Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
163,875 | 20,364,224,698 | IssuesEvent | 2022-02-21 02:21:58 | arielorn/goalert | https://api.github.com/repos/arielorn/goalert | opened | CVE-2021-27515 (Medium) detected in url-parse-1.4.7.tgz | security vulnerability | ## CVE-2021-27515 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /web/src/package.json</p>
<p>Path to vulnerable library: /web/src/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-3.7.2.tgz (Root Library)
- sockjs-client-1.3.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse before 1.5.0 mishandles certain uses of backslash such as http:\/ and interprets the URI as a relative path.
<p>Publish Date: 2021-02-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27515>CVE-2021-27515</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515</a></p>
<p>Release Date: 2021-02-22</p>
<p>Fix Resolution (url-parse): 1.5.0</p>
<p>Direct dependency fix Resolution (webpack-dev-server): 3.8.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-27515 (Medium) detected in url-parse-1.4.7.tgz - ## CVE-2021-27515 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.4.7.tgz</a></p>
<p>Path to dependency file: /web/src/package.json</p>
<p>Path to vulnerable library: /web/src/node_modules/url-parse/package.json</p>
<p>
Dependency Hierarchy:
- webpack-dev-server-3.7.2.tgz (Root Library)
- sockjs-client-1.3.0.tgz
- :x: **url-parse-1.4.7.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
url-parse before 1.5.0 mishandles certain uses of backslash such as http:\/ and interprets the URI as a relative path.
<p>Publish Date: 2021-02-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27515>CVE-2021-27515</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-27515</a></p>
<p>Release Date: 2021-02-22</p>
<p>Fix Resolution (url-parse): 1.5.0</p>
<p>Direct dependency fix Resolution (webpack-dev-server): 3.8.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in url parse tgz cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file web src package json path to vulnerable library web src node modules url parse package json dependency hierarchy webpack dev server tgz root library sockjs client tgz x url parse tgz vulnerable library vulnerability details url parse before mishandles certain uses of backslash such as http and interprets the uri as a relative path publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse direct dependency fix resolution webpack dev server step up your open source security game with whitesource | 0 |
270,912 | 23,547,177,438 | IssuesEvent | 2022-08-21 09:39:28 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | sql: properly assert the emission of structured logging events in event log SQL tests | C-bug A-testing T-sql-experience A-sql-logging-and-telemetry | **Describe the problem**
The `system.eventlog` mechanism is slated for removal in v23.1 (#84983). Yet the misc SQL logging tests in
`pkg/sql/logictest/testdata/logic_test/event_log` still uses it to assert the output of a structured logging event.
**Expected behavior**
The test should assert that a structured event was emitted on the various SQL-related logging channels.
Jira issue: CRDB-17987 | 1.0 | sql: properly assert the emission of structured logging events in event log SQL tests - **Describe the problem**
The `system.eventlog` mechanism is slated for removal in v23.1 (#84983). Yet the misc SQL logging tests in
`pkg/sql/logictest/testdata/logic_test/event_log` still uses it to assert the output of a structured logging event.
**Expected behavior**
The test should assert that a structured event was emitted on the various SQL-related logging channels.
Jira issue: CRDB-17987 | non_priority | sql properly assert the emission of structured logging events in event log sql tests describe the problem the system eventlog mechanism is slated for removal in yet the misc sql logging tests in pkg sql logictest testdata logic test event log still uses it to assert the output of a structured logging event expected behavior the test should assert that a structured event was emitted on the various sql related logging channels jira issue crdb | 0 |
264,794 | 23,139,084,761 | IssuesEvent | 2022-07-28 16:39:36 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Custom splash screen appearing incorrectly on Android | platform:android topic:rendering topic:porting needs testing | ### Godot version
3.4.3
### System information
Android, GLES2
### Issue description
For older versions of Android, the CUSTOM splash screen simply appears for a microsecond or so then disappears. For newer versions, the CUSTOM splash screen appears alright but is not scaled properly to fill whole screen of the phone, despite checking on the box "Fullsize" under the Boot Splash in Project Settings. Also, notice emphasis on CUSTOM, since the preset splash screen works just fine.
### Steps to reproduce
Simple, just change the splash screen, even to a blank colour picture, the export the project to apk and try the game. Try a game with lots of resources to see how the splash screen malfunctions properly.
### Minimal reproduction project
_No response_ | 1.0 | Custom splash screen appearing incorrectly on Android - ### Godot version
3.4.3
### System information
Android, GLES2
### Issue description
For older versions of Android, the CUSTOM splash screen simply appears for a microsecond or so then disappears. For newer versions, the CUSTOM splash screen appears alright but is not scaled properly to fill whole screen of the phone, despite checking on the box "Fullsize" under the Boot Splash in Project Settings. Also, notice emphasis on CUSTOM, since the preset splash screen works just fine.
### Steps to reproduce
Simple, just change the splash screen, even to a blank colour picture, the export the project to apk and try the game. Try a game with lots of resources to see how the splash screen malfunctions properly.
### Minimal reproduction project
_No response_ | non_priority | custom splash screen appearing incorrectly on android godot version system information android issue description for older versions of android the custom splash screen simply appears for a microsecond or so then disappears for newer versions the custom splash screen appears alright but is not scaled properly to fill whole screen of the phone despite checking on the box fullsize under the boot splash in project settings also notice emphasis on custom since the preset splash screen works just fine steps to reproduce simple just change the splash screen even to a blank colour picture the export the project to apk and try the game try a game with lots of resources to see how the splash screen malfunctions properly minimal reproduction project no response | 0 |
164,256 | 13,938,936,109 | IssuesEvent | 2020-10-22 15:51:08 | TwakeApp/Twake | https://api.github.com/repos/TwakeApp/Twake | closed | Documentation missing system requirements | documentation | I've searched your code and documentation and couldn't find any system requirements.
What are the minimum and recommended specs? | 1.0 | Documentation missing system requirements - I've searched your code and documentation and couldn't find any system requirements.
What are the minimum and recommended specs? | non_priority | documentation missing system requirements i ve searched your code and documentation and couldn t find any system requirements what are the minimum and recommended specs | 0 |
313,640 | 23,486,341,240 | IssuesEvent | 2022-08-17 14:41:47 | rectorphp/rector | https://api.github.com/repos/rectorphp/rector | closed | Rector fails with: Child process timed out after 120 seconds | bug parallel Documentation | # Bug Report
Hi!
| Subject | Details |
| :------------- | :---------------------------------------------------------------|
| 0.13.9 | Latest version when issue was observed |
On a random basis my Rector runs end with the following error; also with increased memory; it deals with ~1100 classes.
```
$ ./vendor/bin/rector process --dry-run --memory-limit=1G
...
[ERROR] Could not process "/app/vendor/rector/rector/vendor/symplify/easy-parallel/src/ValueObject/ParallelProcess.php" file, due to: "Child process timed out after 120 seconds". On line: 103
[ERROR] Could not process some files, due to: "Reached system errors count limit of 50, exiting...".
```
Especially when used in CI this lead to failed pipelines.
## Minimal PHP Code Causing Issue
PHP Code is up-to-date, all Rector rules were applied and the runs mostly pass without the above error.
## Expected Behaviour
It should always finish without error.
| 1.0 | Rector fails with: Child process timed out after 120 seconds - # Bug Report
Hi!
| Subject | Details |
| :------------- | :---------------------------------------------------------------|
| 0.13.9 | Latest version when issue was observed |
On a random basis my Rector runs end with the following error; also with increased memory; it deals with ~1100 classes.
```
$ ./vendor/bin/rector process --dry-run --memory-limit=1G
...
[ERROR] Could not process "/app/vendor/rector/rector/vendor/symplify/easy-parallel/src/ValueObject/ParallelProcess.php" file, due to: "Child process timed out after 120 seconds". On line: 103
[ERROR] Could not process some files, due to: "Reached system errors count limit of 50, exiting...".
```
Especially when used in CI this lead to failed pipelines.
## Minimal PHP Code Causing Issue
PHP Code is up-to-date, all Rector rules were applied and the runs mostly pass without the above error.
## Expected Behaviour
It should always finish without error.
| non_priority | rector fails with child process timed out after seconds bug report hi subject details latest version when issue was observed on a random basis my rector runs end with the following error also with increased memory it deals with classes vendor bin rector process dry run memory limit could not process app vendor rector rector vendor symplify easy parallel src valueobject parallelprocess php file due to child process timed out after seconds on line could not process some files due to reached system errors count limit of exiting especially when used in ci this lead to failed pipelines minimal php code causing issue php code is up to date all rector rules were applied and the runs mostly pass without the above error expected behaviour it should always finish without error | 0 |
1,756 | 3,362,194,410 | IssuesEvent | 2015-11-20 03:13:49 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Building roslyn rebuilds all projects every time. | Area-Infrastructure Contributor Pain Resolution-Not Reproducible | Every project gives this error in VS:
```
1>Project 'FakeSign' is not up to date. Error (0x8000FFFF).
1>------ Build started: Project: FakeSign, Configuration: Debug Any CPU ------
2>Project 'CompilersBoundTreeGenerator' is not up to date. Error (0x8000FFFF).
2>------ Build started: Project: CompilersBoundTreeGenerator, Configuration: Debug Any CPU ------
3>Project 'CSharpSyntaxGenerator' is not up to date. Error (0x8000FFFF).
3>------ Build started: Project: CSharpSyntaxGenerator, Configuration: Debug Any CPU ------
4>Project 'CSharpErrorFactsGenerator' is not up to date. Error (0x8000FFFF).
4>------ Build started: Project: CSharpErrorFactsGenerator, Configuration: Debug Any CPU ------
1> FakeSign -> C:\GitHub\roslyn-internal\Open\Binaries\Debug\FakeSign.exe
2> CompilersBoundTreeGenerator -> C:\GitHub\roslyn-internal\Open\Binaries\Debug\BoundTreeGenerator.exe
5>Project 'CodeAnalysis' is not up to date. Error (0x8000FFFF).
5>------ Build started: Project: CodeAnalysis, Configuration: Debug Any CPU ------
6>Project 'InteractiveWindow' is not up to date. Error (0x8000FFFF).
```
i.e. it always thinks that all projects are always out of date. This is a fairly severe productivity hit. This is on the lastest InstallDogfood of very current bits. | 1.0 | Building roslyn rebuilds all projects every time. - Every project gives this error in VS:
```
1>Project 'FakeSign' is not up to date. Error (0x8000FFFF).
1>------ Build started: Project: FakeSign, Configuration: Debug Any CPU ------
2>Project 'CompilersBoundTreeGenerator' is not up to date. Error (0x8000FFFF).
2>------ Build started: Project: CompilersBoundTreeGenerator, Configuration: Debug Any CPU ------
3>Project 'CSharpSyntaxGenerator' is not up to date. Error (0x8000FFFF).
3>------ Build started: Project: CSharpSyntaxGenerator, Configuration: Debug Any CPU ------
4>Project 'CSharpErrorFactsGenerator' is not up to date. Error (0x8000FFFF).
4>------ Build started: Project: CSharpErrorFactsGenerator, Configuration: Debug Any CPU ------
1> FakeSign -> C:\GitHub\roslyn-internal\Open\Binaries\Debug\FakeSign.exe
2> CompilersBoundTreeGenerator -> C:\GitHub\roslyn-internal\Open\Binaries\Debug\BoundTreeGenerator.exe
5>Project 'CodeAnalysis' is not up to date. Error (0x8000FFFF).
5>------ Build started: Project: CodeAnalysis, Configuration: Debug Any CPU ------
6>Project 'InteractiveWindow' is not up to date. Error (0x8000FFFF).
```
i.e. it always thinks that all projects are always out of date. This is a fairly severe productivity hit. This is on the lastest InstallDogfood of very current bits. | non_priority | building roslyn rebuilds all projects every time every project gives this error in vs project fakesign is not up to date error build started project fakesign configuration debug any cpu project compilersboundtreegenerator is not up to date error build started project compilersboundtreegenerator configuration debug any cpu project csharpsyntaxgenerator is not up to date error build started project csharpsyntaxgenerator configuration debug any cpu project csharperrorfactsgenerator is not up to date error build started project csharperrorfactsgenerator configuration debug any cpu fakesign c github roslyn internal open binaries debug fakesign exe compilersboundtreegenerator c github roslyn internal open binaries debug boundtreegenerator exe project codeanalysis is not up to date error build started project codeanalysis configuration debug any cpu project interactivewindow is not up to date error i e it always thinks that all projects are always out of date this is a fairly severe productivity hit this is on the lastest installdogfood of very current bits | 0 |
247,295 | 18,857,568,035 | IssuesEvent | 2021-11-12 08:46:05 | rebeccacxy/pe | https://api.github.com/repos/rebeccacxy/pe | opened | UG error in command syntax – should be "folders" instead of "contacts" | type.DocumentationBug severity.Low | Expected:
`find -folders -invalid_flag CS2103` is equivalent to `find -folders CS2103`
Actual:
`find -folders -invalid_flag CS2103` is equivalent to `find -contacts CS2103`
It should be "folders" instead of "contacts.

<!--session: 1636703556207-4ed05663-8fe5-41b0-b61d-5fbeb8277ea1-->
<!--Version: Web v3.4.1--> | 1.0 | UG error in command syntax – should be "folders" instead of "contacts" - Expected:
`find -folders -invalid_flag CS2103` is equivalent to `find -folders CS2103`
Actual:
`find -folders -invalid_flag CS2103` is equivalent to `find -contacts CS2103`
It should be "folders" instead of "contacts.

<!--session: 1636703556207-4ed05663-8fe5-41b0-b61d-5fbeb8277ea1-->
<!--Version: Web v3.4.1--> | non_priority | ug error in command syntax – should be folders instead of contacts expected find folders invalid flag is equivalent to find folders actual find folders invalid flag is equivalent to find contacts it should be folders instead of contacts | 0 |
47,269 | 24,928,113,292 | IssuesEvent | 2022-10-31 09:18:54 | comunica/comunica-feature-link-traversal | https://api.github.com/repos/comunica/comunica-feature-link-traversal | closed | Excessive re-request of same resource when slash (`/`) uris redirect to the same page | performance 🐌 | #### Issue type:
- :snail: Performance issue <!--Don't change this issue type!-->
____
#### Description:
<!--A clear and concise description of what the issue is.-->
During link traversal the same resource seens to be re-requested *many* times in particular if I run the following script
```ts
// import { QueryEngine } from '@comunica/query-sparql';
import { getOwlClasses, getProperties, predictAllClasses } from './utils';
import { QueryEngine } from '@comunica/query-sparql-link-traversal';
import { DataFactory as DF } from 'n3';
async function main() {
const engine = new QueryEngine();
const WAYBACK_URL = 'http://wayback.archive-it.org/';
function addWayback(action: any): any {
const request = new Request(action.input, action.init);
return {
input: new Request(new URL(`/${request.url}`, WAYBACK_URL), request),
};
}
const results = await engine.queryBindings(`
PREFIX rdfs: <http://www.w3.org/2000/01/rdf-schema#>
PREFIX foaf: <http://xmlns.com/foaf/0.1/>
SELECT ?type WHERE {
foaf:Group (rdfs:subClassOf*/^rdfs:domain/rdfs:range)* ?type
}`,
{
sources: [
"http://xmlns.com/foaf/spec/20140114.rdf"
],
lenient: true,
httpProxyHandler: {
async getProxy(request) {
const res = await fetch(request.input, { method: 'HEAD' });
console.log(res.status)
if (res.status !== 200) {
const newRequest = addWayback(request);
const res = await fetch(newRequest.input, { method: 'HEAD' });
console.log(res.status, res.url)
if (res.status === 200) {
console.log('new request', newRequest.input.toString())
return newRequest;
}
}
console.log('res', request.input.toString(), res.url)
return request;
}
}
}
)
const arr = await results.toArray();
console.log(arr.map(r => r.get('type')))
}
main();
```
Then as a response I get the likes of
```bash
res http://xmlns.com/foaf/0.1/interest http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/icqChatID http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/topic_interest http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/sha1 http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/workInfoHomepage http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/currentProject http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/Document http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/msnChatID http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/logo http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/theme http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/img http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/publications http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/knows http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/page http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/topic http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/pastProject http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/Agent http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/name http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/fundedBy http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/workplaceHomepage http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/aimChatID http://xmlns.com/foaf/0.1/
```
It seems to me that it would be fairly safe in this instance to see that the response URL for `http://xmlns.com/foaf/0.1/interest` is `http://xmlns.com/foaf/0.1/` and then use that cached resource for all future URLs starting with `http://xmlns.com/foaf/0.1/` (or if you want to be safe to a headers request *only* on future URLs to confirm they redirect to the cached page) - I think it would also be safe to have a greater parellisation on the headers requests compared to get requests.
____
#### Environment:
<!--Output of the `comunica-sparql -v` command.-->
<!--If running in a development environment, this must be the output of `node ./packages/actor-init-sparql/bin/query.js -v`--> | True | Excessive re-request of same resource when slash (`/`) uris redirect to the same page - #### Issue type:
- :snail: Performance issue <!--Don't change this issue type!-->
____
#### Description:
<!--A clear and concise description of what the issue is.-->
During link traversal the same resource seens to be re-requested *many* times in particular if I run the following script
```ts
// import { QueryEngine } from '@comunica/query-sparql';
import { getOwlClasses, getProperties, predictAllClasses } from './utils';
import { QueryEngine } from '@comunica/query-sparql-link-traversal';
import { DataFactory as DF } from 'n3';
async function main() {
const engine = new QueryEngine();
const WAYBACK_URL = 'http://wayback.archive-it.org/';
function addWayback(action: any): any {
const request = new Request(action.input, action.init);
return {
input: new Request(new URL(`/${request.url}`, WAYBACK_URL), request),
};
}
const results = await engine.queryBindings(`
PREFIX rdfs: <http://www.w3.org/2000/01/rdf-schema#>
PREFIX foaf: <http://xmlns.com/foaf/0.1/>
SELECT ?type WHERE {
foaf:Group (rdfs:subClassOf*/^rdfs:domain/rdfs:range)* ?type
}`,
{
sources: [
"http://xmlns.com/foaf/spec/20140114.rdf"
],
lenient: true,
httpProxyHandler: {
async getProxy(request) {
const res = await fetch(request.input, { method: 'HEAD' });
console.log(res.status)
if (res.status !== 200) {
const newRequest = addWayback(request);
const res = await fetch(newRequest.input, { method: 'HEAD' });
console.log(res.status, res.url)
if (res.status === 200) {
console.log('new request', newRequest.input.toString())
return newRequest;
}
}
console.log('res', request.input.toString(), res.url)
return request;
}
}
}
)
const arr = await results.toArray();
console.log(arr.map(r => r.get('type')))
}
main();
```
Then as a response I get the likes of
```bash
res http://xmlns.com/foaf/0.1/interest http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/icqChatID http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/topic_interest http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/sha1 http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/workInfoHomepage http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/currentProject http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/Document http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/msnChatID http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/logo http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/theme http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/img http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/publications http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/knows http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/page http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/topic http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/pastProject http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/Agent http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/name http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/fundedBy http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/workplaceHomepage http://xmlns.com/foaf/0.1/
200
res http://xmlns.com/foaf/0.1/aimChatID http://xmlns.com/foaf/0.1/
```
It seems to me that it would be fairly safe in this instance to see that the response URL for `http://xmlns.com/foaf/0.1/interest` is `http://xmlns.com/foaf/0.1/` and then use that cached resource for all future URLs starting with `http://xmlns.com/foaf/0.1/` (or if you want to be safe to a headers request *only* on future URLs to confirm they redirect to the cached page) - I think it would also be safe to have a greater parellisation on the headers requests compared to get requests.
____
#### Environment:
<!--Output of the `comunica-sparql -v` command.-->
<!--If running in a development environment, this must be the output of `node ./packages/actor-init-sparql/bin/query.js -v`--> | non_priority | excessive re request of same resource when slash uris redirect to the same page issue type snail performance issue description during link traversal the same resource seens to be re requested many times in particular if i run the following script ts import queryengine from comunica query sparql import getowlclasses getproperties predictallclasses from utils import queryengine from comunica query sparql link traversal import datafactory as df from async function main const engine new queryengine const wayback url function addwayback action any any const request new request action input action init return input new request new url request url wayback url request const results await engine querybindings prefix rdfs prefix foaf select type where foaf group rdfs subclassof rdfs domain rdfs range type sources lenient true httpproxyhandler async getproxy request const res await fetch request input method head console log res status if res status const newrequest addwayback request const res await fetch newrequest input method head console log res status res url if res status console log new request newrequest input tostring return newrequest console log res request input tostring res url return request const arr await results toarray console log arr map r r get type main then as a response i get the likes of bash res res res res res res res res res res res res res res res res res res res res res it seems to me that it would be fairly safe in this instance to see that the response url for is and then use that cached resource for all future urls starting with or if you want to be safe to a headers request only on future urls to confirm they redirect to the cached page i think it would also be safe to have a greater parellisation on the headers requests compared to get requests environment | 0 |
233,510 | 17,867,863,357 | IssuesEvent | 2021-09-06 11:46:33 | UQdeco2800/2021-ext-studio-2 | https://api.github.com/repos/UQdeco2800/2021-ext-studio-2 | opened | Team 7 - Achievement Records and Storyline | documentation enhancement feature team-7 | **Original Feature**: #4
# **Description**
The idea is to score the record of achievements for each game in local storage, add a brand new achievements screen which shows locked and unlocked achievements (i.e, achievements which have already been encountered during the game). Achievements will also be displayed with the past score history.
## SubFeature/component (optional)
- Achievements screen with locked and unlocked achievements
- Persistent achievements functionality
- Achievements Screen linked with game story
### Examples
- **Achievements Screen linked with game story**: Chapter is unlocked in the Achievements Screen section.
- **Achievements Screen**: Displaying locked and unlocked achievements. (Unlocked achievements are grayed out or annotated with a locked icon).
# **Milestones**
- [ ] Achievements Screen Paper Design (Sept. 7)
- [ ] Achievements Screen Assets (Sept. 8)
- [ ] Storyline Integration with Design Team (Sept. 8)
- [ ] Achievements Screen Final Design (Sept. 9)
- [ ] Persistent Achievements logic (Sept. 10)
- [ ] Coding the Achievements Screen GUI (Sept. 10)
- [ ] Coding unlockable storyline chapters (Sept. 10)
**Completion Deadline:** Sept. 13
# **Members**
- Vishal Gupta (@ThatTechedGuy)
- Akshay Varma (@Butcanudothis)
- Zibo Gong (@Zibo1)
- Kai Wang (@Kaiwang4)
- Aditya Singh Cheema (@addiii4)
| 1.0 | Team 7 - Achievement Records and Storyline - **Original Feature**: #4
# **Description**
The idea is to score the record of achievements for each game in local storage, add a brand new achievements screen which shows locked and unlocked achievements (i.e, achievements which have already been encountered during the game). Achievements will also be displayed with the past score history.
## SubFeature/component (optional)
- Achievements screen with locked and unlocked achievements
- Persistent achievements functionality
- Achievements Screen linked with game story
### Examples
- **Achievements Screen linked with game story**: Chapter is unlocked in the Achievements Screen section.
- **Achievements Screen**: Displaying locked and unlocked achievements. (Unlocked achievements are grayed out or annotated with a locked icon).
# **Milestones**
- [ ] Achievements Screen Paper Design (Sept. 7)
- [ ] Achievements Screen Assets (Sept. 8)
- [ ] Storyline Integration with Design Team (Sept. 8)
- [ ] Achievements Screen Final Design (Sept. 9)
- [ ] Persistent Achievements logic (Sept. 10)
- [ ] Coding the Achievements Screen GUI (Sept. 10)
- [ ] Coding unlockable storyline chapters (Sept. 10)
**Completion Deadline:** Sept. 13
# **Members**
- Vishal Gupta (@ThatTechedGuy)
- Akshay Varma (@Butcanudothis)
- Zibo Gong (@Zibo1)
- Kai Wang (@Kaiwang4)
- Aditya Singh Cheema (@addiii4)
| non_priority | team achievement records and storyline original feature description the idea is to score the record of achievements for each game in local storage add a brand new achievements screen which shows locked and unlocked achievements i e achievements which have already been encountered during the game achievements will also be displayed with the past score history subfeature component optional achievements screen with locked and unlocked achievements persistent achievements functionality achievements screen linked with game story examples achievements screen linked with game story chapter is unlocked in the achievements screen section achievements screen displaying locked and unlocked achievements unlocked achievements are grayed out or annotated with a locked icon milestones achievements screen paper design sept achievements screen assets sept storyline integration with design team sept achievements screen final design sept persistent achievements logic sept coding the achievements screen gui sept coding unlockable storyline chapters sept completion deadline sept members vishal gupta thattechedguy akshay varma butcanudothis zibo gong kai wang aditya singh cheema | 0 |
146,837 | 11,758,481,124 | IssuesEvent | 2020-03-13 15:29:20 | twosixlabs/armory | https://api.github.com/repos/twosixlabs/armory | opened | armory test | docker test cases | Add a "test" command to armory in the` __main__` entrypoint, that runs pytest inside the specified container with the given set of pytest args. This will prevent some of the more complicated volume mounting problems. | 1.0 | armory test - Add a "test" command to armory in the` __main__` entrypoint, that runs pytest inside the specified container with the given set of pytest args. This will prevent some of the more complicated volume mounting problems. | non_priority | armory test add a test command to armory in the main entrypoint that runs pytest inside the specified container with the given set of pytest args this will prevent some of the more complicated volume mounting problems | 0 |
292,564 | 25,223,415,978 | IssuesEvent | 2022-11-14 14:24:40 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: smoketest/secure/multitenant failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.smoketest/secure/multitenant [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7490747?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7490747?buildTab=artifacts#/smoketest/secure/multitenant) on master @ [7f77f57a768a1bc488629234126e9e456bb6ddbb](https://github.com/cockroachdb/cockroach/commits/7f77f57a768a1bc488629234126e9e456bb6ddbb):
```
test artifacts and logs in: /artifacts/smoketest/secure/multitenant/run_1
(test_impl.go:297).Fatalf: error executing 'SELECT crdb_internal.create_tenant($1)': pq: crdb_internal.create_tenant(): could not determine data type of placeholder $1
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=true</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/multi-tenant
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*smoketest/secure/multitenant.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: smoketest/secure/multitenant failed - roachtest.smoketest/secure/multitenant [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7490747?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7490747?buildTab=artifacts#/smoketest/secure/multitenant) on master @ [7f77f57a768a1bc488629234126e9e456bb6ddbb](https://github.com/cockroachdb/cockroach/commits/7f77f57a768a1bc488629234126e9e456bb6ddbb):
```
test artifacts and logs in: /artifacts/smoketest/secure/multitenant/run_1
(test_impl.go:297).Fatalf: error executing 'SELECT crdb_internal.create_tenant($1)': pq: crdb_internal.create_tenant(): could not determine data type of placeholder $1
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=true</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/multi-tenant
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*smoketest/secure/multitenant.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest smoketest secure multitenant failed roachtest smoketest secure multitenant with on master test artifacts and logs in artifacts smoketest secure multitenant run test impl go fatalf error executing select crdb internal create tenant pq crdb internal create tenant could not determine data type of placeholder parameters roachtest cloud gce roachtest cpu roachtest encrypted false roachtest fs roachtest localssd true roachtest ssd help see see cc cockroachdb multi tenant | 0 |
48,275 | 5,950,970,205 | IssuesEvent | 2017-05-26 18:12:09 | rust-lang/rust | https://api.github.com/repos/rust-lang/rust | closed | ICE in nightly with patterns and nested enums | E-needstest I-ICE | ```rust
enum Foo {
Bar { bar: Bar, id: usize }
}
enum Bar {
A, B, C, D, E, F
}
fn test(f: Foo) {
match f {
Foo::Bar { bar: Bar::A, .. } => (),
Foo::Bar { bar: Bar::B, .. } => (),
}
}
```
The `match` doesn't cover all patterns, but instead of triggering an error (like stable does) it panics.
[Playpen link](https://is.gd/6QwCj4)
Version: c8af93f09 2017-01-18
Backtrace:
```
thread 'rustc' panicked at 'assertion failed: !self.is_enum()', C:\bot\slave\nightly-dist-rustc-win-msvc-64\build\src\librustc\ty/mod.rs:1497
stack backtrace:
0: 0x7ffa070208f8 - std::panicking::Location::line::h8c528bbdf4eef8a3
1: 0x7ffa0701fd82 - std::panicking::Location::line::h8c528bbdf4eef8a3
2: 0x7ffa070237bd - std::panicking::rust_panic_with_hook::h7abc6e334345e341
3: 0x7ffa00a82293 - <unknown>
4: 0x7ffa00cfe5d1 - rustc::ty::AdtDef::struct_variant::h3407c5d1765959c4
5: 0x7ffa14c5bbf2 - <rustc_const_eval::pattern::Pattern<'tcx> as core::fmt::Display>::fmt::hd436f1763f102376
6: 0x7ffa07036f31 - core::fmt::write::h17329881d672cff3
7: 0x7ffa14c5617d - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_body::heaaeacf8d46cf425
8: 0x7ffa14c52dc9 - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_expr::h8a811e2d6152dd49
9: 0x7ffa14c51ae5 - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_expr::h8a811e2d6152dd49
10: 0x7ffa14c54130 - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_body::heaaeacf8d46cf425
11: 0x7ffa14c5056d - <rustc_const_eval::check_match::OuterVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_fn::he57f23671b55c8bb
12: 0x7ffa14c3042f - <unknown>
13: 0x7ffa14c3009e - <unknown>
14: 0x7ffa14c2e8d5 - <unknown>
15: 0x7ffa14c50503 - <rustc_const_eval::check_match::OuterVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_fn::he57f23671b55c8bb
16: 0x7ffa14c31ad3 - <unknown>
17: 0x7ffa14c50a7a - rustc_const_eval::check_match::check_crate::h80f0ce25c2e773dc
18: 0x7ffa0cbf6c0e - rustc_driver::driver::count_nodes::h761a1dba824a4f1e
19: 0x7ffa0cb3ad9b - <unknown>
20: 0x7ffa0cbd137c - rustc_driver::driver::compile_input::h44e43be0fc34a1a1
21: 0x7ffa0cc22cdb - rustc_driver::run_compiler::h5e34a930c0929e5c
22: 0x7ffa0caff0ae - <unknown>
23: 0x7ffa07026801 - _rust_maybe_catch_panic
24: 0x7ffa0cb2c6e6 - <unknown>
25: 0x7ffa0701dd2e - std::sys::imp::thread::Thread::new::h7a1b2b1b6bab390a
26: 0x7ffa2a998363 - BaseThreadInitThunk
``` | 1.0 | ICE in nightly with patterns and nested enums - ```rust
enum Foo {
Bar { bar: Bar, id: usize }
}
enum Bar {
A, B, C, D, E, F
}
fn test(f: Foo) {
match f {
Foo::Bar { bar: Bar::A, .. } => (),
Foo::Bar { bar: Bar::B, .. } => (),
}
}
```
The `match` doesn't cover all patterns, but instead of triggering an error (like stable does) it panics.
[Playpen link](https://is.gd/6QwCj4)
Version: c8af93f09 2017-01-18
Backtrace:
```
thread 'rustc' panicked at 'assertion failed: !self.is_enum()', C:\bot\slave\nightly-dist-rustc-win-msvc-64\build\src\librustc\ty/mod.rs:1497
stack backtrace:
0: 0x7ffa070208f8 - std::panicking::Location::line::h8c528bbdf4eef8a3
1: 0x7ffa0701fd82 - std::panicking::Location::line::h8c528bbdf4eef8a3
2: 0x7ffa070237bd - std::panicking::rust_panic_with_hook::h7abc6e334345e341
3: 0x7ffa00a82293 - <unknown>
4: 0x7ffa00cfe5d1 - rustc::ty::AdtDef::struct_variant::h3407c5d1765959c4
5: 0x7ffa14c5bbf2 - <rustc_const_eval::pattern::Pattern<'tcx> as core::fmt::Display>::fmt::hd436f1763f102376
6: 0x7ffa07036f31 - core::fmt::write::h17329881d672cff3
7: 0x7ffa14c5617d - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_body::heaaeacf8d46cf425
8: 0x7ffa14c52dc9 - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_expr::h8a811e2d6152dd49
9: 0x7ffa14c51ae5 - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_expr::h8a811e2d6152dd49
10: 0x7ffa14c54130 - <rustc_const_eval::check_match::MatchVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_body::heaaeacf8d46cf425
11: 0x7ffa14c5056d - <rustc_const_eval::check_match::OuterVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_fn::he57f23671b55c8bb
12: 0x7ffa14c3042f - <unknown>
13: 0x7ffa14c3009e - <unknown>
14: 0x7ffa14c2e8d5 - <unknown>
15: 0x7ffa14c50503 - <rustc_const_eval::check_match::OuterVisitor<'a, 'tcx> as rustc::hir::intravisit::Visitor<'tcx>>::visit_fn::he57f23671b55c8bb
16: 0x7ffa14c31ad3 - <unknown>
17: 0x7ffa14c50a7a - rustc_const_eval::check_match::check_crate::h80f0ce25c2e773dc
18: 0x7ffa0cbf6c0e - rustc_driver::driver::count_nodes::h761a1dba824a4f1e
19: 0x7ffa0cb3ad9b - <unknown>
20: 0x7ffa0cbd137c - rustc_driver::driver::compile_input::h44e43be0fc34a1a1
21: 0x7ffa0cc22cdb - rustc_driver::run_compiler::h5e34a930c0929e5c
22: 0x7ffa0caff0ae - <unknown>
23: 0x7ffa07026801 - _rust_maybe_catch_panic
24: 0x7ffa0cb2c6e6 - <unknown>
25: 0x7ffa0701dd2e - std::sys::imp::thread::Thread::new::h7a1b2b1b6bab390a
26: 0x7ffa2a998363 - BaseThreadInitThunk
``` | non_priority | ice in nightly with patterns and nested enums rust enum foo bar bar bar id usize enum bar a b c d e f fn test f foo match f foo bar bar bar a foo bar bar bar b the match doesn t cover all patterns but instead of triggering an error like stable does it panics version backtrace thread rustc panicked at assertion failed self is enum c bot slave nightly dist rustc win msvc build src librustc ty mod rs stack backtrace std panicking location line std panicking location line std panicking rust panic with hook rustc ty adtdef struct variant as core fmt display fmt core fmt write as rustc hir intravisit visitor visit body as rustc hir intravisit visitor visit expr as rustc hir intravisit visitor visit expr as rustc hir intravisit visitor visit body as rustc hir intravisit visitor visit fn as rustc hir intravisit visitor visit fn rustc const eval check match check crate rustc driver driver count nodes rustc driver driver compile input rustc driver run compiler rust maybe catch panic std sys imp thread thread new basethreadinitthunk | 0 |
404,532 | 27,489,767,991 | IssuesEvent | 2023-03-04 13:23:09 | cleodora-forecasting/cleodora | https://api.github.com/repos/cleodora-forecasting/cleodora | closed | Doc: Update for 0.2.0 | documentation | - [ ] Update cleosrv screenshot
- [x] Update changelog
- [x] Document how to update from 0.1.1 or earlier | 1.0 | Doc: Update for 0.2.0 - - [ ] Update cleosrv screenshot
- [x] Update changelog
- [x] Document how to update from 0.1.1 or earlier | non_priority | doc update for update cleosrv screenshot update changelog document how to update from or earlier | 0 |
141,739 | 18,989,582,726 | IssuesEvent | 2021-11-22 04:37:35 | ChoeMinji/jquery-3.3.0 | https://api.github.com/repos/ChoeMinji/jquery-3.3.0 | opened | WS-2018-0069 (High) detected in is-my-json-valid-2.15.0.tgz | security vulnerability | ## WS-2018-0069 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p></summary>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>Path to dependency file: jquery-3.3.0/package.json</p>
<p>Path to vulnerable library: jquery-3.3.0/node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- npm-4.4.1.tgz (Root Library)
- request-2.79.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/jquery-3.3.0/commit/ceecb0808664406acced37f73d2f7bd52b686a97">ceecb0808664406acced37f73d2f7bd52b686a97</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Version of is-my-json-valid before 1.4.1 or 2.17.2 are vulnerable to regular expression denial of service (ReDoS) via the email validation function.
