Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
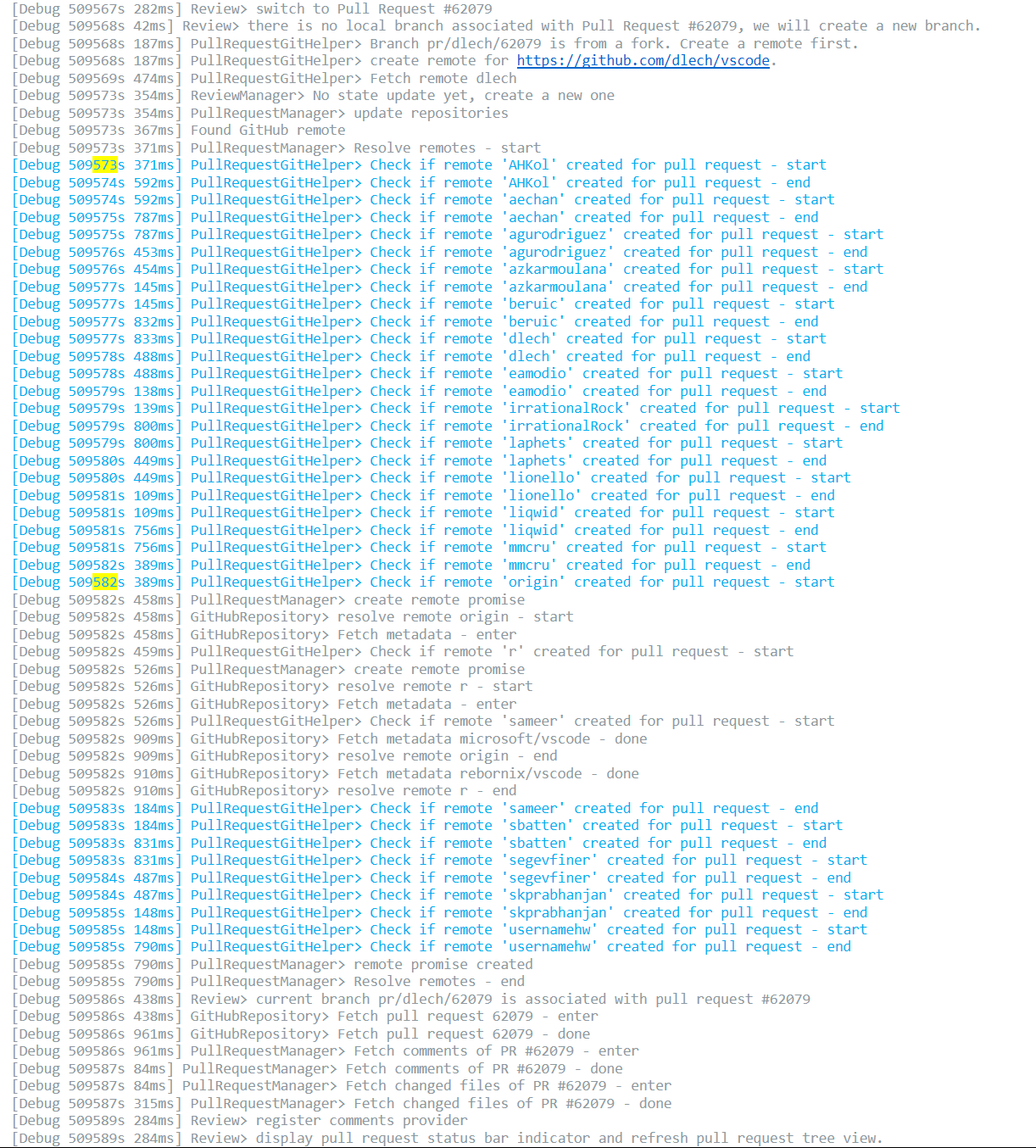
48,944 | 25,910,197,255 | IssuesEvent | 2022-12-15 13:25:01 | microsoft/vscode-pull-request-github | https://api.github.com/repos/microsoft/vscode-pull-request-github | closed | Validating if remote is created for pull request is slow | performance | <!-- Please search existing issues to avoid creating duplicates. -->
<!-- Use Help > Report Issue to prefill these. -->
- Extension version: 0.320.1
- VSCode Version: 1.30 Insiders
- OS: Windows 10
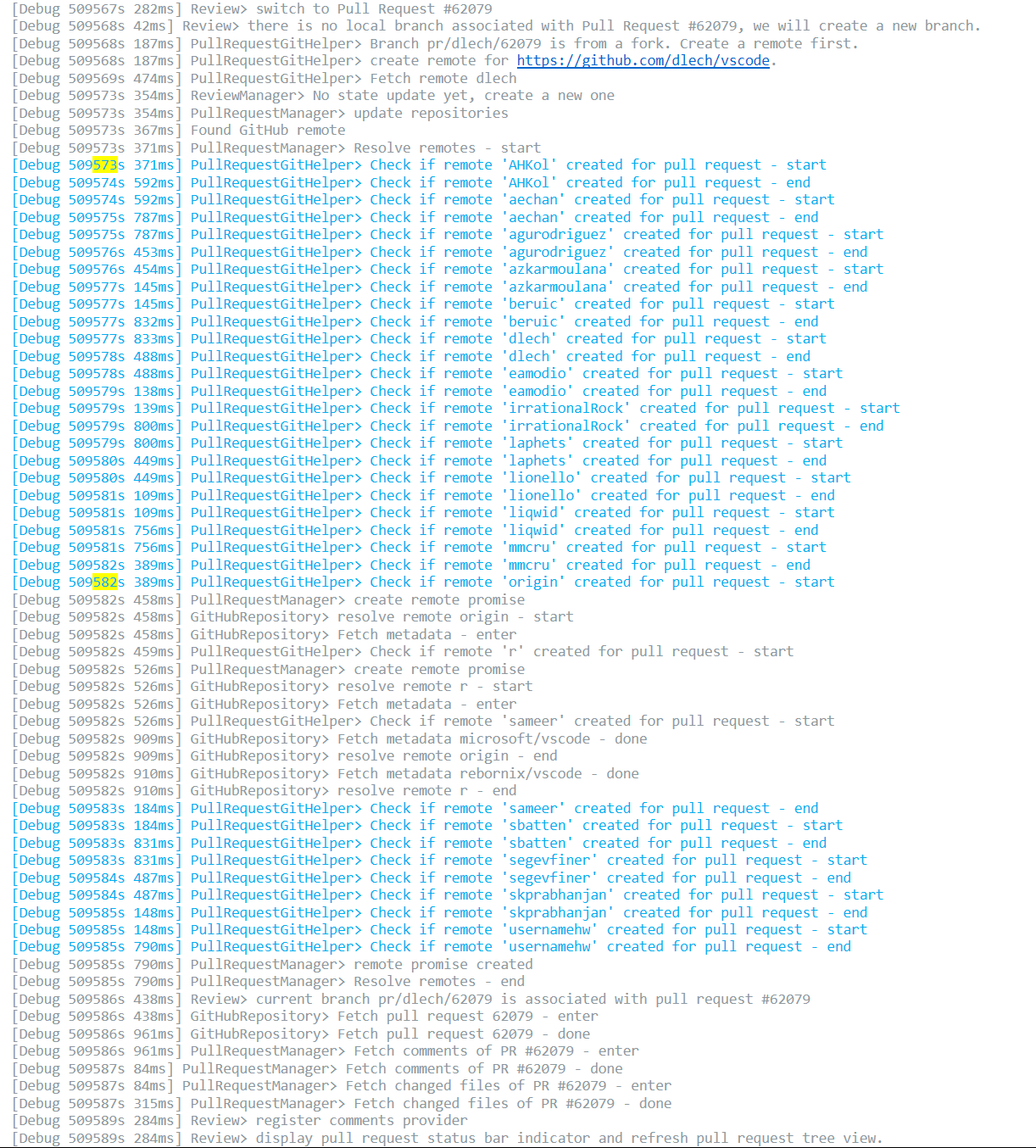
Checkout on my machine now takes 22 seconds and 12s of that is spent in checking if remotes are created for pull request purpose, as I didn't delete them after reviewing the code.
| True | Validating if remote is created for pull request is slow - <!-- Please search existing issues to avoid creating duplicates. -->
<!-- Use Help > Report Issue to prefill these. -->
- Extension version: 0.320.1
- VSCode Version: 1.30 Insiders
- OS: Windows 10
Checkout on my machine now takes 22 seconds and 12s of that is spent in checking if remotes are created for pull request purpose, as I didn't delete them after reviewing the code.
| non_priority | validating if remote is created for pull request is slow report issue to prefill these extension version vscode version insiders os windows checkout on my machine now takes seconds and of that is spent in checking if remotes are created for pull request purpose as i didn t delete them after reviewing the code | 0 |
53,139 | 13,261,006,394 | IssuesEvent | 2020-08-20 19:12:50 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | I3Db - doxygen errors, multiple (Trac #800) | Migrated from Trac combo core defect |
```text
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:35: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:78: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?
/data/i3home/nega/i3/offline-software/src/I3Db/private/I3Db/I3DbOMKey2MBID.cxx:21: warning: no uniquely matching class member found for
I3DbOMKey2MBID::I3DbOMKey2MBID(const string &Host, const string &Username, const string &Password, const string &Database)
Possible candidates:
I3DbOMKey2MBID::I3DbOMKey2MBID(const std::string &Host, const std::string &UserName, const std::string &Password, const std::string &Database)' at line 34 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h
I3DbOMKey2MBID::I3DbOMKey2MBID(const I3DbOMKey2MBID &)' at line 65 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h
todo:-1: warning: multiple use of section label 'todo', (first occurrence: /data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox, line 39)
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:10: warning: Found unknown command `\Id'
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilitiesFactory.h:7: warning: Found unknown command `\Id'
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: argument 'aNoCache' of command @param is not found in the argument list of I3OmDb::ExitInstance(int aNoCahe=0)
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: The following parameters of I3OmDb::ExitInstance(int aNoCahe=0) are not documented:
parameter 'aNoCahe'
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: argument 'aRunSummaryt' of command @param is not found in the argument list of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary)
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: The following parameters of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary) are not documented:
parameter 'aRunSummary'
/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:7: warning: unable to resolve reference to `database<br>' for \ref command
/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:36: warning: unable to resolve reference to `database<br>' for \ref command
```
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/800">https://code.icecube.wisc.edu/projects/icecube/ticket/800</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-02-12T21:20:57",
"_ts": "1423776057987575",
"description": "{{{\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:35: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:78: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?\n/data/i3home/nega/i3/offline-software/src/I3Db/private/I3Db/I3DbOMKey2MBID.cxx:21: warning: no uniquely matching class member found for \n I3DbOMKey2MBID::I3DbOMKey2MBID(const string &Host, const string &Username, const string &Password, const string &Database)\nPossible candidates:\n I3DbOMKey2MBID::I3DbOMKey2MBID(const std::string &Host, const std::string &UserName, const std::string &Password, const std::string &Database)' at line 34 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h\n I3DbOMKey2MBID::I3DbOMKey2MBID(const I3DbOMKey2MBID &)' at line 65 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h\n\ntodo:-1: warning: multiple use of section label 'todo', (first occurrence: /data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox, line 39)\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:10: warning: Found unknown command `\\Id'\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilitiesFactory.h:7: warning: Found unknown command `\\Id'\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: argument 'aNoCache' of command @param is not found in the argument list of I3OmDb::ExitInstance(int aNoCahe=0)\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: The following parameters of I3OmDb::ExitInstance(int aNoCahe=0) are not documented:\n parameter 'aNoCahe'\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: argument 'aRunSummaryt' of command @param is not found in the argument list of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary)\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: The following parameters of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary) are not documented:\n parameter 'aRunSummary'\n/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:7: warning: unable to resolve reference to `database<br>' for \\ref command\n/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:36: warning: unable to resolve reference to `database<br>' for \\ref command\n}}}",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"time": "2014-11-06T19:56:24",
"component": "combo core",
"summary": "I3Db - doxygen errors, multiple",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | I3Db - doxygen errors, multiple (Trac #800) -
```text
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:35: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:78: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?
/data/i3home/nega/i3/offline-software/src/I3Db/private/I3Db/I3DbOMKey2MBID.cxx:21: warning: no uniquely matching class member found for
I3DbOMKey2MBID::I3DbOMKey2MBID(const string &Host, const string &Username, const string &Password, const string &Database)
Possible candidates:
I3DbOMKey2MBID::I3DbOMKey2MBID(const std::string &Host, const std::string &UserName, const std::string &Password, const std::string &Database)' at line 34 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h
I3DbOMKey2MBID::I3DbOMKey2MBID(const I3DbOMKey2MBID &)' at line 65 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h
todo:-1: warning: multiple use of section label 'todo', (first occurrence: /data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox, line 39)
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:10: warning: Found unknown command `\Id'
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilitiesFactory.h:7: warning: Found unknown command `\Id'
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: argument 'aNoCache' of command @param is not found in the argument list of I3OmDb::ExitInstance(int aNoCahe=0)
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: The following parameters of I3OmDb::ExitInstance(int aNoCahe=0) are not documented:
parameter 'aNoCahe'
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: argument 'aRunSummaryt' of command @param is not found in the argument list of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary)
/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: The following parameters of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary) are not documented:
parameter 'aRunSummary'
/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:7: warning: unable to resolve reference to `database<br>' for \ref command
/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:36: warning: unable to resolve reference to `database<br>' for \ref command
```
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/800">https://code.icecube.wisc.edu/projects/icecube/ticket/800</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-02-12T21:20:57",
"_ts": "1423776057987575",
"description": "{{{\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:35: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:78: warning: include file I3Db/I3OmDb/I3OmDbResult_t.h not found, perhaps you forgot to add its directory to INCLUDE_PATH?\n/data/i3home/nega/i3/offline-software/src/I3Db/private/I3Db/I3DbOMKey2MBID.cxx:21: warning: no uniquely matching class member found for \n I3DbOMKey2MBID::I3DbOMKey2MBID(const string &Host, const string &Username, const string &Password, const string &Database)\nPossible candidates:\n I3DbOMKey2MBID::I3DbOMKey2MBID(const std::string &Host, const std::string &UserName, const std::string &Password, const std::string &Database)' at line 34 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h\n I3DbOMKey2MBID::I3DbOMKey2MBID(const I3DbOMKey2MBID &)' at line 65 of file /data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbOMKey2MBID.h\n\ntodo:-1: warning: multiple use of section label 'todo', (first occurrence: /data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox, line 39)\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilities.h:10: warning: Found unknown command `\\Id'\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3DbUtilitiesFactory.h:7: warning: Found unknown command `\\Id'\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: argument 'aNoCache' of command @param is not found in the argument list of I3OmDb::ExitInstance(int aNoCahe=0)\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:257: warning: The following parameters of I3OmDb::ExitInstance(int aNoCahe=0) are not documented:\n parameter 'aNoCahe'\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: argument 'aRunSummaryt' of command @param is not found in the argument list of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary)\n/data/i3home/nega/i3/offline-software/src/I3Db/public/I3Db/I3OmDb/I3OmDb.h:907: warning: The following parameters of I3OmDb::GetRunSummary(time_t aEventTime, RunSummary_t *aRunSummary) are not documented:\n parameter 'aRunSummary'\n/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:7: warning: unable to resolve reference to `database<br>' for \\ref command\n/data/i3home/nega/i3/offline-software/src/I3Db/resources/docs/main.dox:36: warning: unable to resolve reference to `database<br>' for \\ref command\n}}}",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"time": "2014-11-06T19:56:24",
"component": "combo core",
"summary": "I3Db - doxygen errors, multiple",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| non_priority | doxygen errors multiple trac text data nega offline software src public h warning include file t h not found perhaps you forgot to add its directory to include path data nega offline software src public h warning include file t h not found perhaps you forgot to add its directory to include path data nega offline software src private cxx warning no uniquely matching class member found for const string host const string username const string password const string database possible candidates const std string host const std string username const std string password const std string database at line of file data nega offline software src public h const at line of file data nega offline software src public h todo warning multiple use of section label todo first occurrence data nega offline software src resources docs main dox line data nega offline software src public h warning found unknown command id data nega offline software src public h warning found unknown command id data nega offline software src public h warning argument anocache of command param is not found in the argument list of exitinstance int anocahe data nega offline software src public h warning the following parameters of exitinstance int anocahe are not documented parameter anocahe data nega offline software src public h warning argument arunsummaryt of command param is not found in the argument list of getrunsummary time t aeventtime runsummary t arunsummary data nega offline software src public h warning the following parameters of getrunsummary time t aeventtime runsummary t arunsummary are not documented parameter arunsummary data nega offline software src resources docs main dox warning unable to resolve reference to database for ref command data nega offline software src resources docs main dox warning unable to resolve reference to database for ref command migrated from json status closed changetime ts description n data nega offline software src public h warning include file t h not found perhaps you forgot to add its directory to include path n data nega offline software src public h warning include file t h not found perhaps you forgot to add its directory to include path n data nega offline software src private cxx warning no uniquely matching class member found for n const string host const string username const string password const string database npossible candidates n const std string host const std string username const std string password const std string database at line of file data nega offline software src public h n const at line of file data nega offline software src public h n ntodo warning multiple use of section label todo first occurrence data nega offline software src resources docs main dox line n data nega offline software src public h warning found unknown command id n data nega offline software src public h warning found unknown command id n data nega offline software src public h warning argument anocache of command param is not found in the argument list of exitinstance int anocahe n data nega offline software src public h warning the following parameters of exitinstance int anocahe are not documented n parameter anocahe n data nega offline software src public h warning argument arunsummaryt of command param is not found in the argument list of getrunsummary time t aeventtime runsummary t arunsummary n data nega offline software src public h warning the following parameters of getrunsummary time t aeventtime runsummary t arunsummary are not documented n parameter arunsummary n data nega offline software src resources docs main dox warning unable to resolve reference to database for ref command n data nega offline software src resources docs main dox warning unable to resolve reference to database for ref command n reporter nega cc resolution fixed time component combo core summary doxygen errors multiple priority normal keywords milestone owner nega type defect | 0 |
31,674 | 13,612,604,065 | IssuesEvent | 2020-09-23 10:33:04 | SAP/spartacus | https://api.github.com/repos/SAP/spartacus | closed | add events for cds to the events service | event-service team/gladiators | In #5182 we introduced events service.
In this ticket we will add some events for CDS:
- login event. should fire only once, when the user logs in. Different than `AuthService.isUserLoggedIn()`.
- User is on PDP page
- User is on PLP page
- Facet changed on a PLP page (search results, category and brand page) | 1.0 | add events for cds to the events service - In #5182 we introduced events service.
In this ticket we will add some events for CDS:
- login event. should fire only once, when the user logs in. Different than `AuthService.isUserLoggedIn()`.
- User is on PDP page
- User is on PLP page
- Facet changed on a PLP page (search results, category and brand page) | non_priority | add events for cds to the events service in we introduced events service in this ticket we will add some events for cds login event should fire only once when the user logs in different than authservice isuserloggedin user is on pdp page user is on plp page facet changed on a plp page search results category and brand page | 0 |
26,865 | 20,797,663,148 | IssuesEvent | 2022-03-17 10:52:03 | unitaryfund/mitiq | https://api.github.com/repos/unitaryfund/mitiq | opened | mypy CI fail in mitiq_braket | bug infrastructure | Pre-Report Checklist
--------------------
- [x] I am running the latest version of mitiq
- [x] I checked to make sure that this bug has not already been reported
Issue Description
-----------------
CI tests on master fail in `mitiq_braket` with `mypy`.
How to Reproduce
----------------
See the [`test_validate` action](https://github.com/unitaryfund/mitiq/runs/5512635083?check_suite_focus=true).
### Code Snippet
```python
Include a snippet of the mitiq code that produces the error here.
```
### Error Output
```
Additionally, please copy and paste the output of the above code here.
```
Environment Context
-------------------
Use the `about()` function to summarize information on operating system, python version and dependencies.
```python
from mitiq import about
about()
```
Additional Python Environment Details (`pip freeze` or `conda list`):
```
Copy and paste the output of `pip freeze` or `conda list` here.
```
| 1.0 | mypy CI fail in mitiq_braket - Pre-Report Checklist
--------------------
- [x] I am running the latest version of mitiq
- [x] I checked to make sure that this bug has not already been reported
Issue Description
-----------------
CI tests on master fail in `mitiq_braket` with `mypy`.
How to Reproduce
----------------
See the [`test_validate` action](https://github.com/unitaryfund/mitiq/runs/5512635083?check_suite_focus=true).
### Code Snippet
```python
Include a snippet of the mitiq code that produces the error here.
```
### Error Output
```
Additionally, please copy and paste the output of the above code here.
```
Environment Context
-------------------
Use the `about()` function to summarize information on operating system, python version and dependencies.
```python
from mitiq import about
about()
```
Additional Python Environment Details (`pip freeze` or `conda list`):
```
Copy and paste the output of `pip freeze` or `conda list` here.
```
| non_priority | mypy ci fail in mitiq braket pre report checklist i am running the latest version of mitiq i checked to make sure that this bug has not already been reported issue description ci tests on master fail in mitiq braket with mypy how to reproduce see the code snippet python include a snippet of the mitiq code that produces the error here error output additionally please copy and paste the output of the above code here environment context use the about function to summarize information on operating system python version and dependencies python from mitiq import about about additional python environment details pip freeze or conda list copy and paste the output of pip freeze or conda list here | 0 |
115,039 | 9,779,335,005 | IssuesEvent | 2019-06-07 14:17:06 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Complete parser test suite with tests for all supported built-in functions | C: Parser C: Test E: All Editions P: Medium T: Enhancement | With #7755 we now have an integration test which uncovers all supported built-in functions which aren't covered by an existing parser test.
The purpose of this issue is to add any such missing tests. | 1.0 | Complete parser test suite with tests for all supported built-in functions - With #7755 we now have an integration test which uncovers all supported built-in functions which aren't covered by an existing parser test.
The purpose of this issue is to add any such missing tests. | non_priority | complete parser test suite with tests for all supported built in functions with we now have an integration test which uncovers all supported built in functions which aren t covered by an existing parser test the purpose of this issue is to add any such missing tests | 0 |
37,030 | 6,562,566,158 | IssuesEvent | 2017-09-07 17:04:44 | craftercms/craftercms | https://api.github.com/repos/craftercms/craftercms | closed | [docs] Getting Started: Requirements & Supported Platforms | documentation | Please complete the section: Getting Started: Requirements & Supported Platforms.
Point to Requirements under the System Administrator for details, list that only a JVM is needed. | 1.0 | [docs] Getting Started: Requirements & Supported Platforms - Please complete the section: Getting Started: Requirements & Supported Platforms.
Point to Requirements under the System Administrator for details, list that only a JVM is needed. | non_priority | getting started requirements supported platforms please complete the section getting started requirements supported platforms point to requirements under the system administrator for details list that only a jvm is needed | 0 |
134,051 | 18,411,652,408 | IssuesEvent | 2021-10-13 06:47:11 | ChoeMinji/rails-7.0.0.alpha2 | https://api.github.com/repos/ChoeMinji/rails-7.0.0.alpha2 | opened | CVE-2020-28500 (Medium) detected in lodash-4.17.11.tgz | security vulnerability | ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: rails-7.0.0.alpha2/package.json</p>
<p>Path to vulnerable library: rails-7.0.0.alpha2/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- activestorage-7.0.0-alpha2.tgz (Root Library)
- eslint-4.19.1.tgz
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/rails-7.0.0.alpha2/commit/3a3902efe3788aa4f5410d439175653e42f854e6">3a3902efe3788aa4f5410d439175653e42f854e6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash-4.17.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28500 (Medium) detected in lodash-4.17.11.tgz - ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: rails-7.0.0.alpha2/package.json</p>
<p>Path to vulnerable library: rails-7.0.0.alpha2/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- activestorage-7.0.0-alpha2.tgz (Root Library)
- eslint-4.19.1.tgz
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/rails-7.0.0.alpha2/commit/3a3902efe3788aa4f5410d439175653e42f854e6">3a3902efe3788aa4f5410d439175653e42f854e6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Regular Expression Denial of Service (ReDoS) via the toNumber, trim and trimEnd functions.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28500>CVE-2020-28500</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28500</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash-4.17.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file rails package json path to vulnerable library rails node modules lodash package json dependency hierarchy activestorage tgz root library eslint tgz x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash versions prior to are vulnerable to regular expression denial of service redos via the tonumber trim and trimend functions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash step up your open source security game with whitesource | 0 |
16,085 | 20,254,340,796 | IssuesEvent | 2022-02-14 21:18:24 | scikit-learn/scikit-learn | https://api.github.com/repos/scikit-learn/scikit-learn | closed | Multi-target GPR sample_y fails when normalize_y=True | Bug module:gaussian_process | ### Describe the bug
Related to #22174; supposed to have been fixed in [#20761](https://github.com/scikit-learn/scikit-learn/pull/20761)?
See #22199
When using a GPR model for multi-target data, if we set normalize_y=False then sample_y fails.
### Steps/Code to Reproduce
```
import numpy as np
import sklearn
from sklearn.gaussian_process import GaussianProcessRegressor as GPR
print(sklearn.__version__)
X_train = np.random.rand(7,3)
X_test = np.random.rand(4,3)
# ---- Working code ---- #
# n_targets = 1
Y_train = np.random.randn(7,1)
model = GPR(normalize_y=True)
model.fit(X_train, Y_train)
print(model.sample_y(X_test, n_samples=1).shape)
print(model.sample_y(X_test, n_samples=15).shape)
# n_targets = 2
Y_train = np.random.randn(7,2)
model = GPR(normalize_y=False)
model.fit(X_train, Y_train)
print(model.sample_y(X_test, n_samples=1).shape)
print(model.sample_y(X_test, n_samples=15).shape)
# ---- Broken code ---- #
# n_targets = 2
Y_train = np.random.randn(7,2)
model = GPR(normalize_y=True)
model.fit(X_train, Y_train)
print(model.sample_y(X_test, n_samples=1).shape)
print(model.sample_y(X_test, n_samples=15).shape)
```
### Expected Results
GPR.sample_y should result in an array of shape (n_samples_X, n_targets, n_samples_y), so the above code should produce
```
(4, 1, 1)
(4, 1, 15)
(4, 2, 1)
(4, 2, 15)
(4, 2, 1)
(4, 2, 15)
```
### Actual Results
Instead we get an error relating to the shape of the predicted covariance:
```
File "sklearn/gaussian_process/_gpr.py", line 477, in sample_y
y_samples = [
File "sklearn/gaussian_process/_gpr.py", line 478, in <listcomp>
rng.multivariate_normal(y_mean[:, i], y_cov, n_samples).T[:, np.newaxis]
File "mtrand.pyx", line 4069, in numpy.random.mtrand.RandomState.multivariate_normal
ValueError: cov must be 2 dimensional and square
```
### Versions
System:
python: 3.9.5 | packaged by conda-forge | (default, Jun 19 2021, 00:27:35) [Clang 11.1.0 ]
executable: /Users/tnakam10/opt/anaconda3/envs/aerofusion/bin/python
machine: macOS-11.6.1-x86_64-i386-64bit
Python dependencies:
pip: 21.3.1
setuptools: 60.5.0
sklearn: 1.0.2
numpy: 1.19.5
scipy: 1.7.3
Cython: None
pandas: 1.3.5
matplotlib: 3.5.1
joblib: 1.1.0
threadpoolctl: 3.0.0
Built with OpenMP: True | 1.0 | Multi-target GPR sample_y fails when normalize_y=True - ### Describe the bug
Related to #22174; supposed to have been fixed in [#20761](https://github.com/scikit-learn/scikit-learn/pull/20761)?
See #22199
When using a GPR model for multi-target data, if we set normalize_y=False then sample_y fails.
### Steps/Code to Reproduce
```
import numpy as np
import sklearn
from sklearn.gaussian_process import GaussianProcessRegressor as GPR
print(sklearn.__version__)
X_train = np.random.rand(7,3)
X_test = np.random.rand(4,3)
# ---- Working code ---- #
# n_targets = 1
Y_train = np.random.randn(7,1)
model = GPR(normalize_y=True)
model.fit(X_train, Y_train)
print(model.sample_y(X_test, n_samples=1).shape)
print(model.sample_y(X_test, n_samples=15).shape)
# n_targets = 2
Y_train = np.random.randn(7,2)
model = GPR(normalize_y=False)
model.fit(X_train, Y_train)
print(model.sample_y(X_test, n_samples=1).shape)
print(model.sample_y(X_test, n_samples=15).shape)
# ---- Broken code ---- #
# n_targets = 2
Y_train = np.random.randn(7,2)
model = GPR(normalize_y=True)
model.fit(X_train, Y_train)
print(model.sample_y(X_test, n_samples=1).shape)
print(model.sample_y(X_test, n_samples=15).shape)
```
### Expected Results
GPR.sample_y should result in an array of shape (n_samples_X, n_targets, n_samples_y), so the above code should produce
```
(4, 1, 1)
(4, 1, 15)
(4, 2, 1)
(4, 2, 15)
(4, 2, 1)
(4, 2, 15)
```
### Actual Results
Instead we get an error relating to the shape of the predicted covariance:
```
File "sklearn/gaussian_process/_gpr.py", line 477, in sample_y
y_samples = [
File "sklearn/gaussian_process/_gpr.py", line 478, in <listcomp>
rng.multivariate_normal(y_mean[:, i], y_cov, n_samples).T[:, np.newaxis]
File "mtrand.pyx", line 4069, in numpy.random.mtrand.RandomState.multivariate_normal
ValueError: cov must be 2 dimensional and square
```
### Versions
System:
python: 3.9.5 | packaged by conda-forge | (default, Jun 19 2021, 00:27:35) [Clang 11.1.0 ]
executable: /Users/tnakam10/opt/anaconda3/envs/aerofusion/bin/python
machine: macOS-11.6.1-x86_64-i386-64bit
Python dependencies:
pip: 21.3.1
setuptools: 60.5.0
sklearn: 1.0.2
numpy: 1.19.5
scipy: 1.7.3
Cython: None
pandas: 1.3.5
matplotlib: 3.5.1
joblib: 1.1.0
threadpoolctl: 3.0.0
Built with OpenMP: True | non_priority | multi target gpr sample y fails when normalize y true describe the bug related to supposed to have been fixed in see when using a gpr model for multi target data if we set normalize y false then sample y fails steps code to reproduce import numpy as np import sklearn from sklearn gaussian process import gaussianprocessregressor as gpr print sklearn version x train np random rand x test np random rand working code n targets y train np random randn model gpr normalize y true model fit x train y train print model sample y x test n samples shape print model sample y x test n samples shape n targets y train np random randn model gpr normalize y false model fit x train y train print model sample y x test n samples shape print model sample y x test n samples shape broken code n targets y train np random randn model gpr normalize y true model fit x train y train print model sample y x test n samples shape print model sample y x test n samples shape expected results gpr sample y should result in an array of shape n samples x n targets n samples y so the above code should produce actual results instead we get an error relating to the shape of the predicted covariance file sklearn gaussian process gpr py line in sample y y samples file sklearn gaussian process gpr py line in rng multivariate normal y mean y cov n samples t file mtrand pyx line in numpy random mtrand randomstate multivariate normal valueerror cov must be dimensional and square versions system python packaged by conda forge default jun executable users opt envs aerofusion bin python machine macos python dependencies pip setuptools sklearn numpy scipy cython none pandas matplotlib joblib threadpoolctl built with openmp true | 0 |
21,679 | 17,461,957,574 | IssuesEvent | 2021-08-06 11:49:36 | swagger-api/swagger-js | https://api.github.com/repos/swagger-api/swagger-js | closed | SwaggerClient does not work with operations having a body that is not a JSONObject | version: 3.x cat: usability | - OS: macOS
- Environment: Node.js v14.0.0
- Method of installation: npm
- Swagger-Client version: 3.13.7
- Swagger/OpenAPI version: Swagger 2.0
Swagger/OpenAPI definition (**fragment**):
```json
"paths": {
"/observation": {
"post": {
"tags": [
"test-submission-controller"
],
"operationId": "submitObservationUsingPOST",
"consumes": [
"application/json"
],
"produces": [
"application/json"
],
"parameters": [
{
"in": "body",
"name": "request",
"description": "request",
"required": true,
"schema": {
"type": "string"
}
}
],
"responses": {
"200": {
"description": "OK",
"schema": {
"$ref": "#/definitions/TestSubmissionResponse"
}
},
"201": {
"description": "Created"
},
"401": {
"description": "Unauthorized"
},
"403": {
"description": "Forbidden"
},
"404": {
"description": "Not Found"
}
}
}
}
},
```
Swagger-Client usage:
```js
.execute({
operationId: 'submitObservationUsingPOST',
parameters: ...,
})
```
### Describe the bug you're encountering
When the request body is defined as something other than a JSONObject (e.g. JSONString), the client complains about required parameter not being provided.
### Expected behavior
Performing a request should work fine when the request body is not a JSONObject
### Additional context or thoughts
Caused by line 226 in `execute/index.js`:
```js
if (parameter.in === 'body' && parameter.schema && parameter.schema.properties) {
```
where `parameter.schema.properties` is unsurprisingly, falsy. | True | SwaggerClient does not work with operations having a body that is not a JSONObject - - OS: macOS
- Environment: Node.js v14.0.0
- Method of installation: npm
- Swagger-Client version: 3.13.7
- Swagger/OpenAPI version: Swagger 2.0
Swagger/OpenAPI definition (**fragment**):
```json
"paths": {
"/observation": {
"post": {
"tags": [
"test-submission-controller"
],
"operationId": "submitObservationUsingPOST",
"consumes": [
"application/json"
],
"produces": [
"application/json"
],
"parameters": [
{
"in": "body",
"name": "request",
"description": "request",
"required": true,
"schema": {
"type": "string"
}
}
],
"responses": {
"200": {
"description": "OK",
"schema": {
"$ref": "#/definitions/TestSubmissionResponse"
}
},
"201": {
"description": "Created"
},
"401": {
"description": "Unauthorized"
},
"403": {
"description": "Forbidden"
},
"404": {
"description": "Not Found"
}
}
}
}
},
```
Swagger-Client usage:
```js
.execute({
operationId: 'submitObservationUsingPOST',
parameters: ...,
})
```
### Describe the bug you're encountering
When the request body is defined as something other than a JSONObject (e.g. JSONString), the client complains about required parameter not being provided.
### Expected behavior
Performing a request should work fine when the request body is not a JSONObject
### Additional context or thoughts
Caused by line 226 in `execute/index.js`:
```js
if (parameter.in === 'body' && parameter.schema && parameter.schema.properties) {
```
where `parameter.schema.properties` is unsurprisingly, falsy. | non_priority | swaggerclient does not work with operations having a body that is not a jsonobject os macos environment node js method of installation npm swagger client version swagger openapi version swagger swagger openapi definition fragment json paths observation post tags test submission controller operationid submitobservationusingpost consumes application json produces application json parameters in body name request description request required true schema type string responses description ok schema ref definitions testsubmissionresponse description created description unauthorized description forbidden description not found swagger client usage js execute operationid submitobservationusingpost parameters describe the bug you re encountering when the request body is defined as something other than a jsonobject e g jsonstring the client complains about required parameter not being provided expected behavior performing a request should work fine when the request body is not a jsonobject additional context or thoughts caused by line in execute index js js if parameter in body parameter schema parameter schema properties where parameter schema properties is unsurprisingly falsy | 0 |
96,324 | 19,985,859,392 | IssuesEvent | 2022-01-30 16:52:10 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | [Unstable] Lights are ON even if they're OFF | Bug Code | - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Lights are on, even if you uncheck "Is On"
**Steps To Reproduce**
Launch sub editor
Place down a light component
Make sure it's off
Launch test
Light component is on
This is true for all items that have the "Lightcomponent" property | 1.0 | [Unstable] Lights are ON even if they're OFF - - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Lights are on, even if you uncheck "Is On"
**Steps To Reproduce**
Launch sub editor
Place down a light component
Make sure it's off
Launch test
Light component is on
This is true for all items that have the "Lightcomponent" property | non_priority | lights are on even if they re off i have searched the issue tracker to check if the issue has already been reported description lights are on even if you uncheck is on steps to reproduce launch sub editor place down a light component make sure it s off launch test light component is on this is true for all items that have the lightcomponent property | 0 |
137,874 | 18,769,338,601 | IssuesEvent | 2021-11-06 14:44:53 | AlexRogalskiy/github-action-user-contribution | https://api.github.com/repos/AlexRogalskiy/github-action-user-contribution | opened | CVE-2019-10744 (High) detected in lodash-2.4.2.tgz | security vulnerability | ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: github-action-user-contribution/package.json</p>
<p>Path to vulnerable library: github-action-user-contribution/node_modules/dockerfile_lint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- dockerfile_lint-0.3.4.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-user-contribution/commit/aa744014156b1e4ed6a2c7ac856937f7729f7b36">aa744014156b1e4ed6a2c7ac856937f7729f7b36</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-10744 (High) detected in lodash-2.4.2.tgz - ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: github-action-user-contribution/package.json</p>
<p>Path to vulnerable library: github-action-user-contribution/node_modules/dockerfile_lint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- dockerfile_lint-0.3.4.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-user-contribution/commit/aa744014156b1e4ed6a2c7ac856937f7729f7b36">aa744014156b1e4ed6a2c7ac856937f7729f7b36</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in lodash tgz cve high severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file github action user contribution package json path to vulnerable library github action user contribution node modules dockerfile lint node modules lodash package json dependency hierarchy dockerfile lint tgz root library x lodash tgz vulnerable library found in head commit a href vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template step up your open source security game with whitesource | 0 |
109,600 | 13,791,125,447 | IssuesEvent | 2020-10-09 11:37:01 | Rello/audioplayer | https://api.github.com/repos/Rello/audioplayer | closed | Icons not visible with dark theme | design | ### Actual behavior
Icons are black with dark grey background (under firefox not with chrome)
### Steps to reproduce the behavior
1. Use firefox
2. Go to settings -> accessibility -> check dark theme
3. Go to media player
### Additional information (optional)

### Server configuration
**Operating system:**
Debian
**Web server:**
Apache2
**Database:**
MySql
**Nextcloud/ownCloud version:** (see `/status.php`)
20.0.0
**Audio Player version:** (see `/settings/apps`)
2.12.0 | 1.0 | Icons not visible with dark theme - ### Actual behavior
Icons are black with dark grey background (under firefox not with chrome)
### Steps to reproduce the behavior
1. Use firefox
2. Go to settings -> accessibility -> check dark theme
3. Go to media player
### Additional information (optional)

### Server configuration
**Operating system:**
Debian
**Web server:**
Apache2
**Database:**
MySql
**Nextcloud/ownCloud version:** (see `/status.php`)
20.0.0
**Audio Player version:** (see `/settings/apps`)
2.12.0 | non_priority | icons not visible with dark theme actual behavior icons are black with dark grey background under firefox not with chrome steps to reproduce the behavior use firefox go to settings accessibility check dark theme go to media player additional information optional server configuration operating system debian web server database mysql nextcloud owncloud version see status php audio player version see settings apps | 0 |
33,107 | 14,004,249,977 | IssuesEvent | 2020-10-28 16:51:56 | MicrosoftDocs/windowsserverdocs | https://api.github.com/repos/MicrosoftDocs/windowsserverdocs | closed | Server 2019 compatibility | Pri2 remote-desktop-services/tech windows-server-threshold/prod | Hello, can you please update the page with server 2019 compatibility?
I'm interested in migrating a 2012 SH to a 2019 connectionbroker.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 7242a6c0-8f40-bb91-c23e-0081a4d4a94a
* Version Independent ID: 9a1213ac-baf5-c1f3-e735-33a0b818fb6f
* Content: [Supported configurations for Remote Desktop Services](https://docs.microsoft.com/en-us/windows-server/remote/remote-desktop-services/rds-supported-config#feedback)
* Content Source: [WindowsServerDocs/remote/remote-desktop-services/rds-supported-config.md](https://github.com/MicrosoftDocs/windowsserverdocs/blob/master/WindowsServerDocs/remote/remote-desktop-services/rds-supported-config.md)
* Product: **windows-server-threshold**
* Technology: **remote-desktop-services**
* GitHub Login: @lizap
* Microsoft Alias: **elizapo** | 1.0 | Server 2019 compatibility - Hello, can you please update the page with server 2019 compatibility?
I'm interested in migrating a 2012 SH to a 2019 connectionbroker.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 7242a6c0-8f40-bb91-c23e-0081a4d4a94a
* Version Independent ID: 9a1213ac-baf5-c1f3-e735-33a0b818fb6f
* Content: [Supported configurations for Remote Desktop Services](https://docs.microsoft.com/en-us/windows-server/remote/remote-desktop-services/rds-supported-config#feedback)
* Content Source: [WindowsServerDocs/remote/remote-desktop-services/rds-supported-config.md](https://github.com/MicrosoftDocs/windowsserverdocs/blob/master/WindowsServerDocs/remote/remote-desktop-services/rds-supported-config.md)
* Product: **windows-server-threshold**
* Technology: **remote-desktop-services**
* GitHub Login: @lizap
* Microsoft Alias: **elizapo** | non_priority | server compatibility hello can you please update the page with server compatibility i m interested in migrating a sh to a connectionbroker document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product windows server threshold technology remote desktop services github login lizap microsoft alias elizapo | 0 |
52,028 | 12,839,849,238 | IssuesEvent | 2020-07-07 20:00:48 | roc-streaming/roc-toolkit | https://api.github.com/repos/roc-streaming/roc-toolkit | closed | Add Ubuntu 20.04 to CI | build easy hacks help wanted portability | We already have 14.04, 16.04, and 18.04, and now want to add 20.04 as well.
Issue #307 gives an idea how to add a new distro to CI.
The build instructions should be the same as for 18.04, so there is no need to update documentation. | 1.0 | Add Ubuntu 20.04 to CI - We already have 14.04, 16.04, and 18.04, and now want to add 20.04 as well.
Issue #307 gives an idea how to add a new distro to CI.
The build instructions should be the same as for 18.04, so there is no need to update documentation. | non_priority | add ubuntu to ci we already have and and now want to add as well issue gives an idea how to add a new distro to ci the build instructions should be the same as for so there is no need to update documentation | 0 |
185,358 | 14,350,422,711 | IssuesEvent | 2020-11-29 20:48:33 | nucypher/rust-umbral | https://api.github.com/repos/nucypher/rust-umbral | opened | Testing WASM bindings | CI WASM tests | WASM bindings can be tested in two ways:
- from the Rust side (see `#[wasm_bindgen_test]` attribute)
- from the JS side
Do we need only one of those? Both? What JS testing library to use? How to call them from CI?
Testing from the Rust side will increase Rust code coverage. Testing from the JS side is closer to the user experience, but mostly we will be testing how well `wasm-pack` works, since we don't write any JS code directly. Would be nice to test at least the JS example though. | 1.0 | Testing WASM bindings - WASM bindings can be tested in two ways:
- from the Rust side (see `#[wasm_bindgen_test]` attribute)
- from the JS side
Do we need only one of those? Both? What JS testing library to use? How to call them from CI?
Testing from the Rust side will increase Rust code coverage. Testing from the JS side is closer to the user experience, but mostly we will be testing how well `wasm-pack` works, since we don't write any JS code directly. Would be nice to test at least the JS example though. | non_priority | testing wasm bindings wasm bindings can be tested in two ways from the rust side see attribute from the js side do we need only one of those both what js testing library to use how to call them from ci testing from the rust side will increase rust code coverage testing from the js side is closer to the user experience but mostly we will be testing how well wasm pack works since we don t write any js code directly would be nice to test at least the js example though | 0 |
86,385 | 15,755,621,220 | IssuesEvent | 2021-03-31 02:06:09 | senthilbalakrishnanfull/testing | https://api.github.com/repos/senthilbalakrishnanfull/testing | opened | CVE-2020-23849 (Medium) detected in jsoneditor-5.33.0.tgz | security vulnerability | ## CVE-2020-23849 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsoneditor-5.33.0.tgz</b></p></summary>
<p>A web-based tool to view, edit, format, and validate JSON</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsoneditor/-/jsoneditor-5.33.0.tgz">https://registry.npmjs.org/jsoneditor/-/jsoneditor-5.33.0.tgz</a></p>
<p>Path to dependency file: /testing/package.json</p>
<p>Path to vulnerable library: testing/node_modules/jsoneditor/package.json,testing/node_modules/jsoneditor/package.json</p>
<p>
Dependency Hierarchy:
- showroom-0.9.3.tgz (Root Library)
- :x: **jsoneditor-5.33.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Stored XSS was discovered in the tree mode of jsoneditor before 9.0.2 through injecting and executing JavaScript.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-23849>CVE-2020-23849</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=2020-23849">https://cve.mitre.org/cgi-bin/cvename.cgi?name=2020-23849</a></p>
<p>Release Date: 2021-01-11</p>
<p>Fix Resolution: v9.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-23849 (Medium) detected in jsoneditor-5.33.0.tgz - ## CVE-2020-23849 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsoneditor-5.33.0.tgz</b></p></summary>
<p>A web-based tool to view, edit, format, and validate JSON</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsoneditor/-/jsoneditor-5.33.0.tgz">https://registry.npmjs.org/jsoneditor/-/jsoneditor-5.33.0.tgz</a></p>
<p>Path to dependency file: /testing/package.json</p>
<p>Path to vulnerable library: testing/node_modules/jsoneditor/package.json,testing/node_modules/jsoneditor/package.json</p>
<p>
Dependency Hierarchy:
- showroom-0.9.3.tgz (Root Library)
- :x: **jsoneditor-5.33.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Stored XSS was discovered in the tree mode of jsoneditor before 9.0.2 through injecting and executing JavaScript.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-23849>CVE-2020-23849</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=2020-23849">https://cve.mitre.org/cgi-bin/cvename.cgi?name=2020-23849</a></p>
<p>Release Date: 2021-01-11</p>
<p>Fix Resolution: v9.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jsoneditor tgz cve medium severity vulnerability vulnerable library jsoneditor tgz a web based tool to view edit format and validate json library home page a href path to dependency file testing package json path to vulnerable library testing node modules jsoneditor package json testing node modules jsoneditor package json dependency hierarchy showroom tgz root library x jsoneditor tgz vulnerable library vulnerability details stored xss was discovered in the tree mode of jsoneditor before through injecting and executing javascript publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
231,533 | 17,692,823,335 | IssuesEvent | 2021-08-24 12:12:43 | gdcc/dataverse-kubernetes | https://api.github.com/repos/gdcc/dataverse-kubernetes | closed | Enable Maven use for builds and more | enhancement documentation | Inspired by https://github.com/payara/Payara/tree/master/appserver/extras, it would be nice to look into using Maven for images and maybe more.
We could try to compile Dataverse as a submodule. When that submodule would allow for packaging an installation bundle (instead of using automake), it would greatly ease image building and reduce complexity.
It might also be used to replace Skaffold with the right plugins to deploy images to a cluster. (Or integrated with a custom skaffold build call to Maven). IIRC there are Maven plugins for docker-compose, too. | 1.0 | Enable Maven use for builds and more - Inspired by https://github.com/payara/Payara/tree/master/appserver/extras, it would be nice to look into using Maven for images and maybe more.
We could try to compile Dataverse as a submodule. When that submodule would allow for packaging an installation bundle (instead of using automake), it would greatly ease image building and reduce complexity.
It might also be used to replace Skaffold with the right plugins to deploy images to a cluster. (Or integrated with a custom skaffold build call to Maven). IIRC there are Maven plugins for docker-compose, too. | non_priority | enable maven use for builds and more inspired by it would be nice to look into using maven for images and maybe more we could try to compile dataverse as a submodule when that submodule would allow for packaging an installation bundle instead of using automake it would greatly ease image building and reduce complexity it might also be used to replace skaffold with the right plugins to deploy images to a cluster or integrated with a custom skaffold build call to maven iirc there are maven plugins for docker compose too | 0 |
67,775 | 9,099,688,594 | IssuesEvent | 2019-02-20 05:46:53 | gardener/machine-controller-manager | https://api.github.com/repos/gardener/machine-controller-manager | closed | New CP Docs / Implementation Work | area/documentation component/machine-controller-manager exp/beginner needs/review platform/all size/xs status/in-progress topology/seed | Hi,
A few comments on the new CP implementation guide [0]:
- Shouldn't we use a `clone` instead of a `fork` based approach when starting with a new provider? I don't want to start my new CP with the `sampleprovider` commits in the history.
- Also I would start with the target ORG/username right from the beginning. Otherwise I will end up with refactoring my imports e.g. from `gardener` -> `afritzler` -> `gardener`
Regards,
Andreas
[0] https://github.com/gardener/machine-controller-manager/blob/cmi-client/docs/development/new_cp_support.md | 1.0 | New CP Docs / Implementation Work - Hi,
A few comments on the new CP implementation guide [0]:
- Shouldn't we use a `clone` instead of a `fork` based approach when starting with a new provider? I don't want to start my new CP with the `sampleprovider` commits in the history.
- Also I would start with the target ORG/username right from the beginning. Otherwise I will end up with refactoring my imports e.g. from `gardener` -> `afritzler` -> `gardener`
Regards,
Andreas
[0] https://github.com/gardener/machine-controller-manager/blob/cmi-client/docs/development/new_cp_support.md | non_priority | new cp docs implementation work hi a few comments on the new cp implementation guide shouldn t we use a clone instead of a fork based approach when starting with a new provider i don t want to start my new cp with the sampleprovider commits in the history also i would start with the target org username right from the beginning otherwise i will end up with refactoring my imports e g from gardener afritzler gardener regards andreas | 0 |
162,086 | 12,619,360,474 | IssuesEvent | 2020-06-13 00:14:42 | avidrucker/autofocus-exp | https://api.github.com/repos/avidrucker/autofocus-exp | closed | User can focus in on current todo | awaiting tests clarify no-issue-activity question user story | ala the zen design of https://momentumdash.com/
Also called "focus mode", the user sees simply the current most want to do item, and a prompt (or button) to leave the screen / progress forward.
Note: This is not a "screen" per se, but simply a clearing of the console, a display of the current in-progress todo item, and a prompt to hit the enter key to answer the question, "Is there further work left on this todo item? (y/n, or, hit 'q' then 'enter' to quit without saving progress) " where the next "screen" (display) is the return to main menu (prompt).
To sum it up:
- [x] 1. User sees the console cleared
- [x] 2. User sees current in-progress todo item (the cmwtd)
- [ ] 3. User can hit any key to indicate they are "done working for now"
- [ ] 4A. User can answer whether there is work left to do in the future (y/n/quit)
- [ ] 4B. User can quit to indicate that the cmwtd shouldn't be marked as complete
- [ ] 5. User is returned to the main menu | 1.0 | User can focus in on current todo - ala the zen design of https://momentumdash.com/
Also called "focus mode", the user sees simply the current most want to do item, and a prompt (or button) to leave the screen / progress forward.
Note: This is not a "screen" per se, but simply a clearing of the console, a display of the current in-progress todo item, and a prompt to hit the enter key to answer the question, "Is there further work left on this todo item? (y/n, or, hit 'q' then 'enter' to quit without saving progress) " where the next "screen" (display) is the return to main menu (prompt).
To sum it up:
- [x] 1. User sees the console cleared
- [x] 2. User sees current in-progress todo item (the cmwtd)
- [ ] 3. User can hit any key to indicate they are "done working for now"
- [ ] 4A. User can answer whether there is work left to do in the future (y/n/quit)
- [ ] 4B. User can quit to indicate that the cmwtd shouldn't be marked as complete
- [ ] 5. User is returned to the main menu | non_priority | user can focus in on current todo ala the zen design of also called focus mode the user sees simply the current most want to do item and a prompt or button to leave the screen progress forward note this is not a screen per se but simply a clearing of the console a display of the current in progress todo item and a prompt to hit the enter key to answer the question is there further work left on this todo item y n or hit q then enter to quit without saving progress where the next screen display is the return to main menu prompt to sum it up user sees the console cleared user sees current in progress todo item the cmwtd user can hit any key to indicate they are done working for now user can answer whether there is work left to do in the future y n quit user can quit to indicate that the cmwtd shouldn t be marked as complete user is returned to the main menu | 0 |
390,439 | 26,862,527,615 | IssuesEvent | 2023-02-03 19:48:59 | supabase/supabase | https://api.github.com/repos/supabase/supabase | closed | supabase-image-loader docs are incorrect | documentation | # Improve documentation
## Link
https://supabase.com/docs/guides/storage/image-transformations
## Describe the problem
Docs recommend this function for supabase-image-loader:
```
const projectId = '' // your supabase project id
export default function supabaseLoader({ src, width, height, quality }) {
return `https://${projectId}.supabase.co/storage/v1/render/image/public/${src}?width=${width}&height=${
height || 0
}&quality=${quality || 75}`
}
```
However according to nextjs docs, loaders only take src, width and quality as props.
https://nextjs.org/docs/api-reference/next/image#loader
```
A loader is a function returning a URL string for the image, given the following parameters:
src
width
quality
```
## Describe the improvement
Modify the docs to show the correct loader to use.
```
const projectId = '' // your supabase project id
export default function supabaseLoader({ src, width, quality }) {
return `https://${projectId}.supabase.co/storage/v1/render/image/public/${src}?width=${width}&quality=${quality || 75}`
}
```
## Additional context
The height was always undefined if you used the loader suggested. | 1.0 | supabase-image-loader docs are incorrect - # Improve documentation
## Link
https://supabase.com/docs/guides/storage/image-transformations
## Describe the problem
Docs recommend this function for supabase-image-loader:
```
const projectId = '' // your supabase project id
export default function supabaseLoader({ src, width, height, quality }) {
return `https://${projectId}.supabase.co/storage/v1/render/image/public/${src}?width=${width}&height=${
height || 0
}&quality=${quality || 75}`
}
```
However according to nextjs docs, loaders only take src, width and quality as props.
https://nextjs.org/docs/api-reference/next/image#loader
```
A loader is a function returning a URL string for the image, given the following parameters:
src
width
quality
```
## Describe the improvement
Modify the docs to show the correct loader to use.
```
const projectId = '' // your supabase project id
export default function supabaseLoader({ src, width, quality }) {
return `https://${projectId}.supabase.co/storage/v1/render/image/public/${src}?width=${width}&quality=${quality || 75}`
}
```
## Additional context
The height was always undefined if you used the loader suggested. | non_priority | supabase image loader docs are incorrect improve documentation link describe the problem docs recommend this function for supabase image loader const projectid your supabase project id export default function supabaseloader src width height quality return height quality quality however according to nextjs docs loaders only take src width and quality as props a loader is a function returning a url string for the image given the following parameters src width quality describe the improvement modify the docs to show the correct loader to use const projectid your supabase project id export default function supabaseloader src width quality return additional context the height was always undefined if you used the loader suggested | 0 |
235,628 | 25,955,248,572 | IssuesEvent | 2022-12-18 05:42:16 | Dima2022/easybuggy | https://api.github.com/repos/Dima2022/easybuggy | closed | CVE-2015-0254 (High) detected in jstl-1.2.jar - autoclosed | security vulnerability | ## CVE-2015-0254 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jstl-1.2.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/jstl-1.2.jar,/repository/javax/servlet/jstl/1.2/jstl-1.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jstl-1.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/easybuggy/commit/aac8d904642c672c7ec784cc1cbbcf6e9c4c9c3f">aac8d904642c672c7ec784cc1cbbcf6e9c4c9c3f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Standard Taglibs before 1.2.3 allows remote attackers to execute arbitrary code or conduct external XML entity (XXE) attacks via a crafted XSLT extension in a (1) <x:parse> or (2) <x:transform> JSTL XML tag.
<p>Publish Date: 2015-03-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-0254>CVE-2015-0254</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tomcat.apache.org/taglibs/standard/">https://tomcat.apache.org/taglibs/standard/</a></p>
<p>Release Date: 2015-03-09</p>
<p>Fix Resolution: org.apache.taglibs:taglibs-standard-impl:1.2.3</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2015-0254 (High) detected in jstl-1.2.jar - autoclosed - ## CVE-2015-0254 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jstl-1.2.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /target/easybuggy-1-SNAPSHOT/WEB-INF/lib/jstl-1.2.jar,/repository/javax/servlet/jstl/1.2/jstl-1.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jstl-1.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/easybuggy/commit/aac8d904642c672c7ec784cc1cbbcf6e9c4c9c3f">aac8d904642c672c7ec784cc1cbbcf6e9c4c9c3f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Standard Taglibs before 1.2.3 allows remote attackers to execute arbitrary code or conduct external XML entity (XXE) attacks via a crafted XSLT extension in a (1) <x:parse> or (2) <x:transform> JSTL XML tag.
<p>Publish Date: 2015-03-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-0254>CVE-2015-0254</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tomcat.apache.org/taglibs/standard/">https://tomcat.apache.org/taglibs/standard/</a></p>
<p>Release Date: 2015-03-09</p>
<p>Fix Resolution: org.apache.taglibs:taglibs-standard-impl:1.2.3</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in jstl jar autoclosed cve high severity vulnerability vulnerable library jstl jar path to dependency file pom xml path to vulnerable library target easybuggy snapshot web inf lib jstl jar repository javax servlet jstl jstl jar dependency hierarchy x jstl jar vulnerable library found in head commit a href found in base branch master vulnerability details apache standard taglibs before allows remote attackers to execute arbitrary code or conduct external xml entity xxe attacks via a crafted xslt extension in a or jstl xml tag publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache taglibs taglibs standard impl rescue worker helmet automatic remediation is available for this issue | 0 |
190,764 | 14,577,407,051 | IssuesEvent | 2020-12-18 01:58:36 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | mraksoll4/lnd: nursery_store_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [mraksoll4/lnd](https://www.github.com/mraksoll4/lnd) at [nursery_store_test.go](https://github.com/mraksoll4/lnd/blob/e495a1057c2a4b9e3df37f2bac991cedcd64c89a/nursery_store_test.go#L159-L161)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to htlcOutput at line 160 may start a goroutine
[Click here to see the code in its original context.](https://github.com/mraksoll4/lnd/blob/e495a1057c2a4b9e3df37f2bac991cedcd64c89a/nursery_store_test.go#L159-L161)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, htlcOutput := range test.htlcOutputs {
assertCribAtExpiryHeight(t, ns, &htlcOutput)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: e495a1057c2a4b9e3df37f2bac991cedcd64c89a
| 1.0 | mraksoll4/lnd: nursery_store_test.go; 3 LoC -
Found a possible issue in [mraksoll4/lnd](https://www.github.com/mraksoll4/lnd) at [nursery_store_test.go](https://github.com/mraksoll4/lnd/blob/e495a1057c2a4b9e3df37f2bac991cedcd64c89a/nursery_store_test.go#L159-L161)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to htlcOutput at line 160 may start a goroutine
[Click here to see the code in its original context.](https://github.com/mraksoll4/lnd/blob/e495a1057c2a4b9e3df37f2bac991cedcd64c89a/nursery_store_test.go#L159-L161)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, htlcOutput := range test.htlcOutputs {
assertCribAtExpiryHeight(t, ns, &htlcOutput)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: e495a1057c2a4b9e3df37f2bac991cedcd64c89a
| non_priority | lnd nursery store test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to htlcoutput at line may start a goroutine click here to show the line s of go which triggered the analyzer go for htlcoutput range test htlcoutputs assertcribatexpiryheight t ns htlcoutput leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
270,799 | 29,116,036,340 | IssuesEvent | 2023-05-17 01:06:51 | pazhanivel07/frameworks_base_2021-0928 | https://api.github.com/repos/pazhanivel07/frameworks_base_2021-0928 | reopened | CVE-2021-0970 (High) detected in baseandroid-10.0.0_r44 | Mend: dependency security vulnerability | ## CVE-2021-0970 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r44</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_base_2021-0928/commit/098773bdbc80dd36be20c3b38616b8af53e37d78">098773bdbc80dd36be20c3b38616b8af53e37d78</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/location/java/android/location/GpsNavigationMessage.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In createFromParcel of GpsNavigationMessage.java, there is a possible Parcel serialization/deserialization mismatch. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-196970023
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-0970>CVE-2021-0970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0970">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0970</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-0970 (High) detected in baseandroid-10.0.0_r44 - ## CVE-2021-0970 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r44</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/pazhanivel07/frameworks_base_2021-0928/commit/098773bdbc80dd36be20c3b38616b8af53e37d78">098773bdbc80dd36be20c3b38616b8af53e37d78</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/location/java/android/location/GpsNavigationMessage.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In createFromParcel of GpsNavigationMessage.java, there is a possible Parcel serialization/deserialization mismatch. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-196970023
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-0970>CVE-2021-0970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0970">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0970</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in baseandroid cve high severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch master vulnerable source files location java android location gpsnavigationmessage java vulnerability details in createfromparcel of gpsnavigationmessage java there is a possible parcel serialization deserialization mismatch this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend | 0 |
125,665 | 26,710,429,655 | IssuesEvent | 2023-01-27 22:58:21 | phetsims/quadrilateral | https://api.github.com/repos/phetsims/quadrilateral | closed | Keyboard Shortcuts Dialog | dev:code-review | I still need to create a keyboard shortcuts dialog.
This sim has custom interactions, and may have hot keys to get to the check boxes. | 1.0 | Keyboard Shortcuts Dialog - I still need to create a keyboard shortcuts dialog.
This sim has custom interactions, and may have hot keys to get to the check boxes. | non_priority | keyboard shortcuts dialog i still need to create a keyboard shortcuts dialog this sim has custom interactions and may have hot keys to get to the check boxes | 0 |
112,741 | 17,098,861,225 | IssuesEvent | 2021-07-09 08:23:15 | bitbar/remote-device-client | https://api.github.com/repos/bitbar/remote-device-client | closed | CVE-2021-24122 (Medium) detected in tomcat-embed-core-9.0.27.jar - autoclosed | security vulnerability | ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.27.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: remote-device-client/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.27/tomcat-embed-core-9.0.27.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-websocket-2.2.0.RELEASE.jar (Root Library)
- spring-boot-starter-web-2.2.0.RELEASE.jar
- spring-boot-starter-tomcat-2.2.0.RELEASE.jar
- :x: **tomcat-embed-core-9.0.27.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.27","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-websocket:2.2.0.RELEASE;org.springframework.boot:spring-boot-starter-web:2.2.0.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.2.0.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:9.0.27","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-24122","vulnerabilityDetails":"When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-24122 (Medium) detected in tomcat-embed-core-9.0.27.jar - autoclosed - ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.27.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: remote-device-client/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.27/tomcat-embed-core-9.0.27.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-websocket-2.2.0.RELEASE.jar (Root Library)
- spring-boot-starter-web-2.2.0.RELEASE.jar
- spring-boot-starter-tomcat-2.2.0.RELEASE.jar
- :x: **tomcat-embed-core-9.0.27.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"9.0.27","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-websocket:2.2.0.RELEASE;org.springframework.boot:spring-boot-starter-web:2.2.0.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.2.0.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:9.0.27","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-24122","vulnerabilityDetails":"When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in tomcat embed core jar autoclosed cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file remote device client pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter websocket release jar root library spring boot starter web release jar spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in base branch master vulnerability details when serving resources from a network location using the ntfs file system apache tomcat versions to to to and to were susceptible to jsp source code disclosure in some configurations the root cause was the unexpected behaviour of the jre api file getcanonicalpath which in turn was caused by the inconsistent behaviour of the windows api findfirstfilew in some circumstances publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter websocket release org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina basebranches vulnerabilityidentifier cve vulnerabilitydetails when serving resources from a network location using the ntfs file system apache tomcat versions to to to and to were susceptible to jsp source code disclosure in some configurations the root cause was the unexpected behaviour of the jre api file getcanonicalpath which in turn was caused by the inconsistent behaviour of the windows api findfirstfilew in some circumstances vulnerabilityurl | 0 |
250,553 | 18,894,088,089 | IssuesEvent | 2021-11-15 16:02:58 | xournalpp/xournalpp | https://api.github.com/repos/xournalpp/xournalpp | closed | Remove mentions of CppUnit in READMEs | bug papercut documentation | **Is your feature request related to a problem? Please describe.**
After https://github.com/xournalpp/xournalpp/pull/3476 some mentions of CppUnite where forgotten in the READMEs (see https://github.com/xournalpp/xournalpp/pull/3476#issuecomment-966345209)
**Describe the solution you'd like**
Migrate these mentions to refer to gtest.
| 1.0 | Remove mentions of CppUnit in READMEs - **Is your feature request related to a problem? Please describe.**
After https://github.com/xournalpp/xournalpp/pull/3476 some mentions of CppUnite where forgotten in the READMEs (see https://github.com/xournalpp/xournalpp/pull/3476#issuecomment-966345209)
**Describe the solution you'd like**
Migrate these mentions to refer to gtest.
| non_priority | remove mentions of cppunit in readmes is your feature request related to a problem please describe after some mentions of cppunite where forgotten in the readmes see describe the solution you d like migrate these mentions to refer to gtest | 0 |
90,554 | 15,856,202,594 | IssuesEvent | 2021-04-08 01:46:39 | AnhaaD/auth-client | https://api.github.com/repos/AnhaaD/auth-client | opened | WS-2019-0333 (High) detected in handlebars-4.1.2.tgz | security vulnerability | ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /auth-client/package.json</p>
<p>Path to vulnerable library: auth-client/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- karma-coverage-istanbul-reporter-1.4.3.tgz (Root Library)
- istanbul-api-1.3.7.tgz
- istanbul-reports-1.5.1.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it's possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08>WS-2019-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1325">https://www.npmjs.com/advisories/1325</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0333 (High) detected in handlebars-4.1.2.tgz - ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /auth-client/package.json</p>
<p>Path to vulnerable library: auth-client/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- karma-coverage-istanbul-reporter-1.4.3.tgz (Root Library)
- istanbul-api-1.3.7.tgz
- istanbul-reports-1.5.1.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it's possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08>WS-2019-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1325">https://www.npmjs.com/advisories/1325</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in handlebars tgz ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file auth client package json path to vulnerable library auth client node modules handlebars package json dependency hierarchy karma coverage istanbul reporter tgz root library istanbul api tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details in handlebars versions prior to are vulnerable to prototype pollution using a malicious template it s possbile to add or modify properties to the object prototype this can also lead to dos and rce in certain conditions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
41,119 | 16,623,318,134 | IssuesEvent | 2021-06-03 06:16:26 | microsoft/BotFramework-Composer | https://api.github.com/repos/microsoft/BotFramework-Composer | closed | LUIS build fails with reason "undefined" after adding the 11th phrase list | Bot Services Team: Platform Type: Bug customer-replied-to customer-reported | ## Describe the bug
LUIS build fails with reason "undefined" after adding the 11th phrase list.
## Version
Version: 1.4.0
Electron: 8.2.4
Chrome: 80.0.3987.165
NodeJS: 12.13.0
V8: 8.0.426.27-electron.0
## Browser
- [X] Electron distribution
- [ ] Chrome
- [ ] Safari
- [ ] Firefox
- [ ] Edge
## OS
- [ ] macOS
- [X] Windows
- [ ] Ubuntu
## To Reproduce
Steps to reproduce the behavior:
1. Go to any intent trigger(s) and add 11 simple phrase lists
2. Click on 'Start Bot'
3. Once it fails to start, click on 'See Details'
4. See error "Luis build failed: undefined"
## Expected behavior
I expect to see an informative error message with a reason as to why it failed.
In this case, the luis.ai portal shows "BadArgument: The phraselist features allowed per model cannot exceed the limit 10.".
## Screenshots
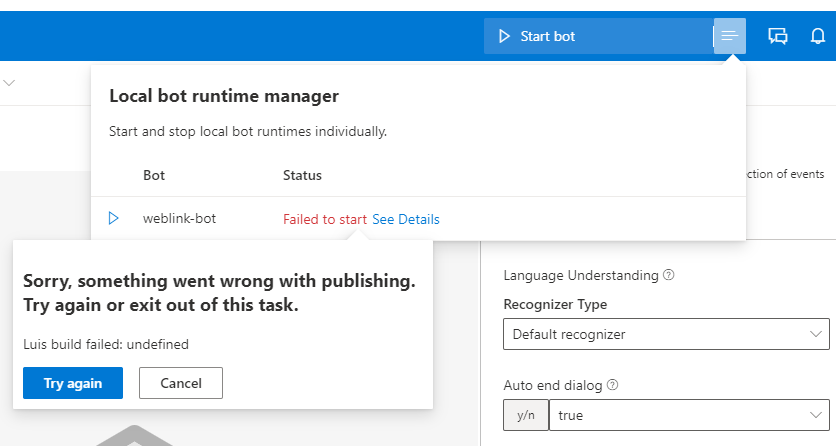 | 1.0 | LUIS build fails with reason "undefined" after adding the 11th phrase list - ## Describe the bug
LUIS build fails with reason "undefined" after adding the 11th phrase list.
## Version
Version: 1.4.0
Electron: 8.2.4
Chrome: 80.0.3987.165
NodeJS: 12.13.0
V8: 8.0.426.27-electron.0
## Browser
- [X] Electron distribution
- [ ] Chrome
- [ ] Safari
- [ ] Firefox
- [ ] Edge
## OS
- [ ] macOS
- [X] Windows
- [ ] Ubuntu
## To Reproduce
Steps to reproduce the behavior:
1. Go to any intent trigger(s) and add 11 simple phrase lists
2. Click on 'Start Bot'
3. Once it fails to start, click on 'See Details'
4. See error "Luis build failed: undefined"
## Expected behavior
I expect to see an informative error message with a reason as to why it failed.
In this case, the luis.ai portal shows "BadArgument: The phraselist features allowed per model cannot exceed the limit 10.".
## Screenshots
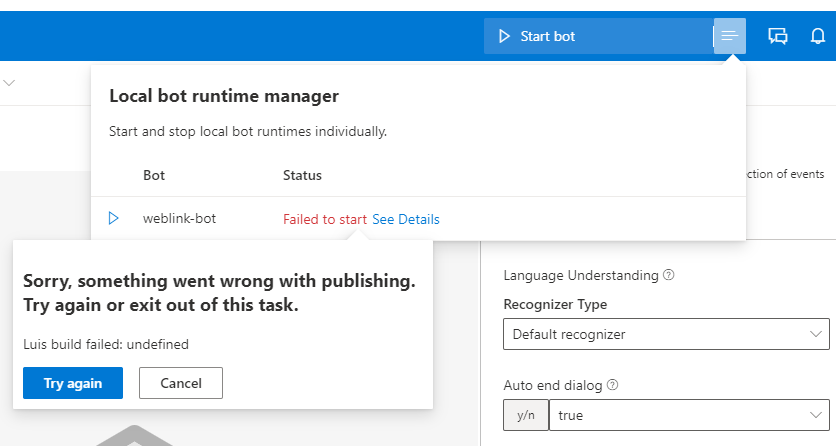 | non_priority | luis build fails with reason undefined after adding the phrase list describe the bug luis build fails with reason undefined after adding the phrase list version version electron chrome nodejs electron browser electron distribution chrome safari firefox edge os macos windows ubuntu to reproduce steps to reproduce the behavior go to any intent trigger s and add simple phrase lists click on start bot once it fails to start click on see details see error luis build failed undefined expected behavior i expect to see an informative error message with a reason as to why it failed in this case the luis ai portal shows badargument the phraselist features allowed per model cannot exceed the limit screenshots | 0 |
5,739 | 20,913,263,523 | IssuesEvent | 2022-03-24 11:11:01 | tikv/tikv | https://api.github.com/repos/tikv/tikv | closed | Entry count of raft-engine seems not right | type/bug severity/moderate found/automation | ## Bug Report
<!-- Thanks for your bug report! Don't worry if you can't fill out all the sections. -->
The entry count keep increasing. After the tikv is restarted, it goes down.
### What version of TiKV are you using?
<!-- You can run `tikv-server --version` -->
e1fae9469b33ff1ec4fd66aa143a21a5f30f5aa3
### What operating system and CPU are you using?
<!-- If you're using Linux, you can run `cat /proc/cpuinfo` -->
### Steps to reproduce
<!-- If possible, provide a recipe for reproducing the error. A complete runnable program is good. -->
1. Run go-tpc workload
### What did you expect?
The entry count should not increase at all time.
### What did happened?

| 1.0 | Entry count of raft-engine seems not right - ## Bug Report
<!-- Thanks for your bug report! Don't worry if you can't fill out all the sections. -->
The entry count keep increasing. After the tikv is restarted, it goes down.
### What version of TiKV are you using?
<!-- You can run `tikv-server --version` -->
e1fae9469b33ff1ec4fd66aa143a21a5f30f5aa3
### What operating system and CPU are you using?
<!-- If you're using Linux, you can run `cat /proc/cpuinfo` -->
### Steps to reproduce
<!-- If possible, provide a recipe for reproducing the error. A complete runnable program is good. -->
1. Run go-tpc workload
### What did you expect?
The entry count should not increase at all time.
### What did happened?

