Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3
values | title stringlengths 2 665 | labels stringlengths 4 554 | body stringlengths 3 235k | index stringclasses 6
values | text_combine stringlengths 96 235k | label stringclasses 2
values | text stringlengths 96 196k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
24,650 | 17,552,189,998 | IssuesEvent | 2021-08-13 00:10:51 | scala-js/scala-js-dom | https://api.github.com/repos/scala-js/scala-js-dom | closed | GH Action Release fails | infrastructure | @armanbilge Release failed on the `series/v1.x` branch, seemingly cos of SJS 0.6.x. I know it's just SNAPSHOT release but if it doesn't work, pushing a v1.2.0 tag wont work either sadly.
https://github.com/scala-js/scala-js-dom/actions/runs/1125835306 | 1.0 | GH Action Release fails - @armanbilge Release failed on the `series/v1.x` branch, seemingly cos of SJS 0.6.x. I know it's just SNAPSHOT release but if it doesn't work, pushing a v1.2.0 tag wont work either sadly.
https://github.com/scala-js/scala-js-dom/actions/runs/1125835306 | infrastructure | gh action release fails armanbilge release failed on the series x branch seemingly cos of sjs x i know it s just snapshot release but if it doesn t work pushing a tag wont work either sadly | 1 |
4,055 | 4,789,239,172 | IssuesEvent | 2016-10-30 23:27:34 | dst-academy/docker-dontstarvetogether | https://api.github.com/repos/dst-academy/docker-dontstarvetogether | closed | Optimize repository names | enhancement infrastructure | For a better forking experience and better identification overall we should rename the repository before releasing the final version. In addition the Docker Hub name should be clearer.
Suggestions for GitHub:
- `dst-academy/dst-server-docker`
- `dst-academy/docker-dst-server`
- `dst-academy/dont-starve-together-docker... | 1.0 | Optimize repository names - For a better forking experience and better identification overall we should rename the repository before releasing the final version. In addition the Docker Hub name should be clearer.
Suggestions for GitHub:
- `dst-academy/dst-server-docker`
- `dst-academy/docker-dst-server`
- `dst-academy... | infrastructure | optimize repository names for a better forking experience and better identification overall we should rename the repository before releasing the final version in addition the docker hub name should be clearer suggestions for github dst academy dst server docker dst academy docker dst server dst academy... | 1 |
2,634 | 3,790,108,481 | IssuesEvent | 2016-03-21 20:17:49 | elmsln/elmsln | https://api.github.com/repos/elmsln/elmsln | closed | support drush concurrency in elmsln-upgrade-sites | enhancement infrastructure scale / performance | server specs:
2 processors, 6 gigs of ram
php 5.6 mysql 5.5 opcache in place
drush has built in support for concurrency so that you can process multiple calls in a alias target. As elmsln's upgrade routine is built on @ elmsln which is a lazy loaded, very big alias grouping (of sub-groupings of sites) we could sta... | 1.0 | support drush concurrency in elmsln-upgrade-sites - server specs:
2 processors, 6 gigs of ram
php 5.6 mysql 5.5 opcache in place
drush has built in support for concurrency so that you can process multiple calls in a alias target. As elmsln's upgrade routine is built on @ elmsln which is a lazy loaded, very big ali... | infrastructure | support drush concurrency in elmsln upgrade sites server specs processors gigs of ram php mysql opcache in place drush has built in support for concurrency so that you can process multiple calls in a alias target as elmsln s upgrade routine is built on elmsln which is a lazy loaded very big ali... | 1 |
1,564 | 3,268,382,207 | IssuesEvent | 2015-10-23 11:07:22 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Please merge revision 1a7528174263af0a95d7edf51c01a2b3d1b568ff into dev channel | Area-Infrastructure MergeToDev | @ricowind @whesse @kasperl
This fixes a constant evaluation bug which could cause an analyzer crash when analyzing code containing malformed constant expressions. See #24645.
Revision to be merged: 1a7528174263af0a95d7edf51c01a2b3d1b568ff
There is a minor merge conflict. I've uploaded a CL with the correct m... | 1.0 | Please merge revision 1a7528174263af0a95d7edf51c01a2b3d1b568ff into dev channel - @ricowind @whesse @kasperl
This fixes a constant evaluation bug which could cause an analyzer crash when analyzing code containing malformed constant expressions. See #24645.
Revision to be merged: 1a7528174263af0a95d7edf51c01a2b3d... | infrastructure | please merge revision into dev channel ricowind whesse kasperl this fixes a constant evaluation bug which could cause an analyzer crash when analyzing code containing malformed constant expressions see revision to be merged there is a minor merge conflict i ve uploaded a cl with the correct m... | 1 |
31,587 | 25,903,311,165 | IssuesEvent | 2022-12-15 08:12:19 | deckhouse/deckhouse | https://api.github.com/repos/deckhouse/deckhouse | opened | [cloud-provider-aws] Add disable_api_termination to master nodes | type/enhancement area/cluster-and-infrastructure source/internal-client status/needs-triage | ### Preflight Checklist
- [X] I agree to follow the [Code of Conduct](https://github.com/deckhouse/deckhouse/blob/main/CODE_OF_CONDUCT.md) that this project adheres to.
- [X] I have searched the [issue tracker](https://github.com/deckhouse/deckhouse/issues) for an issue that matches the one I want to file, without suc... | 1.0 | [cloud-provider-aws] Add disable_api_termination to master nodes - ### Preflight Checklist
- [X] I agree to follow the [Code of Conduct](https://github.com/deckhouse/deckhouse/blob/main/CODE_OF_CONDUCT.md) that this project adheres to.
- [X] I have searched the [issue tracker](https://github.com/deckhouse/deckhouse/is... | infrastructure | add disable api termination to master nodes preflight checklist i agree to follow the that this project adheres to i have searched the for an issue that matches the one i want to file without success use case why is this important there was a case when all control plane nodes were ac... | 1 |
12,373 | 9,753,863,178 | IssuesEvent | 2019-06-04 10:07:05 | Altinn/altinn-studio | https://api.github.com/repos/Altinn/altinn-studio | closed | Set up load balancing for SBL Bridge | draft infrastructure sbl sbl-bridge team-steam team-tamagotchi user-story | **Functional architect/designer:** @-mention
**Technical architect:** @-mention
**Description**
The platform integration application should be loadbalanced between the portal servers in the test environment.
**Technical considerations**
- Which loadbalancer will we use?
- Should only be aviable internal
**... | 1.0 | Set up load balancing for SBL Bridge - **Functional architect/designer:** @-mention
**Technical architect:** @-mention
**Description**
The platform integration application should be loadbalanced between the portal servers in the test environment.
**Technical considerations**
- Which loadbalancer will we use?
... | infrastructure | set up load balancing for sbl bridge functional architect designer mention technical architect mention description the platform integration application should be loadbalanced between the portal servers in the test environment technical considerations which loadbalancer will we use ... | 1 |
6,217 | 6,258,907,792 | IssuesEvent | 2017-07-14 16:43:12 | servo/servo | https://api.github.com/repos/servo/servo | closed | Add tidy to support crates' CI | A-infrastructure B-meta | Superseding https://github.com/servo/servo/issues/861
- [ ] set up CI to automatically deploy new tidy versions to pypi when the source is changed
- [ ] Update list of all support crates and add it here
- [ ] check whether tidy is run by their CI and add it if not | 1.0 | Add tidy to support crates' CI - Superseding https://github.com/servo/servo/issues/861
- [ ] set up CI to automatically deploy new tidy versions to pypi when the source is changed
- [ ] Update list of all support crates and add it here
- [ ] check whether tidy is run by their CI and add it if not | infrastructure | add tidy to support crates ci superseding set up ci to automatically deploy new tidy versions to pypi when the source is changed update list of all support crates and add it here check whether tidy is run by their ci and add it if not | 1 |
11,804 | 9,430,400,017 | IssuesEvent | 2019-04-12 08:56:38 | vsechnovcloudu/chaosgunsonline | https://api.github.com/repos/vsechnovcloudu/chaosgunsonline | opened | Containerization and deployment of server | infrastructure | Dockerfile ready, but we need to deploy it somewhere.
Proposal: AWS Fargate | 1.0 | Containerization and deployment of server - Dockerfile ready, but we need to deploy it somewhere.
Proposal: AWS Fargate | infrastructure | containerization and deployment of server dockerfile ready but we need to deploy it somewhere proposal aws fargate | 1 |
20,404 | 3,812,082,739 | IssuesEvent | 2016-03-27 09:29:49 | QualiSystems/vCenterShell | https://api.github.com/repos/QualiSystems/vCenterShell | closed | Delete a resource that is endpoint of a CVC - vlan is held in vlan pool till reservation ends | bug Connectivity P2 ready to test | ### Issue details
Delete resource that is part of active P2P connection such that its VLAN should be released.
VLAN is still held in Vlan Items table until reservation ends, if delete VM resource (not remove, but delete through client or API)
### Steps to reproduce
Have a P2P connection between two apps. Co... | 1.0 | Delete a resource that is endpoint of a CVC - vlan is held in vlan pool till reservation ends - ### Issue details
Delete resource that is part of active P2P connection such that its VLAN should be released.
VLAN is still held in Vlan Items table until reservation ends, if delete VM resource (not remove, but delet... | non_infrastructure | delete a resource that is endpoint of a cvc vlan is held in vlan pool till reservation ends issue details delete resource that is part of active connection such that its vlan should be released vlan is still held in vlan items table until reservation ends if delete vm resource not remove but delete ... | 0 |
11,357 | 9,115,980,832 | IssuesEvent | 2019-02-22 07:28:58 | radare/radare2 | https://api.github.com/repos/radare/radare2 | opened | Automate merging easy and test-passing pull requests | infrastructure question | For example if all tests are passing, coverage is not decreased, amount of changes is not big, PR was reviewed, it can merge automatically.
There is a bot for that:
https://mergify.io/
https://github.com/apps/mergify
| 1.0 | Automate merging easy and test-passing pull requests - For example if all tests are passing, coverage is not decreased, amount of changes is not big, PR was reviewed, it can merge automatically.
There is a bot for that:
https://mergify.io/
https://github.com/apps/mergify
| infrastructure | automate merging easy and test passing pull requests for example if all tests are passing coverage is not decreased amount of changes is not big pr was reviewed it can merge automatically there is a bot for that | 1 |
31,769 | 26,107,086,998 | IssuesEvent | 2022-12-27 14:33:22 | treeverse/lakeFS | https://api.github.com/repos/treeverse/lakeFS | closed | RouterFS: should we use "provided" for hadoop- dependencies? | infrastructure area/client/spark team/ecosystem | In RouterFS:
- Check if it makes sense to use provided dependencies.
- If we use provided, how do we compile?
- ~For hadoopFs~ and RouterFS (lower priority)
EDIT: was already done for HadoopFS (#4357)
| 1.0 | RouterFS: should we use "provided" for hadoop- dependencies? - In RouterFS:
- Check if it makes sense to use provided dependencies.
- If we use provided, how do we compile?
- ~For hadoopFs~ and RouterFS (lower priority)
EDIT: was already done for HadoopFS (#4357)
| infrastructure | routerfs should we use provided for hadoop dependencies in routerfs check if it makes sense to use provided dependencies if we use provided how do we compile for hadoopfs and routerfs lower priority edit was already done for hadoopfs | 1 |
344,889 | 10,349,714,597 | IssuesEvent | 2019-09-04 23:36:23 | oslc-op/oslc-specs | https://api.github.com/repos/oslc-op/oslc-specs | opened | Consider defining a more general approach than a fixed JSON-LD format | Core: TRS Jira: access-control Priority: High Xtra: Jira | For the TRS spec, can we use a more general approach?
