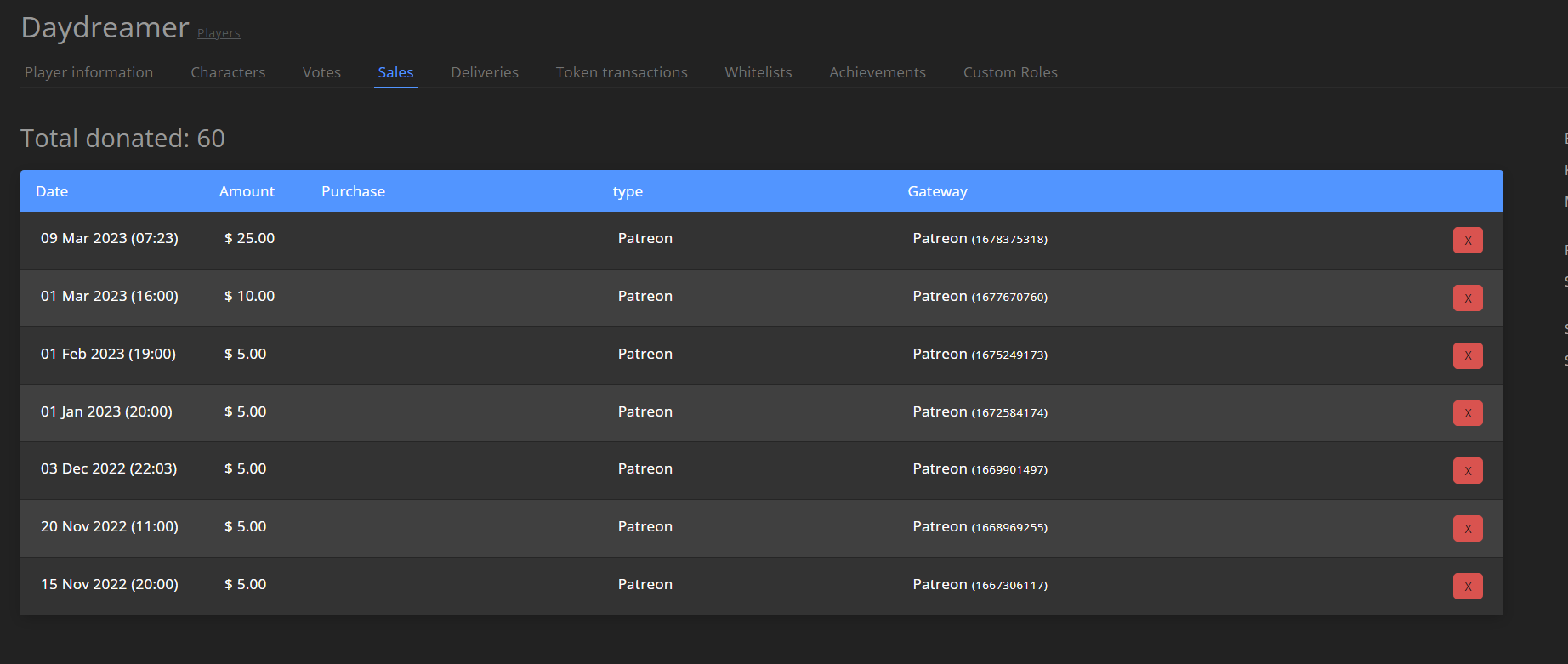
In addition, this part of GSA recognizes that Daydreamer is at the Juvie Nycta tier.
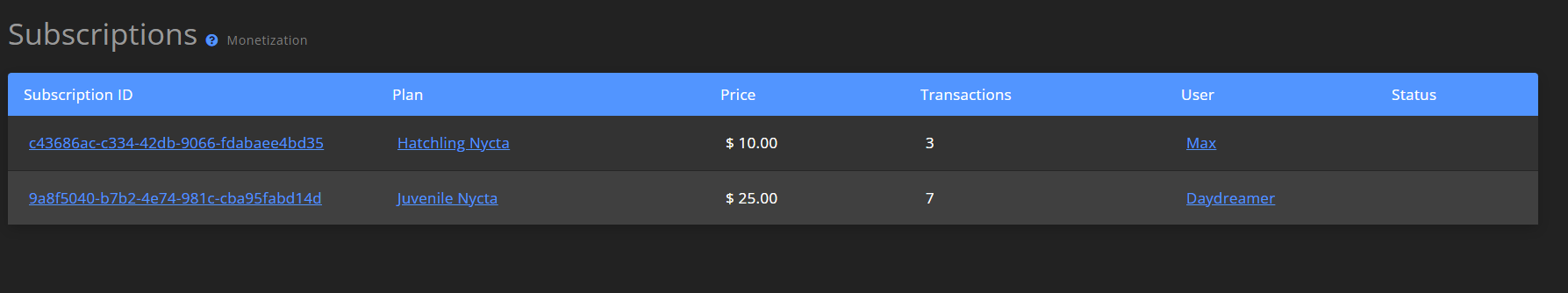
I've also pushed for a few sync attempts through the dashboard, but it doesn't seem to update the aforementioned tasks/triggers.