| non_priority | entry count of raft engine seems not right bug report the entry count keep increasing after the tikv is restarted it goes down what version of tikv are you using what operating system and cpu are you using steps to reproduce run go tpc workload what did you expect the entry count should not increase at all time what did happened | 0 |
46,834 | 7,292,667,543 | IssuesEvent | 2018-02-25 04:19:43 | BoiseState/interfaith-donation | https://api.github.com/repos/BoiseState/interfaith-donation | closed | Create documentation for Docker and Docker Compose | devops documentation | Create documentation explaining Docker and how to use it for this application.
**Acceptance Criteria:**
- [x] Documentation is created detailing how to start the Docker containers
- [x] Documentation is created about useful tools and tips for Docker container use | 1.0 | Create documentation for Docker and Docker Compose - Create documentation explaining Docker and how to use it for this application.
**Acceptance Criteria:**
- [x] Documentation is created detailing how to start the Docker containers
- [x] Documentation is created about useful tools and tips for Docker container use | non_priority | create documentation for docker and docker compose create documentation explaining docker and how to use it for this application acceptance criteria documentation is created detailing how to start the docker containers documentation is created about useful tools and tips for docker container use | 0 |
247,977 | 18,858,015,695 | IssuesEvent | 2021-11-12 09:17:23 | TLChicken/pe | https://api.github.com/repos/TLChicken/pe | opened | Inconsistent ellipsis in UG Command Formats | severity.VeryLow type.DocumentationBug | 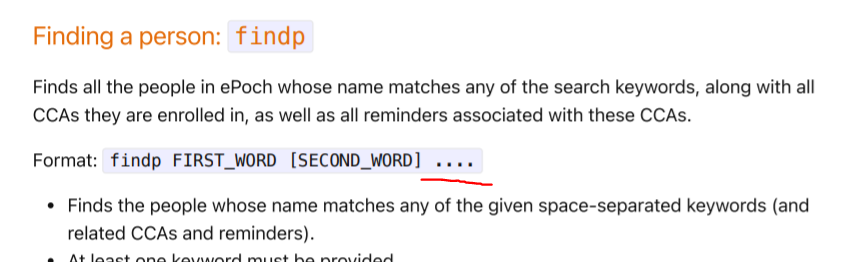
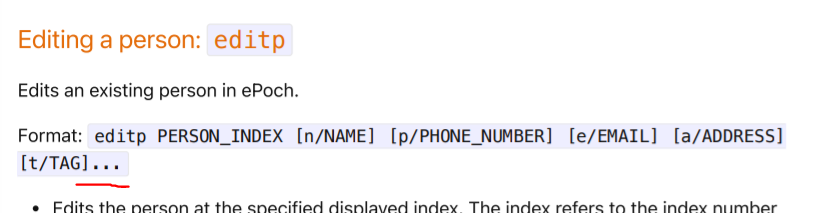
As we can see here in `findp`, a space then 4 dots are used but in `editp`, there is no leading space and there is only 3 dots. The functionality of the dots appears to be the same, however this may indicate to the user that the dots mean different things. (Eg: findp is supposed to take in mor eparameters than editp)
<!--session: 1636703263327-e6c50568-a8c4-46cc-9014-76ab75bad2fb-->
<!--Version: Web v3.4.1--> | 1.0 | Inconsistent ellipsis in UG Command Formats - 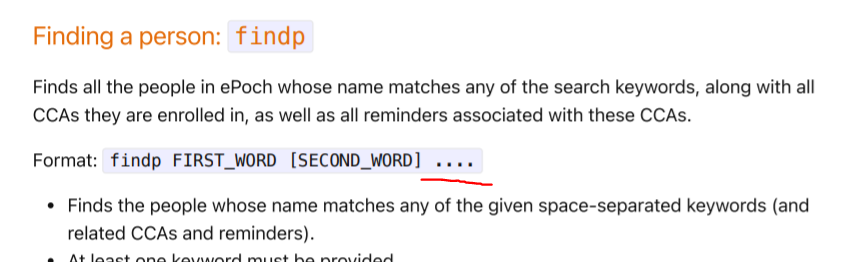
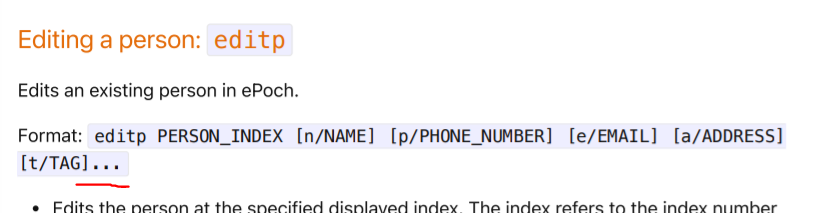
As we can see here in `findp`, a space then 4 dots are used but in `editp`, there is no leading space and there is only 3 dots. The functionality of the dots appears to be the same, however this may indicate to the user that the dots mean different things. (Eg: findp is supposed to take in mor eparameters than editp)
<!--session: 1636703263327-e6c50568-a8c4-46cc-9014-76ab75bad2fb-->
<!--Version: Web v3.4.1--> | non_priority | inconsistent ellipsis in ug command formats as we can see here in findp a space then dots are used but in editp there is no leading space and there is only dots the functionality of the dots appears to be the same however this may indicate to the user that the dots mean different things eg findp is supposed to take in mor eparameters than editp | 0 |
78,988 | 15,586,091,994 | IssuesEvent | 2021-03-18 01:09:16 | vlaship/async | https://api.github.com/repos/vlaship/async | opened | CVE-2020-11996 (High) detected in tomcat-embed-core-9.0.26.jar | security vulnerability | ## CVE-2020-11996 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.26.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: async/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.26/6312ba542bc58fa9ee789a43516ce4d862548a6b/tomcat-embed-core-9.0.26.jar,/root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.26/6312ba542bc58fa9ee789a43516ce4d862548a6b/tomcat-embed-core-9.0.26.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.9.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.1.9.RELEASE.jar
- tomcat-embed-websocket-9.0.26.jar
- :x: **tomcat-embed-core-9.0.26.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A specially crafted sequence of HTTP/2 requests sent to Apache Tomcat 10.0.0-M1 to 10.0.0-M5, 9.0.0.M1 to 9.0.35 and 8.5.0 to 8.5.55 could trigger high CPU usage for several seconds. If a sufficient number of such requests were made on concurrent HTTP/2 connections, the server could become unresponsive.
<p>Publish Date: 2020-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11996>CVE-2020-11996</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r5541ef6b6b68b49f76fc4c45695940116da2bcbe0312ef204a00a2e0%40%3Cannounce.tomcat.apache.org%3E,http://tomcat.apache.org/security-10.html">https://lists.apache.org/thread.html/r5541ef6b6b68b49f76fc4c45695940116da2bcbe0312ef204a00a2e0%40%3Cannounce.tomcat.apache.org%3E,http://tomcat.apache.org/security-10.html</a></p>
<p>Release Date: 2020-06-26</p>
<p>Fix Resolution: org.apache.tomcat:tomcat-coyote:10.0.0-M6,9.0.36,8.5.56,org.apache.tomcat.embed:org.apache.tomcat.embed:10.0.0-M6,9.0.36,8.5.56</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11996 (High) detected in tomcat-embed-core-9.0.26.jar - ## CVE-2020-11996 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.26.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: async/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.26/6312ba542bc58fa9ee789a43516ce4d862548a6b/tomcat-embed-core-9.0.26.jar,/root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.26/6312ba542bc58fa9ee789a43516ce4d862548a6b/tomcat-embed-core-9.0.26.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.9.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.1.9.RELEASE.jar
- tomcat-embed-websocket-9.0.26.jar
- :x: **tomcat-embed-core-9.0.26.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A specially crafted sequence of HTTP/2 requests sent to Apache Tomcat 10.0.0-M1 to 10.0.0-M5, 9.0.0.M1 to 9.0.35 and 8.5.0 to 8.5.55 could trigger high CPU usage for several seconds. If a sufficient number of such requests were made on concurrent HTTP/2 connections, the server could become unresponsive.
<p>Publish Date: 2020-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11996>CVE-2020-11996</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r5541ef6b6b68b49f76fc4c45695940116da2bcbe0312ef204a00a2e0%40%3Cannounce.tomcat.apache.org%3E,http://tomcat.apache.org/security-10.html">https://lists.apache.org/thread.html/r5541ef6b6b68b49f76fc4c45695940116da2bcbe0312ef204a00a2e0%40%3Cannounce.tomcat.apache.org%3E,http://tomcat.apache.org/security-10.html</a></p>
<p>Release Date: 2020-06-26</p>
<p>Fix Resolution: org.apache.tomcat:tomcat-coyote:10.0.0-M6,9.0.36,8.5.56,org.apache.tomcat.embed:org.apache.tomcat.embed:10.0.0-M6,9.0.36,8.5.56</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file async build gradle path to vulnerable library root gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar root gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar tomcat embed websocket jar x tomcat embed core jar vulnerable library vulnerability details a specially crafted sequence of http requests sent to apache tomcat to to and to could trigger high cpu usage for several seconds if a sufficient number of such requests were made on concurrent http connections the server could become unresponsive publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat tomcat coyote org apache tomcat embed org apache tomcat embed step up your open source security game with whitesource | 0 |
322,834 | 23,924,857,911 | IssuesEvent | 2022-09-09 21:05:02 | AlecTroemel/junk-drawer | https://api.github.com/repos/AlecTroemel/junk-drawer | closed | write docs | documentation | My thought with this is to fill in the doc strings for all the public macros and functions, so that you can do stuff like
```janet
(doc "add-component")
```
I think that, combined with any missing examples would be enough to close this out... since I dont want to maintain a whole separate markdown files and the source here is pretty readable IMO. | 1.0 | write docs - My thought with this is to fill in the doc strings for all the public macros and functions, so that you can do stuff like
```janet
(doc "add-component")
```
I think that, combined with any missing examples would be enough to close this out... since I dont want to maintain a whole separate markdown files and the source here is pretty readable IMO. | non_priority | write docs my thought with this is to fill in the doc strings for all the public macros and functions so that you can do stuff like janet doc add component i think that combined with any missing examples would be enough to close this out since i dont want to maintain a whole separate markdown files and the source here is pretty readable imo | 0 |
41,347 | 10,704,449,242 | IssuesEvent | 2019-10-24 11:46:13 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | Documentation for pushing native library to central | Area/BuildTools BetaTesting Type/Docs | **Description:**
We need to have documentation on interoperability support and pushing native library to central
**Steps to reproduce:**
N/A
**Affected Versions:**
jballerin 1.0 beta
| 1.0 | Documentation for pushing native library to central - **Description:**
We need to have documentation on interoperability support and pushing native library to central
**Steps to reproduce:**
N/A
**Affected Versions:**
jballerin 1.0 beta
| non_priority | documentation for pushing native library to central description we need to have documentation on interoperability support and pushing native library to central steps to reproduce n a affected versions jballerin beta | 0 |
17,643 | 10,098,145,716 | IssuesEvent | 2019-07-28 12:48:05 | Shuunen/bergerac-roads | https://api.github.com/repos/Shuunen/bergerac-roads | closed | CVE-2018-3774 High Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2018-3774 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.2.0.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>path: /bergerac-roads/node_modules/cypress/dist/Cypress/resources/app/packages/server/node_modules/url-parse/package.json</p>
<p>
<p>Library home page: <a href=https://registry.npmjs.org/url-parse/-/url-parse-1.2.0.tgz>https://registry.npmjs.org/url-parse/-/url-parse-1.2.0.tgz</a></p>
Dependency Hierarchy:
- :x: **url-parse-1.2.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect parsing in url-parse <1.4.3 returns wrong hostname which leads to multiple vulnerabilities such as SSRF, Open Redirect, Bypass Authentication Protocol.
<p>Publish Date: 2018-08-12
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3774>CVE-2018-3774</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/unshiftio/url-parse/commit/53b1794e54d0711ceb52505e0f74145270570d5a#diff-168726dbe96b3ce427e7fedce31bb0bc">https://github.com/unshiftio/url-parse/commit/53b1794e54d0711ceb52505e0f74145270570d5a#diff-168726dbe96b3ce427e7fedce31bb0bc</a></p>
<p>Release Date: 2018-07-29</p>
<p>Fix Resolution: Replace or update the following files: index.js, test.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-3774 High Severity Vulnerability detected by WhiteSource - ## CVE-2018-3774 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.2.0.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>path: /bergerac-roads/node_modules/cypress/dist/Cypress/resources/app/packages/server/node_modules/url-parse/package.json</p>
<p>
<p>Library home page: <a href=https://registry.npmjs.org/url-parse/-/url-parse-1.2.0.tgz>https://registry.npmjs.org/url-parse/-/url-parse-1.2.0.tgz</a></p>
Dependency Hierarchy:
- :x: **url-parse-1.2.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect parsing in url-parse <1.4.3 returns wrong hostname which leads to multiple vulnerabilities such as SSRF, Open Redirect, Bypass Authentication Protocol.
<p>Publish Date: 2018-08-12
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3774>CVE-2018-3774</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/unshiftio/url-parse/commit/53b1794e54d0711ceb52505e0f74145270570d5a#diff-168726dbe96b3ce427e7fedce31bb0bc">https://github.com/unshiftio/url-parse/commit/53b1794e54d0711ceb52505e0f74145270570d5a#diff-168726dbe96b3ce427e7fedce31bb0bc</a></p>
<p>Release Date: 2018-07-29</p>
<p>Fix Resolution: Replace or update the following files: index.js, test.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments path bergerac roads node modules cypress dist cypress resources app packages server node modules url parse package json library home page a href dependency hierarchy x url parse tgz vulnerable library vulnerability details incorrect parsing in url parse returns wrong hostname which leads to multiple vulnerabilities such as ssrf open redirect bypass authentication protocol publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following files index js test js step up your open source security game with whitesource | 0 |
25,903 | 7,759,130,867 | IssuesEvent | 2018-05-31 22:00:56 | xamarin/xamarin-android | https://api.github.com/repos/xamarin/xamarin-android | opened | [Aapt2] Can't operate across drives on Windows | Area: App+Library Build | ### Steps to Reproduce
See VSTS build here: http://build.devdiv.io/1735992
1. Create a project into `E:\` or some secondary drive with Aapt2 enabled
2. Your system has `%TEMP%` in `C:\`
3. `aapt2.exe` fails an error such as:
```
error APT0000: failed to create directory 'C:\Users\myuser\AppData\Local\Temp\3\hyxjnzdb.0d1\xamarin\forms_performance_integration'.
```
Other links about this:
- https://stackoverflow.com/questions/46512990/gradle-error-failed-to-create-directory
- https://github.com/xamarin/xamarin-android/pull/1757
### Expected Behavior
`Aapt2` works even if you have the project on a second drive.
### Actual Behavior
`Aapt` fails.
### Version Information
I was using `xamarin-android/master/1cbac614061df022d93fcff2384afdbba813e37e`.
Don't know what we should even do about this, but I thought I would file it... | 1.0 | [Aapt2] Can't operate across drives on Windows - ### Steps to Reproduce
See VSTS build here: http://build.devdiv.io/1735992
1. Create a project into `E:\` or some secondary drive with Aapt2 enabled
2. Your system has `%TEMP%` in `C:\`
3. `aapt2.exe` fails an error such as:
```
error APT0000: failed to create directory 'C:\Users\myuser\AppData\Local\Temp\3\hyxjnzdb.0d1\xamarin\forms_performance_integration'.
```
Other links about this:
- https://stackoverflow.com/questions/46512990/gradle-error-failed-to-create-directory
- https://github.com/xamarin/xamarin-android/pull/1757
### Expected Behavior
`Aapt2` works even if you have the project on a second drive.
### Actual Behavior
`Aapt` fails.
### Version Information
I was using `xamarin-android/master/1cbac614061df022d93fcff2384afdbba813e37e`.
Don't know what we should even do about this, but I thought I would file it... | non_priority | can t operate across drives on windows steps to reproduce see vsts build here create a project into e or some secondary drive with enabled your system has temp in c exe fails an error such as error failed to create directory c users myuser appdata local temp hyxjnzdb xamarin forms performance integration other links about this expected behavior works even if you have the project on a second drive actual behavior aapt fails version information i was using xamarin android master don t know what we should even do about this but i thought i would file it | 0 |
170,648 | 20,883,795,000 | IssuesEvent | 2022-03-23 01:13:43 | snowdensb/dependabot-core | https://api.github.com/repos/snowdensb/dependabot-core | reopened | CVE-2017-0249 (High) detected in system.net.http.4.3.0.nupkg | security vulnerability | ## CVE-2017-0249 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>system.net.http.4.3.0.nupkg</b></p></summary>
<p>Provides a programming interface for modern HTTP applications, including HTTP client components that...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.net.http.4.3.0.nupkg">https://api.nuget.org/packages/system.net.http.4.3.0.nupkg</a></p>
<p>Path to dependency file: /nuget/spec/fixtures/csproj/basic.csproj</p>
<p>Path to vulnerable library: /usr/share/dotnet/sdk/NuGetFallbackFolder/system.net.http/4.3.0/system.net.http.4.3.0.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.extensions.platformabstractions.1.1.0.nupkg (Root Library)
- netstandard.library.1.6.1.nupkg
- :x: **system.net.http.4.3.0.nupkg** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An elevation of privilege vulnerability exists when the ASP.NET Core fails to properly sanitize web requests.
<p>Publish Date: 2017-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-0249>CVE-2017-0249</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/aspnet/Announcements/issues/239">https://github.com/aspnet/Announcements/issues/239</a></p>
<p>Release Date: 2017-05-12</p>
<p>Fix Resolution: System.Text.Encodings.Web - 4.0.1,4.3.1;System.Net.Http - 4.1.2,4.3.2;System.Net.Http.WinHttpHandler - 4.0.2,4.3.1;System.Net.Security - 4.0.1,4.3.1;System.Net.WebSockets.Client - 4.0.1,4.3.1;Microsoft.AspNetCore.Mvc - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Core - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Abstractions - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ApiExplorer - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Cors - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.DataAnnotations - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Json - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Xml - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Localization - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor.Host - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.TagHelpers - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ViewFeatures - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.WebApiCompatShim - 1.0.4,1.1.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Nuget","packageName":"System.Net.Http","packageVersion":"4.3.0","packageFilePaths":["/nuget/spec/fixtures/csproj/basic.csproj"],"isTransitiveDependency":true,"dependencyTree":"Microsoft.Extensions.PlatformAbstractions:1.1.0;NETStandard.Library:1.6.1;System.Net.Http:4.3.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"System.Text.Encodings.Web - 4.0.1,4.3.1;System.Net.Http - 4.1.2,4.3.2;System.Net.Http.WinHttpHandler - 4.0.2,4.3.1;System.Net.Security - 4.0.1,4.3.1;System.Net.WebSockets.Client - 4.0.1,4.3.1;Microsoft.AspNetCore.Mvc - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Core - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Abstractions - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ApiExplorer - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Cors - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.DataAnnotations - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Json - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Xml - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Localization - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor.Host - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.TagHelpers - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ViewFeatures - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.WebApiCompatShim - 1.0.4,1.1.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-0249","vulnerabilityDetails":"An elevation of privilege vulnerability exists when the ASP.NET Core fails to properly sanitize web requests.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-0249","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-0249 (High) detected in system.net.http.4.3.0.nupkg - ## CVE-2017-0249 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>system.net.http.4.3.0.nupkg</b></p></summary>
<p>Provides a programming interface for modern HTTP applications, including HTTP client components that...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.net.http.4.3.0.nupkg">https://api.nuget.org/packages/system.net.http.4.3.0.nupkg</a></p>
<p>Path to dependency file: /nuget/spec/fixtures/csproj/basic.csproj</p>
<p>Path to vulnerable library: /usr/share/dotnet/sdk/NuGetFallbackFolder/system.net.http/4.3.0/system.net.http.4.3.0.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.extensions.platformabstractions.1.1.0.nupkg (Root Library)
- netstandard.library.1.6.1.nupkg
- :x: **system.net.http.4.3.0.nupkg** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An elevation of privilege vulnerability exists when the ASP.NET Core fails to properly sanitize web requests.
<p>Publish Date: 2017-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-0249>CVE-2017-0249</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/aspnet/Announcements/issues/239">https://github.com/aspnet/Announcements/issues/239</a></p>
<p>Release Date: 2017-05-12</p>
<p>Fix Resolution: System.Text.Encodings.Web - 4.0.1,4.3.1;System.Net.Http - 4.1.2,4.3.2;System.Net.Http.WinHttpHandler - 4.0.2,4.3.1;System.Net.Security - 4.0.1,4.3.1;System.Net.WebSockets.Client - 4.0.1,4.3.1;Microsoft.AspNetCore.Mvc - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Core - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Abstractions - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ApiExplorer - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Cors - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.DataAnnotations - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Json - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Xml - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Localization - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor.Host - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.TagHelpers - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ViewFeatures - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.WebApiCompatShim - 1.0.4,1.1.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Nuget","packageName":"System.Net.Http","packageVersion":"4.3.0","packageFilePaths":["/nuget/spec/fixtures/csproj/basic.csproj"],"isTransitiveDependency":true,"dependencyTree":"Microsoft.Extensions.PlatformAbstractions:1.1.0;NETStandard.Library:1.6.1;System.Net.Http:4.3.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"System.Text.Encodings.Web - 4.0.1,4.3.1;System.Net.Http - 4.1.2,4.3.2;System.Net.Http.WinHttpHandler - 4.0.2,4.3.1;System.Net.Security - 4.0.1,4.3.1;System.Net.WebSockets.Client - 4.0.1,4.3.1;Microsoft.AspNetCore.Mvc - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Core - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Abstractions - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ApiExplorer - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Cors - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.DataAnnotations - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Json - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Xml - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Localization - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor.Host - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.TagHelpers - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ViewFeatures - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.WebApiCompatShim - 1.0.4,1.1.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-0249","vulnerabilityDetails":"An elevation of privilege vulnerability exists when the ASP.NET Core fails to properly sanitize web requests.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-0249","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in system net http nupkg cve high severity vulnerability vulnerable library system net http nupkg provides a programming interface for modern http applications including http client components that library home page a href path to dependency file nuget spec fixtures csproj basic csproj path to vulnerable library usr share dotnet sdk nugetfallbackfolder system net http system net http nupkg dependency hierarchy microsoft extensions platformabstractions nupkg root library netstandard library nupkg x system net http nupkg vulnerable library found in base branch main vulnerability details an elevation of privilege vulnerability exists when the asp net core fails to properly sanitize web requests publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution system text encodings web system net http system net http winhttphandler system net security system net websockets client microsoft aspnetcore mvc microsoft aspnetcore mvc core microsoft aspnetcore mvc abstractions microsoft aspnetcore mvc apiexplorer microsoft aspnetcore mvc cors microsoft aspnetcore mvc dataannotations microsoft aspnetcore mvc formatters json microsoft aspnetcore mvc formatters xml microsoft aspnetcore mvc localization microsoft aspnetcore mvc razor host microsoft aspnetcore mvc razor microsoft aspnetcore mvc taghelpers microsoft aspnetcore mvc viewfeatures microsoft aspnetcore mvc webapicompatshim isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree microsoft extensions platformabstractions netstandard library system net http isminimumfixversionavailable true minimumfixversion system text encodings web system net http system net http winhttphandler system net security system net websockets client microsoft aspnetcore mvc microsoft aspnetcore mvc core microsoft aspnetcore mvc abstractions microsoft aspnetcore mvc apiexplorer microsoft aspnetcore mvc cors microsoft aspnetcore mvc dataannotations microsoft aspnetcore mvc formatters json microsoft aspnetcore mvc formatters xml microsoft aspnetcore mvc localization microsoft aspnetcore mvc razor host microsoft aspnetcore mvc razor microsoft aspnetcore mvc taghelpers microsoft aspnetcore mvc viewfeatures microsoft aspnetcore mvc webapicompatshim isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails an elevation of privilege vulnerability exists when the asp net core fails to properly sanitize web requests vulnerabilityurl | 0 |
113,419 | 24,416,067,818 | IssuesEvent | 2022-10-05 15:59:03 | dwp/design-system | https://api.github.com/repos/dwp/design-system | closed | Find an address: Designs | 🔗 component find an address/postcode | ## What
Sub task for Find my address by postcode/house number #237. Designing the journey and screens where typeahead/autocomplete is not used i.e. a non JavaScript journey.
## Why
After discussion with Sarat from common capabilities team working on the the SRA formerly (ARA) lookup, there appears to be deprioritised looking into research for the component. The address lookup requires further development. In the mean time there are examples of address lookup being used which could be published and and in the future be enhanced by any typeahead functionality.
## Done when
- [x] Reach out to designers using the find an address component and gather insights
- [x] Analyse insights and rough out steps and fields for a user journey
- [x] Review with design system team
- [x] Update design content and layout based on review
- [x] Document design decisions
- [x] Build pages
- [x] Collate feedback from designers and accessibility team on solution
- [x] Update designs based on feedback
## Outcomes
- Designs for a find an address journey
## Who needs to know about this
- Design System team
- Design community
- Accessibility team
## Related stories
#237
## Anything else
[Mural board](https://app.mural.co/t/dwpdigital7412/m/dwpdigital7412/1657636707008/e8e422d466ec6f13e6b101899d14a9cf630b0500?sender=ub2947a7492ef409e91952034)
| 1.0 | Find an address: Designs - ## What
Sub task for Find my address by postcode/house number #237. Designing the journey and screens where typeahead/autocomplete is not used i.e. a non JavaScript journey.
## Why
After discussion with Sarat from common capabilities team working on the the SRA formerly (ARA) lookup, there appears to be deprioritised looking into research for the component. The address lookup requires further development. In the mean time there are examples of address lookup being used which could be published and and in the future be enhanced by any typeahead functionality.
## Done when
- [x] Reach out to designers using the find an address component and gather insights
- [x] Analyse insights and rough out steps and fields for a user journey
- [x] Review with design system team
- [x] Update design content and layout based on review
- [x] Document design decisions
- [x] Build pages
- [x] Collate feedback from designers and accessibility team on solution
- [x] Update designs based on feedback
## Outcomes
- Designs for a find an address journey
## Who needs to know about this
- Design System team
- Design community
- Accessibility team
## Related stories
#237
## Anything else
[Mural board](https://app.mural.co/t/dwpdigital7412/m/dwpdigital7412/1657636707008/e8e422d466ec6f13e6b101899d14a9cf630b0500?sender=ub2947a7492ef409e91952034)
| non_priority | find an address designs what sub task for find my address by postcode house number designing the journey and screens where typeahead autocomplete is not used i e a non javascript journey why after discussion with sarat from common capabilities team working on the the sra formerly ara lookup there appears to be deprioritised looking into research for the component the address lookup requires further development in the mean time there are examples of address lookup being used which could be published and and in the future be enhanced by any typeahead functionality done when reach out to designers using the find an address component and gather insights analyse insights and rough out steps and fields for a user journey review with design system team update design content and layout based on review document design decisions build pages collate feedback from designers and accessibility team on solution update designs based on feedback outcomes designs for a find an address journey who needs to know about this design system team design community accessibility team related stories anything else | 0 |
289,911 | 32,006,099,873 | IssuesEvent | 2023-09-21 14:55:44 | TreyM-WSS/concord | https://api.github.com/repos/TreyM-WSS/concord | opened | CVE-2023-40167 (Medium) detected in jetty-http-9.4.26.v20200117.jar | Mend: dependency security vulnerability | ## CVE-2023-40167 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-http-9.4.26.v20200117.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: /server/queue-client/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.26.v20200117/jetty-http-9.4.26.v20200117.jar,/home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.26.v20200117/jetty-http-9.4.26.v20200117.jar</p>
<p>
Dependency Hierarchy:
- concord-queue-client-1.55.1-SNAPSHOT.jar (Root Library)
- jetty-client-9.4.26.v20200117.jar
- :x: **jetty-http-9.4.26.v20200117.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TreyM-WSS/concord/commit/cfb756aae811651de93ac8a69c7191e48bb4960f">cfb756aae811651de93ac8a69c7191e48bb4960f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Jetty is a Java based web server and servlet engine. Prior to versions 9.4.52, 10.0.16, 11.0.16, and 12.0.1, Jetty accepts the `+` character proceeding the content-length value in a HTTP/1 header field. This is more permissive than allowed by the RFC and other servers routinely reject such requests with 400 responses. There is no known exploit scenario, but it is conceivable that request smuggling could result if jetty is used in combination with a server that does not close the connection after sending such a 400 response. Versions 9.4.52, 10.0.16, 11.0.16, and 12.0.1 contain a patch for this issue. There is no workaround as there is no known exploit scenario.
<p>Publish Date: 2023-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-40167>CVE-2023-40167</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eclipse/jetty.project/security/advisories/GHSA-hmr7-m48g-48f6">https://github.com/eclipse/jetty.project/security/advisories/GHSA-hmr7-m48g-48f6</a></p>
<p>Release Date: 2023-09-15</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-http:9.4.52.v20230823,10.0.16,11.0.16,12.0.1</p>
</p>
</details>
<p></p>
| True | CVE-2023-40167 (Medium) detected in jetty-http-9.4.26.v20200117.jar - ## CVE-2023-40167 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-http-9.4.26.v20200117.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: /server/queue-client/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.26.v20200117/jetty-http-9.4.26.v20200117.jar,/home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.26.v20200117/jetty-http-9.4.26.v20200117.jar</p>
<p>
Dependency Hierarchy:
- concord-queue-client-1.55.1-SNAPSHOT.jar (Root Library)
- jetty-client-9.4.26.v20200117.jar
- :x: **jetty-http-9.4.26.v20200117.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TreyM-WSS/concord/commit/cfb756aae811651de93ac8a69c7191e48bb4960f">cfb756aae811651de93ac8a69c7191e48bb4960f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Jetty is a Java based web server and servlet engine. Prior to versions 9.4.52, 10.0.16, 11.0.16, and 12.0.1, Jetty accepts the `+` character proceeding the content-length value in a HTTP/1 header field. This is more permissive than allowed by the RFC and other servers routinely reject such requests with 400 responses. There is no known exploit scenario, but it is conceivable that request smuggling could result if jetty is used in combination with a server that does not close the connection after sending such a 400 response. Versions 9.4.52, 10.0.16, 11.0.16, and 12.0.1 contain a patch for this issue. There is no workaround as there is no known exploit scenario.
<p>Publish Date: 2023-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-40167>CVE-2023-40167</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eclipse/jetty.project/security/advisories/GHSA-hmr7-m48g-48f6">https://github.com/eclipse/jetty.project/security/advisories/GHSA-hmr7-m48g-48f6</a></p>
<p>Release Date: 2023-09-15</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-http:9.4.52.v20230823,10.0.16,11.0.16,12.0.1</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in jetty http jar cve medium severity vulnerability vulnerable library jetty http jar the eclipse jetty project library home page a href path to dependency file server queue client pom xml path to vulnerable library home wss scanner repository org eclipse jetty jetty http jetty http jar home wss scanner repository org eclipse jetty jetty http jetty http jar dependency hierarchy concord queue client snapshot jar root library jetty client jar x jetty http jar vulnerable library found in head commit a href found in base branch master vulnerability details jetty is a java based web server and servlet engine prior to versions and jetty accepts the character proceeding the content length value in a http header field this is more permissive than allowed by the rfc and other servers routinely reject such requests with responses there is no known exploit scenario but it is conceivable that request smuggling could result if jetty is used in combination with a server that does not close the connection after sending such a response versions and contain a patch for this issue there is no workaround as there is no known exploit scenario publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org eclipse jetty jetty http | 0 |
342,099 | 30,608,190,081 | IssuesEvent | 2023-07-23 09:21:51 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix device.test_as_ivy_dev | Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix device.test_as_ivy_dev - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5635199425/job/15265896193"><img src=https://img.shields.io/badge/-success-success></a>
| non_priority | fix device test as ivy dev jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 0 |
39,763 | 8,683,559,683 | IssuesEvent | 2018-12-02 19:13:27 | theimpossibleastronaut/rmw | https://api.github.com/repos/theimpossibleastronaut/rmw | opened | purge function can be split into two or more functions | code-refactoring good first issue help wanted pri:normal | https://github.com/theimpossibleastronaut/rmw/blob/7456e89d561e0d3467d74abade865ea29ab74ad0/src/purging_rmw.c#L159
This function is far longer than it needs to be. Best to chop it up.
If you want some ideas on the first step, let me know.
If you have ideas on how to split it, run them by me first.
Before trying to make 3 or 4 functions out of it, let's just do one a time, i.e. wait for the first one to get approved and merged, etc. | 1.0 | purge function can be split into two or more functions - https://github.com/theimpossibleastronaut/rmw/blob/7456e89d561e0d3467d74abade865ea29ab74ad0/src/purging_rmw.c#L159
This function is far longer than it needs to be. Best to chop it up.
If you want some ideas on the first step, let me know.
If you have ideas on how to split it, run them by me first.
Before trying to make 3 or 4 functions out of it, let's just do one a time, i.e. wait for the first one to get approved and merged, etc. | non_priority | purge function can be split into two or more functions this function is far longer than it needs to be best to chop it up if you want some ideas on the first step let me know if you have ideas on how to split it run them by me first before trying to make or functions out of it let s just do one a time i e wait for the first one to get approved and merged etc | 0 |
313,453 | 23,475,585,013 | IssuesEvent | 2022-08-17 05:29:22 | greysonlalonde/sweetpotato | https://api.github.com/repos/greysonlalonde/sweetpotato | closed | Add kwarg checking for state, style, str kwargs | documentation enhancement help wanted | - **I'm submitting a ...**
- [ ] `🐛 Bug report`
- [x] `🚀 Feature request`
- [ ] `⚒️ Support request`
- **What is the current behavior?**
kwargs passed to components render as the given type.
- **What is the expected behavior?**
a kwarg with a substring like `'prop.'` or `'state.'` would invoke a helper method to render the kwarg as is in the .js file.
- **What is the motivation / use case for changing the behavior?**
ease of use/ enhanced functionality.
| 1.0 | Add kwarg checking for state, style, str kwargs - - **I'm submitting a ...**
- [ ] `🐛 Bug report`
- [x] `🚀 Feature request`
- [ ] `⚒️ Support request`
- **What is the current behavior?**
kwargs passed to components render as the given type.
- **What is the expected behavior?**
a kwarg with a substring like `'prop.'` or `'state.'` would invoke a helper method to render the kwarg as is in the .js file.
- **What is the motivation / use case for changing the behavior?**
ease of use/ enhanced functionality.
| non_priority | add kwarg checking for state style str kwargs i m submitting a 🐛 bug report 🚀 feature request ⚒️ support request what is the current behavior kwargs passed to components render as the given type what is the expected behavior a kwarg with a substring like prop or state would invoke a helper method to render the kwarg as is in the js file what is the motivation use case for changing the behavior ease of use enhanced functionality | 0 |
136,661 | 18,751,012,084 | IssuesEvent | 2021-11-05 01:56:32 | ChoeMinji/react | https://api.github.com/repos/ChoeMinji/react | opened | CVE-2021-23807 (Medium) detected in jsonpointer-4.0.1.tgz, jsonpointer-4.1.0.tgz | security vulnerability | ## CVE-2021-23807 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jsonpointer-4.0.1.tgz</b>, <b>jsonpointer-4.1.0.tgz</b></p></summary>
<p>
<details><summary><b>jsonpointer-4.0.1.tgz</b></p></summary>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz</a></p>
<p>Path to dependency file: react/package.json</p>
<p>Path to vulnerable library: react/node_modules/jsonpointer/package.json,react/fixtures/eslint/node_modules/jsonpointer/package.json,react/fixtures/fiber-debugger/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-0.9.5.tgz (Root Library)
- fsevents-1.0.17.tgz
- node-pre-gyp-0.6.32.tgz
- request-2.79.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.15.0.tgz
- :x: **jsonpointer-4.0.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>jsonpointer-4.1.0.tgz</b></p></summary>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.1.0.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.1.0.tgz</a></p>
<p>Path to dependency file: react/fixtures/ssr/package.json</p>
<p>Path to vulnerable library: react/fixtures/ssr/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-0.9.5.tgz (Root Library)
- eslint-3.16.1.tgz
- is-my-json-valid-2.20.5.tgz
- :x: **jsonpointer-4.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.
<p>Publish Date: 2021-11-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807>CVE-2021-23807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution: jsonpointer - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23807 (Medium) detected in jsonpointer-4.0.1.tgz, jsonpointer-4.1.0.tgz - ## CVE-2021-23807 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jsonpointer-4.0.1.tgz</b>, <b>jsonpointer-4.1.0.tgz</b></p></summary>
<p>
<details><summary><b>jsonpointer-4.0.1.tgz</b></p></summary>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz</a></p>
<p>Path to dependency file: react/package.json</p>
<p>Path to vulnerable library: react/node_modules/jsonpointer/package.json,react/fixtures/eslint/node_modules/jsonpointer/package.json,react/fixtures/fiber-debugger/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-0.9.5.tgz (Root Library)
- fsevents-1.0.17.tgz
- node-pre-gyp-0.6.32.tgz
- request-2.79.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.15.0.tgz
- :x: **jsonpointer-4.0.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>jsonpointer-4.1.0.tgz</b></p></summary>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.1.0.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.1.0.tgz</a></p>
<p>Path to dependency file: react/fixtures/ssr/package.json</p>
<p>Path to vulnerable library: react/fixtures/ssr/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-0.9.5.tgz (Root Library)
- eslint-3.16.1.tgz
- is-my-json-valid-2.20.5.tgz
- :x: **jsonpointer-4.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.
<p>Publish Date: 2021-11-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807>CVE-2021-23807</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution: jsonpointer - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jsonpointer tgz jsonpointer tgz cve medium severity vulnerability vulnerable libraries jsonpointer tgz jsonpointer tgz jsonpointer tgz simple json addressing library home page a href path to dependency file react package json path to vulnerable library react node modules jsonpointer package json react fixtures eslint node modules jsonpointer package json react fixtures fiber debugger node modules jsonpointer package json dependency hierarchy react scripts tgz root library fsevents tgz node pre gyp tgz request tgz har validator tgz is my json valid tgz x jsonpointer tgz vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file react fixtures ssr package json path to vulnerable library react fixtures ssr node modules jsonpointer package json dependency hierarchy react scripts tgz root library eslint tgz is my json valid tgz x jsonpointer tgz vulnerable library found in base branch main vulnerability details this affects the package jsonpointer before a type confusion vulnerability can lead to a bypass of a previous prototype pollution fix when the pointer components are arrays publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jsonpointer step up your open source security game with whitesource | 0 |
79,217 | 9,853,909,214 | IssuesEvent | 2019-06-19 15:40:43 | openopps/OpenOppsTasks | https://api.github.com/repos/openopps/OpenOppsTasks | closed | login.gov: Help content for Open Opps + login.gov | Content Design Waiting for release | **Old Trello URL:** https://trello.com/c/CvJuiUcx/316-logingov-help-content-for-open-opps-logingov
The following help center links will need to be updated for the login.gov release:
1) How to create an account - I think this is a separate card already just need to verify
https://usajobs.github.io/openopps-help/account/
| 1.0 | login.gov: Help content for Open Opps + login.gov - **Old Trello URL:** https://trello.com/c/CvJuiUcx/316-logingov-help-content-for-open-opps-logingov
The following help center links will need to be updated for the login.gov release:
1) How to create an account - I think this is a separate card already just need to verify
https://usajobs.github.io/openopps-help/account/
| non_priority | login gov help content for open opps login gov old trello url the following help center links will need to be updated for the login gov release how to create an account i think this is a separate card already just need to verify | 0 |
50,159 | 26,501,870,982 | IssuesEvent | 2023-01-18 10:53:39 | llvm/llvm-project | https://api.github.com/repos/llvm/llvm-project | closed | [RISCV] Generalize performFP_TO_INTCombine to vectors | backend:RISC-V performance | We have custom lowering for (`fp_to_int (ftrunc X)`) and variants in the scalar domain. Unless I'm missing something, we can extend this handling into the vector domain as well.
Unlike the scalar domain, we don't have static rounding modes for vector ops for all the variants. `ftrunc` is the only one directly supported via static rounding. For all the others, we'd have to preserve the rounding mode, change it, then change it back. That's relatively expensive, but, I think, probably still worthwhile.
Here's a test with current codegen inline:
```llvm
define <vscale x 1 x i64> @trunc_nxv1f64_to_si(<vscale x 1 x double> %x) {
; CHECK-LABEL: trunc_nxv1f64_to_si:
; CHECK: # %bb.0:
; CHECK-NEXT: vsetvli a0, zero, e64, m1, ta, mu
; CHECK-NEXT: vfcvt.rtz.x.f.v v9, v8
; CHECK-NEXT: vfcvt.f.x.v v9, v9
; CHECK-NEXT: lui a0, %hi(.LCPI15_0)
; CHECK-NEXT: fld ft0, %lo(.LCPI15_0)(a0)
; CHECK-NEXT: vmflt.vv v0, v9, v8
; CHECK-NEXT: lui a0, %hi(.LCPI15_1)
; CHECK-NEXT: fld ft1, %lo(.LCPI15_1)(a0)
; CHECK-NEXT: vfadd.vf v10, v9, ft0
; CHECK-NEXT: vmerge.vvm v9, v9, v10, v0
; CHECK-NEXT: vfabs.v v10, v8
; CHECK-NEXT: vmflt.vf v0, v10, ft1
; CHECK-NEXT: vfsgnj.vv v9, v9, v8
; CHECK-NEXT: vmerge.vvm v8, v8, v9, v0
; CHECK-NEXT: vfcvt.rtz.x.f.v v8, v8
; CHECK-NEXT: ret
%a = call <vscale x 1 x double> @llvm.trunc.nxv1f64(<vscale x 1 x double> %x)
%b = fptosi <vscale x 1 x double> %a to <vscale x 1 x i64>
ret <vscale x 1 x i64> %b
}
define <vscale x 1 x i64> @si_only(<vscale x 1 x double> %x) {
; CHECK-LABEL: si_only:
; CHECK: # %bb.0:
; CHECK-NEXT: vsetvli a0, zero, e64, m1, ta, mu
; CHECK-NEXT: vfcvt.rtz.x.f.v v8, v8
; CHECK-NEXT: ret
%b = fptosi <vscale x 1 x double> %x to <vscale x 1 x i64>
ret <vscale x 1 x i64> %b
}
```
Unless I'm missing something, we should be able to emit the same codegen for these two.
Note there's also a SAT version of this transform. We should do the same there. | True | [RISCV] Generalize performFP_TO_INTCombine to vectors - We have custom lowering for (`fp_to_int (ftrunc X)`) and variants in the scalar domain. Unless I'm missing something, we can extend this handling into the vector domain as well.
Unlike the scalar domain, we don't have static rounding modes for vector ops for all the variants. `ftrunc` is the only one directly supported via static rounding. For all the others, we'd have to preserve the rounding mode, change it, then change it back. That's relatively expensive, but, I think, probably still worthwhile.
Here's a test with current codegen inline:
```llvm
define <vscale x 1 x i64> @trunc_nxv1f64_to_si(<vscale x 1 x double> %x) {
; CHECK-LABEL: trunc_nxv1f64_to_si:
; CHECK: # %bb.0:
; CHECK-NEXT: vsetvli a0, zero, e64, m1, ta, mu
; CHECK-NEXT: vfcvt.rtz.x.f.v v9, v8
; CHECK-NEXT: vfcvt.f.x.v v9, v9
; CHECK-NEXT: lui a0, %hi(.LCPI15_0)
; CHECK-NEXT: fld ft0, %lo(.LCPI15_0)(a0)
; CHECK-NEXT: vmflt.vv v0, v9, v8
; CHECK-NEXT: lui a0, %hi(.LCPI15_1)
; CHECK-NEXT: fld ft1, %lo(.LCPI15_1)(a0)
; CHECK-NEXT: vfadd.vf v10, v9, ft0
; CHECK-NEXT: vmerge.vvm v9, v9, v10, v0
; CHECK-NEXT: vfabs.v v10, v8
; CHECK-NEXT: vmflt.vf v0, v10, ft1
; CHECK-NEXT: vfsgnj.vv v9, v9, v8
; CHECK-NEXT: vmerge.vvm v8, v8, v9, v0
; CHECK-NEXT: vfcvt.rtz.x.f.v v8, v8
; CHECK-NEXT: ret
%a = call <vscale x 1 x double> @llvm.trunc.nxv1f64(<vscale x 1 x double> %x)
%b = fptosi <vscale x 1 x double> %a to <vscale x 1 x i64>
ret <vscale x 1 x i64> %b
}
define <vscale x 1 x i64> @si_only(<vscale x 1 x double> %x) {
; CHECK-LABEL: si_only:
; CHECK: # %bb.0:
; CHECK-NEXT: vsetvli a0, zero, e64, m1, ta, mu
; CHECK-NEXT: vfcvt.rtz.x.f.v v8, v8
; CHECK-NEXT: ret
%b = fptosi <vscale x 1 x double> %x to <vscale x 1 x i64>
ret <vscale x 1 x i64> %b
}
```
Unless I'm missing something, we should be able to emit the same codegen for these two.
Note there's also a SAT version of this transform. We should do the same there. | non_priority | generalize performfp to intcombine to vectors we have custom lowering for fp to int ftrunc x and variants in the scalar domain unless i m missing something we can extend this handling into the vector domain as well unlike the scalar domain we don t have static rounding modes for vector ops for all the variants ftrunc is the only one directly supported via static rounding for all the others we d have to preserve the rounding mode change it then change it back that s relatively expensive but i think probably still worthwhile here s a test with current codegen inline llvm define trunc to si x check label trunc to si check bb check next vsetvli zero ta mu check next vfcvt rtz x f v check next vfcvt f x v check next lui hi check next fld lo check next vmflt vv check next lui hi check next fld lo check next vfadd vf check next vmerge vvm check next vfabs v check next vmflt vf check next vfsgnj vv check next vmerge vvm check next vfcvt rtz x f v check next ret a call llvm trunc x b fptosi a to ret b define si only x check label si only check bb check next vsetvli zero ta mu check next vfcvt rtz x f v check next ret b fptosi x to ret b unless i m missing something we should be able to emit the same codegen for these two note there s also a sat version of this transform we should do the same there | 0 |
260,450 | 22,621,697,739 | IssuesEvent | 2022-06-30 07:04:31 | openfoodfacts/smooth-app | https://api.github.com/repos/openfoodfacts/smooth-app | closed | Add a test that placeholder are preserved in translations | good first issue P1 tests | ### What
- Add a test that placeholder are preserved:
- "share_product_text": "Have a look at this product on Open Food Facts: {url}",
"share_product_text": "Open Food Facts'teki bu ürüne bir göz atın",
https://github.com/openfoodfacts/smooth-app/pull/2384
https://github.com/openfoodfacts/smooth-app/pull/2389/commits/2bb16c82b5d1c8286977fe6b6beaa9963d2884d7 | 1.0 | Add a test that placeholder are preserved in translations - ### What
- Add a test that placeholder are preserved:
- "share_product_text": "Have a look at this product on Open Food Facts: {url}",
"share_product_text": "Open Food Facts'teki bu ürüne bir göz atın",
https://github.com/openfoodfacts/smooth-app/pull/2384
https://github.com/openfoodfacts/smooth-app/pull/2389/commits/2bb16c82b5d1c8286977fe6b6beaa9963d2884d7 | non_priority | add a test that placeholder are preserved in translations what add a test that placeholder are preserved share product text have a look at this product on open food facts url share product text open food facts teki bu ürüne bir göz atın | 0 |
12,177 | 14,741,968,154 | IssuesEvent | 2021-01-07 11:28:18 | kdjstudios/SABillingGitlab | https://api.github.com/repos/kdjstudios/SABillingGitlab | closed | Dynamic Draft Invoice - Late Fees | anc-process anp-1.5 ant-enhancement | In GitLab by @kdjstudios on Feb 28, 2019, 10:24
**Submitted by:** Kyle
**Helpdesk:** NA
**Server:** All
**Client/Site:** ALL
**Account:** ALL
**Issue:**
IN #1302 we found the possibility that when adjusting items on the draft invoice, the late fee is not updating dynamically. Below is the test case document which contains those scenarios.
`Existing Functionality of Late Fee`: [Existing Functionality of Late Fee](https://docs.google.com/spreadsheets/d/1Rx-6jyVIIUqEFDMxnP4Zwe5CIL8Vvcsz-XKGtshFbvg/edit?usp=sharing)
`Draft Invoice Test Cases`: [Draft Invoice Test Cases](https://docs.google.com/spreadsheets/d/13pJPni78oybFgp2wN69gSSj7eFGerI6b6m50p8mwn7Q/edit?usp=sharing) | 1.0 | Dynamic Draft Invoice - Late Fees - In GitLab by @kdjstudios on Feb 28, 2019, 10:24
**Submitted by:** Kyle
**Helpdesk:** NA
**Server:** All
**Client/Site:** ALL
**Account:** ALL
**Issue:**
IN #1302 we found the possibility that when adjusting items on the draft invoice, the late fee is not updating dynamically. Below is the test case document which contains those scenarios.
`Existing Functionality of Late Fee`: [Existing Functionality of Late Fee](https://docs.google.com/spreadsheets/d/1Rx-6jyVIIUqEFDMxnP4Zwe5CIL8Vvcsz-XKGtshFbvg/edit?usp=sharing)
`Draft Invoice Test Cases`: [Draft Invoice Test Cases](https://docs.google.com/spreadsheets/d/13pJPni78oybFgp2wN69gSSj7eFGerI6b6m50p8mwn7Q/edit?usp=sharing) | non_priority | dynamic draft invoice late fees in gitlab by kdjstudios on feb submitted by kyle helpdesk na server all client site all account all issue in we found the possibility that when adjusting items on the draft invoice the late fee is not updating dynamically below is the test case document which contains those scenarios existing functionality of late fee draft invoice test cases | 0 |
16,670 | 21,774,829,000 | IssuesEvent | 2022-05-13 12:51:22 | camunda/feel-scala | https://api.github.com/repos/camunda/feel-scala | opened | range function before/after are failing with date and time objects | type: bug team/process-automation | **Describe the bug**
The FEEL expression
`after(date and time(now()), date and time(today(),time("14:00:00")))`
fails with
`14:44:02.988 [main] WARN org.camunda.feel.FeelEngine - Suppressed failure: illegal arguments: List(ValDateTime(2022-05-13T14:44:02.987611+02:00[Europe/Berlin]))
14:44:02.990 [main] WARN org.camunda.feel.FeelEngine - Suppressed failure: illegal arguments: List(ValNull, ValLocalDateTime(2022-05-13T14:00))`
**Expected behavior**
range functions work as documented
**Environment**
* FEEL engine version: Ammonite Repl 2.5.3 (Scala 2.13.8 Java 11.0.13) | also: zeebe_8.0.1
| 1.0 | range function before/after are failing with date and time objects - **Describe the bug**
The FEEL expression
`after(date and time(now()), date and time(today(),time("14:00:00")))`
fails with
`14:44:02.988 [main] WARN org.camunda.feel.FeelEngine - Suppressed failure: illegal arguments: List(ValDateTime(2022-05-13T14:44:02.987611+02:00[Europe/Berlin]))
14:44:02.990 [main] WARN org.camunda.feel.FeelEngine - Suppressed failure: illegal arguments: List(ValNull, ValLocalDateTime(2022-05-13T14:00))`
**Expected behavior**
range functions work as documented
**Environment**
* FEEL engine version: Ammonite Repl 2.5.3 (Scala 2.13.8 Java 11.0.13) | also: zeebe_8.0.1
| non_priority | range function before after are failing with date and time objects describe the bug the feel expression after date and time now date and time today time fails with warn org camunda feel feelengine suppressed failure illegal arguments list valdatetime warn org camunda feel feelengine suppressed failure illegal arguments list valnull vallocaldatetime expected behavior range functions work as documented environment feel engine version ammonite repl scala java also zeebe | 0 |
70,434 | 30,666,812,289 | IssuesEvent | 2023-07-25 18:56:43 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | IT Support: UKG class at 8;30 | Workgroup: HR Type: IT Support Service: Tech Services | ## Device & User Information (first name and last initial, no last names)
HR
## What's the problem?
HR was having a class at 8:30
## What did you do to resolve the issue
I went around helping users get into the system | 2.0 | IT Support: UKG class at 8;30 - ## Device & User Information (first name and last initial, no last names)
HR
## What's the problem?
HR was having a class at 8:30
## What did you do to resolve the issue
I went around helping users get into the system | non_priority | it support ukg class at device user information first name and last initial no last names hr what s the problem hr was having a class at what did you do to resolve the issue i went around helping users get into the system | 0 |
251,306 | 18,945,837,771 | IssuesEvent | 2021-11-18 10:04:17 | mdabrowski1990/uds | https://api.github.com/repos/mdabrowski1990/uds | closed | CAN Packet | documentation enhancement CAN | ## Requires
#78
#79
#96
## Description
As a user, I would like to have dedicated UDS Packet implementation for CAN, so I could easily communicate using CAN bus.
As a user, I would like CAN Packet and CAN Packet Record classes have support for [python-can frames](https://python-can.readthedocs.io/en/master/message.html#module-can), so I could easily use python-can with this package.
As a user, I would like to have UDS Packet and UDS Packet Record implementations supporting all possible CAN addressings (Normal, Extended, Mixed, etc.) and bus types (CLASSIC CAN and CAN-FD), so I could use it in all possible situations.
As a developer, I would like to have CAN Packet classes that inherits after `AbstractUdsPacket` class, so I have CAN packet implementation separated.
As a developer, I would like to have CAN Packet Record classes that inherits after `AbstractUdsPacketRecord` class, so I have CAN packet record implementation separated.
As a developer, I would like to have flexible implementation of CAN Packet Record, so it supports [python-can frame](https://python-can.readthedocs.io/en/master/message.html#module-can) but it is also extendable and could provide support for other CAN libraries that could be used in the future.
## Test Strategy
Unit Tests:
- 100% code coverage for CAN Packets specific code
Integration Tests:
- GIVEN python-can frame that carries diagnostic message, WHEN I provide this frame to CAN Packet Record, THEN I can create CAN Packet Record object and read all relevant information from it.
- GIVEN python-can frame that obviously carries non diagnostic message, WHEN I provide this frame to CAN Packet Record, THEN and error is raised.
## Acceptance Criteria
- UDS Packet and UDS Packet Record for CAN bus are Integrated with [python-can frame](https://python-can.readthedocs.io/en/master/message.html#module-can)
- UDS Packet and UDS Packet Record supports all CAN configurations:
- all bus types (CLASSIC CAN and CAN-FD)
- all [addressings types](https://can-isotp.readthedocs.io/en/latest/isotp/addressing.html#addressing-modes) (including Normal, Fixed, Mixed)
- User Documentation is updated:
- [UDS Packet Definition](https://uds.readthedocs.io/en/latest/pages/messages.html#uds-packet-definition) for CAN is documented
- [UDS Packet Record](https://uds.readthedocs.io/en/latest/pages/messages.html#uds-packet-record) for CAN is documented
- [UDS Packet Type](https://uds.readthedocs.io/en/latest/pages/messages.html#uds-packet-type) for CAN is documented
- CAN Packets and their types are described in [knowledge base](https://uds.readthedocs.io/en/latest/pages/knowledge_base.html#uds-packet). | 1.0 | CAN Packet - ## Requires
#78
#79
#96
## Description
As a user, I would like to have dedicated UDS Packet implementation for CAN, so I could easily communicate using CAN bus.
As a user, I would like CAN Packet and CAN Packet Record classes have support for [python-can frames](https://python-can.readthedocs.io/en/master/message.html#module-can), so I could easily use python-can with this package.
As a user, I would like to have UDS Packet and UDS Packet Record implementations supporting all possible CAN addressings (Normal, Extended, Mixed, etc.) and bus types (CLASSIC CAN and CAN-FD), so I could use it in all possible situations.
As a developer, I would like to have CAN Packet classes that inherits after `AbstractUdsPacket` class, so I have CAN packet implementation separated.
As a developer, I would like to have CAN Packet Record classes that inherits after `AbstractUdsPacketRecord` class, so I have CAN packet record implementation separated.
As a developer, I would like to have flexible implementation of CAN Packet Record, so it supports [python-can frame](https://python-can.readthedocs.io/en/master/message.html#module-can) but it is also extendable and could provide support for other CAN libraries that could be used in the future.
## Test Strategy
Unit Tests:
- 100% code coverage for CAN Packets specific code
Integration Tests:
- GIVEN python-can frame that carries diagnostic message, WHEN I provide this frame to CAN Packet Record, THEN I can create CAN Packet Record object and read all relevant information from it.
- GIVEN python-can frame that obviously carries non diagnostic message, WHEN I provide this frame to CAN Packet Record, THEN and error is raised.
## Acceptance Criteria
- UDS Packet and UDS Packet Record for CAN bus are Integrated with [python-can frame](https://python-can.readthedocs.io/en/master/message.html#module-can)
- UDS Packet and UDS Packet Record supports all CAN configurations:
- all bus types (CLASSIC CAN and CAN-FD)
- all [addressings types](https://can-isotp.readthedocs.io/en/latest/isotp/addressing.html#addressing-modes) (including Normal, Fixed, Mixed)
- User Documentation is updated:
- [UDS Packet Definition](https://uds.readthedocs.io/en/latest/pages/messages.html#uds-packet-definition) for CAN is documented
- [UDS Packet Record](https://uds.readthedocs.io/en/latest/pages/messages.html#uds-packet-record) for CAN is documented
- [UDS Packet Type](https://uds.readthedocs.io/en/latest/pages/messages.html#uds-packet-type) for CAN is documented
- CAN Packets and their types are described in [knowledge base](https://uds.readthedocs.io/en/latest/pages/knowledge_base.html#uds-packet). | non_priority | can packet requires description as a user i would like to have dedicated uds packet implementation for can so i could easily communicate using can bus as a user i would like can packet and can packet record classes have support for so i could easily use python can with this package as a user i would like to have uds packet and uds packet record implementations supporting all possible can addressings normal extended mixed etc and bus types classic can and can fd so i could use it in all possible situations as a developer i would like to have can packet classes that inherits after abstractudspacket class so i have can packet implementation separated as a developer i would like to have can packet record classes that inherits after abstractudspacketrecord class so i have can packet record implementation separated as a developer i would like to have flexible implementation of can packet record so it supports but it is also extendable and could provide support for other can libraries that could be used in the future test strategy unit tests code coverage for can packets specific code integration tests given python can frame that carries diagnostic message when i provide this frame to can packet record then i can create can packet record object and read all relevant information from it given python can frame that obviously carries non diagnostic message when i provide this frame to can packet record then and error is raised acceptance criteria uds packet and uds packet record for can bus are integrated with uds packet and uds packet record supports all can configurations all bus types classic can and can fd all including normal fixed mixed user documentation is updated for can is documented for can is documented for can is documented can packets and their types are described in | 0 |
43,015 | 5,561,111,738 | IssuesEvent | 2017-03-24 21:26:30 | Calligre/attendee-web | https://api.github.com/repos/Calligre/attendee-web | opened | Social integration on post when not authenticated with services. | design | 
See image: I am not authenticated with twitter.
Either:
- the twitter button should be hidden
- the twitter button should prompt me to sign in with twitter as well
- NOTE: this requires a bunch of auth flow changes and we may need to pay auth0 for this feature | 1.0 | Social integration on post when not authenticated with services. - 
See image: I am not authenticated with twitter.
Either:
- the twitter button should be hidden
- the twitter button should prompt me to sign in with twitter as well
- NOTE: this requires a bunch of auth flow changes and we may need to pay auth0 for this feature | non_priority | social integration on post when not authenticated with services see image i am not authenticated with twitter either the twitter button should be hidden the twitter button should prompt me to sign in with twitter as well note this requires a bunch of auth flow changes and we may need to pay for this feature | 0 |
94,121 | 19,483,829,632 | IssuesEvent | 2021-12-26 00:03:44 | nwplus/admin | https://api.github.com/repos/nwplus/admin | closed | List page | qr_code_scanner | Requirements:
- uses #152 for dropdown
- has functional search box
- implement two lists (one of hackers that meet condition, the other of hackers that don't)
- each list item should be the hacker's name and their email
- there should be a count badge as well
- this issue also includes fetching the list of Applicants from nwHacks 2022 and populating it in the app

 | 1.0 | List page - Requirements:
- uses #152 for dropdown
- has functional search box
- implement two lists (one of hackers that meet condition, the other of hackers that don't)
- each list item should be the hacker's name and their email
- there should be a count badge as well
- this issue also includes fetching the list of Applicants from nwHacks 2022 and populating it in the app

