Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 2 665 | labels stringlengths 4 554 | body stringlengths 3 235k | index stringclasses 6 values | text_combine stringlengths 96 235k | label stringclasses 2 values | text stringlengths 96 196k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
309,644 | 9,477,759,854 | IssuesEvent | 2019-04-19 19:50:42 | sagesharp/outreachy-django-wagtail | https://api.github.com/repos/sagesharp/outreachy-django-wagtail | closed | Show missing information on the project/community preview | future-work low priority | Have a list of things that are default text, with links like "Fill out this field on the Project/Community Information page" | 1.0 | Show missing information on the project/community preview - Have a list of things that are default text, with links like "Fill out this field on the Project/Community Information page" | non_infrastructure | show missing information on the project community preview have a list of things that are default text with links like fill out this field on the project community information page | 0 |
27,505 | 21,796,498,674 | IssuesEvent | 2022-05-15 18:07:48 | lorenzwalthert/precommit | https://api.github.com/repos/lorenzwalthert/precommit | closed | Failure with latest roxygen2 | Complexity: Low Priority: Critical Status: WIP Type: Infrastructure | Not sure why this didn't turn up in my revdepchecks; so please let me know if there's anything I can do to help.
══ Failed tests ════════════════════════════════════════════════════════════════
── Failure (test-hook-roxygenize.R:95:3): roxygenize works in general ──────────
`roxygenize_with_cache(list(getwd()), dirs = dirs_R.cache("roxygenize"))` produced no output
── Failure (test-hook-roxygenize.R:163:3): warns if there is any other warning ──
`roxygenize_with_cache(list(getwd()), dirs = dirs_R.cache("roxygenize"))` produced unexpected warnings.
Expected match: Missing name
Actual values:
* [blur.R:4] Block must have a @name
ℹ Either document an existing object or manually specify with @name
── Failure (test-hooks.R:293:1): (code run outside of `test_that()`) ───────────
paste(contents, collapse = "\n") does not match "Writing flie.Rd".
Actual value: ""
Backtrace:
▆
1. └─precommit:::run_test(...) at test-hooks.R:293:0
2. └─precommit:::run_test_impl(...)
3. └─precommit:::hook_state_assert(...)
4. └─purrr::map2(...)
5. └─precommit .f(.x[[1L]], .y[[1L]], ...)
6. └─testthat::expect_match(...)
7. └─testthat:::expect_match_(...)
| 1.0 | Failure with latest roxygen2 - Not sure why this didn't turn up in my revdepchecks; so please let me know if there's anything I can do to help.
══ Failed tests ════════════════════════════════════════════════════════════════
── Failure (test-hook-roxygenize.R:95:3): roxygenize works in general ──────────
`roxygenize_with_cache(list(getwd()), dirs = dirs_R.cache("roxygenize"))` produced no output
── Failure (test-hook-roxygenize.R:163:3): warns if there is any other warning ──
`roxygenize_with_cache(list(getwd()), dirs = dirs_R.cache("roxygenize"))` produced unexpected warnings.
Expected match: Missing name
Actual values:
* [blur.R:4] Block must have a @name
ℹ Either document an existing object or manually specify with @name
── Failure (test-hooks.R:293:1): (code run outside of `test_that()`) ───────────
paste(contents, collapse = "\n") does not match "Writing flie.Rd".
Actual value: ""
Backtrace:
▆
1. └─precommit:::run_test(...) at test-hooks.R:293:0
2. └─precommit:::run_test_impl(...)
3. └─precommit:::hook_state_assert(...)
4. └─purrr::map2(...)
5. └─precommit .f(.x[[1L]], .y[[1L]], ...)
6. └─testthat::expect_match(...)
7. └─testthat:::expect_match_(...)
| infrastructure | failure with latest not sure why this didn t turn up in my revdepchecks so please let me know if there s anything i can do to help ══ failed tests ════════════════════════════════════════════════════════════════ ── failure test hook roxygenize r roxygenize works in general ────────── roxygenize with cache list getwd dirs dirs r cache roxygenize produced no output ── failure test hook roxygenize r warns if there is any other warning ── roxygenize with cache list getwd dirs dirs r cache roxygenize produced unexpected warnings expected match missing name actual values block must have a name ℹ either document an existing object or manually specify with name ── failure test hooks r code run outside of test that ─────────── paste contents collapse n does not match writing flie rd actual value backtrace ▆ └─precommit run test at test hooks r └─precommit run test impl └─precommit hook state assert └─purrr └─precommit f x y └─testthat expect match └─testthat expect match | 1 |
243,595 | 7,859,522,448 | IssuesEvent | 2018-06-21 16:52:01 | cds-snc/vac-benefits-directory | https://api.github.com/repos/cds-snc/vac-benefits-directory | closed | Skipping GE questions produces some funny results | High Priority bug | Start GE
Click Next
Click Next
Click Deceased
Nothing is selected on result page.
Should next only be clickable if something was selected? | 1.0 | Skipping GE questions produces some funny results - Start GE
Click Next
Click Next
Click Deceased
Nothing is selected on result page.
Should next only be clickable if something was selected? | non_infrastructure | skipping ge questions produces some funny results start ge click next click next click deceased nothing is selected on result page should next only be clickable if something was selected | 0 |
32,695 | 26,914,073,910 | IssuesEvent | 2023-02-07 04:00:11 | WordPress/performance | https://api.github.com/repos/WordPress/performance | closed | Benefit from static analysis | [Type] Bug Infrastructure [Focus] Images Needs Triage | ## Bug Description
There are errors in the code.
e.g. `webp_uploads_update_image_onchange`: _Callback expects 5 parameters, $accepted_args is set to 7._
## Steps to reproduce
1. `composer require --dev szepeviktor/phpstan-wordpress`
2. `vendor/bin/phpstan analyse -c vendor/szepeviktor/phpstan-wordpress/extension.neon admin/ modules/ server-timing/ *.php --level=0` then raise level by one
3. Benefit!
Please consider using PHPStan.
Thank you!
| 1.0 | Benefit from static analysis - ## Bug Description
There are errors in the code.
e.g. `webp_uploads_update_image_onchange`: _Callback expects 5 parameters, $accepted_args is set to 7._
## Steps to reproduce
1. `composer require --dev szepeviktor/phpstan-wordpress`
2. `vendor/bin/phpstan analyse -c vendor/szepeviktor/phpstan-wordpress/extension.neon admin/ modules/ server-timing/ *.php --level=0` then raise level by one
3. Benefit!
Please consider using PHPStan.
Thank you!
| infrastructure | benefit from static analysis bug description there are errors in the code e g webp uploads update image onchange callback expects parameters accepted args is set to steps to reproduce composer require dev szepeviktor phpstan wordpress vendor bin phpstan analyse c vendor szepeviktor phpstan wordpress extension neon admin modules server timing php level then raise level by one benefit please consider using phpstan thank you | 1 |
239,010 | 18,257,469,837 | IssuesEvent | 2021-10-03 09:21:01 | oprogram/LibreNote | https://api.github.com/repos/oprogram/LibreNote | closed | Access Denied? [Docker] | documentation | Alright so, I've recently been "stalking" this project because it caught my interest but haven't tried it for myself until yesterday. I downloaded the source code and I set up everything perfectly fine (I'm trying the docker step). Now this is where the interesting part starts.
Setting up Redis was flawless. No issues. But here's the problem; `docker pull ghcr.io/librenotebot/librenote:latest` -> _Output;_ `Error response from daemon: Head "https://ghcr.io/v2/librenotebot/librenote/manifests/latest": denied`
It seems like I cannot pull the content? I'm using the latest nodeJS version and the WebStorm IDE. The Redis docker is fully functional and I am using a windows machine. I have also tried setting it up on my kali linux virtual machine but without success (needed to upgrade node and I was too lazy to do it)
Any suggestions on what I should do?
**I'm more active in discord so if I do not respond here you can contact me over there!**
Fakado#8525 | 1.0 | Access Denied? [Docker] - Alright so, I've recently been "stalking" this project because it caught my interest but haven't tried it for myself until yesterday. I downloaded the source code and I set up everything perfectly fine (I'm trying the docker step). Now this is where the interesting part starts.
Setting up Redis was flawless. No issues. But here's the problem; `docker pull ghcr.io/librenotebot/librenote:latest` -> _Output;_ `Error response from daemon: Head "https://ghcr.io/v2/librenotebot/librenote/manifests/latest": denied`
It seems like I cannot pull the content? I'm using the latest nodeJS version and the WebStorm IDE. The Redis docker is fully functional and I am using a windows machine. I have also tried setting it up on my kali linux virtual machine but without success (needed to upgrade node and I was too lazy to do it)
Any suggestions on what I should do?
**I'm more active in discord so if I do not respond here you can contact me over there!**
Fakado#8525 | non_infrastructure | access denied alright so i ve recently been stalking this project because it caught my interest but haven t tried it for myself until yesterday i downloaded the source code and i set up everything perfectly fine i m trying the docker step now this is where the interesting part starts setting up redis was flawless no issues but here s the problem docker pull ghcr io librenotebot librenote latest output error response from daemon head denied it seems like i cannot pull the content i m using the latest nodejs version and the webstorm ide the redis docker is fully functional and i am using a windows machine i have also tried setting it up on my kali linux virtual machine but without success needed to upgrade node and i was too lazy to do it any suggestions on what i should do i m more active in discord so if i do not respond here you can contact me over there fakado | 0 |
86 | 2,517,758,443 | IssuesEvent | 2015-01-16 16:58:37 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | Set up directory listings for the distribution directory on s3 | A-infrastructure | Add a cronjob invoking https://github.com/nagisa/s3-directory-listing/ to the build master. | 1.0 | Set up directory listings for the distribution directory on s3 - Add a cronjob invoking https://github.com/nagisa/s3-directory-listing/ to the build master. | infrastructure | set up directory listings for the distribution directory on add a cronjob invoking to the build master | 1 |
81,865 | 7,806,083,822 | IssuesEvent | 2018-06-11 13:05:15 | ethersphere/go-ethereum | https://api.github.com/repos/ethersphere/go-ethereum | opened | Storage benchmark tests are failing: | bug test | Storage tests are failing:
```
--- FAIL: BenchmarkMemStoreGet_1_5k
common_test.go:199: mget failed: chunk not found
--- FAIL: BenchmarkMemStoreGet_8_5k
common_test.go:199: mget failed: chunk not found
FAIL
```
Lot of errors in logs:
```
ERROR[06-11|14:20:16.168137|swarm/storage/ldbstore.go:571] spawn batch write (9661 entries): unable to write batch: leveldb: closed
```
| 1.0 | Storage benchmark tests are failing: - Storage tests are failing:
```
--- FAIL: BenchmarkMemStoreGet_1_5k
common_test.go:199: mget failed: chunk not found
--- FAIL: BenchmarkMemStoreGet_8_5k
common_test.go:199: mget failed: chunk not found
FAIL
```
Lot of errors in logs:
```
ERROR[06-11|14:20:16.168137|swarm/storage/ldbstore.go:571] spawn batch write (9661 entries): unable to write batch: leveldb: closed
```
| non_infrastructure | storage benchmark tests are failing storage tests are failing fail benchmarkmemstoreget common test go mget failed chunk not found fail benchmarkmemstoreget common test go mget failed chunk not found fail lot of errors in logs error spawn batch write entries unable to write batch leveldb closed | 0 |
42,036 | 12,867,875,851 | IssuesEvent | 2020-07-10 07:48:49 | benchmarkdebricked/sentry | https://api.github.com/repos/benchmarkdebricked/sentry | opened | CVE-2020-10379 (High) detected in Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2020-10379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/43/5a/904f2cc20ef9f9ba05f9ff1fb3dfadb1e6923e3bf6f8c8363d5dc3a179ab/Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/43/5a/904f2cc20ef9f9ba05f9ff1fb3dfadb1e6923e3bf6f8c8363d5dc3a179ab/Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/sentry</p>
<p>Path to vulnerable library: /sentry</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/sentry/commit/3f63a21af8bb1c66de6f859ad79ababfd2c21a46">3f63a21af8bb1c66de6f859ad79ababfd2c21a46</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Pillow before 7.1.0, there are two Buffer Overflows in libImaging/TiffDecode.c.
<p>Publish Date: 2020-06-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10379>CVE-2020-10379</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/python-pillow/Pillow/commit/41b554bc56982ee4f30238a7677c0f4ff90a73a8">https://github.com/python-pillow/Pillow/commit/41b554bc56982ee4f30238a7677c0f4ff90a73a8</a></p>
<p>Release Date: 2020-06-25</p>
<p>Fix Resolution: 7.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-10379 (High) detected in Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2020-10379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/43/5a/904f2cc20ef9f9ba05f9ff1fb3dfadb1e6923e3bf6f8c8363d5dc3a179ab/Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/43/5a/904f2cc20ef9f9ba05f9ff1fb3dfadb1e6923e3bf6f8c8363d5dc3a179ab/Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/sentry</p>
<p>Path to vulnerable library: /sentry</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-4.2.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/sentry/commit/3f63a21af8bb1c66de6f859ad79ababfd2c21a46">3f63a21af8bb1c66de6f859ad79ababfd2c21a46</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Pillow before 7.1.0, there are two Buffer Overflows in libImaging/TiffDecode.c.
<p>Publish Date: 2020-06-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10379>CVE-2020-10379</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/python-pillow/Pillow/commit/41b554bc56982ee4f30238a7677c0f4ff90a73a8">https://github.com/python-pillow/Pillow/commit/41b554bc56982ee4f30238a7677c0f4ff90a73a8</a></p>
<p>Release Date: 2020-06-25</p>
<p>Fix Resolution: 7.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in pillow whl cve high severity vulnerability vulnerable library pillow whl python imaging library fork library home page a href path to dependency file tmp ws scm sentry path to vulnerable library sentry dependency hierarchy x pillow whl vulnerable library found in head commit a href vulnerability details in pillow before there are two buffer overflows in libimaging tiffdecode c publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
140,717 | 18,908,733,734 | IssuesEvent | 2021-11-16 11:54:58 | lyubov888L/long-term-system | https://api.github.com/repos/lyubov888L/long-term-system | opened | WS-2020-0044 (High) detected in decompress-4.2.0.tgz | security vulnerability | ## WS-2020-0044 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>decompress-4.2.0.tgz</b></p></summary>
<p>Extracting archives made easy</p>
<p>Library home page: <a href="https://registry.npmjs.org/decompress/-/decompress-4.2.0.tgz">https://registry.npmjs.org/decompress/-/decompress-4.2.0.tgz</a></p>
<p>Path to dependency file: long-term-system/package.json</p>
<p>Path to vulnerable library: long-term-system/node_modules/decompress/package.json</p>
<p>
Dependency Hierarchy:
- gulp-imagemin-7.1.0.tgz (Root Library)
- imagemin-gifsicle-7.0.0.tgz
- gifsicle-5.0.0.tgz
- bin-build-3.0.0.tgz
- :x: **decompress-4.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lyubov888L/long-term-system/commit/70ceacee09bde0d9b6f809a77010ad55db64e593">70ceacee09bde0d9b6f809a77010ad55db64e593</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
decompress in all its versions is vulnerable to arbitrary file write. the package fails to prevent an extraction of files with relative paths which allows attackers to write to any folder in the system.
<p>Publish Date: 2020-03-08
<p>URL: <a href=https://github.com/kevva/decompress/issues/71>WS-2020-0044</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/kevva/decompress/issues/71">https://github.com/kevva/decompress/issues/71</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 4.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0044 (High) detected in decompress-4.2.0.tgz - ## WS-2020-0044 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>decompress-4.2.0.tgz</b></p></summary>
<p>Extracting archives made easy</p>
<p>Library home page: <a href="https://registry.npmjs.org/decompress/-/decompress-4.2.0.tgz">https://registry.npmjs.org/decompress/-/decompress-4.2.0.tgz</a></p>
<p>Path to dependency file: long-term-system/package.json</p>
<p>Path to vulnerable library: long-term-system/node_modules/decompress/package.json</p>
<p>
Dependency Hierarchy:
- gulp-imagemin-7.1.0.tgz (Root Library)
- imagemin-gifsicle-7.0.0.tgz
- gifsicle-5.0.0.tgz
- bin-build-3.0.0.tgz
- :x: **decompress-4.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lyubov888L/long-term-system/commit/70ceacee09bde0d9b6f809a77010ad55db64e593">70ceacee09bde0d9b6f809a77010ad55db64e593</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
decompress in all its versions is vulnerable to arbitrary file write. the package fails to prevent an extraction of files with relative paths which allows attackers to write to any folder in the system.
<p>Publish Date: 2020-03-08
<p>URL: <a href=https://github.com/kevva/decompress/issues/71>WS-2020-0044</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/kevva/decompress/issues/71">https://github.com/kevva/decompress/issues/71</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 4.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | ws high detected in decompress tgz ws high severity vulnerability vulnerable library decompress tgz extracting archives made easy library home page a href path to dependency file long term system package json path to vulnerable library long term system node modules decompress package json dependency hierarchy gulp imagemin tgz root library imagemin gifsicle tgz gifsicle tgz bin build tgz x decompress tgz vulnerable library found in head commit a href found in base branch main vulnerability details decompress in all its versions is vulnerable to arbitrary file write the package fails to prevent an extraction of files with relative paths which allows attackers to write to any folder in the system publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
227,667 | 25,099,271,505 | IssuesEvent | 2022-11-08 12:30:01 | netlify/build | https://api.github.com/repos/netlify/build | closed | Ensure Netlify API token is not passed to build command | security security-risk: low Owner: Pillar-Developer-Workflow | The `--token` passed in the CLI could be used inside build command and plugins by using `ps`. This token is only valid during the duration of the build, and can only perform a limited set of read-only endpoints, so this is only a minor security concern.
Instead, we should pass it as an environment variable, and remove that environment variable from the child processes (build command and plugins). | True | Ensure Netlify API token is not passed to build command - The `--token` passed in the CLI could be used inside build command and plugins by using `ps`. This token is only valid during the duration of the build, and can only perform a limited set of read-only endpoints, so this is only a minor security concern.
Instead, we should pass it as an environment variable, and remove that environment variable from the child processes (build command and plugins). | non_infrastructure | ensure netlify api token is not passed to build command the token passed in the cli could be used inside build command and plugins by using ps this token is only valid during the duration of the build and can only perform a limited set of read only endpoints so this is only a minor security concern instead we should pass it as an environment variable and remove that environment variable from the child processes build command and plugins | 0 |
20,322 | 13,822,291,486 | IssuesEvent | 2020-10-13 04:42:45 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | Accept csv weather files | interface/infrastructure newfeature | Creating the space-separated column-width-fixed (.met) weather files is regularly causing problems. Why does Apsim not accept the widely used and accepted (and much more fail safe) csv format (and extension)?
In addition, Apsim could to the calculation which is currently done in the separate program tav_amp. | 1.0 | Accept csv weather files - Creating the space-separated column-width-fixed (.met) weather files is regularly causing problems. Why does Apsim not accept the widely used and accepted (and much more fail safe) csv format (and extension)?
In addition, Apsim could to the calculation which is currently done in the separate program tav_amp. | infrastructure | accept csv weather files creating the space separated column width fixed met weather files is regularly causing problems why does apsim not accept the widely used and accepted and much more fail safe csv format and extension in addition apsim could to the calculation which is currently done in the separate program tav amp | 1 |
26,017 | 19,567,934,286 | IssuesEvent | 2022-01-04 05:09:08 | leavemealone-app/roadmap | https://api.github.com/repos/leavemealone-app/roadmap | closed | Fix Rollups database limitations | infrastructure | When a single rollup gets too big (over 16MB) then it essentially stops rolling up new emails. This can easily happen in a 100+ sender Rollup that's sent weekly for example.
This is a limitation of how I structured the data. It needs fixing ASAP as some users are starting to hit this limitation. | 1.0 | Fix Rollups database limitations - When a single rollup gets too big (over 16MB) then it essentially stops rolling up new emails. This can easily happen in a 100+ sender Rollup that's sent weekly for example.
This is a limitation of how I structured the data. It needs fixing ASAP as some users are starting to hit this limitation. | infrastructure | fix rollups database limitations when a single rollup gets too big over then it essentially stops rolling up new emails this can easily happen in a sender rollup that s sent weekly for example this is a limitation of how i structured the data it needs fixing asap as some users are starting to hit this limitation | 1 |
71,585 | 8,666,051,055 | IssuesEvent | 2018-11-29 02:08:22 | OfficeDev/office-ui-fabric-react | https://api.github.com/repos/OfficeDev/office-ui-fabric-react | closed | Panel doesn't handle onOuterClick | Component: Panel Needs: Author Feedback Resolution: By Design | <!-- 🚨 STOP 🚨 𝗦𝗧𝗢𝗣 🚨 𝑺𝑻𝑶𝑷 🚨
We’re here to help, but we need a few things from you!
Please help us reduce duplicates by doing the following steps before logging an issue:
* Search: https://github.com/OfficeDev/office-ui-fabric-react/search?type=Issues
* Search by area or component: https://github.com/OfficeDev/office-ui-fabric-react/issues/labels
Please provide a reproduction of the bug in a codepen, if possible. Here’s how:
* Goto https://aka.ms/fabricpen for a starting codepen
* You can also use the "Export to Codepen" feature for the various components in our documentation site.
* Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links if the repro occurs with an example.
(A permanent link is preferable to "use the website" as the website can change)
Note that if you do not provide enough information to reproduce the issue, we may not be able to take action on your report.
-->
### Environment Information
<!--
** If using the website, note that the website is often behind. You can find the current version the website uses at the home page (i.e. at the landing page of uifabric.io).
-->
- __Package version(s)__: 6.106.3
- __Browser and OS versions__: Chrome 70, Windows 10
### Please provide a reproduction of the bug in a codepen:
https://codepen.io/anon/pen/jQpamP
#### Actual behavior:
Panel doesn't handle onOuterClick function. Nothing happened after clicks outside the component.
#### Expected behavior:
Panel handle onOuterClick function after clicks outside this component.
#### Priorities and help requested:
Are you willing to submit a PR to fix? No
Requested priority: High
Products/sites affected: (if applicable)
| 1.0 | Panel doesn't handle onOuterClick - <!-- 🚨 STOP 🚨 𝗦𝗧𝗢𝗣 🚨 𝑺𝑻𝑶𝑷 🚨
We’re here to help, but we need a few things from you!
Please help us reduce duplicates by doing the following steps before logging an issue:
* Search: https://github.com/OfficeDev/office-ui-fabric-react/search?type=Issues
* Search by area or component: https://github.com/OfficeDev/office-ui-fabric-react/issues/labels
Please provide a reproduction of the bug in a codepen, if possible. Here’s how:
* Goto https://aka.ms/fabricpen for a starting codepen
* You can also use the "Export to Codepen" feature for the various components in our documentation site.
* Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links if the repro occurs with an example.
(A permanent link is preferable to "use the website" as the website can change)
Note that if you do not provide enough information to reproduce the issue, we may not be able to take action on your report.
-->
### Environment Information
<!--
** If using the website, note that the website is often behind. You can find the current version the website uses at the home page (i.e. at the landing page of uifabric.io).
-->
- __Package version(s)__: 6.106.3
- __Browser and OS versions__: Chrome 70, Windows 10
### Please provide a reproduction of the bug in a codepen:
https://codepen.io/anon/pen/jQpamP
#### Actual behavior:
Panel doesn't handle onOuterClick function. Nothing happened after clicks outside the component.
#### Expected behavior:
Panel handle onOuterClick function after clicks outside this component.
#### Priorities and help requested:
Are you willing to submit a PR to fix? No
Requested priority: High
Products/sites affected: (if applicable)
| non_infrastructure | panel doesn t handle onouterclick 🚨 stop 🚨 𝗦𝗧𝗢𝗣 🚨 𝑺𝑻𝑶𝑷 🚨 we’re here to help but we need a few things from you please help us reduce duplicates by doing the following steps before logging an issue search search by area or component please provide a reproduction of the bug in a codepen if possible here’s how goto for a starting codepen you can also use the export to codepen feature for the various components in our documentation site alternatively you can also use to get permanent repro links if the repro occurs with an example a permanent link is preferable to use the website as the website can change note that if you do not provide enough information to reproduce the issue we may not be able to take action on your report environment information if using the website note that the website is often behind you can find the current version the website uses at the home page i e at the landing page of uifabric io package version s browser and os versions chrome windows please provide a reproduction of the bug in a codepen actual behavior panel doesn t handle onouterclick function nothing happened after clicks outside the component expected behavior panel handle onouterclick function after clicks outside this component priorities and help requested are you willing to submit a pr to fix no requested priority high products sites affected if applicable | 0 |
25,017 | 18,045,536,299 | IssuesEvent | 2021-09-18 20:46:15 | Kavignon/developer-senzu-bean | https://api.github.com/repos/Kavignon/developer-senzu-bean | opened | Create GitHub Action file and establish CI/CD pipeline | enhancement good first issue Infrastructure CI | As for like any project, we want to make sure that whatever is in a pull request is of sound quality before merging it in. So, we'll want a basic CI pipeline which will take of the following:
- [ ] Restores the packages used by the executable (dotnet restore)
- [ ] Validates that the solution can build (dotnet build)
- [ ] Confirms that all the tests are successful across **every** test project (dotnet test)
- [ ] Publishes the executable to a zip file that can be distributed on this repository (dotnet publish) | 1.0 | Create GitHub Action file and establish CI/CD pipeline - As for like any project, we want to make sure that whatever is in a pull request is of sound quality before merging it in. So, we'll want a basic CI pipeline which will take of the following:
- [ ] Restores the packages used by the executable (dotnet restore)
- [ ] Validates that the solution can build (dotnet build)
- [ ] Confirms that all the tests are successful across **every** test project (dotnet test)
- [ ] Publishes the executable to a zip file that can be distributed on this repository (dotnet publish) | infrastructure | create github action file and establish ci cd pipeline as for like any project we want to make sure that whatever is in a pull request is of sound quality before merging it in so we ll want a basic ci pipeline which will take of the following restores the packages used by the executable dotnet restore validates that the solution can build dotnet build confirms that all the tests are successful across every test project dotnet test publishes the executable to a zip file that can be distributed on this repository dotnet publish | 1 |
3,905 | 4,705,908,789 | IssuesEvent | 2016-10-13 15:41:10 | matthiasbeyer/imag | https://api.github.com/repos/matthiasbeyer/imag | opened | Rewrite libimagentrylink interface | complexity/high kind/enhancement kind/feature kind/infrastructure kind/nicetohave kind/refactor part/lib/imagentrylink release/hard-required | Some things that come up:
* The `get_internal_links()` (and other) function(s) should return iterators
* There should be iterators that do special stuff, for example
* An iterator that `Store::delete()`s `FileLockEntry`s that do not contain any link to other FLEs anymore
* An iterator that filters for items that are linked to a certain set of entries
* ... possibly more
That would help greatly in #733 !
I will mark that as hard required feature for the next (0.3.0) release therefor.
---
This issue should be solved in two steps:
- [ ] Refactor the interface of `libimagentrylink` to return Iterator objects rather than `Vec`s
- [ ] Add more iterator types to do special things, like GC and so on. | 1.0 | Rewrite libimagentrylink interface - Some things that come up:
* The `get_internal_links()` (and other) function(s) should return iterators
* There should be iterators that do special stuff, for example
* An iterator that `Store::delete()`s `FileLockEntry`s that do not contain any link to other FLEs anymore
* An iterator that filters for items that are linked to a certain set of entries
* ... possibly more
That would help greatly in #733 !
I will mark that as hard required feature for the next (0.3.0) release therefor.
---
This issue should be solved in two steps:
- [ ] Refactor the interface of `libimagentrylink` to return Iterator objects rather than `Vec`s
- [ ] Add more iterator types to do special things, like GC and so on. | infrastructure | rewrite libimagentrylink interface some things that come up the get internal links and other function s should return iterators there should be iterators that do special stuff for example an iterator that store delete s filelockentry s that do not contain any link to other fles anymore an iterator that filters for items that are linked to a certain set of entries possibly more that would help greatly in i will mark that as hard required feature for the next release therefor this issue should be solved in two steps refactor the interface of libimagentrylink to return iterator objects rather than vec s add more iterator types to do special things like gc and so on | 1 |
12,543 | 9,819,392,738 | IssuesEvent | 2019-06-13 21:52:33 | eventespresso/event-espresso-core | https://api.github.com/repos/eventespresso/event-espresso-core | opened | Changes sometimes not applied when calling the save method | category:models-and-data-infrastructure type:bug 🐞 | Easiest to show with a a quick example:
`add_action('AHEE__Extend_Events_Admin_Page___duplicate_event__after', 'updateacfanddatetime', 10, 2);
function updateacfanddatetime($new_event, $orig_event) {
$new_datetimes = $new_event->get_many_related('Datetime');
foreach ($new_datetimes as $new_dtt) {
$newdate = new DateTime(date("Y-m-d",strtotime($new_dtt->start_date()))) ;
$newdateplusone = date_format($newdate->add(new DateInterval('P1D')), 'F d, Y');
$new_dtt->set_start_date($newdateplusone);
$new_dtt->set_end_date($newdateplusone);
$new_dtt->save();
}
}
`
The above adds a single date onto your events datetimes when you duplicate an event, however, the change is not saved as `set_end_date` does not set a `_has_changes` flag in `EE_Base_Class.class.php::save()`.
So for the above to work as is, you'd need to add something like:
`$new_dtt->set('DTT_EVT_start', $new_dtt->start_date_and_time());
$new_dtt->set('DTT_EVT_end', $new_dtt->end_date_and_time());`
just before the `save()` call, as `set()` sets the `_has_changes` flag it all then works fine.
Spoke about this a little with Darren, take a look here
See: https://eventespresso.slack.com/archives/C080L8G68/p1560423687230700
(Darren replies a little below)
Posting convo here in case we hit slack limit:
> tony [12:01 PM]
Found something that (I think) is a little strange with Datetimes.
A user is updating datetimes by 1 day when you duplicate the event and is doing it like this:
`function updateacfanddatetime($new_event, $orig_event) {
$new_datetimes = $new_event->get_many_related('Datetime');
foreach ($new_datetimes as $new_dtt) {
$newdate = new DateTime(date("Y-m-d",strtotime($new_dtt->start_date()))) ;
$newdateplusone = date_format($newdate->add(new DateInterval('P1D')), 'F d, Y');
$new_dtt->set_start_date($newdateplusone);
$new_dtt->set_end_date($newdateplusone);
}
}`
(edited)
Which apart from missing `$new_dtt->save();` I would have through worked, right?
Echoing out `$new_dtt->start_date_and_time()` and `$new_dtt->start_end_and_time()` both before and after the change shows the date is updated, but save fails.
Did some digging and in `EE_Base_Class.class.php::save()` it checks `$this->_has_changes` before doing any updates, which is false after the above, hence the fail, so the only way to update the datetime is using something like `$new_dtt->set('DTT_EVT_start', $new_dtt->start_date_and_time());` because it sets `_has_changes`.
Is that expected?
darren [3:34 PM]
tony re the above, ya that looks like a bug… I’m trying to trace when `_has_changes` was added. the problem is `_set_date_time` modifies the internal field values on a `EE_Base_Class` instance directly rather than going through `_set`. So as you discovered `_has_changes` isn’t flagged and the save won’t happen.
so `EE_Base_Class::_set_date_time` needs to set the `_has_changes` flag as well. (edited)
tony [3:36 PM]
Kk thanks for checking. I can do a ticket in a little, wasnt sure if I was missing something
darren [3:51 PM]
So tony looks like the `$_has_changes` property was added here: https://events.codebasehq.com/projects/event-espresso/tickets/10167
I’m looking now to see if it existed in the `_set_date_time` method at one point.
(commits made in 2016 but not actually merged to master until 2017)
ya I’ve looked through git history and it looks like `_set_date_time` (or `_clear_cached_property` which should probably mark `_has_changes` as well) never had any flag or accounted for `_has_changes`. If/when you create the ticket, can you copy/paste in the above too please? It’s good for reference. | 1.0 | Changes sometimes not applied when calling the save method - Easiest to show with a a quick example:
`add_action('AHEE__Extend_Events_Admin_Page___duplicate_event__after', 'updateacfanddatetime', 10, 2);
function updateacfanddatetime($new_event, $orig_event) {
$new_datetimes = $new_event->get_many_related('Datetime');
foreach ($new_datetimes as $new_dtt) {
$newdate = new DateTime(date("Y-m-d",strtotime($new_dtt->start_date()))) ;
$newdateplusone = date_format($newdate->add(new DateInterval('P1D')), 'F d, Y');
$new_dtt->set_start_date($newdateplusone);
$new_dtt->set_end_date($newdateplusone);
$new_dtt->save();
}
}
`
The above adds a single date onto your events datetimes when you duplicate an event, however, the change is not saved as `set_end_date` does not set a `_has_changes` flag in `EE_Base_Class.class.php::save()`.
So for the above to work as is, you'd need to add something like:
`$new_dtt->set('DTT_EVT_start', $new_dtt->start_date_and_time());
$new_dtt->set('DTT_EVT_end', $new_dtt->end_date_and_time());`
just before the `save()` call, as `set()` sets the `_has_changes` flag it all then works fine.
Spoke about this a little with Darren, take a look here
See: https://eventespresso.slack.com/archives/C080L8G68/p1560423687230700
(Darren replies a little below)
Posting convo here in case we hit slack limit:
> tony [12:01 PM]
Found something that (I think) is a little strange with Datetimes.
A user is updating datetimes by 1 day when you duplicate the event and is doing it like this:
`function updateacfanddatetime($new_event, $orig_event) {
$new_datetimes = $new_event->get_many_related('Datetime');
foreach ($new_datetimes as $new_dtt) {
$newdate = new DateTime(date("Y-m-d",strtotime($new_dtt->start_date()))) ;
$newdateplusone = date_format($newdate->add(new DateInterval('P1D')), 'F d, Y');
$new_dtt->set_start_date($newdateplusone);
$new_dtt->set_end_date($newdateplusone);
}
}`
(edited)
Which apart from missing `$new_dtt->save();` I would have through worked, right?