Jim says it is brittle...
---
_Migrated from https://issues.oasis-open.org/browse/OSLCCORE-79 (opened by @sarabura; previously assigned to @jamsden)_
| 1.0 | Consider defining a more general approach than a fixed JSON-LD format - For the TRS spec, can we use a more general approach?
Jim says it is brittle...
---
_Migrated from https://issues.oasis-open.org/browse/OSLCCORE-79 (opened by @sarabura; previously assigned to @jamsden)_
| non_infrastructure | consider defining a more general approach than a fixed json ld format for the trs spec can we use a more general approach jim says it is brittle migrated from opened by sarabura previously assigned to jamsden | 0 |
504,609 | 14,620,295,026 | IssuesEvent | 2020-12-22 19:27:20 | googleapis/elixir-google-api | https://api.github.com/repos/googleapis/elixir-google-api | closed | Synthesis failed for Content | autosynth failure priority: p1 type: bug | Hello! Autosynth couldn't regenerate Content. :broken_heart:
Here's the output from running `synth.py`:
```
ionsListResponse to clients/content/lib/google_api/content/v21/model/settlementtransactions_list_response.ex.
Writing ShipmentInvoice to clients/content/lib/google_api/content/v21/model/shipment_invoice.ex.
Wri... | 1.0 | Synthesis failed for Content - Hello! Autosynth couldn't regenerate Content. :broken_heart:
Here's the output from running `synth.py`:
```
ionsListResponse to clients/content/lib/google_api/content/v21/model/settlementtransactions_list_response.ex.
Writing ShipmentInvoice to clients/content/lib/google_api/content/v21... | non_infrastructure | synthesis failed for content hello autosynth couldn t regenerate content broken heart here s the output from running synth py ionslistresponse to clients content lib google api content model settlementtransactions list response ex writing shipmentinvoice to clients content lib google api content mod... | 0 |
5,093 | 5,435,260,130 | IssuesEvent | 2017-03-05 15:33:03 | AdguardTeam/AdguardFilters | https://api.github.com/repos/AdguardTeam/AdguardFilters | closed | adblock.ro filter | Infrastructure |
Want to inform this is a new Romanian filter list https://www.adblock.ro/, on our website you can find all details, may need to use translation tools because is written in Romanian. This is a Public list, and anyone can contribute on our GitHub open project.
Our Website: https://www.adblock.ro/
Github Project: h... | 1.0 | adblock.ro filter -
Want to inform this is a new Romanian filter list https://www.adblock.ro/, on our website you can find all details, may need to use translation tools because is written in Romanian. This is a Public list, and anyone can contribute on our GitHub open project.
Our Website: https://www.adblock.ro/... | infrastructure | adblock ro filter want to inform this is a new romanian filter list on our website you can find all details may need to use translation tools because is written in romanian this is a public list and anyone can contribute on our github open project our website github project | 1 |
3,286 | 4,187,972,579 | IssuesEvent | 2016-06-23 19:09:41 | SemanticMediaWiki/SemanticMediaWiki | https://api.github.com/repos/SemanticMediaWiki/SemanticMediaWiki | closed | Leave SourceForge? | discussion infrastructure | SourceForge has become a rather controversial provider of software downloads [0][1][2] and is now routinely blocked by e.g. uBlock [3] as well as at least one corporate firewall I know.
Would it make sense to leave SourceForge and use GitHub to distribute tar balls instead?
[0] http://www.howtogeek.com/218764/war... | 1.0 | Leave SourceForge? - SourceForge has become a rather controversial provider of software downloads [0][1][2] and is now routinely blocked by e.g. uBlock [3] as well as at least one corporate firewall I know.
Would it make sense to leave SourceForge and use GitHub to distribute tar balls instead?
[0] http://www.how... | infrastructure | leave sourceforge sourceforge has become a rather controversial provider of software downloads and is now routinely blocked by e g ublock as well as at least one corporate firewall i know would it make sense to leave sourceforge and use github to distribute tar balls instead | 1 |
6,279 | 8,652,736,797 | IssuesEvent | 2018-11-27 08:59:54 | gooddata/gooddata-java | https://api.github.com/repos/gooddata/gooddata-java | opened | Mutable DTOs can't honour equals semantics | backward incompatible | The core concept of gooddata-java - mutable dtos is effectively preventing such objects to have valid `equals` method. It's a question how this issue should be resolved:
:question: make the DTOs immutable and provide copy constrcutors/builders
:question: stay on the current state - the equals is only implemented on... | True | Mutable DTOs can't honour equals semantics - The core concept of gooddata-java - mutable dtos is effectively preventing such objects to have valid `equals` method. It's a question how this issue should be resolved:
:question: make the DTOs immutable and provide copy constrcutors/builders
:question: stay on the curr... | non_infrastructure | mutable dtos can t honour equals semantics the core concept of gooddata java mutable dtos is effectively preventing such objects to have valid equals method it s a question how this issue should be resolved question make the dtos immutable and provide copy constrcutors builders question stay on the curr... | 0 |
31,384 | 25,601,993,145 | IssuesEvent | 2022-12-01 21:07:07 | gothick/omm | https://api.github.com/repos/gothick/omm | opened | Should we persist beanstalkd? | infrastructure beanstalk | Should we persist beanstalkd? (if we do, there’s a recommended cookbook: https://github.com/djoos-cookbooks/beanstalkd) “Yes; if you choose, you can use the “-b” option, and beanstalkd will write all jobs to a binlog. If the power goes out, you can restart beanstalkd with the same option and it will recover the content... | 1.0 | Should we persist beanstalkd? - Should we persist beanstalkd? (if we do, there’s a recommended cookbook: https://github.com/djoos-cookbooks/beanstalkd) “Yes; if you choose, you can use the “-b” option, and beanstalkd will write all jobs to a binlog. If the power goes out, you can restart beanstalkd with the same option... | infrastructure | should we persist beanstalkd should we persist beanstalkd if we do there’s a recommended cookbook “yes if you choose you can use the “ b” option and beanstalkd will write all jobs to a binlog if the power goes out you can restart beanstalkd with the same option and it will recover the contents of the log ... | 1 |
417,204 | 28,110,195,695 | IssuesEvent | 2023-03-31 06:26:02 | dsja612/ped | https://api.github.com/repos/dsja612/ped | opened | [UG] The image showed in the `Deleting a person` section is outdated | severity.Low type.DocumentationBug | The image showed in the `Deleting a person` section is outdated, and does not reflect the changes in the new UI.
### DG Screenshot
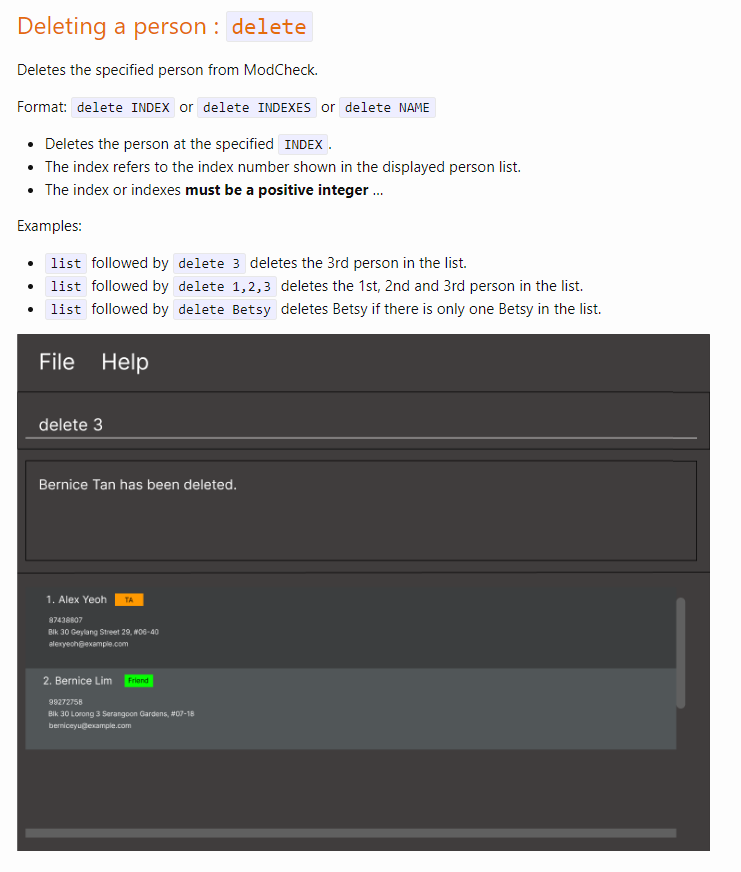
### ModCheck Screenshot

### ... | non_infrastructure | the image showed in the deleting a person section is outdated the image showed in the deleting a person section is outdated and does not reflect the changes in the new ui dg screenshot modcheck screenshot | 0 |
529,312 | 15,386,160,488 | IssuesEvent | 2021-03-03 07:47:37 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | opened | Error when creating a new API from scratch by a user with Creator only permission | API-M 4.0.0 Priority/High Type/Bug | ### Description:
Below error popup is displayed in Publisher UI when a user with Creator only permissions creates an API from scratch at the point of clicking on the CREATE button.

The browser console s... | 1.0 | Error when creating a new API from scratch by a user with Creator only permission - ### Description:
Below error popup is displayed in Publisher UI when a user with Creator only permissions creates an API from scratch at the point of clicking on the CREATE button.
</sup>
---
_TODO: add basic details about this VPS on next weeks_ | 1.0 | VPS Águia Pescadora Alpha - - https://github.com/fititnt/cplp-aiops/issues/17 <sup>(Portuguese)</sup>
---
_TODO: add basic details about this VPS on next weeks_ | infrastructure | vps águia pescadora alpha portuguese todo add basic details about this vps on next weeks | 1 |
117,582 | 11,950,458,110 | IssuesEvent | 2020-04-03 15:14:15 | Azure/azure-devops-cli-extension | https://api.github.com/repos/Azure/azure-devops-cli-extension | opened | [Documentation] Include azure devops documentation in top level command group details. | documentation | In each of the top level commands - az boards, az pipelines, az repos, az artifacts and az devops, we include the line indicating that this command is a part of azure-devops extension. In addition to this, we need to include the link out to the documentation - https://docs.microsoft.com/en-us/azure/devops/cli/?view=azu... | 1.0 | [Documentation] Include azure devops documentation in top level command group details. - In each of the top level commands - az boards, az pipelines, az repos, az artifacts and az devops, we include the line indicating that this command is a part of azure-devops extension. In addition to this, we need to include the li... | non_infrastructure | include azure devops documentation in top level command group details in each of the top level commands az boards az pipelines az repos az artifacts and az devops we include the line indicating that this command is a part of azure devops extension in addition to this we need to include the link out to the ... | 0 |
32,572 | 26,802,892,813 | IssuesEvent | 2023-02-01 16:13:54 | microsoft/WindowsAppSDK | https://api.github.com/repos/microsoft/WindowsAppSDK | closed | DevCheck doesn't verify VS components | feature area-Infrastructure | `tools\DevCheck.ps1` (conveniently accessible by running `tools\DevCheck.cmd`) verifies the local development environment is ready and often can (and will) update the environment as needed e.g. make sure the TAEF service is installed.
Building ProjectReunion.sln and others in the repository require many Visual Studi... | 1.0 | DevCheck doesn't verify VS components - `tools\DevCheck.ps1` (conveniently accessible by running `tools\DevCheck.cmd`) verifies the local development environment is ready and often can (and will) update the environment as needed e.g. make sure the TAEF service is installed.