 | non_priority | list page requirements uses for dropdown has functional search box implement two lists one of hackers that meet condition the other of hackers that don t each list item should be the hacker s name and their email there should be a count badge as well this issue also includes fetching the list of applicants from nwhacks and populating it in the app | 0 |
12,996 | 9,820,080,029 | IssuesEvent | 2019-06-14 00:48:18 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Issues invoking Register-AZureRMAutomationDSCNode after AzureRM.Automation upgrade to 5.1.1 | Automation Service Attention automation-dsc | ### Description
After upgrading AzureRM.Automation module to 5.1.1 (and all depending as AzureRM.Profile) all our DSC processes are failing with an strange pending parameter output. Tested from Azure DSC and local with same modules version and we get the same response
### Script/Steps for Reproduction
Register-AzureRmAutomationDscNode -ResourceGroupName $DSCRGName -AutomationAccountName $AutomationAccountName -AzureVMName $VMName -ConfigurationModeFrequencyMins 30 -verbose -RebootNodeIfNeeded $true -ConfigurationMode "ApplyandMonitor" -AzureVMResourceGroup $VMRGName -NodeConfigurationName $DSCConfiguration
All variable typeas and values seems correct
### Module Version
Directory: C:\Users\username\Documents\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 5.1.1 AzureRM.Automation {Get-AzureRMAutomationHybridWorkerGroup, Get-AzureRmAutomationJobOutputRecord, Import-AzureRmAutomationDscNodeConfiguration, Export-AzureRmAutomationDscConfiguration...}
Script 5.5.1 AzureRM.profile {Disable-AzureRmDataCollection, Disable-AzureRmContextAutosave, Enable-AzureRmDataCollection, Enable-AzureRmContextAutosave...}
Directory: C:\Program Files\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 5.6.0 AzureRM
Script 0.6.5 AzureRM.AnalysisServices {Resume-AzureRmAnalysisServicesServer, Suspend-AzureRmAnalysisServicesServer, Get-AzureRmAnalysisServicesServer, Remove-AzureRmAnalysisServicesServer...}
Script 5.1.1 AzureRM.ApiManagement {Add-AzureRmApiManagementRegion, Get-AzureRmApiManagementSsoToken, New-AzureRmApiManagementHostnameConfiguration, New-AzureRmApiManagementRegion...}
Script 0.1.2 AzureRM.ApplicationInsights {Get-AzureRmApplicationInsights, New-AzureRmApplicationInsights, Remove-AzureRmApplicationInsights, Set-AzureRmApplicationInsightsPricingPlan...}
Script 4.3.1 AzureRM.Automation {Get-AzureRMAutomationHybridWorkerGroup, Get-AzureRmAutomationJobOutputRecord, Import-AzureRmAutomationDscNodeConfiguration, Export-AzureRmAutomationDscConfiguration...}
Script 4.0.3 AzureRM.Backup {Backup-AzureRmBackupItem, Enable-AzureRmBackupContainerReregistration, Get-AzureRmBackupContainer, Register-AzureRmBackupContainer...}
Script 4.0.5 AzureRM.Batch {Remove-AzureRmBatchAccount, Get-AzureRmBatchAccount, Get-AzureRmBatchAccountKeys, New-AzureRmBatchAccount...}
Script 0.14.0 AzureRM.Billing {Get-AzureRmBillingInvoice, Get-AzureRmBillingPeriod}
Script 4.2.1 AzureRM.Cdn {Get-AzureRmCdnProfile, Get-AzureRmCdnProfileSsoUrl, New-AzureRmCdnProfile, Remove-AzureRmCdnProfile...}
Script 0.9.3 AzureRM.CognitiveServices {Get-AzureRmCognitiveServicesAccount, Get-AzureRmCognitiveServicesAccountKey, Get-AzureRmCognitiveServicesAccountSkus, New-AzureRmCognitiveServicesAccount...}
Script 4.5.0 AzureRM.Compute {Remove-AzureRmAvailabilitySet, Get-AzureRmAvailabilitySet, New-AzureRmAvailabilitySet, Update-AzureRmAvailabilitySet...}
Script 0.3.0 AzureRM.Consumption Get-AzureRmConsumptionUsageDetail
Script 0.2.4 AzureRM.ContainerInstance {New-AzureRmContainerGroup, Get-AzureRmContainerGroup, Remove-AzureRmContainerGroup, Get-AzureRmContainerInstanceLog}
Script 1.0.3 AzureRM.ContainerRegistry {New-AzureRmContainerRegistry, Get-AzureRmContainerRegistry, Update-AzureRmContainerRegistry, Remove-AzureRmContainerRegistry...}
Script 4.2.1 AzureRM.DataFactories {Remove-AzureRmDataFactory, Get-AzureRmDataFactoryRun, Get-AzureRmDataFactorySlice, Save-AzureRmDataFactoryLog...}
Script 0.5.2 AzureRM.DataFactoryV2 {Set-AzureRmDataFactoryV2, Update-AzureRmDataFactoryV2, Get-AzureRmDataFactoryV2, Remove-AzureRmDataFactoryV2...}
Script 4.2.2 AzureRM.DataLakeAnalytics {Get-AzureRmDataLakeAnalyticsDataSource, New-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogSecret...}
Script 5.1.1 AzureRM.DataLakeStore {Get-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreFirewallRule, Set-AzureRmDataLakeStoreTrustedIdProvider...}
Script 4.0.3 AzureRM.DevTestLabs {Get-AzureRmDtlAllowedVMSizesPolicy, Get-AzureRmDtlAutoShutdownPolicy, Get-AzureRmDtlAutoStartPolicy, Get-AzureRmDtlVMsPerLabPolicy...}
Script 4.1.1 AzureRM.Dns {Get-AzureRmDnsRecordSet, New-AzureRmDnsRecordConfig, Remove-AzureRmDnsRecordSet, Set-AzureRmDnsRecordSet...}
Script 0.3.1 AzureRM.EventGrid {New-AzureRmEventGridTopic, Get-AzureRmEventGridTopic, Set-AzureRmEventGridTopic, New-AzureRmEventGridTopicKey...}
Script 0.6.2 AzureRM.EventHub {New-AzureRmEventHubNamespace, Get-AzureRmEventHubNamespace, Set-AzureRmEventHubNamespace, Remove-AzureRmEventHubNamespace...}
Script 4.1.1 AzureRM.HDInsight {Get-AzureRmHDInsightJob, New-AzureRmHDInsightSqoopJobDefinition, Wait-AzureRmHDInsightJob, New-AzureRmHDInsightStreamingMapReduceJobDefinition...}
Script 4.0.3 AzureRM.Insights {Get-AzureRmMetricDefinition, Get-AzureRmMetric, Remove-AzureRmLogProfile, Get-AzureRmLogProfile...}
Script 3.1.1 AzureRM.IotHub {Add-AzureRmIotHubKey, Get-AzureRmIotHubEventHubConsumerGroup, Get-AzureRmIotHubConnectionString, Get-AzureRmIotHubJob...}
Script 4.2.1 AzureRM.KeyVault {Add-AzureKeyVaultCertificate, Set-AzureKeyVaultCertificateAttribute, Stop-AzureKeyVaultCertificateOperation, Get-AzureKeyVaultCertificateOperation...}
Script 4.0.2 AzureRM.LogicApp {Get-AzureRmIntegrationAccountAgreement, Get-AzureRmIntegrationAccountCallbackUrl, Get-AzureRmIntegrationAccountCertificate, Get-AzureRmIntegrationAccount...}
Script 0.17.1 AzureRM.MachineLearning {Move-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentPlanUsageHistory, Remove-AzureRmMlCommitmentPlan...}
Script 0.4.1 AzureRM.MachineLearningCompute {Get-AzureRmMlOpCluster, Get-AzureRmMlOpClusterKey, Test-AzureRmMlOpClusterSystemServicesUpdateAvailability, Update-AzureRmMlOpClusterSystemService...}
Script 0.2.0 AzureRM.MarketplaceOrdering {Get-AzureRmMarketplaceTerms, Set-AzureRmMarketplaceTerms}
Script 0.9.1 AzureRM.Media {Sync-AzureRmMediaServiceStorageKeys, Set-AzureRmMediaServiceKey, Get-AzureRmMediaServiceKeys, Get-AzureRmMediaServiceNameAvailability...}
Script 5.4.1 AzureRM.Network {Add-AzureRmApplicationGatewayAuthenticationCertificate, Get-AzureRmApplicationGatewayAuthenticationCertificate, New-AzureRmApplicationGatewayAuthenticationCertificate, Remove-AzureRmApplicationGatewayAuthenti...
Script 4.1.0 AzureRM.NotificationHubs {Get-AzureRmNotificationHub, Get-AzureRmNotificationHubAuthorizationRules, Get-AzureRmNotificationHubListKeys, Get-AzureRmNotificationHubPNSCredentials...}
Script 4.3.1 AzureRM.OperationalInsights {New-AzureRmOperationalInsightsAzureActivityLogDataSource, New-AzureRmOperationalInsightsCustomLogDataSource, Disable-AzureRmOperationalInsightsLinuxCustomLogCollection, Disable-AzureRmOperationalInsightsIISLo...
Script 4.1.3 AzureRM.PowerBIEmbedded {Remove-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollectionAccessKeys, Get-AzureRmPowerBIWorkspace...}
Script 4.5.0 AzureRM.profile {Disable-AzureRmDataCollection, Disable-AzureRmContextAutosave, Enable-AzureRmDataCollection, Enable-AzureRmContextAutosave...}
Script 4.1.1 AzureRM.RecoveryServices {Get-AzureRmRecoveryServicesBackupProperty, Get-AzureRmRecoveryServicesVault, Get-AzureRmRecoveryServicesVaultSettingsFile, New-AzureRmRecoveryServicesVault...}
Script 4.1.1 AzureRM.RecoveryServices.Backup {Backup-AzureRmRecoveryServicesBackupItem, Get-AzureRmRecoveryServicesBackupManagementServer, Get-AzureRmRecoveryServicesBackupContainer, Unregister-AzureRmRecoveryServicesBackupContainer...}
Script 0.2.3 AzureRM.RecoveryServices.SiteRec... {Edit-AzureRmRecoveryServicesAsrRecoveryPlan, Get-AzureRmRecoveryServicesAsrAlertSetting, Get-AzureRmRecoveryServicesAsrEvent, Get-AzureRmRecoveryServicesAsrFabric...}
Script 4.1.1 AzureRM.RedisCache {Remove-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCacheScheduleEntry, Get-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCachePatchSchedule...}
Script 0.3.2 AzureRM.Relay {New-AzureRmRelayNamespace, Get-AzureRmRelayNamespace, Set-AzureRmRelayNamespace, Remove-AzureRmRelayNamespace...}
Script 5.5.1 AzureRM.Resources {Get-AzureRmProviderOperation, Remove-AzureRmRoleAssignment, Get-AzureRmRoleAssignment, New-AzureRmRoleAssignment...}
Script 0.16.2 AzureRM.Scheduler {Disable-AzureRmSchedulerJobCollection, Enable-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJob...}
Script 4.1.1 AzureRM.ServerManagement {Invoke-AzureRmServerManagementPowerShellCommand, Get-AzureRmServerManagementSession, New-AzureRmServerManagementSession, Remove-AzureRmServerManagementSession...}
Script 0.6.3 AzureRM.ServiceBus {New-AzureRmServiceBusNamespace, Get-AzureRmServiceBusNamespace, Set-AzureRmServiceBusNamespace, Remove-AzureRmServiceBusNamespace...}
Script 0.3.3 AzureRM.ServiceFabric {Add-AzureRmServiceFabricApplicationCertificate, Add-AzureRmServiceFabricClientCertificate, Add-AzureRmServiceFabricClusterCertificate, Add-AzureRmServiceFabricNode...}
Script 5.0.5 AzureRM.SiteRecovery {Get-AzureRmSiteRecoveryFabric, New-AzureRmSiteRecoveryFabric, Remove-AzureRmSiteRecoveryFabric, Stop-AzureRmSiteRecoveryJob...}
Script 4.3.1 AzureRM.Sql {Get-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseTransparentDataEncryptionActivity, Set-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseUpgradeHint...}
Script 4.2.2 AzureRM.Storage {Get-AzureRmStorageAccount, Get-AzureRmStorageAccountKey, New-AzureRmStorageAccount, New-AzureRmStorageAccountKey...}
Script 4.0.3 AzureRM.StreamAnalytics {Get-AzureRmStreamAnalyticsFunction, Get-AzureRmStreamAnalyticsDefaultFunctionDefinition, New-AzureRmStreamAnalyticsFunction, Remove-AzureRmStreamAnalyticsFunction...}
Script 4.0.0 AzureRM.Tags {Remove-AzureRmTag, Get-AzureRmTag, New-AzureRmTag}
Script 4.0.2 AzureRM.TrafficManager {Disable-AzureRmTrafficManagerEndpoint, Enable-AzureRmTrafficManagerEndpoint, Set-AzureRmTrafficManagerEndpoint, Get-AzureRmTrafficManagerEndpoint...}
Script 4.0.1 AzureRM.UsageAggregates Get-UsageAggregates
Script 4.2.1 AzureRM.Websites {Get-AzureRmAppServicePlan, Set-AzureRmAppServicePlan, New-AzureRmAppServicePlan, Remove-AzureRmAppServicePlan...}
Directory: C:\Program Files (x86)\Microsoft SDKs\Azure\PowerShell\ResourceManager\AzureResourceManager
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 0.6.1 AzureRM.AnalysisServices {Resume-AzureRmAnalysisServicesServer, Suspend-AzureRmAnalysisServicesServer, Get-AzureRmAnalysisServicesServer, Remove-AzureRmAnalysisServicesServer...}
Script 5.0.1 AzureRM.ApiManagement {Add-AzureRmApiManagementRegion, Get-AzureRmApiManagementSsoToken, New-AzureRmApiManagementHostnameConfiguration, New-AzureRmApiManagementRegion...}
Script 0.1.0 AzureRM.ApplicationInsights {Get-AzureRmApplicationInsights, New-AzureRmApplicationInsights, Remove-AzureRmApplicationInsights, Set-AzureRmApplicationInsightsPricingPlan...}
Script 4.1.1 AzureRM.Automation {Get-AzureRMAutomationHybridWorkerGroup, Get-AzureRmAutomationJobOutputRecord, Import-AzureRmAutomationDscNodeConfiguration, Export-AzureRmAutomationDscConfiguration...}
Script 4.0.1 AzureRM.Backup {Backup-AzureRmBackupItem, Enable-AzureRmBackupContainerReregistration, Get-AzureRmBackupContainer, Register-AzureRmBackupContainer...}
Script 4.0.3 AzureRM.Batch {Remove-AzureRmBatchAccount, Get-AzureRmBatchAccount, Get-AzureRmBatchAccountKeys, New-AzureRmBatchAccount...}
Script 0.14.0 AzureRM.Billing {Get-AzureRmBillingInvoice, Get-AzureRmBillingPeriod}
Script 4.0.0 AzureRM.Cdn {Get-AzureRmCdnProfile, Get-AzureRmCdnProfileSsoUrl, New-AzureRmCdnProfile, Remove-AzureRmCdnProfile...}
Script 0.9.0 AzureRM.CognitiveServices {Get-AzureRmCognitiveServicesAccount, Get-AzureRmCognitiveServicesAccountKey, Get-AzureRmCognitiveServicesAccountSkus, New-AzureRmCognitiveServicesAccount...}
Script 4.1.1 AzureRM.Compute {Remove-AzureRmAvailabilitySet, Get-AzureRmAvailabilitySet, New-AzureRmAvailabilitySet, Update-AzureRmAvailabilitySet...}
Script 0.3.0 AzureRM.Consumption Get-AzureRmConsumptionUsageDetail
Script 0.2.1 AzureRM.ContainerInstance {New-AzureRmContainerGroup, Get-AzureRmContainerGroup, Remove-AzureRmContainerGroup, Get-AzureRmContainerInstanceLog}
Script 1.0.1 AzureRM.ContainerRegistry {New-AzureRmContainerRegistry, Get-AzureRmContainerRegistry, Update-AzureRmContainerRegistry, Remove-AzureRmContainerRegistry...}
Script 4.0.3 AzureRM.DataFactories {Remove-AzureRmDataFactory, Get-AzureRmDataFactoryRun, Get-AzureRmDataFactorySlice, Save-AzureRmDataFactoryLog...}
Script 0.4.1 AzureRM.DataFactoryV2 {Set-AzureRmDataFactoryV2, Update-AzureRmDataFactoryV2, Get-AzureRmDataFactoryV2, Remove-AzureRmDataFactoryV2...}
Script 4.1.1 AzureRM.DataLakeAnalytics {Get-AzureRmDataLakeAnalyticsDataSource, New-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogSecret...}
Script 5.0.0 AzureRM.DataLakeStore {Get-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreFirewallRule, Set-AzureRmDataLakeStoreTrustedIdProvider...}
Script 4.0.0 AzureRM.DevTestLabs {Get-AzureRmDtlAllowedVMSizesPolicy, Get-AzureRmDtlAutoShutdownPolicy, Get-AzureRmDtlAutoStartPolicy, Get-AzureRmDtlVMsPerLabPolicy...}
Script 4.0.0 AzureRM.Dns {Get-AzureRmDnsRecordSet, New-AzureRmDnsRecordConfig, Remove-AzureRmDnsRecordSet, Set-AzureRmDnsRecordSet...}
Script 0.2.0 AzureRM.EventGrid {New-AzureRmEventGridTopic, Get-AzureRmEventGridTopic, Set-AzureRmEventGridTopic, New-AzureRmEventGridTopicKey...}
Script 0.5.0 AzureRM.EventHub {New-AzureRmEventHubNamespace, Get-AzureRmEventHubNamespace, Set-AzureRmEventHubNamespace, Remove-AzureRmEventHubNamespace...}
Script 4.0.1 AzureRM.HDInsight {Get-AzureRmHDInsightJob, New-AzureRmHDInsightSqoopJobDefinition, Wait-AzureRmHDInsightJob, New-AzureRmHDInsightStreamingMapReduceJobDefinition...}
Script 4.0.0 AzureRM.Insights {Get-AzureRmMetricDefinition, Get-AzureRmMetric, Remove-AzureRmLogProfile, Get-AzureRmLogProfile...}
Script 3.0.0 AzureRM.IotHub {Add-AzureRmIotHubKey, Get-AzureRmIotHubEventHubConsumerGroup, Get-AzureRmIotHubConnectionString, Get-AzureRmIotHubJob...}
Script 4.0.1 AzureRM.KeyVault {Add-AzureKeyVaultCertificate, Set-AzureKeyVaultCertificateAttribute, Stop-AzureKeyVaultCertificateOperation, Get-AzureKeyVaultCertificateOperation...}
Script 4.0.0 AzureRM.LogicApp {Get-AzureRmIntegrationAccountAgreement, Get-AzureRmIntegrationAccountCallbackUrl, Get-AzureRmIntegrationAccountCertificate, Get-AzureRmIntegrationAccount...}
Script 0.16.0 AzureRM.MachineLearning {Move-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentPlanUsageHistory, Remove-AzureRmMlCommitmentPlan...}
Script 0.3.1 AzureRM.MachineLearningCompute {Get-AzureRmMlOpCluster, Get-AzureRmMlOpClusterKey, Test-AzureRmMlOpClusterSystemServicesUpdateAvailability, Update-AzureRmMlOpClusterSystemService...}
Script 0.2.0 AzureRM.MarketplaceOrdering {Get-AzureRmMarketplaceTerms, Set-AzureRmMarketplaceTerms}
Script 0.8.0 AzureRM.Media {Sync-AzureRmMediaServiceStorageKeys, Set-AzureRmMediaServiceKey, Get-AzureRmMediaServiceKeys, Get-AzureRmMediaServiceNameAvailability...}
Script 5.0.0 AzureRM.Network {Add-AzureRmApplicationGatewayAuthenticationCertificate, Get-AzureRmApplicationGatewayAuthenticationCertificate, New-AzureRmApplicationGatewayAuthenticationCertificate, Remove-AzureRmApplicationGatewayAuthenti...
Script 4.0.0 AzureRM.NotificationHubs {Get-AzureRmNotificationHub, Get-AzureRmNotificationHubAuthorizationRules, Get-AzureRmNotificationHubListKeys, Get-AzureRmNotificationHubPNSCredentials...}
Script 4.0.0 AzureRM.OperationalInsights {New-AzureRmOperationalInsightsAzureActivityLogDataSource, New-AzureRmOperationalInsightsCustomLogDataSource, Disable-AzureRmOperationalInsightsLinuxCustomLogCollection, Disable-AzureRmOperationalInsightsIISLo...
Script 4.1.1 AzureRM.PowerBIEmbedded {Remove-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollectionAccessKeys, Get-AzureRmPowerBIWorkspace...}
Script 4.1.1 AzureRM.Profile {Disable-AzureRmDataCollection, Disable-AzureRmContextAutosave, Enable-AzureRmDataCollection, Enable-AzureRmContextAutosave...}
Script 4.0.1 AzureRM.RecoveryServices {Get-AzureRmRecoveryServicesBackupProperty, Get-AzureRmRecoveryServicesVault, Get-AzureRmRecoveryServicesVaultSettingsFile, New-AzureRmRecoveryServicesVault...}
Script 4.0.3 AzureRM.RecoveryServices.Backup {Backup-AzureRmRecoveryServicesBackupItem, Get-AzureRmRecoveryServicesBackupManagementServer, Get-AzureRmRecoveryServicesBackupContainer, Unregister-AzureRmRecoveryServicesBackupContainer...}
Script 0.2.1 AzureRM.RecoveryServices.SiteRec... {Edit-AzureRmRecoveryServicesAsrRecoveryPlan, Get-AzureRmRecoveryServicesAsrAlertSetting, Get-AzureRmRecoveryServicesAsrEvent, Get-AzureRmRecoveryServicesAsrFabric...}
Script 4.0.1 AzureRM.RedisCache {Remove-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCacheScheduleEntry, Get-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCachePatchSchedule...}
Script 0.3.0 AzureRM.Relay {New-AzureRmRelayNamespace, Get-AzureRmRelayNamespace, Set-AzureRmRelayNamespace, Remove-AzureRmRelayNamespace...}
Script 5.1.1 AzureRM.Resources {Get-AzureRmProviderOperation, Remove-AzureRmRoleAssignment, Get-AzureRmRoleAssignment, New-AzureRmRoleAssignment...}
Script 0.16.0 AzureRM.Scheduler {Disable-AzureRmSchedulerJobCollection, Enable-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJob...}
Script 4.0.0 AzureRM.ServerManagement {Invoke-AzureRmServerManagementPowerShellCommand, Get-AzureRmServerManagementSession, New-AzureRmServerManagementSession, Remove-AzureRmServerManagementSession...}
Script 0.5.0 AzureRM.ServiceBus {New-AzureRmServiceBusNamespace, Get-AzureRmServiceBusNamespace, Set-AzureRmServiceBusNamespace, Remove-AzureRmServiceBusNamespace...}
Script 0.3.0 AzureRM.ServiceFabric {Add-AzureRmServiceFabricApplicationCertificate, Add-AzureRmServiceFabricClientCertificate, Add-AzureRmServiceFabricClusterCertificate, Add-AzureRmServiceFabricNode...}
Script 5.0.3 AzureRM.SiteRecovery {Get-AzureRmSiteRecoveryFabric, New-AzureRmSiteRecoveryFabric, Remove-AzureRmSiteRecoveryFabric, Stop-AzureRmSiteRecoveryJob...}
Script 4.1.1 AzureRM.Sql {Get-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseTransparentDataEncryptionActivity, Set-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseUpgradeHint...}
Script 4.0.1 AzureRM.Storage {Get-AzureRmStorageAccount, Get-AzureRmStorageAccountKey, New-AzureRmStorageAccount, New-AzureRmStorageAccountKey...}
Script 4.0.1 AzureRM.StreamAnalytics {Get-AzureRmStreamAnalyticsFunction, Get-AzureRmStreamAnalyticsDefaultFunctionDefinition, New-AzureRmStreamAnalyticsFunction, Remove-AzureRmStreamAnalyticsFunction...}
Script 4.0.0 AzureRM.Tags {Remove-AzureRmTag, Get-AzureRmTag, New-AzureRmTag}
Script 4.0.0 AzureRM.TrafficManager {Disable-AzureRmTrafficManagerEndpoint, Enable-AzureRmTrafficManagerEndpoint, Set-AzureRmTrafficManagerEndpoint, Get-AzureRmTrafficManagerEndpoint...}
Script 4.0.0 AzureRM.UsageAggregates Get-UsageAggregates
Script 4.0.0 AzureRM.Websites {Get-AzureRmAppServicePlan, Set-AzureRmAppServicePlan, New-AzureRmAppServicePlan, Remove-AzureRmAppServicePlan...}
### Environment Data
Name Value
---- -----
PSVersion 5.1.17134.228
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.17134.228
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
### Debug Output
PS C:\WINDOWS\system32> Register-AzureRmAutomationDscNode -ResourceGroupName "Management" -AutomationAccountName $AutomationAccountName -AzureVMName $VM.Name -ConfigurationModeFrequencyMins 30 -verbose -RebootNodeIfNeeded $true -ConfigurationMode "ApplyandMonitor" -Azure
VMResourceGroup $VM.ResourceGroupName -NodeConfigurationName $DSCConfiguration
DEBUG: 1:05:13 PM - RegisterAzureAutomationDscNode begin processing with ParameterSet '__AllParameterSets'.
DEBUG: 1:05:13 PM - using account id xxx.xxxxxx@xxxxx.xxxxx'...
DEBUG: ResourceGroupName: Management, AutomationAccountName: XXXXXXDSCAccount, AzureVMName: BPO-tst-web-vm1, NodeConfigurationName: , ConfigurationMode: ApplyandMonitor, ConfigurationModeFrequencyMins: 30, RefreshFrequencyMins: 30, RebootNodeIfNeeded: True,
ActionAfterReboot: ContinueConfiguration, AllowModuleOverwrite: False, AzureVMResourceGroup: BPO-TST-RG, AzureVMLocation:
DEBUG: [Common.Authentication]: Authenticating using Account: 'xxxxxx.xxxxxxx@xxxxxxx.xxxxx', environment: 'AzureCloud', tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2'
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: - TokenCache: Serializing token cache with 11 items.
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: - TokenCache: Serializing token cache with 11 items.
DEBUG: [Common.Authentication]: Authenticating using configuration values: Domain: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', Endpoint: 'https://login.microsoftonline.com/', ClientId: '1950a258-227b-4e31-a9cf-717495945fc2', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob',
ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthrity: 'True'
DEBUG: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/eff0a260-dfdb-4f2f-b34c-99ac2d5994c2/', CorrelationId: '00000000-0000-0000-0000-000000000000', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: '1950a258-227b-4e31-a9cf-717495945fc2', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - AcquireTokenHandlerBase: === Token Acquisition started:
Authority: https://login.microsoftonline.com/eff0a260-dfdb-4f2f-b34c-99ac2d5994c2/
Resource: https://management.core.windows.net/
ClientId: 1950a258-227b-4e31-a9cf-717495945fc2
CacheType: Microsoft.Azure.Commands.Common.Authentication.ProtectedFileTokenCache (11 items)
Authentication Target: User
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: - TokenCache: Deserialized 11 items to token cache.
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Verbose: 1 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: Looking up cache for a token...
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: An item matching the requested resource was found in the cache
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Verbose: 1 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: 25.1839195683333 minutes left until token in cache expires
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: A matching item (access token or refresh token or both) was found in the cache
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - AcquireTokenHandlerBase: === Token Acquisition finished successfully. An access token was retuned:
Access Token Hash: +DpNw3JYcV8gEcfhMtZbGJNuO+EGCK+Gb7yIvhrXpes=
Refresh Token Hash: LmCG7qQxsMvWB9F3beUo1f1YKDARBdKF9++w2uEP+iE=
Expiration Time: 09/04/2018 11:30:24 +00:00
User Hash: UYR4zJR2D/Z6MW1iYf1/Y6QOvhTx62Yiqjo1kPGvP+I=
DEBUG: [Common.Authentication]: Received token with LoginType 'LiveId', Tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', UserId: 'xxxxxx.xxxxxx@xxxxxx.xxxx'
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '09/04/2018 11:30:24 +00:00', MultipleResource? 'True', Tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', UserId: 'xxxxxxx.xxxxxxx@xxxxxxxx.xxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxx.xxxxx@xxxxxx.xxxx', Name: , IdProvider: 'https://sts.windows.net/6ddd3f38-9d37-43ee-86b5-ffb8ab55b538/', Uid: '52344aec-a5b0-40d9-be62-75662479b218'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '09/04/2018 11:30:24 +00:00' Comparing to '09/04/2018 11:05:13 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:25:11.0351741'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxDSCAccount?api-version=2015-10-31
Headers:
Accept : application/json
x-ms-version : 2014-06-01
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Pragma : no-cache
ocp-automation-accountid : 52284d28-a55f-4996-840f-2babfc532f10
x-ms-request-id : be12d902-2844-4cbc-b577-af241f7b9aae
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-ratelimit-remaining-subscription-reads: 11997
x-ms-correlation-request-id : 8b2a1a3c-e484-4964-a695-bd56bf8ad4a9
x-ms-routing-request-id : WESTEUROPE:20180904T110511Z:8b2a1a3c-e484-4964-a695-bd56bf8ad4a9
X-Content-Type-Options : nosniff
Cache-Control : no-cache
Date : Tue, 04 Sep 2018 11:05:11 GMT
Server : Microsoft-IIS/8.5
X-AspNet-Version : 4.0.30319
X-Powered-By : ASP.NET
Body:
{
"name": "xxxxxxDSCAccount",
"id": "/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxxDSCAccount",
"type": "Microsoft.Automation/AutomationAccounts",
"location": "westeurope",
"tags": {},
"etag": null,
"properties": {
"sku": {
"name": "Basic",
"family": null,
"capacity": null
},
"state": "Ok",
"RegistrationUrl": "https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10",
"creationTime": "2018-07-25T09:24:01.16+02:00",
"lastModifiedBy": null,
"lastModifiedTime": "2018-08-08T09:08:12.34+02:00"
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '09/04/2018 11:30:24 +00:00', MultipleResource? 'True', Tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', UserId: 'xxxxxx.xxxxxx@xxxxxx.xxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxx.xxxxx@xxxxxxx.xxxxx', Name: , IdProvider: 'https://sts.windows.net/6ddd3f38-9d37-43ee-86b5-ffb8ab55b538/', Uid: '52344aec-a5b0-40d9-be62-75662479b218'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '09/04/2018 11:30:24 +00:00' Comparing to '09/04/2018 11:05:13 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:25:10.8352773'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxxDSCAccount/agentRegistrationInformation?api-version=2015-10-31
Headers:
Accept : application/json
x-ms-version : 2014-06-01
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Pragma : no-cache
x-ms-request-id : 44915726-8761-479e-954b-d765a81f5aa7
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-ratelimit-remaining-subscription-reads: 11996
x-ms-correlation-request-id : 0ee2cb8a-2fd6-4ab0-831c-d01987c27527
x-ms-routing-request-id : WESTEUROPE:20180904T110511Z:0ee2cb8a-2fd6-4ab0-831c-d01987c27527
X-Content-Type-Options : nosniff
Cache-Control : no-cache
Date : Tue, 04 Sep 2018 11:05:11 GMT
Server : Microsoft-IIS/8.5
X-AspNet-Version : 4.0.30319
X-Powered-By : ASP.NET
Body:
{
"id":
"/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxDSCAccount/agentRegistrationInformation/https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532
f10",
"keys": {
"primary": "jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==",
"secondary": "LxeYAlMCbV7lSqHRSRV/mNAYgBBaN1vJAiwewxh1JAnO1Vy3Ugo58U6iYN4yfWpOLLB39Se413enAPlSGrCl1g=="
},
"endpoint": "https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10",
"dscMetaConfiguration": "\r\n\tinstance of MSFT_WebDownloadManager as $MSFT_WebDownloadManager1ref\r\n\t{\r\n\tResourceID = \"[ConfigurationRepositoryWeb]AzureAutomationDSC\";\r\n\t SourceInfo =
\"C:\\\\OaaS-RegistrationMetaConfig2.ps1::20::9::ConfigurationRepositoryWeb\";\r\n\t RegistrationKey = \"jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==\"; \r\n\t ServerURL =
\"https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10\";\r\n\t};\r\n\r\n\tinstance of MSFT_WebResourceManager as $MSFT_WebResourceManager1ref\r\n\t{\r\n\t SourceInfo =
\"C:\\\\OaaS-RegistrationMetaConfig2.ps1::27::9::ResourceRepositoryWeb\";\r\n\t ServerURL = \"https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10\";\r\n\t ResourceID = \"[ResourceRepositoryWeb]AzureAutomationDSC\";\r\n\t
RegistrationKey = \"jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==\"; \r\n\t};\r\n\r\n\tinstance of MSFT_WebReportManager as $MSFT_WebReportManager1ref\r\n\t{\r\n\t SourceInfo =
\"C:\\\\OaaS-RegistrationMetaConfig2.ps1::34::9::ReportServerWeb\";\r\n\t ServerURL = \"https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10\";\r\n\t ResourceID = \"[ReportServerWeb]AzureAutomationDSC\";\r\n\t RegistrationKey
= \"jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==\"; \r\n\t};\r\n\r\n\tinstance of MSFT_DSCMetaConfiguration as $MSFT_DSCMetaConfiguration1ref\r\n\t{\r\n\t RefreshMode = \"Pull\";\r\n\t AllowModuleOverwrite = False;\r\n\t
ActionAfterReboot = \"ContinueConfiguration\";\r\n\t RefreshFrequencyMins = 30;\r\n\t RebootNodeIfNeeded = False;\r\n\t ConfigurationModeFrequencyMins = 15;\r\n\t ConfigurationMode = \"ApplyAndMonitor\";\r\n\r\n\t ResourceModuleManagers = {\r\n\t
$MSFT_WebResourceManager1ref \r\n\t};\r\n\t ReportManagers = {\r\n\t $MSFT_WebReportManager1ref \r\n\t };\r\n\t ConfigurationDownloadManagers = {\r\n\t $MSFT_WebDownloadManager1ref \r\n\t };\r\n\t};\r\n\r\n\tinstance of OMI_ConfigurationDocument\r\n\t{\r\n\t
Version=\"2.0.0\";\r\n\t MinimumCompatibleVersion = \"2.0.0\";\r\n\t CompatibleVersionAdditionalProperties= { \"MSFT_DSCMetaConfiguration:StatusRetentionTimeInDays\" };\r\n\t Author=\"azureautomation\";\r\n\t GenerationDate=\"04/17/2015 11:41:09\";\r\n\t
GenerationHost=\"azureautomation-01\";\r\n\t Name=\"RegistrationMetaConfig\";\r\n\t};\r\n\t"
}
Register-AzureRmAutomationDscNode : Cannot process command because of one or more missing mandatory parameters: ResourceGroupName TemplateFile.
At line:1 char:1
+ Register-AzureRmAutomationDscNode -ResourceGroupName "Management" -Au ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : CloseError: (:) [Register-AzureRmAutomationDscNode], ParameterBindingException
+ FullyQualifiedErrorId : Microsoft.Azure.Commands.Automation.Cmdlet.RegisterAzureAutomationDscNode
DEBUG: AzureQoSEvent: CommandName - Register-AzureRmAutomationDscNode; IsSuccess - False; Duration - 00:00:02.2772300; Exception - System.Management.Automation.ParameterBindingException: Cannot process command because of one or more missing mandatory parameters:
ResourceGroupName TemplateFile.
at System.Management.Automation.Runspaces.PipelineBase.Invoke(IEnumerable input)
at System.Management.Automation.PowerShell.Worker.ConstructPipelineAndDoWork(Runspace rs, Boolean performSyncInvoke)
at System.Management.Automation.PowerShell.Worker.CreateRunspaceIfNeededAndDoWork(Runspace rsToUse, Boolean isSync)
at System.Management.Automation.PowerShell.CoreInvokeHelper[TInput,TOutput](PSDataCollection`1 input, PSDataCollection`1 output, PSInvocationSettings settings)
at System.Management.Automation.PowerShell.CoreInvoke[TInput,TOutput](PSDataCollection`1 input, PSDataCollection`1 output, PSInvocationSettings settings)
at System.Management.Automation.PowerShell.Invoke(IEnumerable input, PSInvocationSettings settings)
at Microsoft.Azure.Commands.Automation.Common.AutomationClient.RegisterDscNode(String resourceGroupName, String automationAccountName, String azureVMName, String nodeconfigurationName, String configurationMode, Int32 configurationModeFrequencyMins, Int32
refreshFrequencyMins, Boolean rebootFlag, String actionAfterReboot, Boolean moduleOverwriteFlag, String azureVmResourceGroup, String azureVmLocation)
at Microsoft.Azure.Commands.Automation.Cmdlet.RegisterAzureAutomationDscNode.ExecuteCmdlet()
at Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord();
DEBUG: Finish sending metric.
DEBUG: 1:05:16 PM - RegisterAzureAutomationDscNode end processing.
DEBUG: 1:05:16 PM - RegisterAzureAutomationDscNode end processing.
| 1.0 | Issues invoking Register-AZureRMAutomationDSCNode after AzureRM.Automation upgrade to 5.1.1 - ### Description
After upgrading AzureRM.Automation module to 5.1.1 (and all depending as AzureRM.Profile) all our DSC processes are failing with an strange pending parameter output. Tested from Azure DSC and local with same modules version and we get the same response
### Script/Steps for Reproduction
Register-AzureRmAutomationDscNode -ResourceGroupName $DSCRGName -AutomationAccountName $AutomationAccountName -AzureVMName $VMName -ConfigurationModeFrequencyMins 30 -verbose -RebootNodeIfNeeded $true -ConfigurationMode "ApplyandMonitor" -AzureVMResourceGroup $VMRGName -NodeConfigurationName $DSCConfiguration
All variable typeas and values seems correct
### Module Version
Directory: C:\Users\username\Documents\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 5.1.1 AzureRM.Automation {Get-AzureRMAutomationHybridWorkerGroup, Get-AzureRmAutomationJobOutputRecord, Import-AzureRmAutomationDscNodeConfiguration, Export-AzureRmAutomationDscConfiguration...}
Script 5.5.1 AzureRM.profile {Disable-AzureRmDataCollection, Disable-AzureRmContextAutosave, Enable-AzureRmDataCollection, Enable-AzureRmContextAutosave...}
Directory: C:\Program Files\WindowsPowerShell\Modules
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 5.6.0 AzureRM
Script 0.6.5 AzureRM.AnalysisServices {Resume-AzureRmAnalysisServicesServer, Suspend-AzureRmAnalysisServicesServer, Get-AzureRmAnalysisServicesServer, Remove-AzureRmAnalysisServicesServer...}
Script 5.1.1 AzureRM.ApiManagement {Add-AzureRmApiManagementRegion, Get-AzureRmApiManagementSsoToken, New-AzureRmApiManagementHostnameConfiguration, New-AzureRmApiManagementRegion...}
Script 0.1.2 AzureRM.ApplicationInsights {Get-AzureRmApplicationInsights, New-AzureRmApplicationInsights, Remove-AzureRmApplicationInsights, Set-AzureRmApplicationInsightsPricingPlan...}
Script 4.3.1 AzureRM.Automation {Get-AzureRMAutomationHybridWorkerGroup, Get-AzureRmAutomationJobOutputRecord, Import-AzureRmAutomationDscNodeConfiguration, Export-AzureRmAutomationDscConfiguration...}
Script 4.0.3 AzureRM.Backup {Backup-AzureRmBackupItem, Enable-AzureRmBackupContainerReregistration, Get-AzureRmBackupContainer, Register-AzureRmBackupContainer...}
Script 4.0.5 AzureRM.Batch {Remove-AzureRmBatchAccount, Get-AzureRmBatchAccount, Get-AzureRmBatchAccountKeys, New-AzureRmBatchAccount...}
Script 0.14.0 AzureRM.Billing {Get-AzureRmBillingInvoice, Get-AzureRmBillingPeriod}
Script 4.2.1 AzureRM.Cdn {Get-AzureRmCdnProfile, Get-AzureRmCdnProfileSsoUrl, New-AzureRmCdnProfile, Remove-AzureRmCdnProfile...}
Script 0.9.3 AzureRM.CognitiveServices {Get-AzureRmCognitiveServicesAccount, Get-AzureRmCognitiveServicesAccountKey, Get-AzureRmCognitiveServicesAccountSkus, New-AzureRmCognitiveServicesAccount...}
Script 4.5.0 AzureRM.Compute {Remove-AzureRmAvailabilitySet, Get-AzureRmAvailabilitySet, New-AzureRmAvailabilitySet, Update-AzureRmAvailabilitySet...}
Script 0.3.0 AzureRM.Consumption Get-AzureRmConsumptionUsageDetail
Script 0.2.4 AzureRM.ContainerInstance {New-AzureRmContainerGroup, Get-AzureRmContainerGroup, Remove-AzureRmContainerGroup, Get-AzureRmContainerInstanceLog}
Script 1.0.3 AzureRM.ContainerRegistry {New-AzureRmContainerRegistry, Get-AzureRmContainerRegistry, Update-AzureRmContainerRegistry, Remove-AzureRmContainerRegistry...}
Script 4.2.1 AzureRM.DataFactories {Remove-AzureRmDataFactory, Get-AzureRmDataFactoryRun, Get-AzureRmDataFactorySlice, Save-AzureRmDataFactoryLog...}
Script 0.5.2 AzureRM.DataFactoryV2 {Set-AzureRmDataFactoryV2, Update-AzureRmDataFactoryV2, Get-AzureRmDataFactoryV2, Remove-AzureRmDataFactoryV2...}
Script 4.2.2 AzureRM.DataLakeAnalytics {Get-AzureRmDataLakeAnalyticsDataSource, New-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogSecret...}
Script 5.1.1 AzureRM.DataLakeStore {Get-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreFirewallRule, Set-AzureRmDataLakeStoreTrustedIdProvider...}
Script 4.0.3 AzureRM.DevTestLabs {Get-AzureRmDtlAllowedVMSizesPolicy, Get-AzureRmDtlAutoShutdownPolicy, Get-AzureRmDtlAutoStartPolicy, Get-AzureRmDtlVMsPerLabPolicy...}
Script 4.1.1 AzureRM.Dns {Get-AzureRmDnsRecordSet, New-AzureRmDnsRecordConfig, Remove-AzureRmDnsRecordSet, Set-AzureRmDnsRecordSet...}
Script 0.3.1 AzureRM.EventGrid {New-AzureRmEventGridTopic, Get-AzureRmEventGridTopic, Set-AzureRmEventGridTopic, New-AzureRmEventGridTopicKey...}
Script 0.6.2 AzureRM.EventHub {New-AzureRmEventHubNamespace, Get-AzureRmEventHubNamespace, Set-AzureRmEventHubNamespace, Remove-AzureRmEventHubNamespace...}
Script 4.1.1 AzureRM.HDInsight {Get-AzureRmHDInsightJob, New-AzureRmHDInsightSqoopJobDefinition, Wait-AzureRmHDInsightJob, New-AzureRmHDInsightStreamingMapReduceJobDefinition...}
Script 4.0.3 AzureRM.Insights {Get-AzureRmMetricDefinition, Get-AzureRmMetric, Remove-AzureRmLogProfile, Get-AzureRmLogProfile...}
Script 3.1.1 AzureRM.IotHub {Add-AzureRmIotHubKey, Get-AzureRmIotHubEventHubConsumerGroup, Get-AzureRmIotHubConnectionString, Get-AzureRmIotHubJob...}
Script 4.2.1 AzureRM.KeyVault {Add-AzureKeyVaultCertificate, Set-AzureKeyVaultCertificateAttribute, Stop-AzureKeyVaultCertificateOperation, Get-AzureKeyVaultCertificateOperation...}
Script 4.0.2 AzureRM.LogicApp {Get-AzureRmIntegrationAccountAgreement, Get-AzureRmIntegrationAccountCallbackUrl, Get-AzureRmIntegrationAccountCertificate, Get-AzureRmIntegrationAccount...}
Script 0.17.1 AzureRM.MachineLearning {Move-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentPlanUsageHistory, Remove-AzureRmMlCommitmentPlan...}
Script 0.4.1 AzureRM.MachineLearningCompute {Get-AzureRmMlOpCluster, Get-AzureRmMlOpClusterKey, Test-AzureRmMlOpClusterSystemServicesUpdateAvailability, Update-AzureRmMlOpClusterSystemService...}
Script 0.2.0 AzureRM.MarketplaceOrdering {Get-AzureRmMarketplaceTerms, Set-AzureRmMarketplaceTerms}
Script 0.9.1 AzureRM.Media {Sync-AzureRmMediaServiceStorageKeys, Set-AzureRmMediaServiceKey, Get-AzureRmMediaServiceKeys, Get-AzureRmMediaServiceNameAvailability...}
Script 5.4.1 AzureRM.Network {Add-AzureRmApplicationGatewayAuthenticationCertificate, Get-AzureRmApplicationGatewayAuthenticationCertificate, New-AzureRmApplicationGatewayAuthenticationCertificate, Remove-AzureRmApplicationGatewayAuthenti...
Script 4.1.0 AzureRM.NotificationHubs {Get-AzureRmNotificationHub, Get-AzureRmNotificationHubAuthorizationRules, Get-AzureRmNotificationHubListKeys, Get-AzureRmNotificationHubPNSCredentials...}
Script 4.3.1 AzureRM.OperationalInsights {New-AzureRmOperationalInsightsAzureActivityLogDataSource, New-AzureRmOperationalInsightsCustomLogDataSource, Disable-AzureRmOperationalInsightsLinuxCustomLogCollection, Disable-AzureRmOperationalInsightsIISLo...
Script 4.1.3 AzureRM.PowerBIEmbedded {Remove-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollectionAccessKeys, Get-AzureRmPowerBIWorkspace...}
Script 4.5.0 AzureRM.profile {Disable-AzureRmDataCollection, Disable-AzureRmContextAutosave, Enable-AzureRmDataCollection, Enable-AzureRmContextAutosave...}
Script 4.1.1 AzureRM.RecoveryServices {Get-AzureRmRecoveryServicesBackupProperty, Get-AzureRmRecoveryServicesVault, Get-AzureRmRecoveryServicesVaultSettingsFile, New-AzureRmRecoveryServicesVault...}
Script 4.1.1 AzureRM.RecoveryServices.Backup {Backup-AzureRmRecoveryServicesBackupItem, Get-AzureRmRecoveryServicesBackupManagementServer, Get-AzureRmRecoveryServicesBackupContainer, Unregister-AzureRmRecoveryServicesBackupContainer...}
Script 0.2.3 AzureRM.RecoveryServices.SiteRec... {Edit-AzureRmRecoveryServicesAsrRecoveryPlan, Get-AzureRmRecoveryServicesAsrAlertSetting, Get-AzureRmRecoveryServicesAsrEvent, Get-AzureRmRecoveryServicesAsrFabric...}
Script 4.1.1 AzureRM.RedisCache {Remove-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCacheScheduleEntry, Get-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCachePatchSchedule...}
Script 0.3.2 AzureRM.Relay {New-AzureRmRelayNamespace, Get-AzureRmRelayNamespace, Set-AzureRmRelayNamespace, Remove-AzureRmRelayNamespace...}
Script 5.5.1 AzureRM.Resources {Get-AzureRmProviderOperation, Remove-AzureRmRoleAssignment, Get-AzureRmRoleAssignment, New-AzureRmRoleAssignment...}
Script 0.16.2 AzureRM.Scheduler {Disable-AzureRmSchedulerJobCollection, Enable-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJob...}
Script 4.1.1 AzureRM.ServerManagement {Invoke-AzureRmServerManagementPowerShellCommand, Get-AzureRmServerManagementSession, New-AzureRmServerManagementSession, Remove-AzureRmServerManagementSession...}
Script 0.6.3 AzureRM.ServiceBus {New-AzureRmServiceBusNamespace, Get-AzureRmServiceBusNamespace, Set-AzureRmServiceBusNamespace, Remove-AzureRmServiceBusNamespace...}
Script 0.3.3 AzureRM.ServiceFabric {Add-AzureRmServiceFabricApplicationCertificate, Add-AzureRmServiceFabricClientCertificate, Add-AzureRmServiceFabricClusterCertificate, Add-AzureRmServiceFabricNode...}
Script 5.0.5 AzureRM.SiteRecovery {Get-AzureRmSiteRecoveryFabric, New-AzureRmSiteRecoveryFabric, Remove-AzureRmSiteRecoveryFabric, Stop-AzureRmSiteRecoveryJob...}
Script 4.3.1 AzureRM.Sql {Get-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseTransparentDataEncryptionActivity, Set-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseUpgradeHint...}
Script 4.2.2 AzureRM.Storage {Get-AzureRmStorageAccount, Get-AzureRmStorageAccountKey, New-AzureRmStorageAccount, New-AzureRmStorageAccountKey...}
Script 4.0.3 AzureRM.StreamAnalytics {Get-AzureRmStreamAnalyticsFunction, Get-AzureRmStreamAnalyticsDefaultFunctionDefinition, New-AzureRmStreamAnalyticsFunction, Remove-AzureRmStreamAnalyticsFunction...}
Script 4.0.0 AzureRM.Tags {Remove-AzureRmTag, Get-AzureRmTag, New-AzureRmTag}
Script 4.0.2 AzureRM.TrafficManager {Disable-AzureRmTrafficManagerEndpoint, Enable-AzureRmTrafficManagerEndpoint, Set-AzureRmTrafficManagerEndpoint, Get-AzureRmTrafficManagerEndpoint...}
Script 4.0.1 AzureRM.UsageAggregates Get-UsageAggregates
Script 4.2.1 AzureRM.Websites {Get-AzureRmAppServicePlan, Set-AzureRmAppServicePlan, New-AzureRmAppServicePlan, Remove-AzureRmAppServicePlan...}
Directory: C:\Program Files (x86)\Microsoft SDKs\Azure\PowerShell\ResourceManager\AzureResourceManager
ModuleType Version Name ExportedCommands
---------- ------- ---- ----------------
Script 0.6.1 AzureRM.AnalysisServices {Resume-AzureRmAnalysisServicesServer, Suspend-AzureRmAnalysisServicesServer, Get-AzureRmAnalysisServicesServer, Remove-AzureRmAnalysisServicesServer...}
Script 5.0.1 AzureRM.ApiManagement {Add-AzureRmApiManagementRegion, Get-AzureRmApiManagementSsoToken, New-AzureRmApiManagementHostnameConfiguration, New-AzureRmApiManagementRegion...}
Script 0.1.0 AzureRM.ApplicationInsights {Get-AzureRmApplicationInsights, New-AzureRmApplicationInsights, Remove-AzureRmApplicationInsights, Set-AzureRmApplicationInsightsPricingPlan...}
Script 4.1.1 AzureRM.Automation {Get-AzureRMAutomationHybridWorkerGroup, Get-AzureRmAutomationJobOutputRecord, Import-AzureRmAutomationDscNodeConfiguration, Export-AzureRmAutomationDscConfiguration...}
Script 4.0.1 AzureRM.Backup {Backup-AzureRmBackupItem, Enable-AzureRmBackupContainerReregistration, Get-AzureRmBackupContainer, Register-AzureRmBackupContainer...}
Script 4.0.3 AzureRM.Batch {Remove-AzureRmBatchAccount, Get-AzureRmBatchAccount, Get-AzureRmBatchAccountKeys, New-AzureRmBatchAccount...}
Script 0.14.0 AzureRM.Billing {Get-AzureRmBillingInvoice, Get-AzureRmBillingPeriod}
Script 4.0.0 AzureRM.Cdn {Get-AzureRmCdnProfile, Get-AzureRmCdnProfileSsoUrl, New-AzureRmCdnProfile, Remove-AzureRmCdnProfile...}
Script 0.9.0 AzureRM.CognitiveServices {Get-AzureRmCognitiveServicesAccount, Get-AzureRmCognitiveServicesAccountKey, Get-AzureRmCognitiveServicesAccountSkus, New-AzureRmCognitiveServicesAccount...}
Script 4.1.1 AzureRM.Compute {Remove-AzureRmAvailabilitySet, Get-AzureRmAvailabilitySet, New-AzureRmAvailabilitySet, Update-AzureRmAvailabilitySet...}
Script 0.3.0 AzureRM.Consumption Get-AzureRmConsumptionUsageDetail
Script 0.2.1 AzureRM.ContainerInstance {New-AzureRmContainerGroup, Get-AzureRmContainerGroup, Remove-AzureRmContainerGroup, Get-AzureRmContainerInstanceLog}
Script 1.0.1 AzureRM.ContainerRegistry {New-AzureRmContainerRegistry, Get-AzureRmContainerRegistry, Update-AzureRmContainerRegistry, Remove-AzureRmContainerRegistry...}
Script 4.0.3 AzureRM.DataFactories {Remove-AzureRmDataFactory, Get-AzureRmDataFactoryRun, Get-AzureRmDataFactorySlice, Save-AzureRmDataFactoryLog...}
Script 0.4.1 AzureRM.DataFactoryV2 {Set-AzureRmDataFactoryV2, Update-AzureRmDataFactoryV2, Get-AzureRmDataFactoryV2, Remove-AzureRmDataFactoryV2...}
Script 4.1.1 AzureRM.DataLakeAnalytics {Get-AzureRmDataLakeAnalyticsDataSource, New-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogCredential, Remove-AzureRmDataLakeAnalyticsCatalogSecret...}
Script 5.0.0 AzureRM.DataLakeStore {Get-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreTrustedIdProvider, Remove-AzureRmDataLakeStoreFirewallRule, Set-AzureRmDataLakeStoreTrustedIdProvider...}
Script 4.0.0 AzureRM.DevTestLabs {Get-AzureRmDtlAllowedVMSizesPolicy, Get-AzureRmDtlAutoShutdownPolicy, Get-AzureRmDtlAutoStartPolicy, Get-AzureRmDtlVMsPerLabPolicy...}
Script 4.0.0 AzureRM.Dns {Get-AzureRmDnsRecordSet, New-AzureRmDnsRecordConfig, Remove-AzureRmDnsRecordSet, Set-AzureRmDnsRecordSet...}
Script 0.2.0 AzureRM.EventGrid {New-AzureRmEventGridTopic, Get-AzureRmEventGridTopic, Set-AzureRmEventGridTopic, New-AzureRmEventGridTopicKey...}
Script 0.5.0 AzureRM.EventHub {New-AzureRmEventHubNamespace, Get-AzureRmEventHubNamespace, Set-AzureRmEventHubNamespace, Remove-AzureRmEventHubNamespace...}
Script 4.0.1 AzureRM.HDInsight {Get-AzureRmHDInsightJob, New-AzureRmHDInsightSqoopJobDefinition, Wait-AzureRmHDInsightJob, New-AzureRmHDInsightStreamingMapReduceJobDefinition...}
Script 4.0.0 AzureRM.Insights {Get-AzureRmMetricDefinition, Get-AzureRmMetric, Remove-AzureRmLogProfile, Get-AzureRmLogProfile...}
Script 3.0.0 AzureRM.IotHub {Add-AzureRmIotHubKey, Get-AzureRmIotHubEventHubConsumerGroup, Get-AzureRmIotHubConnectionString, Get-AzureRmIotHubJob...}
Script 4.0.1 AzureRM.KeyVault {Add-AzureKeyVaultCertificate, Set-AzureKeyVaultCertificateAttribute, Stop-AzureKeyVaultCertificateOperation, Get-AzureKeyVaultCertificateOperation...}
Script 4.0.0 AzureRM.LogicApp {Get-AzureRmIntegrationAccountAgreement, Get-AzureRmIntegrationAccountCallbackUrl, Get-AzureRmIntegrationAccountCertificate, Get-AzureRmIntegrationAccount...}
Script 0.16.0 AzureRM.MachineLearning {Move-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentAssociation, Get-AzureRmMlCommitmentPlanUsageHistory, Remove-AzureRmMlCommitmentPlan...}
Script 0.3.1 AzureRM.MachineLearningCompute {Get-AzureRmMlOpCluster, Get-AzureRmMlOpClusterKey, Test-AzureRmMlOpClusterSystemServicesUpdateAvailability, Update-AzureRmMlOpClusterSystemService...}
Script 0.2.0 AzureRM.MarketplaceOrdering {Get-AzureRmMarketplaceTerms, Set-AzureRmMarketplaceTerms}
Script 0.8.0 AzureRM.Media {Sync-AzureRmMediaServiceStorageKeys, Set-AzureRmMediaServiceKey, Get-AzureRmMediaServiceKeys, Get-AzureRmMediaServiceNameAvailability...}
Script 5.0.0 AzureRM.Network {Add-AzureRmApplicationGatewayAuthenticationCertificate, Get-AzureRmApplicationGatewayAuthenticationCertificate, New-AzureRmApplicationGatewayAuthenticationCertificate, Remove-AzureRmApplicationGatewayAuthenti...
Script 4.0.0 AzureRM.NotificationHubs {Get-AzureRmNotificationHub, Get-AzureRmNotificationHubAuthorizationRules, Get-AzureRmNotificationHubListKeys, Get-AzureRmNotificationHubPNSCredentials...}
Script 4.0.0 AzureRM.OperationalInsights {New-AzureRmOperationalInsightsAzureActivityLogDataSource, New-AzureRmOperationalInsightsCustomLogDataSource, Disable-AzureRmOperationalInsightsLinuxCustomLogCollection, Disable-AzureRmOperationalInsightsIISLo...
Script 4.1.1 AzureRM.PowerBIEmbedded {Remove-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollection, Get-AzureRmPowerBIWorkspaceCollectionAccessKeys, Get-AzureRmPowerBIWorkspace...}
Script 4.1.1 AzureRM.Profile {Disable-AzureRmDataCollection, Disable-AzureRmContextAutosave, Enable-AzureRmDataCollection, Enable-AzureRmContextAutosave...}
Script 4.0.1 AzureRM.RecoveryServices {Get-AzureRmRecoveryServicesBackupProperty, Get-AzureRmRecoveryServicesVault, Get-AzureRmRecoveryServicesVaultSettingsFile, New-AzureRmRecoveryServicesVault...}
Script 4.0.3 AzureRM.RecoveryServices.Backup {Backup-AzureRmRecoveryServicesBackupItem, Get-AzureRmRecoveryServicesBackupManagementServer, Get-AzureRmRecoveryServicesBackupContainer, Unregister-AzureRmRecoveryServicesBackupContainer...}
Script 0.2.1 AzureRM.RecoveryServices.SiteRec... {Edit-AzureRmRecoveryServicesAsrRecoveryPlan, Get-AzureRmRecoveryServicesAsrAlertSetting, Get-AzureRmRecoveryServicesAsrEvent, Get-AzureRmRecoveryServicesAsrFabric...}
Script 4.0.1 AzureRM.RedisCache {Remove-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCacheScheduleEntry, Get-AzureRmRedisCachePatchSchedule, New-AzureRmRedisCachePatchSchedule...}
Script 0.3.0 AzureRM.Relay {New-AzureRmRelayNamespace, Get-AzureRmRelayNamespace, Set-AzureRmRelayNamespace, Remove-AzureRmRelayNamespace...}
Script 5.1.1 AzureRM.Resources {Get-AzureRmProviderOperation, Remove-AzureRmRoleAssignment, Get-AzureRmRoleAssignment, New-AzureRmRoleAssignment...}
Script 0.16.0 AzureRM.Scheduler {Disable-AzureRmSchedulerJobCollection, Enable-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJobCollection, Get-AzureRmSchedulerJob...}
Script 4.0.0 AzureRM.ServerManagement {Invoke-AzureRmServerManagementPowerShellCommand, Get-AzureRmServerManagementSession, New-AzureRmServerManagementSession, Remove-AzureRmServerManagementSession...}
Script 0.5.0 AzureRM.ServiceBus {New-AzureRmServiceBusNamespace, Get-AzureRmServiceBusNamespace, Set-AzureRmServiceBusNamespace, Remove-AzureRmServiceBusNamespace...}
Script 0.3.0 AzureRM.ServiceFabric {Add-AzureRmServiceFabricApplicationCertificate, Add-AzureRmServiceFabricClientCertificate, Add-AzureRmServiceFabricClusterCertificate, Add-AzureRmServiceFabricNode...}
Script 5.0.3 AzureRM.SiteRecovery {Get-AzureRmSiteRecoveryFabric, New-AzureRmSiteRecoveryFabric, Remove-AzureRmSiteRecoveryFabric, Stop-AzureRmSiteRecoveryJob...}
Script 4.1.1 AzureRM.Sql {Get-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseTransparentDataEncryptionActivity, Set-AzureRmSqlDatabaseTransparentDataEncryption, Get-AzureRmSqlDatabaseUpgradeHint...}
Script 4.0.1 AzureRM.Storage {Get-AzureRmStorageAccount, Get-AzureRmStorageAccountKey, New-AzureRmStorageAccount, New-AzureRmStorageAccountKey...}
Script 4.0.1 AzureRM.StreamAnalytics {Get-AzureRmStreamAnalyticsFunction, Get-AzureRmStreamAnalyticsDefaultFunctionDefinition, New-AzureRmStreamAnalyticsFunction, Remove-AzureRmStreamAnalyticsFunction...}
Script 4.0.0 AzureRM.Tags {Remove-AzureRmTag, Get-AzureRmTag, New-AzureRmTag}
Script 4.0.0 AzureRM.TrafficManager {Disable-AzureRmTrafficManagerEndpoint, Enable-AzureRmTrafficManagerEndpoint, Set-AzureRmTrafficManagerEndpoint, Get-AzureRmTrafficManagerEndpoint...}
Script 4.0.0 AzureRM.UsageAggregates Get-UsageAggregates
Script 4.0.0 AzureRM.Websites {Get-AzureRmAppServicePlan, Set-AzureRmAppServicePlan, New-AzureRmAppServicePlan, Remove-AzureRmAppServicePlan...}
### Environment Data
Name Value
---- -----
PSVersion 5.1.17134.228
PSEdition Desktop
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0...}
BuildVersion 10.0.17134.228
CLRVersion 4.0.30319.42000
WSManStackVersion 3.0
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
### Debug Output
PS C:\WINDOWS\system32> Register-AzureRmAutomationDscNode -ResourceGroupName "Management" -AutomationAccountName $AutomationAccountName -AzureVMName $VM.Name -ConfigurationModeFrequencyMins 30 -verbose -RebootNodeIfNeeded $true -ConfigurationMode "ApplyandMonitor" -Azure
VMResourceGroup $VM.ResourceGroupName -NodeConfigurationName $DSCConfiguration
DEBUG: 1:05:13 PM - RegisterAzureAutomationDscNode begin processing with ParameterSet '__AllParameterSets'.
DEBUG: 1:05:13 PM - using account id xxx.xxxxxx@xxxxx.xxxxx'...
DEBUG: ResourceGroupName: Management, AutomationAccountName: XXXXXXDSCAccount, AzureVMName: BPO-tst-web-vm1, NodeConfigurationName: , ConfigurationMode: ApplyandMonitor, ConfigurationModeFrequencyMins: 30, RefreshFrequencyMins: 30, RebootNodeIfNeeded: True,
ActionAfterReboot: ContinueConfiguration, AllowModuleOverwrite: False, AzureVMResourceGroup: BPO-TST-RG, AzureVMLocation:
DEBUG: [Common.Authentication]: Authenticating using Account: 'xxxxxx.xxxxxxx@xxxxxxx.xxxxx', environment: 'AzureCloud', tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2'
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: - TokenCache: Serializing token cache with 11 items.
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: - TokenCache: Serializing token cache with 11 items.
DEBUG: [Common.Authentication]: Authenticating using configuration values: Domain: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', Endpoint: 'https://login.microsoftonline.com/', ClientId: '1950a258-227b-4e31-a9cf-717495945fc2', ClientRedirect: 'urn:ietf:wg:oauth:2.0:oob',
ResourceClientUri: 'https://management.core.windows.net/', ValidateAuthrity: 'True'
DEBUG: [Common.Authentication]: Acquiring token using context with Authority 'https://login.microsoftonline.com/eff0a260-dfdb-4f2f-b34c-99ac2d5994c2/', CorrelationId: '00000000-0000-0000-0000-000000000000', ValidateAuthority: 'True'
DEBUG: [Common.Authentication]: Acquiring token using AdalConfiguration with Domain: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', AdEndpoint: 'https://login.microsoftonline.com/', ClientId: '1950a258-227b-4e31-a9cf-717495945fc2', ClientRedirectUri: urn:ietf:wg:oauth:2.0:oob
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - AcquireTokenHandlerBase: === Token Acquisition started:
Authority: https://login.microsoftonline.com/eff0a260-dfdb-4f2f-b34c-99ac2d5994c2/
Resource: https://management.core.windows.net/
ClientId: 1950a258-227b-4e31-a9cf-717495945fc2
CacheType: Microsoft.Azure.Commands.Common.Authentication.ProtectedFileTokenCache (11 items)
Authentication Target: User
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: - TokenCache: Deserialized 11 items to token cache.
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Verbose: 1 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: Looking up cache for a token...
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: An item matching the requested resource was found in the cache
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Verbose: 1 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: 25.1839195683333 minutes left until token in cache expires
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - TokenCache: A matching item (access token or refresh token or both) was found in the cache
DEBUG: Microsoft.IdentityModel.Clients.ActiveDirectory Information: 2 :
DEBUG: 09/04/2018 11:05:13: 6a3d6fe2-7adf-4db9-99db-868d2bffa383 - AcquireTokenHandlerBase: === Token Acquisition finished successfully. An access token was retuned:
Access Token Hash: +DpNw3JYcV8gEcfhMtZbGJNuO+EGCK+Gb7yIvhrXpes=
Refresh Token Hash: LmCG7qQxsMvWB9F3beUo1f1YKDARBdKF9++w2uEP+iE=
Expiration Time: 09/04/2018 11:30:24 +00:00
User Hash: UYR4zJR2D/Z6MW1iYf1/Y6QOvhTx62Yiqjo1kPGvP+I=
DEBUG: [Common.Authentication]: Received token with LoginType 'LiveId', Tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', UserId: 'xxxxxx.xxxxxx@xxxxxx.xxxx'
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '09/04/2018 11:30:24 +00:00', MultipleResource? 'True', Tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', UserId: 'xxxxxxx.xxxxxxx@xxxxxxxx.xxxxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxxxxx.xxxxx@xxxxxx.xxxx', Name: , IdProvider: 'https://sts.windows.net/6ddd3f38-9d37-43ee-86b5-ffb8ab55b538/', Uid: '52344aec-a5b0-40d9-be62-75662479b218'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '09/04/2018 11:30:24 +00:00' Comparing to '09/04/2018 11:05:13 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:25:11.0351741'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxDSCAccount?api-version=2015-10-31
Headers:
Accept : application/json
x-ms-version : 2014-06-01
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Pragma : no-cache
ocp-automation-accountid : 52284d28-a55f-4996-840f-2babfc532f10
x-ms-request-id : be12d902-2844-4cbc-b577-af241f7b9aae
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-ratelimit-remaining-subscription-reads: 11997
x-ms-correlation-request-id : 8b2a1a3c-e484-4964-a695-bd56bf8ad4a9
x-ms-routing-request-id : WESTEUROPE:20180904T110511Z:8b2a1a3c-e484-4964-a695-bd56bf8ad4a9
X-Content-Type-Options : nosniff
Cache-Control : no-cache
Date : Tue, 04 Sep 2018 11:05:11 GMT
Server : Microsoft-IIS/8.5
X-AspNet-Version : 4.0.30319
X-Powered-By : ASP.NET
Body:
{
"name": "xxxxxxDSCAccount",
"id": "/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxxDSCAccount",
"type": "Microsoft.Automation/AutomationAccounts",
"location": "westeurope",
"tags": {},
"etag": null,
"properties": {
"sku": {
"name": "Basic",
"family": null,
"capacity": null
},
"state": "Ok",
"RegistrationUrl": "https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10",
"creationTime": "2018-07-25T09:24:01.16+02:00",
"lastModifiedBy": null,
"lastModifiedTime": "2018-08-08T09:08:12.34+02:00"
}
}
DEBUG: [Common.Authentication]: Renewing Token with Type: 'Bearer', Expiry: '09/04/2018 11:30:24 +00:00', MultipleResource? 'True', Tenant: 'eff0a260-dfdb-4f2f-b34c-99ac2d5994c2', UserId: 'xxxxxx.xxxxxx@xxxxxx.xxxx'
DEBUG: [Common.Authentication]: User info for token DisplayId: 'xxxx.xxxxx@xxxxxxx.xxxxx', Name: , IdProvider: 'https://sts.windows.net/6ddd3f38-9d37-43ee-86b5-ffb8ab55b538/', Uid: '52344aec-a5b0-40d9-be62-75662479b218'
DEBUG: [Common.Authentication]: Checking token expiration, token expires '09/04/2018 11:30:24 +00:00' Comparing to '09/04/2018 11:05:13 +00:00' With threshold '00:05:00', calculated time until token expiry: '00:25:10.8352773'
DEBUG: ============================ HTTP REQUEST ============================
HTTP Method:
GET
Absolute Uri:
https://management.azure.com/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxxDSCAccount/agentRegistrationInformation?api-version=2015-10-31
Headers:
Accept : application/json
x-ms-version : 2014-06-01
Body:
DEBUG: ============================ HTTP RESPONSE ============================
Status Code:
OK
Headers:
Pragma : no-cache
x-ms-request-id : 44915726-8761-479e-954b-d765a81f5aa7
Strict-Transport-Security : max-age=31536000; includeSubDomains
x-ms-ratelimit-remaining-subscription-reads: 11996
x-ms-correlation-request-id : 0ee2cb8a-2fd6-4ab0-831c-d01987c27527
x-ms-routing-request-id : WESTEUROPE:20180904T110511Z:0ee2cb8a-2fd6-4ab0-831c-d01987c27527
X-Content-Type-Options : nosniff
Cache-Control : no-cache
Date : Tue, 04 Sep 2018 11:05:11 GMT
Server : Microsoft-IIS/8.5
X-AspNet-Version : 4.0.30319
X-Powered-By : ASP.NET
Body:
{
"id":
"/subscriptions/53ef36be-4ab5-4a7d-8223-0ed2d8bbedc5/resourceGroups/Management/providers/Microsoft.Automation/automationAccounts/xxxxxxDSCAccount/agentRegistrationInformation/https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532
f10",
"keys": {
"primary": "jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==",
"secondary": "LxeYAlMCbV7lSqHRSRV/mNAYgBBaN1vJAiwewxh1JAnO1Vy3Ugo58U6iYN4yfWpOLLB39Se413enAPlSGrCl1g=="
},
"endpoint": "https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10",
"dscMetaConfiguration": "\r\n\tinstance of MSFT_WebDownloadManager as $MSFT_WebDownloadManager1ref\r\n\t{\r\n\tResourceID = \"[ConfigurationRepositoryWeb]AzureAutomationDSC\";\r\n\t SourceInfo =
\"C:\\\\OaaS-RegistrationMetaConfig2.ps1::20::9::ConfigurationRepositoryWeb\";\r\n\t RegistrationKey = \"jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==\"; \r\n\t ServerURL =
\"https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10\";\r\n\t};\r\n\r\n\tinstance of MSFT_WebResourceManager as $MSFT_WebResourceManager1ref\r\n\t{\r\n\t SourceInfo =
\"C:\\\\OaaS-RegistrationMetaConfig2.ps1::27::9::ResourceRepositoryWeb\";\r\n\t ServerURL = \"https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10\";\r\n\t ResourceID = \"[ResourceRepositoryWeb]AzureAutomationDSC\";\r\n\t
RegistrationKey = \"jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==\"; \r\n\t};\r\n\r\n\tinstance of MSFT_WebReportManager as $MSFT_WebReportManager1ref\r\n\t{\r\n\t SourceInfo =
\"C:\\\\OaaS-RegistrationMetaConfig2.ps1::34::9::ReportServerWeb\";\r\n\t ServerURL = \"https://we-agentservice-prod-1.azure-automation.net/accounts/52284d28-a55f-4996-840f-2babfc532f10\";\r\n\t ResourceID = \"[ReportServerWeb]AzureAutomationDSC\";\r\n\t RegistrationKey
= \"jiQFiCLeWfTFqfqLpdbxqGj/gUP62r/ZBB5+wZgjk2CleQh5xAT58ERRD4+Uwb0DLnWjQDO9OWIU0PyfuuknnA==\"; \r\n\t};\r\n\r\n\tinstance of MSFT_DSCMetaConfiguration as $MSFT_DSCMetaConfiguration1ref\r\n\t{\r\n\t RefreshMode = \"Pull\";\r\n\t AllowModuleOverwrite = False;\r\n\t
ActionAfterReboot = \"ContinueConfiguration\";\r\n\t RefreshFrequencyMins = 30;\r\n\t RebootNodeIfNeeded = False;\r\n\t ConfigurationModeFrequencyMins = 15;\r\n\t ConfigurationMode = \"ApplyAndMonitor\";\r\n\r\n\t ResourceModuleManagers = {\r\n\t
$MSFT_WebResourceManager1ref \r\n\t};\r\n\t ReportManagers = {\r\n\t $MSFT_WebReportManager1ref \r\n\t };\r\n\t ConfigurationDownloadManagers = {\r\n\t $MSFT_WebDownloadManager1ref \r\n\t };\r\n\t};\r\n\r\n\tinstance of OMI_ConfigurationDocument\r\n\t{\r\n\t
Version=\"2.0.0\";\r\n\t MinimumCompatibleVersion = \"2.0.0\";\r\n\t CompatibleVersionAdditionalProperties= { \"MSFT_DSCMetaConfiguration:StatusRetentionTimeInDays\" };\r\n\t Author=\"azureautomation\";\r\n\t GenerationDate=\"04/17/2015 11:41:09\";\r\n\t
GenerationHost=\"azureautomation-01\";\r\n\t Name=\"RegistrationMetaConfig\";\r\n\t};\r\n\t"
}
Register-AzureRmAutomationDscNode : Cannot process command because of one or more missing mandatory parameters: ResourceGroupName TemplateFile.
At line:1 char:1
+ Register-AzureRmAutomationDscNode -ResourceGroupName "Management" -Au ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : CloseError: (:) [Register-AzureRmAutomationDscNode], ParameterBindingException
+ FullyQualifiedErrorId : Microsoft.Azure.Commands.Automation.Cmdlet.RegisterAzureAutomationDscNode
DEBUG: AzureQoSEvent: CommandName - Register-AzureRmAutomationDscNode; IsSuccess - False; Duration - 00:00:02.2772300; Exception - System.Management.Automation.ParameterBindingException: Cannot process command because of one or more missing mandatory parameters:
ResourceGroupName TemplateFile.
at System.Management.Automation.Runspaces.PipelineBase.Invoke(IEnumerable input)
at System.Management.Automation.PowerShell.Worker.ConstructPipelineAndDoWork(Runspace rs, Boolean performSyncInvoke)
at System.Management.Automation.PowerShell.Worker.CreateRunspaceIfNeededAndDoWork(Runspace rsToUse, Boolean isSync)
at System.Management.Automation.PowerShell.CoreInvokeHelper[TInput,TOutput](PSDataCollection`1 input, PSDataCollection`1 output, PSInvocationSettings settings)
at System.Management.Automation.PowerShell.CoreInvoke[TInput,TOutput](PSDataCollection`1 input, PSDataCollection`1 output, PSInvocationSettings settings)
at System.Management.Automation.PowerShell.Invoke(IEnumerable input, PSInvocationSettings settings)
at Microsoft.Azure.Commands.Automation.Common.AutomationClient.RegisterDscNode(String resourceGroupName, String automationAccountName, String azureVMName, String nodeconfigurationName, String configurationMode, Int32 configurationModeFrequencyMins, Int32
refreshFrequencyMins, Boolean rebootFlag, String actionAfterReboot, Boolean moduleOverwriteFlag, String azureVmResourceGroup, String azureVmLocation)
at Microsoft.Azure.Commands.Automation.Cmdlet.RegisterAzureAutomationDscNode.ExecuteCmdlet()
at Microsoft.WindowsAzure.Commands.Utilities.Common.AzurePSCmdlet.ProcessRecord();
DEBUG: Finish sending metric.
DEBUG: 1:05:16 PM - RegisterAzureAutomationDscNode end processing.
DEBUG: 1:05:16 PM - RegisterAzureAutomationDscNode end processing.
| non_priority | issues invoking register azurermautomationdscnode after azurerm automation upgrade to description after upgrading azurerm automation module to and all depending as azurerm profile all our dsc processes are failing with an strange pending parameter output tested from azure dsc and local with same modules version and we get the same response script steps for reproduction register azurermautomationdscnode resourcegroupname dscrgname automationaccountname automationaccountname azurevmname vmname configurationmodefrequencymins verbose rebootnodeifneeded true configurationmode applyandmonitor azurevmresourcegroup vmrgname nodeconfigurationname dscconfiguration all variable typeas and values seems correct module version directory c users username documents windowspowershell modules moduletype version name exportedcommands script azurerm automation get azurermautomationhybridworkergroup get azurermautomationjoboutputrecord import azurermautomationdscnodeconfiguration export azurermautomationdscconfiguration script azurerm profile disable azurermdatacollection disable azurermcontextautosave enable azurermdatacollection enable azurermcontextautosave directory c program files windowspowershell modules moduletype version name exportedcommands script azurerm script azurerm analysisservices resume azurermanalysisservicesserver suspend azurermanalysisservicesserver get azurermanalysisservicesserver remove azurermanalysisservicesserver script azurerm apimanagement add azurermapimanagementregion get azurermapimanagementssotoken new azurermapimanagementhostnameconfiguration new azurermapimanagementregion script azurerm applicationinsights get azurermapplicationinsights new azurermapplicationinsights remove azurermapplicationinsights set azurermapplicationinsightspricingplan script azurerm automation get azurermautomationhybridworkergroup get azurermautomationjoboutputrecord import azurermautomationdscnodeconfiguration export azurermautomationdscconfiguration script azurerm backup backup azurermbackupitem enable azurermbackupcontainerreregistration get azurermbackupcontainer register azurermbackupcontainer script azurerm batch remove azurermbatchaccount get azurermbatchaccount get azurermbatchaccountkeys new azurermbatchaccount script azurerm billing get azurermbillinginvoice get azurermbillingperiod script azurerm cdn get azurermcdnprofile get azurermcdnprofilessourl new azurermcdnprofile remove azurermcdnprofile script azurerm cognitiveservices get azurermcognitiveservicesaccount get azurermcognitiveservicesaccountkey get azurermcognitiveservicesaccountskus new azurermcognitiveservicesaccount script azurerm compute remove azurermavailabilityset get azurermavailabilityset new azurermavailabilityset update azurermavailabilityset script azurerm consumption get azurermconsumptionusagedetail script azurerm containerinstance new azurermcontainergroup get azurermcontainergroup remove azurermcontainergroup get azurermcontainerinstancelog script azurerm containerregistry new azurermcontainerregistry get azurermcontainerregistry update azurermcontainerregistry remove azurermcontainerregistry script azurerm datafactories remove azurermdatafactory get azurermdatafactoryrun get azurermdatafactoryslice save azurermdatafactorylog script azurerm set update get remove script azurerm datalakeanalytics get azurermdatalakeanalyticsdatasource new azurermdatalakeanalyticscatalogcredential remove azurermdatalakeanalyticscatalogcredential remove azurermdatalakeanalyticscatalogsecret script azurerm datalakestore get azurermdatalakestoretrustedidprovider remove azurermdatalakestoretrustedidprovider remove azurermdatalakestorefirewallrule set azurermdatalakestoretrustedidprovider script azurerm devtestlabs get azurermdtlallowedvmsizespolicy get azurermdtlautoshutdownpolicy get azurermdtlautostartpolicy get azurermdtlvmsperlabpolicy script azurerm dns get azurermdnsrecordset new azurermdnsrecordconfig remove azurermdnsrecordset set azurermdnsrecordset script azurerm eventgrid new azurermeventgridtopic get azurermeventgridtopic set azurermeventgridtopic new azurermeventgridtopickey script azurerm eventhub new azurermeventhubnamespace get azurermeventhubnamespace set azurermeventhubnamespace remove azurermeventhubnamespace script azurerm hdinsight get azurermhdinsightjob new azurermhdinsightsqoopjobdefinition wait azurermhdinsightjob new azurermhdinsightstreamingmapreducejobdefinition script azurerm insights get azurermmetricdefinition get azurermmetric remove azurermlogprofile get azurermlogprofile script azurerm iothub add azurermiothubkey get azurermiothubeventhubconsumergroup get azurermiothubconnectionstring get azurermiothubjob script azurerm keyvault add azurekeyvaultcertificate set azurekeyvaultcertificateattribute stop azurekeyvaultcertificateoperation get azurekeyvaultcertificateoperation script azurerm logicapp get azurermintegrationaccountagreement get azurermintegrationaccountcallbackurl get azurermintegrationaccountcertificate get azurermintegrationaccount script azurerm machinelearning move azurermmlcommitmentassociation get azurermmlcommitmentassociation get azurermmlcommitmentplanusagehistory remove azurermmlcommitmentplan script azurerm machinelearningcompute get azurermmlopcluster get azurermmlopclusterkey test azurermmlopclustersystemservicesupdateavailability update azurermmlopclustersystemservice script azurerm marketplaceordering get azurermmarketplaceterms set azurermmarketplaceterms script azurerm media sync azurermmediaservicestoragekeys set azurermmediaservicekey get azurermmediaservicekeys get azurermmediaservicenameavailability script azurerm network add azurermapplicationgatewayauthenticationcertificate get azurermapplicationgatewayauthenticationcertificate new azurermapplicationgatewayauthenticationcertificate remove azurermapplicationgatewayauthenti script azurerm notificationhubs get azurermnotificationhub get azurermnotificationhubauthorizationrules get azurermnotificationhublistkeys get azurermnotificationhubpnscredentials script azurerm operationalinsights new azurermoperationalinsightsazureactivitylogdatasource new azurermoperationalinsightscustomlogdatasource disable azurermoperationalinsightslinuxcustomlogcollection disable azurermoperationalinsightsiislo script azurerm powerbiembedded remove azurermpowerbiworkspacecollection get azurermpowerbiworkspacecollection get azurermpowerbiworkspacecollectionaccesskeys get azurermpowerbiworkspace script azurerm profile disable azurermdatacollection disable azurermcontextautosave enable azurermdatacollection enable azurermcontextautosave script azurerm recoveryservices get azurermrecoveryservicesbackupproperty get azurermrecoveryservicesvault get azurermrecoveryservicesvaultsettingsfile new azurermrecoveryservicesvault script azurerm recoveryservices backup backup azurermrecoveryservicesbackupitem get azurermrecoveryservicesbackupmanagementserver get azurermrecoveryservicesbackupcontainer unregister azurermrecoveryservicesbackupcontainer script azurerm recoveryservices siterec edit azurermrecoveryservicesasrrecoveryplan get azurermrecoveryservicesasralertsetting get azurermrecoveryservicesasrevent get azurermrecoveryservicesasrfabric script azurerm rediscache remove azurermrediscachepatchschedule new azurermrediscachescheduleentry get azurermrediscachepatchschedule new azurermrediscachepatchschedule script azurerm relay new azurermrelaynamespace get azurermrelaynamespace set azurermrelaynamespace remove azurermrelaynamespace script azurerm resources get azurermprovideroperation remove azurermroleassignment get azurermroleassignment new azurermroleassignment script azurerm scheduler disable azurermschedulerjobcollection enable azurermschedulerjobcollection get azurermschedulerjobcollection get azurermschedulerjob script azurerm servermanagement invoke azurermservermanagementpowershellcommand get azurermservermanagementsession new azurermservermanagementsession remove azurermservermanagementsession script azurerm servicebus new azurermservicebusnamespace get azurermservicebusnamespace set azurermservicebusnamespace remove azurermservicebusnamespace script azurerm servicefabric add azurermservicefabricapplicationcertificate add azurermservicefabricclientcertificate add azurermservicefabricclustercertificate add azurermservicefabricnode script azurerm siterecovery get azurermsiterecoveryfabric new azurermsiterecoveryfabric remove azurermsiterecoveryfabric stop azurermsiterecoveryjob script azurerm sql get azurermsqldatabasetransparentdataencryption get azurermsqldatabasetransparentdataencryptionactivity set azurermsqldatabasetransparentdataencryption get azurermsqldatabaseupgradehint script azurerm storage get azurermstorageaccount get azurermstorageaccountkey new azurermstorageaccount new azurermstorageaccountkey script azurerm streamanalytics get azurermstreamanalyticsfunction get azurermstreamanalyticsdefaultfunctiondefinition new azurermstreamanalyticsfunction remove azurermstreamanalyticsfunction script azurerm tags remove azurermtag get azurermtag new azurermtag script azurerm trafficmanager disable azurermtrafficmanagerendpoint enable azurermtrafficmanagerendpoint set azurermtrafficmanagerendpoint get azurermtrafficmanagerendpoint script azurerm usageaggregates get usageaggregates script azurerm websites get azurermappserviceplan set azurermappserviceplan new azurermappserviceplan remove azurermappserviceplan directory c program files microsoft sdks azure powershell resourcemanager azureresourcemanager moduletype version name exportedcommands script azurerm analysisservices resume azurermanalysisservicesserver suspend azurermanalysisservicesserver get azurermanalysisservicesserver remove azurermanalysisservicesserver script azurerm apimanagement add azurermapimanagementregion get azurermapimanagementssotoken new azurermapimanagementhostnameconfiguration new azurermapimanagementregion script azurerm applicationinsights get azurermapplicationinsights new azurermapplicationinsights remove azurermapplicationinsights set azurermapplicationinsightspricingplan script azurerm automation get azurermautomationhybridworkergroup get azurermautomationjoboutputrecord import azurermautomationdscnodeconfiguration export azurermautomationdscconfiguration script azurerm backup backup azurermbackupitem enable azurermbackupcontainerreregistration get azurermbackupcontainer register azurermbackupcontainer script azurerm batch remove azurermbatchaccount get azurermbatchaccount get azurermbatchaccountkeys new azurermbatchaccount script azurerm billing get azurermbillinginvoice get azurermbillingperiod script azurerm cdn get azurermcdnprofile get azurermcdnprofilessourl new azurermcdnprofile remove azurermcdnprofile script azurerm cognitiveservices get azurermcognitiveservicesaccount get azurermcognitiveservicesaccountkey get azurermcognitiveservicesaccountskus new azurermcognitiveservicesaccount script azurerm compute remove azurermavailabilityset get azurermavailabilityset new azurermavailabilityset update azurermavailabilityset script azurerm consumption get azurermconsumptionusagedetail script azurerm containerinstance new azurermcontainergroup get azurermcontainergroup remove azurermcontainergroup get azurermcontainerinstancelog script azurerm containerregistry new azurermcontainerregistry get azurermcontainerregistry update azurermcontainerregistry remove azurermcontainerregistry script azurerm datafactories remove azurermdatafactory get azurermdatafactoryrun get azurermdatafactoryslice save azurermdatafactorylog script azurerm set update get remove script azurerm datalakeanalytics get azurermdatalakeanalyticsdatasource new azurermdatalakeanalyticscatalogcredential remove azurermdatalakeanalyticscatalogcredential remove azurermdatalakeanalyticscatalogsecret script azurerm datalakestore get azurermdatalakestoretrustedidprovider remove azurermdatalakestoretrustedidprovider remove azurermdatalakestorefirewallrule set azurermdatalakestoretrustedidprovider script azurerm devtestlabs get azurermdtlallowedvmsizespolicy get azurermdtlautoshutdownpolicy get azurermdtlautostartpolicy get azurermdtlvmsperlabpolicy script azurerm dns get azurermdnsrecordset new azurermdnsrecordconfig remove azurermdnsrecordset set azurermdnsrecordset script azurerm eventgrid new azurermeventgridtopic get azurermeventgridtopic set azurermeventgridtopic new azurermeventgridtopickey script azurerm eventhub new azurermeventhubnamespace get azurermeventhubnamespace set azurermeventhubnamespace remove azurermeventhubnamespace script azurerm hdinsight get azurermhdinsightjob new azurermhdinsightsqoopjobdefinition wait azurermhdinsightjob new azurermhdinsightstreamingmapreducejobdefinition script azurerm insights get azurermmetricdefinition get azurermmetric remove azurermlogprofile get azurermlogprofile script azurerm iothub add azurermiothubkey get azurermiothubeventhubconsumergroup get azurermiothubconnectionstring get azurermiothubjob script azurerm keyvault add azurekeyvaultcertificate set azurekeyvaultcertificateattribute stop azurekeyvaultcertificateoperation get azurekeyvaultcertificateoperation script azurerm logicapp get azurermintegrationaccountagreement get azurermintegrationaccountcallbackurl get azurermintegrationaccountcertificate get azurermintegrationaccount script azurerm machinelearning move azurermmlcommitmentassociation get azurermmlcommitmentassociation get azurermmlcommitmentplanusagehistory remove azurermmlcommitmentplan script azurerm machinelearningcompute get azurermmlopcluster get azurermmlopclusterkey test azurermmlopclustersystemservicesupdateavailability update azurermmlopclustersystemservice script azurerm marketplaceordering get azurermmarketplaceterms set azurermmarketplaceterms script azurerm media sync azurermmediaservicestoragekeys set azurermmediaservicekey get azurermmediaservicekeys get azurermmediaservicenameavailability script azurerm network add azurermapplicationgatewayauthenticationcertificate get azurermapplicationgatewayauthenticationcertificate new azurermapplicationgatewayauthenticationcertificate remove azurermapplicationgatewayauthenti script azurerm notificationhubs get azurermnotificationhub get azurermnotificationhubauthorizationrules get azurermnotificationhublistkeys get azurermnotificationhubpnscredentials script azurerm operationalinsights new azurermoperationalinsightsazureactivitylogdatasource new azurermoperationalinsightscustomlogdatasource disable azurermoperationalinsightslinuxcustomlogcollection disable azurermoperationalinsightsiislo script azurerm powerbiembedded remove azurermpowerbiworkspacecollection get azurermpowerbiworkspacecollection get azurermpowerbiworkspacecollectionaccesskeys get azurermpowerbiworkspace script azurerm profile disable azurermdatacollection disable azurermcontextautosave enable azurermdatacollection enable azurermcontextautosave script azurerm recoveryservices get azurermrecoveryservicesbackupproperty get azurermrecoveryservicesvault get azurermrecoveryservicesvaultsettingsfile new azurermrecoveryservicesvault script azurerm recoveryservices backup backup azurermrecoveryservicesbackupitem get azurermrecoveryservicesbackupmanagementserver get azurermrecoveryservicesbackupcontainer unregister azurermrecoveryservicesbackupcontainer script azurerm recoveryservices siterec edit azurermrecoveryservicesasrrecoveryplan get azurermrecoveryservicesasralertsetting get azurermrecoveryservicesasrevent get azurermrecoveryservicesasrfabric script azurerm rediscache remove azurermrediscachepatchschedule new azurermrediscachescheduleentry get azurermrediscachepatchschedule new azurermrediscachepatchschedule script azurerm relay new azurermrelaynamespace get azurermrelaynamespace set azurermrelaynamespace remove azurermrelaynamespace script azurerm resources get azurermprovideroperation remove azurermroleassignment get azurermroleassignment new azurermroleassignment script azurerm scheduler disable azurermschedulerjobcollection enable azurermschedulerjobcollection get azurermschedulerjobcollection get azurermschedulerjob script azurerm servermanagement invoke azurermservermanagementpowershellcommand get azurermservermanagementsession new azurermservermanagementsession remove azurermservermanagementsession script azurerm servicebus new azurermservicebusnamespace get azurermservicebusnamespace set azurermservicebusnamespace remove azurermservicebusnamespace script azurerm servicefabric add azurermservicefabricapplicationcertificate add azurermservicefabricclientcertificate add azurermservicefabricclustercertificate add azurermservicefabricnode script azurerm siterecovery get azurermsiterecoveryfabric new azurermsiterecoveryfabric remove azurermsiterecoveryfabric stop azurermsiterecoveryjob script azurerm sql get azurermsqldatabasetransparentdataencryption get azurermsqldatabasetransparentdataencryptionactivity set azurermsqldatabasetransparentdataencryption get azurermsqldatabaseupgradehint script azurerm storage get azurermstorageaccount get azurermstorageaccountkey new azurermstorageaccount new azurermstorageaccountkey script azurerm streamanalytics get azurermstreamanalyticsfunction get azurermstreamanalyticsdefaultfunctiondefinition new azurermstreamanalyticsfunction remove azurermstreamanalyticsfunction script azurerm tags remove azurermtag get azurermtag new azurermtag script azurerm trafficmanager disable azurermtrafficmanagerendpoint enable azurermtrafficmanagerendpoint set azurermtrafficmanagerendpoint get azurermtrafficmanagerendpoint script azurerm usageaggregates get usageaggregates script azurerm websites get azurermappserviceplan set azurermappserviceplan new azurermappserviceplan remove azurermappserviceplan environment data name value psversion psedition desktop pscompatibleversions buildversion clrversion wsmanstackversion psremotingprotocolversion serializationversion debug output ps c windows register azurermautomationdscnode resourcegroupname management automationaccountname automationaccountname azurevmname vm name configurationmodefrequencymins verbose rebootnodeifneeded true configurationmode applyandmonitor azure vmresourcegroup vm resourcegroupname nodeconfigurationname dscconfiguration debug pm registerazureautomationdscnode begin processing with parameterset allparametersets debug pm using account id xxx xxxxxx xxxxx xxxxx debug resourcegroupname management automationaccountname xxxxxxdscaccount azurevmname bpo tst web nodeconfigurationname configurationmode applyandmonitor configurationmodefrequencymins refreshfrequencymins rebootnodeifneeded true actionafterreboot continueconfiguration allowmoduleoverwrite false azurevmresourcegroup bpo tst rg azurevmlocation debug authenticating using account xxxxxx xxxxxxx xxxxxxx xxxxx environment azurecloud tenant dfdb debug microsoft identitymodel clients activedirectory information debug tokencache serializing token cache with items debug microsoft identitymodel clients activedirectory information debug tokencache serializing token cache with items debug authenticating using configuration values domain dfdb endpoint clientid clientredirect urn ietf wg oauth oob resourceclienturi validateauthrity true debug acquiring token using context with authority correlationid validateauthority true debug acquiring token using adalconfiguration with domain dfdb adendpoint clientid clientredirecturi urn ietf wg oauth oob debug microsoft identitymodel clients activedirectory information debug acquiretokenhandlerbase token acquisition started authority resource clientid cachetype microsoft azure commands common authentication protectedfiletokencache items authentication target user debug microsoft identitymodel clients activedirectory information debug tokencache deserialized items to token cache debug microsoft identitymodel clients activedirectory verbose debug tokencache looking up cache for a token debug microsoft identitymodel clients activedirectory information debug tokencache an item matching the requested resource was found in the cache debug microsoft identitymodel clients activedirectory verbose debug tokencache minutes left until token in cache expires debug microsoft identitymodel clients activedirectory information debug tokencache a matching item access token or refresh token or both was found in the cache debug microsoft identitymodel clients activedirectory information debug acquiretokenhandlerbase token acquisition finished successfully an access token was retuned access token hash egck refresh token hash ie expiration time user hash i debug received token with logintype liveid tenant dfdb userid xxxxxx xxxxxx xxxxxx xxxx debug renewing token with type bearer expiry multipleresource true tenant dfdb userid xxxxxxx xxxxxxx xxxxxxxx xxxxxx debug user info for token displayid xxxxxxx xxxxx xxxxxx xxxx name idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers accept application json x ms version body debug http response status code ok headers pragma no cache ocp automation accountid x ms request id strict transport security max age includesubdomains x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id westeurope x content type options nosniff cache control no cache date tue sep gmt server microsoft iis x aspnet version x powered by asp net body name xxxxxxdscaccount id subscriptions resourcegroups management providers microsoft automation automationaccounts xxxxxxxdscaccount type microsoft automation automationaccounts location westeurope tags etag null properties sku name basic family null capacity null state ok registrationurl creationtime lastmodifiedby null lastmodifiedtime debug renewing token with type bearer expiry multipleresource true tenant dfdb userid xxxxxx xxxxxx xxxxxx xxxx debug user info for token displayid xxxx xxxxx xxxxxxx xxxxx name idprovider uid debug checking token expiration token expires comparing to with threshold calculated time until token expiry debug http request http method get absolute uri headers accept application json x ms version body debug http response status code ok headers pragma no cache x ms request id strict transport security max age includesubdomains x ms ratelimit remaining subscription reads x ms correlation request id x ms routing request id westeurope x content type options nosniff cache control no cache date tue sep gmt server microsoft iis x aspnet version x powered by asp net body id subscriptions resourcegroups management providers microsoft automation automationaccounts xxxxxxdscaccount agentregistrationinformation keys primary jiqficlewftfqfqlpdbxqgj secondary endpoint dscmetaconfiguration r n tinstance of msft webdownloadmanager as msft r n t r n tresourceid azureautomationdsc r n t sourceinfo c oaas configurationrepositoryweb r n t registrationkey jiqficlewftfqfqlpdbxqgj r n t serverurl of msft webresourcemanager as msft r n t r n t sourceinfo c oaas resourcerepositoryweb r n t serverurl resourceid azureautomationdsc r n t registrationkey jiqficlewftfqfqlpdbxqgj r n t r n r n tinstance of msft webreportmanager as msft r n t r n t sourceinfo c oaas reportserverweb r n t serverurl resourceid azureautomationdsc r n t registrationkey jiqficlewftfqfqlpdbxqgj r n t r n r n tinstance of msft dscmetaconfiguration as msft r n t r n t refreshmode pull r n t allowmoduleoverwrite false r n t actionafterreboot continueconfiguration r n t refreshfrequencymins r n t rebootnodeifneeded false r n t configurationmodefrequencymins r n t configurationmode applyandmonitor r n r n t resourcemodulemanagers r n t msft r n t r n t reportmanagers r n t msft r n t r n t configurationdownloadmanagers r n t msft r n t r n t r n r n tinstance of omi configurationdocument r n t r n t version r n t minimumcompatibleversion r n t compatibleversionadditionalproperties msft dscmetaconfiguration statusretentiontimeindays r n t author azureautomation r n t generationdate r n t generationhost azureautomation r n t name registrationmetaconfig r n t r n t register azurermautomationdscnode cannot process command because of one or more missing mandatory parameters resourcegroupname templatefile at line char register azurermautomationdscnode resourcegroupname management au categoryinfo closeerror parameterbindingexception fullyqualifiederrorid microsoft azure commands automation cmdlet registerazureautomationdscnode debug azureqosevent commandname register azurermautomationdscnode issuccess false duration exception system management automation parameterbindingexception cannot process command because of one or more missing mandatory parameters resourcegroupname templatefile at system management automation runspaces pipelinebase invoke ienumerable input at system management automation powershell worker constructpipelineanddowork runspace rs boolean performsyncinvoke at system management automation powershell worker createrunspaceifneededanddowork runspace rstouse boolean issync at system management automation powershell coreinvokehelper psdatacollection input psdatacollection output psinvocationsettings settings at system management automation powershell coreinvoke psdatacollection input psdatacollection output psinvocationsettings settings at system management automation powershell invoke ienumerable input psinvocationsettings settings at microsoft azure commands automation common automationclient registerdscnode string resourcegroupname string automationaccountname string azurevmname string nodeconfigurationname string configurationmode configurationmodefrequencymins refreshfrequencymins boolean rebootflag string actionafterreboot boolean moduleoverwriteflag string azurevmresourcegroup string azurevmlocation at microsoft azure commands automation cmdlet registerazureautomationdscnode executecmdlet at microsoft windowsazure commands utilities common azurepscmdlet processrecord debug finish sending metric debug pm registerazureautomationdscnode end processing debug pm registerazureautomationdscnode end processing | 0 |
138,942 | 11,222,590,889 | IssuesEvent | 2020-01-07 20:32:57 | Sp2000/colplus-repo | https://api.github.com/repos/Sp2000/colplus-repo | closed | Conversion report 2019-11-25 | report testing | Here's the [stats diff]() for the 2019-11-26 draft with the following notable changes between 2019-11-26 and 2019-09-19:
- FishBase lost ~6000 common names
- Scarabs may have lost its database ID in ac-export.zip (?), so appears missing in the stats diff but it still [shows up in management classification on the database page](http://workbench.catalogueoflife.org/col_plus/details/database/id/500). For Scarabs, in the AC_Interface the database info is missing on the species pages (see 2nd screenshot below).

