Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
4,510 | 2,730,491,706 | IssuesEvent | 2015-04-16 15:09:25 | uscensusbureau/citysdk | https://api.github.com/repos/uscensusbureau/citysdk | closed | ZIP to FIPS service | bus-4 dev-1 test user stories | As a developer, I don't want to use zip codes to access Census data rather than FIPs codes. | 1.0 | ZIP to FIPS service - As a developer, I don't want to use zip codes to access Census data rather than FIPs codes. | non_priority | zip to fips service as a developer i don t want to use zip codes to access census data rather than fips codes | 0 |
38,771 | 5,198,640,325 | IssuesEvent | 2017-01-23 18:41:16 | Azure/azure-service-bus-dotnet | https://api.github.com/repos/Azure/azure-service-bus-dotnet | closed | Failing CI / Unit Tests | testing | These tests are currently failing in AppVeyor:
* .NET Core:
* QueueClientTests.BasicRenewLockTest("non-partitioned-queue")
* QueueClientTests.BasicRenewLockTest("partitioned-queue")
* QueueClientTests.PeekLockDeferTest("partitioned-queue")
* TopicClientTests.TopicClientRenewLockTestCase("non-partitioned-topic")
* TopicClientTests.TopicClientRenewLockTestCase("partitioned-topic")
* TopicClientTests.TopicClientPeekLockDeferTestCase("non-partitioned-topic")
* TopicClientTests.TopicClientPeekLockWithAbandonTestCase("partitioned-topic")
* .NET 4.5.1
* QueueClientTests.PeekLockWithAbandonTest("non-partitioned-queue")
* QueueClientTests.PeekLockWithAbandonTest("partitioned-queue")
* QueueClientTests.PeekLockDeferTest("partitioned-queue")
* TopicClientTests.TopicClientPeekLockWithAbandonTestCase("non-partitioned-topic")
Here are the details of the tests: https://ci.appveyor.com/project/jtaubensee/azure-service-bus-dotnet/build/1.0.79/tests
| 1.0 | Failing CI / Unit Tests - These tests are currently failing in AppVeyor:
* .NET Core:
* QueueClientTests.BasicRenewLockTest("non-partitioned-queue")
* QueueClientTests.BasicRenewLockTest("partitioned-queue")
* QueueClientTests.PeekLockDeferTest("partitioned-queue")
* TopicClientTests.TopicClientRenewLockTestCase("non-partitioned-topic")
* TopicClientTests.TopicClientRenewLockTestCase("partitioned-topic")
* TopicClientTests.TopicClientPeekLockDeferTestCase("non-partitioned-topic")
* TopicClientTests.TopicClientPeekLockWithAbandonTestCase("partitioned-topic")
* .NET 4.5.1
* QueueClientTests.PeekLockWithAbandonTest("non-partitioned-queue")
* QueueClientTests.PeekLockWithAbandonTest("partitioned-queue")
* QueueClientTests.PeekLockDeferTest("partitioned-queue")
* TopicClientTests.TopicClientPeekLockWithAbandonTestCase("non-partitioned-topic")
Here are the details of the tests: https://ci.appveyor.com/project/jtaubensee/azure-service-bus-dotnet/build/1.0.79/tests
| non_priority | failing ci unit tests these tests are currently failing in appveyor net core queueclienttests basicrenewlocktest non partitioned queue queueclienttests basicrenewlocktest partitioned queue queueclienttests peeklockdefertest partitioned queue topicclienttests topicclientrenewlocktestcase non partitioned topic topicclienttests topicclientrenewlocktestcase partitioned topic topicclienttests topicclientpeeklockdefertestcase non partitioned topic topicclienttests topicclientpeeklockwithabandontestcase partitioned topic net queueclienttests peeklockwithabandontest non partitioned queue queueclienttests peeklockwithabandontest partitioned queue queueclienttests peeklockdefertest partitioned queue topicclienttests topicclientpeeklockwithabandontestcase non partitioned topic here are the details of the tests | 0 |
256,197 | 19,403,060,680 | IssuesEvent | 2021-12-19 14:32:18 | opensemanticsearch/open-semantic-search | https://api.github.com/repos/opensemanticsearch/open-semantic-search | closed | Provide full documentation in the packages and docker images | enhancement ui packaging documentation | Since by #381 the full documentation as markdown (and so by mkdocs static html site available), provide full documentation in the packages and docker images and link to the (local) documents in UI. | 1.0 | Provide full documentation in the packages and docker images - Since by #381 the full documentation as markdown (and so by mkdocs static html site available), provide full documentation in the packages and docker images and link to the (local) documents in UI. | non_priority | provide full documentation in the packages and docker images since by the full documentation as markdown and so by mkdocs static html site available provide full documentation in the packages and docker images and link to the local documents in ui | 0 |
317,287 | 27,224,487,370 | IssuesEvent | 2023-02-21 08:44:28 | akka/akka-http | https://api.github.com/repos/akka/akka-http | closed | Now that Route.asyncHandler is deprecated, there is now no way to avoid the default ExceptionHandler | 3 - in progress t:testing | Previously, with `Route.asyncHandler`, I would describe an `ExceptionHandler({ case t => _ => Future.failed(t) })` for use with ScalaTest, to permit bubbling failure assertions out.
It would be nice to have a variant of `Route.toFunction` that avoids this catch-all that turns exceptions into `StatusCodes.InternalServerError`, even if it is just for testing.
Guidance here would be appreciated, I am happy to do the work. Thank you! | 1.0 | Now that Route.asyncHandler is deprecated, there is now no way to avoid the default ExceptionHandler - Previously, with `Route.asyncHandler`, I would describe an `ExceptionHandler({ case t => _ => Future.failed(t) })` for use with ScalaTest, to permit bubbling failure assertions out.
It would be nice to have a variant of `Route.toFunction` that avoids this catch-all that turns exceptions into `StatusCodes.InternalServerError`, even if it is just for testing.
Guidance here would be appreciated, I am happy to do the work. Thank you! | non_priority | now that route asynchandler is deprecated there is now no way to avoid the default exceptionhandler previously with route asynchandler i would describe an exceptionhandler case t future failed t for use with scalatest to permit bubbling failure assertions out it would be nice to have a variant of route tofunction that avoids this catch all that turns exceptions into statuscodes internalservererror even if it is just for testing guidance here would be appreciated i am happy to do the work thank you | 0 |
69,694 | 8,444,921,886 | IssuesEvent | 2018-10-18 19:53:59 | revelrylabs/incentivize | https://api.github.com/repos/revelrylabs/incentivize | closed | Discover page hard to look at | design in progress points:8 | ## Background
The Discover page needs to be a place where users get excited about contributing to projects. See https://www.kickstarter.com/ for some inspiration. It ought to feel like shopping in a sense.
## Scenario: Update the layout of the Discover page with a new design
- [ ] When I look at the discover page
- [ ] Then I am interested in browing projects
- [ ] And I understand what it is I'm looking at
## Scenario: Developer/Designer Tasks
- [ ] Pick a new layout/design for the discover page
- [ ] Implement it | 1.0 | Discover page hard to look at - ## Background
The Discover page needs to be a place where users get excited about contributing to projects. See https://www.kickstarter.com/ for some inspiration. It ought to feel like shopping in a sense.
## Scenario: Update the layout of the Discover page with a new design
- [ ] When I look at the discover page
- [ ] Then I am interested in browing projects
- [ ] And I understand what it is I'm looking at
## Scenario: Developer/Designer Tasks
- [ ] Pick a new layout/design for the discover page
- [ ] Implement it | non_priority | discover page hard to look at background the discover page needs to be a place where users get excited about contributing to projects see for some inspiration it ought to feel like shopping in a sense scenario update the layout of the discover page with a new design when i look at the discover page then i am interested in browing projects and i understand what it is i m looking at scenario developer designer tasks pick a new layout design for the discover page implement it | 0 |
911 | 2,520,599,510 | IssuesEvent | 2015-01-19 05:57:42 | codeformuenster/codeformuenster.github.io_old | https://api.github.com/repos/codeformuenster/codeformuenster.github.io_old | closed | CSS verbessern und eigenen Stil entwickeln | design Difficulty: ★ Prio: ★★ ready | Das CSS ist aktuell vom Anual Report von Code for America.
Entweder nehmen wir den Stil von codeforde oder wir entwickeln einen eigenen.
Die CSS muss ein wenig aufgeräumt werden.
Achtung! Es ist SASS :) | 1.0 | CSS verbessern und eigenen Stil entwickeln - Das CSS ist aktuell vom Anual Report von Code for America.
Entweder nehmen wir den Stil von codeforde oder wir entwickeln einen eigenen.
Die CSS muss ein wenig aufgeräumt werden.
Achtung! Es ist SASS :) | non_priority | css verbessern und eigenen stil entwickeln das css ist aktuell vom anual report von code for america entweder nehmen wir den stil von codeforde oder wir entwickeln einen eigenen die css muss ein wenig aufgeräumt werden achtung es ist sass | 0 |
295,605 | 25,488,181,514 | IssuesEvent | 2022-11-26 17:52:17 | burningmantech/ranger-clubhouse-web | https://api.github.com/repos/burningmantech/ranger-clubhouse-web | closed | People By Status Change modification to handle 2020 extension | Please Test Show Stopper | Due to the 2020 world crises, the decision has been made to extend Clubhouse status changes by one year.
The People By Status Change report will need to compensate for the 2020 extension. E.g., if Hubcap was last active in 2017, he would be marked as inactive post the 2020 event. However, with the ordered extension, he will not be marked inactive until 2021.
| 1.0 | People By Status Change modification to handle 2020 extension - Due to the 2020 world crises, the decision has been made to extend Clubhouse status changes by one year.
The People By Status Change report will need to compensate for the 2020 extension. E.g., if Hubcap was last active in 2017, he would be marked as inactive post the 2020 event. However, with the ordered extension, he will not be marked inactive until 2021.
| non_priority | people by status change modification to handle extension due to the world crises the decision has been made to extend clubhouse status changes by one year the people by status change report will need to compensate for the extension e g if hubcap was last active in he would be marked as inactive post the event however with the ordered extension he will not be marked inactive until | 0 |
230,279 | 25,460,315,016 | IssuesEvent | 2022-11-24 18:04:24 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] Proofpoint: Watch Out for Nighthawk Hacking Tool Abuse | SecurityWeek Stale |
Security researchers at Proofpoint are calling attention to the discovery of a commercial red-teaming tool called Nighthawk, warning that the command-and-control framework is likely to be abused by threat actors.
[read more](https://www.securityweek.com/proofpoint-watch-out-nighthawk-hacking-tool-abuse)
<https://www.securityweek.com/proofpoint-watch-out-nighthawk-hacking-tool-abuse>
| True | [SecurityWeek] Proofpoint: Watch Out for Nighthawk Hacking Tool Abuse -
Security researchers at Proofpoint are calling attention to the discovery of a commercial red-teaming tool called Nighthawk, warning that the command-and-control framework is likely to be abused by threat actors.
[read more](https://www.securityweek.com/proofpoint-watch-out-nighthawk-hacking-tool-abuse)
<https://www.securityweek.com/proofpoint-watch-out-nighthawk-hacking-tool-abuse>
| non_priority | proofpoint watch out for nighthawk hacking tool abuse security researchers at proofpoint are calling attention to the discovery of a commercial red teaming tool called nighthawk warning that the command and control framework is likely to be abused by threat actors | 0 |
11,729 | 3,220,190,599 | IssuesEvent | 2015-10-08 13:52:39 | softlayer/sl-ember-behavior | https://api.github.com/repos/softlayer/sl-ember-behavior | opened | Registered templates need to be unregistered in unit tests | bug ready tests | * "Renders content when isUnable() returns true" test in *tests/unit/components/sl-unable-test.js*
* "'Renders content when isAble() returns true'" test in *tests/unit/components/sl-able-test.js*
Syntax example:
`this.registry.unregister( 'template:test-template' );` | 1.0 | Registered templates need to be unregistered in unit tests - * "Renders content when isUnable() returns true" test in *tests/unit/components/sl-unable-test.js*
* "'Renders content when isAble() returns true'" test in *tests/unit/components/sl-able-test.js*
Syntax example:
`this.registry.unregister( 'template:test-template' );` | non_priority | registered templates need to be unregistered in unit tests renders content when isunable returns true test in tests unit components sl unable test js renders content when isable returns true test in tests unit components sl able test js syntax example this registry unregister template test template | 0 |
68,626 | 14,941,146,736 | IssuesEvent | 2021-01-25 19:19:21 | DWG61868/dagger-browser | https://api.github.com/repos/DWG61868/dagger-browser | opened | CVE-2019-16769 (Medium) detected in serialize-javascript-1.9.1.tgz | security vulnerability | ## CVE-2019-16769 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular expressions and functions.</p>
<p>Library home page: <a href="https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz">https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz</a></p>
<p>Path to dependency file: dagger-browser/browser/package.json</p>
<p>Path to vulnerable library: dagger-browser/browser/node_modules/serialize-javascript/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- terser-webpack-plugin-1.4.1.tgz
- :x: **serialize-javascript-1.9.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DWG61868/dagger-browser/commit/1b365bcdf87aff79a6694987cd838c2895b3f081">1b365bcdf87aff79a6694987cd838c2895b3f081</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The serialize-javascript npm package before version 2.1.1 is vulnerable to Cross-site Scripting (XSS). It does not properly mitigate against unsafe characters in serialized regular expressions. This vulnerability is not affected on Node.js environment since Node.js's implementation of RegExp.prototype.toString() backslash-escapes all forward slashes in regular expressions. If serialized data of regular expression objects are used in an environment other than Node.js, it is affected by this vulnerability.
<p>Publish Date: 2019-12-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16769>CVE-2019-16769</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: v2.1.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"serialize-javascript","packageVersion":"1.9.1","isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;terser-webpack-plugin:1.4.1;serialize-javascript:1.9.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.1.1"}],"vulnerabilityIdentifier":"CVE-2019-16769","vulnerabilityDetails":"The serialize-javascript npm package before version 2.1.1 is vulnerable to Cross-site Scripting (XSS). It does not properly mitigate against unsafe characters in serialized regular expressions. This vulnerability is not affected on Node.js environment since Node.js\u0027s implementation of RegExp.prototype.toString() backslash-escapes all forward slashes in regular expressions. If serialized data of regular expression objects are used in an environment other than Node.js, it is affected by this vulnerability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16769","cvss3Severity":"medium","cvss3Score":"5.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-16769 (Medium) detected in serialize-javascript-1.9.1.tgz - ## CVE-2019-16769 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular expressions and functions.</p>
<p>Library home page: <a href="https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz">https://registry.npmjs.org/serialize-javascript/-/serialize-javascript-1.9.1.tgz</a></p>
<p>Path to dependency file: dagger-browser/browser/package.json</p>
<p>Path to vulnerable library: dagger-browser/browser/node_modules/serialize-javascript/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.2.0.tgz (Root Library)
- terser-webpack-plugin-1.4.1.tgz
- :x: **serialize-javascript-1.9.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/DWG61868/dagger-browser/commit/1b365bcdf87aff79a6694987cd838c2895b3f081">1b365bcdf87aff79a6694987cd838c2895b3f081</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The serialize-javascript npm package before version 2.1.1 is vulnerable to Cross-site Scripting (XSS). It does not properly mitigate against unsafe characters in serialized regular expressions. This vulnerability is not affected on Node.js environment since Node.js's implementation of RegExp.prototype.toString() backslash-escapes all forward slashes in regular expressions. If serialized data of regular expression objects are used in an environment other than Node.js, it is affected by this vulnerability.
<p>Publish Date: 2019-12-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16769>CVE-2019-16769</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16769</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: v2.1.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"serialize-javascript","packageVersion":"1.9.1","isTransitiveDependency":true,"dependencyTree":"react-scripts:3.2.0;terser-webpack-plugin:1.4.1;serialize-javascript:1.9.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.1.1"}],"vulnerabilityIdentifier":"CVE-2019-16769","vulnerabilityDetails":"The serialize-javascript npm package before version 2.1.1 is vulnerable to Cross-site Scripting (XSS). It does not properly mitigate against unsafe characters in serialized regular expressions. This vulnerability is not affected on Node.js environment since Node.js\u0027s implementation of RegExp.prototype.toString() backslash-escapes all forward slashes in regular expressions. If serialized data of regular expression objects are used in an environment other than Node.js, it is affected by this vulnerability.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16769","cvss3Severity":"medium","cvss3Score":"5.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in serialize javascript tgz cve medium severity vulnerability vulnerable library serialize javascript tgz serialize javascript to a superset of json that includes regular expressions and functions library home page a href path to dependency file dagger browser browser package json path to vulnerable library dagger browser browser node modules serialize javascript package json dependency hierarchy react scripts tgz root library terser webpack plugin tgz x serialize javascript tgz vulnerable library found in head commit a href found in base branch main vulnerability details the serialize javascript npm package before version is vulnerable to cross site scripting xss it does not properly mitigate against unsafe characters in serialized regular expressions this vulnerability is not affected on node js environment since node js s implementation of regexp prototype tostring backslash escapes all forward slashes in regular expressions if serialized data of regular expression objects are used in an environment other than node js it is affected by this vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails the serialize javascript npm package before version is vulnerable to cross site scripting xss it does not properly mitigate against unsafe characters in serialized regular expressions this vulnerability is not affected on node js environment since node js implementation of regexp prototype tostring backslash escapes all forward slashes in regular expressions if serialized data of regular expression objects are used in an environment other than node js it is affected by this vulnerability vulnerabilityurl | 0 |
80,028 | 29,871,779,345 | IssuesEvent | 2023-06-20 08:58:23 | vector-im/element-android | https://api.github.com/repos/vector-im/element-android | closed | "In reply to" has translation against the Matrix spec | T-Defect A-Timeline S-Tolerable O-Occasional Z-Localisation | ### Steps to reproduce
1. Reply to a message
2. Get a reply to the reply
### Outcome
#### What did you expect?
`In reply to` should not be translated based on this issue: https://github.com/vector-im/element-android/issues/3163#issuecomment-817660485
#### What happened instead?
`In reply to` is translated. Please check `に返信` under the username of the author of the post.
I have searched the string in files related to the existing translation, but I cannot not detect which one corresponds to this translation.
### Your phone model
_No response_
### Operating system version
_No response_
### Application version and app store
_No response_
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | "In reply to" has translation against the Matrix spec - ### Steps to reproduce
1. Reply to a message
2. Get a reply to the reply
### Outcome
#### What did you expect?
`In reply to` should not be translated based on this issue: https://github.com/vector-im/element-android/issues/3163#issuecomment-817660485
#### What happened instead?
`In reply to` is translated. Please check `に返信` under the username of the author of the post.
I have searched the string in files related to the existing translation, but I cannot not detect which one corresponds to this translation.
### Your phone model
_No response_
### Operating system version
_No response_
### Application version and app store
_No response_
### Homeserver
_No response_
### Will you send logs?
No | non_priority | in reply to has translation against the matrix spec steps to reproduce reply to a message get a reply to the reply outcome what did you expect in reply to should not be translated based on this issue what happened instead in reply to is translated please check に返信 under the username of the author of the post i have searched the string in files related to the existing translation but i cannot not detect which one corresponds to this translation your phone model no response operating system version no response application version and app store no response homeserver no response will you send logs no | 0 |
211,523 | 23,833,131,486 | IssuesEvent | 2022-09-06 01:06:00 | dmyers87/camunda-message-streaming | https://api.github.com/repos/dmyers87/camunda-message-streaming | opened | CVE-2022-38749 (Medium) detected in snakeyaml-1.25.jar | security vulnerability | ## CVE-2022-38749 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.25.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /messaging/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.25/snakeyaml-1.25.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.25/snakeyaml-1.25.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-jdbc-2.2.5.RELEASE.jar (Root Library)
- spring-boot-starter-2.2.5.RELEASE.jar
- :x: **snakeyaml-1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/camunda-message-streaming/commit/41e27a1fe9f0949f331a284bafd06fdaefba62e0">41e27a1fe9f0949f331a284bafd06fdaefba62e0</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open">https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
</details>
<p></p>
| True | CVE-2022-38749 (Medium) detected in snakeyaml-1.25.jar - ## CVE-2022-38749 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.25.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /messaging/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.25/snakeyaml-1.25.jar,/home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.25/snakeyaml-1.25.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-jdbc-2.2.5.RELEASE.jar (Root Library)
- spring-boot-starter-2.2.5.RELEASE.jar
- :x: **snakeyaml-1.25.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/camunda-message-streaming/commit/41e27a1fe9f0949f331a284bafd06fdaefba62e0">41e27a1fe9f0949f331a284bafd06fdaefba62e0</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open">https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in snakeyaml jar cve medium severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file messaging pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy spring boot starter jdbc release jar root library spring boot starter release jar x snakeyaml jar vulnerable library found in head commit a href found in base branch develop vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml | 0 |
156,633 | 24,624,956,548 | IssuesEvent | 2022-10-16 11:56:30 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | Allow Create Migration History table option on Ensure Created | closed-by-design | Describe what is not working as expected.
EnsureCreated doesn't create a migration history file
Migrate requires one or will attempt to run migrations whose schema has already been implemented in the database via EnsureCreated, causing the database to throw "already exists" errors.
Technically there is no reason to use EnsureCreated plus Migrate. Migrate does the same job.
However there's no compile time way to know about the confusing side effect.
Would it be possible to have an a parameter in EnsureCreated to just go ahead and build the migrationhistory file to protect against this problem?
Or is it possible for EF Core to wrap the database error inside of an EF Core error when the database throws "already exists" when Migrate is run?
```
Exception message:
Stack trace:
```
### Steps to reproduce
Include a complete code listing (or project/solution) that we can run to reproduce the issue.
Partial code listings, or multiple fragments of code, will slow down our response or cause us to push the issue back to you to provide code to reproduce the issue.
```c#
Console.WriteLine("Hello World!");
```
### Further technical details
EF Core version: (found in project.csproj or packages.config)
Database Provider: (e.g. Microsoft.EntityFrameworkCore.SqlServer)
Operating system:
IDE: (e.g. Visual Studio 2015)
| 1.0 | Allow Create Migration History table option on Ensure Created - Describe what is not working as expected.
EnsureCreated doesn't create a migration history file
Migrate requires one or will attempt to run migrations whose schema has already been implemented in the database via EnsureCreated, causing the database to throw "already exists" errors.
Technically there is no reason to use EnsureCreated plus Migrate. Migrate does the same job.
However there's no compile time way to know about the confusing side effect.
Would it be possible to have an a parameter in EnsureCreated to just go ahead and build the migrationhistory file to protect against this problem?
Or is it possible for EF Core to wrap the database error inside of an EF Core error when the database throws "already exists" when Migrate is run?
```
Exception message:
Stack trace:
```
### Steps to reproduce
Include a complete code listing (or project/solution) that we can run to reproduce the issue.
Partial code listings, or multiple fragments of code, will slow down our response or cause us to push the issue back to you to provide code to reproduce the issue.
```c#
Console.WriteLine("Hello World!");
```
### Further technical details
EF Core version: (found in project.csproj or packages.config)
Database Provider: (e.g. Microsoft.EntityFrameworkCore.SqlServer)
Operating system:
IDE: (e.g. Visual Studio 2015)
| non_priority | allow create migration history table option on ensure created describe what is not working as expected ensurecreated doesn t create a migration history file migrate requires one or will attempt to run migrations whose schema has already been implemented in the database via ensurecreated causing the database to throw already exists errors technically there is no reason to use ensurecreated plus migrate migrate does the same job however there s no compile time way to know about the confusing side effect would it be possible to have an a parameter in ensurecreated to just go ahead and build the migrationhistory file to protect against this problem or is it possible for ef core to wrap the database error inside of an ef core error when the database throws already exists when migrate is run exception message stack trace steps to reproduce include a complete code listing or project solution that we can run to reproduce the issue partial code listings or multiple fragments of code will slow down our response or cause us to push the issue back to you to provide code to reproduce the issue c console writeline hello world further technical details ef core version found in project csproj or packages config database provider e g microsoft entityframeworkcore sqlserver operating system ide e g visual studio | 0 |
197,183 | 15,631,841,448 | IssuesEvent | 2021-03-22 05:47:43 | TheThingsIndustries/lorawan-stack-docs | https://api.github.com/repos/TheThingsIndustries/lorawan-stack-docs | opened | Improve CLI doc UI | documentation | <!--
Thanks for submitting this documentation request. Please fill the template
below, otherwise we will not be able to process this request.
-->
#### Summary
<!-- Summarize the request in a few sentences: -->
A user built his own CLI docs and recommended we make our own CLI doc navigation more similar for ease of use -> http://descartes.co.uk/TTSv3CLI.html
| 1.0 | Improve CLI doc UI - <!--
Thanks for submitting this documentation request. Please fill the template
below, otherwise we will not be able to process this request.
