Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
84,545 | 15,724,685,654 | IssuesEvent | 2021-03-29 09:06:02 | crouchr/learnage | https://api.github.com/repos/crouchr/learnage | opened | CVE-2015-2170 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2015-2170 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>winpenpackclamwin-0.97.2</b>, <b>clamav-develclamav-0.90.1</b>, <b>clamav-develclamav-0.98.4</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The upx decoder in ClamAV before 0.98.7 allows remote attackers to cause a denial of service (crash) via a crafted file.
<p>Publish Date: 2015-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-2170>CVE-2015-2170</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2170">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2170</a></p>
<p>Release Date: 2015-05-12</p>
<p>Fix Resolution: 0.98.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-2170 (Medium) detected in multiple libraries - ## CVE-2015-2170 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>winpenpackclamwin-0.97.2</b>, <b>clamav-develclamav-0.90.1</b>, <b>clamav-develclamav-0.98.4</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The upx decoder in ClamAV before 0.98.7 allows remote attackers to cause a denial of service (crash) via a crafted file.
<p>Publish Date: 2015-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-2170>CVE-2015-2170</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2170">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-2170</a></p>
<p>Release Date: 2015-05-12</p>
<p>Fix Resolution: 0.98.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries winpenpackclamwin clamav develclamav clamav develclamav vulnerability details the upx decoder in clamav before allows remote attackers to cause a denial of service crash via a crafted file publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
40,806 | 5,316,764,638 | IssuesEvent | 2017-02-13 20:45:16 | dotnet/roslyn-project-system | https://api.github.com/repos/dotnet/roslyn-project-system | opened | Create integration “restore after project file edits” test | Test | We need to create an integration test verifying “restore after project file edits” features. | 1.0 | Create integration “restore after project file edits” test - We need to create an integration test verifying “restore after project file edits” features. | non_priority | create integration “restore after project file edits” test we need to create an integration test verifying “restore after project file edits” features | 0 |
323,157 | 23,936,746,612 | IssuesEvent | 2022-09-11 10:44:36 | loraandar/frontend | https://api.github.com/repos/loraandar/frontend | opened | Sposób przechowywania dokumentacji w Gicie | documentation good first issue question | Należy opracować sposób przechowywania dokumentacji alternatywny do A. C.; najlepiej umoźliwiający opublikowanie jej w Sieci | 1.0 | Sposób przechowywania dokumentacji w Gicie - Należy opracować sposób przechowywania dokumentacji alternatywny do A. C.; najlepiej umoźliwiający opublikowanie jej w Sieci | non_priority | sposób przechowywania dokumentacji w gicie należy opracować sposób przechowywania dokumentacji alternatywny do a c najlepiej umoźliwiający opublikowanie jej w sieci | 0 |
241,133 | 18,427,959,155 | IssuesEvent | 2021-10-14 02:10:02 | brendenwest/cascade | https://api.github.com/repos/brendenwest/cascade | closed | Research UI Library for Reach Native | documentation | ### Description
Research the best UI libraries for React Native.
Find alternatives and prepare a very small presentation/explanation for your teammates.
Try to have done by Sunday's meeting on the 10th.
NOTE:
- No PR will be needed, just a meeting/approval from team
### Acceptance Criteria
- [ ] Library is approved by team | 1.0 | Research UI Library for Reach Native - ### Description
Research the best UI libraries for React Native.
Find alternatives and prepare a very small presentation/explanation for your teammates.
Try to have done by Sunday's meeting on the 10th.
NOTE:
- No PR will be needed, just a meeting/approval from team
### Acceptance Criteria
- [ ] Library is approved by team | non_priority | research ui library for reach native description research the best ui libraries for react native find alternatives and prepare a very small presentation explanation for your teammates try to have done by sunday s meeting on the note no pr will be needed just a meeting approval from team acceptance criteria library is approved by team | 0 |
104,649 | 8,996,419,894 | IssuesEvent | 2019-02-02 01:18:19 | Ben12345rocks/VotingPlugin | https://api.github.com/repos/Ben12345rocks/VotingPlugin | closed | Crash with VotingPlugin v5.16.3 | Needs Testing Possible Bug | Looks like the server got stuck with VotingPlugin while executing an event.
Log:
https://gist.github.com/mart-r/0ca48dff367ddd8dbd0fa95f955ad2ef | 1.0 | Crash with VotingPlugin v5.16.3 - Looks like the server got stuck with VotingPlugin while executing an event.
Log:
https://gist.github.com/mart-r/0ca48dff367ddd8dbd0fa95f955ad2ef | non_priority | crash with votingplugin looks like the server got stuck with votingplugin while executing an event log | 0 |
285,192 | 31,080,068,339 | IssuesEvent | 2023-08-13 00:57:17 | vital-ws/java-goof | https://api.github.com/repos/vital-ws/java-goof | opened | struts2-core-2.3.20.jar: 25 vulnerabilities (highest severity is: 10.0) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p></summary>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (struts2-core version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2017-5638](https://www.mend.io/vulnerability-database/CVE-2017-5638) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 10.0 | struts2-core-2.3.20.jar | Direct | 2.3.32 | ✅ |
| [CVE-2016-3082](https://www.mend.io/vulnerability-database/CVE-2016-3082) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.20.3 | ✅ |
| [CVE-2021-31805](https://www.mend.io/vulnerability-database/CVE-2021-31805) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | org.apache.struts:struts2-core:2.5.30 | ✅ |
| [CVE-2016-6795](https://www.mend.io/vulnerability-database/CVE-2016-6795) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.31 | ✅ |
| [CVE-2019-0230](https://www.mend.io/vulnerability-database/CVE-2019-0230) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.5.22 | ✅ |
| [CVE-2016-3087](https://www.mend.io/vulnerability-database/CVE-2016-3087) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.20.3 | ✅ |
| [CVE-2017-12611](https://www.mend.io/vulnerability-database/CVE-2017-12611) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.34 | ✅ |
| [CVE-2016-4436](https://www.mend.io/vulnerability-database/CVE-2016-4436) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2020-17530](https://www.mend.io/vulnerability-database/CVE-2020-17530) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.5.26 | ✅ |
| [CVE-2016-4430](https://www.mend.io/vulnerability-database/CVE-2016-4430) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2016-3081](https://www.mend.io/vulnerability-database/CVE-2016-3081) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | struts2-core-2.3.20.jar | Direct | 2.3.20.3 | ✅ |
| [CVE-2018-11776](https://www.mend.io/vulnerability-database/CVE-2018-11776) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | struts2-core-2.3.20.jar | Direct | 2.3.35 | ✅ |
| [CVE-2016-4431](https://www.mend.io/vulnerability-database/CVE-2016-4431) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2016-4433](https://www.mend.io/vulnerability-database/CVE-2016-4433) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2017-9804](https://www.mend.io/vulnerability-database/CVE-2017-9804) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.34 | ✅ |
| [CVE-2019-0233](https://www.mend.io/vulnerability-database/CVE-2019-0233) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.5.22 | ✅ |
| [CVE-2017-9787](https://www.mend.io/vulnerability-database/CVE-2017-9787) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.33 | ✅ |
| [CVE-2015-5209](https://www.mend.io/vulnerability-database/CVE-2015-5209) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.24.1 | ✅ |
| [CVE-2023-34396](https://www.mend.io/vulnerability-database/CVE-2023-34396) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.5.31 | ✅ |
| [CVE-2023-34149](https://www.mend.io/vulnerability-database/CVE-2023-34149) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | struts2-core-2.3.20.jar | Direct | 2.5.31 | ✅ |
| [CVE-2016-4003](https://www.mend.io/vulnerability-database/CVE-2016-4003) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | struts2-core-2.3.20.jar | Direct | 2.3.28 | ✅ |
| [CVE-2015-2992](https://www.mend.io/vulnerability-database/CVE-2015-2992) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | struts2-core-2.3.20.jar | Direct | 2.3.20.1 | ✅ |
| [CVE-2015-5169](https://www.mend.io/vulnerability-database/CVE-2015-5169) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | struts2-core-2.3.20.jar | Direct | 2.3.20.1 | ✅ |
| [CVE-2016-3093](https://www.mend.io/vulnerability-database/CVE-2016-3093) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | struts2-core-2.3.20.jar | Direct | 2.3.24.3 | ✅ |
| [CVE-2016-4465](https://www.mend.io/vulnerability-database/CVE-2016-4465) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-5638</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Jakarta Multipart parser in Apache Struts 2 2.3.x before 2.3.32 and 2.5.x before 2.5.10.1 has incorrect exception handling and error-message generation during file-upload attempts, which allows remote attackers to execute arbitrary commands via a crafted Content-Type, Content-Disposition, or Content-Length HTTP header, as exploited in the wild in March 2017 with a Content-Type header containing a #cmd= string.
<p>Publish Date: 2017-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-5638>CVE-2017-5638</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-03-11</p>
<p>Fix Resolution: 2.3.32</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-3082</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XSLTResult in Apache Struts 2.x before 2.3.20.2, 2.3.24.x before 2.3.24.2, and 2.3.28.x before 2.3.28.1 allows remote attackers to execute arbitrary code via the stylesheet location parameter.
<p>Publish Date: 2016-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3082>CVE-2016-3082</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-04-26</p>
<p>Fix Resolution: 2.3.20.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-31805</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The fix issued for CVE-2020-17530 was incomplete. So from Apache Struts 2.0.0 to 2.5.29, still some of the tag’s attributes could perform a double evaluation if a developer applied forced OGNL evaluation by using the %{...} syntax. Using forced OGNL evaluation on untrusted user input can lead to a Remote Code Execution and security degradation.
<p>Publish Date: 2022-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-31805>CVE-2021-31805</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/WW/S2-062">https://cwiki.apache.org/confluence/display/WW/S2-062</a></p>
<p>Release Date: 2022-04-12</p>
<p>Fix Resolution: org.apache.struts:struts2-core:2.5.30</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-6795</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In the Convention plugin in Apache Struts 2.3.x before 2.3.31, and 2.5.x before 2.5.5, it is possible to prepare a special URL which will be used for path traversal and execution of arbitrary code on server side.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-6795>CVE-2016-6795</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-10-18</p>
<p>Fix Resolution: 2.3.31</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-0230</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.0.0 to 2.5.20 forced double OGNL evaluation, when evaluated on raw user input in tag attributes, may lead to remote code execution.
<p>Publish Date: 2020-09-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-0230>CVE-2019-0230</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/ww/s2-059">https://cwiki.apache.org/confluence/display/ww/s2-059</a></p>
<p>Release Date: 2020-09-14</p>
<p>Fix Resolution: 2.5.22</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-3087</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.3.19 to 2.3.20.2, 2.3.21 to 2.3.24.1, and 2.3.25 to 2.3.28, when Dynamic Method Invocation is enabled, allow remote attackers to execute arbitrary code via vectors related to an ! (exclamation mark) operator to the REST Plugin.
<p>Publish Date: 2016-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3087>CVE-2016-3087</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-06-07</p>
<p>Fix Resolution: 2.3.20.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-12611</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Struts 2.0.0 through 2.3.33 and 2.5 through 2.5.10.1, using an unintentional expression in a Freemarker tag instead of string literals can lead to a RCE attack.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-12611>CVE-2017-12611</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/WW/S2-053">https://cwiki.apache.org/confluence/display/WW/S2-053</a></p>
<p>Release Date: 2017-09-07</p>
<p>Fix Resolution: 2.3.34</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-4436</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 before 2.3.29 and 2.5.x before 2.5.1 allow attackers to have unspecified impact via vectors related to improper action name clean up.
<p>Publish Date: 2016-10-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4436>CVE-2016-4436</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-10-03</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-17530</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forced OGNL evaluation, when evaluated on raw user input in tag attributes, may lead to remote code execution. Affected software : Apache Struts 2.0.0 - Struts 2.5.25.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-17530>CVE-2020-17530</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/WW/S2-061">https://cwiki.apache.org/confluence/display/WW/S2-061</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 2.5.26</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-4430</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 2.3.20 through 2.3.28.1 mishandles token validation, which allows remote attackers to conduct cross-site request forgery (CSRF) attacks via unspecified vectors.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4430>CVE-2016-4430</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-4430">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-4430</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-3081</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.3.19 to 2.3.20.2, 2.3.21 to 2.3.24.1, and 2.3.25 to 2.3.28, when Dynamic Method Invocation is enabled, allow remote attackers to execute arbitrary code via method: prefix, related to chained expressions.
<p>Publish Date: 2016-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3081>CVE-2016-3081</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-04-26</p>
<p>Fix Resolution: 2.3.20.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2018-11776</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts versions 2.3 to 2.3.34 and 2.5 to 2.5.16 suffer from possible Remote Code Execution when alwaysSelectFullNamespace is true (either by user or a plugin like Convention Plugin) and then: results are used with no namespace and in same time, its upper package have no or wildcard namespace and similar to results, same possibility when using url tag which doesn't have value and action set and in same time, its upper package have no or wildcard namespace.
<p>Publish Date: 2018-08-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11776>CVE-2018-11776</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-11776">https://nvd.nist.gov/vuln/detail/CVE-2018-11776</a></p>
<p>Release Date: 2018-08-22</p>
<p>Fix Resolution: 2.3.35</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-4431</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 2.3.20 through 2.3.28.1 allows remote attackers to bypass intended access restrictions and conduct redirection attacks by leveraging a default method.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4431>CVE-2016-4431</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-4433</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 2.3.20 through 2.3.28.1 allows remote attackers to bypass intended access restrictions and conduct redirection attacks via a crafted request.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4433>CVE-2016-4433</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2017-9804</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Struts 2.3.7 through 2.3.33 and 2.5 through 2.5.12, if an application allows entering a URL in a form field and built-in URLValidator is used, it is possible to prepare a special URL which will be used to overload server process when performing validation of the URL. NOTE: this vulnerability exists because of an incomplete fix for S2-047 / CVE-2017-7672.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-9804>CVE-2017-9804</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-09-05</p>
<p>Fix Resolution: 2.3.34</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2019-0233</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An access permission override in Apache Struts 2.0.0 to 2.5.20 may cause a Denial of Service when performing a file upload.
<p>Publish Date: 2020-09-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-0233>CVE-2019-0233</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/ww/s2-060">https://cwiki.apache.org/confluence/display/ww/s2-060</a></p>
<p>Release Date: 2020-09-14</p>
<p>Fix Resolution: 2.5.22</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2017-9787</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When using a Spring AOP functionality to secure Struts actions it is possible to perform a DoS attack. Solution is to upgrade to Apache Struts version 2.5.12 or 2.3.33.
<p>Publish Date: 2017-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-9787>CVE-2017-9787</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-07-13</p>
<p>Fix Resolution: 2.3.33</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2015-5209</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.x before 2.3.24.1 allows remote attackers to manipulate Struts internals, alter user sessions, or affect container settings via vectors involving a top object.
<p>Publish Date: 2017-08-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-5209>CVE-2015-5209</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-5209">https://nvd.nist.gov/vuln/detail/CVE-2015-5209</a></p>
<p>Release Date: 2017-08-29</p>
<p>Fix Resolution: 2.3.24.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-34396</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Allocation of Resources Without Limits or Throttling vulnerability in Apache Software Foundation Apache Struts.This issue affects Apache Struts: through 2.5.30, through 6.1.2.
Upgrade to Struts 2.5.31 or 6.1.2.1 or greater
<p>Publish Date: 2023-06-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-34396>CVE-2023-34396</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-4g42-gqrg-4633">https://github.com/advisories/GHSA-4g42-gqrg-4633</a></p>
<p>Release Date: 2023-06-14</p>
<p>Fix Resolution: 2.5.31</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-34149</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Allocation of Resources Without Limits or Throttling vulnerability in Apache Software Foundation Apache Struts.This issue affects Apache Struts: through 2.5.30, through 6.1.2.
Upgrade to Struts 2.5.31 or 6.1.2.1 or greater.
<p>Publish Date: 2023-06-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-34149>CVE-2023-34149</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-8f6x-v685-g2xc">https://github.com/advisories/GHSA-8f6x-v685-g2xc</a></p>
<p>Release Date: 2023-06-14</p>
<p>Fix Resolution: 2.5.31</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-4003</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in the URLDecoder function in JRE before 1.8, as used in Apache Struts 2.x before 2.3.28, when using a single byte page encoding, allows remote attackers to inject arbitrary web script or HTML via multi-byte characters in a url-encoded parameter.
<p>Publish Date: 2016-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4003>CVE-2016-4003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-04-12</p>
<p>Fix Resolution: 2.3.28</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2015-2992</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts before 2.3.20 has a cross-site scripting (XSS) vulnerability.
<p>Publish Date: 2020-02-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-2992>CVE-2015-2992</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-2992">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-2992</a></p>
<p>Release Date: 2020-02-27</p>
<p>Fix Resolution: 2.3.20.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2015-5169</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in Apache Struts before 2.3.20.
<p>Publish Date: 2017-09-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-5169>CVE-2015-5169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5169">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5169</a></p>
<p>Release Date: 2017-09-25</p>
<p>Fix Resolution: 2.3.20.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-3093</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.0.0 through 2.3.24.1 does not properly cache method references when used with OGNL before 3.0.12, which allows remote attackers to cause a denial of service (block access to a web site) via unspecified vectors.
<p>Publish Date: 2016-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3093>CVE-2016-3093</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-3093">https://nvd.nist.gov/vuln/detail/CVE-2016-3093</a></p>
<p>Release Date: 2016-06-07</p>
<p>Fix Resolution: 2.3.24.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-4465</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The URLValidator class in Apache Struts 2 2.3.20 through 2.3.28.1 and 2.5.x before 2.5.1 allows remote attackers to cause a denial of service via a null value for a URL field.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4465>CVE-2016-4465</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | struts2-core-2.3.20.jar: 25 vulnerabilities (highest severity is: 10.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p></summary>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (struts2-core version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2017-5638](https://www.mend.io/vulnerability-database/CVE-2017-5638) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 10.0 | struts2-core-2.3.20.jar | Direct | 2.3.32 | ✅ |
| [CVE-2016-3082](https://www.mend.io/vulnerability-database/CVE-2016-3082) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.20.3 | ✅ |
| [CVE-2021-31805](https://www.mend.io/vulnerability-database/CVE-2021-31805) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | org.apache.struts:struts2-core:2.5.30 | ✅ |
| [CVE-2016-6795](https://www.mend.io/vulnerability-database/CVE-2016-6795) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.31 | ✅ |
| [CVE-2019-0230](https://www.mend.io/vulnerability-database/CVE-2019-0230) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.5.22 | ✅ |
| [CVE-2016-3087](https://www.mend.io/vulnerability-database/CVE-2016-3087) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.20.3 | ✅ |
| [CVE-2017-12611](https://www.mend.io/vulnerability-database/CVE-2017-12611) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.34 | ✅ |
| [CVE-2016-4436](https://www.mend.io/vulnerability-database/CVE-2016-4436) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2020-17530](https://www.mend.io/vulnerability-database/CVE-2020-17530) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> Critical | 9.8 | struts2-core-2.3.20.jar | Direct | 2.5.26 | ✅ |
| [CVE-2016-4430](https://www.mend.io/vulnerability-database/CVE-2016-4430) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.8 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2016-3081](https://www.mend.io/vulnerability-database/CVE-2016-3081) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | struts2-core-2.3.20.jar | Direct | 2.3.20.3 | ✅ |
| [CVE-2018-11776](https://www.mend.io/vulnerability-database/CVE-2018-11776) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 8.1 | struts2-core-2.3.20.jar | Direct | 2.3.35 | ✅ |
| [CVE-2016-4431](https://www.mend.io/vulnerability-database/CVE-2016-4431) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2016-4433](https://www.mend.io/vulnerability-database/CVE-2016-4433) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
| [CVE-2017-9804](https://www.mend.io/vulnerability-database/CVE-2017-9804) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.34 | ✅ |
| [CVE-2019-0233](https://www.mend.io/vulnerability-database/CVE-2019-0233) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.5.22 | ✅ |
| [CVE-2017-9787](https://www.mend.io/vulnerability-database/CVE-2017-9787) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.33 | ✅ |
| [CVE-2015-5209](https://www.mend.io/vulnerability-database/CVE-2015-5209) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.3.24.1 | ✅ |
| [CVE-2023-34396](https://www.mend.io/vulnerability-database/CVE-2023-34396) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | struts2-core-2.3.20.jar | Direct | 2.5.31 | ✅ |
| [CVE-2023-34149](https://www.mend.io/vulnerability-database/CVE-2023-34149) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.5 | struts2-core-2.3.20.jar | Direct | 2.5.31 | ✅ |
| [CVE-2016-4003](https://www.mend.io/vulnerability-database/CVE-2016-4003) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | struts2-core-2.3.20.jar | Direct | 2.3.28 | ✅ |
| [CVE-2015-2992](https://www.mend.io/vulnerability-database/CVE-2015-2992) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | struts2-core-2.3.20.jar | Direct | 2.3.20.1 | ✅ |
| [CVE-2015-5169](https://www.mend.io/vulnerability-database/CVE-2015-5169) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | struts2-core-2.3.20.jar | Direct | 2.3.20.1 | ✅ |
| [CVE-2016-3093](https://www.mend.io/vulnerability-database/CVE-2016-3093) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | struts2-core-2.3.20.jar | Direct | 2.3.24.3 | ✅ |
| [CVE-2016-4465](https://www.mend.io/vulnerability-database/CVE-2016-4465) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 5.3 | struts2-core-2.3.20.jar | Direct | 2.3.29 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-5638</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Jakarta Multipart parser in Apache Struts 2 2.3.x before 2.3.32 and 2.5.x before 2.5.10.1 has incorrect exception handling and error-message generation during file-upload attempts, which allows remote attackers to execute arbitrary commands via a crafted Content-Type, Content-Disposition, or Content-Length HTTP header, as exploited in the wild in March 2017 with a Content-Type header containing a #cmd= string.
<p>Publish Date: 2017-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-5638>CVE-2017-5638</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>10.0</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-03-11</p>
<p>Fix Resolution: 2.3.32</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-3082</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XSLTResult in Apache Struts 2.x before 2.3.20.2, 2.3.24.x before 2.3.24.2, and 2.3.28.x before 2.3.28.1 allows remote attackers to execute arbitrary code via the stylesheet location parameter.
<p>Publish Date: 2016-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3082>CVE-2016-3082</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-04-26</p>
<p>Fix Resolution: 2.3.20.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2021-31805</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The fix issued for CVE-2020-17530 was incomplete. So from Apache Struts 2.0.0 to 2.5.29, still some of the tag’s attributes could perform a double evaluation if a developer applied forced OGNL evaluation by using the %{...} syntax. Using forced OGNL evaluation on untrusted user input can lead to a Remote Code Execution and security degradation.
<p>Publish Date: 2022-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-31805>CVE-2021-31805</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/WW/S2-062">https://cwiki.apache.org/confluence/display/WW/S2-062</a></p>
<p>Release Date: 2022-04-12</p>
<p>Fix Resolution: org.apache.struts:struts2-core:2.5.30</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-6795</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In the Convention plugin in Apache Struts 2.3.x before 2.3.31, and 2.5.x before 2.5.5, it is possible to prepare a special URL which will be used for path traversal and execution of arbitrary code on server side.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-6795>CVE-2016-6795</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-10-18</p>
<p>Fix Resolution: 2.3.31</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2019-0230</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.0.0 to 2.5.20 forced double OGNL evaluation, when evaluated on raw user input in tag attributes, may lead to remote code execution.
<p>Publish Date: 2020-09-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-0230>CVE-2019-0230</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/ww/s2-059">https://cwiki.apache.org/confluence/display/ww/s2-059</a></p>
<p>Release Date: 2020-09-14</p>
<p>Fix Resolution: 2.5.22</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-3087</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.3.19 to 2.3.20.2, 2.3.21 to 2.3.24.1, and 2.3.25 to 2.3.28, when Dynamic Method Invocation is enabled, allow remote attackers to execute arbitrary code via vectors related to an ! (exclamation mark) operator to the REST Plugin.
<p>Publish Date: 2016-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3087>CVE-2016-3087</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-06-07</p>
<p>Fix Resolution: 2.3.20.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2017-12611</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Struts 2.0.0 through 2.3.33 and 2.5 through 2.5.10.1, using an unintentional expression in a Freemarker tag instead of string literals can lead to a RCE attack.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-12611>CVE-2017-12611</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/WW/S2-053">https://cwiki.apache.org/confluence/display/WW/S2-053</a></p>
<p>Release Date: 2017-09-07</p>
<p>Fix Resolution: 2.3.34</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2016-4436</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 before 2.3.29 and 2.5.x before 2.5.1 allow attackers to have unspecified impact via vectors related to improper action name clean up.
<p>Publish Date: 2016-10-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4436>CVE-2016-4436</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-10-03</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png?' width=19 height=20> CVE-2020-17530</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Forced OGNL evaluation, when evaluated on raw user input in tag attributes, may lead to remote code execution. Affected software : Apache Struts 2.0.0 - Struts 2.5.25.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-17530>CVE-2020-17530</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/WW/S2-061">https://cwiki.apache.org/confluence/display/WW/S2-061</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 2.5.26</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-4430</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 2.3.20 through 2.3.28.1 mishandles token validation, which allows remote attackers to conduct cross-site request forgery (CSRF) attacks via unspecified vectors.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4430>CVE-2016-4430</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-4430">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-4430</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-3081</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.3.19 to 2.3.20.2, 2.3.21 to 2.3.24.1, and 2.3.25 to 2.3.28, when Dynamic Method Invocation is enabled, allow remote attackers to execute arbitrary code via method: prefix, related to chained expressions.
<p>Publish Date: 2016-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3081>CVE-2016-3081</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-04-26</p>
<p>Fix Resolution: 2.3.20.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2018-11776</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts versions 2.3 to 2.3.34 and 2.5 to 2.5.16 suffer from possible Remote Code Execution when alwaysSelectFullNamespace is true (either by user or a plugin like Convention Plugin) and then: results are used with no namespace and in same time, its upper package have no or wildcard namespace and similar to results, same possibility when using url tag which doesn't have value and action set and in same time, its upper package have no or wildcard namespace.
<p>Publish Date: 2018-08-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-11776>CVE-2018-11776</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-11776">https://nvd.nist.gov/vuln/detail/CVE-2018-11776</a></p>
<p>Release Date: 2018-08-22</p>
<p>Fix Resolution: 2.3.35</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-4431</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 2.3.20 through 2.3.28.1 allows remote attackers to bypass intended access restrictions and conduct redirection attacks by leveraging a default method.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4431>CVE-2016-4431</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2016-4433</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2 2.3.20 through 2.3.28.1 allows remote attackers to bypass intended access restrictions and conduct redirection attacks via a crafted request.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4433>CVE-2016-4433</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2017-9804</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Struts 2.3.7 through 2.3.33 and 2.5 through 2.5.12, if an application allows entering a URL in a form field and built-in URLValidator is used, it is possible to prepare a special URL which will be used to overload server process when performing validation of the URL. NOTE: this vulnerability exists because of an incomplete fix for S2-047 / CVE-2017-7672.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-9804>CVE-2017-9804</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-09-05</p>
<p>Fix Resolution: 2.3.34</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2019-0233</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An access permission override in Apache Struts 2.0.0 to 2.5.20 may cause a Denial of Service when performing a file upload.
<p>Publish Date: 2020-09-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-0233>CVE-2019-0233</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cwiki.apache.org/confluence/display/ww/s2-060">https://cwiki.apache.org/confluence/display/ww/s2-060</a></p>
<p>Release Date: 2020-09-14</p>
<p>Fix Resolution: 2.5.22</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2017-9787</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
When using a Spring AOP functionality to secure Struts actions it is possible to perform a DoS attack. Solution is to upgrade to Apache Struts version 2.5.12 or 2.3.33.
<p>Publish Date: 2017-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-9787>CVE-2017-9787</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-07-13</p>
<p>Fix Resolution: 2.3.33</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2015-5209</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.x before 2.3.24.1 allows remote attackers to manipulate Struts internals, alter user sessions, or affect container settings via vectors involving a top object.
<p>Publish Date: 2017-08-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-5209>CVE-2015-5209</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-5209">https://nvd.nist.gov/vuln/detail/CVE-2015-5209</a></p>
<p>Release Date: 2017-08-29</p>
<p>Fix Resolution: 2.3.24.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2023-34396</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Allocation of Resources Without Limits or Throttling vulnerability in Apache Software Foundation Apache Struts.This issue affects Apache Struts: through 2.5.30, through 6.1.2.
Upgrade to Struts 2.5.31 or 6.1.2.1 or greater
<p>Publish Date: 2023-06-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-34396>CVE-2023-34396</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-4g42-gqrg-4633">https://github.com/advisories/GHSA-4g42-gqrg-4633</a></p>
<p>Release Date: 2023-06-14</p>
<p>Fix Resolution: 2.5.31</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2023-34149</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Allocation of Resources Without Limits or Throttling vulnerability in Apache Software Foundation Apache Struts.This issue affects Apache Struts: through 2.5.30, through 6.1.2.
Upgrade to Struts 2.5.31 or 6.1.2.1 or greater.
<p>Publish Date: 2023-06-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-34149>CVE-2023-34149</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-8f6x-v685-g2xc">https://github.com/advisories/GHSA-8f6x-v685-g2xc</a></p>
<p>Release Date: 2023-06-14</p>
<p>Fix Resolution: 2.5.31</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-4003</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in the URLDecoder function in JRE before 1.8, as used in Apache Struts 2.x before 2.3.28, when using a single byte page encoding, allows remote attackers to inject arbitrary web script or HTML via multi-byte characters in a url-encoded parameter.
<p>Publish Date: 2016-04-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4003>CVE-2016-4003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-04-12</p>
<p>Fix Resolution: 2.3.28</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2015-2992</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts before 2.3.20 has a cross-site scripting (XSS) vulnerability.
<p>Publish Date: 2020-02-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-2992>CVE-2015-2992</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-2992">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2015-2992</a></p>
<p>Release Date: 2020-02-27</p>
<p>Fix Resolution: 2.3.20.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2015-5169</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in Apache Struts before 2.3.20.
<p>Publish Date: 2017-09-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-5169>CVE-2015-5169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5169">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-5169</a></p>
<p>Release Date: 2017-09-25</p>
<p>Fix Resolution: 2.3.20.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-3093</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Struts 2.0.0 through 2.3.24.1 does not properly cache method references when used with OGNL before 3.0.12, which allows remote attackers to cause a denial of service (block access to a web site) via unspecified vectors.
<p>Publish Date: 2016-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3093>CVE-2016-3093</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-3093">https://nvd.nist.gov/vuln/detail/CVE-2016-3093</a></p>
<p>Release Date: 2016-06-07</p>
<p>Fix Resolution: 2.3.24.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-4465</summary>
### Vulnerable Library - <b>struts2-core-2.3.20.jar</b></p>
<p>Apache Struts 2</p>
<p>Path to dependency file: /todolist-goof/todolist-web-struts/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts2-core/2.3.20/struts2-core-2.3.20.jar,/todolist-goof/todolist-web-struts/target/todolist/WEB-INF/lib/struts2-core-2.3.20.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.3.20.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The URLValidator class in Apache Struts 2 2.3.20 through 2.3.28.1 and 2.5.x before 2.5.1 allows remote attackers to cause a denial of service via a null value for a URL field.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4465>CVE-2016-4465</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: 2.3.29</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | core jar vulnerabilities highest severity is vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar vulnerabilities cve severity cvss dependency type fixed in core version remediation available critical core jar direct critical core jar direct critical core jar direct org apache struts core critical core jar direct critical core jar direct critical core jar direct critical core jar direct critical core jar direct critical core jar direct high core jar direct high core jar direct high core jar direct high core jar direct high core jar direct high core jar direct high core jar direct high core jar direct high core jar direct high core jar direct medium core jar direct medium core jar direct medium core jar direct medium core jar direct medium core jar direct medium core jar direct details cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details the jakarta multipart parser in apache struts x before and x before has incorrect exception handling and error message generation during file upload attempts which allows remote attackers to execute arbitrary commands via a crafted content type content disposition or content length http header as exploited in the wild in march with a content type header containing a cmd string publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details xsltresult in apache struts x before x before and x before allows remote attackers to execute arbitrary code via the stylesheet location parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details the fix issued for cve was incomplete so from apache struts to still some of the tag’s attributes could perform a double evaluation if a developer applied forced ognl evaluation by using the syntax using forced ognl evaluation on untrusted user input can lead to a remote code execution and security degradation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache struts core rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details in the convention plugin in apache struts x before and x before it is possible to prepare a special url which will be used for path traversal and execution of arbitrary code on server side publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts to forced double ognl evaluation when evaluated on raw user input in tag attributes may lead to remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts to to and to when dynamic method invocation is enabled allow remote attackers to execute arbitrary code via vectors related to an exclamation mark operator to the rest plugin publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details in apache struts through and through using an unintentional expression in a freemarker tag instead of string literals can lead to a rce attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts before and x before allow attackers to have unspecified impact via vectors related to improper action name clean up publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details forced ognl evaluation when evaluated on raw user input in tag attributes may lead to remote code execution affected software apache struts struts publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts through mishandles token validation which allows remote attackers to conduct cross site request forgery csrf attacks via unspecified vectors publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts to to and to when dynamic method invocation is enabled allow remote attackers to execute arbitrary code via method prefix related to chained expressions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts versions to and to suffer from possible remote code execution when alwaysselectfullnamespace is true either by user or a plugin like convention plugin and then results are used with no namespace and in same time its upper package have no or wildcard namespace and similar to results same possibility when using url tag which doesn t have value and action set and in same time its upper package have no or wildcard namespace publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts through allows remote attackers to bypass intended access restrictions and conduct redirection attacks by leveraging a default method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts through allows remote attackers to bypass intended access restrictions and conduct redirection attacks via a crafted request publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details in apache struts through and through if an application allows entering a url in a form field and built in urlvalidator is used it is possible to prepare a special url which will be used to overload server process when performing validation of the url note this vulnerability exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details an access permission override in apache struts to may cause a denial of service when performing a file upload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details when using a spring aop functionality to secure struts actions it is possible to perform a dos attack solution is to upgrade to apache struts version or publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts x before allows remote attackers to manipulate struts internals alter user sessions or affect container settings via vectors involving a top object publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details allocation of resources without limits or throttling vulnerability in apache software foundation apache struts this issue affects apache struts through through upgrade to struts or or greater publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details allocation of resources without limits or throttling vulnerability in apache software foundation apache struts this issue affects apache struts through through upgrade to struts or or greater publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details cross site scripting xss vulnerability in the urldecoder function in jre before as used in apache struts x before when using a single byte page encoding allows remote attackers to inject arbitrary web script or html via multi byte characters in a url encoded parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts before has a cross site scripting xss vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details cross site scripting xss vulnerability in apache struts before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details apache struts through does not properly cache method references when used with ognl before which allows remote attackers to cause a denial of service block access to a web site via unspecified vectors publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library core jar apache struts path to dependency file todolist goof todolist web struts pom xml path to vulnerable library home wss scanner repository org apache struts core core jar todolist goof todolist web struts target todolist web inf lib core jar dependency hierarchy x core jar vulnerable library found in base branch main vulnerability details the urlvalidator class in apache struts through and x before allows remote attackers to cause a denial of service via a null value for a url field publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
360,818 | 25,312,019,813 | IssuesEvent | 2022-11-17 18:14:07 | kubernetes-sigs/cluster-api | https://api.github.com/repos/kubernetes-sigs/cluster-api | closed | Add `failureDomain` as a required field in the machine controller docs | kind/documentation triage/accepted | /kind bug
The [infra machine provider contract](https://cluster-api.sigs.k8s.io/developer/providers/machine-infrastructure.html) lists `failureDomain` as a required contract field. It's not listed in the [machine controller](https://cluster-api.sigs.k8s.io/developer/architecture/controllers/machine.html) section however, and it should be added in order to be consistent. | 1.0 | Add `failureDomain` as a required field in the machine controller docs - /kind bug
The [infra machine provider contract](https://cluster-api.sigs.k8s.io/developer/providers/machine-infrastructure.html) lists `failureDomain` as a required contract field. It's not listed in the [machine controller](https://cluster-api.sigs.k8s.io/developer/architecture/controllers/machine.html) section however, and it should be added in order to be consistent. | non_priority | add failuredomain as a required field in the machine controller docs kind bug the lists failuredomain as a required contract field it s not listed in the section however and it should be added in order to be consistent | 0 |
8,670 | 12,219,032,615 | IssuesEvent | 2020-05-01 20:42:44 | Diego448/scholar-control | https://api.github.com/repos/Diego448/scholar-control | closed | Create payments registry view | requirement | Create both the template and the required functions to create the view | 1.0 | Create payments registry view - Create both the template and the required functions to create the view | non_priority | create payments registry view create both the template and the required functions to create the view | 0 |
365,545 | 25,541,308,849 | IssuesEvent | 2022-11-29 15:29:38 | lieion/OpenSource_Final_Project | https://api.github.com/repos/lieion/OpenSource_Final_Project | closed | 현재 진행상황 Update | documentation | #
+ **Term Server 관련 개발 정보**
현재 개발 완료된 정보
~~1. 각 카페 별 json file~~
json 파일이 필요하기 때문에 디렉토리 구조를 public 내부에 json 파일 폴더를 추가하였습니다.(./public/json)
~~2. Blue Port 가격 계산~~
가격 계산 구조가 Post로 주문한 음료의 개수를 각각 보내고 서버에서 가격을 계산한 뒤에 응답으로 그 가격을 보내면 출력해주는 방식으로 구현하였습니다.
~~3. Blue Port 주문~~
~~4. myPage에서 Blue Port 주문정보 출력~~
개발 예정 정보
_1. 카페 관리자_
카페 관리하는 입장에서의 페이지 제작, 신고 추가 (~29)
_2.다른 카페 부분 구현_
Blue Port 카페만 구현되었기 때문에 다른 카페 부분도 구현 필요 (~30)
+ **Suggestion**
다른 카페 부분도 구조가 비슷해서 변수만 수정하면 구현하는데 문제가 없을 것 같습니다.
+ **Additional Info**
개발할 시 주의해야 할 사항, 다른 file과의 dependency 등 추가적으로 알려줘야 할 내용
jquery를 사용하기 때문에 충돌이 나는 경우
`<script src="https://code.jquery.com/jquery-1.12.4.js"></script>`
`<script src="https://code.jquery.com/ui/1.12.1/jquery-ui.js"></script>`
head에 불러오지 않아서 일어나는 일이 잦았습니다.
이번 업데이트 이후 file storage 관련 npm 'fs'를 추가로 더 사용합니다.
`npm install fs` 이 요구됩니다.
Object에 더 필요한 property가 더 있다면 추가하도록 하겠습니다.
#
| 1.0 | 현재 진행상황 Update - #
+ **Term Server 관련 개발 정보**
현재 개발 완료된 정보
~~1. 각 카페 별 json file~~
json 파일이 필요하기 때문에 디렉토리 구조를 public 내부에 json 파일 폴더를 추가하였습니다.(./public/json)
~~2. Blue Port 가격 계산~~
가격 계산 구조가 Post로 주문한 음료의 개수를 각각 보내고 서버에서 가격을 계산한 뒤에 응답으로 그 가격을 보내면 출력해주는 방식으로 구현하였습니다.
~~3. Blue Port 주문~~
~~4. myPage에서 Blue Port 주문정보 출력~~
개발 예정 정보
_1. 카페 관리자_
카페 관리하는 입장에서의 페이지 제작, 신고 추가 (~29)
_2.다른 카페 부분 구현_
Blue Port 카페만 구현되었기 때문에 다른 카페 부분도 구현 필요 (~30)
+ **Suggestion**
다른 카페 부분도 구조가 비슷해서 변수만 수정하면 구현하는데 문제가 없을 것 같습니다.
+ **Additional Info**
개발할 시 주의해야 할 사항, 다른 file과의 dependency 등 추가적으로 알려줘야 할 내용
jquery를 사용하기 때문에 충돌이 나는 경우
`<script src="https://code.jquery.com/jquery-1.12.4.js"></script>`
`<script src="https://code.jquery.com/ui/1.12.1/jquery-ui.js"></script>`
head에 불러오지 않아서 일어나는 일이 잦았습니다.
이번 업데이트 이후 file storage 관련 npm 'fs'를 추가로 더 사용합니다.
`npm install fs` 이 요구됩니다.
Object에 더 필요한 property가 더 있다면 추가하도록 하겠습니다.
#
| non_priority | 현재 진행상황 update term server 관련 개발 정보 현재 개발 완료된 정보 각 카페 별 json file json 파일이 필요하기 때문에 디렉토리 구조를 public 내부에 json 파일 폴더를 추가하였습니다 public json blue port 가격 계산 가격 계산 구조가 post로 주문한 음료의 개수를 각각 보내고 서버에서 가격을 계산한 뒤에 응답으로 그 가격을 보내면 출력해주는 방식으로 구현하였습니다 blue port 주문 mypage에서 blue port 주문정보 출력 개발 예정 정보 카페 관리자 카페 관리하는 입장에서의 페이지 제작 신고 추가 다른 카페 부분 구현 blue port 카페만 구현되었기 때문에 다른 카페 부분도 구현 필요 suggestion 다른 카페 부분도 구조가 비슷해서 변수만 수정하면 구현하는데 문제가 없을 것 같습니다 additional info 개발할 시 주의해야 할 사항 다른 file과의 dependency 등 추가적으로 알려줘야 할 내용 jquery를 사용하기 때문에 충돌이 나는 경우 script src script src head에 불러오지 않아서 일어나는 일이 잦았습니다 이번 업데이트 이후 file storage 관련 npm fs 를 추가로 더 사용합니다 npm install fs 이 요구됩니다 object에 더 필요한 property가 더 있다면 추가하도록 하겠습니다 | 0 |
112,958 | 11,783,764,698 | IssuesEvent | 2020-03-17 06:38:59 | meeshkan/json-schema-poet | https://api.github.com/repos/meeshkan/json-schema-poet | opened | Add documentation of function signatures | documentation | <!-- If you have any questions while filling out this issue template, please feel free to reach out to us through the [Unmock Community Gitter](https://gitter.im/unmock/community) -->
### Description
Document function signatures in README.
<!-- Tell us all about your feature idea and give an example of how it'd be used -->
### Motivation
Because it is not clear what certain functions, like `oneOf`, do. Brought to my attention by https://github.com/shaabans | 1.0 | Add documentation of function signatures - <!-- If you have any questions while filling out this issue template, please feel free to reach out to us through the [Unmock Community Gitter](https://gitter.im/unmock/community) -->
### Description
Document function signatures in README.
<!-- Tell us all about your feature idea and give an example of how it'd be used -->
### Motivation
Because it is not clear what certain functions, like `oneOf`, do. Brought to my attention by https://github.com/shaabans | non_priority | add documentation of function signatures description document function signatures in readme motivation because it is not clear what certain functions like oneof do brought to my attention by | 0 |
101,817 | 31,683,462,085 | IssuesEvent | 2023-09-08 03:16:19 | discoverfinancial/a11y-theme-builder | https://api.github.com/repos/discoverfinancial/a11y-theme-builder | opened | [REQUEST] New Request Title | enhancement good first issue theme builder app | <!-- Request Content -->
## Suggestion/Concern
This issue is to build a MUI Masonry-based molecule which would allow other molecules (e.g. cards, images) to display in a fluid layout system.
For information on how to extend our atomic components, please read: https://discoverfinancial.github.io/a11y-theme-builder/developers/add-atomic-elements/#extending-the-user-interface
## Proposed Solution
| 1.0 | [REQUEST] New Request Title - <!-- Request Content -->
## Suggestion/Concern
This issue is to build a MUI Masonry-based molecule which would allow other molecules (e.g. cards, images) to display in a fluid layout system.
For information on how to extend our atomic components, please read: https://discoverfinancial.github.io/a11y-theme-builder/developers/add-atomic-elements/#extending-the-user-interface
## Proposed Solution
| non_priority | new request title suggestion concern this issue is to build a mui masonry based molecule which would allow other molecules e g cards images to display in a fluid layout system for information on how to extend our atomic components please read proposed solution | 0 |
83,784 | 7,881,595,563 | IssuesEvent | 2018-06-26 19:36:14 | openworm/ChannelWorm | https://api.github.com/repos/openworm/ChannelWorm | closed | Create tests for verifying proper database behavior | in progress testing | With @travs:
- Can we create new entries?
- Can we retrieve entires?
- Can we update entires?
- Can we delete entries?
| 1.0 | Create tests for verifying proper database behavior - With @travs:
- Can we create new entries?
- Can we retrieve entires?
- Can we update entires?
- Can we delete entries?
| non_priority | create tests for verifying proper database behavior with travs can we create new entries can we retrieve entires can we update entires can we delete entries | 0 |
5,722 | 3,976,030,638 | IssuesEvent | 2016-05-05 09:27:41 | Virtual-Labs/fab-laboratory-coep | https://api.github.com/repos/Virtual-Labs/fab-laboratory-coep | closed | QA_Identification of Prehistoric handaxe_Quiz_smk | Category: Usability Developed By: VLEAD Release Number: Production Severity: S3 Status: Open | Defect Description :
In the Quiz page of "Identification of Prehistoric handaxe" experiment, in the 3rd questions options "Quiz_handaxe.html" is present instead it should be removed from the page
Actual Result :
In the Quiz page of "Identification of Prehistoric handaxe" experiment, in the 3rd questions options "Quiz_handaxe.html" is present
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/anthropology-iitg/blob/master/test-cases/integration_test-cases/Identification%20of%20Prehistoric%20handaxe/Identification%20of%20Prehistoric%20handaxe_17_Quiz_smk.org | True | QA_Identification of Prehistoric handaxe_Quiz_smk - Defect Description :
In the Quiz page of "Identification of Prehistoric handaxe" experiment, in the 3rd questions options "Quiz_handaxe.html" is present instead it should be removed from the page
Actual Result :
In the Quiz page of "Identification of Prehistoric handaxe" experiment, in the 3rd questions options "Quiz_handaxe.html" is present
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers: Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Test Step Link:
https://github.com/Virtual-Labs/anthropology-iitg/blob/master/test-cases/integration_test-cases/Identification%20of%20Prehistoric%20handaxe/Identification%20of%20Prehistoric%20handaxe_17_Quiz_smk.org | non_priority | qa identification of prehistoric handaxe quiz smk defect description in the quiz page of identification of prehistoric handaxe experiment in the questions options quiz handaxe html is present instead it should be removed from the page actual result in the quiz page of identification of prehistoric handaxe experiment in the questions options quiz handaxe html is present environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor test step link | 0 |
152,258 | 23,940,355,510 | IssuesEvent | 2022-09-11 20:20:47 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | DSN: Iterate on Lovell content model | Design Content model ⭐️ Facilities Needs refining Content VA Lovell | Once all the existing Lovell content notes have been [collated](https://github.com/department-of-veterans-affairs/va.gov-cms/issues/9850), we will have a better sense of where there are gaps in our knowledge that may require additional research / conversations with Lovell SMEs, back-end engineers
- Audit legacy Lovell site?
| 1.0 | DSN: Iterate on Lovell content model - Once all the existing Lovell content notes have been [collated](https://github.com/department-of-veterans-affairs/va.gov-cms/issues/9850), we will have a better sense of where there are gaps in our knowledge that may require additional research / conversations with Lovell SMEs, back-end engineers
- Audit legacy Lovell site?
| non_priority | dsn iterate on lovell content model once all the existing lovell content notes have been we will have a better sense of where there are gaps in our knowledge that may require additional research conversations with lovell smes back end engineers audit legacy lovell site | 0 |
68,945 | 17,482,294,867 | IssuesEvent | 2021-08-09 05:47:20 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug] Deploy Preview - List widget - On overlapping of items and outer border it is observed that there is no smooth movement back separating them | Bug Widgets Low UI Building Pod Needs Triaging List Widget Deploy Preview | ## Description
Deploy Preview - List Widget - It is observed that On overlapping of items and outer border it is observed that there is no smooth movement back separating them
**Expected Result:**
When the item container is dragged below the pagination section and after that it should be smoother to separate item container with the list widget container
**Actual Result:**
If the item container are dragged beyond list widget container it is difficult to bring back the item container
### Steps to reproduce the behaviour:
1.Launch Appmsith app in the Deploy preview - https://deploy-preview-4189--appsmith-editor-ce.netlify.app/
2.Drag and Drop list widget
3.Select any item container
4.Drag the item container beyond pagination area
5.Try to pull back the item container and observe
**Videolink:**
https://www.loom.com/share/79fa2896884242fbbef2da7029917c00
### Important Details
Version: [14.1 (16611.1.21.161.3)]
OS: [MacOS]
Browser [Safari]
Environment [Deploy Preview] | 1.0 | [Bug] Deploy Preview - List widget - On overlapping of items and outer border it is observed that there is no smooth movement back separating them - ## Description
Deploy Preview - List Widget - It is observed that On overlapping of items and outer border it is observed that there is no smooth movement back separating them
**Expected Result:**
When the item container is dragged below the pagination section and after that it should be smoother to separate item container with the list widget container
**Actual Result:**
If the item container are dragged beyond list widget container it is difficult to bring back the item container
### Steps to reproduce the behaviour:
1.Launch Appmsith app in the Deploy preview - https://deploy-preview-4189--appsmith-editor-ce.netlify.app/
2.Drag and Drop list widget
3.Select any item container
4.Drag the item container beyond pagination area
5.Try to pull back the item container and observe
**Videolink:**
https://www.loom.com/share/79fa2896884242fbbef2da7029917c00
### Important Details
Version: [14.1 (16611.1.21.161.3)]
OS: [MacOS]
Browser [Safari]
Environment [Deploy Preview] | non_priority | deploy preview list widget on overlapping of items and outer border it is observed that there is no smooth movement back separating them description deploy preview list widget it is observed that on overlapping of items and outer border it is observed that there is no smooth movement back separating them expected result when the item container is dragged below the pagination section and after that it should be smoother to separate item container with the list widget container actual result if the item container are dragged beyond list widget container it is difficult to bring back the item container steps to reproduce the behaviour launch appmsith app in the deploy preview drag and drop list widget select any item container drag the item container beyond pagination area try to pull back the item container and observe videolink important details version os browser environment | 0 |
109,556 | 11,645,397,956 | IssuesEvent | 2020-03-01 01:05:58 | NGCP/GCS | https://api.github.com/repos/NGCP/GCS | closed | Add coverage | documentation enhancement | istanbul + coveralls
- [x] install packages and add to project
- [x] add bot to comment on PR for coverage | 1.0 | Add coverage - istanbul + coveralls
- [x] install packages and add to project
- [x] add bot to comment on PR for coverage | non_priority | add coverage istanbul coveralls install packages and add to project add bot to comment on pr for coverage | 0 |
37,521 | 10,023,978,738 | IssuesEvent | 2019-07-16 20:37:06 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | pip install tf-nightly-2.0-preview No matching distribution found for python 3.7 | 2.0 stat:awaiting tensorflower subtype:macOS type:build/install | Has anything changed with the pip naming of this? I see it was updated 7 hours ago and I think it worked yesterday.
Could also be something to do with the pip chain. | 1.0 | pip install tf-nightly-2.0-preview No matching distribution found for python 3.7 - Has anything changed with the pip naming of this? I see it was updated 7 hours ago and I think it worked yesterday.
Could also be something to do with the pip chain. | non_priority | pip install tf nightly preview no matching distribution found for python has anything changed with the pip naming of this i see it was updated hours ago and i think it worked yesterday could also be something to do with the pip chain | 0 |
106,512 | 16,681,659,850 | IssuesEvent | 2021-06-08 01:04:28 | mrcelewis/flink | https://api.github.com/repos/mrcelewis/flink | opened | CVE-2021-23362 (Medium) detected in hosted-git-info-2.8.8.tgz | security vulnerability | ## CVE-2021-23362 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hosted-git-info-2.8.8.tgz</b></p></summary>
<p>Provides metadata and conversions from repository urls for Github, Bitbucket and Gitlab</p>
<p>Library home page: <a href="https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz">https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz</a></p>
<p>Path to dependency file: flink/flink-runtime-web/web-dashboard/package.json</p>
<p>Path to vulnerable library: flink/flink-runtime-web/web-dashboard/node_modules/hosted-git-info/package.json</p>
<p>
Dependency Hierarchy:
- gulp-browserify-0.5.1.tgz (Root Library)
- gulp-util-2.2.20.tgz
- dateformat-1.0.12.tgz
- meow-3.7.0.tgz
- normalize-package-data-2.5.0.tgz
- :x: **hosted-git-info-2.8.8.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362>CVE-2021-23362</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-43f8-2h32-f4cj">https://github.com/advisories/GHSA-43f8-2h32-f4cj</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: hosted-git-info - 2.8.9,3.0.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hosted-git-info","packageVersion":"2.8.8","packageFilePaths":["/flink-runtime-web/web-dashboard/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-browserify:0.5.1;gulp-util:2.2.20;dateformat:1.0.12;meow:3.7.0;normalize-package-data:2.5.0;hosted-git-info:2.8.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hosted-git-info - 2.8.9,3.0.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23362","vulnerabilityDetails":"The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-23362 (Medium) detected in hosted-git-info-2.8.8.tgz - ## CVE-2021-23362 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hosted-git-info-2.8.8.tgz</b></p></summary>
<p>Provides metadata and conversions from repository urls for Github, Bitbucket and Gitlab</p>
<p>Library home page: <a href="https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz">https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz</a></p>
<p>Path to dependency file: flink/flink-runtime-web/web-dashboard/package.json</p>
<p>Path to vulnerable library: flink/flink-runtime-web/web-dashboard/node_modules/hosted-git-info/package.json</p>
<p>
Dependency Hierarchy:
- gulp-browserify-0.5.1.tgz (Root Library)
- gulp-util-2.2.20.tgz
- dateformat-1.0.12.tgz
- meow-3.7.0.tgz
- normalize-package-data-2.5.0.tgz
- :x: **hosted-git-info-2.8.8.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362>CVE-2021-23362</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-43f8-2h32-f4cj">https://github.com/advisories/GHSA-43f8-2h32-f4cj</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: hosted-git-info - 2.8.9,3.0.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hosted-git-info","packageVersion":"2.8.8","packageFilePaths":["/flink-runtime-web/web-dashboard/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-browserify:0.5.1;gulp-util:2.2.20;dateformat:1.0.12;meow:3.7.0;normalize-package-data:2.5.0;hosted-git-info:2.8.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hosted-git-info - 2.8.9,3.0.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23362","vulnerabilityDetails":"The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in hosted git info tgz cve medium severity vulnerability vulnerable library hosted git info tgz provides metadata and conversions from repository urls for github bitbucket and gitlab library home page a href path to dependency file flink flink runtime web web dashboard package json path to vulnerable library flink flink runtime web web dashboard node modules hosted git info package json dependency hierarchy gulp browserify tgz root library gulp util tgz dateformat tgz meow tgz normalize package data tgz x hosted git info tgz vulnerable library found in base branch master vulnerability details the package hosted git info before are vulnerable to regular expression denial of service redos via regular expression shortcutmatch in the fromurl function in index js the affected regular expression exhibits polynomial worst case time complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hosted git info isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree gulp browserify gulp util dateformat meow normalize package data hosted git info isminimumfixversionavailable true minimumfixversion hosted git info basebranches vulnerabilityidentifier cve vulnerabilitydetails the package hosted git info before are vulnerable to regular expression denial of service redos via regular expression shortcutmatch in the fromurl function in index js the affected regular expression exhibits polynomial worst case time complexity vulnerabilityurl | 0 |
50,718 | 26,752,250,592 | IssuesEvent | 2023-01-30 20:36:51 | status-im/status-desktop | https://api.github.com/repos/status-im/status-desktop | closed | [getChats] refactor chats models to only be one layer, with categories being sections | Chat refactor E:PerformanceImprovements S:4 | This would be a relatively big refactor of the chat model and QML, but with the goal of simplificating.
This is meant as both a proposal, and a task once we agree on doing it.
As it is right now, the Chat is a bit complex, because we have a need to have a model, that has a submodel, for the categories and the chats.
Then in the QML, we need to have ListViews inside ListViews to display it.
That is a bit complex and it also limits some features we would like to do, like drag and drop in the Chat list.
My proposal, which has been thought of in conjunction with @alexandraB99 and @iurimatias, would be to flatten the Chat model. ie we only have one model per chat section (or channel group) that would contain all channels.
To display the categories, we would use the `section` attribute of the ListView component.
Since we now use the new `getChats` API, this is even simpler than before, because the API gives us the chats directly per section. So we'd be able to populate the model directly.
One small use case that needs a special handling is the case of an empty category. Since we want to show those as well, we'd need to populate it with an "empty chat", which would basically be resolved as an invisible item. @alexandraB99 has done a small test and found it to be doable easily.
With this new flattened model, we hope to remove a lot of the complexity, clean up some code and enable the drag and drop in the chat list.
Let me know if doing this would bring some undesired side effects that I haven't thought about, if you have reservations or just any questions or comments. | True | [getChats] refactor chats models to only be one layer, with categories being sections - This would be a relatively big refactor of the chat model and QML, but with the goal of simplificating.
This is meant as both a proposal, and a task once we agree on doing it.
As it is right now, the Chat is a bit complex, because we have a need to have a model, that has a submodel, for the categories and the chats.
Then in the QML, we need to have ListViews inside ListViews to display it.
That is a bit complex and it also limits some features we would like to do, like drag and drop in the Chat list.
My proposal, which has been thought of in conjunction with @alexandraB99 and @iurimatias, would be to flatten the Chat model. ie we only have one model per chat section (or channel group) that would contain all channels.
To display the categories, we would use the `section` attribute of the ListView component.
Since we now use the new `getChats` API, this is even simpler than before, because the API gives us the chats directly per section. So we'd be able to populate the model directly.
One small use case that needs a special handling is the case of an empty category. Since we want to show those as well, we'd need to populate it with an "empty chat", which would basically be resolved as an invisible item. @alexandraB99 has done a small test and found it to be doable easily.
With this new flattened model, we hope to remove a lot of the complexity, clean up some code and enable the drag and drop in the chat list.
Let me know if doing this would bring some undesired side effects that I haven't thought about, if you have reservations or just any questions or comments. | non_priority | refactor chats models to only be one layer with categories being sections this would be a relatively big refactor of the chat model and qml but with the goal of simplificating this is meant as both a proposal and a task once we agree on doing it as it is right now the chat is a bit complex because we have a need to have a model that has a submodel for the categories and the chats then in the qml we need to have listviews inside listviews to display it that is a bit complex and it also limits some features we would like to do like drag and drop in the chat list my proposal which has been thought of in conjunction with and iurimatias would be to flatten the chat model ie we only have one model per chat section or channel group that would contain all channels to display the categories we would use the section attribute of the listview component since we now use the new getchats api this is even simpler than before because the api gives us the chats directly per section so we d be able to populate the model directly one small use case that needs a special handling is the case of an empty category since we want to show those as well we d need to populate it with an empty chat which would basically be resolved as an invisible item has done a small test and found it to be doable easily with this new flattened model we hope to remove a lot of the complexity clean up some code and enable the drag and drop in the chat list let me know if doing this would bring some undesired side effects that i haven t thought about if you have reservations or just any questions or comments | 0 |
59,002 | 24,626,552,294 | IssuesEvent | 2022-10-16 15:44:11 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | config appservice list: value at null instead of the one that I see in portal | Web Apps Service Attention customer-reported needs-team-attention Auto-Assign | ## Describe the bug
**Command Name**
`az webapp config appsettings list`
**Errors:**
Return `"value": null` instead of the correct one for some environment variables
```json
{
"name": "DOCKER_REGISTRY_SERVER_PASSWORD",
"slotSetting": false,
"value": null
},
```
## To Reproduce:
Steps to reproduce the behavior. Note that argument values have been redacted, as they may contain sensitive information.
- `az webapp config appsettings list --name {} --resource-group {}`
## Expected Behavior
Having the right value that I see in portal.azure.com:
```json
{
"name": "DOCKER_REGISTRY_SERVER_PASSWORD",
"slotSetting": false,
"value": "@Microsoft.KeyVault(VaultName=xxxxxxxxxxx;SecretName=xxxxxxxx)"
},
```
## Environment Summary
```
macOS-12.5.1-x86_64-i386-64bit, Darwin 21.6.0
Python 3.10.6
Installer: HOMEBREW
azure-cli 2.39.0
```
## Additional Context
<!--Please don't remove this:-->
<!--auto-generated-->
| 1.0 | config appservice list: value at null instead of the one that I see in portal - ## Describe the bug
**Command Name**
`az webapp config appsettings list`
**Errors:**
Return `"value": null` instead of the correct one for some environment variables
```json
{
"name": "DOCKER_REGISTRY_SERVER_PASSWORD",
"slotSetting": false,
"value": null
},
```
## To Reproduce:
Steps to reproduce the behavior. Note that argument values have been redacted, as they may contain sensitive information.
- `az webapp config appsettings list --name {} --resource-group {}`
## Expected Behavior
Having the right value that I see in portal.azure.com:
```json
{
"name": "DOCKER_REGISTRY_SERVER_PASSWORD",
"slotSetting": false,
"value": "@Microsoft.KeyVault(VaultName=xxxxxxxxxxx;SecretName=xxxxxxxx)"
},
```
## Environment Summary
```
macOS-12.5.1-x86_64-i386-64bit, Darwin 21.6.0
Python 3.10.6
Installer: HOMEBREW
azure-cli 2.39.0
```
## Additional Context
<!--Please don't remove this:-->
<!--auto-generated-->
| non_priority | config appservice list value at null instead of the one that i see in portal describe the bug command name az webapp config appsettings list errors return value null instead of the correct one for some environment variables json name docker registry server password slotsetting false value null to reproduce steps to reproduce the behavior note that argument values have been redacted as they may contain sensitive information az webapp config appsettings list name resource group expected behavior having the right value that i see in portal azure com json name docker registry server password slotsetting false value microsoft keyvault vaultname xxxxxxxxxxx secretname xxxxxxxx environment summary macos darwin python installer homebrew azure cli additional context | 0 |
67,242 | 14,859,104,413 | IssuesEvent | 2021-01-18 17:52:47 | fuzzdbunit/fuzzdbunit | https://api.github.com/repos/fuzzdbunit/fuzzdbunit | opened | CVE-2020-36180 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-36180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: fuzzdbunit/samples/sample-selenium-test/build.gradle</p>
<p>Path to vulnerable library: /tmp/ws-ua_20210118174829_XFXYQM/downloadResource_ONNCEJ/20210118175102/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- selenium-jupiter-3.3.5.jar (Root Library)
- docker-client-8.16.0.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fuzzdbunit/fuzzdbunit/commit/ddf69c6b4c2883e52c646aaf0bfc16845f74b017">ddf69c6b4c2883e52c646aaf0bfc16845f74b017</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180>CVE-2020-36180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/3004">https://github.com/FasterXML/jackson-databind/issues/3004</a></p>
<p>Release Date: 2021-01-07</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-36180 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-36180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: fuzzdbunit/samples/sample-selenium-test/build.gradle</p>
<p>Path to vulnerable library: /tmp/ws-ua_20210118174829_XFXYQM/downloadResource_ONNCEJ/20210118175102/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- selenium-jupiter-3.3.5.jar (Root Library)
- docker-client-8.16.0.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fuzzdbunit/fuzzdbunit/commit/ddf69c6b4c2883e52c646aaf0bfc16845f74b017">ddf69c6b4c2883e52c646aaf0bfc16845f74b017</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180>CVE-2020-36180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/3004">https://github.com/FasterXML/jackson-databind/issues/3004</a></p>
<p>Release Date: 2021-01-07</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file fuzzdbunit samples sample selenium test build gradle path to vulnerable library tmp ws ua xfxyqm downloadresource onncej jackson databind jar dependency hierarchy selenium jupiter jar root library docker client jar x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons cpdsadapter driveradaptercpds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
28,895 | 11,706,020,170 | IssuesEvent | 2020-03-07 19:25:37 | vlaship/spark | https://api.github.com/repos/vlaship/spark | opened | CVE-2018-14720 (High) detected in jackson-databind-2.6.7.1.jar | security vulnerability | ## CVE-2018-14720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/spark/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.7.1/306775aeb5164835a1dcbdf3f945587045cfb3b5/jackson-databind-2.6.7.1.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.7.1/306775aeb5164835a1dcbdf3f945587045cfb3b5/jackson-databind-2.6.7.1.jar</p>
<p>
Dependency Hierarchy:
- spark-sql_2.12-2.4.4.jar (Root Library)
- :x: **jackson-databind-2.6.7.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vlaship/spark/commit/2d517982709d6cf8718c3af48ef079795b448bd9">2d517982709d6cf8718c3af48ef079795b448bd9</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow attackers to conduct external XML entity (XXE) attacks by leveraging failure to block unspecified JDK classes from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14720>CVE-2018-14720</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14720">https://nvd.nist.gov/vuln/detail/CVE-2018-14720</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-14720 (High) detected in jackson-databind-2.6.7.1.jar - ## CVE-2018-14720 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/spark/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.7.1/306775aeb5164835a1dcbdf3f945587045cfb3b5/jackson-databind-2.6.7.1.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.7.1/306775aeb5164835a1dcbdf3f945587045cfb3b5/jackson-databind-2.6.7.1.jar</p>
<p>
Dependency Hierarchy:
- spark-sql_2.12-2.4.4.jar (Root Library)
- :x: **jackson-databind-2.6.7.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vlaship/spark/commit/2d517982709d6cf8718c3af48ef079795b448bd9">2d517982709d6cf8718c3af48ef079795b448bd9</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow attackers to conduct external XML entity (XXE) attacks by leveraging failure to block unspecified JDK classes from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14720>CVE-2018-14720</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-14720">https://nvd.nist.gov/vuln/detail/CVE-2018-14720</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm spark build gradle path to vulnerable library root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spark sql jar root library x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before might allow attackers to conduct external xml entity xxe attacks by leveraging failure to block unspecified jdk classes from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
19,024 | 6,664,254,112 | IssuesEvent | 2017-10-02 19:26:26 | hackersatcambridge/hac-website | https://api.github.com/repos/hackersatcambridge/hac-website | opened | Auto-generation of .env files for development | build system | Is there a way we can generate the .env file with all the dev info automatically, and update with new info if it needs it?
We could at least give more descriptive errors if the environment variables are missing, maybe if the user is building in development, we could point them to the README? | 1.0 | Auto-generation of .env files for development - Is there a way we can generate the .env file with all the dev info automatically, and update with new info if it needs it?
We could at least give more descriptive errors if the environment variables are missing, maybe if the user is building in development, we could point them to the README? | non_priority | auto generation of env files for development is there a way we can generate the env file with all the dev info automatically and update with new info if it needs it we could at least give more descriptive errors if the environment variables are missing maybe if the user is building in development we could point them to the readme | 0 |
114,173 | 11,839,488,543 | IssuesEvent | 2020-03-23 17:14:12 | openZH/covid_19 | https://api.github.com/repos/openZH/covid_19 | closed | A quick script for computing latest totals | documentation | In the directory with data:
```shell
for f in *.csv; do awk -F , '{if ($5) { print $1, $3, $5; }}' "$f" | tail -1; done | awk 'BEGIN { sum = 0; } { sum += $3; } END { print sum; }'
```
6262
Getting latest confirmed cases by subdivision:
```shell
for f in *.csv; do awk -F , '{if ($5) { print $1, $3, $5; }}' "$f" | tail -1; done | sort -r -n -k 3
```
```
2020-03-20 VD 1432
2020-03-21 TI 918
2020-03-20 GE 873
2020-03-20 ZH 773
2020-03-20 BE 377
2020-03-21 BS 299
2020-03-21 BL 282
2020-03-20 VS 282
2020-03-20 GR 213
2020-03-20 AG 165
2020-03-20 NE 159
2020-03-21 LU 109
2020-03-20 SG 98
2020-03-21 TG 56
2020-03-20 ZG 48
2020-03-20 FL 40
2020-03-20 JU 29
2020-03-20 NW 28
2020-03-19 GL 17
2020-03-20 SH 14
2020-03-15 SZ 13
2020-03-21 UR 12
2020-03-18 AR 11
2020-03-09 FR 11
2020-03-14 AI 2
2020-03-13 OW 1
```
Feel free to include it in the repo, or readme. Public Domain. Signed off, Witold Baryluk.
| 1.0 | A quick script for computing latest totals - In the directory with data:
```shell
for f in *.csv; do awk -F , '{if ($5) { print $1, $3, $5; }}' "$f" | tail -1; done | awk 'BEGIN { sum = 0; } { sum += $3; } END { print sum; }'
```
6262
Getting latest confirmed cases by subdivision:
```shell
for f in *.csv; do awk -F , '{if ($5) { print $1, $3, $5; }}' "$f" | tail -1; done | sort -r -n -k 3
```
```
2020-03-20 VD 1432
2020-03-21 TI 918
2020-03-20 GE 873
2020-03-20 ZH 773
2020-03-20 BE 377
2020-03-21 BS 299
2020-03-21 BL 282
2020-03-20 VS 282
2020-03-20 GR 213
2020-03-20 AG 165
2020-03-20 NE 159
2020-03-21 LU 109
2020-03-20 SG 98
2020-03-21 TG 56
2020-03-20 ZG 48
2020-03-20 FL 40
2020-03-20 JU 29
2020-03-20 NW 28
2020-03-19 GL 17
2020-03-20 SH 14
2020-03-15 SZ 13
2020-03-21 UR 12
2020-03-18 AR 11
2020-03-09 FR 11
2020-03-14 AI 2
2020-03-13 OW 1
```
Feel free to include it in the repo, or readme. Public Domain. Signed off, Witold Baryluk.
| non_priority | a quick script for computing latest totals in the directory with data shell for f in csv do awk f if print f tail done awk begin sum sum end print sum getting latest confirmed cases by subdivision shell for f in csv do awk f if print f tail done sort r n k vd ti ge zh be bs bl vs gr ag ne lu sg tg zg fl ju nw gl sh sz ur ar fr ai ow feel free to include it in the repo or readme public domain signed off witold baryluk | 0 |
182,763 | 21,676,487,976 | IssuesEvent | 2022-05-08 19:55:00 | samq-wsdemo/cassandra | https://api.github.com/repos/samq-wsdemo/cassandra | opened | CVE-2022-24823 (Medium) detected in netty-all-4.0.44.Final.jar | security vulnerability | ## CVE-2022-24823 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-all-4.0.44.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to vulnerable library: /lib/netty-all-4.0.44.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.44.Final.jar** (Vulnerable Library)
<p>Found in base branch: <b>palantir-cassandra-2.2.18</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an open-source, asynchronous event-driven network application framework. The package `io.netty:netty-codec-http` prior to version 4.1.77.Final contains an insufficient fix for CVE-2021-21290. When Netty's multipart decoders are used local information disclosure can occur via the local system temporary directory if temporary storing uploads on the disk is enabled. This only impacts applications running on Java version 6 and lower. Additionally, this vulnerability impacts code running on Unix-like systems, and very old versions of Mac OSX and Windows as they all share the system temporary directory between all users. Version 4.1.77.Final contains a patch for this vulnerability. As a workaround, specify one's own `java.io.tmpdir` when starting the JVM or use DefaultHttpDataFactory.setBaseDir(...) to set the directory to something that is only readable by the current user.
<p>Publish Date: 2022-05-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24823>CVE-2022-24823</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24823">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24823</a></p>
<p>Release Date: 2022-05-06</p>
<p>Fix Resolution: io.netty:netty-all;io.netty:netty-common - 4.1.77.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.44.Final","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.44.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all;io.netty:netty-common - 4.1.77.Final","isBinary":true}],"baseBranches":["palantir-cassandra-2.2.18"],"vulnerabilityIdentifier":"CVE-2022-24823","vulnerabilityDetails":"Netty is an open-source, asynchronous event-driven network application framework. The package `io.netty:netty-codec-http` prior to version 4.1.77.Final contains an insufficient fix for CVE-2021-21290. When Netty\u0027s multipart decoders are used local information disclosure can occur via the local system temporary directory if temporary storing uploads on the disk is enabled. This only impacts applications running on Java version 6 and lower. Additionally, this vulnerability impacts code running on Unix-like systems, and very old versions of Mac OSX and Windows as they all share the system temporary directory between all users. Version 4.1.77.Final contains a patch for this vulnerability. As a workaround, specify one\u0027s own `java.io.tmpdir` when starting the JVM or use DefaultHttpDataFactory.setBaseDir(...) to set the directory to something that is only readable by the current user.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24823","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-24823 (Medium) detected in netty-all-4.0.44.Final.jar - ## CVE-2022-24823 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-all-4.0.44.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to vulnerable library: /lib/netty-all-4.0.44.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.44.Final.jar** (Vulnerable Library)
<p>Found in base branch: <b>palantir-cassandra-2.2.18</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an open-source, asynchronous event-driven network application framework. The package `io.netty:netty-codec-http` prior to version 4.1.77.Final contains an insufficient fix for CVE-2021-21290. When Netty's multipart decoders are used local information disclosure can occur via the local system temporary directory if temporary storing uploads on the disk is enabled. This only impacts applications running on Java version 6 and lower. Additionally, this vulnerability impacts code running on Unix-like systems, and very old versions of Mac OSX and Windows as they all share the system temporary directory between all users. Version 4.1.77.Final contains a patch for this vulnerability. As a workaround, specify one's own `java.io.tmpdir` when starting the JVM or use DefaultHttpDataFactory.setBaseDir(...) to set the directory to something that is only readable by the current user.
<p>Publish Date: 2022-05-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24823>CVE-2022-24823</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24823">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24823</a></p>
<p>Release Date: 2022-05-06</p>
<p>Fix Resolution: io.netty:netty-all;io.netty:netty-common - 4.1.77.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.44.Final","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.44.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all;io.netty:netty-common - 4.1.77.Final","isBinary":true}],"baseBranches":["palantir-cassandra-2.2.18"],"vulnerabilityIdentifier":"CVE-2022-24823","vulnerabilityDetails":"Netty is an open-source, asynchronous event-driven network application framework. The package `io.netty:netty-codec-http` prior to version 4.1.77.Final contains an insufficient fix for CVE-2021-21290. When Netty\u0027s multipart decoders are used local information disclosure can occur via the local system temporary directory if temporary storing uploads on the disk is enabled. This only impacts applications running on Java version 6 and lower. Additionally, this vulnerability impacts code running on Unix-like systems, and very old versions of Mac OSX and Windows as they all share the system temporary directory between all users. Version 4.1.77.Final contains a patch for this vulnerability. As a workaround, specify one\u0027s own `java.io.tmpdir` when starting the JVM or use DefaultHttpDataFactory.setBaseDir(...) to set the directory to something that is only readable by the current user.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24823","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in netty all final jar cve medium severity vulnerability vulnerable library netty all final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients library home page a href path to vulnerable library lib netty all final jar dependency hierarchy x netty all final jar vulnerable library found in base branch palantir cassandra vulnerability details netty is an open source asynchronous event driven network application framework the package io netty netty codec http prior to version final contains an insufficient fix for cve when netty s multipart decoders are used local information disclosure can occur via the local system temporary directory if temporary storing uploads on the disk is enabled this only impacts applications running on java version and lower additionally this vulnerability impacts code running on unix like systems and very old versions of mac osx and windows as they all share the system temporary directory between all users version final contains a patch for this vulnerability as a workaround specify one s own java io tmpdir when starting the jvm or use defaulthttpdatafactory setbasedir to set the directory to something that is only readable by the current user publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io netty netty all io netty netty common final isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree io netty netty all final isminimumfixversionavailable true minimumfixversion io netty netty all io netty netty common final isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails netty is an open source asynchronous event driven network application framework the package io netty netty codec http prior to version final contains an insufficient fix for cve when netty multipart decoders are used local information disclosure can occur via the local system temporary directory if temporary storing uploads on the disk is enabled this only impacts applications running on java version and lower additionally this vulnerability impacts code running on unix like systems and very old versions of mac osx and windows as they all share the system temporary directory between all users version final contains a patch for this vulnerability as a workaround specify one own java io tmpdir when starting the jvm or use defaulthttpdatafactory setbasedir to set the directory to something that is only readable by the current user vulnerabilityurl | 0 |
20,096 | 3,538,544,113 | IssuesEvent | 2016-01-18 10:24:56 | owncloud/client | https://api.github.com/repos/owncloud/client | closed | Resume button when synchronization fails | Design & UX Enhancement | In Setting/Account, when the synchronization has failed, there is a pause button to click on, then a "resume" button is shown.
Would it be more clear if it was a "resume" button in the first place? | 1.0 | Resume button when synchronization fails - In Setting/Account, when the synchronization has failed, there is a pause button to click on, then a "resume" button is shown.
Would it be more clear if it was a "resume" button in the first place? | non_priority | resume button when synchronization fails in setting account when the synchronization has failed there is a pause button to click on then a resume button is shown would it be more clear if it was a resume button in the first place | 0 |
93,825 | 11,811,324,357 | IssuesEvent | 2020-03-19 17:59:38 | ethereum/ethereum-org-website | https://api.github.com/repos/ethereum/ethereum-org-website | closed | Update list styles | Type: Design Type: Feature | **Describe the solution you'd like**
<!-- A clear and concise description of what you want to happen. -->
See the [Figma file](https://www.figma.com/file/rQK2dt9eaLOMmvTOf5ifdr/Ethereum.org-Style-Guide-RC1?node-id=602%3A1) style guide for implementation details.
- [ ] Text list (with & without bullets)
- [ ] Link list (with & without bullets)
- [ ] Text & description list (with & without bullets)
**Additional context**
<!-- Add any other context or screenshots about the feature request here. -->
Part #753, the output of #668 (see [Figma file](https://www.figma.com/file/rQK2dt9eaLOMmvTOf5ifdr/Ethereum.org-Style-Guide-RC1?node-id=602%3A1
)) | 1.0 | Update list styles - **Describe the solution you'd like**
<!-- A clear and concise description of what you want to happen. -->
See the [Figma file](https://www.figma.com/file/rQK2dt9eaLOMmvTOf5ifdr/Ethereum.org-Style-Guide-RC1?node-id=602%3A1) style guide for implementation details.
- [ ] Text list (with & without bullets)
- [ ] Link list (with & without bullets)
- [ ] Text & description list (with & without bullets)
**Additional context**
<!-- Add any other context or screenshots about the feature request here. -->
Part #753, the output of #668 (see [Figma file](https://www.figma.com/file/rQK2dt9eaLOMmvTOf5ifdr/Ethereum.org-Style-Guide-RC1?node-id=602%3A1
)) | non_priority | update list styles describe the solution you d like see the style guide for implementation details text list with without bullets link list with without bullets text description list with without bullets additional context part the output of see | 0 |
14,720 | 9,438,168,601 | IssuesEvent | 2019-04-13 21:01:57 | Electron-Cash/Electron-Cash | https://api.github.com/repos/Electron-Cash/Electron-Cash | opened | We probably need to raise the gap limit for change to 20 | CashShuffle UX and usability enhancement | __The problem:__ CashShuffle can potentially create situations where users have address gaps in their "change" account larger than the default gap limit for change of **6**. There is no getting around this: Each tentative shuffle (of which there may be up to 6 pending on a default install .. 1 for each of the 6 tiers) reserves **2** change addresses ahead of time. If only the *last* shuffle succeeds, there could be a gap as large as 10 in the change addresses (actually 11 since the Send tab also reserves a change address of its own).
Subsequent shuffles or spends may use up these empty addresses in the gap -- but until they happen the wallet is in an in-between state where recovery becomes problematic and/or annoying for users.
__Problem impact:__ Users restoring a wallet that has such a gap may think they are missing funds. They currently need to go into Wallet -> Scan beyond gap... to recover their funds. This is something even a pro user (say like Amaury or Jonald or Mark) may forget to do and may panic at first and curse the software. The software should never require the user to end up in such a situation.
__The solution:__ Make the gap limit for change 20. The default of 6 is an "Electrumism" of just being very conservative. It is arbitrary. Raising it to 20 would solve this problem for users.
__Background:__ There is no "standard' gap limit for change -- historically 20 was used as a gap limit for receiving. The 6 number appears to be arbitrary. (BIP44)[https://github.com/bitcoin/bips/blob/master/bip-0044.mediawiki] (which is an incomplete proposal) mentions a 20 address gap limit and leaves change unspecified.
Bitcoin Core and Bitcoin ABC internally have an effective gap limit of 1000.
_Rationale:__ Right now effectively we are acting like the gap limit is >6 because of CashShuffle (we are acting like it's 12). But in our code we have it set to 6. This is a bug. Setting it to 20 rights the wrongs.
__Summary:__ Let's set the gap limit for change to 20 (to match receiving). It will fix things. | True | We probably need to raise the gap limit for change to 20 - __The problem:__ CashShuffle can potentially create situations where users have address gaps in their "change" account larger than the default gap limit for change of **6**. There is no getting around this: Each tentative shuffle (of which there may be up to 6 pending on a default install .. 1 for each of the 6 tiers) reserves **2** change addresses ahead of time. If only the *last* shuffle succeeds, there could be a gap as large as 10 in the change addresses (actually 11 since the Send tab also reserves a change address of its own).
Subsequent shuffles or spends may use up these empty addresses in the gap -- but until they happen the wallet is in an in-between state where recovery becomes problematic and/or annoying for users.
__Problem impact:__ Users restoring a wallet that has such a gap may think they are missing funds. They currently need to go into Wallet -> Scan beyond gap... to recover their funds. This is something even a pro user (say like Amaury or Jonald or Mark) may forget to do and may panic at first and curse the software. The software should never require the user to end up in such a situation.
__The solution:__ Make the gap limit for change 20. The default of 6 is an "Electrumism" of just being very conservative. It is arbitrary. Raising it to 20 would solve this problem for users.
__Background:__ There is no "standard' gap limit for change -- historically 20 was used as a gap limit for receiving. The 6 number appears to be arbitrary. (BIP44)[https://github.com/bitcoin/bips/blob/master/bip-0044.mediawiki] (which is an incomplete proposal) mentions a 20 address gap limit and leaves change unspecified.
Bitcoin Core and Bitcoin ABC internally have an effective gap limit of 1000.
_Rationale:__ Right now effectively we are acting like the gap limit is >6 because of CashShuffle (we are acting like it's 12). But in our code we have it set to 6. This is a bug. Setting it to 20 rights the wrongs.
__Summary:__ Let's set the gap limit for change to 20 (to match receiving). It will fix things. | non_priority | we probably need to raise the gap limit for change to the problem cashshuffle can potentially create situations where users have address gaps in their change account larger than the default gap limit for change of there is no getting around this each tentative shuffle of which there may be up to pending on a default install for each of the tiers reserves change addresses ahead of time if only the last shuffle succeeds there could be a gap as large as in the change addresses actually since the send tab also reserves a change address of its own subsequent shuffles or spends may use up these empty addresses in the gap but until they happen the wallet is in an in between state where recovery becomes problematic and or annoying for users problem impact users restoring a wallet that has such a gap may think they are missing funds they currently need to go into wallet scan beyond gap to recover their funds this is something even a pro user say like amaury or jonald or mark may forget to do and may panic at first and curse the software the software should never require the user to end up in such a situation the solution make the gap limit for change the default of is an electrumism of just being very conservative it is arbitrary raising it to would solve this problem for users background there is no standard gap limit for change historically was used as a gap limit for receiving the number appears to be arbitrary which is an incomplete proposal mentions a address gap limit and leaves change unspecified bitcoin core and bitcoin abc internally have an effective gap limit of rationale right now effectively we are acting like the gap limit is because of cashshuffle we are acting like it s but in our code we have it set to this is a bug setting it to rights the wrongs summary let s set the gap limit for change to to match receiving it will fix things | 0 |
136,518 | 19,831,128,731 | IssuesEvent | 2022-01-20 12:07:08 | RRZE-Webteam/FAU-Einrichtungen | https://api.github.com/repos/RRZE-Webteam/FAU-Einrichtungen | opened | Ghostbutton-Hover | enhancement Diskussion Design | Derzeit hat das Ghostbutton bei der Hoverfarbe die Hover-Farbe des normalen Buttons.
Bei einem normalen Button wird als Hintergrundfarbe die "dunkler"-Farbe verwenden und beim Hover die "dunkelste".
Bei dem Ghostbutton ist die normale Farbe aber transparent, bzw auf dem Standardhintergrund eben weiß.
Damit ist aber Sprung beim Hovern gleich auf die dunkelste Farne zu krass.
Normal, ohne Hover:
Hover bei Zentral:

Hover bei Phil:
Die Frage wäre daher, ob man bei dem Ghostbottons als Hoverfarbe daher nicht stattdessen entweder die
"ci-hell" nimmt, wie bei den Linkhover im Textcontent oder aber die erste dunklere Farbe.
Das sähe dann entweder so aus (ci-hell):
Zentral:

Phil:
oder so (dunkler):
Zentral:

Phil:

Am besten vor Release 2.0 klären, da die Ghostbuttons neu sind und eine Gewöhnung an etwas was man dann in 2.1 ändert ungünstig wäre.
| 1.0 | Ghostbutton-Hover - Derzeit hat das Ghostbutton bei der Hoverfarbe die Hover-Farbe des normalen Buttons.
Bei einem normalen Button wird als Hintergrundfarbe die "dunkler"-Farbe verwenden und beim Hover die "dunkelste".
Bei dem Ghostbutton ist die normale Farbe aber transparent, bzw auf dem Standardhintergrund eben weiß.
Damit ist aber Sprung beim Hovern gleich auf die dunkelste Farne zu krass.
Normal, ohne Hover:
Hover bei Zentral:

Hover bei Phil:
Die Frage wäre daher, ob man bei dem Ghostbottons als Hoverfarbe daher nicht stattdessen entweder die
"ci-hell" nimmt, wie bei den Linkhover im Textcontent oder aber die erste dunklere Farbe.
Das sähe dann entweder so aus (ci-hell):
Zentral:

Phil:
oder so (dunkler):
Zentral:

Phil:

Am besten vor Release 2.0 klären, da die Ghostbuttons neu sind und eine Gewöhnung an etwas was man dann in 2.1 ändert ungünstig wäre.
| non_priority | ghostbutton hover derzeit hat das ghostbutton bei der hoverfarbe die hover farbe des normalen buttons bei einem normalen button wird als hintergrundfarbe die dunkler farbe verwenden und beim hover die dunkelste bei dem ghostbutton ist die normale farbe aber transparent bzw auf dem standardhintergrund eben weiß damit ist aber sprung beim hovern gleich auf die dunkelste farne zu krass normal ohne hover hover bei zentral hover bei phil die frage wäre daher ob man bei dem ghostbottons als hoverfarbe daher nicht stattdessen entweder die ci hell nimmt wie bei den linkhover im textcontent oder aber die erste dunklere farbe das sähe dann entweder so aus ci hell zentral phil oder so dunkler zentral phil am besten vor release klären da die ghostbuttons neu sind und eine gewöhnung an etwas was man dann in ändert ungünstig wäre | 0 |
298,086 | 25,785,556,428 | IssuesEvent | 2022-12-09 20:01:40 | ValveSoftware/steam-for-linux | https://api.github.com/repos/ValveSoftware/steam-for-linux | closed | Games with initial selection dialog window don't start | Steam client Need Retest Distro Family: Ubuntu | #### Your system information
* Steam client version (build number or date): 1667429911
* Distribution (e.g. Ubuntu): Kubuntu 22.04
* Opted into Steam client beta?: [Yes/No] Yes
* Have you checked for system updates?: [Yes/No] Yes
#### Please describe your issue in as much detail as possible:
Testing the new beta client with "-gamepadui" option. Games with an initial selection dialog window (e.g. "Relicta") fail to start.
Starting the same game on the Steam Deck (Relicta is Verified), the selection dialog box is shown. After making the selection, the game starts.
#### Steps for reproducing this issue:
1. Start Steam with "-gamepadui" option
2. Select and start a game that presents an initial selection dialog window (e.g. Relicta)
3. Observe that the "Play" button changes to "Cancel", but nothing more happens, even after waiting for two minutes.
| 1.0 | Games with initial selection dialog window don't start - #### Your system information
* Steam client version (build number or date): 1667429911
* Distribution (e.g. Ubuntu): Kubuntu 22.04
* Opted into Steam client beta?: [Yes/No] Yes
* Have you checked for system updates?: [Yes/No] Yes
#### Please describe your issue in as much detail as possible:
Testing the new beta client with "-gamepadui" option. Games with an initial selection dialog window (e.g. "Relicta") fail to start.
Starting the same game on the Steam Deck (Relicta is Verified), the selection dialog box is shown. After making the selection, the game starts.
#### Steps for reproducing this issue:
1. Start Steam with "-gamepadui" option
2. Select and start a game that presents an initial selection dialog window (e.g. Relicta)
3. Observe that the "Play" button changes to "Cancel", but nothing more happens, even after waiting for two minutes.
| non_priority | games with initial selection dialog window don t start your system information steam client version build number or date distribution e g ubuntu kubuntu opted into steam client beta yes have you checked for system updates yes please describe your issue in as much detail as possible testing the new beta client with gamepadui option games with an initial selection dialog window e g relicta fail to start starting the same game on the steam deck relicta is verified the selection dialog box is shown after making the selection the game starts steps for reproducing this issue start steam with gamepadui option select and start a game that presents an initial selection dialog window e g relicta observe that the play button changes to cancel but nothing more happens even after waiting for two minutes | 0 |
101,303 | 16,503,208,397 | IssuesEvent | 2021-05-25 16:16:04 | idonthaveafifaaddiction/automerge-conflict-detector-plugin | https://api.github.com/repos/idonthaveafifaaddiction/automerge-conflict-detector-plugin | opened | CVE-2021-27290 (High) detected in ssri-6.0.1.tgz, ssri-7.1.0.tgz | security vulnerability | ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ssri-6.0.1.tgz</b>, <b>ssri-7.1.0.tgz</b></p></summary>
<p>
<details><summary><b>ssri-6.0.1.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz">https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz</a></p>
<p>Path to dependency file: automerge-conflict-detector-plugin/package.json</p>
<p>Path to vulnerable library: automerge-conflict-detector-plugin/node_modules/ssri/package.json</p>
<p>
Dependency Hierarchy:
- webpack-4.41.5.tgz (Root Library)
- terser-webpack-plugin-1.4.4.tgz
- cacache-12.0.4.tgz
- :x: **ssri-6.0.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ssri-7.1.0.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz">https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz</a></p>
<p>Path to dependency file: automerge-conflict-detector-plugin/package.json</p>
<p>Path to vulnerable library: automerge-conflict-detector-plugin/node_modules/cacache/node_modules/ssri/package.json</p>
<p>
Dependency Hierarchy:
- terser-webpack-plugin-2.2.1.tgz (Root Library)
- cacache-13.0.1.tgz
- :x: **ssri-7.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/automerge-conflict-detector-plugin/commit/b54fd03fd52baedb4e95e356419a51cd677014b1">b54fd03fd52baedb4e95e356419a51cd677014b1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290>CVE-2021-27290</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: ssri - 6.0.2,8.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ssri","packageVersion":"6.0.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"webpack:4.41.5;terser-webpack-plugin:1.4.4;cacache:12.0.4;ssri:6.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ssri - 6.0.2,8.0.1"},{"packageType":"javascript/Node.js","packageName":"ssri","packageVersion":"7.1.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"terser-webpack-plugin:2.2.1;cacache:13.0.1;ssri:7.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ssri - 6.0.2,8.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-27290","vulnerabilityDetails":"ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-27290 (High) detected in ssri-6.0.1.tgz, ssri-7.1.0.tgz - ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ssri-6.0.1.tgz</b>, <b>ssri-7.1.0.tgz</b></p></summary>
<p>
<details><summary><b>ssri-6.0.1.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz">https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz</a></p>
<p>Path to dependency file: automerge-conflict-detector-plugin/package.json</p>
<p>Path to vulnerable library: automerge-conflict-detector-plugin/node_modules/ssri/package.json</p>
<p>
Dependency Hierarchy:
- webpack-4.41.5.tgz (Root Library)
- terser-webpack-plugin-1.4.4.tgz
- cacache-12.0.4.tgz
- :x: **ssri-6.0.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>ssri-7.1.0.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz">https://registry.npmjs.org/ssri/-/ssri-7.1.0.tgz</a></p>
<p>Path to dependency file: automerge-conflict-detector-plugin/package.json</p>
<p>Path to vulnerable library: automerge-conflict-detector-plugin/node_modules/cacache/node_modules/ssri/package.json</p>
<p>
Dependency Hierarchy:
- terser-webpack-plugin-2.2.1.tgz (Root Library)
- cacache-13.0.1.tgz
- :x: **ssri-7.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/automerge-conflict-detector-plugin/commit/b54fd03fd52baedb4e95e356419a51cd677014b1">b54fd03fd52baedb4e95e356419a51cd677014b1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290>CVE-2021-27290</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: ssri - 6.0.2,8.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ssri","packageVersion":"6.0.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"webpack:4.41.5;terser-webpack-plugin:1.4.4;cacache:12.0.4;ssri:6.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ssri - 6.0.2,8.0.1"},{"packageType":"javascript/Node.js","packageName":"ssri","packageVersion":"7.1.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"terser-webpack-plugin:2.2.1;cacache:13.0.1;ssri:7.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ssri - 6.0.2,8.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-27290","vulnerabilityDetails":"ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in ssri tgz ssri tgz cve high severity vulnerability vulnerable libraries ssri tgz ssri tgz ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spec library home page a href path to dependency file automerge conflict detector plugin package json path to vulnerable library automerge conflict detector plugin node modules ssri package json dependency hierarchy webpack tgz root library terser webpack plugin tgz cacache tgz x ssri tgz vulnerable library ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spec library home page a href path to dependency file automerge conflict detector plugin package json path to vulnerable library automerge conflict detector plugin node modules cacache node modules ssri package json dependency hierarchy terser webpack plugin tgz root library cacache tgz x ssri tgz vulnerable library found in head commit a href found in base branch master vulnerability details ssri fixed in processes sris using a regular expression which is vulnerable to a denial of service malicious sris could take an extremely long time to process leading to denial of service this issue only affects consumers using the strict option publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ssri isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree webpack terser webpack plugin cacache ssri isminimumfixversionavailable true minimumfixversion ssri packagetype javascript node js packagename ssri packageversion packagefilepaths istransitivedependency true dependencytree terser webpack plugin cacache ssri isminimumfixversionavailable true minimumfixversion ssri basebranches vulnerabilityidentifier cve vulnerabilitydetails ssri fixed in processes sris using a regular expression which is vulnerable to a denial of service malicious sris could take an extremely long time to process leading to denial of service this issue only affects consumers using the strict option vulnerabilityurl | 0 |
38,703 | 8,952,343,428 | IssuesEvent | 2019-01-25 16:17:30 | svigerske/ipopt-donotuse | https://api.github.com/repos/svigerske/ipopt-donotuse | closed | wget not found when building IPOPT on MinGW/MSYS | Ipopt defect | Issue created by migration from Trac.
Original creator: jdpipe
Original creation time: 2010-05-06 07:38:33
Assignee: ipopt-team
Version: 3.8
I use the 'wget' from the GnuWin32 project, which by default installs in c:\Program Files\GnuWin32\bin. I then add that folder to my PATH in MSYS and all GnuWin32 commands are then available straight away. These are much easier to install than the MSYS/MinGW stuff, and work fine.
Problem is that the various 'get.PACKAGENAME' scripts in the ThirdParty section of IPOPT fail to detect my 'wget', because the call 'which wget | wc -w' returns a number more than 1, but a value of 1 is the only allowable.
The solution to this bug, I believe, is a to simply change 'wc -w' to 'wc -l' for all of these 'wget' calls. Alternatively, I wonder if the return value of the 'which' command can be checked?
For ease of building, maybe a 'get.ThirdParty' script could be provided that automatically downloaded all possible third-party libraries (except HSL which can't be automated...easily).
| 1.0 | wget not found when building IPOPT on MinGW/MSYS - Issue created by migration from Trac.
Original creator: jdpipe
Original creation time: 2010-05-06 07:38:33
Assignee: ipopt-team
Version: 3.8
I use the 'wget' from the GnuWin32 project, which by default installs in c:\Program Files\GnuWin32\bin. I then add that folder to my PATH in MSYS and all GnuWin32 commands are then available straight away. These are much easier to install than the MSYS/MinGW stuff, and work fine.
Problem is that the various 'get.PACKAGENAME' scripts in the ThirdParty section of IPOPT fail to detect my 'wget', because the call 'which wget | wc -w' returns a number more than 1, but a value of 1 is the only allowable.
The solution to this bug, I believe, is a to simply change 'wc -w' to 'wc -l' for all of these 'wget' calls. Alternatively, I wonder if the return value of the 'which' command can be checked?
For ease of building, maybe a 'get.ThirdParty' script could be provided that automatically downloaded all possible third-party libraries (except HSL which can't be automated...easily).
| non_priority | wget not found when building ipopt on mingw msys issue created by migration from trac original creator jdpipe original creation time assignee ipopt team version i use the wget from the project which by default installs in c program files bin i then add that folder to my path in msys and all commands are then available straight away these are much easier to install than the msys mingw stuff and work fine problem is that the various get packagename scripts in the thirdparty section of ipopt fail to detect my wget because the call which wget wc w returns a number more than but a value of is the only allowable the solution to this bug i believe is a to simply change wc w to wc l for all of these wget calls alternatively i wonder if the return value of the which command can be checked for ease of building maybe a get thirdparty script could be provided that automatically downloaded all possible third party libraries except hsl which can t be automated easily | 0 |
238,350 | 18,239,141,071 | IssuesEvent | 2021-10-01 10:41:29 | microsoft/CCF | https://api.github.com/repos/microsoft/CCF | opened | JS: Document API stability | documentation versioning | https://microsoft.github.io/CCF/main/overview/release_policy.html
This covers C++ only currently. For JS, some statements should be made as well.
I'd like to take an approach similar to how globals in Node.JS / W3C Web APIs work and are evolved, which roughly means there are no `v2` etc. suffixes. Evolving in JS is often doable in a backwards-compatible way as additional parameters can be added without breaking existing usage and/or `options` objects as last argument are used which are easier to evolve. So the promise would be that we never break old APIs, though we may deprecate and remove APIs and replace them with differently named ones, if it really is too awkward to extend/change behaviour of an existing API.
@eddyashton Does this make sense? | 1.0 | JS: Document API stability - https://microsoft.github.io/CCF/main/overview/release_policy.html
This covers C++ only currently. For JS, some statements should be made as well.
I'd like to take an approach similar to how globals in Node.JS / W3C Web APIs work and are evolved, which roughly means there are no `v2` etc. suffixes. Evolving in JS is often doable in a backwards-compatible way as additional parameters can be added without breaking existing usage and/or `options` objects as last argument are used which are easier to evolve. So the promise would be that we never break old APIs, though we may deprecate and remove APIs and replace them with differently named ones, if it really is too awkward to extend/change behaviour of an existing API.
@eddyashton Does this make sense? | non_priority | js document api stability this covers c only currently for js some statements should be made as well i d like to take an approach similar to how globals in node js web apis work and are evolved which roughly means there are no etc suffixes evolving in js is often doable in a backwards compatible way as additional parameters can be added without breaking existing usage and or options objects as last argument are used which are easier to evolve so the promise would be that we never break old apis though we may deprecate and remove apis and replace them with differently named ones if it really is too awkward to extend change behaviour of an existing api eddyashton does this make sense | 0 |
6,751 | 6,627,675,437 | IssuesEvent | 2017-09-23 06:55:21 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | opened | visiting about:preferences#search should not set cookies | needs-triage privacy security | i noticed that opening about:preferences#search causes cookies to be set for various sites, probably because Brave is making requests to load their favicons:

we should not load the favicons remotely | True | visiting about:preferences#search should not set cookies - i noticed that opening about:preferences#search causes cookies to be set for various sites, probably because Brave is making requests to load their favicons:

we should not load the favicons remotely | non_priority | visiting about preferences search should not set cookies i noticed that opening about preferences search causes cookies to be set for various sites probably because brave is making requests to load their favicons we should not load the favicons remotely | 0 |
81,252 | 7,776,860,824 | IssuesEvent | 2018-06-05 09:22:53 | ubtue/tuefind | https://api.github.com/repos/ubtue/tuefind | closed | Doppelpunkt in zweisprachigen Titeln | ready for testing | Bei der Zs PPN 094083746 ist folgendes aufgefallen:
Neuere Aufsatztitel werden immer in zwei Sprachen angezeigt, verbunden mit " = ". Wenn der Titel keinen Untertitel enthält, wird dennoch vor dem " = " auch noch ein Doppelpunkt angezeigt, der da nicht hingehört.
Beispiel:
https://relbib.de/Record/451549988 | 1.0 | Doppelpunkt in zweisprachigen Titeln - Bei der Zs PPN 094083746 ist folgendes aufgefallen:
Neuere Aufsatztitel werden immer in zwei Sprachen angezeigt, verbunden mit " = ". Wenn der Titel keinen Untertitel enthält, wird dennoch vor dem " = " auch noch ein Doppelpunkt angezeigt, der da nicht hingehört.
Beispiel:
https://relbib.de/Record/451549988 | non_priority | doppelpunkt in zweisprachigen titeln bei der zs ppn ist folgendes aufgefallen neuere aufsatztitel werden immer in zwei sprachen angezeigt verbunden mit wenn der titel keinen untertitel enthält wird dennoch vor dem auch noch ein doppelpunkt angezeigt der da nicht hingehört beispiel | 0 |
2,640 | 8,072,848,824 | IssuesEvent | 2018-08-06 17:17:19 | dotnet/docs | https://api.github.com/repos/dotnet/docs | closed | Definition of POCO | Area - Architecture e-books Source - Docs.ms kudos | One thing that confused me here is the definition of POCO classes. I always thought a POCO class was one that had no methods, and just a bunch of properties with getters and setters. So I was wondering where the domain logic would be.
You eventually clarify it by saying
> It is important to note that this is a domain entity implemented as a POCO class. It does not have any direct dependency on Entity Framework Core or any other infrastructure framework.
But I think it would be improved if you define what you mean by a POCO class earlier in the book.
Thanks for a great book though, it solidified a lot of the DDD concepts for me.
---
#### Document details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 49c9fdb0-f078-2030-204d-67d016b22c8d
* Version Independent ID: c37e4177-f0bd-de19-f53b-f597fbadcef0
* Content: [Implementing a microservice domain model with .NET Core](https://docs.microsoft.com/en-gb/dotnet/standard/microservices-architecture/microservice-ddd-cqrs-patterns/net-core-microservice-domain-model)
* Content Source: [docs/standard/microservices-architecture/microservice-ddd-cqrs-patterns/net-core-microservice-domain-model.md](https://github.com/dotnet/docs/blob/master/docs/standard/microservices-architecture/microservice-ddd-cqrs-patterns/net-core-microservice-domain-model.md)
* Product: **dotnet**
* GitHub Login: @CESARDELATORRE
* Microsoft Alias: **wiwagn** | 1.0 | Definition of POCO - One thing that confused me here is the definition of POCO classes. I always thought a POCO class was one that had no methods, and just a bunch of properties with getters and setters. So I was wondering where the domain logic would be.
You eventually clarify it by saying
> It is important to note that this is a domain entity implemented as a POCO class. It does not have any direct dependency on Entity Framework Core or any other infrastructure framework.
But I think it would be improved if you define what you mean by a POCO class earlier in the book.
Thanks for a great book though, it solidified a lot of the DDD concepts for me.
---
#### Document details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 49c9fdb0-f078-2030-204d-67d016b22c8d
* Version Independent ID: c37e4177-f0bd-de19-f53b-f597fbadcef0
* Content: [Implementing a microservice domain model with .NET Core](https://docs.microsoft.com/en-gb/dotnet/standard/microservices-architecture/microservice-ddd-cqrs-patterns/net-core-microservice-domain-model)
* Content Source: [docs/standard/microservices-architecture/microservice-ddd-cqrs-patterns/net-core-microservice-domain-model.md](https://github.com/dotnet/docs/blob/master/docs/standard/microservices-architecture/microservice-ddd-cqrs-patterns/net-core-microservice-domain-model.md)
* Product: **dotnet**
* GitHub Login: @CESARDELATORRE
* Microsoft Alias: **wiwagn** | non_priority | definition of poco one thing that confused me here is the definition of poco classes i always thought a poco class was one that had no methods and just a bunch of properties with getters and setters so i was wondering where the domain logic would be you eventually clarify it by saying gt it is important to note that this is a domain entity implemented as a poco class it does not have any direct dependency on entity framework core or any other infrastructure framework but i think it would be improved if you define what you mean by a poco class earlier in the book thanks for a great book though it solidified a lot of the ddd concepts for me document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product dotnet github login cesardelatorre microsoft alias wiwagn | 0 |
212,164 | 16,474,435,429 | IssuesEvent | 2021-05-24 01:42:01 | dominickpastore/pymd4c | https://api.github.com/repos/dominickpastore/pymd4c | closed | Enum names in docs not links | bug documentation | Enum names in the callback section on the pure parsing page are not clickable links.
Edit: Turns out this isn't specific to those particular identifiers—the API pages didn't generate properly, so all API links are broken. Oops. | 1.0 | Enum names in docs not links - Enum names in the callback section on the pure parsing page are not clickable links.
Edit: Turns out this isn't specific to those particular identifiers—the API pages didn't generate properly, so all API links are broken. Oops. | non_priority | enum names in docs not links enum names in the callback section on the pure parsing page are not clickable links edit turns out this isn t specific to those particular identifiers mdash the api pages didn t generate properly so all api links are broken oops | 0 |
342,888 | 30,642,726,679 | IssuesEvent | 2023-07-25 00:12:04 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix jax_numpy_linalg.test_jax_inv | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix jax_numpy_linalg.test_jax_inv - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5574012988/jobs/10182065230"><img src=https://img.shields.io/badge/-success-success></a>
| non_priority | fix jax numpy linalg test jax inv numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
73,919 | 15,286,453,334 | IssuesEvent | 2021-02-23 14:43:21 | wouter140/PortfolioSite | https://api.github.com/repos/wouter140/PortfolioSite | closed | CVE-2018-19839 (Medium) detected in node-sass-4.13.1.tgz, CSS::Sass-v3.4.11 | security vulnerability | ## CVE-2018-19839 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/PortfolioSite/package.json</p>
<p>Path to vulnerable library: /PortfolioSite/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.13.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/wouter140/PortfolioSite/commit/5e211947fdfe3701bd2dc55db9ed2cf44fc06c98">5e211947fdfe3701bd2dc55db9ed2cf44fc06c98</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, the function handle_error in sass_context.cpp allows attackers to cause a denial-of-service resulting from a heap-based buffer over-read via a crafted sass file.
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19839>CVE-2018-19839</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19839">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19839</a></p>
<p>Release Date: 2020-03-20</p>
<p>Fix Resolution: LibSass - 3.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19839 (Medium) detected in node-sass-4.13.1.tgz, CSS::Sass-v3.4.11 - ## CVE-2018-19839 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/PortfolioSite/package.json</p>
<p>Path to vulnerable library: /PortfolioSite/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.13.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/wouter140/PortfolioSite/commit/5e211947fdfe3701bd2dc55db9ed2cf44fc06c98">5e211947fdfe3701bd2dc55db9ed2cf44fc06c98</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, the function handle_error in sass_context.cpp allows attackers to cause a denial-of-service resulting from a heap-based buffer over-read via a crafted sass file.
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19839>CVE-2018-19839</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19839">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19839</a></p>
<p>Release Date: 2020-03-20</p>
<p>Fix Resolution: LibSass - 3.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz css sass cve medium severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm portfoliosite package json path to vulnerable library portfoliosite node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href vulnerability details in libsass prior to the function handle error in sass context cpp allows attackers to cause a denial of service resulting from a heap based buffer over read via a crafted sass file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
21,126 | 16,578,551,615 | IssuesEvent | 2021-05-31 08:36:44 | aquarist-labs/aquarium | https://api.github.com/repos/aquarist-labs/aquarium | closed | glass: 'Join existing cluster' page helper(s) | aqr: Would Have enhancement glass milestone: nice to have prio: low usability | I think it would be nice to add a hint telling where the security token can be found to the 'Join existing cluster' page:

I'm wondering if we should also add a note about how to get the IP address or FQDN.
| True | glass: 'Join existing cluster' page helper(s) - I think it would be nice to add a hint telling where the security token can be found to the 'Join existing cluster' page:

I'm wondering if we should also add a note about how to get the IP address or FQDN.
| non_priority | glass join existing cluster page helper s i think it would be nice to add a hint telling where the security token can be found to the join existing cluster page i m wondering if we should also add a note about how to get the ip address or fqdn | 0 |
356,285 | 25,176,156,972 | IssuesEvent | 2022-11-11 09:26:29 | phyliciachristel/pe | https://api.github.com/repos/phyliciachristel/pe | opened | Edit in UG does not show that module can be added multiple times | severity.Low type.DocumentationBug | App shows multiple modules for a person:

UG does not show this for module:

Confusing as user would not know how to edit to allocate multiple modules
<!--session: 1668153114756-9b7bce4c-4378-4d16-ae7d-02a3792f38df-->
<!--Version: Web v3.4.4--> | 1.0 | Edit in UG does not show that module can be added multiple times - App shows multiple modules for a person:

UG does not show this for module:

Confusing as user would not know how to edit to allocate multiple modules
<!--session: 1668153114756-9b7bce4c-4378-4d16-ae7d-02a3792f38df-->
<!--Version: Web v3.4.4--> | non_priority | edit in ug does not show that module can be added multiple times app shows multiple modules for a person ug does not show this for module confusing as user would not know how to edit to allocate multiple modules | 0 |
55,110 | 13,524,851,339 | IssuesEvent | 2020-09-15 12:11:57 | GetTerminus/terminus-oss | https://api.github.com/repos/GetTerminus/terminus-oss | closed | Verify storybook is a passable replacement for standalone docs | Focus: build Goal: Process Improvement Type: chore | Since storybook now generates API docs from compodoc, we can likely stop publishing the standalone docs.
Need to do a pass over to make sure there isn't anything important that will be lost. If there is, possibly we can add a standalone storybook page. | 1.0 | Verify storybook is a passable replacement for standalone docs - Since storybook now generates API docs from compodoc, we can likely stop publishing the standalone docs.
Need to do a pass over to make sure there isn't anything important that will be lost. If there is, possibly we can add a standalone storybook page. | non_priority | verify storybook is a passable replacement for standalone docs since storybook now generates api docs from compodoc we can likely stop publishing the standalone docs need to do a pass over to make sure there isn t anything important that will be lost if there is possibly we can add a standalone storybook page | 0 |
48,925 | 5,989,914,841 | IssuesEvent | 2017-06-02 09:53:23 | innosoft-pro/label-them | https://api.github.com/repos/innosoft-pro/label-them | closed | Strange naming | enhancement To be tested and closed | Somehow in JSON output we have entities called such as `jsonPoints` or `jsonParams`, while it sounds obvious. | 1.0 | Strange naming - Somehow in JSON output we have entities called such as `jsonPoints` or `jsonParams`, while it sounds obvious. | non_priority | strange naming somehow in json output we have entities called such as jsonpoints or jsonparams while it sounds obvious | 0 |
327,867 | 28,085,900,338 | IssuesEvent | 2023-03-30 09:44:47 | saladuit/minishell | https://api.github.com/repos/saladuit/minishell | closed | 🧪Test lexical analyzer | 🧪test | Some steps to achieve the lexical analyzer:
- [x] Write the production rules in BNF
- [x] Generate a program that is able to parse that [Tree sitter?](https://tree-sitter.github.io/tree-sitter/creating-parsers) | 1.0 | 🧪Test lexical analyzer - Some steps to achieve the lexical analyzer:
- [x] Write the production rules in BNF
- [x] Generate a program that is able to parse that [Tree sitter?](https://tree-sitter.github.io/tree-sitter/creating-parsers) | non_priority | 🧪test lexical analyzer some steps to achieve the lexical analyzer write the production rules in bnf generate a program that is able to parse that | 0 |
126,585 | 17,947,247,964 | IssuesEvent | 2021-09-12 02:51:50 | corbantjoyce/website | https://api.github.com/repos/corbantjoyce/website | opened | WS-2021-0153 (High) detected in ejs-2.7.4.tgz | security vulnerability | ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: website/package.json</p>
<p>Path to vulnerable library: website/node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.3.tgz (Root Library)
- workbox-webpack-plugin-5.1.4.tgz
- workbox-build-5.1.4.tgz
- rollup-plugin-off-main-thread-1.4.2.tgz
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/corbantjoyce/website/commit/e82dfbeb7218e3ae5399d7e6464aeb3e3c23eb49">e82dfbeb7218e3ae5399d7e6464aeb3e3c23eb49</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0153 (High) detected in ejs-2.7.4.tgz - ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: website/package.json</p>
<p>Path to vulnerable library: website/node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.3.tgz (Root Library)
- workbox-webpack-plugin-5.1.4.tgz
- workbox-build-5.1.4.tgz
- rollup-plugin-off-main-thread-1.4.2.tgz
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/corbantjoyce/website/commit/e82dfbeb7218e3ae5399d7e6464aeb3e3c23eb49">e82dfbeb7218e3ae5399d7e6464aeb3e3c23eb49</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in ejs tgz ws high severity vulnerability vulnerable library ejs tgz embedded javascript templates library home page a href path to dependency file website package json path to vulnerable library website node modules ejs package json dependency hierarchy react scripts tgz root library workbox webpack plugin tgz workbox build tgz rollup plugin off main thread tgz x ejs tgz vulnerable library found in head commit a href found in base branch master vulnerability details arbitrary code injection vulnerability was found in ejs before caused by filename which isn t sanitized for display publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ejs step up your open source security game with whitesource | 0 |
155,759 | 13,632,946,195 | IssuesEvent | 2020-09-24 20:31:40 | openstax/cnx-recipes | https://api.github.com/repos/openstax/cnx-recipes | closed | corn theme - boxed note with class and title | documentation theme:corn z.archive.baked.styles | 
Same specs here (#2191) but the title of the note+numbering is bold and the `<title>` of the note is not bold
If the feature has numbering, numbering follows #.# schema. Resets every chapter (1.1, 1.2, 1.3, 2.1, 2.2, etc)
Used in Calculus frequently.
### Boxed note
color: G1: `#F4F7F4`
### Theorem Title
color: B2: `#1E7E91`
font type: roboto slab
style: bold
font size: font-scale(0)
### Title from `<title>`
style: not bold
color: B2: `#1E7E91`
font type: roboto slab
font size: font-scale(0)
### Line between title and text
height: 1px (0.09rem?)
color: Grey1: `#F1F1F1`
### Padding
top, left, bottom, right: v-grid(.5)
# Alternative color schema
See Problem Solving Strategy feature in Calculus
background is B4: `#F7FAFB`; title color: B1: `#093D4C` | 1.0 | corn theme - boxed note with class and title - 
Same specs here (#2191) but the title of the note+numbering is bold and the `<title>` of the note is not bold
If the feature has numbering, numbering follows #.# schema. Resets every chapter (1.1, 1.2, 1.3, 2.1, 2.2, etc)
Used in Calculus frequently.
### Boxed note
color: G1: `#F4F7F4`
### Theorem Title
color: B2: `#1E7E91`
font type: roboto slab
style: bold
font size: font-scale(0)
### Title from `<title>`
style: not bold
color: B2: `#1E7E91`
font type: roboto slab
font size: font-scale(0)
### Line between title and text
height: 1px (0.09rem?)
color: Grey1: `#F1F1F1`
### Padding
top, left, bottom, right: v-grid(.5)
# Alternative color schema
See Problem Solving Strategy feature in Calculus
background is B4: `#F7FAFB`; title color: B1: `#093D4C` | non_priority | corn theme boxed note with class and title same specs here but the title of the note numbering is bold and the of the note is not bold if the feature has numbering numbering follows schema resets every chapter etc used in calculus frequently boxed note color theorem title color font type roboto slab style bold font size font scale title from style not bold color font type roboto slab font size font scale line between title and text height color padding top left bottom right v grid alternative color schema see problem solving strategy feature in calculus background is title color | 0 |
172,858 | 21,056,328,513 | IssuesEvent | 2022-04-01 03:58:37 | themagicalmammal/YOLOv4-pytorch | https://api.github.com/repos/themagicalmammal/YOLOv4-pytorch | opened | CVE-2021-41496 (High) detected in numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-41496 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl</b></p></summary>
<p>NumPy is the fundamental package for array computing with Python.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/4a/e34fce8f18c0e052c2b49f1b3713469d855f7662d58ae2b82a88341e865b/numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/00/4a/e34fce8f18c0e052c2b49f1b3713469d855f7662d58ae2b82a88341e865b/numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/themagicalmammal/YOLOv4-pytorch/commit/a60256c1d38244c95a7a8f32f56cf76f9b0814ad">a60256c1d38244c95a7a8f32f56cf76f9b0814ad</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** Buffer overflow in the array_from_pyobj function of fortranobject.c in NumPy < 1.19, which allows attackers to conduct a Denial of Service attacks by carefully constructing an array with negative values. NOTE: The vendor does not agree this is a vulnerability; the negative dimensions can only be created by an already privileged user (or internally).
<p>Publish Date: 2021-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41496>CVE-2021-41496</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-41496">https://nvd.nist.gov/vuln/detail/CVE-2021-41496</a></p>
<p>Release Date: 2021-12-17</p>
<p>Fix Resolution: autovizwidget - 0.12.7;numpy - 1.22.0rc1;numcodecs - 0.6.2;numpy-base - 1.11.3;numpy - 1.17.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-41496 (High) detected in numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl - ## CVE-2021-41496 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl</b></p></summary>
<p>NumPy is the fundamental package for array computing with Python.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/4a/e34fce8f18c0e052c2b49f1b3713469d855f7662d58ae2b82a88341e865b/numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/00/4a/e34fce8f18c0e052c2b49f1b3713469d855f7662d58ae2b82a88341e865b/numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **numpy-1.17.3-cp37-cp37m-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/themagicalmammal/YOLOv4-pytorch/commit/a60256c1d38244c95a7a8f32f56cf76f9b0814ad">a60256c1d38244c95a7a8f32f56cf76f9b0814ad</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** Buffer overflow in the array_from_pyobj function of fortranobject.c in NumPy < 1.19, which allows attackers to conduct a Denial of Service attacks by carefully constructing an array with negative values. NOTE: The vendor does not agree this is a vulnerability; the negative dimensions can only be created by an already privileged user (or internally).
<p>Publish Date: 2021-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-41496>CVE-2021-41496</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-41496">https://nvd.nist.gov/vuln/detail/CVE-2021-41496</a></p>
<p>Release Date: 2021-12-17</p>
<p>Fix Resolution: autovizwidget - 0.12.7;numpy - 1.22.0rc1;numcodecs - 0.6.2;numpy-base - 1.11.3;numpy - 1.17.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in numpy whl cve high severity vulnerability vulnerable library numpy whl numpy is the fundamental package for array computing with python library home page a href path to dependency file requirements txt path to vulnerable library requirements txt requirements txt dependency hierarchy x numpy whl vulnerable library found in head commit a href found in base branch master vulnerability details disputed buffer overflow in the array from pyobj function of fortranobject c in numpy which allows attackers to conduct a denial of service attacks by carefully constructing an array with negative values note the vendor does not agree this is a vulnerability the negative dimensions can only be created by an already privileged user or internally publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution autovizwidget numpy numcodecs numpy base numpy step up your open source security game with whitesource | 0 |
84,315 | 10,514,423,514 | IssuesEvent | 2019-09-28 00:35:35 | OfficeDev/office-ui-fabric-react | https://api.github.com/repos/OfficeDev/office-ui-fabric-react | closed | [Panel] Footer not rendering in the footer area | Component: Panel Resolution: By Design Type: Question ❔ | <!--
Thanks for contacting us! We're here to help.
Before you report an issue, check if it's been reported before:
* Search: https://github.com/OfficeDev/office-ui-fabric-react/search?type=Issues
* Search by area or component: https://github.com/OfficeDev/office-ui-fabric-react/issues/labels
Note that if you do not provide enough information to reproduce the issue, we may not be able to take action on your report.
-->
### Environment Information
- **Package version(s)**: 7.39.1
- **Browser and OS versions**: (fill this out if relevant)
### Please provide a reproduction of the bug in a codepen:
<!--
Providing an isolated reproduction of the bug in a codepen makes it much easier for us to help you. Here are some ways to get started:
* Go to https://aka.ms/fabricpen for a starter codepen
* You can also use the "Export to Codepen" feature for the various components in our documentation site.
* See http://codepen.io/dzearing/pens/public/?grid_type=list for a variety of examples
Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links if the repro occurs with an example.
(A permanent link is preferable to "use the website" as the website can change.)
-->
https://codepen.io/riosn/pen/yLBWyOK
#### Actual behavior:
Footer content is rendered where main content ends.
#### Expected behavior:
Footer content should be rendered at the bottom.
### Priorities and help requested:
Are you willing to submit a PR to fix? (No)
Requested priority: (High)
Products/sites affected: (if applicable)
PowerApps, Dynamics CRM | 1.0 | [Panel] Footer not rendering in the footer area - <!--
Thanks for contacting us! We're here to help.
Before you report an issue, check if it's been reported before:
* Search: https://github.com/OfficeDev/office-ui-fabric-react/search?type=Issues
* Search by area or component: https://github.com/OfficeDev/office-ui-fabric-react/issues/labels
Note that if you do not provide enough information to reproduce the issue, we may not be able to take action on your report.
-->
### Environment Information
- **Package version(s)**: 7.39.1
- **Browser and OS versions**: (fill this out if relevant)
### Please provide a reproduction of the bug in a codepen:
<!--
Providing an isolated reproduction of the bug in a codepen makes it much easier for us to help you. Here are some ways to get started:
* Go to https://aka.ms/fabricpen for a starter codepen
* You can also use the "Export to Codepen" feature for the various components in our documentation site.
* See http://codepen.io/dzearing/pens/public/?grid_type=list for a variety of examples
Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links if the repro occurs with an example.
(A permanent link is preferable to "use the website" as the website can change.)
-->
https://codepen.io/riosn/pen/yLBWyOK
#### Actual behavior:
Footer content is rendered where main content ends.
#### Expected behavior:
Footer content should be rendered at the bottom.
### Priorities and help requested:
Are you willing to submit a PR to fix? (No)
Requested priority: (High)
Products/sites affected: (if applicable)
PowerApps, Dynamics CRM | non_priority | footer not rendering in the footer area thanks for contacting us we re here to help before you report an issue check if it s been reported before search search by area or component note that if you do not provide enough information to reproduce the issue we may not be able to take action on your report environment information package version s browser and os versions fill this out if relevant please provide a reproduction of the bug in a codepen providing an isolated reproduction of the bug in a codepen makes it much easier for us to help you here are some ways to get started go to for a starter codepen you can also use the export to codepen feature for the various components in our documentation site see for a variety of examples alternatively you can also use to get permanent repro links if the repro occurs with an example a permanent link is preferable to use the website as the website can change actual behavior footer content is rendered where main content ends expected behavior footer content should be rendered at the bottom priorities and help requested are you willing to submit a pr to fix no requested priority high products sites affected if applicable powerapps dynamics crm | 0 |
5,357 | 19,295,477,955 | IssuesEvent | 2021-12-12 14:15:31 | Azure/PSRule.Rules.Azure | https://api.github.com/repos/Azure/PSRule.Rules.Azure | closed | Automation accounts should enable diagnostic logs | rule: automation-account | # Rule request
Automation accounts should enable the following diagnostic logs:
- JobLogs
- JobStreams
- DSCNodeStatus
- Metrics
## Applies to the following
The rule applies to the following:
- Resource type: **Microsoft.Automation/automationAccounts**
## Additional context
[Template reference](https://docs.microsoft.com/en-us/azure/templates/microsoft.automation/automationaccounts?tabs=bicep)
| 1.0 | Automation accounts should enable diagnostic logs - # Rule request
Automation accounts should enable the following diagnostic logs:
- JobLogs
- JobStreams
- DSCNodeStatus
- Metrics
## Applies to the following
The rule applies to the following:
- Resource type: **Microsoft.Automation/automationAccounts**
## Additional context
[Template reference](https://docs.microsoft.com/en-us/azure/templates/microsoft.automation/automationaccounts?tabs=bicep)
| non_priority | automation accounts should enable diagnostic logs rule request automation accounts should enable the following diagnostic logs joblogs jobstreams dscnodestatus metrics applies to the following the rule applies to the following resource type microsoft automation automationaccounts additional context | 0 |
11,587 | 5,041,460,377 | IssuesEvent | 2016-12-19 10:25:16 | opencv/opencv | https://api.github.com/repos/opencv/opencv | closed | (EXAMPLE_GPU) video_writer compile error. | bug category: build/install category: gpu (cuda) easy | <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
This is a template helping you to create an issue which can be processed as quickly as possible. This is the bug reporting section for the OpenCV library.
-->
##### System information (version)
<!-- Example
- OpenCV => 3.1
- Operating System / Platform => Windows 64 Bit
- Compiler => Visual Studio 2015
-->
- OpenCV => Latest
- Operating System / Platform => Windows 64 Bit
- Compiler => Visual Studio 2015 Update 3
##### Detailed description
<!-- your description -->
(EXAMPLE_GPU) video_writer compile error.
Source: video_writer.cpp : Line42
##### Steps to reproduce
Check the BUILD_EXAMPLES on CMake, and build.
Error code:
```.cpp
42: TickMeter tm;
```
Fixed code:
```.cpp
42: cv::TickMeter tm;
```
<!-- to add code example fence it with triple backticks and optional file extension
```.cpp
// C++ code example
```
or attach as .txt or .zip file
--> | 1.0 | (EXAMPLE_GPU) video_writer compile error. - <!--
If you have a question rather than reporting a bug please go to http://answers.opencv.org where you get much faster responses.
If you need further assistance please read [How To Contribute](https://github.com/opencv/opencv/wiki/How_to_contribute).
This is a template helping you to create an issue which can be processed as quickly as possible. This is the bug reporting section for the OpenCV library.
-->
##### System information (version)
<!-- Example
- OpenCV => 3.1
- Operating System / Platform => Windows 64 Bit
- Compiler => Visual Studio 2015
-->
- OpenCV => Latest
- Operating System / Platform => Windows 64 Bit
- Compiler => Visual Studio 2015 Update 3
##### Detailed description
<!-- your description -->
(EXAMPLE_GPU) video_writer compile error.
Source: video_writer.cpp : Line42
##### Steps to reproduce
Check the BUILD_EXAMPLES on CMake, and build.
Error code:
```.cpp
42: TickMeter tm;
```
Fixed code:
```.cpp
42: cv::TickMeter tm;
```
<!-- to add code example fence it with triple backticks and optional file extension
```.cpp
// C++ code example
```
or attach as .txt or .zip file
--> | non_priority | example gpu video writer compile error if you have a question rather than reporting a bug please go to where you get much faster responses if you need further assistance please read this is a template helping you to create an issue which can be processed as quickly as possible this is the bug reporting section for the opencv library system information version example opencv operating system platform windows bit compiler visual studio opencv latest operating system platform windows bit compiler visual studio update detailed description example gpu video writer compile error source video writer cpp steps to reproduce check the build examples on cmake and build error code cpp tickmeter tm fixed code cpp cv tickmeter tm to add code example fence it with triple backticks and optional file extension cpp c code example or attach as txt or zip file | 0 |
64,066 | 8,709,227,398 | IssuesEvent | 2018-12-06 13:23:08 | tripal/tripal | https://api.github.com/repos/tripal/tripal | closed | migrate satellite documentation in markdown into RTD | PR Submitted documentation | * Move documentation for contirbuting, testing, etc, into RTD
* Have sub-README link out to RTD instead
pre-approved after discussion with @tripal/project-managent-commitee-pmc | 1.0 | migrate satellite documentation in markdown into RTD - * Move documentation for contirbuting, testing, etc, into RTD
* Have sub-README link out to RTD instead
pre-approved after discussion with @tripal/project-managent-commitee-pmc | non_priority | migrate satellite documentation in markdown into rtd move documentation for contirbuting testing etc into rtd have sub readme link out to rtd instead pre approved after discussion with tripal project managent commitee pmc | 0 |
18,429 | 10,964,503,923 | IssuesEvent | 2019-11-27 22:50:37 | microsoft/botframework-solutions | https://api.github.com/repos/microsoft/botframework-solutions | closed | There was an error while connecting the Skill to the Assistant: Error: Some of the cultures provided to connect from the Skill are not available or aren't supported by your VA. Make sure you have a Dispatch for the cultures you are trying to connect, and that your Skill has a LUIS model for that culture | Bot Services Type: Bug customer-replied-to customer-reported | #### What project is affected?
Virtual Assistant and point of Interest skill
#### What language is this in?
csharp
#### What happens?
There was an error while connecting the Skill to the Assistant:
Error: Some of the cultures provided to connect from the Skill are not available or aren't supported by your VA.
Make sure you have a Dispatch for the cultures you are trying to connect, and that your Skill has a LUIS model for that culture
#### What are the steps to reproduce this issue?
I have updated the botskills and current version is botskills 1.0.10
And also Tried the Botskills connect without languages "en-us"
#### What were you expecting to happen?
Connect the skill to VA through Botskill command
#### Can you share any logs, error output, etc.?
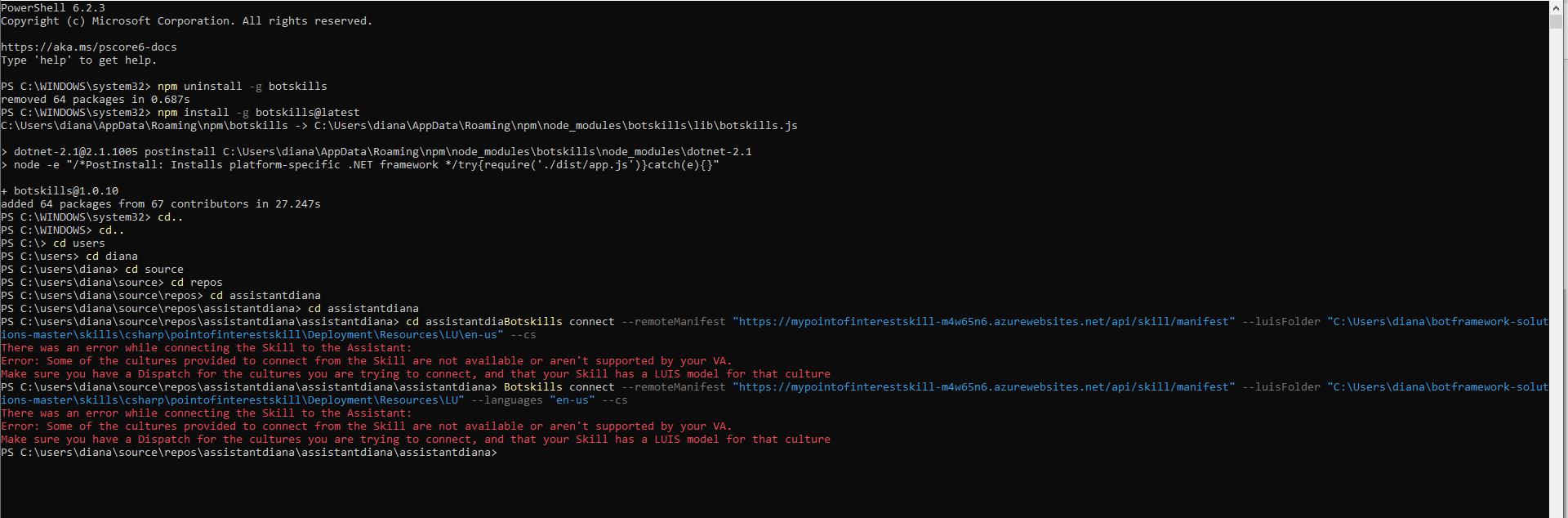
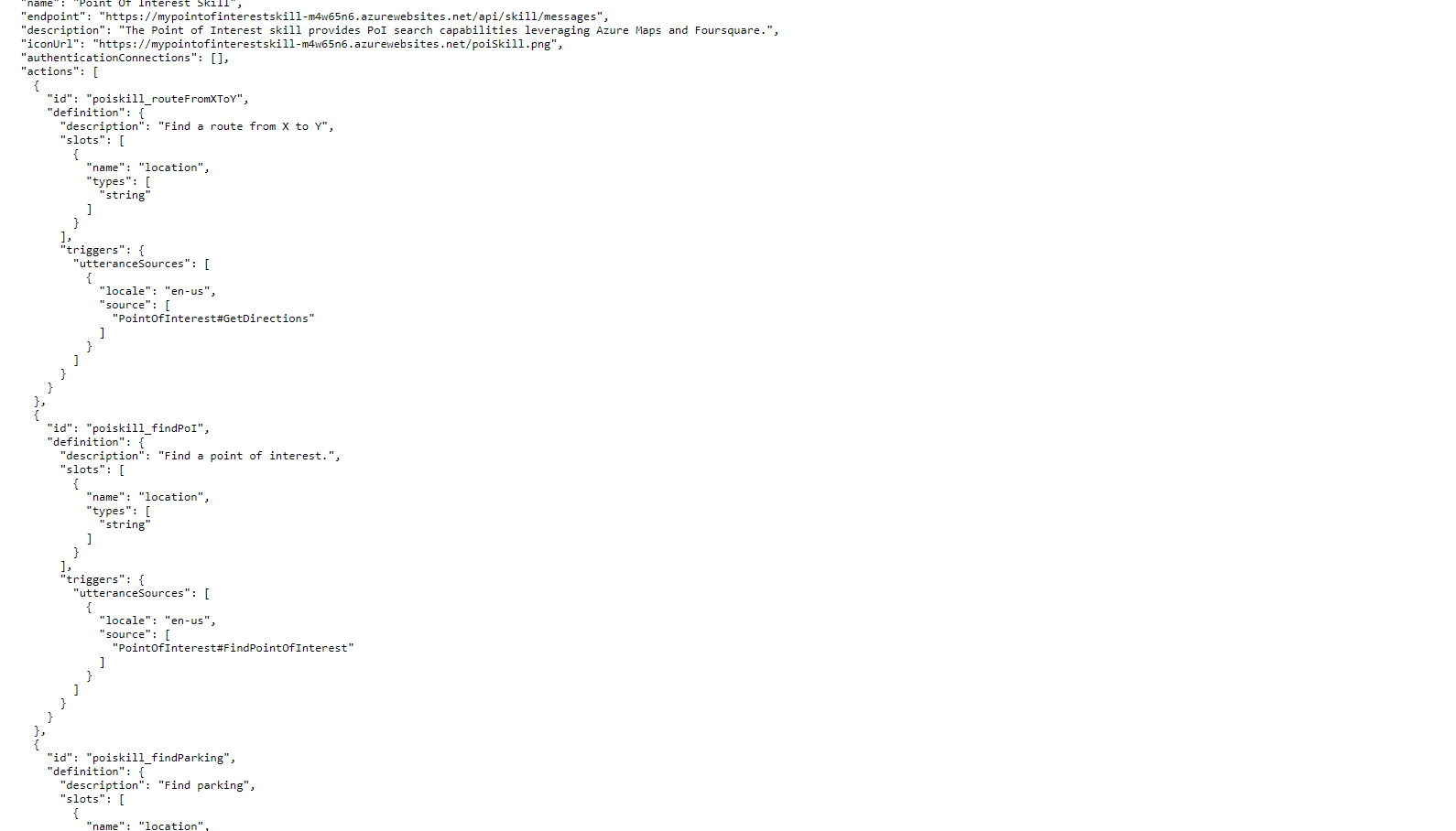
#### Any screenshots or additional context?
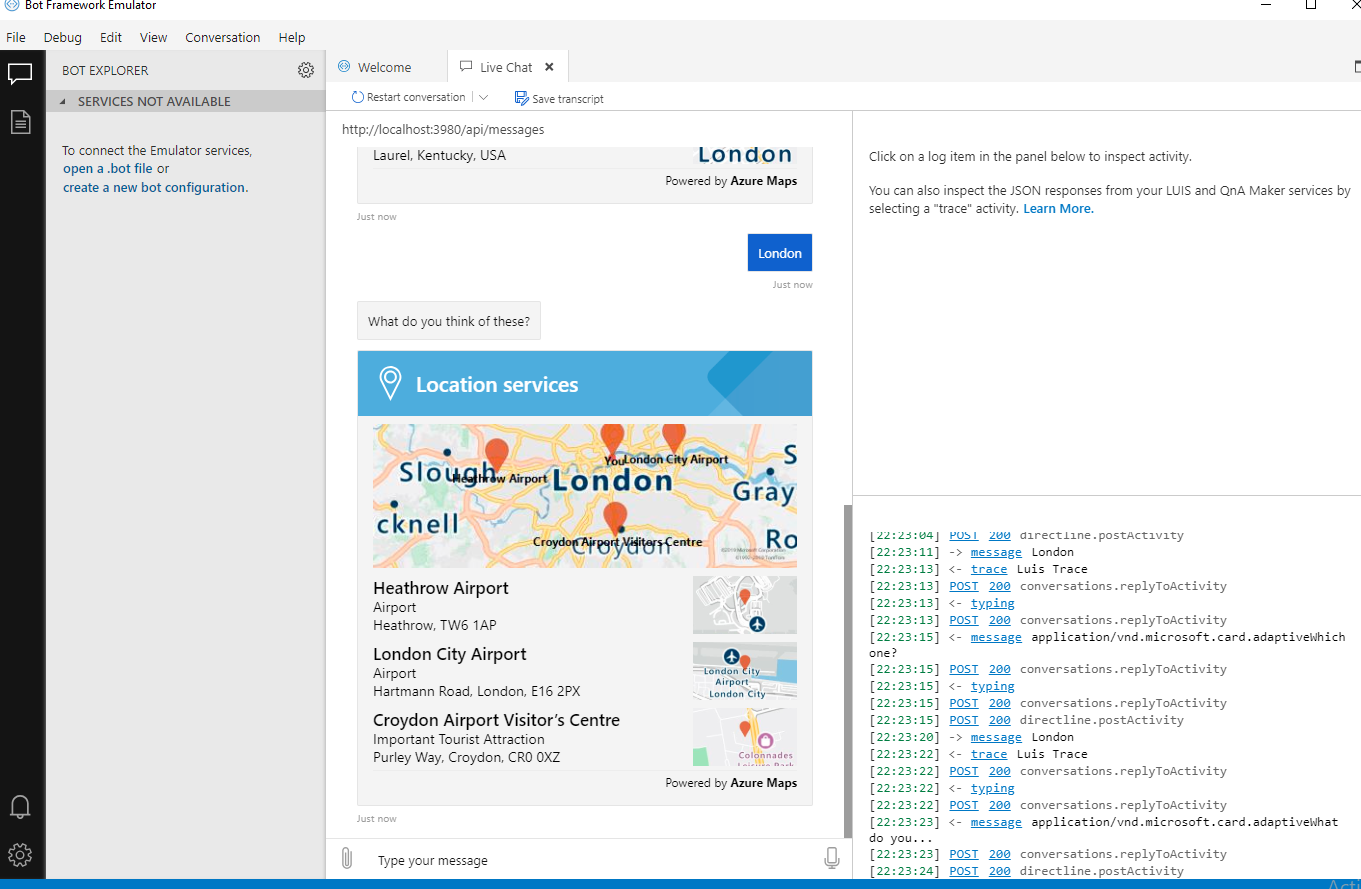
Please help. Thank you
| 1.0 | There was an error while connecting the Skill to the Assistant: Error: Some of the cultures provided to connect from the Skill are not available or aren't supported by your VA. Make sure you have a Dispatch for the cultures you are trying to connect, and that your Skill has a LUIS model for that culture - #### What project is affected?
Virtual Assistant and point of Interest skill
#### What language is this in?
csharp
#### What happens?
There was an error while connecting the Skill to the Assistant:
Error: Some of the cultures provided to connect from the Skill are not available or aren't supported by your VA.
Make sure you have a Dispatch for the cultures you are trying to connect, and that your Skill has a LUIS model for that culture
#### What are the steps to reproduce this issue?
I have updated the botskills and current version is botskills 1.0.10
And also Tried the Botskills connect without languages "en-us"
#### What were you expecting to happen?
Connect the skill to VA through Botskill command
#### Can you share any logs, error output, etc.?
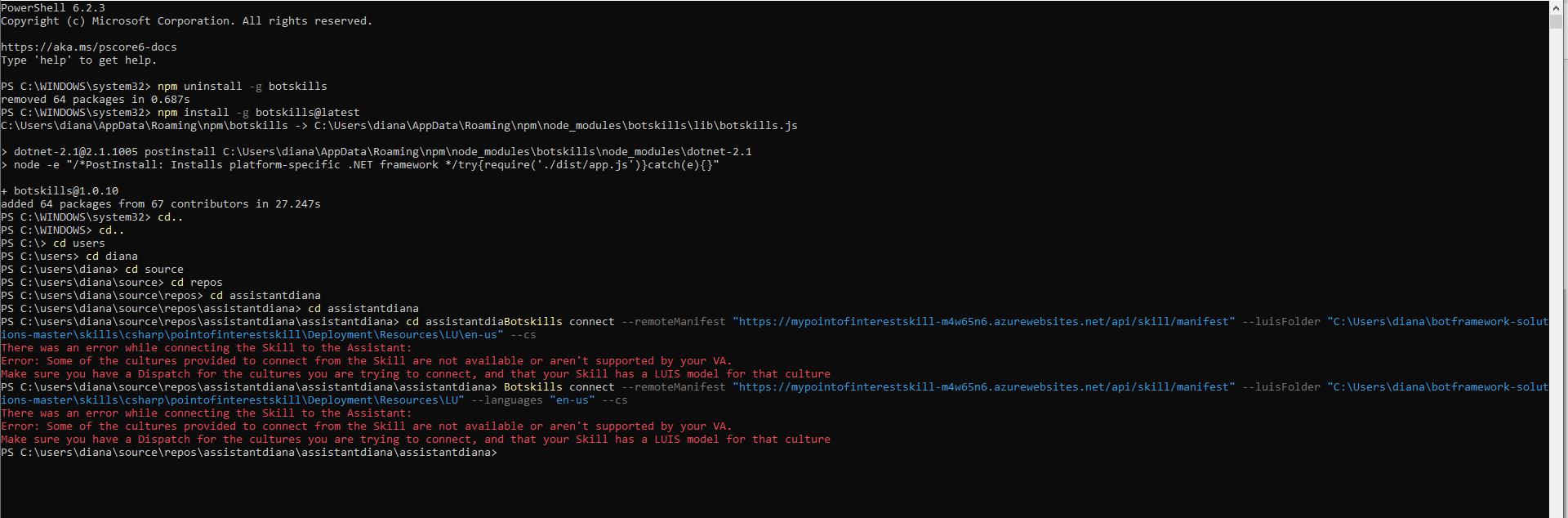
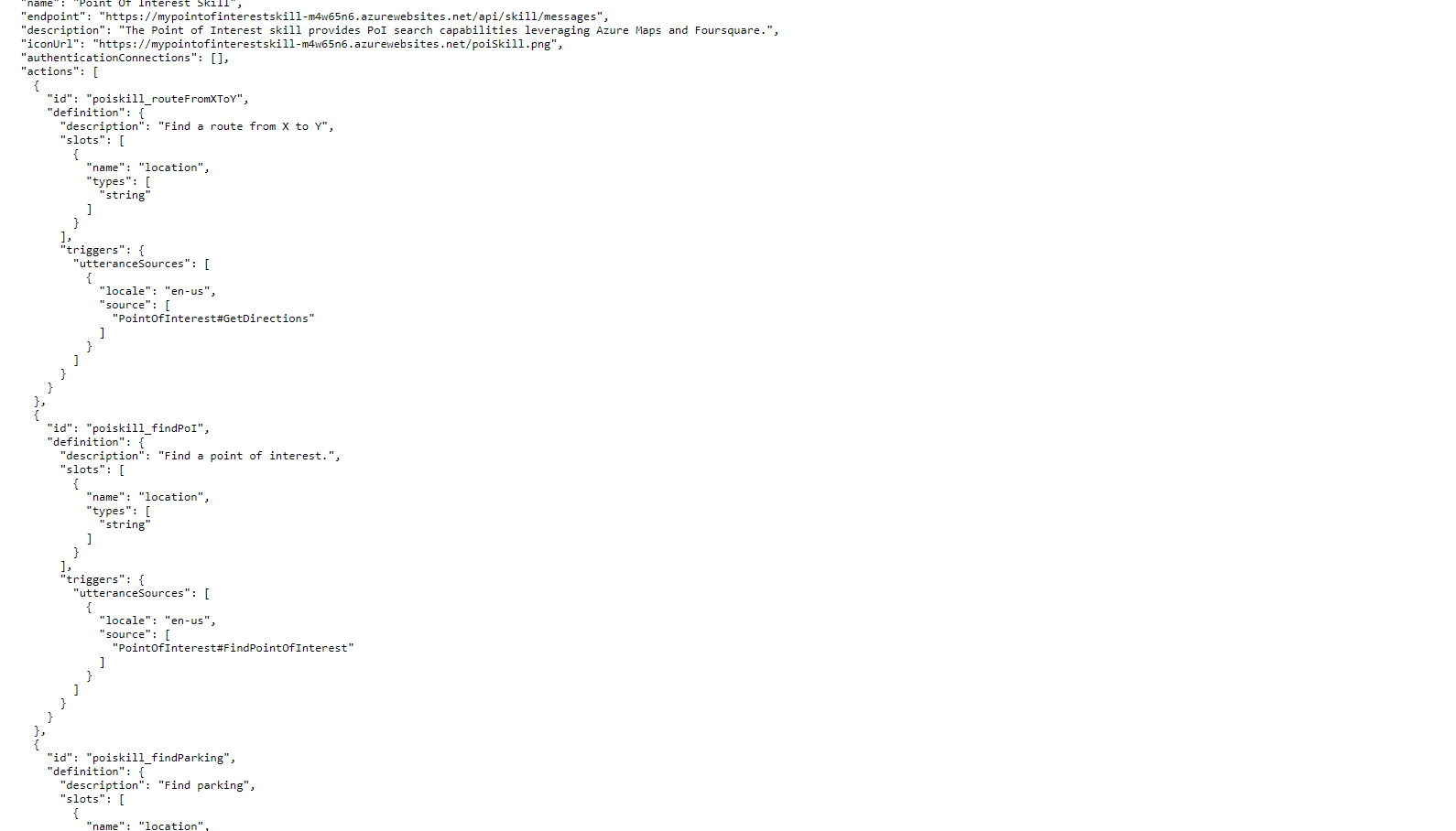
#### Any screenshots or additional context?
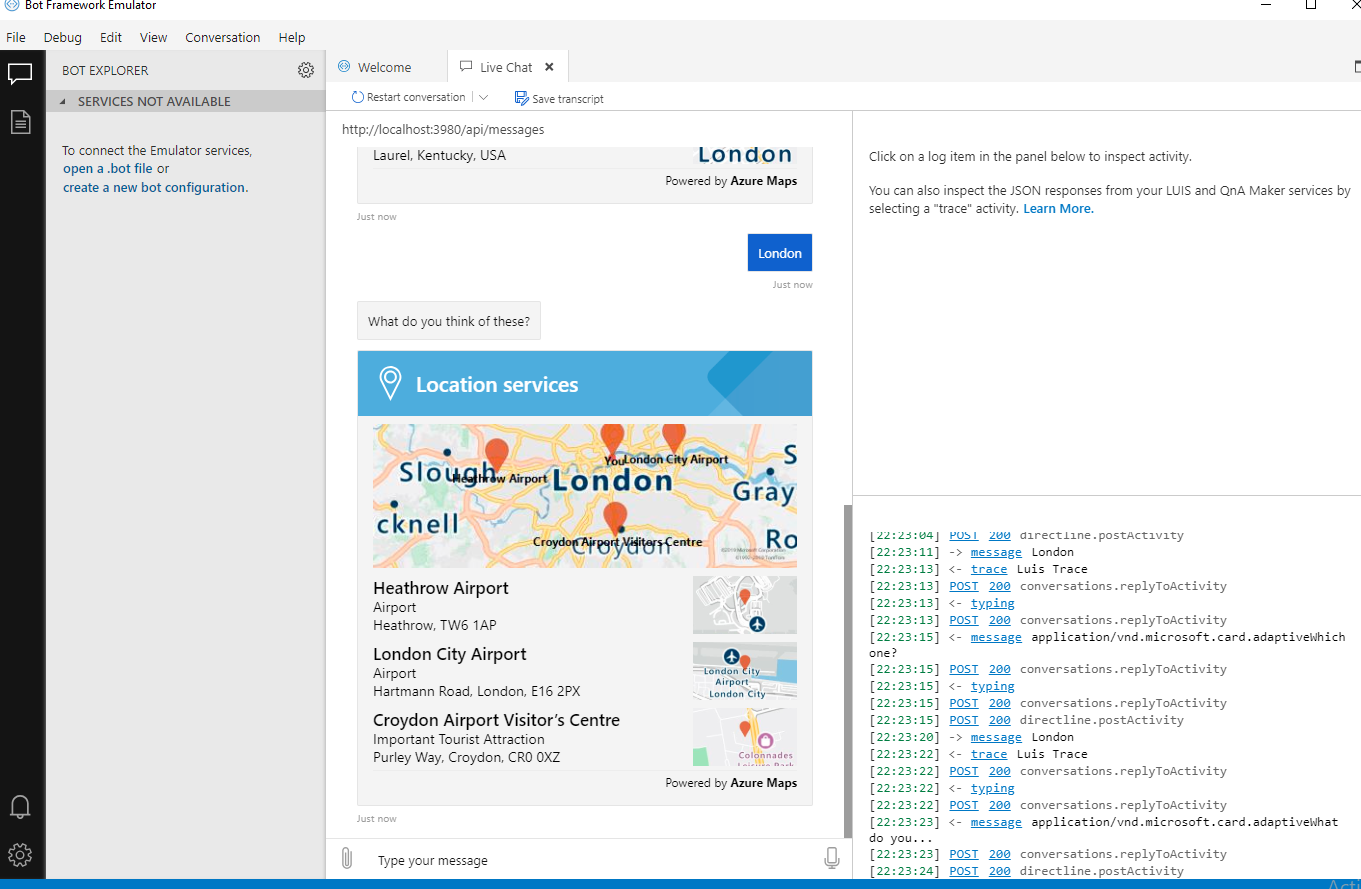
Please help. Thank you
| non_priority | there was an error while connecting the skill to the assistant error some of the cultures provided to connect from the skill are not available or aren t supported by your va make sure you have a dispatch for the cultures you are trying to connect and that your skill has a luis model for that culture what project is affected virtual assistant and point of interest skill what language is this in csharp what happens there was an error while connecting the skill to the assistant error some of the cultures provided to connect from the skill are not available or aren t supported by your va make sure you have a dispatch for the cultures you are trying to connect and that your skill has a luis model for that culture what are the steps to reproduce this issue i have updated the botskills and current version is botskills and also tried the botskills connect without languages en us what were you expecting to happen connect the skill to va through botskill command can you share any logs error output etc any screenshots or additional context please help thank you | 0 |
226,329 | 18,012,130,070 | IssuesEvent | 2021-09-16 09:48:32 | t3rn/t3rn | https://api.github.com/repos/t3rn/t3rn | closed | Unit tests remaining functionalities of Circuit | circuit :green_circle: contracts :memo: test :test_tube: | ## Description
Cover following scenarios with unit tests
### Contracts registry [Beqa]
- [ ] purge fails (contract missing + non-root user case)
- [ ] add_new_contract fails (contract already exists + non-root user case)
### Execution delivery
- [x] register gateway fail and success; 4 different tests for each header and block size combination [Maciej]
- [ ] submit_step_confirmation fail and success; 4 different tests for each header and block size combination [Maciej]
- [ ] dry_run_single_contract; other success paths, other failure paths [Devanshu]
- [ ] preload_bunch_of_contracts [Devanshu]
- [ ] run_single_contract [Devanshu]
- [ ] pre_run_bunch_until_break; depends on above two functions [Devanshu]
- [ ] retrieve_gateway_pointer [Beqa]
- [ ] retrieve_gateway_protocol [Beqa]
- [ ] dry_run_whole_xtx [Beqa] | 2.0 | Unit tests remaining functionalities of Circuit - ## Description
Cover following scenarios with unit tests
### Contracts registry [Beqa]
- [ ] purge fails (contract missing + non-root user case)
- [ ] add_new_contract fails (contract already exists + non-root user case)
### Execution delivery
- [x] register gateway fail and success; 4 different tests for each header and block size combination [Maciej]
- [ ] submit_step_confirmation fail and success; 4 different tests for each header and block size combination [Maciej]
- [ ] dry_run_single_contract; other success paths, other failure paths [Devanshu]
- [ ] preload_bunch_of_contracts [Devanshu]
- [ ] run_single_contract [Devanshu]
- [ ] pre_run_bunch_until_break; depends on above two functions [Devanshu]
- [ ] retrieve_gateway_pointer [Beqa]
- [ ] retrieve_gateway_protocol [Beqa]
- [ ] dry_run_whole_xtx [Beqa] | non_priority | unit tests remaining functionalities of circuit description cover following scenarios with unit tests contracts registry purge fails contract missing non root user case add new contract fails contract already exists non root user case execution delivery register gateway fail and success different tests for each header and block size combination submit step confirmation fail and success different tests for each header and block size combination dry run single contract other success paths other failure paths preload bunch of contracts run single contract pre run bunch until break depends on above two functions retrieve gateway pointer retrieve gateway protocol dry run whole xtx | 0 |
35,867 | 17,295,287,821 | IssuesEvent | 2021-07-25 15:49:08 | verilator/verilator | https://api.github.com/repos/verilator/verilator | closed | Any changes for multi-threading since v4.204? | area: performance status: assigned | We use verilator to simulate a large RISC-V core.
Previously we were using v4.204 and it can produce 16-thread simulator. However, when we upgrade to v4.210, it fails and says
```
%Warning-UNOPTTHREADS: Thread scheduler is unable to provide requested parallelism; suggest asking for fewer threads.
```
Are there any changes for multi-threading since v4.204? Is it expected that the optimal number of threads is reduced for v4.210? | True | Any changes for multi-threading since v4.204? - We use verilator to simulate a large RISC-V core.
Previously we were using v4.204 and it can produce 16-thread simulator. However, when we upgrade to v4.210, it fails and says
```
%Warning-UNOPTTHREADS: Thread scheduler is unable to provide requested parallelism; suggest asking for fewer threads.
```
Are there any changes for multi-threading since v4.204? Is it expected that the optimal number of threads is reduced for v4.210? | non_priority | any changes for multi threading since we use verilator to simulate a large risc v core previously we were using and it can produce thread simulator however when we upgrade to it fails and says warning unoptthreads thread scheduler is unable to provide requested parallelism suggest asking for fewer threads are there any changes for multi threading since is it expected that the optimal number of threads is reduced for | 0 |
164,382 | 13,941,615,677 | IssuesEvent | 2020-10-22 19:41:26 | prebuild/prebuild-install | https://api.github.com/repos/prebuild/prebuild-install | closed | Document cross platform options | documentation good first issue | I tried to build an electron application for Windows on Linux. It depends on one native module, but luckily it uses `prebuild`. So I thought it should work in theory. However it wasn't as simple as I expected. There are no parameters to set the target platform for prebuild-install. So it will automatically install for the current platform.
But then I found out that actually there ARE parameters to specify the platforms, they are just not in the docs. (More of the story: https://github.com/electron/electron-rebuild/issues/176#issuecomment-705445381).
With following command everything works fine:
`(cd node_modules/@thiagoelg/node-printer && node /home/myuser/myapp/src/electron/node_modules/prebuild-install/bin.js --platform=win32 --arch=x64 --target=10.1.3 --runtime=electron --verbose --force)`
So my main request here is to add those to the docs and CLI help.
Also the call above is very incovenient. I cd into the dependency to trick prebuild-install to think it's a project root dir. Otherwise it tries to fetch a prebuild binary for the project (myapp) itself.
However I see a bigger problem here: Luckily, the dependency has a prebuild version for Linux. If it didn't I assume it wouldn't work, although I don't need a Linux binary for my application at all. The reason for my assumption:
Before calling `prebuild-install` with different target platform (see command above) I have to run `npm install` and this will automatically call a hook that runs `prebuild-install` but WITHOUT target platform. If there was no Linux-build, the entire `npm install` would abort and the node_module directory for that dependency wouldn't exist. I checked this assumption in a proof-of-concept by using a different version of my dependency that has no Linux build.
I could workaround this by removing `--force` and try to build the module from source. But this would be absolutely unnecessary, as I don't need the Linux version at all.
My idea is to allow a project configuration that tells prebuild-install that you have specific target platforms / archs. If available, prebuild-install should consider those settings. If not, it should work like before and fetch the modules for the platform it's running on.
Maybe in package.json. Maybe it could re-use electron-builder's syntax. I also can see prebuild has a config file itself but it seems it's only for configuring a project to provide prebuild itself. Maybe you could also allow it to tell "I will not provide prebuild myself, but I have dependencies that do" | 1.0 | Document cross platform options - I tried to build an electron application for Windows on Linux. It depends on one native module, but luckily it uses `prebuild`. So I thought it should work in theory. However it wasn't as simple as I expected. There are no parameters to set the target platform for prebuild-install. So it will automatically install for the current platform.
But then I found out that actually there ARE parameters to specify the platforms, they are just not in the docs. (More of the story: https://github.com/electron/electron-rebuild/issues/176#issuecomment-705445381).
With following command everything works fine:
`(cd node_modules/@thiagoelg/node-printer && node /home/myuser/myapp/src/electron/node_modules/prebuild-install/bin.js --platform=win32 --arch=x64 --target=10.1.3 --runtime=electron --verbose --force)`
So my main request here is to add those to the docs and CLI help.
Also the call above is very incovenient. I cd into the dependency to trick prebuild-install to think it's a project root dir. Otherwise it tries to fetch a prebuild binary for the project (myapp) itself.
However I see a bigger problem here: Luckily, the dependency has a prebuild version for Linux. If it didn't I assume it wouldn't work, although I don't need a Linux binary for my application at all. The reason for my assumption:
Before calling `prebuild-install` with different target platform (see command above) I have to run `npm install` and this will automatically call a hook that runs `prebuild-install` but WITHOUT target platform. If there was no Linux-build, the entire `npm install` would abort and the node_module directory for that dependency wouldn't exist. I checked this assumption in a proof-of-concept by using a different version of my dependency that has no Linux build.
I could workaround this by removing `--force` and try to build the module from source. But this would be absolutely unnecessary, as I don't need the Linux version at all.
My idea is to allow a project configuration that tells prebuild-install that you have specific target platforms / archs. If available, prebuild-install should consider those settings. If not, it should work like before and fetch the modules for the platform it's running on.
Maybe in package.json. Maybe it could re-use electron-builder's syntax. I also can see prebuild has a config file itself but it seems it's only for configuring a project to provide prebuild itself. Maybe you could also allow it to tell "I will not provide prebuild myself, but I have dependencies that do" | non_priority | document cross platform options i tried to build an electron application for windows on linux it depends on one native module but luckily it uses prebuild so i thought it should work in theory however it wasn t as simple as i expected there are no parameters to set the target platform for prebuild install so it will automatically install for the current platform but then i found out that actually there are parameters to specify the platforms they are just not in the docs more of the story with following command everything works fine cd node modules thiagoelg node printer node home myuser myapp src electron node modules prebuild install bin js platform arch target runtime electron verbose force so my main request here is to add those to the docs and cli help also the call above is very incovenient i cd into the dependency to trick prebuild install to think it s a project root dir otherwise it tries to fetch a prebuild binary for the project myapp itself however i see a bigger problem here luckily the dependency has a prebuild version for linux if it didn t i assume it wouldn t work although i don t need a linux binary for my application at all the reason for my assumption before calling prebuild install with different target platform see command above i have to run npm install and this will automatically call a hook that runs prebuild install but without target platform if there was no linux build the entire npm install would abort and the node module directory for that dependency wouldn t exist i checked this assumption in a proof of concept by using a different version of my dependency that has no linux build i could workaround this by removing force and try to build the module from source but this would be absolutely unnecessary as i don t need the linux version at all my idea is to allow a project configuration that tells prebuild install that you have specific target platforms archs if available prebuild install should consider those settings if not it should work like before and fetch the modules for the platform it s running on maybe in package json maybe it could re use electron builder s syntax i also can see prebuild has a config file itself but it seems it s only for configuring a project to provide prebuild itself maybe you could also allow it to tell i will not provide prebuild myself but i have dependencies that do | 0 |
46,182 | 13,055,864,181 | IssuesEvent | 2020-07-30 02:57:47 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | Update CMAKE project docs (Trac #702) | Incomplete Migration Migrated from Trac defect documentation | Migrated from https://code.icecube.wisc.edu/ticket/702
```json
{
"status": "closed",
"changetime": "2015-02-11T19:23:39",
"description": "The cmake project docs are old and crufty and need some updating.\n\n",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1423682619623426",
"component": "documentation",
"summary": "Update CMAKE project docs",
"priority": "normal",
"keywords": "",
"time": "2012-11-06T02:12:20",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
| 1.0 | Update CMAKE project docs (Trac #702) - Migrated from https://code.icecube.wisc.edu/ticket/702
```json
{
"status": "closed",
"changetime": "2015-02-11T19:23:39",
"description": "The cmake project docs are old and crufty and need some updating.\n\n",
"reporter": "blaufuss",
"cc": "",
"resolution": "fixed",
"_ts": "1423682619623426",
"component": "documentation",
"summary": "Update CMAKE project docs",
"priority": "normal",
"keywords": "",
"time": "2012-11-06T02:12:20",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
| non_priority | update cmake project docs trac migrated from json status closed changetime description the cmake project docs are old and crufty and need some updating n n reporter blaufuss cc resolution fixed ts component documentation summary update cmake project docs priority normal keywords time milestone owner nega type defect | 0 |
171,006 | 27,046,006,272 | IssuesEvent | 2023-02-13 09:49:50 | alexdeploy/developer-portfolio | https://api.github.com/repos/alexdeploy/developer-portfolio | closed | [Projects page] Set a width limit to projects filters tab. | design | If multiple techs are added to filters tab, there is an overwidth with text.
it would be necessary to create a line break every time it reaches the end of the window width.
[Projects page](https://github.com/alexdeploy/developer-portfolio/blob/main/pages/projects.vue) line 37 | 1.0 | [Projects page] Set a width limit to projects filters tab. - If multiple techs are added to filters tab, there is an overwidth with text.
it would be necessary to create a line break every time it reaches the end of the window width.
[Projects page](https://github.com/alexdeploy/developer-portfolio/blob/main/pages/projects.vue) line 37 | non_priority | set a width limit to projects filters tab if multiple techs are added to filters tab there is an overwidth with text it would be necessary to create a line break every time it reaches the end of the window width line | 0 |
99,197 | 12,405,175,759 | IssuesEvent | 2020-05-21 16:48:12 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | No way to scroll search scopes/filters with a mouse | design team/search team/web | Reported by https://app.hubspot.com/contacts/2762526/company/693777200
A user reported they were unable to scroll repo filters and search scopes. Since we lack any visual indicator that the row is scrollable, or any buttons to scroll left and right, this only works if a user has a trackpad, or a mouse that has provides a scroll device that supports left-right scrolling. | 1.0 | No way to scroll search scopes/filters with a mouse - Reported by https://app.hubspot.com/contacts/2762526/company/693777200
A user reported they were unable to scroll repo filters and search scopes. Since we lack any visual indicator that the row is scrollable, or any buttons to scroll left and right, this only works if a user has a trackpad, or a mouse that has provides a scroll device that supports left-right scrolling. | non_priority | no way to scroll search scopes filters with a mouse reported by a user reported they were unable to scroll repo filters and search scopes since we lack any visual indicator that the row is scrollable or any buttons to scroll left and right this only works if a user has a trackpad or a mouse that has provides a scroll device that supports left right scrolling | 0 |
122,396 | 10,221,857,526 | IssuesEvent | 2019-08-16 03:47:17 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | opened | Time module, current time parsing fails | Area/StandardLibs BetaTesting Type/Question | **Description:**
Is the following code snippet valid?
```ballerina
time:Time currentTime = time:currentTime();
var k = time:parse(time:toString(currentTime), "yyyy-MM-dd'T'HH:mm:ss.SSSZ");
io:println(k);
```
It prints the following, but I expect it to parse the current time properly.
```
error {ballerina/time}TimeError message=parse date "2019-08-16T09:15:01.758+05:30" for the format "yyyy-MM-dd'T'HH:mm:ss.SSSZ" failed:Text '2019-08-16T09:15:01.758+05:30' c
ould not be parsed at index 23
```
**Affected Versions:**
Ballerina 1.0.0-beta-SNAPSHOT
| 1.0 | Time module, current time parsing fails - **Description:**
Is the following code snippet valid?
```ballerina
time:Time currentTime = time:currentTime();
var k = time:parse(time:toString(currentTime), "yyyy-MM-dd'T'HH:mm:ss.SSSZ");
io:println(k);
```
It prints the following, but I expect it to parse the current time properly.
```
error {ballerina/time}TimeError message=parse date "2019-08-16T09:15:01.758+05:30" for the format "yyyy-MM-dd'T'HH:mm:ss.SSSZ" failed:Text '2019-08-16T09:15:01.758+05:30' c
ould not be parsed at index 23
```
**Affected Versions:**
Ballerina 1.0.0-beta-SNAPSHOT
| non_priority | time module current time parsing fails description is the following code snippet valid ballerina time time currenttime time currenttime var k time parse time tostring currenttime yyyy mm dd t hh mm ss sssz io println k it prints the following but i expect it to parse the current time properly error ballerina time timeerror message parse date for the format yyyy mm dd t hh mm ss sssz failed text c ould not be parsed at index affected versions ballerina beta snapshot | 0 |
56,527 | 6,992,169,990 | IssuesEvent | 2017-12-15 04:53:00 | MyEtherWallet/MyEtherWallet | https://api.github.com/repos/MyEtherWallet/MyEtherWallet | closed | Make unlock header expand / collapse more obvious | design/research enhancement | The + / - symbol next to the header that allows you to change wallets is a little too subtle. Make a button or icon that makes this feature a little more obvious. | 1.0 | Make unlock header expand / collapse more obvious - The + / - symbol next to the header that allows you to change wallets is a little too subtle. Make a button or icon that makes this feature a little more obvious. | non_priority | make unlock header expand collapse more obvious the symbol next to the header that allows you to change wallets is a little too subtle make a button or icon that makes this feature a little more obvious | 0 |
251,583 | 21,511,687,887 | IssuesEvent | 2022-04-28 05:39:12 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | opened | Intermittent UI test failure - < CrashReportingTest. privateBrowsingUseAppWhileTabIsCrashedTest > | b:crash eng:intermittent-test eng:ui-test | ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/7426066978220056767/executions/bs.3f14b5803425fc45/testcases/1)
### Stacktrace:
04-27 15:14:32.458: D/AndroidRuntime(14707): --------- beginning of crash
04-27 15:14:32.459: E/AndroidRuntime(14707): FATAL EXCEPTION: main
04-27 15:14:32.459: E/AndroidRuntime(14707): Process: org.mozilla.fenix.debug:mozilla.components.lib.crash.CrashHandler, PID: 14707
04-27 15:14:32.459: E/AndroidRuntime(14707): android.app.RemoteServiceException: Context.startForegroundService() did not then call Service.startForeground(): ServiceRecord{8705358 u0 org.mozilla.fenix.debug/mozilla.components.lib.crash.handler.CrashHandlerService}
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.app.ActivityThread$H.handleMessage(ActivityThread.java:2005)
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.os.Handler.dispatchMessage(Handler.java:106)
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.os.Looper.loop(Looper.java:223)
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.app.ActivityThread.main(ActivityThread.java:7656)
04-27 15:14:32.459: E/AndroidRuntime(14707): at java.lang.reflect.Method.invoke(Native Method)
04-27 15:14:32.459: E/AndroidRuntime(14707): at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:592)
04-27 15:14:32.459: E/AndroidRuntime(14707): at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:947)
04-27 15:14:32.460: E/ExceptionHandler(14707): Uncaught exception handled:
04-27 15:14:32.460: E/ExceptionHandler(14707): android.app.RemoteServiceException: Context.startForegroundService() did not then call Service.startForeground(): ServiceRecord{8705358 u0 org.mozilla.fenix.debug/mozilla.components.lib.crash.handler.CrashHandlerService}
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.app.ActivityThread$H.handleMessage(ActivityThread.java:2005)
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.os.Handler.dispatchMessage(Handler.java:106)
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.os.Looper.loop(Looper.java:223)
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.app.ActivityThread.main(ActivityThread.java:7656)
04-27 15:14:32.460: E/ExceptionHandler(14707): at java.lang.reflect.Method.invoke(Native Method)
04-27 15:14:32.460: E/ExceptionHandler(14707): at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:592)
04-27 15:14:32.460: E/ExceptionHandler(14707): at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:947)
04-27 15:14:32.461: I/mozac/CrashReporter(14707): Received crash: UncaughtExceptionCrash(timestamp=1651072472461, throwable=android.app.RemoteServiceException: Context.startForegroundService() did not then call Service.startForeground(): ServiceRecord{8705358 u0 org.mozilla.fenix.debug/mozilla.components.lib.crash.handler.CrashHandlerService}, breadcrumbs=[], uuid=d6941988-aa12-4b5d-b9e5-24549fe6a6ae)
04-27 15:14:32.491: I/mozac/CrashReporter(14707): Received crash: NativeCodeCrash(timestamp=1651072472491, minidumpPath=/data/user/0/org.mozilla.fenix.debug/files/mozilla/Crash Reports/pending/4e9806dd-723a-9234-7243-fb7e89df0b56.dmp, minidumpSuccess=false, extrasPath=/data/user/0/org.mozilla.fenix.debug/files/mozilla/Crash Reports/pending/4e9806dd-723a-9234-7243-fb7e89df0b56.extra, processType=FOREGROUND_CHILD, breadcrumbs=[], uuid=5e59ec3a-1a33-48d2-9616-c8db401f9b47)
04-27 15:14:32.520: I/Choreographer(11599): Skipped 32 frames! The application may be doing too much work on its main thread.
04-27 15:14:32.546: I/tombstoned(283): received crash request for pid 14707
04-27 15:14:32.546: I/tombstoned(283): found intercept fd 512 for pid 14707 and type kDebuggerdJavaBacktrace
04-27 15:14:32.547: I/sh.CrashHandle(14707): Wrote stack traces to tombstoned
04-27 15:14:32.547: I/system_server(483): libdebuggerd_client: done dumping process 14707
04-27 15:14:32.556: I/ActivityManager(483): Done dumping
04-27 15:14:32.557: E/ActivityManager(483): ANR in org.mozilla.fenix.debug:mozilla.components.lib.crash.CrashHandler
04-27 15:14:32.557: E/ActivityManager(483): PID: 14707
### Build: 4/27 Main
| 2.0 | Intermittent UI test failure - < CrashReportingTest. privateBrowsingUseAppWhileTabIsCrashedTest > - ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/7426066978220056767/executions/bs.3f14b5803425fc45/testcases/1)
### Stacktrace:
04-27 15:14:32.458: D/AndroidRuntime(14707): --------- beginning of crash
04-27 15:14:32.459: E/AndroidRuntime(14707): FATAL EXCEPTION: main
04-27 15:14:32.459: E/AndroidRuntime(14707): Process: org.mozilla.fenix.debug:mozilla.components.lib.crash.CrashHandler, PID: 14707
04-27 15:14:32.459: E/AndroidRuntime(14707): android.app.RemoteServiceException: Context.startForegroundService() did not then call Service.startForeground(): ServiceRecord{8705358 u0 org.mozilla.fenix.debug/mozilla.components.lib.crash.handler.CrashHandlerService}
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.app.ActivityThread$H.handleMessage(ActivityThread.java:2005)
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.os.Handler.dispatchMessage(Handler.java:106)
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.os.Looper.loop(Looper.java:223)
04-27 15:14:32.459: E/AndroidRuntime(14707): at android.app.ActivityThread.main(ActivityThread.java:7656)
04-27 15:14:32.459: E/AndroidRuntime(14707): at java.lang.reflect.Method.invoke(Native Method)
04-27 15:14:32.459: E/AndroidRuntime(14707): at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:592)
04-27 15:14:32.459: E/AndroidRuntime(14707): at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:947)
04-27 15:14:32.460: E/ExceptionHandler(14707): Uncaught exception handled:
04-27 15:14:32.460: E/ExceptionHandler(14707): android.app.RemoteServiceException: Context.startForegroundService() did not then call Service.startForeground(): ServiceRecord{8705358 u0 org.mozilla.fenix.debug/mozilla.components.lib.crash.handler.CrashHandlerService}
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.app.ActivityThread$H.handleMessage(ActivityThread.java:2005)
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.os.Handler.dispatchMessage(Handler.java:106)
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.os.Looper.loop(Looper.java:223)
04-27 15:14:32.460: E/ExceptionHandler(14707): at android.app.ActivityThread.main(ActivityThread.java:7656)
04-27 15:14:32.460: E/ExceptionHandler(14707): at java.lang.reflect.Method.invoke(Native Method)
04-27 15:14:32.460: E/ExceptionHandler(14707): at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:592)
04-27 15:14:32.460: E/ExceptionHandler(14707): at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:947)
04-27 15:14:32.461: I/mozac/CrashReporter(14707): Received crash: UncaughtExceptionCrash(timestamp=1651072472461, throwable=android.app.RemoteServiceException: Context.startForegroundService() did not then call Service.startForeground(): ServiceRecord{8705358 u0 org.mozilla.fenix.debug/mozilla.components.lib.crash.handler.CrashHandlerService}, breadcrumbs=[], uuid=d6941988-aa12-4b5d-b9e5-24549fe6a6ae)
04-27 15:14:32.491: I/mozac/CrashReporter(14707): Received crash: NativeCodeCrash(timestamp=1651072472491, minidumpPath=/data/user/0/org.mozilla.fenix.debug/files/mozilla/Crash Reports/pending/4e9806dd-723a-9234-7243-fb7e89df0b56.dmp, minidumpSuccess=false, extrasPath=/data/user/0/org.mozilla.fenix.debug/files/mozilla/Crash Reports/pending/4e9806dd-723a-9234-7243-fb7e89df0b56.extra, processType=FOREGROUND_CHILD, breadcrumbs=[], uuid=5e59ec3a-1a33-48d2-9616-c8db401f9b47)
04-27 15:14:32.520: I/Choreographer(11599): Skipped 32 frames! The application may be doing too much work on its main thread.
04-27 15:14:32.546: I/tombstoned(283): received crash request for pid 14707
04-27 15:14:32.546: I/tombstoned(283): found intercept fd 512 for pid 14707 and type kDebuggerdJavaBacktrace
04-27 15:14:32.547: I/sh.CrashHandle(14707): Wrote stack traces to tombstoned
04-27 15:14:32.547: I/system_server(483): libdebuggerd_client: done dumping process 14707
04-27 15:14:32.556: I/ActivityManager(483): Done dumping
04-27 15:14:32.557: E/ActivityManager(483): ANR in org.mozilla.fenix.debug:mozilla.components.lib.crash.CrashHandler
04-27 15:14:32.557: E/ActivityManager(483): PID: 14707
### Build: 4/27 Main
| non_priority | intermittent ui test failure firebase test run stacktrace d androidruntime beginning of crash e androidruntime fatal exception main e androidruntime process org mozilla fenix debug mozilla components lib crash crashhandler pid e androidruntime android app remoteserviceexception context startforegroundservice did not then call service startforeground servicerecord org mozilla fenix debug mozilla components lib crash handler crashhandlerservice e androidruntime at android app activitythread h handlemessage activitythread java e androidruntime at android os handler dispatchmessage handler java e androidruntime at android os looper loop looper java e androidruntime at android app activitythread main activitythread java e androidruntime at java lang reflect method invoke native method e androidruntime at com android internal os runtimeinit methodandargscaller run runtimeinit java e androidruntime at com android internal os zygoteinit main zygoteinit java e exceptionhandler uncaught exception handled e exceptionhandler android app remoteserviceexception context startforegroundservice did not then call service startforeground servicerecord org mozilla fenix debug mozilla components lib crash handler crashhandlerservice e exceptionhandler at android app activitythread h handlemessage activitythread java e exceptionhandler at android os handler dispatchmessage handler java e exceptionhandler at android os looper loop looper java e exceptionhandler at android app activitythread main activitythread java e exceptionhandler at java lang reflect method invoke native method e exceptionhandler at com android internal os runtimeinit methodandargscaller run runtimeinit java e exceptionhandler at com android internal os zygoteinit main zygoteinit java i mozac crashreporter received crash uncaughtexceptioncrash timestamp throwable android app remoteserviceexception context startforegroundservice did not then call service startforeground servicerecord org mozilla fenix debug mozilla components lib crash handler crashhandlerservice breadcrumbs uuid i mozac crashreporter received crash nativecodecrash timestamp minidumppath data user org mozilla fenix debug files mozilla crash reports pending dmp minidumpsuccess false extraspath data user org mozilla fenix debug files mozilla crash reports pending extra processtype foreground child breadcrumbs uuid i choreographer skipped frames the application may be doing too much work on its main thread i tombstoned received crash request for pid i tombstoned found intercept fd for pid and type kdebuggerdjavabacktrace i sh crashhandle wrote stack traces to tombstoned i system server libdebuggerd client done dumping process i activitymanager done dumping e activitymanager anr in org mozilla fenix debug mozilla components lib crash crashhandler e activitymanager pid build main | 0 |
