Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
310,771 | 26,741,904,856 | IssuesEvent | 2023-01-30 13:33:35 | hotosm/fAIr | https://api.github.com/repos/hotosm/fAIr | closed | Create API endpoint to gather the folder structure of training along with its no of files | component ; backend status : testing Feature Request | - Info included on #47 | 1.0 | Create API endpoint to gather the folder structure of training along with its no of files - - Info included on #47 | non_priority | create api endpoint to gather the folder structure of training along with its no of files info included on | 0 |
62,850 | 26,186,576,280 | IssuesEvent | 2023-01-03 01:46:16 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | Cannot create App plan in sub A for ASEv3 in Sub B | Service Attention App Services app-service-ase | ### **This is autogenerated. Please review and update as needed.**
## Describe the bug
**Command Name**
`az appservice plan create`
**Errors:**
```
App service environment 'subscriptions/<subB>/resourceGroups/ase-rg/providers/Microsoft.Web/hostingEnvironments/begimase' not found in subscription.
```
## To Reproduce:
Steps to reproduce the behavior. Note that argument values have been redacted, as they may contain sensitive information.
- _Put any pre-requisite steps here..._
- `az appservice plan create --name {} --resource-group {} --app-service-environment {} --location {} --number-of-workers {} --sku {}`
## Expected Behavior
## Environment Summary
```
Windows-10-10.0.22000-SP0
Python 3.8.9
Installer: MSI
azure-cli 2.29.0
Extensions:
aks-preview 0.5.34
```
## Additional Context
<!--Please don't remove this:-->
<!--auto-generated-->
| 3.0 | Cannot create App plan in sub A for ASEv3 in Sub B - ### **This is autogenerated. Please review and update as needed.**
## Describe the bug
**Command Name**
`az appservice plan create`
**Errors:**
```
App service environment 'subscriptions/<subB>/resourceGroups/ase-rg/providers/Microsoft.Web/hostingEnvironments/begimase' not found in subscription.
```
## To Reproduce:
Steps to reproduce the behavior. Note that argument values have been redacted, as they may contain sensitive information.
- _Put any pre-requisite steps here..._
- `az appservice plan create --name {} --resource-group {} --app-service-environment {} --location {} --number-of-workers {} --sku {}`
## Expected Behavior
## Environment Summary
```
Windows-10-10.0.22000-SP0
Python 3.8.9
Installer: MSI
azure-cli 2.29.0
Extensions:
aks-preview 0.5.34
```
## Additional Context
<!--Please don't remove this:-->
<!--auto-generated-->
| non_priority | cannot create app plan in sub a for in sub b this is autogenerated please review and update as needed describe the bug command name az appservice plan create errors app service environment subscriptions resourcegroups ase rg providers microsoft web hostingenvironments begimase not found in subscription to reproduce steps to reproduce the behavior note that argument values have been redacted as they may contain sensitive information put any pre requisite steps here az appservice plan create name resource group app service environment location number of workers sku expected behavior environment summary windows python installer msi azure cli extensions aks preview additional context | 0 |
316,205 | 23,619,439,177 | IssuesEvent | 2022-08-24 19:00:27 | tidymodels/probably | https://api.github.com/repos/tidymodels/probably | closed | Update vignette for recent releases of probably and yardstick | documentation | The [`where-to-use` vignette](https://github.com/tidymodels/probably/blob/master/vignettes/where-to-use.Rmd) is now a bit out-of-date in how it discusses probably and yardstick working together and needs to be updated, both in code and narrative.
For example, comments like this:
https://github.com/tidymodels/probably/blob/98fbe4acd5a75c16a2ef5b1aa1303e904484fb1f/vignettes/where-to-use.Rmd#L137-L138 | 1.0 | Update vignette for recent releases of probably and yardstick - The [`where-to-use` vignette](https://github.com/tidymodels/probably/blob/master/vignettes/where-to-use.Rmd) is now a bit out-of-date in how it discusses probably and yardstick working together and needs to be updated, both in code and narrative.
For example, comments like this:
https://github.com/tidymodels/probably/blob/98fbe4acd5a75c16a2ef5b1aa1303e904484fb1f/vignettes/where-to-use.Rmd#L137-L138 | non_priority | update vignette for recent releases of probably and yardstick the is now a bit out of date in how it discusses probably and yardstick working together and needs to be updated both in code and narrative for example comments like this | 0 |
253,209 | 19,095,478,014 | IssuesEvent | 2021-11-29 16:15:12 | nss-day-cohort-50/bangazon-api-cameronpwhite | https://api.github.com/repos/nss-day-cohort-50/bangazon-api-cameronpwhite | opened | TEST: Delete payment type | documentation enhancement | Add a test to the `tests/payment.py` module that verifies that a payment type can be deleted.
| 1.0 | TEST: Delete payment type - Add a test to the `tests/payment.py` module that verifies that a payment type can be deleted.
| non_priority | test delete payment type add a test to the tests payment py module that verifies that a payment type can be deleted | 0 |
139,861 | 31,799,311,067 | IssuesEvent | 2023-09-13 10:02:01 | arduino/arduino-cli | https://api.github.com/repos/arduino/arduino-cli | opened | Log `Required tool` with `debug` severity instead of `info` | type: enhancement topic: code | ### Describe the request
Please relax the daemon logger and print the `Required tool` with the `debug` level.
Currently, I have the `info` level set in the CLI config, and when the LS is running, touching the editor once triggers so many tools log messages—then formatting the code once more. Can you relax and print these messages with a `debug` severity?
### Describe the current behavior
Currently, it's with `info` level.
https://github.com/arduino/arduino-cli/assets/1405703/74b90b75-a4f6-4bb0-8ff4-e805d9566630
### Arduino CLI version
3f5c0eb2
### Operating system
macOS
### Operating system version
13.5.2
### Additional context
_No response_
### Issue checklist
- [X] I searched for previous requests in [the issue tracker](https://github.com/arduino/arduino-cli/issues?q=)
- [X] I verified the feature was still missing when using the [nightly build](https://arduino.github.io/arduino-cli/dev/installation/#nightly-builds)
- [X] My request contains all necessary details | 1.0 | Log `Required tool` with `debug` severity instead of `info` - ### Describe the request
Please relax the daemon logger and print the `Required tool` with the `debug` level.
Currently, I have the `info` level set in the CLI config, and when the LS is running, touching the editor once triggers so many tools log messages—then formatting the code once more. Can you relax and print these messages with a `debug` severity?
### Describe the current behavior
Currently, it's with `info` level.
https://github.com/arduino/arduino-cli/assets/1405703/74b90b75-a4f6-4bb0-8ff4-e805d9566630
### Arduino CLI version
3f5c0eb2
### Operating system
macOS
### Operating system version
13.5.2
### Additional context
_No response_
### Issue checklist
- [X] I searched for previous requests in [the issue tracker](https://github.com/arduino/arduino-cli/issues?q=)
- [X] I verified the feature was still missing when using the [nightly build](https://arduino.github.io/arduino-cli/dev/installation/#nightly-builds)
- [X] My request contains all necessary details | non_priority | log required tool with debug severity instead of info describe the request please relax the daemon logger and print the required tool with the debug level currently i have the info level set in the cli config and when the ls is running touching the editor once triggers so many tools log messages—then formatting the code once more can you relax and print these messages with a debug severity describe the current behavior currently it s with info level arduino cli version operating system macos operating system version additional context no response issue checklist i searched for previous requests in i verified the feature was still missing when using the my request contains all necessary details | 0 |
313,000 | 26,893,974,935 | IssuesEvent | 2023-02-06 10:59:47 | TestIntegrations/TestForwarding | https://api.github.com/repos/TestIntegrations/TestForwarding | opened | Hav | forwardeddddddTest ddw | # :clipboard: Bug Details
>Hav
key | value
--|--
Reported At | 2023-02-06 10:59:31 UTC
Email | shussein@instabug.com
Categories | Report a bug, sssss, jj
Tags | forwardeddddddTest, ddw
App Version | 1.0 (4)
Session Duration | 77479
Device | Simulator, iOS 15.5
Display | 414x736 (@3x)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/birdy-demo-app/beta/bugs/9301?utm_source=github&utm_medium=integrations) :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
CPU Load | 13.1%
Used Memory | 100.0% - 0.36/0.36 GB
Used Storage | 96.8% - 225.93/233.47 GB
Connectivity | WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/birdy-demo-app/beta/bugs/9301?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
Age: 18
Logged in: True
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
10:59:23 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:35:39 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:30:30 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:28:56 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:28:04 Top View: ViewController
13:28:04 Application: DidBecomeActive
13:28:04 Application: SceneDidActivate
13:28:04 Application: WillEnterForeground
13:28:04 Application: SceneWillConnect
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/birdy-demo-app/beta/bugs/9301?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/19578560/e6ee4debf29c65fe31bb93c49a043fb2_original/28794530/2023020612592774539400.jpg?Expires=4831354786&Signature=XPp416wl7gu3SXpzqwCo0G~zXB06BWt0O2aF3A3lr6LVte92EFPNKkjO8S9UBe6Xgy86ILVtJIQXy3nGJKDDXqF-6DMq7fUUuPhxQjoOFr5ogvCb-P17kADgla9y7LUumwxhc2dZL1QE2FtTIPqQtfzHObNreA4FBEPx5aLZkZWhuYQeQ0A2xhWJoc787vlu9-1kZF39EKt0MYd8olr4Ih~4pMPaXV~KjxemnA9Z6AZdWqOAH76LKS6XAejtow5gaVknJEv2n4xwytp9j~qzwSQx-sK~6U~hSfxH1c9bdxHI7W9qAcmZNaWizW3AFk4~6EPdon3W~OFU36jcNBSb6w__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using AFNetworking or Alamofire, [**check the details mentioned here**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations#section-requests-not-appearing-in-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations).
4. **Console Log**: when enabled you will see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations). | 1.0 | Hav - # :clipboard: Bug Details
>Hav
key | value
--|--
Reported At | 2023-02-06 10:59:31 UTC
Email | shussein@instabug.com
Categories | Report a bug, sssss, jj
Tags | forwardeddddddTest, ddw
App Version | 1.0 (4)
Session Duration | 77479
Device | Simulator, iOS 15.5
Display | 414x736 (@3x)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/birdy-demo-app/beta/bugs/9301?utm_source=github&utm_medium=integrations) :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
CPU Load | 13.1%
Used Memory | 100.0% - 0.36/0.36 GB
Used Storage | 96.8% - 225.93/233.47 GB
Connectivity | WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/birdy-demo-app/beta/bugs/9301?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
Age: 18
Logged in: True
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
10:59:23 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:35:39 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:30:30 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:28:56 Tap in Floating Button of type IBGInvocationFloatingView in ViewController
13:28:04 Top View: ViewController
13:28:04 Application: DidBecomeActive
13:28:04 Application: SceneDidActivate
13:28:04 Application: WillEnterForeground
13:28:04 Application: SceneWillConnect
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/birdy-demo-app/beta/bugs/9301?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/19578560/e6ee4debf29c65fe31bb93c49a043fb2_original/28794530/2023020612592774539400.jpg?Expires=4831354786&Signature=XPp416wl7gu3SXpzqwCo0G~zXB06BWt0O2aF3A3lr6LVte92EFPNKkjO8S9UBe6Xgy86ILVtJIQXy3nGJKDDXqF-6DMq7fUUuPhxQjoOFr5ogvCb-P17kADgla9y7LUumwxhc2dZL1QE2FtTIPqQtfzHObNreA4FBEPx5aLZkZWhuYQeQ0A2xhWJoc787vlu9-1kZF39EKt0MYd8olr4Ih~4pMPaXV~KjxemnA9Z6AZdWqOAH76LKS6XAejtow5gaVknJEv2n4xwytp9j~qzwSQx-sK~6U~hSfxH1c9bdxHI7W9qAcmZNaWizW3AFk4~6EPdon3W~OFU36jcNBSb6w__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using AFNetworking or Alamofire, [**check the details mentioned here**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations#section-requests-not-appearing-in-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations).
4. **Console Log**: when enabled you will see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/ios-logging?utm_source=github&utm_medium=integrations). | non_priority | hav clipboard bug details hav key value reported at utc email shussein instabug com categories report a bug sssss jj tags forwardeddddddtest ddw app version session duration device simulator ios display point right point left chart with downwards trend session profiler here is what the app was doing right before the bug was reported key value cpu load used memory gb used storage gb connectivity wifi battery unplugged orientation portrait find all the changes that happened in the parameters mentioned above during the last seconds before the bug was reported here point right point left bust in silhouette user info user attributes age logged in true mag right logs user steps here are the last steps done by the user right before the bug was reported tap in floating button of type ibginvocationfloatingview in viewcontroller tap in floating button of type ibginvocationfloatingview in viewcontroller tap in floating button of type ibginvocationfloatingview in viewcontroller tap in floating button of type ibginvocationfloatingview in viewcontroller top view viewcontroller application didbecomeactive application scenedidactivate application willenterforeground application scenewillconnect find all the user steps done by the user throughout the session here point right point left camera images warning looking for more details network log we are unable to capture your network requests automatically if you are using afnetworking or alamofire user events start capturing custom user events to send them along with each report instabug log start adding instabug logs to see them right inside each report you receive console log when enabled you will see them right inside each report you receive | 0 |
78,411 | 27,511,429,855 | IssuesEvent | 2023-03-06 09:06:25 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Remove Sexual Content from the Room Directory (NSFW) | T-Defect S-Critical O-Frequent A-Safety | ### Your use case
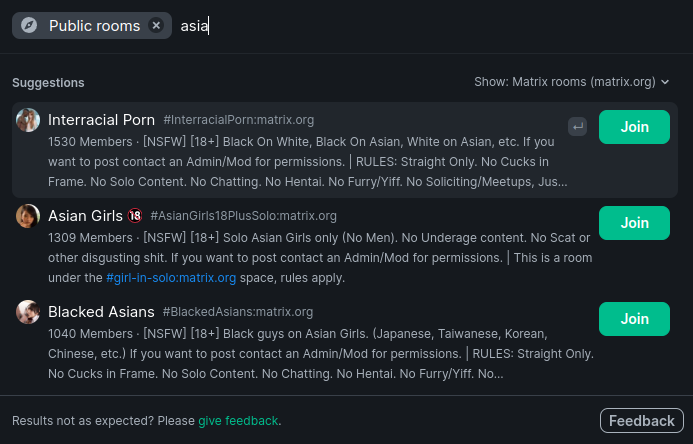
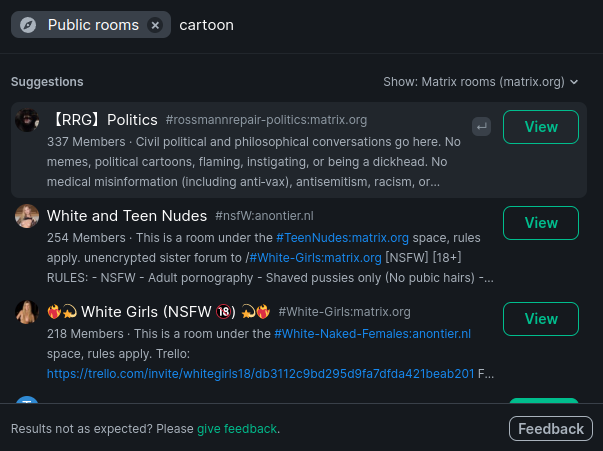
Matrix.org homeserver seems to not have its own issue tracker and my message in Matrix HQ has been ignored so I will report here as that's what the Element app suggests. I ask you to remove sexual content from the public room search as there is a high probability of users discovering such content unintentionally and the content that does get discovered is just a pure PR disaster waiting to happen.
For example I wouldn't want an Asian person to feel objectified the moment they join matrix:
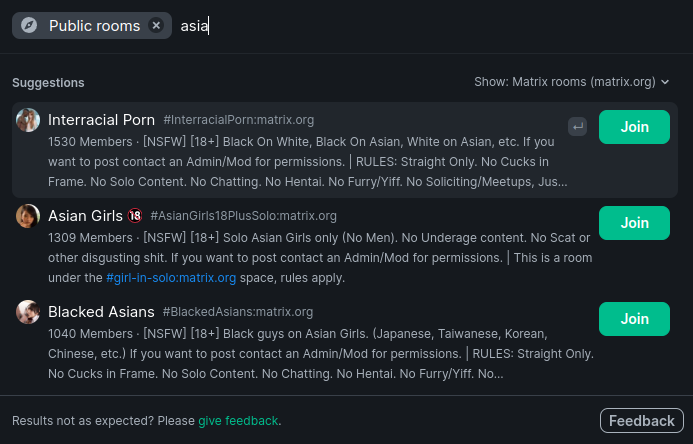
Or a minor to discover sex related rooms the moment they search "cartoon":
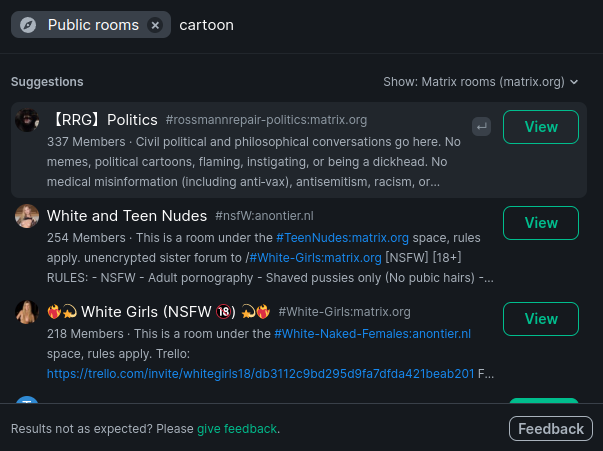
Those innocent search queries returning a slew of fetishistic content is utterly inappropriate for a network that strives to be inclusive for all kinds of people. Therefore I propose to ban NSFW content from the public room search on Matrix.org homeserver.
### Have you considered any alternatives?
Offer a toggle that is off by default if it is technically possible
### Additional context
_No response_ | 1.0 | Remove Sexual Content from the Room Directory (NSFW) - ### Your use case
Matrix.org homeserver seems to not have its own issue tracker and my message in Matrix HQ has been ignored so I will report here as that's what the Element app suggests. I ask you to remove sexual content from the public room search as there is a high probability of users discovering such content unintentionally and the content that does get discovered is just a pure PR disaster waiting to happen.
For example I wouldn't want an Asian person to feel objectified the moment they join matrix:
Or a minor to discover sex related rooms the moment they search "cartoon":
Those innocent search queries returning a slew of fetishistic content is utterly inappropriate for a network that strives to be inclusive for all kinds of people. Therefore I propose to ban NSFW content from the public room search on Matrix.org homeserver.
### Have you considered any alternatives?
Offer a toggle that is off by default if it is technically possible
### Additional context
_No response_ | non_priority | remove sexual content from the room directory nsfw your use case matrix org homeserver seems to not have its own issue tracker and my message in matrix hq has been ignored so i will report here as that s what the element app suggests i ask you to remove sexual content from the public room search as there is a high probability of users discovering such content unintentionally and the content that does get discovered is just a pure pr disaster waiting to happen for example i wouldn t want an asian person to feel objectified the moment they join matrix or a minor to discover sex related rooms the moment they search cartoon those innocent search queries returning a slew of fetishistic content is utterly inappropriate for a network that strives to be inclusive for all kinds of people therefore i propose to ban nsfw content from the public room search on matrix org homeserver have you considered any alternatives offer a toggle that is off by default if it is technically possible additional context no response | 0 |
146,354 | 23,051,587,252 | IssuesEvent | 2022-07-24 18:04:44 | penumbra-zone/penumbra | https://api.github.com/repos/penumbra-zone/penumbra | closed | NCT frontier snapshot endpoint for `pd` | A-node A-client C-enhancement E-med C-design A-TCT | **Is your feature request related to a problem? Please describe.**
Motivation is the same as #1128, solution desired is simpler.
If you absolutely know that you don't have any transactions before a certain date (say, you generated your spendkey on that date), it would be nice to not have to sync the entirety of the chain, but rather to start processing at that date.
**Describe the solution you'd like**
`pd` could track every epoch-boundary NCT frontier in sidecar non-consensus storage, and provide a gRPC endpoint to let you request the one for a given epoch, alongside a proof of inclusion of that frontier's root in the JMT.
(some details copied from #1128)
Implementing this would require writing a non-incremental (de)serialization function for solely the frontier of the NCT, into a protobuf representation. Some details about this are discussed in https://github.com/penumbra-zone/penumbra/issues/1082, which I previously closed as low-priority and negligible impact. Because this would not be consensus critical information, we could choose to include or not include cached internal node hashes in the frontier; either choice is fine, and can be altered at will.
On the view-client side, when the view service is started in this checkpointed mode, it should request the checkpoint for the most recent epoch prior to the block desired to start at, and proceed synchronizing from there. In order to prevent leaking information about which height is desired, the client could issue an additional number of random chaff requests to the endpoint, distributed so that the desired request is randomly ordered in the chaff, and cannot be reasonably distinguished in the distribution.
To make this process automatic, we can have key generation store in the custody file the block height at which the keys were generated (check the block height, then generate the keys, to ensure that they only existed before that moment). This way, if you reset your view state, this extra data is present in the custody file and can still be used to resume from that moment in time rather than zero.
**Describe alternatives you've considered**
#1128 is an alternative, but it's not necessary to store this in consensus, as pointed out by @hdevalence.
On the point about automating this via custody, we could instead choose to disable this feature by default and require the user to explicitly opt-in when initializing `pviewd` or `pcli` for the first time.
| 1.0 | NCT frontier snapshot endpoint for `pd` - **Is your feature request related to a problem? Please describe.**
Motivation is the same as #1128, solution desired is simpler.
If you absolutely know that you don't have any transactions before a certain date (say, you generated your spendkey on that date), it would be nice to not have to sync the entirety of the chain, but rather to start processing at that date.
**Describe the solution you'd like**
`pd` could track every epoch-boundary NCT frontier in sidecar non-consensus storage, and provide a gRPC endpoint to let you request the one for a given epoch, alongside a proof of inclusion of that frontier's root in the JMT.
(some details copied from #1128)
Implementing this would require writing a non-incremental (de)serialization function for solely the frontier of the NCT, into a protobuf representation. Some details about this are discussed in https://github.com/penumbra-zone/penumbra/issues/1082, which I previously closed as low-priority and negligible impact. Because this would not be consensus critical information, we could choose to include or not include cached internal node hashes in the frontier; either choice is fine, and can be altered at will.
On the view-client side, when the view service is started in this checkpointed mode, it should request the checkpoint for the most recent epoch prior to the block desired to start at, and proceed synchronizing from there. In order to prevent leaking information about which height is desired, the client could issue an additional number of random chaff requests to the endpoint, distributed so that the desired request is randomly ordered in the chaff, and cannot be reasonably distinguished in the distribution.
To make this process automatic, we can have key generation store in the custody file the block height at which the keys were generated (check the block height, then generate the keys, to ensure that they only existed before that moment). This way, if you reset your view state, this extra data is present in the custody file and can still be used to resume from that moment in time rather than zero.
**Describe alternatives you've considered**
#1128 is an alternative, but it's not necessary to store this in consensus, as pointed out by @hdevalence.
On the point about automating this via custody, we could instead choose to disable this feature by default and require the user to explicitly opt-in when initializing `pviewd` or `pcli` for the first time.
| non_priority | nct frontier snapshot endpoint for pd is your feature request related to a problem please describe motivation is the same as solution desired is simpler if you absolutely know that you don t have any transactions before a certain date say you generated your spendkey on that date it would be nice to not have to sync the entirety of the chain but rather to start processing at that date describe the solution you d like pd could track every epoch boundary nct frontier in sidecar non consensus storage and provide a grpc endpoint to let you request the one for a given epoch alongside a proof of inclusion of that frontier s root in the jmt some details copied from implementing this would require writing a non incremental de serialization function for solely the frontier of the nct into a protobuf representation some details about this are discussed in which i previously closed as low priority and negligible impact because this would not be consensus critical information we could choose to include or not include cached internal node hashes in the frontier either choice is fine and can be altered at will on the view client side when the view service is started in this checkpointed mode it should request the checkpoint for the most recent epoch prior to the block desired to start at and proceed synchronizing from there in order to prevent leaking information about which height is desired the client could issue an additional number of random chaff requests to the endpoint distributed so that the desired request is randomly ordered in the chaff and cannot be reasonably distinguished in the distribution to make this process automatic we can have key generation store in the custody file the block height at which the keys were generated check the block height then generate the keys to ensure that they only existed before that moment this way if you reset your view state this extra data is present in the custody file and can still be used to resume from that moment in time rather than zero describe alternatives you ve considered is an alternative but it s not necessary to store this in consensus as pointed out by hdevalence on the point about automating this via custody we could instead choose to disable this feature by default and require the user to explicitly opt in when initializing pviewd or pcli for the first time | 0 |
297,218 | 25,710,231,151 | IssuesEvent | 2022-12-07 05:47:47 | dotnet/msbuild | https://api.github.com/repos/dotnet/msbuild | opened | DeleteFiles function doesn't delete first file directory when second file is in the subfolder of first file | bug needs-triage test | ### Issue Description
There's a bug in the cleanup logic here. Specifically, it creates the source and dest files, and at the end of the test, it calls Helpers.DeleteFiles(sourceFile, destFile); That method loops through each file and deletes it if it exists, then deletes the directory containing it if it's empty...but when we delete the source file, the directory isn't empty; it has the destination folder/file. When we delete the destination file, its folder just contains the destination file, so we delete that. Afterwards, the source folder never gets deleted. That means we can't write to it.
https://github.com/dotnet/msbuild/blob/c5532da3a3c99817e70d95fe9e07302ba72ee523/src/Shared/UnitTests/ObjectModelHelpers.cs#L1818-L1833 | 1.0 | DeleteFiles function doesn't delete first file directory when second file is in the subfolder of first file - ### Issue Description
There's a bug in the cleanup logic here. Specifically, it creates the source and dest files, and at the end of the test, it calls Helpers.DeleteFiles(sourceFile, destFile); That method loops through each file and deletes it if it exists, then deletes the directory containing it if it's empty...but when we delete the source file, the directory isn't empty; it has the destination folder/file. When we delete the destination file, its folder just contains the destination file, so we delete that. Afterwards, the source folder never gets deleted. That means we can't write to it.
https://github.com/dotnet/msbuild/blob/c5532da3a3c99817e70d95fe9e07302ba72ee523/src/Shared/UnitTests/ObjectModelHelpers.cs#L1818-L1833 | non_priority | deletefiles function doesn t delete first file directory when second file is in the subfolder of first file issue description there s a bug in the cleanup logic here specifically it creates the source and dest files and at the end of the test it calls helpers deletefiles sourcefile destfile that method loops through each file and deletes it if it exists then deletes the directory containing it if it s empty but when we delete the source file the directory isn t empty it has the destination folder file when we delete the destination file its folder just contains the destination file so we delete that afterwards the source folder never gets deleted that means we can t write to it | 0 |
12,594 | 4,506,156,255 | IssuesEvent | 2016-09-02 01:55:58 | Jeremy-Barnes/Critters | https://api.github.com/repos/Jeremy-Barnes/Critters | opened | Server: Personal Messages | Code feature | Create server endpoint to allow users to send a message to other users.
Add new messages to the long polling notification system. | 1.0 | Server: Personal Messages - Create server endpoint to allow users to send a message to other users.
Add new messages to the long polling notification system. | non_priority | server personal messages create server endpoint to allow users to send a message to other users add new messages to the long polling notification system | 0 |
141,458 | 21,524,084,867 | IssuesEvent | 2022-04-28 16:37:32 | dotnet/iot | https://api.github.com/repos/dotnet/iot | closed | [Proposal] Support OpenDrain and OpenCollector options for GPIO PinMode | Design Discussion api-suggestion area-System.Device.Gpio | GPIO `PinMode` currently only supports Input, Output, InputPullDown and InputPullUp. There are other scenarios where outputs are open-drain and open-collector types and the API should accommodate.
## Rationale and Usage
I/O expanders are a good example where they have different types of I/O within a particular family and are differentiated by part numbers for the family. In many cases, a user's hardware will be configured with the basic Input or Output `PinMode` values along with attaching external resistors for pull-up/down functionality. However, you can utilize internal circuitry in binding devices to perform this. For example, the MCP23X09/MCP23X18 devices have open-drain outputs. Therefore, you could update the GPIO Pull-up Resistor Configuration Register (GPPU) when opening pins when using as a controller.
## Example
You could have something similar below based on the [IGpioControllerProvider proposal](https://github.com/dotnet/iot/issues/125).
```csharp
var connectionSettings = new SpiConnectionSettings(0, 0);
var spiDevice = new UnixSpiDevice(connectionSettings);
var mcp23Sxx = new Mcp23Sxx(0, spiDevice);
GpioController mcp23SxxController = mcp23Sxx.GetDefaultGpioController();
// Now when you call the GpioController methods, the master controller will send
// the respective SPI commands to the binding behind the scenes to update its I/O.
//
// The code below would interact with the MCP23XXX related registers (IODIR, GPIO, GPPU, etc.)
// to configure the pin as an output and write the value.
mcp23SxxController.SetPinMode(1, PinMode.OpenDrainPullUp);
mcp23SxxController.Write(1, PinValue.High);
```
## Proposed Change
Update the GPIO `PinMode` to include the new values. Summaries were left out for simplicity.
```csharp
public enum PinMode
{
Input,
Output,
InputPullDown,
InputPullUp,
// The following are the proposed additions.
OutputOpenDrain,
OutputOpenDrainPullUp,
OutputOpenCollector,
OutputOpenCollectorPullDown
}
```
I have not checked throughout API, but will also need to update logic that checks if PinMode is of specific type. For example, the GpioController.Write methods verify the mode is equal to Output before writing.
```csharp
// From GpioController.cs file.
if (_driver.GetPinMode(pinNumber) != PinMode.Output)
{
throw new InvalidOperationException("Can not write to a pin that is not set to Output mode.");
}
```
## Open Questions
1. [Windows.Devices.Gpio.GpioPinDriveMode](https://docs.microsoft.com/en-us/uwp/api/windows.devices.gpio.gpiopindrivemode) is similar to `System.Device.Gpio.PinMode`. It already includes current `PinMode` values and the values being proposed. However, the names are slightly different for the open-collector types. The question is should we stay consistent to Windows.Devices.Gpio (OutputOpenSource and OutputOpenSourcePullDown) or use OutputOpenCollector and OutputOpenCollectorPullDown? I've mainly seen references to open-collector and not open-source while researching related content. I'm not sure what the best approach would be in this case and would be content either way. Open-source mentioned here during [this Libgpiod session](https://youtu.be/cdTLewJCL1Y?list=PLbzoR-pLrL6pISWAq-1cXP4_UZAyRtesk&t=14m).
## References
https://blog.digilentinc.com/open-collector-vs-open-drain/
**Section 1.5**: http://ww1.microchip.com/downloads/en/DeviceDoc/20002121C.pdf
https://docs.microsoft.com/en-us/uwp/api/windows.devices.gpio.gpiopindrivemode
| 1.0 | [Proposal] Support OpenDrain and OpenCollector options for GPIO PinMode - GPIO `PinMode` currently only supports Input, Output, InputPullDown and InputPullUp. There are other scenarios where outputs are open-drain and open-collector types and the API should accommodate.
## Rationale and Usage
I/O expanders are a good example where they have different types of I/O within a particular family and are differentiated by part numbers for the family. In many cases, a user's hardware will be configured with the basic Input or Output `PinMode` values along with attaching external resistors for pull-up/down functionality. However, you can utilize internal circuitry in binding devices to perform this. For example, the MCP23X09/MCP23X18 devices have open-drain outputs. Therefore, you could update the GPIO Pull-up Resistor Configuration Register (GPPU) when opening pins when using as a controller.
## Example
You could have something similar below based on the [IGpioControllerProvider proposal](https://github.com/dotnet/iot/issues/125).
```csharp
var connectionSettings = new SpiConnectionSettings(0, 0);
var spiDevice = new UnixSpiDevice(connectionSettings);
var mcp23Sxx = new Mcp23Sxx(0, spiDevice);
GpioController mcp23SxxController = mcp23Sxx.GetDefaultGpioController();
// Now when you call the GpioController methods, the master controller will send
// the respective SPI commands to the binding behind the scenes to update its I/O.
//
// The code below would interact with the MCP23XXX related registers (IODIR, GPIO, GPPU, etc.)
// to configure the pin as an output and write the value.
mcp23SxxController.SetPinMode(1, PinMode.OpenDrainPullUp);
mcp23SxxController.Write(1, PinValue.High);
```
## Proposed Change
Update the GPIO `PinMode` to include the new values. Summaries were left out for simplicity.
```csharp
public enum PinMode
{
Input,
Output,
InputPullDown,
InputPullUp,
// The following are the proposed additions.
OutputOpenDrain,
OutputOpenDrainPullUp,
OutputOpenCollector,
OutputOpenCollectorPullDown
}
```
I have not checked throughout API, but will also need to update logic that checks if PinMode is of specific type. For example, the GpioController.Write methods verify the mode is equal to Output before writing.
```csharp
// From GpioController.cs file.
if (_driver.GetPinMode(pinNumber) != PinMode.Output)
{
throw new InvalidOperationException("Can not write to a pin that is not set to Output mode.");
}
```
## Open Questions
1. [Windows.Devices.Gpio.GpioPinDriveMode](https://docs.microsoft.com/en-us/uwp/api/windows.devices.gpio.gpiopindrivemode) is similar to `System.Device.Gpio.PinMode`. It already includes current `PinMode` values and the values being proposed. However, the names are slightly different for the open-collector types. The question is should we stay consistent to Windows.Devices.Gpio (OutputOpenSource and OutputOpenSourcePullDown) or use OutputOpenCollector and OutputOpenCollectorPullDown? I've mainly seen references to open-collector and not open-source while researching related content. I'm not sure what the best approach would be in this case and would be content either way. Open-source mentioned here during [this Libgpiod session](https://youtu.be/cdTLewJCL1Y?list=PLbzoR-pLrL6pISWAq-1cXP4_UZAyRtesk&t=14m).
## References
https://blog.digilentinc.com/open-collector-vs-open-drain/
**Section 1.5**: http://ww1.microchip.com/downloads/en/DeviceDoc/20002121C.pdf
https://docs.microsoft.com/en-us/uwp/api/windows.devices.gpio.gpiopindrivemode
| non_priority | support opendrain and opencollector options for gpio pinmode gpio pinmode currently only supports input output inputpulldown and inputpullup there are other scenarios where outputs are open drain and open collector types and the api should accommodate rationale and usage i o expanders are a good example where they have different types of i o within a particular family and are differentiated by part numbers for the family in many cases a user s hardware will be configured with the basic input or output pinmode values along with attaching external resistors for pull up down functionality however you can utilize internal circuitry in binding devices to perform this for example the devices have open drain outputs therefore you could update the gpio pull up resistor configuration register gppu when opening pins when using as a controller example you could have something similar below based on the csharp var connectionsettings new spiconnectionsettings var spidevice new unixspidevice connectionsettings var new spidevice gpiocontroller getdefaultgpiocontroller now when you call the gpiocontroller methods the master controller will send the respective spi commands to the binding behind the scenes to update its i o the code below would interact with the related registers iodir gpio gppu etc to configure the pin as an output and write the value setpinmode pinmode opendrainpullup write pinvalue high proposed change update the gpio pinmode to include the new values summaries were left out for simplicity csharp public enum pinmode input output inputpulldown inputpullup the following are the proposed additions outputopendrain outputopendrainpullup outputopencollector outputopencollectorpulldown i have not checked throughout api but will also need to update logic that checks if pinmode is of specific type for example the gpiocontroller write methods verify the mode is equal to output before writing csharp from gpiocontroller cs file if driver getpinmode pinnumber pinmode output throw new invalidoperationexception can not write to a pin that is not set to output mode open questions is similar to system device gpio pinmode it already includes current pinmode values and the values being proposed however the names are slightly different for the open collector types the question is should we stay consistent to windows devices gpio outputopensource and outputopensourcepulldown or use outputopencollector and outputopencollectorpulldown i ve mainly seen references to open collector and not open source while researching related content i m not sure what the best approach would be in this case and would be content either way open source mentioned here during references section | 0 |
57,642 | 7,086,941,784 | IssuesEvent | 2018-01-11 16:16:30 | 18F/dol-whd-14c | https://api.github.com/repos/18F/dol-whd-14c | closed | As a WHD Security Officer, I would like each User's session to timeout from inactivity set to WHD policies | Milestone 1 Security Visual Design WHD Provide Requirements required to go live | Refer to prototype here for behavior: https://preview.uxpin.com/6dc6e8912fdaeb32cdfefa6e237f0d300d960588#/pages/77031627/simulate/no-panels?mode=i
**Note:** On the first page, click anywhere on the dark modal background to simulate the session expiring.
Descripition:
In Ref to NIST Control AC-12, The WHD Organiation Defined Perameter (ODP) will be provided so that it can be enforced by the information system - 15 mins of inactivity
TODO WHD Provide clarification on 15 min vs 60 min (DIT); WHD business needs to provide clarification on what should happen with "Application Status". Also what UX behavior do we expect in terms of a popup or something to remind user that session is about to timeout?
Tasks:
- [ ] User session timeout value is configured in web.config and provided to UI through some existing means (API?)
- [ ] Implement web server session timeout
- [ ] Create running task to track timeout
- [ ] Create alert/notification to user at a set interval before the timeout occurs, following 508 standards
- [x] Alert should go by USWDS
Acceptance Criteria: After 60 minutes of inactivity any logged in user should be automatically logged out and their session should be terminated. At a set interval before that timeout, alert should be thrown to current logged in user that in x interval (minutes) they will be logged out and their session terminated.
Considerations:
1. Application Status
WHD Business position: Filled out Application Status values must be saved.
IT position: Currently Application Status values are saved when moving to the next page. Hence fair to expect values must not be saved. In addition saving values in weird states left by the user is a complex problem and needs workflow/context implementation internally and not recommended.
2. Role: Any logged in User
| 1.0 | As a WHD Security Officer, I would like each User's session to timeout from inactivity set to WHD policies - Refer to prototype here for behavior: https://preview.uxpin.com/6dc6e8912fdaeb32cdfefa6e237f0d300d960588#/pages/77031627/simulate/no-panels?mode=i
**Note:** On the first page, click anywhere on the dark modal background to simulate the session expiring.
Descripition:
In Ref to NIST Control AC-12, The WHD Organiation Defined Perameter (ODP) will be provided so that it can be enforced by the information system - 15 mins of inactivity
TODO WHD Provide clarification on 15 min vs 60 min (DIT); WHD business needs to provide clarification on what should happen with "Application Status". Also what UX behavior do we expect in terms of a popup or something to remind user that session is about to timeout?
Tasks:
- [ ] User session timeout value is configured in web.config and provided to UI through some existing means (API?)
- [ ] Implement web server session timeout
- [ ] Create running task to track timeout
- [ ] Create alert/notification to user at a set interval before the timeout occurs, following 508 standards
- [x] Alert should go by USWDS
Acceptance Criteria: After 60 minutes of inactivity any logged in user should be automatically logged out and their session should be terminated. At a set interval before that timeout, alert should be thrown to current logged in user that in x interval (minutes) they will be logged out and their session terminated.
Considerations:
1. Application Status
WHD Business position: Filled out Application Status values must be saved.
IT position: Currently Application Status values are saved when moving to the next page. Hence fair to expect values must not be saved. In addition saving values in weird states left by the user is a complex problem and needs workflow/context implementation internally and not recommended.
2. Role: Any logged in User
| non_priority | as a whd security officer i would like each user s session to timeout from inactivity set to whd policies refer to prototype here for behavior note on the first page click anywhere on the dark modal background to simulate the session expiring descripition in ref to nist control ac the whd organiation defined perameter odp will be provided so that it can be enforced by the information system mins of inactivity todo whd provide clarification on min vs min dit whd business needs to provide clarification on what should happen with application status also what ux behavior do we expect in terms of a popup or something to remind user that session is about to timeout tasks user session timeout value is configured in web config and provided to ui through some existing means api implement web server session timeout create running task to track timeout create alert notification to user at a set interval before the timeout occurs following standards alert should go by uswds acceptance criteria after minutes of inactivity any logged in user should be automatically logged out and their session should be terminated at a set interval before that timeout alert should be thrown to current logged in user that in x interval minutes they will be logged out and their session terminated considerations application status whd business position filled out application status values must be saved it position currently application status values are saved when moving to the next page hence fair to expect values must not be saved in addition saving values in weird states left by the user is a complex problem and needs workflow context implementation internally and not recommended role any logged in user | 0 |
70,695 | 9,437,948,388 | IssuesEvent | 2019-04-13 19:09:25 | django-mptt/django-mptt | https://api.github.com/repos/django-mptt/django-mptt | closed | Order of insertion causes new roots to get the same tree_id when order_insertion_by is defined | Broken Tree Documentation | Using `django-mptt 0.8.4`
With this model:
```
from django.db import models
from mptt.models import MPTTModel, TreeForeignKey
class Node(MPTTModel):
name = models.CharField(max_length=50)
parent = TreeForeignKey('self', null=True, blank=True, related_name='children', db_index=True)
class MPTTMeta:
order_insertion_by = ['name']
```
And these tests:
```
from django.test import TestCase
from .models import Node
class NodeTest(TestCase):
def test_multiple_roots_in_order(self):
r1 = Node.objects.create(name='A', parent=None)
r2 = Node.objects.create(name='B', parent=None)
self.assertNotEqual(r1.tree_id, r2.tree_id)
def test_multiple_roots_in_reverse_order(self):
r1 = Node.objects.create(name='B', parent=None)
r2 = Node.objects.create(name='A', parent=None)
self.assertNotEqual(r1.tree_id, r2.tree_id)
```
When the nodes are inserted "in order" (A before B), they go into separate trees. When the nodes are inserted in reverse order, they go into the same tree:
```
Creating test database for alias 'default'...