- "CoL Management Classification" is missing in the AC_Interface classification tree, although [GSD 500 is present](http://workbench.catalogueoflife.org/col_plus/details/database/id/500)
- Lost ~30 synonyms in WSCP
- There's lots of small improvements where stats previously were off by usually less than 10 species and now match. MOWD stats now match exactly (66 taxa improvement)
- World Ferns lost 221 species, 81 infraspecies, 618 synonyms
- World Plants lost 599 species, 194 infraspecies, 1082 synonyms
- Fossil Ginkgoales lost 100 extinct species
- StaphBase improved by ~700 synonyms | 1.0 | Conversion report 2019-11-25 - Here's the [stats diff]() for the 2019-11-26 draft with the following notable changes between 2019-11-26 and 2019-09-19:
- FishBase lost ~6000 common names
- Scarabs may have lost its database ID in ac-export.zip (?), so appears missing in the stats diff but it still [shows up in management classification on the database page](http://workbench.catalogueoflife.org/col_plus/details/database/id/500). For Scarabs, in the AC_Interface the database info is missing on the species pages (see 2nd screenshot below).

- "CoL Management Classification" is missing in the AC_Interface classification tree, although [GSD 500 is present](http://workbench.catalogueoflife.org/col_plus/details/database/id/500)
- Lost ~30 synonyms in WSCP
- There's lots of small improvements where stats previously were off by usually less than 10 species and now match. MOWD stats now match exactly (66 taxa improvement)
- World Ferns lost 221 species, 81 infraspecies, 618 synonyms
- World Plants lost 599 species, 194 infraspecies, 1082 synonyms
- Fossil Ginkgoales lost 100 extinct species
- StaphBase improved by ~700 synonyms | non_priority | conversion report here s the for the draft with the following notable changes between and fishbase lost common names scarabs may have lost its database id in ac export zip so appears missing in the stats diff but it still for scarabs in the ac interface the database info is missing on the species pages see screenshot below col management classification is missing in the ac interface classification tree although lost synonyms in wscp there s lots of small improvements where stats previously were off by usually less than species and now match mowd stats now match exactly taxa improvement world ferns lost species infraspecies synonyms world plants lost species infraspecies synonyms fossil ginkgoales lost extinct species staphbase improved by synonyms | 0 |
231,637 | 25,525,472,684 | IssuesEvent | 2022-11-29 01:37:01 | kapseliboi/WeiPay | https://api.github.com/repos/kapseliboi/WeiPay | reopened | CVE-2020-7789 (Medium) detected in node-notifier-5.4.0.tgz | security vulnerability | ## CVE-2020-7789 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-notifier-5.4.0.tgz</b></p></summary>
<p>A Node.js module for sending notifications on native Mac, Windows (post and pre 8) and Linux (or Growl as fallback)</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.0.tgz">https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-notifier/package.json</p>
<p>
Dependency Hierarchy:
- react-native-0.55.4.tgz (Root Library)
- :x: **node-notifier-5.4.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>stable</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package node-notifier before 9.0.0. It allows an attacker to run arbitrary commands on Linux machines due to the options params not being sanitised when being passed an array.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7789>CVE-2020-7789</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (node-notifier): 5.4.4</p>
<p>Direct dependency fix Resolution (react-native): 0.56.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7789 (Medium) detected in node-notifier-5.4.0.tgz - ## CVE-2020-7789 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-notifier-5.4.0.tgz</b></p></summary>
<p>A Node.js module for sending notifications on native Mac, Windows (post and pre 8) and Linux (or Growl as fallback)</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.0.tgz">https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-notifier/package.json</p>
<p>
Dependency Hierarchy:
- react-native-0.55.4.tgz (Root Library)
- :x: **node-notifier-5.4.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>stable</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package node-notifier before 9.0.0. It allows an attacker to run arbitrary commands on Linux machines due to the options params not being sanitised when being passed an array.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7789>CVE-2020-7789</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (node-notifier): 5.4.4</p>
<p>Direct dependency fix Resolution (react-native): 0.56.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node notifier tgz cve medium severity vulnerability vulnerable library node notifier tgz a node js module for sending notifications on native mac windows post and pre and linux or growl as fallback library home page a href path to dependency file package json path to vulnerable library node modules node notifier package json dependency hierarchy react native tgz root library x node notifier tgz vulnerable library found in base branch stable vulnerability details this affects the package node notifier before it allows an attacker to run arbitrary commands on linux machines due to the options params not being sanitised when being passed an array publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node notifier direct dependency fix resolution react native step up your open source security game with mend | 0 |
195,055 | 14,701,112,634 | IssuesEvent | 2021-01-04 11:18:29 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | coinexchain/cet-sdk: modules/bancorlite/internal/keepers/keeper_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [coinexchain/cet-sdk](https://www.github.com/coinexchain/cet-sdk) at [modules/bancorlite/internal/keepers/keeper_test.go](https://github.com/coinexchain/cet-sdk/blob/be74ddd3fc86a8968a73a7da79d7aebc7f0ac0df/modules/bancorlite/internal/keepers/keeper_test.go#L265-L267)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> function call at line 266 passes reference to p to third-party code
[Click here to see the code in its original context.](https://github.com/coinexchain/cet-sdk/blob/be74ddd3fc86a8968a73a7da79d7aebc7f0ac0df/modules/bancorlite/internal/keepers/keeper_test.go#L265-L267)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, p := range bi {
keeper.Save(ctx, &p)
}
```
</details>
<details>
<summary>Click here to show extra information the analyzer produced.</summary>
```
No path was found through the callgraph that could lead to a function which writes a pointer argument.
The following graphviz dot graph describes paths through the callgraph that could lead to a function which passes a pointer to third-party code:
digraph G {
"(Save, 2)" -> {}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: be74ddd3fc86a8968a73a7da79d7aebc7f0ac0df
| 1.0 | coinexchain/cet-sdk: modules/bancorlite/internal/keepers/keeper_test.go; 3 LoC -
Found a possible issue in [coinexchain/cet-sdk](https://www.github.com/coinexchain/cet-sdk) at [modules/bancorlite/internal/keepers/keeper_test.go](https://github.com/coinexchain/cet-sdk/blob/be74ddd3fc86a8968a73a7da79d7aebc7f0ac0df/modules/bancorlite/internal/keepers/keeper_test.go#L265-L267)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> function call at line 266 passes reference to p to third-party code
[Click here to see the code in its original context.](https://github.com/coinexchain/cet-sdk/blob/be74ddd3fc86a8968a73a7da79d7aebc7f0ac0df/modules/bancorlite/internal/keepers/keeper_test.go#L265-L267)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, p := range bi {
keeper.Save(ctx, &p)
}
```
</details>
<details>
<summary>Click here to show extra information the analyzer produced.</summary>
```
No path was found through the callgraph that could lead to a function which writes a pointer argument.
The following graphviz dot graph describes paths through the callgraph that could lead to a function which passes a pointer to third-party code:
digraph G {
"(Save, 2)" -> {}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: be74ddd3fc86a8968a73a7da79d7aebc7f0ac0df
| non_priority | coinexchain cet sdk modules bancorlite internal keepers keeper test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call at line passes reference to p to third party code click here to show the line s of go which triggered the analyzer go for p range bi keeper save ctx p click here to show extra information the analyzer produced no path was found through the callgraph that could lead to a function which writes a pointer argument the following graphviz dot graph describes paths through the callgraph that could lead to a function which passes a pointer to third party code digraph g save leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
1,856 | 2,575,435,627 | IssuesEvent | 2015-02-11 23:04:00 | ThibaultLatrille/ControverSciences | https://api.github.com/repos/ThibaultLatrille/ControverSciences | closed | Caractères restants | ** to do design | Vert/rouge et indiquer combien en trop
Sur la page http://0.0.0.0:3000/comments/3/edit
Par : T. Lorin
Navigateur : chrome modern linux webkit | 1.0 | Caractères restants - Vert/rouge et indiquer combien en trop
Sur la page http://0.0.0.0:3000/comments/3/edit
Par : T. Lorin
Navigateur : chrome modern linux webkit | non_priority | caractères restants vert rouge et indiquer combien en trop sur la page par t lorin navigateur chrome modern linux webkit | 0 |
204,310 | 15,896,884,107 | IssuesEvent | 2021-04-11 19:00:26 | AJStacy/Adze | https://api.github.com/repos/AJStacy/Adze | closed | Add documentation for unit testing | documentation enhancement | Write documentation explaining global environment variables that can be used for toggling logs during unit testing. | 1.0 | Add documentation for unit testing - Write documentation explaining global environment variables that can be used for toggling logs during unit testing. | non_priority | add documentation for unit testing write documentation explaining global environment variables that can be used for toggling logs during unit testing | 0 |
328,222 | 28,106,140,851 | IssuesEvent | 2023-03-31 00:58:07 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | reopened | DISABLED test_vmapvjpvjp_linalg_lu_cuda_float32 (__main__.TestOperatorsCUDA) | triaged module: flaky-tests skipped module: functorch | Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_vmapvjpvjp_linalg_lu_cuda_float32&suite=TestOperatorsCUDA) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/8873086538).
Over the past 3 hours, it has been determined flaky in 1 workflow(s) with 1 failures and 1 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT BE ALARMED IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_vmapvjpvjp_linalg_lu_cuda_float32`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
cc @zou3519 @Chillee @samdow @soumith | 1.0 | DISABLED test_vmapvjpvjp_linalg_lu_cuda_float32 (__main__.TestOperatorsCUDA) - Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_vmapvjpvjp_linalg_lu_cuda_float32&suite=TestOperatorsCUDA) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/8873086538).
Over the past 3 hours, it has been determined flaky in 1 workflow(s) with 1 failures and 1 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT BE ALARMED IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_vmapvjpvjp_linalg_lu_cuda_float32`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
cc @zou3519 @Chillee @samdow @soumith | non_priority | disabled test vmapvjpvjp linalg lu cuda main testoperatorscuda platforms linux this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with failures and successes debugging instructions after clicking on the recent samples link do not be alarmed if the ci is green we now shield flaky tests from developers so ci will thus be green but it will be harder to parse the logs to find relevant log snippets click on the workflow logs linked above click on the test step of the job so that it is expanded otherwise the grepping will not work grep for test vmapvjpvjp linalg lu cuda there should be several instances run as flaky tests are rerun in ci from which you can study the logs cc chillee samdow soumith | 0 |
3,517 | 6,492,117,666 | IssuesEvent | 2017-08-21 11:56:09 | Cxbx-Reloaded/Cxbx-Reloaded | https://api.github.com/repos/Cxbx-Reloaded/Cxbx-Reloaded | closed | Starsky And Hutch - reaches the menu but the graphics are broken | game-compatibility | Merge PR #307 is merged, Starsky And Hutch reaches the menu but the graphics are broken.


[Xbe.txt](https://github.com/Cxbx-Reloaded/Cxbx-Reloaded/files/887128/Xbe.txt)
[KrnlDebug.txt](https://github.com/Cxbx-Reloaded/Cxbx-Reloaded/files/887131/KrnlDebug.txt)
| True | Starsky And Hutch - reaches the menu but the graphics are broken - Merge PR #307 is merged, Starsky And Hutch reaches the menu but the graphics are broken.


[Xbe.txt](https://github.com/Cxbx-Reloaded/Cxbx-Reloaded/files/887128/Xbe.txt)
[KrnlDebug.txt](https://github.com/Cxbx-Reloaded/Cxbx-Reloaded/files/887131/KrnlDebug.txt)
| non_priority | starsky and hutch reaches the menu but the graphics are broken merge pr is merged starsky and hutch reaches the menu but the graphics are broken | 0 |
21,768 | 17,687,962,991 | IssuesEvent | 2021-08-24 06:03:03 | ZcashFoundation/zebra | https://api.github.com/repos/ZcashFoundation/zebra | opened | Zebra panics when git checkout has been modified | C-bug A-rust S-needs-triage P-Medium I-panic I-usability | ## Description
Sometimes when I run Zebra with a modified git checkout, it panics with a semver error.
This is probably a bug in how we convert git semver to Rust semver.
I'll fix this eventually, when it gets annoying enough.
This is unexpected work in Sprint 17.
TODO <details>
### Steps to Reproduce
I tried this:
[behavior or code sample that causes the bug]
```sh
copy and paste the exact commands or code here
```
### Expected Behaviour
I expected to see this happen: [explanation]
### Actual Behaviour
Instead, this happened: [explanation]
### Zebra Logs
<!--
Copy and paste the last 100 Zebra log lines.
Or upload the full logs to https://gist.github.com/ and add a link to them here.
-->
<details>
```
copy and paste the logs here
```
</details>
## Environment
### Zebra Version
<!--
For bugs in `zebrad`, run `zebrad version`.
For bugs in the `zebra` libraries, list the `zebra` crate versions.
You can get this information using cargo-tree:
cargo install cargo-tree
cargo tree | grep zebra
-->
</details>
### Operating System
This behavior might have changed because the `libgit2` crate version is unpinned, or because my version of `git` stores different metadata in `.git`.
```
$ uname -a
Linux ... 5.4.122 #1-NixOS SMP Wed May 26 10:05:21 UTC 2021 x86_64 GNU/Linux`
$ git --version
git version 2.32.0
$ cargo tree | rg git2
├── git2 v0.13.17
│ ├── libgit2-sys v0.12.19+1.1.0
``` | True | Zebra panics when git checkout has been modified - ## Description
Sometimes when I run Zebra with a modified git checkout, it panics with a semver error.
This is probably a bug in how we convert git semver to Rust semver.
I'll fix this eventually, when it gets annoying enough.
This is unexpected work in Sprint 17.
TODO <details>
### Steps to Reproduce
I tried this:
[behavior or code sample that causes the bug]
```sh
copy and paste the exact commands or code here
```
### Expected Behaviour
I expected to see this happen: [explanation]
### Actual Behaviour
Instead, this happened: [explanation]
### Zebra Logs
<!--
Copy and paste the last 100 Zebra log lines.
Or upload the full logs to https://gist.github.com/ and add a link to them here.
-->
<details>
```
copy and paste the logs here
```
</details>
## Environment
### Zebra Version
<!--
For bugs in `zebrad`, run `zebrad version`.
For bugs in the `zebra` libraries, list the `zebra` crate versions.
You can get this information using cargo-tree:
cargo install cargo-tree
cargo tree | grep zebra
-->
</details>
### Operating System
This behavior might have changed because the `libgit2` crate version is unpinned, or because my version of `git` stores different metadata in `.git`.
```
$ uname -a
Linux ... 5.4.122 #1-NixOS SMP Wed May 26 10:05:21 UTC 2021 x86_64 GNU/Linux`
$ git --version
git version 2.32.0
$ cargo tree | rg git2
├── git2 v0.13.17
│ ├── libgit2-sys v0.12.19+1.1.0
``` | non_priority | zebra panics when git checkout has been modified description sometimes when i run zebra with a modified git checkout it panics with a semver error this is probably a bug in how we convert git semver to rust semver i ll fix this eventually when it gets annoying enough this is unexpected work in sprint todo steps to reproduce i tried this sh copy and paste the exact commands or code here expected behaviour i expected to see this happen actual behaviour instead this happened zebra logs copy and paste the last zebra log lines or upload the full logs to and add a link to them here copy and paste the logs here environment zebra version for bugs in zebrad run zebrad version for bugs in the zebra libraries list the zebra crate versions you can get this information using cargo tree cargo install cargo tree cargo tree grep zebra operating system this behavior might have changed because the crate version is unpinned or because my version of git stores different metadata in git uname a linux nixos smp wed may utc gnu linux git version git version cargo tree rg ├── │ ├── sys | 0 |
52,508 | 7,768,026,542 | IssuesEvent | 2018-06-03 13:43:00 | barrucadu/dejafu | https://api.github.com/repos/barrucadu/dejafu | closed | Quick intro to heap profiling in CONTRIBUTING file | T: documentation | I just had to check the GHC docs for the appropriate incantation, would be good to have a small note in the CONTRIBUTING file about some useful flags. | 1.0 | Quick intro to heap profiling in CONTRIBUTING file - I just had to check the GHC docs for the appropriate incantation, would be good to have a small note in the CONTRIBUTING file about some useful flags. | non_priority | quick intro to heap profiling in contributing file i just had to check the ghc docs for the appropriate incantation would be good to have a small note in the contributing file about some useful flags | 0 |
1,156 | 2,532,542,880 | IssuesEvent | 2015-01-23 16:46:17 | autotest/autotest-docker | https://api.github.com/repos/autotest/autotest-docker | opened | New test: Docker events for exec_create and exec_start | New Feature Docker Test On Milestone | Likely just need to add these to existing events test | 1.0 | New test: Docker events for exec_create and exec_start - Likely just need to add these to existing events test | non_priority | new test docker events for exec create and exec start likely just need to add these to existing events test | 0 |
322,708 | 23,919,820,489 | IssuesEvent | 2022-09-09 15:45:32 | JanssenProject/jans | https://api.github.com/repos/JanssenProject/jans | closed | docs(config-api): auto generation of swagger spec | comp-docker-jans-config-api area-documentation | Incorporate auto generation of swagger spec for endpoint
| 1.0 | docs(config-api): auto generation of swagger spec - Incorporate auto generation of swagger spec for endpoint
| non_priority | docs config api auto generation of swagger spec incorporate auto generation of swagger spec for endpoint | 0 |
131,376 | 18,245,019,515 | IssuesEvent | 2021-10-01 17:10:46 | sveltejs/kit | https://api.github.com/repos/sveltejs/kit | closed | XSS using data-url when doing SSR | bug security | ### Describe the bug
It is possible to inject a script tag in `data-url` in the `svelte-data` script tag.
E.g. if we have the search term in the query params https://www.google.com/search?q=Svelte we can create a malicious term that inject a script tag while SSR.
Happens on Firefox, Brave and Chrome, but Safari seems to protect against my POC, however it should be possible to circumvent it in other scenarios.
### Reproduction
#### Minimal example
##### term.js
```js
export const term = '/asdf?search="></script><script>alert(1)</script><script type="application/json';
```
##### index.svelte
```html
<script context="module">
import { term } from './term';
export async function load({ fetch }) {
const res = await fetch(term);
return {
props: {
results: await res.json()
}
};
}
</script>
<h1>Supersearch</h1>
```
#### Deployed POC using query params
POC Deployed: https://debug-app.vkrae.workers.dev/?search=%22%3E%3C/script%3E%3Cscript%3Ealert(1)%3C/script%3E%3Cscript%20type=%22application/json
POC Code: https://github.com/valterkraemer/debug-app/commit/1cc04c89d033bd31c0fb3ccb88ef8bb039128507
### Logs
_No response_
### System Info
```shell
System:
OS: macOS 11.6
CPU: (8) arm64 Apple M1
Memory: 144.72 MB / 8.00 GB
Shell: 5.8 - /bin/zsh
Binaries:
Node: 14.17.6 - ~/.nvm/versions/node/v14.17.6/bin/node
npm: 6.14.15 - ~/.nvm/versions/node/v14.17.6/bin/npm
Browsers:
Brave Browser: 93.1.29.79
Chrome: 94.0.4606.61
Firefox: 92.0.1
Safari: 14.1.2
npmPackages:
@sveltejs/adapter-cloudflare-workers: ^1.0.0-next.21 => 1.0.0-next.23
@sveltejs/kit: next => 1.0.0-next.178
svelte: ^3.42.6 => 3.43.1
```
### Severity
serious, but I can work around it
### Additional Information
_No response_ | True | XSS using data-url when doing SSR - ### Describe the bug
It is possible to inject a script tag in `data-url` in the `svelte-data` script tag.
E.g. if we have the search term in the query params https://www.google.com/search?q=Svelte we can create a malicious term that inject a script tag while SSR.
Happens on Firefox, Brave and Chrome, but Safari seems to protect against my POC, however it should be possible to circumvent it in other scenarios.
### Reproduction
#### Minimal example
##### term.js
```js
export const term = '/asdf?search="></script><script>alert(1)</script><script type="application/json';
```
##### index.svelte
```html
<script context="module">
import { term } from './term';
export async function load({ fetch }) {
const res = await fetch(term);
return {
props: {
results: await res.json()
}
};
}
</script>
<h1>Supersearch</h1>
```
#### Deployed POC using query params
POC Deployed: https://debug-app.vkrae.workers.dev/?search=%22%3E%3C/script%3E%3Cscript%3Ealert(1)%3C/script%3E%3Cscript%20type=%22application/json
POC Code: https://github.com/valterkraemer/debug-app/commit/1cc04c89d033bd31c0fb3ccb88ef8bb039128507
### Logs
_No response_
### System Info
```shell
System:
OS: macOS 11.6
CPU: (8) arm64 Apple M1
Memory: 144.72 MB / 8.00 GB
Shell: 5.8 - /bin/zsh
Binaries:
Node: 14.17.6 - ~/.nvm/versions/node/v14.17.6/bin/node
npm: 6.14.15 - ~/.nvm/versions/node/v14.17.6/bin/npm
Browsers:
Brave Browser: 93.1.29.79
Chrome: 94.0.4606.61
Firefox: 92.0.1
Safari: 14.1.2
npmPackages:
@sveltejs/adapter-cloudflare-workers: ^1.0.0-next.21 => 1.0.0-next.23
@sveltejs/kit: next => 1.0.0-next.178
svelte: ^3.42.6 => 3.43.1
```
### Severity
serious, but I can work around it
### Additional Information
_No response_ | non_priority | xss using data url when doing ssr describe the bug it is possible to inject a script tag in data url in the svelte data script tag e g if we have the search term in the query params we can create a malicious term that inject a script tag while ssr happens on firefox brave and chrome but safari seems to protect against my poc however it should be possible to circumvent it in other scenarios reproduction minimal example term js js export const term asdf search alert script type application json index svelte html import term from term export async function load fetch const res await fetch term return props results await res json supersearch deployed poc using query params poc deployed poc code logs no response system info shell system os macos cpu apple memory mb gb shell bin zsh binaries node nvm versions node bin node npm nvm versions node bin npm browsers brave browser chrome firefox safari npmpackages sveltejs adapter cloudflare workers next next sveltejs kit next next svelte severity serious but i can work around it additional information no response | 0 |
68,353 | 8,263,330,202 | IssuesEvent | 2018-09-14 01:43:04 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Parentheses can be removed (IDE0047) false-positives | Area-IDE Bug Need Design Review Resolution-Won't Fix | Following code produces false-positive when `dotnet_style_parentheses_in_relational_binary_operators` is set to `always_for_clarity`.
```csharp
public static bool Foo(int a, int b, bool c)
{
return (a == b) == c;
}
```
Since the rule is set to always for clarity, my assumption is that the code is indeed fine as-is.
I understand that the analyzer cannot always guess the parenthesis right in these situations and should ignore the statement rather than producing the message.
**Version Used**:
* Visual Studio: 15.8.0
* Roslyn: 2.9.0.63208 (958f2354)
**Steps to Reproduce**:
1. Set `dotnet_style_parentheses_in_relational_binary_operators` to `always_for_clarity` in `.editorconfig`
2. Copy the code above to the editor
**Expected Behavior**:
No message, actually I'd prefer if the analyzer reported an issue if the parenthesis is missing (but this might be too strict to say for every scenario).
**Actual Behavior**:
IDE0047 is reported.
**Notes:**
Originally posted to: MicrosoftDocs/visualstudio-docs#1392
Related to: #29454 | 1.0 | Parentheses can be removed (IDE0047) false-positives - Following code produces false-positive when `dotnet_style_parentheses_in_relational_binary_operators` is set to `always_for_clarity`.
```csharp
public static bool Foo(int a, int b, bool c)
{
return (a == b) == c;
}
```
Since the rule is set to always for clarity, my assumption is that the code is indeed fine as-is.
I understand that the analyzer cannot always guess the parenthesis right in these situations and should ignore the statement rather than producing the message.
**Version Used**:
* Visual Studio: 15.8.0
* Roslyn: 2.9.0.63208 (958f2354)
**Steps to Reproduce**:
1. Set `dotnet_style_parentheses_in_relational_binary_operators` to `always_for_clarity` in `.editorconfig`
2. Copy the code above to the editor
**Expected Behavior**:
No message, actually I'd prefer if the analyzer reported an issue if the parenthesis is missing (but this might be too strict to say for every scenario).
**Actual Behavior**:
IDE0047 is reported.
**Notes:**
Originally posted to: MicrosoftDocs/visualstudio-docs#1392
Related to: #29454 | non_priority | parentheses can be removed false positives following code produces false positive when dotnet style parentheses in relational binary operators is set to always for clarity csharp public static bool foo int a int b bool c return a b c since the rule is set to always for clarity my assumption is that the code is indeed fine as is i understand that the analyzer cannot always guess the parenthesis right in these situations and should ignore the statement rather than producing the message version used visual studio roslyn steps to reproduce set dotnet style parentheses in relational binary operators to always for clarity in editorconfig copy the code above to the editor expected behavior no message actually i d prefer if the analyzer reported an issue if the parenthesis is missing but this might be too strict to say for every scenario actual behavior is reported notes originally posted to microsoftdocs visualstudio docs related to | 0 |
2,949 | 12,876,081,568 | IssuesEvent | 2020-07-11 02:27:10 | home-assistant/core | https://api.github.com/repos/home-assistant/core | closed | State triggers with "for" fail to trigger after reboot | integration: automation | <!-- READ THIS FIRST:
- If you need additional help with this template, please refer to https://www.home-assistant.io/help/reporting_issues/
- Make sure you are running the latest version of Home Assistant before reporting an issue: https://github.com/home-assistant/core/releases
- Do not report issues for integrations if you are using custom components or integrations.
- Provide as many details as possible. Paste logs, configuration samples and code into the backticks.
DO NOT DELETE ANY TEXT from this template! Otherwise, your issue may be closed without comment.
-->
## The problem
<!--
Describe the issue you are experiencing here to communicate to the
maintainers. Tell us what you were trying to do and what happened.
-->
If a state trigger has "for" time on it, it will fail to trigger after a reboot. Let's say I want and automation to run 5 minutes after a light turns on. If HA is rebooted 1 minute after the light turns on, the automation will never run.
This makes automations with "for" unreliable.
## Environment
<!--
Provide details about the versions you are using, which helps us to reproduce
and find the issue quicker. Version information is found in the
Home Assistant frontend: Developer tools -> Info.
-->
- Home Assistant Core release with the issue: 0.112.2
- Last working Home Assistant Core release (if known):
- Operating environment (OS/Container/Supervised/Core): Tested in docker and venv.
- Integration causing this issue: automation
- Link to integration documentation on our website:
## Problem-relevant `configuration.yaml`
<!--
An example configuration that caused the problem for you. Fill this out even
if it seems unimportant to you. Please be sure to remove personal information
like passwords, private URLs and other credentials.
-->
```yaml
automation:
trigger:
platform: state
entity_id: switch.desk
to: "on"
for: "00:00:05"
```
## Traceback/Error logs
<!--
If you come across any trace or error logs, please provide them.
-->
```txt
```
## Additional information
I think HA only sets up the timer when the entity's state changes. It should also do it after a reboot.
| 1.0 | State triggers with "for" fail to trigger after reboot - <!-- READ THIS FIRST:
- If you need additional help with this template, please refer to https://www.home-assistant.io/help/reporting_issues/
- Make sure you are running the latest version of Home Assistant before reporting an issue: https://github.com/home-assistant/core/releases
- Do not report issues for integrations if you are using custom components or integrations.
- Provide as many details as possible. Paste logs, configuration samples and code into the backticks.
DO NOT DELETE ANY TEXT from this template! Otherwise, your issue may be closed without comment.
-->
## The problem
<!--
Describe the issue you are experiencing here to communicate to the
maintainers. Tell us what you were trying to do and what happened.
-->
If a state trigger has "for" time on it, it will fail to trigger after a reboot. Let's say I want and automation to run 5 minutes after a light turns on. If HA is rebooted 1 minute after the light turns on, the automation will never run.
This makes automations with "for" unreliable.
## Environment
<!--
Provide details about the versions you are using, which helps us to reproduce
and find the issue quicker. Version information is found in the
Home Assistant frontend: Developer tools -> Info.
-->
- Home Assistant Core release with the issue: 0.112.2
- Last working Home Assistant Core release (if known):
- Operating environment (OS/Container/Supervised/Core): Tested in docker and venv.
- Integration causing this issue: automation
- Link to integration documentation on our website:
## Problem-relevant `configuration.yaml`
<!--
An example configuration that caused the problem for you. Fill this out even
if it seems unimportant to you. Please be sure to remove personal information
like passwords, private URLs and other credentials.
-->
```yaml
automation:
trigger:
platform: state
entity_id: switch.desk
to: "on"
for: "00:00:05"
```
## Traceback/Error logs
<!--
If you come across any trace or error logs, please provide them.
-->
```txt
```
## Additional information
I think HA only sets up the timer when the entity's state changes. It should also do it after a reboot.
| non_priority | state triggers with for fail to trigger after reboot read this first if you need additional help with this template please refer to make sure you are running the latest version of home assistant before reporting an issue do not report issues for integrations if you are using custom components or integrations provide as many details as possible paste logs configuration samples and code into the backticks do not delete any text from this template otherwise your issue may be closed without comment the problem describe the issue you are experiencing here to communicate to the maintainers tell us what you were trying to do and what happened if a state trigger has for time on it it will fail to trigger after a reboot let s say i want and automation to run minutes after a light turns on if ha is rebooted minute after the light turns on the automation will never run this makes automations with for unreliable environment provide details about the versions you are using which helps us to reproduce and find the issue quicker version information is found in the home assistant frontend developer tools info home assistant core release with the issue last working home assistant core release if known operating environment os container supervised core tested in docker and venv integration causing this issue automation link to integration documentation on our website problem relevant configuration yaml an example configuration that caused the problem for you fill this out even if it seems unimportant to you please be sure to remove personal information like passwords private urls and other credentials yaml automation trigger platform state entity id switch desk to on for traceback error logs if you come across any trace or error logs please provide them txt additional information i think ha only sets up the timer when the entity s state changes it should also do it after a reboot | 0 |
83,242 | 7,867,927,223 | IssuesEvent | 2018-06-23 15:05:36 | jbeard4/SCION | https://api.github.com/repos/jbeard4/SCION | closed | fail test/scxml-test-framework/test/w3c-ecma/test294.txml.scxml | 2.0.0 Node v0.10.24 Tests fail feature:donedata | [https://github.com/jbeard4/scxml-test-framework/tree/master/test/scxml-test-framework/test/w3c-ecma/test294.txml.scxml](https://github.com/jbeard4/scxml-test-framework/tree/master/test/scxml-test-framework/test/w3c-ecma/test294.txml.scxml)
**Error** <code><pre>{
"name": "AssertionError",
"actual": [
"s02"
],
"expected": [
"pass"
],
"operator": "deepEqual",
"message": "[\"s02\"] deepEqual [\"pass\"]"
}</code></pre>
**Data**: <code><pre>{
"sessionToken": 512,
"nextConfiguration": [
"s02"
]
}</code></pre>
**scxml**:
``` xml
<?xml version="1.0" encoding="UTF-8"?>
<!-- test that a param inside donedata ends up in the data field of the done event and
that content inside donedata sets the full value of the event.data field -->
<scxml xmlns="http://www.w3.org/2005/07/scxml" xmlns:conf="http://www.w3.org/2005/scxml-conformance" version="1.0" datamodel="ecmascript" initial="s0">
<datamodel>
<data id="Var1" expr="0"/>
</datamodel>
<state id="s0" initial="s01">
<transition event="done.state.s0" cond="_event.data['Var1']==1" target="s1">
</transition>
<transition event="done.state.s0" target="fail">
</transition>
<state id="s01">
<transition target="s02"/>
</state>
<final id="s02">
<donedata>
<param name="Var1" expr="1"/>
</donedata>
</final>
</state>
<state id="s1" initial="s11">
<transition event="done.state.s1" cond="_event.data === 'foo'" target="pass">
</transition>
<transition event="done.state.s1" target="fail">
</transition>
<state id="s11">
<transition target="s12"/>
</state>
<final id="s12">
<donedata>
<content>foo</content>
</donedata>
</final>
</state>
<final id="pass"><onentry><log label="Outcome" expr="'pass'"/></onentry></final>
<final id="fail"><onentry><log label="Outcome" expr="'fail'"/></onentry></final>
</scxml>
```
**JSON**: <code><pre>{
"initialConfiguration": [
"pass"
],
"events": []
}</code></pre>
| 1.0 | fail test/scxml-test-framework/test/w3c-ecma/test294.txml.scxml - [https://github.com/jbeard4/scxml-test-framework/tree/master/test/scxml-test-framework/test/w3c-ecma/test294.txml.scxml](https://github.com/jbeard4/scxml-test-framework/tree/master/test/scxml-test-framework/test/w3c-ecma/test294.txml.scxml)
**Error** <code><pre>{
"name": "AssertionError",
"actual": [
"s02"
],
"expected": [
"pass"
],
"operator": "deepEqual",
"message": "[\"s02\"] deepEqual [\"pass\"]"
}</code></pre>
**Data**: <code><pre>{
"sessionToken": 512,
"nextConfiguration": [
"s02"
]
}</code></pre>
**scxml**:
``` xml
<?xml version="1.0" encoding="UTF-8"?>
<!-- test that a param inside donedata ends up in the data field of the done event and
that content inside donedata sets the full value of the event.data field -->
<scxml xmlns="http://www.w3.org/2005/07/scxml" xmlns:conf="http://www.w3.org/2005/scxml-conformance" version="1.0" datamodel="ecmascript" initial="s0">
<datamodel>
<data id="Var1" expr="0"/>
</datamodel>
<state id="s0" initial="s01">
<transition event="done.state.s0" cond="_event.data['Var1']==1" target="s1">
</transition>
<transition event="done.state.s0" target="fail">
</transition>
<state id="s01">
<transition target="s02"/>
</state>
<final id="s02">
<donedata>
<param name="Var1" expr="1"/>
</donedata>
</final>
</state>
<state id="s1" initial="s11">
<transition event="done.state.s1" cond="_event.data === 'foo'" target="pass">
</transition>
<transition event="done.state.s1" target="fail">
</transition>
<state id="s11">
<transition target="s12"/>
</state>
<final id="s12">
<donedata>
<content>foo</content>
</donedata>
</final>
</state>
<final id="pass"><onentry><log label="Outcome" expr="'pass'"/></onentry></final>
<final id="fail"><onentry><log label="Outcome" expr="'fail'"/></onentry></final>
</scxml>
```
**JSON**: <code><pre>{
"initialConfiguration": [
"pass"
],
"events": []
}</code></pre>
| non_priority | fail test scxml test framework test ecma txml scxml error name assertionerror actual expected pass operator deepequal message deepequal data sessiontoken nextconfiguration scxml xml test that a param inside donedata ends up in the data field of the done event and that content inside donedata sets the full value of the event data field foo json initialconfiguration pass events | 0 |
238,072 | 19,696,120,322 | IssuesEvent | 2022-01-12 12:20:02 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [test-failed]: Chrome X-Pack UI Functional Tests1.x-pack/test/functional/apps/ml/anomaly_detection/saved_search_job·ts - machine learning anomaly detection saved search with lucene query job creation loads the multi metric wizard for the source data | :ml failed-test test-cloud | **Version: 7.16.0**
**Class: Chrome X-Pack UI Functional Tests1.x-pack/test/functional/apps/ml/anomaly_detection/saved_search_job·ts**
**Stack Trace:**
```
Error: retry.tryForTime timeout: TimeoutError: Waiting for element to be located By(css selector, [data-test-subj="savedObjectTitleft_farequote_lucene"])
Wait timed out after 10041ms
at /var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/node_modules/selenium-webdriver/lib/webdriver.js:895:17
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at onFailure (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/test/common/services/retry/retry_for_success.ts:17:9)
at retryForSuccess (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/test/common/services/retry/retry_for_success.ts:59:13)
at RetryService.tryForTime (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/test/common/services/retry/retry.ts:22:12)
at Object.selectSource (test/functional/services/ml/job_source_selection.ts:28:7)
at Object.selectSourceForAnomalyDetectionJob (test/functional/services/ml/job_source_selection.ts:35:7)
at Context.<anonymous> (test/functional/apps/ml/anomaly_detection/saved_search_job.ts:300:11)
at Object.apply (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/wrap_function.js:87:16)
```
**Other test failures:**
- machine learning anomaly detection saved search with lucene query job creation navigates through the multi metric wizard and sets all needed fields
- machine learning anomaly detection saved search with lucene query job creation runs the job and displays it correctly in the job list
- machine learning anomaly detection saved search with kuery query job creation loads the multi metric wizard for the source data
- machine learning anomaly detection saved search with kuery query job creation navigates through the multi metric wizard and sets all needed fields
- machine learning anomaly detection saved search with kuery query job creation runs the job and displays it correctly in the job list
_Test Report: https://internal-ci.elastic.co/view/Stack%20Tests/job/elastic+estf-cloud-kibana-tests/2636/testReport/_ | 2.0 | [test-failed]: Chrome X-Pack UI Functional Tests1.x-pack/test/functional/apps/ml/anomaly_detection/saved_search_job·ts - machine learning anomaly detection saved search with lucene query job creation loads the multi metric wizard for the source data - **Version: 7.16.0**
**Class: Chrome X-Pack UI Functional Tests1.x-pack/test/functional/apps/ml/anomaly_detection/saved_search_job·ts**
**Stack Trace:**
```
Error: retry.tryForTime timeout: TimeoutError: Waiting for element to be located By(css selector, [data-test-subj="savedObjectTitleft_farequote_lucene"])
Wait timed out after 10041ms
at /var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/node_modules/selenium-webdriver/lib/webdriver.js:895:17
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at onFailure (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/test/common/services/retry/retry_for_success.ts:17:9)
at retryForSuccess (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/test/common/services/retry/retry_for_success.ts:59:13)
at RetryService.tryForTime (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/test/common/services/retry/retry.ts:22:12)
at Object.selectSource (test/functional/services/ml/job_source_selection.ts:28:7)
at Object.selectSourceForAnomalyDetectionJob (test/functional/services/ml/job_source_selection.ts:35:7)
at Context.<anonymous> (test/functional/apps/ml/anomaly_detection/saved_search_job.ts:300:11)
at Object.apply (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackGrp3/TASK/saas_run_kibana_tests/node/ess-testing/ci/cloud/common/build/kibana/node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/wrap_function.js:87:16)
```
**Other test failures:**
- machine learning anomaly detection saved search with lucene query job creation navigates through the multi metric wizard and sets all needed fields
- machine learning anomaly detection saved search with lucene query job creation runs the job and displays it correctly in the job list
- machine learning anomaly detection saved search with kuery query job creation loads the multi metric wizard for the source data
- machine learning anomaly detection saved search with kuery query job creation navigates through the multi metric wizard and sets all needed fields
- machine learning anomaly detection saved search with kuery query job creation runs the job and displays it correctly in the job list
_Test Report: https://internal-ci.elastic.co/view/Stack%20Tests/job/elastic+estf-cloud-kibana-tests/2636/testReport/_ | non_priority | chrome x pack ui functional x pack test functional apps ml anomaly detection saved search job·ts machine learning anomaly detection saved search with lucene query job creation loads the multi metric wizard for the source data version class chrome x pack ui functional x pack test functional apps ml anomaly detection saved search job·ts stack trace error retry tryfortime timeout timeouterror waiting for element to be located by css selector wait timed out after at var lib jenkins workspace elastic estf cloud kibana tests job task saas run kibana tests node ess testing ci cloud common build kibana node modules selenium webdriver lib webdriver js at runmicrotasks at processticksandrejections node internal process task queues at onfailure var lib jenkins workspace elastic estf cloud kibana tests job task saas run kibana tests node ess testing ci cloud common build kibana test common services retry retry for success ts at retryforsuccess var lib jenkins workspace elastic estf cloud kibana tests job task saas run kibana tests node ess testing ci cloud common build kibana test common services retry retry for success ts at retryservice tryfortime var lib jenkins workspace elastic estf cloud kibana tests job task saas run kibana tests node ess testing ci cloud common build kibana test common services retry retry ts at object selectsource test functional services ml job source selection ts at object selectsourceforanomalydetectionjob test functional services ml job source selection ts at context test functional apps ml anomaly detection saved search job ts at object apply var lib jenkins workspace elastic estf cloud kibana tests job task saas run kibana tests node ess testing ci cloud common build kibana node modules kbn test target node functional test runner lib mocha wrap function js other test failures machine learning anomaly detection saved search with lucene query job creation navigates through the multi metric wizard and sets all needed fields machine learning anomaly detection saved search with lucene query job creation runs the job and displays it correctly in the job list machine learning anomaly detection saved search with kuery query job creation loads the multi metric wizard for the source data machine learning anomaly detection saved search with kuery query job creation navigates through the multi metric wizard and sets all needed fields machine learning anomaly detection saved search with kuery query job creation runs the job and displays it correctly in the job list test report | 0 |
18,539 | 4,283,966,838 | IssuesEvent | 2016-07-15 15:09:40 | mamontov-cpp/saddy-graphics-engine-2d | https://api.github.com/repos/mamontov-cpp/saddy-graphics-engine-2d | closed | [atalsgen,exporter,ifaceed] Move those to /tools | documentation enhancement | This was a mistake to have thos here. So, to fix such folder should be moved to tools to ensure, that plugins will contain only static libraries | 1.0 | [atalsgen,exporter,ifaceed] Move those to /tools - This was a mistake to have thos here. So, to fix such folder should be moved to tools to ensure, that plugins will contain only static libraries | non_priority | move those to tools this was a mistake to have thos here so to fix such folder should be moved to tools to ensure that plugins will contain only static libraries | 0 |
183,817 | 14,959,283,621 | IssuesEvent | 2021-01-27 02:48:45 | RaeStichter/note-taker | https://api.github.com/repos/RaeStichter/note-taker | closed | User Story | documentation | AS A small business owner
I WANT to be able to write and save notes
SO THAT I can organize my thoughts and keep track of tasks I need to complete | 1.0 | User Story - AS A small business owner
I WANT to be able to write and save notes
SO THAT I can organize my thoughts and keep track of tasks I need to complete | non_priority | user story as a small business owner i want to be able to write and save notes so that i can organize my thoughts and keep track of tasks i need to complete | 0 |
265,200 | 28,262,290,886 | IssuesEvent | 2023-04-07 01:07:31 | t2kx/juice-shop | https://api.github.com/repos/t2kx/juice-shop | opened | CVE-2023-0842 (Medium) detected in xml2js-0.4.23.tgz | Mend: dependency security vulnerability | ## CVE-2023-0842 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xml2js-0.4.23.tgz</b></p></summary>
<p>Simple XML to JavaScript object converter.</p>
<p>Library home page: <a href="https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz">https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/xml2js/package.json</p>
<p>
Dependency Hierarchy:
- webdriver-manager-12.1.7.tgz (Root Library)
- :x: **xml2js-0.4.23.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/t2kx/juice-shop/commit/892c07158a9eaff6c38e82269f691bf26b48b694">892c07158a9eaff6c38e82269f691bf26b48b694</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
xml2js version 0.4.23 allows an external attacker to edit or add new properties to an object. This is possible because the application does not properly validate incoming JSON keys, thus allowing the __proto__ property to be edited.
<p>Publish Date: 2023-04-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0842>CVE-2023-0842</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-0842 (Medium) detected in xml2js-0.4.23.tgz - ## CVE-2023-0842 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xml2js-0.4.23.tgz</b></p></summary>
<p>Simple XML to JavaScript object converter.</p>
<p>Library home page: <a href="https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz">https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/xml2js/package.json</p>
<p>
Dependency Hierarchy:
- webdriver-manager-12.1.7.tgz (Root Library)
- :x: **xml2js-0.4.23.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/t2kx/juice-shop/commit/892c07158a9eaff6c38e82269f691bf26b48b694">892c07158a9eaff6c38e82269f691bf26b48b694</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
xml2js version 0.4.23 allows an external attacker to edit or add new properties to an object. This is possible because the application does not properly validate incoming JSON keys, thus allowing the __proto__ property to be edited.
<p>Publish Date: 2023-04-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0842>CVE-2023-0842</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tgz cve medium severity vulnerability vulnerable library tgz simple xml to javascript object converter library home page a href path to dependency file package json path to vulnerable library node modules package json dependency hierarchy webdriver manager tgz root library x tgz vulnerable library found in head commit a href found in base branch master vulnerability details version allows an external attacker to edit or add new properties to an object this is possible because the application does not properly validate incoming json keys thus allowing the proto property to be edited publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
37,555 | 10,029,018,201 | IssuesEvent | 2019-07-17 13:04:49 | ovh-ux/manager | https://api.github.com/repos/ovh-ux/manager | closed | Set `yarn` engine to `>=1.17.3` | build | **Is your feature request related to a problem? Please describe.**
Yarn recently published an article on their blog that refer to a vulnerability (see: Additional context).
**Describe the solution you'd like**
Update the `yarn` entry from the `engines` part of the `package.json` file.
```diff
diff --git a/package.json b/package.json
index a5df24c28786..7b655c1a7b0b 100644
--- a/package.json
+++ b/package.json
@@ -67,6 +67,6 @@
},
"engines": {
"node": ">=8.11",
- "yarn": ">=1.12.3"
+ "yarn": ">=1.17.3"
}
}
```
**Describe alternatives you've considered**
Update also the Docker image used in our CI/CD system.
**Additional context**
Blog post: https://yarnpkg.com/blog/2019/07/12/recommended-security-update/
| 1.0 | Set `yarn` engine to `>=1.17.3` - **Is your feature request related to a problem? Please describe.**
Yarn recently published an article on their blog that refer to a vulnerability (see: Additional context).
**Describe the solution you'd like**
Update the `yarn` entry from the `engines` part of the `package.json` file.
```diff
diff --git a/package.json b/package.json
index a5df24c28786..7b655c1a7b0b 100644
--- a/package.json
+++ b/package.json
@@ -67,6 +67,6 @@
},
"engines": {
"node": ">=8.11",
- "yarn": ">=1.12.3"
+ "yarn": ">=1.17.3"
}
}
```
**Describe alternatives you've considered**
Update also the Docker image used in our CI/CD system.
**Additional context**
Blog post: https://yarnpkg.com/blog/2019/07/12/recommended-security-update/
| non_priority | set yarn engine to is your feature request related to a problem please describe yarn recently published an article on their blog that refer to a vulnerability see additional context describe the solution you d like update the yarn entry from the engines part of the package json file diff diff git a package json b package json index a package json b package json engines node yarn yarn describe alternatives you ve considered update also the docker image used in our ci cd system additional context blog post | 0 |
45,809 | 9,816,681,788 | IssuesEvent | 2019-06-13 15:07:30 | startsole/StartSOLE-web-app | https://api.github.com/repos/startsole/StartSOLE-web-app | opened | Make a dashboard for a ring leader | better code enhancement/feature | If a user is a ringleader they should be able to see a dashboard that displays info about users in a ring. This is a revision of the google-docs-backed dashboard implemented in code and using the database.
Need to start by looking at the current dashboard and what data come in and how we want it to look | 1.0 | Make a dashboard for a ring leader - If a user is a ringleader they should be able to see a dashboard that displays info about users in a ring. This is a revision of the google-docs-backed dashboard implemented in code and using the database.
Need to start by looking at the current dashboard and what data come in and how we want it to look | non_priority | make a dashboard for a ring leader if a user is a ringleader they should be able to see a dashboard that displays info about users in a ring this is a revision of the google docs backed dashboard implemented in code and using the database need to start by looking at the current dashboard and what data come in and how we want it to look | 0 |
77,284 | 14,762,744,108 | IssuesEvent | 2021-01-09 05:34:24 | TravelMapping/DataProcessing | https://api.github.com/repos/TravelMapping/DataProcessing | closed | nmp lists | Python code organization efficiency nmps pending speed | ```Python
if len(nmps) > 0:
if w.near_miss_points is None:
w.near_miss_points = nmps
else:
w.near_miss_points.extend(nmps)
for other_w in nmps:
if other_w.near_miss_points is None:
other_w.near_miss_points = [ w ]
else:
other_w.near_miss_points.append(w)
```
**Why:**
* init `Waypoint.near_miss_points` to `None`,
* set `nmps = all_waypoints.near_miss_waypoints(w, 0.0005)`,
* check `nmps` length,
* check whether `w.near_miss_points is None` *(it will be, since this is a brand new waypoint not yet added to the QuadTree)*,
* set `w.near_miss_points = nmps`, and
* check whether `other_w.near_miss_points is None` & do stuff...
**When we can:**
* init `Waypoint.near_miss_points` to `[]`,
* dispense with the `nmps` list altogether,
* just set `w.near_miss_points = all_waypoints.near_miss_waypoints(w, 0.0005)`, and
* simply append `w` to `other_w`'s list? | 1.0 | nmp lists - ```Python
if len(nmps) > 0:
if w.near_miss_points is None:
w.near_miss_points = nmps
else:
w.near_miss_points.extend(nmps)
for other_w in nmps:
if other_w.near_miss_points is None:
other_w.near_miss_points = [ w ]
else:
other_w.near_miss_points.append(w)
```
**Why:**
* init `Waypoint.near_miss_points` to `None`,
* set `nmps = all_waypoints.near_miss_waypoints(w, 0.0005)`,
* check `nmps` length,
* check whether `w.near_miss_points is None` *(it will be, since this is a brand new waypoint not yet added to the QuadTree)*,
* set `w.near_miss_points = nmps`, and
* check whether `other_w.near_miss_points is None` & do stuff...
**When we can:**
* init `Waypoint.near_miss_points` to `[]`,
* dispense with the `nmps` list altogether,
* just set `w.near_miss_points = all_waypoints.near_miss_waypoints(w, 0.0005)`, and
* simply append `w` to `other_w`'s list? | non_priority | nmp lists python if len nmps if w near miss points is none w near miss points nmps else w near miss points extend nmps for other w in nmps if other w near miss points is none other w near miss points else other w near miss points append w why init waypoint near miss points to none set nmps all waypoints near miss waypoints w check nmps length check whether w near miss points is none it will be since this is a brand new waypoint not yet added to the quadtree set w near miss points nmps and check whether other w near miss points is none do stuff when we can init waypoint near miss points to dispense with the nmps list altogether just set w near miss points all waypoints near miss waypoints w and simply append w to other w s list | 0 |
151,859 | 23,884,579,460 | IssuesEvent | 2022-09-08 06:26:53 | hackforla/website | https://api.github.com/repos/hackforla/website | opened | Auditing the inconsistency of text components in the Getting StartedPage | P-Feature: Getting Started role: design Ready for Milestone size: 1pt | ### Overview
We need to audit the Getting Started page to know which ones have text elements that are missing text components.
### Action Items
- [ ] Find the page on the left panel of Figma
- [ ] Find the most recent Figma frame/version of that page (It should have a pink frame around it)
- [ ] For any texts that do not have the text components, make a line at the side of the texts and indicate what type of text component it is (See Sample of Audit Figma for more instructions)
- [ ] Review with Design Lead when finished auditing
### Resources/Instructions
- [Getting Started Figma](https://www.figma.com/file/0RRPy1Ph7HafI3qOITg0Mr/Hack-for-LA-Website?node-id=13%3A0)
- [Sample of Audit Figma](https://www.figma.com/file/0RRPy1Ph7HafI3qOITg0Mr/Hack-for-LA-Website?node-id=19750%3A127093)
- [Design Systems](https://www.figma.com/file/0RRPy1Ph7HafI3qOITg0Mr/Hack-for-LA-Website?node-id=3686%3A93)
| 1.0 | Auditing the inconsistency of text components in the Getting StartedPage - ### Overview
We need to audit the Getting Started page to know which ones have text elements that are missing text components.
### Action Items
- [ ] Find the page on the left panel of Figma
- [ ] Find the most recent Figma frame/version of that page (It should have a pink frame around it)
- [ ] For any texts that do not have the text components, make a line at the side of the texts and indicate what type of text component it is (See Sample of Audit Figma for more instructions)
- [ ] Review with Design Lead when finished auditing
### Resources/Instructions
- [Getting Started Figma](https://www.figma.com/file/0RRPy1Ph7HafI3qOITg0Mr/Hack-for-LA-Website?node-id=13%3A0)
- [Sample of Audit Figma](https://www.figma.com/file/0RRPy1Ph7HafI3qOITg0Mr/Hack-for-LA-Website?node-id=19750%3A127093)
- [Design Systems](https://www.figma.com/file/0RRPy1Ph7HafI3qOITg0Mr/Hack-for-LA-Website?node-id=3686%3A93)
| non_priority | auditing the inconsistency of text components in the getting startedpage overview we need to audit the getting started page to know which ones have text elements that are missing text components action items find the page on the left panel of figma find the most recent figma frame version of that page it should have a pink frame around it for any texts that do not have the text components make a line at the side of the texts and indicate what type of text component it is see sample of audit figma for more instructions review with design lead when finished auditing resources instructions | 0 |
128,342 | 12,370,449,333 | IssuesEvent | 2020-05-18 16:49:17 | trilinos/Trilinos | https://api.github.com/repos/trilinos/Trilinos | closed | What is the latest trilinos version and where? | impacting: documentation | Your site
https://trilinos.github.io/
claims 12.12 as the latest but I have 12.14.
However, I can't find either for download on
https://github.com/trilinos/trilinos.github.io
there are zero releases. | 1.0 | What is the latest trilinos version and where? - Your site
https://trilinos.github.io/
claims 12.12 as the latest but I have 12.14.
However, I can't find either for download on
https://github.com/trilinos/trilinos.github.io
there are zero releases. | non_priority | what is the latest trilinos version and where your site claims as the latest but i have however i can t find either for download on there are zero releases | 0 |
415,311 | 28,029,463,861 | IssuesEvent | 2023-03-28 11:23:43 | brixxt27/inception | https://api.github.com/repos/brixxt27/inception | opened | inception | documentation | # To do
- [ ] 가상머신과 도커의 차이
- [ ] hacky patch 란?
- [ ] makefile 로 docker-compose.yml 을 실행하여 dockerfile 을 호출하는 방법
- [ ] 왜 컨테이너에는 독립적인 프로그램만 담겨 있어야 하는가?
- [ ] docker volume 세팅 방법
- [ ] container 의 crash 상황에 restart 하는 방법
- [ ] daemon 작동 방식과 이것을 사용하는 것이 좋은지 나쁜지 알아보기
- [ ] PID1 과 dockerfile 을 작성하기 위한 최고의 방법 알아보기 | 1.0 | inception - # To do
- [ ] 가상머신과 도커의 차이
- [ ] hacky patch 란?
- [ ] makefile 로 docker-compose.yml 을 실행하여 dockerfile 을 호출하는 방법
- [ ] 왜 컨테이너에는 독립적인 프로그램만 담겨 있어야 하는가?
- [ ] docker volume 세팅 방법
- [ ] container 의 crash 상황에 restart 하는 방법
- [ ] daemon 작동 방식과 이것을 사용하는 것이 좋은지 나쁜지 알아보기
- [ ] PID1 과 dockerfile 을 작성하기 위한 최고의 방법 알아보기 | non_priority | inception to do 가상머신과 도커의 차이 hacky patch 란 makefile 로 docker compose yml 을 실행하여 dockerfile 을 호출하는 방법 왜 컨테이너에는 독립적인 프로그램만 담겨 있어야 하는가 docker volume 세팅 방법 container 의 crash 상황에 restart 하는 방법 daemon 작동 방식과 이것을 사용하는 것이 좋은지 나쁜지 알아보기 과 dockerfile 을 작성하기 위한 최고의 방법 알아보기 | 0 |
340,510 | 24,657,577,834 | IssuesEvent | 2022-10-18 02:02:48 | pitzzahh/automated-teller-machine-API | https://api.github.com/repos/pitzzahh/automated-teller-machine-API | closed | Outdated comment | documentation | The comments forgetClientByAccountNumber() found in AtmDAO, AtmDAOImplementation, and AtmService does not contain the latest info about the method changes | 1.0 | Outdated comment - The comments forgetClientByAccountNumber() found in AtmDAO, AtmDAOImplementation, and AtmService does not contain the latest info about the method changes | non_priority | outdated comment the comments forgetclientbyaccountnumber found in atmdao atmdaoimplementation and atmservice does not contain the latest info about the method changes | 0 |
161,060 | 13,805,686,345 | IssuesEvent | 2020-10-11 14:42:27 | czafikm/AFP-Team-6 | https://api.github.com/repos/czafikm/AFP-Team-6 | closed | Use case egyszerűsítése | documentation | Use case diagramot kellene egyszerűsíteni, azaz minden szerepkörhöz legyen feltüntetve ,hogy milyen szolgáltatást vehet igénybe és milyet nem valamint az is ,hogy milyen funkciókat tud használni.
**AC:**
Legyen szinkronban a funkciók listájával (srs.md-ben található) és tartalmazza az alábbiakat is:
- Tiltott szolgáltatások:
- Engedélyezett szolgáltatások:
- Szerepkörökhöz tartozó funkciók:
| 1.0 | Use case egyszerűsítése - Use case diagramot kellene egyszerűsíteni, azaz minden szerepkörhöz legyen feltüntetve ,hogy milyen szolgáltatást vehet igénybe és milyet nem valamint az is ,hogy milyen funkciókat tud használni.
**AC:**
Legyen szinkronban a funkciók listájával (srs.md-ben található) és tartalmazza az alábbiakat is:
- Tiltott szolgáltatások:
- Engedélyezett szolgáltatások:
- Szerepkörökhöz tartozó funkciók:
| non_priority | use case egyszerűsítése use case diagramot kellene egyszerűsíteni azaz minden szerepkörhöz legyen feltüntetve hogy milyen szolgáltatást vehet igénybe és milyet nem valamint az is hogy milyen funkciókat tud használni ac legyen szinkronban a funkciók listájával srs md ben található és tartalmazza az alábbiakat is tiltott szolgáltatások engedélyezett szolgáltatások szerepkörökhöz tartozó funkciók | 0 |
274,293 | 29,992,824,381 | IssuesEvent | 2023-06-26 01:06:42 | panasalap/linux-4.19.72_1 | https://api.github.com/repos/panasalap/linux-4.19.72_1 | opened | CVE-2023-35788 (High) detected in linux-yoctov5.4.51 | Mend: dependency security vulnerability | ## CVE-2023-35788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/cls_flower.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/cls_flower.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in fl_set_geneve_opt in net/sched/cls_flower.c in the Linux kernel before 6.3.7. It allows an out-of-bounds write in the flower classifier code via TCA_FLOWER_KEY_ENC_OPTS_GENEVE packets. This may result in denial of service or privilege escalation.
<p>Publish Date: 2023-06-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-35788>CVE-2023-35788</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-35788">https://www.cve.org/CVERecord?id=CVE-2023-35788</a></p>
<p>Release Date: 2023-06-16</p>
<p>Fix Resolution: v4.19.285,v5.4.246,v5.10.183,v5.15.116,v6.1.33</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-35788 (High) detected in linux-yoctov5.4.51 - ## CVE-2023-35788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/cls_flower.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/sched/cls_flower.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in fl_set_geneve_opt in net/sched/cls_flower.c in the Linux kernel before 6.3.7. It allows an out-of-bounds write in the flower classifier code via TCA_FLOWER_KEY_ENC_OPTS_GENEVE packets. This may result in denial of service or privilege escalation.
<p>Publish Date: 2023-06-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-35788>CVE-2023-35788</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-35788">https://www.cve.org/CVERecord?id=CVE-2023-35788</a></p>
<p>Release Date: 2023-06-16</p>
<p>Fix Resolution: v4.19.285,v5.4.246,v5.10.183,v5.15.116,v6.1.33</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux cve high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in base branch master vulnerable source files net sched cls flower c net sched cls flower c vulnerability details an issue was discovered in fl set geneve opt in net sched cls flower c in the linux kernel before it allows an out of bounds write in the flower classifier code via tca flower key enc opts geneve packets this may result in denial of service or privilege escalation publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
38,938 | 5,205,477,018 | IssuesEvent | 2017-01-24 18:02:49 | brunobuzzi/OrbeonPersistenceLayer | https://api.github.com/repos/brunobuzzi/OrbeonPersistenceLayer | closed | Import data from Orbeon 2016.2 with MySQL and export it as CSV | analyze testing web app | The export process has not been tested with new Orbeon database schema for 2016.2 | 1.0 | Import data from Orbeon 2016.2 with MySQL and export it as CSV - The export process has not been tested with new Orbeon database schema for 2016.2 | non_priority | import data from orbeon with mysql and export it as csv the export process has not been tested with new orbeon database schema for | 0 |
27,919 | 6,916,510,201 | IssuesEvent | 2017-11-29 02:59:31 | ElinamLLC/SharpVectors | https://api.github.com/repos/ElinamLLC/SharpVectors | closed | Issue with embedded bitmap unsing SharpVectors.Runtime in the VS designer | bug CodePlexMigrationInitiated Impact: Low | Embedded bitmap images via SharpVectors.Runtime work fine at runtime, but in the VS2010 designer I get:
System.InvalidOperationException
BitmapImage has not been initialized. Call the BeginInit method, set the appropriate properties, and then call the EndInit method.
I couldn't figure out, where this is going wrong. I've attached a sample project.
#### Attachments
[Test.zip](https://www.codeplex.com/Download/AttachmentDownload.ashx?ProjectName=sharpvectors&WorkItemId=543&FileAttachmentId=95)
[EmbeddedBitmapSource.cs](https://www.codeplex.com/Download/AttachmentDownload.ashx?ProjectName=sharpvectors&WorkItemId=543&FileAttachmentId=103)
#### This work item was migrated from CodePlex
CodePlex work item ID: '543'
Vote count: '3'
| 1.0 | Issue with embedded bitmap unsing SharpVectors.Runtime in the VS designer - Embedded bitmap images via SharpVectors.Runtime work fine at runtime, but in the VS2010 designer I get:
System.InvalidOperationException
BitmapImage has not been initialized. Call the BeginInit method, set the appropriate properties, and then call the EndInit method.
I couldn't figure out, where this is going wrong. I've attached a sample project.
#### Attachments
[Test.zip](https://www.codeplex.com/Download/AttachmentDownload.ashx?ProjectName=sharpvectors&WorkItemId=543&FileAttachmentId=95)
[EmbeddedBitmapSource.cs](https://www.codeplex.com/Download/AttachmentDownload.ashx?ProjectName=sharpvectors&WorkItemId=543&FileAttachmentId=103)
#### This work item was migrated from CodePlex
CodePlex work item ID: '543'
Vote count: '3'
| non_priority | issue with embedded bitmap unsing sharpvectors runtime in the vs designer embedded bitmap images via sharpvectors runtime work fine at runtime but in the designer i get system invalidoperationexception bitmapimage has not been initialized call the begininit method set the appropriate properties and then call the endinit method i couldn t figure out where this is going wrong i ve attached a sample project attachments this work item was migrated from codeplex codeplex work item id vote count | 0 |
2,817 | 3,882,729,864 | IssuesEvent | 2016-04-13 11:08:16 | versionpress/versionpress | https://api.github.com/repos/versionpress/versionpress | closed | Build frontend on `gulp build` | improvement in review minor scope:dev-infrastructure size:xs | Built ZIP should contain up-to-date version of the frontend. Now it just copies already built version if there is any. | 1.0 | Build frontend on `gulp build` - Built ZIP should contain up-to-date version of the frontend. Now it just copies already built version if there is any. | non_priority | build frontend on gulp build built zip should contain up to date version of the frontend now it just copies already built version if there is any | 0 |
96,131 | 27,755,601,275 | IssuesEvent | 2023-03-16 02:03:20 | apple/swift | https://api.github.com/repos/apple/swift | closed | Result builder with `if`-statement accepted even if builder does not has `buildIf` if closure has explicit `return` | bug type checker result builders triage needed | The following code is accepted even though it shouldn’t be
```swift
@resultBuilder
struct MyBuilder {
static func buildBlock() -> () { }
}
func takeBuilder(@MyBuilder body: () -> Int) {}
func testAcceptColorTagged() {
takeBuilder { () -> Int in
if true {
return 0
} else {
return 9
}
}
}
```
The problem is that `matchResultBuilder` returns `None` in case of `ResultBuilderBodyPreCheck::HasReturnStmt` when not in diagnostic mode, which then causes us to type check the closure as a regular closure and not as a result builder at all. | 1.0 | Result builder with `if`-statement accepted even if builder does not has `buildIf` if closure has explicit `return` - The following code is accepted even though it shouldn’t be
```swift
@resultBuilder
struct MyBuilder {
static func buildBlock() -> () { }
}
func takeBuilder(@MyBuilder body: () -> Int) {}
func testAcceptColorTagged() {
takeBuilder { () -> Int in
if true {
return 0
} else {
return 9
}
}
}
```
The problem is that `matchResultBuilder` returns `None` in case of `ResultBuilderBodyPreCheck::HasReturnStmt` when not in diagnostic mode, which then causes us to type check the closure as a regular closure and not as a result builder at all. | non_priority | result builder with if statement accepted even if builder does not has buildif if closure has explicit return the following code is accepted even though it shouldn’t be swift resultbuilder struct mybuilder static func buildblock func takebuilder mybuilder body int func testacceptcolortagged takebuilder int in if true return else return the problem is that matchresultbuilder returns none in case of resultbuilderbodyprecheck hasreturnstmt when not in diagnostic mode which then causes us to type check the closure as a regular closure and not as a result builder at all | 0 |
97,012 | 8,639,968,694 | IssuesEvent | 2018-11-23 23:13:09 | HolmanA/cat-chat | https://api.github.com/repos/HolmanA/cat-chat | closed | Unit test template files | testing | It would be nice to have example unit test files for each main component of our application. | 1.0 | Unit test template files - It would be nice to have example unit test files for each main component of our application. | non_priority | unit test template files it would be nice to have example unit test files for each main component of our application | 0 |
147 | 4,098,822,879 | IssuesEvent | 2016-06-03 09:56:34 | eclipse/smarthome | https://api.github.com/repos/eclipse/smarthome | closed | RuleRegistry contains two entries after creating a rule based on template | Automation bug | The "create rule by template" feature is broken - the rule registry contains two entries with the same ruleid afterwards which causes all kinds of problems.
This bug has been introduced by https://github.com/eclipse/smarthome/pull/1500 - @danchom could you please have a look? | 1.0 | RuleRegistry contains two entries after creating a rule based on template - The "create rule by template" feature is broken - the rule registry contains two entries with the same ruleid afterwards which causes all kinds of problems.
This bug has been introduced by https://github.com/eclipse/smarthome/pull/1500 - @danchom could you please have a look? | non_priority | ruleregistry contains two entries after creating a rule based on template the create rule by template feature is broken the rule registry contains two entries with the same ruleid afterwards which causes all kinds of problems this bug has been introduced by danchom could you please have a look | 0 |
186,475 | 14,394,699,687 | IssuesEvent | 2020-12-03 01:55:10 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | itsivareddy/terrafrom-Oci: oci/core_vcn_test.go; 16 LoC | fresh small test |
Found a possible issue in [itsivareddy/terrafrom-Oci](https://www.github.com/itsivareddy/terrafrom-Oci) at [oci/core_vcn_test.go](https://github.com/itsivareddy/terrafrom-Oci/blob/075608a9e201ee0e32484da68d5ba5370dfde1be/oci/core_vcn_test.go#L296-L311)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/itsivareddy/terrafrom-Oci/blob/075608a9e201ee0e32484da68d5ba5370dfde1be/oci/core_vcn_test.go#L296-L311)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, vcnId := range vcnIds {
if ok := SweeperDefaultResourceId[vcnId]; !ok {
deleteVcnRequest := oci_core.DeleteVcnRequest{}
deleteVcnRequest.VcnId = &vcnId
deleteVcnRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "core")
_, error := virtualNetworkClient.DeleteVcn(context.Background(), deleteVcnRequest)
if error != nil {
fmt.Printf("Error deleting Vcn %s %s, It is possible that the resource is already deleted. Please verify manually \n", vcnId, error)
continue
}
waitTillCondition(testAccProvider, &vcnId, vcnSweepWaitCondition, time.Duration(3*time.Minute),
vcnSweepResponseFetchOperation, "core", true)
}
}
```
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to vcnId is reassigned at line 300
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 075608a9e201ee0e32484da68d5ba5370dfde1be
| 1.0 | itsivareddy/terrafrom-Oci: oci/core_vcn_test.go; 16 LoC -
Found a possible issue in [itsivareddy/terrafrom-Oci](https://www.github.com/itsivareddy/terrafrom-Oci) at [oci/core_vcn_test.go](https://github.com/itsivareddy/terrafrom-Oci/blob/075608a9e201ee0e32484da68d5ba5370dfde1be/oci/core_vcn_test.go#L296-L311)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/itsivareddy/terrafrom-Oci/blob/075608a9e201ee0e32484da68d5ba5370dfde1be/oci/core_vcn_test.go#L296-L311)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, vcnId := range vcnIds {
if ok := SweeperDefaultResourceId[vcnId]; !ok {
deleteVcnRequest := oci_core.DeleteVcnRequest{}
deleteVcnRequest.VcnId = &vcnId
deleteVcnRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "core")
_, error := virtualNetworkClient.DeleteVcn(context.Background(), deleteVcnRequest)
if error != nil {
fmt.Printf("Error deleting Vcn %s %s, It is possible that the resource is already deleted. Please verify manually \n", vcnId, error)
continue
}
waitTillCondition(testAccProvider, &vcnId, vcnSweepWaitCondition, time.Duration(3*time.Minute),
vcnSweepResponseFetchOperation, "core", true)
}
}
```
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to vcnId is reassigned at line 300
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 075608a9e201ee0e32484da68d5ba5370dfde1be
| non_priority | itsivareddy terrafrom oci oci core vcn test go loc found a possible issue in at the below snippet of go code triggered static analysis which searches for goroutines and or defer statements which capture loop variables click here to show the line s of go which triggered the analyzer go for vcnid range vcnids if ok sweeperdefaultresourceid ok deletevcnrequest oci core deletevcnrequest deletevcnrequest vcnid vcnid deletevcnrequest requestmetadata retrypolicy getretrypolicy true core error virtualnetworkclient deletevcn context background deletevcnrequest if error nil fmt printf error deleting vcn s s it is possible that the resource is already deleted please verify manually n vcnid error continue waittillcondition testaccprovider vcnid vcnsweepwaitcondition time duration time minute vcnsweepresponsefetchoperation core true below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to vcnid is reassigned at line leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
55,444 | 6,900,252,416 | IssuesEvent | 2017-11-24 17:25:37 | Ronneesley/redesocial | https://api.github.com/repos/Ronneesley/redesocial | closed | Como fazer AJAX com jQuery? | Banco de dados Design Pesquisa | Mostrar o que é AJAX e como fazê-lo **COM** o uso de **jQuery**.
Envio de dados com método POST e GET.
3 estrelas em *design*
2 estrelas em pesquisa (relatório de 3 páginas)
Se fizer com exemplo ligado a um BD vale 5 estrelas em *design* e 1 estrela em BD.
Entrega: **10/11** | 1.0 | Como fazer AJAX com jQuery? - Mostrar o que é AJAX e como fazê-lo **COM** o uso de **jQuery**.
Envio de dados com método POST e GET.
3 estrelas em *design*
2 estrelas em pesquisa (relatório de 3 páginas)
Se fizer com exemplo ligado a um BD vale 5 estrelas em *design* e 1 estrela em BD.
Entrega: **10/11** | non_priority | como fazer ajax com jquery mostrar o que é ajax e como fazê lo com o uso de jquery envio de dados com método post e get estrelas em design estrelas em pesquisa relatório de páginas se fizer com exemplo ligado a um bd vale estrelas em design e estrela em bd entrega | 0 |
363,653 | 25,460,472,519 | IssuesEvent | 2022-11-24 18:16:02 | redpanda-data/documentation | https://api.github.com/repos/redpanda-data/documentation | opened | engine: Provide more context in internal search results | documentation website engine usability improvement | ### Describe the Issue
When you enter a query into our search box, the results don't differentiate between Cloud and Platform. It would be useful to configure Algolia to display the product to which the search result applies.
### Updates to existing documentation
<!--
Provide the URL of the page(s) to which the updates apply.
Which topic(s) should be updated?
What is the requested fix? Describe what is wrong in the existing doc and include screenshots if possible. Then provide the correct information.
Is this request to document an existing Redpanda feature that is not currently documented?
-->
### New feature or content gap requests
### If new feature, in which release is it included or expected?
### If the requested update is from customer feedback or a Community slack conversation, provide a link:
### Additional notes
<!--
Documentation Issues must be distinct and not overlap. If filing an Issue for a feature that spans platform and cloud, you must file two separate Issues. Each Issue will drive the new content in GitHub for the respective platform or cloud doc.
Include:
- Relevant GitHub issues and pull requests
- Dependencies on other features or components
- Specific Redpanda contributors to notify
-->
| 1.0 | engine: Provide more context in internal search results - ### Describe the Issue
When you enter a query into our search box, the results don't differentiate between Cloud and Platform. It would be useful to configure Algolia to display the product to which the search result applies.
### Updates to existing documentation
<!--
Provide the URL of the page(s) to which the updates apply.
Which topic(s) should be updated?
What is the requested fix? Describe what is wrong in the existing doc and include screenshots if possible. Then provide the correct information.
Is this request to document an existing Redpanda feature that is not currently documented?
-->
### New feature or content gap requests
### If new feature, in which release is it included or expected?
### If the requested update is from customer feedback or a Community slack conversation, provide a link:
### Additional notes
<!--
Documentation Issues must be distinct and not overlap. If filing an Issue for a feature that spans platform and cloud, you must file two separate Issues. Each Issue will drive the new content in GitHub for the respective platform or cloud doc.
Include:
- Relevant GitHub issues and pull requests
- Dependencies on other features or components
- Specific Redpanda contributors to notify
-->
| non_priority | engine provide more context in internal search results describe the issue when you enter a query into our search box the results don t differentiate between cloud and platform it would be useful to configure algolia to display the product to which the search result applies updates to existing documentation provide the url of the page s to which the updates apply which topic s should be updated what is the requested fix describe what is wrong in the existing doc and include screenshots if possible then provide the correct information is this request to document an existing redpanda feature that is not currently documented new feature or content gap requests if new feature in which release is it included or expected if the requested update is from customer feedback or a community slack conversation provide a link additional notes documentation issues must be distinct and not overlap if filing an issue for a feature that spans platform and cloud you must file two separate issues each issue will drive the new content in github for the respective platform or cloud doc include relevant github issues and pull requests dependencies on other features or components specific redpanda contributors to notify | 0 |
26,924 | 13,155,477,827 | IssuesEvent | 2020-08-10 08:58:12 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | closed | Bazel deadlocks hosts with large numbers of cores | team-Performance untriaged | ### Description of the problem / feature request:
Bazel appears to be incredibly sensitive to the number of cores available on the local machine: at high core counts (>=64), bazel will predictably deadlock, often bringing the machine down with it, if there is any I/O latency or contention. We have experienced this consistently on multiple Linux hosts, both physical and virtual -- although it happens at a much greater frequency on virtual machines, even when provisioned to be fairly isolated and running on SSDs. On a GCE n1-highcpu-64 (96 core, 57GB RAM, 100GB SSD VM, we can trigger this deadlock for roughly 80% of builds of our project (which includes part of TensorFlow and LLVM as deps, and has on the order of ~7000 actions). In such a configuration, the deadlock usually occurs after ~2000-3000 actions and always with the same pattern. Bazel will report that "128 jobs running" but watching top will show very low utilization (say 16-30 processes), high CPU usage of the Bazel Java process (200-400%), and the tendency for jobs to "get lost", eventually with no active jobs running (from the perspective of top).
On internal developer specialist workstations (with normal disks, not SSD), the occurrence is 100% and happens much sooner in a build.
I have found two workarounds that help the problem:
1. Set the `--output_base` to a directory on tmpfs (under `/dev/shm`), making sure that it is sized appropriately.
2. Set `--spawn_strategy=standalone`
For the first, this seems to make things relatively reliable. Looking at top, bazel gets close to saturating all cores (90-95% consistent utilization). For the second, it seems to help but deadlocks still occur at a lower rate. When not triggering a deadlock, the utilization seems relatively high. I have a low sample count for the second option.
Note also that we maintain roughly parallel CMake/Ninja builds for a substantial fraction of the code, have never had any such issues with it, and in general, it is much more reliable at utilizing all available cores for cc compilation jobs than Bazel is. This is a fairly apples to apples comparison running on the same systems.
I have no real knowledge of bazel internals, but all of the evidence I have seen suggests that at high core counts, Bazel is extremely sensitive to I/O latency, the presence of which exacerbates some kind of locking issue which can turn into a flood which does something *really bad* causing machines to become unresponsive with no obvious resource contention. I have seen such machines eventually wake back up after an hour or so on occasion if an external agent kills processes.
### Feature requests: what underlying problem are you trying to solve with this feature?
Bazel should operate reliably regardless of the machine size.
### Bugs: what's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
Comment out [this line](https://github.com/google/mlir-release-tools/blob/85004fbbbc040735de9c426d2bc9299bf0e4860b/scripts/automation/iree_tf_python_manylinux_build.sh#L19) and run our build pipeline. Based on internal, ad-hoc testing, I suspect that this can be easily triggered on affected machines by building TensorFlow, or another such project with ~thousands of actions.
Alternatively, building our project on such a machine repros easily: https://google.github.io/iree/get-started/getting-started-linux-bazel
### What operating system are you running Bazel on?
Various. Most commonly Debian 10.
### What's the output of `bazel info release`?
Various - we've experienced this over many versions over ~months.
Here is one:
release 3.3.1
### If `bazel info release` returns "development version" or "(@non-git)", tell us how you built Bazel.
N/A - although I have also experienced this with custom build bazel versions on exotic configs.
### What's the output of `git remote get-url origin ; git rev-parse master ; git rev-parse HEAD` ?
https://github.com/google/iree.git
c96bbb1d38d3fe81230e38ce3214d80b922ba4c3
c96bbb1d38d3fe81230e38ce3214d80b922ba4c3
### Have you found anything relevant by searching the web?
No.
### Any other information, logs, or outputs that you want to share?
I can followup with artifacts you think might be valuable. I have not found anything worthwhile, and when it gets into a really bad state, I'm often on a remote ssh connection and the machine locks to the point that it is hard to do much. | True | Bazel deadlocks hosts with large numbers of cores - ### Description of the problem / feature request:
Bazel appears to be incredibly sensitive to the number of cores available on the local machine: at high core counts (>=64), bazel will predictably deadlock, often bringing the machine down with it, if there is any I/O latency or contention. We have experienced this consistently on multiple Linux hosts, both physical and virtual -- although it happens at a much greater frequency on virtual machines, even when provisioned to be fairly isolated and running on SSDs. On a GCE n1-highcpu-64 (96 core, 57GB RAM, 100GB SSD VM, we can trigger this deadlock for roughly 80% of builds of our project (which includes part of TensorFlow and LLVM as deps, and has on the order of ~7000 actions). In such a configuration, the deadlock usually occurs after ~2000-3000 actions and always with the same pattern. Bazel will report that "128 jobs running" but watching top will show very low utilization (say 16-30 processes), high CPU usage of the Bazel Java process (200-400%), and the tendency for jobs to "get lost", eventually with no active jobs running (from the perspective of top).
On internal developer specialist workstations (with normal disks, not SSD), the occurrence is 100% and happens much sooner in a build.
I have found two workarounds that help the problem:
1. Set the `--output_base` to a directory on tmpfs (under `/dev/shm`), making sure that it is sized appropriately.
2. Set `--spawn_strategy=standalone`
For the first, this seems to make things relatively reliable. Looking at top, bazel gets close to saturating all cores (90-95% consistent utilization). For the second, it seems to help but deadlocks still occur at a lower rate. When not triggering a deadlock, the utilization seems relatively high. I have a low sample count for the second option.
Note also that we maintain roughly parallel CMake/Ninja builds for a substantial fraction of the code, have never had any such issues with it, and in general, it is much more reliable at utilizing all available cores for cc compilation jobs than Bazel is. This is a fairly apples to apples comparison running on the same systems.
I have no real knowledge of bazel internals, but all of the evidence I have seen suggests that at high core counts, Bazel is extremely sensitive to I/O latency, the presence of which exacerbates some kind of locking issue which can turn into a flood which does something *really bad* causing machines to become unresponsive with no obvious resource contention. I have seen such machines eventually wake back up after an hour or so on occasion if an external agent kills processes.
### Feature requests: what underlying problem are you trying to solve with this feature?
Bazel should operate reliably regardless of the machine size.
### Bugs: what's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
Comment out [this line](https://github.com/google/mlir-release-tools/blob/85004fbbbc040735de9c426d2bc9299bf0e4860b/scripts/automation/iree_tf_python_manylinux_build.sh#L19) and run our build pipeline. Based on internal, ad-hoc testing, I suspect that this can be easily triggered on affected machines by building TensorFlow, or another such project with ~thousands of actions.
Alternatively, building our project on such a machine repros easily: https://google.github.io/iree/get-started/getting-started-linux-bazel
### What operating system are you running Bazel on?
Various. Most commonly Debian 10.
### What's the output of `bazel info release`?
Various - we've experienced this over many versions over ~months.
Here is one:
release 3.3.1
### If `bazel info release` returns "development version" or "(@non-git)", tell us how you built Bazel.
N/A - although I have also experienced this with custom build bazel versions on exotic configs.
### What's the output of `git remote get-url origin ; git rev-parse master ; git rev-parse HEAD` ?
https://github.com/google/iree.git
c96bbb1d38d3fe81230e38ce3214d80b922ba4c3
c96bbb1d38d3fe81230e38ce3214d80b922ba4c3
### Have you found anything relevant by searching the web?
No.
### Any other information, logs, or outputs that you want to share?
I can followup with artifacts you think might be valuable. I have not found anything worthwhile, and when it gets into a really bad state, I'm often on a remote ssh connection and the machine locks to the point that it is hard to do much. | non_priority | bazel deadlocks hosts with large numbers of cores description of the problem feature request bazel appears to be incredibly sensitive to the number of cores available on the local machine at high core counts bazel will predictably deadlock often bringing the machine down with it if there is any i o latency or contention we have experienced this consistently on multiple linux hosts both physical and virtual although it happens at a much greater frequency on virtual machines even when provisioned to be fairly isolated and running on ssds on a gce highcpu core ram ssd vm we can trigger this deadlock for roughly of builds of our project which includes part of tensorflow and llvm as deps and has on the order of actions in such a configuration the deadlock usually occurs after actions and always with the same pattern bazel will report that jobs running but watching top will show very low utilization say processes high cpu usage of the bazel java process and the tendency for jobs to get lost eventually with no active jobs running from the perspective of top on internal developer specialist workstations with normal disks not ssd the occurrence is and happens much sooner in a build i have found two workarounds that help the problem set the output base to a directory on tmpfs under dev shm making sure that it is sized appropriately set spawn strategy standalone for the first this seems to make things relatively reliable looking at top bazel gets close to saturating all cores consistent utilization for the second it seems to help but deadlocks still occur at a lower rate when not triggering a deadlock the utilization seems relatively high i have a low sample count for the second option note also that we maintain roughly parallel cmake ninja builds for a substantial fraction of the code have never had any such issues with it and in general it is much more reliable at utilizing all available cores for cc compilation jobs than bazel is this is a fairly apples to apples comparison running on the same systems i have no real knowledge of bazel internals but all of the evidence i have seen suggests that at high core counts bazel is extremely sensitive to i o latency the presence of which exacerbates some kind of locking issue which can turn into a flood which does something really bad causing machines to become unresponsive with no obvious resource contention i have seen such machines eventually wake back up after an hour or so on occasion if an external agent kills processes feature requests what underlying problem are you trying to solve with this feature bazel should operate reliably regardless of the machine size bugs what s the simplest easiest way to reproduce this bug please provide a minimal example if possible comment out and run our build pipeline based on internal ad hoc testing i suspect that this can be easily triggered on affected machines by building tensorflow or another such project with thousands of actions alternatively building our project on such a machine repros easily what operating system are you running bazel on various most commonly debian what s the output of bazel info release various we ve experienced this over many versions over months here is one release if bazel info release returns development version or non git tell us how you built bazel n a although i have also experienced this with custom build bazel versions on exotic configs what s the output of git remote get url origin git rev parse master git rev parse head have you found anything relevant by searching the web no any other information logs or outputs that you want to share i can followup with artifacts you think might be valuable i have not found anything worthwhile and when it gets into a really bad state i m often on a remote ssh connection and the machine locks to the point that it is hard to do much | 0 |
302,391 | 26,141,065,282 | IssuesEvent | 2022-12-29 18:31:44 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | closed | Release 4.4.0 - Alpha 2 - Footprint Metrics - ACTIVE-RESPONSE (2.5d) | team/cicd/automation type/release release test/4.4.0 | ## Footprint metrics information
| | |
|---------------------------------|--------------------------------------------|
| **Main release candidate issue #** | #15746 |
| **Main footprint metrics issue #** | #15752 |
| **Version** | 4.4.0 |
| **Release candidate #** | Alpha 2 |
| **Tag** | https://github.com/wazuh/wazuh/tree/v4.4.0-alpha2 |
## Stress test documentation
### Packages used
- Repository: `packages-dev.wazuh.com`
- Package path: `pre-release`
- Package revision: `1`
- **Jenkins build**: https://ci.wazuh.info/job/Test_stress/3692/
---
<details><summary>Manager</summary>
+ <details><summary>Plots</summary>
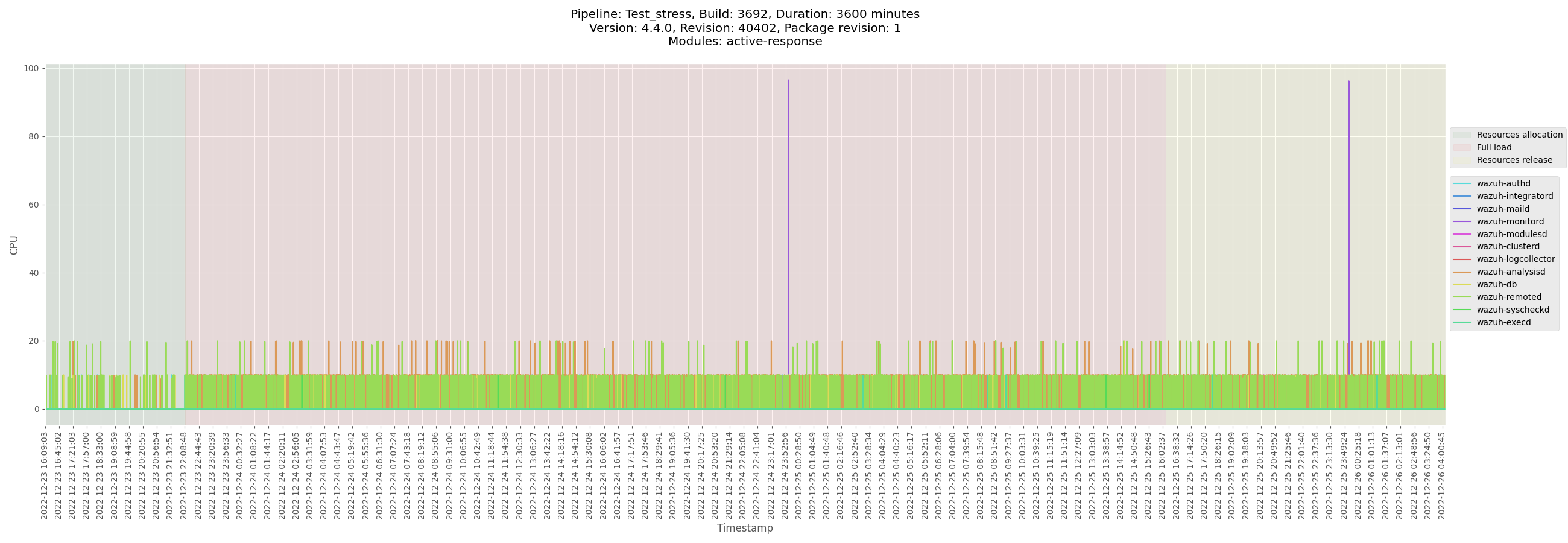
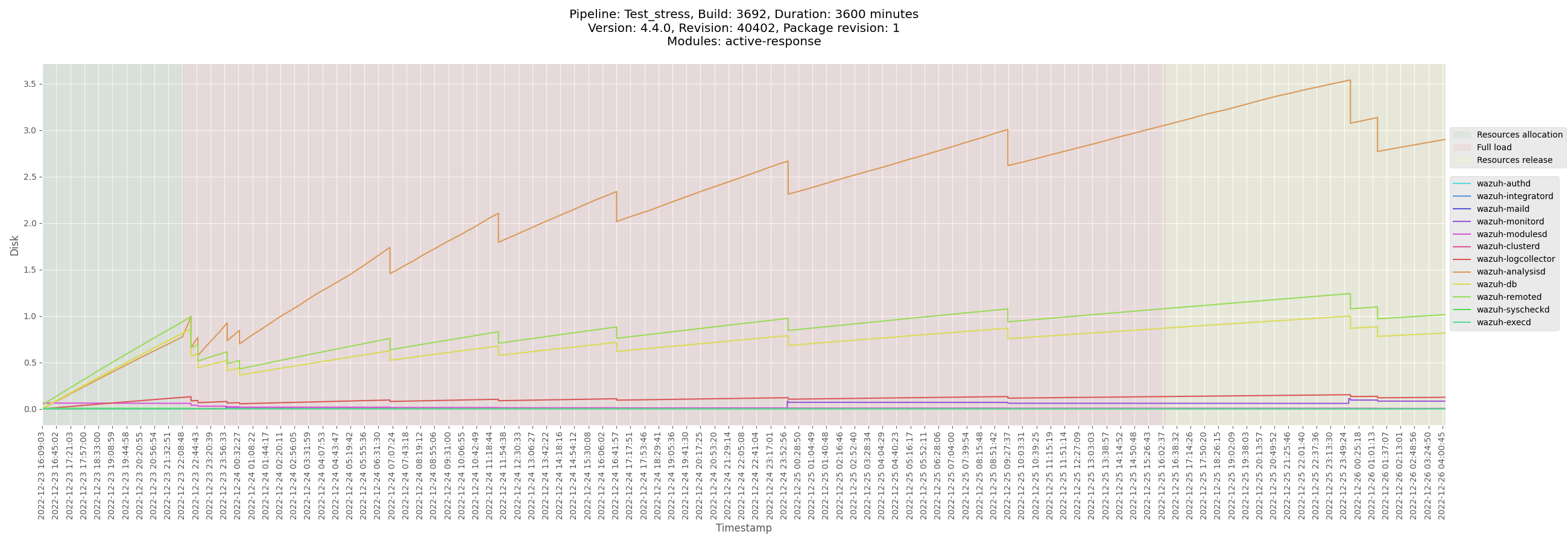
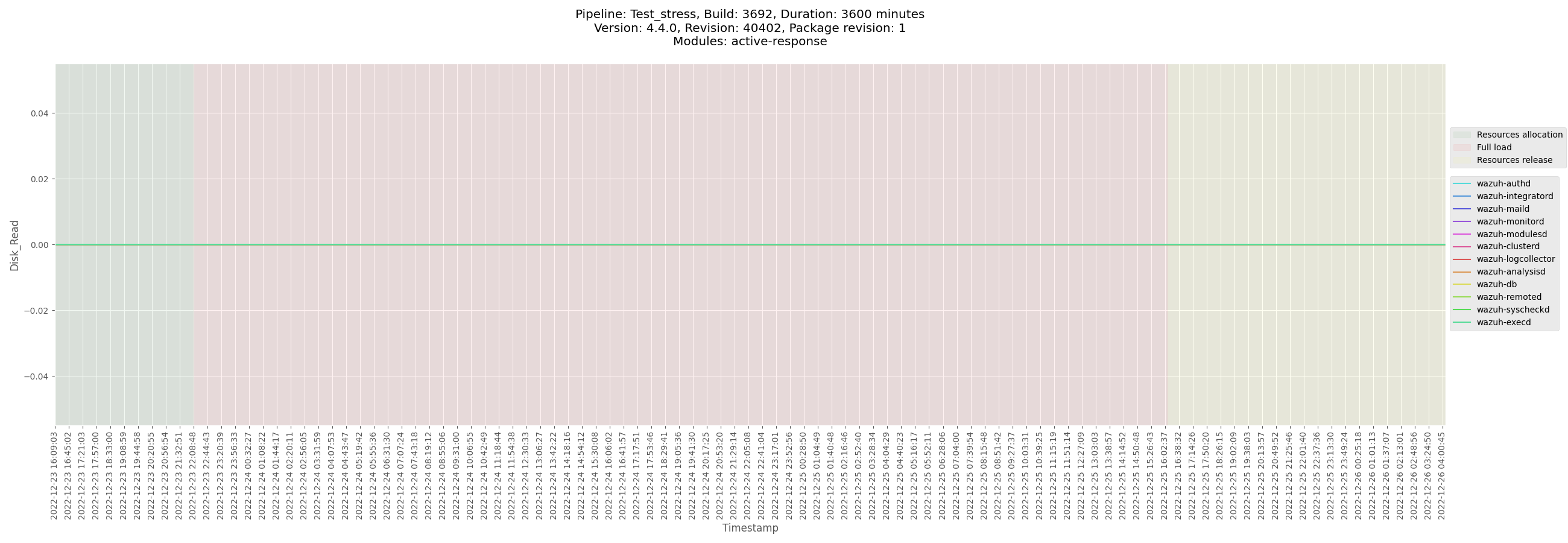
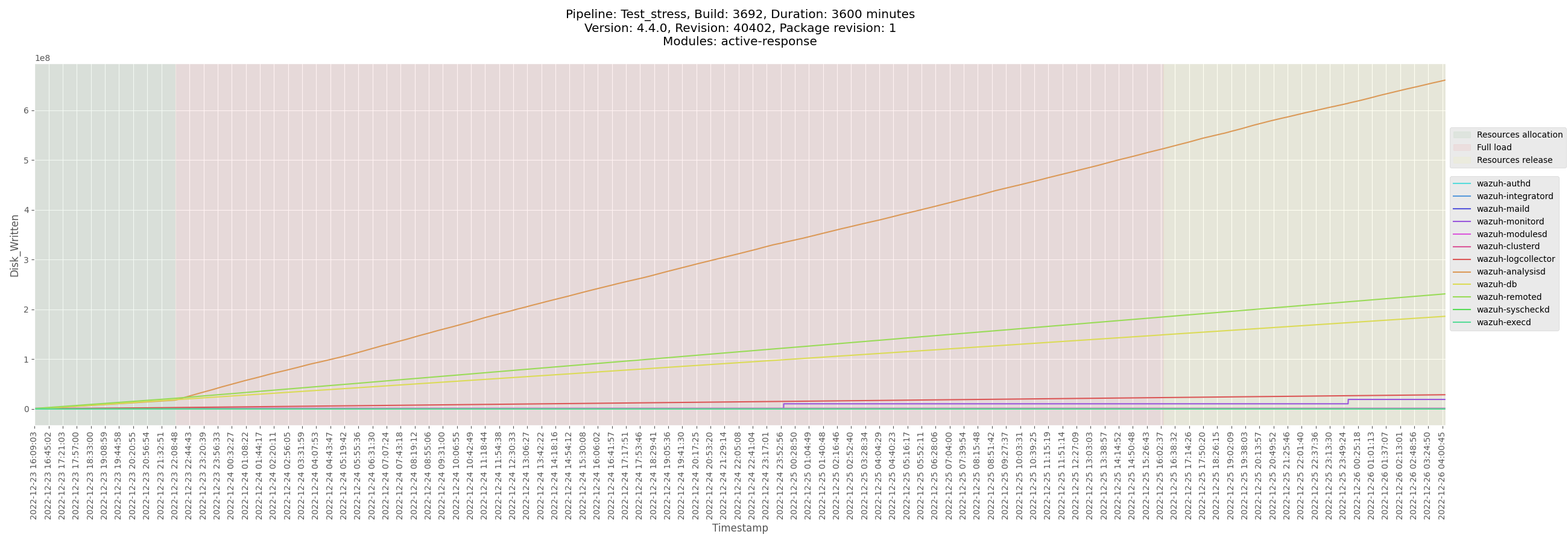
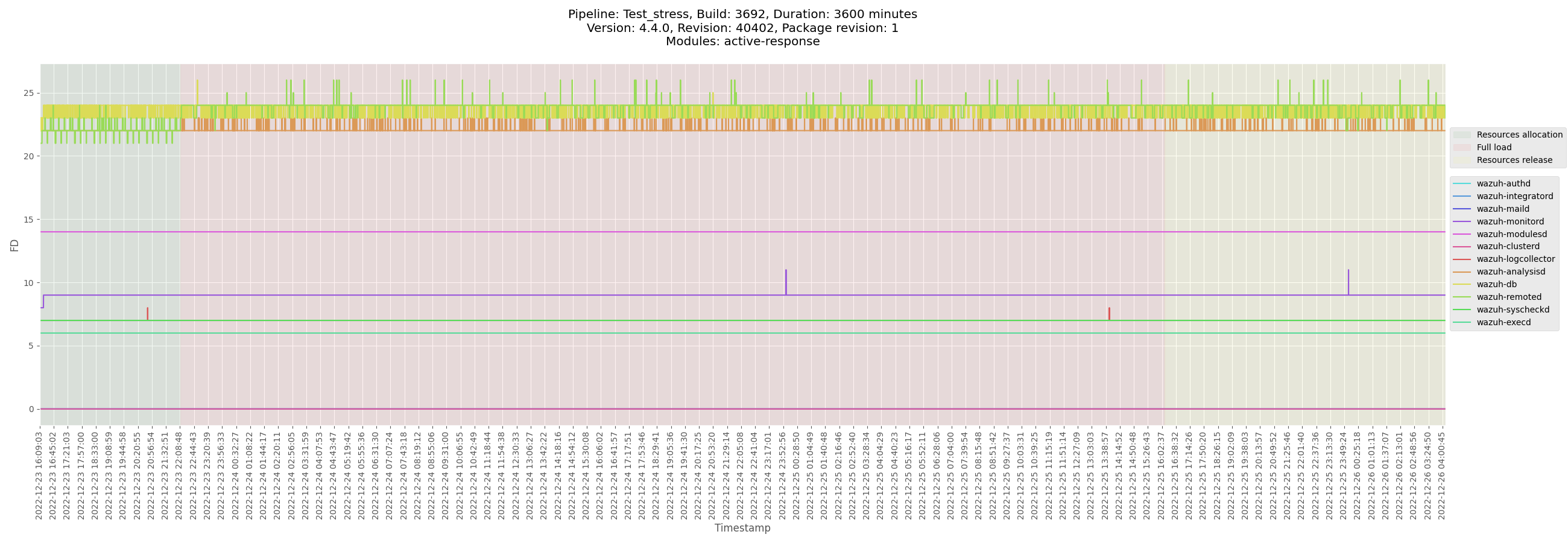

