Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
2,905 | 3,696,678,689 | IssuesEvent | 2016-02-27 04:41:53 | dotnet/wcf | https://api.github.com/repos/dotnet/wcf | opened | Investigate regressions in HelloWorld and Duplex (NetTcp) throughput | performance | We see about 8% regression on rc3 23822 running on dnx build 16551 comparing to rc3 23811 running on dnx build16496. More investigations needed to determine if this is due to CLR / corefx / or WCF itself. | True | Investigate regressions in HelloWorld and Duplex (NetTcp) throughput - We see about 8% regression on rc3 23822 running on dnx build 16551 comparing to rc3 23811 running on dnx build16496. More investigations needed to determine if this is due to CLR / corefx / or WCF itself. | non_priority | investigate regressions in helloworld and duplex nettcp throughput we see about regression on running on dnx build comparing to running on dnx more investigations needed to determine if this is due to clr corefx or wcf itself | 0 |
57,956 | 8,215,501,023 | IssuesEvent | 2018-09-05 05:52:12 | SwissDataScienceCenter/renku | https://api.github.com/repos/SwissDataScienceCenter/renku | closed | update "running the platform" doc | documentation | Plenty of old information in https://renku.readthedocs.io/en/latest/developer/setup.html -- clean it up and give instructions for deploying with helm. | 1.0 | update "running the platform" doc - Plenty of old information in https://renku.readthedocs.io/en/latest/developer/setup.html -- clean it up and give instructions for deploying with helm. | non_priority | update running the platform doc plenty of old information in clean it up and give instructions for deploying with helm | 0 |
104,014 | 11,387,505,373 | IssuesEvent | 2020-01-29 15:08:05 | vtex-apps/io-documentation | https://api.github.com/repos/vtex-apps/io-documentation | closed | vtex-apps/admin-cms has no documentation yet | no-documentation | [vtex-apps/admin-cms](https://github.com/vtex-apps/admin-cms) hasn't created any README file yet or is not using Docs Builder | 1.0 | vtex-apps/admin-cms has no documentation yet - [vtex-apps/admin-cms](https://github.com/vtex-apps/admin-cms) hasn't created any README file yet or is not using Docs Builder | non_priority | vtex apps admin cms has no documentation yet hasn t created any readme file yet or is not using docs builder | 0 |
43,964 | 17,775,017,915 | IssuesEvent | 2021-08-30 18:03:04 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | System.DirectoryServices.Protocols kerberos authentication for ldapconnection in kubernetes | area-System.DirectoryServices untriaged | ### Description
Hi, I'm trying to make a ldap search with kerberos authentication in kubernetes environment. The pod is using redhat as OS.
Code I used for the search looks like:
` var atrris = new string[] { "name" };
var filter = "(&(objectCategory=person)(objectClass=user))";
var id = new LdapDirectoryIdentifier("dc.test.com", 389);
var ldapConnection = new System.DirectoryServices.Protocols.LdapConnection(id, null, AuthType.Kerberos);
try
{
var searchRequest = new SearchRequest("DC=test,DC=com", filter, SearchScope.Subtree, atrris);
ldapConnection.Bind();
var res = (SearchResponse)ldapConnection.SendRequest(searchRequest);
}
catch (Exception ex)
{
_logger.LogInformation($"Test: {ex.Message}, {ex.StackTrace}, {ex.InnerException}");
}`
I can make the search if running command in the pod. For example:
ldapsearch -h dc.test.rpa -b "dc=test,dc=com" -s sub -a always "(objectSid=S-1-5-21-3015680287-1561686406-2361570444-1105)"
If run 'klist' on the pod, I can get the tgt (which is not expired). Here is an example.
`Ticket cache: FILE:/etc/krb5cc_1000
Default principal: sqlsp@TEST.RPA
Valid starting Expires Service principal
08/27/21 18:45:22 08/28/21 04:45:22 krbtgt/TEST.COM@TEST.COM
renew until 08/28/21 18:45:22
08/27/21 23:53:00 08/28/21 04:45:22 ldap/dc.test.com@TEST.COM
renew until 08/28/21 18:45:22`
But, if I run the above code for the ldap search, I can see the exception:
`The feature is not supported. , at System.DirectoryServices.Protocols.LdapConnection.BindHelper(NetworkCredential newCredential, Boolean needSetCredential)`
Is kerberos auth for ldap connection supported in kubernetes env?
Am I using the right code for it or there should be more configs needed?
Meanwhile, is there a documentation on how yo setup for the AuthType.Kerberos?
Thanks!
### Configuration
* Which version of .NET is the code running on?
.NET5
* What OS and version, and what distro if applicable?
RedHst RHEL8.1
| 1.0 | System.DirectoryServices.Protocols kerberos authentication for ldapconnection in kubernetes - ### Description
Hi, I'm trying to make a ldap search with kerberos authentication in kubernetes environment. The pod is using redhat as OS.
Code I used for the search looks like:
` var atrris = new string[] { "name" };
var filter = "(&(objectCategory=person)(objectClass=user))";
var id = new LdapDirectoryIdentifier("dc.test.com", 389);
var ldapConnection = new System.DirectoryServices.Protocols.LdapConnection(id, null, AuthType.Kerberos);
try
{
var searchRequest = new SearchRequest("DC=test,DC=com", filter, SearchScope.Subtree, atrris);
ldapConnection.Bind();
var res = (SearchResponse)ldapConnection.SendRequest(searchRequest);
}
catch (Exception ex)
{
_logger.LogInformation($"Test: {ex.Message}, {ex.StackTrace}, {ex.InnerException}");
}`
I can make the search if running command in the pod. For example:
ldapsearch -h dc.test.rpa -b "dc=test,dc=com" -s sub -a always "(objectSid=S-1-5-21-3015680287-1561686406-2361570444-1105)"
If run 'klist' on the pod, I can get the tgt (which is not expired). Here is an example.
`Ticket cache: FILE:/etc/krb5cc_1000
Default principal: sqlsp@TEST.RPA
Valid starting Expires Service principal
08/27/21 18:45:22 08/28/21 04:45:22 krbtgt/TEST.COM@TEST.COM
renew until 08/28/21 18:45:22
08/27/21 23:53:00 08/28/21 04:45:22 ldap/dc.test.com@TEST.COM
renew until 08/28/21 18:45:22`
But, if I run the above code for the ldap search, I can see the exception:
`The feature is not supported. , at System.DirectoryServices.Protocols.LdapConnection.BindHelper(NetworkCredential newCredential, Boolean needSetCredential)`
Is kerberos auth for ldap connection supported in kubernetes env?
Am I using the right code for it or there should be more configs needed?
Meanwhile, is there a documentation on how yo setup for the AuthType.Kerberos?
Thanks!
### Configuration
* Which version of .NET is the code running on?
.NET5
* What OS and version, and what distro if applicable?
RedHst RHEL8.1
| non_priority | system directoryservices protocols kerberos authentication for ldapconnection in kubernetes description hi i m trying to make a ldap search with kerberos authentication in kubernetes environment the pod is using redhat as os code i used for the search looks like var atrris new string name var filter objectcategory person objectclass user var id new ldapdirectoryidentifier dc test com var ldapconnection new system directoryservices protocols ldapconnection id null authtype kerberos try var searchrequest new searchrequest dc test dc com filter searchscope subtree atrris ldapconnection bind var res searchresponse ldapconnection sendrequest searchrequest catch exception ex logger loginformation test ex message ex stacktrace ex innerexception i can make the search if running command in the pod for example ldapsearch h dc test rpa b dc test dc com s sub a always objectsid s if run klist on the pod i can get the tgt which is not expired here is an example ticket cache file etc default principal sqlsp test rpa valid starting expires service principal krbtgt test com test com renew until ldap dc test com test com renew until but if i run the above code for the ldap search i can see the exception the feature is not supported at system directoryservices protocols ldapconnection bindhelper networkcredential newcredential boolean needsetcredential is kerberos auth for ldap connection supported in kubernetes env am i using the right code for it or there should be more configs needed meanwhile is there a documentation on how yo setup for the authtype kerberos thanks configuration which version of net is the code running on what os and version and what distro if applicable redhst | 0 |
187,503 | 22,045,781,032 | IssuesEvent | 2022-05-30 01:25:13 | little-apps/SerializableModel | https://api.github.com/repos/little-apps/SerializableModel | closed | CVE-2018-14041 (Medium) detected in bootstrap-3.3.7-3.3.13.min.js - autoclosed | security vulnerability | ## CVE-2018-14041 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7-3.3.13.min.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.7-3.3.13/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.7-3.3.13/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /SerializableModel/vendor/phpunit/php-code-coverage/src/Report/Html/Renderer/Template/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7-3.3.13.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/little-apps/SerializableModel/commit/d24e2596eb1a71a465b708fbf7645b0698026e82">d24e2596eb1a71a465b708fbf7645b0698026e82</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-target property of scrollspy.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14041>CVE-2018-14041</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14041">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14041</a></p>
<p>Release Date: 2019-06-12</p>
<p>Fix Resolution: 4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-14041 (Medium) detected in bootstrap-3.3.7-3.3.13.min.js - autoclosed - ## CVE-2018-14041 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.7-3.3.13.min.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.7-3.3.13/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.7-3.3.13/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /SerializableModel/vendor/phpunit/php-code-coverage/src/Report/Html/Renderer/Template/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.7-3.3.13.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/little-apps/SerializableModel/commit/d24e2596eb1a71a465b708fbf7645b0698026e82">d24e2596eb1a71a465b708fbf7645b0698026e82</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-target property of scrollspy.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14041>CVE-2018-14041</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14041">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14041</a></p>
<p>Release Date: 2019-06-12</p>
<p>Fix Resolution: 4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bootstrap min js autoclosed cve medium severity vulnerability vulnerable library bootstrap min js google styled theme for bootstrap library home page a href path to vulnerable library serializablemodel vendor phpunit php code coverage src report html renderer template js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href vulnerability details in bootstrap before xss is possible in the data target property of scrollspy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
175,628 | 14,533,530,837 | IssuesEvent | 2020-12-15 00:47:22 | vuejs/vue-cli | https://api.github.com/repos/vuejs/vue-cli | closed | inline iframe not working for webpack DevServer | documentation | ### Version
4.5.8
### Environment info
```
Environment Info:
System:
OS: macOS 11.0.1
CPU: (12) x64 Intel(R) Core(TM) i7-9750H CPU @ 2.60GHz
Binaries:
Node: 15.0.1 - /usr/local/bin/node
Yarn: 1.22.10 - /usr/local/bin/yarn
npm: 6.14.8 - /usr/local/bin/npm
Browsers:
Chrome: 87.0.4280.40
Edge: Not Found
Firefox: 78.4.0
Safari: 14.0.1
npmPackages:
@types/vue-moment: 4.0.1 => 4.0.1
@vue/babel-helper-vue-jsx-merge-props: 1.2.1
@vue/babel-helper-vue-transform-on: 1.0.0-rc.2
@vue/babel-plugin-jsx: 1.0.0-rc.3
@vue/babel-plugin-transform-vue-jsx: 1.2.1
@vue/babel-preset-app: 4.5.8
@vue/babel-preset-jsx: 1.2.3
@vue/babel-sugar-composition-api-inject-h: 1.2.1
@vue/babel-sugar-composition-api-render-instance: 1.2.1
@vue/babel-sugar-functional-vue: 1.2.2
@vue/babel-sugar-inject-h: 1.2.2
@vue/babel-sugar-v-model: 1.2.3
@vue/babel-sugar-v-on: 1.2.3
@vue/cli-overlay: 4.5.8
@vue/cli-plugin-babel: 4.5.8 => 4.5.8
@vue/cli-plugin-e2e-cypress: 4.5.8 => 4.5.8
@vue/cli-plugin-eslint: 4.5.8 => 4.5.8
@vue/cli-plugin-pwa: 4.5.8 => 4.5.8
@vue/cli-plugin-router: 4.5.8 => 4.5.8
@vue/cli-plugin-typescript: 4.5.8 => 4.5.8
@vue/cli-plugin-unit-jest: 4.5.8 => 4.5.8
@vue/cli-plugin-vuex: 4.5.8 => 4.5.8
@vue/cli-service: 4.5.8 => 4.5.8
@vue/cli-shared-utils: 4.5.8
@vue/component-compiler-utils: 3.2.0
@vue/eslint-config-standard: 5.1.2 => 5.1.2
@vue/eslint-config-typescript: 7.0.0 => 7.0.0
@vue/preload-webpack-plugin: 1.1.2
@vue/test-utils: 1.1.1 => 1.1.1
@vue/web-component-wrapper: 1.2.0
eslint-plugin-vue: 7.1.0 => 7.1.0
jest-serializer-vue: 2.0.2
js-cookie-vue: 1.0.5 => 1.0.5
typescript: 4.0.5 => 4.0.5
vue: 2.6.12 => 2.6.12
vue-class-component: 7.2.6 => 7.2.6
vue-cli-plugin-moment: 0.1.1 => 0.1.1
vue-cli-plugin-vuetify: 2.0.7 => 2.0.7
vue-eslint-parser: 7.0.0 (7.1.1)
vue-hot-reload-api: 2.3.4
vue-jest: 3.0.7
vue-loader: 15.9.3 (16.0.0-beta.9)
vue-moment: 4.1.0 => 4.1.0
vue-property-decorator: 9.0.2 => 9.0.2
vue-router: 3.4.7 => 3.4.7
vue-style-loader: 4.1.2
vue-template-compiler: 2.6.12 => 2.6.12
vue-template-es2015-compiler: 1.9.1
vuetify: 2.3.15 => 2.3.15
vuex: 3.5.1 => 3.5.1
vuex-class: 0.3.2 => 0.3.2
npmGlobalPackages:
@vue/cli: Not Found
```
### Steps to reproduce
Set `devServer.inline=false` in `vue.config.js`
### What is expected?
Should have an iframe with a notification bar to give messages about the build
### What is actually happening?
Nothing
---
The [DevServer](https://webpack.js.org/configuration/dev-server/#devserverinline) documentation describes an option called "inline", that, if disabled, "uses an `<iframe>` under a notification bar with messages about the build". When I set `devServer.inline=false` in my `vue.config.js`, I don't see a notification bar in my app.
<!-- generated by vue-issues. DO NOT REMOVE --> | 1.0 | inline iframe not working for webpack DevServer - ### Version
4.5.8
### Environment info
```
Environment Info:
System:
OS: macOS 11.0.1
CPU: (12) x64 Intel(R) Core(TM) i7-9750H CPU @ 2.60GHz
Binaries:
Node: 15.0.1 - /usr/local/bin/node
Yarn: 1.22.10 - /usr/local/bin/yarn
npm: 6.14.8 - /usr/local/bin/npm
Browsers:
Chrome: 87.0.4280.40
Edge: Not Found
Firefox: 78.4.0
Safari: 14.0.1
npmPackages:
@types/vue-moment: 4.0.1 => 4.0.1
@vue/babel-helper-vue-jsx-merge-props: 1.2.1
@vue/babel-helper-vue-transform-on: 1.0.0-rc.2
@vue/babel-plugin-jsx: 1.0.0-rc.3
@vue/babel-plugin-transform-vue-jsx: 1.2.1
@vue/babel-preset-app: 4.5.8
@vue/babel-preset-jsx: 1.2.3
@vue/babel-sugar-composition-api-inject-h: 1.2.1
@vue/babel-sugar-composition-api-render-instance: 1.2.1
@vue/babel-sugar-functional-vue: 1.2.2
@vue/babel-sugar-inject-h: 1.2.2
@vue/babel-sugar-v-model: 1.2.3
@vue/babel-sugar-v-on: 1.2.3
@vue/cli-overlay: 4.5.8
@vue/cli-plugin-babel: 4.5.8 => 4.5.8
@vue/cli-plugin-e2e-cypress: 4.5.8 => 4.5.8
@vue/cli-plugin-eslint: 4.5.8 => 4.5.8
@vue/cli-plugin-pwa: 4.5.8 => 4.5.8
@vue/cli-plugin-router: 4.5.8 => 4.5.8
@vue/cli-plugin-typescript: 4.5.8 => 4.5.8
@vue/cli-plugin-unit-jest: 4.5.8 => 4.5.8
@vue/cli-plugin-vuex: 4.5.8 => 4.5.8
@vue/cli-service: 4.5.8 => 4.5.8
@vue/cli-shared-utils: 4.5.8
@vue/component-compiler-utils: 3.2.0
@vue/eslint-config-standard: 5.1.2 => 5.1.2
@vue/eslint-config-typescript: 7.0.0 => 7.0.0
@vue/preload-webpack-plugin: 1.1.2
@vue/test-utils: 1.1.1 => 1.1.1
@vue/web-component-wrapper: 1.2.0
eslint-plugin-vue: 7.1.0 => 7.1.0
jest-serializer-vue: 2.0.2
js-cookie-vue: 1.0.5 => 1.0.5
typescript: 4.0.5 => 4.0.5
vue: 2.6.12 => 2.6.12
vue-class-component: 7.2.6 => 7.2.6
vue-cli-plugin-moment: 0.1.1 => 0.1.1
vue-cli-plugin-vuetify: 2.0.7 => 2.0.7
vue-eslint-parser: 7.0.0 (7.1.1)
vue-hot-reload-api: 2.3.4
vue-jest: 3.0.7
vue-loader: 15.9.3 (16.0.0-beta.9)
vue-moment: 4.1.0 => 4.1.0
vue-property-decorator: 9.0.2 => 9.0.2
vue-router: 3.4.7 => 3.4.7
vue-style-loader: 4.1.2
vue-template-compiler: 2.6.12 => 2.6.12
vue-template-es2015-compiler: 1.9.1
vuetify: 2.3.15 => 2.3.15
vuex: 3.5.1 => 3.5.1
vuex-class: 0.3.2 => 0.3.2
npmGlobalPackages:
@vue/cli: Not Found
```
### Steps to reproduce
Set `devServer.inline=false` in `vue.config.js`
### What is expected?
Should have an iframe with a notification bar to give messages about the build
### What is actually happening?
Nothing
---
The [DevServer](https://webpack.js.org/configuration/dev-server/#devserverinline) documentation describes an option called "inline", that, if disabled, "uses an `<iframe>` under a notification bar with messages about the build". When I set `devServer.inline=false` in my `vue.config.js`, I don't see a notification bar in my app.
<!-- generated by vue-issues. DO NOT REMOVE --> | non_priority | inline iframe not working for webpack devserver version environment info environment info system os macos cpu intel r core tm cpu binaries node usr local bin node yarn usr local bin yarn npm usr local bin npm browsers chrome edge not found firefox safari npmpackages types vue moment vue babel helper vue jsx merge props vue babel helper vue transform on rc vue babel plugin jsx rc vue babel plugin transform vue jsx vue babel preset app vue babel preset jsx vue babel sugar composition api inject h vue babel sugar composition api render instance vue babel sugar functional vue vue babel sugar inject h vue babel sugar v model vue babel sugar v on vue cli overlay vue cli plugin babel vue cli plugin cypress vue cli plugin eslint vue cli plugin pwa vue cli plugin router vue cli plugin typescript vue cli plugin unit jest vue cli plugin vuex vue cli service vue cli shared utils vue component compiler utils vue eslint config standard vue eslint config typescript vue preload webpack plugin vue test utils vue web component wrapper eslint plugin vue jest serializer vue js cookie vue typescript vue vue class component vue cli plugin moment vue cli plugin vuetify vue eslint parser vue hot reload api vue jest vue loader beta vue moment vue property decorator vue router vue style loader vue template compiler vue template compiler vuetify vuex vuex class npmglobalpackages vue cli not found steps to reproduce set devserver inline false in vue config js what is expected should have an iframe with a notification bar to give messages about the build what is actually happening nothing the documentation describes an option called inline that if disabled uses an under a notification bar with messages about the build when i set devserver inline false in my vue config js i don t see a notification bar in my app | 0 |
24,231 | 12,056,766,472 | IssuesEvent | 2020-04-15 14:54:29 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [APM] Document agents and versions section to service maps | Feature:Service Maps Team:apm v7.7.0 | Lets add an additional section to the service maps documentation to specify what agents and the minimum version for each agent that will have support for service maps. I expect this list to change as we add additional support across the agents.
| 1.0 | [APM] Document agents and versions section to service maps - Lets add an additional section to the service maps documentation to specify what agents and the minimum version for each agent that will have support for service maps. I expect this list to change as we add additional support across the agents.
| non_priority | document agents and versions section to service maps lets add an additional section to the service maps documentation to specify what agents and the minimum version for each agent that will have support for service maps i expect this list to change as we add additional support across the agents | 0 |
57,371 | 8,178,592,825 | IssuesEvent | 2018-08-28 14:13:18 | nlesc-dirac/sagecal | https://api.github.com/repos/nlesc-dirac/sagecal | closed | a short tutorial can be added | Documentation | it would be very useful to have a short tutorial which explains how to use the code. We have an example but it could be more explanatory. | 1.0 | a short tutorial can be added - it would be very useful to have a short tutorial which explains how to use the code. We have an example but it could be more explanatory. | non_priority | a short tutorial can be added it would be very useful to have a short tutorial which explains how to use the code we have an example but it could be more explanatory | 0 |
195,098 | 15,500,446,831 | IssuesEvent | 2021-03-11 09:19:49 | Tekipeps/aul-forum | https://api.github.com/repos/Tekipeps/aul-forum | closed | reduce readme.md length | documentation good first issue | @BidemiEnoch you could move the content from Development - Testing from README.md to CONTRIBUTING.md and add `# CONTRUBUTING` stating to view the CONTRIBUTING.md file with a link to it.. | 1.0 | reduce readme.md length - @BidemiEnoch you could move the content from Development - Testing from README.md to CONTRIBUTING.md and add `# CONTRUBUTING` stating to view the CONTRIBUTING.md file with a link to it.. | non_priority | reduce readme md length bidemienoch you could move the content from development testing from readme md to contributing md and add contrubuting stating to view the contributing md file with a link to it | 0 |
276,227 | 30,386,250,568 | IssuesEvent | 2023-07-13 01:09:35 | mahithagj/WebGoat | https://api.github.com/repos/mahithagj/WebGoat | opened | jquery-2.1.4.min.js: 4 vulnerabilities (highest severity is: 6.1) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-11023](https://www.mend.io/vulnerability-database/CVE-2020-11023) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jquery - 3.5.0;jquery-rails - 4.4.0 | ❌ |
| [CVE-2020-11022](https://www.mend.io/vulnerability-database/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://www.mend.io/vulnerability-database/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jQuery - 3.0.0 | ❌ |
| [CVE-2019-11358](https://www.mend.io/vulnerability-database/CVE-2019-11358) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jquery - 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-11023</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11022">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11022</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - 3.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-11358</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: jquery - 3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | jquery-2.1.4.min.js: 4 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2020-11023](https://www.mend.io/vulnerability-database/CVE-2020-11023) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jquery - 3.5.0;jquery-rails - 4.4.0 | ❌ |
| [CVE-2020-11022](https://www.mend.io/vulnerability-database/CVE-2020-11022) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jQuery - 3.5.0 | ❌ |
| [CVE-2015-9251](https://www.mend.io/vulnerability-database/CVE-2015-9251) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jQuery - 3.0.0 | ❌ |
| [CVE-2019-11358](https://www.mend.io/vulnerability-database/CVE-2019-11358) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-2.1.4.min.js | Direct | jquery - 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-11023</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2020-11022</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11022">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11022</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2015-9251</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - 3.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-11358</summary>
### Vulnerable Library - <b>jquery-2.1.4.min.js</b></p>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to vulnerable library: /target/classes/webgoat/static/js/libs/jquery-2.1.4.min.js,/src/main/resources/webgoat/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: jquery - 3.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | jquery min js vulnerabilities highest severity is vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library target classes webgoat static js libs jquery min js src main resources webgoat static js libs jquery min js vulnerabilities cve severity cvss dependency type fixed in jquery version remediation available medium jquery min js direct jquery jquery rails medium jquery min js direct jquery medium jquery min js direct jquery medium jquery min js direct jquery details cve vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library target classes webgoat static js libs jquery min js src main resources webgoat static js libs jquery min js dependency hierarchy x jquery min js vulnerable library found in base branch main vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery jquery rails step up your open source security game with mend cve vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library target classes webgoat static js libs jquery min js src main resources webgoat static js libs jquery min js dependency hierarchy x jquery min js vulnerable library found in base branch main vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with mend cve vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library target classes webgoat static js libs jquery min js src main resources webgoat static js libs jquery min js dependency hierarchy x jquery min js vulnerable library found in base branch main vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with mend cve vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library target classes webgoat static js libs jquery min js src main resources webgoat static js libs jquery min js dependency hierarchy x jquery min js vulnerable library found in base branch main vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with mend | 0 |
100,523 | 11,198,316,230 | IssuesEvent | 2020-01-03 15:38:38 | spacepy/spacepy | https://api.github.com/repos/spacepy/spacepy | opened | Sign Python 3 statement | documentation | Once #265 is accepted we should sign the [Python 3 statement](https://python3statement.org/). I'll submit the PR there at that time, but making a note here so I don't forget. | 1.0 | Sign Python 3 statement - Once #265 is accepted we should sign the [Python 3 statement](https://python3statement.org/). I'll submit the PR there at that time, but making a note here so I don't forget. | non_priority | sign python statement once is accepted we should sign the i ll submit the pr there at that time but making a note here so i don t forget | 0 |
56,044 | 6,952,755,799 | IssuesEvent | 2017-12-06 18:33:42 | BraveUX/braveux | https://api.github.com/repos/BraveUX/braveux | opened | Stretch Portal Case Study: Make it tangible | Case Study design dev stretch | <img width="400" alt="screen shot 2017-12-06 at 1 32 33 pm" src="https://user-images.githubusercontent.com/31738798/33678511-efb75df8-da89-11e7-952a-8a0e397cdb49.png">
not sure if "intuitive way" is the right way to put it? or at least the word "way" could be replaced. | 1.0 | Stretch Portal Case Study: Make it tangible - <img width="400" alt="screen shot 2017-12-06 at 1 32 33 pm" src="https://user-images.githubusercontent.com/31738798/33678511-efb75df8-da89-11e7-952a-8a0e397cdb49.png">
not sure if "intuitive way" is the right way to put it? or at least the word "way" could be replaced. | non_priority | stretch portal case study make it tangible img width alt screen shot at pm src not sure if intuitive way is the right way to put it or at least the word way could be replaced | 0 |
89,166 | 25,599,956,222 | IssuesEvent | 2022-12-01 19:15:35 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | Periodic Failure - development - Windows [debug_pipe]/debug | needs-triage periodic_failure/development kind/periodicbuildfailure | ### Build URL: https://jenkins.build.o3de.org/job/O3DE_periodic-incremental-daily/job/development/99/
### Identified problems:
* **Windows [debug_pipe] - debug**
* **Log URL**: https://jenkins.build.o3de.org/blue/rest/organizations/jenkins/pipelines/O3DE_periodic-incremental-daily/pipelines/development/runs/99/nodes/1190//log
* **Warning is treated as an error**
[2022-09-13T05:53:02.977Z] D:\workspace\o3de\Code\Tools\SceneAPI\SceneUI\CommonWidgets\SceneSettingsCard.h(125,69): error C2220: the following warning is treated as an error [D:\workspace\o3de\build\windows\Code\Tools\SceneAPI\SceneUI\SceneUI.vcxproj]
[2022-09-13T05:53:07.231Z] D:\workspace\o3de\build\windows\Code\Tools\SceneAPI\SceneUI\SceneUI_autogen\include_debug\DLGSA3MWPO\../../../../../../../../../Code/Tools/SceneAPI/SceneUI/CommonWidgets/SceneSettingsCard.h(125,69): error C2220: the following warning is treated as an error [D:\workspace\o3de\build\windows\Code\Tools\SceneAPI\SceneUI\SceneUI.vcxproj]
| 1.0 | Periodic Failure - development - Windows [debug_pipe]/debug - ### Build URL: https://jenkins.build.o3de.org/job/O3DE_periodic-incremental-daily/job/development/99/
### Identified problems:
* **Windows [debug_pipe] - debug**
* **Log URL**: https://jenkins.build.o3de.org/blue/rest/organizations/jenkins/pipelines/O3DE_periodic-incremental-daily/pipelines/development/runs/99/nodes/1190//log
* **Warning is treated as an error**
[2022-09-13T05:53:02.977Z] D:\workspace\o3de\Code\Tools\SceneAPI\SceneUI\CommonWidgets\SceneSettingsCard.h(125,69): error C2220: the following warning is treated as an error [D:\workspace\o3de\build\windows\Code\Tools\SceneAPI\SceneUI\SceneUI.vcxproj]
[2022-09-13T05:53:07.231Z] D:\workspace\o3de\build\windows\Code\Tools\SceneAPI\SceneUI\SceneUI_autogen\include_debug\DLGSA3MWPO\../../../../../../../../../Code/Tools/SceneAPI/SceneUI/CommonWidgets/SceneSettingsCard.h(125,69): error C2220: the following warning is treated as an error [D:\workspace\o3de\build\windows\Code\Tools\SceneAPI\SceneUI\SceneUI.vcxproj]
| non_priority | periodic failure development windows debug build url identified problems windows debug log url warning is treated as an error d workspace code tools sceneapi sceneui commonwidgets scenesettingscard h error the following warning is treated as an error d workspace build windows code tools sceneapi sceneui sceneui autogen include debug code tools sceneapi sceneui commonwidgets scenesettingscard h error the following warning is treated as an error | 0 |
237,457 | 19,635,833,111 | IssuesEvent | 2022-01-08 08:53:56 | Sifchain/sifnode | https://api.github.com/repos/Sifchain/sifnode | opened | [Testing] Peg in a bunch of assets into TestNet | Testing Team | We recently had to re-build TestNet. As such, we need to re-run the scripts to peg in a bunch of assets, like we did last time (as all balances have been reset). | 1.0 | [Testing] Peg in a bunch of assets into TestNet - We recently had to re-build TestNet. As such, we need to re-run the scripts to peg in a bunch of assets, like we did last time (as all balances have been reset). | non_priority | peg in a bunch of assets into testnet we recently had to re build testnet as such we need to re run the scripts to peg in a bunch of assets like we did last time as all balances have been reset | 0 |
143,323 | 13,060,045,185 | IssuesEvent | 2020-07-30 11:45:18 | aler9/rtsp-simple-server | https://api.github.com/repos/aler9/rtsp-simple-server | closed | Service for Debian buster on arm64 | documentation | ## Which version are you using?
rtsp-simple-server_v0.9.3_linux_arm64.tar.gz
Here my service for debian10 buster (armbian) that works fine
```
wget https://github.com/aler9/rtsp-simple-server/releases/download/v0.9.4/rtsp-simple-server_v0.9.4_linux_arm64.tar.gz
tar zxvf rtsp-simple-server_v0.9.4_linux_arm64.tar.gz
install rtsp-simple-server /usr/local/bin/
cp rtsp-simple-server.yml /usr/local/etc/
```
now create a service with
`mcedit /etc/systemd/system/rtsp-simple-server.service`
and write:
```
[Unit]
Description=RTSP Simple Server service on local port 8554
After=network.target
[Service]
User=root
WorkingDirectory=/
ExecStart=/usr/local/bin/rtsp-simple-server /usr/local/etc/rtsp-simple-server.yml
TimeoutStopSec=10
[Install]
WantedBy=multi-user.target
```
then
```
systemctl enable rtsp-simple-server.service
systemctl start rtsp-simple-server.service
```
I hope to help
I will open some questions in other tickets
regards
MaX
| 1.0 | Service for Debian buster on arm64 - ## Which version are you using?
rtsp-simple-server_v0.9.3_linux_arm64.tar.gz
Here my service for debian10 buster (armbian) that works fine
```
wget https://github.com/aler9/rtsp-simple-server/releases/download/v0.9.4/rtsp-simple-server_v0.9.4_linux_arm64.tar.gz
tar zxvf rtsp-simple-server_v0.9.4_linux_arm64.tar.gz
install rtsp-simple-server /usr/local/bin/
cp rtsp-simple-server.yml /usr/local/etc/
```
now create a service with
`mcedit /etc/systemd/system/rtsp-simple-server.service`
and write:
```
[Unit]
Description=RTSP Simple Server service on local port 8554
After=network.target
[Service]
User=root
WorkingDirectory=/
ExecStart=/usr/local/bin/rtsp-simple-server /usr/local/etc/rtsp-simple-server.yml
TimeoutStopSec=10
[Install]
WantedBy=multi-user.target
```
then
```
systemctl enable rtsp-simple-server.service
systemctl start rtsp-simple-server.service
```
I hope to help
I will open some questions in other tickets
regards
MaX
| non_priority | service for debian buster on which version are you using rtsp simple server linux tar gz here my service for buster armbian that works fine wget tar zxvf rtsp simple server linux tar gz install rtsp simple server usr local bin cp rtsp simple server yml usr local etc now create a service with mcedit etc systemd system rtsp simple server service and write description rtsp simple server service on local port after network target user root workingdirectory execstart usr local bin rtsp simple server usr local etc rtsp simple server yml timeoutstopsec wantedby multi user target then systemctl enable rtsp simple server service systemctl start rtsp simple server service i hope to help i will open some questions in other tickets regards max | 0 |
137,658 | 12,768,784,398 | IssuesEvent | 2020-06-30 01:35:19 | cilium/cilium | https://api.github.com/repos/cilium/cilium | opened | Document how to wildcard labels in identity logic | area/documentation | Add documentation with the specific steps / syntax for how the `--labels` option can be configured. | 1.0 | Document how to wildcard labels in identity logic - Add documentation with the specific steps / syntax for how the `--labels` option can be configured. | non_priority | document how to wildcard labels in identity logic add documentation with the specific steps syntax for how the labels option can be configured | 0 |
55,646 | 13,647,704,233 | IssuesEvent | 2020-09-26 04:56:13 | TerryCavanagh/diceydungeonsbeta | https://api.github.com/repos/TerryCavanagh/diceydungeonsbeta | closed | Sad Verse and Sonic Wave are identical except size and Sad Verse's lack of PU counterpart | v0.6: 28th June Build | Ice Shard and Snowball at least have differing upgrades. Ice Shard and Ice Crystal are also identical (and Ice Crystal lacks a PU counterpart), but Ice Crystal is bestowed by Crystallize, which should be enough of a difference. | 1.0 | Sad Verse and Sonic Wave are identical except size and Sad Verse's lack of PU counterpart - Ice Shard and Snowball at least have differing upgrades. Ice Shard and Ice Crystal are also identical (and Ice Crystal lacks a PU counterpart), but Ice Crystal is bestowed by Crystallize, which should be enough of a difference. | non_priority | sad verse and sonic wave are identical except size and sad verse s lack of pu counterpart ice shard and snowball at least have differing upgrades ice shard and ice crystal are also identical and ice crystal lacks a pu counterpart but ice crystal is bestowed by crystallize which should be enough of a difference | 0 |
111,561 | 17,029,045,237 | IssuesEvent | 2021-07-04 06:56:03 | turkdevops/grafana | https://api.github.com/repos/turkdevops/grafana | opened | WS-2021-0153 (High) detected in ejs-2.7.4.tgz, ejs-2.7.1.tgz | security vulnerability | ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ejs-2.7.4.tgz</b>, <b>ejs-2.7.1.tgz</b></p></summary>
<p>
<details><summary><b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: grafana/yarn.lock</p>
<p>Path to vulnerable library: grafana/node_modules/ejs/package.json,grafana/node_modules/ejs</p>
<p>
Dependency Hierarchy:
- @grafana/ui-6.7.0-pre.tgz (Root Library)
- react-5.3.9.tgz
- core-5.3.9.tgz
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>ejs-2.7.1.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.1.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/ejs</p>
<p>
Dependency Hierarchy:
- webpack-bundle-analyzer-3.3.2.tgz (Root Library)
- :x: **ejs-2.7.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/dbebc475a6020320f663bf0fd4a87fa26c1bca88">dbebc475a6020320f663bf0fd4a87fa26c1bca88</a></p>
<p>Found in base branch: <b>datasource-meta</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0153 (High) detected in ejs-2.7.4.tgz, ejs-2.7.1.tgz - ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ejs-2.7.4.tgz</b>, <b>ejs-2.7.1.tgz</b></p></summary>
<p>
<details><summary><b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: grafana/yarn.lock</p>
<p>Path to vulnerable library: grafana/node_modules/ejs/package.json,grafana/node_modules/ejs</p>
<p>
Dependency Hierarchy:
- @grafana/ui-6.7.0-pre.tgz (Root Library)
- react-5.3.9.tgz
- core-5.3.9.tgz
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>ejs-2.7.1.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.1.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/ejs</p>
<p>
Dependency Hierarchy:
- webpack-bundle-analyzer-3.3.2.tgz (Root Library)
- :x: **ejs-2.7.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/dbebc475a6020320f663bf0fd4a87fa26c1bca88">dbebc475a6020320f663bf0fd4a87fa26c1bca88</a></p>
<p>Found in base branch: <b>datasource-meta</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in ejs tgz ejs tgz ws high severity vulnerability vulnerable libraries ejs tgz ejs tgz ejs tgz embedded javascript templates library home page a href path to dependency file grafana yarn lock path to vulnerable library grafana node modules ejs package json grafana node modules ejs dependency hierarchy grafana ui pre tgz root library react tgz core tgz x ejs tgz vulnerable library ejs tgz embedded javascript templates library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules ejs dependency hierarchy webpack bundle analyzer tgz root library x ejs tgz vulnerable library found in head commit a href found in base branch datasource meta vulnerability details arbitrary code injection vulnerability was found in ejs before caused by filename which isn t sanitized for display publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ejs step up your open source security game with whitesource | 0 |
318,127 | 27,288,796,722 | IssuesEvent | 2023-02-23 15:15:19 | hashicorp/terraform-provider-google | https://api.github.com/repos/hashicorp/terraform-provider-google | opened | Failing test(s): TestAccAccessContextManagerAccessPolicyIamPolicy | test failure | <!--- This is a template for reporting test failures on nightly builds. It should only be used by core contributors who have access to our CI/CD results. --->
### Failure rates
- 30% since 2023-02-04
### Impacted tests
<!-- List all impacted tests for searchability. The title of the issue can instead list one or more groups of tests, or describe the overall root cause. -->
- TestAccAccessContextManagerAccessPolicyIamPolicy
### Affected Resource(s)
<!--- List the affected resources and data sources. Use google_* if all resources or data sources are affected. --->
* google_access_context_manager_access_policy_iam_policy
### Nightly build test history
<!-- Link to the test failure(s) page ie https://ci-oss.hashicorp.engineering/test/4373437493444570564?currentProjectId=GoogleCloudBeta&branch=%3Cdefault%3E -->
- [Link](https://ci-oss.hashicorp.engineering/viewLog.html?buildId=376246&tab=buildResultsDiv&buildTypeId=GoogleCloud_ProviderGoogleCloudGoogleProject#testNameId-6957108147711246159)
<!-- The error message that displays in the tests tab, for reference -->
### Message(s)
```
=== RUN TestAccAccessContextManagerAccessPolicyIamPolicy
testing_new.go:84: Error running post-test destroy, there may be dangling resources: exit status 1
Error: Error setting IAM policy for accesscontextmanager accesspolicy "accessPolicies/1004069631272": googleapi: Error 409: The operation was aborted.
--- FAIL: TestAccAccessContextManagerAccessPolicyIamPolicy (36.29s)
FAIL
```
| 1.0 | Failing test(s): TestAccAccessContextManagerAccessPolicyIamPolicy - <!--- This is a template for reporting test failures on nightly builds. It should only be used by core contributors who have access to our CI/CD results. --->
### Failure rates
- 30% since 2023-02-04
### Impacted tests
<!-- List all impacted tests for searchability. The title of the issue can instead list one or more groups of tests, or describe the overall root cause. -->
- TestAccAccessContextManagerAccessPolicyIamPolicy
### Affected Resource(s)
<!--- List the affected resources and data sources. Use google_* if all resources or data sources are affected. --->
* google_access_context_manager_access_policy_iam_policy
### Nightly build test history
<!-- Link to the test failure(s) page ie https://ci-oss.hashicorp.engineering/test/4373437493444570564?currentProjectId=GoogleCloudBeta&branch=%3Cdefault%3E -->
- [Link](https://ci-oss.hashicorp.engineering/viewLog.html?buildId=376246&tab=buildResultsDiv&buildTypeId=GoogleCloud_ProviderGoogleCloudGoogleProject#testNameId-6957108147711246159)
<!-- The error message that displays in the tests tab, for reference -->
### Message(s)
```
=== RUN TestAccAccessContextManagerAccessPolicyIamPolicy
testing_new.go:84: Error running post-test destroy, there may be dangling resources: exit status 1
Error: Error setting IAM policy for accesscontextmanager accesspolicy "accessPolicies/1004069631272": googleapi: Error 409: The operation was aborted.
