Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
107,679 | 23,465,318,256 | IssuesEvent | 2022-08-16 16:13:46 | objectos/objectos | https://api.github.com/repos/objectos/objectos | closed | AsciiDoc Lexer | t:feature c:code a:objectos-asciidoc | ## Improvements
- [x] #66
- [x] #68
## Test cases
- [x] tc01: support apostrophe (subs)
- [ ] tc02: support apostrophe (no subs) | 1.0 | AsciiDoc Lexer - ## Improvements
- [x] #66
- [x] #68
## Test cases
- [x] tc01: support apostrophe (subs)
- [ ] tc02: support apostrophe (no subs) | non_priority | asciidoc lexer improvements test cases support apostrophe subs support apostrophe no subs | 0 |
298,408 | 25,824,143,742 | IssuesEvent | 2022-12-12 11:42:46 | nodejs/node | https://api.github.com/repos/nodejs/node | closed | Investigate flaky parallel/test-process-wrap on macos | flaky-test | Seems to time out frequently as of late.
```
12:08:43 not ok 2473 parallel/test-process-wrap
12:08:43 ---
12:08:43 duration_ms: 120.72
12:08:43 severity: fail
12:08:43 exitcode: -15
12:08:43 stack: |-
12:08:43 timeout
12:08:43 (node:25456) internal/test/binding: These APIs are for internal testing only. Do not use them.
12:08:43 (Use `node --trace-warnings ...` to show where the warning was created)
```
Example run: https://ci.nodejs.org/job/node-test-commit-osx/49092/nodes=osx1015/console
It's a really old test (f01b241057567818160f8cd4f58cf9cafdccf1ed from 2011) that's testing internal implementation details that don't need testing so maybe it should just go. | 1.0 | Investigate flaky parallel/test-process-wrap on macos - Seems to time out frequently as of late.
```
12:08:43 not ok 2473 parallel/test-process-wrap
12:08:43 ---
12:08:43 duration_ms: 120.72
12:08:43 severity: fail
12:08:43 exitcode: -15
12:08:43 stack: |-
12:08:43 timeout
12:08:43 (node:25456) internal/test/binding: These APIs are for internal testing only. Do not use them.
12:08:43 (Use `node --trace-warnings ...` to show where the warning was created)
```
Example run: https://ci.nodejs.org/job/node-test-commit-osx/49092/nodes=osx1015/console
It's a really old test (f01b241057567818160f8cd4f58cf9cafdccf1ed from 2011) that's testing internal implementation details that don't need testing so maybe it should just go. | non_priority | investigate flaky parallel test process wrap on macos seems to time out frequently as of late not ok parallel test process wrap duration ms severity fail exitcode stack timeout node internal test binding these apis are for internal testing only do not use them use node trace warnings to show where the warning was created example run it s a really old test from that s testing internal implementation details that don t need testing so maybe it should just go | 0 |
57,692 | 6,554,170,054 | IssuesEvent | 2017-09-06 03:45:56 | Microsoft/vsts-tasks | https://api.github.com/repos/Microsoft/vsts-tasks | closed | Run functional tests - Side by side VS15 and VS17 Test agent installations cause intermittent failures | Area: Test | I have 2 release definitions that fail to run tests intermittently.
Here is the log from the task:
[25_Run system tests on target.txt](https://github.com/Microsoft/vsts-tasks/files/1257202/25_Run.system.tests.on.target.txt)
Here is the log from Test Agent host:
[DTAExecutionHost.exe.txt](https://github.com/Microsoft/vsts-tasks/files/1257215/DTAExecutionHost.exe.txt)
Here is test agent deployment task configuration:

We use VS17 TA to run the tests, but the test VM still has a VS15 Update 3 TA installed on it.
We have other release definitions, which were running tests on VS15 Update 3 TA with VS17 TA installed on the same VM. They were also failing until we uninstalled VS17 TA. We do not run tests in parallel on same machines. | 1.0 | Run functional tests - Side by side VS15 and VS17 Test agent installations cause intermittent failures - I have 2 release definitions that fail to run tests intermittently.