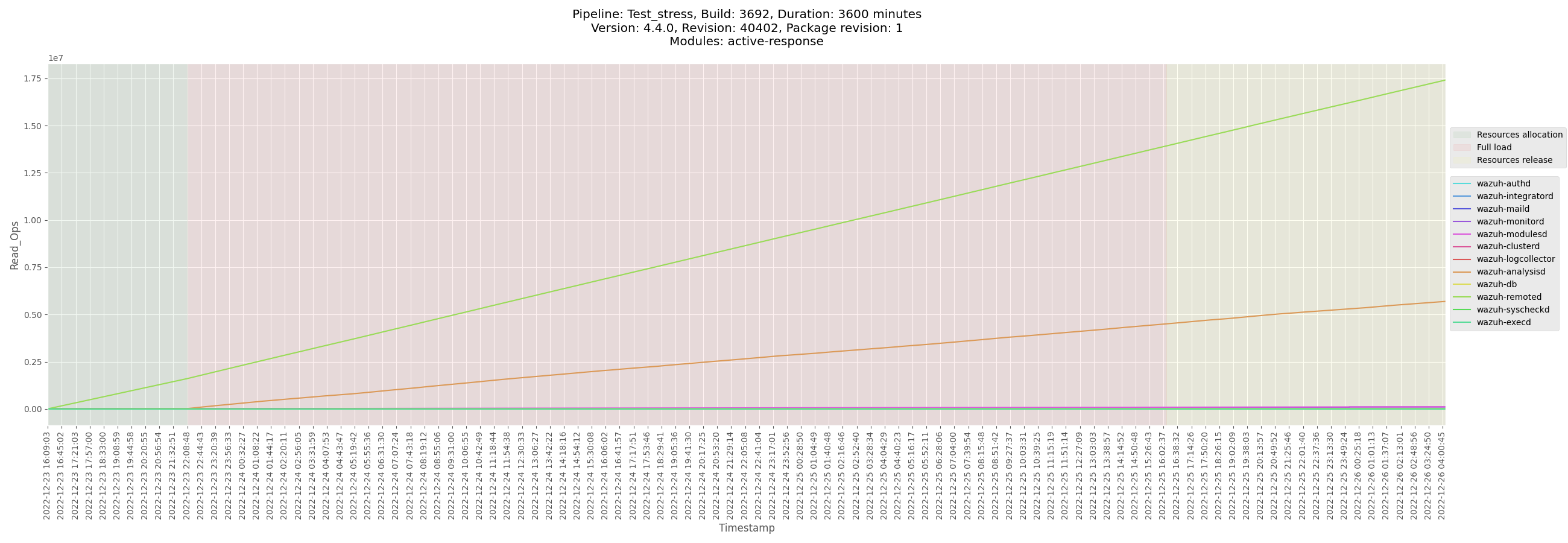
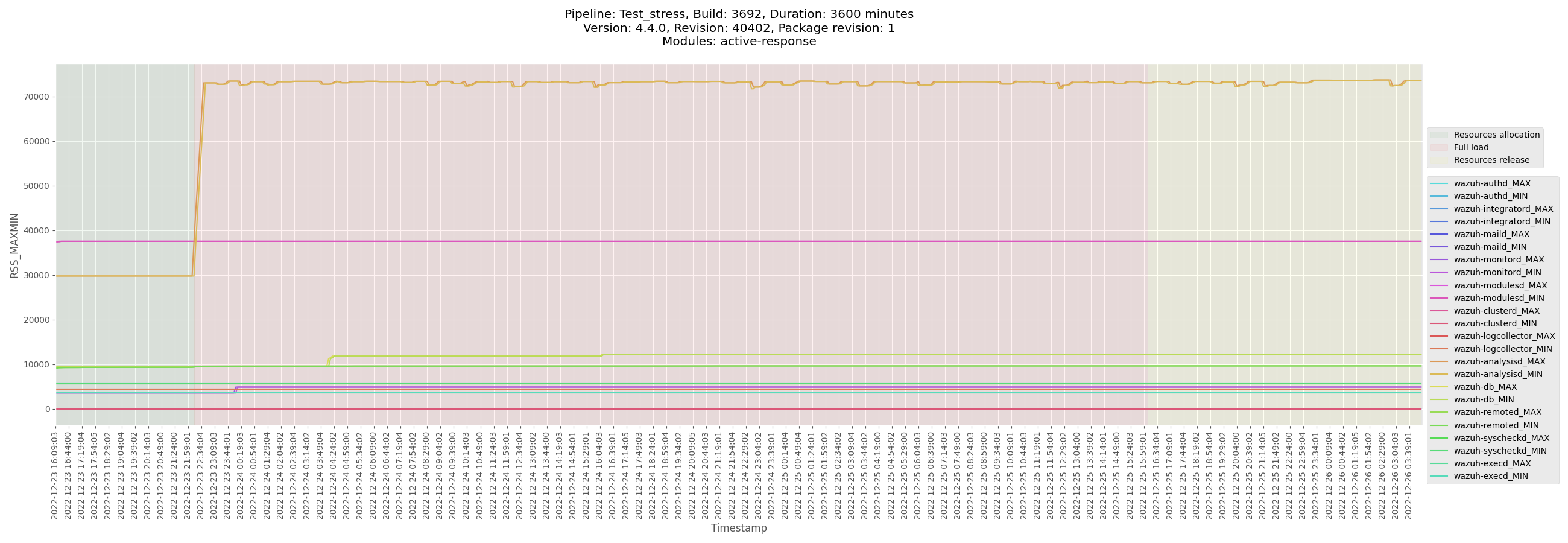
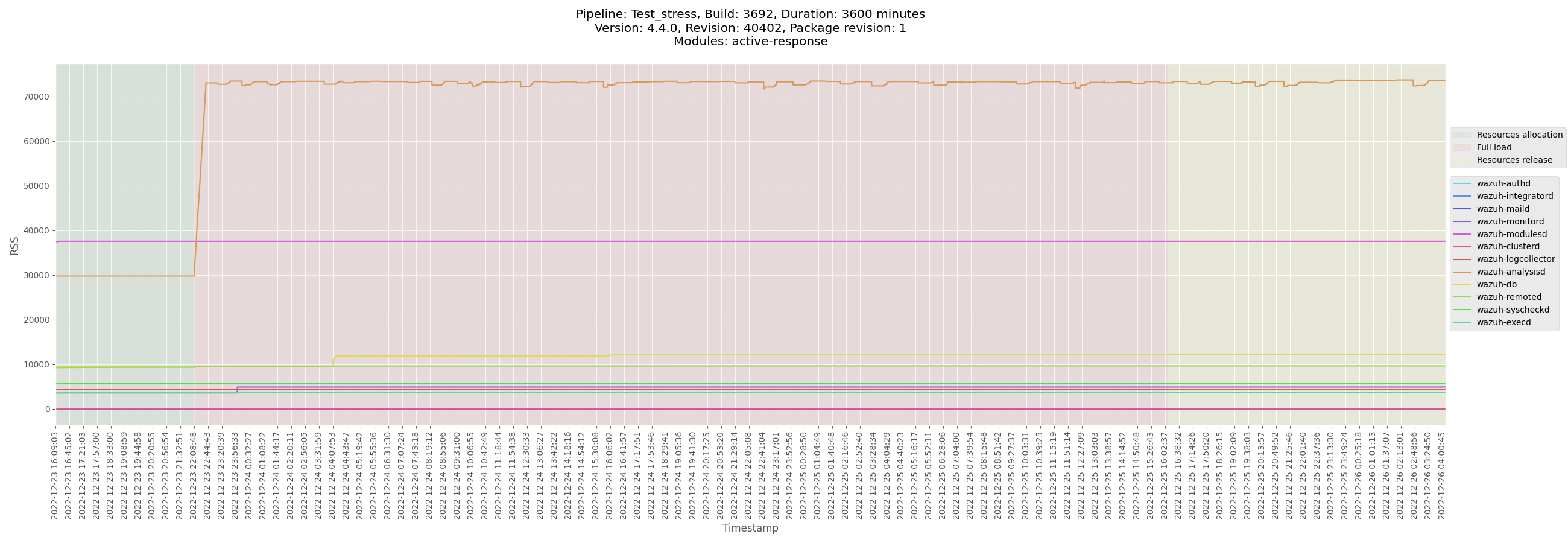
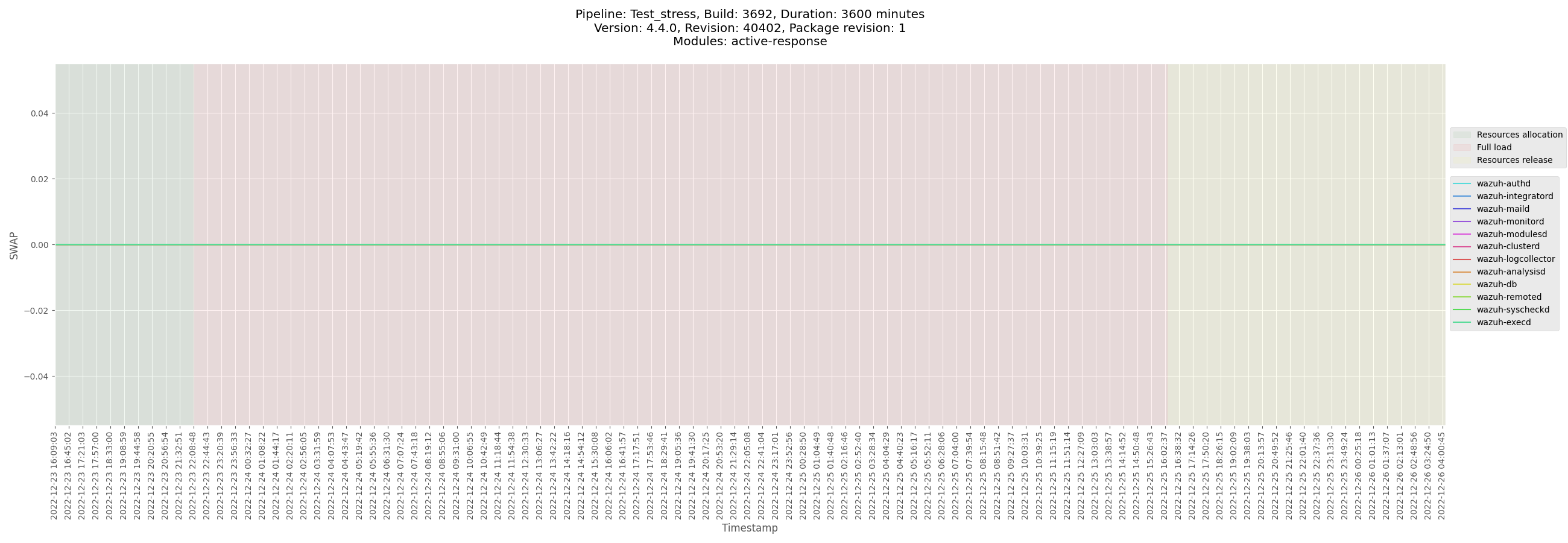
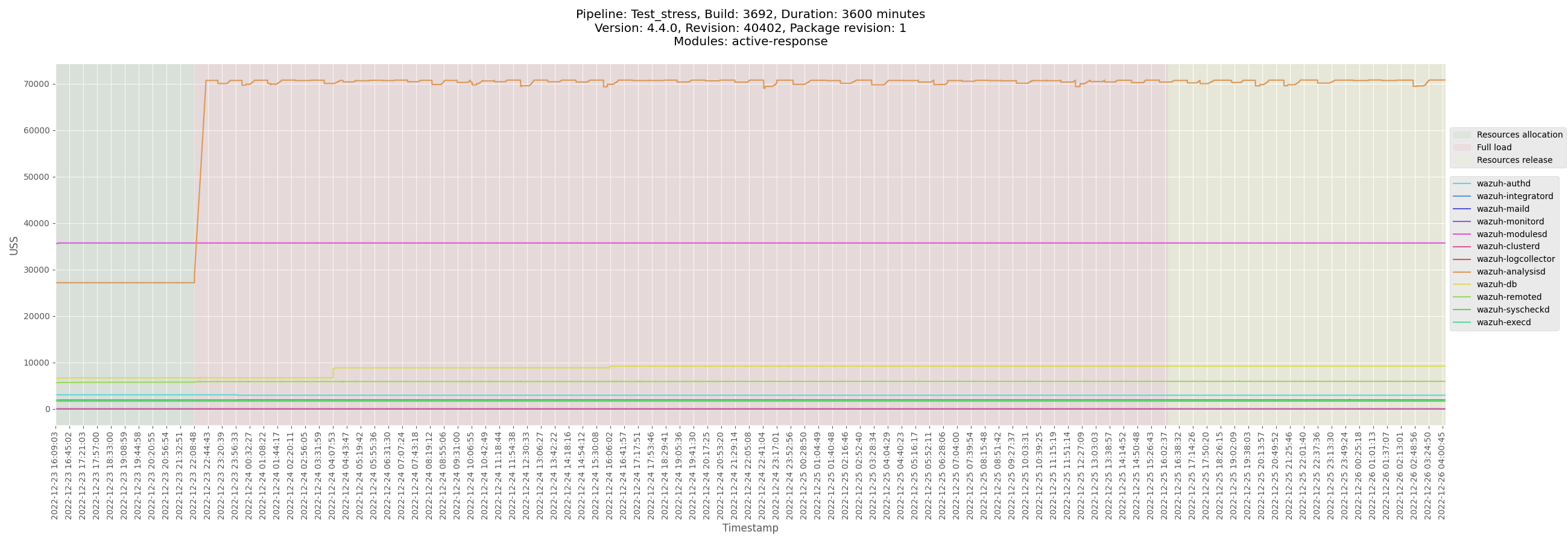

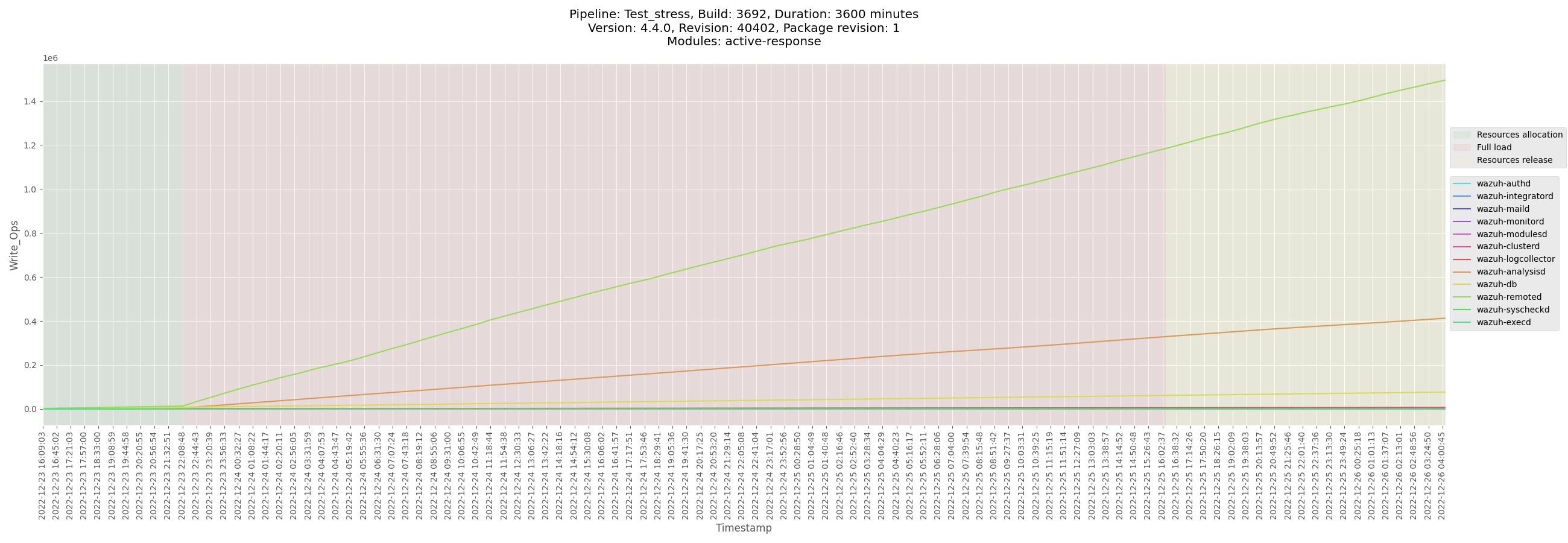
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_manager_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/logs/ossec_Test_stress_B3692_manager_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-manager-Test_stress_B3692_manager-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/data/monitor-manager-Test_stress_B3692_manager-pre-release.csv)
[Test_stress_B3692_manager_analysisd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/data/Test_stress_B3692_manager_analysisd_state.csv)
[Test_stress_B3692_manager_remoted_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/data/Test_stress_B3692_manager_remoted_state.csv)
</details>
</details>
<details><summary>Centos agent</summary>
+ <details><summary>Plots</summary>



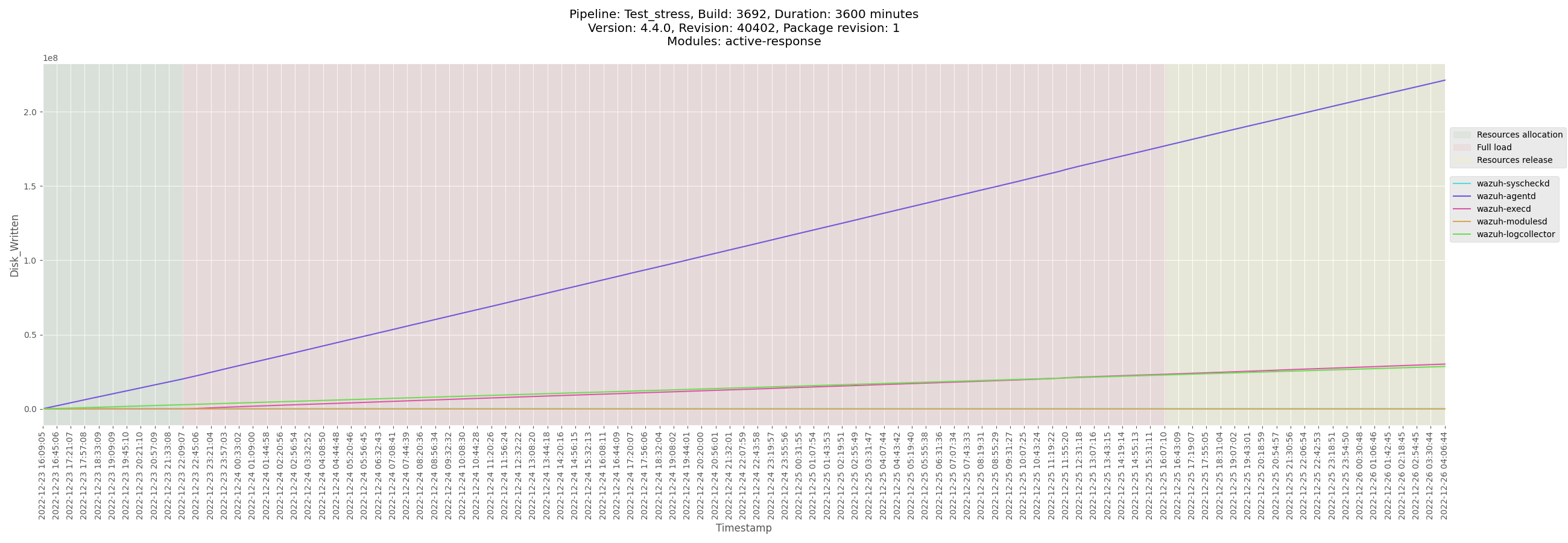
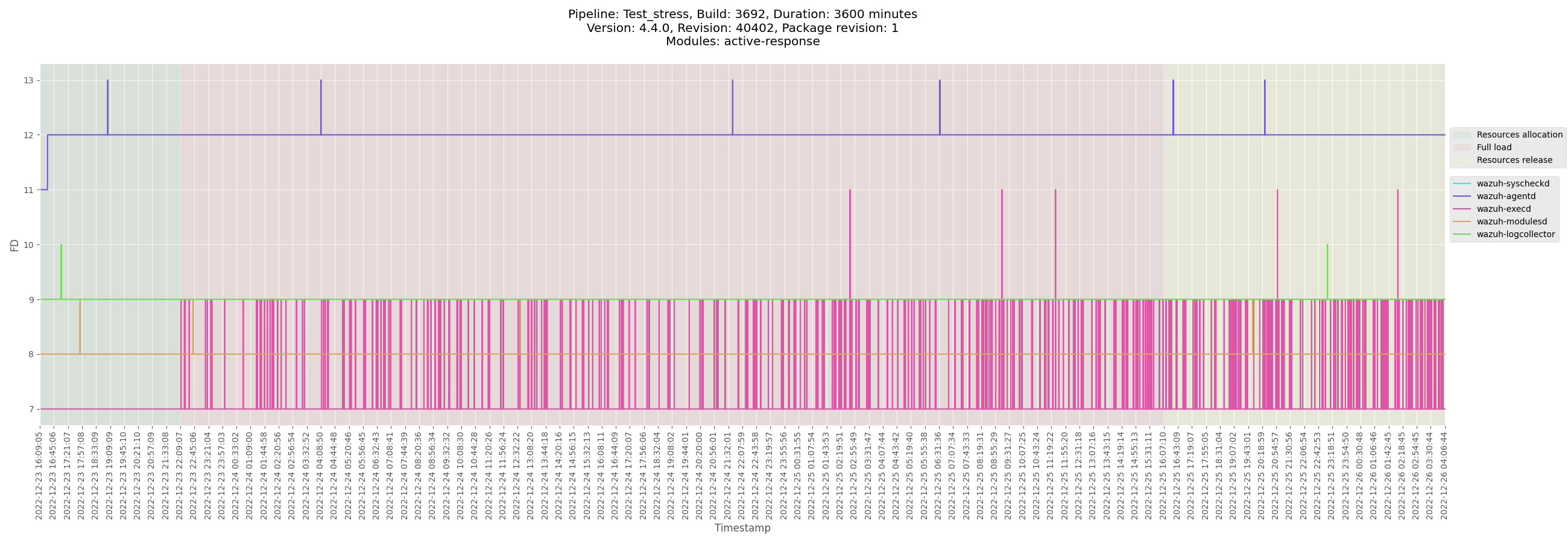
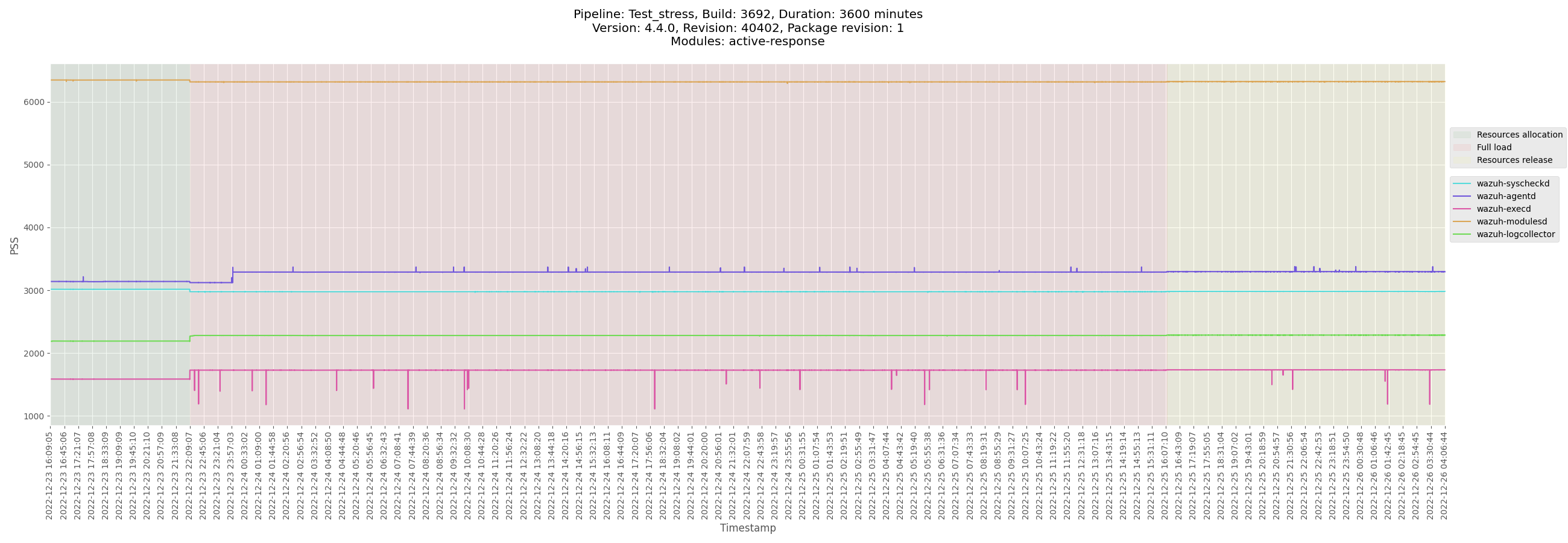
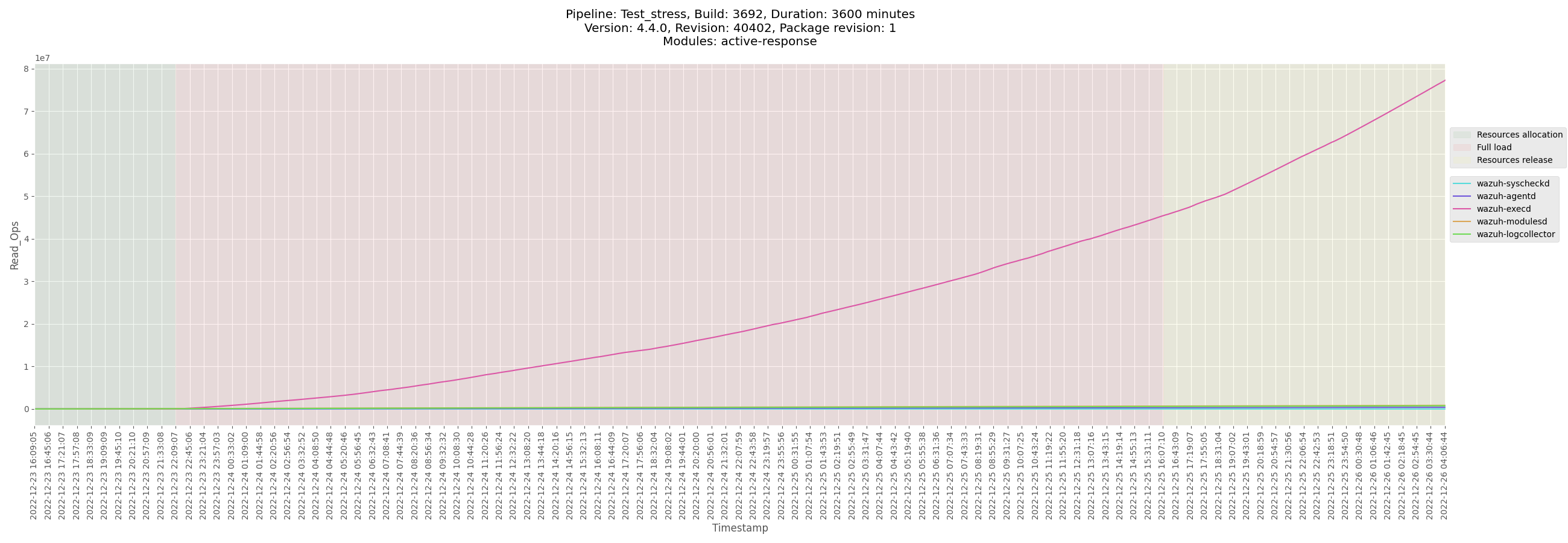
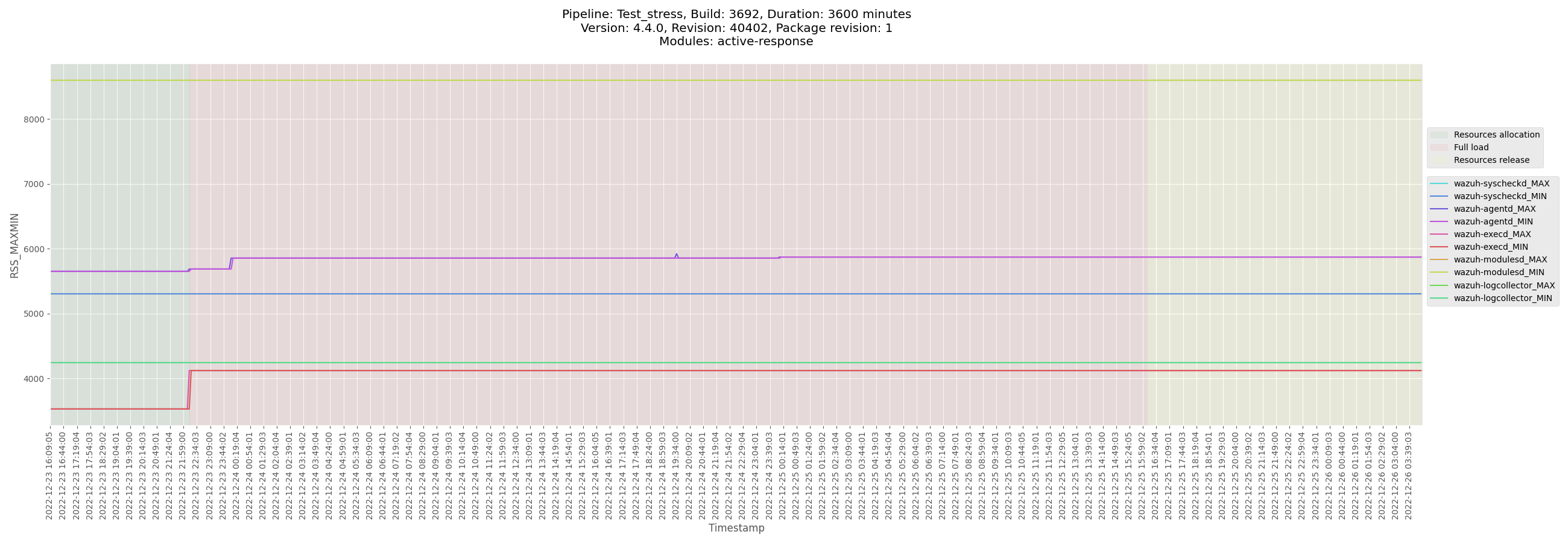
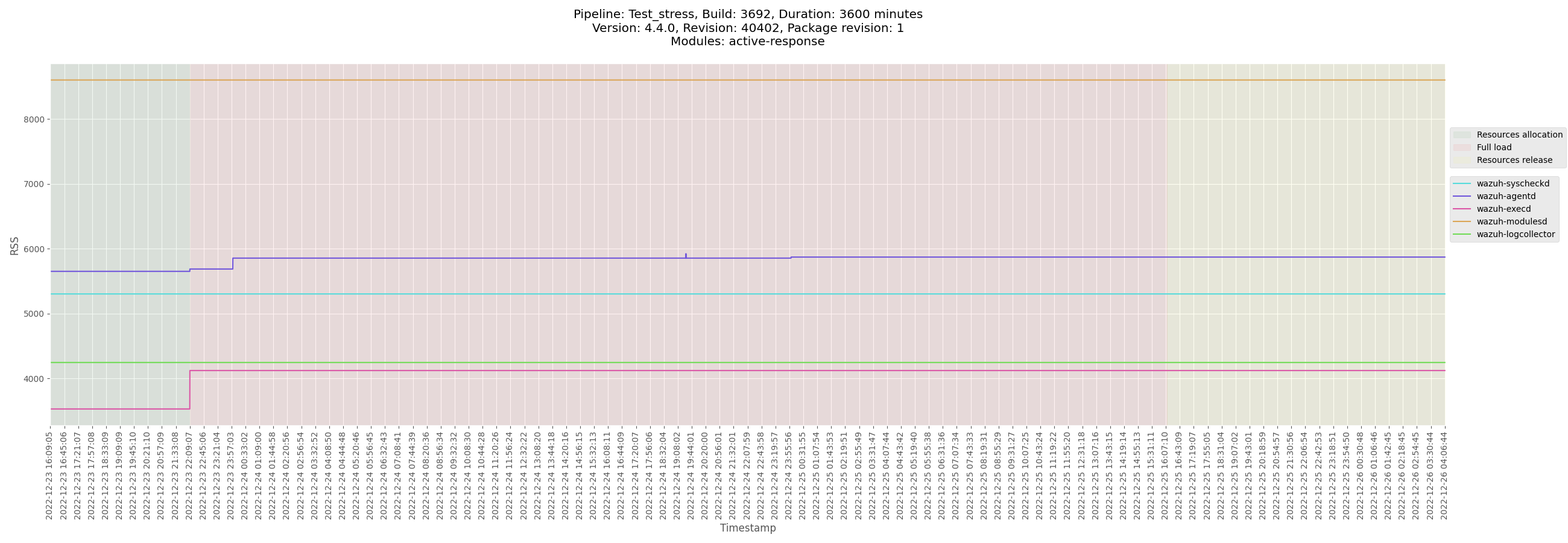
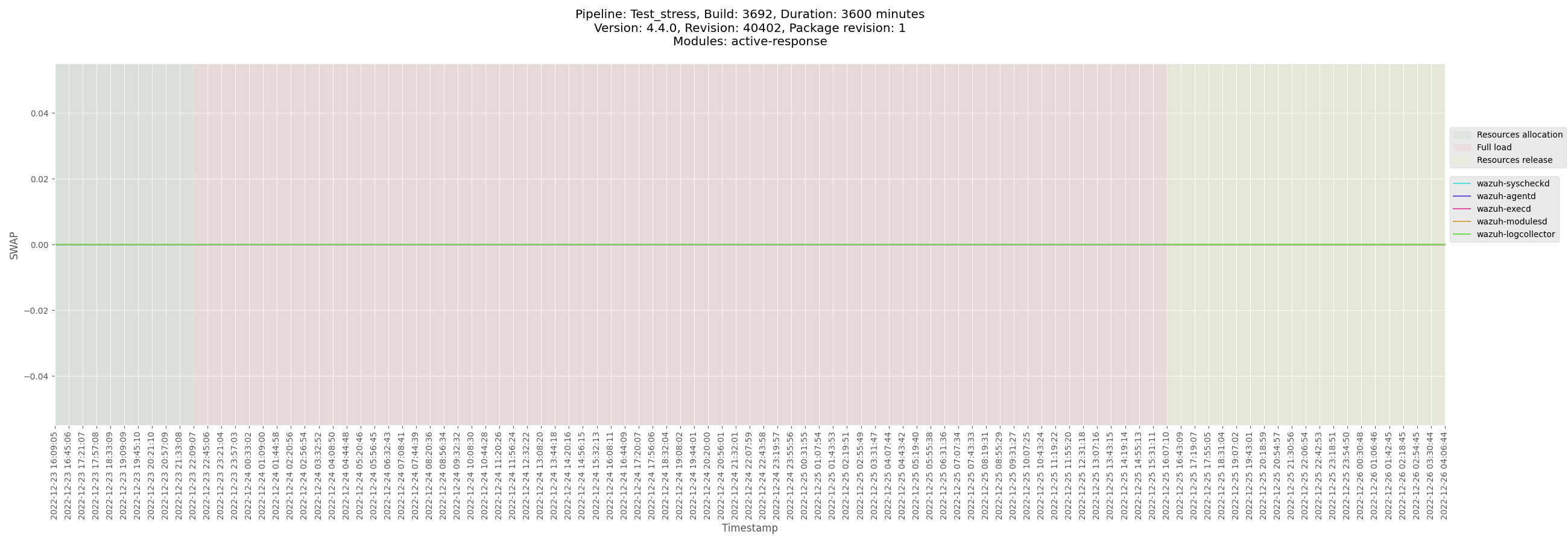
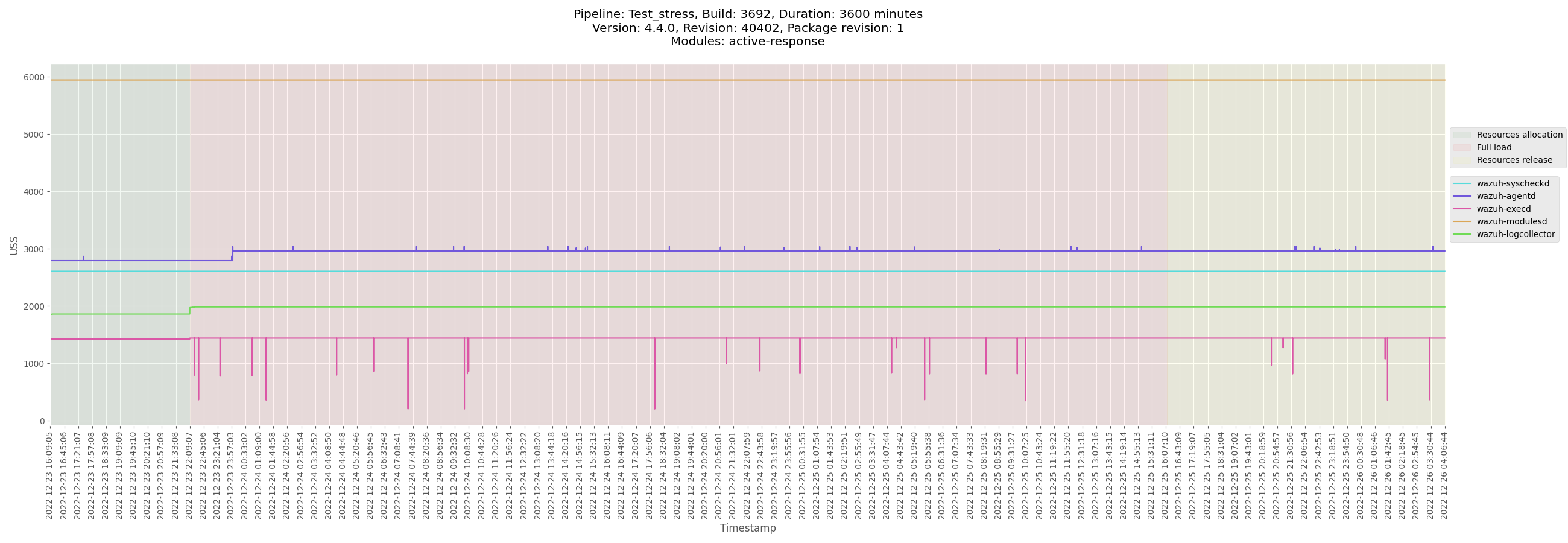
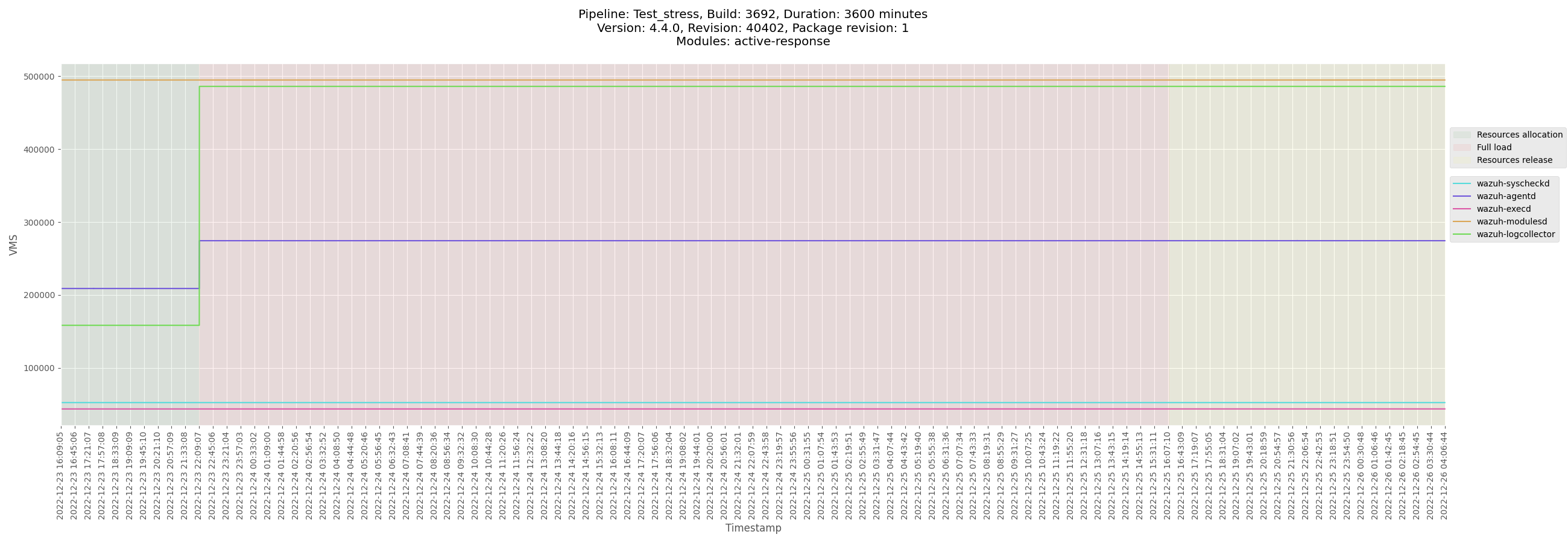
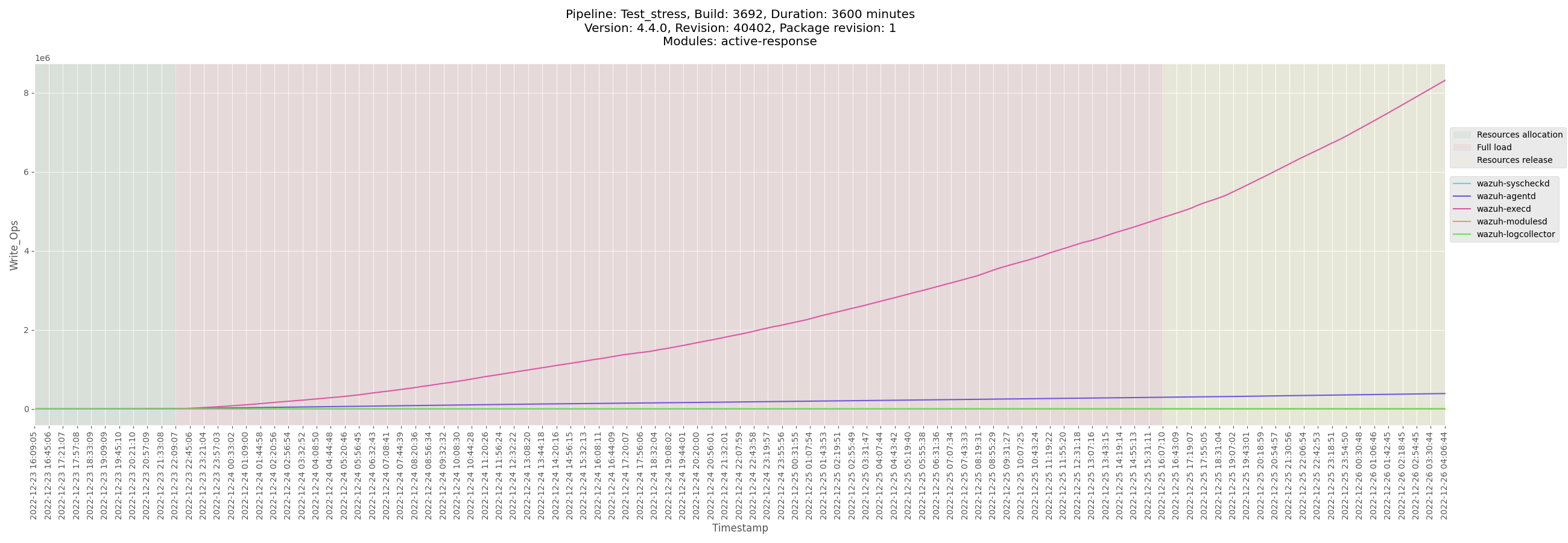