-->
#### Summary
<!-- Summarize the request in a few sentences: -->
A user built his own CLI docs and recommended we make our own CLI doc navigation more similar for ease of use -> http://descartes.co.uk/TTSv3CLI.html
| non_priority | improve cli doc ui thanks for submitting this documentation request please fill the template below otherwise we will not be able to process this request summary a user built his own cli docs and recommended we make our own cli doc navigation more similar for ease of use | 0 |
213,721 | 24,016,347,226 | IssuesEvent | 2022-09-15 01:21:01 | JMD60260/llsolidaires | https://api.github.com/repos/JMD60260/llsolidaires | opened | WS-2019-0425 (Medium) detected in mocha-2.2.5.js | security vulnerability | ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.2.5.js</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/mocha/2.2.5/mocha.js">https://cdnjs.cloudflare.com/ajax/libs/mocha/2.2.5/mocha.js</a></p>
<p>Path to dependency file: /node_modules/js-base64/.attic/test-moment/index.html</p>
<p>Path to vulnerable library: /node_modules/js-base64/.attic/test-moment/index.html</p>
<p>
Dependency Hierarchy:
- :x: **mocha-2.2.5.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: v6.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0425 (Medium) detected in mocha-2.2.5.js - ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-2.2.5.js</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/mocha/2.2.5/mocha.js">https://cdnjs.cloudflare.com/ajax/libs/mocha/2.2.5/mocha.js</a></p>
<p>Path to dependency file: /node_modules/js-base64/.attic/test-moment/index.html</p>
<p>Path to vulnerable library: /node_modules/js-base64/.attic/test-moment/index.html</p>
<p>
Dependency Hierarchy:
- :x: **mocha-2.2.5.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: v6.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in mocha js ws medium severity vulnerability vulnerable library mocha js simple flexible fun test framework library home page a href path to dependency file node modules js attic test moment index html path to vulnerable library node modules js attic test moment index html dependency hierarchy x mocha js vulnerable library vulnerability details mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
252,801 | 21,632,104,043 | IssuesEvent | 2022-05-05 10:48:33 | Tencent/bk-ci | https://api.github.com/repos/Tencent/bk-ci | closed | fix: agent build_tmp 目录权限问题 | kind/bug for gray for test done area/ci/agent tested grayed streams/tested streams/for test streams/for gray streams/done streams/stage/uat doing | <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!-->
**What happened**:
假设Mac下以root身份启动agent, 并在.agent.properties 配置指定了devops.slave.user=user00
agent启动时会创建 build_tmp目录,并设置777权限,是为了方便指定用户都可以公开读写该构建临时目录。
但一般Linux/Mac机器上都会有umask 权限掩码, 并且大多是0022 , 这就会导致设置 0777 都会被改成0755
最终导致指定了用户无法使用该build_tmp目录进行写操作
**What you expected to happen**:
build_tmp 支持所有用户写
**How to reproduce it (as minimally and precisely as possible)**:
按上述操作,假设以root身份启动agent, 并在.agent.properties 配置指定了devops.slave.user=user00
**Anything else we need to know?**:
最佳建议: 不以root/管理员身份安装和启动agent,仅使用其他需要的帐号安装。
**Environment**:
- bk-ci version (use `cat VERSION` in installed dir): v1.8.x
- Cloud provider or hardware configuration:
- OS (e.g: `cat /etc/os-release`): Linux/Mac
- Kernel (e.g. `uname -a`):
- Install tools:
- Others: | 4.0 | fix: agent build_tmp 目录权限问题 - <!-- Please use this template while reporting a bug and provide as much info as possible. Not doing so may result in your bug not being addressed in a timely manner. Thanks!-->
**What happened**:
假设Mac下以root身份启动agent, 并在.agent.properties 配置指定了devops.slave.user=user00
agent启动时会创建 build_tmp目录,并设置777权限,是为了方便指定用户都可以公开读写该构建临时目录。
但一般Linux/Mac机器上都会有umask 权限掩码, 并且大多是0022 , 这就会导致设置 0777 都会被改成0755
最终导致指定了用户无法使用该build_tmp目录进行写操作
**What you expected to happen**:
build_tmp 支持所有用户写
**How to reproduce it (as minimally and precisely as possible)**:
按上述操作,假设以root身份启动agent, 并在.agent.properties 配置指定了devops.slave.user=user00
**Anything else we need to know?**:
最佳建议: 不以root/管理员身份安装和启动agent,仅使用其他需要的帐号安装。
**Environment**:
- bk-ci version (use `cat VERSION` in installed dir): v1.8.x
- Cloud provider or hardware configuration:
- OS (e.g: `cat /etc/os-release`): Linux/Mac
- Kernel (e.g. `uname -a`):
- Install tools:
- Others: | non_priority | fix agent build tmp 目录权限问题 what happened 假设mac下以root身份启动agent 并在 agent properties 配置指定了devops slave user agent启动时会创建 build tmp目录, ,是为了方便指定用户都可以公开读写该构建临时目录。 但一般linux mac机器上都会有umask 权限掩码, , 这就会导致设置 最终导致指定了用户无法使用该build tmp目录进行写操作 what you expected to happen build tmp 支持所有用户写 how to reproduce it as minimally and precisely as possible 按上述操作 假设以root身份启动agent 并在 agent properties 配置指定了devops slave user anything else we need to know 最佳建议: 不以root 管理员身份安装和启动agent,仅使用其他需要的帐号安装。 environment bk ci version use cat version in installed dir x cloud provider or hardware configuration os e g cat etc os release linux mac kernel e g uname a install tools others | 0 |
697 | 3,039,713,234 | IssuesEvent | 2015-08-07 10:51:10 | opencb/cellbase | https://api.github.com/repos/opencb/cellbase | closed | REST query param 'assembly' needs to be parsed | enhancement web services | Some species have now several assemblies, a query param 'assembly' exists and needs to be automatically parsed. | 1.0 | REST query param 'assembly' needs to be parsed - Some species have now several assemblies, a query param 'assembly' exists and needs to be automatically parsed. | non_priority | rest query param assembly needs to be parsed some species have now several assemblies a query param assembly exists and needs to be automatically parsed | 0 |
65,860 | 12,692,754,849 | IssuesEvent | 2020-06-22 00:27:38 | sehyunchung/til | https://api.github.com/repos/sehyunchung/til | opened | Vertical rulers in vscode | vscode | `settings.json`에 아래 코드를 추가하면,
```json
"editor.rulers": [
80,
100,
120
],
```
위와 같이 80, 100, 120자 위치에 세로줄이 생긴다.
```json
"workbench.colorCustomizations": {
"editorRuler.foreground": "#ff4081"
}
```
세로줄의 컬러를 커스텀 할 수도 있다. | 1.0 | Vertical rulers in vscode - `settings.json`에 아래 코드를 추가하면,
```json
"editor.rulers": [
80,
100,
120
],
```
위와 같이 80, 100, 120자 위치에 세로줄이 생긴다.
```json
"workbench.colorCustomizations": {
"editorRuler.foreground": "#ff4081"
}
```
세로줄의 컬러를 커스텀 할 수도 있다. | non_priority | vertical rulers in vscode settings json 에 아래 코드를 추가하면 json editor rulers 위와 같이 위치에 세로줄이 생긴다 json workbench colorcustomizations editorruler foreground 세로줄의 컬러를 커스텀 할 수도 있다 | 0 |
2,003 | 7,137,597,367 | IssuesEvent | 2018-01-23 11:35:40 | Tendrl/documentation | https://api.github.com/repos/Tendrl/documentation | closed | Give details about services, languages, protocols | architecture documentation | Looking at the diagram on Tendrl Core Components:
- Is Central Store etcd?
- Is Tendrl Application Instance a Go binary?
- Are the arrows between big boxes etcd clients?
- What protocol are the arrows within nodes?
| 1.0 | Give details about services, languages, protocols - Looking at the diagram on Tendrl Core Components:
- Is Central Store etcd?
- Is Tendrl Application Instance a Go binary?
- Are the arrows between big boxes etcd clients?
- What protocol are the arrows within nodes?
| non_priority | give details about services languages protocols looking at the diagram on tendrl core components is central store etcd is tendrl application instance a go binary are the arrows between big boxes etcd clients what protocol are the arrows within nodes | 0 |
11,653 | 5,064,796,989 | IssuesEvent | 2016-12-23 08:52:15 | raphw/byte-buddy | https://api.github.com/repos/raphw/byte-buddy | closed | Byte Buddy 1.5.11 does not published to Maven Central Repository | build | Probably the cause is a timestamp inconsistency of the artifact files.
Time will tell?
#### maven-metadata.xml in [Maven Central Repository](https://repo.maven.apache.org/maven2/net/bytebuddy/byte-buddy/)
```xml
<metadata modelVersion="1.1.0">
<groupId>net.bytebuddy</groupId>
<artifactId>byte-buddy</artifactId>
<versioning>
<latest>1.5.11</latest>
<release>1.5.11</release>
<versions>
[...]
<version>1.5.10</version>
<version>1.5.11</version>
</versions>
<lastUpdated>20161220163144</lastUpdated>
</versioning>
</metadata>
```
#### Timestamp of artifact files in [Sonatype OSSRH Release Repository](https://oss.sonatype.org/content/repositories/releases/net/bytebuddy/byte-buddy/)
```
byte-buddy-1.5.10.pom: Tue Dec 20 16:30:33 UTC 2016
byte-buddy-1.5.11.pom: Tue Dec 20 13:26:17 UTC 2016
```
| 1.0 | Byte Buddy 1.5.11 does not published to Maven Central Repository - Probably the cause is a timestamp inconsistency of the artifact files.
Time will tell?
#### maven-metadata.xml in [Maven Central Repository](https://repo.maven.apache.org/maven2/net/bytebuddy/byte-buddy/)
```xml
<metadata modelVersion="1.1.0">
<groupId>net.bytebuddy</groupId>
<artifactId>byte-buddy</artifactId>
<versioning>
<latest>1.5.11</latest>
<release>1.5.11</release>
<versions>
[...]
<version>1.5.10</version>
<version>1.5.11</version>
</versions>
<lastUpdated>20161220163144</lastUpdated>
</versioning>
</metadata>
```
#### Timestamp of artifact files in [Sonatype OSSRH Release Repository](https://oss.sonatype.org/content/repositories/releases/net/bytebuddy/byte-buddy/)
```
byte-buddy-1.5.10.pom: Tue Dec 20 16:30:33 UTC 2016
byte-buddy-1.5.11.pom: Tue Dec 20 13:26:17 UTC 2016
```
| non_priority | byte buddy does not published to maven central repository probably the cause is a timestamp inconsistency of the artifact files time will tell maven metadata xml in xml net bytebuddy byte buddy timestamp of artifact files in byte buddy pom tue dec utc byte buddy pom tue dec utc | 0 |
60,286 | 14,533,656,557 | IssuesEvent | 2020-12-15 01:05:21 | yaeljacobs67/cncjs | https://api.github.com/repos/yaeljacobs67/cncjs | opened | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz | security vulnerability | ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: /cncjs/package.json</p>
<p>Path to vulnerable library: cncjs/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- eslint-import-resolver-webpack-0.8.4.tgz (Root Library)
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.4.1","isTransitiveDependency":true,"dependencyTree":"eslint-import-resolver-webpack:0.8.4;node-libs-browser:2.2.1;crypto-browserify:3.12.0;browserify-sign:4.0.4;elliptic:6.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.2"}],"vulnerabilityIdentifier":"WS-2019-0427","vulnerabilityDetails":"The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2","vulnerabilityUrl":"https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz - ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: /cncjs/package.json</p>
<p>Path to vulnerable library: cncjs/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- eslint-import-resolver-webpack-0.8.4.tgz (Root Library)
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.4.1","isTransitiveDependency":true,"dependencyTree":"eslint-import-resolver-webpack:0.8.4;node-libs-browser:2.2.1;crypto-browserify:3.12.0;browserify-sign:4.0.4;elliptic:6.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.2"}],"vulnerabilityIdentifier":"WS-2019-0427","vulnerabilityDetails":"The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2","vulnerabilityUrl":"https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file cncjs package json path to vulnerable library cncjs node modules elliptic package json dependency hierarchy eslint import resolver webpack tgz root library node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library vulnerability details the function getnaf in elliptic library has information leakage this issue is mitigated in version publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails the function getnaf in elliptic library has information leakage this issue is mitigated in version vulnerabilityurl | 0 |
320,265 | 23,805,454,931 | IssuesEvent | 2022-09-04 00:44:28 | solipsis-project/mizu-client | https://api.github.com/repos/solipsis-project/mizu-client | opened | Improve .mizurc configuration file | documentation | Currently, the .mizurc file contains a set of flags that get added to all mizu commands. This means that it's currently only good for flags that are accepted by all commands.
- [ ] Allow flags in .mizurc that aren't required by all actions. (This may require a change in yargs)
- [ ] On startup, warn the user if the .mizurc file contains unknown keys (this will help prevent against typos)
- [ ] Provide sensible defaults for missing flags (like database type and database location)
- [ ] Document how to manipulate .mizurc via the `mizu config` command (uses [yargs-command-config](https://www.npmjs.com/package/yargs-command-config?activeTab=readme)) | 1.0 | Improve .mizurc configuration file - Currently, the .mizurc file contains a set of flags that get added to all mizu commands. This means that it's currently only good for flags that are accepted by all commands.
- [ ] Allow flags in .mizurc that aren't required by all actions. (This may require a change in yargs)
- [ ] On startup, warn the user if the .mizurc file contains unknown keys (this will help prevent against typos)
- [ ] Provide sensible defaults for missing flags (like database type and database location)
- [ ] Document how to manipulate .mizurc via the `mizu config` command (uses [yargs-command-config](https://www.npmjs.com/package/yargs-command-config?activeTab=readme)) | non_priority | improve mizurc configuration file currently the mizurc file contains a set of flags that get added to all mizu commands this means that it s currently only good for flags that are accepted by all commands allow flags in mizurc that aren t required by all actions this may require a change in yargs on startup warn the user if the mizurc file contains unknown keys this will help prevent against typos provide sensible defaults for missing flags like database type and database location document how to manipulate mizurc via the mizu config command uses | 0 |
101,112 | 12,643,066,844 | IssuesEvent | 2020-06-16 09:12:13 | easably/platform-player-extension | https://api.github.com/repos/easably/platform-player-extension | closed | make instruction for extension in choosen language | design | The language should be changed by default from landing
| 1.0 | make instruction for extension in choosen language - The language should be changed by default from landing
| non_priority | make instruction for extension in choosen language the language should be changed by default from landing | 0 |
77,633 | 10,012,036,711 | IssuesEvent | 2019-07-15 12:15:31 | tidyverse/dplyr | https://api.github.com/repos/tidyverse/dplyr | closed | Mark rowwise() + do() as questioning | data frame documentation tidy-dev-day :nerd_face: | And recommend alternatives
Using same style as rlang documentation
| 1.0 | Mark rowwise() + do() as questioning - And recommend alternatives
Using same style as rlang documentation
| non_priority | mark rowwise do as questioning and recommend alternatives using same style as rlang documentation | 0 |
17,403 | 10,027,911,000 | IssuesEvent | 2019-07-17 10:18:16 | lil-kira/MikaelaBot | https://api.github.com/repos/lil-kira/MikaelaBot | closed | CVE-2017-1000048 (High) detected in qs-6.2.3.tgz | security vulnerability | ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.2.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.2.3.tgz">https://registry.npmjs.org/qs/-/qs-6.2.3.tgz</a></p>
<p>Path to dependency file: /MikaelaBot/package.json</p>
<p>Path to vulnerable library: /tmp/git/MikaelaBot/node_modules/google-auth-library/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- youtube-api-2.0.10.tgz (Root Library)
- googleapis-5.2.1.tgz
- google-auth-library-0.9.10.tgz
- request-2.74.0.tgz
- :x: **qs-6.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lil-kira/MikaelaBot/commit/f84a9e4a35304227b78cc0d7b1f54296b607b9de">f84a9e4a35304227b78cc0d7b1f54296b607b9de</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6">https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6</a></p>
<p>Release Date: 2017-03-06</p>
<p>Fix Resolution: Replace or update the following files: parse.js, parse.js, utils.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-1000048 (High) detected in qs-6.2.3.tgz - ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.2.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.2.3.tgz">https://registry.npmjs.org/qs/-/qs-6.2.3.tgz</a></p>
<p>Path to dependency file: /MikaelaBot/package.json</p>
<p>Path to vulnerable library: /tmp/git/MikaelaBot/node_modules/google-auth-library/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- youtube-api-2.0.10.tgz (Root Library)
- googleapis-5.2.1.tgz
- google-auth-library-0.9.10.tgz
- request-2.74.0.tgz
- :x: **qs-6.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lil-kira/MikaelaBot/commit/f84a9e4a35304227b78cc0d7b1f54296b607b9de">f84a9e4a35304227b78cc0d7b1f54296b607b9de</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6">https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6</a></p>
<p>Release Date: 2017-03-06</p>
<p>Fix Resolution: Replace or update the following files: parse.js, parse.js, utils.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in qs tgz cve high severity vulnerability vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file mikaelabot package json path to vulnerable library tmp git mikaelabot node modules google auth library node modules qs package json dependency hierarchy youtube api tgz root library googleapis tgz google auth library tgz request tgz x qs tgz vulnerable library found in head commit a href vulnerability details the web framework using ljharb s qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following files parse js parse js utils js step up your open source security game with whitesource | 0 |
23,401 | 16,110,372,577 | IssuesEvent | 2021-04-27 20:18:03 | ampproject/amp.dev | https://api.github.com/repos/ampproject/amp.dev | closed | blog post redirects from ampproject.org don't work | Category: Infrastructure P1: High Type: Bug | ## Description of the issue found on ampproject.org
A blog post link clicked from ampproject.org that would redirect to amp.dev goes to the main blog page instead of the specific blog post
## How do we reproduce the issue?
Please provide the steps to reproduce the issue:
1. - Google Search: [Standardizing lessons learned from AMP]
2. Click first link: https://www.ampproject.org/latest/blog/standardizing-lessons-learned-from-amp/
3. Goes to https://blog.amp.dev/
What browser are you using? Chrome
What O/S are you using?
| 1.0 | blog post redirects from ampproject.org don't work - ## Description of the issue found on ampproject.org
A blog post link clicked from ampproject.org that would redirect to amp.dev goes to the main blog page instead of the specific blog post
## How do we reproduce the issue?
Please provide the steps to reproduce the issue:
1. - Google Search: [Standardizing lessons learned from AMP]
2. Click first link: https://www.ampproject.org/latest/blog/standardizing-lessons-learned-from-amp/
3. Goes to https://blog.amp.dev/
What browser are you using? Chrome
What O/S are you using?
| non_priority | blog post redirects from ampproject org don t work description of the issue found on ampproject org a blog post link clicked from ampproject org that would redirect to amp dev goes to the main blog page instead of the specific blog post how do we reproduce the issue please provide the steps to reproduce the issue google search click first link goes to what browser are you using chrome what o s are you using | 0 |
174,342 | 27,623,113,594 | IssuesEvent | 2023-03-10 02:58:59 | quicwg/multipath | https://api.github.com/repos/quicwg/multipath | closed | Regular ACK frames when multipath has been negotiated | design | # Introduction
It should be allowed to send regular ACK frames also after multipath has been negotiated.
# Reasoning
Sending acknowledgments over other paths than where the packet was received is complex, which is recognised in the Packet Scheduling section of the draft. A straight-forward implementation may therefore never send cross-path acknowledgments. Allowing it to use regular ACK frames would reduce the special-case code for multipath mode and also save at least one byte on every acknowledgment.
The specification should be updated to (explicitly) say that an endpoint MAY send regular ACK frames also after multipath has been negotiated. | 1.0 | Regular ACK frames when multipath has been negotiated - # Introduction
It should be allowed to send regular ACK frames also after multipath has been negotiated.
# Reasoning
Sending acknowledgments over other paths than where the packet was received is complex, which is recognised in the Packet Scheduling section of the draft. A straight-forward implementation may therefore never send cross-path acknowledgments. Allowing it to use regular ACK frames would reduce the special-case code for multipath mode and also save at least one byte on every acknowledgment.
The specification should be updated to (explicitly) say that an endpoint MAY send regular ACK frames also after multipath has been negotiated. | non_priority | regular ack frames when multipath has been negotiated introduction it should be allowed to send regular ack frames also after multipath has been negotiated reasoning sending acknowledgments over other paths than where the packet was received is complex which is recognised in the packet scheduling section of the draft a straight forward implementation may therefore never send cross path acknowledgments allowing it to use regular ack frames would reduce the special case code for multipath mode and also save at least one byte on every acknowledgment the specification should be updated to explicitly say that an endpoint may send regular ack frames also after multipath has been negotiated | 0 |
20,120 | 3,793,576,391 | IssuesEvent | 2016-03-22 14:24:37 | RestComm/restcomm-web-sdk | https://api.github.com/repos/RestComm/restcomm-web-sdk | closed | Improvements in the logging of webrtc-client.html load test application | in progress load testing framework | Right now if a Device error occurs we don't see the error.
Also replaced webrtcomm and jain-sip-js with latest versios and also used non-debug library versions | 1.0 | Improvements in the logging of webrtc-client.html load test application - Right now if a Device error occurs we don't see the error.
Also replaced webrtcomm and jain-sip-js with latest versios and also used non-debug library versions | non_priority | improvements in the logging of webrtc client html load test application right now if a device error occurs we don t see the error also replaced webrtcomm and jain sip js with latest versios and also used non debug library versions | 0 |
30,777 | 13,309,864,161 | IssuesEvent | 2020-08-26 05:16:39 | woowacourse-teams/2020-doran-doran | https://api.github.com/repos/woowacourse-teams/2020-doran-doran | closed | 페이지에서 사용자의 확대를 방지한다. | :bug: Bug :dolphin: Front 👩👩👧👦 Service | ## 목적
앱을 사용하다보면 원하지않는 상황에 확대가 되어 사용자의 불편함을 유발할 수 있다.
이를 방지한다.
## 상세 작업내용
- [x] index.html header에 확대를 방지하는 코드를 추가한다.
## 주의사항
| 1.0 | 페이지에서 사용자의 확대를 방지한다. - ## 목적
앱을 사용하다보면 원하지않는 상황에 확대가 되어 사용자의 불편함을 유발할 수 있다.
이를 방지한다.
## 상세 작업내용
- [x] index.html header에 확대를 방지하는 코드를 추가한다.
## 주의사항
| non_priority | 페이지에서 사용자의 확대를 방지한다 목적 앱을 사용하다보면 원하지않는 상황에 확대가 되어 사용자의 불편함을 유발할 수 있다 이를 방지한다 상세 작업내용 index html header에 확대를 방지하는 코드를 추가한다 주의사항 | 0 |
6,226 | 3,776,332,529 | IssuesEvent | 2016-03-17 16:20:34 | aldebaran/qibuild | https://api.github.com/repos/aldebaran/qibuild | opened | qibuild list-config should give better output when there is no build config yet | easy qibuild | Currently it displays:
```
$ qibuild list-configs
Known configs
<empty>
```
This is a bit confusing | 1.0 | qibuild list-config should give better output when there is no build config yet - Currently it displays:
```
$ qibuild list-configs
Known configs
<empty>
```
This is a bit confusing | non_priority | qibuild list config should give better output when there is no build config yet currently it displays qibuild list configs known configs this is a bit confusing | 0 |
119,398 | 10,041,454,008 | IssuesEvent | 2019-07-18 22:54:33 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Backport: In airgap setup with private registry, cluster fails to provision - Error: No such image: registry:443/rancher/rke-tools:v0.1.34 | [zube]: To Test area/air-gapped kind/bug team/ca | Backport https://github.com/rancher/rancher/issues/21621 | 1.0 | Backport: In airgap setup with private registry, cluster fails to provision - Error: No such image: registry:443/rancher/rke-tools:v0.1.34 - Backport https://github.com/rancher/rancher/issues/21621 | non_priority | backport in airgap setup with private registry cluster fails to provision error no such image registry rancher rke tools backport | 0 |
147,264 | 23,191,634,532 | IssuesEvent | 2022-08-01 13:09:01 | DXgovernance/DAVI | https://api.github.com/repos/DXgovernance/DAVI | closed | Discussions view | Design | On the main page of guilds right now we show just active proposals in a large card with proposal details. These will of course have their own discussions but I think its important also to separate discussions which are not yet on chain proposals.
Perhaps this should be a list underneath? This can include key metrics like most recent post time, number of comments, tags and in future even how many times the discussion has gone to a vote. | 1.0 | Discussions view - On the main page of guilds right now we show just active proposals in a large card with proposal details. These will of course have their own discussions but I think its important also to separate discussions which are not yet on chain proposals.
Perhaps this should be a list underneath? This can include key metrics like most recent post time, number of comments, tags and in future even how many times the discussion has gone to a vote. | non_priority | discussions view on the main page of guilds right now we show just active proposals in a large card with proposal details these will of course have their own discussions but i think its important also to separate discussions which are not yet on chain proposals perhaps this should be a list underneath this can include key metrics like most recent post time number of comments tags and in future even how many times the discussion has gone to a vote | 0 |
45,125 | 18,425,120,694 | IssuesEvent | 2021-10-13 20:53:28 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | Add CR3 download script to Dev Toolbox | Type: Data Impact: 2-Major Service: Dev Need: 2-Should Have Workgroup: VZ Product: Vision Zero Crash Data System | When Service Request come in for CR3 any Dev should be able to run a script to download them and send them back to the requester.
@frankhereford has a script he runs that we would like to have added to the Dev Toolbox.
- We'll need to make sure that it's refactored and written in python so that it's inline with the stack that we're using.
- We'll need to document it so that Devs can run the script
Came out of #3931 discussion. | 1.0 | Add CR3 download script to Dev Toolbox - When Service Request come in for CR3 any Dev should be able to run a script to download them and send them back to the requester.
@frankhereford has a script he runs that we would like to have added to the Dev Toolbox.
- We'll need to make sure that it's refactored and written in python so that it's inline with the stack that we're using.
- We'll need to document it so that Devs can run the script
Came out of #3931 discussion. | non_priority | add download script to dev toolbox when service request come in for any dev should be able to run a script to download them and send them back to the requester frankhereford has a script he runs that we would like to have added to the dev toolbox we ll need to make sure that it s refactored and written in python so that it s inline with the stack that we re using we ll need to document it so that devs can run the script came out of discussion | 0 |
48,263 | 10,226,402,674 | IssuesEvent | 2019-08-16 17:43:42 | google/shaka-player | https://api.github.com/repos/google/shaka-player | closed | Check for text language match after filtering in Player | code health | In `lib/player.js` there is a TODO with very little context. We can use this issue to explore the intent of the TODO and then update the TODO with the issue number.
https://github.com/google/shaka-player/blob/master/lib/player.js#L2869
```
// Create empty object first and initialize the fields through
// [] to allow field names to be expressions.
// TODO: This feedback system for language matches could be cleaned up.
let languageMatches = {};
languageMatches[ContentType.AUDIO] = false;
languageMatches[ContentType.TEXT] = false;
let variants = StreamUtils.filterVariantsByConfig(
period.variants,
this.currentAudioLanguage_,
this.currentVariantRole_,
this.currentAudioChannelCount_,
languageMatches);
``` | 1.0 | Check for text language match after filtering in Player - In `lib/player.js` there is a TODO with very little context. We can use this issue to explore the intent of the TODO and then update the TODO with the issue number.
https://github.com/google/shaka-player/blob/master/lib/player.js#L2869
```
// Create empty object first and initialize the fields through
// [] to allow field names to be expressions.