| 1.0 | Patreon - Upgrades to Higher Tiers Only Being Partially Completed - So - situation is that I had a player increase their patronage to a higher tier, but the actual actions that are supposed to take place when the system recognizes the upgrade did not take place.
When the system recognizes the user as this tier, this is what actions are supposed to execute.
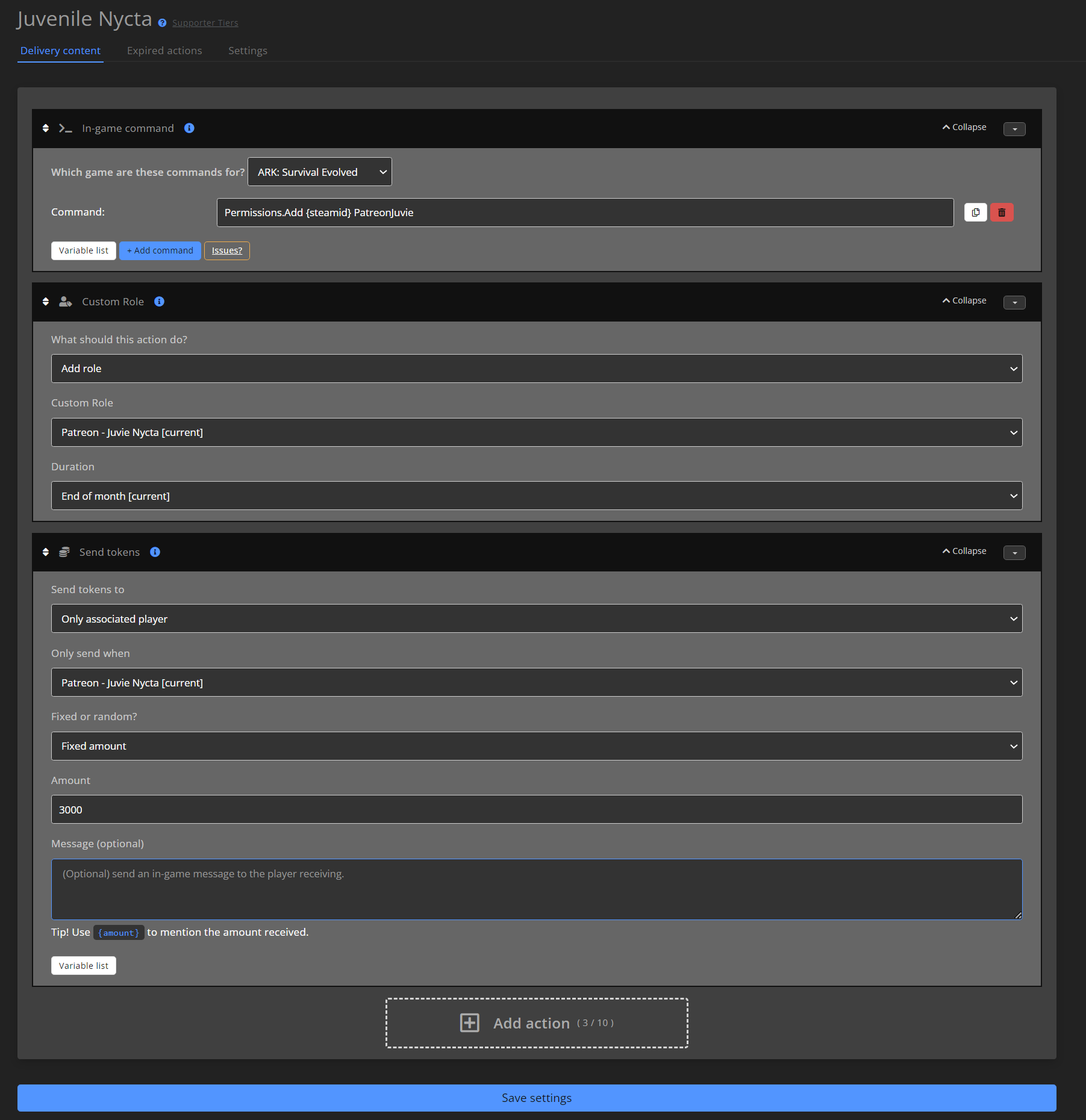
This is the character in question - unfortunately, while my list of subscribers is starting to grow, this is the only example I have, as they are the only one that has increased their Patronage during the month. Here is a list of their roles they have - they still have the Supporter and Hatchling roles, when those should have been removed when they had "stopped" those Patreon tiers.