<p>Publish Date: 2018-02-14
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976>WS-2018-0069</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/572">https://nodesecurity.io/advisories/572</a></p>
<p>Release Date: 2018-02-14</p>
<p>Fix Resolution: 1.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2018-0069 (High) detected in is-my-json-valid-2.15.0.tgz - ## WS-2018-0069 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p></summary>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>Path to dependency file: jquery-3.3.0/package.json</p>
<p>Path to vulnerable library: jquery-3.3.0/node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- npm-4.4.1.tgz (Root Library)
- request-2.79.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/jquery-3.3.0/commit/ceecb0808664406acced37f73d2f7bd52b686a97">ceecb0808664406acced37f73d2f7bd52b686a97</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Version of is-my-json-valid before 1.4.1 or 2.17.2 are vulnerable to regular expression denial of service (ReDoS) via the email validation function.
<p>Publish Date: 2018-02-14
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976>WS-2018-0069</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/572">https://nodesecurity.io/advisories/572</a></p>
<p>Release Date: 2018-02-14</p>
<p>Fix Resolution: 1.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in is my json valid tgz ws high severity vulnerability vulnerable library is my json valid tgz a jsonschema validator that uses code generation to be extremely fast library home page a href path to dependency file jquery package json path to vulnerable library jquery node modules npm node modules request node modules har validator node modules is my json valid package json dependency hierarchy npm tgz root library request tgz har validator tgz x is my json valid tgz vulnerable library found in head commit a href found in base branch master vulnerability details version of is my json valid before or are vulnerable to regular expression denial of service redos via the email validation function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
236,643 | 26,033,720,025 | IssuesEvent | 2022-12-22 01:10:14 | pazhanivel07/frameworks_av-CVE-2020-0242_CVE-2020-0243 | https://api.github.com/repos/pazhanivel07/frameworks_av-CVE-2020-0242_CVE-2020-0243 | closed | CVE-2022-20418 (Medium) detected in avandroid-10.0.0_r37 - autoclosed | security vulnerability | ## CVE-2022-20418 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-10.0.0_r37</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/av>https://android.googlesource.com/platform/frameworks/av</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/media/libstagefright/rtsp/AAVCAssembler.cpp</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/media/libstagefright/rtsp/AAVCAssembler.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In pickStartSeq of AAVCAssembler.cpp, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12L Android-13Android ID: A-231986464
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20418>CVE-2022-20418</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/av/+/91fddd9386c2e50e6fed87af2bed8b33da058a24">https://android.googlesource.com/platform/frameworks/av/+/91fddd9386c2e50e6fed87af2bed8b33da058a24</a></p>
<p>Release Date: 2022-10-11</p>
<p>Fix Resolution: android-13.0.0_r7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-20418 (Medium) detected in avandroid-10.0.0_r37 - autoclosed - ## CVE-2022-20418 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-10.0.0_r37</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/av>https://android.googlesource.com/platform/frameworks/av</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/media/libstagefright/rtsp/AAVCAssembler.cpp</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/media/libstagefright/rtsp/AAVCAssembler.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In pickStartSeq of AAVCAssembler.cpp, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12L Android-13Android ID: A-231986464
<p>Publish Date: 2022-10-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20418>CVE-2022-20418</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/av/+/91fddd9386c2e50e6fed87af2bed8b33da058a24">https://android.googlesource.com/platform/frameworks/av/+/91fddd9386c2e50e6fed87af2bed8b33da058a24</a></p>
<p>Release Date: 2022-10-11</p>
<p>Fix Resolution: android-13.0.0_r7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in avandroid autoclosed cve medium severity vulnerability vulnerable library avandroid library home page a href found in base branch master vulnerable source files media libstagefright rtsp aavcassembler cpp media libstagefright rtsp aavcassembler cpp vulnerability details in pickstartseq of aavcassembler cpp there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend | 0 |
54,343 | 6,810,370,036 | IssuesEvent | 2017-11-05 04:36:53 | pandas-dev/pandas | https://api.github.com/repos/pandas-dev/pandas | closed | Regression: to_csv and multiindex columns with header kw | API Design Bug IO CSV MultiIndex Output-Formatting Regression | This used to work (October 2012), but doesn't anymore:
``` python
from pandas import DataFrame
import numpy as np
import StringIO
a = ["a","b","a","b","a","b","a","b","a","b","a","b"]
b = ["c","d","e","c","d","e","c","d","e","c","d","e"]
c = [1,2,3,4,5,6,7,8,9,10,11,12]
d = list(reversed(c))
df = DataFrame({"a":a, "b":b, "c":c, "d":d})
_agg_funs = [np.mean, np.std, np.min, np.max]
groupby_variables = ["a","b"]
df_grouped = df.groupby(groupby_variables, as_index=True).agg(_agg_funs)
output = StringIO.StringIO()
df_grouped.to_csv(output, header=[var + "_" + agg for (var, agg) in df_grouped.columns])
index = output.getvalue().split("\n")[0].split(",")
expected_index = groupby_variables + [var + "_" + agg for (var, agg) in df_grouped.columns]
print(index == expected_index) # This was true in October 2012!
print(index)
print(expected_index)
False
['', '', 'c', 'c', 'c', 'c', 'd', 'd', 'd', 'd']
['a', 'b', 'c_mean', 'c_std', 'c_amin', 'c_amax', 'd_mean', 'd_std', 'd_amin', 'd_amax']
```
Probably related to #3575
| 1.0 | Regression: to_csv and multiindex columns with header kw - This used to work (October 2012), but doesn't anymore:
``` python
from pandas import DataFrame
import numpy as np
import StringIO
a = ["a","b","a","b","a","b","a","b","a","b","a","b"]
b = ["c","d","e","c","d","e","c","d","e","c","d","e"]
c = [1,2,3,4,5,6,7,8,9,10,11,12]
d = list(reversed(c))
df = DataFrame({"a":a, "b":b, "c":c, "d":d})
_agg_funs = [np.mean, np.std, np.min, np.max]
groupby_variables = ["a","b"]
df_grouped = df.groupby(groupby_variables, as_index=True).agg(_agg_funs)
output = StringIO.StringIO()
df_grouped.to_csv(output, header=[var + "_" + agg for (var, agg) in df_grouped.columns])
index = output.getvalue().split("\n")[0].split(",")
expected_index = groupby_variables + [var + "_" + agg for (var, agg) in df_grouped.columns]
print(index == expected_index) # This was true in October 2012!
print(index)
print(expected_index)
False
['', '', 'c', 'c', 'c', 'c', 'd', 'd', 'd', 'd']
['a', 'b', 'c_mean', 'c_std', 'c_amin', 'c_amax', 'd_mean', 'd_std', 'd_amin', 'd_amax']
```
Probably related to #3575
| non_priority | regression to csv and multiindex columns with header kw this used to work october but doesn t anymore python from pandas import dataframe import numpy as np import stringio a b c d list reversed c df dataframe a a b b c c d d agg funs groupby variables df grouped df groupby groupby variables as index true agg agg funs output stringio stringio df grouped to csv output header index output getvalue split n split expected index groupby variables print index expected index this was true in october print index print expected index false probably related to | 0 |
165,260 | 12,835,645,734 | IssuesEvent | 2020-07-07 13:13:07 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] XPackRestIT.test {p0=ml/delete_expired_data/Test delete expired data with unknown job id} failure master | :ml >test-failure | Test times out.
**Build scan**:
https://gradle-enterprise.elastic.co/s/nuarmaeswwers
**Repro line**:
```
./gradlew ':x-pack:plugin:integTestRunner' --tests "org.elasticsearch.xpack.test.rest.XPackRestIT.test {p0=ml/delete_expired_data/Test delete expired data with unknown job id}" \
-Dtests.seed=3CB3A0963BA8B500 \
-Dtests.security.manager=true \
-Dtests.locale=el-CY \
-Dtests.timezone=Africa/Sao_Tome \
-Druntime.java=11 \
-Dtests.rest.blacklist=getting_started/10_monitor_cluster_health/*
```
**Reproduces locally?**:
No
**Applicable branches**:
master
**Failure history**:
**Failure excerpt**:
```
java.lang.Exception: Test abandoned because suite timeout was reached. |
```
<details><summary>jstack</summary>
<p>
```
[2020-07-07T07:28:57,589][INFO ][o.e.x.t.r.XPackRestIT ] [test] [p0=ml/delete_expired_data/Test delete expired data with unknown job id] before test
Ιουλ 07, 2020 7:28:58 ΠΜ com.carrotsearch.randomizedtesting.ThreadLeakControl$2 evaluate
WARNING: Suite execution timed out: org.elasticsearch.xpack.test.rest.XPackRestIT
==== jstack at approximately timeout time ====
"main" ID=1 WAITING on java.util.concurrent.CountDownLatch$Sync@47252ff9
at java.base@11.0.2/jdk.internal.misc.Unsafe.park(Native Method)
- waiting on java.util.concurrent.CountDownLatch$Sync@47252ff9
at java.base@11.0.2/java.util.concurrent.locks.LockSupport.park(LockSupport.java:194)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer.parkAndCheckInterrupt(AbstractQueuedSynchronizer.java:885)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedInterruptibly(AbstractQueuedSynchronizer.java:1039)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer.acquireSharedInterruptibly(AbstractQueuedSynchronizer.java:1345)
at java.base@11.0.2/java.util.concurrent.CountDownLatch.await(CountDownLatch.java:232)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.execute(TestWorker.java:73)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.execute(TestWorker.java:47)
at org.gradle.process.internal.worker.child.ActionExecutionWorker.execute(ActionExecutionWorker.java:56)
at org.gradle.process.internal.worker.child.SystemApplicationClassLoaderWorker.call(SystemApplicationClassLoaderWorker.java:133)
at org.gradle.process.internal.worker.child.SystemApplicationClassLoaderWorker.call(SystemApplicationClassLoaderWorker.java:71)
at app//worker.org.gradle.process.internal.worker.GradleWorkerMain.run(GradleWorkerMain.java:69)
at app//worker.org.gradle.process.internal.worker.GradleWorkerMain.main(GradleWorkerMain.java:74)
"Reference Handler" ID=2 RUNNABLE
at java.base@11.0.2/java.lang.ref.Reference.waitForReferencePendingList(Native Method)
at java.base@11.0.2/java.lang.ref.Reference.processPendingReferences(Reference.java:241)
at java.base@11.0.2/java.lang.ref.Reference$ReferenceHandler.run(Reference.java:213)
"Finalizer" ID=3 WAITING on java.lang.ref.ReferenceQueue$Lock@53468bca
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- waiting on java.lang.ref.ReferenceQueue$Lock@53468bca
at java.base@11.0.2/java.lang.ref.ReferenceQueue.remove(ReferenceQueue.java:155)
at java.base@11.0.2/java.lang.ref.ReferenceQueue.remove(ReferenceQueue.java:176)
at java.base@11.0.2/java.lang.ref.Finalizer$FinalizerThread.run(Finalizer.java:170)
"Signal Dispatcher" ID=4 RUNNABLE
"Common-Cleaner" ID=11 TIMED_WAITING on java.lang.ref.ReferenceQueue$Lock@126707c9
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- timed waiting on java.lang.ref.ReferenceQueue$Lock@126707c9
at java.base@11.0.2/java.lang.ref.ReferenceQueue.remove(ReferenceQueue.java:155)
at java.base@11.0.2/jdk.internal.ref.CleanerImpl.run(CleanerImpl.java:148)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
at java.base@11.0.2/jdk.internal.misc.InnocuousThread.run(InnocuousThread.java:134)
"Test worker" ID=13 WAITING on com.carrotsearch.randomizedtesting.RandomizedRunner$2@addf938
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- waiting on com.carrotsearch.randomizedtesting.RandomizedRunner$2@addf938
at java.base@11.0.2/java.lang.Thread.join(Thread.java:1305)
at java.base@11.0.2/java.lang.Thread.join(Thread.java:1379)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.runSuite(RandomizedRunner.java:647)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.run(RandomizedRunner.java:504)
at org.gradle.api.internal.tasks.testing.junit.JUnitTestClassExecutor.runTestClass(JUnitTestClassExecutor.java:110)
at org.gradle.api.internal.tasks.testing.junit.JUnitTestClassExecutor.execute(JUnitTestClassExecutor.java:58)
at org.gradle.api.internal.tasks.testing.junit.JUnitTestClassExecutor.execute(JUnitTestClassExecutor.java:38)
at org.gradle.api.internal.tasks.testing.junit.AbstractJUnitTestClassProcessor.processTestClass(AbstractJUnitTestClassProcessor.java:62)
at org.gradle.api.internal.tasks.testing.SuiteTestClassProcessor.processTestClass(SuiteTestClassProcessor.java:51)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base@11.0.2/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.2/java.lang.reflect.Method.invoke(Method.java:566)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.dispatch.ContextClassLoaderDispatch.dispatch(ContextClassLoaderDispatch.java:33)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy2.processTestClass(Unknown Source)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.processTestClass(TestWorker.java:119)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base@11.0.2/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.2/java.lang.reflect.Method.invoke(Method.java:566)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:182)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:164)
at org.gradle.internal.remote.internal.hub.MessageHub$Handler.run(MessageHub.java:414)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
Locked synchronizers:
- java.util.concurrent.ThreadPoolExecutor$Worker@45b4c3a9
"/127.0.0.1:54358 to /127.0.0.1:54357 workers Thread 2" ID=14 WAITING on java.util.concurrent.locks.AbstractQueuedSynchronizer$ConditionObject@76d285bd
at java.base@11.0.2/jdk.internal.misc.Unsafe.park(Native Method)
- waiting on java.util.concurrent.locks.AbstractQueuedSynchronizer$ConditionObject@76d285bd
at java.base@11.0.2/java.util.concurrent.locks.LockSupport.park(LockSupport.java:194)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer$ConditionObject.await(AbstractQueuedSynchronizer.java:2081)
at org.gradle.internal.remote.internal.hub.queue.EndPointQueue.take(EndPointQueue.java:49)
at org.gradle.internal.remote.internal.hub.MessageHub$ConnectionDispatch.run(MessageHub.java:322)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
Locked synchronizers:
- java.util.concurrent.ThreadPoolExecutor$Worker@5552768b
"/127.0.0.1:54358 to /127.0.0.1:54357 workers Thread 3" ID=15 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@6be5b6ec
- locked sun.nio.ch.KQueueSelectorImpl@26697f84
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:141)
at org.gradle.internal.remote.internal.inet.SocketConnection$SocketInputStream.read(SocketConnection.java:185)
at com.esotericsoftware.kryo.io.Input.fill(Input.java:146)
at com.esotericsoftware.kryo.io.Input.require(Input.java:178)
at com.esotericsoftware.kryo.io.Input.readByte(Input.java:295)
at org.gradle.internal.serialize.kryo.KryoBackedDecoder.readByte(KryoBackedDecoder.java:82)
at org.gradle.internal.remote.internal.hub.InterHubMessageSerializer$MessageReader.read(InterHubMessageSerializer.java:64)
at org.gradle.internal.remote.internal.hub.InterHubMessageSerializer$MessageReader.read(InterHubMessageSerializer.java:52)
at org.gradle.internal.remote.internal.inet.SocketConnection.receive(SocketConnection.java:81)
at org.gradle.internal.remote.internal.hub.MessageHub$ConnectionReceive.run(MessageHub.java:270)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
Locked synchronizers:
- java.util.concurrent.ThreadPoolExecutor$Worker@1356d4d4
"SUITE-XPackRestIT-seed#[3CB3A0963BA8B500]" ID=45 RUNNABLE
at java.management@11.0.2/sun.management.ThreadImpl.dumpThreads0(Native Method)
at java.management@11.0.2/sun.management.ThreadImpl.dumpAllThreads(ThreadImpl.java:502)
at java.management@11.0.2/sun.management.ThreadImpl.dumpAllThreads(ThreadImpl.java:490)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.formatThreadStacksFull(ThreadLeakControl.java:688)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.access$1000(ThreadLeakControl.java:67)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$2.evaluate(ThreadLeakControl.java:422)
- locked java.lang.Object@44f4f999
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.runSuite(RandomizedRunner.java:716)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.access$200(RandomizedRunner.java:138)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$2.run(RandomizedRunner.java:637)
"TEST-XPackRestIT.test-seed#[3CB3A0963BA8B500]" ID=46 WAITING on org.apache.http.concurrent.BasicFuture@2e0653d
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- waiting on org.apache.http.concurrent.BasicFuture@2e0653d
at java.base@11.0.2/java.lang.Object.wait(Object.java:328)
at app//org.apache.http.concurrent.BasicFuture.get(BasicFuture.java:82)
at app//org.apache.http.impl.nio.client.FutureWrapper.get(FutureWrapper.java:70)
at app//org.elasticsearch.client.RestClient.performRequest(RestClient.java:255)
at app//org.elasticsearch.client.RestClient.performRequest(RestClient.java:246)
at app//org.elasticsearch.test.rest.yaml.ClientYamlTestClient.callApi(ClientYamlTestClient.java:186)
at app//org.elasticsearch.test.rest.yaml.ClientYamlTestExecutionContext.callApiInternal(ClientYamlTestExecutionContext.java:169)
at app//org.elasticsearch.test.rest.yaml.ClientYamlTestExecutionContext.callApi(ClientYamlTestExecutionContext.java:101)
at app//org.elasticsearch.test.rest.yaml.section.DoSection.execute(DoSection.java:279)
at app//org.elasticsearch.test.rest.yaml.ESClientYamlSuiteTestCase.executeSection(ESClientYamlSuiteTestCase.java:407)
at app//org.elasticsearch.test.rest.yaml.ESClientYamlSuiteTestCase.test(ESClientYamlSuiteTestCase.java:382)
at jdk.internal.reflect.GeneratedMethodAccessor16.invoke(Unknown Source)
at java.base@11.0.2/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.2/java.lang.reflect.Method.invoke(Method.java:566)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$8.evaluate(RandomizedRunner.java:946)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:982)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//org.apache.lucene.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:49)
at app//org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at app//org.apache.lucene.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:48)
at app//org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at app//org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:824)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:475)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
at app//org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//org.apache.lucene.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:41)
at app//com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at app//com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//org.apache.lucene.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
at app//org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at app//org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at app//org.apache.lucene.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:54)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:831)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$$Lambda$133/0x0000000800296040.run(Unknown Source)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"pool-4-thread-1" ID=47 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@5d61db90
- locked sun.nio.ch.KQueueSelectorImpl@30190ae7
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor.execute(AbstractMultiworkerIOReactor.java:343)
at app//org.apache.http.impl.nio.conn.PoolingNHttpClientConnectionManager.execute(PoolingNHttpClientConnectionManager.java:221)
at app//org.apache.http.impl.nio.client.CloseableHttpAsyncClientBase$1.run(CloseableHttpAsyncClientBase.java:64)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 25" ID=48 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@5342054c
- locked sun.nio.ch.KQueueSelectorImpl@520a4b94
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 26" ID=49 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@164b71e
- locked sun.nio.ch.KQueueSelectorImpl@79d2cbe7
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 27" ID=50 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@3af9d9f4
- locked sun.nio.ch.KQueueSelectorImpl@3a2f73d4
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 28" ID=51 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@1ed7efc8
- locked sun.nio.ch.KQueueSelectorImpl@71359206
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 29" ID=52 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@577d3ad
- locked sun.nio.ch.KQueueSelectorImpl@4487b104
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 30" ID=53 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@658fbff3
- locked sun.nio.ch.KQueueSelectorImpl@38f7a4e6
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 31" ID=54 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@3a6f2ee
- locked sun.nio.ch.KQueueSelectorImpl@7ad07c0f
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 32" ID=55 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@62383481
- locked sun.nio.ch.KQueueSelectorImpl@676d7cb4
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"pool-5-thread-1" ID=60 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@53e8d335
- locked sun.nio.ch.KQueueSelectorImpl@2aa1ed43
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor.execute(AbstractMultiworkerIOReactor.java:343)
at app//org.apache.http.impl.nio.conn.PoolingNHttpClientConnectionManager.execute(PoolingNHttpClientConnectionManager.java:221)
at app//org.apache.http.impl.nio.client.CloseableHttpAsyncClientBase$1.run(CloseableHttpAsyncClientBase.java:64)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 33" ID=56 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@99e48aa
- locked sun.nio.ch.KQueueSelectorImpl@59a0df1
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 34" ID=57 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@10fe070c
- locked sun.nio.ch.KQueueSelectorImpl@35103ba5
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 35" ID=58 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@4eb0feb5
- locked sun.nio.ch.KQueueSelectorImpl@1b908717
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 36" ID=59 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7bb6350e
- locked sun.nio.ch.KQueueSelectorImpl@4fcfe4ce
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 37" ID=61 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@643eed4
- locked sun.nio.ch.KQueueSelectorImpl@19f47934
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 38" ID=62 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@53202141
- locked sun.nio.ch.KQueueSelectorImpl@6379467f
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 39" ID=63 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7a55318a
- locked sun.nio.ch.KQueueSelectorImpl@40d2da2d
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 40" ID=64 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@122ac15f
- locked sun.nio.ch.KQueueSelectorImpl@3bc937db
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 41" ID=65 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@68c39849
- locked sun.nio.ch.KQueueSelectorImpl@3e9624ce
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 42" ID=66 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7af23a7a
- locked sun.nio.ch.KQueueSelectorImpl@877ad10
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 43" ID=67 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7c026d87
- locked sun.nio.ch.KQueueSelectorImpl@733d969d
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 44" ID=68 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@18f7536a
- locked sun.nio.ch.KQueueSelectorImpl@2ddd7249
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 45" ID=69 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@425c5c20
- locked sun.nio.ch.KQueueSelectorImpl@5d4aa388
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 46" ID=70 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7f04d748
- locked sun.nio.ch.KQueueSelectorImpl@390dbddb
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 47" ID=71 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@19104b86
- locked sun.nio.ch.KQueueSelectorImpl@11cefdcf
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 48" ID=72 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@48a9c629
- locked sun.nio.ch.KQueueSelectorImpl@1c9e4982
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
^^==============================================
REPRODUCE WITH: ./gradlew ':x-pack:plugin:integTestRunner' --tests "org.elasticsearch.xpack.test.rest.XPackRestIT.test {p0=ml/delete_expired_data/Test delete expired data with unknown job id}" -Dtests.seed=3CB3A0963BA8B500 -Dtests.security.manager=true -Dtests.locale=el-CY -Dtests.timezone=Africa/Sao_Tome -Druntime.java=11 -Dtests.rest.blacklist=getting_started/10_monitor_cluster_health/*
```
</p>
</details>
| 1.0 | [CI] XPackRestIT.test {p0=ml/delete_expired_data/Test delete expired data with unknown job id} failure master - Test times out.
**Build scan**:
https://gradle-enterprise.elastic.co/s/nuarmaeswwers
**Repro line**:
```
./gradlew ':x-pack:plugin:integTestRunner' --tests "org.elasticsearch.xpack.test.rest.XPackRestIT.test {p0=ml/delete_expired_data/Test delete expired data with unknown job id}" \
-Dtests.seed=3CB3A0963BA8B500 \
-Dtests.security.manager=true \
-Dtests.locale=el-CY \
-Dtests.timezone=Africa/Sao_Tome \
-Druntime.java=11 \
-Dtests.rest.blacklist=getting_started/10_monitor_cluster_health/*
```
**Reproduces locally?**:
No
**Applicable branches**:
master
**Failure history**:
**Failure excerpt**:
```
java.lang.Exception: Test abandoned because suite timeout was reached. |
```
<details><summary>jstack</summary>
<p>
```
[2020-07-07T07:28:57,589][INFO ][o.e.x.t.r.XPackRestIT ] [test] [p0=ml/delete_expired_data/Test delete expired data with unknown job id] before test
Ιουλ 07, 2020 7:28:58 ΠΜ com.carrotsearch.randomizedtesting.ThreadLeakControl$2 evaluate
WARNING: Suite execution timed out: org.elasticsearch.xpack.test.rest.XPackRestIT
==== jstack at approximately timeout time ====
"main" ID=1 WAITING on java.util.concurrent.CountDownLatch$Sync@47252ff9
at java.base@11.0.2/jdk.internal.misc.Unsafe.park(Native Method)
- waiting on java.util.concurrent.CountDownLatch$Sync@47252ff9
at java.base@11.0.2/java.util.concurrent.locks.LockSupport.park(LockSupport.java:194)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer.parkAndCheckInterrupt(AbstractQueuedSynchronizer.java:885)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer.doAcquireSharedInterruptibly(AbstractQueuedSynchronizer.java:1039)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer.acquireSharedInterruptibly(AbstractQueuedSynchronizer.java:1345)
at java.base@11.0.2/java.util.concurrent.CountDownLatch.await(CountDownLatch.java:232)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.execute(TestWorker.java:73)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.execute(TestWorker.java:47)
at org.gradle.process.internal.worker.child.ActionExecutionWorker.execute(ActionExecutionWorker.java:56)
at org.gradle.process.internal.worker.child.SystemApplicationClassLoaderWorker.call(SystemApplicationClassLoaderWorker.java:133)
at org.gradle.process.internal.worker.child.SystemApplicationClassLoaderWorker.call(SystemApplicationClassLoaderWorker.java:71)
at app//worker.org.gradle.process.internal.worker.GradleWorkerMain.run(GradleWorkerMain.java:69)
at app//worker.org.gradle.process.internal.worker.GradleWorkerMain.main(GradleWorkerMain.java:74)
"Reference Handler" ID=2 RUNNABLE
at java.base@11.0.2/java.lang.ref.Reference.waitForReferencePendingList(Native Method)
at java.base@11.0.2/java.lang.ref.Reference.processPendingReferences(Reference.java:241)
at java.base@11.0.2/java.lang.ref.Reference$ReferenceHandler.run(Reference.java:213)
"Finalizer" ID=3 WAITING on java.lang.ref.ReferenceQueue$Lock@53468bca
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- waiting on java.lang.ref.ReferenceQueue$Lock@53468bca
at java.base@11.0.2/java.lang.ref.ReferenceQueue.remove(ReferenceQueue.java:155)
at java.base@11.0.2/java.lang.ref.ReferenceQueue.remove(ReferenceQueue.java:176)
at java.base@11.0.2/java.lang.ref.Finalizer$FinalizerThread.run(Finalizer.java:170)
"Signal Dispatcher" ID=4 RUNNABLE
"Common-Cleaner" ID=11 TIMED_WAITING on java.lang.ref.ReferenceQueue$Lock@126707c9
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- timed waiting on java.lang.ref.ReferenceQueue$Lock@126707c9
at java.base@11.0.2/java.lang.ref.ReferenceQueue.remove(ReferenceQueue.java:155)
at java.base@11.0.2/jdk.internal.ref.CleanerImpl.run(CleanerImpl.java:148)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
at java.base@11.0.2/jdk.internal.misc.InnocuousThread.run(InnocuousThread.java:134)
"Test worker" ID=13 WAITING on com.carrotsearch.randomizedtesting.RandomizedRunner$2@addf938
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- waiting on com.carrotsearch.randomizedtesting.RandomizedRunner$2@addf938
at java.base@11.0.2/java.lang.Thread.join(Thread.java:1305)
at java.base@11.0.2/java.lang.Thread.join(Thread.java:1379)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.runSuite(RandomizedRunner.java:647)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.run(RandomizedRunner.java:504)
at org.gradle.api.internal.tasks.testing.junit.JUnitTestClassExecutor.runTestClass(JUnitTestClassExecutor.java:110)
at org.gradle.api.internal.tasks.testing.junit.JUnitTestClassExecutor.execute(JUnitTestClassExecutor.java:58)
at org.gradle.api.internal.tasks.testing.junit.JUnitTestClassExecutor.execute(JUnitTestClassExecutor.java:38)
at org.gradle.api.internal.tasks.testing.junit.AbstractJUnitTestClassProcessor.processTestClass(AbstractJUnitTestClassProcessor.java:62)
at org.gradle.api.internal.tasks.testing.SuiteTestClassProcessor.processTestClass(SuiteTestClassProcessor.java:51)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base@11.0.2/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.2/java.lang.reflect.Method.invoke(Method.java:566)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.dispatch.ContextClassLoaderDispatch.dispatch(ContextClassLoaderDispatch.java:33)
at org.gradle.internal.dispatch.ProxyDispatchAdapter$DispatchingInvocationHandler.invoke(ProxyDispatchAdapter.java:94)
at com.sun.proxy.$Proxy2.processTestClass(Unknown Source)
at org.gradle.api.internal.tasks.testing.worker.TestWorker.processTestClass(TestWorker.java:119)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base@11.0.2/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base@11.0.2/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.2/java.lang.reflect.Method.invoke(Method.java:566)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:36)
at org.gradle.internal.dispatch.ReflectionDispatch.dispatch(ReflectionDispatch.java:24)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:182)
at org.gradle.internal.remote.internal.hub.MessageHubBackedObjectConnection$DispatchWrapper.dispatch(MessageHubBackedObjectConnection.java:164)
at org.gradle.internal.remote.internal.hub.MessageHub$Handler.run(MessageHub.java:414)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
Locked synchronizers:
- java.util.concurrent.ThreadPoolExecutor$Worker@45b4c3a9
"/127.0.0.1:54358 to /127.0.0.1:54357 workers Thread 2" ID=14 WAITING on java.util.concurrent.locks.AbstractQueuedSynchronizer$ConditionObject@76d285bd
at java.base@11.0.2/jdk.internal.misc.Unsafe.park(Native Method)
- waiting on java.util.concurrent.locks.AbstractQueuedSynchronizer$ConditionObject@76d285bd
at java.base@11.0.2/java.util.concurrent.locks.LockSupport.park(LockSupport.java:194)
at java.base@11.0.2/java.util.concurrent.locks.AbstractQueuedSynchronizer$ConditionObject.await(AbstractQueuedSynchronizer.java:2081)
at org.gradle.internal.remote.internal.hub.queue.EndPointQueue.take(EndPointQueue.java:49)
at org.gradle.internal.remote.internal.hub.MessageHub$ConnectionDispatch.run(MessageHub.java:322)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
Locked synchronizers:
- java.util.concurrent.ThreadPoolExecutor$Worker@5552768b
"/127.0.0.1:54358 to /127.0.0.1:54357 workers Thread 3" ID=15 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@6be5b6ec
- locked sun.nio.ch.KQueueSelectorImpl@26697f84
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:141)
at org.gradle.internal.remote.internal.inet.SocketConnection$SocketInputStream.read(SocketConnection.java:185)
at com.esotericsoftware.kryo.io.Input.fill(Input.java:146)
at com.esotericsoftware.kryo.io.Input.require(Input.java:178)
at com.esotericsoftware.kryo.io.Input.readByte(Input.java:295)
at org.gradle.internal.serialize.kryo.KryoBackedDecoder.readByte(KryoBackedDecoder.java:82)
at org.gradle.internal.remote.internal.hub.InterHubMessageSerializer$MessageReader.read(InterHubMessageSerializer.java:64)
at org.gradle.internal.remote.internal.hub.InterHubMessageSerializer$MessageReader.read(InterHubMessageSerializer.java:52)
at org.gradle.internal.remote.internal.inet.SocketConnection.receive(SocketConnection.java:81)
at org.gradle.internal.remote.internal.hub.MessageHub$ConnectionReceive.run(MessageHub.java:270)
at org.gradle.internal.concurrent.ExecutorPolicy$CatchAndRecordFailures.onExecute(ExecutorPolicy.java:64)
at org.gradle.internal.concurrent.ManagedExecutorImpl$1.run(ManagedExecutorImpl.java:48)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base@11.0.2/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at org.gradle.internal.concurrent.ThreadFactoryImpl$ManagedThreadRunnable.run(ThreadFactoryImpl.java:56)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
Locked synchronizers:
- java.util.concurrent.ThreadPoolExecutor$Worker@1356d4d4
"SUITE-XPackRestIT-seed#[3CB3A0963BA8B500]" ID=45 RUNNABLE
at java.management@11.0.2/sun.management.ThreadImpl.dumpThreads0(Native Method)
at java.management@11.0.2/sun.management.ThreadImpl.dumpAllThreads(ThreadImpl.java:502)
at java.management@11.0.2/sun.management.ThreadImpl.dumpAllThreads(ThreadImpl.java:490)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.formatThreadStacksFull(ThreadLeakControl.java:688)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.access$1000(ThreadLeakControl.java:67)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$2.evaluate(ThreadLeakControl.java:422)
- locked java.lang.Object@44f4f999
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.runSuite(RandomizedRunner.java:716)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.access$200(RandomizedRunner.java:138)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$2.run(RandomizedRunner.java:637)
"TEST-XPackRestIT.test-seed#[3CB3A0963BA8B500]" ID=46 WAITING on org.apache.http.concurrent.BasicFuture@2e0653d
at java.base@11.0.2/java.lang.Object.wait(Native Method)
- waiting on org.apache.http.concurrent.BasicFuture@2e0653d
at java.base@11.0.2/java.lang.Object.wait(Object.java:328)
at app//org.apache.http.concurrent.BasicFuture.get(BasicFuture.java:82)
at app//org.apache.http.impl.nio.client.FutureWrapper.get(FutureWrapper.java:70)
at app//org.elasticsearch.client.RestClient.performRequest(RestClient.java:255)
at app//org.elasticsearch.client.RestClient.performRequest(RestClient.java:246)
at app//org.elasticsearch.test.rest.yaml.ClientYamlTestClient.callApi(ClientYamlTestClient.java:186)
at app//org.elasticsearch.test.rest.yaml.ClientYamlTestExecutionContext.callApiInternal(ClientYamlTestExecutionContext.java:169)
at app//org.elasticsearch.test.rest.yaml.ClientYamlTestExecutionContext.callApi(ClientYamlTestExecutionContext.java:101)
at app//org.elasticsearch.test.rest.yaml.section.DoSection.execute(DoSection.java:279)
at app//org.elasticsearch.test.rest.yaml.ESClientYamlSuiteTestCase.executeSection(ESClientYamlSuiteTestCase.java:407)
at app//org.elasticsearch.test.rest.yaml.ESClientYamlSuiteTestCase.test(ESClientYamlSuiteTestCase.java:382)
at jdk.internal.reflect.GeneratedMethodAccessor16.invoke(Unknown Source)
at java.base@11.0.2/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.2/java.lang.reflect.Method.invoke(Method.java:566)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$8.evaluate(RandomizedRunner.java:946)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:982)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//org.apache.lucene.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:49)
at app//org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at app//org.apache.lucene.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:48)
at app//org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at app//org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:824)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:475)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
at app//com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
at app//org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//org.apache.lucene.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:41)
at app//com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at app//com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//org.apache.lucene.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
at app//org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at app//org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at app//org.apache.lucene.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:54)
at app//com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:831)
at app//com.carrotsearch.randomizedtesting.ThreadLeakControl$$Lambda$133/0x0000000800296040.run(Unknown Source)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"pool-4-thread-1" ID=47 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@5d61db90
- locked sun.nio.ch.KQueueSelectorImpl@30190ae7
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor.execute(AbstractMultiworkerIOReactor.java:343)
at app//org.apache.http.impl.nio.conn.PoolingNHttpClientConnectionManager.execute(PoolingNHttpClientConnectionManager.java:221)
at app//org.apache.http.impl.nio.client.CloseableHttpAsyncClientBase$1.run(CloseableHttpAsyncClientBase.java:64)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 25" ID=48 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@5342054c
- locked sun.nio.ch.KQueueSelectorImpl@520a4b94
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 26" ID=49 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@164b71e
- locked sun.nio.ch.KQueueSelectorImpl@79d2cbe7
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 27" ID=50 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@3af9d9f4
- locked sun.nio.ch.KQueueSelectorImpl@3a2f73d4
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 28" ID=51 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@1ed7efc8
- locked sun.nio.ch.KQueueSelectorImpl@71359206
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 29" ID=52 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@577d3ad
- locked sun.nio.ch.KQueueSelectorImpl@4487b104
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 30" ID=53 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@658fbff3
- locked sun.nio.ch.KQueueSelectorImpl@38f7a4e6
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 31" ID=54 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@3a6f2ee
- locked sun.nio.ch.KQueueSelectorImpl@7ad07c0f
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 32" ID=55 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@62383481
- locked sun.nio.ch.KQueueSelectorImpl@676d7cb4
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"pool-5-thread-1" ID=60 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@53e8d335
- locked sun.nio.ch.KQueueSelectorImpl@2aa1ed43
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor.execute(AbstractMultiworkerIOReactor.java:343)
at app//org.apache.http.impl.nio.conn.PoolingNHttpClientConnectionManager.execute(PoolingNHttpClientConnectionManager.java:221)
at app//org.apache.http.impl.nio.client.CloseableHttpAsyncClientBase$1.run(CloseableHttpAsyncClientBase.java:64)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 33" ID=56 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@99e48aa
- locked sun.nio.ch.KQueueSelectorImpl@59a0df1
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 34" ID=57 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@10fe070c
- locked sun.nio.ch.KQueueSelectorImpl@35103ba5