--- FAIL: TestAccAccessContextManagerAccessPolicyIamPolicy (36.29s)
FAIL
```
| non_priority | failing test s testaccaccesscontextmanageraccesspolicyiampolicy failure rates since impacted tests testaccaccesscontextmanageraccesspolicyiampolicy affected resource s google access context manager access policy iam policy nightly build test history message s run testaccaccesscontextmanageraccesspolicyiampolicy testing new go error running post test destroy there may be dangling resources exit status error error setting iam policy for accesscontextmanager accesspolicy accesspolicies googleapi error the operation was aborted fail testaccaccesscontextmanageraccesspolicyiampolicy fail | 0 |
318,505 | 23,724,332,014 | IssuesEvent | 2022-08-30 18:05:52 | tidymodels/parsnip | https://api.github.com/repos/tidymodels/parsnip | closed | Internals bug? `will_make_matrix()` returns `False` when given a matrix | documentation | Hello, I'm working on a PR to address #765. While doing so I ran into an issue with `will_make_matrix()`. Shouldn't the return value be True if `y` is a matrix or a vector?
When `y` is a numeric matrix it fails this check and converts it to a vector. This is stripping the colname of `y` whenever it is passed to function later down the line such as `xgb_train()`
https://github.com/tidymodels/parsnip/blob/f0810910d0b69141af12c66ae210ec0880f95323/R/convert_data.R#L326-L336 | 1.0 | Internals bug? `will_make_matrix()` returns `False` when given a matrix - Hello, I'm working on a PR to address #765. While doing so I ran into an issue with `will_make_matrix()`. Shouldn't the return value be True if `y` is a matrix or a vector?
When `y` is a numeric matrix it fails this check and converts it to a vector. This is stripping the colname of `y` whenever it is passed to function later down the line such as `xgb_train()`
https://github.com/tidymodels/parsnip/blob/f0810910d0b69141af12c66ae210ec0880f95323/R/convert_data.R#L326-L336 | non_priority | internals bug will make matrix returns false when given a matrix hello i m working on a pr to address while doing so i ran into an issue with will make matrix shouldn t the return value be true if y is a matrix or a vector when y is a numeric matrix it fails this check and converts it to a vector this is stripping the colname of y whenever it is passed to function later down the line such as xgb train | 0 |
174,184 | 13,461,367,852 | IssuesEvent | 2020-09-09 14:44:04 | WoWManiaUK/Redemption | https://api.github.com/repos/WoWManiaUK/Redemption | closed | [Pet] Argent Squire acts as a vendor before being upgraded | Fix - Tester Confirmed | **Links:**
https://wow-mania.org/armory/?item=44998
https://wow-mania.org/armory/?npc=33238
**What is Happening:**
The Argent Squire pet as bought without the upgrade, acts as a continual vendor. This is incorrect:
https://www.wowhead.com/item=44998/argent-squire#comments:id=637445

Once upgraded using the [Argent Pony Bridle](https://wow-mania.org/armory/?item=47541), the Squire acts correctly, being able to act as a vendor every 3 hours.
**What Should happen:**
The Vendor attribute on the Argent Squire should ONLY be available after upgrading. Before upgrade, he should be a standard "pet".
https://www.wowhead.com/item=44998/argent-squire#comments:id=748403

| 1.0 | [Pet] Argent Squire acts as a vendor before being upgraded - **Links:**
https://wow-mania.org/armory/?item=44998
https://wow-mania.org/armory/?npc=33238
**What is Happening:**
The Argent Squire pet as bought without the upgrade, acts as a continual vendor. This is incorrect:
https://www.wowhead.com/item=44998/argent-squire#comments:id=637445

Once upgraded using the [Argent Pony Bridle](https://wow-mania.org/armory/?item=47541), the Squire acts correctly, being able to act as a vendor every 3 hours.
**What Should happen:**
The Vendor attribute on the Argent Squire should ONLY be available after upgrading. Before upgrade, he should be a standard "pet".
https://www.wowhead.com/item=44998/argent-squire#comments:id=748403

| non_priority | argent squire acts as a vendor before being upgraded links what is happening the argent squire pet as bought without the upgrade acts as a continual vendor this is incorrect once upgraded using the the squire acts correctly being able to act as a vendor every hours what should happen the vendor attribute on the argent squire should only be available after upgrading before upgrade he should be a standard pet | 0 |
45,256 | 18,503,950,724 | IssuesEvent | 2021-10-19 16:21:37 | microsoftgraph/msgraph-sdk-powershell | https://api.github.com/repos/microsoftgraph/msgraph-sdk-powershell | closed | Using the existing ref content for New-MgEntitlementManagementAccessPackageResourceRequest does not help work with the cmdlet. Error returned not intuitive to guide user to resolution. | question service issue Needs: Attention :wave: | New-MgEntitlementManagementAccessPackageResourceRequest -CatalogId '54152ecb-c65d-47f2-8a4d-ba2732de0a7b' -RequestType "AdminAdd"
New-MgEntitlementManagementAccessPackageResourceRequest : Value cannot be null.
Parameter name: resource
At line:1 char:1
+ New-MgEntitlementManagementAccessPackageResourceRequest -CatalogId '5 ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: ({ body = Micros...sourceRequest }:<>f__AnonymousType59`1) [New-MgEntitleme..._CreateExpanded], RestException`1
+ FullyQualifiedErrorId : ArgumentNullException,Microsoft.Graph.PowerShell.Cmdlets.NewMgEntitlementManagementAccessPackageResourceRequest_CreateExpanded
There is no parameter named resources as per the error and the ref content does not correctly highlight the required parameters.
| 1.0 | Using the existing ref content for New-MgEntitlementManagementAccessPackageResourceRequest does not help work with the cmdlet. Error returned not intuitive to guide user to resolution. - New-MgEntitlementManagementAccessPackageResourceRequest -CatalogId '54152ecb-c65d-47f2-8a4d-ba2732de0a7b' -RequestType "AdminAdd"
New-MgEntitlementManagementAccessPackageResourceRequest : Value cannot be null.
Parameter name: resource
At line:1 char:1
+ New-MgEntitlementManagementAccessPackageResourceRequest -CatalogId '5 ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: ({ body = Micros...sourceRequest }:<>f__AnonymousType59`1) [New-MgEntitleme..._CreateExpanded], RestException`1
+ FullyQualifiedErrorId : ArgumentNullException,Microsoft.Graph.PowerShell.Cmdlets.NewMgEntitlementManagementAccessPackageResourceRequest_CreateExpanded
There is no parameter named resources as per the error and the ref content does not correctly highlight the required parameters.
| non_priority | using the existing ref content for new mgentitlementmanagementaccesspackageresourcerequest does not help work with the cmdlet error returned not intuitive to guide user to resolution new mgentitlementmanagementaccesspackageresourcerequest catalogid requesttype adminadd new mgentitlementmanagementaccesspackageresourcerequest value cannot be null parameter name resource at line char new mgentitlementmanagementaccesspackageresourcerequest catalogid categoryinfo invalidoperation body micros sourcerequest f restexception fullyqualifiederrorid argumentnullexception microsoft graph powershell cmdlets newmgentitlementmanagementaccesspackageresourcerequest createexpanded there is no parameter named resources as per the error and the ref content does not correctly highlight the required parameters | 0 |
55,538 | 11,441,537,767 | IssuesEvent | 2020-02-05 11:54:45 | GooglingTheCancerGenome/CNN | https://api.github.com/repos/GooglingTheCancerGenome/CNN | opened | Update test environment | code enhancement | - [ ] OS: `trusty` -> `xenial`
- [ ] Python: `3.6` -> `3.7`
- [ ] docker images: `gtcg/sv-callers-*` -> `gtcg/xenon-*` | 1.0 | Update test environment - - [ ] OS: `trusty` -> `xenial`
- [ ] Python: `3.6` -> `3.7`
- [ ] docker images: `gtcg/sv-callers-*` -> `gtcg/xenon-*` | non_priority | update test environment os trusty xenial python docker images gtcg sv callers gtcg xenon | 0 |
96,855 | 28,031,198,974 | IssuesEvent | 2023-03-28 12:30:41 | tutao/tutanota | https://api.github.com/repos/tutao/tutanota | closed | Migrate to Rollup 3 | maintenance build | Rollup 3 has been out for a while and it's likely that support for Rollup 2 with the plugins will diminish soon. All of them seem to have versions for Rollup 3.
As far as I can see, there are a few changes to the plugin API which impacts our check plugins for the chunking and imports. | 1.0 | Migrate to Rollup 3 - Rollup 3 has been out for a while and it's likely that support for Rollup 2 with the plugins will diminish soon. All of them seem to have versions for Rollup 3.
As far as I can see, there are a few changes to the plugin API which impacts our check plugins for the chunking and imports. | non_priority | migrate to rollup rollup has been out for a while and it s likely that support for rollup with the plugins will diminish soon all of them seem to have versions for rollup as far as i can see there are a few changes to the plugin api which impacts our check plugins for the chunking and imports | 0 |
324,231 | 27,790,371,832 | IssuesEvent | 2023-03-17 08:26:15 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | opened | com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest.readsFromMongo_withoutId_twoSteps | Type: Test-Failure Source: Internal Team: Platform | Failed on pr-builder (oracle-11): https://jenkins.hazelcast.com/job/Hazelcast-pr-builder/17222/testReport/junit/com.hazelcast.jet.sql.impl.connector.mongodb/MongoStreamSqlConnectorTest/readsFromMongo_withoutId_twoSteps/
<details><summary>Stacktrace:</summary>
```
java.lang.AssertionError:
Expecting actual:
[Row{[Anakin, Skywalker, insert]}]
to contain exactly in any order:
[Row{[Luke, Skywalker, insert]}, Row{[Anakin, Skywalker, insert]}]
but could not find the following elements:
[Row{[Luke, Skywalker, insert]}]
at com.hazelcast.jet.sql.SqlTestSupport.assertRowsEventuallyInAnyOrder(SqlTestSupport.java:289)
at com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest.readsFromMongo(MongoStreamSqlConnectorTest.java:109)
at com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest.readsFromMongo_withoutId_twoSteps(MongoStreamSqlConnectorTest.java:56)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:115)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:107)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.lang.Thread.run(Thread.java:750)
```
</details>
<details><summary>Standard output:</summary>
```
Finished Running Test: readsFromMongo_withId_oneStep in 2.736 seconds.
Started Running Test: readsFromMongo_withoutId_twoSteps
09:01:31,980 DEBUG |readsFromMongo_withoutId_twoSteps| - [CalciteSqlOptimizer] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Before logical opt:
LogicalCalc(expr#0..4=[{inputs}], expr#5=[?0], expr#6=[=($t2, $t5)], expr#7=[CAST($t3):VARCHAR CHARACTER SET "UTF-16LE"], expr#8=[_UTF-16LE'true':VARCHAR CHARACTER SET "UTF-16LE"], expr#9=[=($t7, $t8)], expr#10=[AND($t6, $t3, $t9)], firstName=[$t1], lastName=[$t2], operation=[$t4], $condition=[$t10])
LogicalTableScan(table=[[hazelcast, public, readsFromMongo_withoutId_twoSteps[projects=[$0, $1, $2, $3, $4]]]])
09:01:31,988 DEBUG |readsFromMongo_withoutId_twoSteps| - [CalciteSqlOptimizer] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] After logical opt:
FullScanLogicalRel(table=[[hazelcast, public, readsFromMongo_withoutId_twoSteps[projects=[$1, $2, $4], filter=AND(=($2, ?0), $3, =(CAST($3):VARCHAR CHARACTER SET "UTF-16LE", _UTF-16LE'true'))]]])
09:01:32,003 DEBUG |readsFromMongo_withoutId_twoSteps| - [CalciteSqlOptimizer] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] After physical opt:
FullScanPhysicalRel(table=[[hazelcast, public, readsFromMongo_withoutId_twoSteps[projects=[$1, $2, $4], filter=AND(=($2, ?0), $3, =(CAST($3):VARCHAR CHARACTER SET "UTF-16LE", _UTF-16LE'true'))]]], discriminator=[0])
09:01:32,077 DEBUG |readsFromMongo_withoutId_twoSteps| - [LightMasterContext] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Start executing light job 098e-a8a3-f781-0001, execution graph in DOT format:
digraph DAG {
"Select (readsFromMongo_withoutId_twoSteps)" [localParallelism=2];
"ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})" [localParallelism=2];
"ClientSink" [localParallelism=1];
"Select (readsFromMongo_withoutId_twoSteps)" -> "ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})" [label="isolated", queueSize=1024];
"ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})" -> "ClientSink" [label="distributed to [127.0.0.1]:5701-partitioned", queueSize=1024];
}
HINT: You can use graphviz or http://viz-js.com to visualize the printed graph.
09:01:32,077 DEBUG |readsFromMongo_withoutId_twoSteps| - [LightMasterContext] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Building execution plan for 098e-a8a3-f781-0001
09:01:32,077 DEBUG || - [LightMasterContext] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Built execution plans for 098e-a8a3-f781-0001
09:01:32,086 DEBUG || - [InitExecutionOperation] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Initializing execution plan for job 098e-a8a3-f781-0001, execution 098e-a8a3-f781-0001 from [127.0.0.1]:5701
09:01:32,098 DEBUG || - [JobExecutionService] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-2 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Execution plan for light job ID=098e-a8a3-f781-0001, jobName='098e-a8a3-f781-0001', executionId=098e-a8a3-f781-0001 initialized, will start the execution
09:01:32,101 INFO || - [ReadMongoP] hz.MongoStreamSqlConnectorTest_hardcore_benz.jet.blocking.thread-0 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] [098e-a8a3-f781-0001/Select (readsFromMongo_withoutId_twoSteps)#1] (Re)connecting to MongoDB
09:01:32,116 INFO || - [ReadMongoP] hz.MongoStreamSqlConnectorTest_hardcore_benz.jet.blocking.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] [098e-a8a3-f781-0001/Select (readsFromMongo_withoutId_twoSteps)#0] (Re)connecting to MongoDB
09:01:32,855 WARN || - [ManagementCenterPublisher] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Too long value in the metric descriptor found, maximum is 255: ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})
09:01:34,268 DEBUG || - [JobRepository] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Job cleanup took 5ms
09:01:39,263 DEBUG || - [JobRepository] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-9 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Job cleanup took 0ms
09:01:41,916 DEBUG || - [TaskletExecutionService] hz.MongoStreamSqlConnectorTest_hardcore_benz.jet.cooperative.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Job was cancelled by the user.
09:01:42,262 INFO |readsFromMongo_withoutId_twoSteps| - [SqlTestSupport] Time-limited test - Removing 1 cached plans in SqlTestSupport.@After
09:01:42,266 INFO |readsFromMongo_withoutId_twoSteps| - [SimpleTestInClusterSupport] Time-limited test - Ditching 1 jobs in SimpleTestInClusterSupport.@After: [098e-a8a3-f781-0001]
09:01:42,266 DEBUG |readsFromMongo_withoutId_twoSteps| - [AbstractJobProxy] Time-limited test - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Sending CANCEL_FORCEFUL request for job 098e-a8a3-f781-0001 (name ??)
09:01:42,275 DEBUG || - [JobExecutionService] ForkJoinPool.commonPool-worker-4 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Completed execution of job '098e-a8a3-f781-0001', execution 098e-a8a3-f781-0001
09:01:42,275 DEBUG || - [JobExecutionService] ForkJoinPool.commonPool-worker-4 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Execution of job '098e-a8a3-f781-0001', execution 098e-a8a3-f781-0001 completed with failure
java.util.concurrent.CompletionException: java.util.concurrent.CancellationException
at java.util.concurrent.CompletableFuture.encodeThrowable(CompletableFuture.java:292) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.completeThrowable(CompletableFuture.java:308) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:783) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:750) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.completeExceptionally(CompletableFuture.java:1990) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.util.NonCompletableFuture.internalCompleteExceptionally(NonCompletableFuture.java:72) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$ExecutionTracker.taskletDone(TaskletExecutionService.java:498) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$BlockingWorker.run(TaskletExecutionService.java:330) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511) ~[?:1.8.0_351]
at java.util.concurrent.FutureTask.run(FutureTask.java:266) ~[?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149) ~[?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624) ~[?:1.8.0_351]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
Caused by: java.util.concurrent.CancellationException
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
... 1 more
09:01:42,276 WARN || - [InitExecutionOperation] ForkJoinPool.commonPool-worker-4 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException: null
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
09:01:42,277 WARN || - [JoinSubmittedJobOperation] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException: null
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
09:01:42,277 WARN || - [SubmitJobOperation] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException: null
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
09:01:42,278 WARN || - [JobCoordinationService] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-7 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
com.hazelcast.jet.core.JobNotFoundException: Job with id 098e-a8a3-f781-0001 not found
at com.hazelcast.jet.impl.JobCoordinationService.lambda$callWithJob$49(JobCoordinationService.java:1025) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.submitToCoordinatorThread(JobCoordinationService.java:1439) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.callWithJob(JobCoordinationService.java:977) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$getJobIds$21(JobCoordinationService.java:542) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$submitToCoordinatorThread$58(JobCoordinationService.java:1451) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CompletableFutureTask.run(CompletableFutureTask.java:64) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CachedExecutorServiceDelegate$Worker.run(CachedExecutorServiceDelegate.java:217) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149) [?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624) [?:1.8.0_351]
at java.lang.Thread.run(Thread.java:750) [?:1.8.0_351]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.executeRun(HazelcastManagedThread.java:76) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.run(HazelcastManagedThread.java:111) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
09:01:42,278 WARN || - [JobCoordinationService] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-5 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
com.hazelcast.jet.core.JobNotFoundException: Job with id 098e-a8a3-f781-0001 not found
at com.hazelcast.jet.impl.JobCoordinationService.lambda$callWithJob$49(JobCoordinationService.java:1025) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.submitToCoordinatorThread(JobCoordinationService.java:1439) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.callWithJob(JobCoordinationService.java:977) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$getJobIds$21(JobCoordinationService.java:542) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$submitToCoordinatorThread$58(JobCoordinationService.java:1451) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CompletableFutureTask.run(CompletableFutureTask.java:64) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CachedExecutorServiceDelegate$Worker.run(CachedExecutorServiceDelegate.java:217) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149) [?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624) [?:1.8.0_351]
at java.lang.Thread.run(Thread.java:750) [?:1.8.0_351]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.executeRun(HazelcastManagedThread.java:76) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.run(HazelcastManagedThread.java:111) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
09:01:42,279 INFO |readsFromMongo_withoutId_twoSteps| - [SimpleTestInClusterSupport] Time-limited test - Destroying 1 distributed objects in SimpleTestInClusterSupport.@After: [hz:impl:mapService/__sql.catalog]
BuildInfo right after readsFromMongo_withoutId_twoSteps(com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest): BuildInfo{version='5.3.0-SNAPSHOT', build='20230316', buildNumber=20230316, revision=a4f86ee, enterprise=false, serializationVersion=1}
Hiccups measured while running test 'readsFromMongo_withoutId_twoSteps(com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest):'
09:01:30, accumulated pauses: 128 ms, max pause: 12 ms, pauses over 1000 ms: 0
09:01:35, accumulated pauses: 181 ms, max pause: 9 ms, pauses over 1000 ms: 0
09:01:40, accumulated pauses: 370 ms, max pause: 307 ms, pauses over 1000 ms: 0
No metrics recorded during the test
```
</details>
Standard output can be found here - https://s3.console.aws.amazon.com/s3/buckets/j-artifacts/Hazelcast-pr-builder/17222/
| 1.0 | com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest.readsFromMongo_withoutId_twoSteps - Failed on pr-builder (oracle-11): https://jenkins.hazelcast.com/job/Hazelcast-pr-builder/17222/testReport/junit/com.hazelcast.jet.sql.impl.connector.mongodb/MongoStreamSqlConnectorTest/readsFromMongo_withoutId_twoSteps/
<details><summary>Stacktrace:</summary>
```
java.lang.AssertionError:
Expecting actual:
[Row{[Anakin, Skywalker, insert]}]
to contain exactly in any order:
[Row{[Luke, Skywalker, insert]}, Row{[Anakin, Skywalker, insert]}]
but could not find the following elements:
[Row{[Luke, Skywalker, insert]}]
at com.hazelcast.jet.sql.SqlTestSupport.assertRowsEventuallyInAnyOrder(SqlTestSupport.java:289)
at com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest.readsFromMongo(MongoStreamSqlConnectorTest.java:109)
at com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest.readsFromMongo_withoutId_twoSteps(MongoStreamSqlConnectorTest.java:56)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:59)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:56)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:115)
at com.hazelcast.test.FailOnTimeoutStatement$CallableStatement.call(FailOnTimeoutStatement.java:107)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.lang.Thread.run(Thread.java:750)
```
</details>
<details><summary>Standard output:</summary>
```
Finished Running Test: readsFromMongo_withId_oneStep in 2.736 seconds.
Started Running Test: readsFromMongo_withoutId_twoSteps
09:01:31,980 DEBUG |readsFromMongo_withoutId_twoSteps| - [CalciteSqlOptimizer] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Before logical opt:
LogicalCalc(expr#0..4=[{inputs}], expr#5=[?0], expr#6=[=($t2, $t5)], expr#7=[CAST($t3):VARCHAR CHARACTER SET "UTF-16LE"], expr#8=[_UTF-16LE'true':VARCHAR CHARACTER SET "UTF-16LE"], expr#9=[=($t7, $t8)], expr#10=[AND($t6, $t3, $t9)], firstName=[$t1], lastName=[$t2], operation=[$t4], $condition=[$t10])
LogicalTableScan(table=[[hazelcast, public, readsFromMongo_withoutId_twoSteps[projects=[$0, $1, $2, $3, $4]]]])
09:01:31,988 DEBUG |readsFromMongo_withoutId_twoSteps| - [CalciteSqlOptimizer] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] After logical opt:
FullScanLogicalRel(table=[[hazelcast, public, readsFromMongo_withoutId_twoSteps[projects=[$1, $2, $4], filter=AND(=($2, ?0), $3, =(CAST($3):VARCHAR CHARACTER SET "UTF-16LE", _UTF-16LE'true'))]]])
09:01:32,003 DEBUG |readsFromMongo_withoutId_twoSteps| - [CalciteSqlOptimizer] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] After physical opt:
FullScanPhysicalRel(table=[[hazelcast, public, readsFromMongo_withoutId_twoSteps[projects=[$1, $2, $4], filter=AND(=($2, ?0), $3, =(CAST($3):VARCHAR CHARACTER SET "UTF-16LE", _UTF-16LE'true'))]]], discriminator=[0])
09:01:32,077 DEBUG |readsFromMongo_withoutId_twoSteps| - [LightMasterContext] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Start executing light job 098e-a8a3-f781-0001, execution graph in DOT format:
digraph DAG {
"Select (readsFromMongo_withoutId_twoSteps)" [localParallelism=2];
"ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})" [localParallelism=2];
"ClientSink" [localParallelism=1];
"Select (readsFromMongo_withoutId_twoSteps)" -> "ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})" [label="isolated", queueSize=1024];
"ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})" -> "ClientSink" [label="distributed to [127.0.0.1]:5701-partitioned", queueSize=1024];
}
HINT: You can use graphviz or http://viz-js.com to visualize the printed graph.
09:01:32,077 DEBUG |readsFromMongo_withoutId_twoSteps| - [LightMasterContext] Thread-17 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Building execution plan for 098e-a8a3-f781-0001
09:01:32,077 DEBUG || - [LightMasterContext] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Built execution plans for 098e-a8a3-f781-0001
09:01:32,086 DEBUG || - [InitExecutionOperation] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Initializing execution plan for job 098e-a8a3-f781-0001, execution 098e-a8a3-f781-0001 from [127.0.0.1]:5701
09:01:32,098 DEBUG || - [JobExecutionService] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-2 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Execution plan for light job ID=098e-a8a3-f781-0001, jobName='098e-a8a3-f781-0001', executionId=098e-a8a3-f781-0001 initialized, will start the execution
09:01:32,101 INFO || - [ReadMongoP] hz.MongoStreamSqlConnectorTest_hardcore_benz.jet.blocking.thread-0 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] [098e-a8a3-f781-0001/Select (readsFromMongo_withoutId_twoSteps)#1] (Re)connecting to MongoDB
09:01:32,116 INFO || - [ReadMongoP] hz.MongoStreamSqlConnectorTest_hardcore_benz.jet.blocking.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] [098e-a8a3-f781-0001/Select (readsFromMongo_withoutId_twoSteps)#0] (Re)connecting to MongoDB
09:01:32,855 WARN || - [ManagementCenterPublisher] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Too long value in the metric descriptor found, maximum is 255: ProjectAndFilter(MongoTable{databaseName='sqlConnectorTest', collectionName='readsFromMongo_withoutId_twoSteps', connectionString='mongodb://172.17.0.1:51403', options={connectionString=mongodb://172.17.0.1:51403, database=sqlConnectorTest, collection=readsFromMongo_withoutId_twoSteps, startAt=now}, streaming=true})
09:01:34,268 DEBUG || - [JobRepository] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-8 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Job cleanup took 5ms
09:01:39,263 DEBUG || - [JobRepository] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-9 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Job cleanup took 0ms
09:01:41,916 DEBUG || - [TaskletExecutionService] hz.MongoStreamSqlConnectorTest_hardcore_benz.jet.cooperative.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Job was cancelled by the user.
09:01:42,262 INFO |readsFromMongo_withoutId_twoSteps| - [SqlTestSupport] Time-limited test - Removing 1 cached plans in SqlTestSupport.@After
09:01:42,266 INFO |readsFromMongo_withoutId_twoSteps| - [SimpleTestInClusterSupport] Time-limited test - Ditching 1 jobs in SimpleTestInClusterSupport.@After: [098e-a8a3-f781-0001]
09:01:42,266 DEBUG |readsFromMongo_withoutId_twoSteps| - [AbstractJobProxy] Time-limited test - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Sending CANCEL_FORCEFUL request for job 098e-a8a3-f781-0001 (name ??)
09:01:42,275 DEBUG || - [JobExecutionService] ForkJoinPool.commonPool-worker-4 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Completed execution of job '098e-a8a3-f781-0001', execution 098e-a8a3-f781-0001
09:01:42,275 DEBUG || - [JobExecutionService] ForkJoinPool.commonPool-worker-4 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] Execution of job '098e-a8a3-f781-0001', execution 098e-a8a3-f781-0001 completed with failure
java.util.concurrent.CompletionException: java.util.concurrent.CancellationException
at java.util.concurrent.CompletableFuture.encodeThrowable(CompletableFuture.java:292) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.completeThrowable(CompletableFuture.java:308) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.uniWhenComplete(CompletableFuture.java:783) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture$UniWhenComplete.tryFire(CompletableFuture.java:750) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.postComplete(CompletableFuture.java:488) ~[?:1.8.0_351]
at java.util.concurrent.CompletableFuture.completeExceptionally(CompletableFuture.java:1990) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.util.NonCompletableFuture.internalCompleteExceptionally(NonCompletableFuture.java:72) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$ExecutionTracker.taskletDone(TaskletExecutionService.java:498) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$BlockingWorker.run(TaskletExecutionService.java:330) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511) ~[?:1.8.0_351]
at java.util.concurrent.FutureTask.run(FutureTask.java:266) ~[?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149) ~[?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624) ~[?:1.8.0_351]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
Caused by: java.util.concurrent.CancellationException
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
... 1 more
09:01:42,276 WARN || - [InitExecutionOperation] ForkJoinPool.commonPool-worker-4 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException: null
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
09:01:42,277 WARN || - [JoinSubmittedJobOperation] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException: null
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
09:01:42,277 WARN || - [SubmitJobOperation] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-1 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
java.util.concurrent.CancellationException: null
at com.hazelcast.jet.sql.impl.processors.RootResultConsumerSink.tryProcess(RootResultConsumerSink.java:97) ~[classes/:?]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.lambda$stateMachineStep$2(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.util.Util.doWithClassLoader(Util.java:547) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:334) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.stateMachineStep(ProcessorTasklet.java:328) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.ProcessorTasklet.call(ProcessorTasklet.java:291) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.runTasklet(TaskletExecutionService.java:404) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.CopyOnWriteArrayList.forEach(CopyOnWriteArrayList.java:895) ~[?:1.8.0_351]
at com.hazelcast.jet.impl.execution.TaskletExecutionService$CooperativeWorker.run(TaskletExecutionService.java:369) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.lang.Thread.run(Thread.java:750) ~[?:1.8.0_351]
09:01:42,278 WARN || - [JobCoordinationService] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-7 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
com.hazelcast.jet.core.JobNotFoundException: Job with id 098e-a8a3-f781-0001 not found
at com.hazelcast.jet.impl.JobCoordinationService.lambda$callWithJob$49(JobCoordinationService.java:1025) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.submitToCoordinatorThread(JobCoordinationService.java:1439) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.callWithJob(JobCoordinationService.java:977) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$getJobIds$21(JobCoordinationService.java:542) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$submitToCoordinatorThread$58(JobCoordinationService.java:1451) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CompletableFutureTask.run(CompletableFutureTask.java:64) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CachedExecutorServiceDelegate$Worker.run(CachedExecutorServiceDelegate.java:217) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149) [?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624) [?:1.8.0_351]
at java.lang.Thread.run(Thread.java:750) [?:1.8.0_351]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.executeRun(HazelcastManagedThread.java:76) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.run(HazelcastManagedThread.java:111) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
09:01:42,278 WARN || - [JobCoordinationService] hz.MongoStreamSqlConnectorTest_hardcore_benz.cached.thread-5 - [127.0.0.1]:5701 [dev] [5.3.0-SNAPSHOT] null
com.hazelcast.jet.core.JobNotFoundException: Job with id 098e-a8a3-f781-0001 not found
at com.hazelcast.jet.impl.JobCoordinationService.lambda$callWithJob$49(JobCoordinationService.java:1025) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.submitToCoordinatorThread(JobCoordinationService.java:1439) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.callWithJob(JobCoordinationService.java:977) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$getJobIds$21(JobCoordinationService.java:542) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.jet.impl.JobCoordinationService.lambda$submitToCoordinatorThread$58(JobCoordinationService.java:1451) ~[hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CompletableFutureTask.run(CompletableFutureTask.java:64) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.CachedExecutorServiceDelegate$Worker.run(CachedExecutorServiceDelegate.java:217) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149) [?:1.8.0_351]
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624) [?:1.8.0_351]
at java.lang.Thread.run(Thread.java:750) [?:1.8.0_351]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.executeRun(HazelcastManagedThread.java:76) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
at com.hazelcast.internal.util.executor.HazelcastManagedThread.run(HazelcastManagedThread.java:111) [hazelcast-5.3.0-SNAPSHOT.jar:5.3.0-SNAPSHOT]
09:01:42,279 INFO |readsFromMongo_withoutId_twoSteps| - [SimpleTestInClusterSupport] Time-limited test - Destroying 1 distributed objects in SimpleTestInClusterSupport.@After: [hz:impl:mapService/__sql.catalog]
BuildInfo right after readsFromMongo_withoutId_twoSteps(com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest): BuildInfo{version='5.3.0-SNAPSHOT', build='20230316', buildNumber=20230316, revision=a4f86ee, enterprise=false, serializationVersion=1}
Hiccups measured while running test 'readsFromMongo_withoutId_twoSteps(com.hazelcast.jet.sql.impl.connector.mongodb.MongoStreamSqlConnectorTest):'
09:01:30, accumulated pauses: 128 ms, max pause: 12 ms, pauses over 1000 ms: 0
09:01:35, accumulated pauses: 181 ms, max pause: 9 ms, pauses over 1000 ms: 0
09:01:40, accumulated pauses: 370 ms, max pause: 307 ms, pauses over 1000 ms: 0
No metrics recorded during the test
```
</details>
Standard output can be found here - https://s3.console.aws.amazon.com/s3/buckets/j-artifacts/Hazelcast-pr-builder/17222/
| non_priority | com hazelcast jet sql impl connector mongodb mongostreamsqlconnectortest readsfrommongo withoutid twosteps failed on pr builder oracle stacktrace java lang assertionerror expecting actual to contain exactly in any order row but could not find the following elements at com hazelcast jet sql sqltestsupport assertrowseventuallyinanyorder sqltestsupport java at com hazelcast jet sql impl connector mongodb mongostreamsqlconnectortest readsfrommongo mongostreamsqlconnectortest java at com hazelcast jet sql impl connector mongodb mongostreamsqlconnectortest readsfrommongo withoutid twosteps mongostreamsqlconnectortest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at com hazelcast test failontimeoutstatement callablestatement call failontimeoutstatement java at com hazelcast test failontimeoutstatement callablestatement call failontimeoutstatement java at java util concurrent futuretask run futuretask java at java lang thread run thread java standard output finished running test readsfrommongo withid onestep in seconds started running test readsfrommongo withoutid twosteps debug readsfrommongo withoutid twosteps thread before logical opt logicalcalc expr expr expr expr expr expr expr firstname lastname operation condition logicaltablescan table debug readsfrommongo withoutid twosteps thread after logical opt fullscanlogicalrel table filter and cast varchar character set utf utf true debug readsfrommongo withoutid twosteps thread after physical opt fullscanphysicalrel table filter and cast varchar character set utf utf true discriminator debug readsfrommongo withoutid twosteps thread start executing light job execution graph in dot format digraph dag select readsfrommongo withoutid twosteps projectandfilter mongotable databasename sqlconnectortest collectionname readsfrommongo withoutid twosteps connectionstring mongodb options connectionstring mongodb database sqlconnectortest collection readsfrommongo withoutid twosteps startat now streaming true clientsink select readsfrommongo withoutid twosteps projectandfilter mongotable databasename sqlconnectortest collectionname readsfrommongo withoutid twosteps connectionstring mongodb options connectionstring mongodb database sqlconnectortest collection readsfrommongo withoutid twosteps startat now streaming true projectandfilter mongotable databasename sqlconnectortest collectionname readsfrommongo withoutid twosteps connectionstring mongodb options connectionstring mongodb database sqlconnectortest collection readsfrommongo withoutid twosteps startat now streaming true clientsink partitioned queuesize hint you can use graphviz or to visualize the printed graph debug readsfrommongo withoutid twosteps thread building execution plan for debug hz mongostreamsqlconnectortest hardcore benz cached thread built execution plans for debug hz mongostreamsqlconnectortest hardcore benz cached thread initializing execution plan for job execution from debug hz mongostreamsqlconnectortest hardcore benz cached thread execution plan for light job id jobname executionid initialized will start the execution info hz mongostreamsqlconnectortest hardcore benz jet blocking thread re connecting to mongodb info hz mongostreamsqlconnectortest hardcore benz jet blocking thread re connecting to mongodb warn hz mongostreamsqlconnectortest hardcore benz cached thread too long value in the metric descriptor found maximum is projectandfilter mongotable databasename sqlconnectortest collectionname readsfrommongo withoutid twosteps connectionstring mongodb options connectionstring mongodb database sqlconnectortest collection readsfrommongo withoutid twosteps startat now streaming true debug hz mongostreamsqlconnectortest hardcore benz cached thread job cleanup took debug hz mongostreamsqlconnectortest hardcore benz cached thread job cleanup took debug hz mongostreamsqlconnectortest hardcore benz jet cooperative thread job was cancelled by the user info readsfrommongo withoutid twosteps time limited test removing cached plans in sqltestsupport after info readsfrommongo withoutid twosteps time limited test ditching jobs in simpletestinclustersupport after debug readsfrommongo withoutid twosteps time limited test sending cancel forceful request for job name debug forkjoinpool commonpool worker completed execution of job execution debug forkjoinpool commonpool worker execution of job execution completed with failure java util concurrent completionexception java util concurrent cancellationexception at java util concurrent completablefuture encodethrowable completablefuture java at java util concurrent completablefuture completethrowable completablefuture java at java util concurrent completablefuture uniwhencomplete completablefuture java at java util concurrent completablefuture uniwhencomplete tryfire completablefuture java at java util concurrent completablefuture postcomplete completablefuture java at java util concurrent completablefuture completeexceptionally completablefuture java at com hazelcast jet impl util noncompletablefuture internalcompleteexceptionally noncompletablefuture java at com hazelcast jet impl execution taskletexecutionservice executiontracker taskletdone taskletexecutionservice java at com hazelcast jet impl execution taskletexecutionservice blockingworker run taskletexecutionservice java at java util concurrent executors runnableadapter call executors java at java util concurrent futuretask run futuretask java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java caused by java util concurrent cancellationexception at com hazelcast jet sql impl processors rootresultconsumersink tryprocess rootresultconsumersink java at com hazelcast jet impl execution processortasklet lambda statemachinestep processortasklet java at com hazelcast jet impl util util dowithclassloader util java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet call processortasklet java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker runtasklet taskletexecutionservice java at java util concurrent copyonwritearraylist foreach copyonwritearraylist java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker run taskletexecutionservice java more warn forkjoinpool commonpool worker null java util concurrent cancellationexception null at com hazelcast jet sql impl processors rootresultconsumersink tryprocess rootresultconsumersink java at com hazelcast jet impl execution processortasklet lambda statemachinestep processortasklet java at com hazelcast jet impl util util dowithclassloader util java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet call processortasklet java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker runtasklet taskletexecutionservice java at java util concurrent copyonwritearraylist foreach copyonwritearraylist java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker run taskletexecutionservice java at java lang thread run thread java warn hz mongostreamsqlconnectortest hardcore benz cached thread null java util concurrent cancellationexception null at com hazelcast jet sql impl processors rootresultconsumersink tryprocess rootresultconsumersink java at com hazelcast jet impl execution processortasklet lambda statemachinestep processortasklet java at com hazelcast jet impl util util dowithclassloader util java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet call processortasklet java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker runtasklet taskletexecutionservice java at java util concurrent copyonwritearraylist foreach copyonwritearraylist java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker run taskletexecutionservice java at java lang thread run thread java warn hz mongostreamsqlconnectortest hardcore benz cached thread null java util concurrent cancellationexception null at com hazelcast jet sql impl processors rootresultconsumersink tryprocess rootresultconsumersink java at com hazelcast jet impl execution processortasklet lambda statemachinestep processortasklet java at com hazelcast jet impl util util dowithclassloader util java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet statemachinestep processortasklet java at com hazelcast jet impl execution processortasklet call processortasklet java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker runtasklet taskletexecutionservice java at java util concurrent copyonwritearraylist foreach copyonwritearraylist java at com hazelcast jet impl execution taskletexecutionservice cooperativeworker run taskletexecutionservice java at java lang thread run thread java warn hz mongostreamsqlconnectortest hardcore benz cached thread null com hazelcast jet core jobnotfoundexception job with id not found at com hazelcast jet impl jobcoordinationservice lambda callwithjob jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice submittocoordinatorthread jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice callwithjob jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice lambda getjobids jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice lambda submittocoordinatorthread jobcoordinationservice java at com hazelcast internal util executor completablefuturetask run completablefuturetask java at com hazelcast internal util executor cachedexecutorservicedelegate worker run cachedexecutorservicedelegate java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java at com hazelcast internal util executor hazelcastmanagedthread executerun hazelcastmanagedthread java at com hazelcast internal util executor hazelcastmanagedthread run hazelcastmanagedthread java warn hz mongostreamsqlconnectortest hardcore benz cached thread null com hazelcast jet core jobnotfoundexception job with id not found at com hazelcast jet impl jobcoordinationservice lambda callwithjob jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice submittocoordinatorthread jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice callwithjob jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice lambda getjobids jobcoordinationservice java at com hazelcast jet impl jobcoordinationservice lambda submittocoordinatorthread jobcoordinationservice java at com hazelcast internal util executor completablefuturetask run completablefuturetask java at com hazelcast internal util executor cachedexecutorservicedelegate worker run cachedexecutorservicedelegate java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java at com hazelcast internal util executor hazelcastmanagedthread executerun hazelcastmanagedthread java at com hazelcast internal util executor hazelcastmanagedthread run hazelcastmanagedthread java info readsfrommongo withoutid twosteps time limited test destroying distributed objects in simpletestinclustersupport after buildinfo right after readsfrommongo withoutid twosteps com hazelcast jet sql impl connector mongodb mongostreamsqlconnectortest buildinfo version snapshot build buildnumber revision enterprise false serializationversion hiccups measured while running test readsfrommongo withoutid twosteps com hazelcast jet sql impl connector mongodb mongostreamsqlconnectortest accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms accumulated pauses ms max pause ms pauses over ms no metrics recorded during the test standard output can be found here | 0 |
75,525 | 9,285,216,591 | IssuesEvent | 2019-03-21 06:00:11 | OfficeDev/office-ui-fabric-react | https://api.github.com/repos/OfficeDev/office-ui-fabric-react | closed | SplitButton in Touch doesn't work correctly | Component: Button Needs: Author Feedback Resolution: By Design no-recent-activity | <!--
Thanks for contacting us! We're here to help.
Before you report an issue, check if it's been reported before:
* Search: https://github.com/OfficeDev/office-ui-fabric-react/search?type=Issues
* Search by area or component: https://github.com/OfficeDev/office-ui-fabric-react/issues/labels
Please provide a reproduction of the bug in a codepen, if possible. Here’s how:
* Goto https://aka.ms/fabricpen for a starting codepen
* You can also use the "Export to Codepen" feature for the various components in our documentation site.
* Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links if the repro occurs with an example.
(A permanent link is preferable to "use the website" as the website can change)
Note that if you do not provide enough information to reproduce the issue, we may not be able to take action on your report.