Building ProjectReunion.sln and others in ... | infrastructure | devcheck doesn t verify vs components tools devcheck conveniently accessible by running tools devcheck cmd verifies the local development environment is ready and often can and will update the environment as needed e g make sure the taef service is installed building projectreunion sln and others in th... | 1 |
81,478 | 3,591,421,460 | IssuesEvent | 2016-02-01 11:41:02 | thesgc/chembiohub_helpdesk | https://api.github.com/repos/thesgc/chembiohub_helpdesk | closed | Asked to define assays in the sub project - which I can only select one. Then when I add an assay I | app: AssayReg For Andy and Paul Review name: Karen priority: Medium status: New | Asked to define assays in the sub project - which I can only select one. Then when I add an assay I can choose a template of any type - shouldn't they be restricted to the assay type I've defined? | 1.0 | Asked to define assays in the sub project - which I can only select one. Then when I add an assay I - Asked to define assays in the sub project - which I can only select one. Then when I add an assay I can choose a template of any type - shouldn't they be restricted to the assay type I've defined? | non_infrastructure | asked to define assays in the sub project which i can only select one then when i add an assay i asked to define assays in the sub project which i can only select one then when i add an assay i can choose a template of any type shouldn t they be restricted to the assay type i ve defined | 0 |
287,863 | 24,869,061,963 | IssuesEvent | 2022-10-27 14:02:15 | iho-ohi/S-101_Portrayal-Catalogue | https://api.github.com/repos/iho-ohi/S-101_Portrayal-Catalogue | closed | Measured Distance Value (row 61 main) | enhancement test PC 1.0.2 | 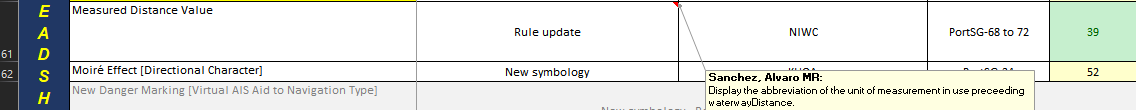
Rule update DistanceMark.lua.
NOTE: Sanchez, Alvaro MR:
Display the abbreviation of the unit of measurement in use preceeding waterwayDistance.
 - 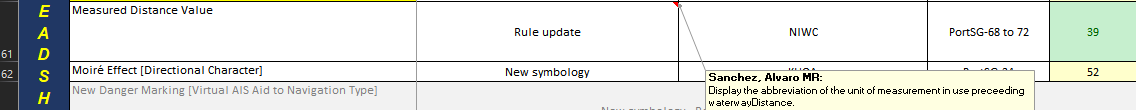
Rule update DistanceMark.lua.
NOTE: Sanchez, Alvaro MR:
Display the abbreviation of the unit of measurement in use preceeding waterwayDistance.
 | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-3.2-py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home ... | True | Django-3.2-py3-none-any.whl: 16 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-3.2-py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that e... | non_infrastructure | django none any whl vulnerabilities highest severity is vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file requirements txt path to vulner... | 0 |
307,176 | 9,414,250,969 | IssuesEvent | 2019-04-10 09:42:24 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | Add dependencies check on first start. | Medium Priority | Add dependencies check on first game start.
All needed software installed, and available.
To exclude this situation.
Player install game from steam, installing .net is not succeed.
Result - singleplayer silence not working, return to main menu after launch.
Only after player try to launch server manually, they s... | 1.0 | Add dependencies check on first start. - Add dependencies check on first game start.
All needed software installed, and available.
To exclude this situation.
Player install game from steam, installing .net is not succeed.
Result - singleplayer silence not working, return to main menu after launch.
Only after pla... | non_infrastructure | add dependencies check on first start add dependencies check on first game start all needed software installed and available to exclude this situation player install game from steam installing net is not succeed result singleplayer silence not working return to main menu after launch only after pla... | 0 |
19,584 | 3,227,243,090 | IssuesEvent | 2015-10-11 01:10:00 | krashanoff/cleanrip | https://api.github.com/repos/krashanoff/cleanrip | closed | Error checking | auto-migrated Priority-Medium Type-Defect | ```
1.0.4
Would it be possible to add the option to do error checking? Since the DVD
speed is more than half slower than most USB drives this shouldn't affect
speed. Anyway this would be an option so users could turn it off. I had
problems with a corrupt FAT32 drive, only got the second chunk and the program
di... | 1.0 | Error checking - ```
1.0.4
Would it be possible to add the option to do error checking? Since the DVD
speed is more than half slower than most USB drives this shouldn't affect
speed. Anyway this would be an option so users could turn it off. I had
problems with a corrupt FAT32 drive, only got the second chunk an... | non_infrastructure | error checking would it be possible to add the option to do error checking since the dvd speed is more than half slower than most usb drives this shouldn t affect speed anyway this would be an option so users could turn it off i had problems with a corrupt drive only got the second chunk and th... | 0 |
7,444 | 6,961,838,903 | IssuesEvent | 2017-12-08 11:04:18 | servicecatalog/oscm | https://api.github.com/repos/servicecatalog/oscm | closed | Remove exported projects from fb_tomee_maven branch | infrastructure | Remove projects which are exported to following repositories
https://github.com/servicecatalog/oscm-interfaces
https://github.com/servicecatalog/oscm-commons
https://github.com/servicecatalog/oscm-app
Check if unittests are also exported. | 1.0 | Remove exported projects from fb_tomee_maven branch - Remove projects which are exported to following repositories
https://github.com/servicecatalog/oscm-interfaces
https://github.com/servicecatalog/oscm-commons
https://github.com/servicecatalog/oscm-app
Check if unittests are also exported. | infrastructure | remove exported projects from fb tomee maven branch remove projects which are exported to following repositories check if unittests are also exported | 1 |
28,048 | 22,783,006,371 | IssuesEvent | 2022-07-08 22:45:45 | ProjectPythia/pythia-foundations | https://api.github.com/repos/ProjectPythia/pythia-foundations | opened | Foundations should be citable with a DOI | infrastructure | As I mused about over at https://github.com/ProjectPythiaCookbooks/projectpythiacookbooks.github.io/issues/15, the Foundations book should be citable with a DOI pointing to specific tagged versions of the book. Zenodo makes this pretty simple.
We would need to create a tagged Release of the source repo. I think this... | 1.0 | Foundations should be citable with a DOI - As I mused about over at https://github.com/ProjectPythiaCookbooks/projectpythiacookbooks.github.io/issues/15, the Foundations book should be citable with a DOI pointing to specific tagged versions of the book. Zenodo makes this pretty simple.
We would need to create a tagg... | infrastructure | foundations should be citable with a doi as i mused about over at the foundations book should be citable with a doi pointing to specific tagged versions of the book zenodo makes this pretty simple we would need to create a tagged release of the source repo i think this would be a good summer goal once we get... | 1 |
343,106 | 10,325,343,564 | IssuesEvent | 2019-09-01 16:34:02 | thonny/thonny | https://api.github.com/repos/thonny/thonny | closed | Investigate function call keyword argument completion | feature low priority | **[Original report](https://bitbucket.org/bitbucket-issue-migration\thonny-issues.zip/issue/300) by me.**
----------------------------------------
See https://github.com/srusskih/SublimeJEDI and https://github.com/davidhalter/jedi-vim
| 1.0 | Investigate function call keyword argument completion - **[Original report](https://bitbucket.org/bitbucket-issue-migration\thonny-issues.zip/issue/300) by me.**
----------------------------------------
See https://github.com/srusskih/SublimeJEDI and https://github.com/davidhalter/jedi-vim
| non_infrastructure | investigate function call keyword argument completion by me see and | 0 |
19,175 | 13,198,902,050 | IssuesEvent | 2020-08-14 04:05:02 | vuejs/vetur | https://api.github.com/repos/vuejs/vetur | closed | Clean up CI output | infrastructure | https://github.com/microsoft/vscode/blob/34dee12ff383689d9d5e62f6b263ed644e4df44d/src/vs/workbench/api/common/extHostTypes.ts#L1012-L1016
Need to validate that all symbols have a `name`
```
name must not be falsy: Error: name must not be falsy
at Function.validate (/Users/pine/Code/mine/vetur/vetur/.vsc... | 1.0 | Clean up CI output - https://github.com/microsoft/vscode/blob/34dee12ff383689d9d5e62f6b263ed644e4df44d/src/vs/workbench/api/common/extHostTypes.ts#L1012-L1016
Need to validate that all symbols have a `name`
```
name must not be falsy: Error: name must not be falsy
at Function.validate (/Users/pine/Code/... | infrastructure | clean up ci output need to validate that all symbols have a name name must not be falsy error name must not be falsy at function validate users pine code mine vetur vetur vscode test vscode visual studio code app contents resources app out vs workbench services extensions node exten... | 1 |
5,420 | 5,641,613,846 | IssuesEvent | 2017-04-06 19:07:01 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Tests are Hanging | Area-Infrastructure Flaky Test Urgency-Soon | There seems to be an intermittent problem with hanging vsi tests. As an example, see the logs saved in "\\mlangfs1\public\frsilb\logs\Jenkins Hang". These are from a debug and release build of https://github.com/dotnet/roslyn/pull/18454. | 1.0 | Tests are Hanging - There seems to be an intermittent problem with hanging vsi tests. As an example, see the logs saved in "\\mlangfs1\public\frsilb\logs\Jenkins Hang". These are from a debug and release build of https://github.com/dotnet/roslyn/pull/18454. | infrastructure | tests are hanging there seems to be an intermittent problem with hanging vsi tests as an example see the logs saved in public frsilb logs jenkins hang these are from a debug and release build of | 1 |
20,119 | 13,673,186,408 | IssuesEvent | 2020-09-29 09:30:03 | google/web-stories-wp | https://api.github.com/repos/google/web-stories-wp | opened | Package Reorganization | Pod: WP & Infra Type: Infrastructure Type: Task | ## Task Description
Our current repository structure has organically grown over the past year to a point where we have multiple different "packages" spread across different folders. Some of them are pretty self-contained and could be easily published standalone (e.g. all the Karma packages), others are a bit more in... | 1.0 | Package Reorganization - ## Task Description
Our current repository structure has organically grown over the past year to a point where we have multiple different "packages" spread across different folders. Some of them are pretty self-contained and could be easily published standalone (e.g. all the Karma packages),... | infrastructure | package reorganization task description our current repository structure has organically grown over the past year to a point where we have multiple different packages spread across different folders some of them are pretty self contained and could be easily published standalone e g all the karma packages ... | 1 |
25,721 | 4,424,912,298 | IssuesEvent | 2016-08-16 14:03:15 | PowerDNS/pdns | https://api.github.com/repos/PowerDNS/pdns | closed | Boost context path and namespace changed in boost 1.61 | defect rec | Reported by @IngoThierack in #4014
```
checking for Boost headers version >= 1.35.0... /opt/lib/boost/1.61-4.8//include
checking for Boost's header version... 1_61
checking for the flags needed to use pthreads... conftest.cpp: In function 'int main()':
conftest.cpp:33:24: warning: null argument where non-null r... | 1.0 | Boost context path and namespace changed in boost 1.61 - Reported by @IngoThierack in #4014
```
checking for Boost headers version >= 1.35.0... /opt/lib/boost/1.61-4.8//include
checking for Boost's header version... 1_61
checking for the flags needed to use pthreads... conftest.cpp: In function 'int main()':
co... | non_infrastructure | boost context path and namespace changed in boost reported by ingothierack in checking for boost headers version opt lib boost include checking for boost s header version checking for the flags needed to use pthreads conftest cpp in function int main conftest ... | 0 |
96,511 | 10,934,396,431 | IssuesEvent | 2019-11-24 11:19:21 | roundcube/roundcubemail | https://api.github.com/repos/roundcube/roundcubemail | closed | Wrong file ownerships after upgrade as root | C: Documentation C: Installer bug | When upgrading Roundcube as root via
```
wget https://github.com/roundcube/roundcubemail/releases/download/1.4.0/roundcubemail-1.4.0-complete.tar.gz
tar xf roundcubemail-1.4.0-complete.tar.gz
./roundcubemail-1.4.0/bin/installto.sh DESTDIR
```
the installed files have the ownership pair `501:80`, which is probably... | 1.0 | Wrong file ownerships after upgrade as root - When upgrading Roundcube as root via
```
wget https://github.com/roundcube/roundcubemail/releases/download/1.4.0/roundcubemail-1.4.0-complete.tar.gz
tar xf roundcubemail-1.4.0-complete.tar.gz
./roundcubemail-1.4.0/bin/installto.sh DESTDIR
```
the installed files have ... | non_infrastructure | wrong file ownerships after upgrade as root when upgrading roundcube as root via wget tar xf roundcubemail complete tar gz roundcubemail bin installto sh destdir the installed files have the ownership pair which is probably always invalid please either set the ownership after ... | 0 |
27,224 | 21,477,294,143 | IssuesEvent | 2022-04-26 14:38:23 | OpenEnergyPlatform/ontology | https://api.github.com/repos/OpenEnergyPlatform/ontology | opened | Locating term-tracker for imported modules | external ontology organisation To do ontology infrastructure | ## Description of the issue
`term tracker items` added in PR #1086 (all related to imported ontologies) are located in the `oeo.omn`-file and not in the defining ontology. As these are the only ones located there, this grew my suspicion.