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 35" ID=58 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@4eb0feb5
- locked sun.nio.ch.KQueueSelectorImpl@1b908717
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 36" ID=59 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7bb6350e
- locked sun.nio.ch.KQueueSelectorImpl@4fcfe4ce
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 37" ID=61 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@643eed4
- locked sun.nio.ch.KQueueSelectorImpl@19f47934
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 38" ID=62 RUNNABLE (in native code)
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@53202141
- locked sun.nio.ch.KQueueSelectorImpl@6379467f
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 39" ID=63 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7a55318a
- locked sun.nio.ch.KQueueSelectorImpl@40d2da2d
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 40" ID=64 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@122ac15f
- locked sun.nio.ch.KQueueSelectorImpl@3bc937db
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 41" ID=65 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@68c39849
- locked sun.nio.ch.KQueueSelectorImpl@3e9624ce
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 42" ID=66 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7af23a7a
- locked sun.nio.ch.KQueueSelectorImpl@877ad10
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 43" ID=67 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7c026d87
- locked sun.nio.ch.KQueueSelectorImpl@733d969d
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 44" ID=68 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@18f7536a
- locked sun.nio.ch.KQueueSelectorImpl@2ddd7249
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 45" ID=69 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@425c5c20
- locked sun.nio.ch.KQueueSelectorImpl@5d4aa388
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 46" ID=70 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@7f04d748
- locked sun.nio.ch.KQueueSelectorImpl@390dbddb
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 47" ID=71 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@19104b86
- locked sun.nio.ch.KQueueSelectorImpl@11cefdcf
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
"I/O dispatcher 48" ID=72 RUNNABLE
at java.base@11.0.2/sun.nio.ch.KQueue.poll(Native Method)
at java.base@11.0.2/sun.nio.ch.KQueueSelectorImpl.doSelect(KQueueSelectorImpl.java:122)
at java.base@11.0.2/sun.nio.ch.SelectorImpl.lockAndDoSelect(SelectorImpl.java:124)
- locked sun.nio.ch.Util$2@48a9c629
- locked sun.nio.ch.KQueueSelectorImpl@1c9e4982
at java.base@11.0.2/sun.nio.ch.SelectorImpl.select(SelectorImpl.java:136)
at app//org.apache.http.impl.nio.reactor.AbstractIOReactor.execute(AbstractIOReactor.java:255)
at app//org.apache.http.impl.nio.reactor.BaseIOReactor.execute(BaseIOReactor.java:104)
at app//org.apache.http.impl.nio.reactor.AbstractMultiworkerIOReactor$Worker.run(AbstractMultiworkerIOReactor.java:591)
at java.base@11.0.2/java.lang.Thread.run(Thread.java:834)
^^==============================================
REPRODUCE WITH: ./gradlew ':x-pack:plugin:integTestRunner' --tests "org.elasticsearch.xpack.test.rest.XPackRestIT.test {p0=ml/delete_expired_data/Test delete expired data with unknown job id}" -Dtests.seed=3CB3A0963BA8B500 -Dtests.security.manager=true -Dtests.locale=el-CY -Dtests.timezone=Africa/Sao_Tome -Druntime.java=11 -Dtests.rest.blacklist=getting_started/10_monitor_cluster_health/*
```
</p>
</details>
| non_priority | xpackrestit test ml delete expired data test delete expired data with unknown job id failure master test times out build scan repro line gradlew x pack plugin integtestrunner tests org elasticsearch xpack test rest xpackrestit test ml delete expired data test delete expired data with unknown job id dtests seed dtests security manager true dtests locale el cy dtests timezone africa sao tome druntime java dtests rest blacklist getting started monitor cluster health reproduces locally no applicable branches master failure history failure excerpt java lang exception test abandoned because suite timeout was reached jstack before test ιουλ πμ com carrotsearch randomizedtesting threadleakcontrol evaluate warning suite execution timed out org elasticsearch xpack test rest xpackrestit jstack at approximately timeout time main id waiting on java util concurrent countdownlatch sync at java base jdk internal misc unsafe park native method waiting on java util concurrent countdownlatch sync at java base java util concurrent locks locksupport park locksupport java at java base java util concurrent locks abstractqueuedsynchronizer parkandcheckinterrupt abstractqueuedsynchronizer java at java base java util concurrent locks abstractqueuedsynchronizer doacquiresharedinterruptibly abstractqueuedsynchronizer java at java base java util concurrent locks abstractqueuedsynchronizer acquiresharedinterruptibly abstractqueuedsynchronizer java at java base java util concurrent countdownlatch await countdownlatch java at org gradle api internal tasks testing worker testworker execute testworker java at org gradle api internal tasks testing worker testworker execute testworker java at org gradle process internal worker child actionexecutionworker execute actionexecutionworker java at org gradle process internal worker child systemapplicationclassloaderworker call systemapplicationclassloaderworker java at org gradle process internal worker child systemapplicationclassloaderworker call systemapplicationclassloaderworker java at app worker org gradle process internal worker gradleworkermain run gradleworkermain java at app worker org gradle process internal worker gradleworkermain main gradleworkermain java reference handler id runnable at java base java lang ref reference waitforreferencependinglist native method at java base java lang ref reference processpendingreferences reference java at java base java lang ref reference referencehandler run reference java finalizer id waiting on java lang ref referencequeue lock at java base java lang object wait native method waiting on java lang ref referencequeue lock at java base java lang ref referencequeue remove referencequeue java at java base java lang ref referencequeue remove referencequeue java at java base java lang ref finalizer finalizerthread run finalizer java signal dispatcher id runnable common cleaner id timed waiting on java lang ref referencequeue lock at java base java lang object wait native method timed waiting on java lang ref referencequeue lock at java base java lang ref referencequeue remove referencequeue java at java base jdk internal ref cleanerimpl run cleanerimpl java at java base java lang thread run thread java at java base jdk internal misc innocuousthread run innocuousthread java test worker id waiting on com carrotsearch randomizedtesting randomizedrunner at java base java lang object wait native method waiting on com carrotsearch randomizedtesting randomizedrunner at java base java lang thread join thread java at java base java lang thread join thread java at app com carrotsearch randomizedtesting randomizedrunner runsuite randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner run randomizedrunner java at org gradle api internal tasks testing junit junittestclassexecutor runtestclass junittestclassexecutor java at org gradle api internal tasks testing junit junittestclassexecutor execute junittestclassexecutor java at org gradle api internal tasks testing junit junittestclassexecutor execute junittestclassexecutor java at org gradle api internal tasks testing junit abstractjunittestclassprocessor processtestclass abstractjunittestclassprocessor java at org gradle api internal tasks testing suitetestclassprocessor processtestclass suitetestclassprocessor java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal dispatch contextclassloaderdispatch dispatch contextclassloaderdispatch java at org gradle internal dispatch proxydispatchadapter dispatchinginvocationhandler invoke proxydispatchadapter java at com sun proxy processtestclass unknown source at org gradle api internal tasks testing worker testworker processtestclass testworker java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal dispatch reflectiondispatch dispatch reflectiondispatch java at org gradle internal remote internal hub messagehubbackedobjectconnection dispatchwrapper dispatch messagehubbackedobjectconnection java at org gradle internal remote internal hub messagehubbackedobjectconnection dispatchwrapper dispatch messagehubbackedobjectconnection java at org gradle internal remote internal hub messagehub handler run messagehub java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java base java lang thread run thread java locked synchronizers java util concurrent threadpoolexecutor worker to workers thread id waiting on java util concurrent locks abstractqueuedsynchronizer conditionobject at java base jdk internal misc unsafe park native method waiting on java util concurrent locks abstractqueuedsynchronizer conditionobject at java base java util concurrent locks locksupport park locksupport java at java base java util concurrent locks abstractqueuedsynchronizer conditionobject await abstractqueuedsynchronizer java at org gradle internal remote internal hub queue endpointqueue take endpointqueue java at org gradle internal remote internal hub messagehub connectiondispatch run messagehub java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java base java lang thread run thread java locked synchronizers java util concurrent threadpoolexecutor worker to workers thread id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at org gradle internal remote internal inet socketconnection socketinputstream read socketconnection java at com esotericsoftware kryo io input fill input java at com esotericsoftware kryo io input require input java at com esotericsoftware kryo io input readbyte input java at org gradle internal serialize kryo kryobackeddecoder readbyte kryobackeddecoder java at org gradle internal remote internal hub interhubmessageserializer messagereader read interhubmessageserializer java at org gradle internal remote internal hub interhubmessageserializer messagereader read interhubmessageserializer java at org gradle internal remote internal inet socketconnection receive socketconnection java at org gradle internal remote internal hub messagehub connectionreceive run messagehub java at org gradle internal concurrent executorpolicy catchandrecordfailures onexecute executorpolicy java at org gradle internal concurrent managedexecutorimpl run managedexecutorimpl java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at org gradle internal concurrent threadfactoryimpl managedthreadrunnable run threadfactoryimpl java at java base java lang thread run thread java locked synchronizers java util concurrent threadpoolexecutor worker suite xpackrestit seed id runnable at java management sun management threadimpl native method at java management sun management threadimpl dumpallthreads threadimpl java at java management sun management threadimpl dumpallthreads threadimpl java at app com carrotsearch randomizedtesting threadleakcontrol formatthreadstacksfull threadleakcontrol java at app com carrotsearch randomizedtesting threadleakcontrol access threadleakcontrol java at app com carrotsearch randomizedtesting threadleakcontrol evaluate threadleakcontrol java locked java lang object at app com carrotsearch randomizedtesting randomizedrunner runsuite randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner access randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner run randomizedrunner java test xpackrestit test seed id waiting on org apache http concurrent basicfuture at java base java lang object wait native method waiting on org apache http concurrent basicfuture at java base java lang object wait object java at app org apache http concurrent basicfuture get basicfuture java at app org apache http impl nio client futurewrapper get futurewrapper java at app org elasticsearch client restclient performrequest restclient java at app org elasticsearch client restclient performrequest restclient java at app org elasticsearch test rest yaml clientyamltestclient callapi clientyamltestclient java at app org elasticsearch test rest yaml clientyamltestexecutioncontext callapiinternal clientyamltestexecutioncontext java at app org elasticsearch test rest yaml clientyamltestexecutioncontext callapi clientyamltestexecutioncontext java at app org elasticsearch test rest yaml section dosection execute dosection java at app org elasticsearch test rest yaml esclientyamlsuitetestcase executesection esclientyamlsuitetestcase java at app org elasticsearch test rest yaml esclientyamlsuitetestcase test esclientyamlsuitetestcase java at jdk internal reflect invoke unknown source at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at app com carrotsearch randomizedtesting randomizedrunner invoke randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at app com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at app org apache lucene util testrulesetupteardownchained evaluate testrulesetupteardownchained java at app org apache lucene util abstractbeforeafterrule evaluate abstractbeforeafterrule java at app org apache lucene util testrulethreadandtestname evaluate testrulethreadandtestname java at app org apache lucene util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at app org apache lucene util testrulemarkfailure evaluate testrulemarkfailure java at app com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at app com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at app com carrotsearch randomizedtesting threadleakcontrol forktimeoutingtask threadleakcontrol java at app com carrotsearch randomizedtesting threadleakcontrol evaluate threadleakcontrol java at app com carrotsearch randomizedtesting randomizedrunner runsingletest randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at app com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at app org apache lucene util abstractbeforeafterrule evaluate abstractbeforeafterrule java at app com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at app org apache lucene util testrulestoreclassname evaluate testrulestoreclassname java at app com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at app com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at app com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at app com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at app org apache lucene util testruleassertionsrequired evaluate testruleassertionsrequired java at app org apache lucene util testrulemarkfailure evaluate testrulemarkfailure java at app org apache lucene util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at app org apache lucene util testruleignoretestsuites evaluate testruleignoretestsuites java at app com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at app com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at app com carrotsearch randomizedtesting threadleakcontrol lambda forktimeoutingtask threadleakcontrol java at app com carrotsearch randomizedtesting threadleakcontrol lambda run unknown source at java base java lang thread run thread java pool thread id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractmultiworkerioreactor execute abstractmultiworkerioreactor java at app org apache http impl nio conn poolingnhttpclientconnectionmanager execute poolingnhttpclientconnectionmanager java at app org apache http impl nio client closeablehttpasyncclientbase run closeablehttpasyncclientbase java at java base java lang thread run thread java i o dispatcher id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java pool thread id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractmultiworkerioreactor execute abstractmultiworkerioreactor java at app org apache http impl nio conn poolingnhttpclientconnectionmanager execute poolingnhttpclientconnectionmanager java at app org apache http impl nio client closeablehttpasyncclientbase run closeablehttpasyncclientbase java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable in native code at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java i o dispatcher id runnable at java base sun nio ch kqueue poll native method at java base sun nio ch kqueueselectorimpl doselect kqueueselectorimpl java at java base sun nio ch selectorimpl lockanddoselect selectorimpl java locked sun nio ch util locked sun nio ch kqueueselectorimpl at java base sun nio ch selectorimpl select selectorimpl java at app org apache http impl nio reactor abstractioreactor execute abstractioreactor java at app org apache http impl nio reactor baseioreactor execute baseioreactor java at app org apache http impl nio reactor abstractmultiworkerioreactor worker run abstractmultiworkerioreactor java at java base java lang thread run thread java reproduce with gradlew x pack plugin integtestrunner tests org elasticsearch xpack test rest xpackrestit test ml delete expired data test delete expired data with unknown job id dtests seed dtests security manager true dtests locale el cy dtests timezone africa sao tome druntime java dtests rest blacklist getting started monitor cluster health | 0 |
123,663 | 16,522,401,583 | IssuesEvent | 2021-05-26 15:49:59 | circlesland/o-platform | https://api.github.com/repos/circlesland/o-platform | reopened | Separate Process navigation from actual bottom navigation (code wise) | Process redesign | let's have separate components for the bottom nav (website and dapps also separate) and process navigation.
| 1.0 | Separate Process navigation from actual bottom navigation (code wise) - let's have separate components for the bottom nav (website and dapps also separate) and process navigation.
| non_priority | separate process navigation from actual bottom navigation code wise let s have separate components for the bottom nav website and dapps also separate and process navigation | 0 |
257,726 | 27,563,811,769 | IssuesEvent | 2023-03-08 01:08:14 | rsoreq/cwa-server | https://api.github.com/repos/rsoreq/cwa-server | opened | CVE-2021-25122 (High) detected in tomcat-embed-core-9.0.35.jar | security vulnerability | ## CVE-2021-25122 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.35.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /services/submission/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.35/tomcat-embed-core-9.0.35.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.0.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.3.0.RELEASE.jar
- :x: **tomcat-embed-core-9.0.35.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When responding to new h2c connection requests, Apache Tomcat versions 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41 and 8.5.0 to 8.5.61 could duplicate request headers and a limited amount of request body from one request to another meaning user A and user B could both see the results of user A's request.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-25122>CVE-2021-25122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.43</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.3.9.RELEASE</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2021-25122 (High) detected in tomcat-embed-core-9.0.35.jar - ## CVE-2021-25122 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.35.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /services/submission/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.35/tomcat-embed-core-9.0.35.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.0.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.3.0.RELEASE.jar
- :x: **tomcat-embed-core-9.0.35.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When responding to new h2c connection requests, Apache Tomcat versions 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41 and 8.5.0 to 8.5.61 could duplicate request headers and a limited amount of request body from one request to another meaning user A and user B could both see the results of user A's request.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-25122>CVE-2021-25122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r7b95bc248603360501f18c8eb03bb6001ec0ee3296205b34b07105b7%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.43</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.3.9.RELEASE</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file services submission pom xml path to vulnerable library root repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in base branch master vulnerability details when responding to new connection requests apache tomcat versions to to and to could duplicate request headers and a limited amount of request body from one request to another meaning user a and user b could both see the results of user a s request publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core direct dependency fix resolution org springframework boot spring boot starter web release rescue worker helmet automatic remediation is available for this issue | 0 |
22,383 | 6,245,883,017 | IssuesEvent | 2017-07-13 01:29:34 | xceedsoftware/wpftoolkit | https://api.github.com/repos/xceedsoftware/wpftoolkit | closed | childwindow start-up location issue | CodePlex | <b>lilgbolahan[CodePlex]</b> <br />The childwin.WindowStartupLocation enum is messed up. nbspVersion: 1.6 releasenbspChildWindow.WindowStartupLocation = WindowStartupLocation.Manual will centralize the window while ChildWindow.WindowStartupLocation = WindowStartupLocation.CenterScreen is vice
versa.nbspPlese can this be fixed asap
| 1.0 | childwindow start-up location issue - <b>lilgbolahan[CodePlex]</b> <br />The childwin.WindowStartupLocation enum is messed up. nbspVersion: 1.6 releasenbspChildWindow.WindowStartupLocation = WindowStartupLocation.Manual will centralize the window while ChildWindow.WindowStartupLocation = WindowStartupLocation.CenterScreen is vice
versa.nbspPlese can this be fixed asap
| non_priority | childwindow start up location issue lilgbolahan the childwin windowstartuplocation enum is messed up nbspversion releasenbspchildwindow windowstartuplocation windowstartuplocation manual will centralize the window while childwindow windowstartuplocation windowstartuplocation centerscreen is vice versa nbspplese can this be fixed asap | 0 |
411,584 | 27,825,979,691 | IssuesEvent | 2023-03-19 19:18:17 | evanofslack/analogdb | https://api.github.com/repos/evanofslack/analogdb | closed | Update docs for API | documentation | Currently https://www.analogdb.com/docs redirects to https://api.analogdb.com/ which has outdated docs. These should be updated. | 1.0 | Update docs for API - Currently https://www.analogdb.com/docs redirects to https://api.analogdb.com/ which has outdated docs. These should be updated. | non_priority | update docs for api currently redirects to which has outdated docs these should be updated | 0 |
179,494 | 13,884,260,939 | IssuesEvent | 2020-10-18 15:27:39 | ImagingDataCommons/IDC-WebApp | https://api.github.com/repos/ImagingDataCommons/IDC-WebApp | closed | Click on Landing Page Bar Goes to Explorer With That Filter | MVP merged testing needed testing passed | E.g. click on Brain on the Landing page takes you to brain in the Explorer. Need to be able to launch the Explorer with a specified filter set. | 2.0 | Click on Landing Page Bar Goes to Explorer With That Filter - E.g. click on Brain on the Landing page takes you to brain in the Explorer. Need to be able to launch the Explorer with a specified filter set. | non_priority | click on landing page bar goes to explorer with that filter e g click on brain on the landing page takes you to brain in the explorer need to be able to launch the explorer with a specified filter set | 0 |
178,355 | 13,775,471,404 | IssuesEvent | 2020-10-08 08:03:39 | hazelcast/hazelcast-jet | https://api.github.com/repos/hazelcast/hazelcast-jet | opened | Do proper cleanup in Docker-based tests | test-failure | Do proper resource cleanup in Docker-based tests.
Docker volumes and exited containers are not removed after the tests and they consume system resources.
```
$ docker ps -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
0efa39e27b27 debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago affectionate_ritchie
a3fefde5c41b debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago nifty_golick
0f6c9e9ea4ca debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago sleepy_franklin
1246b3187cd8 debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (137) 2 hours ago hopeful_jackson
259841aef88c debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago clever_varahamihira
c6b25248a8b4 debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago epic_spence
e801b2344e00 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago determined_mccarthy
f011ebea7db1 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago amazing_newton
2a49a2b85b38 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago romantic_torvalds
1d7dc98e4dc5 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (137) 3 hours ago elegant_lumiere
a75794a5bf8e debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago gracious_johnson
```
| 1.0 | Do proper cleanup in Docker-based tests - Do proper resource cleanup in Docker-based tests.
Docker volumes and exited containers are not removed after the tests and they consume system resources.
```
$ docker ps -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
0efa39e27b27 debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago affectionate_ritchie
a3fefde5c41b debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago nifty_golick
0f6c9e9ea4ca debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago sleepy_franklin
1246b3187cd8 debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (137) 2 hours ago hopeful_jackson
259841aef88c debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago clever_varahamihira
c6b25248a8b4 debezium/example-mysql:1.2 "docker-entrypoint.s…" 2 hours ago Exited (0) 2 hours ago epic_spence
e801b2344e00 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago determined_mccarthy
f011ebea7db1 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago amazing_newton
2a49a2b85b38 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago romantic_torvalds
1d7dc98e4dc5 debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (137) 3 hours ago elegant_lumiere
a75794a5bf8e debezium/example-mysql:1.2 "docker-entrypoint.s…" 3 hours ago Exited (0) 3 hours ago gracious_johnson
```
| non_priority | do proper cleanup in docker based tests do proper resource cleanup in docker based tests docker volumes and exited containers are not removed after the tests and they consume system resources docker ps a container id image command created status ports names debezium example mysql docker entrypoint s… hours ago exited hours ago affectionate ritchie debezium example mysql docker entrypoint s… hours ago exited hours ago nifty golick debezium example mysql docker entrypoint s… hours ago exited hours ago sleepy franklin debezium example mysql docker entrypoint s… hours ago exited hours ago hopeful jackson debezium example mysql docker entrypoint s… hours ago exited hours ago clever varahamihira debezium example mysql docker entrypoint s… hours ago exited hours ago epic spence debezium example mysql docker entrypoint s… hours ago exited hours ago determined mccarthy debezium example mysql docker entrypoint s… hours ago exited hours ago amazing newton debezium example mysql docker entrypoint s… hours ago exited hours ago romantic torvalds debezium example mysql docker entrypoint s… hours ago exited hours ago elegant lumiere debezium example mysql docker entrypoint s… hours ago exited hours ago gracious johnson | 0 |
207,548 | 23,458,622,918 | IssuesEvent | 2022-08-16 11:10:26 | Gal-Doron/Baragon-test-6 | https://api.github.com/repos/Gal-Doron/Baragon-test-6 | opened | google-api-client-1.25.0.jar: 2 vulnerabilities (highest severity is: 9.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google-api-client-1.25.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.25.0/google-oauth-client-1.25.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-7692](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7692) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | google-oauth-client-1.25.0.jar | Transitive | 1.30.10 | ✅ |
| [CVE-2021-22573](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22573) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | google-oauth-client-1.25.0.jar | Transitive | 1.35.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7692</summary>
### Vulnerable Library - <b>google-oauth-client-1.25.0.jar</b></p>
<p>Google OAuth Client Library for Java. Functionality that works on all supported Java platforms,
including Java 5 (or higher) desktop (SE) and web (EE), Android, and Google App Engine.</p>
<p>Library home page: <a href="https://github.com/google/google-oauth-java-client">https://github.com/google/google-oauth-java-client</a></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.25.0/google-oauth-client-1.25.0.jar</p>
<p>
Dependency Hierarchy:
- google-api-client-1.25.0.jar (Root Library)
- :x: **google-oauth-client-1.25.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
PKCE support is not implemented in accordance with the RFC for OAuth 2.0 for Native Apps. Without the use of PKCE, the authorization code returned by an authorization server is not enough to guarantee that the client that issued the initial authorization request is the one that will be authorized. An attacker is able to obtain the authorization code using a malicious app on the client-side and use it to gain authorization to the protected resource. This affects the package com.google.oauth-client:google-oauth-client before 1.31.0.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7692>CVE-2020-7692</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution (com.google.oauth-client:google-oauth-client): 1.31.0</p>
<p>Direct dependency fix Resolution (com.google.api-client:google-api-client): 1.30.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22573</summary>
### Vulnerable Library - <b>google-oauth-client-1.25.0.jar</b></p>
<p>Google OAuth Client Library for Java. Functionality that works on all supported Java platforms,
including Java 5 (or higher) desktop (SE) and web (EE), Android, and Google App Engine.</p>
<p>Library home page: <a href="https://github.com/google/google-oauth-java-client">https://github.com/google/google-oauth-java-client</a></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.25.0/google-oauth-client-1.25.0.jar</p>
<p>
Dependency Hierarchy:
- google-api-client-1.25.0.jar (Root Library)
- :x: **google-oauth-client-1.25.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The vulnerability is that IDToken verifier does not verify if token is properly signed. Signature verification makes sure that the token's payload comes from valid provider, not from someone else. An attacker can provide a compromised token with custom payload. The token will pass the validation on the client side. We recommend upgrading to version 1.33.3 or above
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22573>CVE-2021-22573</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-22573">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-22573</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution (com.google.oauth-client:google-oauth-client): 1.33.3</p>
<p>Direct dependency fix Resolution (com.google.api-client:google-api-client): 1.35.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | google-api-client-1.25.0.jar: 2 vulnerabilities (highest severity is: 9.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google-api-client-1.25.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.25.0/google-oauth-client-1.25.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-7692](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7692) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.1 | google-oauth-client-1.25.0.jar | Transitive | 1.30.10 | ✅ |
| [CVE-2021-22573](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22573) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | google-oauth-client-1.25.0.jar | Transitive | 1.35.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7692</summary>
### Vulnerable Library - <b>google-oauth-client-1.25.0.jar</b></p>
<p>Google OAuth Client Library for Java. Functionality that works on all supported Java platforms,
including Java 5 (or higher) desktop (SE) and web (EE), Android, and Google App Engine.</p>
<p>Library home page: <a href="https://github.com/google/google-oauth-java-client">https://github.com/google/google-oauth-java-client</a></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.25.0/google-oauth-client-1.25.0.jar</p>
<p>
Dependency Hierarchy:
- google-api-client-1.25.0.jar (Root Library)
- :x: **google-oauth-client-1.25.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
PKCE support is not implemented in accordance with the RFC for OAuth 2.0 for Native Apps. Without the use of PKCE, the authorization code returned by an authorization server is not enough to guarantee that the client that issued the initial authorization request is the one that will be authorized. An attacker is able to obtain the authorization code using a malicious app on the client-side and use it to gain authorization to the protected resource. This affects the package com.google.oauth-client:google-oauth-client before 1.31.0.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7692>CVE-2020-7692</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution (com.google.oauth-client:google-oauth-client): 1.31.0</p>
<p>Direct dependency fix Resolution (com.google.api-client:google-api-client): 1.30.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22573</summary>
### Vulnerable Library - <b>google-oauth-client-1.25.0.jar</b></p>
<p>Google OAuth Client Library for Java. Functionality that works on all supported Java platforms,
including Java 5 (or higher) desktop (SE) and web (EE), Android, and Google App Engine.</p>
<p>Library home page: <a href="https://github.com/google/google-oauth-java-client">https://github.com/google/google-oauth-java-client</a></p>
<p>Path to dependency file: /BaragonService/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.25.0/google-oauth-client-1.25.0.jar</p>
<p>
Dependency Hierarchy:
- google-api-client-1.25.0.jar (Root Library)
- :x: **google-oauth-client-1.25.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-6/commit/10c20000fec2ffa6628601aaf45fbbd85b996de2">10c20000fec2ffa6628601aaf45fbbd85b996de2</a></p>
<p>Found in base branch: <b>basepom-upgrade</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The vulnerability is that IDToken verifier does not verify if token is properly signed. Signature verification makes sure that the token's payload comes from valid provider, not from someone else. An attacker can provide a compromised token with custom payload. The token will pass the validation on the client side. We recommend upgrading to version 1.33.3 or above
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22573>CVE-2021-22573</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-22573">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-22573</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution (com.google.oauth-client:google-oauth-client): 1.33.3</p>
<p>Direct dependency fix Resolution (com.google.api-client:google-api-client): 1.35.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | google api client jar vulnerabilities highest severity is vulnerable library google api client jar path to dependency file baragonservice pom xml path to vulnerable library home wss scanner repository com google oauth client google oauth client google oauth client jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high google oauth client jar transitive high google oauth client jar transitive details cve vulnerable library google oauth client jar google oauth client library for java functionality that works on all supported java platforms including java or higher desktop se and web ee android and google app engine library home page a href path to dependency file baragonservice pom xml path to vulnerable library home wss scanner repository com google oauth client google oauth client google oauth client jar dependency hierarchy google api client jar root library x google oauth client jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details pkce support is not implemented in accordance with the rfc for oauth for native apps without the use of pkce the authorization code returned by an authorization server is not enough to guarantee that the client that issued the initial authorization request is the one that will be authorized an attacker is able to obtain the authorization code using a malicious app on the client side and use it to gain authorization to the protected resource this affects the package com google oauth client google oauth client before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution com google oauth client google oauth client direct dependency fix resolution com google api client google api client rescue worker helmet automatic remediation is available for this issue cve vulnerable library google oauth client jar google oauth client library for java functionality that works on all supported java platforms including java or higher desktop se and web ee android and google app engine library home page a href path to dependency file baragonservice pom xml path to vulnerable library home wss scanner repository com google oauth client google oauth client google oauth client jar dependency hierarchy google api client jar root library x google oauth client jar vulnerable library found in head commit a href found in base branch basepom upgrade vulnerability details the vulnerability is that idtoken verifier does not verify if token is properly signed signature verification makes sure that the token s payload comes from valid provider not from someone else an attacker can provide a compromised token with custom payload the token will pass the validation on the client side we recommend upgrading to version or above publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google oauth client google oauth client direct dependency fix resolution com google api client google api client rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
23,387 | 3,838,034,290 | IssuesEvent | 2016-04-02 04:24:05 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | button captions should be all-caps | affects: material design customer: gallery fix pending ⚠ bug | The "Launch Demo" button and the "Disabled" button for both raised and flat buttons, and the Action button on the snackbar, should all be uppercase, but are not. | 1.0 | button captions should be all-caps - The "Launch Demo" button and the "Disabled" button for both raised and flat buttons, and the Action button on the snackbar, should all be uppercase, but are not. | non_priority | button captions should be all caps the launch demo button and the disabled button for both raised and flat buttons and the action button on the snackbar should all be uppercase but are not | 0 |
126,784 | 10,435,593,292 | IssuesEvent | 2019-09-17 17:38:28 | bitcoin/bitcoin | https://api.github.com/repos/bitcoin/bitcoin | closed | feature_block and p2p_permissions time out | Tests | Current master, on travis:
https://travis-ci.org/bitcoin/bitcoin/builds/578612449
https://travis-ci.org/bitcoin/bitcoin/builds/578444718
https://travis-ci.org/bitcoin/bitcoin/builds/577975853
Reported by @mzumsande in https://github.com/bitcoin/bitcoin/pull/16756#issuecomment-526748925 | 1.0 | feature_block and p2p_permissions time out - Current master, on travis:
https://travis-ci.org/bitcoin/bitcoin/builds/578612449
https://travis-ci.org/bitcoin/bitcoin/builds/578444718
https://travis-ci.org/bitcoin/bitcoin/builds/577975853
Reported by @mzumsande in https://github.com/bitcoin/bitcoin/pull/16756#issuecomment-526748925 | non_priority | feature block and permissions time out current master on travis reported by mzumsande in | 0 |
355,541 | 25,175,963,085 | IssuesEvent | 2022-11-11 09:17:19 | teoyuqi/pe | https://api.github.com/repos/teoyuqi/pe | opened | Incorrect code format in `edit` | type.DocumentationBug severity.Low | In the `edit` command section, the `...` symbol is placed after the `as/` prefix despite it not being a prefix that can be used multiple times.

<!--session: 1668154174404-06fc7f6c-3ad6-41d2-a33c-d1034ca8be81-->
<!--Version: Web v3.4.4--> | 1.0 | Incorrect code format in `edit` - In the `edit` command section, the `...` symbol is placed after the `as/` prefix despite it not being a prefix that can be used multiple times.

