Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
56,835 | 6,529,981,575 | IssuesEvent | 2017-08-30 13:43:02 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed tests on master: testrace/TestLogic, testrace/TestLogic/distsql, testrace/TestLogic/distsql/fk | Robot test-failure | The following tests appear to have failed:
[#318512](https://teamcity.cockroachdb.com/viewLog.html?buildId=318512):
```
--- FAIL: testrace/TestLogic (544.850s)
<autogenerated>:10: test logs captured to: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestLogic105657545
<autogenerated>:9: use -show-logs to present logs inline
--- FAIL: testrace/TestLogic/distsql (1.910s)
null
--- FAIL: testrace/TestLogic/distsql/fk (61.430s)
logic_test.go:1728:
testdata/logic_test/fk:721: expected success, but found
pq: restart transaction: HandledRetryableTxnError: TransactionRetryError: retry txn "sql txn" id=1471c8ee key=/Table/SystemConfigSpan/Start rw=true pri=0.01109298 iso=SERIALIZABLE stat=PENDING epo=0 ts=1502214442.885034914,1 orig=1502214442.882029031,0 max=1502214442.882029031,0 wto=false rop=false seq=10
logic_test.go:1739:
testdata/logic_test/fk:721: error in statement, skipping to next file
```
Please assign, take a look and update the issue accordingly. | 1.0 | teamcity: failed tests on master: testrace/TestLogic, testrace/TestLogic/distsql, testrace/TestLogic/distsql/fk - The following tests appear to have failed:
[#318512](https://teamcity.cockroachdb.com/viewLog.html?buildId=318512):
```
--- FAIL: testrace/TestLogic (544.850s)
<autogenerated>:10: test logs captured to: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestLogic105657545
<autogenerated>:9: use -show-logs to present logs inline
--- FAIL: testrace/TestLogic/distsql (1.910s)
null
--- FAIL: testrace/TestLogic/distsql/fk (61.430s)
logic_test.go:1728:
testdata/logic_test/fk:721: expected success, but found
pq: restart transaction: HandledRetryableTxnError: TransactionRetryError: retry txn "sql txn" id=1471c8ee key=/Table/SystemConfigSpan/Start rw=true pri=0.01109298 iso=SERIALIZABLE stat=PENDING epo=0 ts=1502214442.885034914,1 orig=1502214442.882029031,0 max=1502214442.882029031,0 wto=false rop=false seq=10
logic_test.go:1739:
testdata/logic_test/fk:721: error in statement, skipping to next file
```
Please assign, take a look and update the issue accordingly. | non_priority | teamcity failed tests on master testrace testlogic testrace testlogic distsql testrace testlogic distsql fk the following tests appear to have failed fail testrace testlogic test logs captured to go src github com cockroachdb cockroach artifacts use show logs to present logs inline fail testrace testlogic distsql null fail testrace testlogic distsql fk logic test go testdata logic test fk expected success but found pq restart transaction handledretryabletxnerror transactionretryerror retry txn sql txn id key table systemconfigspan start rw true pri iso serializable stat pending epo ts orig max wto false rop false seq logic test go testdata logic test fk error in statement skipping to next file please assign take a look and update the issue accordingly | 0 |
394,803 | 27,040,796,035 | IssuesEvent | 2023-02-13 05:04:37 | jrodriguezlagos/git_web_practice | https://api.github.com/repos/jrodriguezlagos/git_web_practice | closed | Un commit que no sigue la convención de código o FIX a realizar | documentation | La convención del mensaje del último commit no es la esperada:
`Merge branch 'master' of https://github.com/jrodriguezlagos/git_web_practice into master`
Recuerde que debe tener el siguiente formato: `<Identificador de la corrección>: <Comentario>`
Para realizar la corrección del mensaje de commit ejecute los comandos `git commit --amend` y `git push -f`
Este issue es solo un recordatorio de la convención de comentarios en los commits y puede ser cerrado. | 1.0 | Un commit que no sigue la convención de código o FIX a realizar - La convención del mensaje del último commit no es la esperada:
`Merge branch 'master' of https://github.com/jrodriguezlagos/git_web_practice into master`
Recuerde que debe tener el siguiente formato: `<Identificador de la corrección>: <Comentario>`
Para realizar la corrección del mensaje de commit ejecute los comandos `git commit --amend` y `git push -f`
Este issue es solo un recordatorio de la convención de comentarios en los commits y puede ser cerrado. | non_priority | un commit que no sigue la convención de código o fix a realizar la convención del mensaje del último commit no es la esperada merge branch master of into master recuerde que debe tener el siguiente formato para realizar la corrección del mensaje de commit ejecute los comandos git commit amend y git push f este issue es solo un recordatorio de la convención de comentarios en los commits y puede ser cerrado | 0 |
251,127 | 21,419,107,475 | IssuesEvent | 2022-04-22 13:56:28 | TheGameCreators/GameGuruRepo | https://api.github.com/repos/TheGameCreators/GameGuruRepo | opened | Drag camera settings FAR slider to 1 and get a CRASH | bug Max CRASH! Test Game | Create a new terrain level, drop in a building, run test level then grab the far distance and slider it down to 1, it will crash at that point. | 1.0 | Drag camera settings FAR slider to 1 and get a CRASH - Create a new terrain level, drop in a building, run test level then grab the far distance and slider it down to 1, it will crash at that point. | non_priority | drag camera settings far slider to and get a crash create a new terrain level drop in a building run test level then grab the far distance and slider it down to it will crash at that point | 0 |
195,033 | 22,281,639,728 | IssuesEvent | 2022-06-11 01:19:55 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | reopened | CVE-2021-38202 (High) detected in linuxv4.19 | security vulnerability | ## CVE-2021-38202 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
fs/nfsd/trace.h in the Linux kernel before 5.13.4 might allow remote attackers to cause a denial of service (out-of-bounds read in strlen) by sending NFS traffic when the trace event framework is being used for nfsd.
<p>Publish Date: 2021-08-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-38202>CVE-2021-38202</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-38202">https://www.linuxkernelcves.com/cves/CVE-2021-38202</a></p>
<p>Release Date: 2021-08-08</p>
<p>Fix Resolution: v5.13.4,v5.14-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-38202 (High) detected in linuxv4.19 - ## CVE-2021-38202 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
fs/nfsd/trace.h in the Linux kernel before 5.13.4 might allow remote attackers to cause a denial of service (out-of-bounds read in strlen) by sending NFS traffic when the trace event framework is being used for nfsd.
<p>Publish Date: 2021-08-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-38202>CVE-2021-38202</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-38202">https://www.linuxkernelcves.com/cves/CVE-2021-38202</a></p>
<p>Release Date: 2021-08-08</p>
<p>Fix Resolution: v5.13.4,v5.14-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in cve high severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details fs nfsd trace h in the linux kernel before might allow remote attackers to cause a denial of service out of bounds read in strlen by sending nfs traffic when the trace event framework is being used for nfsd publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
390,052 | 26,845,507,459 | IssuesEvent | 2023-02-03 06:29:39 | o3de/o3de.org | https://api.github.com/repos/o3de/o3de.org | closed | [DOCS] Document how to use source control for projects | feature/installer kind/documentation kind/install triage/accepted kind/onboarding | ## Describe the issue briefly
Create content for a drafted page.
Page metadata:
title: "Projects and Source Control"
weight: 500
draft: true
Related issues:
https://github.com/o3de/o3de.org/issues/1509
https://github.com/o3de/o3de.org/issues/964
## Which page(s) / section(s) are affected?
content\docs\user-guide\project-config\project-source-control.md | 1.0 | [DOCS] Document how to use source control for projects - ## Describe the issue briefly
Create content for a drafted page.
Page metadata:
title: "Projects and Source Control"
weight: 500
draft: true
Related issues:
https://github.com/o3de/o3de.org/issues/1509
https://github.com/o3de/o3de.org/issues/964
## Which page(s) / section(s) are affected?
content\docs\user-guide\project-config\project-source-control.md | non_priority | document how to use source control for projects describe the issue briefly create content for a drafted page page metadata title projects and source control weight draft true related issues which page s section s are affected content docs user guide project config project source control md | 0 |
197,350 | 15,651,022,437 | IssuesEvent | 2021-03-23 09:42:28 | alan-turing-institute/sktime | https://api.github.com/repos/alan-turing-institute/sktime | closed | [DOC] automated generation of estimators table | documentation good first issue | #### Describe the issue linked to the documentation
Following an idea by @lynssi, we could think about generating the estimators.md automatically following some parsing convention and automated document compilation.
This would be extremely useful i.m.o., as such an auto-generated table would automatically give a look-up of any papers/documents describing algorithms, perhaps tutorials too, and who is currently the maintainer.
It would also be important since the current version is not too well-curated, since it requires much manual intervention.
#### Suggest a potential alternative/fix
I´m not sure how this would practically work though.
It would require an html or md page to be generated, based on pre-defined tags and hierarchies. | 1.0 | [DOC] automated generation of estimators table - #### Describe the issue linked to the documentation
Following an idea by @lynssi, we could think about generating the estimators.md automatically following some parsing convention and automated document compilation.
This would be extremely useful i.m.o., as such an auto-generated table would automatically give a look-up of any papers/documents describing algorithms, perhaps tutorials too, and who is currently the maintainer.
It would also be important since the current version is not too well-curated, since it requires much manual intervention.
#### Suggest a potential alternative/fix
I´m not sure how this would practically work though.
It would require an html or md page to be generated, based on pre-defined tags and hierarchies. | non_priority | automated generation of estimators table describe the issue linked to the documentation following an idea by lynssi we could think about generating the estimators md automatically following some parsing convention and automated document compilation this would be extremely useful i m o as such an auto generated table would automatically give a look up of any papers documents describing algorithms perhaps tutorials too and who is currently the maintainer it would also be important since the current version is not too well curated since it requires much manual intervention suggest a potential alternative fix i´m not sure how this would practically work though it would require an html or md page to be generated based on pre defined tags and hierarchies | 0 |
291,213 | 21,918,040,857 | IssuesEvent | 2022-05-22 05:55:39 | vjiranek/Natural-Language-Understanding-for-Multiple-Languages | https://api.github.com/repos/vjiranek/Natural-Language-Understanding-for-Multiple-Languages | opened | Upload of Yaml File | documentation enhancement | Please upload the yaml file as soon as possible for the translation of the user utterances! | 1.0 | Upload of Yaml File - Please upload the yaml file as soon as possible for the translation of the user utterances! | non_priority | upload of yaml file please upload the yaml file as soon as possible for the translation of the user utterances | 0 |
77,226 | 7,569,447,982 | IssuesEvent | 2018-04-23 04:34:22 | s-newman/skitter | https://api.github.com/repos/s-newman/skitter | closed | Test User Searching | required test | We need to make sure that user searching works as expected. This will test the `/userSearch` API endpoint. | 1.0 | Test User Searching - We need to make sure that user searching works as expected. This will test the `/userSearch` API endpoint. | non_priority | test user searching we need to make sure that user searching works as expected this will test the usersearch api endpoint | 0 |
33,719 | 4,857,685,136 | IssuesEvent | 2016-11-12 18:56:31 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed tests on master: testrace (proposer evaluated kv)/TestRemoveRangeWithoutGC | Robot test-failure | The following tests appear to have failed:
[#46372](https://teamcity.cockroachdb.com/viewLog.html?buildId=46372):
```
--- FAIL: testrace (proposer evaluated kv)/TestRemoveRangeWithoutGC (0.003s)
Race detected!
I161111 23:06:42.336442 21568 storage/engine/rocksdb.go:340 opening in memory rocksdb instance
I161111 23:06:42.337446 21568 gossip/gossip.go:237 [n?] initial resolvers: []
W161111 23:06:42.337535 21568 gossip/gossip.go:1055 [n?] no resolvers found; use --join to specify a connected node
I161111 23:06:42.337683 21568 base/node_id.go:62 NodeID set to 1
I161111 23:06:42.347308 21568 storage/store.go:1187 [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I161111 23:06:42.347524 21568 gossip/gossip.go:280 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:43886" > attrs:<> locality:<>
I161111 23:06:42.349298 21637 storage/replica_proposal.go:328 [s1,r1/1:/M{in-ax}] new range lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 900.000124ms following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0s [physicalTime=1970-01-01 00:00:00.000000123 +0000 UTC]
I161111 23:06:42.351679 21568 storage/engine/rocksdb.go:340 opening in memory rocksdb instance
I161111 23:06:42.352673 21568 gossip/gossip.go:237 [n?] initial resolvers: [127.0.0.1:43886]
W161111 23:06:42.352762 21568 gossip/gossip.go:1057 [n?] no incoming or outgoing connections
I161111 23:06:42.352918 21568 base/node_id.go:62 NodeID set to 2
I161111 23:06:42.357176 21535 gossip/client.go:125 [n2] started gossip client to 127.0.0.1:43886
I161111 23:06:42.359353 21568 storage/store.go:1187 [n2,s2]: failed initial metrics computation: [n2,s2]: system config not yet available
I161111 23:06:42.359545 21568 gossip/gossip.go:280 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:48452" > attrs:<> locality:<>
I161111 23:06:42.364585 21568 storage/replica_raftstorage.go:445 [s1,r1/1:/M{in-ax}] generated snapshot f29772df at index 13 in 126.105��s.
I161111 23:06:42.366649 21568 storage/store.go:3126 [s1,r1/1:/M{in-ax}] streamed snapshot: kv pairs: 32, log entries: 3
I161111 23:06:42.367996 21417 storage/replica_raftstorage.go:589 [s2,r1/?:{-}] applying preemptive snapshot at index 13 (id=f29772df, encoded size=16, 1 rocksdb batches, 3 log entries)
I161111 23:06:42.368988 21417 storage/replica_raftstorage.go:592 [s2,r1/?:/M{in-ax}] applied preemptive snapshot in 0.001s
I161111 23:06:42.372358 21568 storage/replica_command.go:3245 [s1,r1/1:/M{in-ax}] change replicas: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I161111 23:06:42.376708 21679 storage/replica.go:2055 [s1,r1/1:/M{in-ax}] proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I161111 23:06:42.509446 21781 storage/raft_transport.go:432 raft transport stream to node 1 established
I161111 23:06:42.522955 21568 storage/replica_command.go:3245 [s1,r1/1:/M{in-ax}] change replicas: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:3
I161111 23:06:42.529057 21753 storage/replica.go:2055 [s1,r1/1:/M{in-ax}] proposing REMOVE_REPLICA {NodeID:1 StoreID:1 ReplicaID:1}: [{NodeID:2 StoreID:2 ReplicaID:2}]
E161111 23:06:42.531291 21641 storage/replica_proposal.go:520 [s1,r1/1:/M{in-ax}] unable to add to replica GC queue: queue disabled
I161111 23:06:42.533276 21568 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.533364 21568 util/stop/stopper.go:468 quiescing; tasks left:
1 kv/txn_coord_sender.go:918
E161111 23:06:42.539643 21667 storage/node_liveness.go:141 [hb] failed liveness heartbeat: node unavailable; try another peer
W161111 23:06:42.544720 21768 storage/store.go:2987 [s2] got error from range 1, replica {1 1 1}: storage/raft_transport.go:258: unable to accept Raft message from {NodeID:2 StoreID:2 ReplicaID:2}: no handler registered for {NodeID:1 StoreID:1 ReplicaID:1}
==================
WARNING: DATA RACE
Write at 0x00c4200123b0 by goroutine 323:
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).populateDB()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:603 +0x37d
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).restartStore()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:827 +0x220
github.com/cockroachdb/cockroach/pkg/storage_test.TestRemoveRangeWithoutGC()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_raft_test.go:2558 +0x6cb
testing.tRunner()
/usr/local/go/src/testing/testing.go:610 +0xc9
Previous read at 0x00c4200123b0 by goroutine 317:
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).RangeLookup()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:579 +0x82
github.com/cockroachdb/cockroach/pkg/kv.(*rangeDescriptorCache).performRangeLookup()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_cache.go:443 +0x559
github.com/cockroachdb/cockroach/pkg/kv.(*rangeDescriptorCache).lookupRangeDescriptorInternal()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_cache.go:327 +0x649
github.com/cockroachdb/cockroach/pkg/kv.(*rangeDescriptorCache).LookupRangeDescriptor()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_cache.go:266 +0xb3
github.com/cockroachdb/cockroach/pkg/kv.(*DistSender).getDescriptor()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/dist_sender.go:401 +0xc3
github.com/cockroachdb/cockroach/pkg/kv.(*RangeIterator).Seek()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_iter.go:132 +0x3f5
github.com/cockroachdb/cockroach/pkg/kv.(*DistSender).divideAndSendBatchToRanges()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/dist_sender.go:670 +0x248
github.com/cockroachdb/cockroach/pkg/kv.(*DistSender).Send()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/dist_sender.go:576 +0x32e
github.com/cockroachdb/cockroach/pkg/kv.(*TxnCoordSender).Send()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/txn_coord_sender.go:416 +0x7f1
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).sendInternal()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:585 +0x16e
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).send()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:709 +0x63c
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).(github.com/cockroachdb/cockroach/pkg/internal/client.send)-fm()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:311 +0x7c
github.com/cockroachdb/cockroach/pkg/internal/client.sendAndFill()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/db.go:416 +0x1ab
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).Run()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:311 +0xfd
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).updateLiveness.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:307 +0x54e
github.com/cockroachdb/cockroach/pkg/internal/client.(*DB).Txn.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/db.go:466 +0x46
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).Exec()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:518 +0x233
github.com/cockroachdb/cockroach/pkg/internal/client.(*DB).Txn()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/db.go:467 +0x297
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).updateLiveness()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:308 +0x158
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).heartbeat()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:188 +0x4ed
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).StartHeartbeat.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:140 +0x3b4
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:196 +0x8a
Goroutine 323 (running) created at:
testing.(*T).Run()
/usr/local/go/src/testing/testing.go:646 +0x52f
testing.RunTests.func1()
/usr/local/go/src/testing/testing.go:793 +0xb9
testing.tRunner()
/usr/local/go/src/testing/testing.go:610 +0xc9
testing.RunTests()
/usr/local/go/src/testing/testing.go:799 +0x4ba
testing.(*M).Run()
/usr/local/go/src/testing/testing.go:743 +0x12f
github.com/cockroachdb/cockroach/pkg/storage_test.TestMain()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/main_test.go:57 +0x286
main.main()
github.com/cockroachdb/cockroach/pkg/storage/_test/_testmain.go:752 +0x1b5
Goroutine 317 (running) created at:
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker()
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:197 +0x73
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).StartHeartbeat()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:152 +0x122
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).addStore()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:776 +0x178b
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).Start()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:299 +0xab6
github.com/cockroachdb/cockroach/pkg/storage_test.TestRemoveRangeWithoutGC()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_raft_test.go:2523 +0x225
testing.tRunner()
/usr/local/go/src/testing/testing.go:610 +0xc9
==================
E161111 23:06:42.548643 21568 storage/store.go:1050 [n1,s1,r1/?:/M{in-ax}]: unable to add replica to GC queue: queue disabled
W161111 23:06:42.552379 21820 storage/replica.go:3804 [s1] could not acquire lease for range gossip: range 1 was not found
W161111 23:06:42.552464 21820 storage/store.go:1236 [s1] error gossiping system config: range 1 was not found
W161111 23:06:42.552599 21819 storage/replica.go:3804 [s1] could not acquire lease for range gossip: range 1 was not found
W161111 23:06:42.552680 21819 storage/store.go:1236 [s1] error gossiping first range descriptor: range 1 was not found
I161111 23:06:42.760809 21697 storage/replica_proposal.go:328 [s2,r1/2:/M{in-ax}] new range lease replica {2 2 2} 1970-01-01 00:00:00.900000124 +0000 UTC 240h0m1.800000003s following replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 900.000124ms [physicalTime=1970-01-11 00:00:01.800000126 +0000 UTC]
I161111 23:06:42.766166 21787 util/stop/stopper.go:468 quiescing; tasks left:
1 storage/client_test.go:501
I161111 23:06:42.766838 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
E161111 23:06:42.767103 21593 storage/node_liveness.go:141 [hb] failed liveness heartbeat: node unavailable; try another peer
E161111 23:06:42.767742 21593 storage/node_liveness.go:141 [hb] failed liveness heartbeat: node unavailable; try another peer
I161111 23:06:42.768247 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.769591 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.770699 21531 http2_server.go:276 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:43886->127.0.0.1:54496: use of closed network connection
I161111 23:06:42.770982 21611 http2_server.go:276 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:48452->127.0.0.1:55511: use of closed network connection
I161111 23:06:42.771362 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.771650 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
```
Please assign, take a look and update the issue accordingly. | 1.0 | teamcity: failed tests on master: testrace (proposer evaluated kv)/TestRemoveRangeWithoutGC - The following tests appear to have failed:
[#46372](https://teamcity.cockroachdb.com/viewLog.html?buildId=46372):
```
--- FAIL: testrace (proposer evaluated kv)/TestRemoveRangeWithoutGC (0.003s)
Race detected!
I161111 23:06:42.336442 21568 storage/engine/rocksdb.go:340 opening in memory rocksdb instance
I161111 23:06:42.337446 21568 gossip/gossip.go:237 [n?] initial resolvers: []
W161111 23:06:42.337535 21568 gossip/gossip.go:1055 [n?] no resolvers found; use --join to specify a connected node
I161111 23:06:42.337683 21568 base/node_id.go:62 NodeID set to 1
I161111 23:06:42.347308 21568 storage/store.go:1187 [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I161111 23:06:42.347524 21568 gossip/gossip.go:280 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:43886" > attrs:<> locality:<>
I161111 23:06:42.349298 21637 storage/replica_proposal.go:328 [s1,r1/1:/M{in-ax}] new range lease replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 900.000124ms following replica {0 0 0} 1970-01-01 00:00:00 +0000 UTC 0s [physicalTime=1970-01-01 00:00:00.000000123 +0000 UTC]
I161111 23:06:42.351679 21568 storage/engine/rocksdb.go:340 opening in memory rocksdb instance
I161111 23:06:42.352673 21568 gossip/gossip.go:237 [n?] initial resolvers: [127.0.0.1:43886]
W161111 23:06:42.352762 21568 gossip/gossip.go:1057 [n?] no incoming or outgoing connections
I161111 23:06:42.352918 21568 base/node_id.go:62 NodeID set to 2
I161111 23:06:42.357176 21535 gossip/client.go:125 [n2] started gossip client to 127.0.0.1:43886
I161111 23:06:42.359353 21568 storage/store.go:1187 [n2,s2]: failed initial metrics computation: [n2,s2]: system config not yet available
I161111 23:06:42.359545 21568 gossip/gossip.go:280 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:48452" > attrs:<> locality:<>
I161111 23:06:42.364585 21568 storage/replica_raftstorage.go:445 [s1,r1/1:/M{in-ax}] generated snapshot f29772df at index 13 in 126.105��s.
I161111 23:06:42.366649 21568 storage/store.go:3126 [s1,r1/1:/M{in-ax}] streamed snapshot: kv pairs: 32, log entries: 3
I161111 23:06:42.367996 21417 storage/replica_raftstorage.go:589 [s2,r1/?:{-}] applying preemptive snapshot at index 13 (id=f29772df, encoded size=16, 1 rocksdb batches, 3 log entries)
I161111 23:06:42.368988 21417 storage/replica_raftstorage.go:592 [s2,r1/?:/M{in-ax}] applied preemptive snapshot in 0.001s
I161111 23:06:42.372358 21568 storage/replica_command.go:3245 [s1,r1/1:/M{in-ax}] change replicas: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I161111 23:06:42.376708 21679 storage/replica.go:2055 [s1,r1/1:/M{in-ax}] proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I161111 23:06:42.509446 21781 storage/raft_transport.go:432 raft transport stream to node 1 established
I161111 23:06:42.522955 21568 storage/replica_command.go:3245 [s1,r1/1:/M{in-ax}] change replicas: read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:3
I161111 23:06:42.529057 21753 storage/replica.go:2055 [s1,r1/1:/M{in-ax}] proposing REMOVE_REPLICA {NodeID:1 StoreID:1 ReplicaID:1}: [{NodeID:2 StoreID:2 ReplicaID:2}]
E161111 23:06:42.531291 21641 storage/replica_proposal.go:520 [s1,r1/1:/M{in-ax}] unable to add to replica GC queue: queue disabled
I161111 23:06:42.533276 21568 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.533364 21568 util/stop/stopper.go:468 quiescing; tasks left:
1 kv/txn_coord_sender.go:918
E161111 23:06:42.539643 21667 storage/node_liveness.go:141 [hb] failed liveness heartbeat: node unavailable; try another peer
W161111 23:06:42.544720 21768 storage/store.go:2987 [s2] got error from range 1, replica {1 1 1}: storage/raft_transport.go:258: unable to accept Raft message from {NodeID:2 StoreID:2 ReplicaID:2}: no handler registered for {NodeID:1 StoreID:1 ReplicaID:1}
==================
WARNING: DATA RACE
Write at 0x00c4200123b0 by goroutine 323:
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).populateDB()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:603 +0x37d
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).restartStore()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:827 +0x220
github.com/cockroachdb/cockroach/pkg/storage_test.TestRemoveRangeWithoutGC()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_raft_test.go:2558 +0x6cb
testing.tRunner()
/usr/local/go/src/testing/testing.go:610 +0xc9
Previous read at 0x00c4200123b0 by goroutine 317:
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).RangeLookup()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:579 +0x82
github.com/cockroachdb/cockroach/pkg/kv.(*rangeDescriptorCache).performRangeLookup()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_cache.go:443 +0x559
github.com/cockroachdb/cockroach/pkg/kv.(*rangeDescriptorCache).lookupRangeDescriptorInternal()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_cache.go:327 +0x649
github.com/cockroachdb/cockroach/pkg/kv.(*rangeDescriptorCache).LookupRangeDescriptor()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_cache.go:266 +0xb3
github.com/cockroachdb/cockroach/pkg/kv.(*DistSender).getDescriptor()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/dist_sender.go:401 +0xc3
github.com/cockroachdb/cockroach/pkg/kv.(*RangeIterator).Seek()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/range_iter.go:132 +0x3f5
github.com/cockroachdb/cockroach/pkg/kv.(*DistSender).divideAndSendBatchToRanges()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/dist_sender.go:670 +0x248
github.com/cockroachdb/cockroach/pkg/kv.(*DistSender).Send()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/dist_sender.go:576 +0x32e
github.com/cockroachdb/cockroach/pkg/kv.(*TxnCoordSender).Send()
/go/src/github.com/cockroachdb/cockroach/pkg/kv/txn_coord_sender.go:416 +0x7f1
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).sendInternal()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:585 +0x16e
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).send()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:709 +0x63c
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).(github.com/cockroachdb/cockroach/pkg/internal/client.send)-fm()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:311 +0x7c
github.com/cockroachdb/cockroach/pkg/internal/client.sendAndFill()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/db.go:416 +0x1ab
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).Run()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:311 +0xfd
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).updateLiveness.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:307 +0x54e
github.com/cockroachdb/cockroach/pkg/internal/client.(*DB).Txn.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/db.go:466 +0x46
github.com/cockroachdb/cockroach/pkg/internal/client.(*Txn).Exec()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/txn.go:518 +0x233
github.com/cockroachdb/cockroach/pkg/internal/client.(*DB).Txn()
/go/src/github.com/cockroachdb/cockroach/pkg/internal/client/db.go:467 +0x297
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).updateLiveness()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:308 +0x158
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).heartbeat()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:188 +0x4ed
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).StartHeartbeat.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:140 +0x3b4
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:196 +0x8a
Goroutine 323 (running) created at:
testing.(*T).Run()
/usr/local/go/src/testing/testing.go:646 +0x52f
testing.RunTests.func1()
/usr/local/go/src/testing/testing.go:793 +0xb9
testing.tRunner()
/usr/local/go/src/testing/testing.go:610 +0xc9
testing.RunTests()
/usr/local/go/src/testing/testing.go:799 +0x4ba
testing.(*M).Run()
/usr/local/go/src/testing/testing.go:743 +0x12f
github.com/cockroachdb/cockroach/pkg/storage_test.TestMain()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/main_test.go:57 +0x286
main.main()
github.com/cockroachdb/cockroach/pkg/storage/_test/_testmain.go:752 +0x1b5
Goroutine 317 (running) created at:
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker()
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:197 +0x73
github.com/cockroachdb/cockroach/pkg/storage.(*NodeLiveness).StartHeartbeat()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/node_liveness.go:152 +0x122
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).addStore()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:776 +0x178b
github.com/cockroachdb/cockroach/pkg/storage_test.(*multiTestContext).Start()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_test.go:299 +0xab6
github.com/cockroachdb/cockroach/pkg/storage_test.TestRemoveRangeWithoutGC()
/go/src/github.com/cockroachdb/cockroach/pkg/storage/client_raft_test.go:2523 +0x225
testing.tRunner()
/usr/local/go/src/testing/testing.go:610 +0xc9
==================
E161111 23:06:42.548643 21568 storage/store.go:1050 [n1,s1,r1/?:/M{in-ax}]: unable to add replica to GC queue: queue disabled
W161111 23:06:42.552379 21820 storage/replica.go:3804 [s1] could not acquire lease for range gossip: range 1 was not found
W161111 23:06:42.552464 21820 storage/store.go:1236 [s1] error gossiping system config: range 1 was not found
W161111 23:06:42.552599 21819 storage/replica.go:3804 [s1] could not acquire lease for range gossip: range 1 was not found
W161111 23:06:42.552680 21819 storage/store.go:1236 [s1] error gossiping first range descriptor: range 1 was not found
I161111 23:06:42.760809 21697 storage/replica_proposal.go:328 [s2,r1/2:/M{in-ax}] new range lease replica {2 2 2} 1970-01-01 00:00:00.900000124 +0000 UTC 240h0m1.800000003s following replica {1 1 1} 1970-01-01 00:00:00 +0000 UTC 900.000124ms [physicalTime=1970-01-11 00:00:01.800000126 +0000 UTC]
I161111 23:06:42.766166 21787 util/stop/stopper.go:468 quiescing; tasks left:
1 storage/client_test.go:501
I161111 23:06:42.766838 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
E161111 23:06:42.767103 21593 storage/node_liveness.go:141 [hb] failed liveness heartbeat: node unavailable; try another peer
E161111 23:06:42.767742 21593 storage/node_liveness.go:141 [hb] failed liveness heartbeat: node unavailable; try another peer
I161111 23:06:42.768247 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.769591 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.770699 21531 http2_server.go:276 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:43886->127.0.0.1:54496: use of closed network connection
I161111 23:06:42.770982 21611 http2_server.go:276 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:48452->127.0.0.1:55511: use of closed network connection
I161111 23:06:42.771362 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
I161111 23:06:42.771650 21785 util/stop/stopper.go:396 stop has been called, stopping or quiescing all running tasks
```
Please assign, take a look and update the issue accordingly. | non_priority | teamcity failed tests on master testrace proposer evaluated kv testremoverangewithoutgc the following tests appear to have failed fail testrace proposer evaluated kv testremoverangewithoutgc race detected storage engine rocksdb go opening in memory rocksdb instance gossip gossip go initial resolvers gossip gossip go no resolvers found use join to specify a connected node base node id go nodeid set to storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality storage replica proposal go new range lease replica utc following replica utc storage engine rocksdb go opening in memory rocksdb instance gossip gossip go initial resolvers gossip gossip go no incoming or outgoing connections base node id go nodeid set to gossip client go started gossip client to storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality storage replica raftstorage go generated snapshot at index in ��s storage store go streamed snapshot kv pairs log entries storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas read existing descriptor range id start key end key replicas next replica id storage replica go proposing add replica nodeid storeid replicaid storage raft transport go raft transport stream to node established storage replica command go change replicas read existing descriptor range id start key end key replicas replicas next replica id storage replica go proposing remove replica nodeid storeid replicaid storage replica proposal go unable to add to replica gc queue queue disabled util stop stopper go stop has been called stopping or quiescing all running tasks util stop stopper go quiescing tasks left kv txn coord sender go storage node liveness go failed liveness heartbeat node unavailable try another peer storage store go got error from range replica storage raft transport go unable to accept raft message from nodeid storeid replicaid no handler registered for nodeid storeid replicaid warning data race write at by goroutine github com cockroachdb cockroach pkg storage test multitestcontext populatedb go src github com cockroachdb cockroach pkg storage client test go github com cockroachdb cockroach pkg storage test multitestcontext restartstore go src github com cockroachdb cockroach pkg storage client test go github com cockroachdb cockroach pkg storage test testremoverangewithoutgc go src github com cockroachdb cockroach pkg storage client raft test go testing trunner usr local go src testing testing go previous read at by goroutine github com cockroachdb cockroach pkg storage test multitestcontext rangelookup go src github com cockroachdb cockroach pkg storage client test go github com cockroachdb cockroach pkg kv rangedescriptorcache performrangelookup go src github com cockroachdb cockroach pkg kv range cache go github com cockroachdb cockroach pkg kv rangedescriptorcache lookuprangedescriptorinternal go src github com cockroachdb cockroach pkg kv range cache go github com cockroachdb cockroach pkg kv rangedescriptorcache lookuprangedescriptor go src github com cockroachdb cockroach pkg kv range cache go github com cockroachdb cockroach pkg kv distsender getdescriptor go src github com cockroachdb cockroach pkg kv dist sender go github com cockroachdb cockroach pkg kv rangeiterator seek go src github com cockroachdb cockroach pkg kv range iter go github com cockroachdb cockroach pkg kv distsender divideandsendbatchtoranges go src github com cockroachdb cockroach pkg kv dist sender go github com cockroachdb cockroach pkg kv distsender send go src github com cockroachdb cockroach pkg kv dist sender go github com cockroachdb cockroach pkg kv txncoordsender send go src github com cockroachdb cockroach pkg kv txn coord sender go github com cockroachdb cockroach pkg internal client txn sendinternal go src github com cockroachdb cockroach pkg internal client txn go github com cockroachdb cockroach pkg internal client txn send go src github com cockroachdb cockroach pkg internal client txn go github com cockroachdb cockroach pkg internal client txn github com cockroachdb cockroach pkg internal client send fm go src github com cockroachdb cockroach pkg internal client txn go github com cockroachdb cockroach pkg internal client sendandfill go src github com cockroachdb cockroach pkg internal client db go github com cockroachdb cockroach pkg internal client txn run go src github com cockroachdb cockroach pkg internal client txn go github com cockroachdb cockroach pkg storage nodeliveness updateliveness go src github com cockroachdb cockroach pkg storage node liveness go github com cockroachdb cockroach pkg internal client db txn go src github com cockroachdb cockroach pkg internal client db go github com cockroachdb cockroach pkg internal client txn exec go src github com cockroachdb cockroach pkg internal client txn go github com cockroachdb cockroach pkg internal client db txn go src github com cockroachdb cockroach pkg internal client db go github com cockroachdb cockroach pkg storage nodeliveness updateliveness go src github com cockroachdb cockroach pkg storage node liveness go github com cockroachdb cockroach pkg storage nodeliveness heartbeat go src github com cockroachdb cockroach pkg storage node liveness go github com cockroachdb cockroach pkg storage nodeliveness startheartbeat go src github com cockroachdb cockroach pkg storage node liveness go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine running created at testing t run usr local go src testing testing go testing runtests usr local go src testing testing go testing trunner usr local go src testing testing go testing runtests usr local go src testing testing go testing m run usr local go src testing testing go github com cockroachdb cockroach pkg storage test testmain go src github com cockroachdb cockroach pkg storage main test go main main github com cockroachdb cockroach pkg storage test testmain go goroutine running created at github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go github com cockroachdb cockroach pkg storage nodeliveness startheartbeat go src github com cockroachdb cockroach pkg storage node liveness go github com cockroachdb cockroach pkg storage test multitestcontext addstore go src github com cockroachdb cockroach pkg storage client test go github com cockroachdb cockroach pkg storage test multitestcontext start go src github com cockroachdb cockroach pkg storage client test go github com cockroachdb cockroach pkg storage test testremoverangewithoutgc go src github com cockroachdb cockroach pkg storage client raft test go testing trunner usr local go src testing testing go storage store go unable to add replica to gc queue queue disabled storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping system config range was not found storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping first range descriptor range was not found storage replica proposal go new range lease replica utc following replica utc util stop stopper go quiescing tasks left storage client test go util stop stopper go stop has been called stopping or quiescing all running tasks storage node liveness go failed liveness heartbeat node unavailable try another peer storage node liveness go failed liveness heartbeat node unavailable try another peer util stop stopper go stop has been called stopping or quiescing all running tasks util stop stopper go stop has been called stopping or quiescing all running tasks server go transport handlestreams failed to read frame read tcp use of closed network connection server go transport handlestreams failed to read frame read tcp use of closed network connection util stop stopper go stop has been called stopping or quiescing all running tasks util stop stopper go stop has been called stopping or quiescing all running tasks please assign take a look and update the issue accordingly | 0 |
38,549 | 4,970,459,328 | IssuesEvent | 2016-12-05 16:05:39 | blockstack/designs | https://api.github.com/repos/blockstack/designs | opened | create microsoft 1-click release blog image | design production | Create Microsoft 1-click release blog image.
Image will be appearing on the blog
- https://blogs.microsoft.com/
No image size dimensions provided
Sample image: (from Microsoft blog)
ms-sample-image-640x348

| 1.0 | create microsoft 1-click release blog image - Create Microsoft 1-click release blog image.
Image will be appearing on the blog
- https://blogs.microsoft.com/
No image size dimensions provided
Sample image: (from Microsoft blog)
ms-sample-image-640x348

| non_priority | create microsoft click release blog image create microsoft click release blog image image will be appearing on the blog no image size dimensions provided sample image from microsoft blog ms sample image | 0 |
139,662 | 31,723,357,061 | IssuesEvent | 2023-09-10 17:08:34 | h4sh5/pypi-auto-scanner | https://api.github.com/repos/h4sh5/pypi-auto-scanner | opened | hictkpy 0.0.2 has 4 GuardDog issues | guarddog code-execution exec-base64 | https://pypi.org/project/hictkpy
https://inspector.pypi.io/project/hictkpy
```{
"dependency": "hictkpy",
"version": "0.0.2",
"result": {
"issues": 4,
"errors": {},
"results": {
"code-execution": [
{
"location": "hictkpy-0.0.2/setup.py:127",
"code": " subprocess.run([\"conan\", \"profile\", \"detect\"], check=False)",
"message": "This package is executing OS commands in the setup.py file"
},
{
"location": "hictkpy-0.0.2/setup.py:128",
"code": " subprocess.run([\"conan\", \"profile\", \"detect\", \"--name\", self.plat_name], check=False)",
"message": "This package is executing OS commands in the setup.py file"
},
{
"location": "hictkpy-0.0.2/setup.py:129",
"code": " subprocess.run(\n [\n \"conan\",\n \"install\",\n ext.sourcedir,\n f\"-pr:b=default\",\n f\"-pr:h={self.plat_name}\",\n ... )",
"message": "This package is executing OS commands in the setup.py file"
}
],
"exec-base64": [
{
"location": "hictkpy-0.0.2/setup.py:149",
"code": " subprocess.run([\"cmake\", ext.sourcedir, *cmake_args], cwd=build_temp, check=True)",
"message": "This package contains a call to the `eval` function with a `base64` encoded string as argument.\nThis is a common method used to hide a malicious payload in a module as static analysis will not decode the\nstring.\n"
}
]
},
"path": "/tmp/tmpu2r1kcaz/hictkpy"
}
}``` | 1.0 | hictkpy 0.0.2 has 4 GuardDog issues - https://pypi.org/project/hictkpy
https://inspector.pypi.io/project/hictkpy
```{
"dependency": "hictkpy",
"version": "0.0.2",
"result": {
"issues": 4,
"errors": {},
"results": {
"code-execution": [
{
"location": "hictkpy-0.0.2/setup.py:127",
"code": " subprocess.run([\"conan\", \"profile\", \"detect\"], check=False)",
"message": "This package is executing OS commands in the setup.py file"
},
{
"location": "hictkpy-0.0.2/setup.py:128",
"code": " subprocess.run([\"conan\", \"profile\", \"detect\", \"--name\", self.plat_name], check=False)",
"message": "This package is executing OS commands in the setup.py file"
},
{
"location": "hictkpy-0.0.2/setup.py:129",
"code": " subprocess.run(\n [\n \"conan\",\n \"install\",\n ext.sourcedir,\n f\"-pr:b=default\",\n f\"-pr:h={self.plat_name}\",\n ... )",
"message": "This package is executing OS commands in the setup.py file"
}
],
"exec-base64": [
{
"location": "hictkpy-0.0.2/setup.py:149",
"code": " subprocess.run([\"cmake\", ext.sourcedir, *cmake_args], cwd=build_temp, check=True)",
"message": "This package contains a call to the `eval` function with a `base64` encoded string as argument.\nThis is a common method used to hide a malicious payload in a module as static analysis will not decode the\nstring.\n"
}
]
},
"path": "/tmp/tmpu2r1kcaz/hictkpy"
}
}``` | non_priority | hictkpy has guarddog issues dependency hictkpy version result issues errors results code execution location hictkpy setup py code subprocess run check false message this package is executing os commands in the setup py file location hictkpy setup py code subprocess run check false message this package is executing os commands in the setup py file location hictkpy setup py code subprocess run n n conan n install n ext sourcedir n f pr b default n f pr h self plat name n message this package is executing os commands in the setup py file exec location hictkpy setup py code subprocess run cwd build temp check true message this package contains a call to the eval function with a encoded string as argument nthis is a common method used to hide a malicious payload in a module as static analysis will not decode the nstring n path tmp hictkpy | 0 |
13,640 | 10,369,154,867 | IssuesEvent | 2019-09-07 23:40:15 | perl6/problem-solving | https://api.github.com/repos/perl6/problem-solving | closed | pl6anet.org will be discontinued breaking "Recent Blog Posts" on perl6.org | infrastructure | Currently the right hand side of the perl6.org website "Recent Blog Posts" is dependent on an external system "pl6anet.org" via
https://github.com/perl6/perl6.org/blob/master/fetch-recent-blog-posts.pl
This system will be closing down in about 30 days time and will need someone to work on a replacement if the "Recent Blog Posts" box is to continue.
Hosting a replacement is easy and details are at
https://github.com/stmuk/pl6anet.org
| 1.0 | pl6anet.org will be discontinued breaking "Recent Blog Posts" on perl6.org - Currently the right hand side of the perl6.org website "Recent Blog Posts" is dependent on an external system "pl6anet.org" via
https://github.com/perl6/perl6.org/blob/master/fetch-recent-blog-posts.pl
This system will be closing down in about 30 days time and will need someone to work on a replacement if the "Recent Blog Posts" box is to continue.
Hosting a replacement is easy and details are at
https://github.com/stmuk/pl6anet.org
| non_priority | org will be discontinued breaking recent blog posts on org currently the right hand side of the org website recent blog posts is dependent on an external system org via this system will be closing down in about days time and will need someone to work on a replacement if the recent blog posts box is to continue hosting a replacement is easy and details are at | 0 |
54,837 | 13,960,445,927 | IssuesEvent | 2020-10-24 21:07:12 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | opened | 'configure' fails on Kernel 5.8 with no module support | Status: Triage Needed Type: Defect | ### System information
Type | Version/Name
--- | ---
Distribution Name | Gentoo
Linux Kernel | 5.8+
Architecture | amd64
ZFS Version | 0.8.6-staging, 2.0.0-rc4
### Describe the problem you're observing
Configure fails when used in builtin mode for Linux 5.8 and 5.9 when those have no support for loadable modules.
It works on Linux 5.7 and lower with the same ZFS versions mentioned earlier.
The command I use:
```console
$ ./configure --with-linux=/path/to/linux-stable.git --enable-linux-builtin
[...]
checking kernel source directory... /path/to/linux-stable.git
checking kernel build directory... /path/to/linux-stable.git
checking kernel source version... 5.8.16
checking kernel file name for module symbols... NONE
checking whether modules can be built... no
configure: error:
*** Unable to build an empty module.
*** Please run 'make scripts' inside the kernel source tree.
```
### Include any warning/errors/backtraces from the system logs
Here is the extract of `config.log`:
```
configure:49874: checking whether modules can be built
configure:49935:
KBUILD_MODPOST_NOFINAL= KBUILD_MODPOST_WARN=
make modules -k -j8 -C /path/to/linux-stable.git
M=/path/to/zfs.git/build/conftest >build/conftest/build.log 2>&1
configure:49938: $? = 2
configure:49941: test -f build/conftest/conftest.o
configure:49944: $? = 1
configure:49952: result: no
configure:49959: error:
*** Unable to build an empty module.
*** Please run 'make scripts' inside the kernel source tree.
```
More interestingly, here is the content of `build/conftest/build.log`:
```
make: Entering directory '/path/to/linux-stable.git'
make[1]: *** No rule to make target '/path/to/zfs.git/build/conftest/modules.order', needed by '/path/to/zfs.git/build/conftest/Module.symvers'.
WARNING: Symbol version dump "Module.symvers" is missing.
Modules may not have dependencies or modversions.
make[1]: Target '__modpost' not remade because of errors.
make: *** [Makefile:1665: modules] Error 2
make: Leaving directory '/path/to/linux-stable.git'
```
### Further analysis in kernel changes
Of course this sudden breakage cannot be attributed to ZFS but this has a direct impact when you want to compile ZFS in a standalone kernel.
I did a little bisect in the kernel sources between 5.7 and 5.8 and found that the following commit is responsible:
- https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=436b2ac603d58504f38041a0cd8adb5aeace992b
It seems to be part of a bigger refactoring around modpost performed by Masahiro Yamada (@masahir0y).
There may be a workaround but honestly I don't fully understand what really causes this issue. | 1.0 | 'configure' fails on Kernel 5.8 with no module support - ### System information
Type | Version/Name
--- | ---
Distribution Name | Gentoo
Linux Kernel | 5.8+
Architecture | amd64
ZFS Version | 0.8.6-staging, 2.0.0-rc4
### Describe the problem you're observing
Configure fails when used in builtin mode for Linux 5.8 and 5.9 when those have no support for loadable modules.
It works on Linux 5.7 and lower with the same ZFS versions mentioned earlier.
The command I use:
```console
$ ./configure --with-linux=/path/to/linux-stable.git --enable-linux-builtin
[...]
checking kernel source directory... /path/to/linux-stable.git
checking kernel build directory... /path/to/linux-stable.git
checking kernel source version... 5.8.16
checking kernel file name for module symbols... NONE
checking whether modules can be built... no
configure: error:
*** Unable to build an empty module.
*** Please run 'make scripts' inside the kernel source tree.
```
### Include any warning/errors/backtraces from the system logs
Here is the extract of `config.log`:
```
configure:49874: checking whether modules can be built
configure:49935:
KBUILD_MODPOST_NOFINAL= KBUILD_MODPOST_WARN=
make modules -k -j8 -C /path/to/linux-stable.git
M=/path/to/zfs.git/build/conftest >build/conftest/build.log 2>&1
configure:49938: $? = 2
configure:49941: test -f build/conftest/conftest.o
configure:49944: $? = 1
configure:49952: result: no
configure:49959: error:
*** Unable to build an empty module.
*** Please run 'make scripts' inside the kernel source tree.
```
More interestingly, here is the content of `build/conftest/build.log`:
```
make: Entering directory '/path/to/linux-stable.git'
make[1]: *** No rule to make target '/path/to/zfs.git/build/conftest/modules.order', needed by '/path/to/zfs.git/build/conftest/Module.symvers'.
WARNING: Symbol version dump "Module.symvers" is missing.
Modules may not have dependencies or modversions.
make[1]: Target '__modpost' not remade because of errors.
make: *** [Makefile:1665: modules] Error 2
make: Leaving directory '/path/to/linux-stable.git'
```
### Further analysis in kernel changes
Of course this sudden breakage cannot be attributed to ZFS but this has a direct impact when you want to compile ZFS in a standalone kernel.
I did a little bisect in the kernel sources between 5.7 and 5.8 and found that the following commit is responsible:
- https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=436b2ac603d58504f38041a0cd8adb5aeace992b
It seems to be part of a bigger refactoring around modpost performed by Masahiro Yamada (@masahir0y).
There may be a workaround but honestly I don't fully understand what really causes this issue. | non_priority | configure fails on kernel with no module support system information type version name distribution name gentoo linux kernel architecture zfs version staging describe the problem you re observing configure fails when used in builtin mode for linux and when those have no support for loadable modules it works on linux and lower with the same zfs versions mentioned earlier the command i use console configure with linux path to linux stable git enable linux builtin checking kernel source directory path to linux stable git checking kernel build directory path to linux stable git checking kernel source version checking kernel file name for module symbols none checking whether modules can be built no configure error unable to build an empty module please run make scripts inside the kernel source tree include any warning errors backtraces from the system logs here is the extract of config log configure checking whether modules can be built configure kbuild modpost nofinal kbuild modpost warn make modules k c path to linux stable git m path to zfs git build conftest build conftest build log configure configure test f build conftest conftest o configure configure result no configure error unable to build an empty module please run make scripts inside the kernel source tree more interestingly here is the content of build conftest build log make entering directory path to linux stable git make no rule to make target path to zfs git build conftest modules order needed by path to zfs git build conftest module symvers warning symbol version dump module symvers is missing modules may not have dependencies or modversions make target modpost not remade because of errors make error make leaving directory path to linux stable git further analysis in kernel changes of course this sudden breakage cannot be attributed to zfs but this has a direct impact when you want to compile zfs in a standalone kernel i did a little bisect in the kernel sources between and and found that the following commit is responsible it seems to be part of a bigger refactoring around modpost performed by masahiro yamada there may be a workaround but honestly i don t fully understand what really causes this issue | 0 |
139,645 | 12,877,091,444 | IssuesEvent | 2020-07-11 09:00:59 | rotki/rotki | https://api.github.com/repos/rotki/rotki | opened | Update Usage Guide to reflect new rotki data dir (PR #1135) | documentation | ## Problem Definition
The usage guide should be updated to reflect the new default directory for rotki data as per #1135.
Also include the logs directory somewhere. | 1.0 | Update Usage Guide to reflect new rotki data dir (PR #1135) - ## Problem Definition
The usage guide should be updated to reflect the new default directory for rotki data as per #1135.