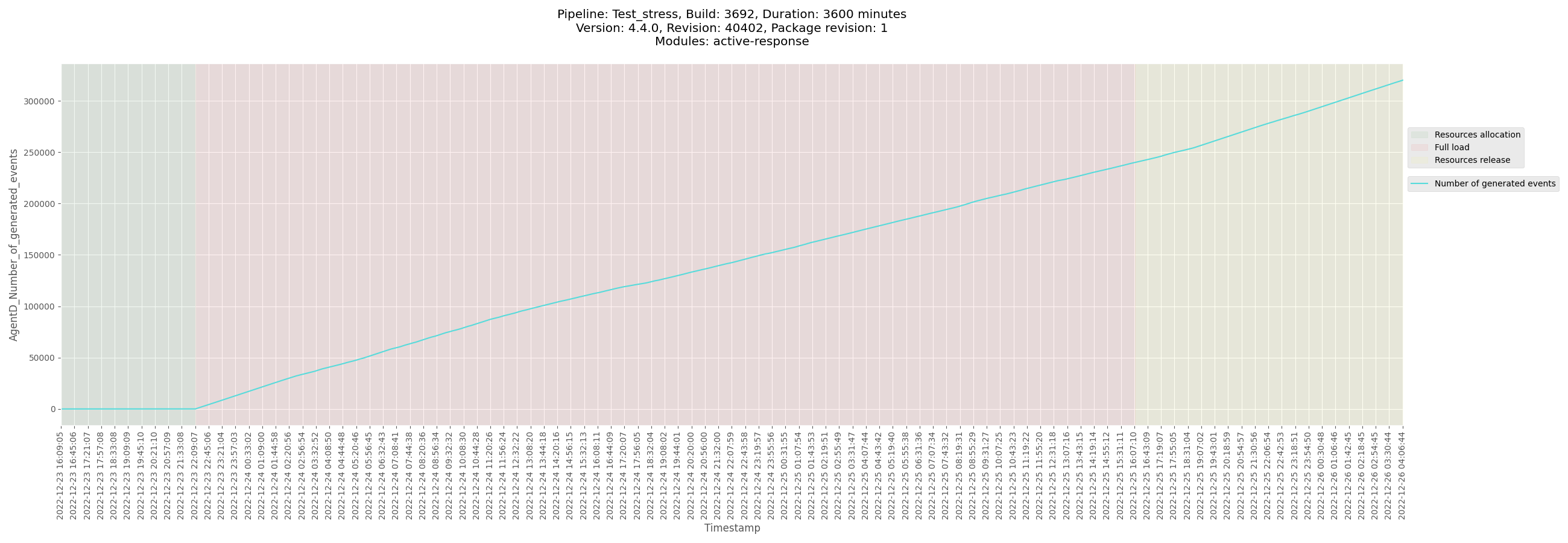

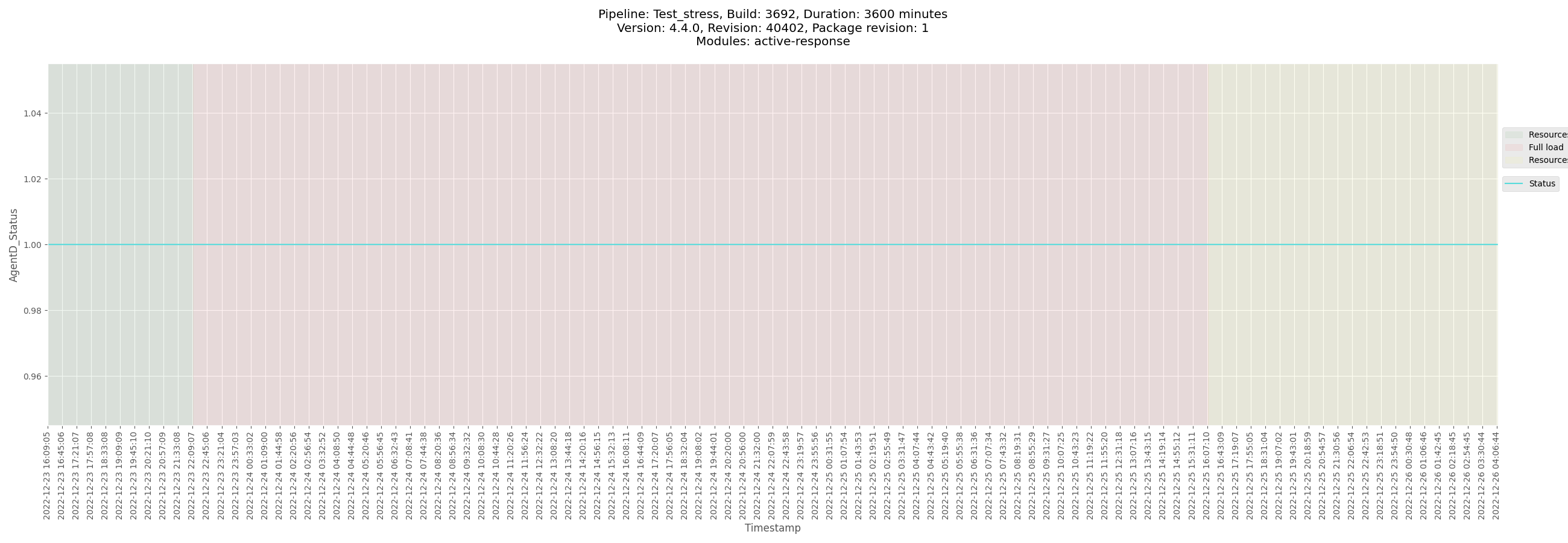
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_centos_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_centos/logs/ossec_Test_stress_B3692_centos_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3692_centos-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_centos/data/monitor-agent-Test_stress_B3692_centos-pre-release.csv)
[Test_stress_B3692_centos_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_centos/data/Test_stress_B3692_centos_agentd_state.csv)
</details>
</details>
<details><summary>Ubuntu agent</summary>
+ <details><summary>Plots</summary>
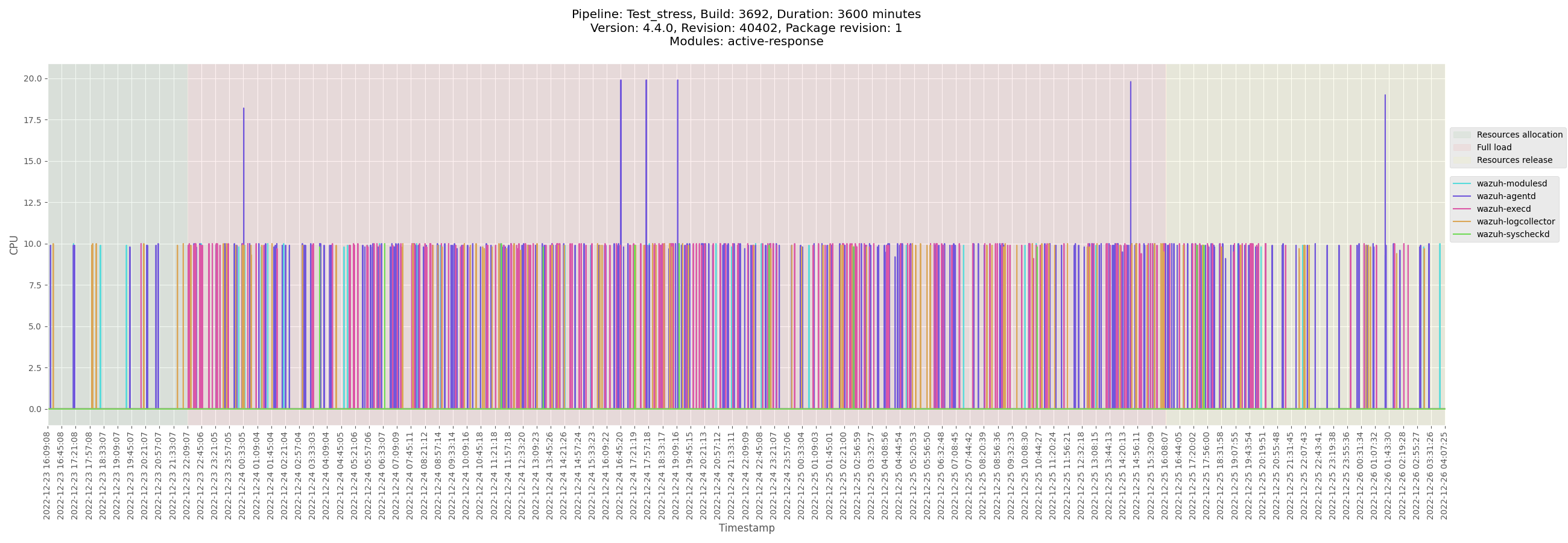

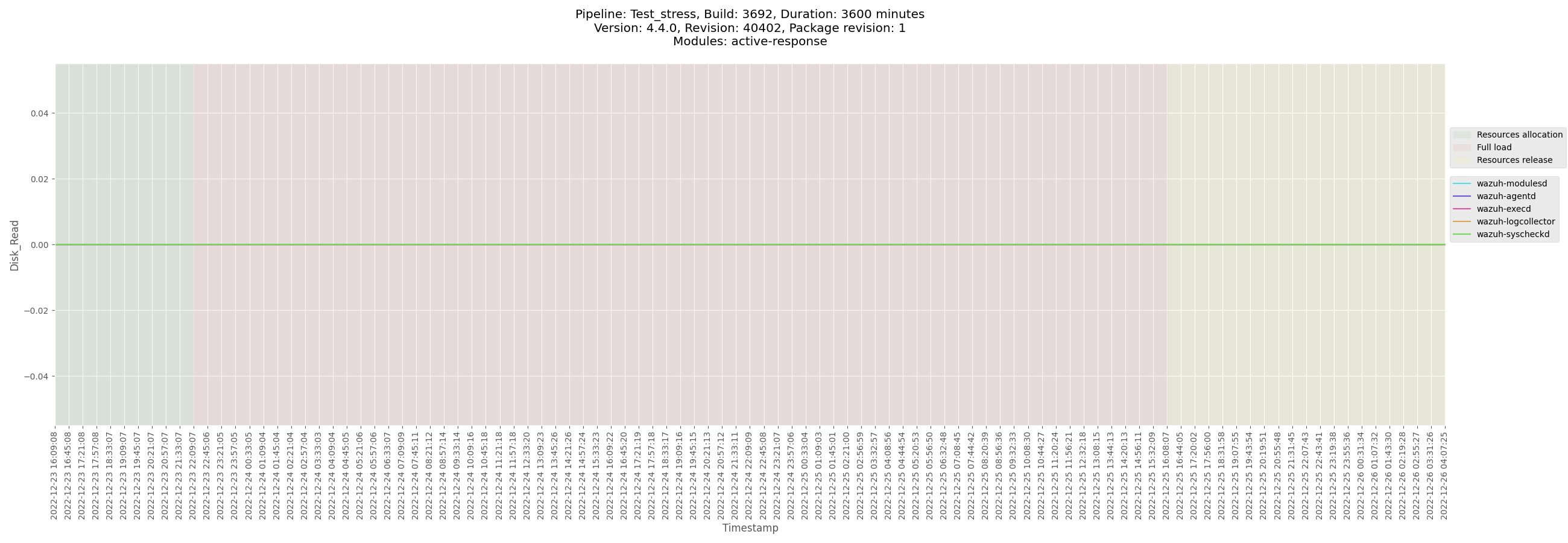

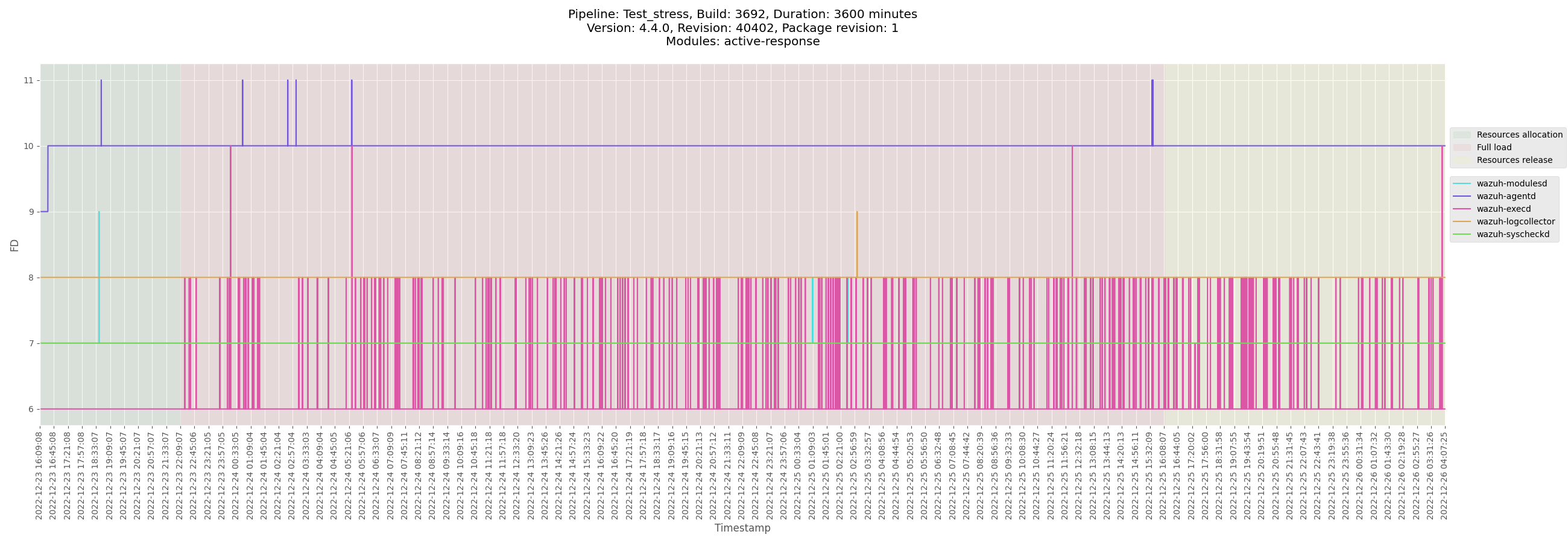
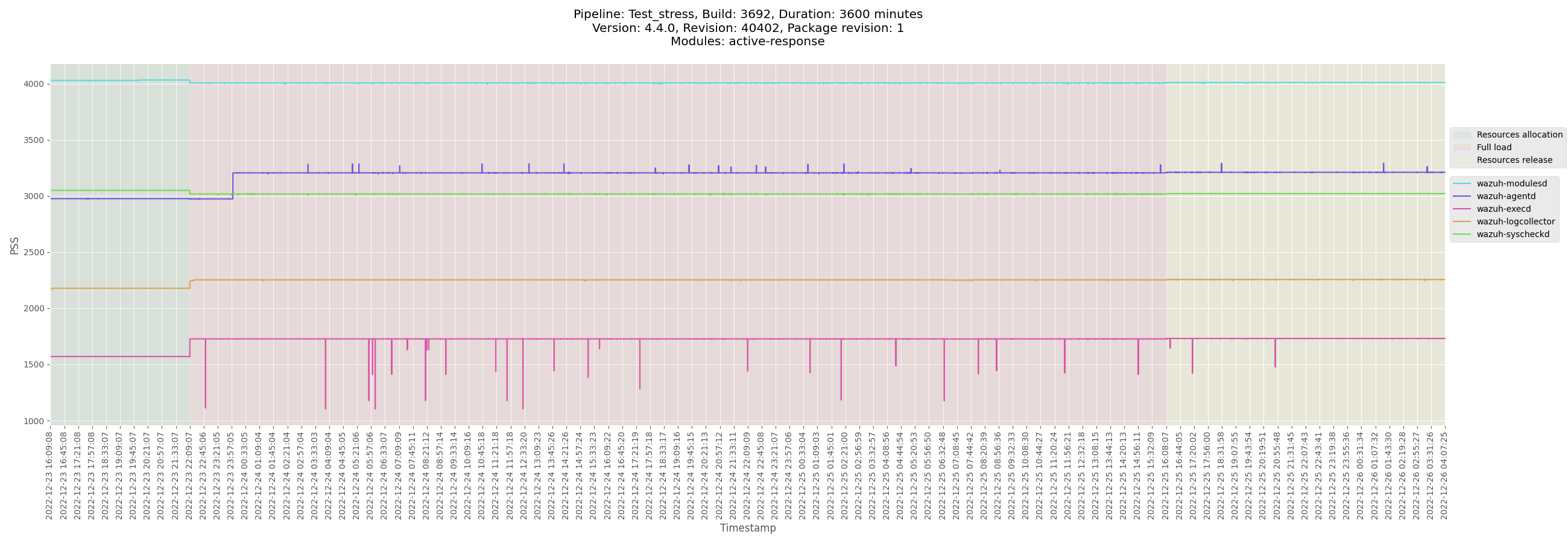


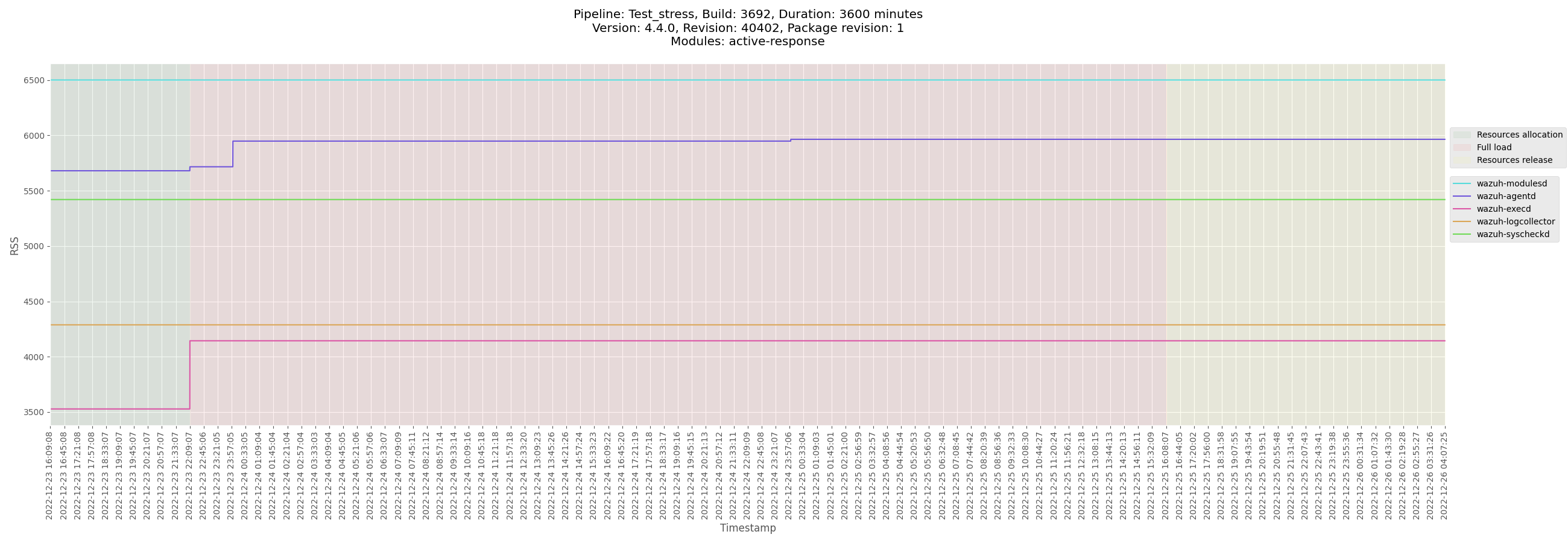
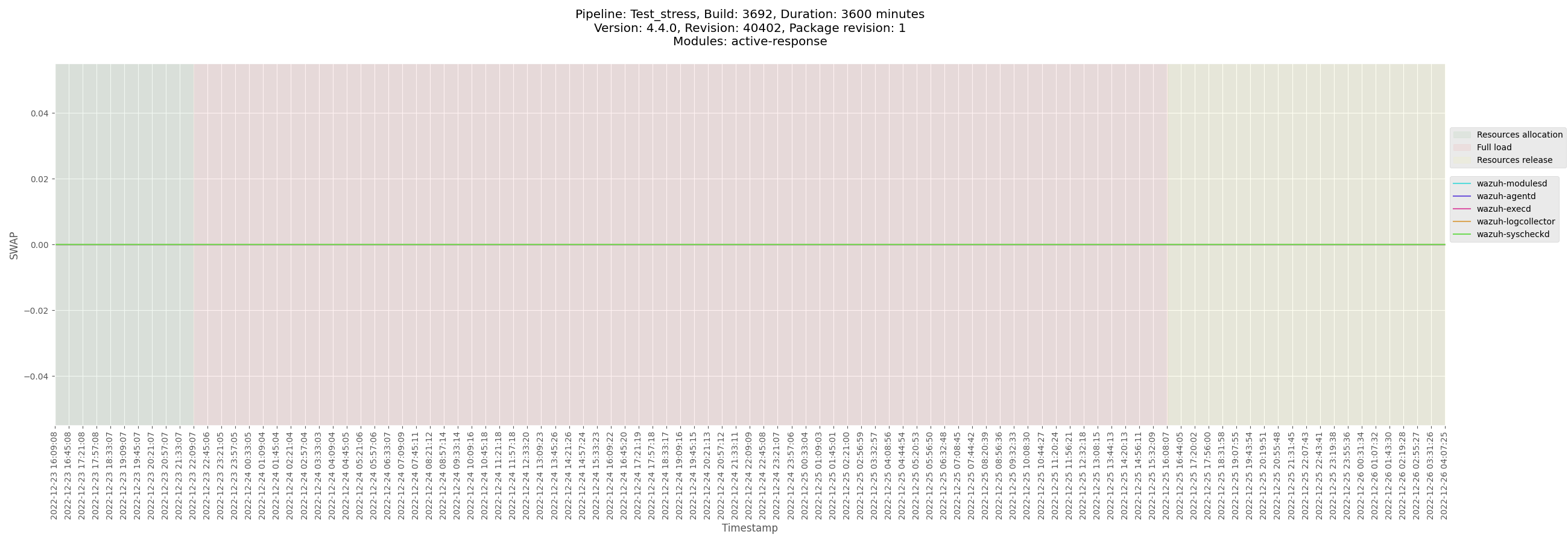
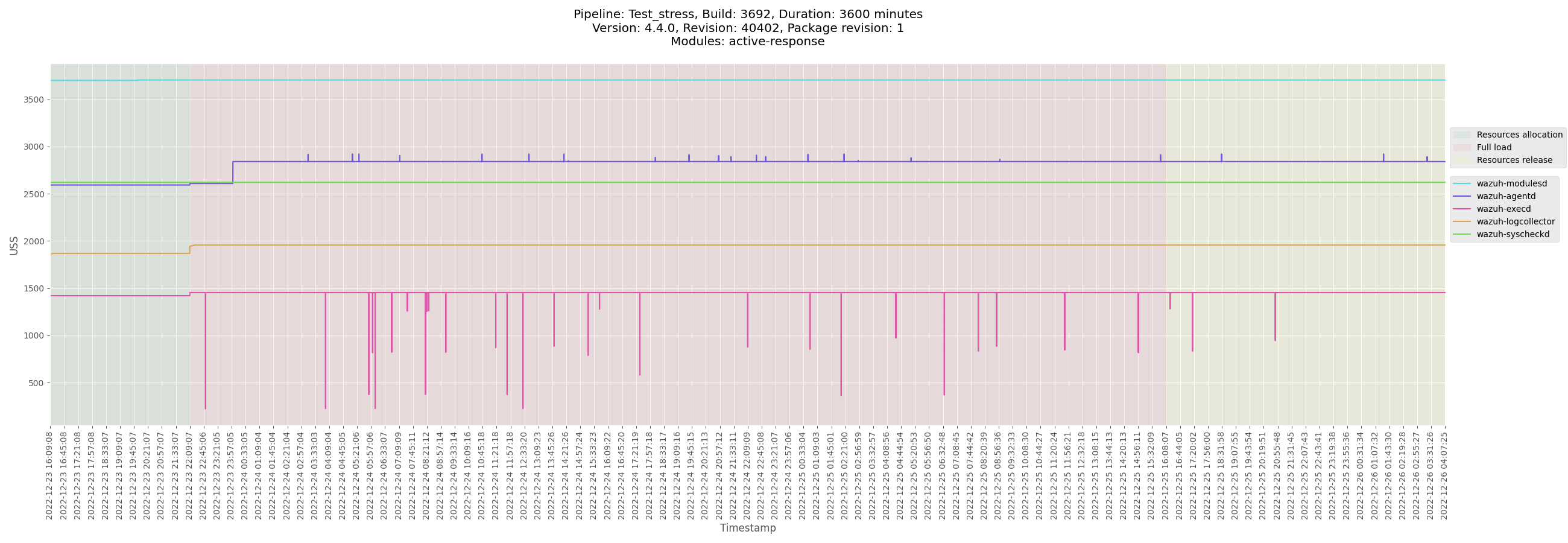
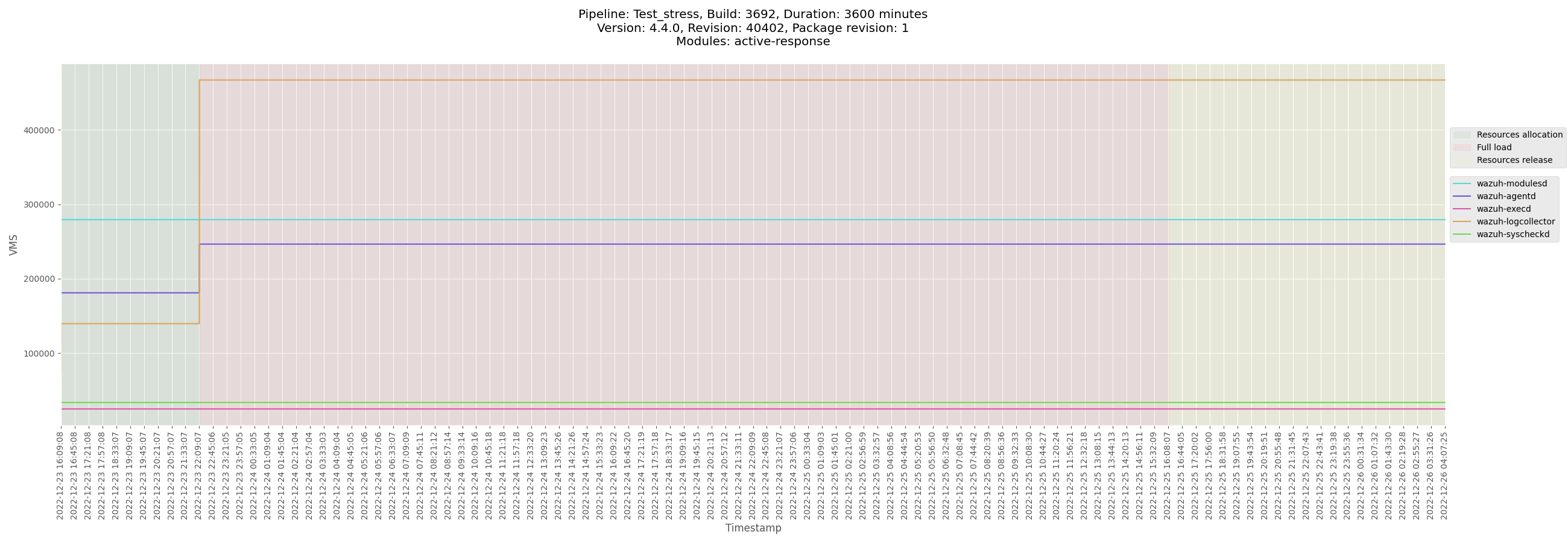
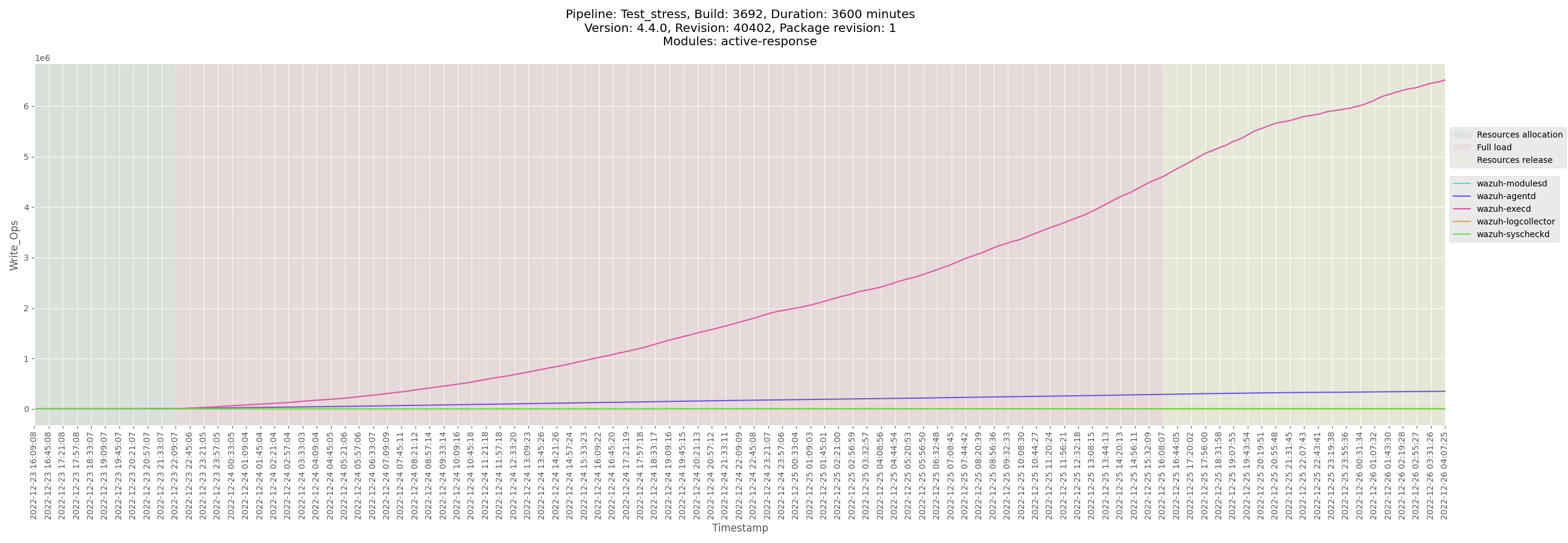

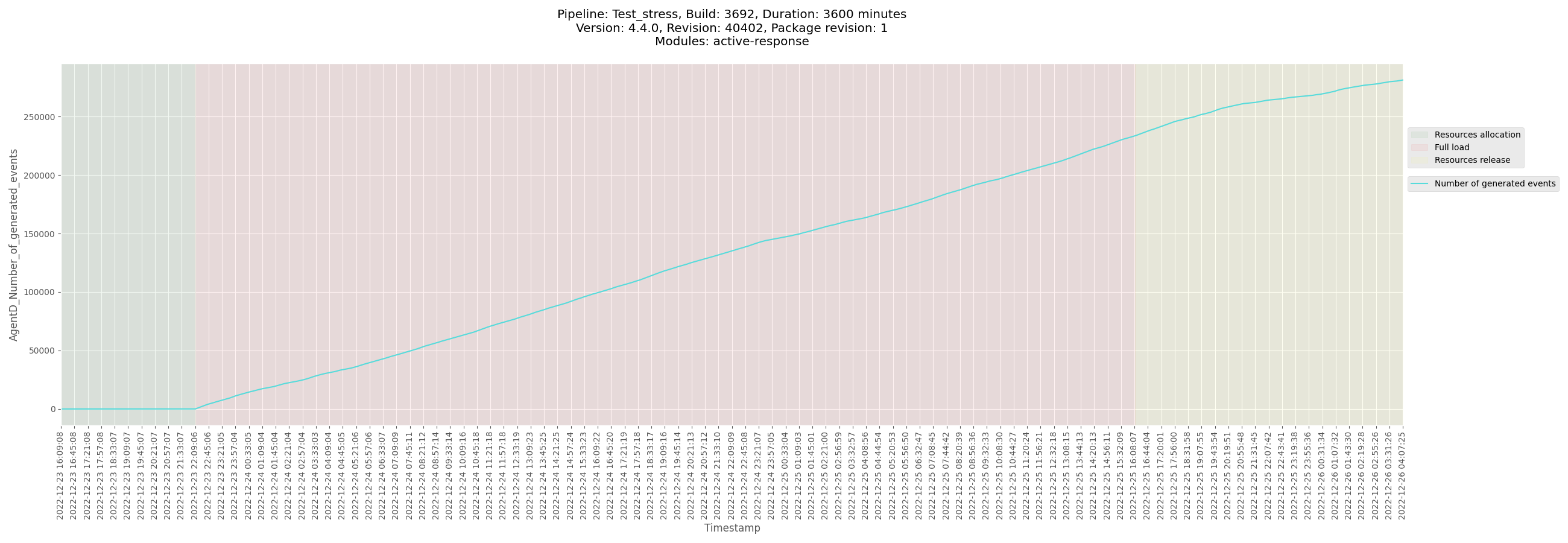
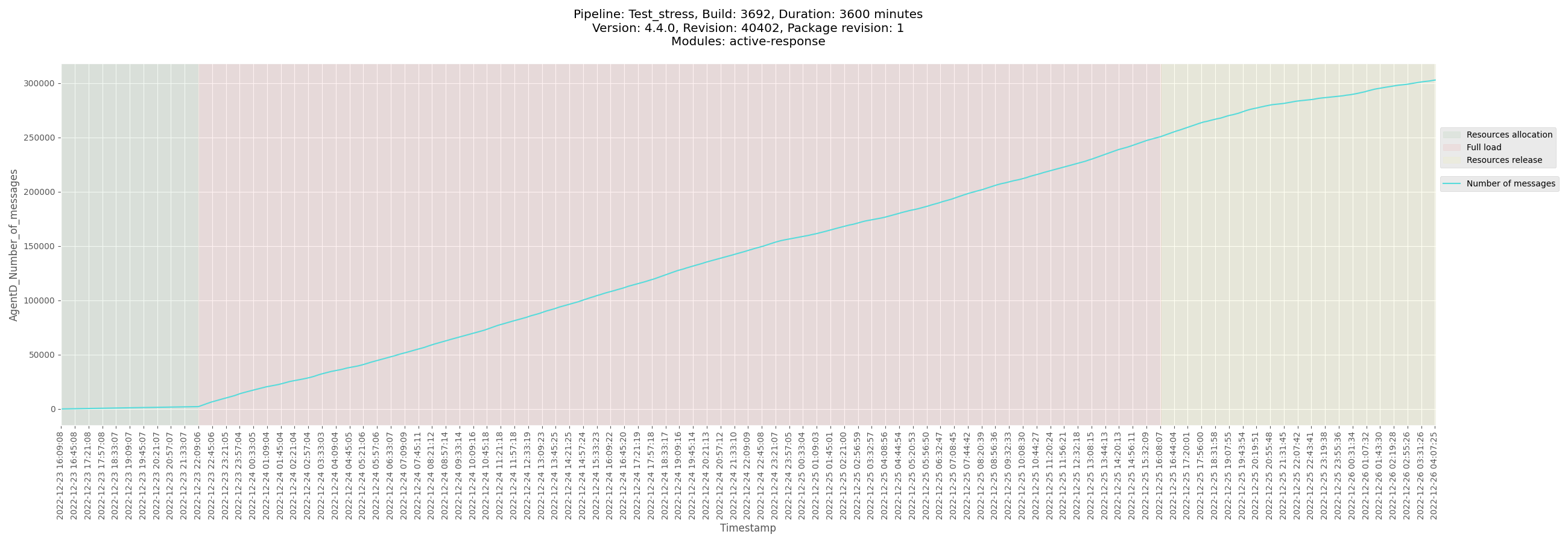
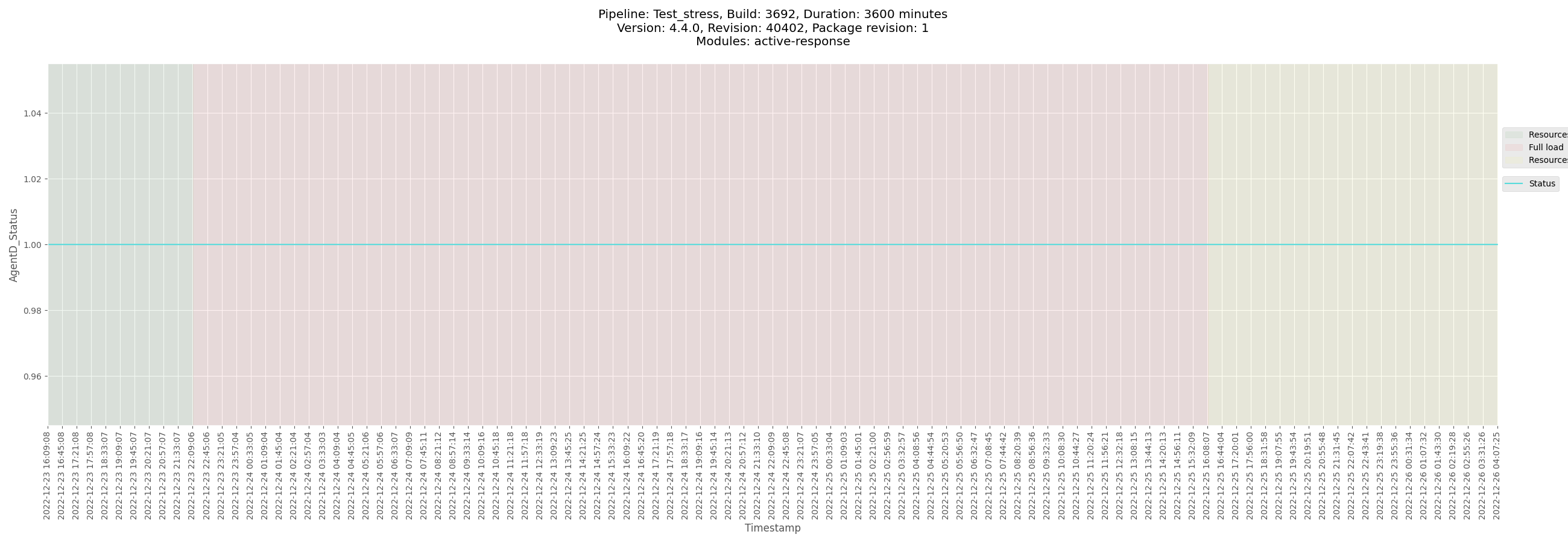
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_ubuntu_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_ubuntu/logs/ossec_Test_stress_B3692_ubuntu_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3692_ubuntu-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_ubuntu/data/monitor-agent-Test_stress_B3692_ubuntu-pre-release.csv)
[Test_stress_B3692_ubuntu_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_ubuntu/data/Test_stress_B3692_ubuntu_agentd_state.csv)
</details>
</details>
<details><summary>Windows agent</summary>
+ <details><summary>Plots</summary>
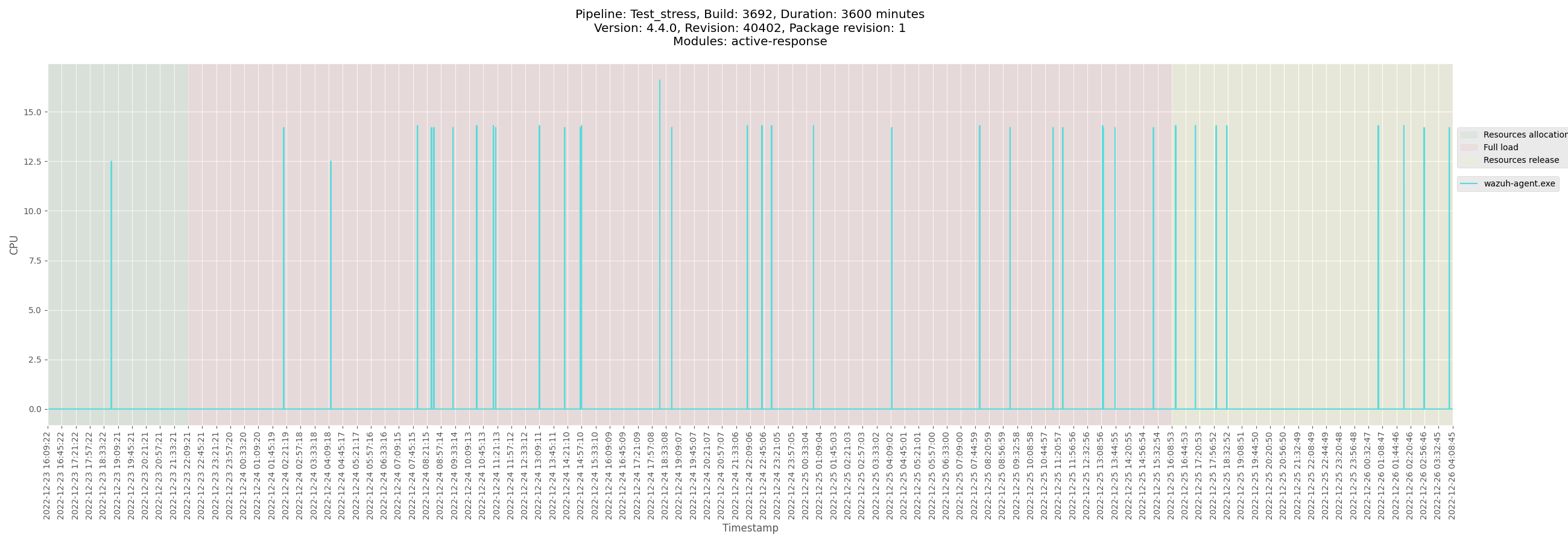
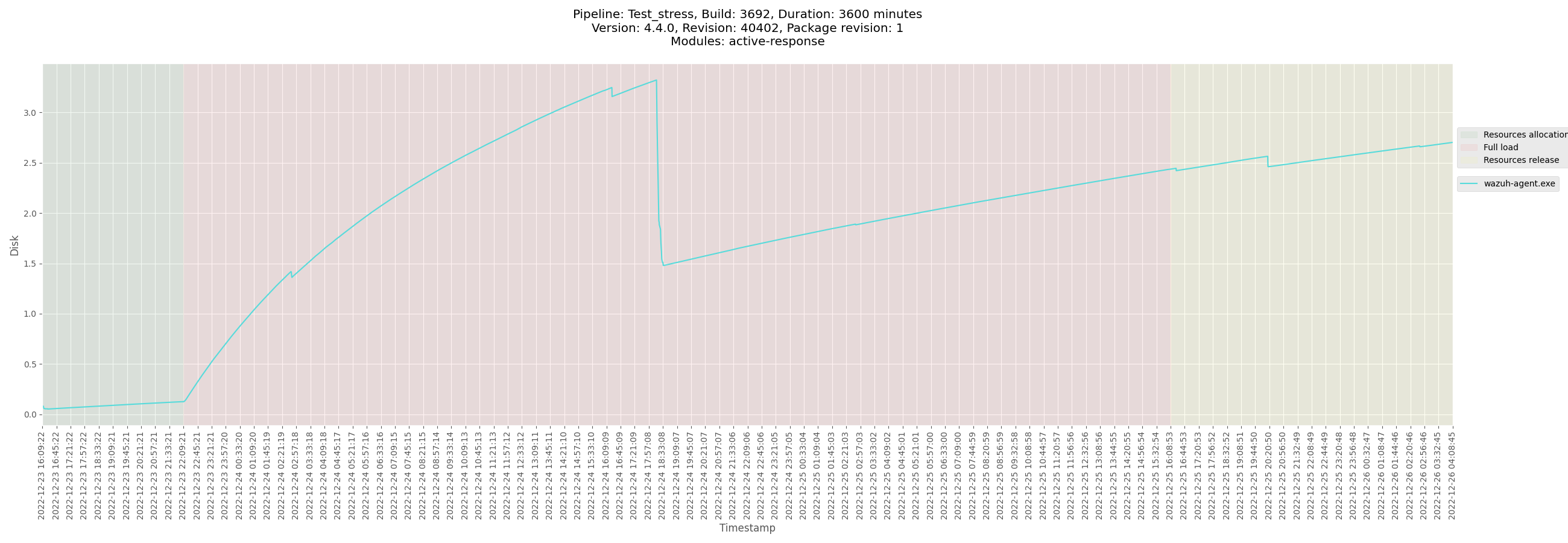
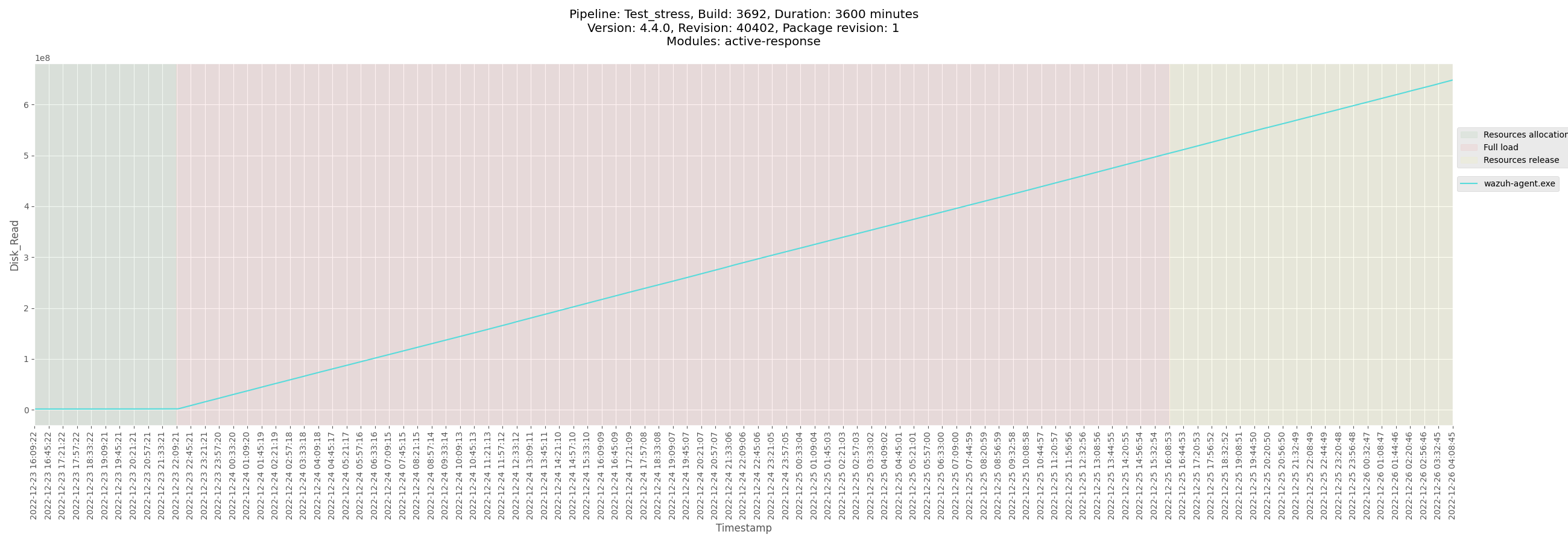
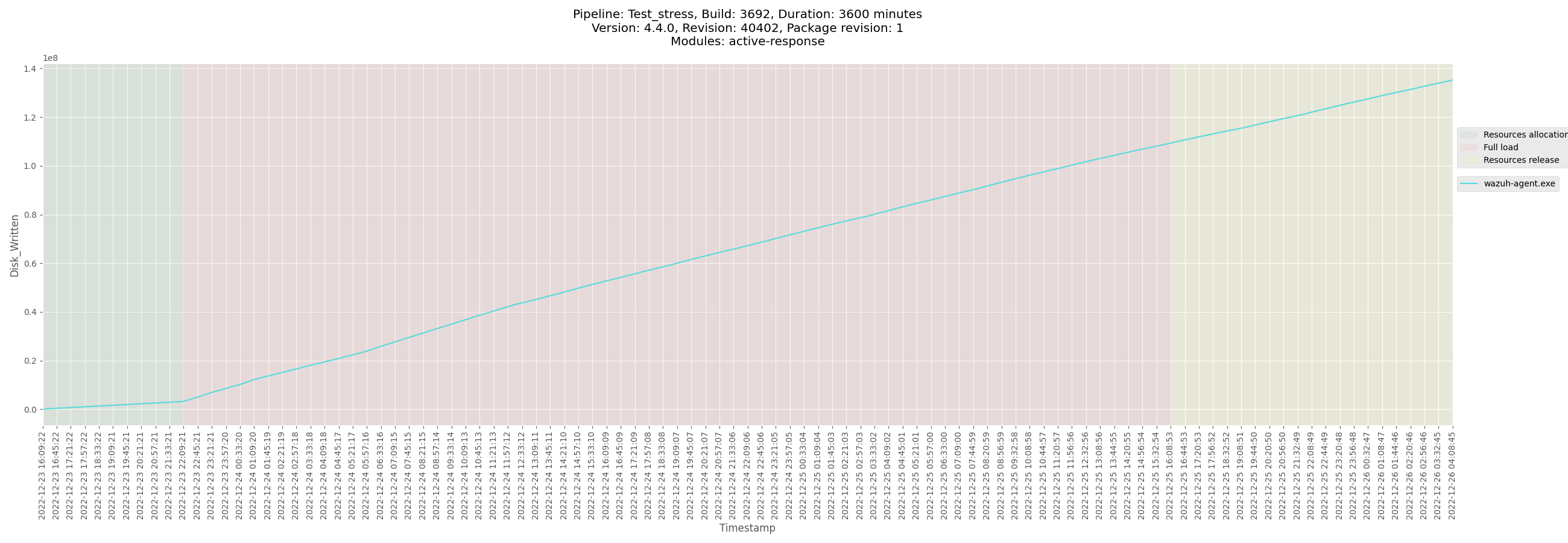
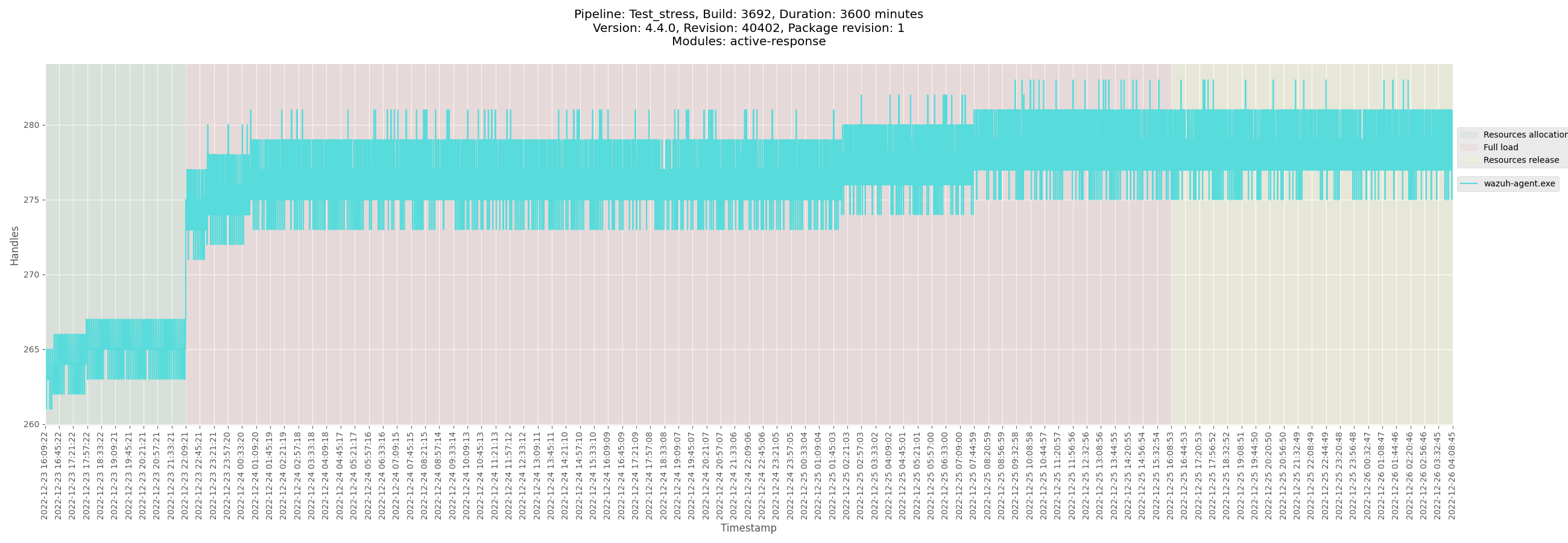
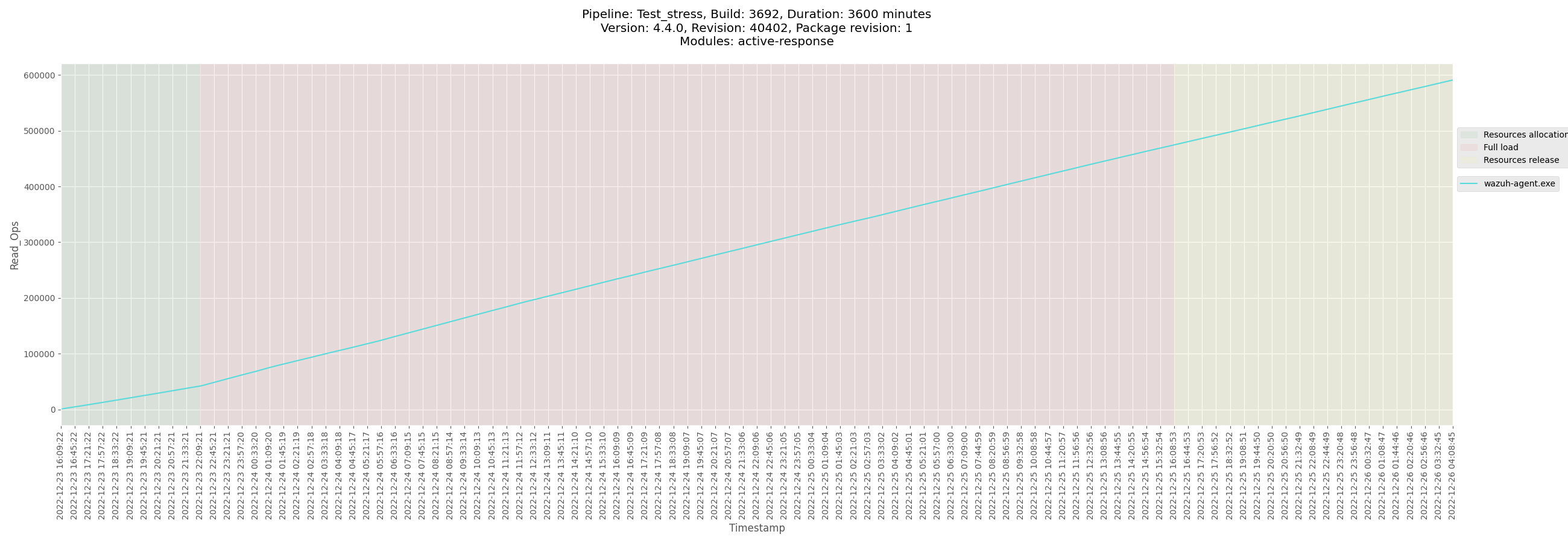
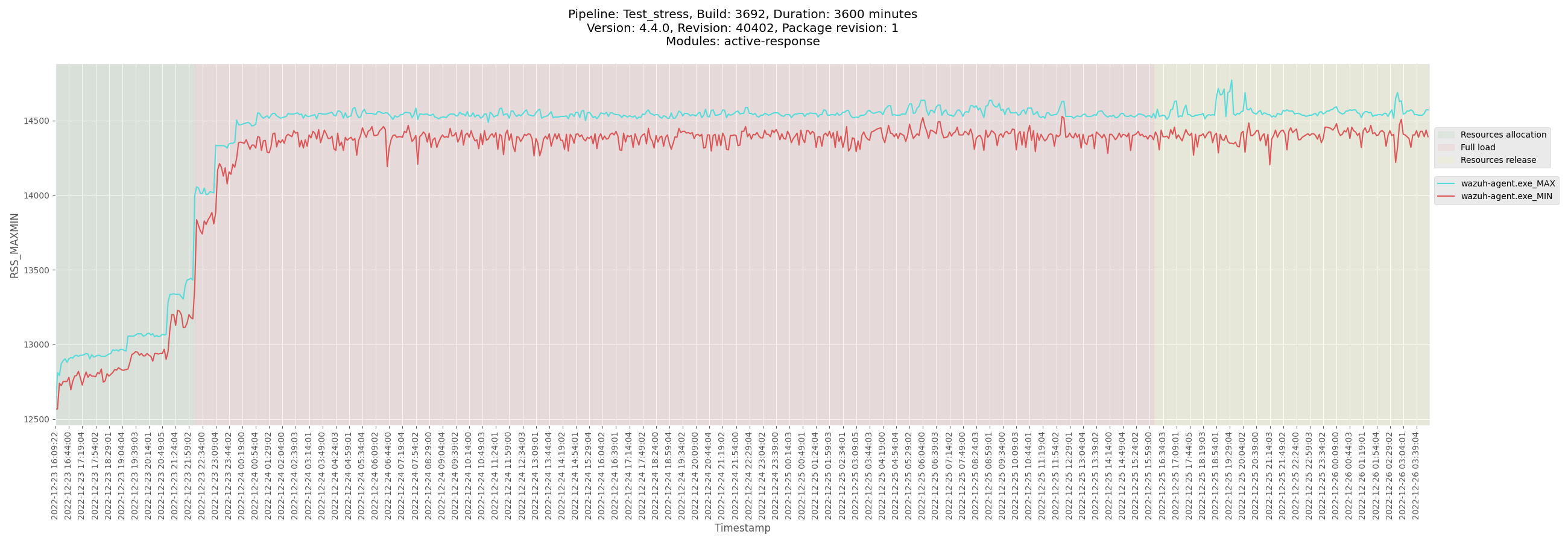
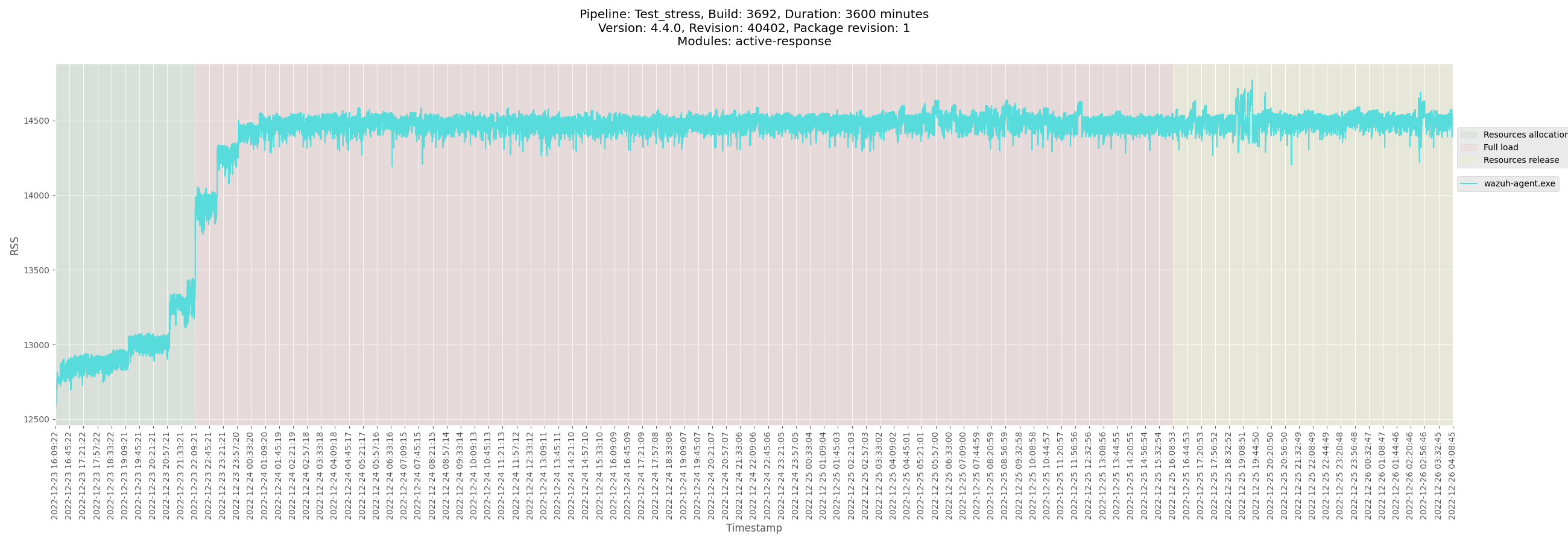
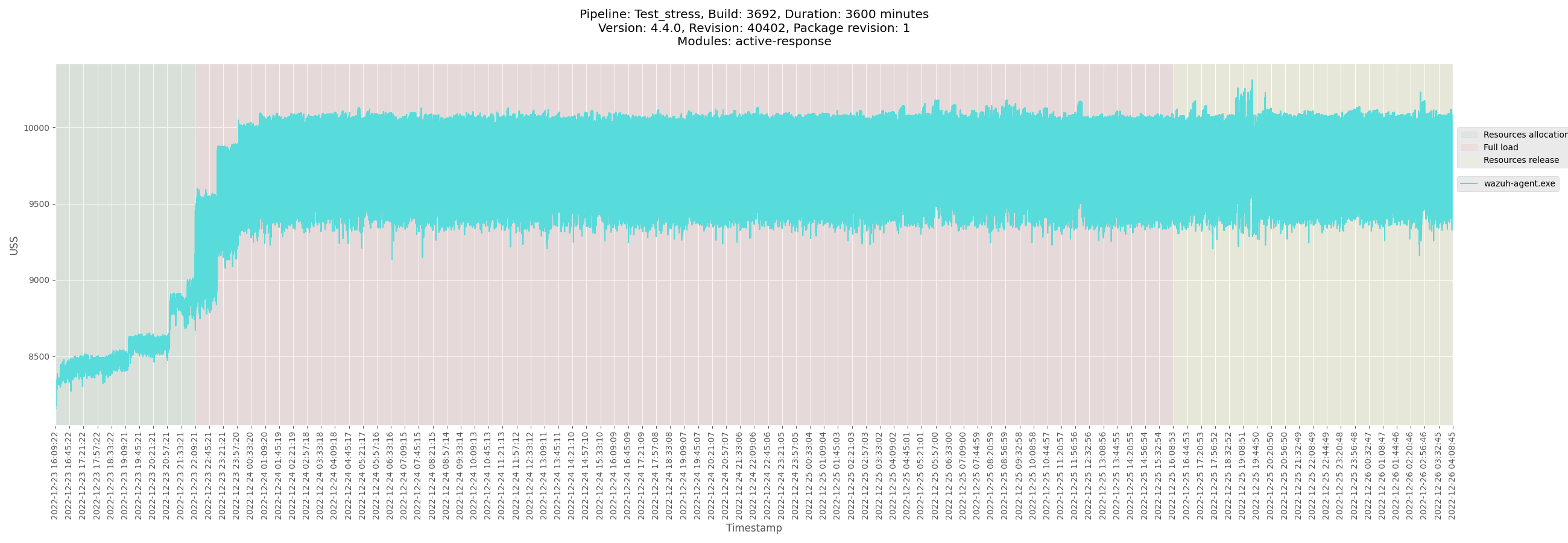
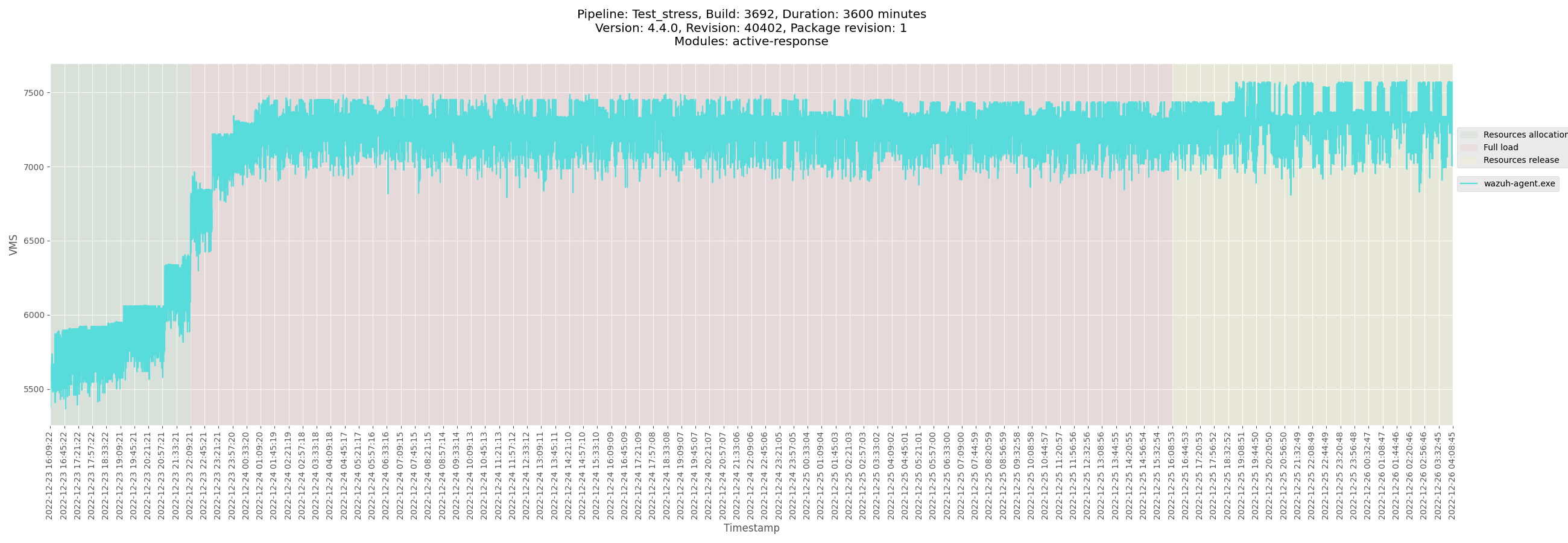
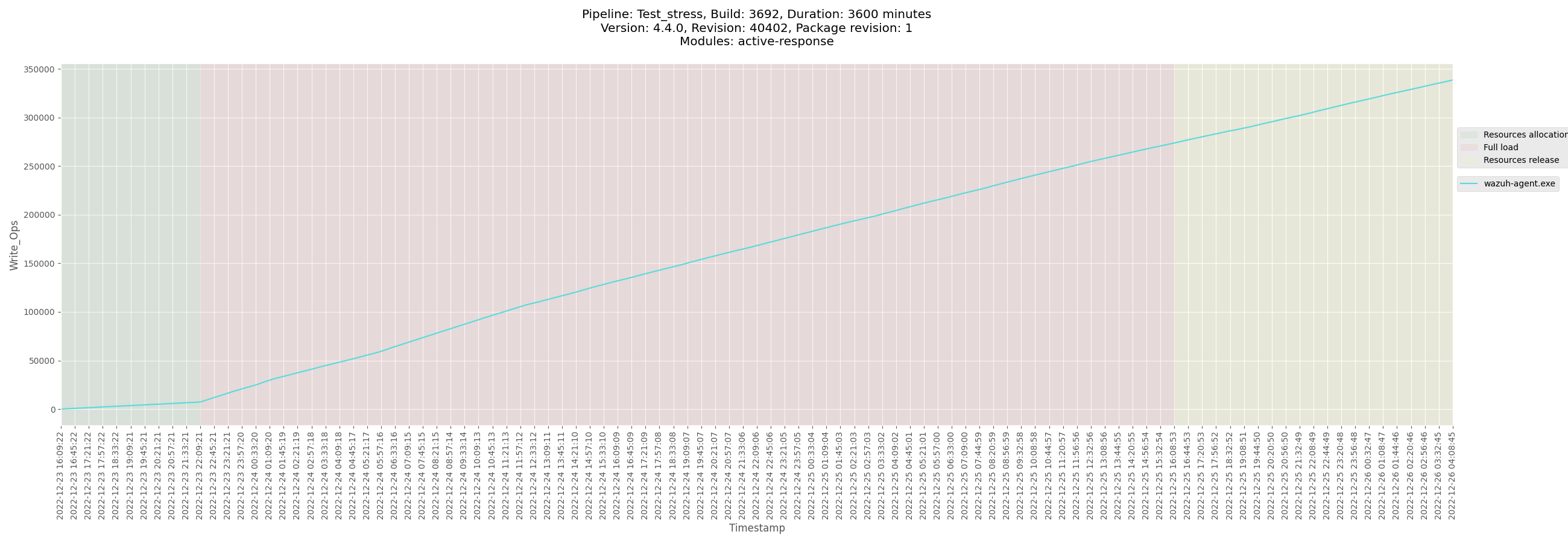
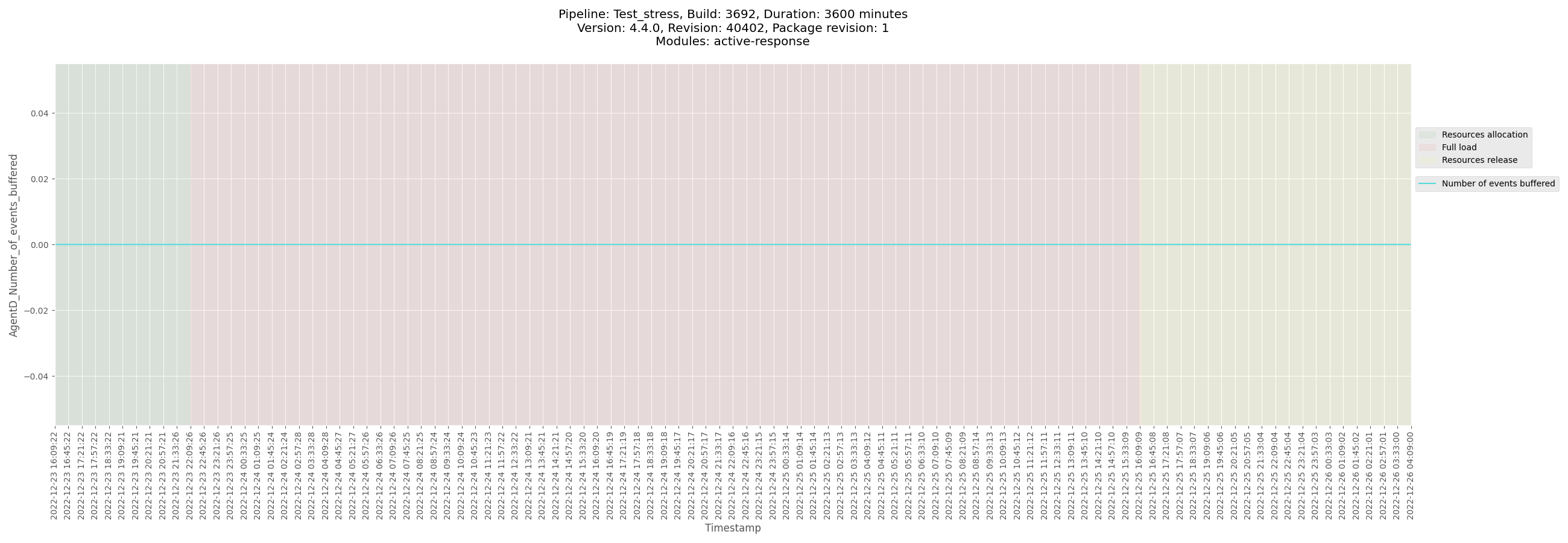
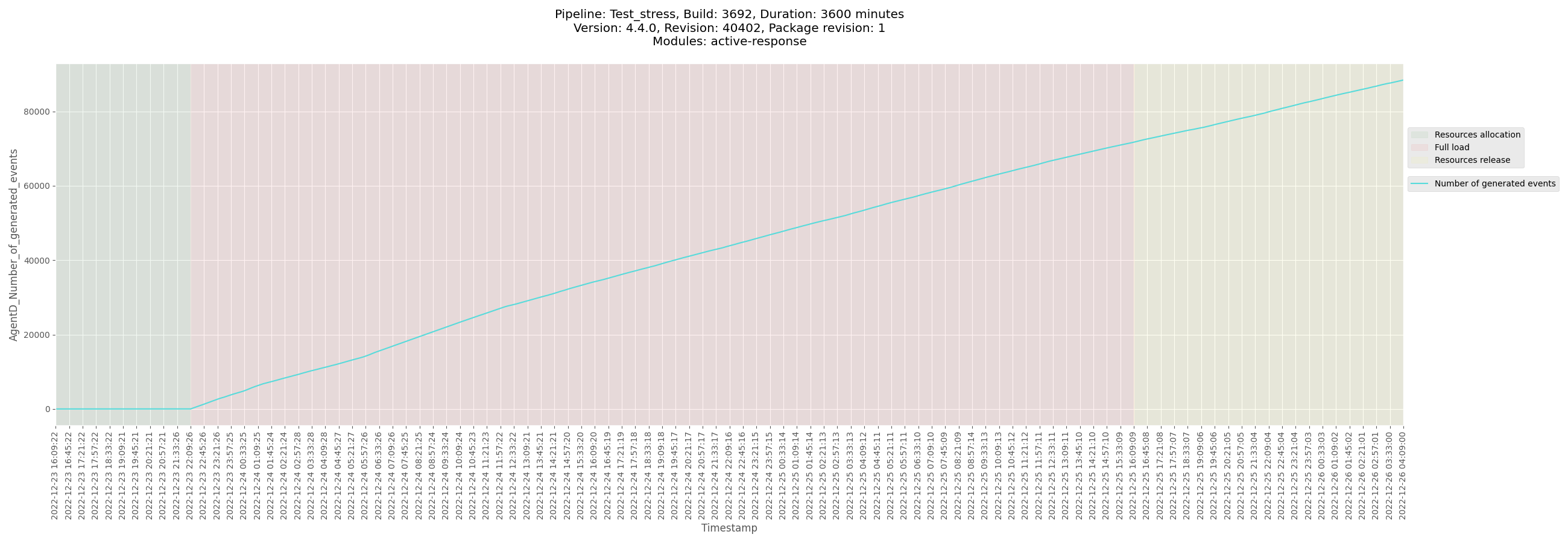
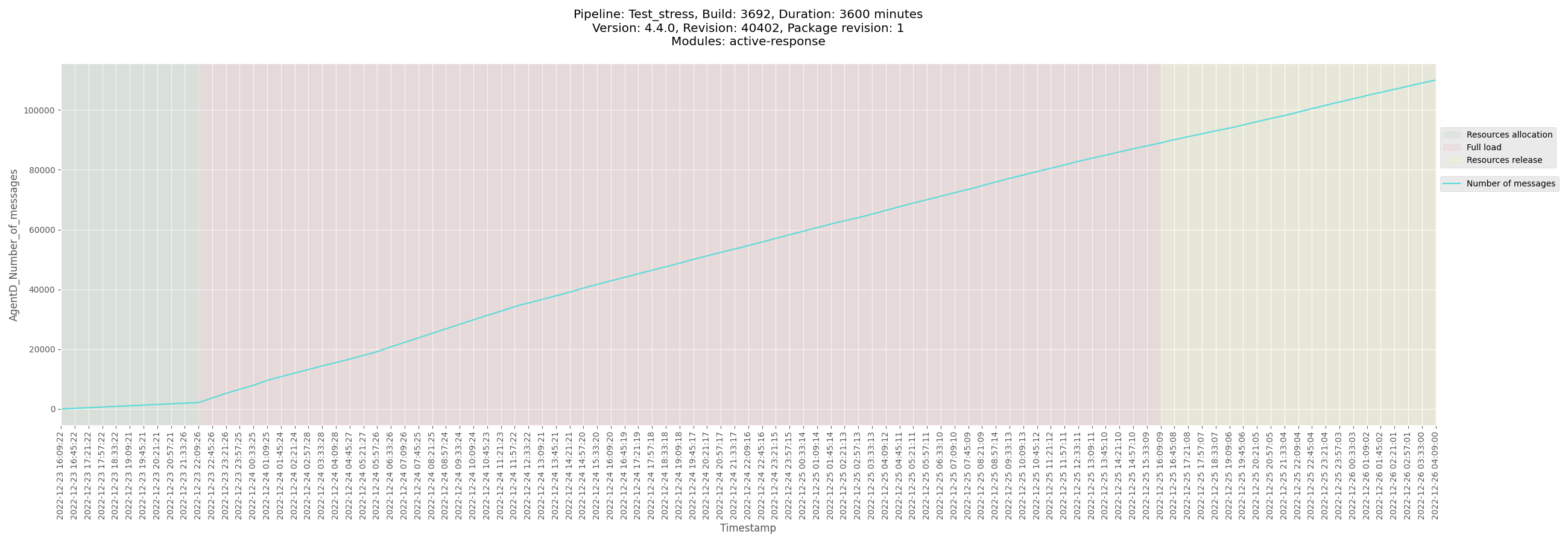
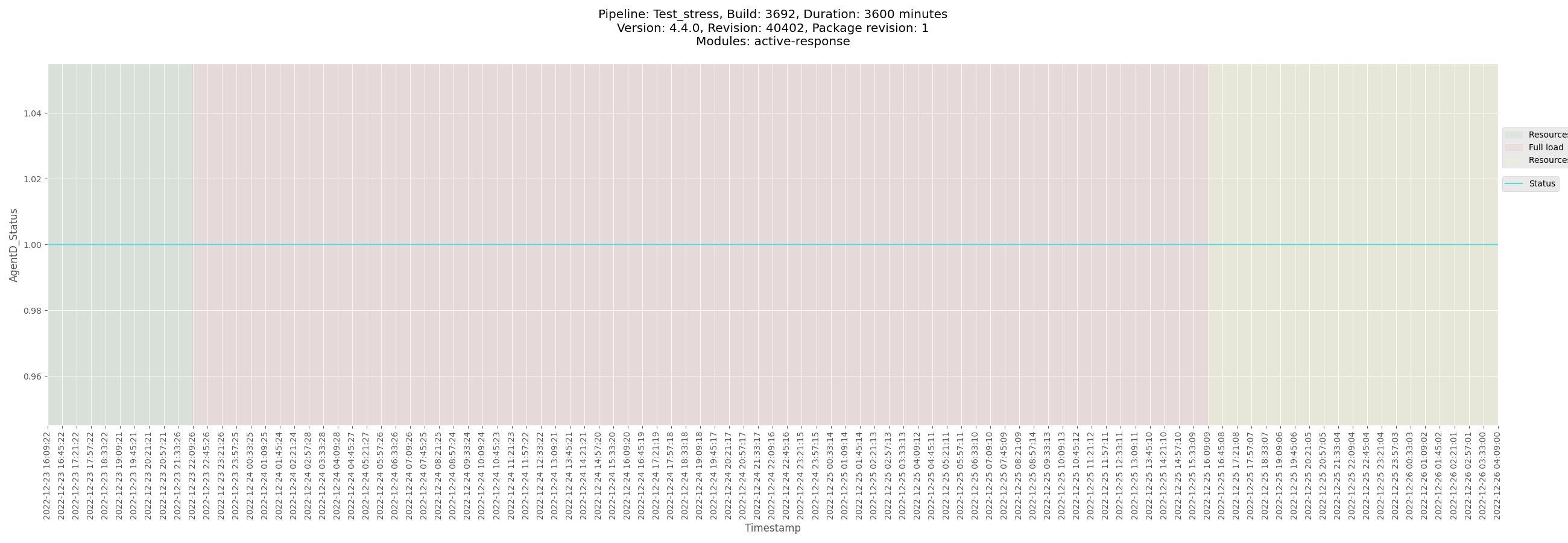
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_windows_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_windows/logs/ossec_Test_stress_B3692_windows_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-winagent-Test_stress_B3692_windows-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_windows/data/monitor-winagent-Test_stress_B3692_windows-pre-release.csv)
[Test_stress_B3692_windows_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_windows/data/Test_stress_B3692_windows_agentd_state.csv)
</details>
</details>
<details><summary>macOS agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details>
<details><summary>Solaris agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details> | 1.0 | Release 4.4.0 - Alpha 2 - Footprint Metrics - ACTIVE-RESPONSE (2.5d) - ## Footprint metrics information
| | |
|---------------------------------|--------------------------------------------|
| **Main release candidate issue #** | #15746 |
| **Main footprint metrics issue #** | #15752 |
| **Version** | 4.4.0 |
| **Release candidate #** | Alpha 2 |
| **Tag** | https://github.com/wazuh/wazuh/tree/v4.4.0-alpha2 |
## Stress test documentation
### Packages used
- Repository: `packages-dev.wazuh.com`
- Package path: `pre-release`
- Package revision: `1`
- **Jenkins build**: https://ci.wazuh.info/job/Test_stress/3692/
---
<details><summary>Manager</summary>
+ <details><summary>Plots</summary>
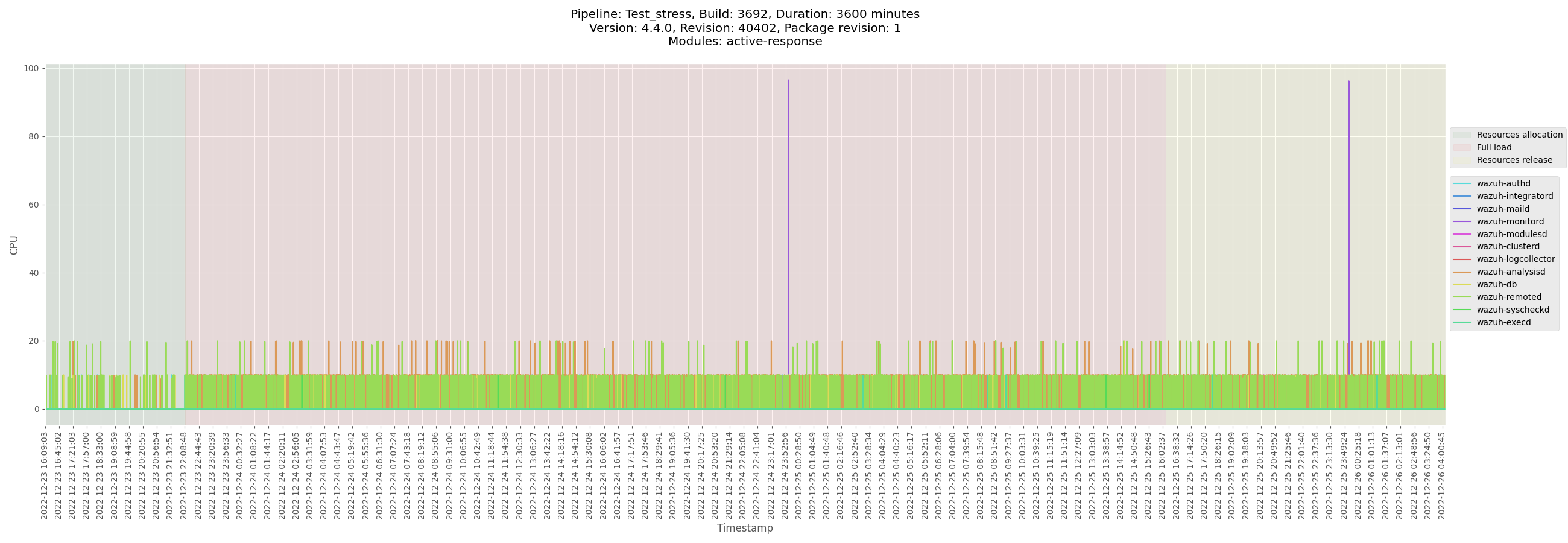
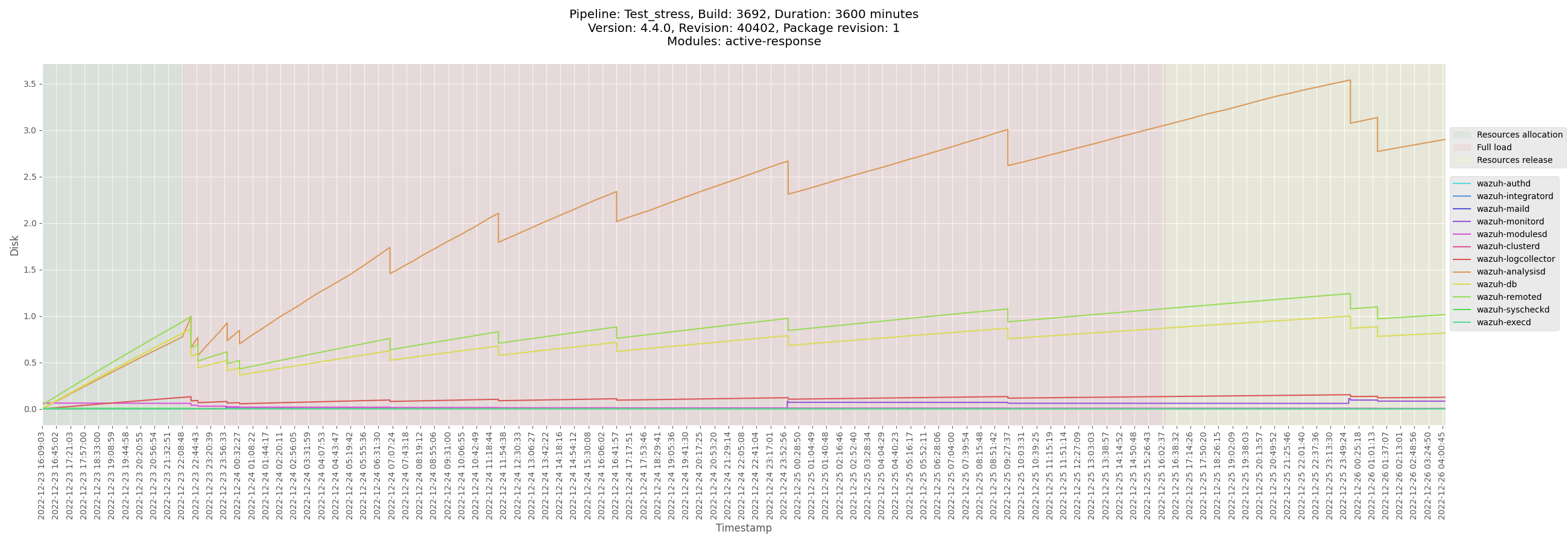
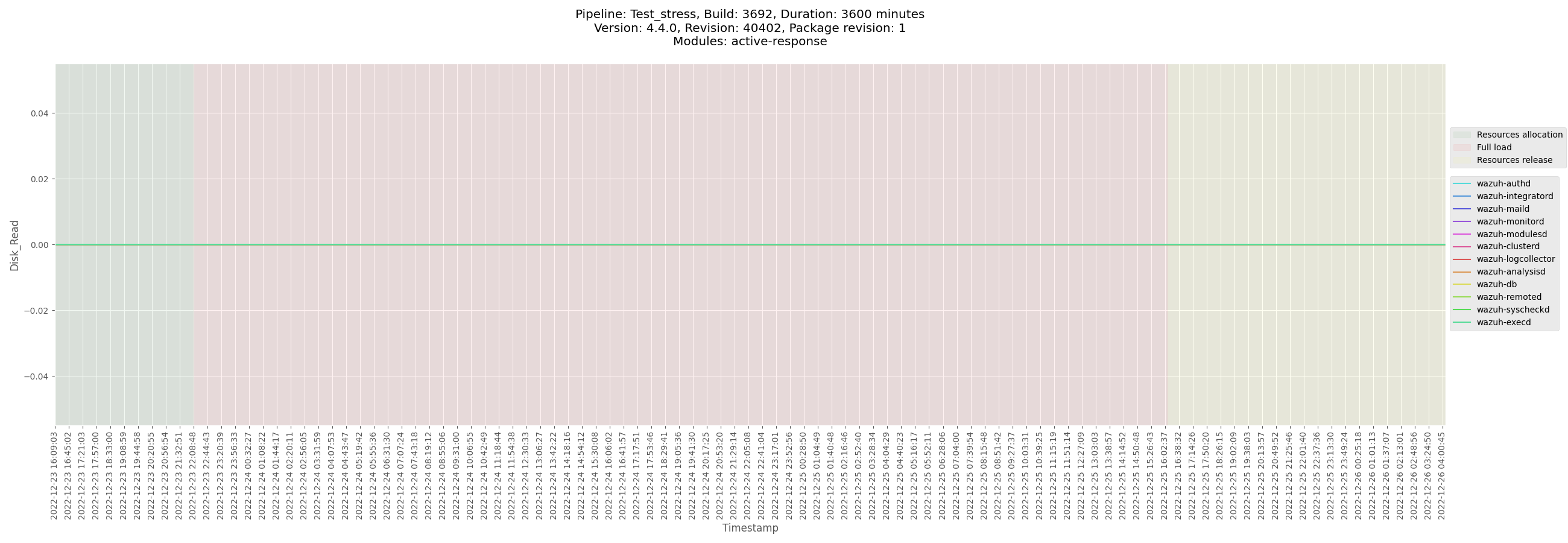
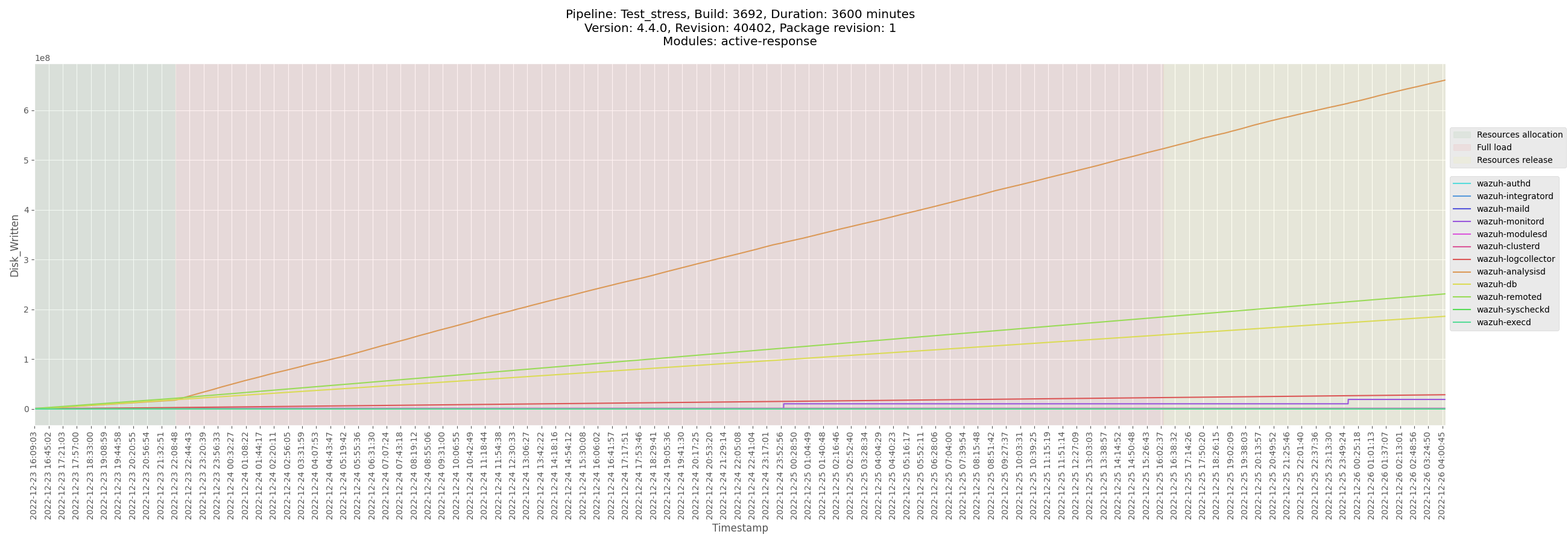
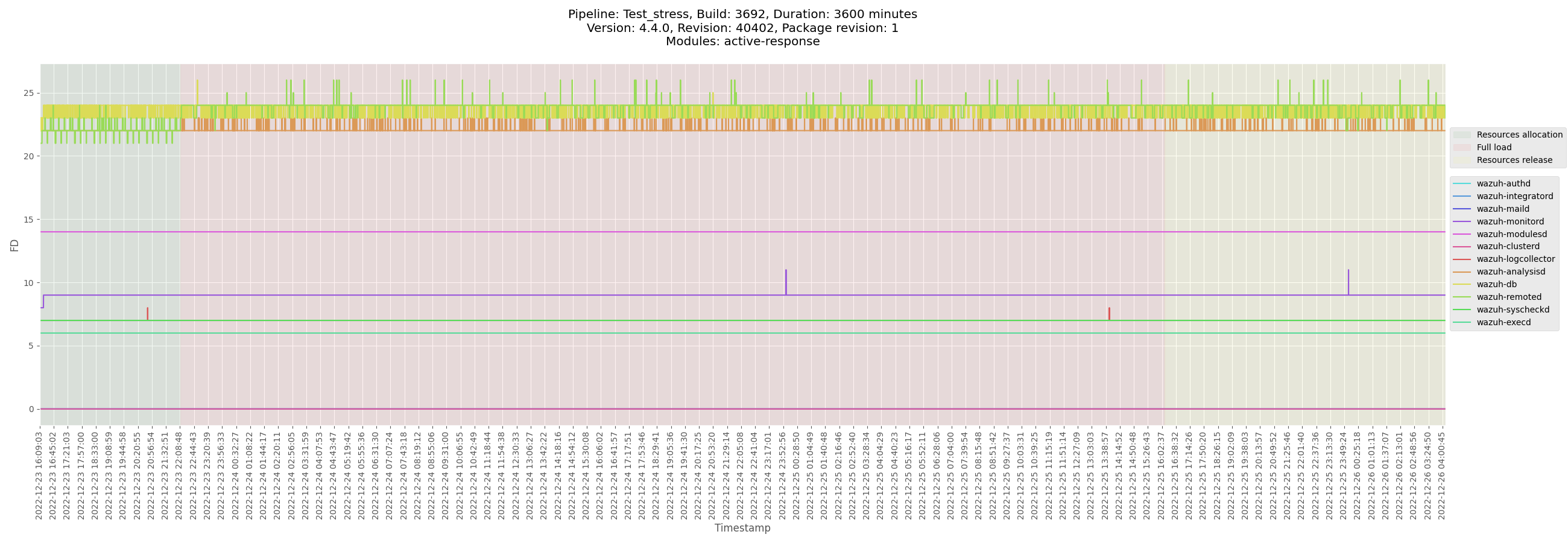