<!--session: 1668154174404-06fc7f6c-3ad6-41d2-a33c-d1034ca8be81-->
<!--Version: Web v3.4.4--> | non_priority | incorrect code format in edit in the edit command section the symbol is placed after the as prefix despite it not being a prefix that can be used multiple times | 0 |
389,796 | 26,834,128,709 | IssuesEvent | 2023-02-02 18:05:44 | NetAppDocs/storagegrid-116 | https://api.github.com/repos/NetAppDocs/storagegrid-116 | closed | Suggestion to include pre-upgrade check reference page with list of checks and recommendations / troubleshooting steps | documentation good first issue | Page: [StorageGRID 11.6 Documentation](https://docs.netapp.com/us-en/storagegrid-116/index.html)
Example of pre-upgrade check failures:
https://kb.netapp.com/Advice_and_Troubleshooting/Hybrid_Cloud_Infrastructure/StorageGRID/StorageGRID_11.7_upgrade_precheck_reports_CIFS_audit_warnings | 1.0 | Suggestion to include pre-upgrade check reference page with list of checks and recommendations / troubleshooting steps - Page: [StorageGRID 11.6 Documentation](https://docs.netapp.com/us-en/storagegrid-116/index.html)
Example of pre-upgrade check failures:
https://kb.netapp.com/Advice_and_Troubleshooting/Hybrid_Cloud_Infrastructure/StorageGRID/StorageGRID_11.7_upgrade_precheck_reports_CIFS_audit_warnings | non_priority | suggestion to include pre upgrade check reference page with list of checks and recommendations troubleshooting steps page example of pre upgrade check failures | 0 |
282,750 | 21,315,942,204 | IssuesEvent | 2022-04-16 09:18:41 | cristoforows/pe | https://api.github.com/repos/cristoforows/pe | opened | Consistency in command | type.DocumentationBug severity.VeryLow | perhaps makes them to 'medicine' or change the rest which are also targeting plural object to also use plural in the command ,eg. view medicine
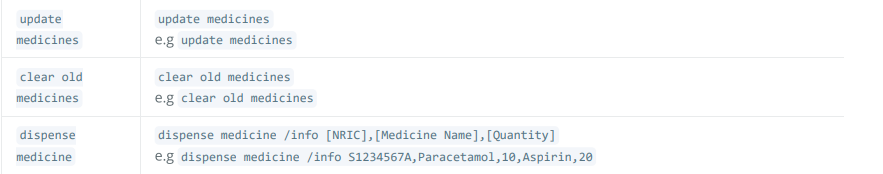
<!--session: 1650096027977-a32ed089-155e-444a-b94b-7c25c7cb1e12-->
<!--Version: Web v3.4.2--> | 1.0 | Consistency in command - perhaps makes them to 'medicine' or change the rest which are also targeting plural object to also use plural in the command ,eg. view medicine
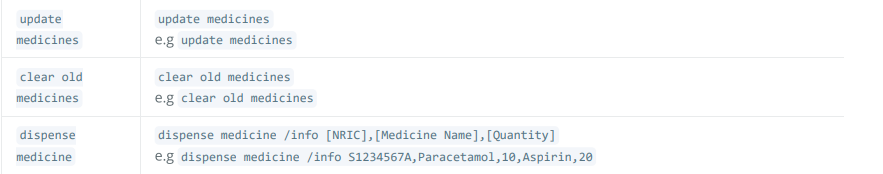
<!--session: 1650096027977-a32ed089-155e-444a-b94b-7c25c7cb1e12-->
<!--Version: Web v3.4.2--> | non_priority | consistency in command perhaps makes them to medicine or change the rest which are also targeting plural object to also use plural in the command eg view medicine | 0 |
330,656 | 28,479,268,325 | IssuesEvent | 2023-04-18 00:14:55 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: API Integration Tests.test/api_integration/apis/data_views/deprecations/scripted_fields·ts - apis index_patterns scripted_fields_deprecations scripted field deprecations no scripted fields deprecations | failed-test | A test failed on a tracked branch
```
Error: expected 1 to equal 0
at Assertion.assert (expect.js:100:11)
at Assertion.apply (expect.js:227:8)
at Assertion.be (expect.js:69:22)
at Context.<anonymous> (scripted_fields.ts:37:48)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/29018#01879188-ac03-447e-9c89-408deb9dd304)
<!-- kibanaCiData = {"failed-test":{"test.class":"API Integration Tests.test/api_integration/apis/data_views/deprecations/scripted_fields·ts","test.name":"apis index_patterns scripted_fields_deprecations scripted field deprecations no scripted fields deprecations","test.failCount":1}} --> | 1.0 | Failing test: API Integration Tests.test/api_integration/apis/data_views/deprecations/scripted_fields·ts - apis index_patterns scripted_fields_deprecations scripted field deprecations no scripted fields deprecations - A test failed on a tracked branch
```
Error: expected 1 to equal 0
at Assertion.assert (expect.js:100:11)
at Assertion.apply (expect.js:227:8)
at Assertion.be (expect.js:69:22)
at Context.<anonymous> (scripted_fields.ts:37:48)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/29018#01879188-ac03-447e-9c89-408deb9dd304)
<!-- kibanaCiData = {"failed-test":{"test.class":"API Integration Tests.test/api_integration/apis/data_views/deprecations/scripted_fields·ts","test.name":"apis index_patterns scripted_fields_deprecations scripted field deprecations no scripted fields deprecations","test.failCount":1}} --> | non_priority | failing test api integration tests test api integration apis data views deprecations scripted fields·ts apis index patterns scripted fields deprecations scripted field deprecations no scripted fields deprecations a test failed on a tracked branch error expected to equal at assertion assert expect js at assertion apply expect js at assertion be expect js at context scripted fields ts at runmicrotasks at processticksandrejections node internal process task queues at object apply wrap function js first failure | 0 |
226,442 | 24,947,134,716 | IssuesEvent | 2022-11-01 01:54:11 | directoryxx/Laravel-UUID-CRUD-Login | https://api.github.com/repos/directoryxx/Laravel-UUID-CRUD-Login | opened | CVE-2022-37620 (Medium) detected in html-minifier-3.5.21.tgz | security vulnerability | ## CVE-2022-37620 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>html-minifier-3.5.21.tgz</b></p></summary>
<p>Highly configurable, well-tested, JavaScript-based HTML minifier.</p>
<p>Library home page: <a href="https://registry.npmjs.org/html-minifier/-/html-minifier-3.5.21.tgz">https://registry.npmjs.org/html-minifier/-/html-minifier-3.5.21.tgz</a></p>
<p>Path to dependency file: /Laravel-UUID-CRUD-Login/package.json</p>
<p>Path to vulnerable library: /node_modules/html-minifier/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-4.1.2.tgz (Root Library)
- html-loader-0.5.5.tgz
- :x: **html-minifier-3.5.21.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Regular Expression Denial of Service (ReDoS) flaw was found in kangax html-minifier 4.0.0 via the candidate variable in htmlminifier.js.
<p>Publish Date: 2022-10-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37620>CVE-2022-37620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-37620 (Medium) detected in html-minifier-3.5.21.tgz - ## CVE-2022-37620 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>html-minifier-3.5.21.tgz</b></p></summary>
<p>Highly configurable, well-tested, JavaScript-based HTML minifier.</p>
<p>Library home page: <a href="https://registry.npmjs.org/html-minifier/-/html-minifier-3.5.21.tgz">https://registry.npmjs.org/html-minifier/-/html-minifier-3.5.21.tgz</a></p>
<p>Path to dependency file: /Laravel-UUID-CRUD-Login/package.json</p>
<p>Path to vulnerable library: /node_modules/html-minifier/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-4.1.2.tgz (Root Library)
- html-loader-0.5.5.tgz
- :x: **html-minifier-3.5.21.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Regular Expression Denial of Service (ReDoS) flaw was found in kangax html-minifier 4.0.0 via the candidate variable in htmlminifier.js.
<p>Publish Date: 2022-10-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-37620>CVE-2022-37620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in html minifier tgz cve medium severity vulnerability vulnerable library html minifier tgz highly configurable well tested javascript based html minifier library home page a href path to dependency file laravel uuid crud login package json path to vulnerable library node modules html minifier package json dependency hierarchy laravel mix tgz root library html loader tgz x html minifier tgz vulnerable library vulnerability details a regular expression denial of service redos flaw was found in kangax html minifier via the candidate variable in htmlminifier js publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
185,311 | 14,349,331,442 | IssuesEvent | 2020-11-29 16:10:27 | aio-libs/aiosmtpd | https://api.github.com/repos/aio-libs/aiosmtpd | closed | Using GitHub Actions -- replace Travis CI integration? | administrivia integration pr-available testing | I've created the YAML script to drive GitHub Actions (GA) testing, in commit c7630ae + 3b10324 (the latter because I didn't realize before that GA cancels everything in the matrix if any one of them fails.)
As you can [see here](https://github.com/aio-libs/aiosmtpd/actions), the tests passes for the current HEAD of `master`.
(You can manually trigger it to run by clicking on "aiosmtpd CI" on the left sidebar, then click "Run workflow".)
I don't know how to integrate them to the PR system, though. And/or how to replace Travis CI automatic testing of PR and pushes-to-PR. | 1.0 | Using GitHub Actions -- replace Travis CI integration? - I've created the YAML script to drive GitHub Actions (GA) testing, in commit c7630ae + 3b10324 (the latter because I didn't realize before that GA cancels everything in the matrix if any one of them fails.)
As you can [see here](https://github.com/aio-libs/aiosmtpd/actions), the tests passes for the current HEAD of `master`.
(You can manually trigger it to run by clicking on "aiosmtpd CI" on the left sidebar, then click "Run workflow".)
I don't know how to integrate them to the PR system, though. And/or how to replace Travis CI automatic testing of PR and pushes-to-PR. | non_priority | using github actions replace travis ci integration i ve created the yaml script to drive github actions ga testing in commit the latter because i didn t realize before that ga cancels everything in the matrix if any one of them fails as you can the tests passes for the current head of master you can manually trigger it to run by clicking on aiosmtpd ci on the left sidebar then click run workflow i don t know how to integrate them to the pr system though and or how to replace travis ci automatic testing of pr and pushes to pr | 0 |
119,305 | 25,505,074,480 | IssuesEvent | 2022-11-28 08:48:43 | 5l1D3R/Veracode-Github-integration | https://api.github.com/repos/5l1D3R/Veracode-Github-integration | opened | Improper Neutralization of CRLF Sequences in HTTP Headers ('HTTP Request/Response Splitting') ('CRLF Injection') [VID:39] | VeracodeFlaw: Medium Veracode Policy Scan | **Filename:** UserController.java
**Line:** 631
**CWE:** 113 (Improper Neutralization of CRLF Sequences in HTTP Headers ('HTTP Request/Response Splitting') ('CRLF Injection'))
<span>This call to javax.servlet.http.HttpServletResponse.addCookie() contains an HTTP response splitting flaw. Writing untrusted input into an HTTP header allows an attacker to manipulate the HTTP response rendered by the browser, to inject additional headers or an entire response body into the response stream. Injecting headers can be used to trick various security mechanisms in browsers into allowing XSS style attacks. Injecting entire response bodies can not only cause XSS attacks to succeed but may even poison the cache of any intermediary proxies between the clients and the application server. The first argument to addCookie() contains tainted data from the variable cookie. The tainted data originated from earlier calls to javax.servlet.http.HttpServletRequest.getCookies, and AnnotationVirtualController.vc_annotation_entry.</span> <span>Escape, encode, or remove carriage return and line feed characters from untrusted data before inclusion in HTTP response headers. Whenever possible, use a security library such as ESAPI that provides safe versions of addHeader(), etc. that will automatically remove unexpected carriage returns and line feeds and can be configured to use HTML entity encoding for non-alphanumeric data. Alternatively, some of the XSS escaping functions from the OWASP Java Encoder project will also sanitize CRLF sequences. Only create a custom blocklist when absolutely necessary. Always validate untrusted input to ensure that it conforms to the expected format, using centralized data validation routines when possible.</span> <span>References: <a href="https://cwe.mitre.org/data/definitions/113.html">CWE</a> <a href="https://owasp.org/www-community/attacks/HTTP_Response_Splitting">OWASP</a> <a href="https://docs.veracode.com/r/review_cleansers">Supported Cleansers</a></span> | 2.0 | Improper Neutralization of CRLF Sequences in HTTP Headers ('HTTP Request/Response Splitting') ('CRLF Injection') [VID:39] - **Filename:** UserController.java
**Line:** 631
**CWE:** 113 (Improper Neutralization of CRLF Sequences in HTTP Headers ('HTTP Request/Response Splitting') ('CRLF Injection'))
<span>This call to javax.servlet.http.HttpServletResponse.addCookie() contains an HTTP response splitting flaw. Writing untrusted input into an HTTP header allows an attacker to manipulate the HTTP response rendered by the browser, to inject additional headers or an entire response body into the response stream. Injecting headers can be used to trick various security mechanisms in browsers into allowing XSS style attacks. Injecting entire response bodies can not only cause XSS attacks to succeed but may even poison the cache of any intermediary proxies between the clients and the application server. The first argument to addCookie() contains tainted data from the variable cookie. The tainted data originated from earlier calls to javax.servlet.http.HttpServletRequest.getCookies, and AnnotationVirtualController.vc_annotation_entry.</span> <span>Escape, encode, or remove carriage return and line feed characters from untrusted data before inclusion in HTTP response headers. Whenever possible, use a security library such as ESAPI that provides safe versions of addHeader(), etc. that will automatically remove unexpected carriage returns and line feeds and can be configured to use HTML entity encoding for non-alphanumeric data. Alternatively, some of the XSS escaping functions from the OWASP Java Encoder project will also sanitize CRLF sequences. Only create a custom blocklist when absolutely necessary. Always validate untrusted input to ensure that it conforms to the expected format, using centralized data validation routines when possible.</span> <span>References: <a href="https://cwe.mitre.org/data/definitions/113.html">CWE</a> <a href="https://owasp.org/www-community/attacks/HTTP_Response_Splitting">OWASP</a> <a href="https://docs.veracode.com/r/review_cleansers">Supported Cleansers</a></span> | non_priority | improper neutralization of crlf sequences in http headers http request response splitting crlf injection filename usercontroller java line cwe improper neutralization of crlf sequences in http headers http request response splitting crlf injection this call to javax servlet http httpservletresponse addcookie contains an http response splitting flaw writing untrusted input into an http header allows an attacker to manipulate the http response rendered by the browser to inject additional headers or an entire response body into the response stream injecting headers can be used to trick various security mechanisms in browsers into allowing xss style attacks injecting entire response bodies can not only cause xss attacks to succeed but may even poison the cache of any intermediary proxies between the clients and the application server the first argument to addcookie contains tainted data from the variable cookie the tainted data originated from earlier calls to javax servlet http httpservletrequest getcookies and annotationvirtualcontroller vc annotation entry escape encode or remove carriage return and line feed characters from untrusted data before inclusion in http response headers whenever possible use a security library such as esapi that provides safe versions of addheader etc that will automatically remove unexpected carriage returns and line feeds and can be configured to use html entity encoding for non alphanumeric data alternatively some of the xss escaping functions from the owasp java encoder project will also sanitize crlf sequences only create a custom blocklist when absolutely necessary always validate untrusted input to ensure that it conforms to the expected format using centralized data validation routines when possible references | 0 |
38,380 | 6,669,026,822 | IssuesEvent | 2017-10-03 17:51:45 | creativedisturbance/podcasts | https://api.github.com/repos/creativedisturbance/podcasts | closed | MIT Forms for Future Labs Africa Channel- BETA access | ARTECA Documentation | Creating an issue to document processes needed for Future Labs Africa to publish their podcasts on ARTECA.
-New Collaboration Agreement
-MIT Podcast form
Getting Teagan Bristow and Jepchumba II free beta access to ARTECA | 1.0 | MIT Forms for Future Labs Africa Channel- BETA access - Creating an issue to document processes needed for Future Labs Africa to publish their podcasts on ARTECA.
-New Collaboration Agreement
-MIT Podcast form
Getting Teagan Bristow and Jepchumba II free beta access to ARTECA | non_priority | mit forms for future labs africa channel beta access creating an issue to document processes needed for future labs africa to publish their podcasts on arteca new collaboration agreement mit podcast form getting teagan bristow and jepchumba ii free beta access to arteca | 0 |
33,664 | 9,199,272,504 | IssuesEvent | 2019-03-07 14:36:24 | quicklisp/quicklisp-projects | https://api.github.com/repos/quicklisp/quicklisp-projects | closed | Please Add cl-markless | canbuild | cl-markless is an implementation of the [Markless](https://github.com/shirakumo/markless) document markup standard.
Author: Nicolas Hafner
Documentation: https://shirakumo.github.io/cl-markless/
Repository: https://github.com/Shirakumo/cl-markless | 1.0 | Please Add cl-markless - cl-markless is an implementation of the [Markless](https://github.com/shirakumo/markless) document markup standard.
Author: Nicolas Hafner
Documentation: https://shirakumo.github.io/cl-markless/
Repository: https://github.com/Shirakumo/cl-markless | non_priority | please add cl markless cl markless is an implementation of the document markup standard author nicolas hafner documentation repository | 0 |
81,224 | 10,113,532,589 | IssuesEvent | 2019-07-30 16:57:19 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [AppBar] Multiple UIBarButtonItems take a lot of horizontal space | Needs design input [AppBar] type:Feature request | ### Overview
let appBar = MDCAppBar()
...
navigationItem.rightBarButtonItems = [moreItem, searchItem, filterItem]
3 buttons take more than a half of the screen width.
Solution - UIBarButtonItem(customView: view) where view has fixed size.
Other UIBarButtonItem initializers produce the mentioned issue.
### Reproduction steps
- see code above
### Operating system and device
- iPhone
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/117179403](http://b/117179403) | 1.0 | [AppBar] Multiple UIBarButtonItems take a lot of horizontal space - ### Overview
let appBar = MDCAppBar()
...
navigationItem.rightBarButtonItems = [moreItem, searchItem, filterItem]
3 buttons take more than a half of the screen width.
Solution - UIBarButtonItem(customView: view) where view has fixed size.
Other UIBarButtonItem initializers produce the mentioned issue.
### Reproduction steps
- see code above
### Operating system and device
- iPhone
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/117179403](http://b/117179403) | non_priority | multiple uibarbuttonitems take a lot of horizontal space overview let appbar mdcappbar navigationitem rightbarbuttonitems buttons take more than a half of the screen width solution uibarbuttonitem customview view where view has fixed size other uibarbuttonitem initializers produce the mentioned issue reproduction steps see code above operating system and device iphone internal data associated internal bug | 0 |
230,902 | 18,723,625,340 | IssuesEvent | 2021-11-03 14:19:34 | hashgraph/hedera-services | https://api.github.com/repos/hashgraph/hedera-services | closed | HTS-Restart-Performance-Hotspot-10k-61m fails with `FREEZE_ALREADY_SCHEDULED` | Test Development Regression Test config failure | ### Description
`TokenTransfersLoadProvider` EET suit ends with a `freezeOnly()` spec. So when using multiple clients one of accepted response codes must be `FREEZE_ALREADY_SCHEDULED` as one of the other clients might have already scheduled a freeze when this clients freeze request is handled.
### Steps to reproduce
Run `HTS-Restart-Performance-Hotspot-10k-61m` with multiple clients
### Additional context
_No response_
### Hedera network
other
### Version
v0.20.0
### Operating system
_No response_ | 2.0 | HTS-Restart-Performance-Hotspot-10k-61m fails with `FREEZE_ALREADY_SCHEDULED` - ### Description
`TokenTransfersLoadProvider` EET suit ends with a `freezeOnly()` spec. So when using multiple clients one of accepted response codes must be `FREEZE_ALREADY_SCHEDULED` as one of the other clients might have already scheduled a freeze when this clients freeze request is handled.
### Steps to reproduce
Run `HTS-Restart-Performance-Hotspot-10k-61m` with multiple clients
### Additional context
_No response_
### Hedera network
other
### Version
v0.20.0
### Operating system
_No response_ | non_priority | hts restart performance hotspot fails with freeze already scheduled description tokentransfersloadprovider eet suit ends with a freezeonly spec so when using multiple clients one of accepted response codes must be freeze already scheduled as one of the other clients might have already scheduled a freeze when this clients freeze request is handled steps to reproduce run hts restart performance hotspot with multiple clients additional context no response hedera network other version operating system no response | 0 |
6,632 | 4,403,454,848 | IssuesEvent | 2016-08-11 07:59:29 | qfeys/ThrottleControlledAvionics | https://api.github.com/repos/qfeys/ThrottleControlledAvionics | closed | TCA activates the part it is installed into; if that part also has ModuleEngines, engines are fired. | usability issue | I've been running into a problem that I believe I have isolated to TCA and mod ships with integrated engines. With TCA, all engines load in "active" state, and since the game defaults to 50% throttle, bad things happen before I am able to tap "X." When using the Endurance mod, both the Lander and the Ranger immediately leap forward and nose-dive into the ground as soon as the loading is complete. Mod command pods that are equipped with integrated SuperDraco engines automatically fire up resulting in spectacular destruction of the entire launch system. | True | TCA activates the part it is installed into; if that part also has ModuleEngines, engines are fired. - I've been running into a problem that I believe I have isolated to TCA and mod ships with integrated engines. With TCA, all engines load in "active" state, and since the game defaults to 50% throttle, bad things happen before I am able to tap "X." When using the Endurance mod, both the Lander and the Ranger immediately leap forward and nose-dive into the ground as soon as the loading is complete. Mod command pods that are equipped with integrated SuperDraco engines automatically fire up resulting in spectacular destruction of the entire launch system. | non_priority | tca activates the part it is installed into if that part also has moduleengines engines are fired i ve been running into a problem that i believe i have isolated to tca and mod ships with integrated engines with tca all engines load in active state and since the game defaults to throttle bad things happen before i am able to tap x when using the endurance mod both the lander and the ranger immediately leap forward and nose dive into the ground as soon as the loading is complete mod command pods that are equipped with integrated superdraco engines automatically fire up resulting in spectacular destruction of the entire launch system | 0 |
118,411 | 9,986,417,610 | IssuesEvent | 2019-07-10 19:02:40 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | closed | Test_openjdk12_j9_extended.system_s390x_linux MathLoadTest JIT crash | arch:z comp:jit test failure | https://ci.eclipse.org/openj9/job/Test_openjdk12_j9_extended.system_s390x_linux_Nightly/71
MathLoadTest_all_0
```
MLT stderr Unhandled exception
MLT stderr Type=Segmentation error vmState=0x00000000
MLT stderr J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=00802ac0 Signal_Code=00000001
MLT stderr Handler1=000003FF7ECCA458 Handler2=000003FF7E8A7E98 InaccessibleAddress=000358000C848000
MLT stderr gpr0=000000000000000D gpr1=00000000000002F5 gpr2=0000000074B7AD28 gpr3=0000000000000006
MLT stderr gpr4=00000000000A6800 gpr5=000000000046E3B0 gpr6=0000000074B7AD3A gpr7=0003580000000035
MLT stderr gpr8=0000000000000100 gpr9=0000000000000006 gpr10=000000000C8488C8 gpr11=000358000000000D
MLT stderr gpr12=0000000000000005 gpr13=0000000000463F00 gpr14=000003FF5EF97644 gpr15=000003FF7E37E478
MLT stderr psw=000003FF5F0BAD18 mask=0705100180000000 fpc=00b8ff00 bea=000003FF5F0BC522
MLT stderr fpr0 000000000e176298 (f: 236413600.000000, d: 1.168038e-315)
MLT stderr fpr1 377fcdf96e760ac5 (f: 1853229824.000000, d: 2.281867e-41)
MLT stderr fpr2 0000005f00000044 (f: 68.000000, d: 2.015896e-312)
MLT stderr fpr3 3faca77511ce8399 (f: 298746784.000000, d: 5.596510e-02)
MLT stderr fpr4 42c0000000000000 (f: 0.000000, d: 3.518437e+13)
MLT stderr fpr5 3d7b182886ac0ce1 (f: 2259422464.000000, d: 1.540137e-12)
MLT stderr fpr6 0000000000000000 (f: 0.000000, d: 0.000000e+00)
MLT stderr fpr7 3c00000000000000 (f: 0.000000, d: 1.084202e-19)
MLT stderr fpr8 40734413509f79fe (f: 1352628736.000000, d: 3.082547e+02)
MLT stderr fpr9 3fc1640c43cb4edb (f: 1137397504.000000, d: 1.358657e-01)
MLT stderr fpr10 000003ff7e340000 (f: 2117337088.000000, d: 2.171848e-311)
MLT stderr fpr11 000003ffd0d7f153 (f: 3503812864.000000, d: 2.172533e-311)
MLT stderr fpr12 00000000000f35f8 (f: 996856.000000, d: 4.925123e-318)
MLT stderr fpr13 000003fff64fcc48 (f: 4132424704.000000, d: 2.172843e-311)
MLT stderr fpr14 0000000000000022 (f: 34.000000, d: 1.679823e-322)
MLT stderr fpr15 000003ffd5d7de78 (f: 3587694080.000000, d: 2.172574e-311)
MLT stderr
MLT stderr Compiled_method=java/math/BigInteger.<init>([CII)V
MLT stderr Target=2_90_20190623_72 (Linux 4.4.0-141-generic)
MLT stderr CPU=s390x (4 logical CPUs) (0x1e9a00000 RAM)
MLT stderr ----------- Stack Backtrace -----------
MLT stderr (0x000003FF5F0BAD18 [<unknown>+0x0])
``` | 1.0 | Test_openjdk12_j9_extended.system_s390x_linux MathLoadTest JIT crash - https://ci.eclipse.org/openj9/job/Test_openjdk12_j9_extended.system_s390x_linux_Nightly/71
MathLoadTest_all_0
```
MLT stderr Unhandled exception
MLT stderr Type=Segmentation error vmState=0x00000000
MLT stderr J9Generic_Signal_Number=00000018 Signal_Number=0000000b Error_Value=00802ac0 Signal_Code=00000001
MLT stderr Handler1=000003FF7ECCA458 Handler2=000003FF7E8A7E98 InaccessibleAddress=000358000C848000
MLT stderr gpr0=000000000000000D gpr1=00000000000002F5 gpr2=0000000074B7AD28 gpr3=0000000000000006
MLT stderr gpr4=00000000000A6800 gpr5=000000000046E3B0 gpr6=0000000074B7AD3A gpr7=0003580000000035
MLT stderr gpr8=0000000000000100 gpr9=0000000000000006 gpr10=000000000C8488C8 gpr11=000358000000000D
MLT stderr gpr12=0000000000000005 gpr13=0000000000463F00 gpr14=000003FF5EF97644 gpr15=000003FF7E37E478
MLT stderr psw=000003FF5F0BAD18 mask=0705100180000000 fpc=00b8ff00 bea=000003FF5F0BC522
MLT stderr fpr0 000000000e176298 (f: 236413600.000000, d: 1.168038e-315)
MLT stderr fpr1 377fcdf96e760ac5 (f: 1853229824.000000, d: 2.281867e-41)
MLT stderr fpr2 0000005f00000044 (f: 68.000000, d: 2.015896e-312)
MLT stderr fpr3 3faca77511ce8399 (f: 298746784.000000, d: 5.596510e-02)
MLT stderr fpr4 42c0000000000000 (f: 0.000000, d: 3.518437e+13)
MLT stderr fpr5 3d7b182886ac0ce1 (f: 2259422464.000000, d: 1.540137e-12)
MLT stderr fpr6 0000000000000000 (f: 0.000000, d: 0.000000e+00)
MLT stderr fpr7 3c00000000000000 (f: 0.000000, d: 1.084202e-19)
MLT stderr fpr8 40734413509f79fe (f: 1352628736.000000, d: 3.082547e+02)
MLT stderr fpr9 3fc1640c43cb4edb (f: 1137397504.000000, d: 1.358657e-01)
MLT stderr fpr10 000003ff7e340000 (f: 2117337088.000000, d: 2.171848e-311)
MLT stderr fpr11 000003ffd0d7f153 (f: 3503812864.000000, d: 2.172533e-311)
MLT stderr fpr12 00000000000f35f8 (f: 996856.000000, d: 4.925123e-318)
MLT stderr fpr13 000003fff64fcc48 (f: 4132424704.000000, d: 2.172843e-311)
MLT stderr fpr14 0000000000000022 (f: 34.000000, d: 1.679823e-322)
MLT stderr fpr15 000003ffd5d7de78 (f: 3587694080.000000, d: 2.172574e-311)
MLT stderr
MLT stderr Compiled_method=java/math/BigInteger.<init>([CII)V
MLT stderr Target=2_90_20190623_72 (Linux 4.4.0-141-generic)
MLT stderr CPU=s390x (4 logical CPUs) (0x1e9a00000 RAM)
MLT stderr ----------- Stack Backtrace -----------
MLT stderr (0x000003FF5F0BAD18 [<unknown>+0x0])
``` | non_priority | test extended system linux mathloadtest jit crash mathloadtest all mlt stderr unhandled exception mlt stderr type segmentation error vmstate mlt stderr signal number signal number error value signal code mlt stderr inaccessibleaddress mlt stderr mlt stderr mlt stderr mlt stderr mlt stderr psw mask fpc bea mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr f d mlt stderr mlt stderr compiled method java math biginteger cii v mlt stderr target linux generic mlt stderr cpu logical cpus ram mlt stderr stack backtrace mlt stderr | 0 |
170,655 | 20,883,797,774 | IssuesEvent | 2022-03-23 01:13:59 | snowdensb/dependabot-core | https://api.github.com/repos/snowdensb/dependabot-core | reopened | WS-2020-0003 (High) detected in phpunit/phpunit-6.5.5 | security vulnerability | ## WS-2020-0003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>phpunit/phpunit-6.5.5</b></p></summary>
<p>The PHP Unit Testing framework.</p>
<p>
Dependency Hierarchy:
- :x: **phpunit/phpunit-6.5.5** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/dependabot-core/commit/ba8cd9078c8ce0cb202767d627706711237abf71">ba8cd9078c8ce0cb202767d627706711237abf71</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Some autoupgrade module ZIP archives have been built with phpunit dev dependencies. PHPUnit contains a php script that would allow an attacker to perform RCE on a webserver.
<p>Publish Date: 2019-12-10
<p>URL: <a href=https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f>WS-2020-0003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f">https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f</a></p>
<p>Release Date: 2020-01-09</p>
<p>Fix Resolution: 7.5.19,8.5.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"PHP","packageName":"phpunit/phpunit","packageVersion":"6.5.5","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"phpunit/phpunit:6.5.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"7.5.19,8.5.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0003","vulnerabilityDetails":"Some autoupgrade module ZIP archives have been built with phpunit dev dependencies. PHPUnit contains a php script that would allow an attacker to perform RCE on a webserver.","vulnerabilityUrl":"https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | WS-2020-0003 (High) detected in phpunit/phpunit-6.5.5 - ## WS-2020-0003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>phpunit/phpunit-6.5.5</b></p></summary>
<p>The PHP Unit Testing framework.</p>
<p>
Dependency Hierarchy:
- :x: **phpunit/phpunit-6.5.5** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/dependabot-core/commit/ba8cd9078c8ce0cb202767d627706711237abf71">ba8cd9078c8ce0cb202767d627706711237abf71</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Some autoupgrade module ZIP archives have been built with phpunit dev dependencies. PHPUnit contains a php script that would allow an attacker to perform RCE on a webserver.
<p>Publish Date: 2019-12-10
<p>URL: <a href=https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f>WS-2020-0003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f">https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f</a></p>
<p>Release Date: 2020-01-09</p>
<p>Fix Resolution: 7.5.19,8.5.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"PHP","packageName":"phpunit/phpunit","packageVersion":"6.5.5","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"phpunit/phpunit:6.5.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"7.5.19,8.5.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0003","vulnerabilityDetails":"Some autoupgrade module ZIP archives have been built with phpunit dev dependencies. PHPUnit contains a php script that would allow an attacker to perform RCE on a webserver.","vulnerabilityUrl":"https://github.com/PrestaShop/autoupgrade/security/advisories/GHSA-wqq8-mqj9-697f","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in phpunit phpunit ws high severity vulnerability vulnerable library phpunit phpunit the php unit testing framework dependency hierarchy x phpunit phpunit vulnerable library found in head commit a href found in base branch main vulnerability details some autoupgrade module zip archives have been built with phpunit dev dependencies phpunit contains a php script that would allow an attacker to perform rce on a webserver publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree phpunit phpunit isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier ws vulnerabilitydetails some autoupgrade module zip archives have been built with phpunit dev dependencies phpunit contains a php script that would allow an attacker to perform rce on a webserver vulnerabilityurl | 0 |
127,260 | 10,456,229,700 | IssuesEvent | 2019-09-20 00:09:18 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Unnecessary space in `Remove` button for widget menus in NTP | QA/Test-Plan-Specified QA/Yes bug feature/user-interface | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description
<!--Provide a brief description of the issue-->
Unnecessary space in `Remove` button for widget menus in NTP
## Steps to Reproduce
<!--Please add a series of steps to reproduce the issue-->
1. Open brave 0.70.97
2. Open a few websites so that top tiles shown in NTP
3. Open an NTP
4. Click on Widget icon for `Remove`
5. Unnecessary space in `Remove` button for widget menus
## Actual result:
<!--Please add screenshots if needed-->
Unnecessary space in `Remove` button for widget menus in NTP



## Expected result:
Trim the `Remove` button
## Reproduces how often:
<!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
Always
## Brave version (brave://version info)
<!--For installed build, please copy Brave, Revision and OS from brave://version and paste here. If building from source please mention it along with brave://version details-->
Brave | 0.70.97 Chromium: 77.0.3865.65 (Official Build) beta (64-bit)
-- | --
Revision | 87a331a3169cab563505fb44011058b904011ba1-refs/branch-heads/3865@{#726}
OS | Windows 10 OS Version 1803 (Build 17134.1006)
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current release? NA
- Can you reproduce this issue with the beta channel? Yes
- Can you reproduce this issue with the dev channel? Yes
- Can you reproduce this issue with the nightly channel? Yes
## Other Additional Information:
- Does the issue resolve itself when disabling Brave Shields? NA
- Does the issue resolve itself when disabling Brave Rewards? NA
- Is the issue reproducible on the latest version of Chrome? NA
## Miscellaneous Information:
<!--Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue-->
@brave/legacy_qa @karenkliu | 1.0 | Unnecessary space in `Remove` button for widget menus in NTP - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description
<!--Provide a brief description of the issue-->
Unnecessary space in `Remove` button for widget menus in NTP
## Steps to Reproduce
<!--Please add a series of steps to reproduce the issue-->
1. Open brave 0.70.97
2. Open a few websites so that top tiles shown in NTP
3. Open an NTP
4. Click on Widget icon for `Remove`
5. Unnecessary space in `Remove` button for widget menus
## Actual result:
<!--Please add screenshots if needed-->
Unnecessary space in `Remove` button for widget menus in NTP



## Expected result:
Trim the `Remove` button
## Reproduces how often:
<!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
Always
## Brave version (brave://version info)
<!--For installed build, please copy Brave, Revision and OS from brave://version and paste here. If building from source please mention it along with brave://version details-->
Brave | 0.70.97 Chromium: 77.0.3865.65 (Official Build) beta (64-bit)
-- | --
Revision | 87a331a3169cab563505fb44011058b904011ba1-refs/branch-heads/3865@{#726}
OS | Windows 10 OS Version 1803 (Build 17134.1006)
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current release? NA
- Can you reproduce this issue with the beta channel? Yes
- Can you reproduce this issue with the dev channel? Yes
- Can you reproduce this issue with the nightly channel? Yes
## Other Additional Information:
- Does the issue resolve itself when disabling Brave Shields? NA
- Does the issue resolve itself when disabling Brave Rewards? NA
- Is the issue reproducible on the latest version of Chrome? NA
## Miscellaneous Information:
<!--Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue-->
@brave/legacy_qa @karenkliu | non_priority | unnecessary space in remove button for widget menus in ntp have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will only be reopened after sufficient info is provided description unnecessary space in remove button for widget menus in ntp steps to reproduce open brave open a few websites so that top tiles shown in ntp open an ntp click on widget icon for remove unnecessary space in remove button for widget menus actual result unnecessary space in remove button for widget menus in ntp expected result trim the remove button reproduces how often always brave version brave version info brave chromium official build beta bit revision refs branch heads os windows os version build version channel information can you reproduce this issue with the current release na can you reproduce this issue with the beta channel yes can you reproduce this issue with the dev channel yes can you reproduce this issue with the nightly channel yes other additional information does the issue resolve itself when disabling brave shields na does the issue resolve itself when disabling brave rewards na is the issue reproducible on the latest version of chrome na miscellaneous information brave legacy qa karenkliu | 0 |
352,602 | 32,079,643,569 | IssuesEvent | 2023-09-25 13:12:55 | fingerprintjs/fingerprintjs-pro-flutter | https://api.github.com/repos/fingerprintjs/fingerprintjs-pro-flutter | closed | Android native plugin doesn't support AGP 8.0 | released released on @test | Android Flutter plugins should add namespace under android inside the build configuration for the app.
Something like [this](https://github.com/fluttercommunity/plus_plugins/pull/1704/files).