Also include the logs directory somewhere. | non_priority | update usage guide to reflect new rotki data dir pr problem definition the usage guide should be updated to reflect the new default directory for rotki data as per also include the logs directory somewhere | 0 |
328,283 | 28,111,079,611 | IssuesEvent | 2023-03-31 07:13:54 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix jax_numpy_linalg.test_jax_numpy_solve | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4544908745/jobs/8011554145" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_jax/test_jax_numpy_linalg.py::test_jax_numpy_solve[cpu-ivy.functional.backends.torch-False-False]</summary>
2023-03-28T15:54:01.1757903Z E TypeError: to_native() got an unexpected keyword argument 'dtype'
2023-03-28T15:54:01.1762236Z E ivy.utils.exceptions.IvyBackendException: jax: nested_map: to_native() got an unexpected keyword argument 'dtype'
2023-03-28T15:54:01.1768439Z E ivy.utils.exceptions.IvyBackendException: jax: nested_map: jax: nested_map: to_native() got an unexpected keyword argument 'dtype'
2023-03-28T15:54:01.1769027Z E Falsifying example: test_jax_numpy_solve(
2023-03-28T15:54:01.1769528Z E dtype_and_data=(['float64'], [array([[0., 1., 0.],
2023-03-28T15:54:01.1769906Z E [1., 0., 1.]])]),
2023-03-28T15:54:01.1770436Z E fn_tree='ivy.functional.frontends.jax.numpy.linalg.solve',
2023-03-28T15:54:01.1770939Z E test_flags=FrontendFunctionTestFlags(
2023-03-28T15:54:01.1771326Z E num_positional_args=0,
2023-03-28T15:54:01.1771653Z E with_out=False,
2023-03-28T15:54:01.1771984Z E inplace=False,
2023-03-28T15:54:01.1772307Z E as_variable=[False],
2023-03-28T15:54:01.1772646Z E native_arrays=[False],
2023-03-28T15:54:01.1772999Z E generate_frontend_arrays=False,
2023-03-28T15:54:01.1773329Z E ),
2023-03-28T15:54:01.1773666Z E on_device='cpu',
2023-03-28T15:54:01.1774017Z E frontend='jax',
2023-03-28T15:54:01.1774311Z E )
2023-03-28T15:54:01.1774562Z E
2023-03-28T15:54:01.1775268Z E You can reproduce this example by temporarily adding @reproduce_failure('6.70.1', b'AXicY2DADhhJFgUAAJ4ABA==') as a decorator on your test case
</details>
| 1.0 | Fix jax_numpy_linalg.test_jax_numpy_solve - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4544908745/jobs/8011554145" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4526951745/jobs/7972435662" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_jax/test_jax_numpy_linalg.py::test_jax_numpy_solve[cpu-ivy.functional.backends.torch-False-False]</summary>
2023-03-28T15:54:01.1757903Z E TypeError: to_native() got an unexpected keyword argument 'dtype'
2023-03-28T15:54:01.1762236Z E ivy.utils.exceptions.IvyBackendException: jax: nested_map: to_native() got an unexpected keyword argument 'dtype'
2023-03-28T15:54:01.1768439Z E ivy.utils.exceptions.IvyBackendException: jax: nested_map: jax: nested_map: to_native() got an unexpected keyword argument 'dtype'
2023-03-28T15:54:01.1769027Z E Falsifying example: test_jax_numpy_solve(
2023-03-28T15:54:01.1769528Z E dtype_and_data=(['float64'], [array([[0., 1., 0.],
2023-03-28T15:54:01.1769906Z E [1., 0., 1.]])]),
2023-03-28T15:54:01.1770436Z E fn_tree='ivy.functional.frontends.jax.numpy.linalg.solve',
2023-03-28T15:54:01.1770939Z E test_flags=FrontendFunctionTestFlags(
2023-03-28T15:54:01.1771326Z E num_positional_args=0,
2023-03-28T15:54:01.1771653Z E with_out=False,
2023-03-28T15:54:01.1771984Z E inplace=False,
2023-03-28T15:54:01.1772307Z E as_variable=[False],
2023-03-28T15:54:01.1772646Z E native_arrays=[False],
2023-03-28T15:54:01.1772999Z E generate_frontend_arrays=False,
2023-03-28T15:54:01.1773329Z E ),
2023-03-28T15:54:01.1773666Z E on_device='cpu',
2023-03-28T15:54:01.1774017Z E frontend='jax',
2023-03-28T15:54:01.1774311Z E )
2023-03-28T15:54:01.1774562Z E
2023-03-28T15:54:01.1775268Z E You can reproduce this example by temporarily adding @reproduce_failure('6.70.1', b'AXicY2DADhhJFgUAAJ4ABA==') as a decorator on your test case
</details>
| non_priority | fix jax numpy linalg test jax numpy solve tensorflow img src torch img src numpy img src jax img src failed ivy tests test ivy test frontends test jax test jax numpy linalg py test jax numpy solve e typeerror to native got an unexpected keyword argument dtype e ivy utils exceptions ivybackendexception jax nested map to native got an unexpected keyword argument dtype e ivy utils exceptions ivybackendexception jax nested map jax nested map to native got an unexpected keyword argument dtype e falsifying example test jax numpy solve e dtype and data e e fn tree ivy functional frontends jax numpy linalg solve e test flags frontendfunctiontestflags e num positional args e with out false e inplace false e as variable e native arrays e generate frontend arrays false e e on device cpu e frontend jax e e e you can reproduce this example by temporarily adding reproduce failure b as a decorator on your test case | 0 |
77,421 | 21,791,300,146 | IssuesEvent | 2022-05-15 00:00:27 | eccentricdevotion/TARDIS | https://api.github.com/repos/eccentricdevotion/TARDIS | closed | Unable to travel to biome | bug build available | ### Describe the bug
Biome, cave, and village travel all appear to be broken on the newest version of the plugin on 1.18.2 servers. 'Could not find biome within distance and time limits!' even when searching the biome one is inside of.
### To Reproduce
1. Be on a 1.18.2 server with the latest version of the plugin
2. Attempt to travel to a specific biome, a village, or a cave
3. Error will arise
### Screenshots
_No response_
### Log files
```
Paste configs or paste.gg link here!
```
### '/tardis version' output
TARDIS Build #2429 | 1.0 | Unable to travel to biome - ### Describe the bug
Biome, cave, and village travel all appear to be broken on the newest version of the plugin on 1.18.2 servers. 'Could not find biome within distance and time limits!' even when searching the biome one is inside of.
### To Reproduce
1. Be on a 1.18.2 server with the latest version of the plugin
2. Attempt to travel to a specific biome, a village, or a cave
3. Error will arise
### Screenshots
_No response_
### Log files
```
Paste configs or paste.gg link here!
```
### '/tardis version' output
TARDIS Build #2429 | non_priority | unable to travel to biome describe the bug biome cave and village travel all appear to be broken on the newest version of the plugin on servers could not find biome within distance and time limits even when searching the biome one is inside of to reproduce be on a server with the latest version of the plugin attempt to travel to a specific biome a village or a cave error will arise screenshots no response log files paste configs or paste gg link here tardis version output tardis build | 0 |
116,048 | 24,850,167,755 | IssuesEvent | 2022-10-26 19:19:07 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Infer Tuple item names from method names | help wanted Area-IDE Feature Request IDE-CodeStyle | The issue in #28928 has been fixed for anonymous types, but not for tuples.
If I write this:
`var x = (GetType(), Enabled);`
'x' will have the two fields 'Item1' and 'Enabled'. and if I use the pulp suggestions to add the tuple declaration instead of var, it will be:
`(Type, bool Enabled) x = (GetType(), Enabled);`
You can infer the name from method names the same way you did in #28928 so 'x' declaration becomes:
'(Type Type, bool Enabled);`
and please fix that in the pulp suggestions too.
| 1.0 | Infer Tuple item names from method names - The issue in #28928 has been fixed for anonymous types, but not for tuples.
If I write this:
`var x = (GetType(), Enabled);`
'x' will have the two fields 'Item1' and 'Enabled'. and if I use the pulp suggestions to add the tuple declaration instead of var, it will be:
`(Type, bool Enabled) x = (GetType(), Enabled);`
You can infer the name from method names the same way you did in #28928 so 'x' declaration becomes:
'(Type Type, bool Enabled);`
and please fix that in the pulp suggestions too.
| non_priority | infer tuple item names from method names the issue in has been fixed for anonymous types but not for tuples if i write this var x gettype enabled x will have the two fields and enabled and if i use the pulp suggestions to add the tuple declaration instead of var it will be type bool enabled x gettype enabled you can infer the name from method names the same way you did in so x declaration becomes type type bool enabled and please fix that in the pulp suggestions too | 0 |
161,138 | 13,806,824,982 | IssuesEvent | 2020-10-11 19:17:46 | NiliStein/DNASimulator | https://api.github.com/repos/NiliStein/DNASimulator | opened | Error Simulation Algorithm (Initial Guidelines) | documentation | # Error Simulation Algorithm
> NOTE: The following is missing the clustering correcting code, thus should be modified later to have it.
## General Guidelines:
0. Duplication of each input strand to the desired amount
For each copy:
1. Error raffle
2. Selection of error location
3. Error injection
And finally write the output to a file.
### 0. Duplication of input strands
This step is required to produce strands for modifications, but should not necessarily happen before the rest of the algorithm.
It's acceptable as well to create a duplicated strand to work with at each iteration of the algorithm.
### 1. Error Raffle
Each strand has a chance of a sole error occurrence, independent of previous happenings and not affecting the following.
> NOTE: We should check probabilities of each error sub-types occurrences as well.
The error is drawn as below.
Let:
* **d** - be the probability of **deletion** error occurrence. (0<d<1)
* **i** - be the probability of **insertion** error occurrence. (0<i<1)
* **s** - be the probability of **substitution** error occurrence. (0<s<1)
And let **n** be the complementary probability to error occurrence (of all types), that is the probability to receive a strand with no errors. (0<n<1)
That implies for the beginning that `d + i + s + n = 1`. (⭐)
1. Sort `{d, i, s, n}` from low to high.
* Notation: `x1 = min{d, i, s, n}`, `x2`, `x3`, `x4 = max{d, i, s, n}`
2. Let `x <- x4 - x1`
3. Draw a random number in the range `(0,x]`
> (⭐) Implies that `0<=x<=1`
4. Check the value of x:
1. If `x` in the range `(0 , x1]` - choose the error corresponding to x1
2. If `x` in the range `(x1 , x1+x2]` - choose the error corresponding to x2
3. If `x` in the range `(x1+x2 , x1+x2+x3]` - choose the error corresponding to x3
4. If `x` in the range `(x1+x2+x3 , x]` - choose the error corresponding to x4
### 2. Selection of Error Location
Assuming that each error might occur anywhere on the strand uniformly:
1. Let `len` be the length of the input strand.
2. Let `index <- random(0,len-1)` be the index of error (beginning) location in the strand, while random is a uniform random function.
### Error Injection
* For deletion:
1. Go to `index` base of the duplicated strand.
1. For multiple base deletions: draw a number between `[1,max_deletion]`, where `max_deletion` is the highest number of bases that can be deleted on a single strand synthesis deletion error. (NOTE: Check probabilities. This step might be implemented as a distinct error in the error raffle step)
2. Delete the base(s) in that index (and to the right) and shift left the content to the right.
* For insertion:
1. Go to `index` base of the duplicated strand.
1. For multiple base insertions: draw a number `k` between `[1,max_insertion]`, where `max_insertion` is the highest number of bases that can be inserted in a single strand synthesis insertion error. (NOTE: Check probabilities. This step might be implemented as a distinct error in the error raffle step)
2. Randomize an insertion sequence in length of `k`.
2. Shift right (`k`) base(s) from that index and fill the gap with the sequence.
* For substitution:
1. Go to `index` character of the duplicated strand.
2. Draw a substituting base (in a similar manner to the error raffle, but for base subsitutions).
3. Replace the base in `index` with the new base.
| 1.0 | Error Simulation Algorithm (Initial Guidelines) - # Error Simulation Algorithm
> NOTE: The following is missing the clustering correcting code, thus should be modified later to have it.
## General Guidelines:
0. Duplication of each input strand to the desired amount
For each copy:
1. Error raffle
2. Selection of error location
3. Error injection
And finally write the output to a file.
### 0. Duplication of input strands
This step is required to produce strands for modifications, but should not necessarily happen before the rest of the algorithm.
It's acceptable as well to create a duplicated strand to work with at each iteration of the algorithm.
### 1. Error Raffle
Each strand has a chance of a sole error occurrence, independent of previous happenings and not affecting the following.
> NOTE: We should check probabilities of each error sub-types occurrences as well.
The error is drawn as below.
Let:
* **d** - be the probability of **deletion** error occurrence. (0<d<1)
* **i** - be the probability of **insertion** error occurrence. (0<i<1)
* **s** - be the probability of **substitution** error occurrence. (0<s<1)
And let **n** be the complementary probability to error occurrence (of all types), that is the probability to receive a strand with no errors. (0<n<1)
That implies for the beginning that `d + i + s + n = 1`. (⭐)
1. Sort `{d, i, s, n}` from low to high.
* Notation: `x1 = min{d, i, s, n}`, `x2`, `x3`, `x4 = max{d, i, s, n}`
2. Let `x <- x4 - x1`
3. Draw a random number in the range `(0,x]`
> (⭐) Implies that `0<=x<=1`
4. Check the value of x:
1. If `x` in the range `(0 , x1]` - choose the error corresponding to x1
2. If `x` in the range `(x1 , x1+x2]` - choose the error corresponding to x2
3. If `x` in the range `(x1+x2 , x1+x2+x3]` - choose the error corresponding to x3
4. If `x` in the range `(x1+x2+x3 , x]` - choose the error corresponding to x4
### 2. Selection of Error Location
Assuming that each error might occur anywhere on the strand uniformly:
1. Let `len` be the length of the input strand.
2. Let `index <- random(0,len-1)` be the index of error (beginning) location in the strand, while random is a uniform random function.
### Error Injection
* For deletion:
1. Go to `index` base of the duplicated strand.
1. For multiple base deletions: draw a number between `[1,max_deletion]`, where `max_deletion` is the highest number of bases that can be deleted on a single strand synthesis deletion error. (NOTE: Check probabilities. This step might be implemented as a distinct error in the error raffle step)
2. Delete the base(s) in that index (and to the right) and shift left the content to the right.
* For insertion:
1. Go to `index` base of the duplicated strand.
1. For multiple base insertions: draw a number `k` between `[1,max_insertion]`, where `max_insertion` is the highest number of bases that can be inserted in a single strand synthesis insertion error. (NOTE: Check probabilities. This step might be implemented as a distinct error in the error raffle step)
2. Randomize an insertion sequence in length of `k`.
2. Shift right (`k`) base(s) from that index and fill the gap with the sequence.
* For substitution:
1. Go to `index` character of the duplicated strand.
2. Draw a substituting base (in a similar manner to the error raffle, but for base subsitutions).
3. Replace the base in `index` with the new base.
| non_priority | error simulation algorithm initial guidelines error simulation algorithm note the following is missing the clustering correcting code thus should be modified later to have it general guidelines duplication of each input strand to the desired amount for each copy error raffle selection of error location error injection and finally write the output to a file duplication of input strands this step is required to produce strands for modifications but should not necessarily happen before the rest of the algorithm it s acceptable as well to create a duplicated strand to work with at each iteration of the algorithm error raffle each strand has a chance of a sole error occurrence independent of previous happenings and not affecting the following note we should check probabilities of each error sub types occurrences as well the error is drawn as below let d be the probability of deletion error occurrence d i be the probability of insertion error occurrence i s be the probability of substitution error occurrence s and let n be the complementary probability to error occurrence of all types that is the probability to receive a strand with no errors n that implies for the beginning that d i s n ⭐ sort d i s n from low to high notation min d i s n max d i s n let x draw a random number in the range x ⭐ implies that x check the value of x if x in the range choose the error corresponding to if x in the range choose the error corresponding to if x in the range choose the error corresponding to if x in the range x choose the error corresponding to selection of error location assuming that each error might occur anywhere on the strand uniformly let len be the length of the input strand let index random len be the index of error beginning location in the strand while random is a uniform random function error injection for deletion go to index base of the duplicated strand for multiple base deletions draw a number between where max deletion is the highest number of bases that can be deleted on a single strand synthesis deletion error note check probabilities this step might be implemented as a distinct error in the error raffle step delete the base s in that index and to the right and shift left the content to the right for insertion go to index base of the duplicated strand for multiple base insertions draw a number k between where max insertion is the highest number of bases that can be inserted in a single strand synthesis insertion error note check probabilities this step might be implemented as a distinct error in the error raffle step randomize an insertion sequence in length of k shift right k base s from that index and fill the gap with the sequence for substitution go to index character of the duplicated strand draw a substituting base in a similar manner to the error raffle but for base subsitutions replace the base in index with the new base | 0 |
60,892 | 8,474,389,840 | IssuesEvent | 2018-10-24 16:01:50 | polkadot-js/api | https://api.github.com/repos/polkadot-js/api | closed | Unable to get examples to work when not following instructions | documentation help wanted question | I can get all the examples to work if I **follow the instructions** in https://polkadot.js.org/api/examples/, by starting a Polkadot Node with `polkadot --dev`, and then in the folder of each example running `yarn; yarn run start`
However, if I **"do my own thing"** to try the examples in a separate folder, I get errors. For example if I create a package.json with `yarn init -y`. Add all dependencies `yarn add bn.js @polkadot/api @polkadot/api-provider @polkadot/storage @polkadot/extrinsics -W`. Install all dependences in node_modules with `yarn`. Start a Polkadot Node with `polkadot --dev`. And then copy/paste the code from each example into a test.js file and run it with `node test.js`.
I can successfully get "Simple Connect" and "Generate Accounts" example code to work.
However I get errors when I run the other examples as follows:
* "Listen to blocks" example code as it just returns #0 (even thought it's already at block #180,000).
* "Listen to balance change" example code, it returns error `TypeError: Cannot read property 'public' of undefined` (in relation to the argument that 's provided `storage.staking.public.freeBalanceOf`).
* "Read Storage" example code returns error `TypeError: Cannot read property 'public' of undefined` (in relation to argument `storage.session.public.validators`).
* "Craft Extrinsic" example code returns error `Error: Cannot find module '@polkadot/extrinsics/codec/encode'` (even after performing `yarn add @polkadot/extrinsics`).
* "Transfer DOTs" example code returns error `Error: Cannot find module '@polkadot/extrinsics/codec/encode/uncheckedLength'
` | 1.0 | Unable to get examples to work when not following instructions - I can get all the examples to work if I **follow the instructions** in https://polkadot.js.org/api/examples/, by starting a Polkadot Node with `polkadot --dev`, and then in the folder of each example running `yarn; yarn run start`
However, if I **"do my own thing"** to try the examples in a separate folder, I get errors. For example if I create a package.json with `yarn init -y`. Add all dependencies `yarn add bn.js @polkadot/api @polkadot/api-provider @polkadot/storage @polkadot/extrinsics -W`. Install all dependences in node_modules with `yarn`. Start a Polkadot Node with `polkadot --dev`. And then copy/paste the code from each example into a test.js file and run it with `node test.js`.
I can successfully get "Simple Connect" and "Generate Accounts" example code to work.
However I get errors when I run the other examples as follows:
* "Listen to blocks" example code as it just returns #0 (even thought it's already at block #180,000).
* "Listen to balance change" example code, it returns error `TypeError: Cannot read property 'public' of undefined` (in relation to the argument that 's provided `storage.staking.public.freeBalanceOf`).
* "Read Storage" example code returns error `TypeError: Cannot read property 'public' of undefined` (in relation to argument `storage.session.public.validators`).
* "Craft Extrinsic" example code returns error `Error: Cannot find module '@polkadot/extrinsics/codec/encode'` (even after performing `yarn add @polkadot/extrinsics`).
* "Transfer DOTs" example code returns error `Error: Cannot find module '@polkadot/extrinsics/codec/encode/uncheckedLength'
` | non_priority | unable to get examples to work when not following instructions i can get all the examples to work if i follow the instructions in by starting a polkadot node with polkadot dev and then in the folder of each example running yarn yarn run start however if i do my own thing to try the examples in a separate folder i get errors for example if i create a package json with yarn init y add all dependencies yarn add bn js polkadot api polkadot api provider polkadot storage polkadot extrinsics w install all dependences in node modules with yarn start a polkadot node with polkadot dev and then copy paste the code from each example into a test js file and run it with node test js i can successfully get simple connect and generate accounts example code to work however i get errors when i run the other examples as follows listen to blocks example code as it just returns even thought it s already at block listen to balance change example code it returns error typeerror cannot read property public of undefined in relation to the argument that s provided storage staking public freebalanceof read storage example code returns error typeerror cannot read property public of undefined in relation to argument storage session public validators craft extrinsic example code returns error error cannot find module polkadot extrinsics codec encode even after performing yarn add polkadot extrinsics transfer dots example code returns error error cannot find module polkadot extrinsics codec encode uncheckedlength | 0 |
61,717 | 25,706,871,782 | IssuesEvent | 2022-12-07 01:42:40 | dockstore/dockstore | https://api.github.com/repos/dockstore/dockstore | opened | A java.lang.Error in processing a workflow causes Dockstore to report it was successfully processed | bug web-service | **Describe the bug**
If a java.lang.Error occurs in processing a workflow, Dockstore reports the workflow as having been successfully processed. But the version is not updated, nor the workflow created if needed.
In this real world case, a WDL had a circular import, which caused a legitimate StackOverflowError from the Cromwell Java code.
Problem looks to be [here](https://github.com/dockstore/dockstore/blob/ba888a658a93a6561fdc0fe7279f6332dbfcd7a3/dockstore-webservice/src/main/java/io/dockstore/webservice/resources/AbstractWorkflowResource.java#L372) -- a StackOverFlowError is not an Exception, so the code falls through to `finally`, where it creates an event saying all is good.
Possibly the root cause of both #5272 and #5273 , although this needs to be verified.
**To Reproduce**
Steps to reproduce the behavior:
It happened with this workflow: https://github.com/aofarrel/fairyland/blob/f057d043b5b56d5259e1bbb2a89c4bbc1fc7e0e9/ld-pruning/ld-pruning-wf.wdl, but it might be hard to reproduce with that one.
1. Create a workflow that imports itself (you'll probably need to do an http import, but maybe not).
2. Register with Dockstore, push
3. Look at the GitHub app logs -- is says the push was successful, but the workflow doesn't show up.
**Expected behavior**
There should be an error in the GitHub app logs.
**Additional context**
[Webservice](https://github.com/dockstore/dockstore/releases/tag/1.13.1) - 1.13.1
[UI](https://github.com/dockstore/dockstore-ui2/releases/tag/2.10.1) - 2.10.1
[Compose Setup](https://github.com/dockstore/compose_setup/releases/tag/1.13.1) - 1.13.1
[Deploy](https://github.com/dockstore/dockstore-deploy/releases/tag/1.13.2) - 1.13.2 | 1.0 | A java.lang.Error in processing a workflow causes Dockstore to report it was successfully processed - **Describe the bug**
If a java.lang.Error occurs in processing a workflow, Dockstore reports the workflow as having been successfully processed. But the version is not updated, nor the workflow created if needed.
In this real world case, a WDL had a circular import, which caused a legitimate StackOverflowError from the Cromwell Java code.
Problem looks to be [here](https://github.com/dockstore/dockstore/blob/ba888a658a93a6561fdc0fe7279f6332dbfcd7a3/dockstore-webservice/src/main/java/io/dockstore/webservice/resources/AbstractWorkflowResource.java#L372) -- a StackOverFlowError is not an Exception, so the code falls through to `finally`, where it creates an event saying all is good.
Possibly the root cause of both #5272 and #5273 , although this needs to be verified.
**To Reproduce**
Steps to reproduce the behavior:
It happened with this workflow: https://github.com/aofarrel/fairyland/blob/f057d043b5b56d5259e1bbb2a89c4bbc1fc7e0e9/ld-pruning/ld-pruning-wf.wdl, but it might be hard to reproduce with that one.
1. Create a workflow that imports itself (you'll probably need to do an http import, but maybe not).
2. Register with Dockstore, push
3. Look at the GitHub app logs -- is says the push was successful, but the workflow doesn't show up.
**Expected behavior**
There should be an error in the GitHub app logs.
**Additional context**
[Webservice](https://github.com/dockstore/dockstore/releases/tag/1.13.1) - 1.13.1
[UI](https://github.com/dockstore/dockstore-ui2/releases/tag/2.10.1) - 2.10.1
[Compose Setup](https://github.com/dockstore/compose_setup/releases/tag/1.13.1) - 1.13.1
[Deploy](https://github.com/dockstore/dockstore-deploy/releases/tag/1.13.2) - 1.13.2 | non_priority | a java lang error in processing a workflow causes dockstore to report it was successfully processed describe the bug if a java lang error occurs in processing a workflow dockstore reports the workflow as having been successfully processed but the version is not updated nor the workflow created if needed in this real world case a wdl had a circular import which caused a legitimate stackoverflowerror from the cromwell java code problem looks to be a stackoverflowerror is not an exception so the code falls through to finally where it creates an event saying all is good possibly the root cause of both and although this needs to be verified to reproduce steps to reproduce the behavior it happened with this workflow but it might be hard to reproduce with that one create a workflow that imports itself you ll probably need to do an http import but maybe not register with dockstore push look at the github app logs is says the push was successful but the workflow doesn t show up expected behavior there should be an error in the github app logs additional context | 0 |
210,846 | 16,387,662,196 | IssuesEvent | 2021-05-17 12:38:31 | f-lab-edu/awesome-wiki | https://api.github.com/repos/f-lab-edu/awesome-wiki | closed | 공통 코드 포맷 지정 | documentation | ### 개요
공통 코드 포맷 및 detekt 규칙을 프로젝트 root 에 추가한다.
### AS-IS
모두들 사용할 수 있는 코드 포맷과 detekt 규칙이 없음.
### TO-BE
공통 코드포맷을 지정해 모든 참여자들이 코드 리뷰 시간에 스타일보다는 그 내용에 좀 더 집중할 수 있도록 돕는다.
| 1.0 | 공통 코드 포맷 지정 - ### 개요
공통 코드 포맷 및 detekt 규칙을 프로젝트 root 에 추가한다.
### AS-IS
모두들 사용할 수 있는 코드 포맷과 detekt 규칙이 없음.
### TO-BE
공통 코드포맷을 지정해 모든 참여자들이 코드 리뷰 시간에 스타일보다는 그 내용에 좀 더 집중할 수 있도록 돕는다.
| non_priority | 공통 코드 포맷 지정 개요 공통 코드 포맷 및 detekt 규칙을 프로젝트 root 에 추가한다 as is 모두들 사용할 수 있는 코드 포맷과 detekt 규칙이 없음 to be 공통 코드포맷을 지정해 모든 참여자들이 코드 리뷰 시간에 스타일보다는 그 내용에 좀 더 집중할 수 있도록 돕는다 | 0 |
25,232 | 7,657,136,191 | IssuesEvent | 2018-05-10 18:37:24 | angular/angular-cli | https://api.github.com/repos/angular/angular-cli | closed | Module not found: Error: Can't resolve ... (using custom path) | comp: cli/build | <!--
We will close this issue if you don't provide the needed information.
For feature requests, delete the form below and describe the requirements and use case.
-->
### Versions
```
Angular CLI: 6.0.0
Node: 8.9.4
OS: win32 x64
Angular: 6.0.0
... animations, cli, common, compiler, compiler-cli, core, forms
... http, language-service, platform-browser
... platform-browser-dynamic, router
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.6.0
@angular-devkit/build-angular 0.6.0
@angular-devkit/build-optimizer 0.6.0
@angular-devkit/core 0.6.0
@angular-devkit/schematics 0.6.0
@ngtools/webpack 6.0.0
@schematics/angular 0.6.0
@schematics/update 0.6.0
rxjs 6.1.0
typescript 2.7.2
webpack 4.6.0
```
### Repro steps
<!--
Simple steps to reproduce this bug.
Please include: commands run, packages added, related code changes.
A link to a sample repo would help too.
-->
* ng new pathtest
* add my-common module
* add Utils folder and service file
* add baseUrl and paths to tsconfig.app.json and tsconfig.json
Sample repo at https://github.com/clabough/Angular6PathIssue
### Observed behavior
`ng build`
```
chunk {main} main.js, main.js.map (main) 12 kB [initial] [rendered]
chunk {polyfills} polyfills.js, polyfills.js.map (polyfills) 227 kB [initial] [rendered]
chunk {runtime} runtime.js, runtime.js.map (runtime) 5.4 kB [entry] [rendered]
chunk {styles} styles.js, styles.js.map (styles) 15.6 kB [initial] [rendered]
chunk {vendor} vendor.js, vendor.js.map (vendor) 3.05 MB [initial] [rendered]
ERROR in ./src/app/app.component.ts
Module not found: Error: Can't resolve 'C:\Local Files\pathTest\src\app\my-common\Utils' in 'C:\Local Files\pathTest\src\app'
```
### Desired behavior
Successful build
| 1.0 | Module not found: Error: Can't resolve ... (using custom path) - <!--
We will close this issue if you don't provide the needed information.
For feature requests, delete the form below and describe the requirements and use case.
-->
### Versions
```
Angular CLI: 6.0.0
Node: 8.9.4
OS: win32 x64
Angular: 6.0.0
... animations, cli, common, compiler, compiler-cli, core, forms
... http, language-service, platform-browser
... platform-browser-dynamic, router
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.6.0
@angular-devkit/build-angular 0.6.0
@angular-devkit/build-optimizer 0.6.0
@angular-devkit/core 0.6.0
@angular-devkit/schematics 0.6.0
@ngtools/webpack 6.0.0
@schematics/angular 0.6.0
@schematics/update 0.6.0
rxjs 6.1.0
typescript 2.7.2
webpack 4.6.0
```
### Repro steps
<!--
Simple steps to reproduce this bug.
Please include: commands run, packages added, related code changes.
A link to a sample repo would help too.
-->
* ng new pathtest
* add my-common module
* add Utils folder and service file
* add baseUrl and paths to tsconfig.app.json and tsconfig.json
Sample repo at https://github.com/clabough/Angular6PathIssue
### Observed behavior
`ng build`
```
chunk {main} main.js, main.js.map (main) 12 kB [initial] [rendered]
chunk {polyfills} polyfills.js, polyfills.js.map (polyfills) 227 kB [initial] [rendered]
chunk {runtime} runtime.js, runtime.js.map (runtime) 5.4 kB [entry] [rendered]
chunk {styles} styles.js, styles.js.map (styles) 15.6 kB [initial] [rendered]
chunk {vendor} vendor.js, vendor.js.map (vendor) 3.05 MB [initial] [rendered]
ERROR in ./src/app/app.component.ts
Module not found: Error: Can't resolve 'C:\Local Files\pathTest\src\app\my-common\Utils' in 'C:\Local Files\pathTest\src\app'
```
### Desired behavior
Successful build
| non_priority | module not found error can t resolve using custom path we will close this issue if you don t provide the needed information for feature requests delete the form below and describe the requirements and use case versions angular cli node os angular animations cli common compiler compiler cli core forms http language service platform browser platform browser dynamic router package version angular devkit architect angular devkit build angular angular devkit build optimizer angular devkit core angular devkit schematics ngtools webpack schematics angular schematics update rxjs typescript webpack repro steps simple steps to reproduce this bug please include commands run packages added related code changes a link to a sample repo would help too ng new pathtest add my common module add utils folder and service file add baseurl and paths to tsconfig app json and tsconfig json sample repo at observed behavior ng build chunk main main js main js map main kb chunk polyfills polyfills js polyfills js map polyfills kb chunk runtime runtime js runtime js map runtime kb chunk styles styles js styles js map styles kb chunk vendor vendor js vendor js map vendor mb error in src app app component ts module not found error can t resolve c local files pathtest src app my common utils in c local files pathtest src app desired behavior successful build | 0 |
61,022 | 6,721,341,261 | IssuesEvent | 2017-10-16 11:19:28 | codepress/admin-columns-issues | https://api.github.com/repos/codepress/admin-columns-issues | closed | Ranged date filtering for more content types | Status: Needs Testing Type: Improvement | Ranged date filtering:
- [x] Post publish date (Since 4.0)
- [x] Comment publish date
- [x] User register date
| 1.0 | Ranged date filtering for more content types - Ranged date filtering:
- [x] Post publish date (Since 4.0)
- [x] Comment publish date
- [x] User register date
| non_priority | ranged date filtering for more content types ranged date filtering post publish date since comment publish date user register date | 0 |
153,184 | 24,084,533,486 | IssuesEvent | 2022-09-19 09:42:58 | nextunicorn-inc/nu-packages | https://api.github.com/repos/nextunicorn-inc/nu-packages | closed | 🔨 REFACTOR: foundation의 font-weight, font-size 사용법을 통일하고 jsdoc을 추가한다. | 🔨 REFACTOR 🌱DESIGN | ## 🚩 변경사항
- FontWeight의 값 타입을 number가 아닌 emotion의 css 타입으로 변경한다.
- FontSize에 주석을 추가한다.
- FontWeight에 angles 접두어를 제거하고 주석을 추가한다.
<br/>
## 🌐 참고 자료
-
<br/>
| 1.0 | 🔨 REFACTOR: foundation의 font-weight, font-size 사용법을 통일하고 jsdoc을 추가한다. - ## 🚩 변경사항
- FontWeight의 값 타입을 number가 아닌 emotion의 css 타입으로 변경한다.
- FontSize에 주석을 추가한다.
- FontWeight에 angles 접두어를 제거하고 주석을 추가한다.
<br/>
## 🌐 참고 자료
-
<br/>
| non_priority | 🔨 refactor foundation의 font weight font size 사용법을 통일하고 jsdoc을 추가한다 🚩 변경사항 fontweight의 값 타입을 number가 아닌 emotion의 css 타입으로 변경한다 fontsize에 주석을 추가한다 fontweight에 angles 접두어를 제거하고 주석을 추가한다 🌐 참고 자료 | 0 |
126,249 | 26,810,215,999 | IssuesEvent | 2023-02-01 21:40:47 | starperov-net/universal_flash_cards_chatbot | https://api.github.com/repos/starperov-net/universal_flash_cards_chatbot | opened | unite duplicate code in /study and /selftest | Yana code_refactoring | Винести дублюючий код у файлі study.py та quick_self_test.py в окремі функції. | 1.0 | unite duplicate code in /study and /selftest - Винести дублюючий код у файлі study.py та quick_self_test.py в окремі функції. | non_priority | unite duplicate code in study and selftest винести дублюючий код у файлі study py та quick self test py в окремі функції | 0 |
43,199 | 23,142,918,113 | IssuesEvent | 2022-07-28 20:26:26 | PowerShell/PowerShellGet | https://api.github.com/repos/PowerShell/PowerShellGet | closed | [Performance improvements for find/install] Fix IEnumerable issues | Area-Find Area-Install feature_request Issue-Performance | ### Summary of the new feature / enhancement
Misuse of IEnumerable is causing multiple server hits in 'Find'.
- LINQ is generics and can cause multiple compiled methods calling search APIs.
- Find code always returned IEnumerable interface, causing LINQ calls to call
search APIs multiple times to manipulate IEnumerable as collections.
- Dependency search returns IEnumerable which is then used as collection and calls server X times.
retrievedPkgs = pkgMetadataResource.GetMetadataAsync(...)
if (retrievedPkgs == null || retrievedPkgs.Count() == 0) ...
foundPackagesMetadata.AddRange(retrievedPkgs.ToList());
### Proposed technical implementation details (optional)
_No response_ | True | [Performance improvements for find/install] Fix IEnumerable issues - ### Summary of the new feature / enhancement
Misuse of IEnumerable is causing multiple server hits in 'Find'.
- LINQ is generics and can cause multiple compiled methods calling search APIs.
- Find code always returned IEnumerable interface, causing LINQ calls to call
search APIs multiple times to manipulate IEnumerable as collections.
- Dependency search returns IEnumerable which is then used as collection and calls server X times.
retrievedPkgs = pkgMetadataResource.GetMetadataAsync(...)
if (retrievedPkgs == null || retrievedPkgs.Count() == 0) ...
foundPackagesMetadata.AddRange(retrievedPkgs.ToList());
### Proposed technical implementation details (optional)
_No response_ | non_priority | fix ienumerable issues summary of the new feature enhancement misuse of ienumerable is causing multiple server hits in find linq is generics and can cause multiple compiled methods calling search apis find code always returned ienumerable interface causing linq calls to call search apis multiple times to manipulate ienumerable as collections dependency search returns ienumerable which is then used as collection and calls server x times retrievedpkgs pkgmetadataresource getmetadataasync if retrievedpkgs null retrievedpkgs count foundpackagesmetadata addrange retrievedpkgs tolist proposed technical implementation details optional no response | 0 |
239,285 | 18,268,199,231 | IssuesEvent | 2021-10-04 10:57:40 | ConorMFinn/CO600-SeriousCyberSec | https://api.github.com/repos/ConorMFinn/CO600-SeriousCyberSec | closed | Create a Video showcasing the game | documentation report | ## Expected Behaviour
Part of the final corpus of materials
There should be a video created that showcases how the game plays and how it works.
## Actual Behaviour
Missing
## Steps to Reproduce Behaviour
1. Check not there.
| 1.0 | Create a Video showcasing the game - ## Expected Behaviour
Part of the final corpus of materials
There should be a video created that showcases how the game plays and how it works.
## Actual Behaviour
Missing
## Steps to Reproduce Behaviour
1. Check not there.
| non_priority | create a video showcasing the game expected behaviour part of the final corpus of materials there should be a video created that showcases how the game plays and how it works actual behaviour missing steps to reproduce behaviour check not there | 0 |
181,275 | 30,655,761,932 | IssuesEvent | 2023-07-25 12:02:33 | status-im/status-desktop | https://api.github.com/repos/status-im/status-desktop | closed | [Community Overview] Update Control Node help page URL opened by `Learn more` button | ui-team C2 E:DesktopCommunityOverviewRedesign | ### Description
The current URL is https://help.status.im/en/status-communities/about-the-control-node-in-status-communities, but it's subject to change.
The domain will definitely change to `status.app`, but the URL layout needs to be discussed with the Status Web team.
### Context
Regarding the URL, please, be aware that our documentation website (Status Help, https://help.status.im/) is now being moved to the new Status web. I don't know the new URLs for any given doc on the new website. @prichodko, @marcelines, @felicio, guys, can you please help us here? 🙏
_Originally posted by @jorge-campo in https://github.com/status-im/status-desktop/pull/11430#discussion_r1255772780_
| 1.0 | [Community Overview] Update Control Node help page URL opened by `Learn more` button - ### Description
The current URL is https://help.status.im/en/status-communities/about-the-control-node-in-status-communities, but it's subject to change.
The domain will definitely change to `status.app`, but the URL layout needs to be discussed with the Status Web team.
### Context
Regarding the URL, please, be aware that our documentation website (Status Help, https://help.status.im/) is now being moved to the new Status web. I don't know the new URLs for any given doc on the new website. @prichodko, @marcelines, @felicio, guys, can you please help us here? 🙏
_Originally posted by @jorge-campo in https://github.com/status-im/status-desktop/pull/11430#discussion_r1255772780_
| non_priority | update control node help page url opened by learn more button description the current url is but it s subject to change the domain will definitely change to status app but the url layout needs to be discussed with the status web team context regarding the url please be aware that our documentation website status help is now being moved to the new status web i don t know the new urls for any given doc on the new website prichodko marcelines felicio guys can you please help us here 🙏 originally posted by jorge campo in | 0 |
13,428 | 23,082,901,743 | IssuesEvent | 2022-07-26 08:50:57 | goharbor/harbor | https://api.github.com/repos/goharbor/harbor | closed | Add current version and fixed version columns in export CVE data csv_file | kind/requirement target/2.6.0 area/cve-export | Currently it is not possible to distinguish between cases where the CVE ID and package are the same but the version is different.
<img width="1062" alt="图片" src="https://user-images.githubusercontent.com/72076317/179457118-363823f6-c5dc-4d94-9928-bc6d1faff51e.png">
| 1.0 | Add current version and fixed version columns in export CVE data csv_file - Currently it is not possible to distinguish between cases where the CVE ID and package are the same but the version is different.
<img width="1062" alt="图片" src="https://user-images.githubusercontent.com/72076317/179457118-363823f6-c5dc-4d94-9928-bc6d1faff51e.png">
| non_priority | add current version and fixed version columns in export cve data csv file currently it is not possible to distinguish between cases where the cve id and package are the same but the version is different img width alt 图片 src | 0 |
418,283 | 28,114,251,835 | IssuesEvent | 2023-03-31 09:31:51 | moseslee9012/ped | https://api.github.com/repos/moseslee9012/ped | opened | Wrong output under `add` command in UG | severity.Low type.DocumentationBug | 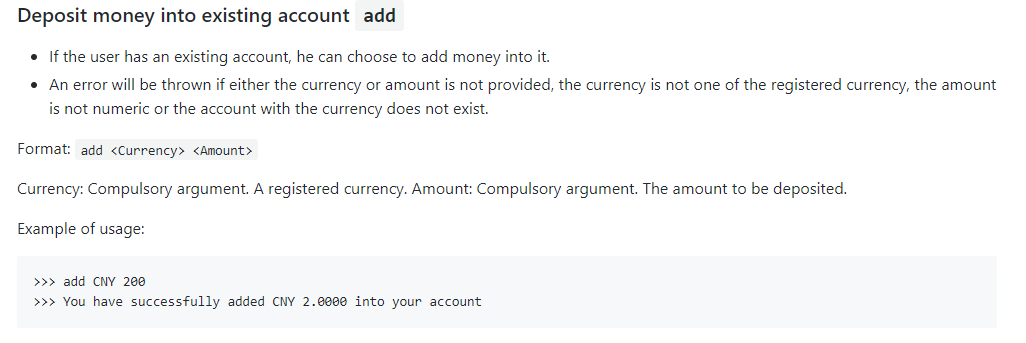
In the UG, when the user adds CNY 200, the output shows `You have successfully added CNY 2.0000 into your account`, but the correct output should be `You have successfully added CNY 200.00 into your account`, as shown below

<!--session: 1680252511905-8af0b136-cf99-4d93-9bc6-63426293b215-->
<!--Version: Web v3.4.7--> | 1.0 | Wrong output under `add` command in UG - 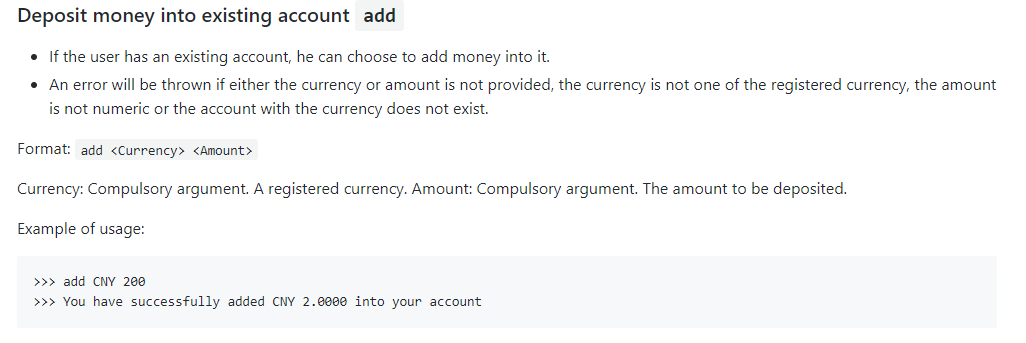
In the UG, when the user adds CNY 200, the output shows `You have successfully added CNY 2.0000 into your account`, but the correct output should be `You have successfully added CNY 200.00 into your account`, as shown below

<!--session: 1680252511905-8af0b136-cf99-4d93-9bc6-63426293b215-->
<!--Version: Web v3.4.7--> | non_priority | wrong output under add command in ug in the ug when the user adds cny the output shows you have successfully added cny into your account but the correct output should be you have successfully added cny into your account as shown below | 0 |
30,885 | 11,860,110,569 | IssuesEvent | 2020-03-25 14:25:41 | BrianMcDonaldWS/genie | https://api.github.com/repos/BrianMcDonaldWS/genie | opened | CVE-2017-16028 (Medium) detected in randomatic-1.1.6.tgz | security vulnerability | ## CVE-2017-16028 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>randomatic-1.1.6.tgz</b></p></summary>
<p>Generate randomized strings of a specified length, fast. Only the length is necessary, but you can optionally generate patterns using any combination of numeric, alpha-numeric, alphabetical, special or custom characters.</p>
<p>Library home page: <a href="https://registry.npmjs.org/randomatic/-/randomatic-1.1.6.tgz">https://registry.npmjs.org/randomatic/-/randomatic-1.1.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/genie/genie-ui/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/genie/genie-ui/node_modules/randomatic/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-1.16.5.tgz (Root Library)
- http-proxy-middleware-0.17.4.tgz
- micromatch-2.3.11.tgz
- braces-1.8.5.tgz
- expand-range-1.8.2.tgz
- fill-range-2.2.3.tgz
- :x: **randomatic-1.1.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BrianMcDonaldWS/genie/commit/568866fb6e52bc93c68e71b643c3271128773566">568866fb6e52bc93c68e71b643c3271128773566</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
react-native-meteor-oauth is a library for Oauth2 login to a Meteor server in React Native. The oauth Random Token is generated using a non-cryptographically strong RNG (Math.random()).
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16028>CVE-2017-16028</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/157">https://nodesecurity.io/advisories/157</a></p>
<p>Release Date: 2017-04-14</p>
<p>Fix Resolution: Update to version 3.0.0 or later.</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"randomatic","packageVersion":"1.1.6","isTransitiveDependency":true,"dependencyTree":"webpack-dev-server:1.16.5;http-proxy-middleware:0.17.4;micromatch:2.3.11;braces:1.8.5;expand-range:1.8.2;fill-range:2.2.3;randomatic:1.1.6","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2017-16028","vulnerabilityDetails":"react-native-meteor-oauth is a library for Oauth2 login to a Meteor server in React Native. The oauth Random Token is generated using a non-cryptographically strong RNG (Math.random()).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16028","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-16028 (Medium) detected in randomatic-1.1.6.tgz - ## CVE-2017-16028 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>randomatic-1.1.6.tgz</b></p></summary>
<p>Generate randomized strings of a specified length, fast. Only the length is necessary, but you can optionally generate patterns using any combination of numeric, alpha-numeric, alphabetical, special or custom characters.</p>
<p>Library home page: <a href="https://registry.npmjs.org/randomatic/-/randomatic-1.1.6.tgz">https://registry.npmjs.org/randomatic/-/randomatic-1.1.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/genie/genie-ui/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/genie/genie-ui/node_modules/randomatic/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-1.16.5.tgz (Root Library)
- http-proxy-middleware-0.17.4.tgz
- micromatch-2.3.11.tgz
- braces-1.8.5.tgz
- expand-range-1.8.2.tgz
- fill-range-2.2.3.tgz
- :x: **randomatic-1.1.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BrianMcDonaldWS/genie/commit/568866fb6e52bc93c68e71b643c3271128773566">568866fb6e52bc93c68e71b643c3271128773566</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
react-native-meteor-oauth is a library for Oauth2 login to a Meteor server in React Native. The oauth Random Token is generated using a non-cryptographically strong RNG (Math.random()).
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16028>CVE-2017-16028</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/157">https://nodesecurity.io/advisories/157</a></p>
<p>Release Date: 2017-04-14</p>
<p>Fix Resolution: Update to version 3.0.0 or later.</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"randomatic","packageVersion":"1.1.6","isTransitiveDependency":true,"dependencyTree":"webpack-dev-server:1.16.5;http-proxy-middleware:0.17.4;micromatch:2.3.11;braces:1.8.5;expand-range:1.8.2;fill-range:2.2.3;randomatic:1.1.6","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2017-16028","vulnerabilityDetails":"react-native-meteor-oauth is a library for Oauth2 login to a Meteor server in React Native. The oauth Random Token is generated using a non-cryptographically strong RNG (Math.random()).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16028","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in randomatic tgz cve medium severity vulnerability vulnerable library randomatic tgz generate randomized strings of a specified length fast only the length is necessary but you can optionally generate patterns using any combination of numeric alpha numeric alphabetical special or custom characters library home page a href path to dependency file tmp ws scm genie genie ui package json path to vulnerable library tmp ws scm genie genie ui node modules randomatic package json dependency hierarchy webpack dev server tgz root library http proxy middleware tgz micromatch tgz braces tgz expand range tgz fill range tgz x randomatic tgz vulnerable library found in head commit a href vulnerability details react native meteor oauth is a library for login to a meteor server in react native the oauth random token is generated using a non cryptographically strong rng math random publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution update to version or later isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails react native meteor oauth is a library for login to a meteor server in react native the oauth random token is generated using a non cryptographically strong rng math random vulnerabilityurl | 0 |
36,830 | 8,176,855,517 | IssuesEvent | 2018-08-28 08:54:32 | openvstorage/framework | https://api.github.com/repos/openvstorage/framework | closed | The GUI mode sometimes reverts to undefined instead of the default full | state_codecomplete type_bug | The GUI mode sometimes reverts to undefined instead of the default full.
http://<ip>/#undefined/<more stuff> instead of http://<ip>/#full/<more stuff>
It happens sometimes, not yet discovered why.
http://jira.openvstorage.com/browse/OVS-2748
| 1.0 | The GUI mode sometimes reverts to undefined instead of the default full - The GUI mode sometimes reverts to undefined instead of the default full.
http://<ip>/#undefined/<more stuff> instead of http://<ip>/#full/<more stuff>
It happens sometimes, not yet discovered why.
http://jira.openvstorage.com/browse/OVS-2748
| non_priority | the gui mode sometimes reverts to undefined instead of the default full the gui mode sometimes reverts to undefined instead of the default full stuff instead of stuff it happens sometimes not yet discovered why | 0 |
67,360 | 12,948,664,603 | IssuesEvent | 2020-07-19 05:40:00 | EdenServer/community | https://api.github.com/repos/EdenServer/community | closed | Yhoator Mandragora levels too low! | in-code-review | ### Checklist
<!--
Don't edit or delete this section, but tick the boxes after you have submitted your issue.
If you are impatient and want to tick boxes before you submit your issue, use an x WITHOUT spaces like this: - [x]
If there are unticked boxes a developer may not address the issue and/or may close the issue without comment.
Make sure you comply with the checklist (as in you're not just ticking boxes you actually do the checklist) and then start writing in the details section below.
-->
- [X] I have searched for existing issues for issues like this one. The issue has not been posted. (Duplicate reports slow down development.)
- [X] I have provided reproducable steps. (No "as the title says" posts please. Provide reproducable steps even if it seems like a waste of time.)