18,733 | 10,279,480,024 | IssuesEvent | 2019-08-25 23:37:47 | olivialancaster/spring-boot | https://api.github.com/repos/olivialancaster/spring-boot | opened | CVE-2019-10072 (High) detected in tomcat-embed-core-9.0.13.jar | security vulnerability | ## CVE-2019-10072 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.13.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /spring-boot/spring-boot-project/spring-boot-starters/spring-boot-starter-hateoas/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-9.0.13.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/olivialancaster/spring-boot/commit/06c21dded737831cbb881513825fdf4325a51765">06c21dded737831cbb881513825fdf4325a51765</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2019-0199 was incomplete and did not address HTTP/2 connection window exhaustion on write in Apache Tomcat versions 9.0.0.M1 to 9.0.19 and 8.5.0 to 8.5.40 . By not sending WINDOW_UPDATE messages for the connection window (stream 0) clients were able to cause server-side threads to block eventually leading to thread exhaustion and a DoS.
<p>Publish Date: 2019-06-21
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10072>CVE-2019-10072</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://tomcat.apache.org/security-8.html#Fixed_in_Apache_Tomcat_8.5.41">http://tomcat.apache.org/security-8.html#Fixed_in_Apache_Tomcat_8.5.41</a></p>
<p>Release Date: 2019-06-21</p>
<p>Fix Resolution: 8.5.41,9.0.20</p>
</p>
</details>
<p></p>
| True | CVE-2019-10072 (High) detected in tomcat-embed-core-9.0.13.jar - ## CVE-2019-10072 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.13.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /spring-boot/spring-boot-project/spring-boot-starters/spring-boot-starter-hateoas/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar,/root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.13/tomcat-embed-core-9.0.13.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-9.0.13.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/olivialancaster/spring-boot/commit/06c21dded737831cbb881513825fdf4325a51765">06c21dded737831cbb881513825fdf4325a51765</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2019-0199 was incomplete and did not address HTTP/2 connection window exhaustion on write in Apache Tomcat versions 9.0.0.M1 to 9.0.19 and 8.5.0 to 8.5.40 . By not sending WINDOW_UPDATE messages for the connection window (stream 0) clients were able to cause server-side threads to block eventually leading to thread exhaustion and a DoS.
<p>Publish Date: 2019-06-21
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10072>CVE-2019-10072</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://tomcat.apache.org/security-8.html#Fixed_in_Apache_Tomcat_8.5.41">http://tomcat.apache.org/security-8.html#Fixed_in_Apache_Tomcat_8.5.41</a></p>
<p>Release Date: 2019-06-21</p>
<p>Fix Resolution: 8.5.41,9.0.20</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file spring boot spring boot project spring boot starters spring boot starter hateoas pom xml path to vulnerable library root repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar repository org apache tomcat embed tomcat embed core tomcat embed core jar root repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy x tomcat embed core jar vulnerable library found in head commit a href vulnerability details the fix for cve was incomplete and did not address http connection window exhaustion on write in apache tomcat versions to and to by not sending window update messages for the connection window stream clients were able to cause server side threads to block eventually leading to thread exhaustion and a dos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
147,186 | 11,778,066,502 | IssuesEvent | 2020-03-16 15:45:16 | apache/skywalking | https://api.github.com/repos/apache/skywalking | closed | [Refactor] E2E test framework | enhancement test | According to the feedbacks from our developers, committers and PMCs, especially from @JaredTan95 , the E2E framework is rather unfriendly to our contributors, especially new contributors, therefore I'm refactoring the E2E test framework, the goals are:
- more debuggable, locally, in IDE
- more intuitive, adopt well known technologies to let people get started more quickly
- less verbose/duplicated codes
I've had a runnable version and may need some time to refactor the remains test cases, hope it would be ready soon, anyone who has more ideas about how the new E2E tests should work (friendly), please let me know | 1.0 | [Refactor] E2E test framework - According to the feedbacks from our developers, committers and PMCs, especially from @JaredTan95 , the E2E framework is rather unfriendly to our contributors, especially new contributors, therefore I'm refactoring the E2E test framework, the goals are:
- more debuggable, locally, in IDE
- more intuitive, adopt well known technologies to let people get started more quickly
- less verbose/duplicated codes
I've had a runnable version and may need some time to refactor the remains test cases, hope it would be ready soon, anyone who has more ideas about how the new E2E tests should work (friendly), please let me know | non_priority | test framework according to the feedbacks from our developers committers and pmcs especially from the framework is rather unfriendly to our contributors especially new contributors therefore i m refactoring the test framework the goals are more debuggable locally in ide more intuitive adopt well known technologies to let people get started more quickly less verbose duplicated codes i ve had a runnable version and may need some time to refactor the remains test cases hope it would be ready soon anyone who has more ideas about how the new tests should work friendly please let me know | 0 |
103,235 | 8,883,685,490 | IssuesEvent | 2019-01-14 16:14:57 | edenlabllc/ehealth.web | https://api.github.com/repos/edenlabllc/ehealth.web | closed | New template for capitation contract | FE [zube]: In Test epic/reimbursement_contracts | As NHS Admin i want new template to be used for all capitation contracts so contracts will comply with legal requirements
[Договір (1).doc](https://zube.io/files/edenlabllc/a12ff1585293e3f4b861196363c5b98a-dogovir-1.doc) | 1.0 | New template for capitation contract - As NHS Admin i want new template to be used for all capitation contracts so contracts will comply with legal requirements
[Договір (1).doc](https://zube.io/files/edenlabllc/a12ff1585293e3f4b861196363c5b98a-dogovir-1.doc) | non_priority | new template for capitation contract as nhs admin i want new template to be used for all capitation contracts so contracts will comply with legal requirements | 0 |
27,230 | 27,870,967,516 | IssuesEvent | 2023-03-21 13:27:15 | informalsystems/quint | https://api.github.com/repos/informalsystems/quint | closed | Change output order in "quint run --invariant=..." | usability Fsimulator (phase 5a) | I use invariant checking for some basic checks. It gives me
```
[ok] No violation found (32000ms).
You may increase --max-samples and --max-steps.
See the example:
```
... followed by a trace of 20 steps.
That is, in my terminal, I always need to scroll up to figure out whether it is OK. It would be great to give the "ok" response at the very end of the output, so that one can easily get the most important information. | True | Change output order in "quint run --invariant=..." - I use invariant checking for some basic checks. It gives me
```
[ok] No violation found (32000ms).
You may increase --max-samples and --max-steps.
See the example:
```
... followed by a trace of 20 steps.
That is, in my terminal, I always need to scroll up to figure out whether it is OK. It would be great to give the "ok" response at the very end of the output, so that one can easily get the most important information. | non_priority | change output order in quint run invariant i use invariant checking for some basic checks it gives me no violation found you may increase max samples and max steps see the example followed by a trace of steps that is in my terminal i always need to scroll up to figure out whether it is ok it would be great to give the ok response at the very end of the output so that one can easily get the most important information | 0 |
48,222 | 6,084,084,242 | IssuesEvent | 2017-06-17 00:25:51 | 18F/crime-data-explorer | https://api.github.com/repos/18F/crime-data-explorer | closed | Selecting DC from the homepage breaks the app | bug workflow: design-review | Attempting to select DC from the drop-down menu on the homepage breaks the app. Not only is navigation to DC data affected, but it puts the app in a state where no other states are accessible without refreshing the page. You can access DC data from within the Explorer, but only if you navigate to DC from another state. While DC state data appears to load, I have been unable to load DC agency data.
https://crime-data-explorer-demo.fr.cloud.gov/explorer/state/district-of-columbia/violent-crime | 1.0 | Selecting DC from the homepage breaks the app - Attempting to select DC from the drop-down menu on the homepage breaks the app. Not only is navigation to DC data affected, but it puts the app in a state where no other states are accessible without refreshing the page. You can access DC data from within the Explorer, but only if you navigate to DC from another state. While DC state data appears to load, I have been unable to load DC agency data.
https://crime-data-explorer-demo.fr.cloud.gov/explorer/state/district-of-columbia/violent-crime | non_priority | selecting dc from the homepage breaks the app attempting to select dc from the drop down menu on the homepage breaks the app not only is navigation to dc data affected but it puts the app in a state where no other states are accessible without refreshing the page you can access dc data from within the explorer but only if you navigate to dc from another state while dc state data appears to load i have been unable to load dc agency data | 0 |
55,751 | 8,028,841,366 | IssuesEvent | 2018-07-27 14:12:44 | pnp/pnpjs | https://api.github.com/repos/pnp/pnpjs | closed | 'The specified program requires a newer version of Windows' error | area: documentation status: answered type: question | Thank you for reporting an issue, suggesting an enhancement, or asking a question. We appreciate your feedback - to help the team understand your
needs please complete the below template to ensure we have the details to help. Thanks!
**Please check out the [Docs](https://pnp.github.io/pnpjs/) to see if your question is already addressed there. This will help us ensure our documentation covers the most frequent questions.**
### Category
- Bug
### Version
Please specify what version of the library you are using: 1.1.2
### Expected / Desired Behavior / Question
Add a column to a list.
### Observed Behavior
Attempting to add multiple columns to a list in a set of Promise.all() calls, many throw an error - body contents:-
```
{ error:
{ code: '-2147023746, Microsoft.SharePoint.SPException',
message:
{ lang: 'en-US',
value: 'The specified program requires a newer version of Windows. (Exception from HRESULT: 0x8007047E)' }
}
}
```
### Steps to Reproduce
Trying to create columns on a new list:-
```
retvar.push(sp.web.lists.getById(listID).fields.addText("Department", 255, {
Description: "Department of person making request.",
EnforceUniqueValues: false,
Required: true,
DefaultFormula: ''
}));
return Promise.all(retvar);
```
I am setting multiple headers as per previous issues found online:-
```
sp.setup({
sp: {
fetchClientFactory: () => {
return new SPFetchClient(config[rtFlag].siteURL, config[rtFlag].appID, config[rtFlag].appSecret);
},
headers: {
"accept": "application/json;odata=verbose",
"content-type": "application/json;odata=verbose",
"odata-version": "3.0",
"UserAgent": "ISV|OurCompany|ListCreator/1.0"
}
},
});
``` | 1.0 | 'The specified program requires a newer version of Windows' error - Thank you for reporting an issue, suggesting an enhancement, or asking a question. We appreciate your feedback - to help the team understand your
needs please complete the below template to ensure we have the details to help. Thanks!
**Please check out the [Docs](https://pnp.github.io/pnpjs/) to see if your question is already addressed there. This will help us ensure our documentation covers the most frequent questions.**
### Category
- Bug
### Version
Please specify what version of the library you are using: 1.1.2
### Expected / Desired Behavior / Question
Add a column to a list.
### Observed Behavior
Attempting to add multiple columns to a list in a set of Promise.all() calls, many throw an error - body contents:-
```
{ error:
{ code: '-2147023746, Microsoft.SharePoint.SPException',
message:
{ lang: 'en-US',
value: 'The specified program requires a newer version of Windows. (Exception from HRESULT: 0x8007047E)' }
}
}
```
### Steps to Reproduce
Trying to create columns on a new list:-
```
retvar.push(sp.web.lists.getById(listID).fields.addText("Department", 255, {
Description: "Department of person making request.",
EnforceUniqueValues: false,
Required: true,
DefaultFormula: ''
}));
return Promise.all(retvar);
```
I am setting multiple headers as per previous issues found online:-
```
sp.setup({
sp: {
fetchClientFactory: () => {
return new SPFetchClient(config[rtFlag].siteURL, config[rtFlag].appID, config[rtFlag].appSecret);
},
headers: {
"accept": "application/json;odata=verbose",
"content-type": "application/json;odata=verbose",
"odata-version": "3.0",
"UserAgent": "ISV|OurCompany|ListCreator/1.0"
}
},
});
``` | non_priority | the specified program requires a newer version of windows error thank you for reporting an issue suggesting an enhancement or asking a question we appreciate your feedback to help the team understand your needs please complete the below template to ensure we have the details to help thanks please check out the to see if your question is already addressed there this will help us ensure our documentation covers the most frequent questions category bug version please specify what version of the library you are using expected desired behavior question add a column to a list observed behavior attempting to add multiple columns to a list in a set of promise all calls many throw an error body contents error code microsoft sharepoint spexception message lang en us value the specified program requires a newer version of windows exception from hresult steps to reproduce trying to create columns on a new list retvar push sp web lists getbyid listid fields addtext department description department of person making request enforceuniquevalues false required true defaultformula return promise all retvar i am setting multiple headers as per previous issues found online sp setup sp fetchclientfactory return new spfetchclient config siteurl config appid config appsecret headers accept application json odata verbose content type application json odata verbose odata version useragent isv ourcompany listcreator | 0 |
18,511 | 11,011,656,877 | IssuesEvent | 2019-12-04 16:41:28 | cityofaustin/atd-vz-data | https://api.github.com/repos/cityofaustin/atd-vz-data | closed | VZE add new "Geocoder Provider" column to crash table | Project: Vision Zero Crash Data System Service: Dev Workgroup: VZ | When going through their QA/QC processes, our customers need an easy way to see which crash records have or have not been manually updated. We need to add a column to the crash records table that shows which Geocoder Provider the record is using. Expanding this to the Geocoder Provider will help address other use cases in the future.  | 1.0 | VZE add new "Geocoder Provider" column to crash table - When going through their QA/QC processes, our customers need an easy way to see which crash records have or have not been manually updated. We need to add a column to the crash records table that shows which Geocoder Provider the record is using. Expanding this to the Geocoder Provider will help address other use cases in the future.  | non_priority | vze add new geocoder provider column to crash table when going through their qa qc processes our customers need an easy way to see which crash records have or have not been manually updated we need to add a column to the crash records table that shows which geocoder provider the record is using expanding this to the geocoder provider will help address other use cases in the future | 0 |
277,323 | 24,059,767,867 | IssuesEvent | 2022-09-16 20:52:13 | jooohneth/fusion-finance | https://api.github.com/repos/jooohneth/fusion-finance | closed | Mock FusionCore for liquidate function test | test | Generate a mock ETH price for a borrow position to be able to get liquidated | 1.0 | Mock FusionCore for liquidate function test - Generate a mock ETH price for a borrow position to be able to get liquidated | non_priority | mock fusioncore for liquidate function test generate a mock eth price for a borrow position to be able to get liquidated | 0 |
68,241 | 8,235,685,425 | IssuesEvent | 2018-09-09 08:01:11 | Microsoft/vscode-cpptools | https://api.github.com/repos/Microsoft/vscode-cpptools | closed | when you define new struct type without name, the ouline display _unnamed_struct_1afa_1 info | Language Service by design question | **Type: LanguageService**
<!----- Input information below ----->
<!--
**Please review existing issues and our documentation at https://github.com/Microsoft/vscode-cpptools/tree/master/Documentation prior to filing an issue.**
-->
**Describe the bug**
- OS and Version: macos 10.13
- VS Code Version: 1.27.0
- C/C++ Extension Version: 0.18.1
**Detail Test Issue description**
When you define a new struct type without name, just like typedef struct { ... } MyNewBufferContext. the ouline of VS Code display _unnamed_struct_1afa_1 and its field variables and MyNewBufferContext. is it ok? or just only display MyNewBufferContext and its field variables.
C source code:
```C
typedef struct {
BufferContext base;
Context *pAppCtx;
}MyBufferContext;
```
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
only display MyNewBufferContext and its field variables.
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
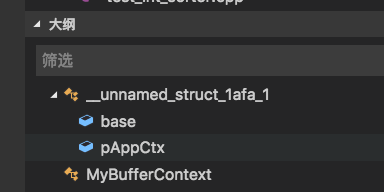
**Additional context**
<!--
*Call Stacks: For bugs like crashes, deadlocks, infinite loops, etc. that we are not able to repro and for which the call stack may be useful, please attach a debugger and/or create a dmp and provide the call stacks. Starting with 0.17.3, Windows binaries have symbols available in VS Code by setting your "symbolSearchPath" to "http://msdl.microsoft.com/download/symbols".*
Add any other context about the problem here including log messages in your Output window ("C_Cpp.loggingLevel": "Debug" in settings.json).
-->
None | 1.0 | when you define new struct type without name, the ouline display _unnamed_struct_1afa_1 info - **Type: LanguageService**
<!----- Input information below ----->
<!--
**Please review existing issues and our documentation at https://github.com/Microsoft/vscode-cpptools/tree/master/Documentation prior to filing an issue.**
-->
**Describe the bug**
- OS and Version: macos 10.13
- VS Code Version: 1.27.0
- C/C++ Extension Version: 0.18.1
**Detail Test Issue description**
When you define a new struct type without name, just like typedef struct { ... } MyNewBufferContext. the ouline of VS Code display _unnamed_struct_1afa_1 and its field variables and MyNewBufferContext. is it ok? or just only display MyNewBufferContext and its field variables.
C source code:
```C
typedef struct {
BufferContext base;
Context *pAppCtx;
}MyBufferContext;
```
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
only display MyNewBufferContext and its field variables.
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
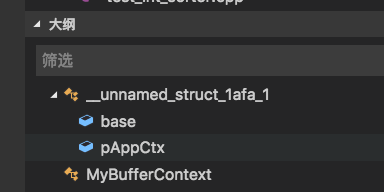
**Additional context**
<!--
*Call Stacks: For bugs like crashes, deadlocks, infinite loops, etc. that we are not able to repro and for which the call stack may be useful, please attach a debugger and/or create a dmp and provide the call stacks. Starting with 0.17.3, Windows binaries have symbols available in VS Code by setting your "symbolSearchPath" to "http://msdl.microsoft.com/download/symbols".*
Add any other context about the problem here including log messages in your Output window ("C_Cpp.loggingLevel": "Debug" in settings.json).
-->
None | non_priority | when you define new struct type without name the ouline display unnamed struct info type languageservice please review existing issues and our documentation at prior to filing an issue describe the bug os and version macos vs code version c c extension version detail test issue description when you define a new struct type without name just like typedef struct mynewbuffercontext the ouline of vs code display unnamed struct and its field variables and mynewbuffercontext is it ok or just only display mynewbuffercontext and its field variables c source code c typedef struct buffercontext base context pappctx mybuffercontext expected behavior only display mynewbuffercontext and its field variables screenshots additional context call stacks for bugs like crashes deadlocks infinite loops etc that we are not able to repro and for which the call stack may be useful please attach a debugger and or create a dmp and provide the call stacks starting with windows binaries have symbols available in vs code by setting your symbolsearchpath to add any other context about the problem here including log messages in your output window c cpp logginglevel debug in settings json none | 0 |
24,028 | 5,012,673,152 | IssuesEvent | 2016-12-13 12:08:56 | IgniteUI/ignite-ui | https://api.github.com/repos/IgniteUI/ignite-ui | closed | Unclear and/or wrong descriptions in igToolbar API | api documentation status: in-development toolbar | 1) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#options:allowCollapsing
2) It is not clear which is the expandButtonIcon http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#options:expandButtonIcon
- better be smth like "the expand/collapse button icon"
3) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#options:isExpanded
- needs better description
4) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#events:collapsing
- desc is wrong !
5) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#events:toolbarComboOpening
- needs better desc
6) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#methods:getItem make the descriptiong consistent with the removeItem method
| 1.0 | Unclear and/or wrong descriptions in igToolbar API - 1) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#options:allowCollapsing
2) It is not clear which is the expandButtonIcon http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#options:expandButtonIcon
- better be smth like "the expand/collapse button icon"
3) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#options:isExpanded
- needs better description
4) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#events:collapsing
- desc is wrong !
5) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#events:toolbarComboOpening
- needs better desc
6) http://www.igniteui.com/help/api/2016.2/ui.igtoolbar#methods:getItem make the descriptiong consistent with the removeItem method
| non_priority | unclear and or wrong descriptions in igtoolbar api it is not clear which is the expandbuttonicon better be smth like the expand collapse button icon needs better description desc is wrong needs better desc make the descriptiong consistent with the removeitem method | 0 |
4,672 | 6,760,460,561 | IssuesEvent | 2017-10-24 20:42:47 | nukturnal/gvive | https://api.github.com/repos/nukturnal/gvive | closed | Passport NoImage Flags Disregarded | api service bug | The `incp` flag for picture blob is disregarded by the GVIVE webservice for Passport Authentications. Pictures are returned regardless of whether the flag is turned on or off.
I will follow up with an official email to the team to sort this out. Until then I will artificially handle this within the wrapper to make the gem behave uniformly across various Identities if user decides to turn on the flags or vice versa through the gem. | 1.0 | Passport NoImage Flags Disregarded - The `incp` flag for picture blob is disregarded by the GVIVE webservice for Passport Authentications. Pictures are returned regardless of whether the flag is turned on or off.
I will follow up with an official email to the team to sort this out. Until then I will artificially handle this within the wrapper to make the gem behave uniformly across various Identities if user decides to turn on the flags or vice versa through the gem. | non_priority | passport noimage flags disregarded the incp flag for picture blob is disregarded by the gvive webservice for passport authentications pictures are returned regardless of whether the flag is turned on or off i will follow up with an official email to the team to sort this out until then i will artificially handle this within the wrapper to make the gem behave uniformly across various identities if user decides to turn on the flags or vice versa through the gem | 0 |
20,212 | 10,678,771,316 | IssuesEvent | 2019-10-21 17:56:39 | elmsln/lrnwebcomponents | https://api.github.com/repos/elmsln/lrnwebcomponents | closed | Make gizmo display more efficient and cleaner to read | a11y enhancement performance ux | So it's supposed to look like the android app fly out on a phone, and instead when we hover stuff it's needlessly animating and doing a lot of JS we don't care much about. | True | Make gizmo display more efficient and cleaner to read - So it's supposed to look like the android app fly out on a phone, and instead when we hover stuff it's needlessly animating and doing a lot of JS we don't care much about. | non_priority | make gizmo display more efficient and cleaner to read so it s supposed to look like the android app fly out on a phone and instead when we hover stuff it s needlessly animating and doing a lot of js we don t care much about | 0 |
82,054 | 31,883,455,607 | IssuesEvent | 2023-09-16 17:04:09 | zuzukin/whl2conda | https://api.github.com/repos/zuzukin/whl2conda | closed | install does not create entry point | defect status: invalid component: install | `whl2conda install` into an environment adds the package just using
`conda install <pkg>` after installing dependencies but it appears that
the conda install doesn't install the entry points.
| 1.0 | install does not create entry point - `whl2conda install` into an environment adds the package just using
`conda install <pkg>` after installing dependencies but it appears that
the conda install doesn't install the entry points.
| non_priority | install does not create entry point install into an environment adds the package just using conda install after installing dependencies but it appears that the conda install doesn t install the entry points | 0 |
264,967 | 28,214,170,941 | IssuesEvent | 2023-04-05 07:42:23 | hshivhare67/platform_device_renesas_kernel_v4.19.72 | https://api.github.com/repos/hshivhare67/platform_device_renesas_kernel_v4.19.72 | closed | CVE-2020-9391 (Medium) detected in linuxlinux-4.19.279 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-9391 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.279</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel 5.4 and 5.5 through 5.5.6 on the AArch64 architecture. It ignores the top byte in the address passed to the brk system call, potentially moving the memory break downwards when the application expects it to move upwards, aka CID-dcde237319e6. This has been observed to cause heap corruption with the GNU C Library malloc implementation.
<p>Publish Date: 2020-02-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9391>CVE-2020-9391</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-9391">https://www.linuxkernelcves.com/cves/CVE-2020-9391</a></p>
<p>Release Date: 2020-02-25</p>
<p>Fix Resolution: v5.6-rc3,v5.4.23,v5.5.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-9391 (Medium) detected in linuxlinux-4.19.279 - autoclosed - ## CVE-2020-9391 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.279</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mremap.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel 5.4 and 5.5 through 5.5.6 on the AArch64 architecture. It ignores the top byte in the address passed to the brk system call, potentially moving the memory break downwards when the application expects it to move upwards, aka CID-dcde237319e6. This has been observed to cause heap corruption with the GNU C Library malloc implementation.
<p>Publish Date: 2020-02-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9391>CVE-2020-9391</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-9391">https://www.linuxkernelcves.com/cves/CVE-2020-9391</a></p>
<p>Release Date: 2020-02-25</p>
<p>Fix Resolution: v5.6-rc3,v5.4.23,v5.5.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux autoclosed cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch main vulnerable source files mm mremap c mm mremap c vulnerability details an issue was discovered in the linux kernel and through on the architecture it ignores the top byte in the address passed to the brk system call potentially moving the memory break downwards when the application expects it to move upwards aka cid this has been observed to cause heap corruption with the gnu c library malloc implementation publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
88,804 | 8,178,377,426 | IssuesEvent | 2018-08-28 13:40:17 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed tests on master: test/TestShowTraceReplica | C-test-failure O-robot | The following tests appear to have failed:
[#853175](https://teamcity.cockroachdb.com/viewLog.html?buildId=853175):
```
--- FAIL: test/TestShowTraceReplica (56.880s)
------- Stdout: -------
W180822 02:45:08.896090 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:08.914399 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:08.914705 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:08.914765 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:08.924394 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:08.924513 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:08.924573 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
I180822 02:45:08.930005 158345 util/stop/stopper.go:537 [n?] quiescing; tasks left:
1 [async] storage.pendingLeaseRequest: requesting lease
I180822 02:45:08.930637 158345 server/node.go:373 [n?] **** cluster a9379584-4fcf-40c2-8feb-f1f399f5d3e9 has been created
I180822 02:45:08.930660 158345 server/server.go:1401 [n?] **** add additional nodes by specifying --join=127.0.0.1:36021
I180822 02:45:08.930817 158345 gossip/gossip.go:382 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:36021" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905908930753221
I180822 02:45:08.932713 158345 storage/store.go:1541 [n1,s1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I180822 02:45:08.934417 158345 server/node.go:476 [n1] initialized store [n1,s1]: disk (capacity=512 MiB, available=512 MiB, used=0 B, logicalBytes=6.9 KiB), ranges=1, leases=1, queries=0.00, writes=0.00, bytesPerReplica={p10=7103.00 p25=7103.00 p50=7103.00 p75=7103.00 p90=7103.00 pMax=7103.00}, writesPerReplica={p10=0.00 p25=0.00 p50=0.00 p75=0.00 p90=0.00 pMax=0.00}
I180822 02:45:08.934503 158345 storage/stores.go:242 [n1] read 0 node addresses from persistent storage
I180822 02:45:08.934607 158345 server/node.go:697 [n1] connecting to gossip network to verify cluster ID...
I180822 02:45:08.934648 158345 server/node.go:722 [n1] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:08.934677 158345 server/node.go:546 [n1] node=1: started with [n1=<in-mem>] engine(s) and attributes []
I180822 02:45:08.934985 158345 server/status/recorder.go:652 [n1] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:08.936436 158433 storage/replica_command.go:289 [split,n1,s1,r1/1:/M{in-ax}] initiating a split of this range at key /System/"" [r2]
I180822 02:45:08.936773 158345 server/server.go:1807 [n1] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:08.938980 158594 server/status/recorder.go:652 [n1,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:08.940118 158345 server/server.go:1538 [n1] starting https server at 127.0.0.1:36377 (use: 127.0.0.1:36377)
I180822 02:45:08.942728 158345 server/server.go:1540 [n1] starting grpc/postgres server at 127.0.0.1:36021
I180822 02:45:08.943780 158345 server/server.go:1541 [n1] advertising CockroachDB node at 127.0.0.1:36021
I180822 02:45:09.138194 158408 storage/replica_command.go:289 [split,n1,s1,r2/1:/{System/-Max}] initiating a split of this range at key /System/NodeLiveness [r3]
I180822 02:45:09.159639 158378 storage/replica_command.go:289 [split,n1,s1,r3/1:/{System/NodeL…-Max}] initiating a split of this range at key /System/NodeLivenessMax [r4]
W180822 02:45:09.160842 158375 storage/intent_resolver.go:668 [n1,s1] failed to push during intent resolution: failed to push "sql txn" id=5d8995aa key=/Table/SystemConfigSpan/Start rw=true pri=0.00786353 iso=SERIALIZABLE stat=PENDING epo=0 ts=1534905909.140242610,0 orig=1534905909.140242610,0 max=1534905909.140242610,0 wto=false rop=false seq=6
I180822 02:45:09.176781 157118 storage/replica_command.go:289 [split,n1,s1,r4/1:/{System/NodeL…-Max}] initiating a split of this range at key /System/tsd [r5]
I180822 02:45:09.177818 158599 sql/event_log.go:126 [n1,intExec=optInToDiagnosticsStatReporting] Event: "set_cluster_setting", target: 0, info: {SettingName:diagnostics.reporting.enabled Value:true User:root}
I180822 02:45:09.199663 158661 storage/replica_command.go:289 [split,n1,s1,r5/1:/{System/tsd-Max}] initiating a split of this range at key /System/"tse" [r6]
I180822 02:45:09.210577 158604 storage/replica_command.go:289 [split,n1,s1,r6/1:/{System/tse-Max}] initiating a split of this range at key /Table/SystemConfigSpan/Start [r7]
I180822 02:45:09.218989 158383 storage/replica_command.go:289 [split,n1,s1,r7/1:/{Table/System…-Max}] initiating a split of this range at key /Table/11 [r8]
I180822 02:45:09.226652 158696 storage/replica_command.go:289 [split,n1,s1,r8/1:/{Table/11-Max}] initiating a split of this range at key /Table/12 [r9]
I180822 02:45:09.234841 158644 sql/event_log.go:126 [n1,intExec=set-setting] Event: "set_cluster_setting", target: 0, info: {SettingName:version Value:$1 User:root}
I180822 02:45:09.242665 158678 storage/replica_command.go:289 [split,n1,s1,r9/1:/{Table/12-Max}] initiating a split of this range at key /Table/13 [r10]
I180822 02:45:09.251750 158723 storage/replica_command.go:289 [split,n1,s1,r10/1:/{Table/13-Max}] initiating a split of this range at key /Table/14 [r11]
I180822 02:45:09.253502 158655 sql/event_log.go:126 [n1,intExec=disableNetTrace] Event: "set_cluster_setting", target: 0, info: {SettingName:trace.debug.enable Value:false User:root}
I180822 02:45:09.267578 158742 storage/replica_command.go:289 [split,n1,s1,r11/1:/{Table/14-Max}] initiating a split of this range at key /Table/15 [r12]
I180822 02:45:09.287164 158726 storage/replica_command.go:289 [split,n1,s1,r12/1:/{Table/15-Max}] initiating a split of this range at key /Table/16 [r13]
I180822 02:45:09.293807 158713 storage/replica_command.go:289 [split,n1,s1,r13/1:/{Table/16-Max}] initiating a split of this range at key /Table/17 [r14]
I180822 02:45:09.305946 158757 sql/event_log.go:126 [n1,intExec=initializeClusterSecret] Event: "set_cluster_setting", target: 0, info: {SettingName:cluster.secret Value:gen_random_uuid()::STRING User:root}
I180822 02:45:09.306648 158734 storage/replica_command.go:289 [split,n1,s1,r14/1:/{Table/17-Max}] initiating a split of this range at key /Table/18 [r15]
I180822 02:45:09.316139 158789 sql/event_log.go:126 [n1,intExec=create-default-db] Event: "create_database", target: 50, info: {DatabaseName:defaultdb Statement:CREATE DATABASE IF NOT EXISTS defaultdb User:root}
I180822 02:45:09.320870 158777 sql/event_log.go:126 [n1,intExec=create-default-db] Event: "create_database", target: 51, info: {DatabaseName:postgres Statement:CREATE DATABASE IF NOT EXISTS postgres User:root}
I180822 02:45:09.323984 158345 server/server.go:1594 [n1] done ensuring all necessary migrations have run
I180822 02:45:09.324594 158345 server/server.go:1597 [n1] serving sql connections
I180822 02:45:09.329653 158803 sql/event_log.go:126 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36021} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905908930753221 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905908930753221 LastUp:1534905908930753221}
I180822 02:45:09.330111 158785 server/server_update.go:67 [n1] no need to upgrade, cluster already at the newest version
I180822 02:45:09.338745 158805 storage/replica_command.go:289 [split,n1,s1,r15/1:/{Table/18-Max}] initiating a split of this range at key /Table/19 [r16]
I180822 02:45:09.346484 158808 storage/replica_command.go:289 [split,n1,s1,r16/1:/{Table/19-Max}] initiating a split of this range at key /Table/20 [r17]
I180822 02:45:09.354532 158811 storage/replica_command.go:289 [split,n1,s1,r17/1:/{Table/20-Max}] initiating a split of this range at key /Table/21 [r18]
I180822 02:45:09.359077 158824 storage/replica_command.go:289 [split,n1,s1,r18/1:/{Table/21-Max}] initiating a split of this range at key /Table/22 [r19]
I180822 02:45:09.366472 158885 storage/replica_command.go:289 [split,n1,s1,r19/1:/{Table/22-Max}] initiating a split of this range at key /Table/23 [r20]
I180822 02:45:09.372342 158762 storage/replica_command.go:289 [split,n1,s1,r20/1:/{Table/23-Max}] initiating a split of this range at key /Table/50 [r21]
I180822 02:45:09.376710 158917 storage/replica_command.go:289 [split,n1,s1,r21/1:/{Table/50-Max}] initiating a split of this range at key /Table/51 [r22]
W180822 02:45:09.388446 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:09.436671 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:09.436820 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.436841 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.452621 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:09.452679 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:09.452689 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
W180822 02:45:09.452774 158345 gossip/gossip.go:1362 [n?] no incoming or outgoing connections
I180822 02:45:09.452825 158345 server/server.go:1403 [n?] no stores bootstrapped and --join flag specified, awaiting init command.
I180822 02:45:09.466224 158836 gossip/client.go:129 [n?] started gossip client to 127.0.0.1:36021
I180822 02:45:09.466733 158870 gossip/server.go:217 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:44707}
I180822 02:45:09.467220 158345 server/node.go:697 [n?] connecting to gossip network to verify cluster ID...
I180822 02:45:09.467254 158345 server/node.go:722 [n?] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:09.467554 158994 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.468782 158881 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.469412 158345 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.470138 158345 server/node.go:428 [n?] new node allocated ID 2
I180822 02:45:09.470224 158345 gossip/gossip.go:382 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:44707" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905909470146464
I180822 02:45:09.470274 158345 storage/stores.go:242 [n2] read 0 node addresses from persistent storage
I180822 02:45:09.470306 158345 storage/stores.go:261 [n2] wrote 1 node addresses to persistent storage
I180822 02:45:09.471143 158998 storage/stores.go:261 [n1] wrote 1 node addresses to persistent storage
I180822 02:45:09.471961 158345 server/node.go:672 [n2] bootstrapped store [n2,s2]
I180822 02:45:09.472073 158345 server/node.go:546 [n2] node=2: started with [] engine(s) and attributes []
I180822 02:45:09.472306 158345 server/status/recorder.go:652 [n2] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.472339 158345 server/server.go:1807 [n2] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:09.472409 158345 server/server.go:1538 [n2] starting https server at 127.0.0.1:46099 (use: 127.0.0.1:46099)
I180822 02:45:09.472426 158345 server/server.go:1540 [n2] starting grpc/postgres server at 127.0.0.1:44707
I180822 02:45:09.472441 158345 server/server.go:1541 [n2] advertising CockroachDB node at 127.0.0.1:44707
I180822 02:45:09.476501 159083 server/status/recorder.go:652 [n2,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.484622 158345 server/server.go:1594 [n2] done ensuring all necessary migrations have run
I180822 02:45:09.484660 158345 server/server.go:1597 [n2] serving sql connections
W180822 02:45:09.528792 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:09.530588 159112 sql/event_log.go:126 [n2] Event: "node_join", target: 2, info: {Descriptor:{NodeID:2 Address:{NetworkField:tcp AddressField:127.0.0.1:44707} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905909470146464 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905909470146464 LastUp:1534905909470146464}
I180822 02:45:09.531153 159110 server/server_update.go:67 [n2] no need to upgrade, cluster already at the newest version
I180822 02:45:09.535213 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:09.535320 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.535334 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.537535 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:09.537552 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:09.537561 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
W180822 02:45:09.537624 158345 gossip/gossip.go:1362 [n?] no incoming or outgoing connections
I180822 02:45:09.537657 158345 server/server.go:1403 [n?] no stores bootstrapped and --join flag specified, awaiting init command.
I180822 02:45:09.555538 159171 gossip/client.go:129 [n?] started gossip client to 127.0.0.1:36021
I180822 02:45:09.566299 159227 gossip/server.go:217 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:39899}
I180822 02:45:09.566935 158345 server/node.go:697 [n?] connecting to gossip network to verify cluster ID...
I180822 02:45:09.566979 158345 server/node.go:722 [n?] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:09.567287 159244 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.568721 159243 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.572675 158345 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.573436 159142 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n2 established
I180822 02:45:09.574467 158345 server/node.go:428 [n?] new node allocated ID 3
I180822 02:45:09.574536 158345 gossip/gossip.go:382 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:39899" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905909574478010
I180822 02:45:09.574580 158345 storage/stores.go:242 [n3] read 0 node addresses from persistent storage
I180822 02:45:09.574615 158345 storage/stores.go:261 [n3] wrote 2 node addresses to persistent storage
I180822 02:45:09.575798 158718 storage/stores.go:261 [n1] wrote 2 node addresses to persistent storage
I180822 02:45:09.576120 158719 storage/stores.go:261 [n2] wrote 2 node addresses to persistent storage
I180822 02:45:09.579849 158345 server/node.go:672 [n3] bootstrapped store [n3,s3]
I180822 02:45:09.580110 158345 server/node.go:546 [n3] node=3: started with [] engine(s) and attributes []
I180822 02:45:09.580830 158345 server/status/recorder.go:652 [n3] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.580876 158345 server/server.go:1807 [n3] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:09.580972 158345 server/server.go:1538 [n3] starting https server at 127.0.0.1:40575 (use: 127.0.0.1:40575)
I180822 02:45:09.584849 158345 server/server.go:1540 [n3] starting grpc/postgres server at 127.0.0.1:39899
I180822 02:45:09.584929 158345 server/server.go:1541 [n3] advertising CockroachDB node at 127.0.0.1:39899
I180822 02:45:09.583601 159367 server/status/recorder.go:652 [n3,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.594496 158345 server/server.go:1594 [n3] done ensuring all necessary migrations have run
I180822 02:45:09.594524 158345 server/server.go:1597 [n3] serving sql connections
W180822 02:45:09.627465 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:09.668348 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:09.674150 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.674178 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.676251 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:09.676281 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:09.676289 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
W180822 02:45:09.676364 158345 gossip/gossip.go:1362 [n?] no incoming or outgoing connections
I180822 02:45:09.676413 158345 server/server.go:1403 [n?] no stores bootstrapped and --join flag specified, awaiting init command.
I180822 02:45:09.668857 159383 sql/event_log.go:126 [n3] Event: "node_join", target: 3, info: {Descriptor:{NodeID:3 Address:{NetworkField:tcp AddressField:127.0.0.1:39899} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905909574478010 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905909574478010 LastUp:1534905909574478010}
I180822 02:45:09.673098 159474 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n1 established
I180822 02:45:09.673657 159381 server/server_update.go:67 [n3] no need to upgrade, cluster already at the newest version
I180822 02:45:09.698002 159482 gossip/client.go:129 [n?] started gossip client to 127.0.0.1:36021
I180822 02:45:09.698566 159409 gossip/server.go:217 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:40015}
I180822 02:45:09.699147 158345 server/node.go:697 [n?] connecting to gossip network to verify cluster ID...
I180822 02:45:09.699187 158345 server/node.go:722 [n?] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:09.699463 159534 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.700864 159533 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.701457 158345 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.702160 158345 server/node.go:428 [n?] new node allocated ID 4
I180822 02:45:09.702246 158345 gossip/gossip.go:382 [n4] NodeDescriptor set to node_id:4 address:<network_field:"tcp" address_field:"127.0.0.1:40015" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905909702181761
I180822 02:45:09.702303 158345 storage/stores.go:242 [n4] read 0 node addresses from persistent storage
I180822 02:45:09.702350 158345 storage/stores.go:261 [n4] wrote 3 node addresses to persistent storage
I180822 02:45:09.703285 159540 storage/stores.go:261 [n1] wrote 3 node addresses to persistent storage
I180822 02:45:09.703793 159358 storage/stores.go:261 [n2] wrote 3 node addresses to persistent storage
I180822 02:45:09.704593 158345 server/node.go:672 [n4] bootstrapped store [n4,s4]
I180822 02:45:09.704687 158345 server/node.go:546 [n4] node=4: started with [] engine(s) and attributes []
I180822 02:45:09.704888 158345 server/status/recorder.go:652 [n4] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.704911 158345 server/server.go:1807 [n4] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:09.704982 158345 server/server.go:1538 [n4] starting https server at 127.0.0.1:42991 (use: 127.0.0.1:42991)
I180822 02:45:09.704996 158345 server/server.go:1540 [n4] starting grpc/postgres server at 127.0.0.1:40015
I180822 02:45:09.705008 158345 server/server.go:1541 [n4] advertising CockroachDB node at 127.0.0.1:40015
I180822 02:45:09.707331 159637 server/status/recorder.go:652 [n4,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.711351 159541 storage/stores.go:261 [n3] wrote 3 node addresses to persistent storage
I180822 02:45:09.717042 158345 server/server.go:1594 [n4] done ensuring all necessary migrations have run
I180822 02:45:09.717123 158345 server/server.go:1597 [n4] serving sql connections
I180822 02:45:09.723229 159475 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n3 established
I180822 02:45:09.747908 159716 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n3 established
I180822 02:45:09.771402 159717 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n4 established
I180822 02:45:09.772325 159547 sql/event_log.go:126 [n4] Event: "node_join", target: 4, info: {Descriptor:{NodeID:4 Address:{NetworkField:tcp AddressField:127.0.0.1:40015} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905909702181761 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905909702181761 LastUp:1534905909702181761}
I180822 02:45:09.772951 159545 server/server_update.go:67 [n4] no need to upgrade, cluster already at the newest version
I180822 02:45:09.779764 159786 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n1 established
I180822 02:45:09.809361 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 0, info: {Target:.default Config:constraints: [+n4] User:root}
I180822 02:45:09.826809 159785 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n4 established
I180822 02:45:09.832895 159784 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n2 established
I180822 02:45:09.849545 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_database", target: 52, info: {DatabaseName:d Statement:CREATE DATABASE d User:root}
I180822 02:45:09.850629 159776 storage/replica_command.go:289 [split,n1,s1,r22/1:/{Table/51-Max}] initiating a split of this range at key /Table/52 [r23]
I180822 02:45:09.857202 159818 storage/replica_raftstorage.go:538 [replicate,n1,s1,r22/1:/Table/5{1-2}] generated preemptive snapshot 7f8ef362 at index 15
I180822 02:45:09.857969 159818 storage/store_snapshot.go:655 [replicate,n1,s1,r22/1:/Table/5{1-2}] streamed snapshot to (n4,s4):?: kv pairs: 9, log entries: 5, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.858896 159677 storage/replica_raftstorage.go:782 [n4,s4,r22/?:{-}] applying preemptive snapshot at index 15 (id=7f8ef362, encoded size=2321, 1 rocksdb batches, 5 log entries)
I180822 02:45:09.860089 159677 storage/replica_raftstorage.go:788 [n4,s4,r22/?:/Table/5{1-2}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=1ms]
I180822 02:45:09.860624 159818 storage/replica_command.go:803 [replicate,n1,s1,r22/1:/Table/5{1-2}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r22:/Table/5{1-2} [(n1,s1):1, next=2, gen=842354566152]
I180822 02:45:09.866127 159818 storage/replica.go:3743 [n1,s1,r22/1:/Table/5{1-2}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.868444 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_table", target: 53, info: {TableName:d.public.t1 Statement:CREATE TABLE d.public.t1 (a INT PRIMARY KEY) User:root}
I180822 02:45:09.869195 159909 storage/replica_command.go:289 [split,n1,s1,r23/1:/{Table/52-Max}] initiating a split of this range at key /Table/53 [r24]
I180822 02:45:09.870600 159555 rpc/nodedialer/nodedialer.go:92 [n4] connection to n1 established
I180822 02:45:09.872397 159825 storage/replica_range_lease.go:554 [replicate,n1,s1,r22/1:/Table/5{1-2}] transferring lease to s4
I180822 02:45:09.873209 159825 storage/replica_range_lease.go:617 [replicate,n1,s1,r22/1:/Table/5{1-2}] done transferring lease to s4: <nil>
I180822 02:45:09.876010 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_table", target: 54, info: {TableName:d.public.t2 Statement:CREATE TABLE d.public.t2 (a INT PRIMARY KEY) User:root}
I180822 02:45:09.877328 159841 storage/replica_command.go:289 [split,n1,s1,r24/1:/{Table/53-Max}] initiating a split of this range at key /Table/54 [r25]
I180822 02:45:09.880827 159559 storage/replica_proposal.go:214 [n4,s4,r22/2:/Table/5{1-2}] new range lease repl=(n4,s4):2 seq=3 start=1534905909.872443081,0 epo=1 pro=1534905909.872446544,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:09.887440 159903 storage/replica_raftstorage.go:538 [replicate,n1,s1,r23/1:/Table/5{2-3}] generated preemptive snapshot 78d69c74 at index 16
I180822 02:45:09.888034 159903 storage/store_snapshot.go:655 [replicate,n1,s1,r23/1:/Table/5{2-3}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 6, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.889435 159942 storage/replica_raftstorage.go:782 [n4,s4,r23/?:{-}] applying preemptive snapshot at index 16 (id=78d69c74, encoded size=2078, 1 rocksdb batches, 6 log entries)
I180822 02:45:09.889641 159942 storage/replica_raftstorage.go:788 [n4,s4,r23/?:/Table/5{2-3}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:09.890052 159903 storage/replica_command.go:803 [replicate,n1,s1,r23/1:/Table/5{2-3}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r23:/Table/5{2-3} [(n1,s1):1, next=2, gen=842362934016]
I180822 02:45:09.892772 159903 storage/replica.go:3743 [n1,s1,r23/1:/Table/5{2-3}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.895363 160027 storage/replica_range_lease.go:554 [replicate,n1,s1,r23/1:/Table/5{2-3}] transferring lease to s4
I180822 02:45:09.896128 160027 storage/replica_range_lease.go:617 [replicate,n1,s1,r23/1:/Table/5{2-3}] done transferring lease to s4: <nil>
I180822 02:45:09.896469 159946 storage/replica_raftstorage.go:538 [replicate,n1,s1,r25/1:/{Table/54-Max}] generated preemptive snapshot 4f870146 at index 11
I180822 02:45:09.897183 159568 storage/replica_proposal.go:214 [n4,s4,r23/2:/Table/5{2-3}] new range lease repl=(n4,s4):2 seq=3 start=1534905909.895408651,0 epo=1 pro=1534905909.895412489,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:09.897309 159946 storage/store_snapshot.go:655 [replicate,n1,s1,r25/1:/{Table/54-Max}] streamed snapshot to (n4,s4):?: kv pairs: 7, log entries: 1, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.897614 160011 storage/replica_raftstorage.go:782 [n4,s4,r25/?:{-}] applying preemptive snapshot at index 11 (id=4f870146, encoded size=369, 1 rocksdb batches, 1 log entries)
I180822 02:45:09.897806 160011 storage/replica_raftstorage.go:788 [n4,s4,r25/?:/{Table/54-Max}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:09.898350 159946 storage/replica_command.go:803 [replicate,n1,s1,r25/1:/{Table/54-Max}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r25:/{Table/54-Max} [(n1,s1):1, next=2, gen=0]
I180822 02:45:09.899260 159870 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n4 established
I180822 02:45:09.900183 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_table", target: 55, info: {TableName:d.public.t3 Statement:CREATE TABLE d.public.t3 (a INT PRIMARY KEY) User:root}