Steps to reproduce
- Create a new Flutter Application (empty)
- Use Android Studio's "AGP Upgrade Assistant" to upgrade to Gradle 8
- flutter pub add fpjs_pro_plugin
Also check official android documentation [here](https://developer.android.com/build/publish-library/prep-lib-release#choose-namespace).
| 1.0 | Android native plugin doesn't support AGP 8.0 - Android Flutter plugins should add namespace under android inside the build configuration for the app.
Something like [this](https://github.com/fluttercommunity/plus_plugins/pull/1704/files).
Steps to reproduce
- Create a new Flutter Application (empty)
- Use Android Studio's "AGP Upgrade Assistant" to upgrade to Gradle 8
- flutter pub add fpjs_pro_plugin
Also check official android documentation [here](https://developer.android.com/build/publish-library/prep-lib-release#choose-namespace).
| non_priority | android native plugin doesn t support agp android flutter plugins should add namespace under android inside the build configuration for the app something like steps to reproduce create a new flutter application empty use android studio s agp upgrade assistant to upgrade to gradle flutter pub add fpjs pro plugin also check official android documentation | 0 |
65,430 | 6,963,676,197 | IssuesEvent | 2017-12-08 18:22:53 | sttDB/sttDB-client | https://api.github.com/repos/sttDB/sttDB-client | closed | Create angular App | feature testing | - Create angular 4 app
- Migrate last prototype to app
## Test:
- [x] Are links broken?
- [x] Collaborators ok?
- [x] Upload page
- [ ] Query page | 1.0 | Create angular App - - Create angular 4 app
- Migrate last prototype to app
## Test:
- [x] Are links broken?
- [x] Collaborators ok?
- [x] Upload page
- [ ] Query page | non_priority | create angular app create angular app migrate last prototype to app test are links broken collaborators ok upload page query page | 0 |
125,660 | 10,349,047,928 | IssuesEvent | 2019-09-04 21:18:55 | vincaslt/vscode-highlight-matching-tag | https://api.github.com/repos/vincaslt/vscode-highlight-matching-tag | closed | Doesn't work more | test data needed | Unfortunately doesn't work more, was so beautiful...
In my Django Templates, before, everything worked perfectly, but now doesn't work. | 1.0 | Doesn't work more - Unfortunately doesn't work more, was so beautiful...
In my Django Templates, before, everything worked perfectly, but now doesn't work. | non_priority | doesn t work more unfortunately doesn t work more was so beautiful in my django templates before everything worked perfectly but now doesn t work | 0 |
228,822 | 17,481,345,545 | IssuesEvent | 2021-08-09 03:16:00 | browneli003/jest-another-RPG | https://api.github.com/repos/browneli003/jest-another-RPG | opened | Consolidate the code | documentation | ##We don't yet know exactly what this step entails, but we do know that we'll need to refactor our code after the tests pass, so we'll create this issue as a placeholder. | 1.0 | Consolidate the code - ##We don't yet know exactly what this step entails, but we do know that we'll need to refactor our code after the tests pass, so we'll create this issue as a placeholder. | non_priority | consolidate the code we don t yet know exactly what this step entails but we do know that we ll need to refactor our code after the tests pass so we ll create this issue as a placeholder | 0 |
48,921 | 7,465,147,266 | IssuesEvent | 2018-04-02 02:14:57 | apollo-rsps/apollo | https://api.github.com/repos/apollo-rsps/apollo | opened | Improve plugin documentation | documentation kotlin | This is an epic that involves:
- Introductory information ("what are plugins and why do they exist")
- Information for developing, testing, and releasing plugins
- In-code documentation for plugin APIs.
See #330, #392. | 1.0 | Improve plugin documentation - This is an epic that involves:
- Introductory information ("what are plugins and why do they exist")
- Information for developing, testing, and releasing plugins
- In-code documentation for plugin APIs.
See #330, #392. | non_priority | improve plugin documentation this is an epic that involves introductory information what are plugins and why do they exist information for developing testing and releasing plugins in code documentation for plugin apis see | 0 |
260,306 | 19,664,428,890 | IssuesEvent | 2022-01-10 20:41:15 | JoelMon/scriptx | https://api.github.com/repos/JoelMon/scriptx | opened | Mention Known Problems on README.md | documentation good first issue | Mention the problems one might run into while working with some books of the Bible.
See issue #30 as an example. | 1.0 | Mention Known Problems on README.md - Mention the problems one might run into while working with some books of the Bible.
See issue #30 as an example. | non_priority | mention known problems on readme md mention the problems one might run into while working with some books of the bible see issue as an example | 0 |
180,821 | 14,814,104,088 | IssuesEvent | 2021-01-14 03:52:11 | amzn/selling-partner-api-docs | https://api.github.com/repos/amzn/selling-partner-api-docs | opened | [BUG] /fba/inventory/v1/summaries inaccurate data | bug documentation | **If you need help troubleshooting a problem with Selling Partner APIs, please [open a support case](https://developer.amazonservices.com/support). Issues are for reporting documentation bugs and enhancements only.**
By calling /fba/inventory/v1/summaries API, it is found that there is a great delay in getting inventory data and background data, some of which are about two days late
| 1.0 | [BUG] /fba/inventory/v1/summaries inaccurate data - **If you need help troubleshooting a problem with Selling Partner APIs, please [open a support case](https://developer.amazonservices.com/support). Issues are for reporting documentation bugs and enhancements only.**
By calling /fba/inventory/v1/summaries API, it is found that there is a great delay in getting inventory data and background data, some of which are about two days late
| non_priority | fba inventory summaries inaccurate data if you need help troubleshooting a problem with selling partner apis please issues are for reporting documentation bugs and enhancements only by calling fba inventory summaries api it is found that there is a great delay in getting inventory data and background data some of which are about two days late | 0 |
32,349 | 26,644,908,547 | IssuesEvent | 2023-01-25 09:13:22 | pymor/pymor | https://api.github.com/repos/pymor/pymor | closed | Switch to github super linter | infrastructure | I've disabled the branch protection for it until I figure out the best way to solve the problem | 1.0 | Switch to github super linter - I've disabled the branch protection for it until I figure out the best way to solve the problem | non_priority | switch to github super linter i ve disabled the branch protection for it until i figure out the best way to solve the problem | 0 |
63,442 | 7,721,750,231 | IssuesEvent | 2018-05-24 06:57:56 | zayne72/blog | https://api.github.com/repos/zayne72/blog | opened | 设计模式之单例模式 | Design pattern | ### 一、什么是设计模式
#### 1. 定义
GoF:设计模式是在面向对象软件设计过程中针对特定问题的简洁而优雅的解决方案。
也可以理解为,**是对前人经验的一种总结,当我们封装一个函数时,是在复用代码;而当使用一个设计模式时,是在复用他人的经验**
#### 2. 分类
《设计模式》一书将设计模式分为三类:
- 创建型模式
单例模式、抽象工厂模式、建造者模式、工厂模式、原型模式
- 结构型模式
适配器模式、桥接模式、装饰模式、组合模式、外观模式、享元模式、代理模式
- 行为型模式
模版方法模式、命令模式、迭代器模式、观察者模式、中介者模式、备忘录模式、解释器模式、状态模式、策略模式、职责链模式、访问者模式
#### 3. 优点
- [x] 行之有效的解决方法
- [x] 易于修改和维护
- [x] 便于交流和沟通
### 二、单例模式
此次学习目标为单例模式
#### 什么是单例模式
保证一个类仅有一个实例,并提供一个访问它的全局访问点
文字定义总是晦涩难懂的,还是看代码:
```JS
// 皇帝,一国之主,有且只有一个
function Emperor() {
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
}
Emperor.prototype.say = function() {
console.log(this.name + this.id + ' : 择日再议');
};
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!')
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = new Emperor();
m1.say();
e1.say(); //每次皇帝的id都不一样
var m2 = new Minister('李大人');
var e2 = new Emperor();
m2.say();
e2.say(); //每次皇帝的id都不一样
var m3 = new Minister('王大人');
var e3 = new Emperor();
m3.say();
e3.say(); //每次皇帝的id都不一样
```
以上,每次皇帝(Emperor实例)得到的都是不一样的id,这样显然是不行的,以单例模式定义来理解,一个类只能实例化出一个对象,不管你实例化多少次`Emperor`,最终所有实例应该都是同一个
如何保证`Emperor`实例的唯一性,有两种做法
- 方法一
直接在函数里返回对象的形式来实现:
```JS
// 皇帝,一国之主,有且只有一个
function Emperor() {
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
// 保存着Emperor的实例
this.instance = null;
}
Emperor.getInstance = function() {
// 首次进入,实例化Emperor,并返回
if(!this.instance) {
this.instance = new Emperor();
}
return this.instance;
};
Emperor.prototype.say = function() {
console.log(this.name + this.id + ' : 择日再议');
};
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!');
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = Emperor.getInstance();
m1.say();
e1.say(); // 每次输出一致,保存了第一次的id
var m2 = new Minister('李大人');
var e2 = Emperor.getInstance();
m2.say();
e2.say(); // 每次输出一致,保存了第一次的id
var m3 = new Minister('王大人');
var e3 = Emperor.getInstance();
m3.say();
e3.say(); // 每次输出一致,保存了第一次的id
```
不难发现,以上代码中的`instance`并非私有成员,在外部是可以随意修改的,存在一定的安全隐患,私有化`instance`:
```JS
// 皇帝,一国之主,有且只有一个
function Emperor() {
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
}
Emperor.getInstance = (function() {
var instance = null;
return function() {
if(!instance) {
instance = new Emperor();
}
return instance;
};
})();
Emperor.prototype.say = function() {
console.log(this.name + this.id + ' : 择日再议');
};
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!');
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = Emperor.getInstance();
m1.say();
e1.say(); // 每次输出一致,保存了第一次的id
var m2 = new Minister('李大人');
var e2 = Emperor.getInstance();
m2.say();
e2.say(); // 每次输出一致,保存了第一次的id
var m3 = new Minister('王大人');
var e3 = Emperor.getInstance();
m3.say();
e3.say(); // 每次输出一致,保存了第一次的id
```
问题又来了,每次我们必须通过`Emperor.getInstance()`这样的静态访问获取对象而非使用`new`构造函数形式来获取,这就要求我们必须得知道`Emperor`是单例模式,同时还必须得知道通过`.getInstance()`方法才能获取到单例对象,如何通过`new`运算符正常获取对象?见第二种做法
- 方法二
```JS
// 皇帝,一国之主,有且只有一个
var Emperor = (function() {
var instance = null;
// 与全局的Emperor没有任何关系
function Emperor() {
if(instance) {
return instance;
}
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
return instance = this;
}
Emperor.prototype.say = function() {
console.log(this.name + this.id + ': 择日再议!');
};
return Emperor;
})();
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!');
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = new Emperor();
m1.say();
e1.say(); // 每次输出一致
var m2 = new Minister('李大人');
var e2 = new Emperor();
m2.say();
e2.say(); // 每次输出一致
var m3 = new Minister('王大人');
var e3 = new Emperor();
m3.say();
e3.say(); // 每次输出一致
```
以上,类似当想创建`Emperor`这样的只能实例化唯一对象的类的时候,就需要单例模式,而单例模式的原理其实就是,在每次创建之前需要判断一下是否存在,不存在就直接创建,存在的话,就把已经创建了的返回出去
| 1.0 | 设计模式之单例模式 - ### 一、什么是设计模式
#### 1. 定义
GoF:设计模式是在面向对象软件设计过程中针对特定问题的简洁而优雅的解决方案。
也可以理解为,**是对前人经验的一种总结,当我们封装一个函数时,是在复用代码;而当使用一个设计模式时,是在复用他人的经验**
#### 2. 分类
《设计模式》一书将设计模式分为三类:
- 创建型模式
单例模式、抽象工厂模式、建造者模式、工厂模式、原型模式
- 结构型模式
适配器模式、桥接模式、装饰模式、组合模式、外观模式、享元模式、代理模式
- 行为型模式
模版方法模式、命令模式、迭代器模式、观察者模式、中介者模式、备忘录模式、解释器模式、状态模式、策略模式、职责链模式、访问者模式
#### 3. 优点
- [x] 行之有效的解决方法
- [x] 易于修改和维护
- [x] 便于交流和沟通
### 二、单例模式
此次学习目标为单例模式
#### 什么是单例模式
保证一个类仅有一个实例,并提供一个访问它的全局访问点
文字定义总是晦涩难懂的,还是看代码:
```JS
// 皇帝,一国之主,有且只有一个
function Emperor() {
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
}
Emperor.prototype.say = function() {
console.log(this.name + this.id + ' : 择日再议');
};
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!')
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = new Emperor();
m1.say();
e1.say(); //每次皇帝的id都不一样
var m2 = new Minister('李大人');
var e2 = new Emperor();
m2.say();
e2.say(); //每次皇帝的id都不一样
var m3 = new Minister('王大人');
var e3 = new Emperor();
m3.say();
e3.say(); //每次皇帝的id都不一样
```
以上,每次皇帝(Emperor实例)得到的都是不一样的id,这样显然是不行的,以单例模式定义来理解,一个类只能实例化出一个对象,不管你实例化多少次`Emperor`,最终所有实例应该都是同一个
如何保证`Emperor`实例的唯一性,有两种做法
- 方法一
直接在函数里返回对象的形式来实现:
```JS
// 皇帝,一国之主,有且只有一个
function Emperor() {
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
// 保存着Emperor的实例
this.instance = null;
}
Emperor.getInstance = function() {
// 首次进入,实例化Emperor,并返回
if(!this.instance) {
this.instance = new Emperor();
}
return this.instance;
};
Emperor.prototype.say = function() {
console.log(this.name + this.id + ' : 择日再议');
};
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!');
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = Emperor.getInstance();
m1.say();
e1.say(); // 每次输出一致,保存了第一次的id
var m2 = new Minister('李大人');
var e2 = Emperor.getInstance();
m2.say();
e2.say(); // 每次输出一致,保存了第一次的id
var m3 = new Minister('王大人');
var e3 = Emperor.getInstance();
m3.say();
e3.say(); // 每次输出一致,保存了第一次的id
```
不难发现,以上代码中的`instance`并非私有成员,在外部是可以随意修改的,存在一定的安全隐患,私有化`instance`:
```JS
// 皇帝,一国之主,有且只有一个
function Emperor() {
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
}
Emperor.getInstance = (function() {
var instance = null;
return function() {
if(!instance) {
instance = new Emperor();
}
return instance;
};
})();
Emperor.prototype.say = function() {
console.log(this.name + this.id + ' : 择日再议');
};
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!');
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = Emperor.getInstance();
m1.say();
e1.say(); // 每次输出一致,保存了第一次的id
var m2 = new Minister('李大人');
var e2 = Emperor.getInstance();
m2.say();
e2.say(); // 每次输出一致,保存了第一次的id
var m3 = new Minister('王大人');
var e3 = Emperor.getInstance();
m3.say();
e3.say(); // 每次输出一致,保存了第一次的id
```
问题又来了,每次我们必须通过`Emperor.getInstance()`这样的静态访问获取对象而非使用`new`构造函数形式来获取,这就要求我们必须得知道`Emperor`是单例模式,同时还必须得知道通过`.getInstance()`方法才能获取到单例对象,如何通过`new`运算符正常获取对象?见第二种做法
- 方法二
```JS
// 皇帝,一国之主,有且只有一个
var Emperor = (function() {
var instance = null;
// 与全局的Emperor没有任何关系
function Emperor() {
if(instance) {
return instance;
}
this.name = '皇帝';
this.id = Math.floor(Math.random() * 10);
return instance = this;
}
Emperor.prototype.say = function() {
console.log(this.name + this.id + ': 择日再议!');
};
return Emperor;
})();
// 大臣,国之栋梁,多多益善
function Minister(name) {
this.name = name;
}
Minister.prototype.say = function() {
console.log(this.name + ': 陛下,臣附议!');
};
// 对某国事,三名大臣集体附议
var m1 = new Minister('张大人');
var e1 = new Emperor();
m1.say();
e1.say(); // 每次输出一致
var m2 = new Minister('李大人');
var e2 = new Emperor();
m2.say();
e2.say(); // 每次输出一致
var m3 = new Minister('王大人');
var e3 = new Emperor();
m3.say();
e3.say(); // 每次输出一致
```
以上,类似当想创建`Emperor`这样的只能实例化唯一对象的类的时候,就需要单例模式,而单例模式的原理其实就是,在每次创建之前需要判断一下是否存在,不存在就直接创建,存在的话,就把已经创建了的返回出去
| non_priority | 设计模式之单例模式 一、什么是设计模式 定义 gof:设计模式是在面向对象软件设计过程中针对特定问题的简洁而优雅的解决方案。 也可以理解为, 是对前人经验的一种总结,当我们封装一个函数时,是在复用代码;而当使用一个设计模式时,是在复用他人的经验 分类 《设计模式》一书将设计模式分为三类 创建型模式 单例模式、抽象工厂模式、建造者模式、工厂模式、原型模式 结构型模式 适配器模式、桥接模式、装饰模式、组合模式、外观模式、享元模式、代理模式 行为型模式 模版方法模式、命令模式、迭代器模式、观察者模式、中介者模式、备忘录模式、解释器模式、状态模式、策略模式、职责链模式、访问者模式 优点 行之有效的解决方法 易于修改和维护 便于交流和沟通 二、单例模式 此次学习目标为单例模式 什么是单例模式 保证一个类仅有一个实例,并提供一个访问它的全局访问点 文字定义总是晦涩难懂的 还是看代码: js 皇帝 一国之主 有且只有一个 function emperor this name 皇帝 this id math floor math random emperor prototype say function console log this name this id 择日再议 大臣 国之栋梁 多多益善 function minister name this name name minister prototype say function console log this name 陛下 臣附议 对某国事 三名大臣集体附议 var new minister 张大人 var new emperor say say 每次皇帝的id都不一样 var new minister 李大人 var new emperor say say 每次皇帝的id都不一样 var new minister 王大人 var new emperor say say 每次皇帝的id都不一样 以上 每次皇帝 emperor实例 得到的都是不一样的id 这样显然是不行的 以单例模式定义来理解 一个类只能实例化出一个对象 不管你实例化多少次 emperor 最终所有实例应该都是同一个 如何保证 emperor 实例的唯一性 有两种做法 方法一 直接在函数里返回对象的形式来实现 js 皇帝 一国之主 有且只有一个 function emperor this name 皇帝 this id math floor math random 保存着emperor的实例 this instance null emperor getinstance function 首次进入 实例化emperor 并返回 if this instance this instance new emperor return this instance emperor prototype say function console log this name this id 择日再议 大臣 国之栋梁 多多益善 function minister name this name name minister prototype say function console log this name 陛下 臣附议 对某国事 三名大臣集体附议 var new minister 张大人 var emperor getinstance say say 每次输出一致 保存了第一次的id var new minister 李大人 var emperor getinstance say say 每次输出一致 保存了第一次的id var new minister 王大人 var emperor getinstance say say 每次输出一致 保存了第一次的id 不难发现 以上代码中的 instance 并非私有成员 在外部是可以随意修改的 存在一定的安全隐患 私有化 instance js 皇帝 一国之主 有且只有一个 function emperor this name 皇帝 this id math floor math random emperor getinstance function var instance null return function if instance instance new emperor return instance emperor prototype say function console log this name this id 择日再议 大臣 国之栋梁 多多益善 function minister name this name name minister prototype say function console log this name 陛下 臣附议 对某国事 三名大臣集体附议 var new minister 张大人 var emperor getinstance say say 每次输出一致 保存了第一次的id var new minister 李大人 var emperor getinstance say say 每次输出一致 保存了第一次的id var new minister 王大人 var emperor getinstance say say 每次输出一致 保存了第一次的id 问题又来了 每次我们必须通过 emperor getinstance 这样的静态访问获取对象而非使用 new 构造函数形式来获取 这就要求我们必须得知道 emperor 是单例模式 同时还必须得知道通过 getinstance 方法才能获取到单例对象 如何通过 new 运算符正常获取对象 见第二种做法 方法二 js 皇帝 一国之主 有且只有一个 var emperor function var instance null 与全局的emperor没有任何关系 function emperor if instance return instance this name 皇帝 this id math floor math random return instance this emperor prototype say function console log this name this id 择日再议 return emperor 大臣 国之栋梁 多多益善 function minister name this name name minister prototype say function console log this name 陛下 臣附议 对某国事 三名大臣集体附议 var new minister 张大人 var new emperor say say 每次输出一致 var new minister 李大人 var new emperor say say 每次输出一致 var new minister 王大人 var new emperor say say 每次输出一致 以上 类似当想创建 emperor 这样的只能实例化唯一对象的类的时候 就需要单例模式 而单例模式的原理其实就是 在每次创建之前需要判断一下是否存在 不存在就直接创建 存在的话 就把已经创建了的返回出去 | 0 |
42,764 | 11,259,453,582 | IssuesEvent | 2020-01-13 08:22:20 | line/armeria | https://api.github.com/repos/line/armeria | closed | Using ClientFactoryOptions causes NPE during client connection | defect | `ClientFactoryOptions.DEFAULT` overrides the defaults set by `ClientFactoryBuilder` which causes NPE (at `HttpChannelPool` constructor) during client connection, which makes `ClientFactoryOptions` impossible to use.
**The code to reproduce the issue:**
```
ClientFactoryBuilder clientFactoryBuilder = ClientFactory.builder();
clientFactoryBuilder.options(ClientFactoryOptions.of()); // or any other "of" method
clientBuilder.factory(clientFactoryBuilder.build());
```
**The exception thrown during client connect:**
```
java.lang.NullPointerException
at com.linecorp.armeria.client.HttpChannelPool.<init>(HttpChannelPool.java:109)
```
**The code that throws NPE (`HttpChannelPool.<init>`):**
```
this.connectTimeoutMillis = (Integer)baseBootstrap.config().options().get(ChannelOption.CONNECT_TIMEOUT_MILLIS);
```
**Analysis:**
`ClientFactoryBuilder` sets some defaults during the construction [`ClientFactory.builder()` --> `new ClientFactoryBuilder()`].
More specifically it sets `CHANNEL_OPTIONS` with a default `CONNECT_TIMEOUT_MILLIS` as following:
```
connectTimeoutMillis(Flags.defaultConnectTimeoutMillis());
```
In the debugger I see the following after executing `ClientFactory.builder()`:
```
options = {java.util.LinkedHashMap@2624} size = 1
{com.linecorp.armeria.client.ClientFactoryOption@2629} "CHANNEL_OPTIONS" -> {com.linecorp.armeria.client.ClientFactoryOptionValue@2630} "CHANNEL_OPTIONS={CONNECT_TIMEOUT_MILLIS=>3200}"
```
On a contrary, `ClientFactoryOptions` defines its own set of defaults (via its `DEFAULT_OPTIONS`) which defines empty `CHANNEL_OPTIONS` as following:
```
ClientFactoryOption.CHANNEL_OPTIONS.newValue(new Object2ObjectArrayMap<>()),
```
When `ClientFactoryBuilder#options()` method invoked with any `ClientFactoryOptions` it will override previous `CHANNEL_OPTIONS` default.
Then, it empties `CHANNEL_OPTIONS`, while `CONNECT_TIMEOUT_MILLIS` expected by `HttpChannelPool` and possibly by other places.
In the debugger I see the following after executing `clientFactoryBuilder.options(ClientFactoryOptions.of())`:
```
{com.linecorp.armeria.client.ClientFactoryOption@2629} "CHANNEL_OPTIONS" -> {com.linecorp.armeria.client.ClientFactoryOptionValue@2688} "CHANNEL_OPTIONS={}"
```
**Expectation:**
1. The use of `ClientFactoryOptions` should not cause any failure. `ClientFactoryOptions` defaults should not override any defaults set by `ClientFactoryBuilder`.
2. The solution should only take those options defined by the user and apply those to `ClientFactoryBuilder`.
3. `HttpChannelPool` should not fail with NPE when some expected configurations are missing. It should provide reasonable problem indication or/and fall back to a default.
**Current Workaround:**
Avoid using `ClientFactoryOptions` and use individual user defined options as a collection of `ClientFactoryOptions` and add those to `ClientFactoryBuilder` via `ClientFactoryBuilder#option()` method as following:
```
Collection<ClientFactoryOptionValue<?>> clientFactoryOptions = ...
if (clientFactoryOptions != null && !clientFactoryOptions.isEmpty()) {
clientFactoryOptions.forEach(clientFactoryBuilder::option);
}
clientBuilder.factory(clientFactoryBuilder.build());
```
| 1.0 | Using ClientFactoryOptions causes NPE during client connection - `ClientFactoryOptions.DEFAULT` overrides the defaults set by `ClientFactoryBuilder` which causes NPE (at `HttpChannelPool` constructor) during client connection, which makes `ClientFactoryOptions` impossible to use.
**The code to reproduce the issue:**
```
ClientFactoryBuilder clientFactoryBuilder = ClientFactory.builder();
clientFactoryBuilder.options(ClientFactoryOptions.of()); // or any other "of" method
clientBuilder.factory(clientFactoryBuilder.build());
```
**The exception thrown during client connect:**
```
java.lang.NullPointerException
at com.linecorp.armeria.client.HttpChannelPool.<init>(HttpChannelPool.java:109)
```
**The code that throws NPE (`HttpChannelPool.<init>`):**
```
this.connectTimeoutMillis = (Integer)baseBootstrap.config().options().get(ChannelOption.CONNECT_TIMEOUT_MILLIS);
```
**Analysis:**
`ClientFactoryBuilder` sets some defaults during the construction [`ClientFactory.builder()` --> `new ClientFactoryBuilder()`].
More specifically it sets `CHANNEL_OPTIONS` with a default `CONNECT_TIMEOUT_MILLIS` as following:
```
connectTimeoutMillis(Flags.defaultConnectTimeoutMillis());
```
In the debugger I see the following after executing `ClientFactory.builder()`:
```
options = {java.util.LinkedHashMap@2624} size = 1
{com.linecorp.armeria.client.ClientFactoryOption@2629} "CHANNEL_OPTIONS" -> {com.linecorp.armeria.client.ClientFactoryOptionValue@2630} "CHANNEL_OPTIONS={CONNECT_TIMEOUT_MILLIS=>3200}"
```
On a contrary, `ClientFactoryOptions` defines its own set of defaults (via its `DEFAULT_OPTIONS`) which defines empty `CHANNEL_OPTIONS` as following:
```
ClientFactoryOption.CHANNEL_OPTIONS.newValue(new Object2ObjectArrayMap<>()),
```
When `ClientFactoryBuilder#options()` method invoked with any `ClientFactoryOptions` it will override previous `CHANNEL_OPTIONS` default.
Then, it empties `CHANNEL_OPTIONS`, while `CONNECT_TIMEOUT_MILLIS` expected by `HttpChannelPool` and possibly by other places.
In the debugger I see the following after executing `clientFactoryBuilder.options(ClientFactoryOptions.of())`:
```
{com.linecorp.armeria.client.ClientFactoryOption@2629} "CHANNEL_OPTIONS" -> {com.linecorp.armeria.client.ClientFactoryOptionValue@2688} "CHANNEL_OPTIONS={}"
```
**Expectation:**
1. The use of `ClientFactoryOptions` should not cause any failure. `ClientFactoryOptions` defaults should not override any defaults set by `ClientFactoryBuilder`.
2. The solution should only take those options defined by the user and apply those to `ClientFactoryBuilder`.
3. `HttpChannelPool` should not fail with NPE when some expected configurations are missing. It should provide reasonable problem indication or/and fall back to a default.
**Current Workaround:**
Avoid using `ClientFactoryOptions` and use individual user defined options as a collection of `ClientFactoryOptions` and add those to `ClientFactoryBuilder` via `ClientFactoryBuilder#option()` method as following:
```
Collection<ClientFactoryOptionValue<?>> clientFactoryOptions = ...
if (clientFactoryOptions != null && !clientFactoryOptions.isEmpty()) {
clientFactoryOptions.forEach(clientFactoryBuilder::option);
}
clientBuilder.factory(clientFactoryBuilder.build());
```
| non_priority | using clientfactoryoptions causes npe during client connection clientfactoryoptions default overrides the defaults set by clientfactorybuilder which causes npe at httpchannelpool constructor during client connection which makes clientfactoryoptions impossible to use the code to reproduce the issue clientfactorybuilder clientfactorybuilder clientfactory builder clientfactorybuilder options clientfactoryoptions of or any other of method clientbuilder factory clientfactorybuilder build the exception thrown during client connect java lang nullpointerexception at com linecorp armeria client httpchannelpool httpchannelpool java the code that throws npe httpchannelpool this connecttimeoutmillis integer basebootstrap config options get channeloption connect timeout millis analysis clientfactorybuilder sets some defaults during the construction more specifically it sets channel options with a default connect timeout millis as following connecttimeoutmillis flags defaultconnecttimeoutmillis in the debugger i see the following after executing clientfactory builder options java util linkedhashmap size com linecorp armeria client clientfactoryoption channel options com linecorp armeria client clientfactoryoptionvalue channel options connect timeout millis on a contrary clientfactoryoptions defines its own set of defaults via its default options which defines empty channel options as following clientfactoryoption channel options newvalue new when clientfactorybuilder options method invoked with any clientfactoryoptions it will override previous channel options default then it empties channel options while connect timeout millis expected by httpchannelpool and possibly by other places in the debugger i see the following after executing clientfactorybuilder options clientfactoryoptions of com linecorp armeria client clientfactoryoption channel options com linecorp armeria client clientfactoryoptionvalue channel options expectation the use of clientfactoryoptions should not cause any failure clientfactoryoptions defaults should not override any defaults set by clientfactorybuilder the solution should only take those options defined by the user and apply those to clientfactorybuilder httpchannelpool should not fail with npe when some expected configurations are missing it should provide reasonable problem indication or and fall back to a default current workaround avoid using clientfactoryoptions and use individual user defined options as a collection of clientfactoryoptions and add those to clientfactorybuilder via clientfactorybuilder option method as following collection clientfactoryoptions if clientfactoryoptions null clientfactoryoptions isempty clientfactoryoptions foreach clientfactorybuilder option clientbuilder factory clientfactorybuilder build | 0 |
21,389 | 7,010,310,057 | IssuesEvent | 2017-12-19 22:38:56 | GLVis/glvis | https://api.github.com/repos/GLVis/glvis | closed | CMake LibPNG define | bug building | Hi,
I compiled GLVis with CMake and noticed screenshots weren't following the build parameters.
In the cmake file https://github.com/GLVis/glvis/blob/master/CMakeLists.txt#L160
The define for libpng should read
```
list(APPEND _glvis_compile_defs "GLVIS_USE_LIBPNG")
```
where `GLVIS_USE_PNG` -> ```GLVIS_USE_LIBPNG```
Thanks
| 1.0 | CMake LibPNG define - Hi,
I compiled GLVis with CMake and noticed screenshots weren't following the build parameters.
In the cmake file https://github.com/GLVis/glvis/blob/master/CMakeLists.txt#L160
The define for libpng should read
```
list(APPEND _glvis_compile_defs "GLVIS_USE_LIBPNG")
```
where `GLVIS_USE_PNG` -> ```GLVIS_USE_LIBPNG```
Thanks
| non_priority | cmake libpng define hi i compiled glvis with cmake and noticed screenshots weren t following the build parameters in the cmake file the define for libpng should read list append glvis compile defs glvis use libpng where glvis use png glvis use libpng thanks | 0 |
45,500 | 7,187,857,457 | IssuesEvent | 2018-02-02 07:46:31 | django/channels | https://api.github.com/repos/django/channels | closed | Add reference documentation for all decorators | documentation exp/intermediate | I've seen a few different decorators used (like `channel_session`) in the docs, but don't have good reference information for them. | 1.0 | Add reference documentation for all decorators - I've seen a few different decorators used (like `channel_session`) in the docs, but don't have good reference information for them. | non_priority | add reference documentation for all decorators i ve seen a few different decorators used like channel session in the docs but don t have good reference information for them | 0 |
6,659 | 9,781,415,824 | IssuesEvent | 2019-06-07 19:43:23 | brucemiller/LaTeXML | https://api.github.com/repos/brucemiller/LaTeXML | closed | subequations environment results in invalid XHTML | bug postprocessing schema | The minimal LaTeX file `subeqs.tex`:
```
\documentclass{article}
\usepackage{amsmath}
\begin{document}
\begin{subequations}
\begin{align}
1 &= 1\\
2 &= 2
\end{align}
\end{subequations}
\end{document}
```
converted to XHTML using
```
latexml --dest=subeqs.xml subeqs.tex ; latexmlpost --dest=subeqs.xhtml subeqs.xml
```
results in invalid XHTML. The errors are
```
Line 19, Column 20: document type does not allow element "tbody" here
<tbody id="S0.E1.1"><tr class="ltx_equation ltx_eqn_row ltx_align_baseline">
```
and the same for `Line 25, Column 20` when checking the syntax on `https://validator.w3.org/#validate-by-upload`.
Note that this is new in `LaTeXML` version 0.8.3. Version 0.8.2 inserted `tbody` in the proper place and just once whereas 0.8.3 seems to add a (misplaced) `tbody` for each sub-equation. | 1.0 | subequations environment results in invalid XHTML - The minimal LaTeX file `subeqs.tex`:
```
\documentclass{article}
\usepackage{amsmath}
\begin{document}
\begin{subequations}
\begin{align}
1 &= 1\\
2 &= 2
\end{align}
\end{subequations}
\end{document}
```
converted to XHTML using
```
latexml --dest=subeqs.xml subeqs.tex ; latexmlpost --dest=subeqs.xhtml subeqs.xml
```
results in invalid XHTML. The errors are
```
Line 19, Column 20: document type does not allow element "tbody" here
<tbody id="S0.E1.1"><tr class="ltx_equation ltx_eqn_row ltx_align_baseline">
```
and the same for `Line 25, Column 20` when checking the syntax on `https://validator.w3.org/#validate-by-upload`.
Note that this is new in `LaTeXML` version 0.8.3. Version 0.8.2 inserted `tbody` in the proper place and just once whereas 0.8.3 seems to add a (misplaced) `tbody` for each sub-equation. | non_priority | subequations environment results in invalid xhtml the minimal latex file subeqs tex documentclass article usepackage amsmath begin document begin subequations begin align end align end subequations end document converted to xhtml using latexml dest subeqs xml subeqs tex latexmlpost dest subeqs xhtml subeqs xml results in invalid xhtml the errors are line column document type does not allow element tbody here and the same for line column when checking the syntax on note that this is new in latexml version version inserted tbody in the proper place and just once whereas seems to add a misplaced tbody for each sub equation | 0 |
46,779 | 24,717,663,971 | IssuesEvent | 2022-10-20 08:18:19 | claroline/Claroline | https://api.github.com/repos/claroline/Claroline | opened | [Workspace] removes the WorkspaceOptions entity | Refactoring Performances | | Q | A
| ------------- | ---
| Bug report? | no
| Version? | all
The `Workspace` entity has a One-to-One relationship with a `WorkspaceOptions` entity to store some option in a json encoded format.
- This has a negative impact on performances (DB queries / serialization of props...).
- Most of the workspaces options are directly set on the `Workspace` entity.
- Poor readability and hard to migrate if some of the embedded options change.
This is an easy pick but I will need to create an updater to migrate the options and this will be an huge one for the platforms.
| True | [Workspace] removes the WorkspaceOptions entity - | Q | A
| ------------- | ---
| Bug report? | no
| Version? | all
The `Workspace` entity has a One-to-One relationship with a `WorkspaceOptions` entity to store some option in a json encoded format.
- This has a negative impact on performances (DB queries / serialization of props...).
- Most of the workspaces options are directly set on the `Workspace` entity.
- Poor readability and hard to migrate if some of the embedded options change.