- [X] I have provided my client version in the details. (type /ver into your game window)
### Details
/ver 30181205_1
The mob Yhoator Mandragora has it's levels set too low. They are current 33-35 (I think) when they should be 35-37 as per [this wiki page](https://ffxiclopedia.fandom.com/wiki/Yhoator_Mandragora).
Here are some checks I did during an exp party earlier today:
To duplicate simply check them and you will see they are too low in level.
As a result of this the camp dies very fast and there isn't really enough of a gap between Yuhtunga Mandragoras and these.
Please consider reverting their levels to the era-accurate 35-37. Thanks!
| 1.0 | Yhoator Mandragora levels too low! - ### Checklist
<!--
Don't edit or delete this section, but tick the boxes after you have submitted your issue.
If you are impatient and want to tick boxes before you submit your issue, use an x WITHOUT spaces like this: - [x]
If there are unticked boxes a developer may not address the issue and/or may close the issue without comment.
Make sure you comply with the checklist (as in you're not just ticking boxes you actually do the checklist) and then start writing in the details section below.
-->
- [X] I have searched for existing issues for issues like this one. The issue has not been posted. (Duplicate reports slow down development.)
- [X] I have provided reproducable steps. (No "as the title says" posts please. Provide reproducable steps even if it seems like a waste of time.)
- [X] I have provided my client version in the details. (type /ver into your game window)
### Details
/ver 30181205_1
The mob Yhoator Mandragora has it's levels set too low. They are current 33-35 (I think) when they should be 35-37 as per [this wiki page](https://ffxiclopedia.fandom.com/wiki/Yhoator_Mandragora).
Here are some checks I did during an exp party earlier today:
To duplicate simply check them and you will see they are too low in level.
As a result of this the camp dies very fast and there isn't really enough of a gap between Yuhtunga Mandragoras and these.
Please consider reverting their levels to the era-accurate 35-37. Thanks!
| non_priority | yhoator mandragora levels too low checklist don t edit or delete this section but tick the boxes after you have submitted your issue if you are impatient and want to tick boxes before you submit your issue use an x without spaces like this if there are unticked boxes a developer may not address the issue and or may close the issue without comment make sure you comply with the checklist as in you re not just ticking boxes you actually do the checklist and then start writing in the details section below i have searched for existing issues for issues like this one the issue has not been posted duplicate reports slow down development i have provided reproducable steps no as the title says posts please provide reproducable steps even if it seems like a waste of time i have provided my client version in the details type ver into your game window details ver the mob yhoator mandragora has it s levels set too low they are current i think when they should be as per here are some checks i did during an exp party earlier today to duplicate simply check them and you will see they are too low in level as a result of this the camp dies very fast and there isn t really enough of a gap between yuhtunga mandragoras and these please consider reverting their levels to the era accurate thanks | 0 |
55,389 | 30,728,345,286 | IssuesEvent | 2023-07-27 21:51:14 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | Web engine fallback font initialization adds too much to first frame time. | from: performance template | In profiling the counter demo
`flutter run -d chrome --profile`
I see 80-100ms is spent in the first frame in [FallbackFontManager.createNotoFontTree](https://github.com/flutter/engine/blob/9a935ecbf73a9df9cf76ef234a4f7cd62b1da854/lib/web_ui/lib/src/engine/font_fallbacks.dart#L59)
(This is on Chrome 115.0.5790.110 (Official Build) (64-bit) in Linux, on a powerful workstation, but I don't think the problem is specific to that configuration)
The code constructs an interval tree of ~25k nodes.
- [ ] The initialization happens even if fallback fonts are not needed (as in the counter demo). Perhaps the initialization could be lazy, or async with substeps.
- [x] Half of the time is spent in sorting. I have recently improved sorting and expect that to reduce from ~50ms to ~10ms https://github.com/dart-lang/sdk/commit/74242b1b6ceb9ff7666e66ea75921a871a692be9
- [ ] 10-15% of the time is spent copying lists via `sublist` in the recursive [makeBalancedTree](https://github.com/flutter/engine/blob/9a935ecbf73a9df9cf76ef234a4f7cd62b1da854/lib/web_ui/lib/src/engine/interval_tree.dart#L41). Rewriting `makeBalancedTree` to use a _[start,end)_ range as parameters could completely remove this overhead.
- [ ] `NotoFont._unpackFontRange` takes ~10%. I am working on a new encoding which _should_ be faster because it parses fewer characters, but it still has to allocate ~25k ranges.
A more complicated idea would be to try to avoid the interval tree. The interval tree has ~25k nodes but if this is transformed into a non-overlapping range tree, there would be ~22k nodes. The nodes would then need to map to the set of fonts supporting the code point (range). This tree would be directly useful and could be 'unpacked' in approximately the same time as the aggregate calls to `NotoFont._unpackFontRange`. If the fallback algorithm was modified to not need `NotoFont.contains`, so the ranges list was not needed, this unpacking could replace `_unpackFontRange`.
The fallback algorithm has some inefficiencies too, but I am not sure how important that is, since one remedy is to bundle a font covering the missing code-points. | True | Web engine fallback font initialization adds too much to first frame time. - In profiling the counter demo
`flutter run -d chrome --profile`
I see 80-100ms is spent in the first frame in [FallbackFontManager.createNotoFontTree](https://github.com/flutter/engine/blob/9a935ecbf73a9df9cf76ef234a4f7cd62b1da854/lib/web_ui/lib/src/engine/font_fallbacks.dart#L59)
(This is on Chrome 115.0.5790.110 (Official Build) (64-bit) in Linux, on a powerful workstation, but I don't think the problem is specific to that configuration)
The code constructs an interval tree of ~25k nodes.
- [ ] The initialization happens even if fallback fonts are not needed (as in the counter demo). Perhaps the initialization could be lazy, or async with substeps.
- [x] Half of the time is spent in sorting. I have recently improved sorting and expect that to reduce from ~50ms to ~10ms https://github.com/dart-lang/sdk/commit/74242b1b6ceb9ff7666e66ea75921a871a692be9
- [ ] 10-15% of the time is spent copying lists via `sublist` in the recursive [makeBalancedTree](https://github.com/flutter/engine/blob/9a935ecbf73a9df9cf76ef234a4f7cd62b1da854/lib/web_ui/lib/src/engine/interval_tree.dart#L41). Rewriting `makeBalancedTree` to use a _[start,end)_ range as parameters could completely remove this overhead.
- [ ] `NotoFont._unpackFontRange` takes ~10%. I am working on a new encoding which _should_ be faster because it parses fewer characters, but it still has to allocate ~25k ranges.
A more complicated idea would be to try to avoid the interval tree. The interval tree has ~25k nodes but if this is transformed into a non-overlapping range tree, there would be ~22k nodes. The nodes would then need to map to the set of fonts supporting the code point (range). This tree would be directly useful and could be 'unpacked' in approximately the same time as the aggregate calls to `NotoFont._unpackFontRange`. If the fallback algorithm was modified to not need `NotoFont.contains`, so the ranges list was not needed, this unpacking could replace `_unpackFontRange`.
The fallback algorithm has some inefficiencies too, but I am not sure how important that is, since one remedy is to bundle a font covering the missing code-points. | non_priority | web engine fallback font initialization adds too much to first frame time in profiling the counter demo flutter run d chrome profile i see is spent in the first frame in this is on chrome official build bit in linux on a powerful workstation but i don t think the problem is specific to that configuration the code constructs an interval tree of nodes the initialization happens even if fallback fonts are not needed as in the counter demo perhaps the initialization could be lazy or async with substeps half of the time is spent in sorting i have recently improved sorting and expect that to reduce from to of the time is spent copying lists via sublist in the recursive rewriting makebalancedtree to use a start end range as parameters could completely remove this overhead notofont unpackfontrange takes i am working on a new encoding which should be faster because it parses fewer characters but it still has to allocate ranges a more complicated idea would be to try to avoid the interval tree the interval tree has nodes but if this is transformed into a non overlapping range tree there would be nodes the nodes would then need to map to the set of fonts supporting the code point range this tree would be directly useful and could be unpacked in approximately the same time as the aggregate calls to notofont unpackfontrange if the fallback algorithm was modified to not need notofont contains so the ranges list was not needed this unpacking could replace unpackfontrange the fallback algorithm has some inefficiencies too but i am not sure how important that is since one remedy is to bundle a font covering the missing code points | 0 |
224,705 | 24,784,467,029 | IssuesEvent | 2022-10-24 08:39:22 | sast-automation-dev/django-43 | https://api.github.com/repos/sast-automation-dev/django-43 | opened | bootstrap-3.2.0.js: 6 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.2.0.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: Feb 20, 2019 4:29:00 PM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Feb 20, 2019 4:29:00 PM</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: Jul 13, 2018 2:29:00 PM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Jul 13, 2018 2:29:00 PM</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: Jan 9, 2019 5:29:00 AM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: Jan 9, 2019 5:29:00 AM</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: Jul 13, 2018 2:29:00 PM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Jul 13, 2018 2:29:00 PM</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: Jan 9, 2019 5:29:00 AM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: Jan 9, 2019 5:29:00 AM</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: Jan 9, 2019 5:29:00 AM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Jan 9, 2019 5:29:00 AM</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | True | bootstrap-3.2.0.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.2.0.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: Feb 20, 2019 4:29:00 PM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Feb 20, 2019 4:29:00 PM</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: Jul 13, 2018 2:29:00 PM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Jul 13, 2018 2:29:00 PM</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: Jan 9, 2019 5:29:00 AM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: Jan 9, 2019 5:29:00 AM</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: Jul 13, 2018 2:29:00 PM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Jul 13, 2018 2:29:00 PM</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: Jan 9, 2019 5:29:00 AM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: Jan 9, 2019 5:29:00 AM</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/django-43/commit/18e90f87c1f38d7b1e596a0112997abe5054d696">18e90f87c1f38d7b1e596a0112997abe5054d696</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: Jan 9, 2019 5:29:00 AM
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: Jan 9, 2019 5:29:00 AM</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | non_priority | bootstrap js vulnerabilities highest severity is vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in bootstrap version remediation available medium bootstrap js direct bootstrap bootstrap sass medium bootstrap js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap js direct bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter medium bootstrap js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap js direct bootstrap medium bootstrap js direct details cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date feb pm url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date feb pm fix resolution bootstrap bootstrap sass cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date jul pm url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date jul pm fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date jan am url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date jan am fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date jul pm url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date jul pm fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date jan am url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date jan am fix resolution bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date jan am url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date jan am fix resolution | 0 |
53,460 | 22,796,180,172 | IssuesEvent | 2022-07-10 18:57:39 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | APPSETTING_DEFAULT_OS error when trying to upgrade from Debain 9 to Debian 11 | app-service/svc triaged cxp product-question Pri1 | I am trying to follow the steps in this doc to ensure my app is running smoothly for the transition to Debian 11. However, I am not able to perform step 2 successfully. I get the following error when running this command
`az webapp config appsettings set -g MyResourceGroup -n MyUniqueApp --settings APPSETTING_DEFAULT_OS=bullseye --debug`
` {"Code":"BadRequest","Message":"AppSetting with name 'APPSETTING_DEFAULT_OS' is not allowed.","Target":null,"Details":[{"Message":"AppSetting with name 'APPSETTING_DEFAULT_OS' is not allowed."},{"Code":"BadRequest"},{"ErrorEntity":{"ExtendedCode":"04072","MessageTemplate":"AppSetting with name '{0}' is not allowed.","Parameters":["APPSETTING_DEFAULT_OS"],"Code":"BadRequest","Message":"AppSetting with name 'APPSETTING_DEFAULT_OS' is not allowed."}}],"Innererror":null}
`
How can I make this change in my staging slot to ensure that my app is still working with Debian 11? I tried the same thing through the UI, and got the same error:
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 53dd65b1-6f9d-9431-5850-9cee636aeabd
* Version Independent ID: 0012e819-bb2b-2955-d87b-d6f145fb6af7
* Content: [Overview - Azure App Service](https://docs.microsoft.com/en-us/azure/app-service/overview#debian-9-end-of-life)
* Content Source: [articles/app-service/overview.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/app-service/overview.md)
* Service: **app-service**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | 1.0 | APPSETTING_DEFAULT_OS error when trying to upgrade from Debain 9 to Debian 11 - I am trying to follow the steps in this doc to ensure my app is running smoothly for the transition to Debian 11. However, I am not able to perform step 2 successfully. I get the following error when running this command
`az webapp config appsettings set -g MyResourceGroup -n MyUniqueApp --settings APPSETTING_DEFAULT_OS=bullseye --debug`
` {"Code":"BadRequest","Message":"AppSetting with name 'APPSETTING_DEFAULT_OS' is not allowed.","Target":null,"Details":[{"Message":"AppSetting with name 'APPSETTING_DEFAULT_OS' is not allowed."},{"Code":"BadRequest"},{"ErrorEntity":{"ExtendedCode":"04072","MessageTemplate":"AppSetting with name '{0}' is not allowed.","Parameters":["APPSETTING_DEFAULT_OS"],"Code":"BadRequest","Message":"AppSetting with name 'APPSETTING_DEFAULT_OS' is not allowed."}}],"Innererror":null}
`
How can I make this change in my staging slot to ensure that my app is still working with Debian 11? I tried the same thing through the UI, and got the same error:
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 53dd65b1-6f9d-9431-5850-9cee636aeabd
* Version Independent ID: 0012e819-bb2b-2955-d87b-d6f145fb6af7
* Content: [Overview - Azure App Service](https://docs.microsoft.com/en-us/azure/app-service/overview#debian-9-end-of-life)
* Content Source: [articles/app-service/overview.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/app-service/overview.md)
* Service: **app-service**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | non_priority | appsetting default os error when trying to upgrade from debain to debian i am trying to follow the steps in this doc to ensure my app is running smoothly for the transition to debian however i am not able to perform step successfully i get the following error when running this command az webapp config appsettings set g myresourcegroup n myuniqueapp settings appsetting default os bullseye debug code badrequest message appsetting with name appsetting default os is not allowed target null details code badrequest message appsetting with name appsetting default os is not allowed innererror null how can i make this change in my staging slot to ensure that my app is still working with debian i tried the same thing through the ui and got the same error document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service app service github login cephalin microsoft alias cephalin | 0 |
66,584 | 8,953,682,817 | IssuesEvent | 2019-01-25 20:13:22 | coq/coq | https://api.github.com/repos/coq/coq | closed | Documentation doesn't explain clearly enough how to use options and the difference between flags and options. | kind: documentation | <!-- Thank you for your contribution.
Please complete the following information when reporting a bug. -->
#### Version 8.8
<!-- You can get this information by running `coqtop -v`. -->
#### Operating system Windows 10
#### Description of the problem
The command `Set Printing Compact Contexts on." is documented but not accepted in Coqtop. Should be made to work or removed from the doc. If the option is removed, references to it in the comments before Printer.bld_sign_env and pr_context_limit_compact and use of the option value in Printer.should_compact should also be removed.
https://coq.inria.fr/distrib/current/refman/proof-engine/vernacular-commands.html?highlight=compact#coq:opt.printing-compact-contexts
```
Unnamed_thm < Set Printing Compact Contexts on.
Toplevel input, characters 0-33:
> Set Printing Compact Contexts on.
> ^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
Warning: There is no option Printing Compact Contexts on.
[unknown-option,option]
```
| 1.0 | Documentation doesn't explain clearly enough how to use options and the difference between flags and options. - <!-- Thank you for your contribution.
Please complete the following information when reporting a bug. -->
#### Version 8.8
<!-- You can get this information by running `coqtop -v`. -->
#### Operating system Windows 10
#### Description of the problem
The command `Set Printing Compact Contexts on." is documented but not accepted in Coqtop. Should be made to work or removed from the doc. If the option is removed, references to it in the comments before Printer.bld_sign_env and pr_context_limit_compact and use of the option value in Printer.should_compact should also be removed.
https://coq.inria.fr/distrib/current/refman/proof-engine/vernacular-commands.html?highlight=compact#coq:opt.printing-compact-contexts
```
Unnamed_thm < Set Printing Compact Contexts on.
Toplevel input, characters 0-33:
> Set Printing Compact Contexts on.
> ^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
Warning: There is no option Printing Compact Contexts on.
[unknown-option,option]
```
| non_priority | documentation doesn t explain clearly enough how to use options and the difference between flags and options thank you for your contribution please complete the following information when reporting a bug version operating system windows description of the problem the command set printing compact contexts on is documented but not accepted in coqtop should be made to work or removed from the doc if the option is removed references to it in the comments before printer bld sign env and pr context limit compact and use of the option value in printer should compact should also be removed unnamed thm set printing compact contexts on toplevel input characters set printing compact contexts on warning there is no option printing compact contexts on | 0 |
177,420 | 21,475,382,220 | IssuesEvent | 2022-04-26 13:16:22 | pazhanivel07/frameworks_base_Aosp10_r33_CVE-2021-0315 | https://api.github.com/repos/pazhanivel07/frameworks_base_Aosp10_r33_CVE-2021-0315 | opened | CVE-2021-0928 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-0928 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>baseandroid-10.0.0_r46</b>, <b>baseandroid-10.0.0_r46</b>, <b>baseandroid-10.0.0_r46</b>, <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In createFromParcel of OutputConfiguration.java, there is a possible parcel serialization/deserialization mismatch due to improper input validation. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-9Android ID: A-188675581
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0928>CVE-2021-0928</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-0928 (High) detected in multiple libraries - ## CVE-2021-0928 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>baseandroid-10.0.0_r46</b>, <b>baseandroid-10.0.0_r46</b>, <b>baseandroid-10.0.0_r46</b>, <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In createFromParcel of OutputConfiguration.java, there is a possible parcel serialization/deserialization mismatch due to improper input validation. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-9Android ID: A-188675581
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0928>CVE-2021-0928</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries baseandroid baseandroid baseandroid baseandroid vulnerability details in createfromparcel of outputconfiguration java there is a possible parcel serialization deserialization mismatch due to improper input validation this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
30,018 | 14,370,511,966 | IssuesEvent | 2020-12-01 11:11:58 | pounard/goat-query | https://api.github.com/repos/pounard/goat-query | closed | Optimize AbstractSqlWriter::rewriteQueryAndParameters() | enhancement needs evaluation performance | This method is historically the oldest piece of this whole component. It has been rewrote or improved many times, but today, we cannot really make it faster anymore as it exists.
In some benchmarks, this method execution time takes up to 1/3rd of query formatting, prepare, execute, which is huge.
Some leads we can follow:
- make this a component which can be replaced,
- write default implementation to be the current one,
- write an optional parser not using preg and benchmark, whereas this could be a nice improvement for PHP8 + JIT (this is a purely arbitrary assumption) it may be much much slower than preg,
- write an external optional implementation using c, rust, I don't care the language, based upon a parsing framework such as nom (rust), or any other, and plug it using FFI,
- any other ideas?
| True | Optimize AbstractSqlWriter::rewriteQueryAndParameters() - This method is historically the oldest piece of this whole component. It has been rewrote or improved many times, but today, we cannot really make it faster anymore as it exists.
In some benchmarks, this method execution time takes up to 1/3rd of query formatting, prepare, execute, which is huge.
Some leads we can follow:
- make this a component which can be replaced,
- write default implementation to be the current one,
- write an optional parser not using preg and benchmark, whereas this could be a nice improvement for PHP8 + JIT (this is a purely arbitrary assumption) it may be much much slower than preg,
- write an external optional implementation using c, rust, I don't care the language, based upon a parsing framework such as nom (rust), or any other, and plug it using FFI,
- any other ideas?
| non_priority | optimize abstractsqlwriter rewritequeryandparameters this method is historically the oldest piece of this whole component it has been rewrote or improved many times but today we cannot really make it faster anymore as it exists in some benchmarks this method execution time takes up to of query formatting prepare execute which is huge some leads we can follow make this a component which can be replaced write default implementation to be the current one write an optional parser not using preg and benchmark whereas this could be a nice improvement for jit this is a purely arbitrary assumption it may be much much slower than preg write an external optional implementation using c rust i don t care the language based upon a parsing framework such as nom rust or any other and plug it using ffi any other ideas | 0 |
281,782 | 30,888,948,021 | IssuesEvent | 2023-08-04 02:03:00 | nidhi7598/linux-4.1.15_CVE-2019-10220 | https://api.github.com/repos/nidhi7598/linux-4.1.15_CVE-2019-10220 | reopened | CVE-2017-16994 (Medium) detected in linuxlinux-4.4.302 | Mend: dependency security vulnerability | ## CVE-2017-16994 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.1.15_CVE-2019-10220/commit/6a0d304d962ca933d73f507ce02157ef2791851c">6a0d304d962ca933d73f507ce02157ef2791851c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/pagewalk.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/pagewalk.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The walk_hugetlb_range function in mm/pagewalk.c in the Linux kernel before 4.14.2 mishandles holes in hugetlb ranges, which allows local users to obtain sensitive information from uninitialized kernel memory via crafted use of the mincore() system call.
<p>Publish Date: 2017-11-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-16994>CVE-2017-16994</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16994">https://nvd.nist.gov/vuln/detail/CVE-2017-16994</a></p>
<p>Release Date: 2017-11-27</p>
<p>Fix Resolution: 4.14.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-16994 (Medium) detected in linuxlinux-4.4.302 - ## CVE-2017-16994 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.1.15_CVE-2019-10220/commit/6a0d304d962ca933d73f507ce02157ef2791851c">6a0d304d962ca933d73f507ce02157ef2791851c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/pagewalk.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/pagewalk.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The walk_hugetlb_range function in mm/pagewalk.c in the Linux kernel before 4.14.2 mishandles holes in hugetlb ranges, which allows local users to obtain sensitive information from uninitialized kernel memory via crafted use of the mincore() system call.
<p>Publish Date: 2017-11-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-16994>CVE-2017-16994</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16994">https://nvd.nist.gov/vuln/detail/CVE-2017-16994</a></p>
<p>Release Date: 2017-11-27</p>
<p>Fix Resolution: 4.14.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files mm pagewalk c mm pagewalk c vulnerability details the walk hugetlb range function in mm pagewalk c in the linux kernel before mishandles holes in hugetlb ranges which allows local users to obtain sensitive information from uninitialized kernel memory via crafted use of the mincore system call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
132,337 | 10,741,627,192 | IssuesEvent | 2019-10-29 20:38:46 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [TEST] IndexLifecycleInitialisationTests#testExplainExecution failing | :Core/Features/ILM+SLM >test-failure | Build scan: https://gradle.com/s/dxhi5ukbyipee
Relevant output:
```
org.elasticsearch.xpack.ilm.IndexLifecycleInitialisationTests > testExplainExecution FAILED
java.time.format.DateTimeParseException: Text '2019-07-29T06:54Z' could not be parsed at index 16
at __randomizedtesting.SeedInfo.seed([9D5B884C7F0F4F4E:97A5C8C9D42F1CBF]:0)
at java.time.format.DateTimeFormatter.parseResolved0(DateTimeFormatter.java:1949)
at java.time.format.DateTimeFormatter.parse(DateTimeFormatter.java:1851)
at java.time.Instant.parse(Instant.java:395)
at org.elasticsearch.xpack.ilm.IndexLifecycleInitialisationTests.testExplainExecution(IndexLifecycleInitialisationTests.java:219)
REPRODUCE WITH: ./gradlew :x-pack:plugin:ilm:test --tests "org.elasticsearch.xpack.ilm.IndexLifecycleInitialisationTests.testExplainExecution" -Dtests.seed=9D5B884C7F0F4F4E -Dtests.security.manager=true -Dtests.locale=es-CL -Dtests.timezone=America/St_Lucia -Dcompiler.java=12 -Druntime.java=8
``` | 1.0 | [TEST] IndexLifecycleInitialisationTests#testExplainExecution failing - Build scan: https://gradle.com/s/dxhi5ukbyipee
Relevant output:
```
org.elasticsearch.xpack.ilm.IndexLifecycleInitialisationTests > testExplainExecution FAILED
java.time.format.DateTimeParseException: Text '2019-07-29T06:54Z' could not be parsed at index 16
at __randomizedtesting.SeedInfo.seed([9D5B884C7F0F4F4E:97A5C8C9D42F1CBF]:0)
at java.time.format.DateTimeFormatter.parseResolved0(DateTimeFormatter.java:1949)
at java.time.format.DateTimeFormatter.parse(DateTimeFormatter.java:1851)
at java.time.Instant.parse(Instant.java:395)
at org.elasticsearch.xpack.ilm.IndexLifecycleInitialisationTests.testExplainExecution(IndexLifecycleInitialisationTests.java:219)
REPRODUCE WITH: ./gradlew :x-pack:plugin:ilm:test --tests "org.elasticsearch.xpack.ilm.IndexLifecycleInitialisationTests.testExplainExecution" -Dtests.seed=9D5B884C7F0F4F4E -Dtests.security.manager=true -Dtests.locale=es-CL -Dtests.timezone=America/St_Lucia -Dcompiler.java=12 -Druntime.java=8
``` | non_priority | indexlifecycleinitialisationtests testexplainexecution failing build scan relevant output org elasticsearch xpack ilm indexlifecycleinitialisationtests testexplainexecution failed java time format datetimeparseexception text could not be parsed at index at randomizedtesting seedinfo seed at java time format datetimeformatter datetimeformatter java at java time format datetimeformatter parse datetimeformatter java at java time instant parse instant java at org elasticsearch xpack ilm indexlifecycleinitialisationtests testexplainexecution indexlifecycleinitialisationtests java reproduce with gradlew x pack plugin ilm test tests org elasticsearch xpack ilm indexlifecycleinitialisationtests testexplainexecution dtests seed dtests security manager true dtests locale es cl dtests timezone america st lucia dcompiler java druntime java | 0 |
11,507 | 4,233,768,632 | IssuesEvent | 2016-07-05 09:14:19 | Elorfin/MusicTools | https://api.github.com/repos/Elorfin/MusicTools | closed | [Insight] The response should be redirected after posting data to an action - in src/…/Controller/LessonController.php, line 55 | code-style | **[in src/LessonBundle/Controller/LessonController.php, line 55](https://github.com/Elorfin/MusicTools/blob/a48c683d35f7ec6b7a338aec7e230fc4d8ff356c/src/LessonBundle/Controller/LessonController.php#L55)**
> The `createAction()` method allows POST requests, but does not redirect the user. It is a common best practice to call a redirect after a POST action.
```php
* @return JsonApiResponse
*
* @Route("")
* @Method("POST")
*/
public function createAction()
{
}
/**
```
---------------------
_Posted from [SensioLabsInsight](https://insight.sensiolabs.com/projects/74bd74a9-b6fc-4b4e-9eb6-146748ab49db/analyses/33)_ | 1.0 | [Insight] The response should be redirected after posting data to an action - in src/…/Controller/LessonController.php, line 55 - **[in src/LessonBundle/Controller/LessonController.php, line 55](https://github.com/Elorfin/MusicTools/blob/a48c683d35f7ec6b7a338aec7e230fc4d8ff356c/src/LessonBundle/Controller/LessonController.php#L55)**
> The `createAction()` method allows POST requests, but does not redirect the user. It is a common best practice to call a redirect after a POST action.
```php
* @return JsonApiResponse
*
* @Route("")
* @Method("POST")
*/
public function createAction()
{
}
/**
```
---------------------
_Posted from [SensioLabsInsight](https://insight.sensiolabs.com/projects/74bd74a9-b6fc-4b4e-9eb6-146748ab49db/analyses/33)_ | non_priority | the response should be redirected after posting data to an action in src … controller lessoncontroller php line the createaction method allows post requests but does not redirect the user it is a common best practice to call a redirect after a post action php return jsonapiresponse route method post public function createaction posted from | 0 |
198,466 | 15,710,280,726 | IssuesEvent | 2021-03-27 01:11:49 | thanhphuongIT/APP_DIEMDANH | https://api.github.com/repos/thanhphuongIT/APP_DIEMDANH | closed | Phân tích nghiệp vụ quản lý sinh viên | documentation | - Tìm kiếm và tra cứu thông tin sinh viên
- Sắp xếp thời khóa biểu cho sinh viên
- Lọc danh sách sinh viên theo yêu cầu
- Kiểm tra thông tin sinh viên (văng, tham gia) theo ngày/tháng/năm và môn học
| 1.0 | Phân tích nghiệp vụ quản lý sinh viên - - Tìm kiếm và tra cứu thông tin sinh viên
- Sắp xếp thời khóa biểu cho sinh viên
- Lọc danh sách sinh viên theo yêu cầu
- Kiểm tra thông tin sinh viên (văng, tham gia) theo ngày/tháng/năm và môn học
| non_priority | phân tích nghiệp vụ quản lý sinh viên tìm kiếm và tra cứu thông tin sinh viên sắp xếp thời khóa biểu cho sinh viên lọc danh sách sinh viên theo yêu cầu kiểm tra thông tin sinh viên văng tham gia theo ngày tháng năm và môn học | 0 |
51,566 | 6,534,749,975 | IssuesEvent | 2017-08-31 12:10:02 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Generic Enums (Not sure if this is the right place for this) | Area-Language Design Resolution-Duplicate | Recently I was trying to implement something like a Generic Enum Property. I looked at Enum and TEnum but they did not seem to provide what I needed. Is there any work to make Enums more flexible to work with (a la Java)? Thanks! | 1.0 | Generic Enums (Not sure if this is the right place for this) - Recently I was trying to implement something like a Generic Enum Property. I looked at Enum and TEnum but they did not seem to provide what I needed. Is there any work to make Enums more flexible to work with (a la Java)? Thanks! | non_priority | generic enums not sure if this is the right place for this recently i was trying to implement something like a generic enum property i looked at enum and tenum but they did not seem to provide what i needed is there any work to make enums more flexible to work with a la java thanks | 0 |
19,304 | 4,375,752,741 | IssuesEvent | 2016-08-05 01:31:50 | san650/ember-cli-page-object | https://api.github.com/repos/san650/ember-cli-page-object | closed | Go to source code links are broken in the website | bug documentation help wanted | Each method in the API documentation has a link to the source code, right now those links are broken. See http://ember-cli-page-object.js.org/docs/v1.4.x/api/helpers#getcontext
Expected URL
https://github.com/san650/ember-cli-page-object/blob/f6764e1741c7d2964c1cba26ae375c672ad45d02/addon/helpers.js#L300-L309
Actual URL
http://ember-cli-page-object.js.org/docs/v1.4.x/api/undefined/blob/f6764e1741c7d2964c1cba26ae375c672ad45d02/addon/helpers.js#L300-L309 | 1.0 | Go to source code links are broken in the website - Each method in the API documentation has a link to the source code, right now those links are broken. See http://ember-cli-page-object.js.org/docs/v1.4.x/api/helpers#getcontext
Expected URL
https://github.com/san650/ember-cli-page-object/blob/f6764e1741c7d2964c1cba26ae375c672ad45d02/addon/helpers.js#L300-L309
Actual URL
http://ember-cli-page-object.js.org/docs/v1.4.x/api/undefined/blob/f6764e1741c7d2964c1cba26ae375c672ad45d02/addon/helpers.js#L300-L309 | non_priority | go to source code links are broken in the website each method in the api documentation has a link to the source code right now those links are broken see expected url actual url | 0 |
14,869 | 9,430,890,630 | IssuesEvent | 2019-04-12 10:07:16 | Alfresco/alfresco-data-model | https://api.github.com/repos/Alfresco/alfresco-data-model | closed | CVE-2017-12624 Medium Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2017-12624 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cxf-rt-frontend-jaxrs-3.0.16.jar</b></p></summary>
<p>Apache CXF Runtime JAX-RS Frontend</p>
<p>Library home page: <a href="http://cxf.apache.org">http://cxf.apache.org</a></p>
<p>Path to dependency file: /alfresco-data-model/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/cxf/cxf-rt-frontend-jaxrs/3.0.16/cxf-rt-frontend-jaxrs-3.0.16.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.17-20180201-alfresco-patched.jar (Root Library)
- cxf-rt-rs-client-3.0.16.jar
- :x: **cxf-rt-frontend-jaxrs-3.0.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Alfresco/alfresco-data-model/commit/cbfe8041c3ecbbf176a5208a087cb87e8ad2504f">cbfe8041c3ecbbf176a5208a087cb87e8ad2504f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache CXF supports sending and receiving attachments via either the JAX-WS or JAX-RS specifications. It is possible to craft a message attachment header that could lead to a Denial of Service (DoS) attack on a CXF web service provider. Both JAX-WS and JAX-RS services are vulnerable to this attack. From Apache CXF 3.2.1 and 3.1.14, message attachment headers that are greater than 300 characters will be rejected by default. This value is configurable via the property "attachment-max-header-size".
<p>Publish Date: 2017-11-14
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12624>CVE-2017-12624</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12624">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12624</a></p>
<p>Release Date: 2017-11-14</p>
<p>Fix Resolution: 3.2.1, 3.1.14</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isOpenPROnNewVersion":false,"isPackageBased":true,"packages":[{"packageType":"Java","groupId":"org.apache.cxf","packageName":"cxf-rt-frontend-jaxrs","packageVersion":"3.0.16","isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.17-20180201-alfresco-patched;org.apache.cxf:cxf-rt-rs-client:3.0.16;org.apache.cxf:cxf-rt-frontend-jaxrs:3.0.16","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.2.1, 3.1.14"}],"vulnerabilityIdentifier":"CVE-2017-12624","vulnerabilityDetails":"Apache CXF supports sending and receiving attachments via either the JAX-WS or JAX-RS specifications. It is possible to craft a message attachment header that could lead to a Denial of Service (DoS) attack on a CXF web service provider. Both JAX-WS and JAX-RS services are vulnerable to this attack. From Apache CXF 3.2.1 and 3.1.14, message attachment headers that are greater than 300 characters will be rejected by default. This value is configurable via the property \"attachment-max-header-size\".","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-12624 Medium Severity Vulnerability detected by WhiteSource - ## CVE-2017-12624 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cxf-rt-frontend-jaxrs-3.0.16.jar</b></p></summary>
<p>Apache CXF Runtime JAX-RS Frontend</p>
<p>Library home page: <a href="http://cxf.apache.org">http://cxf.apache.org</a></p>
<p>Path to dependency file: /alfresco-data-model/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/cxf/cxf-rt-frontend-jaxrs/3.0.16/cxf-rt-frontend-jaxrs-3.0.16.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.17-20180201-alfresco-patched.jar (Root Library)
- cxf-rt-rs-client-3.0.16.jar
- :x: **cxf-rt-frontend-jaxrs-3.0.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Alfresco/alfresco-data-model/commit/cbfe8041c3ecbbf176a5208a087cb87e8ad2504f">cbfe8041c3ecbbf176a5208a087cb87e8ad2504f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache CXF supports sending and receiving attachments via either the JAX-WS or JAX-RS specifications. It is possible to craft a message attachment header that could lead to a Denial of Service (DoS) attack on a CXF web service provider. Both JAX-WS and JAX-RS services are vulnerable to this attack. From Apache CXF 3.2.1 and 3.1.14, message attachment headers that are greater than 300 characters will be rejected by default. This value is configurable via the property "attachment-max-header-size".
<p>Publish Date: 2017-11-14
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12624>CVE-2017-12624</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12624">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-12624</a></p>
<p>Release Date: 2017-11-14</p>
<p>Fix Resolution: 3.2.1, 3.1.14</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isOpenPROnNewVersion":false,"isPackageBased":true,"packages":[{"packageType":"Java","groupId":"org.apache.cxf","packageName":"cxf-rt-frontend-jaxrs","packageVersion":"3.0.16","isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.17-20180201-alfresco-patched;org.apache.cxf:cxf-rt-rs-client:3.0.16;org.apache.cxf:cxf-rt-frontend-jaxrs:3.0.16","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.2.1, 3.1.14"}],"vulnerabilityIdentifier":"CVE-2017-12624","vulnerabilityDetails":"Apache CXF supports sending and receiving attachments via either the JAX-WS or JAX-RS specifications. It is possible to craft a message attachment header that could lead to a Denial of Service (DoS) attack on a CXF web service provider. Both JAX-WS and JAX-RS services are vulnerable to this attack. From Apache CXF 3.2.1 and 3.1.14, message attachment headers that are greater than 300 characters will be rejected by default. This value is configurable via the property \"attachment-max-header-size\".","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium severity vulnerability detected by whitesource cve medium severity vulnerability vulnerable library cxf rt frontend jaxrs jar apache cxf runtime jax rs frontend library home page a href path to dependency file alfresco data model pom xml path to vulnerable library root repository org apache cxf cxf rt frontend jaxrs cxf rt frontend jaxrs jar dependency hierarchy tika parsers alfresco patched jar root library cxf rt rs client jar x cxf rt frontend jaxrs jar vulnerable library found in head commit a href vulnerability details apache cxf supports sending and receiving attachments via either the jax ws or jax rs specifications it is possible to craft a message attachment header that could lead to a denial of service dos attack on a cxf web service provider both jax ws and jax rs services are vulnerable to this attack from apache cxf and message attachment headers that are greater than characters will be rejected by default this value is configurable via the property attachment max header size publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource isopenpronvulnerability true isopenpronnewversion false ispackagebased true packages vulnerabilityidentifier cve vulnerabilitydetails apache cxf supports sending and receiving attachments via either the jax ws or jax rs specifications it is possible to craft a message attachment header that could lead to a denial of service dos attack on a cxf web service provider both jax ws and jax rs services are vulnerable to this attack from apache cxf and message attachment headers that are greater than characters will be rejected by default this value is configurable via the property attachment max header size medium a high ac low pr none s unchanged c none ui required av local i none extradata | 0 |