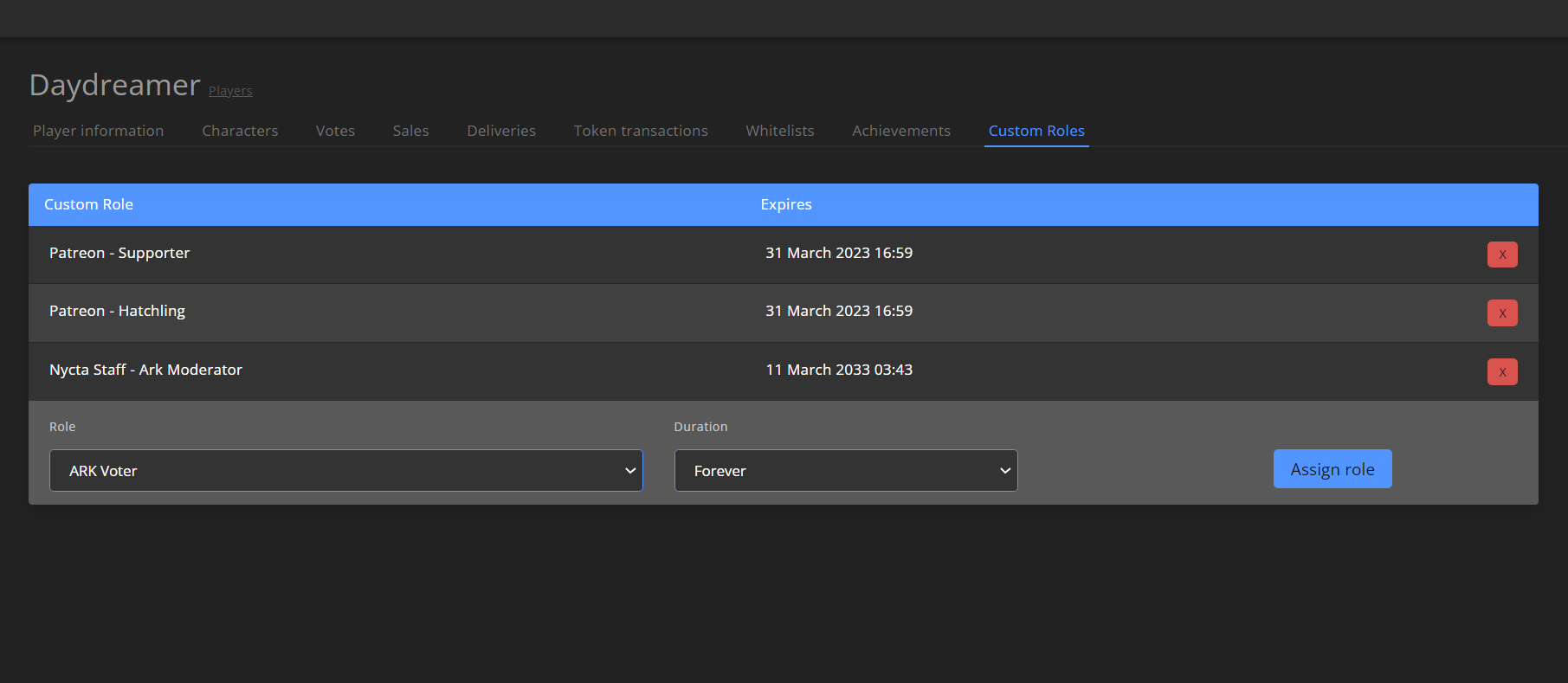
They still have the Supporter and Hatchling roles, when those should have been removed when they had "stopped" those Patreon tiers.