// TODO: This feedback system for language matches could be cleaned up.
let languageMatches = {};
languageMatches[ContentType.AUDIO] = false;
languageMatches[ContentType.TEXT] = false;
let variants = StreamUtils.filterVariantsByConfig(
period.variants,
this.currentAudioLanguage_,
this.currentVariantRole_,
this.currentAudioChannelCount_,
languageMatches);
``` | non_priority | check for text language match after filtering in player in lib player js there is a todo with very little context we can use this issue to explore the intent of the todo and then update the todo with the issue number create empty object first and initialize the fields through to allow field names to be expressions todo this feedback system for language matches could be cleaned up let languagematches languagematches false languagematches false let variants streamutils filtervariantsbyconfig period variants this currentaudiolanguage this currentvariantrole this currentaudiochannelcount languagematches | 0 |
65,465 | 19,529,884,085 | IssuesEvent | 2021-12-30 14:50:50 | Siryu6/test-DefectDojo | https://api.github.com/repos/Siryu6/test-DefectDojo | closed | ajinabraham.njsscan.xss_node.express_xss | security / high defectdojo |
*Title*: [ajinabraham.njsscan.xss_node.express_xss|http://localhost:8080/finding/2]
*Defect Dojo link:* http://localhost:8080/finding/2 (2)
*Severity:* High
*CWE:* [CWE-79|https://cwe.mitre.org/data/definitions/79.html]
*CVE:* Unknown
*Product/Engagement/Test:* [Test-DefectDojo|http://localhost:8080/product/5] / [AdHoc Import - Thu, 30 Dec 2021 14:28:59|http://localhost:8080/engagement/3] / [Semgrep JSON Report|http://localhost:8080/test/2]
*Branch/Tag:*
*BuildID:*
*Commit hash:*
*Systems/Endpoints*:
* localhost:7000
*Description*:
**Result message:** Untrusted User Input in Response will result in Reflected Cross Site Scripting Vulnerability.
**Snippet:**
``` res.send(req.params.xss)```
*Mitigation*:
None
*Impact*:
None
*Steps to reproduce*:
None
*References*:
None
*Reporter:* [Admin User (admin) (admin@defectdojo.local)|mailto:admin@defectdojo.local]
| 1.0 | ajinabraham.njsscan.xss_node.express_xss -
*Title*: [ajinabraham.njsscan.xss_node.express_xss|http://localhost:8080/finding/2]
*Defect Dojo link:* http://localhost:8080/finding/2 (2)
*Severity:* High
*CWE:* [CWE-79|https://cwe.mitre.org/data/definitions/79.html]
*CVE:* Unknown
*Product/Engagement/Test:* [Test-DefectDojo|http://localhost:8080/product/5] / [AdHoc Import - Thu, 30 Dec 2021 14:28:59|http://localhost:8080/engagement/3] / [Semgrep JSON Report|http://localhost:8080/test/2]
*Branch/Tag:*
*BuildID:*
*Commit hash:*
*Systems/Endpoints*:
* localhost:7000
*Description*:
**Result message:** Untrusted User Input in Response will result in Reflected Cross Site Scripting Vulnerability.
**Snippet:**
``` res.send(req.params.xss)```
*Mitigation*:
None
*Impact*:
None
*Steps to reproduce*:
None
*References*:
None
*Reporter:* [Admin User (admin) (admin@defectdojo.local)|mailto:admin@defectdojo.local]
| non_priority | ajinabraham njsscan xss node express xss title defect dojo link severity high cwe cve unknown product engagement test branch tag buildid commit hash systems endpoints localhost description result message untrusted user input in response will result in reflected cross site scripting vulnerability snippet res send req params xss mitigation none impact none steps to reproduce none references none reporter | 0 |
131,061 | 12,474,157,239 | IssuesEvent | 2020-05-29 09:09:09 | keera-studios/keera-hails | https://api.github.com/repos/keera-studios/keera-hails | opened | Typo in README | bug documentation enhancement good first issue hacktoberfest help wanted | "Reactive value are data holders" should be "Reactive values are" or "A Reactive Value is a" | 1.0 | Typo in README - "Reactive value are data holders" should be "Reactive values are" or "A Reactive Value is a" | non_priority | typo in readme reactive value are data holders should be reactive values are or a reactive value is a | 0 |
278,517 | 30,702,344,849 | IssuesEvent | 2023-07-27 01:22:15 | Nivaskumark/CVE-2020-0074-frameworks_base | https://api.github.com/repos/Nivaskumark/CVE-2020-0074-frameworks_base | reopened | CVE-2022-20457 (Medium) detected in baseandroid-11.0.0_r39 | Mend: dependency security vulnerability | ## CVE-2022-20457 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-11.0.0_r39</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/CVE-2020-0074-frameworks_base/commit/f63c00c11df9fe4c62ee2ed7d5f72e3a7ebec027">f63c00c11df9fe4c62ee2ed7d5f72e3a7ebec027</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/services/core/java/com/android/server/StorageManagerService.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In getMountModeInternal of StorageManagerService.java, there is a possible prevention of package installation due to improper input validation. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-13Android ID: A-243924784
<p>Publish Date: 2022-11-08
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20457>CVE-2022-20457</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/docs/security/bulletin/2022-11-01">https://source.android.com/docs/security/bulletin/2022-11-01</a></p>
<p>Release Date: 2022-11-08</p>
<p>Fix Resolution: android-13.0.0_r12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-20457 (Medium) detected in baseandroid-11.0.0_r39 - ## CVE-2022-20457 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-11.0.0_r39</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/CVE-2020-0074-frameworks_base/commit/f63c00c11df9fe4c62ee2ed7d5f72e3a7ebec027">f63c00c11df9fe4c62ee2ed7d5f72e3a7ebec027</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/services/core/java/com/android/server/StorageManagerService.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In getMountModeInternal of StorageManagerService.java, there is a possible prevention of package installation due to improper input validation. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-13Android ID: A-243924784
<p>Publish Date: 2022-11-08
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20457>CVE-2022-20457</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/docs/security/bulletin/2022-11-01">https://source.android.com/docs/security/bulletin/2022-11-01</a></p>
<p>Release Date: 2022-11-08</p>
<p>Fix Resolution: android-13.0.0_r12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in baseandroid cve medium severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch master vulnerable source files services core java com android server storagemanagerservice java vulnerability details in getmountmodeinternal of storagemanagerservice java there is a possible prevention of package installation due to improper input validation this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend | 0 |
39,325 | 12,663,367,782 | IssuesEvent | 2020-06-18 01:07:39 | jgeraigery/pnc | https://api.github.com/repos/jgeraigery/pnc | opened | CVE-2018-19837 (Medium) detected in node-sass-4.11.0.tgz | security vulnerability | ## CVE-2018-19837 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.11.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, Sass::Eval::operator()(Sass::Binary_Expression*) inside eval.cpp allows attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, because of certain incorrect parsing of '%' as a modulo operator in parser.cpp.
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19837>CVE-2018-19837</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19837">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19837</a></p>
<p>Fix Resolution: 3.5.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.11.0","isTransitiveDependency":false,"dependencyTree":"node-sass:4.11.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.5.5"}],"vulnerabilityIdentifier":"CVE-2018-19837","vulnerabilityDetails":"In LibSass prior to 3.5.5, Sass::Eval::operator()(Sass::Binary_Expression*) inside eval.cpp allows attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, because of certain incorrect parsing of \u0027%\u0027 as a modulo operator in parser.cpp.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19837","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-19837 (Medium) detected in node-sass-4.11.0.tgz - ## CVE-2018-19837 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.11.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, Sass::Eval::operator()(Sass::Binary_Expression*) inside eval.cpp allows attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, because of certain incorrect parsing of '%' as a modulo operator in parser.cpp.
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19837>CVE-2018-19837</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19837">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19837</a></p>
<p>Fix Resolution: 3.5.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.11.0","isTransitiveDependency":false,"dependencyTree":"node-sass:4.11.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.5.5"}],"vulnerabilityIdentifier":"CVE-2018-19837","vulnerabilityDetails":"In LibSass prior to 3.5.5, Sass::Eval::operator()(Sass::Binary_Expression*) inside eval.cpp allows attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, because of certain incorrect parsing of \u0027%\u0027 as a modulo operator in parser.cpp.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19837","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in node sass tgz cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href dependency hierarchy x node sass tgz vulnerable library vulnerability details in libsass prior to sass eval operator sass binary expression inside eval cpp allows attackers to cause a denial of service resulting from stack consumption via a crafted sass file because of certain incorrect parsing of as a modulo operator in parser cpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails in libsass prior to sass eval operator sass binary expression inside eval cpp allows attackers to cause a denial of service resulting from stack consumption via a crafted sass file because of certain incorrect parsing of as a modulo operator in parser cpp vulnerabilityurl | 0 |
439,876 | 30,719,767,666 | IssuesEvent | 2023-07-27 15:10:07 | jaredhendrickson13/pfsense-api | https://api.github.com/repos/jaredhendrickson13/pfsense-api | closed | Is there any recommended api client? | documentation |
Is there a recommended API client you would suggest? I work more with Node.js, but could not find any client for Node.js. Is there any page with the client libraries connecting to the API?
Thank you for the wonderful package!
| 1.0 | Is there any recommended api client? -
Is there a recommended API client you would suggest? I work more with Node.js, but could not find any client for Node.js. Is there any page with the client libraries connecting to the API?
Thank you for the wonderful package!
| non_priority | is there any recommended api client is there a recommended api client you would suggest i work more with node js but could not find any client for node js is there any page with the client libraries connecting to the api thank you for the wonderful package | 0 |
143,601 | 11,570,454,730 | IssuesEvent | 2020-02-20 19:32:49 | CBICA/CaPTk | https://api.github.com/repos/CBICA/CaPTk | closed | Loading CaPTk on cluster | Testathon-Feb-2020 wontfix | **Describe the bug**
When trying to load CaPTk on the cluster using: module load captk/1.7.6, an error message appears saying no such file or directory
**To Reproduce**
Steps to reproduce the behavior:
1. On cluster type: module load captk/1.7.6
2. type: captk
**Expected behavior**
captk should load
**Error message **
WARNING: Trying to run CaPTk GUI using software rendering - this might not work on all systems and in those cases, only the CLI will be available.
[0220/113047.396168:WARNING:stack_trace_posix.cc(699)] Failed to open file: /scratch/chitalir/#5898244 (deleted)
Error: No such file or directory
qt.qpa.xcb: QXcbConnection: XCB error: 145 (Unknown), sequence: 175, resource id: 0, major code: 139 (Unknown), minor code: 20
ApplicationPreferences::DisplayPreferences()
font = ""
theme = ""
ApplicationPreferences::DisplayPreferences()
font = "Sans Serif,9,-1,5,50,0,0,0,0,0"
theme = "Dark"
ApplicationPreferences::DisplayPreferences()
font = "Sans Serif,9,-1,5,50,0,0,0,0,0"
theme = "Dark"
p11-kit: couldn't list directory: /etc/pki/ca-trust/source/anchors: Permission denied
The X11 connection broke: I/O error (code 1)
XIO: fatal IO error 0 (Success) on X server "170.166.98.52:16.0"
after 710 requests (710 known processed) with 0 events remaining.
**CaPTk Version**
1.7.6
**Desktop (please complete the following information):**
Windows
| 1.0 | Loading CaPTk on cluster - **Describe the bug**
When trying to load CaPTk on the cluster using: module load captk/1.7.6, an error message appears saying no such file or directory
**To Reproduce**
Steps to reproduce the behavior:
1. On cluster type: module load captk/1.7.6
2. type: captk
**Expected behavior**
captk should load
**Error message **
WARNING: Trying to run CaPTk GUI using software rendering - this might not work on all systems and in those cases, only the CLI will be available.
[0220/113047.396168:WARNING:stack_trace_posix.cc(699)] Failed to open file: /scratch/chitalir/#5898244 (deleted)
Error: No such file or directory
qt.qpa.xcb: QXcbConnection: XCB error: 145 (Unknown), sequence: 175, resource id: 0, major code: 139 (Unknown), minor code: 20
ApplicationPreferences::DisplayPreferences()
font = ""
theme = ""
ApplicationPreferences::DisplayPreferences()
font = "Sans Serif,9,-1,5,50,0,0,0,0,0"
theme = "Dark"
ApplicationPreferences::DisplayPreferences()
font = "Sans Serif,9,-1,5,50,0,0,0,0,0"
theme = "Dark"
p11-kit: couldn't list directory: /etc/pki/ca-trust/source/anchors: Permission denied
The X11 connection broke: I/O error (code 1)
XIO: fatal IO error 0 (Success) on X server "170.166.98.52:16.0"
after 710 requests (710 known processed) with 0 events remaining.
**CaPTk Version**
1.7.6
**Desktop (please complete the following information):**
Windows
| non_priority | loading captk on cluster describe the bug when trying to load captk on the cluster using module load captk an error message appears saying no such file or directory to reproduce steps to reproduce the behavior on cluster type module load captk type captk expected behavior captk should load error message warning trying to run captk gui using software rendering this might not work on all systems and in those cases only the cli will be available failed to open file scratch chitalir deleted error no such file or directory qt qpa xcb qxcbconnection xcb error unknown sequence resource id major code unknown minor code applicationpreferences displaypreferences font theme applicationpreferences displaypreferences font sans serif theme dark applicationpreferences displaypreferences font sans serif theme dark kit couldn t list directory etc pki ca trust source anchors permission denied the connection broke i o error code xio fatal io error success on x server after requests known processed with events remaining captk version desktop please complete the following information windows | 0 |
60,971 | 6,719,788,379 | IssuesEvent | 2017-10-16 03:27:10 | red/red | https://api.github.com/repos/red/red | closed | It is not possible to unselect value in TEXT-LIST on macOS | GUI status.built status.tested type.bug | This code:
```
view [t: text-list data ["a" "b" "c" "d"] button "unselect" [t/selected: none show t]]
```
will unselect value in `text-list` when pressing `[unselect]` button. At least under Windows, but it does nothing under macOS. | 1.0 | It is not possible to unselect value in TEXT-LIST on macOS - This code:
```
view [t: text-list data ["a" "b" "c" "d"] button "unselect" [t/selected: none show t]]
```
will unselect value in `text-list` when pressing `[unselect]` button. At least under Windows, but it does nothing under macOS. | non_priority | it is not possible to unselect value in text list on macos this code view button unselect will unselect value in text list when pressing button at least under windows but it does nothing under macos | 0 |
211,534 | 23,833,138,386 | IssuesEvent | 2022-09-06 01:06:53 | rsoreq/assertj-core | https://api.github.com/repos/rsoreq/assertj-core | opened | CVE-2022-38749 (Medium) detected in snakeyaml-1.21.jar | security vulnerability | ## CVE-2022-38749 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.21.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to vulnerable library: /target/local-repo/org/yaml/snakeyaml/1.21/snakeyaml-1.21.jar</p>
<p>
Dependency Hierarchy:
- :x: **snakeyaml-1.21.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/assertj-core/commit/0970b0b9328fa33f24679a08024d5baa8c82ae65">0970b0b9328fa33f24679a08024d5baa8c82ae65</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open">https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
</details>
<p></p>
| True | CVE-2022-38749 (Medium) detected in snakeyaml-1.21.jar - ## CVE-2022-38749 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.21.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to vulnerable library: /target/local-repo/org/yaml/snakeyaml/1.21/snakeyaml-1.21.jar</p>
<p>
Dependency Hierarchy:
- :x: **snakeyaml-1.21.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/assertj-core/commit/0970b0b9328fa33f24679a08024d5baa8c82ae65">0970b0b9328fa33f24679a08024d5baa8c82ae65</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Using snakeYAML to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow.
<p>Publish Date: 2022-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-38749>CVE-2022-38749</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open">https://bitbucket.org/snakeyaml/snakeyaml/issues/525/got-stackoverflowerror-for-many-open</a></p>
<p>Release Date: 2022-09-05</p>
<p>Fix Resolution: org.yaml:snakeyaml:1.31</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in snakeyaml jar cve medium severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to vulnerable library target local repo org yaml snakeyaml snakeyaml jar dependency hierarchy x snakeyaml jar vulnerable library found in head commit a href found in base branch main vulnerability details using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml | 0 |
191,828 | 14,596,491,069 | IssuesEvent | 2020-12-20 16:04:07 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | hello-mr-code/terraform-oci: oci/cloud_guard_target_test.go; 16 LoC | fresh small test |
Found a possible issue in [hello-mr-code/terraform-oci](https://www.github.com/hello-mr-code/terraform-oci) at [oci/cloud_guard_target_test.go](https://github.com/hello-mr-code/terraform-oci/blob/2f6aa93ef8643328af454512a5fe78ab006697f0/oci/cloud_guard_target_test.go#L447-L462)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to targetId is reassigned at line 451
[Click here to see the code in its original context.](https://github.com/hello-mr-code/terraform-oci/blob/2f6aa93ef8643328af454512a5fe78ab006697f0/oci/cloud_guard_target_test.go#L447-L462)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, targetId := range targetIds {
if ok := SweeperDefaultResourceId[targetId]; !ok {
deleteTargetRequest := oci_cloud_guard.DeleteTargetRequest{}
deleteTargetRequest.TargetId = &targetId
deleteTargetRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "cloud_guard")
_, error := cloudGuardClient.DeleteTarget(context.Background(), deleteTargetRequest)
if error != nil {
fmt.Printf("Error deleting Target %s %s, It is possible that the resource is already deleted. Please verify manually \n", targetId, error)
continue
}
waitTillCondition(testAccProvider, &targetId, targetSweepWaitCondition, time.Duration(3*time.Minute),
targetSweepResponseFetchOperation, "cloud_guard", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 2f6aa93ef8643328af454512a5fe78ab006697f0
| 1.0 | hello-mr-code/terraform-oci: oci/cloud_guard_target_test.go; 16 LoC -
Found a possible issue in [hello-mr-code/terraform-oci](https://www.github.com/hello-mr-code/terraform-oci) at [oci/cloud_guard_target_test.go](https://github.com/hello-mr-code/terraform-oci/blob/2f6aa93ef8643328af454512a5fe78ab006697f0/oci/cloud_guard_target_test.go#L447-L462)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to targetId is reassigned at line 451
[Click here to see the code in its original context.](https://github.com/hello-mr-code/terraform-oci/blob/2f6aa93ef8643328af454512a5fe78ab006697f0/oci/cloud_guard_target_test.go#L447-L462)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, targetId := range targetIds {
if ok := SweeperDefaultResourceId[targetId]; !ok {
deleteTargetRequest := oci_cloud_guard.DeleteTargetRequest{}
deleteTargetRequest.TargetId = &targetId
deleteTargetRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "cloud_guard")
_, error := cloudGuardClient.DeleteTarget(context.Background(), deleteTargetRequest)
if error != nil {
fmt.Printf("Error deleting Target %s %s, It is possible that the resource is already deleted. Please verify manually \n", targetId, error)
continue
}
waitTillCondition(testAccProvider, &targetId, targetSweepWaitCondition, time.Duration(3*time.Minute),
targetSweepResponseFetchOperation, "cloud_guard", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 2f6aa93ef8643328af454512a5fe78ab006697f0
| non_priority | hello mr code terraform oci oci cloud guard target test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to targetid is reassigned at line click here to show the line s of go which triggered the analyzer go for targetid range targetids if ok sweeperdefaultresourceid ok deletetargetrequest oci cloud guard deletetargetrequest deletetargetrequest targetid targetid deletetargetrequest requestmetadata retrypolicy getretrypolicy true cloud guard error cloudguardclient deletetarget context background deletetargetrequest if error nil fmt printf error deleting target s s it is possible that the resource is already deleted please verify manually n targetid error continue waittillcondition testaccprovider targetid targetsweepwaitcondition time duration time minute targetsweepresponsefetchoperation cloud guard true leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
97,307 | 12,227,056,281 | IssuesEvent | 2020-05-03 13:44:31 | chakra-ui/chakra-ui | https://api.github.com/repos/chakra-ui/chakra-ui | closed | How to reduce the spacing in the menu | Topic: Design and UX ✍️ Type: Question ❓ | If I change the size of the button, the spacing increases. How can I reduce this spacing?
<img width="360" alt="Screenshot 2020-02-17 at 1 43 30 AM" src="https://user-images.githubusercontent.com/15448192/74611999-12404e00-5127-11ea-9ce2-afd309c3687d.png">
| 1.0 | How to reduce the spacing in the menu - If I change the size of the button, the spacing increases. How can I reduce this spacing?
<img width="360" alt="Screenshot 2020-02-17 at 1 43 30 AM" src="https://user-images.githubusercontent.com/15448192/74611999-12404e00-5127-11ea-9ce2-afd309c3687d.png">
| non_priority | how to reduce the spacing in the menu if i change the size of the button the spacing increases how can i reduce this spacing img width alt screenshot at am src | 0 |
390,703 | 26,869,653,094 | IssuesEvent | 2023-02-04 09:43:12 | p2panda/p2panda | https://api.github.com/repos/p2panda/p2panda | closed | Write a whole bunch of nice doc-string examples | documentation p2panda-rs | Especially after some got lost after the refactoring in: https://github.com/p2panda/p2panda/pull/415 | 1.0 | Write a whole bunch of nice doc-string examples - Especially after some got lost after the refactoring in: https://github.com/p2panda/p2panda/pull/415 | non_priority | write a whole bunch of nice doc string examples especially after some got lost after the refactoring in | 0 |
80,064 | 9,977,140,474 | IssuesEvent | 2019-07-09 16:31:02 | ParabolInc/action | https://api.github.com/repos/ParabolInc/action | closed | handle single-card groups better | design | the group name "New Group" is a sad one
AC
- single card groups are handled better, maybe we make folks pick a title, or assign a better auto-generated title
effort: 11 points
| 1.0 | handle single-card groups better - the group name "New Group" is a sad one
AC
- single card groups are handled better, maybe we make folks pick a title, or assign a better auto-generated title
effort: 11 points
| non_priority | handle single card groups better the group name new group is a sad one ac single card groups are handled better maybe we make folks pick a title or assign a better auto generated title effort points | 0 |
67,448 | 16,984,269,646 | IssuesEvent | 2021-06-30 12:45:41 | ng-bootstrap/ng-bootstrap | https://api.github.com/repos/ng-bootstrap/ng-bootstrap | closed | Angular 12 support | breaking change type: build | ### Feature description:
[Angular 12](https://github.com/angular/angular/releases/tag/12.0.0) is released & I have successfully upgraded one of my small project using ng-bootstrap `9.1.1` & Angular `12.0.0`, but having official support would be good & Thank you for this great library.
### Versions of Angular, ng-bootstrap and Bootstrap:
Angular: 12.0.0
ng-bootstrap: 9.1.1
Bootstrap: 4.6.0
| 1.0 | Angular 12 support - ### Feature description:
[Angular 12](https://github.com/angular/angular/releases/tag/12.0.0) is released & I have successfully upgraded one of my small project using ng-bootstrap `9.1.1` & Angular `12.0.0`, but having official support would be good & Thank you for this great library.
### Versions of Angular, ng-bootstrap and Bootstrap:
Angular: 12.0.0
ng-bootstrap: 9.1.1
Bootstrap: 4.6.0
| non_priority | angular support feature description is released i have successfully upgraded one of my small project using ng bootstrap angular but having official support would be good thank you for this great library versions of angular ng bootstrap and bootstrap angular ng bootstrap bootstrap | 0 |
82,159 | 10,272,362,509 | IssuesEvent | 2019-08-23 16:14:10 | calidadudea/Diseno | https://api.github.com/repos/calidadudea/Diseno | closed | Hacer casos de uso y diagramas de secuencia | documentation | Yo como diseñador quiero desarrollar los casos de uso y los diagramas de secuencia que describirán la funcionalidad de la aplicación. | 1.0 | Hacer casos de uso y diagramas de secuencia - Yo como diseñador quiero desarrollar los casos de uso y los diagramas de secuencia que describirán la funcionalidad de la aplicación. | non_priority | hacer casos de uso y diagramas de secuencia yo como diseñador quiero desarrollar los casos de uso y los diagramas de secuencia que describirán la funcionalidad de la aplicación | 0 |
367,932 | 25,769,480,052 | IssuesEvent | 2022-12-09 06:25:19 | freesewing/freesewing | https://api.github.com/repos/freesewing/freesewing | opened | [docs]: Point.slope() documentation is missing | :book: documentation | ### Where can we see the problem? 🤔
https://freesewing.dev/reference/api/point
### Are you a FreeSewing patron? 😃
No, I am not 😞
### Suggested content
_No response_
### Additional context
_No response_ | 1.0 | [docs]: Point.slope() documentation is missing - ### Where can we see the problem? 🤔
https://freesewing.dev/reference/api/point
### Are you a FreeSewing patron? 😃
No, I am not 😞
### Suggested content
_No response_
### Additional context
_No response_ | non_priority | point slope documentation is missing where can we see the problem 🤔 are you a freesewing patron 😃 no i am not 😞 suggested content no response additional context no response | 0 |
212,723 | 16,475,508,788 | IssuesEvent | 2021-05-24 04:41:52 | tektoncd/cli | https://api.github.com/repos/tektoncd/cli | closed | TestClusterTaskInteractiveStartE2E/Start_ClusterTask_with_flags consistently fails | area/testing kind/bug kind/flake | `TestClusterTaskInteractiveStartE2E/Start_ClusterTask_with_flags` consistently fails on the CI, I am not sure why, but I am willing to skip it in order to unblock PRs and release.
/cc @tektoncd/cli-maintainers
/kind test | 1.0 | TestClusterTaskInteractiveStartE2E/Start_ClusterTask_with_flags consistently fails - `TestClusterTaskInteractiveStartE2E/Start_ClusterTask_with_flags` consistently fails on the CI, I am not sure why, but I am willing to skip it in order to unblock PRs and release.