How does the general policy concerning `term tracker items` and imported ont... | 1.0 | Locating term-tracker for imported modules - ## Description of the issue
`term tracker items` added in PR #1086 (all related to imported ontologies) are located in the `oeo.omn`-file and not in the defining ontology. As these are the only ones located there, this grew my suspicion.
How does the general policy con... | infrastructure | locating term tracker for imported modules description of the issue term tracker items added in pr all related to imported ontologies are located in the oeo omn file and not in the defining ontology as these are the only ones located there this grew my suspicion how does the general policy concer... | 1 |
801 | 2,915,634,473 | IssuesEvent | 2015-06-23 13:36:53 | deconst/deconst-docs | https://api.github.com/repos/deconst/deconst-docs | opened | Shipping checklist for systemd infra overhaul | infrastructure | The infrastructure overhaul in deconst/deploy#38 will take some care to :shipit:. Running Ansible on the existing hosts won't work because:
* It changes the names of server groups and load balancers because it implements #99 along the way.
* I've fiddled with the names of the systemd units that we're creating and... | 1.0 | Shipping checklist for systemd infra overhaul - The infrastructure overhaul in deconst/deploy#38 will take some care to :shipit:. Running Ansible on the existing hosts won't work because:
* It changes the names of server groups and load balancers because it implements #99 along the way.
* I've fiddled with the na... | infrastructure | shipping checklist for systemd infra overhaul the infrastructure overhaul in deconst deploy will take some care to shipit running ansible on the existing hosts won t work because it changes the names of server groups and load balancers because it implements along the way i ve fiddled with the name... | 1 |
179,234 | 13,852,063,504 | IssuesEvent | 2020-10-15 05:42:16 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | closed | The layout of the descriptions in the 'Sign In' dialog is unsightly when using device code flow sign-in | :beetle: regression 🧪 testing | **Storage Explorer Version:** 1.16.0-dev
**Build**: 20201012.5
**Branch**: main
**Platform/OS:** Windows 10/ MacOS Catalina
**Architecture**: ia32/x64
**Regression From:** Previous release (1.15.1)
**Steps to reproduce:**
1. Launch Storage Explorer -> Open 'Settings -> Application' -> Enable the setting 'Use ... | 1.0 | The layout of the descriptions in the 'Sign In' dialog is unsightly when using device code flow sign-in - **Storage Explorer Version:** 1.16.0-dev
**Build**: 20201012.5
**Branch**: main
**Platform/OS:** Windows 10/ MacOS Catalina
**Architecture**: ia32/x64
**Regression From:** Previous release (1.15.1)
**Steps... | non_infrastructure | the layout of the descriptions in the sign in dialog is unsightly when using device code flow sign in storage explorer version dev build branch main platform os windows macos catalina architecture regression from previous release steps to reproduce ... | 0 |
162,049 | 20,164,363,796 | IssuesEvent | 2022-02-10 01:45:43 | kapseliboi/dapp | https://api.github.com/repos/kapseliboi/dapp | opened | CVE-2021-27290 (High) detected in ssri-7.1.0.tgz, ssri-6.0.1.tgz | security vulnerability | ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ssri-7.1.0.tgz</b>, <b>ssri-6.0.1.tgz</b></p></summary>
<p>
<details><summary><b>ssri-7.1.0.tgz</b></p></summary>
<... | True | CVE-2021-27290 (High) detected in ssri-7.1.0.tgz, ssri-6.0.1.tgz - ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ssri-7.1.0.tgz</b>, <b>ssri-6.0.1.tgz</b></p></sum... | non_infrastructure | cve high detected in ssri tgz ssri tgz cve high severity vulnerability vulnerable libraries ssri tgz ssri tgz ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spe... | 0 |
159,681 | 25,031,477,935 | IssuesEvent | 2022-11-04 12:46:19 | webaverse/app | https://api.github.com/repos/webaverse/app | closed | Art: Title Deeds | design | A special type of Card is the Title Deed, which grants the right to use (and restrict access to) real estate on The Street.
The information it might display include:
* Season / Zone at the top
* Title nam... | 1.0 | Art: Title Deeds - A special type of Card is the Title Deed, which grants the right to use (and restrict access to) real estate on The Street.
The information it might display include:
* Season / Zone at t... | non_infrastructure | art title deeds a special type of card is the title deed which grants the right to use and restrict access to real estate on the street the information it might display include season zone at the top title name transaction date hash string certified to description signed by on ... | 0 |
28,030 | 22,773,601,863 | IssuesEvent | 2022-07-08 12:29:02 | airyhq/airy | https://api.github.com/repos/airyhq/airy | closed | Create endpoints to install components | infrastructure | Create an endpoint that receives a request to install a component and then the controller would deploy the appropriate helm chart for it | 1.0 | Create endpoints to install components - Create an endpoint that receives a request to install a component and then the controller would deploy the appropriate helm chart for it | infrastructure | create endpoints to install components create an endpoint that receives a request to install a component and then the controller would deploy the appropriate helm chart for it | 1 |
290,897 | 8,909,438,671 | IssuesEvent | 2019-01-18 06:17:04 | artemii235/SuperNET | https://api.github.com/repos/artemii235/SuperNET | opened | Remove the hardcoded wait timeout in swaps. | High priority bug | Calculate it properly depending on coins used. E.G. it should be higher for BTC due to high blocktime. Current 1000 seconds timeout is not usable in many cases. | 1.0 | Remove the hardcoded wait timeout in swaps. - Calculate it properly depending on coins used. E.G. it should be higher for BTC due to high blocktime. Current 1000 seconds timeout is not usable in many cases. | non_infrastructure | remove the hardcoded wait timeout in swaps calculate it properly depending on coins used e g it should be higher for btc due to high blocktime current seconds timeout is not usable in many cases | 0 |
253,547 | 19,122,949,085 | IssuesEvent | 2021-12-01 01:56:47 | Encapsule/arcccore | https://api.github.com/repos/Encapsule/arcccore | closed | arccore.disciminator should allow override of ID, name, and description | enhancement documentation test discriminator | ... so it's even remotely feasible to differentiate between different discriminator filter instances at runtime under the debugger without having to compare the associated target filter arrays. | 1.0 | arccore.disciminator should allow override of ID, name, and description - ... so it's even remotely feasible to differentiate between different discriminator filter instances at runtime under the debugger without having to compare the associated target filter arrays. | non_infrastructure | arccore disciminator should allow override of id name and description so it s even remotely feasible to differentiate between different discriminator filter instances at runtime under the debugger without having to compare the associated target filter arrays | 0 |
635,991 | 20,516,812,337 | IssuesEvent | 2022-03-01 12:39:39 | kytos-ng/topology | https://api.github.com/repos/kytos-ng/topology | opened | PortMod should be sent when an interface is disabled or enabled | enhancement priority_major | Currently, when an interface is disabled even tough the `enabled` state will be set as false, a `PortMod` OpenFlow message isn't being sent, as a result it's possible to have an interface `enabled: False`, and `active: True`, since it won't actually administratively disable the interface on the switch.
When impleme... | 1.0 | PortMod should be sent when an interface is disabled or enabled - Currently, when an interface is disabled even tough the `enabled` state will be set as false, a `PortMod` OpenFlow message isn't being sent, as a result it's possible to have an interface `enabled: False`, and `active: True`, since it won't actually adm... | non_infrastructure | portmod should be sent when an interface is disabled or enabled currently when an interface is disabled even tough the enabled state will be set as false a portmod openflow message isn t being sent as a result it s possible to have an interface enabled false and active true since it won t actually adm... | 0 |
233,516 | 17,868,202,384 | IssuesEvent | 2021-09-06 12:11:36 | reactor/reactor-core | https://api.github.com/repos/reactor/reactor-core | closed | errorContinue javadoc sometimes badly placed within `@TAGS` section | type/documentation | Since #2333, the onDiscard support and onErrorContinue support tags have been turned into plain paragraphs.
Unfortunately, some of the old tags were not placed at the beginning of the tags section, and the search-and-replacement has left these as paragraphs inside the block tag section.
These paragraphs are still... | 1.0 | errorContinue javadoc sometimes badly placed within `@TAGS` section - Since #2333, the onDiscard support and onErrorContinue support tags have been turned into plain paragraphs.
Unfortunately, some of the old tags were not placed at the beginning of the tags section, and the search-and-replacement has left these as ... | non_infrastructure | errorcontinue javadoc sometimes badly placed within tags section since the ondiscard support and onerrorcontinue support tags have been turned into plain paragraphs unfortunately some of the old tags were not placed at the beginning of the tags section and the search and replacement has left these as par... | 0 |
99,026 | 11,103,419,997 | IssuesEvent | 2019-12-17 03:47:00 | pytorch/fairseq | https://api.github.com/repos/pytorch/fairseq | closed | Please correct the minimum required Python version | documentation | The main [README file](https://github.com/pytorch/fairseq/blob/50cf3bb596abba70a0770ad2308fed0f4d32a002/README.md#requirements-and-installation) of this repo claims the minimum required Python version is 3.5, but the code occasionally uses a trailing comma at the end of a function's argument list and that's a syntax fe... | 1.0 | Please correct the minimum required Python version - The main [README file](https://github.com/pytorch/fairseq/blob/50cf3bb596abba70a0770ad2308fed0f4d32a002/README.md#requirements-and-installation) of this repo claims the minimum required Python version is 3.5, but the code occasionally uses a trailing comma at the end... | non_infrastructure | please correct the minimum required python version the main of this repo claims the minimum required python version is but the code occasionally uses a trailing comma at the end of a function s argument list and that s a syntax feature that was here is an example therefore the code currently does no... | 0 |
4,716 | 2,610,143,801 | IssuesEvent | 2015-02-26 18:45:19 | chrsmith/hedgewars | https://api.github.com/repos/chrsmith/hedgewars | closed | bad team name filtering while editing | auto-migrated Priority-Low Type-Defect | ```
i try to set team name which contains special characters. the ones that are not
allowed in windows's file names make team disappear from the list when saved.
no warnings are raised.