256,439 | 19,412,714,317 | IssuesEvent | 2021-12-20 11:23:02 | Tobats1992/polyfills.io-tobats1992 | https://api.github.com/repos/Tobats1992/polyfills.io-tobats1992 | closed | beam.mw.polyfills.bf99d438b005d57b2b31.js | documentation | (window.webpackJsonp=window.webpackJsonp||[]).push([[2],{1:function(e,t,n){e.exports=n("hN/g")},"hN/g":function(e,t,n){"use strict";n.r(t),n("pDpN")},pDpN:function(e,t,n){var o,r;void 0===(r="function"==typeof(o=function(){"use strict";!function(e){const t=e.performance;function n(e){t&&t.mark&&t.mark(e)}function o(e,n){t&&t.measure&&t.measure(e,n)}n("Zone");const r=e.__Zone_symbol_prefix||"__zone_symbol__";function s(e){return r+e}const i=!0===e[s("forceDuplicateZoneCheck")];if(e.Zone){if(i||"function"!=typeof e.Zone.__symbol__)throw new Error("Zone already loaded.");return e.Zone}class a{constructor(e,t){this._parent=e,this._name=t?t.name||"unnamed":"<root>",this._properties=t&&t.properties||{},this._zoneDelegate=new l(this,this._parent&&this._parent._zoneDelegate,t)}static assertZonePatched(){if(e.Promise!==C.ZoneAwarePromise)throw new Error("Zone.js has detected that ZoneAwarePromise `(window|global).Promise` has been overwritten.\nMost likely cause is that a Promise polyfill has been loaded after Zone.js (Polyfilling Promise api is not necessary when zone.js is loaded. If you must load one, do so before loading zone.js.)")}static get root(){let e=a.current;for(;e.parent;)e=e.parent;return e}static get current(){return z.zone}static get currentTask(){return j}static __load_patch(t,r){if(C.hasOwnProperty(t)){if(i)throw Error("Already loaded patch: "+t)}else if(!e["__Zone_disable_"+t]){const s="Zone:"+t;n(s),C[t]=r(e,a,O),o(s,s)}}get parent(){return this._parent}get name(){return this._name}get(e){const t=this.getZoneWith(e);if(t)return t._properties[e]}getZoneWith(e){let t=this;for(;t;){if(t._properties.hasOwnProperty(e))return t;t=t._parent}return null}fork(e){if(!e)throw new Error("ZoneSpec required!");return this._zoneDelegate.fork(this,e)}wrap(e,t){if("function"!=typeof e)throw new Error("Expecting function got: "+e);const n=this._zoneDelegate.intercept(this,e,t),o=this;return function(){return o.runGuarded(n,this,arguments,t)}}run(e,t,n,o){z={parent:z,zone:this};try{return this._zoneDelegate.invoke(this,e,t,n,o)}finally{z=z.parent}}runGuarded(e,t=null,n,o){z={parent:z,zone:this};try{try{return this._zoneDelegate.invoke(this,e,t,n,o)}catch(r){if(this._zoneDelegate.handleError(this,r))throw r}}finally{z=z.parent}}runTask(e,t,n){if(e.zone!=this)throw new Error("A task can only be run in the zone of creation! (Creation: "+(e.zone||y).name+"; Execution: "+this.name+")");if(e.state===v&&(e.type===P||e.type===D))return;const o=e.state!=E;o&&e._transitionTo(E,T),e.runCount++;const r=j;j=e,z={parent:z,zone:this};try{e.type==D&&e.data&&!e.data.isPeriodic&&(e.cancelFn=void 0);try{return this._zoneDelegate.invokeTask(this,e,t,n)}catch(s){if(this._zoneDelegate.handleError(this,s))throw s}}finally{e.state!==v&&e.state!==Z&&(e.type==P||e.data&&e.data.isPeriodic?o&&e._transitionTo(T,E):(e.runCount=0,this._updateTaskCount(e,-1),o&&e._transitionTo(v,E,v))),z=z.parent,j=r}}scheduleTask(e){if(e.zone&&e.zone!==this){let t=this;for(;t;){if(t===e.zone)throw Error(`can not reschedule task to ${this.name} which is descendants of the original zone ${e.zone.name}`);t=t.parent}}e._transitionTo(b,v);const t=[];e._zoneDelegates=t,e._zone=this;try{e=this._zoneDelegate.scheduleTask(this,e)}catch(n){throw e._transitionTo(Z,b,v),this._zoneDelegate.handleError(this,n),n}return e._zoneDelegates===t&&this._updateTaskCount(e,1),e.state==b&&e._transitionTo(T,b),e}scheduleMicroTask(e,t,n,o){return this.scheduleTask(new u(S,e,t,n,o,void 0))}scheduleMacroTask(e,t,n,o,r){return this.scheduleTask(new u(D,e,t,n,o,r))}scheduleEventTask(e,t,n,o,r){return this.scheduleTask(new u(P,e,t,n,o,r))}cancelTask(e){if(e.zone!=this)throw new Error("A task can only be cancelled in the zone of creation! (Creation: "+(e.zone||y).name+"; Execution: "+this.name+")");e._transitionTo(w,T,E);try{this._zoneDelegate.cancelTask(this,e)}catch(t){throw e._transitionTo(Z,w),this._zoneDelegate.handleError(this,t),t}return this._updateTaskCount(e,-1),e._transitionTo(v,w),e.runCount=0,e}_updateTaskCount(e,t){const n=e._zoneDelegates;-1==t&&(e._zoneDelegates=null);for(let o=0;o<n.length;o++)n[o]._updateTaskCount(e.type,t)}}a.__symbol__=s;const c={name:"",onHasTask:(e,t,n,o)=>e.hasTask(n,o),onScheduleTask:(e,t,n,o)=>e.scheduleTask(n,o),onInvokeTask:(e,t,n,o,r,s)=>e.invokeTask(n,o,r,s),onCancelTask:(e,t,n,o)=>e.cancelTask(n,o)};class l{constructor(e,t,n){this._taskCounts={microTask:0,macroTask:0,eventTask:0},this.zone=e,this._parentDelegate=t,this._forkZS=n&&(n&&n.onFork?n:t._forkZS),this._forkDlgt=n&&(n.onFork?t:t._forkDlgt),this._forkCurrZone=n&&(n.onFork?this.zone:t._forkCurrZone),this._interceptZS=n&&(n.onIntercept?n:t._interceptZS),this._interceptDlgt=n&&(n.onIntercept?t:t._interceptDlgt),this._interceptCurrZone=n&&(n.onIntercept?this.zone:t._interceptCurrZone),this._invokeZS=n&&(n.onInvoke?n:t._invokeZS),this._invokeDlgt=n&&(n.onInvoke?t:t._invokeDlgt),this._invokeCurrZone=n&&(n.onInvoke?this.zone:t._invokeCurrZone),this._handleErrorZS=n&&(n.onHandleError?n:t._handleErrorZS),this._handleErrorDlgt=n&&(n.onHandleError?t:t._handleErrorDlgt),this._handleErrorCurrZone=n&&(n.onHandleError?this.zone:t._handleErrorCurrZone),this._scheduleTaskZS=n&&(n.onScheduleTask?n:t._scheduleTaskZS),this._scheduleTaskDlgt=n&&(n.onScheduleTask?t:t._scheduleTaskDlgt),this._scheduleTaskCurrZone=n&&(n.onScheduleTask?this.zone:t._scheduleTaskCurrZone),this._invokeTaskZS=n&&(n.onInvokeTask?n:t._invokeTaskZS),this._invokeTaskDlgt=n&&(n.onInvokeTask?t:t._invokeTaskDlgt),this._invokeTaskCurrZone=n&&(n.onInvokeTask?this.zone:t._invokeTaskCurrZone),this._cancelTaskZS=n&&(n.onCancelTask?n:t._cancelTaskZS),this._cancelTaskDlgt=n&&(n.onCancelTask?t:t._cancelTaskDlgt),this._cancelTaskCurrZone=n&&(n.onCancelTask?this.zone:t._cancelTaskCurrZone),this._hasTaskZS=null,this._hasTaskDlgt=null,this._hasTaskDlgtOwner=null,this._hasTaskCurrZone=null;const o=n&&n.onHasTask;(o||t&&t._hasTaskZS)&&(this._hasTaskZS=o?n:c,this._hasTaskDlgt=t,this._hasTaskDlgtOwner=this,this._hasTaskCurrZone=e,n.onScheduleTask||(this._scheduleTaskZS=c,this._scheduleTaskDlgt=t,this._scheduleTaskCurrZone=this.zone),n.onInvokeTask||(this._invokeTaskZS=c,this._invokeTaskDlgt=t,this._invokeTaskCurrZone=this.zone),n.onCancelTask||(this._cancelTaskZS=c,this._cancelTaskDlgt=t,this._cancelTaskCurrZone=this.zone))}fork(e,t){return this._forkZS?this._forkZS.onFork(this._forkDlgt,this.zone,e,t):new a(e,t)}intercept(e,t,n){return this._interceptZS?this._interceptZS.onIntercept(this._interceptDlgt,this._interceptCurrZone,e,t,n):t}invoke(e,t,n,o,r){return this._invokeZS?this._invokeZS.onInvoke(this._invokeDlgt,this._invokeCurrZone,e,t,n,o,r):t.apply(n,o)}handleError(e,t){return!this._handleErrorZS||this._handleErrorZS.onHandleError(this._handleErrorDlgt,this._handleErrorCurrZone,e,t)}scheduleTask(e,t){let n=t;if(this._scheduleTaskZS)this._hasTaskZS&&n._zoneDelegates.push(this._hasTaskDlgtOwner),n=this._scheduleTaskZS.onScheduleTask(this._scheduleTaskDlgt,this._scheduleTaskCurrZone,e,t),n||(n=t);else if(t.scheduleFn)t.scheduleFn(t);else{if(t.type!=S)throw new Error("Task is missing scheduleFn.");k(t)}return n}invokeTask(e,t,n,o){return this._invokeTaskZS?this._invokeTaskZS.onInvokeTask(this._invokeTaskDlgt,this._invokeTaskCurrZone,e,t,n,o):t.callback.apply(n,o)}cancelTask(e,t){let n;if(this._cancelTaskZS)n=this._cancelTaskZS.onCancelTask(this._cancelTaskDlgt,this._cancelTaskCurrZone,e,t);else{if(!t.cancelFn)throw Error("Task is not cancelable");n=t.cancelFn(t)}return n}hasTask(e,t){try{this._hasTaskZS&&this._hasTaskZS.onHasTask(this._hasTaskDlgt,this._hasTaskCurrZone,e,t)}catch(n){this.handleError(e,n)}}_updateTaskCount(e,t){const n=this._taskCounts,o=n[e],r=n[e]=o+t;if(r<0)throw new Error("More tasks executed then were scheduled.");0!=o&&0!=r||this.hasTask(this.zone,{microTask:n.microTask>0,macroTask:n.macroTask>0,eventTask:n.eventTask>0,change:e})}}class u{constructor(t,n,o,r,s,i){if(this._zone=null,this.runCount=0,this._zoneDelegates=null,this._state="notScheduled",this.type=t,this.source=n,this.data=r,this.scheduleFn=s,this.cancelFn=i,!o)throw new Error("callback is not defined");this.callback=o;const a=this;this.invoke=t===P&&r&&r.useG?u.invokeTask:function(){return u.invokeTask.call(e,a,this,arguments)}}static invokeTask(e,t,n){e||(e=this),I++;try{return e.runCount++,e.zone.runTask(e,t,n)}finally{1==I&&m(),I--}}get zone(){return this._zone}get state(){return this._state}cancelScheduleRequest(){this._transitionTo(v,b)}_transitionTo(e,t,n){if(this._state!==t&&this._state!==n)throw new Error(`${this.type} '${this.source}': can not transition to '${e}', expecting state '${t}'${n?" or '"+n+"'":""}, was '${this._state}'.`);this._state=e,e==v&&(this._zoneDelegates=null)}toString(){return this.data&&void 0!==this.data.handleId?this.data.handleId.toString():Object.prototype.toString.call(this)}toJSON(){return{type:this.type,state:this.state,source:this.source,zone:this.zone.name,runCount:this.runCount}}}const h=s("setTimeout"),p=s("Promise"),f=s("then");let d,g=[],_=!1;function k(t){if(0===I&&0===g.length)if(d||e[p]&&(d=e[p].resolve(0)),d){let e=d[f];e||(e=d.then),e.call(d,m)}else e[h](m,0);t&&g.push(t)}function m(){if(!_){for(_=!0;g.length;){const t=g;g=[];for(let n=0;n<t.length;n++){const o=t[n];try{o.zone.runTask(o,null,null)}catch(e){O.onUnhandledError(e)}}}O.microtaskDrainDone(),_=!1}}const y={name:"NO ZONE"},v="notScheduled",b="scheduling",T="scheduled",E="running",w="canceling",Z="unknown",S="microTask",D="macroTask",P="eventTask",C={},O={symbol:s,currentZoneFrame:()=>z,onUnhandledError:N,microtaskDrainDone:N,scheduleMicroTask:k,showUncaughtError:()=>!a[s("ignoreConsoleErrorUncaughtError")],patchEventTarget:()=>[],patchOnProperties:N,patchMethod:()=>N,bindArguments:()=>[],patchThen:()=>N,patchMacroTask:()=>N,setNativePromise:e=>{e&&"function"==typeof e.resolve&&(d=e.resolve(0))},patchEventPrototype:()=>N,isIEOrEdge:()=>!1,getGlobalObjects:()=>{},ObjectDefineProperty:()=>N,ObjectGetOwnPropertyDescriptor:()=>{},ObjectCreate:()=>{},ArraySlice:()=>[],patchClass:()=>N,wrapWithCurrentZone:()=>N,filterProperties:()=>[],attachOriginToPatched:()=>N,_redefineProperty:()=>N,patchCallbacks:()=>N};let z={parent:null,zone:new a(null,null)},j=null,I=0;function N(){}o("Zone","Zone"),e.Zone=a}("undefined"!=typeof window&&window||"undefined"!=typeof self&&self||global),Zone.__load_patch("ZoneAwarePromise",(e,t,n)=>{const o=Object.getOwnPropertyDescriptor,r=Object.defineProperty,s=n.symbol,i=[],a=!0===e[s("DISABLE_WRAPPING_UNCAUGHT_PROMISE_REJECTION")],c=s("Promise"),l=s("then");n.onUnhandledError=e=>{if(n.showUncaughtError()){const t=e&&e.rejection;t?console.error("Unhandled Promise rejection:",t instanceof Error?t.message:t,"; Zone:",e.zone.name,"; Task:",e.task&&e.task.source,"; Value:",t,t instanceof Error?t.stack:void 0):console.error(e)}},n.microtaskDrainDone=()=>{for(;i.length;){const t=i.shift();try{t.zone.runGuarded(()=>{throw t})}catch(e){h(e)}}};const u=s("unhandledPromiseRejectionHandler");function h(e){n.onUnhandledError(e);try{const n=t[u];"function"==typeof n&&n.call(this,e)}catch(o){}}function p(e){return e&&e.then}function f(e){return e}function d(e){return O.reject(e)}const g=s("state"),_=s("value"),k=s("finally"),m=s("parentPromiseValue"),y=s("parentPromiseState"),v=null,b=!0,T=!1;function E(e,t){return n=>{try{Z(e,t,n)}catch(o){Z(e,!1,o)}}}const w=s("currentTaskTrace");function Z(e,o,s){const c=function(){let e=!1;return function(t){return function(){e||(e=!0,t.apply(null,arguments))}}}();if(e===s)throw new TypeError("Promise resolved with itself");if(e[g]===v){let h=null;try{"object"!=typeof s&&"function"!=typeof s||(h=s&&s.then)}catch(u){return c(()=>{Z(e,!1,u)})(),e}if(o!==T&&s instanceof O&&s.hasOwnProperty(g)&&s.hasOwnProperty(_)&&s[g]!==v)D(s),Z(e,s[g],s[_]);else if(o!==T&&"function"==typeof h)try{h.call(s,c(E(e,o)),c(E(e,!1)))}catch(u){c(()=>{Z(e,!1,u)})()}else{e[g]=o;const c=e[_];if(e[_]=s,e[k]===k&&o===b&&(e[g]=e[y],e[_]=e[m]),o===T&&s instanceof Error){const e=t.currentTask&&t.currentTask.data&&t.currentTask.data.__creationTrace__;e&&r(s,w,{configurable:!0,enumerable:!1,writable:!0,value:e})}for(let t=0;t<c.length;)P(e,c[t++],c[t++],c[t++],c[t++]);if(0==c.length&&o==T){e[g]=0;let o=s;if(!a)try{throw new Error("Uncaught (in promise): "+((l=s)&&l.toString===Object.prototype.toString?(l.constructor&&l.constructor.name||"")+": "+JSON.stringify(l):l?l.toString():Object.prototype.toString.call(l))+(s&&s.stack?"\n"+s.stack:""))}catch(u){o=u}o.rejection=s,o.promise=e,o.zone=t.current,o.task=t.currentTask,i.push(o),n.scheduleMicroTask()}}}var l;return e}const S=s("rejectionHandledHandler");function D(e){if(0===e[g]){try{const n=t[S];n&&"function"==typeof n&&n.call(this,{rejection:e[_],promise:e})}catch(n){}e[g]=T;for(let t=0;t<i.length;t++)e===i[t].promise&&i.splice(t,1)}}function P(e,t,n,o,r){D(e);const s=e[g],i=s?"function"==typeof o?o:f:"function"==typeof r?r:d;t.scheduleMicroTask("Promise.then",()=>{try{const o=e[_],r=!!n&&k===n[k];r&&(n[m]=o,n[y]=s);const a=t.run(i,void 0,r&&i!==d&&i!==f?[]:[o]);Z(n,!0,a)}catch(o){Z(n,!1,o)}},n)}const C=function(){};class O{static toString(){return"function ZoneAwarePromise() { [native code] }"}static resolve(e){return Z(new this(null),b,e)}static reject(e){return Z(new this(null),T,e)}static race(e){let t,n,o=new this((e,o)=>{t=e,n=o});function r(e){t(e)}function s(e){n(e)}for(let i of e)p(i)||(i=this.resolve(i)),i.then(r,s);return o}static all(e){return O.allWithCallback(e)}static allSettled(e){return(this&&this.prototype instanceof O?this:O).allWithCallback(e,{thenCallback:e=>({status:"fulfilled",value:e}),errorCallback:e=>({status:"rejected",reason:e})})}static allWithCallback(e,t){let n,o,r=new this((e,t)=>{n=e,o=t}),s=2,i=0;const a=[];for(let l of e){p(l)||(l=this.resolve(l));const e=i;try{l.then(o=>{a[e]=t?t.thenCallback(o):o,s--,0===s&&n(a)},r=>{t?(a[e]=t.errorCallback(r),s--,0===s&&n(a)):o(r)})}catch(c){o(c)}s++,i++}return s-=2,0===s&&n(a),r}constructor(e){const t=this;if(!(t instanceof O))throw new Error("Must be an instanceof Promise.");t[g]=v,t[_]=[];try{e&&e(E(t,b),E(t,T))}catch(n){Z(t,!1,n)}}get[Symbol.toStringTag](){return"Promise"}get[Symbol.species](){return O}then(e,n){let o=this.constructor[Symbol.species];o&&"function"==typeof o||(o=this.constructor||O);const r=new o(C),s=t.current;return this[g]==v?this[_].push(s,r,e,n):P(this,s,r,e,n),r}catch(e){return this.then(null,e)}finally(e){let n=this.constructor[Symbol.species];n&&"function"==typeof n||(n=O);const o=new n(C);o[k]=k;const r=t.current;return this[g]==v?this[_].push(r,o,e,e):P(this,r,o,e,e),o}}O.resolve=O.resolve,O.reject=O.reject,O.race=O.race,O.all=O.all;const z=e[c]=e.Promise,j=t.__symbol__("ZoneAwarePromise");let I=o(e,"Promise");I&&!I.configurable||(I&&delete I.writable,I&&delete I.value,I||(I={configurable:!0,enumerable:!0}),I.get=function(){return e[j]?e[j]:e[c]},I.set=function(t){t===O?e[j]=t:(e[c]=t,t.prototype[l]||R(t),n.setNativePromise(t))},r(e,"Promise",I)),e.Promise=O;const N=s("thenPatched");function R(e){const t=e.prototype,n=o(t,"then");if(n&&(!1===n.writable||!n.configurable))return;const r=t.then;t[l]=r,e.prototype.then=function(e,t){return new O((e,t)=>{r.call(this,e,t)}).then(e,t)},e[N]=!0}if(n.patchThen=R,z){R(z);const t=e.fetch;"function"==typeof t&&(e[n.symbol("fetch")]=t,e.fetch=(x=t,function(){let e=x.apply(this,arguments);if(e instanceof O)return e;let t=e.constructor;return t[N]||R(t),e}))}var x;return Promise[t.__symbol__("uncaughtPromiseErrors")]=i,O});const e=Object.getOwnPropertyDescriptor,t=Object.defineProperty,n=Object.getPrototypeOf,o=Object.create,r=Array.prototype.slice,s="addEventListener",i="removeEventListener",a=Zone.__symbol__(s),c=Zone.__symbol__(i),l="true",u="false",h=Zone.__symbol__("");function p(e,t){return Zone.current.wrap(e,t)}function f(e,t,n,o,r){return Zone.current.scheduleMacroTask(e,t,n,o,r)}const d=Zone.__symbol__,g="undefined"!=typeof window,_=g?window:void 0,k=g&&_||"object"==typeof self&&self||global,m=[null];function y(e,t){for(let n=e.length-1;n>=0;n--)"function"==typeof e[n]&&(e[n]=p(e[n],t+"_"+n));return e}function v(e){return!e||!1!==e.writable&&!("function"==typeof e.get&&void 0===e.set)}const b="undefined"!=typeof WorkerGlobalScope&&self instanceof WorkerGlobalScope,T=!("nw"in k)&&void 0!==k.process&&"[object process]"==={}.toString.call(k.process),E=!T&&!b&&!(!g||!_.HTMLElement),w=void 0!==k.process&&"[object process]"==={}.toString.call(k.process)&&!b&&!(!g||!_.HTMLElement),Z={},S=function(e){if(!(e=e||k.event))return;let t=Z[e.type];t||(t=Z[e.type]=d("ON_PROPERTY"+e.type));const n=this||e.target||k,o=n[t];let r;if(E&&n===_&&"error"===e.type){const t=e;r=o&&o.call(this,t.message,t.filename,t.lineno,t.colno,t.error),!0===r&&e.preventDefault()}else r=o&&o.apply(this,arguments),null==r||r||e.preventDefault();return r};function D(n,o,r){let s=e(n,o);if(!s&&r&&e(r,o)&&(s={enumerable:!0,configurable:!0}),!s||!s.configurable)return;const i=d("on"+o+"patched");if(n.hasOwnProperty(i)&&n[i])return;delete s.writable,delete s.value;const a=s.get,c=s.set,l=o.substr(2);let u=Z[l];u||(u=Z[l]=d("ON_PROPERTY"+l)),s.set=function(e){let t=this;t||n!==k||(t=k),t&&(t[u]&&t.removeEventListener(l,S),c&&c.apply(t,m),"function"==typeof e?(t[u]=e,t.addEventListener(l,S,!1)):t[u]=null)},s.get=function(){let e=this;if(e||n!==k||(e=k),!e)return null;const t=e[u];if(t)return t;if(a){let t=a&&a.call(this);if(t)return s.set.call(this,t),"function"==typeof e.removeAttribute&&e.removeAttribute(o),t}return null},t(n,o,s),n[i]=!0}function P(e,t,n){if(t)for(let o=0;o<t.length;o++)D(e,"on"+t[o],n);else{const t=[];for(const n in e)"on"==n.substr(0,2)&&t.push(n);for(let o=0;o<t.length;o++)D(e,t[o],n)}}const C=d("originalInstance");function O(e){const n=k[e];if(!n)return;k[d(e)]=n,k[e]=function(){const t=y(arguments,e);switch(t.length){case 0:this[C]=new n;break;case 1:this[C]=new n(t[0]);break;case 2:this[C]=new n(t[0],t[1]);break;case 3:this[C]=new n(t[0],t[1],t[2]);break;case 4:this[C]=new n(t[0],t[1],t[2],t[3]);break;default:throw new Error("Arg list too long.")}},I(k[e],n);const o=new n(function(){});let r;for(r in o)"XMLHttpRequest"===e&&"responseBlob"===r||function(n){"function"==typeof o[n]?k[e].prototype[n]=function(){return this[C][n].apply(this[C],arguments)}:t(k[e].prototype,n,{set:function(t){"function"==typeof t?(this[C][n]=p(t,e+"."+n),I(this[C][n],t)):this[C][n]=t},get:function(){return this[C][n]}})}(r);for(r in n)"prototype"!==r&&n.hasOwnProperty(r)&&(k[e][r]=n[r])}function z(t,o,r){let s=t;for(;s&&!s.hasOwnProperty(o);)s=n(s);!s&&t[o]&&(s=t);const i=d(o);let a=null;if(s&&!(a=s[i])&&(a=s[i]=s[o],v(s&&e(s,o)))){const e=r(a,i,o);s[o]=function(){return e(this,arguments)},I(s[o],a)}return a}function j(e,t,n){let o=null;function r(e){const t=e.data;return t.args[t.cbIdx]=function(){e.invoke.apply(this,arguments)},o.apply(t.target,t.args),e}o=z(e,t,e=>function(t,o){const s=n(t,o);return s.cbIdx>=0&&"function"==typeof o[s.cbIdx]?f(s.name,o[s.cbIdx],s,r):e.apply(t,o)})}function I(e,t){e[d("OriginalDelegate")]=t}let N=!1,R=!1;function x(){try{const e=_.navigator.userAgent;if(-1!==e.indexOf("MSIE ")||-1!==e.indexOf("Trident/"))return!0}catch(e){}return!1}function M(){if(N)return R;N=!0;try{const e=_.navigator.userAgent;-1===e.indexOf("MSIE ")&&-1===e.indexOf("Trident/")&&-1===e.indexOf("Edge/")||(R=!0)}catch(e){}return R}Zone.__load_patch("toString",e=>{const t=Function.prototype.toString,n=d("OriginalDelegate"),o=d("Promise"),r=d("Error"),s=function(){if("function"==typeof this){const s=this[n];if(s)return"function"==typeof s?t.call(s):Object.prototype.toString.call(s);if(this===Promise){const n=e[o];if(n)return t.call(n)}if(this===Error){const n=e[r];if(n)return t.call(n)}}return t.call(this)};s[n]=t,Function.prototype.toString=s;const i=Object.prototype.toString;Object.prototype.toString=function(){return this instanceof Promise?"[object Promise]":i.call(this)}});let L=!1;if("undefined"!=typeof window)try{const e=Object.defineProperty({},"passive",{get:function(){L=!0}});window.addEventListener("test",e,e),window.removeEventListener("test",e,e)}catch(he){L=!1}const A={useG:!0},H={},F={},G=new RegExp("^"+h+"(\\w+)(true|false)$"),B=d("propagationStopped");function q(e,t){const n=(t?t(e):e)+u,o=(t?t(e):e)+l,r=h+n,s=h+o;H[e]={},H[e].false=r,H[e].true=s}function W(e,t,o){const r=o&&o.add||s,a=o&&o.rm||i,c=o&&o.listeners||"eventListeners",p=o&&o.rmAll||"removeAllListeners",f=d(r),g="."+r+":",_=function(e,t,n){if(e.isRemoved)return;const o=e.callback;"object"==typeof o&&o.handleEvent&&(e.callback=e=>o.handleEvent(e),e.originalDelegate=o),e.invoke(e,t,[n]);const r=e.options;r&&"object"==typeof r&&r.once&&t[a].call(t,n.type,e.originalDelegate?e.originalDelegate:e.callback,r)},k=function(t){if(!(t=t||e.event))return;const n=this||t.target||e,o=n[H[t.type].false];if(o)if(1===o.length)_(o[0],n,t);else{const e=o.slice();for(let o=0;o<e.length&&(!t||!0!==t[B]);o++)_(e[o],n,t)}},m=function(t){if(!(t=t||e.event))return;const n=this||t.target||e,o=n[H[t.type].true];if(o)if(1===o.length)_(o[0],n,t);else{const e=o.slice();for(let o=0;o<e.length&&(!t||!0!==t[B]);o++)_(e[o],n,t)}};function y(t,o){if(!t)return!1;let s=!0;o&&void 0!==o.useG&&(s=o.useG);const i=o&&o.vh;let _=!0;o&&void 0!==o.chkDup&&(_=o.chkDup);let y=!1;o&&void 0!==o.rt&&(y=o.rt);let v=t;for(;v&&!v.hasOwnProperty(r);)v=n(v);if(!v&&t[r]&&(v=t),!v)return!1;if(v[f])return!1;const b=o&&o.eventNameToString,E={},w=v[f]=v[r],Z=v[d(a)]=v[a],S=v[d(c)]=v[c],D=v[d(p)]=v[p];let P;function C(e,t){return!L&&"object"==typeof e&&e?!!e.capture:L&&t?"boolean"==typeof e?{capture:e,passive:!0}:e?"object"==typeof e&&!1!==e.passive?Object.assign(Object.assign({},e),{passive:!0}):e:{passive:!0}:e}o&&o.prepend&&(P=v[d(o.prepend)]=v[o.prepend]);const O=s?function(e){if(!E.isExisting)return w.call(E.target,E.eventName,E.capture?m:k,E.options)}:function(e){return w.call(E.target,E.eventName,e.invoke,E.options)},z=s?function(e){if(!e.isRemoved){const t=H[e.eventName];let n;t&&(n=t[e.capture?l:u]);const o=n&&e.target[n];if(o)for(let r=0;r<o.length;r++)if(o[r]===e){o.splice(r,1),e.isRemoved=!0,0===o.length&&(e.allRemoved=!0,e.target[n]=null);break}}if(e.allRemoved)return Z.call(e.target,e.eventName,e.capture?m:k,e.options)}:function(e){return Z.call(e.target,e.eventName,e.invoke,e.options)},j=o&&o.diff?o.diff:function(e,t){const n=typeof t;return"function"===n&&e.callback===t||"object"===n&&e.originalDelegate===t},N=Zone[d("BLACK_LISTED_EVENTS")],R=e[d("PASSIVE_EVENTS")],x=function(t,n,r,a,c=!1,h=!1){return function(){const p=this||e;let f=arguments[0];o&&o.transferEventName&&(f=o.transferEventName(f));let d=arguments[1];if(!d)return t.apply(this,arguments);if(T&&"uncaughtException"===f)return t.apply(this,arguments);let g=!1;if("function"!=typeof d){if(!d.handleEvent)return t.apply(this,arguments);g=!0}if(i&&!i(t,d,p,arguments))return;const k=L&&!!R&&-1!==R.indexOf(f),m=C(arguments[2],k);if(N)for(let e=0;e<N.length;e++)if(f===N[e])return k?t.call(p,f,d,m):t.apply(this,arguments);const y=!!m&&("boolean"==typeof m||m.capture),v=!(!m||"object"!=typeof m)&&m.once,w=Zone.current;let Z=H[f];Z||(q(f,b),Z=H[f]);const S=Z[y?l:u];let D,P=p[S],O=!1;if(P){if(O=!0,_)for(let e=0;e<P.length;e++)if(j(P[e],d))return}else P=p[S]=[];const z=p.constructor.name,I=F[z];I&&(D=I[f]),D||(D=z+n+(b?b(f):f)),E.options=m,v&&(E.options.once=!1),E.target=p,E.capture=y,E.eventName=f,E.isExisting=O;const x=s?A:void 0;x&&(x.taskData=E);const M=w.scheduleEventTask(D,d,x,r,a);return E.target=null,x&&(x.taskData=null),v&&(m.once=!0),(L||"boolean"!=typeof M.options)&&(M.options=m),M.target=p,M.capture=y,M.eventName=f,g&&(M.originalDelegate=d),h?P.unshift(M):P.push(M),c?p:void 0}};return v[r]=x(w,g,O,z,y),P&&(v.prependListener=x(P,".prependListener:",function(e){return P.call(E.target,E.eventName,e.invoke,E.options)},z,y,!0)),v[a]=function(){const t=this||e;let n=arguments[0];o&&o.transferEventName&&(n=o.transferEventName(n));const r=arguments[2],s=!!r&&("boolean"==typeof r||r.capture),a=arguments[1];if(!a)return Z.apply(this,arguments);if(i&&!i(Z,a,t,arguments))return;const c=H[n];let p;c&&(p=c[s?l:u]);const f=p&&t[p];if(f)for(let e=0;e<f.length;e++){const o=f[e];if(j(o,a))return f.splice(e,1),o.isRemoved=!0,0===f.length&&(o.allRemoved=!0,t[p]=null,"string"==typeof n)&&(t[h+"ON_PROPERTY"+n]=null),o.zone.cancelTask(o),y?t:void 0}return Z.apply(this,arguments)},v[c]=function(){const t=this||e;let n=arguments[0];o&&o.transferEventName&&(n=o.transferEventName(n));const r=[],s=U(t,b?b(n):n);for(let e=0;e<s.length;e++){const t=s[e];r.push(t.originalDelegate?t.originalDelegate:t.callback)}return r},v[p]=function(){const t=this||e;let n=arguments[0];if(n){o&&o.transferEventName&&(n=o.transferEventName(n));const e=H[n];if(e){const o=t[e.false],r=t[e.true];if(o){const e=o.slice();for(let t=0;t<e.length;t++){const o=e[t];this[a].call(this,n,o.originalDelegate?o.originalDelegate:o.callback,o.options)}}if(r){const e=r.slice();for(let t=0;t<e.length;t++){const o=e[t];this[a].call(this,n,o.originalDelegate?o.originalDelegate:o.callback,o.options)}}}}else{const e=Object.keys(t);for(let t=0;t<e.length;t++){const n=G.exec(e[t]);let o=n&&n[1];o&&"removeListener"!==o&&this[p].call(this,o)}this[p].call(this,"removeListener")}if(y)return this},I(v[r],w),I(v[a],Z),D&&I(v[p],D),S&&I(v[c],S),!0}let v=[];for(let n=0;n<t.length;n++)v[n]=y(t[n],o);return v}function U(e,t){if(!t){const n=[];for(let o in e){const r=G.exec(o);let s=r&&r[1];if(s&&(!t||s===t)){const t=e[o];if(t)for(let e=0;e<t.length;e++)n.push(t[e])}}return n}let n=H[t];n||(q(t),n=H[t]);const o=e[n.false],r=e[n.true];return o?r?o.concat(r):o.slice():r?r.slice():[]}function V(e,t){const n=e.Event;n&&n.prototype&&t.patchMethod(n.prototype,"stopImmediatePropagation",e=>function(t,n){t[B]=!0,e&&e.apply(t,n)})}function $(e,t,n,o,r){const s=Zone.__symbol__(o);if(t[s])return;const i=t[s]=t[o];t[o]=function(s,a,c){return a&&a.prototype&&r.forEach(function(t){const r=`${n}.${o}::`+t,s=a.prototype;if(s.hasOwnProperty(t)){const n=e.ObjectGetOwnPropertyDescriptor(s,t);n&&n.value?(n.value=e.wrapWithCurrentZone(n.value,r),e._redefineProperty(a.prototype,t,n)):s[t]&&(s[t]=e.wrapWithCurrentZone(s[t],r))}else s[t]&&(s[t]=e.wrapWithCurrentZone(s[t],r))}),i.call(t,s,a,c)},e.attachOriginToPatched(t[o],i)}const X=["absolutedeviceorientation","afterinput","afterprint","appinstalled","beforeinstallprompt","beforeprint","beforeunload","devicelight","devicemotion","deviceorientation","deviceorientationabsolute","deviceproximity","hashchange","languagechange","message","mozbeforepaint","offline","online","paint","pageshow","pagehide","popstate","rejectionhandled","storage","unhandledrejection","unload","userproximity","vrdisplayconnected","vrdisplaydisconnected","vrdisplaypresentchange"],J=["encrypted","waitingforkey","msneedkey","mozinterruptbegin","mozinterruptend"],Y=["load"],K=["blur","error","focus","load","resize","scroll","messageerror"],Q=["bounce","finish","start"],ee=["loadstart","progress","abort","error","load","progress","timeout","loadend","readystatechange"],te=["upgradeneeded","complete","abort","success","error","blocked","versionchange","close"],ne=["close","error","open","message"],oe=["error","message"],re=["abort","animationcancel","animationend","animationiteration","auxclick","beforeinput","blur","cancel","canplay","canplaythrough","change","compositionstart","compositionupdate","compositionend","cuechange","click","close","contextmenu","curechange","dblclick","drag","dragend","dragenter","dragexit","dragleave","dragover","drop","durationchange","emptied","ended","error","focus","focusin","focusout","gotpointercapture","input","invalid","keydown","keypress","keyup","load","loadstart","loadeddata","loadedmetadata","lostpointercapture","mousedown","mouseenter","mouseleave","mousemove","mouseout","mouseover","mouseup","mousewheel","orientationchange","pause","play","playing","pointercancel","pointerdown","pointerenter","pointerleave","pointerlockchange","mozpointerlockchange","webkitpointerlockerchange","pointerlockerror","mozpointerlockerror","webkitpointerlockerror","pointermove","pointout","pointerover","pointerup","progress","ratechange","reset","resize","scroll","seeked","seeking","select","selectionchange","selectstart","show","sort","stalled","submit","suspend","timeupdate","volumechange","touchcancel","touchmove","touchstart","touchend","transitioncancel","transitionend","waiting","wheel"].concat(["webglcontextrestored","webglcontextlost","webglcontextcreationerror"],["autocomplete","autocompleteerror"],["toggle"],["afterscriptexecute","beforescriptexecute","DOMContentLoaded","freeze","fullscreenchange","mozfullscreenchange","webkitfullscreenchange","msfullscreenchange","fullscreenerror","mozfullscreenerror","webkitfullscreenerror","msfullscreenerror","readystatechange","visibilitychange","resume"],X,["beforecopy","beforecut","beforepaste","copy","cut","paste","dragstart","loadend","animationstart","search","transitionrun","transitionstart","webkitanimationend","webkitanimationiteration","webkitanimationstart","webkittransitionend"],["activate","afterupdate","ariarequest","beforeactivate","beforedeactivate","beforeeditfocus","beforeupdate","cellchange","controlselect","dataavailable","datasetchanged","datasetcomplete","errorupdate","filterchange","layoutcomplete","losecapture","move","moveend","movestart","propertychange","resizeend","resizestart","rowenter","rowexit","rowsdelete","rowsinserted","command","compassneedscalibration","deactivate","help","mscontentzoom","msmanipulationstatechanged","msgesturechange","msgesturedoubletap","msgestureend","msgesturehold","msgesturestart","msgesturetap","msgotpointercapture","msinertiastart","mslostpointercapture","mspointercancel","mspointerdown","mspointerenter","mspointerhover","mspointerleave","mspointermove","mspointerout","mspointerover","mspointerup","pointerout","mssitemodejumplistitemremoved","msthumbnailclick","stop","storagecommit"]);function se(e,t,n){if(!n||0===n.length)return t;const o=n.filter(t=>t.target===e);if(!o||0===o.length)return t;const r=o[0].ignoreProperties;return t.filter(e=>-1===r.indexOf(e))}function ie(e,t,n,o){e&&P(e,se(e,t,n),o)}function ae(e,t){if(T&&!w)return;if(Zone[e.symbol("patchEvents")])return;const o="undefined"!=typeof WebSocket,r=t.__Zone_ignore_on_properties;if(E){const e=window,t=x?[{target:e,ignoreProperties:["error"]}]:[];ie(e,re.concat(["messageerror"]),r?r.concat(t):r,n(e)),ie(Document.prototype,re,r),void 0!==e.SVGElement&&ie(e.SVGElement.prototype,re,r),ie(Element.prototype,re,r),ie(HTMLElement.prototype,re,r),ie(HTMLMediaElement.prototype,J,r),ie(HTMLFrameSetElement.prototype,X.concat(K),r),ie(HTMLBodyElement.prototype,X.concat(K),r),ie(HTMLFrameElement.prototype,Y,r),ie(HTMLIFrameElement.prototype,Y,r);const o=e.HTMLMarqueeElement;o&&ie(o.prototype,Q,r);const s=e.Worker;s&&ie(s.prototype,oe,r)}const s=t.XMLHttpRequest;s&&ie(s.prototype,ee,r);const i=t.XMLHttpRequestEventTarget;i&&ie(i&&i.prototype,ee,r),"undefined"!=typeof IDBIndex&&(ie(IDBIndex.prototype,te,r),ie(IDBRequest.prototype,te,r),ie(IDBOpenDBRequest.prototype,te,r),ie(IDBDatabase.prototype,te,r),ie(IDBTransaction.prototype,te,r),ie(IDBCursor.prototype,te,r)),o&&ie(WebSocket.prototype,ne,r)}Zone.__load_patch("util",(n,a,c)=>{c.patchOnProperties=P,c.patchMethod=z,c.bindArguments=y,c.patchMacroTask=j;const f=a.__symbol__("BLACK_LISTED_EVENTS"),d=a.__symbol__("UNPATCHED_EVENTS");n[d]&&(n[f]=n[d]),n[f]&&(a[f]=a[d]=n[f]),c.patchEventPrototype=V,c.patchEventTarget=W,c.isIEOrEdge=M,c.ObjectDefineProperty=t,c.ObjectGetOwnPropertyDescriptor=e,c.ObjectCreate=o,c.ArraySlice=r,c.patchClass=O,c.wrapWithCurrentZone=p,c.filterProperties=se,c.attachOriginToPatched=I,c._redefineProperty=Object.defineProperty,c.patchCallbacks=$,c.getGlobalObjects=()=>({globalSources:F,zoneSymbolEventNames:H,eventNames:re,isBrowser:E,isMix:w,isNode:T,TRUE_STR:l,FALSE_STR:u,ZONE_SYMBOL_PREFIX:h,ADD_EVENT_LISTENER_STR:s,REMOVE_EVENT_LISTENER_STR:i})});const ce=d("zoneTask");function le(e,t,n,o){let r=null,s=null;n+=o;const i={};function a(t){const n=t.data;return n.args[0]=function(){try{t.invoke.apply(this,arguments)}finally{t.data&&t.data.isPeriodic||("number"==typeof n.handleId?delete i[n.handleId]:n.handleId&&(n.handleId[ce]=null))}},n.handleId=r.apply(e,n.args),t}function c(e){return s(e.data.handleId)}r=z(e,t+=o,n=>function(r,s){if("function"==typeof s[0]){const e=f(t,s[0],{isPeriodic:"Interval"===o,delay:"Timeout"===o||"Interval"===o?s[1]||0:void 0,args:s},a,c);if(!e)return e;const n=e.data.handleId;return"number"==typeof n?i[n]=e:n&&(n[ce]=e),n&&n.ref&&n.unref&&"function"==typeof n.ref&&"function"==typeof n.unref&&(e.ref=n.ref.bind(n),e.unref=n.unref.bind(n)),"number"==typeof n||n?n:e}return n.apply(e,s)}),s=z(e,n,t=>function(n,o){const r=o[0];let s;"number"==typeof r?s=i[r]:(s=r&&r[ce],s||(s=r)),s&&"string"==typeof s.type?"notScheduled"!==s.state&&(s.cancelFn&&s.data.isPeriodic||0===s.runCount)&&("number"==typeof r?delete i[r]:r&&(r[ce]=null),s.zone.cancelTask(s)):t.apply(e,o)})}function ue(e,t){if(Zone[t.symbol("patchEventTarget")])return;const{eventNames:n,zoneSymbolEventNames:o,TRUE_STR:r,FALSE_STR:s,ZONE_SYMBOL_PREFIX:i}=t.getGlobalObjects();for(let c=0;c<n.length;c++){const e=n[c],t=i+(e+s),a=i+(e+r);o[e]={},o[e][s]=t,o[e][r]=a}const a=e.EventTarget;return a&&a.prototype?(t.patchEventTarget(e,[a&&a.prototype]),!0):void 0}Zone.__load_patch("legacy",e=>{const t=e[Zone.__symbol__("legacyPatch")];t&&t()}),Zone.__load_patch("timers",e=>{const t="set",n="clear";le(e,t,n,"Timeout"),le(e,t,n,"Interval"),le(e,t,n,"Immediate")}),Zone.__load_patch("requestAnimationFrame",e=>{le(e,"request","cancel","AnimationFrame"),le(e,"mozRequest","mozCancel","AnimationFrame"),le(e,"webkitRequest","webkitCancel","AnimationFrame")}),Zone.__load_patch("blocking",(e,t)=>{const n=["alert","prompt","confirm"];for(let o=0;o<n.length;o++)z(e,n[o],(n,o,r)=>function(o,s){return t.current.run(n,e,s,r)})}),Zone.__load_patch("EventTarget",(e,t,n)=>{(function(e,t){t.patchEventPrototype(e,t)})(e,n),ue(e,n);const o=e.XMLHttpRequestEventTarget;o&&o.prototype&&n.patchEventTarget(e,[o.prototype]),O("MutationObserver"),O("WebKitMutationObserver"),O("IntersectionObserver"),O("FileReader")}),Zone.__load_patch("on_property",(e,t,n)=>{ae(n,e)}),Zone.__load_patch("customElements",(e,t,n)=>{!function(e,t){const{isBrowser:n,isMix:o}=t.getGlobalObjects();(n||o)&&e.customElements&&"customElements"in e&&t.patchCallbacks(t,e.customElements,"customElements","define",["connectedCallback","disconnectedCallback","adoptedCallback","attributeChangedCallback"])}(e,n)}),Zone.__load_patch("XHR",(e,t)=>{!function(e){const u=e.XMLHttpRequest;if(!u)return;const h=u.prototype;let p=h[a],g=h[c];if(!p){const t=e.XMLHttpRequestEventTarget;if(t){const e=t.prototype;p=e[a],g=e[c]}}const _="readystatechange",k="scheduled";function m(e){const o=e.data,i=o.target;i[s]=!1,i[l]=!1;const u=i[r];p||(p=i[a],g=i[c]),u&&g.call(i,_,u);const h=i[r]=()=>{if(i.readyState===i.DONE)if(!o.aborted&&i[s]&&e.state===k){const n=i[t.__symbol__("loadfalse")];if(n&&n.length>0){const r=e.invoke;e.invoke=function(){const n=i[t.__symbol__("loadfalse")];for(let t=0;t<n.length;t++)n[t]===e&&n.splice(t,1);o.aborted||e.state!==k||r.call(e)},n.push(e)}else e.invoke()}else o.aborted||!1!==i[s]||(i[l]=!0)};return p.call(i,_,h),i[n]||(i[n]=e),w.apply(i,o.args),i[s]=!0,e}function y(){}function v(e){const t=e.data;return t.aborted=!0,Z.apply(t.target,t.args)}const b=z(h,"open",()=>function(e,t){return e[o]=0==t[2],e[i]=t[1],b.apply(e,t)}),T=d("fetchTaskAborting"),E=d("fetchTaskScheduling"),w=z(h,"send",()=>function(e,n){if(!0===t.current[E])return w.apply(e,n);if(e[o])return w.apply(e,n);{const t={target:e,url:e[i],isPeriodic:!1,args:n,aborted:!1},o=f("XMLHttpRequest.send",y,t,m,v);e&&!0===e[l]&&!t.aborted&&o.state===k&&o.invoke()}}),Z=z(h,"abort",()=>function(e,o){const r=e[n];if(r&&"string"==typeof r.type){if(null==r.cancelFn||r.data&&r.data.aborted)return;r.zone.cancelTask(r)}else if(!0===t.current[T])return Z.apply(e,o)})}(e);const n=d("xhrTask"),o=d("xhrSync"),r=d("xhrListener"),s=d("xhrScheduled"),i=d("xhrURL"),l=d("xhrErrorBeforeScheduled")}),Zone.__load_patch("geolocation",t=>{t.navigator&&t.navigator.geolocation&&function(t,n){const o=t.constructor.name;for(let r=0;r<n.length;r++){const s=n[r],i=t[s];if(i){if(!v(e(t,s)))continue;t[s]=(e=>{const t=function(){return e.apply(this,y(arguments,o+"."+s))};return I(t,e),t})(i)}}}(t.navigator.geolocation,["getCurrentPosition","watchPosition"])}),Zone.__load_patch("PromiseRejectionEvent",(e,t)=>{function n(t){return function(n){U(e,t).forEach(o=>{const r=e.PromiseRejectionEvent;if(r){const e=new r(t,{promise:n.promise,reason:n.rejection});o.invoke(e)}})}}e.PromiseRejectionEvent&&(t[d("unhandledPromiseRejectionHandler")]=n("unhandledrejection"),t[d("rejectionHandledHandler")]=n("rejectionhandled"))})})?o.call(t,n,t,e):o)||(e.exports=r)}},[[1,0]]]); | 1.0 | beam.mw.polyfills.bf99d438b005d57b2b31.js - (window.webpackJsonp=window.webpackJsonp||[]).push([[2],{1:function(e,t,n){e.exports=n("hN/g")},"hN/g":function(e,t,n){"use strict";n.r(t),n("pDpN")},pDpN:function(e,t,n){var o,r;void 0===(r="function"==typeof(o=function(){"use strict";!function(e){const t=e.performance;function n(e){t&&t.mark&&t.mark(e)}function o(e,n){t&&t.measure&&t.measure(e,n)}n("Zone");const r=e.__Zone_symbol_prefix||"__zone_symbol__";function s(e){return r+e}const i=!0===e[s("forceDuplicateZoneCheck")];if(e.Zone){if(i||"function"!=typeof e.Zone.__symbol__)throw new Error("Zone already loaded.");return e.Zone}class a{constructor(e,t){this._parent=e,this._name=t?t.name||"unnamed":"<root>",this._properties=t&&t.properties||{},this._zoneDelegate=new l(this,this._parent&&this._parent._zoneDelegate,t)}static assertZonePatched(){if(e.Promise!==C.ZoneAwarePromise)throw new Error("Zone.js has detected that ZoneAwarePromise `(window|global).Promise` has been overwritten.\nMost likely cause is that a Promise polyfill has been loaded after Zone.js (Polyfilling Promise api is not necessary when zone.js is loaded. If you must load one, do so before loading zone.js.)")}static get root(){let e=a.current;for(;e.parent;)e=e.parent;return e}static get current(){return z.zone}static get currentTask(){return j}static __load_patch(t,r){if(C.hasOwnProperty(t)){if(i)throw Error("Already loaded patch: "+t)}else if(!e["__Zone_disable_"+t]){const s="Zone:"+t;n(s),C[t]=r(e,a,O),o(s,s)}}get parent(){return this._parent}get name(){return this._name}get(e){const t=this.getZoneWith(e);if(t)return t._properties[e]}getZoneWith(e){let t=this;for(;t;){if(t._properties.hasOwnProperty(e))return t;t=t._parent}return null}fork(e){if(!e)throw new Error("ZoneSpec required!");return this._zoneDelegate.fork(this,e)}wrap(e,t){if("function"!=typeof e)throw new Error("Expecting function got: "+e);const n=this._zoneDelegate.intercept(this,e,t),o=this;return function(){return o.runGuarded(n,this,arguments,t)}}run(e,t,n,o){z={parent:z,zone:this};try{return this._zoneDelegate.invoke(this,e,t,n,o)}finally{z=z.parent}}runGuarded(e,t=null,n,o){z={parent:z,zone:this};try{try{return this._zoneDelegate.invoke(this,e,t,n,o)}catch(r){if(this._zoneDelegate.handleError(this,r))throw r}}finally{z=z.parent}}runTask(e,t,n){if(e.zone!=this)throw new Error("A task can only be run in the zone of creation! (Creation: "+(e.zone||y).name+"; Execution: "+this.name+")");if(e.state===v&&(e.type===P||e.type===D))return;const o=e.state!=E;o&&e._transitionTo(E,T),e.runCount++;const r=j;j=e,z={parent:z,zone:this};try{e.type==D&&e.data&&!e.data.isPeriodic&&(e.cancelFn=void 0);try{return this._zoneDelegate.invokeTask(this,e,t,n)}catch(s){if(this._zoneDelegate.handleError(this,s))throw s}}finally{e.state!==v&&e.state!==Z&&(e.type==P||e.data&&e.data.isPeriodic?o&&e._transitionTo(T,E):(e.runCount=0,this._updateTaskCount(e,-1),o&&e._transitionTo(v,E,v))),z=z.parent,j=r}}scheduleTask(e){if(e.zone&&e.zone!==this){let t=this;for(;t;){if(t===e.zone)throw Error(`can not reschedule task to ${this.name} which is descendants of the original zone ${e.zone.name}`);t=t.parent}}e._transitionTo(b,v);const t=[];e._zoneDelegates=t,e._zone=this;try{e=this._zoneDelegate.scheduleTask(this,e)}catch(n){throw e._transitionTo(Z,b,v),this._zoneDelegate.handleError(this,n),n}return e._zoneDelegates===t&&this._updateTaskCount(e,1),e.state==b&&e._transitionTo(T,b),e}scheduleMicroTask(e,t,n,o){return this.scheduleTask(new u(S,e,t,n,o,void 0))}scheduleMacroTask(e,t,n,o,r){return this.scheduleTask(new u(D,e,t,n,o,r))}scheduleEventTask(e,t,n,o,r){return this.scheduleTask(new u(P,e,t,n,o,r))}cancelTask(e){if(e.zone!=this)throw new Error("A task can only be cancelled in the zone of creation! (Creation: "+(e.zone||y).name+"; Execution: "+this.name+")");e._transitionTo(w,T,E);try{this._zoneDelegate.cancelTask(this,e)}catch(t){throw e._transitionTo(Z,w),this._zoneDelegate.handleError(this,t),t}return this._updateTaskCount(e,-1),e._transitionTo(v,w),e.runCount=0,e}_updateTaskCount(e,t){const n=e._zoneDelegates;-1==t&&(e._zoneDelegates=null);for(let o=0;o<n.length;o++)n[o]._updateTaskCount(e.type,t)}}a.__symbol__=s;const c={name:"",onHasTask:(e,t,n,o)=>e.hasTask(n,o),onScheduleTask:(e,t,n,o)=>e.scheduleTask(n,o),onInvokeTask:(e,t,n,o,r,s)=>e.invokeTask(n,o,r,s),onCancelTask:(e,t,n,o)=>e.cancelTask(n,o)};class l{constructor(e,t,n){this._taskCounts={microTask:0,macroTask:0,eventTask:0},this.zone=e,this._parentDelegate=t,this._forkZS=n&&(n&&n.onFork?n:t._forkZS),this._forkDlgt=n&&(n.onFork?t:t._forkDlgt),this._forkCurrZone=n&&(n.onFork?this.zone:t._forkCurrZone),this._interceptZS=n&&(n.onIntercept?n:t._interceptZS),this._interceptDlgt=n&&(n.onIntercept?t:t._interceptDlgt),this._interceptCurrZone=n&&(n.onIntercept?this.zone:t._interceptCurrZone),this._invokeZS=n&&(n.onInvoke?n:t._invokeZS),this._invokeDlgt=n&&(n.onInvoke?t:t._invokeDlgt),this._invokeCurrZone=n&&(n.onInvoke?this.zone:t._invokeCurrZone),this._handleErrorZS=n&&(n.onHandleError?n:t._handleErrorZS),this._handleErrorDlgt=n&&(n.onHandleError?t:t._handleErrorDlgt),this._handleErrorCurrZone=n&&(n.onHandleError?this.zone:t._handleErrorCurrZone),this._scheduleTaskZS=n&&(n.onScheduleTask?n:t._scheduleTaskZS),this._scheduleTaskDlgt=n&&(n.onScheduleTask?t:t._scheduleTaskDlgt),this._scheduleTaskCurrZone=n&&(n.onScheduleTask?this.zone:t._scheduleTaskCurrZone),this._invokeTaskZS=n&&(n.onInvokeTask?n:t._invokeTaskZS),this._invokeTaskDlgt=n&&(n.onInvokeTask?t:t._invokeTaskDlgt),this._invokeTaskCurrZone=n&&(n.onInvokeTask?this.zone:t._invokeTaskCurrZone),this._cancelTaskZS=n&&(n.onCancelTask?n:t._cancelTaskZS),this._cancelTaskDlgt=n&&(n.onCancelTask?t:t._cancelTaskDlgt),this._cancelTaskCurrZone=n&&(n.onCancelTask?this.zone:t._cancelTaskCurrZone),this._hasTaskZS=null,this._hasTaskDlgt=null,this._hasTaskDlgtOwner=null,this._hasTaskCurrZone=null;const o=n&&n.onHasTask;(o||t&&t._hasTaskZS)&&(this._hasTaskZS=o?n:c,this._hasTaskDlgt=t,this._hasTaskDlgtOwner=this,this._hasTaskCurrZone=e,n.onScheduleTask||(this._scheduleTaskZS=c,this._scheduleTaskDlgt=t,this._scheduleTaskCurrZone=this.zone),n.onInvokeTask||(this._invokeTaskZS=c,this._invokeTaskDlgt=t,this._invokeTaskCurrZone=this.zone),n.onCancelTask||(this._cancelTaskZS=c,this._cancelTaskDlgt=t,this._cancelTaskCurrZone=this.zone))}fork(e,t){return this._forkZS?this._forkZS.onFork(this._forkDlgt,this.zone,e,t):new a(e,t)}intercept(e,t,n){return this._interceptZS?this._interceptZS.onIntercept(this._interceptDlgt,this._interceptCurrZone,e,t,n):t}invoke(e,t,n,o,r){return this._invokeZS?this._invokeZS.onInvoke(this._invokeDlgt,this._invokeCurrZone,e,t,n,o,r):t.apply(n,o)}handleError(e,t){return!this._handleErrorZS||this._handleErrorZS.onHandleError(this._handleErrorDlgt,this._handleErrorCurrZone,e,t)}scheduleTask(e,t){let n=t;if(this._scheduleTaskZS)this._hasTaskZS&&n._zoneDelegates.push(this._hasTaskDlgtOwner),n=this._scheduleTaskZS.onScheduleTask(this._scheduleTaskDlgt,this._scheduleTaskCurrZone,e,t),n||(n=t);else if(t.scheduleFn)t.scheduleFn(t);else{if(t.type!=S)throw new Error("Task is missing scheduleFn.");k(t)}return n}invokeTask(e,t,n,o){return this._invokeTaskZS?this._invokeTaskZS.onInvokeTask(this._invokeTaskDlgt,this._invokeTaskCurrZone,e,t,n,o):t.callback.apply(n,o)}cancelTask(e,t){let n;if(this._cancelTaskZS)n=this._cancelTaskZS.onCancelTask(this._cancelTaskDlgt,this._cancelTaskCurrZone,e,t);else{if(!t.cancelFn)throw Error("Task is not cancelable");n=t.cancelFn(t)}return n}hasTask(e,t){try{this._hasTaskZS&&this._hasTaskZS.onHasTask(this._hasTaskDlgt,this._hasTaskCurrZone,e,t)}catch(n){this.handleError(e,n)}}_updateTaskCount(e,t){const n=this._taskCounts,o=n[e],r=n[e]=o+t;if(r<0)throw new Error("More tasks executed then were scheduled.");0!=o&&0!=r||this.hasTask(this.zone,{microTask:n.microTask>0,macroTask:n.macroTask>0,eventTask:n.eventTask>0,change:e})}}class u{constructor(t,n,o,r,s,i){if(this._zone=null,this.runCount=0,this._zoneDelegates=null,this._state="notScheduled",this.type=t,this.source=n,this.data=r,this.scheduleFn=s,this.cancelFn=i,!o)throw new Error("callback is not defined");this.callback=o;const a=this;this.invoke=t===P&&r&&r.useG?u.invokeTask:function(){return u.invokeTask.call(e,a,this,arguments)}}static invokeTask(e,t,n){e||(e=this),I++;try{return e.runCount++,e.zone.runTask(e,t,n)}finally{1==I&&m(),I--}}get zone(){return this._zone}get state(){return this._state}cancelScheduleRequest(){this._transitionTo(v,b)}_transitionTo(e,t,n){if(this._state!==t&&this._state!==n)throw new Error(`${this.type} '${this.source}': can not transition to '${e}', expecting state '${t}'${n?" or '"+n+"'":""}, was '${this._state}'.`);this._state=e,e==v&&(this._zoneDelegates=null)}toString(){return this.data&&void 0!==this.data.handleId?this.data.handleId.toString():Object.prototype.toString.call(this)}toJSON(){return{type:this.type,state:this.state,source:this.source,zone:this.zone.name,runCount:this.runCount}}}const h=s("setTimeout"),p=s("Promise"),f=s("then");let d,g=[],_=!1;function k(t){if(0===I&&0===g.length)if(d||e[p]&&(d=e[p].resolve(0)),d){let e=d[f];e||(e=d.then),e.call(d,m)}else e[h](m,0);t&&g.push(t)}function m(){if(!_){for(_=!0;g.length;){const t=g;g=[];for(let n=0;n<t.length;n++){const o=t[n];try{o.zone.runTask(o,null,null)}catch(e){O.onUnhandledError(e)}}}O.microtaskDrainDone(),_=!1}}const y={name:"NO ZONE"},v="notScheduled",b="scheduling",T="scheduled",E="running",w="canceling",Z="unknown",S="microTask",D="macroTask",P="eventTask",C={},O={symbol:s,currentZoneFrame:()=>z,onUnhandledError:N,microtaskDrainDone:N,scheduleMicroTask:k,showUncaughtError:()=>!a[s("ignoreConsoleErrorUncaughtError")],patchEventTarget:()=>[],patchOnProperties:N,patchMethod:()=>N,bindArguments:()=>[],patchThen:()=>N,patchMacroTask:()=>N,setNativePromise:e=>{e&&"function"==typeof e.resolve&&(d=e.resolve(0))},patchEventPrototype:()=>N,isIEOrEdge:()=>!1,getGlobalObjects:()=>{},ObjectDefineProperty:()=>N,ObjectGetOwnPropertyDescriptor:()=>{},ObjectCreate:()=>{},ArraySlice:()=>[],patchClass:()=>N,wrapWithCurrentZone:()=>N,filterProperties:()=>[],attachOriginToPatched:()=>N,_redefineProperty:()=>N,patchCallbacks:()=>N};let z={parent:null,zone:new a(null,null)},j=null,I=0;function N(){}o("Zone","Zone"),e.Zone=a}("undefined"!=typeof window&&window||"undefined"!=typeof self&&self||global),Zone.__load_patch("ZoneAwarePromise",(e,t,n)=>{const o=Object.getOwnPropertyDescriptor,r=Object.defineProperty,s=n.symbol,i=[],a=!0===e[s("DISABLE_WRAPPING_UNCAUGHT_PROMISE_REJECTION")],c=s("Promise"),l=s("then");n.onUnhandledError=e=>{if(n.showUncaughtError()){const t=e&&e.rejection;t?console.error("Unhandled Promise rejection:",t instanceof Error?t.message:t,"; Zone:",e.zone.name,"; Task:",e.task&&e.task.source,"; Value:",t,t instanceof Error?t.stack:void 0):console.error(e)}},n.microtaskDrainDone=()=>{for(;i.length;){const t=i.shift();try{t.zone.runGuarded(()=>{throw t})}catch(e){h(e)}}};const u=s("unhandledPromiseRejectionHandler");function h(e){n.onUnhandledError(e);try{const n=t[u];"function"==typeof n&&n.call(this,e)}catch(o){}}function p(e){return e&&e.then}function f(e){return e}function d(e){return O.reject(e)}const g=s("state"),_=s("value"),k=s("finally"),m=s("parentPromiseValue"),y=s("parentPromiseState"),v=null,b=!0,T=!1;function E(e,t){return n=>{try{Z(e,t,n)}catch(o){Z(e,!1,o)}}}const w=s("currentTaskTrace");function Z(e,o,s){const c=function(){let e=!1;return function(t){return function(){e||(e=!0,t.apply(null,arguments))}}}();if(e===s)throw new TypeError("Promise resolved with itself");if(e[g]===v){let h=null;try{"object"!=typeof s&&"function"!=typeof s||(h=s&&s.then)}catch(u){return c(()=>{Z(e,!1,u)})(),e}if(o!==T&&s instanceof O&&s.hasOwnProperty(g)&&s.hasOwnProperty(_)&&s[g]!==v)D(s),Z(e,s[g],s[_]);else if(o!==T&&"function"==typeof h)try{h.call(s,c(E(e,o)),c(E(e,!1)))}catch(u){c(()=>{Z(e,!1,u)})()}else{e[g]=o;const c=e[_];if(e[_]=s,e[k]===k&&o===b&&(e[g]=e[y],e[_]=e[m]),o===T&&s instanceof Error){const e=t.currentTask&&t.currentTask.data&&t.currentTask.data.