/cc @tektoncd/cli-maintainers
/kind test | non_priority | start clustertask with flags consistently fails start clustertask with flags consistently fails on the ci i am not sure why but i am willing to skip it in order to unblock prs and release cc tektoncd cli maintainers kind test | 0 |
237,874 | 26,085,423,193 | IssuesEvent | 2022-12-26 01:43:34 | faizulho/sanity-jigsaw-blog | https://api.github.com/repos/faizulho/sanity-jigsaw-blog | opened | CVE-2022-37603 (High) detected in loader-utils-1.4.0.tgz, loader-utils-1.1.0.tgz | security vulnerability | ## CVE-2022-37603 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>loader-utils-1.4.0.tgz</b>, <b>loader-utils-1.1.0.tgz</b></p></summary>
<p>
<details><summary><b>loader-utils-1.4.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>Path to dependency file: /web/package.json</p>
<p>Path to vulnerable library: /web/node_modules/loader-utils/package.json,/studio/node_modules/babel-loader/node_modules/loader-utils/package.json</p>
<p>
Dependency Hierarchy:
- sass-loader-7.3.1.tgz (Root Library)
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>loader-utils-1.1.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.1.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.1.0.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/loader-utils/package.json</p>
<p>
Dependency Hierarchy:
- core-1.150.7.tgz (Root Library)
- server-1.150.1.tgz
- css-loader-0.28.12.tgz
- :x: **loader-utils-1.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/faizulho/sanity-jigsaw-blog/commit/3182c6ae26644fb8cb51607fa8ee35d62c0c59d7">3182c6ae26644fb8cb51607fa8ee35d62c0c59d7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the url variable in interpolateName.js.
<p>Publish Date: 2022-10-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37603>CVE-2022-37603</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-3rfm-jhwj-7488">https://github.com/advisories/GHSA-3rfm-jhwj-7488</a></p>
<p>Release Date: 2022-10-14</p>
<p>Fix Resolution (loader-utils): 2.0.4</p>
<p>Direct dependency fix Resolution (sass-loader): 8.0.0</p><p>Fix Resolution (loader-utils): 2.0.4</p>
<p>Direct dependency fix Resolution (@sanity/core): 2.21.12-purple-unicorn.1300</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-37603 (High) detected in loader-utils-1.4.0.tgz, loader-utils-1.1.0.tgz - ## CVE-2022-37603 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>loader-utils-1.4.0.tgz</b>, <b>loader-utils-1.1.0.tgz</b></p></summary>
<p>
<details><summary><b>loader-utils-1.4.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>Path to dependency file: /web/package.json</p>
<p>Path to vulnerable library: /web/node_modules/loader-utils/package.json,/studio/node_modules/babel-loader/node_modules/loader-utils/package.json</p>
<p>
Dependency Hierarchy:
- sass-loader-7.3.1.tgz (Root Library)
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>loader-utils-1.1.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.1.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.1.0.tgz</a></p>
<p>Path to dependency file: /studio/package.json</p>
<p>Path to vulnerable library: /studio/node_modules/loader-utils/package.json</p>
<p>
Dependency Hierarchy:
- core-1.150.7.tgz (Root Library)
- server-1.150.1.tgz
- css-loader-0.28.12.tgz
- :x: **loader-utils-1.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/faizulho/sanity-jigsaw-blog/commit/3182c6ae26644fb8cb51607fa8ee35d62c0c59d7">3182c6ae26644fb8cb51607fa8ee35d62c0c59d7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Regular expression denial of service (ReDoS) flaw was found in Function interpolateName in interpolateName.js in webpack loader-utils 2.0.0 via the url variable in interpolateName.js.
<p>Publish Date: 2022-10-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37603>CVE-2022-37603</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-3rfm-jhwj-7488">https://github.com/advisories/GHSA-3rfm-jhwj-7488</a></p>
<p>Release Date: 2022-10-14</p>
<p>Fix Resolution (loader-utils): 2.0.4</p>
<p>Direct dependency fix Resolution (sass-loader): 8.0.0</p><p>Fix Resolution (loader-utils): 2.0.4</p>
<p>Direct dependency fix Resolution (@sanity/core): 2.21.12-purple-unicorn.1300</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in loader utils tgz loader utils tgz cve high severity vulnerability vulnerable libraries loader utils tgz loader utils tgz loader utils tgz utils for webpack loaders library home page a href path to dependency file web package json path to vulnerable library web node modules loader utils package json studio node modules babel loader node modules loader utils package json dependency hierarchy sass loader tgz root library x loader utils tgz vulnerable library loader utils tgz utils for webpack loaders library home page a href path to dependency file studio package json path to vulnerable library studio node modules loader utils package json dependency hierarchy core tgz root library server tgz css loader tgz x loader utils tgz vulnerable library found in head commit a href found in base branch main vulnerability details a regular expression denial of service redos flaw was found in function interpolatename in interpolatename js in webpack loader utils via the url variable in interpolatename js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution loader utils direct dependency fix resolution sass loader fix resolution loader utils direct dependency fix resolution sanity core purple unicorn step up your open source security game with mend | 0 |
131,670 | 18,358,293,096 | IssuesEvent | 2021-10-08 22:00:18 | cagov/design-system | https://api.github.com/repos/cagov/design-system | closed | ODI huddle/brown bag content design principle presentation | Content Design Presentations | Do a dry run of presenting on our Design System content principles in preparation for a soft launch with the Digital Web Services group.
- Highlight the principles themselves
- The structure we used
- The reasons behind them
- One or two key ways to achieve them
- How we intend to use them | 1.0 | ODI huddle/brown bag content design principle presentation - Do a dry run of presenting on our Design System content principles in preparation for a soft launch with the Digital Web Services group.
- Highlight the principles themselves
- The structure we used
- The reasons behind them
- One or two key ways to achieve them
- How we intend to use them | non_priority | odi huddle brown bag content design principle presentation do a dry run of presenting on our design system content principles in preparation for a soft launch with the digital web services group highlight the principles themselves the structure we used the reasons behind them one or two key ways to achieve them how we intend to use them | 0 |
6,622 | 4,387,476,860 | IssuesEvent | 2016-08-08 15:53:45 | MISP/MISP | https://api.github.com/repos/MISP/MISP | opened | Do not apply regexp for path to pdb attribute type | bug usability | ### Work environment
| Questions | Answers
|---------------------------|--------------------
| Type of issue | Bug
| MISP version / git hash | 2.4.49 (misppriv as of 08 AUG)
### Expected behavior
- PDB path attributes are not generified using regexps.
### Actual behavior
- PDB path attributes are generified using regexps (**C:\Users\mr.tekide\Documents\** becomes **%USERPROFILE%\Documents\**).
### Steps to reproduce the behavior
- Add a PDB path attribute to a stock install of MISP.
- For example: _C:\Users\mr.tekide\Documents\Visual Studio 2013\Projects\paccrypt11njratmalii\paccryptalipnahzade\obj\Debug\LManager.pdb_ from [here](https://citizenlab.org/2016/08/group5-syria/).
The whole point of PDB paths is to preserve unique/identifying informations such as the user-names. | True | Do not apply regexp for path to pdb attribute type - ### Work environment
| Questions | Answers
|---------------------------|--------------------
| Type of issue | Bug
| MISP version / git hash | 2.4.49 (misppriv as of 08 AUG)
### Expected behavior
- PDB path attributes are not generified using regexps.
### Actual behavior
- PDB path attributes are generified using regexps (**C:\Users\mr.tekide\Documents\** becomes **%USERPROFILE%\Documents\**).
### Steps to reproduce the behavior
- Add a PDB path attribute to a stock install of MISP.
- For example: _C:\Users\mr.tekide\Documents\Visual Studio 2013\Projects\paccrypt11njratmalii\paccryptalipnahzade\obj\Debug\LManager.pdb_ from [here](https://citizenlab.org/2016/08/group5-syria/).
The whole point of PDB paths is to preserve unique/identifying informations such as the user-names. | non_priority | do not apply regexp for path to pdb attribute type work environment questions answers type of issue bug misp version git hash misppriv as of aug expected behavior pdb path attributes are not generified using regexps actual behavior pdb path attributes are generified using regexps c users mr tekide documents becomes userprofile documents steps to reproduce the behavior add a pdb path attribute to a stock install of misp for example c users mr tekide documents visual studio projects paccryptalipnahzade obj debug lmanager pdb from the whole point of pdb paths is to preserve unique identifying informations such as the user names | 0 |
22,090 | 3,933,424,809 | IssuesEvent | 2016-04-25 19:04:35 | GCSO2/D3S-INVENTORY | https://api.github.com/repos/GCSO2/D3S-INVENTORY | closed | Cloud - Inventory Transfer Report: Adjustments | ready for gio to test | linked to #29
Please do the following tweaks on the Inventory Adjustment Report
- Remove Core Column
- Remove Unit Cost and Total Cost
- Add part location from the From inventory (so that employee can find the physical part)
- Add barcode after Part#
- After UOM add a column with header Revised, and a line so that user can write the revised quantity.
- Make every other line with gray background as example below
- Add Total number of lines (parts) at the bottom.


| 1.0 | Cloud - Inventory Transfer Report: Adjustments - linked to #29
Please do the following tweaks on the Inventory Adjustment Report
- Remove Core Column
- Remove Unit Cost and Total Cost
- Add part location from the From inventory (so that employee can find the physical part)
- Add barcode after Part#
- After UOM add a column with header Revised, and a line so that user can write the revised quantity.
- Make every other line with gray background as example below
- Add Total number of lines (parts) at the bottom.


| non_priority | cloud inventory transfer report adjustments linked to please do the following tweaks on the inventory adjustment report remove core column remove unit cost and total cost add part location from the from inventory so that employee can find the physical part add barcode after part after uom add a column with header revised and a line so that user can write the revised quantity make every other line with gray background as example below add total number of lines parts at the bottom | 0 |
150,084 | 23,597,710,021 | IssuesEvent | 2022-08-23 21:01:22 | carbon-design-system/carbon-platform | https://api.github.com/repos/carbon-design-system/carbon-platform | closed | WIP: [Tech Design] Replace fs cache with redis | role: dev 🤖 type: tech design 🏗️ | # Feature technical design
## Summary
**Summary**
The web app uses a [Node.js cache-manager](https://www.npmjs.com/package/cache-manager) to cache all GitHub responses to prevent the web app from getting GitHub API rate limited. These GitHub requests vary from fetching repository information, traversing GitHub trees, to primarily fetching GitHub file content to read carbon.yml files and MDX files for web page content.
We're currently using a file system store engine (https://www.npmjs.com/package/cache-manager-fs-hash), which was chosen during v1 preview prototyping as a quick and easy way to prevent GitHub API rate limits.
As we index more content (asset documentation pages), each GitHub request per MDX file adds to the amount of cached responses. Our current build pipeline does not persist cached files written to disk between builds.
As the amount of indexed content grows, so does the risk of our production GitHub access tokens getting rate limited which could leave us with a production environment void of all content.
**Potential solution**
To mitigate that risk, until we can create proper back-end services for this, what if we added Redis stores for staging and production? It looks like we could use a Redis store listed here: https://github.com/BryanDonovan/node-cache-manager#store-engines
Those Redis store engines _should_ share the same API as `cache-manager-fs-hash`, so that _should_ require minimal web app changes.
We could keep the [1 hour TTL](https://github.com/carbon-design-system/carbon-platform/blob/main/services/web-app/lib/file-cache.js#L24) for cached responses, so for Next.js ISR pages, content from GitHub would be at most 1 hour stale.
With a Redis cache, our production builds should be faster because there's a greater chance of a cache hit.
We could use a Redis cache for local development too, or for simplicity, keep that with the current file system cache.
**TL;DR:**
In the event that our production environment gets rate limited by GitHub, because the Redis cache would be persisted, we wouldn't lose web app content between deploys. Also, it would be neat to see how many keys would get cached in Redis, to give us a better idea of to-be infrastructure needs to manage GitHub content.
TODO: vv Everything below this vv
## Research
- [ ] Approved?
- **Unanswered questions**
- List any unknowns and unanswered questions that need answers prior to beginning development
- **New technologies**
- List new technologies that need to be explored in detail before beginning development
- **Proofs of concept**
- List proofs of concept that need to be completed before beginning development
## UI/UX design
Does this feature have any associated UI/UX? If so, describe any design that needs to be
completed/red-lined prior to development.
## APIs
- [ ] Approved?
- **Programmatic APIs**
- List any APIs that will be developed and made available in the `@carbon-platform/api` package,
including function/class/method names, parameters, and return values.
- **Messages**
- List any new/changed RabbitMQ messages introduced by this feature, the message payload structure
associated with them, whether they are queries or emits, and their expected return values (for
queries).
## Test strategy
- [ ] Approved?
How will the new feature be tested? (e.g. unit tests, manual verification, automated e2e testing,
etc.)
What interesting edge cases should be considered and tested?
## Security
- [ ] Approved?
What new data is created/stored/collected/transmitted by this feature? How is that data secured? Who
is allowed to access it? How is that access controlled?
Think like a hacker. How might someone attempt to break or abuse this feature?
## Error handling
Ignore the happy path. What can go wrong with this feature? How will the error conditions manifest
through the APIs? How will users be informed about these errors?
## Logging
- [ ] Approved?
Detail any FFDC data (info, warning, error, debug logs) to be captured by this feature.
## File and code layout
- [ ] Approved?
Describe how the files and code for this feature will fit into the rest of the mono repo. Will there
be a new package/service? Are there existing files/directories in which the new logic should live?
## Issue and work breakdown
- [ ] Approved?
List any issues that should be created prior to starting work on this feature
- **Epics**
- ...
- **Issues**
- ...
| 1.0 | WIP: [Tech Design] Replace fs cache with redis - # Feature technical design
## Summary
**Summary**
The web app uses a [Node.js cache-manager](https://www.npmjs.com/package/cache-manager) to cache all GitHub responses to prevent the web app from getting GitHub API rate limited. These GitHub requests vary from fetching repository information, traversing GitHub trees, to primarily fetching GitHub file content to read carbon.yml files and MDX files for web page content.
We're currently using a file system store engine (https://www.npmjs.com/package/cache-manager-fs-hash), which was chosen during v1 preview prototyping as a quick and easy way to prevent GitHub API rate limits.
As we index more content (asset documentation pages), each GitHub request per MDX file adds to the amount of cached responses. Our current build pipeline does not persist cached files written to disk between builds.
As the amount of indexed content grows, so does the risk of our production GitHub access tokens getting rate limited which could leave us with a production environment void of all content.
**Potential solution**
To mitigate that risk, until we can create proper back-end services for this, what if we added Redis stores for staging and production? It looks like we could use a Redis store listed here: https://github.com/BryanDonovan/node-cache-manager#store-engines
Those Redis store engines _should_ share the same API as `cache-manager-fs-hash`, so that _should_ require minimal web app changes.
We could keep the [1 hour TTL](https://github.com/carbon-design-system/carbon-platform/blob/main/services/web-app/lib/file-cache.js#L24) for cached responses, so for Next.js ISR pages, content from GitHub would be at most 1 hour stale.
With a Redis cache, our production builds should be faster because there's a greater chance of a cache hit.
We could use a Redis cache for local development too, or for simplicity, keep that with the current file system cache.
**TL;DR:**
In the event that our production environment gets rate limited by GitHub, because the Redis cache would be persisted, we wouldn't lose web app content between deploys. Also, it would be neat to see how many keys would get cached in Redis, to give us a better idea of to-be infrastructure needs to manage GitHub content.
TODO: vv Everything below this vv
## Research
- [ ] Approved?
- **Unanswered questions**
- List any unknowns and unanswered questions that need answers prior to beginning development
- **New technologies**
- List new technologies that need to be explored in detail before beginning development
- **Proofs of concept**
- List proofs of concept that need to be completed before beginning development
## UI/UX design
Does this feature have any associated UI/UX? If so, describe any design that needs to be
completed/red-lined prior to development.
## APIs
- [ ] Approved?
- **Programmatic APIs**
- List any APIs that will be developed and made available in the `@carbon-platform/api` package,
including function/class/method names, parameters, and return values.
- **Messages**
- List any new/changed RabbitMQ messages introduced by this feature, the message payload structure
associated with them, whether they are queries or emits, and their expected return values (for
queries).
## Test strategy
- [ ] Approved?
How will the new feature be tested? (e.g. unit tests, manual verification, automated e2e testing,
etc.)
What interesting edge cases should be considered and tested?
## Security
- [ ] Approved?
What new data is created/stored/collected/transmitted by this feature? How is that data secured? Who
is allowed to access it? How is that access controlled?
Think like a hacker. How might someone attempt to break or abuse this feature?
## Error handling
Ignore the happy path. What can go wrong with this feature? How will the error conditions manifest
through the APIs? How will users be informed about these errors?
## Logging
- [ ] Approved?
Detail any FFDC data (info, warning, error, debug logs) to be captured by this feature.
## File and code layout
- [ ] Approved?
Describe how the files and code for this feature will fit into the rest of the mono repo. Will there
be a new package/service? Are there existing files/directories in which the new logic should live?
## Issue and work breakdown
- [ ] Approved?
List any issues that should be created prior to starting work on this feature
- **Epics**
- ...
- **Issues**
- ...
| non_priority | wip replace fs cache with redis feature technical design summary summary the web app uses a to cache all github responses to prevent the web app from getting github api rate limited these github requests vary from fetching repository information traversing github trees to primarily fetching github file content to read carbon yml files and mdx files for web page content we re currently using a file system store engine which was chosen during preview prototyping as a quick and easy way to prevent github api rate limits as we index more content asset documentation pages each github request per mdx file adds to the amount of cached responses our current build pipeline does not persist cached files written to disk between builds as the amount of indexed content grows so does the risk of our production github access tokens getting rate limited which could leave us with a production environment void of all content potential solution to mitigate that risk until we can create proper back end services for this what if we added redis stores for staging and production it looks like we could use a redis store listed here those redis store engines should share the same api as cache manager fs hash so that should require minimal web app changes we could keep the for cached responses so for next js isr pages content from github would be at most hour stale with a redis cache our production builds should be faster because there s a greater chance of a cache hit we could use a redis cache for local development too or for simplicity keep that with the current file system cache tl dr in the event that our production environment gets rate limited by github because the redis cache would be persisted we wouldn t lose web app content between deploys also it would be neat to see how many keys would get cached in redis to give us a better idea of to be infrastructure needs to manage github content todo vv everything below this vv research approved unanswered questions list any unknowns and unanswered questions that need answers prior to beginning development new technologies list new technologies that need to be explored in detail before beginning development proofs of concept list proofs of concept that need to be completed before beginning development ui ux design does this feature have any associated ui ux if so describe any design that needs to be completed red lined prior to development apis approved programmatic apis list any apis that will be developed and made available in the carbon platform api package including function class method names parameters and return values messages list any new changed rabbitmq messages introduced by this feature the message payload structure associated with them whether they are queries or emits and their expected return values for queries test strategy approved how will the new feature be tested e g unit tests manual verification automated testing etc what interesting edge cases should be considered and tested security approved what new data is created stored collected transmitted by this feature how is that data secured who is allowed to access it how is that access controlled think like a hacker how might someone attempt to break or abuse this feature error handling ignore the happy path what can go wrong with this feature how will the error conditions manifest through the apis how will users be informed about these errors logging approved detail any ffdc data info warning error debug logs to be captured by this feature file and code layout approved describe how the files and code for this feature will fit into the rest of the mono repo will there be a new package service are there existing files directories in which the new logic should live issue and work breakdown approved list any issues that should be created prior to starting work on this feature epics issues | 0 |
42,043 | 17,019,563,110 | IssuesEvent | 2021-07-02 16:40:16 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | IT Support: Upgrade Lauren S. user roles in system | Product: Human Resources Service: Apps Type: IT Support Workgroup: HR | Nathan B.
HR
Emailed
>Lauren will assume Acting DM duties starting next Tuesday (Anthony is retiring). Can you please provide her the same approval rights that Anthony had.
| 1.0 | IT Support: Upgrade Lauren S. user roles in system - Nathan B.
HR
Emailed
>Lauren will assume Acting DM duties starting next Tuesday (Anthony is retiring). Can you please provide her the same approval rights that Anthony had.
| non_priority | it support upgrade lauren s user roles in system nathan b hr emailed lauren will assume acting dm duties starting next tuesday anthony is retiring can you please provide her the same approval rights that anthony had | 0 |
59,983 | 6,668,722,232 | IssuesEvent | 2017-10-03 16:45:19 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | sql/distsqlplan: TestDistAggregationTable/VARIANCE/dec1/50 failed under stress | Robot test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/b36405997c61ed77cf758863c55a73c3db833461
Parameters:
```
TAGS=
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=367016&tab=buildLog
```
``` | 1.0 | sql/distsqlplan: TestDistAggregationTable/VARIANCE/dec1/50 failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/b36405997c61ed77cf758863c55a73c3db833461
Parameters:
```
TAGS=
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=367016&tab=buildLog
```
``` | non_priority | sql distsqlplan testdistaggregationtable variance failed under stress sha parameters tags goflags stress build found a failed test | 0 |
82,745 | 10,276,387,732 | IssuesEvent | 2019-08-24 16:52:23 | backdrop/backdrop-issues | https://api.github.com/repos/backdrop/backdrop-issues | closed | [UX] Remove the hover color from header account links in Basis | design good first issue needs - more feedback pr - ready to be committed pr - works for me status - has pull request type - task | While testing https://github.com/backdrop/backdrop-issues/issues/3209 I found it distracting that the account links in the Header area had a hover color. I would prefer that they have an underline while hovered.
I was distracted by the big color block, especially when it does not reach the top of the menu area. I don't think we should treat them the same way as the main menu.
---
PR by @jenlampton: https://github.com/backdrop/backdrop/pull/2822 | 1.0 | [UX] Remove the hover color from header account links in Basis - While testing https://github.com/backdrop/backdrop-issues/issues/3209 I found it distracting that the account links in the Header area had a hover color. I would prefer that they have an underline while hovered.
I was distracted by the big color block, especially when it does not reach the top of the menu area. I don't think we should treat them the same way as the main menu.
---
PR by @jenlampton: https://github.com/backdrop/backdrop/pull/2822 | non_priority | remove the hover color from header account links in basis while testing i found it distracting that the account links in the header area had a hover color i would prefer that they have an underline while hovered i was distracted by the big color block especially when it does not reach the top of the menu area i don t think we should treat them the same way as the main menu pr by jenlampton | 0 |
302,481 | 26,147,177,487 | IssuesEvent | 2022-12-30 07:33:06 | AvaLido/mpc-controller | https://api.github.com/repos/AvaLido/mpc-controller | closed | mpc_controller_mpc_keygen_done_total had value 2 for mpc-controller 3 even keygen request was triggered once | internal-testnet p2 | mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7001", job="mpc-controller-01"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7002", job="mpc-controller-02"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7003", job="mpc-controller-03"}
2
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7004", job="mpc-controller-04"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7005", job="mpc-controller-05"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7006", job="mpc-controller-06"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7007", job="mpc-controller-07"}
1
| 1.0 | mpc_controller_mpc_keygen_done_total had value 2 for mpc-controller 3 even keygen request was triggered once - mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7001", job="mpc-controller-01"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7002", job="mpc-controller-02"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7003", job="mpc-controller-03"}
2
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7004", job="mpc-controller-04"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7005", job="mpc-controller-05"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7006", job="mpc-controller-06"}
1
mpc_controller_mpc_keygen_done_total{instance="127.0.0.1:7007", job="mpc-controller-07"}
1
| non_priority | mpc controller mpc keygen done total had value for mpc controller even keygen request was triggered once mpc controller mpc keygen done total instance job mpc controller mpc controller mpc keygen done total instance job mpc controller mpc controller mpc keygen done total instance job mpc controller mpc controller mpc keygen done total instance job mpc controller mpc controller mpc keygen done total instance job mpc controller mpc controller mpc keygen done total instance job mpc controller mpc controller mpc keygen done total instance job mpc controller | 0 |
270,273 | 28,960,475,280 | IssuesEvent | 2023-05-10 01:45:11 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | reopened | CVE-2019-12378 (Medium) detected in linuxlinux-4.19.6 | Mend: dependency security vulnerability | ## CVE-2019-12378 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** An issue was discovered in ip6_ra_control in net/ipv6/ipv6_sockglue.c in the Linux kernel through 5.1.5. There is an unchecked kmalloc of new_ra, which might allow an attacker to cause a denial of service (NULL pointer dereference and system crash). NOTE: This has been disputed as not an issue.
<p>Publish Date: 2019-05-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-12378>CVE-2019-12378</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378</a></p>
<p>Release Date: 2019-06-10</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-12378 (Medium) detected in linuxlinux-4.19.6 - ## CVE-2019-12378 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv6/ipv6_sockglue.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** An issue was discovered in ip6_ra_control in net/ipv6/ipv6_sockglue.c in the Linux kernel through 5.1.5. There is an unchecked kmalloc of new_ra, which might allow an attacker to cause a denial of service (NULL pointer dereference and system crash). NOTE: This has been disputed as not an issue.