team name effect
------------------------------------------------------
\team saves as "team". seems ... | 1.0 | bad team name filtering while editing - ```
i try to set team name which contains special characters. the ones that are not
allowed in windows's file names make team disappear from the list when saved.
no warnings are raised.
team name effect
------------------------------------------------------
\team ... | non_infrastructure | bad team name filtering while editing i try to set team name which contains special characters the ones that are not allowed in windows s file names make team disappear from the list when saved no warnings are raised team name effect team ... | 0 |
35,507 | 31,770,011,955 | IssuesEvent | 2023-09-12 11:10:07 | Tonomy-Foundation/Tonomy-ID-Management | https://api.github.com/repos/Tonomy-Foundation/Tonomy-ID-Management | opened | Telos UK onboarding - learn their tech stack | infrastructure | Acceptance criteria
- [ ] read the wiki http://wiki.advantapro.com/index.php?title=Main_Page
- [ ] go through source repositories:
- [ ] https://gitlab.com/advantaproductions/telos-configs
- [ ] https://gitlab.com/advantaproductions/ansible
- [ ] https://github.com/varilink/telos-eosio
- [ ] Get access to commun... | 1.0 | Telos UK onboarding - learn their tech stack - Acceptance criteria
- [ ] read the wiki http://wiki.advantapro.com/index.php?title=Main_Page
- [ ] go through source repositories:
- [ ] https://gitlab.com/advantaproductions/telos-configs
- [ ] https://gitlab.com/advantaproductions/ansible
- [ ] https://github.com/... | infrastructure | telos uk onboarding learn their tech stack acceptance criteria read the wiki go through source repositories get access to communication groups introduce yourself get access to hetzner iaas | 1 |
31,047 | 25,293,239,522 | IssuesEvent | 2022-11-17 03:11:56 | alan-turing-institute/the-turing-way | https://api.github.com/repos/alan-turing-institute/the-turing-way | opened | Proposal: delete `figure_list.md` | idea-for-discussion infrastructure | https://github.com/alan-turing-institute/the-turing-way/blob/main/book/website/figures/_figure-list.md
---
- When the book started, it had [17 different figures](https://github.com/alan-turing-institute/the-turing-way/blob/840067db4839e59019183f84853a2fa4efca2413/website/_site/assets/figures/figure_list.md). As o... | 1.0 | Proposal: delete `figure_list.md` - https://github.com/alan-turing-institute/the-turing-way/blob/main/book/website/figures/_figure-list.md
---
- When the book started, it had [17 different figures](https://github.com/alan-turing-institute/the-turing-way/blob/840067db4839e59019183f84853a2fa4efca2413/website/_site/... | infrastructure | proposal delete figure list md when the book started it had as of today it has despite that file is only it is currently i argue that instead of updating it we remove it since i am not convinced of its utility | 1 |
717,811 | 24,692,062,106 | IssuesEvent | 2022-10-19 09:16:18 | frequenz-floss/frequenz-sdk-python | https://api.github.com/repos/frequenz-floss/frequenz-sdk-python | opened | Fix typing for Actor's `join()` method | priority:low type:bug part:actor | ### What happened?
When calling the `join()` method of an actor (or `_stop()` or probably any method defined by the `@actor` decorator) we get an error from `mypy` complaining about the method not existing in the actor class, for example:
```
test.py:10: error: "SampleActor" has no attribute "join"
```
### What ... | 1.0 | Fix typing for Actor's `join()` method - ### What happened?
When calling the `join()` method of an actor (or `_stop()` or probably any method defined by the `@actor` decorator) we get an error from `mypy` complaining about the method not existing in the actor class, for example:
```
test.py:10: error: "SampleActor... | non_infrastructure | fix typing for actor s join method what happened when calling the join method of an actor or stop or probably any method defined by the actor decorator we get an error from mypy complaining about the method not existing in the actor class for example test py error sampleactor ... | 0 |
101,217 | 12,675,514,227 | IssuesEvent | 2020-06-19 01:58:36 | greatnewcls/KNLWKKGOTE62XGFSVAZIMVUH | https://api.github.com/repos/greatnewcls/KNLWKKGOTE62XGFSVAZIMVUH | closed | P3+H8jpQDZrmhv17Y2SazyIhJ9i9GmieyftaV8IHUhQFmz0xlCtfn32XcVCpYv/aYW3ZVkIF1wZm4vpWsgEpEiNnMRQ4OlYi3f5d2w6hL7U2sk43WFYZjwfnkbh6Jhu8R721lmOpsjtqmlR80gD7ohXHJZ3KXr9LCmzT80t4E4g= | design | +k4fzIXQSVCCeujhvJiVjcG8e+QbeH+ne+b+zGtk1PmC5ywkwjGHrYEOViTZeCHxfcjWVBl0IMf4VjoBSWf60d/ZnEeJ8esS+W19MpO679SuDnBLjReeVd4/dsjzj1LyNmj9ivHeVLQ0ylOMUgVW0fC8MWEEK7PheutnK2DAT7GItL1wno87570FyQoSry4lziTn6CO8kr6u8Z4U7Fg5HgfJOWcyKIk1QBB29DIXBwD+fHtascDmyaNm4ltdw/oK4UAqz/FU4DfB4GEb5LtEY30JambpnvjOoKq+PjWzvan7IaMkigaifSYY9ePk87Kg... | 1.0 | P3+H8jpQDZrmhv17Y2SazyIhJ9i9GmieyftaV8IHUhQFmz0xlCtfn32XcVCpYv/aYW3ZVkIF1wZm4vpWsgEpEiNnMRQ4OlYi3f5d2w6hL7U2sk43WFYZjwfnkbh6Jhu8R721lmOpsjtqmlR80gD7ohXHJZ3KXr9LCmzT80t4E4g= - +k4fzIXQSVCCeujhvJiVjcG8e+QbeH+ne+b+zGtk1PmC5ywkwjGHrYEOViTZeCHxfcjWVBl0IMf4VjoBSWf60d/ZnEeJ8esS+W19MpO679SuDnBLjReeVd4/dsjzj1LyNmj9ivHeVLQ0ylOMU... | non_infrastructure | qbeh ne b rrhhgrafbkdre ewf urjx u pikrgolh rz ea frk xlctmsbiae yon q ezq k pxejmfmkllxot j qp t ngclotukl... | 0 |
45,260 | 5,916,237,250 | IssuesEvent | 2017-05-22 09:59:00 | canonical-ols/build.snapcraft.io | https://api.github.com/repos/canonical-ols/build.snapcraft.io | closed | [footer] social media icons are warm grey | Status: Triaged Visual design | The footer is still using the warm grey from old ubuntu.com
---
Copied from Trello card: https://trello.com/c/AyjUMqTc/297-footer-social-media-icons-are-warm-grey
Labels: design | 1.0 | [footer] social media icons are warm grey - The footer is still using the warm grey from old ubuntu.com
---
Copied from Trello card: https://trello.com/c/AyjUMqTc/297-footer-social-media-icons-are-warm-grey
Labels: design | non_infrastructure | social media icons are warm grey the footer is still using the warm grey from old ubuntu com copied from trello card labels design | 0 |
7,590 | 7,979,283,560 | IssuesEvent | 2018-07-17 21:09:18 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Backup and restore | assigned-to-author container-service/svc doc-enhancement in-progress triaged | Hi,
I am using a persistent volume with an Azure disk in an Azure Kubernetes Service AKS cluster.
How do I backup and restore that disk?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d1ac572f-c613-71fc-580a-2805b740b793
* Version Independ... | 1.0 | Backup and restore - Hi,
I am using a persistent volume with an Azure disk in an Azure Kubernetes Service AKS cluster.
How do I backup and restore that disk?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d1ac572f-c613-71fc-580a-2805b740b7... | non_infrastructure | backup and restore hi i am using a persistent volume with an azure disk in an azure kubernetes service aks cluster how do i backup and restore that disk document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id... | 0 |
958 | 3,010,756,528 | IssuesEvent | 2015-07-28 14:45:09 | dotnet/wcf | https://api.github.com/repos/dotnet/wcf | opened | Move code to ensure the Bridge is running into a custom build task | Infrastructure test bug | Currently the code to check whether the Bridge is running and launch it lives in ensureBridge.ps1, and it is called via CMD files from build.cmd.
This task is to create a custom build task that does the same work. Reasons are:
- MSBuild command line properties are available (such as BridgeURL)
- The Bridge will l... | 1.0 | Move code to ensure the Bridge is running into a custom build task - Currently the code to check whether the Bridge is running and launch it lives in ensureBridge.ps1, and it is called via CMD files from build.cmd.
This task is to create a custom build task that does the same work. Reasons are:
- MSBuild command l... | infrastructure | move code to ensure the bridge is running into a custom build task currently the code to check whether the bridge is running and launch it lives in ensurebridge and it is called via cmd files from build cmd this task is to create a custom build task that does the same work reasons are msbuild command lin... | 1 |
29,931 | 24,404,247,157 | IssuesEvent | 2022-10-05 06:12:49 | dart-lang/site-www | https://api.github.com/repos/dart-lang/site-www | closed | Fix or remove html_proof.rb | infrastructure p3-low help wanted e1-hours | As of April 16, 2019, `./deploy/html_proof.rb` fails. It hasn't changed, so I suspect a ruby change. Here's the output (with `./` substituted for my directory path details):
```
$ ./deploy/html_proof.rb
./deploy/urls/get_all.rb:3:in `require_relative': cannot load such file --
./deploy/urls/old_site_urls (LoadE... | 1.0 | Fix or remove html_proof.rb - As of April 16, 2019, `./deploy/html_proof.rb` fails. It hasn't changed, so I suspect a ruby change. Here's the output (with `./` substituted for my directory path details):
```
$ ./deploy/html_proof.rb
./deploy/urls/get_all.rb:3:in `require_relative': cannot load such file --
./de... | infrastructure | fix or remove html proof rb as of april deploy html proof rb fails it hasn t changed so i suspect a ruby change here s the output with substituted for my directory path details deploy html proof rb deploy urls get all rb in require relative cannot load such file deploy... | 1 |
13,883 | 10,519,890,614 | IssuesEvent | 2019-09-29 21:07:37 | oppia/oppia-android | https://api.github.com/repos/oppia/oppia-android | closed | Introduce interface for ExplorationDataController | Priority: Essential Status: In implementation Type: Improvement Where: Infrastructure Workstream: Domain Interface | This is tracking introducing a stubbed interface for #113 without the real implementation being complete. | 1.0 | Introduce interface for ExplorationDataController - This is tracking introducing a stubbed interface for #113 without the real implementation being complete. | infrastructure | introduce interface for explorationdatacontroller this is tracking introducing a stubbed interface for without the real implementation being complete | 1 |
21,444 | 14,570,381,506 | IssuesEvent | 2020-12-17 14:19:22 | cds-snc/covid-alert-server-staging-terraform | https://api.github.com/repos/cds-snc/covid-alert-server-staging-terraform | closed | Upgrade to 0.14.2 terraform | high priority infrastructure unplanned work | Due to a known issue with TF and WAFv2 upgrading to the latest TF version 0.14.2 should speed up plan's and applys.
https://github.com/hashicorp/terraform-provider-aws/issues/14062 | 1.0 | Upgrade to 0.14.2 terraform - Due to a known issue with TF and WAFv2 upgrading to the latest TF version 0.14.2 should speed up plan's and applys.
https://github.com/hashicorp/terraform-provider-aws/issues/14062 | infrastructure | upgrade to terraform due to a known issue with tf and upgrading to the latest tf version should speed up plan s and applys | 1 |
32,033 | 26,371,984,876 | IssuesEvent | 2023-01-11 21:33:11 | ejgallego/coq-serapi | https://api.github.com/repos/ejgallego/coq-serapi | closed | Missing build dependency on mathcomp's ssreflect | kind: bug kind: testing kind: infrastructure | While trying to package coq-serapi for Debian, it turns out tests/genarg/move.v wants mathcomp's ssrnat and eqtype.