.F
======================================================================
FAIL: test_multiple_roots_in_reverse_order (my_app.tests.NodeTest)
----------------------------------------------------------------------
Traceback (most recent call last):
File "/Users/cmermingas/django_projects/mptt_test/my_app/tests.py", line 16, in test_multiple_roots_in_reverse_order
self.assertNotEqual(r1.tree_id, r2.tree_id)
AssertionError: 1 == 1
----------------------------------------------------------------------
Ran 2 tests in 0.007s
FAILED (failures=1)
Destroying test database for alias 'default'...
```
If someone is willing to coach me a bit, I am willing to create a pull request and work on this.
Please let me know if I am doing something wrong. I'm pretty new here.
- Edited: I had a "suspected problem" and a potential fix here. I removed it after discovering that I was totally wrong.
| 1.0 | Order of insertion causes new roots to get the same tree_id when order_insertion_by is defined - Using `django-mptt 0.8.4`
With this model:
```
from django.db import models
from mptt.models import MPTTModel, TreeForeignKey
class Node(MPTTModel):
name = models.CharField(max_length=50)
parent = TreeForeignKey('self', null=True, blank=True, related_name='children', db_index=True)
class MPTTMeta:
order_insertion_by = ['name']
```
And these tests:
```
from django.test import TestCase
from .models import Node
class NodeTest(TestCase):
def test_multiple_roots_in_order(self):
r1 = Node.objects.create(name='A', parent=None)
r2 = Node.objects.create(name='B', parent=None)
self.assertNotEqual(r1.tree_id, r2.tree_id)
def test_multiple_roots_in_reverse_order(self):
r1 = Node.objects.create(name='B', parent=None)
r2 = Node.objects.create(name='A', parent=None)
self.assertNotEqual(r1.tree_id, r2.tree_id)
```
When the nodes are inserted "in order" (A before B), they go into separate trees. When the nodes are inserted in reverse order, they go into the same tree:
```
Creating test database for alias 'default'...
.F
======================================================================
FAIL: test_multiple_roots_in_reverse_order (my_app.tests.NodeTest)
----------------------------------------------------------------------
Traceback (most recent call last):
File "/Users/cmermingas/django_projects/mptt_test/my_app/tests.py", line 16, in test_multiple_roots_in_reverse_order
self.assertNotEqual(r1.tree_id, r2.tree_id)
AssertionError: 1 == 1
----------------------------------------------------------------------
Ran 2 tests in 0.007s
FAILED (failures=1)
Destroying test database for alias 'default'...
```
If someone is willing to coach me a bit, I am willing to create a pull request and work on this.
Please let me know if I am doing something wrong. I'm pretty new here.
- Edited: I had a "suspected problem" and a potential fix here. I removed it after discovering that I was totally wrong.
| non_priority | order of insertion causes new roots to get the same tree id when order insertion by is defined using django mptt with this model from django db import models from mptt models import mpttmodel treeforeignkey class node mpttmodel name models charfield max length parent treeforeignkey self null true blank true related name children db index true class mpttmeta order insertion by and these tests from django test import testcase from models import node class nodetest testcase def test multiple roots in order self node objects create name a parent none node objects create name b parent none self assertnotequal tree id tree id def test multiple roots in reverse order self node objects create name b parent none node objects create name a parent none self assertnotequal tree id tree id when the nodes are inserted in order a before b they go into separate trees when the nodes are inserted in reverse order they go into the same tree creating test database for alias default f fail test multiple roots in reverse order my app tests nodetest traceback most recent call last file users cmermingas django projects mptt test my app tests py line in test multiple roots in reverse order self assertnotequal tree id tree id assertionerror ran tests in failed failures destroying test database for alias default if someone is willing to coach me a bit i am willing to create a pull request and work on this please let me know if i am doing something wrong i m pretty new here edited i had a suspected problem and a potential fix here i removed it after discovering that i was totally wrong | 0 |
159,978 | 20,086,694,626 | IssuesEvent | 2022-02-05 04:03:08 | jtimberlake/rei-cedar | https://api.github.com/repos/jtimberlake/rei-cedar | opened | CVE-2021-32803 (High) detected in tar-6.1.0.tgz | security vulnerability | ## CVE-2021-32803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-6.1.0.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-6.1.0.tgz">https://registry.npmjs.org/tar/-/tar-6.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-6.0.0.tgz (Root Library)
- node-gyp-7.1.2.tgz
- :x: **tar-6.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/rei-cedar/commit/9c0c2cadda2965ff0d2cb956635474ae9161ddfe">9c0c2cadda2965ff0d2cb956635474ae9161ddfe</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803>CVE-2021-32803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw">https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution: tar - 3.2.3, 4.4.15, 5.0.7, 6.1.2</p>
</p>
</details>
<p></p>
| True | CVE-2021-32803 (High) detected in tar-6.1.0.tgz - ## CVE-2021-32803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-6.1.0.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-6.1.0.tgz">https://registry.npmjs.org/tar/-/tar-6.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-6.0.0.tgz (Root Library)
- node-gyp-7.1.2.tgz
- :x: **tar-6.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/rei-cedar/commit/9c0c2cadda2965ff0d2cb956635474ae9161ddfe">9c0c2cadda2965ff0d2cb956635474ae9161ddfe</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.2, 5.0.7, 4.4.15, and 3.2.3 has an arbitrary File Creation/Overwrite vulnerability via insufficient symlink protection. `node-tar` aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary `stat` calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory. This order of operations resulted in the directory being created and added to the `node-tar` directory cache. When a directory is present in the directory cache, subsequent calls to mkdir for that directory are skipped. However, this is also where `node-tar` checks for symlinks occur. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass `node-tar` symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.3, 4.4.15, 5.0.7 and 6.1.2.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32803>CVE-2021-32803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw">https://github.com/npm/node-tar/security/advisories/GHSA-r628-mhmh-qjhw</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution: tar - 3.2.3, 4.4.15, 5.0.7, 6.1.2</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules tar package json dependency hierarchy node sass tgz root library node gyp tgz x tar tgz vulnerable library found in head commit a href vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite vulnerability via insufficient symlink protection node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory this order of operations resulted in the directory being created and added to the node tar directory cache when a directory is present in the directory cache subsequent calls to mkdir for that directory are skipped however this is also where node tar checks for symlinks occur by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite this issue was addressed in releases and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar | 0 |
216,578 | 24,281,576,575 | IssuesEvent | 2022-09-28 17:54:09 | liorzilberg/struts | https://api.github.com/repos/liorzilberg/struts | opened | CVE-2016-1000027 (High) detected in spring-web-4.3.13.RELEASE.jar | security vulnerability | ## CVE-2016-1000027 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /plugins/async/pom.xml</p>
<p>Path to vulnerable library: /.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.3.13.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/liorzilberg/struts/commit/6950763af860884188f4080d19a18c5ede16cd74">6950763af860884188f4080d19a18c5ede16cd74</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Spring Framework through 5.3.16 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required. NOTE: the vendor's position is that untrusted data is not an intended use case. The product's behavior will not be changed because some users rely on deserialization of trusted data.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000027>CVE-2016-1000027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-1000027">https://nvd.nist.gov/vuln/detail/CVE-2016-1000027</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: 4.3.26.RELEASE</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2016-1000027 (High) detected in spring-web-4.3.13.RELEASE.jar - ## CVE-2016-1000027 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /plugins/async/pom.xml</p>
<p>Path to vulnerable library: /.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar,/.m2/repository/org/springframework/spring-web/4.3.13.RELEASE/spring-web-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.3.13.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/liorzilberg/struts/commit/6950763af860884188f4080d19a18c5ede16cd74">6950763af860884188f4080d19a18c5ede16cd74</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Spring Framework through 5.3.16 suffers from a potential remote code execution (RCE) issue if used for Java deserialization of untrusted data. Depending on how the library is implemented within a product, this issue may or not occur, and authentication may be required. NOTE: the vendor's position is that untrusted data is not an intended use case. The product's behavior will not be changed because some users rely on deserialization of trusted data.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000027>CVE-2016-1000027</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-1000027">https://nvd.nist.gov/vuln/detail/CVE-2016-1000027</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: 4.3.26.RELEASE</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve high detected in spring web release jar cve high severity vulnerability vulnerable library spring web release jar spring web library home page a href path to dependency file plugins async pom xml path to vulnerable library repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar repository org springframework spring web release spring web release jar repository org springframework spring web release spring web release jar repository org springframework spring web release spring web release jar repository org springframework spring web release spring web release jar repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar repository org springframework spring web release spring web release jar dependency hierarchy x spring web release jar vulnerable library found in head commit a href found in base branch master vulnerability details pivotal spring framework through suffers from a potential remote code execution rce issue if used for java deserialization of untrusted data depending on how the library is implemented within a product this issue may or not occur and authentication may be required note the vendor s position is that untrusted data is not an intended use case the product s behavior will not be changed because some users rely on deserialization of trusted data publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution release check this box to open an automated fix pr | 0 |
8,134 | 2,868,985,749 | IssuesEvent | 2015-06-05 22:23:10 | dart-lang/pub | https://api.github.com/repos/dart-lang/pub | closed | Building project results in dart packages not being in appropriate location | AsDesigned bug | _Originally opened as dart-lang/sdk#21127_
*This issue was originally filed by daniel.robinson.open...@gmail.com*
_____
1. Get latest from https://github.com/0xor1/purity_oauth2/tree/integration-test
2. run pub build
3. run build/test/integration/bin/host.dart
Expect the program to start running, but it fails as it cannot find the packages directory, if I manually copy the packages folder from build/test to build/test/integration/bin then it does work:
Unhandled exception:
Uncaught Error: FileSystemException: Cannot open file, path = 'D:\Projects\purity_oauth2\build\test\integration\bin\packages\purity\host.dart' (OS Error: The system cannot find the path specified.
Dart Editor version 1.6.0.release (STABLE)
Dart SDK version 1.6.0
Windows 8.1 x64 | 1.0 | Building project results in dart packages not being in appropriate location - _Originally opened as dart-lang/sdk#21127_
*This issue was originally filed by daniel.robinson.open...@gmail.com*
_____
1. Get latest from https://github.com/0xor1/purity_oauth2/tree/integration-test
2. run pub build
3. run build/test/integration/bin/host.dart
Expect the program to start running, but it fails as it cannot find the packages directory, if I manually copy the packages folder from build/test to build/test/integration/bin then it does work:
Unhandled exception:
Uncaught Error: FileSystemException: Cannot open file, path = 'D:\Projects\purity_oauth2\build\test\integration\bin\packages\purity\host.dart' (OS Error: The system cannot find the path specified.
Dart Editor version 1.6.0.release (STABLE)
Dart SDK version 1.6.0
Windows 8.1 x64 | non_priority | building project results in dart packages not being in appropriate location originally opened as dart lang sdk this issue was originally filed by daniel robinson open gmail com get latest from run pub build run build test integration bin host dart expect the program to start running but it fails as it cannot find the packages directory if i manually copy the packages folder from build test to build test integration bin then it does work unhandled exception uncaught error filesystemexception cannot open file path d projects purity build test integration bin packages purity host dart os error the system cannot find the path specified dart editor version release stable dart sdk version windows | 0 |
169,719 | 20,841,884,031 | IssuesEvent | 2022-03-21 01:45:43 | violasarah2000/satx2 | https://api.github.com/repos/violasarah2000/satx2 | opened | CVE-2022-24773 (Medium) detected in node-forge-0.9.0.tgz | security vulnerability | ## CVE-2022-24773 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz</a></p>
<p>Path to dependency file: /integration/angular_cli/package.json</p>
<p>Path to vulnerable library: /integration/angular_cli/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.901.12.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- selfsigned-1.10.7.tgz
- :x: **node-forge-0.9.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not properly check `DigestInfo` for a proper ASN.1 structure. This can lead to successful verification with signatures that contain invalid structures but a valid digest. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773>CVE-2022-24773</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: node-forge - 1.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-24773 (Medium) detected in node-forge-0.9.0.tgz - ## CVE-2022-24773 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.9.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.9.0.tgz</a></p>
<p>Path to dependency file: /integration/angular_cli/package.json</p>
<p>Path to vulnerable library: /integration/angular_cli/node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.901.12.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- selfsigned-1.10.7.tgz
- :x: **node-forge-0.9.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. Prior to version 1.3.0, RSA PKCS#1 v1.5 signature verification code does not properly check `DigestInfo` for a proper ASN.1 structure. This can lead to successful verification with signatures that contain invalid structures but a valid digest. The issue has been addressed in `node-forge` version 1.3.0. There are currently no known workarounds.
<p>Publish Date: 2022-03-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-24773>CVE-2022-24773</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-24773</a></p>
<p>Release Date: 2022-03-18</p>
<p>Fix Resolution: node-forge - 1.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node forge tgz cve medium severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file integration angular cli package json path to vulnerable library integration angular cli node modules node forge package json dependency hierarchy build angular tgz root library webpack dev server tgz selfsigned tgz x node forge tgz vulnerable library found in base branch master vulnerability details forge also called node forge is a native implementation of transport layer security in javascript prior to version rsa pkcs signature verification code does not properly check digestinfo for a proper asn structure this can lead to successful verification with signatures that contain invalid structures but a valid digest the issue has been addressed in node forge version there are currently no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge step up your open source security game with whitesource | 0 |
257,520 | 27,563,797,157 | IssuesEvent | 2023-03-08 01:07:11 | samqws-marketing/uber_RIBs | https://api.github.com/repos/samqws-marketing/uber_RIBs | opened | error_prone_core-2.3.3.jar: 3 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>error_prone_core-2.3.3.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /android/demos/memory-leaks/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (error_prone_core version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-3509](https://www.mend.io/vulnerability-database/CVE-2022-3509) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | 2.11.0 | ✅ |
| [CVE-2022-3171](https://www.mend.io/vulnerability-database/CVE-2022-3171) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | 2.11.0 | ✅ |
| [CVE-2021-22569](https://www.mend.io/vulnerability-database/CVE-2021-22569) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | protobuf-java-3.4.0.jar | Transitive | 2.11.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3509</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /android/tutorials/tutorial2/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- error_prone_core-2.3.3.jar (Root Library)
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue similar to CVE-2022-3171, but with textformat in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3509>CVE-2022-3509</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509</a></p>
<p>Release Date: 2022-12-12</p>
<p>Fix Resolution (com.google.protobuf:protobuf-java): 3.16.3</p>
<p>Direct dependency fix Resolution (com.google.errorprone:error_prone_core): 2.11.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3171</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /android/tutorials/tutorial2/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- error_prone_core-2.3.3.jar (Root Library)
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue with binary data in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3171>CVE-2022-3171</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4h5-3hr4-j3g2">https://github.com/advisories/GHSA-h4h5-3hr4-j3g2</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution (com.google.protobuf:protobuf-java): 3.16.3</p>
<p>Direct dependency fix Resolution (com.google.errorprone:error_prone_core): 2.11.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22569</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /android/tutorials/tutorial2/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- error_prone_core-2.3.3.jar (Root Library)
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in protobuf-java allowed the interleaving of com.google.protobuf.UnknownFieldSet fields in such a way that would be processed out of order. A small malicious payload can occupy the parser for several minutes by creating large numbers of short-lived objects that cause frequent, repeated pauses. We recommend upgrading libraries beyond the vulnerable versions.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22569>CVE-2021-22569</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wrvw-hg22-4m67">https://github.com/advisories/GHSA-wrvw-hg22-4m67</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution (com.google.protobuf:protobuf-java): 3.16.1</p>
<p>Direct dependency fix Resolution (com.google.errorprone:error_prone_core): 2.11.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | error_prone_core-2.3.3.jar: 3 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>error_prone_core-2.3.3.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /android/demos/memory-leaks/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (error_prone_core version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-3509](https://www.mend.io/vulnerability-database/CVE-2022-3509) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | 2.11.0 | ✅ |
| [CVE-2022-3171](https://www.mend.io/vulnerability-database/CVE-2022-3171) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | protobuf-java-3.4.0.jar | Transitive | 2.11.0 | ✅ |
| [CVE-2021-22569](https://www.mend.io/vulnerability-database/CVE-2021-22569) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | protobuf-java-3.4.0.jar | Transitive | 2.11.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3509</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /android/tutorials/tutorial2/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- error_prone_core-2.3.3.jar (Root Library)
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue similar to CVE-2022-3171, but with textformat in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-12-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3509>CVE-2022-3509</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3509</a></p>
<p>Release Date: 2022-12-12</p>
<p>Fix Resolution (com.google.protobuf:protobuf-java): 3.16.3</p>
<p>Direct dependency fix Resolution (com.google.errorprone:error_prone_core): 2.11.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-3171</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /android/tutorials/tutorial2/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- error_prone_core-2.3.3.jar (Root Library)
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A parsing issue with binary data in protobuf-java core and lite versions prior to 3.21.7, 3.20.3, 3.19.6 and 3.16.3 can lead to a denial of service attack. Inputs containing multiple instances of non-repeated embedded messages with repeated or unknown fields causes objects to be converted back-n-forth between mutable and immutable forms, resulting in potentially long garbage collection pauses. We recommend updating to the versions mentioned above.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-3171>CVE-2022-3171</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h4h5-3hr4-j3g2">https://github.com/advisories/GHSA-h4h5-3hr4-j3g2</a></p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution (com.google.protobuf:protobuf-java): 3.16.3</p>
<p>Direct dependency fix Resolution (com.google.errorprone:error_prone_core): 2.11.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-22569</summary>
### Vulnerable Library - <b>protobuf-java-3.4.0.jar</b></p>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding structured data in an
efficient yet extensible format.</p>
<p>Library home page: <a href="https://developers.google.com/protocol-buffers/">https://developers.google.com/protocol-buffers/</a></p>
<p>Path to dependency file: /android/tutorials/tutorial2/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.google.protobuf/protobuf-java/3.4.0/b32aba0cbe737a4ca953f71688725972e3ee927c/protobuf-java-3.4.0.jar</p>
<p>
Dependency Hierarchy:
- error_prone_core-2.3.3.jar (Root Library)
- :x: **protobuf-java-3.4.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/uber_RIBs/commit/e6102a9df66ccc997345788bbf970a06b9de359e">e6102a9df66ccc997345788bbf970a06b9de359e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An issue in protobuf-java allowed the interleaving of com.google.protobuf.UnknownFieldSet fields in such a way that would be processed out of order. A small malicious payload can occupy the parser for several minutes by creating large numbers of short-lived objects that cause frequent, repeated pauses. We recommend upgrading libraries beyond the vulnerable versions.
<p>Publish Date: 2022-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-22569>CVE-2021-22569</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-wrvw-hg22-4m67">https://github.com/advisories/GHSA-wrvw-hg22-4m67</a></p>
<p>Release Date: 2022-01-10</p>
<p>Fix Resolution (com.google.protobuf:protobuf-java): 3.16.1</p>
<p>Direct dependency fix Resolution (com.google.errorprone:error_prone_core): 2.11.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | error prone core jar vulnerabilities highest severity is vulnerable library error prone core jar path to dependency file android demos memory leaks build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in error prone core version remediation available high protobuf java jar transitive high protobuf java jar transitive medium protobuf java jar transitive details cve vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file android tutorials build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy error prone core jar root library x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details a parsing issue similar to cve but with textformat in protobuf java core and lite versions prior to and can lead to a denial of service attack inputs containing multiple instances of non repeated embedded messages with repeated or unknown fields causes objects to be converted back n forth between mutable and immutable forms resulting in potentially long garbage collection pauses we recommend updating to the versions mentioned above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java direct dependency fix resolution com google errorprone error prone core rescue worker helmet automatic remediation is available for this issue cve vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file android tutorials build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy error prone core jar root library x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details a parsing issue with binary data in protobuf java core and lite versions prior to and can lead to a denial of service attack inputs containing multiple instances of non repeated embedded messages with repeated or unknown fields causes objects to be converted back n forth between mutable and immutable forms resulting in potentially long garbage collection pauses we recommend updating to the versions mentioned above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java direct dependency fix resolution com google errorprone error prone core rescue worker helmet automatic remediation is available for this issue cve vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to dependency file android tutorials build gradle path to vulnerable library home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar home wss scanner gradle caches modules files com google protobuf protobuf java protobuf java jar dependency hierarchy error prone core jar root library x protobuf java jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue in protobuf java allowed the interleaving of com google protobuf unknownfieldset fields in such a way that would be processed out of order a small malicious payload can occupy the parser for several minutes by creating large numbers of short lived objects that cause frequent repeated pauses we recommend upgrading libraries beyond the vulnerable versions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google protobuf protobuf java direct dependency fix resolution com google errorprone error prone core rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
57,974 | 11,812,095,802 | IssuesEvent | 2020-03-19 19:28:15 | mozilla/foundation.mozilla.org | https://api.github.com/repos/mozilla/foundation.mozilla.org | closed | clean up <a href="#"> | code cleanup engineering | Under HTML5 rules, the `<a>` element is a purely navigational element, and adding `href="#"` tells the browser to navigatet to the top of the document, which is almost never the intended behaviour when `<a href="#">` is used, so let's find all instances of `<a href="#" ...>` and make sure we replace them with correctly semantically marked up code instead (which will almost always be `<button>`)
Marked as small effort, but this might turn out to be an invalid assessment. | 1.0 | clean up <a href="#"> - Under HTML5 rules, the `<a>` element is a purely navigational element, and adding `href="#"` tells the browser to navigatet to the top of the document, which is almost never the intended behaviour when `<a href="#">` is used, so let's find all instances of `<a href="#" ...>` and make sure we replace them with correctly semantically marked up code instead (which will almost always be `<button>`)
Marked as small effort, but this might turn out to be an invalid assessment. | non_priority | clean up under rules the element is a purely navigational element and adding href tells the browser to navigatet to the top of the document which is almost never the intended behaviour when is used so let s find all instances of and make sure we replace them with correctly semantically marked up code instead which will almost always be marked as small effort but this might turn out to be an invalid assessment | 0 |
121,809 | 26,035,858,044 | IssuesEvent | 2022-12-22 04:51:44 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | LSRA Reg Optional: Folding of operations using a tree temp | enhancement tenet-performance area-CodeGen-coreclr optimization | Say we have the following expr
a = (b + (c + (d+ (e+f))))
in LIR form
t0 = e+f
t1 = t0+d
t2 = t1+c
a = t2+b
Say it is profitable to not to allocate a reg to Use position of '+' in (e+f). That is tree temp t0 needs to be spilled to memory. Furthermore it is profitable to not to allocate a reg to both use and def positions of '+' in (t0+d) and (t1+c)
Since all of these tree temps are not live at the same time, using a single tree temp, we can generate the following
reg = e+f
spill reg to stack location given by spill tmp1
add [addr of tmp1], reg of d
add [add or tmp1], reg of c
mov a'reg, b's reg
add a'reg, [addr of tmp1]
To perform such an optimization, LSRA would need to annotate a tree node with a spill temp number that codegen is supposed to use for spill/reload purposes.
category:cq
theme:register-allocator
skill-level:expert
cost:medium | 1.0 | LSRA Reg Optional: Folding of operations using a tree temp - Say we have the following expr
a = (b + (c + (d+ (e+f))))
in LIR form
t0 = e+f
t1 = t0+d
t2 = t1+c
a = t2+b
Say it is profitable to not to allocate a reg to Use position of '+' in (e+f). That is tree temp t0 needs to be spilled to memory. Furthermore it is profitable to not to allocate a reg to both use and def positions of '+' in (t0+d) and (t1+c)
Since all of these tree temps are not live at the same time, using a single tree temp, we can generate the following
reg = e+f
spill reg to stack location given by spill tmp1
add [addr of tmp1], reg of d
add [add or tmp1], reg of c
mov a'reg, b's reg
add a'reg, [addr of tmp1]
To perform such an optimization, LSRA would need to annotate a tree node with a spill temp number that codegen is supposed to use for spill/reload purposes.
category:cq
theme:register-allocator
skill-level:expert
cost:medium | non_priority | lsra reg optional folding of operations using a tree temp say we have the following expr a b c d e f in lir form e f d c a b say it is profitable to not to allocate a reg to use position of in e f that is tree temp needs to be spilled to memory furthermore it is profitable to not to allocate a reg to both use and def positions of in d and c since all of these tree temps are not live at the same time using a single tree temp we can generate the following reg e f spill reg to stack location given by spill add reg of d add reg of c mov a reg b s reg add a reg to perform such an optimization lsra would need to annotate a tree node with a spill temp number that codegen is supposed to use for spill reload purposes category cq theme register allocator skill level expert cost medium | 0 |
60,715 | 14,909,094,152 | IssuesEvent | 2021-01-22 07:19:36 | timrockefeller/timrockefeller.github.io | https://api.github.com/repos/timrockefeller/timrockefeller.github.io | opened | SFM-notes | 外野 - wryyyyyyyyyY! | /2019/09/12/CG/3Drebuild/SFM-notes/ Gitalk | https://blog.iik.moe/2019/09/12/CG/3Drebuild/SFM-notes/
OverallStructure from motion (SFM) is a photogrammetric range imaging technique for estimating three-dimensional structures from two-dimensional image sequences that may be coupled with local motion s | 1.0 | SFM-notes | 外野 - wryyyyyyyyyY! - https://blog.iik.moe/2019/09/12/CG/3Drebuild/SFM-notes/
OverallStructure from motion (SFM) is a photogrammetric range imaging technique for estimating three-dimensional structures from two-dimensional image sequences that may be coupled with local motion s | non_priority | sfm notes 外野 wryyyyyyyyyy overallstructure from motion sfm is a photogrammetric range imaging technique for estimating three dimensional structures from two dimensional image sequences that may be coupled with local motion s | 0 |
132,836 | 18,766,063,137 | IssuesEvent | 2021-11-06 00:40:58 | Call-for-Code-for-Racial-Justice/TakeTwo | https://api.github.com/repos/Call-for-Code-for-Racial-Justice/TakeTwo | closed | Provide alternate/ recommendations that are not racially biased | stale design-thinking | ### Background on the problem the feature will solve/improved user experience
People who use TakeTwo might not only want to detect racially biased content but receive help on how to debias their content.
### Describe the solution you'd like
A solution that uses ML models, updated the API and updates the UI to provide the user with terms that are alternatives to the detected racially biased content
Related to : https://github.com/Call-for-Code-for-Racial-Justice/TakeTwo-DataScience/issues/20
### Tasks
- update ML models
- update API output
- update any UIDescription of the development tasks needed to complete this issue, including tests,
### Acceptance Criteria
Standards we believe this issue must reach to be considered complete and ready for a pull request. E.g precisely all the user should be able to do with this update, performance requirements, security requirements, etc as appropriate.
- As a user, if content I've input for analysis is found to be biased, I receive accurate alternatives that are unbiased to replace them with
| 1.0 | Provide alternate/ recommendations that are not racially biased - ### Background on the problem the feature will solve/improved user experience
People who use TakeTwo might not only want to detect racially biased content but receive help on how to debias their content.
### Describe the solution you'd like
A solution that uses ML models, updated the API and updates the UI to provide the user with terms that are alternatives to the detected racially biased content
Related to : https://github.com/Call-for-Code-for-Racial-Justice/TakeTwo-DataScience/issues/20
### Tasks
- update ML models
- update API output
- update any UIDescription of the development tasks needed to complete this issue, including tests,
### Acceptance Criteria
Standards we believe this issue must reach to be considered complete and ready for a pull request. E.g precisely all the user should be able to do with this update, performance requirements, security requirements, etc as appropriate.
- As a user, if content I've input for analysis is found to be biased, I receive accurate alternatives that are unbiased to replace them with
| non_priority | provide alternate recommendations that are not racially biased background on the problem the feature will solve improved user experience people who use taketwo might not only want to detect racially biased content but receive help on how to debias their content describe the solution you d like a solution that uses ml models updated the api and updates the ui to provide the user with terms that are alternatives to the detected racially biased content related to tasks update ml models update api output update any uidescription of the development tasks needed to complete this issue including tests acceptance criteria standards we believe this issue must reach to be considered complete and ready for a pull request e g precisely all the user should be able to do with this update performance requirements security requirements etc as appropriate as a user if content i ve input for analysis is found to be biased i receive accurate alternatives that are unbiased to replace them with | 0 |
1,707 | 3,897,006,716 | IssuesEvent | 2016-04-16 04:56:54 | ChagasCo/enw-angular | https://api.github.com/repos/ChagasCo/enw-angular | closed | test: have a go session form validation | test:services | ### Test For:
1. length of fields don't exceed database limits, asserts an error
2. submitting empty fields, asserts an error
3. submitting with filled fields, asserts success
4. submitting with filled fields expect for optional fields, asserts success
5. when submitted, check if success message displays (protractor) | 1.0 | test: have a go session form validation - ### Test For:
1. length of fields don't exceed database limits, asserts an error
2. submitting empty fields, asserts an error
3. submitting with filled fields, asserts success
4. submitting with filled fields expect for optional fields, asserts success
5. when submitted, check if success message displays (protractor) | non_priority | test have a go session form validation test for length of fields don t exceed database limits asserts an error submitting empty fields asserts an error submitting with filled fields asserts success submitting with filled fields expect for optional fields asserts success when submitted check if success message displays protractor | 0 |
62,668 | 14,656,558,300 | IssuesEvent | 2020-12-28 13:41:36 | fu1771695yongxie/Rocket.Chat | https://api.github.com/repos/fu1771695yongxie/Rocket.Chat | opened | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz | security vulnerability | ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: Rocket.Chat/package.json</p>
<p>Path to vulnerable library: Rocket.Chat/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- blockstack-19.3.0.tgz (Root Library)
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/Rocket.Chat/commit/60c2c8d370f1dbf301090daf20046b9ecd2435f4">60c2c8d370f1dbf301090daf20046b9ecd2435f4</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz - ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: Rocket.Chat/package.json</p>
<p>Path to vulnerable library: Rocket.Chat/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- blockstack-19.3.0.tgz (Root Library)
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/fu1771695yongxie/Rocket.Chat/commit/60c2c8d370f1dbf301090daf20046b9ecd2435f4">60c2c8d370f1dbf301090daf20046b9ecd2435f4</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file rocket chat package json path to vulnerable library rocket chat node modules elliptic package json dependency hierarchy blockstack tgz root library x elliptic tgz vulnerable library found in head commit a href found in base branch develop vulnerability details the function getnaf in elliptic library has information leakage this issue is mitigated in version publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
95,717 | 16,096,928,191 | IssuesEvent | 2021-04-27 02:09:12 | CoolBreeze613/adaptive-images | https://api.github.com/repos/CoolBreeze613/adaptive-images | opened | WS-2019-0063 (High) detected in js-yaml-2.0.5.tgz, js-yaml-3.4.6.tgz | security vulnerability | ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>js-yaml-2.0.5.tgz</b>, <b>js-yaml-3.4.6.tgz</b></p></summary>
<p>
<details><summary><b>js-yaml-2.0.5.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-2.0.5.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-2.0.5.tgz</a></p>
<p>Path to dependency file: /adaptive-images/package.json</p>
<p>Path to vulnerable library: adaptive-images/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **js-yaml-2.0.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>js-yaml-3.4.6.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.4.6.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.4.6.tgz</a></p>
<p>Path to dependency file: /adaptive-images/package.json</p>
<p>Path to vulnerable library: adaptive-images/node_modules/jscs/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jscs-2.8.0.tgz (Root Library)
- jscs-2.11.0.tgz
- :x: **js-yaml-3.4.6.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Js-yaml prior to 3.13.1 are vulnerable to Code Injection. The load() function may execute arbitrary code injected through a malicious YAML file.
<p>Publish Date: 2019-04-05
<p>URL: <a href=https://github.com/nodeca/js-yaml/pull/480>WS-2019-0063</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/813">https://www.npmjs.com/advisories/813</a></p>
<p>Release Date: 2019-04-05</p>
<p>Fix Resolution: js-yaml - 3.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0063 (High) detected in js-yaml-2.0.5.tgz, js-yaml-3.4.6.tgz - ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>js-yaml-2.0.5.tgz</b>, <b>js-yaml-3.4.6.tgz</b></p></summary>
<p>
<details><summary><b>js-yaml-2.0.5.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-2.0.5.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-2.0.5.tgz</a></p>
<p>Path to dependency file: /adaptive-images/package.json</p>
<p>Path to vulnerable library: adaptive-images/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **js-yaml-2.0.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>js-yaml-3.4.6.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registry.npmjs.org/js-yaml/-/js-yaml-3.4.6.tgz">https://registry.npmjs.org/js-yaml/-/js-yaml-3.4.6.tgz</a></p>
<p>Path to dependency file: /adaptive-images/package.json</p>
<p>Path to vulnerable library: adaptive-images/node_modules/jscs/node_modules/js-yaml/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jscs-2.8.0.tgz (Root Library)
- jscs-2.11.0.tgz
- :x: **js-yaml-3.4.6.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Js-yaml prior to 3.13.1 are vulnerable to Code Injection. The load() function may execute arbitrary code injected through a malicious YAML file.
<p>Publish Date: 2019-04-05
<p>URL: <a href=https://github.com/nodeca/js-yaml/pull/480>WS-2019-0063</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/813">https://www.npmjs.com/advisories/813</a></p>
<p>Release Date: 2019-04-05</p>
<p>Fix Resolution: js-yaml - 3.13.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in js yaml tgz js yaml tgz ws high severity vulnerability vulnerable libraries js yaml tgz js yaml tgz js yaml tgz yaml parser and serializer library home page a href path to dependency file adaptive images package json path to vulnerable library adaptive images node modules js yaml package json dependency hierarchy grunt tgz root library x js yaml tgz vulnerable library js yaml tgz yaml parser and serializer library home page a href path to dependency file adaptive images package json path to vulnerable library adaptive images node modules jscs node modules js yaml package json dependency hierarchy grunt jscs tgz root library jscs tgz x js yaml tgz vulnerable library vulnerability details js yaml prior to are vulnerable to code injection the load function may execute arbitrary code injected through a malicious yaml file publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution js yaml step up your open source security game with whitesource | 0 |
70,310 | 23,112,217,952 | IssuesEvent | 2022-07-27 13:54:37 | vector-im/element-ios | https://api.github.com/repos/vector-im/element-ios | opened | Dark or black themes: Can't automatically change status bar color. | T-Defect | ### Steps to reproduce
1. Set iOS as light theme, Element as dark or dark theme;
2. Go back to any position in the Element.
### Outcome
#### What did you expect?
Even if the iOS theme is light and the Element is dark or black, the status bar should respond appropriately to the current interface color.
#### What happened instead?
As shown, the status bar is still black when the Element has a dark or black theme.

### Your phone model
iPhone 6s
### Operating system version
iOS 14.0.1
### Application version
Element 1.8.24
### Homeserver
Synapse 1.63.0
### Will you send logs?
No | 1.0 | Dark or black themes: Can't automatically change status bar color. - ### Steps to reproduce
1. Set iOS as light theme, Element as dark or dark theme;
2. Go back to any position in the Element.
### Outcome
#### What did you expect?
Even if the iOS theme is light and the Element is dark or black, the status bar should respond appropriately to the current interface color.
#### What happened instead?
As shown, the status bar is still black when the Element has a dark or black theme.

### Your phone model
iPhone 6s
### Operating system version
iOS 14.0.1
### Application version
Element 1.8.24
### Homeserver
Synapse 1.63.0
### Will you send logs?
No | non_priority | dark or black themes can t automatically change status bar color steps to reproduce set ios as light theme element as dark or dark theme go back to any position in the element outcome what did you expect even if the ios theme is light and the element is dark or black the status bar should respond appropriately to the current interface color what happened instead as shown the status bar is still black when the element has a dark or black theme your phone model iphone operating system version ios application version element homeserver synapse will you send logs no | 0 |
66,683 | 8,958,392,421 | IssuesEvent | 2019-01-27 13:58:02 | ZetaGlest/zetaglest-source | https://api.github.com/repos/ZetaGlest/zetaglest-source | closed | Documenting Code | announcement documentation help wanted wip | Documentation is currently very sparse in the zetaglest code. If you're working on some code, please try to comment undocumented code that you have learnt about. It will be greatly appreciated!
Thanks! | 1.0 | Documenting Code - Documentation is currently very sparse in the zetaglest code. If you're working on some code, please try to comment undocumented code that you have learnt about. It will be greatly appreciated!
Thanks! | non_priority | documenting code documentation is currently very sparse in the zetaglest code if you re working on some code please try to comment undocumented code that you have learnt about it will be greatly appreciated thanks | 0 |
88,558 | 25,462,160,377 | IssuesEvent | 2022-11-24 20:58:44 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | Build 87 for 8.5 with status FAILURE | automation ci-reported Team:Elastic-Agent-Data-Plane build-failures |
## :broken_heart: Tests Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//pipeline) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//tests) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//changes) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//artifacts) [](http://beats_null.docs-preview.app.elstc.co/diff) [](https://ci-stats.elastic.co/app/apm/services/beats-ci/transactions/view?rangeFrom=2022-11-22T17:37:33.591Z&rangeTo=2022-11-22T17:57:33.591Z&transactionName=BUILD+Beats%2Fbeats%2F8.5&transactionType=job&latencyAggregationType=avg&traceId=35e4f3ba64a0f60d8f4d952f0b3aef63&transactionId=5d6e6dc970ac9433)
<!-- BUILD SUMMARY-->
<details><summary>Expand to view the summary</summary>
<p>
#### Build stats
* Start Time: 2022-11-22T17:47:33.591+0000
* Duration: 106 min 45 sec
#### Test stats :test_tube:
| Test | Results |
| ------------ | :-----------------------------: |
| Failed | 2 |
| Passed | 25572 |
| Skipped | 2267 |
| Total | 27841 |
</p>
</details>
<!-- TEST RESULTS IF ANY-->
### Test errors [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//tests)
<details><summary>Expand to view the tests failures</summary><p>
##### `Build&Test / metricbeat-goIntegTest / TestFetch – github.com/elastic/beats/v7/metricbeat/module/nginx/stubstatus`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestFetch
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_memcached_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 27a5c62ad37b
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (914 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:33: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_memcached_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 84a8b9eb28a6
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (918 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:33: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_memcached_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 8f08f7445797
Ign http://httpredir.debian.org jessie InRelease
Get:1 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:2 http://security.debian.org jessie/updates InRelease [44.9 kB]
Get:3 http://httpredir.debian.org jessie Release [77.3 kB]
Get:4 http://nginx.org jessie InRelease [2865 B]
Ign http://security.debian.org jessie/updates InRelease
Ign http://httpredir.debian.org jessie Release
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Get:6 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Get:7 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Fetched 10.3 MB in 10s (950 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:33: failed to start service "nginx: exit status 1
stubstatus_integration_test.go:33: getting host for nginx: no container running for service
--- FAIL: TestFetch (122.65s)
```
</p></details>
</ul>
##### `Build&Test / metricbeat-goIntegTest / TestData – github.com/elastic/beats/v7/metricbeat/module/nginx/stubstatus`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestData
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 60f1f0fd4d07
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 10s (943 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
�[91mE: There are problems and -y was used without --force-yes
�[0m0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
Service "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:50: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 54f3014974dc
Ign http://httpredir.debian.org jessie InRelease
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Get:2 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:3 http://nginx.org jessie InRelease [2865 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (918 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:50: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 0e1a34f34d48
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (926 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:50: failed to start service "nginx: exit status 1
stubstatus_integration_test.go:50: getting host for nginx: no container running for service
--- FAIL: TestData (120.87s)
```
</p></details>
</ul>
</p></details>
<!-- STEPS ERRORS IF ANY -->
### Steps errors [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//pipeline)
<details><summary>Expand to view the steps failures</summary>
<p>
##### `metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 32 min 45 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/14325/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 22 min 27 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/20716/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 22 min 29 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/20819/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `Error signal`
<ul>
<li>Took 0 min 0 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/20835/log/?start=0">here</a></li>
<li>Description: <code>Error "hudson.AbortException: script returned exit code 1"</code></l1>
</ul>
</p>
</details>
| 1.0 | Build 87 for 8.5 with status FAILURE -
## :broken_heart: Tests Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//pipeline) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//tests) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//changes) [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//artifacts) [](http://beats_null.docs-preview.app.elstc.co/diff) [](https://ci-stats.elastic.co/app/apm/services/beats-ci/transactions/view?rangeFrom=2022-11-22T17:37:33.591Z&rangeTo=2022-11-22T17:57:33.591Z&transactionName=BUILD+Beats%2Fbeats%2F8.5&transactionType=job&latencyAggregationType=avg&traceId=35e4f3ba64a0f60d8f4d952f0b3aef63&transactionId=5d6e6dc970ac9433)
<!-- BUILD SUMMARY-->
<details><summary>Expand to view the summary</summary>
<p>
#### Build stats
* Start Time: 2022-11-22T17:47:33.591+0000
* Duration: 106 min 45 sec
#### Test stats :test_tube:
| Test | Results |
| ------------ | :-----------------------------: |
| Failed | 2 |
| Passed | 25572 |
| Skipped | 2267 |
| Total | 27841 |
</p>
</details>
<!-- TEST RESULTS IF ANY-->
### Test errors [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//tests)
<details><summary>Expand to view the tests failures</summary><p>
##### `Build&Test / metricbeat-goIntegTest / TestFetch – github.com/elastic/beats/v7/metricbeat/module/nginx/stubstatus`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestFetch
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_memcached_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 27a5c62ad37b
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (914 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:33: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_memcached_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 84a8b9eb28a6
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (918 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:33: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_memcached_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 8f08f7445797
Ign http://httpredir.debian.org jessie InRelease
Get:1 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:2 http://security.debian.org jessie/updates InRelease [44.9 kB]
Get:3 http://httpredir.debian.org jessie Release [77.3 kB]
Get:4 http://nginx.org jessie InRelease [2865 B]
Ign http://security.debian.org jessie/updates InRelease
Ign http://httpredir.debian.org jessie Release
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Get:6 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Get:7 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Fetched 10.3 MB in 10s (950 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:33: failed to start service "nginx: exit status 1
stubstatus_integration_test.go:33: getting host for nginx: no container running for service
--- FAIL: TestFetch (122.65s)
```
</p></details>
</ul>
##### `Build&Test / metricbeat-goIntegTest / TestData – github.com/elastic/beats/v7/metricbeat/module/nginx/stubstatus`
<ul>
<details><summary>Expand to view the error details</summary><p>
```
Failed
```
</p></details>
<details><summary>Expand to view the stacktrace</summary><p>
```
=== RUN TestData
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 60f1f0fd4d07
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 10s (943 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
�[91mE: There are problems and -y was used without --force-yes
�[0m0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
Service "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:50: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 54f3014974dc
Ign http://httpredir.debian.org jessie InRelease
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Get:2 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:3 http://nginx.org jessie InRelease [2865 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (918 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:50: failed to start service "nginx: exit status 1
Found orphan containers (metricbeat_8_5_3_8ed8d49939-snapshot_nats-routes_1, metricbeat_8_5_3_8ed8d49939-snapshot_nats_1, metricbeat_8_5_3_8ed8d49939-snapshot_mysql_1, metricbeat_8_5_3_8ed8d49939-snapshot_munin_1, metricbeat_8_5_3_8ed8d49939-snapshot_mongodb_1, metricbeat_8_5_3_8ed8d49939-snapshot_logstash_1, metricbeat_8_5_3_8ed8d49939-snapshot_kafka_1) for this project. If you removed or renamed this service in your compose file, you can run this command with the --remove-orphans flag to clean it up.