-->
### Environment Information
- __Package version(s)__: (fill this out)
- __Browser and OS versions__: (fill this out if relevant)
### Please provide a reproduction of the bug in a codepen:
<!-- Goto https://aka.ms/fabricpen for a starting codepen -->
<!-- See http://codepen.io/dzearing/pens/public/?grid_type=list for a variety of examples -->
<!-- Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links. -->
#### Actual behavior:
https://codepen.io/anon/pen/oVBORo
Click Hello World with mouse
Notice Alert pops up saying hello
Now tap with touch
Notice drop down appears instead with other options
<!-- fill this out -->
#### Expected behavior:
Tapping with touch should do the same thing as clicking with mouse
<!-- fill this out -->
#### Priorities and help requested:
Are you willing to submit a PR to fix? (Yes, No)
No
Requested priority: (Blocking, High, Normal, Low)
High
Products/sites affected: (if applicable)
Office UI Fabric. Discovered on Sharepoint. | 1.0 | SplitButton in Touch doesn't work correctly - <!--
Thanks for contacting us! We're here to help.
Before you report an issue, check if it's been reported before:
* Search: https://github.com/OfficeDev/office-ui-fabric-react/search?type=Issues
* Search by area or component: https://github.com/OfficeDev/office-ui-fabric-react/issues/labels
Please provide a reproduction of the bug in a codepen, if possible. Here’s how:
* Goto https://aka.ms/fabricpen for a starting codepen
* You can also use the "Export to Codepen" feature for the various components in our documentation site.
* Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links if the repro occurs with an example.
(A permanent link is preferable to "use the website" as the website can change)
Note that if you do not provide enough information to reproduce the issue, we may not be able to take action on your report.
-->
### Environment Information
- __Package version(s)__: (fill this out)
- __Browser and OS versions__: (fill this out if relevant)
### Please provide a reproduction of the bug in a codepen:
<!-- Goto https://aka.ms/fabricpen for a starting codepen -->
<!-- See http://codepen.io/dzearing/pens/public/?grid_type=list for a variety of examples -->
<!-- Alternatively, you can also use https://aka.ms/fabricdemo to get permanent repro links. -->
#### Actual behavior:
https://codepen.io/anon/pen/oVBORo
Click Hello World with mouse
Notice Alert pops up saying hello
Now tap with touch
Notice drop down appears instead with other options
<!-- fill this out -->
#### Expected behavior:
Tapping with touch should do the same thing as clicking with mouse
<!-- fill this out -->
#### Priorities and help requested:
Are you willing to submit a PR to fix? (Yes, No)
No
Requested priority: (Blocking, High, Normal, Low)
High
Products/sites affected: (if applicable)
Office UI Fabric. Discovered on Sharepoint. | non_priority | splitbutton in touch doesn t work correctly thanks for contacting us we re here to help before you report an issue check if it s been reported before search search by area or component please provide a reproduction of the bug in a codepen if possible here’s how goto for a starting codepen you can also use the export to codepen feature for the various components in our documentation site alternatively you can also use to get permanent repro links if the repro occurs with an example a permanent link is preferable to use the website as the website can change note that if you do not provide enough information to reproduce the issue we may not be able to take action on your report environment information package version s fill this out browser and os versions fill this out if relevant please provide a reproduction of the bug in a codepen actual behavior click hello world with mouse notice alert pops up saying hello now tap with touch notice drop down appears instead with other options expected behavior tapping with touch should do the same thing as clicking with mouse priorities and help requested are you willing to submit a pr to fix yes no no requested priority blocking high normal low high products sites affected if applicable office ui fabric discovered on sharepoint | 0 |
410,978 | 27,808,941,760 | IssuesEvent | 2023-03-17 23:53:11 | cosmos/interchain-security | https://api.github.com/repos/cosmos/interchain-security | closed | docs: elaborate slashing mechanisms in ICS | documentation enhancement | ## Summary
Add a documentation page outlining the slashing in ICS.
## Problem Definition
At present, the slashing mechanisms used in ICS are not clearly outlined.
## Proposal
Write and publish docs outlining the slashing mechanisms in ICS and their implications.
The final work should include:
- double signing and an example of submitting an equivocation proposal
- downtime slashing and an overview of chain parameters tied to slashing (signed blocks window)
- if applicabe specify default values
Linked to: #750
____
#### For Admin Use
- [x] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
- [ ] Is a spike necessary to map out how the issue should be approached? | 1.0 | docs: elaborate slashing mechanisms in ICS - ## Summary
Add a documentation page outlining the slashing in ICS.
## Problem Definition
At present, the slashing mechanisms used in ICS are not clearly outlined.
## Proposal
Write and publish docs outlining the slashing mechanisms in ICS and their implications.
The final work should include:
- double signing and an example of submitting an equivocation proposal
- downtime slashing and an overview of chain parameters tied to slashing (signed blocks window)
- if applicabe specify default values
Linked to: #750
____
#### For Admin Use
- [x] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
- [ ] Is a spike necessary to map out how the issue should be approached? | non_priority | docs elaborate slashing mechanisms in ics summary add a documentation page outlining the slashing in ics problem definition at present the slashing mechanisms used in ics are not clearly outlined proposal write and publish docs outlining the slashing mechanisms in ics and their implications the final work should include double signing and an example of submitting an equivocation proposal downtime slashing and an overview of chain parameters tied to slashing signed blocks window if applicabe specify default values linked to for admin use not duplicate issue appropriate labels applied appropriate contributors tagged contributor assigned self assigned is a spike necessary to map out how the issue should be approached | 0 |
237,912 | 26,085,448,876 | IssuesEvent | 2022-12-26 01:46:46 | t2kx/juice-shop | https://api.github.com/repos/t2kx/juice-shop | opened | CVE-2022-46175 (High) detected in json5-2.1.3.tgz, json5-1.0.1.tgz | security vulnerability | ## CVE-2022-46175 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>json5-2.1.3.tgz</b>, <b>json5-1.0.1.tgz</b></p></summary>
<p>
<details><summary><b>json5-2.1.3.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-2.1.3.tgz">https://registry.npmjs.org/json5/-/json5-2.1.3.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json,/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.803.26.tgz (Root Library)
- core-7.8.7.tgz
- :x: **json5-2.1.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>json5-1.0.1.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-1.0.1.tgz">https://registry.npmjs.org/json5/-/json5-1.0.1.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /frontend/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.803.26.tgz (Root Library)
- loader-utils-1.2.3.tgz
- :x: **json5-1.0.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/t2kx/juice-shop/commit/892c07158a9eaff6c38e82269f691bf26b48b694">892c07158a9eaff6c38e82269f691bf26b48b694</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later.
<p>Publish Date: 2022-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-46175>CVE-2022-46175</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-46175">https://www.cve.org/CVERecord?id=CVE-2022-46175</a></p>
<p>Release Date: 2022-12-24</p>
<p>Fix Resolution: json5 - 2.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-46175 (High) detected in json5-2.1.3.tgz, json5-1.0.1.tgz - ## CVE-2022-46175 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>json5-2.1.3.tgz</b>, <b>json5-1.0.1.tgz</b></p></summary>
<p>
<details><summary><b>json5-2.1.3.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-2.1.3.tgz">https://registry.npmjs.org/json5/-/json5-2.1.3.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /node_modules/json5/package.json,/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.803.26.tgz (Root Library)
- core-7.8.7.tgz
- :x: **json5-2.1.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>json5-1.0.1.tgz</b></p></summary>
<p>JSON for humans.</p>
<p>Library home page: <a href="https://registry.npmjs.org/json5/-/json5-1.0.1.tgz">https://registry.npmjs.org/json5/-/json5-1.0.1.tgz</a></p>
<p>Path to dependency file: /frontend/package.json</p>
<p>Path to vulnerable library: /frontend/node_modules/json5/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.803.26.tgz (Root Library)
- loader-utils-1.2.3.tgz
- :x: **json5-1.0.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/t2kx/juice-shop/commit/892c07158a9eaff6c38e82269f691bf26b48b694">892c07158a9eaff6c38e82269f691bf26b48b694</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JSON5 is an extension to the popular JSON file format that aims to be easier to write and maintain by hand (e.g. for config files). The `parse` method of the JSON5 library before and including version `2.2.1` does not restrict parsing of keys named `__proto__`, allowing specially crafted strings to pollute the prototype of the resulting object. This vulnerability pollutes the prototype of the object returned by `JSON5.parse` and not the global Object prototype, which is the commonly understood definition of Prototype Pollution. However, polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations. This vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from `JSON5.parse`. The actual impact will depend on how applications utilize the returned object and how they filter unwanted keys, but could include denial of service, cross-site scripting, elevation of privilege, and in extreme cases, remote code execution. `JSON5.parse` should restrict parsing of `__proto__` keys when parsing JSON strings to objects. As a point of reference, the `JSON.parse` method included in JavaScript ignores `__proto__` keys. Simply changing `JSON5.parse` to `JSON.parse` in the examples above mitigates this vulnerability. This vulnerability is patched in json5 version 2.2.2 and later.
<p>Publish Date: 2022-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-46175>CVE-2022-46175</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-46175">https://www.cve.org/CVERecord?id=CVE-2022-46175</a></p>
<p>Release Date: 2022-12-24</p>
<p>Fix Resolution: json5 - 2.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tgz tgz cve high severity vulnerability vulnerable libraries tgz tgz tgz json for humans library home page a href path to dependency file frontend package json path to vulnerable library node modules package json node modules package json dependency hierarchy build angular tgz root library core tgz x tgz vulnerable library tgz json for humans library home page a href path to dependency file frontend package json path to vulnerable library frontend node modules package json dependency hierarchy build angular tgz root library loader utils tgz x tgz vulnerable library found in head commit a href found in base branch master vulnerability details is an extension to the popular json file format that aims to be easier to write and maintain by hand e g for config files the parse method of the library before and including version does not restrict parsing of keys named proto allowing specially crafted strings to pollute the prototype of the resulting object this vulnerability pollutes the prototype of the object returned by parse and not the global object prototype which is the commonly understood definition of prototype pollution however polluting the prototype of a single object can have significant security impact for an application if the object is later used in trusted operations this vulnerability could allow an attacker to set arbitrary and unexpected keys on the object returned from parse the actual impact will depend on how applications utilize the returned object and how they filter unwanted keys but could include denial of service cross site scripting elevation of privilege and in extreme cases remote code execution parse should restrict parsing of proto keys when parsing json strings to objects as a point of reference the json parse method included in javascript ignores proto keys simply changing parse to json parse in the examples above mitigates this vulnerability this vulnerability is patched in version and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
127,240 | 18,010,353,914 | IssuesEvent | 2021-09-16 07:53:05 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | opened | CVE-2018-1000028 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2018-1000028 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/auth.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/auth.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Linux kernel version after commit bdcf0a423ea1 - 4.15-rc4+, 4.14.8+, 4.9.76+, 4.4.111+ contains a Incorrect Access Control vulnerability in NFS server (nfsd) that can result in remote users reading or writing files they should not be able to via NFS. This attack appear to be exploitable via NFS server must export a filesystem with the "rootsquash" options enabled. This vulnerability appears to have been fixed in after commit 1995266727fa.
<p>Publish Date: 2018-02-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000028>CVE-2018-1000028</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000028">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000028</a></p>
<p>Release Date: 2018-02-09</p>
<p>Fix Resolution: v4.15</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-1000028 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2018-1000028 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/auth.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/nfsd/auth.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Linux kernel version after commit bdcf0a423ea1 - 4.15-rc4+, 4.14.8+, 4.9.76+, 4.4.111+ contains a Incorrect Access Control vulnerability in NFS server (nfsd) that can result in remote users reading or writing files they should not be able to via NFS. This attack appear to be exploitable via NFS server must export a filesystem with the "rootsquash" options enabled. This vulnerability appears to have been fixed in after commit 1995266727fa.
<p>Publish Date: 2018-02-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000028>CVE-2018-1000028</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000028">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000028</a></p>
<p>Release Date: 2018-02-09</p>
<p>Fix Resolution: v4.15</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href vulnerable source files fs nfsd auth c fs nfsd auth c vulnerability details linux kernel version after commit contains a incorrect access control vulnerability in nfs server nfsd that can result in remote users reading or writing files they should not be able to via nfs this attack appear to be exploitable via nfs server must export a filesystem with the rootsquash options enabled this vulnerability appears to have been fixed in after commit publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
346 | 3,193,798,824 | IssuesEvent | 2015-09-30 08:20:05 | netvl/xml-rs | https://api.github.com/repos/netvl/xml-rs | closed | Finish writer with proper namespacing support | absolutely required architecture | I need to finish the XML writer and add proper namespaces support to it. It currently does work, but only in basic cases. Also its configuration is mostly unused. | 1.0 | Finish writer with proper namespacing support - I need to finish the XML writer and add proper namespaces support to it. It currently does work, but only in basic cases. Also its configuration is mostly unused. | non_priority | finish writer with proper namespacing support i need to finish the xml writer and add proper namespaces support to it it currently does work but only in basic cases also its configuration is mostly unused | 0 |
10,055 | 3,995,915,288 | IssuesEvent | 2016-05-10 17:00:40 | scenarioo/scenarioo | https://api.github.com/repos/scenarioo/scenarioo | reopened | Prevent caching of static resources | 1 - Ready enhancement important Prio-1 Ready-to-Code | HTML templates ("partials") stick in the cache each time after updating to a new Scenarioo version. Only clearing the entire browser cache helps. This is very annoying and for the demo deployments it means that you might not see the latest features even if they are deployed.
Therefore I propose to add a query string to all templates. We could use the Git revision as a parameter (?rev=1234xyz). Any other ideas?
I got the query idea from here: https://groups.google.com/forum/#!msg/angular/wMRtJZ7R480/5bFH_ZhgdRwJ
### Tasks
* Is ETAG a valid option, also supported by IE 10 and newer?
* What config options does Tomcat support?
* Is a ServletFilter an option?
* How do other web apps do this (e.g. Outlook Web App)?
* What is AngularJS best practice?
<!---
@huboard:{"order":56.609375,"milestone_order":276,"custom_state":""}
-->
| 1.0 | Prevent caching of static resources - HTML templates ("partials") stick in the cache each time after updating to a new Scenarioo version. Only clearing the entire browser cache helps. This is very annoying and for the demo deployments it means that you might not see the latest features even if they are deployed.
Therefore I propose to add a query string to all templates. We could use the Git revision as a parameter (?rev=1234xyz). Any other ideas?
I got the query idea from here: https://groups.google.com/forum/#!msg/angular/wMRtJZ7R480/5bFH_ZhgdRwJ
### Tasks
* Is ETAG a valid option, also supported by IE 10 and newer?
* What config options does Tomcat support?
* Is a ServletFilter an option?
* How do other web apps do this (e.g. Outlook Web App)?
* What is AngularJS best practice?
<!---
@huboard:{"order":56.609375,"milestone_order":276,"custom_state":""}
-->
| non_priority | prevent caching of static resources html templates partials stick in the cache each time after updating to a new scenarioo version only clearing the entire browser cache helps this is very annoying and for the demo deployments it means that you might not see the latest features even if they are deployed therefore i propose to add a query string to all templates we could use the git revision as a parameter rev any other ideas i got the query idea from here tasks is etag a valid option also supported by ie and newer what config options does tomcat support is a servletfilter an option how do other web apps do this e g outlook web app what is angularjs best practice huboard order milestone order custom state | 0 |
28,024 | 4,350,656,210 | IssuesEvent | 2016-07-31 11:45:37 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | stress: failed test in cockroach/storage/storage.test: TestGossipFirstRange | Robot test-failure | Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/cf1708206ce61409aebecb2238ee4e9148935fef
Stress build found a failed test:
```
=== RUN TestGossipFirstRange
I160731 05:25:31.977436 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
W160731 05:25:31.979802 gossip/gossip.go:1006 not connected to cluster; use --join to specify a connected node
I160731 05:25:31.980602 server/node.go:397 store store=0:0 ([]=) not bootstrapped
I160731 05:25:31.982107 storage/replica_command.go:1741 store=1:1 ([]=) range=1 [/Min-/Max): new range lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 408317h25m36.481654554s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-07-31 05:25:31.982072919 +0000 UTC]
I160731 05:25:31.982539 server/node.go:323 **** cluster {b165ad48-224a-48e7-a420-2222f1a7e76c} has been created
I160731 05:25:31.982553 server/node.go:324 **** add additional nodes by specifying --join=127.0.0.1:36998
I160731 05:25:31.983003 storage/store.go:2774 system config not yet available
I160731 05:25:31.983038 server/node.go:410 initialized store store=1:1 ([]=): {Capacity:536870912 Available:536870912 RangeCount:0}
I160731 05:25:31.983052 server/node.go:298 node ID 1 initialized
I160731 05:25:31.983090 storage/stores.go:302 read 0 node addresses from persistent storage
I160731 05:25:31.983133 server/node.go:533 connecting to gossip network to verify cluster ID...
I160731 05:25:31.983220 server/node.go:554 node connected via gossip and verified as part of cluster {"b165ad48-224a-48e7-a420-2222f1a7e76c"}
I160731 05:25:31.983252 server/node.go:351 node=1: started with [[]=] engine(s) and attributes []
I160731 05:25:31.983271 server/server.go:427 starting https server at 127.0.0.1:36364
I160731 05:25:31.983282 server/server.go:428 starting grpc/postgres server at 127.0.0.1:36998
I160731 05:25:31.983528 sql/event_log.go:103 Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36998} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942731983233312}
I160731 05:25:31.993425 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
I160731 05:25:31.994219 sql/event_log.go:103 Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36998} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942731983233312}
W160731 05:25:31.995498 gossip/gossip.go:1006 not connected to cluster; use --join to specify a connected node
I160731 05:25:31.996224 server/node.go:397 store store=0:0 ([]=) not bootstrapped
I160731 05:25:31.996248 gossip/client.go:75 starting client to 127.0.0.1:36998
I160731 05:25:31.996276 storage/stores.go:302 read 0 node addresses from persistent storage
I160731 05:25:31.996292 server/node.go:533 connecting to gossip network to verify cluster ID...
I160731 05:25:32.008252 server/node.go:554 node connected via gossip and verified as part of cluster {"b165ad48-224a-48e7-a420-2222f1a7e76c"}
I160731 05:25:32.009177 storage/stores.go:317 wrote 1 node addresses to persistent storage
I160731 05:25:32.010043 kv/dist_sender.go:310 unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I160731 05:25:32.010594 server/node.go:292 new node allocated ID 2
I160731 05:25:32.010649 server/node.go:351 node=2: started with [[]=] engine(s) and attributes []
I160731 05:25:32.010671 server/server.go:427 starting https server at 127.0.0.1:35463
I160731 05:25:32.010681 server/server.go:428 starting grpc/postgres server at 127.0.0.1:32853
I160731 05:25:32.010793 sql/event_log.go:103 Event: "node_join", target: 2, info: {Descriptor:{NodeID:2 Address:{NetworkField:tcp AddressField:127.0.0.1:32853} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942732032764757}
I160731 05:25:32.011154 storage/stores.go:317 wrote 1 node addresses to persistent storage
I160731 05:25:32.021034 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
I160731 05:25:32.022445 server/node.go:516 bootstrapped store store=2:2 ([]=)
W160731 05:25:32.023179 gossip/gossip.go:1006 not connected to cluster; use --join to specify a connected node
I160731 05:25:32.023888 gossip/client.go:75 starting client to 127.0.0.1:36998
I160731 05:25:32.023986 server/node.go:397 store store=0:0 ([]=) not bootstrapped
I160731 05:25:32.024010 storage/stores.go:302 read 0 node addresses from persistent storage
I160731 05:25:32.024025 server/node.go:533 connecting to gossip network to verify cluster ID...
I160731 05:25:32.033896 server/node.go:554 node connected via gossip and verified as part of cluster {"b165ad48-224a-48e7-a420-2222f1a7e76c"}
I160731 05:25:32.033928 storage/stores.go:317 wrote 1 node addresses to persistent storage
I160731 05:25:32.033956 storage/stores.go:317 wrote 2 node addresses to persistent storage
I160731 05:25:32.035176 kv/dist_sender.go:310 unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I160731 05:25:32.036044 server/node.go:292 new node allocated ID 3
I160731 05:25:32.036123 server/node.go:351 node=3: started with [[]=] engine(s) and attributes []
I160731 05:25:32.036146 server/server.go:427 starting https server at 127.0.0.1:45564
I160731 05:25:32.036156 server/server.go:428 starting grpc/postgres server at 127.0.0.1:44276
I160731 05:25:32.036319 sql/event_log.go:103 Event: "node_join", target: 3, info: {Descriptor:{NodeID:3 Address:{NetworkField:tcp AddressField:127.0.0.1:44276} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942732036110214}
I160731 05:25:32.036427 storage/stores.go:317 wrote 2 node addresses to persistent storage
I160731 05:25:32.036663 storage/stores.go:317 wrote 2 node addresses to persistent storage
I160731 05:25:32.049293 server/node.go:516 bootstrapped store store=3:3 ([]=)
I160731 05:25:32.063388 storage/replica_raftstorage.go:467 generated snapshot for range 1 at index 34 in 3.324313ms. encoded size=160649, 553 KV pairs, 24 log entries
I160731 05:25:32.064286 storage/replica_command.go:3206 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I160731 05:25:32.064670 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.064809 storage/log.go:84 Range Event: "add", range: 1, info: {"AddReplica":{"node_id":2,"store_id":2,"replica_id":2},"UpdatedDesc":{"range_id":1,"end_key":"//8=","replicas":[{"node_id":1,"store_id":1,"replica_id":1},{"node_id":2,"store_id":2,"replica_id":2}],"next_replica_id":3}}
I160731 05:25:32.065875 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/6/1,/Min), pErr=<nil>
I160731 05:25:32.066128 storage/replica.go:1419 store=1:1 ([]=) range=1 [/Min-/Max): proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2} for range 1: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I160731 05:25:32.066397 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.066561 storage/replica_raftstorage.go:588 store=2:2 ([]=) range=1 [/Min-/Min): with replicaID [?], applying preemptive snapshot for range 1 at index 34 (encoded size=160649, 553 KV pairs, 24 log entries)
I160731 05:25:32.068376 storage/replica_raftstorage.go:591 store=2:2 ([]=) range=1 [/Min-/Max): with replicaID [?], applied preemptive snapshot for range 1 in 1.780146ms
I160731 05:25:32.080957 storage/replica_raftstorage.go:467 generated snapshot for range 1 at index 37 in 1.944077ms. encoded size=162913, 561 KV pairs, 27 log entries
I160731 05:25:32.081355 storage/replica_command.go:3206 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:3
I160731 05:25:32.082857 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.082937 storage/replica_raftstorage.go:588 store=3:3 ([]=) range=1 [/Min-/Min): with replicaID [?], applying preemptive snapshot for range 1 at index 37 (encoded size=162913, 561 KV pairs, 27 log entries)
I160731 05:25:32.083070 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/6/1,/Min), pErr=<nil>
I160731 05:25:32.083279 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.083302 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.083455 storage/log.go:84 Range Event: "add", range: 1, info: {"AddReplica":{"node_id":3,"store_id":3,"replica_id":3},"UpdatedDesc":{"range_id":1,"end_key":"//8=","replicas":[{"node_id":1,"store_id":1,"replica_id":1},{"node_id":2,"store_id":2,"replica_id":2},{"node_id":3,"store_id":3,"replica_id":3}],"next_replica_id":4}}
I160731 05:25:32.083601 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.083740 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.084452 storage/replica_raftstorage.go:591 store=3:3 ([]=) range=1 [/Min-/Max): with replicaID [?], applied preemptive snapshot for range 1 in 1.484945ms
I160731 05:25:32.084849 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/6/1,/Min), pErr=<nil>
I160731 05:25:32.085225 storage/replica.go:1419 store=1:1 ([]=) range=1 [/Min-/Max): proposing ADD_REPLICA {NodeID:3 StoreID:3 ReplicaID:3} for range 1: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2} {NodeID:3 StoreID:3 ReplicaID:3}]
I160731 05:25:32.085240 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/6/1,/Min), pErr=<nil>
I160731 05:25:32.085878 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.086223 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.086445 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.087458 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.087631 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/6/1,/Min), pErr=<nil>
I160731 05:25:32.087821 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.087837 storage/replica_command.go:1757 range 1: replicaID 1 transfer raft leadership to replicaID 2
I160731 05:25:32.088100 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.088359 storage/replica_command.go:1741 store=2:2 ([]=) range=1 [/Min-/Max): new range lease replica {2 2 2} 2016-07-31 05:25:32.086320174 +0000 UTC 4.55s following replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 408317h25m36.481654554s [physicalTime=2016-07-31 05:25:32.088325874 +0000 UTC]
I160731 05:25:32.135097 storage/replica_command.go:3206 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > replicas:<node_id:3 store_id:3 replica_id:3 > next_replica_id:4
I160731 05:25:32.136428 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.136686 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.136724 storage/log.go:84 Range Event: "remove", range: 1, info: {"RemovedReplica":{"node_id":1,"store_id":1,"replica_id":1},"UpdatedDesc":{"range_id":1,"end_key":"//8=","replicas":[{"node_id":3,"store_id":3,"replica_id":3},{"node_id":2,"store_id":2,"replica_id":2}],"next_replica_id":4}}
I160731 05:25:32.136893 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.139783 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/6/1,/Min), pErr=<nil>
I160731 05:25:32.139968 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/6/1,/Min), pErr=<nil>
I160731 05:25:32.140154 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/6/1,/Min), pErr=<nil>
I160731 05:25:32.140370 storage/replica.go:1419 store=2:2 ([]=) range=1 [/Min-/Max): proposing REMOVE_REPLICA {NodeID:1 StoreID:1 ReplicaID:1} for range 1: [{NodeID:3 StoreID:3 ReplicaID:3} {NodeID:2 StoreID:2 ReplicaID:2}]
I160731 05:25:32.141129 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.141313 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.141466 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
W160731 05:25:32.141648 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 2} closed by the remote: rpc error: code = 2 desc = range 1: discarding message from {NodeID:1 StoreID:1 ReplicaID:1}, older than NextReplicaID 4
I160731 05:25:32.141662 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.141699 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.142075 stopper.go:408 quiesceing; tasks left:
2 gossip/infostore.go:276
1 storage/queue.go:427
I160731 05:25:32.142183 stopper.go:408 quiesceing; tasks left:
1 storage/queue.go:427
1 gossip/infostore.go:276
I160731 05:25:32.142284 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
W160731 05:25:32.142294 storage/replica.go:337 range 1: outgoing raft transport stream to {3 3 3} closed by the remote: rpc error: code = 13 desc = transport is closing
W160731 05:25:32.142299 storage/replica.go:337 range 1: outgoing raft transport stream to {1 1 1} closed by the remote: <nil>
I160731 05:25:32.142318 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:44276->127.0.0.1:60122: use of closed network connection
I160731 05:25:32.142350 http2_client.go:1019 transport: http2Client.notifyError got notified that the client transport was broken EOF.
W160731 05:25:32.142355 storage/replica.go:337 range 1: outgoing raft transport stream to {3 3 0} closed by the remote: rpc error: code = 13 desc = transport is closing
I160731 05:25:32.142360 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
W160731 05:25:32.142379 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 2} closed by the remote: <nil>
W160731 05:25:32.142386 storage/replica.go:337 range 1: outgoing raft transport stream to {3 3 3} closed by the remote: <nil>
I160731 05:25:32.142399 stopper.go:408 quiesceing; tasks left:
1 storage/queue.go:427
E160731 05:25:32.142406 storage/queue.go:497 [replicaGC] on store=1:1 ([]=) range=1 [/Min-/Max): failed to send RPC: sending to all 3 replicas failed; last error: rpc error: code = 13 desc = transport is closing
I160731 05:25:32.142412 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
W160731 05:25:32.142438 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 0} closed by the remote: rpc error: code = 13 desc = transport is closing
I160731 05:25:32.142460 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
I160731 05:25:32.142477 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:36998->127.0.0.1:52884: use of closed network connection
I160731 05:25:32.142489 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
I160731 05:25:32.142527 /go/src/google.golang.org/grpc/clientconn.go:416 Failed to dial 127.0.0.1:36998: grpc: the connection is closing; please retry.
I160731 05:25:32.142547 /go/src/google.golang.org/grpc/clientconn.go:594 grpc: addrConn.resetTransport failed to create client transport: connection error: desc = "transport: dial tcp 127.0.0.1:44276: getsockopt: connection refused"; Reconnecting to {"127.0.0.1:44276" <nil>}
I160731 05:25:32.142559 /go/src/google.golang.org/grpc/clientconn.go:416 Failed to dial 127.0.0.1:44276: grpc: the connection is closing; please retry.
W160731 05:25:32.142585 storage/replica.go:337 range 1: outgoing raft transport stream to {1 1 1} closed by the remote: <nil>
I160731 05:25:32.142601 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
I160731 05:25:32.142674 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
--- FAIL: TestGossipFirstRange (5.18s)
leaktest.go:105: Leaked goroutine: goroutine 86886 [select]:
google.golang.org/grpc/transport.(*http2Client).controller(0xc82633ae00)
/go/src/google.golang.org/grpc/transport/http2_client.go:965 +0x5e0
created by google.golang.org/grpc/transport.newHTTP2Client
/go/src/google.golang.org/grpc/transport/http2_client.go:206 +0x14bd
```
Run Details:
```
0 runs so far, 0 failures, over 5s
0 runs so far, 0 failures, over 10s
0 runs so far, 0 failures, over 15s
0 runs so far, 0 failures, over 20s
0 runs so far, 0 failures, over 25s
0 runs so far, 0 failures, over 30s
0 runs so far, 0 failures, over 35s
0 runs so far, 0 failures, over 40s
0 runs so far, 0 failures, over 45s
0 runs so far, 0 failures, over 50s
0 runs so far, 0 failures, over 55s
0 runs so far, 0 failures, over 1m0s
0 runs so far, 0 failures, over 1m5s
0 runs so far, 0 failures, over 1m10s
0 runs so far, 0 failures, over 1m15s
6 runs so far, 0 failures, over 1m20s
15 runs so far, 0 failures, over 1m25s
15 runs so far, 0 failures, over 1m30s
15 runs so far, 0 failures, over 1m35s
15 runs so far, 0 failures, over 1m40s
15 runs so far, 0 failures, over 1m45s
15 runs so far, 0 failures, over 1m50s
15 runs so far, 0 failures, over 1m55s
15 runs so far, 0 failures, over 2m0s
15 runs so far, 0 failures, over 2m5s
15 runs so far, 0 failures, over 2m10s
15 runs so far, 0 failures, over 2m15s
15 runs so far, 0 failures, over 2m20s
15 runs so far, 0 failures, over 2m25s
15 runs so far, 0 failures, over 2m30s
15 runs so far, 0 failures, over 2m35s
26 runs so far, 0 failures, over 2m40s
29 runs so far, 0 failures, over 2m45s
29 runs so far, 0 failures, over 2m50s
29 runs so far, 0 failures, over 2m55s
29 runs so far, 0 failures, over 3m0s
29 runs so far, 0 failures, over 3m5s
29 runs so far, 0 failures, over 3m10s
29 runs so far, 0 failures, over 3m15s
29 runs so far, 0 failures, over 3m20s
29 runs so far, 0 failures, over 3m25s
29 runs so far, 0 failures, over 3m30s
29 runs so far, 0 failures, over 3m35s
29 runs so far, 0 failures, over 3m40s
29 runs so far, 0 failures, over 3m45s
29 runs so far, 0 failures, over 3m50s
40 runs so far, 0 failures, over 3m55s
43 runs so far, 0 failures, over 4m0s
43 runs so far, 0 failures, over 4m5s
43 runs so far, 0 failures, over 4m10s
43 runs so far, 0 failures, over 4m15s
43 runs so far, 0 failures, over 4m20s
43 runs so far, 0 failures, over 4m25s
43 runs so far, 0 failures, over 4m30s
43 runs so far, 0 failures, over 4m35s
43 runs so far, 0 failures, over 4m40s
43 runs so far, 0 failures, over 4m45s
43 runs so far, 0 failures, over 4m50s
43 runs so far, 0 failures, over 4m55s
43 runs so far, 0 failures, over 5m0s
44 runs so far, 0 failures, over 5m5s
53 runs so far, 0 failures, over 5m10s
56 runs so far, 0 failures, over 5m15s
56 runs so far, 0 failures, over 5m20s
56 runs so far, 0 failures, over 5m25s
56 runs so far, 0 failures, over 5m30s
56 runs so far, 0 failures, over 5m35s
56 runs so far, 0 failures, over 5m40s
56 runs so far, 0 failures, over 5m45s
56 runs so far, 0 failures, over 5m50s
56 runs so far, 0 failures, over 5m55s
56 runs so far, 0 failures, over 6m0s
56 runs so far, 0 failures, over 6m5s
56 runs so far, 0 failures, over 6m10s
56 runs so far, 0 failures, over 6m15s
59 runs so far, 0 failures, over 6m20s
68 runs completed, 1 failures, over 6m24s
FAIL
```
Please assign, take a look and update the issue accordingly. | 1.0 | stress: failed test in cockroach/storage/storage.test: TestGossipFirstRange - Binary: cockroach/static-tests.tar.gz sha: https://github.com/cockroachdb/cockroach/commits/cf1708206ce61409aebecb2238ee4e9148935fef
Stress build found a failed test:
```
=== RUN TestGossipFirstRange
I160731 05:25:31.977436 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
W160731 05:25:31.979802 gossip/gossip.go:1006 not connected to cluster; use --join to specify a connected node
I160731 05:25:31.980602 server/node.go:397 store store=0:0 ([]=) not bootstrapped
I160731 05:25:31.982107 storage/replica_command.go:1741 store=1:1 ([]=) range=1 [/Min-/Max): new range lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 408317h25m36.481654554s following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0 [physicalTime=2016-07-31 05:25:31.982072919 +0000 UTC]
I160731 05:25:31.982539 server/node.go:323 **** cluster {b165ad48-224a-48e7-a420-2222f1a7e76c} has been created
I160731 05:25:31.982553 server/node.go:324 **** add additional nodes by specifying --join=127.0.0.1:36998
I160731 05:25:31.983003 storage/store.go:2774 system config not yet available
I160731 05:25:31.983038 server/node.go:410 initialized store store=1:1 ([]=): {Capacity:536870912 Available:536870912 RangeCount:0}
I160731 05:25:31.983052 server/node.go:298 node ID 1 initialized
I160731 05:25:31.983090 storage/stores.go:302 read 0 node addresses from persistent storage
I160731 05:25:31.983133 server/node.go:533 connecting to gossip network to verify cluster ID...
I160731 05:25:31.983220 server/node.go:554 node connected via gossip and verified as part of cluster {"b165ad48-224a-48e7-a420-2222f1a7e76c"}
I160731 05:25:31.983252 server/node.go:351 node=1: started with [[]=] engine(s) and attributes []
I160731 05:25:31.983271 server/server.go:427 starting https server at 127.0.0.1:36364
I160731 05:25:31.983282 server/server.go:428 starting grpc/postgres server at 127.0.0.1:36998
I160731 05:25:31.983528 sql/event_log.go:103 Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36998} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942731983233312}
I160731 05:25:31.993425 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
I160731 05:25:31.994219 sql/event_log.go:103 Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:36998} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942731983233312}
W160731 05:25:31.995498 gossip/gossip.go:1006 not connected to cluster; use --join to specify a connected node
I160731 05:25:31.996224 server/node.go:397 store store=0:0 ([]=) not bootstrapped
I160731 05:25:31.996248 gossip/client.go:75 starting client to 127.0.0.1:36998
I160731 05:25:31.996276 storage/stores.go:302 read 0 node addresses from persistent storage
I160731 05:25:31.996292 server/node.go:533 connecting to gossip network to verify cluster ID...
I160731 05:25:32.008252 server/node.go:554 node connected via gossip and verified as part of cluster {"b165ad48-224a-48e7-a420-2222f1a7e76c"}
I160731 05:25:32.009177 storage/stores.go:317 wrote 1 node addresses to persistent storage
I160731 05:25:32.010043 kv/dist_sender.go:310 unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I160731 05:25:32.010594 server/node.go:292 new node allocated ID 2
I160731 05:25:32.010649 server/node.go:351 node=2: started with [[]=] engine(s) and attributes []
I160731 05:25:32.010671 server/server.go:427 starting https server at 127.0.0.1:35463
I160731 05:25:32.010681 server/server.go:428 starting grpc/postgres server at 127.0.0.1:32853
I160731 05:25:32.010793 sql/event_log.go:103 Event: "node_join", target: 2, info: {Descriptor:{NodeID:2 Address:{NetworkField:tcp AddressField:127.0.0.1:32853} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942732032764757}
I160731 05:25:32.011154 storage/stores.go:317 wrote 1 node addresses to persistent storage
I160731 05:25:32.021034 storage/engine/rocksdb.go:353 opening in memory rocksdb instance
I160731 05:25:32.022445 server/node.go:516 bootstrapped store store=2:2 ([]=)
W160731 05:25:32.023179 gossip/gossip.go:1006 not connected to cluster; use --join to specify a connected node
I160731 05:25:32.023888 gossip/client.go:75 starting client to 127.0.0.1:36998
I160731 05:25:32.023986 server/node.go:397 store store=0:0 ([]=) not bootstrapped
I160731 05:25:32.024010 storage/stores.go:302 read 0 node addresses from persistent storage
I160731 05:25:32.024025 server/node.go:533 connecting to gossip network to verify cluster ID...