__creationTrace__;e&&r(s,w,{configurable:!0,enumerable:!1,writable:!0,value:e})}for(let t=0;t<c.length;)P(e,c[t++],c[t++],c[t++],c[t++]);if(0==c.length&&o==T){e[g]=0;let o=s;if(!a)try{throw new Error("Uncaught (in promise): "+((l=s)&&l.toString===Object.prototype.toString?(l.constructor&&l.constructor.name||"")+": "+JSON.stringify(l):l?l.toString():Object.prototype.toString.call(l))+(s&&s.stack?"\n"+s.stack:""))}catch(u){o=u}o.rejection=s,o.promise=e,o.zone=t.current,o.task=t.currentTask,i.push(o),n.scheduleMicroTask()}}}var l;return e}const S=s("rejectionHandledHandler");function D(e){if(0===e[g]){try{const n=t[S];n&&"function"==typeof n&&n.call(this,{rejection:e[_],promise:e})}catch(n){}e[g]=T;for(let t=0;t<i.length;t++)e===i[t].promise&&i.splice(t,1)}}function P(e,t,n,o,r){D(e);const s=e[g],i=s?"function"==typeof o?o:f:"function"==typeof r?r:d;t.scheduleMicroTask("Promise.then",()=>{try{const o=e[_],r=!!n&&k===n[k];r&&(n[m]=o,n[y]=s);const a=t.run(i,void 0,r&&i!==d&&i!==f?[]:[o]);Z(n,!0,a)}catch(o){Z(n,!1,o)}},n)}const C=function(){};class O{static toString(){return"function ZoneAwarePromise() { [native code] }"}static resolve(e){return Z(new this(null),b,e)}static reject(e){return Z(new this(null),T,e)}static race(e){let t,n,o=new this((e,o)=>{t=e,n=o});function r(e){t(e)}function s(e){n(e)}for(let i of e)p(i)||(i=this.resolve(i)),i.then(r,s);return o}static all(e){return O.allWithCallback(e)}static allSettled(e){return(this&&this.prototype instanceof O?this:O).allWithCallback(e,{thenCallback:e=>({status:"fulfilled",value:e}),errorCallback:e=>({status:"rejected",reason:e})})}static allWithCallback(e,t){let n,o,r=new this((e,t)=>{n=e,o=t}),s=2,i=0;const a=[];for(let l of e){p(l)||(l=this.resolve(l));const e=i;try{l.then(o=>{a[e]=t?t.thenCallback(o):o,s--,0===s&&n(a)},r=>{t?(a[e]=t.errorCallback(r),s--,0===s&&n(a)):o(r)})}catch(c){o(c)}s++,i++}return s-=2,0===s&&n(a),r}constructor(e){const t=this;if(!(t instanceof O))throw new Error("Must be an instanceof Promise.");t[g]=v,t[_]=[];try{e&&e(E(t,b),E(t,T))}catch(n){Z(t,!1,n)}}get[Symbol.toStringTag](){return"Promise"}get[Symbol.species](){return O}then(e,n){let o=this.constructor[Symbol.species];o&&"function"==typeof o||(o=this.constructor||O);const r=new o(C),s=t.current;return this[g]==v?this[_].push(s,r,e,n):P(this,s,r,e,n),r}catch(e){return this.then(null,e)}finally(e){let n=this.constructor[Symbol.species];n&&"function"==typeof n||(n=O);const o=new n(C);o[k]=k;const r=t.current;return this[g]==v?this[_].push(r,o,e,e):P(this,r,o,e,e),o}}O.resolve=O.resolve,O.reject=O.reject,O.race=O.race,O.all=O.all;const z=e[c]=e.Promise,j=t.__symbol__("ZoneAwarePromise");let I=o(e,"Promise");I&&!I.configurable||(I&&delete I.writable,I&&delete I.value,I||(I={configurable:!0,enumerable:!0}),I.get=function(){return e[j]?e[j]:e[c]},I.set=function(t){t===O?e[j]=t:(e[c]=t,t.prototype[l]||R(t),n.setNativePromise(t))},r(e,"Promise",I)),e.Promise=O;const N=s("thenPatched");function R(e){const t=e.prototype,n=o(t,"then");if(n&&(!1===n.writable||!n.configurable))return;const r=t.then;t[l]=r,e.prototype.then=function(e,t){return new O((e,t)=>{r.call(this,e,t)}).then(e,t)},e[N]=!0}if(n.patchThen=R,z){R(z);const t=e.fetch;"function"==typeof t&&(e[n.symbol("fetch")]=t,e.fetch=(x=t,function(){let e=x.apply(this,arguments);if(e instanceof O)return e;let t=e.constructor;return t[N]||R(t),e}))}var x;return Promise[t.__symbol__("uncaughtPromiseErrors")]=i,O});const e=Object.getOwnPropertyDescriptor,t=Object.defineProperty,n=Object.getPrototypeOf,o=Object.create,r=Array.prototype.slice,s="addEventListener",i="removeEventListener",a=Zone.__symbol__(s),c=Zone.__symbol__(i),l="true",u="false",h=Zone.__symbol__("");function p(e,t){return Zone.current.wrap(e,t)}function f(e,t,n,o,r){return Zone.current.scheduleMacroTask(e,t,n,o,r)}const d=Zone.__symbol__,g="undefined"!=typeof window,_=g?window:void 0,k=g&&_||"object"==typeof self&&self||global,m=[null];function y(e,t){for(let n=e.length-1;n>=0;n--)"function"==typeof e[n]&&(e[n]=p(e[n],t+"_"+n));return e}function v(e){return!e||!1!==e.writable&&!("function"==typeof e.get&&void 0===e.set)}const b="undefined"!=typeof WorkerGlobalScope&&self instanceof WorkerGlobalScope,T=!("nw"in k)&&void 0!==k.process&&"[object process]"==={}.toString.call(k.process),E=!T&&!b&&!(!g||!_.HTMLElement),w=void 0!==k.process&&"[object process]"==={}.toString.call(k.process)&&!b&&!(!g||!_.HTMLElement),Z={},S=function(e){if(!(e=e||k.event))return;let t=Z[e.type];t||(t=Z[e.type]=d("ON_PROPERTY"+e.type));const n=this||e.target||k,o=n[t];let r;if(E&&n===_&&"error"===e.type){const t=e;r=o&&o.call(this,t.message,t.filename,t.lineno,t.colno,t.error),!0===r&&e.preventDefault()}else r=o&&o.apply(this,arguments),null==r||r||e.preventDefault();return r};function D(n,o,r){let s=e(n,o);if(!s&&r&&e(r,o)&&(s={enumerable:!0,configurable:!0}),!s||!s.configurable)return;const i=d("on"+o+"patched");if(n.hasOwnProperty(i)&&n[i])return;delete s.writable,delete s.value;const a=s.get,c=s.set,l=o.substr(2);let u=Z[l];u||(u=Z[l]=d("ON_PROPERTY"+l)),s.set=function(e){let t=this;t||n!==k||(t=k),t&&(t[u]&&t.removeEventListener(l,S),c&&c.apply(t,m),"function"==typeof e?(t[u]=e,t.addEventListener(l,S,!1)):t[u]=null)},s.get=function(){let e=this;if(e||n!==k||(e=k),!e)return null;const t=e[u];if(t)return t;if(a){let t=a&&a.call(this);if(t)return s.set.call(this,t),"function"==typeof e.removeAttribute&&e.removeAttribute(o),t}return null},t(n,o,s),n[i]=!0}function P(e,t,n){if(t)for(let o=0;o<t.length;o++)D(e,"on"+t[o],n);else{const t=[];for(const n in e)"on"==n.substr(0,2)&&t.push(n);for(let o=0;o<t.length;o++)D(e,t[o],n)}}const C=d("originalInstance");function O(e){const n=k[e];if(!n)return;k[d(e)]=n,k[e]=function(){const t=y(arguments,e);switch(t.length){case 0:this[C]=new n;break;case 1:this[C]=new n(t[0]);break;case 2:this[C]=new n(t[0],t[1]);break;case 3:this[C]=new n(t[0],t[1],t[2]);break;case 4:this[C]=new n(t[0],t[1],t[2],t[3]);break;default:throw new Error("Arg list too long.")}},I(k[e],n);const o=new n(function(){});let r;for(r in o)"XMLHttpRequest"===e&&"responseBlob"===r||function(n){"function"==typeof o[n]?k[e].prototype[n]=function(){return this[C][n].apply(this[C],arguments)}:t(k[e].prototype,n,{set:function(t){"function"==typeof t?(this[C][n]=p(t,e+"."+n),I(this[C][n],t)):this[C][n]=t},get:function(){return this[C][n]}})}(r);for(r in n)"prototype"!==r&&n.hasOwnProperty(r)&&(k[e][r]=n[r])}function z(t,o,r){let s=t;for(;s&&!s.hasOwnProperty(o);)s=n(s);!s&&t[o]&&(s=t);const i=d(o);let a=null;if(s&&!(a=s[i])&&(a=s[i]=s[o],v(s&&e(s,o)))){const e=r(a,i,o);s[o]=function(){return e(this,arguments)},I(s[o],a)}return a}function j(e,t,n){let o=null;function r(e){const t=e.data;return t.args[t.cbIdx]=function(){e.invoke.apply(this,arguments)},o.apply(t.target,t.args),e}o=z(e,t,e=>function(t,o){const s=n(t,o);return s.cbIdx>=0&&"function"==typeof o[s.cbIdx]?f(s.name,o[s.cbIdx],s,r):e.apply(t,o)})}function I(e,t){e[d("OriginalDelegate")]=t}let N=!1,R=!1;function x(){try{const e=_.navigator.userAgent;if(-1!==e.indexOf("MSIE ")||-1!==e.indexOf("Trident/"))return!0}catch(e){}return!1}function M(){if(N)return R;N=!0;try{const e=_.navigator.userAgent;-1===e.indexOf("MSIE ")&&-1===e.indexOf("Trident/")&&-1===e.indexOf("Edge/")||(R=!0)}catch(e){}return R}Zone.__load_patch("toString",e=>{const t=Function.prototype.toString,n=d("OriginalDelegate"),o=d("Promise"),r=d("Error"),s=function(){if("function"==typeof this){const s=this[n];if(s)return"function"==typeof s?t.call(s):Object.prototype.toString.call(s);if(this===Promise){const n=e[o];if(n)return t.call(n)}if(this===Error){const n=e[r];if(n)return t.call(n)}}return t.call(this)};s[n]=t,Function.prototype.toString=s;const i=Object.prototype.toString;Object.prototype.toString=function(){return this instanceof Promise?"[object Promise]":i.call(this)}});let L=!1;if("undefined"!=typeof window)try{const e=Object.defineProperty({},"passive",{get:function(){L=!0}});window.addEventListener("test",e,e),window.removeEventListener("test",e,e)}catch(he){L=!1}const A={useG:!0},H={},F={},G=new RegExp("^"+h+"(\\w+)(true|false)$"),B=d("propagationStopped");function q(e,t){const n=(t?t(e):e)+u,o=(t?t(e):e)+l,r=h+n,s=h+o;H[e]={},H[e].false=r,H[e].true=s}function W(e,t,o){const r=o&&o.add||s,a=o&&o.rm||i,c=o&&o.listeners||"eventListeners",p=o&&o.rmAll||"removeAllListeners",f=d(r),g="."+r+":",_=function(e,t,n){if(e.isRemoved)return;const o=e.callback;"object"==typeof o&&o.handleEvent&&(e.callback=e=>o.handleEvent(e),e.originalDelegate=o),e.invoke(e,t,[n]);const r=e.options;r&&"object"==typeof r&&r.once&&t[a].call(t,n.type,e.originalDelegate?e.originalDelegate:e.callback,r)},k=function(t){if(!(t=t||e.event))return;const n=this||t.target||e,o=n[H[t.type].false];if(o)if(1===o.length)_(o[0],n,t);else{const e=o.slice();for(let o=0;o<e.length&&(!t||!0!==t[B]);o++)_(e[o],n,t)}},m=function(t){if(!(t=t||e.event))return;const n=this||t.target||e,o=n[H[t.type].true];if(o)if(1===o.length)_(o[0],n,t);else{const e=o.slice();for(let o=0;o<e.length&&(!t||!0!==t[B]);o++)_(e[o],n,t)}};function y(t,o){if(!t)return!1;let s=!0;o&&void 0!==o.useG&&(s=o.useG);const i=o&&o.vh;let _=!0;o&&void 0!==o.chkDup&&(_=o.chkDup);let y=!1;o&&void 0!==o.rt&&(y=o.rt);let v=t;for(;v&&!v.hasOwnProperty(r);)v=n(v);if(!v&&t[r]&&(v=t),!v)return!1;if(v[f])return!1;const b=o&&o.eventNameToString,E={},w=v[f]=v[r],Z=v[d(a)]=v[a],S=v[d(c)]=v[c],D=v[d(p)]=v[p];let P;function C(e,t){return!L&&"object"==typeof e&&e?!!e.capture:L&&t?"boolean"==typeof e?{capture:e,passive:!0}:e?"object"==typeof e&&!1!==e.passive?Object.assign(Object.assign({},e),{passive:!0}):e:{passive:!0}:e}o&&o.prepend&&(P=v[d(o.prepend)]=v[o.prepend]);const O=s?function(e){if(!E.isExisting)return w.call(E.target,E.eventName,E.capture?m:k,E.options)}:function(e){return w.call(E.target,E.eventName,e.invoke,E.options)},z=s?function(e){if(!e.isRemoved){const t=H[e.eventName];let n;t&&(n=t[e.capture?l:u]);const o=n&&e.target[n];if(o)for(let r=0;r<o.length;r++)if(o[r]===e){o.splice(r,1),e.isRemoved=!0,0===o.length&&(e.allRemoved=!0,e.target[n]=null);break}}if(e.allRemoved)return Z.call(e.target,e.eventName,e.capture?m:k,e.options)}:function(e){return Z.call(e.target,e.eventName,e.invoke,e.options)},j=o&&o.diff?o.diff:function(e,t){const n=typeof t;return"function"===n&&e.callback===t||"object"===n&&e.originalDelegate===t},N=Zone[d("BLACK_LISTED_EVENTS")],R=e[d("PASSIVE_EVENTS")],x=function(t,n,r,a,c=!1,h=!1){return function(){const p=this||e;let f=arguments[0];o&&o.transferEventName&&(f=o.transferEventName(f));let d=arguments[1];if(!d)return t.apply(this,arguments);if(T&&"uncaughtException"===f)return t.apply(this,arguments);let g=!1;if("function"!=typeof d){if(!d.handleEvent)return t.apply(this,arguments);g=!0}if(i&&!i(t,d,p,arguments))return;const k=L&&!!R&&-1!==R.indexOf(f),m=C(arguments[2],k);if(N)for(let e=0;e<N.length;e++)if(f===N[e])return k?t.call(p,f,d,m):t.apply(this,arguments);const y=!!m&&("boolean"==typeof m||m.capture),v=!(!m||"object"!=typeof m)&&m.once,w=Zone.current;let Z=H[f];Z||(q(f,b),Z=H[f]);const S=Z[y?l:u];let D,P=p[S],O=!1;if(P){if(O=!0,_)for(let e=0;e<P.length;e++)if(j(P[e],d))return}else P=p[S]=[];const z=p.constructor.name,I=F[z];I&&(D=I[f]),D||(D=z+n+(b?b(f):f)),E.options=m,v&&(E.options.once=!1),E.target=p,E.capture=y,E.eventName=f,E.isExisting=O;const x=s?A:void 0;x&&(x.taskData=E);const M=w.scheduleEventTask(D,d,x,r,a);return E.target=null,x&&(x.taskData=null),v&&(m.once=!0),(L||"boolean"!=typeof M.options)&&(M.options=m),M.target=p,M.capture=y,M.eventName=f,g&&(M.originalDelegate=d),h?P.unshift(M):P.push(M),c?p:void 0}};return v[r]=x(w,g,O,z,y),P&&(v.prependListener=x(P,".prependListener:",function(e){return P.call(E.target,E.eventName,e.invoke,E.options)},z,y,!0)),v[a]=function(){const t=this||e;let n=arguments[0];o&&o.transferEventName&&(n=o.transferEventName(n));const r=arguments[2],s=!!r&&("boolean"==typeof r||r.capture),a=arguments[1];if(!a)return Z.apply(this,arguments);if(i&&!i(Z,a,t,arguments))return;const c=H[n];let p;c&&(p=c[s?l:u]);const f=p&&t[p];if(f)for(let e=0;e<f.length;e++){const o=f[e];if(j(o,a))return f.splice(e,1),o.isRemoved=!0,0===f.length&&(o.allRemoved=!0,t[p]=null,"string"==typeof n)&&(t[h+"ON_PROPERTY"+n]=null),o.zone.cancelTask(o),y?t:void 0}return Z.apply(this,arguments)},v[c]=function(){const t=this||e;let n=arguments[0];o&&o.transferEventName&&(n=o.transferEventName(n));const r=[],s=U(t,b?b(n):n);for(let e=0;e<s.length;e++){const t=s[e];r.push(t.originalDelegate?t.originalDelegate:t.callback)}return r},v[p]=function(){const t=this||e;let n=arguments[0];if(n){o&&o.transferEventName&&(n=o.transferEventName(n));const e=H[n];if(e){const o=t[e.false],r=t[e.true];if(o){const e=o.slice();for(let t=0;t<e.length;t++){const o=e[t];this[a].call(this,n,o.originalDelegate?o.originalDelegate:o.callback,o.options)}}if(r){const e=r.slice();for(let t=0;t<e.length;t++){const o=e[t];this[a].call(this,n,o.originalDelegate?o.originalDelegate:o.callback,o.options)}}}}else{const e=Object.keys(t);for(let t=0;t<e.length;t++){const n=G.exec(e[t]);let o=n&&n[1];o&&"removeListener"!==o&&this[p].call(this,o)}this[p].call(this,"removeListener")}if(y)return this},I(v[r],w),I(v[a],Z),D&&I(v[p],D),S&&I(v[c],S),!0}let v=[];for(let n=0;n<t.length;n++)v[n]=y(t[n],o);return v}function U(e,t){if(!t){const n=[];for(let o in e){const r=G.exec(o);let s=r&&r[1];if(s&&(!t||s===t)){const t=e[o];if(t)for(let e=0;e<t.length;e++)n.push(t[e])}}return n}let n=H[t];n||(q(t),n=H[t]);const o=e[n.false],r=e[n.true];return o?r?o.concat(r):o.slice():r?r.slice():[]}function V(e,t){const n=e.Event;n&&n.prototype&&t.patchMethod(n.prototype,"stopImmediatePropagation",e=>function(t,n){t[B]=!0,e&&e.apply(t,n)})}function $(e,t,n,o,r){const s=Zone.__symbol__(o);if(t[s])return;const i=t[s]=t[o];t[o]=function(s,a,c){return a&&a.prototype&&r.forEach(function(t){const r=`${n}.${o}::`+t,s=a.prototype;if(s.hasOwnProperty(t)){const n=e.ObjectGetOwnPropertyDescriptor(s,t);n&&n.value?(n.value=e.wrapWithCurrentZone(n.value,r),e._redefineProperty(a.prototype,t,n)):s[t]&&(s[t]=e.wrapWithCurrentZone(s[t],r))}else s[t]&&(s[t]=e.wrapWithCurrentZone(s[t],r))}),i.call(t,s,a,c)},e.attachOriginToPatched(t[o],i)}const X=["absolutedeviceorientation","afterinput","afterprint","appinstalled","beforeinstallprompt","beforeprint","beforeunload","devicelight","devicemotion","deviceorientation","deviceorientationabsolute","deviceproximity","hashchange","languagechange","message","mozbeforepaint","offline","online","paint","pageshow","pagehide","popstate","rejectionhandled","storage","unhandledrejection","unload","userproximity","vrdisplayconnected","vrdisplaydisconnected","vrdisplaypresentchange"],J=["encrypted","waitingforkey","msneedkey","mozinterruptbegin","mozinterruptend"],Y=["load"],K=["blur","error","focus","load","resize","scroll","messageerror"],Q=["bounce","finish","start"],ee=["loadstart","progress","abort","error","load","progress","timeout","loadend","readystatechange"],te=["upgradeneeded","complete","abort","success","error","blocked","versionchange","close"],ne=["close","error","open","message"],oe=["error","message"],re=["abort","animationcancel","animationend","animationiteration","auxclick","beforeinput","blur","cancel","canplay","canplaythrough","change","compositionstart","compositionupdate","compositionend","cuechange","click","close","contextmenu","curechange","dblclick","drag","dragend","dragenter","dragexit","dragleave","dragover","drop","durationchange","emptied","ended","error","focus","focusin","focusout","gotpointercapture","input","invalid","keydown","keypress","keyup","load","loadstart","loadeddata","loadedmetadata","lostpointercapture","mousedown","mouseenter","mouseleave","mousemove","mouseout","mouseover","mouseup","mousewheel","orientationchange","pause","play","playing","pointercancel","pointerdown","pointerenter","pointerleave","pointerlockchange","mozpointerlockchange","webkitpointerlockerchange","pointerlockerror","mozpointerlockerror","webkitpointerlockerror","pointermove","pointout","pointerover","pointerup","progress","ratechange","reset","resize","scroll","seeked","seeking","select","selectionchange","selectstart","show","sort","stalled","submit","suspend","timeupdate","volumechange","touchcancel","touchmove","touchstart","touchend","transitioncancel","transitionend","waiting","wheel"].concat(["webglcontextrestored","webglcontextlost","webglcontextcreationerror"],["autocomplete","autocompleteerror"],["toggle"],["afterscriptexecute","beforescriptexecute","DOMContentLoaded","freeze","fullscreenchange","mozfullscreenchange","webkitfullscreenchange","msfullscreenchange","fullscreenerror","mozfullscreenerror","webkitfullscreenerror","msfullscreenerror","readystatechange","visibilitychange","resume"],X,["beforecopy","beforecut","beforepaste","copy","cut","paste","dragstart","loadend","animationstart","search","transitionrun","transitionstart","webkitanimationend","webkitanimationiteration","webkitanimationstart","webkittransitionend"],["activate","afterupdate","ariarequest","beforeactivate","beforedeactivate","beforeeditfocus","beforeupdate","cellchange","controlselect","dataavailable","datasetchanged","datasetcomplete","errorupdate","filterchange","layoutcomplete","losecapture","move","moveend","movestart","propertychange","resizeend","resizestart","rowenter","rowexit","rowsdelete","rowsinserted","command","compassneedscalibration","deactivate","help","mscontentzoom","msmanipulationstatechanged","msgesturechange","msgesturedoubletap","msgestureend","msgesturehold","msgesturestart","msgesturetap","msgotpointercapture","msinertiastart","mslostpointercapture","mspointercancel","mspointerdown","mspointerenter","mspointerhover","mspointerleave","mspointermove","mspointerout","mspointerover","mspointerup","pointerout","mssitemodejumplistitemremoved","msthumbnailclick","stop","storagecommit"]);function se(e,t,n){if(!n||0===n.length)return t;const o=n.filter(t=>t.target===e);if(!o||0===o.length)return t;const r=o[0].ignoreProperties;return t.filter(e=>-1===r.indexOf(e))}function ie(e,t,n,o){e&&P(e,se(e,t,n),o)}function ae(e,t){if(T&&!w)return;if(Zone[e.symbol("patchEvents")])return;const o="undefined"!=typeof WebSocket,r=t.__Zone_ignore_on_properties;if(E){const e=window,t=x?[{target:e,ignoreProperties:["error"]}]:[];ie(e,re.concat(["messageerror"]),r?r.concat(t):r,n(e)),ie(Document.prototype,re,r),void 0!==e.SVGElement&&ie(e.SVGElement.prototype,re,r),ie(Element.prototype,re,r),ie(HTMLElement.prototype,re,r),ie(HTMLMediaElement.prototype,J,r),ie(HTMLFrameSetElement.prototype,X.concat(K),r),ie(HTMLBodyElement.prototype,X.concat(K),r),ie(HTMLFrameElement.prototype,Y,r),ie(HTMLIFrameElement.prototype,Y,r);const o=e.HTMLMarqueeElement;o&&ie(o.prototype,Q,r);const s=e.Worker;s&&ie(s.prototype,oe,r)}const s=t.XMLHttpRequest;s&&ie(s.prototype,ee,r);const i=t.XMLHttpRequestEventTarget;i&&ie(i&&i.prototype,ee,r),"undefined"!=typeof IDBIndex&&(ie(IDBIndex.prototype,te,r),ie(IDBRequest.prototype,te,r),ie(IDBOpenDBRequest.prototype,te,r),ie(IDBDatabase.prototype,te,r),ie(IDBTransaction.prototype,te,r),ie(IDBCursor.prototype,te,r)),o&&ie(WebSocket.prototype,ne,r)}Zone.__load_patch("util",(n,a,c)=>{c.patchOnProperties=P,c.patchMethod=z,c.bindArguments=y,c.patchMacroTask=j;const f=a.__symbol__("BLACK_LISTED_EVENTS"),d=a.__symbol__("UNPATCHED_EVENTS");n[d]&&(n[f]=n[d]),n[f]&&(a[f]=a[d]=n[f]),c.patchEventPrototype=V,c.patchEventTarget=W,c.isIEOrEdge=M,c.ObjectDefineProperty=t,c.ObjectGetOwnPropertyDescriptor=e,c.ObjectCreate=o,c.ArraySlice=r,c.patchClass=O,c.wrapWithCurrentZone=p,c.filterProperties=se,c.attachOriginToPatched=I,c._redefineProperty=Object.defineProperty,c.patchCallbacks=$,c.getGlobalObjects=()=>({globalSources:F,zoneSymbolEventNames:H,eventNames:re,isBrowser:E,isMix:w,isNode:T,TRUE_STR:l,FALSE_STR:u,ZONE_SYMBOL_PREFIX:h,ADD_EVENT_LISTENER_STR:s,REMOVE_EVENT_LISTENER_STR:i})});const ce=d("zoneTask");function le(e,t,n,o){let r=null,s=null;n+=o;const i={};function a(t){const n=t.data;return n.args[0]=function(){try{t.invoke.apply(this,arguments)}finally{t.data&&t.data.isPeriodic||("number"==typeof n.handleId?delete i[n.handleId]:n.handleId&&(n.handleId[ce]=null))}},n.handleId=r.apply(e,n.args),t}function c(e){return s(e.data.handleId)}r=z(e,t+=o,n=>function(r,s){if("function"==typeof s[0]){const e=f(t,s[0],{isPeriodic:"Interval"===o,delay:"Timeout"===o||"Interval"===o?s[1]||0:void 0,args:s},a,c);if(!e)return e;const n=e.data.handleId;return"number"==typeof n?i[n]=e:n&&(n[ce]=e),n&&n.ref&&n.unref&&"function"==typeof n.ref&&"function"==typeof n.unref&&(e.ref=n.ref.bind(n),e.unref=n.unref.bind(n)),"number"==typeof n||n?n:e}return n.apply(e,s)}),s=z(e,n,t=>function(n,o){const r=o[0];let s;"number"==typeof r?s=i[r]:(s=r&&r[ce],s||(s=r)),s&&"string"==typeof s.type?"notScheduled"!==s.state&&(s.cancelFn&&s.data.isPeriodic||0===s.runCount)&&("number"==typeof r?delete i[r]:r&&(r[ce]=null),s.zone.cancelTask(s)):t.apply(e,o)})}function ue(e,t){if(Zone[t.symbol("patchEventTarget")])return;const{eventNames:n,zoneSymbolEventNames:o,TRUE_STR:r,FALSE_STR:s,ZONE_SYMBOL_PREFIX:i}=t.getGlobalObjects();for(let c=0;c<n.length;c++){const e=n[c],t=i+(e+s),a=i+(e+r);o[e]={},o[e][s]=t,o[e][r]=a}const a=e.EventTarget;return a&&a.prototype?(t.patchEventTarget(e,[a&&a.prototype]),!0):void 0}Zone.__load_patch("legacy",e=>{const t=e[Zone.__symbol__("legacyPatch")];t&&t()}),Zone.__load_patch("timers",e=>{const t="set",n="clear";le(e,t,n,"Timeout"),le(e,t,n,"Interval"),le(e,t,n,"Immediate")}),Zone.__load_patch("requestAnimationFrame",e=>{le(e,"request","cancel","AnimationFrame"),le(e,"mozRequest","mozCancel","AnimationFrame"),le(e,"webkitRequest","webkitCancel","AnimationFrame")}),Zone.__load_patch("blocking",(e,t)=>{const n=["alert","prompt","confirm"];for(let o=0;o<n.length;o++)z(e,n[o],(n,o,r)=>function(o,s){return t.current.run(n,e,s,r)})}),Zone.__load_patch("EventTarget",(e,t,n)=>{(function(e,t){t.patchEventPrototype(e,t)})(e,n),ue(e,n);const o=e.XMLHttpRequestEventTarget;o&&o.prototype&&n.patchEventTarget(e,[o.prototype]),O("MutationObserver"),O("WebKitMutationObserver"),O("IntersectionObserver"),O("FileReader")}),Zone.__load_patch("on_property",(e,t,n)=>{ae(n,e)}),Zone.__load_patch("customElements",(e,t,n)=>{!function(e,t){const{isBrowser:n,isMix:o}=t.getGlobalObjects();(n||o)&&e.customElements&&"customElements"in e&&t.patchCallbacks(t,e.customElements,"customElements","define",["connectedCallback","disconnectedCallback","adoptedCallback","attributeChangedCallback"])}(e,n)}),Zone.__load_patch("XHR",(e,t)=>{!function(e){const u=e.XMLHttpRequest;if(!u)return;const h=u.prototype;let p=h[a],g=h[c];if(!p){const t=e.XMLHttpRequestEventTarget;if(t){const e=t.prototype;p=e[a],g=e[c]}}const _="readystatechange",k="scheduled";function m(e){const o=e.data,i=o.target;i[s]=!1,i[l]=!1;const u=i[r];p||(p=i[a],g=i[c]),u&&g.call(i,_,u);const h=i[r]=()=>{if(i.readyState===i.DONE)if(!o.aborted&&i[s]&&e.state===k){const n=i[t.__symbol__("loadfalse")];if(n&&n.length>0){const r=e.invoke;e.invoke=function(){const n=i[t.__symbol__("loadfalse")];for(let t=0;t<n.length;t++)n[t]===e&&n.splice(t,1);o.aborted||e.state!==k||r.call(e)},n.push(e)}else e.invoke()}else o.aborted||!1!==i[s]||(i[l]=!0)};return p.call(i,_,h),i[n]||(i[n]=e),w.apply(i,o.args),i[s]=!0,e}function y(){}function v(e){const t=e.data;return t.aborted=!0,Z.apply(t.target,t.args)}const b=z(h,"open",()=>function(e,t){return e[o]=0==t[2],e[i]=t[1],b.apply(e,t)}),T=d("fetchTaskAborting"),E=d("fetchTaskScheduling"),w=z(h,"send",()=>function(e,n){if(!0===t.current[E])return w.apply(e,n);if(e[o])return w.apply(e,n);{const t={target:e,url:e[i],isPeriodic:!1,args:n,aborted:!1},o=f("XMLHttpRequest.send",y,t,m,v);e&&!0===e[l]&&!t.aborted&&o.state===k&&o.invoke()}}),Z=z(h,"abort",()=>function(e,o){const r=e[n];if(r&&"string"==typeof r.type){if(null==r.cancelFn||r.data&&r.data.aborted)return;r.zone.cancelTask(r)}else if(!0===t.current[T])return Z.apply(e,o)})}(e);const n=d("xhrTask"),o=d("xhrSync"),r=d("xhrListener"),s=d("xhrScheduled"),i=d("xhrURL"),l=d("xhrErrorBeforeScheduled")}),Zone.__load_patch("geolocation",t=>{t.navigator&&t.navigator.geolocation&&function(t,n){const o=t.constructor.name;for(let r=0;r<n.length;r++){const s=n[r],i=t[s];if(i){if(!v(e(t,s)))continue;t[s]=(e=>{const t=function(){return e.apply(this,y(arguments,o+"."+s))};return I(t,e),t})(i)}}}(t.navigator.geolocation,["getCurrentPosition","watchPosition"])}),Zone.__load_patch("PromiseRejectionEvent",(e,t)=>{function n(t){return function(n){U(e,t).forEach(o=>{const r=e.PromiseRejectionEvent;if(r){const e=new r(t,{promise:n.promise,reason:n.rejection});o.invoke(e)}})}}e.PromiseRejectionEvent&&(t[d("unhandledPromiseRejectionHandler")]=n("unhandledrejection"),t[d("rejectionHandledHandler")]=n("rejectionhandled"))})})?o.call(t,n,t,e):o)||(e.exports=r)}},[[1,0]]]); | non_priority | beam mw polyfills js window webpackjsonp window webpackjsonp push function e t n e exports n hn g hn g function e t n use strict n r t n pdpn pdpn function e t n var o r void r function typeof o function use strict function e const t e performance function n e t t mark t mark e function o e n t t measure t measure e n n zone const r e zone symbol prefix zone symbol function s e return r e const i e if e zone if i function typeof e zone symbol throw new error zone already loaded return e zone class a constructor e t this parent e this name t t name unnamed this properties t t properties this zonedelegate new l this this parent this parent zonedelegate t static assertzonepatched if e promise c zoneawarepromise throw new error zone js has detected that zoneawarepromise window global promise has been overwritten nmost likely cause is that a promise polyfill has been loaded after zone js polyfilling promise api is not necessary when zone js is loaded if you must load one do so before loading zone js static get root let e a current for e parent e e parent return e static get current return z zone static get currenttask return j static load patch t r if c hasownproperty t if i throw error already loaded patch t else if e const s zone t n s c r e a o o s s get parent return this parent get name return this name get e const t this getzonewith e if t return t properties getzonewith e let t this for t if t properties hasownproperty e return t t t parent return null fork e if e throw new error zonespec required return this zonedelegate fork this e wrap e t if function typeof e throw new error expecting function got e const n this zonedelegate intercept this e t o this return function return o runguarded n this arguments t run e t n o z parent z zone this try return this zonedelegate invoke this e t n o finally z z parent runguarded e t null n o z parent z zone this try try return this zonedelegate invoke this e t n o catch r if this zonedelegate handleerror this r throw r finally z z parent runtask e t n if e zone this throw new error a task can only be run in the zone of creation creation e zone y name execution this name if e state v e type p e type d return const o e state e o e transitionto e t e runcount const r j j e z parent z zone this try e type d e data e data isperiodic e cancelfn void try return this zonedelegate invoketask this e t n catch s if this zonedelegate handleerror this s throw s finally e state v e state z e type p e data e data isperiodic o e transitionto t e e runcount this updatetaskcount e o e transitionto v e v z z parent j r scheduletask e if e zone e zone this let t this for t if t e zone throw error can not reschedule task to this name which is descendants of the original zone e zone name t t parent e transitionto b v const t e zonedelegates t e zone this try e this zonedelegate scheduletask this e catch n throw e transitionto z b v this zonedelegate handleerror this n n return e zonedelegates t this updatetaskcount e e state b e transitionto t b e schedulemicrotask e t n o return this scheduletask new u s e t n o void schedulemacrotask e t n o r return this scheduletask new u d e t n o r scheduleeventtask e t n o r return this scheduletask new u p e t n o r canceltask e if e zone this throw new error a task can only be cancelled in the zone of creation creation e zone y name execution this name e transitionto w t e try this zonedelegate canceltask this e catch t throw e transitionto z w this zonedelegate handleerror this t t return this updatetaskcount e e transitionto v w e runcount e updatetaskcount e t const n e zonedelegates t e zonedelegates null for let o o e hastask n o onscheduletask e t n o e scheduletask n o oninvoketask e t n o r s e invoketask n o r s oncanceltask e t n o e canceltask n o class l constructor e t n this taskcounts microtask macrotask eventtask this zone e this parentdelegate t this forkzs n n n onfork n t forkzs this forkdlgt n n onfork t t forkdlgt this forkcurrzone n n onfork this zone t forkcurrzone this interceptzs n n onintercept n t interceptzs this interceptdlgt n n onintercept t t interceptdlgt this interceptcurrzone n n onintercept this zone t interceptcurrzone this invokezs n n oninvoke n t invokezs this invokedlgt n n oninvoke t t invokedlgt this invokecurrzone n n oninvoke this zone t invokecurrzone this handleerrorzs n n onhandleerror n t handleerrorzs this handleerrordlgt n n onhandleerror t t handleerrordlgt this handleerrorcurrzone n n onhandleerror this zone t handleerrorcurrzone this scheduletaskzs n n onscheduletask n t scheduletaskzs this scheduletaskdlgt n n onscheduletask t t scheduletaskdlgt this scheduletaskcurrzone n n onscheduletask this zone t scheduletaskcurrzone this invoketaskzs n n oninvoketask n t invoketaskzs this invoketaskdlgt n n oninvoketask t t invoketaskdlgt this invoketaskcurrzone n n oninvoketask this zone t invoketaskcurrzone this canceltaskzs n n oncanceltask n t canceltaskzs this canceltaskdlgt n n oncanceltask t t canceltaskdlgt this canceltaskcurrzone n n oncanceltask this zone t canceltaskcurrzone this hastaskzs null this hastaskdlgt null this hastaskdlgtowner null this hastaskcurrzone null const o n n onhastask o t t hastaskzs this hastaskzs o n c this hastaskdlgt t this hastaskdlgtowner this this hastaskcurrzone e n onscheduletask this scheduletaskzs c this scheduletaskdlgt t this scheduletaskcurrzone this zone n oninvoketask this invoketaskzs c this invoketaskdlgt t this invoketaskcurrzone this zone n oncanceltask this canceltaskzs c this canceltaskdlgt t this canceltaskcurrzone this zone fork e t return this forkzs this forkzs onfork this forkdlgt this zone e t new a e t intercept e t n return this interceptzs this interceptzs onintercept this interceptdlgt this interceptcurrzone e t n t invoke e t n o r return this invokezs this invokezs oninvoke this invokedlgt this invokecurrzone e t n o r t apply n o handleerror e t return this handleerrorzs this handleerrorzs onhandleerror this handleerrordlgt this handleerrorcurrzone e t scheduletask e t let n t if this scheduletaskzs this hastaskzs n zonedelegates push this hastaskdlgtowner n this scheduletaskzs onscheduletask this scheduletaskdlgt this scheduletaskcurrzone e t n n t else if t schedulefn t schedulefn t else if t type s throw new error task is missing schedulefn k t return n invoketask e t n o return this invoketaskzs this invoketaskzs oninvoketask this invoketaskdlgt this invoketaskcurrzone e t n o t callback apply n o canceltask e t let n if this canceltaskzs n this canceltaskzs oncanceltask this canceltaskdlgt this canceltaskcurrzone e t else if t cancelfn throw error task is not cancelable n t cancelfn t return n hastask e t try this hastaskzs this hastaskzs onhastask this hastaskdlgt this hastaskcurrzone e t catch n this handleerror e n updatetaskcount e t const n this taskcounts o n r n o t if r macrotask n macrotask eventtask n eventtask change e class u constructor t n o r s i if this zone null this runcount this zonedelegates null this state notscheduled this type t this source n this data r this schedulefn s this cancelfn i o throw new error callback is not defined this callback o const a this this invoke t p r r useg u invoketask function return u invoketask call e a this arguments static invoketask e t n e e this i try return e runcount e zone runtask e t n finally i m i get zone return this zone get state return this state cancelschedulerequest this transitionto v b transitionto e t n if this state t this state n throw new error this type this source can not transition to e expecting state t n or n was this state this state e e v this zonedelegates null tostring return this data void this data handleid this data handleid tostring object prototype tostring call this tojson return type this type state this state source this source zone this zone name runcount this runcount const h s settimeout p s promise f s then let d g function k t if i g length if d e d e resolve d let e d e e d then e call d m else e m t g push t function m if for g length const t g g for let n n z onunhandlederror n microtaskdraindone n schedulemicrotask k showuncaughterror a patcheventtarget patchonproperties n patchmethod n bindarguments patchthen n patchmacrotask n setnativepromise e e function typeof e resolve d e resolve patcheventprototype n isieoredge getglobalobjects objectdefineproperty n objectgetownpropertydescriptor objectcreate arrayslice patchclass n wrapwithcurrentzone n filterproperties attachorigintopatched n redefineproperty n patchcallbacks n let z parent null zone new a null null j null i function n o zone zone e zone a undefined typeof window window undefined typeof self self global zone load patch zoneawarepromise e t n const o object getownpropertydescriptor r object defineproperty s n symbol i a e c s promise l s then n onunhandlederror e if n showuncaughterror const t e e rejection t console error unhandled promise rejection t instanceof error t message t zone e zone name task e task e task source value t t instanceof error t stack void console error e n microtaskdraindone for i length const t i shift try t zone runguarded throw t catch e h e const u s unhandledpromiserejectionhandler function h e n onunhandlederror e try const n t function typeof n n call this e catch o function p e return e e then function f e return e function d e return o reject e const g s state s value k s finally m s parentpromisevalue y s parentpromisestate v null b t function e e t return n try z e t n catch o z e o const w s currenttasktrace function z e o s const c function let e return function t return function e e t apply null arguments if e s throw new typeerror promise resolved with itself if e v let h null try object typeof s function typeof s h s s then catch u return c z e u e if o t s instanceof o s hasownproperty g s hasownproperty s v d s z e s s else if o t function typeof h try h call s c e e o c e e catch u c z e u else e o const c e if e s e k o b e e e e o t s instanceof error const e t currenttask t currenttask data t currenttask data creationtrace e r s w configurable enumerable writable value e for let t t try const o e r n k n r n o n s const a t run i void r i d i f z n a catch o z n o n const c function class o static tostring return function zoneawarepromise static resolve e return z new this null b e static reject e return z new this null t e static race e let t n o new this e o t e n o function r e t e function s e n e for let i of e p i i this resolve i i then r s return o static all e return o allwithcallback e static allsettled e return this this prototype instanceof o this o allwithcallback e thencallback e status fulfilled value e errorcallback e status rejected reason e static allwithcallback e t let n o r new this e t n e o t s i const a for let l of e p l l this resolve l const e i try l then o a t t thencallback o o s s n a r t a t errorcallback r s s n a o r catch c o c s i return s s n a r constructor e const t this if t instanceof o throw new error must be an instanceof promise t v t try e e e t b e t t catch n z t n get return promise get return o then e n let o this constructor o function typeof o o this constructor o const r new o c s t current return this v this push s r e n p this s r e n r catch e return this then null e finally e let n this constructor n function typeof n n o const o new n c o k const r t current return this v this push r o e e p this r o e e o o resolve o resolve o reject o reject o race o race o all o all const z e e promise j t symbol zoneawarepromise let i o e promise i i configurable i delete i writable i delete i value i i configurable enumerable i get function return e e e i set function t t o e t e t t prototype r t n setnativepromise t r e promise i e promise o const n s thenpatched function r e const t e prototype n o t then if n n writable n configurable return const r t then t r e prototype then function e t return new o e t r call this e t then e t e if n patchthen r z r z const t e fetch function typeof t e t e fetch x t function let e x apply this arguments if e instanceof o return e let t e constructor return t r t e var x return promise i o const e object getownpropertydescriptor t object defineproperty n object getprototypeof o object create r array prototype slice s addeventlistener i removeeventlistener a zone symbol s c zone symbol i l true u false h zone symbol function p e t return zone current wrap e t function f e t n o r return zone current schedulemacrotask e t n o r const d zone symbol g undefined typeof window g window void k g object typeof self self global m function y e t for let n e length n n function typeof e e p e t n return e function v e return e e writable function typeof e get void e set const b undefined typeof workerglobalscope self instanceof workerglobalscope t nw in k void k process tostring call k process e t b g htmlelement w void k process tostring call k process b g htmlelement z s function e if e e k event return let t z t t z d on property e type const n this e target k o n let r if e n error e type const t e r o o call this t message t filename t lineno t colno t error r e preventdefault else r o o apply this arguments null r r e preventdefault return r function d n o r let s e n o if s r e r o s enumerable configurable s s configurable return const i d on o patched if n hasownproperty i n return delete s writable delete s value const a s get c s set l o substr let u z u u z d on property l s set function e let t this t n k t k t t t removeeventlistener l s c c apply t m function typeof e t e t addeventlistener l s t null s get function let e this if e n k e k e return null const t e if t return t if a let t a a call this if t return s set call this t function typeof e removeattribute e removeattribute o t return null t n o s n function p e t n if t for let o o function t o const s n t o return s cbidx function typeof o f s name o s r e apply t o function i e t e t let n r function x try const e navigator useragent if e indexof msie e indexof trident return catch e return function m if n return r n try const e navigator useragent e indexof msie e indexof trident e indexof edge r catch e return r zone load patch tostring e const t function prototype tostring n d originaldelegate o d promise r d error s function if function typeof this const s this if s return function typeof s t call s object prototype tostring call s if this promise const n e if n return t call n if this error const n e if n return t call n return t call this s t function prototype tostring s const i object prototype tostring object prototype tostring function return this instanceof promise i call this let l if undefined typeof window try const e object defineproperty passive get function l window addeventlistener test e e window removeeventlistener test e e catch he l const a useg h f g new regexp h w true false b d propagationstopped function q e t const n t t e e u o t t e e l r h n s h o h h false r h true s function w e t o const r o o add s a o o rm i c o o listeners eventlisteners p o o rmall removealllisteners f d r g r function e t n if e isremoved return const o e callback object typeof o o handleevent e callback e o handleevent e e originaldelegate o e invoke e t const r e options r object typeof r r once t call t n type e originaldelegate e originaldelegate e callback r k function t if t t e event return const n this t target e o n false if o if o length o n t else const e o slice for let o o function t n t e e apply t n function e t n o r const s zone symbol o if t return const i t t t function s a c return a a prototype r foreach function t const r n o t s a prototype if s hasownproperty t const n e objectgetownpropertydescriptor s t n n value n value e wrapwithcurrentzone n value r e redefineproperty a prototype t n s s e wrapwithcurrentzone s r else s s e wrapwithcurrentzone s r i call t s a c e attachorigintopatched t i const x j y k q ee te ne oe re concat x function se e t n if n n length return t const o n filter t t target e if o o length return t const r o ignoreproperties return t filter e r indexof e function ie e t n o e p e se e t n o function ae e t if t w return if zone return const o undefined typeof websocket r t zone ignore on properties if e const e window t x ie e re concat r r concat t r n e ie document prototype re r void e svgelement ie e svgelement prototype re r ie element prototype re r ie htmlelement prototype re r ie htmlmediaelement prototype j r ie htmlframesetelement prototype x concat k r ie htmlbodyelement prototype x concat k r ie htmlframeelement prototype y r ie htmliframeelement prototype y r const o e htmlmarqueeelement o ie o prototype q r const s e worker s ie s prototype oe r const s t xmlhttprequest s ie s prototype ee r const i t xmlhttprequesteventtarget i ie i i prototype ee r undefined typeof idbindex ie idbindex prototype te r ie idbrequest prototype te r ie idbopendbrequest prototype te r ie idbdatabase prototype te r ie idbtransaction prototype te r ie idbcursor prototype te r o ie websocket prototype ne r zone load patch util n a c c patchonproperties p c patchmethod z c bindarguments y c patchmacrotask j const f a symbol black listed events d a symbol unpatched events n n n n a a n c patcheventprototype v c patcheventtarget w c isieoredge m c objectdefineproperty t c objectgetownpropertydescriptor e c objectcreate o c arrayslice r c patchclass o c wrapwithcurrentzone p c filterproperties se c attachorigintopatched i c redefineproperty object defineproperty c patchcallbacks c getglobalobjects globalsources f zonesymboleventnames h eventnames re isbrowser e ismix w isnode t true str l false str u zone symbol prefix h add event listener str s remove event listener str i const ce d zonetask function le e t n o let r null s null n o const i function a t const n t data return n args function try t invoke apply this arguments finally t data t data isperiodic number typeof n handleid delete i n handleid n handleid null n handleid r apply e n args t function c e return s e data handleid r z e t o n function r s if function typeof s const e f t s isperiodic interval o delay timeout o interval o s void args s a c if e return e const n e data handleid return number typeof n i e n n e n n ref n unref function typeof n ref function typeof n unref e ref n ref bind n e unref n unref bind n number typeof n n n e return n apply e s s z e n t function n o const r o let s number typeof r s i s r r s s r s string typeof s type notscheduled s state s cancelfn s data isperiodic s runcount number typeof r delete i r r null s zone canceltask s t apply e o function ue e t if zone return const eventnames n zonesymboleventnames o true str r false str s zone symbol prefix i t getglobalobjects for let c c const t e t t zone load patch timers e const t set n clear le e t n timeout le e t n interval le e t n immediate zone load patch requestanimationframe e le e request cancel animationframe le e mozrequest mozcancel animationframe le e webkitrequest webkitcancel animationframe zone load patch blocking e t const n for let o o function o s return t current run n e s r zone load patch eventtarget e t n function e t t patcheventprototype e t e n ue e n const o e xmlhttprequesteventtarget o o prototype n patcheventtarget e o mutationobserver o webkitmutationobserver o intersectionobserver o filereader zone load patch on property e t n ae n e zone load patch customelements e t n function e t const isbrowser n ismix o t getglobalobjects n o e customelements customelements in e t patchcallbacks t e customelements customelements define e n zone load patch xhr e t function e const u e xmlhttprequest if u return const h u prototype let p h g h if p const t e xmlhttprequesteventtarget if t const e t prototype p e g e const readystatechange k scheduled function m e const o e data i o target i i const u i p p i g i u g call i u const h i if i readystate i done if o aborted i e state k const n i if n n length const r e invoke e invoke function const n i for let t t function e t return e t e t b apply e t t d fetchtaskaborting e d fetchtaskscheduling w z h send function e n if t current return w apply e n if e return w apply e n const t target e url e isperiodic args n aborted o f xmlhttprequest send y t m v e e t aborted o state k o invoke z z h abort function e o const r e if r string typeof r type if null r cancelfn r data r data aborted return r zone canceltask r else if t current return z apply e o e const n d xhrtask o d xhrsync r d xhrlistener s d xhrscheduled i d xhrurl l d xhrerrorbeforescheduled zone load patch geolocation t t navigator t navigator geolocation function t n const o t constructor name for let r r const t function return e apply this y arguments o s return i t e t i t navigator geolocation zone load patch promiserejectionevent e t function n t return function n u e t foreach o const r e promiserejectionevent if r const e new r t promise n promise reason n rejection o invoke e e promiserejectionevent t n unhandledrejection t n rejectionhandled o call t n t e o e exports r | 0 |
66,707 | 27,556,151,857 | IssuesEvent | 2023-03-07 18:05:09 | ovh/terraform-provider-ovh | https://api.github.com/repos/ovh/terraform-provider-ovh | closed | Unable to complete operation on subnet during Terraform destroy | Product: Managed Kubernetes Service Product: Network Status: Missing inputs | Hi,
I'm running Terraform 1.38 that has created kubernetes cluster on a private network and subnet.