Echoing out `$new_dtt->start_date_and_time()` and `$new_dtt->start_end_and_time()` both before and after the change shows the date is updated, but save fails.
Did some digging and in `EE_Base_Class.class.php::save()` it checks `$this->_has_changes` before doing any updates, which is false after the above, hence the fail, so the only way to update the datetime is using something like `$new_dtt->set('DTT_EVT_start', $new_dtt->start_date_and_time());` because it sets `_has_changes`.
Is that expected?
darren [3:34 PM]
tony re the above, ya that looks like a bug… I’m trying to trace when `_has_changes` was added. the problem is `_set_date_time` modifies the internal field values on a `EE_Base_Class` instance directly rather than going through `_set`. So as you discovered `_has_changes` isn’t flagged and the save won’t happen.
so `EE_Base_Class::_set_date_time` needs to set the `_has_changes` flag as well. (edited)
tony [3:36 PM]
Kk thanks for checking. I can do a ticket in a little, wasnt sure if I was missing something
darren [3:51 PM]
So tony looks like the `$_has_changes` property was added here: https://events.codebasehq.com/projects/event-espresso/tickets/10167
I’m looking now to see if it existed in the `_set_date_time` method at one point.
(commits made in 2016 but not actually merged to master until 2017)
ya I’ve looked through git history and it looks like `_set_date_time` (or `_clear_cached_property` which should probably mark `_has_changes` as well) never had any flag or accounted for `_has_changes`. If/when you create the ticket, can you copy/paste in the above too please? It’s good for reference. | infrastructure | changes sometimes not applied when calling the save method easiest to show with a a quick example add action ahee extend events admin page duplicate event after updateacfanddatetime function updateacfanddatetime new event orig event new datetimes new event get many related datetime foreach new datetimes as new dtt newdate new datetime date y m d strtotime new dtt start date newdateplusone date format newdate add new dateinterval f d y new dtt set start date newdateplusone new dtt set end date newdateplusone new dtt save the above adds a single date onto your events datetimes when you duplicate an event however the change is not saved as set end date does not set a has changes flag in ee base class class php save so for the above to work as is you d need to add something like new dtt set dtt evt start new dtt start date and time new dtt set dtt evt end new dtt end date and time just before the save call as set sets the has changes flag it all then works fine spoke about this a little with darren take a look here see darren replies a little below posting convo here in case we hit slack limit tony found something that i think is a little strange with datetimes a user is updating datetimes by day when you duplicate the event and is doing it like this function updateacfanddatetime new event orig event new datetimes new event get many related datetime foreach new datetimes as new dtt newdate new datetime date y m d strtotime new dtt start date newdateplusone date format newdate add new dateinterval f d y new dtt set start date newdateplusone new dtt set end date newdateplusone edited which apart from missing new dtt save i would have through worked right echoing out new dtt start date and time and new dtt start end and time both before and after the change shows the date is updated but save fails did some digging and in ee base class class php save it checks this has changes before doing any updates which is false after the above hence the fail so the only way to update the datetime is using something like new dtt set dtt evt start new dtt start date and time because it sets has changes is that expected darren tony re the above ya that looks like a bug… i’m trying to trace when has changes was added the problem is set date time modifies the internal field values on a ee base class instance directly rather than going through set so as you discovered has changes isn’t flagged and the save won’t happen so ee base class set date time needs to set the has changes flag as well edited tony kk thanks for checking i can do a ticket in a little wasnt sure if i was missing something darren so tony looks like the has changes property was added here i’m looking now to see if it existed in the set date time method at one point commits made in but not actually merged to master until ya i’ve looked through git history and it looks like set date time or clear cached property which should probably mark has changes as well never had any flag or accounted for has changes if when you create the ticket can you copy paste in the above too please it’s good for reference | 1 |
27,510 | 4,317,433,983 | IssuesEvent | 2016-07-23 09:27:33 | openshift/origin | https://api.github.com/repos/openshift/origin | opened | should run a deployment to completion and then scale to zero [Conformance] | area/tests component/deployments kind/test-flake | Because of the latest changes in deployment logs
```
STEP: verifying the scale is updated on the deployment config
STEP: deploying a few more times
Jul 22 22:07:25.246: INFO: Running 'oc deploy --namespace=extended-test-cli-deployment-f3mzp-9tfjf --config=/tmp/openshift/extended-test-cli-deployment-f3mzp-9tfjf-user.kubeconfig --latest --follow deployment-test'
Jul 22 22:07:45.721: INFO: Error running &{/data/src/github.com/openshift/origin/_output/local/bin/linux/amd64/oc [oc deploy --namespace=extended-test-cli-deployment-f3mzp-9tfjf --config=/tmp/openshift/extended-test-cli-deployment-f3mzp-9tfjf-user.kubeconfig --latest --follow deployment-test] [] Started deployment #2
Error from server: The get operation against ReplicationController could not be completed at this time, please try again.
Started deployment #2
Error from server: The get operation against ReplicationController could not be completed at this time, please try again.
[] <nil> 0xc820d49f20 exit status 1 <nil> true [0xc82002f208 0xc82002f230 0xc82002f230] [0xc82002f208 0xc82002f230] [0xc82002f210 0xc82002f228] [0xa7ed60 0xa7eec0] 0xc8202c1080}:
Started deployment #2
Error from server: The get operation against ReplicationController could not be completed at this time, please try again.
```
• Failure [63.861 seconds]
deploymentconfigs
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:598
with test deployments
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:252
should run a deployment to completion and then scale to zero [Conformance] [It]
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:251
Expected error:
<*exec.ExitError | 0xc820d49f80>: {
ProcessState: {
pid: 4354,
status: 256,
rusage: {
Utime: {Sec: 0, Usec: 120189},
Stime: {Sec: 0, Usec: 20722},
Maxrss: 28188,
Ixrss: 0,
Idrss: 0,
Isrss: 0,
Minflt: 6714,
Majflt: 0,
Nswap: 0,
Inblock: 0,
Oublock: 0,
Msgsnd: 0,
Msgrcv: 0,
Nsignals: 0,
Nvcsw: 2160,
Nivcsw: 15,
},
},
Stderr: nil,
}
exit status 1
not to have occurred
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:240
------------------------------
``` | 2.0 | should run a deployment to completion and then scale to zero [Conformance] - Because of the latest changes in deployment logs
```
STEP: verifying the scale is updated on the deployment config
STEP: deploying a few more times
Jul 22 22:07:25.246: INFO: Running 'oc deploy --namespace=extended-test-cli-deployment-f3mzp-9tfjf --config=/tmp/openshift/extended-test-cli-deployment-f3mzp-9tfjf-user.kubeconfig --latest --follow deployment-test'
Jul 22 22:07:45.721: INFO: Error running &{/data/src/github.com/openshift/origin/_output/local/bin/linux/amd64/oc [oc deploy --namespace=extended-test-cli-deployment-f3mzp-9tfjf --config=/tmp/openshift/extended-test-cli-deployment-f3mzp-9tfjf-user.kubeconfig --latest --follow deployment-test] [] Started deployment #2
Error from server: The get operation against ReplicationController could not be completed at this time, please try again.
Started deployment #2
Error from server: The get operation against ReplicationController could not be completed at this time, please try again.
[] <nil> 0xc820d49f20 exit status 1 <nil> true [0xc82002f208 0xc82002f230 0xc82002f230] [0xc82002f208 0xc82002f230] [0xc82002f210 0xc82002f228] [0xa7ed60 0xa7eec0] 0xc8202c1080}:
Started deployment #2
Error from server: The get operation against ReplicationController could not be completed at this time, please try again.
```
• Failure [63.861 seconds]
deploymentconfigs
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:598
with test deployments
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:252
should run a deployment to completion and then scale to zero [Conformance] [It]
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:251
Expected error:
<*exec.ExitError | 0xc820d49f80>: {
ProcessState: {
pid: 4354,
status: 256,
rusage: {
Utime: {Sec: 0, Usec: 120189},
Stime: {Sec: 0, Usec: 20722},
Maxrss: 28188,
Ixrss: 0,
Idrss: 0,
Isrss: 0,
Minflt: 6714,
Majflt: 0,
Nswap: 0,
Inblock: 0,
Oublock: 0,
Msgsnd: 0,
Msgrcv: 0,
Nsignals: 0,
Nvcsw: 2160,
Nivcsw: 15,
},
},
Stderr: nil,
}
exit status 1
not to have occurred
/data/src/github.com/openshift/origin/test/extended/deployments/deployments.go:240
------------------------------
``` | non_infrastructure | should run a deployment to completion and then scale to zero because of the latest changes in deployment logs step verifying the scale is updated on the deployment config step deploying a few more times jul info running oc deploy namespace extended test cli deployment config tmp openshift extended test cli deployment user kubeconfig latest follow deployment test jul info error running data src github com openshift origin output local bin linux oc started deployment error from server the get operation against replicationcontroller could not be completed at this time please try again started deployment error from server the get operation against replicationcontroller could not be completed at this time please try again exit status true started deployment error from server the get operation against replicationcontroller could not be completed at this time please try again • failure deploymentconfigs data src github com openshift origin test extended deployments deployments go with test deployments data src github com openshift origin test extended deployments deployments go should run a deployment to completion and then scale to zero data src github com openshift origin test extended deployments deployments go expected error processstate pid status rusage utime sec usec stime sec usec maxrss ixrss idrss isrss minflt majflt nswap inblock oublock msgsnd msgrcv nsignals nvcsw nivcsw stderr nil exit status not to have occurred data src github com openshift origin test extended deployments deployments go | 0 |
162,758 | 20,246,696,677 | IssuesEvent | 2022-02-14 14:22:12 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [Security Solution] The user is able create different integration policies with same name by just adding leading/trailing spaces. It results in further conflicts while updating anyone | bug v8.0.0 impact:medium Team:Fleet Team: SecuritySolution Team:Onboarding and Lifecycle Mgt OLM Sprint | **Description:**
The user is able create different integration policies with same name by just adding leading/trailing spaces. It results in further conflicts while updating anyone
**Build Details:**
```
Kibana version: 8.0.0 SNAPSHOT
Build: 48868
Commit: a29e0164a4af4d3135910cac9e6caa4478af5f3b
Artifact page: https://artifacts-api.elastic.co/v1/search/8.0.0-SNAPSHOT
```
**Browser Details:**
All
**Preconditions:**
1. Kibana user should be logged in.
**Steps to Reproduce:**
1. Navigate to the Integrations tab from the left side navigation on Kibana
2. Select the Endpoint Security integration
3. Create multiple integrations for different policies with the same name but add space either leading or trailing.
Example: `Security` and `Security `
4. After installing agents on both policies, make changes in one policy and observe the second policy gets the exact same changes
5. Also observe, the agent which was installed later, would go to offline state with error: 400 Bad Request.
**Impacted Test case:**
N/A
**Actual Result:**
1. Policies are allowed with the same name
2. If it is expected, the changes done in one policy are being reflected in another policy. And also, the endpoint goes in an offline state
**Expected Result:**
1. Policies should not be allowed with the same name
2. If it is expected, the changes done in one policy should not be reflected in another policy. And also, the endpoint should not go in an offline state
**What's working:**
N/A
**What's not working:**
N/A
**Screen Recording:**

**Logs:**
N/A
## Solution
From @kevinlog's comment below https://github.com/elastic/kibana/issues/122015#issuecomment-1006895304
### Make a change in Fleet to trim leading and trailing spaces
This seems like the easiest fix and would eliminate all issue discussed in this ticket. Would we be able to make a change to Fleet to trim spaces before attempting to save a package policy name? | True | [Security Solution] The user is able create different integration policies with same name by just adding leading/trailing spaces. It results in further conflicts while updating anyone - **Description:**
The user is able create different integration policies with same name by just adding leading/trailing spaces. It results in further conflicts while updating anyone
**Build Details:**
```
Kibana version: 8.0.0 SNAPSHOT
Build: 48868
Commit: a29e0164a4af4d3135910cac9e6caa4478af5f3b
Artifact page: https://artifacts-api.elastic.co/v1/search/8.0.0-SNAPSHOT
```
**Browser Details:**
All
**Preconditions:**
1. Kibana user should be logged in.
**Steps to Reproduce:**
1. Navigate to the Integrations tab from the left side navigation on Kibana
2. Select the Endpoint Security integration
3. Create multiple integrations for different policies with the same name but add space either leading or trailing.
Example: `Security` and `Security `
4. After installing agents on both policies, make changes in one policy and observe the second policy gets the exact same changes
5. Also observe, the agent which was installed later, would go to offline state with error: 400 Bad Request.
**Impacted Test case:**
N/A
**Actual Result:**
1. Policies are allowed with the same name
2. If it is expected, the changes done in one policy are being reflected in another policy. And also, the endpoint goes in an offline state
**Expected Result:**
1. Policies should not be allowed with the same name
2. If it is expected, the changes done in one policy should not be reflected in another policy. And also, the endpoint should not go in an offline state
**What's working:**
N/A
**What's not working:**
N/A
**Screen Recording:**

**Logs:**
N/A
## Solution
From @kevinlog's comment below https://github.com/elastic/kibana/issues/122015#issuecomment-1006895304
### Make a change in Fleet to trim leading and trailing spaces
This seems like the easiest fix and would eliminate all issue discussed in this ticket. Would we be able to make a change to Fleet to trim spaces before attempting to save a package policy name? | non_infrastructure | the user is able create different integration policies with same name by just adding leading trailing spaces it results in further conflicts while updating anyone description the user is able create different integration policies with same name by just adding leading trailing spaces it results in further conflicts while updating anyone build details kibana version snapshot build commit artifact page browser details all preconditions kibana user should be logged in steps to reproduce navigate to the integrations tab from the left side navigation on kibana select the endpoint security integration create multiple integrations for different policies with the same name but add space either leading or trailing example security and security after installing agents on both policies make changes in one policy and observe the second policy gets the exact same changes also observe the agent which was installed later would go to offline state with error bad request impacted test case n a actual result policies are allowed with the same name if it is expected the changes done in one policy are being reflected in another policy and also the endpoint goes in an offline state expected result policies should not be allowed with the same name if it is expected the changes done in one policy should not be reflected in another policy and also the endpoint should not go in an offline state what s working n a what s not working n a screen recording logs n a solution from kevinlog s comment below make a change in fleet to trim leading and trailing spaces this seems like the easiest fix and would eliminate all issue discussed in this ticket would we be able to make a change to fleet to trim spaces before attempting to save a package policy name | 0 |
10,642 | 8,662,885,360 | IssuesEvent | 2018-11-28 16:02:26 | LibreTime/libretime | https://api.github.com/repos/LibreTime/libretime | closed | Issues at summertime UK changeover. | bug feedback-needed infrastructure php | My station settings are:
Hardware clock UTC, Unix Time UTC, Libre Station Time UTC, Admin UTC
I am in the UK.
I had a show set for midnight until one. It displayed midnight until 2am, overlapping another show I could not edit to a sensible state.
At 1 am exactly the station went silent
I switched the admin interface time to Europe London and a 1 hour gap appeared in the schedule, which I was able to fill and station playout commenced.
Weird stuff:
The UK time changes to summertime @ 2AM not 1AM
EVERYTHING was set to UTC, so nothing should care about UK summer time.
AT 2.5.2 didn't care. LT does.
| 1.0 | Issues at summertime UK changeover. - My station settings are:
Hardware clock UTC, Unix Time UTC, Libre Station Time UTC, Admin UTC
I am in the UK.
I had a show set for midnight until one. It displayed midnight until 2am, overlapping another show I could not edit to a sensible state.
At 1 am exactly the station went silent
I switched the admin interface time to Europe London and a 1 hour gap appeared in the schedule, which I was able to fill and station playout commenced.
Weird stuff:
The UK time changes to summertime @ 2AM not 1AM
EVERYTHING was set to UTC, so nothing should care about UK summer time.
AT 2.5.2 didn't care. LT does.
| infrastructure | issues at summertime uk changeover my station settings are hardware clock utc unix time utc libre station time utc admin utc i am in the uk i had a show set for midnight until one it displayed midnight until overlapping another show i could not edit to a sensible state at am exactly the station went silent i switched the admin interface time to europe london and a hour gap appeared in the schedule which i was able to fill and station playout commenced weird stuff the uk time changes to summertime not everything was set to utc so nothing should care about uk summer time at didn t care lt does | 1 |
219,395 | 17,089,532,031 | IssuesEvent | 2021-07-08 15:38:58 | urapadmin/kiosk | https://api.github.com/repos/urapadmin/kiosk | closed | pdf image upload unexpected error | bug kiosk test-stage | I attempted to upload an image with no checked boxes about how to find context or time to URAP (dangerous, but I would have deleted it). I did not expect it to fail and I do not really understand the message. This might be a ticket about a message needing more information, not a bigger problem, but I cannot tell.

This is on LDB's Mac, in kiosk 0.11.12. Happened with PVD 0.12.3, too, but I cannot isolate what makes it happen. I thought at first I might have tried to upload pdfs that weren't actually on my computer, were cloud files in dropbox. But I discovered quite to my surprise that those I can actually upload successfully; I see them in the dialog box when I am choosing files to upload as having 0 bytes, and then I choose them and they upload properly and are there, and then it is clear that kiosk triggered a two step thing - downloading it to my computer (where subsequently it is no longer 0 bytes) and uploading it to the file repository. So, that's quite cool. But it means I haven't a clue as to why I am sometimes getting that message. | 1.0 | pdf image upload unexpected error - I attempted to upload an image with no checked boxes about how to find context or time to URAP (dangerous, but I would have deleted it). I did not expect it to fail and I do not really understand the message. This might be a ticket about a message needing more information, not a bigger problem, but I cannot tell.

This is on LDB's Mac, in kiosk 0.11.12. Happened with PVD 0.12.3, too, but I cannot isolate what makes it happen. I thought at first I might have tried to upload pdfs that weren't actually on my computer, were cloud files in dropbox. But I discovered quite to my surprise that those I can actually upload successfully; I see them in the dialog box when I am choosing files to upload as having 0 bytes, and then I choose them and they upload properly and are there, and then it is clear that kiosk triggered a two step thing - downloading it to my computer (where subsequently it is no longer 0 bytes) and uploading it to the file repository. So, that's quite cool. But it means I haven't a clue as to why I am sometimes getting that message. | non_infrastructure | pdf image upload unexpected error i attempted to upload an image with no checked boxes about how to find context or time to urap dangerous but i would have deleted it i did not expect it to fail and i do not really understand the message this might be a ticket about a message needing more information not a bigger problem but i cannot tell this is on ldb s mac in kiosk happened with pvd too but i cannot isolate what makes it happen i thought at first i might have tried to upload pdfs that weren t actually on my computer were cloud files in dropbox but i discovered quite to my surprise that those i can actually upload successfully i see them in the dialog box when i am choosing files to upload as having bytes and then i choose them and they upload properly and are there and then it is clear that kiosk triggered a two step thing downloading it to my computer where subsequently it is no longer bytes and uploading it to the file repository so that s quite cool but it means i haven t a clue as to why i am sometimes getting that message | 0 |
28,068 | 22,832,954,929 | IssuesEvent | 2022-07-12 14:21:26 | opendp/opendp | https://api.github.com/repos/opendp/opendp | closed | Change the default python bindings' int type from i32 to C long | OpenDP Core Effort 1 - Small :coffee: CATEGORY: Infrastructure | When you create an integer array in numpy, it defaults to the bit depth of a C long on your system. On most systems this is an i64, meaning the default dtype of numpy integer arrays isn't the same as the default dtype on int transformations and measurements. This is just annoying to work with, because you have to set domains manually throughout the pipeline, or cast data before invocation. | 1.0 | Change the default python bindings' int type from i32 to C long - When you create an integer array in numpy, it defaults to the bit depth of a C long on your system. On most systems this is an i64, meaning the default dtype of numpy integer arrays isn't the same as the default dtype on int transformations and measurements. This is just annoying to work with, because you have to set domains manually throughout the pipeline, or cast data before invocation. | infrastructure | change the default python bindings int type from to c long when you create an integer array in numpy it defaults to the bit depth of a c long on your system on most systems this is an meaning the default dtype of numpy integer arrays isn t the same as the default dtype on int transformations and measurements this is just annoying to work with because you have to set domains manually throughout the pipeline or cast data before invocation | 1 |
370,827 | 25,926,228,868 | IssuesEvent | 2022-12-16 04:53:00 | 0xGhazy/PyPass | https://api.github.com/repos/0xGhazy/PyPass | opened | Document the project well | documentation | documentation process consists of the following:
1- Define project structure.
2- Document each function, method, and class with docstring.
3- Writing a Guide for newcomers to help them in contributing to PyPass project.
5- Provide project digrams. | 1.0 | Document the project well - documentation process consists of the following:
1- Define project structure.
2- Document each function, method, and class with docstring.
3- Writing a Guide for newcomers to help them in contributing to PyPass project.
5- Provide project digrams. | non_infrastructure | document the project well documentation process consists of the following define project structure document each function method and class with docstring writing a guide for newcomers to help them in contributing to pypass project provide project digrams | 0 |
2,895 | 3,954,312,570 | IssuesEvent | 2016-04-29 16:30:51 | dotnet/wcf | https://api.github.com/repos/dotnet/wcf | opened | Clean MSBuild target should close SelfHostedWcfService and cleanup | Infrastructure suggestion | Running either clean.cmd or 'build /t:Clean' should cause the SelfHostedWcfService.exe to terminate (if running) and all test certificates, firewall rules, and SSL port associations used for testing should to be removed.
Reason: this allows the normal MSBuild semantics to be used to stop the self-hosted service and cleanup. And this would allow a CI or PR job to start with a clean to assure a clean state. This also allows the dev using a manually started self-hosted service to assure it is closed when doing modify/rebuild/retest iterations.
Proposed solution is to use the new build.override.targets just to add a new target into the normal clean target dependency list. | 1.0 | Clean MSBuild target should close SelfHostedWcfService and cleanup - Running either clean.cmd or 'build /t:Clean' should cause the SelfHostedWcfService.exe to terminate (if running) and all test certificates, firewall rules, and SSL port associations used for testing should to be removed.
Reason: this allows the normal MSBuild semantics to be used to stop the self-hosted service and cleanup. And this would allow a CI or PR job to start with a clean to assure a clean state. This also allows the dev using a manually started self-hosted service to assure it is closed when doing modify/rebuild/retest iterations.
Proposed solution is to use the new build.override.targets just to add a new target into the normal clean target dependency list. | infrastructure | clean msbuild target should close selfhostedwcfservice and cleanup running either clean cmd or build t clean should cause the selfhostedwcfservice exe to terminate if running and all test certificates firewall rules and ssl port associations used for testing should to be removed reason this allows the normal msbuild semantics to be used to stop the self hosted service and cleanup and this would allow a ci or pr job to start with a clean to assure a clean state this also allows the dev using a manually started self hosted service to assure it is closed when doing modify rebuild retest iterations proposed solution is to use the new build override targets just to add a new target into the normal clean target dependency list | 1 |
2,727 | 3,828,998,194 | IssuesEvent | 2016-03-31 08:50:41 | sindresorhus/refined-github | https://api.github.com/repos/sindresorhus/refined-github | closed | Use LGTM.co service | infrastructure under discussion | https://lgtm.co/ is a very neat service which works really well with GitHub Commit Status API and GitHub protected branches. Basically when a new PR is opened it will set the status of the PR to failed and it will keep listening to comments on the PR. When a certain regex check is detected in the comments by enough maintainers it will set the PR status to green which will allow the merge (based on GitHub protected branches settings).
So this is very useful for detecting if maintainers have approved the change and setting common rules like what text to be detected as an approval and how many maintainers need to approve before it's marked as approved.
I encourage you to go through the documentation and enable it.
@sindresorhus What do you think? Since you have admin rights to the repository you'd need to set it up and configure protected branches. With protected branches admins could merge a PR even if required checks have failed and collaborators cannot. I believe this would help you even more and ease you in the future when working with more collaborators. If not sure it's useful in general you could at least try it on this repo to see whether it's worth it adding on more of your repos. | 1.0 | Use LGTM.co service - https://lgtm.co/ is a very neat service which works really well with GitHub Commit Status API and GitHub protected branches. Basically when a new PR is opened it will set the status of the PR to failed and it will keep listening to comments on the PR. When a certain regex check is detected in the comments by enough maintainers it will set the PR status to green which will allow the merge (based on GitHub protected branches settings).
So this is very useful for detecting if maintainers have approved the change and setting common rules like what text to be detected as an approval and how many maintainers need to approve before it's marked as approved.
I encourage you to go through the documentation and enable it.
@sindresorhus What do you think? Since you have admin rights to the repository you'd need to set it up and configure protected branches. With protected branches admins could merge a PR even if required checks have failed and collaborators cannot. I believe this would help you even more and ease you in the future when working with more collaborators. If not sure it's useful in general you could at least try it on this repo to see whether it's worth it adding on more of your repos. | infrastructure | use lgtm co service is a very neat service which works really well with github commit status api and github protected branches basically when a new pr is opened it will set the status of the pr to failed and it will keep listening to comments on the pr when a certain regex check is detected in the comments by enough maintainers it will set the pr status to green which will allow the merge based on github protected branches settings so this is very useful for detecting if maintainers have approved the change and setting common rules like what text to be detected as an approval and how many maintainers need to approve before it s marked as approved i encourage you to go through the documentation and enable it sindresorhus what do you think since you have admin rights to the repository you d need to set it up and configure protected branches with protected branches admins could merge a pr even if required checks have failed and collaborators cannot i believe this would help you even more and ease you in the future when working with more collaborators if not sure it s useful in general you could at least try it on this repo to see whether it s worth it adding on more of your repos | 1 |
108,388 | 23,598,676,828 | IssuesEvent | 2022-08-23 22:10:29 | MetaMask/design-tokens | https://api.github.com/repos/MetaMask/design-tokens | closed | Fix fonts in storybook github pages | bug documentation code | ### **Description**
Fonts are broken on storybook github page. Should be Euclid.
<img width="1440" alt="Screen Shot 2022-07-19 at 8 47 44 AM" src="https://user-images.githubusercontent.com/8112138/179793462-0da485cf-33c0-46f7-b43b-953c0552bdf6.png">
### **Technical Details**
- debug and fix font issue in storybook on github pages
### **Acceptance Criteria**
- Storybook github page should display correct font without needing it to be on your machine
| 1.0 | Fix fonts in storybook github pages - ### **Description**
Fonts are broken on storybook github page. Should be Euclid.
<img width="1440" alt="Screen Shot 2022-07-19 at 8 47 44 AM" src="https://user-images.githubusercontent.com/8112138/179793462-0da485cf-33c0-46f7-b43b-953c0552bdf6.png">
### **Technical Details**
- debug and fix font issue in storybook on github pages
### **Acceptance Criteria**
- Storybook github page should display correct font without needing it to be on your machine
| non_infrastructure | fix fonts in storybook github pages description fonts are broken on storybook github page should be euclid img width alt screen shot at am src technical details debug and fix font issue in storybook on github pages acceptance criteria storybook github page should display correct font without needing it to be on your machine | 0 |
51,971 | 27,321,487,227 | IssuesEvent | 2023-02-24 20:16:31 | python/cpython | https://api.github.com/repos/python/cpython | closed | Add internal API for fast module access from heap type methods | type-feature performance extension-modules expert-C-API | See [topic on Discourse](https://discuss.python.org/t/a-fast-variant-of-pytype-getmodule/23377?u=erlendaasland).
For CPython internal usage, we've got `_PyModule_GetState`, which is a fast variant of `PyModule_GetState`, the module check in the latter is simply an assert in the former.
For `PyType_GetModuleState`, there are three `if`s (two of them implicitly in `PyType_GetModule`):
1. check that the given type is a heap type
2. check that the given type has an associated module
3. check that the result of `PyType_GetModule` is not `NULL`
For stdlib core extension modules, all of these conditions are always true (AFAIK). With a fast static inlined variant, for example `_PyType_GetModuleState`, with a fast variant of `PyType_GetModule` inlined, where all three conditions are `assert()`ed, we can speed up a heap type methods that need to access module state.
<!-- gh-linked-prs -->
### Linked PRs
* gh-101477
* gh-102188
<!-- /gh-linked-prs -->
| True | Add internal API for fast module access from heap type methods - See [topic on Discourse](https://discuss.python.org/t/a-fast-variant-of-pytype-getmodule/23377?u=erlendaasland).
For CPython internal usage, we've got `_PyModule_GetState`, which is a fast variant of `PyModule_GetState`, the module check in the latter is simply an assert in the former.
For `PyType_GetModuleState`, there are three `if`s (two of them implicitly in `PyType_GetModule`):
1. check that the given type is a heap type
2. check that the given type has an associated module
3. check that the result of `PyType_GetModule` is not `NULL`
For stdlib core extension modules, all of these conditions are always true (AFAIK). With a fast static inlined variant, for example `_PyType_GetModuleState`, with a fast variant of `PyType_GetModule` inlined, where all three conditions are `assert()`ed, we can speed up a heap type methods that need to access module state.
<!-- gh-linked-prs -->
### Linked PRs
* gh-101477
* gh-102188
<!-- /gh-linked-prs -->
| non_infrastructure | add internal api for fast module access from heap type methods see for cpython internal usage we ve got pymodule getstate which is a fast variant of pymodule getstate the module check in the latter is simply an assert in the former for pytype getmodulestate there are three if s two of them implicitly in pytype getmodule check that the given type is a heap type check that the given type has an associated module check that the result of pytype getmodule is not null for stdlib core extension modules all of these conditions are always true afaik with a fast static inlined variant for example pytype getmodulestate with a fast variant of pytype getmodule inlined where all three conditions are assert ed we can speed up a heap type methods that need to access module state linked prs gh gh | 0 |
17,122 | 12,228,448,253 | IssuesEvent | 2020-05-03 19:28:26 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | "./build.sh --subset" throw unbound variable error | area-Infrastructure-libraries untriaged | I wanted to list all the subsets, so I triedSteps to repro.
```
./build.sh --subset`
```
But I got an error:
```
/Users/hugh/Documents/GitHub/runtime/eng/build.sh: line 111: $2: unbound variable
```
Would be good to fix this | 1.0 | "./build.sh --subset" throw unbound variable error - I wanted to list all the subsets, so I triedSteps to repro.
```
./build.sh --subset`
```
But I got an error:
```
/Users/hugh/Documents/GitHub/runtime/eng/build.sh: line 111: $2: unbound variable
```
Would be good to fix this | infrastructure | build sh subset throw unbound variable error i wanted to list all the subsets so i triedsteps to repro build sh subset but i got an error users hugh documents github runtime eng build sh line unbound variable would be good to fix this | 1 |
31,896 | 26,227,823,568 | IssuesEvent | 2023-01-04 20:29:58 | microsoft/TypeScript | https://api.github.com/repos/microsoft/TypeScript | closed | Feature request: publish git release tags during NPM package release process | Bug Infrastructure | # Suggestion
<!--
Please fill in each section completely. Thank you!
-->
## 🔍 Search Terms
<!--
💡 Did you know? TypeScript has over 2,000 open suggestions!
🔎 Please search thoroughly before logging new feature requests as most common ideas already have a proposal in progress.
The "Common Feature Requests" section of the FAQ lists many popular requests: https://github.com/Microsoft/TypeScript/wiki/FAQ#common-feature-requests
Replace the text below:
-->
`git` `tag` `release`
## ✅ Viability Checklist
<!--
Suggestions that don't meet all these criteria are very, very unlikely to be accepted.
We always recommend reviewing the TypeScript design goals before investing time writing
a proposal for ideas outside the scope of the project.
-->
My suggestion meets these guidelines:
* [x] This wouldn't be a breaking change in existing TypeScript/JavaScript code
* [x] This wouldn't change the runtime behavior of existing JavaScript code
* [x] This could be implemented without emitting different JS based on the types of the expressions
* [x] This isn't a runtime feature (e.g. library functionality, non-ECMAScript syntax with JavaScript output, new syntax sugar for JS, etc.)
* [x] This feature would agree with the rest of [TypeScript's Design Goals](https://github.com/Microsoft/TypeScript/wiki/TypeScript-Design-Goals).
## ⭐ Suggestion
<!-- A summary of what you'd like to see added or changed -->
As part of the process for release of `typescript` packages to NPM, push a corresponding `git` tag to this repository.
## 📃 Motivating Example
<!--
If you were announcing this feature in a blog post, what's a short explanation that shows
a developer why this feature improves the language?
-->
Version 4.9.3 of `typescript` is currently available on NPM and it is not immediately clear what `git` commit version that corresponds to in this repository.
## 💻 Use Cases
<!--
What do you want to use this for?
What shortcomings exist with current approaches?
What workarounds are you using in the meantime?
-->
This would be useful during dependency and upgrade review - for example, when looking for potential functionality, compatibility, performance, security and transitive dependency implications of a version upgrade.
With the current approach, `git` tags _are_ published, although that occurs some variable amount of time after package publication to NPM taken place. It's possible that some users do upgrade before a `git` tag is published -- and it's also possible that they could review the contents of the release themselves to perform non-source-controlled review. | 1.0 | Feature request: publish git release tags during NPM package release process - # Suggestion
<!--
Please fill in each section completely. Thank you!
-->
## 🔍 Search Terms
<!--
💡 Did you know? TypeScript has over 2,000 open suggestions!
🔎 Please search thoroughly before logging new feature requests as most common ideas already have a proposal in progress.
The "Common Feature Requests" section of the FAQ lists many popular requests: https://github.com/Microsoft/TypeScript/wiki/FAQ#common-feature-requests
Replace the text below:
-->
`git` `tag` `release`
## ✅ Viability Checklist
<!--
Suggestions that don't meet all these criteria are very, very unlikely to be accepted.
We always recommend reviewing the TypeScript design goals before investing time writing
a proposal for ideas outside the scope of the project.
-->
My suggestion meets these guidelines:
* [x] This wouldn't be a breaking change in existing TypeScript/JavaScript code
* [x] This wouldn't change the runtime behavior of existing JavaScript code
* [x] This could be implemented without emitting different JS based on the types of the expressions
* [x] This isn't a runtime feature (e.g. library functionality, non-ECMAScript syntax with JavaScript output, new syntax sugar for JS, etc.)