Building nginx
Step 1/6 : ARG NGINX_VERSION
Step 2/6 : FROM nginx:${NGINX_VERSION}
---> c8c29d842c09
Step 3/6 : RUN sed -i "/jessie-updates/d" /etc/apt/sources.list
---> Using cache
---> 2f66c4dd5344
Step 4/6 : RUN apt-get update && apt-get install -y curl
---> Running in 0e1a34f34d48
Get:1 http://security.debian.org jessie/updates InRelease [44.9 kB]
Ign http://httpredir.debian.org jessie InRelease
Get:2 http://nginx.org jessie InRelease [2865 B]
Get:3 http://httpredir.debian.org jessie Release.gpg [1652 B]
Get:4 http://httpredir.debian.org jessie Release [77.3 kB]
Ign http://security.debian.org jessie/updates InRelease
Get:5 http://security.debian.org jessie/updates/main amd64 Packages [992 kB]
Ign http://nginx.org jessie InRelease
Ign http://httpredir.debian.org jessie Release
Get:6 http://nginx.org jessie/nginx amd64 Packages [62.1 kB]
Get:7 http://httpredir.debian.org jessie/main amd64 Packages [9098 kB]
Fetched 10.3 MB in 11s (926 kB/s)
Reading package lists...
�[91mW: GPG error: http://security.debian.org jessie/updates InRelease: The following signatures were invalid: KEYEXPIRED 1668892417 The following signatures couldn"t be verified because the public key is not available: NO_PUBKEY AA8E81B4331F7F50
W: GPG error: http://nginx.org jessie InRelease: The following signatures were invalid: KEYEXPIRED 1471427554
W: GPG error: http://httpredir.debian.org jessie Release: The following signatures were invalid: KEYEXPIRED 1668891673
�[0mReading package lists...
Building dependency tree...
Reading state information...
The following extra packages will be installed:
krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28 libgssapi-krb5-2
libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3 libkrb5support0
libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2 libsasl2-modules
libsasl2-modules-db libssh2-1 libtasn1-6
Suggested packages:
gnutls-bin krb5-doc krb5-user libsasl2-modules-otp libsasl2-modules-ldap
libsasl2-modules-sql libsasl2-modules-gssapi-mit
libsasl2-modules-gssapi-heimdal
The following NEW packages will be installed:
curl krb5-locales libcurl3 libffi6 libgmp10 libgnutls-deb0-28
libgssapi-krb5-2 libhogweed2 libidn11 libk5crypto3 libkeyutils1 libkrb5-3
libkrb5support0 libldap-2.4-2 libnettle4 libp11-kit0 librtmp1 libsasl2-2
libsasl2-modules libsasl2-modules-db libssh2-1 libtasn1-6
0 upgraded, 22 newly installed, 0 to remove and 77 not upgraded.
Need to get 6027 kB of archives.
After this operation, 11.4 MB of additional disk space will be used.
WARNING: The following packages cannot be authenticated!
libgmp10 libnettle4 libhogweed2 libffi6 libp11-kit0 libtasn1-6
libgnutls-deb0-28 libkeyutils1 libkrb5support0 libk5crypto3 libkrb5-3
libgssapi-krb5-2 libidn11 libsasl2-modules-db libsasl2-2 libldap-2.4-2
librtmp1 libssh2-1 libcurl3 krb5-locales curl libsasl2-modules
�[91mE: There are problems and -y was used without --force-yes
�[0mService "nginx" failed to build: The command "/bin/sh -c apt-get update && apt-get install -y curl" returned a non-zero code: 100
stubstatus_integration_test.go:50: failed to start service "nginx: exit status 1
stubstatus_integration_test.go:50: getting host for nginx: no container running for service
--- FAIL: TestData (120.87s)
```
</p></details>
</ul>
</p></details>
<!-- STEPS ERRORS IF ANY -->
### Steps errors [](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.5/detail/8.5/87//pipeline)
<details><summary>Expand to view the steps failures</summary>
<p>
##### `metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 32 min 45 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/14325/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 22 min 27 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/20716/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `metricbeat-goIntegTest - mage goIntegTest`
<ul>
<li>Took 22 min 29 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/20819/log/?start=0">here</a></li>
<li>Description: <code>mage goIntegTest</code></l1>
</ul>
##### `Error signal`
<ul>
<li>Took 0 min 0 sec . View more details <a href="https://beats-ci.elastic.co//blue/rest/organizations/jenkins/pipelines/Beats/pipelines/beats/pipelines/8.5/runs/87/steps/20835/log/?start=0">here</a></li>
<li>Description: <code>Error "hudson.AbortException: script returned exit code 1"</code></l1>
</ul>
</p>
</details>
| non_priority | build for with status failure broken heart tests failed the below badges are clickable and redirect to their specific view in the ci or docs expand to view the summary build stats start time duration min sec test stats test tube test results failed passed skipped total test errors expand to view the tests failures build test metricbeat gointegtest testfetch – github com elastic beats metricbeat module nginx stubstatus expand to view the error details failed expand to view the stacktrace run testfetch found orphan containers metricbeat snapshot nats routes metricbeat snapshot nats metricbeat snapshot mysql metricbeat snapshot munin metricbeat snapshot mongodb metricbeat snapshot memcached metricbeat snapshot logstash metricbeat snapshot kafka for this project if you removed or renamed this service in your compose file you can run this command with the remove orphans flag to clean it up building nginx step arg nginx version step from nginx nginx version step run sed i jessie updates d etc apt sources list using cache step run apt get update apt get install y curl running in get jessie updates inrelease ign jessie inrelease get jessie inrelease get jessie release gpg get jessie release ign jessie updates inrelease get jessie updates main packages ign jessie inrelease ign jessie release get jessie nginx packages get jessie main packages fetched mb in kb s reading package lists � gpg error jessie updates inrelease the following signatures were invalid keyexpired the following signatures couldn t be verified because the public key is not available no pubkey w gpg error jessie inrelease the following signatures were invalid keyexpired w gpg error jessie release the following signatures were invalid keyexpired � package lists building dependency tree reading state information the following extra packages will be installed locales libgnutls libgssapi libldap modules modules db suggested packages gnutls bin doc user modules otp modules ldap modules sql modules gssapi mit modules gssapi heimdal the following new packages will be installed curl locales libgnutls libgssapi libldap modules modules db upgraded newly installed to remove and not upgraded need to get kb of archives after this operation mb of additional disk space will be used warning the following packages cannot be authenticated libgnutls libgssapi modules db libldap locales curl modules � there are problems and y was used without force yes � nginx failed to build the command bin sh c apt get update apt get install y curl returned a non zero code stubstatus integration test go failed to start service nginx exit status found orphan containers metricbeat snapshot nats routes metricbeat snapshot nats metricbeat snapshot mysql metricbeat snapshot munin metricbeat snapshot mongodb metricbeat snapshot memcached metricbeat snapshot logstash metricbeat snapshot kafka for this project if you removed or renamed this service in your compose file you can run this command with the remove orphans flag to clean it up building nginx step arg nginx version step from nginx nginx version step run sed i jessie updates d etc apt sources list using cache step run apt get update apt get install y curl running in get jessie updates inrelease ign jessie inrelease get jessie inrelease get jessie release gpg get jessie release ign jessie updates inrelease get jessie updates main packages ign jessie inrelease ign jessie release get jessie nginx packages get jessie main packages fetched mb in kb s reading package lists � gpg error jessie updates inrelease the following signatures were invalid keyexpired the following signatures couldn t be verified because the public key is not available no pubkey w gpg error jessie inrelease the following signatures were invalid keyexpired w gpg error jessie release the following signatures were invalid keyexpired � package lists building dependency tree reading state information the following extra packages will be installed locales libgnutls libgssapi libldap modules modules db suggested packages gnutls bin doc user modules otp modules ldap modules sql modules gssapi mit modules gssapi heimdal the following new packages will be installed curl locales libgnutls libgssapi libldap modules modules db upgraded newly installed to remove and not upgraded need to get kb of archives after this operation mb of additional disk space will be used warning the following packages cannot be authenticated libgnutls libgssapi modules db libldap locales curl modules � there are problems and y was used without force yes � nginx failed to build the command bin sh c apt get update apt get install y curl returned a non zero code stubstatus integration test go failed to start service nginx exit status found orphan containers metricbeat snapshot nats routes metricbeat snapshot nats metricbeat snapshot mysql metricbeat snapshot munin metricbeat snapshot mongodb metricbeat snapshot memcached metricbeat snapshot logstash metricbeat snapshot kafka for this project if you removed or renamed this service in your compose file you can run this command with the remove orphans flag to clean it up building nginx step arg nginx version step from nginx nginx version step run sed i jessie updates d etc apt sources list using cache step run apt get update apt get install y curl running in ign jessie inrelease get jessie release gpg get jessie updates inrelease get jessie release get jessie inrelease ign jessie updates inrelease ign jessie release get jessie updates main packages ign jessie inrelease get jessie main packages get jessie nginx packages fetched mb in kb s reading package lists � gpg error jessie updates inrelease the following signatures were invalid keyexpired the following signatures couldn t be verified because the public key is not available no pubkey w gpg error jessie release the following signatures were invalid keyexpired w gpg error jessie inrelease the following signatures were invalid keyexpired � package lists building dependency tree reading state information the following extra packages will be installed locales libgnutls libgssapi libldap modules modules db suggested packages gnutls bin doc user modules otp modules ldap modules sql modules gssapi mit modules gssapi heimdal the following new packages will be installed curl locales libgnutls libgssapi libldap modules modules db upgraded newly installed to remove and not upgraded need to get kb of archives after this operation mb of additional disk space will be used warning the following packages cannot be authenticated libgnutls libgssapi modules db libldap locales curl modules � there are problems and y was used without force yes � nginx failed to build the command bin sh c apt get update apt get install y curl returned a non zero code stubstatus integration test go failed to start service nginx exit status stubstatus integration test go getting host for nginx no container running for service fail testfetch build test metricbeat gointegtest testdata – github com elastic beats metricbeat module nginx stubstatus expand to view the error details failed expand to view the stacktrace run testdata found orphan containers metricbeat snapshot nats routes metricbeat snapshot nats metricbeat snapshot mysql metricbeat snapshot munin metricbeat snapshot mongodb metricbeat snapshot logstash metricbeat snapshot kafka for this project if you removed or renamed this service in your compose file you can run this command with the remove orphans flag to clean it up building nginx step arg nginx version step from nginx nginx version step run sed i jessie updates d etc apt sources list using cache step run apt get update apt get install y curl running in get jessie updates inrelease ign jessie inrelease get jessie inrelease get jessie release gpg get jessie release ign jessie updates inrelease get jessie updates main packages ign jessie inrelease ign jessie release get jessie nginx packages get jessie main packages fetched mb in kb s reading package lists � gpg error jessie updates inrelease the following signatures were invalid keyexpired the following signatures couldn t be verified because the public key is not available no pubkey w gpg error jessie inrelease the following signatures were invalid keyexpired w gpg error jessie release the following signatures were invalid keyexpired � package lists building dependency tree reading state information the following extra packages will be installed locales libgnutls libgssapi libldap modules modules db suggested packages gnutls bin doc user modules otp modules ldap modules sql modules gssapi mit modules gssapi heimdal the following new packages will be installed curl locales libgnutls libgssapi libldap modules modules db � there are problems and y was used without force yes � upgraded newly installed to remove and not upgraded need to get kb of archives after this operation mb of additional disk space will be used warning the following packages cannot be authenticated libgnutls libgssapi modules db libldap locales curl modules service nginx failed to build the command bin sh c apt get update apt get install y curl returned a non zero code stubstatus integration test go failed to start service nginx exit status found orphan containers metricbeat snapshot nats routes metricbeat snapshot nats metricbeat snapshot mysql metricbeat snapshot munin metricbeat snapshot mongodb metricbeat snapshot logstash metricbeat snapshot kafka for this project if you removed or renamed this service in your compose file you can run this command with the remove orphans flag to clean it up building nginx step arg nginx version step from nginx nginx version step run sed i jessie updates d etc apt sources list using cache step run apt get update apt get install y curl running in ign jessie inrelease get jessie updates inrelease get jessie release gpg get jessie inrelease get jessie release ign jessie updates inrelease get jessie updates main packages ign jessie inrelease ign jessie release get jessie nginx packages get jessie main packages fetched mb in kb s reading package lists � gpg error jessie updates inrelease the following signatures were invalid keyexpired the following signatures couldn t be verified because the public key is not available no pubkey w gpg error jessie inrelease the following signatures were invalid keyexpired w gpg error jessie release the following signatures were invalid keyexpired � package lists building dependency tree reading state information the following extra packages will be installed locales libgnutls libgssapi libldap modules modules db suggested packages gnutls bin doc user modules otp modules ldap modules sql modules gssapi mit modules gssapi heimdal the following new packages will be installed curl locales libgnutls libgssapi libldap modules modules db upgraded newly installed to remove and not upgraded need to get kb of archives after this operation mb of additional disk space will be used warning the following packages cannot be authenticated libgnutls libgssapi modules db libldap locales curl modules � there are problems and y was used without force yes � nginx failed to build the command bin sh c apt get update apt get install y curl returned a non zero code stubstatus integration test go failed to start service nginx exit status found orphan containers metricbeat snapshot nats routes metricbeat snapshot nats metricbeat snapshot mysql metricbeat snapshot munin metricbeat snapshot mongodb metricbeat snapshot logstash metricbeat snapshot kafka for this project if you removed or renamed this service in your compose file you can run this command with the remove orphans flag to clean it up building nginx step arg nginx version step from nginx nginx version step run sed i jessie updates d etc apt sources list using cache step run apt get update apt get install y curl running in get jessie updates inrelease ign jessie inrelease get jessie inrelease get jessie release gpg get jessie release ign jessie updates inrelease get jessie updates main packages ign jessie inrelease ign jessie release get jessie nginx packages get jessie main packages fetched mb in kb s reading package lists � gpg error jessie updates inrelease the following signatures were invalid keyexpired the following signatures couldn t be verified because the public key is not available no pubkey w gpg error jessie inrelease the following signatures were invalid keyexpired w gpg error jessie release the following signatures were invalid keyexpired � package lists building dependency tree reading state information the following extra packages will be installed locales libgnutls libgssapi libldap modules modules db suggested packages gnutls bin doc user modules otp modules ldap modules sql modules gssapi mit modules gssapi heimdal the following new packages will be installed curl locales libgnutls libgssapi libldap modules modules db upgraded newly installed to remove and not upgraded need to get kb of archives after this operation mb of additional disk space will be used warning the following packages cannot be authenticated libgnutls libgssapi modules db libldap locales curl modules � there are problems and y was used without force yes � nginx failed to build the command bin sh c apt get update apt get install y curl returned a non zero code stubstatus integration test go failed to start service nginx exit status stubstatus integration test go getting host for nginx no container running for service fail testdata steps errors expand to view the steps failures metricbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest metricbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest metricbeat gointegtest mage gointegtest took min sec view more details a href description mage gointegtest error signal took min sec view more details a href description error hudson abortexception script returned exit code | 0 |
220,693 | 24,565,381,258 | IssuesEvent | 2022-10-13 02:10:17 | dgee2/dgee2.github.io | https://api.github.com/repos/dgee2/dgee2.github.io | closed | CVE-2022-0235 (Medium) detected in node-fetch-2.6.1.tgz - autoclosed | security vulnerability | ## CVE-2022-0235 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-fetch-2.6.1.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-3.2.1.tgz (Root Library)
- gatsby-cli-3.2.0.tgz
- :x: **node-fetch-2.6.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution (node-fetch): 2.6.7</p>
<p>Direct dependency fix Resolution (gatsby): 4.17.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0235 (Medium) detected in node-fetch-2.6.1.tgz - autoclosed - ## CVE-2022-0235 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-fetch-2.6.1.tgz</b></p></summary>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-3.2.1.tgz (Root Library)
- gatsby-cli-3.2.0.tgz
- :x: **node-fetch-2.6.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution (node-fetch): 2.6.7</p>
<p>Direct dependency fix Resolution (gatsby): 4.17.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node fetch tgz autoclosed cve medium severity vulnerability vulnerable library node fetch tgz a light weight module that brings window fetch to node js library home page a href path to dependency file package json path to vulnerable library node modules node fetch package json dependency hierarchy gatsby tgz root library gatsby cli tgz x node fetch tgz vulnerable library found in base branch master vulnerability details node fetch is vulnerable to exposure of sensitive information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node fetch direct dependency fix resolution gatsby step up your open source security game with mend | 0 |
70,361 | 15,085,547,328 | IssuesEvent | 2021-02-05 18:51:06 | mthbernardes/shaggy-rogers | https://api.github.com/repos/mthbernardes/shaggy-rogers | reopened | CVE-2019-16335 (High) detected in jackson-databind-2.9.6.jar | security vulnerability | ## CVE-2019-16335 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: shaggy-rogers/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- pantomime-2.11.0.jar (Root Library)
- tika-parsers-1.19.1.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mthbernardes/shaggy-rogers/commit/f72a5cb259e01c0ac208ba3a95eee5232c30fe6c">f72a5cb259e01c0ac208ba3a95eee5232c30fe6c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-16335 (High) detected in jackson-databind-2.9.6.jar - ## CVE-2019-16335 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: shaggy-rogers/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- pantomime-2.11.0.jar (Root Library)
- tika-parsers-1.19.1.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mthbernardes/shaggy-rogers/commit/f72a5cb259e01c0ac208ba3a95eee5232c30fe6c">f72a5cb259e01c0ac208ba3a95eee5232c30fe6c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x">https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file shaggy rogers pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy pantomime jar root library tika parsers jar x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
258,386 | 27,563,936,898 | IssuesEvent | 2023-03-08 01:17:13 | habusha/CIOIL | https://api.github.com/repos/habusha/CIOIL | closed | CVE-2022-41915 (Medium) detected in netty-codec-http-4.1.29.Final.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2022-41915 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.29.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /infra_github/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty-codec-http/4.1.29.Final/netty-codec-http-4.1.29.Final.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-netflix-eureka-client-2.0.1.RELEASE.jar (Root Library)
- spring-cloud-starter-netflix-ribbon-2.0.1.RELEASE.jar
- ribbon-2.2.5.jar
- rxnetty-0.4.9.jar
- :x: **netty-codec-http-4.1.29.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/habusha/CIOIL/commit/a676271c34e978872269bbce91d5a1e5211b6419">a676271c34e978872269bbce91d5a1e5211b6419</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty project is an event-driven asynchronous network application framework. Starting in version 4.1.83.Final and prior to 4.1.86.Final, when calling `DefaultHttpHeadesr.set` with an _iterator_ of values, header value validation was not performed, allowing malicious header values in the iterator to perform HTTP Response Splitting. This issue has been patched in version 4.1.86.Final. Integrators can work around the issue by changing the `DefaultHttpHeaders.set(CharSequence, Iterator<?>)` call, into a `remove()` call, and call `add()` in a loop over the iterator of values.
<p>Publish Date: 2022-12-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41915>CVE-2022-41915</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-12-13</p>
<p>Fix Resolution (io.netty:netty-codec-http): 4.1.86.Final</p>
<p>Direct dependency fix Resolution (org.springframework.cloud:spring-cloud-starter-netflix-eureka-client): 2.0.2.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-41915 (Medium) detected in netty-codec-http-4.1.29.Final.jar - autoclosed - ## CVE-2022-41915 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.29.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /infra_github/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty-codec-http/4.1.29.Final/netty-codec-http-4.1.29.Final.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-netflix-eureka-client-2.0.1.RELEASE.jar (Root Library)
- spring-cloud-starter-netflix-ribbon-2.0.1.RELEASE.jar
- ribbon-2.2.5.jar
- rxnetty-0.4.9.jar
- :x: **netty-codec-http-4.1.29.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/habusha/CIOIL/commit/a676271c34e978872269bbce91d5a1e5211b6419">a676271c34e978872269bbce91d5a1e5211b6419</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty project is an event-driven asynchronous network application framework. Starting in version 4.1.83.Final and prior to 4.1.86.Final, when calling `DefaultHttpHeadesr.set` with an _iterator_ of values, header value validation was not performed, allowing malicious header values in the iterator to perform HTTP Response Splitting. This issue has been patched in version 4.1.86.Final. Integrators can work around the issue by changing the `DefaultHttpHeaders.set(CharSequence, Iterator<?>)` call, into a `remove()` call, and call `add()` in a loop over the iterator of values.
<p>Publish Date: 2022-12-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41915>CVE-2022-41915</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-12-13</p>
<p>Fix Resolution (io.netty:netty-codec-http): 4.1.86.Final</p>
<p>Direct dependency fix Resolution (org.springframework.cloud:spring-cloud-starter-netflix-eureka-client): 2.0.2.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in netty codec http final jar autoclosed cve medium severity vulnerability vulnerable library netty codec http final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients library home page a href path to dependency file infra github pom xml path to vulnerable library home wss scanner repository io netty netty codec http final netty codec http final jar dependency hierarchy spring cloud starter netflix eureka client release jar root library spring cloud starter netflix ribbon release jar ribbon jar rxnetty jar x netty codec http final jar vulnerable library found in head commit a href found in base branch master vulnerability details netty project is an event driven asynchronous network application framework starting in version final and prior to final when calling defaulthttpheadesr set with an iterator of values header value validation was not performed allowing malicious header values in the iterator to perform http response splitting this issue has been patched in version final integrators can work around the issue by changing the defaulthttpheaders set charsequence iterator call into a remove call and call add in a loop over the iterator of values publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution io netty netty codec http final direct dependency fix resolution org springframework cloud spring cloud starter netflix eureka client release step up your open source security game with mend | 0 |
247,462 | 20,980,838,769 | IssuesEvent | 2022-03-28 19:45:36 | geneontology/minerva | https://api.github.com/repos/geneontology/minerva | closed | include git revision and tbox ontology version in status service output | enhancement ready for testing | We frequently have issues that would be clarified by knowing what version of Minerva is running, or what release of the ontology is loaded, e.g. #466. | 1.0 | include git revision and tbox ontology version in status service output - We frequently have issues that would be clarified by knowing what version of Minerva is running, or what release of the ontology is loaded, e.g. #466. | non_priority | include git revision and tbox ontology version in status service output we frequently have issues that would be clarified by knowing what version of minerva is running or what release of the ontology is loaded e g | 0 |
23,228 | 4,003,818,919 | IssuesEvent | 2016-05-12 02:55:13 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | stress: failed test in cockroach/sql/sql.test: TestRaceWithBackfill | Robot test-failure | Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/2f7d0f60f694357e12322c70e4c8f78c2ca8e81d
Stress build found a failed test:
```
=== RUN TestRaceWithBackfill
W160501 06:39:52.006373 gossip/gossip.go:892 not connected to cluster; use --join to specify a connected node
I160501 06:39:52.006944 storage/engine/rocksdb.go:137 opening in memory rocksdb instance
I160501 06:39:52.007976 server/node.go:399 store store=0:0 ([]=) not bootstrapped
W160501 06:39:52.009116 gossip/gossip.go:892 not connected to cluster; use --join to specify a connected node
I160501 06:39:52.009322 storage/replica_command.go:1440 range 1: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.009024277s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.009256983 +0000 UTC]
I160501 06:39:52.009650 server/node.go:325 **** cluster {378faa32-c044-473d-8b16-fed6f29aad93} has been created
I160501 06:39:52.009666 server/node.go:326 **** add additional nodes by specifying --join=127.0.0.1:34422
W160501 06:39:52.009676 gossip/gossip.go:892 not connected to cluster; use --join to specify a connected node
I160501 06:39:52.010218 server/node.go:412 initialized store store=1:1 ([]=): {Capacity:10365558784 Available:8079773696 RangeCount:0}
I160501 06:39:52.010247 server/node.go:300 node ID 1 initialized
I160501 06:39:52.010304 storage/stores.go:287 read 0 node addresses from persistent storage
I160501 06:39:52.010365 server/node.go:533 connecting to gossip network to verify cluster ID...
I160501 06:39:52.010889 server/node.go:554 node connected via gossip and verified as part of cluster {"378faa32-c044-473d-8b16-fed6f29aad93"}
I160501 06:39:52.010926 server/node.go:353 [node=1] Started node with [[]=] engine(s) and attributes []
I160501 06:39:52.010969 server/server.go:375 starting https server at 127.0.0.1:45659
I160501 06:39:52.010989 server/server.go:376 starting grpc/postgres server at 127.0.0.1:34422
I160501 06:39:52.011312 storage/split_queue.go:100 splitting range=1 [/Min-/Max) at keys [/Table/11/0 /Table/12/0 /Table/13/0 /Table/14/0]
I160501 06:39:52.012227 storage/replica_command.go:1902 initiating a split of range=1 [/Min-/Max) at key /Table/11
I160501 06:39:52.017267 storage/replica_command.go:1440 range 2: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.109885608s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.017221628 +0000 UTC]
I160501 06:39:52.017387 storage/replica_command.go:1902 initiating a split of range=2 [/Table/11-/Max) at key /Table/12
I160501 06:39:52.059856 server/updates.go:147 No previous updates check time.
I160501 06:39:52.063790 storage/replica_command.go:1440 range 3: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.11351013s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.06368907 +0000 UTC]
I160501 06:39:52.063904 storage/replica_command.go:1902 initiating a split of range=3 [/Table/12-/Max) at key /Table/13
I160501 06:39:52.075311 storage/replica_command.go:1440 range 4: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.12505264s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.075265126 +0000 UTC]
I160501 06:39:52.075426 storage/replica_command.go:1902 initiating a split of range=4 [/Table/13-/Max) at key /Table/14
I160501 06:39:52.127299 storage/replica_command.go:1440 range 5: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.176952639s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.127252019 +0000 UTC]
I160501 06:39:52.127787 storage/split_queue.go:100 splitting range=5 [/Table/14-/Max) at keys [/Table/50/0]
I160501 06:39:52.128051 storage/replica_command.go:1902 initiating a split of range=5 [/Table/14-/Max) at key /Table/50
I160501 06:39:52.138718 storage/replica_command.go:1440 range 6: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.188441709s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.138670163 +0000 UTC]
I160501 06:39:52.138832 storage/split_queue.go:100 splitting range=6 [/Table/50-/Max) at keys [/Table/51/0]
I160501 06:39:52.139112 storage/replica_command.go:1902 initiating a split of range=6 [/Table/50-/Max) at key /Table/51
I160501 06:39:52.157112 storage/replica_command.go:1440 range 7: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.206872203s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.157069201 +0000 UTC]
I160501 06:39:53.009340 gossip/gossip.go:918 starting client to 127.0.0.1:34422
I160501 06:39:53.009871 gossip/client.go:86 closing client to node 1 (127.0.0.1:34422): gossip/client.go:180: stopping outgoing client to node 1 (127.0.0.1:34422); loopback connection
I160501 06:39:54.414416 sql/lease.go:218 publish (count leases): descID=51 name=test version=5 count=1
I160501 06:39:54.820511 sql/lease.go:218 publish (count leases): descID=51 name=test version=6 count=1
I160501 06:39:54.949845 sql/lease.go:218 publish (count leases): descID=51 name=test version=7 count=1
I160501 06:39:54.973047 sql/lease.go:218 publish (count leases): descID=51 name=test version=8 count=1
I160501 06:39:55.297607 stopper.go:352 draining; tasks left:
1 server/node.go:782
1 kv/txn_coord_sender.go:895
I160501 06:39:55.297972 stopper.go:352 draining; tasks left:
1 server/node.go:782
W160501 06:39:55.299691 sql/schema_changer.go:208 node unavailable; try another peer
W160501 06:39:55.299769 sql/schema_changer.go:174 node unavailable; try another peer
W160501 06:39:55.299790 sql/session.go:290 Error executing schema change: sql/schema_changer.go:233: error purging mutation: node unavailable; try another peer, after error: node unavailable; try another peer
--- FAIL: TestRaceWithBackfill (3.31s)
schema_changer_test.go:451: schema change ALTER TABLE t.test ADD COLUMN x DECIMAL DEFAULT (DECIMAL '1.4') took 448.999589ms
schema_changer_test.go:496: pq: duplicate key value (k)=(2522) violates unique constraint "primary"
schema_changer_test.go:449: pq: sql/schema_changer.go:233: error purging mutation: node unavailable; try another peer, after error: node unavailable; try another peer
schema_changer_test.go:451: schema change ALTER TABLE t.test DROP pi took 357.037042ms
```
Run Details:
```
0 runs so far, 0 failures, over 5s
0 runs so far, 0 failures, over 10s
0 runs so far, 0 failures, over 15s
0 runs so far, 0 failures, over 20s
0 runs so far, 0 failures, over 25s
0 runs so far, 0 failures, over 30s
0 runs so far, 0 failures, over 35s
12 runs so far, 0 failures, over 40s
16 runs so far, 0 failures, over 45s
16 runs so far, 0 failures, over 50s
16 runs so far, 0 failures, over 55s
16 runs so far, 0 failures, over 1m0s
16 runs so far, 0 failures, over 1m5s
16 runs so far, 0 failures, over 1m10s
16 runs so far, 0 failures, over 1m15s
30 runs so far, 0 failures, over 1m20s
32 runs so far, 0 failures, over 1m25s
32 runs so far, 0 failures, over 1m30s
32 runs so far, 0 failures, over 1m35s
32 runs so far, 0 failures, over 1m40s
32 runs so far, 0 failures, over 1m45s
32 runs so far, 0 failures, over 1m50s
35 runs so far, 0 failures, over 1m55s
47 runs so far, 0 failures, over 2m0s
48 runs so far, 0 failures, over 2m5s
48 runs so far, 0 failures, over 2m10s
48 runs so far, 0 failures, over 2m15s
48 runs so far, 0 failures, over 2m20s
48 runs so far, 0 failures, over 2m25s
48 runs so far, 0 failures, over 2m30s
53 runs so far, 0 failures, over 2m35s
62 runs so far, 0 failures, over 2m40s
64 runs so far, 0 failures, over 2m45s
64 runs so far, 0 failures, over 2m50s
64 runs so far, 0 failures, over 2m55s
64 runs so far, 0 failures, over 3m0s
64 runs so far, 0 failures, over 3m5s
65 runs so far, 0 failures, over 3m10s
71 runs so far, 0 failures, over 3m15s
79 runs so far, 0 failures, over 3m20s
80 runs so far, 0 failures, over 3m25s
80 runs so far, 0 failures, over 3m30s
80 runs so far, 0 failures, over 3m35s
80 runs so far, 0 failures, over 3m40s
80 runs so far, 0 failures, over 3m45s
82 runs so far, 0 failures, over 3m50s
86 runs so far, 0 failures, over 3m55s
95 runs completed, 1 failures, over 3m59s
FAIL
```
Please assign, take a look and update the issue accordingly. | 1.0 | stress: failed test in cockroach/sql/sql.test: TestRaceWithBackfill - Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/2f7d0f60f694357e12322c70e4c8f78c2ca8e81d
Stress build found a failed test:
```
=== RUN TestRaceWithBackfill
W160501 06:39:52.006373 gossip/gossip.go:892 not connected to cluster; use --join to specify a connected node
I160501 06:39:52.006944 storage/engine/rocksdb.go:137 opening in memory rocksdb instance
I160501 06:39:52.007976 server/node.go:399 store store=0:0 ([]=) not bootstrapped
W160501 06:39:52.009116 gossip/gossip.go:892 not connected to cluster; use --join to specify a connected node
I160501 06:39:52.009322 storage/replica_command.go:1440 range 1: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.009024277s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.009256983 +0000 UTC]
I160501 06:39:52.009650 server/node.go:325 **** cluster {378faa32-c044-473d-8b16-fed6f29aad93} has been created
I160501 06:39:52.009666 server/node.go:326 **** add additional nodes by specifying --join=127.0.0.1:34422
W160501 06:39:52.009676 gossip/gossip.go:892 not connected to cluster; use --join to specify a connected node
I160501 06:39:52.010218 server/node.go:412 initialized store store=1:1 ([]=): {Capacity:10365558784 Available:8079773696 RangeCount:0}
I160501 06:39:52.010247 server/node.go:300 node ID 1 initialized
I160501 06:39:52.010304 storage/stores.go:287 read 0 node addresses from persistent storage
I160501 06:39:52.010365 server/node.go:533 connecting to gossip network to verify cluster ID...
I160501 06:39:52.010889 server/node.go:554 node connected via gossip and verified as part of cluster {"378faa32-c044-473d-8b16-fed6f29aad93"}
I160501 06:39:52.010926 server/node.go:353 [node=1] Started node with [[]=] engine(s) and attributes []
I160501 06:39:52.010969 server/server.go:375 starting https server at 127.0.0.1:45659
I160501 06:39:52.010989 server/server.go:376 starting grpc/postgres server at 127.0.0.1:34422
I160501 06:39:52.011312 storage/split_queue.go:100 splitting range=1 [/Min-/Max) at keys [/Table/11/0 /Table/12/0 /Table/13/0 /Table/14/0]
I160501 06:39:52.012227 storage/replica_command.go:1902 initiating a split of range=1 [/Min-/Max) at key /Table/11
I160501 06:39:52.017267 storage/replica_command.go:1440 range 2: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.109885608s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.017221628 +0000 UTC]
I160501 06:39:52.017387 storage/replica_command.go:1902 initiating a split of range=2 [/Table/11-/Max) at key /Table/12
I160501 06:39:52.059856 server/updates.go:147 No previous updates check time.
I160501 06:39:52.063790 storage/replica_command.go:1440 range 3: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.11351013s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.06368907 +0000 UTC]
I160501 06:39:52.063904 storage/replica_command.go:1902 initiating a split of range=3 [/Table/12-/Max) at key /Table/13
I160501 06:39:52.075311 storage/replica_command.go:1440 range 4: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.12505264s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.075265126 +0000 UTC]
I160501 06:39:52.075426 storage/replica_command.go:1902 initiating a split of range=4 [/Table/13-/Max) at key /Table/14
I160501 06:39:52.127299 storage/replica_command.go:1440 range 5: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.176952639s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.127252019 +0000 UTC]
I160501 06:39:52.127787 storage/split_queue.go:100 splitting range=5 [/Table/14-/Max) at keys [/Table/50/0]
I160501 06:39:52.128051 storage/replica_command.go:1902 initiating a split of range=5 [/Table/14-/Max) at key /Table/50
I160501 06:39:52.138718 storage/replica_command.go:1440 range 6: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.188441709s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.138670163 +0000 UTC]
I160501 06:39:52.138832 storage/split_queue.go:100 splitting range=6 [/Table/50-/Max) at keys [/Table/51/0]
I160501 06:39:52.139112 storage/replica_command.go:1902 initiating a split of range=6 [/Table/50-/Max) at key /Table/51
I160501 06:39:52.157112 storage/replica_command.go:1440 range 7: new leader lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 406134h39m53.206872203s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-05-01 06:39:52.157069201 +0000 UTC]
I160501 06:39:53.009340 gossip/gossip.go:918 starting client to 127.0.0.1:34422
I160501 06:39:53.009871 gossip/client.go:86 closing client to node 1 (127.0.0.1:34422): gossip/client.go:180: stopping outgoing client to node 1 (127.0.0.1:34422); loopback connection
I160501 06:39:54.414416 sql/lease.go:218 publish (count leases): descID=51 name=test version=5 count=1
I160501 06:39:54.820511 sql/lease.go:218 publish (count leases): descID=51 name=test version=6 count=1
I160501 06:39:54.949845 sql/lease.go:218 publish (count leases): descID=51 name=test version=7 count=1
I160501 06:39:54.973047 sql/lease.go:218 publish (count leases): descID=51 name=test version=8 count=1
I160501 06:39:55.297607 stopper.go:352 draining; tasks left:
1 server/node.go:782
1 kv/txn_coord_sender.go:895
I160501 06:39:55.297972 stopper.go:352 draining; tasks left:
1 server/node.go:782
W160501 06:39:55.299691 sql/schema_changer.go:208 node unavailable; try another peer
W160501 06:39:55.299769 sql/schema_changer.go:174 node unavailable; try another peer
W160501 06:39:55.299790 sql/session.go:290 Error executing schema change: sql/schema_changer.go:233: error purging mutation: node unavailable; try another peer, after error: node unavailable; try another peer
--- FAIL: TestRaceWithBackfill (3.31s)
schema_changer_test.go:451: schema change ALTER TABLE t.test ADD COLUMN x DECIMAL DEFAULT (DECIMAL '1.4') took 448.999589ms
schema_changer_test.go:496: pq: duplicate key value (k)=(2522) violates unique constraint "primary"
schema_changer_test.go:449: pq: sql/schema_changer.go:233: error purging mutation: node unavailable; try another peer, after error: node unavailable; try another peer
schema_changer_test.go:451: schema change ALTER TABLE t.test DROP pi took 357.037042ms
```
Run Details:
```
0 runs so far, 0 failures, over 5s
0 runs so far, 0 failures, over 10s
0 runs so far, 0 failures, over 15s
0 runs so far, 0 failures, over 20s
0 runs so far, 0 failures, over 25s
0 runs so far, 0 failures, over 30s
0 runs so far, 0 failures, over 35s
12 runs so far, 0 failures, over 40s
16 runs so far, 0 failures, over 45s
16 runs so far, 0 failures, over 50s
16 runs so far, 0 failures, over 55s
16 runs so far, 0 failures, over 1m0s
16 runs so far, 0 failures, over 1m5s
16 runs so far, 0 failures, over 1m10s
16 runs so far, 0 failures, over 1m15s
30 runs so far, 0 failures, over 1m20s
32 runs so far, 0 failures, over 1m25s
32 runs so far, 0 failures, over 1m30s
32 runs so far, 0 failures, over 1m35s
32 runs so far, 0 failures, over 1m40s
32 runs so far, 0 failures, over 1m45s
32 runs so far, 0 failures, over 1m50s
35 runs so far, 0 failures, over 1m55s
47 runs so far, 0 failures, over 2m0s
48 runs so far, 0 failures, over 2m5s
48 runs so far, 0 failures, over 2m10s
48 runs so far, 0 failures, over 2m15s
48 runs so far, 0 failures, over 2m20s
48 runs so far, 0 failures, over 2m25s
48 runs so far, 0 failures, over 2m30s
53 runs so far, 0 failures, over 2m35s
62 runs so far, 0 failures, over 2m40s
64 runs so far, 0 failures, over 2m45s
64 runs so far, 0 failures, over 2m50s
64 runs so far, 0 failures, over 2m55s
64 runs so far, 0 failures, over 3m0s
64 runs so far, 0 failures, over 3m5s
65 runs so far, 0 failures, over 3m10s
71 runs so far, 0 failures, over 3m15s
79 runs so far, 0 failures, over 3m20s
80 runs so far, 0 failures, over 3m25s
80 runs so far, 0 failures, over 3m30s
80 runs so far, 0 failures, over 3m35s
80 runs so far, 0 failures, over 3m40s
80 runs so far, 0 failures, over 3m45s
82 runs so far, 0 failures, over 3m50s
86 runs so far, 0 failures, over 3m55s
95 runs completed, 1 failures, over 3m59s
FAIL
```
Please assign, take a look and update the issue accordingly. | non_priority | stress failed test in cockroach sql sql test testracewithbackfill binary cockroach static tests tar gz sha stress build found a failed test run testracewithbackfill gossip gossip go not connected to cluster use join to specify a connected node storage engine rocksdb go opening in memory rocksdb instance server node go store store not bootstrapped gossip gossip go not connected to cluster use join to specify a connected node storage replica command go range new leader lease replica utc following replica utc server node go cluster has been created server node go add additional nodes by specifying join gossip gossip go not connected to cluster use join to specify a connected node server node go initialized store store capacity available rangecount server node go node id initialized storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go started node with engine s and attributes server server go starting https server at server server go starting grpc postgres server at storage split queue go splitting range storage replica command go initiating a split of range min max at key table storage replica command go range new leader lease replica utc following replica utc storage replica command go initiating a split of range table max at key table server updates go no previous updates check time storage replica command go range new leader lease replica utc following replica utc storage replica command go initiating a split of range table max at key table storage replica command go range new leader lease replica utc following replica utc storage replica command go initiating a split of range table max at key table storage replica command go range new leader lease replica utc following replica utc storage split queue go splitting range storage replica command go initiating a split of range table max at key table storage replica command go range new leader lease replica utc following replica utc storage split queue go splitting range storage replica command go initiating a split of range table max at key table storage replica command go range new leader lease replica utc following replica utc gossip gossip go starting client to gossip client go closing client to node gossip client go stopping outgoing client to node loopback connection sql lease go publish count leases descid name test version count sql lease go publish count leases descid name test version count sql lease go publish count leases descid name test version count sql lease go publish count leases descid name test version count stopper go draining tasks left server node go kv txn coord sender go stopper go draining tasks left server node go sql schema changer go node unavailable try another peer sql schema changer go node unavailable try another peer sql session go error executing schema change sql schema changer go error purging mutation node unavailable try another peer after error node unavailable try another peer fail testracewithbackfill schema changer test go schema change alter table t test add column x decimal default decimal took schema changer test go pq duplicate key value k violates unique constraint primary schema changer test go pq sql schema changer go error purging mutation node unavailable try another peer after error node unavailable try another peer schema changer test go schema change alter table t test drop pi took run details runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs completed failures over fail please assign take a look and update the issue accordingly | 0 |
76,932 | 26,674,153,370 | IssuesEvent | 2023-01-26 12:59:10 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | java.util.concurrent.CancellationException when loading from GenericMapStore | Type: Defect Source: Internal to-jira Team: Platform | <!--
Thanks for reporting your issue. Please share with us the following information, to help us resolve your issue quickly and efficiently.