However it is consistently failing at the final resources.
The error message is
Error: calling DELETE /cloud/project/id/network/private/netId/subnet/subnetId:
"Unable to complete operation on subnet subnetId: One or more ports have an IP allocation from this subnet."
terraform -v
Terraform v1.3.8
on windows_amd64
+ provider registry.terraform.io/hashicorp/helm v2.9.0
+ provider registry.terraform.io/ovh/ovh v0.27.0
steps to produce
1. terraform apply create kubernetes cluster on private network and subnet.
2. terraform destroy.
I beleve the ovh provider has a timing issue. It should probably retry with expotential back-off or is returning before the kubernetes cluster is actually deleted. | 1.0 | Unable to complete operation on subnet during Terraform destroy - Hi,
I'm running Terraform 1.38 that has created kubernetes cluster on a private network and subnet.
However it is consistently failing at the final resources.
The error message is
Error: calling DELETE /cloud/project/id/network/private/netId/subnet/subnetId:
"Unable to complete operation on subnet subnetId: One or more ports have an IP allocation from this subnet."
terraform -v
Terraform v1.3.8
on windows_amd64
+ provider registry.terraform.io/hashicorp/helm v2.9.0
+ provider registry.terraform.io/ovh/ovh v0.27.0
steps to produce
1. terraform apply create kubernetes cluster on private network and subnet.
2. terraform destroy.
I beleve the ovh provider has a timing issue. It should probably retry with expotential back-off or is returning before the kubernetes cluster is actually deleted. | non_priority | unable to complete operation on subnet during terraform destroy hi i m running terraform that has created kubernetes cluster on a private network and subnet however it is consistently failing at the final resources the error message is error calling delete cloud project id network private netid subnet subnetid unable to complete operation on subnet subnetid one or more ports have an ip allocation from this subnet terraform v terraform on windows provider registry terraform io hashicorp helm provider registry terraform io ovh ovh steps to produce terraform apply create kubernetes cluster on private network and subnet terraform destroy i beleve the ovh provider has a timing issue it should probably retry with expotential back off or is returning before the kubernetes cluster is actually deleted | 0 |
99,800 | 21,043,480,464 | IssuesEvent | 2022-03-31 14:12:08 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | railgun firing order ambiguous | Art Code Design | - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
New players are likely to be mislead about what shells fire in which order for railgun.
- when on the periscope, there is no UI indicating which railgun shell is going to be fired (leftmost)
- in the loader, no UI indicating which shell is going to be fired (also leftmost)
- -loader is even more ambiguous due to the empty slot appearing on the right side
the common case of loaded shells being all the same (ex: all 5 being empty regular shells) doesn't help the situation either
**Steps To Reproduce**
1. Ask multiple new players to describe the railgun / shells.
**Version**
yes
**Additional information**
something like this idk


| 1.0 | railgun firing order ambiguous - - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
New players are likely to be mislead about what shells fire in which order for railgun.
- when on the periscope, there is no UI indicating which railgun shell is going to be fired (leftmost)
- in the loader, no UI indicating which shell is going to be fired (also leftmost)
- -loader is even more ambiguous due to the empty slot appearing on the right side
the common case of loaded shells being all the same (ex: all 5 being empty regular shells) doesn't help the situation either
**Steps To Reproduce**
1. Ask multiple new players to describe the railgun / shells.
**Version**
yes
**Additional information**
something like this idk


| non_priority | railgun firing order ambiguous i have searched the issue tracker to check if the issue has already been reported description new players are likely to be mislead about what shells fire in which order for railgun when on the periscope there is no ui indicating which railgun shell is going to be fired leftmost in the loader no ui indicating which shell is going to be fired also leftmost loader is even more ambiguous due to the empty slot appearing on the right side the common case of loaded shells being all the same ex all being empty regular shells doesn t help the situation either steps to reproduce ask multiple new players to describe the railgun shells version yes additional information something like this idk | 0 |
5,288 | 5,555,440,804 | IssuesEvent | 2017-03-24 04:59:38 | akvo/akvo-flow | https://api.github.com/repos/akvo/akvo-flow | opened | CI project build via Docker | Deployment & infrastructure | We can have consistent/reproducible via Docker container.
- [ ] Use a Docker image to have all the necessary components for the build: JDK, Ruby, Node.js, Ant, Leinigen, etc
- [ ] Expose the host folders `$HOME/.m2` and `$HOME/.cache` to avoid the need to downloading dependencies and/or caching those in the Docker image itself (reducing the size of the image). We also advantage of the CI caching capabilities. https://docs.travis-ci.com/user/caching#Arbitrary-directories
The idea is to publish `akvo/flow-build` image in the public Docker registry, and use it as part of the build process: https://docs.travis-ci.com/user/docker/ | 1.0 | CI project build via Docker - We can have consistent/reproducible via Docker container.
- [ ] Use a Docker image to have all the necessary components for the build: JDK, Ruby, Node.js, Ant, Leinigen, etc
- [ ] Expose the host folders `$HOME/.m2` and `$HOME/.cache` to avoid the need to downloading dependencies and/or caching those in the Docker image itself (reducing the size of the image). We also advantage of the CI caching capabilities. https://docs.travis-ci.com/user/caching#Arbitrary-directories
The idea is to publish `akvo/flow-build` image in the public Docker registry, and use it as part of the build process: https://docs.travis-ci.com/user/docker/ | non_priority | ci project build via docker we can have consistent reproducible via docker container use a docker image to have all the necessary components for the build jdk ruby node js ant leinigen etc expose the host folders home and home cache to avoid the need to downloading dependencies and or caching those in the docker image itself reducing the size of the image we also advantage of the ci caching capabilities the idea is to publish akvo flow build image in the public docker registry and use it as part of the build process | 0 |
28,189 | 5,217,129,365 | IssuesEvent | 2017-01-26 12:52:57 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Listbox: select all option does not work well when using the filter | defect | <!--
- IF YOU DON'T FILL OUT THE FOLLOWING INFORMATION WE MIGHT CLOSE YOUR ISSUE WITHOUT INVESTIGATING.
- IF YOU'D LIKE TO SECURE OUR RESPONSE, YOU MAY CONSIDER PRIMENG PRO SUPPORT WHERE SUPPORT IS PROVIDED WITHIN 4 hours.
-->
**I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
I tried to build a Plunkr Case for it but i encountered importing the Listbox module.
Any help with it will be much appreciated.
**Current behavior**
Filter the multi-select, you will see that the list box shows all items that *contains* the entered filter
but clicking will only select items that *begins* with the entered filter.
**Expected behavior**
Select-all should select all options you currently see on the listbox.
**Minimal reproduction of the problem with instructions**
1. Go to the documentation of Listbox:
http://www.primefaces.org/primeng/#/listbox
use the Advanced (Multiple, Checkbox and Filter) demo.
2. In the filter enter the letter 'r' => (you will see only options that contains the letter 'r', which is good)
3. Click on select-all => only Rome will be selected.
**What is the motivation / use case for changing the behavior?**
We think that selecting all items once you use the filter if a very common
and important case in this component.
It definitely the case for us...
| 1.0 | Listbox: select all option does not work well when using the filter - <!--
- IF YOU DON'T FILL OUT THE FOLLOWING INFORMATION WE MIGHT CLOSE YOUR ISSUE WITHOUT INVESTIGATING.
- IF YOU'D LIKE TO SECURE OUR RESPONSE, YOU MAY CONSIDER PRIMENG PRO SUPPORT WHERE SUPPORT IS PROVIDED WITHIN 4 hours.
-->
**I'm submitting a ...** (check one with "x")
```
[x] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
I tried to build a Plunkr Case for it but i encountered importing the Listbox module.
Any help with it will be much appreciated.
**Current behavior**
Filter the multi-select, you will see that the list box shows all items that *contains* the entered filter
but clicking will only select items that *begins* with the entered filter.
**Expected behavior**
Select-all should select all options you currently see on the listbox.
**Minimal reproduction of the problem with instructions**
1. Go to the documentation of Listbox:
http://www.primefaces.org/primeng/#/listbox
use the Advanced (Multiple, Checkbox and Filter) demo.
2. In the filter enter the letter 'r' => (you will see only options that contains the letter 'r', which is good)
3. Click on select-all => only Rome will be selected.
**What is the motivation / use case for changing the behavior?**
We think that selecting all items once you use the filter if a very common
and important case in this component.
It definitely the case for us...
| non_priority | listbox select all option does not work well when using the filter if you don t fill out the following information we might close your issue without investigating if you d like to secure our response you may consider primeng pro support where support is provided within hours i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see plunkr case bug reports i tried to build a plunkr case for it but i encountered importing the listbox module any help with it will be much appreciated current behavior filter the multi select you will see that the list box shows all items that contains the entered filter but clicking will only select items that begins with the entered filter expected behavior select all should select all options you currently see on the listbox minimal reproduction of the problem with instructions go to the documentation of listbox use the advanced multiple checkbox and filter demo in the filter enter the letter r you will see only options that contains the letter r which is good click on select all only rome will be selected what is the motivation use case for changing the behavior we think that selecting all items once you use the filter if a very common and important case in this component it definitely the case for us | 0 |
43,680 | 23,328,304,422 | IssuesEvent | 2022-08-09 00:37:01 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | storage: optimize `pointSynthesizingIter` initialization | C-performance A-kv-replication A-storage T-storage | Optimize initialization and use of `pointSynthesizingIter` in `pebbleMVCCScanner`. For example, consider pooling it together with the scanner, and add a function to avoid seeking the underlying iterator when switching to point synthesis. I.e. this:
https://github.com/cockroachdb/cockroach/blob/745208894239f140d7990e980807c7313e284dd4/pkg/storage/pebble_mvcc_scanner.go#L1160-L1170
Jira issue: CRDB-17625
Epic CRDB-2624 | True | storage: optimize `pointSynthesizingIter` initialization - Optimize initialization and use of `pointSynthesizingIter` in `pebbleMVCCScanner`. For example, consider pooling it together with the scanner, and add a function to avoid seeking the underlying iterator when switching to point synthesis. I.e. this:
https://github.com/cockroachdb/cockroach/blob/745208894239f140d7990e980807c7313e284dd4/pkg/storage/pebble_mvcc_scanner.go#L1160-L1170
Jira issue: CRDB-17625
Epic CRDB-2624 | non_priority | storage optimize pointsynthesizingiter initialization optimize initialization and use of pointsynthesizingiter in pebblemvccscanner for example consider pooling it together with the scanner and add a function to avoid seeking the underlying iterator when switching to point synthesis i e this jira issue crdb epic crdb | 0 |
10,458 | 4,073,840,453 | IssuesEvent | 2016-05-28 01:49:47 | oppia/oppia | https://api.github.com/repos/oppia/oppia | closed | Textbox underline shortcut doesn't work. | bug: minor frontend/rich-text-editor starter project TODO: code | The keyboard shortcut Command-U on a Mac does not engage the underline method in text boxes. The shortcuts for Bold and Italic both work. | 1.0 | Textbox underline shortcut doesn't work. - The keyboard shortcut Command-U on a Mac does not engage the underline method in text boxes. The shortcuts for Bold and Italic both work. | non_priority | textbox underline shortcut doesn t work the keyboard shortcut command u on a mac does not engage the underline method in text boxes the shortcuts for bold and italic both work | 0 |
134,477 | 10,917,197,841 | IssuesEvent | 2019-11-21 14:45:22 | proarc/proarc | https://api.github.com/repos/proarc/proarc | closed | eČlánek - jednoduchý formulář | 6 k testování Release-3.5.14 | Ve zjednodušeném formuláři pro ečlánek zmizela možnost vybrat, jestli o recenzovaný nebo nerecenzovaný článek.
| 1.0 | eČlánek - jednoduchý formulář - Ve zjednodušeném formuláři pro ečlánek zmizela možnost vybrat, jestli o recenzovaný nebo nerecenzovaný článek.
| non_priority | ečlánek jednoduchý formulář ve zjednodušeném formuláři pro ečlánek zmizela možnost vybrat jestli o recenzovaný nebo nerecenzovaný článek | 0 |
83,420 | 16,167,184,557 | IssuesEvent | 2021-05-01 18:40:37 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] After deleting the last item, the empty state layout still has filter for trashed items activated | No Code Attached Yet | ### Steps to reproduce the issue
The following describes the issue for com_content, but we have it elsewhere, too.
It is like that on J3 since long time and so some kind of expected behaviour, i.e. not been introduced by the new empty states in J4.
But I think it's confusing and annoying the user, so we should take a chance to change that with J4.
1. Have some articles so the articles list view in backend shows items.
2. Trash all articles.
3. Filter for trashed items.
4. Select all trashed articles and empty trash.
Result: The empty state layout is shown. No filter tool bar is shown, but there is still the filter for trashed items active, as you will see in the next step-
5. Use the "New" button to create a new article.
6. See that the status of the new article is "Trashed".
7. Change it to "Published".
6. Use the "Save & Close" button.
Result: The article list view is shown, The filter tool bar is visible, the filter for trashed items is set, and so the new article is not shown. That's confusing.
Alternatively you could skip step 6, then the article would be visible but have "Trashed" status, that's the same annoying.
### Expected result
When the last item is deleted so that the empty state layout is show, all active filters are cleared.
### Actual result
See above steps to reproduce.
### System information (as much as possible)
Current 4.0-dev.
### Additional comments
This issue has not been introduced by the empty states like I first thought because I didn't remember that this issue was confusing me long time ago in J3. | 1.0 | [4.0] After deleting the last item, the empty state layout still has filter for trashed items activated - ### Steps to reproduce the issue
The following describes the issue for com_content, but we have it elsewhere, too.
It is like that on J3 since long time and so some kind of expected behaviour, i.e. not been introduced by the new empty states in J4.
But I think it's confusing and annoying the user, so we should take a chance to change that with J4.
1. Have some articles so the articles list view in backend shows items.
2. Trash all articles.
3. Filter for trashed items.
4. Select all trashed articles and empty trash.
Result: The empty state layout is shown. No filter tool bar is shown, but there is still the filter for trashed items active, as you will see in the next step-
5. Use the "New" button to create a new article.
6. See that the status of the new article is "Trashed".
7. Change it to "Published".
6. Use the "Save & Close" button.
Result: The article list view is shown, The filter tool bar is visible, the filter for trashed items is set, and so the new article is not shown. That's confusing.
Alternatively you could skip step 6, then the article would be visible but have "Trashed" status, that's the same annoying.
### Expected result
When the last item is deleted so that the empty state layout is show, all active filters are cleared.
### Actual result
See above steps to reproduce.
### System information (as much as possible)
Current 4.0-dev.
### Additional comments
This issue has not been introduced by the empty states like I first thought because I didn't remember that this issue was confusing me long time ago in J3. | non_priority | after deleting the last item the empty state layout still has filter for trashed items activated steps to reproduce the issue the following describes the issue for com content but we have it elsewhere too it is like that on since long time and so some kind of expected behaviour i e not been introduced by the new empty states in but i think it s confusing and annoying the user so we should take a chance to change that with have some articles so the articles list view in backend shows items trash all articles filter for trashed items select all trashed articles and empty trash result the empty state layout is shown no filter tool bar is shown but there is still the filter for trashed items active as you will see in the next step use the new button to create a new article see that the status of the new article is trashed change it to published use the save close button result the article list view is shown the filter tool bar is visible the filter for trashed items is set and so the new article is not shown that s confusing alternatively you could skip step then the article would be visible but have trashed status that s the same annoying expected result when the last item is deleted so that the empty state layout is show all active filters are cleared actual result see above steps to reproduce system information as much as possible current dev additional comments this issue has not been introduced by the empty states like i first thought because i didn t remember that this issue was confusing me long time ago in | 0 |
187,327 | 14,427,551,320 | IssuesEvent | 2020-12-06 04:45:40 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | pbolla0818/oci_terraform: oci/core_boot_volume_backup_test.go; 16 LoC | fresh small test |
Found a possible issue in [pbolla0818/oci_terraform](https://www.github.com/pbolla0818/oci_terraform) at [oci/core_boot_volume_backup_test.go](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/core_boot_volume_backup_test.go#L293-L308)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to bootVolumeBackupId is reassigned at line 297
[Click here to see the code in its original context.](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/core_boot_volume_backup_test.go#L293-L308)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, bootVolumeBackupId := range bootVolumeBackupIds {
if ok := SweeperDefaultResourceId[bootVolumeBackupId]; !ok {
deleteBootVolumeBackupRequest := oci_core.DeleteBootVolumeBackupRequest{}
deleteBootVolumeBackupRequest.BootVolumeBackupId = &bootVolumeBackupId
deleteBootVolumeBackupRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "core")
_, error := blockstorageClient.DeleteBootVolumeBackup(context.Background(), deleteBootVolumeBackupRequest)
if error != nil {
fmt.Printf("Error deleting BootVolumeBackup %s %s, It is possible that the resource is already deleted. Please verify manually \n", bootVolumeBackupId, error)
continue
}
waitTillCondition(testAccProvider, &bootVolumeBackupId, bootVolumeBackupSweepWaitCondition, time.Duration(3*time.Minute),
bootVolumeBackupSweepResponseFetchOperation, "core", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c233d54c5fe32f12c234d6dceefba0a9b4ab3022
| 1.0 | pbolla0818/oci_terraform: oci/core_boot_volume_backup_test.go; 16 LoC -
Found a possible issue in [pbolla0818/oci_terraform](https://www.github.com/pbolla0818/oci_terraform) at [oci/core_boot_volume_backup_test.go](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/core_boot_volume_backup_test.go#L293-L308)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to bootVolumeBackupId is reassigned at line 297
[Click here to see the code in its original context.](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/core_boot_volume_backup_test.go#L293-L308)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, bootVolumeBackupId := range bootVolumeBackupIds {
if ok := SweeperDefaultResourceId[bootVolumeBackupId]; !ok {
deleteBootVolumeBackupRequest := oci_core.DeleteBootVolumeBackupRequest{}
deleteBootVolumeBackupRequest.BootVolumeBackupId = &bootVolumeBackupId
deleteBootVolumeBackupRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "core")
_, error := blockstorageClient.DeleteBootVolumeBackup(context.Background(), deleteBootVolumeBackupRequest)
if error != nil {
fmt.Printf("Error deleting BootVolumeBackup %s %s, It is possible that the resource is already deleted. Please verify manually \n", bootVolumeBackupId, error)
continue
}
waitTillCondition(testAccProvider, &bootVolumeBackupId, bootVolumeBackupSweepWaitCondition, time.Duration(3*time.Minute),
bootVolumeBackupSweepResponseFetchOperation, "core", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c233d54c5fe32f12c234d6dceefba0a9b4ab3022
| non_priority | oci terraform oci core boot volume backup test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to bootvolumebackupid is reassigned at line click here to show the line s of go which triggered the analyzer go for bootvolumebackupid range bootvolumebackupids if ok sweeperdefaultresourceid ok deletebootvolumebackuprequest oci core deletebootvolumebackuprequest deletebootvolumebackuprequest bootvolumebackupid bootvolumebackupid deletebootvolumebackuprequest requestmetadata retrypolicy getretrypolicy true core error blockstorageclient deletebootvolumebackup context background deletebootvolumebackuprequest if error nil fmt printf error deleting bootvolumebackup s s it is possible that the resource is already deleted please verify manually n bootvolumebackupid error continue waittillcondition testaccprovider bootvolumebackupid bootvolumebackupsweepwaitcondition time duration time minute bootvolumebackupsweepresponsefetchoperation core true leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
151,030 | 19,648,281,082 | IssuesEvent | 2022-01-10 01:20:52 | dogegarden/landing | https://api.github.com/repos/dogegarden/landing | closed | WS-2022-0007 (Medium) detected in node-forge-0.10.0.tgz - autoclosed | security vulnerability | ## WS-2022-0007 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.10.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-8.3.1.tgz (Root Library)
- firestore-2.2.1.tgz
- grpc-js-1.2.12.tgz
- google-auth-library-6.1.6.tgz
- gtoken-5.2.1.tgz
- google-p12-pem-3.0.3.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In node-forge before 1.0.0 he regex used for the forge.util.parseUrl API would not properly parse certain inputs resulting in a parsed data structure that could lead to undesired behavior.
<p>Publish Date: 2022-01-08
<p>URL: <a href=https://github.com/digitalbazaar/forge/commit/db8016c805371e72b06d8e2edfe0ace0df934a5e>WS-2022-0007</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-gf8q-jrpm-jvxq">https://github.com/advisories/GHSA-gf8q-jrpm-jvxq</a></p>
<p>Release Date: 2022-01-08</p>
<p>Fix Resolution: node-forge - 1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2022-0007 (Medium) detected in node-forge-0.10.0.tgz - autoclosed - ## WS-2022-0007 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.10.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PKI, message digests, and various utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz">https://registry.npmjs.org/node-forge/-/node-forge-0.10.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-forge/package.json</p>
<p>
Dependency Hierarchy:
- firebase-8.3.1.tgz (Root Library)
- firestore-2.2.1.tgz
- grpc-js-1.2.12.tgz
- google-auth-library-6.1.6.tgz
- gtoken-5.2.1.tgz
- google-p12-pem-3.0.3.tgz
- :x: **node-forge-0.10.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In node-forge before 1.0.0 he regex used for the forge.util.parseUrl API would not properly parse certain inputs resulting in a parsed data structure that could lead to undesired behavior.
<p>Publish Date: 2022-01-08
<p>URL: <a href=https://github.com/digitalbazaar/forge/commit/db8016c805371e72b06d8e2edfe0ace0df934a5e>WS-2022-0007</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-gf8q-jrpm-jvxq">https://github.com/advisories/GHSA-gf8q-jrpm-jvxq</a></p>
<p>Release Date: 2022-01-08</p>
<p>Fix Resolution: node-forge - 1.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in node forge tgz autoclosed ws medium severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file package json path to vulnerable library node modules node forge package json dependency hierarchy firebase tgz root library firestore tgz grpc js tgz google auth library tgz gtoken tgz google pem tgz x node forge tgz vulnerable library found in base branch master vulnerability details in node forge before he regex used for the forge util parseurl api would not properly parse certain inputs resulting in a parsed data structure that could lead to undesired behavior publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node forge step up your open source security game with whitesource | 0 |
92,385 | 11,634,325,776 | IssuesEvent | 2020-02-28 10:09:05 | ieee-ihuthess/managing_the_branch | https://api.github.com/repos/ieee-ihuthess/managing_the_branch | opened | Create logos for github teams | design committee | We have some two teams:
- current active members
- dev_squad
I believe it would be nice if we had a cool profile pic for the `dev_squad`.
If there is any good idea, current active members can have their own too :grin:
> References https://github.com/orgs/ieee-ihuthess/teams/dev_squad
> References https://github.com/orgs/ieee-ihuthess/teams/current-active-members | 1.0 | Create logos for github teams - We have some two teams:
- current active members
- dev_squad
I believe it would be nice if we had a cool profile pic for the `dev_squad`.
If there is any good idea, current active members can have their own too :grin:
> References https://github.com/orgs/ieee-ihuthess/teams/dev_squad
> References https://github.com/orgs/ieee-ihuthess/teams/current-active-members | non_priority | create logos for github teams we have some two teams current active members dev squad i believe it would be nice if we had a cool profile pic for the dev squad if there is any good idea current active members can have their own too grin references references | 0 |
67,987 | 9,107,017,488 | IssuesEvent | 2019-02-21 02:23:12 | cyberark/docs-cyberark-conjur-service-broker | https://api.github.com/repos/cyberark/docs-cyberark-conjur-service-broker | closed | Docs include description of CONJUR_FOLLOWER_URL environment variable | component/pcf defined kind/documentation triage/duplicate | The Conjur service broker can now be configured with the `CONJUR_FOLLOWER_URL` environment variable, which should be set to the URL of a load balancer managing Conjur followers when using a high availability cluster. During the bind request, it will be returned to the application as the URL with which to communicate with Conjur. | 1.0 | Docs include description of CONJUR_FOLLOWER_URL environment variable - The Conjur service broker can now be configured with the `CONJUR_FOLLOWER_URL` environment variable, which should be set to the URL of a load balancer managing Conjur followers when using a high availability cluster. During the bind request, it will be returned to the application as the URL with which to communicate with Conjur. | non_priority | docs include description of conjur follower url environment variable the conjur service broker can now be configured with the conjur follower url environment variable which should be set to the url of a load balancer managing conjur followers when using a high availability cluster during the bind request it will be returned to the application as the url with which to communicate with conjur | 0 |
7,390 | 3,538,248,883 | IssuesEvent | 2016-01-18 08:54:56 | OpenRIAServices/TestIssues | https://api.github.com/repos/OpenRIAServices/TestIssues | opened | Enable Entity Framework Proxy Generation On SubmitChanges Crud Operations | CodePlex | <sub>This issue was imported from [CodePlex](http://openriaservices.codeplex.com/workitem/20)</sub>
**[Gatolus](https://github.com/Gatolus)** <sup>wrote 2013-11-13 at 08:28</sup>
As we know Proxygeneration are turned off on EF5 when Using RIA Services
DataContext.Configuration.LazyLoadingEnabled = true;
DataContext.Configuration.ProxyCreationEnabled = true;
This Forces me to do this and it creates Nasty Bugs when it have been missed.
if (MilkTest == null)
{
```
DCtx.Entry(this).Reference(x => x.MilkTest).Load();
```
}
It is not a issue on querys. But on SubmitChanges we need Proxygeneration Enabled.
Possible Fix..
I know that WCF is Creating the entity's themselves And not EF . But I would like to Find an way to Simply Import(Property By Property) the Entitys from the ChangedSet Incomming from the WCF request into the Same Entity Loaded from the Proxy Enabled EF Datacontext . | 1.0 | Enable Entity Framework Proxy Generation On SubmitChanges Crud Operations - <sub>This issue was imported from [CodePlex](http://openriaservices.codeplex.com/workitem/20)</sub>
**[Gatolus](https://github.com/Gatolus)** <sup>wrote 2013-11-13 at 08:28</sup>
As we know Proxygeneration are turned off on EF5 when Using RIA Services
DataContext.Configuration.LazyLoadingEnabled = true;
DataContext.Configuration.ProxyCreationEnabled = true;
This Forces me to do this and it creates Nasty Bugs when it have been missed.
if (MilkTest == null)
{
```
DCtx.Entry(this).Reference(x => x.MilkTest).Load();
```
}
It is not a issue on querys. But on SubmitChanges we need Proxygeneration Enabled.
Possible Fix..
I know that WCF is Creating the entity's themselves And not EF . But I would like to Find an way to Simply Import(Property By Property) the Entitys from the ChangedSet Incomming from the WCF request into the Same Entity Loaded from the Proxy Enabled EF Datacontext . | non_priority | enable entity framework proxy generation on submitchanges crud operations this issue was imported from wrote at as we know proxygeneration are turned off on when using ria services datacontext configuration lazyloadingenabled true datacontext configuration proxycreationenabled true this forces me to do this and it creates nasty bugs when it have been missed if milktest null dctx entry this reference x x milktest load it is not a issue on querys but on submitchanges we need proxygeneration enabled possible fix i know that wcf is creating the entity s themselves and not ef but i would like to find an way to simply import property by property the entitys from the changedset incomming from the wcf request into the same entity loaded from the proxy enabled ef datacontext | 0 |
246,893 | 20,924,189,743 | IssuesEvent | 2022-03-24 20:37:19 | Uuvana-Studios/longvinter-windows-client | https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client | closed | Bugged container in my new tent | bug Not Tested | **Describe the bug**
I used to have another tent but it got deleted (i'm pretty sure it's not from the timer)
i recently got another tent and when i entered it for the first time some of my old stuff was there including a radiator, a workbench (out of bounds) and a container in the middle of the room that had some of my old stuff
i cannot remove this container and i'm pretty sure that when trying to remove it it dupes itself by dropping but not disapearing (the item is stuck under it so not exploiting by taking 'em)
**To Reproduce**
not sure if you can reproduce it unless your tent gets removed unnaturally
**Expected behavior**
i expected an empty tent
**Screenshots**
the container is the one in the middle. i'v taken care of the workbench (couldn't get it back tho)
**Desktop (please complete the following information):**
- OS: windows 10
- Game Version beta 1.0.1
- Steam Version steapAPI 020
| 1.0 | Bugged container in my new tent - **Describe the bug**
I used to have another tent but it got deleted (i'm pretty sure it's not from the timer)
i recently got another tent and when i entered it for the first time some of my old stuff was there including a radiator, a workbench (out of bounds) and a container in the middle of the room that had some of my old stuff
i cannot remove this container and i'm pretty sure that when trying to remove it it dupes itself by dropping but not disapearing (the item is stuck under it so not exploiting by taking 'em)
**To Reproduce**
not sure if you can reproduce it unless your tent gets removed unnaturally
**Expected behavior**
i expected an empty tent
**Screenshots**
the container is the one in the middle. i'v taken care of the workbench (couldn't get it back tho)
**Desktop (please complete the following information):**
- OS: windows 10
- Game Version beta 1.0.1
- Steam Version steapAPI 020
| non_priority | bugged container in my new tent describe the bug i used to have another tent but it got deleted i m pretty sure it s not from the timer i recently got another tent and when i entered it for the first time some of my old stuff was there including a radiator a workbench out of bounds and a container in the middle of the room that had some of my old stuff i cannot remove this container and i m pretty sure that when trying to remove it it dupes itself by dropping but not disapearing the item is stuck under it so not exploiting by taking em to reproduce not sure if you can reproduce it unless your tent gets removed unnaturally expected behavior i expected an empty tent screenshots the container is the one in the middle i v taken care of the workbench couldn t get it back tho desktop please complete the following information os windows game version beta steam version steapapi | 0 |
51,430 | 13,635,122,598 | IssuesEvent | 2020-09-25 01:57:48 | nasifimtiazohi/openmrs-module-reporting-1.20.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-reporting-1.20.0 | opened | CVE-2018-7489 (High) detected in jackson-databind-2.9.0.jar | security vulnerability | ## CVE-2018-7489 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: openmrs-module-reporting-1.20.0/api-2.2/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.0/jackson-databind-2.9.0.jar</p>
<p>
Dependency Hierarchy:
- openmrs-api-2.2.0.jar (Root Library)
- :x: **jackson-databind-2.9.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-reporting-1.20.0/commit/43757d56a9ab9f7202e297fea95f1861af41888c">43757d56a9ab9f7202e297fea95f1861af41888c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind before 2.7.9.3, 2.8.x before 2.8.11.1 and 2.9.x before 2.9.5 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 deserialization flaw. This is exploitable by sending maliciously crafted JSON input to the readValue method of the ObjectMapper, bypassing a blacklist that is ineffective if the c3p0 libraries are available in the classpath.
<p>Publish Date: 2018-02-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-7489>CVE-2018-7489</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-7489">https://nvd.nist.gov/vuln/detail/CVE-2018-7489</a></p>
<p>Release Date: 2018-02-26</p>
<p>Fix Resolution: 2.8.11.1,2.9.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-7489 (High) detected in jackson-databind-2.9.0.jar - ## CVE-2018-7489 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: openmrs-module-reporting-1.20.0/api-2.2/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.0/jackson-databind-2.9.0.jar</p>
<p>
Dependency Hierarchy:
- openmrs-api-2.2.0.jar (Root Library)
- :x: **jackson-databind-2.9.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-reporting-1.20.0/commit/43757d56a9ab9f7202e297fea95f1861af41888c">43757d56a9ab9f7202e297fea95f1861af41888c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind before 2.7.9.3, 2.8.x before 2.8.11.1 and 2.9.x before 2.9.5 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 deserialization flaw. This is exploitable by sending maliciously crafted JSON input to the readValue method of the ObjectMapper, bypassing a blacklist that is ineffective if the c3p0 libraries are available in the classpath.
<p>Publish Date: 2018-02-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-7489>CVE-2018-7489</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-7489">https://nvd.nist.gov/vuln/detail/CVE-2018-7489</a></p>
<p>Release Date: 2018-02-26</p>
<p>Fix Resolution: 2.8.11.1,2.9.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file openmrs module reporting api pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy openmrs api jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind before x before and x before allows unauthenticated remote code execution because of an incomplete fix for the cve deserialization flaw this is exploitable by sending maliciously crafted json input to the readvalue method of the objectmapper bypassing a blacklist that is ineffective if the libraries are available in the classpath publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
58,643 | 14,342,882,189 | IssuesEvent | 2020-11-28 06:01:34 | mgh3326/making_page | https://api.github.com/repos/mgh3326/making_page | opened | CVE-2020-7595 (High) detected in nokogiri-1.10.5.gem | security vulnerability | ## CVE-2020-7595 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.5.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.5.gem">https://rubygems.org/gems/nokogiri-1.10.5.gem</a></p>
<p>
Dependency Hierarchy:
- web-console-4.0.1.gem (Root Library)
- actionview-6.0.1.gem
- rails-dom-testing-2.0.3.gem
- :x: **nokogiri-1.10.5.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mgh3326/making_page/commit/2968cc2abbf69556605e8e0e7fb089f2c5bd93f3">2968cc2abbf69556605e8e0e7fb089f2c5bd93f3</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
xmlStringLenDecodeEntities in parser.c in libxml2 2.9.10 has an infinite loop in a certain end-of-file situation.
<p>Publish Date: 2020-01-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7595>CVE-2020-7595</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7595">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7595</a></p>
<p>Release Date: 2020-01-21</p>
<p>Fix Resolution: 5.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7595 (High) detected in nokogiri-1.10.5.gem - ## CVE-2020-7595 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.5.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.5.gem">https://rubygems.org/gems/nokogiri-1.10.5.gem</a></p>
<p>
Dependency Hierarchy:
- web-console-4.0.1.gem (Root Library)
- actionview-6.0.1.gem
- rails-dom-testing-2.0.3.gem
- :x: **nokogiri-1.10.5.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mgh3326/making_page/commit/2968cc2abbf69556605e8e0e7fb089f2c5bd93f3">2968cc2abbf69556605e8e0e7fb089f2c5bd93f3</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
xmlStringLenDecodeEntities in parser.c in libxml2 2.9.10 has an infinite loop in a certain end-of-file situation.
<p>Publish Date: 2020-01-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7595>CVE-2020-7595</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7595">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7595</a></p>
<p>Release Date: 2020-01-21</p>
<p>Fix Resolution: 5.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in nokogiri gem cve high severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href dependency hierarchy web console gem root library actionview gem rails dom testing gem x nokogiri gem vulnerable library found in head commit a href vulnerability details xmlstringlendecodeentities in parser c in has an infinite loop in a certain end of file situation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
136,084 | 18,722,305,943 | IssuesEvent | 2021-11-03 13:09:45 | KDWSS/dd-trace-java | https://api.github.com/repos/KDWSS/dd-trace-java | opened | CVE-2018-11040 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2018-11040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-4.3.7.RELEASE.jar</b>, <b>spring-web-4.3.13.RELEASE.jar</b>, <b>spring-web-5.0.4.RELEASE.jar</b>, <b>spring-webmvc-4.3.13.RELEASE.jar</b>, <b>spring-web-5.0.0.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-web-4.3.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/http-url-connection/http-url-connection.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.springframework/spring-web/4.3.7.RELEASE/7b69fc68cdb74c1c92f72905af6995696fcb56aa/spring-web-4.3.7.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.3.7.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/4.3.13.RELEASE/7cd084992d546165ede3e99bc31ee49c937f0ce7/spring-web-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- :x: **spring-web-4.3.13.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.0.4.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.0.4.RELEASE/9565bbc67bf1a850a6505deaa5103931712a7b80/spring-web-5.0.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-webflux-5.0.4.RELEASE.jar (Root Library)
- :x: **spring-web-5.0.4.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-webmvc-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Web MVC</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.springframework/spring-webmvc/4.3.13.RELEASE/87a095c7a1d13fe433ae6712787238c1dbaa6919/spring-webmvc-4.3.13.RELEASE.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-webmvc/4.3.13.RELEASE/87a095c7a1d13fe433ae6712787238c1dbaa6919/spring-webmvc-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- :x: **spring-webmvc-4.3.13.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.0.0.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-rabbit/spring-rabbit.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.0.0.RELEASE/f5c2d9d5668534c308a1ca4eda070cd01320af65/spring-web-5.0.0.RELEASE.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.0.0.RELEASE/f5c2d9d5668534c308a1ca4eda070cd01320af65/spring-web-5.0.0.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-2.0.0.RELEASE.jar (Root Library)
- :x: **spring-web-5.0.0.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0.x prior to 5.0.7 and 4.3.x prior to 4.3.18 and older unsupported versions, allows web applications to enable cross-domain requests via JSONP (JSON with Padding) through AbstractJsonpResponseBodyAdvice for REST controllers and MappingJackson2JsonView for browser requests. Both are not enabled by default in Spring Framework nor Spring Boot, however, when MappingJackson2JsonView is configured in an application, JSONP support is automatically ready to use through the "jsonp" and "callback" JSONP parameters, enabling cross-domain requests.
<p>Publish Date: 2018-06-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11040>CVE-2018-11040</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040</a></p>
<p>Release Date: 2018-06-25</p>
<p>Fix Resolution: org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.3.7.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/http-url-connection/http-url-connection.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:4.3.7.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.3.13.RELEASE","packageFilePaths":["/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.9.RELEASE;org.springframework:spring-web:4.3.13.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.0.4.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework:spring-webflux:5.0.4.RELEASE;org.springframework:spring-web:5.0.4.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-webmvc","packageVersion":"4.3.13.RELEASE","packageFilePaths":["/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.9.RELEASE;org.springframework:spring-webmvc:4.3.13.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.0.0.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/spring-rabbit/spring-rabbit.gradle","/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.amqp:spring-rabbit:2.0.0.RELEASE;org.springframework:spring-web:5.0.0.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-11040","vulnerabilityDetails":"Spring Framework, versions 5.0.x prior to 5.0.7 and 4.3.x prior to 4.3.18 and older unsupported versions, allows web applications to enable cross-domain requests via JSONP (JSON with Padding) through AbstractJsonpResponseBodyAdvice for REST controllers and MappingJackson2JsonView for browser requests. Both are not enabled by default in Spring Framework nor Spring Boot, however, when MappingJackson2JsonView is configured in an application, JSONP support is automatically ready to use through the \"jsonp\" and \"callback\" JSONP parameters, enabling cross-domain requests.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11040","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-11040 (Medium) detected in multiple libraries - ## CVE-2018-11040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-4.3.7.RELEASE.jar</b>, <b>spring-web-4.3.13.RELEASE.jar</b>, <b>spring-web-5.0.4.RELEASE.jar</b>, <b>spring-webmvc-4.3.13.RELEASE.jar</b>, <b>spring-web-5.0.0.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-web-4.3.7.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/http-url-connection/http-url-connection.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.springframework/spring-web/4.3.7.RELEASE/7b69fc68cdb74c1c92f72905af6995696fcb56aa/spring-web-4.3.7.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.3.7.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/4.3.13.RELEASE/7cd084992d546165ede3e99bc31ee49c937f0ce7/spring-web-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- :x: **spring-web-4.3.13.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.0.4.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.0.4.RELEASE/9565bbc67bf1a850a6505deaa5103931712a7b80/spring-web-5.0.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-webflux-5.0.4.RELEASE.jar (Root Library)
- :x: **spring-web-5.0.4.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-webmvc-4.3.13.RELEASE.jar</b></p></summary>
<p>Spring Web MVC</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.springframework/spring-webmvc/4.3.13.RELEASE/87a095c7a1d13fe433ae6712787238c1dbaa6919/spring-webmvc-4.3.13.RELEASE.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-webmvc/4.3.13.RELEASE/87a095c7a1d13fe433ae6712787238c1dbaa6919/spring-webmvc-4.3.13.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.9.RELEASE.jar (Root Library)
- :x: **spring-webmvc-4.3.13.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-web-5.0.0.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: dd-trace-java/dd-java-agent/instrumentation/spring-rabbit/spring-rabbit.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.0.0.RELEASE/f5c2d9d5668534c308a1ca4eda070cd01320af65/spring-web-5.0.0.RELEASE.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/5.0.0.RELEASE/f5c2d9d5668534c308a1ca4eda070cd01320af65/spring-web-5.0.0.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-rabbit-2.0.0.RELEASE.jar (Root Library)
- :x: **spring-web-5.0.0.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/KDWSS/dd-trace-java/commit/2819174635979a19573ec0ce8e3e2b63a3848079">2819174635979a19573ec0ce8e3e2b63a3848079</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework, versions 5.0.x prior to 5.0.7 and 4.3.x prior to 4.3.18 and older unsupported versions, allows web applications to enable cross-domain requests via JSONP (JSON with Padding) through AbstractJsonpResponseBodyAdvice for REST controllers and MappingJackson2JsonView for browser requests. Both are not enabled by default in Spring Framework nor Spring Boot, however, when MappingJackson2JsonView is configured in an application, JSONP support is automatically ready to use through the "jsonp" and "callback" JSONP parameters, enabling cross-domain requests.
<p>Publish Date: 2018-06-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11040>CVE-2018-11040</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11040</a></p>
<p>Release Date: 2018-06-25</p>
<p>Fix Resolution: org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.3.7.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/http-url-connection/http-url-connection.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:4.3.7.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.3.13.RELEASE","packageFilePaths":["/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.9.RELEASE;org.springframework:spring-web:4.3.13.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.0.4.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework:spring-webflux:5.0.4.RELEASE;org.springframework:spring-web:5.0.4.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-webmvc","packageVersion":"4.3.13.RELEASE","packageFilePaths":["/dd-java-agent/appsec/weblog/weblog-spring-app/weblog-spring-app.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.9.RELEASE;org.springframework:spring-webmvc:4.3.13.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"5.0.0.RELEASE","packageFilePaths":["/dd-java-agent/instrumentation/spring-rabbit/spring-rabbit.gradle","/dd-java-agent/instrumentation/spring-webflux-5/spring-webflux-5.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.amqp:spring-rabbit:2.0.0.RELEASE;org.springframework:spring-web:5.0.0.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-webmvc:5.0.7.RELEASE,4.3.18.RELEASE,org.springframework:spring-websocket:5.0.7.RELEASE,4.3.18.RELEASE"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-11040","vulnerabilityDetails":"Spring Framework, versions 5.0.x prior to 5.0.7 and 4.3.x prior to 4.3.18 and older unsupported versions, allows web applications to enable cross-domain requests via JSONP (JSON with Padding) through AbstractJsonpResponseBodyAdvice for REST controllers and MappingJackson2JsonView for browser requests. Both are not enabled by default in Spring Framework nor Spring Boot, however, when MappingJackson2JsonView is configured in an application, JSONP support is automatically ready to use through the \"jsonp\" and \"callback\" JSONP parameters, enabling cross-domain requests.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11040","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries spring web release jar spring web release jar spring web release jar spring webmvc release jar spring web release jar spring web release jar spring web library home page a href path to dependency file dd trace java dd java agent instrumentation http url connection http url connection gradle path to vulnerable library caches modules files org springframework spring web release spring web release jar dependency hierarchy x spring web release jar vulnerable library spring web release jar spring web library home page a href path to dependency file dd trace java dd java agent appsec weblog weblog spring app weblog spring app gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web release spring web release jar dependency hierarchy spring boot starter web release jar root library x spring web release jar vulnerable library spring web release jar spring web library home page a href path to dependency file dd trace java dd java agent instrumentation spring webflux spring webflux gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web release spring web release jar dependency hierarchy spring webflux release jar root library x spring web release jar vulnerable library spring webmvc release jar spring web mvc library home page a href path to dependency file dd trace java dd java agent appsec weblog weblog spring app weblog spring app gradle path to vulnerable library caches modules files org springframework spring webmvc release spring webmvc release jar home wss scanner gradle caches modules files org springframework spring webmvc release spring webmvc release jar dependency hierarchy spring boot starter web release jar root library x spring webmvc release jar vulnerable library spring web release jar spring web library home page a href path to dependency file dd trace java dd java agent instrumentation spring rabbit spring rabbit gradle path to vulnerable library home wss scanner gradle caches modules files org springframework spring web release spring web release jar home wss scanner gradle caches modules files org springframework spring web release spring web release jar dependency hierarchy spring rabbit release jar root library x spring web release jar vulnerable library found in head commit a href found in base branch master vulnerability details spring framework versions x prior to and x prior to and older unsupported versions allows web applications to enable cross domain requests via jsonp json with padding through abstractjsonpresponsebodyadvice for rest controllers and for browser requests both are not enabled by default in spring framework nor spring boot however when is configured in an application jsonp support is automatically ready to use through the jsonp and callback jsonp parameters enabling cross domain requests publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework spring webflux release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release packagetype java groupid org springframework packagename spring webmvc packageversion release packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring webmvc release isminimumfixversionavailable true minimumfixversion org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release packagetype java groupid org springframework packagename spring web packageversion release packagefilepaths istransitivedependency true dependencytree org springframework amqp spring rabbit release org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web release release org springframework spring webmvc release release org springframework spring websocket release release basebranches vulnerabilityidentifier cve vulnerabilitydetails spring framework versions x prior to and x prior to and older unsupported versions allows web applications to enable cross domain requests via jsonp json with padding through abstractjsonpresponsebodyadvice for rest controllers and for browser requests both are not enabled by default in spring framework nor spring boot however when is configured in an application jsonp support is automatically ready to use through the jsonp and callback jsonp parameters enabling cross domain requests vulnerabilityurl | 0 |
90,425 | 15,856,153,466 | IssuesEvent | 2021-04-08 01:39:12 | hiucimon/PF2Client | https://api.github.com/repos/hiucimon/PF2Client | opened | CVE-2020-8124 (Medium) detected in url-parse-1.4.3.tgz | security vulnerability | ## CVE-2020-8124 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.3.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.3.tgz</a></p>
<p>Path to dependency file: /PF2Client/package.json</p>
<p>Path to vulnerable library: PF2Client/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.6.8.tgz (Root Library)
- webpack-dev-server-3.1.5.tgz
- sockjs-client-1.1.5.tgz
- :x: **url-parse-1.4.3.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Insufficient validation and sanitization of user input exists in url-parse npm package version 1.4.4 and earlier may allow attacker to bypass security checks.
<p>Publish Date: 2020-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8124>CVE-2020-8124</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8124">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8124</a></p>
<p>Release Date: 2020-02-04</p>
<p>Fix Resolution: url-parse - 1.4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-8124 (Medium) detected in url-parse-1.4.3.tgz - ## CVE-2020-8124 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.3.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.3.tgz</a></p>
<p>Path to dependency file: /PF2Client/package.json</p>
<p>Path to vulnerable library: PF2Client/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.6.8.tgz (Root Library)
- webpack-dev-server-3.1.5.tgz
- sockjs-client-1.1.5.tgz
- :x: **url-parse-1.4.3.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Insufficient validation and sanitization of user input exists in url-parse npm package version 1.4.4 and earlier may allow attacker to bypass security checks.