* [x] This feature would agree with the rest of [TypeScript's Design Goals](https://github.com/Microsoft/TypeScript/wiki/TypeScript-Design-Goals).
## ⭐ Suggestion
<!-- A summary of what you'd like to see added or changed -->
As part of the process for release of `typescript` packages to NPM, push a corresponding `git` tag to this repository.
## 📃 Motivating Example
<!--
If you were announcing this feature in a blog post, what's a short explanation that shows
a developer why this feature improves the language?
-->
Version 4.9.3 of `typescript` is currently available on NPM and it is not immediately clear what `git` commit version that corresponds to in this repository.
## 💻 Use Cases
<!--
What do you want to use this for?
What shortcomings exist with current approaches?
What workarounds are you using in the meantime?
-->
This would be useful during dependency and upgrade review - for example, when looking for potential functionality, compatibility, performance, security and transitive dependency implications of a version upgrade.
With the current approach, `git` tags _are_ published, although that occurs some variable amount of time after package publication to NPM taken place. It's possible that some users do upgrade before a `git` tag is published -- and it's also possible that they could review the contents of the release themselves to perform non-source-controlled review. | infrastructure | feature request publish git release tags during npm package release process suggestion please fill in each section completely thank you 🔍 search terms 💡 did you know typescript has over open suggestions 🔎 please search thoroughly before logging new feature requests as most common ideas already have a proposal in progress the common feature requests section of the faq lists many popular requests replace the text below git tag release ✅ viability checklist suggestions that don t meet all these criteria are very very unlikely to be accepted we always recommend reviewing the typescript design goals before investing time writing a proposal for ideas outside the scope of the project my suggestion meets these guidelines this wouldn t be a breaking change in existing typescript javascript code this wouldn t change the runtime behavior of existing javascript code this could be implemented without emitting different js based on the types of the expressions this isn t a runtime feature e g library functionality non ecmascript syntax with javascript output new syntax sugar for js etc this feature would agree with the rest of ⭐ suggestion as part of the process for release of typescript packages to npm push a corresponding git tag to this repository 📃 motivating example if you were announcing this feature in a blog post what s a short explanation that shows a developer why this feature improves the language version of typescript is currently available on npm and it is not immediately clear what git commit version that corresponds to in this repository 💻 use cases what do you want to use this for what shortcomings exist with current approaches what workarounds are you using in the meantime this would be useful during dependency and upgrade review for example when looking for potential functionality compatibility performance security and transitive dependency implications of a version upgrade with the current approach git tags are published although that occurs some variable amount of time after package publication to npm taken place it s possible that some users do upgrade before a git tag is published and it s also possible that they could review the contents of the release themselves to perform non source controlled review | 1 |
325,072 | 24,033,272,658 | IssuesEvent | 2022-09-15 16:43:46 | codestates-seb/seb39_main_001 | https://api.github.com/repos/codestates-seb/seb39_main_001 | opened | [SCR-005] 모집자 지원자 수락/거절 | documentation BE | - [ ] PATCH /applications/{application-id}
- [ ] DELETE /applications/{application-id}
- | 1.0 | [SCR-005] 모집자 지원자 수락/거절 - - [ ] PATCH /applications/{application-id}
- [ ] DELETE /applications/{application-id}
- | non_infrastructure | 모집자 지원자 수락 거절 patch applications application id delete applications application id | 0 |
24,836 | 17,838,217,191 | IssuesEvent | 2021-09-03 06:20:14 | Budibase/budibase | https://api.github.com/repos/Budibase/budibase | closed | QA Test Environment | infrastructure qa | - EC2 instance in AWS
- Run the whole docker compose stack
- Potentially run PG, MongoDB and other popular data sources on the box
- Allow targeting from the automated tests
- test.budi.live | 1.0 | QA Test Environment - - EC2 instance in AWS
- Run the whole docker compose stack
- Potentially run PG, MongoDB and other popular data sources on the box
- Allow targeting from the automated tests
- test.budi.live | infrastructure | qa test environment instance in aws run the whole docker compose stack potentially run pg mongodb and other popular data sources on the box allow targeting from the automated tests test budi live | 1 |
45,797 | 9,815,665,206 | IssuesEvent | 2019-06-13 13:09:31 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | vscode.executeCodeLensProvider command doesn't correctly return merge conflicts code lens | bug editor-code-lens | Version: 1.36.0-insider (system setup)
Commit: c089daa858f34631f5f827ff8a0313bf1e2ded6d
Date: 2019-06-07T05:19:15.188Z
Electron: 4.2.3
Chrome: 69.0.3497.128
Node.js: 10.11.0
V8: 6.9.427.31-electron.0
OS: Windows_NT x64 10.0.17763
Steps to Reproduce:
1. Create an extension to query for code lenses. E.g. `codeLenses = await vscode.commands.executeCommand<vscode.CodeLens[]>('vscode.executeCodeLensProvider', uri, Number.MAX_VALUE);`
2. Query for code lenses in a document that has merge conflicts.
EXPECTED (and the behavior in stable):
Returns merge conflicts code lenses. E.g.
```
{
"range": [
{
"line": 5,
"character": 0
},
{
"line": 10,
"character": 0
}
],
"command": {
"command": "merge-conflict.accept.current",
"title": "Accept Current Change",
"arguments": [
"known-conflict",
{
"range": [
{
"line": 5,
"character": 0
},
{
"line": 10,
"character": 0
}
],
"current": {
"header": [
{
"line": 5,
"character": 0
},
{
"line": 5,
"character": 12
}
],
"decoratorContent": [
{
"line": 6,
"character": 0
},
{
"line": 6,
"character": 14
}
],
"content": [
{
"line": 6,
"character": 0
},
{
"line": 7,
"character": 0
}
],
"name": "HEAD"
},
"incoming": {
"header": [
{
"line": 9,
"character": 0
},
{
"line": 9,
"character": 10
}
],
"decoratorContent": [
{
"line": 8,
"character": 0
},
{
"line": 8,
"character": 14
}
],
"content": [
{
"line": 8,
"character": 0
},
{
"line": 9,
"character": 0
}
],
"name": "b2"
},
"commonAncestors": [],
"splitter": [
{
"line": 7,
"character": 0
},
{
"line": 7,
"character": 7
}
]
}
]
}
}
```
ACTUAL (behavior in insiders):
Merge conflict code lenses only contain a range. E.g.
```
{
"range": [
{
"line": 5,
"character": 0
},
{
"line": 10,
"character": 0
}
]
}
```
| 1.0 | vscode.executeCodeLensProvider command doesn't correctly return merge conflicts code lens - Version: 1.36.0-insider (system setup)
Commit: c089daa858f34631f5f827ff8a0313bf1e2ded6d
Date: 2019-06-07T05:19:15.188Z
Electron: 4.2.3
Chrome: 69.0.3497.128
Node.js: 10.11.0
V8: 6.9.427.31-electron.0
OS: Windows_NT x64 10.0.17763
Steps to Reproduce:
1. Create an extension to query for code lenses. E.g. `codeLenses = await vscode.commands.executeCommand<vscode.CodeLens[]>('vscode.executeCodeLensProvider', uri, Number.MAX_VALUE);`
2. Query for code lenses in a document that has merge conflicts.
EXPECTED (and the behavior in stable):
Returns merge conflicts code lenses. E.g.
```
{
"range": [
{
"line": 5,
"character": 0
},
{
"line": 10,
"character": 0
}
],
"command": {
"command": "merge-conflict.accept.current",
"title": "Accept Current Change",
"arguments": [
"known-conflict",
{
"range": [
{
"line": 5,
"character": 0
},
{
"line": 10,
"character": 0
}
],
"current": {
"header": [
{
"line": 5,
"character": 0
},
{
"line": 5,
"character": 12
}
],
"decoratorContent": [
{
"line": 6,
"character": 0
},
{
"line": 6,
"character": 14
}
],
"content": [
{
"line": 6,
"character": 0
},
{
"line": 7,
"character": 0
}
],
"name": "HEAD"
},
"incoming": {
"header": [
{
"line": 9,
"character": 0
},
{
"line": 9,
"character": 10
}
],
"decoratorContent": [
{
"line": 8,
"character": 0
},
{
"line": 8,
"character": 14
}
],
"content": [
{
"line": 8,
"character": 0
},
{
"line": 9,
"character": 0
}
],
"name": "b2"
},
"commonAncestors": [],
"splitter": [
{
"line": 7,
"character": 0
},
{
"line": 7,
"character": 7
}
]
}
]
}
}
```
ACTUAL (behavior in insiders):
Merge conflict code lenses only contain a range. E.g.
```
{
"range": [
{
"line": 5,
"character": 0
},
{
"line": 10,
"character": 0
}
]
}
```
| non_infrastructure | vscode executecodelensprovider command doesn t correctly return merge conflicts code lens version insider system setup commit date electron chrome node js electron os windows nt steps to reproduce create an extension to query for code lenses e g codelenses await vscode commands executecommand vscode executecodelensprovider uri number max value query for code lenses in a document that has merge conflicts expected and the behavior in stable returns merge conflicts code lenses e g range line character line character command command merge conflict accept current title accept current change arguments known conflict range line character line character current header line character line character decoratorcontent line character line character content line character line character name head incoming header line character line character decoratorcontent line character line character content line character line character name commonancestors splitter line character line character actual behavior in insiders merge conflict code lenses only contain a range e g range line character line character | 0 |
9,147 | 12,203,198,130 | IssuesEvent | 2020-04-30 10:11:25 | MHRA/products | https://api.github.com/repos/MHRA/products | closed | AUTOMATIC BATCH PROCESS - Create service informs State Manager on completion / error | EPIC - Auto Batch Process :oncoming_automobile: HIGH PRIORITY :arrow_double_up: TASK :rescue_worker_helmet: | ### User want
As a user
I want to see up to date documents on the products website
So I can make informed decisions
**Customer acceptance criteria**
**Technical acceptance criteria**
Create service calls the state Manager with the status of the upload - either failed or successful.
**Data acceptance criteria**
**Testing acceptance criteria**
**Size**
S
**Value**
**Effort**
### Exit Criteria met
- [x] Backlog
- [x] Discovery
- [x] DUXD
- [ ] Development
- [ ] Quality Assurance
- [ ] Release and Validate | 1.0 | AUTOMATIC BATCH PROCESS - Create service informs State Manager on completion / error - ### User want
As a user
I want to see up to date documents on the products website
So I can make informed decisions
**Customer acceptance criteria**
**Technical acceptance criteria**
Create service calls the state Manager with the status of the upload - either failed or successful.
**Data acceptance criteria**
**Testing acceptance criteria**
**Size**
S
**Value**
**Effort**
### Exit Criteria met
- [x] Backlog
- [x] Discovery
- [x] DUXD
- [ ] Development
- [ ] Quality Assurance
- [ ] Release and Validate | non_infrastructure | automatic batch process create service informs state manager on completion error user want as a user i want to see up to date documents on the products website so i can make informed decisions customer acceptance criteria technical acceptance criteria create service calls the state manager with the status of the upload either failed or successful data acceptance criteria testing acceptance criteria size s value effort exit criteria met backlog discovery duxd development quality assurance release and validate | 0 |
29,620 | 24,116,412,820 | IssuesEvent | 2022-09-20 15:02:17 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Release-only build has errors due to ResolvedMatchingContract when re-compiling in Visual Studio | area-Infrastructure-libraries | When opening a library project with Visual Studio against a previously-build release-only (runtime and libraries) build the following error occurs:
```
Error ResolvedMatchingContract 'C:\git\runtime\artifacts\bin\System.Private.CoreLib\ref\Debug\net7.0\System.Private.CoreLib.dll' did not exist. System.Private.CoreLib C:\Users\sharter\.nuget\packages\microsoft.dotnet.apicompat\8.0.0-beta.22455.1\build\Microsoft.DotNet.ApiCompat.targets 35
```
So it is trying to use the `debug` version of `System.Private.CoreLib` (which does not exist) instead of the `release` version.
Not sure if this applies to all libraries or not.
## Repro
On a clean enlistment:
```
build -s clr+libs+libs.tests -c Release
```
- Open `C:\git\runtime\src\libraries\System.Reflection\System.Reflection.sln` in VS
- Change build to `release`
- Build
Result: the above error plus attempting to run the tests from withing VS results in a silent failure because the default is to not run when there is a build error. The `Test` error output shows:
```
Aborting test run due to build failures. Please see the build output for more details.
```
| 1.0 | Release-only build has errors due to ResolvedMatchingContract when re-compiling in Visual Studio - When opening a library project with Visual Studio against a previously-build release-only (runtime and libraries) build the following error occurs:
```
Error ResolvedMatchingContract 'C:\git\runtime\artifacts\bin\System.Private.CoreLib\ref\Debug\net7.0\System.Private.CoreLib.dll' did not exist. System.Private.CoreLib C:\Users\sharter\.nuget\packages\microsoft.dotnet.apicompat\8.0.0-beta.22455.1\build\Microsoft.DotNet.ApiCompat.targets 35
```
So it is trying to use the `debug` version of `System.Private.CoreLib` (which does not exist) instead of the `release` version.
Not sure if this applies to all libraries or not.
## Repro
On a clean enlistment:
```
build -s clr+libs+libs.tests -c Release
```
- Open `C:\git\runtime\src\libraries\System.Reflection\System.Reflection.sln` in VS
- Change build to `release`
- Build
Result: the above error plus attempting to run the tests from withing VS results in a silent failure because the default is to not run when there is a build error. The `Test` error output shows:
```
Aborting test run due to build failures. Please see the build output for more details.
```
| infrastructure | release only build has errors due to resolvedmatchingcontract when re compiling in visual studio when opening a library project with visual studio against a previously build release only runtime and libraries build the following error occurs error resolvedmatchingcontract c git runtime artifacts bin system private corelib ref debug system private corelib dll did not exist system private corelib c users sharter nuget packages microsoft dotnet apicompat beta build microsoft dotnet apicompat targets so it is trying to use the debug version of system private corelib which does not exist instead of the release version not sure if this applies to all libraries or not repro on a clean enlistment build s clr libs libs tests c release open c git runtime src libraries system reflection system reflection sln in vs change build to release build result the above error plus attempting to run the tests from withing vs results in a silent failure because the default is to not run when there is a build error the test error output shows aborting test run due to build failures please see the build output for more details | 1 |
6,609 | 6,530,169,795 | IssuesEvent | 2017-08-30 14:18:30 | twosigma/beakerx | https://api.github.com/repos/twosigma/beakerx | closed | Changes in js files appear only after beakerx-install | Infrastructure Priority High | To make any changes in JS files and see the effect in running application developer needs to do following steps:
1. run webpack build `webpack` in js dir
2. run `beakerx-install` cmd in root dir
Before only webpack build was required.
It complicate working with js files. | 1.0 | Changes in js files appear only after beakerx-install - To make any changes in JS files and see the effect in running application developer needs to do following steps:
1. run webpack build `webpack` in js dir
2. run `beakerx-install` cmd in root dir
Before only webpack build was required.
It complicate working with js files. | infrastructure | changes in js files appear only after beakerx install to make any changes in js files and see the effect in running application developer needs to do following steps run webpack build webpack in js dir run beakerx install cmd in root dir before only webpack build was required it complicate working with js files | 1 |
83,069 | 7,860,759,201 | IssuesEvent | 2018-06-21 21:05:44 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | EKS bugs for v2.0.3 | area/ui kind/bug status/resolved status/to-test version/2.0 | Version: master 6/19
- Regions should be limited to `us-east-1` and `us-west-2`
- After entering Region, Access Key and Secret Key the button is `Next: Authenticate & select a network` which is false, because you can select `Instance Type`, Min and Max ASG size
<img width="1269" alt="screen shot 2018-06-19 at 16 00 11" src="https://user-images.githubusercontent.com/2620179/41601908-df906804-73d9-11e8-8869-7c8423abbc1e.png">
| 1.0 | EKS bugs for v2.0.3 - Version: master 6/19
- Regions should be limited to `us-east-1` and `us-west-2`
- After entering Region, Access Key and Secret Key the button is `Next: Authenticate & select a network` which is false, because you can select `Instance Type`, Min and Max ASG size
<img width="1269" alt="screen shot 2018-06-19 at 16 00 11" src="https://user-images.githubusercontent.com/2620179/41601908-df906804-73d9-11e8-8869-7c8423abbc1e.png">
| non_infrastructure | eks bugs for version master regions should be limited to us east and us west after entering region access key and secret key the button is next authenticate select a network which is false because you can select instance type min and max asg size img width alt screen shot at src | 0 |
8,517 | 7,465,092,220 | IssuesEvent | 2018-04-02 01:48:12 | unitedhubs/material-ui-form | https://api.github.com/repos/unitedhubs/material-ui-form | closed | webpack-dev-server refresh on react-router Route other than / | bug help wanted infrastructure | refreshing the page while on say `http://localhost:8080/misc-props` breaks the site. how to fix this? is there "pass-thru" functionality in webpack-dev-server? | 1.0 | webpack-dev-server refresh on react-router Route other than / - refreshing the page while on say `http://localhost:8080/misc-props` breaks the site. how to fix this? is there "pass-thru" functionality in webpack-dev-server? | infrastructure | webpack dev server refresh on react router route other than refreshing the page while on say breaks the site how to fix this is there pass thru functionality in webpack dev server | 1 |
25,703 | 19,011,299,584 | IssuesEvent | 2021-11-23 09:37:07 | informalsystems/ibc-rs | https://api.github.com/repos/informalsystems/ibc-rs | closed | gm-connector for e2e testing in Rust | testing infrastructure P-low | <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberation
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Crate
relayer
gm-connector
## Summary
gm-connector is a Rust library that allows Rust tests to start/stop/manage SDK networks through `gm` (Gaiad Manager).
## Problem Definition
e2e testing in Rust is complex and it has dependencies completely unrelated to Rust (or to the code we oversee): network binaries, configuration, ports, etc.
During developer testing it is possible to contain these dependencies with `gm` Gaiad Manager. `gm` allows the user to describe multiple network nodes and their dependencies on each other in a simple TOML file.
`gm-connector` should allow the developer to do the same in Rust tests either ran locally or in CI. `gm-connector` deals with telling `gm` to start/stop any network nodes as well as it returns endpoints to the developer for RPC, gRPC and other connection types.
Subsequently, `gm-connector` should also allow the developer to read/change the network configuration of each node.
What problems may be addressed by introducing this feature?
e2e testing now uses a lot of different kind of dependencies (Python, network binaries, etc). The relevant dependencies are lowered.
What benefits does IBC-rs stand to gain by including this feature?
Easier e2e testing using Rust native tools.
Are there any disadvantages of including this feature?
Yet another Rust library to maintain. (Fortunately, it is only used in testing.)
## Proposal
Write an initial version of `gm-connector` and see if it resolves dependencies as expected.
<!-- Detailed description of requirements of implementation -->
## Acceptance Criteria
At least one e2e test can be run successfully without invoking Python.
<!-- What's the definition of "done" for this issue? -->
____
#### For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate milestone (priority) applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
| 1.0 | gm-connector for e2e testing in Rust - <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberation
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Crate
relayer
gm-connector
## Summary
gm-connector is a Rust library that allows Rust tests to start/stop/manage SDK networks through `gm` (Gaiad Manager).
## Problem Definition
e2e testing in Rust is complex and it has dependencies completely unrelated to Rust (or to the code we oversee): network binaries, configuration, ports, etc.
During developer testing it is possible to contain these dependencies with `gm` Gaiad Manager. `gm` allows the user to describe multiple network nodes and their dependencies on each other in a simple TOML file.
`gm-connector` should allow the developer to do the same in Rust tests either ran locally or in CI. `gm-connector` deals with telling `gm` to start/stop any network nodes as well as it returns endpoints to the developer for RPC, gRPC and other connection types.
Subsequently, `gm-connector` should also allow the developer to read/change the network configuration of each node.
What problems may be addressed by introducing this feature?
e2e testing now uses a lot of different kind of dependencies (Python, network binaries, etc). The relevant dependencies are lowered.
What benefits does IBC-rs stand to gain by including this feature?
Easier e2e testing using Rust native tools.
Are there any disadvantages of including this feature?
Yet another Rust library to maintain. (Fortunately, it is only used in testing.)
## Proposal
Write an initial version of `gm-connector` and see if it resolves dependencies as expected.
<!-- Detailed description of requirements of implementation -->
## Acceptance Criteria
At least one e2e test can be run successfully without invoking Python.
<!-- What's the definition of "done" for this issue? -->
____
#### For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate milestone (priority) applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
| infrastructure | gm connector for testing in rust ☺ v ✰ thanks for opening an issue ✰ v before smashing the submit button please review the template v word of caution poorly thought out proposals may be rejected v without deliberation ☺ crate relayer gm connector summary gm connector is a rust library that allows rust tests to start stop manage sdk networks through gm gaiad manager problem definition testing in rust is complex and it has dependencies completely unrelated to rust or to the code we oversee network binaries configuration ports etc during developer testing it is possible to contain these dependencies with gm gaiad manager gm allows the user to describe multiple network nodes and their dependencies on each other in a simple toml file gm connector should allow the developer to do the same in rust tests either ran locally or in ci gm connector deals with telling gm to start stop any network nodes as well as it returns endpoints to the developer for rpc grpc and other connection types subsequently gm connector should also allow the developer to read change the network configuration of each node what problems may be addressed by introducing this feature testing now uses a lot of different kind of dependencies python network binaries etc the relevant dependencies are lowered what benefits does ibc rs stand to gain by including this feature easier testing using rust native tools are there any disadvantages of including this feature yet another rust library to maintain fortunately it is only used in testing proposal write an initial version of gm connector and see if it resolves dependencies as expected acceptance criteria at least one test can be run successfully without invoking python for admin use not duplicate issue appropriate labels applied appropriate milestone priority applied appropriate contributors tagged contributor assigned self assigned | 1 |
22,758 | 10,772,083,453 | IssuesEvent | 2019-11-02 12:39:01 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 75: sqlite-3.28.0: 1 advisory | 1.severity: security | [search](https://search.nix.gsc.io/?q=sqlite&i=fosho&repos=nixos-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=sqlite+in%3Apath&type=Code)
* [x] [CVE-2019-16168](https://nvd.nist.gov/vuln/detail/CVE-2019-16168) (nixos-unstable, nixos-19.03)
Scanned versions: nixos-unstable: e19054ab3cd; nixos-19.03: cf018a7c558. May contain false positives.
| True | Vulnerability roundup 75: sqlite-3.28.0: 1 advisory - [search](https://search.nix.gsc.io/?q=sqlite&i=fosho&repos=nixos-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=sqlite+in%3Apath&type=Code)
* [x] [CVE-2019-16168](https://nvd.nist.gov/vuln/detail/CVE-2019-16168) (nixos-unstable, nixos-19.03)
Scanned versions: nixos-unstable: e19054ab3cd; nixos-19.03: cf018a7c558. May contain false positives.
| non_infrastructure | vulnerability roundup sqlite advisory nixos unstable nixos scanned versions nixos unstable nixos may contain false positives | 0 |
3,026 | 4,018,254,168 | IssuesEvent | 2016-05-16 09:39:18 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | opened | Make browser testing more resilient by checking test loading | area-infrastructure P3 low Type: enhancement | Our hardest failures to find are those where a browser test times out because it doesn't load.
The sequence of actions that should happen is:
Driver page requests a test URL from the controller
Driver page fetches that URL from the file server
The page loads, in an iframe or window
The page reports that it started (entered main).
The driver page, test controller, and file server could communicate more, so that when one of these steps doesn't happen, we detect it and report details about the problem. If the driver page writes a URL to the iframe's address, but it doesn't get the started message, it should return fuller data about the browser state, or perhaps close and reopen the iframe.
| 1.0 | Make browser testing more resilient by checking test loading - Our hardest failures to find are those where a browser test times out because it doesn't load.
The sequence of actions that should happen is:
Driver page requests a test URL from the controller
Driver page fetches that URL from the file server
The page loads, in an iframe or window
The page reports that it started (entered main).
The driver page, test controller, and file server could communicate more, so that when one of these steps doesn't happen, we detect it and report details about the problem. If the driver page writes a URL to the iframe's address, but it doesn't get the started message, it should return fuller data about the browser state, or perhaps close and reopen the iframe.
| infrastructure | make browser testing more resilient by checking test loading our hardest failures to find are those where a browser test times out because it doesn t load the sequence of actions that should happen is driver page requests a test url from the controller driver page fetches that url from the file server the page loads in an iframe or window the page reports that it started entered main the driver page test controller and file server could communicate more so that when one of these steps doesn t happen we detect it and report details about the problem if the driver page writes a url to the iframe s address but it doesn t get the started message it should return fuller data about the browser state or perhaps close and reopen the iframe | 1 |
6,605 | 6,529,802,757 | IssuesEvent | 2017-08-30 13:07:01 | nanoframework/Home | https://api.github.com/repos/nanoframework/Home | closed | General code review on Core Library | area-Core-Library area-Infrastructure-and-Organization | From nf-class-libraries created by [josesimoes](https://github.com/josesimoes) : nanoframework/nf-class-libraries#39
This task is to be split into multiple ones. The goal is to perform a review checking for:
- [ ] review methods (naming, declaration, existence, compliant with official version)
- [ ] general code update (evaluate if the best approach is there, if anything should be moved to/from native)
- [x] review documentation (correctness of the comments, matching the official documentation
The classes/structs to review are:
(_check the ones that are reviewed as work progresses_)
- [x] System.BitConverter
- [x] System.AppDomain
- [x] System.AppDomainUnloadedException
- [x] System.ApplicationException
- [x] System.ArgumentException
- [x] System.ArgumentNullException
- [x] System.ArgumentOutOfRangeException
- [x] System.Array
- [x] System.AssemblyInfo2
- [x] System.AsyncCallback
- [x] System.Attribute
- [x] System.AttributeTargets
- [x] System.AttributeUsageAttribute
- [x] System.Boolean
- [x] System.Byte
- [x] System.Char
- [x] System.ComponentModel.EditorBrowsableAttribute
- [x] System.Convert
- [x] System.CLSCompliantAttribute
- [x] System.DateTime
- [x] System.DayOfWeek
- [x] System.DBNull
- [x] System.Decimal
- [x] System.Delegate
- [x] System.Diagnostics.ConditionalAttribute
- [x] System.Diagnostics.Debugger
- [x] System.Diagnostics.DebuggerAttributes
- [x] System.Double
- [x] System.Enum
- [x] System.Exception
- [x] System.FlagsAttribute
- [x] System.GC
- [x] System.Guid
- [x] System.IAsyncResult
- [x] System.ICloneable
- [x] System.IComparable
- [x] System.ICustomFormatter
- [x] System.IDisposable
- [x] System.IFormatProvider
- [x] System.IFormattable
- [x] System.IndexOutOfRangeException
- [x] System.Int16
- [x] System.Int32
- [x] System.Int64
- [x] System.IntPtr
- [x] System.InvalidCastException
- [x] System.InvalidOperationException
- [x] System.MarshalByRefObject
- [x] System.Math
- [x] System.MulticastDelegate
- [x] System.NonSerializedAttribute
- [x] System.NotImplementedException
- [x] System.NotSupportedException
- [x] System.NullReferenceException
- [x] System.Number
- [x] System.Object
- [x] System.ObjectDisposedException
- [x] System.ObsoleteAttribute
- [x] System.OutOfMemoryException
- [x] System.ParamArrayAttribute
- [x] System.Random
- [x] System.RuntimeArgumentHandle
- [x] System.RuntimeFieldHandle
- [x] System.RuntimeMethodHandle
- [x] System.RuntimeType
- [x] System.RuntimeTypeHandle
- [x] System.TargetFrameworkAttribute
- [x] System.SByte
- [x] System.SerializableAttribute
- [x] System.Single
- [x] System.String
- [x] System.SystemException
- [x] System.Text.Decoder
- [x] System.Text.Encoding
- [x] System.Text.StringBuilder
- [x] System.Text.UTF8Decoder
- [x] System.Text.UTF8Encoding
- [x] System.ThreadAttributes
- [x] System.TimeSpan
- [x] System.TimeZone
- [x] System.Type
- [x] System.TypeCode
- [x] System.TypedReference
- [x] System.UInt16
- [x] System.UInt32
- [x] System.UInt64
- [x] System.UIntPtr
- [x] System.ValueType
- [x] System.Version
- [x] System.Void
- [x] System.WeakReference
- [x] System.Collections.ArrayList
- [x] System.Collections.DictionaryEntry
- [x] System.Collections.Hashtable
- [x] System.Collections.ICollection
- [x] System.Collections.IComparer
- [x] System.Collections.IDictionary
- [x] System.Collections.IEqualityComparer
- [x] System.Collections.IEnumerable
- [x] System.Collections.IEnumerator
- [x] System.Collections.IList
- [x] System.Collections.Queue
- [x] System.Collections.Stack
- [x] System.IO.IOException
- [x] System.IO.SeekOrigin
- [x] System.IO.Stream
- [x] System.Globalization.CultureInfo
- [ ] System.Globalization.Resources.CultureInfo.resx
- [x] System.Globalization.CultureTypes
- [x] System.Globalization.DateTimeFormat
- [x] System.Globalization.DateTimeFormatInfo
- [x] System.Globalization.DaylightTime
- [x] System.Globalization.NumberFormatInfo
- [x] System.Reflection.Assembly
- [x] System.Reflection.AssemblyAttributes
- [x] System.Reflection.AssemblyNameFlags
- [x] System.Reflection.AssemblyReflectionAttributes
- [x] System.Reflection.Binder
- [x] System.Reflection.BindingFlags
- [x] System.Reflection.ConstructorInfo
- [x] System.Reflection.DefaultMemberAttribute
- [x] System.Reflection.FieldInfo
- [x] System.Reflection.FieldReflectionAttributes
- [x] System.Reflection.IReflect
- [x] System.Reflection.MemberInfo
- [x] System.Reflection.MethodImplAttributes
- [x] System.Reflection.MemberTypes
- [x] System.Reflection.MethodBase
- [x] System.Reflection.MethodInfo
- [x] System.Reflection.PropertyInfo
- [x] System.Reflection.RuntimeConstructorInfo
- [x] System.Reflection.RuntimeFieldInfo
- [x] System.Reflection.RuntimeMethodInfo
- [x] System.Resources.ResourceManager
- [x] System.Runtime.CompilerServices.AccessedThroughPropertyAttribute
- [x] System.Runtime.CompilerServices.ExtensionAttribute
- [x] System.Runtime.CompilerServices.MethodImplAttribute
- [x] System.Runtime.CompilerServices.IndexerNameAttribute
- [x] System.Runtime.CompilerServices.InternalsVisibleToAttribute
- [x] System.Runtime.CompilerServices.RuntimeHelpers
- [x] System.Runtime.InteropServices.Attributes
- [x] System.Runtime.InteropServices.CharSet
- [x] System.Runtime.InteropServices.LayoutKind
- [x] System.Runtime.Remoting.__TransparentProxy
- [x] System.Runtime.Remoting.RemotingServices
- [x] System.Threading.AutoResetEvent
- [x] System.Threading.Interlocked
- [x] System.Threading.ManualResetEvent
- [x] System.Threading.Monitor
- [x] System.Threading.Thread
- [x] System.Threading.ThreadAbortException
- [x] System.Threading.ThreadPriority
- [x] System.Threading.ThreadStart
- [x] System.Threading.ThreadState
- [x] System.Threading.Timer
- [x] System.Threading.Timeout
- [x] System.Threading.WaitHandle
| 1.0 | General code review on Core Library - From nf-class-libraries created by [josesimoes](https://github.com/josesimoes) : nanoframework/nf-class-libraries#39
This task is to be split into multiple ones. The goal is to perform a review checking for:
- [ ] review methods (naming, declaration, existence, compliant with official version)
- [ ] general code update (evaluate if the best approach is there, if anything should be moved to/from native)
- [x] review documentation (correctness of the comments, matching the official documentation
The classes/structs to review are:
(_check the ones that are reviewed as work progresses_)
- [x] System.BitConverter
- [x] System.AppDomain
- [x] System.AppDomainUnloadedException
- [x] System.ApplicationException
- [x] System.ArgumentException
- [x] System.ArgumentNullException
- [x] System.ArgumentOutOfRangeException
- [x] System.Array
- [x] System.AssemblyInfo2
- [x] System.AsyncCallback
- [x] System.Attribute
- [x] System.AttributeTargets
- [x] System.AttributeUsageAttribute
- [x] System.Boolean
- [x] System.Byte
- [x] System.Char
- [x] System.ComponentModel.EditorBrowsableAttribute
- [x] System.Convert
- [x] System.CLSCompliantAttribute
- [x] System.DateTime
- [x] System.DayOfWeek
- [x] System.DBNull
- [x] System.Decimal
- [x] System.Delegate
- [x] System.Diagnostics.ConditionalAttribute
- [x] System.Diagnostics.Debugger
- [x] System.Diagnostics.DebuggerAttributes
- [x] System.Double
- [x] System.Enum
- [x] System.Exception
- [x] System.FlagsAttribute
- [x] System.GC
- [x] System.Guid
- [x] System.IAsyncResult
- [x] System.ICloneable
- [x] System.IComparable
- [x] System.ICustomFormatter
- [x] System.IDisposable
- [x] System.IFormatProvider
- [x] System.IFormattable
- [x] System.IndexOutOfRangeException
- [x] System.Int16
- [x] System.Int32
- [x] System.Int64
- [x] System.IntPtr
- [x] System.InvalidCastException
- [x] System.InvalidOperationException
- [x] System.MarshalByRefObject
- [x] System.Math
- [x] System.MulticastDelegate
- [x] System.NonSerializedAttribute
- [x] System.NotImplementedException
- [x] System.NotSupportedException
- [x] System.NullReferenceException
- [x] System.Number
- [x] System.Object
- [x] System.ObjectDisposedException
- [x] System.ObsoleteAttribute
- [x] System.OutOfMemoryException
- [x] System.ParamArrayAttribute
- [x] System.Random
- [x] System.RuntimeArgumentHandle
- [x] System.RuntimeFieldHandle
- [x] System.RuntimeMethodHandle
- [x] System.RuntimeType
- [x] System.RuntimeTypeHandle
- [x] System.TargetFrameworkAttribute
- [x] System.SByte
- [x] System.SerializableAttribute
- [x] System.Single
- [x] System.String
- [x] System.SystemException
- [x] System.Text.Decoder
- [x] System.Text.Encoding
- [x] System.Text.StringBuilder
- [x] System.Text.UTF8Decoder
- [x] System.Text.UTF8Encoding
- [x] System.ThreadAttributes
- [x] System.TimeSpan
- [x] System.TimeZone
- [x] System.Type
- [x] System.TypeCode
- [x] System.TypedReference
- [x] System.UInt16
- [x] System.UInt32
- [x] System.UInt64
- [x] System.UIntPtr
- [x] System.ValueType
- [x] System.Version
- [x] System.Void
- [x] System.WeakReference
- [x] System.Collections.ArrayList
- [x] System.Collections.DictionaryEntry
- [x] System.Collections.Hashtable
- [x] System.Collections.ICollection
- [x] System.Collections.IComparer
- [x] System.Collections.IDictionary
- [x] System.Collections.IEqualityComparer
- [x] System.Collections.IEnumerable
- [x] System.Collections.IEnumerator
- [x] System.Collections.IList
- [x] System.Collections.Queue
- [x] System.Collections.Stack
- [x] System.IO.IOException
- [x] System.IO.SeekOrigin
- [x] System.IO.Stream
- [x] System.Globalization.CultureInfo
- [ ] System.Globalization.Resources.CultureInfo.resx
- [x] System.Globalization.CultureTypes
- [x] System.Globalization.DateTimeFormat
- [x] System.Globalization.DateTimeFormatInfo
- [x] System.Globalization.DaylightTime
- [x] System.Globalization.NumberFormatInfo
- [x] System.Reflection.Assembly
- [x] System.Reflection.AssemblyAttributes
- [x] System.Reflection.AssemblyNameFlags
- [x] System.Reflection.AssemblyReflectionAttributes
- [x] System.Reflection.Binder
- [x] System.Reflection.BindingFlags
- [x] System.Reflection.ConstructorInfo
- [x] System.Reflection.DefaultMemberAttribute
- [x] System.Reflection.FieldInfo
- [x] System.Reflection.FieldReflectionAttributes
- [x] System.Reflection.IReflect
- [x] System.Reflection.MemberInfo
- [x] System.Reflection.MethodImplAttributes
- [x] System.Reflection.MemberTypes
- [x] System.Reflection.MethodBase
- [x] System.Reflection.MethodInfo
- [x] System.Reflection.PropertyInfo
- [x] System.Reflection.RuntimeConstructorInfo
- [x] System.Reflection.RuntimeFieldInfo
- [x] System.Reflection.RuntimeMethodInfo
- [x] System.Resources.ResourceManager
- [x] System.Runtime.CompilerServices.AccessedThroughPropertyAttribute
- [x] System.Runtime.CompilerServices.ExtensionAttribute
- [x] System.Runtime.CompilerServices.MethodImplAttribute
- [x] System.Runtime.CompilerServices.IndexerNameAttribute
- [x] System.Runtime.CompilerServices.InternalsVisibleToAttribute
- [x] System.Runtime.CompilerServices.RuntimeHelpers
- [x] System.Runtime.InteropServices.Attributes
- [x] System.Runtime.InteropServices.CharSet
- [x] System.Runtime.InteropServices.LayoutKind
- [x] System.Runtime.Remoting.__TransparentProxy
- [x] System.Runtime.Remoting.RemotingServices
- [x] System.Threading.AutoResetEvent
- [x] System.Threading.Interlocked
- [x] System.Threading.ManualResetEvent
- [x] System.Threading.Monitor
- [x] System.Threading.Thread
- [x] System.Threading.ThreadAbortException
- [x] System.Threading.ThreadPriority
- [x] System.Threading.ThreadStart
- [x] System.Threading.ThreadState
- [x] System.Threading.Timer
- [x] System.Threading.Timeout
- [x] System.Threading.WaitHandle
| infrastructure | general code review on core library from nf class libraries created by nanoframework nf class libraries this task is to be split into multiple ones the goal is to perform a review checking for review methods naming declaration existence compliant with official version general code update evaluate if the best approach is there if anything should be moved to from native review documentation correctness of the comments matching the official documentation the classes structs to review are check the ones that are reviewed as work progresses system bitconverter system appdomain system appdomainunloadedexception system applicationexception system argumentexception system argumentnullexception system argumentoutofrangeexception system array system system asynccallback system attribute system attributetargets system attributeusageattribute system boolean system byte system char system componentmodel editorbrowsableattribute system convert system clscompliantattribute system datetime system dayofweek system dbnull system decimal system delegate system diagnostics conditionalattribute system diagnostics debugger system diagnostics debuggerattributes system double system enum system exception system flagsattribute system gc system guid system iasyncresult system icloneable system icomparable system icustomformatter system idisposable system iformatprovider system iformattable system indexoutofrangeexception system system system system intptr system invalidcastexception system invalidoperationexception system marshalbyrefobject system math system multicastdelegate system nonserializedattribute system notimplementedexception system notsupportedexception system nullreferenceexception system number system object system objectdisposedexception system obsoleteattribute system outofmemoryexception system paramarrayattribute system random system runtimeargumenthandle system runtimefieldhandle system runtimemethodhandle system runtimetype system runtimetypehandle system targetframeworkattribute system sbyte system serializableattribute system single system string system systemexception system text decoder system text encoding system text stringbuilder system text system text system threadattributes system timespan system timezone system type system typecode system typedreference system system system system uintptr system valuetype system version system void system weakreference system collections arraylist system collections dictionaryentry system collections hashtable system collections icollection system collections icomparer system collections idictionary system collections iequalitycomparer system collections ienumerable system collections ienumerator system collections ilist system collections queue system collections stack system io ioexception system io seekorigin system io stream system globalization cultureinfo system globalization resources cultureinfo resx system globalization culturetypes system globalization datetimeformat system globalization datetimeformatinfo system globalization daylighttime system globalization numberformatinfo system reflection assembly system reflection assemblyattributes system reflection assemblynameflags system reflection assemblyreflectionattributes system reflection binder system reflection bindingflags system reflection constructorinfo system reflection defaultmemberattribute system reflection fieldinfo system reflection fieldreflectionattributes system reflection ireflect system reflection memberinfo system reflection methodimplattributes system reflection membertypes system reflection methodbase system reflection methodinfo system reflection propertyinfo system reflection runtimeconstructorinfo system reflection runtimefieldinfo system reflection runtimemethodinfo system resources resourcemanager system runtime compilerservices accessedthroughpropertyattribute system runtime compilerservices extensionattribute system runtime compilerservices methodimplattribute system runtime compilerservices indexernameattribute system runtime compilerservices internalsvisibletoattribute system runtime compilerservices runtimehelpers system runtime interopservices attributes system runtime interopservices charset system runtime interopservices layoutkind system runtime remoting transparentproxy system runtime remoting remotingservices system threading autoresetevent system threading interlocked system threading manualresetevent system threading monitor system threading thread system threading threadabortexception system threading threadpriority system threading threadstart system threading threadstate system threading timer system threading timeout system threading waithandle | 1 |
15,817 | 11,715,691,557 | IssuesEvent | 2020-03-09 14:32:01 | Graylog2/graylog2-server | https://api.github.com/repos/Graylog2/graylog2-server | opened | Remove `integration-test` module | improvement infrastructure | The current `integration-tests` module will be superseded by this: https://github.com/Graylog2/graylog2-server/pull/7561
We should re-implement the tests actually worth keeping in the new system and delete the module. | 1.0 | Remove `integration-test` module - The current `integration-tests` module will be superseded by this: https://github.com/Graylog2/graylog2-server/pull/7561
We should re-implement the tests actually worth keeping in the new system and delete the module. | infrastructure | remove integration test module the current integration tests module will be superseded by this we should re implement the tests actually worth keeping in the new system and delete the module | 1 |
58,738 | 11,905,173,579 | IssuesEvent | 2020-03-30 18:06:12 | home-assistant/brands | https://api.github.com/repos/home-assistant/brands | opened | Hisense AEH-W4A1 is missing brand images | domain-missing has-codeowner has-config-flow |
## The problem
The Hisense AEH-W4A1 integration does not have brand images in
this repository.