I160731 05:25:32.033896 server/node.go:554 node connected via gossip and verified as part of cluster {"b165ad48-224a-48e7-a420-2222f1a7e76c"}
I160731 05:25:32.033928 storage/stores.go:317 wrote 1 node addresses to persistent storage
I160731 05:25:32.033956 storage/stores.go:317 wrote 2 node addresses to persistent storage
I160731 05:25:32.035176 kv/dist_sender.go:310 unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I160731 05:25:32.036044 server/node.go:292 new node allocated ID 3
I160731 05:25:32.036123 server/node.go:351 node=3: started with [[]=] engine(s) and attributes []
I160731 05:25:32.036146 server/server.go:427 starting https server at 127.0.0.1:45564
I160731 05:25:32.036156 server/server.go:428 starting grpc/postgres server at 127.0.0.1:44276
I160731 05:25:32.036319 sql/event_log.go:103 Event: "node_join", target: 3, info: {Descriptor:{NodeID:3 Address:{NetworkField:tcp AddressField:127.0.0.1:44276} Attrs:} ClusterID:{UUID:b165ad48-224a-48e7-a420-2222f1a7e76c} StartedAt:1469942732036110214}
I160731 05:25:32.036427 storage/stores.go:317 wrote 2 node addresses to persistent storage
I160731 05:25:32.036663 storage/stores.go:317 wrote 2 node addresses to persistent storage
I160731 05:25:32.049293 server/node.go:516 bootstrapped store store=3:3 ([]=)
I160731 05:25:32.063388 storage/replica_raftstorage.go:467 generated snapshot for range 1 at index 34 in 3.324313ms. encoded size=160649, 553 KV pairs, 24 log entries
I160731 05:25:32.064286 storage/replica_command.go:3206 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I160731 05:25:32.064670 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.064809 storage/log.go:84 Range Event: "add", range: 1, info: {"AddReplica":{"node_id":2,"store_id":2,"replica_id":2},"UpdatedDesc":{"range_id":1,"end_key":"//8=","replicas":[{"node_id":1,"store_id":1,"replica_id":1},{"node_id":2,"store_id":2,"replica_id":2}],"next_replica_id":3}}
I160731 05:25:32.065875 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/6/1,/Min), pErr=<nil>
I160731 05:25:32.066128 storage/replica.go:1419 store=1:1 ([]=) range=1 [/Min-/Max): proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2} for range 1: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I160731 05:25:32.066397 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.066561 storage/replica_raftstorage.go:588 store=2:2 ([]=) range=1 [/Min-/Min): with replicaID [?], applying preemptive snapshot for range 1 at index 34 (encoded size=160649, 553 KV pairs, 24 log entries)
I160731 05:25:32.068376 storage/replica_raftstorage.go:591 store=2:2 ([]=) range=1 [/Min-/Max): with replicaID [?], applied preemptive snapshot for range 1 in 1.780146ms
I160731 05:25:32.080957 storage/replica_raftstorage.go:467 generated snapshot for range 1 at index 37 in 1.944077ms. encoded size=162913, 561 KV pairs, 27 log entries
I160731 05:25:32.081355 storage/replica_command.go:3206 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:3
I160731 05:25:32.082857 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.082937 storage/replica_raftstorage.go:588 store=3:3 ([]=) range=1 [/Min-/Min): with replicaID [?], applying preemptive snapshot for range 1 at index 37 (encoded size=162913, 561 KV pairs, 27 log entries)
I160731 05:25:32.083070 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.064115Z/163421657712066560/6/1,/Min), pErr=<nil>
I160731 05:25:32.083279 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.083302 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.083455 storage/log.go:84 Range Event: "add", range: 1, info: {"AddReplica":{"node_id":3,"store_id":3,"replica_id":3},"UpdatedDesc":{"range_id":1,"end_key":"//8=","replicas":[{"node_id":1,"store_id":1,"replica_id":1},{"node_id":2,"store_id":2,"replica_id":2},{"node_id":3,"store_id":3,"replica_id":3}],"next_replica_id":4}}
I160731 05:25:32.083601 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.083740 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.084452 storage/replica_raftstorage.go:591 store=3:3 ([]=) range=1 [/Min-/Max): with replicaID [?], applied preemptive snapshot for range 1 in 1.484945ms
I160731 05:25:32.084849 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/6/1,/Min), pErr=<nil>
I160731 05:25:32.085225 storage/replica.go:1419 store=1:1 ([]=) range=1 [/Min-/Max): proposing ADD_REPLICA {NodeID:3 StoreID:3 ReplicaID:3} for range 1: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2} {NodeID:3 StoreID:3 ReplicaID:3}]
I160731 05:25:32.085240 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/6/1,/Min), pErr=<nil>
I160731 05:25:32.085878 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.086223 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.086445 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.087458 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.087631 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.081101Z/163421657772982272/6/1,/Min), pErr=<nil>
I160731 05:25:32.087821 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.087837 storage/replica_command.go:1757 range 1: replicaID 1 transfer raft leadership to replicaID 2
I160731 05:25:32.088100 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.088359 storage/replica_command.go:1741 store=2:2 ([]=) range=1 [/Min-/Max): new range lease replica {2 2 2} 2016-07-31 05:25:32.086320174 +0000 UTC 4.55s following replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 408317h25m36.481654554s [physicalTime=2016-07-31 05:25:32.088325874 +0000 UTC]
I160731 05:25:32.135097 storage/replica_command.go:3206 store=1:1 ([]=) range=1 [/Min-/Max): change replicas of 1: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > replicas:<node_id:3 store_id:3 replica_id:3 > next_replica_id:4
I160731 05:25:32.136428 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.136686 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.136724 storage/log.go:84 Range Event: "remove", range: 1, info: {"RemovedReplica":{"node_id":1,"store_id":1,"replica_id":1},"UpdatedDesc":{"range_id":1,"end_key":"//8=","replicas":[{"node_id":3,"store_id":3,"replica_id":3},{"node_id":2,"store_id":2,"replica_id":2}],"next_replica_id":4}}
I160731 05:25:32.136893 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: BeginTransaction [/Local/Range/""/RangeDescriptor,/Min), ConditionalPut [/Local/Range/""/RangeDescriptor,/Min), Put [/Meta2/Max,/Min), Put [/Meta1/Max,/Min), pErr=<nil>
I160731 05:25:32.139783 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/6/1,/Min), pErr=<nil>
I160731 05:25:32.139968 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/6/1,/Min), pErr=<nil>
I160731 05:25:32.140154 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/0,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/2/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/3/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/4/1,/Min), ConditionalPut [/Table/13/1/2016-07-31T05:25:32.134587Z/163421657952190464/6/1,/Min), pErr=<nil>
I160731 05:25:32.140370 storage/replica.go:1419 store=2:2 ([]=) range=1 [/Min-/Max): proposing REMOVE_REPLICA {NodeID:1 StoreID:1 ReplicaID:1} for range 1: [{NodeID:3 StoreID:3 ReplicaID:3} {NodeID:2 StoreID:2 ReplicaID:2}]
I160731 05:25:32.141129 storage/replica.go:1982 store=2:2 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.141313 storage/replica.go:1982 store=1:1 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
I160731 05:25:32.141466 storage/replica.go:1982 store=3:3 ([]=) range=1 [/Min-/Max): applied part of replica change txn: EndTransaction [/Local/Range/""/RangeDescriptor,/Min), pErr=<nil>
W160731 05:25:32.141648 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 2} closed by the remote: rpc error: code = 2 desc = range 1: discarding message from {NodeID:1 StoreID:1 ReplicaID:1}, older than NextReplicaID 4
I160731 05:25:32.141662 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.141699 storage/replica_command.go:2995 unable to gossip first range; hasLease=false, err=<nil>
I160731 05:25:32.142075 stopper.go:408 quiesceing; tasks left:
2 gossip/infostore.go:276
1 storage/queue.go:427
I160731 05:25:32.142183 stopper.go:408 quiesceing; tasks left:
1 storage/queue.go:427
1 gossip/infostore.go:276
I160731 05:25:32.142284 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
W160731 05:25:32.142294 storage/replica.go:337 range 1: outgoing raft transport stream to {3 3 3} closed by the remote: rpc error: code = 13 desc = transport is closing
W160731 05:25:32.142299 storage/replica.go:337 range 1: outgoing raft transport stream to {1 1 1} closed by the remote: <nil>
I160731 05:25:32.142318 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:44276->127.0.0.1:60122: use of closed network connection
I160731 05:25:32.142350 http2_client.go:1019 transport: http2Client.notifyError got notified that the client transport was broken EOF.
W160731 05:25:32.142355 storage/replica.go:337 range 1: outgoing raft transport stream to {3 3 0} closed by the remote: rpc error: code = 13 desc = transport is closing
I160731 05:25:32.142360 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
W160731 05:25:32.142379 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 2} closed by the remote: <nil>
W160731 05:25:32.142386 storage/replica.go:337 range 1: outgoing raft transport stream to {3 3 3} closed by the remote: <nil>
I160731 05:25:32.142399 stopper.go:408 quiesceing; tasks left:
1 storage/queue.go:427
E160731 05:25:32.142406 storage/queue.go:497 [replicaGC] on store=1:1 ([]=) range=1 [/Min-/Max): failed to send RPC: sending to all 3 replicas failed; last error: rpc error: code = 13 desc = transport is closing
I160731 05:25:32.142412 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
W160731 05:25:32.142438 storage/replica.go:337 range 1: outgoing raft transport stream to {2 2 0} closed by the remote: rpc error: code = 13 desc = transport is closing
I160731 05:25:32.142460 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
I160731 05:25:32.142477 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:36998->127.0.0.1:52884: use of closed network connection
I160731 05:25:32.142489 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
I160731 05:25:32.142527 /go/src/google.golang.org/grpc/clientconn.go:416 Failed to dial 127.0.0.1:36998: grpc: the connection is closing; please retry.
I160731 05:25:32.142547 /go/src/google.golang.org/grpc/clientconn.go:594 grpc: addrConn.resetTransport failed to create client transport: connection error: desc = "transport: dial tcp 127.0.0.1:44276: getsockopt: connection refused"; Reconnecting to {"127.0.0.1:44276" <nil>}
I160731 05:25:32.142559 /go/src/google.golang.org/grpc/clientconn.go:416 Failed to dial 127.0.0.1:44276: grpc: the connection is closing; please retry.
W160731 05:25:32.142585 storage/replica.go:337 range 1: outgoing raft transport stream to {1 1 1} closed by the remote: <nil>
I160731 05:25:32.142601 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
I160731 05:25:32.142674 http2_server.go:268 transport: http2Server.HandleStreams failed to read frame: EOF
--- FAIL: TestGossipFirstRange (5.18s)
leaktest.go:105: Leaked goroutine: goroutine 86886 [select]:
google.golang.org/grpc/transport.(*http2Client).controller(0xc82633ae00)
/go/src/google.golang.org/grpc/transport/http2_client.go:965 +0x5e0
created by google.golang.org/grpc/transport.newHTTP2Client
/go/src/google.golang.org/grpc/transport/http2_client.go:206 +0x14bd
```
Run Details:
```
0 runs so far, 0 failures, over 5s
0 runs so far, 0 failures, over 10s
0 runs so far, 0 failures, over 15s
0 runs so far, 0 failures, over 20s
0 runs so far, 0 failures, over 25s
0 runs so far, 0 failures, over 30s
0 runs so far, 0 failures, over 35s
0 runs so far, 0 failures, over 40s
0 runs so far, 0 failures, over 45s
0 runs so far, 0 failures, over 50s
0 runs so far, 0 failures, over 55s
0 runs so far, 0 failures, over 1m0s
0 runs so far, 0 failures, over 1m5s
0 runs so far, 0 failures, over 1m10s
0 runs so far, 0 failures, over 1m15s
6 runs so far, 0 failures, over 1m20s
15 runs so far, 0 failures, over 1m25s
15 runs so far, 0 failures, over 1m30s
15 runs so far, 0 failures, over 1m35s
15 runs so far, 0 failures, over 1m40s
15 runs so far, 0 failures, over 1m45s
15 runs so far, 0 failures, over 1m50s
15 runs so far, 0 failures, over 1m55s
15 runs so far, 0 failures, over 2m0s
15 runs so far, 0 failures, over 2m5s
15 runs so far, 0 failures, over 2m10s
15 runs so far, 0 failures, over 2m15s
15 runs so far, 0 failures, over 2m20s
15 runs so far, 0 failures, over 2m25s
15 runs so far, 0 failures, over 2m30s
15 runs so far, 0 failures, over 2m35s
26 runs so far, 0 failures, over 2m40s
29 runs so far, 0 failures, over 2m45s
29 runs so far, 0 failures, over 2m50s
29 runs so far, 0 failures, over 2m55s
29 runs so far, 0 failures, over 3m0s
29 runs so far, 0 failures, over 3m5s
29 runs so far, 0 failures, over 3m10s
29 runs so far, 0 failures, over 3m15s
29 runs so far, 0 failures, over 3m20s
29 runs so far, 0 failures, over 3m25s
29 runs so far, 0 failures, over 3m30s
29 runs so far, 0 failures, over 3m35s
29 runs so far, 0 failures, over 3m40s
29 runs so far, 0 failures, over 3m45s
29 runs so far, 0 failures, over 3m50s
40 runs so far, 0 failures, over 3m55s
43 runs so far, 0 failures, over 4m0s
43 runs so far, 0 failures, over 4m5s
43 runs so far, 0 failures, over 4m10s
43 runs so far, 0 failures, over 4m15s
43 runs so far, 0 failures, over 4m20s
43 runs so far, 0 failures, over 4m25s
43 runs so far, 0 failures, over 4m30s
43 runs so far, 0 failures, over 4m35s
43 runs so far, 0 failures, over 4m40s
43 runs so far, 0 failures, over 4m45s
43 runs so far, 0 failures, over 4m50s
43 runs so far, 0 failures, over 4m55s
43 runs so far, 0 failures, over 5m0s
44 runs so far, 0 failures, over 5m5s
53 runs so far, 0 failures, over 5m10s
56 runs so far, 0 failures, over 5m15s
56 runs so far, 0 failures, over 5m20s
56 runs so far, 0 failures, over 5m25s
56 runs so far, 0 failures, over 5m30s
56 runs so far, 0 failures, over 5m35s
56 runs so far, 0 failures, over 5m40s
56 runs so far, 0 failures, over 5m45s
56 runs so far, 0 failures, over 5m50s
56 runs so far, 0 failures, over 5m55s
56 runs so far, 0 failures, over 6m0s
56 runs so far, 0 failures, over 6m5s
56 runs so far, 0 failures, over 6m10s
56 runs so far, 0 failures, over 6m15s
59 runs so far, 0 failures, over 6m20s
68 runs completed, 1 failures, over 6m24s
FAIL
```
Please assign, take a look and update the issue accordingly. | non_priority | stress failed test in cockroach storage storage test testgossipfirstrange binary cockroach static tests tar gz sha stress build found a failed test run testgossipfirstrange storage engine rocksdb go opening in memory rocksdb instance gossip gossip go not connected to cluster use join to specify a connected node server node go store store not bootstrapped storage replica command go store range server node go cluster has been created server node go add additional nodes by specifying join storage store go system config not yet available server node go initialized store store capacity available rangecount server node go node id initialized storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go node started with engine s and attributes server server go starting https server at server server go starting grpc postgres server at sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs clusterid uuid startedat storage engine rocksdb go opening in memory rocksdb instance sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs clusterid uuid startedat gossip gossip go not connected to cluster use join to specify a connected node server node go store store not bootstrapped gossip client go starting client to storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster storage stores go wrote node addresses to persistent storage kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping server node go new node allocated id server node go node started with engine s and attributes server server go starting https server at server server go starting grpc postgres server at sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs clusterid uuid startedat storage stores go wrote node addresses to persistent storage storage engine rocksdb go opening in memory rocksdb instance server node go bootstrapped store store gossip gossip go not connected to cluster use join to specify a connected node gossip client go starting client to server node go store store not bootstrapped storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping server node go new node allocated id server node go node started with engine s and attributes server server go starting https server at server server go starting grpc postgres server at sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs clusterid uuid startedat storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage server node go bootstrapped store store storage replica raftstorage go generated snapshot for range at index in encoded size kv pairs log entries storage replica command go store range min max change replicas of read existing descriptor range id start key end key replicas next replica id storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage log go range event add range info addreplica node id store id replica id updateddesc range id end key replicas next replica id storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica raftstorage go store range applying preemptive snapshot for range at index encoded size kv pairs log entries storage replica raftstorage go store range applied preemptive snapshot for range in storage replica raftstorage go generated snapshot for range at index in encoded size kv pairs log entries storage replica command go store range min max change replicas of read existing descriptor range id start key end key replicas replicas next replica id storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage replica raftstorage go store range applying preemptive snapshot for range at index encoded size kv pairs log entries storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage log go range event add range info addreplica node id store id replica id updateddesc range id end key replicas next replica id storage replica command go unable to gossip first range haslease false err storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage replica raftstorage go store range applied preemptive snapshot for range in storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica command go unable to gossip first range haslease false err storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica command go range replicaid transfer raft leadership to replicaid storage replica command go unable to gossip first range haslease false err storage replica command go store range storage replica command go store range min max change replicas of read existing descriptor range id start key end key replicas replicas replicas next replica id storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage log go range event remove range info removedreplica node id store id replica id updateddesc range id end key replicas next replica id storage replica go store range min max applied part of replica change txn begintransaction local range rangedescriptor min conditionalput local range rangedescriptor min put max min put max min perr storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range min max applied part of replica change txn conditionalput table min conditionalput table min conditionalput table min conditionalput table min conditionalput table min perr storage replica go store range storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica go store range min max applied part of replica change txn endtransaction local range rangedescriptor min perr storage replica go range outgoing raft transport stream to closed by the remote rpc error code desc range discarding message from nodeid storeid replicaid older than nextreplicaid storage replica command go unable to gossip first range haslease false err storage replica command go unable to gossip first range haslease false err stopper go quiesceing tasks left gossip infostore go storage queue go stopper go quiesceing tasks left storage queue go gossip infostore go server go transport handlestreams failed to read frame eof storage replica go range outgoing raft transport stream to closed by the remote rpc error code desc transport is closing storage replica go range outgoing raft transport stream to closed by the remote server go transport handlestreams failed to read frame read tcp use of closed network connection client go transport notifyerror got notified that the client transport was broken eof storage replica go range outgoing raft transport stream to closed by the remote rpc error code desc transport is closing server go transport handlestreams failed to read frame eof storage replica go range outgoing raft transport stream to closed by the remote storage replica go range outgoing raft transport stream to closed by the remote stopper go quiesceing tasks left storage queue go storage queue go on store range min max failed to send rpc sending to all replicas failed last error rpc error code desc transport is closing server go transport handlestreams failed to read frame eof storage replica go range outgoing raft transport stream to closed by the remote rpc error code desc transport is closing server go transport handlestreams failed to read frame eof server go transport handlestreams failed to read frame read tcp use of closed network connection server go transport handlestreams failed to read frame eof go src google golang org grpc clientconn go failed to dial grpc the connection is closing please retry go src google golang org grpc clientconn go grpc addrconn resettransport failed to create client transport connection error desc transport dial tcp getsockopt connection refused reconnecting to go src google golang org grpc clientconn go failed to dial grpc the connection is closing please retry storage replica go range outgoing raft transport stream to closed by the remote server go transport handlestreams failed to read frame eof server go transport handlestreams failed to read frame eof fail testgossipfirstrange leaktest go leaked goroutine goroutine google golang org grpc transport controller go src google golang org grpc transport client go created by google golang org grpc transport go src google golang org grpc transport client go run details runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs so far failures over runs completed failures over fail please assign take a look and update the issue accordingly | 0 |
20,034 | 10,583,399,418 | IssuesEvent | 2019-10-08 13:39:04 | citusdata/citus | https://api.github.com/repos/citusdata/citus | opened | Do not read from pg_dist_object for non-distributed functions multiple times | performance | We currently keep a record in `DistObjectCacheHash` for every function OID that we evaluate. However, we never mark the entry as valid for non-distributed functions and this causes us to read from pg_dist_object again instead of taking advantage of the cache when the function is not distributed.
https://github.com/citusdata/citus/blob/master/src/backend/distributed/utils/metadata_cache.c#L1004 | True | Do not read from pg_dist_object for non-distributed functions multiple times - We currently keep a record in `DistObjectCacheHash` for every function OID that we evaluate. However, we never mark the entry as valid for non-distributed functions and this causes us to read from pg_dist_object again instead of taking advantage of the cache when the function is not distributed.
https://github.com/citusdata/citus/blob/master/src/backend/distributed/utils/metadata_cache.c#L1004 | non_priority | do not read from pg dist object for non distributed functions multiple times we currently keep a record in distobjectcachehash for every function oid that we evaluate however we never mark the entry as valid for non distributed functions and this causes us to read from pg dist object again instead of taking advantage of the cache when the function is not distributed | 0 |
326,828 | 24,103,457,810 | IssuesEvent | 2022-09-20 04:35:38 | Face-Recognition-App-SD/Face-Recognition-Mobile | https://api.github.com/repos/Face-Recognition-App-SD/Face-Recognition-Mobile | opened | things to add to our read me file | documentation | Please list the things that you think will be needed for our read me here, write them, add them to read me file and check them off the list as you do
- [ ] steps to add aws vault
- [ ] | 1.0 | things to add to our read me file - Please list the things that you think will be needed for our read me here, write them, add them to read me file and check them off the list as you do
- [ ] steps to add aws vault
- [ ] | non_priority | things to add to our read me file please list the things that you think will be needed for our read me here write them add them to read me file and check them off the list as you do steps to add aws vault | 0 |
310,071 | 26,697,839,191 | IssuesEvent | 2023-01-27 11:57:38 | Uuvana-Studios/longvinter-windows-client | https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client | opened | can attack others in the safe zone of Nora Island. | Bug Not Tested | **Describe the bug**
Can attack others in the safe zone of Nora Island.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'Norra supply'
2. climbing over the cliff from below.
3. Can hit others
**Expected behavior**
A few users are killing a lot of users through this 'hanging'.
**Screenshots**
[https://youtu.be/EYJ8Vis3VKw](url)
**Desktop (please complete the following information):**
It doesn't affect the OS or version so...
**Additional context**
| 1.0 | can attack others in the safe zone of Nora Island. - **Describe the bug**
Can attack others in the safe zone of Nora Island.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'Norra supply'
2. climbing over the cliff from below.
3. Can hit others
**Expected behavior**
A few users are killing a lot of users through this 'hanging'.
**Screenshots**
[https://youtu.be/EYJ8Vis3VKw](url)
**Desktop (please complete the following information):**
It doesn't affect the OS or version so...
**Additional context**
| non_priority | can attack others in the safe zone of nora island describe the bug can attack others in the safe zone of nora island to reproduce steps to reproduce the behavior go to norra supply climbing over the cliff from below can hit others expected behavior a few users are killing a lot of users through this hanging screenshots url desktop please complete the following information it doesn t affect the os or version so additional context | 0 |
70,509 | 7,190,123,187 | IssuesEvent | 2018-02-02 16:13:38 | sjtug/lug | https://api.github.com/repos/sjtug/lug | closed | worker_test: TestUtilityRlimit fails occasionally | bug test | ```
? github.com/sjtug/lug [no test files]
ok github.com/sjtug/lug/config 0.002s
? github.com/sjtug/lug/exporter [no test files]
ok github.com/sjtug/lug/helper 0.006s
ok github.com/sjtug/lug/manager 6.004s
--- FAIL: TestUtilityRlimit (0.33s)
Error Trace: worker_test.go:94
Error: Should be true
time="2018-02-02T23:50:12+08:00" level=info msg="start execution" worker=shell
time="2018-02-02T23:50:12+08:00" level=info msg="Exporter initialized"
time="2018-02-02T23:50:12+08:00" level=info msg=succeed worker=shell
time="2018-02-02T23:50:12+08:00" level=info msg="Stderr: " worker=shell
FAIL
FAIL github.com/sjtug/lug/worker 1.340s
``` | 1.0 | worker_test: TestUtilityRlimit fails occasionally - ```
? github.com/sjtug/lug [no test files]
ok github.com/sjtug/lug/config 0.002s
? github.com/sjtug/lug/exporter [no test files]
ok github.com/sjtug/lug/helper 0.006s
ok github.com/sjtug/lug/manager 6.004s
--- FAIL: TestUtilityRlimit (0.33s)
Error Trace: worker_test.go:94
Error: Should be true
time="2018-02-02T23:50:12+08:00" level=info msg="start execution" worker=shell
time="2018-02-02T23:50:12+08:00" level=info msg="Exporter initialized"
time="2018-02-02T23:50:12+08:00" level=info msg=succeed worker=shell
time="2018-02-02T23:50:12+08:00" level=info msg="Stderr: " worker=shell
FAIL
FAIL github.com/sjtug/lug/worker 1.340s
``` | non_priority | worker test testutilityrlimit fails occasionally github com sjtug lug ok github com sjtug lug config github com sjtug lug exporter ok github com sjtug lug helper ok github com sjtug lug manager fail testutilityrlimit error trace worker test go error should be true time level info msg start execution worker shell time level info msg exporter initialized time level info msg succeed worker shell time level info msg stderr worker shell fail fail github com sjtug lug worker | 0 |
39,012 | 10,277,568,131 | IssuesEvent | 2019-08-25 06:11:01 | microsoft/qsharp-compiler | https://api.github.com/repos/microsoft/qsharp-compiler | closed | Allow to easily test compiler modifications | Area-Build Resolution-Done enhancement | It would be nice if there was as setup to easily test whether the compiler generates code that can be executed on various targets without having to build the compiler package each time. | 1.0 | Allow to easily test compiler modifications - It would be nice if there was as setup to easily test whether the compiler generates code that can be executed on various targets without having to build the compiler package each time. | non_priority | allow to easily test compiler modifications it would be nice if there was as setup to easily test whether the compiler generates code that can be executed on various targets without having to build the compiler package each time | 0 |
5,690 | 3,637,980,270 | IssuesEvent | 2016-02-12 13:44:52 | avTranscoder/avTranscoder | https://api.github.com/repos/avTranscoder/avTranscoder | closed | Launch pyTest on ubuntu with project built with libav | bug build prio:major | <a href="https://github.com/cchampet"><img src="https://avatars.githubusercontent.com/u/2589095?v=3" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [cchampet](https://github.com/cchampet)**
_Thursday Apr 09, 2015 at 16:50 GMT_
_Originally opened as https://github.com/mikrosimage/avTranscoder/issues/158_
----
Travis CI crash when it launches pyTests.
https://github.com/cchampet/avTranscoder/commit/a262d51925cca880f9b7b0b99a73e1f65489a089
<!---
@huboard:{"order":42.59375,"milestone_order":90.5,"custom_state":""}
-->
| 1.0 | Launch pyTest on ubuntu with project built with libav - <a href="https://github.com/cchampet"><img src="https://avatars.githubusercontent.com/u/2589095?v=3" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [cchampet](https://github.com/cchampet)**
_Thursday Apr 09, 2015 at 16:50 GMT_
_Originally opened as https://github.com/mikrosimage/avTranscoder/issues/158_
----
Travis CI crash when it launches pyTests.
https://github.com/cchampet/avTranscoder/commit/a262d51925cca880f9b7b0b99a73e1f65489a089
<!---
@huboard:{"order":42.59375,"milestone_order":90.5,"custom_state":""}
-->
| non_priority | launch pytest on ubuntu with project built with libav issue by thursday apr at gmt originally opened as travis ci crash when it launches pytests huboard order milestone order custom state | 0 |
94,599 | 16,010,731,574 | IssuesEvent | 2021-04-20 10:12:08 | wagner-deoliveira/proofy-react-app | https://api.github.com/repos/wagner-deoliveira/proofy-react-app | closed | CVE-2021-27290 (High) detected in ssri-6.0.1.tgz | security vulnerability | ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ssri-6.0.1.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz">https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz</a></p>
<p>Path to dependency file: proofy-react-app/package.json</p>
<p>Path to vulnerable library: proofy-react-app/node_modules/webpack/node_modules/ssri/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.3.tgz (Root Library)
- webpack-4.44.2.tgz
- terser-webpack-plugin-1.4.5.tgz
- cacache-12.0.4.tgz
- :x: **ssri-6.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/wagner-deoliveira/proofy-react-app/commit/de9af1cd15fc99bfbfec317c0ae8971c684a43c5">de9af1cd15fc99bfbfec317c0ae8971c684a43c5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290>CVE-2021-27290</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: v8.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-27290 (High) detected in ssri-6.0.1.tgz - ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ssri-6.0.1.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and verifies integrity metadata according to the SRI spec.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz">https://registry.npmjs.org/ssri/-/ssri-6.0.1.tgz</a></p>
<p>Path to dependency file: proofy-react-app/package.json</p>
<p>Path to vulnerable library: proofy-react-app/node_modules/webpack/node_modules/ssri/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.3.tgz (Root Library)
- webpack-4.44.2.tgz
- terser-webpack-plugin-1.4.5.tgz
- cacache-12.0.4.tgz
- :x: **ssri-6.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/wagner-deoliveira/proofy-react-app/commit/de9af1cd15fc99bfbfec317c0ae8971c684a43c5">de9af1cd15fc99bfbfec317c0ae8971c684a43c5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ssri 5.2.2-8.0.0, fixed in 8.0.1, processes SRIs using a regular expression which is vulnerable to a denial of service. Malicious SRIs could take an extremely long time to process, leading to denial of service. This issue only affects consumers using the strict option.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27290>CVE-2021-27290</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27290</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: v8.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in ssri tgz cve high severity vulnerability vulnerable library ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spec library home page a href path to dependency file proofy react app package json path to vulnerable library proofy react app node modules webpack node modules ssri package json dependency hierarchy react scripts tgz root library webpack tgz terser webpack plugin tgz cacache tgz x ssri tgz vulnerable library found in head commit a href found in base branch master vulnerability details ssri fixed in processes sris using a regular expression which is vulnerable to a denial of service malicious sris could take an extremely long time to process leading to denial of service this issue only affects consumers using the strict option publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
87,926 | 10,560,490,654 | IssuesEvent | 2019-10-04 14:00:05 | fack2/ptfb-griffinot | https://api.github.com/repos/fack2/ptfb-griffinot | closed | Potential App Pages/Flow | documentation | # Context
In the workshops on Thursday, we originally spoke about a website flow which would involve the team creating a login, finding a video hosting service, creating a quiz to take the user to the correct level, tracking progress, and leaving space for a potential payment system in the future. By the end of the workshop, particularly when creating the flow/page content outlined below, I was concerned about the amount of work that this project might involve.
Kim then proposed that an alternative could be to create the login and questionnaire system, but leave the videos (and therefore the payment system) on Teachable, and use links within our app to send people to the Teachable videos. This is not ideal, since it would require the user to have both a Teachable login and an app login, but it could be a good solution for an MVP.
This idea only came up at the end of the session, so we were not able to explore it further. I think an important part of the beginning of this design process will be deciding what you all as a team of developers think it is better for this first sprint.
# Potential App Flow (/draft potential user stories)
- User arrives on landing page, and is directed to login or to take the questionnaire
- User takes the questionnaire
- User arrives on a results page (could be the sign up page?) explaining the level that they should start on and asking for account details as well as some information about how often they want to practice, what goals they have, and their current thoughts about their child's progress
- User is directed to a main page/their profile page, where they can watch some introductory videos that explain the app's process
- User watches some education videos to learn more about what they are doing
- User then watches some activity videos in order to prepare for delivering the activities to their child
- User completes the activites and then returns to the app to record progress or results
- If the level is finished, the user is shown their goals and asked for some reflection on progress. They are then prompted to start the next level
- User can see progress on the main page
- User can browse and review resources if they need more help
# App pages and content
(Each title is a new page, and each bullet is something that should be available in the page)
### Landing page
- Call to action to go to questionnaire
- button to login
### Log in page
- email
- password
- link to questionnaire before signing up
### Questionnaire
- As described in "where to start flowchart"
- include breakpoints for each letter (A, B, C, etc)
### Results
- Sign up page (need to confirm this on Sunday)
- email
- password
- questions for the user:
- how many days do you want to practice?
- for how long?
- what are your overall goals for your child at the moment?(Choose 2 from a list of 10-15 prepoulated choices)
- Rate child's current level (how are they currently performing) with these goals from 1-10
- what is your satisfaction with that? from 1-10
- (payment page in future)
### Profile/Main page
- Introduction videos
- brief copy about process
- goals
- some form of progress tracking
- level that you're working on
- link to education videos
- potentially links to individual pages for videos (either on our site or Teachable)
- link to activity videos
- potentially links to individual pages for activities(either on our site or Teachable)
- final 'activity' to review goals set in sign-up, and re-answer questions relating to their chosen two goals
- i.e. "Rate child's current level (how are they currently performing) with these goals, and what is your satisfaction with that?"
- (if level finished but next level not paid for) link to pay for next level
- Resources page
- Education Videos (by level)
- list of videos
- title
- video
- indication of whether it has been watched
- Activity Videos (by level)
- list of warmups (by level)
- title
- videos or text/image
- list of activities
- title
- video
- text about goal/target
- some way of recording child's progress/achievement
- indication of completion
### Resources page
- basic list of various support resources
| 1.0 | Potential App Pages/Flow - # Context
In the workshops on Thursday, we originally spoke about a website flow which would involve the team creating a login, finding a video hosting service, creating a quiz to take the user to the correct level, tracking progress, and leaving space for a potential payment system in the future. By the end of the workshop, particularly when creating the flow/page content outlined below, I was concerned about the amount of work that this project might involve.
Kim then proposed that an alternative could be to create the login and questionnaire system, but leave the videos (and therefore the payment system) on Teachable, and use links within our app to send people to the Teachable videos. This is not ideal, since it would require the user to have both a Teachable login and an app login, but it could be a good solution for an MVP.
This idea only came up at the end of the session, so we were not able to explore it further. I think an important part of the beginning of this design process will be deciding what you all as a team of developers think it is better for this first sprint.
# Potential App Flow (/draft potential user stories)
- User arrives on landing page, and is directed to login or to take the questionnaire
- User takes the questionnaire
- User arrives on a results page (could be the sign up page?) explaining the level that they should start on and asking for account details as well as some information about how often they want to practice, what goals they have, and their current thoughts about their child's progress
- User is directed to a main page/their profile page, where they can watch some introductory videos that explain the app's process
- User watches some education videos to learn more about what they are doing
- User then watches some activity videos in order to prepare for delivering the activities to their child
- User completes the activites and then returns to the app to record progress or results
- If the level is finished, the user is shown their goals and asked for some reflection on progress. They are then prompted to start the next level
- User can see progress on the main page
- User can browse and review resources if they need more help
# App pages and content
(Each title is a new page, and each bullet is something that should be available in the page)
### Landing page
- Call to action to go to questionnaire
- button to login
### Log in page
- email
- password
- link to questionnaire before signing up
### Questionnaire
- As described in "where to start flowchart"
- include breakpoints for each letter (A, B, C, etc)
### Results
- Sign up page (need to confirm this on Sunday)
- email
- password
- questions for the user:
- how many days do you want to practice?
- for how long?
- what are your overall goals for your child at the moment?(Choose 2 from a list of 10-15 prepoulated choices)
- Rate child's current level (how are they currently performing) with these goals from 1-10
- what is your satisfaction with that? from 1-10
- (payment page in future)
### Profile/Main page
- Introduction videos
- brief copy about process
- goals
- some form of progress tracking
- level that you're working on
- link to education videos
- potentially links to individual pages for videos (either on our site or Teachable)
- link to activity videos
- potentially links to individual pages for activities(either on our site or Teachable)
- final 'activity' to review goals set in sign-up, and re-answer questions relating to their chosen two goals
- i.e. "Rate child's current level (how are they currently performing) with these goals, and what is your satisfaction with that?"
- (if level finished but next level not paid for) link to pay for next level
- Resources page
- Education Videos (by level)
- list of videos
- title
- video
- indication of whether it has been watched
- Activity Videos (by level)
- list of warmups (by level)
- title
- videos or text/image
- list of activities
- title
- video
- text about goal/target
- some way of recording child's progress/achievement
- indication of completion
### Resources page
- basic list of various support resources
| non_priority | potential app pages flow context in the workshops on thursday we originally spoke about a website flow which would involve the team creating a login finding a video hosting service creating a quiz to take the user to the correct level tracking progress and leaving space for a potential payment system in the future by the end of the workshop particularly when creating the flow page content outlined below i was concerned about the amount of work that this project might involve kim then proposed that an alternative could be to create the login and questionnaire system but leave the videos and therefore the payment system on teachable and use links within our app to send people to the teachable videos this is not ideal since it would require the user to have both a teachable login and an app login but it could be a good solution for an mvp this idea only came up at the end of the session so we were not able to explore it further i think an important part of the beginning of this design process will be deciding what you all as a team of developers think it is better for this first sprint potential app flow draft potential user stories user arrives on landing page and is directed to login or to take the questionnaire user takes the questionnaire user arrives on a results page could be the sign up page explaining the level that they should start on and asking for account details as well as some information about how often they want to practice what goals they have and their current thoughts about their child s progress user is directed to a main page their profile page where they can watch some introductory videos that explain the app s process user watches some education videos to learn more about what they are doing user then watches some activity videos in order to prepare for delivering the activities to their child user completes the activites and then returns to the app to record progress or results if the level is finished the user is shown their goals and asked for some reflection on progress they are then prompted to start the next level user can see progress on the main page user can browse and review resources if they need more help app pages and content each title is a new page and each bullet is something that should be available in the page landing page call to action to go to questionnaire button to login log in page email password link to questionnaire before signing up questionnaire as described in where to start flowchart include breakpoints for each letter a b c etc results sign up page need to confirm this on sunday email password questions for the user how many days do you want to practice for how long what are your overall goals for your child at the moment choose from a list of prepoulated choices rate child s current level how are they currently performing with these goals from what is your satisfaction with that from payment page in future profile main page introduction videos brief copy about process goals some form of progress tracking level that you re working on link to education videos potentially links to individual pages for videos either on our site or teachable link to activity videos potentially links to individual pages for activities either on our site or teachable final activity to review goals set in sign up and re answer questions relating to their chosen two goals i e rate child s current level how are they currently performing with these goals and what is your satisfaction with that if level finished but next level not paid for link to pay for next level resources page education videos by level list of videos title video indication of whether it has been watched activity videos by level list of warmups by level title videos or text image list of activities title video text about goal target some way of recording child s progress achievement indication of completion resources page basic list of various support resources | 0 |
34,284 | 29,189,977,165 | IssuesEvent | 2023-05-19 18:58:13 | woocommerce/woocommerce | https://api.github.com/repos/woocommerce/woocommerce | opened | Investigate E2E Package Infrastructure & Processes | type: task tool: monorepo infrastructure | ### Description
Before we can begin to adopt ownership over the package infrastructure and processes related to the various E2E packages we will need a deep understanding of it. We will need to dive into the various packages and testing directories in `plugins/woocommerce/tests/e2e` to figure out the specific differences and areas of improvement that we can provide.
* `package.json` scripts in packages and WooCommerce Core. There is some notable overlap with their usage of `wp-env` and we need to consider how it interacts with our own as a development environment.
* `e2e` vs `e2e-pw`: There's currently the current playwright E2E tests, but, also the older Puppeteer ones. We should check with Solaris and see if the old E2E tests are even used, and if they aren't, should we consider removing them?
* How do they manage changelogs and releases for packages? If we align them here we can start using our GH Action to release these packages more easily.
* What GitHub Actions exist in support of E2E tests? What kind of overlap is there here and are there ways that we can streamline/combine them based on our own experience with GitHub Actions?
* What kind of unused dependencies do the E2E packages have?
* Some of these packages are used externally but are no longer used internally. I speak mostly of the `e2e-environment`. Is this something we should consider deprecating in favor of people using something simpler like `wp-env`?
### Acceptance Criteria
Given the political nature of these changes we will need to:
* Reach out to Solaris to develop a proposal that makes sense.
* Publish a proposal for how to move forward, what Solaris should own and what Atlas should own. Make it clear what benefits exist and consequences exist so that good decisions can be made about how to proceed. | 1.0 | Investigate E2E Package Infrastructure & Processes - ### Description
Before we can begin to adopt ownership over the package infrastructure and processes related to the various E2E packages we will need a deep understanding of it. We will need to dive into the various packages and testing directories in `plugins/woocommerce/tests/e2e` to figure out the specific differences and areas of improvement that we can provide.
* `package.json` scripts in packages and WooCommerce Core. There is some notable overlap with their usage of `wp-env` and we need to consider how it interacts with our own as a development environment.
* `e2e` vs `e2e-pw`: There's currently the current playwright E2E tests, but, also the older Puppeteer ones. We should check with Solaris and see if the old E2E tests are even used, and if they aren't, should we consider removing them?
* How do they manage changelogs and releases for packages? If we align them here we can start using our GH Action to release these packages more easily.
* What GitHub Actions exist in support of E2E tests? What kind of overlap is there here and are there ways that we can streamline/combine them based on our own experience with GitHub Actions?
* What kind of unused dependencies do the E2E packages have?
* Some of these packages are used externally but are no longer used internally. I speak mostly of the `e2e-environment`. Is this something we should consider deprecating in favor of people using something simpler like `wp-env`?
### Acceptance Criteria
Given the political nature of these changes we will need to:
* Reach out to Solaris to develop a proposal that makes sense.
* Publish a proposal for how to move forward, what Solaris should own and what Atlas should own. Make it clear what benefits exist and consequences exist so that good decisions can be made about how to proceed. | non_priority | investigate package infrastructure processes description before we can begin to adopt ownership over the package infrastructure and processes related to the various packages we will need a deep understanding of it we will need to dive into the various packages and testing directories in plugins woocommerce tests to figure out the specific differences and areas of improvement that we can provide package json scripts in packages and woocommerce core there is some notable overlap with their usage of wp env and we need to consider how it interacts with our own as a development environment vs pw there s currently the current playwright tests but also the older puppeteer ones we should check with solaris and see if the old tests are even used and if they aren t should we consider removing them how do they manage changelogs and releases for packages if we align them here we can start using our gh action to release these packages more easily what github actions exist in support of tests what kind of overlap is there here and are there ways that we can streamline combine them based on our own experience with github actions what kind of unused dependencies do the packages have some of these packages are used externally but are no longer used internally i speak mostly of the environment is this something we should consider deprecating in favor of people using something simpler like wp env acceptance criteria given the political nature of these changes we will need to reach out to solaris to develop a proposal that makes sense publish a proposal for how to move forward what solaris should own and what atlas should own make it clear what benefits exist and consequences exist so that good decisions can be made about how to proceed | 0 |
40,445 | 16,482,935,963 | IssuesEvent | 2021-05-24 14:08:26 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Reporting fails on large dashboards | Feature:Reporting Team:AppServices Team:Reporting Services bug | **Kibana version**: 7.13.0 BC9
**Elasticsearch version**: 7.13.0 BC9
**Server OS version**: Ubuntu
**Browser version**: Chrome latest
**Original install method (e.g. download page, yum, from source, etc.)**:
Staging
**Description of the problem including expected versus actual behavior**:
Reports error on large dashboard.
**Steps to reproduce**:
1. Install ES/Kibana
2. Generate report on a large dashboard
**Provide logs and/or server output (if relevant)**:
```
{"type":"log","@timestamp":"2021-05-24T13:51:22+00:00","tags":["info","plugins","reporting","chromium-stderr"],"pid":18555,"message":"[0524/135122.246386:ERROR:gpu_init.cc(426)] Passthrough is not supported, GL is swiftshader"}
{"type":"log","@timestamp":"2021-05-24T13:49:47+00:00","tags":["error","plugins","reporting","printable_pdf","execute-job","kp2o13no0ebf8f5fe5fcpubj"],"pid":18555,"message":"Error: Protocol error (Page.captureScreenshot): Unable to capture screenshot\n at /home/vagrant/kibana-7.13.0-linux-x86_64/node_modules/puppeteer/lib/cjs/puppeteer/common/Connection.js:208:63\n at new Promise (<anonymous>)\n at CDPSession.send (/home/vagrant/kibana-7.13.0-linux-x86_64/node_modules/puppeteer/lib/cjs/puppeteer/common/Connection.js:207:16)\n at Page._screenshotTask (/home/vagrant/kibana-7.13.0-linux-x86_64/node_modules/puppeteer/lib/cjs/puppeteer/common/Page.js:1105:43)\n at runMicrotasks (<anonymous>)\n at processTicksAndRejections (internal/process/task_queues.js:93:5)"}
```

| 2.0 | Reporting fails on large dashboards - **Kibana version**: 7.13.0 BC9
**Elasticsearch version**: 7.13.0 BC9
**Server OS version**: Ubuntu
**Browser version**: Chrome latest
**Original install method (e.g. download page, yum, from source, etc.)**:
Staging
**Description of the problem including expected versus actual behavior**:
Reports error on large dashboard.