<p>Publish Date: 2019-05-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-12378>CVE-2019-12378</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378</a></p>
<p>Release Date: 2019-06-10</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files net sockglue c net sockglue c vulnerability details disputed an issue was discovered in ra control in net sockglue c in the linux kernel through there is an unchecked kmalloc of new ra which might allow an attacker to cause a denial of service null pointer dereference and system crash note this has been disputed as not an issue publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
277,699 | 24,096,525,179 | IssuesEvent | 2022-09-19 19:16:54 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: unoptimized-query-oracle/disable-rules=half failed | C-test-failure O-robot O-roachtest branch-master T-sql-queries | roachtest.unoptimized-query-oracle/disable-rules=half [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6433129?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6433129?buildTab=artifacts#/unoptimized-query-oracle/disable-rules=half) on master @ [773568fbda06ba9be9fb1bc34a331f21c8891ffa](https://github.com/cockroachdb/cockroach/commits/773568fbda06ba9be9fb1bc34a331f21c8891ffa):
```
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "Infinity,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-5603543133744",
| "919124",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "Infinity,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,NULL,-5603543133",
| "744919124",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| }
| sql: SELECT
| tab_2767.col2_3 AS col_7639,
| 0:::OID AS col_7640,
| '01ef01ef-01ef-01ef-01ef-01ef01ef01ef':::UUID AS col_7641,
| tab_2767.col2_2 AS col_7642,
| ((-5603543133744919124):::INT8::INT8 / 1:::DECIMAL::DECIMAL)::DECIMAL AS col_7643,
| (-6.839896181776363352E+23):::DECIMAL AS col_7644
| FROM
| defaultdb.public.table2@[0] AS tab_2767
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.leafError
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #87779 roachtest: unoptimized-query-oracle/disable-rules=half failed [C-test-failure O-roachtest O-robot T-sql-queries branch-release-22.2 release-blocker]
- #86790 roachtest.unoptimized-query-oracle/disable-rules=half failed due to extra precision decimals [C-test-failure T-sql-queries]
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*unoptimized-query-oracle/disable-rules=half.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-19556 | 2.0 | roachtest: unoptimized-query-oracle/disable-rules=half failed - roachtest.unoptimized-query-oracle/disable-rules=half [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6433129?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/6433129?buildTab=artifacts#/unoptimized-query-oracle/disable-rules=half) on master @ [773568fbda06ba9be9fb1bc34a331f21c8891ffa](https://github.com/cockroachdb/cockroach/commits/773568fbda06ba9be9fb1bc34a331f21c8891ffa):
```
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "Infinity,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-5603543133744",
| "919124",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "Infinity,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,NULL,-5603543133",
| "744919124",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| strings.Join({
| "NaN,0,01ef01ef-01ef-01ef-01ef-01ef01ef01ef,0,-560354313374491912",
| "4",
| + ".0",
| ",-6.839896181776363352E+23",
| }, ""),
| }
| sql: SELECT
| tab_2767.col2_3 AS col_7639,
| 0:::OID AS col_7640,
| '01ef01ef-01ef-01ef-01ef-01ef01ef01ef':::UUID AS col_7641,
| tab_2767.col2_2 AS col_7642,
| ((-5603543133744919124):::INT8::INT8 / 1:::DECIMAL::DECIMAL)::DECIMAL AS col_7643,
| (-6.839896181776363352E+23):::DECIMAL AS col_7644
| FROM
| defaultdb.public.table2@[0] AS tab_2767
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *withstack.withStack (4) *errutil.leafError
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #87779 roachtest: unoptimized-query-oracle/disable-rules=half failed [C-test-failure O-roachtest O-robot T-sql-queries branch-release-22.2 release-blocker]
- #86790 roachtest.unoptimized-query-oracle/disable-rules=half failed due to extra precision decimals [C-test-failure T-sql-queries]
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*unoptimized-query-oracle/disable-rules=half.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-19556 | non_priority | roachtest unoptimized query oracle disable rules half failed roachtest unoptimized query oracle disable rules half with on master strings join infinity strings join infinity null strings join nan strings join nan strings join nan strings join nan sql select tab as col oid as col uuid as col tab as col decimal decimal decimal as col decimal as col from defaultdb public as tab error types withstack withstack errutil withprefix withstack withstack errutil leaferror parameters roachtest cloud gce roachtest cpu roachtest ssd help see see same failure on other branches roachtest unoptimized query oracle disable rules half failed roachtest unoptimized query oracle disable rules half failed due to extra precision decimals cc cockroachdb sql queries jira issue crdb | 0 |
185,467 | 14,355,088,236 | IssuesEvent | 2020-11-30 09:36:54 | mirage/mirage-tcpip | https://api.github.com/repos/mirage/mirage-tcpip | closed | use bisect to test coverage of the tcpip tests | Testing enhancement | instructions from @djs55 on the mailing list below:
---
I've been having a lot of fun with bisect[1] recently-- I've been using it to see which parts of the mirage-block-volume[2] and shared-block-ring[3] libraries are completely untouched by their unit tests. I found the following game to be quite addictive:
1. "make coverage", and load result in web-browser
2. spot a big chunk of obvious red (danger, danger, danger)
3. (thinking carefully about what could go wrong) devise an interesting test to stress the red bits (obviously you could cover it with a 'noddy' test but there is probably no point)
4. "make coverage", reload in browser and see the red go green!
I've hooked it up with coveralls.io (admittedly in a bit of a hacky way[4]) such that the master branch is firmly in "development" mode, linking against bisect, and without checking in the oasis autogen rubbish. The .travis.yml runs both the travisci-skeleton script and then invokes ocveralls[5] to upload the results.
I've added a separate "make release" step which removes bisect and checks in the autogen (presumably into a release branch). Perhaps eventually this could make a github pull request (with the "hub" tool?) and make an opam package?
I think the game is made even more addictive when the coveralls badge changes colour, see:
https://coveralls.io/r/mirage/mirage-block-volume?branch=master
Here's an example bisect report (the code is a work-in-progress):
http://dave.recoil.org/tmp/report/file0000.html
If you haven't given bisect a go -- I recommend playing with it.
Also, if you can think of a nicer way to integrate this -- I admit using 'sed' on the _oasis file is a bit of a hack -- please let me know!
Cheers,
Dave
[1] http://bisect.x9c.fr
[2] https://github.com/mirage/mirage-block-volume
[3] https://github.com/mirage/shared-block-ring
[4] https://github.com/mirage/shared-block-ring/commit/67b9f3100be8e4e9732dd79b7c1cc5352a61d478
[5] https://github.com/sagotch/ocveralls
| 1.0 | use bisect to test coverage of the tcpip tests - instructions from @djs55 on the mailing list below:
---
I've been having a lot of fun with bisect[1] recently-- I've been using it to see which parts of the mirage-block-volume[2] and shared-block-ring[3] libraries are completely untouched by their unit tests. I found the following game to be quite addictive:
1. "make coverage", and load result in web-browser
2. spot a big chunk of obvious red (danger, danger, danger)
3. (thinking carefully about what could go wrong) devise an interesting test to stress the red bits (obviously you could cover it with a 'noddy' test but there is probably no point)
4. "make coverage", reload in browser and see the red go green!
I've hooked it up with coveralls.io (admittedly in a bit of a hacky way[4]) such that the master branch is firmly in "development" mode, linking against bisect, and without checking in the oasis autogen rubbish. The .travis.yml runs both the travisci-skeleton script and then invokes ocveralls[5] to upload the results.
I've added a separate "make release" step which removes bisect and checks in the autogen (presumably into a release branch). Perhaps eventually this could make a github pull request (with the "hub" tool?) and make an opam package?
I think the game is made even more addictive when the coveralls badge changes colour, see:
https://coveralls.io/r/mirage/mirage-block-volume?branch=master
Here's an example bisect report (the code is a work-in-progress):
http://dave.recoil.org/tmp/report/file0000.html
If you haven't given bisect a go -- I recommend playing with it.
Also, if you can think of a nicer way to integrate this -- I admit using 'sed' on the _oasis file is a bit of a hack -- please let me know!
Cheers,
Dave
[1] http://bisect.x9c.fr
[2] https://github.com/mirage/mirage-block-volume
[3] https://github.com/mirage/shared-block-ring
[4] https://github.com/mirage/shared-block-ring/commit/67b9f3100be8e4e9732dd79b7c1cc5352a61d478
[5] https://github.com/sagotch/ocveralls
| non_priority | use bisect to test coverage of the tcpip tests instructions from on the mailing list below i ve been having a lot of fun with bisect recently i ve been using it to see which parts of the mirage block volume and shared block ring libraries are completely untouched by their unit tests i found the following game to be quite addictive make coverage and load result in web browser spot a big chunk of obvious red danger danger danger thinking carefully about what could go wrong devise an interesting test to stress the red bits obviously you could cover it with a noddy test but there is probably no point make coverage reload in browser and see the red go green i ve hooked it up with coveralls io admittedly in a bit of a hacky way such that the master branch is firmly in development mode linking against bisect and without checking in the oasis autogen rubbish the travis yml runs both the travisci skeleton script and then invokes ocveralls to upload the results i ve added a separate make release step which removes bisect and checks in the autogen presumably into a release branch perhaps eventually this could make a github pull request with the hub tool and make an opam package i think the game is made even more addictive when the coveralls badge changes colour see here s an example bisect report the code is a work in progress if you haven t given bisect a go i recommend playing with it also if you can think of a nicer way to integrate this i admit using sed on the oasis file is a bit of a hack please let me know cheers dave | 0 |
23,240 | 3,783,471,943 | IssuesEvent | 2016-03-19 05:11:26 | playframework/playframework | https://api.github.com/repos/playframework/playframework | closed | [play-scala 2.5.0] ERR_CONTENT_LENGTH_MISMATCH error occurs on Heroku when the response is greater than 85kb | defect | The demo project source code is here [https://github.com/joymufeng/play250](https://github.com/joymufeng/play250). And the demo application on Heroku is:
```
http://play250.herokuapp.com/getResponse?len=99000
```
You can change the len parameter to control the response length. If the response length is lower than 85kb, it works well, otherwise ERR_CONTENT_LENGTH_MISMATCH error occurs in the browser. | 1.0 | [play-scala 2.5.0] ERR_CONTENT_LENGTH_MISMATCH error occurs on Heroku when the response is greater than 85kb - The demo project source code is here [https://github.com/joymufeng/play250](https://github.com/joymufeng/play250). And the demo application on Heroku is:
```
http://play250.herokuapp.com/getResponse?len=99000
```
You can change the len parameter to control the response length. If the response length is lower than 85kb, it works well, otherwise ERR_CONTENT_LENGTH_MISMATCH error occurs in the browser. | non_priority | err content length mismatch error occurs on heroku when the response is greater than the demo project source code is here and the demo application on heroku is you can change the len parameter to control the response length if the response length is lower than it works well otherwise err content length mismatch error occurs in the browser | 0 |
101,295 | 21,641,911,588 | IssuesEvent | 2022-05-05 19:44:49 | apple/swift | https://api.github.com/repos/apple/swift | closed | [SR-15496] Code completion not suggesting members of parameter to closure | bug CodeCompletion FoundByStressTester |
| | |
|------------------|-----------------|
|Previous ID | SR-15496 |
|Radar | rdar://85602411 |
|Original Reporter | @ahoppen |
|Type | Bug |
<details>
<summary>Additional Detail from JIRA</summary>
| | |
|------------------|-----------------|
|Votes | 0 |
|Component/s | CodeCompletion |
|Labels | Bug, FoundByStressTester |
|Assignee | None |
|Priority | Medium |
md5: 40df6f8ed07123e264ce52e6673e2e52
</details>
**is duplicated by**:
* [SR-15999](https://bugs.swift.org/browse/SR-15999) Missing dot member completion inside closure
**Issue Description:**
The following new test case fails. When removing replacing either `let ranges` or `let nsRange` by `_`, the test case passes.
``` java
// RUN: %swift-ide-test --code-completion --code-completion-token COMPLETE --source-filename %s | %FileCheck %s
public func test() {
let ranges = compactMap { (match) in
let nsRange = match.#^COMPLETE^#
}
}
struct Foo {
var x: String
}
func compactMap(_ transform: (Foo) -> Void) {
fatalError()
}
// CHECK: Begin completions, 2 items
// CHECK-DAG: Keyword[self]/CurrNominal: self[#Foo#];
// CHECK-DAG: Decl[InstanceVar]/CurrNominal: x[#String#];
// CHECK: End completions
```
| 1.0 | [SR-15496] Code completion not suggesting members of parameter to closure -
| | |
|------------------|-----------------|
|Previous ID | SR-15496 |
|Radar | rdar://85602411 |
|Original Reporter | @ahoppen |
|Type | Bug |
<details>
<summary>Additional Detail from JIRA</summary>
| | |
|------------------|-----------------|
|Votes | 0 |
|Component/s | CodeCompletion |
|Labels | Bug, FoundByStressTester |
|Assignee | None |
|Priority | Medium |
md5: 40df6f8ed07123e264ce52e6673e2e52
</details>
**is duplicated by**:
* [SR-15999](https://bugs.swift.org/browse/SR-15999) Missing dot member completion inside closure
**Issue Description:**
The following new test case fails. When removing replacing either `let ranges` or `let nsRange` by `_`, the test case passes.
``` java
// RUN: %swift-ide-test --code-completion --code-completion-token COMPLETE --source-filename %s | %FileCheck %s
public func test() {
let ranges = compactMap { (match) in
let nsRange = match.#^COMPLETE^#
}
}
struct Foo {
var x: String
}
func compactMap(_ transform: (Foo) -> Void) {
fatalError()
}
// CHECK: Begin completions, 2 items
// CHECK-DAG: Keyword[self]/CurrNominal: self[#Foo#];
// CHECK-DAG: Decl[InstanceVar]/CurrNominal: x[#String#];
// CHECK: End completions
```
| non_priority | code completion not suggesting members of parameter to closure previous id sr radar rdar original reporter ahoppen type bug additional detail from jira votes component s codecompletion labels bug foundbystresstester assignee none priority medium is duplicated by missing dot member completion inside closure issue description the following new test case fails when removing replacing either let ranges or let nsrange by the test case passes java run swift ide test code completion code completion token complete source filename s filecheck s public func test let ranges compactmap match in let nsrange match complete struct foo var x string func compactmap transform foo void fatalerror check begin completions items check dag keyword currnominal self check dag decl currnominal x check end completions | 0 |
124,093 | 26,396,924,865 | IssuesEvent | 2023-01-12 20:20:38 | microsoft/cadl | https://api.github.com/repos/microsoft/cadl | closed | Update default collectionFormat and add encoding string to header and query parameters | :pushpin: DPG Impact WS: Language Completeness WS: Code Generation Required for DPG 1.0 | Implementation issue for: https://github.com/Azure/cadl-azure/issues/1790
- Add optional parameters to query and header decorators for format
- for query, format can be 'csv', 'multi', default should be multi
- for header, only csv is allowed (and should be default)
- target parameter/property must be a string array (or equivalent) type
- Add support in OpenAPI3 emitter for this additional data
- for header, add `style: simple` to the parameter object (csv)
- for query
- add style: form for csv
- add style: form and explode: true for multi
- Add support in cadl-autorest for this additional data (should emit collectionFormat: csv | multi in the schema) | 1.0 | Update default collectionFormat and add encoding string to header and query parameters - Implementation issue for: https://github.com/Azure/cadl-azure/issues/1790
- Add optional parameters to query and header decorators for format
- for query, format can be 'csv', 'multi', default should be multi
- for header, only csv is allowed (and should be default)
- target parameter/property must be a string array (or equivalent) type
- Add support in OpenAPI3 emitter for this additional data
- for header, add `style: simple` to the parameter object (csv)
- for query
- add style: form for csv
- add style: form and explode: true for multi
- Add support in cadl-autorest for this additional data (should emit collectionFormat: csv | multi in the schema) | non_priority | update default collectionformat and add encoding string to header and query parameters implementation issue for add optional parameters to query and header decorators for format for query format can be csv multi default should be multi for header only csv is allowed and should be default target parameter property must be a string array or equivalent type add support in emitter for this additional data for header add style simple to the parameter object csv for query add style form for csv add style form and explode true for multi add support in cadl autorest for this additional data should emit collectionformat csv multi in the schema | 0 |
37,930 | 12,510,052,651 | IssuesEvent | 2020-06-02 17:57:16 | alpersonalwebsite/react-todo-board | https://api.github.com/repos/alpersonalwebsite/react-todo-board | opened | WS-2019-0424 (Medium) detected in elliptic-6.5.2.tgz | security vulnerability | ## WS-2019-0424 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/react-todo-board/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/react-todo-board/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- webpack-4.29.6.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/alpersonalwebsite/react-todo-board/commit/f2c1d3a9e288d32170d4f46102dc017d7a555b33">f2c1d3a9e288d32170d4f46102dc017d7a555b33</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
all versions of elliptic are vulnerable to Timing Attack through side-channels.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0424 (Medium) detected in elliptic-6.5.2.tgz - ## WS-2019-0424 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.2.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/react-todo-board/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/react-todo-board/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.1.tgz (Root Library)
- webpack-4.29.6.tgz
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.0.tgz
- :x: **elliptic-6.5.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/alpersonalwebsite/react-todo-board/commit/f2c1d3a9e288d32170d4f46102dc017d7a555b33">f2c1d3a9e288d32170d4f46102dc017d7a555b33</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
all versions of elliptic are vulnerable to Timing Attack through side-channels.
<p>Publish Date: 2019-11-13
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0424</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file tmp ws scm react todo board package json path to vulnerable library tmp ws scm react todo board node modules elliptic package json dependency hierarchy react scripts tgz root library webpack tgz node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in head commit a href vulnerability details all versions of elliptic are vulnerable to timing attack through side channels publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact none for more information on scores click a href step up your open source security game with whitesource | 0 |
31,436 | 11,939,265,344 | IssuesEvent | 2020-04-02 14:58:13 | icgc-argo/workflow-docs | https://api.github.com/repos/icgc-argo/workflow-docs | closed | Update Dockerfile security workflow-docs | security | Refer to program-service Dockerfile:
https://github.com/icgc-argo/program-service/blob/develop/Dockerfile
The main process must run as user $APP_UID, not as root | True | Update Dockerfile security workflow-docs - Refer to program-service Dockerfile:
https://github.com/icgc-argo/program-service/blob/develop/Dockerfile
The main process must run as user $APP_UID, not as root | non_priority | update dockerfile security workflow docs refer to program service dockerfile the main process must run as user app uid not as root | 0 |
256,333 | 27,561,652,470 | IssuesEvent | 2023-03-07 22:37:59 | samqws-marketing/nutanix_Nutanix-Calm-Jenkins-Plugin | https://api.github.com/repos/samqws-marketing/nutanix_Nutanix-Calm-Jenkins-Plugin | closed | CVE-2019-10320 (Medium) detected in credentials-2.1.16.jar - autoclosed | security vulnerability | ## CVE-2019-10320 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>credentials-2.1.16.jar</b></p></summary>
<p>This plugin allows you to store credentials in Jenkins.</p>
<p>Library home page: <a href="https://wiki.jenkins.io/display/JENKINS/Credentials+Plugin">https://wiki.jenkins.io/display/JENKINS/Credentials+Plugin</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /plugins/credentials/2.1.16/credentials-2.1.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **credentials-2.1.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/nutanix_Nutanix-Calm-Jenkins-Plugin/commit/b89f901a0279722a24085f8135e181bd1555459a">b89f901a0279722a24085f8135e181bd1555459a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Jenkins Credentials Plugin 2.1.18 and earlier allowed users with permission to create or update credentials to confirm the existence of files on the Jenkins master with an attacker-specified path, and obtain the certificate content of files containing a PKCS#12 certificate.
<p>Publish Date: 2019-05-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10320>CVE-2019-10320</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10320">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10320</a></p>
<p>Release Date: 2019-06-11</p>
<p>Fix Resolution: org.jenkins-ci.plugins:credentials:2.1.8</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2019-10320 (Medium) detected in credentials-2.1.16.jar - autoclosed - ## CVE-2019-10320 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>credentials-2.1.16.jar</b></p></summary>
<p>This plugin allows you to store credentials in Jenkins.</p>
<p>Library home page: <a href="https://wiki.jenkins.io/display/JENKINS/Credentials+Plugin">https://wiki.jenkins.io/display/JENKINS/Credentials+Plugin</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /plugins/credentials/2.1.16/credentials-2.1.16.jar</p>
<p>
Dependency Hierarchy:
- :x: **credentials-2.1.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/nutanix_Nutanix-Calm-Jenkins-Plugin/commit/b89f901a0279722a24085f8135e181bd1555459a">b89f901a0279722a24085f8135e181bd1555459a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Jenkins Credentials Plugin 2.1.18 and earlier allowed users with permission to create or update credentials to confirm the existence of files on the Jenkins master with an attacker-specified path, and obtain the certificate content of files containing a PKCS#12 certificate.
<p>Publish Date: 2019-05-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10320>CVE-2019-10320</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10320">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10320</a></p>
<p>Release Date: 2019-06-11</p>
<p>Fix Resolution: org.jenkins-ci.plugins:credentials:2.1.8</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in credentials jar autoclosed cve medium severity vulnerability vulnerable library credentials jar this plugin allows you to store credentials in jenkins library home page a href path to dependency file pom xml path to vulnerable library plugins credentials credentials jar dependency hierarchy x credentials jar vulnerable library found in head commit a href found in base branch master vulnerability details jenkins credentials plugin and earlier allowed users with permission to create or update credentials to confirm the existence of files on the jenkins master with an attacker specified path and obtain the certificate content of files containing a pkcs certificate publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org jenkins ci plugins credentials check this box to open an automated fix pr | 0 |
319,063 | 23,753,149,849 | IssuesEvent | 2022-08-31 22:56:21 | gbowne1/radio_logger | https://api.github.com/repos/gbowne1/radio_logger | opened | Fix darkMode || lightMode | bug documentation enhancement help wanted good first issue question | Use the FontAwesome or Bootstrap Glyphicon toggle icon to implement a darkmode and lightmode toggle switch. I have added both of the FontAwesome Toggle On and Toggle Off Icons.
use the included theme.js and/or a darkmode.js // lightmode.js | 1.0 | Fix darkMode || lightMode - Use the FontAwesome or Bootstrap Glyphicon toggle icon to implement a darkmode and lightmode toggle switch. I have added both of the FontAwesome Toggle On and Toggle Off Icons.
use the included theme.js and/or a darkmode.js // lightmode.js | non_priority | fix darkmode lightmode use the fontawesome or bootstrap glyphicon toggle icon to implement a darkmode and lightmode toggle switch i have added both of the fontawesome toggle on and toggle off icons use the included theme js and or a darkmode js lightmode js | 0 |
85,735 | 10,679,052,557 | IssuesEvent | 2019-10-21 18:30:04 | eBay/skin | https://api.github.com/repos/eBay/skin | closed | Textbox: change disabled textbox color to @color-grey3 (DS6) | design system: DS6.5 fellowship: good first issue module: textbox status: merged | Simple change.
Current:
`@textbox-control-disabled-color: @color-grey1;`
Proposed
`@textbox-control-disabled-color: @color-grey3;`
| 1.0 | Textbox: change disabled textbox color to @color-grey3 (DS6) - Simple change.
Current:
`@textbox-control-disabled-color: @color-grey1;`
Proposed
`@textbox-control-disabled-color: @color-grey3;`
| non_priority | textbox change disabled textbox color to color simple change current textbox control disabled color color proposed textbox control disabled color color | 0 |
184,340 | 31,860,392,875 | IssuesEvent | 2023-09-15 10:27:20 | dev-launchers/dev-launchers-platform | https://api.github.com/repos/dev-launchers/dev-launchers-platform | opened | Usability Testing Planning and Setup for Dev Launchers Mobile Navigation | Universal Design | This ticket is dedicated to the initial planning and setup required for conducting usability testing of the mobile navigation of Dev Launchers. The goal is to enhance the usability, intuitiveness, and accessibility of mobile navigation.
**Acceptance criteria:**
The following outcomes have been created:
- Usability testing plan
- Discussion guide
- Screening & recruiting communications & logistics
| 1.0 | Usability Testing Planning and Setup for Dev Launchers Mobile Navigation - This ticket is dedicated to the initial planning and setup required for conducting usability testing of the mobile navigation of Dev Launchers. The goal is to enhance the usability, intuitiveness, and accessibility of mobile navigation.
**Acceptance criteria:**
The following outcomes have been created:
- Usability testing plan
- Discussion guide
- Screening & recruiting communications & logistics
| non_priority | usability testing planning and setup for dev launchers mobile navigation this ticket is dedicated to the initial planning and setup required for conducting usability testing of the mobile navigation of dev launchers the goal is to enhance the usability intuitiveness and accessibility of mobile navigation acceptance criteria the following outcomes have been created usability testing plan discussion guide screening recruiting communications logistics | 0 |
45,153 | 7,163,930,872 | IssuesEvent | 2018-01-29 09:28:57 | SkyLined/BugId | https://api.github.com/repos/SkyLined/BugId | closed | Create a how-to for using cBugId in your own framework | documentation enhancement help wanted | I should explain how to integrate BugId into a framework by instantiating cBugId and adding callbacks. | 1.0 | Create a how-to for using cBugId in your own framework - I should explain how to integrate BugId into a framework by instantiating cBugId and adding callbacks. | non_priority | create a how to for using cbugid in your own framework i should explain how to integrate bugid into a framework by instantiating cbugid and adding callbacks | 0 |
151,865 | 12,060,742,841 | IssuesEvent | 2020-04-15 21:52:46 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | tests: Windows packet fragmentation issue | kind/failing-test sig/windows | <!-- Please only use this template for submitting reports about failing tests in Kubernetes CI jobs -->
**Which jobs are failing**:
sig-windows#flannel-overlay-windows-master
**Which test(s) are failing**:
[sig-api-machinery] AdmissionWebhook [Privileged:ClusterAdmin] should deny crd creation [Conformance]
**Since when has it been failing**:
Unknown.
**Testgrid link**:
https://testgrid.k8s.io/sig-windows#flannel-overlay-windows-master
**Reason for failure**:
There seems to be an issue regarding packet fragmentation on Windows that occurs especially when using flannel vxlan. This can also be reproduced manually:
kubectl create namespace ns1
kubectl create -f pods/agnhost_linux.yaml -n ns1 # https://paste.ubuntu.com/p/wqhvmpx9S7/
kubectl create -f pods/agnhost_windows.yaml -n ns1 # https://paste.ubuntu.com/p/YrbpwtqBdM/
kubectl create -f pods/services.yaml -n ns1 # https://paste.ubuntu.com/p/wTxnSTws4P/
# wait for the pods to spawn...
sleep 10
sudo apt install jq
linux_pod_ip=`kubectl get -o json -n ns1 pod/linux-agnhost | jq '.status.podIP' | sed 's/"//g'`
linux_host_ip=`kubectl get -o json -n ns1 pod/linux-agnhost | jq '.status.hostIP' | sed 's/"//g'`
windows_pod_ip=`kubectl get -o json -n ns1 pod/windows-agnhost | jq '.status.podIP' | sed 's/"//g'`
windows_host_ip=`kubectl get -o json -n ns1 pod/windows-agnhost | jq '.status.hostIP' | sed 's/"//g'`
cluster_ip=`kubectl get -o json -n ns1 service/node-port-service | jq '.spec.clusterIP' | sed 's/"//g'`
# check the MTU in the containers: it should be 1450 when using flannel vxlan, and 1500 when using flannel l2bridge.
kubectl exec -n ns1 windows-agnhost -- netsh int ipv4 show subint
kubectl exec -n ns1 linux-agnhost -- ifconfig
# the following pings work
ping -c 3 $windows_pod_ip
ping -c 3 -s 1342 $windows_pod_ip
# the following pings work in l2bridge, but not in vxlan.
ping -c 3 -s 1344 $windows_pod_ip
ping -c 3 -s 1400 $windows_pod_ip
ping -c 3 -s 1600 $windows_pod_ip
# the following pings work
kubectl exec -n ns1 windows-agnhost -- ping -n 3 $linux_pod_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1342 $linux_pod_ip
# the following pings work in l2bridge, but not in vxlan.
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1344 $linux_pod_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1400 $linux_pod_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1600 $linux_pod_ip
# the following pings work
kubectl exec -n ns1 windows-agnhost -- ping -n 3 $windows_host_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1422 $windows_host_ip
# the following pings should work, but do not.
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1424 $windows_host_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1600 $windows_host_ip
# the following ping works
kubectl exec -n ns1 linux-agnhost -- ping -c 3 -s 1900 $linux_host_ip
# msg to be used in the tests below
msg=$(cat /dev/urandom | tr -dc 'a-zA-Z0-9' | fold -w 1900 | head -n 1)
# for UDP, the following command should work
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$linux_pod_ip&port=8081&protocol=udp&request=echo%20hi"
# when the message is larger, it won't work anymore in azure-vnet-cni v1.0.27.
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$linux_pod_ip&port=8081&protocol=udp&request=echo%20$msg"
# for flannel l2bridge, this does not work
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$cluster_ip&port=90&protocol=udp&request=echo%20$msg"
# but if the message is shorter, it works:
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$cluster_ip&port=90&protocol=udp&request=echo%20hi"
The mentioned test fails because ``kube-apiserver`` will send a 1400+ bytes packet to the pod which should deny the crd creation (which is higher than the 1342 bytes limit observed), and it never gets any reply.