-->
**Describe the bug**
Given a configured `external-data-store` and corresponding `map-store` for connecting a DB such as Postgres or MySQL, when loading the data from the external store (i.e. by calling `hz.getMap()`), some warnings for `java.util.concurrent.CancellationException` are logged. They may be unnecessary and confusing, because it implies that a query/job was canceled by the user (which is not the case).
Data is still loaded successfully in the map.
Example:
```
Jan 26, 2023 7:29:42 AM com.hazelcast.jet.impl.operation.InitExecutionOperation
WARNING: [10.0.0.29]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334)
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291)
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404)
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895)
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369)
at java.lang.Thread.run(Thread.java:750)
```
**Expected behavior**
`java.util.concurrent.CancellationException` are not logged when successfully loading from the external store.
**To Reproduce**
Config and code snippets of a reporoducer:
hazelcast.xml:
```
...
<external-data-store name="postgres">
<class-name>com.hazelcast.datastore.JdbcDataStoreFactory</class-name>
<properties>
<property name="jdbcUrl">jdbc:postgresql://127.0.0.1:5432/test</property>
<property name="username">postgres</property>
<property name="password">****</property>
</properties>
</external-data-store>
...
<map name="people">
<map-store enabled="true">
<class-name>com.hazelcast.mapstore.GenericMapStore</class-name>
<properties>
<property name="external-data-store-ref">postgres</property>
</properties>
</map-store>
</map>
...
```
HZ member code:
```
HazelcastInstance hz = Hazelcast.newHazelcastInstance();
IMap<Integer, GenericRecord> map = hz.getMap("people");
map.values().stream().forEach(v -> System.out.println(v));
System.out.println(">>>>>>>>>>> DONE");
hz.shutdown();
```
**Additional context**
The issue seems to be related to [this method](https://github.com/hazelcast/hazelcast/blob/fc2271c3a19a6a048c26613152870d4c85fa222b/extensions/mapstore/src/main/java/com/hazelcast/mapstore/GenericMapStore.java#L255) in `GenericMapStore`. The `SqlResult` is closed without consuming the iterator. Similar behavior can be triggered from a client/embedded member with:
```
try (SqlResult result = hz.getSql().execute("SELECT * FROM people")) {
SqlRowMetadata rowMetadata = result.getRowMetadata();
System.out.println(rowMetadata);
}
```
<!--
Add any other context about the problem here.
Common details that we're often interested in:
- Detailed description of the steps to reproduce your issue
- Logs and stack traces, if available
- Hazelcast version that you use (e.g. 3.4, also specify whether it is a minor release or the latest snapshot)
- If available, integration module versions (e.g. Tomcat, Jetty, Spring, Hibernate). Also, include their detailed configuration information such as web.xml, Hibernate configuration and `context.xml` for Spring
- Cluster size, i.e. the number of Hazelcast cluster members
- Number of the clients
- Version of Java. It is also helpful to mention the JVM parameters
- Operating system. If it is Linux, kernel version is helpful
- Unit test with the `hazelcast.xml` file. If you could include a unit test which reproduces your issue, we would be grateful
-->
| 1.0 | java.util.concurrent.CancellationException when loading from GenericMapStore - <!--
Thanks for reporting your issue. Please share with us the following information, to help us resolve your issue quickly and efficiently.
-->
**Describe the bug**
Given a configured `external-data-store` and corresponding `map-store` for connecting a DB such as Postgres or MySQL, when loading the data from the external store (i.e. by calling `hz.getMap()`), some warnings for `java.util.concurrent.CancellationException` are logged. They may be unnecessary and confusing, because it implies that a query/job was canceled by the user (which is not the case).
Data is still loaded successfully in the map.
Example:
```
Jan 26, 2023 7:29:42 AM com.hazelcast.jet.impl.operation.InitExecutionOperation
WARNING: [10.0.0.29]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334)
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328)
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291)
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404)
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895)
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369)
at java.lang.Thread.run(Thread.java:750)
```
**Expected behavior**
`java.util.concurrent.CancellationException` are not logged when successfully loading from the external store.
**To Reproduce**
Config and code snippets of a reporoducer:
hazelcast.xml:
```
...
<external-data-store name="postgres">
<class-name>com.hazelcast.datastore.JdbcDataStoreFactory</class-name>
<properties>
<property name="jdbcUrl">jdbc:postgresql://127.0.0.1:5432/test</property>
<property name="username">postgres</property>
<property name="password">****</property>
</properties>
</external-data-store>
...
<map name="people">
<map-store enabled="true">
<class-name>com.hazelcast.mapstore.GenericMapStore</class-name>
<properties>
<property name="external-data-store-ref">postgres</property>
</properties>
</map-store>
</map>
...
```
HZ member code:
```
HazelcastInstance hz = Hazelcast.newHazelcastInstance();
IMap<Integer, GenericRecord> map = hz.getMap("people");
map.values().stream().forEach(v -> System.out.println(v));
System.out.println(">>>>>>>>>>> DONE");
hz.shutdown();
```
**Additional context**
The issue seems to be related to [this method](https://github.com/hazelcast/hazelcast/blob/fc2271c3a19a6a048c26613152870d4c85fa222b/extensions/mapstore/src/main/java/com/hazelcast/mapstore/GenericMapStore.java#L255) in `GenericMapStore`. The `SqlResult` is closed without consuming the iterator. Similar behavior can be triggered from a client/embedded member with:
```
try (SqlResult result = hz.getSql().execute("SELECT * FROM people")) {
SqlRowMetadata rowMetadata = result.getRowMetadata();
System.out.println(rowMetadata);
}
```
<!--
Add any other context about the problem here.
Common details that we're often interested in:
- Detailed description of the steps to reproduce your issue
- Logs and stack traces, if available
- Hazelcast version that you use (e.g. 3.4, also specify whether it is a minor release or the latest snapshot)
- If available, integration module versions (e.g. Tomcat, Jetty, Spring, Hibernate). Also, include their detailed configuration information such as web.xml, Hibernate configuration and `context.xml` for Spring
- Cluster size, i.e. the number of Hazelcast cluster members
- Number of the clients
- Version of Java. It is also helpful to mention the JVM parameters
- Operating system. If it is Linux, kernel version is helpful
- Unit test with the `hazelcast.xml` file. If you could include a unit test which reproduces your issue, we would be grateful
-->
| non_priority | java util concurrent cancellationexception when loading from genericmapstore thanks for reporting your issue please share with us the following information to help us resolve your issue quickly and efficiently describe the bug given a configured external data store and corresponding map store for connecting a db such as postgres or mysql when loading the data from the external store i e by calling hz getmap some warnings for java util concurrent cancellationexception are logged they may be unnecessary and confusing because it implies that a query job was canceled by the user which is not the case data is still loaded successfully in the map example jan am com hazelcast jet impl operation initexecutionoperation warning null java util concurrent cancellationexception at com hazelcast jet sql impl processors rootresultconsumersink tryprocess rootresultconsumersink java at com hazelcast jet impl execution processortasklet lambda statemachinestep processortasklet java at com hazelcast jet impl util util dowithclassloader util java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet call processortasklet java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker runtasklet taskletexecutionservice java at java util concurrent copyonwritearraylist foreach copyonwritearraylist java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker run taskletexecutionservice java at java lang thread run thread java expected behavior java util concurrent cancellationexception are not logged when successfully loading from the external store to reproduce config and code snippets of a reporoducer hazelcast xml com hazelcast datastore jdbcdatastorefactory jdbc postgresql test postgres com hazelcast mapstore genericmapstore postgres hz member code hazelcastinstance hz hazelcast newhazelcastinstance imap map hz getmap people map values stream foreach v system out println v system out println done hz shutdown additional context the issue seems to be related to in genericmapstore the sqlresult is closed without consuming the iterator similar behavior can be triggered from a client embedded member with try sqlresult result hz getsql execute select from people sqlrowmetadata rowmetadata result getrowmetadata system out println rowmetadata add any other context about the problem here common details that we re often interested in detailed description of the steps to reproduce your issue logs and stack traces if available hazelcast version that you use e g also specify whether it is a minor release or the latest snapshot if available integration module versions e g tomcat jetty spring hibernate also include their detailed configuration information such as web xml hibernate configuration and context xml for spring cluster size i e the number of hazelcast cluster members number of the clients version of java it is also helpful to mention the jvm parameters operating system if it is linux kernel version is helpful unit test with the hazelcast xml file if you could include a unit test which reproduces your issue we would be grateful | 0 |
46,049 | 13,148,590,199 | IssuesEvent | 2020-08-08 22:36:01 | AlexRogalskiy/ws-documents | https://api.github.com/repos/AlexRogalskiy/ws-documents | closed | WS-2016-7062 (Medium) detected in plexus-utils-1.1.jar | security vulnerability | ## WS-2016-7062 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>plexus-utils-1.1.jar</b></p></summary>
<p>null</p>
<p>Path to dependency file: /tmp/ws-scm/ws-documents/modules/commons/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/codehaus/plexus/plexus-utils/1.1/plexus-utils-1.1.jar</p>
<p>
Dependency Hierarchy:
- wsdl4j-1.6.3.wso2v3.jar (Root Library)
- maven-artifact-2.0.5.jar
- :x: **plexus-utils-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/ws-documents/commit/7ae3202b2ad66e00260af930086ca05fa5f4b29f">7ae3202b2ad66e00260af930086ca05fa5f4b29f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Security vulnerability found in plexus-utils before 3.0.24. XML injection found in XmlWriterUtil.java.
<p>Publish Date: 2016-05-07
<p>URL: <a href=https://github.com/codehaus-plexus/plexus-utils/commit/f933e5e78dc2637e485447ed821fe14904f110de>WS-2016-7062</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/codehaus-plexus/plexus-utils/commit/f933e5e78dc2637e485447ed821fe14904f110de">https://github.com/codehaus-plexus/plexus-utils/commit/f933e5e78dc2637e485447ed821fe14904f110de</a></p>
<p>Release Date: 2019-09-26</p>
<p>Fix Resolution: 3.0.24</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2016-7062 (Medium) detected in plexus-utils-1.1.jar - ## WS-2016-7062 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>plexus-utils-1.1.jar</b></p></summary>
<p>null</p>
<p>Path to dependency file: /tmp/ws-scm/ws-documents/modules/commons/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/codehaus/plexus/plexus-utils/1.1/plexus-utils-1.1.jar</p>
<p>
Dependency Hierarchy:
- wsdl4j-1.6.3.wso2v3.jar (Root Library)
- maven-artifact-2.0.5.jar
- :x: **plexus-utils-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/ws-documents/commit/7ae3202b2ad66e00260af930086ca05fa5f4b29f">7ae3202b2ad66e00260af930086ca05fa5f4b29f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Security vulnerability found in plexus-utils before 3.0.24. XML injection found in XmlWriterUtil.java.
<p>Publish Date: 2016-05-07
<p>URL: <a href=https://github.com/codehaus-plexus/plexus-utils/commit/f933e5e78dc2637e485447ed821fe14904f110de>WS-2016-7062</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/codehaus-plexus/plexus-utils/commit/f933e5e78dc2637e485447ed821fe14904f110de">https://github.com/codehaus-plexus/plexus-utils/commit/f933e5e78dc2637e485447ed821fe14904f110de</a></p>
<p>Release Date: 2019-09-26</p>
<p>Fix Resolution: 3.0.24</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in plexus utils jar ws medium severity vulnerability vulnerable library plexus utils jar null path to dependency file tmp ws scm ws documents modules commons pom xml path to vulnerable library home wss scanner repository org codehaus plexus plexus utils plexus utils jar dependency hierarchy jar root library maven artifact jar x plexus utils jar vulnerable library found in head commit a href vulnerability details security vulnerability found in plexus utils before xml injection found in xmlwriterutil java publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
51,780 | 13,211,305,439 | IssuesEvent | 2020-08-15 22:11:02 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | libarchive - falls back to system lib when using I3_PORTS (Trac #1031) | Incomplete Migration Migrated from Trac defect tools/ports | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1031">https://code.icecube.wisc.edu/projects/icecube/ticket/1031</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:26",
"_ts": "1550067086520250",
"description": "this is on the new suse bot, and causes conflicts w/ its libxml2 dependency.\n\nhaven't i fixed this before?",
"reporter": "nega",
"cc": "",
"resolution": "invalid",
"time": "2015-06-24T21:20:33",
"component": "tools/ports",
"summary": "libarchive - falls back to system lib when using I3_PORTS",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | libarchive - falls back to system lib when using I3_PORTS (Trac #1031) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/1031">https://code.icecube.wisc.edu/projects/icecube/ticket/1031</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:26",
"_ts": "1550067086520250",
"description": "this is on the new suse bot, and causes conflicts w/ its libxml2 dependency.\n\nhaven't i fixed this before?",
"reporter": "nega",
"cc": "",
"resolution": "invalid",
"time": "2015-06-24T21:20:33",
"component": "tools/ports",
"summary": "libarchive - falls back to system lib when using I3_PORTS",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| non_priority | libarchive falls back to system lib when using ports trac migrated from json status closed changetime ts description this is on the new suse bot and causes conflicts w its dependency n nhaven t i fixed this before reporter nega cc resolution invalid time component tools ports summary libarchive falls back to system lib when using ports priority normal keywords milestone owner nega type defect | 0 |
28,072 | 31,552,874,826 | IssuesEvent | 2023-09-02 09:13:52 | buggregator/frontend | https://api.github.com/repos/buggregator/frontend | closed | FR: Ability to pause profiles autorefresh. | module:xhprof feature usability | It's hard to find a specific profile when the profiles page in autorefreshing mode. It is necessary to add the ability to pause the loading of a new profiles. For example, you can pause it when the scroll down and trigger it back when it scrolls back on top. | True | FR: Ability to pause profiles autorefresh. - It's hard to find a specific profile when the profiles page in autorefreshing mode. It is necessary to add the ability to pause the loading of a new profiles. For example, you can pause it when the scroll down and trigger it back when it scrolls back on top. | non_priority | fr ability to pause profiles autorefresh it s hard to find a specific profile when the profiles page in autorefreshing mode it is necessary to add the ability to pause the loading of a new profiles for example you can pause it when the scroll down and trigger it back when it scrolls back on top | 0 |
261,300 | 22,717,773,967 | IssuesEvent | 2022-07-06 05:01:02 | Merck/metalite.ae | https://api.github.com/repos/Merck/metalite.ae | closed | Independent Testing for prop_test_mn.R | independent test | Test plan:
- Test if the output matches that from SAS under
+ different test types (one-sided or two-sided)
+ different alpha | 1.0 | Independent Testing for prop_test_mn.R - Test plan:
- Test if the output matches that from SAS under
+ different test types (one-sided or two-sided)
+ different alpha | non_priority | independent testing for prop test mn r test plan test if the output matches that from sas under different test types one sided or two sided different alpha | 0 |
43,209 | 11,569,199,051 | IssuesEvent | 2020-02-20 17:07:23 | NREL/EnergyPlus | https://api.github.com/repos/NREL/EnergyPlus | closed | "Other" heating subcategory appears (incorrectly) | Defect | Issue overview
--------------
See IDF below where >12 GJ of energy appears in an "Other" heating subcategory in the End Uses By Subcategory output table. The subcategory is being automatically created. Across several hundred test IDFs, this is the _only_ file where this subcategory appears. In every other test file, heating energy correctly shows up in the "General" subcategory. (This particular test file includes a complex set of HVAC systems serving a single conditioned zone.)
[in.idf.txt](https://github.com/NREL/EnergyPlus/files/3725469/in.idf.txt)
### Details
Some additional details for this issue (if relevant):
- Windows 10
- Version 9.2.0-921312fa1d
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [ ] Defect file added (list location of defect file here)
- [ ] Ticket added to Pivotal for defect (development team task)
- [ ] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect)
| 1.0 | "Other" heating subcategory appears (incorrectly) - Issue overview
--------------
See IDF below where >12 GJ of energy appears in an "Other" heating subcategory in the End Uses By Subcategory output table. The subcategory is being automatically created. Across several hundred test IDFs, this is the _only_ file where this subcategory appears. In every other test file, heating energy correctly shows up in the "General" subcategory. (This particular test file includes a complex set of HVAC systems serving a single conditioned zone.)
[in.idf.txt](https://github.com/NREL/EnergyPlus/files/3725469/in.idf.txt)
### Details
Some additional details for this issue (if relevant):
- Windows 10
- Version 9.2.0-921312fa1d
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [ ] Defect file added (list location of defect file here)
- [ ] Ticket added to Pivotal for defect (development team task)
- [ ] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect)
| non_priority | other heating subcategory appears incorrectly issue overview see idf below where gj of energy appears in an other heating subcategory in the end uses by subcategory output table the subcategory is being automatically created across several hundred test idfs this is the only file where this subcategory appears in every other test file heating energy correctly shows up in the general subcategory this particular test file includes a complex set of hvac systems serving a single conditioned zone details some additional details for this issue if relevant windows version checklist add to this list or remove from it as applicable this is a simple templated set of guidelines defect file added list location of defect file here ticket added to pivotal for defect development team task pull request created the pull request will have additional tasks related to reviewing changes that fix this defect | 0 |
20,848 | 27,626,784,129 | IssuesEvent | 2023-03-10 07:36:28 | core-wg/oscore-key-update | https://api.github.com/repos/core-wg/oscore-key-update | closed | Extend 4.3 about multiple CTX_NEW | KUDOS Processing | A newly derived CTX_NEW replaces any potential already stored CTX_NEW. | 1.0 | Extend 4.3 about multiple CTX_NEW - A newly derived CTX_NEW replaces any potential already stored CTX_NEW. | non_priority | extend about multiple ctx new a newly derived ctx new replaces any potential already stored ctx new | 0 |
81,020 | 15,598,681,389 | IssuesEvent | 2021-03-18 18:24:53 | BCDevOps/developer-experience | https://api.github.com/repos/BCDevOps/developer-experience | closed | Aporeto STRA Remediation - Backup and Restore | aporeto security | Create restore instructions/playbook to re-import policies and other details in the event a re-build is required.
Test restore process. | True | Aporeto STRA Remediation - Backup and Restore - Create restore instructions/playbook to re-import policies and other details in the event a re-build is required.
Test restore process. | non_priority | aporeto stra remediation backup and restore create restore instructions playbook to re import policies and other details in the event a re build is required test restore process | 0 |
98,424 | 11,082,852,761 | IssuesEvent | 2019-12-13 13:10:53 | Open-EO/openeo-processes | https://api.github.com/repos/Open-EO/openeo-processes | closed | filter_bands / load_collection / reduce: Contradicting language regarding bands | accepted documentation | Originates from https://github.com/Open-EO/openeo-api/issues/208
There's contradicting wording regarding dimension type bands, especially when reading filter_bands and load_collection.
reduce / filter:
> For multi-spectral imagery there is usually a separate dimension of type `bands` for the bands.
filter_bands:
> The data cube is expected to have only one dimension of type `bands`.
load_collection (which unfortunately contradicts to filter_bands above):
> Applies to all dimensions of type `bands` if there are multiple of them.
It's still valid as it's just a recommendation on how the passed data cube should look like, but I should double-check the language here. | 1.0 | filter_bands / load_collection / reduce: Contradicting language regarding bands - Originates from https://github.com/Open-EO/openeo-api/issues/208
There's contradicting wording regarding dimension type bands, especially when reading filter_bands and load_collection.
reduce / filter:
> For multi-spectral imagery there is usually a separate dimension of type `bands` for the bands.
filter_bands:
> The data cube is expected to have only one dimension of type `bands`.
load_collection (which unfortunately contradicts to filter_bands above):
> Applies to all dimensions of type `bands` if there are multiple of them.
It's still valid as it's just a recommendation on how the passed data cube should look like, but I should double-check the language here. | non_priority | filter bands load collection reduce contradicting language regarding bands originates from there s contradicting wording regarding dimension type bands especially when reading filter bands and load collection reduce filter for multi spectral imagery there is usually a separate dimension of type bands for the bands filter bands the data cube is expected to have only one dimension of type bands load collection which unfortunately contradicts to filter bands above applies to all dimensions of type bands if there are multiple of them it s still valid as it s just a recommendation on how the passed data cube should look like but i should double check the language here | 0 |
208,828 | 23,660,817,233 | IssuesEvent | 2022-08-26 15:24:01 | MinaProtocol/mina | https://api.github.com/repos/MinaProtocol/mina | closed | Require block reward in every block? | daemon security consider-for-closing stale triage | Currently it is up to block producers whether they want to include a block reward or not. I think faithfully implementing the [economics whitepaper](https://codaprotocol.com/static/pdf/economicsWP.pdf) demands that block producers not have the power to stop inflation independently of on-chain governance. I think it also weakens consensus? I believe that if the main chain inflates slower than adversarial side chains can, the side chain stake distribution might become favorable (although I don't see how to execute this attack without triggering the epoch density comparison). | True | Require block reward in every block? - Currently it is up to block producers whether they want to include a block reward or not. I think faithfully implementing the [economics whitepaper](https://codaprotocol.com/static/pdf/economicsWP.pdf) demands that block producers not have the power to stop inflation independently of on-chain governance. I think it also weakens consensus? I believe that if the main chain inflates slower than adversarial side chains can, the side chain stake distribution might become favorable (although I don't see how to execute this attack without triggering the epoch density comparison). | non_priority | require block reward in every block currently it is up to block producers whether they want to include a block reward or not i think faithfully implementing the demands that block producers not have the power to stop inflation independently of on chain governance i think it also weakens consensus i believe that if the main chain inflates slower than adversarial side chains can the side chain stake distribution might become favorable although i don t see how to execute this attack without triggering the epoch density comparison | 0 |
156,027 | 19,803,785,206 | IssuesEvent | 2022-01-19 02:44:29 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Rework Role and LimitedRole to support more general limiting | :Security/Authorization Team:Security | The `LimitedRole` limits what a `Role` can authorize by intersecting it privileges with an additional set of privileges. This concept is useful in general and we plan to leverage it in more features. However the current implementation only works for one level of limiting and this prevents its general usefulness. For example, an API key already has one level of limiting. So it is not possible to further limiting it which might be useful in cases like derived API keys, cross-cluster API keys.
We should remove the above constraint by reworking the implementation of `Role` and `LimitedRole`. | True | Rework Role and LimitedRole to support more general limiting - The `LimitedRole` limits what a `Role` can authorize by intersecting it privileges with an additional set of privileges. This concept is useful in general and we plan to leverage it in more features. However the current implementation only works for one level of limiting and this prevents its general usefulness. For example, an API key already has one level of limiting. So it is not possible to further limiting it which might be useful in cases like derived API keys, cross-cluster API keys.
We should remove the above constraint by reworking the implementation of `Role` and `LimitedRole`. | non_priority | rework role and limitedrole to support more general limiting the limitedrole limits what a role can authorize by intersecting it privileges with an additional set of privileges this concept is useful in general and we plan to leverage it in more features however the current implementation only works for one level of limiting and this prevents its general usefulness for example an api key already has one level of limiting so it is not possible to further limiting it which might be useful in cases like derived api keys cross cluster api keys we should remove the above constraint by reworking the implementation of role and limitedrole | 0 |
26,760 | 4,778,168,095 | IssuesEvent | 2016-10-27 18:28:35 | wheeler-microfluidics/microdrop | https://api.github.com/repos/wheeler-microfluidics/microdrop | closed | Error importing device from svg (Trac #137) | defect microdrop Migrated from Trac | From the error log:
[WARNING]: The following paths could not be parsed properly have been ignore
d:
Error parsing problem device.svg:5385, loop needs 3 or more verts
<path xmlns="http://www.w3.org/2000/svg" xmlns:inkscape="http://www.inkscape
.org/namespaces/inkscape" xmlns:dc="http://purl.org/dc/elements/1.1/" xmlns:cc="
http://creativecommons.org/ns#" xmlns:rdf="http://www.w3.org/1999/02/22-rdf-synt
ax-ns#" xmlns:svg="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/19
99/xlink" xmlns:sodipodi="http://sodipodi.sourceforge.net/DTD/sodipodi-0.dtd" in
kscape:connector-curvature="0" style="fill:none;stroke:http://microfluidics.utoronto.ca/microdrop/ticket/0;stroke-width:0.1;
stroke-miterlimit:4;stroke-dasharray:none" d="M185.46948 288.025L185.46948 288.0
25" id="path5113"/>
Note also that the program shows a warning box, but is left in a bad state with the file dialog still open.
Migrated from http://microfluidics.utoronto.ca/microdrop/ticket/137
```json
{
"status": "closed",
"changetime": "2014-04-17T19:39:01",
"description": "From the error log:\n\n[WARNING]: The following paths could not be parsed properly have been ignore\nd:\n Error parsing problem device.svg:5385, loop needs 3 or more verts\n <path xmlns=\"http://www.w3.org/2000/svg\" xmlns:inkscape=\"http://www.inkscape\n.org/namespaces/inkscape\" xmlns:dc=\"http://purl.org/dc/elements/1.1/\" xmlns:cc=\"\nhttp://creativecommons.org/ns#\" xmlns:rdf=\"http://www.w3.org/1999/02/22-rdf-synt\nax-ns#\" xmlns:svg=\"http://www.w3.org/2000/svg\" xmlns:xlink=\"http://www.w3.org/19\n99/xlink\" xmlns:sodipodi=\"http://sodipodi.sourceforge.net/DTD/sodipodi-0.dtd\" in\nkscape:connector-curvature=\"0\" style=\"fill:none;stroke:#000000;stroke-width:0.1;\nstroke-miterlimit:4;stroke-dasharray:none\" d=\"M185.46948 288.025L185.46948 288.0\n25\" id=\"path5113\"/>\n\nNote also that the program shows a warning box, but is left in a bad state with the file dialog still open.",
"reporter": "ryan",
"cc": "",
"resolution": "fixed",
"_ts": "1397763541728826",
"component": "microdrop",
"summary": "Error importing device from svg",
"priority": "major",
"keywords": "",
"version": "0.1",
"time": "2013-02-27T19:16:09",
"milestone": "Microdrop 1.0",
"owner": "",
"type": "defect"
}
```
| 1.0 | Error importing device from svg (Trac #137) - From the error log:
[WARNING]: The following paths could not be parsed properly have been ignore
d:
Error parsing problem device.svg:5385, loop needs 3 or more verts
<path xmlns="http://www.w3.org/2000/svg" xmlns:inkscape="http://www.inkscape
.org/namespaces/inkscape" xmlns:dc="http://purl.org/dc/elements/1.1/" xmlns:cc="
http://creativecommons.org/ns#" xmlns:rdf="http://www.w3.org/1999/02/22-rdf-synt
ax-ns#" xmlns:svg="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/19
99/xlink" xmlns:sodipodi="http://sodipodi.sourceforge.net/DTD/sodipodi-0.dtd" in
kscape:connector-curvature="0" style="fill:none;stroke:http://microfluidics.utoronto.ca/microdrop/ticket/0;stroke-width:0.1;
stroke-miterlimit:4;stroke-dasharray:none" d="M185.46948 288.025L185.46948 288.0
25" id="path5113"/>
Note also that the program shows a warning box, but is left in a bad state with the file dialog still open.
Migrated from http://microfluidics.utoronto.ca/microdrop/ticket/137
```json
{
"status": "closed",
"changetime": "2014-04-17T19:39:01",
"description": "From the error log:\n\n[WARNING]: The following paths could not be parsed properly have been ignore\nd:\n Error parsing problem device.svg:5385, loop needs 3 or more verts\n <path xmlns=\"http://www.w3.org/2000/svg\" xmlns:inkscape=\"http://www.inkscape\n.org/namespaces/inkscape\" xmlns:dc=\"http://purl.org/dc/elements/1.1/\" xmlns:cc=\"\nhttp://creativecommons.org/ns#\" xmlns:rdf=\"http://www.w3.org/1999/02/22-rdf-synt\nax-ns#\" xmlns:svg=\"http://www.w3.org/2000/svg\" xmlns:xlink=\"http://www.w3.org/19\n99/xlink\" xmlns:sodipodi=\"http://sodipodi.sourceforge.net/DTD/sodipodi-0.dtd\" in\nkscape:connector-curvature=\"0\" style=\"fill:none;stroke:#000000;stroke-width:0.1;\nstroke-miterlimit:4;stroke-dasharray:none\" d=\"M185.46948 288.025L185.46948 288.0\n25\" id=\"path5113\"/>\n\nNote also that the program shows a warning box, but is left in a bad state with the file dialog still open.",
"reporter": "ryan",
"cc": "",
"resolution": "fixed",
"_ts": "1397763541728826",
"component": "microdrop",
"summary": "Error importing device from svg",
"priority": "major",
"keywords": "",
"version": "0.1",
"time": "2013-02-27T19:16:09",
"milestone": "Microdrop 1.0",
"owner": "",
"type": "defect"
}
```
| non_priority | error importing device from svg trac from the error log the following paths could not be parsed properly have been ignore d error parsing problem device svg loop needs or more verts path xmlns xmlns inkscape org namespaces inkscape xmlns dc xmlns cc xmlns rdf ax ns xmlns svg xmlns xlink xlink xmlns sodipodi in kscape connector curvature style fill none stroke stroke miterlimit stroke dasharray none d id note also that the program shows a warning box but is left in a bad state with the file dialog still open migrated from json status closed changetime description from the error log n n the following paths could not be parsed properly have been ignore nd n error parsing problem device svg loop needs or more verts n n nnote also that the program shows a warning box but is left in a bad state with the file dialog still open reporter ryan cc resolution fixed ts component microdrop summary error importing device from svg priority major keywords version time milestone microdrop owner type defect | 0 |
384,754 | 26,601,961,030 | IssuesEvent | 2023-01-23 16:21:49 | root-project/root | https://api.github.com/repos/root-project/root | closed | Document TROOT::SetBatch | improvement in:Documentation | It's currently completely undocumented: https://root.cern/doc/master/classTROOT.html#a78c012ca4694a4e0694735e48866be8d but we use it in several tutorials so users ask what it does. | 1.0 | Document TROOT::SetBatch - It's currently completely undocumented: https://root.cern/doc/master/classTROOT.html#a78c012ca4694a4e0694735e48866be8d but we use it in several tutorials so users ask what it does. | non_priority | document troot setbatch it s currently completely undocumented but we use it in several tutorials so users ask what it does | 0 |
34,738 | 12,294,713,480 | IssuesEvent | 2020-05-11 01:15:31 | doc-ai/nlp.js | https://api.github.com/repos/doc-ai/nlp.js | opened | WS-2020-0070 (High) detected in lodash-4.17.11.tgz | security vulnerability | ## WS-2020-0070 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: /nlp.js/package.json</p>
<p>Path to vulnerable library: /tmp/git/nlp.js/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- eslint-5.16.0.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
a prototype pollution vulnerability in lodash. It allows an attacker to inject properties on Object.prototype
<p>Publish Date: 2020-04-28
<p>URL: <a href=https://hackerone.com/reports/712065>WS-2020-0070</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.11","isTransitiveDependency":true,"dependencyTree":"eslint:5.16.0;lodash:4.17.11","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"WS-2020-0070","vulnerabilityDetails":"a prototype pollution vulnerability in lodash. It allows an attacker to inject properties on Object.prototype","vulnerabilityUrl":"https://hackerone.com/reports/712065","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | WS-2020-0070 (High) detected in lodash-4.17.11.tgz - ## WS-2020-0070 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: /nlp.js/package.json</p>
<p>Path to vulnerable library: /tmp/git/nlp.js/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- eslint-5.16.0.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
a prototype pollution vulnerability in lodash. It allows an attacker to inject properties on Object.prototype
<p>Publish Date: 2020-04-28
<p>URL: <a href=https://hackerone.com/reports/712065>WS-2020-0070</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.11","isTransitiveDependency":true,"dependencyTree":"eslint:5.16.0;lodash:4.17.11","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"WS-2020-0070","vulnerabilityDetails":"a prototype pollution vulnerability in lodash. It allows an attacker to inject properties on Object.prototype","vulnerabilityUrl":"https://hackerone.com/reports/712065","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in lodash tgz ws high severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file nlp js package json path to vulnerable library tmp git nlp js node modules lodash package json dependency hierarchy eslint tgz root library x lodash tgz vulnerable library vulnerability details a prototype pollution vulnerability in lodash it allows an attacker to inject properties on object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails a prototype pollution vulnerability in lodash it allows an attacker to inject properties on object prototype vulnerabilityurl | 0 |
424,188 | 29,045,530,719 | IssuesEvent | 2023-05-13 14:04:17 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [Docs] Inconsistency in xCluster replication docs | area/documentation status/awaiting-triage temp/docs-migration |
Marko Rajcevic 10:24 AM
Some confusion on the docs regarding Read Replicas and eventual consistency. The table below under multi-region deployments shows the consistency level for read replicas set to “eventual consistency” although within the read replica docs there is a section specifically calling out that read replicas (timeline-consistent) are different than eventual consistency.
Believe i found an inconsistency in our xCluster replication docs. We call out transactional atomicity as a limitation and then go on to call out atomicity of transactions as a transactional guarantee. Seems contradictory.
[https://docs.yugabyte.com/latest/architecture/docdb-replication/async-replication/#root](https://docs.yugabyte.com/latest/architecture/docdb-replication/async-replication/#root)
alan: 1 hour ago
the guarantee is for single-shard only — not distributed transactions | 1.0 | [Docs] Inconsistency in xCluster replication docs -
Marko Rajcevic 10:24 AM
Some confusion on the docs regarding Read Replicas and eventual consistency. The table below under multi-region deployments shows the consistency level for read replicas set to “eventual consistency” although within the read replica docs there is a section specifically calling out that read replicas (timeline-consistent) are different than eventual consistency.
Believe i found an inconsistency in our xCluster replication docs. We call out transactional atomicity as a limitation and then go on to call out atomicity of transactions as a transactional guarantee. Seems contradictory.
[https://docs.yugabyte.com/latest/architecture/docdb-replication/async-replication/#root](https://docs.yugabyte.com/latest/architecture/docdb-replication/async-replication/#root)
alan: 1 hour ago
the guarantee is for single-shard only — not distributed transactions | non_priority | inconsistency in xcluster replication docs marko rajcevic am some confusion on the docs regarding read replicas and eventual consistency the table below under multi region deployments shows the consistency level for read replicas set to “eventual consistency” although within the read replica docs there is a section specifically calling out that read replicas timeline consistent are different than eventual consistency believe i found an inconsistency in our xcluster replication docs we call out transactional atomicity as a limitation and then go on to call out atomicity of transactions as a transactional guarantee seems contradictory alan hour ago the guarantee is for single shard only — not distributed transactions | 0 |
7,348 | 10,482,866,327 | IssuesEvent | 2019-09-24 13:02:27 | dita-ot/dita-ot | https://api.github.com/repos/dita-ot/dita-ot | closed | JPEG image resolution | enhancement preprocess stale | ## Expected Behavior
I'm developing DITA to WordprocessingML plug-in. To convert `<image>` to the `<w:drawing>` the image resolution information is indispensable for JPEG image.
## Actual Behavior
[https://github.com/dita-ot/dita-ot/blob/develop/src/main/java/org/dita/dost/writer/ImageMetadataFilter.java](
) currently support only PNG image file resolution. It does not return the JPEG resolution.
As a result the plug-in cannot get correct image size, moreover I cannot implement image/@scale attribute.
<image href="image/tys125f.jpg" id="image_tdk_5tg_dbb" scale="20" placement="inline" class="- topic/image " xtrf="file:/D:/SVN/pdf5/testdata-ooxml/20170907-image/cImageTest.dita" xtrc="image:4;20:74" dita-ot:image-width="1200" dita-ot:image-height="1600"/>
## Possible Solution
Add the code to get the resolution of JPEG image.
## Steps to Reproduce
1. Make a topic that contains image element that contains the href attribute to the JPEG image file.
2. Execute Jarno's plugin com.elovirta.ooxml
3. Confirm that the topic file in temp directory does not contain dita-ot:horizontal-dpi and dita-ot:vertical-dpi attribute. for JPEG image
## Environment
* DITA-OT version: 2.5.1
* Operating system and version: Windows 10 64bit
* How did you run DITA-OT? From oXygen or command-line
* Transformation type: com.elovirta.ooxml
| 1.0 | JPEG image resolution - ## Expected Behavior
I'm developing DITA to WordprocessingML plug-in. To convert `<image>` to the `<w:drawing>` the image resolution information is indispensable for JPEG image.
## Actual Behavior
[https://github.com/dita-ot/dita-ot/blob/develop/src/main/java/org/dita/dost/writer/ImageMetadataFilter.java](
) currently support only PNG image file resolution. It does not return the JPEG resolution.
As a result the plug-in cannot get correct image size, moreover I cannot implement image/@scale attribute.
<image href="image/tys125f.jpg" id="image_tdk_5tg_dbb" scale="20" placement="inline" class="- topic/image " xtrf="file:/D:/SVN/pdf5/testdata-ooxml/20170907-image/cImageTest.dita" xtrc="image:4;20:74" dita-ot:image-width="1200" dita-ot:image-height="1600"/>
## Possible Solution
Add the code to get the resolution of JPEG image.
## Steps to Reproduce
1. Make a topic that contains image element that contains the href attribute to the JPEG image file.
2. Execute Jarno's plugin com.elovirta.ooxml
3. Confirm that the topic file in temp directory does not contain dita-ot:horizontal-dpi and dita-ot:vertical-dpi attribute. for JPEG image
## Environment
* DITA-OT version: 2.5.1
* Operating system and version: Windows 10 64bit
* How did you run DITA-OT? From oXygen or command-line
* Transformation type: com.elovirta.ooxml
| non_priority | jpeg image resolution expected behavior i m developing dita to wordprocessingml plug in to convert to the the image resolution information is indispensable for jpeg image actual behavior currently support only png image file resolution it does not return the jpeg resolution as a result the plug in cannot get correct image size moreover i cannot implement image scale attribute possible solution add the code to get the resolution of jpeg image steps to reproduce make a topic that contains image element that contains the href attribute to the jpeg image file execute jarno s plugin com elovirta ooxml confirm that the topic file in temp directory does not contain dita ot horizontal dpi and dita ot vertical dpi attribute for jpeg image environment dita ot version operating system and version windows how did you run dita ot from oxygen or command line transformation type com elovirta ooxml | 0 |
316,553 | 23,638,011,613 | IssuesEvent | 2022-08-25 14:42:38 | Big-Life-Lab/PHES-ODM | https://api.github.com/repos/Big-Life-Lab/PHES-ODM | opened | Review approach to record time-specific measure | documentation for discussion | There are different options for recording time-specific measures such as flow rates.
Provide documentation and examples of these options and review to ensure all options can be recorded. | 1.0 | Review approach to record time-specific measure - There are different options for recording time-specific measures such as flow rates.