**Steps to reproduce**:
1. Install ES/Kibana
2. Generate report on a large dashboard
**Provide logs and/or server output (if relevant)**:
```
{"type":"log","@timestamp":"2021-05-24T13:51:22+00:00","tags":["info","plugins","reporting","chromium-stderr"],"pid":18555,"message":"[0524/135122.246386:ERROR:gpu_init.cc(426)] Passthrough is not supported, GL is swiftshader"}
{"type":"log","@timestamp":"2021-05-24T13:49:47+00:00","tags":["error","plugins","reporting","printable_pdf","execute-job","kp2o13no0ebf8f5fe5fcpubj"],"pid":18555,"message":"Error: Protocol error (Page.captureScreenshot): Unable to capture screenshot\n at /home/vagrant/kibana-7.13.0-linux-x86_64/node_modules/puppeteer/lib/cjs/puppeteer/common/Connection.js:208:63\n at new Promise (<anonymous>)\n at CDPSession.send (/home/vagrant/kibana-7.13.0-linux-x86_64/node_modules/puppeteer/lib/cjs/puppeteer/common/Connection.js:207:16)\n at Page._screenshotTask (/home/vagrant/kibana-7.13.0-linux-x86_64/node_modules/puppeteer/lib/cjs/puppeteer/common/Page.js:1105:43)\n at runMicrotasks (<anonymous>)\n at processTicksAndRejections (internal/process/task_queues.js:93:5)"}
```

| non_priority | reporting fails on large dashboards kibana version elasticsearch version server os version ubuntu browser version chrome latest original install method e g download page yum from source etc staging description of the problem including expected versus actual behavior reports error on large dashboard steps to reproduce install es kibana generate report on a large dashboard provide logs and or server output if relevant type log timestamp tags pid message passthrough is not supported gl is swiftshader type log timestamp tags pid message error protocol error page capturescreenshot unable to capture screenshot n at home vagrant kibana linux node modules puppeteer lib cjs puppeteer common connection js n at new promise n at cdpsession send home vagrant kibana linux node modules puppeteer lib cjs puppeteer common connection js n at page screenshottask home vagrant kibana linux node modules puppeteer lib cjs puppeteer common page js n at runmicrotasks n at processticksandrejections internal process task queues js | 0 |
44,866 | 12,415,767,622 | IssuesEvent | 2020-05-22 16:50:27 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Dropdowns and MultiSelects open inconsistently or not at all when using a wrapped-label layout | defect | **I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case**
https://stackblitz.com/edit/github-6wsadz
**Current behavior**
After surrounding a `p-dropdown` or `p-multiSelect` with a `label` tag, clicking on the dropdown icon or any portion of the multiSelect no longer expands their options.
**Expected behavior**
The components should behave the same regardless of whether they are wrapped in a `label` tag or not.
**Minimal reproduction of the problem with instructions**
1. Insert a `p-dropdown` or `p-multiSelect` in HTML and provide it an array of options.
2. Surround the component with a HTML `label` tag and add some arbitrary label.
3. Observe as the component no longer expands to show its options when clicked.
See example here: https://stackblitz.com/edit/github-6wsadz
**What is the motivation / use case for changing the behavior?**
My organization would like to implement a wrapped-label form framework so labels and inputs are automatically associated with one another and we no longer have to provide "for" and "id" tags on our labels/inputs. It will save us a lot of headache and boilerplate code in the long run.
**Please tell us about your environment:**
* **OS:** Windows 10
* **IDE:** Visual Studio Code
* **Package Manager:** NPM
* **HTTP Server:** Apache Tomcat
* **Angular version:** 7.2.7, verified on 9.0.0-rc4
* **PrimeNG version:** 7.1.0, verified on 9.0.0-rc1
* **Browser:** verified on [Chrome 79.0.3945.117 | Firefox 72.0.1 | Edge 79.0.309.65 | IE 11.535.18362.0]
* **Language:** [TypeScript 3.2.4 | ES6/7]
* **Node (for AoT issues):** `node --version` = v10.16.3
| 1.0 | Dropdowns and MultiSelects open inconsistently or not at all when using a wrapped-label layout - **I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case**
https://stackblitz.com/edit/github-6wsadz
**Current behavior**
After surrounding a `p-dropdown` or `p-multiSelect` with a `label` tag, clicking on the dropdown icon or any portion of the multiSelect no longer expands their options.
**Expected behavior**
The components should behave the same regardless of whether they are wrapped in a `label` tag or not.
**Minimal reproduction of the problem with instructions**
1. Insert a `p-dropdown` or `p-multiSelect` in HTML and provide it an array of options.
2. Surround the component with a HTML `label` tag and add some arbitrary label.
3. Observe as the component no longer expands to show its options when clicked.
See example here: https://stackblitz.com/edit/github-6wsadz
**What is the motivation / use case for changing the behavior?**
My organization would like to implement a wrapped-label form framework so labels and inputs are automatically associated with one another and we no longer have to provide "for" and "id" tags on our labels/inputs. It will save us a lot of headache and boilerplate code in the long run.
**Please tell us about your environment:**
* **OS:** Windows 10
* **IDE:** Visual Studio Code
* **Package Manager:** NPM
* **HTTP Server:** Apache Tomcat
* **Angular version:** 7.2.7, verified on 9.0.0-rc4
* **PrimeNG version:** 7.1.0, verified on 9.0.0-rc1
* **Browser:** verified on [Chrome 79.0.3945.117 | Firefox 72.0.1 | Edge 79.0.309.65 | IE 11.535.18362.0]
* **Language:** [TypeScript 3.2.4 | ES6/7]
* **Node (for AoT issues):** `node --version` = v10.16.3
| non_priority | dropdowns and multiselects open inconsistently or not at all when using a wrapped label layout i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see plunkr case current behavior after surrounding a p dropdown or p multiselect with a label tag clicking on the dropdown icon or any portion of the multiselect no longer expands their options expected behavior the components should behave the same regardless of whether they are wrapped in a label tag or not minimal reproduction of the problem with instructions insert a p dropdown or p multiselect in html and provide it an array of options surround the component with a html label tag and add some arbitrary label observe as the component no longer expands to show its options when clicked see example here what is the motivation use case for changing the behavior my organization would like to implement a wrapped label form framework so labels and inputs are automatically associated with one another and we no longer have to provide for and id tags on our labels inputs it will save us a lot of headache and boilerplate code in the long run please tell us about your environment os windows ide visual studio code package manager npm http server apache tomcat angular version verified on primeng version verified on browser verified on language node for aot issues node version | 0 |
117,818 | 9,960,225,186 | IssuesEvent | 2019-07-06 14:41:19 | TeamAmaze/AmazeFileManager | https://api.github.com/repos/TeamAmaze/AmazeFileManager | reopened | Issues copying to SD card | test on master | When I try to copy/paste a file from the internal storage to my SD card, an empty file (size: 0 byte) appears on my SD card that I can't open but with the right name.
I tried to do the same thing with the same file, but this time from the Android built-in file manager, and it worked. I can open the file, and it's written that it has a positive size on the built-in manager. But Amaze File Manager, after a refresh, still shows that the file is empty and I can't open it from there.
So then, I tried to copy/paste another file from my internal storage to my SD card using Amaze File Manager but trying to open it from the built-in file manager and indeed, there, the file is normal in my SD card even though AFM considers it as empty
I have a Xiaomi Mi A1 with Android 8.0
| 1.0 | Issues copying to SD card - When I try to copy/paste a file from the internal storage to my SD card, an empty file (size: 0 byte) appears on my SD card that I can't open but with the right name.
I tried to do the same thing with the same file, but this time from the Android built-in file manager, and it worked. I can open the file, and it's written that it has a positive size on the built-in manager. But Amaze File Manager, after a refresh, still shows that the file is empty and I can't open it from there.
So then, I tried to copy/paste another file from my internal storage to my SD card using Amaze File Manager but trying to open it from the built-in file manager and indeed, there, the file is normal in my SD card even though AFM considers it as empty
I have a Xiaomi Mi A1 with Android 8.0
| non_priority | issues copying to sd card when i try to copy paste a file from the internal storage to my sd card an empty file size byte appears on my sd card that i can t open but with the right name i tried to do the same thing with the same file but this time from the android built in file manager and it worked i can open the file and it s written that it has a positive size on the built in manager but amaze file manager after a refresh still shows that the file is empty and i can t open it from there so then i tried to copy paste another file from my internal storage to my sd card using amaze file manager but trying to open it from the built in file manager and indeed there the file is normal in my sd card even though afm considers it as empty i have a xiaomi mi with android | 0 |
9,467 | 3,286,724,976 | IssuesEvent | 2015-10-29 05:24:29 | web-animations/web-animations-js | https://api.github.com/repos/web-animations/web-animations-js | closed | what is the actual browser support for _this_ library? | Documentation | Browser support is pretty obfuscated. I go to this page: https://www.polymer-project.org/0.5/resources/compatibility.html
That page shows chrome as being the only supported browser for web animations. But i read further down to the polyfill browser support section which then directs me to a web components polyfill or a compatability matrix: https://github.com/WebComponents/webcomponentsjs#browser-support
That matrix only mentions: Custom Elements, HTML Imports, Shadow DOM and Templates.
No mention of the web animation API. And now I'm confused, do I need a webcomponents polyfill to use the web-animations polyfill?
So where can I find the actual browser support of _this_ library as a standalone? | 1.0 | what is the actual browser support for _this_ library? - Browser support is pretty obfuscated. I go to this page: https://www.polymer-project.org/0.5/resources/compatibility.html
That page shows chrome as being the only supported browser for web animations. But i read further down to the polyfill browser support section which then directs me to a web components polyfill or a compatability matrix: https://github.com/WebComponents/webcomponentsjs#browser-support
That matrix only mentions: Custom Elements, HTML Imports, Shadow DOM and Templates.
No mention of the web animation API. And now I'm confused, do I need a webcomponents polyfill to use the web-animations polyfill?
So where can I find the actual browser support of _this_ library as a standalone? | non_priority | what is the actual browser support for this library browser support is pretty obfuscated i go to this page that page shows chrome as being the only supported browser for web animations but i read further down to the polyfill browser support section which then directs me to a web components polyfill or a compatability matrix that matrix only mentions custom elements html imports shadow dom and templates no mention of the web animation api and now i m confused do i need a webcomponents polyfill to use the web animations polyfill so where can i find the actual browser support of this library as a standalone | 0 |
101,960 | 21,884,029,982 | IssuesEvent | 2022-05-19 16:44:03 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | reopened | Some mods hash calculation did not match expected hash | Bug Code Modding | - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
When update some mods, the console will report errors after download, like this:
Hash calculation for content package "EK | Armory" didn't match expected hash (F1CAED0F482D5F30F637C3AF0C5140B7 != 1CA92A30D1DB5E36FB98D3D9D49DB548)
**Steps To Reproduce**
Update some mods. some will have this error (not always).
**Version**
v0.17.12.0 windows
**Additional information**
It does not seem to be solved by the re-download function.I'm not sure if this has any effect on online play.
| 1.0 | Some mods hash calculation did not match expected hash - - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
When update some mods, the console will report errors after download, like this:
Hash calculation for content package "EK | Armory" didn't match expected hash (F1CAED0F482D5F30F637C3AF0C5140B7 != 1CA92A30D1DB5E36FB98D3D9D49DB548)
**Steps To Reproduce**
Update some mods. some will have this error (not always).
**Version**
v0.17.12.0 windows
**Additional information**
It does not seem to be solved by the re-download function.I'm not sure if this has any effect on online play.
| non_priority | some mods hash calculation did not match expected hash i have searched the issue tracker to check if the issue has already been reported description when update some mods the console will report errors after download like this hash calculation for content package ek armory didn t match expected hash steps to reproduce update some mods some will have this error not always version windows additional information it does not seem to be solved by the re download function i m not sure if this has any effect on online play | 0 |
73,630 | 15,277,903,973 | IssuesEvent | 2021-02-23 00:17:06 | Watemlifts/redash | https://api.github.com/repos/Watemlifts/redash | closed | CVE-2013-7459 (High) detected in pycrypto-2.6.1.tar.gz - autoclosed | security vulnerability | ## CVE-2013-7459 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pycrypto-2.6.1.tar.gz</b></p></summary>
<p>Cryptographic modules for Python.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/60/db/645aa9af249f059cc3a368b118de33889219e0362141e75d4eaf6f80f163/pycrypto-2.6.1.tar.gz">https://files.pythonhosted.org/packages/60/db/645aa9af249f059cc3a368b118de33889219e0362141e75d4eaf6f80f163/pycrypto-2.6.1.tar.gz</a></p>
<p>Path to dependency file: redash/redash/handlers</p>
<p>Path to vulnerable library: redash/redash/handlers,redash/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **pycrypto-2.6.1.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Watemlifts/redash/commit/f364fa4a64743076f075151eae4c972928dac50c">f364fa4a64743076f075151eae4c972928dac50c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Heap-based buffer overflow in the ALGnew function in block_templace.c in Python Cryptography Toolkit (aka pycrypto) allows remote attackers to execute arbitrary code as demonstrated by a crafted iv parameter to cryptmsg.py.
<p>Publish Date: 2017-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7459>CVE-2013-7459</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security.gentoo.org/glsa/201702-14">https://security.gentoo.org/glsa/201702-14</a></p>
<p>Release Date: 2017-02-20</p>
<p>Fix Resolution: All PyCrypto users should upgrade to the latest version >= pycrypto-2.6.1-r2
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2013-7459 (High) detected in pycrypto-2.6.1.tar.gz - autoclosed - ## CVE-2013-7459 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pycrypto-2.6.1.tar.gz</b></p></summary>
<p>Cryptographic modules for Python.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/60/db/645aa9af249f059cc3a368b118de33889219e0362141e75d4eaf6f80f163/pycrypto-2.6.1.tar.gz">https://files.pythonhosted.org/packages/60/db/645aa9af249f059cc3a368b118de33889219e0362141e75d4eaf6f80f163/pycrypto-2.6.1.tar.gz</a></p>
<p>Path to dependency file: redash/redash/handlers</p>
<p>Path to vulnerable library: redash/redash/handlers,redash/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **pycrypto-2.6.1.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Watemlifts/redash/commit/f364fa4a64743076f075151eae4c972928dac50c">f364fa4a64743076f075151eae4c972928dac50c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Heap-based buffer overflow in the ALGnew function in block_templace.c in Python Cryptography Toolkit (aka pycrypto) allows remote attackers to execute arbitrary code as demonstrated by a crafted iv parameter to cryptmsg.py.
<p>Publish Date: 2017-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-7459>CVE-2013-7459</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security.gentoo.org/glsa/201702-14">https://security.gentoo.org/glsa/201702-14</a></p>
<p>Release Date: 2017-02-20</p>
<p>Fix Resolution: All PyCrypto users should upgrade to the latest version >= pycrypto-2.6.1-r2
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in pycrypto tar gz autoclosed cve high severity vulnerability vulnerable library pycrypto tar gz cryptographic modules for python library home page a href path to dependency file redash redash handlers path to vulnerable library redash redash handlers redash requirements txt dependency hierarchy x pycrypto tar gz vulnerable library found in head commit a href vulnerability details heap based buffer overflow in the algnew function in block templace c in python cryptography toolkit aka pycrypto allows remote attackers to execute arbitrary code as demonstrated by a crafted iv parameter to cryptmsg py publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution all pycrypto users should upgrade to the latest version pycrypto step up your open source security game with whitesource | 0 |
82,124 | 23,676,676,485 | IssuesEvent | 2022-08-28 07:21:15 | junit-pioneer/junit-pioneer | https://api.github.com/repos/junit-pioneer/junit-pioneer | closed | Include JUnit 5.9 in build | 📖 theme: build 🚦 status: in progress 🏗️ type: task ⚙️ component: Pioneer | JUnit 5.9.0-RC1 has been released:
https://junit.org/junit5/docs/snapshot/release-notes/#release-notes-5.9.0-RC1
So the final release is probably just around the corner.
Including 5.9.0-RC1 into our build:
https://github.com/junit-pioneer/junit-pioneer/pull/651/commits/12edd783323165fd6b514942a909a691bc2c2dca
Currently causes the following error:
```text
/home/runner/work/junit-pioneer/junit-pioneer/src/test/java/org/junitpioneer/internal/TestExtensionContext.java:33: error: TestExtensionContext is not abstract and does not override abstract method getExecutableInvoker() in ExtensionContext
public class TestExtensionContext implements ExtensionContext {
```
We should fix this and include JUnit 5.9 in our build. | 1.0 | Include JUnit 5.9 in build - JUnit 5.9.0-RC1 has been released:
https://junit.org/junit5/docs/snapshot/release-notes/#release-notes-5.9.0-RC1
So the final release is probably just around the corner.
Including 5.9.0-RC1 into our build:
https://github.com/junit-pioneer/junit-pioneer/pull/651/commits/12edd783323165fd6b514942a909a691bc2c2dca
Currently causes the following error:
```text
/home/runner/work/junit-pioneer/junit-pioneer/src/test/java/org/junitpioneer/internal/TestExtensionContext.java:33: error: TestExtensionContext is not abstract and does not override abstract method getExecutableInvoker() in ExtensionContext
public class TestExtensionContext implements ExtensionContext {
```
We should fix this and include JUnit 5.9 in our build. | non_priority | include junit in build junit has been released so the final release is probably just around the corner including into our build currently causes the following error text home runner work junit pioneer junit pioneer src test java org junitpioneer internal testextensioncontext java error testextensioncontext is not abstract and does not override abstract method getexecutableinvoker in extensioncontext public class testextensioncontext implements extensioncontext we should fix this and include junit in our build | 0 |
63,111 | 15,435,490,550 | IssuesEvent | 2021-03-07 09:06:20 | BlueBrain/nmodl | https://api.github.com/repos/BlueBrain/nmodl | closed | Issue while building on Apple M1 with AppleClang 12 | bug build-system | Building todays master on vanila Apple M1 with apple clang:
```sh
bb-fvff266jq05n:build kumbhar$ cmake .. -DCMAKE_INSTALL_PREFIX=$HOME/nmodl
-- The CXX compiler identification is AppleClang 12.0.0.12000032
-- Detecting CXX compiler ABI info
-- Detecting CXX compiler ABI info - done
-- Check for working CXX compiler: /Library/Developer/CommandLineTools/usr/bin/c++ - skipped
-- Detecting CXX compile features
-- Detecting CXX compile features - done
-- CHECKING FOR FLEX/BISON
-- Found FLEX: /opt/homebrew/opt/flex/bin/flex (found suitable version "2.6.4", minimum required is "2.6")
-- Found BISON: /opt/homebrew/opt/bison/bin/bison (found suitable version "3.7.5", minimum required is "3.0")
-- Adding Flex include path as : /opt/homebrew/opt/flex/include/
-- Found Git: /usr/bin/git (found version "2.24.3 (Apple Git-128)")
-- Sub-project : using fmt from "/Users/kumbhar/nmodl/ext/fmt"
-- Sub-project : using spdlog from "/Users/kumbhar/nmodl/ext/spdlog"
-- Sub-project : using pybind11 from "/Users/kumbhar/nmodl/ext/pybind11"
-- pybind11 v2.6.1
-- Found PythonInterp: /opt/homebrew/bin/python3.9 (found version "3.9.2")
-- Found PythonLibs: /opt/homebrew/opt/python@3.9/Frameworks/Python.framework/Versions/3.9/lib/libpython3.9.dylib
-- Performing Test HAS_FLTO
-- Performing Test HAS_FLTO - Success
-- Performing Test HAS_FLTO_THIN
-- Performing Test HAS_FLTO_THIN - Success
-- Sub-project : using cli11 from "/Users/kumbhar/nmodl/ext/cli11"
-- Sub-project : using eigen from "/Users/kumbhar/nmodl/ext/eigen"
-- Version: 6.2.0
-- Build type:
-- CXX_STANDARD: 11
-- Performing Test has_std_11_flag
-- Performing Test has_std_11_flag - Success
-- Performing Test has_std_0x_flag
-- Performing Test has_std_0x_flag - Success
-- Performing Test SUPPORTS_USER_DEFINED_LITERALS
-- Performing Test SUPPORTS_USER_DEFINED_LITERALS - Success
-- Performing Test FMT_HAS_VARIANT
-- Performing Test FMT_HAS_VARIANT - Success
-- Required features: cxx_variadic_templates
-- Performing Test HAS_NULLPTR_WARNING
-- Performing Test HAS_NULLPTR_WARNING - Success
-- Looking for strtod_l
-- Looking for strtod_l - found
-- Sub-project : using hpc-coding-conventions from "/Users/kumbhar/nmodl/cmake/hpc-coding-conventions"
-- NMODL_FORMATTING: OFF
-- NMODL_FORMATTING_ON: all
-- NMODL_FORMATTING_CPP_CHANGES_ONLY: OFF
-- NMODL_TEST_FORMATTING: OFF
-- NMODL_FORMATTING_NO_SUBMODULES: ON
-- NMODL_CLANG_FORMAT: OFF
-- NMODL_CMAKE_FORMAT: OFF
-- NMODL_GIT_HOOKS: OFF
-- NMODL_GIT_COMMIT_HOOKS:
-- NMODL_GIT_PUSH_HOOKS: courtesy-msg
-- NMODL_STATIC_ANALYSIS: OFF
-- NMODL_TEST_STATIC_ANALYSIS: OFF
-- Could NOT find ClangFormat (missing: ClangFormat_EXECUTABLE)
-- CHECKING FOR PYTHON
-- Found PythonInterp: /opt/homebrew/bin/python3.9 (found suitable version "3.9.2", minimum required is "3.5")
--
-- Configured NMODL 0.2 (791b8a1 2021-02-25 08:23:25 +0100)
--
-- Some things you can do now:
-- --------------------+--------------------------------------------------------
-- Command | Description
-- --------------------+--------------------------------------------------------
-- make | Build the project
-- make test | Run unit tests
-- make install | Will install NMODL to: /Users/kumbhar/nmodl
-- --------------------+--------------------------------------------------------
-- Build option | Status
-- --------------------+--------------------------------------------------------
-- CXX COMPILER | /Library/Developer/CommandLineTools/usr/bin/c++
-- COMPILE FLAGS |
-- Build Type |
-- Legacy Units | OFF
-- Python Bindings | ON
-- Flex | /opt/homebrew/opt/flex/bin/flex
-- Bison | /opt/homebrew/opt/bison/bin/bison
-- Python | /opt/homebrew/bin/python3.9
-- --------------+--------------------------------------------------------------
-- See documentation : https://github.com/BlueBrain/nmodl/
-- --------------+--------------------------------------------------------------
--
-- Configuring done
-- Generating done
-- Build files have been written to: /Users/kumbhar/nmodl/build
```
But while building I see:
```sh
bb-fvff266jq05n:build kumbhar$ make
Scanning dependencies of target util_obj
[ 1%] Building CXX object src/utils/CMakeFiles/util_obj.dir/common_utils.cpp.o
[ 1%] Building CXX object src/utils/CMakeFiles/util_obj.dir/file_library.cpp.o
[ 2%] Building CXX object src/utils/CMakeFiles/util_obj.dir/logger.cpp.o
[ 2%] Building CXX object src/utils/CMakeFiles/util_obj.dir/perf_stat.cpp.o
[ 3%] Building CXX object src/utils/CMakeFiles/util_obj.dir/table_data.cpp.o
[ 3%] Building CXX object src/utils/CMakeFiles/util_obj.dir/__/config/config.cpp.o
[ 3%] Built target util_obj
....
Scanning dependencies of target testlexer
[ 26%] Building CXX object test/unit/CMakeFiles/testlexer.dir/lexer/tokens.cpp.o
In file included from /Users/kumbhar/nmodl/test/unit/lexer/tokens.cpp:12:
/Users/kumbhar/nmodl/ext/catch/catch.hpp:4167:13: error: invalid token in expression
CATCH_BREAK_INTO_DEBUGGER();
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1392:75: note: expanded from macro 'CATCH_BREAK_INTO_DEBUGGER'
#define CATCH_BREAK_INTO_DEBUGGER() if( Catch::isDebuggerActive() ) { CATCH_TRAP(); }
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1371:34: note: expanded from macro 'CATCH_TRAP'
#define CATCH_TRAP() __asm__("int $3\n" : : ) /* NOLINT */
^
<inline asm>:1:6: note: instantiated into assembly here
int $3
^
In file included from /Users/kumbhar/nmodl/test/unit/lexer/tokens.cpp:12:
/Users/kumbhar/nmodl/ext/catch/catch.hpp:4167:13: error: invalid operand
CATCH_BREAK_INTO_DEBUGGER();
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1392:75: note: expanded from macro 'CATCH_BREAK_INTO_DEBUGGER'
#define CATCH_BREAK_INTO_DEBUGGER() if( Catch::isDebuggerActive() ) { CATCH_TRAP(); }
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1371:34: note: expanded from macro 'CATCH_TRAP'
#define CATCH_TRAP() __asm__("int $3\n" : : ) /* NOLINT */
^
<inline asm>:1:6: note: instantiated into assembly here
int $3
^
...
```
| 1.0 | Issue while building on Apple M1 with AppleClang 12 - Building todays master on vanila Apple M1 with apple clang:
```sh
bb-fvff266jq05n:build kumbhar$ cmake .. -DCMAKE_INSTALL_PREFIX=$HOME/nmodl
-- The CXX compiler identification is AppleClang 12.0.0.12000032
-- Detecting CXX compiler ABI info
-- Detecting CXX compiler ABI info - done
-- Check for working CXX compiler: /Library/Developer/CommandLineTools/usr/bin/c++ - skipped
-- Detecting CXX compile features
-- Detecting CXX compile features - done
-- CHECKING FOR FLEX/BISON
-- Found FLEX: /opt/homebrew/opt/flex/bin/flex (found suitable version "2.6.4", minimum required is "2.6")
-- Found BISON: /opt/homebrew/opt/bison/bin/bison (found suitable version "3.7.5", minimum required is "3.0")
-- Adding Flex include path as : /opt/homebrew/opt/flex/include/
-- Found Git: /usr/bin/git (found version "2.24.3 (Apple Git-128)")
-- Sub-project : using fmt from "/Users/kumbhar/nmodl/ext/fmt"
-- Sub-project : using spdlog from "/Users/kumbhar/nmodl/ext/spdlog"
-- Sub-project : using pybind11 from "/Users/kumbhar/nmodl/ext/pybind11"
-- pybind11 v2.6.1
-- Found PythonInterp: /opt/homebrew/bin/python3.9 (found version "3.9.2")
-- Found PythonLibs: /opt/homebrew/opt/python@3.9/Frameworks/Python.framework/Versions/3.9/lib/libpython3.9.dylib
-- Performing Test HAS_FLTO
-- Performing Test HAS_FLTO - Success
-- Performing Test HAS_FLTO_THIN
-- Performing Test HAS_FLTO_THIN - Success
-- Sub-project : using cli11 from "/Users/kumbhar/nmodl/ext/cli11"
-- Sub-project : using eigen from "/Users/kumbhar/nmodl/ext/eigen"
-- Version: 6.2.0
-- Build type:
-- CXX_STANDARD: 11
-- Performing Test has_std_11_flag
-- Performing Test has_std_11_flag - Success
-- Performing Test has_std_0x_flag
-- Performing Test has_std_0x_flag - Success
-- Performing Test SUPPORTS_USER_DEFINED_LITERALS
-- Performing Test SUPPORTS_USER_DEFINED_LITERALS - Success
-- Performing Test FMT_HAS_VARIANT
-- Performing Test FMT_HAS_VARIANT - Success
-- Required features: cxx_variadic_templates
-- Performing Test HAS_NULLPTR_WARNING
-- Performing Test HAS_NULLPTR_WARNING - Success
-- Looking for strtod_l
-- Looking for strtod_l - found
-- Sub-project : using hpc-coding-conventions from "/Users/kumbhar/nmodl/cmake/hpc-coding-conventions"
-- NMODL_FORMATTING: OFF
-- NMODL_FORMATTING_ON: all
-- NMODL_FORMATTING_CPP_CHANGES_ONLY: OFF
-- NMODL_TEST_FORMATTING: OFF
-- NMODL_FORMATTING_NO_SUBMODULES: ON
-- NMODL_CLANG_FORMAT: OFF
-- NMODL_CMAKE_FORMAT: OFF
-- NMODL_GIT_HOOKS: OFF
-- NMODL_GIT_COMMIT_HOOKS:
-- NMODL_GIT_PUSH_HOOKS: courtesy-msg
-- NMODL_STATIC_ANALYSIS: OFF
-- NMODL_TEST_STATIC_ANALYSIS: OFF
-- Could NOT find ClangFormat (missing: ClangFormat_EXECUTABLE)
-- CHECKING FOR PYTHON
-- Found PythonInterp: /opt/homebrew/bin/python3.9 (found suitable version "3.9.2", minimum required is "3.5")
--
-- Configured NMODL 0.2 (791b8a1 2021-02-25 08:23:25 +0100)
--
-- Some things you can do now:
-- --------------------+--------------------------------------------------------
-- Command | Description
-- --------------------+--------------------------------------------------------
-- make | Build the project
-- make test | Run unit tests
-- make install | Will install NMODL to: /Users/kumbhar/nmodl
-- --------------------+--------------------------------------------------------
-- Build option | Status
-- --------------------+--------------------------------------------------------
-- CXX COMPILER | /Library/Developer/CommandLineTools/usr/bin/c++
-- COMPILE FLAGS |
-- Build Type |
-- Legacy Units | OFF
-- Python Bindings | ON
-- Flex | /opt/homebrew/opt/flex/bin/flex
-- Bison | /opt/homebrew/opt/bison/bin/bison
-- Python | /opt/homebrew/bin/python3.9
-- --------------+--------------------------------------------------------------
-- See documentation : https://github.com/BlueBrain/nmodl/
-- --------------+--------------------------------------------------------------
--
-- Configuring done
-- Generating done
-- Build files have been written to: /Users/kumbhar/nmodl/build
```
But while building I see:
```sh
bb-fvff266jq05n:build kumbhar$ make
Scanning dependencies of target util_obj
[ 1%] Building CXX object src/utils/CMakeFiles/util_obj.dir/common_utils.cpp.o
[ 1%] Building CXX object src/utils/CMakeFiles/util_obj.dir/file_library.cpp.o
[ 2%] Building CXX object src/utils/CMakeFiles/util_obj.dir/logger.cpp.o
[ 2%] Building CXX object src/utils/CMakeFiles/util_obj.dir/perf_stat.cpp.o
[ 3%] Building CXX object src/utils/CMakeFiles/util_obj.dir/table_data.cpp.o
[ 3%] Building CXX object src/utils/CMakeFiles/util_obj.dir/__/config/config.cpp.o
[ 3%] Built target util_obj
....
Scanning dependencies of target testlexer
[ 26%] Building CXX object test/unit/CMakeFiles/testlexer.dir/lexer/tokens.cpp.o
In file included from /Users/kumbhar/nmodl/test/unit/lexer/tokens.cpp:12:
/Users/kumbhar/nmodl/ext/catch/catch.hpp:4167:13: error: invalid token in expression
CATCH_BREAK_INTO_DEBUGGER();
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1392:75: note: expanded from macro 'CATCH_BREAK_INTO_DEBUGGER'
#define CATCH_BREAK_INTO_DEBUGGER() if( Catch::isDebuggerActive() ) { CATCH_TRAP(); }
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1371:34: note: expanded from macro 'CATCH_TRAP'
#define CATCH_TRAP() __asm__("int $3\n" : : ) /* NOLINT */
^
<inline asm>:1:6: note: instantiated into assembly here
int $3
^
In file included from /Users/kumbhar/nmodl/test/unit/lexer/tokens.cpp:12:
/Users/kumbhar/nmodl/ext/catch/catch.hpp:4167:13: error: invalid operand
CATCH_BREAK_INTO_DEBUGGER();
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1392:75: note: expanded from macro 'CATCH_BREAK_INTO_DEBUGGER'
#define CATCH_BREAK_INTO_DEBUGGER() if( Catch::isDebuggerActive() ) { CATCH_TRAP(); }
^
/Users/kumbhar/nmodl/ext/catch/catch.hpp:1371:34: note: expanded from macro 'CATCH_TRAP'
#define CATCH_TRAP() __asm__("int $3\n" : : ) /* NOLINT */
^
<inline asm>:1:6: note: instantiated into assembly here
int $3
^
...
```
| non_priority | issue while building on apple with appleclang building todays master on vanila apple with apple clang sh bb build kumbhar cmake dcmake install prefix home nmodl the cxx compiler identification is appleclang detecting cxx compiler abi info detecting cxx compiler abi info done check for working cxx compiler library developer commandlinetools usr bin c skipped detecting cxx compile features detecting cxx compile features done checking for flex bison found flex opt homebrew opt flex bin flex found suitable version minimum required is found bison opt homebrew opt bison bin bison found suitable version minimum required is adding flex include path as opt homebrew opt flex include found git usr bin git found version apple git sub project using fmt from users kumbhar nmodl ext fmt sub project using spdlog from users kumbhar nmodl ext spdlog sub project using from users kumbhar nmodl ext found pythoninterp opt homebrew bin found version found pythonlibs opt homebrew opt python frameworks python framework versions lib dylib performing test has flto performing test has flto success performing test has flto thin performing test has flto thin success sub project using from users kumbhar nmodl ext sub project using eigen from users kumbhar nmodl ext eigen version build type cxx standard performing test has std flag performing test has std flag success performing test has std flag performing test has std flag success performing test supports user defined literals performing test supports user defined literals success performing test fmt has variant performing test fmt has variant success required features cxx variadic templates performing test has nullptr warning performing test has nullptr warning success looking for strtod l looking for strtod l found sub project using hpc coding conventions from users kumbhar nmodl cmake hpc coding conventions nmodl formatting off nmodl formatting on all nmodl formatting cpp changes only off nmodl test formatting off nmodl formatting no submodules on nmodl clang format off nmodl cmake format off nmodl git hooks off nmodl git commit hooks nmodl git push hooks courtesy msg nmodl static analysis off nmodl test static analysis off could not find clangformat missing clangformat executable checking for python found pythoninterp opt homebrew bin found suitable version minimum required is configured nmodl some things you can do now command description make build the project make test run unit tests make install will install nmodl to users kumbhar nmodl build option status cxx compiler library developer commandlinetools usr bin c compile flags build type legacy units off python bindings on flex opt homebrew opt flex bin flex bison opt homebrew opt bison bin bison python opt homebrew bin see documentation configuring done generating done build files have been written to users kumbhar nmodl build but while building i see sh bb build kumbhar make scanning dependencies of target util obj building cxx object src utils cmakefiles util obj dir common utils cpp o building cxx object src utils cmakefiles util obj dir file library cpp o building cxx object src utils cmakefiles util obj dir logger cpp o building cxx object src utils cmakefiles util obj dir perf stat cpp o building cxx object src utils cmakefiles util obj dir table data cpp o building cxx object src utils cmakefiles util obj dir config config cpp o built target util obj scanning dependencies of target testlexer building cxx object test unit cmakefiles testlexer dir lexer tokens cpp o in file included from users kumbhar nmodl test unit lexer tokens cpp users kumbhar nmodl ext catch catch hpp error invalid token in expression catch break into debugger users kumbhar nmodl ext catch catch hpp note expanded from macro catch break into debugger define catch break into debugger if catch isdebuggeractive catch trap users kumbhar nmodl ext catch catch hpp note expanded from macro catch trap define catch trap asm int n nolint note instantiated into assembly here int in file included from users kumbhar nmodl test unit lexer tokens cpp users kumbhar nmodl ext catch catch hpp error invalid operand catch break into debugger users kumbhar nmodl ext catch catch hpp note expanded from macro catch break into debugger define catch break into debugger if catch isdebuggeractive catch trap users kumbhar nmodl ext catch catch hpp note expanded from macro catch trap define catch trap asm int n nolint note instantiated into assembly here int | 0 |
147,235 | 13,203,853,243 | IssuesEvent | 2020-08-14 14:52:34 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | Acceptance tests do not seem to adopt local schema changes for development | documentation provider | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
- terraform v0.12.24
- terraform-provider-aws master
### Expected Behavior
Acceptance tests adopt local schema changes when running.
### Actual Behavior
Acceptance tests ignore local schema changes when running.
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. Pull the latest terraform-provider-aws and modify any `Schema`.
2. Run the acceptance tests related to the schema, and see accs ignore the changes
### Important Factoids
First I used terraform v0.12.24 and saw this behavior. After switching to v0.12.29, this seems not to happen anymore. I feel this issue occurred after updating Terraform Plugin SDK, but not pretty sure if that really is the case.
If there is a dependency on the terraform version, it would be nice if we update [the documentation](https://github.com/terraform-providers/terraform-provider-aws/blob/master/docs/DEVELOPMENT.md) for developers. Thank you! 👍
| 1.0 | Acceptance tests do not seem to adopt local schema changes for development - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
- terraform v0.12.24
- terraform-provider-aws master
### Expected Behavior
Acceptance tests adopt local schema changes when running.
### Actual Behavior
Acceptance tests ignore local schema changes when running.
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. Pull the latest terraform-provider-aws and modify any `Schema`.
2. Run the acceptance tests related to the schema, and see accs ignore the changes
### Important Factoids
First I used terraform v0.12.24 and saw this behavior. After switching to v0.12.29, this seems not to happen anymore. I feel this issue occurred after updating Terraform Plugin SDK, but not pretty sure if that really is the case.
If there is a dependency on the terraform version, it would be nice if we update [the documentation](https://github.com/terraform-providers/terraform-provider-aws/blob/master/docs/DEVELOPMENT.md) for developers. Thank you! 👍
| non_priority | acceptance tests do not seem to adopt local schema changes for development please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one of these scenarios we recommend opening an issue in the instead community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform cli and terraform aws provider version terraform terraform provider aws master expected behavior acceptance tests adopt local schema changes when running actual behavior acceptance tests ignore local schema changes when running steps to reproduce pull the latest terraform provider aws and modify any schema run the acceptance tests related to the schema and see accs ignore the changes important factoids first i used terraform and saw this behavior after switching to this seems not to happen anymore i feel this issue occurred after updating terraform plugin sdk but not pretty sure if that really is the case if there is a dependency on the terraform version it would be nice if we update for developers thank you 👍 | 0 |
42,932 | 11,102,595,497 | IssuesEvent | 2019-12-17 00:37:46 | NoahAGonzales/vys-phys-convertor | https://api.github.com/repos/NoahAGonzales/vys-phys-convertor | closed | Recommend settings | building | Recommend settings such as the base height, height, and smoothing based on the scale and the picture and general. | 1.0 | Recommend settings - Recommend settings such as the base height, height, and smoothing based on the scale and the picture and general. | non_priority | recommend settings recommend settings such as the base height height and smoothing based on the scale and the picture and general | 0 |
212,654 | 23,934,096,198 | IssuesEvent | 2022-09-11 01:02:19 | brightcove/cloud-custodian | https://api.github.com/repos/brightcove/cloud-custodian | closed | CVE-2022-29217 (High) detected in PyJWT-1.7.1-py2.py3-none-any.whl - autoclosed | security vulnerability | ## CVE-2022-29217 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyJWT-1.7.1-py2.py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /tools/c7n_azure/requirements.txt</p>
<p>Path to vulnerable library: /tools/c7n_azure/requirements.txt,/tools/c7n_azure/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **PyJWT-1.7.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>brightcove</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
PyJWT is a Python implementation of RFC 7519. PyJWT supports multiple different JWT signing algorithms. With JWT, an attacker submitting the JWT token can choose the used signing algorithm. The PyJWT library requires that the application chooses what algorithms are supported. The application can specify `jwt.algorithms.get_default_algorithms()` to get support for all algorithms, or specify a single algorithm. The issue is not that big as `algorithms=jwt.algorithms.get_default_algorithms()` has to be used. Users should upgrade to v2.4.0 to receive a patch for this issue. As a workaround, always be explicit with the algorithms that are accepted and expected when decoding.
<p>Publish Date: 2022-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29217>CVE-2022-29217</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217</a></p>
<p>Release Date: 2022-05-24</p>
<p>Fix Resolution: PyJWT - 2.4.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"PyJWT","packageVersion":"1.7.1","packageFilePaths":["/tools/c7n_azure/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"PyJWT:1.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"PyJWT - 2.4.0","isBinary":false}],"baseBranches":["brightcove"],"vulnerabilityIdentifier":"CVE-2022-29217","vulnerabilityDetails":"PyJWT is a Python implementation of RFC 7519. PyJWT supports multiple different JWT signing algorithms. With JWT, an attacker submitting the JWT token can choose the used signing algorithm. The PyJWT library requires that the application chooses what algorithms are supported. The application can specify `jwt.algorithms.get_default_algorithms()` to get support for all algorithms, or specify a single algorithm. The issue is not that big as `algorithms\u003djwt.algorithms.get_default_algorithms()` has to be used. Users should upgrade to v2.4.0 to receive a patch for this issue. As a workaround, always be explicit with the algorithms that are accepted and expected when decoding.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29217","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-29217 (High) detected in PyJWT-1.7.1-py2.py3-none-any.whl - autoclosed - ## CVE-2022-29217 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyJWT-1.7.1-py2.py3-none-any.whl</b></p></summary>
<p>JSON Web Token implementation in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/87/8b/6a9f14b5f781697e51259d81657e6048fd31a113229cf346880bb7545565/PyJWT-1.7.1-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /tools/c7n_azure/requirements.txt</p>
<p>Path to vulnerable library: /tools/c7n_azure/requirements.txt,/tools/c7n_azure/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **PyJWT-1.7.1-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>brightcove</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
PyJWT is a Python implementation of RFC 7519. PyJWT supports multiple different JWT signing algorithms. With JWT, an attacker submitting the JWT token can choose the used signing algorithm. The PyJWT library requires that the application chooses what algorithms are supported. The application can specify `jwt.algorithms.get_default_algorithms()` to get support for all algorithms, or specify a single algorithm. The issue is not that big as `algorithms=jwt.algorithms.get_default_algorithms()` has to be used. Users should upgrade to v2.4.0 to receive a patch for this issue. As a workaround, always be explicit with the algorithms that are accepted and expected when decoding.