I guess the opam file needs a dep on coq-mathcomp-ssreflect in addition to what is already declared. | 1.0 | Missing build dependency on mathcomp's ssreflect - While trying to package coq-serapi for Debian, it turns out tests/genarg/move.v wants mathcomp's ssrnat and eqtype.
I guess the opam file needs a dep on coq-mathcomp-ssreflect in addition to what is already declared. | infrastructure | missing build dependency on mathcomp s ssreflect while trying to package coq serapi for debian it turns out tests genarg move v wants mathcomp s ssrnat and eqtype i guess the opam file needs a dep on coq mathcomp ssreflect in addition to what is already declared | 1 |
26,517 | 20,187,799,050 | IssuesEvent | 2022-02-11 00:44:05 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | Disable BlazorTemplates.Tests from running in quarantined pipelines | task area-infrastructure area-blazor | These tests were disabled in the helix environment via https://github.com/dotnet/aspnetcore/pull/38814/files#diff-0ccc4599c1cd44580f93ef1ab4182e747b297872577a970d651be18220d91768R13. This issue tracks disabling the tests from the quarantined pipelines as well until we're able to make some improvements to the underlying... | 1.0 | Disable BlazorTemplates.Tests from running in quarantined pipelines - These tests were disabled in the helix environment via https://github.com/dotnet/aspnetcore/pull/38814/files#diff-0ccc4599c1cd44580f93ef1ab4182e747b297872577a970d651be18220d91768R13. This issue tracks disabling the tests from the quarantined pipeline... | infrastructure | disable blazortemplates tests from running in quarantined pipelines these tests were disabled in the helix environment via this issue tracks disabling the tests from the quarantined pipelines as well until we re able to make some improvements to the underlying test suite related | 1 |
211,429 | 23,823,171,297 | IssuesEvent | 2022-09-05 12:58:27 | hugo-fixit/FixIt | https://api.github.com/repos/hugo-fixit/FixIt | opened | Fix code scanning alert - Potentially unsafe external link | security | <!-- Warning: The suggested title contains the alert rule name. This can expose security information. -->
Tracking issue for:
- [ ] https://github.com/hugo-fixit/FixIt/security/code-scanning/6
Salution:
- [ ] Using built-in link template
- [ ] Add front matter `[noreferrer=true]` only for `friends` type
| True | Fix code scanning alert - Potentially unsafe external link - <!-- Warning: The suggested title contains the alert rule name. This can expose security information. -->
Tracking issue for:
- [ ] https://github.com/hugo-fixit/FixIt/security/code-scanning/6
Salution:
- [ ] Using built-in link template
- [ ] Add fr... | non_infrastructure | fix code scanning alert potentially unsafe external link tracking issue for salution using built in link template add front matter only for friends type | 0 |
527,029 | 15,307,350,856 | IssuesEvent | 2021-02-24 20:46:25 | hetic-newsroom/heticiens.news | https://api.github.com/repos/hetic-newsroom/heticiens.news | closed | Optimize SEO | UI enhancement low-priority | Add JSON-LD Schema tags to improve ranking.
Suggested tags: Article, Organization
Look at schema.org | 1.0 | Optimize SEO - Add JSON-LD Schema tags to improve ranking.
Suggested tags: Article, Organization
Look at schema.org | non_infrastructure | optimize seo add json ld schema tags to improve ranking suggested tags article organization look at schema org | 0 |
9,200 | 7,867,042,770 | IssuesEvent | 2018-06-23 02:40:40 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | crossgen.sh: line 80: $2: unbound variable | area-Infrastructure bug os-windows-wsl | When trying to run `build.sh` on a clean check out from WSL. | 1.0 | crossgen.sh: line 80: $2: unbound variable - When trying to run `build.sh` on a clean check out from WSL. | infrastructure | crossgen sh line unbound variable when trying to run build sh on a clean check out from wsl | 1 |
17,393 | 12,339,840,249 | IssuesEvent | 2020-05-14 18:50:18 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Restore failing intermittently on build | area-Infrastructure blocking-clean-ci untriaged | Restore is failing intermittently
```
F:\workspace\_work\1\s\.dotnet\sdk\5.0.100-preview.5.20251.2\NuGet.targets(128,5): error : Cannot create a file when that file already exists. [F:\workspace\_work\1\s\src\libraries\restore\binplacePackages\binplacePackages.depproj]
##[error].dotnet\sdk\5.0.100-preview.5.2025... | 1.0 | Restore failing intermittently on build - Restore is failing intermittently
```
F:\workspace\_work\1\s\.dotnet\sdk\5.0.100-preview.5.20251.2\NuGet.targets(128,5): error : Cannot create a file when that file already exists. [F:\workspace\_work\1\s\src\libraries\restore\binplacePackages\binplacePackages.depproj]
#... | infrastructure | restore failing intermittently on build restore is failing intermittently f workspace work s dotnet sdk preview nuget targets error cannot create a file when that file already exists dotnet sdk preview nuget targets error netcore engineering telemetry re... | 1 |
22,229 | 15,054,631,312 | IssuesEvent | 2021-02-03 17:41:03 | google/web-stories-wp | https://api.github.com/repos/google/web-stories-wp | closed | PHP 8 Compatibility | Epic Group: WordPress P1 Pod: WP & Infra Type: Infrastructure Type: Task | <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Task Description
Once PHP 8 is out and the WordPress PHPUnit test suite supports it, we should make sure the plugin works smoothly on PHP 8.
... | 1.0 | PHP 8 Compatibility - <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Task Description
Once PHP 8 is out and the WordPress PHPUnit test suite supports it, we should make sure the plugin work... | infrastructure | php compatibility task description once php is out and the wordpress phpunit test suite supports it we should make sure the plugin works smoothly on php ci ensure unit tests can be run with php update local dev environment to support php necessary update tests to... | 1 |
2,482 | 3,699,050,107 | IssuesEvent | 2016-02-28 18:53:17 | m-labs/artiq | https://api.github.com/repos/m-labs/artiq | closed | use Xvnc with QEMU | area:infrastructure prio:1-low | Having to compile and install the hacky VNC client is inconvenient, and it lacks features like mouse motion events plus special keys get stuck at times.
Alternatively, fix the QEMU VNC bugs.
| 1.0 | use Xvnc with QEMU - Having to compile and install the hacky VNC client is inconvenient, and it lacks features like mouse motion events plus special keys get stuck at times.
Alternatively, fix the QEMU VNC bugs.
| infrastructure | use xvnc with qemu having to compile and install the hacky vnc client is inconvenient and it lacks features like mouse motion events plus special keys get stuck at times alternatively fix the qemu vnc bugs | 1 |
16,062 | 11,812,374,512 | IssuesEvent | 2020-03-19 20:02:24 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Changes to CoreCLR workflow | Discussion area-Infrastructure-coreclr | PR #31701 is changing the developer workflow for CoreCLR to help increase reliability, reduce local build times, and move us closer to a place where we can better parallelize CI to improve build times.
The largest part of the change is that the `build.cmd` and `build.sh` scripts under `src/coreclr` will be **depreca... | 1.0 | Changes to CoreCLR workflow - PR #31701 is changing the developer workflow for CoreCLR to help increase reliability, reduce local build times, and move us closer to a place where we can better parallelize CI to improve build times.
The largest part of the change is that the `build.cmd` and `build.sh` scripts under `... | infrastructure | changes to coreclr workflow pr is changing the developer workflow for coreclr to help increase reliability reduce local build times and move us closer to a place where we can better parallelize ci to improve build times the largest part of the change is that the build cmd and build sh scripts under src ... | 1 |
87,705 | 3,757,176,058 | IssuesEvent | 2016-03-13 20:40:18 | svof/svof | https://api.github.com/repos/svof/svof | opened | Consider new tree scenario against 2 handed | enhancement low priority medium difficulty up for grabs | reported by Aerek
> A Touch Tree scenario for curing when you ONLY have 2H fractures and no other affs would be useful. I can't figure out how to script this, myself | 1.0 | Consider new tree scenario against 2 handed - reported by Aerek
> A Touch Tree scenario for curing when you ONLY have 2H fractures and no other affs would be useful. I can't figure out how to script this, myself | non_infrastructure | consider new tree scenario against handed reported by aerek a touch tree scenario for curing when you only have fractures and no other affs would be useful i can t figure out how to script this myself | 0 |
630 | 2,798,583,331 | IssuesEvent | 2015-05-12 19:23:24 | new-day-international/reddit | https://api.github.com/repos/new-day-international/reddit | closed | Investigate using fewer cloud search instances | Infrastructure | From @inflector
> Attached please find the usage report for September. It looks like we've got stuff firing off every hour uploading and somehow querying CloudSearch, what might be causing this? Are we getting spiders doing searches?
> Also, we seem to be getting separate charges for each of the different dev, t... | 1.0 | Investigate using fewer cloud search instances - From @inflector
> Attached please find the usage report for September. It looks like we've got stuff firing off every hour uploading and somehow querying CloudSearch, what might be causing this? Are we getting spiders doing searches?
> Also, we seem to be getting ... | infrastructure | investigate using fewer cloud search instances from inflector attached please find the usage report for september it looks like we ve got stuff firing off every hour uploading and somehow querying cloudsearch what might be causing this are we getting spiders doing searches also we seem to be getting ... | 1 |
217,405 | 24,334,897,568 | IssuesEvent | 2022-10-01 01:07:10 | H-459/test4Gal | https://api.github.com/repos/H-459/test4Gal | closed | CVE-2020-7692 (High) detected in google-oauth-client-1.25.0.jar - autoclosed | security vulnerability | ## CVE-2020-7692 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google-oauth-client-1.25.0.jar</b></p></summary>
<p>Google OAuth Client Library for Java. Functionality that works on a... | True | CVE-2020-7692 (High) detected in google-oauth-client-1.25.0.jar - autoclosed - ## CVE-2020-7692 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google-oauth-client-1.25.0.jar</b></p></s... | non_infrastructure | cve high detected in google oauth client jar autoclosed cve high severity vulnerability vulnerable library google oauth client jar google oauth client library for java functionality that works on all supported java platforms including java or higher desktop se and ... | 0 |
16,419 | 5,233,716,001 | IssuesEvent | 2017-01-30 13:47:18 | SemsTestOrg/combinearchive-web | https://api.github.com/repos/SemsTestOrg/combinearchive-web | closed | fetch instead of upload | code feature request fixed migrated minor | ## Trac Ticket #133
**component:** code
**owner:** somebody
**reporter:** martin
**created:** 2015-09-23 09:30:48
**milestone:**
**type:** feature request
**version:**
**keywords:**
add an option to fetch a file from URL. users do not need to download model from eg biomodels, but can simply provide a link..
howe... | 1.0 | fetch instead of upload - ## Trac Ticket #133
**component:** code
**owner:** somebody
**reporter:** martin
**created:** 2015-09-23 09:30:48
**milestone:**
**type:** feature request
**version:**
**keywords:**
add an option to fetch a file from URL. users do not need to download model from eg biomodels, but can simpl... | non_infrastructure | fetch instead of upload trac ticket component code owner somebody reporter martin created milestone type feature request version keywords add an option to fetch a file from url users do not need to download model from eg biomodels but can simply provide ... | 0 |
15,227 | 11,423,150,998 | IssuesEvent | 2020-02-03 15:25:31 | reservix-ui/marigold | https://api.github.com/repos/reservix-ui/marigold | closed | Setup jest + testing-library | infrastructure | We can base it on the following setup form `tsdx`:
https://github.com/jaredpalmer/tsdx/blob/ce3ff8e23b77515ca09d32cb01273531acebf9ab/src/createJestConfig.ts#L5-L19
Also, install `@testing-library`!
| 1.0 | Setup jest + testing-library - We can base it on the following setup form `tsdx`:
https://github.com/jaredpalmer/tsdx/blob/ce3ff8e23b77515ca09d32cb01273531acebf9ab/src/createJestConfig.ts#L5-L19
Also, install `@testing-library`!
| infrastructure | setup jest testing library we can base it on the following setup form tsdx also install testing library | 1 |
14,360 | 10,765,263,091 | IssuesEvent | 2019-11-01 10:32:18 | tunapanda/swag | https://api.github.com/repos/tunapanda/swag | closed | Database structure & design | backend points:5 priority:highest type:infrastructure | As an engineer, I would like a database with a logical structure to store the relational data for Wikonnect.