Provide documentation and examples of these options and review to ensure all options can be recorded. | non_priority | review approach to record time specific measure there are different options for recording time specific measures such as flow rates provide documentation and examples of these options and review to ensure all options can be recorded | 0 |
83,817 | 16,374,211,606 | IssuesEvent | 2021-05-15 19:21:17 | M-Yankov/SimpleTracker | https://api.github.com/repos/M-Yankov/SimpleTracker | opened | Xamarin Forms | code refactoring research | What are the benefits if the app is like Xamarin Forms structure ?
Is only the benefit for cross platform development ? _I am not targeting the iOS at all_ | 1.0 | Xamarin Forms - What are the benefits if the app is like Xamarin Forms structure ?
Is only the benefit for cross platform development ? _I am not targeting the iOS at all_ | non_priority | xamarin forms what are the benefits if the app is like xamarin forms structure is only the benefit for cross platform development i am not targeting the ios at all | 0 |
193,400 | 14,652,443,433 | IssuesEvent | 2020-12-28 01:48:19 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | anssihalmeaho/funl: funl/fumap_test.go; 8 LoC | fresh test tiny |
Found a possible issue in [anssihalmeaho/funl](https://www.github.com/anssihalmeaho/funl) at [funl/fumap_test.go](https:%2F%2Fgithub.com%2Fanssihalmeaho%2Ffunl%2Fblob%2F029086da3fa4cdbced826af1562612238a904da9%2Ffunl%2Ffumap_test.go%23L230-L237)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to num was used in a composite literal at line 233
[Click here to see the code in its original context.](https:%2F%2Fgithub.com%2Fanssihalmeaho%2Ffunl%2Fblob%2F029086da3fa4cdbced826af1562612238a904da9%2Ffunl%2Ffumap_test.go%23L230-L237)
<details>
<summary>Click here to show the 8 line(s) of Go which triggered the analyzer.</summary>
```go
for _, num := range nums {
val := Item{Type: ValueItem, Data: Value{Kind: StringValue, Data: fmt.Sprintf("val-%v", num.Data.(Value).Data)}}
mapItem := Item{Type: ValueItem, Data: mapval}
mapval = handlePutOP(nil, []*Item{&mapItem, &num, &val})
if mapval.Kind != MapValue {
t.Errorf("Map assumed, got: %d", mapval.Kind)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 029086da3fa4cdbced826af1562612238a904da9
| 1.0 | anssihalmeaho/funl: funl/fumap_test.go; 8 LoC -
Found a possible issue in [anssihalmeaho/funl](https://www.github.com/anssihalmeaho/funl) at [funl/fumap_test.go](https:%2F%2Fgithub.com%2Fanssihalmeaho%2Ffunl%2Fblob%2F029086da3fa4cdbced826af1562612238a904da9%2Ffunl%2Ffumap_test.go%23L230-L237)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to num was used in a composite literal at line 233
[Click here to see the code in its original context.](https:%2F%2Fgithub.com%2Fanssihalmeaho%2Ffunl%2Fblob%2F029086da3fa4cdbced826af1562612238a904da9%2Ffunl%2Ffumap_test.go%23L230-L237)
<details>
<summary>Click here to show the 8 line(s) of Go which triggered the analyzer.</summary>
```go
for _, num := range nums {
val := Item{Type: ValueItem, Data: Value{Kind: StringValue, Data: fmt.Sprintf("val-%v", num.Data.(Value).Data)}}
mapItem := Item{Type: ValueItem, Data: mapval}
mapval = handlePutOP(nil, []*Item{&mapItem, &num, &val})
if mapval.Kind != MapValue {
t.Errorf("Map assumed, got: %d", mapval.Kind)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 029086da3fa4cdbced826af1562612238a904da9
| non_priority | anssihalmeaho funl funl fumap test go loc found a possible issue in at https com test go below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to num was used in a composite literal at line https com test go click here to show the line s of go which triggered the analyzer go for num range nums val item type valueitem data value kind stringvalue data fmt sprintf val v num data value data mapitem item type valueitem data mapval mapval handleputop nil item mapitem num val if mapval kind mapvalue t errorf map assumed got d mapval kind leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
240,257 | 20,019,840,808 | IssuesEvent | 2022-02-01 15:27:18 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Crash closing many stacked tabs with tab groups disabled | crash feature/new-tab QA/Yes release-notes/exclude QA/Test-Plan-Specified OS/Android feature/brave-news | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description <!-- Provide a brief description of the issue -->
Crash closing many stacked tabs with tab groups disabled
## Steps to reproduce <!-- Please add a series of steps to reproduce the issue -->
1. install `1.37.5`
2. launch Brave
3. tap through onboarding
4. tap on the 3-dots menu on the bottom toolbar
5. tap `Settings`
6. tap `Appearance`
7. tap to set `Enable Tab Groups` to `Off`
8. tap `RELAUNCH NOW`
9. swipe down
10. tap to `Show Brave News`
11. open a bunch of new-tab pages
12. now, tap to close/undo/open new ones
13. repeat steps 11-2 until you crash
## Actual result <!-- Please add screenshots if needed -->
Crash:
```
2022-01-28 00:44:10.863 5331-5347/? I/ActivityManager: Start proc 26122:com.brave.browser_nightly:sandboxed_process13/u0i920 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService13
2022-01-28 00:44:10.924 26122-26122/? W/boxed_process13: type=1400 audit(0.0:13703): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c152,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:10.936 26122-26122/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process13 isIsolated=true
2022-01-28 00:44:15.524 5331-5347/? I/ActivityManager: Start proc 26152:com.brave.browser_nightly:sandboxed_process14/u0i921 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService14
2022-01-28 00:44:15.607 26152-26152/? W/boxed_process14: type=1400 audit(0.0:13704): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c153,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:15.642 26152-26152/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process14 isIsolated=true
2022-01-28 00:44:17.777 5331-5347/? I/ActivityManager: Start proc 26246:com.brave.browser_nightly:sandboxed_process15/u0i922 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService15
2022-01-28 00:44:17.847 26246-26246/? W/boxed_process15: type=1400 audit(0.0:13705): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c154,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:17.861 26246-26246/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process15 isIsolated=true
2022-01-28 00:44:19.027 5331-5347/? I/ActivityManager: Start proc 26283:com.brave.browser_nightly:sandboxed_process16/u0i923 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService16
2022-01-28 00:44:19.157 26283-26283/? W/boxed_process16: type=1400 audit(0.0:13706): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c155,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:19.179 26283-26283/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process16 isIsolated=true
2022-01-28 00:44:20.384 5331-5347/? I/ActivityManager: Start proc 26310:com.brave.browser_nightly:sandboxed_process17/u0i924 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService17
2022-01-28 00:44:20.487 26310-26310/? W/boxed_process17: type=1400 audit(0.0:13707): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c156,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:20.500 26310-26310/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process17 isIsolated=true
2022-01-28 00:44:21.653 5331-5347/? I/ActivityManager: Start proc 26340:com.brave.browser_nightly:sandboxed_process18/u0i925 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService18
2022-01-28 00:44:21.741 26340-26340/? W/boxed_process18: type=1400 audit(0.0:13708): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c157,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:21.753 26340-26340/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process18 isIsolated=true
2022-01-28 00:44:23.027 25638-25638/? E/AndroidRuntime: FATAL EXCEPTION: main
Process: com.brave.browser_nightly, PID: 25638
java.lang.ClassCastException: com.google.android.material.textview.MaterialTextView cannot be cast to android.widget.ScrollView
at Zu0.m(chromium-MonochromePublic.apk-canary-413700523:10)
at fg.run(chromium-MonochromePublic.apk-canary-413700523:3)
at android.os.Handler.handleCallback(Handler.java:873)
at android.os.Handler.dispatchMessage(Handler.java:99)
at android.os.Looper.loop(Looper.java:193)
at android.app.ActivityThread.main(ActivityThread.java:6718)
at java.lang.reflect.Method.invoke(Native Method)
at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:493)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:858)
2022-01-28 00:44:24.179 5331-7481/? W/ActivityManager: Force finishing activity com.brave.browser_nightly/com.google.android.apps.chrome.Main
2022-01-28 00:44:24.400 5331-5405/? W/InputDispatcher: channel 'e5a2956 com.brave.browser_nightly/com.google.android.apps.chrome.Main (server)' ~ Consumer closed input channel or an error occurred. events=0xd
2022-01-28 00:44:24.400 5331-5405/? E/InputDispatcher: channel 'e5a2956 com.brave.browser_nightly/com.google.android.apps.chrome.Main (server)' ~ Channel is unrecoverably broken and will be disposed!
2022-01-28 00:44:24.403 5331-5652/? I/WindowManager: WIN DEATH: Window{e5a2956 u0 com.brave.browser_nightly/com.google.android.apps.chrome.Main}
2022-01-28 00:44:24.403 5331-5652/? W/InputDispatcher: Attempted to unregister already unregistered input channel 'e5a2956 com.brave.browser_nightly/com.google.android.apps.chrome.Main (server)'
2022-01-28 00:44:24.403 5331-9294/? I/ActivityManager: Process com.brave.browser_nightly (pid 25638) has died: vis +99TOP
```
## Expected result
No crash
## Issue reproduces how often <!-- [Easily reproduced/Intermittent issue/No steps to reproduce] -->
100% with time & patience
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current Play Store version?
- Can you reproduce this issue with the current Play Store Beta version?
- Can you reproduce this issue with the current Play Store Nightly version?
## Device details
- Install type (ARM, x86): `arm64`
- Device type (Phone, Tablet, Phablet): `Google Pixel XL` phone
- Android version: `9.0`
## Brave version
1.37.5, Chromium 98.0.4758.74`
cc @alexsafe @srirambv @kjozwiak | 1.0 | Crash closing many stacked tabs with tab groups disabled - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description <!-- Provide a brief description of the issue -->
Crash closing many stacked tabs with tab groups disabled
## Steps to reproduce <!-- Please add a series of steps to reproduce the issue -->
1. install `1.37.5`
2. launch Brave
3. tap through onboarding
4. tap on the 3-dots menu on the bottom toolbar
5. tap `Settings`
6. tap `Appearance`
7. tap to set `Enable Tab Groups` to `Off`
8. tap `RELAUNCH NOW`
9. swipe down
10. tap to `Show Brave News`
11. open a bunch of new-tab pages
12. now, tap to close/undo/open new ones
13. repeat steps 11-2 until you crash
## Actual result <!-- Please add screenshots if needed -->
Crash:
```
2022-01-28 00:44:10.863 5331-5347/? I/ActivityManager: Start proc 26122:com.brave.browser_nightly:sandboxed_process13/u0i920 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService13
2022-01-28 00:44:10.924 26122-26122/? W/boxed_process13: type=1400 audit(0.0:13703): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c152,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:10.936 26122-26122/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process13 isIsolated=true
2022-01-28 00:44:15.524 5331-5347/? I/ActivityManager: Start proc 26152:com.brave.browser_nightly:sandboxed_process14/u0i921 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService14
2022-01-28 00:44:15.607 26152-26152/? W/boxed_process14: type=1400 audit(0.0:13704): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c153,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:15.642 26152-26152/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process14 isIsolated=true
2022-01-28 00:44:17.777 5331-5347/? I/ActivityManager: Start proc 26246:com.brave.browser_nightly:sandboxed_process15/u0i922 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService15
2022-01-28 00:44:17.847 26246-26246/? W/boxed_process15: type=1400 audit(0.0:13705): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c154,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:17.861 26246-26246/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process15 isIsolated=true
2022-01-28 00:44:19.027 5331-5347/? I/ActivityManager: Start proc 26283:com.brave.browser_nightly:sandboxed_process16/u0i923 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService16
2022-01-28 00:44:19.157 26283-26283/? W/boxed_process16: type=1400 audit(0.0:13706): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c155,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:19.179 26283-26283/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process16 isIsolated=true
2022-01-28 00:44:20.384 5331-5347/? I/ActivityManager: Start proc 26310:com.brave.browser_nightly:sandboxed_process17/u0i924 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService17
2022-01-28 00:44:20.487 26310-26310/? W/boxed_process17: type=1400 audit(0.0:13707): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c156,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:20.500 26310-26310/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process17 isIsolated=true
2022-01-28 00:44:21.653 5331-5347/? I/ActivityManager: Start proc 26340:com.brave.browser_nightly:sandboxed_process18/u0i925 for service com.brave.browser_nightly/org.chromium.content.app.SandboxedProcessService18
2022-01-28 00:44:21.741 26340-26340/? W/boxed_process18: type=1400 audit(0.0:13708): avc: denied { getattr } for path="/data/data/com.brave.browser_nightly" dev="sda35" ino=396560 scontext=u:r:isolated_app:s0:c157,c259,c512,c768 tcontext=u:object_r:app_data_file:s0:c135,c257,c512,c768 tclass=dir permissive=0
2022-01-28 00:44:21.753 26340-26340/? I/cr_SplitCompatApp: Launched version=98.1.37.5 minSdkVersion=24 isBundle=false processName=com.brave.browser_nightly:sandboxed_process18 isIsolated=true
2022-01-28 00:44:23.027 25638-25638/? E/AndroidRuntime: FATAL EXCEPTION: main
Process: com.brave.browser_nightly, PID: 25638
java.lang.ClassCastException: com.google.android.material.textview.MaterialTextView cannot be cast to android.widget.ScrollView
at Zu0.m(chromium-MonochromePublic.apk-canary-413700523:10)
at fg.run(chromium-MonochromePublic.apk-canary-413700523:3)
at android.os.Handler.handleCallback(Handler.java:873)
at android.os.Handler.dispatchMessage(Handler.java:99)
at android.os.Looper.loop(Looper.java:193)
at android.app.ActivityThread.main(ActivityThread.java:6718)
at java.lang.reflect.Method.invoke(Native Method)
at com.android.internal.os.RuntimeInit$MethodAndArgsCaller.run(RuntimeInit.java:493)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:858)
2022-01-28 00:44:24.179 5331-7481/? W/ActivityManager: Force finishing activity com.brave.browser_nightly/com.google.android.apps.chrome.Main
2022-01-28 00:44:24.400 5331-5405/? W/InputDispatcher: channel 'e5a2956 com.brave.browser_nightly/com.google.android.apps.chrome.Main (server)' ~ Consumer closed input channel or an error occurred. events=0xd
2022-01-28 00:44:24.400 5331-5405/? E/InputDispatcher: channel 'e5a2956 com.brave.browser_nightly/com.google.android.apps.chrome.Main (server)' ~ Channel is unrecoverably broken and will be disposed!
2022-01-28 00:44:24.403 5331-5652/? I/WindowManager: WIN DEATH: Window{e5a2956 u0 com.brave.browser_nightly/com.google.android.apps.chrome.Main}
2022-01-28 00:44:24.403 5331-5652/? W/InputDispatcher: Attempted to unregister already unregistered input channel 'e5a2956 com.brave.browser_nightly/com.google.android.apps.chrome.Main (server)'
2022-01-28 00:44:24.403 5331-9294/? I/ActivityManager: Process com.brave.browser_nightly (pid 25638) has died: vis +99TOP
```
## Expected result
No crash
## Issue reproduces how often <!-- [Easily reproduced/Intermittent issue/No steps to reproduce] -->
100% with time & patience
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current Play Store version?
- Can you reproduce this issue with the current Play Store Beta version?
- Can you reproduce this issue with the current Play Store Nightly version?
## Device details
- Install type (ARM, x86): `arm64`
- Device type (Phone, Tablet, Phablet): `Google Pixel XL` phone
- Android version: `9.0`
## Brave version
1.37.5, Chromium 98.0.4758.74`
cc @alexsafe @srirambv @kjozwiak | non_priority | crash closing many stacked tabs with tab groups disabled have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will only be reopened after sufficient info is provided description crash closing many stacked tabs with tab groups disabled steps to reproduce install launch brave tap through onboarding tap on the dots menu on the bottom toolbar tap settings tap appearance tap to set enable tab groups to off tap relaunch now swipe down tap to show brave news open a bunch of new tab pages now tap to close undo open new ones repeat steps until you crash actual result crash i activitymanager start proc com brave browser nightly sandboxed for service com brave browser nightly org chromium content app w boxed type audit avc denied getattr for path data data com brave browser nightly dev ino scontext u r isolated app tcontext u object r app data file tclass dir permissive i cr splitcompatapp launched version minsdkversion isbundle false processname com brave browser nightly sandboxed isisolated true i activitymanager start proc com brave browser nightly sandboxed for service com brave browser nightly org chromium content app w boxed type audit avc denied getattr for path data data com brave browser nightly dev ino scontext u r isolated app tcontext u object r app data file tclass dir permissive i cr splitcompatapp launched version minsdkversion isbundle false processname com brave browser nightly sandboxed isisolated true i activitymanager start proc com brave browser nightly sandboxed for service com brave browser nightly org chromium content app w boxed type audit avc denied getattr for path data data com brave browser nightly dev ino scontext u r isolated app tcontext u object r app data file tclass dir permissive i cr splitcompatapp launched version minsdkversion isbundle false processname com brave browser nightly sandboxed isisolated true i activitymanager start proc com brave browser nightly sandboxed for service com brave browser nightly org chromium content app w boxed type audit avc denied getattr for path data data com brave browser nightly dev ino scontext u r isolated app tcontext u object r app data file tclass dir permissive i cr splitcompatapp launched version minsdkversion isbundle false processname com brave browser nightly sandboxed isisolated true i activitymanager start proc com brave browser nightly sandboxed for service com brave browser nightly org chromium content app w boxed type audit avc denied getattr for path data data com brave browser nightly dev ino scontext u r isolated app tcontext u object r app data file tclass dir permissive i cr splitcompatapp launched version minsdkversion isbundle false processname com brave browser nightly sandboxed isisolated true i activitymanager start proc com brave browser nightly sandboxed for service com brave browser nightly org chromium content app w boxed type audit avc denied getattr for path data data com brave browser nightly dev ino scontext u r isolated app tcontext u object r app data file tclass dir permissive i cr splitcompatapp launched version minsdkversion isbundle false processname com brave browser nightly sandboxed isisolated true e androidruntime fatal exception main process com brave browser nightly pid java lang classcastexception com google android material textview materialtextview cannot be cast to android widget scrollview at m chromium monochromepublic apk canary at fg run chromium monochromepublic apk canary at android os handler handlecallback handler java at android os handler dispatchmessage handler java at android os looper loop looper java at android app activitythread main activitythread java at java lang reflect method invoke native method at com android internal os runtimeinit methodandargscaller run runtimeinit java at com android internal os zygoteinit main zygoteinit java w activitymanager force finishing activity com brave browser nightly com google android apps chrome main w inputdispatcher channel com brave browser nightly com google android apps chrome main server consumer closed input channel or an error occurred events e inputdispatcher channel com brave browser nightly com google android apps chrome main server channel is unrecoverably broken and will be disposed i windowmanager win death window com brave browser nightly com google android apps chrome main w inputdispatcher attempted to unregister already unregistered input channel com brave browser nightly com google android apps chrome main server i activitymanager process com brave browser nightly pid has died vis expected result no crash issue reproduces how often with time patience version channel information can you reproduce this issue with the current play store version can you reproduce this issue with the current play store beta version can you reproduce this issue with the current play store nightly version device details install type arm device type phone tablet phablet google pixel xl phone android version brave version chromium cc alexsafe srirambv kjozwiak | 0 |
87,782 | 17,375,528,215 | IssuesEvent | 2021-07-30 20:26:49 | kitsudaiki/libKitsunemimiSakuraNetwork | https://api.github.com/repos/kitsudaiki/libKitsunemimiSakuraNetwork | closed | refactor and cleanup process for closing sessions | API-breaking Code cleanup / QA | ## Cleanup-request
### Description
The closing of sessions is not really stable at the moment and has to be cleaned and slightly refactored.
| 1.0 | refactor and cleanup process for closing sessions - ## Cleanup-request
### Description
The closing of sessions is not really stable at the moment and has to be cleaned and slightly refactored.
| non_priority | refactor and cleanup process for closing sessions cleanup request description the closing of sessions is not really stable at the moment and has to be cleaned and slightly refactored | 0 |
313,922 | 26,962,562,239 | IssuesEvent | 2023-02-08 19:24:29 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | closed | [FormRecognizer] Remove IgnoreServiceError attribute for "Generic error during training" | Client Cognitive - Form Recognizer test-reliability | ## Error information
Error code: 3014
Error message: Generic error during training.
When: after a model-training LRO finishes.
API version: v2.0 ([confirmed](https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1592631&view=logs&j=4fdea57c-dd88-576f-325a-03d0fa6bffa4&t=a4ecc073-dd68-51ff-f619-b7e68a44a8f8&l=565)) and possibly v2.1 (needs further investigation).
apim-request-id: bdefd7ca-7b2b-4fc6-aca0-b168ba6f9a43
Example: https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1575344&view=logs&j=01d5a77e-6e85-5280-0e9f-af5629bd443f&t=1e514895-521a-57d8-4030-b9d8f4f46b20&l=85060
## Additional details
This is a flaky service error that doesn't happen often, but it's frequent enough to happen on every test pipeline run. The service team has already been notified about it ([discussion here](https://teams.microsoft.com/l/message/19:88f2d9dea2344075b5d4bc34d82a3d1c@thread.skype/1652910631452?tenantId=72f988bf-86f1-41af-91ab-2d7cd011db47&groupId=3e17dcb0-4257-4a30-b843-77f47f1d4121&parentMessageId=1652910631452&teamName=Azure%20SDK&channelName=Service%20-%20Form%20Recognizer&createdTime=1652910631452)).
This error won't make our pipeline fail anymore since it's been suppressed with the `IgnoreServiceError` attribute in our test project. The attribute is set on the class level (instead of single method) because it can happen on any test that trains a model, which includes most of our tests.
## Action items
Once the service has fixed this issue on their side, we must remove the `IgnoreServiceError` attribute from the following classes:
- `FormRecognizerSamples`
- `FormTrainingClientLiveTests`
- `RecognizeCustomFormsLiveTests` | 1.0 | [FormRecognizer] Remove IgnoreServiceError attribute for "Generic error during training" - ## Error information
Error code: 3014
Error message: Generic error during training.
When: after a model-training LRO finishes.
API version: v2.0 ([confirmed](https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1592631&view=logs&j=4fdea57c-dd88-576f-325a-03d0fa6bffa4&t=a4ecc073-dd68-51ff-f619-b7e68a44a8f8&l=565)) and possibly v2.1 (needs further investigation).
apim-request-id: bdefd7ca-7b2b-4fc6-aca0-b168ba6f9a43
Example: https://dev.azure.com/azure-sdk/internal/_build/results?buildId=1575344&view=logs&j=01d5a77e-6e85-5280-0e9f-af5629bd443f&t=1e514895-521a-57d8-4030-b9d8f4f46b20&l=85060
## Additional details
This is a flaky service error that doesn't happen often, but it's frequent enough to happen on every test pipeline run. The service team has already been notified about it ([discussion here](https://teams.microsoft.com/l/message/19:88f2d9dea2344075b5d4bc34d82a3d1c@thread.skype/1652910631452?tenantId=72f988bf-86f1-41af-91ab-2d7cd011db47&groupId=3e17dcb0-4257-4a30-b843-77f47f1d4121&parentMessageId=1652910631452&teamName=Azure%20SDK&channelName=Service%20-%20Form%20Recognizer&createdTime=1652910631452)).
This error won't make our pipeline fail anymore since it's been suppressed with the `IgnoreServiceError` attribute in our test project. The attribute is set on the class level (instead of single method) because it can happen on any test that trains a model, which includes most of our tests.
## Action items
Once the service has fixed this issue on their side, we must remove the `IgnoreServiceError` attribute from the following classes:
- `FormRecognizerSamples`
- `FormTrainingClientLiveTests`
- `RecognizeCustomFormsLiveTests` | non_priority | remove ignoreserviceerror attribute for generic error during training error information error code error message generic error during training when after a model training lro finishes api version and possibly needs further investigation apim request id example additional details this is a flaky service error that doesn t happen often but it s frequent enough to happen on every test pipeline run the service team has already been notified about it this error won t make our pipeline fail anymore since it s been suppressed with the ignoreserviceerror attribute in our test project the attribute is set on the class level instead of single method because it can happen on any test that trains a model which includes most of our tests action items once the service has fixed this issue on their side we must remove the ignoreserviceerror attribute from the following classes formrecognizersamples formtrainingclientlivetests recognizecustomformslivetests | 0 |
141,229 | 18,956,965,228 | IssuesEvent | 2021-11-18 21:32:47 | CliffCrerar/aws-amplift-starter | https://api.github.com/repos/CliffCrerar/aws-amplift-starter | opened | CVE-2020-7656 (Medium) detected in jquery-1.7.1.min.js | security vulnerability | ## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>Path to dependency file: aws-amplift-starter/node_modules/sockjs/examples/express/index.html</p>
<p>Path to vulnerable library: /node_modules/sockjs/examples/express/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/CliffCrerar/aws-amplift-starter/commit/1c99251524518f24892aa666395393a8251c80a2">1c99251524518f24892aa666395393a8251c80a2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-q4m3-2j7h-f7xw">https://github.com/advisories/GHSA-q4m3-2j7h-f7xw</a></p>
<p>Release Date: 2020-05-28</p>
<p>Fix Resolution: jquery - 1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7656 (Medium) detected in jquery-1.7.1.min.js - ## CVE-2020-7656 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.1/jquery.min.js</a></p>
<p>Path to dependency file: aws-amplift-starter/node_modules/sockjs/examples/express/index.html</p>
<p>Path to vulnerable library: /node_modules/sockjs/examples/express/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/CliffCrerar/aws-amplift-starter/commit/1c99251524518f24892aa666395393a8251c80a2">1c99251524518f24892aa666395393a8251c80a2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jquery prior to 1.9.0 allows Cross-site Scripting attacks via the load method. The load method fails to recognize and remove "<script>" HTML tags that contain a whitespace character, i.e: "</script >", which results in the enclosed script logic to be executed.
<p>Publish Date: 2020-05-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7656>CVE-2020-7656</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-q4m3-2j7h-f7xw">https://github.com/advisories/GHSA-q4m3-2j7h-f7xw</a></p>
<p>Release Date: 2020-05-28</p>
<p>Fix Resolution: jquery - 1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file aws amplift starter node modules sockjs examples express index html path to vulnerable library node modules sockjs examples express index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery prior to allows cross site scripting attacks via the load method the load method fails to recognize and remove html tags that contain a whitespace character i e which results in the enclosed script logic to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
39,147 | 10,308,320,604 | IssuesEvent | 2019-08-29 10:39:12 | gitpod-io/gitpod | https://api.github.com/repos/gitpod-io/gitpod | reopened | Docker support | docker-build enhancement | The default image(s) should include some sort of docker support, so I can run `docker build`, as well as `docker start` to run either my own service (and expose ports as usual) or its requirements. | 1.0 | Docker support - The default image(s) should include some sort of docker support, so I can run `docker build`, as well as `docker start` to run either my own service (and expose ports as usual) or its requirements. | non_priority | docker support the default image s should include some sort of docker support so i can run docker build as well as docker start to run either my own service and expose ports as usual or its requirements | 0 |
452,601 | 32,062,766,535 | IssuesEvent | 2023-09-24 21:03:48 | r-yeh/grocery-spending-tracker | https://api.github.com/repos/r-yeh/grocery-spending-tracker | closed | Conceive Problem Statement - Input/Output | documentation | See discord #general for chat notes on problem statement and project motivation.
develop problem statement and add to [ProblemStatementAndGoals](https://github.com/r-yeh/grocery-spending-tracker/tree/master/docs/ProblemStatementAndGoals).
| 1.0 | Conceive Problem Statement - Input/Output - See discord #general for chat notes on problem statement and project motivation.
develop problem statement and add to [ProblemStatementAndGoals](https://github.com/r-yeh/grocery-spending-tracker/tree/master/docs/ProblemStatementAndGoals).
| non_priority | conceive problem statement input output see discord general for chat notes on problem statement and project motivation develop problem statement and add to | 0 |
443,503 | 30,921,721,535 | IssuesEvent | 2023-08-06 01:28:48 | danthegoodman1/icedb | https://api.github.com/repos/danthegoodman1/icedb | closed | adjustable `row_group_size` | documentation enhancement | Should be able to set a `row_group_size` override in the initialization of the icedb class | 1.0 | adjustable `row_group_size` - Should be able to set a `row_group_size` override in the initialization of the icedb class | non_priority | adjustable row group size should be able to set a row group size override in the initialization of the icedb class | 0 |
71,497 | 8,658,383,927 | IssuesEvent | 2018-11-28 00:44:58 | byucs340ta/Fall2018 | https://api.github.com/repos/byucs340ta/Fall2018 | opened | Check marks for initial destination card draw is reset when another player chooses theirs | P4: Aesthetic or Design Flaw Team 3 | Player one had two cards selected and player two had two cards selected. When player two picked their cards and selected DONE the checkmarks on player one's cards were reset. | 1.0 | Check marks for initial destination card draw is reset when another player chooses theirs - Player one had two cards selected and player two had two cards selected. When player two picked their cards and selected DONE the checkmarks on player one's cards were reset. | non_priority | check marks for initial destination card draw is reset when another player chooses theirs player one had two cards selected and player two had two cards selected when player two picked their cards and selected done the checkmarks on player one s cards were reset | 0 |
142,972 | 13,046,654,515 | IssuesEvent | 2020-07-29 09:21:39 | SneakyWhoami/159251 | https://api.github.com/repos/SneakyWhoami/159251 | opened | hardcore log ("issue" so it's not in repo, attached until marking time) | documentation | ```bash
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2330
git init
Initialized empty Git repository in /home/sneaky/Desktop/159251/Tutorial 1- Git/.git/
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2331
git add *.py
warning: CRLF will be replaced by LF in Simplecalculator.py.
The file will have its original line endings in your working directory
warning: CRLF will be replaced by LF in leapYear.py.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2332
git commit -am "Add python leapYear and SimpleCalculator utilities"
[master (root-commit) c6795b6] Add python leapYear and SimpleCalculator utilities
2 files changed, 54 insertions(+)
create mode 100755 Simplecalculator.py
create mode 100755 leapYear.py
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout -b FirstBranch
Switched to a new branch 'FirstBranch'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2336
git add *java
warning: CRLF will be replaced by LF in leapYear.java.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2337
git commit -m "add java leapYear thing"
[FirstBranch ad9646d] add java leapYear thing
1 file changed, 19 insertions(+)
create mode 100755 leapYear.java
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout -b SecondBranch
Switched to a new branch 'SecondBranch'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2340
git add HelloWorldInCpp.cpp README.txt .DS_Store
warning: CRLF will be replaced by LF in HelloWorldInCpp.cpp.
The file will have its original line endings in your working directory
warning: CRLF will be replaced by LF in README.txt.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2341
git commit -m "add c++, README, apple metadata"
[SecondBranch 29f81d2] add c++, README, apple metadata
3 files changed, 11 insertions(+)
create mode 100644 .DS_Store
create mode 100755 HelloWorldInCpp.cpp
create mode 100755 README.txt
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout master
Switched to branch 'master'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git merge FirstBranch SecondBranch
Updating c6795b6..29f81d2
Fast-forward
.DS_Store | Bin 0 -> 6148 bytes
HelloWorldInCpp.cpp | 7 +++++++
README.txt | 4 ++++
leapYear.java | 19 +++++++++++++++++++
4 files changed, 30 insertions(+)
create mode 100644 .DS_Store
create mode 100755 HelloWorldInCpp.cpp
create mode 100755 README.txt
create mode 100755 leapYear.java
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git branch -d FirstBranch SecondBranch
Deleted branch FirstBranch (was ad9646d).
Deleted branch SecondBranch (was 29f81d2).
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git log
commit 29f81d2e1fa8501d2d6d10315bb4ddedd8d124e2 (HEAD -> master)
Author: Chris <git@chris-nz.com>
Date: Wed Jul 29 20:43:34 2020 +1200
add c++, README, apple metadata
commit ad9646de6c72ec711dc5fc988b2a22705b1ea97a
Author: Chris <git@chris-nz.com>
Date: Wed Jul 29 20:43:06 2020 +1200
add java leapYear thing
commit c6795b63dad5fd3aacebb1471c59d61d0c927257
Author: Chris <git@chris-nz.com>
Date: Wed Jul 29 20:42:47 2020 +1200
Add python leapYear and SimpleCalculator utilities
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git show branch --all
fatal: ambiguous argument 'branch': unknown revision or path not in the working tree.
Use '--' to separate paths from revisions, like this:
'git <command> [<revision>...] -- [<file>...]'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git show-branch --all
[master] add c++, README, apple metadata
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git ls-tree -r master --name-only
.DS_Store
HelloWorldInCpp.cpp
README.txt
Simplecalculator.py
leapYear.java
leapYear.py
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ cp -R . /tmp
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ echo 'print("done")' >> leapYear.py
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout -b feature-2
Switched to a new branch 'feature-2'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git diff leapYear.py
warning: CRLF will be replaced by LF in leapYear.py.
The file will have its original line endings in your working directory
diff --git a/leapYear.py b/leapYear.py
index 21d25f0..f97b98c 100755
--- a/leapYear.py
+++ b/leapYear.py
@@ -14,3 +14,4 @@ else:
print("{0} is not a leap year".format(year))
print("done")
+print("done")
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git add leapYear.py
warning: CRLF will be replaced by LF in leapYear.py.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git commit -m "Changed leapYear.py"
[feature-2 7547352] Changed leapYear.py
1 file changed, 1 insertion(+)
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout master
Switched to branch 'master'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git merge feature-2
Updating 29f81d2..7547352
Fast-forward
leapYear.py | 1 +
1 file changed, 1 insertion(+)
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git branch -d feature-2
Deleted branch feature-2 (was 7547352).
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git log --all --oneline --graph --decorate
* 7547352 (HEAD -> master) Changed leapYear.py
* 29f81d2 add c++, README, apple metadata
* ad9646d add java leapYear thing
* c6795b6 Add python leapYear and SimpleCalculator utilities
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git tag -a "0.9" -m "Create 0.9 release for testing"
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git remote add origin git@github.com:SneakyWhoami/159251.git
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git push -u origin all
error: src refspec all does not match any
error: failed to push some refs to 'git@github.com:SneakyWhoami/159251.git'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git push -u origin --all
Enumerating objects: 15, done.
Counting objects: 100% (15/15), done.
Delta compression using up to 4 threads
Compressing objects: 100% (14/14), done.
Writing objects: 100% (15/15), 2.00 KiB | 2.00 MiB/s, done.
Total 15 (delta 4), reused 0 (delta 0)
remote: Resolving deltas: 100% (4/4), done.
To github.com:SneakyWhoami/159251.git
* [new branch] master -> master
Branch 'master' set up to track remote branch 'master' from 'origin'.
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git push origin --tags
Enumerating objects: 1, done.
Counting objects: 100% (1/1), done.
Writing objects: 100% (1/1), 166 bytes | 166.00 KiB/s, done.
Total 1 (delta 0), reused 0 (delta 0)
To github.com:SneakyWhoami/159251.git
* [new tag] 0.9 -> 0.9
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$
``` | 1.0 | hardcore log ("issue" so it's not in repo, attached until marking time) - ```bash
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2330
git init
Initialized empty Git repository in /home/sneaky/Desktop/159251/Tutorial 1- Git/.git/
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2331
git add *.py
warning: CRLF will be replaced by LF in Simplecalculator.py.
The file will have its original line endings in your working directory
warning: CRLF will be replaced by LF in leapYear.py.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2332
git commit -am "Add python leapYear and SimpleCalculator utilities"
[master (root-commit) c6795b6] Add python leapYear and SimpleCalculator utilities
2 files changed, 54 insertions(+)
create mode 100755 Simplecalculator.py
create mode 100755 leapYear.py
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout -b FirstBranch
Switched to a new branch 'FirstBranch'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2336
git add *java
warning: CRLF will be replaced by LF in leapYear.java.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2337
git commit -m "add java leapYear thing"
[FirstBranch ad9646d] add java leapYear thing
1 file changed, 19 insertions(+)
create mode 100755 leapYear.java
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout -b SecondBranch
Switched to a new branch 'SecondBranch'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2340
git add HelloWorldInCpp.cpp README.txt .DS_Store
warning: CRLF will be replaced by LF in HelloWorldInCpp.cpp.
The file will have its original line endings in your working directory
warning: CRLF will be replaced by LF in README.txt.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ !2341
git commit -m "add c++, README, apple metadata"
[SecondBranch 29f81d2] add c++, README, apple metadata
3 files changed, 11 insertions(+)
create mode 100644 .DS_Store
create mode 100755 HelloWorldInCpp.cpp
create mode 100755 README.txt
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout master
Switched to branch 'master'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git merge FirstBranch SecondBranch
Updating c6795b6..29f81d2
Fast-forward
.DS_Store | Bin 0 -> 6148 bytes
HelloWorldInCpp.cpp | 7 +++++++
README.txt | 4 ++++
leapYear.java | 19 +++++++++++++++++++
4 files changed, 30 insertions(+)
create mode 100644 .DS_Store
create mode 100755 HelloWorldInCpp.cpp
create mode 100755 README.txt
create mode 100755 leapYear.java
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git branch -d FirstBranch SecondBranch
Deleted branch FirstBranch (was ad9646d).
Deleted branch SecondBranch (was 29f81d2).
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git log
commit 29f81d2e1fa8501d2d6d10315bb4ddedd8d124e2 (HEAD -> master)
Author: Chris <git@chris-nz.com>
Date: Wed Jul 29 20:43:34 2020 +1200
add c++, README, apple metadata
commit ad9646de6c72ec711dc5fc988b2a22705b1ea97a
Author: Chris <git@chris-nz.com>
Date: Wed Jul 29 20:43:06 2020 +1200
add java leapYear thing
commit c6795b63dad5fd3aacebb1471c59d61d0c927257
Author: Chris <git@chris-nz.com>
Date: Wed Jul 29 20:42:47 2020 +1200
Add python leapYear and SimpleCalculator utilities
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git show branch --all
fatal: ambiguous argument 'branch': unknown revision or path not in the working tree.
Use '--' to separate paths from revisions, like this:
'git <command> [<revision>...] -- [<file>...]'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git show-branch --all
[master] add c++, README, apple metadata
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git ls-tree -r master --name-only
.DS_Store
HelloWorldInCpp.cpp
README.txt
Simplecalculator.py
leapYear.java
leapYear.py
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ cp -R . /tmp
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ echo 'print("done")' >> leapYear.py
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout -b feature-2
Switched to a new branch 'feature-2'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git diff leapYear.py
warning: CRLF will be replaced by LF in leapYear.py.
The file will have its original line endings in your working directory
diff --git a/leapYear.py b/leapYear.py
index 21d25f0..f97b98c 100755
--- a/leapYear.py
+++ b/leapYear.py
@@ -14,3 +14,4 @@ else:
print("{0} is not a leap year".format(year))
print("done")
+print("done")
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git add leapYear.py
warning: CRLF will be replaced by LF in leapYear.py.
The file will have its original line endings in your working directory
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git commit -m "Changed leapYear.py"
[feature-2 7547352] Changed leapYear.py
1 file changed, 1 insertion(+)
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git checkout master
Switched to branch 'master'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git merge feature-2
Updating 29f81d2..7547352
Fast-forward
leapYear.py | 1 +
1 file changed, 1 insertion(+)
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git branch -d feature-2
Deleted branch feature-2 (was 7547352).
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git log --all --oneline --graph --decorate
* 7547352 (HEAD -> master) Changed leapYear.py
* 29f81d2 add c++, README, apple metadata
* ad9646d add java leapYear thing
* c6795b6 Add python leapYear and SimpleCalculator utilities
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git tag -a "0.9" -m "Create 0.9 release for testing"
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git remote add origin git@github.com:SneakyWhoami/159251.git
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git push -u origin all
error: src refspec all does not match any
error: failed to push some refs to 'git@github.com:SneakyWhoami/159251.git'
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git push -u origin --all
Enumerating objects: 15, done.
Counting objects: 100% (15/15), done.
Delta compression using up to 4 threads
Compressing objects: 100% (14/14), done.
Writing objects: 100% (15/15), 2.00 KiB | 2.00 MiB/s, done.
Total 15 (delta 4), reused 0 (delta 0)
remote: Resolving deltas: 100% (4/4), done.
To github.com:SneakyWhoami/159251.git
* [new branch] master -> master
Branch 'master' set up to track remote branch 'master' from 'origin'.
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$ git push origin --tags
Enumerating objects: 1, done.
Counting objects: 100% (1/1), done.
Writing objects: 100% (1/1), 166 bytes | 166.00 KiB/s, done.