<p>Publish Date: 2022-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29217>CVE-2022-29217</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29217</a></p>
<p>Release Date: 2022-05-24</p>
<p>Fix Resolution: PyJWT - 2.4.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"PyJWT","packageVersion":"1.7.1","packageFilePaths":["/tools/c7n_azure/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"PyJWT:1.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"PyJWT - 2.4.0","isBinary":false}],"baseBranches":["brightcove"],"vulnerabilityIdentifier":"CVE-2022-29217","vulnerabilityDetails":"PyJWT is a Python implementation of RFC 7519. PyJWT supports multiple different JWT signing algorithms. With JWT, an attacker submitting the JWT token can choose the used signing algorithm. The PyJWT library requires that the application chooses what algorithms are supported. The application can specify `jwt.algorithms.get_default_algorithms()` to get support for all algorithms, or specify a single algorithm. The issue is not that big as `algorithms\u003djwt.algorithms.get_default_algorithms()` has to be used. Users should upgrade to v2.4.0 to receive a patch for this issue. As a workaround, always be explicit with the algorithms that are accepted and expected when decoding.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29217","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in pyjwt none any whl autoclosed cve high severity vulnerability vulnerable library pyjwt none any whl json web token implementation in python library home page a href path to dependency file tools azure requirements txt path to vulnerable library tools azure requirements txt tools azure requirements txt dependency hierarchy x pyjwt none any whl vulnerable library found in base branch brightcove vulnerability details pyjwt is a python implementation of rfc pyjwt supports multiple different jwt signing algorithms with jwt an attacker submitting the jwt token can choose the used signing algorithm the pyjwt library requires that the application chooses what algorithms are supported the application can specify jwt algorithms get default algorithms to get support for all algorithms or specify a single algorithm the issue is not that big as algorithms jwt algorithms get default algorithms has to be used users should upgrade to to receive a patch for this issue as a workaround always be explicit with the algorithms that are accepted and expected when decoding publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pyjwt check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree pyjwt isminimumfixversionavailable true minimumfixversion pyjwt isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails pyjwt is a python implementation of rfc pyjwt supports multiple different jwt signing algorithms with jwt an attacker submitting the jwt token can choose the used signing algorithm the pyjwt library requires that the application chooses what algorithms are supported the application can specify jwt algorithms get default algorithms to get support for all algorithms or specify a single algorithm the issue is not that big as algorithms algorithms get default algorithms has to be used users should upgrade to to receive a patch for this issue as a workaround always be explicit with the algorithms that are accepted and expected when decoding vulnerabilityurl | 0 |
124,216 | 16,597,053,292 | IssuesEvent | 2021-06-01 14:36:06 | readthedocs/sphinx-hoverxref | https://api.github.com/repos/readthedocs/sphinx-hoverxref | opened | Figure it out a good way to remove `title=` attribute on intersphinx nodes | Improvement Needed: design decision | I originally removed the `node['reftitle']` attribute because it makes the browser show the default tooltip (browser's built-in) and immediately after that our tooltip was shown. This behavior is a little confusing and it's not _styled_ in my opinion. That's why I removed it.
However, removing this attribute made other extensions break (`sphinx.ext.inheritance_diagram`) which expects that attribute exists.
I went back in [`0a75b73` (#86)](https://github.com/readthedocs/sphinx-hoverxref/pull/86/commits/0a75b73d1fd7969dc5c838fb0093e130de774dd3) and I'm opening this issue to find a better solution to avoid this.
We could:
1. define it as `node['reftitle'] = ''`
* it makes the browser to not show the built-in tooltip
* I'm not sure about the accessibility implication it has
* is the HTML still valid? It will generate a `<a title="">` tag
2. use javascript to remove all the `title=` from tags with `.hoverxref .external` on document load
3. other ideas?
See https://github.com/readthedocs/sphinx-hoverxref/pull/86#issuecomment-852136211 | 1.0 | Figure it out a good way to remove `title=` attribute on intersphinx nodes - I originally removed the `node['reftitle']` attribute because it makes the browser show the default tooltip (browser's built-in) and immediately after that our tooltip was shown. This behavior is a little confusing and it's not _styled_ in my opinion. That's why I removed it.
However, removing this attribute made other extensions break (`sphinx.ext.inheritance_diagram`) which expects that attribute exists.
I went back in [`0a75b73` (#86)](https://github.com/readthedocs/sphinx-hoverxref/pull/86/commits/0a75b73d1fd7969dc5c838fb0093e130de774dd3) and I'm opening this issue to find a better solution to avoid this.
We could:
1. define it as `node['reftitle'] = ''`
* it makes the browser to not show the built-in tooltip
* I'm not sure about the accessibility implication it has
* is the HTML still valid? It will generate a `<a title="">` tag
2. use javascript to remove all the `title=` from tags with `.hoverxref .external` on document load
3. other ideas?
See https://github.com/readthedocs/sphinx-hoverxref/pull/86#issuecomment-852136211 | non_priority | figure it out a good way to remove title attribute on intersphinx nodes i originally removed the node attribute because it makes the browser show the default tooltip browser s built in and immediately after that our tooltip was shown this behavior is a little confusing and it s not styled in my opinion that s why i removed it however removing this attribute made other extensions break sphinx ext inheritance diagram which expects that attribute exists i went back in and i m opening this issue to find a better solution to avoid this we could define it as node it makes the browser to not show the built in tooltip i m not sure about the accessibility implication it has is the html still valid it will generate a tag use javascript to remove all the title from tags with hoverxref external on document load other ideas see | 0 |
10,099 | 26,269,882,326 | IssuesEvent | 2023-01-06 15:59:26 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Gorilla WebSocket has been archived | kind/feature sig/architecture area/code-organization needs-triage | ### What would you like to be added?
Replace wesocket package from gorila to
- https://github.com/nhooyr/websocket
### Why is this needed?
gorila websocket has been archived | 1.0 | Gorilla WebSocket has been archived - ### What would you like to be added?
Replace wesocket package from gorila to
- https://github.com/nhooyr/websocket
### Why is this needed?
gorila websocket has been archived | non_priority | gorilla websocket has been archived what would you like to be added replace wesocket package from gorila to why is this needed gorila websocket has been archived | 0 |
1,582 | 6,572,347,582 | IssuesEvent | 2017-09-11 01:36:06 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Debconf to (be able to) perform dpkg-reconfigure | affects_2.1 feature_idea waiting_on_maintainer | ##### ISSUE TYPE
Feature Idea
##### COMPONENT NAME
debconf
##### ANSIBLE VERSION
```
ansible 2.1.1.0
```
##### CONFIGURATION
N/A
##### OS / ENVIRONMENT
Debian 8.5 Jessie
##### SUMMARY
debconf only sets configuration parameters, but can't execute/set them.
##### STEPS TO REPRODUCE
```
- name: Enable unattended security updates
debconf: name=unattended-upgrades
question="unattended-upgrades/enable_auto_updates"
value=true
vtype=boolean
reconfigure=true
```
##### EXPECTED RESULTS
```
- name: Enable unattended security updates
debconf: name=unattended-upgrades
question="unattended-upgrades/enable_auto_updates"
value=true
vtype=boolean
- name: Reconfigure unattended upgrades with dpkg
command: '/usr/sbin/dpkg-reconfigure --frontend noninteractive unattended-upgrades'
```
##### ACTUAL RESULTS
Variable is being set in debconf, but it's not actually applied to the package.
| True | Debconf to (be able to) perform dpkg-reconfigure - ##### ISSUE TYPE
Feature Idea
##### COMPONENT NAME
debconf
##### ANSIBLE VERSION
```
ansible 2.1.1.0
```
##### CONFIGURATION
N/A
##### OS / ENVIRONMENT
Debian 8.5 Jessie
##### SUMMARY
debconf only sets configuration parameters, but can't execute/set them.
##### STEPS TO REPRODUCE
```
- name: Enable unattended security updates
debconf: name=unattended-upgrades
question="unattended-upgrades/enable_auto_updates"
value=true
vtype=boolean
reconfigure=true
```
##### EXPECTED RESULTS
```
- name: Enable unattended security updates
debconf: name=unattended-upgrades
question="unattended-upgrades/enable_auto_updates"
value=true
vtype=boolean
- name: Reconfigure unattended upgrades with dpkg
command: '/usr/sbin/dpkg-reconfigure --frontend noninteractive unattended-upgrades'
```
##### ACTUAL RESULTS
Variable is being set in debconf, but it's not actually applied to the package.
| non_priority | debconf to be able to perform dpkg reconfigure issue type feature idea component name debconf ansible version ansible configuration n a os environment debian jessie summary debconf only sets configuration parameters but can t execute set them steps to reproduce name enable unattended security updates debconf name unattended upgrades question unattended upgrades enable auto updates value true vtype boolean reconfigure true expected results name enable unattended security updates debconf name unattended upgrades question unattended upgrades enable auto updates value true vtype boolean name reconfigure unattended upgrades with dpkg command usr sbin dpkg reconfigure frontend noninteractive unattended upgrades actual results variable is being set in debconf but it s not actually applied to the package | 0 |
68,814 | 13,184,909,237 | IssuesEvent | 2020-08-12 20:20:14 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | com_search returns text in results containing breaks in words | No Code Attached Yet | ### Steps to reproduce the issue
Publish article with 400 characters
```
This product is meant for educational purposes only. Any resemblance to real persons, living or dead is purely coincidental. Void where prohibited. Some assembly required. List each check separately by bank number. Batteries not included.
The 'Ledger'
Contents may settle during shipment. Use only as directed. No other warranty expressed or implied. Do not use while operating a motor vehicle or heavy equipment. Postage will be paid by addressee. Subject to CARB approval.
```
Use the standard joomla search component to search for *shipment*
### Expected result
Search text results returns
```
... bank number. Batteries not included.
The 'Ledger'
Contents may settle during <span class="highlight">shipment</span>. Use only as directed. No other warranty expressed or implied. Do not use while operating a motor vehicle or heavy ...
````
### Actual result
Search text results returns text without the last character heavy => heav
```
... bank number. Batteries not included.
The 'Ledger'
Contents may settle during <span class="highlight">shipment</span>. Use only as directed. No other warranty expressed or implied. Do not use while operating a motor vehicle or heav ...
```
### System information (as much as possible)
Joomla 3.9.20
### Additional comments
The function _remove_accents_ in administrator\components\com_search\helpers\search.php can change the length of the string which is used for searching.
By changing **The 'Ledger'** to **The Ledger'**, the string is shortened by 1 character (`preg_replace("/[\"'^]([a-z])/ui", '\1', $str);`)
The start position and length from the match in the modified string are used to return a portion of the original string, thus producing breaks in the middle of words.
The same thing can happen with the transliteration of the string in the *remove_accents* function.
By replacing `ü => ue, ä => ae, æ => ae, et cetera` the modified string is lengthened
### Solution
Check if the modified string is lengthened or shortened and use this for the calculation of starting position and length of the original string. | 1.0 | com_search returns text in results containing breaks in words - ### Steps to reproduce the issue
Publish article with 400 characters
```
This product is meant for educational purposes only. Any resemblance to real persons, living or dead is purely coincidental. Void where prohibited. Some assembly required. List each check separately by bank number. Batteries not included.
The 'Ledger'
Contents may settle during shipment. Use only as directed. No other warranty expressed or implied. Do not use while operating a motor vehicle or heavy equipment. Postage will be paid by addressee. Subject to CARB approval.
```
Use the standard joomla search component to search for *shipment*
### Expected result
Search text results returns
```
... bank number. Batteries not included.
The 'Ledger'
Contents may settle during <span class="highlight">shipment</span>. Use only as directed. No other warranty expressed or implied. Do not use while operating a motor vehicle or heavy ...
````
### Actual result
Search text results returns text without the last character heavy => heav
```
... bank number. Batteries not included.
The 'Ledger'
Contents may settle during <span class="highlight">shipment</span>. Use only as directed. No other warranty expressed or implied. Do not use while operating a motor vehicle or heav ...
```
### System information (as much as possible)
Joomla 3.9.20
### Additional comments
The function _remove_accents_ in administrator\components\com_search\helpers\search.php can change the length of the string which is used for searching.
By changing **The 'Ledger'** to **The Ledger'**, the string is shortened by 1 character (`preg_replace("/[\"'^]([a-z])/ui", '\1', $str);`)
The start position and length from the match in the modified string are used to return a portion of the original string, thus producing breaks in the middle of words.
The same thing can happen with the transliteration of the string in the *remove_accents* function.
By replacing `ü => ue, ä => ae, æ => ae, et cetera` the modified string is lengthened
### Solution
Check if the modified string is lengthened or shortened and use this for the calculation of starting position and length of the original string. | non_priority | com search returns text in results containing breaks in words steps to reproduce the issue publish article with characters this product is meant for educational purposes only any resemblance to real persons living or dead is purely coincidental void where prohibited some assembly required list each check separately by bank number batteries not included the ledger contents may settle during shipment use only as directed no other warranty expressed or implied do not use while operating a motor vehicle or heavy equipment postage will be paid by addressee subject to carb approval use the standard joomla search component to search for shipment expected result search text results returns bank number batteries not included the ledger contents may settle during shipment use only as directed no other warranty expressed or implied do not use while operating a motor vehicle or heavy actual result search text results returns text without the last character heavy heav bank number batteries not included the ledger contents may settle during shipment use only as directed no other warranty expressed or implied do not use while operating a motor vehicle or heav system information as much as possible joomla additional comments the function remove accents in administrator components com search helpers search php can change the length of the string which is used for searching by changing the ledger to the ledger the string is shortened by character preg replace ui str the start position and length from the match in the modified string are used to return a portion of the original string thus producing breaks in the middle of words the same thing can happen with the transliteration of the string in the remove accents function by replacing ü ue ä ae æ ae et cetera the modified string is lengthened solution check if the modified string is lengthened or shortened and use this for the calculation of starting position and length of the original string | 0 |
177,729 | 21,509,166,117 | IssuesEvent | 2022-04-28 01:11:39 | farooqmir/React-Redux-Demonstration-with-api | https://api.github.com/repos/farooqmir/React-Redux-Demonstration-with-api | closed | WS-2019-0331 (Medium) detected in handlebars-4.1.2.tgz - autoclosed | security vulnerability | ## WS-2019-0331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /React-Redux-Demonstration-with-api/package.json</p>
<p>Path to vulnerable library: React-Redux-Demonstration-with-api/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-24.8.0.tgz (Root Library)
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.4.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.2. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0331 (Medium) detected in handlebars-4.1.2.tgz - autoclosed - ## WS-2019-0331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /React-Redux-Demonstration-with-api/package.json</p>
<p>Path to vulnerable library: React-Redux-Demonstration-with-api/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-24.8.0.tgz (Root Library)
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.4.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.2. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/d54137810a49939fd2ad01a91a34e182ece4528e>WS-2019-0331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1316">https://www.npmjs.com/advisories/1316</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in handlebars tgz autoclosed ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file react redux demonstration with api package json path to vulnerable library react redux demonstration with api node modules handlebars package json dependency hierarchy jest cli tgz root library core tgz reporters tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details arbitrary code execution vulnerability found in handlebars before lookup helper fails to validate templates attack may submit templates that execute arbitrary javascript in the system publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
174,698 | 27,710,660,824 | IssuesEvent | 2023-03-14 14:04:09 | JaviTrek/AW-Competitive | https://api.github.com/repos/JaviTrek/AW-Competitive | closed | Render unit building menu correctly | Easy Medium Graphic Design Frontend Javascript | When the user clicks on a factory, a menu very similar to this should pop up

It only lets the user select units it can afford with their current funds and greys out other options | 1.0 | Render unit building menu correctly - When the user clicks on a factory, a menu very similar to this should pop up

It only lets the user select units it can afford with their current funds and greys out other options | non_priority | render unit building menu correctly when the user clicks on a factory a menu very similar to this should pop up it only lets the user select units it can afford with their current funds and greys out other options | 0 |
313,316 | 26,917,615,189 | IssuesEvent | 2023-02-07 08:04:36 | eclipse/sumo | https://api.github.com/repos/eclipse/sumo | opened | Refactor additional test | a:netedit c:testsystem | - [ ] access
- [ ] busstop
- [ ] calibrator
- [ ] calibratorflow
- [ ] calibratorlane
- [ ] chargingstation
- [ ] containerstop
- [ ] detentry
- [ ] detexit
- [ ] e1detector
- [ ] e1instantdetector
- [ ] e2detector
- [ ] e2multilanedetector
- [ ] e3detector
- [ ] parkingarea
- [ ] parkingspace
- [ ] rerouter
- [ ] rerouterelements
- [ ] routeprobe
- [ ] trainstop
- [ ] vaporizer
- [ ] variablespeedsign
| 1.0 | Refactor additional test - - [ ] access
- [ ] busstop
- [ ] calibrator
- [ ] calibratorflow
- [ ] calibratorlane
- [ ] chargingstation
- [ ] containerstop
- [ ] detentry
- [ ] detexit
- [ ] e1detector
- [ ] e1instantdetector
- [ ] e2detector
- [ ] e2multilanedetector
- [ ] e3detector
- [ ] parkingarea
- [ ] parkingspace
- [ ] rerouter
- [ ] rerouterelements
- [ ] routeprobe
- [ ] trainstop
- [ ] vaporizer
- [ ] variablespeedsign
| non_priority | refactor additional test access busstop calibrator calibratorflow calibratorlane chargingstation containerstop detentry detexit parkingarea parkingspace rerouter rerouterelements routeprobe trainstop vaporizer variablespeedsign | 0 |
9,413 | 6,284,251,690 | IssuesEvent | 2017-07-19 07:11:45 | integration-team-iiith/physical-chemistry-responsive-lab | https://api.github.com/repos/integration-team-iiith/physical-chemistry-responsive-lab | closed | QA_Instrumentation and working principles of infra red spectroscopy using salt plates_Experiment_Beam-Splitter-is-not-included | category : Usability Developed by : VLEAD Severity : S1 Status : Resolved | Defect Description :
In the experiment section of "Instrumentation and working principles of infra red spectroscopy using salt plates" experiment, Beam Splitter is not included in the converted experiment. Where as in the original experiment the Beam Splitter is provided.
Actual Result :
In the experiment section of "Instrumentation and working principles of infra red spectroscopy using salt plates" experiment, Beam Splitter is not included in the converted experiment. Where as in the original experiment the Beam Splitter is provided. Refer the attachment for the details.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers:Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Attachments:
**In the screen shot right side image is from the original experiment that has Beam Splitter**
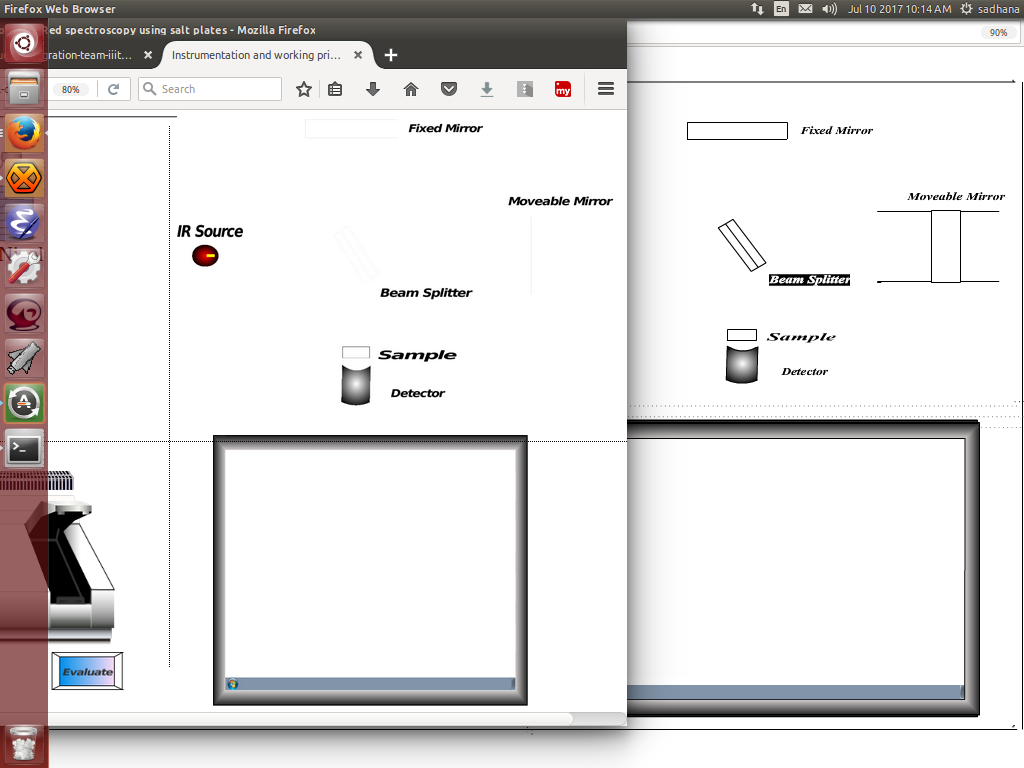
| True | QA_Instrumentation and working principles of infra red spectroscopy using salt plates_Experiment_Beam-Splitter-is-not-included - Defect Description :
In the experiment section of "Instrumentation and working principles of infra red spectroscopy using salt plates" experiment, Beam Splitter is not included in the converted experiment. Where as in the original experiment the Beam Splitter is provided.
Actual Result :
In the experiment section of "Instrumentation and working principles of infra red spectroscopy using salt plates" experiment, Beam Splitter is not included in the converted experiment. Where as in the original experiment the Beam Splitter is provided. Refer the attachment for the details.
Environment :
OS: Windows 7, Ubuntu-16.04,Centos-6
Browsers:Firefox-42.0,Chrome-47.0,chromium-45.0
Bandwidth : 100Mbps
Hardware Configuration:8GBRAM ,
Processor:i5
Attachments:
**In the screen shot right side image is from the original experiment that has Beam Splitter**
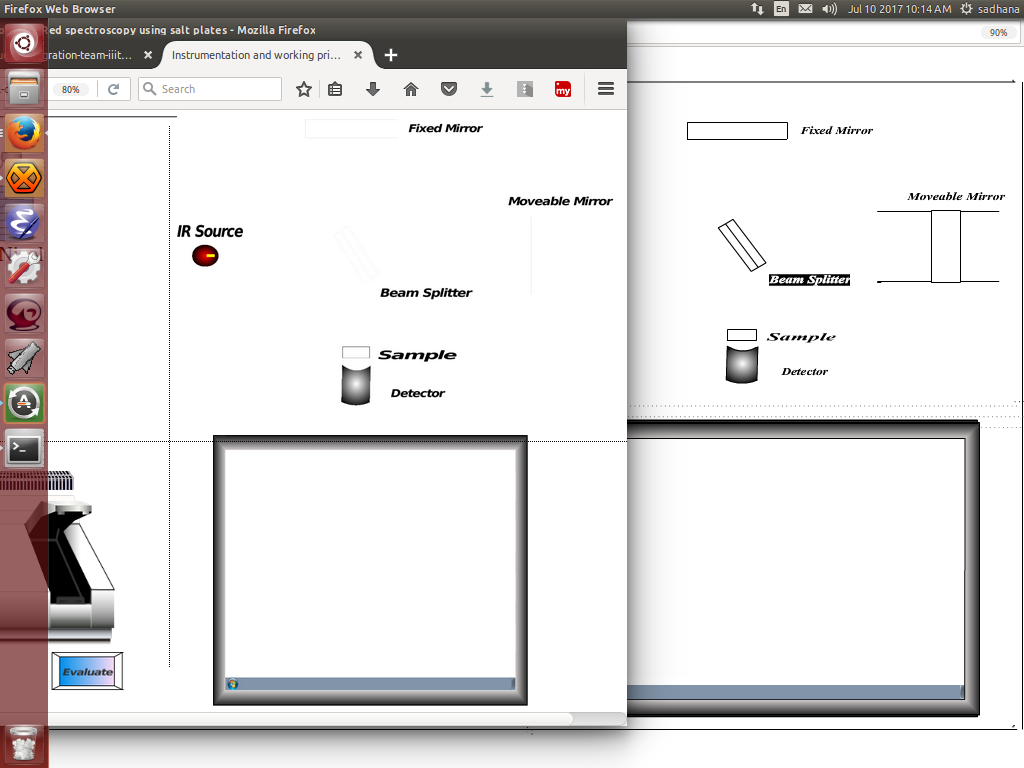
| non_priority | qa instrumentation and working principles of infra red spectroscopy using salt plates experiment beam splitter is not included defect description in the experiment section of instrumentation and working principles of infra red spectroscopy using salt plates experiment beam splitter is not included in the converted experiment where as in the original experiment the beam splitter is provided actual result in the experiment section of instrumentation and working principles of infra red spectroscopy using salt plates experiment beam splitter is not included in the converted experiment where as in the original experiment the beam splitter is provided refer the attachment for the details environment os windows ubuntu centos browsers firefox chrome chromium bandwidth hardware configuration processor attachments in the screen shot right side image is from the original experiment that has beam splitter | 0 |
161,988 | 12,603,042,176 | IssuesEvent | 2020-06-11 12:50:29 | Chiniga/pa-queue-ph | https://api.github.com/repos/Chiniga/pa-queue-ph | closed | Add action completed messages | P1 enhancement ready for testing | Add messages when adding/editing/deleting players to notify users of completed actions. | 1.0 | Add action completed messages - Add messages when adding/editing/deleting players to notify users of completed actions. | non_priority | add action completed messages add messages when adding editing deleting players to notify users of completed actions | 0 |
362,999 | 25,403,016,961 | IssuesEvent | 2022-11-22 13:29:45 | Heigvd/colab | https://api.github.com/repos/Heigvd/colab | closed | Brainstormer sur la portée de la documentation (fonctionnel + visuel) | documentation canWeClose? brainstorm first | à discuter
- séparer ce qui vient du projet / de la carte parente / de la carte
- définir l'ordre nécessaire pour les catégories et les documents | 1.0 | Brainstormer sur la portée de la documentation (fonctionnel + visuel) - à discuter
- séparer ce qui vient du projet / de la carte parente / de la carte
- définir l'ordre nécessaire pour les catégories et les documents | non_priority | brainstormer sur la portée de la documentation fonctionnel visuel à discuter séparer ce qui vient du projet de la carte parente de la carte définir l ordre nécessaire pour les catégories et les documents | 0 |
12,786 | 3,645,718,081 | IssuesEvent | 2016-02-15 15:46:34 | canjs/canjs | https://api.github.com/repos/canjs/canjs | opened | can.view.preload docs could use improvement | Documentation | The docs for can.view.preload can only be found by hitting this URL directly: https://canjs.com/docs/can.view.preload.html
Also, a usage example would be very helpful. | 1.0 | can.view.preload docs could use improvement - The docs for can.view.preload can only be found by hitting this URL directly: https://canjs.com/docs/can.view.preload.html
Also, a usage example would be very helpful. | non_priority | can view preload docs could use improvement the docs for can view preload can only be found by hitting this url directly also a usage example would be very helpful | 0 |
208,793 | 23,654,450,677 | IssuesEvent | 2022-08-26 09:49:43 | finos/FDC3-conformance-framework | https://api.github.com/repos/finos/FDC3-conformance-framework | closed | CVE-2021-23424 (High) detected in ansi-html-0.0.7.tgz | security vulnerability | ## CVE-2021-23424 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-html-0.0.7.tgz</b></p></summary>
<p>An elegant lib that converts the chalked (ANSI) text to HTML.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-html/-/ansi-html-0.0.7.tgz">https://registry.npmjs.org/ansi-html/-/ansi-html-0.0.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ansi-html/package.json</p>
<p>
Dependency Hierarchy:
- @fdc3-conformance-framework/app-1.0.0.tgz (Root Library)
- react-scripts-4.0.3.tgz
- webpack-dev-server-3.11.1.tgz
- :x: **ansi-html-0.0.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/finos/FDC3-conformance-framework/commit/464478c8d773c9f1db106df334cccbe96b76f1e7">464478c8d773c9f1db106df334cccbe96b76f1e7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects all versions of package ansi-html. If an attacker provides a malicious string, it will get stuck processing the input for an extremely long time.
<p>Publish Date: 2021-08-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23424>CVE-2021-23424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-23424">https://nvd.nist.gov/vuln/detail/CVE-2021-23424</a></p>
<p>Release Date: 2021-08-18</p>
<p>Fix Resolution: VueJS.NetCore - 1.1.1;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;Fable.Template.Elmish.React - 0.1.6;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;Envisia.DotNet.Templates - 3.0.1</p>
</p>
</details>
<p></p>
| True | CVE-2021-23424 (High) detected in ansi-html-0.0.7.tgz - ## CVE-2021-23424 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansi-html-0.0.7.tgz</b></p></summary>
<p>An elegant lib that converts the chalked (ANSI) text to HTML.</p>
<p>Library home page: <a href="https://registry.npmjs.org/ansi-html/-/ansi-html-0.0.7.tgz">https://registry.npmjs.org/ansi-html/-/ansi-html-0.0.7.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ansi-html/package.json</p>
<p>
Dependency Hierarchy:
- @fdc3-conformance-framework/app-1.0.0.tgz (Root Library)
- react-scripts-4.0.3.tgz
- webpack-dev-server-3.11.1.tgz
- :x: **ansi-html-0.0.7.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/finos/FDC3-conformance-framework/commit/464478c8d773c9f1db106df334cccbe96b76f1e7">464478c8d773c9f1db106df334cccbe96b76f1e7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects all versions of package ansi-html. If an attacker provides a malicious string, it will get stuck processing the input for an extremely long time.
<p>Publish Date: 2021-08-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23424>CVE-2021-23424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-23424">https://nvd.nist.gov/vuln/detail/CVE-2021-23424</a></p>
<p>Release Date: 2021-08-18</p>
<p>Fix Resolution: VueJS.NetCore - 1.1.1;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;Fable.Template.Elmish.React - 0.1.6;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;Envisia.DotNet.Templates - 3.0.1</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in ansi html tgz cve high severity vulnerability vulnerable library ansi html tgz an elegant lib that converts the chalked ansi text to html library home page a href path to dependency file package json path to vulnerable library node modules ansi html package json dependency hierarchy conformance framework app tgz root library react scripts tgz webpack dev server tgz x ansi html tgz vulnerable library found in head commit a href found in base branch main vulnerability details this affects all versions of package ansi html if an attacker provides a malicious string it will get stuck processing the input for an extremely long time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution vuejs netcore indianadavy vuejswebapitemplate csharp nordron angulartemplate corevuewebtest dotnetng template fable template elmish react safe template gr pagerender razor envisia dotnet templates | 0 |
21,948 | 6,227,571,452 | IssuesEvent | 2017-07-10 21:03:41 | XceedBoucherS/TestImport5 | https://api.github.com/repos/XceedBoucherS/TestImport5 | closed | MaskedTextBox - IsEditable set to false allows paste / delete | CodePlex | <b>Stride[CodePlex]</b> <br />Good morning Brian,
nbsp
Great toolkit! Something I noticed when using the MaskedTextBox is when the IsEditable property is set to false I am still able to paste and delete data in the TextBox. MaskedTextBox.cs, TextBox_PreviewTextInput, checks if TextBox.IsReadOnly is false before
preceding but TextBox_PreviewKeyDown and Paste do not.
nbsp
Thanks,
-Donna
| 1.0 | MaskedTextBox - IsEditable set to false allows paste / delete - <b>Stride[CodePlex]</b> <br />Good morning Brian,
nbsp
Great toolkit! Something I noticed when using the MaskedTextBox is when the IsEditable property is set to false I am still able to paste and delete data in the TextBox. MaskedTextBox.cs, TextBox_PreviewTextInput, checks if TextBox.IsReadOnly is false before
preceding but TextBox_PreviewKeyDown and Paste do not.
nbsp
Thanks,
-Donna
| non_priority | maskedtextbox iseditable set to false allows paste delete stride good morning brian nbsp great toolkit something i noticed when using the maskedtextbox is when the iseditable property is set to false i am still able to paste and delete data in the textbox maskedtextbox cs textbox previewtextinput checks if textbox isreadonly is false before preceding but textbox previewkeydown and paste do not nbsp thanks donna | 0 |
213,690 | 16,532,760,946 | IssuesEvent | 2021-05-27 08:14:58 | telerik/kendo-ui-core | https://api.github.com/repos/telerik/kendo-ui-core | opened | Extend Gantt documentation on sorting and reordering of tasks | C: Gantt Documentation S: Wrappers (ASP.NET Core) | Extend the [Gantt documentation](https://docs.telerik.com/aspnet-core/html-helpers/scheduling/gantt/overview) with details on sorting and reordering tasks. | 1.0 | Extend Gantt documentation on sorting and reordering of tasks - Extend the [Gantt documentation](https://docs.telerik.com/aspnet-core/html-helpers/scheduling/gantt/overview) with details on sorting and reordering tasks. | non_priority | extend gantt documentation on sorting and reordering of tasks extend the with details on sorting and reordering tasks | 0 |
75,220 | 15,396,378,414 | IssuesEvent | 2021-03-03 20:33:17 | jgeraigery/experian-java | https://api.github.com/repos/jgeraigery/experian-java | closed | CVE-2017-17485 (High) detected in jackson-databind-2.9.2.jar - autoclosed | security vulnerability | ## CVE-2017-17485 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/44cf7628c83393be837f883c680a5bea55efbf37">44cf7628c83393be837f883c680a5bea55efbf37</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind through 2.8.10 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 deserialization flaw. This is exploitable by sending maliciously crafted JSON input to the readValue method of the ObjectMapper, bypassing a blacklist that is ineffective if the Spring libraries are available in the classpath.
<p>Publish Date: 2018-01-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-17485>CVE-2017-17485</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/commit/bb45fb16709018842f858f1a6e1118676aaa34bd#diff-727a6e8db3603b95f185697108af6c48">https://github.com/FasterXML/jackson-databind/commit/bb45fb16709018842f858f1a6e1118676aaa34bd#diff-727a6e8db3603b95f185697108af6c48</a></p>
<p>Release Date: 2017-12-19</p>
<p>Fix Resolution: Replace or update the following files: AbstractApplicationContext.java, AbstractPointcutAdvisor.java, BogusApplicationContext.java, SubTypeValidator.java, BogusPointcutAdvisor.java, IllegalTypesCheckTest.java</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","packageFilePaths":["/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-17485","vulnerabilityDetails":"FasterXML jackson-databind through 2.8.10 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 deserialization flaw. This is exploitable by sending maliciously crafted JSON input to the readValue method of the ObjectMapper, bypassing a blacklist that is ineffective if the Spring libraries are available in the classpath.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-17485","cvss2Severity":"high","cvss2Score":"7.5","extraData":{}}</REMEDIATE> --> | True | CVE-2017-17485 (High) detected in jackson-databind-2.9.2.jar - autoclosed - ## CVE-2017-17485 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/44cf7628c83393be837f883c680a5bea55efbf37">44cf7628c83393be837f883c680a5bea55efbf37</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind through 2.8.10 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 deserialization flaw. This is exploitable by sending maliciously crafted JSON input to the readValue method of the ObjectMapper, bypassing a blacklist that is ineffective if the Spring libraries are available in the classpath.
<p>Publish Date: 2018-01-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-17485>CVE-2017-17485</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/commit/bb45fb16709018842f858f1a6e1118676aaa34bd#diff-727a6e8db3603b95f185697108af6c48">https://github.com/FasterXML/jackson-databind/commit/bb45fb16709018842f858f1a6e1118676aaa34bd#diff-727a6e8db3603b95f185697108af6c48</a></p>
<p>Release Date: 2017-12-19</p>
<p>Fix Resolution: Replace or update the following files: AbstractApplicationContext.java, AbstractPointcutAdvisor.java, BogusApplicationContext.java, SubTypeValidator.java, BogusPointcutAdvisor.java, IllegalTypesCheckTest.java</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","packageFilePaths":["/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-17485","vulnerabilityDetails":"FasterXML jackson-databind through 2.8.10 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 deserialization flaw. This is exploitable by sending maliciously crafted JSON input to the readValue method of the ObjectMapper, bypassing a blacklist that is ineffective if the Spring libraries are available in the classpath.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-17485","cvss2Severity":"high","cvss2Score":"7.5","extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file experian java mavenworkspace bis services lib bis services base pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind through and x through allows unauthenticated remote code execution because of an incomplete fix for the cve deserialization flaw this is exploitable by sending maliciously crafted json input to the readvalue method of the objectmapper bypassing a blacklist that is ineffective if the spring libraries are available in the classpath publish date url a href cvss score details base score metrics not available suggested fix type change files origin a href release date fix resolution replace or update the following files abstractapplicationcontext java abstractpointcutadvisor java bogusapplicationcontext java subtypevalidator java boguspointcutadvisor java illegaltypeschecktest java isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind through and x through allows unauthenticated remote code execution because of an incomplete fix for the cve deserialization flaw this is exploitable by sending maliciously crafted json input to the readvalue method of the objectmapper bypassing a blacklist that is ineffective if the spring libraries are available in the classpath vulnerabilityurl | 0 |
52,773 | 6,277,154,422 | IssuesEvent | 2017-07-18 11:27:13 | Princeton-CDH/derrida-django | https://api.github.com/repos/Princeton-CDH/derrida-django | closed | interventions: tag annotation text as illegible | awaiting testing | As an intervention data editor, I would like to be able to tag a verbal intervention as “illegible” so that I can clearly indicate when the text is unreadable.
| 1.0 | interventions: tag annotation text as illegible - As an intervention data editor, I would like to be able to tag a verbal intervention as “illegible” so that I can clearly indicate when the text is unreadable.
| non_priority | interventions tag annotation text as illegible as an intervention data editor i would like to be able to tag a verbal intervention as “illegible” so that i can clearly indicate when the text is unreadable | 0 |
107,601 | 23,447,624,208 | IssuesEvent | 2022-08-15 21:25:52 | Sage-Bionetworks/challenge-registry | https://api.github.com/repos/Sage-Bionetworks/challenge-registry | closed | Invite the developer to rebuild the devcontainer when devcontainer.json uses an image different from the one used | dev/devcontainer vscode chore | Errors may occur if the tools provided by the dev container and the tools expected by the code base (defined in `devcontainer.json`) are not in sync. We had a similar issue with node packages, which we solved by automatically running `yarn install --frozen-lockfile` when switching or rebasing branches. Here we can't do that automatically for devcontainer as the developer needs to shutdown the devcontainer and rebuild it.
The idea is display a message in the terminal if the image version defined in `devcontainer.json` and the version of the current dev container are not the same.
cc: @rrchai (following our discussion on Friday) | 1.0 | Invite the developer to rebuild the devcontainer when devcontainer.json uses an image different from the one used - Errors may occur if the tools provided by the dev container and the tools expected by the code base (defined in `devcontainer.json`) are not in sync. We had a similar issue with node packages, which we solved by automatically running `yarn install --frozen-lockfile` when switching or rebasing branches. Here we can't do that automatically for devcontainer as the developer needs to shutdown the devcontainer and rebuild it.
The idea is display a message in the terminal if the image version defined in `devcontainer.json` and the version of the current dev container are not the same.
cc: @rrchai (following our discussion on Friday) | non_priority | invite the developer to rebuild the devcontainer when devcontainer json uses an image different from the one used errors may occur if the tools provided by the dev container and the tools expected by the code base defined in devcontainer json are not in sync we had a similar issue with node packages which we solved by automatically running yarn install frozen lockfile when switching or rebasing branches here we can t do that automatically for devcontainer as the developer needs to shutdown the devcontainer and rebuild it the idea is display a message in the terminal if the image version defined in devcontainer json and the version of the current dev container are not the same cc rrchai following our discussion on friday | 0 |
171,026 | 27,051,379,872 | IssuesEvent | 2023-02-13 13:28:59 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Slow animation on fab transition | framework a: animation f: material design team: gallery has reproducible steps P4 found in release: 3.3 found in release: 3.6 | ## Steps to Reproduce
In the gallery example of a fab transition using a tabview, using gesture instead of tapping the tab produce a really slow animation on the fab.