I180822 02:45:09.902444 160017 storage/replica_command.go:289 [split,n1,s1,r25/1:/{Table/54-Max}] initiating a split of this range at key /Table/55 [r26]
I180822 02:45:09.903518 159946 storage/replica.go:3743 [n1,s1,r25/1:/{Table/54-Max}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.904150 160071 storage/replica_raftstorage.go:538 [replicate,n1,s1,r24/1:/Table/5{3-4}] generated preemptive snapshot 9ee9e085 at index 16
I180822 02:45:09.905055 160071 storage/store_snapshot.go:655 [replicate,n1,s1,r24/1:/Table/5{3-4}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 6, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.915871 160074 storage/replica_raftstorage.go:782 [n4,s4,r24/?:{-}] applying preemptive snapshot at index 16 (id=9ee9e085, encoded size=2078, 1 rocksdb batches, 6 log entries)
I180822 02:45:09.916150 160074 storage/replica_raftstorage.go:788 [n4,s4,r24/?:/Table/5{3-4}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:09.919554 160071 storage/replica_command.go:803 [replicate,n1,s1,r24/1:/Table/5{3-4}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r24:/Table/5{3-4} [(n1,s1):1, next=2, gen=842366453288]
I180822 02:45:09.922015 160017 storage/split_queue.go:135 [split,n1,s1,r25/1:/{Table/54-Max}] split saw concurrent descriptor modification; maybe retrying
I180822 02:45:09.922182 160078 storage/replica_command.go:289 [split,n1,s1,r25/1:/{Table/54-Max}] initiating a split of this range at key /Table/55 [r27]
I180822 02:45:09.934699 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 53, info: {Target:d.t1 Config:constraints: [+n1] User:root}
I180822 02:45:09.936195 160045 rpc/nodedialer/nodedialer.go:92 [consistencyChecker,n1,s1,r1/1:/{Min-System/}] connection to n1 established
I180822 02:45:09.937732 159966 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n2 established
I180822 02:45:09.938161 160071 storage/replica.go:3743 [n1,s1,r24/1:/Table/5{3-4}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.938649 159967 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n3 established
I180822 02:45:09.944873 160164 storage/replica_range_lease.go:554 [replicate,n1,s1,r25/1:/Table/5{4-5}] transferring lease to s4
I180822 02:45:09.946017 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 54, info: {Target:d.t2 Config:constraints: [+n2] User:root}
I180822 02:45:09.946424 160164 storage/replica_range_lease.go:617 [replicate,n1,s1,r25/1:/Table/5{4-5}] done transferring lease to s4: <nil>
I180822 02:45:09.946885 160156 storage/replica_command.go:803 [replicate,n1,s1,r24/1:/Table/5{3-4}] change replicas (REMOVE_REPLICA (n4,s4):2): read existing descriptor r24:/Table/5{3-4} [(n1,s1):1, (n4,s4):2, next=3, gen=842413132040]
I180822 02:45:09.948180 159588 storage/replica_proposal.go:214 [n4,s4,r25/2:/Table/5{4-5}] new range lease repl=(n4,s4):2 seq=3 start=1534905909.944897194,0 epo=1 pro=1534905909.944900936,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:09.951782 160156 storage/replica.go:3743 [n1,s1,r24/1:/Table/5{3-4}] proposing REMOVE_REPLICA((n4,s4):2): updated=[(n1,s1):1] next=3
E180822 02:45:09.952676 160161 storage/queue.go:788 [replicate,n1,s1,r27/1:/{Table/55-Max}] no removable replicas from range that needs a removal: [raft progress unknown]
I180822 02:45:09.953577 159938 storage/store.go:3745 [n4,s4,r24/2:/Table/5{3-4}] added to replica GC queue (peer suggestion)
I180822 02:45:09.953903 160194 storage/store.go:2632 [replicaGC,n4,s4,r24/2:/Table/5{3-4}] removing replica
I180822 02:45:09.953940 160137 storage/replica_raftstorage.go:538 [replicate,n1,s1,r1/1:/{Min-System/}] generated preemptive snapshot 2cd7f1b1 at index 90
I180822 02:45:09.954132 160194 storage/replica.go:880 [replicaGC,n4,s4,r24/2:/Table/5{3-4}] removed 7 (0+7) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:09.954364 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 55, info: {Target:d.t3 Config:constraints: [+n3] User:root}
--- FAIL: test/TestShowTraceReplica: TestShowTraceReplica/UPSERT_INTO_d.t2_VALUES_(1) (45.430s)
show_trace_replica_test.go:101: condition failed to evaluate within 45s: UPSERT INTO d.t2 VALUES (1): got [[4 4]] expected [[2 2]]
goroutine 160202 [running]:
runtime/debug.Stack(0xa7a358200, 0xc4222834d0, 0x2a98280)
/usr/local/go/src/runtime/debug/stack.go:24 +0xa7
github.com/cockroachdb/cockroach/pkg/testutils.SucceedsSoon(0x2ae7580, 0xc423f67b30, 0xc4227c23e0)
/go/src/github.com/cockroachdb/cockroach/pkg/testutils/soon.go:50 +0x10d
github.com/cockroachdb/cockroach/pkg/sql_test.TestShowTraceReplica.func2(0xc423f67b30)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/show_trace_replica_test.go:101 +0x9d
testing.tRunner(0xc423f67b30, 0xc4227c23a0)
/usr/local/go/src/testing/testing.go:777 +0xd0
created by testing.(*T).Run
/usr/local/go/src/testing/testing.go:824 +0x2e0
------- Stdout: -------
I180822 02:45:10.012981 160263 storage/replica_range_lease.go:554 [replicate,n1,s1,r1/1:/{Min-System/}] transferring lease to s3
I180822 02:45:10.015071 160263 storage/replica_range_lease.go:617 [replicate,n1,s1,r1/1:/{Min-System/}] done transferring lease to s3: <nil>
I180822 02:45:10.937427 160330 storage/replica_raftstorage.go:538 [replicate,n1,s1,r10/1:/Table/1{3-4}] generated preemptive snapshot dea55734 at index 64
I180822 02:45:10.939646 160330 storage/store_snapshot.go:655 [replicate,n1,s1,r10/1:/Table/1{3-4}] streamed snapshot to (n4,s4):?: kv pairs: 189, log entries: 54, rate-limit: 2.0 MiB/sec, 2ms
I180822 02:45:10.940327 160129 storage/replica_raftstorage.go:782 [n4,s4,r10/?:{-}] applying preemptive snapshot at index 64 (id=dea55734, encoded size=57008, 1 rocksdb batches, 54 log entries)
I180822 02:45:10.941048 160129 storage/replica_raftstorage.go:788 [n4,s4,r10/?:/Table/1{3-4}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:10.941598 160330 storage/replica_command.go:803 [replicate,n1,s1,r10/1:/Table/1{3-4}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r10:/Table/1{3-4} [(n1,s1):1, next=2, gen=842448414080]
I180822 02:45:10.948269 160330 storage/replica.go:3743 [n1,s1,r10/1:/Table/1{3-4}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:10.954821 160376 storage/replica_range_lease.go:554 [replicate,n1,s1,r10/1:/Table/1{3-4}] transferring lease to s4
I180822 02:45:10.955857 160376 storage/replica_range_lease.go:617 [replicate,n1,s1,r10/1:/Table/1{3-4}] done transferring lease to s4: <nil>
I180822 02:45:10.956127 159574 storage/replica_proposal.go:214 [n4,s4,r10/2:/Table/1{3-4}] new range lease repl=(n4,s4):2 seq=3 start=1534905910.954962824,0 epo=1 pro=1534905910.954966814,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:11.581479 160379 storage/replica_command.go:803 [replicate,n3,s3,r1/2:/{Min-System/}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r1:/{Min-System/} [(n1,s1):1, (n3,s3):2, next=3, gen=842353732432]
I180822 02:45:11.644535 160379 storage/replica.go:3743 [n3,s3,r1/2:/{Min-System/}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n3,s3):2] next=3
I180822 02:45:11.647846 160277 storage/store.go:3745 [n1,s1,r1/1:/{Min-System/}] added to replica GC queue (peer suggestion)
I180822 02:45:11.647896 160408 storage/store.go:2632 [replicaGC,n1,s1,r1/1:/{Min-System/}] removing replica
I180822 02:45:11.648327 160408 storage/replica.go:880 [replicaGC,n1,s1,r1/1:/{Min-System/}] removed 37 (27+10) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:12.706634 160411 storage/replica_range_lease.go:554 [replicate,n4,s4,r25/2:/Table/5{4-5}] transferring lease to s1
I180822 02:45:12.707913 160411 storage/replica_range_lease.go:617 [replicate,n4,s4,r25/2:/Table/5{4-5}] done transferring lease to s1: <nil>
I180822 02:45:12.708406 158500 storage/replica_proposal.go:214 [n1,s1,r25/1:/Table/5{4-5}] new range lease repl=(n1,s1):1 seq=4 start=1534905912.706654906,0 epo=1 pro=1534905912.706658979,0 following repl=(n4,s4):2 seq=3 start=1534905909.944897194,0 epo=1 pro=1534905909.944900936,0
I180822 02:45:12.939909 160429 storage/replica_raftstorage.go:538 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] generated preemptive snapshot 6c20b96e at index 54
I180822 02:45:12.941234 160429 storage/store_snapshot.go:655 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] streamed snapshot to (n4,s4):?: kv pairs: 47, log entries: 44, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:12.942076 160432 storage/replica_raftstorage.go:782 [n4,s4,r4/?:{-}] applying preemptive snapshot at index 54 (id=6c20b96e, encoded size=137413, 1 rocksdb batches, 44 log entries)
I180822 02:45:12.943230 160432 storage/replica_raftstorage.go:788 [n4,s4,r4/?:/System/{NodeLive…-tsd}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=1ms]
I180822 02:45:12.943706 160429 storage/replica_command.go:803 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r4:/System/{NodeLivenessMax-tsd} [(n1,s1):1, next=2, gen=842354567632]
I180822 02:45:13.009951 160429 storage/replica.go:3743 [n1,s1,r4/1:/System/{NodeLive…-tsd}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:13.016311 160510 storage/replica_range_lease.go:554 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] transferring lease to s4
I180822 02:45:13.017140 160510 storage/replica_range_lease.go:617 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] done transferring lease to s4: <nil>
I180822 02:45:13.017437 159556 storage/replica_proposal.go:214 [n4,s4,r4/2:/System/{NodeLive…-tsd}] new range lease repl=(n4,s4):2 seq=3 start=1534905913.016336904,0 epo=1 pro=1534905913.016339599,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:13.215154 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[4 4] [1 1]] expected [[2 2]]
I180822 02:45:13.712236 160462 storage/replica_command.go:803 [replicate,n4,s4,r22/2:/Table/5{1-2}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r22:/Table/5{1-2} [(n1,s1):1, (n4,s4):2, next=3, gen=842389309568]
I180822 02:45:13.738132 160352 rpc/nodedialer/nodedialer.go:92 [consistencyChecker,n4,s4,r22/2:/Table/5{1-2}] connection to n4 established
I180822 02:45:13.776417 160462 storage/replica.go:3743 [n4,s4,r22/2:/Table/5{1-2}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:13.780090 159823 storage/store.go:3745 [n1,s1,r22/1:/Table/5{1-2}] added to replica GC queue (peer suggestion)
I180822 02:45:13.780173 160563 storage/store.go:2632 [replicaGC,n1,s1,r22/1:/Table/5{1-2}] removing replica
I180822 02:45:13.780440 160563 storage/replica.go:880 [replicaGC,n1,s1,r22/1:/Table/5{1-2}] removed 8 (0+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:13.938878 160571 storage/replica_raftstorage.go:538 [replicate,n1,s1,r14/1:/Table/1{7-8}] generated preemptive snapshot bc2ef860 at index 18
I180822 02:45:13.940145 160571 storage/store_snapshot.go:655 [replicate,n1,s1,r14/1:/Table/1{7-8}] streamed snapshot to (n4,s4):?: kv pairs: 9, log entries: 8, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:13.940619 160579 storage/replica_raftstorage.go:782 [n4,s4,r14/?:{-}] applying preemptive snapshot at index 18 (id=bc2ef860, encoded size=2552, 1 rocksdb batches, 8 log entries)
I180822 02:45:13.940881 160579 storage/replica_raftstorage.go:788 [n4,s4,r14/?:/Table/1{7-8}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:13.941436 160571 storage/replica_command.go:803 [replicate,n1,s1,r14/1:/Table/1{7-8}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r14:/Table/1{7-8} [(n1,s1):1, next=2, gen=842390025728]
I180822 02:45:13.947071 160571 storage/replica.go:3743 [n1,s1,r14/1:/Table/1{7-8}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:13.950682 160573 storage/replica_range_lease.go:554 [replicate,n1,s1,r14/1:/Table/1{7-8}] transferring lease to s4
I180822 02:45:13.952595 160573 storage/replica_range_lease.go:617 [replicate,n1,s1,r14/1:/Table/1{7-8}] done transferring lease to s4: <nil>
I180822 02:45:13.952912 159607 storage/replica_proposal.go:214 [n4,s4,r14/2:/Table/1{7-8}] new range lease repl=(n4,s4):2 seq=3 start=1534905913.951818050,0 epo=1 pro=1534905913.951821769,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:14.219604 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:14.711437 160601 storage/replica_command.go:803 [replicate,n4,s4,r23/2:/Table/5{2-3}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r23:/Table/5{2-3} [(n1,s1):1, (n4,s4):2, next=3, gen=842414329880]
I180822 02:45:14.725307 160601 storage/replica.go:3743 [n4,s4,r23/2:/Table/5{2-3}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:14.734784 159823 storage/store.go:3745 [n1,s1,r23/1:/Table/5{2-3}] added to replica GC queue (peer suggestion)
I180822 02:45:14.735302 160676 storage/store.go:2632 [replicaGC,n1,s1,r23/1:/Table/5{2-3}] removing replica
I180822 02:45:14.735698 160676 storage/replica.go:880 [replicaGC,n1,s1,r23/1:/Table/5{2-3}] removed 8 (0+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:14.939216 160696 storage/replica_raftstorage.go:538 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] generated preemptive snapshot f6e33119 at index 62
I180822 02:45:14.940782 160696 storage/store_snapshot.go:655 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] streamed snapshot to (n4,s4):?: kv pairs: 76, log entries: 52, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:14.951735 160662 storage/replica_raftstorage.go:782 [n4,s4,r7/?:{-}] applying preemptive snapshot at index 62 (id=f6e33119, encoded size=28052, 1 rocksdb batches, 52 log entries)
I180822 02:45:14.952264 160662 storage/replica_raftstorage.go:788 [n4,s4,r7/?:/Table/{SystemCon…-11}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:14.952890 160696 storage/replica_command.go:803 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r7:/Table/{SystemConfigSpan/Start-11} [(n1,s1):1, next=2, gen=842392433488]
I180822 02:45:14.961800 160696 storage/replica.go:3743 [n1,s1,r7/1:/Table/{SystemCon…-11}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:14.973080 160761 storage/replica_range_lease.go:554 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] transferring lease to s4
I180822 02:45:14.974268 160761 storage/replica_range_lease.go:617 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] done transferring lease to s4: <nil>
I180822 02:45:14.974504 159582 storage/replica_proposal.go:214 [n4,s4,r7/2:/Table/{SystemCon…-11}] new range lease repl=(n4,s4):2 seq=3 start=1534905914.973103765,0 epo=1 pro=1534905914.973107378,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:15.223274 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:15.712508 160787 storage/replica_command.go:803 [replicate,n4,s4,r10/2:/Table/1{3-4}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r10:/Table/1{3-4} [(n1,s1):1, (n4,s4):2, next=3, gen=842397780040]
I180822 02:45:15.789362 160787 storage/replica.go:3743 [n4,s4,r10/2:/Table/1{3-4}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:15.793698 159823 storage/store.go:3745 [n1,s1,r10/1:/Table/1{3-4}] added to replica GC queue (peer suggestion)
I180822 02:45:15.793833 160704 storage/store.go:2632 [replicaGC,n1,s1,r10/1:/Table/1{3-4}] removing replica
I180822 02:45:15.794223 160704 storage/replica.go:880 [replicaGC,n1,s1,r10/1:/Table/1{3-4}] removed 228 (220+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:15.939068 160710 storage/replica_raftstorage.go:538 [replicate,n1,s1,r19/1:/Table/2{2-3}] generated preemptive snapshot 46c9ce27 at index 16
I180822 02:45:15.940245 160710 storage/store_snapshot.go:655 [replicate,n1,s1,r19/1:/Table/2{2-3}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 6, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:15.941271 160811 storage/replica_raftstorage.go:782 [n4,s4,r19/?:{-}] applying preemptive snapshot at index 16 (id=46c9ce27, encoded size=2109, 1 rocksdb batches, 6 log entries)
I180822 02:45:15.941506 160811 storage/replica_raftstorage.go:788 [n4,s4,r19/?:/Table/2{2-3}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:15.945188 160710 storage/replica_command.go:803 [replicate,n1,s1,r19/1:/Table/2{2-3}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r19:/Table/2{2-3} [(n1,s1):1, next=2, gen=842424010808]
I180822 02:45:16.011232 160710 storage/replica.go:3743 [n1,s1,r19/1:/Table/2{2-3}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:16.018641 160892 storage/replica_range_lease.go:554 [replicate,n1,s1,r19/1:/Table/2{2-3}] transferring lease to s4
I180822 02:45:16.019519 160892 storage/replica_range_lease.go:617 [replicate,n1,s1,r19/1:/Table/2{2-3}] done transferring lease to s4: <nil>
I180822 02:45:16.020722 159610 storage/replica_proposal.go:214 [n4,s4,r19/2:/Table/2{2-3}] new range lease repl=(n4,s4):2 seq=3 start=1534905916.018662892,0 epo=1 pro=1534905916.018667618,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:16.227147 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:16.940522 160898 storage/replica_raftstorage.go:538 [replicate,n1,s1,r9/1:/Table/1{2-3}] generated preemptive snapshot 9d4e84bd at index 52
I180822 02:45:16.942200 160898 storage/store_snapshot.go:655 [replicate,n1,s1,r9/1:/Table/1{2-3}] streamed snapshot to (n4,s4):?: kv pairs: 100, log entries: 42, rate-limit: 2.0 MiB/sec, 2ms
I180822 02:45:16.942828 160901 storage/replica_raftstorage.go:782 [n4,s4,r9/?:{-}] applying preemptive snapshot at index 52 (id=9d4e84bd, encoded size=34353, 1 rocksdb batches, 42 log entries)
I180822 02:45:16.943382 160901 storage/replica_raftstorage.go:788 [n4,s4,r9/?:/Table/1{2-3}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:16.943936 160898 storage/replica_command.go:803 [replicate,n1,s1,r9/1:/Table/1{2-3}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r9:/Table/1{2-3} [(n1,s1):1, next=2, gen=842363826640]
I180822 02:45:16.953007 160898 storage/replica.go:3743 [n1,s1,r9/1:/Table/1{2-3}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:16.975746 161080 storage/replica_range_lease.go:554 [replicate,n1,s1,r9/1:/Table/1{2-3}] transferring lease to s4
I180822 02:45:16.976622 159564 storage/replica_proposal.go:214 [n4,s4,r9/2:/Table/1{2-3}] new range lease repl=(n4,s4):2 seq=3 start=1534905916.975760342,0 epo=1 pro=1534905916.975765007,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:16.978976 161080 storage/replica_range_lease.go:617 [replicate,n1,s1,r9/1:/Table/1{2-3}] done transferring lease to s4: <nil>
I180822 02:45:17.230831 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:17.944059 158540 storage/replica_proposal.go:214 [n1,s1,r18/1:/Table/2{1-2}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905917.943663211,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:17.944872 161126 storage/replica_raftstorage.go:538 [replicate,n1,s1,r18/1:/Table/2{1-2}] generated preemptive snapshot 9aecac46 at index 17
I180822 02:45:17.946399 161126 storage/store_snapshot.go:655 [replicate,n1,s1,r18/1:/Table/2{1-2}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 7, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:17.946868 161086 storage/replica_raftstorage.go:782 [n4,s4,r18/?:{-}] applying preemptive snapshot at index 17 (id=9aecac46, encoded size=2437, 1 rocksdb batches, 7 log entries)
I180822 02:45:17.947132 161086 storage/replica_raftstorage.go:788 [n4,s4,r18/?:/Table/2{1-2}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:17.947563 161126 storage/replica_command.go:803 [replicate,n1,s1,r18/1:/Table/2{1-2}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r18:/Table/2{1-2} [(n1,s1):1, next=2, gen=842354476208]
I180822 02:45:17.956356 161126 storage/replica.go:3743 [n1,s1,r18/1:/Table/2{1-2}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:17.960699 161154 storage/replica_range_lease.go:554 [replicate,n1,s1,r18/1:/Table/2{1-2}] transferring lease to s4
I180822 02:45:17.961606 161154 storage/replica_range_lease.go:617 [replicate,n1,s1,r18/1:/Table/2{1-2}] done transferring lease to s4: <nil>
I180822 02:45:17.962644 159580 storage/replica_proposal.go:214 [n4,s4,r18/2:/Table/2{1-2}] new range lease repl=(n4,s4):2 seq=4 start=1534905917.960761933,0 epo=1 pro=1534905917.960765548,0 following repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905917.943663211,0
I180822 02:45:18.234190 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:18.941334 158576 server/status/runtime.go:433 [n1] runtime stats: 274 MiB RSS, 1256 goroutines, 42 MiB/42 MiB/113 MiB GO alloc/idle/total, 37 MiB/74 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1043x)
I180822 02:45:18.944612 158505 storage/replica_proposal.go:214 [n1,s1,r16/1:/Table/{19-20}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905918.944227918,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:18.946983 161164 storage/replica_raftstorage.go:538 [replicate,n1,s1,r16/1:/Table/{19-20}] generated preemptive snapshot 6c55d88b at index 19
I180822 02:45:18.947772 161164 storage/store_snapshot.go:655 [replicate,n1,s1,r16/1:/Table/{19-20}] streamed snapshot to (n4,s4):?: kv pairs: 9, log entries: 9, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:18.948196 161168 storage/replica_raftstorage.go:782 [n4,s4,r16/?:{-}] applying preemptive snapshot at index 19 (id=6c55d88b, encoded size=2554, 1 rocksdb batches, 9 log entries)
I180822 02:45:18.948488 161168 storage/replica_raftstorage.go:788 [n4,s4,r16/?:/Table/{19-20}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:18.948990 161164 storage/replica_command.go:803 [replicate,n1,s1,r16/1:/Table/{19-20}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r16:/Table/{19-20} [(n1,s1):1, next=2, gen=842362935984]
I180822 02:45:18.967671 161164 storage/replica.go:3743 [n1,s1,r16/1:/Table/{19-20}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:18.989174 161369 storage/replica_range_lease.go:554 [replicate,n1,s1,r16/1:/Table/{19-20}] transferring lease to s4
I180822 02:45:18.989591 158512 storage/replica_proposal.go:214 [n1,s1,r5/1:/System/ts{d-e}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905918.989267642,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:18.989968 161369 storage/replica_range_lease.go:617 [replicate,n1,s1,r16/1:/Table/{19-20}] done transferring lease to s4: <nil>
I180822 02:45:18.990162 159597 storage/replica_proposal.go:214 [n4,s4,r16/2:/Table/{19-20}] new range lease repl=(n4,s4):2 seq=4 start=1534905918.989236242,0 epo=1 pro=1534905918.989241356,0 following repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905918.944227918,0
I180822 02:45:19.133952 158594 server/status/recorder.go:652 [n1,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
W180822 02:45:19.145717 158594 server/node.go:886 [n1,summaries] health alerts detected: {Alerts:[{StoreID:1 Category:METRICS Description:queue.replicate.process.failure Value:1}]}
I180822 02:45:19.237821 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:19.474061 159081 server/status/runtime.go:433 [n2] runtime stats: 275 MiB RSS, 1256 goroutines, 51 MiB/34 MiB/113 MiB GO alloc/idle/total, 38 MiB/75 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1043x)
I180822 02:45:19.484680 159083 server/status/recorder.go:652 [n2,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:19.584286 159365 server/status/runtime.go:433 [n3] runtime stats: 275 MiB RSS, 1256 goroutines, 57 MiB/28 MiB/113 MiB GO alloc/idle/total, 39 MiB/75 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1043x)
I180822 02:45:19.603340 159367 server/status/recorder.go:652 [n3,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:19.706726 159635 server/status/runtime.go:433 [n4] runtime stats: 275 MiB RSS, 1256 goroutines, 34 MiB/46 MiB/113 MiB GO alloc/idle/total, 39 MiB/75 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1044x)
I180822 02:45:19.724433 159637 server/status/recorder.go:652 [n4,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:19.945139 158548 storage/replica_proposal.go:214 [n1,s1,r11/1:/Table/1{4-5}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905919.944715296,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:19.946655 161421 storage/replica_raftstorage.go:538 [replicate,n1,s1,r11/1:/Table/1{4-5}] generated preemptive snapshot 4ac1ebcd at index 21
I180822 02:45:19.949091 161421 storage/store_snapshot.go:655 [replicate,n1,s1,r11/1:/Table/1{4-5}] streamed snapshot to (n4,s4):?: kv pairs: 10, log entries: 11, rate-limit: 2.0 MiB/sec, 2ms
I180822 02:45:19.949584 161426 storage/replica_raftstorage.go:782 [n4,s4,r11/?:{-}] applying preemptive snapshot at index 21 (id=4ac1ebcd, encoded size=3096, 1 rocksdb batches, 11 log entries)
I180822 02:45:19.949857 161426 storage/replica_raftstorage.go:788 [n4,s4,r11/?:/Table/1{4-5}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:19.950383 161421 storage/replica_command.go:803 [replicate,n1,s1,r11/1:/Table/1{4-5}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r11:/Table/1{4-5} [(n1,s1):1, next=2, gen=842425789696]
I180822 02:45:19.959551 161421 storage/replica.go:3743 [n1,s1,r11/1:/Table/1{4-5}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:19.973357 161543 storage/replica_range_lease.go:554 [replicate,n1,s1,r11/1:/Table/1{4-5}] transferring lease to s4
I180822 02:45:19.974316 159566 storage/replica_proposal.go:214 [n4,s4,r11/2:/Table/1{4-5}] new range lease repl=(n4,s4):2 seq=4 start=1534905919.973415499,0 epo=1 pro=1534905919.973419509,0 following repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905919.944715296,0
I180822 02:45:19.976701 161543 storage/replica_range_lease.go:617 [replicate,n1,s1,r11/1:/Table/1{4-5}] done transferring lease to s4: <nil>
I180822 02:45:20.241862 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:20.715455 161387 storage/replica_command.go:803 [replicate,n4,s4,r14/2:/Table/1{7-8}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r14:/Table/1{7-8} [(n1,s1):1, (n4,s4):2, next=3, gen=842355192504]
I180822 02:45:20.721048 161387 storage/replica.go:3743 [n4,s4,r14/2:/Table/1{7-8}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:20.725609 161389 storage/store.go:2632 [replicaGC,n1,s1,r14/1:/Table/1{7-8}] removing replica
I180822 02:45:20.725882 161389 storage/replica.go:880 [replicaGC,n1,s1,r14/1:/Table/1{7-8}] removed 8 (0+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:20.945591 158506 storage/replica_proposal.go:214 [n1,s1,r6/1:/{System/tse-Table/System…}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905920.945157546,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:20.947273 161455 storage/replica_raftstorage.go:538 [replicate,n1,s1,r6/1:/{System/tse-Table/System…}] generated preemptive snapshot e68bb8f3 at index 21
I180822 02:45:20.949023 161455 storage/store_snapshot.go:655 [replicate,n1,s1,r6/1:/{System/tse-Table/System…}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 11, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:20.949542 161548 storage/replica_raftstorage.go:782 [n4,s4,r6/?:{-}] applying preemptive snapshot at index 21 (id=e68bb8f3, encoded size=5408, 1 r
```
Please assign, take a look and update the issue accordingly.
| 1.0 | teamcity: failed tests on master: test/TestShowTraceReplica - The following tests appear to have failed:
[#853175](https://teamcity.cockroachdb.com/viewLog.html?buildId=853175):
```
--- FAIL: test/TestShowTraceReplica (56.880s)
------- Stdout: -------
W180822 02:45:08.896090 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:08.914399 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:08.914705 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:08.914765 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:08.924394 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:08.924513 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:08.924573 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
I180822 02:45:08.930005 158345 util/stop/stopper.go:537 [n?] quiescing; tasks left:
1 [async] storage.pendingLeaseRequest: requesting lease
I180822 02:45:08.930637 158345 server/node.go:373 [n?] **** cluster a9379584-4fcf-40c2-8feb-f1f399f5d3e9 has been created
I180822 02:45:08.930660 158345 server/server.go:1401 [n?] **** add additional nodes by specifying --join=127.0.0.1:36021
I180822 02:45:08.930817 158345 gossip/gossip.go:382 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:36021" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905908930753221
I180822 02:45:08.932713 158345 storage/store.go:1541 [n1,s1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I180822 02:45:08.934417 158345 server/node.go:476 [n1] initialized store [n1,s1]: disk (capacity=512 MiB, available=512 MiB, used=0 B, logicalBytes=6.9 KiB), ranges=1, leases=1, queries=0.00, writes=0.00, bytesPerReplica={p10=7103.00 p25=7103.00 p50=7103.00 p75=7103.00 p90=7103.00 pMax=7103.00}, writesPerReplica={p10=0.00 p25=0.00 p50=0.00 p75=0.00 p90=0.00 pMax=0.00}
I180822 02:45:08.934503 158345 storage/stores.go:242 [n1] read 0 node addresses from persistent storage
I180822 02:45:08.934607 158345 server/node.go:697 [n1] connecting to gossip network to verify cluster ID...
I180822 02:45:08.934648 158345 server/node.go:722 [n1] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:08.934677 158345 server/node.go:546 [n1] node=1: started with [n1=<in-mem>] engine(s) and attributes []
I180822 02:45:08.934985 158345 server/status/recorder.go:652 [n1] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:08.936436 158433 storage/replica_command.go:289 [split,n1,s1,r1/1:/M{in-ax}] initiating a split of this range at key /System/"" [r2]
I180822 02:45:08.936773 158345 server/server.go:1807 [n1] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:08.938980 158594 server/status/recorder.go:652 [n1,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:08.940118 158345 server/server.go:1538 [n1] starting https server at 127.0.0.1:36377 (use: 127.0.0.1:36377)
I180822 02:45:08.942728 158345 server/server.go:1540 [n1] starting grpc/postgres server at 127.0.0.1:36021
I180822 02:45:08.943780 158345 server/server.go:1541 [n1] advertising CockroachDB node at 127.0.0.1:36021
I180822 02:45:09.138194 158408 storage/replica_command.go:289 [split,n1,s1,r2/1:/{System/-Max}] initiating a split of this range at key /System/NodeLiveness [r3]
I180822 02:45:09.159639 158378 storage/replica_command.go:289 [split,n1,s1,r3/1:/{System/NodeL…-Max}] initiating a split of this range at key /System/NodeLivenessMax [r4]
W180822 02:45:09.160842 158375 storage/intent_resolver.go:668 [n1,s1] failed to push during intent resolution: failed to push "sql txn" id=5d8995aa key=/Table/SystemConfigSpan/Start rw=true pri=0.00786353 iso=SERIALIZABLE stat=PENDING epo=0 ts=1534905909.140242610,0 orig=1534905909.140242610,0 max=1534905909.140242610,0 wto=false rop=false seq=6
I180822 02:45:09.176781 157118 storage/replica_command.go:289 [split,n1,s1,r4/1:/{System/NodeL…-Max}] initiating a split of this range at key /System/tsd [r5]
I180822 02:45:09.177818 158599 sql/event_log.go:126 [n1,intExec=optInToDiagnosticsStatReporting] Event: "set_cluster_setting", target: 0, info: {SettingName:diagnostics.reporting.enabled Value:true User:root}
I180822 02:45:09.199663 158661 storage/replica_command.go:289 [split,n1,s1,r5/1:/{System/tsd-Max}] initiating a split of this range at key /System/"tse" [r6]
I180822 02:45:09.210577 158604 storage/replica_command.go:289 [split,n1,s1,r6/1:/{System/tse-Max}] initiating a split of this range at key /Table/SystemConfigSpan/Start [r7]
I180822 02:45:09.218989 158383 storage/replica_command.go:289 [split,n1,s1,r7/1:/{Table/System…-Max}] initiating a split of this range at key /Table/11 [r8]
I180822 02:45:09.226652 158696 storage/replica_command.go:289 [split,n1,s1,r8/1:/{Table/11-Max}] initiating a split of this range at key /Table/12 [r9]
I180822 02:45:09.234841 158644 sql/event_log.go:126 [n1,intExec=set-setting] Event: "set_cluster_setting", target: 0, info: {SettingName:version Value:$1 User:root}
I180822 02:45:09.242665 158678 storage/replica_command.go:289 [split,n1,s1,r9/1:/{Table/12-Max}] initiating a split of this range at key /Table/13 [r10]
I180822 02:45:09.251750 158723 storage/replica_command.go:289 [split,n1,s1,r10/1:/{Table/13-Max}] initiating a split of this range at key /Table/14 [r11]
I180822 02:45:09.253502 158655 sql/event_log.go:126 [n1,intExec=disableNetTrace] Event: "set_cluster_setting", target: 0, info: {SettingName:trace.debug.enable Value:false User:root}
I180822 02:45:09.267578 158742 storage/replica_command.go:289 [split,n1,s1,r11/1:/{Table/14-Max}] initiating a split of this range at key /Table/15 [r12]
I180822 02:45:09.287164 158726 storage/replica_command.go:289 [split,n1,s1,r12/1:/{Table/15-Max}] initiating a split of this range at key /Table/16 [r13]
I180822 02:45:09.293807 158713 storage/replica_command.go:289 [split,n1,s1,r13/1:/{Table/16-Max}] initiating a split of this range at key /Table/17 [r14]
I180822 02:45:09.305946 158757 sql/event_log.go:126 [n1,intExec=initializeClusterSecret] Event: "set_cluster_setting", target: 0, info: {SettingName:cluster.secret Value:gen_random_uuid()::STRING User:root}
I180822 02:45:09.306648 158734 storage/replica_command.go:289 [split,n1,s1,r14/1:/{Table/17-Max}] initiating a split of this range at key /Table/18 [r15]
I180822 02:45:09.316139 158789 sql/event_log.go:126 [n1,intExec=create-default-db] Event: "create_database", target: 50, info: {DatabaseName:defaultdb Statement:CREATE DATABASE IF NOT EXISTS defaultdb User:root}
I180822 02:45:09.320870 158777 sql/event_log.go:126 [n1,intExec=create-default-db] Event: "create_database", target: 51, info: {DatabaseName:postgres Statement:CREATE DATABASE IF NOT EXISTS postgres User:root}
I180822 02:45:09.323984 158345 server/server.go:1594 [n1] done ensuring all necessary migrations have run
I180822 02:45:09.324594 158345 server/server.go:1597 [n1] serving sql connections
I180822 02:45:09.329653 158803 sql/event_log.go:126 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36021} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905908930753221 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905908930753221 LastUp:1534905908930753221}
I180822 02:45:09.330111 158785 server/server_update.go:67 [n1] no need to upgrade, cluster already at the newest version
I180822 02:45:09.338745 158805 storage/replica_command.go:289 [split,n1,s1,r15/1:/{Table/18-Max}] initiating a split of this range at key /Table/19 [r16]
I180822 02:45:09.346484 158808 storage/replica_command.go:289 [split,n1,s1,r16/1:/{Table/19-Max}] initiating a split of this range at key /Table/20 [r17]
I180822 02:45:09.354532 158811 storage/replica_command.go:289 [split,n1,s1,r17/1:/{Table/20-Max}] initiating a split of this range at key /Table/21 [r18]
I180822 02:45:09.359077 158824 storage/replica_command.go:289 [split,n1,s1,r18/1:/{Table/21-Max}] initiating a split of this range at key /Table/22 [r19]
I180822 02:45:09.366472 158885 storage/replica_command.go:289 [split,n1,s1,r19/1:/{Table/22-Max}] initiating a split of this range at key /Table/23 [r20]
I180822 02:45:09.372342 158762 storage/replica_command.go:289 [split,n1,s1,r20/1:/{Table/23-Max}] initiating a split of this range at key /Table/50 [r21]
I180822 02:45:09.376710 158917 storage/replica_command.go:289 [split,n1,s1,r21/1:/{Table/50-Max}] initiating a split of this range at key /Table/51 [r22]
W180822 02:45:09.388446 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:09.436671 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:09.436820 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.436841 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.452621 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:09.452679 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:09.452689 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
W180822 02:45:09.452774 158345 gossip/gossip.go:1362 [n?] no incoming or outgoing connections
I180822 02:45:09.452825 158345 server/server.go:1403 [n?] no stores bootstrapped and --join flag specified, awaiting init command.
I180822 02:45:09.466224 158836 gossip/client.go:129 [n?] started gossip client to 127.0.0.1:36021
I180822 02:45:09.466733 158870 gossip/server.go:217 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:44707}
I180822 02:45:09.467220 158345 server/node.go:697 [n?] connecting to gossip network to verify cluster ID...
I180822 02:45:09.467254 158345 server/node.go:722 [n?] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:09.467554 158994 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.468782 158881 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.469412 158345 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.470138 158345 server/node.go:428 [n?] new node allocated ID 2
I180822 02:45:09.470224 158345 gossip/gossip.go:382 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:44707" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905909470146464
I180822 02:45:09.470274 158345 storage/stores.go:242 [n2] read 0 node addresses from persistent storage
I180822 02:45:09.470306 158345 storage/stores.go:261 [n2] wrote 1 node addresses to persistent storage
I180822 02:45:09.471143 158998 storage/stores.go:261 [n1] wrote 1 node addresses to persistent storage
I180822 02:45:09.471961 158345 server/node.go:672 [n2] bootstrapped store [n2,s2]
I180822 02:45:09.472073 158345 server/node.go:546 [n2] node=2: started with [] engine(s) and attributes []
I180822 02:45:09.472306 158345 server/status/recorder.go:652 [n2] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.472339 158345 server/server.go:1807 [n2] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:09.472409 158345 server/server.go:1538 [n2] starting https server at 127.0.0.1:46099 (use: 127.0.0.1:46099)
I180822 02:45:09.472426 158345 server/server.go:1540 [n2] starting grpc/postgres server at 127.0.0.1:44707
I180822 02:45:09.472441 158345 server/server.go:1541 [n2] advertising CockroachDB node at 127.0.0.1:44707
I180822 02:45:09.476501 159083 server/status/recorder.go:652 [n2,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.484622 158345 server/server.go:1594 [n2] done ensuring all necessary migrations have run
I180822 02:45:09.484660 158345 server/server.go:1597 [n2] serving sql connections
W180822 02:45:09.528792 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:09.530588 159112 sql/event_log.go:126 [n2] Event: "node_join", target: 2, info: {Descriptor:{NodeID:2 Address:{NetworkField:tcp AddressField:127.0.0.1:44707} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905909470146464 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905909470146464 LastUp:1534905909470146464}
I180822 02:45:09.531153 159110 server/server_update.go:67 [n2] no need to upgrade, cluster already at the newest version
I180822 02:45:09.535213 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:09.535320 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.535334 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.537535 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:09.537552 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:09.537561 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
W180822 02:45:09.537624 158345 gossip/gossip.go:1362 [n?] no incoming or outgoing connections
I180822 02:45:09.537657 158345 server/server.go:1403 [n?] no stores bootstrapped and --join flag specified, awaiting init command.
I180822 02:45:09.555538 159171 gossip/client.go:129 [n?] started gossip client to 127.0.0.1:36021
I180822 02:45:09.566299 159227 gossip/server.go:217 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:39899}
I180822 02:45:09.566935 158345 server/node.go:697 [n?] connecting to gossip network to verify cluster ID...
I180822 02:45:09.566979 158345 server/node.go:722 [n?] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:09.567287 159244 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.568721 159243 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.572675 158345 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.573436 159142 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n2 established
I180822 02:45:09.574467 158345 server/node.go:428 [n?] new node allocated ID 3
I180822 02:45:09.574536 158345 gossip/gossip.go:382 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:39899" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905909574478010
I180822 02:45:09.574580 158345 storage/stores.go:242 [n3] read 0 node addresses from persistent storage
I180822 02:45:09.574615 158345 storage/stores.go:261 [n3] wrote 2 node addresses to persistent storage
I180822 02:45:09.575798 158718 storage/stores.go:261 [n1] wrote 2 node addresses to persistent storage
I180822 02:45:09.576120 158719 storage/stores.go:261 [n2] wrote 2 node addresses to persistent storage
I180822 02:45:09.579849 158345 server/node.go:672 [n3] bootstrapped store [n3,s3]
I180822 02:45:09.580110 158345 server/node.go:546 [n3] node=3: started with [] engine(s) and attributes []
I180822 02:45:09.580830 158345 server/status/recorder.go:652 [n3] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.580876 158345 server/server.go:1807 [n3] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:09.580972 158345 server/server.go:1538 [n3] starting https server at 127.0.0.1:40575 (use: 127.0.0.1:40575)
I180822 02:45:09.584849 158345 server/server.go:1540 [n3] starting grpc/postgres server at 127.0.0.1:39899
I180822 02:45:09.584929 158345 server/server.go:1541 [n3] advertising CockroachDB node at 127.0.0.1:39899
I180822 02:45:09.583601 159367 server/status/recorder.go:652 [n3,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.594496 158345 server/server.go:1594 [n3] done ensuring all necessary migrations have run
I180822 02:45:09.594524 158345 server/server.go:1597 [n3] serving sql connections
W180822 02:45:09.627465 158345 server/status/runtime.go:294 [n?] Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
I180822 02:45:09.668348 158345 server/server.go:830 [n?] monitoring forward clock jumps based on server.clock.forward_jump_check_enabled
I180822 02:45:09.674150 158345 base/addr_validation.go:260 [n?] server certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.674178 158345 base/addr_validation.go:300 [n?] web UI certificate addresses: IP=127.0.0.1,::1; DNS=localhost,*.local; CN=node
I180822 02:45:09.676251 158345 server/config.go:496 [n?] 1 storage engine initialized
I180822 02:45:09.676281 158345 server/config.go:499 [n?] RocksDB cache size: 128 MiB
I180822 02:45:09.676289 158345 server/config.go:499 [n?] store 0: in-memory, size 0 B
W180822 02:45:09.676364 158345 gossip/gossip.go:1362 [n?] no incoming or outgoing connections
I180822 02:45:09.676413 158345 server/server.go:1403 [n?] no stores bootstrapped and --join flag specified, awaiting init command.
I180822 02:45:09.668857 159383 sql/event_log.go:126 [n3] Event: "node_join", target: 3, info: {Descriptor:{NodeID:3 Address:{NetworkField:tcp AddressField:127.0.0.1:39899} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905909574478010 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905909574478010 LastUp:1534905909574478010}
I180822 02:45:09.673098 159474 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n1 established
I180822 02:45:09.673657 159381 server/server_update.go:67 [n3] no need to upgrade, cluster already at the newest version
I180822 02:45:09.698002 159482 gossip/client.go:129 [n?] started gossip client to 127.0.0.1:36021
I180822 02:45:09.698566 159409 gossip/server.go:217 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:40015}
I180822 02:45:09.699147 158345 server/node.go:697 [n?] connecting to gossip network to verify cluster ID...
I180822 02:45:09.699187 158345 server/node.go:722 [n?] node connected via gossip and verified as part of cluster "a9379584-4fcf-40c2-8feb-f1f399f5d3e9"
I180822 02:45:09.699463 159534 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.700864 159533 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.701457 158345 kv/dist_sender.go:345 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I180822 02:45:09.702160 158345 server/node.go:428 [n?] new node allocated ID 4
I180822 02:45:09.702246 158345 gossip/gossip.go:382 [n4] NodeDescriptor set to node_id:4 address:<network_field:"tcp" address_field:"127.0.0.1:40015" > attrs:<> locality:<> ServerVersion:<major_val:2 minor_val:0 patch:0 unstable:12 > build_tag:"v2.1.0-alpha.20180702-1890-g749187a" started_at:1534905909702181761
I180822 02:45:09.702303 158345 storage/stores.go:242 [n4] read 0 node addresses from persistent storage
I180822 02:45:09.702350 158345 storage/stores.go:261 [n4] wrote 3 node addresses to persistent storage
I180822 02:45:09.703285 159540 storage/stores.go:261 [n1] wrote 3 node addresses to persistent storage
I180822 02:45:09.703793 159358 storage/stores.go:261 [n2] wrote 3 node addresses to persistent storage
I180822 02:45:09.704593 158345 server/node.go:672 [n4] bootstrapped store [n4,s4]
I180822 02:45:09.704687 158345 server/node.go:546 [n4] node=4: started with [] engine(s) and attributes []
I180822 02:45:09.704888 158345 server/status/recorder.go:652 [n4] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.704911 158345 server/server.go:1807 [n4] Could not start heap profiler worker due to: directory to store profiles could not be determined
I180822 02:45:09.704982 158345 server/server.go:1538 [n4] starting https server at 127.0.0.1:42991 (use: 127.0.0.1:42991)
I180822 02:45:09.704996 158345 server/server.go:1540 [n4] starting grpc/postgres server at 127.0.0.1:40015
I180822 02:45:09.705008 158345 server/server.go:1541 [n4] advertising CockroachDB node at 127.0.0.1:40015
I180822 02:45:09.707331 159637 server/status/recorder.go:652 [n4,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:09.711351 159541 storage/stores.go:261 [n3] wrote 3 node addresses to persistent storage
I180822 02:45:09.717042 158345 server/server.go:1594 [n4] done ensuring all necessary migrations have run
I180822 02:45:09.717123 158345 server/server.go:1597 [n4] serving sql connections
I180822 02:45:09.723229 159475 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n3 established
I180822 02:45:09.747908 159716 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n3 established
I180822 02:45:09.771402 159717 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n4 established
I180822 02:45:09.772325 159547 sql/event_log.go:126 [n4] Event: "node_join", target: 4, info: {Descriptor:{NodeID:4 Address:{NetworkField:tcp AddressField:127.0.0.1:40015} Attrs: Locality: ServerVersion:2.0-12 BuildTag:v2.1.0-alpha.20180702-1890-g749187a StartedAt:1534905909702181761 LocalityAddress:[]} ClusterID:a9379584-4fcf-40c2-8feb-f1f399f5d3e9 StartedAt:1534905909702181761 LastUp:1534905909702181761}
I180822 02:45:09.772951 159545 server/server_update.go:67 [n4] no need to upgrade, cluster already at the newest version
I180822 02:45:09.779764 159786 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n1 established
I180822 02:45:09.809361 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 0, info: {Target:.default Config:constraints: [+n4] User:root}
I180822 02:45:09.826809 159785 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n4 established
I180822 02:45:09.832895 159784 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n2 established
I180822 02:45:09.849545 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_database", target: 52, info: {DatabaseName:d Statement:CREATE DATABASE d User:root}
I180822 02:45:09.850629 159776 storage/replica_command.go:289 [split,n1,s1,r22/1:/{Table/51-Max}] initiating a split of this range at key /Table/52 [r23]
I180822 02:45:09.857202 159818 storage/replica_raftstorage.go:538 [replicate,n1,s1,r22/1:/Table/5{1-2}] generated preemptive snapshot 7f8ef362 at index 15
I180822 02:45:09.857969 159818 storage/store_snapshot.go:655 [replicate,n1,s1,r22/1:/Table/5{1-2}] streamed snapshot to (n4,s4):?: kv pairs: 9, log entries: 5, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.858896 159677 storage/replica_raftstorage.go:782 [n4,s4,r22/?:{-}] applying preemptive snapshot at index 15 (id=7f8ef362, encoded size=2321, 1 rocksdb batches, 5 log entries)
I180822 02:45:09.860089 159677 storage/replica_raftstorage.go:788 [n4,s4,r22/?:/Table/5{1-2}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=1ms]
I180822 02:45:09.860624 159818 storage/replica_command.go:803 [replicate,n1,s1,r22/1:/Table/5{1-2}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r22:/Table/5{1-2} [(n1,s1):1, next=2, gen=842354566152]
I180822 02:45:09.866127 159818 storage/replica.go:3743 [n1,s1,r22/1:/Table/5{1-2}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.868444 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_table", target: 53, info: {TableName:d.public.t1 Statement:CREATE TABLE d.public.t1 (a INT PRIMARY KEY) User:root}
I180822 02:45:09.869195 159909 storage/replica_command.go:289 [split,n1,s1,r23/1:/{Table/52-Max}] initiating a split of this range at key /Table/53 [r24]
I180822 02:45:09.870600 159555 rpc/nodedialer/nodedialer.go:92 [n4] connection to n1 established
I180822 02:45:09.872397 159825 storage/replica_range_lease.go:554 [replicate,n1,s1,r22/1:/Table/5{1-2}] transferring lease to s4
I180822 02:45:09.873209 159825 storage/replica_range_lease.go:617 [replicate,n1,s1,r22/1:/Table/5{1-2}] done transferring lease to s4: <nil>
I180822 02:45:09.876010 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_table", target: 54, info: {TableName:d.public.t2 Statement:CREATE TABLE d.public.t2 (a INT PRIMARY KEY) User:root}
I180822 02:45:09.877328 159841 storage/replica_command.go:289 [split,n1,s1,r24/1:/{Table/53-Max}] initiating a split of this range at key /Table/54 [r25]
I180822 02:45:09.880827 159559 storage/replica_proposal.go:214 [n4,s4,r22/2:/Table/5{1-2}] new range lease repl=(n4,s4):2 seq=3 start=1534905909.872443081,0 epo=1 pro=1534905909.872446544,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:09.887440 159903 storage/replica_raftstorage.go:538 [replicate,n1,s1,r23/1:/Table/5{2-3}] generated preemptive snapshot 78d69c74 at index 16
I180822 02:45:09.888034 159903 storage/store_snapshot.go:655 [replicate,n1,s1,r23/1:/Table/5{2-3}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 6, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.889435 159942 storage/replica_raftstorage.go:782 [n4,s4,r23/?:{-}] applying preemptive snapshot at index 16 (id=78d69c74, encoded size=2078, 1 rocksdb batches, 6 log entries)
I180822 02:45:09.889641 159942 storage/replica_raftstorage.go:788 [n4,s4,r23/?:/Table/5{2-3}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:09.890052 159903 storage/replica_command.go:803 [replicate,n1,s1,r23/1:/Table/5{2-3}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r23:/Table/5{2-3} [(n1,s1):1, next=2, gen=842362934016]
I180822 02:45:09.892772 159903 storage/replica.go:3743 [n1,s1,r23/1:/Table/5{2-3}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.895363 160027 storage/replica_range_lease.go:554 [replicate,n1,s1,r23/1:/Table/5{2-3}] transferring lease to s4
I180822 02:45:09.896128 160027 storage/replica_range_lease.go:617 [replicate,n1,s1,r23/1:/Table/5{2-3}] done transferring lease to s4: <nil>
I180822 02:45:09.896469 159946 storage/replica_raftstorage.go:538 [replicate,n1,s1,r25/1:/{Table/54-Max}] generated preemptive snapshot 4f870146 at index 11
I180822 02:45:09.897183 159568 storage/replica_proposal.go:214 [n4,s4,r23/2:/Table/5{2-3}] new range lease repl=(n4,s4):2 seq=3 start=1534905909.895408651,0 epo=1 pro=1534905909.895412489,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:09.897309 159946 storage/store_snapshot.go:655 [replicate,n1,s1,r25/1:/{Table/54-Max}] streamed snapshot to (n4,s4):?: kv pairs: 7, log entries: 1, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.897614 160011 storage/replica_raftstorage.go:782 [n4,s4,r25/?:{-}] applying preemptive snapshot at index 11 (id=4f870146, encoded size=369, 1 rocksdb batches, 1 log entries)
I180822 02:45:09.897806 160011 storage/replica_raftstorage.go:788 [n4,s4,r25/?:/{Table/54-Max}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:09.898350 159946 storage/replica_command.go:803 [replicate,n1,s1,r25/1:/{Table/54-Max}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r25:/{Table/54-Max} [(n1,s1):1, next=2, gen=0]
I180822 02:45:09.899260 159870 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n4 established
I180822 02:45:09.900183 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "create_table", target: 55, info: {TableName:d.public.t3 Statement:CREATE TABLE d.public.t3 (a INT PRIMARY KEY) User:root}
I180822 02:45:09.902444 160017 storage/replica_command.go:289 [split,n1,s1,r25/1:/{Table/54-Max}] initiating a split of this range at key /Table/55 [r26]
I180822 02:45:09.903518 159946 storage/replica.go:3743 [n1,s1,r25/1:/{Table/54-Max}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.904150 160071 storage/replica_raftstorage.go:538 [replicate,n1,s1,r24/1:/Table/5{3-4}] generated preemptive snapshot 9ee9e085 at index 16
I180822 02:45:09.905055 160071 storage/store_snapshot.go:655 [replicate,n1,s1,r24/1:/Table/5{3-4}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 6, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:09.915871 160074 storage/replica_raftstorage.go:782 [n4,s4,r24/?:{-}] applying preemptive snapshot at index 16 (id=9ee9e085, encoded size=2078, 1 rocksdb batches, 6 log entries)
I180822 02:45:09.916150 160074 storage/replica_raftstorage.go:788 [n4,s4,r24/?:/Table/5{3-4}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:09.919554 160071 storage/replica_command.go:803 [replicate,n1,s1,r24/1:/Table/5{3-4}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r24:/Table/5{3-4} [(n1,s1):1, next=2, gen=842366453288]
I180822 02:45:09.922015 160017 storage/split_queue.go:135 [split,n1,s1,r25/1:/{Table/54-Max}] split saw concurrent descriptor modification; maybe retrying
I180822 02:45:09.922182 160078 storage/replica_command.go:289 [split,n1,s1,r25/1:/{Table/54-Max}] initiating a split of this range at key /Table/55 [r27]
I180822 02:45:09.934699 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 53, info: {Target:d.t1 Config:constraints: [+n1] User:root}
I180822 02:45:09.936195 160045 rpc/nodedialer/nodedialer.go:92 [consistencyChecker,n1,s1,r1/1:/{Min-System/}] connection to n1 established
I180822 02:45:09.937732 159966 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n2 established
I180822 02:45:09.938161 160071 storage/replica.go:3743 [n1,s1,r24/1:/Table/5{3-4}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:09.938649 159967 rpc/nodedialer/nodedialer.go:92 [ct-client] connection to n3 established
I180822 02:45:09.944873 160164 storage/replica_range_lease.go:554 [replicate,n1,s1,r25/1:/Table/5{4-5}] transferring lease to s4
I180822 02:45:09.946017 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 54, info: {Target:d.t2 Config:constraints: [+n2] User:root}
I180822 02:45:09.946424 160164 storage/replica_range_lease.go:617 [replicate,n1,s1,r25/1:/Table/5{4-5}] done transferring lease to s4: <nil>
I180822 02:45:09.946885 160156 storage/replica_command.go:803 [replicate,n1,s1,r24/1:/Table/5{3-4}] change replicas (REMOVE_REPLICA (n4,s4):2): read existing descriptor r24:/Table/5{3-4} [(n1,s1):1, (n4,s4):2, next=3, gen=842413132040]