Total 1 (delta 0), reused 0 (delta 0)
To github.com:SneakyWhoami/159251.git
* [new tag] 0.9 -> 0.9
sneaky@yellow:~/Desktop/159251/Tutorial 1- Git$
``` | non_priority | hardcore log issue so it s not in repo attached until marking time bash sneaky yellow desktop tutorial git git init initialized empty git repository in home sneaky desktop tutorial git git sneaky yellow desktop tutorial git git add py warning crlf will be replaced by lf in simplecalculator py the file will have its original line endings in your working directory warning crlf will be replaced by lf in leapyear py the file will have its original line endings in your working directory sneaky yellow desktop tutorial git git commit am add python leapyear and simplecalculator utilities add python leapyear and simplecalculator utilities files changed insertions create mode simplecalculator py create mode leapyear py sneaky yellow desktop tutorial git git checkout b firstbranch switched to a new branch firstbranch sneaky yellow desktop tutorial git git add java warning crlf will be replaced by lf in leapyear java the file will have its original line endings in your working directory sneaky yellow desktop tutorial git git commit m add java leapyear thing add java leapyear thing file changed insertions create mode leapyear java sneaky yellow desktop tutorial git git checkout b secondbranch switched to a new branch secondbranch sneaky yellow desktop tutorial git git add helloworldincpp cpp readme txt ds store warning crlf will be replaced by lf in helloworldincpp cpp the file will have its original line endings in your working directory warning crlf will be replaced by lf in readme txt the file will have its original line endings in your working directory sneaky yellow desktop tutorial git git commit m add c readme apple metadata add c readme apple metadata files changed insertions create mode ds store create mode helloworldincpp cpp create mode readme txt sneaky yellow desktop tutorial git git checkout master switched to branch master sneaky yellow desktop tutorial git git merge firstbranch secondbranch updating fast forward ds store bin bytes helloworldincpp cpp readme txt leapyear java files changed insertions create mode ds store create mode helloworldincpp cpp create mode readme txt create mode leapyear java sneaky yellow desktop tutorial git git branch d firstbranch secondbranch deleted branch firstbranch was deleted branch secondbranch was sneaky yellow desktop tutorial git git log commit head master author chris date wed jul add c readme apple metadata commit author chris date wed jul add java leapyear thing commit author chris date wed jul add python leapyear and simplecalculator utilities sneaky yellow desktop tutorial git git show branch all fatal ambiguous argument branch unknown revision or path not in the working tree use to separate paths from revisions like this git sneaky yellow desktop tutorial git git show branch all add c readme apple metadata sneaky yellow desktop tutorial git git ls tree r master name only ds store helloworldincpp cpp readme txt simplecalculator py leapyear java leapyear py sneaky yellow desktop tutorial git cp r tmp sneaky yellow desktop tutorial git echo print done leapyear py sneaky yellow desktop tutorial git git checkout b feature switched to a new branch feature sneaky yellow desktop tutorial git git diff leapyear py warning crlf will be replaced by lf in leapyear py the file will have its original line endings in your working directory diff git a leapyear py b leapyear py index a leapyear py b leapyear py else print is not a leap year format year print done print done sneaky yellow desktop tutorial git git add leapyear py warning crlf will be replaced by lf in leapyear py the file will have its original line endings in your working directory sneaky yellow desktop tutorial git git commit m changed leapyear py changed leapyear py file changed insertion sneaky yellow desktop tutorial git git checkout master switched to branch master sneaky yellow desktop tutorial git git merge feature updating fast forward leapyear py file changed insertion sneaky yellow desktop tutorial git git branch d feature deleted branch feature was sneaky yellow desktop tutorial git git log all oneline graph decorate head master changed leapyear py add c readme apple metadata add java leapyear thing add python leapyear and simplecalculator utilities sneaky yellow desktop tutorial git git tag a m create release for testing sneaky yellow desktop tutorial git git remote add origin git github com sneakywhoami git sneaky yellow desktop tutorial git git push u origin all error src refspec all does not match any error failed to push some refs to git github com sneakywhoami git sneaky yellow desktop tutorial git git push u origin all enumerating objects done counting objects done delta compression using up to threads compressing objects done writing objects kib mib s done total delta reused delta remote resolving deltas done to github com sneakywhoami git master master branch master set up to track remote branch master from origin sneaky yellow desktop tutorial git git push origin tags enumerating objects done counting objects done writing objects bytes kib s done total delta reused delta to github com sneakywhoami git sneaky yellow desktop tutorial git | 0 |
134,602 | 18,475,012,895 | IssuesEvent | 2021-10-18 05:54:45 | samq-ghdemo/JS-DEMO | https://api.github.com/repos/samq-ghdemo/JS-DEMO | closed | WS-2019-0493 (High) detected in handlebars-4.0.5.tgz - autoclosed | security vulnerability | ## WS-2019-0493 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: JS-DEMO/package.json</p>
<p>Path to vulnerable library: JS-DEMO/node_modules/nyc/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- grunt-if-0.2.0.tgz (Root Library)
- grunt-contrib-nodeunit-1.0.0.tgz
- nodeunit-0.9.5.tgz
- tap-7.1.2.tgz
- nyc-7.1.0.tgz
- istanbul-reports-1.0.0-alpha.8.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-DEMO/commit/65c8bc8e7543b27d85a7808be0b83c7d68219bb7">65c8bc8e7543b27d85a7808be0b83c7d68219bb7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-14
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0493</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-11-14</p>
<p>Fix Resolution: handlebars - 3.0.8,4.5.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.0.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-if:0.2.0;grunt-contrib-nodeunit:1.0.0;nodeunit:0.9.5;tap:7.1.2;nyc:7.1.0;istanbul-reports:1.0.0-alpha.8;handlebars:4.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"handlebars - 3.0.8,4.5.2"}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2019-0493","vulnerabilityDetails":"handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package\u0027s lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.","vulnerabilityUrl":"https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0493 (High) detected in handlebars-4.0.5.tgz - autoclosed - ## WS-2019-0493 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.5.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.5.tgz</a></p>
<p>Path to dependency file: JS-DEMO/package.json</p>
<p>Path to vulnerable library: JS-DEMO/node_modules/nyc/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- grunt-if-0.2.0.tgz (Root Library)
- grunt-contrib-nodeunit-1.0.0.tgz
- nodeunit-0.9.5.tgz
- tap-7.1.2.tgz
- nyc-7.1.0.tgz
- istanbul-reports-1.0.0-alpha.8.tgz
- :x: **handlebars-4.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-DEMO/commit/65c8bc8e7543b27d85a7808be0b83c7d68219bb7">65c8bc8e7543b27d85a7808be0b83c7d68219bb7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-14
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0493</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-11-14</p>
<p>Fix Resolution: handlebars - 3.0.8,4.5.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.0.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-if:0.2.0;grunt-contrib-nodeunit:1.0.0;nodeunit:0.9.5;tap:7.1.2;nyc:7.1.0;istanbul-reports:1.0.0-alpha.8;handlebars:4.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"handlebars - 3.0.8,4.5.2"}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2019-0493","vulnerabilityDetails":"handlebars before 3.0.8 and 4.x before 4.5.2 is vulnerable to Arbitrary Code Execution. The package\u0027s lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system.","vulnerabilityUrl":"https://github.com/handlebars-lang/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in handlebars tgz autoclosed ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules nyc node modules handlebars package json dependency hierarchy grunt if tgz root library grunt contrib nodeunit tgz nodeunit tgz tap tgz nyc tgz istanbul reports alpha tgz x handlebars tgz vulnerable library found in head commit a href found in base branch main vulnerability details handlebars before and x before is vulnerable to arbitrary code execution the package s lookup helper fails to properly validate templates allowing attackers to submit templates that execute arbitrary javascript in the system publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree grunt if grunt contrib nodeunit nodeunit tap nyc istanbul reports alpha handlebars isminimumfixversionavailable true minimumfixversion handlebars basebranches vulnerabilityidentifier ws vulnerabilitydetails handlebars before and x before is vulnerable to arbitrary code execution the package lookup helper fails to properly validate templates allowing attackers to submit templates that execute arbitrary javascript in the system vulnerabilityurl | 0 |
20,944 | 27,805,232,913 | IssuesEvent | 2023-03-17 19:13:25 | Azure/azure-sdk-tools | https://api.github.com/repos/Azure/azure-sdk-tools | closed | Implement an existing fabricbot rules using github actions. | Central-EngSys GitHub Event Processor | We're looking at moving from FabricBot into GitHub Actions. This issue is for tracking the work to do this.
| 1.0 | Implement an existing fabricbot rules using github actions. - We're looking at moving from FabricBot into GitHub Actions. This issue is for tracking the work to do this.
| non_priority | implement an existing fabricbot rules using github actions we re looking at moving from fabricbot into github actions this issue is for tracking the work to do this | 0 |
259,830 | 19,634,463,285 | IssuesEvent | 2022-01-08 02:51:59 | HealthScreening/HealthScreeningBot | https://api.github.com/repos/HealthScreening/HealthScreeningBot | closed | [Feature Request]: Contributing a Guide: Suggest use of the script over manually adding an entry | documentation enhancement manually filed feature | ### Description
There is a script that automatically builds the guide list in a specific order.
### Describe the solution you'd like
The script should be used 100% of the time.
### Describe alternatives you've considered
_No response_ | 1.0 | [Feature Request]: Contributing a Guide: Suggest use of the script over manually adding an entry - ### Description
There is a script that automatically builds the guide list in a specific order.
### Describe the solution you'd like
The script should be used 100% of the time.
### Describe alternatives you've considered
_No response_ | non_priority | contributing a guide suggest use of the script over manually adding an entry description there is a script that automatically builds the guide list in a specific order describe the solution you d like the script should be used of the time describe alternatives you ve considered no response | 0 |
215,917 | 24,197,961,913 | IssuesEvent | 2022-09-24 06:11:30 | mkevenaar/OctoPrint-Slack | https://api.github.com/repos/mkevenaar/OctoPrint-Slack | closed | CVE-2022-1430 (High) detected in OctoPrint-1.7.2-py2.py3-none-any.whl - autoclosed | security vulnerability | ## CVE-2022-1430 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>OctoPrint-1.7.2-py2.py3-none-any.whl</b></p></summary>
<p>The snappy web interface for your 3D printer</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/85/f9/643f8de22bc50d11afee9560e0557859f0af7993c79cd4794c79bcd4d8c4/OctoPrint-1.7.2-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/85/f9/643f8de22bc50d11afee9560e0557859f0af7993c79cd4794c79bcd4d8c4/OctoPrint-1.7.2-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt,/tmp/ws-scm/OctoPrint-Slack</p>
<p>
Dependency Hierarchy:
- :x: **OctoPrint-1.7.2-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-site Scripting (XSS) - DOM in GitHub repository octoprint/octoprint prior to 1.8.0.
<p>Publish Date: 2022-05-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1430>CVE-2022-1430</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-1430">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-1430</a></p>
<p>Release Date: 2022-05-18</p>
<p>Fix Resolution: OctoPrint - 1.8.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-1430 (High) detected in OctoPrint-1.7.2-py2.py3-none-any.whl - autoclosed - ## CVE-2022-1430 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>OctoPrint-1.7.2-py2.py3-none-any.whl</b></p></summary>
<p>The snappy web interface for your 3D printer</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/85/f9/643f8de22bc50d11afee9560e0557859f0af7993c79cd4794c79bcd4d8c4/OctoPrint-1.7.2-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/85/f9/643f8de22bc50d11afee9560e0557859f0af7993c79cd4794c79bcd4d8c4/OctoPrint-1.7.2-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt,/tmp/ws-scm/OctoPrint-Slack</p>
<p>
Dependency Hierarchy:
- :x: **OctoPrint-1.7.2-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-site Scripting (XSS) - DOM in GitHub repository octoprint/octoprint prior to 1.8.0.
<p>Publish Date: 2022-05-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1430>CVE-2022-1430</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-1430">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-1430</a></p>
<p>Release Date: 2022-05-18</p>
<p>Fix Resolution: OctoPrint - 1.8.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in octoprint none any whl autoclosed cve high severity vulnerability vulnerable library octoprint none any whl the snappy web interface for your printer library home page a href path to dependency file requirements txt path to vulnerable library requirements txt tmp ws scm octoprint slack dependency hierarchy x octoprint none any whl vulnerable library found in base branch develop vulnerability details cross site scripting xss dom in github repository octoprint octoprint prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution octoprint step up your open source security game with mend | 0 |
289,228 | 24,969,006,938 | IssuesEvent | 2022-11-01 22:20:04 | bazelbuild/intellij | https://api.github.com/repos/bazelbuild/intellij | closed | Add Missing Gutter Icons for Runnable/Testable Targets | type: bug product: IntelliJ more-data-needed topic: testing | Example:
<img width="568" alt="image" src="https://user-images.githubusercontent.com/1097794/175791841-76cff735-e5af-4fd7-94d2-aba8f8694257.png">
Note that in this example, `intellij_integration_test_suite` is in fact runnable, despite missing gutter icons:
<img width="585" alt="image" src="https://user-images.githubusercontent.com/1097794/175791857-d54a001d-7e99-4b8c-8ead-e4e67d8711fa.png"> | 1.0 | Add Missing Gutter Icons for Runnable/Testable Targets - Example:
<img width="568" alt="image" src="https://user-images.githubusercontent.com/1097794/175791841-76cff735-e5af-4fd7-94d2-aba8f8694257.png">
Note that in this example, `intellij_integration_test_suite` is in fact runnable, despite missing gutter icons:
<img width="585" alt="image" src="https://user-images.githubusercontent.com/1097794/175791857-d54a001d-7e99-4b8c-8ead-e4e67d8711fa.png"> | non_priority | add missing gutter icons for runnable testable targets example img width alt image src note that in this example intellij integration test suite is in fact runnable despite missing gutter icons img width alt image src | 0 |
43,530 | 17,618,416,183 | IssuesEvent | 2021-08-18 12:43:14 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Linux php 8 containers now use nginx rather than apache | app-service/svc triaged cxp awaiting-product-team-response docs-experience Pri2 |
This guide works fine for deploying a laravel app to php 7.x on a linux based app service but when using the php 8.0 stack the container seems to use nginx rather than apache so the prescribed step of adding a .htaccess file doesn't work anymore. Is there an easy way of acheiving the same result (eg pointing the app root at wwwroot/public) with nginx? The only ways I can find to do this would involve altering files that won't end up persisting.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: a3209bb1-99cd-9e32-ae48-2605831aee02
* Version Independent ID: 743bc03e-d0d1-1e9e-acb1-52ae01daa0cc
* Content: [Configure PHP apps - Azure App Service](https://docs.microsoft.com/en-us/azure/app-service/configure-language-php)
* Content Source: [articles/app-service/configure-language-php.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/app-service/configure-language-php.md)
* Service: **app-service**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | 1.0 | Linux php 8 containers now use nginx rather than apache -
This guide works fine for deploying a laravel app to php 7.x on a linux based app service but when using the php 8.0 stack the container seems to use nginx rather than apache so the prescribed step of adding a .htaccess file doesn't work anymore. Is there an easy way of acheiving the same result (eg pointing the app root at wwwroot/public) with nginx? The only ways I can find to do this would involve altering files that won't end up persisting.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: a3209bb1-99cd-9e32-ae48-2605831aee02
* Version Independent ID: 743bc03e-d0d1-1e9e-acb1-52ae01daa0cc
* Content: [Configure PHP apps - Azure App Service](https://docs.microsoft.com/en-us/azure/app-service/configure-language-php)
* Content Source: [articles/app-service/configure-language-php.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/app-service/configure-language-php.md)
* Service: **app-service**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | non_priority | linux php containers now use nginx rather than apache this guide works fine for deploying a laravel app to php x on a linux based app service but when using the php stack the container seems to use nginx rather than apache so the prescribed step of adding a htaccess file doesn t work anymore is there an easy way of acheiving the same result eg pointing the app root at wwwroot public with nginx the only ways i can find to do this would involve altering files that won t end up persisting document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service app service github login cephalin microsoft alias cephalin | 0 |
149,213 | 11,885,906,017 | IssuesEvent | 2020-03-27 20:38:35 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | opened | Test case to check that kernel scrubs CPU registers of any sensitive data | area: Tests enhancement | I'm developing a test case to check that kernel scrubs CPU registers of any sensitive data.
I'm using a syscall and 0xDEADBEEF value, which should be written to registers, and after returning from system call into test code, as I expect that 0xDEADBEEF should be replaced with another value.
That will prove kernel scrubs CPU registers.
**I made the system call, and right before return from the system call, I'm writing into the registers special value 0xDEADBEEF**
```
size_t z_impl_string_nlen(char *src, size_t maxlen, int *err)
{
size_t ret;
ret = z_user_string_nlen(src, maxlen, err);
#if defined(CONFIG_X86)
__asm__ volatile (
"movl $0xDEADBEEF, %ebx;\n\t"
"movl $0xDEADBEEF, %ecx;\n\t"
"movl $0xDEADBEEF, %edx;\n\t"
//"movl $0xDEADBEEF, %esi;\n\t"
//"movl $0xDEADBEEF, %edi;\n\t"
//"movl $0xDEADBEEF, %esp;\n\t"
//"movl $0xDEADBEEF, %ebp;\n\t"
);
#elif defined(CONFIG_X86_64)
__asm__ volatile (
"movq $0xDEADBEEF, %rbx;\n\t"
"movq $0xDEADBEEF, %rcx;\n\t"
"movq $0xDEADBEEF, %rdx;\n\t"
);
#elif defined(CONFIG_ARM)
__asm__ volatile (
"mov r2, #100;\n\t"
);
#elif defined(CONFIG_ARC)
__asm__ volatile (
);
#else
#error "Not implemented for this architecture"
zassert_unreachable("Write to control register fault");
#endif
return ret;
}
```
**Then after exit from the system call in main test function, I check registers again for that value.**
```
void test_after_syscall_cpu_scrubs_regs(void)
{
int err;
size_t ret;
ret = string_nlen(user_string, BUF_SIZE, &err);
#if defined(CONFIG_X86)
int ebx_val;
int ecx_val;
int edx_val;
__asm__ volatile (
"\t movl %%ebx,%0" : "=r"(ebx_val));
__asm__ volatile (
"\t movl %%ecx,%0" : "=r"(ecx_val));
__asm__ volatile (
"\t movl %%edx,%0" : "=r"(edx_val));
printk("\nReg ebx val user mode 0x%x\n", ebx_val);
printk("\nReg ecx val user mode 0x%x\n", ecx_val);
printk("\nReg edx val user mode 0x%x\n", edx_val);
#elif defined(CONFIG_X86_64)
long int rbx_val;
long int rcx_val;
long int rdx_val;
__asm__ volatile(
"\t movq %%rbx,%0" : "=r"(rbx_val));
__asm__ volatile(
"\t movq %%rcx,%0" : "=r"(rcx_val));
__asm__ volatile(
"\t movq %%rdx,%0" : "=r"(rdx_val));
printk("\nReg rbx val user mode 0x%lx\n", rbx_val);
printk("\nReg rcx val user mode 0x%lx\n", rcx_val);
printk("\nReg rdx val user mode 0x%lx\n", rdx_val);
#elif defined(CONFIG_ARM)
int r0_val;
__asm__ volatile (
"\t mov %%r2,%0" : "=r"(r0_val));
#elif defined(CONFIG_ARC)
__asm__ volatile (
);
#else
#error "Not implemented for this architecture"
zassert_unreachable("Write to control register fault");
#endif
}
```
**It is my rough demo, code can be dirty, but main idea should be clear. I'm not good at ARM, ARC registers, so does anybody knows what registers necessary to check and how to do that?** That test seems to be platform dependant, so different architectures are using different registers to store sensitive data. That test will verify that sensitive data won't remain in CPU's registers after returning from a system call.
| 1.0 | Test case to check that kernel scrubs CPU registers of any sensitive data - I'm developing a test case to check that kernel scrubs CPU registers of any sensitive data.
I'm using a syscall and 0xDEADBEEF value, which should be written to registers, and after returning from system call into test code, as I expect that 0xDEADBEEF should be replaced with another value.
That will prove kernel scrubs CPU registers.
**I made the system call, and right before return from the system call, I'm writing into the registers special value 0xDEADBEEF**
```
size_t z_impl_string_nlen(char *src, size_t maxlen, int *err)
{
size_t ret;
ret = z_user_string_nlen(src, maxlen, err);
#if defined(CONFIG_X86)
__asm__ volatile (
"movl $0xDEADBEEF, %ebx;\n\t"
"movl $0xDEADBEEF, %ecx;\n\t"
"movl $0xDEADBEEF, %edx;\n\t"
//"movl $0xDEADBEEF, %esi;\n\t"
//"movl $0xDEADBEEF, %edi;\n\t"
//"movl $0xDEADBEEF, %esp;\n\t"
//"movl $0xDEADBEEF, %ebp;\n\t"
);
#elif defined(CONFIG_X86_64)
__asm__ volatile (
"movq $0xDEADBEEF, %rbx;\n\t"
"movq $0xDEADBEEF, %rcx;\n\t"
"movq $0xDEADBEEF, %rdx;\n\t"
);
#elif defined(CONFIG_ARM)
__asm__ volatile (
"mov r2, #100;\n\t"
);
#elif defined(CONFIG_ARC)
__asm__ volatile (
);
#else
#error "Not implemented for this architecture"
zassert_unreachable("Write to control register fault");
#endif
return ret;
}
```
**Then after exit from the system call in main test function, I check registers again for that value.**
```
void test_after_syscall_cpu_scrubs_regs(void)
{
int err;
size_t ret;
ret = string_nlen(user_string, BUF_SIZE, &err);
#if defined(CONFIG_X86)
int ebx_val;
int ecx_val;
int edx_val;
__asm__ volatile (
"\t movl %%ebx,%0" : "=r"(ebx_val));
__asm__ volatile (
"\t movl %%ecx,%0" : "=r"(ecx_val));
__asm__ volatile (
"\t movl %%edx,%0" : "=r"(edx_val));
printk("\nReg ebx val user mode 0x%x\n", ebx_val);
printk("\nReg ecx val user mode 0x%x\n", ecx_val);
printk("\nReg edx val user mode 0x%x\n", edx_val);
#elif defined(CONFIG_X86_64)
long int rbx_val;
long int rcx_val;
long int rdx_val;
__asm__ volatile(
"\t movq %%rbx,%0" : "=r"(rbx_val));
__asm__ volatile(
"\t movq %%rcx,%0" : "=r"(rcx_val));
__asm__ volatile(
"\t movq %%rdx,%0" : "=r"(rdx_val));
printk("\nReg rbx val user mode 0x%lx\n", rbx_val);
printk("\nReg rcx val user mode 0x%lx\n", rcx_val);
printk("\nReg rdx val user mode 0x%lx\n", rdx_val);
#elif defined(CONFIG_ARM)
int r0_val;
__asm__ volatile (
"\t mov %%r2,%0" : "=r"(r0_val));
#elif defined(CONFIG_ARC)
__asm__ volatile (
);
#else
#error "Not implemented for this architecture"
zassert_unreachable("Write to control register fault");
#endif
}
```
**It is my rough demo, code can be dirty, but main idea should be clear. I'm not good at ARM, ARC registers, so does anybody knows what registers necessary to check and how to do that?** That test seems to be platform dependant, so different architectures are using different registers to store sensitive data. That test will verify that sensitive data won't remain in CPU's registers after returning from a system call.
| non_priority | test case to check that kernel scrubs cpu registers of any sensitive data i m developing a test case to check that kernel scrubs cpu registers of any sensitive data i m using a syscall and value which should be written to registers and after returning from system call into test code as i expect that should be replaced with another value that will prove kernel scrubs cpu registers i made the system call and right before return from the system call i m writing into the registers special value size t z impl string nlen char src size t maxlen int err size t ret ret z user string nlen src maxlen err if defined config asm volatile movl ebx n t movl ecx n t movl edx n t movl esi n t movl edi n t movl esp n t movl ebp n t elif defined config asm volatile movq rbx n t movq rcx n t movq rdx n t elif defined config arm asm volatile mov n t elif defined config arc asm volatile else error not implemented for this architecture zassert unreachable write to control register fault endif return ret then after exit from the system call in main test function i check registers again for that value void test after syscall cpu scrubs regs void int err size t ret ret string nlen user string buf size err if defined config int ebx val int ecx val int edx val asm volatile t movl ebx r ebx val asm volatile t movl ecx r ecx val asm volatile t movl edx r edx val printk nreg ebx val user mode x n ebx val printk nreg ecx val user mode x n ecx val printk nreg edx val user mode x n edx val elif defined config long int rbx val long int rcx val long int rdx val asm volatile t movq rbx r rbx val asm volatile t movq rcx r rcx val asm volatile t movq rdx r rdx val printk nreg rbx val user mode lx n rbx val printk nreg rcx val user mode lx n rcx val printk nreg rdx val user mode lx n rdx val elif defined config arm int val asm volatile t mov r val elif defined config arc asm volatile else error not implemented for this architecture zassert unreachable write to control register fault endif it is my rough demo code can be dirty but main idea should be clear i m not good at arm arc registers so does anybody knows what registers necessary to check and how to do that that test seems to be platform dependant so different architectures are using different registers to store sensitive data that test will verify that sensitive data won t remain in cpu s registers after returning from a system call | 0 |
449,296 | 31,837,641,484 | IssuesEvent | 2023-09-14 14:24:16 | mohammadjaloudi/WRO-FUTURE-ENGINEERS-2023 | https://api.github.com/repos/mohammadjaloudi/WRO-FUTURE-ENGINEERS-2023 | opened | WRO-FUTURE-ENGINEERS-2023 | documentation | WRO-FUTURE-ENGINEERS-2023 this template is for our competition , if you like you can use it as a reference later in other years , I hope this will help you | 1.0 | WRO-FUTURE-ENGINEERS-2023 - WRO-FUTURE-ENGINEERS-2023 this template is for our competition , if you like you can use it as a reference later in other years , I hope this will help you | non_priority | wro future engineers wro future engineers this template is for our competition if you like you can use it as a reference later in other years i hope this will help you | 0 |
18,003 | 12,728,329,353 | IssuesEvent | 2020-06-25 02:13:25 | edgi-govdata-archiving/EEW_Planning | https://api.github.com/repos/edgi-govdata-archiving/EEW_Planning | reopened | Switch database meeting link? | coordination infrastructure | @lourdesvera - It looks like I'll be coordinating the Tuesday 1pm database meetings. I think we might as well go ahead and switch to using the same link as the 2pm sprint meetings, and ask the sprint team to jump on at 1:45/1:50 so we can overlap. That's the idea right?
The problem is that while I can change the info on the google calendar, I don't know how to update the Slackbot / if I have access to it. Is there a writeup somewhere on how to do this?
cc: @Frijol
┆Issue is synchronized with this [Trello card](https://trello.com/c/eVYEEpf7)
| 1.0 | Switch database meeting link? - @lourdesvera - It looks like I'll be coordinating the Tuesday 1pm database meetings. I think we might as well go ahead and switch to using the same link as the 2pm sprint meetings, and ask the sprint team to jump on at 1:45/1:50 so we can overlap. That's the idea right?
The problem is that while I can change the info on the google calendar, I don't know how to update the Slackbot / if I have access to it. Is there a writeup somewhere on how to do this?
cc: @Frijol
┆Issue is synchronized with this [Trello card](https://trello.com/c/eVYEEpf7)
| non_priority | switch database meeting link lourdesvera it looks like i ll be coordinating the tuesday database meetings i think we might as well go ahead and switch to using the same link as the sprint meetings and ask the sprint team to jump on at so we can overlap that s the idea right the problem is that while i can change the info on the google calendar i don t know how to update the slackbot if i have access to it is there a writeup somewhere on how to do this cc frijol ┆issue is synchronized with this | 0 |
50,632 | 10,542,897,496 | IssuesEvent | 2019-10-02 14:02:49 | openvalidation/openvalidation | https://api.github.com/repos/openvalidation/openvalidation | opened | ONE_OF -> EXACTLY_ONE_OF | OV-lang codegen enhancement refactor | <!--- Thank you for using openVALIDATION! -->
## Expected Behavior
<!--- If you're describing a bug, tell us what should happen -->
<!--- If you're suggesting a change/improvement, tell us how it should work -->
There should be two distinct framework functions `EXACTLY_ONE_OF` and `AT_LEAST_ONE_OF`.
## Current Behavior
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If describing a bug, also provide console output if possible -->
<!--- If suggesting a change/improvement, explain the difference from current behavior -->
There is no `EXACTLY_ONE_OF`, instead there is `ONE_OF` which behaves equivalently to `AT_LEAST_ONE_OF` on most cases and like an exactly-one-of function in some others (python FW).
## Possible Solution
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change -->
Rename `ONE_OF` to `EXACTLY_ONE_OF` everywhere and re-define it accordingly where needed.
Requires changes in:
- Framework templates
- function enums for AST
- some thoughtful changes to one-of aliases in language/culture resources
## Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most useful in the real world -->
duh
| 1.0 | ONE_OF -> EXACTLY_ONE_OF - <!--- Thank you for using openVALIDATION! -->
## Expected Behavior
<!--- If you're describing a bug, tell us what should happen -->
<!--- If you're suggesting a change/improvement, tell us how it should work -->
There should be two distinct framework functions `EXACTLY_ONE_OF` and `AT_LEAST_ONE_OF`.
## Current Behavior
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If describing a bug, also provide console output if possible -->
<!--- If suggesting a change/improvement, explain the difference from current behavior -->
There is no `EXACTLY_ONE_OF`, instead there is `ONE_OF` which behaves equivalently to `AT_LEAST_ONE_OF` on most cases and like an exactly-one-of function in some others (python FW).
## Possible Solution
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change -->
Rename `ONE_OF` to `EXACTLY_ONE_OF` everywhere and re-define it accordingly where needed.
Requires changes in:
- Framework templates
- function enums for AST
- some thoughtful changes to one-of aliases in language/culture resources
## Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most useful in the real world -->
duh
| non_priority | one of exactly one of expected behavior there should be two distinct framework functions exactly one of and at least one of current behavior there is no exactly one of instead there is one of which behaves equivalently to at least one of on most cases and like an exactly one of function in some others python fw possible solution rename one of to exactly one of everywhere and re define it accordingly where needed requires changes in framework templates function enums for ast some thoughtful changes to one of aliases in language culture resources context duh | 0 |
22,863 | 7,239,357,930 | IssuesEvent | 2018-02-13 17:14:02 | vaadin/framework8-issues | https://api.github.com/repos/vaadin/framework8-issues | closed | Add TestBench smoke tests for archetypes | Integration and IDE support Project packaging build release stale | Run a small smoke test on each archetype after building it. This can either be in the archetype project or a separate subproject of the top-level archetypes project.
| 1.0 | Add TestBench smoke tests for archetypes - Run a small smoke test on each archetype after building it. This can either be in the archetype project or a separate subproject of the top-level archetypes project.
| non_priority | add testbench smoke tests for archetypes run a small smoke test on each archetype after building it this can either be in the archetype project or a separate subproject of the top level archetypes project | 0 |
103,714 | 8,940,773,727 | IssuesEvent | 2019-01-24 01:11:55 | apache/incubator-mxnet | https://api.github.com/repos/apache/incubator-mxnet | closed | ARM QEMU test in CI failed unrelated PR | ARM CI Question Test | ## Description
Test with ARM QEMU fails with some kind of network interruption...
Makes wonder about these network issues where dependencies fail to download... should we put in a retry function, so that we don't have to restart our PRs when there's a transient error?
## Error
```
runtime_functions.py: 2018-11-26 03:47:02,687 ['run_ut_py3_qemu']
⢎⡑ ⣰⡀ ⢀⣀ ⡀⣀ ⣰⡀ ⠄ ⣀⡀ ⢀⡀ ⡎⢱ ⣏⡉ ⡷⢾ ⡇⢸
⠢⠜ ⠘⠤ ⠣⠼ ⠏ ⠘⠤ ⠇ ⠇⠸ ⣑⡺ ⠣⠪ ⠧⠤ ⠇⠸ ⠣⠜
runtime_functions.py: 2018-11-26 03:47:02,765 Starting VM, ssh port redirected to localhost:2222 (inside docker, not exposed by default)
runtime_functions.py: 2018-11-26 03:47:02,765 Starting in non-interactive mode. Terminal output is disabled.
runtime_functions.py: 2018-11-26 03:47:02,766 waiting for ssh to be open in the VM (timeout 300s)
runtime_functions.py: 2018-11-26 03:47:46,729 wait_ssh_open: port 127.0.0.1:2222 is open and ssh is ready
runtime_functions.py: 2018-11-26 03:47:46,729 VM is online and SSH is up
runtime_functions.py: 2018-11-26 03:47:46,729 Provisioning the VM with artifacts and sources
ssh_exchange_identification: read: Connection reset by peer
rsync: safe_write failed to write 4 bytes to socket [sender]: Broken pipe (32)
rsync error: unexplained error (code 255) at io.c(320) [sender=3.1.1]
runtime_functions.py: 2018-11-26 03:47:46,916 Shutdown via ssh
ssh_exchange_identification: read: Connection reset by peer
Traceback (most recent call last):
File "./runtime_functions.py", line 66, in run_ut_py3_qemu
qemu_provision(vm.ssh_port)
File "/work/vmcontrol.py", line 186, in qemu_provision
qemu_rsync(ssh_port, x, 'mxnet_dist/')
File "/work/vmcontrol.py", line 175, in qemu_rsync
check_call(['rsync', '-e', 'ssh -o StrictHostKeyChecking=no -p{}'.format(ssh_port), '-a', local_path, 'qemu@localhost:{}'.format(remote_path)])
File "/usr/lib/python3.5/subprocess.py", line 581, in check_call
raise CalledProcessError(retcode, cmd)
subprocess.CalledProcessError: Command '['rsync', '-e', 'ssh -o StrictHostKeyChecking=no -p2222', '-a', '/work/mxnet/build/mxnet-1.4.0-py2.py3-none-any.whl', 'qemu@localhost:mxnet_dist/']' returned non-zero exit status 255
``` | 1.0 | ARM QEMU test in CI failed unrelated PR - ## Description
Test with ARM QEMU fails with some kind of network interruption...
Makes wonder about these network issues where dependencies fail to download... should we put in a retry function, so that we don't have to restart our PRs when there's a transient error?
## Error
```
runtime_functions.py: 2018-11-26 03:47:02,687 ['run_ut_py3_qemu']
⢎⡑ ⣰⡀ ⢀⣀ ⡀⣀ ⣰⡀ ⠄ ⣀⡀ ⢀⡀ ⡎⢱ ⣏⡉ ⡷⢾ ⡇⢸
⠢⠜ ⠘⠤ ⠣⠼ ⠏ ⠘⠤ ⠇ ⠇⠸ ⣑⡺ ⠣⠪ ⠧⠤ ⠇⠸ ⠣⠜
runtime_functions.py: 2018-11-26 03:47:02,765 Starting VM, ssh port redirected to localhost:2222 (inside docker, not exposed by default)
runtime_functions.py: 2018-11-26 03:47:02,765 Starting in non-interactive mode. Terminal output is disabled.
runtime_functions.py: 2018-11-26 03:47:02,766 waiting for ssh to be open in the VM (timeout 300s)
runtime_functions.py: 2018-11-26 03:47:46,729 wait_ssh_open: port 127.0.0.1:2222 is open and ssh is ready
runtime_functions.py: 2018-11-26 03:47:46,729 VM is online and SSH is up
runtime_functions.py: 2018-11-26 03:47:46,729 Provisioning the VM with artifacts and sources
ssh_exchange_identification: read: Connection reset by peer
rsync: safe_write failed to write 4 bytes to socket [sender]: Broken pipe (32)
rsync error: unexplained error (code 255) at io.c(320) [sender=3.1.1]
runtime_functions.py: 2018-11-26 03:47:46,916 Shutdown via ssh
ssh_exchange_identification: read: Connection reset by peer
Traceback (most recent call last):
File "./runtime_functions.py", line 66, in run_ut_py3_qemu
qemu_provision(vm.ssh_port)
File "/work/vmcontrol.py", line 186, in qemu_provision
qemu_rsync(ssh_port, x, 'mxnet_dist/')
File "/work/vmcontrol.py", line 175, in qemu_rsync
check_call(['rsync', '-e', 'ssh -o StrictHostKeyChecking=no -p{}'.format(ssh_port), '-a', local_path, 'qemu@localhost:{}'.format(remote_path)])
File "/usr/lib/python3.5/subprocess.py", line 581, in check_call
raise CalledProcessError(retcode, cmd)
subprocess.CalledProcessError: Command '['rsync', '-e', 'ssh -o StrictHostKeyChecking=no -p2222', '-a', '/work/mxnet/build/mxnet-1.4.0-py2.py3-none-any.whl', 'qemu@localhost:mxnet_dist/']' returned non-zero exit status 255
``` | non_priority | arm qemu test in ci failed unrelated pr description test with arm qemu fails with some kind of network interruption makes wonder about these network issues where dependencies fail to download should we put in a retry function so that we don t have to restart our prs when there s a transient error error runtime functions py ⢎⡑ ⣰⡀ ⢀⣀ ⡀⣀ ⣰⡀ ⠄ ⣀⡀ ⢀⡀ ⡎⢱ ⣏⡉ ⡷⢾ ⡇⢸ ⠢⠜ ⠘⠤ ⠣⠼ ⠏ ⠘⠤ ⠇ ⠇⠸ ⣑⡺ ⠣⠪ ⠧⠤ ⠇⠸ ⠣⠜ runtime functions py starting vm ssh port redirected to localhost inside docker not exposed by default runtime functions py starting in non interactive mode terminal output is disabled runtime functions py waiting for ssh to be open in the vm timeout runtime functions py wait ssh open port is open and ssh is ready runtime functions py vm is online and ssh is up runtime functions py provisioning the vm with artifacts and sources ssh exchange identification read connection reset by peer rsync safe write failed to write bytes to socket broken pipe rsync error unexplained error code at io c runtime functions py shutdown via ssh ssh exchange identification read connection reset by peer traceback most recent call last file runtime functions py line in run ut qemu qemu provision vm ssh port file work vmcontrol py line in qemu provision qemu rsync ssh port x mxnet dist file work vmcontrol py line in qemu rsync check call file usr lib subprocess py line in check call raise calledprocesserror retcode cmd subprocess calledprocesserror command returned non zero exit status | 0 |
12,693 | 3,640,442,130 | IssuesEvent | 2016-02-13 00:17:20 | OfficeDev/Office-UI-Fabric | https://api.github.com/repos/OfficeDev/Office-UI-Fabric | closed | List and List Grid are not valid HTML 5 | documentation VSO | Only **li** elements are allowed under **ul **but both List and List Grid have **div **directly under **ul**
As a workaround, tried using with bootstrap list-unstyled and surrounding the **div **with an **li **and it seems to work but the in the List Grid the short versions of the text that end with "..." don't work well since there is plenty of space but it displays just one letter of the name Ex. "S..." when there is room for "Smith" to display.
I am trying to use fabric inside an Excel Task Pane app but I can't use it | 1.0 | List and List Grid are not valid HTML 5 - Only **li** elements are allowed under **ul **but both List and List Grid have **div **directly under **ul**
As a workaround, tried using with bootstrap list-unstyled and surrounding the **div **with an **li **and it seems to work but the in the List Grid the short versions of the text that end with "..." don't work well since there is plenty of space but it displays just one letter of the name Ex. "S..." when there is room for "Smith" to display.
I am trying to use fabric inside an Excel Task Pane app but I can't use it | non_priority | list and list grid are not valid html only li elements are allowed under ul but both list and list grid have div directly under ul as a workaround tried using with bootstrap list unstyled and surrounding the div with an li and it seems to work but the in the list grid the short versions of the text that end with don t work well since there is plenty of space but it displays just one letter of the name ex s when there is room for smith to display i am trying to use fabric inside an excel task pane app but i can t use it | 0 |
16,037 | 4,006,769,137 | IssuesEvent | 2016-05-12 15:53:04 | mileszs/wicked_pdf | https://api.github.com/repos/mileszs/wicked_pdf | closed | Compatibility issues in production with wkhtmltopdf-binary | needs-documentation | I have recently experienced issues getting wicked_pdf to work in production mode.
In particular, supplying one or more of the following arguments will cause the pdf render to fail.
cover: render_to_string('reports/cover.pdf.erb'),
this will fail with the following error (it will however work on a blank value such as '', suggesting the parameter is accepted just not the argument.
Error: Failed to execute: ["/home/mja/.rvm/gems/ruby-2.3.0/bin/wkhtmltopdf", "-q"]
Error: undefined method `<' for nil:NilClass
In addition. Any use of the toc: arguement (even an empty hash) will cause the same above error.
I have also noticed that assets will not be correctly displayed by wicked_pdf using this binary unless
config.assets.compile = true.
Note that above issues only occur in production, making the issue deceptively difficult to identify.
gem 'wicked_pdf', github: 'mileszs/wicked_pdf' (both branches have same issue).
gem 'wkhtmltopdf-binary'
I have also tried manually installing the wkhtmltopdf from the binaries (0.12.2.1) and statically setting the exe path, but the same issue is present.
Rails 4.2.6
Ruby 2.3.0 | 1.0 | Compatibility issues in production with wkhtmltopdf-binary - I have recently experienced issues getting wicked_pdf to work in production mode.
In particular, supplying one or more of the following arguments will cause the pdf render to fail.
cover: render_to_string('reports/cover.pdf.erb'),
this will fail with the following error (it will however work on a blank value such as '', suggesting the parameter is accepted just not the argument.
Error: Failed to execute: ["/home/mja/.rvm/gems/ruby-2.3.0/bin/wkhtmltopdf", "-q"]
Error: undefined method `<' for nil:NilClass
In addition. Any use of the toc: arguement (even an empty hash) will cause the same above error.
I have also noticed that assets will not be correctly displayed by wicked_pdf using this binary unless
config.assets.compile = true.
Note that above issues only occur in production, making the issue deceptively difficult to identify.
gem 'wicked_pdf', github: 'mileszs/wicked_pdf' (both branches have same issue).
gem 'wkhtmltopdf-binary'
I have also tried manually installing the wkhtmltopdf from the binaries (0.12.2.1) and statically setting the exe path, but the same issue is present.