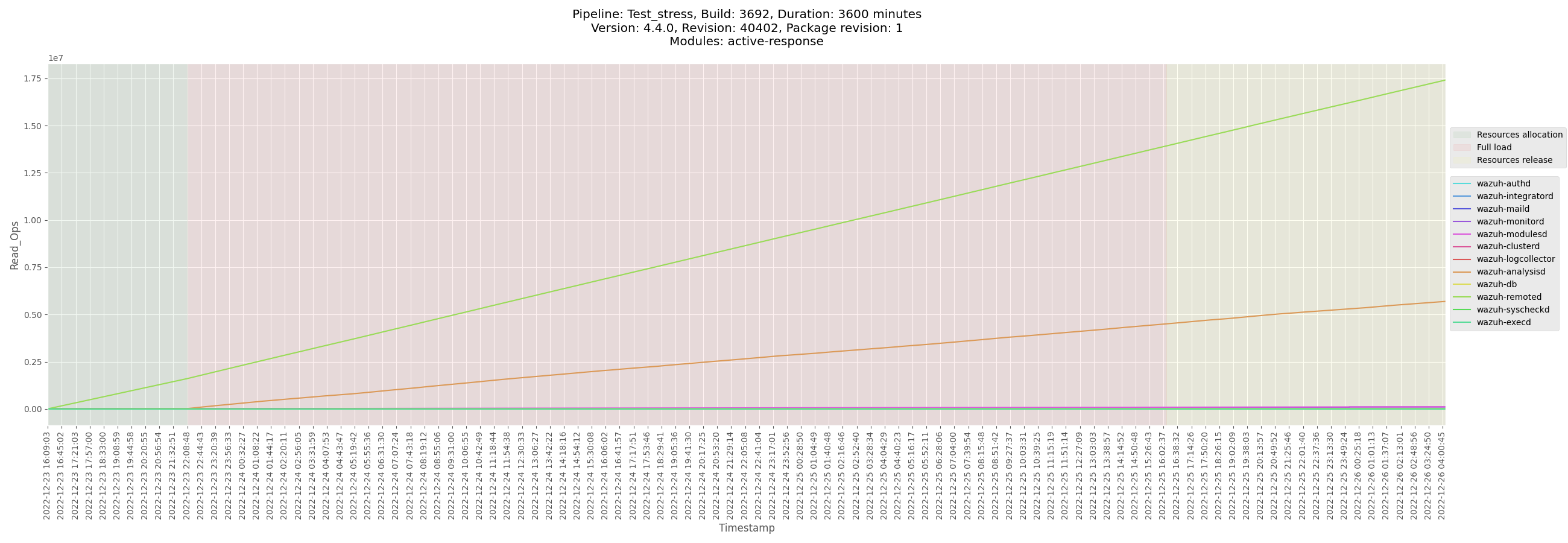
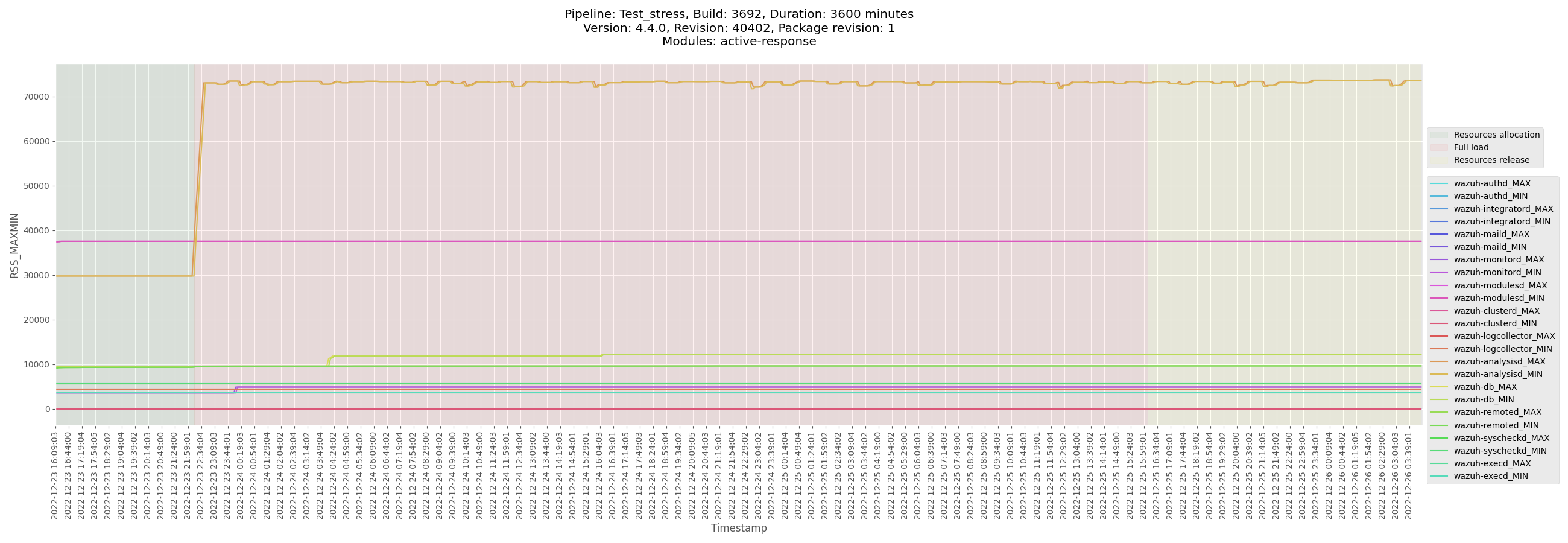
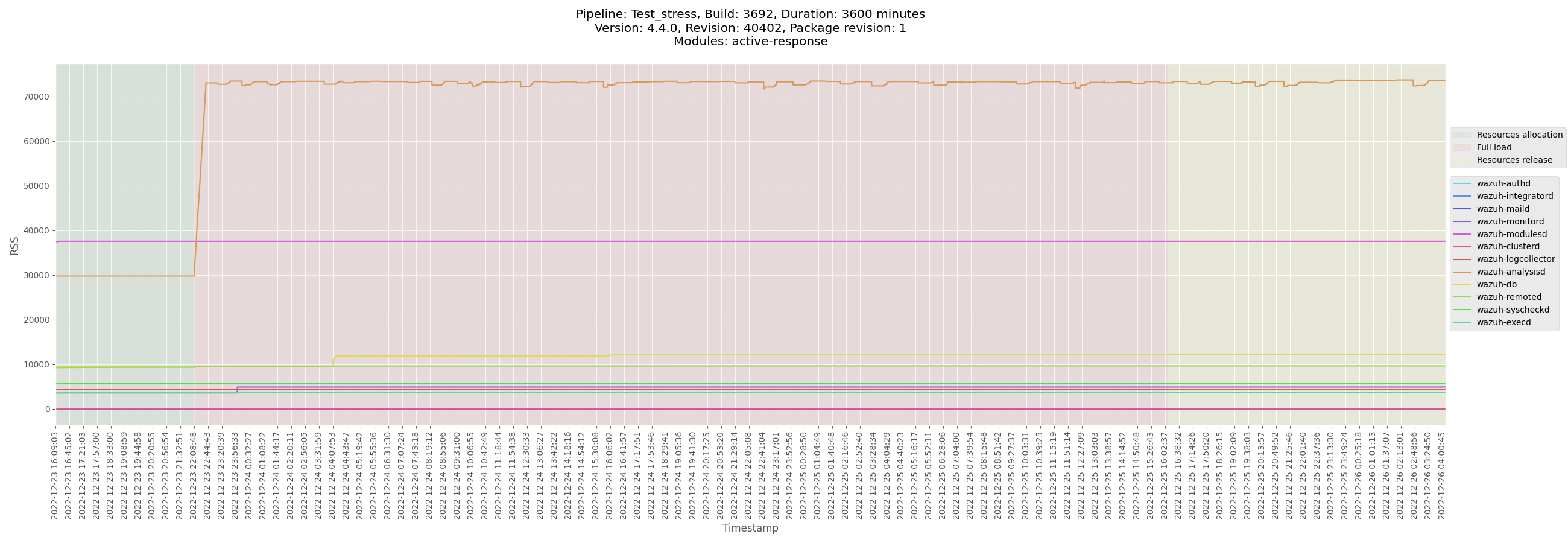
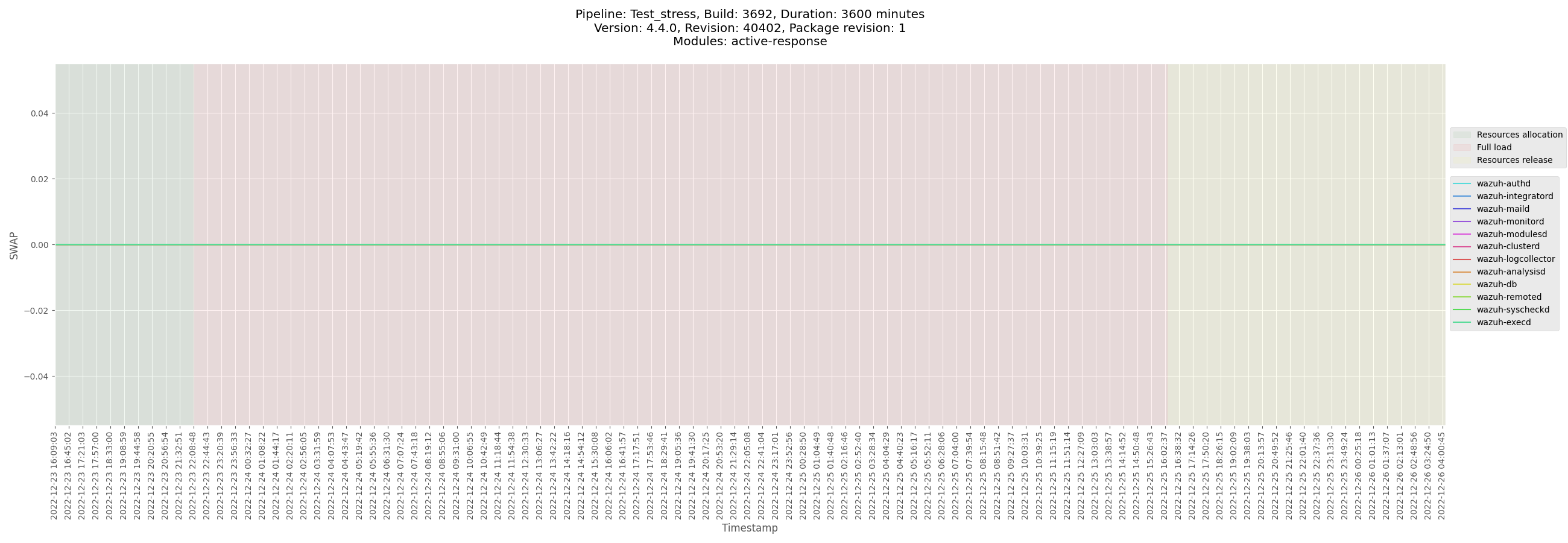
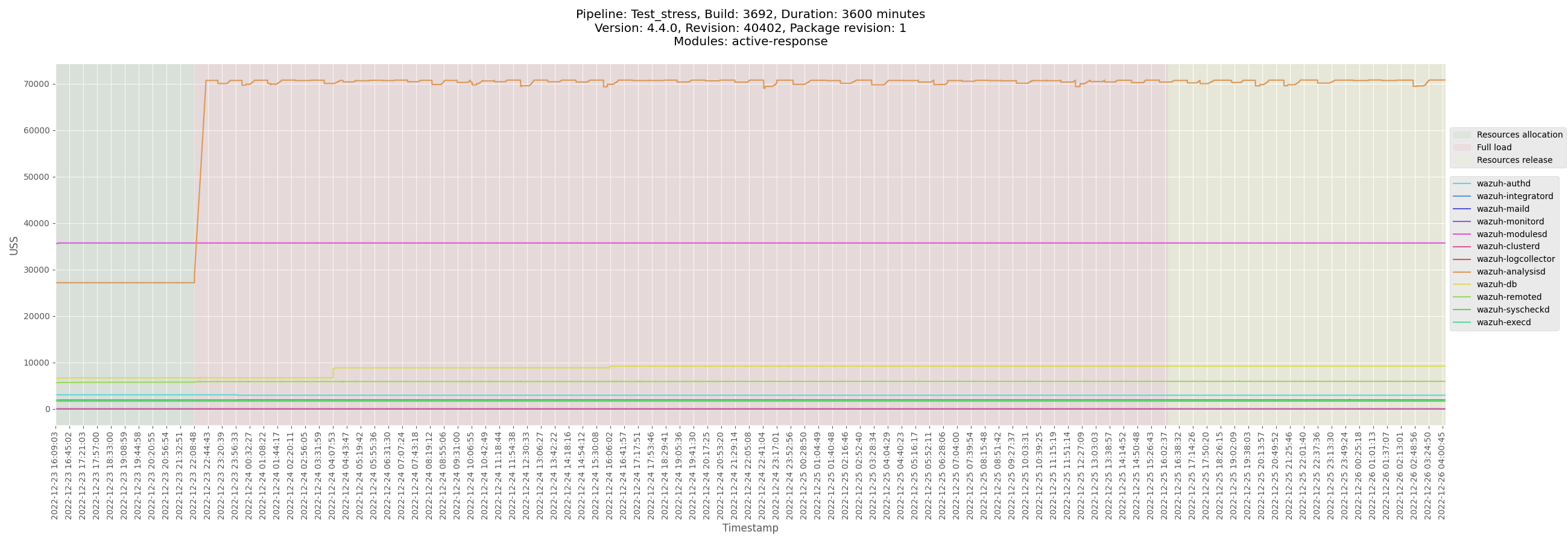

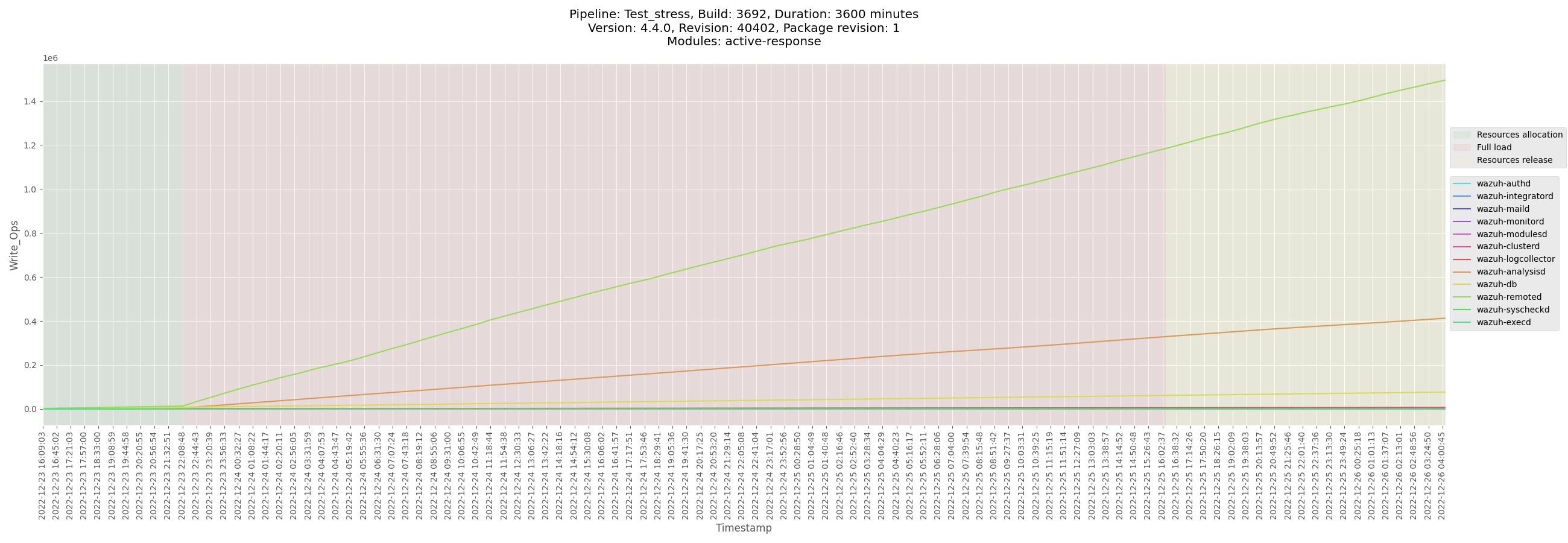
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_manager_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/logs/ossec_Test_stress_B3692_manager_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-manager-Test_stress_B3692_manager-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/data/monitor-manager-Test_stress_B3692_manager-pre-release.csv)
[Test_stress_B3692_manager_analysisd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/data/Test_stress_B3692_manager_analysisd_state.csv)
[Test_stress_B3692_manager_remoted_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_manager_centos/data/Test_stress_B3692_manager_remoted_state.csv)
</details>
</details>
<details><summary>Centos agent</summary>
+ <details><summary>Plots</summary>



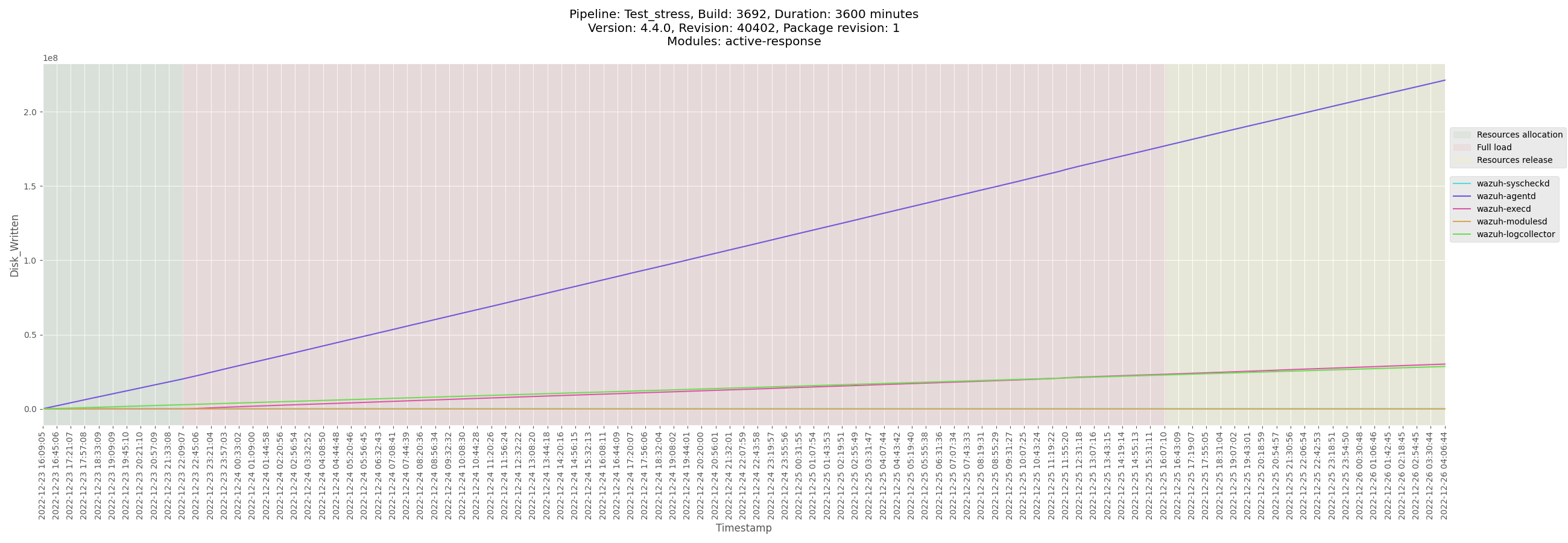
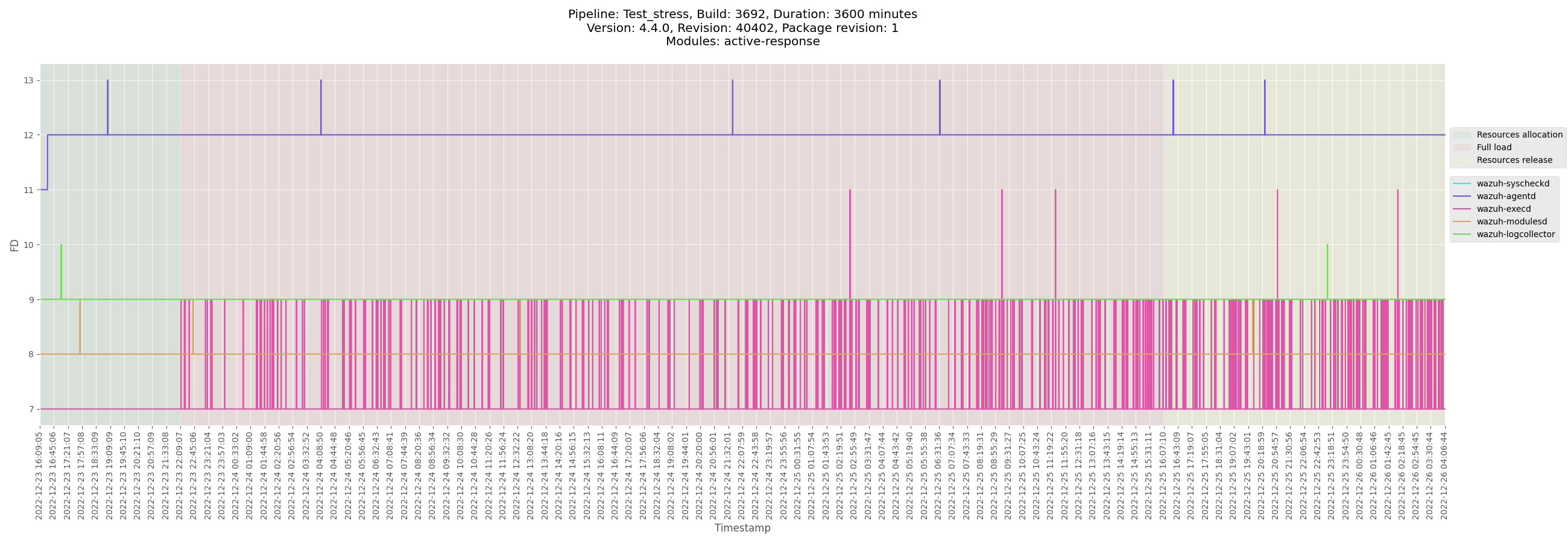
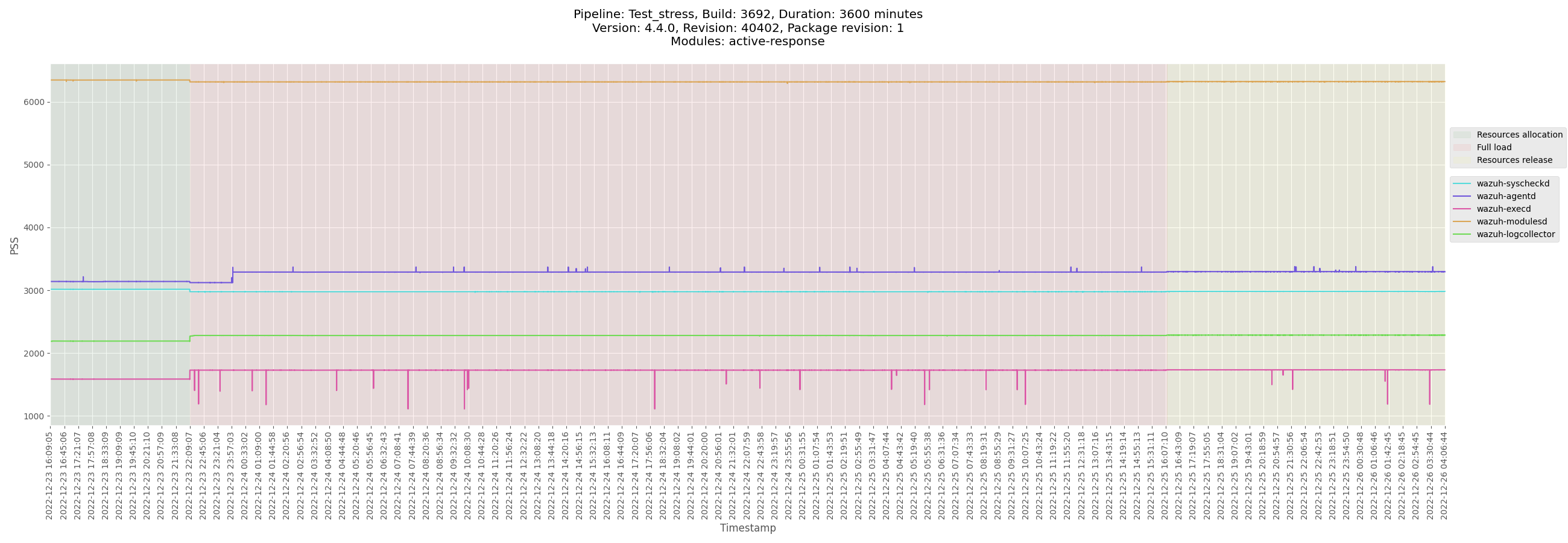
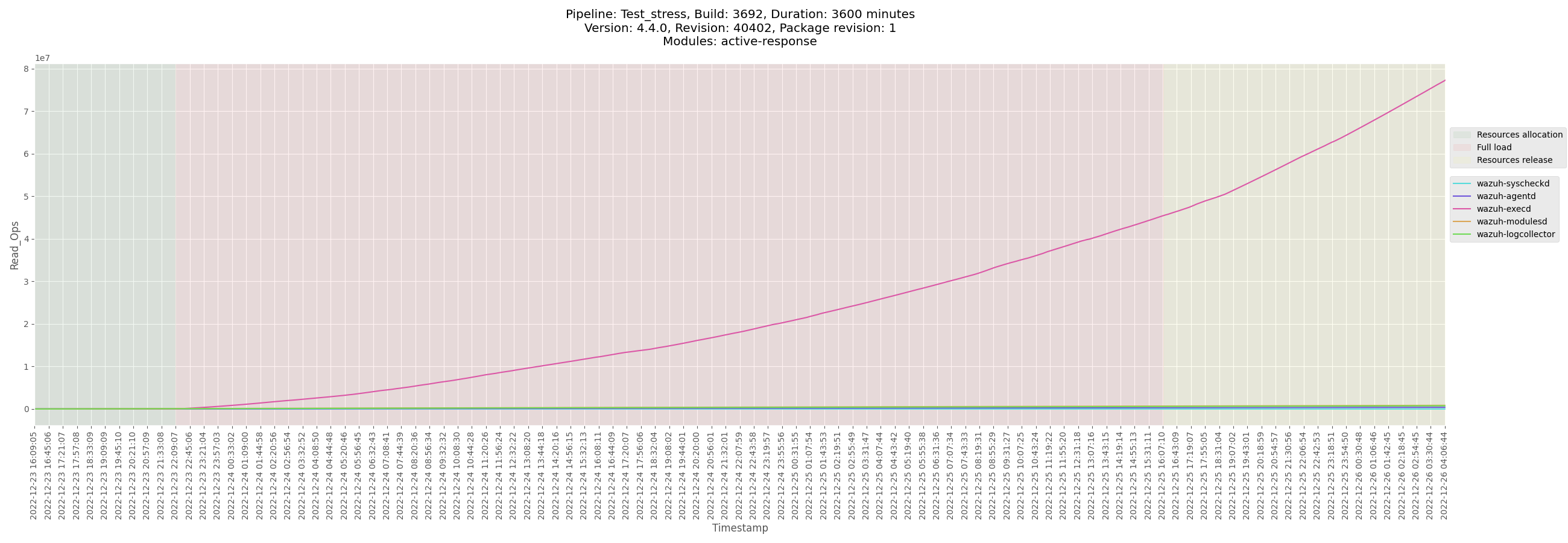
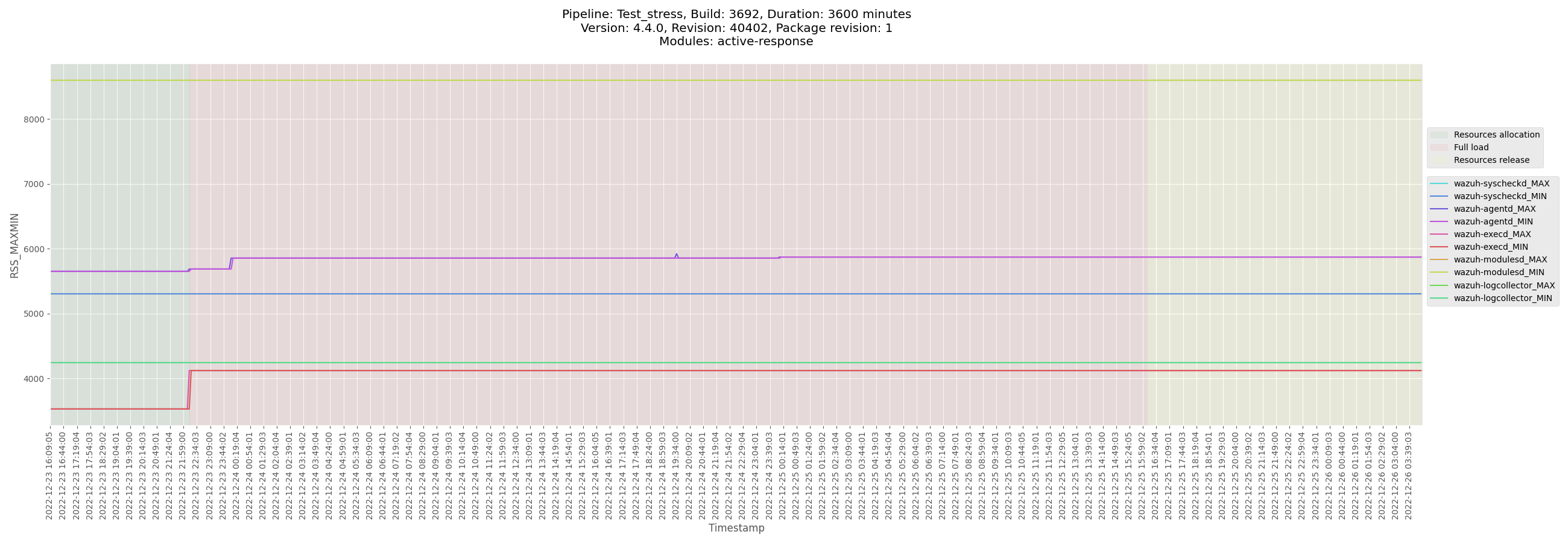
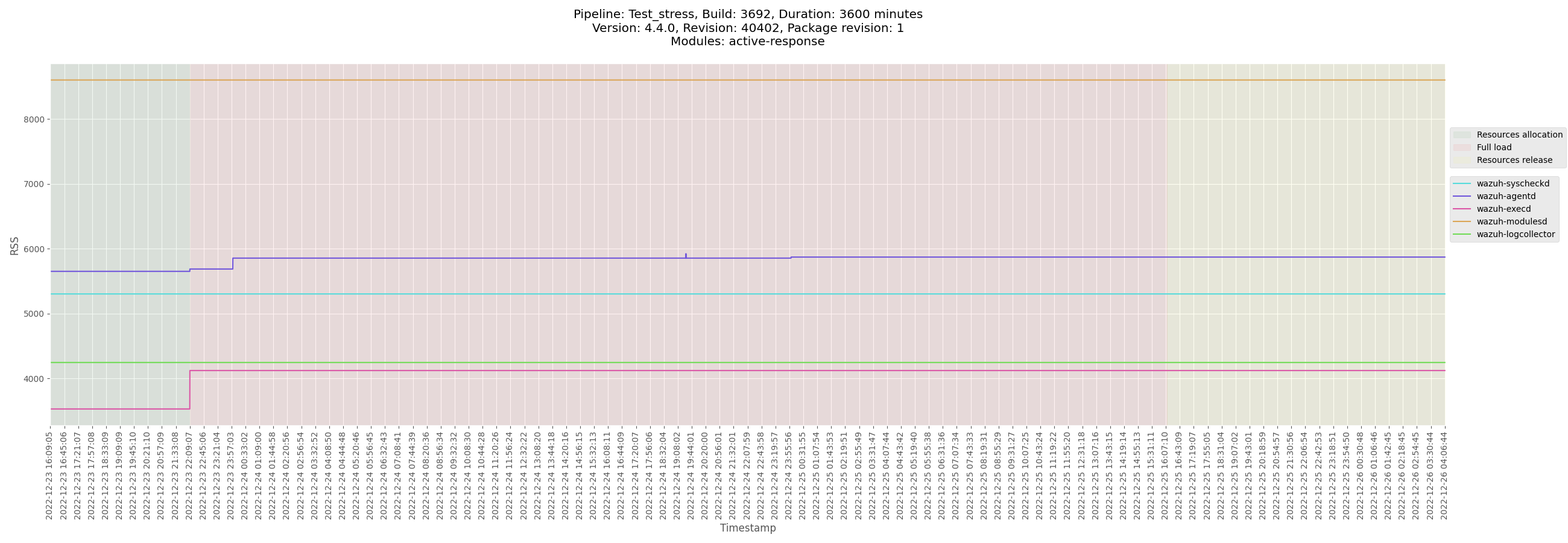
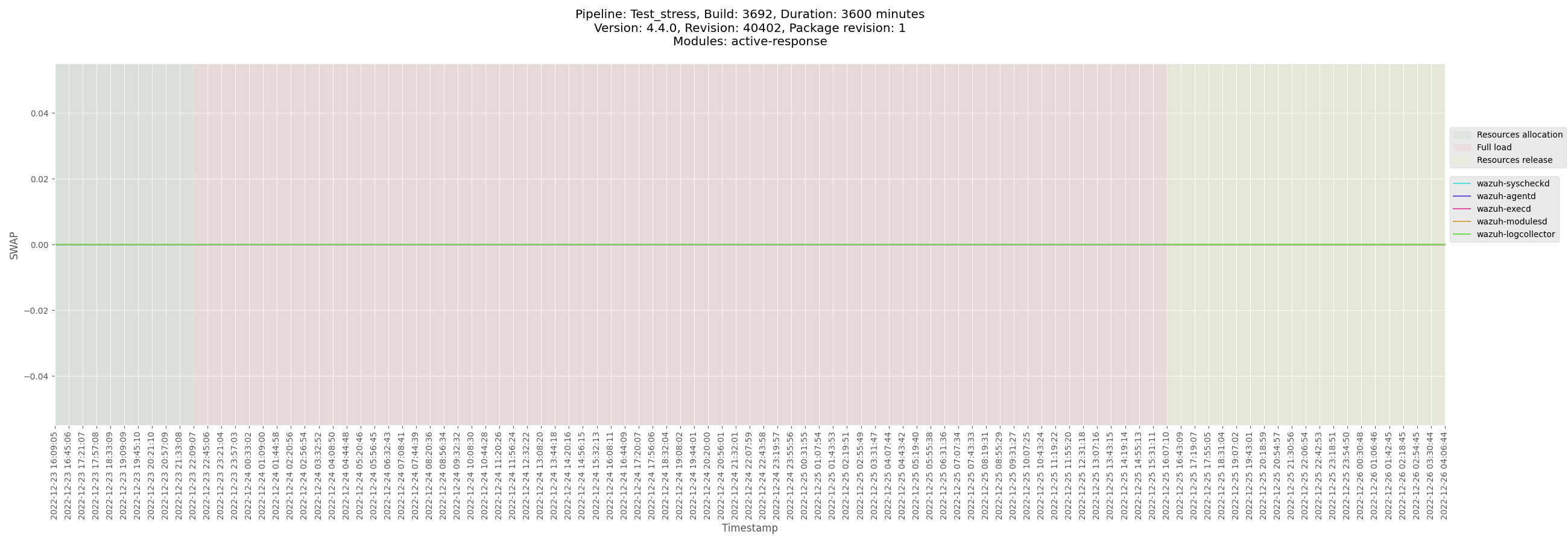
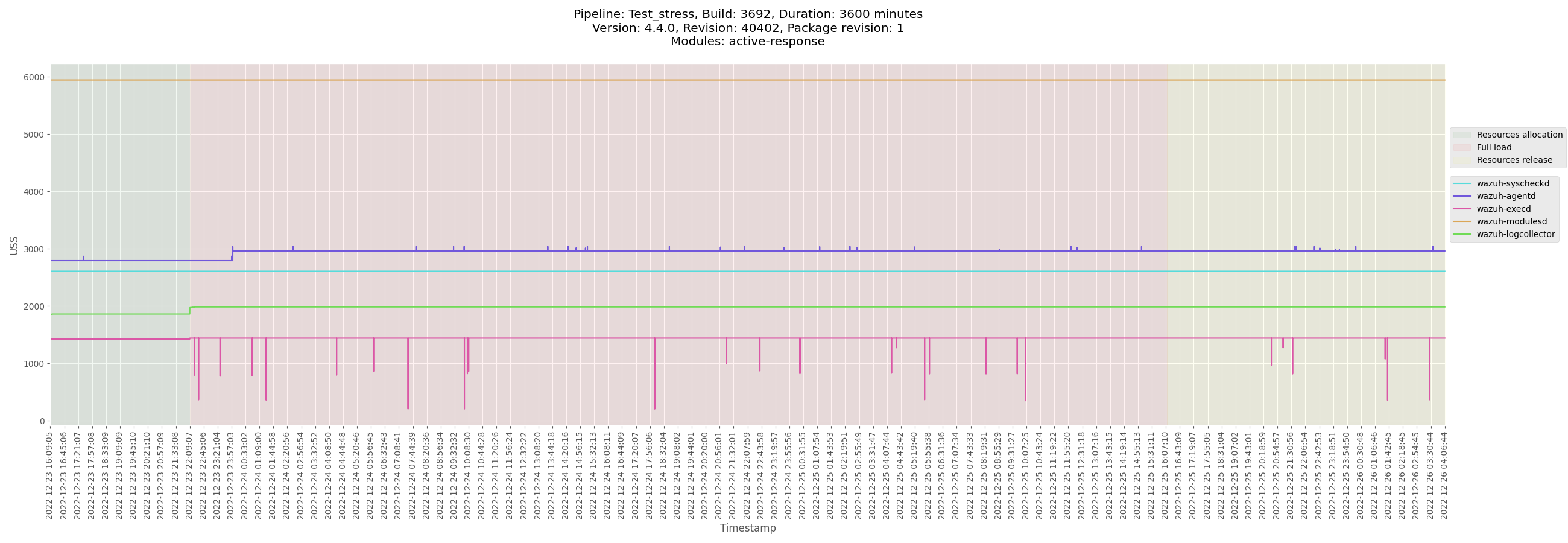
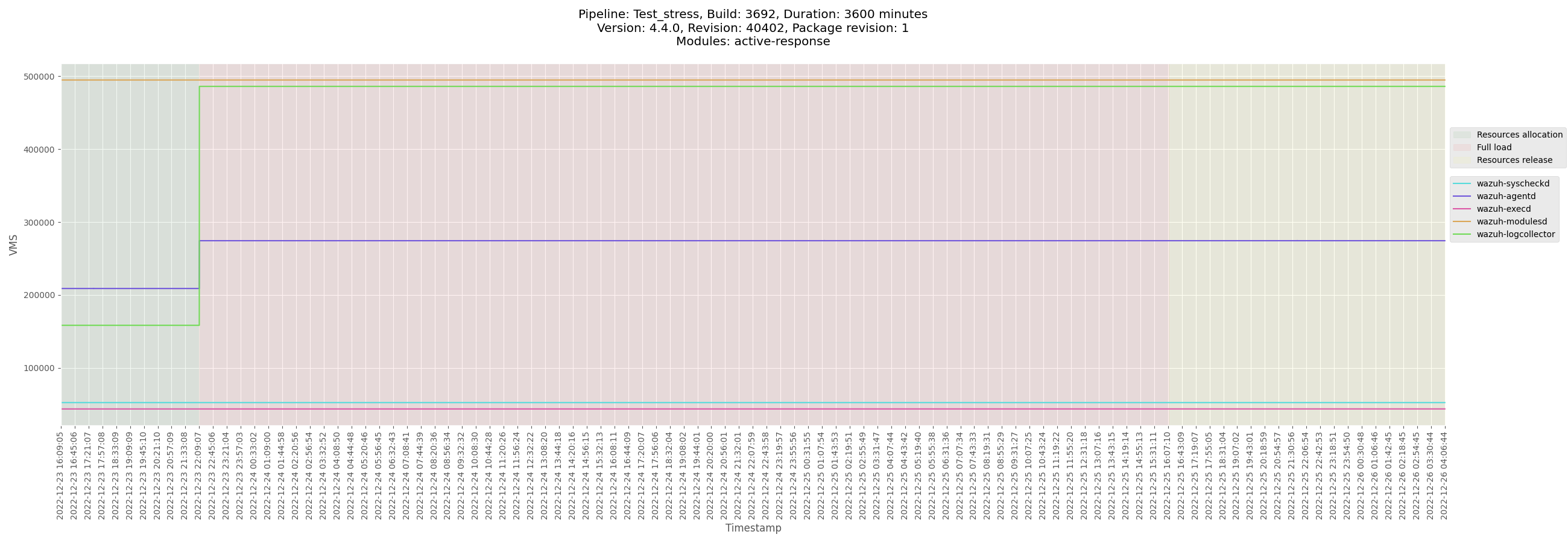
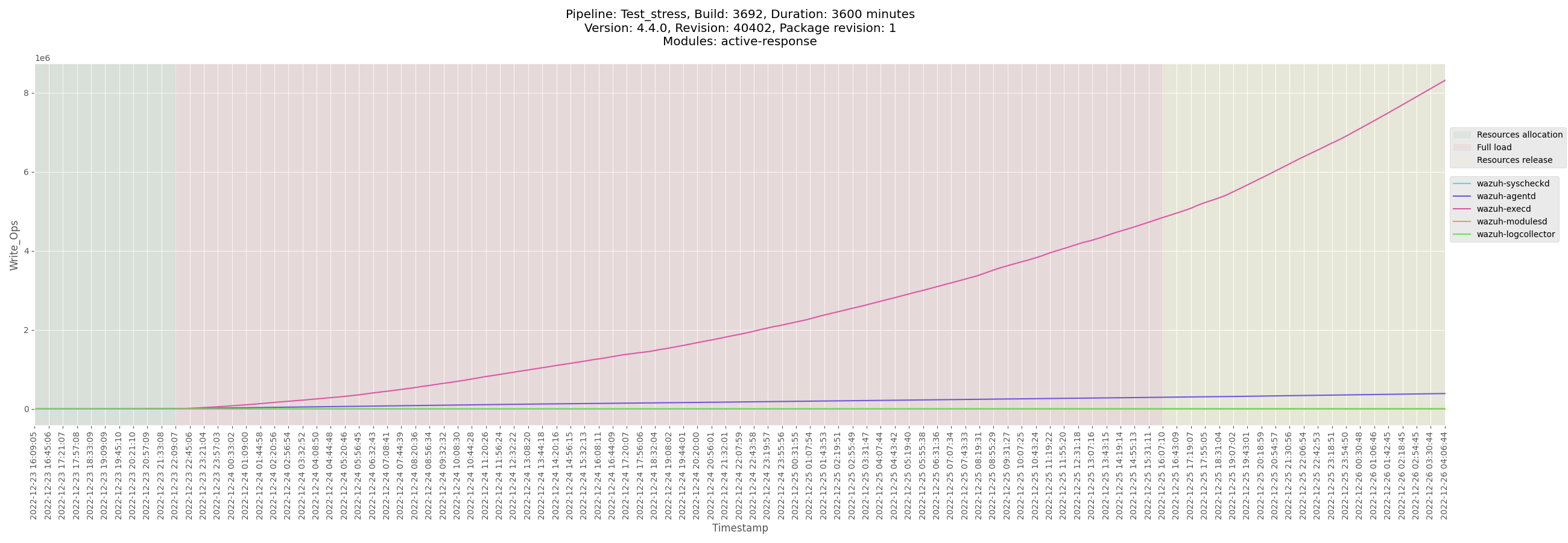

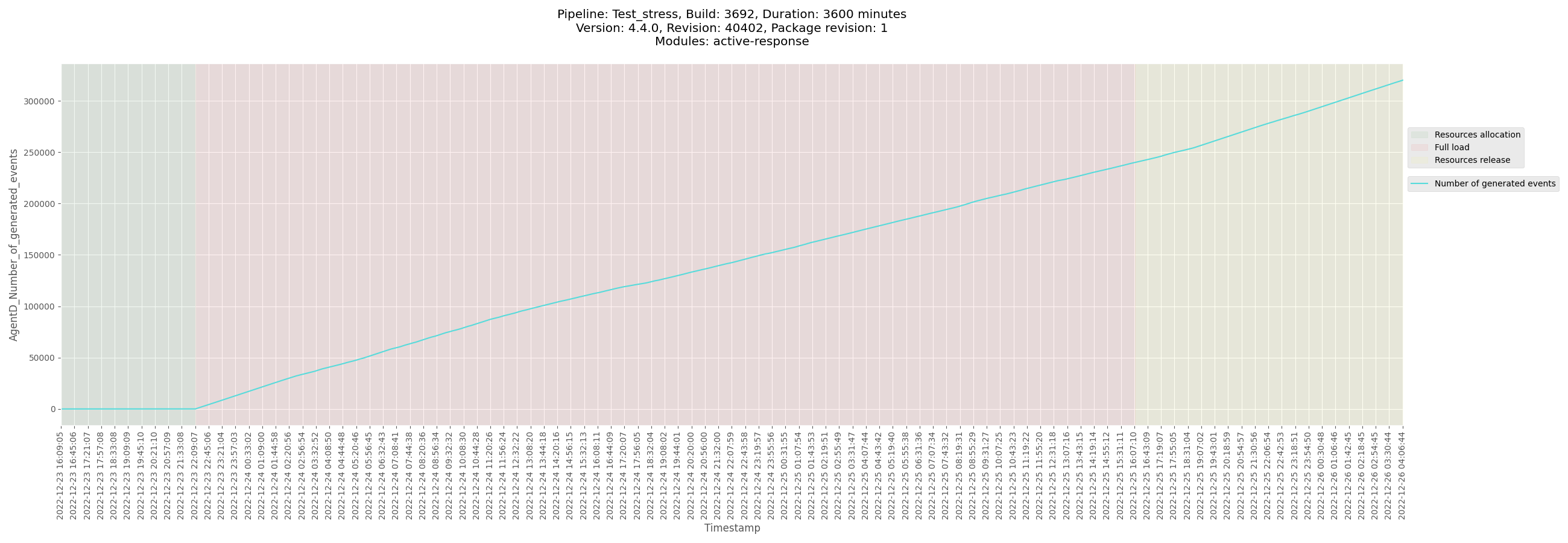

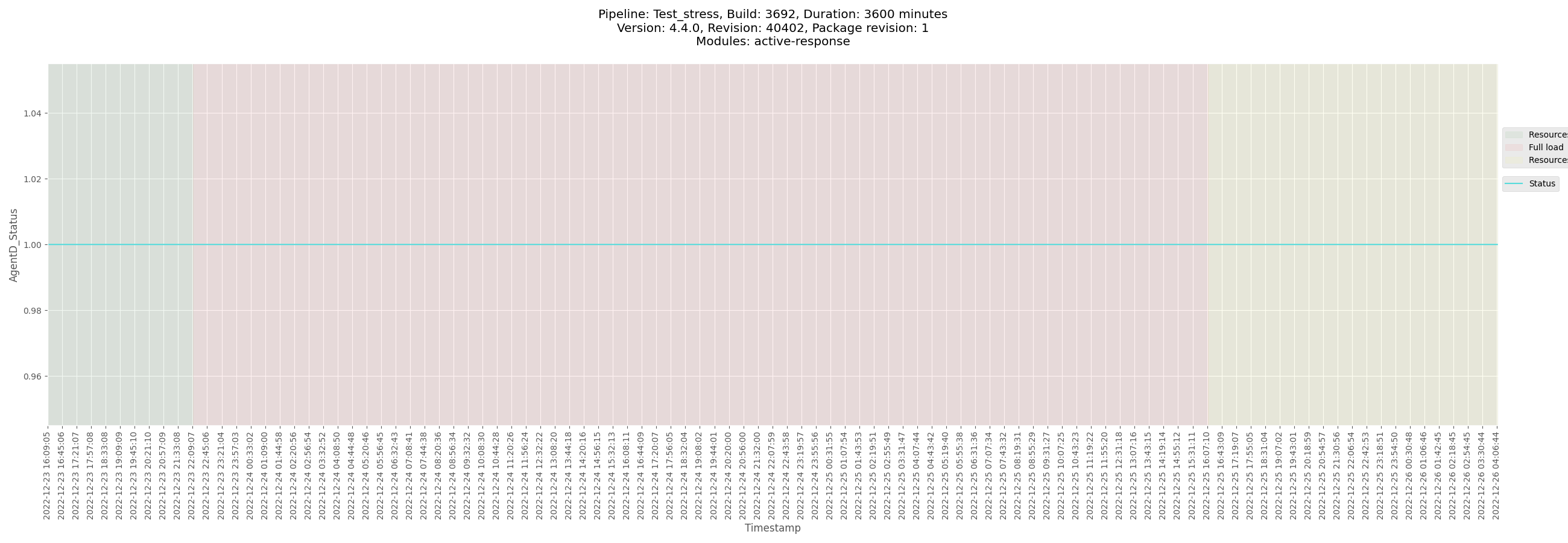
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_centos_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_centos/logs/ossec_Test_stress_B3692_centos_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3692_centos-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_centos/data/monitor-agent-Test_stress_B3692_centos-pre-release.csv)
[Test_stress_B3692_centos_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_centos/data/Test_stress_B3692_centos_agentd_state.csv)
</details>
</details>
<details><summary>Ubuntu agent</summary>
+ <details><summary>Plots</summary>
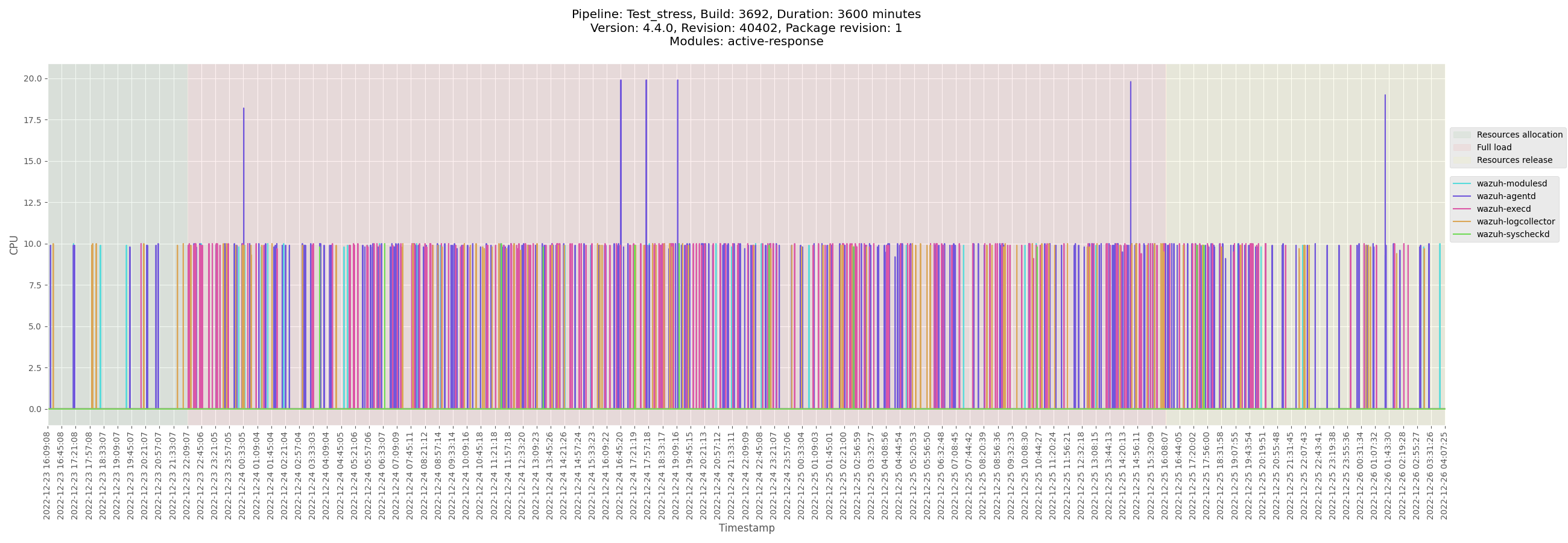

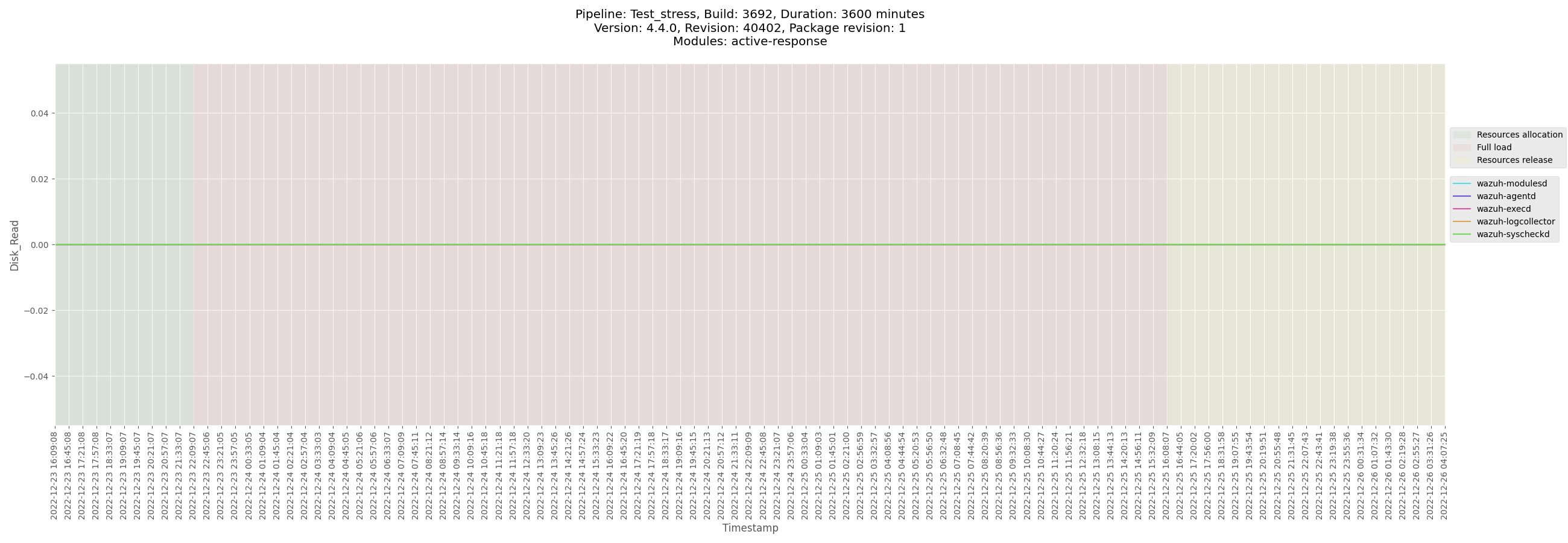

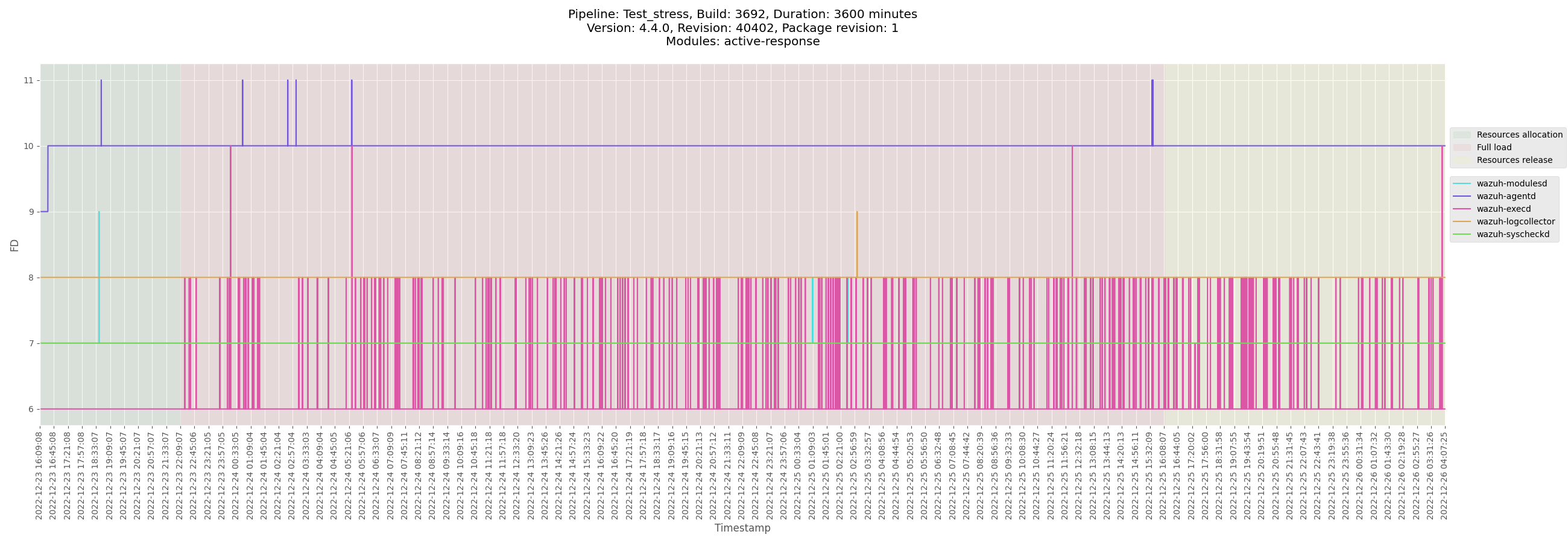
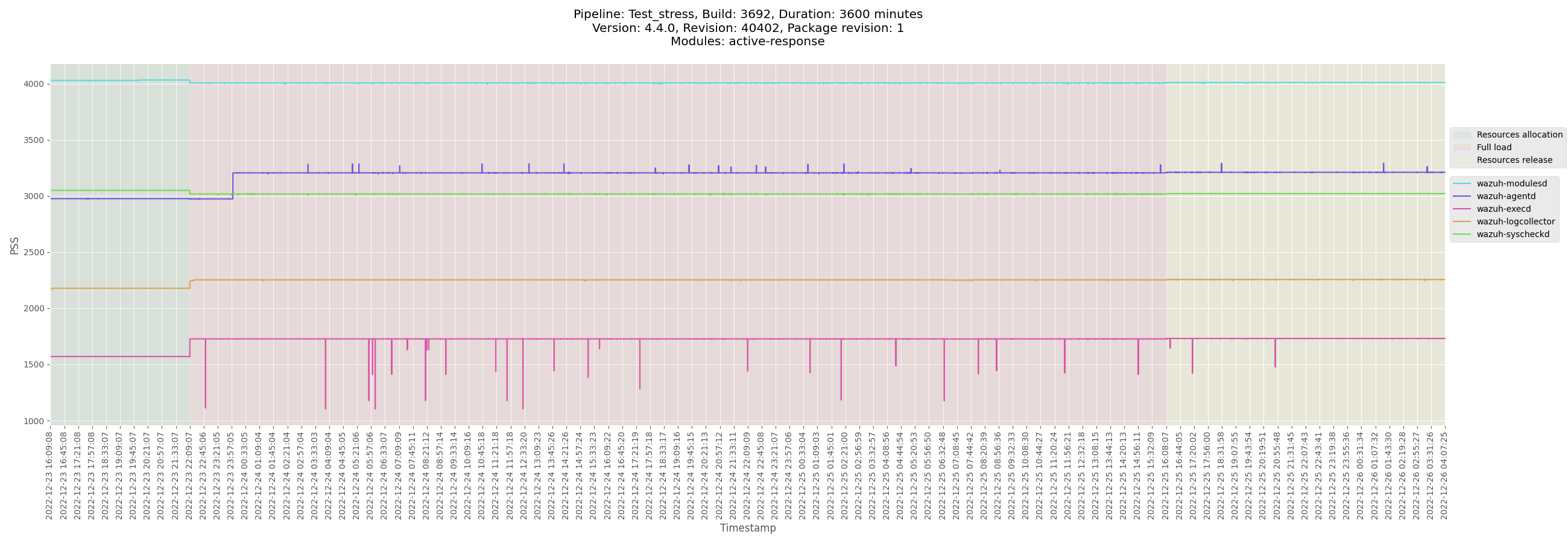