I180822 02:45:09.948180 159588 storage/replica_proposal.go:214 [n4,s4,r25/2:/Table/5{4-5}] new range lease repl=(n4,s4):2 seq=3 start=1534905909.944897194,0 epo=1 pro=1534905909.944900936,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:09.951782 160156 storage/replica.go:3743 [n1,s1,r24/1:/Table/5{3-4}] proposing REMOVE_REPLICA((n4,s4):2): updated=[(n1,s1):1] next=3
E180822 02:45:09.952676 160161 storage/queue.go:788 [replicate,n1,s1,r27/1:/{Table/55-Max}] no removable replicas from range that needs a removal: [raft progress unknown]
I180822 02:45:09.953577 159938 storage/store.go:3745 [n4,s4,r24/2:/Table/5{3-4}] added to replica GC queue (peer suggestion)
I180822 02:45:09.953903 160194 storage/store.go:2632 [replicaGC,n4,s4,r24/2:/Table/5{3-4}] removing replica
I180822 02:45:09.953940 160137 storage/replica_raftstorage.go:538 [replicate,n1,s1,r1/1:/{Min-System/}] generated preemptive snapshot 2cd7f1b1 at index 90
I180822 02:45:09.954132 160194 storage/replica.go:880 [replicaGC,n4,s4,r24/2:/Table/5{3-4}] removed 7 (0+7) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:09.954364 159713 sql/event_log.go:126 [n1,client=127.0.0.1:55780,user=root] Event: "set_zone_config", target: 55, info: {Target:d.t3 Config:constraints: [+n3] User:root}
--- FAIL: test/TestShowTraceReplica: TestShowTraceReplica/UPSERT_INTO_d.t2_VALUES_(1) (45.430s)
show_trace_replica_test.go:101: condition failed to evaluate within 45s: UPSERT INTO d.t2 VALUES (1): got [[4 4]] expected [[2 2]]
goroutine 160202 [running]:
runtime/debug.Stack(0xa7a358200, 0xc4222834d0, 0x2a98280)
/usr/local/go/src/runtime/debug/stack.go:24 +0xa7
github.com/cockroachdb/cockroach/pkg/testutils.SucceedsSoon(0x2ae7580, 0xc423f67b30, 0xc4227c23e0)
/go/src/github.com/cockroachdb/cockroach/pkg/testutils/soon.go:50 +0x10d
github.com/cockroachdb/cockroach/pkg/sql_test.TestShowTraceReplica.func2(0xc423f67b30)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/show_trace_replica_test.go:101 +0x9d
testing.tRunner(0xc423f67b30, 0xc4227c23a0)
/usr/local/go/src/testing/testing.go:777 +0xd0
created by testing.(*T).Run
/usr/local/go/src/testing/testing.go:824 +0x2e0
------- Stdout: -------
I180822 02:45:10.012981 160263 storage/replica_range_lease.go:554 [replicate,n1,s1,r1/1:/{Min-System/}] transferring lease to s3
I180822 02:45:10.015071 160263 storage/replica_range_lease.go:617 [replicate,n1,s1,r1/1:/{Min-System/}] done transferring lease to s3: <nil>
I180822 02:45:10.937427 160330 storage/replica_raftstorage.go:538 [replicate,n1,s1,r10/1:/Table/1{3-4}] generated preemptive snapshot dea55734 at index 64
I180822 02:45:10.939646 160330 storage/store_snapshot.go:655 [replicate,n1,s1,r10/1:/Table/1{3-4}] streamed snapshot to (n4,s4):?: kv pairs: 189, log entries: 54, rate-limit: 2.0 MiB/sec, 2ms
I180822 02:45:10.940327 160129 storage/replica_raftstorage.go:782 [n4,s4,r10/?:{-}] applying preemptive snapshot at index 64 (id=dea55734, encoded size=57008, 1 rocksdb batches, 54 log entries)
I180822 02:45:10.941048 160129 storage/replica_raftstorage.go:788 [n4,s4,r10/?:/Table/1{3-4}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:10.941598 160330 storage/replica_command.go:803 [replicate,n1,s1,r10/1:/Table/1{3-4}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r10:/Table/1{3-4} [(n1,s1):1, next=2, gen=842448414080]
I180822 02:45:10.948269 160330 storage/replica.go:3743 [n1,s1,r10/1:/Table/1{3-4}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:10.954821 160376 storage/replica_range_lease.go:554 [replicate,n1,s1,r10/1:/Table/1{3-4}] transferring lease to s4
I180822 02:45:10.955857 160376 storage/replica_range_lease.go:617 [replicate,n1,s1,r10/1:/Table/1{3-4}] done transferring lease to s4: <nil>
I180822 02:45:10.956127 159574 storage/replica_proposal.go:214 [n4,s4,r10/2:/Table/1{3-4}] new range lease repl=(n4,s4):2 seq=3 start=1534905910.954962824,0 epo=1 pro=1534905910.954966814,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:11.581479 160379 storage/replica_command.go:803 [replicate,n3,s3,r1/2:/{Min-System/}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r1:/{Min-System/} [(n1,s1):1, (n3,s3):2, next=3, gen=842353732432]
I180822 02:45:11.644535 160379 storage/replica.go:3743 [n3,s3,r1/2:/{Min-System/}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n3,s3):2] next=3
I180822 02:45:11.647846 160277 storage/store.go:3745 [n1,s1,r1/1:/{Min-System/}] added to replica GC queue (peer suggestion)
I180822 02:45:11.647896 160408 storage/store.go:2632 [replicaGC,n1,s1,r1/1:/{Min-System/}] removing replica
I180822 02:45:11.648327 160408 storage/replica.go:880 [replicaGC,n1,s1,r1/1:/{Min-System/}] removed 37 (27+10) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:12.706634 160411 storage/replica_range_lease.go:554 [replicate,n4,s4,r25/2:/Table/5{4-5}] transferring lease to s1
I180822 02:45:12.707913 160411 storage/replica_range_lease.go:617 [replicate,n4,s4,r25/2:/Table/5{4-5}] done transferring lease to s1: <nil>
I180822 02:45:12.708406 158500 storage/replica_proposal.go:214 [n1,s1,r25/1:/Table/5{4-5}] new range lease repl=(n1,s1):1 seq=4 start=1534905912.706654906,0 epo=1 pro=1534905912.706658979,0 following repl=(n4,s4):2 seq=3 start=1534905909.944897194,0 epo=1 pro=1534905909.944900936,0
I180822 02:45:12.939909 160429 storage/replica_raftstorage.go:538 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] generated preemptive snapshot 6c20b96e at index 54
I180822 02:45:12.941234 160429 storage/store_snapshot.go:655 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] streamed snapshot to (n4,s4):?: kv pairs: 47, log entries: 44, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:12.942076 160432 storage/replica_raftstorage.go:782 [n4,s4,r4/?:{-}] applying preemptive snapshot at index 54 (id=6c20b96e, encoded size=137413, 1 rocksdb batches, 44 log entries)
I180822 02:45:12.943230 160432 storage/replica_raftstorage.go:788 [n4,s4,r4/?:/System/{NodeLive…-tsd}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=1ms]
I180822 02:45:12.943706 160429 storage/replica_command.go:803 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r4:/System/{NodeLivenessMax-tsd} [(n1,s1):1, next=2, gen=842354567632]
I180822 02:45:13.009951 160429 storage/replica.go:3743 [n1,s1,r4/1:/System/{NodeLive…-tsd}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:13.016311 160510 storage/replica_range_lease.go:554 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] transferring lease to s4
I180822 02:45:13.017140 160510 storage/replica_range_lease.go:617 [replicate,n1,s1,r4/1:/System/{NodeLive…-tsd}] done transferring lease to s4: <nil>
I180822 02:45:13.017437 159556 storage/replica_proposal.go:214 [n4,s4,r4/2:/System/{NodeLive…-tsd}] new range lease repl=(n4,s4):2 seq=3 start=1534905913.016336904,0 epo=1 pro=1534905913.016339599,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:13.215154 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[4 4] [1 1]] expected [[2 2]]
I180822 02:45:13.712236 160462 storage/replica_command.go:803 [replicate,n4,s4,r22/2:/Table/5{1-2}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r22:/Table/5{1-2} [(n1,s1):1, (n4,s4):2, next=3, gen=842389309568]
I180822 02:45:13.738132 160352 rpc/nodedialer/nodedialer.go:92 [consistencyChecker,n4,s4,r22/2:/Table/5{1-2}] connection to n4 established
I180822 02:45:13.776417 160462 storage/replica.go:3743 [n4,s4,r22/2:/Table/5{1-2}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:13.780090 159823 storage/store.go:3745 [n1,s1,r22/1:/Table/5{1-2}] added to replica GC queue (peer suggestion)
I180822 02:45:13.780173 160563 storage/store.go:2632 [replicaGC,n1,s1,r22/1:/Table/5{1-2}] removing replica
I180822 02:45:13.780440 160563 storage/replica.go:880 [replicaGC,n1,s1,r22/1:/Table/5{1-2}] removed 8 (0+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:13.938878 160571 storage/replica_raftstorage.go:538 [replicate,n1,s1,r14/1:/Table/1{7-8}] generated preemptive snapshot bc2ef860 at index 18
I180822 02:45:13.940145 160571 storage/store_snapshot.go:655 [replicate,n1,s1,r14/1:/Table/1{7-8}] streamed snapshot to (n4,s4):?: kv pairs: 9, log entries: 8, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:13.940619 160579 storage/replica_raftstorage.go:782 [n4,s4,r14/?:{-}] applying preemptive snapshot at index 18 (id=bc2ef860, encoded size=2552, 1 rocksdb batches, 8 log entries)
I180822 02:45:13.940881 160579 storage/replica_raftstorage.go:788 [n4,s4,r14/?:/Table/1{7-8}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:13.941436 160571 storage/replica_command.go:803 [replicate,n1,s1,r14/1:/Table/1{7-8}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r14:/Table/1{7-8} [(n1,s1):1, next=2, gen=842390025728]
I180822 02:45:13.947071 160571 storage/replica.go:3743 [n1,s1,r14/1:/Table/1{7-8}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:13.950682 160573 storage/replica_range_lease.go:554 [replicate,n1,s1,r14/1:/Table/1{7-8}] transferring lease to s4
I180822 02:45:13.952595 160573 storage/replica_range_lease.go:617 [replicate,n1,s1,r14/1:/Table/1{7-8}] done transferring lease to s4: <nil>
I180822 02:45:13.952912 159607 storage/replica_proposal.go:214 [n4,s4,r14/2:/Table/1{7-8}] new range lease repl=(n4,s4):2 seq=3 start=1534905913.951818050,0 epo=1 pro=1534905913.951821769,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:14.219604 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:14.711437 160601 storage/replica_command.go:803 [replicate,n4,s4,r23/2:/Table/5{2-3}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r23:/Table/5{2-3} [(n1,s1):1, (n4,s4):2, next=3, gen=842414329880]
I180822 02:45:14.725307 160601 storage/replica.go:3743 [n4,s4,r23/2:/Table/5{2-3}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:14.734784 159823 storage/store.go:3745 [n1,s1,r23/1:/Table/5{2-3}] added to replica GC queue (peer suggestion)
I180822 02:45:14.735302 160676 storage/store.go:2632 [replicaGC,n1,s1,r23/1:/Table/5{2-3}] removing replica
I180822 02:45:14.735698 160676 storage/replica.go:880 [replicaGC,n1,s1,r23/1:/Table/5{2-3}] removed 8 (0+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:14.939216 160696 storage/replica_raftstorage.go:538 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] generated preemptive snapshot f6e33119 at index 62
I180822 02:45:14.940782 160696 storage/store_snapshot.go:655 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] streamed snapshot to (n4,s4):?: kv pairs: 76, log entries: 52, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:14.951735 160662 storage/replica_raftstorage.go:782 [n4,s4,r7/?:{-}] applying preemptive snapshot at index 62 (id=f6e33119, encoded size=28052, 1 rocksdb batches, 52 log entries)
I180822 02:45:14.952264 160662 storage/replica_raftstorage.go:788 [n4,s4,r7/?:/Table/{SystemCon…-11}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:14.952890 160696 storage/replica_command.go:803 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r7:/Table/{SystemConfigSpan/Start-11} [(n1,s1):1, next=2, gen=842392433488]
I180822 02:45:14.961800 160696 storage/replica.go:3743 [n1,s1,r7/1:/Table/{SystemCon…-11}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:14.973080 160761 storage/replica_range_lease.go:554 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] transferring lease to s4
I180822 02:45:14.974268 160761 storage/replica_range_lease.go:617 [replicate,n1,s1,r7/1:/Table/{SystemCon…-11}] done transferring lease to s4: <nil>
I180822 02:45:14.974504 159582 storage/replica_proposal.go:214 [n4,s4,r7/2:/Table/{SystemCon…-11}] new range lease repl=(n4,s4):2 seq=3 start=1534905914.973103765,0 epo=1 pro=1534905914.973107378,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:15.223274 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:15.712508 160787 storage/replica_command.go:803 [replicate,n4,s4,r10/2:/Table/1{3-4}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r10:/Table/1{3-4} [(n1,s1):1, (n4,s4):2, next=3, gen=842397780040]
I180822 02:45:15.789362 160787 storage/replica.go:3743 [n4,s4,r10/2:/Table/1{3-4}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:15.793698 159823 storage/store.go:3745 [n1,s1,r10/1:/Table/1{3-4}] added to replica GC queue (peer suggestion)
I180822 02:45:15.793833 160704 storage/store.go:2632 [replicaGC,n1,s1,r10/1:/Table/1{3-4}] removing replica
I180822 02:45:15.794223 160704 storage/replica.go:880 [replicaGC,n1,s1,r10/1:/Table/1{3-4}] removed 228 (220+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:15.939068 160710 storage/replica_raftstorage.go:538 [replicate,n1,s1,r19/1:/Table/2{2-3}] generated preemptive snapshot 46c9ce27 at index 16
I180822 02:45:15.940245 160710 storage/store_snapshot.go:655 [replicate,n1,s1,r19/1:/Table/2{2-3}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 6, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:15.941271 160811 storage/replica_raftstorage.go:782 [n4,s4,r19/?:{-}] applying preemptive snapshot at index 16 (id=46c9ce27, encoded size=2109, 1 rocksdb batches, 6 log entries)
I180822 02:45:15.941506 160811 storage/replica_raftstorage.go:788 [n4,s4,r19/?:/Table/2{2-3}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:15.945188 160710 storage/replica_command.go:803 [replicate,n1,s1,r19/1:/Table/2{2-3}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r19:/Table/2{2-3} [(n1,s1):1, next=2, gen=842424010808]
I180822 02:45:16.011232 160710 storage/replica.go:3743 [n1,s1,r19/1:/Table/2{2-3}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:16.018641 160892 storage/replica_range_lease.go:554 [replicate,n1,s1,r19/1:/Table/2{2-3}] transferring lease to s4
I180822 02:45:16.019519 160892 storage/replica_range_lease.go:617 [replicate,n1,s1,r19/1:/Table/2{2-3}] done transferring lease to s4: <nil>
I180822 02:45:16.020722 159610 storage/replica_proposal.go:214 [n4,s4,r19/2:/Table/2{2-3}] new range lease repl=(n4,s4):2 seq=3 start=1534905916.018662892,0 epo=1 pro=1534905916.018667618,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:16.227147 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:16.940522 160898 storage/replica_raftstorage.go:538 [replicate,n1,s1,r9/1:/Table/1{2-3}] generated preemptive snapshot 9d4e84bd at index 52
I180822 02:45:16.942200 160898 storage/store_snapshot.go:655 [replicate,n1,s1,r9/1:/Table/1{2-3}] streamed snapshot to (n4,s4):?: kv pairs: 100, log entries: 42, rate-limit: 2.0 MiB/sec, 2ms
I180822 02:45:16.942828 160901 storage/replica_raftstorage.go:782 [n4,s4,r9/?:{-}] applying preemptive snapshot at index 52 (id=9d4e84bd, encoded size=34353, 1 rocksdb batches, 42 log entries)
I180822 02:45:16.943382 160901 storage/replica_raftstorage.go:788 [n4,s4,r9/?:/Table/1{2-3}] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:16.943936 160898 storage/replica_command.go:803 [replicate,n1,s1,r9/1:/Table/1{2-3}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r9:/Table/1{2-3} [(n1,s1):1, next=2, gen=842363826640]
I180822 02:45:16.953007 160898 storage/replica.go:3743 [n1,s1,r9/1:/Table/1{2-3}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:16.975746 161080 storage/replica_range_lease.go:554 [replicate,n1,s1,r9/1:/Table/1{2-3}] transferring lease to s4
I180822 02:45:16.976622 159564 storage/replica_proposal.go:214 [n4,s4,r9/2:/Table/1{2-3}] new range lease repl=(n4,s4):2 seq=3 start=1534905916.975760342,0 epo=1 pro=1534905916.975765007,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:16.978976 161080 storage/replica_range_lease.go:617 [replicate,n1,s1,r9/1:/Table/1{2-3}] done transferring lease to s4: <nil>
I180822 02:45:17.230831 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:17.944059 158540 storage/replica_proposal.go:214 [n1,s1,r18/1:/Table/2{1-2}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905917.943663211,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:17.944872 161126 storage/replica_raftstorage.go:538 [replicate,n1,s1,r18/1:/Table/2{1-2}] generated preemptive snapshot 9aecac46 at index 17
I180822 02:45:17.946399 161126 storage/store_snapshot.go:655 [replicate,n1,s1,r18/1:/Table/2{1-2}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 7, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:17.946868 161086 storage/replica_raftstorage.go:782 [n4,s4,r18/?:{-}] applying preemptive snapshot at index 17 (id=9aecac46, encoded size=2437, 1 rocksdb batches, 7 log entries)
I180822 02:45:17.947132 161086 storage/replica_raftstorage.go:788 [n4,s4,r18/?:/Table/2{1-2}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:17.947563 161126 storage/replica_command.go:803 [replicate,n1,s1,r18/1:/Table/2{1-2}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r18:/Table/2{1-2} [(n1,s1):1, next=2, gen=842354476208]
I180822 02:45:17.956356 161126 storage/replica.go:3743 [n1,s1,r18/1:/Table/2{1-2}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:17.960699 161154 storage/replica_range_lease.go:554 [replicate,n1,s1,r18/1:/Table/2{1-2}] transferring lease to s4
I180822 02:45:17.961606 161154 storage/replica_range_lease.go:617 [replicate,n1,s1,r18/1:/Table/2{1-2}] done transferring lease to s4: <nil>
I180822 02:45:17.962644 159580 storage/replica_proposal.go:214 [n4,s4,r18/2:/Table/2{1-2}] new range lease repl=(n4,s4):2 seq=4 start=1534905917.960761933,0 epo=1 pro=1534905917.960765548,0 following repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905917.943663211,0
I180822 02:45:18.234190 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:18.941334 158576 server/status/runtime.go:433 [n1] runtime stats: 274 MiB RSS, 1256 goroutines, 42 MiB/42 MiB/113 MiB GO alloc/idle/total, 37 MiB/74 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1043x)
I180822 02:45:18.944612 158505 storage/replica_proposal.go:214 [n1,s1,r16/1:/Table/{19-20}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905918.944227918,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:18.946983 161164 storage/replica_raftstorage.go:538 [replicate,n1,s1,r16/1:/Table/{19-20}] generated preemptive snapshot 6c55d88b at index 19
I180822 02:45:18.947772 161164 storage/store_snapshot.go:655 [replicate,n1,s1,r16/1:/Table/{19-20}] streamed snapshot to (n4,s4):?: kv pairs: 9, log entries: 9, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:18.948196 161168 storage/replica_raftstorage.go:782 [n4,s4,r16/?:{-}] applying preemptive snapshot at index 19 (id=6c55d88b, encoded size=2554, 1 rocksdb batches, 9 log entries)
I180822 02:45:18.948488 161168 storage/replica_raftstorage.go:788 [n4,s4,r16/?:/Table/{19-20}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:18.948990 161164 storage/replica_command.go:803 [replicate,n1,s1,r16/1:/Table/{19-20}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r16:/Table/{19-20} [(n1,s1):1, next=2, gen=842362935984]
I180822 02:45:18.967671 161164 storage/replica.go:3743 [n1,s1,r16/1:/Table/{19-20}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:18.989174 161369 storage/replica_range_lease.go:554 [replicate,n1,s1,r16/1:/Table/{19-20}] transferring lease to s4
I180822 02:45:18.989591 158512 storage/replica_proposal.go:214 [n1,s1,r5/1:/System/ts{d-e}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905918.989267642,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:18.989968 161369 storage/replica_range_lease.go:617 [replicate,n1,s1,r16/1:/Table/{19-20}] done transferring lease to s4: <nil>
I180822 02:45:18.990162 159597 storage/replica_proposal.go:214 [n4,s4,r16/2:/Table/{19-20}] new range lease repl=(n4,s4):2 seq=4 start=1534905918.989236242,0 epo=1 pro=1534905918.989241356,0 following repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905918.944227918,0
I180822 02:45:19.133952 158594 server/status/recorder.go:652 [n1,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
W180822 02:45:19.145717 158594 server/node.go:886 [n1,summaries] health alerts detected: {Alerts:[{StoreID:1 Category:METRICS Description:queue.replicate.process.failure Value:1}]}
I180822 02:45:19.237821 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:19.474061 159081 server/status/runtime.go:433 [n2] runtime stats: 275 MiB RSS, 1256 goroutines, 51 MiB/34 MiB/113 MiB GO alloc/idle/total, 38 MiB/75 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1043x)
I180822 02:45:19.484680 159083 server/status/recorder.go:652 [n2,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:19.584286 159365 server/status/runtime.go:433 [n3] runtime stats: 275 MiB RSS, 1256 goroutines, 57 MiB/28 MiB/113 MiB GO alloc/idle/total, 39 MiB/75 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1043x)
I180822 02:45:19.603340 159367 server/status/recorder.go:652 [n3,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:19.706726 159635 server/status/runtime.go:433 [n4] runtime stats: 275 MiB RSS, 1256 goroutines, 34 MiB/46 MiB/113 MiB GO alloc/idle/total, 39 MiB/75 MiB CGO alloc/total, 0.00cgo/sec, 0.00/0.00 %(u/s)time, 0.00 %gc (1044x)
I180822 02:45:19.724433 159637 server/status/recorder.go:652 [n4,summaries] available memory from cgroups (8.0 EiB) exceeds system memory 16 GiB, using system memory
I180822 02:45:19.945139 158548 storage/replica_proposal.go:214 [n1,s1,r11/1:/Table/1{4-5}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905919.944715296,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:19.946655 161421 storage/replica_raftstorage.go:538 [replicate,n1,s1,r11/1:/Table/1{4-5}] generated preemptive snapshot 4ac1ebcd at index 21
I180822 02:45:19.949091 161421 storage/store_snapshot.go:655 [replicate,n1,s1,r11/1:/Table/1{4-5}] streamed snapshot to (n4,s4):?: kv pairs: 10, log entries: 11, rate-limit: 2.0 MiB/sec, 2ms
I180822 02:45:19.949584 161426 storage/replica_raftstorage.go:782 [n4,s4,r11/?:{-}] applying preemptive snapshot at index 21 (id=4ac1ebcd, encoded size=3096, 1 rocksdb batches, 11 log entries)
I180822 02:45:19.949857 161426 storage/replica_raftstorage.go:788 [n4,s4,r11/?:/Table/1{4-5}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180822 02:45:19.950383 161421 storage/replica_command.go:803 [replicate,n1,s1,r11/1:/Table/1{4-5}] change replicas (ADD_REPLICA (n4,s4):2): read existing descriptor r11:/Table/1{4-5} [(n1,s1):1, next=2, gen=842425789696]
I180822 02:45:19.959551 161421 storage/replica.go:3743 [n1,s1,r11/1:/Table/1{4-5}] proposing ADD_REPLICA((n4,s4):2): updated=[(n1,s1):1 (n4,s4):2] next=3
I180822 02:45:19.973357 161543 storage/replica_range_lease.go:554 [replicate,n1,s1,r11/1:/Table/1{4-5}] transferring lease to s4
I180822 02:45:19.974316 159566 storage/replica_proposal.go:214 [n4,s4,r11/2:/Table/1{4-5}] new range lease repl=(n4,s4):2 seq=4 start=1534905919.973415499,0 epo=1 pro=1534905919.973419509,0 following repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905919.944715296,0
I180822 02:45:19.976701 161543 storage/replica_range_lease.go:617 [replicate,n1,s1,r11/1:/Table/1{4-5}] done transferring lease to s4: <nil>
I180822 02:45:20.241862 160202 sql/show_trace_replica_test.go:101 SucceedsSoon: UPSERT INTO d.t2 VALUES (1): got [[1 1]] expected [[2 2]]
I180822 02:45:20.715455 161387 storage/replica_command.go:803 [replicate,n4,s4,r14/2:/Table/1{7-8}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r14:/Table/1{7-8} [(n1,s1):1, (n4,s4):2, next=3, gen=842355192504]
I180822 02:45:20.721048 161387 storage/replica.go:3743 [n4,s4,r14/2:/Table/1{7-8}] proposing REMOVE_REPLICA((n1,s1):1): updated=[(n4,s4):2] next=3
I180822 02:45:20.725609 161389 storage/store.go:2632 [replicaGC,n1,s1,r14/1:/Table/1{7-8}] removing replica
I180822 02:45:20.725882 161389 storage/replica.go:880 [replicaGC,n1,s1,r14/1:/Table/1{7-8}] removed 8 (0+8) keys in 0ms [clear=0ms commit=0ms]
I180822 02:45:20.945591 158506 storage/replica_proposal.go:214 [n1,s1,r6/1:/{System/tse-Table/System…}] new range lease repl=(n1,s1):1 seq=3 start=1534905908.932491474,0 epo=1 pro=1534905920.945157546,0 following repl=(n1,s1):1 seq=2 start=1534905908.932491474,0 exp=1534905917.933033848,0 pro=1534905908.933054254,0
I180822 02:45:20.947273 161455 storage/replica_raftstorage.go:538 [replicate,n1,s1,r6/1:/{System/tse-Table/System…}] generated preemptive snapshot e68bb8f3 at index 21
I180822 02:45:20.949023 161455 storage/store_snapshot.go:655 [replicate,n1,s1,r6/1:/{System/tse-Table/System…}] streamed snapshot to (n4,s4):?: kv pairs: 8, log entries: 11, rate-limit: 2.0 MiB/sec, 1ms
I180822 02:45:20.949542 161548 storage/replica_raftstorage.go:782 [n4,s4,r6/?:{-}] applying preemptive snapshot at index 21 (id=e68bb8f3, encoded size=5408, 1 r
```
Please assign, take a look and update the issue accordingly.
| non_priority | teamcity failed tests on master test testshowtracereplica the following tests appear to have failed fail test testshowtracereplica stdout server status runtime go could not parse build timestamp parsing time as cannot parse as server server go monitoring forward clock jumps based on server clock forward jump check enabled base addr validation go server certificate addresses ip dns localhost local cn node base addr validation go web ui certificate addresses ip dns localhost local cn node server config go storage engine initialized server config go rocksdb cache size mib server config go store in memory size b util stop stopper go quiescing tasks left storage pendingleaserequest requesting lease server node go cluster has been created server server go add additional nodes by specifying join gossip gossip go nodedescriptor set to node id address attrs locality serverversion build tag alpha started at storage store go failed initial metrics computation system config not yet available server node go initialized store disk capacity mib available mib used b logicalbytes kib ranges leases queries writes bytesperreplica pmax writesperreplica pmax storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go node started with engine s and attributes server status recorder go available memory from cgroups eib exceeds system memory gib using system memory storage replica command go initiating a split of this range at key system server server go could not start heap profiler worker due to directory to store profiles could not be determined server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server server go starting https server at use server server go starting grpc postgres server at server server go advertising cockroachdb node at storage replica command go initiating a split of this range at key system nodeliveness storage replica command go initiating a split of this range at key system nodelivenessmax storage intent resolver go failed to push during intent resolution failed to push sql txn id key table systemconfigspan start rw true pri iso serializable stat pending epo ts orig max wto false rop false seq storage replica command go initiating a split of this range at key system tsd sql event log go event set cluster setting target info settingname diagnostics reporting enabled value true user root storage replica command go initiating a split of this range at key system tse storage replica command go initiating a split of this range at key table systemconfigspan start storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table sql event log go event set cluster setting target info settingname version value user root storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table sql event log go event set cluster setting target info settingname trace debug enable value false user root storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table sql event log go event set cluster setting target info settingname cluster secret value gen random uuid string user root storage replica command go initiating a split of this range at key table sql event log go event create database target info databasename defaultdb statement create database if not exists defaultdb user root sql event log go event create database target info databasename postgres statement create database if not exists postgres user root server server go done ensuring all necessary migrations have run server server go serving sql connections sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality serverversion buildtag alpha startedat localityaddress clusterid startedat lastup server server update go no need to upgrade cluster already at the newest version storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table storage replica command go initiating a split of this range at key table server status runtime go could not parse build timestamp parsing time as cannot parse as server server go monitoring forward clock jumps based on server clock forward jump check enabled base addr validation go server certificate addresses ip dns localhost local cn node base addr validation go web ui certificate addresses ip dns localhost local cn node server config go storage engine initialized server config go rocksdb cache size mib server config go store in memory size b gossip gossip go no incoming or outgoing connections server server go no stores bootstrapped and join flag specified awaiting init command gossip client go started gossip client to gossip server go received initial cluster verification connection from tcp server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping server node go new node allocated id gossip gossip go nodedescriptor set to node id address attrs locality serverversion build tag alpha started at storage stores go read node addresses from persistent storage storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage server node go bootstrapped store server node go node started with engine s and attributes server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server server go could not start heap profiler worker due to directory to store profiles could not be determined server server go starting https server at use server server go starting grpc postgres server at server server go advertising cockroachdb node at server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server server go done ensuring all necessary migrations have run server server go serving sql connections server status runtime go could not parse build timestamp parsing time as cannot parse as sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality serverversion buildtag alpha startedat localityaddress clusterid startedat lastup server server update go no need to upgrade cluster already at the newest version server server go monitoring forward clock jumps based on server clock forward jump check enabled base addr validation go server certificate addresses ip dns localhost local cn node base addr validation go web ui certificate addresses ip dns localhost local cn node server config go storage engine initialized server config go rocksdb cache size mib server config go store in memory size b gossip gossip go no incoming or outgoing connections server server go no stores bootstrapped and join flag specified awaiting init command gossip client go started gossip client to gossip server go received initial cluster verification connection from tcp server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping rpc nodedialer nodedialer go connection to established server node go new node allocated id gossip gossip go nodedescriptor set to node id address attrs locality serverversion build tag alpha started at storage stores go read node addresses from persistent storage storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage server node go bootstrapped store server node go node started with engine s and attributes server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server server go could not start heap profiler worker due to directory to store profiles could not be determined server server go starting https server at use server server go starting grpc postgres server at server server go advertising cockroachdb node at server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server server go done ensuring all necessary migrations have run server server go serving sql connections server status runtime go could not parse build timestamp parsing time as cannot parse as server server go monitoring forward clock jumps based on server clock forward jump check enabled base addr validation go server certificate addresses ip dns localhost local cn node base addr validation go web ui certificate addresses ip dns localhost local cn node server config go storage engine initialized server config go rocksdb cache size mib server config go store in memory size b gossip gossip go no incoming or outgoing connections server server go no stores bootstrapped and join flag specified awaiting init command sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality serverversion buildtag alpha startedat localityaddress clusterid startedat lastup rpc nodedialer nodedialer go connection to established server server update go no need to upgrade cluster already at the newest version gossip client go started gossip client to gossip server go received initial cluster verification connection from tcp server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping server node go new node allocated id gossip gossip go nodedescriptor set to node id address attrs locality serverversion build tag alpha started at storage stores go read node addresses from persistent storage storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage server node go bootstrapped store server node go node started with engine s and attributes server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server server go could not start heap profiler worker due to directory to store profiles could not be determined server server go starting https server at use server server go starting grpc postgres server at server server go advertising cockroachdb node at server status recorder go available memory from cgroups eib exceeds system memory gib using system memory storage stores go wrote node addresses to persistent storage server server go done ensuring all necessary migrations have run server server go serving sql connections rpc nodedialer nodedialer go connection to established rpc nodedialer nodedialer go connection to established rpc nodedialer nodedialer go connection to established sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality serverversion buildtag alpha startedat localityaddress clusterid startedat lastup server server update go no need to upgrade cluster already at the newest version rpc nodedialer nodedialer go connection to established sql event log go event set zone config target info target default config constraints user root rpc nodedialer nodedialer go connection to established rpc nodedialer nodedialer go connection to established sql event log go event create database target info databasename d statement create database d user root storage replica command go initiating a split of this range at key table storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next sql event log go event create table target info tablename d public statement create table d public a int primary key user root storage replica command go initiating a split of this range at key table rpc nodedialer nodedialer go connection to established storage replica range lease go transferring lease to storage replica range lease go done transferring lease to sql event log go event create table target info tablename d public statement create table d public a int primary key user root storage replica command go initiating a split of this range at key table storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica raftstorage go generated preemptive snapshot at index storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table max rpc nodedialer nodedialer go connection to established sql event log go event create table target info tablename d public statement create table d public a int primary key user root storage replica command go initiating a split of this range at key table storage replica go proposing add replica updated next storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage split queue go split saw concurrent descriptor modification maybe retrying storage replica command go initiating a split of this range at key table sql event log go event set zone config target info target d config constraints user root rpc nodedialer nodedialer go connection to established rpc nodedialer nodedialer go connection to established storage replica go proposing add replica updated next rpc nodedialer nodedialer go connection to established storage replica range lease go transferring lease to sql event log go event set zone config target info target d config constraints user root storage replica range lease go done transferring lease to storage replica command go change replicas remove replica read existing descriptor table storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica go proposing remove replica updated next storage queue go no removable replicas from range that needs a removal storage store go added to replica gc queue peer suggestion storage store go removing replica storage replica raftstorage go generated preemptive snapshot at index storage replica go removed keys in sql event log go event set zone config target info target d config constraints user root fail test testshowtracereplica testshowtracereplica upsert into d values show trace replica test go condition failed to evaluate within upsert into d values got expected goroutine runtime debug stack usr local go src runtime debug stack go github com cockroachdb cockroach pkg testutils succeedssoon go src github com cockroachdb cockroach pkg testutils soon go github com cockroachdb cockroach pkg sql test testshowtracereplica go src github com cockroachdb cockroach pkg sql show trace replica test go testing trunner usr local go src testing testing go created by testing t run usr local go src testing testing go stdout storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica command go change replicas remove replica read existing descriptor min system storage replica go proposing remove replica updated next storage store go added to replica gc queue peer suggestion storage store go removing replica storage replica go removed keys in storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start epo pro storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor system nodelivenessmax tsd storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro sql show trace replica test go succeedssoon upsert into d values got expected storage replica command go change replicas remove replica read existing descriptor table rpc nodedialer nodedialer go connection to established storage replica go proposing remove replica updated next storage store go added to replica gc queue peer suggestion storage store go removing replica storage replica go removed keys in storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro sql show trace replica test go succeedssoon upsert into d values got expected storage replica command go change replicas remove replica read existing descriptor table storage replica go proposing remove replica updated next storage store go added to replica gc queue peer suggestion storage store go removing replica storage replica go removed keys in storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table systemconfigspan start storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro sql show trace replica test go succeedssoon upsert into d values got expected storage replica command go change replicas remove replica read existing descriptor table storage replica go proposing remove replica updated next storage store go added to replica gc queue peer suggestion storage store go removing replica storage replica go removed keys in storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro sql show trace replica test go succeedssoon upsert into d values got expected storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica range lease go done transferring lease to sql show trace replica test go succeedssoon upsert into d values got expected storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start epo pro sql show trace replica test go succeedssoon upsert into d values got expected server status runtime go runtime stats mib rss goroutines mib mib mib go alloc idle total mib mib cgo alloc total sec u s time gc storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start epo pro server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server node go health alerts detected alerts sql show trace replica test go succeedssoon upsert into d values got expected server status runtime go runtime stats mib rss goroutines mib mib mib go alloc idle total mib mib cgo alloc total sec u s time gc server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server status runtime go runtime stats mib rss goroutines mib mib mib go alloc idle total mib mib cgo alloc total sec u s time gc server status recorder go available memory from cgroups eib exceeds system memory gib using system memory server status runtime go runtime stats mib rss goroutines mib mib mib go alloc idle total mib mib cgo alloc total sec u s time gc server status recorder go available memory from cgroups eib exceeds system memory gib using system memory storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next storage replica range lease go transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start epo pro storage replica range lease go done transferring lease to sql show trace replica test go succeedssoon upsert into d values got expected storage replica command go change replicas remove replica read existing descriptor table storage replica go proposing remove replica updated next storage store go removing replica storage replica go removed keys in storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica raftstorage go generated preemptive snapshot at index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size r please assign take a look and update the issue accordingly | 0 |
16,017 | 5,197,863,940 | IssuesEvent | 2017-01-23 16:38:55 | ftc-9773/ftc_app_9773_velocity_vortex | https://api.github.com/repos/ftc-9773/ftc_app_9773_velocity_vortex | opened | Create a "Debuggable" Interface to turn on/off debug messages | Code Refactor Help Wanted | The purpose of this interface is to control the display of debug messages globally and on a per-class basis.
- Add a new interface to the util package: "Debuggable"
- This interface will have only one method : debugMsg(....) which will take the same parameters DbgLog.msg or DbgLog.error -- i.e. 1 format string and multiple values.
- All classes under teamcode/ will implement this interface.
- Within each class, the debugMsg implementation checks for the global "debug" flag and invokes DbgLog.msg only if the "debug" flag is set.
| 1.0 | Create a "Debuggable" Interface to turn on/off debug messages - The purpose of this interface is to control the display of debug messages globally and on a per-class basis.
- Add a new interface to the util package: "Debuggable"
- This interface will have only one method : debugMsg(....) which will take the same parameters DbgLog.msg or DbgLog.error -- i.e. 1 format string and multiple values.
- All classes under teamcode/ will implement this interface.
- Within each class, the debugMsg implementation checks for the global "debug" flag and invokes DbgLog.msg only if the "debug" flag is set.
| non_priority | create a debuggable interface to turn on off debug messages the purpose of this interface is to control the display of debug messages globally and on a per class basis add a new interface to the util package debuggable this interface will have only one method debugmsg which will take the same parameters dbglog msg or dbglog error i e format string and multiple values all classes under teamcode will implement this interface within each class the debugmsg implementation checks for the global debug flag and invokes dbglog msg only if the debug flag is set | 0 |
80,442 | 15,586,285,704 | IssuesEvent | 2021-03-18 01:35:39 | Bangtrongtuyet/spring-cloud-netflix | https://api.github.com/repos/Bangtrongtuyet/spring-cloud-netflix | opened | CVE-2020-9548 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-9548 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /spring-cloud-netflix/spring-cloud-starter-netflix/spring-cloud-starter-netflix-eureka-client/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- archaius-core-0.7.6.jar (Root Library)
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.6,2.9.10.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-9548 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-9548 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /spring-cloud-netflix/spring-cloud-starter-netflix/spring-cloud-starter-netflix-eureka-client/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar,2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- archaius-core-0.7.6.jar (Root Library)
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.6,2.9.10.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file spring cloud netflix spring cloud starter netflix spring cloud starter netflix eureka client pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy archaius core jar root library x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to br com anteros dbcp anterosdbcpconfig aka anteros core publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
38,033 | 10,132,189,083 | IssuesEvent | 2019-08-01 21:36:17 | MicrosoftDocs/visualstudio-docs | https://api.github.com/repos/MicrosoftDocs/visualstudio-docs | closed | target a specific installation-directory of .NET instead of defaulting to the GAC | Pri1 area - msbuild doc-bug needs-more-info unspecified/svc | This WWWpage does not mention any way to target a specific installation-directory of, say, V4.0 .NET assemblies instead of defaulting to the Global Assembly Cache (which is malfunctioning in 2 projects (out of 17) when building Mono's current Embeddinator-4000 from a totally fresh install.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 1a80e5d7-2db7-48c0-e8b6-ca8c3ff30017
* Version Independent ID: ad64635b-06d5-1b87-8f02-80cf25c12520
* [Content](https://docs.microsoft.com/en-us/visualstudio/msbuild/msbuild-target-framework-and-target-platform)
* [Content Source](https://github.com/MicrosoftDocs/visualstudio-docs-pr/blob/live/docs/msbuild/msbuild-target-framework-and-target-platform.md)
* Service: unspecified | 1.0 | target a specific installation-directory of .NET instead of defaulting to the GAC - This WWWpage does not mention any way to target a specific installation-directory of, say, V4.0 .NET assemblies instead of defaulting to the Global Assembly Cache (which is malfunctioning in 2 projects (out of 17) when building Mono's current Embeddinator-4000 from a totally fresh install.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 1a80e5d7-2db7-48c0-e8b6-ca8c3ff30017
* Version Independent ID: ad64635b-06d5-1b87-8f02-80cf25c12520
* [Content](https://docs.microsoft.com/en-us/visualstudio/msbuild/msbuild-target-framework-and-target-platform)
* [Content Source](https://github.com/MicrosoftDocs/visualstudio-docs-pr/blob/live/docs/msbuild/msbuild-target-framework-and-target-platform.md)
* Service: unspecified | non_priority | target a specific installation directory of net instead of defaulting to the gac this wwwpage does not mention any way to target a specific installation directory of say net assemblies instead of defaulting to the global assembly cache which is malfunctioning in projects out of when building mono s current embeddinator from a totally fresh install document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id service unspecified | 0 |
27,223 | 21,477,066,245 | IssuesEvent | 2022-04-26 14:28:38 | OpenEnergyPlatform/ontology | https://api.github.com/repos/OpenEnergyPlatform/ontology | opened | Potential overwriting of attributes in imported modules | question external ontology To do ontology infrastructure | ## Description of the issue
Changes introduced in #1086 (e.g. adding `Inverse Of`) reside in `ro-module` which is an **imported module**.
The content of the `ro-module` is automatically extracted via ROBOT [🤖](https://github.com/OpenEnergyPlatform/ontology/wiki/ROBOT-as-commandline-tool).
Inspecting the `extract-ro-module.sh`-script, I have NOT seen any precaution checking for potential changes BEFORE recreating the `ro-module` from scratch/source.
From my perspective this means: **As soon as the script is run, all previous edits are lost immediately.**
Can someone comment whether this is true or if there any taken measures I'm not aware of?
@jannahastings, @stap-m, @MGlauer
## Ideas of solution
In case I'm right about my assumption, I see the following options:
1. implement a diff check in the script and merge changes
2. change the location of implementation of attributes in imported modules
| 1.0 | Potential overwriting of attributes in imported modules - ## Description of the issue
Changes introduced in #1086 (e.g. adding `Inverse Of`) reside in `ro-module` which is an **imported module**.
The content of the `ro-module` is automatically extracted via ROBOT [🤖](https://github.com/OpenEnergyPlatform/ontology/wiki/ROBOT-as-commandline-tool).
Inspecting the `extract-ro-module.sh`-script, I have NOT seen any precaution checking for potential changes BEFORE recreating the `ro-module` from scratch/source.
From my perspective this means: **As soon as the script is run, all previous edits are lost immediately.**
Can someone comment whether this is true or if there any taken measures I'm not aware of?
@jannahastings, @stap-m, @MGlauer
## Ideas of solution
In case I'm right about my assumption, I see the following options:
1. implement a diff check in the script and merge changes
2. change the location of implementation of attributes in imported modules
| non_priority | potential overwriting of attributes in imported modules description of the issue changes introduced in e g adding inverse of reside in ro module which is an imported module the content of the ro module is automatically extracted via robot inspecting the extract ro module sh script i have not seen any precaution checking for potential changes before recreating the ro module from scratch source from my perspective this means as soon as the script is run all previous edits are lost immediately can someone comment whether this is true or if there any taken measures i m not aware of jannahastings stap m mglauer ideas of solution in case i m right about my assumption i see the following options implement a diff check in the script and merge changes change the location of implementation of attributes in imported modules | 0 |
55,087 | 13,521,952,163 | IssuesEvent | 2020-09-15 07:50:38 | googleapis/nodejs-cloudbuild | https://api.github.com/repos/googleapis/nodejs-cloudbuild | closed | Cloud Builder Node.js createBuild API example | api: cloudbuild type: question | I am trying to replicate the [create build python example](https://github.com/googleapis/python-cloudbuild/issues/30) using Node.js. The example enables a cloud function to call Cloud Build without setting a trigger based on a gcloud command.
My assumption was that the runtime libraries would have parity between Python/Node? However when I try the example in Node.js I am unable to initiate a build. Example code used below:
```
// Imports the Google Cloud client library
const {CloudBuildClient} = require('@google-cloud/cloudbuild');
// Creates a client
const cb = new CloudBuildClient();
// Add a project ID from the environment - std PROJECT_ID definition based on homepage
const PROJECT_ID = process.env.PROJECT_ID || 'PRJ_ERROR';
// Process the function
async function step_one_function() {
// Starts a build against the branch provided.
console.log(`Project ID: ${PROJECT_ID}`);
const build = {
"steps": [
{
"name": "bash",
"args": ["echo", "Hello Cloud Build"],
}
],
}
// Call the createBuild function
const [resp] = await cb.createBuild(PROJECT_ID, build );
console.log(`Response: ${resp}`);
}
```
package.json
```
"dependencies": {
"@google-cloud/cloudbuild": "^2.0.3"
},
```
I believe I need to supply the build parameter as a `google.devtools.cloudbuild.v1.ICreateBuildRequest` however, I am not clear how to create the build object based on the documentation. I tried to keep the example simple to illustrate the issue.
Would someone be able to clarify how this variable is defined and how to utilise the createBuild function to get a similar outcome to the Python version of the library?
Many thanks
Rich
| 1.0 | Cloud Builder Node.js createBuild API example - I am trying to replicate the [create build python example](https://github.com/googleapis/python-cloudbuild/issues/30) using Node.js. The example enables a cloud function to call Cloud Build without setting a trigger based on a gcloud command.
My assumption was that the runtime libraries would have parity between Python/Node? However when I try the example in Node.js I am unable to initiate a build. Example code used below:
```
// Imports the Google Cloud client library
const {CloudBuildClient} = require('@google-cloud/cloudbuild');
// Creates a client
const cb = new CloudBuildClient();
// Add a project ID from the environment - std PROJECT_ID definition based on homepage
const PROJECT_ID = process.env.PROJECT_ID || 'PRJ_ERROR';
// Process the function
async function step_one_function() {
// Starts a build against the branch provided.
console.log(`Project ID: ${PROJECT_ID}`);
const build = {
"steps": [
{
"name": "bash",
"args": ["echo", "Hello Cloud Build"],
}
],
}
// Call the createBuild function
const [resp] = await cb.createBuild(PROJECT_ID, build );
console.log(`Response: ${resp}`);
}
```
package.json
```
"dependencies": {
"@google-cloud/cloudbuild": "^2.0.3"
},
```
I believe I need to supply the build parameter as a `google.devtools.cloudbuild.v1.ICreateBuildRequest` however, I am not clear how to create the build object based on the documentation. I tried to keep the example simple to illustrate the issue.
Would someone be able to clarify how this variable is defined and how to utilise the createBuild function to get a similar outcome to the Python version of the library?
Many thanks
Rich
| non_priority | cloud builder node js createbuild api example i am trying to replicate the using node js the example enables a cloud function to call cloud build without setting a trigger based on a gcloud command my assumption was that the runtime libraries would have parity between python node however when i try the example in node js i am unable to initiate a build example code used below imports the google cloud client library const cloudbuildclient require google cloud cloudbuild creates a client const cb new cloudbuildclient add a project id from the environment std project id definition based on homepage const project id process env project id prj error process the function async function step one function starts a build against the branch provided console log project id project id const build steps name bash args call the createbuild function const await cb createbuild project id build console log response resp package json dependencies google cloud cloudbuild i believe i need to supply the build parameter as a google devtools cloudbuild icreatebuildrequest however i am not clear how to create the build object based on the documentation i tried to keep the example simple to illustrate the issue would someone be able to clarify how this variable is defined and how to utilise the createbuild function to get a similar outcome to the python version of the library many thanks rich | 0 |