Rails 4.2.6
Ruby 2.3.0 | non_priority | compatibility issues in production with wkhtmltopdf binary i have recently experienced issues getting wicked pdf to work in production mode in particular supplying one or more of the following arguments will cause the pdf render to fail cover render to string reports cover pdf erb this will fail with the following error it will however work on a blank value such as suggesting the parameter is accepted just not the argument error failed to execute error undefined method for nil nilclass in addition any use of the toc arguement even an empty hash will cause the same above error i have also noticed that assets will not be correctly displayed by wicked pdf using this binary unless config assets compile true note that above issues only occur in production making the issue deceptively difficult to identify gem wicked pdf github mileszs wicked pdf both branches have same issue gem wkhtmltopdf binary i have also tried manually installing the wkhtmltopdf from the binaries and statically setting the exe path but the same issue is present rails ruby | 0 |
14,268 | 3,815,269,661 | IssuesEvent | 2016-03-28 17:12:22 | bounswe/bounswe2016group2 | https://api.github.com/repos/bounswe/bounswe2016group2 | opened | Use Case Diagrams | documentation enhancement | All use cases, at least 2 substantial cases that are elaborated with actors, description, data, stimulus, response, and comments. | 1.0 | Use Case Diagrams - All use cases, at least 2 substantial cases that are elaborated with actors, description, data, stimulus, response, and comments. | non_priority | use case diagrams all use cases at least substantial cases that are elaborated with actors description data stimulus response and comments | 0 |
59,545 | 14,599,233,321 | IssuesEvent | 2020-12-21 03:33:47 | FashionFreedom/Seamly2D | https://api.github.com/repos/FashionFreedom/Seamly2D | opened | Build: Typos | build | Lots of typos encountered when building debian distro. See here: [https://salsa.debian.org/debian/pkg-seamly2d/-/jobs/1261725](https://salsa.debian.org/debian/pkg-seamly2d/-/jobs/1261725)
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Calulation Calculation
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d InformationS Information
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Openning Opening
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Reseting Resetting
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Uknown Unknown
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d availiable available
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d betwen between
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d childern children
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d containe contained
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d formating formatting
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d orgin origin
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d overriden overridden
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d prefered preferred
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d unknow unknown
I: seamly2d: spelling-error-in-binary usr/bin/seamlyme betwen between
I: seamly2d: spelling-error-in-binary usr/bin/seamlyme openning opening
I: seamly2d: spelling-error-in-binary usr/lib/libqmuparser.so.2.5.0 preceeded preceded
I: seamly2d: typo-in-manual-page usr/share/man/man1/seamly2d.1.gz availiable available
I: seamly2d: typo-in-manual-page usr/share/man/man1/seamlyme.1.gz availiable available
| 1.0 | Build: Typos - Lots of typos encountered when building debian distro. See here: [https://salsa.debian.org/debian/pkg-seamly2d/-/jobs/1261725](https://salsa.debian.org/debian/pkg-seamly2d/-/jobs/1261725)
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Calulation Calculation
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d InformationS Information
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Openning Opening
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Reseting Resetting
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d Uknown Unknown
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d availiable available
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d betwen between
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d childern children
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d containe contained
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d formating formatting
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d orgin origin
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d overriden overridden
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d prefered preferred
I: seamly2d: spelling-error-in-binary usr/bin/seamly2d unknow unknown
I: seamly2d: spelling-error-in-binary usr/bin/seamlyme betwen between
I: seamly2d: spelling-error-in-binary usr/bin/seamlyme openning opening
I: seamly2d: spelling-error-in-binary usr/lib/libqmuparser.so.2.5.0 preceeded preceded
I: seamly2d: typo-in-manual-page usr/share/man/man1/seamly2d.1.gz availiable available
I: seamly2d: typo-in-manual-page usr/share/man/man1/seamlyme.1.gz availiable available
| non_priority | build typos lots of typos encountered when building debian distro see here i spelling error in binary usr bin calulation calculation i spelling error in binary usr bin informations information i spelling error in binary usr bin openning opening i spelling error in binary usr bin reseting resetting i spelling error in binary usr bin uknown unknown i spelling error in binary usr bin availiable available i spelling error in binary usr bin betwen between i spelling error in binary usr bin childern children i spelling error in binary usr bin containe contained i spelling error in binary usr bin formating formatting i spelling error in binary usr bin orgin origin i spelling error in binary usr bin overriden overridden i spelling error in binary usr bin prefered preferred i spelling error in binary usr bin unknow unknown i spelling error in binary usr bin seamlyme betwen between i spelling error in binary usr bin seamlyme openning opening i spelling error in binary usr lib libqmuparser so preceeded preceded i typo in manual page usr share man gz availiable available i typo in manual page usr share man seamlyme gz availiable available | 0 |
43,883 | 17,759,182,422 | IssuesEvent | 2021-08-29 11:10:56 | apolloconfig/apollo | https://api.github.com/repos/apolloconfig/apollo | closed | Apollo organization related content needs to be updated | area/docker area/configservice area/client area/portal area/adminservice good first issue area/demo area/document | Because the organization of the apollo repository has changed, the related content also needs to change.
### So, I think we have those steps or things need to update:
- [x] remove `ctrip` profile.
- [ ] refactor java package name.
@apolloconfig/committers @apolloconfig/pmc FYI | 2.0 | Apollo organization related content needs to be updated - Because the organization of the apollo repository has changed, the related content also needs to change.
### So, I think we have those steps or things need to update:
- [x] remove `ctrip` profile.
- [ ] refactor java package name.
@apolloconfig/committers @apolloconfig/pmc FYI | non_priority | apollo organization related content needs to be updated because the organization of the apollo repository has changed the related content also needs to change so i think we have those steps or things need to update remove ctrip profile refactor java package name apolloconfig committers apolloconfig pmc fyi | 0 |
286,879 | 31,780,264,335 | IssuesEvent | 2023-09-12 16:54:48 | dotnet/announcements | https://api.github.com/repos/dotnet/announcements | opened | .NET September 2023 Updates | Security Patch-Tuesday Monthly-Update .NET 6.0 .NET 7.0 | Microsoft released the following [.NET Updates in September 2023](https://devblogs.microsoft.com/dotnet/september-2023-updates/).
<h2>.NET Releases </h2>
<h3> .NET August Updates </h3>
* [.NET 7.0.11 and .NET SDK 7.0.401](https://github.com/dotnet/core/blob/main/release-notes/7.0/7.0.11/7.0.11.md) ([Download](https://dotnet.microsoft.com/download/dotnet-core/7.0))
* [.NET 6.0.22 and .NET SDK 6.0.414](https://github.com/dotnet/core/blob/main/release-notes/6.0/6.0.22/6.0.22.md) ([Download](https://dotnet.microsoft.com/download/dotnet-core/6.0))
This issue will be updated if there are any additional releases during the month.
| True | .NET September 2023 Updates - Microsoft released the following [.NET Updates in September 2023](https://devblogs.microsoft.com/dotnet/september-2023-updates/).
<h2>.NET Releases </h2>
<h3> .NET August Updates </h3>
* [.NET 7.0.11 and .NET SDK 7.0.401](https://github.com/dotnet/core/blob/main/release-notes/7.0/7.0.11/7.0.11.md) ([Download](https://dotnet.microsoft.com/download/dotnet-core/7.0))
* [.NET 6.0.22 and .NET SDK 6.0.414](https://github.com/dotnet/core/blob/main/release-notes/6.0/6.0.22/6.0.22.md) ([Download](https://dotnet.microsoft.com/download/dotnet-core/6.0))
This issue will be updated if there are any additional releases during the month.
| non_priority | net september updates microsoft released the following net releases net august updates this issue will be updated if there are any additional releases during the month | 0 |
247,992 | 26,771,155,468 | IssuesEvent | 2023-01-31 14:13:15 | billmcchesney1/linkerd2 | https://api.github.com/repos/billmcchesney1/linkerd2 | opened | CVE-2022-25881 (Medium) detected in http-cache-semantics-4.1.0.tgz | security vulnerability | ## CVE-2022-25881 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-cache-semantics-4.1.0.tgz</b></p></summary>
<p>Parses Cache-Control and other headers. Helps building correct HTTP caches and proxies</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz">https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz</a></p>
<p>Path to dependency file: /web/app/package.json</p>
<p>Path to vulnerable library: /web/app/node_modules/http-cache-semantics/package.json</p>
<p>
Dependency Hierarchy:
- webdriverio-6.1.2.tgz (Root Library)
- webdriver-6.1.2.tgz
- got-10.7.0.tgz
- cacheable-request-7.0.1.tgz
- :x: **http-cache-semantics-4.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects versions of the package http-cache-semantics before 4.1.1. The issue can be exploited via malicious request header values sent to a server, when that server reads the cache policy from the request using this library.
<p>Publish Date: 2023-01-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25881>CVE-2022-25881</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-25881">https://www.cve.org/CVERecord?id=CVE-2022-25881</a></p>
<p>Release Date: 2023-01-31</p>
<p>Fix Resolution: http-cache-semantics - 4.1.1</p>
</p>
</details>
<p></p>
| True | CVE-2022-25881 (Medium) detected in http-cache-semantics-4.1.0.tgz - ## CVE-2022-25881 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-cache-semantics-4.1.0.tgz</b></p></summary>
<p>Parses Cache-Control and other headers. Helps building correct HTTP caches and proxies</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz">https://registry.npmjs.org/http-cache-semantics/-/http-cache-semantics-4.1.0.tgz</a></p>
<p>Path to dependency file: /web/app/package.json</p>
<p>Path to vulnerable library: /web/app/node_modules/http-cache-semantics/package.json</p>
<p>
Dependency Hierarchy:
- webdriverio-6.1.2.tgz (Root Library)
- webdriver-6.1.2.tgz
- got-10.7.0.tgz
- cacheable-request-7.0.1.tgz
- :x: **http-cache-semantics-4.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects versions of the package http-cache-semantics before 4.1.1. The issue can be exploited via malicious request header values sent to a server, when that server reads the cache policy from the request using this library.
<p>Publish Date: 2023-01-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25881>CVE-2022-25881</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-25881">https://www.cve.org/CVERecord?id=CVE-2022-25881</a></p>
<p>Release Date: 2023-01-31</p>
<p>Fix Resolution: http-cache-semantics - 4.1.1</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in http cache semantics tgz cve medium severity vulnerability vulnerable library http cache semantics tgz parses cache control and other headers helps building correct http caches and proxies library home page a href path to dependency file web app package json path to vulnerable library web app node modules http cache semantics package json dependency hierarchy webdriverio tgz root library webdriver tgz got tgz cacheable request tgz x http cache semantics tgz vulnerable library found in base branch main vulnerability details this affects versions of the package http cache semantics before the issue can be exploited via malicious request header values sent to a server when that server reads the cache policy from the request using this library publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution http cache semantics | 0 |
97,675 | 16,237,900,629 | IssuesEvent | 2021-05-07 04:48:23 | three11/optisize | https://api.github.com/repos/three11/optisize | closed | CVE-2021-23343 (Medium) detected in path-parse-1.0.6.tgz | security vulnerability | ## CVE-2021-23343 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>Path to dependency file: optisize/package.json</p>
<p>Path to vulnerable library: optisize/node_modules/path-parse/package.json</p>
<p>
Dependency Hierarchy:
- tape-5.2.2.tgz (Root Library)
- resolve-2.0.0-next.3.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/three11/optisize/commit/6c980b1cbe19f16918186dfa254526e6a2bcefbf">6c980b1cbe19f16918186dfa254526e6a2bcefbf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23343 (Medium) detected in path-parse-1.0.6.tgz - ## CVE-2021-23343 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>Path to dependency file: optisize/package.json</p>
<p>Path to vulnerable library: optisize/node_modules/path-parse/package.json</p>
<p>
Dependency Hierarchy:
- tape-5.2.2.tgz (Root Library)
- resolve-2.0.0-next.3.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/three11/optisize/commit/6c980b1cbe19f16918186dfa254526e6a2bcefbf">6c980b1cbe19f16918186dfa254526e6a2bcefbf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in path parse tgz cve medium severity vulnerability vulnerable library path parse tgz node js path parse ponyfill library home page a href path to dependency file optisize package json path to vulnerable library optisize node modules path parse package json dependency hierarchy tape tgz root library resolve next tgz x path parse tgz vulnerable library found in head commit a href found in base branch master vulnerability details all versions of package path parse are vulnerable to regular expression denial of service redos via splitdevicere splittailre and splitpathre regular expressions redos exhibits polynomial worst case time complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href step up your open source security game with whitesource | 0 |
317,703 | 27,258,715,440 | IssuesEvent | 2023-02-22 13:28:13 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: X-Pack Endpoint API Integration Tests.x-pack/test/security_solution_endpoint_api_int/apis/policy·ts - Endpoint plugin Endpoint policy api GET /api/endpoint/policy_response "before all" hook for "should return one policy response for an id" | failed-test | A test failed on a tracked branch
```
AggregateError:
Error: Bulk doc failure [operation=create]:
doc: {"@timestamp":1588443706336,"agent":{"id":"a10ac658-a3bc-4ac6-944a-68d9bd1c5a5e","version":"1.0.0-local.20200416.0"},"ecs":{"version":"1.4.0"},"elastic":{"agent":{"id":"cbdba168-19d8-4f9c-8e97-7222709e868f"}},"Endpoint":{"policy":{"applied":{"actions":{"configure_elasticsearch_connection":{"message":"elasticsearch comms configured successfully","status":"success"},"configure_kernel":{"message":"Failed to configure kernel","status":"failure"},"configure_logging":{"message":"Successfully configured logging","status":"success"},"configure_malware":{"message":"Unexpected error configuring malware","status":"failure"},"connect_kernel":{"message":"Successfully initialized minifilter","status":"success"},"detect_file_open_events":{"message":"Successfully stopped file open event reporting","status":"success"},"detect_file_write_events":{"message":"Failed to stop file write event reporting","status":"success"},"detect_image_load_events":{"message":"Successfuly started image load event reporting","status":"success"},"detect_process_events":{"message":"Successfully started process event reporting","status":"success"},"download_global_artifacts":{"message":"Failed to download EXE model","status":"success"},"download_model":{"message":"Failed to apply a portion of the configuration (kernel)","status":"success"},"ingest_events_config":{"message":"Failed to apply a portion of the configuration (kernel)","status":"success"},"load_config":{"message":"successfully parsed configuration","status":"success"},"load_malware_model":{"message":"Error deserializing EXE model; no valid malware model installed","status":"success"},"read_elasticsearch_config":{"message":"Successfully read Elasticsearch configuration","status":"success"},"read_events_config":{"message":"Successfully read events configuration","status":"success"},"read_kernel_config":{"message":"Succesfully read kernel configuration","status":"success"},"read_logging_config":{"message":"field (logging.debugview) not found in config","status":"success"},"read_malware_config":{"message":"Successfully read malware detect configuration","status":"success"},"workflow":{"message":"Failed to apply a portion of the configuration (kernel)","status":"success"}},"id":"C2A9093E-E289-4C0A-AA44-8C32A414FA7A","response":{"configurations":{"events":{"concerned_actions":["load_config","configure_malware"],"status":"warning"},"logging":{"concerned_actions":["detect_image_load_events","load_malware_model","detect_file_write_events"],"status":"warning"},"malware":{"concerned_actions":["detect_file_write_events","detect_file_write_events"],"status":"failure"},"streaming":{"concerned_actions":["configure_malware","configure_kernel","connect_kernel"],"status":"warning"}}},"status":"success","version":"94a10ce9-91c2-469b-823e-2e07df374b67","name":"With Eventing"}}},"event":{"created":1588443706336,"id":"ab279ea5-a1da-4253-ac2a-77ad4427d5d6","kind":"state","category":["host"],"type":["change"],"module":"endpoint","action":"endpoint_policy_response","dataset":"endpoint.policy"},"host":{"id":"4f3b9858-a96d-49d8-a326-230d7763d767","hostname":"Host-mhbzzuy86f","name":"Host-mhbzzuy86f","architecture":"hnezzm3ol9","ip":["10.78.120.83"],"mac":["62-6a-18-23-26-2d","34-5a-d0-72-41-52"],"os":{"name":"windows 10.0","full":"Windows 10","version":"10.0","platform":"Windows","family":"Windows","Ext":{"variant":"Windows Pro"}}}}
error: {"type":"illegal_argument_exception","reason":"pipeline with id [metrics-endpoint.policy-8.7.0-next] does not exist"}
at Array.map (<anonymous>)
at indexDocs (index_doc_records_stream.ts:62:13)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Writable.write [as _write] (index_doc_records_stream.ts:76:9)
at indexDocs (index_doc_records_stream.ts:62:13)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Writable.write [as _write] (index_doc_records_stream.ts:76:9)
```
First failure: [CI Build - 8.7](https://buildkite.com/elastic/kibana-on-merge/builds/27367#0186791c-aec8-44c4-b765-35d1af0f6b54)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Endpoint API Integration Tests.x-pack/test/security_solution_endpoint_api_int/apis/policy·ts","test.name":"Endpoint plugin Endpoint policy api GET /api/endpoint/policy_response \"before all\" hook for \"should return one policy response for an id\"","test.failCount":1}} --> | 1.0 | Failing test: X-Pack Endpoint API Integration Tests.x-pack/test/security_solution_endpoint_api_int/apis/policy·ts - Endpoint plugin Endpoint policy api GET /api/endpoint/policy_response "before all" hook for "should return one policy response for an id" - A test failed on a tracked branch
```
AggregateError:
Error: Bulk doc failure [operation=create]:
doc: {"@timestamp":1588443706336,"agent":{"id":"a10ac658-a3bc-4ac6-944a-68d9bd1c5a5e","version":"1.0.0-local.20200416.0"},"ecs":{"version":"1.4.0"},"elastic":{"agent":{"id":"cbdba168-19d8-4f9c-8e97-7222709e868f"}},"Endpoint":{"policy":{"applied":{"actions":{"configure_elasticsearch_connection":{"message":"elasticsearch comms configured successfully","status":"success"},"configure_kernel":{"message":"Failed to configure kernel","status":"failure"},"configure_logging":{"message":"Successfully configured logging","status":"success"},"configure_malware":{"message":"Unexpected error configuring malware","status":"failure"},"connect_kernel":{"message":"Successfully initialized minifilter","status":"success"},"detect_file_open_events":{"message":"Successfully stopped file open event reporting","status":"success"},"detect_file_write_events":{"message":"Failed to stop file write event reporting","status":"success"},"detect_image_load_events":{"message":"Successfuly started image load event reporting","status":"success"},"detect_process_events":{"message":"Successfully started process event reporting","status":"success"},"download_global_artifacts":{"message":"Failed to download EXE model","status":"success"},"download_model":{"message":"Failed to apply a portion of the configuration (kernel)","status":"success"},"ingest_events_config":{"message":"Failed to apply a portion of the configuration (kernel)","status":"success"},"load_config":{"message":"successfully parsed configuration","status":"success"},"load_malware_model":{"message":"Error deserializing EXE model; no valid malware model installed","status":"success"},"read_elasticsearch_config":{"message":"Successfully read Elasticsearch configuration","status":"success"},"read_events_config":{"message":"Successfully read events configuration","status":"success"},"read_kernel_config":{"message":"Succesfully read kernel configuration","status":"success"},"read_logging_config":{"message":"field (logging.debugview) not found in config","status":"success"},"read_malware_config":{"message":"Successfully read malware detect configuration","status":"success"},"workflow":{"message":"Failed to apply a portion of the configuration (kernel)","status":"success"}},"id":"C2A9093E-E289-4C0A-AA44-8C32A414FA7A","response":{"configurations":{"events":{"concerned_actions":["load_config","configure_malware"],"status":"warning"},"logging":{"concerned_actions":["detect_image_load_events","load_malware_model","detect_file_write_events"],"status":"warning"},"malware":{"concerned_actions":["detect_file_write_events","detect_file_write_events"],"status":"failure"},"streaming":{"concerned_actions":["configure_malware","configure_kernel","connect_kernel"],"status":"warning"}}},"status":"success","version":"94a10ce9-91c2-469b-823e-2e07df374b67","name":"With Eventing"}}},"event":{"created":1588443706336,"id":"ab279ea5-a1da-4253-ac2a-77ad4427d5d6","kind":"state","category":["host"],"type":["change"],"module":"endpoint","action":"endpoint_policy_response","dataset":"endpoint.policy"},"host":{"id":"4f3b9858-a96d-49d8-a326-230d7763d767","hostname":"Host-mhbzzuy86f","name":"Host-mhbzzuy86f","architecture":"hnezzm3ol9","ip":["10.78.120.83"],"mac":["62-6a-18-23-26-2d","34-5a-d0-72-41-52"],"os":{"name":"windows 10.0","full":"Windows 10","version":"10.0","platform":"Windows","family":"Windows","Ext":{"variant":"Windows Pro"}}}}
error: {"type":"illegal_argument_exception","reason":"pipeline with id [metrics-endpoint.policy-8.7.0-next] does not exist"}
at Array.map (<anonymous>)
at indexDocs (index_doc_records_stream.ts:62:13)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Writable.write [as _write] (index_doc_records_stream.ts:76:9)
at indexDocs (index_doc_records_stream.ts:62:13)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Writable.write [as _write] (index_doc_records_stream.ts:76:9)
```
First failure: [CI Build - 8.7](https://buildkite.com/elastic/kibana-on-merge/builds/27367#0186791c-aec8-44c4-b765-35d1af0f6b54)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Endpoint API Integration Tests.x-pack/test/security_solution_endpoint_api_int/apis/policy·ts","test.name":"Endpoint plugin Endpoint policy api GET /api/endpoint/policy_response \"before all\" hook for \"should return one policy response for an id\"","test.failCount":1}} --> | non_priority | failing test x pack endpoint api integration tests x pack test security solution endpoint api int apis policy·ts endpoint plugin endpoint policy api get api endpoint policy response before all hook for should return one policy response for an id a test failed on a tracked branch aggregateerror error bulk doc failure doc timestamp agent id version local ecs version elastic agent id endpoint policy applied actions configure elasticsearch connection message elasticsearch comms configured successfully status success configure kernel message failed to configure kernel status failure configure logging message successfully configured logging status success configure malware message unexpected error configuring malware status failure connect kernel message successfully initialized minifilter status success detect file open events message successfully stopped file open event reporting status success detect file write events message failed to stop file write event reporting status success detect image load events message successfuly started image load event reporting status success detect process events message successfully started process event reporting status success download global artifacts message failed to download exe model status success download model message failed to apply a portion of the configuration kernel status success ingest events config message failed to apply a portion of the configuration kernel status success load config message successfully parsed configuration status success load malware model message error deserializing exe model no valid malware model installed status success read elasticsearch config message successfully read elasticsearch configuration status success read events config message successfully read events configuration status success read kernel config message succesfully read kernel configuration status success read logging config message field logging debugview not found in config status success read malware config message successfully read malware detect configuration status success workflow message failed to apply a portion of the configuration kernel status success id response configurations events concerned actions status warning logging concerned actions status warning malware concerned actions status failure streaming concerned actions status warning status success version name with eventing event created id kind state category type module endpoint action endpoint policy response dataset endpoint policy host id hostname host name host architecture ip mac os name windows full windows version platform windows family windows ext variant windows pro error type illegal argument exception reason pipeline with id does not exist at array map at indexdocs index doc records stream ts at runmicrotasks at processticksandrejections node internal process task queues at writable write index doc records stream ts at indexdocs index doc records stream ts at runmicrotasks at processticksandrejections node internal process task queues at writable write index doc records stream ts first failure | 0 |
179,995 | 14,730,230,818 | IssuesEvent | 2021-01-06 12:52:36 | cloudskiff/driftctl | https://api.github.com/repos/cloudskiff/driftctl | closed | 'kind/documentation' tags aren't automatically added | kind/documentation | **Description**
'kind/documentation' tags aren't automatically added for Documentation type of issues
| 1.0 | 'kind/documentation' tags aren't automatically added - **Description**
'kind/documentation' tags aren't automatically added for Documentation type of issues
| non_priority | kind documentation tags aren t automatically added description kind documentation tags aren t automatically added for documentation type of issues | 0 |
211,406 | 23,817,991,753 | IssuesEvent | 2022-09-05 08:38:46 | sast-automation-dev/soundcloud-redux-333 | https://api.github.com/repos/sast-automation-dev/soundcloud-redux-333 | opened | helmet-3.8.1.tgz: 2 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>helmet-3.8.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/connect/node_modules/debug/package.json,/node_modules/express/node_modules/debug/package.json,/node_modules/finalhandler/node_modules/debug/package.json,/node_modules/send/node_modules/debug/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-333/commit/39fff905eda1da74897903d06eb5d4cc3ae423d3">39fff905eda1da74897903d06eb5d4cc3ae423d3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [WS-2019-0289](https://github.com/helmetjs/csp/compare/v2.9.0...v2.9.1) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | helmet-csp-2.5.1.tgz | Transitive | 3.21.0 | ✅ |
| [CVE-2017-16137](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | debug-2.6.7.tgz | Transitive | 3.8.2 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2019-0289</summary>
### Vulnerable Library - <b>helmet-csp-2.5.1.tgz</b></p>
<p>Content Security Policy middleware.</p>
<p>Library home page: <a href="https://registry.npmjs.org/helmet-csp/-/helmet-csp-2.5.1.tgz">https://registry.npmjs.org/helmet-csp/-/helmet-csp-2.5.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/helmet-csp/package.json</p>
<p>
Dependency Hierarchy:
- helmet-3.8.1.tgz (Root Library)
- :x: **helmet-csp-2.5.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-333/commit/39fff905eda1da74897903d06eb5d4cc3ae423d3">39fff905eda1da74897903d06eb5d4cc3ae423d3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Helmet-csp before 2.9.1 is vulnerable to a Configuration Override affecting the application's Content Security Policy (CSP). The package's browser sniffing for Firefox deletes the default-src CSP policy, which is the fallback policy. This allows an attacker to remove an application's default CSP, possibly rendering the application vulnerable to Cross-Site Scripting.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/helmetjs/csp/compare/v2.9.0...v2.9.1>WS-2019-0289</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1176">https://www.npmjs.com/advisories/1176</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution (helmet-csp): 2.9.1</p>
<p>Direct dependency fix Resolution (helmet): 3.21.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16137</summary>
### Vulnerable Library - <b>debug-2.6.7.tgz</b></p>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-2.6.7.tgz">https://registry.npmjs.org/debug/-/debug-2.6.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/connect/node_modules/debug/package.json,/node_modules/express/node_modules/debug/package.json,/node_modules/finalhandler/node_modules/debug/package.json,/node_modules/send/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- helmet-3.8.1.tgz (Root Library)
- connect-3.6.2.tgz
- :x: **debug-2.6.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-333/commit/39fff905eda1da74897903d06eb5d4cc3ae423d3">39fff905eda1da74897903d06eb5d4cc3ae423d3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (debug): 2.6.9</p>
<p>Direct dependency fix Resolution (helmet): 3.8.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | helmet-3.8.1.tgz: 2 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>helmet-3.8.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/connect/node_modules/debug/package.json,/node_modules/express/node_modules/debug/package.json,/node_modules/finalhandler/node_modules/debug/package.json,/node_modules/send/node_modules/debug/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-333/commit/39fff905eda1da74897903d06eb5d4cc3ae423d3">39fff905eda1da74897903d06eb5d4cc3ae423d3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [WS-2019-0289](https://github.com/helmetjs/csp/compare/v2.9.0...v2.9.1) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | helmet-csp-2.5.1.tgz | Transitive | 3.21.0 | ✅ |
| [CVE-2017-16137](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | debug-2.6.7.tgz | Transitive | 3.8.2 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2019-0289</summary>
### Vulnerable Library - <b>helmet-csp-2.5.1.tgz</b></p>
<p>Content Security Policy middleware.</p>
<p>Library home page: <a href="https://registry.npmjs.org/helmet-csp/-/helmet-csp-2.5.1.tgz">https://registry.npmjs.org/helmet-csp/-/helmet-csp-2.5.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/helmet-csp/package.json</p>
<p>
Dependency Hierarchy:
- helmet-3.8.1.tgz (Root Library)
- :x: **helmet-csp-2.5.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-333/commit/39fff905eda1da74897903d06eb5d4cc3ae423d3">39fff905eda1da74897903d06eb5d4cc3ae423d3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Helmet-csp before 2.9.1 is vulnerable to a Configuration Override affecting the application's Content Security Policy (CSP). The package's browser sniffing for Firefox deletes the default-src CSP policy, which is the fallback policy. This allows an attacker to remove an application's default CSP, possibly rendering the application vulnerable to Cross-Site Scripting.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/helmetjs/csp/compare/v2.9.0...v2.9.1>WS-2019-0289</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1176">https://www.npmjs.com/advisories/1176</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution (helmet-csp): 2.9.1</p>
<p>Direct dependency fix Resolution (helmet): 3.21.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16137</summary>
### Vulnerable Library - <b>debug-2.6.7.tgz</b></p>
<p>small debugging utility</p>
<p>Library home page: <a href="https://registry.npmjs.org/debug/-/debug-2.6.7.tgz">https://registry.npmjs.org/debug/-/debug-2.6.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/connect/node_modules/debug/package.json,/node_modules/express/node_modules/debug/package.json,/node_modules/finalhandler/node_modules/debug/package.json,/node_modules/send/node_modules/debug/package.json</p>
<p>
Dependency Hierarchy:
- helmet-3.8.1.tgz (Root Library)
- connect-3.6.2.tgz
- :x: **debug-2.6.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/soundcloud-redux-333/commit/39fff905eda1da74897903d06eb5d4cc3ae423d3">39fff905eda1da74897903d06eb5d4cc3ae423d3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16137>CVE-2017-16137</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137">https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution (debug): 2.6.9</p>
<p>Direct dependency fix Resolution (helmet): 3.8.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | helmet tgz vulnerabilities highest severity is vulnerable library helmet tgz path to dependency file package json path to vulnerable library node modules connect node modules debug package json node modules express node modules debug package json node modules finalhandler node modules debug package json node modules send node modules debug package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium helmet csp tgz transitive medium debug tgz transitive details ws vulnerable library helmet csp tgz content security policy middleware library home page a href path to dependency file package json path to vulnerable library node modules helmet csp package json dependency hierarchy helmet tgz root library x helmet csp tgz vulnerable library found in head commit a href found in base branch master vulnerability details helmet csp before is vulnerable to a configuration override affecting the application s content security policy csp the package s browser sniffing for firefox deletes the default src csp policy which is the fallback policy this allows an attacker to remove an application s default csp possibly rendering the application vulnerable to cross site scripting publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution helmet csp direct dependency fix resolution helmet rescue worker helmet automatic remediation is available for this issue cve vulnerable library debug tgz small debugging utility library home page a href path to dependency file package json path to vulnerable library node modules connect node modules debug package json node modules express node modules debug package json node modules finalhandler node modules debug package json node modules send node modules debug package json dependency hierarchy helmet tgz root library connect tgz x debug tgz vulnerable library found in head commit a href found in base branch master vulnerability details the debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter it takes around characters to block for seconds making this a low severity issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution debug direct dependency fix resolution helmet rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
70,292 | 9,395,467,562 | IssuesEvent | 2019-04-08 02:44:40 | vuejs/jp.vuejs.org | https://api.github.com/repos/vuejs/jp.vuejs.org | closed | [Doc]: Use immediate watcher in serverless blog cookbook post | assigned documentation | 本家のドキュメントに更新がありました:page_facing_up:
Original:https://github.com/vuejs/vuejs.org/commit/9a9006413d4c5b2b7887f342ea1a573238dae6c2 | 1.0 | [Doc]: Use immediate watcher in serverless blog cookbook post - 本家のドキュメントに更新がありました:page_facing_up:
Original:https://github.com/vuejs/vuejs.org/commit/9a9006413d4c5b2b7887f342ea1a573238dae6c2 | non_priority | use immediate watcher in serverless blog cookbook post 本家のドキュメントに更新がありました page facing up original | 0 |
30,618 | 8,568,165,285 | IssuesEvent | 2018-11-10 18:49:28 | wilburt/flutter_paystack | https://api.github.com/repos/wilburt/flutter_paystack | closed | Android dependency issues preventing build | build-failure | Awesome plugin. Although I am not able to build on Android. It throws this error
FAILURE: Build failed with an exception.
* What went wrong:
Execution failed for task ':app:preDebugBuild'.
> Android dependency 'com.android.support:support-fragment' has different version for the compile (27.1.1) and runtime (28.0.0) classpath. You should manually set the same version via DependencyResolution
* Try:
Run with --stacktrace option to get the stack trace. Run with --info or --debug option to get more log output. Run with --scan to get full insights.
* Get more help at https://help.gradle.org
BUILD FAILED in 1s
Finished with error: Gradle task assembleDebug failed with exit code 1
Any advice on how to solve this is highly appreciated. Thanks. | 1.0 | Android dependency issues preventing build - Awesome plugin. Although I am not able to build on Android. It throws this error
FAILURE: Build failed with an exception.
* What went wrong:
Execution failed for task ':app:preDebugBuild'.
> Android dependency 'com.android.support:support-fragment' has different version for the compile (27.1.1) and runtime (28.0.0) classpath. You should manually set the same version via DependencyResolution
* Try:
Run with --stacktrace option to get the stack trace. Run with --info or --debug option to get more log output. Run with --scan to get full insights.
* Get more help at https://help.gradle.org
BUILD FAILED in 1s
Finished with error: Gradle task assembleDebug failed with exit code 1
Any advice on how to solve this is highly appreciated. Thanks. | non_priority | android dependency issues preventing build awesome plugin although i am not able to build on android it throws this error failure build failed with an exception what went wrong execution failed for task app predebugbuild android dependency com android support support fragment has different version for the compile and runtime classpath you should manually set the same version via dependencyresolution try run with stacktrace option to get the stack trace run with info or debug option to get more log output run with scan to get full insights get more help at build failed in finished with error gradle task assembledebug failed with exit code any advice on how to solve this is highly appreciated thanks | 0 |
285,229 | 21,509,090,282 | IssuesEvent | 2022-04-28 01:03:15 | enoren5/tarot_juicer | https://api.github.com/repos/enoren5/tarot_juicer | closed | Sysadmin and Heroku: Install DDOS protection tech (free tier) including SSL + answer questions | documentation enhancement | Install DDOS protection (free) along with SSL for the free tier. https://www.cloudflare.com/plans/#overview
I also require answers to these questions:
1. How easy is it to upgrade / scale to higher tiers when the time comes?
2. Is there a way to scale up/down as traffic increases/decreases sporadically?
3. Is there a way to completely turn off the DDOS protection with a switch and turn it back on? If so, where is it?
| 1.0 | Sysadmin and Heroku: Install DDOS protection tech (free tier) including SSL + answer questions - Install DDOS protection (free) along with SSL for the free tier. https://www.cloudflare.com/plans/#overview
I also require answers to these questions:
1. How easy is it to upgrade / scale to higher tiers when the time comes?
2. Is there a way to scale up/down as traffic increases/decreases sporadically?
3. Is there a way to completely turn off the DDOS protection with a switch and turn it back on? If so, where is it?
| non_priority | sysadmin and heroku install ddos protection tech free tier including ssl answer questions install ddos protection free along with ssl for the free tier i also require answers to these questions how easy is it to upgrade scale to higher tiers when the time comes is there a way to scale up down as traffic increases decreases sporadically is there a way to completely turn off the ddos protection with a switch and turn it back on if so where is it | 0 |
64,332 | 26,693,304,815 | IssuesEvent | 2023-01-27 08:03:16 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | closed | Azure Service Bus - Not able to publish the message to service bus in azure using node SDK | question customer-reported Client Service Bus needs-author-feedback no-recent-activity | Packages: "@azure/service-bus": "^7.7.2", @azure/identity": "^3.0.0"
Operating System: MacOs Monterey Version 12.6.1
Node Version: v18.12.1
**Environment Setup**
Running the service bus in Private VNET with the private end point configured and trying to access it from local machine with VPN.
**Describe the bug**
Not able to publish the message using connection_string (shared access policies) to the service bus, but able to do all the management level activities (creation of topic, creation of subscription)
**Observed error message:**
ServiceBusError: [connection-4] Sender "testtopic3-9b192bd4-5991-3b4f-837b-38886eedd68f" with address "testtopic3", was not able to send the message right now, due to operation timeout.
retryable: true,
code: 'ServiceTimeout'
**ServiceBus Explorer**
Tried connecting to Service Bus via Service Bus explorer using connection_string, able to list the topic, subscriptions created and able to publish the message to topic and receive the message the message from subscription through service bus explorer successfully, facing the issue while publishing the message through SDK (attached the screenshot of error).
**Reproducible Example:**
**Service Bus client**
```
const sClient = new ServiceBusClient(connection_string);
```
**Publish Message to Topic**
```
const publishMessageToTopic = async () => {
try {
const sender = sClient.createSender(topic_name);
const message = {
body: {
firstName: "Albert",
lastName: "Einstein",
},
};
const res = await sender.sendMessages(message);
sender.close();
} catch (error) {
console.log(error);
} finally {
sClient.close();
}
};
publishMessageToTopic();
```
**Service Bus Explorer Screenshot**
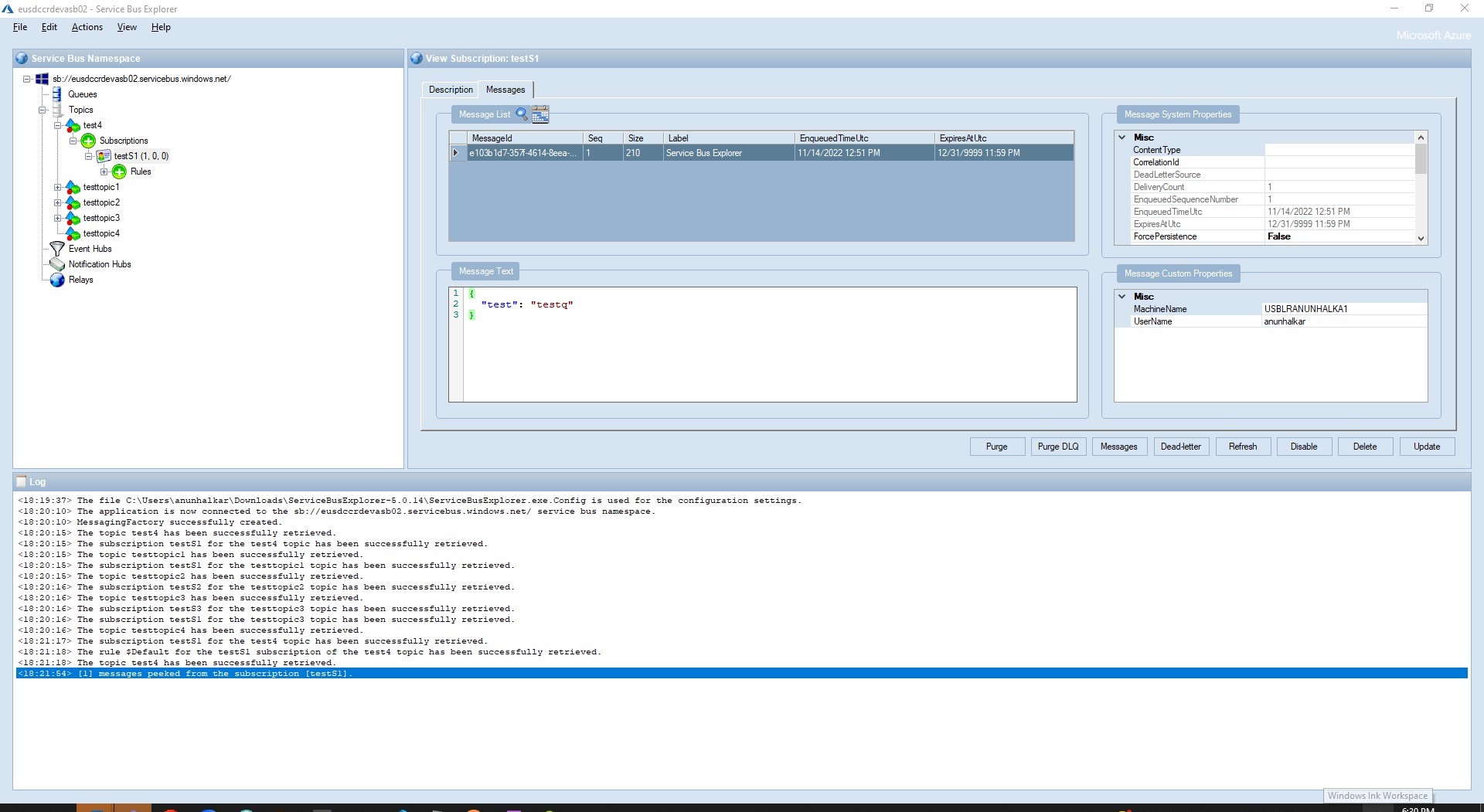
**Error Message Screenshot**
<img width="1005" alt="Screenshot 2022-11-14 at 7 16 37 PM" src="https://user-images.githubusercontent.com/100764604/201676013-7412440f-f0ef-4445-97ba-caff3b5e7618.png">
| 1.0 | Azure Service Bus - Not able to publish the message to service bus in azure using node SDK - Packages: "@azure/service-bus": "^7.7.2", @azure/identity": "^3.0.0"
Operating System: MacOs Monterey Version 12.6.1
Node Version: v18.12.1
**Environment Setup**
Running the service bus in Private VNET with the private end point configured and trying to access it from local machine with VPN.