This is an easy pick but I will need to create an updater to migrate the options and this will be an huge one for the platforms.
| non_priority | removes the workspaceoptions entity q a bug report no version all the workspace entity has a one to one relationship with a workspaceoptions entity to store some option in a json encoded format this has a negative impact on performances db queries serialization of props most of the workspaces options are directly set on the workspace entity poor readability and hard to migrate if some of the embedded options change this is an easy pick but i will need to create an updater to migrate the options and this will be an huge one for the platforms | 0 |
91,389 | 8,304,130,369 | IssuesEvent | 2018-09-21 20:01:15 | mozilla/iris | https://api.github.com/repos/mozilla/iris | opened | Investigate and fix failing unti_test/firefox_build_apis test case | test case | This test case is failing every time on all platforms. | 1.0 | Investigate and fix failing unti_test/firefox_build_apis test case - This test case is failing every time on all platforms. | non_priority | investigate and fix failing unti test firefox build apis test case this test case is failing every time on all platforms | 0 |
271,658 | 23,620,525,272 | IssuesEvent | 2022-08-24 20:03:38 | sqlalchemy/sqlalchemy | https://api.github.com/repos/sqlalchemy/sqlalchemy | opened | Pypy test seem to fail (at least on windows) | tests windows pypy | Trying to add support for pypy wheels via cibuildwheel, but currently the test are failing at least on windows.
See attachment [broken-tests.txt](https://github.com/sqlalchemy/sqlalchemy/files/9419100/broken-tests.txt) for details on broken test. I have not yet tested locally to see what's up.
This is somewhat blocking for #6702 unless we decide to skip tests on pypy
| 1.0 | Pypy test seem to fail (at least on windows) - Trying to add support for pypy wheels via cibuildwheel, but currently the test are failing at least on windows.
See attachment [broken-tests.txt](https://github.com/sqlalchemy/sqlalchemy/files/9419100/broken-tests.txt) for details on broken test. I have not yet tested locally to see what's up.
This is somewhat blocking for #6702 unless we decide to skip tests on pypy
| non_priority | pypy test seem to fail at least on windows trying to add support for pypy wheels via cibuildwheel but currently the test are failing at least on windows see attachment for details on broken test i have not yet tested locally to see what s up this is somewhat blocking for unless we decide to skip tests on pypy | 0 |
122,382 | 10,221,097,126 | IssuesEvent | 2019-08-15 23:55:39 | MicrosoftDocs/visualstudio-docs | https://api.github.com/repos/MicrosoftDocs/visualstudio-docs | closed | Missing UI for toggling assembly-based discovery of tests | Pri1 doc-bug visual-studio-windows/prod vs-ide-test/tech | 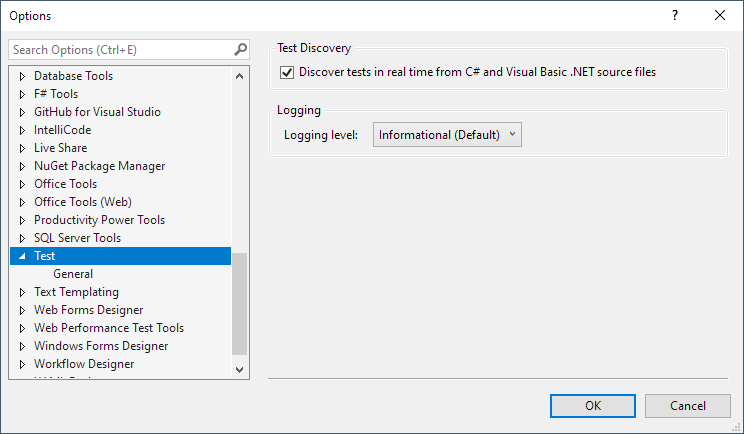
If it's no longer needed, then the relevant docs should be fixed.
Otherwise, there should be some information as to how to display it.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: b1fa1671-f27f-484e-8994-ceb85b1a73d6
* Version Independent ID: 5b90e41e-b4ba-7cb7-b798-59ea1ae38eb4
* Content: [Test Explorer FAQ - Visual Studio](https://docs.microsoft.com/en-us/visualstudio/test/test-explorer-faq?view=vs-2019)
* Content Source: [docs/test/test-explorer-faq.md](https://github.com/MicrosoftDocs/visualstudio-docs/blob/master/docs/test/test-explorer-faq.md)
* Product: **visual-studio-windows**
* Technology: **vs-ide-test**
* GitHub Login: @kendrahavens
* Microsoft Alias: **kehavens** | 1.0 | Missing UI for toggling assembly-based discovery of tests - 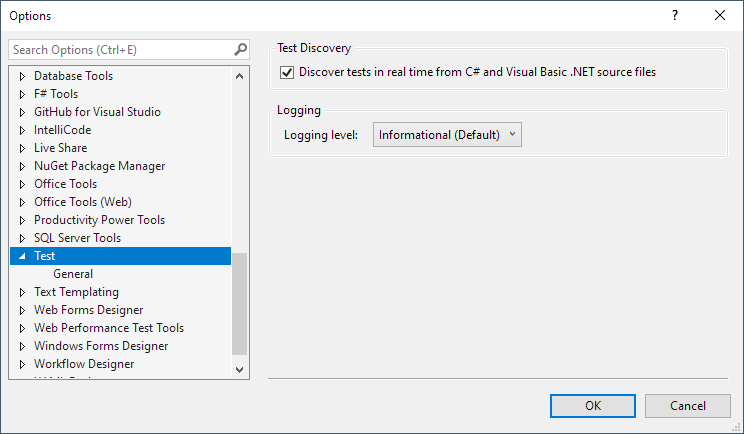
If it's no longer needed, then the relevant docs should be fixed.
Otherwise, there should be some information as to how to display it.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: b1fa1671-f27f-484e-8994-ceb85b1a73d6
* Version Independent ID: 5b90e41e-b4ba-7cb7-b798-59ea1ae38eb4
* Content: [Test Explorer FAQ - Visual Studio](https://docs.microsoft.com/en-us/visualstudio/test/test-explorer-faq?view=vs-2019)
* Content Source: [docs/test/test-explorer-faq.md](https://github.com/MicrosoftDocs/visualstudio-docs/blob/master/docs/test/test-explorer-faq.md)
* Product: **visual-studio-windows**
* Technology: **vs-ide-test**
* GitHub Login: @kendrahavens
* Microsoft Alias: **kehavens** | non_priority | missing ui for toggling assembly based discovery of tests if it s no longer needed then the relevant docs should be fixed otherwise there should be some information as to how to display it document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product visual studio windows technology vs ide test github login kendrahavens microsoft alias kehavens | 0 |
16,744 | 9,873,253,172 | IssuesEvent | 2019-06-22 12:48:52 | FreshRSS/FreshRSS | https://api.github.com/repos/FreshRSS/FreshRSS | closed | E-Mail as username not possible during dirst time installation | Critical :skull_and_crossbones: Security :shield: | With the fix for #2407 i can use a e-mail address as username. This works perfectly, if i add a user in a old installation. However, when i add a new user during first time installation, the @ and dot signs are removed from the username and the user is created without that signs. This prevents the user from logging in. | True | E-Mail as username not possible during dirst time installation - With the fix for #2407 i can use a e-mail address as username. This works perfectly, if i add a user in a old installation. However, when i add a new user during first time installation, the @ and dot signs are removed from the username and the user is created without that signs. This prevents the user from logging in. | non_priority | e mail as username not possible during dirst time installation with the fix for i can use a e mail address as username this works perfectly if i add a user in a old installation however when i add a new user during first time installation the and dot signs are removed from the username and the user is created without that signs this prevents the user from logging in | 0 |
187,865 | 14,433,400,641 | IssuesEvent | 2020-12-07 04:44:51 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | rakutentech/kafka-firehose-nozzle: kafka_test.go; 62 LoC | fresh medium test |
Found a possible issue in [rakutentech/kafka-firehose-nozzle](https://www.github.com/rakutentech/kafka-firehose-nozzle) at [kafka_test.go](https://github.com/rakutentech/kafka-firehose-nozzle/blob/b877eca0f25fc98548634fda5e9d78743b4b20b6/kafka_test.go#L166-L227)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable tc used in defer or goroutine at line 213
[Click here to see the code in its original context.](https://github.com/rakutentech/kafka-firehose-nozzle/blob/b877eca0f25fc98548634fda5e9d78743b4b20b6/kafka_test.go#L166-L227)
<details>
<summary>Click here to show the 62 line(s) of Go which triggered the analyzer.</summary>
```go
for _, tc := range cases {
leader := sarama.NewMockBroker(t, int32(1))
success := new(sarama.ProduceResponse)
success.AddTopicPartition(tc.topic, int32(0), sarama.ErrNoError)
leader.Returns(success)
meta := new(sarama.MetadataResponse)
meta.AddTopicPartition(tc.topic, int32(0), leader.BrokerID(), nil, nil, sarama.ErrNoError)
meta.AddBroker(leader.Addr(), int32(1))
seed := sarama.NewMockBroker(t, int32(0))
seed.Returns(meta)
tc.config.Kafka.Brokers = []string{seed.Addr()}
// Create new kafka producer
stats := NewStats()
producer, err := NewKafkaProducer(nil, stats, tc.config)
if err != nil {
t.Fatalf("err: %s", err)
}
if tc.config.Kafka.Compression == "gzip" &&
producer.(*KafkaProducer).config.Producer.Compression != sarama.CompressionGZIP {
t.Fatalf("gzip compression is not set on producer")
} else if tc.config.Kafka.Compression == "snappy" &&
producer.(*KafkaProducer).config.Producer.Compression != sarama.CompressionSnappy {
t.Fatalf("snappy compression is not set on producer")
} else if (tc.config.Kafka.Compression == "none" || tc.config.Kafka.Compression == "") &&
producer.(*KafkaProducer).config.Producer.Compression != sarama.CompressionNone {
t.Fatalf("none compression is not set on producer")
}
// Create test eventCh where producer gets actual message
eventCh := make(chan *events.Envelope)
// Start producing
ctx, cancel := context.WithCancel(context.Background())
defer cancel()
go func() {
producer.Produce(ctx, eventCh)
}()
// Send event to producer
go func() {
// Create test event and send it to channel
eventCh <- tc.event
}()
select {
case err := <-producer.Errors():
if err != nil {
t.Fatalf("expect err to be nil: %s", err)
}
case msg := <-producer.Successes():
if msg.Topic != tc.topic {
t.Fatalf("expect %q to be eq %q", msg.Topic, tc.topic)
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: b877eca0f25fc98548634fda5e9d78743b4b20b6
| 1.0 | rakutentech/kafka-firehose-nozzle: kafka_test.go; 62 LoC -
Found a possible issue in [rakutentech/kafka-firehose-nozzle](https://www.github.com/rakutentech/kafka-firehose-nozzle) at [kafka_test.go](https://github.com/rakutentech/kafka-firehose-nozzle/blob/b877eca0f25fc98548634fda5e9d78743b4b20b6/kafka_test.go#L166-L227)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable tc used in defer or goroutine at line 213
[Click here to see the code in its original context.](https://github.com/rakutentech/kafka-firehose-nozzle/blob/b877eca0f25fc98548634fda5e9d78743b4b20b6/kafka_test.go#L166-L227)
<details>
<summary>Click here to show the 62 line(s) of Go which triggered the analyzer.</summary>
```go
for _, tc := range cases {
leader := sarama.NewMockBroker(t, int32(1))
success := new(sarama.ProduceResponse)
success.AddTopicPartition(tc.topic, int32(0), sarama.ErrNoError)
leader.Returns(success)
meta := new(sarama.MetadataResponse)
meta.AddTopicPartition(tc.topic, int32(0), leader.BrokerID(), nil, nil, sarama.ErrNoError)
meta.AddBroker(leader.Addr(), int32(1))
seed := sarama.NewMockBroker(t, int32(0))
seed.Returns(meta)
tc.config.Kafka.Brokers = []string{seed.Addr()}
// Create new kafka producer
stats := NewStats()
producer, err := NewKafkaProducer(nil, stats, tc.config)
if err != nil {
t.Fatalf("err: %s", err)
}
if tc.config.Kafka.Compression == "gzip" &&
producer.(*KafkaProducer).config.Producer.Compression != sarama.CompressionGZIP {
t.Fatalf("gzip compression is not set on producer")
} else if tc.config.Kafka.Compression == "snappy" &&
producer.(*KafkaProducer).config.Producer.Compression != sarama.CompressionSnappy {
t.Fatalf("snappy compression is not set on producer")
} else if (tc.config.Kafka.Compression == "none" || tc.config.Kafka.Compression == "") &&
producer.(*KafkaProducer).config.Producer.Compression != sarama.CompressionNone {
t.Fatalf("none compression is not set on producer")
}
// Create test eventCh where producer gets actual message
eventCh := make(chan *events.Envelope)
// Start producing
ctx, cancel := context.WithCancel(context.Background())
defer cancel()
go func() {
producer.Produce(ctx, eventCh)
}()
// Send event to producer
go func() {
// Create test event and send it to channel
eventCh <- tc.event
}()
select {
case err := <-producer.Errors():
if err != nil {
t.Fatalf("expect err to be nil: %s", err)
}
case msg := <-producer.Successes():
if msg.Topic != tc.topic {
t.Fatalf("expect %q to be eq %q", msg.Topic, tc.topic)
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: b877eca0f25fc98548634fda5e9d78743b4b20b6
| non_priority | rakutentech kafka firehose nozzle kafka test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable tc used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for tc range cases leader sarama newmockbroker t success new sarama produceresponse success addtopicpartition tc topic sarama errnoerror leader returns success meta new sarama metadataresponse meta addtopicpartition tc topic leader brokerid nil nil sarama errnoerror meta addbroker leader addr seed sarama newmockbroker t seed returns meta tc config kafka brokers string seed addr create new kafka producer stats newstats producer err newkafkaproducer nil stats tc config if err nil t fatalf err s err if tc config kafka compression gzip producer kafkaproducer config producer compression sarama compressiongzip t fatalf gzip compression is not set on producer else if tc config kafka compression snappy producer kafkaproducer config producer compression sarama compressionsnappy t fatalf snappy compression is not set on producer else if tc config kafka compression none tc config kafka compression producer kafkaproducer config producer compression sarama compressionnone t fatalf none compression is not set on producer create test eventch where producer gets actual message eventch make chan events envelope start producing ctx cancel context withcancel context background defer cancel go func producer produce ctx eventch send event to producer go func create test event and send it to channel eventch tc event select case err producer errors if err nil t fatalf expect err to be nil s err case msg producer successes if msg topic tc topic t fatalf expect q to be eq q msg topic tc topic leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
199,440 | 22,693,330,861 | IssuesEvent | 2022-07-05 01:14:07 | benlazarine/subspace | https://api.github.com/repos/benlazarine/subspace | opened | CVE-2020-14330 (Medium) detected in ansible-2.9.1.tar.gz | security vulnerability | ## CVE-2020-14330 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.1.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/4b/c5/fb70a2d9817eb48c358a67952ed3a1869e5cda8a5e4f1911cffc75f42375/ansible-2.9.1.tar.gz">https://files.pythonhosted.org/packages/4b/c5/fb70a2d9817eb48c358a67952ed3a1869e5cda8a5e4f1911cffc75f42375/ansible-2.9.1.tar.gz</a></p>
<p>Path to dependency file: /tmp/ws-scm/subspace</p>
<p>Path to vulnerable library: /subspace,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.1.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An Improper Output Neutralization for Logs flaw was found in Ansible when using the uri module, where sensitive data is exposed to content and json output. This flaw allows an attacker to access the logs or outputs of performed tasks to read keys used in playbooks from other users within the uri module. The highest threat from this vulnerability is to data confidentiality.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14330>CVE-2020-14330</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-14330 (Medium) detected in ansible-2.9.1.tar.gz - ## CVE-2020-14330 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.1.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/4b/c5/fb70a2d9817eb48c358a67952ed3a1869e5cda8a5e4f1911cffc75f42375/ansible-2.9.1.tar.gz">https://files.pythonhosted.org/packages/4b/c5/fb70a2d9817eb48c358a67952ed3a1869e5cda8a5e4f1911cffc75f42375/ansible-2.9.1.tar.gz</a></p>
<p>Path to dependency file: /tmp/ws-scm/subspace</p>
<p>Path to vulnerable library: /subspace,/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.1.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An Improper Output Neutralization for Logs flaw was found in Ansible when using the uri module, where sensitive data is exposed to content and json output. This flaw allows an attacker to access the logs or outputs of performed tasks to read keys used in playbooks from other users within the uri module. The highest threat from this vulnerability is to data confidentiality.
<p>Publish Date: 2020-09-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14330>CVE-2020-14330</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2020-14330</a></p>
<p>Release Date: 2020-09-11</p>
<p>Fix Resolution: 2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in ansible tar gz cve medium severity vulnerability vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file tmp ws scm subspace path to vulnerable library subspace requirements txt dependency hierarchy x ansible tar gz vulnerable library vulnerability details an improper output neutralization for logs flaw was found in ansible when using the uri module where sensitive data is exposed to content and json output this flaw allows an attacker to access the logs or outputs of performed tasks to read keys used in playbooks from other users within the uri module the highest threat from this vulnerability is to data confidentiality publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
74,834 | 25,348,377,447 | IssuesEvent | 2022-11-19 13:22:21 | scoutplan/scoutplan | https://api.github.com/repos/scoutplan/scoutplan | closed | [Scoutplan Production/production] ActionView::Template::Error: Net::ReadTimeout with #<TCPSocket:(closed)> | defect | ## Backtrace
line 87 of [PROJECT_ROOT]/app/views/layouts/mailer.html.erb: block in _app_views_layouts_mailer_html_erb___4458926536717683142_91880
line 86 of [PROJECT_ROOT]/app/views/layouts/mailer.html.erb: _app_views_layouts_mailer_html_erb___4458926536717683142_91880
line 55 of [PROJECT_ROOT]/app/mailers/member_mailer.rb: daily_reminder_email
[View full backtrace and more info at honeybadger.io](https://app.honeybadger.io/projects/97676/faults/90481918) | 1.0 | [Scoutplan Production/production] ActionView::Template::Error: Net::ReadTimeout with #<TCPSocket:(closed)> - ## Backtrace
line 87 of [PROJECT_ROOT]/app/views/layouts/mailer.html.erb: block in _app_views_layouts_mailer_html_erb___4458926536717683142_91880
line 86 of [PROJECT_ROOT]/app/views/layouts/mailer.html.erb: _app_views_layouts_mailer_html_erb___4458926536717683142_91880
line 55 of [PROJECT_ROOT]/app/mailers/member_mailer.rb: daily_reminder_email
[View full backtrace and more info at honeybadger.io](https://app.honeybadger.io/projects/97676/faults/90481918) | non_priority | actionview template error net readtimeout with backtrace line of app views layouts mailer html erb block in app views layouts mailer html erb line of app views layouts mailer html erb app views layouts mailer html erb line of app mailers member mailer rb daily reminder email | 0 |
296,537 | 22,305,853,111 | IssuesEvent | 2022-06-13 12:59:34 | proyectoalba/alba | https://api.github.com/repos/proyectoalba/alba | closed | Informes y consultas ? | Documentation | Según la comunidad de Alba, una de las utilidades más populares de la aplicación es la generación de informes. Es manifiestamente mejorable el wikimanual en este aspecto !https://github.com/proyectoalba/alba/wiki/Informes-y-consultas
| 1.0 | Informes y consultas ? - Según la comunidad de Alba, una de las utilidades más populares de la aplicación es la generación de informes. Es manifiestamente mejorable el wikimanual en este aspecto !https://github.com/proyectoalba/alba/wiki/Informes-y-consultas
| non_priority | informes y consultas según la comunidad de alba una de las utilidades más populares de la aplicación es la generación de informes es manifiestamente mejorable el wikimanual en este aspecto | 0 |
134,167 | 10,885,361,332 | IssuesEvent | 2019-11-18 10:14:42 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | A strange symbol shows on Retry Transfers dialog | :gear: blobs 🧪 testing | **Storage Explorer Version:** 1.11.1
**Build:** [20191116.1](https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=3250060)
**Branch:** hotfix/1.11.1
**Platform/OS:** Windows 10/ Linux Ubuntu 18.04/macOS High Sierra
**Architecture:** ia32/x64
**Regression From:** Not a regression
**Steps to reproduce:**
1. Expand one storage account -> Blob Containers.
2. Create a new blob container -> Upload one file.
3. Upload the same file -> Select 'Do not upload' -> Apply.
4. Click 'Retry Transfers...' in Activities panel -> Check the source path on Retry Transfers dialog.
**Expect Experience:**
No strange symbol shows.
**Actual Experience:**
A strange symbol shows.
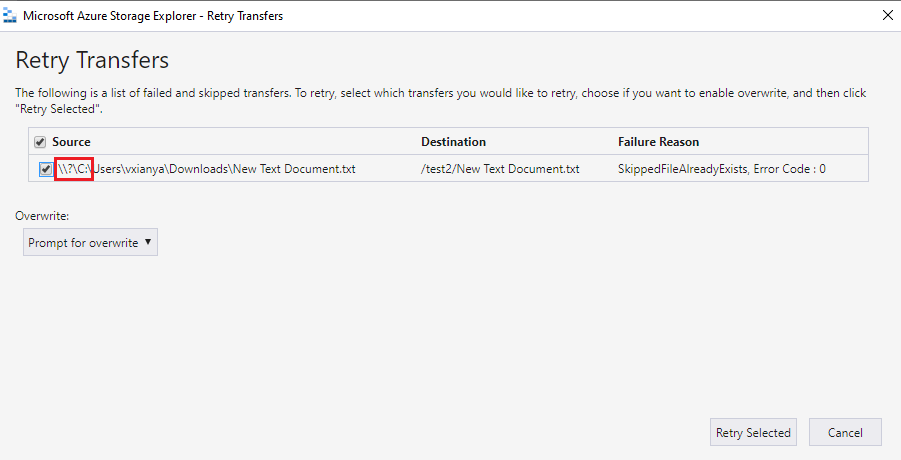
| 1.0 | A strange symbol shows on Retry Transfers dialog - **Storage Explorer Version:** 1.11.1
**Build:** [20191116.1](https://devdiv.visualstudio.com/DevDiv/_build/results?buildId=3250060)
**Branch:** hotfix/1.11.1
**Platform/OS:** Windows 10/ Linux Ubuntu 18.04/macOS High Sierra
**Architecture:** ia32/x64
**Regression From:** Not a regression
**Steps to reproduce:**
1. Expand one storage account -> Blob Containers.
2. Create a new blob container -> Upload one file.
3. Upload the same file -> Select 'Do not upload' -> Apply.
4. Click 'Retry Transfers...' in Activities panel -> Check the source path on Retry Transfers dialog.
**Expect Experience:**
No strange symbol shows.
**Actual Experience:**
A strange symbol shows.
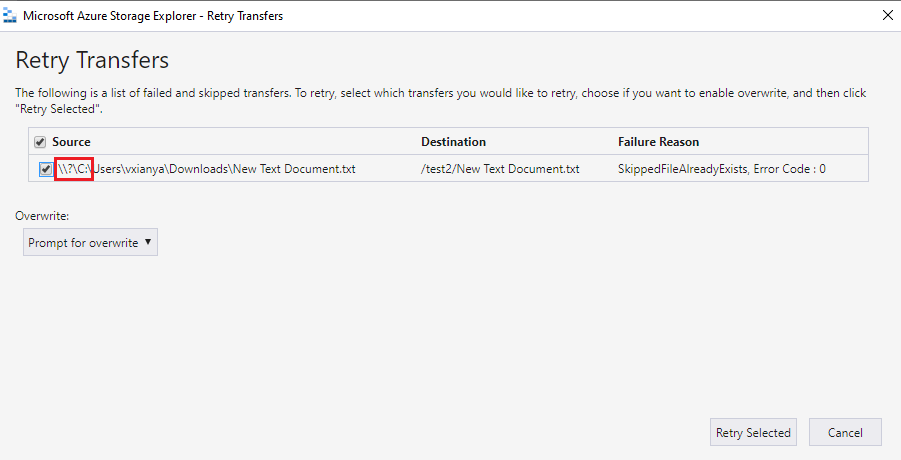
| non_priority | a strange symbol shows on retry transfers dialog storage explorer version build branch hotfix platform os windows linux ubuntu macos high sierra architecture regression from not a regression steps to reproduce expand one storage account blob containers create a new blob container upload one file upload the same file select do not upload apply click retry transfers in activities panel check the source path on retry transfers dialog expect experience no strange symbol shows actual experience a strange symbol shows | 0 |
50,393 | 26,620,654,570 | IssuesEvent | 2023-01-24 10:57:54 | scalableminds/webknossos | https://api.github.com/repos/scalableminds/webknossos | closed | speed up dataset list request | enhancement backend performance | We should do some profiling and optimize the performance for the dataset list request. | True | speed up dataset list request - We should do some profiling and optimize the performance for the dataset list request. | non_priority | speed up dataset list request we should do some profiling and optimize the performance for the dataset list request | 0 |
99,052 | 16,418,653,772 | IssuesEvent | 2021-05-19 09:50:16 | MicrosoftDocs/CloudAppSecurityDocs | https://api.github.com/repos/MicrosoftDocs/CloudAppSecurityDocs | closed | Optionally Validating the Signature | Pri2 cloud-app-security/svc |
When optionally validating the signature of the powershell script LogCollectorInstaller.ps1, the name of signer is "Microsoft Azure Code Sign" rather than "Microsoft Corportation" and the Digital Signature Information records that "A certificate chain processed, but terminated in a root certificate which is not trusted by the trust provider". The countersignatures Name of Signer is "Microsoft Time-Stamp Service"
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: e4f7c304-9777-e8d6-1e49-e80ea333c072
* Version Independent ID: c659f6d0-9011-fd40-d33e-090a719e82da
* Content: [Roll out continuous reports for Cloud App Security using a Docker on Windows](https://docs.microsoft.com/en-us/cloud-app-security/discovery-docker-windows#validate-signature)
* Content Source: [CloudAppSecurityDocs/discovery-docker-windows.md](https://github.com/Microsoft/CloudAppSecurityDocs/blob/master/CloudAppSecurityDocs/discovery-docker-windows.md)
* Service: **cloud-app-security**
* GitHub Login: @dcurwin
* Microsoft Alias: **dacurwin** | True | Optionally Validating the Signature -
When optionally validating the signature of the powershell script LogCollectorInstaller.ps1, the name of signer is "Microsoft Azure Code Sign" rather than "Microsoft Corportation" and the Digital Signature Information records that "A certificate chain processed, but terminated in a root certificate which is not trusted by the trust provider". The countersignatures Name of Signer is "Microsoft Time-Stamp Service"
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: e4f7c304-9777-e8d6-1e49-e80ea333c072
* Version Independent ID: c659f6d0-9011-fd40-d33e-090a719e82da
* Content: [Roll out continuous reports for Cloud App Security using a Docker on Windows](https://docs.microsoft.com/en-us/cloud-app-security/discovery-docker-windows#validate-signature)
* Content Source: [CloudAppSecurityDocs/discovery-docker-windows.md](https://github.com/Microsoft/CloudAppSecurityDocs/blob/master/CloudAppSecurityDocs/discovery-docker-windows.md)
* Service: **cloud-app-security**
* GitHub Login: @dcurwin
* Microsoft Alias: **dacurwin** | non_priority | optionally validating the signature when optionally validating the signature of the powershell script logcollectorinstaller the name of signer is microsoft azure code sign rather than microsoft corportation and the digital signature information records that a certificate chain processed but terminated in a root certificate which is not trusted by the trust provider the countersignatures name of signer is microsoft time stamp service document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service cloud app security github login dcurwin microsoft alias dacurwin | 0 |
47,928 | 7,360,192,089 | IssuesEvent | 2018-03-10 16:04:20 | CanalTP/navitia | https://api.github.com/repos/CanalTP/navitia | opened | Journey.Section.type should be an enum | documentation enhancement schema | It is a `string` at this time.
In proto it is called `SectionType` | 1.0 | Journey.Section.type should be an enum - It is a `string` at this time.
In proto it is called `SectionType` | non_priority | journey section type should be an enum it is a string at this time in proto it is called sectiontype | 0 |
253,602 | 19,142,980,583 | IssuesEvent | 2021-12-02 02:26:59 | cloudfoundry/cf-k8s-controllers | https://api.github.com/repos/cloudfoundry/cf-k8s-controllers | closed | [Feature]: Platform Operator can see instructions to manually install HNC in the README | documentation | ### Blockers/Dependencies
_No response_
### Background
**As a** platform operator
**I want** instructions to manually install HNC
**So that** I can install all of the dependencies for cf-k8s-controllers
### Acceptance Criteria
**GIVEN** that I am trying to install the cf-k8s-controllers
**WHEN I** follow the instructions in the README
**THEN I** can install HNC on my cluster
### Dev Notes
_No response_ | 1.0 | [Feature]: Platform Operator can see instructions to manually install HNC in the README - ### Blockers/Dependencies
_No response_
### Background
**As a** platform operator
**I want** instructions to manually install HNC
**So that** I can install all of the dependencies for cf-k8s-controllers
### Acceptance Criteria
**GIVEN** that I am trying to install the cf-k8s-controllers
**WHEN I** follow the instructions in the README
**THEN I** can install HNC on my cluster
### Dev Notes
_No response_ | non_priority | platform operator can see instructions to manually install hnc in the readme blockers dependencies no response background as a platform operator i want instructions to manually install hnc so that i can install all of the dependencies for cf controllers acceptance criteria given that i am trying to install the cf controllers when i follow the instructions in the readme then i can install hnc on my cluster dev notes no response | 0 |
314,445 | 23,522,411,035 | IssuesEvent | 2022-08-19 07:32:34 | among-neighbors/AN-backend | https://api.github.com/repos/among-neighbors/AN-backend | closed | smtp Service 추가 | documentation enhancement | 회원가입 시 인증코드를 생성하여 인증메일을 전송하고 서버에 해당 코드를 저장하는 메일 서비스를 추가합니다.
서버에서 생성된 인증 코드를 클라이언트가 기입하고 회원가입을 인가받는 방식으로 동작합니다. | 1.0 | smtp Service 추가 - 회원가입 시 인증코드를 생성하여 인증메일을 전송하고 서버에 해당 코드를 저장하는 메일 서비스를 추가합니다.
서버에서 생성된 인증 코드를 클라이언트가 기입하고 회원가입을 인가받는 방식으로 동작합니다. | non_priority | smtp service 추가 회원가입 시 인증코드를 생성하여 인증메일을 전송하고 서버에 해당 코드를 저장하는 메일 서비스를 추가합니다 서버에서 생성된 인증 코드를 클라이언트가 기입하고 회원가입을 인가받는 방식으로 동작합니다 | 0 |
1,185 | 13,634,351,343 | IssuesEvent | 2020-09-24 23:35:50 | Azure/azure-sdk-for-java | https://api.github.com/repos/Azure/azure-sdk-for-java | opened | Ensure all Key Vault models align correctly with the Swagger specification | Client KeyVault tenet-reliability | Issue #14513 showed that the Key Vault Keys library had issues when deserializing a couple models (fixed by #15375), so it would be a worthwhile effort to further look into the rest of the models in Keys, Certificates and Secrets to ensure everything conforms to the service's Swagger specification. | True | Ensure all Key Vault models align correctly with the Swagger specification - Issue #14513 showed that the Key Vault Keys library had issues when deserializing a couple models (fixed by #15375), so it would be a worthwhile effort to further look into the rest of the models in Keys, Certificates and Secrets to ensure everything conforms to the service's Swagger specification. | non_priority | ensure all key vault models align correctly with the swagger specification issue showed that the key vault keys library had issues when deserializing a couple models fixed by so it would be a worthwhile effort to further look into the rest of the models in keys certificates and secrets to ensure everything conforms to the service s swagger specification | 0 |
216,570 | 24,281,573,350 | IssuesEvent | 2022-09-28 17:53:59 | liorzilberg/swagger-parser | https://api.github.com/repos/liorzilberg/swagger-parser | closed | CVE-2018-19361 (High) detected in jackson-databind-2.9.5.jar - autoclosed | security vulnerability | ## CVE-2018-19361 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/target/lib/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/liorzilberg/swagger-parser/commits/9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b">9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the openjpa class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19361>CVE-2018-19361</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19361 (High) detected in jackson-databind-2.9.5.jar - autoclosed - ## CVE-2018-19361 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/target/lib/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/liorzilberg/swagger-parser/commits/9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b">9f26f497b26e4c9500e5ea2d717d2c01e05b5d7b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the openjpa class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19361>CVE-2018-19361</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19361</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar target lib jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the openjpa class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
264,706 | 20,029,616,878 | IssuesEvent | 2022-02-02 02:57:39 | JCSDA/pycrtm | https://api.github.com/repos/JCSDA/pycrtm | closed | Create pyCRTM flowcharts | documentation | Create a set of flowcharts for the pyCRTM Forwad- and K-Matrix functions to iilustrate their functionality. | 1.0 | Create pyCRTM flowcharts - Create a set of flowcharts for the pyCRTM Forwad- and K-Matrix functions to iilustrate their functionality. | non_priority | create pycrtm flowcharts create a set of flowcharts for the pycrtm forwad and k matrix functions to iilustrate their functionality | 0 |
89 | 3,576,794,814 | IssuesEvent | 2016-01-27 20:52:32 | eclipse/smarthome | https://api.github.com/repos/eclipse/smarthome | closed | Automation API should not prevent the use of Declarative Services | Automation | The BaseModuleHandlerFactory expects the bundle context in its constructor. This prevents declaring handler factories through DS. This should be changed to a setBundleContext method, see https://github.com/eclipse/smarthome/issues/908#issuecomment-174288786.
@danchom Could you have a look at that, please? | 1.0 | Automation API should not prevent the use of Declarative Services - The BaseModuleHandlerFactory expects the bundle context in its constructor. This prevents declaring handler factories through DS. This should be changed to a setBundleContext method, see https://github.com/eclipse/smarthome/issues/908#issuecomment-174288786.
@danchom Could you have a look at that, please? | non_priority | automation api should not prevent the use of declarative services the basemodulehandlerfactory expects the bundle context in its constructor this prevents declaring handler factories through ds this should be changed to a setbundlecontext method see danchom could you have a look at that please | 0 |
352,722 | 25,080,169,054 | IssuesEvent | 2022-11-07 18:34:50 | kg-construct/rml-target-source-spec | https://api.github.com/repos/kg-construct/rml-target-source-spec | closed | more concrete examples of reference formulations | documentation enhancement proposal | the reference formulations were introduced in RML but they were never clarified in the end.
now that we have seen some opportunities wrt what to add in the reference formulation, it might be good to introduce some more concrete examples in the spec | 1.0 | more concrete examples of reference formulations - the reference formulations were introduced in RML but they were never clarified in the end.
now that we have seen some opportunities wrt what to add in the reference formulation, it might be good to introduce some more concrete examples in the spec | non_priority | more concrete examples of reference formulations the reference formulations were introduced in rml but they were never clarified in the end now that we have seen some opportunities wrt what to add in the reference formulation it might be good to introduce some more concrete examples in the spec | 0 |
29,596 | 5,654,812,674 | IssuesEvent | 2017-04-09 12:28:03 | getnikola/nikola | https://api.github.com/repos/getnikola/nikola | reopened | Where can I find what default fields are available in templates? | documentation help wanted question | For example, in templates, we have `${header.html_site_title()}` for the site title. Where can I find the whole list? | 1.0 | Where can I find what default fields are available in templates? - For example, in templates, we have `${header.html_site_title()}` for the site title. Where can I find the whole list? | non_priority | where can i find what default fields are available in templates for example in templates we have header html site title for the site title where can i find the whole list | 0 |
237,818 | 18,169,094,816 | IssuesEvent | 2021-09-27 17:45:08 | adafruit/Adafruit_CircuitPython_PYOA | https://api.github.com/repos/adafruit/Adafruit_CircuitPython_PYOA | opened | Missing Type Annotations | good first issue documentation | There are missing type annotations for some functions in this library.