- [ ] Knex migrations
| 1.0 | Database structure & design - As an engineer, I would like a database with a logical structure to store the relational data for Wikonnect.
- [ ] Knex migrations
| infrastructure | database structure design as an engineer i would like a database with a logical structure to store the relational data for wikonnect knex migrations | 1 |
653,011 | 21,568,612,099 | IssuesEvent | 2022-05-02 04:19:24 | solgenomics/sgn | https://api.github.com/repos/solgenomics/sgn | closed | Implement a generation advancement tool | Type: Feature Request Priority: High | Expected Behavior <!-- Describe the desired or expected behavour here. -->
--------------------------------------------------------------------------
An important feature for breeders is to track generation advancement of populations (F1,F2, F3....)
A useful feature would be to include automatically this F level inc... | 1.0 | Implement a generation advancement tool - Expected Behavior <!-- Describe the desired or expected behavour here. -->
--------------------------------------------------------------------------
An important feature for breeders is to track generation advancement of populations (F1,F2, F3....)
A useful feature would be... | non_infrastructure | implement a generation advancement tool expected behavior an important feature for breeders is to track generation advancement of populations a useful feature would be to include automatically this f level incrementation to p... | 0 |
11,595 | 9,306,961,366 | IssuesEvent | 2019-03-25 11:00:12 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [InfraUI] Infrastructure UI not loading in Kibana 7.0 | :Infra UI :infrastructure | As part of Beats testing I was trying a variety of Elasticsearch / Kibana / Beats versions, which led me to discover the Infrastructure UI isn't working in Kibana `7.0` (Logs is unaffected).
The Infrastructure UI renders fine in Kibana `6.7`, `7.x` and `master` but **not** `7.0`.
On `7.0` I see the following:
... | 1.0 | [InfraUI] Infrastructure UI not loading in Kibana 7.0 - As part of Beats testing I was trying a variety of Elasticsearch / Kibana / Beats versions, which led me to discover the Infrastructure UI isn't working in Kibana `7.0` (Logs is unaffected).
The Infrastructure UI renders fine in Kibana `6.7`, `7.x` and `master`... | infrastructure | infrastructure ui not loading in kibana as part of beats testing i was trying a variety of elasticsearch kibana beats versions which led me to discover the infrastructure ui isn t working in kibana logs is unaffected the infrastructure ui renders fine in kibana x and master but n... | 1 |
1,173 | 3,061,982,734 | IssuesEvent | 2015-08-16 04:10:14 | jquery/esprima | https://api.github.com/repos/jquery/esprima | closed | Integrate codecov.io | infrastructure | With [Codecov.io](https://codecov.io/) integration, there can be two benefits:
* Coverage information is prominent in every pull request
* Code coverage dashboard is available for more detailed information
Any possible coverage regression can be easily tracked. | 1.0 | Integrate codecov.io - With [Codecov.io](https://codecov.io/) integration, there can be two benefits:
* Coverage information is prominent in every pull request
* Code coverage dashboard is available for more detailed information
Any possible coverage regression can be easily tracked. | infrastructure | integrate codecov io with integration there can be two benefits coverage information is prominent in every pull request code coverage dashboard is available for more detailed information any possible coverage regression can be easily tracked | 1 |
294,736 | 9,040,107,654 | IssuesEvent | 2019-02-10 13:37:22 | opencv/opencv | https://api.github.com/repos/opencv/opencv | opened | G-API: vagrind tests crashed | bug category: g-api priority: high | [Build](http://pullrequest.opencv.org/buildbot/builders/master_valgrind-lin64-debug/builds/10146).
opencv_test_gapi:
```
[ RUN ] SobelXYTestFluid/SobelXYTest.AccuracyTest/0, where GetParam() = (compare_f, 8UC1, 3, 1280x720, -1, 1, 0, 0, { gapi.kernel_package })
==13111== Warning: set address range perms: lar... | 1.0 | G-API: vagrind tests crashed - [Build](http://pullrequest.opencv.org/buildbot/builders/master_valgrind-lin64-debug/builds/10146).
opencv_test_gapi:
```
[ RUN ] SobelXYTestFluid/SobelXYTest.AccuracyTest/0, where GetParam() = (compare_f, 8UC1, 3, 1280x720, -1, 1, 0, 0, { gapi.kernel_package })
==13111== Warnin... | non_infrastructure | g api vagrind tests crashed opencv test gapi sobelxytestfluid sobelxytest accuracytest where getparam compare f gapi kernel package warning set address range perms large range undefined warning set address range perms large range ... | 0 |
152,328 | 23,952,709,560 | IssuesEvent | 2022-09-12 12:51:00 | kedro-org/kedro-viz | https://api.github.com/repos/kedro-org/kedro-viz | closed | Develop a brief to inform our approach for branding | Issue: Feature Request Design: Research | ## Description
We're doing a holistic evaluation of the Kedro brand to understand our positioning and messaging. The outcome of this exercise will be a brief that would be used to answer:
- Why are we doing this? Why is this exercise important?
- What pain points we have with our current brand?
- What key message... | 1.0 | Develop a brief to inform our approach for branding - ## Description
We're doing a holistic evaluation of the Kedro brand to understand our positioning and messaging. The outcome of this exercise will be a brief that would be used to answer:
- Why are we doing this? Why is this exercise important?
- What pain poin... | non_infrastructure | develop a brief to inform our approach for branding description we re doing a holistic evaluation of the kedro brand to understand our positioning and messaging the outcome of this exercise will be a brief that would be used to answer why are we doing this why is this exercise important what pain poin... | 0 |
19,533 | 13,261,772,275 | IssuesEvent | 2020-08-20 20:30:22 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | remove the need for svn:externals (and merge the icetray repository back into the main one) (Trac #1546) | Migrated from Trac enhancement infrastructure | We discussed the possibility of removing the need for svn:externals in the usual meta-projects at the software session in Copenhagen (they might still make sense for more specialized uses and/or meta-projects). The idea is to move all relevant project trunks directly into "combo" and start releasing the whole meta-proj... | 1.0 | remove the need for svn:externals (and merge the icetray repository back into the main one) (Trac #1546) - We discussed the possibility of removing the need for svn:externals in the usual meta-projects at the software session in Copenhagen (they might still make sense for more specialized uses and/or meta-projects). Th... | infrastructure | remove the need for svn externals and merge the icetray repository back into the main one trac we discussed the possibility of removing the need for svn externals in the usual meta projects at the software session in copenhagen they might still make sense for more specialized uses and or meta projects the i... | 1 |
28,924 | 23,613,070,552 | IssuesEvent | 2022-08-24 13:53:14 | spring-projects/spring-batch | https://api.github.com/repos/spring-projects/spring-batch | closed | Deprecate Hibernate support | type: task in: infrastructure | Due to https://github.com/spring-projects/spring-framework/issues/28813, we are intending to deprecate Hibernate support in Spring Batch in v5.0 for removal in v5.2. | 1.0 | Deprecate Hibernate support - Due to https://github.com/spring-projects/spring-framework/issues/28813, we are intending to deprecate Hibernate support in Spring Batch in v5.0 for removal in v5.2. | infrastructure | deprecate hibernate support due to we are intending to deprecate hibernate support in spring batch in for removal in | 1 |
5,211 | 5,521,091,881 | IssuesEvent | 2017-03-19 12:42:50 | Daniel-Mietchen/ideas | https://api.github.com/repos/Daniel-Mietchen/ideas | opened | Ideas for "resolve authors" | 5min far-future infrastructure Wikidata | as per
https://tools.wmflabs.org/sourcemd/new_resolve_authors.php
- add "toggle all"
- display author names known via P50 | 1.0 | Ideas for "resolve authors" - as per
https://tools.wmflabs.org/sourcemd/new_resolve_authors.php
- add "toggle all"
- display author names known via P50 | infrastructure | ideas for resolve authors as per add toggle all display author names known via | 1 |
49,813 | 3,004,504,077 | IssuesEvent | 2015-07-26 00:58:50 | wwivbbs/wwiv | https://api.github.com/repos/wwivbbs/wwiv | closed | Taglines, OpenEdit/MSGINFO editor | 5.0 auto-migrated FSED low priority sourceforge TAGLINES | Build 1099
OS Win7 32
Taglines are no longer generated with OpenEdit. Taglines are configured on, but they don't present.
Original comment by: mmunson79 | 1.0 | Taglines, OpenEdit/MSGINFO editor - Build 1099
OS Win7 32
Taglines are no longer generated with OpenEdit. Taglines are configured on, but they don't present.
Original comment by: mmunson79 | non_infrastructure | taglines openedit msginfo editor build os taglines are no longer generated with openedit taglines are configured on but they don t present original comment by | 0 |
26,945 | 13,160,493,601 | IssuesEvent | 2020-08-10 17:42:12 | yalelibrary/YUL-DC | https://api.github.com/repos/yalelibrary/YUL-DC | closed | deploy-sql and deploy-solr not working through cam tool | bug performance team | # Acceptant #
These two scripts should run the same both in and out of the camerata cli and produce the same results either way. | True | deploy-sql and deploy-solr not working through cam tool - # Acceptant #
These two scripts should run the same both in and out of the camerata cli and produce the same results either way. | non_infrastructure | deploy sql and deploy solr not working through cam tool acceptant these two scripts should run the same both in and out of the camerata cli and produce the same results either way | 0 |
97,889 | 28,962,238,926 | IssuesEvent | 2023-05-10 04:15:50 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | `pytorch setup.py develop` fails on M1 macbooks with `fatal error: 'omp.h' file not found` | module: build triaged module: macos module: arm | ### 🐛 Describe the bug
On my M1 macbook, running `pytorch setup.py develop` with a clean build resulted in the error `fatal error: 'omp.h' file not found`
To get the build to successfully run, I had to instead invoke `USE_OPENMP=0 python setup.py develop`
The error message:
```
(base) ➜ pytorch git:(zain... | 1.0 | `pytorch setup.py develop` fails on M1 macbooks with `fatal error: 'omp.h' file not found` - ### 🐛 Describe the bug
On my M1 macbook, running `pytorch setup.py develop` with a clean build resulted in the error `fatal error: 'omp.h' file not found`
To get the build to successfully run, I had to instead invoke `US... | non_infrastructure | pytorch setup py develop fails on macbooks with fatal error omp h file not found 🐛 describe the bug on my macbook running pytorch setup py develop with a clean build resulted in the error fatal error omp h file not found to get the build to successfully run i had to instead invoke use ... | 0 |
83,181 | 3,631,622,060 | IssuesEvent | 2016-02-11 02:54:11 | umple/umple | https://api.github.com/repos/umple/umple | closed | Have myenv default to `local` when building | Diffic-Easy enhancement Maintainability Priority-Low | ## Description
Currently, myenv defaults to `cc`. This is a very specific case and most people are building via local developments. When building this way, one often types commands by hand.