This issue does not occur when using flannel l2bridge, the test passes, as seen here: https://testgrid.k8s.io/sig-windows#containerd-l2bridge-windows-master
**Anything else we need to know**:
We've sent a PR which adds 2 E2E tests that sends larger HTTP / UDP packets in order to detect and check for this issue: https://github.com/kubernetes/kubernetes/pull/83680 .
As expected, the tests fail when using Windows nodes with flannel vxlan. The HTTP test passes when using Windows nodes with azure CNI, or flannel l2bridge, however the UDP test does not, which may indicate a different issue. Both the HTTP and the UDP tests pass when using Linux nodes / pods with azure CNI, flannel l2bridge, or flannel overlay.
/sig windows
| 1.0 | tests: Windows packet fragmentation issue - <!-- Please only use this template for submitting reports about failing tests in Kubernetes CI jobs -->
**Which jobs are failing**:
sig-windows#flannel-overlay-windows-master
**Which test(s) are failing**:
[sig-api-machinery] AdmissionWebhook [Privileged:ClusterAdmin] should deny crd creation [Conformance]
**Since when has it been failing**:
Unknown.
**Testgrid link**:
https://testgrid.k8s.io/sig-windows#flannel-overlay-windows-master
**Reason for failure**:
There seems to be an issue regarding packet fragmentation on Windows that occurs especially when using flannel vxlan. This can also be reproduced manually:
kubectl create namespace ns1
kubectl create -f pods/agnhost_linux.yaml -n ns1 # https://paste.ubuntu.com/p/wqhvmpx9S7/
kubectl create -f pods/agnhost_windows.yaml -n ns1 # https://paste.ubuntu.com/p/YrbpwtqBdM/
kubectl create -f pods/services.yaml -n ns1 # https://paste.ubuntu.com/p/wTxnSTws4P/
# wait for the pods to spawn...
sleep 10
sudo apt install jq
linux_pod_ip=`kubectl get -o json -n ns1 pod/linux-agnhost | jq '.status.podIP' | sed 's/"//g'`
linux_host_ip=`kubectl get -o json -n ns1 pod/linux-agnhost | jq '.status.hostIP' | sed 's/"//g'`
windows_pod_ip=`kubectl get -o json -n ns1 pod/windows-agnhost | jq '.status.podIP' | sed 's/"//g'`
windows_host_ip=`kubectl get -o json -n ns1 pod/windows-agnhost | jq '.status.hostIP' | sed 's/"//g'`
cluster_ip=`kubectl get -o json -n ns1 service/node-port-service | jq '.spec.clusterIP' | sed 's/"//g'`
# check the MTU in the containers: it should be 1450 when using flannel vxlan, and 1500 when using flannel l2bridge.
kubectl exec -n ns1 windows-agnhost -- netsh int ipv4 show subint
kubectl exec -n ns1 linux-agnhost -- ifconfig
# the following pings work
ping -c 3 $windows_pod_ip
ping -c 3 -s 1342 $windows_pod_ip
# the following pings work in l2bridge, but not in vxlan.
ping -c 3 -s 1344 $windows_pod_ip
ping -c 3 -s 1400 $windows_pod_ip
ping -c 3 -s 1600 $windows_pod_ip
# the following pings work
kubectl exec -n ns1 windows-agnhost -- ping -n 3 $linux_pod_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1342 $linux_pod_ip
# the following pings work in l2bridge, but not in vxlan.
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1344 $linux_pod_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1400 $linux_pod_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1600 $linux_pod_ip
# the following pings work
kubectl exec -n ns1 windows-agnhost -- ping -n 3 $windows_host_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1422 $windows_host_ip
# the following pings should work, but do not.
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1424 $windows_host_ip
kubectl exec -n ns1 windows-agnhost -- ping -n 3 -l 1600 $windows_host_ip
# the following ping works
kubectl exec -n ns1 linux-agnhost -- ping -c 3 -s 1900 $linux_host_ip
# msg to be used in the tests below
msg=$(cat /dev/urandom | tr -dc 'a-zA-Z0-9' | fold -w 1900 | head -n 1)
# for UDP, the following command should work
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$linux_pod_ip&port=8081&protocol=udp&request=echo%20hi"
# when the message is larger, it won't work anymore in azure-vnet-cni v1.0.27.
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$linux_pod_ip&port=8081&protocol=udp&request=echo%20$msg"
# for flannel l2bridge, this does not work
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$cluster_ip&port=90&protocol=udp&request=echo%20$msg"
# but if the message is shorter, it works:
kubectl exec -n ns1 windows-agnhost -- curl.exe -s "http://127.0.0.1:8080/dial?host=$cluster_ip&port=90&protocol=udp&request=echo%20hi"
The mentioned test fails because ``kube-apiserver`` will send a 1400+ bytes packet to the pod which should deny the crd creation (which is higher than the 1342 bytes limit observed), and it never gets any reply.
This issue does not occur when using flannel l2bridge, the test passes, as seen here: https://testgrid.k8s.io/sig-windows#containerd-l2bridge-windows-master
**Anything else we need to know**:
We've sent a PR which adds 2 E2E tests that sends larger HTTP / UDP packets in order to detect and check for this issue: https://github.com/kubernetes/kubernetes/pull/83680 .
As expected, the tests fail when using Windows nodes with flannel vxlan. The HTTP test passes when using Windows nodes with azure CNI, or flannel l2bridge, however the UDP test does not, which may indicate a different issue. Both the HTTP and the UDP tests pass when using Linux nodes / pods with azure CNI, flannel l2bridge, or flannel overlay.
/sig windows
| non_priority | tests windows packet fragmentation issue which jobs are failing sig windows flannel overlay windows master which test s are failing admissionwebhook should deny crd creation since when has it been failing unknown testgrid link reason for failure there seems to be an issue regarding packet fragmentation on windows that occurs especially when using flannel vxlan this can also be reproduced manually kubectl create namespace kubectl create f pods agnhost linux yaml n kubectl create f pods agnhost windows yaml n kubectl create f pods services yaml n wait for the pods to spawn sleep sudo apt install jq linux pod ip kubectl get o json n pod linux agnhost jq status podip sed s g linux host ip kubectl get o json n pod linux agnhost jq status hostip sed s g windows pod ip kubectl get o json n pod windows agnhost jq status podip sed s g windows host ip kubectl get o json n pod windows agnhost jq status hostip sed s g cluster ip kubectl get o json n service node port service jq spec clusterip sed s g check the mtu in the containers it should be when using flannel vxlan and when using flannel kubectl exec n windows agnhost netsh int show subint kubectl exec n linux agnhost ifconfig the following pings work ping c windows pod ip ping c s windows pod ip the following pings work in but not in vxlan ping c s windows pod ip ping c s windows pod ip ping c s windows pod ip the following pings work kubectl exec n windows agnhost ping n linux pod ip kubectl exec n windows agnhost ping n l linux pod ip the following pings work in but not in vxlan kubectl exec n windows agnhost ping n l linux pod ip kubectl exec n windows agnhost ping n l linux pod ip kubectl exec n windows agnhost ping n l linux pod ip the following pings work kubectl exec n windows agnhost ping n windows host ip kubectl exec n windows agnhost ping n l windows host ip the following pings should work but do not kubectl exec n windows agnhost ping n l windows host ip kubectl exec n windows agnhost ping n l windows host ip the following ping works kubectl exec n linux agnhost ping c s linux host ip msg to be used in the tests below msg cat dev urandom tr dc a za fold w head n for udp the following command should work kubectl exec n windows agnhost curl exe s when the message is larger it won t work anymore in azure vnet cni kubectl exec n windows agnhost curl exe s for flannel this does not work kubectl exec n windows agnhost curl exe s but if the message is shorter it works kubectl exec n windows agnhost curl exe s the mentioned test fails because kube apiserver will send a bytes packet to the pod which should deny the crd creation which is higher than the bytes limit observed and it never gets any reply this issue does not occur when using flannel the test passes as seen here anything else we need to know we ve sent a pr which adds tests that sends larger http udp packets in order to detect and check for this issue as expected the tests fail when using windows nodes with flannel vxlan the http test passes when using windows nodes with azure cni or flannel however the udp test does not which may indicate a different issue both the http and the udp tests pass when using linux nodes pods with azure cni flannel or flannel overlay sig windows | 0 |
15,569 | 8,960,506,271 | IssuesEvent | 2019-01-28 06:15:06 | fomkin/korolev | https://api.github.com/repos/fomkin/korolev | closed | File inputs streaming | feature performance | Sometime we need to upload large files (larger than 1G). Currently we are need to save the file in memory to parse `FormData`. Also `FormDataCodec` works very slow. Parsing of 300mb form on my MacBook Pro 2018 takes 30 seconds.
The idea is to add `access.downloadFile` method which will run `FileReader.readAsDataURL` on a frontend, then send it with `XmlHttpRequest` (which supports blobs) to server side where it will handled as streamed body. | True | File inputs streaming - Sometime we need to upload large files (larger than 1G). Currently we are need to save the file in memory to parse `FormData`. Also `FormDataCodec` works very slow. Parsing of 300mb form on my MacBook Pro 2018 takes 30 seconds.
The idea is to add `access.downloadFile` method which will run `FileReader.readAsDataURL` on a frontend, then send it with `XmlHttpRequest` (which supports blobs) to server side where it will handled as streamed body. | non_priority | file inputs streaming sometime we need to upload large files larger than currently we are need to save the file in memory to parse formdata also formdatacodec works very slow parsing of form on my macbook pro takes seconds the idea is to add access downloadfile method which will run filereader readasdataurl on a frontend then send it with xmlhttprequest which supports blobs to server side where it will handled as streamed body | 0 |
116,243 | 11,905,122,831 | IssuesEvent | 2020-03-30 18:00:54 | rideskip/anchor | https://api.github.com/repos/rideskip/anchor | closed | Console Readme | documentation | Hello,
I am really impressed with your job! I really enjoy using it!
I found small mistake in Readme file for console, first argument in example is string but should be " a valid C symbol name"
this part:
```
CONSOLE_STR_ARG_DEF("port", "The port <A,B,C>"),
```
should be:
```
CONSOLE_STR_ARG_DEF(port, "The port <A,B,C>"),
```
etc. | 1.0 | Console Readme - Hello,
I am really impressed with your job! I really enjoy using it!
I found small mistake in Readme file for console, first argument in example is string but should be " a valid C symbol name"
this part:
```
CONSOLE_STR_ARG_DEF("port", "The port <A,B,C>"),
```
should be:
```
CONSOLE_STR_ARG_DEF(port, "The port <A,B,C>"),
```
etc. | non_priority | console readme hello i am really impressed with your job i really enjoy using it i found small mistake in readme file for console first argument in example is string but should be a valid c symbol name this part console str arg def port the port should be console str arg def port the port etc | 0 |
79,380 | 10,121,390,922 | IssuesEvent | 2019-07-31 15:31:54 | zalando/skipper | https://api.github.com/repos/zalando/skipper | closed | Document egress specific feature | documentation | - [x] `bearerinjector` filter needs to be documented in user docs
- [x] skipper as sidecar and egress features should be documented
- [x] link from filter reference bearerinjector, circuit breaker filters to the egress feature manual with backref | 1.0 | Document egress specific feature - - [x] `bearerinjector` filter needs to be documented in user docs
- [x] skipper as sidecar and egress features should be documented
- [x] link from filter reference bearerinjector, circuit breaker filters to the egress feature manual with backref | non_priority | document egress specific feature bearerinjector filter needs to be documented in user docs skipper as sidecar and egress features should be documented link from filter reference bearerinjector circuit breaker filters to the egress feature manual with backref | 0 |
51,434 | 6,159,451,501 | IssuesEvent | 2017-06-29 00:22:27 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | Test: multi root explorer | multi-root testplan-item | - [x] win - @alexandrudima
- [x] mac - @aefernandes
- [x] linux - @bpasero
Complexity: 4
Refs: https://github.com/Microsoft/vscode/pull/29030
This milestone we have started to work on the multi root experience, currently this is only available on insiders. Verify:
* Quickly check that the single root explorer is the same as before
* You can nicely transition from single root to multi root (from File menu, from explorer context menu, via global action)
* View state is preserved in the explorer between restarts (focus, expand state, opened editor)
* The active file is always revealed when switching between editors
* You can drag and drop in the explorer (also between different roots)
* All the context menu actions make sense (check the ones for the roots as well as clicking into the empty space outside any root)
* All the explorer actions (top right) make sense and target the currently selected element
* Deleting, renaming, adding file should work as before
* Check the case when you have the same folder opened twice - once the parent and once any of its children (try to rename / delete something in that folder, both parents should get updated)
* Have a `files.exclude` setting in each folder and make sure that it is exactly respected in each folder
* Delete the root folder in some other tool while vscode is open. Make sure vscode handles this case gracefully
* Be creative in trying to break the explorer | 1.0 | Test: multi root explorer - - [x] win - @alexandrudima
- [x] mac - @aefernandes
- [x] linux - @bpasero
Complexity: 4
Refs: https://github.com/Microsoft/vscode/pull/29030
This milestone we have started to work on the multi root experience, currently this is only available on insiders. Verify:
* Quickly check that the single root explorer is the same as before
* You can nicely transition from single root to multi root (from File menu, from explorer context menu, via global action)
* View state is preserved in the explorer between restarts (focus, expand state, opened editor)
* The active file is always revealed when switching between editors
* You can drag and drop in the explorer (also between different roots)
* All the context menu actions make sense (check the ones for the roots as well as clicking into the empty space outside any root)
* All the explorer actions (top right) make sense and target the currently selected element
* Deleting, renaming, adding file should work as before
* Check the case when you have the same folder opened twice - once the parent and once any of its children (try to rename / delete something in that folder, both parents should get updated)
* Have a `files.exclude` setting in each folder and make sure that it is exactly respected in each folder
* Delete the root folder in some other tool while vscode is open. Make sure vscode handles this case gracefully
* Be creative in trying to break the explorer | non_priority | test multi root explorer win alexandrudima mac aefernandes linux bpasero complexity refs this milestone we have started to work on the multi root experience currently this is only available on insiders verify quickly check that the single root explorer is the same as before you can nicely transition from single root to multi root from file menu from explorer context menu via global action view state is preserved in the explorer between restarts focus expand state opened editor the active file is always revealed when switching between editors you can drag and drop in the explorer also between different roots all the context menu actions make sense check the ones for the roots as well as clicking into the empty space outside any root all the explorer actions top right make sense and target the currently selected element deleting renaming adding file should work as before check the case when you have the same folder opened twice once the parent and once any of its children try to rename delete something in that folder both parents should get updated have a files exclude setting in each folder and make sure that it is exactly respected in each folder delete the root folder in some other tool while vscode is open make sure vscode handles this case gracefully be creative in trying to break the explorer | 0 |
153,550 | 19,708,283,701 | IssuesEvent | 2022-01-13 01:18:39 | Rossb0b/web-agency | https://api.github.com/repos/Rossb0b/web-agency | opened | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz | security vulnerability | ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /web-agency/package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json,/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- webpack-encore-0.28.2.tgz (Root Library)
- webpack-dev-server-3.10.3.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /web-agency/package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json,/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- webpack-encore-0.28.2.tgz (Root Library)
- webpack-dev-server-3.10.3.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz cve high severity vulnerability vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file web agency package json path to vulnerable library node modules glob parent package json node modules glob parent package json dependency hierarchy webpack encore tgz root library webpack dev server tgz chokidar tgz x glob parent tgz vulnerable library vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent step up your open source security game with whitesource | 0 |
73,202 | 9,652,947,850 | IssuesEvent | 2019-05-18 22:05:59 | rust-lang-nursery/mdBook | https://api.github.com/repos/rust-lang-nursery/mdBook | closed | build > preprocess ? i think it not working, and preprocessor help me | A-Documentation | ### 1. [mdbook doc site](https://rust-lang-nursery.github.io/mdBook/format/config.html#build-options) say
That **preprocess** can handle the preprocess
``` toml
[build]
build-dir = "build"
create-missing = false
use-default-preprocessors = false # no use default pre, then
preprocess = ["links"] # preprocess was not working
```
But,`preprocess = ["links"]` no working
### 2. src/config.rs about `BuildConfig` even without field of preprocess [->ref](https://github.com/rust-lang-nursery/mdBook/blob/master/src/config.rs#L391)
>Am i right, i a Rookie of Rust
``` rust
#[derive(Debug, Clone, PartialEq, Serialize, Deserialize)]
#[serde(default, rename_all = "kebab-case")]
pub struct BuildConfig {
/// Where to put built artefacts relative to the book's root directory.
pub build_dir: PathBuf,
/// Should non-existent markdown files specified in `SETTINGS.md` be created
/// if they don't exist?
pub create_missing: bool,
/// Should the default preprocessors always be used when they are
/// compatible with the renderer?
pub use_default_preprocessors: bool,
}
```
## 3. Solve
### With `[preprocessor.***]`
``` toml
[build]
build-dir = "build"
create-missing = false
use-default-preprocessors = false
[preprocessor.links] # 🌟 ok, it working
```
I found the key:*preprocessor* in [src/book/mod.rs :: determine_preprocessors](https://sourcegraph.com/github.com/rust-lang-nursery/mdBook@master/-/blob/src/book/mod.rs#L367)
``` rust
fn determine_preprocessors(config: &Config) -> Result<Vec<Box<Preprocessor>>> {
--
| let mut preprocessors = Vec::new();
|
| if config.build.use_default_preprocessors {
| preprocessors.extend(default_preprocessors());
| }
|
| if let Some(preprocessor_table) =
❤️| config.get("preprocessor").and_then(\|v\| v.as_table())
| {
| for key in preprocessor_table.keys() {
| match key.as_ref() {
| "links" => {
| preprocessors.push(Box::new(LinkPreprocessor::new()))
| }
| "index" => {
| preprocessors.push(Box::new(IndexPreprocessor::new()))
| }
| name => preprocessors.push(interpret_custom_preprocessor(
| name,
| &preprocessor_table[name],
| )),
| }
| }
| }
|
| Ok(preprocessors)
| }
```
### Is that Docs wrong ?
| 1.0 | build > preprocess ? i think it not working, and preprocessor help me - ### 1. [mdbook doc site](https://rust-lang-nursery.github.io/mdBook/format/config.html#build-options) say
That **preprocess** can handle the preprocess
``` toml
[build]
build-dir = "build"
create-missing = false
use-default-preprocessors = false # no use default pre, then
preprocess = ["links"] # preprocess was not working
```
But,`preprocess = ["links"]` no working
### 2. src/config.rs about `BuildConfig` even without field of preprocess [->ref](https://github.com/rust-lang-nursery/mdBook/blob/master/src/config.rs#L391)
>Am i right, i a Rookie of Rust
``` rust
#[derive(Debug, Clone, PartialEq, Serialize, Deserialize)]
#[serde(default, rename_all = "kebab-case")]
pub struct BuildConfig {
/// Where to put built artefacts relative to the book's root directory.
pub build_dir: PathBuf,
/// Should non-existent markdown files specified in `SETTINGS.md` be created
/// if they don't exist?
pub create_missing: bool,
/// Should the default preprocessors always be used when they are
/// compatible with the renderer?
pub use_default_preprocessors: bool,
}
```
## 3. Solve
### With `[preprocessor.***]`
``` toml
[build]
build-dir = "build"
create-missing = false
use-default-preprocessors = false
[preprocessor.links] # 🌟 ok, it working
```
I found the key:*preprocessor* in [src/book/mod.rs :: determine_preprocessors](https://sourcegraph.com/github.com/rust-lang-nursery/mdBook@master/-/blob/src/book/mod.rs#L367)
``` rust
fn determine_preprocessors(config: &Config) -> Result<Vec<Box<Preprocessor>>> {
--
| let mut preprocessors = Vec::new();
|
| if config.build.use_default_preprocessors {
| preprocessors.extend(default_preprocessors());
| }
|
| if let Some(preprocessor_table) =
❤️| config.get("preprocessor").and_then(\|v\| v.as_table())
| {
| for key in preprocessor_table.keys() {
| match key.as_ref() {
| "links" => {
| preprocessors.push(Box::new(LinkPreprocessor::new()))
| }
| "index" => {
| preprocessors.push(Box::new(IndexPreprocessor::new()))
| }
| name => preprocessors.push(interpret_custom_preprocessor(
| name,
| &preprocessor_table[name],
| )),
| }
| }
| }
|
| Ok(preprocessors)
| }
```
### Is that Docs wrong ?
| non_priority | build preprocess i think it not working and preprocessor help me say that preprocess can handle the preprocess toml build dir build create missing false use default preprocessors false no use default pre then preprocess preprocess was not working but preprocess no working src config rs about buildconfig even without field of preprocess am i right i a rookie of rust rust pub struct buildconfig where to put built artefacts relative to the book s root directory pub build dir pathbuf should non existent markdown files specified in settings md be created if they don t exist pub create missing bool should the default preprocessors always be used when they are compatible with the renderer pub use default preprocessors bool solve with toml build dir build create missing false use default preprocessors false 🌟 ok it working i found the key preprocessor in rust fn determine preprocessors config config result let mut preprocessors vec new if config build use default preprocessors preprocessors extend default preprocessors if let some preprocessor table ❤️ config get preprocessor and then v v as table for key in preprocessor table keys match key as ref links preprocessors push box new linkpreprocessor new index preprocessors push box new indexpreprocessor new name preprocessors push interpret custom preprocessor name preprocessor table ok preprocessors is that docs wrong ? | 0 |
122,184 | 17,692,856,209 | IssuesEvent | 2021-08-24 12:15:08 | gdcc/dataverse-kubernetes | https://api.github.com/repos/gdcc/dataverse-kubernetes | closed | Look into security scans for container images | enhancement security | ~~Free plan for OSS at https://snyk.io~~
~~And nice lables via shield.io~~
Snyk only offers up to 100 scans for OSS.
After some reading, we should go with [Clair](https://github.com/quay/clair) or [Anchore Engine](https://github.com/anchore/anchore-engine).
See also https://kubedex.com/follow-up-container-scanning-comparison | True | Look into security scans for container images - ~~Free plan for OSS at https://snyk.io~~
~~And nice lables via shield.io~~
Snyk only offers up to 100 scans for OSS.
After some reading, we should go with [Clair](https://github.com/quay/clair) or [Anchore Engine](https://github.com/anchore/anchore-engine).
See also https://kubedex.com/follow-up-container-scanning-comparison | non_priority | look into security scans for container images free plan for oss at and nice lables via shield io snyk only offers up to scans for oss after some reading we should go with or see also | 0 |
28,537 | 5,287,421,212 | IssuesEvent | 2017-02-08 12:17:48 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | closed | Multiple exception handlers is emitted incorrectly if the caught exceptions have the same variable name | defect in progress | If there are multiple exception handlers with the same caught exceptions' variable names on the same level, invalid JS code is generated and `ErrorException: adas is not defined` is thrown.
Might be related to #343, #929, #2223.
### Steps To Reproduce
http://deck.net/25cecc7fd9aaf5936ddffbce68832a59/top
```c#
public class App
{
public static void Main()
{
try
{
}
catch (Exception e)
{
throw;
}
try
{
}
catch (Exception e)
{
throw;
}
}
}
```
### Expected Result
```js
Bridge.assembly("Demo", function ($asm, globals) {
"use strict";
Bridge.define("Demo.App", {
$main: function () {
try {
}
catch (e) {
e = System.Exception.create(e);
throw e;
}
try {
}
catch (e1) {
e1 = System.Exception.create(e1);
throw e1;
}
}
});
});
```
### Actual Result
```js
Bridge.assembly("Demo", function ($asm, globals) {
"use strict";
Bridge.define("Demo.App", {
$main: function () {
try {
}
catch (e) {
e = System.Exception.create(e);
throw e;
}
try {
}
catch (e1) {
e1 = System.Exception.create(e1);
throw e;
}
}
});
});
```
| 1.0 | Multiple exception handlers is emitted incorrectly if the caught exceptions have the same variable name - If there are multiple exception handlers with the same caught exceptions' variable names on the same level, invalid JS code is generated and `ErrorException: adas is not defined` is thrown.
Might be related to #343, #929, #2223.