The `typing` module does not exist on CircuitPython devices so the import needs to be wrapped in try/except to catch the error for missing import. There is an example of how that is done here:
```python
try:
from typing import List, Tuple
except ImportError:
pass
```
Once imported the typing annotations for the argument type(s), and return type(s) can be added to the function signature. Here is an example of a function that has had this done already:
```python
def wrap_text_to_pixels(
string: str, max_width: int, font=None, indent0: str = "", indent1: str = ""
) -> List[str]:
```
If you are new to Git or Github we have a guide about contributing to our projects here: https://learn.adafruit.com/contribute-to-circuitpython-with-git-and-github
There is also a guide that covers our CI utilities and how to run them locally to ensure they will pass in Github Actions here: https://learn.adafruit.com/creating-and-sharing-a-circuitpython-library/check-your-code In particular the pages: `Sharing docs on ReadTheDocs` and `Check your code with pre-commit` contain the tools to install and commands to run locally to run the checks.
If you are attempting to resolve this issue and need help, you can post a comment on this issue and tag both @foamyguy and @kattni or reach out to us on Discord: https://adafru.it/discord in the `#circuitpython-dev` channel.
The following locations are reported by mypy to be missing type annotations:
- [ ] adafruit_pyoa.py:113
- [ ] adafruit_pyoa.py:195
- [ ] adafruit_pyoa.py:212
- [ ] adafruit_pyoa.py:219
- [ ] adafruit_pyoa.py:233
- [ ] adafruit_pyoa.py:245
- [ ] adafruit_pyoa.py:282
- [ ] adafruit_pyoa.py:324
- [ ] adafruit_pyoa.py:361
- [ ] adafruit_pyoa.py:392
- [ ] adafruit_pyoa.py:427
- [ ] adafruit_pyoa.py:444 | 1.0 | Missing Type Annotations - There are missing type annotations for some functions in this library.
The `typing` module does not exist on CircuitPython devices so the import needs to be wrapped in try/except to catch the error for missing import. There is an example of how that is done here:
```python
try:
from typing import List, Tuple
except ImportError:
pass
```
Once imported the typing annotations for the argument type(s), and return type(s) can be added to the function signature. Here is an example of a function that has had this done already:
```python
def wrap_text_to_pixels(
string: str, max_width: int, font=None, indent0: str = "", indent1: str = ""
) -> List[str]:
```
If you are new to Git or Github we have a guide about contributing to our projects here: https://learn.adafruit.com/contribute-to-circuitpython-with-git-and-github
There is also a guide that covers our CI utilities and how to run them locally to ensure they will pass in Github Actions here: https://learn.adafruit.com/creating-and-sharing-a-circuitpython-library/check-your-code In particular the pages: `Sharing docs on ReadTheDocs` and `Check your code with pre-commit` contain the tools to install and commands to run locally to run the checks.
If you are attempting to resolve this issue and need help, you can post a comment on this issue and tag both @foamyguy and @kattni or reach out to us on Discord: https://adafru.it/discord in the `#circuitpython-dev` channel.
The following locations are reported by mypy to be missing type annotations:
- [ ] adafruit_pyoa.py:113
- [ ] adafruit_pyoa.py:195
- [ ] adafruit_pyoa.py:212
- [ ] adafruit_pyoa.py:219
- [ ] adafruit_pyoa.py:233
- [ ] adafruit_pyoa.py:245
- [ ] adafruit_pyoa.py:282
- [ ] adafruit_pyoa.py:324
- [ ] adafruit_pyoa.py:361
- [ ] adafruit_pyoa.py:392
- [ ] adafruit_pyoa.py:427
- [ ] adafruit_pyoa.py:444 | non_priority | missing type annotations there are missing type annotations for some functions in this library the typing module does not exist on circuitpython devices so the import needs to be wrapped in try except to catch the error for missing import there is an example of how that is done here python try from typing import list tuple except importerror pass once imported the typing annotations for the argument type s and return type s can be added to the function signature here is an example of a function that has had this done already python def wrap text to pixels string str max width int font none str str list if you are new to git or github we have a guide about contributing to our projects here there is also a guide that covers our ci utilities and how to run them locally to ensure they will pass in github actions here in particular the pages sharing docs on readthedocs and check your code with pre commit contain the tools to install and commands to run locally to run the checks if you are attempting to resolve this issue and need help you can post a comment on this issue and tag both foamyguy and kattni or reach out to us on discord in the circuitpython dev channel the following locations are reported by mypy to be missing type annotations adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py adafruit pyoa py | 0 |
235,423 | 25,934,456,682 | IssuesEvent | 2022-12-16 12:56:59 | uthrapathi/extrernal_expat_Demo_uthra | https://api.github.com/repos/uthrapathi/extrernal_expat_Demo_uthra | opened | CVE-2022-43680 (High) detected in expatexpat-2.2.6 | security vulnerability | ## CVE-2022-43680 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>expatexpat-2.2.6</b></p></summary>
<p>
<p>Fast XML parser library in C</p>
<p>Library home page: <a href=https://sourceforge.net/projects/expat/>https://sourceforge.net/projects/expat/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/uthrapathi/extrernal_expat_Demo_uthra/commit/3618c82de7712730b01ffd25210b441827930f93">3618c82de7712730b01ffd25210b441827930f93</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/xmlparse.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In libexpat through 2.4.9, there is a use-after free caused by overeager destruction of a shared DTD in XML_ExternalEntityParserCreate in out-of-memory situations.
<p>Publish Date: 2022-10-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-43680>CVE-2022-43680</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-43680 (High) detected in expatexpat-2.2.6 - ## CVE-2022-43680 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>expatexpat-2.2.6</b></p></summary>
<p>
<p>Fast XML parser library in C</p>
<p>Library home page: <a href=https://sourceforge.net/projects/expat/>https://sourceforge.net/projects/expat/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/uthrapathi/extrernal_expat_Demo_uthra/commit/3618c82de7712730b01ffd25210b441827930f93">3618c82de7712730b01ffd25210b441827930f93</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/lib/xmlparse.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In libexpat through 2.4.9, there is a use-after free caused by overeager destruction of a shared DTD in XML_ExternalEntityParserCreate in out-of-memory situations.
<p>Publish Date: 2022-10-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-43680>CVE-2022-43680</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in expatexpat cve high severity vulnerability vulnerable library expatexpat fast xml parser library in c library home page a href found in head commit a href found in base branch master vulnerable source files lib xmlparse c vulnerability details in libexpat through there is a use after free caused by overeager destruction of a shared dtd in xml externalentityparsercreate in out of memory situations publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
4,974 | 11,912,377,033 | IssuesEvent | 2020-03-31 10:09:52 | SUSE/doc-caasp | https://api.github.com/repos/SUSE/doc-caasp | closed | [doc] 2.2.6.1 Mirror Configuration | ArchitectureGuide DeploymentGuide Enhancement Reported v4 wontfix | 2.2.6.1 Mirror Configuration
https://www.suse.com/documentation/suse-caasp-3/singlehtml/book_caasp_deployment/book_caasp_deployment.html#sec.deploy.scenarios.airgap.container-registry.mirror
The text is rather complex, it would be great to have a picture outlining the setup with internal/external registries and how they are interconnected together and with CaaSP.
| 1.0 | [doc] 2.2.6.1 Mirror Configuration - 2.2.6.1 Mirror Configuration
https://www.suse.com/documentation/suse-caasp-3/singlehtml/book_caasp_deployment/book_caasp_deployment.html#sec.deploy.scenarios.airgap.container-registry.mirror
The text is rather complex, it would be great to have a picture outlining the setup with internal/external registries and how they are interconnected together and with CaaSP.
| non_priority | mirror configuration mirror configuration the text is rather complex it would be great to have a picture outlining the setup with internal external registries and how they are interconnected together and with caasp | 0 |
86,067 | 24,755,896,076 | IssuesEvent | 2022-10-21 17:41:37 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Follow up on mono toolchain workload PR feedback | area-Build-mono in-pr | Looks like we missed some feedback from Viktor on this PR: https://github.com/dotnet/runtime/pull/51327#pullrequestreview-651576417
We should address it. | 1.0 | Follow up on mono toolchain workload PR feedback - Looks like we missed some feedback from Viktor on this PR: https://github.com/dotnet/runtime/pull/51327#pullrequestreview-651576417
We should address it. | non_priority | follow up on mono toolchain workload pr feedback looks like we missed some feedback from viktor on this pr we should address it | 0 |
306,714 | 23,170,034,439 | IssuesEvent | 2022-07-30 15:10:33 | lepoco/wpfui | https://api.github.com/repos/lepoco/wpfui | closed | Getting started tutorial link from the main webpage is incorrect and warns user about site security | bug documentation | **Describe the bug**
I am unable to view the getting started tutorial on the web page. When I click "see our tutorial" I get the following:
The connection for this site is not secure
wpf.ui.lepo.co uses an unsupported protocol.
ERR_SSL_VERSION_OR_CIPHER_MISMATCH
The target URL of the website is https://wpf.ui.lepo.co/documentation/tutorial
**To Reproduce**
Steps to reproduce the behavior:
1. Go to [https://wpfui.lepo.co/documentation/](https://wpfui.lepo.co/documentation/)
2. Click on 'see our tutorial'
3. See error
**Expected behavior**
You go to the tutorial.
**Desktop (please complete the following information):**
- OS: Windows 11, Edge Browser
**Additional context**
It appears that the link is simply broken.
The expected URL is https://wpfui.lepo.co/documentation/tutorial
The link goes to https://wpf.ui.lepo.co/documentation/tutorial | 1.0 | Getting started tutorial link from the main webpage is incorrect and warns user about site security - **Describe the bug**
I am unable to view the getting started tutorial on the web page. When I click "see our tutorial" I get the following:
The connection for this site is not secure
wpf.ui.lepo.co uses an unsupported protocol.
ERR_SSL_VERSION_OR_CIPHER_MISMATCH
The target URL of the website is https://wpf.ui.lepo.co/documentation/tutorial
**To Reproduce**
Steps to reproduce the behavior:
1. Go to [https://wpfui.lepo.co/documentation/](https://wpfui.lepo.co/documentation/)
2. Click on 'see our tutorial'
3. See error
**Expected behavior**
You go to the tutorial.
**Desktop (please complete the following information):**
- OS: Windows 11, Edge Browser
**Additional context**
It appears that the link is simply broken.
The expected URL is https://wpfui.lepo.co/documentation/tutorial
The link goes to https://wpf.ui.lepo.co/documentation/tutorial | non_priority | getting started tutorial link from the main webpage is incorrect and warns user about site security describe the bug i am unable to view the getting started tutorial on the web page when i click see our tutorial i get the following the connection for this site is not secure wpf ui lepo co uses an unsupported protocol err ssl version or cipher mismatch the target url of the website is to reproduce steps to reproduce the behavior go to click on see our tutorial see error expected behavior you go to the tutorial desktop please complete the following information os windows edge browser additional context it appears that the link is simply broken the expected url is the link goes to | 0 |
182,743 | 14,148,383,792 | IssuesEvent | 2020-11-10 22:27:05 | blockstack/stacks-blockchain | https://api.github.com/repos/blockstack/stacks-blockchain | opened | [TESTNET BUG]: microblock key derivation not working as expected | bug testnet | ## Describe the bug
After starting a miner, it joins a pre-existing STX network and syncs to the latest burnchain tip and STX tip just fine, but it does not start mining operations until a large amount of time has passed (depending on the STX height). The logs also emit the following WARNing messages:
```
WARN [1605045926.632094] [src/chainstate/stacks/db/blocks.rs:4474] [ThreadId(6)] Encountered invalid block: Invalid stacks block 578e9e2772ea55729cc14d494489d2a0da3194bf/565ecf8e66aa840e5aa796e9c835bbfa114c62c7880926bb8a07450ce01020ff -- already used microblock pubkey hash 2215229e86136fefeaa254273b1f0d150daa7645
WARN [1605046028.992105] [src/chainstate/stacks/db/blocks.rs:4474] [ThreadId(6)] Encountered invalid block: Invalid stacks block a5003e2351e9f136d29d60f5954f2c24f576fcab/12c051ca6974e3e2842b6f4af2297c564344419e1c21846ea1fbb43d3bf685c3 -- already used microblock pubkey hash e74aa54918ad8d5ae6dd1fe569b1d47ad114ff6d
WARN [1605046165.423254] [src/chainstate/stacks/db/blocks.rs:4474] [ThreadId(6)] Encountered invalid block: Invalid stacks block 951278dc8633c5d36f27a70296221842a24b0ce1/3dacc68a79ac279eefc01de9d766150b3d29f5139555af82ea50e052bc56b0da -- already used microblock pubkey hash ee95f3f535c2acbf8160c0971383c993eb24924b
```
## Steps To Reproduce
1. Start a BTC node, a krypton miner, and a krypton follower which uses the miner as a bootstrap_node. These should be the _only_ two nodes on the network.
2. Wait until the burnchain and STX chain progresses consistently to verify it's working as expected.
3. Terminate the miner, and start it back up after it has fully terminated.
4. Observe the miner syncing to the burnchain tip and STX tip.
5. Once the miner is fully synced, check the logs for the errors and record the amount of time it takes for the STX tip to progress. The burnchain tip will continue progressing at a normal rate.
## Expected behavior
The miner should resume mining operations quickly after it's finished syncing with the STX network.
## Environment
- Used the stacks-burnchain docker image `blockstack/stacks-blockchain:v23.0.0.9-krypton-stretch`
## Additional context
After discussing this with @kantai and @lgalabru in Discord, it appears the microblock keypair is not being derived, taking into account the block height. Once the keypair was rejected 60 times (the STX tip height at the time of testing), the miner would continue on to mine block 61, and so on at a normal rate. but until then, the miner is effectively stalled.
This bug seems to occur even if the `mine_microblocks` config property is set to `false`.
----
If you think this is eligible for a [bug bounty](https://testnet.blockstack.org/bounties), please check the relevant boxes below:
### Critical, Launch Blocking Bugs
**Consensus critical bugs**
- [ ] Can cause a chain split
- [ ] Can cause an invalid transaction to get mined
- [ ] Can cause an invalid block to get accepted
- [X] Can cause a node to stall
**State corruption**
- [ ] Can modify a smart contract’s data maps and data vars without a `contract-call?
**Stolen funds**
- [ ] Any address losing STX without a corresponding transfer
- [ ] Modify token balances and NFT ownership in other contracts without a `contract-call?`
**Take control and/or bring network to a halt**
- [ ] Take control and/or bring network to a halt
### Major, Launch Blocking Bugs
**Major bugs**
- [ ] Performance or correctness bugs that don’t rise to P0 level
- [ ] Stress test or DoS attacks that slow things down enough
- [ ] Resource exhaustion
- [X] Expected functionality doesn’t work in obvious ways (important to be super specific with this wording)
| 1.0 | [TESTNET BUG]: microblock key derivation not working as expected - ## Describe the bug
After starting a miner, it joins a pre-existing STX network and syncs to the latest burnchain tip and STX tip just fine, but it does not start mining operations until a large amount of time has passed (depending on the STX height). The logs also emit the following WARNing messages:
```
WARN [1605045926.632094] [src/chainstate/stacks/db/blocks.rs:4474] [ThreadId(6)] Encountered invalid block: Invalid stacks block 578e9e2772ea55729cc14d494489d2a0da3194bf/565ecf8e66aa840e5aa796e9c835bbfa114c62c7880926bb8a07450ce01020ff -- already used microblock pubkey hash 2215229e86136fefeaa254273b1f0d150daa7645
WARN [1605046028.992105] [src/chainstate/stacks/db/blocks.rs:4474] [ThreadId(6)] Encountered invalid block: Invalid stacks block a5003e2351e9f136d29d60f5954f2c24f576fcab/12c051ca6974e3e2842b6f4af2297c564344419e1c21846ea1fbb43d3bf685c3 -- already used microblock pubkey hash e74aa54918ad8d5ae6dd1fe569b1d47ad114ff6d
WARN [1605046165.423254] [src/chainstate/stacks/db/blocks.rs:4474] [ThreadId(6)] Encountered invalid block: Invalid stacks block 951278dc8633c5d36f27a70296221842a24b0ce1/3dacc68a79ac279eefc01de9d766150b3d29f5139555af82ea50e052bc56b0da -- already used microblock pubkey hash ee95f3f535c2acbf8160c0971383c993eb24924b
```
## Steps To Reproduce
1. Start a BTC node, a krypton miner, and a krypton follower which uses the miner as a bootstrap_node. These should be the _only_ two nodes on the network.
2. Wait until the burnchain and STX chain progresses consistently to verify it's working as expected.
3. Terminate the miner, and start it back up after it has fully terminated.
4. Observe the miner syncing to the burnchain tip and STX tip.
5. Once the miner is fully synced, check the logs for the errors and record the amount of time it takes for the STX tip to progress. The burnchain tip will continue progressing at a normal rate.
## Expected behavior
The miner should resume mining operations quickly after it's finished syncing with the STX network.
## Environment
- Used the stacks-burnchain docker image `blockstack/stacks-blockchain:v23.0.0.9-krypton-stretch`
## Additional context
After discussing this with @kantai and @lgalabru in Discord, it appears the microblock keypair is not being derived, taking into account the block height. Once the keypair was rejected 60 times (the STX tip height at the time of testing), the miner would continue on to mine block 61, and so on at a normal rate. but until then, the miner is effectively stalled.
This bug seems to occur even if the `mine_microblocks` config property is set to `false`.
----
If you think this is eligible for a [bug bounty](https://testnet.blockstack.org/bounties), please check the relevant boxes below:
### Critical, Launch Blocking Bugs
**Consensus critical bugs**
- [ ] Can cause a chain split
- [ ] Can cause an invalid transaction to get mined
- [ ] Can cause an invalid block to get accepted
- [X] Can cause a node to stall
**State corruption**
- [ ] Can modify a smart contract’s data maps and data vars without a `contract-call?
**Stolen funds**
- [ ] Any address losing STX without a corresponding transfer
- [ ] Modify token balances and NFT ownership in other contracts without a `contract-call?`
**Take control and/or bring network to a halt**
- [ ] Take control and/or bring network to a halt
### Major, Launch Blocking Bugs
**Major bugs**
- [ ] Performance or correctness bugs that don’t rise to P0 level
- [ ] Stress test or DoS attacks that slow things down enough
- [ ] Resource exhaustion
- [X] Expected functionality doesn’t work in obvious ways (important to be super specific with this wording)
| non_priority | microblock key derivation not working as expected describe the bug after starting a miner it joins a pre existing stx network and syncs to the latest burnchain tip and stx tip just fine but it does not start mining operations until a large amount of time has passed depending on the stx height the logs also emit the following warning messages warn encountered invalid block invalid stacks block already used microblock pubkey hash warn encountered invalid block invalid stacks block already used microblock pubkey hash warn encountered invalid block invalid stacks block already used microblock pubkey hash steps to reproduce start a btc node a krypton miner and a krypton follower which uses the miner as a bootstrap node these should be the only two nodes on the network wait until the burnchain and stx chain progresses consistently to verify it s working as expected terminate the miner and start it back up after it has fully terminated observe the miner syncing to the burnchain tip and stx tip once the miner is fully synced check the logs for the errors and record the amount of time it takes for the stx tip to progress the burnchain tip will continue progressing at a normal rate expected behavior the miner should resume mining operations quickly after it s finished syncing with the stx network environment used the stacks burnchain docker image blockstack stacks blockchain krypton stretch additional context after discussing this with kantai and lgalabru in discord it appears the microblock keypair is not being derived taking into account the block height once the keypair was rejected times the stx tip height at the time of testing the miner would continue on to mine block and so on at a normal rate but until then the miner is effectively stalled this bug seems to occur even if the mine microblocks config property is set to false if you think this is eligible for a please check the relevant boxes below critical launch blocking bugs consensus critical bugs can cause a chain split can cause an invalid transaction to get mined can cause an invalid block to get accepted can cause a node to stall state corruption can modify a smart contract’s data maps and data vars without a contract call stolen funds any address losing stx without a corresponding transfer modify token balances and nft ownership in other contracts without a contract call take control and or bring network to a halt take control and or bring network to a halt major launch blocking bugs major bugs performance or correctness bugs that don’t rise to level stress test or dos attacks that slow things down enough resource exhaustion expected functionality doesn’t work in obvious ways important to be super specific with this wording | 0 |
150,047 | 19,598,545,017 | IssuesEvent | 2022-01-05 21:10:23 | opensearch-project/OpenSearch-Dashboards | https://api.github.com/repos/opensearch-project/OpenSearch-Dashboards | closed | CVE-2019-6283 (Medium) detected in node-sass-4.13.1.tgz - autoclosed | security vulnerability medium severity | ## CVE-2019-6283 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz</a></p>
<p>
Dependency Hierarchy:
- @osd/optimizer-1.0.0.tgz (Root Library)
- :x: **node-sass-4.13.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/opensearch-project/OpenSearch-Dashboards/commit/4fd064970b66ce555f48c22dfab6ed965d0e260a">4fd064970b66ce555f48c22dfab6ed965d0e260a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::parenthese_scope in prelexer.hpp.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6283>CVE-2019-6283</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.6.0">https://github.com/sass/libsass/releases/tag/3.6.0</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: libsass - 3.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.13.1","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"@osd/optimizer:1.0.0;node-sass:4.13.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"libsass - 3.6.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-6283","vulnerabilityDetails":"In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::parenthese_scope in prelexer.hpp.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6283","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-6283 (Medium) detected in node-sass-4.13.1.tgz - autoclosed - ## CVE-2019-6283 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz</a></p>
<p>
Dependency Hierarchy:
- @osd/optimizer-1.0.0.tgz (Root Library)
- :x: **node-sass-4.13.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/opensearch-project/OpenSearch-Dashboards/commit/4fd064970b66ce555f48c22dfab6ed965d0e260a">4fd064970b66ce555f48c22dfab6ed965d0e260a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::parenthese_scope in prelexer.hpp.
<p>Publish Date: 2019-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6283>CVE-2019-6283</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.6.0">https://github.com/sass/libsass/releases/tag/3.6.0</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: libsass - 3.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.13.1","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"@osd/optimizer:1.0.0;node-sass:4.13.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"libsass - 3.6.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-6283","vulnerabilityDetails":"In LibSass 3.5.5, a heap-based buffer over-read exists in Sass::Prelexer::parenthese_scope in prelexer.hpp.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-6283","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in node sass tgz autoclosed cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href dependency hierarchy osd optimizer tgz root library x node sass tgz vulnerable library found in head commit a href found in base branch main vulnerability details in libsass a heap based buffer over read exists in sass prelexer parenthese scope in prelexer hpp publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree osd optimizer node sass isminimumfixversionavailable true minimumfixversion libsass isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in libsass a heap based buffer over read exists in sass prelexer parenthese scope in prelexer hpp vulnerabilityurl | 0 |
74,865 | 15,377,647,684 | IssuesEvent | 2021-03-02 17:19:53 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | SSLStream should not use the ArrayPool for it's internal buffers | area-System.Net.Security tenet-performance untriaged | ### Description
Today SSLStream uses a 4K buffer for the TLS handshake and a 16K buffer for the reading TLS frames. These buffers come from the array pool today which makes it really easy to exhaust the buckets in the shared array pool for those commonly used sizes. This affects websocket and any other scenario that results in a large number of long lived concurrent connections.
### Regression?
No.
### Data
A demo of 5000 websocket connections connected to an ASP.NET Core server using Kestrel:
Here's a heap dump sorted by inclusive size. Most of what is being held onto is array pool buffers.

On top of that, I took a trace of the same set of connections and you can see the ArrayPool event source says the number of buffers allocated is 5000. The buffers are all 32K in size (because of how the SslSteam adds the FrameOverhead).

Allocation profile of 5000 websocket connections. You can see the array pool has the most byte[] allocations.

They're mostly in the handshake and reading (I'm not writing in this app), just sitting mostly idle with ping pongs:

### Analysis
We shouldn't use the array pool buffers for reads that may take a long time. That means both for the handshake and the encryption/decryption:
https://github.com/dotnet/runtime/blob/5dacf1e3fdbe0769fd54ef4070af6b3477243d75/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs#L1040
The handshake will end up doing the same for 8K buffers in the pool but potentially for a much shorter duration as clients negotiate quickly and there's a timeout to complete the handshake (in kestrel). | True | SSLStream should not use the ArrayPool for it's internal buffers - ### Description
Today SSLStream uses a 4K buffer for the TLS handshake and a 16K buffer for the reading TLS frames. These buffers come from the array pool today which makes it really easy to exhaust the buckets in the shared array pool for those commonly used sizes. This affects websocket and any other scenario that results in a large number of long lived concurrent connections.
### Regression?
No.
### Data
A demo of 5000 websocket connections connected to an ASP.NET Core server using Kestrel:
Here's a heap dump sorted by inclusive size. Most of what is being held onto is array pool buffers.

On top of that, I took a trace of the same set of connections and you can see the ArrayPool event source says the number of buffers allocated is 5000. The buffers are all 32K in size (because of how the SslSteam adds the FrameOverhead).

Allocation profile of 5000 websocket connections. You can see the array pool has the most byte[] allocations.

They're mostly in the handshake and reading (I'm not writing in this app), just sitting mostly idle with ping pongs:

### Analysis
We shouldn't use the array pool buffers for reads that may take a long time. That means both for the handshake and the encryption/decryption:
https://github.com/dotnet/runtime/blob/5dacf1e3fdbe0769fd54ef4070af6b3477243d75/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs#L1040
The handshake will end up doing the same for 8K buffers in the pool but potentially for a much shorter duration as clients negotiate quickly and there's a timeout to complete the handshake (in kestrel). | non_priority | sslstream should not use the arraypool for it s internal buffers description today sslstream uses a buffer for the tls handshake and a buffer for the reading tls frames these buffers come from the array pool today which makes it really easy to exhaust the buckets in the shared array pool for those commonly used sizes this affects websocket and any other scenario that results in a large number of long lived concurrent connections regression no data a demo of websocket connections connected to an asp net core server using kestrel here s a heap dump sorted by inclusive size most of what is being held onto is array pool buffers on top of that i took a trace of the same set of connections and you can see the arraypool event source says the number of buffers allocated is the buffers are all in size because of how the sslsteam adds the frameoverhead allocation profile of websocket connections you can see the array pool has the most byte allocations they re mostly in the handshake and reading i m not writing in this app just sitting mostly idle with ping pongs analysis we shouldn t use the array pool buffers for reads that may take a long time that means both for the handshake and the encryption decryption the handshake will end up doing the same for buffers in the pool but potentially for a much shorter duration as clients negotiate quickly and there s a timeout to complete the handshake in kestrel | 0 |
43,709 | 11,799,790,838 | IssuesEvent | 2020-03-18 16:26:56 | primefaces/primeng | https://api.github.com/repos/primefaces/primeng | closed | Table and TreeTable footer with vertical scroll might be misaligned with header and body | defect | **I'm submitting a ...** (check one with "x")
```
[ x ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
https://stackblitz.com/edit/github-jkqfkq
**Current behavior**
TreeTable footer is always misaligned with header and body when vertical scroll is enabled.
This bug was introduced in primeng v9.0.0.
It worked before in primeng v8.1.1.

**Expected behavior**
TreeTable footer is aligned with header and body when vertical scroll is enabled.
Column resize should be taken care as well.
**Minimal reproduction of the problem with instructions**
The column in footer was misaligned from the beginning. Resizing columns did not fix the misalignment.
**Please tell us about your environment:**
* **Angular version:** 9.0.4
* **PrimeNG version:** 9.0.0 | 1.0 | Table and TreeTable footer with vertical scroll might be misaligned with header and body - **I'm submitting a ...** (check one with "x")
```
[ x ] bug report => Search github for a similar issue or PR before submitting
[ ] feature request => Please check if request is not on the roadmap already https://github.com/primefaces/primeng/wiki/Roadmap
[ ] support request => Please do not submit support request here, instead see http://forum.primefaces.org/viewforum.php?f=35
```
**Plunkr Case (Bug Reports)**
https://stackblitz.com/edit/github-jkqfkq
**Current behavior**
TreeTable footer is always misaligned with header and body when vertical scroll is enabled.
This bug was introduced in primeng v9.0.0.
It worked before in primeng v8.1.1.

**Expected behavior**
TreeTable footer is aligned with header and body when vertical scroll is enabled.
Column resize should be taken care as well.
**Minimal reproduction of the problem with instructions**
The column in footer was misaligned from the beginning. Resizing columns did not fix the misalignment.
**Please tell us about your environment:**
* **Angular version:** 9.0.4
* **PrimeNG version:** 9.0.0 | non_priority | table and treetable footer with vertical scroll might be misaligned with header and body i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request please check if request is not on the roadmap already support request please do not submit support request here instead see plunkr case bug reports current behavior treetable footer is always misaligned with header and body when vertical scroll is enabled this bug was introduced in primeng it worked before in primeng expected behavior treetable footer is aligned with header and body when vertical scroll is enabled column resize should be taken care as well minimal reproduction of the problem with instructions the column in footer was misaligned from the beginning resizing columns did not fix the misalignment please tell us about your environment angular version primeng version | 0 |
2,738 | 2,631,965,470 | IssuesEvent | 2015-03-07 16:59:50 | breaker27/smarthomatic | https://api.github.com/repos/breaker27/smarthomatic | closed | SoilMoistureMeter: Variable DENOISE_WINDOW_PERMILL | Feature Firmware Testing | This variable (currently fixed in source code) tells in which way the resulting humidity (in percent from 0 to 100) is smoothed. I have several SoilMoistureMeters and some show "jumps" from 1-2%, some 8-10%. This has to do with the thickness of Isolation above the sensor plates, the humidity range of the soil where you use it, and humidity values seem to change much when plants are above a radiator.
Default could be around 8%, values should be adjustable via e2p. | 1.0 | SoilMoistureMeter: Variable DENOISE_WINDOW_PERMILL - This variable (currently fixed in source code) tells in which way the resulting humidity (in percent from 0 to 100) is smoothed. I have several SoilMoistureMeters and some show "jumps" from 1-2%, some 8-10%. This has to do with the thickness of Isolation above the sensor plates, the humidity range of the soil where you use it, and humidity values seem to change much when plants are above a radiator.
Default could be around 8%, values should be adjustable via e2p. | non_priority | soilmoisturemeter variable denoise window permill this variable currently fixed in source code tells in which way the resulting humidity in percent from to is smoothed i have several soilmoisturemeters and some show jumps from some this has to do with the thickness of isolation above the sensor plates the humidity range of the soil where you use it and humidity values seem to change much when plants are above a radiator default could be around values should be adjustable via | 0 |
152,393 | 19,681,385,921 | IssuesEvent | 2022-01-11 17:05:34 | OSWeekends/batimagen | https://api.github.com/repos/OSWeekends/batimagen | opened | CVE-2021-33502 (High) detected in normalize-url-3.3.0.tgz | security vulnerability | ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-3.3.0.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-3.3.0.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-3.3.0.tgz</a></p>
<p>
Dependency Hierarchy:
- snyk-1.192.5.tgz (Root Library)
- git-url-parse-11.1.2.tgz
- git-up-4.0.1.tgz
- parse-url-5.0.1.tgz
- :x: **normalize-url-3.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/OSWeekends/batimagen/git/commits/91935c9712dc7108a8e93a1a03524ff430afe66b">91935c9712dc7108a8e93a1a03524ff430afe66b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution: normalize-url - 4.5.1, 5.3.1, 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33502 (High) detected in normalize-url-3.3.0.tgz - ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-3.3.0.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-3.3.0.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-3.3.0.tgz</a></p>
<p>
Dependency Hierarchy:
- snyk-1.192.5.tgz (Root Library)
- git-url-parse-11.1.2.tgz
- git-up-4.0.1.tgz
- parse-url-5.0.1.tgz
- :x: **normalize-url-3.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/OSWeekends/batimagen/git/commits/91935c9712dc7108a8e93a1a03524ff430afe66b">91935c9712dc7108a8e93a1a03524ff430afe66b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution: normalize-url - 4.5.1, 5.3.1, 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in normalize url tgz cve high severity vulnerability vulnerable library normalize url tgz normalize a url library home page a href dependency hierarchy snyk tgz root library git url parse tgz git up tgz parse url tgz x normalize url tgz vulnerable library found in head commit a href vulnerability details the normalize url package before x before and x before for node js has a redos regular expression denial of service issue because it has exponential performance for data urls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution normalize url step up your open source security game with whitesource | 0 |
108,584 | 13,641,726,025 | IssuesEvent | 2020-09-25 14:33:25 | cityofaustin/techstack | https://api.github.com/repos/cityofaustin/techstack | opened | Doc collection: keyword filter | Content type: Official document Feature: Search Team: Design | ## Overview
Nick's ready to tackle keyword search on `Official document collections`, and since we did some wide exploration for filtering a few months ago, we already have a head start on that effort. Let's get the specs and criteria ready to hand off to dev by the end of this sprint.
## Components
- Label for the field group
- EN: ""
- ES: ""
- Text input field
- Any states: focus/active, error
## Criteria
Abstract branch:
Dev criteria collection:
| 1.0 | Doc collection: keyword filter - ## Overview
Nick's ready to tackle keyword search on `Official document collections`, and since we did some wide exploration for filtering a few months ago, we already have a head start on that effort. Let's get the specs and criteria ready to hand off to dev by the end of this sprint.
## Components
- Label for the field group
- EN: ""
- ES: ""
- Text input field
- Any states: focus/active, error
## Criteria
Abstract branch:
Dev criteria collection:
| non_priority | doc collection keyword filter overview nick s ready to tackle keyword search on official document collections and since we did some wide exploration for filtering a few months ago we already have a head start on that effort let s get the specs and criteria ready to hand off to dev by the end of this sprint components label for the field group en es text input field any states focus active error criteria abstract branch dev criteria collection | 0 |
14,008 | 3,791,634,825 | IssuesEvent | 2016-03-22 04:22:20 | derek-damron/transform | https://api.github.com/repos/derek-damron/transform | opened | Improve transform's value proposition | Documentation Enhancement Idea | Still a bit amorphous, but some initial word vomit:
- What problem(s) does it solve?
- Why should people use it?
- Does it really:
- Save coding time?
- Make code more readable?
- Reduce coding errors? | 1.0 | Improve transform's value proposition - Still a bit amorphous, but some initial word vomit:
- What problem(s) does it solve?
- Why should people use it?
- Does it really:
- Save coding time?
- Make code more readable?