In contrast, when working with a build environment when scripting, e.g. Travis, or CC, you're writing scripts where it is s... | 1.0 | Have myenv default to `local` when building - ## Description
Currently, myenv defaults to `cc`. This is a very specific case and most people are building via local developments. When building this way, one often types commands by hand.
In contrast, when working with a build environment when scripting, e.g. Travi... | non_infrastructure | have myenv default to local when building description currently myenv defaults to cc this is a very specific case and most people are building via local developments when building this way one often types commands by hand in contrast when working with a build environment when scripting e g travi... | 0 |
256,248 | 27,557,388,492 | IssuesEvent | 2023-03-07 19:02:21 | occmundial/atomic-icons | https://api.github.com/repos/occmundial/atomic-icons | closed | CVE-2022-21681 (High) detected in marked-2.1.3.tgz - autoclosed | security vulnerability | ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-2.1.3.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://reg... | True | CVE-2022-21681 (High) detected in marked-2.1.3.tgz - autoclosed - ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-2.1.3.tgz</b></p></summary>
<p>A markdown par... | non_infrastructure | cve high detected in marked tgz autoclosed cve high severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file package json path to vulnerable library node modules marked package json ... | 0 |
7,259 | 6,808,939,520 | IssuesEvent | 2017-11-04 10:50:29 | HaCSBCU/hacsbcu.github.io | https://api.github.com/repos/HaCSBCU/hacsbcu.github.io | opened | HTTP Strict Transport Security | SECURITY | HTTP Strict Transport Security (HSTS) header not implemented.
https://wiki.mozilla.org/Security/Guidelines/Web_Security#HTTP_Strict_Transport_Security | True | HTTP Strict Transport Security - HTTP Strict Transport Security (HSTS) header not implemented.
https://wiki.mozilla.org/Security/Guidelines/Web_Security#HTTP_Strict_Transport_Security | non_infrastructure | http strict transport security http strict transport security hsts header not implemented | 0 |
18,376 | 12,961,009,816 | IssuesEvent | 2020-07-20 15:06:33 | gnosis/safe-ios | https://api.github.com/repos/gnosis/safe-ios | opened | Remove non-inclusive language | infrastructure | - "master" branch -> "main" branch
- "masterCopy" -> "primaryCopy"
- "whitelist" -> "allow list"
- "blacklist" -> "deny list" | 1.0 | Remove non-inclusive language - - "master" branch -> "main" branch
- "masterCopy" -> "primaryCopy"
- "whitelist" -> "allow list"
- "blacklist" -> "deny list" | infrastructure | remove non inclusive language master branch main branch mastercopy primarycopy whitelist allow list blacklist deny list | 1 |
211,866 | 23,850,202,518 | IssuesEvent | 2022-09-06 17:10:53 | CMSgov/mdct-mcr | https://api.github.com/repos/CMSgov/mdct-mcr | closed | SHF - mdct-mcr - main - MEDIUM - S3.12 S3 access control lists (ACLs) should not be used to manage user access to buckets | security-hub main | **************************************************************
__This issue was generated from Security Hub data and is managed through automation.__
Please do not edit the title or body of this issue, or remove the security-hub tag. All other edits/comments are welcome.
Finding Id: arn:aws:securityhub:us-east-1:44671... | True | SHF - mdct-mcr - main - MEDIUM - S3.12 S3 access control lists (ACLs) should not be used to manage user access to buckets - **************************************************************
__This issue was generated from Security Hub data and is managed through automation.__
Please do not edit the title or body of this i... | non_infrastructure | shf mdct mcr main medium access control lists acls should not be used to manage user access to buckets this issue was generated from security hub data and is managed through automation please do not edit the title or body of this issu... | 0 |
49,974 | 10,436,936,378 | IssuesEvent | 2019-09-17 20:44:05 | eclipse/che | https://api.github.com/repos/eclipse/che | closed | Cover "Dashboard / Workspace Details / Overview" part of test plan by selenium test | kind/task lifecycle/stale status/code-review team/che-qe | ### Description
We have the test plan where described all use cases for dashboard:
https://docs.google.com/document/d/1aXUAWFOOylrk-_nO5Iqm77M0Viu8ykCjaQMtJuEBvUA/edit#heading=h.wf4eguoewmmg
We should cover the "Dashboard / Workspace Details / Overview" page by selenium test according to use cases which described ... | 1.0 | Cover "Dashboard / Workspace Details / Overview" part of test plan by selenium test - ### Description
We have the test plan where described all use cases for dashboard:
https://docs.google.com/document/d/1aXUAWFOOylrk-_nO5Iqm77M0Viu8ykCjaQMtJuEBvUA/edit#heading=h.wf4eguoewmmg
We should cover the "Dashboard / Works... | non_infrastructure | cover dashboard workspace details overview part of test plan by selenium test description we have the test plan where described all use cases for dashboard we should cover the dashboard workspace details overview page by selenium test according to use cases which described in the test plan | 0 |
15,916 | 11,765,443,123 | IssuesEvent | 2020-03-14 17:25:12 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Microsoft.Bcl.AsyncInterfaces | area-Infrastructure-libraries customer assistance |
Microsoft.Bcl.AsyncInterfaces has dependency on System.Threading.Tasks.Extensions >= 4.5.2, and it works fine with 4.5.2 version. However if upgraded to 4.5.3 app will throw below exception
```
Unhandled Exception: System.IO.FileLoadException: Could not load file or assembly 'System.Threading.Tasks.Extensions, ... | 1.0 | Microsoft.Bcl.AsyncInterfaces -
Microsoft.Bcl.AsyncInterfaces has dependency on System.Threading.Tasks.Extensions >= 4.5.2, and it works fine with 4.5.2 version. However if upgraded to 4.5.3 app will throw below exception
```
Unhandled Exception: System.IO.FileLoadException: Could not load file or assembly 'Sys... | infrastructure | microsoft bcl asyncinterfaces microsoft bcl asyncinterfaces has dependency on system threading tasks extensions and it works fine with version however if upgraded to app will throw below exception unhandled exception system io fileloadexception could not load file or assembly sys... | 1 |
34,715 | 6,367,713,826 | IssuesEvent | 2017-08-01 07:15:52 | symfony/symfony-docs | https://api.github.com/repos/symfony/symfony-docs | closed | [BrowserKit] Emulate back/forward browser navigation | BrowserKit hasPR Missing Documentation | See https://github.com/symfony/symfony/pull/22341.
BrowserKit now behaves as normal browsers, so let's check if we mention anywhere the old behavior as something specific to Symfony. | 1.0 | [BrowserKit] Emulate back/forward browser navigation - See https://github.com/symfony/symfony/pull/22341.
BrowserKit now behaves as normal browsers, so let's check if we mention anywhere the old behavior as something specific to Symfony. | non_infrastructure | emulate back forward browser navigation see browserkit now behaves as normal browsers so let s check if we mention anywhere the old behavior as something specific to symfony | 0 |
42,895 | 12,958,898,562 | IssuesEvent | 2020-07-20 12:10:11 | mdsaj/LP-AngularSpring | https://api.github.com/repos/mdsaj/LP-AngularSpring | closed | CVE-2019-14379 (High) detected in jackson-databind-2.9.7.jar | security vulnerability | ## CVE-2019-14379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.7.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14379 (High) detected in jackson-databind-2.9.7.jar - ## CVE-2019-14379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.7.jar</b></p></summary>
<p>General... | non_infrastructure | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm lp angularspring an... | 0 |
27,015 | 21,006,088,770 | IssuesEvent | 2022-03-29 22:50:19 | opensearch-project/k-NN | https://api.github.com/repos/opensearch-project/k-NN | closed | Apply spotless on whole project and get rid of ratchet | Infrastructure | Currently, we only apply spotless check on files that are touched only by the PR. The goal of this was to maintain git history.
However, I think we should just make one large spotless apply commit (as suggested here https://github.com/opensearch-project/k-NN/pull/328#discussion_r836714040) so that PRs dont contain c... | 1.0 | Apply spotless on whole project and get rid of ratchet - Currently, we only apply spotless check on files that are touched only by the PR. The goal of this was to maintain git history.
However, I think we should just make one large spotless apply commit (as suggested here https://github.com/opensearch-project/k-NN/p... | infrastructure | apply spotless on whole project and get rid of ratchet currently we only apply spotless check on files that are touched only by the pr the goal of this was to maintain git history however i think we should just make one large spotless apply commit as suggested here so that prs dont contain changes unrelated... | 1 |
19,161 | 13,196,120,149 | IssuesEvent | 2020-08-13 20:00:45 | microsoft/react-native-windows | https://api.github.com/repos/microsoft/react-native-windows | closed | Support direct debugging when using Chakra in VS Code. | Area: Debug Infrastructure Proposal | <!-- This is a template for new feature or API proposals for React Native Windows. Use this to submit new API/component requests or behavior updates that are specific to Windows-only. For feature requests to React Native, go [here](https://github.com/react-native-community/discussions-and-proposals) instead.
It's f... | 1.0 | Support direct debugging when using Chakra in VS Code. - <!-- This is a template for new feature or API proposals for React Native Windows. Use this to submit new API/component requests or behavior updates that are specific to Windows-only. For feature requests to React Native, go [here](https://github.com/react-native... | infrastructure | support direct debugging when using chakra in vs code this is a template for new feature or api proposals for react native windows use this to submit new api component requests or behavior updates that are specific to windows only for feature requests to react native go instead it s fine if you don ... | 1 |
18,761 | 13,096,273,699 | IssuesEvent | 2020-08-03 15:25:03 | knative/docs | https://api.github.com/repos/knative/docs | closed | First Eventing Example is Too Complicated | kind/epic kind/eventing kind/infrastructure kind/sample lifecycle/frozen |
**Describe the change you'd like to see**
The landing page points to an eventing example that deals with the kubernetes event source. I think it is too complicated.
A simple cronjob event source should suffice. It would avoid having to setup service accounts and role binding for the k8s source to work.
**Add... | 1.0 | First Eventing Example is Too Complicated -
**Describe the change you'd like to see**
The landing page points to an eventing example that deals with the kubernetes event source. I think it is too complicated.
A simple cronjob event source should suffice. It would avoid having to setup service accounts and role ... | infrastructure | first eventing example is too complicated describe the change you d like to see the landing page points to an eventing example that deals with the kubernetes event source i think it is too complicated a simple cronjob event source should suffice it would avoid having to setup service accounts and role ... | 1 |
165,514 | 6,277,681,600 | IssuesEvent | 2017-07-18 12:50:46 | vanilla-framework/vanilla-framework | https://api.github.com/repos/vanilla-framework/vanilla-framework | closed | Link to Grid page in strip documentation | Priority: High Status: Review | From [the “Strip” reference](https://docs.vanillaframework.io/en/patterns/strip): “The strip pattern provides a full width strip container in which to wrap a row. A strip can have light (`.p-strip--light`) or dark (`.p-strip--dark`) grey background. A `.p-strip` container should always be the parent of a `.row` and nev... | 1.0 | Link to Grid page in strip documentation - From [the “Strip” reference](https://docs.vanillaframework.io/en/patterns/strip): “The strip pattern provides a full width strip container in which to wrap a row. A strip can have light (`.p-strip--light`) or dark (`.p-strip--dark`) grey background. A `.p-strip` container shou... | non_infrastructure | link to grid page in strip documentation from “the strip pattern provides a full width strip container in which to wrap a row a strip can have light p strip light or dark p strip dark grey background a p strip container should always be the parent of a row and never the other way around ” o... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.