### Steps To Reproduce
http://deck.net/25cecc7fd9aaf5936ddffbce68832a59/top
```c#
public class App
{
public static void Main()
{
try
{
}
catch (Exception e)
{
throw;
}
try
{
}
catch (Exception e)
{
throw;
}
}
}
```
### Expected Result
```js
Bridge.assembly("Demo", function ($asm, globals) {
"use strict";
Bridge.define("Demo.App", {
$main: function () {
try {
}
catch (e) {
e = System.Exception.create(e);
throw e;
}
try {
}
catch (e1) {
e1 = System.Exception.create(e1);
throw e1;
}
}
});
});
```
### Actual Result
```js
Bridge.assembly("Demo", function ($asm, globals) {
"use strict";
Bridge.define("Demo.App", {
$main: function () {
try {
}
catch (e) {
e = System.Exception.create(e);
throw e;
}
try {
}
catch (e1) {
e1 = System.Exception.create(e1);
throw e;
}
}
});
});
```
| non_priority | multiple exception handlers is emitted incorrectly if the caught exceptions have the same variable name if there are multiple exception handlers with the same caught exceptions variable names on the same level invalid js code is generated and errorexception adas is not defined is thrown might be related to steps to reproduce c public class app public static void main try catch exception e throw try catch exception e throw expected result js bridge assembly demo function asm globals use strict bridge define demo app main function try catch e e system exception create e throw e try catch system exception create throw actual result js bridge assembly demo function asm globals use strict bridge define demo app main function try catch e e system exception create e throw e try catch system exception create throw e | 0 |
146,165 | 22,973,370,945 | IssuesEvent | 2022-07-20 06:32:13 | vector-im/element-ios | https://api.github.com/repos/vector-im/element-ios | closed | Remove permission popups on a new sign in/up | X-Needs-Design feature:privacy Z-Papercuts Z-Visibility-1 Z-Impact-1 Z-D1 | We currently display 2 permission popups after logging in on a fresh app install:
- [x] Contact access. We should ask it only if the users go to the people tab. This is a regression
- [ ] Logs gathering. We should ask later after several uses. We need to check what element-android does.
This is too much for a new user. We should remove them. | 1.0 | Remove permission popups on a new sign in/up - We currently display 2 permission popups after logging in on a fresh app install:
- [x] Contact access. We should ask it only if the users go to the people tab. This is a regression
- [ ] Logs gathering. We should ask later after several uses. We need to check what element-android does.
This is too much for a new user. We should remove them. | non_priority | remove permission popups on a new sign in up we currently display permission popups after logging in on a fresh app install contact access we should ask it only if the users go to the people tab this is a regression logs gathering we should ask later after several uses we need to check what element android does this is too much for a new user we should remove them | 0 |
79,060 | 9,819,280,737 | IssuesEvent | 2019-06-13 21:31:22 | AiursoftWeb/Kahla.App | https://api.github.com/repos/AiursoftWeb/Kahla.App | closed | Page displays obsolete info when accepted friend request. | Bug Invalid design | [//]: <Don't delete any header! Please fill out the form or your bug report will not be considered!>
## Environment
- Environment: `Staging(Pre-release)\Production`
- Last git commit: 075a232f44693a6701882ba15e9e25fa4e0246d4
- Platform: `Web Desktop\Web Mobile\Electron\Cordova\PWA`
- Browser: `Chrome\Edge\Firefox\Safari\Others`
## How to repro
- Step 1: Sign in an account.
- Step 2: Go to my friends -> My requests
- Step 3: Accept one friend request.
- Step 4: Go back to `my friends` page.
And then I can't find this new friend.
## Expected situation
I expect that I can always get the latest info in the `my friends` page.
## Other information
Nothing.
| 1.0 | Page displays obsolete info when accepted friend request. - [//]: <Don't delete any header! Please fill out the form or your bug report will not be considered!>
## Environment
- Environment: `Staging(Pre-release)\Production`
- Last git commit: 075a232f44693a6701882ba15e9e25fa4e0246d4
- Platform: `Web Desktop\Web Mobile\Electron\Cordova\PWA`
- Browser: `Chrome\Edge\Firefox\Safari\Others`
## How to repro
- Step 1: Sign in an account.
- Step 2: Go to my friends -> My requests
- Step 3: Accept one friend request.
- Step 4: Go back to `my friends` page.
And then I can't find this new friend.
## Expected situation
I expect that I can always get the latest info in the `my friends` page.
## Other information
Nothing.
| non_priority | page displays obsolete info when accepted friend request environment environment staging pre release production last git commit platform web desktop web mobile electron cordova pwa browser chrome edge firefox safari others how to repro step sign in an account step go to my friends my requests step accept one friend request step go back to my friends page and then i can t find this new friend expected situation i expect that i can always get the latest info in the my friends page other information nothing | 0 |
216,571 | 24,281,573,667 | IssuesEvent | 2022-09-28 17:54:00 | liorzilberg/struts | https://api.github.com/repos/liorzilberg/struts | opened | CVE-2018-1272 (High) detected in spring-core-4.3.13.RELEASE.jar | security vulnerability | ## CVE-2018-1272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /apps/showcase/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.13.RELEASE/spring-core-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.13.RELEASE/spring-core-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- struts2-spring-plugin-2.6-SNAPSHOT.jar (Root Library)
- :x: **spring-core-4.3.13.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/liorzilberg/struts/commit/6950763af860884188f4080d19a18c5ede16cd74">6950763af860884188f4080d19a18c5ede16cd74</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.
<p>Publish Date: 2018-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1272>CVE-2018-1272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2018-1272">https://tanzu.vmware.com/security/cve-2018-1272</a></p>
<p>Release Date: 2018-04-06</p>
<p>Fix Resolution: org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE</p>
</p>
</details>
<p></p>
| True | CVE-2018-1272 (High) detected in spring-core-4.3.13.RELEASE.jar - ## CVE-2018-1272 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /apps/showcase/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.13.RELEASE/spring-core-4.3.13.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-core/4.3.13.RELEASE/spring-core-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- struts2-spring-plugin-2.6-SNAPSHOT.jar (Root Library)
- :x: **spring-core-4.3.13.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/liorzilberg/struts/commit/6950763af860884188f4080d19a18c5ede16cd74">6950763af860884188f4080d19a18c5ede16cd74</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0 prior to 5.0.5 and versions 4.3 prior to 4.3.15 and older unsupported versions, provide client-side support for multipart requests. When Spring MVC or Spring WebFlux server application (server A) receives input from a remote client, and then uses that input to make a multipart request to another server (server B), it can be exposed to an attack, where an extra multipart is inserted in the content of the request from server A, causing server B to use the wrong value for a part it expects. This could to lead privilege escalation, for example, if the part content represents a username or user roles.
<p>Publish Date: 2018-04-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1272>CVE-2018-1272</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2018-1272">https://tanzu.vmware.com/security/cve-2018-1272</a></p>
<p>Release Date: 2018-04-06</p>
<p>Fix Resolution: org.springframework:spring-core:4.3.15.RELEASE,5.0.5.RELEASE;org.springframework:spring-web:4.3.15.RELEASE,5.0.5.RELEASE</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in spring core release jar cve high severity vulnerability vulnerable library spring core release jar spring core library home page a href path to dependency file apps showcase pom xml path to vulnerable library home wss scanner repository org springframework spring core release spring core release jar home wss scanner repository org springframework spring core release spring core release jar dependency hierarchy spring plugin snapshot jar root library x spring core release jar vulnerable library found in head commit a href found in base branch master vulnerability details spring framework versions prior to and versions prior to and older unsupported versions provide client side support for multipart requests when spring mvc or spring webflux server application server a receives input from a remote client and then uses that input to make a multipart request to another server server b it can be exposed to an attack where an extra multipart is inserted in the content of the request from server a causing server b to use the wrong value for a part it expects this could to lead privilege escalation for example if the part content represents a username or user roles publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring core release release org springframework spring web release release | 0 |
14,312 | 24,764,445,855 | IssuesEvent | 2022-10-22 10:24:18 | Flackozi/ISPW | https://api.github.com/repos/Flackozi/ISPW | opened | FR | Functional Requirements | The system shall add the missing ingredients in the recipes saved by the premium user in the shopping list. | 1.0 | FR - The system shall add the missing ingredients in the recipes saved by the premium user in the shopping list. | non_priority | fr the system shall add the missing ingredients in the recipes saved by the premium user in the shopping list | 0 |
8,721 | 3,210,435,642 | IssuesEvent | 2015-10-06 02:52:05 | elixir-lang/ecto | https://api.github.com/repos/elixir-lang/ecto | closed | Document query and model prefix | Kind:Documentation Level:Starter | We have this feature for some time now, but it seems it's not documented. We should explain how to use prefix for queries and for models. | 1.0 | Document query and model prefix - We have this feature for some time now, but it seems it's not documented. We should explain how to use prefix for queries and for models. | non_priority | document query and model prefix we have this feature for some time now but it seems it s not documented we should explain how to use prefix for queries and for models | 0 |
222,462 | 24,708,940,160 | IssuesEvent | 2022-10-19 21:51:44 | lukebrogan-mend/bag-of-holding | https://api.github.com/repos/lukebrogan-mend/bag-of-holding | closed | WS-2017-0266 (Low) detected in http-signature-0.10.1.tgz - autoclosed | security vulnerability | ## WS-2017-0266 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-signature-0.10.1.tgz</b></p></summary>
<p>Reference implementation of Joyent's HTTP Signature scheme.</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz">https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pangyp/node_modules/http-signature/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-1.3.3.tgz (Root Library)
- node-sass-2.1.1.tgz
- pangyp-2.3.3.tgz
- request-2.51.0.tgz
- :x: **http-signature-0.10.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/bag-of-holding/commit/fd67f5ea4245a25511650d4bf41a6c699a799144">fd67f5ea4245a25511650d4bf41a6c699a799144</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
http-signature before version 1.0.0 are vulnerable to timing attack, which may lead to information disclosure.
<p>Publish Date: 2015-01-22
<p>URL: <a href=https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56>WS-2017-0266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2015-01-22</p>
<p>Fix Resolution (http-signature): 1.0.0</p>
<p>Direct dependency fix Resolution (gulp-sass): 2.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | WS-2017-0266 (Low) detected in http-signature-0.10.1.tgz - autoclosed - ## WS-2017-0266 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-signature-0.10.1.tgz</b></p></summary>
<p>Reference implementation of Joyent's HTTP Signature scheme.</p>
<p>Library home page: <a href="https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz">https://registry.npmjs.org/http-signature/-/http-signature-0.10.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/pangyp/node_modules/http-signature/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-1.3.3.tgz (Root Library)
- node-sass-2.1.1.tgz
- pangyp-2.3.3.tgz
- request-2.51.0.tgz
- :x: **http-signature-0.10.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/bag-of-holding/commit/fd67f5ea4245a25511650d4bf41a6c699a799144">fd67f5ea4245a25511650d4bf41a6c699a799144</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
http-signature before version 1.0.0 are vulnerable to timing attack, which may lead to information disclosure.
<p>Publish Date: 2015-01-22
<p>URL: <a href=https://github.com/joyent/node-http-signature/commit/78ab1da232f31f695f5c362d863593a143aa8b56>WS-2017-0266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2015-01-22</p>
<p>Fix Resolution (http-signature): 1.0.0</p>
<p>Direct dependency fix Resolution (gulp-sass): 2.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | ws low detected in http signature tgz autoclosed ws low severity vulnerability vulnerable library http signature tgz reference implementation of joyent s http signature scheme library home page a href path to dependency file package json path to vulnerable library node modules pangyp node modules http signature package json dependency hierarchy gulp sass tgz root library node sass tgz pangyp tgz request tgz x http signature tgz vulnerable library found in head commit a href found in base branch master vulnerability details http signature before version are vulnerable to timing attack which may lead to information disclosure publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution http signature direct dependency fix resolution gulp sass rescue worker helmet automatic remediation is available for this issue | 0 |
136,443 | 18,734,120,636 | IssuesEvent | 2021-11-04 03:42:36 | Dima2022/kaltura-sample-code | https://api.github.com/repos/Dima2022/kaltura-sample-code | opened | CVE-2021-25122 (High) detected in tomcat-embed-core-8.5.16.jar | security vulnerability | ## CVE-2021-25122 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.16.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: kaltura-sample-code/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.16/tomcat-embed-core-8.5.16.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.6.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.6.RELEASE.jar
- :x: **tomcat-embed-core-8.5.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/kaltura-sample-code/commit/e022312630d07a000d07ace8bd86a7f0590a0f65">e022312630d07a000d07ace8bd86a7f0590a0f65</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When responding to new h2c connection requests, Apache Tomcat versions 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41 and 8.5.0 to 8.5.61 could duplicate request headers and a limited amount of request body from one request to another meaning user A and user B could both see the results of user A's request.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25122>CVE-2021-25122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:8.5.62,9.0.42,10.0.2;org.apache.tomcat:tomcat-coyote:8.5.62,9.0.42,10.0.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.16","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.6.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.6.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.16","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:8.5.62,9.0.42,10.0.2;org.apache.tomcat:tomcat-coyote:8.5.62,9.0.42,10.0.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-25122","vulnerabilityDetails":"When responding to new h2c connection requests, Apache Tomcat versions 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41 and 8.5.0 to 8.5.61 could duplicate request headers and a limited amount of request body from one request to another meaning user A and user B could both see the results of user A\u0027s request.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25122","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-25122 (High) detected in tomcat-embed-core-8.5.16.jar - ## CVE-2021-25122 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.16.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: kaltura-sample-code/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.16/tomcat-embed-core-8.5.16.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.6.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.6.RELEASE.jar
- :x: **tomcat-embed-core-8.5.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/kaltura-sample-code/commit/e022312630d07a000d07ace8bd86a7f0590a0f65">e022312630d07a000d07ace8bd86a7f0590a0f65</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When responding to new h2c connection requests, Apache Tomcat versions 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41 and 8.5.0 to 8.5.61 could duplicate request headers and a limited amount of request body from one request to another meaning user A and user B could both see the results of user A's request.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25122>CVE-2021-25122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:8.5.62,9.0.42,10.0.2;org.apache.tomcat:tomcat-coyote:8.5.62,9.0.42,10.0.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.16","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.6.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.6.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.16","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:8.5.62,9.0.42,10.0.2;org.apache.tomcat:tomcat-coyote:8.5.62,9.0.42,10.0.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-25122","vulnerabilityDetails":"When responding to new h2c connection requests, Apache Tomcat versions 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41 and 8.5.0 to 8.5.61 could duplicate request headers and a limited amount of request body from one request to another meaning user A and user B could both see the results of user A\u0027s request.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25122","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file kaltura sample code pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details when responding to new connection requests apache tomcat versions to to and to could duplicate request headers and a limited amount of request body from one request to another meaning user a and user b could both see the results of user a s request publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat coyote isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat embed tomcat embed core org apache tomcat tomcat coyote basebranches vulnerabilityidentifier cve vulnerabilitydetails when responding to new connection requests apache tomcat versions to to and to could duplicate request headers and a limited amount of request body from one request to another meaning user a and user b could both see the results of user a request vulnerabilityurl | 0 |
271,239 | 23,592,439,290 | IssuesEvent | 2022-08-23 16:14:43 | katilingban/mozambique-s3m | https://api.github.com/repos/katilingban/mozambique-s3m | opened | add GitHub Actions workflow to test data processing and analysis workflows | data cleaning data analysis testing | Curent GHA workflow is for daily data quality checks only. Will be good to add a workflow for testing data processing and analysis steps. | 1.0 | add GitHub Actions workflow to test data processing and analysis workflows - Curent GHA workflow is for daily data quality checks only. Will be good to add a workflow for testing data processing and analysis steps. | non_priority | add github actions workflow to test data processing and analysis workflows curent gha workflow is for daily data quality checks only will be good to add a workflow for testing data processing and analysis steps | 0 |
55,672 | 6,916,006,733 | IssuesEvent | 2017-11-29 00:08:44 | Microsoft/TypeScript | https://api.github.com/repos/Microsoft/TypeScript | closed | TS2454 and var hoisting | Design Limitation | <!-- BUGS: Please use this template. -->
<!-- QUESTIONS: This is not a general support forum! Ask Qs at http://stackoverflow.com/questions/tagged/typescript -->
<!-- SUGGESTIONS: See https://github.com/Microsoft/TypeScript-wiki/blob/master/Writing-Good-Design-Proposals.md -->
<!-- Please try to reproduce the issue with `typescript@next`. It may have already been fixed. -->
**TypeScript Version:** 2.6.1
**Code**
I have some code vaguely similar to the following, which takes advantage of `var` hoisting; `strictNullChecks` is enabled:
```ts
if (input.a) {
var a = doSomething(input.a); // returns a string
}
if (input.b) {
var b = doSomethingElse(input.b); // returns a string
}
if (input.c) {
var c = doAThirdThing(input.c); // returns a string
}
let options = {
a, // error TS2454: Variable 'a' is used before being assigned
b, // error TS2454: Variable 'b' is used before being assigned
c // error TS2454: Variable 'c' is used before being assigned
};
```
**Expected behavior:**
`a`, `b`, and `c` should probably have implicit types of `string | undefined`, and no errors should be thrown.
**Actual behavior:**
`a`, `b`, and `c` have implicit types of `string`, and TS2454 is thrown.
-----
For the moment, explicitly setting the types with `var a: string | undefined = ...` is a workaround, but I'm not a fan of how verbose that is, and I don't believe it should be needed. | 1.0 | TS2454 and var hoisting - <!-- BUGS: Please use this template. -->
<!-- QUESTIONS: This is not a general support forum! Ask Qs at http://stackoverflow.com/questions/tagged/typescript -->
<!-- SUGGESTIONS: See https://github.com/Microsoft/TypeScript-wiki/blob/master/Writing-Good-Design-Proposals.md -->
<!-- Please try to reproduce the issue with `typescript@next`. It may have already been fixed. -->
**TypeScript Version:** 2.6.1
**Code**
I have some code vaguely similar to the following, which takes advantage of `var` hoisting; `strictNullChecks` is enabled:
```ts
if (input.a) {
var a = doSomething(input.a); // returns a string
}
if (input.b) {
var b = doSomethingElse(input.b); // returns a string
}
if (input.c) {
var c = doAThirdThing(input.c); // returns a string
}
let options = {
a, // error TS2454: Variable 'a' is used before being assigned
b, // error TS2454: Variable 'b' is used before being assigned
c // error TS2454: Variable 'c' is used before being assigned
};
```
**Expected behavior:**
`a`, `b`, and `c` should probably have implicit types of `string | undefined`, and no errors should be thrown.
**Actual behavior:**
`a`, `b`, and `c` have implicit types of `string`, and TS2454 is thrown.
-----
For the moment, explicitly setting the types with `var a: string | undefined = ...` is a workaround, but I'm not a fan of how verbose that is, and I don't believe it should be needed. | non_priority | and var hoisting typescript version code i have some code vaguely similar to the following which takes advantage of var hoisting strictnullchecks is enabled ts if input a var a dosomething input a returns a string if input b var b dosomethingelse input b returns a string if input c var c doathirdthing input c returns a string let options a error variable a is used before being assigned b error variable b is used before being assigned c error variable c is used before being assigned expected behavior a b and c should probably have implicit types of string undefined and no errors should be thrown actual behavior a b and c have implicit types of string and is thrown for the moment explicitly setting the types with var a string undefined is a workaround but i m not a fan of how verbose that is and i don t believe it should be needed | 0 |
4,199 | 6,758,166,773 | IssuesEvent | 2017-10-24 13:25:42 | support-project/knowledge | https://api.github.com/repos/support-project/knowledge | closed | テンプレートのタグ初期値のお願い | [Status] 3.merged [Type] 1.requirement | テンプレートへの機能追加のお願いです。
* タグの初期値を設定できるようにしていただけないでしょうか。タグ付けルールがある程度強制されて、良いように思います。もしくは、コンテンツの初期値が設定できれば、タグの代わりに検索に掛かるようにキーワードを入れておくこともできます。
* テキストエリアにMarkdownで入力できないようなので、コンテンツエリア項目の追加が欲しいです。ただ、この要望もコンテンツの初期値が設定できれば済む問題かもしれません。
ご検討のほどよろしくお願いいたします。 | 1.0 | テンプレートのタグ初期値のお願い - テンプレートへの機能追加のお願いです。
* タグの初期値を設定できるようにしていただけないでしょうか。タグ付けルールがある程度強制されて、良いように思います。もしくは、コンテンツの初期値が設定できれば、タグの代わりに検索に掛かるようにキーワードを入れておくこともできます。
* テキストエリアにMarkdownで入力できないようなので、コンテンツエリア項目の追加が欲しいです。ただ、この要望もコンテンツの初期値が設定できれば済む問題かもしれません。
ご検討のほどよろしくお願いいたします。 | non_priority | テンプレートのタグ初期値のお願い テンプレートへの機能追加のお願いです。 タグの初期値を設定できるようにしていただけないでしょうか。タグ付けルールがある程度強制されて、良いように思います。もしくは、コンテンツの初期値が設定できれば、タグの代わりに検索に掛かるようにキーワードを入れておくこともできます。 テキストエリアにmarkdownで入力できないようなので、コンテンツエリア項目の追加が欲しいです。ただ、この要望もコンテンツの初期値が設定できれば済む問題かもしれません。 ご検討のほどよろしくお願いいたします。 | 0 |
24,042 | 12,196,234,501 | IssuesEvent | 2020-04-29 18:43:53 | kframework/kore | https://api.github.com/repos/kframework/kore | closed | No branching in K-EQUAL hooks | appetite: M feature performance | After kframework/k#1151
The implementations of the K-EQUAL hooks should not branch, but expect concrete arguments.
---
- [ ] Concrete implementation of `==K` in the backend.
The built-in implementation of `==K` should apply only to concrete (constructor-like) arguments. Given concrete arguments, its value should be `true` or `false` by comparing patterns using Haskell equality.
- [ ] Symbolic implementation of `==K` in the frontend.
The rules are `rule A ==K B => true requires true #And {A #Equals B}` and `rule A ==K B => false [owise]`. These should go in a `K-EQUAL-SYMBOLIC` module with the `symbolic` and `kore` attributes to avoid interfering with the LLVM or Java backends. | True | No branching in K-EQUAL hooks - After kframework/k#1151
The implementations of the K-EQUAL hooks should not branch, but expect concrete arguments.
---
- [ ] Concrete implementation of `==K` in the backend.
The built-in implementation of `==K` should apply only to concrete (constructor-like) arguments. Given concrete arguments, its value should be `true` or `false` by comparing patterns using Haskell equality.
- [ ] Symbolic implementation of `==K` in the frontend.
The rules are `rule A ==K B => true requires true #And {A #Equals B}` and `rule A ==K B => false [owise]`. These should go in a `K-EQUAL-SYMBOLIC` module with the `symbolic` and `kore` attributes to avoid interfering with the LLVM or Java backends. | non_priority | no branching in k equal hooks after kframework k the implementations of the k equal hooks should not branch but expect concrete arguments concrete implementation of k in the backend the built in implementation of k should apply only to concrete constructor like arguments given concrete arguments its value should be true or false by comparing patterns using haskell equality symbolic implementation of k in the frontend the rules are rule a k b true requires true and a equals b and rule a k b false these should go in a k equal symbolic module with the symbolic and kore attributes to avoid interfering with the llvm or java backends | 0 |
92,408 | 8,363,267,600 | IssuesEvent | 2018-10-03 19:12:59 | aspnet/Templating | https://api.github.com/repos/aspnet/Templating | closed | Test failure: MvcTemplate_NoAuth_Works_NetFramework_ForFSharpTemplate | 1 - Ready Branch:master PRI: 1 - Required duplicate task test-failure | This test [fails](http://aspnetci/viewLog.html?buildId=557861&buildTypeId=Lite_UniverseTest) occasionally with the following error:
```
System.AggregateException : One or more errors occurred. (An error occurred while sending the request.)
---- System.Net.Http.HttpRequestException : An error occurred while sending the request.
-------- System.IO.IOException : Unable to read data from the transport connection: An existing connection was forcibly closed by the remote host..
------------ System.Net.Sockets.SocketException : An existing connection was forcibly closed by the remote host.
at System.Threading.Tasks.Task.ThrowIfExceptional(Boolean includeTaskCanceledExceptions)
at System.Threading.Tasks.Task`1.GetResultCore(Boolean waitCompletionNotification)
at Templates.Test.Helpers.AspNetProcess.AssertStatusCode(String requestUrl, HttpStatusCode statusCode, String acceptContentType) in /_/test/Templates.Test/Helpers/AspNetProcess.cs:line 168
at Templates.Test.Helpers.AspNetProcess.AssertOk(String requestUrl) in /_/test/Templates.Test/Helpers/AspNetProcess.cs:line 152
at Templates.Test.MvcTemplateTest.MvcTemplate_NoAuthImpl(String targetFrameworkOverride, String languageOverride, Boolean noHttps) in /_/test/Templates.Test/MvcTemplateTest.cs:line 78
at Templates.Test.MvcTemplateTest.MvcTemplate_NoAuth_Works_NetFramework_ForFSharpTemplate() in /_/test/Templates.Test/MvcTemplateTest.cs:line 24
----- Inner Stack Trace -----
at System.Net.Http.HttpConnection.SendAsyncCore(HttpRequestMessage request, CancellationToken cancellationToken)
at System.Net.Http.HttpConnectionPool.SendWithNtConnectionAuthAsync(HttpConnection connection, HttpRequestMessage request, Boolean doRequestAuth, CancellationToken cancellationToken)
at System.Net.Http.HttpConnectionPool.SendWithRetryAsync(HttpRequestMessage request, Boolean doRequestAuth, CancellationToken cancellationToken)
at System.Net.Http.RedirectHandler.SendAsync(HttpRequestMessage request, CancellationToken cancellationToken)
at System.Net.Http.HttpClient.FinishSendAsyncBuffered(Task`1 sendTask, HttpRequestMessage request, CancellationTokenSource cts, Boolean disposeCts)
----- Inner Stack Trace -----
at System.Net.Sockets.Socket.AwaitableSocketAsyncEventArgs.ThrowException(SocketError error)
at System.Net.Sockets.Socket.AwaitableSocketAsyncEventArgs.GetResult(Int16 token)
at System.Net.Http.HttpConnection.FillAsync()
at System.Net.Http.HttpConnection.ReadNextResponseHeaderLineAsync(Boolean foldedHeadersAllowed)
at System.Net.Http.HttpConnection.SendAsyncCore(HttpRequestMessage request, CancellationToken cancellationToken)
----- Inner Stack Trace -----
------- Stdout: -------
==> C:\b\w\33bdfc1cae7b2a38\.dotnet\x64\dotnet.exe new mvc --debug:custom-hive "C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\.templateengine" --target-framework-override net461 -lang F# [C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22]
The template "ASP.NET Core Web App (Model-View-Controller)" was created successfully.
This template contains technologies from parties other than Microsoft, see https://aka.ms/aspnetcore-template-3pn-210 for details.
Processing post-creation actions...
Running 'dotnet restore' on C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj...
Restoring packages for C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj...