## Flutter Doctor
```
[✓] Flutter (on Mac OS X 10.12.6 16G16b, locale es-ES, channel master)
• Flutter at /Users/arcas/Documents/Desarrollo/flutter
• Framework revision 7ada46677b (6 days ago), 2017-06-14 11:25:03 -0700
• Engine revision 4f5d6fab11
• Tools Dart version 1.24.0-dev.6.7
[✓] Android toolchain - develop for Android devices (Android SDK 25.0.3)
• Android SDK at /Users/arcas/Library/Android/sdk
• Platform android-25, build-tools 25.0.3
• Java binary at: /Applications/Android Studio.app/Contents/jre/jdk/Contents/Home/bin/java
• Java version OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[-] iOS toolchain - develop for iOS devices (Xcode 8.3.3)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 8.3.3, Build version 8E3004b
✗ libimobiledevice and ideviceinstaller are not installed or require updating. To update, run:
brew update
brew uninstall --ignore-dependencies libimobiledevice
brew install --HEAD libimobiledevice
brew install ideviceinstaller
✗ ios-deploy not installed. To install:
brew update
brew install ios-deploy
• CocoaPods version 1.2.1
[✓] Android Studio (version 2.3)
• Android Studio at /Applications/Android Studio.app/Contents
• Gradle version 3.2
• Java version OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[✓] IntelliJ IDEA Community Edition (version 2017.1.4)
• Flutter plugin version 14.0
• Dart plugin version 171.4694.29
[-] WebStorm (version 2016.3.1)
✗ Flutter plugin not installed; this adds Flutter specific functionality.
• For information about managing plugins, see
https://www.jetbrains.com/help/idea/managing-plugins.html
✗ This install is older than the minimum recommended version of 2017.1.0.
[✓] Connected devices
• Redmi Note 3 • f71a59a0 • android-arm • Android 7.1.1 (API 25)
> For more information about diagnosing and reporting Flutter bugs, please see [https://flutter.io/bug-reports/](https://flutter.io/bug-reports/).
``` | 1.0 | Slow animation on fab transition - ## Steps to Reproduce
In the gallery example of a fab transition using a tabview, using gesture instead of tapping the tab produce a really slow animation on the fab.
## Flutter Doctor
```
[✓] Flutter (on Mac OS X 10.12.6 16G16b, locale es-ES, channel master)
• Flutter at /Users/arcas/Documents/Desarrollo/flutter
• Framework revision 7ada46677b (6 days ago), 2017-06-14 11:25:03 -0700
• Engine revision 4f5d6fab11
• Tools Dart version 1.24.0-dev.6.7
[✓] Android toolchain - develop for Android devices (Android SDK 25.0.3)
• Android SDK at /Users/arcas/Library/Android/sdk
• Platform android-25, build-tools 25.0.3
• Java binary at: /Applications/Android Studio.app/Contents/jre/jdk/Contents/Home/bin/java
• Java version OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[-] iOS toolchain - develop for iOS devices (Xcode 8.3.3)
• Xcode at /Applications/Xcode.app/Contents/Developer
• Xcode 8.3.3, Build version 8E3004b
✗ libimobiledevice and ideviceinstaller are not installed or require updating. To update, run:
brew update
brew uninstall --ignore-dependencies libimobiledevice
brew install --HEAD libimobiledevice
brew install ideviceinstaller
✗ ios-deploy not installed. To install:
brew update
brew install ios-deploy
• CocoaPods version 1.2.1
[✓] Android Studio (version 2.3)
• Android Studio at /Applications/Android Studio.app/Contents
• Gradle version 3.2
• Java version OpenJDK Runtime Environment (build 1.8.0_112-release-b06)
[✓] IntelliJ IDEA Community Edition (version 2017.1.4)
• Flutter plugin version 14.0
• Dart plugin version 171.4694.29
[-] WebStorm (version 2016.3.1)
✗ Flutter plugin not installed; this adds Flutter specific functionality.
• For information about managing plugins, see
https://www.jetbrains.com/help/idea/managing-plugins.html
✗ This install is older than the minimum recommended version of 2017.1.0.
[✓] Connected devices
• Redmi Note 3 • f71a59a0 • android-arm • Android 7.1.1 (API 25)
> For more information about diagnosing and reporting Flutter bugs, please see [https://flutter.io/bug-reports/](https://flutter.io/bug-reports/).
``` | non_priority | slow animation on fab transition steps to reproduce in the gallery example of a fab transition using a tabview using gesture instead of tapping the tab produce a really slow animation on the fab flutter doctor flutter on mac os x locale es es channel master • flutter at users arcas documents desarrollo flutter • framework revision days ago • engine revision • tools dart version dev android toolchain develop for android devices android sdk • android sdk at users arcas library android sdk • platform android build tools • java binary at applications android studio app contents jre jdk contents home bin java • java version openjdk runtime environment build release ios toolchain develop for ios devices xcode • xcode at applications xcode app contents developer • xcode build version ✗ libimobiledevice and ideviceinstaller are not installed or require updating to update run brew update brew uninstall ignore dependencies libimobiledevice brew install head libimobiledevice brew install ideviceinstaller ✗ ios deploy not installed to install brew update brew install ios deploy • cocoapods version android studio version • android studio at applications android studio app contents • gradle version • java version openjdk runtime environment build release intellij idea community edition version • flutter plugin version • dart plugin version webstorm version ✗ flutter plugin not installed this adds flutter specific functionality • for information about managing plugins see ✗ this install is older than the minimum recommended version of connected devices • redmi note • • android arm • android api for more information about diagnosing and reporting flutter bugs please see | 0 |
230,871 | 17,649,779,759 | IssuesEvent | 2021-08-20 11:34:05 | eth-cscs/reframe | https://api.github.com/repos/eth-cscs/reframe | opened | Order options in alphabetical order in both the help message and the man page | prio: normal documentation | Within their respective groups, not globally. | 1.0 | Order options in alphabetical order in both the help message and the man page - Within their respective groups, not globally. | non_priority | order options in alphabetical order in both the help message and the man page within their respective groups not globally | 0 |
67,796 | 7,060,282,127 | IssuesEvent | 2018-01-05 07:54:58 | EnMasseProject/enmasse | https://api.github.com/repos/EnMasseProject/enmasse | opened | System-tests: standard: new test for io.enmasse.systemtest.standard.TopicTest#testRestApiForMulticast | test development | test could be based on: https://github.com/EnMasseProject/enmasse/blob/master/systemtests/src/test/java/io/enmasse/systemtest/standard/QueueTest.java#L89 | 1.0 | System-tests: standard: new test for io.enmasse.systemtest.standard.TopicTest#testRestApiForMulticast - test could be based on: https://github.com/EnMasseProject/enmasse/blob/master/systemtests/src/test/java/io/enmasse/systemtest/standard/QueueTest.java#L89 | non_priority | system tests standard new test for io enmasse systemtest standard topictest testrestapiformulticast test could be based on | 0 |
100,084 | 16,481,416,506 | IssuesEvent | 2021-05-24 12:13:17 | yoswein/WebGoat_2.0 | https://api.github.com/repos/yoswein/WebGoat_2.0 | opened | CVE-2020-7793 (High) detected in ua-parser-js-0.7.17.tgz | security vulnerability | ## CVE-2020-7793 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ua-parser-js-0.7.17.tgz</b></p></summary>
<p>Lightweight JavaScript-based user-agent string parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.17.tgz">https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.17.tgz</a></p>
<p>Path to dependency file: WebGoat_2.0/docs/package.json</p>
<p>Path to vulnerable library: WebGoat_2.0/docs/node_modules/ua-parser-js/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.26.3.tgz (Root Library)
- :x: **ua-parser-js-0.7.17.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/yoswein/WebGoat_2.0/commit/4d038f6521e1205e037211e7c3dcc92a82448d22">4d038f6521e1205e037211e7c3dcc92a82448d22</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package ua-parser-js before 0.7.23 are vulnerable to Regular Expression Denial of Service (ReDoS) in multiple regexes (see linked commit for more info).
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7793>CVE-2020-7793</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/faisalman/ua-parser-js/commit/6d1f26df051ba681463ef109d36c9cf0f7e32b18">https://github.com/faisalman/ua-parser-js/commit/6d1f26df051ba681463ef109d36c9cf0f7e32b18</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 0.7.23</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ua-parser-js","packageVersion":"0.7.17","packageFilePaths":["/docs/package.json"],"isTransitiveDependency":true,"dependencyTree":"browser-sync:2.26.3;ua-parser-js:0.7.17","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.7.23"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7793","vulnerabilityDetails":"The package ua-parser-js before 0.7.23 are vulnerable to Regular Expression Denial of Service (ReDoS) in multiple regexes (see linked commit for more info).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7793","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7793 (High) detected in ua-parser-js-0.7.17.tgz - ## CVE-2020-7793 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ua-parser-js-0.7.17.tgz</b></p></summary>
<p>Lightweight JavaScript-based user-agent string parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.17.tgz">https://registry.npmjs.org/ua-parser-js/-/ua-parser-js-0.7.17.tgz</a></p>
<p>Path to dependency file: WebGoat_2.0/docs/package.json</p>
<p>Path to vulnerable library: WebGoat_2.0/docs/node_modules/ua-parser-js/package.json</p>
<p>
Dependency Hierarchy:
- browser-sync-2.26.3.tgz (Root Library)
- :x: **ua-parser-js-0.7.17.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/yoswein/WebGoat_2.0/commit/4d038f6521e1205e037211e7c3dcc92a82448d22">4d038f6521e1205e037211e7c3dcc92a82448d22</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package ua-parser-js before 0.7.23 are vulnerable to Regular Expression Denial of Service (ReDoS) in multiple regexes (see linked commit for more info).
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7793>CVE-2020-7793</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/faisalman/ua-parser-js/commit/6d1f26df051ba681463ef109d36c9cf0f7e32b18">https://github.com/faisalman/ua-parser-js/commit/6d1f26df051ba681463ef109d36c9cf0f7e32b18</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 0.7.23</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ua-parser-js","packageVersion":"0.7.17","packageFilePaths":["/docs/package.json"],"isTransitiveDependency":true,"dependencyTree":"browser-sync:2.26.3;ua-parser-js:0.7.17","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.7.23"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-7793","vulnerabilityDetails":"The package ua-parser-js before 0.7.23 are vulnerable to Regular Expression Denial of Service (ReDoS) in multiple regexes (see linked commit for more info).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7793","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in ua parser js tgz cve high severity vulnerability vulnerable library ua parser js tgz lightweight javascript based user agent string parser library home page a href path to dependency file webgoat docs package json path to vulnerable library webgoat docs node modules ua parser js package json dependency hierarchy browser sync tgz root library x ua parser js tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package ua parser js before are vulnerable to regular expression denial of service redos in multiple regexes see linked commit for more info publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree browser sync ua parser js isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails the package ua parser js before are vulnerable to regular expression denial of service redos in multiple regexes see linked commit for more info vulnerabilityurl | 0 |
175,899 | 27,990,270,403 | IssuesEvent | 2023-03-27 02:39:19 | MetaMask/metamask-mobile | https://api.github.com/repos/MetaMask/metamask-mobile | closed | [Mobile] Create component: Label | design-system | ### **Description**
Componentize `Label` according to the insight report
Example Screenshot:
<img width="332" alt="Screenshot 2023-02-01 at 3 06 44 PM" src="https://user-images.githubusercontent.com/8112138/216186483-ae0579df-b884-4b5f-8ab5-6ec8c72fc5c4.png">
### **Technical Details**
Unless audited by Design System - Place component in `components-temp` directory location in `app/component-library/components-temp` directory.
- Component Structure (Assume `Label` = your component's name)
- Under `Label` directory
- [ ] `Label`.tsx - Actual component file.
- [ ] `Label`.types.ts - Includes all TypeScript related types/interfaces/enums etc.
- [ ] `Label`.styles.ts - Includes styles for the `Label` component.
- [ ] `Label`.test.tsx - Includes both snapshots AND unit tests.
- [ ] `Label`.stories.ts - Includes stories for the `Label` component.
- [ ] `Label`.constants.ts - Includes any constants that is used in any `Label` file. For example, test IDs for tests, mappings for the component, etc.
- [ ] `Label`.utils.ts - Includes any utility functions specific to be used with the `NAME` component.
- [ ] index.ts - Exports both `Label` component as default and anything else such as types, test IDs, etc if needed.
- [ ] README.md - Documentation on how the `Label` component will be used and the props associated with it.
- Caveat
- Components may differ in terms of files to include depending on what is needed.
- For example - you might not need a constants file or a styles file depending on how the component is built.
- A more specific example - you can omit the styles file if your component doesn't require styles. Just use your best judgement.
- Refer to an example component such as `AvatarFavicon` for more details.
### **Acceptance Criteria**
- [ ] Snapshot and unit tests pass
- [ ] Storybook shows interactive version of component. Include screenshot or video in pull request for visual reference.
- [ ] Component structure should resemble the structure listed in the Technical Details section above.
### **References**
- [Figma](https://www.figma.com/file/HKpPKij9V3TpsyMV1TpV7C/DS-Components?node-id=7294%3A25180&t=QqFU9YJamwcKLvul-1)
- [FigJam Audit & Insight Report](https://www.figma.com/file/aGW8sk6X6Jf9ac0MRMD4kX/TextField-Audit?node-id=0%3A1&t=ULa7Q5OYfNcoF78F-1)
| 1.0 | [Mobile] Create component: Label - ### **Description**
Componentize `Label` according to the insight report
Example Screenshot:
<img width="332" alt="Screenshot 2023-02-01 at 3 06 44 PM" src="https://user-images.githubusercontent.com/8112138/216186483-ae0579df-b884-4b5f-8ab5-6ec8c72fc5c4.png">
### **Technical Details**
Unless audited by Design System - Place component in `components-temp` directory location in `app/component-library/components-temp` directory.
- Component Structure (Assume `Label` = your component's name)
- Under `Label` directory
- [ ] `Label`.tsx - Actual component file.
- [ ] `Label`.types.ts - Includes all TypeScript related types/interfaces/enums etc.
- [ ] `Label`.styles.ts - Includes styles for the `Label` component.
- [ ] `Label`.test.tsx - Includes both snapshots AND unit tests.
- [ ] `Label`.stories.ts - Includes stories for the `Label` component.
- [ ] `Label`.constants.ts - Includes any constants that is used in any `Label` file. For example, test IDs for tests, mappings for the component, etc.
- [ ] `Label`.utils.ts - Includes any utility functions specific to be used with the `NAME` component.
- [ ] index.ts - Exports both `Label` component as default and anything else such as types, test IDs, etc if needed.
- [ ] README.md - Documentation on how the `Label` component will be used and the props associated with it.
- Caveat
- Components may differ in terms of files to include depending on what is needed.
- For example - you might not need a constants file or a styles file depending on how the component is built.
- A more specific example - you can omit the styles file if your component doesn't require styles. Just use your best judgement.
- Refer to an example component such as `AvatarFavicon` for more details.
### **Acceptance Criteria**
- [ ] Snapshot and unit tests pass
- [ ] Storybook shows interactive version of component. Include screenshot or video in pull request for visual reference.
- [ ] Component structure should resemble the structure listed in the Technical Details section above.
### **References**
- [Figma](https://www.figma.com/file/HKpPKij9V3TpsyMV1TpV7C/DS-Components?node-id=7294%3A25180&t=QqFU9YJamwcKLvul-1)
- [FigJam Audit & Insight Report](https://www.figma.com/file/aGW8sk6X6Jf9ac0MRMD4kX/TextField-Audit?node-id=0%3A1&t=ULa7Q5OYfNcoF78F-1)
| non_priority | create component label description componentize label according to the insight report example screenshot img width alt screenshot at pm src technical details unless audited by design system place component in components temp directory location in app component library components temp directory component structure assume label your component s name under label directory label tsx actual component file label types ts includes all typescript related types interfaces enums etc label styles ts includes styles for the label component label test tsx includes both snapshots and unit tests label stories ts includes stories for the label component label constants ts includes any constants that is used in any label file for example test ids for tests mappings for the component etc label utils ts includes any utility functions specific to be used with the name component index ts exports both label component as default and anything else such as types test ids etc if needed readme md documentation on how the label component will be used and the props associated with it caveat components may differ in terms of files to include depending on what is needed for example you might not need a constants file or a styles file depending on how the component is built a more specific example you can omit the styles file if your component doesn t require styles just use your best judgement refer to an example component such as avatarfavicon for more details acceptance criteria snapshot and unit tests pass storybook shows interactive version of component include screenshot or video in pull request for visual reference component structure should resemble the structure listed in the technical details section above references | 0 |
165,155 | 12,830,275,711 | IssuesEvent | 2020-07-07 01:39:17 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: schemachange/during/tpcc failed | C-test-failure O-roachtest O-robot branch-release-19.2 release-blocker | [(roachtest).schemachange/during/tpcc failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1902166&tab=buildLog) on [release-19.2@93ac4d8875d10ed865b4c5252c209a8048e0d65c](https://github.com/cockroachdb/cockroach/commits/93ac4d8875d10ed865b4c5252c209a8048e0d65c):
```
| 9200.0s 0 43.0 50.8 1073.7 1275.1 1543.5 1543.5 delivery
| 9200.0s 0 389.8 507.5 1208.0 1811.9 2013.3 2281.7 newOrder
| 9200.0s 0 45.0 50.8 104.9 335.5 637.5 637.5 orderStatus
| 9200.0s 0 505.8 507.5 738.2 1208.0 1409.3 2818.6 payment
| 9200.0s 0 47.0 50.8 436.2 1275.1 1342.2 1342.2 stockLevel
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 9201.0s 0 37.0 50.8 973.1 1409.3 2147.5 2147.5 delivery
| 9201.0s 0 550.1 507.5 1275.1 1946.2 2281.7 2684.4 newOrder
| 9201.0s 0 48.0 50.8 130.0 285.2 503.3 503.3 orderStatus
| 9201.0s 0 463.1 507.5 738.2 1208.0 1409.3 1677.7 payment
| 9201.0s 0 42.0 50.8 335.5 1073.7 1208.0 1208.0 stockLevel
Wraps: (5) secondary error attachment
| signal: killed
| (1) signal: killed
| Error types: (1) *exec.ExitError
Wraps: (6) context canceled
Error types: (1) *withstack.withStack (2) *safedetails.withSafeDetails (3) *errutil.withMessage (4) *main.withCommandDetails (5) *secondary.withSecondaryError (6) *errors.errorString
cluster.go:2444,tpcc.go:168,schemachange.go:416,test_runner.go:753: monitor failure: monitor task failed: Goexit() was called
(1) attached stack trace
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2432
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2440
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:168
| main.makeSchemaChangeDuringTPCC.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/schemachange.go:416
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:753
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2488
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2385
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5222
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) Goexit() was called
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *errors.errorString
Failed to find issue assignee:
couldn't find GitHub commits for user email lucy@cockroachlabs.com
```
<details><summary>More</summary><p>
Artifacts: [/schemachange/during/tpcc](https://teamcity.cockroachdb.com/viewLog.html?buildId=1902166&tab=artifacts#/schemachange/during/tpcc)
Related:
- #47979 roachtest: schemachange/during/tpcc failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-20.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-20.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47653 roachtest: schemachange/during/tpcc failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004171855_v20.1.0-rc.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004171855_v20.1.0-rc.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47614 roachtest: schemachange/during/tpcc failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Aschemachange%2Fduring%2Ftpcc.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: schemachange/during/tpcc failed - [(roachtest).schemachange/during/tpcc failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1902166&tab=buildLog) on [release-19.2@93ac4d8875d10ed865b4c5252c209a8048e0d65c](https://github.com/cockroachdb/cockroach/commits/93ac4d8875d10ed865b4c5252c209a8048e0d65c):
```
| 9200.0s 0 43.0 50.8 1073.7 1275.1 1543.5 1543.5 delivery
| 9200.0s 0 389.8 507.5 1208.0 1811.9 2013.3 2281.7 newOrder
| 9200.0s 0 45.0 50.8 104.9 335.5 637.5 637.5 orderStatus
| 9200.0s 0 505.8 507.5 738.2 1208.0 1409.3 2818.6 payment
| 9200.0s 0 47.0 50.8 436.2 1275.1 1342.2 1342.2 stockLevel
| _elapsed___errors__ops/sec(inst)___ops/sec(cum)__p50(ms)__p95(ms)__p99(ms)_pMax(ms)
| 9201.0s 0 37.0 50.8 973.1 1409.3 2147.5 2147.5 delivery
| 9201.0s 0 550.1 507.5 1275.1 1946.2 2281.7 2684.4 newOrder
| 9201.0s 0 48.0 50.8 130.0 285.2 503.3 503.3 orderStatus
| 9201.0s 0 463.1 507.5 738.2 1208.0 1409.3 1677.7 payment
| 9201.0s 0 42.0 50.8 335.5 1073.7 1208.0 1208.0 stockLevel
Wraps: (5) secondary error attachment
| signal: killed
| (1) signal: killed
| Error types: (1) *exec.ExitError
Wraps: (6) context canceled
Error types: (1) *withstack.withStack (2) *safedetails.withSafeDetails (3) *errutil.withMessage (4) *main.withCommandDetails (5) *secondary.withSecondaryError (6) *errors.errorString
cluster.go:2444,tpcc.go:168,schemachange.go:416,test_runner.go:753: monitor failure: monitor task failed: Goexit() was called
(1) attached stack trace
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2432
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2440
| main.runTPCC
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:168
| main.makeSchemaChangeDuringTPCC.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/schemachange.go:416
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:753
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2488
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2385
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5222
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) Goexit() was called
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *errors.errorString
Failed to find issue assignee:
couldn't find GitHub commits for user email lucy@cockroachlabs.com
```
<details><summary>More</summary><p>
Artifacts: [/schemachange/during/tpcc](https://teamcity.cockroachdb.com/viewLog.html?buildId=1902166&tab=artifacts#/schemachange/during/tpcc)
Related:
- #47979 roachtest: schemachange/during/tpcc failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-20.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-20.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47653 roachtest: schemachange/during/tpcc failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202004171855_v20.1.0-rc.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202004171855_v20.1.0-rc.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #47614 roachtest: schemachange/during/tpcc failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Aschemachange%2Fduring%2Ftpcc.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | roachtest schemachange during tpcc failed on delivery neworder orderstatus payment stocklevel elapsed errors ops sec inst ops sec cum ms ms ms pmax ms delivery neworder orderstatus payment stocklevel wraps secondary error attachment signal killed signal killed error types exec exiterror wraps context canceled error types withstack withstack safedetails withsafedetails errutil withmessage main withcommanddetails secondary withsecondaryerror errors errorstring cluster go tpcc go schemachange go test runner go monitor failure monitor task failed goexit was called attached stack trace main monitor waite home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main runtpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main makeschemachangeduringtpcc home agent work go src github com cockroachdb cockroach pkg cmd roachtest schemachange go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go wraps monitor failure wraps attached stack trace main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go wraps monitor task failed wraps attached stack trace main init home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go runtime doinit usr local go src runtime proc go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps goexit was called error types withstack withstack errutil withmessage withstack withstack errutil withmessage withstack withstack errors errorstring failed to find issue assignee couldn t find github commits for user email lucy cockroachlabs com more artifacts related roachtest schemachange during tpcc failed roachtest schemachange during tpcc failed roachtest schemachange during tpcc failed powered by | 0 |
283,961 | 30,913,574,692 | IssuesEvent | 2023-08-05 02:17:09 | Satheesh575555/linux-4.1.15_CVE-2022-45934 | https://api.github.com/repos/Satheesh575555/linux-4.1.15_CVE-2022-45934 | reopened | CVE-2016-4485 (High) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2016-4485 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/linux-4.1.15_CVE-2022-45934/commit/7c0b143b43394df131d83e9aecb3c5518edc127a">7c0b143b43394df131d83e9aecb3c5518edc127a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/llc/af_llc.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/llc/af_llc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The llc_cmsg_rcv function in net/llc/af_llc.c in the Linux kernel before 4.5.5 does not initialize a certain data structure, which allows attackers to obtain sensitive information from kernel stack memory by reading a message.
<p>Publish Date: 2016-05-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4485>CVE-2016-4485</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-4485">https://nvd.nist.gov/vuln/detail/CVE-2016-4485</a></p>
<p>Release Date: 2016-05-23</p>
<p>Fix Resolution: 4.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-4485 (High) detected in linuxlinux-4.6 - ## CVE-2016-4485 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Satheesh575555/linux-4.1.15_CVE-2022-45934/commit/7c0b143b43394df131d83e9aecb3c5518edc127a">7c0b143b43394df131d83e9aecb3c5518edc127a</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/llc/af_llc.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/llc/af_llc.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The llc_cmsg_rcv function in net/llc/af_llc.c in the Linux kernel before 4.5.5 does not initialize a certain data structure, which allows attackers to obtain sensitive information from kernel stack memory by reading a message.
<p>Publish Date: 2016-05-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-4485>CVE-2016-4485</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-4485">https://nvd.nist.gov/vuln/detail/CVE-2016-4485</a></p>
<p>Release Date: 2016-05-23</p>
<p>Fix Resolution: 4.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files net llc af llc c net llc af llc c vulnerability details the llc cmsg rcv function in net llc af llc c in the linux kernel before does not initialize a certain data structure which allows attackers to obtain sensitive information from kernel stack memory by reading a message publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
130,771 | 10,652,867,037 | IssuesEvent | 2019-10-17 13:26:55 | scality/metalk8s | https://api.github.com/repos/scality/metalk8s | closed | Update the repository list on Ubuntu machines deployed by Vagrant | easy enhancement moonshot tests | <!-- Please only use this template for submitting improvement requests, and make sure it is linked to the relevant GitHub Project. -->
**Component**: Vagrant
<!-- E.g. 'salt', 'containers', 'kubernetes', 'build', 'tests'... -->
**Why this is needed**:
Canonical moved some packages on their repositories. For our tests on our Vagrant environment, we need to install python2.7 but we need to update the repo list first, installation fail if we don't do it.
**What should be done**: Permit to execute a command to update the repo list before to launch the python2.7 installation
**Implementation proposal** (strongly recommended):
Modify the Vagrant file to add the execution of `apt update`
**Test plan**:
- Launch `vagrant up Ubuntu1`
- Verify that the VM installation is well executed | 1.0 | Update the repository list on Ubuntu machines deployed by Vagrant - <!-- Please only use this template for submitting improvement requests, and make sure it is linked to the relevant GitHub Project. -->
**Component**: Vagrant
<!-- E.g. 'salt', 'containers', 'kubernetes', 'build', 'tests'... -->
**Why this is needed**:
Canonical moved some packages on their repositories. For our tests on our Vagrant environment, we need to install python2.7 but we need to update the repo list first, installation fail if we don't do it.
**What should be done**: Permit to execute a command to update the repo list before to launch the python2.7 installation
**Implementation proposal** (strongly recommended):
Modify the Vagrant file to add the execution of `apt update`
**Test plan**:
- Launch `vagrant up Ubuntu1`
- Verify that the VM installation is well executed | non_priority | update the repository list on ubuntu machines deployed by vagrant component vagrant why this is needed canonical moved some packages on their repositories for our tests on our vagrant environment we need to install but we need to update the repo list first installation fail if we don t do it what should be done permit to execute a command to update the repo list before to launch the installation implementation proposal strongly recommended modify the vagrant file to add the execution of apt update test plan launch vagrant up verify that the vm installation is well executed | 0 |
40,093 | 8,728,193,292 | IssuesEvent | 2018-12-10 16:45:52 | modin-project/modin | https://api.github.com/repos/modin-project/modin | closed | Refactor io.py into a module | Code Quality :100: good first issue :beginner: | ### Describe the problem
<!-- Describe the problem clearly here. -->
`modin.pandas.io` is currently a bit messy and needs a refactor. Ideally, we would refactor it into a module with python files for each backend (currently only Pandas on Ray).
This issue would be good for a first time contributor, so please feel free to reply to this thread with any questions if you are interested.
### Source code / logs
[Link to source](https://github.com/modin-project/modin/blob/master/modin/pandas/io.py)
| 1.0 | Refactor io.py into a module - ### Describe the problem
<!-- Describe the problem clearly here. -->
`modin.pandas.io` is currently a bit messy and needs a refactor. Ideally, we would refactor it into a module with python files for each backend (currently only Pandas on Ray).
This issue would be good for a first time contributor, so please feel free to reply to this thread with any questions if you are interested.
### Source code / logs
[Link to source](https://github.com/modin-project/modin/blob/master/modin/pandas/io.py)
| non_priority | refactor io py into a module describe the problem modin pandas io is currently a bit messy and needs a refactor ideally we would refactor it into a module with python files for each backend currently only pandas on ray this issue would be good for a first time contributor so please feel free to reply to this thread with any questions if you are interested source code logs | 0 |
89,803 | 18,045,462,038 | IssuesEvent | 2021-09-18 20:29:02 | julz0815/veracode-flaws-to-issues | https://api.github.com/repos/julz0815/veracode-flaws-to-issues | closed | Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') ('SQL Injection') [VID:20] | VeracodeFlaw: High Veracode Policy Scan | **Filename:** https://github.com/julz0815/veracode-flaws-to-issues/blob/d80f36548eefc759f32d8f170fdde9e3c4af2f1e/src/main/java/com/veracode/verademo/controller/UserController.java#L251
**Line:** 251
**CWE:** 89 (Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') ('SQL Injection'))
<span>This database query contains a SQL injection flaw. The call to java.sql.Statement.executeQuery() constructs a dynamic SQL query using a variable derived from untrusted input. An attacker could exploit this flaw to execute arbitrary SQL queries against the database. The first argument to executeQuery() contains tainted data from the variable sql. The tainted data originated from an earlier call to AnnotationVirtualController.vc_annotation_entry.</span> <span>Avoid dynamically constructing SQL queries. Instead, use parameterized prepared statements to prevent the database from interpreting the contents of bind variables as part of the query. Always validate untrusted input to ensure that it conforms to the expected format, using centralized data validation routines when possible.</span> <span>References: <a href="https://cwe.mitre.org/data/definitions/89.html">CWE</a> <a href="https://www.owasp.org/index.php/SQL_injection">OWASP</a> <a href="https://webappsec.pbworks.com/SQL-Injection">WASC</a></span> | 2.0 | Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') ('SQL Injection') [VID:20] - **Filename:** https://github.com/julz0815/veracode-flaws-to-issues/blob/d80f36548eefc759f32d8f170fdde9e3c4af2f1e/src/main/java/com/veracode/verademo/controller/UserController.java#L251
**Line:** 251
**CWE:** 89 (Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection') ('SQL Injection'))
<span>This database query contains a SQL injection flaw. The call to java.sql.Statement.executeQuery() constructs a dynamic SQL query using a variable derived from untrusted input. An attacker could exploit this flaw to execute arbitrary SQL queries against the database. The first argument to executeQuery() contains tainted data from the variable sql. The tainted data originated from an earlier call to AnnotationVirtualController.vc_annotation_entry.</span> <span>Avoid dynamically constructing SQL queries. Instead, use parameterized prepared statements to prevent the database from interpreting the contents of bind variables as part of the query. Always validate untrusted input to ensure that it conforms to the expected format, using centralized data validation routines when possible.</span> <span>References: <a href="https://cwe.mitre.org/data/definitions/89.html">CWE</a> <a href="https://www.owasp.org/index.php/SQL_injection">OWASP</a> <a href="https://webappsec.pbworks.com/SQL-Injection">WASC</a></span> | non_priority | improper neutralization of special elements used in an sql command sql injection sql injection filename line cwe improper neutralization of special elements used in an sql command sql injection sql injection this database query contains a sql injection flaw the call to java sql statement executequery constructs a dynamic sql query using a variable derived from untrusted input an attacker could exploit this flaw to execute arbitrary sql queries against the database the first argument to executequery contains tainted data from the variable sql the tainted data originated from an earlier call to annotationvirtualcontroller vc annotation entry avoid dynamically constructing sql queries instead use parameterized prepared statements to prevent the database from interpreting the contents of bind variables as part of the query always validate untrusted input to ensure that it conforms to the expected format using centralized data validation routines when possible references a href a href a href | 0 |
184,348 | 21,784,873,252 | IssuesEvent | 2022-05-14 01:38:04 | onokatio/blog.katio.net | https://api.github.com/repos/onokatio/blog.katio.net | closed | CVE-2021-35065 (High) detected in glob-parent-3.1.0.tgz - autoclosed | security vulnerability | ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.10.5.tgz (Root Library)
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package glob-parent before 6.0.1 are vulnerable to Regular Expression Denial of Service (ReDoS)
<p>Publish Date: 2021-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35065>CVE-2021-35065</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/gulpjs/glob-parent/pull/49">https://github.com/gulpjs/glob-parent/pull/49</a></p>
<p>Release Date: 2021-06-22</p>
<p>Fix Resolution: glob-parent - 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-35065 (High) detected in glob-parent-3.1.0.tgz - autoclosed - ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- cli-7.10.5.tgz (Root Library)
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package glob-parent before 6.0.1 are vulnerable to Regular Expression Denial of Service (ReDoS)
<p>Publish Date: 2021-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-35065>CVE-2021-35065</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/gulpjs/glob-parent/pull/49">https://github.com/gulpjs/glob-parent/pull/49</a></p>
<p>Release Date: 2021-06-22</p>
<p>Fix Resolution: glob-parent - 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz autoclosed cve high severity vulnerability vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file package json path to vulnerable library node modules glob parent package json dependency hierarchy cli tgz root library chokidar tgz x glob parent tgz vulnerable library found in base branch master vulnerability details the package glob parent before are vulnerable to regular expression denial of service redos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent step up your open source security game with whitesource | 0 |
68,874 | 8,357,976,130 | IssuesEvent | 2018-10-03 00:00:17 | vavr-io/vavr | https://api.github.com/repos/vavr-io/vavr | closed | Streams are not lazy enough | !BACK-COMPAT design/refactoring/improvement «vavr-collection» | Recently I've faced with an issue with Vavr Streams design. Streams are implemented in a such way that head of the stream is eager and not lazy. Most of the time it's not a big deal, but there are some cases when this behavior can produce a lot of useless calculations.
The example I've faced with is the following:
Suppose there is a large map that maps some keys to streams of data. There is a function that accepts the map and filter it's values in a lazy manner (since the values are Streams). Since Steams are eager to the head, the filtering will be eager until first element that satisfies the predicate will be found. And that is going to be done for every element in the map. In my case it's quite common case that all values in streams can be filtered out completely, so, basically that means that this operation will not be lazy, but completely eager.
The user guide states that
> Stream implementation is a lazy linked list. Values are computed only when needed
so it may be understood that Stream head will be computed only on read and not on steam creation. Even if the documentation explicitly states
> A Stream is composed of a head element and a lazy evaluated tail Stream
it's still not obvious why to make this collection half lazy - half eager, to make users to always keep this behavior in mind.
So the main question is: Is such behavior designed and fixed or it is possible to change it in the future to make streams lazy?
P. S. If latter I could try to improve that to make Streams fully lazy and in case of success I could prepare PR.
P. P. S. Also it's just strange to have a lazy collection that calculates it's first element in eager way. I've also faced with the situation where I have to deal with errors when stream is created (in case of exception happens during head calculations) and in the place where the Stream is actually used (where other elements are calculated). This was also unexpected to have. | 1.0 | Streams are not lazy enough - Recently I've faced with an issue with Vavr Streams design. Streams are implemented in a such way that head of the stream is eager and not lazy. Most of the time it's not a big deal, but there are some cases when this behavior can produce a lot of useless calculations.
The example I've faced with is the following:
Suppose there is a large map that maps some keys to streams of data. There is a function that accepts the map and filter it's values in a lazy manner (since the values are Streams). Since Steams are eager to the head, the filtering will be eager until first element that satisfies the predicate will be found. And that is going to be done for every element in the map. In my case it's quite common case that all values in streams can be filtered out completely, so, basically that means that this operation will not be lazy, but completely eager.
The user guide states that
> Stream implementation is a lazy linked list. Values are computed only when needed
so it may be understood that Stream head will be computed only on read and not on steam creation. Even if the documentation explicitly states
> A Stream is composed of a head element and a lazy evaluated tail Stream
it's still not obvious why to make this collection half lazy - half eager, to make users to always keep this behavior in mind.
So the main question is: Is such behavior designed and fixed or it is possible to change it in the future to make streams lazy?
P. S. If latter I could try to improve that to make Streams fully lazy and in case of success I could prepare PR.
P. P. S. Also it's just strange to have a lazy collection that calculates it's first element in eager way. I've also faced with the situation where I have to deal with errors when stream is created (in case of exception happens during head calculations) and in the place where the Stream is actually used (where other elements are calculated). This was also unexpected to have. | non_priority | streams are not lazy enough recently i ve faced with an issue with vavr streams design streams are implemented in a such way that head of the stream is eager and not lazy most of the time it s not a big deal but there are some cases when this behavior can produce a lot of useless calculations the example i ve faced with is the following suppose there is a large map that maps some keys to streams of data there is a function that accepts the map and filter it s values in a lazy manner since the values are streams since steams are eager to the head the filtering will be eager until first element that satisfies the predicate will be found and that is going to be done for every element in the map in my case it s quite common case that all values in streams can be filtered out completely so basically that means that this operation will not be lazy but completely eager the user guide states that stream implementation is a lazy linked list values are computed only when needed so it may be understood that stream head will be computed only on read and not on steam creation even if the documentation explicitly states a stream is composed of a head element and a lazy evaluated tail stream it s still not obvious why to make this collection half lazy half eager to make users to always keep this behavior in mind so the main question is is such behavior designed and fixed or it is possible to change it in the future to make streams lazy p s if latter i could try to improve that to make streams fully lazy and in case of success i could prepare pr p p s also it s just strange to have a lazy collection that calculates it s first element in eager way i ve also faced with the situation where i have to deal with errors when stream is created in case of exception happens during head calculations and in the place where the stream is actually used where other elements are calculated this was also unexpected to have | 0 |
81,695 | 15,789,087,816 | IssuesEvent | 2021-04-01 21:59:23 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Superpmi asmdiff is slow for windows arm64 | area-CodeGen-coreclr needs further triage | ```
python repo\src\coreclr\scripts\superpmi.py asmdiffs -target_arch arm64 -base_jit_path base_path\clrjit_win_arm64_x64.dll -diff_j
it_path diff_path\clrjit_win_arm64_x64.dll -jit_name clrjit_win_arm64_x64.dll
```
This takes a long time to complete (it completes successfully). In my run, I didn't see any other issue like https://github.com/dotnet/jitutils/issues/309, but need to figure out why it is slow. | 1.0 | Superpmi asmdiff is slow for windows arm64 - ```
python repo\src\coreclr\scripts\superpmi.py asmdiffs -target_arch arm64 -base_jit_path base_path\clrjit_win_arm64_x64.dll -diff_j
it_path diff_path\clrjit_win_arm64_x64.dll -jit_name clrjit_win_arm64_x64.dll
```
This takes a long time to complete (it completes successfully). In my run, I didn't see any other issue like https://github.com/dotnet/jitutils/issues/309, but need to figure out why it is slow. | non_priority | superpmi asmdiff is slow for windows python repo src coreclr scripts superpmi py asmdiffs target arch base jit path base path clrjit win dll diff j it path diff path clrjit win dll jit name clrjit win dll this takes a long time to complete it completes successfully in my run i didn t see any other issue like but need to figure out why it is slow | 0 |
249,249 | 18,858,175,544 | IssuesEvent | 2021-11-12 09:28:10 | kahhe/pe | https://api.github.com/repos/kahhe/pe | opened | UG: Card Page hyperlink does not work under "Intermediate page" Section | severity.VeryLow type.DocumentationBug |
Hyper link does not work because markdown format is wrong
```
card Manage your holding cards. You can refer to detailed introduction about card here [Card Page](#card page)
```
<!--session: 1636703720023-d7d9b39a-b355-4313-953b-916be653625d-->
<!--Version: Web v3.4.1--> | 1.0 | UG: Card Page hyperlink does not work under "Intermediate page" Section -
Hyper link does not work because markdown format is wrong
```
card Manage your holding cards. You can refer to detailed introduction about card here [Card Page](#card page)
```
<!--session: 1636703720023-d7d9b39a-b355-4313-953b-916be653625d-->
<!--Version: Web v3.4.1--> | non_priority | ug card page hyperlink does not work under intermediate page section hyper link does not work because markdown format is wrong card manage your holding cards you can refer to detailed introduction about card here card page | 0 |
8,322 | 5,623,108,461 | IssuesEvent | 2017-04-04 14:18:41 | zaproxy/zaproxy | https://api.github.com/repos/zaproxy/zaproxy | closed | Missing Help details Options Connection screen | bug Component-Docs Usability | https://github.com/zaproxy/zap-core-help/wiki/HelpUiDialogsOptionsConnection
Doesn't have any details as to how the "Default User Agent" is used, or info on the "Security Protocols" section. | True | Missing Help details Options Connection screen - https://github.com/zaproxy/zap-core-help/wiki/HelpUiDialogsOptionsConnection
Doesn't have any details as to how the "Default User Agent" is used, or info on the "Security Protocols" section. | non_priority | missing help details options connection screen doesn t have any details as to how the default user agent is used or info on the security protocols section | 0 |
8,305 | 26,672,611,380 | IssuesEvent | 2023-01-26 11:39:51 | Accenture/sfmc-devtools | https://api.github.com/repos/Accenture/sfmc-devtools | opened | [BUG] if downloading a single automation's details fails, the entire automation retrieve is canceled | bug c/automation | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
you run `mcdev retrieve ... automation` and it gets a list of available automations. Then, it proceeds to download the details for each of them separately.