65,292 | 19,324,545,285 | IssuesEvent | 2021-12-14 09:56:36 | vector-im/element-android | https://api.github.com/repos/vector-im/element-android | closed | [VoIP] Echo from loudspeaker during call | T-Defect A-VoIP S-Major O-Occasional X-Needs-Info | #### Describe the bug
Observed when having a call between two Element-Android devices. Enabling the loudspeaker causes the other person to hear an echo of their own voice, and vice-versa.
#### To Reproduce
Steps to reproduce the behavior:
1. Call from Element-Android on Device1.
2. When user on Device2 picks up, either or both then switch audio to loudspeaker.
3. Either one or both hear an echo of their own voice.
#### Expected behavior
No echo when using the loudspeaker.
#### Smartphone (please complete the following information):
- Device: multiple devices
- OS: multiple OSs
#### Additional context
- App version and store: 1.1.7 - F-Droid & Play Store
- Homeserver: matrix.org, fairydust.space | 1.0 | [VoIP] Echo from loudspeaker during call - #### Describe the bug
Observed when having a call between two Element-Android devices. Enabling the loudspeaker causes the other person to hear an echo of their own voice, and vice-versa.
#### To Reproduce
Steps to reproduce the behavior:
1. Call from Element-Android on Device1.
2. When user on Device2 picks up, either or both then switch audio to loudspeaker.
3. Either one or both hear an echo of their own voice.
#### Expected behavior
No echo when using the loudspeaker.
#### Smartphone (please complete the following information):
- Device: multiple devices
- OS: multiple OSs
#### Additional context
- App version and store: 1.1.7 - F-Droid & Play Store
- Homeserver: matrix.org, fairydust.space | non_priority | echo from loudspeaker during call describe the bug observed when having a call between two element android devices enabling the loudspeaker causes the other person to hear an echo of their own voice and vice versa to reproduce steps to reproduce the behavior call from element android on when user on picks up either or both then switch audio to loudspeaker either one or both hear an echo of their own voice expected behavior no echo when using the loudspeaker smartphone please complete the following information device multiple devices os multiple oss additional context app version and store f droid play store homeserver matrix org fairydust space | 0 |
12,885 | 3,664,679,591 | IssuesEvent | 2016-02-19 12:58:15 | Itseez/opencv | https://api.github.com/repos/Itseez/opencv | closed | Content missing in the OpenCV-Python Tutorials/Mathematical Tools in OpenCV | category: documentation question | The content of "OpenCV 3.0.0-dev documentation » OpenCV-Python Tutorials » Core Operations » Mathematical Tools in OpenCV" seems to be missing now.
Please help. | 1.0 | Content missing in the OpenCV-Python Tutorials/Mathematical Tools in OpenCV - The content of "OpenCV 3.0.0-dev documentation » OpenCV-Python Tutorials » Core Operations » Mathematical Tools in OpenCV" seems to be missing now.
Please help. | non_priority | content missing in the opencv python tutorials mathematical tools in opencv the content of opencv dev documentation » opencv python tutorials » core operations » mathematical tools in opencv seems to be missing now please help | 0 |
59,413 | 24,757,950,460 | IssuesEvent | 2022-10-21 19:48:14 | orcoastalmgmt/tool_sealevelrise_planning | https://api.github.com/repos/orcoastalmgmt/tool_sealevelrise_planning | closed | Create new set of "Impacted Assets" layers | Enhancement Layers Web Service | We can no longer rely on the older services created by Julie, as they do not cover the Columbia River estuary. In addition, we have new assets such as buildings to add, in addition to new categories of assets not previously considered (such as parks and parking lots).
All this to say that we will need to build a new set of coast-wide point, line and polygon feature classes that cover all of the assets we are interesting in. | 1.0 | Create new set of "Impacted Assets" layers - We can no longer rely on the older services created by Julie, as they do not cover the Columbia River estuary. In addition, we have new assets such as buildings to add, in addition to new categories of assets not previously considered (such as parks and parking lots).
All this to say that we will need to build a new set of coast-wide point, line and polygon feature classes that cover all of the assets we are interesting in. | non_priority | create new set of impacted assets layers we can no longer rely on the older services created by julie as they do not cover the columbia river estuary in addition we have new assets such as buildings to add in addition to new categories of assets not previously considered such as parks and parking lots all this to say that we will need to build a new set of coast wide point line and polygon feature classes that cover all of the assets we are interesting in | 0 |
32,089 | 26,417,906,826 | IssuesEvent | 2023-01-13 17:27:42 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Skip dotnet CLI first run logic when executing tests | area-Infrastructure | In https://github.com/dotnet/runtime/pull/80510#issuecomment-1382160934 we saw a failure because some NuGet migration code failed to run during the dotnet CLI first run experience:
```
+ dotnet /datadisks/disk1/work/ADFC09B1/p/xunit/xunit.console.dll JIT/HardwareIntrinsics/JIT.HardwareIntrinsics.XUnitWrapper.dll -parallel collections -nocolor -noshadow -xml testResults.xml -trait TestGroup=JIT.HardwareIntrinsics.Arm.ArmBase
Microsoft.DotNet.XUnitConsoleRunner v2.5.0 (64-bit .NET 7.0.2)
Discovering: JIT.HardwareIntrinsics.XUnitWrapper (method display = ClassAndMethod, method display options = None)
Discovered: JIT.HardwareIntrinsics.XUnitWrapper (found 6 of 362 test cases)
Starting: JIT.HardwareIntrinsics.XUnitWrapper (parallel test collections = on, max threads = 2)
JIT/HardwareIntrinsics/Arm/ArmBase.Arm64/ArmBase.Arm64_ro/ArmBase.Arm64_ro.sh [FAIL]
System.IO.IOException: The system cannot open the device or file specified. : 'NuGet-Migrations'
at System.Threading.Mutex.CreateMutexCore(Boolean initiallyOwned, String name, Boolean& createdNew)
at System.Threading.Mutex..ctor(Boolean initiallyOwned, String name)
at NuGet.Common.Migrations.MigrationRunner.Run()
at Microsoft.DotNet.Configurer.DotnetFirstTimeUseConfigurer.Configure()
at Microsoft.DotNet.Cli.Program.ConfigureDotNetForFirstTimeUse(IFirstTimeUseNoticeSentinel firstTimeUseNoticeSentinel, IAspNetCertificateSentinel aspNetCertificateSentinel, IFileSentinel toolPathSentinel, Boolean isDotnetBeingInvokedFromNativeInstaller, DotnetFirstRunConfiguration dotnetFirstRunConfiguration, IEnvironmentProvider environmentProvider, Dictionary`2 performanceMeasurements)
at Microsoft.DotNet.Cli.Program.ProcessArgs(String[] args, TimeSpan startupTime, ITelemetry telemetryClient)
at Microsoft.DotNet.Cli.Program.Main(String[] args)
Return code: 1
```
We should look into disabling the first run experience via the `DOTNET_SKIP_FIRST_TIME_EXPERIENCE=1` env var, it doesn't make sense to run that for the tests. | 1.0 | Skip dotnet CLI first run logic when executing tests - In https://github.com/dotnet/runtime/pull/80510#issuecomment-1382160934 we saw a failure because some NuGet migration code failed to run during the dotnet CLI first run experience:
```
+ dotnet /datadisks/disk1/work/ADFC09B1/p/xunit/xunit.console.dll JIT/HardwareIntrinsics/JIT.HardwareIntrinsics.XUnitWrapper.dll -parallel collections -nocolor -noshadow -xml testResults.xml -trait TestGroup=JIT.HardwareIntrinsics.Arm.ArmBase
Microsoft.DotNet.XUnitConsoleRunner v2.5.0 (64-bit .NET 7.0.2)
Discovering: JIT.HardwareIntrinsics.XUnitWrapper (method display = ClassAndMethod, method display options = None)
Discovered: JIT.HardwareIntrinsics.XUnitWrapper (found 6 of 362 test cases)
Starting: JIT.HardwareIntrinsics.XUnitWrapper (parallel test collections = on, max threads = 2)
JIT/HardwareIntrinsics/Arm/ArmBase.Arm64/ArmBase.Arm64_ro/ArmBase.Arm64_ro.sh [FAIL]
System.IO.IOException: The system cannot open the device or file specified. : 'NuGet-Migrations'
at System.Threading.Mutex.CreateMutexCore(Boolean initiallyOwned, String name, Boolean& createdNew)
at System.Threading.Mutex..ctor(Boolean initiallyOwned, String name)
at NuGet.Common.Migrations.MigrationRunner.Run()
at Microsoft.DotNet.Configurer.DotnetFirstTimeUseConfigurer.Configure()
at Microsoft.DotNet.Cli.Program.ConfigureDotNetForFirstTimeUse(IFirstTimeUseNoticeSentinel firstTimeUseNoticeSentinel, IAspNetCertificateSentinel aspNetCertificateSentinel, IFileSentinel toolPathSentinel, Boolean isDotnetBeingInvokedFromNativeInstaller, DotnetFirstRunConfiguration dotnetFirstRunConfiguration, IEnvironmentProvider environmentProvider, Dictionary`2 performanceMeasurements)
at Microsoft.DotNet.Cli.Program.ProcessArgs(String[] args, TimeSpan startupTime, ITelemetry telemetryClient)
at Microsoft.DotNet.Cli.Program.Main(String[] args)
Return code: 1
```
We should look into disabling the first run experience via the `DOTNET_SKIP_FIRST_TIME_EXPERIENCE=1` env var, it doesn't make sense to run that for the tests. | non_priority | skip dotnet cli first run logic when executing tests in we saw a failure because some nuget migration code failed to run during the dotnet cli first run experience dotnet datadisks work p xunit xunit console dll jit hardwareintrinsics jit hardwareintrinsics xunitwrapper dll parallel collections nocolor noshadow xml testresults xml trait testgroup jit hardwareintrinsics arm armbase microsoft dotnet xunitconsolerunner bit net discovering jit hardwareintrinsics xunitwrapper method display classandmethod method display options none discovered jit hardwareintrinsics xunitwrapper found of test cases starting jit hardwareintrinsics xunitwrapper parallel test collections on max threads jit hardwareintrinsics arm armbase armbase ro armbase ro sh system io ioexception the system cannot open the device or file specified nuget migrations at system threading mutex createmutexcore boolean initiallyowned string name boolean creatednew at system threading mutex ctor boolean initiallyowned string name at nuget common migrations migrationrunner run at microsoft dotnet configurer dotnetfirsttimeuseconfigurer configure at microsoft dotnet cli program configuredotnetforfirsttimeuse ifirsttimeusenoticesentinel firsttimeusenoticesentinel iaspnetcertificatesentinel aspnetcertificatesentinel ifilesentinel toolpathsentinel boolean isdotnetbeinginvokedfromnativeinstaller dotnetfirstrunconfiguration dotnetfirstrunconfiguration ienvironmentprovider environmentprovider dictionary performancemeasurements at microsoft dotnet cli program processargs string args timespan startuptime itelemetry telemetryclient at microsoft dotnet cli program main string args return code we should look into disabling the first run experience via the dotnet skip first time experience env var it doesn t make sense to run that for the tests | 0 |
327,074 | 24,116,810,481 | IssuesEvent | 2022-09-20 15:17:58 | davidalvarezcastro/TFM_IRRIAPP | https://api.github.com/repos/davidalvarezcastro/TFM_IRRIAPP | closed | Video demostración proyecto | documentation | Preparar el video demostración a mostrar durante la presentación del proyecto.
- guión
- partes
- mostrar organización del sistema (base de datos relacional)
- mostrar controladores (arduino + sensores)
- recogida de datos en el sistema (eventos en el broker y almacenamiento en mongo mediante el `recollector`)
- interfaz web (gestión de autorización y zonas/controladores + visualización de datos)
- mostrar el funcionamiento del `actuator` (raspberry pi + gestión del relé) | 1.0 | Video demostración proyecto - Preparar el video demostración a mostrar durante la presentación del proyecto.
- guión
- partes
- mostrar organización del sistema (base de datos relacional)
- mostrar controladores (arduino + sensores)
- recogida de datos en el sistema (eventos en el broker y almacenamiento en mongo mediante el `recollector`)
- interfaz web (gestión de autorización y zonas/controladores + visualización de datos)
- mostrar el funcionamiento del `actuator` (raspberry pi + gestión del relé) | non_priority | video demostración proyecto preparar el video demostración a mostrar durante la presentación del proyecto guión partes mostrar organización del sistema base de datos relacional mostrar controladores arduino sensores recogida de datos en el sistema eventos en el broker y almacenamiento en mongo mediante el recollector interfaz web gestión de autorización y zonas controladores visualización de datos mostrar el funcionamiento del actuator raspberry pi gestión del relé | 0 |
68,193 | 8,229,411,499 | IssuesEvent | 2018-09-07 09:18:13 | monero-project/kovri | https://api.github.com/repos/monero-project/kovri | closed | Rewrite Identity implementation | design libcore maintenance | **By submitting this issue, I confirm the following:**
- I have read and understood the [contributor guide](https://github.com/monero-project/kovri/blob/master/doc/CONTRIBUTING.md).
- I have checked that the issue I am reporting can be replicated or that the feature I am suggesting is not present.
- I have checked opened or recently closed [pull requests](https://github.com/monero-project/kovri/pulls) for existing solutions/implementations to my issue/suggestion.
_Place an X inside the bracket to confirm_
- [X] I confirm.
---
If I had to vote for one of the most questionably dangerous, ugliest, least functional, and least maintainable areas of this codebase, I could give a strong vote for our current identity implementation. It's error prone and confusing (to say the least). It's not a lot of code but it's important code - so it should be solid code (as should the other areas that tie into it).
Noticed especially during #364, we can put this issue toward a later release milestone but ideas for improvements in the meantime are welcome. One solution includes over-arching libcore design refactor but let's not get carried away (for now) 😄
| 1.0 | Rewrite Identity implementation - **By submitting this issue, I confirm the following:**
- I have read and understood the [contributor guide](https://github.com/monero-project/kovri/blob/master/doc/CONTRIBUTING.md).
- I have checked that the issue I am reporting can be replicated or that the feature I am suggesting is not present.
- I have checked opened or recently closed [pull requests](https://github.com/monero-project/kovri/pulls) for existing solutions/implementations to my issue/suggestion.
_Place an X inside the bracket to confirm_
- [X] I confirm.
---
If I had to vote for one of the most questionably dangerous, ugliest, least functional, and least maintainable areas of this codebase, I could give a strong vote for our current identity implementation. It's error prone and confusing (to say the least). It's not a lot of code but it's important code - so it should be solid code (as should the other areas that tie into it).
Noticed especially during #364, we can put this issue toward a later release milestone but ideas for improvements in the meantime are welcome. One solution includes over-arching libcore design refactor but let's not get carried away (for now) 😄
| non_priority | rewrite identity implementation by submitting this issue i confirm the following i have read and understood the i have checked that the issue i am reporting can be replicated or that the feature i am suggesting is not present i have checked opened or recently closed for existing solutions implementations to my issue suggestion place an x inside the bracket to confirm i confirm if i had to vote for one of the most questionably dangerous ugliest least functional and least maintainable areas of this codebase i could give a strong vote for our current identity implementation it s error prone and confusing to say the least it s not a lot of code but it s important code so it should be solid code as should the other areas that tie into it noticed especially during we can put this issue toward a later release milestone but ideas for improvements in the meantime are welcome one solution includes over arching libcore design refactor but let s not get carried away for now 😄 | 0 |
24,754 | 24,235,905,957 | IssuesEvent | 2022-09-26 23:14:27 | vanjac/chromafiler | https://api.github.com/repos/vanjac/chromafiler | opened | Common context menu | enhancement usability | All window types should have a context menu accessible through the toolbar, Shift+F10, or right-clicking the background. This would include commands currently available only through keyboard shortcuts or the toolbar (Settings, Refresh, Help...) as well as commands specific to each window type (eg. folder background / selected item context menu).
This would take the place of the settings icon in the toolbar. It would be separate from the proxy menu, system menu, or parent menu. | True | Common context menu - All window types should have a context menu accessible through the toolbar, Shift+F10, or right-clicking the background. This would include commands currently available only through keyboard shortcuts or the toolbar (Settings, Refresh, Help...) as well as commands specific to each window type (eg. folder background / selected item context menu).
This would take the place of the settings icon in the toolbar. It would be separate from the proxy menu, system menu, or parent menu. | non_priority | common context menu all window types should have a context menu accessible through the toolbar shift or right clicking the background this would include commands currently available only through keyboard shortcuts or the toolbar settings refresh help as well as commands specific to each window type eg folder background selected item context menu this would take the place of the settings icon in the toolbar it would be separate from the proxy menu system menu or parent menu | 0 |
72,376 | 19,191,131,651 | IssuesEvent | 2021-12-06 00:37:41 | gradle/gradle | https://api.github.com/repos/gradle/gradle | closed | Consider stopping GitHub Actions jobs on stale commits | a:feature in:building-gradle | cc @JLLeitschuh and @wolfs as majority contributors on [.github/workflows](https://github.com/gradle/gradle/commits/master/.github/workflows).
I've noticed that pushing multiple times to the same forked PR branch will trigger builds for every single commit. Most of the time I'm just fighting with DCO signoffs, but even in other cases if there's a later commit the old ones are not really worth building.
### Expected Behavior
Later pushes could stop earlier builds. This would save resources, might reduce Gradle GitHub costs, and also hopefully slightly affect the environment as well considering the scale of this repo.
### Current Behavior
Each push to a PR will trigger a GitHub Actions build.
https://github.com/gradle/gradle/actions?query=branch%3Astartparams
(1444, 1445 and 1446 were 3 quick pushes trying to satisfy DCO)
### Context
Docs: https://docs.github.com/en/actions/learn-github-actions/workflow-syntax-for-github-actions#concurrency
For example this is what I'm using in most of my projects:
```yaml
on:
push
concurrency:
# Documentation suggests ${{ github.head_ref }}, but that's only available on pull_request/pull_request_target triggers, so using ${{ github.ref }}.
# On master, we want all builds to complete even if merging happens faster to make it easier to discover at which point something broke.
# More info: https://stackoverflow.com/a/68422069/253468:
group: ${{ github.ref == 'refs/heads/master' && format('ci-master-{0}', github.sha) || format('ci-{0}', github.ref) }}
cancel-in-progress: true
```
(replace `ci-` in both places with the name of the workflow to prevent cross-cancellations) | 1.0 | Consider stopping GitHub Actions jobs on stale commits - cc @JLLeitschuh and @wolfs as majority contributors on [.github/workflows](https://github.com/gradle/gradle/commits/master/.github/workflows).
I've noticed that pushing multiple times to the same forked PR branch will trigger builds for every single commit. Most of the time I'm just fighting with DCO signoffs, but even in other cases if there's a later commit the old ones are not really worth building.
### Expected Behavior
Later pushes could stop earlier builds. This would save resources, might reduce Gradle GitHub costs, and also hopefully slightly affect the environment as well considering the scale of this repo.
### Current Behavior
Each push to a PR will trigger a GitHub Actions build.
https://github.com/gradle/gradle/actions?query=branch%3Astartparams
(1444, 1445 and 1446 were 3 quick pushes trying to satisfy DCO)
### Context
Docs: https://docs.github.com/en/actions/learn-github-actions/workflow-syntax-for-github-actions#concurrency
For example this is what I'm using in most of my projects:
```yaml
on:
push
concurrency:
# Documentation suggests ${{ github.head_ref }}, but that's only available on pull_request/pull_request_target triggers, so using ${{ github.ref }}.
# On master, we want all builds to complete even if merging happens faster to make it easier to discover at which point something broke.
# More info: https://stackoverflow.com/a/68422069/253468:
group: ${{ github.ref == 'refs/heads/master' && format('ci-master-{0}', github.sha) || format('ci-{0}', github.ref) }}
cancel-in-progress: true
```
(replace `ci-` in both places with the name of the workflow to prevent cross-cancellations) | non_priority | consider stopping github actions jobs on stale commits cc jlleitschuh and wolfs as majority contributors on i ve noticed that pushing multiple times to the same forked pr branch will trigger builds for every single commit most of the time i m just fighting with dco signoffs but even in other cases if there s a later commit the old ones are not really worth building expected behavior later pushes could stop earlier builds this would save resources might reduce gradle github costs and also hopefully slightly affect the environment as well considering the scale of this repo current behavior each push to a pr will trigger a github actions build and were quick pushes trying to satisfy dco context docs for example this is what i m using in most of my projects yaml on push concurrency documentation suggests github head ref but that s only available on pull request pull request target triggers so using github ref on master we want all builds to complete even if merging happens faster to make it easier to discover at which point something broke more info group github ref refs heads master format ci master github sha format ci github ref cancel in progress true replace ci in both places with the name of the workflow to prevent cross cancellations | 0 |
131,683 | 10,705,838,481 | IssuesEvent | 2019-10-24 14:23:39 | w3c/webrtc-pc | https://api.github.com/repos/w3c/webrtc-pc | closed | iceconnectionstatechange event after PeerConnection.close() is called | Needs Test PR exists | When the `close` method of `RTCPeerConnection` is invoked, user agent runs the following steps[1]:
> ...
> 3. Set `connection.[[IsClosed]]` to true.
> ...
> 11. Set connection's ICE connection state to "closed".
> ...
If I understand correctly, "setting connection's ICE connection state to closed"(step 11) runs the "update the ICE connection state" process[2].
> 1. If `connection.[[IsClosed]]` is true, abort these steps. (**It's always true**)
> 2. Let `newState` be the value of deriving a new state value as described by the `RTCIceConnectionState` enum.
> 3. If connection's ICE connection state is equal to `newState`, abort these steps.
> 4. Set connection's ice connection state to `newState`.
> 5. Fire an event named `iceconnectionstatechange` at `connection`.
As `connection.[[IsClosed]]` is always true in this case, step 2 to step 5 should not be executed. Does it mean user agent should not fire `iceconnectionstatechange` after `PeerConnection.close()` is called?
My observation is Safari doesn't fire `iceconnectionstatechange` after `PeerConnection.close()`, however, Chrome and Firefox do.
[1] https://w3c.github.io/webrtc-pc/#dom-rtcpeerconnection-close
[2] https://w3c.github.io/webrtc-pc/#update-the-ice-connection-state | 1.0 | iceconnectionstatechange event after PeerConnection.close() is called - When the `close` method of `RTCPeerConnection` is invoked, user agent runs the following steps[1]:
> ...
> 3. Set `connection.[[IsClosed]]` to true.
> ...
> 11. Set connection's ICE connection state to "closed".
> ...
If I understand correctly, "setting connection's ICE connection state to closed"(step 11) runs the "update the ICE connection state" process[2].
> 1. If `connection.[[IsClosed]]` is true, abort these steps. (**It's always true**)
> 2. Let `newState` be the value of deriving a new state value as described by the `RTCIceConnectionState` enum.
> 3. If connection's ICE connection state is equal to `newState`, abort these steps.
> 4. Set connection's ice connection state to `newState`.
> 5. Fire an event named `iceconnectionstatechange` at `connection`.
As `connection.[[IsClosed]]` is always true in this case, step 2 to step 5 should not be executed. Does it mean user agent should not fire `iceconnectionstatechange` after `PeerConnection.close()` is called?
My observation is Safari doesn't fire `iceconnectionstatechange` after `PeerConnection.close()`, however, Chrome and Firefox do.
[1] https://w3c.github.io/webrtc-pc/#dom-rtcpeerconnection-close
[2] https://w3c.github.io/webrtc-pc/#update-the-ice-connection-state | non_priority | iceconnectionstatechange event after peerconnection close is called when the close method of rtcpeerconnection is invoked user agent runs the following steps set connection to true set connection s ice connection state to closed if i understand correctly setting connection s ice connection state to closed step runs the update the ice connection state process if connection is true abort these steps it s always true let newstate be the value of deriving a new state value as described by the rtciceconnectionstate enum if connection s ice connection state is equal to newstate abort these steps set connection s ice connection state to newstate fire an event named iceconnectionstatechange at connection as connection is always true in this case step to step should not be executed does it mean user agent should not fire iceconnectionstatechange after peerconnection close is called my observation is safari doesn t fire iceconnectionstatechange after peerconnection close however chrome and firefox do | 0 |
48,753 | 25,794,098,206 | IssuesEvent | 2022-12-10 11:07:20 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Consecutive range checks are not combined | tenet-performance | ### Description
Consider [the following code](https://sharplab.io/#v2:C4LghgzgtgPgxAOwK4BsVgEYoKYAIAmAlhJjgLABQlAAgIwBsu1ATLgIIBCAwgCIBK2YACdC2AG5gUlAN6Vc8pg1yEEwdkKFgAnmwDGu7BAgAKFcADaAXVyZd+AJRyFsigrdMA7DYx3zABmsAam9fWiCQ/HNmcNtIgGZLAG4neQBfSlSgA==) (inspired by https://github.com/dotnet/csharplang/issues/4082#issuecomment-1344991671):
```c#
static int ArrayAccess(int[] abcd)
{
return abcd[0] + abcd[1] + abcd[2] + abcd[3];
}
```
Note that it accesses the array multiple times at increasing indexes, which I think is a relatively common pattern. This results in one range check for every array access:
```asm
L0000: mov eax, [ecx+4]
L0003: test eax, eax
L0005: je short L0025
L0007: mov edx, [ecx+8]
L000a: cmp eax, 1
L000d: jbe short L0025
L000f: add edx, [ecx+0xc]
L0012: cmp eax, 2
L0015: jbe short L0025
L0017: add edx, [ecx+0x10]
L001a: cmp eax, 3
L001d: jbe short L0025
L001f: mov eax, edx
L0021: add eax, [ecx+0x14]
L0024: ret
L0025: call 0x71efa060
L002a: int3
```
This is annoying, because only the check for `abcd[3]` is necessary, since there are no side-effects between the array accesses. Even though these range checks are likely to be well predicted by the CPU, I think it would be nice if they could be elided by the JIT.
This may very well be a duplicate, but I couldn't find it. Or it may not be worth tracking, in which case, feel free to close.
### Configuration
Current SharpLab: Core CLR 7.0.22.51805 on x86
### Regression?
Not that I know of.
| True | Consecutive range checks are not combined - ### Description
Consider [the following code](https://sharplab.io/#v2:C4LghgzgtgPgxAOwK4BsVgEYoKYAIAmAlhJjgLABQlAAgIwBsu1ATLgIIBCAwgCIBK2YACdC2AG5gUlAN6Vc8pg1yEEwdkKFgAnmwDGu7BAgAKFcADaAXVyZd+AJRyFsigrdMA7DYx3zABmsAam9fWiCQ/HNmcNtIgGZLAG4neQBfSlSgA==) (inspired by https://github.com/dotnet/csharplang/issues/4082#issuecomment-1344991671):
```c#
static int ArrayAccess(int[] abcd)
{
return abcd[0] + abcd[1] + abcd[2] + abcd[3];
}
```
Note that it accesses the array multiple times at increasing indexes, which I think is a relatively common pattern. This results in one range check for every array access:
```asm
L0000: mov eax, [ecx+4]
L0003: test eax, eax
L0005: je short L0025
L0007: mov edx, [ecx+8]
L000a: cmp eax, 1
L000d: jbe short L0025
L000f: add edx, [ecx+0xc]
L0012: cmp eax, 2
L0015: jbe short L0025
L0017: add edx, [ecx+0x10]
L001a: cmp eax, 3
L001d: jbe short L0025
L001f: mov eax, edx
L0021: add eax, [ecx+0x14]
L0024: ret
L0025: call 0x71efa060
L002a: int3
```
This is annoying, because only the check for `abcd[3]` is necessary, since there are no side-effects between the array accesses. Even though these range checks are likely to be well predicted by the CPU, I think it would be nice if they could be elided by the JIT.
This may very well be a duplicate, but I couldn't find it. Or it may not be worth tracking, in which case, feel free to close.
### Configuration
Current SharpLab: Core CLR 7.0.22.51805 on x86
### Regression?
Not that I know of.
| non_priority | consecutive range checks are not combined description consider inspired by c static int arrayaccess int abcd return abcd abcd abcd abcd note that it accesses the array multiple times at increasing indexes which i think is a relatively common pattern this results in one range check for every array access asm mov eax test eax eax je short mov edx cmp eax jbe short add edx cmp eax jbe short add edx cmp eax jbe short mov eax edx add eax ret call this is annoying because only the check for abcd is necessary since there are no side effects between the array accesses even though these range checks are likely to be well predicted by the cpu i think it would be nice if they could be elided by the jit this may very well be a duplicate but i couldn t find it or it may not be worth tracking in which case feel free to close configuration current sharplab core clr on regression not that i know of | 0 |
84,009 | 24,196,295,546 | IssuesEvent | 2022-09-24 00:31:43 | tensorflow/tfjs | https://api.github.com/repos/tensorflow/tfjs | closed | No backend found in registry error when trying to launch blazepose | type:build/install | **System information**
- OS: Win 10
- TensorFlow.js installed from: npm
- TensorFlow.js version: ^3.8.0
- CUDA/cuDNN version: 27.21.14.6231
**The problem**
I get an error in vs code when trying to debug/build my ts code referencing blazepose (https://github.com/tensorflow/tfjs-models/tree/master/pose-detection/src/blazepose_tfjs):
`UnhandledPromiseRejectionWarning: Error: No backend found in registry.`
**Exact sequence of commands**
Installed the runtime in vs code and pretty much followed the guides on how to install in the link above:
Installed nodejs, installed ts, installed npm, installed yarn, asked myself why there is so much overhead, ran all yarn commands from the link, setup tsconfig, setup launch.json, setup run and debug window in vs code, had an existential crysis, launched the debugger and error popped up.
**Any other info / logs**
I've started learning js/ts quite literally 3 hours ago. So please, bear with my stupid problem and keep that in mind when answering.
Yes I have seen #3811. But that issue is almost a year old and we are apparently at tf version 3 now. Thats also probably why my issue has come in the first place.
Code in question:
```ts
import * as readline from 'readline';
import * as tf from '@tensorflow/tfjs';
import * as poseDetection from '@tensorflow-models/pose-detection';
// Register WebGL backend.
import '@tensorflow/tfjs-backend-webgl';
async function createModel(image){
const model = poseDetection.SupportedModels.BlazePose;
const detectorConfig = {
runtime: 'tfjs',
enableSmoothing: true,
modelType: 'heavy'
};
var detector = await poseDetection.createDetector(model, detectorConfig);
const estimationConfig = {flipHorizontal: true};
const timestamp = performance.now();
const poses = await detector.estimatePoses(image, estimationConfig, timestamp);
}
createModel(1)
let rl = readline.createInterface({
input: process.stdin,
output: process.stdout
});
rl.question('Is this example useful? [y/n] ', (answer) => {
switch(answer.toLowerCase()) {
case 'y':
console.log('Super!');
break;
case 'n':
console.log('Sorry! :(');
break;
default:
console.log('Invalid answer!');
}
rl.close();
});
```
package.json:
```json
{
"dependencies": {
"@mediapipe/pose": "^0.4.1624666670",
"@tensorflow-models/pose-detection": "^0.0.4",
"@tensorflow/tfjs": "^3.8.0",
"@tensorflow/tfjs-backend-webgl": "^3.8.0"
}
}
```
tsconfig:
```json
{
"compilerOptions": {
"target": "es5",
"module": "commonjs",
"sourceMap": true,
"outDir": "out"
},
"include": ["src/**/*", "out/main.js"],
"exclude": ["node_modules", "**/*.spec.ts"]
}
```
Full error log:
```
(node:6436) UnhandledPromiseRejectionWarning: Error: No backend found in registry.
at Engine.getSortedBackends (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4465:19)
at Engine.initializeBackendsAndReturnBest (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4474:35)
at Engine.get [as backend] (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4280:31)
at Engine.makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4814:35)
at makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5644:19)
at tensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5693:12)
at Object.decodeWeights (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5957:27)
at GraphModel.loadSync (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7762:34)
at GraphModel.<anonymous> (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7737:52)
at step (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:81:23)
(Use `node --trace-warnings ...` to show where the warning was created)
<node_internals>/internal/process/warning.js:44
(node:6436) UnhandledPromiseRejectionWarning: Unhandled promise rejection. This error originated either by throwing inside of an async function without a catch block, or by rejecting a promise which was not handled with .catch(). To terminate the node process on unhandled promise rejection, use the CLI flag `--unhandled-rejections=strict` (see https://nodejs.org/api/cli.html#cli_unhandled_rejections_mode). (rejection id: 1)
<node_internals>/internal/process/warning.js:44
(node:6436) [DEP0018] DeprecationWarning: Unhandled promise rejections are deprecated. In the future, promise rejections that are not handled will terminate the Node.js process with a non-zero exit code.
<node_internals>/internal/process/warning.js:44
Debugger attached.
(node:6436) UnhandledPromiseRejectionWarning: Error: No backend found in registry.
at Engine.getSortedBackends (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4465:19)
at Engine.initializeBackendsAndReturnBest (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4474:35)
at Engine.get [as backend] (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4280:31)
at Engine.makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4814:35)
at makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5644:19)
at tensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5693:12)
at Object.decodeWeights (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5957:27)
at GraphModel.loadSync (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7762:34)
at GraphModel.<anonymous> (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7737:52)
at step (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:81:23)
(Use `node --trace-warnings ...` to show where the warning was created)
(node:6436) UnhandledPromiseRejectionWarning: Unhandled promise rejection. This error originated either by throwing inside of an async function without a catch block, or by rejecting a promise which was not handled with .catch(). To terminate the node process on unhandled promise rejection, use the CLI flag `--unhandled-rejections=strict` (see https://nodejs.org/api/cli.html#cli_unhandled_rejections_mode). (rejection id: 1)
(node:6436) [DEP0018] DeprecationWarning: Unhandled promise rejections are deprecated. In the future, promise rejections that are not handled will terminate the Node.js process with a non-zero exit code.
Process exited with code 1
```
yarn.lock (dunno if that helps)
```lock
# THIS IS AN AUTOGENERATED FILE. DO NOT EDIT THIS FILE DIRECTLY.
# yarn lockfile v1
"@mediapipe/pose@^0.4.1624666670":
version "0.4.1624666670"
resolved "https://registry.yarnpkg.com/@mediapipe/pose/-/pose-0.4.1624666670.tgz#fb6351e1477703b4bc560757e1db1eb0b17e4a29"
integrity sha512-DKROLwNi3DISXIZfnOVF87ObOZ7scaa+juPIDbwy+O3kWIwg0XSkAMkwNGJ+YRETL6QZYNH3KoAEuWS6itxIAw==
"@tensorflow-models/pose-detection@^0.0.4":
version "0.0.4"
resolved "https://registry.yarnpkg.com/@tensorflow-models/pose-detection/-/pose-detection-0.0.4.tgz#bf637367d5b5631a055b989b609fbf916ff721c1"
integrity sha512-7tNhYqCWuo85l8MesVHl9ZytqlqyG+4pc1jhDIF+2PXPOLcbD1G9EOgqU7d2B1Zo1NHi+j3EdDhI6X1dr25iag==
dependencies:
rimraf "^3.0.2"
"@tensorflow/tfjs-backend-cpu@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-backend-cpu/-/tfjs-backend-cpu-3.8.0.tgz#1b0655d5ca1b57370c1ea9586d571f3d63ca7393"
integrity sha512-iSwHrqX0Ixh1kelfmxIgChKft/KrcZk9EMHQcX+878XnX7mxB2HfWUqfiJVIcq+Fyr4I3oE4ncbbpmlKMxA85A==
dependencies:
"@types/seedrandom" "2.4.27"
seedrandom "2.4.3"
"@tensorflow/tfjs-backend-webgl@3.8.0", "@tensorflow/tfjs-backend-webgl@^3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-backend-webgl/-/tfjs-backend-webgl-3.8.0.tgz#35fc3c69979805a0f84a5ffa99fe431512c72f6b"
integrity sha512-Pjv+oWPf+7YS8kz/UFh2QBeD3F74R63AEU48a44LVh63YHXvdRg/M/Mvhjd55Oe0crDbBLej287SgVB8DHjUXg==
dependencies:
"@tensorflow/tfjs-backend-cpu" "3.8.0"
"@types/offscreencanvas" "~2019.3.0"
"@types/seedrandom" "2.4.27"
"@types/webgl-ext" "0.0.30"
"@types/webgl2" "0.0.5"
seedrandom "2.4.3"
"@tensorflow/tfjs-converter@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-converter/-/tfjs-converter-3.8.0.tgz#78dd1c96acd775ceb112cd0c30deb5120a8a7536"
integrity sha512-IWalZtKNfsSHt9He3Tvfje71gwMnFg5msQEiEnAtVnz1Zly0Yi0mycGLp5TPyqPhZCcJ+i9OhgkAlL4sbjP1hw==
"@tensorflow/tfjs-core@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-core/-/tfjs-core-3.8.0.tgz#b7390db21bbcbf4c3da0c540d9318164d987767c"
integrity sha512-0VKqNpnTiXIeOql3dnEyPOxKA9yDA366onv3sphm6k8KAzkr+is+GHOHzmo8mL7+AujiOb6o0J7BYhr7yvpNjA==
dependencies:
"@types/long" "^4.0.1"
"@types/offscreencanvas" "~2019.3.0"
"@types/seedrandom" "2.4.27"
"@types/webgl-ext" "0.0.30"
long "4.0.0"
node-fetch "~2.6.1"
seedrandom "2.4.3"
"@tensorflow/tfjs-data@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-data/-/tfjs-data-3.8.0.tgz#eb60485c35f5e493cab675e3071dc814d1c0dc5d"
integrity sha512-TuzI2ggCKb3lLUAsTGT/CMOkMZgrmgu1dQckEnft621RDJSQTN1o7xC0YLDmuwLwfUmWJax8TvsSxXBy2M5GSg==
dependencies:
"@types/node-fetch" "^2.1.2"
node-fetch "~2.6.1"
"@tensorflow/tfjs-layers@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-layers/-/tfjs-layers-3.8.0.tgz#f8afbc375aacab7457ac5d6a83d5c5b292105681"
integrity sha512-O7r0zkGFM2DTS2NdWhGUrKNgoY1GR7IX5aGIj50SQ8WnPWwY9gaVI7b+euP2Yg7A6kDiFXJIST+MY9EottyqSA==
"@tensorflow/tfjs@^3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs/-/tfjs-3.8.0.tgz#76e9e5447c1d1725bcc25904c2c8c21f615acb0f"
integrity sha512-4tVMEfGT8l8JBei/O0K0j7pcNbWR7C9r6WAuvoFXQBiu6FkwUhnM+rNrBHoh1/UaYKKm1enVbiyAP9+sbSFRaw==
dependencies:
"@tensorflow/tfjs-backend-cpu" "3.8.0"
"@tensorflow/tfjs-backend-webgl" "3.8.0"
"@tensorflow/tfjs-converter" "3.8.0"
"@tensorflow/tfjs-core" "3.8.0"
"@tensorflow/tfjs-data" "3.8.0"
"@tensorflow/tfjs-layers" "3.8.0"
argparse "^1.0.10"
chalk "^4.1.0"
core-js "3"
regenerator-runtime "^0.13.5"
yargs "^16.0.3"
"@types/long@^4.0.1":
version "4.0.1"
resolved "https://registry.yarnpkg.com/@types/long/-/long-4.0.1.tgz#459c65fa1867dafe6a8f322c4c51695663cc55e9"
integrity sha512-5tXH6Bx/kNGd3MgffdmP4dy2Z+G4eaXw0SE81Tq3BNadtnMR5/ySMzX4SLEzHJzSmPNn4HIdpQsBvXMUykr58w==
"@types/node-fetch@^2.1.2":
version "2.5.12"
resolved "https://registry.yarnpkg.com/@types/node-fetch/-/node-fetch-2.5.12.tgz#8a6f779b1d4e60b7a57fb6fd48d84fb545b9cc66"
integrity sha512-MKgC4dlq4kKNa/mYrwpKfzQMB5X3ee5U6fSprkKpToBqBmX4nFZL9cW5jl6sWn+xpRJ7ypWh2yyqqr8UUCstSw==
dependencies:
"@types/node" "*"
form-data "^3.0.0"
"@types/node@*":
version "16.4.1"
resolved "https://registry.yarnpkg.com/@types/node/-/node-16.4.1.tgz#9fad171a5b701613ee8a6f4ece3c88b1034b1b03"
integrity sha512-UW7cbLqf/Wu5XH2RKKY1cHwUNLicIDRLMraYKz+HHAerJ0ZffUEk+fMnd8qU2JaS6cAy0r8tsaf7yqHASf/Y0Q==
"@types/offscreencanvas@~2019.3.0":
version "2019.3.0"
resolved "https://registry.yarnpkg.com/@types/offscreencanvas/-/offscreencanvas-2019.3.0.tgz#3336428ec7e9180cf4566dfea5da04eb586a6553"
integrity sha512-esIJx9bQg+QYF0ra8GnvfianIY8qWB0GBx54PK5Eps6m+xTj86KLavHv6qDhzKcu5UUOgNfJ2pWaIIV7TRUd9Q==
"@types/seedrandom@2.4.27":
version "2.4.27"
resolved "https://registry.yarnpkg.com/@types/seedrandom/-/seedrandom-2.4.27.tgz#9db563937dd86915f69092bc43259d2f48578e41"
integrity sha1-nbVjk33YaRX2kJK8QyWdL0hXjkE=
"@types/webgl-ext@0.0.30":
version "0.0.30"
resolved "https://registry.yarnpkg.com/@types/webgl-ext/-/webgl-ext-0.0.30.tgz#0ce498c16a41a23d15289e0b844d945b25f0fb9d"
integrity sha512-LKVgNmBxN0BbljJrVUwkxwRYqzsAEPcZOe6S2T6ZaBDIrFp0qu4FNlpc5sM1tGbXUYFgdVQIoeLk1Y1UoblyEg==
"@types/webgl2@0.0.5":
version "0.0.5"
resolved "https://registry.yarnpkg.com/@types/webgl2/-/webgl2-0.0.5.tgz#dd925e20ab8ace80eb4b1e46fda5b109c508fb0d"
integrity sha512-oGaKsBbxQOY5+aJFV3KECDhGaXt+yZJt2y/OZsnQGLRkH6Fvr7rv4pCt3SRH1somIHfej/c4u7NSpCyd9x+1Ow==
ansi-regex@^5.0.0:
version "5.0.0"
resolved "https://registry.yarnpkg.com/ansi-regex/-/ansi-regex-5.0.0.tgz#388539f55179bf39339c81af30a654d69f87cb75"
integrity sha512-bY6fj56OUQ0hU1KjFNDQuJFezqKdrAyFdIevADiqrWHwSlbmBNMHp5ak2f40Pm8JTFyM2mqxkG6ngkHO11f/lg==
ansi-styles@^4.0.0, ansi-styles@^4.1.0:
version "4.3.0"
resolved "https://registry.yarnpkg.com/ansi-styles/-/ansi-styles-4.3.0.tgz#edd803628ae71c04c85ae7a0906edad34b648937"
integrity sha512-zbB9rCJAT1rbjiVDb2hqKFHNYLxgtk8NURxZ3IZwD3F6NtxbXZQCnnSi1Lkx+IDohdPlFp222wVALIheZJQSEg==
dependencies:
color-convert "^2.0.1"
argparse@^1.0.10:
version "1.0.10"
resolved "https://registry.yarnpkg.com/argparse/-/argparse-1.0.10.tgz#bcd6791ea5ae09725e17e5ad988134cd40b3d911"
integrity sha512-o5Roy6tNG4SL/FOkCAN6RzjiakZS25RLYFrcMttJqbdd8BWrnA+fGz57iN5Pb06pvBGvl5gQ0B48dJlslXvoTg==
dependencies:
sprintf-js "~1.0.2"
asynckit@^0.4.0:
version "0.4.0"
resolved "https://registry.yarnpkg.com/asynckit/-/asynckit-0.4.0.tgz#c79ed97f7f34cb8f2ba1bc9790bcc366474b4b79"
integrity sha1-x57Zf380y48robyXkLzDZkdLS3k=
balanced-match@^1.0.0:
version "1.0.2"
resolved "https://registry.yarnpkg.com/balanced-match/-/balanced-match-1.0.2.tgz#e83e3a7e3f300b34cb9d87f615fa0cbf357690ee"
integrity sha512-3oSeUO0TMV67hN1AmbXsK4yaqU7tjiHlbxRDZOpH0KW9+CeX4bRAaX0Anxt0tx2MrpRpWwQaPwIlISEJhYU5Pw==
brace-expansion@^1.1.7:
version "1.1.11"
resolved "https://registry.yarnpkg.com/brace-expansion/-/brace-expansion-1.1.11.tgz#3c7fcbf529d87226f3d2f52b966ff5271eb441dd"
integrity sha512-iCuPHDFgrHX7H2vEI/5xpz07zSHB00TpugqhmYtVmMO6518mCuRMoOYFldEBl0g187ufozdaHgWKcYFb61qGiA==
dependencies:
balanced-match "^1.0.0"
concat-map "0.0.1"
chalk@^4.1.0:
version "4.1.1"
resolved "https://registry.yarnpkg.com/chalk/-/chalk-4.1.1.tgz#c80b3fab28bf6371e6863325eee67e618b77e6ad"
integrity sha512-diHzdDKxcU+bAsUboHLPEDQiw0qEe0qd7SYUn3HgcFlWgbDcfLGswOHYeGrHKzG9z6UYf01d9VFMfZxPM1xZSg==
dependencies:
ansi-styles "^4.1.0"
supports-color "^7.1.0"
cliui@^7.0.2:
version "7.0.4"
resolved "https://registry.yarnpkg.com/cliui/-/cliui-7.0.4.tgz#a0265ee655476fc807aea9df3df8df7783808b4f"
integrity sha512-OcRE68cOsVMXp1Yvonl/fzkQOyjLSu/8bhPDfQt0e0/Eb283TKP20Fs2MqoPsr9SwA595rRCA+QMzYc9nBP+JQ==
dependencies:
string-width "^4.2.0"
strip-ansi "^6.0.0"
wrap-ansi "^7.0.0"
color-convert@^2.0.1:
version "2.0.1"
resolved "https://registry.yarnpkg.com/color-convert/-/color-convert-2.0.1.tgz#72d3a68d598c9bdb3af2ad1e84f21d896abd4de3"
integrity sha512-RRECPsj7iu/xb5oKYcsFHSppFNnsj/52OVTRKb4zP5onXwVF3zVmmToNcOfGC+CRDpfK/U584fMg38ZHCaElKQ==
dependencies:
color-name "~1.1.4"
color-name@~1.1.4:
version "1.1.4"
resolved "https://registry.yarnpkg.com/color-name/-/color-name-1.1.4.tgz#c2a09a87acbde69543de6f63fa3995c826c536a2"
integrity sha512-dOy+3AuW3a2wNbZHIuMZpTcgjGuLU/uBL/ubcZF9OXbDo8ff4O8yVp5Bf0efS8uEoYo5q4Fx7dY9OgQGXgAsQA==
combined-stream@^1.0.8:
version "1.0.8"
resolved "https://registry.yarnpkg.com/combined-stream/-/combined-stream-1.0.8.tgz#c3d45a8b34fd730631a110a8a2520682b31d5a7f"
integrity sha512-FQN4MRfuJeHf7cBbBMJFXhKSDq+2kAArBlmRBvcvFE5BB1HZKXtSFASDhdlz9zOYwxh8lDdnvmMOe/+5cdoEdg==
dependencies:
delayed-stream "~1.0.0"
concat-map@0.0.1:
version "0.0.1"
resolved "https://registry.yarnpkg.com/concat-map/-/concat-map-0.0.1.tgz#d8a96bd77fd68df7793a73036a3ba0d5405d477b"
integrity sha1-2Klr13/Wjfd5OnMDajug1UBdR3s=
core-js@3:
version "3.15.2"
resolved "https://registry.yarnpkg.com/core-js/-/core-js-3.15.2.tgz#740660d2ff55ef34ce664d7e2455119c5bdd3d61"
integrity sha512-tKs41J7NJVuaya8DxIOCnl8QuPHx5/ZVbFo1oKgVl1qHFBBrDctzQGtuLjPpRdNTWmKPH6oEvgN/MUID+l485Q==
delayed-stream@~1.0.0:
version "1.0.0"
resolved "https://registry.yarnpkg.com/delayed-stream/-/delayed-stream-1.0.0.tgz#df3ae199acadfb7d440aaae0b29e2272b24ec619"
integrity sha1-3zrhmayt+31ECqrgsp4icrJOxhk=
emoji-regex@^8.0.0:
version "8.0.0"
resolved "https://registry.yarnpkg.com/emoji-regex/-/emoji-regex-8.0.0.tgz#e818fd69ce5ccfcb404594f842963bf53164cc37"
integrity sha512-MSjYzcWNOA0ewAHpz0MxpYFvwg6yjy1NG3xteoqz644VCo/RPgnr1/GGt+ic3iJTzQ8Eu3TdM14SawnVUmGE6A==
escalade@^3.1.1:
version "3.1.1"
resolved "https://registry.yarnpkg.com/escalade/-/escalade-3.1.1.tgz#d8cfdc7000965c5a0174b4a82eaa5c0552742e40"
integrity sha512-k0er2gUkLf8O0zKJiAhmkTnJlTvINGv7ygDNPbeIsX/TJjGJZHuh9B2UxbsaEkmlEo9MfhrSzmhIlhRlI2GXnw==
form-data@^3.0.0:
version "3.0.1"
resolved "https://registry.yarnpkg.com/form-data/-/form-data-3.0.1.tgz#ebd53791b78356a99af9a300d4282c4d5eb9755f"
integrity sha512-RHkBKtLWUVwd7SqRIvCZMEvAMoGUp0XU+seQiZejj0COz3RI3hWP4sCv3gZWWLjJTd7rGwcsF5eKZGii0r/hbg==
dependencies:
asynckit "^0.4.0"
combined-stream "^1.0.8"
mime-types "^2.1.12"
fs.realpath@^1.0.0:
version "1.0.0"
resolved "https://registry.yarnpkg.com/fs.realpath/-/fs.realpath-1.0.0.tgz#1504ad2523158caa40db4a2787cb01411994ea4f"
integrity sha1-FQStJSMVjKpA20onh8sBQRmU6k8=
get-caller-file@^2.0.5:
version "2.0.5"
resolved "https://registry.yarnpkg.com/get-caller-file/-/get-caller-file-2.0.5.tgz#4f94412a82db32f36e3b0b9741f8a97feb031f7e"
integrity sha512-DyFP3BM/3YHTQOCUL/w0OZHR0lpKeGrxotcHWcqNEdnltqFwXVfhEBQ94eIo34AfQpo0rGki4cyIiftY06h2Fg==
glob@^7.1.3:
version "7.1.7"
resolved "https://registry.yarnpkg.com/glob/-/glob-7.1.7.tgz#3b193e9233f01d42d0b3f78294bbeeb418f94a90"
integrity sha512-OvD9ENzPLbegENnYP5UUfJIirTg4+XwMWGaQfQTY0JenxNvvIKP3U3/tAQSPIu/lHxXYSZmpXlUHeqAIdKzBLQ==
dependencies:
fs.realpath "^1.0.0"
inflight "^1.0.4"
inherits "2"
minimatch "^3.0.4"
once "^1.3.0"
path-is-absolute "^1.0.0"
has-flag@^4.0.0:
version "4.0.0"
resolved "https://registry.yarnpkg.com/has-flag/-/has-flag-4.0.0.tgz#944771fd9c81c81265c4d6941860da06bb59479b"
integrity sha512-EykJT/Q1KjTWctppgIAgfSO0tKVuZUjhgMr17kqTumMl6Afv3EISleU7qZUzoXDFTAHTDC4NOoG/ZxU3EvlMPQ==
inflight@^1.0.4:
version "1.0.6"
resolved "https://registry.yarnpkg.com/inflight/-/inflight-1.0.6.tgz#49bd6331d7d02d0c09bc910a1075ba8165b56df9"
integrity sha1-Sb1jMdfQLQwJvJEKEHW6gWW1bfk=
dependencies:
once "^1.3.0"
wrappy "1"
inherits@2:
version "2.0.4"
resolved "https://registry.yarnpkg.com/inherits/-/inherits-2.0.4.tgz#0fa2c64f932917c3433a0ded55363aae37416b7c"
integrity sha512-k/vGaX4/Yla3WzyMCvTQOXYeIHvqOKtnqBduzTHpzpQZzAskKMhZ2K+EnBiSM9zGSoIFeMpXKxa4dYeZIQqewQ==
is-fullwidth-code-point@^3.0.0:
version "3.0.0"
resolved "https://registry.yarnpkg.com/is-fullwidth-code-point/-/is-fullwidth-code-point-3.0.0.tgz#f116f8064fe90b3f7844a38997c0b75051269f1d"
integrity sha512-zymm5+u+sCsSWyD9qNaejV3DFvhCKclKdizYaJUuHA83RLjb7nSuGnddCHGv0hk+KY7BMAlsWeK4Ueg6EV6XQg==
long@4.0.0:
version "4.0.0"
resolved "https://registry.yarnpkg.com/long/-/long-4.0.0.tgz#9a7b71cfb7d361a194ea555241c92f7468d5bf28"
integrity sha512-XsP+KhQif4bjX1kbuSiySJFNAehNxgLb6hPRGJ9QsUr8ajHkuXGdrHmFUTUUXhDwVX2R5bY4JNZEwbUiMhV+MA==
mime-db@1.48.0:
version "1.48.0"
resolved "https://registry.yarnpkg.com/mime-db/-/mime-db-1.48.0.tgz#e35b31045dd7eada3aaad537ed88a33afbef2d1d"
integrity sha512-FM3QwxV+TnZYQ2aRqhlKBMHxk10lTbMt3bBkMAp54ddrNeVSfcQYOOKuGuy3Ddrm38I04If834fOUSq1yzslJQ==
mime-types@^2.1.12:
version "2.1.31"
resolved "https://registry.yarnpkg.com/mime-types/-/mime-types-2.1.31.tgz#a00d76b74317c61f9c2db2218b8e9f8e9c5c9e6b"
integrity sha512-XGZnNzm3QvgKxa8dpzyhFTHmpP3l5YNusmne07VUOXxou9CqUqYa/HBy124RqtVh/O2pECas/MOcsDgpilPOPg==
dependencies:
mime-db "1.48.0"
minimatch@^3.0.4:
version "3.0.4"
resolved "https://registry.yarnpkg.com/minimatch/-/minimatch-3.0.4.tgz#5166e286457f03306064be5497e8dbb0c3d32083"
integrity sha512-yJHVQEhyqPLUTgt9B83PXu6W3rx4MvvHvSUvToogpwoGDOUQ+yDrR0HRot+yOCdCO7u4hX3pWft6kWBBcqh0UA==
dependencies:
brace-expansion "^1.1.7"
node-fetch@~2.6.1:
version "2.6.1"
resolved "https://registry.yarnpkg.com/node-fetch/-/node-fetch-2.6.1.tgz#045bd323631f76ed2e2b55573394416b639a0052"
integrity sha512-V4aYg89jEoVRxRb2fJdAg8FHvI7cEyYdVAh94HH0UIK8oJxUfkjlDQN9RbMx+bEjP7+ggMiFRprSti032Oipxw==
once@^1.3.0:
version "1.4.0"
resolved "https://registry.yarnpkg.com/once/-/once-1.4.0.tgz#583b1aa775961d4b113ac17d9c50baef9dd76bd1"
integrity sha1-WDsap3WWHUsROsF9nFC6753Xa9E=
dependencies:
wrappy "1"
path-is-absolute@^1.0.0:
version "1.0.1"
resolved "https://registry.yarnpkg.com/path-is-absolute/-/path-is-absolute-1.0.1.tgz#174b9268735534ffbc7ace6bf53a5a9e1b5c5f5f"
integrity sha1-F0uSaHNVNP+8es5r9TpanhtcX18=
regenerator-runtime@^0.13.5:
version "0.13.9"
resolved "https://registry.yarnpkg.com/regenerator-runtime/-/regenerator-runtime-0.13.9.tgz#8925742a98ffd90814988d7566ad30ca3b263b52"
integrity sha512-p3VT+cOEgxFsRRA9X4lkI1E+k2/CtnKtU4gcxyaCUreilL/vqI6CdZ3wxVUx3UOUg+gnUOQQcRI7BmSI656MYA==
require-directory@^2.1.1:
version "2.1.1"
resolved "https://registry.yarnpkg.com/require-directory/-/require-directory-2.1.1.tgz#8c64ad5fd30dab1c976e2344ffe7f792a6a6df42"
integrity sha1-jGStX9MNqxyXbiNE/+f3kqam30I=
rimraf@^3.0.2:
version "3.0.2"
resolved "https://registry.yarnpkg.com/rimraf/-/rimraf-3.0.2.tgz#f1a5402ba6220ad52cc1282bac1ae3aa49fd061a"
integrity sha512-JZkJMZkAGFFPP2YqXZXPbMlMBgsxzE8ILs4lMIX/2o0L9UBw9O/Y3o6wFw/i9YLapcUJWwqbi3kdxIPdC62TIA==
dependencies:
glob "^7.1.3"
seedrandom@2.4.3:
version "2.4.3"
resolved "https://registry.yarnpkg.com/seedrandom/-/seedrandom-2.4.3.tgz#2438504dad33917314bff18ac4d794f16d6aaecc"
integrity sha1-JDhQTa0zkXMUv/GKxNeU8W1qrsw=
sprintf-js@~1.0.2:
version "1.0.3"
resolved "https://registry.yarnpkg.com/sprintf-js/-/sprintf-js-1.0.3.tgz#04e6926f662895354f3dd015203633b857297e2c"
integrity sha1-BOaSb2YolTVPPdAVIDYzuFcpfiw=
string-width@^4.1.0, string-width@^4.2.0:
version "4.2.2"
resolved "https://registry.yarnpkg.com/string-width/-/string-width-4.2.2.tgz#dafd4f9559a7585cfba529c6a0a4f73488ebd4c5"
integrity sha512-XBJbT3N4JhVumXE0eoLU9DCjcaF92KLNqTmFCnG1pf8duUxFGwtP6AD6nkjw9a3IdiRtL3E2w3JDiE/xi3vOeA==
dependencies:
emoji-regex "^8.0.0"
is-fullwidth-code-point "^3.0.0"
strip-ansi "^6.0.0"
strip-ansi@^6.0.0:
version "6.0.0"
resolved "https://registry.yarnpkg.com/strip-ansi/-/strip-ansi-6.0.0.tgz#0b1571dd7669ccd4f3e06e14ef1eed26225ae532"
integrity sha512-AuvKTrTfQNYNIctbR1K/YGTR1756GycPsg7b9bdV9Duqur4gv6aKqHXah67Z8ImS7WEz5QVcOtlfW2rZEugt6w==
dependencies:
ansi-regex "^5.0.0"
supports-color@^7.1.0:
version "7.2.0"
resolved "https://registry.yarnpkg.com/supports-color/-/supports-color-7.2.0.tgz#1b7dcdcb32b8138801b3e478ba6a51caa89648da"
integrity sha512-qpCAvRl9stuOHveKsn7HncJRvv501qIacKzQlO/+Lwxc9+0q2wLyv4Dfvt80/DPn2pqOBsJdDiogXGR9+OvwRw==
dependencies:
has-flag "^4.0.0"
wrap-ansi@^7.0.0:
version "7.0.0"
resolved "https://registry.yarnpkg.com/wrap-ansi/-/wrap-ansi-7.0.0.tgz#67e145cff510a6a6984bdf1152911d69d2eb9e43"
integrity sha512-YVGIj2kamLSTxw6NsZjoBxfSwsn0ycdesmc4p+Q21c5zPuZ1pl+NfxVdxPtdHvmNVOQ6XSYG4AUtyt/Fi7D16Q==
dependencies:
ansi-styles "^4.0.0"
string-width "^4.1.0"
strip-ansi "^6.0.0"
wrappy@1:
version "1.0.2"
resolved "https://registry.yarnpkg.com/wrappy/-/wrappy-1.0.2.tgz#b5243d8f3ec1aa35f1364605bc0d1036e30ab69f"
integrity sha1-tSQ9jz7BqjXxNkYFvA0QNuMKtp8=
y18n@^5.0.5:
version "5.0.8"
resolved "https://registry.yarnpkg.com/y18n/-/y18n-5.0.8.tgz#7f4934d0f7ca8c56f95314939ddcd2dd91ce1d55"
integrity sha512-0pfFzegeDWJHJIAmTLRP2DwHjdF5s7jo9tuztdQxAhINCdvS+3nGINqPd00AphqJR/0LhANUS6/+7SCb98YOfA==
yargs-parser@^20.2.2:
version "20.2.9"
resolved "https://registry.yarnpkg.com/yargs-parser/-/yargs-parser-20.2.9.tgz#2eb7dc3b0289718fc295f362753845c41a0c94ee"
integrity sha512-y11nGElTIV+CT3Zv9t7VKl+Q3hTQoT9a1Qzezhhl6Rp21gJ/IVTW7Z3y9EWXhuUBC2Shnf+DX0antecpAwSP8w==
yargs@^16.0.3:
version "16.2.0"
resolved "https://registry.yarnpkg.com/yargs/-/yargs-16.2.0.tgz#1c82bf0f6b6a66eafce7ef30e376f49a12477f66"
integrity sha512-D1mvvtDG0L5ft/jGWkLpG1+m0eQxOfaBvTNELraWj22wSVUMWxZUvYgJYcKh6jGGIkJFhH4IZPQhR4TKpc8mBw==
dependencies:
cliui "^7.0.2"
escalade "^3.1.1"
get-caller-file "^2.0.5"
require-directory "^2.1.1"
string-width "^4.2.0"
y18n "^5.0.5"
yargs-parser "^20.2.2"
```
| 1.0 | No backend found in registry error when trying to launch blazepose - **System information**
- OS: Win 10
- TensorFlow.js installed from: npm
- TensorFlow.js version: ^3.8.0
- CUDA/cuDNN version: 27.21.14.6231
**The problem**
I get an error in vs code when trying to debug/build my ts code referencing blazepose (https://github.com/tensorflow/tfjs-models/tree/master/pose-detection/src/blazepose_tfjs):
`UnhandledPromiseRejectionWarning: Error: No backend found in registry.`
**Exact sequence of commands**
Installed the runtime in vs code and pretty much followed the guides on how to install in the link above:
Installed nodejs, installed ts, installed npm, installed yarn, asked myself why there is so much overhead, ran all yarn commands from the link, setup tsconfig, setup launch.json, setup run and debug window in vs code, had an existential crysis, launched the debugger and error popped up.