**Describe the bug**
Not able to publish the message using connection_string (shared access policies) to the service bus, but able to do all the management level activities (creation of topic, creation of subscription)
**Observed error message:**
ServiceBusError: [connection-4] Sender "testtopic3-9b192bd4-5991-3b4f-837b-38886eedd68f" with address "testtopic3", was not able to send the message right now, due to operation timeout.
retryable: true,
code: 'ServiceTimeout'
**ServiceBus Explorer**
Tried connecting to Service Bus via Service Bus explorer using connection_string, able to list the topic, subscriptions created and able to publish the message to topic and receive the message the message from subscription through service bus explorer successfully, facing the issue while publishing the message through SDK (attached the screenshot of error).
**Reproducible Example:**
**Service Bus client**
```
const sClient = new ServiceBusClient(connection_string);
```
**Publish Message to Topic**
```
const publishMessageToTopic = async () => {
try {
const sender = sClient.createSender(topic_name);
const message = {
body: {
firstName: "Albert",
lastName: "Einstein",
},
};
const res = await sender.sendMessages(message);
sender.close();
} catch (error) {
console.log(error);
} finally {
sClient.close();
}
};
publishMessageToTopic();
```
**Service Bus Explorer Screenshot**
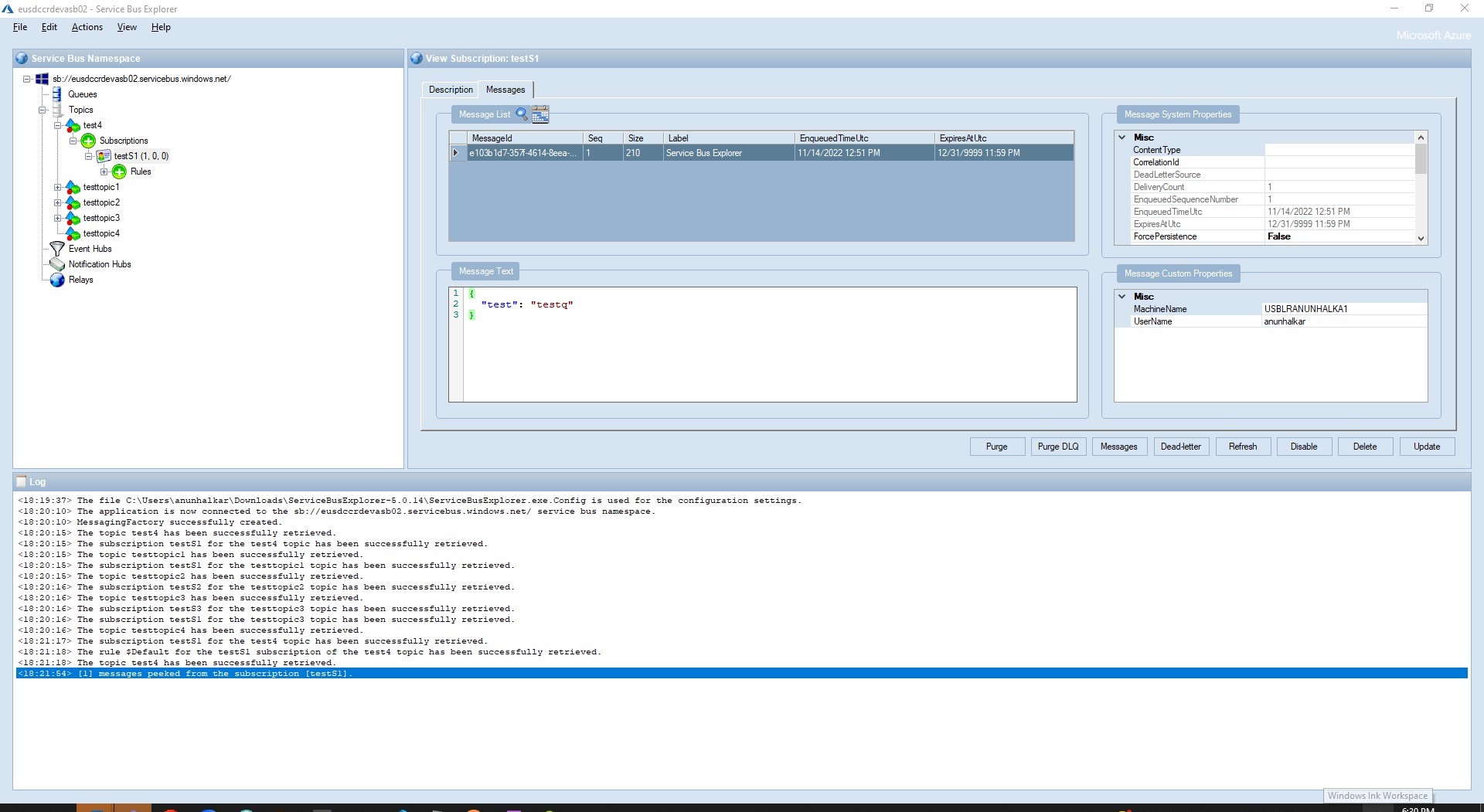
**Error Message Screenshot**
<img width="1005" alt="Screenshot 2022-11-14 at 7 16 37 PM" src="https://user-images.githubusercontent.com/100764604/201676013-7412440f-f0ef-4445-97ba-caff3b5e7618.png">
| non_priority | azure service bus not able to publish the message to service bus in azure using node sdk packages azure service bus azure identity operating system macos monterey version node version environment setup running the service bus in private vnet with the private end point configured and trying to access it from local machine with vpn describe the bug not able to publish the message using connection string shared access policies to the service bus but able to do all the management level activities creation of topic creation of subscription observed error message servicebuserror sender with address was not able to send the message right now due to operation timeout retryable true code servicetimeout servicebus explorer tried connecting to service bus via service bus explorer using connection string able to list the topic subscriptions created and able to publish the message to topic and receive the message the message from subscription through service bus explorer successfully facing the issue while publishing the message through sdk attached the screenshot of error reproducible example service bus client const sclient new servicebusclient connection string publish message to topic const publishmessagetotopic async try const sender sclient createsender topic name const message body firstname albert lastname einstein const res await sender sendmessages message sender close catch error console log error finally sclient close publishmessagetotopic service bus explorer screenshot error message screenshot img width alt screenshot at pm src | 0 |
57,286 | 15,729,436,453 | IssuesEvent | 2021-03-29 14:51:26 | danmar/testissues | https://api.github.com/repos/danmar/testissues | opened | No pair for character ('). Can't process file. File is either invalid or unicode (Trac #261) | Incomplete Migration Migrated from Trac Other defect noone | Migrated from https://trac.cppcheck.net/ticket/261
```json
{
"status": "closed",
"changetime": "2009-04-26T19:23:31",
"description": "Hi,\ni've get a lot of:\n\n{{{\n[.\\file_name.cpp:0]: (error) No pair for character (\"). Can't process file. File is either invalid or unicode, which is currently not supported.\n}}}\n\nwhen using cppcheck rev. 14eff6419451c2e4e666a4922a35662598ef8fa2\n\nI will try to isolate the problem and add small test-case.",
"reporter": "polygon7",
"cc": "",
"resolution": "fixed",
"_ts": "1240773811000000",
"component": "Other",
"summary": "No pair for character ('). Can't process file. File is either invalid or unicode",
"priority": "",
"keywords": "preprocessor",
"time": "2009-04-21T08:20:40",
"milestone": "1.32",
"owner": "noone",
"type": "defect"
}
```
| 1.0 | No pair for character ('). Can't process file. File is either invalid or unicode (Trac #261) - Migrated from https://trac.cppcheck.net/ticket/261
```json
{
"status": "closed",
"changetime": "2009-04-26T19:23:31",
"description": "Hi,\ni've get a lot of:\n\n{{{\n[.\\file_name.cpp:0]: (error) No pair for character (\"). Can't process file. File is either invalid or unicode, which is currently not supported.\n}}}\n\nwhen using cppcheck rev. 14eff6419451c2e4e666a4922a35662598ef8fa2\n\nI will try to isolate the problem and add small test-case.",
"reporter": "polygon7",
"cc": "",
"resolution": "fixed",
"_ts": "1240773811000000",
"component": "Other",
"summary": "No pair for character ('). Can't process file. File is either invalid or unicode",
"priority": "",
"keywords": "preprocessor",
"time": "2009-04-21T08:20:40",
"milestone": "1.32",
"owner": "noone",
"type": "defect"
}
```
| non_priority | no pair for character can t process file file is either invalid or unicode trac migrated from json status closed changetime description hi ni ve get a lot of n n n error no pair for character can t process file file is either invalid or unicode which is currently not supported n n nwhen using cppcheck rev n ni will try to isolate the problem and add small test case reporter cc resolution fixed ts component other summary no pair for character can t process file file is either invalid or unicode priority keywords preprocessor time milestone owner noone type defect | 0 |
147,463 | 19,522,822,230 | IssuesEvent | 2021-12-29 22:26:48 | swagger-api/swagger-codegen | https://api.github.com/repos/swagger-api/swagger-codegen | opened | CVE-2020-36186 (High) detected in multiple libraries | security vulnerability | ## CVE-2020-36186 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.7.8.jar</b>, <b>jackson-databind-2.4.5.jar</b>, <b>jackson-databind-2.6.4.jar</b>, <b>jackson-databind-2.8.8.jar</b>, <b>jackson-databind-2.8.9.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.7.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.fasterxml.jackson.core/jackson-databind/bundles/jackson-databind-2.7.8.jar</p>
<p>
Dependency Hierarchy:
- lagom-scaladsl-api_2.11-1.3.8.jar (Root Library)
- lagom-api_2.11-1.3.8.jar
- play_2.11-2.5.13.jar
- :x: **jackson-databind-2.7.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.4.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /samples/client/petstore/scala/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.4.5/c69c0cb613128c69d84a6a0304ddb9fce82e8242/jackson-databind-2.4.5.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.4.5/c69c0cb613128c69d84a6a0304ddb9fce82e8242/jackson-databind-2.4.5.jar</p>
<p>
Dependency Hierarchy:
- swagger-core-1.5.8.jar (Root Library)
- :x: **jackson-databind-2.4.5.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.6.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /samples/client/petstore/java/jersey1/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.4/f2abadd10891512268b16a1a1a6f81890f3e2976/jackson-databind-2.6.4.jar,/aches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.4/f2abadd10891512268b16a1a1a6f81890f3e2976/jackson-databind-2.6.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.4.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.fasterxml.jackson.core/jackson-databind/bundles/jackson-databind-2.8.8.jar</p>
<p>
Dependency Hierarchy:
- finch-circe_2.11-0.15.1.jar (Root Library)
- circe-jackson28_2.11-0.8.0.jar
- :x: **jackson-databind-2.8.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.fasterxml.jackson.core/jackson-databind/bundles/jackson-databind-2.8.9.jar</p>
<p>
Dependency Hierarchy:
- play-guice_2.12-2.6.3.jar (Root Library)
- play_2.12-2.6.3.jar
- :x: **jackson-databind-2.8.9.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/swagger-api/swagger-codegen/commit/4b7a8d7d7384aa6a27d6309c35ade0916edae7ed">4b7a8d7d7384aa6a27d6309c35ade0916edae7ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186>CVE-2020-36186</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2997">https://github.com/FasterXML/jackson-databind/issues/2997</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.7.8","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"com.lightbend.lagom:lagom-scaladsl-api_2.11:1.3.8;com.lightbend.lagom:lagom-api_2.11:1.3.8;com.typesafe.play:play_2.11:2.5.13;com.fasterxml.jackson.core:jackson-databind:2.7.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.4.5","packageFilePaths":["/samples/client/petstore/scala/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"io.swagger:swagger-core:1.5.8;com.fasterxml.jackson.core:jackson-databind:2.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.4","packageFilePaths":["/samples/client/petstore/java/jersey1/build.gradle"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.8","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"com.github.finagle:finch-circe_2.11:0.15.1;io.circe:circe-jackson28_2.11:0.8.0;com.fasterxml.jackson.core:jackson-databind:2.8.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.9","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"com.typesafe.play:play-guice_2.12:2.6.3;com.typesafe.play:play_2.12:2.6.3;com.fasterxml.jackson.core:jackson-databind:2.8.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-36186","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-36186 (High) detected in multiple libraries - ## CVE-2020-36186 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.7.8.jar</b>, <b>jackson-databind-2.4.5.jar</b>, <b>jackson-databind-2.6.4.jar</b>, <b>jackson-databind-2.8.8.jar</b>, <b>jackson-databind-2.8.9.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.7.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.fasterxml.jackson.core/jackson-databind/bundles/jackson-databind-2.7.8.jar</p>
<p>
Dependency Hierarchy:
- lagom-scaladsl-api_2.11-1.3.8.jar (Root Library)
- lagom-api_2.11-1.3.8.jar
- play_2.11-2.5.13.jar
- :x: **jackson-databind-2.7.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.4.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /samples/client/petstore/scala/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.4.5/c69c0cb613128c69d84a6a0304ddb9fce82e8242/jackson-databind-2.4.5.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.4.5/c69c0cb613128c69d84a6a0304ddb9fce82e8242/jackson-databind-2.4.5.jar</p>
<p>
Dependency Hierarchy:
- swagger-core-1.5.8.jar (Root Library)
- :x: **jackson-databind-2.4.5.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.6.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /samples/client/petstore/java/jersey1/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.4/f2abadd10891512268b16a1a1a6f81890f3e2976/jackson-databind-2.6.4.jar,/aches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.4/f2abadd10891512268b16a1a1a6f81890f3e2976/jackson-databind-2.6.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.4.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.fasterxml.jackson.core/jackson-databind/bundles/jackson-databind-2.8.8.jar</p>
<p>
Dependency Hierarchy:
- finch-circe_2.11-0.15.1.jar (Root Library)
- circe-jackson28_2.11-0.8.0.jar
- :x: **jackson-databind-2.8.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.fasterxml.jackson.core/jackson-databind/bundles/jackson-databind-2.8.9.jar</p>
<p>
Dependency Hierarchy:
- play-guice_2.12-2.6.3.jar (Root Library)
- play_2.12-2.6.3.jar
- :x: **jackson-databind-2.8.9.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/swagger-api/swagger-codegen/commit/4b7a8d7d7384aa6a27d6309c35ade0916edae7ed">4b7a8d7d7384aa6a27d6309c35ade0916edae7ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186>CVE-2020-36186</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2997">https://github.com/FasterXML/jackson-databind/issues/2997</a></p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.7.8","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"com.lightbend.lagom:lagom-scaladsl-api_2.11:1.3.8;com.lightbend.lagom:lagom-api_2.11:1.3.8;com.typesafe.play:play_2.11:2.5.13;com.fasterxml.jackson.core:jackson-databind:2.7.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.4.5","packageFilePaths":["/samples/client/petstore/scala/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"io.swagger:swagger-core:1.5.8;com.fasterxml.jackson.core:jackson-databind:2.4.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.4","packageFilePaths":["/samples/client/petstore/java/jersey1/build.gradle"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.8","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"com.github.finagle:finch-circe_2.11:0.15.1;io.circe:circe-jackson28_2.11:0.8.0;com.fasterxml.jackson.core:jackson-databind:2.8.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.9","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"com.typesafe.play:play-guice_2.12:2.6.3;com.typesafe.play:play_2.12:2.6.3;com.fasterxml.jackson.core:jackson-databind:2.8.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-36186","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.datasources.PerUserPoolDataSource.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library home wss scanner cache com fasterxml jackson core jackson databind bundles jackson databind jar dependency hierarchy lagom scaladsl api jar root library lagom api jar play jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file samples client petstore scala build gradle path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy swagger core jar root library x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file samples client petstore java build gradle path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar aches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library home wss scanner cache com fasterxml jackson core jackson databind bundles jackson databind jar dependency hierarchy finch circe jar root library circe jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library home wss scanner cache com fasterxml jackson core jackson databind bundles jackson databind jar dependency hierarchy play guice jar root library play jar x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp dbcp datasources peruserpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree com lightbend lagom lagom scaladsl api com lightbend lagom lagom api com typesafe play play com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree io swagger swagger core com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree com github finagle finch circe io circe circe com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree com typesafe play play guice com typesafe play play com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp dbcp datasources peruserpooldatasource vulnerabilityurl | 0 |
280,165 | 24,281,806,663 | IssuesEvent | 2022-09-28 18:06:23 | Azure/azure-sdk-for-python | https://api.github.com/repos/Azure/azure-sdk-for-python | closed | [TestProxy] Variables should not require "is_live" awareness | test-enhancement | https://github.com/Azure/azure-sdk-for-python/blob/main/doc/dev/test_proxy_migration_guide.md#record-test-variables
Currently, in order to have a "variables" collection, you need to specify it in the signature and return it from the test method. This means that your test method body has to be aware of whether the test is being run live or not. The test author should not have to have conditional "live" checks as this will bloat the test and make it more difficult to reason about.
It would be preferable if the test author could handle variables in a decorator, preparer, fixture, etc, similar to the woefully misnamed `PowerShellPreparer`. That preparer handles environment variables. If present, it uses those values--otherwise it uses a static value.
A `VariablesPreparer` would function similarly:
- if the test is being played back, it will load the value for the recording's "variables" collection
- if the test is running live, it will generate a random value and store it in the variables collection for playback
For each item in the VariabesPreparer, the author should be able to specify a prefix, if desired, for easier debugging. Using a preparer might also negate the need to modify the test body to return the variables collection, as the variables will not (and should not!) be manipulated in the test method body. | 1.0 | [TestProxy] Variables should not require "is_live" awareness - https://github.com/Azure/azure-sdk-for-python/blob/main/doc/dev/test_proxy_migration_guide.md#record-test-variables
Currently, in order to have a "variables" collection, you need to specify it in the signature and return it from the test method. This means that your test method body has to be aware of whether the test is being run live or not. The test author should not have to have conditional "live" checks as this will bloat the test and make it more difficult to reason about.
It would be preferable if the test author could handle variables in a decorator, preparer, fixture, etc, similar to the woefully misnamed `PowerShellPreparer`. That preparer handles environment variables. If present, it uses those values--otherwise it uses a static value.
A `VariablesPreparer` would function similarly:
- if the test is being played back, it will load the value for the recording's "variables" collection
- if the test is running live, it will generate a random value and store it in the variables collection for playback
For each item in the VariabesPreparer, the author should be able to specify a prefix, if desired, for easier debugging. Using a preparer might also negate the need to modify the test body to return the variables collection, as the variables will not (and should not!) be manipulated in the test method body. | non_priority | variables should not require is live awareness currently in order to have a variables collection you need to specify it in the signature and return it from the test method this means that your test method body has to be aware of whether the test is being run live or not the test author should not have to have conditional live checks as this will bloat the test and make it more difficult to reason about it would be preferable if the test author could handle variables in a decorator preparer fixture etc similar to the woefully misnamed powershellpreparer that preparer handles environment variables if present it uses those values otherwise it uses a static value a variablespreparer would function similarly if the test is being played back it will load the value for the recording s variables collection if the test is running live it will generate a random value and store it in the variables collection for playback for each item in the variabespreparer the author should be able to specify a prefix if desired for easier debugging using a preparer might also negate the need to modify the test body to return the variables collection as the variables will not and should not be manipulated in the test method body | 0 |
431,006 | 30,212,772,766 | IssuesEvent | 2023-07-05 13:48:12 | ykdojo/kaguya | https://api.github.com/repos/ykdojo/kaguya | closed | Move the demo videos up in README | documentation | The demo videos should be right after the initial intro so that we can show people the potential of this project more quickly. | 1.0 | Move the demo videos up in README - The demo videos should be right after the initial intro so that we can show people the potential of this project more quickly. | non_priority | move the demo videos up in readme the demo videos should be right after the initial intro so that we can show people the potential of this project more quickly | 0 |
55,701 | 14,019,816,651 | IssuesEvent | 2020-10-29 18:43:59 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Add easy way to create a certificate from just a cert-PEM | api-approved area-System.Security | ## Background and Motivation
#31944 was a great addition but it is sort of a shame we cannot use it just to create a cert from PEM without private key.
All that is needed is to expose `ExtractCertificateFromPem` publicly.
## Proposed API
```cs
namespace System.Security.Cryptography.X509Certificates
{
partial class X509Certificate2
{
public static X509Certificate2 CreateFromPem(ReadOnlySpan<char> certPem);
}
}
```
## Usage Examples
Cases where I need a single certificate from PEM data that is already in a `System.String` or `ReadOnlySpan<char>`.
## Alternatives
* Using a `X509Certificate2Collection.ImportFromPem` and extracting the single certificate.
* Stripping the header and footer, decoding base64 and feeding to constructor.
* `new X509Certificate2(Encoding.ASCII.GetBytes(certPem))`
| True | Add easy way to create a certificate from just a cert-PEM - ## Background and Motivation
#31944 was a great addition but it is sort of a shame we cannot use it just to create a cert from PEM without private key.
All that is needed is to expose `ExtractCertificateFromPem` publicly.
## Proposed API
```cs
namespace System.Security.Cryptography.X509Certificates
{
partial class X509Certificate2
{
public static X509Certificate2 CreateFromPem(ReadOnlySpan<char> certPem);
}
}
```
## Usage Examples
Cases where I need a single certificate from PEM data that is already in a `System.String` or `ReadOnlySpan<char>`.
## Alternatives
* Using a `X509Certificate2Collection.ImportFromPem` and extracting the single certificate.
* Stripping the header and footer, decoding base64 and feeding to constructor.
* `new X509Certificate2(Encoding.ASCII.GetBytes(certPem))`
| non_priority | add easy way to create a certificate from just a cert pem background and motivation was a great addition but it is sort of a shame we cannot use it just to create a cert from pem without private key all that is needed is to expose extractcertificatefrompem publicly proposed api cs namespace system security cryptography partial class public static createfrompem readonlyspan certpem usage examples cases where i need a single certificate from pem data that is already in a system string or readonlyspan alternatives using a importfrompem and extracting the single certificate stripping the header and footer decoding and feeding to constructor new encoding ascii getbytes certpem | 0 |
80,648 | 30,463,070,509 | IssuesEvent | 2023-07-17 08:26:43 | fernandes-wiraharjo/sneakers.id_web_dev | https://api.github.com/repos/fernandes-wiraharjo/sneakers.id_web_dev | closed | Login : Alert Error Color change to red | Payment styling defect | Dependency #93
Issue : untuk pesan error saat register ataupun login ataupun forgot pass dibikin warna merah saja

| 1.0 | Login : Alert Error Color change to red - Dependency #93
Issue : untuk pesan error saat register ataupun login ataupun forgot pass dibikin warna merah saja

| non_priority | login alert error color change to red dependency issue untuk pesan error saat register ataupun login ataupun forgot pass dibikin warna merah saja | 0 |
206,466 | 15,731,680,186 | IssuesEvent | 2021-03-29 17:22:13 | celo-org/celo-monorepo | https://api.github.com/repos/celo-org/celo-monorepo | closed | [FLAKEY TEST] cli-test -> cli -> releasegold:authorize cmd -> can authorize account signers -> can authorize account attestation signer | FLAKEY cli cli-test devX | FlakeTracker closed this issue after commit fb8da80fbe7ff0444d3f8137c935154dd3677313
Discovered at commit 49261363c5b1ca2107c306fc9564d8474a51e04f
Attempt No. 1:
Error: Some checks didn't pass!
at Object.error (/home/circleci/app/node_modules/@oclif/errors/lib/index.js:26:15)
at CreateAccount.error (/home/circleci/app/node_modules/@oclif/command/lib/command.js:60:23)
at CheckBuilder.<anonymous> (/home/circleci/app/packages/cli/src/utils/checks.ts:226:33)
at Generator.next (<anonymous>)
at fulfilled (/home/circleci/app/packages/cli/src/utils/checks.ts:5:58)
at process._tickCallback (internal/process/next_tick.js:68:7)
Attempt No. 2:
Test Passed!
| 1.0 | [FLAKEY TEST] cli-test -> cli -> releasegold:authorize cmd -> can authorize account signers -> can authorize account attestation signer - FlakeTracker closed this issue after commit fb8da80fbe7ff0444d3f8137c935154dd3677313
Discovered at commit 49261363c5b1ca2107c306fc9564d8474a51e04f
Attempt No. 1:
Error: Some checks didn't pass!
at Object.error (/home/circleci/app/node_modules/@oclif/errors/lib/index.js:26:15)
at CreateAccount.error (/home/circleci/app/node_modules/@oclif/command/lib/command.js:60:23)
at CheckBuilder.<anonymous> (/home/circleci/app/packages/cli/src/utils/checks.ts:226:33)
at Generator.next (<anonymous>)
at fulfilled (/home/circleci/app/packages/cli/src/utils/checks.ts:5:58)
at process._tickCallback (internal/process/next_tick.js:68:7)
Attempt No. 2:
Test Passed!
| non_priority | cli test cli releasegold authorize cmd can authorize account signers can authorize account attestation signer flaketracker closed this issue after commit discovered at commit attempt no error some checks didn t pass at object error home circleci app node modules oclif errors lib index js at createaccount error home circleci app node modules oclif command lib command js at checkbuilder home circleci app packages cli src utils checks ts at generator next at fulfilled home circleci app packages cli src utils checks ts at process tickcallback internal process next tick js attempt no test passed | 0 |
26,929 | 13,156,510,839 | IssuesEvent | 2020-08-10 10:55:40 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Intensive canvas usage leading to app crash | P5 engine perf: memory severe: performance | Hi,
I am trying to create a performant approach for finger drawing to a canvas.
Most examples on the internet / flutter tutorials illustrates an app that samples user touch points and accumulates them in a points array that represents a state. then repainting a CustomPainter with the array of the points.
The problem with this approach is that the paint method in CustomPainter iterates through the points array which becomes very non-performant when crossing X points (X > ~1054).
The right approach for this style of drawing is to draw to a pixel buffer of sort - but i could not find a way to do that with Flutter.
Therefore I came up with the following approach:
1. Draw a given point to a canvas with an initial picture state and then draw a single point.
2. Call endRecording to get the current state of the canvas as a picture.
3. repeat as long as the user is drawing.
Example:
```
Picture _drawPoint(Offset point){
PictureRecorder recorder = PictureRecorder();
Canvas canvas = Canvas(recorder,Rect.fromCenter(center: Offset(0,0),width: 1000,height: 1000));
var paint = Paint()
..color = Colors.blue
..strokeCap = StrokeCap.square
..strokeWidth = 5.0;
if(this._picture != null){
canvas.drawPicture(this._picture);
}
canvas.drawRect(Rect.fromCircle(center: point,radius: 5.0), paint);
final pic = recorder.endRecording();
canvas = null;
recorder = null;
return pic;
}
.......
///call this for every point the finger touches in 'onPanUpdate'
this._picture = this._drawPoint(localPosition);
```
Calling this method causes an app crash after ~1054 points.
So a couple of issues here:
1. The app is crashing. :) (probably issue in memory management)
2. There is no efficient way to continuously drawing into a canvas and render that canvas to the screen - which is a very common task when using 2d graphics library.
**Note**: this approach is not ideal, the best approach is to retain a canvas state which is not possible in Flutter as far as I see.
Thx!!! | True | Intensive canvas usage leading to app crash - Hi,
I am trying to create a performant approach for finger drawing to a canvas.
Most examples on the internet / flutter tutorials illustrates an app that samples user touch points and accumulates them in a points array that represents a state. then repainting a CustomPainter with the array of the points.
The problem with this approach is that the paint method in CustomPainter iterates through the points array which becomes very non-performant when crossing X points (X > ~1054).
The right approach for this style of drawing is to draw to a pixel buffer of sort - but i could not find a way to do that with Flutter.
Therefore I came up with the following approach:
1. Draw a given point to a canvas with an initial picture state and then draw a single point.
2. Call endRecording to get the current state of the canvas as a picture.
3. repeat as long as the user is drawing.
Example:
```
Picture _drawPoint(Offset point){
PictureRecorder recorder = PictureRecorder();
Canvas canvas = Canvas(recorder,Rect.fromCenter(center: Offset(0,0),width: 1000,height: 1000));
var paint = Paint()
..color = Colors.blue
..strokeCap = StrokeCap.square
..strokeWidth = 5.0;
if(this._picture != null){
canvas.drawPicture(this._picture);
}
canvas.drawRect(Rect.fromCircle(center: point,radius: 5.0), paint);
final pic = recorder.endRecording();
canvas = null;
recorder = null;
return pic;
}
.......
///call this for every point the finger touches in 'onPanUpdate'
this._picture = this._drawPoint(localPosition);
```
Calling this method causes an app crash after ~1054 points.
So a couple of issues here:
1. The app is crashing. :) (probably issue in memory management)
2. There is no efficient way to continuously drawing into a canvas and render that canvas to the screen - which is a very common task when using 2d graphics library.
**Note**: this approach is not ideal, the best approach is to retain a canvas state which is not possible in Flutter as far as I see.
Thx!!! | non_priority | intensive canvas usage leading to app crash hi i am trying to create a performant approach for finger drawing to a canvas most examples on the internet flutter tutorials illustrates an app that samples user touch points and accumulates them in a points array that represents a state then repainting a custompainter with the array of the points the problem with this approach is that the paint method in custompainter iterates through the points array which becomes very non performant when crossing x points x the right approach for this style of drawing is to draw to a pixel buffer of sort but i could not find a way to do that with flutter therefore i came up with the following approach draw a given point to a canvas with an initial picture state and then draw a single point call endrecording to get the current state of the canvas as a picture repeat as long as the user is drawing example picture drawpoint offset point picturerecorder recorder picturerecorder canvas canvas canvas recorder rect fromcenter center offset width height var paint paint color colors blue strokecap strokecap square strokewidth if this picture null canvas drawpicture this picture canvas drawrect rect fromcircle center point radius paint final pic recorder endrecording canvas null recorder null return pic call this for every point the finger touches in onpanupdate this picture this drawpoint localposition calling this method causes an app crash after points so a couple of issues here the app is crashing probably issue in memory management there is no efficient way to continuously drawing into a canvas and render that canvas to the screen which is a very common task when using graphics library note this approach is not ideal the best approach is to retain a canvas state which is not possible in flutter as far as i see thx | 0 |
50,272 | 13,505,920,811 | IssuesEvent | 2020-09-14 01:14:33 | jgeraigery/kraft-heinz-merger | https://api.github.com/repos/jgeraigery/kraft-heinz-merger | closed | WS-2017-0330 (Medium) detected in mime-1.2.11.tgz - autoclosed | security vulnerability | ## WS-2017-0330 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mime-1.2.11.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.2.11.tgz">https://registry.npmjs.org/mime/-/mime-1.2.11.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/kraft-heinz-merger/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/kraft-heinz-merger/node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- ft-graphics-deploy-0.1.0.tgz (Root Library)
- s3-4.4.0.tgz
- :x: **mime-1.2.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/kraft-heinz-merger/commit/af6fe510cfa7228a06515d410aeabf6ecca51b7a">af6fe510cfa7228a06515d410aeabf6ecca51b7a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected version of mime (1.0.0 throw 1.4.0 and 2.0.0 throw 2.0.2), are vulnerable to regular expression denial of service.
<p>Publish Date: 2017-09-27
<p>URL: <a href=https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0>WS-2017-0330</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0">https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0</a></p>
<p>Release Date: 2019-04-03</p>
<p>Fix Resolution: 1.4.1,2.0.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mime","packageVersion":"1.2.11","isTransitiveDependency":true,"dependencyTree":"ft-graphics-deploy:0.1.0;s3:4.4.0;mime:1.2.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.1,2.0.3"}],"vulnerabilityIdentifier":"WS-2017-0330","vulnerabilityDetails":"Affected version of mime (1.0.0 throw 1.4.0 and 2.0.0 throw 2.0.2), are vulnerable to regular expression denial of service.","vulnerabilityUrl":"https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | True | WS-2017-0330 (Medium) detected in mime-1.2.11.tgz - autoclosed - ## WS-2017-0330 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mime-1.2.11.tgz</b></p></summary>
<p>A comprehensive library for mime-type mapping</p>
<p>Library home page: <a href="https://registry.npmjs.org/mime/-/mime-1.2.11.tgz">https://registry.npmjs.org/mime/-/mime-1.2.11.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/kraft-heinz-merger/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/kraft-heinz-merger/node_modules/mime/package.json</p>
<p>
Dependency Hierarchy:
- ft-graphics-deploy-0.1.0.tgz (Root Library)
- s3-4.4.0.tgz
- :x: **mime-1.2.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/kraft-heinz-merger/commit/af6fe510cfa7228a06515d410aeabf6ecca51b7a">af6fe510cfa7228a06515d410aeabf6ecca51b7a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Affected version of mime (1.0.0 throw 1.4.0 and 2.0.0 throw 2.0.2), are vulnerable to regular expression denial of service.
<p>Publish Date: 2017-09-27
<p>URL: <a href=https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0>WS-2017-0330</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0">https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0</a></p>
<p>Release Date: 2019-04-03</p>
<p>Fix Resolution: 1.4.1,2.0.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"mime","packageVersion":"1.2.11","isTransitiveDependency":true,"dependencyTree":"ft-graphics-deploy:0.1.0;s3:4.4.0;mime:1.2.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.1,2.0.3"}],"vulnerabilityIdentifier":"WS-2017-0330","vulnerabilityDetails":"Affected version of mime (1.0.0 throw 1.4.0 and 2.0.0 throw 2.0.2), are vulnerable to regular expression denial of service.","vulnerabilityUrl":"https://github.com/broofa/node-mime/commit/1df903fdeb9ae7eaa048795b8d580ce2c98f40b0","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in mime tgz autoclosed ws medium severity vulnerability vulnerable library mime tgz a comprehensive library for mime type mapping library home page a href path to dependency file tmp ws scm kraft heinz merger package json path to vulnerable library tmp ws scm kraft heinz merger node modules mime package json dependency hierarchy ft graphics deploy tgz root library tgz x mime tgz vulnerable library found in head commit a href vulnerability details affected version of mime throw and throw are vulnerable to regular expression denial of service publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails affected version of mime throw and throw are vulnerable to regular expression denial of service vulnerabilityurl | 0 |
82,635 | 7,846,167,032 | IssuesEvent | 2018-06-19 14:48:44 | dpn-admin/EXANode-Acceptance-testing | https://api.github.com/repos/dpn-admin/EXANode-Acceptance-testing | opened | 3.3.1. Transfer tool Test - Fixity | DPN Test | Generate fixity for each test file and compare to Trust log file.
For every file, the tool creates the fixity information (SHA256 checksum) and compares it with the hash calculated server-side after transferring it. | 1.0 | 3.3.1. Transfer tool Test - Fixity - Generate fixity for each test file and compare to Trust log file.
For every file, the tool creates the fixity information (SHA256 checksum) and compares it with the hash calculated server-side after transferring it. | non_priority | transfer tool test fixity generate fixity for each test file and compare to trust log file for every file the tool creates the fixity information checksum and compares it with the hash calculated server side after transferring it | 0 |
84,784 | 15,728,291,581 | IssuesEvent | 2021-03-29 13:39:52 | ssobue/kotlin-boot | https://api.github.com/repos/ssobue/kotlin-boot | closed | CVE-2021-24122 (Medium) detected in tomcat-embed-core-8.5.23.jar | security vulnerability | ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.23.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: /kotlin-boot/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.23/tomcat-embed-core-8.5.23.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.9.RELEASE.jar
- :x: **tomcat-embed-core-8.5.23.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-24122 (Medium) detected in tomcat-embed-core-8.5.23.jar - ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.23.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: /kotlin-boot/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.23/tomcat-embed-core-8.5.23.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.9.RELEASE.jar
- :x: **tomcat-embed-core-8.5.23.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tomcat embed core jar cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file kotlin boot pom xml path to vulnerable library root repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library vulnerability details when serving resources from a network location using the ntfs file system apache tomcat versions to to to and to were susceptible to jsp source code disclosure in some configurations the root cause was the unexpected behaviour of the jre api file getcanonicalpath which in turn was caused by the inconsistent behaviour of the windows api findfirstfilew in some circumstances publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina step up your open source security game with whitesource | 0 |
284,996 | 21,480,447,274 | IssuesEvent | 2022-04-26 17:12:02 | Equipment-and-Tool-Institute/j1939-84 | https://api.github.com/repos/Equipment-and-Tool-Institute/j1939-84 | closed | Part 1 Step 3 Accepting different OBD Compliance values from modules | documentation future enhancement | ```
Start Step 1.3. DM5: Diagnostic readiness 1
09:33:28.9942 Global DM5 Request
09:33:28.9976 18EAFFF9 [3] CE FE 00 (TX)
09:33:28.9989 18FECE55 [8] FF FF 14 00 00 00 00 00
DM5 from DPF Controller (85): OBD Compliance: HD OBD (20), Active Codes: not available, Previously Active Codes: not available
09:33:29.0012 18FECE00 [8] 00 00 14 37 E0 1E A0 1E
DM5 from Engine #1 (0): OBD Compliance: HD OBD (20), Active Codes: 0, Previously Active Codes: 0
09:33:29.0015 18FECE03 [8] 00 00 05 00 00 00 00 00
DM5 from Transmission #1 (3): OBD Compliance: Not intended to meet OBD II requirements (5), Active Codes: 0, Previously Active Codes: 0
09:33:29.0106 18FECE05 [8] 00 01 00 00 00 00 00 00 // 05 is preferred to 00, I believe
DM5 from Shift Console - Primary (5): OBD Compliance: Reserved for SAE/Unknown (0), Active Codes: 0, Previously Active Codes: 1
// We have commonly seen the cluster SA report too
Vehicle Composite of DM5:
A/C system refrigerant not supported, complete
Boost pressure control sys supported, not complete
Catalyst not supported, complete
Cold start aid system not supported, complete
Comprehensive component supported, complete
Diesel Particulate Filter supported, not complete
EGR/VVT system supported, not complete
Evaporative system not supported, complete
Exhaust Gas Sensor supported, not complete
Exhaust Gas Sensor heater supported, complete
Fuel System supported, not complete
Heated catalyst not supported, complete
Misfire supported, not complete
NMHC converting catalyst supported, not complete
NOx catalyst/adsorber supported, not complete
Secondary air system not supported, complete
WARN: 6.1.3.3.a - An ECU responded with a value for OBD Compliance that was not identical to other ECUs. OK for 00 offering for SA 5
```
The spec clearly indicates to warn if the OBD Compliance values is not identical to other ECUs. Does this need to be changed to indicate "...identical other _OBD_ ECUs"? | 1.0 | Part 1 Step 3 Accepting different OBD Compliance values from modules - ```
Start Step 1.3. DM5: Diagnostic readiness 1
09:33:28.9942 Global DM5 Request
09:33:28.9976 18EAFFF9 [3] CE FE 00 (TX)
09:33:28.9989 18FECE55 [8] FF FF 14 00 00 00 00 00
DM5 from DPF Controller (85): OBD Compliance: HD OBD (20), Active Codes: not available, Previously Active Codes: not available
09:33:29.0012 18FECE00 [8] 00 00 14 37 E0 1E A0 1E
DM5 from Engine #1 (0): OBD Compliance: HD OBD (20), Active Codes: 0, Previously Active Codes: 0
09:33:29.0015 18FECE03 [8] 00 00 05 00 00 00 00 00
DM5 from Transmission #1 (3): OBD Compliance: Not intended to meet OBD II requirements (5), Active Codes: 0, Previously Active Codes: 0
09:33:29.0106 18FECE05 [8] 00 01 00 00 00 00 00 00 // 05 is preferred to 00, I believe
DM5 from Shift Console - Primary (5): OBD Compliance: Reserved for SAE/Unknown (0), Active Codes: 0, Previously Active Codes: 1
// We have commonly seen the cluster SA report too
Vehicle Composite of DM5:
A/C system refrigerant not supported, complete
Boost pressure control sys supported, not complete
Catalyst not supported, complete
Cold start aid system not supported, complete
Comprehensive component supported, complete
Diesel Particulate Filter supported, not complete
EGR/VVT system supported, not complete
Evaporative system not supported, complete
Exhaust Gas Sensor supported, not complete
Exhaust Gas Sensor heater supported, complete
Fuel System supported, not complete
Heated catalyst not supported, complete
Misfire supported, not complete
NMHC converting catalyst supported, not complete
NOx catalyst/adsorber supported, not complete
Secondary air system not supported, complete
WARN: 6.1.3.3.a - An ECU responded with a value for OBD Compliance that was not identical to other ECUs. OK for 00 offering for SA 5
```
The spec clearly indicates to warn if the OBD Compliance values is not identical to other ECUs. Does this need to be changed to indicate "...identical other _OBD_ ECUs"? | non_priority | part step accepting different obd compliance values from modules start step diagnostic readiness global request ce fe tx ff ff from dpf controller obd compliance hd obd active codes not available previously active codes not available from engine obd compliance hd obd active codes previously active codes from transmission obd compliance not intended to meet obd ii requirements active codes previously active codes is preferred to i believe from shift console primary obd compliance reserved for sae unknown active codes previously active codes we have commonly seen the cluster sa report too vehicle composite of a c system refrigerant not supported complete boost pressure control sys supported not complete catalyst not supported complete cold start aid system not supported complete comprehensive component supported complete diesel particulate filter supported not complete egr vvt system supported not complete evaporative system not supported complete exhaust gas sensor supported not complete exhaust gas sensor heater supported complete fuel system supported not complete heated catalyst not supported complete misfire supported not complete nmhc converting catalyst supported not complete nox catalyst adsorber supported not complete secondary air system not supported complete warn a an ecu responded with a value for obd compliance that was not identical to other ecus ok for offering for sa the spec clearly indicates to warn if the obd compliance values is not identical to other ecus does this need to be changed to indicate identical other obd ecus | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.