We recently started this Brands repository, to create a centralized storage of all brand-related images. These images are used on our website and the Home Assistant frontend.
The following images are missing and would ideally be added:
- `src/hisense_aehw4a1/icon.png`
- `src/hisense_aehw4a1/logo.png`
- `src/hisense_aehw4a1/icon@2x.png`
- `src/hisense_aehw4a1/logo@2x.png`
For image specifications and requirements, please see [README.md](https://github.com/home-assistant/brands/blob/master/README.md).
## Updating the documentation repository
Our documentation repository already has a logo for this integration, however, it does not meet the image requirements of this new Brands repository.
If adding images to this repository, please open up a PR to the documentation repository as well, removing the `logo: hisense.png` line from this file:
<https://github.com/home-assistant/home-assistant.io/blob/current/source/_integrations/hisense_aehw4a1.markdown>
**Note**: The documentation PR needs to be opened against the `current` branch.
**Note2**: Please leave the actual logo file in the documentation repository. It will be cleaned up differently.
## Additional information
For more information about this repository, read the [README.md](https://github.com/home-assistant/brands/blob/master/README.md) file of this repository. It contains information on how this repository works, and image specification and requirements.
## Codeowner mention
Hi there, @bannhead! Mind taking a look at this issue as it is with an integration (hisense_aehw4a1) you are listed as a [codeowner](https://github.com/home-assistant/core/blob/dev/homeassistant/components/hisense_aehw4a1/manifest.json) for? Thanks!
Resolving this issue is not limited to codeowners! If you want to help us out, feel free to resolve this issue! Thanks already!
| 1.0 | Hisense AEH-W4A1 is missing brand images -
## The problem
The Hisense AEH-W4A1 integration does not have brand images in
this repository.
We recently started this Brands repository, to create a centralized storage of all brand-related images. These images are used on our website and the Home Assistant frontend.
The following images are missing and would ideally be added:
- `src/hisense_aehw4a1/icon.png`
- `src/hisense_aehw4a1/logo.png`
- `src/hisense_aehw4a1/icon@2x.png`
- `src/hisense_aehw4a1/logo@2x.png`
For image specifications and requirements, please see [README.md](https://github.com/home-assistant/brands/blob/master/README.md).
## Updating the documentation repository
Our documentation repository already has a logo for this integration, however, it does not meet the image requirements of this new Brands repository.
If adding images to this repository, please open up a PR to the documentation repository as well, removing the `logo: hisense.png` line from this file:
<https://github.com/home-assistant/home-assistant.io/blob/current/source/_integrations/hisense_aehw4a1.markdown>
**Note**: The documentation PR needs to be opened against the `current` branch.
**Note2**: Please leave the actual logo file in the documentation repository. It will be cleaned up differently.
## Additional information
For more information about this repository, read the [README.md](https://github.com/home-assistant/brands/blob/master/README.md) file of this repository. It contains information on how this repository works, and image specification and requirements.
## Codeowner mention
Hi there, @bannhead! Mind taking a look at this issue as it is with an integration (hisense_aehw4a1) you are listed as a [codeowner](https://github.com/home-assistant/core/blob/dev/homeassistant/components/hisense_aehw4a1/manifest.json) for? Thanks!
Resolving this issue is not limited to codeowners! If you want to help us out, feel free to resolve this issue! Thanks already!
| non_infrastructure | hisense aeh is missing brand images the problem the hisense aeh integration does not have brand images in this repository we recently started this brands repository to create a centralized storage of all brand related images these images are used on our website and the home assistant frontend the following images are missing and would ideally be added src hisense icon png src hisense logo png src hisense icon png src hisense logo png for image specifications and requirements please see updating the documentation repository our documentation repository already has a logo for this integration however it does not meet the image requirements of this new brands repository if adding images to this repository please open up a pr to the documentation repository as well removing the logo hisense png line from this file note the documentation pr needs to be opened against the current branch please leave the actual logo file in the documentation repository it will be cleaned up differently additional information for more information about this repository read the file of this repository it contains information on how this repository works and image specification and requirements codeowner mention hi there bannhead mind taking a look at this issue as it is with an integration hisense you are listed as a for thanks resolving this issue is not limited to codeowners if you want to help us out feel free to resolve this issue thanks already | 0 |
31,148 | 25,371,733,024 | IssuesEvent | 2022-11-21 11:04:12 | Altinn/altinn-platform | https://api.github.com/repos/Altinn/altinn-platform | closed | Remove "old" postgreSQL server from all environments | area/infrastructure | Remove "old" postgreSQL server from all environments from Terraform.
Create a new Tag and deploy to all environments
- [x] AT21
- [x] AT22
- [x] AT23
- [x] AT24
- [x] YT01
- [x] TT02
- [x] PROD | 1.0 | Remove "old" postgreSQL server from all environments - Remove "old" postgreSQL server from all environments from Terraform.
Create a new Tag and deploy to all environments
- [x] AT21
- [x] AT22
- [x] AT23
- [x] AT24
- [x] YT01
- [x] TT02
- [x] PROD | infrastructure | remove old postgresql server from all environments remove old postgresql server from all environments from terraform create a new tag and deploy to all environments prod | 1 |
399,861 | 11,761,892,563 | IssuesEvent | 2020-03-13 23:09:11 | cds-snc/report-a-cybercrime | https://api.github.com/repos/cds-snc/report-a-cybercrime | closed | Remove some unnecessary logging | bug low priority | ## Summary
> The following entry is being logged to standard out at every request, thousands of times a day:
`New Request. {"numberOfSubmissions":0,"numberOfRequests":49,"lastRequested":"2020-03-06T14:33:27.822Z"}
`
## Suggested Fixes
> Reduce the frequency with which this is being logged, or remove it all together if it's determined unvaluable, but it would be nice to see it after every submission to see what the count was up to at that time...
| 1.0 | Remove some unnecessary logging - ## Summary
> The following entry is being logged to standard out at every request, thousands of times a day:
`New Request. {"numberOfSubmissions":0,"numberOfRequests":49,"lastRequested":"2020-03-06T14:33:27.822Z"}
`
## Suggested Fixes
> Reduce the frequency with which this is being logged, or remove it all together if it's determined unvaluable, but it would be nice to see it after every submission to see what the count was up to at that time...
| non_infrastructure | remove some unnecessary logging summary the following entry is being logged to standard out at every request thousands of times a day new request numberofsubmissions numberofrequests lastrequested suggested fixes reduce the frequency with which this is being logged or remove it all together if it s determined unvaluable but it would be nice to see it after every submission to see what the count was up to at that time | 0 |
27,146 | 21,213,553,286 | IssuesEvent | 2022-04-11 03:50:34 | woocommerce/woocommerce | https://api.github.com/repos/woocommerce/woocommerce | opened | Standardize `test` Executor | type: task tool: monorepo infrastructure | <!-- This form is for other issue types specific to the WooCommerce plugin. This is not a support portal. -->
**Prerequisites (mark completed items with an [x]):**
- [x] I have checked that my issue type is not listed here https://github.com/woocommerce/woocommerce/issues/new/choose
- [x] My issue is not a security issue, support request, bug report, enhancement or feature request (Please use the link above if it is).
**Issue Description:**
All of the `test` executors should run unit tests for any language included in a project. [Like the `build` executor](https://github.com/woocommerce/woocommerce/issues/32551), these should use any relevant Nx plugins to better integrate. We should support executing tests using `test-{language}` and then have the `test` executor depend on those languages. They should also depend on the `build` executor so that running tests will automatically build the project when necessary. | 1.0 | Standardize `test` Executor - <!-- This form is for other issue types specific to the WooCommerce plugin. This is not a support portal. -->
**Prerequisites (mark completed items with an [x]):**
- [x] I have checked that my issue type is not listed here https://github.com/woocommerce/woocommerce/issues/new/choose
- [x] My issue is not a security issue, support request, bug report, enhancement or feature request (Please use the link above if it is).
**Issue Description:**
All of the `test` executors should run unit tests for any language included in a project. [Like the `build` executor](https://github.com/woocommerce/woocommerce/issues/32551), these should use any relevant Nx plugins to better integrate. We should support executing tests using `test-{language}` and then have the `test` executor depend on those languages. They should also depend on the `build` executor so that running tests will automatically build the project when necessary. | infrastructure | standardize test executor prerequisites mark completed items with an i have checked that my issue type is not listed here my issue is not a security issue support request bug report enhancement or feature request please use the link above if it is issue description all of the test executors should run unit tests for any language included in a project these should use any relevant nx plugins to better integrate we should support executing tests using test language and then have the test executor depend on those languages they should also depend on the build executor so that running tests will automatically build the project when necessary | 1 |
214,012 | 16,544,565,104 | IssuesEvent | 2021-05-27 21:41:53 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | Question: is there a way to delete the snapshots and keep them too? | Status: Stale Type: Documentation | This is not system-specific: we have several clients with small-ish 1-2TB "data" drives, and we have a storage system with lots of room. What I would like to do is basically incremental backups: snapshot the clients and transfer incremental snapshots to the big box. This is working fine except
* I need to delete old snapshots on the clients to keep disk usage there down
* and I want to keep them on the big box because that's the point.
-- And that's the part I can't get to work: `send -R`/`receive -F` deletes old snapshots on the receiving end. Without them I get
> cannot receive incremental stream: destination has been modified since most recent snapshot
Even `receive -u` does that when the storage system flips from one controller to another (it's a dual-headed setup) -- and `-u` is already suboptimal as you can't browse snapshots, you have to pick one and clone it to browse the files.
So the question is, is there a way around `destination has been modified since most recent snapshot` that I am not aware of? Or is this just not doable?
TIA
| 1.0 | Question: is there a way to delete the snapshots and keep them too? - This is not system-specific: we have several clients with small-ish 1-2TB "data" drives, and we have a storage system with lots of room. What I would like to do is basically incremental backups: snapshot the clients and transfer incremental snapshots to the big box. This is working fine except
* I need to delete old snapshots on the clients to keep disk usage there down
* and I want to keep them on the big box because that's the point.
-- And that's the part I can't get to work: `send -R`/`receive -F` deletes old snapshots on the receiving end. Without them I get
> cannot receive incremental stream: destination has been modified since most recent snapshot
Even `receive -u` does that when the storage system flips from one controller to another (it's a dual-headed setup) -- and `-u` is already suboptimal as you can't browse snapshots, you have to pick one and clone it to browse the files.
So the question is, is there a way around `destination has been modified since most recent snapshot` that I am not aware of? Or is this just not doable?
TIA
| non_infrastructure | question is there a way to delete the snapshots and keep them too this is not system specific we have several clients with small ish data drives and we have a storage system with lots of room what i would like to do is basically incremental backups snapshot the clients and transfer incremental snapshots to the big box this is working fine except i need to delete old snapshots on the clients to keep disk usage there down and i want to keep them on the big box because that s the point and that s the part i can t get to work send r receive f deletes old snapshots on the receiving end without them i get cannot receive incremental stream destination has been modified since most recent snapshot even receive u does that when the storage system flips from one controller to another it s a dual headed setup and u is already suboptimal as you can t browse snapshots you have to pick one and clone it to browse the files so the question is is there a way around destination has been modified since most recent snapshot that i am not aware of or is this just not doable tia | 0 |
24,494 | 12,121,498,775 | IssuesEvent | 2020-04-22 09:24:04 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | AZ CLI support for Security Partner Provider | Network Service Team Support Request | **Resource Provider**
NRP (Microsoft.Network)
**Description of Feature or Work Requested**
Security Partner Provider is a new Top Level Resource in NRP which represents the 3rd Party Security Providers in Virtual Hub.
**Minimum API Version Required**
03-01-2020
**Swagger Link**
https://github.com/Azure/azure-rest-api-specs/blob/master/specification/network/resource-manager/Microsoft.Network/stable/2020-03-01/securityPartnerProvider.json
**Target Date**
May 15th
| 1.0 | AZ CLI support for Security Partner Provider - **Resource Provider**
NRP (Microsoft.Network)
**Description of Feature or Work Requested**
Security Partner Provider is a new Top Level Resource in NRP which represents the 3rd Party Security Providers in Virtual Hub.
**Minimum API Version Required**
03-01-2020
**Swagger Link**
https://github.com/Azure/azure-rest-api-specs/blob/master/specification/network/resource-manager/Microsoft.Network/stable/2020-03-01/securityPartnerProvider.json
**Target Date**
May 15th
| non_infrastructure | az cli support for security partner provider resource provider nrp microsoft network description of feature or work requested security partner provider is a new top level resource in nrp which represents the party security providers in virtual hub minimum api version required swagger link target date may | 0 |
29,779 | 24,263,634,115 | IssuesEvent | 2022-09-28 02:50:54 | C7-Game/Prototype | https://api.github.com/repos/C7-Game/Prototype | closed | Copy all resources at once in Git Actions build | good first issue refactor infrastructure | In the Git Actions build (controlled by export-c7.yml), right now there is a step to copy all the resources ("static files"), on lines 61, 107, and 157. But we have to name each individual file. We could do that for Aztec (1 file) and Babylon (3 files), but as we start adding units and other graphics, it will rapidly become unsustainable.
This card is to refactor that YML (and probably our file structure, putting all static files in a sub-folder of the C7 project) so that we don't have to update that file every time we add a new resource/static file.
Optional bonus points for figuring out how to de-duplicate the copying of static files across Windows/Linux, and maybe Mac. Mac does it a little bit differently right now, so it might not be feasible to do so, at least across all three. Ask JimOfLeisure (Puppeteer on CivFanatics) about the details of why the Mac step thinks different in this regard. | 1.0 | Copy all resources at once in Git Actions build - In the Git Actions build (controlled by export-c7.yml), right now there is a step to copy all the resources ("static files"), on lines 61, 107, and 157. But we have to name each individual file. We could do that for Aztec (1 file) and Babylon (3 files), but as we start adding units and other graphics, it will rapidly become unsustainable.
This card is to refactor that YML (and probably our file structure, putting all static files in a sub-folder of the C7 project) so that we don't have to update that file every time we add a new resource/static file.
Optional bonus points for figuring out how to de-duplicate the copying of static files across Windows/Linux, and maybe Mac. Mac does it a little bit differently right now, so it might not be feasible to do so, at least across all three. Ask JimOfLeisure (Puppeteer on CivFanatics) about the details of why the Mac step thinks different in this regard. | infrastructure | copy all resources at once in git actions build in the git actions build controlled by export yml right now there is a step to copy all the resources static files on lines and but we have to name each individual file we could do that for aztec file and babylon files but as we start adding units and other graphics it will rapidly become unsustainable this card is to refactor that yml and probably our file structure putting all static files in a sub folder of the project so that we don t have to update that file every time we add a new resource static file optional bonus points for figuring out how to de duplicate the copying of static files across windows linux and maybe mac mac does it a little bit differently right now so it might not be feasible to do so at least across all three ask jimofleisure puppeteer on civfanatics about the details of why the mac step thinks different in this regard | 1 |
29,307 | 23,903,009,437 | IssuesEvent | 2022-09-08 20:42:29 | evcc-io/evcc | https://api.github.com/repos/evcc-io/evcc | closed | Add Prometheus Exporter | wontfix infrastructure | Voraussetzung wäre eine generelle Lösung, anwendbar auch für https://github.com/evcc-io/evcc/pull/3749
/cc @bboehmke | 1.0 | Add Prometheus Exporter - Voraussetzung wäre eine generelle Lösung, anwendbar auch für https://github.com/evcc-io/evcc/pull/3749
/cc @bboehmke | infrastructure | add prometheus exporter voraussetzung wäre eine generelle lösung anwendbar auch für cc bboehmke | 1 |
88,066 | 15,800,687,377 | IssuesEvent | 2021-04-03 00:49:32 | DamieFC/linucrash | https://api.github.com/repos/DamieFC/linucrash | closed | CVE-2021-29265 (Medium) detected in rasedac_urgent_for_v5.9_rc6 - autoclosed | security vulnerability | ## CVE-2021-29265 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rasedac_urgent_for_v5.9_rc6</b></p></summary>
<p>
<p>Boris & Tony RAS tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/ras/ras.git>https://git.kernel.org/pub/scm/linux/kernel/git/ras/ras.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/DamieFC/linucrash/commit/8654cdcc113be18daef180e2b92a2e20d8270d54">8654cdcc113be18daef180e2b92a2e20d8270d54</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linucrash/drivers/usb/usbip/stub_dev.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.11.7. usbip_sockfd_store in drivers/usb/usbip/stub_dev.c allows attackers to cause a denial of service (GPF) because the stub-up sequence has race conditions during an update of the local and shared status, aka CID-9380afd6df70.
<p>Publish Date: 2021-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29265>CVE-2021-29265</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-29265">https://www.linuxkernelcves.com/cves/CVE-2021-29265</a></p>
<p>Release Date: 2021-03-26</p>
<p>Fix Resolution: v4.4.262, v4.9.262, v4.14.226, v4.19.181, v5.4.106, v5.10.24, v5.11.7, v5.12-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-29265 (Medium) detected in rasedac_urgent_for_v5.9_rc6 - autoclosed - ## CVE-2021-29265 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rasedac_urgent_for_v5.9_rc6</b></p></summary>
<p>
<p>Boris & Tony RAS tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/ras/ras.git>https://git.kernel.org/pub/scm/linux/kernel/git/ras/ras.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/DamieFC/linucrash/commit/8654cdcc113be18daef180e2b92a2e20d8270d54">8654cdcc113be18daef180e2b92a2e20d8270d54</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>linucrash/drivers/usb/usbip/stub_dev.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.11.7. usbip_sockfd_store in drivers/usb/usbip/stub_dev.c allows attackers to cause a denial of service (GPF) because the stub-up sequence has race conditions during an update of the local and shared status, aka CID-9380afd6df70.
<p>Publish Date: 2021-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29265>CVE-2021-29265</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-29265">https://www.linuxkernelcves.com/cves/CVE-2021-29265</a></p>
<p>Release Date: 2021-03-26</p>
<p>Fix Resolution: v4.4.262, v4.9.262, v4.14.226, v4.19.181, v5.4.106, v5.10.24, v5.11.7, v5.12-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in rasedac urgent for autoclosed cve medium severity vulnerability vulnerable library rasedac urgent for boris tony ras tree library home page a href found in head commit a href found in base branch master vulnerable source files linucrash drivers usb usbip stub dev c vulnerability details an issue was discovered in the linux kernel before usbip sockfd store in drivers usb usbip stub dev c allows attackers to cause a denial of service gpf because the stub up sequence has race conditions during an update of the local and shared status aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
171,473 | 20,964,122,795 | IssuesEvent | 2022-03-28 03:46:35 | nvenkatesh1/SCA_test_JS | https://api.github.com/repos/nvenkatesh1/SCA_test_JS | reopened | lodash-4.15.0.tgz: 7 vulnerabilities (highest severity is: 9.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.15.0.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-10744](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | lodash-4.15.0.tgz | Direct | 4.17.12 | ✅ |
| [CVE-2020-8203](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.4 | lodash-4.15.0.tgz | Direct | 4.17.9 | ✅ |
| [CVE-2021-23337](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | lodash-4.15.0.tgz | Direct | 4.17.21 | ✅ |
| [CVE-2019-1010266](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-4.15.0.tgz | Direct | 4.17.11 | ✅ |
| [CVE-2018-3721](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3721) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-4.15.0.tgz | Direct | 4.17.5 | ✅ |
| [CVE-2018-16487](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | lodash-4.15.0.tgz | Direct | 4.17.11 | ✅ |
| [CVE-2020-28500](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | lodash-4.15.0.tgz | Direct | 4.17.21 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10744</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: 4.17.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8203</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: 4.17.9</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23337</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: 4.17.21</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-1010266</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-3721</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3721>CVE-2018-3721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3721">https://nvd.nist.gov/vuln/detail/CVE-2018-3721</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 4.17.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-16487</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-28500</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: 4.17.21</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.12","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-10744","vulnerabilityDetails":"Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.9","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8203","vulnerabilityDetails":"Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.21","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.11","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-1010266","vulnerabilityDetails":"lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.5","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-3721","vulnerabilityDetails":"lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of \"Object\" via __proto__, causing the addition or modification of an existing property that will exist on all objects.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3721","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.11","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-16487","vulnerabilityDetails":"A prototype pollution vulnerability was found in lodash \u003c4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.21","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.\n WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | lodash-4.15.0.tgz: 7 vulnerabilities (highest severity is: 9.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.15.0.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-10744](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | lodash-4.15.0.tgz | Direct | 4.17.12 | ✅ |
| [CVE-2020-8203](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.4 | lodash-4.15.0.tgz | Direct | 4.17.9 | ✅ |
| [CVE-2021-23337](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | lodash-4.15.0.tgz | Direct | 4.17.21 | ✅ |
| [CVE-2019-1010266](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-4.15.0.tgz | Direct | 4.17.11 | ✅ |
| [CVE-2018-3721](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3721) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-4.15.0.tgz | Direct | 4.17.5 | ✅ |
| [CVE-2018-16487](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | lodash-4.15.0.tgz | Direct | 4.17.11 | ✅ |
| [CVE-2020-28500](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | lodash-4.15.0.tgz | Direct | 4.17.21 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10744</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: 4.17.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8203</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.
<p>Publish Date: 2020-07-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203>CVE-2020-8203</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1523">https://www.npmjs.com/advisories/1523</a></p>
<p>Release Date: 2020-07-15</p>
<p>Fix Resolution: 4.17.9</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23337</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: 4.17.21</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-1010266</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-3721</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3721>CVE-2018-3721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3721">https://nvd.nist.gov/vuln/detail/CVE-2018-3721</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 4.17.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-16487</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-28500</summary>
### Vulnerable Library - <b>lodash-4.15.0.tgz</b></p>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz">https://registry.npmjs.org/lodash/-/lodash-4.15.0.tgz</a></p>
<p>Path to dependency file: /app/compilers/react-compiler/package.json</p>
<p>Path to vulnerable library: /app/compilers/react-compiler/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nvenkatesh1/SCA_test_JS/commit/eb47eeefc02a252a76628fec10a3c26aacb34024">eb47eeefc02a252a76628fec10a3c26aacb34024</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: 4.17.21</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.12","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-10744","vulnerabilityDetails":"Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.9","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8203","vulnerabilityDetails":"Prototype pollution attack when using _.zipObjectDeep in lodash before 4.17.20.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8203","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.21","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.11","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-1010266","vulnerabilityDetails":"lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.5","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-3721","vulnerabilityDetails":"lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of \"Object\" via __proto__, causing the addition or modification of an existing property that will exist on all objects.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3721","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.11","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-16487","vulnerabilityDetails":"A prototype pollution vulnerability was found in lodash \u003c4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.15.0","packageFilePaths":["/app/compilers/react-compiler/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.21","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-28500","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.\n WhiteSource Note: After conducting further research, WhiteSource has determined that CVE-2020-28500 only affects environments with versions 4.0.0 to 4.17.20 of Lodash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_infrastructure | lodash tgz vulnerabilities highest severity is vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high lodash tgz direct high lodash tgz direct high lodash tgz direct medium lodash tgz direct medium lodash tgz direct medium lodash tgz direct medium lodash tgz direct details cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details prototype pollution attack when using zipobjectdeep in lodash before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash node module before suffers from a modification of assumed immutable data maid vulnerability via defaultsdeep merge and mergewith functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details a prototype pollution vulnerability was found in lodash where the functions merge mergewith and defaultsdeep can be tricked into adding or modifying properties of object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file app compilers react compiler package json path to vulnerable library app compilers react compiler node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions whitesource note after conducting further research whitesource has determined that cve only affects environments with versions to of lodash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload vulnerabilityurl istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails prototype pollution attack when using zipobjectdeep in lodash before vulnerabilityurl istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to command injection via the template function vulnerabilityurl istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is vulnerabilityurl istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash node module before suffers from a modification of assumed immutable data maid vulnerability via defaultsdeep merge and mergewith functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects vulnerabilityurl istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a prototype pollution vulnerability was found in lodash where the functions merge mergewith and defaultsdeep can be tricked into adding or modifying properties of object prototype vulnerabilityurl istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions n whitesource note after conducting further research whitesource has determined that cve only affects environments with versions to of lodash vulnerabilityurl | 0 |
71,935 | 13,764,352,036 | IssuesEvent | 2020-10-07 11:57:08 | GoogleCloudPlatform/spring-cloud-gcp | https://api.github.com/repos/GoogleCloudPlatform/spring-cloud-gcp | opened | Update GHActions to remove vuln warning | P3 code-quality dependencies | Our GHActions are spitting out warnings about `add-path` and `set-env`:
> The `add-path` command is deprecated and will be disabled soon. Please upgrade to using Environment Files. For more information see: https://github.blog/changelog/2020-10-01-github-actions-deprecating-set-env-and-add-path-commands/
The fix may be as easy as just bumping the versions of the steps we're using, but needs some investigation on the Environment Files feature. | 1.0 | Update GHActions to remove vuln warning - Our GHActions are spitting out warnings about `add-path` and `set-env`:
> The `add-path` command is deprecated and will be disabled soon. Please upgrade to using Environment Files. For more information see: https://github.blog/changelog/2020-10-01-github-actions-deprecating-set-env-and-add-path-commands/
The fix may be as easy as just bumping the versions of the steps we're using, but needs some investigation on the Environment Files feature. | non_infrastructure | update ghactions to remove vuln warning our ghactions are spitting out warnings about add path and set env the add path command is deprecated and will be disabled soon please upgrade to using environment files for more information see the fix may be as easy as just bumping the versions of the steps we re using but needs some investigation on the environment files feature | 0 |
17,744 | 12,532,777,171 | IssuesEvent | 2020-06-04 16:28:19 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Fix warning 'Executable bit is not set on target script, sourcing instead of executing.' | External area-infrastructure | Part of https://github.com/dotnet/aspnetcore/issues/22240
Happens during 'Setup Private Feed Credentials' on non-windows builds. @dougbu claims this will be fixed by the next Arcade update.