Generating MSBuild file C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\obj\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj.nuget.g.props.
Generating MSBuild file C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\obj\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj.nuget.g.targets.
Restore completed in 857.92 ms for C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj.
Restore succeeded.
Building ASP.NET application...
==> C:\b\w\33bdfc1cae7b2a38\.dotnet\x64\dotnet.exe build --no-restore -c Debug [C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22]
Microsoft (R) Build Engine version 15.8.166+gd4e8d81a88 for .NET Core
Copyright (C) Microsoft Corporation. All rights reserved.
AspNet.Template.468553c732514d0886274b3e73542f22 -> C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\bin\Debug\net461\AspNet.Template.468553c732514d0886274b3e73542f22.exe
Build succeeded.
0 Warning(s)
0 Error(s)
Time Elapsed 00:00:07.64
Running ASP.NET application...
==> C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\bin\Debug\net461\AspNet.Template.468553c732514d0886274b3e73542f22.exe [C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22]
Waiting until ASP.NET application is accepting connections...
info: Microsoft.AspNetCore.DataProtection.KeyManagement.XmlKeyManager[0]
User profile is available. Using 'C:\Users\asplab\AppData\Local\ASP.NET\DataProtection-Keys' as key repository and Windows DPAPI to encrypt keys at rest.
Hosting environment: Development
Content root path: C
...
```
Other tests within that build may have failed with a similar message, but they are not listed here. Check the link above for more info.
This test failed on master.
CC @mkArtakMSFT
This issue was made automatically. If there is a problem contact ryanbrandenburg. | 1.0 | Test failure: MvcTemplate_NoAuth_Works_NetFramework_ForFSharpTemplate - This test [fails](http://aspnetci/viewLog.html?buildId=557861&buildTypeId=Lite_UniverseTest) occasionally with the following error:
```
System.AggregateException : One or more errors occurred. (An error occurred while sending the request.)
---- System.Net.Http.HttpRequestException : An error occurred while sending the request.
-------- System.IO.IOException : Unable to read data from the transport connection: An existing connection was forcibly closed by the remote host..
------------ System.Net.Sockets.SocketException : An existing connection was forcibly closed by the remote host.
at System.Threading.Tasks.Task.ThrowIfExceptional(Boolean includeTaskCanceledExceptions)
at System.Threading.Tasks.Task`1.GetResultCore(Boolean waitCompletionNotification)
at Templates.Test.Helpers.AspNetProcess.AssertStatusCode(String requestUrl, HttpStatusCode statusCode, String acceptContentType) in /_/test/Templates.Test/Helpers/AspNetProcess.cs:line 168
at Templates.Test.Helpers.AspNetProcess.AssertOk(String requestUrl) in /_/test/Templates.Test/Helpers/AspNetProcess.cs:line 152
at Templates.Test.MvcTemplateTest.MvcTemplate_NoAuthImpl(String targetFrameworkOverride, String languageOverride, Boolean noHttps) in /_/test/Templates.Test/MvcTemplateTest.cs:line 78
at Templates.Test.MvcTemplateTest.MvcTemplate_NoAuth_Works_NetFramework_ForFSharpTemplate() in /_/test/Templates.Test/MvcTemplateTest.cs:line 24
----- Inner Stack Trace -----
at System.Net.Http.HttpConnection.SendAsyncCore(HttpRequestMessage request, CancellationToken cancellationToken)
at System.Net.Http.HttpConnectionPool.SendWithNtConnectionAuthAsync(HttpConnection connection, HttpRequestMessage request, Boolean doRequestAuth, CancellationToken cancellationToken)
at System.Net.Http.HttpConnectionPool.SendWithRetryAsync(HttpRequestMessage request, Boolean doRequestAuth, CancellationToken cancellationToken)
at System.Net.Http.RedirectHandler.SendAsync(HttpRequestMessage request, CancellationToken cancellationToken)
at System.Net.Http.HttpClient.FinishSendAsyncBuffered(Task`1 sendTask, HttpRequestMessage request, CancellationTokenSource cts, Boolean disposeCts)
----- Inner Stack Trace -----
at System.Net.Sockets.Socket.AwaitableSocketAsyncEventArgs.ThrowException(SocketError error)
at System.Net.Sockets.Socket.AwaitableSocketAsyncEventArgs.GetResult(Int16 token)
at System.Net.Http.HttpConnection.FillAsync()
at System.Net.Http.HttpConnection.ReadNextResponseHeaderLineAsync(Boolean foldedHeadersAllowed)
at System.Net.Http.HttpConnection.SendAsyncCore(HttpRequestMessage request, CancellationToken cancellationToken)
----- Inner Stack Trace -----
------- Stdout: -------
==> C:\b\w\33bdfc1cae7b2a38\.dotnet\x64\dotnet.exe new mvc --debug:custom-hive "C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\.templateengine" --target-framework-override net461 -lang F# [C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22]
The template "ASP.NET Core Web App (Model-View-Controller)" was created successfully.
This template contains technologies from parties other than Microsoft, see https://aka.ms/aspnetcore-template-3pn-210 for details.
Processing post-creation actions...
Running 'dotnet restore' on C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj...
Restoring packages for C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj...
Generating MSBuild file C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\obj\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj.nuget.g.props.
Generating MSBuild file C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\obj\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj.nuget.g.targets.
Restore completed in 857.92 ms for C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\AspNet.Template.468553c732514d0886274b3e73542f22.fsproj.
Restore succeeded.
Building ASP.NET application...
==> C:\b\w\33bdfc1cae7b2a38\.dotnet\x64\dotnet.exe build --no-restore -c Debug [C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22]
Microsoft (R) Build Engine version 15.8.166+gd4e8d81a88 for .NET Core
Copyright (C) Microsoft Corporation. All rights reserved.
AspNet.Template.468553c732514d0886274b3e73542f22 -> C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\bin\Debug\net461\AspNet.Template.468553c732514d0886274b3e73542f22.exe
Build succeeded.
0 Warning(s)
0 Error(s)
Time Elapsed 00:00:07.64
Running ASP.NET application...
==> C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22\bin\Debug\net461\AspNet.Template.468553c732514d0886274b3e73542f22.exe [C:\b\w\33bdfc1cae7b2a38\modules\Templating\test\Templates.Test\bin\Release\netcoreapp3.0\TestTemplates\AspNet.Template.468553c732514d0886274b3e73542f22]
Waiting until ASP.NET application is accepting connections...
info: Microsoft.AspNetCore.DataProtection.KeyManagement.XmlKeyManager[0]
User profile is available. Using 'C:\Users\asplab\AppData\Local\ASP.NET\DataProtection-Keys' as key repository and Windows DPAPI to encrypt keys at rest.
Hosting environment: Development
Content root path: C
...
```
Other tests within that build may have failed with a similar message, but they are not listed here. Check the link above for more info.
This test failed on master.
CC @mkArtakMSFT
This issue was made automatically. If there is a problem contact ryanbrandenburg. | non_priority | test failure mvctemplate noauth works netframework forfsharptemplate this test occasionally with the following error system aggregateexception one or more errors occurred an error occurred while sending the request system net http httprequestexception an error occurred while sending the request system io ioexception unable to read data from the transport connection an existing connection was forcibly closed by the remote host system net sockets socketexception an existing connection was forcibly closed by the remote host at system threading tasks task throwifexceptional boolean includetaskcanceledexceptions at system threading tasks task getresultcore boolean waitcompletionnotification at templates test helpers aspnetprocess assertstatuscode string requesturl httpstatuscode statuscode string acceptcontenttype in test templates test helpers aspnetprocess cs line at templates test helpers aspnetprocess assertok string requesturl in test templates test helpers aspnetprocess cs line at templates test mvctemplatetest mvctemplate noauthimpl string targetframeworkoverride string languageoverride boolean nohttps in test templates test mvctemplatetest cs line at templates test mvctemplatetest mvctemplate noauth works netframework forfsharptemplate in test templates test mvctemplatetest cs line inner stack trace at system net http httpconnection sendasynccore httprequestmessage request cancellationtoken cancellationtoken at system net http httpconnectionpool sendwithntconnectionauthasync httpconnection connection httprequestmessage request boolean dorequestauth cancellationtoken cancellationtoken at system net http httpconnectionpool sendwithretryasync httprequestmessage request boolean dorequestauth cancellationtoken cancellationtoken at system net http redirecthandler sendasync httprequestmessage request cancellationtoken cancellationtoken at system net http httpclient finishsendasyncbuffered task sendtask httprequestmessage request cancellationtokensource cts boolean disposects inner stack trace at system net sockets socket awaitablesocketasynceventargs throwexception socketerror error at system net sockets socket awaitablesocketasynceventargs getresult token at system net http httpconnection fillasync at system net http httpconnection readnextresponseheaderlineasync boolean foldedheadersallowed at system net http httpconnection sendasynccore httprequestmessage request cancellationtoken cancellationtoken inner stack trace stdout c b w dotnet dotnet exe new mvc debug custom hive c b w modules templating test templates test bin release templateengine target framework override lang f the template asp net core web app model view controller was created successfully this template contains technologies from parties other than microsoft see for details processing post creation actions running dotnet restore on c b w modules templating test templates test bin release testtemplates aspnet template aspnet template fsproj restoring packages for c b w modules templating test templates test bin release testtemplates aspnet template aspnet template fsproj generating msbuild file c b w modules templating test templates test bin release testtemplates aspnet template obj aspnet template fsproj nuget g props generating msbuild file c b w modules templating test templates test bin release testtemplates aspnet template obj aspnet template fsproj nuget g targets restore completed in ms for c b w modules templating test templates test bin release testtemplates aspnet template aspnet template fsproj restore succeeded building asp net application c b w dotnet dotnet exe build no restore c debug microsoft r build engine version for net core copyright c microsoft corporation all rights reserved aspnet template c b w modules templating test templates test bin release testtemplates aspnet template bin debug aspnet template exe build succeeded warning s error s time elapsed running asp net application c b w modules templating test templates test bin release testtemplates aspnet template bin debug aspnet template exe waiting until asp net application is accepting connections info microsoft aspnetcore dataprotection keymanagement xmlkeymanager user profile is available using c users asplab appdata local asp net dataprotection keys as key repository and windows dpapi to encrypt keys at rest hosting environment development content root path c other tests within that build may have failed with a similar message but they are not listed here check the link above for more info this test failed on master cc mkartakmsft this issue was made automatically if there is a problem contact ryanbrandenburg | 0 |
206,316 | 23,374,938,073 | IssuesEvent | 2022-08-11 01:09:51 | snowdensb/CSPBR | https://api.github.com/repos/snowdensb/CSPBR | opened | CVE-2022-31160 (Medium) detected in jquery-ui-1.11.4.js, jquery-ui-1.11.4.min.js | security vulnerability | ## CVE-2022-31160 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-ui-1.11.4.js</b>, <b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>
<details><summary><b>jquery-ui-1.11.4.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.js</a></p>
<p>Path to vulnerable library: /public/plugins/jQueryUI/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.11.4.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js</a></p>
<p>Path to vulnerable library: /public/plugins/jQueryUI/jquery-ui.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.11.4.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/CSPBR/commit/86334f0df744f6cfa35a438987cbb4d18d65b5c2">86334f0df744f6cfa35a438987cbb4d18d65b5c2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery UI is a curated set of user interface interactions, effects, widgets, and themes built on top of jQuery. Versions prior to 1.13.2 are potentially vulnerable to cross-site scripting. Initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label. Calling `.checkboxradio( "refresh" )` on such a widget and the initial HTML contained encoded HTML entities will make them erroneously get decoded. This can lead to potentially executing JavaScript code. The bug has been patched in jQuery UI 1.13.2. To remediate the issue, someone who can change the initial HTML can wrap all the non-input contents of the `label` in a `span`.
<p>Publish Date: 2022-07-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31160>CVE-2022-31160</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160</a></p>
<p>Release Date: 2022-07-20</p>
<p>Fix Resolution: jquery-ui - 1.13.2</p>
</p>
</details>
<p></p>
| True | CVE-2022-31160 (Medium) detected in jquery-ui-1.11.4.js, jquery-ui-1.11.4.min.js - ## CVE-2022-31160 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-ui-1.11.4.js</b>, <b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>
<details><summary><b>jquery-ui-1.11.4.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.js</a></p>
<p>Path to vulnerable library: /public/plugins/jQueryUI/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.11.4.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js</a></p>
<p>Path to vulnerable library: /public/plugins/jQueryUI/jquery-ui.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.11.4.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/CSPBR/commit/86334f0df744f6cfa35a438987cbb4d18d65b5c2">86334f0df744f6cfa35a438987cbb4d18d65b5c2</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery UI is a curated set of user interface interactions, effects, widgets, and themes built on top of jQuery. Versions prior to 1.13.2 are potentially vulnerable to cross-site scripting. Initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label. Calling `.checkboxradio( "refresh" )` on such a widget and the initial HTML contained encoded HTML entities will make them erroneously get decoded. This can lead to potentially executing JavaScript code. The bug has been patched in jQuery UI 1.13.2. To remediate the issue, someone who can change the initial HTML can wrap all the non-input contents of the `label` in a `span`.
<p>Publish Date: 2022-07-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31160>CVE-2022-31160</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160</a></p>
<p>Release Date: 2022-07-20</p>
<p>Fix Resolution: jquery-ui - 1.13.2</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in jquery ui js jquery ui min js cve medium severity vulnerability vulnerable libraries jquery ui js jquery ui min js jquery ui js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to vulnerable library public plugins jqueryui jquery ui js dependency hierarchy x jquery ui js vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to vulnerable library public plugins jqueryui jquery ui min js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery ui is a curated set of user interface interactions effects widgets and themes built on top of jquery versions prior to are potentially vulnerable to cross site scripting initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label calling checkboxradio refresh on such a widget and the initial html contained encoded html entities will make them erroneously get decoded this can lead to potentially executing javascript code the bug has been patched in jquery ui to remediate the issue someone who can change the initial html can wrap all the non input contents of the label in a span publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery ui | 0 |
153,658 | 13,521,988,815 | IssuesEvent | 2020-09-15 07:53:58 | janraasch/hugo-scroll | https://api.github.com/repos/janraasch/hugo-scroll | closed | Incorporating icons, like Academicons | documentation usage question | A suggestion: to make the theme more welcoming to academics looking for a more stylish personal website than other Hugo theme options, consider making it easy to include [Academicons](https://jpswalsh.github.io/academicons/).
I assume it doesn't take many steps to do, if you already know how. The thing is, of course, learning how!
On a related issue, perhaps it is worth mentioning something about font awesome icons too? For example, are are the free ones built-in and ready to incorporate with the right code, like you do in `themes/hugo-scroll/index.html`? Or does the user need to take additional steps to be able to make use of other icons?
| 1.0 | Incorporating icons, like Academicons - A suggestion: to make the theme more welcoming to academics looking for a more stylish personal website than other Hugo theme options, consider making it easy to include [Academicons](https://jpswalsh.github.io/academicons/).
I assume it doesn't take many steps to do, if you already know how. The thing is, of course, learning how!
On a related issue, perhaps it is worth mentioning something about font awesome icons too? For example, are are the free ones built-in and ready to incorporate with the right code, like you do in `themes/hugo-scroll/index.html`? Or does the user need to take additional steps to be able to make use of other icons?
| non_priority | incorporating icons like academicons a suggestion to make the theme more welcoming to academics looking for a more stylish personal website than other hugo theme options consider making it easy to include i assume it doesn t take many steps to do if you already know how the thing is of course learning how on a related issue perhaps it is worth mentioning something about font awesome icons too for example are are the free ones built in and ready to incorporate with the right code like you do in themes hugo scroll index html or does the user need to take additional steps to be able to make use of other icons | 0 |
254,352 | 19,210,811,793 | IssuesEvent | 2021-12-07 01:32:42 | Leo10Gama/RyuNumber | https://api.github.com/repos/Leo10Gama/RyuNumber | closed | Python Docstrings | documentation | Just discovered that docstrings are a thing, I should implement those and a lot more documentation when I get some time. | 1.0 | Python Docstrings - Just discovered that docstrings are a thing, I should implement those and a lot more documentation when I get some time. | non_priority | python docstrings just discovered that docstrings are a thing i should implement those and a lot more documentation when i get some time | 0 |
174,484 | 13,491,754,810 | IssuesEvent | 2020-09-11 16:59:14 | asgiom/cr8-brm-mobile-issues | https://api.github.com/repos/asgiom/cr8-brm-mobile-issues | closed | [BUG] copy tag to clipboard crashes wallet | bug test | **Describe the bug**
When purchasing cr8 i chose xrp and when using the copy button for the tag the wallet will crash. The copy for address works without error.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to buy/sell
2. View pending transaction
3. Click on copy button for tag
Crash
I have a video but not seeing way to upload
**Expected behavior
Copy and paste of tag to work the same way copy and paste of address works.
**Screenshots**
**Smartphone (please complete the following information):**
- Device: iPhonexs
- OS: ios
- OS Version: 13.4.1
- App Version: 0.5.0
**Additional context**
| 1.0 | [BUG] copy tag to clipboard crashes wallet - **Describe the bug**
When purchasing cr8 i chose xrp and when using the copy button for the tag the wallet will crash. The copy for address works without error.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to buy/sell
2. View pending transaction
3. Click on copy button for tag
Crash
I have a video but not seeing way to upload
**Expected behavior
Copy and paste of tag to work the same way copy and paste of address works.
**Screenshots**
**Smartphone (please complete the following information):**
- Device: iPhonexs
- OS: ios
- OS Version: 13.4.1
- App Version: 0.5.0
**Additional context**
| non_priority | copy tag to clipboard crashes wallet describe the bug when purchasing i chose xrp and when using the copy button for the tag the wallet will crash the copy for address works without error to reproduce steps to reproduce the behavior go to buy sell view pending transaction click on copy button for tag crash i have a video but not seeing way to upload expected behavior copy and paste of tag to work the same way copy and paste of address works screenshots smartphone please complete the following information device iphonexs os ios os version app version additional context | 0 |
29,787 | 8,407,516,943 | IssuesEvent | 2018-10-11 21:11:59 | mayn/packerlicious | https://api.github.com/repos/mayn/packerlicious | closed | builder/AmazonEbs add prop decode_authorization_messages | Hacktoberfest builder help wanted | packer v1.3.1 feature sync
add support for https://www.packer.io/docs/builders/amazon-ebs.html#decode_authorization_messages | 1.0 | builder/AmazonEbs add prop decode_authorization_messages - packer v1.3.1 feature sync
add support for https://www.packer.io/docs/builders/amazon-ebs.html#decode_authorization_messages | non_priority | builder amazonebs add prop decode authorization messages packer feature sync add support for | 0 |
222,708 | 17,089,290,243 | IssuesEvent | 2021-07-08 15:23:40 | flyteorg/flyte | https://api.github.com/repos/flyteorg/flyte | closed | [Docs] Docs intersphinx links are confusing in the theme | documentation | **Describe the documentation update**
In the screenshot below, shows an example of the docs from [here](https://docs.flyte.org/projects/cookbook/en/latest/auto_core_basic/files.html). It is not noticeable that some of the library functions/vars are linked and clickable.
In this example, look at the import statement
```python
from flytekit import task, workflow
```
Here `task` and `workflow` are actually clickable and the user can simply click on these words and navigate automatically to flytekit's documentation of them. But because of the theme, the `hyper-link` underscore is missing.
On the other hand, in the dark mode, this is even more confusing. In the same example `flytekit` is underscored, and this is not a link. This leads to users to not click on anything and we are educating them that links are not clickable.
And update would help users to quickly understand concepts and dive deeper if required.
For an example of a better behavior would be to look at `scikit-learn`s [documentation](https://scikit-learn.org/stable/auto_examples/bicluster/plot_spectral_coclustering.html#sphx-glr-auto-examples-bicluster-plot-spectral-coclustering-py). Screenshot below
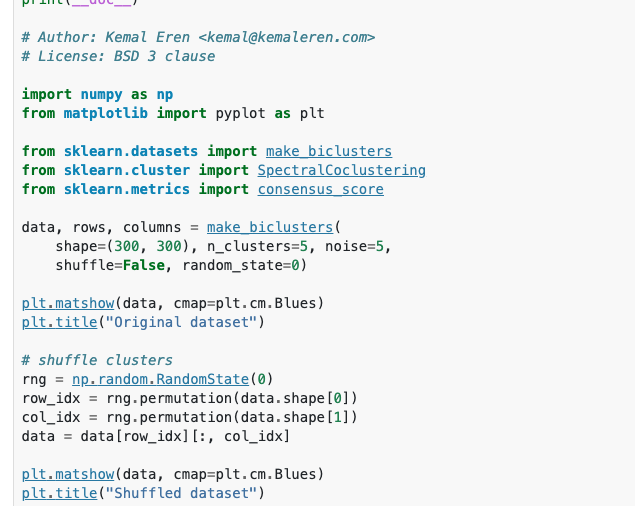
All links here are clickable and simple to understand and follow.
This is probably a simple fix and trying otu different pygments style might help - [here](https://github.com/flyteorg/flytesnacks/blob/master/cookbook/docs/conf.py#L130-L131)
| 1.0 | [Docs] Docs intersphinx links are confusing in the theme - **Describe the documentation update**
In the screenshot below, shows an example of the docs from [here](https://docs.flyte.org/projects/cookbook/en/latest/auto_core_basic/files.html). It is not noticeable that some of the library functions/vars are linked and clickable.
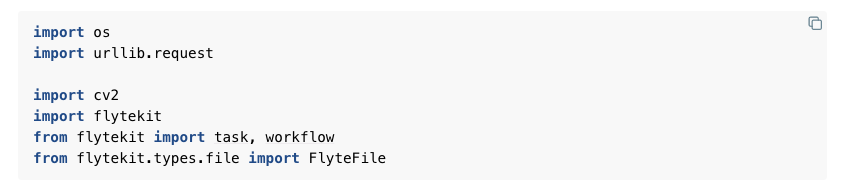
In this example, look at the import statement
```python
from flytekit import task, workflow
```
Here `task` and `workflow` are actually clickable and the user can simply click on these words and navigate automatically to flytekit's documentation of them. But because of the theme, the `hyper-link` underscore is missing.
On the other hand, in the dark mode, this is even more confusing. In the same example `flytekit` is underscored, and this is not a link. This leads to users to not click on anything and we are educating them that links are not clickable.
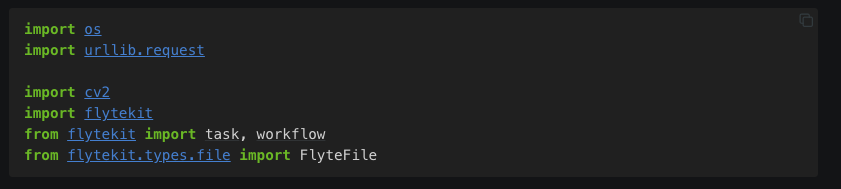
And update would help users to quickly understand concepts and dive deeper if required.
For an example of a better behavior would be to look at `scikit-learn`s [documentation](https://scikit-learn.org/stable/auto_examples/bicluster/plot_spectral_coclustering.html#sphx-glr-auto-examples-bicluster-plot-spectral-coclustering-py). Screenshot below
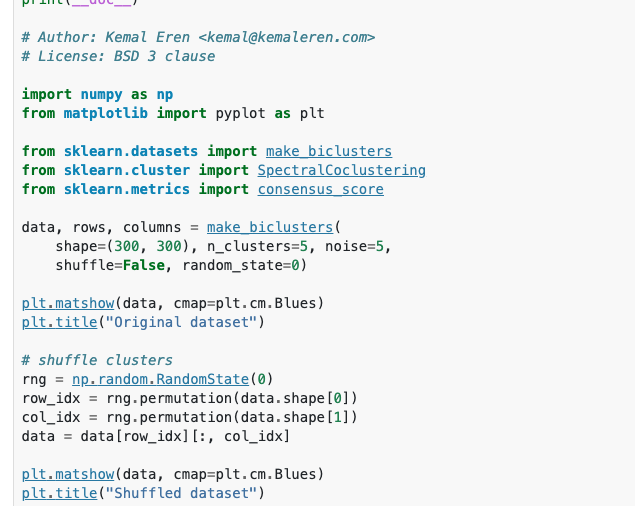
All links here are clickable and simple to understand and follow.
This is probably a simple fix and trying otu different pygments style might help - [here](https://github.com/flyteorg/flytesnacks/blob/master/cookbook/docs/conf.py#L130-L131)
| non_priority | docs intersphinx links are confusing in the theme describe the documentation update in the screenshot below shows an example of the docs from it is not noticeable that some of the library functions vars are linked and clickable in this example look at the import statement python from flytekit import task workflow here task and workflow are actually clickable and the user can simply click on these words and navigate automatically to flytekit s documentation of them but because of the theme the hyper link underscore is missing on the other hand in the dark mode this is even more confusing in the same example flytekit is underscored and this is not a link this leads to users to not click on anything and we are educating them that links are not clickable and update would help users to quickly understand concepts and dive deeper if required for an example of a better behavior would be to look at scikit learn s screenshot below all links here are clickable and simple to understand and follow this is probably a simple fix and trying otu different pygments style might help | 0 |
133,667 | 18,927,569,989 | IssuesEvent | 2021-11-17 11:09:50 | octopusthink/octopusthink.com | https://api.github.com/repos/octopusthink/octopusthink.com | opened | Blog Pagination is unstyled | design | Wheee, we have enough blog posts to show pagination, but unfortunately it's un-styled:
<img width="1295" alt="Screenshot 2021-11-17 at 11 08 36" src="https://user-images.githubusercontent.com/90871/142189567-40d43558-6d01-4cd8-aa82-7ec20677c076.png">
https://octopusthink.com/blog (scroll to the bottom) and you'll see it. | 1.0 | Blog Pagination is unstyled - Wheee, we have enough blog posts to show pagination, but unfortunately it's un-styled:
<img width="1295" alt="Screenshot 2021-11-17 at 11 08 36" src="https://user-images.githubusercontent.com/90871/142189567-40d43558-6d01-4cd8-aa82-7ec20677c076.png">
https://octopusthink.com/blog (scroll to the bottom) and you'll see it. | non_priority | blog pagination is unstyled wheee we have enough blog posts to show pagination but unfortunately it s un styled img width alt screenshot at src scroll to the bottom and you ll see it | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.