- Reduce coding errors? | non_priority | improve transform s value proposition still a bit amorphous but some initial word vomit what problem s does it solve why should people use it does it really save coding time make code more readable reduce coding errors | 0 |
73,884 | 15,286,191,554 | IssuesEvent | 2021-02-23 14:26:04 | idonthaveafifaaddiction/IoT-Smart-Gateway | https://api.github.com/repos/idonthaveafifaaddiction/IoT-Smart-Gateway | opened | CVE-2019-1010266 (Medium) detected in lodash-1.0.2.tgz | security vulnerability | ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: IoT-Smart-Gateway/web/package.json</p>
<p>Path to vulnerable library: IoT-Smart-Gateway/web/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/IoT-Smart-Gateway/commit/085c2936b8c1a6952ca6f0db9eaf75ff33e478a1">085c2936b8c1a6952ca6f0db9eaf75ff33e478a1</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"1.0.2","packageFilePaths":["/web/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp:3.9.1;vinyl-fs:0.3.14;glob-watcher:0.0.6;gaze:0.5.2;globule:0.1.0;lodash:1.0.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.11"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2019-1010266","vulnerabilityDetails":"lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-1010266 (Medium) detected in lodash-1.0.2.tgz - ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: IoT-Smart-Gateway/web/package.json</p>
<p>Path to vulnerable library: IoT-Smart-Gateway/web/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/IoT-Smart-Gateway/commit/085c2936b8c1a6952ca6f0db9eaf75ff33e478a1">085c2936b8c1a6952ca6f0db9eaf75ff33e478a1</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"1.0.2","packageFilePaths":["/web/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp:3.9.1;vinyl-fs:0.3.14;glob-watcher:0.0.6;gaze:0.5.2;globule:0.1.0;lodash:1.0.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.17.11"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2019-1010266","vulnerabilityDetails":"lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file iot smart gateway web package json path to vulnerable library iot smart gateway web node modules globule node modules lodash package json dependency hierarchy gulp tgz root library vinyl fs tgz glob watcher tgz gaze tgz globule tgz x lodash tgz vulnerable library found in head commit a href found in base branch develop vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree gulp vinyl fs glob watcher gaze globule lodash isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is vulnerabilityurl | 0 |
13,419 | 8,916,083,063 | IssuesEvent | 2019-01-19 13:12:45 | effortless-mgmt/EffortlessBackend | https://api.github.com/repos/effortless-mgmt/EffortlessBackend | closed | Extend expiration time of access tokens | enhancement security | The current expiration time is 5 minutes, it should probably be extend a bit. | True | Extend expiration time of access tokens - The current expiration time is 5 minutes, it should probably be extend a bit. | non_priority | extend expiration time of access tokens the current expiration time is minutes it should probably be extend a bit | 0 |
60,865 | 8,470,248,196 | IssuesEvent | 2018-10-24 03:13:21 | bcit-ci/CodeIgniter4 | https://api.github.com/repos/bcit-ci/CodeIgniter4 | closed | Error in user guide for session config | bug documentation | The user guide (libraries/sessions) still describes the CI3 style of configuration (i.e. $sessionDriver = "files" instead of $sessionDriver = 'CodeIgniter\Session\Handlers\FileHandler';
Needs fixing :-/ | 1.0 | Error in user guide for session config - The user guide (libraries/sessions) still describes the CI3 style of configuration (i.e. $sessionDriver = "files" instead of $sessionDriver = 'CodeIgniter\Session\Handlers\FileHandler';
Needs fixing :-/ | non_priority | error in user guide for session config the user guide libraries sessions still describes the style of configuration i e sessiondriver files instead of sessiondriver codeigniter session handlers filehandler needs fixing | 0 |
262,052 | 19,759,963,924 | IssuesEvent | 2022-01-16 08:38:08 | keanuwilliams/inspirational-homepage | https://api.github.com/repos/keanuwilliams/inspirational-homepage | closed | Update History documentation to Include v1.3.0 | documentation | Currently, the history documentation in the Wiki does not have the current version of the application. | 1.0 | Update History documentation to Include v1.3.0 - Currently, the history documentation in the Wiki does not have the current version of the application. | non_priority | update history documentation to include currently the history documentation in the wiki does not have the current version of the application | 0 |
96,460 | 12,130,542,061 | IssuesEvent | 2020-04-23 01:53:48 | reach4help/reach4help | https://api.github.com/repos/reach4help/reach4help | opened | UI of CAV Flow View #2: Requests | UI Design | Since the CAV UX is ready, we are able to start building the UI design of CAV View "Timeline". Referred by the attached image or this [link](https://www.figma.com/file/OiU7Tl4k1YFfqZQXxLaRrl/Reach4Help?node-id=1055%3A235)
 | 1.0 | UI of CAV Flow View #2: Requests - Since the CAV UX is ready, we are able to start building the UI design of CAV View "Timeline". Referred by the attached image or this [link](https://www.figma.com/file/OiU7Tl4k1YFfqZQXxLaRrl/Reach4Help?node-id=1055%3A235)
 | non_priority | ui of cav flow view requests since the cav ux is ready we are able to start building the ui design of cav view timeline referred by the attached image or this | 0 |
18,572 | 3,072,603,030 | IssuesEvent | 2015-08-19 17:45:34 | CocoaPods/CocoaPods | https://api.github.com/repos/CocoaPods/CocoaPods | closed | Missing Required Modules | s2:confirmed t2:defect | I amusing the 0.36.0 beta 2 version of the plugin and working to create an app using an Extension. I want my app framework to be the only part that uses certain cocoa pods. However when I try to import my AppKit into my main project (using swift) the complier complains that it is missing the required modules, which happen to be the cocoapods that I am not including in my main app.


| 1.0 | Missing Required Modules - I amusing the 0.36.0 beta 2 version of the plugin and working to create an app using an Extension. I want my app framework to be the only part that uses certain cocoa pods. However when I try to import my AppKit into my main project (using swift) the complier complains that it is missing the required modules, which happen to be the cocoapods that I am not including in my main app.


| non_priority | missing required modules i amusing the beta version of the plugin and working to create an app using an extension i want my app framework to be the only part that uses certain cocoa pods however when i try to import my appkit into my main project using swift the complier complains that it is missing the required modules which happen to be the cocoapods that i am not including in my main app | 0 |
117,045 | 11,945,660,651 | IssuesEvent | 2020-04-03 06:24:53 | ChesterSim/ped | https://api.github.com/repos/ChesterSim/ped | opened | User Guide info for 'Enter' not clear | severity.Low type.DocumentationBug | 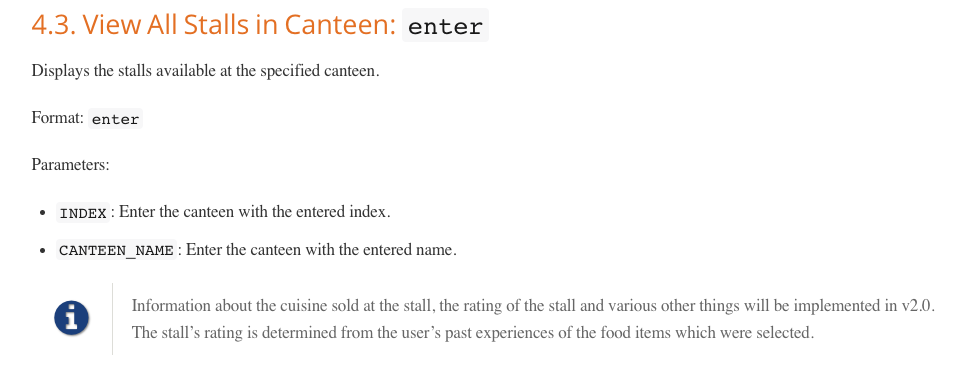
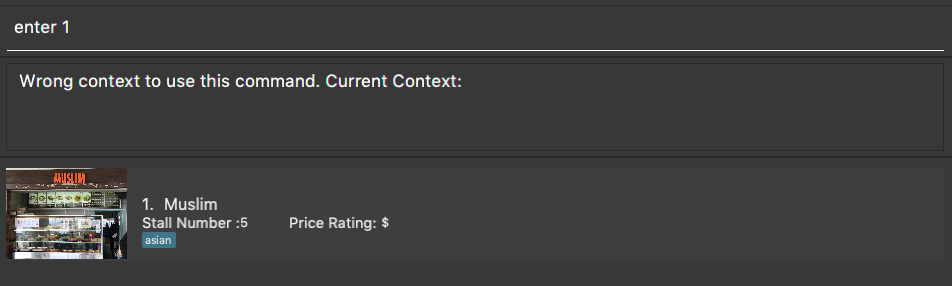
User Guide did not specify that the 'enter' command can be used only in the main screen
| 1.0 | User Guide info for 'Enter' not clear - 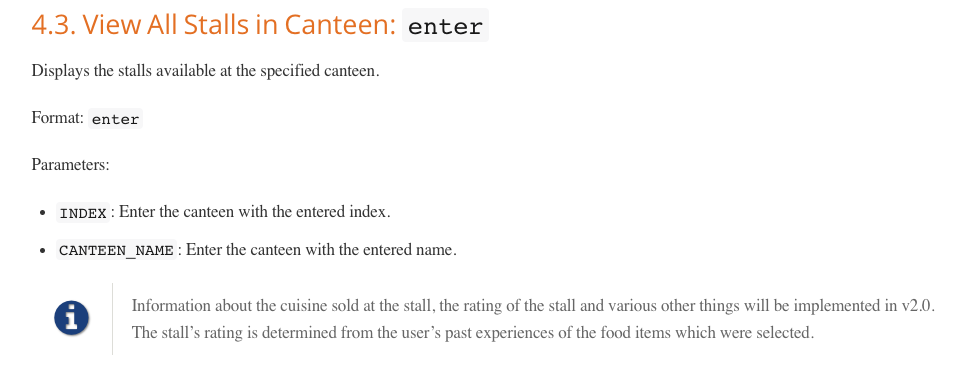
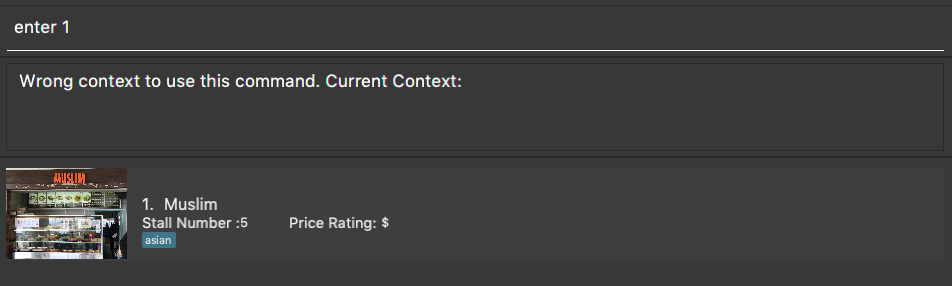
User Guide did not specify that the 'enter' command can be used only in the main screen
| non_priority | user guide info for enter not clear user guide did not specify that the enter command can be used only in the main screen | 0 |
40,491 | 16,487,576,082 | IssuesEvent | 2021-05-24 20:28:58 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | use --network-plugin azure instead of standard kubenet | Pri2 assigned-to-author container-service/svc doc-bug triaged | Could you please add in the docu that for software developers who want to use Azure resources with managed identities, they could better use --network-plugin azure because of a vulnerability: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-1677
See future example here:
https://docs.microsoft.com/en-us/azure/aks/use-azure-ad-pod-identity#before-you-begin
See also here: https://github.com/Azure/aad-pod-identity/issues/949
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 719f4010-810f-b3c7-d807-222b39b20e20
* Version Independent ID: 82ac8cfa-b0a2-c77a-408a-ab9aa2b6bce4
* Content: [Configure kubenet networking in Azure Kubernetes Service (AKS) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/configure-kubenet)
* Content Source: [articles/aks/configure-kubenet.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/configure-kubenet.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **mlearned** | 1.0 | use --network-plugin azure instead of standard kubenet - Could you please add in the docu that for software developers who want to use Azure resources with managed identities, they could better use --network-plugin azure because of a vulnerability: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-1677
See future example here:
https://docs.microsoft.com/en-us/azure/aks/use-azure-ad-pod-identity#before-you-begin
See also here: https://github.com/Azure/aad-pod-identity/issues/949
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 719f4010-810f-b3c7-d807-222b39b20e20
* Version Independent ID: 82ac8cfa-b0a2-c77a-408a-ab9aa2b6bce4
* Content: [Configure kubenet networking in Azure Kubernetes Service (AKS) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/configure-kubenet)
* Content Source: [articles/aks/configure-kubenet.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/configure-kubenet.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **mlearned** | non_priority | use network plugin azure instead of standard kubenet could you please add in the docu that for software developers who want to use azure resources with managed identities they could better use network plugin azure because of a vulnerability see future example here see also here document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login mlearned microsoft alias mlearned | 0 |
41,673 | 16,828,626,205 | IssuesEvent | 2021-06-17 22:45:40 | Rothamsted/knetminer | https://api.github.com/repos/Rothamsted/knetminer | closed | Gene View shows wrong numbers in Evidence column | bug project:web service | In the current master branch, searching with a Genelist but without keywords shows the wrong numbers in the EVIDENCE column of Gene View. Many concept types like Trait, Phenotype, BioProc have always TWO duplicated evidences. On the production it's working as expected. See here comparison of genome API output on dev and live server:
http://babvs72.rothamsted.ac.uk:9100/ws/wheatknet/genome?list=TRAESCS3D02G004100
{"geneTable":"ONDEX-ID\tACCESSION\tGENE NAME\tCHRO\tSTART\tTAXID\tSCORE\tUSER\tQTL\tEVIDENCE\n35264\tTRAESCS3D02G004100\tMFT\t3D\t1733084\t4565\t193.30\tyes\t\tPath__2__Hormone signaling, transpor...//Hormone signaling, transpor...||ProtDomain__2__PEBP_euk//PEBP_euk||Phenotype__2__DECREASED GERMINATION WHEN ...//DECREASED GERMINATION WHEN ...||MolFunc__1__Phosphatidylethanolamine Bi...||CelComp__2__Endoplasmic Reticulum//Endoplasmic Reticulum||**BioProc__2__Abscisic Acid-activated Sig...//Abscisic Acid-activated Sig...**||Gene__2__WRI1//WRI1||Publication__48__PMID:31077147//PMID:30794545//PMID:31012027//PMID:31481195//PMID:30061395//PMID:28254780//PMID:28332758//PMID:29398940//PMID:28240777//PMID:26950112//PMID:27446143//PMID:27293186//PMID:27389636//PMID:26891287//PMID:26873978//PMID:25931984//PMID:24932489//PMID:25464340//PMID:24879400//PMID:24444091||Trait__2__FT10//FT10||Reaction__1__ARF inactivation by AUX/IAA||Protein__2__Q41261//Q41261||SNPEffect__2__START_LOST//START_LOST\n",
https://knetminer.com/wheatknet/genome?list=TRAESCS3D02G004100
{"geneTable":"ONDEX-ID\tACCESSION\tGENE NAME\tCHRO\tSTART\tTAXID\tSCORE\tUSER\tQTL\tEVIDENCE\n35264\tTRAESCS3D02G004100\tMFT\t3D\t1733084\t4565\t183.84\tyes\t\tProtDomain__4__Phosphatidylethanolamine-bd_CS//PEBP//PEBP-like_sf//PEBP_euk||Phenotype__2__DECREASED RATE OF GERMINATION...//DECREASED GERMINATION WHEN GR...||MolFunc__1__Phosphatidylethanolamine Bind...||Gene__36__ERF039//TRAESCS6A02G343300//NFYA8//TRAESCS6D02G268100//TRAESCS2A02G370400//MYB96//TRAESCS4A02G180900//TRAESCS3A02G485400//NFYA6//MKRN//TRAESCS3D02G434700//TULP7//TRAESCS5D02G496300//MFT//TRAESCS4B02G101400//TRAESCS5D02G158300//TRAESCS3A02G486500//NFYB10//MFT//TULP4//TRAESCS1D02G275400//ATMYB69//TRAESCS7D02G259600//ATMYB69//ATMYB69//TRAESCS5A02G491500//NF-YB1//WRI1//TCX2//MFT//MFT//ATY13//TRB1//TRAESCS3B02G533200//TRAESCS7A02G258700//WRI1||**BioProc__13__Regulation Of Timing Of Trans...//Negative Regulation Of Flower...//Cell Differentiation//Inflorescence Development//Response To Abscisic Acid//Photoperiodism, Flowering//Regulation Of Flower Developm...//Short-day Photoperiodism, Flo...//Flower Development//Short-day Photoperiodism//Positive Regulation Of Seed G...//Vegetative To Reproductive Ph...//Abscisic Acid-activated Signa...**||CelComp__3__Nucleus//Cytoplasm//Endoplasmic Reticulum||Publication__46__PMID:30794545//PMID:30061395//PMID:28254780//PMID:27862469//PMID:29398940//PMID:28240777//PMID:26950112//PMID:27446143//PMID:27293186//PMID:27389636//PMID:26891287//PMID:26873978//PMID:25931984//PMID:24932489//PMID:25464340//PMID:24879400//PMID:24444091//PMID:25330236//PMID:24280374//PMID:23590427||Trait__17__Grain germination//Storage 56 days//Mg25//Ca43//Grain yield//Anthesis time//mineral and ion content trait//seed maturation//Seed Dormancy//grain number//flowering time trait//seed dormancy//avrB//Seedling Growth//grain yield trait//Cd114//FT10||Protein__12__Q8VWH2//Q9XH44//Q9XH43//Q656A5//Q93WI9//O82088//Q9ASJ1//AT1G18100.1//Q9XH42//TRAESCS3D02G004100.1//Q9XFK7//Q41261\n" | 1.0 | Gene View shows wrong numbers in Evidence column - In the current master branch, searching with a Genelist but without keywords shows the wrong numbers in the EVIDENCE column of Gene View. Many concept types like Trait, Phenotype, BioProc have always TWO duplicated evidences. On the production it's working as expected. See here comparison of genome API output on dev and live server:
http://babvs72.rothamsted.ac.uk:9100/ws/wheatknet/genome?list=TRAESCS3D02G004100
{"geneTable":"ONDEX-ID\tACCESSION\tGENE NAME\tCHRO\tSTART\tTAXID\tSCORE\tUSER\tQTL\tEVIDENCE\n35264\tTRAESCS3D02G004100\tMFT\t3D\t1733084\t4565\t193.30\tyes\t\tPath__2__Hormone signaling, transpor...//Hormone signaling, transpor...||ProtDomain__2__PEBP_euk//PEBP_euk||Phenotype__2__DECREASED GERMINATION WHEN ...//DECREASED GERMINATION WHEN ...||MolFunc__1__Phosphatidylethanolamine Bi...||CelComp__2__Endoplasmic Reticulum//Endoplasmic Reticulum||**BioProc__2__Abscisic Acid-activated Sig...//Abscisic Acid-activated Sig...**||Gene__2__WRI1//WRI1||Publication__48__PMID:31077147//PMID:30794545//PMID:31012027//PMID:31481195//PMID:30061395//PMID:28254780//PMID:28332758//PMID:29398940//PMID:28240777//PMID:26950112//PMID:27446143//PMID:27293186//PMID:27389636//PMID:26891287//PMID:26873978//PMID:25931984//PMID:24932489//PMID:25464340//PMID:24879400//PMID:24444091||Trait__2__FT10//FT10||Reaction__1__ARF inactivation by AUX/IAA||Protein__2__Q41261//Q41261||SNPEffect__2__START_LOST//START_LOST\n",
https://knetminer.com/wheatknet/genome?list=TRAESCS3D02G004100
{"geneTable":"ONDEX-ID\tACCESSION\tGENE NAME\tCHRO\tSTART\tTAXID\tSCORE\tUSER\tQTL\tEVIDENCE\n35264\tTRAESCS3D02G004100\tMFT\t3D\t1733084\t4565\t183.84\tyes\t\tProtDomain__4__Phosphatidylethanolamine-bd_CS//PEBP//PEBP-like_sf//PEBP_euk||Phenotype__2__DECREASED RATE OF GERMINATION...//DECREASED GERMINATION WHEN GR...||MolFunc__1__Phosphatidylethanolamine Bind...||Gene__36__ERF039//TRAESCS6A02G343300//NFYA8//TRAESCS6D02G268100//TRAESCS2A02G370400//MYB96//TRAESCS4A02G180900//TRAESCS3A02G485400//NFYA6//MKRN//TRAESCS3D02G434700//TULP7//TRAESCS5D02G496300//MFT//TRAESCS4B02G101400//TRAESCS5D02G158300//TRAESCS3A02G486500//NFYB10//MFT//TULP4//TRAESCS1D02G275400//ATMYB69//TRAESCS7D02G259600//ATMYB69//ATMYB69//TRAESCS5A02G491500//NF-YB1//WRI1//TCX2//MFT//MFT//ATY13//TRB1//TRAESCS3B02G533200//TRAESCS7A02G258700//WRI1||**BioProc__13__Regulation Of Timing Of Trans...//Negative Regulation Of Flower...//Cell Differentiation//Inflorescence Development//Response To Abscisic Acid//Photoperiodism, Flowering//Regulation Of Flower Developm...//Short-day Photoperiodism, Flo...//Flower Development//Short-day Photoperiodism//Positive Regulation Of Seed G...//Vegetative To Reproductive Ph...//Abscisic Acid-activated Signa...**||CelComp__3__Nucleus//Cytoplasm//Endoplasmic Reticulum||Publication__46__PMID:30794545//PMID:30061395//PMID:28254780//PMID:27862469//PMID:29398940//PMID:28240777//PMID:26950112//PMID:27446143//PMID:27293186//PMID:27389636//PMID:26891287//PMID:26873978//PMID:25931984//PMID:24932489//PMID:25464340//PMID:24879400//PMID:24444091//PMID:25330236//PMID:24280374//PMID:23590427||Trait__17__Grain germination//Storage 56 days//Mg25//Ca43//Grain yield//Anthesis time//mineral and ion content trait//seed maturation//Seed Dormancy//grain number//flowering time trait//seed dormancy//avrB//Seedling Growth//grain yield trait//Cd114//FT10||Protein__12__Q8VWH2//Q9XH44//Q9XH43//Q656A5//Q93WI9//O82088//Q9ASJ1//AT1G18100.1//Q9XH42//TRAESCS3D02G004100.1//Q9XFK7//Q41261\n" | non_priority | gene view shows wrong numbers in evidence column in the current master branch searching with a genelist but without keywords shows the wrong numbers in the evidence column of gene view many concept types like trait phenotype bioproc have always two duplicated evidences on the production it s working as expected see here comparison of genome api output on dev and live server genetable ondex id taccession tgene name tchro tstart ttaxid tscore tuser tqtl tevidence tmft tyes t tpath hormone signaling transpor hormone signaling transpor protdomain pebp euk pebp euk phenotype decreased germination when decreased germination when molfunc phosphatidylethanolamine bi celcomp endoplasmic reticulum endoplasmic reticulum bioproc abscisic acid activated sig abscisic acid activated sig gene publication pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid trait reaction arf inactivation by aux iaa protein snpeffect start lost start lost n genetable ondex id taccession tgene name tchro tstart ttaxid tscore tuser tqtl tevidence tmft tyes t tprotdomain phosphatidylethanolamine bd cs pebp pebp like sf pebp euk phenotype decreased rate of germination decreased germination when gr molfunc phosphatidylethanolamine bind gene mkrn mft mft nf mft mft bioproc regulation of timing of trans negative regulation of flower cell differentiation inflorescence development response to abscisic acid photoperiodism flowering regulation of flower developm short day photoperiodism flo flower development short day photoperiodism positive regulation of seed g vegetative to reproductive ph abscisic acid activated signa celcomp nucleus cytoplasm endoplasmic reticulum publication pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid pmid trait grain germination storage days grain yield anthesis time mineral and ion content trait seed maturation seed dormancy grain number flowering time trait seed dormancy avrb seedling growth grain yield trait protein n | 0 |
56,464 | 15,105,594,947 | IssuesEvent | 2021-02-08 13:15:49 | SAP/fundamental-styles | https://api.github.com/repos/SAP/fundamental-styles | closed | Quick-view: Header title should be centre aligned | Defect Hunting | **Describe the bug**
Currently header title is not centre aligned. but it should be centre aligned as per fiori spec.
current implementation:
<img width="561" alt="Screenshot 2021-02-08 at 11 11 53 AM" src="https://user-images.githubusercontent.com/57661487/107180358-8cd04080-69fe-11eb-95b2-73c87c24207d.png">
Fiori spec:
<img width="1161" alt="Screenshot 2021-02-08 at 11 02 20 AM" src="https://user-images.githubusercontent.com/57661487/107180379-9659a880-69fe-11eb-9afe-d0414273cd92.png">
> Is this issue related to a specific component?
Quick view
> What version of the Fundamental Library Styles are you using?
v0.16.0-rc.2
> What offering/product do you work on? Any pressing ship or release dates we should be aware of?
> What front-end framework are you implementing in, e.g., Angular, React, etc.?
**To Reproduce**
Steps to reproduce the behavior:
1. Go to https://fundamental-styles.netlify.app/?path=/docs/components-quick-view--popover
**Expected behavior**
Header title should be centre aligned
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Smartphone (please complete the following information):**
- Device: [e.g. iPhone6]
- OS: [e.g. iOS8.1]
- Browser [e.g. stock browser, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the problem here.
| 1.0 | Quick-view: Header title should be centre aligned - **Describe the bug**
Currently header title is not centre aligned. but it should be centre aligned as per fiori spec.
current implementation:
<img width="561" alt="Screenshot 2021-02-08 at 11 11 53 AM" src="https://user-images.githubusercontent.com/57661487/107180358-8cd04080-69fe-11eb-95b2-73c87c24207d.png">
Fiori spec:
<img width="1161" alt="Screenshot 2021-02-08 at 11 02 20 AM" src="https://user-images.githubusercontent.com/57661487/107180379-9659a880-69fe-11eb-9afe-d0414273cd92.png">
> Is this issue related to a specific component?
Quick view
> What version of the Fundamental Library Styles are you using?
v0.16.0-rc.2
> What offering/product do you work on? Any pressing ship or release dates we should be aware of?
> What front-end framework are you implementing in, e.g., Angular, React, etc.?
**To Reproduce**
Steps to reproduce the behavior:
1. Go to https://fundamental-styles.netlify.app/?path=/docs/components-quick-view--popover
**Expected behavior**
Header title should be centre aligned
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Smartphone (please complete the following information):**
- Device: [e.g. iPhone6]
- OS: [e.g. iOS8.1]
- Browser [e.g. stock browser, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the problem here.
| non_priority | quick view header title should be centre aligned describe the bug currently header title is not centre aligned but it should be centre aligned as per fiori spec current implementation img width alt screenshot at am src fiori spec img width alt screenshot at am src is this issue related to a specific component quick view what version of the fundamental library styles are you using rc what offering product do you work on any pressing ship or release dates we should be aware of what front end framework are you implementing in e g angular react etc to reproduce steps to reproduce the behavior go to expected behavior header title should be centre aligned screenshots if applicable add screenshots to help explain your problem desktop please complete the following information os browser version smartphone please complete the following information device os browser version additional context add any other context about the problem here | 0 |
122,436 | 10,222,888,486 | IssuesEvent | 2019-08-16 08:09:00 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | Nothing happens after clicking 'Execute' button for one store procedure | :beetle: regression :gear: cosmosdb 🧪 testing | **Storage Explorer Version:** 1.9.0
**Build:** 20190815.2
**Platform/OS:** Linux Ubuntu 19.04/Windows 10/macOS High Sierra
**Architecture:** ia32/x64
**Regression From:** Previous release(1.9.0)
**Steps to reproduce:**
1. Select one Cosmos DB account which contains Stored Procedures under its collection.
2. Open one stored procedure and click 'Execute'.
3. Check the result.
**Expect Experience:**
The 'Execute Stored Procedure' dialog pops up.
**Actual Experience:**
Nothing happenes. | 1.0 | Nothing happens after clicking 'Execute' button for one store procedure - **Storage Explorer Version:** 1.9.0
**Build:** 20190815.2
**Platform/OS:** Linux Ubuntu 19.04/Windows 10/macOS High Sierra
**Architecture:** ia32/x64
**Regression From:** Previous release(1.9.0)
**Steps to reproduce:**
1. Select one Cosmos DB account which contains Stored Procedures under its collection.
2. Open one stored procedure and click 'Execute'.
3. Check the result.
**Expect Experience:**
The 'Execute Stored Procedure' dialog pops up.
**Actual Experience:**
Nothing happenes. | non_priority | nothing happens after clicking execute button for one store procedure storage explorer version build platform os linux ubuntu windows macos high sierra architecture regression from previous release steps to reproduce select one cosmos db account which contains stored procedures under its collection open one stored procedure and click execute check the result expect experience the execute stored procedure dialog pops up actual experience nothing happenes | 0 |
324,003 | 27,769,050,280 | IssuesEvent | 2023-03-16 13:23:57 | redpanda-data/redpanda | https://api.github.com/repos/redpanda-data/redpanda | closed | ARM: scale tests require more resources than nodes have (`ManyPartitionsTest`.`test_many_partitions`, `ManyClientsTest`.`test_many_clients`) | kind/bug area/tests ci-failure performance | i3en.xlarge has 8GB per vCPU
Is4gen.4xlarge has 6GB per vCPU
Our scale tests do not pass reliably on the weaker arm nodes.
```
FAIL test: ManyPartitionsTest.test_many_partitions (2/3 runs)
failure at 2022-11-20T03:48:19.569Z: RpkException('command /opt/redpanda/bin/rpk topic --brokers ip-172-31-43-14:9092,ip-172-31-32-247:9092,ip-172-31-36-138:9092,ip-172-31-46-34:9092,ip-172-31-36-63:9092,ip-172-31-42-204:9092,ip-172-31-43-72:9092,ip-172-31-40-33:9092,ip-172-31-47-0:9092 describe scale_000000 -p timed out')
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4319#0184917c-c179-4d57-be92-563f4eb9f9c5
failure at 2022-11-21T03:21:08.085Z: RpkException('command /opt/redpanda/bin/rpk topic --brokers ip-172-31-39-61:9092,ip-172-31-44-233:9092,ip-172-31-41-134:9092,ip-172-31-43-92:9092,ip-172-31-43-95:9092,ip-172-31-33-240:9092,ip-172-31-45-166:9092,ip-172-31-44-245:9092,ip-172-31-44-142:9092 describe scale_000000 -p timed out')
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4324#018496a2-e835-4a1e-b9a1-af52a6a95f3b
FAIL test: ManyPartitionsTest.test_many_partitions_compacted (2/3 runs)
failure at 2022-11-20T03:48:19.569Z: <BadLogLines nodes=ip-172-31-36-63(1) example="ERROR 2022-11-19 20:52:54,026 [shard 0] seastar - Failed to allocate 7340032 bytes">
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4319#0184917c-c179-4d57-be92-563f4eb9f9c5
failure at 2022-11-21T03:21:08.085Z: RpkException('command /opt/redpanda/bin/rpk topic --brokers ip-172-31-44-245:9092,ip-172-31-43-92:9092,ip-172-31-39-61:9092,ip-172-31-43-95:9092,ip-172-31-45-166:9092,ip-172-31-44-233:9092,ip-172-31-33-240:9092,ip-172-31-41-134:9092,ip-172-31-44-142:9092 describe scale_000000 -p timed out')
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4324#018496a2-e835-4a1e-b9a1-af52a6a95f3b
```
```
FAIL test: ManyClientsTest.test_many_clients (2/3 runs)
failure at 2022-11-20T03:48:19.569Z: <BadLogLines nodes=ip-172-31-42-204(1) example="ERROR 2022-11-20 01:46:40,286 [shard 1] seastar - Failed to allocate 131072 bytes">
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4319#0184917c-c179-4d57-be92-563f4eb9f9c5
failure at 2022-11-21T03:21:08.085Z: <BadLogLines nodes=ip-172-31-39-61(1) example="ERROR 2022-11-21 01:46:02,937 [shard 0] seastar - Failed to allocate 131072 bytes">
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4324#018496a2-e835-4a1e-b9a1-af52a6a95f3b
``` | 1.0 | ARM: scale tests require more resources than nodes have (`ManyPartitionsTest`.`test_many_partitions`, `ManyClientsTest`.`test_many_clients`) - i3en.xlarge has 8GB per vCPU
Is4gen.4xlarge has 6GB per vCPU
Our scale tests do not pass reliably on the weaker arm nodes.
```
FAIL test: ManyPartitionsTest.test_many_partitions (2/3 runs)
failure at 2022-11-20T03:48:19.569Z: RpkException('command /opt/redpanda/bin/rpk topic --brokers ip-172-31-43-14:9092,ip-172-31-32-247:9092,ip-172-31-36-138:9092,ip-172-31-46-34:9092,ip-172-31-36-63:9092,ip-172-31-42-204:9092,ip-172-31-43-72:9092,ip-172-31-40-33:9092,ip-172-31-47-0:9092 describe scale_000000 -p timed out')
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4319#0184917c-c179-4d57-be92-563f4eb9f9c5
failure at 2022-11-21T03:21:08.085Z: RpkException('command /opt/redpanda/bin/rpk topic --brokers ip-172-31-39-61:9092,ip-172-31-44-233:9092,ip-172-31-41-134:9092,ip-172-31-43-92:9092,ip-172-31-43-95:9092,ip-172-31-33-240:9092,ip-172-31-45-166:9092,ip-172-31-44-245:9092,ip-172-31-44-142:9092 describe scale_000000 -p timed out')
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4324#018496a2-e835-4a1e-b9a1-af52a6a95f3b
FAIL test: ManyPartitionsTest.test_many_partitions_compacted (2/3 runs)
failure at 2022-11-20T03:48:19.569Z: <BadLogLines nodes=ip-172-31-36-63(1) example="ERROR 2022-11-19 20:52:54,026 [shard 0] seastar - Failed to allocate 7340032 bytes">
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4319#0184917c-c179-4d57-be92-563f4eb9f9c5
failure at 2022-11-21T03:21:08.085Z: RpkException('command /opt/redpanda/bin/rpk topic --brokers ip-172-31-44-245:9092,ip-172-31-43-92:9092,ip-172-31-39-61:9092,ip-172-31-43-95:9092,ip-172-31-45-166:9092,ip-172-31-44-233:9092,ip-172-31-33-240:9092,ip-172-31-41-134:9092,ip-172-31-44-142:9092 describe scale_000000 -p timed out')
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4324#018496a2-e835-4a1e-b9a1-af52a6a95f3b
```
```
FAIL test: ManyClientsTest.test_many_clients (2/3 runs)
failure at 2022-11-20T03:48:19.569Z: <BadLogLines nodes=ip-172-31-42-204(1) example="ERROR 2022-11-20 01:46:40,286 [shard 1] seastar - Failed to allocate 131072 bytes">
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4319#0184917c-c179-4d57-be92-563f4eb9f9c5
failure at 2022-11-21T03:21:08.085Z: <BadLogLines nodes=ip-172-31-39-61(1) example="ERROR 2022-11-21 01:46:02,937 [shard 0] seastar - Failed to allocate 131072 bytes">
on (arm64, VM) in job https://buildkite.com/redpanda/vtools/builds/4324#018496a2-e835-4a1e-b9a1-af52a6a95f3b
``` | non_priority | arm scale tests require more resources than nodes have manypartitionstest test many partitions manyclientstest test many clients xlarge has per vcpu has per vcpu our scale tests do not pass reliably on the weaker arm nodes fail test manypartitionstest test many partitions runs failure at rpkexception command opt redpanda bin rpk topic brokers ip ip ip ip ip ip ip ip ip describe scale p timed out on vm in job failure at rpkexception command opt redpanda bin rpk topic brokers ip ip ip ip ip ip ip ip ip describe scale p timed out on vm in job fail test manypartitionstest test many partitions compacted runs failure at on vm in job failure at rpkexception command opt redpanda bin rpk topic brokers ip ip ip ip ip ip ip ip ip describe scale p timed out on vm in job fail test manyclientstest test many clients runs failure at on vm in job failure at on vm in job | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.