Full warning text:
> ##[warning]Executable bit is not set on target script, sourcing instead of executing. More info at https://github.com/Microsoft/azure-pipelines-tasks/blob/master/docs/bashnote.md | 1.0 | Fix warning 'Executable bit is not set on target script, sourcing instead of executing.' - Part of https://github.com/dotnet/aspnetcore/issues/22240
Happens during 'Setup Private Feed Credentials' on non-windows builds. @dougbu claims this will be fixed by the next Arcade update.
Full warning text:
> ##[warning]Executable bit is not set on target script, sourcing instead of executing. More info at https://github.com/Microsoft/azure-pipelines-tasks/blob/master/docs/bashnote.md | infrastructure | fix warning executable bit is not set on target script sourcing instead of executing part of happens during setup private feed credentials on non windows builds dougbu claims this will be fixed by the next arcade update full warning text executable bit is not set on target script sourcing instead of executing more info at | 1 |
10,764 | 8,712,106,418 | IssuesEvent | 2018-12-06 21:12:28 | eventespresso/event-espresso-core | https://api.github.com/repos/eventespresso/event-espresso-core | closed | Fix failing unit test build in master | category:models-and-data-infrastructure category:unit-tests priority:high type:bug 🐞 | <!--
BEFORE POSTING YOUR ISSUE:
- These comments won't show up when you submit the issue.
- Please ensure that what you are reporting is specific to this project.
- Try to add as much detail as possible. Be specific!
- Make sure you read the README.md for the project regarding posting issues.
- Search this repository for issues and pull requests and whether it has been fixed or reported already.
- Ensure you are using the latest code before reporting bugs (unless you are reporting an issue disovered in a branch).
- Disable all plugins and switch to a default theme to ensure its not a plugin/theme conflict issue.
- To report a security issue, please visit this page: https://eventespresso.com/report-a-security-vulnerability/
-->
## Issue Overview
<!-- Describe what this issue is about. -->
There is a failing unit test build being [reported for master](https://travis-ci.org/eventespresso/event-espresso-core/jobs/463442564) and it looks like a test that was introduced with the password protection work recently merged in.
@mnelson4 I've assigned this to you because it should be fixed asap and merged into master so that new pulls based off master or existing pulls bringing in master changes don't have failing test runs.
| 1.0 | Fix failing unit test build in master - <!--
BEFORE POSTING YOUR ISSUE:
- These comments won't show up when you submit the issue.
- Please ensure that what you are reporting is specific to this project.
- Try to add as much detail as possible. Be specific!
- Make sure you read the README.md for the project regarding posting issues.
- Search this repository for issues and pull requests and whether it has been fixed or reported already.
- Ensure you are using the latest code before reporting bugs (unless you are reporting an issue disovered in a branch).
- Disable all plugins and switch to a default theme to ensure its not a plugin/theme conflict issue.
- To report a security issue, please visit this page: https://eventespresso.com/report-a-security-vulnerability/
-->
## Issue Overview
<!-- Describe what this issue is about. -->
There is a failing unit test build being [reported for master](https://travis-ci.org/eventespresso/event-espresso-core/jobs/463442564) and it looks like a test that was introduced with the password protection work recently merged in.
@mnelson4 I've assigned this to you because it should be fixed asap and merged into master so that new pulls based off master or existing pulls bringing in master changes don't have failing test runs.
| infrastructure | fix failing unit test build in master before posting your issue these comments won t show up when you submit the issue please ensure that what you are reporting is specific to this project try to add as much detail as possible be specific make sure you read the readme md for the project regarding posting issues search this repository for issues and pull requests and whether it has been fixed or reported already ensure you are using the latest code before reporting bugs unless you are reporting an issue disovered in a branch disable all plugins and switch to a default theme to ensure its not a plugin theme conflict issue to report a security issue please visit this page issue overview there is a failing unit test build being and it looks like a test that was introduced with the password protection work recently merged in i ve assigned this to you because it should be fixed asap and merged into master so that new pulls based off master or existing pulls bringing in master changes don t have failing test runs | 1 |
21,987 | 11,660,549,314 | IssuesEvent | 2020-03-03 03:43:30 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | VZD: Changed Records Processing | Product: Vision Zero Crash Data System Project: Vision Zero Crash Data System Service: Dev Type: Data Workgroup: VZ migrated | The incoming record changes are stored as a json object in the database; where they show up in a queue where they can be marked as processed. Once marked as processed, we are at the risk the same records will end up in the queue again, since the ETL process will request all records from a 3-day window, where the same record could appear again and since it carries the same differences it will be inserted in the review queue again.
These are some ideas to overcome that issue:
Keeping the records in the database permanently: If the record already exists in the queue, it will not be inserted. We could keep the records in the database permanently; the only risk is to fill up the database with thousands of unnecessary records.
Removing records after some time: We could leave the records there for some time, more than 3 days. This would block the same changes from showing up in the queue, and also solve the problem of keeping the records forever. The only challenge is to write another ETL process that removes all processed records after X amount of time.
*Migrated from [atd-vz-data #561](https://github.com/cityofaustin/atd-vz-data/issues/561)* | 1.0 | VZD: Changed Records Processing - The incoming record changes are stored as a json object in the database; where they show up in a queue where they can be marked as processed. Once marked as processed, we are at the risk the same records will end up in the queue again, since the ETL process will request all records from a 3-day window, where the same record could appear again and since it carries the same differences it will be inserted in the review queue again.
These are some ideas to overcome that issue:
Keeping the records in the database permanently: If the record already exists in the queue, it will not be inserted. We could keep the records in the database permanently; the only risk is to fill up the database with thousands of unnecessary records.
Removing records after some time: We could leave the records there for some time, more than 3 days. This would block the same changes from showing up in the queue, and also solve the problem of keeping the records forever. The only challenge is to write another ETL process that removes all processed records after X amount of time.
*Migrated from [atd-vz-data #561](https://github.com/cityofaustin/atd-vz-data/issues/561)* | non_infrastructure | vzd changed records processing the incoming record changes are stored as a json object in the database where they show up in a queue where they can be marked as processed once marked as processed we are at the risk the same records will end up in the queue again since the etl process will request all records from a day window where the same record could appear again and since it carries the same differences it will be inserted in the review queue again these are some ideas to overcome that issue keeping the records in the database permanently if the record already exists in the queue it will not be inserted we could keep the records in the database permanently the only risk is to fill up the database with thousands of unnecessary records removing records after some time we could leave the records there for some time more than days this would block the same changes from showing up in the queue and also solve the problem of keeping the records forever the only challenge is to write another etl process that removes all processed records after x amount of time migrated from | 0 |
711,959 | 24,480,659,994 | IssuesEvent | 2022-10-08 19:44:05 | json-schema-org/json-schema-spec | https://api.github.com/repos/json-schema-org/json-schema-spec | closed | Reverse direction of "contains" <-> "minContains" / "maxContains" dependency | Priority: High Type: Bug core annotation validation | Note: Other folks (@jdesrosiers ? @karenetheridge ?) came up with this a while ago and apparently I objected to it (which I 100% believe but no longer recall the reason).
JSON Schema has an architectural principle that individual assertion keywords that fail cannot be un-failed. While the assertion result can be manipulated at the schema object level (e.g. by `not` or `oneOf`, which pass when one or more subschemas fail), doing so at the individual keyword level violates the principles of a layered constraint system.
This means that a keyword can only produce an assertion result if it has all of the information necessary to determine the final result. Only `contains` can meet this criteria out of these three keywords, and only if it knows the values of `minContains` and `maxContains`.
This means that `minContains` and `maxContains` cannot produce a failed assertion result. They only exist to provide extra input to `contains`.
One subtlety is that since we describe interactions in terms of annotations (even though they do not need to be implemented that way), and because the absence of a keyword _cannot_ produce an annotation ([§7.3 ¶2](https://www.ietf.org/archive/id/draft-bhutton-json-schema-01.html#name-default-behaviors)), this means that the default `minContains` behavior of `1` must be specified as how `contains` behaves in the absence of `minContains`, not simply as the default value of `minContains`.
To make the behavior of this group of keywords clear, and because `minContains` and `maxContains` no longer have assertion-failing behavior, they should be moved to the applicator vocabulary with `contains`. | 1.0 | Reverse direction of "contains" <-> "minContains" / "maxContains" dependency - Note: Other folks (@jdesrosiers ? @karenetheridge ?) came up with this a while ago and apparently I objected to it (which I 100% believe but no longer recall the reason).
JSON Schema has an architectural principle that individual assertion keywords that fail cannot be un-failed. While the assertion result can be manipulated at the schema object level (e.g. by `not` or `oneOf`, which pass when one or more subschemas fail), doing so at the individual keyword level violates the principles of a layered constraint system.
This means that a keyword can only produce an assertion result if it has all of the information necessary to determine the final result. Only `contains` can meet this criteria out of these three keywords, and only if it knows the values of `minContains` and `maxContains`.
This means that `minContains` and `maxContains` cannot produce a failed assertion result. They only exist to provide extra input to `contains`.
One subtlety is that since we describe interactions in terms of annotations (even though they do not need to be implemented that way), and because the absence of a keyword _cannot_ produce an annotation ([§7.3 ¶2](https://www.ietf.org/archive/id/draft-bhutton-json-schema-01.html#name-default-behaviors)), this means that the default `minContains` behavior of `1` must be specified as how `contains` behaves in the absence of `minContains`, not simply as the default value of `minContains`.
To make the behavior of this group of keywords clear, and because `minContains` and `maxContains` no longer have assertion-failing behavior, they should be moved to the applicator vocabulary with `contains`. | non_infrastructure | reverse direction of contains mincontains maxcontains dependency note other folks jdesrosiers karenetheridge came up with this a while ago and apparently i objected to it which i believe but no longer recall the reason json schema has an architectural principle that individual assertion keywords that fail cannot be un failed while the assertion result can be manipulated at the schema object level e g by not or oneof which pass when one or more subschemas fail doing so at the individual keyword level violates the principles of a layered constraint system this means that a keyword can only produce an assertion result if it has all of the information necessary to determine the final result only contains can meet this criteria out of these three keywords and only if it knows the values of mincontains and maxcontains this means that mincontains and maxcontains cannot produce a failed assertion result they only exist to provide extra input to contains one subtlety is that since we describe interactions in terms of annotations even though they do not need to be implemented that way and because the absence of a keyword cannot produce an annotation this means that the default mincontains behavior of must be specified as how contains behaves in the absence of mincontains not simply as the default value of mincontains to make the behavior of this group of keywords clear and because mincontains and maxcontains no longer have assertion failing behavior they should be moved to the applicator vocabulary with contains | 0 |
17,487 | 3,358,242,359 | IssuesEvent | 2015-11-19 08:21:01 | ramu2016/Q5JAHXVYKMVQJYCRJE6A4ZXH | https://api.github.com/repos/ramu2016/Q5JAHXVYKMVQJYCRJE6A4ZXH | closed | pEMY80EF79eXKa3wokG+8dUFXqAxWDrhN9BMDNbV+lHfd3iU2DUsg1eWOue5Yn6VcXezu+0VjqK0Vb/648OdWihaMxu96A42fsH0uKQ/hXW8QHC9Ri4zhJVQzvAiy0gffeL/kVJe6muXij9ZSrhmLvmIAIoQ9T26ZJwtZmsyzp0= | design | /TTGLigAdRJauBrxJBy0XKFCf/lmJJJ4BwVQ8SioqGyPofRRgrpbIroMKzK8fbyb8nrjTsToRzK0dOETn+d8V6dQCj3qLdzVfLByBifDT0datEVE8buPaDRNBaL64AuV2/QaIiASySYjQMnXLN/+mmI1W/TeIqaOsPqPjZCLhrlK8X7QIIVPhdDQzz1d7/zMC15qE/pxYvIs9wAWp0PRuX1XKs+Y2qBQCo6vH8s8QjLbVQt7h1AFtl7Q84ILNfJyF7b0kg+qpXCZntMWvTVgeswN2Btb5MX9yVZdd7oNyvfjaFGuhW8Lbnwjz5Bf2c2Z6DSuow+kEUCI81Qcl1aqi0p7FFOeaJeIRhTCZ24FXF6unbnwKSkM0XtgXfR8/eeB7rbQFoC0cOsQkjZFJ2CIdA37ytK8qFEm4DuTzBEAnrUK+VFEXlGdPIAMKQqGL+QsI5RGvY9UtndUsSCQ5l/EqcZy3pUbXQHSjhe8Xo1E2nLHsUDDgUcOV5MYVSaF9N749GdNsvtlvjZTPYgbBuQrLFqaoVOPJlSjCbaSViG9xuH54K87usM/Yup/Z3PbH396zvoGJAYuNo3oWi1LU/6lDOcHWroQykjJnI/knOPGsx1FX/0IPV/t6MbaZDtPONWfYTyk082Vre+f2kF+xw2avVhxJYwrbQdKtPlyRbFwxOKY27gR+5Kh6+5q7+NSkRoiMnJZ1gISxRlKL4uRTawJXkn202FpBKeA/6WulHR2P5BUXV3whWSNLx4DZP7o5jl+7/4L4hf/AwQIQpW1R5nMPQ== | 1.0 | pEMY80EF79eXKa3wokG+8dUFXqAxWDrhN9BMDNbV+lHfd3iU2DUsg1eWOue5Yn6VcXezu+0VjqK0Vb/648OdWihaMxu96A42fsH0uKQ/hXW8QHC9Ri4zhJVQzvAiy0gffeL/kVJe6muXij9ZSrhmLvmIAIoQ9T26ZJwtZmsyzp0= - /TTGLigAdRJauBrxJBy0XKFCf/lmJJJ4BwVQ8SioqGyPofRRgrpbIroMKzK8fbyb8nrjTsToRzK0dOETn+d8V6dQCj3qLdzVfLByBifDT0datEVE8buPaDRNBaL64AuV2/QaIiASySYjQMnXLN/+mmI1W/TeIqaOsPqPjZCLhrlK8X7QIIVPhdDQzz1d7/zMC15qE/pxYvIs9wAWp0PRuX1XKs+Y2qBQCo6vH8s8QjLbVQt7h1AFtl7Q84ILNfJyF7b0kg+qpXCZntMWvTVgeswN2Btb5MX9yVZdd7oNyvfjaFGuhW8Lbnwjz5Bf2c2Z6DSuow+kEUCI81Qcl1aqi0p7FFOeaJeIRhTCZ24FXF6unbnwKSkM0XtgXfR8/eeB7rbQFoC0cOsQkjZFJ2CIdA37ytK8qFEm4DuTzBEAnrUK+VFEXlGdPIAMKQqGL+QsI5RGvY9UtndUsSCQ5l/EqcZy3pUbXQHSjhe8Xo1E2nLHsUDDgUcOV5MYVSaF9N749GdNsvtlvjZTPYgbBuQrLFqaoVOPJlSjCbaSViG9xuH54K87usM/Yup/Z3PbH396zvoGJAYuNo3oWi1LU/6lDOcHWroQykjJnI/knOPGsx1FX/0IPV/t6MbaZDtPONWfYTyk082Vre+f2kF+xw2avVhxJYwrbQdKtPlyRbFwxOKY27gR+5Kh6+5q7+NSkRoiMnJZ1gISxRlKL4uRTawJXkn202FpBKeA/6WulHR2P5BUXV3whWSNLx4DZP7o5jl+7/4L4hf/AwQIQpW1R5nMPQ== | non_infrastructure | qaiiasysyjqmnxln vfexlgdpiamkqqgl yup | 0 |
7,138 | 9,423,481,846 | IssuesEvent | 2019-04-11 12:00:19 | ionic-team/capacitor | https://api.github.com/repos/ionic-team/capacitor | closed | Background fetch not working | known incompatible cordova plugin | Hi there! I know capacitor has a way to finish a job called Background Task, but I would like to retrieve the geolocation of the device once in a while.
Basically, make [cordova-plugin-background-fetch](https://github.com/transistorsoft/cordova-plugin-background-fetch) but for some reason, it doesn't work.
I get the log where it gets sent to cordova but the plugin still doesn't work when I do `Debug->Simulate Background Fetch`.
Any ideas or alternative for this?
Thank you! | True | Background fetch not working - Hi there! I know capacitor has a way to finish a job called Background Task, but I would like to retrieve the geolocation of the device once in a while.
Basically, make [cordova-plugin-background-fetch](https://github.com/transistorsoft/cordova-plugin-background-fetch) but for some reason, it doesn't work.
I get the log where it gets sent to cordova but the plugin still doesn't work when I do `Debug->Simulate Background Fetch`.
Any ideas or alternative for this?
Thank you! | non_infrastructure | background fetch not working hi there i know capacitor has a way to finish a job called background task but i would like to retrieve the geolocation of the device once in a while basically make but for some reason it doesn t work i get the log where it gets sent to cordova but the plugin still doesn t work when i do debug simulate background fetch any ideas or alternative for this thank you | 0 |
7,154 | 6,797,176,016 | IssuesEvent | 2017-11-01 21:42:57 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | We should point to the release/2.0.0 version of standard | area-Infrastructure | We are not planning to ship a new stable version of the NETStandard.Library package in the 2.1 timeframe so we need to stick with what is currently shipping from the release/2.0.0 branch in standard repo. | 1.0 | We should point to the release/2.0.0 version of standard - We are not planning to ship a new stable version of the NETStandard.Library package in the 2.1 timeframe so we need to stick with what is currently shipping from the release/2.0.0 branch in standard repo. | infrastructure | we should point to the release version of standard we are not planning to ship a new stable version of the netstandard library package in the timeframe so we need to stick with what is currently shipping from the release branch in standard repo | 1 |
37,089 | 8,229,998,649 | IssuesEvent | 2018-09-07 11:19:50 | contao/core | https://api.github.com/repos/contao/core | closed | Remove support for deprecated user password hashes | defect | We should remove support for sha1 passwords in https://github.com/contao/core/blob/4539b50fd849dda41c58cdf0da2230dffd909c94/system/modules/core/library/Contao/User.php#L383-L388
If someone gets read access to the database, they could brute-force the password of a backend user that has still a sha1 password hash. With the password they could then overtake the server.
Removing support shouldn’t be a problem as it only affects users that didn’t log in for a very long time. | 1.0 | Remove support for deprecated user password hashes - We should remove support for sha1 passwords in https://github.com/contao/core/blob/4539b50fd849dda41c58cdf0da2230dffd909c94/system/modules/core/library/Contao/User.php#L383-L388
If someone gets read access to the database, they could brute-force the password of a backend user that has still a sha1 password hash. With the password they could then overtake the server.
Removing support shouldn’t be a problem as it only affects users that didn’t log in for a very long time. | non_infrastructure | remove support for deprecated user password hashes we should remove support for passwords in if someone gets read access to the database they could brute force the password of a backend user that has still a password hash with the password they could then overtake the server removing support shouldn’t be a problem as it only affects users that didn’t log in for a very long time | 0 |
338,590 | 10,232,020,618 | IssuesEvent | 2019-08-18 14:23:15 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | [Coverity CID :203441]Null pointer dereferences in /subsys/bluetooth/mesh/transport.c | Coverity area: Bluetooth bug priority: medium | Static code scan issues seen in File: /subsys/bluetooth/mesh/transport.c
Category: Null pointer dereferences
Function: bt_mesh_heartbeat_send
Component: Bluetooth
CID: 203441
Please fix or provide comments to square it off in coverity in the link: https://scan9.coverity.com/reports.htm#v32951/p12996 | 1.0 | [Coverity CID :203441]Null pointer dereferences in /subsys/bluetooth/mesh/transport.c - Static code scan issues seen in File: /subsys/bluetooth/mesh/transport.c
Category: Null pointer dereferences
Function: bt_mesh_heartbeat_send
Component: Bluetooth
CID: 203441
Please fix or provide comments to square it off in coverity in the link: https://scan9.coverity.com/reports.htm#v32951/p12996 | non_infrastructure | null pointer dereferences in subsys bluetooth mesh transport c static code scan issues seen in file subsys bluetooth mesh transport c category null pointer dereferences function bt mesh heartbeat send component bluetooth cid please fix or provide comments to square it off in coverity in the link | 0 |
29,402 | 23,985,640,545 | IssuesEvent | 2022-09-13 18:47:57 | cds-snc/scan-files | https://api.github.com/repos/cds-snc/scan-files | closed | Create `WARNING` CloudWatch Alarm metric for `is_clamd_running` function | Infrastructure OKR | # Summary
The [`is_clamd_running` function](https://github.com/cds-snc/scan-files/blob/d8f442275d850ca7394858f3f53332ed3d9249e0/api/clamav_scanner/clamav.py#L323-L341) can have a socket timeout occur when attempting to check if ClamAV daemon is running. This should not be an error condition and is handled as expected by the calling function by triggering the start of the ClamAV daemon process.
As part of this change, we'll add a new CloudWatch alarm metric filter on log warnings to ensure we don't miss a case where the daemon is unable to start.
# Related
* cds-snc/platform-core-services#119 | 1.0 | Create `WARNING` CloudWatch Alarm metric for `is_clamd_running` function - # Summary
The [`is_clamd_running` function](https://github.com/cds-snc/scan-files/blob/d8f442275d850ca7394858f3f53332ed3d9249e0/api/clamav_scanner/clamav.py#L323-L341) can have a socket timeout occur when attempting to check if ClamAV daemon is running. This should not be an error condition and is handled as expected by the calling function by triggering the start of the ClamAV daemon process.
As part of this change, we'll add a new CloudWatch alarm metric filter on log warnings to ensure we don't miss a case where the daemon is unable to start.
# Related
* cds-snc/platform-core-services#119 | infrastructure | create warning cloudwatch alarm metric for is clamd running function summary the can have a socket timeout occur when attempting to check if clamav daemon is running this should not be an error condition and is handled as expected by the calling function by triggering the start of the clamav daemon process as part of this change we ll add a new cloudwatch alarm metric filter on log warnings to ensure we don t miss a case where the daemon is unable to start related cds snc platform core services | 1 |
7,966 | 7,164,607,982 | IssuesEvent | 2018-01-29 11:50:27 | openpaperwork/paperwork | https://api.github.com/repos/openpaperwork/paperwork | closed | Brocken download link | blocking bug infrastructure | On this page
https://openpaper.work/fr/
the linux dowload point here:
https://github.com/openpaperwor//paperwork/#installation
but it should be:
https://github.com/openpaperwork/paperwork/#installation
a 'k' is missing ... | 1.0 | Brocken download link - On this page
https://openpaper.work/fr/
the linux dowload point here:
https://github.com/openpaperwor//paperwork/#installation
but it should be:
https://github.com/openpaperwork/paperwork/#installation
a 'k' is missing ... | infrastructure | brocken download link on this page the linux dowload point here but it should be a k is missing | 1 |
5,102 | 7,714,982,817 | IssuesEvent | 2018-05-23 05:34:21 | PrinceOfAmber/Cyclic | https://api.github.com/repos/PrinceOfAmber/Cyclic | closed | Cyclic Block Placer deletes Better with Mods mini blocks instead of placing them | bug: gameplay done [pending release] mod compatibility | Minecraft version & Mod Version:
Minecraft 1.12.2
Cyclic 1.15.3
Better With Mods 1.18
Single player or Server:
Both
Describe problem (what you were doing / what happened):
Block Placer deletes Better With Mods Mini Blocks instead of placing them.
Mini blocks are siding, moulding, and corners.
Crash log (if any):
None
Originally posted on the SevTech issue tracker. https://github.com/DarkPacks/SevTech-Ages/issues/2538
Maybe provide a block placer blacklist in the config?
| True | Cyclic Block Placer deletes Better with Mods mini blocks instead of placing them - Minecraft version & Mod Version:
Minecraft 1.12.2
Cyclic 1.15.3
Better With Mods 1.18
Single player or Server:
Both
Describe problem (what you were doing / what happened):
Block Placer deletes Better With Mods Mini Blocks instead of placing them.
Mini blocks are siding, moulding, and corners.
Crash log (if any):
None
Originally posted on the SevTech issue tracker. https://github.com/DarkPacks/SevTech-Ages/issues/2538
Maybe provide a block placer blacklist in the config?
| non_infrastructure | cyclic block placer deletes better with mods mini blocks instead of placing them minecraft version mod version minecraft cyclic better with mods single player or server both describe problem what you were doing what happened block placer deletes better with mods mini blocks instead of placing them mini blocks are siding moulding and corners crash log if any none originally posted on the sevtech issue tracker maybe provide a block placer blacklist in the config | 0 |
32,432 | 26,695,578,327 | IssuesEvent | 2023-01-27 10:04:09 | 10up/plugin-check | https://api.github.com/repos/10up/plugin-check | closed | Create Checks class | [Type] Enhancement Infrastructure 15 Milestone 1 | ## Description
The Checks class will be the main class for running checks against a plugin. This class contains all the logic to collect the Plugin and Check contexts, run Preparations ahead of checks, loop over and run all Checks and collect and return the results.
Containing this logic within a single class decoupled from I/O allows this class to be used in the different contexts in which checks can run, such as WP-CLI or in the WordPress admin, without duplicating efforts and logic which is described more in detail in the [Check Orchestration and Execution Approach](https://docs.google.com/document/d/1Mge9i2_EMH7IEJD37vWXX9Uzyaz-p9awD1pI4AQ76Rg/edit?resourcekey=0-y7fxvr6cmxv_QW5xPylGcg#heading=h.d8g2nxbaaltl).
The class will contain a method to return all available checks that can be run against the plugin, which is filterable so developers can extend/modify which checks should run.
Additionally, a method to run a set of checks (by default all checks) should be provided, so the entire suite of checks can be used or a plugin can be tested against one check alone as checks are provided as a list. The method can iterate through the list of checks and execute them. For example, it allows running a single check when a CLI command is executed with one check to test for a plugin and it also allows running a single check as part of running all checks for a plugin when a CLI command or even AJAX requests is initiated to test a plugin for all checks.
The Checks class is also responsible for preparation work ahead of running tests and cleanup after tests have run.
## Acceptance Criteria
- `Checks` class is created and exists at `includes/Checker`
- Protected property `$check_context` should be there which is an instance of `Check_Context`
- Constructor receives the `$plugin_main_file` as an argument
- Method `get_checks` should be created as public and returns the list of checks
- Method `run_check_with_result` should be created as protected and receives `Check $check` and `Check_Result $check_result` as an arguments.
- Method `run_checks` should be created as public and accepts a single parameter `array $checks` which is an array of the check class names to run. The method will loop over the `$checks` array and run each check by calling `run_check_with_result`.
## Tests Coverage
- `get_checks` method returns the list of expected checks
- `run_check_with_result` runs expected check and result is stored as expected
- `run_checks` runs the expected checks based on the parameter passed | 1.0 | Create Checks class - ## Description
The Checks class will be the main class for running checks against a plugin. This class contains all the logic to collect the Plugin and Check contexts, run Preparations ahead of checks, loop over and run all Checks and collect and return the results.
Containing this logic within a single class decoupled from I/O allows this class to be used in the different contexts in which checks can run, such as WP-CLI or in the WordPress admin, without duplicating efforts and logic which is described more in detail in the [Check Orchestration and Execution Approach](https://docs.google.com/document/d/1Mge9i2_EMH7IEJD37vWXX9Uzyaz-p9awD1pI4AQ76Rg/edit?resourcekey=0-y7fxvr6cmxv_QW5xPylGcg#heading=h.d8g2nxbaaltl).
The class will contain a method to return all available checks that can be run against the plugin, which is filterable so developers can extend/modify which checks should run.
Additionally, a method to run a set of checks (by default all checks) should be provided, so the entire suite of checks can be used or a plugin can be tested against one check alone as checks are provided as a list. The method can iterate through the list of checks and execute them. For example, it allows running a single check when a CLI command is executed with one check to test for a plugin and it also allows running a single check as part of running all checks for a plugin when a CLI command or even AJAX requests is initiated to test a plugin for all checks.
The Checks class is also responsible for preparation work ahead of running tests and cleanup after tests have run.
## Acceptance Criteria
- `Checks` class is created and exists at `includes/Checker`
- Protected property `$check_context` should be there which is an instance of `Check_Context`
- Constructor receives the `$plugin_main_file` as an argument
- Method `get_checks` should be created as public and returns the list of checks
- Method `run_check_with_result` should be created as protected and receives `Check $check` and `Check_Result $check_result` as an arguments.
- Method `run_checks` should be created as public and accepts a single parameter `array $checks` which is an array of the check class names to run. The method will loop over the `$checks` array and run each check by calling `run_check_with_result`.
## Tests Coverage
- `get_checks` method returns the list of expected checks
- `run_check_with_result` runs expected check and result is stored as expected
- `run_checks` runs the expected checks based on the parameter passed | infrastructure | create checks class description the checks class will be the main class for running checks against a plugin this class contains all the logic to collect the plugin and check contexts run preparations ahead of checks loop over and run all checks and collect and return the results containing this logic within a single class decoupled from i o allows this class to be used in the different contexts in which checks can run such as wp cli or in the wordpress admin without duplicating efforts and logic which is described more in detail in the the class will contain a method to return all available checks that can be run against the plugin which is filterable so developers can extend modify which checks should run additionally a method to run a set of checks by default all checks should be provided so the entire suite of checks can be used or a plugin can be tested against one check alone as checks are provided as a list the method can iterate through the list of checks and execute them for example it allows running a single check when a cli command is executed with one check to test for a plugin and it also allows running a single check as part of running all checks for a plugin when a cli command or even ajax requests is initiated to test a plugin for all checks the checks class is also responsible for preparation work ahead of running tests and cleanup after tests have run acceptance criteria checks class is created and exists at includes checker protected property check context should be there which is an instance of check context constructor receives the plugin main file as an argument method get checks should be created as public and returns the list of checks method run check with result should be created as protected and receives check check and check result check result as an arguments method run checks should be created as public and accepts a single parameter array checks which is an array of the check class names to run the method will loop over the checks array and run each check by calling run check with result tests coverage get checks method returns the list of expected checks run check with result runs expected check and result is stored as expected run checks runs the expected checks based on the parameter passed | 1 |
13,172 | 10,133,806,725 | IssuesEvent | 2019-08-02 05:09:49 | oppia/oppia-android | https://api.github.com/repos/oppia/oppia-android | opened | Logging system | Priority: Essential Status: Blocked Type: Improvement Where: Infrastructure | There should be an easy-to-use (preferable via fluent pattern) logging system on top of logcat that will be used throughout the app. This should log to a local file specific for the app so that app-level logs can be uploaded with user feedback reports. It's highly preferable to use an existing logging API if one is available rather than building this from scratch. | 1.0 | Logging system - There should be an easy-to-use (preferable via fluent pattern) logging system on top of logcat that will be used throughout the app. This should log to a local file specific for the app so that app-level logs can be uploaded with user feedback reports. It's highly preferable to use an existing logging API if one is available rather than building this from scratch. | infrastructure | logging system there should be an easy to use preferable via fluent pattern logging system on top of logcat that will be used throughout the app this should log to a local file specific for the app so that app level logs can be uploaded with user feedback reports it s highly preferable to use an existing logging api if one is available rather than building this from scratch | 1 |
9,084 | 3,254,095,602 | IssuesEvent | 2015-10-19 22:03:35 | mbraceproject/MBrace.Core | https://api.github.com/repos/mbraceproject/MBrace.Core | opened | Document high level abstractions on website | documentation | A quick high level guide of the different abstractions should be provided on the website, including what each abstraction does and the typical use cases for it. Ideally some simple code examples should be provided as well. | 1.0 | Document high level abstractions on website - A quick high level guide of the different abstractions should be provided on the website, including what each abstraction does and the typical use cases for it. Ideally some simple code examples should be provided as well. | non_infrastructure | document high level abstractions on website a quick high level guide of the different abstractions should be provided on the website including what each abstraction does and the typical use cases for it ideally some simple code examples should be provided as well | 0 |
6,341 | 14,268,585,441 | IssuesEvent | 2020-11-20 22:48:39 | octue/octue-sdk-python | https://api.github.com/repos/octue/octue-sdk-python | closed | CLI raises TypeError when running an app from IDE | architecture decision needed dependencies devops experience (UX) | While running octue 0.1.3 app from IDE:
```
python app.py run
```
Traceback (most recent call last):
File "app.py", line 56, in <module>
octue_cli(args)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 1256, in invoke
Command.invoke(self, ctx)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/decorators.py", line 21, in new_func
return f(get_current_context(), *args, **kwargs)
TypeError: octue_cli() missing 3 required positional arguments: 'data_dir', 'input_dir', and 'tmp_dir' | 1.0 | CLI raises TypeError when running an app from IDE - While running octue 0.1.3 app from IDE:
```
python app.py run
```
Traceback (most recent call last):
File "app.py", line 56, in <module>
octue_cli(args)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 829, in __call__
return self.main(*args, **kwargs)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 782, in main
rv = self.invoke(ctx)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 1256, in invoke
Command.invoke(self, ctx)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 1066, in invoke
return ctx.invoke(self.callback, **ctx.params)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/core.py", line 610, in invoke
return callback(*args, **kwargs)
File "/home/batman/Software/anaconda3/envs/foam_2d_twine/lib/python3.8/site-packages/click/decorators.py", line 21, in new_func
return f(get_current_context(), *args, **kwargs)
TypeError: octue_cli() missing 3 required positional arguments: 'data_dir', 'input_dir', and 'tmp_dir' | non_infrastructure | cli raises typeerror when running an app from ide while running octue app from ide python app py run traceback most recent call last file app py line in octue cli args file home batman software envs foam twine lib site packages click core py line in call return self main args kwargs file home batman software envs foam twine lib site packages click core py line in main rv self invoke ctx file home batman software envs foam twine lib site packages click core py line in invoke command invoke self ctx file home batman software envs foam twine lib site packages click core py line in invoke return ctx invoke self callback ctx params file home batman software envs foam twine lib site packages click core py line in invoke return callback args kwargs file home batman software envs foam twine lib site packages click decorators py line in new func return f get current context args kwargs typeerror octue cli missing required positional arguments data dir input dir and tmp dir | 0 |
3,203 | 4,151,315,430 | IssuesEvent | 2016-06-15 20:12:37 | Azure/autorest | https://api.github.com/repos/Azure/autorest | closed | Standardize process by which each language performs normalization and extension management | Deferred discussion infrastructure | Today, there is a single method: `public override void NormalizeClientModel(ServiceClient serviceClient)` which each code generator implements.