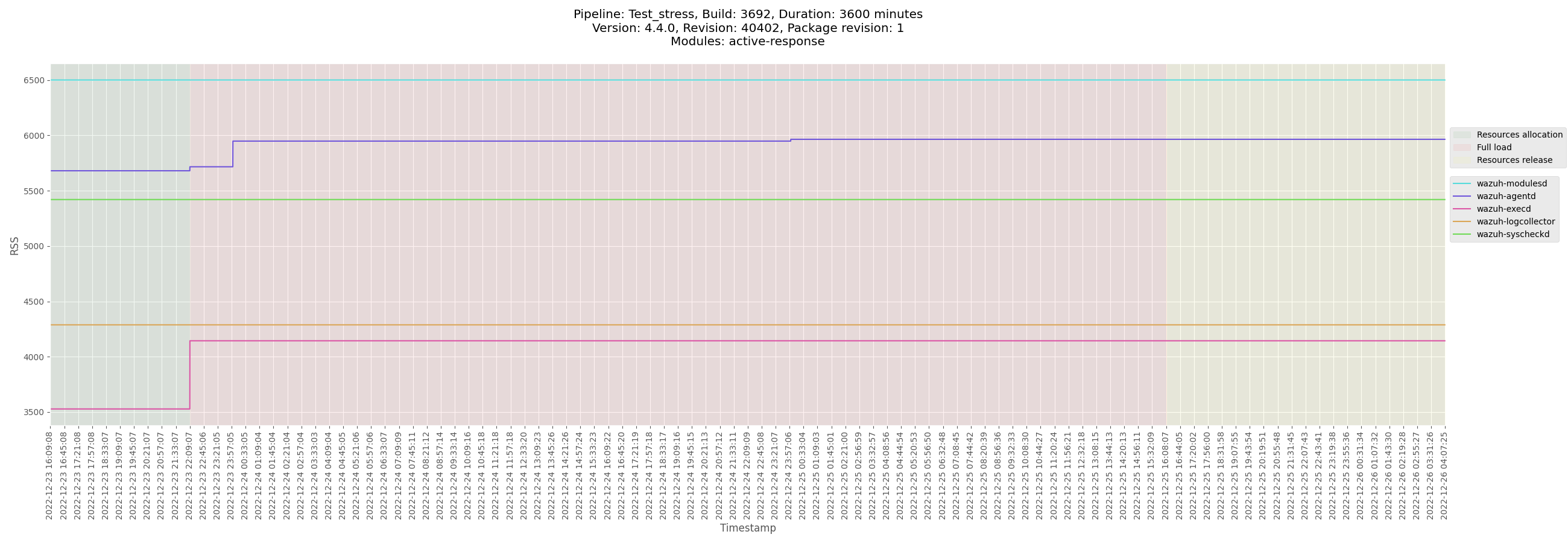
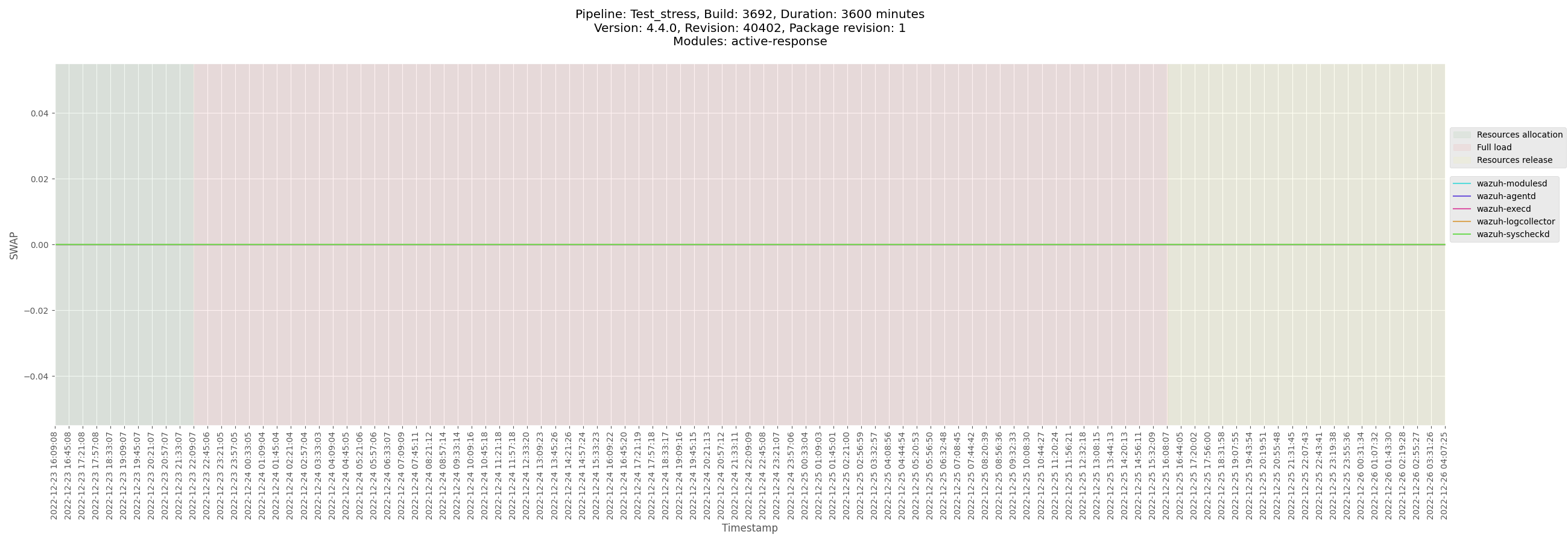
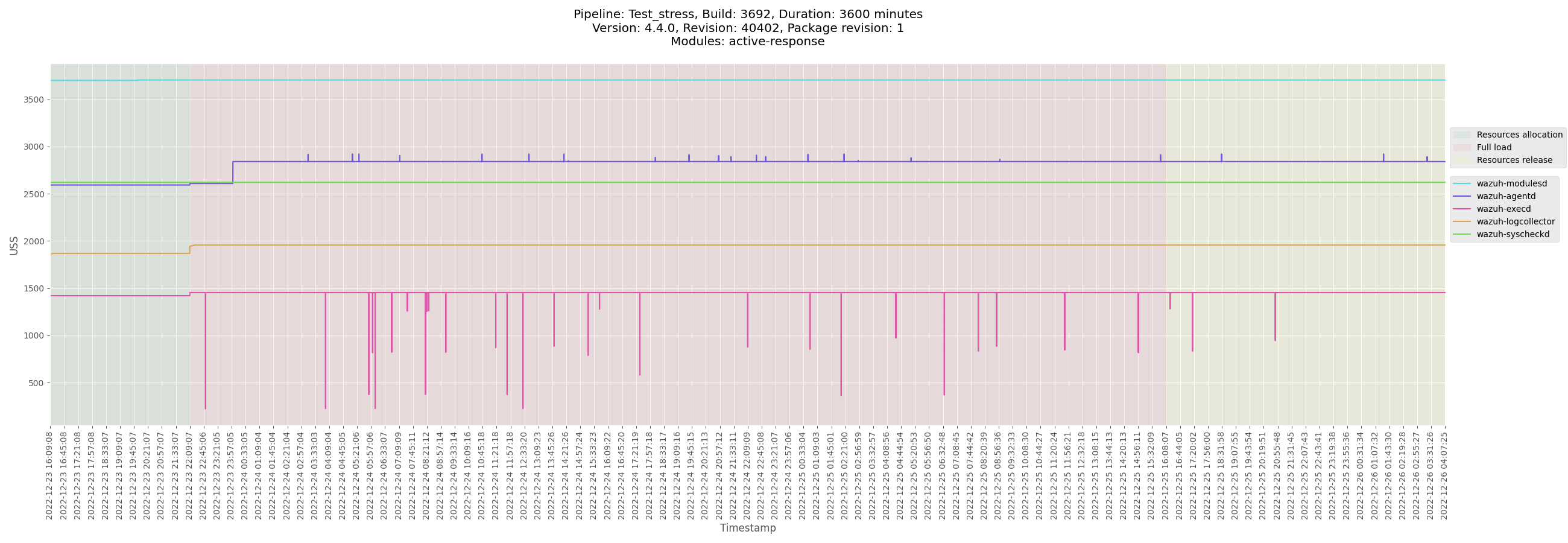
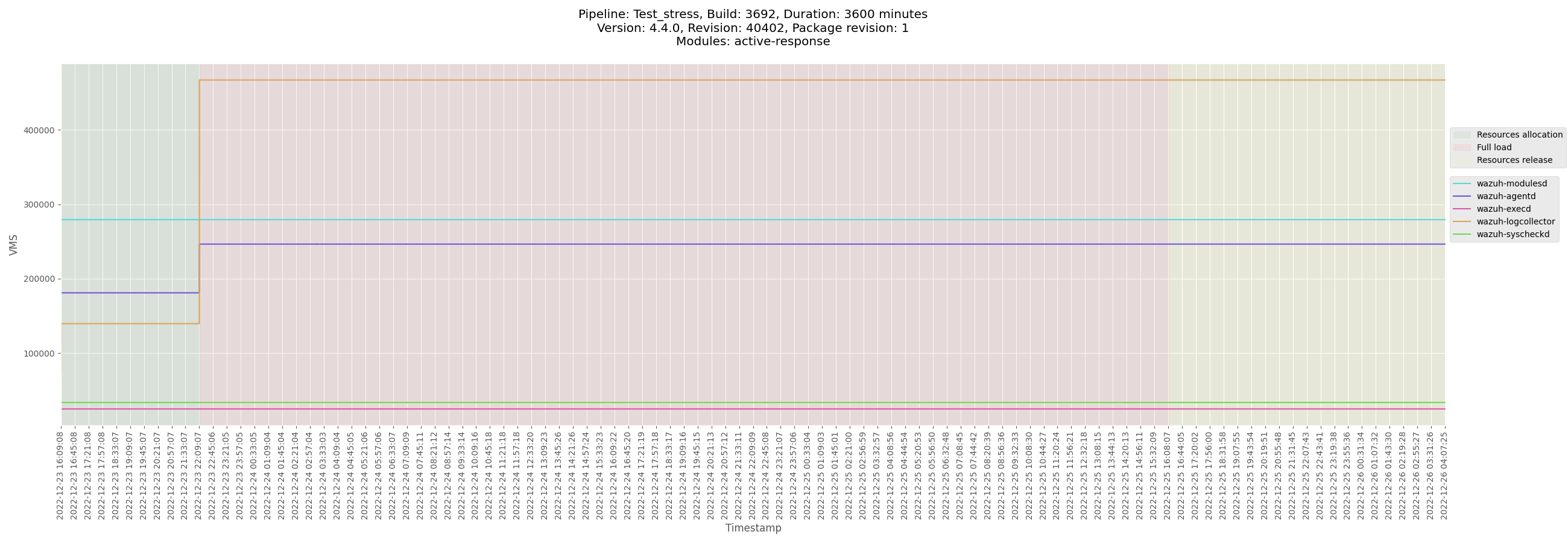
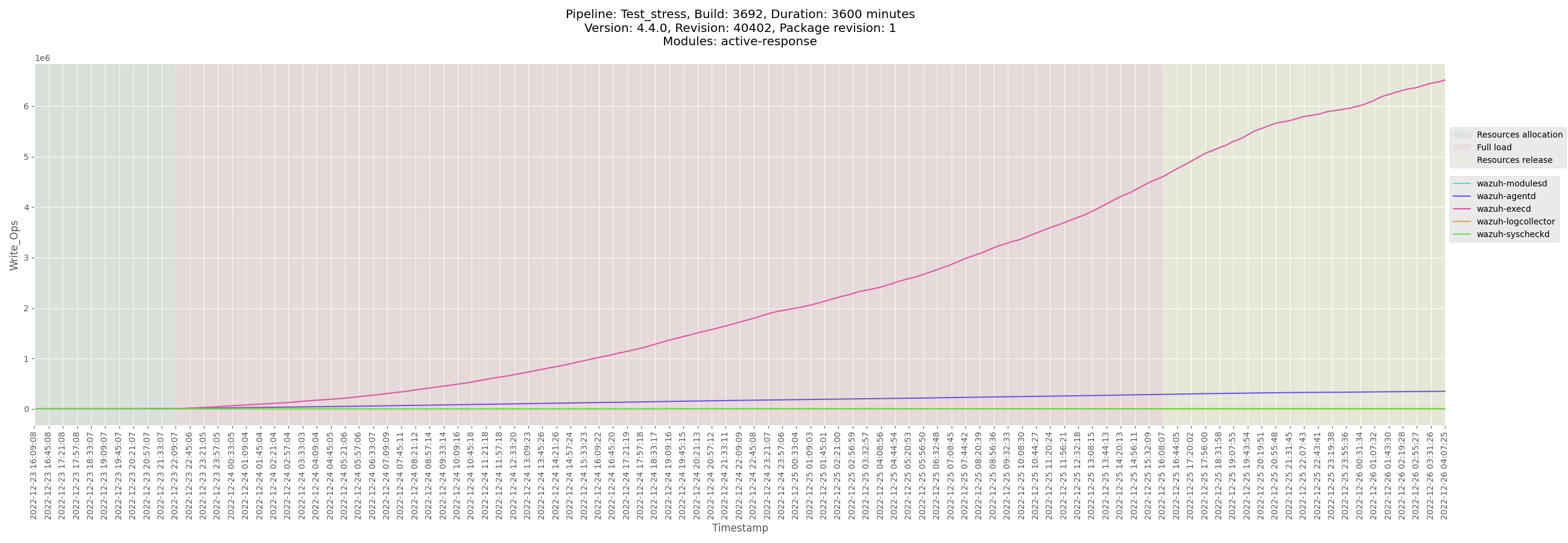

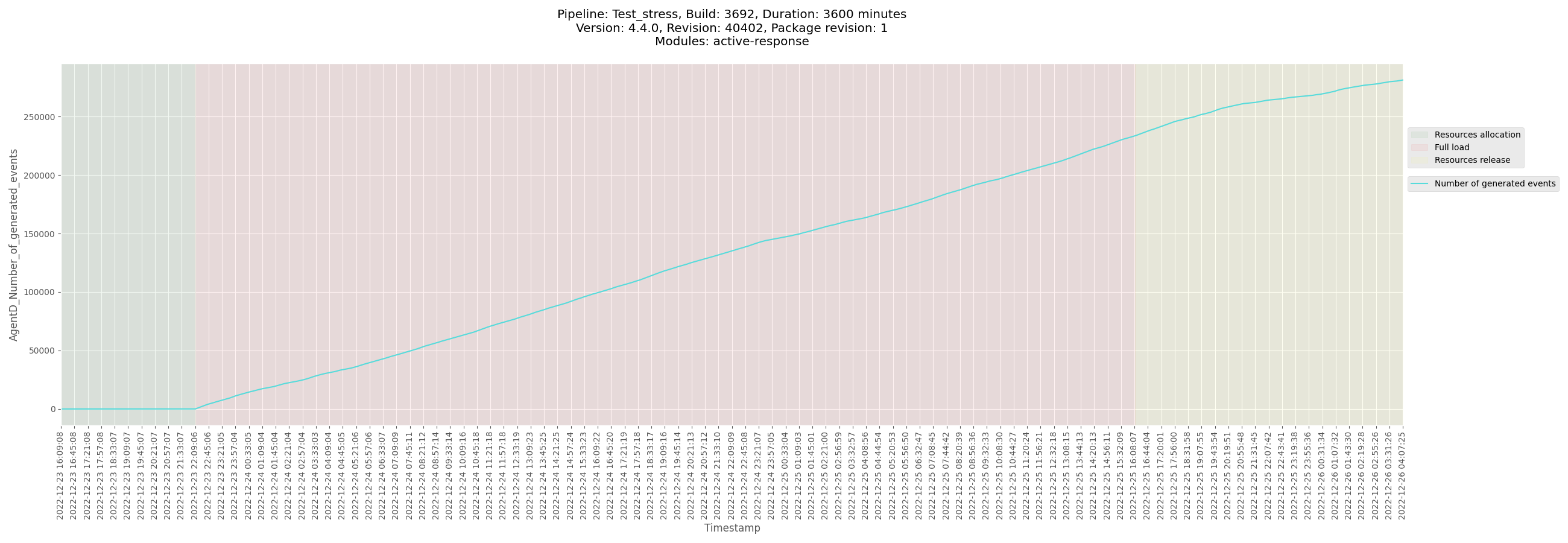
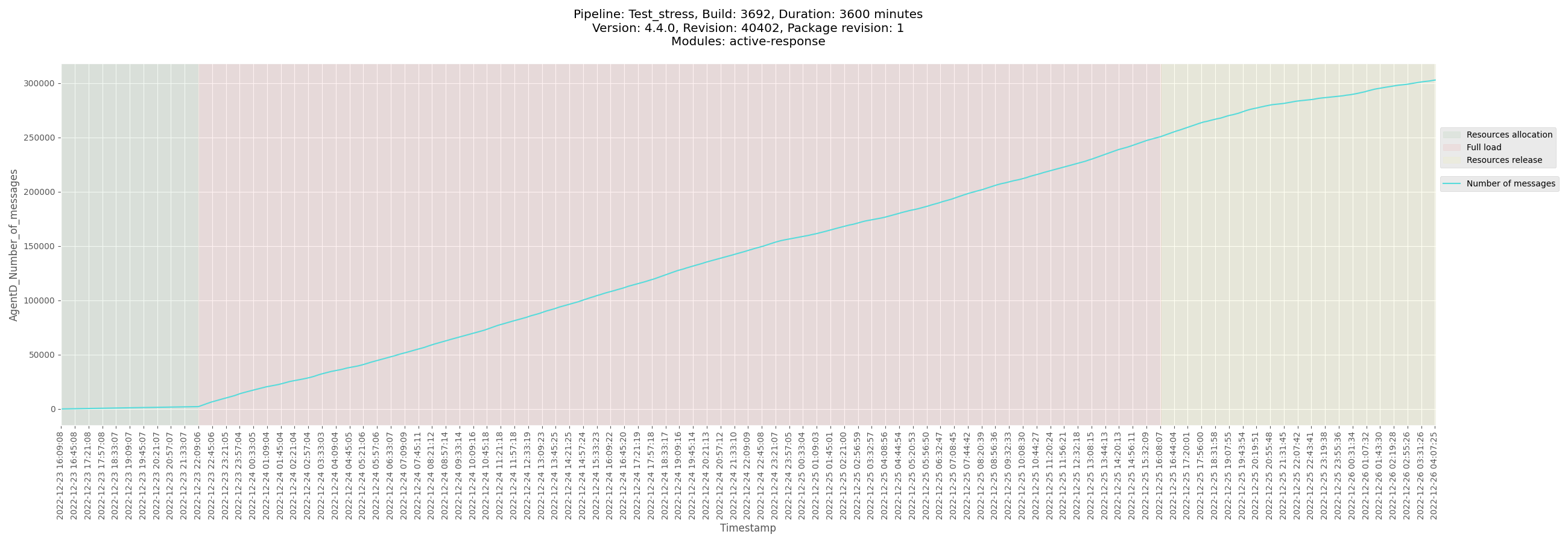
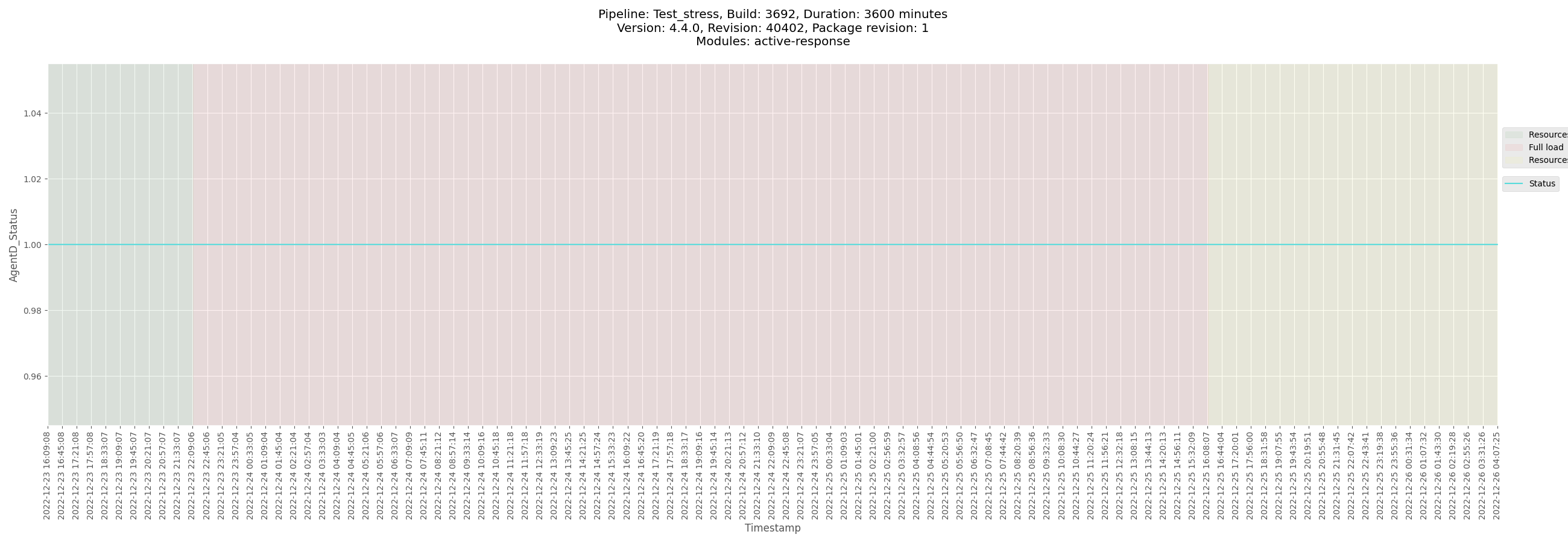
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_ubuntu_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_ubuntu/logs/ossec_Test_stress_B3692_ubuntu_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3692_ubuntu-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_ubuntu/data/monitor-agent-Test_stress_B3692_ubuntu-pre-release.csv)
[Test_stress_B3692_ubuntu_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_ubuntu/data/Test_stress_B3692_ubuntu_agentd_state.csv)
</details>
</details>
<details><summary>Windows agent</summary>
+ <details><summary>Plots</summary>
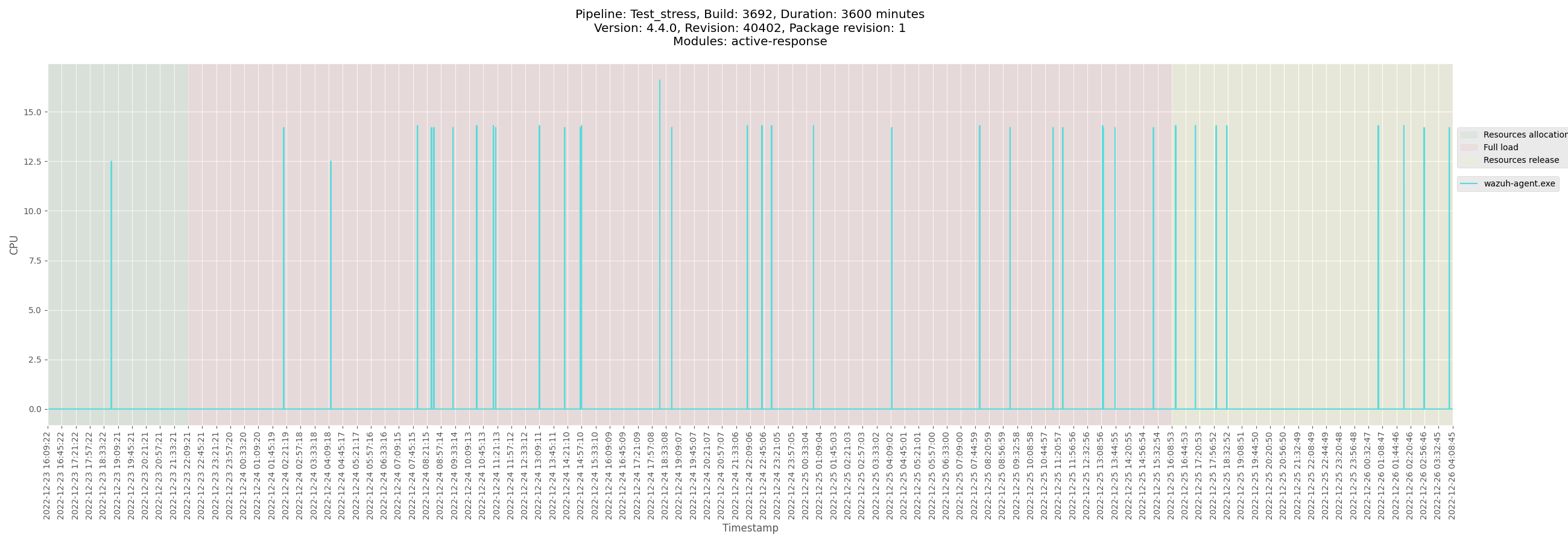
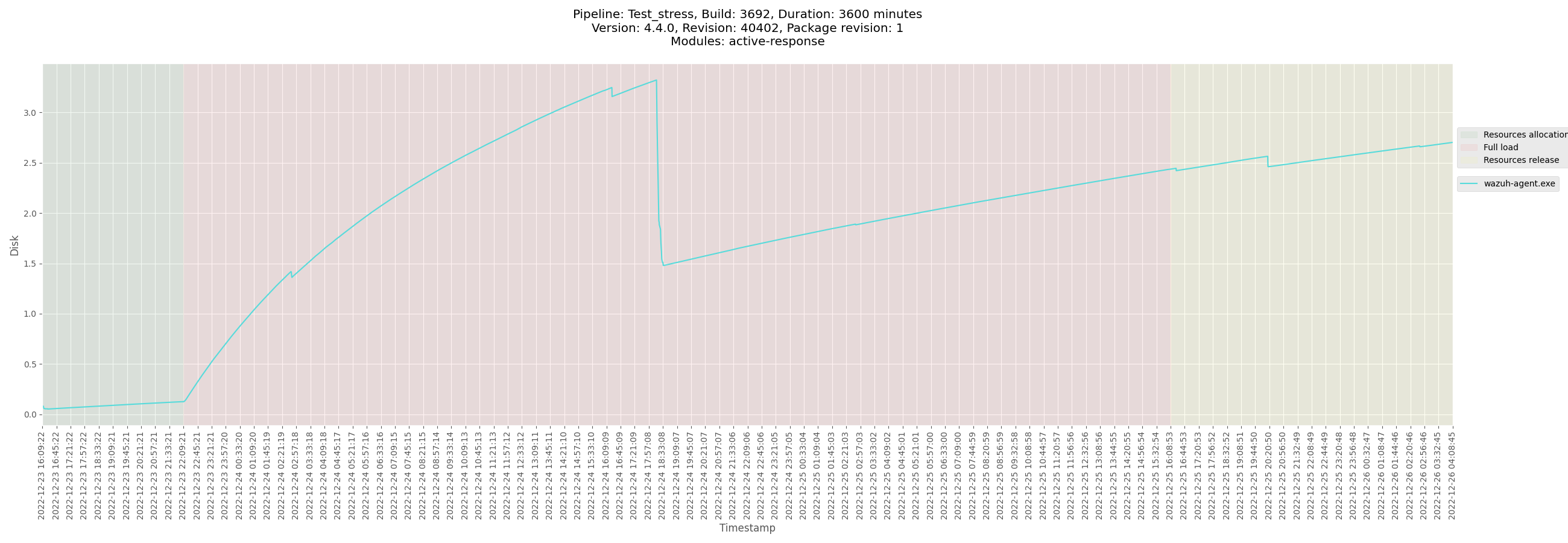
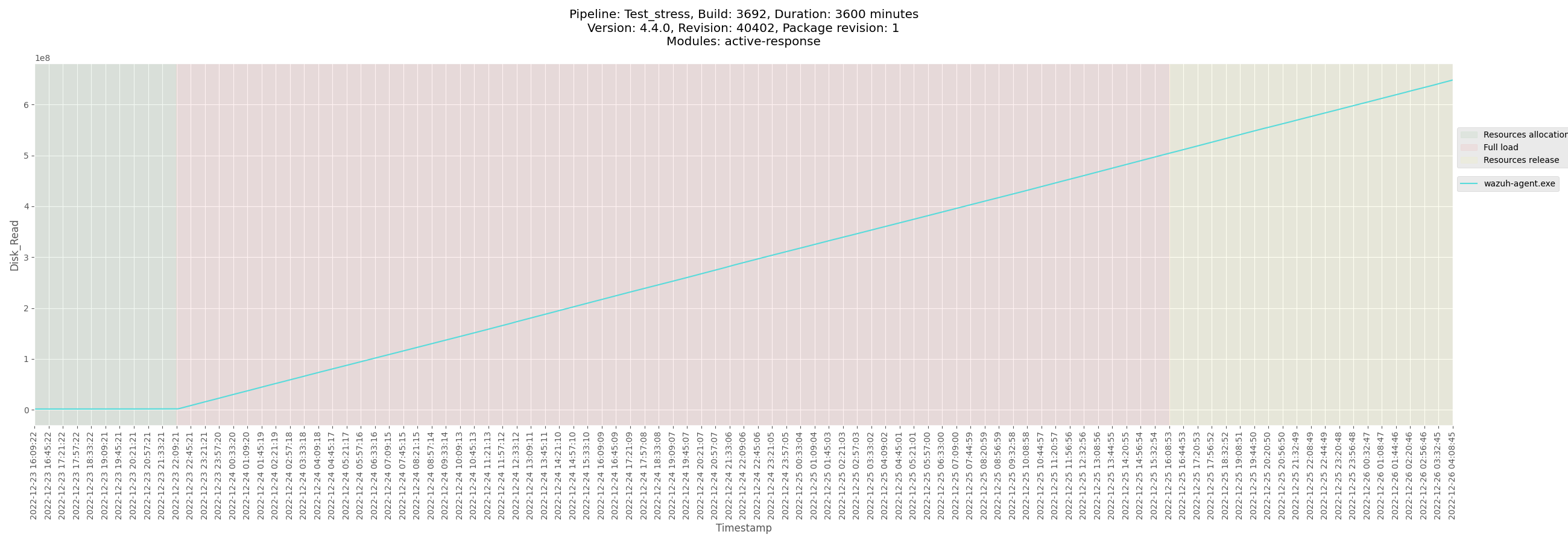
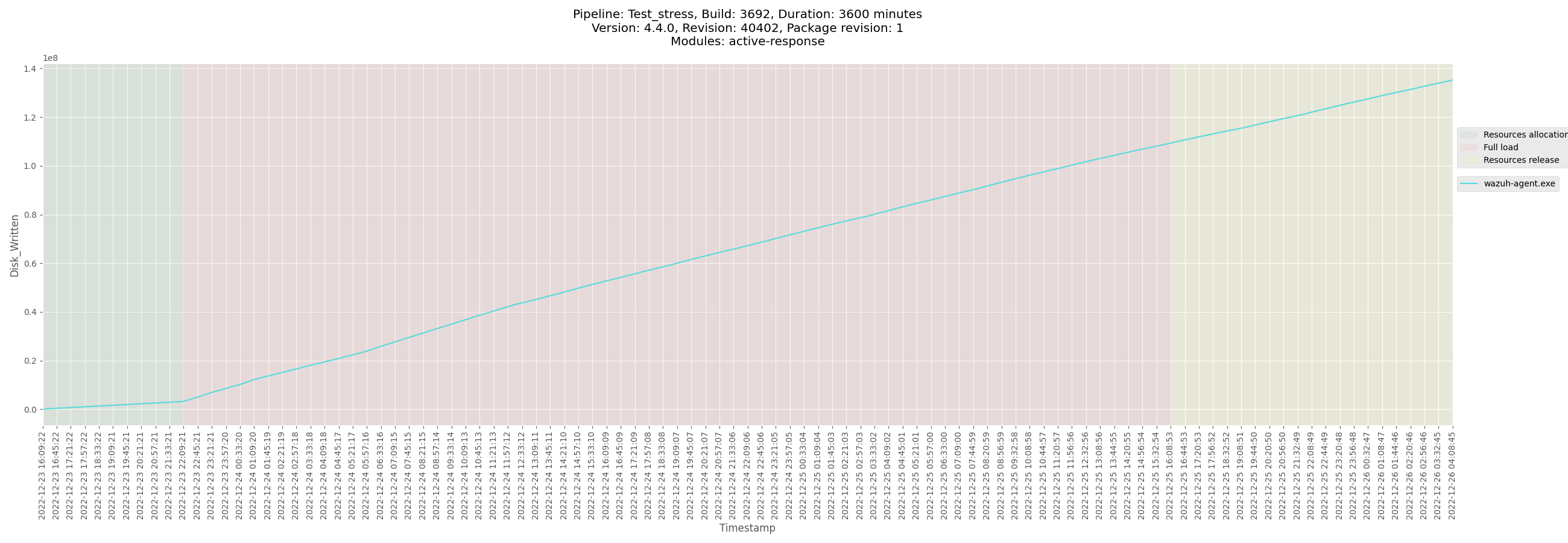
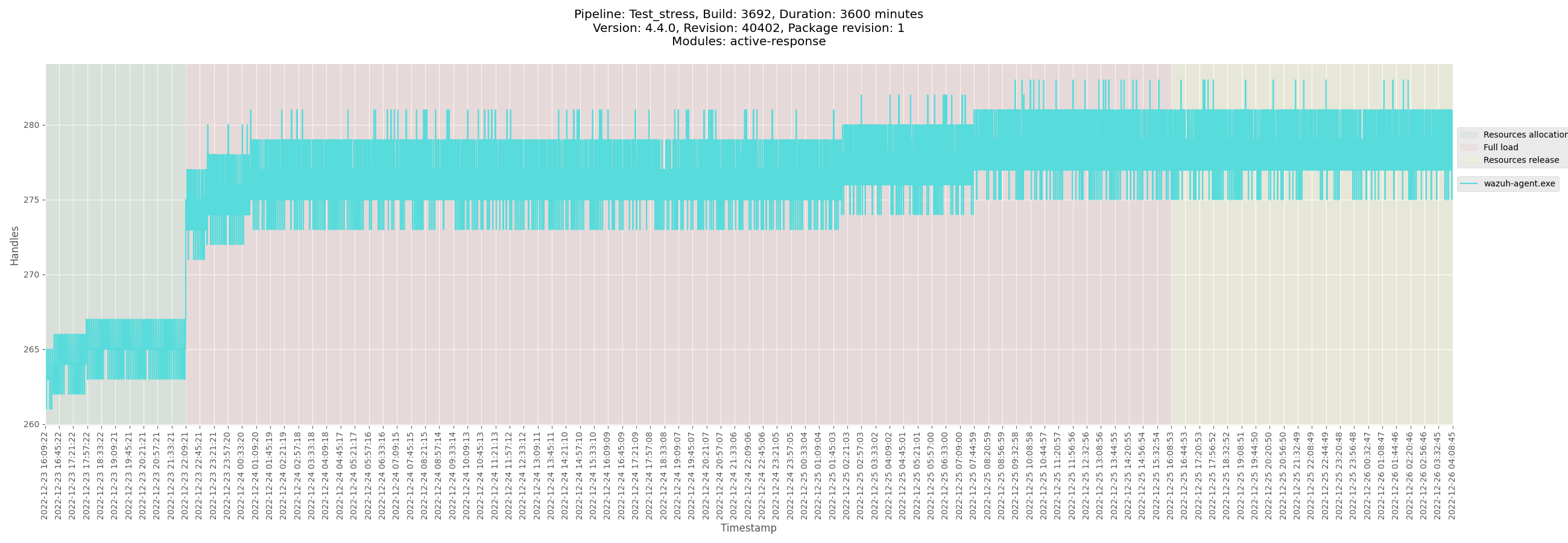
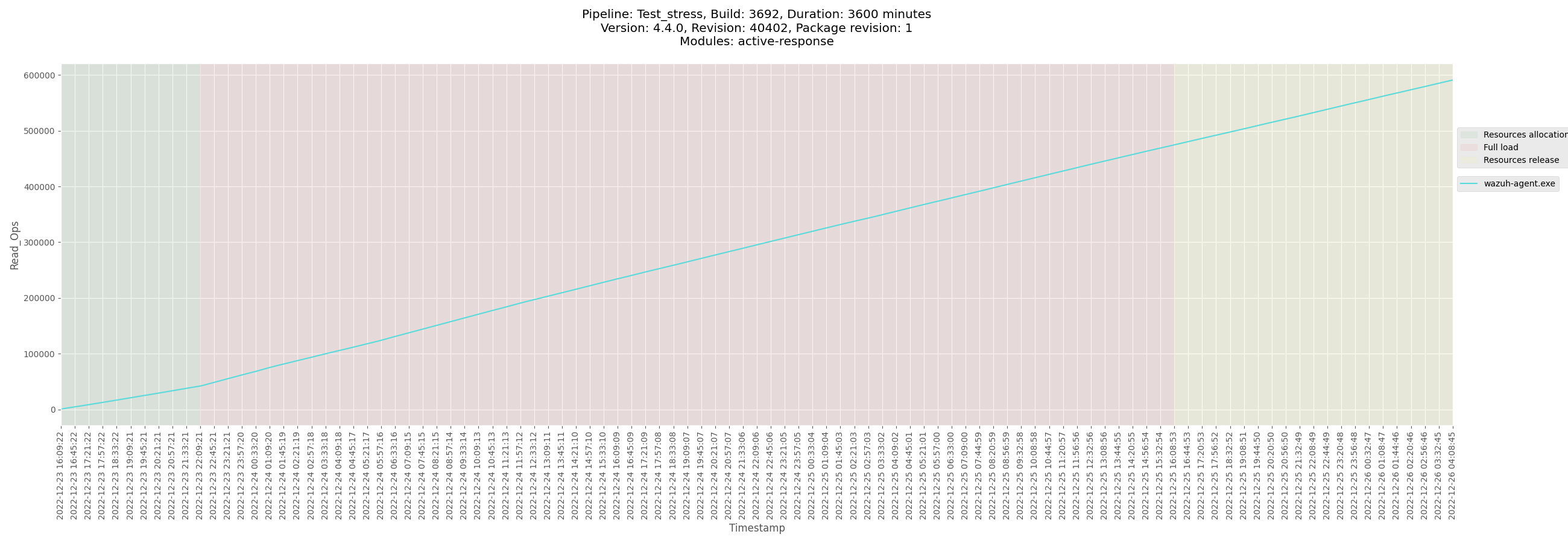
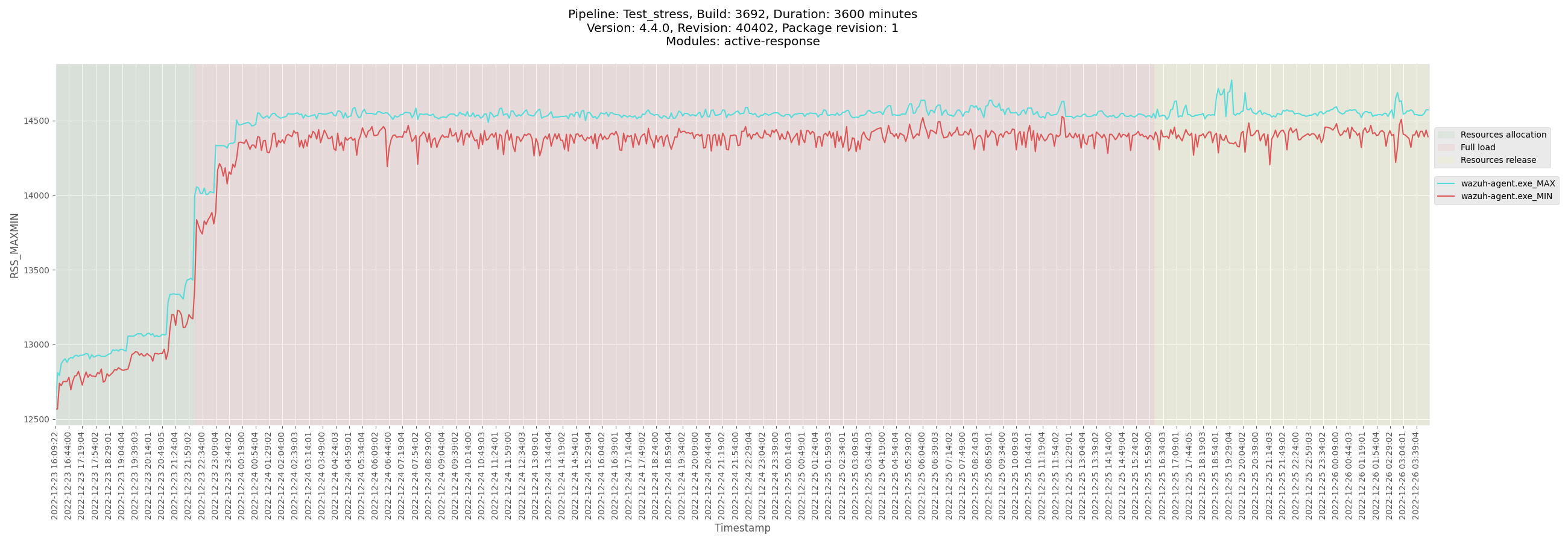
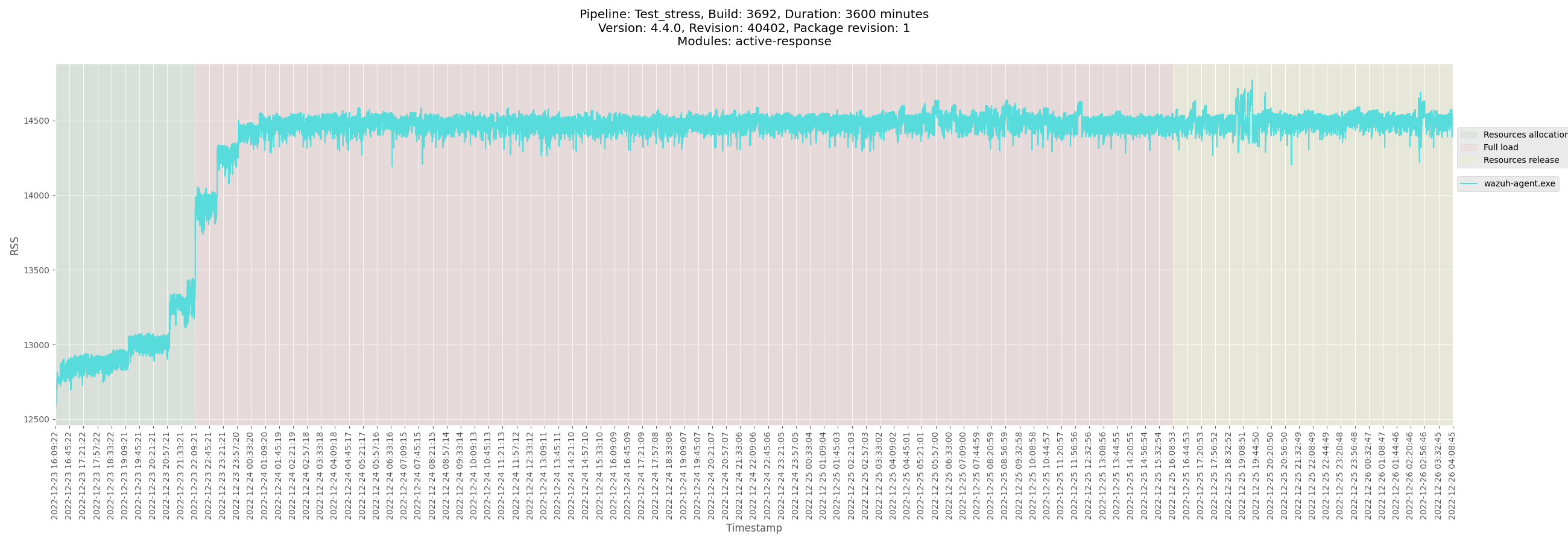
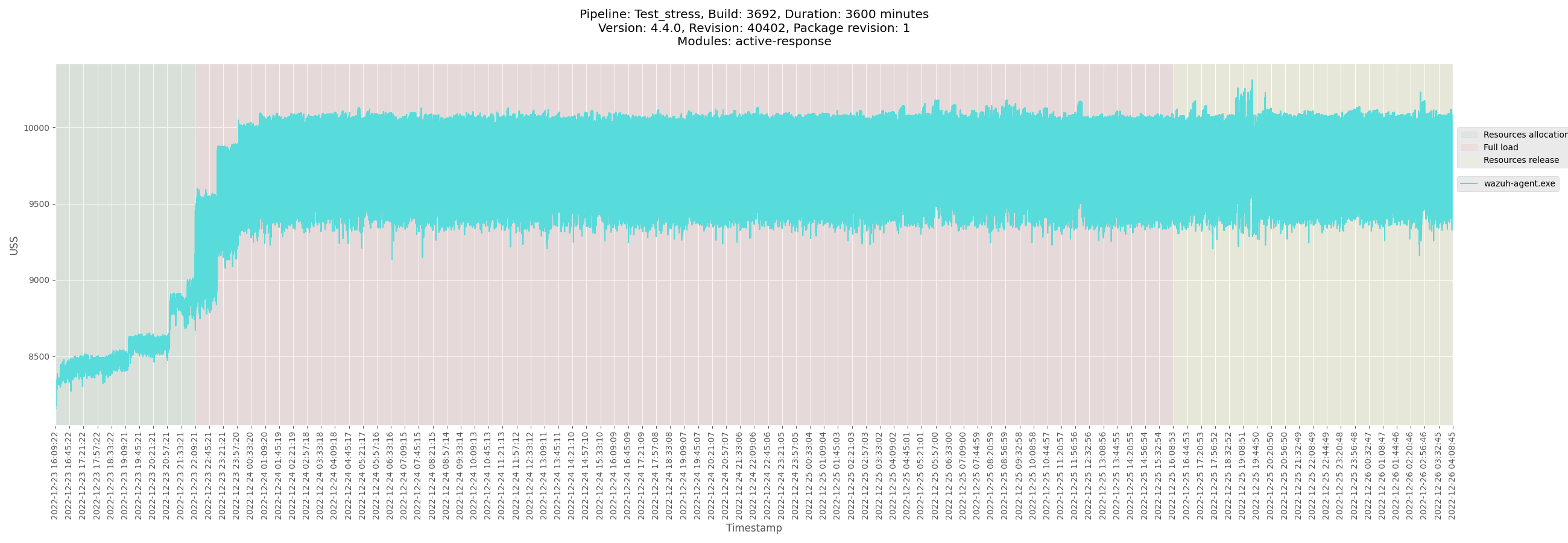
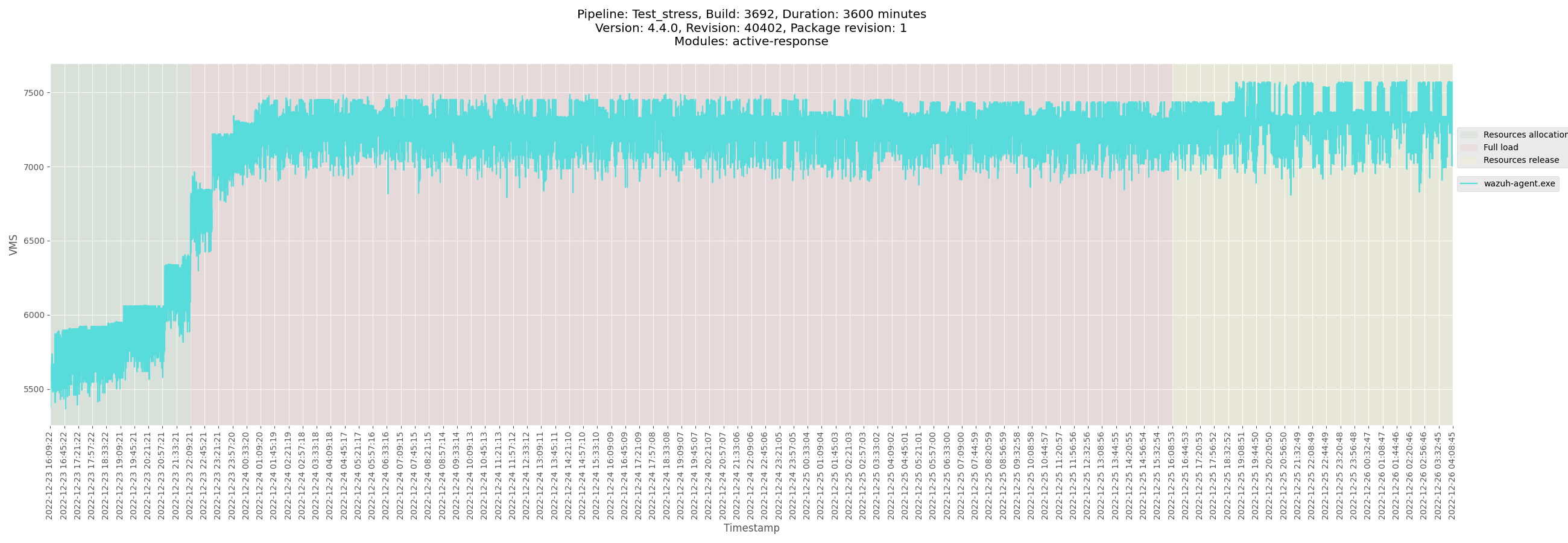
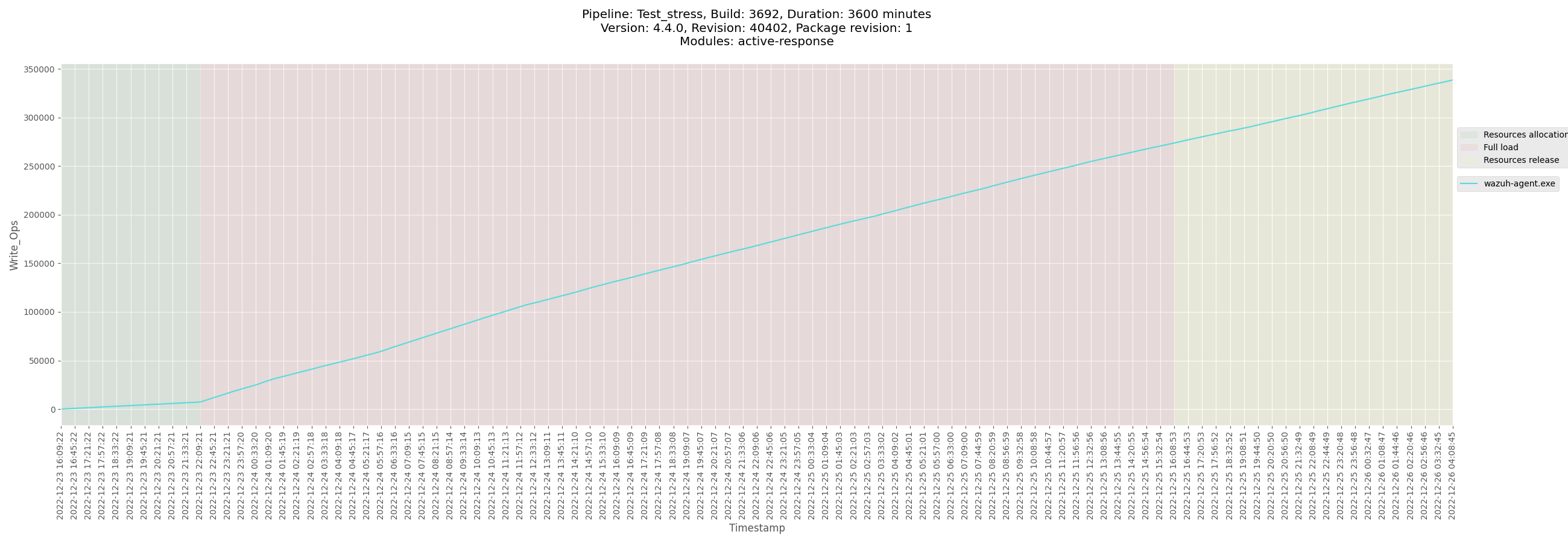
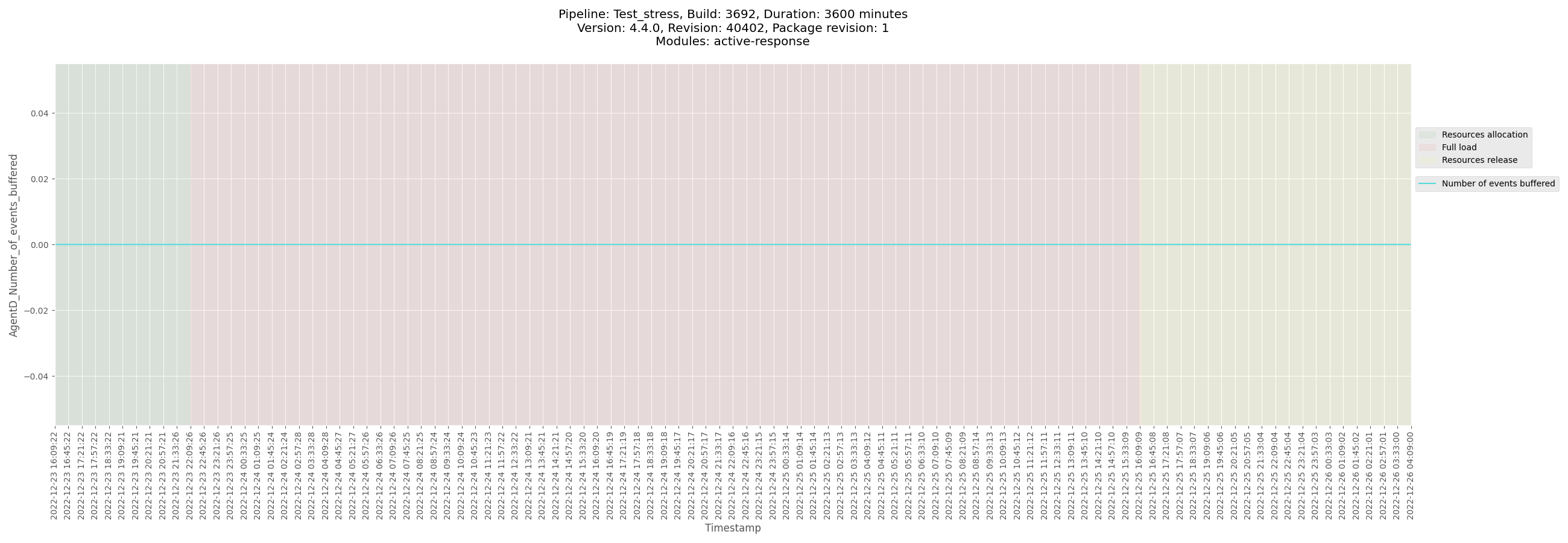
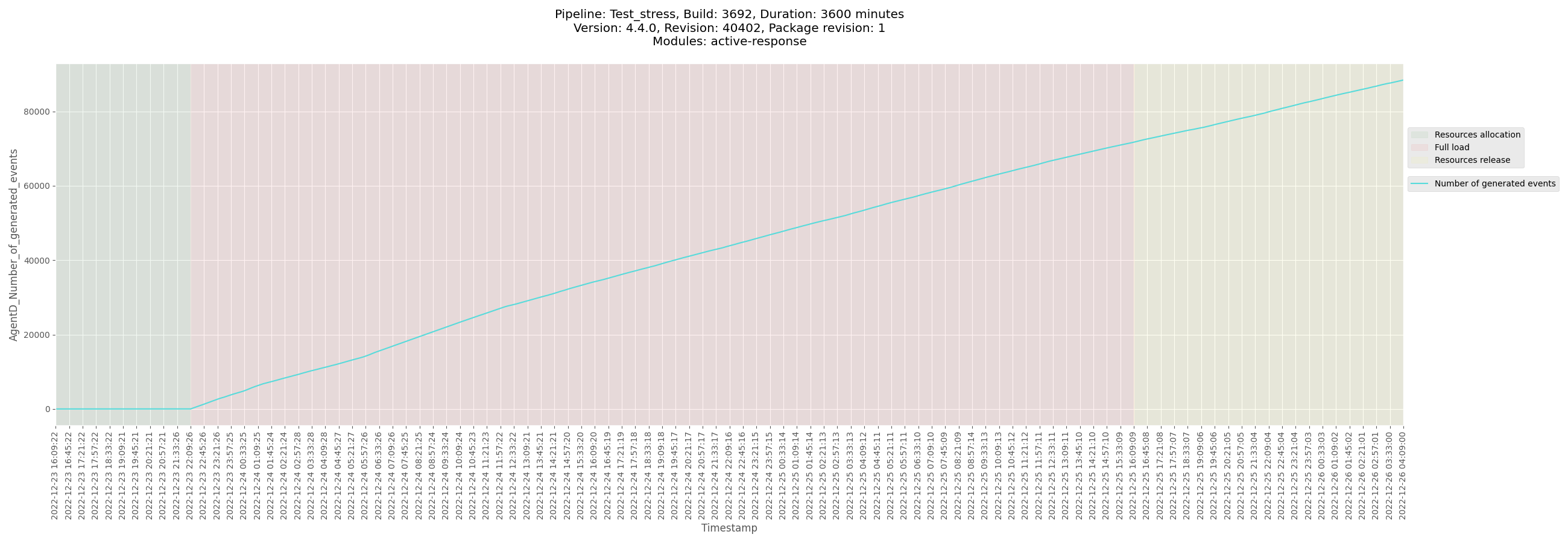
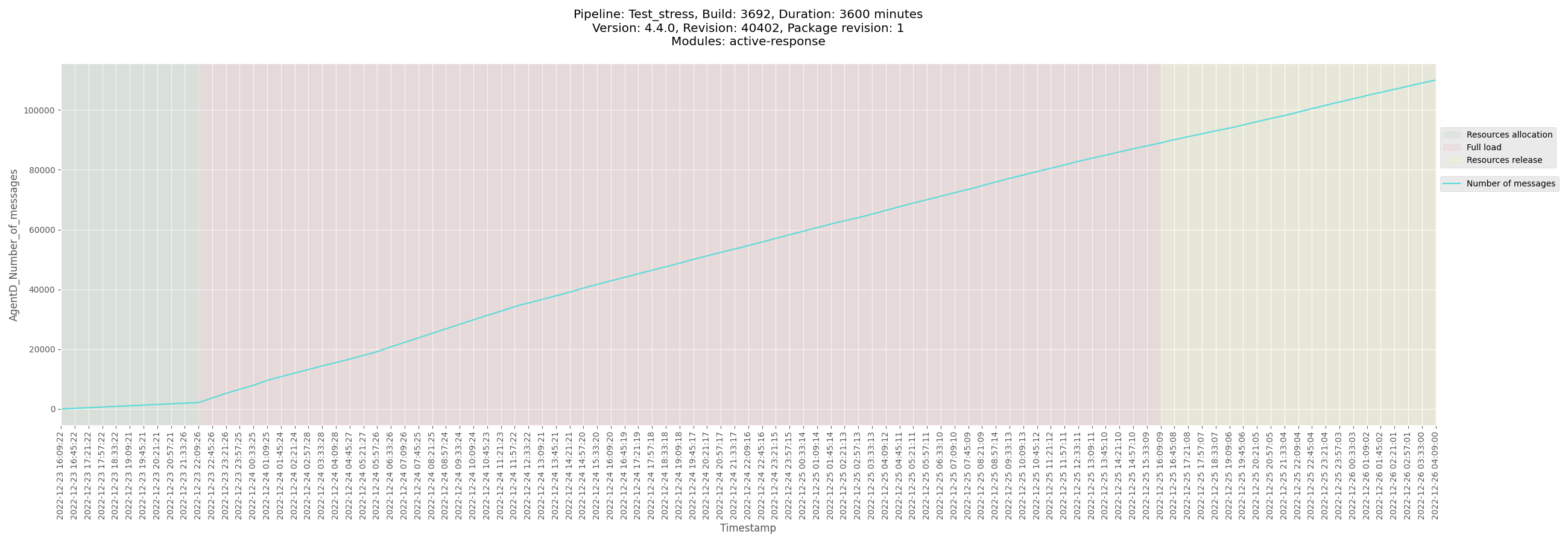
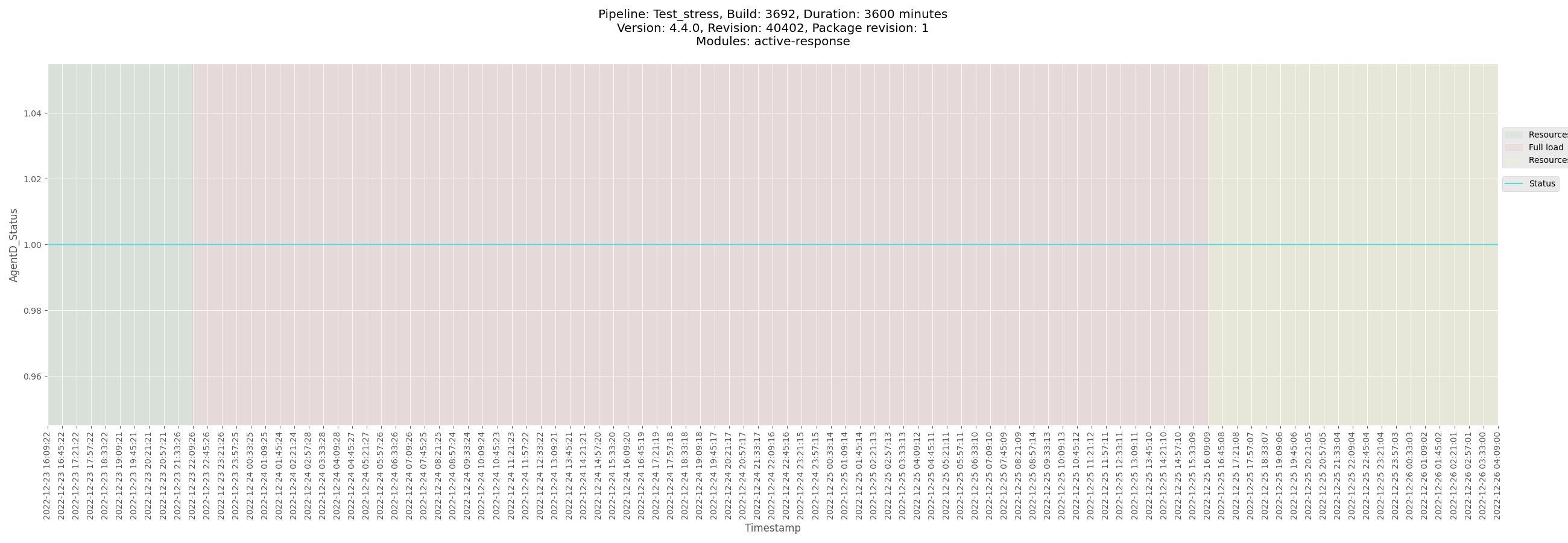
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3692_windows_2022-12-26.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_windows/logs/ossec_Test_stress_B3692_windows_2022-12-26.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-winagent-Test_stress_B3692_windows-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_windows/data/monitor-winagent-Test_stress_B3692_windows-pre-release.csv)
[Test_stress_B3692_windows_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.4.0/B3692-3600m/B3692_agent_windows/data/Test_stress_B3692_windows_agentd_state.csv)
</details>
</details>
<details><summary>macOS agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details>
<details><summary>Solaris agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details> | non_priority | release alpha footprint metrics active response footprint metrics information main release candidate issue main footprint metrics issue version release candidate alpha tag stress test documentation packages used repository packages dev wazuh com package path pre release package revision jenkins build manager plots logs and configuration csv centos agent plots logs and configuration csv ubuntu agent plots logs and configuration csv windows agent plots logs and configuration csv macos agent plots logs and configuration csv solaris agent plots logs and configuration csv | 0 |
204,143 | 23,216,061,164 | IssuesEvent | 2022-08-02 14:10:21 | jgeraigery/LocationIntelligenceSDK-Java | https://api.github.com/repos/jgeraigery/LocationIntelligenceSDK-Java | opened | gson-2.6.2.jar: 2 vulnerabilities (highest severity is: 7.7) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.6.2.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /-2/files-2.1/com.google.code.gson/gson/2.6.2/f1bc476cc167b18e66c297df599b2377131a8947/gson-2.6.2.jar,/.code.gson/gson/jars/gson-2.6.2.jar,/gle/code/gson/gson/2.6.2/gson-2.6.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/LocationIntelligenceSDK-Java/commit/c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558">c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [WS-2021-0419](https://github.com/google/gson/pull/1991) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | gson-2.6.2.jar | Direct | 2.8.9 | ✅ |
| [CVE-2022-25647](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25647) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | gson-2.6.2.jar | Direct | 2.8.9 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2021-0419</summary>
### Vulnerable Library - <b>gson-2.6.2.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /-2/files-2.1/com.google.code.gson/gson/2.6.2/f1bc476cc167b18e66c297df599b2377131a8947/gson-2.6.2.jar,/.code.gson/gson/jars/gson-2.6.2.jar,/gle/code/gson/gson/2.6.2/gson-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **gson-2.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/LocationIntelligenceSDK-Java/commit/c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558">c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Denial of Service vulnerability was discovered in gson before 2.8.9 via the writeReplace() method.
<p>Publish Date: 2021-10-11
<p>URL: <a href=https://github.com/google/gson/pull/1991>WS-2021-0419</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-10-11</p>
<p>Fix Resolution: 2.8.9</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25647</summary>
### Vulnerable Library - <b>gson-2.6.2.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /-2/files-2.1/com.google.code.gson/gson/2.6.2/f1bc476cc167b18e66c297df599b2377131a8947/gson-2.6.2.jar,/.code.gson/gson/jars/gson-2.6.2.jar,/gle/code/gson/gson/2.6.2/gson-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **gson-2.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/LocationIntelligenceSDK-Java/commit/c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558">c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.
<p>Publish Date: 2022-05-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25647>CVE-2022-25647</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`</a></p>
<p>Release Date: 2022-05-01</p>
<p>Fix Resolution: 2.8.9</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | gson-2.6.2.jar: 2 vulnerabilities (highest severity is: 7.7) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.6.2.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /-2/files-2.1/com.google.code.gson/gson/2.6.2/f1bc476cc167b18e66c297df599b2377131a8947/gson-2.6.2.jar,/.code.gson/gson/jars/gson-2.6.2.jar,/gle/code/gson/gson/2.6.2/gson-2.6.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/LocationIntelligenceSDK-Java/commit/c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558">c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [WS-2021-0419](https://github.com/google/gson/pull/1991) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.7 | gson-2.6.2.jar | Direct | 2.8.9 | ✅ |
| [CVE-2022-25647](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25647) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | gson-2.6.2.jar | Direct | 2.8.9 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2021-0419</summary>
### Vulnerable Library - <b>gson-2.6.2.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /-2/files-2.1/com.google.code.gson/gson/2.6.2/f1bc476cc167b18e66c297df599b2377131a8947/gson-2.6.2.jar,/.code.gson/gson/jars/gson-2.6.2.jar,/gle/code/gson/gson/2.6.2/gson-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **gson-2.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/LocationIntelligenceSDK-Java/commit/c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558">c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Denial of Service vulnerability was discovered in gson before 2.8.9 via the writeReplace() method.
<p>Publish Date: 2021-10-11
<p>URL: <a href=https://github.com/google/gson/pull/1991>WS-2021-0419</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-10-11</p>
<p>Fix Resolution: 2.8.9</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25647</summary>
### Vulnerable Library - <b>gson-2.6.2.jar</b></p>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /-2/files-2.1/com.google.code.gson/gson/2.6.2/f1bc476cc167b18e66c297df599b2377131a8947/gson-2.6.2.jar,/.code.gson/gson/jars/gson-2.6.2.jar,/gle/code/gson/gson/2.6.2/gson-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **gson-2.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/LocationIntelligenceSDK-Java/commit/c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558">c8ccfe7ed16e48501f9fd5b1e156a30dce4e7558</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package com.google.code.gson:gson before 2.8.9 are vulnerable to Deserialization of Untrusted Data via the writeReplace() method in internal classes, which may lead to DoS attacks.
<p>Publish Date: 2022-05-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-25647>CVE-2022-25647</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25647`</a></p>
<p>Release Date: 2022-05-01</p>
<p>Fix Resolution: 2.8.9</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | gson jar vulnerabilities highest severity is vulnerable library gson jar gson json library library home page a href path to dependency file build gradle path to vulnerable library files com google code gson gson gson jar code gson gson jars gson jar gle code gson gson gson jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high gson jar direct high gson jar direct details ws vulnerable library gson jar gson json library library home page a href path to dependency file build gradle path to vulnerable library files com google code gson gson gson jar code gson gson jars gson jar gle code gson gson gson jar dependency hierarchy x gson jar vulnerable library found in head commit a href found in base branch master vulnerability details denial of service vulnerability was discovered in gson before via the writereplace method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library gson jar gson json library library home page a href path to dependency file build gradle path to vulnerable library files com google code gson gson gson jar code gson gson jars gson jar gle code gson gson gson jar dependency hierarchy x gson jar vulnerable library found in head commit a href found in base branch master vulnerability details the package com google code gson gson before are vulnerable to deserialization of untrusted data via the writereplace method in internal classes which may lead to dos attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
36,541 | 17,778,373,919 | IssuesEvent | 2021-08-30 22:48:10 | google/iree | https://api.github.com/repos/google/iree | closed | Add Vulkan tracing via Tracy | enhancement ➕ runtime performance ⚡ hal/vulkan | Super hacky (but working) WIP in the benvanik-tracy-vulkan branch. We'll likely want to expose HAL APIs for timestamping and debug groups so that we can get a consistent style of command buffer submission tracking across all backends (not just Vulkan). | True | Add Vulkan tracing via Tracy - Super hacky (but working) WIP in the benvanik-tracy-vulkan branch. We'll likely want to expose HAL APIs for timestamping and debug groups so that we can get a consistent style of command buffer submission tracking across all backends (not just Vulkan). | non_priority | add vulkan tracing via tracy super hacky but working wip in the benvanik tracy vulkan branch we ll likely want to expose hal apis for timestamping and debug groups so that we can get a consistent style of command buffer submission tracking across all backends not just vulkan | 0 |
61,360 | 6,734,304,595 | IssuesEvent | 2017-10-18 17:34:42 | consul/consul | https://api.github.com/repos/consul/consul | closed | Polls - Stats | polls production testable | What
===
- We need add **Poll participation stats** for each poll.
How
===
- We need to include poll stats with this data:
- **TOTAL Nº OF BALLOTS**: this is the total number of participants in this polls (independent of the channel, web or booth)
- The **totals of bottom row** are the sum of each column.
- The **totals of right colum** are the sum of each row.
The percentage of right column are calculated respect to the total of participants in this poll (% of valid vote, white and null, check the values in vertical)
All the rest of percentages are calculated respect to the total of votes in this channel (% of web votes, booth, check the values in horizontal)
💈 The current content of `poll/show` should be maintained on "Information" tab.
It's easier to understand by checking the mockup image.
Screenshots
===
You can see the [mockups here](https://invis.io/MSDWMNAWH) _(image 2)_
Warnings
===
This issue is related with https://github.com/consul/consul/issues/1786 and have some things on common.
Notes
===
- This work has already been done in [Madrid's fork](https://github.com/AyuntamientoMadrid/consul/blob/stable/app/controllers/polls_controller.rb#L34) but needs a little love ❤️
- Something similar to [Budget Stats](https://github.com/consul/consul/pull/1712)
| 1.0 | Polls - Stats - What
===
- We need add **Poll participation stats** for each poll.
How
===
- We need to include poll stats with this data:
- **TOTAL Nº OF BALLOTS**: this is the total number of participants in this polls (independent of the channel, web or booth)
- The **totals of bottom row** are the sum of each column.
- The **totals of right colum** are the sum of each row.
The percentage of right column are calculated respect to the total of participants in this poll (% of valid vote, white and null, check the values in vertical)
All the rest of percentages are calculated respect to the total of votes in this channel (% of web votes, booth, check the values in horizontal)
💈 The current content of `poll/show` should be maintained on "Information" tab.
It's easier to understand by checking the mockup image.
Screenshots
===
You can see the [mockups here](https://invis.io/MSDWMNAWH) _(image 2)_
Warnings
===
This issue is related with https://github.com/consul/consul/issues/1786 and have some things on common.
Notes
===
- This work has already been done in [Madrid's fork](https://github.com/AyuntamientoMadrid/consul/blob/stable/app/controllers/polls_controller.rb#L34) but needs a little love ❤️
- Something similar to [Budget Stats](https://github.com/consul/consul/pull/1712)
| non_priority | polls stats what we need add poll participation stats for each poll how we need to include poll stats with this data total nº of ballots this is the total number of participants in this polls independent of the channel web or booth the totals of bottom row are the sum of each column the totals of right colum are the sum of each row the percentage of right column are calculated respect to the total of participants in this poll of valid vote white and null check the values in vertical all the rest of percentages are calculated respect to the total of votes in this channel of web votes booth check the values in horizontal 💈 the current content of poll show should be maintained on information tab it s easier to understand by checking the mockup image screenshots you can see the image warnings this issue is related with and have some things on common notes this work has already been done in but needs a little love ❤️ something similar to | 0 |
123,610 | 10,276,774,202 | IssuesEvent | 2019-08-24 20:34:23 | dexpenses/dexpenses-extract | https://api.github.com/repos/dexpenses/dexpenses-extract | opened | Implement test receipt ec/wob-daenisches-bettenlager-credit | enhancement test-data | Receipt to implement:
 | 1.0 | Implement test receipt ec/wob-daenisches-bettenlager-credit - Receipt to implement:
 | non_priority | implement test receipt ec wob daenisches bettenlager credit receipt to implement ec wob daenisches bettenlager credit | 0 |
224,362 | 17,691,231,491 | IssuesEvent | 2021-08-24 10:11:03 | eagletrt/telemetria-sender | https://api.github.com/repos/eagletrt/telemetria-sender | closed | Test : can send problem | Test | There was a problem discovered by @Bonnee @mattebit @zabealbe and that I did not remember. Make them pass you the code that revealed that problem, change it if you need to and add a test to the "parziali" to check that it is solved. | 1.0 | Test : can send problem - There was a problem discovered by @Bonnee @mattebit @zabealbe and that I did not remember. Make them pass you the code that revealed that problem, change it if you need to and add a test to the "parziali" to check that it is solved. | non_priority | test can send problem there was a problem discovered by bonnee mattebit zabealbe and that i did not remember make them pass you the code that revealed that problem change it if you need to and add a test to the parziali to check that it is solved | 0 |
35,444 | 6,470,728,777 | IssuesEvent | 2017-08-17 09:47:30 | softwaresaved/lowfat | https://api.github.com/repos/softwaresaved/lowfat | closed | Document workaround for django-dbbackup | bug documentation | Because of https://github.com/django-dbbackup/django-dbbackup/issues/238 ours backup is not being restore properly with the documented instructions. We need to add a note saying
~~~
$ gpg -d backup.dump.gpg > file.dump
$ python manage.py migrate
$ sqlite3 db.sqlite3
> .read file.dump
> .q
~~~ | 1.0 | Document workaround for django-dbbackup - Because of https://github.com/django-dbbackup/django-dbbackup/issues/238 ours backup is not being restore properly with the documented instructions. We need to add a note saying
~~~
$ gpg -d backup.dump.gpg > file.dump
$ python manage.py migrate
$ sqlite3 db.sqlite3
> .read file.dump
> .q
~~~ | non_priority | document workaround for django dbbackup because of ours backup is not being restore properly with the documented instructions we need to add a note saying gpg d backup dump gpg file dump python manage py migrate db read file dump q | 0 |
275,244 | 30,219,264,387 | IssuesEvent | 2023-07-05 17:59:20 | Mosqlimate-project/Data-platform | https://api.github.com/repos/Mosqlimate-project/Data-platform | opened | [API Requests] Limit how many API requests an Anon and a regular User can do per hour | django security API | This issue aims the mitigation of DDoS attacks | True | [API Requests] Limit how many API requests an Anon and a regular User can do per hour - This issue aims the mitigation of DDoS attacks | non_priority | limit how many api requests an anon and a regular user can do per hour this issue aims the mitigation of ddos attacks | 0 |
221,508 | 17,354,492,819 | IssuesEvent | 2021-07-29 12:56:33 | dipu-bd/lightnovel-crawler | https://api.github.com/repos/dipu-bd/lightnovel-crawler | closed | Termux error: Object has no attribute `clearln` | bug testing | **Describe the bug**
When I ran lncrawl from Termux in my Samsung S20FE it came up with error after searching for a novel title. Tried reinstalling older versions but still have same error.

**Let us know**
<!-- Please answer the question below -->
Where did you find this bug?
PIP
What is your novel URL?
Didn't use URL, just search for a novel title using the word hero
If you are using PIP / EXE, what is your APP version ?
2.27.4
2.26.4
If you are using PIP / EXE, what is your operating system ?
<!-- e.g. Windows 7, Windows 10, Ubuntu 20, Mac OS Big Sur etc. -->
Android 11
| 1.0 | Termux error: Object has no attribute `clearln` - **Describe the bug**
When I ran lncrawl from Termux in my Samsung S20FE it came up with error after searching for a novel title. Tried reinstalling older versions but still have same error.

**Let us know**
<!-- Please answer the question below -->
Where did you find this bug?
PIP
What is your novel URL?
Didn't use URL, just search for a novel title using the word hero
If you are using PIP / EXE, what is your APP version ?
2.27.4
2.26.4
If you are using PIP / EXE, what is your operating system ?
<!-- e.g. Windows 7, Windows 10, Ubuntu 20, Mac OS Big Sur etc. -->
Android 11
| non_priority | termux error object has no attribute clearln describe the bug when i ran lncrawl from termux in my samsung it came up with error after searching for a novel title tried reinstalling older versions but still have same error let us know where did you find this bug pip what is your novel url didn t use url just search for a novel title using the word hero if you are using pip exe what is your app version if you are using pip exe what is your operating system android | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.