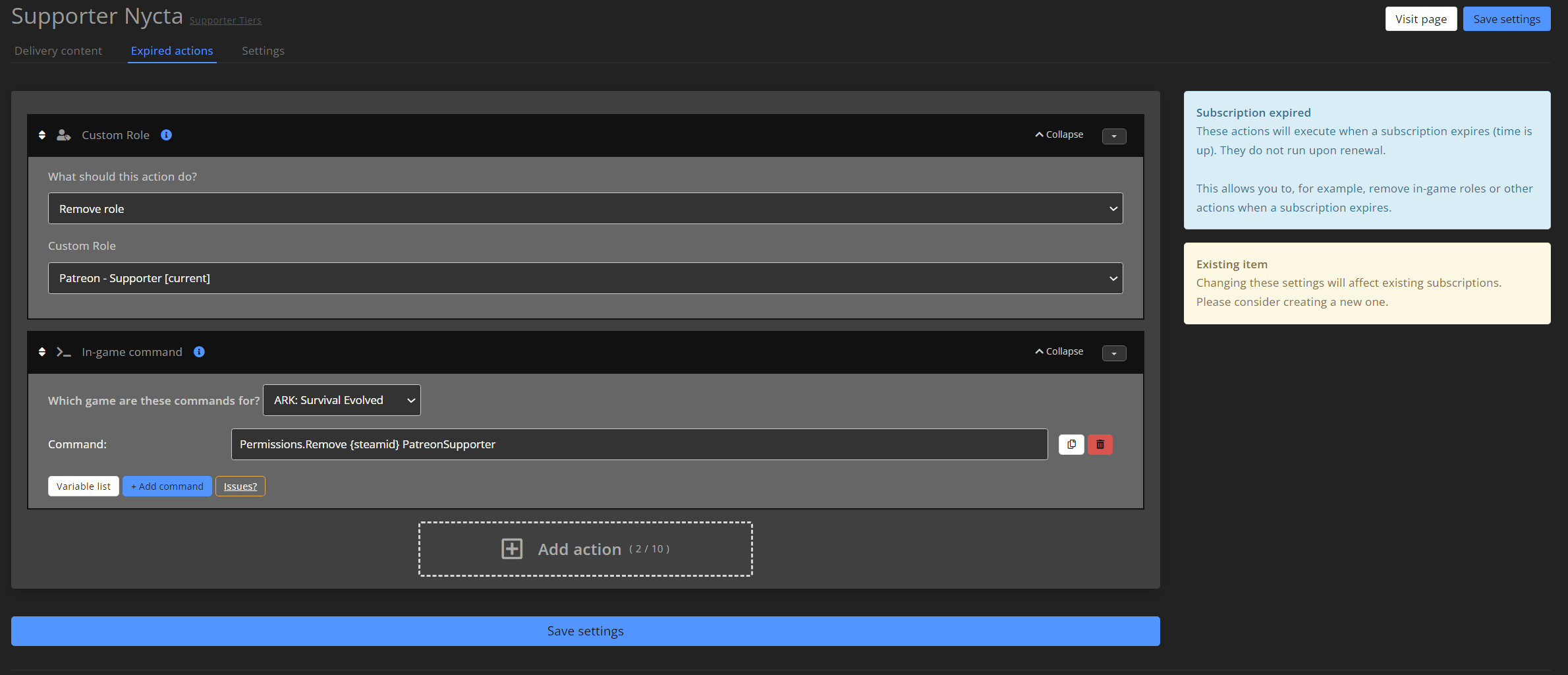
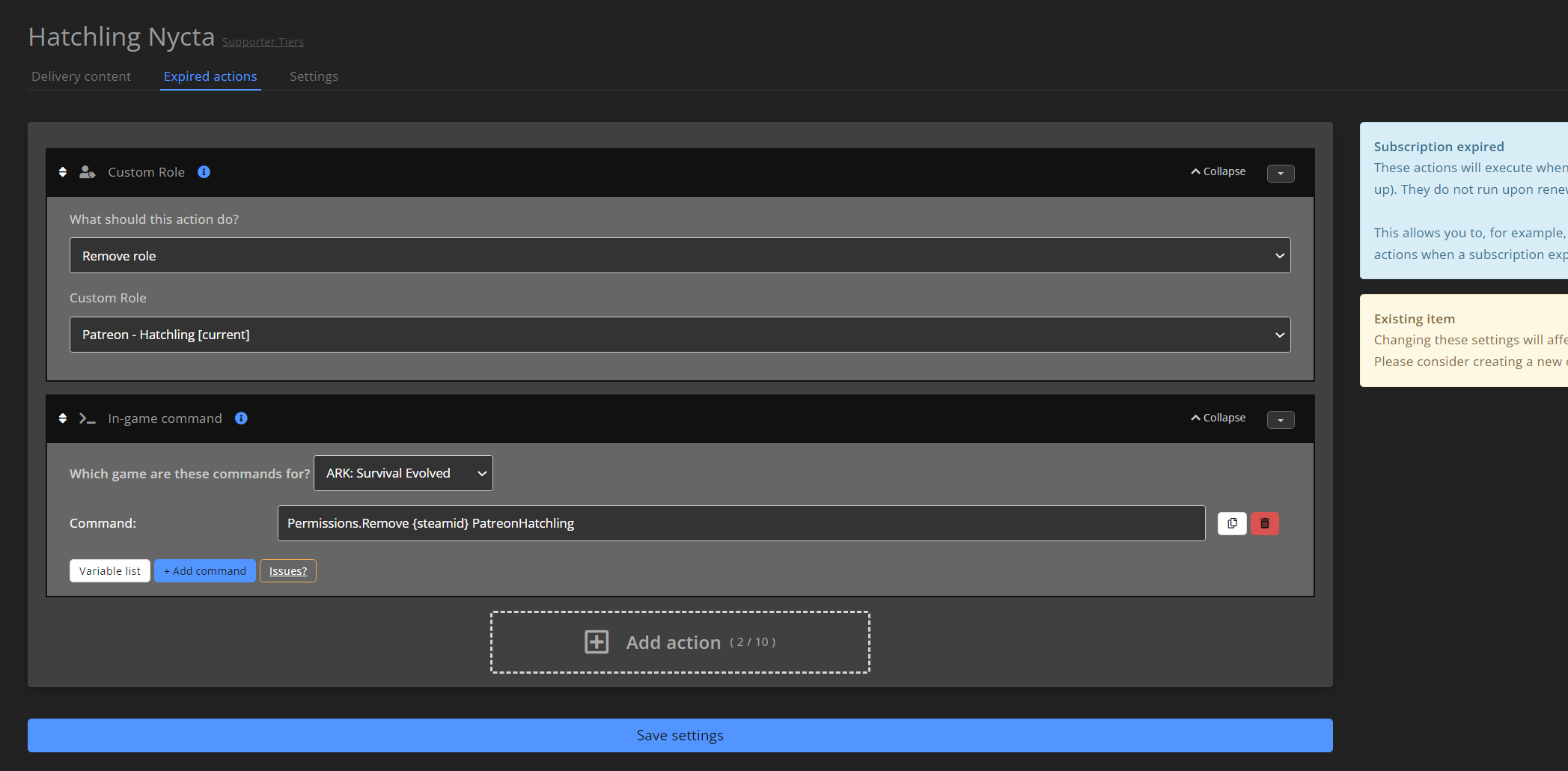
And here is the list of their transactions. Note the increase in Patreon tiers:
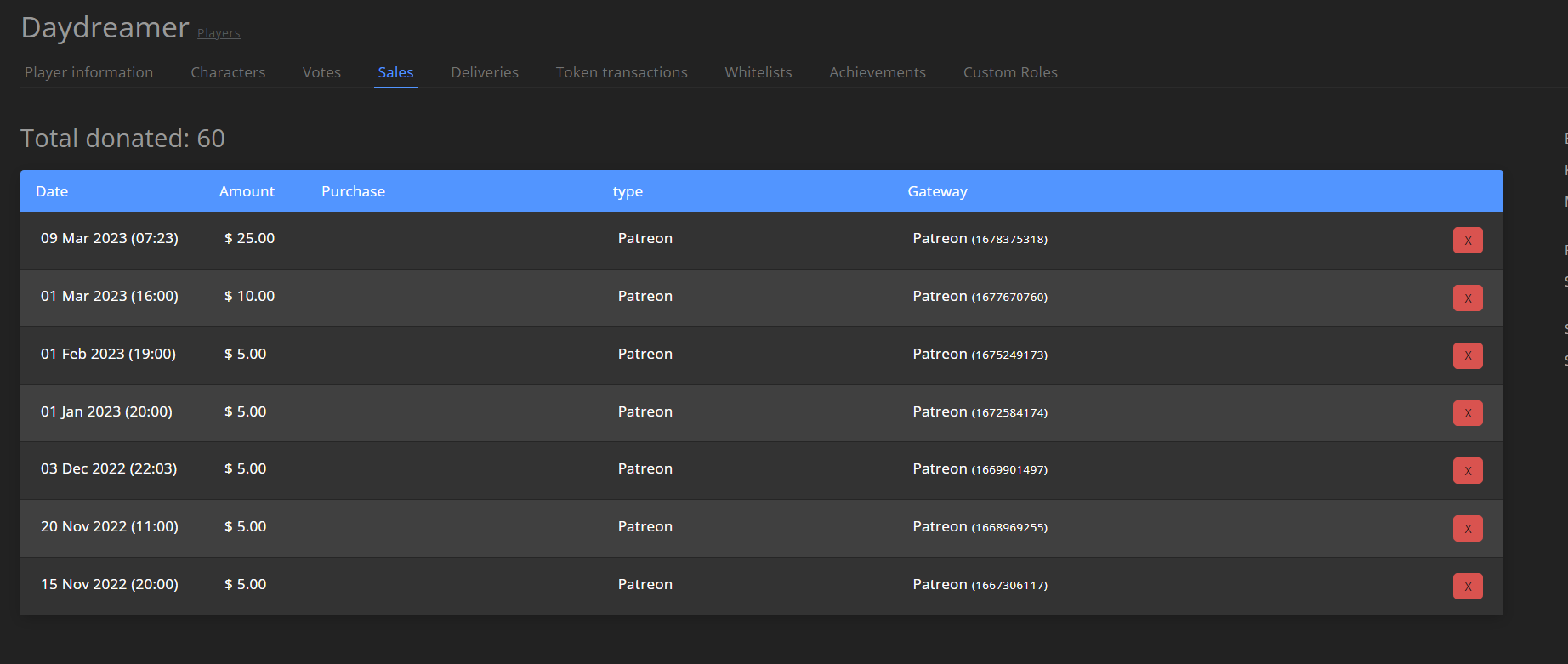
In addition, this part of GSA recognizes that Daydreamer is at the Juvie Nycta tier.