What exactly is done in this method is left entirely up to the code generator (as it should be)... but for many AutoRest languages, they are processing/supporting 90%+ the same set of extensions. The problem is that each language does this process in a somewhat different and complicated manner:
Compare **AzureCSharp:**
```
public override void NormalizeClientModel(ServiceClient serviceClient)
{
AzureExtensions.NormalizeAzureClientModel(serviceClient, Settings, _namer);
_namer.NormalizeClientModel(serviceClient);
_namer.ResolveNameCollisions(serviceClient, Settings.Namespace,
Settings.Namespace + ".Models");
_namer.NormalizePaginatedMethods(serviceClient, pageClasses);
_namer.NormalizeODataMethods(serviceClient);
if (serviceClient != null)
{
foreach (var model in serviceClient.ModelTypes)
{
if (model.Extensions.ContainsKey(AzureExtensions.AzureResourceExtension) &&
(bool)model.Extensions[AzureExtensions.AzureResourceExtension])
{
model.BaseModelType = new CompositeType { Name = "IResource", SerializedName = "IResource" };
}
}
}
}
```
to **NodeJS:**
```
public override void NormalizeClientModel(ServiceClient serviceClient)
{
// MethodNames are normalized explicitly to provide a consitent method name while
// generating cloned methods for long running operations with reserved words. For
// example - beginDeleteMethod() insteadof beginDelete() as delete is a reserved word.
Namer.NormalizeMethodNames(serviceClient);
AzureExtensions.NormalizeAzureClientModel(serviceClient, Settings, Namer);
base.NormalizeClientModel(serviceClient);
NormalizeApiVersion(serviceClient);
NormalizePaginatedMethods(serviceClient);
ExtendAllResourcesToBaseResource(serviceClient);
}
```
to **Python:**
```
public override void NormalizeClientModel(ServiceClient serviceClient)
{
// Don't add pagable/longrunning method since we already handle ourself.
Settings.AddCredentials = true;
AzureExtensions.ProcessClientRequestIdExtension(serviceClient);
AzureExtensions.UpdateHeadMethods(serviceClient);
AzureExtensions.ParseODataExtension(serviceClient);
Extensions.FlattenModels(serviceClient);
ParameterGroupExtensionHelper.AddParameterGroups(serviceClient);
AzureExtensions.AddAzureProperties(serviceClient);
AzureExtensions.SetDefaultResponses(serviceClient);
CorrectFilterParameters(serviceClient);
base.NormalizeClientModel(serviceClient);
NormalizeApiVersion(serviceClient);
NormalizePaginatedMethods(serviceClient);
}
```
(note: Java looks like CSharp basically, which is good!)
So you can see that 3 different languages have 3 very different looking implementations of this method (and Ruby's is different too, I just didn't want to include yet another example):
* NodeJS and Python call the `base.NormalizeClientModel` but CSharp doesn't.
* CSharp and NodeJS use the helper method `AzureExtensions.NormalizeAzureClientModel` but Python doesn't.
* CSharp uses `_namer.NormalizePaginatedMethods(serviceClient)` whereas NodeJS and Python use `NormalizePaginatedMethods(serviceClient)`.
* CSharp does `AzureExtensions.NormalizeAzureClientModel(serviceClient, Settings, _namer)` immediately followed by `_namer.NormalizeClientModel(serviceClient)` -- it's unclear (at least to me) what each of those different calls do and why one needs to happen before the other (until you look at the implementation, then it's clear).
This is a bit of a catchall issue, but **a few concrete improvements would be**:
1. Clarify what the `namer` is for, and use it for those things across all the languages.
2. Make the method structures look a bit more similar (see CSharp + Java for a good example) -- for example things like all Azure generators calling their `base.NormalizeClientModel` (or all of them not).
3. Enable the `AzureExtensions.NormalizeAzureClientModel` method to take a parameter which allows you to opt out of particular bits, so that at least order is enforced even if not all of the extensions are applied (this would allow Python to use it instead of rolling its own I think, and maybe Ruby too).
4. Maybe rename `AzureExtensions.NormalizeAzureClientModel` to something like `AzureExtensions.ApplyAzureClientExtensions` since that's actually what it's doing (I think).
| 1.0 | Standardize process by which each language performs normalization and extension management - Today, there is a single method: `public override void NormalizeClientModel(ServiceClient serviceClient)` which each code generator implements.
What exactly is done in this method is left entirely up to the code generator (as it should be)... but for many AutoRest languages, they are processing/supporting 90%+ the same set of extensions. The problem is that each language does this process in a somewhat different and complicated manner:
Compare **AzureCSharp:**
```
public override void NormalizeClientModel(ServiceClient serviceClient)
{
AzureExtensions.NormalizeAzureClientModel(serviceClient, Settings, _namer);
_namer.NormalizeClientModel(serviceClient);
_namer.ResolveNameCollisions(serviceClient, Settings.Namespace,
Settings.Namespace + ".Models");
_namer.NormalizePaginatedMethods(serviceClient, pageClasses);
_namer.NormalizeODataMethods(serviceClient);
if (serviceClient != null)
{
foreach (var model in serviceClient.ModelTypes)
{
if (model.Extensions.ContainsKey(AzureExtensions.AzureResourceExtension) &&
(bool)model.Extensions[AzureExtensions.AzureResourceExtension])
{
model.BaseModelType = new CompositeType { Name = "IResource", SerializedName = "IResource" };
}
}
}
}
```
to **NodeJS:**
```
public override void NormalizeClientModel(ServiceClient serviceClient)
{
// MethodNames are normalized explicitly to provide a consitent method name while
// generating cloned methods for long running operations with reserved words. For
// example - beginDeleteMethod() insteadof beginDelete() as delete is a reserved word.
Namer.NormalizeMethodNames(serviceClient);
AzureExtensions.NormalizeAzureClientModel(serviceClient, Settings, Namer);
base.NormalizeClientModel(serviceClient);
NormalizeApiVersion(serviceClient);
NormalizePaginatedMethods(serviceClient);
ExtendAllResourcesToBaseResource(serviceClient);
}
```
to **Python:**
```
public override void NormalizeClientModel(ServiceClient serviceClient)
{
// Don't add pagable/longrunning method since we already handle ourself.
Settings.AddCredentials = true;
AzureExtensions.ProcessClientRequestIdExtension(serviceClient);
AzureExtensions.UpdateHeadMethods(serviceClient);
AzureExtensions.ParseODataExtension(serviceClient);
Extensions.FlattenModels(serviceClient);
ParameterGroupExtensionHelper.AddParameterGroups(serviceClient);
AzureExtensions.AddAzureProperties(serviceClient);
AzureExtensions.SetDefaultResponses(serviceClient);
CorrectFilterParameters(serviceClient);
base.NormalizeClientModel(serviceClient);
NormalizeApiVersion(serviceClient);
NormalizePaginatedMethods(serviceClient);
}
```
(note: Java looks like CSharp basically, which is good!)
So you can see that 3 different languages have 3 very different looking implementations of this method (and Ruby's is different too, I just didn't want to include yet another example):
* NodeJS and Python call the `base.NormalizeClientModel` but CSharp doesn't.
* CSharp and NodeJS use the helper method `AzureExtensions.NormalizeAzureClientModel` but Python doesn't.
* CSharp uses `_namer.NormalizePaginatedMethods(serviceClient)` whereas NodeJS and Python use `NormalizePaginatedMethods(serviceClient)`.
* CSharp does `AzureExtensions.NormalizeAzureClientModel(serviceClient, Settings, _namer)` immediately followed by `_namer.NormalizeClientModel(serviceClient)` -- it's unclear (at least to me) what each of those different calls do and why one needs to happen before the other (until you look at the implementation, then it's clear).
This is a bit of a catchall issue, but **a few concrete improvements would be**:
1. Clarify what the `namer` is for, and use it for those things across all the languages.
2. Make the method structures look a bit more similar (see CSharp + Java for a good example) -- for example things like all Azure generators calling their `base.NormalizeClientModel` (or all of them not).
3. Enable the `AzureExtensions.NormalizeAzureClientModel` method to take a parameter which allows you to opt out of particular bits, so that at least order is enforced even if not all of the extensions are applied (this would allow Python to use it instead of rolling its own I think, and maybe Ruby too).
4. Maybe rename `AzureExtensions.NormalizeAzureClientModel` to something like `AzureExtensions.ApplyAzureClientExtensions` since that's actually what it's doing (I think).
| infrastructure | standardize process by which each language performs normalization and extension management today there is a single method public override void normalizeclientmodel serviceclient serviceclient which each code generator implements what exactly is done in this method is left entirely up to the code generator as it should be but for many autorest languages they are processing supporting the same set of extensions the problem is that each language does this process in a somewhat different and complicated manner compare azurecsharp public override void normalizeclientmodel serviceclient serviceclient azureextensions normalizeazureclientmodel serviceclient settings namer namer normalizeclientmodel serviceclient namer resolvenamecollisions serviceclient settings namespace settings namespace models namer normalizepaginatedmethods serviceclient pageclasses namer normalizeodatamethods serviceclient if serviceclient null foreach var model in serviceclient modeltypes if model extensions containskey azureextensions azureresourceextension bool model extensions model basemodeltype new compositetype name iresource serializedname iresource to nodejs public override void normalizeclientmodel serviceclient serviceclient methodnames are normalized explicitly to provide a consitent method name while generating cloned methods for long running operations with reserved words for example begindeletemethod insteadof begindelete as delete is a reserved word namer normalizemethodnames serviceclient azureextensions normalizeazureclientmodel serviceclient settings namer base normalizeclientmodel serviceclient normalizeapiversion serviceclient normalizepaginatedmethods serviceclient extendallresourcestobaseresource serviceclient to python public override void normalizeclientmodel serviceclient serviceclient don t add pagable longrunning method since we already handle ourself settings addcredentials true azureextensions processclientrequestidextension serviceclient azureextensions updateheadmethods serviceclient azureextensions parseodataextension serviceclient extensions flattenmodels serviceclient parametergroupextensionhelper addparametergroups serviceclient azureextensions addazureproperties serviceclient azureextensions setdefaultresponses serviceclient correctfilterparameters serviceclient base normalizeclientmodel serviceclient normalizeapiversion serviceclient normalizepaginatedmethods serviceclient note java looks like csharp basically which is good so you can see that different languages have very different looking implementations of this method and ruby s is different too i just didn t want to include yet another example nodejs and python call the base normalizeclientmodel but csharp doesn t csharp and nodejs use the helper method azureextensions normalizeazureclientmodel but python doesn t csharp uses namer normalizepaginatedmethods serviceclient whereas nodejs and python use normalizepaginatedmethods serviceclient csharp does azureextensions normalizeazureclientmodel serviceclient settings namer immediately followed by namer normalizeclientmodel serviceclient it s unclear at least to me what each of those different calls do and why one needs to happen before the other until you look at the implementation then it s clear this is a bit of a catchall issue but a few concrete improvements would be clarify what the namer is for and use it for those things across all the languages make the method structures look a bit more similar see csharp java for a good example for example things like all azure generators calling their base normalizeclientmodel or all of them not enable the azureextensions normalizeazureclientmodel method to take a parameter which allows you to opt out of particular bits so that at least order is enforced even if not all of the extensions are applied this would allow python to use it instead of rolling its own i think and maybe ruby too maybe rename azureextensions normalizeazureclientmodel to something like azureextensions applyazureclientextensions since that s actually what it s doing i think | 1 |
315,127 | 9,606,822,021 | IssuesEvent | 2019-05-11 13:53:14 | rathena/rathena | https://api.github.com/repos/rathena/rathena | closed | Elemental Manteau Warlock or Socerer? | component:database mode:renewal priority:low type:bug | <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: a348016
<!-- Please specify the rAthena [GitHub hash](https://help.github.com/articles/autolinked-references-and-urls/#commit-shas) on which you encountered this issue.
How to get your GitHub Hash:
1. cd your/rAthena/directory/
2. git rev-parse --short HEAD
3. Copy the resulting hash.
-->
* **Client Date**: 20170517RE
<!-- Please specify the client date you used. -->
* **Server Mode**: RENEWAL
<!-- Which mode does your server use: Pre-Renewal or Renewal? -->
* **Description of Issue**: Elemental Manteau Warlock or Socerer? because on description for Socerer but on database for warlock :)
* Result: <!-- Describe the issue that you experienced in detail. -->
* Expected Result: <!-- Describe what you would expect to happen in detail. -->
* How to Reproduce: <!-- If you have not stated in the description of the result already, please give us a short guide how we can reproduce your issue. -->
* Official Information:<!-- If possible, provide information from official servers (kRO or other sources) which prove that the result is wrong. Please take into account that iRO (especially iRO Wiki) is not always the same as kRO. -->
<!-- * _NOTE: Make sure you quote ``` `@atcommands` ``` just like this so that you do not tag uninvolved GitHub users!_ -->
* **Modifications that may affect results**:
<!-- * Please provide any information that could influence the expected result. -->
<!-- * This can be either configurations you changed, database values you changed, or even external source modifications. -->
| 1.0 | Elemental Manteau Warlock or Socerer? - <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: a348016
<!-- Please specify the rAthena [GitHub hash](https://help.github.com/articles/autolinked-references-and-urls/#commit-shas) on which you encountered this issue.
How to get your GitHub Hash:
1. cd your/rAthena/directory/
2. git rev-parse --short HEAD
3. Copy the resulting hash.
-->
* **Client Date**: 20170517RE
<!-- Please specify the client date you used. -->
* **Server Mode**: RENEWAL
<!-- Which mode does your server use: Pre-Renewal or Renewal? -->
* **Description of Issue**: Elemental Manteau Warlock or Socerer? because on description for Socerer but on database for warlock :)
* Result: <!-- Describe the issue that you experienced in detail. -->
* Expected Result: <!-- Describe what you would expect to happen in detail. -->
* How to Reproduce: <!-- If you have not stated in the description of the result already, please give us a short guide how we can reproduce your issue. -->
* Official Information:<!-- If possible, provide information from official servers (kRO or other sources) which prove that the result is wrong. Please take into account that iRO (especially iRO Wiki) is not always the same as kRO. -->
<!-- * _NOTE: Make sure you quote ``` `@atcommands` ``` just like this so that you do not tag uninvolved GitHub users!_ -->
* **Modifications that may affect results**:
<!-- * Please provide any information that could influence the expected result. -->
<!-- * This can be either configurations you changed, database values you changed, or even external source modifications. -->
| non_infrastructure | elemental manteau warlock or socerer rathena hash please specify the rathena on which you encountered this issue how to get your github hash cd your rathena directory git rev parse short head copy the resulting hash client date server mode renewal description of issue elemental manteau warlock or socerer because on description for socerer but on database for warlock result expected result how to reproduce official information modifications that may affect results | 0 |
101,116 | 30,876,994,976 | IssuesEvent | 2023-08-03 14:53:20 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Assert in System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation | area-System.Net.Sockets blocking-clean-ci in-pr Known Build Error | ## Build Information
Build: https://dev.azure.com/dnceng-public/cbb18261-c48f-4abb-8651-8cdcb5474649/_build/results?buildId=359274
Build error leg or test failing: System.Net.Http.Json.Functional.Tests.WorkItemExecution
Pull request: https://github.com/dotnet/runtime/pull/89537
<!-- Error message template -->
## Error Message
Fill the error message using [step by step known issues guidance](https://github.com/dotnet/arcade/blob/main/Documentation/Projects/Build%20Analysis/KnownIssues.md#how-to-fill-out-a-known-issue-error-section).
<!-- Use ErrorMessage for String.Contains matches. Use ErrorPattern for regex matches (single line/no backtracking). Set BuildRetry to `true` to retry builds with this error. Set ExcludeConsoleLog to `true` to skip helix logs analysis. -->
```json
{
"ErrorMessage": "System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation",
"ErrorPattern": "",
"BuildRetry": false,
"ExcludeConsoleLog": false
}
```
Sample failure log:
```
Process terminated. Assertion failed.
at System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation(IntPtr acceptedFileDescriptor, Memory`1 socketAddress) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/SocketAsyncEventArgs.Unix.cs:line 36
at System.Net.Sockets.SocketAsyncEventArgs.DoOperationAccept(Socket _, SafeSocketHandle handle, SafeSocketHandle acceptHandle, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/SocketAsyncEventArgs.Unix.cs:line 56
at System.Net.Sockets.Socket.AcceptAsync(SocketAsyncEventArgs e, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.cs:line 2695
at System.Net.Sockets.Socket.AwaitableSocketAsyncEventArgs.AcceptAsync(Socket socket, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.Tasks.cs:line 965
at System.Net.Sockets.Socket.AcceptAsync(Socket acceptSocket, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.Tasks.cs:line 70
at System.Net.Sockets.Socket.AcceptAsync() in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.Tasks.cs:line 32
at System.Net.Test.Common.LoopbackServer.EstablishConnectionAsync() in /_/src/libraries/Common/tests/System/Net/Http/LoopbackServer.cs:line 142
at System.Runtime.CompilerServices.AsyncMethodBuilderCore.Start[TStateMachine](TStateMachine& stateMachine) in /_/src/libraries/System.Private.CoreLib/src/System/Runtime/CompilerServices/AsyncMethodBuilderCore.cs:line 38
at System.Net.Test.Common.LoopbackServer.EstablishConnectionAsync()
at System.Net.Test.Common.LoopbackServer.AcceptConnectionAsync(Func`2 funcAsync) in /_/src/libraries/Common/tests/System/Net/Http/LoopbackServer.cs:line 165
at System.Runtime.CompilerServices.AsyncMethodBuilderCore.Start[TStateMachine](TStateMachine& stateMachine) in /_/src/libraries/System.Private.CoreLib/src/System/Runtime/CompilerServices/AsyncMethodBuilderCore.cs:line 38
at System.Net.Test.Common.LoopbackServer.AcceptConnectionAsync(Func`2 funcAsync)
at System.Net.Http.Json.Functional.Tests.HttpClientJsonExtensionsTests.<>c__DisplayClass14_2.<<GetFromJsonAsync_EnforcesTimeout>b__3>d.MoveNext() in /_/src/libraries/System.Net.Http.Json/tests/FunctionalTests/HttpClientJsonExtensionsTests.cs:line 495
at System.Runtime.CompilerServices.AsyncMethodBuilderCore.Start[TStateMachine](TStateMachine& stateMachine) in /_/src/libraries/System.Private.CoreLib/src/System/Runtime/CompilerServices/AsyncMethodBuilderCore.cs:line 38
at System.Net.Http.Json.Functional.Tests.HttpClientJsonExtensionsTests.<>c__DisplayClass14_2.<GetFromJsonAsync_EnforcesTimeout>b__3()
at System.Threading.Tasks.Task`1.InnerInvoke() in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Future.cs:line 501
at System.Threading.Tasks.Task.<>c.<.cctor>b__281_0(Object obj) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2387
at System.Threading.ExecutionContext.RunFromThreadPoolDispatchLoop(Thread threadPoolThread, ExecutionContext executionContext, ContextCallback callback, Object state) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/ExecutionContext.cs:line 264
at System.Threading.Tasks.Task.ExecuteWithThreadLocal(Task& currentTaskSlot, Thread threadPoolThread) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2349
at System.Threading.Tasks.Task.ExecuteEntryUnsafe(Thread threadPoolThread) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2283
at System.Threading.Tasks.Task.ExecuteFromThreadPool(Thread threadPoolThread) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2274
at System.Threading.ThreadPoolWorkQueue.Dispatch() in /_/src/libraries/System.Private.CoreLib/src/System/Threading/ThreadPoolWorkQueue.cs:line 913
at System.Threading.PortableThreadPool.WorkerThread.WorkerThreadStart() in /_/src/libraries/System.Private.CoreLib/src/System/Threading/PortableThreadPool.WorkerThread.NonBrowser.cs:line 58
at System.Threading.Thread.StartCallback() in /_/src/coreclr/System.Private.CoreLib/src/System/Threading/Thread.CoreCLR.cs:line 105
```
Seems to be introduced in https://github.com/dotnet/runtime/commit/e2c6fcfa8a621cbdbc89e1e686a3e4cc39088080#diff-31c708307a9d9c09e7e488a873803e62bfcc91a8d3fa6d9398d3c8bb13cff1afR36 cc @wfurt
<!-- Known issue validation start -->
### Known issue validation
**Build: :mag_right:** https://dev.azure.com/dnceng-public/public/_build/results?buildId=359274
**Error message validated:** `System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation`
**Result validation: :white_check_mark:** Known issue matched with the provided build.
**Validation performed at:** 8/1/2023 8:29:07 PM UTC
<!-- Known issue validation end -->
<!--Known issue error report start -->
### Report
|Build|Definition|Test|Pull Request|
|---|---|---|---|
|[361800](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361800)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361800&view=ms.vss-test-web.build-test-results-tab&runId=7641448&resultId=209030)|dotnet/runtime#89912|
|[361711](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361711)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361711&view=ms.vss-test-web.build-test-results-tab&runId=7639456&resultId=209066)|dotnet/runtime#89630|
|[361700](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361700)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361700&view=ms.vss-test-web.build-test-results-tab&runId=7638942&resultId=209066)|dotnet/runtime#88926|
|[361673](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361673)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361673&view=ms.vss-test-web.build-test-results-tab&runId=7638584&resultId=208916)|dotnet/runtime#86888|
|[361597](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361597)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361597&view=ms.vss-test-web.build-test-results-tab&runId=7636882&resultId=200059)|dotnet/runtime#89841|
|[361610](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361610)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361610&view=ms.vss-test-web.build-test-results-tab&runId=7636786&resultId=200207)|dotnet/runtime#89902|
|[361577](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361577)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361577&view=ms.vss-test-web.build-test-results-tab&runId=7635454&resultId=209030)|dotnet/runtime#89900|
|[361506](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361506)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361506&view=ms.vss-test-web.build-test-results-tab&runId=7634486&resultId=208910)|dotnet/runtime#89869|
|[361496](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361496)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361496&view=ms.vss-test-web.build-test-results-tab&runId=7632000&resultId=208900)|dotnet/runtime#89894|
|[361438](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361438)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361438&view=ms.vss-test-web.build-test-results-tab&runId=7630862&resultId=200386)|dotnet/runtime#89892|
|[361299](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361299)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361299&view=ms.vss-test-web.build-test-results-tab&runId=7627726&resultId=208901)|dotnet/runtime#89882|
|[361145](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361145)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361145&view=ms.vss-test-web.build-test-results-tab&runId=7623524&resultId=200204)|dotnet/runtime#89870|
|[361051](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361051)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361051&view=ms.vss-test-web.build-test-results-tab&runId=7622264&resultId=200201)|dotnet/runtime#87773|
|[360929](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360929)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360929&view=ms.vss-test-web.build-test-results-tab&runId=7618340&resultId=200205)|dotnet/runtime#89863|
|[360734](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360734)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360734&view=ms.vss-test-web.build-test-results-tab&runId=7612920&resultId=209025)|dotnet/runtime#89736|
|[360640](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360640)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360640&view=ms.vss-test-web.build-test-results-tab&runId=7611794&resultId=208959)|dotnet/runtime#89813|
|[360105](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360105)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360105&view=ms.vss-test-web.build-test-results-tab&runId=7597942&resultId=200199)|dotnet/runtime#89636|
|[359917](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359917)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359917&view=ms.vss-test-web.build-test-results-tab&runId=7594830&resultId=208908)|dotnet/runtime#89827|
|[359852](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359852)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359852&view=ms.vss-test-web.build-test-results-tab&runId=7593990&resultId=200199)|dotnet/runtime#89822|
|[359833](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359833)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359833&view=ms.vss-test-web.build-test-results-tab&runId=7593692&resultId=200197)|dotnet/runtime#89689|
|[359830](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359830)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359830&view=ms.vss-test-web.build-test-results-tab&runId=7593536&resultId=200195)|dotnet/runtime#89531|
|[359812](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359812)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359812&view=ms.vss-test-web.build-test-results-tab&runId=7593254&resultId=208913)|dotnet/runtime#89809|
|[359866](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359866)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359866&view=ms.vss-test-web.build-test-results-tab&runId=7591136&resultId=200202)|dotnet/runtime#89799|
|[359677](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359677)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359677&view=ms.vss-test-web.build-test-results-tab&runId=7583548&resultId=209012)|dotnet/runtime#89583|
|[359495](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359495)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359495&view=ms.vss-test-web.build-test-results-tab&runId=7579692&resultId=209045)|dotnet/runtime#89781|
|[359395](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359395)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359395&view=ms.vss-test-web.build-test-results-tab&runId=7579296&resultId=208891)|dotnet/runtime#89630|
|[359274](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359274)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359274&view=ms.vss-test-web.build-test-results-tab&runId=7574852&resultId=200193)|dotnet/runtime#89537|
|[359286](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359286)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359286&view=ms.vss-test-web.build-test-results-tab&runId=7572130&resultId=209009)|dotnet/runtime#87773|
|[358747](https://dev.azure.com/dnceng-public/public/_build/results?buildId=358747)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=358747&view=ms.vss-test-web.build-test-results-tab&runId=7558372&resultId=200335)|dotnet/runtime#89301|
#### Summary
|24-Hour Hit Count|7-Day Hit Count|1-Month Count|
|---|---|---|
|16|29|29|
<!--Known issue error report end --> | 1.0 | Assert in System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation - ## Build Information
Build: https://dev.azure.com/dnceng-public/cbb18261-c48f-4abb-8651-8cdcb5474649/_build/results?buildId=359274
Build error leg or test failing: System.Net.Http.Json.Functional.Tests.WorkItemExecution
Pull request: https://github.com/dotnet/runtime/pull/89537
<!-- Error message template -->
## Error Message
Fill the error message using [step by step known issues guidance](https://github.com/dotnet/arcade/blob/main/Documentation/Projects/Build%20Analysis/KnownIssues.md#how-to-fill-out-a-known-issue-error-section).
<!-- Use ErrorMessage for String.Contains matches. Use ErrorPattern for regex matches (single line/no backtracking). Set BuildRetry to `true` to retry builds with this error. Set ExcludeConsoleLog to `true` to skip helix logs analysis. -->
```json
{
"ErrorMessage": "System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation",
"ErrorPattern": "",
"BuildRetry": false,
"ExcludeConsoleLog": false
}
```
Sample failure log:
```
Process terminated. Assertion failed.
at System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation(IntPtr acceptedFileDescriptor, Memory`1 socketAddress) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/SocketAsyncEventArgs.Unix.cs:line 36
at System.Net.Sockets.SocketAsyncEventArgs.DoOperationAccept(Socket _, SafeSocketHandle handle, SafeSocketHandle acceptHandle, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/SocketAsyncEventArgs.Unix.cs:line 56
at System.Net.Sockets.Socket.AcceptAsync(SocketAsyncEventArgs e, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.cs:line 2695
at System.Net.Sockets.Socket.AwaitableSocketAsyncEventArgs.AcceptAsync(Socket socket, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.Tasks.cs:line 965
at System.Net.Sockets.Socket.AcceptAsync(Socket acceptSocket, CancellationToken cancellationToken) in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.Tasks.cs:line 70
at System.Net.Sockets.Socket.AcceptAsync() in /_/src/libraries/System.Net.Sockets/src/System/Net/Sockets/Socket.Tasks.cs:line 32
at System.Net.Test.Common.LoopbackServer.EstablishConnectionAsync() in /_/src/libraries/Common/tests/System/Net/Http/LoopbackServer.cs:line 142
at System.Runtime.CompilerServices.AsyncMethodBuilderCore.Start[TStateMachine](TStateMachine& stateMachine) in /_/src/libraries/System.Private.CoreLib/src/System/Runtime/CompilerServices/AsyncMethodBuilderCore.cs:line 38
at System.Net.Test.Common.LoopbackServer.EstablishConnectionAsync()
at System.Net.Test.Common.LoopbackServer.AcceptConnectionAsync(Func`2 funcAsync) in /_/src/libraries/Common/tests/System/Net/Http/LoopbackServer.cs:line 165
at System.Runtime.CompilerServices.AsyncMethodBuilderCore.Start[TStateMachine](TStateMachine& stateMachine) in /_/src/libraries/System.Private.CoreLib/src/System/Runtime/CompilerServices/AsyncMethodBuilderCore.cs:line 38
at System.Net.Test.Common.LoopbackServer.AcceptConnectionAsync(Func`2 funcAsync)
at System.Net.Http.Json.Functional.Tests.HttpClientJsonExtensionsTests.<>c__DisplayClass14_2.<<GetFromJsonAsync_EnforcesTimeout>b__3>d.MoveNext() in /_/src/libraries/System.Net.Http.Json/tests/FunctionalTests/HttpClientJsonExtensionsTests.cs:line 495
at System.Runtime.CompilerServices.AsyncMethodBuilderCore.Start[TStateMachine](TStateMachine& stateMachine) in /_/src/libraries/System.Private.CoreLib/src/System/Runtime/CompilerServices/AsyncMethodBuilderCore.cs:line 38
at System.Net.Http.Json.Functional.Tests.HttpClientJsonExtensionsTests.<>c__DisplayClass14_2.<GetFromJsonAsync_EnforcesTimeout>b__3()
at System.Threading.Tasks.Task`1.InnerInvoke() in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Future.cs:line 501
at System.Threading.Tasks.Task.<>c.<.cctor>b__281_0(Object obj) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2387
at System.Threading.ExecutionContext.RunFromThreadPoolDispatchLoop(Thread threadPoolThread, ExecutionContext executionContext, ContextCallback callback, Object state) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/ExecutionContext.cs:line 264
at System.Threading.Tasks.Task.ExecuteWithThreadLocal(Task& currentTaskSlot, Thread threadPoolThread) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2349
at System.Threading.Tasks.Task.ExecuteEntryUnsafe(Thread threadPoolThread) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2283
at System.Threading.Tasks.Task.ExecuteFromThreadPool(Thread threadPoolThread) in /_/src/libraries/System.Private.CoreLib/src/System/Threading/Tasks/Task.cs:line 2274
at System.Threading.ThreadPoolWorkQueue.Dispatch() in /_/src/libraries/System.Private.CoreLib/src/System/Threading/ThreadPoolWorkQueue.cs:line 913
at System.Threading.PortableThreadPool.WorkerThread.WorkerThreadStart() in /_/src/libraries/System.Private.CoreLib/src/System/Threading/PortableThreadPool.WorkerThread.NonBrowser.cs:line 58
at System.Threading.Thread.StartCallback() in /_/src/coreclr/System.Private.CoreLib/src/System/Threading/Thread.CoreCLR.cs:line 105
```
Seems to be introduced in https://github.com/dotnet/runtime/commit/e2c6fcfa8a621cbdbc89e1e686a3e4cc39088080#diff-31c708307a9d9c09e7e488a873803e62bfcc91a8d3fa6d9398d3c8bb13cff1afR36 cc @wfurt