<p>Publish Date: 2020-02-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8124>CVE-2020-8124</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8124">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8124</a></p>
<p>Release Date: 2020-02-04</p>
<p>Fix Resolution: url-parse - 1.4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in url parse tgz cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file package json path to vulnerable library node modules url parse package json dependency hierarchy build angular tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library vulnerability details insufficient validation and sanitization of user input exists in url parse npm package version and earlier may allow attacker to bypass security checks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse step up your open source security game with whitesource | 0 |
82,397 | 15,646,555,366 | IssuesEvent | 2021-03-23 01:11:57 | jgeraigery/redux | https://api.github.com/repos/jgeraigery/redux | closed | CVE-2017-16026 (Medium) detected in request-2.61.0.tgz - autoclosed | security vulnerability | ## CVE-2017-16026 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>request-2.61.0.tgz</b></p></summary>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.61.0.tgz">https://registry.npmjs.org/request/-/request-2.61.0.tgz</a></p>
<p>Path to dependency file: redux/package.json</p>
<p>Path to vulnerable library: redux/node_modules/npm/node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- gitbook-cli-0.3.6.tgz (Root Library)
- npm-2.14.1.tgz
- :x: **request-2.61.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request >=2.2.6 <2.47.0 || >2.51.0 <=2.67.0.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026>CVE-2017-16026</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16026">https://nvd.nist.gov/vuln/detail/CVE-2017-16026</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: 2.47.1,2.67.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"request","packageVersion":"2.61.0","isTransitiveDependency":true,"dependencyTree":"gitbook-cli:0.3.6;npm:2.14.1;request:2.61.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.47.1,2.67.1"}],"vulnerabilityIdentifier":"CVE-2017-16026","vulnerabilityDetails":"Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request \u003e\u003d2.2.6 \u003c2.47.0 || \u003e2.51.0 \u003c\u003d2.67.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-16026 (Medium) detected in request-2.61.0.tgz - autoclosed - ## CVE-2017-16026 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>request-2.61.0.tgz</b></p></summary>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.61.0.tgz">https://registry.npmjs.org/request/-/request-2.61.0.tgz</a></p>
<p>Path to dependency file: redux/package.json</p>
<p>Path to vulnerable library: redux/node_modules/npm/node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- gitbook-cli-0.3.6.tgz (Root Library)
- npm-2.14.1.tgz
- :x: **request-2.61.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request >=2.2.6 <2.47.0 || >2.51.0 <=2.67.0.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026>CVE-2017-16026</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16026">https://nvd.nist.gov/vuln/detail/CVE-2017-16026</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: 2.47.1,2.67.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"request","packageVersion":"2.61.0","isTransitiveDependency":true,"dependencyTree":"gitbook-cli:0.3.6;npm:2.14.1;request:2.61.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.47.1,2.67.1"}],"vulnerabilityIdentifier":"CVE-2017-16026","vulnerabilityDetails":"Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request \u003e\u003d2.2.6 \u003c2.47.0 || \u003e2.51.0 \u003c\u003d2.67.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in request tgz autoclosed cve medium severity vulnerability vulnerable library request tgz simplified http request client library home page a href path to dependency file redux package json path to vulnerable library redux node modules npm node modules request package json dependency hierarchy gitbook cli tgz root library npm tgz x request tgz vulnerable library vulnerability details request is an http client if a request is made using multipart and the body type is a number then the specified number of non zero memory is passed in the body this affects request publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails request is an http client if a request is made using multipart and the body type is a number then the specified number of non zero memory is passed in the body this affects request vulnerabilityurl | 0 |
114,079 | 17,174,031,992 | IssuesEvent | 2021-07-15 09:10:08 | lukebroganws/SecurityShepherd | https://api.github.com/repos/lukebroganws/SecurityShepherd | opened | CVE-2016-7103 (Medium) detected in jquery-ui-1.8.19.min.js, jquery-ui-1.11.4.min.js | security vulnerability | ## CVE-2016-7103 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-ui-1.8.19.min.js</b>, <b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>
<details><summary><b>jquery-ui-1.8.19.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.8.19/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.8.19/jquery-ui.min.js</a></p>
<p>Path to dependency file: SecurityShepherd/src/main/webapp/index.jsp</p>
<p>Path to vulnerable library: SecurityShepherd/src/main/webapp/js/jqueryUI.js,SecurityShepherd/src/main/webapp/js/jqueryUI.js,SecurityShepherd/target/owaspSecurityShepherd/js/jqueryUI.js,SecurityShepherd/target/owaspSecurityShepherd/js/jqueryUI.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.8.19.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js</a></p>
<p>Path to vulnerable library: SecurityShepherd/target/owaspSecurityShepherd/js/jquery-ui.min.js,SecurityShepherd/src/main/webapp/js/jquery-ui.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.11.4.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/SecurityShepherd/commit/501ff4c497d5b9235a7b0370d7895f67064f5952">501ff4c497d5b9235a7b0370d7895f67064f5952</a></p>
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-site scripting (XSS) vulnerability in jQuery UI before 1.12.0 might allow remote attackers to inject arbitrary web script or HTML via the closeText parameter of the dialog function.
<p>Publish Date: 2017-03-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-7103>CVE-2016-7103</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-7103">https://nvd.nist.gov/vuln/detail/CVE-2016-7103</a></p>
<p>Release Date: 2017-03-15</p>
<p>Fix Resolution: 1.12.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jqueryui","packageVersion":"1.8.19","packageFilePaths":["/src/main/webapp/index.jsp","/target/owaspSecurityShepherd/index.jsp"],"isTransitiveDependency":false,"dependencyTree":"jqueryui:1.8.19","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.12.0"},{"packageType":"JavaScript","packageName":"jqueryui","packageVersion":"1.11.4","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jqueryui:1.11.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.12.0"}],"baseBranches":["dev"],"vulnerabilityIdentifier":"CVE-2016-7103","vulnerabilityDetails":"Cross-site scripting (XSS) vulnerability in jQuery UI before 1.12.0 might allow remote attackers to inject arbitrary web script or HTML via the closeText parameter of the dialog function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-7103","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-7103 (Medium) detected in jquery-ui-1.8.19.min.js, jquery-ui-1.11.4.min.js - ## CVE-2016-7103 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-ui-1.8.19.min.js</b>, <b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>
<details><summary><b>jquery-ui-1.8.19.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.8.19/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.8.19/jquery-ui.min.js</a></p>
<p>Path to dependency file: SecurityShepherd/src/main/webapp/index.jsp</p>
<p>Path to vulnerable library: SecurityShepherd/src/main/webapp/js/jqueryUI.js,SecurityShepherd/src/main/webapp/js/jqueryUI.js,SecurityShepherd/target/owaspSecurityShepherd/js/jqueryUI.js,SecurityShepherd/target/owaspSecurityShepherd/js/jqueryUI.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.8.19.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-ui-1.11.4.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.11.4/jquery-ui.min.js</a></p>
<p>Path to vulnerable library: SecurityShepherd/target/owaspSecurityShepherd/js/jquery-ui.min.js,SecurityShepherd/src/main/webapp/js/jquery-ui.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.11.4.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/SecurityShepherd/commit/501ff4c497d5b9235a7b0370d7895f67064f5952">501ff4c497d5b9235a7b0370d7895f67064f5952</a></p>
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-site scripting (XSS) vulnerability in jQuery UI before 1.12.0 might allow remote attackers to inject arbitrary web script or HTML via the closeText parameter of the dialog function.
<p>Publish Date: 2017-03-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-7103>CVE-2016-7103</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-7103">https://nvd.nist.gov/vuln/detail/CVE-2016-7103</a></p>
<p>Release Date: 2017-03-15</p>
<p>Fix Resolution: 1.12.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jqueryui","packageVersion":"1.8.19","packageFilePaths":["/src/main/webapp/index.jsp","/target/owaspSecurityShepherd/index.jsp"],"isTransitiveDependency":false,"dependencyTree":"jqueryui:1.8.19","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.12.0"},{"packageType":"JavaScript","packageName":"jqueryui","packageVersion":"1.11.4","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jqueryui:1.11.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.12.0"}],"baseBranches":["dev"],"vulnerabilityIdentifier":"CVE-2016-7103","vulnerabilityDetails":"Cross-site scripting (XSS) vulnerability in jQuery UI before 1.12.0 might allow remote attackers to inject arbitrary web script or HTML via the closeText parameter of the dialog function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-7103","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery ui min js jquery ui min js cve medium severity vulnerability vulnerable libraries jquery ui min js jquery ui min js jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file securityshepherd src main webapp index jsp path to vulnerable library securityshepherd src main webapp js jqueryui js securityshepherd src main webapp js jqueryui js securityshepherd target owaspsecurityshepherd js jqueryui js securityshepherd target owaspsecurityshepherd js jqueryui js dependency hierarchy x jquery ui min js vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to vulnerable library securityshepherd target owaspsecurityshepherd js jquery ui min js securityshepherd src main webapp js jquery ui min js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch dev vulnerability details cross site scripting xss vulnerability in jquery ui before might allow remote attackers to inject arbitrary web script or html via the closetext parameter of the dialog function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jqueryui isminimumfixversionavailable true minimumfixversion packagetype javascript packagename jqueryui packageversion packagefilepaths istransitivedependency false dependencytree jqueryui isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails cross site scripting xss vulnerability in jquery ui before might allow remote attackers to inject arbitrary web script or html via the closetext parameter of the dialog function vulnerabilityurl | 0 |
54,236 | 7,879,328,581 | IssuesEvent | 2018-06-26 13:07:38 | systers/mentorship-backend | https://api.github.com/repos/systers/mentorship-backend | closed | Update PR template to add check item to update requirement.txt (if needed) | Category: Documentation/Training Difficulty: EASY Program: GSoC Type: Maintenance | ## Description
As a developer,
I need to update the requirements.txt every time I use a new package,
so that I can install all the correct packages to work with the backend.
**Task:** Add check item to Pull Request template checklist, so that the requirements.txt is always updated when needed.
## Acceptance Criteria
### Update
- [x] Update PR template with new check item
## Definition of Done
- [x] All of the required items are completed.
- [x] Submit PR to `develop` branch.
- [x] Approval by 1 mentor.
## Estimation
30 minutes
| 1.0 | Update PR template to add check item to update requirement.txt (if needed) - ## Description
As a developer,
I need to update the requirements.txt every time I use a new package,
so that I can install all the correct packages to work with the backend.
**Task:** Add check item to Pull Request template checklist, so that the requirements.txt is always updated when needed.
## Acceptance Criteria
### Update
- [x] Update PR template with new check item
## Definition of Done
- [x] All of the required items are completed.
- [x] Submit PR to `develop` branch.
- [x] Approval by 1 mentor.
## Estimation
30 minutes
| non_priority | update pr template to add check item to update requirement txt if needed description as a developer i need to update the requirements txt every time i use a new package so that i can install all the correct packages to work with the backend task add check item to pull request template checklist so that the requirements txt is always updated when needed acceptance criteria update update pr template with new check item definition of done all of the required items are completed submit pr to develop branch approval by mentor estimation minutes | 0 |
37,755 | 5,142,581,734 | IssuesEvent | 2017-01-12 13:45:59 | ahmedkaludi/accelerated-mobile-pages | https://api.github.com/repos/ahmedkaludi/accelerated-mobile-pages | closed | Mobile redirection: front page taking too much time to load | Need Testing | when i enable redirection for mobile visitor it take a lot of time to redirect
**REF:**https://wordpress.org/support/topic/on-post-page-next-button-is-not-working/ | 1.0 | Mobile redirection: front page taking too much time to load - when i enable redirection for mobile visitor it take a lot of time to redirect
**REF:**https://wordpress.org/support/topic/on-post-page-next-button-is-not-working/ | non_priority | mobile redirection front page taking too much time to load when i enable redirection for mobile visitor it take a lot of time to redirect ref | 0 |
22,922 | 4,858,083,500 | IssuesEvent | 2016-11-12 23:17:26 | esdscom/sdscom-xml | https://api.github.com/repos/esdscom/sdscom-xml | closed | ProductFunctionCode meaning | documentation refactoring | ProductFunction is split into Code and Description. I am familiar with phrase-based descriptions of product functions. But what are the codes to be used, and why are they encoded as phrases (if they are standardised, which is what I expect from codes)?
| 1.0 | ProductFunctionCode meaning - ProductFunction is split into Code and Description. I am familiar with phrase-based descriptions of product functions. But what are the codes to be used, and why are they encoded as phrases (if they are standardised, which is what I expect from codes)?
| non_priority | productfunctioncode meaning productfunction is split into code and description i am familiar with phrase based descriptions of product functions but what are the codes to be used and why are they encoded as phrases if they are standardised which is what i expect from codes | 0 |
13,514 | 8,530,274,673 | IssuesEvent | 2018-11-03 20:46:26 | pragmatrix/BuildOnSave | https://api.github.com/repos/pragmatrix/BuildOnSave | opened | Dependent Xamarin.iOS library project causes warnings, but everything works. | help wanted usability | The project that causes these warnings is up to date, and is also not in the list that BuildOnSave computed for the rebuild, but nevertheless gets somehow involved and pumps out a mass of warnings. Surprisingly the whole build works: the application can be started immediately _and_ the changes of other dependent library projects were propagated to the build server.
```
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(41,3): warning VSX1000: No enough information has been provided to MSBuild in order to establish a connection to a Remote Server. The project 'ToolboxIOS' will continue building offline
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(67,3): warning : The build signature could not be verified due to an error. If your build fails, please trying rebuilding the solution. Error details: One or more errors occurred.
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : An error occurred getting directory checksum for App
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : Value cannot be null.
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : Parameter name: path2
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : at System.IO.Path.Combine(String path1, String path2, String path3)
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : at Xamarin.Messaging.PlatformPath.GetServerBuildPath(String home, String appName, String sessionId, String path) in E:\A\_work\675\s\External\messaging\src\Xamarin.Messaging.Common\PlatformPath.cs:line 49
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : at Xamarin.Messaging.Ssh.ISshServiceExtensions.<GetDirectoryChecksumAsync>d__4.MoveNext() in E:\A\_work\675\s\External\messaging\src\Xamarin.Messaging.Ssh\Extensions\ISshServiceExtensions.cs:line 52
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : One or more errors occurred.
``` | True | Dependent Xamarin.iOS library project causes warnings, but everything works. - The project that causes these warnings is up to date, and is also not in the list that BuildOnSave computed for the rebuild, but nevertheless gets somehow involved and pumps out a mass of warnings. Surprisingly the whole build works: the application can be started immediately _and_ the changes of other dependent library projects were propagated to the build server.
```
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(41,3): warning VSX1000: No enough information has been provided to MSBuild in order to establish a connection to a Remote Server. The project 'ToolboxIOS' will continue building offline
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(67,3): warning : The build signature could not be verified due to an error. If your build fails, please trying rebuilding the solution. Error details: One or more errors occurred.
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : An error occurred getting directory checksum for App
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : Value cannot be null.
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : Parameter name: path2
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : at System.IO.Path.Combine(String path1, String path2, String path3)
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : at Xamarin.Messaging.PlatformPath.GetServerBuildPath(String home, String appName, String sessionId, String path) in E:\A\_work\675\s\External\messaging\src\Xamarin.Messaging.Common\PlatformPath.cs:line 49
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : at Xamarin.Messaging.Ssh.ISshServiceExtensions.<GetDirectoryChecksumAsync>d__4.MoveNext() in E:\A\_work\675\s\External\messaging\src\Xamarin.Messaging.Ssh\Extensions\ISshServiceExtensions.cs:line 52
C:\Program Files (x86)\Microsoft Visual Studio\2017\Enterprise\MSBuild\Xamarin\iOS\Xamarin.Messaging.targets(82,3): warning : One or more errors occurred.
``` | non_priority | dependent xamarin ios library project causes warnings but everything works the project that causes these warnings is up to date and is also not in the list that buildonsave computed for the rebuild but nevertheless gets somehow involved and pumps out a mass of warnings surprisingly the whole build works the application can be started immediately and the changes of other dependent library projects were propagated to the build server c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning no enough information has been provided to msbuild in order to establish a connection to a remote server the project toolboxios will continue building offline c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning the build signature could not be verified due to an error if your build fails please trying rebuilding the solution error details one or more errors occurred c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning an error occurred getting directory checksum for app c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning value cannot be null c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning parameter name c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning at system io path combine string string string c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning at xamarin messaging platformpath getserverbuildpath string home string appname string sessionid string path in e a work s external messaging src xamarin messaging common platformpath cs line c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning at xamarin messaging ssh isshserviceextensions d movenext in e a work s external messaging src xamarin messaging ssh extensions isshserviceextensions cs line c program files microsoft visual studio enterprise msbuild xamarin ios xamarin messaging targets warning one or more errors occurred | 0 |
16,238 | 11,882,236,806 | IssuesEvent | 2020-03-27 14:05:17 | deptofdefense/solo | https://api.github.com/repos/deptofdefense/solo | opened | Add appropriate NGINX configuration and letsencrypt cert to enable ssl_stapling | infrastructure | Thanks for submitting an issue! Below are a few things you can do to help us more quickly address the issue.
## Checklist
I have…
- [x] described in detail below both the behavior I expected and the behavior I observed.
- [x] thoroughly outlined below the steps to reproduce this issue, including relevant technical details (e.g. device, operating system, browser, browser version).
~~[ ] attached screenshots illustrating relevant behavior.~~
## Expected Behavior
SSL stapling is enabled for deployments
## Observed Behavior
SSL stapling is ignored because of missing SSL certificate information from letsencrypt
## Steps to Reproduce
N/A
## Screenshots
N/A | 1.0 | Add appropriate NGINX configuration and letsencrypt cert to enable ssl_stapling - Thanks for submitting an issue! Below are a few things you can do to help us more quickly address the issue.
## Checklist
I have…
- [x] described in detail below both the behavior I expected and the behavior I observed.
- [x] thoroughly outlined below the steps to reproduce this issue, including relevant technical details (e.g. device, operating system, browser, browser version).
~~[ ] attached screenshots illustrating relevant behavior.~~
## Expected Behavior
SSL stapling is enabled for deployments
## Observed Behavior
SSL stapling is ignored because of missing SSL certificate information from letsencrypt
## Steps to Reproduce
N/A
## Screenshots
N/A | non_priority | add appropriate nginx configuration and letsencrypt cert to enable ssl stapling thanks for submitting an issue below are a few things you can do to help us more quickly address the issue checklist i have… described in detail below both the behavior i expected and the behavior i observed thoroughly outlined below the steps to reproduce this issue including relevant technical details e g device operating system browser browser version attached screenshots illustrating relevant behavior expected behavior ssl stapling is enabled for deployments observed behavior ssl stapling is ignored because of missing ssl certificate information from letsencrypt steps to reproduce n a screenshots n a | 0 |
175,286 | 13,543,342,172 | IssuesEvent | 2020-09-16 18:48:23 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | Tests for Vec256 classes | feature module: cpu module: tests module: vectorization topic: maybe for quansight triaged | ## 🚀 Feature
We should have tests in C++ for the Vec256 classes.
## Motivation
Currently, the Vec256 code is only tested indirectly through operators that use it. This has led to insufficient test coverage and a number of recent bugs in Vec256 and the operators that use it. We should add sufficient test infrastructure so that we can easily add test cases for new functions on Vec256. It's important that the tests cover the different data types (float, double, int32, int64, etc.) and instruction sets (generic, avx, avx2).
This will require changes to CMake since the current test cases don't enable the AVX/AVX2 instruction sets.
cc @VitalyFedyunin | 1.0 | Tests for Vec256 classes - ## 🚀 Feature
We should have tests in C++ for the Vec256 classes.
## Motivation
Currently, the Vec256 code is only tested indirectly through operators that use it. This has led to insufficient test coverage and a number of recent bugs in Vec256 and the operators that use it. We should add sufficient test infrastructure so that we can easily add test cases for new functions on Vec256. It's important that the tests cover the different data types (float, double, int32, int64, etc.) and instruction sets (generic, avx, avx2).
This will require changes to CMake since the current test cases don't enable the AVX/AVX2 instruction sets.
cc @VitalyFedyunin | non_priority | tests for classes 🚀 feature we should have tests in c for the classes motivation currently the code is only tested indirectly through operators that use it this has led to insufficient test coverage and a number of recent bugs in and the operators that use it we should add sufficient test infrastructure so that we can easily add test cases for new functions on it s important that the tests cover the different data types float double etc and instruction sets generic avx this will require changes to cmake since the current test cases don t enable the avx instruction sets cc vitalyfedyunin | 0 |
153,503 | 24,137,375,059 | IssuesEvent | 2022-09-21 12:27:09 | OpenZeppelin/nile | https://api.github.com/repos/OpenZeppelin/nile | opened | Refactor accounts.json and deployments.txt files | enhancement design | Currently, the project is creating these files when setting up accounts or deploying contracts:
**[network].accounts.json** and **[network].deployments.txt**
Room for improvement:
- Format inconsistency (json and txt).
- Structure inconsistency.
- Merging hex and integers (public_key as int, and address as hex).
- Multiple files at the project's root directory (one account and one deployment for each network). Maybe having a folder for deployments would be helpful?
- nile init creating an account.json file that is never used (not having the network) | 1.0 | Refactor accounts.json and deployments.txt files - Currently, the project is creating these files when setting up accounts or deploying contracts:
**[network].accounts.json** and **[network].deployments.txt**
Room for improvement:
- Format inconsistency (json and txt).
- Structure inconsistency.
- Merging hex and integers (public_key as int, and address as hex).
- Multiple files at the project's root directory (one account and one deployment for each network). Maybe having a folder for deployments would be helpful?
- nile init creating an account.json file that is never used (not having the network) | non_priority | refactor accounts json and deployments txt files currently the project is creating these files when setting up accounts or deploying contracts accounts json and deployments txt room for improvement format inconsistency json and txt structure inconsistency merging hex and integers public key as int and address as hex multiple files at the project s root directory one account and one deployment for each network maybe having a folder for deployments would be helpful nile init creating an account json file that is never used not having the network | 0 |
16,806 | 9,888,940,521 | IssuesEvent | 2019-06-25 12:46:29 | orange-cloudfoundry/paas-templates | https://api.github.com/repos/orange-cloudfoundry/paas-templates | closed | SACK Panic CVE | security | ### Expected behavior
As a platform operator, expecting to be protected agains SACK vuln.
### Observed behavior
kernel version 41.0.0-RC2
```
~# hostnamectl status
Static hostname: 5fb0b45e-0246-4892-b10a-dde4cafcb8d3
Transient hostname: status
Icon name: computer-vm
Chassis: vm
Machine ID: 659c0df7d6c8d87f60613e19d2735049
Boot ID: c61ce9cf44154fe6a71bb021be4a49c7
Virtualization: kvm
Operating System: Ubuntu 16.04.6 LTS
Kernel: Linux 4.15.0-50-generic
Architecture: x86-64
```
expected version is linux-image-4.15.0-52-generic 4.15.0-52.56~16.04.1
### references
- https://wiki.ubuntu.com/SecurityTeam/KnowledgeBase/SACKPanic
- https://www.cloudfoundry.org/blog/usn-4001-1/
- https://www.cloudfoundry.org/blog/usn-4012-1/
- https://www.cloudfoundry.org/blog/usn-4015-1/
- https://www.cloudfoundry.org/blog/usn-3999-1/
-https://www.cloudfoundry.org/blog/usn-4001-1/
-https://www.cloudfoundry.org/blog/usn-4008-2/
- https://www.cbronline.com/news/linux-vulnerability-netflix
- https://github.com/cloudfoundry/bosh-linux-stemcell-builder/releases/tag/ubuntu-xenial%2Fv315.48
-https://github.com/cloudfoundry/cflinuxfs3/releases/tag/0.103.0
<!--
### Affected release
Reproduced on version x.y
-->
<!-- specify release note version here -->
<!--
### Traces and logs
Remember this is a public repo. DON'T leak credentials or Orange internal URLs.
Automation may be applied in the future.
* [ ] I have reviewed provided traces against secrets (credentials, internal URLs) that should not be leake, manually of using some tools such as [truffle-hog file:///user/dxa4481/codeprojects/mytraces.txt](https://github.com/dxa4481/truffleHog#truffle-hog)
-->
| True | SACK Panic CVE - ### Expected behavior
As a platform operator, expecting to be protected agains SACK vuln.
### Observed behavior
kernel version 41.0.0-RC2
```
~# hostnamectl status
Static hostname: 5fb0b45e-0246-4892-b10a-dde4cafcb8d3
Transient hostname: status
Icon name: computer-vm
Chassis: vm
Machine ID: 659c0df7d6c8d87f60613e19d2735049
Boot ID: c61ce9cf44154fe6a71bb021be4a49c7
Virtualization: kvm
Operating System: Ubuntu 16.04.6 LTS
Kernel: Linux 4.15.0-50-generic
Architecture: x86-64
```
expected version is linux-image-4.15.0-52-generic 4.15.0-52.56~16.04.1
### references
- https://wiki.ubuntu.com/SecurityTeam/KnowledgeBase/SACKPanic
- https://www.cloudfoundry.org/blog/usn-4001-1/
- https://www.cloudfoundry.org/blog/usn-4012-1/
- https://www.cloudfoundry.org/blog/usn-4015-1/
- https://www.cloudfoundry.org/blog/usn-3999-1/
-https://www.cloudfoundry.org/blog/usn-4001-1/
-https://www.cloudfoundry.org/blog/usn-4008-2/
- https://www.cbronline.com/news/linux-vulnerability-netflix
- https://github.com/cloudfoundry/bosh-linux-stemcell-builder/releases/tag/ubuntu-xenial%2Fv315.48
-https://github.com/cloudfoundry/cflinuxfs3/releases/tag/0.103.0
<!--
### Affected release
Reproduced on version x.y
-->
<!-- specify release note version here -->
<!--
### Traces and logs
Remember this is a public repo. DON'T leak credentials or Orange internal URLs.
Automation may be applied in the future.
* [ ] I have reviewed provided traces against secrets (credentials, internal URLs) that should not be leake, manually of using some tools such as [truffle-hog file:///user/dxa4481/codeprojects/mytraces.txt](https://github.com/dxa4481/truffleHog#truffle-hog)
-->
| non_priority | sack panic cve expected behavior as a platform operator expecting to be protected agains sack vuln observed behavior kernel version hostnamectl status static hostname transient hostname status icon name computer vm chassis vm machine id boot id virtualization kvm operating system ubuntu lts kernel linux generic architecture expected version is linux image generic references affected release reproduced on version x y traces and logs remember this is a public repo don t leak credentials or orange internal urls automation may be applied in the future i have reviewed provided traces against secrets credentials internal urls that should not be leake manually of using some tools such as | 0 |
17,997 | 3,662,606,590 | IssuesEvent | 2016-02-19 00:06:51 | dotnet/wcf | https://api.github.com/repos/dotnet/wcf | opened | PlatformNotSupportedException: Windows Stream Security is not supported | bug NET Native Test Case Failure | |Failing Test Cases |
|--------------------------|
|**Tcp_ClientCredentialTypeTests.SameBinding_DefaultSettings_EchoString**|
|**Tcp_ClientCredentialTypeTests.SameBinding_SecurityModeTransport_EchoString**|
| 1.0 | PlatformNotSupportedException: Windows Stream Security is not supported - |Failing Test Cases |
|--------------------------|
|**Tcp_ClientCredentialTypeTests.SameBinding_DefaultSettings_EchoString**|
|**Tcp_ClientCredentialTypeTests.SameBinding_SecurityModeTransport_EchoString**|
| non_priority | platformnotsupportedexception windows stream security is not supported failing test cases tcp clientcredentialtypetests samebinding defaultsettings echostring tcp clientcredentialtypetests samebinding securitymodetransport echostring | 0 |
155,093 | 24,401,219,301 | IssuesEvent | 2022-10-05 01:42:47 | elementary/website | https://api.github.com/repos/elementary/website | opened | Upgrade Node | Needs Design | ### Problem
Currently, the website runs on Node 12 which hit end of life sometime around 2020 (it has actually scolled off of the releases page of Node's Github). We should switch to a newer supported version of Node and NPM with the project. As of the time of this issue the current LTS is Node 16 however it is scheduled to become the maintenance release before the end of the month.
### Proposal
Adopt either Node 16 or Node 18.
### Prior Art (Optional)
_No response_ | 1.0 | Upgrade Node - ### Problem
Currently, the website runs on Node 12 which hit end of life sometime around 2020 (it has actually scolled off of the releases page of Node's Github). We should switch to a newer supported version of Node and NPM with the project. As of the time of this issue the current LTS is Node 16 however it is scheduled to become the maintenance release before the end of the month.
### Proposal
Adopt either Node 16 or Node 18.
### Prior Art (Optional)
_No response_ | non_priority | upgrade node problem currently the website runs on node which hit end of life sometime around it has actually scolled off of the releases page of node s github we should switch to a newer supported version of node and npm with the project as of the time of this issue the current lts is node however it is scheduled to become the maintenance release before the end of the month proposal adopt either node or node prior art optional no response | 0 |
1,822 | 4,047,269,631 | IssuesEvent | 2016-05-23 03:50:41 | HTBox/MobileKidsIdApp | https://api.github.com/repos/HTBox/MobileKidsIdApp | closed | Create Child Info > Professional Care Provider Screen | P1 requirement | _NOTE_: Issue #12 has been merged into this issue.
**STORY:** As a Kids ID App user, I want to enter information about my child's doctor(s), dentist, therapists and other care providers, so I can share it with authorities should my child go missing.
**ASSUMPTIONS**
User is logged in, and has created at least one child profile.
User has navigated from the Child Info menu screen to "Professional Care Provider" option.
**ACCEPTANCE CRITERIA**
1) The Doctor Info will have fields to enter the following doctor information: Doctor Name, Clinic Name, Address, Phone
2) The Doctor Info will also have fields to enter the following medical info about the child: Medic Alert Info, Allergies, Regular Medications, Psych Meds, Inhaler, Diabetic.
3) All fields except the Inhaler and Diabetic fields are text (up to 255 char) fields.
4) The Inhaler and Diabetic fields are checkbox fields, defaulted to UNchecked.
5) The Dental Info will have fields to enter the following doctor information: Dentist Name, Clinic Name, Address, Phone
6) Additional Professional Care providers can be added, such as psychiatrist, therapist, social worker.
**REFERENCES**
[MCM.pdf](https://github.com/HTBox/MobileKidsIdApp/files/120988/MCM.p)
[Kids ID App screen flow v5.pdf](https://github.com/HTBox/MobileKidsIdApp/files/139742/Kids.ID.App.screen.flow.v5.pdf)
| 1.0 | Create Child Info > Professional Care Provider Screen - _NOTE_: Issue #12 has been merged into this issue.
**STORY:** As a Kids ID App user, I want to enter information about my child's doctor(s), dentist, therapists and other care providers, so I can share it with authorities should my child go missing.
**ASSUMPTIONS**
User is logged in, and has created at least one child profile.
User has navigated from the Child Info menu screen to "Professional Care Provider" option.
**ACCEPTANCE CRITERIA**
1) The Doctor Info will have fields to enter the following doctor information: Doctor Name, Clinic Name, Address, Phone
2) The Doctor Info will also have fields to enter the following medical info about the child: Medic Alert Info, Allergies, Regular Medications, Psych Meds, Inhaler, Diabetic.
3) All fields except the Inhaler and Diabetic fields are text (up to 255 char) fields.
4) The Inhaler and Diabetic fields are checkbox fields, defaulted to UNchecked.
5) The Dental Info will have fields to enter the following doctor information: Dentist Name, Clinic Name, Address, Phone
6) Additional Professional Care providers can be added, such as psychiatrist, therapist, social worker.
**REFERENCES**
[MCM.pdf](https://github.com/HTBox/MobileKidsIdApp/files/120988/MCM.p)
[Kids ID App screen flow v5.pdf](https://github.com/HTBox/MobileKidsIdApp/files/139742/Kids.ID.App.screen.flow.v5.pdf)
| non_priority | create child info professional care provider screen note issue has been merged into this issue story as a kids id app user i want to enter information about my child s doctor s dentist therapists and other care providers so i can share it with authorities should my child go missing assumptions user is logged in and has created at least one child profile user has navigated from the child info menu screen to professional care provider option acceptance criteria the doctor info will have fields to enter the following doctor information doctor name clinic name address phone the doctor info will also have fields to enter the following medical info about the child medic alert info allergies regular medications psych meds inhaler diabetic all fields except the inhaler and diabetic fields are text up to char fields the inhaler and diabetic fields are checkbox fields defaulted to unchecked the dental info will have fields to enter the following doctor information dentist name clinic name address phone additional professional care providers can be added such as psychiatrist therapist social worker references | 0 |
327,674 | 24,147,461,455 | IssuesEvent | 2022-09-21 20:10:44 | mapstruct/mapstruct | https://api.github.com/repos/mapstruct/mapstruct | closed | Use GitHub new Issue Form Templates | documentation | GitHub has added some new Issue Form Templates https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/syntax-for-issue-forms that can allow us to more easily guide our users in creating bug reports or feature requests. | 1.0 | Use GitHub new Issue Form Templates - GitHub has added some new Issue Form Templates https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/syntax-for-issue-forms that can allow us to more easily guide our users in creating bug reports or feature requests. | non_priority | use github new issue form templates github has added some new issue form templates that can allow us to more easily guide our users in creating bug reports or feature requests | 0 |
277,551 | 30,659,354,045 | IssuesEvent | 2023-07-25 14:06:56 | rsoreq/zenbot | https://api.github.com/repos/rsoreq/zenbot | closed | CVE-2021-23413 (Medium) detected in jszip-3.3.0.tgz, jszip-3.5.0.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-23413 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jszip-3.3.0.tgz</b>, <b>jszip-3.5.0.tgz</b></p></summary>
<p>
<details><summary><b>jszip-3.3.0.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz</a></p>
<p>
Dependency Hierarchy:
- snyk-1.386.0.tgz (Root Library)
- snyk-nuget-plugin-1.18.1.tgz
- :x: **jszip-3.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>jszip-3.5.0.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- snyk-1.386.0.tgz (Root Library)
- snyk-mvn-plugin-2.19.1.tgz
- java-call-graph-builder-1.13.1.tgz
- :x: **jszip-3.5.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7a24c0d7b98ee76e6bac827974cff490a7694378">7a24c0d7b98ee76e6bac827974cff490a7694378</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package jszip before 3.7.0. Crafting a new zip file with filenames set to Object prototype values (e.g __proto__, toString, etc) results in a returned object with a modified prototype instance.
<p>Publish Date: 2021-07-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23413>CVE-2021-23413</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413</a></p>
<p>Release Date: 2021-07-25</p>
<p>Fix Resolution (jszip): 3.7.0</p>
<p>Direct dependency fix Resolution (snyk): 1.667.0</p><p>Fix Resolution (jszip): 3.7.0</p>
<p>Direct dependency fix Resolution (snyk): 1.667.0</p>
</p>
</details>
<p></p>
| True | CVE-2021-23413 (Medium) detected in jszip-3.3.0.tgz, jszip-3.5.0.tgz - autoclosed - ## CVE-2021-23413 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jszip-3.3.0.tgz</b>, <b>jszip-3.5.0.tgz</b></p></summary>
<p>
<details><summary><b>jszip-3.3.0.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.3.0.tgz</a></p>
<p>
Dependency Hierarchy:
- snyk-1.386.0.tgz (Root Library)
- snyk-nuget-plugin-1.18.1.tgz
- :x: **jszip-3.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>jszip-3.5.0.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz">https://registry.npmjs.org/jszip/-/jszip-3.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- snyk-1.386.0.tgz (Root Library)
- snyk-mvn-plugin-2.19.1.tgz
- java-call-graph-builder-1.13.1.tgz
- :x: **jszip-3.5.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7a24c0d7b98ee76e6bac827974cff490a7694378">7a24c0d7b98ee76e6bac827974cff490a7694378</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package jszip before 3.7.0. Crafting a new zip file with filenames set to Object prototype values (e.g __proto__, toString, etc) results in a returned object with a modified prototype instance.
<p>Publish Date: 2021-07-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23413>CVE-2021-23413</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23413</a></p>
<p>Release Date: 2021-07-25</p>
<p>Fix Resolution (jszip): 3.7.0</p>
<p>Direct dependency fix Resolution (snyk): 1.667.0</p><p>Fix Resolution (jszip): 3.7.0</p>
<p>Direct dependency fix Resolution (snyk): 1.667.0</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in jszip tgz jszip tgz autoclosed cve medium severity vulnerability vulnerable libraries jszip tgz jszip tgz jszip tgz create read and edit zip files with javascript library home page a href dependency hierarchy snyk tgz root library snyk nuget plugin tgz x jszip tgz vulnerable library jszip tgz create read and edit zip files with javascript library home page a href dependency hierarchy snyk tgz root library snyk mvn plugin tgz java call graph builder tgz x jszip tgz vulnerable library found in head commit a href found in base branch unstable vulnerability details this affects the package jszip before crafting a new zip file with filenames set to object prototype values e g proto tostring etc results in a returned object with a modified prototype instance publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jszip direct dependency fix resolution snyk fix resolution jszip direct dependency fix resolution snyk | 0 |
38,514 | 6,674,104,076 | IssuesEvent | 2017-10-04 17:18:06 | arangodb/arangodb | https://api.github.com/repos/arangodb/arangodb | closed | rocks db config error on startup | 1 Question 3 Documentation 3 RocksDB | ## my environment running ArangoDB
I'm using the latest ArangoDB of the respective release series:
- [X] 3.2
Mode:
- [ ] Cluster
- [X] Single-Server
Storage-Engine:
- [ ] mmfiles
- [X] rocksdb
On this operating system:
- [X] Linux
- [X] other: archlinux
It appears the rocksdb.use-direct-writes option mentioned [here](https://www.arangodb.com/why-arangodb/comparing-rocksdb-mmfiles-storage-engines/) in the "Tuning the RocksDB engine" does not work correctly. The rocksdb.use-direct-reads option works as expected.
```
[rocksdb]
rocksdb.block-cache-size=12G
rocksdb.use-direct-reads=true
rocksdb.use-direct-writes=true
```
```
Oct 03 09:24:08 arangod[9148]: Error while processing config file '//etc/arangodb3/arangod.conf', line #15:
Oct 03 09:24:08 arangod[9148]: unknown option '--rocksdb.use-direct-writes'
Oct 03 09:24:08 arangod[9148]: Did you mean this?
Oct 03 09:24:08 arangod[9148]: --rocksdb.use-direct-reads use O_DIRECT for reading files
``` | 1.0 | rocks db config error on startup - ## my environment running ArangoDB
I'm using the latest ArangoDB of the respective release series:
- [X] 3.2
Mode:
- [ ] Cluster
- [X] Single-Server
Storage-Engine:
- [ ] mmfiles
- [X] rocksdb
On this operating system:
- [X] Linux
- [X] other: archlinux
It appears the rocksdb.use-direct-writes option mentioned [here](https://www.arangodb.com/why-arangodb/comparing-rocksdb-mmfiles-storage-engines/) in the "Tuning the RocksDB engine" does not work correctly. The rocksdb.use-direct-reads option works as expected.
```
[rocksdb]
rocksdb.block-cache-size=12G
rocksdb.use-direct-reads=true
rocksdb.use-direct-writes=true
```
```
Oct 03 09:24:08 arangod[9148]: Error while processing config file '//etc/arangodb3/arangod.conf', line #15:
Oct 03 09:24:08 arangod[9148]: unknown option '--rocksdb.use-direct-writes'
Oct 03 09:24:08 arangod[9148]: Did you mean this?
Oct 03 09:24:08 arangod[9148]: --rocksdb.use-direct-reads use O_DIRECT for reading files
``` | non_priority | rocks db config error on startup my environment running arangodb i m using the latest arangodb of the respective release series mode cluster single server storage engine mmfiles rocksdb on this operating system linux other archlinux it appears the rocksdb use direct writes option mentioned in the tuning the rocksdb engine does not work correctly the rocksdb use direct reads option works as expected rocksdb block cache size rocksdb use direct reads true rocksdb use direct writes true oct arangod error while processing config file etc arangod conf line oct arangod unknown option rocksdb use direct writes oct arangod did you mean this oct arangod rocksdb use direct reads use o direct for reading files | 0 |
442,626 | 30,846,906,022 | IssuesEvent | 2023-08-02 14:16:20 | microsoft/coe-starter-kit | https://api.github.com/repos/microsoft/coe-starter-kit | closed | [CoE Starter Kit - QUESTION] Two Flows that no longer exist is still in documentation | documentation coe-starter-kit | ### Does this question already exist in our backlog?
- [X] I have checked and confirm this is a new question.
### What is your question?
These two flows no longer exist in the installation but they are showing in the documentation:
Command Center App > Get CoE Flows
CLEANUP - Admin | Sync Template v3 (Connection Status)
### What solution are you experiencing the issue with?
Core
### What solution version are you using?
4.8
### What app or flow are you having the issue with?
not sure
### What method are you using to get inventory and telemetry?
None | 1.0 | [CoE Starter Kit - QUESTION] Two Flows that no longer exist is still in documentation - ### Does this question already exist in our backlog?
- [X] I have checked and confirm this is a new question.
### What is your question?
These two flows no longer exist in the installation but they are showing in the documentation:
Command Center App > Get CoE Flows
CLEANUP - Admin | Sync Template v3 (Connection Status)
### What solution are you experiencing the issue with?
Core
### What solution version are you using?
4.8
### What app or flow are you having the issue with?
not sure
### What method are you using to get inventory and telemetry?
None | non_priority | two flows that no longer exist is still in documentation does this question already exist in our backlog i have checked and confirm this is a new question what is your question these two flows no longer exist in the installation but they are showing in the documentation command center app get coe flows cleanup admin sync template connection status what solution are you experiencing the issue with core what solution version are you using what app or flow are you having the issue with not sure what method are you using to get inventory and telemetry none | 0 |
7,172 | 16,903,314,808 | IssuesEvent | 2021-06-24 02:05:40 | MicrosoftDocs/architecture-center | https://api.github.com/repos/MicrosoftDocs/architecture-center | closed | "API Gateway" is referenced but that isnt an azure servivce | architecture-center/svc assigned-to-author azure-guide/subsvc doc-enhancement triaged | Shouldn't this wording either say "API Management" or maybe "Application Gateway" or make a note/link to the https://docs.microsoft.com/en-us/azure/architecture/microservices/design/gateway document and say that it could be any number of technologies....the impression to me is that there is an azure service called 'API Gateway'
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: fccd14ec-192a-ffd8-edec-4296998feb8b
* Version Independent ID: 2bac3769-2613-f739-4796-0737c7cd8919
* Content: [Building microservices on Azure - Azure Architecture Center](https://docs.microsoft.com/en-us/azure/architecture/microservices/)
* Content Source: [docs/microservices/index.md](https://github.com/microsoftdocs/architecture-center/blob/master/docs/microservices/index.md)
* Service: **architecture-center**
* Sub-service: **azure-guide**
* GitHub Login: @doodlemania2
* Microsoft Alias: **pnp** | 1.0 | "API Gateway" is referenced but that isnt an azure servivce - Shouldn't this wording either say "API Management" or maybe "Application Gateway" or make a note/link to the https://docs.microsoft.com/en-us/azure/architecture/microservices/design/gateway document and say that it could be any number of technologies....the impression to me is that there is an azure service called 'API Gateway'
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: fccd14ec-192a-ffd8-edec-4296998feb8b
* Version Independent ID: 2bac3769-2613-f739-4796-0737c7cd8919
* Content: [Building microservices on Azure - Azure Architecture Center](https://docs.microsoft.com/en-us/azure/architecture/microservices/)
* Content Source: [docs/microservices/index.md](https://github.com/microsoftdocs/architecture-center/blob/master/docs/microservices/index.md)
* Service: **architecture-center**
* Sub-service: **azure-guide**
* GitHub Login: @doodlemania2
* Microsoft Alias: **pnp** | non_priority | api gateway is referenced but that isnt an azure servivce shouldn t this wording either say api management or maybe application gateway or make a note link to the document and say that it could be any number of technologies the impression to me is that there is an azure service called api gateway document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id edec version independent id content content source service architecture center sub service azure guide github login microsoft alias pnp | 0 |
47,972 | 13,067,346,340 | IssuesEvent | 2020-07-31 00:10:06 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | Summary of remaining static analysis Issues (Trac #1549) | Migrated from Trac cmake defect |
== Code that is clearly producing incorrect results ==
`CascadeVariables` returns uninitilized data see bug #1529
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7461e5.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-bb648a.html#EndPath
== Code that need improvement ==
Code assumes that the file being read starts with a `#` and contains the number of strings
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6b756c.html#EndPath
code assumes 8 parameters when the number of parameters is a variable
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1e32f9.html#EndPath
code path is confusing and has lots of `#ifdefs`
toprec/private/toprec/laputop/I3LaputopParametrization.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1a61fb.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-cfabfc.html#EndPath
== Code I gave up trying to understand the problem==
PROPOSAL/private/PROPOSAL/Amanda.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-19a21f.html#EndPath
VHESelfVeto/private/clipper/clipper.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-47fef5.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-da4893.html#EndPath
fill-ratio/private/fill-ratio/I3FillRatioLite.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-146975.html#EndPath
icetray/private/icetray/I3Tray.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-fe2e6e.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-873438.html#EndPath
ipdf/private/pybindings/Likelihood.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6148e1.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7d3a26.html#EndPath
mue/private/mue/llhreco.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-b0852c.html#EndPath
dead assignment is the result of `decode()` but i can't tell if `decode()` has side effects or not
payload-parsing/private/payload-parsing/dump-raw-deltacompressed.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-c9677b.html#EndPath
tpx/private/tpx/I3IceTopBaselineModule.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-aaed35.html#EndPath
== copy and paste files with too many problems to list ==
g4-tankresponse/private/g4-tankresponse/triangle/triangle.c
lilliput/private/minimizer/minuit/TMinuit1.cxx
== Memory leaks ==
g4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopDetectorConstruction.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5704c1.html#EndPath
g4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopTank.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-271865.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4e6179.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e17000.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e87022.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f536c8.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f71588.html#EndPath
mue/private/mue/I3mue.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-d05444.html#EndPath
== False Positives ==
complains about an impossible code branch
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-141e17.html#EndPath
clang confuses unix's `open` with `I3::dataio::open` see #1536
clsim/private/make_safeprimes/convert.cxx
dataio/private/dataio/I3MultiWriter.cxx
dataio/private/dataio/I3Writer.cxx
dataio/private/pybindings/I3File.cxx
dataio/private/shovel/Model.cxx
dataio/private/shovel/Model.cxx
dataio/private/shovel/Model.cxx
steamshovel/private/steamshovel/FileService.cpp
clang dosn't understand `G4Exception()`
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1d0a97.html#EndPath
clang doesn't understand Qt memory management see #1537
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4ca3c9.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5c5809.html#EndPath
Migrated from https://code.icecube.wisc.edu/ticket/1549
```json
{
"status": "closed",
"changetime": "2017-04-24T08:39:36",
"description": "\n== Code that is clearly producing incorrect results ==\n`CascadeVariables` returns uninitilized data see bug #1537\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7461e5.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-bb648a.html#EndPath\n\n== Code that need improvement ==\n\nCode assumes that the file being read starts with a `#` and contains the number of strings \nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6b756c.html#EndPath\n\ncode assumes 8 parameters when the number of parameters is a variable\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1e32f9.html#EndPath\n\ncode path is confusing and has lots of `#ifdefs`\ntoprec/private/toprec/laputop/I3LaputopParametrization.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1a61fb.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-cfabfc.html#EndPath\n\n== Code I gave up trying to understand the problem==\nPROPOSAL/private/PROPOSAL/Amanda.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-19a21f.html#EndPath\n\nVHESelfVeto/private/clipper/clipper.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-47fef5.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-da4893.html#EndPath\n\nfill-ratio/private/fill-ratio/I3FillRatioLite.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-146975.html#EndPath\n\nicetray/private/icetray/I3Tray.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-fe2e6e.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-873438.html#EndPath\n\nipdf/private/pybindings/Likelihood.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6148e1.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7d3a26.html#EndPath\n\nmue/private/mue/llhreco.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-b0852c.html#EndPath\n\ndead assignment is the result of `decode()` but i can't tell if `decode()` has side effects or not\npayload-parsing/private/payload-parsing/dump-raw-deltacompressed.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-c9677b.html#EndPath\n\n\n\ntpx/private/tpx/I3IceTopBaselineModule.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-aaed35.html#EndPath\n\n\n== copy and paste files with too many problems to list ==\n\ng4-tankresponse/private/g4-tankresponse/triangle/triangle.c\nlilliput/private/minimizer/minuit/TMinuit1.cxx\n\n== Memory leaks ==\ng4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopDetectorConstruction.cxx\t\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5704c1.html#EndPath\ng4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopTank.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-271865.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4e6179.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e17000.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e87022.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f536c8.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f71588.html#EndPath\n\nmue/private/mue/I3mue.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-d05444.html#EndPath\n\n== False Positives ==\ncomplains about an impossible code branch\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-141e17.html#EndPath\n\nclang confuses unix's `open` with `I3::dataio::open` see #1544\nclsim/private/make_safeprimes/convert.cxx\ndataio/private/dataio/I3MultiWriter.cxx\ndataio/private/dataio/I3Writer.cxx\ndataio/private/pybindings/I3File.cxx\ndataio/private/shovel/Model.cxx\ndataio/private/shovel/Model.cxx\ndataio/private/shovel/Model.cxx\nsteamshovel/private/steamshovel/FileService.cpp\n\nclang dosn't understand `G4Exception()`\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1d0a97.html#EndPath\n\nclang doesn't understand Qt memory management see #1545\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4ca3c9.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5c5809.html#EndPath",
"reporter": "kjmeagher",
"cc": "david.schultz, nega, olivas",
"resolution": "fixed",
"_ts": "1493023176837564",
"component": "cmake",
"summary": "Summary of remaining static analysis Issues",
"priority": "normal",
"keywords": "",
"time": "2016-02-15T10:27:59",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
| 1.0 | Summary of remaining static analysis Issues (Trac #1549) -
== Code that is clearly producing incorrect results ==
`CascadeVariables` returns uninitilized data see bug #1529
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7461e5.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-bb648a.html#EndPath
== Code that need improvement ==
Code assumes that the file being read starts with a `#` and contains the number of strings
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6b756c.html#EndPath
code assumes 8 parameters when the number of parameters is a variable
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1e32f9.html#EndPath
code path is confusing and has lots of `#ifdefs`
toprec/private/toprec/laputop/I3LaputopParametrization.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1a61fb.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-cfabfc.html#EndPath
== Code I gave up trying to understand the problem==
PROPOSAL/private/PROPOSAL/Amanda.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-19a21f.html#EndPath
VHESelfVeto/private/clipper/clipper.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-47fef5.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-da4893.html#EndPath
fill-ratio/private/fill-ratio/I3FillRatioLite.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-146975.html#EndPath
icetray/private/icetray/I3Tray.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-fe2e6e.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-873438.html#EndPath
ipdf/private/pybindings/Likelihood.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6148e1.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7d3a26.html#EndPath
mue/private/mue/llhreco.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-b0852c.html#EndPath
dead assignment is the result of `decode()` but i can't tell if `decode()` has side effects or not
payload-parsing/private/payload-parsing/dump-raw-deltacompressed.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-c9677b.html#EndPath
tpx/private/tpx/I3IceTopBaselineModule.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-aaed35.html#EndPath
== copy and paste files with too many problems to list ==
g4-tankresponse/private/g4-tankresponse/triangle/triangle.c
lilliput/private/minimizer/minuit/TMinuit1.cxx
== Memory leaks ==
g4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopDetectorConstruction.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5704c1.html#EndPath
g4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopTank.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-271865.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4e6179.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e17000.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e87022.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f536c8.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f71588.html#EndPath
mue/private/mue/I3mue.cxx
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-d05444.html#EndPath
== False Positives ==
complains about an impossible code branch
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-141e17.html#EndPath
clang confuses unix's `open` with `I3::dataio::open` see #1536
clsim/private/make_safeprimes/convert.cxx
dataio/private/dataio/I3MultiWriter.cxx
dataio/private/dataio/I3Writer.cxx
dataio/private/pybindings/I3File.cxx
dataio/private/shovel/Model.cxx
dataio/private/shovel/Model.cxx
dataio/private/shovel/Model.cxx
steamshovel/private/steamshovel/FileService.cpp
clang dosn't understand `G4Exception()`
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1d0a97.html#EndPath
clang doesn't understand Qt memory management see #1537
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4ca3c9.html#EndPath
http://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5c5809.html#EndPath
Migrated from https://code.icecube.wisc.edu/ticket/1549
```json
{
"status": "closed",
"changetime": "2017-04-24T08:39:36",
"description": "\n== Code that is clearly producing incorrect results ==\n`CascadeVariables` returns uninitilized data see bug #1537\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7461e5.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-bb648a.html#EndPath\n\n== Code that need improvement ==\n\nCode assumes that the file being read starts with a `#` and contains the number of strings \nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6b756c.html#EndPath\n\ncode assumes 8 parameters when the number of parameters is a variable\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1e32f9.html#EndPath\n\ncode path is confusing and has lots of `#ifdefs`\ntoprec/private/toprec/laputop/I3LaputopParametrization.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1a61fb.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-cfabfc.html#EndPath\n\n== Code I gave up trying to understand the problem==\nPROPOSAL/private/PROPOSAL/Amanda.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-19a21f.html#EndPath\n\nVHESelfVeto/private/clipper/clipper.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-47fef5.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-da4893.html#EndPath\n\nfill-ratio/private/fill-ratio/I3FillRatioLite.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-146975.html#EndPath\n\nicetray/private/icetray/I3Tray.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-fe2e6e.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-873438.html#EndPath\n\nipdf/private/pybindings/Likelihood.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-6148e1.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-7d3a26.html#EndPath\n\nmue/private/mue/llhreco.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-b0852c.html#EndPath\n\ndead assignment is the result of `decode()` but i can't tell if `decode()` has side effects or not\npayload-parsing/private/payload-parsing/dump-raw-deltacompressed.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-c9677b.html#EndPath\n\n\n\ntpx/private/tpx/I3IceTopBaselineModule.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-aaed35.html#EndPath\n\n\n== copy and paste files with too many problems to list ==\n\ng4-tankresponse/private/g4-tankresponse/triangle/triangle.c\nlilliput/private/minimizer/minuit/TMinuit1.cxx\n\n== Memory leaks ==\ng4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopDetectorConstruction.cxx\t\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5704c1.html#EndPath\ng4-tankresponse/private/g4-tankresponse/g4classes/G4IceTopTank.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-271865.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4e6179.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e17000.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-e87022.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f536c8.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-f71588.html#EndPath\n\nmue/private/mue/I3mue.cxx\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-d05444.html#EndPath\n\n== False Positives ==\ncomplains about an impossible code branch\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-141e17.html#EndPath\n\nclang confuses unix's `open` with `I3::dataio::open` see #1544\nclsim/private/make_safeprimes/convert.cxx\ndataio/private/dataio/I3MultiWriter.cxx\ndataio/private/dataio/I3Writer.cxx\ndataio/private/pybindings/I3File.cxx\ndataio/private/shovel/Model.cxx\ndataio/private/shovel/Model.cxx\ndataio/private/shovel/Model.cxx\nsteamshovel/private/steamshovel/FileService.cpp\n\nclang dosn't understand `G4Exception()`\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-1d0a97.html#EndPath\n\nclang doesn't understand Qt memory management see #1545\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-4ca3c9.html#EndPath\nhttp://software.icecube.wisc.edu/static_analysis/2016-02-14-030225-7689-1/report-5c5809.html#EndPath",
"reporter": "kjmeagher",
"cc": "david.schultz, nega, olivas",
"resolution": "fixed",
"_ts": "1493023176837564",
"component": "cmake",
"summary": "Summary of remaining static analysis Issues",
"priority": "normal",
"keywords": "",
"time": "2016-02-15T10:27:59",
"milestone": "Long-Term Future",
"owner": "nega",
"type": "defect"
}
```
| non_priority | summary of remaining static analysis issues trac code that is clearly producing incorrect results cascadevariables returns uninitilized data see bug code that need improvement code assumes that the file being read starts with a and contains the number of strings code assumes parameters when the number of parameters is a variable code path is confusing and has lots of ifdefs toprec private toprec laputop cxx code i gave up trying to understand the problem proposal private proposal amanda cxx vheselfveto private clipper clipper cxx fill ratio private fill ratio cxx icetray private icetray cxx ipdf private pybindings likelihood cxx mue private mue llhreco cxx dead assignment is the result of decode but i can t tell if decode has side effects or not payload parsing private payload parsing dump raw deltacompressed cxx tpx private tpx cxx copy and paste files with too many problems to list tankresponse private tankresponse triangle triangle c lilliput private minimizer minuit cxx memory leaks tankresponse private tankresponse cxx tankresponse private tankresponse cxx mue private mue cxx false positives complains about an impossible code branch clang confuses unix s open with dataio open see clsim private make safeprimes convert cxx dataio private dataio cxx dataio private dataio cxx dataio private pybindings cxx dataio private shovel model cxx dataio private shovel model cxx dataio private shovel model cxx steamshovel private steamshovel fileservice cpp clang dosn t understand clang doesn t understand qt memory management see migrated from json status closed changetime description n code that is clearly producing incorrect results n cascadevariables returns uninitilized data see bug n code that need improvement n ncode assumes that the file being read starts with a and contains the number of strings n assumes parameters when the number of parameters is a variable n path is confusing and has lots of ifdefs ntoprec private toprec laputop cxx n code i gave up trying to understand the problem nproposal private proposal amanda cxx n assignment is the result of decode but i can t tell if decode has side effects or not npayload parsing private payload parsing dump raw deltacompressed cxx n copy and paste files with too many problems to list n tankresponse private tankresponse triangle triangle c nlilliput private minimizer minuit cxx n n memory leaks tankresponse private tankresponse cxx t n false positives ncomplains about an impossible code branch n confuses unix s open with dataio open see nclsim private make safeprimes convert cxx ndataio private dataio cxx ndataio private dataio cxx ndataio private pybindings cxx ndataio private shovel model cxx ndataio private shovel model cxx ndataio private shovel model cxx nsteamshovel private steamshovel fileservice cpp n nclang dosn t understand n doesn t understand qt memory management see n reporter kjmeagher cc david schultz nega olivas resolution fixed ts component cmake summary summary of remaining static analysis issues priority normal keywords time milestone long term future owner nega type defect | 0 |
136,707 | 18,751,452,982 | IssuesEvent | 2021-11-05 02:53:12 | Dima2022/Resiliency-Studio | https://api.github.com/repos/Dima2022/Resiliency-Studio | opened | CVE-2017-5664 (High) detected in tomcat-embed-core-8.5.11.jar | security vulnerability | ## CVE-2017-5664 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.11.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: Resiliency-Studio/resiliency-studio-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.11/tomcat-embed-core-8.5.11.jar,/home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.11/tomcat-embed-core-8.5.11.jar,/home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.11/tomcat-embed-core-8.5.11.jar</p>
<p>
Dependency Hierarchy:
- sdk-java-rest-6.2.0.4-oss.jar (Root Library)
- spring-boot-starter-tomcat-1.5.1.RELEASE.jar
- :x: **tomcat-embed-core-8.5.11.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/Resiliency-Studio/commit/9809d9b7bfdc114eafb0a14d86667f3a76a014e8">9809d9b7bfdc114eafb0a14d86667f3a76a014e8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.