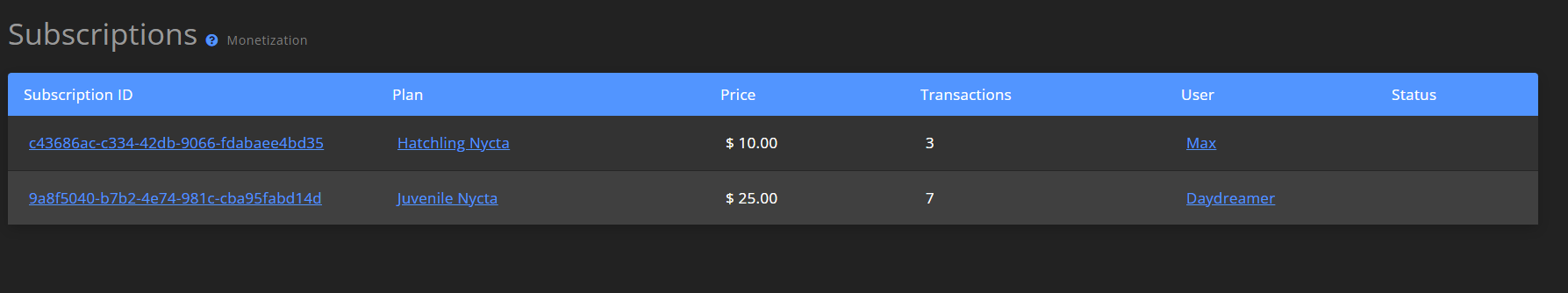
I've also pushed for a few sync attempts through the dashboard, but it doesn't seem to update the aforementioned tasks/triggers.