<!-- Known issue validation start -->
### Known issue validation
**Build: :mag_right:** https://dev.azure.com/dnceng-public/public/_build/results?buildId=359274
**Error message validated:** `System.Net.Sockets.SocketAsyncEventArgs.CompleteAcceptOperation`
**Result validation: :white_check_mark:** Known issue matched with the provided build.
**Validation performed at:** 8/1/2023 8:29:07 PM UTC
<!-- Known issue validation end -->
<!--Known issue error report start -->
### Report
|Build|Definition|Test|Pull Request|
|---|---|---|---|
|[361800](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361800)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361800&view=ms.vss-test-web.build-test-results-tab&runId=7641448&resultId=209030)|dotnet/runtime#89912|
|[361711](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361711)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361711&view=ms.vss-test-web.build-test-results-tab&runId=7639456&resultId=209066)|dotnet/runtime#89630|
|[361700](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361700)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361700&view=ms.vss-test-web.build-test-results-tab&runId=7638942&resultId=209066)|dotnet/runtime#88926|
|[361673](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361673)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361673&view=ms.vss-test-web.build-test-results-tab&runId=7638584&resultId=208916)|dotnet/runtime#86888|
|[361597](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361597)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361597&view=ms.vss-test-web.build-test-results-tab&runId=7636882&resultId=200059)|dotnet/runtime#89841|
|[361610](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361610)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361610&view=ms.vss-test-web.build-test-results-tab&runId=7636786&resultId=200207)|dotnet/runtime#89902|
|[361577](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361577)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361577&view=ms.vss-test-web.build-test-results-tab&runId=7635454&resultId=209030)|dotnet/runtime#89900|
|[361506](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361506)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361506&view=ms.vss-test-web.build-test-results-tab&runId=7634486&resultId=208910)|dotnet/runtime#89869|
|[361496](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361496)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361496&view=ms.vss-test-web.build-test-results-tab&runId=7632000&resultId=208900)|dotnet/runtime#89894|
|[361438](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361438)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361438&view=ms.vss-test-web.build-test-results-tab&runId=7630862&resultId=200386)|dotnet/runtime#89892|
|[361299](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361299)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361299&view=ms.vss-test-web.build-test-results-tab&runId=7627726&resultId=208901)|dotnet/runtime#89882|
|[361145](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361145)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361145&view=ms.vss-test-web.build-test-results-tab&runId=7623524&resultId=200204)|dotnet/runtime#89870|
|[361051](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361051)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=361051&view=ms.vss-test-web.build-test-results-tab&runId=7622264&resultId=200201)|dotnet/runtime#87773|
|[360929](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360929)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360929&view=ms.vss-test-web.build-test-results-tab&runId=7618340&resultId=200205)|dotnet/runtime#89863|
|[360734](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360734)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360734&view=ms.vss-test-web.build-test-results-tab&runId=7612920&resultId=209025)|dotnet/runtime#89736|
|[360640](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360640)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360640&view=ms.vss-test-web.build-test-results-tab&runId=7611794&resultId=208959)|dotnet/runtime#89813|
|[360105](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360105)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=360105&view=ms.vss-test-web.build-test-results-tab&runId=7597942&resultId=200199)|dotnet/runtime#89636|
|[359917](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359917)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359917&view=ms.vss-test-web.build-test-results-tab&runId=7594830&resultId=208908)|dotnet/runtime#89827|
|[359852](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359852)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359852&view=ms.vss-test-web.build-test-results-tab&runId=7593990&resultId=200199)|dotnet/runtime#89822|
|[359833](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359833)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359833&view=ms.vss-test-web.build-test-results-tab&runId=7593692&resultId=200197)|dotnet/runtime#89689|
|[359830](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359830)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359830&view=ms.vss-test-web.build-test-results-tab&runId=7593536&resultId=200195)|dotnet/runtime#89531|
|[359812](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359812)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359812&view=ms.vss-test-web.build-test-results-tab&runId=7593254&resultId=208913)|dotnet/runtime#89809|
|[359866](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359866)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359866&view=ms.vss-test-web.build-test-results-tab&runId=7591136&resultId=200202)|dotnet/runtime#89799|
|[359677](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359677)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359677&view=ms.vss-test-web.build-test-results-tab&runId=7583548&resultId=209012)|dotnet/runtime#89583|
|[359495](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359495)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359495&view=ms.vss-test-web.build-test-results-tab&runId=7579692&resultId=209045)|dotnet/runtime#89781|
|[359395](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359395)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359395&view=ms.vss-test-web.build-test-results-tab&runId=7579296&resultId=208891)|dotnet/runtime#89630|
|[359274](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359274)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359274&view=ms.vss-test-web.build-test-results-tab&runId=7574852&resultId=200193)|dotnet/runtime#89537|
|[359286](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359286)|dotnet/runtime|[System.Net.HttpListener.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=359286&view=ms.vss-test-web.build-test-results-tab&runId=7572130&resultId=209009)|dotnet/runtime#87773|
|[358747](https://dev.azure.com/dnceng-public/public/_build/results?buildId=358747)|dotnet/runtime|[System.Net.Http.Json.Functional.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=358747&view=ms.vss-test-web.build-test-results-tab&runId=7558372&resultId=200335)|dotnet/runtime#89301|
#### Summary
|24-Hour Hit Count|7-Day Hit Count|1-Month Count|
|---|---|---|
|16|29|29|
<!--Known issue error report end --> | non_infrastructure | assert in system net sockets socketasynceventargs completeacceptoperation build information build build error leg or test failing system net http json functional tests workitemexecution pull request error message fill the error message using json errormessage system net sockets socketasynceventargs completeacceptoperation errorpattern buildretry false excludeconsolelog false sample failure log process terminated assertion failed at system net sockets socketasynceventargs completeacceptoperation intptr acceptedfiledescriptor memory socketaddress in src libraries system net sockets src system net sockets socketasynceventargs unix cs line at system net sockets socketasynceventargs dooperationaccept socket safesockethandle handle safesockethandle accepthandle cancellationtoken cancellationtoken in src libraries system net sockets src system net sockets socketasynceventargs unix cs line at system net sockets socket acceptasync socketasynceventargs e cancellationtoken cancellationtoken in src libraries system net sockets src system net sockets socket cs line at system net sockets socket awaitablesocketasynceventargs acceptasync socket socket cancellationtoken cancellationtoken in src libraries system net sockets src system net sockets socket tasks cs line at system net sockets socket acceptasync socket acceptsocket cancellationtoken cancellationtoken in src libraries system net sockets src system net sockets socket tasks cs line at system net sockets socket acceptasync in src libraries system net sockets src system net sockets socket tasks cs line at system net test common loopbackserver establishconnectionasync in src libraries common tests system net http loopbackserver cs line at system runtime compilerservices asyncmethodbuildercore start tstatemachine statemachine in src libraries system private corelib src system runtime compilerservices asyncmethodbuildercore cs line at system net test common loopbackserver establishconnectionasync at system net test common loopbackserver acceptconnectionasync func funcasync in src libraries common tests system net http loopbackserver cs line at system runtime compilerservices asyncmethodbuildercore start tstatemachine statemachine in src libraries system private corelib src system runtime compilerservices asyncmethodbuildercore cs line at system net test common loopbackserver acceptconnectionasync func funcasync at system net http json functional tests httpclientjsonextensionstests c b d movenext in src libraries system net http json tests functionaltests httpclientjsonextensionstests cs line at system runtime compilerservices asyncmethodbuildercore start tstatemachine statemachine in src libraries system private corelib src system runtime compilerservices asyncmethodbuildercore cs line at system net http json functional tests httpclientjsonextensionstests c b at system threading tasks task innerinvoke in src libraries system private corelib src system threading tasks future cs line at system threading tasks task c b object obj in src libraries system private corelib src system threading tasks task cs line at system threading executioncontext runfromthreadpooldispatchloop thread threadpoolthread executioncontext executioncontext contextcallback callback object state in src libraries system private corelib src system threading executioncontext cs line at system threading tasks task executewiththreadlocal task currenttaskslot thread threadpoolthread in src libraries system private corelib src system threading tasks task cs line at system threading tasks task executeentryunsafe thread threadpoolthread in src libraries system private corelib src system threading tasks task cs line at system threading tasks task executefromthreadpool thread threadpoolthread in src libraries system private corelib src system threading tasks task cs line at system threading threadpoolworkqueue dispatch in src libraries system private corelib src system threading threadpoolworkqueue cs line at system threading portablethreadpool workerthread workerthreadstart in src libraries system private corelib src system threading portablethreadpool workerthread nonbrowser cs line at system threading thread startcallback in src coreclr system private corelib src system threading thread coreclr cs line seems to be introduced in cc wfurt known issue validation build mag right error message validated system net sockets socketasynceventargs completeacceptoperation result validation white check mark known issue matched with the provided build validation performed at pm utc report build definition test pull request summary hour hit count day hit count month count | 0 |
11,863 | 9,475,869,252 | IssuesEvent | 2019-04-19 13:08:23 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | InternalsVisibleTo enforcement for external access changes | 3 - Working Area-Infrastructure | BuildBoss should be updated to enforce the new External Access features by validating one of the following is true for every `<InternalsVisibleTo>` in the solution:
1. The target of the IVT is an assembly which is defined and built within Roslyn.sln
2. The source of the IVT is an External Access assembly
3. The IVT element has an attribute `LoadsWithinVisualStudio="false"`
4. The IVT element has a `WorkItem` attribute with a URI to an issue tracking the elimination of the IVT | 1.0 | InternalsVisibleTo enforcement for external access changes - BuildBoss should be updated to enforce the new External Access features by validating one of the following is true for every `<InternalsVisibleTo>` in the solution:
1. The target of the IVT is an assembly which is defined and built within Roslyn.sln
2. The source of the IVT is an External Access assembly
3. The IVT element has an attribute `LoadsWithinVisualStudio="false"`
4. The IVT element has a `WorkItem` attribute with a URI to an issue tracking the elimination of the IVT | infrastructure | internalsvisibleto enforcement for external access changes buildboss should be updated to enforce the new external access features by validating one of the following is true for every in the solution the target of the ivt is an assembly which is defined and built within roslyn sln the source of the ivt is an external access assembly the ivt element has an attribute loadswithinvisualstudio false the ivt element has a workitem attribute with a uri to an issue tracking the elimination of the ivt | 1 |
10,006 | 8,314,904,666 | IssuesEvent | 2018-09-25 01:53:03 | ifmeorg/ifme | https://api.github.com/repos/ifmeorg/ifme | closed | Better CSS optimizations and tree-shaking | hacktoberfest infrastructure performance react ruby on rails | <!--[
Thank you for contributing! Please use this issue template.
Contributor Blurb: https://github.com/ifmeorg/ifme/wiki/Contributor-Blurb
Join Our Slack: https://github.com/ifmeorg/ifme/wiki/Join-Our-Slack
Issue creation is a contribution!
Need help? Post in the #dev channel on Slack
Please use the appropriate labels to tag this issue
]-->
# Description
<!--[Description of issue, this includes a feature suggestion, bug report, code cleanup, and refactoring idea]-->
Better CSS optimizations and tree-shaking, as there's a lot of CSS generated by both Rails and React.
We had something set up in webpack.config.js with the compression-webpack-plugin but we had to disable it cause there was an issue with that package. I recently upgraded to Webpack 3.8.1, I think it might work again?
# Do you want to be the assignee to work on this?
YES
<!--[
You don't have to work on the issue to file an issue!
If you want to, assign yourself to the issue
If you are unable to find your username in the Assignees dropdown, let us know in #dev on Slack
]--> | 1.0 | Better CSS optimizations and tree-shaking - <!--[
Thank you for contributing! Please use this issue template.
Contributor Blurb: https://github.com/ifmeorg/ifme/wiki/Contributor-Blurb
Join Our Slack: https://github.com/ifmeorg/ifme/wiki/Join-Our-Slack
Issue creation is a contribution!
Need help? Post in the #dev channel on Slack
Please use the appropriate labels to tag this issue
]-->
# Description
<!--[Description of issue, this includes a feature suggestion, bug report, code cleanup, and refactoring idea]-->
Better CSS optimizations and tree-shaking, as there's a lot of CSS generated by both Rails and React.
We had something set up in webpack.config.js with the compression-webpack-plugin but we had to disable it cause there was an issue with that package. I recently upgraded to Webpack 3.8.1, I think it might work again?
# Do you want to be the assignee to work on this?
YES
<!--[
You don't have to work on the issue to file an issue!
If you want to, assign yourself to the issue
If you are unable to find your username in the Assignees dropdown, let us know in #dev on Slack
]--> | infrastructure | better css optimizations and tree shaking thank you for contributing please use this issue template contributor blurb join our slack issue creation is a contribution need help post in the dev channel on slack please use the appropriate labels to tag this issue description better css optimizations and tree shaking as there s a lot of css generated by both rails and react we had something set up in webpack config js with the compression webpack plugin but we had to disable it cause there was an issue with that package i recently upgraded to webpack i think it might work again do you want to be the assignee to work on this yes you don t have to work on the issue to file an issue if you want to assign yourself to the issue if you are unable to find your username in the assignees dropdown let us know in dev on slack | 1 |
33,767 | 27,796,720,900 | IssuesEvent | 2023-03-17 13:06:05 | alan-turing-institute/the-turing-way | https://api.github.com/repos/alan-turing-institute/the-turing-way | closed | Broken build | infrastructure | ### Summary
We seem to be getting a broken build on netlify, where accessing [The Turing Way](the-turing-way.netlify.app/) shows an error message: "Page Not Found. Looks like you've followed a broken link or entered a URL that doesn't exist on this site." All our CI checks & Netlify aren't showing that anything is incorrect - is there anything else I am missing here?
<img width="628" alt="Screenshot 2023-03-15 at 09 29 29" src="https://user-images.githubusercontent.com/18509789/225267022-aca25278-8d54-4d25-b2ef-fef5df98653c.png">
Thank you to Alycia Crall of the Carpentries for flagging. | 1.0 | Broken build - ### Summary
We seem to be getting a broken build on netlify, where accessing [The Turing Way](the-turing-way.netlify.app/) shows an error message: "Page Not Found. Looks like you've followed a broken link or entered a URL that doesn't exist on this site." All our CI checks & Netlify aren't showing that anything is incorrect - is there anything else I am missing here?
<img width="628" alt="Screenshot 2023-03-15 at 09 29 29" src="https://user-images.githubusercontent.com/18509789/225267022-aca25278-8d54-4d25-b2ef-fef5df98653c.png">
Thank you to Alycia Crall of the Carpentries for flagging. | infrastructure | broken build summary we seem to be getting a broken build on netlify where accessing the turing way netlify app shows an error message page not found looks like you ve followed a broken link or entered a url that doesn t exist on this site all our ci checks netlify aren t showing that anything is incorrect is there anything else i am missing here img width alt screenshot at src thank you to alycia crall of the carpentries for flagging | 1 |
31,463 | 25,773,010,570 | IssuesEvent | 2022-12-09 09:36:10 | localstack/localstack | https://api.github.com/repos/localstack/localstack | closed | The Locastack connection broken on Kubernetes in M1 Mac. | type: bug status: triage needed area: infrastructure platform: macOS/ARM64 | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Hi team, when I try to build the localstack at the Kubernetes as below by running `kubectl apply -f my-localstack.yaml`
```yaml
# my-localstack.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: localstack
spec:
selector:
matchLabels:
app: localstack
replicas: 1
template:
metadata:
labels:
app: localstack
spec:
containers:
- name: localstack
image: localstack/localstack
resources:
limits:
memory: 500Mi
livenessProbe:
tcpSocket:
port: 4566
readinessProbe:
exec:
command:
- /usr/bin/awslocal
- sts
- get-caller-identity
ports:
- containerPort: 4566
name: edge
env:
- name: SERVICES
value: "kinesis"
---
apiVersion: v1
kind: Service
metadata:
name: localstack
spec:
# selector tells Kubernetes what Deployment this Service
# belongs to
selector:
app: localstack
ports:
- port: 80
targetPort: edge
---
```
I checked the pod log and seems it already start now:
<img width="1233" alt="image" src="https://user-images.githubusercontent.com/96011359/173190909-e38e28d4-5955-46b9-a20d-00a794203ff0.png">
But when I run the `kubectl exec` into the container, and try to run `awslocal kinesis list-streams`, I found the connection is broken.
```shell
root@localstack-78c598d56c-6rwhk:/opt/code/localstack# awslocal kinesis list-streams
Connection was closed before we received a valid response from endpoint URL: "http://localhost:4566/".
root@localstack-78c598d56c-6rwhk:/opt/code/localstack#
```
So although the log said it starts but the real connection is broken, seems a bug, I'm not know whether it's related to my machine.
My environment:
MacOS: M1 Monterey Version 12.2.1
### Expected Behavior
_No response_
### How are you starting LocalStack?
With a docker-compose file
### Steps To Reproduce
Above
### Environment
```markdown
- OS:
- LocalStack:
```
### Anything else?
_No response_ | 1.0 | The Locastack connection broken on Kubernetes in M1 Mac. - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Hi team, when I try to build the localstack at the Kubernetes as below by running `kubectl apply -f my-localstack.yaml`
```yaml
# my-localstack.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: localstack
spec:
selector:
matchLabels:
app: localstack
replicas: 1
template:
metadata:
labels:
app: localstack
spec:
containers:
- name: localstack
image: localstack/localstack
resources:
limits:
memory: 500Mi
livenessProbe:
tcpSocket:
port: 4566
readinessProbe:
exec:
command:
- /usr/bin/awslocal
- sts
- get-caller-identity
ports:
- containerPort: 4566
name: edge
env:
- name: SERVICES
value: "kinesis"
---
apiVersion: v1
kind: Service
metadata:
name: localstack
spec:
# selector tells Kubernetes what Deployment this Service
# belongs to
selector:
app: localstack
ports:
- port: 80
targetPort: edge
---
```
I checked the pod log and seems it already start now:
<img width="1233" alt="image" src="https://user-images.githubusercontent.com/96011359/173190909-e38e28d4-5955-46b9-a20d-00a794203ff0.png">
But when I run the `kubectl exec` into the container, and try to run `awslocal kinesis list-streams`, I found the connection is broken.
```shell
root@localstack-78c598d56c-6rwhk:/opt/code/localstack# awslocal kinesis list-streams
Connection was closed before we received a valid response from endpoint URL: "http://localhost:4566/".
root@localstack-78c598d56c-6rwhk:/opt/code/localstack#
```
So although the log said it starts but the real connection is broken, seems a bug, I'm not know whether it's related to my machine.
My environment:
MacOS: M1 Monterey Version 12.2.1
### Expected Behavior
_No response_
### How are you starting LocalStack?
With a docker-compose file
### Steps To Reproduce
Above
### Environment
```markdown
- OS:
- LocalStack:
```
### Anything else?
_No response_ | infrastructure | the locastack connection broken on kubernetes in mac is there an existing issue for this i have searched the existing issues current behavior hi team when i try to build the localstack at the kubernetes as below by running kubectl apply f my localstack yaml yaml my localstack yaml apiversion apps kind deployment metadata name localstack spec selector matchlabels app localstack replicas template metadata labels app localstack spec containers name localstack image localstack localstack resources limits memory livenessprobe tcpsocket port readinessprobe exec command usr bin awslocal sts get caller identity ports containerport name edge env name services value kinesis apiversion kind service metadata name localstack spec selector tells kubernetes what deployment this service belongs to selector app localstack ports port targetport edge i checked the pod log and seems it already start now img width alt image src but when i run the kubectl exec into the container and try to run awslocal kinesis list streams i found the connection is broken shell root localstack opt code localstack awslocal kinesis list streams connection was closed before we received a valid response from endpoint url root localstack opt code localstack so although the log said it starts but the real connection is broken seems a bug i m not know whether it s related to my machine my environment macos monterey version expected behavior no response how are you starting localstack with a docker compose file steps to reproduce above environment markdown os localstack anything else no response | 1 |
14,858 | 11,204,311,859 | IssuesEvent | 2020-01-05 04:23:08 | casey/intermodal | https://api.github.com/repos/casey/intermodal | opened | Automatically build and upload releases when a version tag is pushed | infrastructure | I've used japaric/trust before. I'm not sure if there's something prebuilt for rust and github actions. I could also consider figuring out how to cross-compile locally, probably using nix. This might have the advantage that I'd get reproducible builds. | 1.0 | Automatically build and upload releases when a version tag is pushed - I've used japaric/trust before. I'm not sure if there's something prebuilt for rust and github actions. I could also consider figuring out how to cross-compile locally, probably using nix. This might have the advantage that I'd get reproducible builds. | infrastructure | automatically build and upload releases when a version tag is pushed i ve used japaric trust before i m not sure if there s something prebuilt for rust and github actions i could also consider figuring out how to cross compile locally probably using nix this might have the advantage that i d get reproducible builds | 1 |
446,788 | 12,878,877,743 | IssuesEvent | 2020-07-11 18:55:08 | grey-software/Material-Math | https://api.github.com/repos/grey-software/Material-Math | closed | Percentage Of Correct Questions | Domain: User Experience Priority: Medium Type: Enhancement | # Overview
Displays the total percentage of questions you got right. | 1.0 | Percentage Of Correct Questions - # Overview
Displays the total percentage of questions you got right. | non_infrastructure | percentage of correct questions overview displays the total percentage of questions you got right | 0 |
245,909 | 26,569,486,421 | IssuesEvent | 2023-01-21 01:09:19 | nidhi7598/linux-3.0.35_CVE-2022-45934 | https://api.github.com/repos/nidhi7598/linux-3.0.35_CVE-2022-45934 | opened | CVE-2020-8649 (Medium) detected in linux-stable-rtv3.8.6 | security vulnerability | ## CVE-2020-8649 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/video/console/vgacon.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/video/console/vgacon.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/video/console/vgacon.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a use-after-free vulnerability in the Linux kernel through 5.5.2 in the vgacon_invert_region function in drivers/video/console/vgacon.c.
<p>Publish Date: 2020-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8649>CVE-2020-8649</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-8649">https://www.linuxkernelcves.com/cves/CVE-2020-8649</a></p>
<p>Release Date: 2020-02-06</p>
<p>Fix Resolution: v5.6-rc5,v3.16.83,v4.14.173,v4.19.109,v4.4.216,v4.9.216,v5.4.25,v5.5.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-8649 (Medium) detected in linux-stable-rtv3.8.6 - ## CVE-2020-8649 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/video/console/vgacon.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/video/console/vgacon.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/video/console/vgacon.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a use-after-free vulnerability in the Linux kernel through 5.5.2 in the vgacon_invert_region function in drivers/video/console/vgacon.c.
<p>Publish Date: 2020-02-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8649>CVE-2020-8649</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-8649">https://www.linuxkernelcves.com/cves/CVE-2020-8649</a></p>
<p>Release Date: 2020-02-06</p>
<p>Fix Resolution: v5.6-rc5,v3.16.83,v4.14.173,v4.19.109,v4.4.216,v4.9.216,v5.4.25,v5.5.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files drivers video console vgacon c drivers video console vgacon c drivers video console vgacon c vulnerability details there is a use after free vulnerability in the linux kernel through in the vgacon invert region function in drivers video console vgacon c publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
74,585 | 25,191,405,155 | IssuesEvent | 2022-11-12 01:54:12 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | spare disk remains in inuse status after replacing the defective disk | Type: Defect Status: Stale | spare disk remains in inuse status after replacing the defective disk
zfs version
zfs-0.8.3-1ubuntu12.12
zfs-kmod-2.1.99-399_g7eebcd2be
uname -r
5.4.0-80-generic
draid2:8d:1s:24c
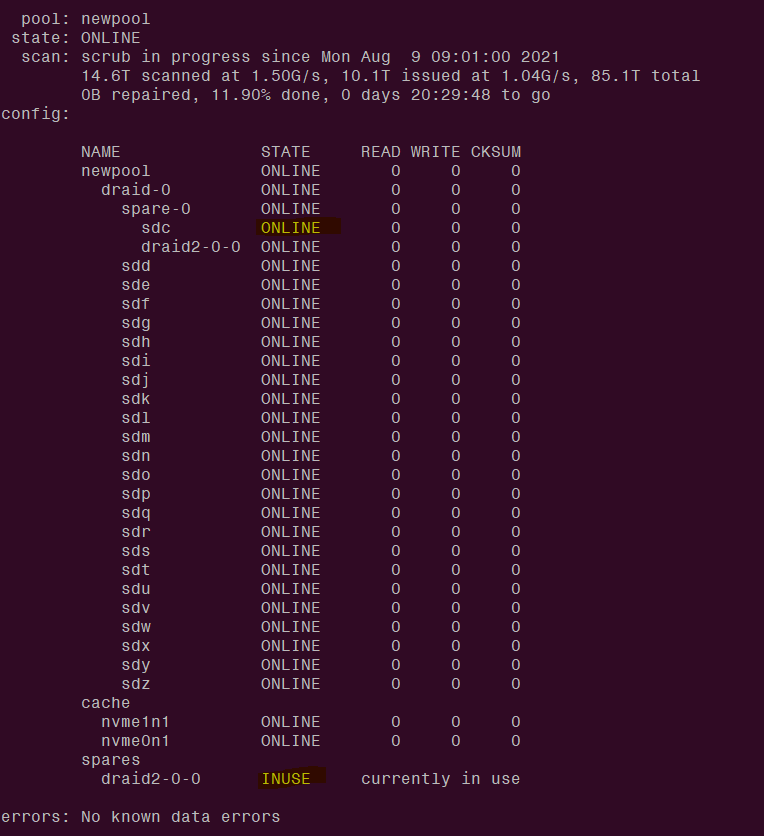
| 1.0 | spare disk remains in inuse status after replacing the defective disk - spare disk remains in inuse status after replacing the defective disk
zfs version
zfs-0.8.3-1ubuntu12.12
zfs-kmod-2.1.99-399_g7eebcd2be
uname -r
5.4.0-80-generic
draid2:8d:1s:24c
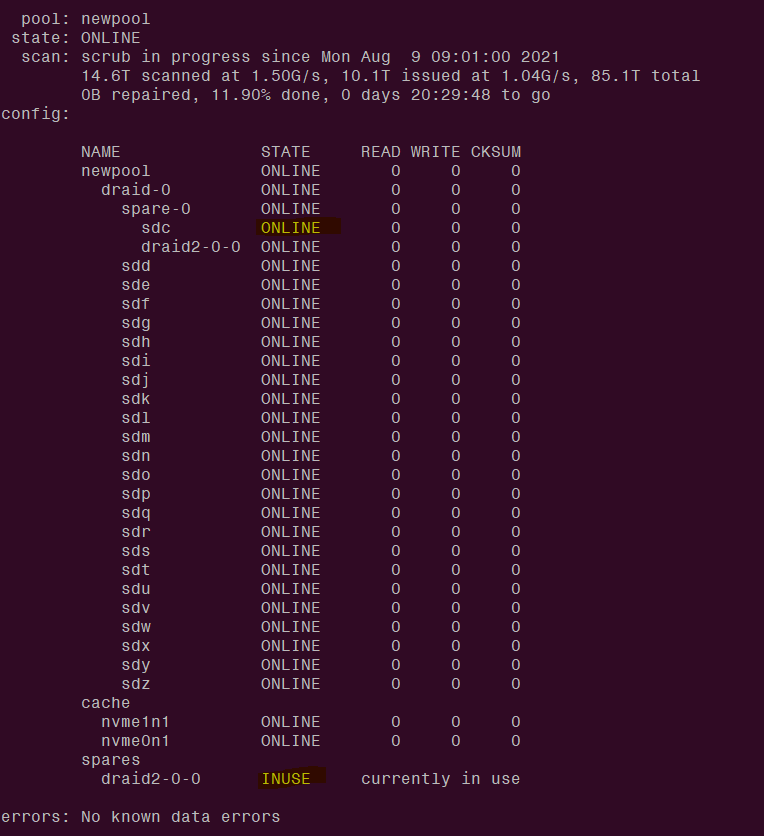
| non_infrastructure | spare disk remains in inuse status after replacing the defective disk spare disk remains in inuse status after replacing the defective disk zfs version zfs zfs kmod uname r generic | 0 |
3,113 | 4,059,092,560 | IssuesEvent | 2016-05-25 08:17:13 | cyberborean/rdfbeans | https://api.github.com/repos/cyberborean/rdfbeans | opened | Test coverage reporting | enhancement infrastructure | In addition to the mere "builds and tests pass" result of Travis, it would be nice to have an idea how well the tests cover the available functionality.
There are several candidate tools in the github ecosystem, e.g. [Coveralls](https://coveralls.io) and [Codecov](https://codecov.io). | 1.0 | Test coverage reporting - In addition to the mere "builds and tests pass" result of Travis, it would be nice to have an idea how well the tests cover the available functionality.
There are several candidate tools in the github ecosystem, e.g. [Coveralls](https://coveralls.io) and [Codecov](https://codecov.io). | infrastructure | test coverage reporting in addition to the mere builds and tests pass result of travis it would be nice to have an idea how well the tests cover the available functionality there are several candidate tools in the github ecosystem e g and | 1 |
215,898 | 24,196,545,713 | IssuesEvent | 2022-09-24 01:16:12 | Killy85/game_ai_trainer | https://api.github.com/repos/Killy85/game_ai_trainer | opened | CVE-2022-35973 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2022-35973 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. If `QuantizedMatMul` is given nonscalar input for: `min_a`, `max_a`, `min_b`, or `max_b` It gives a segfault that can be used to trigger a denial of service attack. We have patched the issue in GitHub commit aca766ac7693bf29ed0df55ad6bfcc78f35e7f48. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-35973>CVE-2022-35973</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-689c-r7h2-fv9v">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-689c-r7h2-fv9v</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-35973 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2022-35973 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. If `QuantizedMatMul` is given nonscalar input for: `min_a`, `max_a`, `min_b`, or `max_b` It gives a segfault that can be used to trigger a denial of service attack. We have patched the issue in GitHub commit aca766ac7693bf29ed0df55ad6bfcc78f35e7f48. The fix will be included in TensorFlow 2.10.0. We will also cherrypick this commit on TensorFlow 2.9.1, TensorFlow 2.8.1, and TensorFlow 2.7.2, as these are also affected and still in supported range. There are no known workarounds for this issue.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-35973>CVE-2022-35973</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-689c-r7h2-fv9v">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-689c-r7h2-fv9v</a></p>
<p>Release Date: 2022-09-16</p>
<p>Fix Resolution: tensorflow - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-cpu - 2.7.2,2.8.1,2.9.1,2.10.0, tensorflow-gpu - 2.7.2,2.8.1,2.9.1,2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an open source platform for machine learning if quantizedmatmul is given nonscalar input for min a max a min b or max b it gives a segfault that can be used to trigger a denial of service attack we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
19,150 | 13,191,780,298 | IssuesEvent | 2020-08-13 12:44:51 | dojopuzzles/dojopuzzles | https://api.github.com/repos/dojopuzzles/dojopuzzles | opened | Configure application to use Docker | help wanted infrastructure | At this moment, the project is deployed in a shared host with a dedicated PostgreSQL database. I want to leave this provider and move the project to a Digital Ocean droplet (or similar). I want to use Docker to orchestrate that so I need a docker-compose.yml file (and the required Dockerfiles) with:
- [ ] Django application
- [ ] PostgreSQL as container
- [ ] Static files running in nginx
As a bonus, a docker-compose-dev.yml file to make configure development environment easier will be good. | 1.0 | Configure application to use Docker - At this moment, the project is deployed in a shared host with a dedicated PostgreSQL database. I want to leave this provider and move the project to a Digital Ocean droplet (or similar). I want to use Docker to orchestrate that so I need a docker-compose.yml file (and the required Dockerfiles) with:
- [ ] Django application
- [ ] PostgreSQL as container
- [ ] Static files running in nginx
As a bonus, a docker-compose-dev.yml file to make configure development environment easier will be good. | infrastructure | configure application to use docker at this moment the project is deployed in a shared host with a dedicated postgresql database i want to leave this provider and move the project to a digital ocean droplet or similar i want to use docker to orchestrate that so i need a docker compose yml file and the required dockerfiles with django application postgresql as container static files running in nginx as a bonus a docker compose dev yml file to make configure development environment easier will be good | 1 |
95,003 | 10,863,592,940 | IssuesEvent | 2019-11-14 15:23:29 | SAP/fundamental-ngx | https://api.github.com/repos/SAP/fundamental-ngx | closed | Documentation Overhaul | documentation enhancement grooming | #### Is this a bug, enhancement, or feature request?
Enhancement
#### Briefly describe your proposal.
- [x] Style like fd-react's next version
- [x] Display version number
- [x] Table-like layout for inputs/outputs etc
- [x] Maybe automatically scrape the files for the properties/methods and display the descriptions using comments in the file? [TSDoc](https://github.com/Microsoft/tsdoc) has a parser. We could use it in a per-file basis. Ideally, we'd do it once when we compile. This needs to be investigated further.
- [x] Tabs for Examples/API at the top. API page should contain tables representing all related child component/service/model etc.
- [x] Tabs to switch between the files of an example, also display file name.
- [x] Use StackBlitz as a playground.
- [x] Have a way to hide/display the code.
- [x] Anchors on all <h> tags, with a link icon to easily share a section of the docs.
- [ ] Table of contents on the right side (as with fd-react). They use [TocBot](https://tscanlin.github.io/tocbot/).
More may be added later | 1.0 | Documentation Overhaul - #### Is this a bug, enhancement, or feature request?
Enhancement
#### Briefly describe your proposal.
- [x] Style like fd-react's next version
- [x] Display version number
- [x] Table-like layout for inputs/outputs etc
- [x] Maybe automatically scrape the files for the properties/methods and display the descriptions using comments in the file? [TSDoc](https://github.com/Microsoft/tsdoc) has a parser. We could use it in a per-file basis. Ideally, we'd do it once when we compile. This needs to be investigated further.
- [x] Tabs for Examples/API at the top. API page should contain tables representing all related child component/service/model etc.
- [x] Tabs to switch between the files of an example, also display file name.
- [x] Use StackBlitz as a playground.
- [x] Have a way to hide/display the code.
- [x] Anchors on all <h> tags, with a link icon to easily share a section of the docs.
- [ ] Table of contents on the right side (as with fd-react). They use [TocBot](https://tscanlin.github.io/tocbot/).
More may be added later | non_infrastructure | documentation overhaul is this a bug enhancement or feature request enhancement briefly describe your proposal style like fd react s next version display version number table like layout for inputs outputs etc maybe automatically scrape the files for the properties methods and display the descriptions using comments in the file has a parser we could use it in a per file basis ideally we d do it once when we compile this needs to be investigated further tabs for examples api at the top api page should contain tables representing all related child component service model etc tabs to switch between the files of an example also display file name use stackblitz as a playground have a way to hide display the code anchors on all tags with a link icon to easily share a section of the docs table of contents on the right side as with fd react they use more may be added later | 0 |
13,365 | 10,221,419,610 | IssuesEvent | 2019-08-16 01:36:04 | pytest-dev/pytest | https://api.github.com/repos/pytest-dev/pytest | closed | Publish GitHub release notes? | type: infrastructure | Any interest in publishing release notes to https://github.com/pytest-dev/pytest/releases?
This would help users follow progress more proactively, especially if using tools such as Sibbell. Currently pages like https://sibbell.com/github/pytest-dev/pytest/3.2.5/ are blank because of the lack of release notes. | 1.0 | Publish GitHub release notes? - Any interest in publishing release notes to https://github.com/pytest-dev/pytest/releases?
This would help users follow progress more proactively, especially if using tools such as Sibbell. Currently pages like https://sibbell.com/github/pytest-dev/pytest/3.2.5/ are blank because of the lack of release notes. | infrastructure | publish github release notes any interest in publishing release notes to this would help users follow progress more proactively especially if using tools such as sibbell currently pages like are blank because of the lack of release notes | 1 |
335,679 | 30,081,752,226 | IssuesEvent | 2023-06-29 04:31:23 | runtimeverification/mir-semantics | https://api.github.com/repos/runtimeverification/mir-semantics | opened | Regenerate MIR outputs of `compiletest-rs/ui` to obtain simpler and cleaner MIR file | kmir-tests | At this moment, we should make use of the `rustc` flags to generate cleaner and less optimized MIR outputs in the `compiletest-rs/ui` suite.
The current generated outputs contains massive comments, `promotes` and debug assertions that are not needed now and in near future.
| 1.0 | Regenerate MIR outputs of `compiletest-rs/ui` to obtain simpler and cleaner MIR file - At this moment, we should make use of the `rustc` flags to generate cleaner and less optimized MIR outputs in the `compiletest-rs/ui` suite.
The current generated outputs contains massive comments, `promotes` and debug assertions that are not needed now and in near future.
| non_infrastructure | regenerate mir outputs of compiletest rs ui to obtain simpler and cleaner mir file at this moment we should make use of the rustc flags to generate cleaner and less optimized mir outputs in the compiletest rs ui suite the current generated outputs contains massive comments promotes and debug assertions that are not needed now and in near future | 0 |
685 | 2,851,421,356 | IssuesEvent | 2015-06-01 06:38:48 | hackndev/zinc | https://api.github.com/repos/hackndev/zinc | closed | Include isr into main zinc rlib | cleanup infrastructure | There are some issues with symbols going missing on OSX during linking (#41). Investigate and fix.