<p>Publish Date: 2017-06-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664>CVE-2017-5664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664</a></p>
<p>Release Date: 2017-06-06</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.11","packageFilePaths":["/resiliency-studio-service/pom.xml","/resiliency-studio-agent/pom.xml","/resiliency-studio-security/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"com.att.ajsc:sdk-java-rest:6.2.0.4-oss;org.springframework.boot:spring-boot-starter-tomcat:1.5.1.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2017-5664","vulnerabilityDetails":"The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-5664 (High) detected in tomcat-embed-core-8.5.11.jar - ## CVE-2017-5664 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-8.5.11.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: Resiliency-Studio/resiliency-studio-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.11/tomcat-embed-core-8.5.11.jar,/home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.11/tomcat-embed-core-8.5.11.jar,/home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/8.5.11/tomcat-embed-core-8.5.11.jar</p>
<p>
Dependency Hierarchy:
- sdk-java-rest-6.2.0.4-oss.jar (Root Library)
- spring-boot-starter-tomcat-1.5.1.RELEASE.jar
- :x: **tomcat-embed-core-8.5.11.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/Resiliency-Studio/commit/9809d9b7bfdc114eafb0a14d86667f3a76a014e8">9809d9b7bfdc114eafb0a14d86667f3a76a014e8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.
<p>Publish Date: 2017-06-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664>CVE-2017-5664</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5664</a></p>
<p>Release Date: 2017-06-06</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.11","packageFilePaths":["/resiliency-studio-service/pom.xml","/resiliency-studio-agent/pom.xml","/resiliency-studio-security/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"com.att.ajsc:sdk-java-rest:6.2.0.4-oss;org.springframework.boot:spring-boot-starter-tomcat:1.5.1.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:9.0.0.M21,8.5.15,8.0.44,7.0.78,org.apache.tomcat:tomcat-catalina:9.0.0.M21,8.5.15,8.0.44,7.0.78"}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2017-5664","vulnerabilityDetails":"The error page mechanism of the Java Servlet Specification requires that, when an error occurs and an error page is configured for the error that occurred, the original request and response are forwarded to the error page. This means that the request is presented to the error page with the original HTTP method. If the error page is a static file, expected behaviour is to serve content of the file as if processing a GET request, regardless of the actual HTTP method. The Default Servlet in Apache Tomcat 9.0.0.M1 to 9.0.0.M20, 8.5.0 to 8.5.14, 8.0.0.RC1 to 8.0.43 and 7.0.0 to 7.0.77 did not do this. Depending on the original request this could lead to unexpected and undesirable results for static error pages including, if the DefaultServlet is configured to permit writes, the replacement or removal of the custom error page. Notes for other user provided error pages: (1) Unless explicitly coded otherwise, JSPs ignore the HTTP method. JSPs used as error pages must must ensure that they handle any error dispatch as a GET request, regardless of the actual method. (2) By default, the response generated by a Servlet does depend on the HTTP method. Custom Servlets used as error pages must ensure that they handle any error dispatch as a GET request, regardless of the actual method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-5664","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file resiliency studio resiliency studio service pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy sdk java rest oss jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in head commit a href vulnerability details the error page mechanism of the java servlet specification requires that when an error occurs and an error page is configured for the error that occurred the original request and response are forwarded to the error page this means that the request is presented to the error page with the original http method if the error page is a static file expected behaviour is to serve content of the file as if processing a get request regardless of the actual http method the default servlet in apache tomcat to to to and to did not do this depending on the original request this could lead to unexpected and undesirable results for static error pages including if the defaultservlet is configured to permit writes the replacement or removal of the custom error page notes for other user provided error pages unless explicitly coded otherwise jsps ignore the http method jsps used as error pages must must ensure that they handle any error dispatch as a get request regardless of the actual method by default the response generated by a servlet does depend on the http method custom servlets used as error pages must ensure that they handle any error dispatch as a get request regardless of the actual method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree com att ajsc sdk java rest oss org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina basebranches vulnerabilityidentifier cve vulnerabilitydetails the error page mechanism of the java servlet specification requires that when an error occurs and an error page is configured for the error that occurred the original request and response are forwarded to the error page this means that the request is presented to the error page with the original http method if the error page is a static file expected behaviour is to serve content of the file as if processing a get request regardless of the actual http method the default servlet in apache tomcat to to to and to did not do this depending on the original request this could lead to unexpected and undesirable results for static error pages including if the defaultservlet is configured to permit writes the replacement or removal of the custom error page notes for other user provided error pages unless explicitly coded otherwise jsps ignore the http method jsps used as error pages must must ensure that they handle any error dispatch as a get request regardless of the actual method by default the response generated by a servlet does depend on the http method custom servlets used as error pages must ensure that they handle any error dispatch as a get request regardless of the actual method vulnerabilityurl | 0 |
128,840 | 10,553,140,655 | IssuesEvent | 2019-10-03 16:33:21 | flutter/flutter | https://api.github.com/repos/flutter/flutter | opened | Fix rendering tests and enable them on CI in Web mode | a: tests ☸ platform-web | We currently skip all `packages/flutter/test/rendering` tests on CI because they fail. We should fix them. | 1.0 | Fix rendering tests and enable them on CI in Web mode - We currently skip all `packages/flutter/test/rendering` tests on CI because they fail. We should fix them. | non_priority | fix rendering tests and enable them on ci in web mode we currently skip all packages flutter test rendering tests on ci because they fail we should fix them | 0 |
340,721 | 30,538,608,813 | IssuesEvent | 2023-07-19 19:23:07 | surveysolutions/surveysolutions | https://api.github.com/repos/surveysolutions/surveysolutions | closed | Hidden questions appear in the PDF transcript of an interview | enhancement testing required immediate pool | **Describe the issue**
Respondent gets the content of the hidden fields included into the interview transcript.
**What steps will reproduce the problem?**
1. Create a questionnaire with a hidden field.
2. Import that questionnaire to HQ
3. Activate web data collection.
4. Create a web assignment preloading the value of the hidden field.
5. Fill out an interview for that web assignment.
6. At completion - pick the PDF transcript. Alternatively, have the settings to have the transcript sent to you on completion in step 3.
**What is the expected result?**
PDF does not contain the hidden question mentioning and the answer preloaded into it.
**What happens instead?**
PDF contains the hidden question mentioning and the answer preloaded into it.
**Environment:**
- Application: Headquarters
- Version: 22.09
| 1.0 | Hidden questions appear in the PDF transcript of an interview - **Describe the issue**
Respondent gets the content of the hidden fields included into the interview transcript.
**What steps will reproduce the problem?**
1. Create a questionnaire with a hidden field.
2. Import that questionnaire to HQ
3. Activate web data collection.
4. Create a web assignment preloading the value of the hidden field.
5. Fill out an interview for that web assignment.
6. At completion - pick the PDF transcript. Alternatively, have the settings to have the transcript sent to you on completion in step 3.
**What is the expected result?**
PDF does not contain the hidden question mentioning and the answer preloaded into it.
**What happens instead?**
PDF contains the hidden question mentioning and the answer preloaded into it.
**Environment:**
- Application: Headquarters
- Version: 22.09
| non_priority | hidden questions appear in the pdf transcript of an interview describe the issue respondent gets the content of the hidden fields included into the interview transcript what steps will reproduce the problem create a questionnaire with a hidden field import that questionnaire to hq activate web data collection create a web assignment preloading the value of the hidden field fill out an interview for that web assignment at completion pick the pdf transcript alternatively have the settings to have the transcript sent to you on completion in step what is the expected result pdf does not contain the hidden question mentioning and the answer preloaded into it what happens instead pdf contains the hidden question mentioning and the answer preloaded into it environment application headquarters version | 0 |
320,850 | 23,828,666,573 | IssuesEvent | 2022-09-05 17:23:58 | open-metadata/OpenMetadata | https://api.github.com/repos/open-metadata/OpenMetadata | closed | Make troubleshooting a top-level section in Try OpenMetadata in Docker | documentation connector-testing | Expand troubleshooting section with a section on the rust error that occurs if you don't upgrade pip to the latest version. | 1.0 | Make troubleshooting a top-level section in Try OpenMetadata in Docker - Expand troubleshooting section with a section on the rust error that occurs if you don't upgrade pip to the latest version. | non_priority | make troubleshooting a top level section in try openmetadata in docker expand troubleshooting section with a section on the rust error that occurs if you don t upgrade pip to the latest version | 0 |
46,965 | 13,056,007,822 | IssuesEvent | 2020-07-30 03:22:31 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | [filterscripts] L2 Monopole Reconstruction throws (Trac #2198) | Incomplete Migration Migrated from Trac combo reconstruction defect | Migrated from https://code.icecube.wisc.edu/ticket/2198
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:18",
"description": "L2 monopole reconstruction is throwing...\n\n\n File \"/home/olivas/icecube/combo/cisystem/build/lib/icecube/filterscripts/offlineL2/level2_Reconstruction_Monopole.py\", line 328, in <lambda>\n If = lambda f: \"FilterMask\" in f and f[\"FilterMask\"][filter_globals.MonopoleFilter].condition_passed and If(f)\nRuntimeError: maximum recursion depth exceeded while calling a Python object\n\n\nI'm guessing this is related to recent activity by flambda.",
"reporter": "olivas",
"cc": "blaufuss",
"resolution": "fixed",
"_ts": "1550067318169976",
"component": "combo reconstruction",
"summary": "[filterscripts] L2 Monopole Reconstruction throws",
"priority": "normal",
"keywords": "",
"time": "2018-10-11T16:15:21",
"milestone": "",
"owner": "flauber",
"type": "defect"
}
```
| 1.0 | [filterscripts] L2 Monopole Reconstruction throws (Trac #2198) - Migrated from https://code.icecube.wisc.edu/ticket/2198
```json
{
"status": "closed",
"changetime": "2019-02-13T14:15:18",
"description": "L2 monopole reconstruction is throwing...\n\n\n File \"/home/olivas/icecube/combo/cisystem/build/lib/icecube/filterscripts/offlineL2/level2_Reconstruction_Monopole.py\", line 328, in <lambda>\n If = lambda f: \"FilterMask\" in f and f[\"FilterMask\"][filter_globals.MonopoleFilter].condition_passed and If(f)\nRuntimeError: maximum recursion depth exceeded while calling a Python object\n\n\nI'm guessing this is related to recent activity by flambda.",
"reporter": "olivas",
"cc": "blaufuss",
"resolution": "fixed",
"_ts": "1550067318169976",
"component": "combo reconstruction",
"summary": "[filterscripts] L2 Monopole Reconstruction throws",
"priority": "normal",
"keywords": "",
"time": "2018-10-11T16:15:21",
"milestone": "",
"owner": "flauber",
"type": "defect"
}
```
| non_priority | monopole reconstruction throws trac migrated from json status closed changetime description monopole reconstruction is throwing n n n file home olivas icecube combo cisystem build lib icecube filterscripts reconstruction monopole py line in n if lambda f filtermask in f and f condition passed and if f nruntimeerror maximum recursion depth exceeded while calling a python object n n ni m guessing this is related to recent activity by flambda reporter olivas cc blaufuss resolution fixed ts component combo reconstruction summary monopole reconstruction throws priority normal keywords time milestone owner flauber type defect | 0 |
195,221 | 15,504,163,131 | IssuesEvent | 2021-03-11 14:00:34 | w3c/wai-statements | https://api.github.com/repos/w3c/wai-statements | closed | [Question]: How to show new form input based on pre-requisite input? | documentation help wanted question | > hide/show conditional text as I introduced the information… things like: I introduced the link and the name above and in the below paragraphs I can mention the variables to write <a href=“http://www.appsurl.pt”>Name of the App</a>; or “The non-compliances and/or the exemptions are listed below” (only appears if I selected the two mentioned options above);
| 1.0 | [Question]: How to show new form input based on pre-requisite input? - > hide/show conditional text as I introduced the information… things like: I introduced the link and the name above and in the below paragraphs I can mention the variables to write <a href=“http://www.appsurl.pt”>Name of the App</a>; or “The non-compliances and/or the exemptions are listed below” (only appears if I selected the two mentioned options above);
| non_priority | how to show new form input based on pre requisite input hide show conditional text as i introduced the information… things like i introduced the link and the name above and in the below paragraphs i can mention the variables to write or “the non compliances and or the exemptions are listed below” only appears if i selected the two mentioned options above | 0 |
142,941 | 19,142,257,731 | IssuesEvent | 2021-12-02 01:05:14 | taddhopkins/maven-project | https://api.github.com/repos/taddhopkins/maven-project | opened | CVE-2021-22096 (Medium) detected in spring-web-4.0.5.RELEASE.jar | security vulnerability | ## CVE-2021-22096 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.0.5.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: maven-project/pom.xml</p>
<p>Path to vulnerable library: epository/org/springframework/spring-web/4.0.5.RELEASE/spring-web-4.0.5.RELEASE.jar,maven-project/target/todo-api-1.0-SNAPSHOT/WEB-INF/lib/spring-web-4.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.0.5.RELEASE.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework versions 5.3.0 - 5.3.10, 5.2.0 - 5.2.17, and older unsupported versions, it is possible for a user to provide malicious input to cause the insertion of additional log entries.
<p>Publish Date: 2021-10-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22096>CVE-2021-22096</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22096">https://tanzu.vmware.com/security/cve-2021-22096</a></p>
<p>Release Date: 2021-10-28</p>
<p>Fix Resolution: org.springframework:spring:5.2.18.RELEASE,5.3.12</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.0.5.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:4.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring:5.2.18.RELEASE,5.3.12","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-22096","vulnerabilityDetails":"In Spring Framework versions 5.3.0 - 5.3.10, 5.2.0 - 5.2.17, and older unsupported versions, it is possible for a user to provide malicious input to cause the insertion of additional log entries.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22096","cvss3Severity":"medium","cvss3Score":"4.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-22096 (Medium) detected in spring-web-4.0.5.RELEASE.jar - ## CVE-2021-22096 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.0.5.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: maven-project/pom.xml</p>
<p>Path to vulnerable library: epository/org/springframework/spring-web/4.0.5.RELEASE/spring-web-4.0.5.RELEASE.jar,maven-project/target/todo-api-1.0-SNAPSHOT/WEB-INF/lib/spring-web-4.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-4.0.5.RELEASE.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework versions 5.3.0 - 5.3.10, 5.2.0 - 5.2.17, and older unsupported versions, it is possible for a user to provide malicious input to cause the insertion of additional log entries.
<p>Publish Date: 2021-10-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22096>CVE-2021-22096</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22096">https://tanzu.vmware.com/security/cve-2021-22096</a></p>
<p>Release Date: 2021-10-28</p>
<p>Fix Resolution: org.springframework:spring:5.2.18.RELEASE,5.3.12</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"4.0.5.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:4.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring:5.2.18.RELEASE,5.3.12","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-22096","vulnerabilityDetails":"In Spring Framework versions 5.3.0 - 5.3.10, 5.2.0 - 5.2.17, and older unsupported versions, it is possible for a user to provide malicious input to cause the insertion of additional log entries.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22096","cvss3Severity":"medium","cvss3Score":"4.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in spring web release jar cve medium severity vulnerability vulnerable library spring web release jar spring web library home page a href path to dependency file maven project pom xml path to vulnerable library epository org springframework spring web release spring web release jar maven project target todo api snapshot web inf lib spring web release jar dependency hierarchy x spring web release jar vulnerable library vulnerability details in spring framework versions and older unsupported versions it is possible for a user to provide malicious input to cause the insertion of additional log entries publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring release check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring release isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in spring framework versions and older unsupported versions it is possible for a user to provide malicious input to cause the insertion of additional log entries vulnerabilityurl | 0 |
62,427 | 25,997,391,089 | IssuesEvent | 2022-12-20 12:45:29 | matrix-org/synapse | https://api.github.com/repos/matrix-org/synapse | closed | Send EDUs to appservices | z-feature A-Application-Service T-Enhancement | Spec bug: https://github.com/matrix-org/matrix-doc/issues/1145
The use case being bridging read receipts, typing notifications, etc to another network.
| 1.0 | Send EDUs to appservices - Spec bug: https://github.com/matrix-org/matrix-doc/issues/1145
The use case being bridging read receipts, typing notifications, etc to another network.
| non_priority | send edus to appservices spec bug the use case being bridging read receipts typing notifications etc to another network | 0 |
183,004 | 21,685,870,798 | IssuesEvent | 2022-05-09 11:13:13 | Project-Books/book-project | https://api.github.com/repos/Project-Books/book-project | closed | Invalidate JWT token after account deletion | bug wontfix spring-security | Currently, JSON Web Tokens (JWTs) are used for passing authentication information. These tokens expire automatically, after a period of time.
Most requests need authorization information; otherwise, the requests are rejected (server returns 403 Forbidden response).
For example, if you want to list users, you will have to send valid authentication information.
The problem is that, after user account deletion, user JWT remains valid (until it expires) and can be used to make requests that normally should be rejected.
Steps to reproduce the issue:
1) Login using Postman (you may wish to create a new user account before, as you will have to delete it later)
https://github.com/Project-Books/book-project/wiki/Connecting-to-the-backend-via-Postman
2) Delete your own account
Using Postman, send a DELETE request to localhost:8080/api/user, having a raw body which contains email and password key/value pairs.
3) Make some requests where you use the JWT that belonged to the account you have just deleted.
Example: GET localhost:8080/api/user/users
Normally, this request should be rejected, but in practice you can successfully retrieve the result, because the JWT that is sent with the request is still valid.
**Additional context**
- Read our contributing guidelines first!
- We'll require you to discuss you implementation approach before being assigned to this
- Branch from `main` and set it as the destination branch in your pull request
| True | Invalidate JWT token after account deletion - Currently, JSON Web Tokens (JWTs) are used for passing authentication information. These tokens expire automatically, after a period of time.
Most requests need authorization information; otherwise, the requests are rejected (server returns 403 Forbidden response).
For example, if you want to list users, you will have to send valid authentication information.
The problem is that, after user account deletion, user JWT remains valid (until it expires) and can be used to make requests that normally should be rejected.
Steps to reproduce the issue:
1) Login using Postman (you may wish to create a new user account before, as you will have to delete it later)
https://github.com/Project-Books/book-project/wiki/Connecting-to-the-backend-via-Postman
2) Delete your own account
Using Postman, send a DELETE request to localhost:8080/api/user, having a raw body which contains email and password key/value pairs.
3) Make some requests where you use the JWT that belonged to the account you have just deleted.
Example: GET localhost:8080/api/user/users
Normally, this request should be rejected, but in practice you can successfully retrieve the result, because the JWT that is sent with the request is still valid.
**Additional context**
- Read our contributing guidelines first!
- We'll require you to discuss you implementation approach before being assigned to this
- Branch from `main` and set it as the destination branch in your pull request
| non_priority | invalidate jwt token after account deletion currently json web tokens jwts are used for passing authentication information these tokens expire automatically after a period of time most requests need authorization information otherwise the requests are rejected server returns forbidden response for example if you want to list users you will have to send valid authentication information the problem is that after user account deletion user jwt remains valid until it expires and can be used to make requests that normally should be rejected steps to reproduce the issue login using postman you may wish to create a new user account before as you will have to delete it later delete your own account using postman send a delete request to localhost api user having a raw body which contains email and password key value pairs make some requests where you use the jwt that belonged to the account you have just deleted example get localhost api user users normally this request should be rejected but in practice you can successfully retrieve the result because the jwt that is sent with the request is still valid additional context read our contributing guidelines first we ll require you to discuss you implementation approach before being assigned to this branch from main and set it as the destination branch in your pull request | 0 |
8,308 | 7,334,580,751 | IssuesEvent | 2018-03-05 23:24:16 | devtools-html/debugger.html | https://api.github.com/repos/devtools-html/debugger.html | closed | prepush script shouldn't run all tests when contributing to /docs/ | infrastructure not-available | It looks like no matter what is the content of the revision we push, we re-run all the tests.
Flow and a complete test suite. But none of this is testing docs, so we can avoid that and make the process be faster. I imagine the same optimization may be applied to other files/folders.
```
$ git push ochameau fix-mcPath
husky > npm run -s prepush (node v7.10.1)
Launching Flow server for /home/alex/debugger.html
Spawned flow server (pid=112604)
Logs will go to /tmp/flow/zShomezSalexzSdebugger.html.log
Monitor logs will go to /tmp/flow/zShomezSalexzSdebugger.html.monitor_log
No errors!
PASS src/actions/tests/pending-breakpoints.spec.js (37.225s)
...
PASS src/components/shared/tests/Badge.spec.js
Test Suites: 89 passed, 89 total
Tests: 542 passed, 542 total
Snapshots: 175 passed, 175 total
Time: 104.048s
Ran all test suites
....
To github.com:ochameau/debugger.html.git
* [new branch] fix-mcPath -> fix-mcPath
``` | 1.0 | prepush script shouldn't run all tests when contributing to /docs/ - It looks like no matter what is the content of the revision we push, we re-run all the tests.
Flow and a complete test suite. But none of this is testing docs, so we can avoid that and make the process be faster. I imagine the same optimization may be applied to other files/folders.
```
$ git push ochameau fix-mcPath
husky > npm run -s prepush (node v7.10.1)
Launching Flow server for /home/alex/debugger.html
Spawned flow server (pid=112604)
Logs will go to /tmp/flow/zShomezSalexzSdebugger.html.log
Monitor logs will go to /tmp/flow/zShomezSalexzSdebugger.html.monitor_log
No errors!
PASS src/actions/tests/pending-breakpoints.spec.js (37.225s)
...
PASS src/components/shared/tests/Badge.spec.js
Test Suites: 89 passed, 89 total
Tests: 542 passed, 542 total
Snapshots: 175 passed, 175 total
Time: 104.048s
Ran all test suites
....
To github.com:ochameau/debugger.html.git
* [new branch] fix-mcPath -> fix-mcPath
``` | non_priority | prepush script shouldn t run all tests when contributing to docs it looks like no matter what is the content of the revision we push we re run all the tests flow and a complete test suite but none of this is testing docs so we can avoid that and make the process be faster i imagine the same optimization may be applied to other files folders git push ochameau fix mcpath husky npm run s prepush node launching flow server for home alex debugger html spawned flow server pid logs will go to tmp flow zshomezsalexzsdebugger html log monitor logs will go to tmp flow zshomezsalexzsdebugger html monitor log no errors pass src actions tests pending breakpoints spec js pass src components shared tests badge spec js test suites passed total tests passed total snapshots passed total time ran all test suites to github com ochameau debugger html git fix mcpath fix mcpath | 0 |
147,159 | 13,201,813,460 | IssuesEvent | 2020-08-14 10:56:06 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Add conditional-expressions subsection about Field<Boolean> | C: Documentation E: All Editions P: Medium R: Fixed T: Enhancement | An FAQ (to be added here, too: https://www.jooq.org/faq) is about how to convert between `Condition` and `Field<Boolean>`. While the answer is simple (use `DSL.condition(Field<Boolean>)` or `DSL.field(Condition)`), it is not obvious to find.
Maybe, it would help if we had a `conditional-expressions` subsection that talks about boolean columns of type `Field<Boolean>`.
The section should be referenced from:
- The FAQ https://www.jooq.org/faq
- A new data type subsection https://www.jooq.org/doc/latest/manual/reference/reference-data-types/
- Condition building section ("create conditions from the DSL") https://www.jooq.org/doc/latest/manual/sql-building/conditional-expressions/condition-building/
----
See also: https://github.com/jOOQ/jOOQ/issues/10490 | 1.0 | Add conditional-expressions subsection about Field<Boolean> - An FAQ (to be added here, too: https://www.jooq.org/faq) is about how to convert between `Condition` and `Field<Boolean>`. While the answer is simple (use `DSL.condition(Field<Boolean>)` or `DSL.field(Condition)`), it is not obvious to find.
Maybe, it would help if we had a `conditional-expressions` subsection that talks about boolean columns of type `Field<Boolean>`.
The section should be referenced from:
- The FAQ https://www.jooq.org/faq
- A new data type subsection https://www.jooq.org/doc/latest/manual/reference/reference-data-types/
- Condition building section ("create conditions from the DSL") https://www.jooq.org/doc/latest/manual/sql-building/conditional-expressions/condition-building/
----
See also: https://github.com/jOOQ/jOOQ/issues/10490 | non_priority | add conditional expressions subsection about field an faq to be added here too is about how to convert between condition and field while the answer is simple use dsl condition field or dsl field condition it is not obvious to find maybe it would help if we had a conditional expressions subsection that talks about boolean columns of type field the section should be referenced from the faq a new data type subsection condition building section create conditions from the dsl see also | 0 |
130,822 | 12,463,587,801 | IssuesEvent | 2020-05-28 10:53:26 | jenkinsci/ui-ux-hackfest-2020 | https://api.github.com/repos/jenkinsci/ui-ux-hackfest-2020 | closed | Convert 'Executor Starvation' wiki page to jenkins.io | documentation | Summary: Please describe what you have done here
## Links
<!-- Link the related pull requests, documentation pages and other materials. -->
Pull request
https://github.com/jenkins-infra/jenkins.io/pull/3384
issue
https://github.com/jenkins-infra/jenkins.io/issues/3193
| 1.0 | Convert 'Executor Starvation' wiki page to jenkins.io - Summary: Please describe what you have done here
## Links
<!-- Link the related pull requests, documentation pages and other materials. -->
Pull request
https://github.com/jenkins-infra/jenkins.io/pull/3384
issue
https://github.com/jenkins-infra/jenkins.io/issues/3193
| non_priority | convert executor starvation wiki page to jenkins io summary please describe what you have done here links pull request issue | 0 |
245,304 | 20,760,454,551 | IssuesEvent | 2022-03-15 15:44:06 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | Refactor how Table rows are mapped to objects for test: Check all fields from the created Task in the Task Management table | testing task e2e-tests | There is a defect in the code regarding how table rows are mapped into Objects causing failures for test Check all fields from the created Task in the Task Management table.
Please refactor the code and make it stable on local and Jenkins. | 2.0 | Refactor how Table rows are mapped to objects for test: Check all fields from the created Task in the Task Management table - There is a defect in the code regarding how table rows are mapped into Objects causing failures for test Check all fields from the created Task in the Task Management table.
Please refactor the code and make it stable on local and Jenkins. | non_priority | refactor how table rows are mapped to objects for test check all fields from the created task in the task management table there is a defect in the code regarding how table rows are mapped into objects causing failures for test check all fields from the created task in the task management table please refactor the code and make it stable on local and jenkins | 0 |
50,154 | 6,329,903,362 | IssuesEvent | 2017-07-26 05:19:38 | rsandor/Solace | https://api.github.com/repos/rsandor/Solace | opened | Skills: Ability Scores | Design | The current design for skills associates each with a major and minor skill. These skill should be used in some way to effect the passives and cooldowns for a skill. A few ideas of how this might work are:
- Chance of success (roll to hit, dodging, etc.)
- Damage scaling
- Buff/Debuff durations
- Casting concentration
There is a fine balance here as the abilities as design thus far give exact potency ranges and bonus percentages. It might be worth removing these from the help file and simply making note of scaling when it occurs. Then, on a case-by-case basis, we could modify various aspects of cooldowns and passives to perform a bit better or worse depending on the ability scores of the character using them. | 1.0 | Skills: Ability Scores - The current design for skills associates each with a major and minor skill. These skill should be used in some way to effect the passives and cooldowns for a skill. A few ideas of how this might work are:
- Chance of success (roll to hit, dodging, etc.)
- Damage scaling
- Buff/Debuff durations
- Casting concentration
There is a fine balance here as the abilities as design thus far give exact potency ranges and bonus percentages. It might be worth removing these from the help file and simply making note of scaling when it occurs. Then, on a case-by-case basis, we could modify various aspects of cooldowns and passives to perform a bit better or worse depending on the ability scores of the character using them. | non_priority | skills ability scores the current design for skills associates each with a major and minor skill these skill should be used in some way to effect the passives and cooldowns for a skill a few ideas of how this might work are chance of success roll to hit dodging etc damage scaling buff debuff durations casting concentration there is a fine balance here as the abilities as design thus far give exact potency ranges and bonus percentages it might be worth removing these from the help file and simply making note of scaling when it occurs then on a case by case basis we could modify various aspects of cooldowns and passives to perform a bit better or worse depending on the ability scores of the character using them | 0 |
8,127 | 5,424,425,713 | IssuesEvent | 2017-03-03 01:08:27 | LibreHealthIO/LibreEHR | https://api.github.com/repos/LibreHealthIO/LibreEHR | closed | Updates to Date functions for consistent Localization | enhancement Usability | Review and integrate update (in progress) to Dates functions.
1) Make sure all dates are stored UTC
2) Add Timezone support at the user and site level
3) Replace DatePicker with newer tools, keep localization support
This is work that is already nearly completed on MI2 private repos and will be pushed to this one for team review.
| True | Updates to Date functions for consistent Localization - Review and integrate update (in progress) to Dates functions.
1) Make sure all dates are stored UTC
2) Add Timezone support at the user and site level
3) Replace DatePicker with newer tools, keep localization support
This is work that is already nearly completed on MI2 private repos and will be pushed to this one for team review.
| non_priority | updates to date functions for consistent localization review and integrate update in progress to dates functions make sure all dates are stored utc add timezone support at the user and site level replace datepicker with newer tools keep localization support this is work that is already nearly completed on private repos and will be pushed to this one for team review | 0 |
46,632 | 11,863,239,267 | IssuesEvent | 2020-03-25 19:20:52 | angular/angular-cli | https://api.github.com/repos/angular/angular-cli | closed | ng build - ES5 bundles -> Unknown helper createSuper | comp: devkit/build-angular freq1: low severity3: broken type: bug/fix | <!--🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅
Oh hi there! 😄
To expedite issue processing please search open and closed issues before submitting a new one.
Existing issues often contain information about workarounds, resolution, or progress updates.
🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅-->
# 🐞 Bug report
### Command (mark with an `x`)
<!-- Can you pin-point the command or commands that are effected by this bug? -->
<!-- ✍️edit: -->
- [ ] new
- [x] build
- [ ] serve
- [ ] test
- [ ] e2e
- [ ] generate
- [ ] add
- [ ] update
- [ ] lint
- [ ] xi18n
- [ ] run
- [ ] config
- [ ] help
- [ ] version
- [ ] doc
### Is this a regression?
<!-- Did this behavior use to work in the previous version? -->
<!-- ✍️--> Yes, the previous version in which this bug was not present was: 9.0.6
### Description
Any `ng build` ends up with `An unhandled exception occurred: C:\my\path\main-es2015.js: Unknown helper createSuper`
## 🔬 Minimal Reproduction
<!--
Simple steps to reproduce this bug.
Please include: commands run (including args), packages added, related code changes.
If reproduction steps are not enough for reproduction of your issue, please create a minimal GitHub repository with the reproduction of the issue.
A good way to make a minimal reproduction is to create a new app via `ng new repro-app` and add the minimum possible code to show the problem.
Share the link to the repo below along with step-by-step instructions to reproduce the problem, as well as expected and actual behavior.
Issues that don't have enough info and can't be reproduced will be closed.
You can read more about issue submission guidelines here: https://github.com/angular/angular-cli/blob/master/CONTRIBUTING.md#-submitting-an-issue
-->
`ng build` or `ng build--prod`
## 🔥 Exception or Error
<pre><code>
Generating ES5 bundles for differential loading...
An unhandled exception occurred: C:\my\path\main-es2015.js: Unknown helper createSuper
See "C:\Users\Me\AppData\Local\Temp\ng-sYZMmM\angular-errors.log" for further details.
</code></pre>
and the angular-errors.log:
<pre>
[error] ReferenceError: C:\my\path\main-es2015.js: Unknown helper createSuper
at loadHelper (C:\my\path\node_modules\@babel\helpers\lib\index.js:225:27)
at Object.ensure (C:\my\path\node_modules\@babel\helpers\lib\index.js:270:3)
at File.addHelper (C:\my\path\node_modules\@babel\core\lib\transformation\file\file.js:203:15)
at pushInheritsToBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:471:384)
at pushConstructorToBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:461:5)
at pushConstructor (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:449:5)
at pushBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:187:11)
at buildBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:133:5)
at classTransformer (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:537:5)
at transformClass (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:573:10)
at PluginPass.ClassExpression (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\index.js:63:54)
at newFn (C:\my\path\node_modules\@babel\traverse\lib\visitors.js:179:21)
at NodePath._call (C:\my\path\node_modules\@babel\traverse\lib\path\context.js:55:20)
at NodePath.call (C:\my\path\node_modules\@babel\traverse\lib\path\context.js:42:17)
at NodePath.visit (C:\my\path\node_modules\@babel\traverse\lib\path\context.js:90:31)
at TraversalContext.visitQueue (C:\my\path\node_modules\@babel\traverse\lib\context.js:112:16)
</pre>
## 🌍 Your Environment
<pre><code>
Angular CLI: 9.0.7
Node: 12.3.1
OS: win32 x64
Angular: 9.0.7
... animations, cli, common, compiler, compiler-cli, core, forms
... language-service, localize, platform-browser
... platform-browser-dynamic, router
Ivy Workspace: Yes
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.900.7
@angular-devkit/build-angular 0.900.7
@angular-devkit/build-optimizer 0.900.7
@angular-devkit/build-webpack 0.900.7
@angular-devkit/core 9.0.7
@angular-devkit/schematics 9.0.7
@angular/cdk 9.1.3
@angular/flex-layout 9.0.0-beta.29
@angular/material 9.1.3
@ngtools/webpack 9.0.7
@schematics/angular 9.0.7
@schematics/update 0.900.7
rxjs 6.5.4
typescript 3.7.5
webpack 4.41.2
</code></pre>
**Anything else relevant?**
Tried to install @babel/compat-data (mentioned [here](https://github.com/angular/angular-cli/issues/17262)) as it seems babel related , did not help
EDIT:
Downgrading to
<pre>
"@angular-devkit/build-angular": "^0.900.6",
"@angular/cli": "^9.0.6",
"@angular/compiler-cli": "^9.0.6",
</pre>
which returned the environment to:
<pre>
Angular CLI: 9.0.6
Node: 12.3.1
OS: win32 x64
Angular: 9.0.7
... animations, common, compiler, core, forms, language-service
... localize, platform-browser, platform-browser-dynamic, router
Ivy Workspace: Yes
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.900.6
@angular-devkit/build-angular 0.900.6
@angular-devkit/build-optimizer 0.900.6
@angular-devkit/build-webpack 0.900.6
@angular-devkit/core 9.0.6
@angular-devkit/schematics 9.0.6
@angular/cdk 9.1.3
@angular/cli 9.0.6
@angular/compiler-cli 9.0.6
@angular/flex-layout 9.0.0-beta.29
@angular/material 9.1.3
@ngtools/webpack 9.0.6
@schematics/angular 9.0.6
@schematics/update 0.900.6
rxjs 6.5.4
typescript 3.7.5
webpack 4.41.2
</pre>
returned the functionality of `ng build` back. | 1.0 | ng build - ES5 bundles -> Unknown helper createSuper - <!--🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅
Oh hi there! 😄
To expedite issue processing please search open and closed issues before submitting a new one.
Existing issues often contain information about workarounds, resolution, or progress updates.
🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅-->
# 🐞 Bug report
### Command (mark with an `x`)
<!-- Can you pin-point the command or commands that are effected by this bug? -->
<!-- ✍️edit: -->
- [ ] new
- [x] build
- [ ] serve
- [ ] test
- [ ] e2e
- [ ] generate
- [ ] add
- [ ] update
- [ ] lint
- [ ] xi18n
- [ ] run
- [ ] config
- [ ] help
- [ ] version
- [ ] doc
### Is this a regression?
<!-- Did this behavior use to work in the previous version? -->
<!-- ✍️--> Yes, the previous version in which this bug was not present was: 9.0.6
### Description
Any `ng build` ends up with `An unhandled exception occurred: C:\my\path\main-es2015.js: Unknown helper createSuper`
## 🔬 Minimal Reproduction
<!--
Simple steps to reproduce this bug.
Please include: commands run (including args), packages added, related code changes.
If reproduction steps are not enough for reproduction of your issue, please create a minimal GitHub repository with the reproduction of the issue.
A good way to make a minimal reproduction is to create a new app via `ng new repro-app` and add the minimum possible code to show the problem.
Share the link to the repo below along with step-by-step instructions to reproduce the problem, as well as expected and actual behavior.
Issues that don't have enough info and can't be reproduced will be closed.
You can read more about issue submission guidelines here: https://github.com/angular/angular-cli/blob/master/CONTRIBUTING.md#-submitting-an-issue
-->
`ng build` or `ng build--prod`
## 🔥 Exception or Error
<pre><code>
Generating ES5 bundles for differential loading...
An unhandled exception occurred: C:\my\path\main-es2015.js: Unknown helper createSuper
See "C:\Users\Me\AppData\Local\Temp\ng-sYZMmM\angular-errors.log" for further details.
</code></pre>
and the angular-errors.log:
<pre>
[error] ReferenceError: C:\my\path\main-es2015.js: Unknown helper createSuper
at loadHelper (C:\my\path\node_modules\@babel\helpers\lib\index.js:225:27)
at Object.ensure (C:\my\path\node_modules\@babel\helpers\lib\index.js:270:3)
at File.addHelper (C:\my\path\node_modules\@babel\core\lib\transformation\file\file.js:203:15)
at pushInheritsToBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:471:384)
at pushConstructorToBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:461:5)
at pushConstructor (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:449:5)
at pushBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:187:11)
at buildBody (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:133:5)
at classTransformer (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:537:5)
at transformClass (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\transformClass.js:573:10)
at PluginPass.ClassExpression (C:\my\path\node_modules\@babel\plugin-transform-classes\lib\index.js:63:54)
at newFn (C:\my\path\node_modules\@babel\traverse\lib\visitors.js:179:21)
at NodePath._call (C:\my\path\node_modules\@babel\traverse\lib\path\context.js:55:20)
at NodePath.call (C:\my\path\node_modules\@babel\traverse\lib\path\context.js:42:17)
at NodePath.visit (C:\my\path\node_modules\@babel\traverse\lib\path\context.js:90:31)
at TraversalContext.visitQueue (C:\my\path\node_modules\@babel\traverse\lib\context.js:112:16)
</pre>
## 🌍 Your Environment
<pre><code>
Angular CLI: 9.0.7
Node: 12.3.1
OS: win32 x64
Angular: 9.0.7
... animations, cli, common, compiler, compiler-cli, core, forms
... language-service, localize, platform-browser
... platform-browser-dynamic, router
Ivy Workspace: Yes
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.900.7
@angular-devkit/build-angular 0.900.7
@angular-devkit/build-optimizer 0.900.7
@angular-devkit/build-webpack 0.900.7
@angular-devkit/core 9.0.7
@angular-devkit/schematics 9.0.7
@angular/cdk 9.1.3
@angular/flex-layout 9.0.0-beta.29
@angular/material 9.1.3
@ngtools/webpack 9.0.7
@schematics/angular 9.0.7
@schematics/update 0.900.7
rxjs 6.5.4
typescript 3.7.5
webpack 4.41.2
</code></pre>
**Anything else relevant?**
Tried to install @babel/compat-data (mentioned [here](https://github.com/angular/angular-cli/issues/17262)) as it seems babel related , did not help
EDIT:
Downgrading to
<pre>
"@angular-devkit/build-angular": "^0.900.6",
"@angular/cli": "^9.0.6",
"@angular/compiler-cli": "^9.0.6",
</pre>
which returned the environment to:
<pre>
Angular CLI: 9.0.6
Node: 12.3.1
OS: win32 x64
Angular: 9.0.7
... animations, common, compiler, core, forms, language-service
... localize, platform-browser, platform-browser-dynamic, router
Ivy Workspace: Yes
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.900.6
@angular-devkit/build-angular 0.900.6
@angular-devkit/build-optimizer 0.900.6
@angular-devkit/build-webpack 0.900.6
@angular-devkit/core 9.0.6
@angular-devkit/schematics 9.0.6
@angular/cdk 9.1.3
@angular/cli 9.0.6
@angular/compiler-cli 9.0.6
@angular/flex-layout 9.0.0-beta.29
@angular/material 9.1.3
@ngtools/webpack 9.0.6
@schematics/angular 9.0.6
@schematics/update 0.900.6
rxjs 6.5.4
typescript 3.7.5
webpack 4.41.2
</pre>
returned the functionality of `ng build` back. | non_priority | ng build bundles unknown helper createsuper 🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅 oh hi there 😄 to expedite issue processing please search open and closed issues before submitting a new one existing issues often contain information about workarounds resolution or progress updates 🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅 🐞 bug report command mark with an x new build serve test generate add update lint run config help version doc is this a regression yes the previous version in which this bug was not present was description any ng build ends up with an unhandled exception occurred c my path main js unknown helper createsuper 🔬 minimal reproduction simple steps to reproduce this bug please include commands run including args packages added related code changes if reproduction steps are not enough for reproduction of your issue please create a minimal github repository with the reproduction of the issue a good way to make a minimal reproduction is to create a new app via ng new repro app and add the minimum possible code to show the problem share the link to the repo below along with step by step instructions to reproduce the problem as well as expected and actual behavior issues that don t have enough info and can t be reproduced will be closed you can read more about issue submission guidelines here ng build or ng build prod 🔥 exception or error generating bundles for differential loading an unhandled exception occurred c my path main js unknown helper createsuper see c users me appdata local temp ng syzmmm angular errors log for further details and the angular errors log referenceerror c my path main js unknown helper createsuper at loadhelper c my path node modules babel helpers lib index js at object ensure c my path node modules babel helpers lib index js at file addhelper c my path node modules babel core lib transformation file file js at pushinheritstobody c my path node modules babel plugin transform classes lib transformclass js at pushconstructortobody c my path node modules babel plugin transform classes lib transformclass js at pushconstructor c my path node modules babel plugin transform classes lib transformclass js at pushbody c my path node modules babel plugin transform classes lib transformclass js at buildbody c my path node modules babel plugin transform classes lib transformclass js at classtransformer c my path node modules babel plugin transform classes lib transformclass js at transformclass c my path node modules babel plugin transform classes lib transformclass js at pluginpass classexpression c my path node modules babel plugin transform classes lib index js at newfn c my path node modules babel traverse lib visitors js at nodepath call c my path node modules babel traverse lib path context js at nodepath call c my path node modules babel traverse lib path context js at nodepath visit c my path node modules babel traverse lib path context js at traversalcontext visitqueue c my path node modules babel traverse lib context js 🌍 your environment angular cli node os angular animations cli common compiler compiler cli core forms language service localize platform browser platform browser dynamic router ivy workspace yes package version angular devkit architect angular devkit build angular angular devkit build optimizer angular devkit build webpack angular devkit core angular devkit schematics angular cdk angular flex layout beta angular material ngtools webpack schematics angular schematics update rxjs typescript webpack anything else relevant tried to install babel compat data mentioned as it seems babel related did not help edit downgrading to angular devkit build angular angular cli angular compiler cli which returned the environment to angular cli node os angular animations common compiler core forms language service localize platform browser platform browser dynamic router ivy workspace yes package version angular devkit architect angular devkit build angular angular devkit build optimizer angular devkit build webpack angular devkit core angular devkit schematics angular cdk angular cli angular compiler cli angular flex layout beta angular material ngtools webpack schematics angular schematics update rxjs typescript webpack returned the functionality of ng build back | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.