If any of these singular downloads ends up failing, no automations are saved to disk
### Expected Behavior
we should handle the error gracefully, tell the user about it and continue processing the rest.
### Steps To Reproduce
1. Go to '...'
2. Click on '....'
3. Run '...'
4. See error...
### Version
4.2.1
### Environment
- OS:
- Node:
- npm:
### Participation
- [X] I am willing to submit a pull request for this issue.
### Additional comments
_No response_ | 1.0 | [BUG] if downloading a single automation's details fails, the entire automation retrieve is canceled - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
you run `mcdev retrieve ... automation` and it gets a list of available automations. Then, it proceeds to download the details for each of them separately.
If any of these singular downloads ends up failing, no automations are saved to disk
### Expected Behavior
we should handle the error gracefully, tell the user about it and continue processing the rest.
### Steps To Reproduce
1. Go to '...'
2. Click on '....'
3. Run '...'
4. See error...
### Version
4.2.1
### Environment
- OS:
- Node:
- npm:
### Participation
- [X] I am willing to submit a pull request for this issue.
### Additional comments
_No response_ | non_priority | if downloading a single automation s details fails the entire automation retrieve is canceled is there an existing issue for this i have searched the existing issues current behavior you run mcdev retrieve automation and it gets a list of available automations then it proceeds to download the details for each of them separately if any of these singular downloads ends up failing no automations are saved to disk expected behavior we should handle the error gracefully tell the user about it and continue processing the rest steps to reproduce go to click on run see error version environment os node npm participation i am willing to submit a pull request for this issue additional comments no response | 0 |
136,294 | 30,516,841,721 | IssuesEvent | 2023-07-19 04:16:27 | SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f | https://api.github.com/repos/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f | opened | Code Security Report: 24 high severity findings, 38 total findings | Mend: code security findings | # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-19 04:13am
**Total Findings:** 38 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 422
**Detected Programming Languages:** 2 (Java*, JavaScript / Node.js)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/f83d8783-8e5a-42e7-91f3-d9316606d958/details).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson4.java:63](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L60
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson2.java:62](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L55
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L59
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson10.java:63](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L52
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Assignment5.java:59](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L51
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Servers.java:72](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L67-L72
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L68
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5a.java:62](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L53
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5.java:73](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L73)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L68-L73
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L65
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L67
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L70
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L73
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionChallenge.java:65](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L63
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5b.java:71](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L66-L71
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L51
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L55
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson3.java:65](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|DOM Based Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|JavaScript / Node.js|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|6|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|14|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|XML External Entity (XXE) Injection|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java*|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|JavaScript / Node.js|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Log Forging|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|System Properties Disclosure|[CWE-497](https://cwe.mitre.org/data/definitions/497.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|1|
| 1.0 | Code Security Report: 24 high severity findings, 38 total findings - # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-19 04:13am
**Total Findings:** 38 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 422
**Detected Programming Languages:** 2 (Java*, JavaScript / Node.js)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/f83d8783-8e5a-42e7-91f3-d9316606d958/details).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson4.java:63](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L60
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson2.java:62](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L55
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L59
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson10.java:63](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L52
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Assignment5.java:59](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L51
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Servers.java:72](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L67-L72
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L68
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5a.java:62](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L53
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5.java:73](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L73)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L68-L73
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L65
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L67
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L70
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5.java#L73
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionChallenge.java:65](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L63
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5b.java:71](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L66-L71
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L51
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L55
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson3.java:65](https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65)
</td><td>1</td><td>2023-07-19 04:16am</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L56
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60
https://github.com/SAST-OldPlatform-DEV/SAST-Test-Repo-861868c1-c1ce-40bc-9329-0dac07b6b57f/blob/e2f5ddd5978ad067e414d3cd5a78a4ba5cce576b/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|DOM Based Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|JavaScript / Node.js|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|6|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|14|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|XML External Entity (XXE) Injection|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java*|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|JavaScript / Node.js|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Log Forging|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|System Properties Disclosure|[CWE-497](https://cwe.mitre.org/data/definitions/497.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|1|
| non_priority | code security report high severity findings total findings code security report scan metadata latest scan total findings new findings resolved findings tested project files detected programming languages java javascript node js check this box to manually trigger a scan most relevant findings the below list presents the most relevant findings that need your attention to view information on the remaining findings navigate to the severity vulnerability type cwe file data flows date high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow findings overview severity vulnerability type cwe language count high dom based cross site scripting node js high path directory traversal high deserialization of untrusted data high sql injection high server side request forgery medium xml external entity xxe injection medium hardcoded password credentials medium error messages information exposure medium weak pseudo random node js low log forging low system properties disclosure low weak hash strength | 0 |
133,007 | 18,792,520,799 | IssuesEvent | 2021-11-08 18:19:15 | getsentry/sentry-docs | https://api.github.com/repos/getsentry/sentry-docs | closed | Silence stack trace do not working | Status: Stale Status: As Designed | ### Core or SDK?
Core Sentry product
### Which part? Which one?
SDK nextJS
### Description
`sentry.client.config.js`:
```
Sentry.init({
dsn: SENTRY_DSN || 'https://nooooooooooooooooooo.ingest.sentry.io/1337',
tracesSampleRate: 1.0,
maxBreadcrumbs: 2,
maxValueLength: 1,
attachStacktrace: false,
autoSessionTracking: false,
});
```
Not working=( I see stack trace in sentry issue and network tabs in my browser.
### Suggested Solution
I want stack trace is off | 1.0 | Silence stack trace do not working - ### Core or SDK?
Core Sentry product
### Which part? Which one?
SDK nextJS
### Description
`sentry.client.config.js`:
```
Sentry.init({
dsn: SENTRY_DSN || 'https://nooooooooooooooooooo.ingest.sentry.io/1337',
tracesSampleRate: 1.0,
maxBreadcrumbs: 2,
maxValueLength: 1,
attachStacktrace: false,
autoSessionTracking: false,
});
```
Not working=( I see stack trace in sentry issue and network tabs in my browser.
### Suggested Solution
I want stack trace is off | non_priority | silence stack trace do not working core or sdk core sentry product which part which one sdk nextjs description sentry client config js sentry init dsn sentry dsn tracessamplerate maxbreadcrumbs maxvaluelength attachstacktrace false autosessiontracking false not working i see stack trace in sentry issue and network tabs in my browser suggested solution i want stack trace is off | 0 |
129,861 | 10,589,310,465 | IssuesEvent | 2019-10-09 05:41:15 | pandas-dev/pandas | https://api.github.com/repos/pandas-dev/pandas | closed | test_time failure in CI logs | CI Unreliable Test | The following failure has shown up a couple times in CI today. Haven't looked in detail but assume it to be an unreliable test.
https://dev.azure.com/pandas-dev/pandas/_build/results?buildId=9836&view=logs&jobId=a69e7846-138e-5465-0656-921e8964615b&taskId=56da51de-fd5a-5466-5244-b5f65d252624&lineStart=42&lineEnd=95&colStart=1&colEnd=64
```
=================================== FAILURES ===================================
_____________________________ TestTSPlot.test_time _____________________________
[gw0] linux -- Python 3.6.6 /home/vsts/miniconda3/envs/pandas-dev/bin/python
self = <pandas.tests.plotting.test_datetimelike.TestTSPlot object at 0x7f2889f69978>
@pytest.mark.slow
def test_time(self):
t = datetime(1, 1, 1, 3, 30, 0)
deltas = np.random.randint(1, 20, 3).cumsum()
ts = np.array([(t + timedelta(minutes=int(x))).time() for x in deltas])
df = DataFrame({'a': np.random.randn(len(ts)),
'b': np.random.randn(len(ts))},
index=ts)
fig, ax = self.plt.subplots()
df.plot(ax=ax)
# verify tick labels
fig.canvas.draw()
ticks = ax.get_xticks()
labels = ax.get_xticklabels()
for t, l in zip(ticks, labels):
m, s = divmod(int(t), 60)
h, m = divmod(m, 60)
rs = l.get_text()
if len(rs) > 0:
if s != 0:
xp = time(h, m, s).strftime('%H:%M:%S')
else:
xp = time(h, m, s).strftime('%H:%M')
assert xp == rs
# change xlim
ax.set_xlim('1:30', '5:00')
# check tick labels again
fig.canvas.draw()
ticks = ax.get_xticks()
labels = ax.get_xticklabels()
for t, l in zip(ticks, labels):
m, s = divmod(int(t), 60)
h, m = divmod(m, 60)
rs = l.get_text()
if len(rs) > 0:
if s != 0:
xp = time(h, m, s).strftime('%H:%M:%S')
else:
xp = time(h, m, s).strftime('%H:%M')
> assert xp == rs
E AssertionError: assert '01:06:40' == '03:40'
E - 01:06:40
E + 03:40
``` | 1.0 | test_time failure in CI logs - The following failure has shown up a couple times in CI today. Haven't looked in detail but assume it to be an unreliable test.
https://dev.azure.com/pandas-dev/pandas/_build/results?buildId=9836&view=logs&jobId=a69e7846-138e-5465-0656-921e8964615b&taskId=56da51de-fd5a-5466-5244-b5f65d252624&lineStart=42&lineEnd=95&colStart=1&colEnd=64
```
=================================== FAILURES ===================================
_____________________________ TestTSPlot.test_time _____________________________
[gw0] linux -- Python 3.6.6 /home/vsts/miniconda3/envs/pandas-dev/bin/python
self = <pandas.tests.plotting.test_datetimelike.TestTSPlot object at 0x7f2889f69978>
@pytest.mark.slow
def test_time(self):
t = datetime(1, 1, 1, 3, 30, 0)
deltas = np.random.randint(1, 20, 3).cumsum()
ts = np.array([(t + timedelta(minutes=int(x))).time() for x in deltas])
df = DataFrame({'a': np.random.randn(len(ts)),
'b': np.random.randn(len(ts))},
index=ts)
fig, ax = self.plt.subplots()
df.plot(ax=ax)
# verify tick labels
fig.canvas.draw()
ticks = ax.get_xticks()
labels = ax.get_xticklabels()
for t, l in zip(ticks, labels):
m, s = divmod(int(t), 60)
h, m = divmod(m, 60)
rs = l.get_text()
if len(rs) > 0:
if s != 0:
xp = time(h, m, s).strftime('%H:%M:%S')
else:
xp = time(h, m, s).strftime('%H:%M')
assert xp == rs
# change xlim
ax.set_xlim('1:30', '5:00')
# check tick labels again
fig.canvas.draw()
ticks = ax.get_xticks()
labels = ax.get_xticklabels()
for t, l in zip(ticks, labels):
m, s = divmod(int(t), 60)
h, m = divmod(m, 60)
rs = l.get_text()
if len(rs) > 0:
if s != 0:
xp = time(h, m, s).strftime('%H:%M:%S')
else:
xp = time(h, m, s).strftime('%H:%M')
> assert xp == rs
E AssertionError: assert '01:06:40' == '03:40'
E - 01:06:40
E + 03:40
``` | non_priority | test time failure in ci logs the following failure has shown up a couple times in ci today haven t looked in detail but assume it to be an unreliable test failures testtsplot test time linux python home vsts envs pandas dev bin python self pytest mark slow def test time self t datetime deltas np random randint cumsum ts np array df dataframe a np random randn len ts b np random randn len ts index ts fig ax self plt subplots df plot ax ax verify tick labels fig canvas draw ticks ax get xticks labels ax get xticklabels for t l in zip ticks labels m s divmod int t h m divmod m rs l get text if len rs if s xp time h m s strftime h m s else xp time h m s strftime h m assert xp rs change xlim ax set xlim check tick labels again fig canvas draw ticks ax get xticks labels ax get xticklabels for t l in zip ticks labels m s divmod int t h m divmod m rs l get text if len rs if s xp time h m s strftime h m s else xp time h m s strftime h m assert xp rs e assertionerror assert e e | 0 |
8,556 | 27,127,411,792 | IssuesEvent | 2023-02-16 06:57:37 | Azure/azure-sdk-tools | https://api.github.com/repos/Azure/azure-sdk-tools | closed | Support latest cadl project folder structure in sdk automation pipeline | SDK Automation | I will only works on sdk automation pipeline framework and js sdk automation script. For other language of sdk, other sdk owners have been working on them. | 1.0 | Support latest cadl project folder structure in sdk automation pipeline - I will only works on sdk automation pipeline framework and js sdk automation script. For other language of sdk, other sdk owners have been working on them. | non_priority | support latest cadl project folder structure in sdk automation pipeline i will only works on sdk automation pipeline framework and js sdk automation script for other language of sdk other sdk owners have been working on them | 0 |
95,555 | 8,563,186,055 | IssuesEvent | 2018-11-09 13:16:06 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | tests: e2e test for the writing flow started to fail | Automated Testing [Type] Bug | Similar to: #6956.
**Describe the bug**
When executing e2e tests two tests fail. It seems like there might be some regression introduced in the code or you can blame me for work done in #8301 🤷♂️ 😄
Let's ensure it has nothing to do with the recently merged PRs.
> FAIL test/e2e/specs/writing-flow.test.js (8.849s)
> ● adding blocks › should clean TinyMCE content
> expect(value).toMatchSnapshot()
> Received value does not match stored snapshot "adding blocks should clean TinyMCE content 1".
> - Snapshot
> + Received
> "<!-- wp:paragraph -->
> - <p><strong></strong></p>
> + <p></p>
> <!-- /wp:paragraph -->"
> 147 | await clickBlockAppender();
> 148 | await pressWithModifier( 'mod', 'b' );
> > 149 | expect( await getEditedPostContent() ).toMatchSnapshot();
> | ^
> 150 |
> 151 | // When returning to Visual mode, backspace in selected block should
> 152 | // reset to the provisional block.
> at Object._callee4$ (test/e2e/specs/writing-flow.test.js:149:42)
> at tryCatch (node_modules/regenerator-runtime/runtime.js:62:40)
> at Generator.invoke [as _invoke] (node_modules/regenerator-runtime/runtime.js:288:22)
> at Generator.prototype.(anonymous function) [as next] (node_modules/regenerator-runtime/runtime.js:114:21)
> at asyncGeneratorStep (test/e2e/specs/writing-flow.test.js:9:103)
> at _next (test/e2e/specs/writing-flow.test.js:11:194)
> ● adding blocks › should clean TinyMCE content
> expect(value).toMatchSnapshot()
> Received value does not match stored snapshot "adding blocks should clean TinyMCE content 2".
> - Snapshot
> + Received
> - "<!-- wp:paragraph -->
> - <p><strong>Inside</strong></p>
> - <!-- /wp:paragraph -->"
> + ""
> 157 | await pressWithModifier( 'mod', 'b' );
> 158 | await page.keyboard.type( 'Inside' );
> > 159 | expect( await getEditedPostContent() ).toMatchSnapshot();
> | ^
> 160 | } );
> 161 | } );
> 162 |
> at Object._callee4$ (test/e2e/specs/writing-flow.test.js:159:42)
> at tryCatch (node_modules/regenerator-runtime/runtime.js:62:40)
> at Generator.invoke [as _invoke] (node_modules/regenerator-runtime/runtime.js:288:22)
> at Generator.prototype.(anonymous function) [as next] (node_modules/regenerator-runtime/runtime.js:114:21)
> at asyncGeneratorStep (test/e2e/specs/writing-flow.test.js:9:103)
> at _next (test/e2e/specs/writing-flow.test.js:11:194)
**To Reproduce**
Steps to reproduce the behavior:
`npm run test-e2e`
**Expected behavior**
Tests pass.
| 1.0 | tests: e2e test for the writing flow started to fail - Similar to: #6956.
**Describe the bug**
When executing e2e tests two tests fail. It seems like there might be some regression introduced in the code or you can blame me for work done in #8301 🤷♂️ 😄
Let's ensure it has nothing to do with the recently merged PRs.
> FAIL test/e2e/specs/writing-flow.test.js (8.849s)
> ● adding blocks › should clean TinyMCE content
> expect(value).toMatchSnapshot()
> Received value does not match stored snapshot "adding blocks should clean TinyMCE content 1".
> - Snapshot
> + Received
> "<!-- wp:paragraph -->
> - <p><strong></strong></p>
> + <p></p>
> <!-- /wp:paragraph -->"
> 147 | await clickBlockAppender();
> 148 | await pressWithModifier( 'mod', 'b' );
> > 149 | expect( await getEditedPostContent() ).toMatchSnapshot();
> | ^
> 150 |
> 151 | // When returning to Visual mode, backspace in selected block should
> 152 | // reset to the provisional block.
> at Object._callee4$ (test/e2e/specs/writing-flow.test.js:149:42)
> at tryCatch (node_modules/regenerator-runtime/runtime.js:62:40)
> at Generator.invoke [as _invoke] (node_modules/regenerator-runtime/runtime.js:288:22)
> at Generator.prototype.(anonymous function) [as next] (node_modules/regenerator-runtime/runtime.js:114:21)
> at asyncGeneratorStep (test/e2e/specs/writing-flow.test.js:9:103)
> at _next (test/e2e/specs/writing-flow.test.js:11:194)
> ● adding blocks › should clean TinyMCE content
> expect(value).toMatchSnapshot()
> Received value does not match stored snapshot "adding blocks should clean TinyMCE content 2".
> - Snapshot
> + Received
> - "<!-- wp:paragraph -->
> - <p><strong>Inside</strong></p>
> - <!-- /wp:paragraph -->"
> + ""
> 157 | await pressWithModifier( 'mod', 'b' );
> 158 | await page.keyboard.type( 'Inside' );
> > 159 | expect( await getEditedPostContent() ).toMatchSnapshot();
> | ^
> 160 | } );
> 161 | } );
> 162 |
> at Object._callee4$ (test/e2e/specs/writing-flow.test.js:159:42)
> at tryCatch (node_modules/regenerator-runtime/runtime.js:62:40)
> at Generator.invoke [as _invoke] (node_modules/regenerator-runtime/runtime.js:288:22)
> at Generator.prototype.(anonymous function) [as next] (node_modules/regenerator-runtime/runtime.js:114:21)
> at asyncGeneratorStep (test/e2e/specs/writing-flow.test.js:9:103)
> at _next (test/e2e/specs/writing-flow.test.js:11:194)
**To Reproduce**
Steps to reproduce the behavior:
`npm run test-e2e`
**Expected behavior**
Tests pass.
| non_priority | tests test for the writing flow started to fail similar to describe the bug when executing tests two tests fail it seems like there might be some regression introduced in the code or you can blame me for work done in 🤷♂️ 😄 let s ensure it has nothing to do with the recently merged prs fail test specs writing flow test js ● adding blocks › should clean tinymce content expect value tomatchsnapshot received value does not match stored snapshot adding blocks should clean tinymce content snapshot received await clickblockappender await presswithmodifier mod b expect await geteditedpostcontent tomatchsnapshot when returning to visual mode backspace in selected block should reset to the provisional block at object test specs writing flow test js at trycatch node modules regenerator runtime runtime js at generator invoke node modules regenerator runtime runtime js at generator prototype anonymous function node modules regenerator runtime runtime js at asyncgeneratorstep test specs writing flow test js at next test specs writing flow test js ● adding blocks › should clean tinymce content expect value tomatchsnapshot received value does not match stored snapshot adding blocks should clean tinymce content snapshot received inside await presswithmodifier mod b await page keyboard type inside expect await geteditedpostcontent tomatchsnapshot at object test specs writing flow test js at trycatch node modules regenerator runtime runtime js at generator invoke node modules regenerator runtime runtime js at generator prototype anonymous function node modules regenerator runtime runtime js at asyncgeneratorstep test specs writing flow test js at next test specs writing flow test js to reproduce steps to reproduce the behavior npm run test expected behavior tests pass | 0 |
126,187 | 12,288,119,927 | IssuesEvent | 2020-05-09 15:20:53 | mynoo1130/MyNutritionist | https://api.github.com/repos/mynoo1130/MyNutritionist | opened | 식단 추천, 요리법 설명 화면 | documentation | 추천 메뉴나 식단 이미지를 눌렀을때 해당 메뉴/식단에 대해 설명하는 화면을 만들어야함
**추천메뉴**
1. 선택하여 들어온 요리(레시피)의 사진 or 동영상이 나오도록 해야함
2. 요리(레시피)가 사진일 경우 옆으로 드래그하여 요리 과정 이미지를 볼 수 있도록 해야함
3. 요리(레시피)의 각 이미지 마다 요리 과정의 상세 설명을 연결하여 이미지를 넘길때마다 상세 설명도 같이 넘겨지도록 해야한다.
**추천 식단**
1. 식단 목록을 가져와 보여주고 각 항목(음식)마다 선택이 가능하게 해야함
2. 선택한 음식의 이미지 및 동영상과 작성자 이름, 요리 난이도, 메뉴 이름, 영양소 정보를 보여줘야함
3. 추천 메뉴에서처럼 선택한 음식이 사진일 경우 이미지가 넘어갈때마다 하단에 상세 설명도 연결되어 같이 넘어가야 한다 | 1.0 | 식단 추천, 요리법 설명 화면 - 추천 메뉴나 식단 이미지를 눌렀을때 해당 메뉴/식단에 대해 설명하는 화면을 만들어야함
**추천메뉴**
1. 선택하여 들어온 요리(레시피)의 사진 or 동영상이 나오도록 해야함
2. 요리(레시피)가 사진일 경우 옆으로 드래그하여 요리 과정 이미지를 볼 수 있도록 해야함
3. 요리(레시피)의 각 이미지 마다 요리 과정의 상세 설명을 연결하여 이미지를 넘길때마다 상세 설명도 같이 넘겨지도록 해야한다.
**추천 식단**
1. 식단 목록을 가져와 보여주고 각 항목(음식)마다 선택이 가능하게 해야함
2. 선택한 음식의 이미지 및 동영상과 작성자 이름, 요리 난이도, 메뉴 이름, 영양소 정보를 보여줘야함
3. 추천 메뉴에서처럼 선택한 음식이 사진일 경우 이미지가 넘어갈때마다 하단에 상세 설명도 연결되어 같이 넘어가야 한다 | non_priority | 식단 추천 요리법 설명 화면 추천 메뉴나 식단 이미지를 눌렀을때 해당 메뉴 식단에 대해 설명하는 화면을 만들어야함 추천메뉴 선택하여 들어온 요리 레시피 의 사진 or 동영상이 나오도록 해야함 요리 레시피 가 사진일 경우 옆으로 드래그하여 요리 과정 이미지를 볼 수 있도록 해야함 요리 레시피 의 각 이미지 마다 요리 과정의 상세 설명을 연결하여 이미지를 넘길때마다 상세 설명도 같이 넘겨지도록 해야한다 추천 식단 식단 목록을 가져와 보여주고 각 항목 음식 마다 선택이 가능하게 해야함 선택한 음식의 이미지 및 동영상과 작성자 이름 요리 난이도 메뉴 이름 영양소 정보를 보여줘야함 추천 메뉴에서처럼 선택한 음식이 사진일 경우 이미지가 넘어갈때마다 하단에 상세 설명도 연결되어 같이 넘어가야 한다 | 0 |
6,297 | 5,352,993,924 | IssuesEvent | 2017-02-20 02:52:26 | weaveworks/scope | https://api.github.com/repos/weaveworks/scope | closed | Changing between topologies feels slow | chore component/ui help-wanted performance | - the load indicator might take too long to show up?
- if a topo has been seen before, and i switch back to it, i should be able to see it right away.
| True | Changing between topologies feels slow - - the load indicator might take too long to show up?
- if a topo has been seen before, and i switch back to it, i should be able to see it right away.
| non_priority | changing between topologies feels slow the load indicator might take too long to show up if a topo has been seen before and i switch back to it i should be able to see it right away | 0 |
156,641 | 12,325,570,657 | IssuesEvent | 2020-05-13 15:14:12 | nasa/cFE | https://api.github.com/repos/nasa/cFE | closed | Unit tests fail to build when MESSAGE_FORMAT_IS_CCSDS_VER_2 is enabled | bug unit test | **Describe the bug**
Unit tests fail to build when MESSAGE_FORMAT_IS_CCSDS_VER_2 is enabled
**To Reproduce**
Enable MESSAGE_FORMAT_IS_CCSDS_VER_2 in `*mission_cfg.h`
Run `make CFLAGS="-m32 -Wno-format" SIMULATION=native ENABLE_UNIT_TESTS=true`
**Expected behavior**
Compilation succeeds, however build actually fails due to missing `#include`
**Code snips**
This can be fixed by doing the following
```
--- a/fsw/cfe-core/ut-stubs/ut_sb_stubs.c
+++ b/fsw/cfe-core/ut-stubs/ut_sb_stubs.c
@@ -34,6 +34,8 @@
*/
#include <string.h>
#include "cfe.h"
+#include "cfe_platform_cfg.h"
+#include "../sb/cfe_sb_msg_id_util.h"
#include "utstubs.h"
```
However, subsequently a checksum error is encountered when running the tests.
This was worked around by doing the following, but unsure if the workaround is correct.
```
--- a/fsw/cfe-core/unit-test/sb_UT.c
+++ b/fsw/cfe-core/unit-test/sb_UT.c
@@ -9456,7 +9456,7 @@ void Test_CFE_SB_ChecksumUtils(void)
#ifndef MESSAGE_FORMAT_IS_CCSDS_VER_2
ExpRtnFrmGet = 0x2f;
#else
- ExpRtnFrmGet = 0x65;
+ ExpRtnFrmGet = 0x61;
#endif
/* Validation expected to return true */
```
**System observed on:**
- Hardware: N/A
- OS: RHEL7
- Versions cFE 6.7.12
**Reporter Info**
John N Pham, Northrop Grumman | 1.0 | Unit tests fail to build when MESSAGE_FORMAT_IS_CCSDS_VER_2 is enabled - **Describe the bug**
Unit tests fail to build when MESSAGE_FORMAT_IS_CCSDS_VER_2 is enabled
**To Reproduce**
Enable MESSAGE_FORMAT_IS_CCSDS_VER_2 in `*mission_cfg.h`
Run `make CFLAGS="-m32 -Wno-format" SIMULATION=native ENABLE_UNIT_TESTS=true`
**Expected behavior**
Compilation succeeds, however build actually fails due to missing `#include`
**Code snips**
This can be fixed by doing the following
```
--- a/fsw/cfe-core/ut-stubs/ut_sb_stubs.c
+++ b/fsw/cfe-core/ut-stubs/ut_sb_stubs.c
@@ -34,6 +34,8 @@
*/
#include <string.h>
#include "cfe.h"
+#include "cfe_platform_cfg.h"
+#include "../sb/cfe_sb_msg_id_util.h"
#include "utstubs.h"
```
However, subsequently a checksum error is encountered when running the tests.
This was worked around by doing the following, but unsure if the workaround is correct.
```
--- a/fsw/cfe-core/unit-test/sb_UT.c
+++ b/fsw/cfe-core/unit-test/sb_UT.c
@@ -9456,7 +9456,7 @@ void Test_CFE_SB_ChecksumUtils(void)
#ifndef MESSAGE_FORMAT_IS_CCSDS_VER_2
ExpRtnFrmGet = 0x2f;
#else
- ExpRtnFrmGet = 0x65;
+ ExpRtnFrmGet = 0x61;
#endif
/* Validation expected to return true */
```
**System observed on:**
- Hardware: N/A
- OS: RHEL7
- Versions cFE 6.7.12
**Reporter Info**
John N Pham, Northrop Grumman | non_priority | unit tests fail to build when message format is ccsds ver is enabled describe the bug unit tests fail to build when message format is ccsds ver is enabled to reproduce enable message format is ccsds ver in mission cfg h run make cflags wno format simulation native enable unit tests true expected behavior compilation succeeds however build actually fails due to missing include code snips this can be fixed by doing the following a fsw cfe core ut stubs ut sb stubs c b fsw cfe core ut stubs ut sb stubs c include include cfe h include cfe platform cfg h include sb cfe sb msg id util h include utstubs h however subsequently a checksum error is encountered when running the tests this was worked around by doing the following but unsure if the workaround is correct a fsw cfe core unit test sb ut c b fsw cfe core unit test sb ut c void test cfe sb checksumutils void ifndef message format is ccsds ver exprtnfrmget else exprtnfrmget exprtnfrmget endif validation expected to return true system observed on hardware n a os versions cfe reporter info john n pham northrop grumman | 0 |
62,410 | 7,575,702,584 | IssuesEvent | 2018-04-24 03:12:33 | nomad-desktop/nomad-simplemenu | https://api.github.com/repos/nomad-desktop/nomad-simplemenu | opened | Arrange order of session buttons to match Plasma logout screen | discussion-design | The order of the session buttons in the menu doesn't match the order of the buttons in the Plasma logout screen:
1. Nomad Simplenu.

2. Plasma logout.

They go in the following order:
1. Suspend
2. Reboot
3. Shutdown
4. Logout | 1.0 | Arrange order of session buttons to match Plasma logout screen - The order of the session buttons in the menu doesn't match the order of the buttons in the Plasma logout screen:
1. Nomad Simplenu.

2. Plasma logout.

They go in the following order:
1. Suspend
2. Reboot
3. Shutdown
4. Logout | non_priority | arrange order of session buttons to match plasma logout screen the order of the session buttons in the menu doesn t match the order of the buttons in the plasma logout screen nomad simplenu plasma logout they go in the following order suspend reboot shutdown logout | 0 |
11,275 | 4,953,949,346 | IssuesEvent | 2016-12-01 16:19:55 | mozilla-mobile/prox | https://api.github.com/repos/mozilla-mobile/prox | closed | mpopova@mozilla.com on build #553: No pictures showing up for the place | 1.0 buddybuild-feedback | Feedback from mpopova@mozilla.com : No pictures showing up for the place
<img src="https://s3-us-west-2.amazonaws.com/buddybuild-screenshots/57f51f8bcaa70a01005412ee/583f131b61760e0100964850/ac37f1e7-99c9-464f-9539-aa0ae4215178.jpg" width="33%" height="33%" /><table><tr><td>Created</td><td>Thu Dec 01 2016 15:17:13 GMT+0000 (UTC)</td></tr><tr><td>CFBundleShortVersion</td><td>1.0</td></tr><tr><td>CFBundleVersion</td><td>1</td></tr><tr><td>App uptime</td><td>37.63069</td></tr><tr><td>Build</td><td>553</td></tr><tr><td>Device type</td><td>iPhone 6s</td></tr><tr><td>Device name</td><td>Maria's iPhone</td></tr><tr><td>Screen size</td><td>375</td></tr><tr><td>Screen size</td><td>375px by 667px</td></tr><tr><td>Battery</td><td>100% Unplugged</td></tr><tr><td>Memory free</td><td>60 MB / 1710 MB</td></tr><tr><td>Disk free</td><td>1016 MB / 11548 MB</td></tr><tr><td>Network IP</td><td>10.5.161.80</td></tr></table>
[Link to buddybuild feedback from build 553](https://dashboard.buddybuild.com/apps/57f51f8bcaa70a01005412ee/feedback?fid=58403ef9035c2501005010b5&bnum=553) | 1.0 | mpopova@mozilla.com on build #553: No pictures showing up for the place - Feedback from mpopova@mozilla.com : No pictures showing up for the place
<img src="https://s3-us-west-2.amazonaws.com/buddybuild-screenshots/57f51f8bcaa70a01005412ee/583f131b61760e0100964850/ac37f1e7-99c9-464f-9539-aa0ae4215178.jpg" width="33%" height="33%" /><table><tr><td>Created</td><td>Thu Dec 01 2016 15:17:13 GMT+0000 (UTC)</td></tr><tr><td>CFBundleShortVersion</td><td>1.0</td></tr><tr><td>CFBundleVersion</td><td>1</td></tr><tr><td>App uptime</td><td>37.63069</td></tr><tr><td>Build</td><td>553</td></tr><tr><td>Device type</td><td>iPhone 6s</td></tr><tr><td>Device name</td><td>Maria's iPhone</td></tr><tr><td>Screen size</td><td>375</td></tr><tr><td>Screen size</td><td>375px by 667px</td></tr><tr><td>Battery</td><td>100% Unplugged</td></tr><tr><td>Memory free</td><td>60 MB / 1710 MB</td></tr><tr><td>Disk free</td><td>1016 MB / 11548 MB</td></tr><tr><td>Network IP</td><td>10.5.161.80</td></tr></table>
[Link to buddybuild feedback from build 553](https://dashboard.buddybuild.com/apps/57f51f8bcaa70a01005412ee/feedback?fid=58403ef9035c2501005010b5&bnum=553) | non_priority | mpopova mozilla com on build no pictures showing up for the place feedback from mpopova mozilla com no pictures showing up for the place created thu dec gmt utc cfbundleshortversion cfbundleversion app uptime build device type iphone device name maria s iphone screen size screen size by battery unplugged memory free mb mb disk free mb mb network ip | 0 |
285,787 | 21,554,693,976 | IssuesEvent | 2022-04-30 07:45:08 | wagtail/wagtail | https://api.github.com/repos/wagtail/wagtail | opened | Automatic redirects | Documentation | Shouldn't this need to change for wagtail 2.16 ? I thought it was automatic redirects from 2.16
https://docs.wagtail.org/en/v2.16.2/reference/pages/model_recipes.html#have-redirects-created-automatically-when-changing-page-slug | 1.0 | Automatic redirects - Shouldn't this need to change for wagtail 2.16 ? I thought it was automatic redirects from 2.16
https://docs.wagtail.org/en/v2.16.2/reference/pages/model_recipes.html#have-redirects-created-automatically-when-changing-page-slug | non_priority | automatic redirects shouldn t this need to change for wagtail i thought it was automatic redirects from | 0 |
147,615 | 13,211,224,955 | IssuesEvent | 2020-08-15 21:38:22 | dankamongmen/notcurses | https://api.github.com/repos/dankamongmen/notcurses | closed | single-character EGCs could be inlined in struct cell->gcluster | documentation enhancement perf | Right now, we only inline ASCII characters, i.e. those encoding to a single UTF-8 byte of 0x00..0x7f. Otherwise, the gcluster is taken as an offset into the egctable, where the EGC is stored as a nul-terminated string. It works well enough.
The vast majority of non-ASCII EGCs are likely to be a single Unicode character mapping to between 2 and 4 UTF-8 bytes (the 21-bit character space already maps to 4 bytes, e.g. `U+1F90C PINCHED FINGERS f0 9f a4 8c`). In the case of a single Unicode character, we can always fit it into the 32-bit `gcluster`, evading the egcplane spillover.
But then what about multicharacter EGCs? Easy: in the case of an ASCII EGC, we're wasting three bytes. All we need is a sentinel ASCII value which we don't actually allow through to the display. 0x00 is already serving a sentinel purpose (transparent glyph channel). We can hijack 0x01 for this purpose. If the first byte of `gcluster` is 0x01, we can interpret the least significant 24 bits as an index into the egcpool. If 16MB is not large enough for an egcpool, we can have the 24-bit values index into a pointer table, whatever (we've addressed this before, see e.g. #425).
To do this safely, we'll want to exclude 0x01 from ever getting into a `cell`, which would mean guarding `CELL_SIMPLE_INITIALIZER`, `cell_load_simple()`, and `cell_load_egc()` from a direct load of 0x01. If a user does it manually, they deserve what's coming to them. As Archimedes said, "do not disturb my [cells]!" | 1.0 | single-character EGCs could be inlined in struct cell->gcluster - Right now, we only inline ASCII characters, i.e. those encoding to a single UTF-8 byte of 0x00..0x7f. Otherwise, the gcluster is taken as an offset into the egctable, where the EGC is stored as a nul-terminated string. It works well enough.
The vast majority of non-ASCII EGCs are likely to be a single Unicode character mapping to between 2 and 4 UTF-8 bytes (the 21-bit character space already maps to 4 bytes, e.g. `U+1F90C PINCHED FINGERS f0 9f a4 8c`). In the case of a single Unicode character, we can always fit it into the 32-bit `gcluster`, evading the egcplane spillover.
But then what about multicharacter EGCs? Easy: in the case of an ASCII EGC, we're wasting three bytes. All we need is a sentinel ASCII value which we don't actually allow through to the display. 0x00 is already serving a sentinel purpose (transparent glyph channel). We can hijack 0x01 for this purpose. If the first byte of `gcluster` is 0x01, we can interpret the least significant 24 bits as an index into the egcpool. If 16MB is not large enough for an egcpool, we can have the 24-bit values index into a pointer table, whatever (we've addressed this before, see e.g. #425).
To do this safely, we'll want to exclude 0x01 from ever getting into a `cell`, which would mean guarding `CELL_SIMPLE_INITIALIZER`, `cell_load_simple()`, and `cell_load_egc()` from a direct load of 0x01. If a user does it manually, they deserve what's coming to them. As Archimedes said, "do not disturb my [cells]!" | non_priority | single character egcs could be inlined in struct cell gcluster right now we only inline ascii characters i e those encoding to a single utf byte of otherwise the gcluster is taken as an offset into the egctable where the egc is stored as a nul terminated string it works well enough the vast majority of non ascii egcs are likely to be a single unicode character mapping to between and utf bytes the bit character space already maps to bytes e g u pinched fingers in the case of a single unicode character we can always fit it into the bit gcluster evading the egcplane spillover but then what about multicharacter egcs easy in the case of an ascii egc we re wasting three bytes all we need is a sentinel ascii value which we don t actually allow through to the display is already serving a sentinel purpose transparent glyph channel we can hijack for this purpose if the first byte of gcluster is we can interpret the least significant bits as an index into the egcpool if is not large enough for an egcpool we can have the bit values index into a pointer table whatever we ve addressed this before see e g to do this safely we ll want to exclude from ever getting into a cell which would mean guarding cell simple initializer cell load simple and cell load egc from a direct load of if a user does it manually they deserve what s coming to them as archimedes said do not disturb my | 0 |
10,932 | 8,817,507,888 | IssuesEvent | 2018-12-31 01:11:00 | codeforboston/cliff-effects | https://api.github.com/repos/codeforboston/cliff-effects | closed | Clean out useless jsdoc comments | feature infrastructure | In:
- [x] /components (knod)
- [x] /forms (knod)
- [x] /data
- [x] /programs
- [x] /utils
- [x] Any others
[knod, 10/23/18: I think the are done at this point, though I'm not sure. I'm pretty sure /utils hasn't been worked on.] | 1.0 | Clean out useless jsdoc comments - In:
- [x] /components (knod)
- [x] /forms (knod)
- [x] /data
- [x] /programs
- [x] /utils
- [x] Any others
[knod, 10/23/18: I think the are done at this point, though I'm not sure. I'm pretty sure /utils hasn't been worked on.] | non_priority | clean out useless jsdoc comments in components knod forms knod data programs utils any others | 0 |
8,041 | 11,310,826,450 | IssuesEvent | 2020-01-19 22:07:01 | cp-api/requirements | https://api.github.com/repos/cp-api/requirements | opened | Annotations about incoming/outgoing links from diagram should be stored in descriptors instead of representations | capella enhancement new requirementsvp | Annotations about incoming/outgoing links from diagram should be stored in descriptors instead of representations
`ECLIPSE-555389` `POLARSYS-2320` `@tto` `2018-12-18` | 1.0 | Annotations about incoming/outgoing links from diagram should be stored in descriptors instead of representations - Annotations about incoming/outgoing links from diagram should be stored in descriptors instead of representations
`ECLIPSE-555389` `POLARSYS-2320` `@tto` `2018-12-18` | non_priority | annotations about incoming outgoing links from diagram should be stored in descriptors instead of representations annotations about incoming outgoing links from diagram should be stored in descriptors instead of representations eclipse polarsys tto | 0 |
5,708 | 7,311,278,389 | IssuesEvent | 2018-02-28 17:16:00 | InFact-coop/BlueCross | https://api.github.com/repos/InFact-coop/BlueCross | closed | New page for specific questions about dog | doggo services | Acceptance Criteria:
- [x] title " Finding a new home for 'Name of Dog' "
- [x] Intro 'We can help you find a new home for 'name of dog' in a couple of different ways. Which would suit you and 'name of dog' best? '
- [x] 1. Home Direct - 'name of dog' will stay with you while we find a him a great new home
- [x] 2. Rehoming Centre - We will look after 'name of dog' at our Rehoming centre until we find him a great new home.
- [x] 3. Unsure - We can talk through the options with you and you can decide what works best for you.
- [x] Separate this from user's details page | 1.0 | New page for specific questions about dog - Acceptance Criteria:
- [x] title " Finding a new home for 'Name of Dog' "
- [x] Intro 'We can help you find a new home for 'name of dog' in a couple of different ways. Which would suit you and 'name of dog' best? '
- [x] 1. Home Direct - 'name of dog' will stay with you while we find a him a great new home
- [x] 2. Rehoming Centre - We will look after 'name of dog' at our Rehoming centre until we find him a great new home.
- [x] 3. Unsure - We can talk through the options with you and you can decide what works best for you.
- [x] Separate this from user's details page | non_priority | new page for specific questions about dog acceptance criteria title finding a new home for name of dog intro we can help you find a new home for name of dog in a couple of different ways which would suit you and name of dog best home direct name of dog will stay with you while we find a him a great new home rehoming centre we will look after name of dog at our rehoming centre until we find him a great new home unsure we can talk through the options with you and you can decide what works best for you separate this from user s details page | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.