- [ ] find source
- [ ] submit fix
- [ ] remove symbol stripping from Rakefile | 1.0 | Include isr into main zinc rlib - There are some issues with symbols going missing on OSX during linking (#41). Investigate and fix.
- [ ] find source
- [ ] submit fix
- [ ] remove symbol stripping from Rakefile | infrastructure | include isr into main zinc rlib there are some issues with symbols going missing on osx during linking investigate and fix find source submit fix remove symbol stripping from rakefile | 1 |
6,391 | 6,378,178,498 | IssuesEvent | 2017-08-02 12:04:26 | hzi-braunschweig/SORMAS-Open | https://api.github.com/repos/hzi-braunschweig/SORMAS-Open | closed | Split 'not connected' snackbar message | Infrastructure sormas-app | We should differentiate whether the user is not connected to the internet or the SORMAS server cannot be reached. | 1.0 | Split 'not connected' snackbar message - We should differentiate whether the user is not connected to the internet or the SORMAS server cannot be reached. | infrastructure | split not connected snackbar message we should differentiate whether the user is not connected to the internet or the sormas server cannot be reached | 1 |
22,733 | 15,415,037,149 | IssuesEvent | 2021-03-05 01:39:33 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Update coreclr build configurations for Fedora 24 and 25 | area-Infrastructure-coreclr question | With Fedora 23 EOL on Dec 20, 2016 the coreclr build configurations should be updated to support source builds on Fedora 24 and 25.
release/1.1.0:
- seems to partially have Fedora 24 but from a quick inspection it may not be complete.
- needs a build configuration for Fedora 25
- build & test status in README.md should include Fedora 24 and 25 instead of 23.
release/1.0.0:
- needs build configurations for Fedora 24 and 25
- build & test status in README.md should include Fedora 24 and 25 instead of 23.
| 1.0 | Update coreclr build configurations for Fedora 24 and 25 - With Fedora 23 EOL on Dec 20, 2016 the coreclr build configurations should be updated to support source builds on Fedora 24 and 25.
release/1.1.0:
- seems to partially have Fedora 24 but from a quick inspection it may not be complete.
- needs a build configuration for Fedora 25
- build & test status in README.md should include Fedora 24 and 25 instead of 23.
release/1.0.0:
- needs build configurations for Fedora 24 and 25
- build & test status in README.md should include Fedora 24 and 25 instead of 23.
| infrastructure | update coreclr build configurations for fedora and with fedora eol on dec the coreclr build configurations should be updated to support source builds on fedora and release seems to partially have fedora but from a quick inspection it may not be complete needs a build configuration for fedora build test status in readme md should include fedora and instead of release needs build configurations for fedora and build test status in readme md should include fedora and instead of | 1 |
82,027 | 10,267,357,356 | IssuesEvent | 2019-08-23 01:14:15 | gatsbyjs/gatsby | https://api.github.com/repos/gatsbyjs/gatsby | closed | [docs][recipes] Sourcing Content: directly importing data (json & yaml) | effort: low impact: high topic: recipes type: documentation | ## Summary
To improve key learning workflows in the Recipes section of the docs, there should be an actionable recipe on directly importing simple JSON and YAML data without GraphQL.
From @KyleAMathews in https://github.com/gatsbyjs/gatsby/issues/11130: "We should emphasize that hard-coded data can be directly imported and that graphql is only necessary when you want db-like functionality e.g. filtering, sorting, pulling bits of data from connected data, and transforming data (images, markdown, dates, etc.)."
This recipe should show how to import JSON and/or YAML data and use it in a component as concisely as possible. There would be a code snippet like `const data = require('../data/cool-data.json')` and an example of how to consume it.
Recipes now follow this format:
- Requirements or prerequisites
- Step-by-step instructions
- Relevant links to any relevant information
- Using Gatsby without GraphQL https://www.gatsbyjs.org/docs/using-gatsby-without-graphql/
- Link to a live example if not already embedded
This recipe should go into a new section of [`docs/docs/recipes.md`](https://github.com/gatsbyjs/gatsby/blob/master/docs/docs/recipes.md) titled "Sourcing Content" (if it hasn't already been created). There is a recipe template in the contributing docs, including tips on adding a new section: https://www.gatsbyjs.org/contributing/docs-templates/#recipes
For reference, the new recipe collection is also listed in a spreadsheet: https://docs.google.com/spreadsheets/d/1yNUQi_-3TsuDtE98hCIJQvLZ6X1YHlDmC-EJwOGxiHk/edit#gid=1252007048 | 1.0 | [docs][recipes] Sourcing Content: directly importing data (json & yaml) - ## Summary
To improve key learning workflows in the Recipes section of the docs, there should be an actionable recipe on directly importing simple JSON and YAML data without GraphQL.
From @KyleAMathews in https://github.com/gatsbyjs/gatsby/issues/11130: "We should emphasize that hard-coded data can be directly imported and that graphql is only necessary when you want db-like functionality e.g. filtering, sorting, pulling bits of data from connected data, and transforming data (images, markdown, dates, etc.)."
This recipe should show how to import JSON and/or YAML data and use it in a component as concisely as possible. There would be a code snippet like `const data = require('../data/cool-data.json')` and an example of how to consume it.
Recipes now follow this format:
- Requirements or prerequisites
- Step-by-step instructions
- Relevant links to any relevant information
- Using Gatsby without GraphQL https://www.gatsbyjs.org/docs/using-gatsby-without-graphql/
- Link to a live example if not already embedded
This recipe should go into a new section of [`docs/docs/recipes.md`](https://github.com/gatsbyjs/gatsby/blob/master/docs/docs/recipes.md) titled "Sourcing Content" (if it hasn't already been created). There is a recipe template in the contributing docs, including tips on adding a new section: https://www.gatsbyjs.org/contributing/docs-templates/#recipes
For reference, the new recipe collection is also listed in a spreadsheet: https://docs.google.com/spreadsheets/d/1yNUQi_-3TsuDtE98hCIJQvLZ6X1YHlDmC-EJwOGxiHk/edit#gid=1252007048 | non_infrastructure | sourcing content directly importing data json yaml summary to improve key learning workflows in the recipes section of the docs there should be an actionable recipe on directly importing simple json and yaml data without graphql from kyleamathews in we should emphasize that hard coded data can be directly imported and that graphql is only necessary when you want db like functionality e g filtering sorting pulling bits of data from connected data and transforming data images markdown dates etc this recipe should show how to import json and or yaml data and use it in a component as concisely as possible there would be a code snippet like const data require data cool data json and an example of how to consume it recipes now follow this format requirements or prerequisites step by step instructions relevant links to any relevant information using gatsby without graphql link to a live example if not already embedded this recipe should go into a new section of titled sourcing content if it hasn t already been created there is a recipe template in the contributing docs including tips on adding a new section for reference the new recipe collection is also listed in a spreadsheet | 0 |
5,904 | 6,032,422,696 | IssuesEvent | 2017-06-09 03:49:56 | zulip/zulip | https://api.github.com/repos/zulip/zulip | opened | Return the correct missing line numbers when running node coverage | area: testing-infrastructure bite size | Currently, the missing lines that are given in `coverage.json` are incorrect and they need to be pulled from a different section of the JSON file. | 1.0 | Return the correct missing line numbers when running node coverage - Currently, the missing lines that are given in `coverage.json` are incorrect and they need to be pulled from a different section of the JSON file. | infrastructure | return the correct missing line numbers when running node coverage currently the missing lines that are given in coverage json are incorrect and they need to be pulled from a different section of the json file | 1 |
166,956 | 12,978,135,992 | IssuesEvent | 2020-07-21 22:06:42 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: Nightly job aborting after running 28 tests | A-testing C-bug | **Describe the problem**
It looks like the last 3 Roachtest Nightly jobs for the master branch quit early after only running 28 tests. Examples: [one](https://teamcity.cockroachdb.com/viewLog.html?buildId=2096175&buildTypeId=Cockroach_Nightlies_WorkloadNightly), [two](https://teamcity.cockroachdb.com/viewLog.html?buildId=2093071&buildTypeId=Cockroach_Nightlies_WorkloadNightly), and [three](https://teamcity.cockroachdb.com/viewLog.html?buildId=2090320&buildTypeId=Cockroach_Nightlies_WorkloadNightly&tab=buildResultsDiv&branch_Cockroach_Nightlies=%3Cdefault%3E).
I don't know if it's the cause of the problem, but I see this in all the logs:
```
[02:23:38][Step 2/2] panic: t.Fatal() was called
[02:23:38][Step 2/2]
[02:23:38][Step 2/2] goroutine 5417 [running]:
[02:23:38][Step 2/2] main.(*test).fatalfInner(0xc000166d80, 0x0, 0x0, 0xc000d4e5b0, 0x1, 0x1)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test.go:279 +0xcd
[02:23:38][Step 2/2] main.FatalIfErr(...)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test.go:285
[02:23:38][Step 2/2] main.(*cluster).Start(0xc000a921e0, 0x4846940, 0xc0006daf00, 0xc000166d80, 0xc0010e5f00, 0x2, 0x2)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:1996 +0xe5
[02:23:38][Step 2/2] main.runDecommission.func5(0x0, 0x0)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/decommission.go:251 +0x926
[02:23:38][Step 2/2] golang.org/x/sync/errgroup.(*Group).Go.func1(0xc000426720, 0xc000d305f0)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x59
[02:23:38][Step 2/2] created by golang.org/x/sync/errgroup.(*Group).Go
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:54 +0x66
[02:23:38][Step 2/2] + upload_stats
[02:23:38][Step 2/2] + [[ master == \m\a\s\t\e\r ]]
[02:23:38][Step 2/2] + bucket=cockroach-nightly-gce
[02:23:38][Step 2/2] + [[ gce == \g\c\e ]]
[02:23:38][Step 2/2] + bucket=cockroach-nightly
[02:23:38][Step 2/2] + cd /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts
[02:23:38][Step 2/2] ++ sed 's/^\.\///'
[02:23:38][Step 2/2] ++ find . -name stats.json
[02:23:38][Step 2/2] + IFS=
[02:23:38][Step 2/2] + read -r f
[02:23:38][Step 2/2] + gsutil cp '' gs://cockroach-nightly/artifacts/20200716-2093071/
[02:23:38][Step 2/2] CommandException: No URLs matched:
[02:23:39][Step 2/2] Process exited with code 1
```
**To Reproduce**
Run a Roachtest Nightly job.
**Expected behavior**
All of the tests should run. There are a few hundred tests.
**Additional context**
The fact that not all tests are being run isn't super obvious. See: #50618 | 1.0 | roachtest: Nightly job aborting after running 28 tests - **Describe the problem**
It looks like the last 3 Roachtest Nightly jobs for the master branch quit early after only running 28 tests. Examples: [one](https://teamcity.cockroachdb.com/viewLog.html?buildId=2096175&buildTypeId=Cockroach_Nightlies_WorkloadNightly), [two](https://teamcity.cockroachdb.com/viewLog.html?buildId=2093071&buildTypeId=Cockroach_Nightlies_WorkloadNightly), and [three](https://teamcity.cockroachdb.com/viewLog.html?buildId=2090320&buildTypeId=Cockroach_Nightlies_WorkloadNightly&tab=buildResultsDiv&branch_Cockroach_Nightlies=%3Cdefault%3E).
I don't know if it's the cause of the problem, but I see this in all the logs:
```
[02:23:38][Step 2/2] panic: t.Fatal() was called
[02:23:38][Step 2/2]
[02:23:38][Step 2/2] goroutine 5417 [running]:
[02:23:38][Step 2/2] main.(*test).fatalfInner(0xc000166d80, 0x0, 0x0, 0xc000d4e5b0, 0x1, 0x1)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test.go:279 +0xcd
[02:23:38][Step 2/2] main.FatalIfErr(...)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test.go:285
[02:23:38][Step 2/2] main.(*cluster).Start(0xc000a921e0, 0x4846940, 0xc0006daf00, 0xc000166d80, 0xc0010e5f00, 0x2, 0x2)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:1996 +0xe5
[02:23:38][Step 2/2] main.runDecommission.func5(0x0, 0x0)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/decommission.go:251 +0x926
[02:23:38][Step 2/2] golang.org/x/sync/errgroup.(*Group).Go.func1(0xc000426720, 0xc000d305f0)
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x59
[02:23:38][Step 2/2] created by golang.org/x/sync/errgroup.(*Group).Go
[02:23:38][Step 2/2] /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:54 +0x66
[02:23:38][Step 2/2] + upload_stats
[02:23:38][Step 2/2] + [[ master == \m\a\s\t\e\r ]]
[02:23:38][Step 2/2] + bucket=cockroach-nightly-gce
[02:23:38][Step 2/2] + [[ gce == \g\c\e ]]
[02:23:38][Step 2/2] + bucket=cockroach-nightly
[02:23:38][Step 2/2] + cd /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts
[02:23:38][Step 2/2] ++ sed 's/^\.\///'
[02:23:38][Step 2/2] ++ find . -name stats.json
[02:23:38][Step 2/2] + IFS=
[02:23:38][Step 2/2] + read -r f
[02:23:38][Step 2/2] + gsutil cp '' gs://cockroach-nightly/artifacts/20200716-2093071/
[02:23:38][Step 2/2] CommandException: No URLs matched:
[02:23:39][Step 2/2] Process exited with code 1
```
**To Reproduce**
Run a Roachtest Nightly job.
**Expected behavior**
All of the tests should run. There are a few hundred tests.
**Additional context**
The fact that not all tests are being run isn't super obvious. See: #50618 | non_infrastructure | roachtest nightly job aborting after running tests describe the problem it looks like the last roachtest nightly jobs for the master branch quit early after only running tests examples and i don t know if it s the cause of the problem but i see this in all the logs panic t fatal was called goroutine main test fatalfinner home agent work go src github com cockroachdb cockroach pkg cmd roachtest test go main fataliferr home agent work go src github com cockroachdb cockroach pkg cmd roachtest test go main cluster start home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main rundecommission home agent work go src github com cockroachdb cockroach pkg cmd roachtest decommission go golang org x sync errgroup group go home agent work go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go created by golang org x sync errgroup group go home agent work go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go upload stats bucket cockroach nightly gce bucket cockroach nightly cd home agent work go src github com cockroachdb cockroach artifacts sed s find name stats json ifs read r f gsutil cp gs cockroach nightly artifacts commandexception no urls matched process exited with code to reproduce run a roachtest nightly job expected behavior all of the tests should run there are a few hundred tests additional context the fact that not all tests are being run isn t super obvious see | 0 |
315,966 | 27,122,957,589 | IssuesEvent | 2023-02-16 01:17:00 | bsc-quantic/rosnet | https://api.github.com/repos/bsc-quantic/rosnet | closed | Design test set | test | - [ ] Unit tests
- [ ] `core`
- [ ] `util`
- [ ] `interface`
- [ ] `array`
- [ ] `BlockArray`
- [x] Constructors
- [ ] `COMPSsArray`
- [ ] Integration tests
- [ ] `numpy`
- [ ] `autoray`
- [ ] `opt_einsum`
- [ ] `quimb`
- [ ] System tests
- [ ] Classical circuits
- [ ] Adder w/o carry
- [ ] QFT
- [ ] Low-frequency, real signal
- [ ] High-frequency, real signal
- [ ] Numerical tests | 1.0 | Design test set - - [ ] Unit tests
- [ ] `core`
- [ ] `util`
- [ ] `interface`
- [ ] `array`
- [ ] `BlockArray`
- [x] Constructors
- [ ] `COMPSsArray`
- [ ] Integration tests
- [ ] `numpy`
- [ ] `autoray`
- [ ] `opt_einsum`
- [ ] `quimb`
- [ ] System tests
- [ ] Classical circuits
- [ ] Adder w/o carry
- [ ] QFT
- [ ] Low-frequency, real signal
- [ ] High-frequency, real signal
- [ ] Numerical tests | non_infrastructure | design test set unit tests core util interface array blockarray constructors compssarray integration tests numpy autoray opt einsum quimb system tests classical circuits adder w o carry qft low frequency real signal high frequency real signal numerical tests | 0 |
71,925 | 18,927,534,403 | IssuesEvent | 2021-11-17 11:07:39 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug]: Input widget of phone number type must read spaces in bound data and accept spaces while entering number | Bug Input Widget App Viewers Pod High Production UI Building Pod | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Currently, phone number type input widget does not read spaces when present in bound data causing an error. Also, one is unable to use spaces in between numbers. This needs to be handled
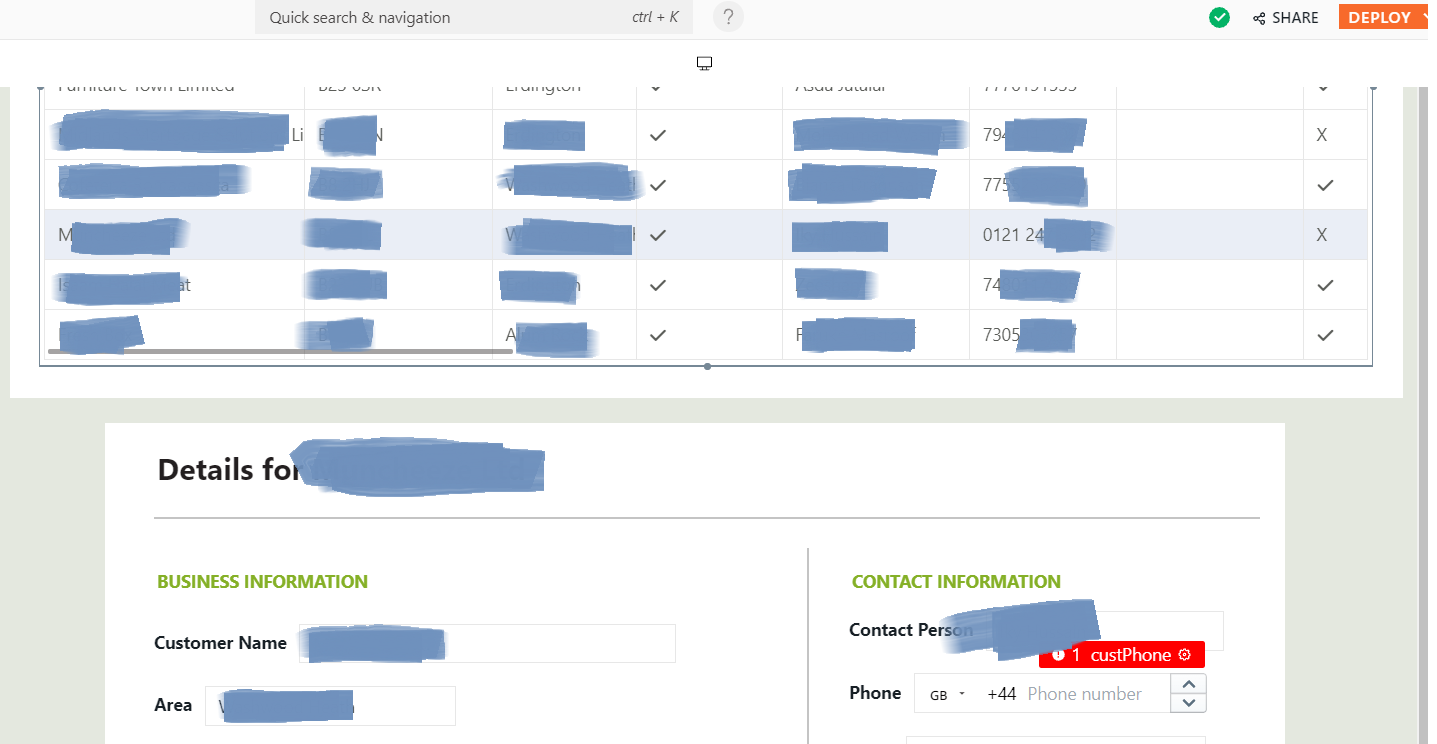
### Steps To Reproduce
```markdown
1. Use a datasource that contains phone numbers that are formatted according to local "readbility" style and bind it to an input widget of Phone number type and observe the error
```
### Environment
Production
### Version
Cloud | 1.0 | [Bug]: Input widget of phone number type must read spaces in bound data and accept spaces while entering number - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
Currently, phone number type input widget does not read spaces when present in bound data causing an error. Also, one is unable to use spaces in between numbers. This needs to be handled
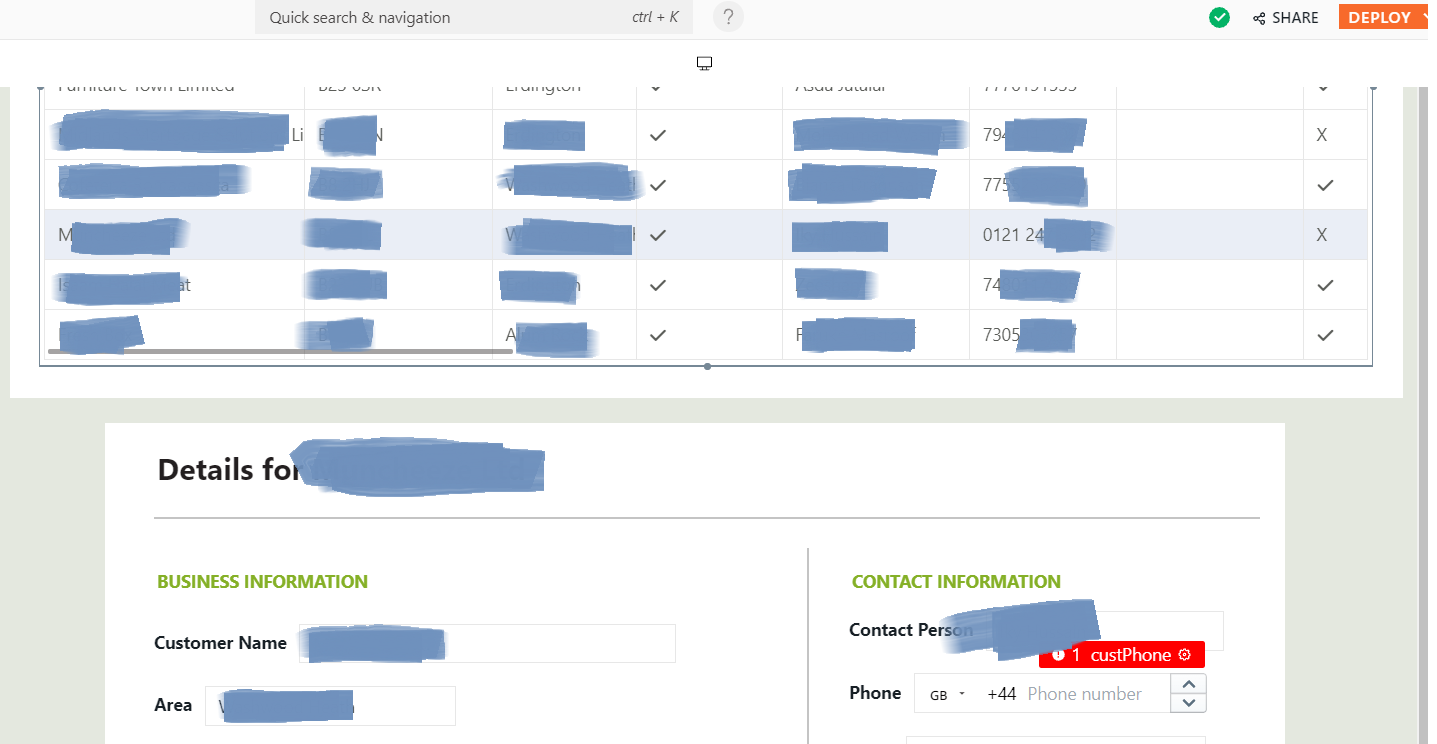
### Steps To Reproduce
```markdown
1. Use a datasource that contains phone numbers that are formatted according to local "readbility" style and bind it to an input widget of Phone number type and observe the error
```
### Environment
Production
### Version
Cloud | non_infrastructure | input widget of phone number type must read spaces in bound data and accept spaces while entering number is there an existing issue for this i have searched the existing issues current behavior currently phone number type input widget does not read spaces when present in bound data causing an error also one is unable to use spaces in between numbers this needs to be handled steps to reproduce markdown use a datasource that contains phone numbers that are formatted according to local readbility style and bind it to an input widget of phone number type and observe the error environment production version cloud | 0 |
133 | 2,534,392,232 | IssuesEvent | 2015-01-24 22:30:26 | RobDixonIII/Bloom | https://api.github.com/repos/RobDixonIII/Bloom | closed | Load Browser Modules into Tab | feature infrastructure | Create a method by which browser modules can be dynamically created and loaded into dock tabs in the application shell. | 1.0 | Load Browser Modules into Tab - Create a method by which browser modules can be dynamically created and loaded into dock tabs in the application shell. | infrastructure | load browser modules into tab create a method by which browser modules can be dynamically created and loaded into dock tabs in the application shell | 1 |
177,729 | 29,045,294,595 | IssuesEvent | 2023-05-13 13:27:37 | Leafwing-Studios/Emergence | https://api.github.com/repos/Leafwing-Studios/Emergence | opened | Add a renewable source and sink of soil | gameplay game design | Dehydrating water / dissolving soil into the water is the most promising generic solution.
Important for building up larger structures.
| 1.0 | Add a renewable source and sink of soil - Dehydrating water / dissolving soil into the water is the most promising generic solution.
Important for building up larger structures.
| non_infrastructure | add a renewable source and sink of soil dehydrating water dissolving soil into the water is the most promising generic solution important for building up larger structures | 0 |
3,117 | 4,063,744,284 | IssuesEvent | 2016-05-26 01:36:19 | pyta-uoft/pyta | https://api.github.com/repos/pyta-uoft/pyta | opened | Improve robustness of module loading | Infrastructure | Right now, if a user types in a module name which is missing, or which has the extension `.py`, the checker will fail. Two changes should be made:
1. Detect if the extension `.py` is added, and if it is, remove it but load the correct module without error.
2. Catch the correct exception when a module is not found, and report a good error message to the user. | 1.0 | Improve robustness of module loading - Right now, if a user types in a module name which is missing, or which has the extension `.py`, the checker will fail. Two changes should be made:
1. Detect if the extension `.py` is added, and if it is, remove it but load the correct module without error.
2. Catch the correct exception when a module is not found, and report a good error message to the user. | infrastructure | improve robustness of module loading right now if a user types in a module name which is missing or which has the extension py the checker will fail two changes should be made detect if the extension py is added and if it is remove it but load the correct module without error catch the correct exception when a module is not found and report a good error message to the user | 1 |
4,125 | 4,822,491,766 | IssuesEvent | 2016-11-05 21:47:47 | stylelint/stylelint | https://api.github.com/repos/stylelint/stylelint | closed | Update Greenkeeper Bot | status: wip type: infrastructure | I discovered today that a couple of unrequired branches created by Greenkeeper had not been deleted, i.e The changes were already covered by semantic versioning so a PR was not required.
Two more occurrences of this have since occurred:
• https://github.com/stylelint/stylelint/commit/76645ec20abc91c53c3f1b728ceeaac23a77881e - https://github.com/stylelint/stylelint/compare/greenkeeper-benchmark-2.1.2
• https://github.com/stylelint/stylelint/commit/f9a51ae659c94087435e0f0b212cb40084bc7a13 - https://github.com/stylelint/stylelint/compare/greenkeeper-lodash-4.16.5
I've not deleted these branches yet in case the Greenkeeper team wanted a peak.
I've pinged @greenkeeperio on [Twitter here](https://twitter.com/netweb/status/793005457254121472) in the hope of a reply 😄
I suspect that part of the reply will be to upgrade to the new _Greenkeeper GitHub Integration_ via https://github.com/integration/greenkeeper which I believe replaces the previous workflow where a repo owner installed and authorised it locally to a centrally managed service on GitHub.
I'll update this issue as I discover more on the new workflow and any reply from @greenkeeperio | 1.0 | Update Greenkeeper Bot - I discovered today that a couple of unrequired branches created by Greenkeeper had not been deleted, i.e The changes were already covered by semantic versioning so a PR was not required.
Two more occurrences of this have since occurred:
• https://github.com/stylelint/stylelint/commit/76645ec20abc91c53c3f1b728ceeaac23a77881e - https://github.com/stylelint/stylelint/compare/greenkeeper-benchmark-2.1.2
• https://github.com/stylelint/stylelint/commit/f9a51ae659c94087435e0f0b212cb40084bc7a13 - https://github.com/stylelint/stylelint/compare/greenkeeper-lodash-4.16.5
I've not deleted these branches yet in case the Greenkeeper team wanted a peak.
I've pinged @greenkeeperio on [Twitter here](https://twitter.com/netweb/status/793005457254121472) in the hope of a reply 😄
I suspect that part of the reply will be to upgrade to the new _Greenkeeper GitHub Integration_ via https://github.com/integration/greenkeeper which I believe replaces the previous workflow where a repo owner installed and authorised it locally to a centrally managed service on GitHub.
I'll update this issue as I discover more on the new workflow and any reply from @greenkeeperio | infrastructure | update greenkeeper bot i discovered today that a couple of unrequired branches created by greenkeeper had not been deleted i e the changes were already covered by semantic versioning so a pr was not required two more occurrences of this have since occurred • • i ve not deleted these branches yet in case the greenkeeper team wanted a peak i ve pinged greenkeeperio on in the hope of a reply 😄 i suspect that part of the reply will be to upgrade to the new greenkeeper github integration via which i believe replaces the previous workflow where a repo owner installed and authorised it locally to a centrally managed service on github i ll update this issue as i discover more on the new workflow and any reply from greenkeeperio | 1 |
214,493 | 24,077,717,424 | IssuesEvent | 2022-09-19 01:03:37 | Bangtrongtuyet/spring-cloud-netflix | https://api.github.com/repos/Bangtrongtuyet/spring-cloud-netflix | opened | CVE-2022-40149 (Medium) detected in jettison-1.3.7.jar | security vulnerability | ## CVE-2022-40149 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.3.7.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /spring-cloud-netflix/spring-cloud-netflix-eureka-server/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-netflix-eureka-server-2.2.0.BUILD-SNAPSHOT.jar (Root Library)
- eureka-client-1.9.8.jar
- :x: **jettison-1.3.7.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40149>CVE-2022-40149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-40149 (Medium) detected in jettison-1.3.7.jar - ## CVE-2022-40149 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.3.7.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /spring-cloud-netflix/spring-cloud-netflix-eureka-server/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar,/root/.m2/repository/org/codehaus/jettison/jettison/1.3.7/jettison-1.3.7.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-netflix-eureka-server-2.2.0.BUILD-SNAPSHOT.jar (Root Library)
- eureka-client-1.9.8.jar
- :x: **jettison-1.3.7.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40149>CVE-2022-40149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_infrastructure | cve medium detected in jettison jar cve medium severity vulnerability vulnerable library jettison jar a stax implementation for json path to dependency file spring cloud netflix spring cloud netflix eureka server pom xml path to vulnerable library root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar root repository org codehaus jettison jettison jettison jar dependency hierarchy spring cloud netflix eureka server build snapshot jar root library eureka client jar x jettison jar vulnerable library vulnerability details those using jettison to parse untrusted xml or json data may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
26,526 | 20,193,581,175 | IssuesEvent | 2022-02-11 08:34:16 | navikt/innbyggerpanelet | https://api.github.com/repos/navikt/innbyggerpanelet | closed | Update github workflows | Priority: HIGH infrastructure | We should consider updating the github workflows and split them up, as they are now always running on each push on every branch. There might be times when we want the workflows to run at different times.
My suggestion:
- Deploy to NAIS runs only when pushing in main or merging to main.
- CI runs on every push, howevery CI needs to pass for a deploy to happen.
- [ ] Update branch rules on main for the eventual change | 1.0 | Update github workflows - We should consider updating the github workflows and split them up, as they are now always running on each push on every branch. There might be times when we want the workflows to run at different times.
My suggestion:
- Deploy to NAIS runs only when pushing in main or merging to main.
- CI runs on every push, howevery CI needs to pass for a deploy to happen.
- [ ] Update branch rules on main for the eventual change | infrastructure | update github workflows we should consider updating the github workflows and split them up as they are now always running on each push on every branch there might be times when we want the workflows to run at different times my suggestion deploy to nais runs only when pushing in main or merging to main ci runs on every push howevery ci needs to pass for a deploy to happen update branch rules on main for the eventual change | 1 |
191,619 | 6,835,583,649 | IssuesEvent | 2017-11-10 02:01:51 | NuGet/Home | https://api.github.com/repos/NuGet/Home | closed | Need to make changes to NuGet when csproj moves to CPS | ClosedAs:WontFix Priority:1 Type:DCR | From @aarnott
I experienced a long hang in VS. I "filed" this against Xamarin but wanted to make you all aware since it took a chain of behaviors for the hang to reproduce:
http://forums.xamarin.com/discussion/52746/xamarin-android-hangs-vs-for-long-periods
Switching csproj.dll to CPS allows for asynchronous design-time builds. But NuGet would also need to switch to CPS' async APIs for reference enumeration in order to avoid such a hang for poorly behaved MSBuild tasks such as Xamarin's.
CC @pilchie
| 1.0 | Need to make changes to NuGet when csproj moves to CPS - From @aarnott
I experienced a long hang in VS. I "filed" this against Xamarin but wanted to make you all aware since it took a chain of behaviors for the hang to reproduce:
http://forums.xamarin.com/discussion/52746/xamarin-android-hangs-vs-for-long-periods
Switching csproj.dll to CPS allows for asynchronous design-time builds. But NuGet would also need to switch to CPS' async APIs for reference enumeration in order to avoid such a hang for poorly behaved MSBuild tasks such as Xamarin's.
CC @pilchie
| non_infrastructure | need to make changes to nuget when csproj moves to cps from aarnott i experienced a long hang in vs i filed this against xamarin but wanted to make you all aware since it took a chain of behaviors for the hang to reproduce switching csproj dll to cps allows for asynchronous design time builds but nuget would also need to switch to cps async apis for reference enumeration in order to avoid such a hang for poorly behaved msbuild tasks such as xamarin s cc pilchie | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.