| non_priority | patreon upgrades to higher tiers only being partially completed so situation is that i had a player increase their patronage to a higher tier but the actual actions that are supposed to take place when the system recognizes the upgrade did not take place when the system recognizes the user as this tier this is what actions are supposed to execute this is the character in question unfortunately while my list of subscribers is starting to grow this is the only example i have as they are the only one that has increased their patronage during the month here is a list of their roles they have they still have the supporter and hatchling roles when those should have been removed when they had stopped those patreon tiers they still have the supporter and hatchling roles when those should have been removed when they had stopped those patreon tiers and here is the list of their transactions note the increase in patreon tiers in addition this part of gsa recognizes that daydreamer is at the juvie nycta tier i ve also pushed for a few sync attempts through the dashboard but it doesn t seem to update the aforementioned tasks triggers | 0 |
16,007 | 9,667,994,572 | IssuesEvent | 2019-05-21 14:20:01 | SitecorePowerShell/Console | https://api.github.com/repos/SitecorePowerShell/Console | closed | Get-User Filter returns no users when no wildcard provided | area-commands area-security | No results:
`Get-User -Filter "exact@email.com"`
Some results:
`Get-User -Filter "exact@*email.com"`
Reported by immanuel79 Slack. | True | Get-User Filter returns no users when no wildcard provided - No results:
`Get-User -Filter "exact@email.com"`
Some results:
`Get-User -Filter "exact@*email.com"`
Reported by immanuel79 Slack. | non_priority | get user filter returns no users when no wildcard provided no results get user filter exact email com some results get user filter exact email com reported by slack | 0 |
119,581 | 17,620,342,127 | IssuesEvent | 2021-08-18 14:38:20 | jgeraigery/experian-java | https://api.github.com/repos/jgeraigery/experian-java | closed | CVE-2018-14719 (High) detected in jackson-databind-2.9.2.jar - autoclosed | security vulnerability | ## CVE-2018-14719 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/9ade2a959068cca30ecfdbb254939af6f67affb1">9ade2a959068cca30ecfdbb254939af6f67affb1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to execute arbitrary code by leveraging failure to block the blaze-ds-opt and blaze-ds-core classes from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14719>CVE-2018-14719</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14719">https://nvd.nist.gov/vuln/detail/CVE-2018-14719</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.7</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","packageFilePaths":["/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.9.7"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-14719","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to execute arbitrary code by leveraging failure to block the blaze-ds-opt and blaze-ds-core classes from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14719","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-14719 (High) detected in jackson-databind-2.9.2.jar - autoclosed - ## CVE-2018-14719 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/9ade2a959068cca30ecfdbb254939af6f67affb1">9ade2a959068cca30ecfdbb254939af6f67affb1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to execute arbitrary code by leveraging failure to block the blaze-ds-opt and blaze-ds-core classes from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14719>CVE-2018-14719</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14719">https://nvd.nist.gov/vuln/detail/CVE-2018-14719</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.7</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","packageFilePaths":["/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.9.7"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-14719","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to execute arbitrary code by leveraging failure to block the blaze-ds-opt and blaze-ds-core classes from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14719","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file experian java mavenworkspace bis services lib bis services base pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow remote attackers to execute arbitrary code by leveraging failure to block the blaze ds opt and blaze ds core classes from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before might allow remote attackers to execute arbitrary code by leveraging failure to block the blaze ds opt and blaze ds core classes from polymorphic deserialization vulnerabilityurl | 0 |
34,808 | 9,475,790,808 | IssuesEvent | 2019-04-19 12:50:23 | codingchili/chili-core | https://api.github.com/repos/codingchili/chili-core | closed | CQEngine, ElasticSearch, MongoDB and Hazelcast as optional dependencies. | build | - [x] move :storage:elastic into :core
- [x] document how to exclude optional dependencies
- [x] document which dependencies that are optional
- [x] make sure to not reference optional dependencies from core features. | 1.0 | CQEngine, ElasticSearch, MongoDB and Hazelcast as optional dependencies. - - [x] move :storage:elastic into :core
- [x] document how to exclude optional dependencies
- [x] document which dependencies that are optional
- [x] make sure to not reference optional dependencies from core features. | non_priority | cqengine elasticsearch mongodb and hazelcast as optional dependencies move storage elastic into core document how to exclude optional dependencies document which dependencies that are optional make sure to not reference optional dependencies from core features | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.