**Any other info / logs**
I've started learning js/ts quite literally 3 hours ago. So please, bear with my stupid problem and keep that in mind when answering.
Yes I have seen #3811. But that issue is almost a year old and we are apparently at tf version 3 now. Thats also probably why my issue has come in the first place.
Code in question:
```ts
import * as readline from 'readline';
import * as tf from '@tensorflow/tfjs';
import * as poseDetection from '@tensorflow-models/pose-detection';
// Register WebGL backend.
import '@tensorflow/tfjs-backend-webgl';
async function createModel(image){
const model = poseDetection.SupportedModels.BlazePose;
const detectorConfig = {
runtime: 'tfjs',
enableSmoothing: true,
modelType: 'heavy'
};
var detector = await poseDetection.createDetector(model, detectorConfig);
const estimationConfig = {flipHorizontal: true};
const timestamp = performance.now();
const poses = await detector.estimatePoses(image, estimationConfig, timestamp);
}
createModel(1)
let rl = readline.createInterface({
input: process.stdin,
output: process.stdout
});
rl.question('Is this example useful? [y/n] ', (answer) => {
switch(answer.toLowerCase()) {
case 'y':
console.log('Super!');
break;
case 'n':
console.log('Sorry! :(');
break;
default:
console.log('Invalid answer!');
}
rl.close();
});
```
package.json:
```json
{
"dependencies": {
"@mediapipe/pose": "^0.4.1624666670",
"@tensorflow-models/pose-detection": "^0.0.4",
"@tensorflow/tfjs": "^3.8.0",
"@tensorflow/tfjs-backend-webgl": "^3.8.0"
}
}
```
tsconfig:
```json
{
"compilerOptions": {
"target": "es5",
"module": "commonjs",
"sourceMap": true,
"outDir": "out"
},
"include": ["src/**/*", "out/main.js"],
"exclude": ["node_modules", "**/*.spec.ts"]
}
```
Full error log:
```
(node:6436) UnhandledPromiseRejectionWarning: Error: No backend found in registry.
at Engine.getSortedBackends (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4465:19)
at Engine.initializeBackendsAndReturnBest (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4474:35)
at Engine.get [as backend] (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4280:31)
at Engine.makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4814:35)
at makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5644:19)
at tensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5693:12)
at Object.decodeWeights (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5957:27)
at GraphModel.loadSync (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7762:34)
at GraphModel.<anonymous> (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7737:52)
at step (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:81:23)
(Use `node --trace-warnings ...` to show where the warning was created)
<node_internals>/internal/process/warning.js:44
(node:6436) UnhandledPromiseRejectionWarning: Unhandled promise rejection. This error originated either by throwing inside of an async function without a catch block, or by rejecting a promise which was not handled with .catch(). To terminate the node process on unhandled promise rejection, use the CLI flag `--unhandled-rejections=strict` (see https://nodejs.org/api/cli.html#cli_unhandled_rejections_mode). (rejection id: 1)
<node_internals>/internal/process/warning.js:44
(node:6436) [DEP0018] DeprecationWarning: Unhandled promise rejections are deprecated. In the future, promise rejections that are not handled will terminate the Node.js process with a non-zero exit code.
<node_internals>/internal/process/warning.js:44
Debugger attached.
(node:6436) UnhandledPromiseRejectionWarning: Error: No backend found in registry.
at Engine.getSortedBackends (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4465:19)
at Engine.initializeBackendsAndReturnBest (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4474:35)
at Engine.get [as backend] (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4280:31)
at Engine.makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:4814:35)
at makeTensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5644:19)
at tensor (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5693:12)
at Object.decodeWeights (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-core\dist\tf-core.node.js:5957:27)
at GraphModel.loadSync (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7762:34)
at GraphModel.<anonymous> (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:7737:52)
at step (c:\Users\Niklas Kolbe\Desktop\Misc Projects\VirtualAvatar\node_modules\@tensorflow\tfjs-converter\dist\tf-converter.node.js:81:23)
(Use `node --trace-warnings ...` to show where the warning was created)
(node:6436) UnhandledPromiseRejectionWarning: Unhandled promise rejection. This error originated either by throwing inside of an async function without a catch block, or by rejecting a promise which was not handled with .catch(). To terminate the node process on unhandled promise rejection, use the CLI flag `--unhandled-rejections=strict` (see https://nodejs.org/api/cli.html#cli_unhandled_rejections_mode). (rejection id: 1)
(node:6436) [DEP0018] DeprecationWarning: Unhandled promise rejections are deprecated. In the future, promise rejections that are not handled will terminate the Node.js process with a non-zero exit code.
Process exited with code 1
```
yarn.lock (dunno if that helps)
```lock
# THIS IS AN AUTOGENERATED FILE. DO NOT EDIT THIS FILE DIRECTLY.
# yarn lockfile v1
"@mediapipe/pose@^0.4.1624666670":
version "0.4.1624666670"
resolved "https://registry.yarnpkg.com/@mediapipe/pose/-/pose-0.4.1624666670.tgz#fb6351e1477703b4bc560757e1db1eb0b17e4a29"
integrity sha512-DKROLwNi3DISXIZfnOVF87ObOZ7scaa+juPIDbwy+O3kWIwg0XSkAMkwNGJ+YRETL6QZYNH3KoAEuWS6itxIAw==
"@tensorflow-models/pose-detection@^0.0.4":
version "0.0.4"
resolved "https://registry.yarnpkg.com/@tensorflow-models/pose-detection/-/pose-detection-0.0.4.tgz#bf637367d5b5631a055b989b609fbf916ff721c1"
integrity sha512-7tNhYqCWuo85l8MesVHl9ZytqlqyG+4pc1jhDIF+2PXPOLcbD1G9EOgqU7d2B1Zo1NHi+j3EdDhI6X1dr25iag==
dependencies:
rimraf "^3.0.2"
"@tensorflow/tfjs-backend-cpu@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-backend-cpu/-/tfjs-backend-cpu-3.8.0.tgz#1b0655d5ca1b57370c1ea9586d571f3d63ca7393"
integrity sha512-iSwHrqX0Ixh1kelfmxIgChKft/KrcZk9EMHQcX+878XnX7mxB2HfWUqfiJVIcq+Fyr4I3oE4ncbbpmlKMxA85A==
dependencies:
"@types/seedrandom" "2.4.27"
seedrandom "2.4.3"
"@tensorflow/tfjs-backend-webgl@3.8.0", "@tensorflow/tfjs-backend-webgl@^3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-backend-webgl/-/tfjs-backend-webgl-3.8.0.tgz#35fc3c69979805a0f84a5ffa99fe431512c72f6b"
integrity sha512-Pjv+oWPf+7YS8kz/UFh2QBeD3F74R63AEU48a44LVh63YHXvdRg/M/Mvhjd55Oe0crDbBLej287SgVB8DHjUXg==
dependencies:
"@tensorflow/tfjs-backend-cpu" "3.8.0"
"@types/offscreencanvas" "~2019.3.0"
"@types/seedrandom" "2.4.27"
"@types/webgl-ext" "0.0.30"
"@types/webgl2" "0.0.5"
seedrandom "2.4.3"
"@tensorflow/tfjs-converter@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-converter/-/tfjs-converter-3.8.0.tgz#78dd1c96acd775ceb112cd0c30deb5120a8a7536"
integrity sha512-IWalZtKNfsSHt9He3Tvfje71gwMnFg5msQEiEnAtVnz1Zly0Yi0mycGLp5TPyqPhZCcJ+i9OhgkAlL4sbjP1hw==
"@tensorflow/tfjs-core@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-core/-/tfjs-core-3.8.0.tgz#b7390db21bbcbf4c3da0c540d9318164d987767c"
integrity sha512-0VKqNpnTiXIeOql3dnEyPOxKA9yDA366onv3sphm6k8KAzkr+is+GHOHzmo8mL7+AujiOb6o0J7BYhr7yvpNjA==
dependencies:
"@types/long" "^4.0.1"
"@types/offscreencanvas" "~2019.3.0"
"@types/seedrandom" "2.4.27"
"@types/webgl-ext" "0.0.30"
long "4.0.0"
node-fetch "~2.6.1"
seedrandom "2.4.3"
"@tensorflow/tfjs-data@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-data/-/tfjs-data-3.8.0.tgz#eb60485c35f5e493cab675e3071dc814d1c0dc5d"
integrity sha512-TuzI2ggCKb3lLUAsTGT/CMOkMZgrmgu1dQckEnft621RDJSQTN1o7xC0YLDmuwLwfUmWJax8TvsSxXBy2M5GSg==
dependencies:
"@types/node-fetch" "^2.1.2"
node-fetch "~2.6.1"
"@tensorflow/tfjs-layers@3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs-layers/-/tfjs-layers-3.8.0.tgz#f8afbc375aacab7457ac5d6a83d5c5b292105681"
integrity sha512-O7r0zkGFM2DTS2NdWhGUrKNgoY1GR7IX5aGIj50SQ8WnPWwY9gaVI7b+euP2Yg7A6kDiFXJIST+MY9EottyqSA==
"@tensorflow/tfjs@^3.8.0":
version "3.8.0"
resolved "https://registry.yarnpkg.com/@tensorflow/tfjs/-/tfjs-3.8.0.tgz#76e9e5447c1d1725bcc25904c2c8c21f615acb0f"
integrity sha512-4tVMEfGT8l8JBei/O0K0j7pcNbWR7C9r6WAuvoFXQBiu6FkwUhnM+rNrBHoh1/UaYKKm1enVbiyAP9+sbSFRaw==
dependencies:
"@tensorflow/tfjs-backend-cpu" "3.8.0"
"@tensorflow/tfjs-backend-webgl" "3.8.0"
"@tensorflow/tfjs-converter" "3.8.0"
"@tensorflow/tfjs-core" "3.8.0"
"@tensorflow/tfjs-data" "3.8.0"
"@tensorflow/tfjs-layers" "3.8.0"
argparse "^1.0.10"
chalk "^4.1.0"
core-js "3"
regenerator-runtime "^0.13.5"
yargs "^16.0.3"
"@types/long@^4.0.1":
version "4.0.1"
resolved "https://registry.yarnpkg.com/@types/long/-/long-4.0.1.tgz#459c65fa1867dafe6a8f322c4c51695663cc55e9"
integrity sha512-5tXH6Bx/kNGd3MgffdmP4dy2Z+G4eaXw0SE81Tq3BNadtnMR5/ySMzX4SLEzHJzSmPNn4HIdpQsBvXMUykr58w==
"@types/node-fetch@^2.1.2":
version "2.5.12"
resolved "https://registry.yarnpkg.com/@types/node-fetch/-/node-fetch-2.5.12.tgz#8a6f779b1d4e60b7a57fb6fd48d84fb545b9cc66"
integrity sha512-MKgC4dlq4kKNa/mYrwpKfzQMB5X3ee5U6fSprkKpToBqBmX4nFZL9cW5jl6sWn+xpRJ7ypWh2yyqqr8UUCstSw==
dependencies:
"@types/node" "*"
form-data "^3.0.0"
"@types/node@*":
version "16.4.1"
resolved "https://registry.yarnpkg.com/@types/node/-/node-16.4.1.tgz#9fad171a5b701613ee8a6f4ece3c88b1034b1b03"
integrity sha512-UW7cbLqf/Wu5XH2RKKY1cHwUNLicIDRLMraYKz+HHAerJ0ZffUEk+fMnd8qU2JaS6cAy0r8tsaf7yqHASf/Y0Q==
"@types/offscreencanvas@~2019.3.0":
version "2019.3.0"
resolved "https://registry.yarnpkg.com/@types/offscreencanvas/-/offscreencanvas-2019.3.0.tgz#3336428ec7e9180cf4566dfea5da04eb586a6553"
integrity sha512-esIJx9bQg+QYF0ra8GnvfianIY8qWB0GBx54PK5Eps6m+xTj86KLavHv6qDhzKcu5UUOgNfJ2pWaIIV7TRUd9Q==
"@types/seedrandom@2.4.27":
version "2.4.27"
resolved "https://registry.yarnpkg.com/@types/seedrandom/-/seedrandom-2.4.27.tgz#9db563937dd86915f69092bc43259d2f48578e41"
integrity sha1-nbVjk33YaRX2kJK8QyWdL0hXjkE=
"@types/webgl-ext@0.0.30":
version "0.0.30"
resolved "https://registry.yarnpkg.com/@types/webgl-ext/-/webgl-ext-0.0.30.tgz#0ce498c16a41a23d15289e0b844d945b25f0fb9d"
integrity sha512-LKVgNmBxN0BbljJrVUwkxwRYqzsAEPcZOe6S2T6ZaBDIrFp0qu4FNlpc5sM1tGbXUYFgdVQIoeLk1Y1UoblyEg==
"@types/webgl2@0.0.5":
version "0.0.5"
resolved "https://registry.yarnpkg.com/@types/webgl2/-/webgl2-0.0.5.tgz#dd925e20ab8ace80eb4b1e46fda5b109c508fb0d"
integrity sha512-oGaKsBbxQOY5+aJFV3KECDhGaXt+yZJt2y/OZsnQGLRkH6Fvr7rv4pCt3SRH1somIHfej/c4u7NSpCyd9x+1Ow==
ansi-regex@^5.0.0:
version "5.0.0"
resolved "https://registry.yarnpkg.com/ansi-regex/-/ansi-regex-5.0.0.tgz#388539f55179bf39339c81af30a654d69f87cb75"
integrity sha512-bY6fj56OUQ0hU1KjFNDQuJFezqKdrAyFdIevADiqrWHwSlbmBNMHp5ak2f40Pm8JTFyM2mqxkG6ngkHO11f/lg==
ansi-styles@^4.0.0, ansi-styles@^4.1.0:
version "4.3.0"
resolved "https://registry.yarnpkg.com/ansi-styles/-/ansi-styles-4.3.0.tgz#edd803628ae71c04c85ae7a0906edad34b648937"
integrity sha512-zbB9rCJAT1rbjiVDb2hqKFHNYLxgtk8NURxZ3IZwD3F6NtxbXZQCnnSi1Lkx+IDohdPlFp222wVALIheZJQSEg==
dependencies:
color-convert "^2.0.1"
argparse@^1.0.10:
version "1.0.10"
resolved "https://registry.yarnpkg.com/argparse/-/argparse-1.0.10.tgz#bcd6791ea5ae09725e17e5ad988134cd40b3d911"
integrity sha512-o5Roy6tNG4SL/FOkCAN6RzjiakZS25RLYFrcMttJqbdd8BWrnA+fGz57iN5Pb06pvBGvl5gQ0B48dJlslXvoTg==
dependencies:
sprintf-js "~1.0.2"
asynckit@^0.4.0:
version "0.4.0"
resolved "https://registry.yarnpkg.com/asynckit/-/asynckit-0.4.0.tgz#c79ed97f7f34cb8f2ba1bc9790bcc366474b4b79"
integrity sha1-x57Zf380y48robyXkLzDZkdLS3k=
balanced-match@^1.0.0:
version "1.0.2"
resolved "https://registry.yarnpkg.com/balanced-match/-/balanced-match-1.0.2.tgz#e83e3a7e3f300b34cb9d87f615fa0cbf357690ee"
integrity sha512-3oSeUO0TMV67hN1AmbXsK4yaqU7tjiHlbxRDZOpH0KW9+CeX4bRAaX0Anxt0tx2MrpRpWwQaPwIlISEJhYU5Pw==
brace-expansion@^1.1.7:
version "1.1.11"
resolved "https://registry.yarnpkg.com/brace-expansion/-/brace-expansion-1.1.11.tgz#3c7fcbf529d87226f3d2f52b966ff5271eb441dd"
integrity sha512-iCuPHDFgrHX7H2vEI/5xpz07zSHB00TpugqhmYtVmMO6518mCuRMoOYFldEBl0g187ufozdaHgWKcYFb61qGiA==
dependencies:
balanced-match "^1.0.0"
concat-map "0.0.1"
chalk@^4.1.0:
version "4.1.1"
resolved "https://registry.yarnpkg.com/chalk/-/chalk-4.1.1.tgz#c80b3fab28bf6371e6863325eee67e618b77e6ad"
integrity sha512-diHzdDKxcU+bAsUboHLPEDQiw0qEe0qd7SYUn3HgcFlWgbDcfLGswOHYeGrHKzG9z6UYf01d9VFMfZxPM1xZSg==
dependencies:
ansi-styles "^4.1.0"
supports-color "^7.1.0"
cliui@^7.0.2:
version "7.0.4"
resolved "https://registry.yarnpkg.com/cliui/-/cliui-7.0.4.tgz#a0265ee655476fc807aea9df3df8df7783808b4f"
integrity sha512-OcRE68cOsVMXp1Yvonl/fzkQOyjLSu/8bhPDfQt0e0/Eb283TKP20Fs2MqoPsr9SwA595rRCA+QMzYc9nBP+JQ==
dependencies:
string-width "^4.2.0"
strip-ansi "^6.0.0"
wrap-ansi "^7.0.0"
color-convert@^2.0.1:
version "2.0.1"
resolved "https://registry.yarnpkg.com/color-convert/-/color-convert-2.0.1.tgz#72d3a68d598c9bdb3af2ad1e84f21d896abd4de3"
integrity sha512-RRECPsj7iu/xb5oKYcsFHSppFNnsj/52OVTRKb4zP5onXwVF3zVmmToNcOfGC+CRDpfK/U584fMg38ZHCaElKQ==
dependencies:
color-name "~1.1.4"
color-name@~1.1.4:
version "1.1.4"
resolved "https://registry.yarnpkg.com/color-name/-/color-name-1.1.4.tgz#c2a09a87acbde69543de6f63fa3995c826c536a2"
integrity sha512-dOy+3AuW3a2wNbZHIuMZpTcgjGuLU/uBL/ubcZF9OXbDo8ff4O8yVp5Bf0efS8uEoYo5q4Fx7dY9OgQGXgAsQA==
combined-stream@^1.0.8:
version "1.0.8"
resolved "https://registry.yarnpkg.com/combined-stream/-/combined-stream-1.0.8.tgz#c3d45a8b34fd730631a110a8a2520682b31d5a7f"
integrity sha512-FQN4MRfuJeHf7cBbBMJFXhKSDq+2kAArBlmRBvcvFE5BB1HZKXtSFASDhdlz9zOYwxh8lDdnvmMOe/+5cdoEdg==
dependencies:
delayed-stream "~1.0.0"
concat-map@0.0.1:
version "0.0.1"
resolved "https://registry.yarnpkg.com/concat-map/-/concat-map-0.0.1.tgz#d8a96bd77fd68df7793a73036a3ba0d5405d477b"
integrity sha1-2Klr13/Wjfd5OnMDajug1UBdR3s=
core-js@3:
version "3.15.2"
resolved "https://registry.yarnpkg.com/core-js/-/core-js-3.15.2.tgz#740660d2ff55ef34ce664d7e2455119c5bdd3d61"
integrity sha512-tKs41J7NJVuaya8DxIOCnl8QuPHx5/ZVbFo1oKgVl1qHFBBrDctzQGtuLjPpRdNTWmKPH6oEvgN/MUID+l485Q==
delayed-stream@~1.0.0:
version "1.0.0"
resolved "https://registry.yarnpkg.com/delayed-stream/-/delayed-stream-1.0.0.tgz#df3ae199acadfb7d440aaae0b29e2272b24ec619"
integrity sha1-3zrhmayt+31ECqrgsp4icrJOxhk=
emoji-regex@^8.0.0:
version "8.0.0"
resolved "https://registry.yarnpkg.com/emoji-regex/-/emoji-regex-8.0.0.tgz#e818fd69ce5ccfcb404594f842963bf53164cc37"
integrity sha512-MSjYzcWNOA0ewAHpz0MxpYFvwg6yjy1NG3xteoqz644VCo/RPgnr1/GGt+ic3iJTzQ8Eu3TdM14SawnVUmGE6A==
escalade@^3.1.1:
version "3.1.1"
resolved "https://registry.yarnpkg.com/escalade/-/escalade-3.1.1.tgz#d8cfdc7000965c5a0174b4a82eaa5c0552742e40"
integrity sha512-k0er2gUkLf8O0zKJiAhmkTnJlTvINGv7ygDNPbeIsX/TJjGJZHuh9B2UxbsaEkmlEo9MfhrSzmhIlhRlI2GXnw==
form-data@^3.0.0:
version "3.0.1"
resolved "https://registry.yarnpkg.com/form-data/-/form-data-3.0.1.tgz#ebd53791b78356a99af9a300d4282c4d5eb9755f"
integrity sha512-RHkBKtLWUVwd7SqRIvCZMEvAMoGUp0XU+seQiZejj0COz3RI3hWP4sCv3gZWWLjJTd7rGwcsF5eKZGii0r/hbg==
dependencies:
asynckit "^0.4.0"
combined-stream "^1.0.8"
mime-types "^2.1.12"
fs.realpath@^1.0.0:
version "1.0.0"
resolved "https://registry.yarnpkg.com/fs.realpath/-/fs.realpath-1.0.0.tgz#1504ad2523158caa40db4a2787cb01411994ea4f"
integrity sha1-FQStJSMVjKpA20onh8sBQRmU6k8=
get-caller-file@^2.0.5:
version "2.0.5"
resolved "https://registry.yarnpkg.com/get-caller-file/-/get-caller-file-2.0.5.tgz#4f94412a82db32f36e3b0b9741f8a97feb031f7e"
integrity sha512-DyFP3BM/3YHTQOCUL/w0OZHR0lpKeGrxotcHWcqNEdnltqFwXVfhEBQ94eIo34AfQpo0rGki4cyIiftY06h2Fg==
glob@^7.1.3:
version "7.1.7"
resolved "https://registry.yarnpkg.com/glob/-/glob-7.1.7.tgz#3b193e9233f01d42d0b3f78294bbeeb418f94a90"
integrity sha512-OvD9ENzPLbegENnYP5UUfJIirTg4+XwMWGaQfQTY0JenxNvvIKP3U3/tAQSPIu/lHxXYSZmpXlUHeqAIdKzBLQ==
dependencies:
fs.realpath "^1.0.0"
inflight "^1.0.4"
inherits "2"
minimatch "^3.0.4"
once "^1.3.0"
path-is-absolute "^1.0.0"
has-flag@^4.0.0:
version "4.0.0"
resolved "https://registry.yarnpkg.com/has-flag/-/has-flag-4.0.0.tgz#944771fd9c81c81265c4d6941860da06bb59479b"
integrity sha512-EykJT/Q1KjTWctppgIAgfSO0tKVuZUjhgMr17kqTumMl6Afv3EISleU7qZUzoXDFTAHTDC4NOoG/ZxU3EvlMPQ==
inflight@^1.0.4:
version "1.0.6"
resolved "https://registry.yarnpkg.com/inflight/-/inflight-1.0.6.tgz#49bd6331d7d02d0c09bc910a1075ba8165b56df9"
integrity sha1-Sb1jMdfQLQwJvJEKEHW6gWW1bfk=
dependencies:
once "^1.3.0"
wrappy "1"
inherits@2:
version "2.0.4"
resolved "https://registry.yarnpkg.com/inherits/-/inherits-2.0.4.tgz#0fa2c64f932917c3433a0ded55363aae37416b7c"
integrity sha512-k/vGaX4/Yla3WzyMCvTQOXYeIHvqOKtnqBduzTHpzpQZzAskKMhZ2K+EnBiSM9zGSoIFeMpXKxa4dYeZIQqewQ==
is-fullwidth-code-point@^3.0.0:
version "3.0.0"
resolved "https://registry.yarnpkg.com/is-fullwidth-code-point/-/is-fullwidth-code-point-3.0.0.tgz#f116f8064fe90b3f7844a38997c0b75051269f1d"
integrity sha512-zymm5+u+sCsSWyD9qNaejV3DFvhCKclKdizYaJUuHA83RLjb7nSuGnddCHGv0hk+KY7BMAlsWeK4Ueg6EV6XQg==
long@4.0.0:
version "4.0.0"
resolved "https://registry.yarnpkg.com/long/-/long-4.0.0.tgz#9a7b71cfb7d361a194ea555241c92f7468d5bf28"
integrity sha512-XsP+KhQif4bjX1kbuSiySJFNAehNxgLb6hPRGJ9QsUr8ajHkuXGdrHmFUTUUXhDwVX2R5bY4JNZEwbUiMhV+MA==
mime-db@1.48.0:
version "1.48.0"
resolved "https://registry.yarnpkg.com/mime-db/-/mime-db-1.48.0.tgz#e35b31045dd7eada3aaad537ed88a33afbef2d1d"
integrity sha512-FM3QwxV+TnZYQ2aRqhlKBMHxk10lTbMt3bBkMAp54ddrNeVSfcQYOOKuGuy3Ddrm38I04If834fOUSq1yzslJQ==
mime-types@^2.1.12:
version "2.1.31"
resolved "https://registry.yarnpkg.com/mime-types/-/mime-types-2.1.31.tgz#a00d76b74317c61f9c2db2218b8e9f8e9c5c9e6b"
integrity sha512-XGZnNzm3QvgKxa8dpzyhFTHmpP3l5YNusmne07VUOXxou9CqUqYa/HBy124RqtVh/O2pECas/MOcsDgpilPOPg==
dependencies:
mime-db "1.48.0"
minimatch@^3.0.4:
version "3.0.4"
resolved "https://registry.yarnpkg.com/minimatch/-/minimatch-3.0.4.tgz#5166e286457f03306064be5497e8dbb0c3d32083"
integrity sha512-yJHVQEhyqPLUTgt9B83PXu6W3rx4MvvHvSUvToogpwoGDOUQ+yDrR0HRot+yOCdCO7u4hX3pWft6kWBBcqh0UA==
dependencies:
brace-expansion "^1.1.7"
node-fetch@~2.6.1:
version "2.6.1"
resolved "https://registry.yarnpkg.com/node-fetch/-/node-fetch-2.6.1.tgz#045bd323631f76ed2e2b55573394416b639a0052"
integrity sha512-V4aYg89jEoVRxRb2fJdAg8FHvI7cEyYdVAh94HH0UIK8oJxUfkjlDQN9RbMx+bEjP7+ggMiFRprSti032Oipxw==
once@^1.3.0:
version "1.4.0"
resolved "https://registry.yarnpkg.com/once/-/once-1.4.0.tgz#583b1aa775961d4b113ac17d9c50baef9dd76bd1"
integrity sha1-WDsap3WWHUsROsF9nFC6753Xa9E=
dependencies:
wrappy "1"
path-is-absolute@^1.0.0:
version "1.0.1"
resolved "https://registry.yarnpkg.com/path-is-absolute/-/path-is-absolute-1.0.1.tgz#174b9268735534ffbc7ace6bf53a5a9e1b5c5f5f"
integrity sha1-F0uSaHNVNP+8es5r9TpanhtcX18=
regenerator-runtime@^0.13.5:
version "0.13.9"
resolved "https://registry.yarnpkg.com/regenerator-runtime/-/regenerator-runtime-0.13.9.tgz#8925742a98ffd90814988d7566ad30ca3b263b52"
integrity sha512-p3VT+cOEgxFsRRA9X4lkI1E+k2/CtnKtU4gcxyaCUreilL/vqI6CdZ3wxVUx3UOUg+gnUOQQcRI7BmSI656MYA==
require-directory@^2.1.1:
version "2.1.1"
resolved "https://registry.yarnpkg.com/require-directory/-/require-directory-2.1.1.tgz#8c64ad5fd30dab1c976e2344ffe7f792a6a6df42"
integrity sha1-jGStX9MNqxyXbiNE/+f3kqam30I=
rimraf@^3.0.2:
version "3.0.2"
resolved "https://registry.yarnpkg.com/rimraf/-/rimraf-3.0.2.tgz#f1a5402ba6220ad52cc1282bac1ae3aa49fd061a"
integrity sha512-JZkJMZkAGFFPP2YqXZXPbMlMBgsxzE8ILs4lMIX/2o0L9UBw9O/Y3o6wFw/i9YLapcUJWwqbi3kdxIPdC62TIA==
dependencies:
glob "^7.1.3"
seedrandom@2.4.3:
version "2.4.3"
resolved "https://registry.yarnpkg.com/seedrandom/-/seedrandom-2.4.3.tgz#2438504dad33917314bff18ac4d794f16d6aaecc"
integrity sha1-JDhQTa0zkXMUv/GKxNeU8W1qrsw=
sprintf-js@~1.0.2:
version "1.0.3"
resolved "https://registry.yarnpkg.com/sprintf-js/-/sprintf-js-1.0.3.tgz#04e6926f662895354f3dd015203633b857297e2c"
integrity sha1-BOaSb2YolTVPPdAVIDYzuFcpfiw=
string-width@^4.1.0, string-width@^4.2.0:
version "4.2.2"
resolved "https://registry.yarnpkg.com/string-width/-/string-width-4.2.2.tgz#dafd4f9559a7585cfba529c6a0a4f73488ebd4c5"
integrity sha512-XBJbT3N4JhVumXE0eoLU9DCjcaF92KLNqTmFCnG1pf8duUxFGwtP6AD6nkjw9a3IdiRtL3E2w3JDiE/xi3vOeA==
dependencies:
emoji-regex "^8.0.0"
is-fullwidth-code-point "^3.0.0"
strip-ansi "^6.0.0"
strip-ansi@^6.0.0:
version "6.0.0"
resolved "https://registry.yarnpkg.com/strip-ansi/-/strip-ansi-6.0.0.tgz#0b1571dd7669ccd4f3e06e14ef1eed26225ae532"
integrity sha512-AuvKTrTfQNYNIctbR1K/YGTR1756GycPsg7b9bdV9Duqur4gv6aKqHXah67Z8ImS7WEz5QVcOtlfW2rZEugt6w==
dependencies:
ansi-regex "^5.0.0"
supports-color@^7.1.0:
version "7.2.0"
resolved "https://registry.yarnpkg.com/supports-color/-/supports-color-7.2.0.tgz#1b7dcdcb32b8138801b3e478ba6a51caa89648da"
integrity sha512-qpCAvRl9stuOHveKsn7HncJRvv501qIacKzQlO/+Lwxc9+0q2wLyv4Dfvt80/DPn2pqOBsJdDiogXGR9+OvwRw==
dependencies:
has-flag "^4.0.0"
wrap-ansi@^7.0.0:
version "7.0.0"
resolved "https://registry.yarnpkg.com/wrap-ansi/-/wrap-ansi-7.0.0.tgz#67e145cff510a6a6984bdf1152911d69d2eb9e43"
integrity sha512-YVGIj2kamLSTxw6NsZjoBxfSwsn0ycdesmc4p+Q21c5zPuZ1pl+NfxVdxPtdHvmNVOQ6XSYG4AUtyt/Fi7D16Q==
dependencies:
ansi-styles "^4.0.0"
string-width "^4.1.0"
strip-ansi "^6.0.0"
wrappy@1:
version "1.0.2"
resolved "https://registry.yarnpkg.com/wrappy/-/wrappy-1.0.2.tgz#b5243d8f3ec1aa35f1364605bc0d1036e30ab69f"
integrity sha1-tSQ9jz7BqjXxNkYFvA0QNuMKtp8=
y18n@^5.0.5:
version "5.0.8"
resolved "https://registry.yarnpkg.com/y18n/-/y18n-5.0.8.tgz#7f4934d0f7ca8c56f95314939ddcd2dd91ce1d55"
integrity sha512-0pfFzegeDWJHJIAmTLRP2DwHjdF5s7jo9tuztdQxAhINCdvS+3nGINqPd00AphqJR/0LhANUS6/+7SCb98YOfA==
yargs-parser@^20.2.2:
version "20.2.9"
resolved "https://registry.yarnpkg.com/yargs-parser/-/yargs-parser-20.2.9.tgz#2eb7dc3b0289718fc295f362753845c41a0c94ee"
integrity sha512-y11nGElTIV+CT3Zv9t7VKl+Q3hTQoT9a1Qzezhhl6Rp21gJ/IVTW7Z3y9EWXhuUBC2Shnf+DX0antecpAwSP8w==
yargs@^16.0.3:
version "16.2.0"
resolved "https://registry.yarnpkg.com/yargs/-/yargs-16.2.0.tgz#1c82bf0f6b6a66eafce7ef30e376f49a12477f66"
integrity sha512-D1mvvtDG0L5ft/jGWkLpG1+m0eQxOfaBvTNELraWj22wSVUMWxZUvYgJYcKh6jGGIkJFhH4IZPQhR4TKpc8mBw==
dependencies:
cliui "^7.0.2"
escalade "^3.1.1"
get-caller-file "^2.0.5"
require-directory "^2.1.1"
string-width "^4.2.0"
y18n "^5.0.5"
yargs-parser "^20.2.2"
```
| non_priority | no backend found in registry error when trying to launch blazepose system information os win tensorflow js installed from npm tensorflow js version cuda cudnn version the problem i get an error in vs code when trying to debug build my ts code referencing blazepose unhandledpromiserejectionwarning error no backend found in registry exact sequence of commands installed the runtime in vs code and pretty much followed the guides on how to install in the link above installed nodejs installed ts installed npm installed yarn asked myself why there is so much overhead ran all yarn commands from the link setup tsconfig setup launch json setup run and debug window in vs code had an existential crysis launched the debugger and error popped up any other info logs i ve started learning js ts quite literally hours ago so please bear with my stupid problem and keep that in mind when answering yes i have seen but that issue is almost a year old and we are apparently at tf version now thats also probably why my issue has come in the first place code in question ts import as readline from readline import as tf from tensorflow tfjs import as posedetection from tensorflow models pose detection register webgl backend import tensorflow tfjs backend webgl async function createmodel image const model posedetection supportedmodels blazepose const detectorconfig runtime tfjs enablesmoothing true modeltype heavy var detector await posedetection createdetector model detectorconfig const estimationconfig fliphorizontal true const timestamp performance now const poses await detector estimateposes image estimationconfig timestamp createmodel let rl readline createinterface input process stdin output process stdout rl question is this example useful answer switch answer tolowercase case y console log super break case n console log sorry break default console log invalid answer rl close package json json dependencies mediapipe pose tensorflow models pose detection tensorflow tfjs tensorflow tfjs backend webgl tsconfig json compileroptions target module commonjs sourcemap true outdir out include exclude full error log node unhandledpromiserejectionwarning error no backend found in registry at engine getsortedbackends c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at engine initializebackendsandreturnbest c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at engine get c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at engine maketensor c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at maketensor c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at tensor c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at object decodeweights c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at graphmodel loadsync c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs converter dist tf converter node js at graphmodel c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs converter dist tf converter node js at step c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs converter dist tf converter node js use node trace warnings to show where the warning was created internal process warning js node unhandledpromiserejectionwarning unhandled promise rejection this error originated either by throwing inside of an async function without a catch block or by rejecting a promise which was not handled with catch to terminate the node process on unhandled promise rejection use the cli flag unhandled rejections strict see rejection id internal process warning js node deprecationwarning unhandled promise rejections are deprecated in the future promise rejections that are not handled will terminate the node js process with a non zero exit code internal process warning js debugger attached node unhandledpromiserejectionwarning error no backend found in registry at engine getsortedbackends c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at engine initializebackendsandreturnbest c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at engine get c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at engine maketensor c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at maketensor c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at tensor c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at object decodeweights c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs core dist tf core node js at graphmodel loadsync c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs converter dist tf converter node js at graphmodel c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs converter dist tf converter node js at step c users niklas kolbe desktop misc projects virtualavatar node modules tensorflow tfjs converter dist tf converter node js use node trace warnings to show where the warning was created node unhandledpromiserejectionwarning unhandled promise rejection this error originated either by throwing inside of an async function without a catch block or by rejecting a promise which was not handled with catch to terminate the node process on unhandled promise rejection use the cli flag unhandled rejections strict see rejection id node deprecationwarning unhandled promise rejections are deprecated in the future promise rejections that are not handled will terminate the node js process with a non zero exit code process exited with code yarn lock dunno if that helps lock this is an autogenerated file do not edit this file directly yarn lockfile mediapipe pose version resolved integrity jupidbwy tensorflow models pose detection version resolved integrity dependencies rimraf tensorflow tfjs backend cpu version resolved integrity dependencies types seedrandom seedrandom tensorflow tfjs backend webgl tensorflow tfjs backend webgl version resolved integrity pjv owpf m dependencies tensorflow tfjs backend cpu types offscreencanvas types seedrandom types webgl ext types seedrandom tensorflow tfjs converter version resolved integrity tensorflow tfjs core version resolved integrity is dependencies types long types offscreencanvas types seedrandom types webgl ext long node fetch seedrandom tensorflow tfjs data version resolved integrity dependencies types node fetch node fetch tensorflow tfjs layers version resolved integrity tensorflow tfjs version resolved integrity sbsfraw dependencies tensorflow tfjs backend cpu tensorflow tfjs backend webgl tensorflow tfjs converter tensorflow tfjs core tensorflow tfjs data tensorflow tfjs layers argparse chalk core js regenerator runtime yargs types long version resolved integrity types node fetch version resolved integrity dependencies types node form data types node version resolved integrity types offscreencanvas version resolved integrity types seedrandom version resolved integrity types webgl ext version resolved integrity types version resolved integrity ansi regex version resolved integrity lg ansi styles ansi styles version resolved integrity dependencies color convert argparse version resolved integrity dependencies sprintf js asynckit version resolved integrity balanced match version resolved integrity brace expansion version resolved integrity dependencies balanced match concat map chalk version resolved integrity dihzddkxcu dependencies ansi styles supports color cliui version resolved integrity fzkqoyjlsu jq dependencies string width strip ansi wrap ansi color convert version resolved integrity crdpfk dependencies color name color name version resolved integrity doy ubl combined stream version resolved integrity dependencies delayed stream concat map version resolved integrity core js version resolved integrity muid delayed stream version resolved integrity emoji regex version resolved integrity ggt escalade version resolved integrity form data version resolved integrity hbg dependencies asynckit combined stream mime types fs realpath version resolved integrity get caller file version resolved integrity glob version resolved integrity taqspiu lhxxyszmpxluheqaidkzblq dependencies fs realpath inflight inherits minimatch once path is absolute has flag version resolved integrity eykjt inflight version resolved integrity dependencies once wrappy inherits version resolved integrity k is fullwidth code point version resolved integrity u long version resolved integrity xsp ma mime db version resolved integrity mime types version resolved integrity mocsdgpilpopg dependencies mime db minimatch version resolved integrity dependencies brace expansion node fetch version resolved integrity once version resolved integrity dependencies wrappy path is absolute version resolved integrity regenerator runtime version resolved integrity require directory version resolved integrity rimraf version resolved integrity dependencies glob seedrandom version resolved integrity sprintf js version resolved integrity string width string width version resolved integrity dependencies emoji regex is fullwidth code point strip ansi strip ansi version resolved integrity dependencies ansi regex supports color version resolved integrity ovwrw dependencies has flag wrap ansi version resolved integrity dependencies ansi styles string width strip ansi wrappy version resolved integrity version resolved integrity yargs parser version resolved integrity yargs version resolved integrity dependencies cliui escalade get caller file require directory string width yargs parser | 0 |
55,778 | 6,921,954,270 | IssuesEvent | 2017-11-30 00:23:19 | pecon94/AsteroidsPlus | https://api.github.com/repos/pecon94/AsteroidsPlus | closed | Sound effect for explosions | Sound Design | Need sounds to go off when any object explodes.
Example: asteroids exploding or ships getting hit. | 1.0 | Sound effect for explosions - Need sounds to go off when any object explodes.
Example: asteroids exploding or ships getting hit. | non_priority | sound effect for explosions need sounds to go off when any object explodes example asteroids exploding or ships getting hit | 0 |
233,368 | 18,976,547,578 | IssuesEvent | 2021-11-20 04:12:03 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | Unexpected semilocon makes rustdoc to produce false negatives | T-rustdoc C-bug A-doctests | <!--
Thank you for filing a bug report! 🐛 Please provide a short summary of the bug,
along with any information you feel relevant to replicating the bug.
-->
I tried this code:
```rust
/// ```rust
/// struct S {}; // unexpected semicolon after struct def
///
/// fn main() {
/// assert_eq!(0, 1);
/// }
/// ```
mod m {}
```
```
cargo test
```
I expected to see this happen:
```
running 0 tests
test result: ok. 0 passed; 0 failed; 0 ignored; 0 measured; 0 filtered out; finished in 0.00s
running 1 test
test src/lib.rs - m (line 1) ... FAILED
failures:
---- src/lib.rs - m (line 1) stdout ----
error: expected item, found `;`
--> src/lib.rs:6:12
|
2 | struct S {};
| ^ help: remove this semicolon
|
= help: braced struct declarations are not followed by a semicolon
error: aborting due to previous error
Couldn't compile the test.
failures:
src/lib.rs - m (line 1)
test result: FAILED. 0 passed; 1 failed; 0 ignored; 0 measured; 0 filtered out; finished in 0.29s
```
Instead, this happened:
```
running 0 tests
test result: ok. 0 passed; 0 failed; 0 ignored; 0 measured; 0 filtered out; finished in 0.00s
running 1 test
test src/lib.rs - m (line 1) ... ok
test result: ok. 1 passed; 0 failed; 0 ignored; 0 measured; 0 filtered out; finished in 1.06s
```
### Meta
<!--
If you're using the stable version of the compiler, you should also check if the
bug also exists in the beta or nightly versions.
-->
`rustc --version --verbose`:
```
binary: rustc
commit-hash: c8dfcfe046a7680554bf4eb612bad840e7631c4b
commit-date: 2021-09-06
host: x86_64-unknown-linux-gnu
release: 1.55.0
LLVM version: 12.0.1
```
Also, reproduces on [playground](https://play.rust-lang.org/?version=stable&mode=debug&edition=2021&gist=d229f821f3a532bfaf6c1790da28c0c6) (1.56.1 / 1.57.0-beta.3 / 1.58.0-nightly)
Putting struct def after the `main` function makes rustdoc to behave as expected:
```rust
/// ```rust
/// fn main() {
/// assert_eq!(0, 1);
/// }
///
/// struct S {}; // unexpected semicolon after struct def
/// ```
mod m {}
```
Implicit `main` function does the assertion correctly.
```rust
/// ```rust
/// struct S {}; // semicolon is OK here
/// assert_eq!(0, 1);
/// ```
mod m {}
``` | 1.0 | Unexpected semilocon makes rustdoc to produce false negatives - <!--
Thank you for filing a bug report! 🐛 Please provide a short summary of the bug,
along with any information you feel relevant to replicating the bug.
-->
I tried this code:
```rust
/// ```rust
/// struct S {}; // unexpected semicolon after struct def
///
/// fn main() {
/// assert_eq!(0, 1);
/// }
/// ```
mod m {}
```
```
cargo test
```
I expected to see this happen:
```
running 0 tests
test result: ok. 0 passed; 0 failed; 0 ignored; 0 measured; 0 filtered out; finished in 0.00s
running 1 test
test src/lib.rs - m (line 1) ... FAILED
failures:
---- src/lib.rs - m (line 1) stdout ----
error: expected item, found `;`
--> src/lib.rs:6:12
|
2 | struct S {};
| ^ help: remove this semicolon
|
= help: braced struct declarations are not followed by a semicolon
error: aborting due to previous error
Couldn't compile the test.
failures:
src/lib.rs - m (line 1)
test result: FAILED. 0 passed; 1 failed; 0 ignored; 0 measured; 0 filtered out; finished in 0.29s
```
Instead, this happened:
```
running 0 tests
test result: ok. 0 passed; 0 failed; 0 ignored; 0 measured; 0 filtered out; finished in 0.00s
running 1 test
test src/lib.rs - m (line 1) ... ok
test result: ok. 1 passed; 0 failed; 0 ignored; 0 measured; 0 filtered out; finished in 1.06s
```
### Meta
<!--
If you're using the stable version of the compiler, you should also check if the
bug also exists in the beta or nightly versions.
-->
`rustc --version --verbose`:
```
binary: rustc
commit-hash: c8dfcfe046a7680554bf4eb612bad840e7631c4b
commit-date: 2021-09-06
host: x86_64-unknown-linux-gnu
release: 1.55.0
LLVM version: 12.0.1
```
Also, reproduces on [playground](https://play.rust-lang.org/?version=stable&mode=debug&edition=2021&gist=d229f821f3a532bfaf6c1790da28c0c6) (1.56.1 / 1.57.0-beta.3 / 1.58.0-nightly)
Putting struct def after the `main` function makes rustdoc to behave as expected:
```rust
/// ```rust
/// fn main() {
/// assert_eq!(0, 1);
/// }
///
/// struct S {}; // unexpected semicolon after struct def
/// ```
mod m {}
```
Implicit `main` function does the assertion correctly.
```rust
/// ```rust
/// struct S {}; // semicolon is OK here
/// assert_eq!(0, 1);
/// ```
mod m {}
``` | non_priority | unexpected semilocon makes rustdoc to produce false negatives thank you for filing a bug report 🐛 please provide a short summary of the bug along with any information you feel relevant to replicating the bug i tried this code rust rust struct s unexpected semicolon after struct def fn main assert eq mod m cargo test i expected to see this happen running tests test result ok passed failed ignored measured filtered out finished in running test test src lib rs m line failed failures src lib rs m line stdout error expected item found src lib rs struct s help remove this semicolon help braced struct declarations are not followed by a semicolon error aborting due to previous error couldn t compile the test failures src lib rs m line test result failed passed failed ignored measured filtered out finished in instead this happened running tests test result ok passed failed ignored measured filtered out finished in running test test src lib rs m line ok test result ok passed failed ignored measured filtered out finished in meta if you re using the stable version of the compiler you should also check if the bug also exists in the beta or nightly versions rustc version verbose binary rustc commit hash commit date host unknown linux gnu release llvm version also reproduces on beta nightly putting struct def after the main function makes rustdoc to behave as expected rust rust fn main assert eq struct s unexpected semicolon after struct def mod m implicit main function does the assertion correctly rust rust struct s semicolon is ok here assert eq mod m | 0 |
44,026 | 13,047,868,481 | IssuesEvent | 2020-07-29 11:30:30 | rsoreq/zaproxy | https://api.github.com/repos/rsoreq/zaproxy | opened | CVE-2020-10968 (High) detected in jackson-databind-2.9.10.jar, jackson-databind-2.9.2.jar | security vulnerability | ## CVE-2020-10968 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.10.jar</b>, <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/zaproxy</p>
<p>Path to vulnerable library: /tmp/ws-ua_20200729112444_WCAEYA/downloadResource_JMENZF/20200729112922/jackson-databind-2.9.10.jar</p>
<p>
Dependency Hierarchy:
- wiremock-jre8-2.25.1.jar (Root Library)
- zjsonpatch-0.4.4.jar
- :x: **jackson-databind-2.9.10.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/zaproxy/buildSrc/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.2/1d8d8cb7cf26920ba57fb61fa56da88cc123b21f/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- kotlin-reflect-1.3.72.jar (Root Library)
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zaproxy/commit/faf0234fff2dbd2142cc463fc90d7e58bcf20cd0">faf0234fff2dbd2142cc463fc90d7e58bcf20cd0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968>CVE-2020-10968</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10968">https://nvd.nist.gov/vuln/detail/CVE-2020-10968</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: jackson-databind-2.9.10.4</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.10","isTransitiveDependency":true,"dependencyTree":"com.github.tomakehurst:wiremock-jre8:2.25.1;com.flipkart.zjsonpatch:zjsonpatch:0.4.4;com.fasterxml.jackson.core:jackson-databind:2.9.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jackson-databind-2.9.10.4"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","isTransitiveDependency":true,"dependencyTree":"org.jetbrains.kotlin:kotlin-reflect:1.3.72;com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jackson-databind-2.9.10.4"}],"vulnerabilityIdentifier":"CVE-2020-10968","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-10968 (High) detected in jackson-databind-2.9.10.jar, jackson-databind-2.9.2.jar - ## CVE-2020-10968 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.10.jar</b>, <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/zaproxy</p>
<p>Path to vulnerable library: /tmp/ws-ua_20200729112444_WCAEYA/downloadResource_JMENZF/20200729112922/jackson-databind-2.9.10.jar</p>
<p>
Dependency Hierarchy:
- wiremock-jre8-2.25.1.jar (Root Library)
- zjsonpatch-0.4.4.jar
- :x: **jackson-databind-2.9.10.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/zaproxy/buildSrc/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.2/1d8d8cb7cf26920ba57fb61fa56da88cc123b21f/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- kotlin-reflect-1.3.72.jar (Root Library)
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zaproxy/commit/faf0234fff2dbd2142cc463fc90d7e58bcf20cd0">faf0234fff2dbd2142cc463fc90d7e58bcf20cd0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968>CVE-2020-10968</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10968">https://nvd.nist.gov/vuln/detail/CVE-2020-10968</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: jackson-databind-2.9.10.4</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.10","isTransitiveDependency":true,"dependencyTree":"com.github.tomakehurst:wiremock-jre8:2.25.1;com.flipkart.zjsonpatch:zjsonpatch:0.4.4;com.fasterxml.jackson.core:jackson-databind:2.9.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jackson-databind-2.9.10.4"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","isTransitiveDependency":true,"dependencyTree":"org.jetbrains.kotlin:kotlin-reflect:1.3.72;com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jackson-databind-2.9.10.4"}],"vulnerabilityIdentifier":"CVE-2020-10968","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm zaproxy path to vulnerable library tmp ws ua wcaeya downloadresource jmenzf jackson databind jar dependency hierarchy wiremock jar root library zjsonpatch jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm zaproxy buildsrc build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy kotlin reflect jar root library x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org aoju bus proxy provider remoting rmiprovider aka bus proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jackson databind isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org aoju bus proxy provider remoting rmiprovider aka bus proxy vulnerabilityurl | 0 |
25,570 | 4,162,244,745 | IssuesEvent | 2016-06-17 19:37:15 | grpc/grpc | https://api.github.com/repos/grpc/grpc | opened | Python tests should not complete with reference cycles | cleanup python test | According to @kpayson64 [in this comment](https://github.com/grpc/grpc/pull/6857#issuecomment-225091528) our unit tests currently have cyclic object graphs after testing completes. We should clean that up; while it's true that the garbage collector will get to it eventually, I doubt that we need it and it's just a weird platform-dependent obstacle right now. | 1.0 | Python tests should not complete with reference cycles - According to @kpayson64 [in this comment](https://github.com/grpc/grpc/pull/6857#issuecomment-225091528) our unit tests currently have cyclic object graphs after testing completes. We should clean that up; while it's true that the garbage collector will get to it eventually, I doubt that we need it and it's just a weird platform-dependent obstacle right now. | non_priority | python tests should not complete with reference cycles according to our unit tests currently have cyclic object graphs after testing completes we should clean that up while it s true that the garbage collector will get to it eventually i doubt that we need it and it s just a weird platform dependent obstacle right now | 0 |
116,055 | 14,918,686,088 | IssuesEvent | 2021-01-22 22:11:52 | pangeo-forge/pangeo-forge | https://api.github.com/repos/pangeo-forge/pangeo-forge | opened | Support incremental appending | design question recipe enhancement | Currently, when a recipe is run, it will always cache all of the inputs and write all of the chunks. However, it would be nice to have an option where, if the target already exists, it only write NEW chunks. This raises some design questions.
- Currently, the target is never read until we start to execute the recipe (not until the `prepare_target` stage). However, for this to work, the `iter_inputs()` and `iter_chunks()` methods needs to know _which_ inputs and chunks to process. In order to build the pipeline for execution, this information needs to already be inside the recipe object. So this implies that we need open the target in `__post_init__`. Could this cause problems?
- How do we align the recipe with the target? For the standard [NetCDFZarrSequential](https://pangeo-forge.readthedocs.io/en/latest/tutorials/netcdf_zarr_sequential.html) recipe, it may be as simple as looking at the length of the sequence dimension: if the target has 100 items but the recipe has 120, we assume the last 20 need to be appended. But are there edge cases to worry about?
This intersects a bit with the "versioning" question in #3.
If we agree on the answers to the questions above, I think we can move ahead with implementing incremental updates to the `NetCDFZarrSequentialRecipe` class. | 1.0 | Support incremental appending - Currently, when a recipe is run, it will always cache all of the inputs and write all of the chunks. However, it would be nice to have an option where, if the target already exists, it only write NEW chunks. This raises some design questions.
- Currently, the target is never read until we start to execute the recipe (not until the `prepare_target` stage). However, for this to work, the `iter_inputs()` and `iter_chunks()` methods needs to know _which_ inputs and chunks to process. In order to build the pipeline for execution, this information needs to already be inside the recipe object. So this implies that we need open the target in `__post_init__`. Could this cause problems?
- How do we align the recipe with the target? For the standard [NetCDFZarrSequential](https://pangeo-forge.readthedocs.io/en/latest/tutorials/netcdf_zarr_sequential.html) recipe, it may be as simple as looking at the length of the sequence dimension: if the target has 100 items but the recipe has 120, we assume the last 20 need to be appended. But are there edge cases to worry about?
This intersects a bit with the "versioning" question in #3.
If we agree on the answers to the questions above, I think we can move ahead with implementing incremental updates to the `NetCDFZarrSequentialRecipe` class. | non_priority | support incremental appending currently when a recipe is run it will always cache all of the inputs and write all of the chunks however it would be nice to have an option where if the target already exists it only write new chunks this raises some design questions currently the target is never read until we start to execute the recipe not until the prepare target stage however for this to work the iter inputs and iter chunks methods needs to know which inputs and chunks to process in order to build the pipeline for execution this information needs to already be inside the recipe object so this implies that we need open the target in post init could this cause problems how do we align the recipe with the target for the standard recipe it may be as simple as looking at the length of the sequence dimension if the target has items but the recipe has we assume the last need to be appended but are there edge cases to worry about this intersects a bit with the versioning question in if we agree on the answers to the questions above i think we can move ahead with implementing incremental updates to the netcdfzarrsequentialrecipe class | 0 |
313,899 | 26,961,486,012 | IssuesEvent | 2023-02-08 18:32:48 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | opened | Refactor VerifyAllowedTenantEnforcementCredentials test to reduce permutations | Azure.Identity test-enhancement MQ | TenantIdResolver covers all the permutations, each credential test need only validate that the resolver gets invoked properly and its result is used for the tenantId. | 1.0 | Refactor VerifyAllowedTenantEnforcementCredentials test to reduce permutations - TenantIdResolver covers all the permutations, each credential test need only validate that the resolver gets invoked properly and its result is used for the tenantId. | non_priority | refactor verifyallowedtenantenforcementcredentials test to reduce permutations tenantidresolver covers all the permutations each credential test need only validate that the resolver gets invoked properly and its result is used for the tenantid | 0 |
78,343 | 15,569,971,230 | IssuesEvent | 2021-03-17 01:25:23 | jrrk/riscv-linux | https://api.github.com/repos/jrrk/riscv-linux | opened | CVE-2019-2025 (High) detected in aspeedaspeed-4.19-devicetree-no-fsi | security vulnerability | ## CVE-2019-2025 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>aspeedaspeed-4.19-devicetree-no-fsi</b></p></summary>
<p>
<p>ASPEED ARM SoC development</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git>https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (6)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In binder_thread_read of binder.c, there is a possible use-after-free due to improper locking. This could lead to local escalation of privilege in the kernel with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-116855682References: Upstream kernel
<p>Publish Date: 2019-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2025>CVE-2019-2025</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d">https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d</a></p>
<p>Release Date: 2019-03-05</p>
<p>Fix Resolution: v4.20-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-2025 (High) detected in aspeedaspeed-4.19-devicetree-no-fsi - ## CVE-2019-2025 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>aspeedaspeed-4.19-devicetree-no-fsi</b></p></summary>
<p>
<p>ASPEED ARM SoC development</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git>https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (6)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.h</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/android/binder_alloc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In binder_thread_read of binder.c, there is a possible use-after-free due to improper locking. This could lead to local escalation of privilege in the kernel with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-116855682References: Upstream kernel
<p>Publish Date: 2019-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2025>CVE-2019-2025</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d">https://github.com/torvalds/linux/commit/910b0797fa9e8af09c44a3fa36cb310ba7a7218d</a></p>
<p>Release Date: 2019-03-05</p>
<p>Fix Resolution: v4.20-rc5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in aspeedaspeed devicetree no fsi cve high severity vulnerability vulnerable library aspeedaspeed devicetree no fsi aspeed arm soc development library home page a href vulnerable source files riscv linux drivers android binder c riscv linux drivers android binder c riscv linux drivers android binder alloc c riscv linux drivers android binder alloc h riscv linux drivers android binder alloc h riscv linux drivers android binder alloc c vulnerability details in binder thread read of binder c there is a possible use after free due to improper locking this could lead to local escalation of privilege in the kernel with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android kernelandroid id a upstream kernel publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
217,715 | 24,348,946,579 | IssuesEvent | 2022-10-02 17:50:39 | venkateshreddypala/NeverNote | https://api.github.com/repos/venkateshreddypala/NeverNote | opened | CVE-2020-25649 (High) detected in jackson-databind-2.10.2.jar | security vulnerability | ## CVE-2020-25649 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.10.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.2/jackson-databind-2.10.2.jar</p>
<p>
Dependency Hierarchy:
- jjwt-0.9.1.jar (Root Library)
- :x: **jackson-databind-2.10.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/venkateshreddypala/NeverNote/commit/5221eede5346114f03f90b149d4c90e211459561">5221eede5346114f03f90b149d4c90e211459561</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in FasterXML Jackson Databind, where it did not have entity expansion secured properly. This flaw allows vulnerability to XML external entity (XXE) attacks. The highest threat from this vulnerability is data integrity.
<p>Publish Date: 2020-12-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25649>CVE-2020-25649</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-12-03</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.4,2.9.10.7,2.10.5.1,2.11.0.rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-25649 (High) detected in jackson-databind-2.10.2.jar - ## CVE-2020-25649 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.10.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.2/jackson-databind-2.10.2.jar</p>
<p>
Dependency Hierarchy:
- jjwt-0.9.1.jar (Root Library)
- :x: **jackson-databind-2.10.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/venkateshreddypala/NeverNote/commit/5221eede5346114f03f90b149d4c90e211459561">5221eede5346114f03f90b149d4c90e211459561</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in FasterXML Jackson Databind, where it did not have entity expansion secured properly. This flaw allows vulnerability to XML external entity (XXE) attacks. The highest threat from this vulnerability is data integrity.
<p>Publish Date: 2020-12-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25649>CVE-2020-25649</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-12-03</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.4,2.9.10.7,2.10.5.1,2.11.0.rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy jjwt jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was found in fasterxml jackson databind where it did not have entity expansion secured properly this flaw allows vulnerability to xml external entity xxe attacks the highest threat from this vulnerability is data integrity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with mend | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.