Here is the log from the task:
[25_Run system tests on target.txt](https://github.com/Microsoft/vsts-tasks/files/1257202/25_Run.system.tests.on.target.txt)
Here is the log from Test Agent host:
[DTAExecutionHost.exe.txt](https://github.com/Microsoft/vsts-tasks/files/1257215/DTAExecutionHost.exe.txt)
Here is test agent deployment task configuration:

We use VS17 TA to run the tests, but the test VM still has a VS15 Update 3 TA installed on it.
We have other release definitions, which were running tests on VS15 Update 3 TA with VS17 TA installed on the same VM. They were also failing until we uninstalled VS17 TA. We do not run tests in parallel on same machines. | non_priority | run functional tests side by side and test agent installations cause intermittent failures i have release definitions that fail to run tests intermittently here is the log from the task here is the log from test agent host here is test agent deployment task configuration we use ta to run the tests but the test vm still has a update ta installed on it we have other release definitions which were running tests on update ta with ta installed on the same vm they were also failing until we uninstalled ta we do not run tests in parallel on same machines | 0 |
220,152 | 24,562,396,980 | IssuesEvent | 2022-10-12 21:41:29 | MValle21/Intelehealth-WebApp | https://api.github.com/repos/MValle21/Intelehealth-WebApp | opened | CVE-2019-11358 (Medium) detected in jquery-3.3.1.slim.min.js | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.3.1.slim.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.slim.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.slim.min.js</a></p>
<p>Path to dependency file: /src/index.html</p>
<p>Path to vulnerable library: /src/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.slim.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: jquery - 3.4.0</p>
</p>
</details>
<p></p>
| True | CVE-2019-11358 (Medium) detected in jquery-3.3.1.slim.min.js - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.3.1.slim.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.slim.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.slim.min.js</a></p>
<p>Path to dependency file: /src/index.html</p>
<p>Path to vulnerable library: /src/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.slim.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: jquery - 3.4.0</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in jquery slim min js cve medium severity vulnerability vulnerable library jquery slim min js javascript library for dom operations library home page a href path to dependency file src index html path to vulnerable library src index html dependency hierarchy x jquery slim min js vulnerable library found in base branch master vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery | 0 |
247,412 | 20,977,736,526 | IssuesEvent | 2022-03-28 16:42:26 | PalisadoesFoundation/talawa-admin | https://api.github.com/repos/PalisadoesFoundation/talawa-admin | closed | Code Coverage: Create tests for OrganizationPeople.tsx | good first issue test points 01 | The Talawa-Admin code base needs to be 100% reliable. This means we need to have 100% test code coverage.
Tests need to be written for file `src/screens/OrganizationPeople/OrganizationPeople.tsx`
- When complete, all methods, classes and/or functions in the file will need to be tested.
- These tests must be placed in a single file with the name `src/screens/OrganizationPeople/OrganizationPeople.test.tsx`. You may need to create the appropriate directory structure to do this.
### IMPORTANT:
Please refer to the parent issue on how to implement these tests correctly:
- #241
### PR Acceptance Criteria
- When complete this file must show **100%** coverage when merged into the code base. This will be clearly visible when you submit your PR.
- [The current code coverage for the file can be found here](https://codecov.io/gh/PalisadoesFoundation/talawa-admin/tree/develop/src/screens/OrganizationPeople/). If the file isn't found in this directory, or there is a 404 error, then tests have not been created.
- Create a code coverage account for your repo's preferred branch to generate the values when you do your commits for that branch to your repo.
- _**NOTE:**_ Make sure you select the correct branch when you do the setup, or else the reporting will fail. You must also create a `CODECOV` GitHub secret for your repo as part of the process.
- The PR will show a report for the code coverage for the file you have added. You can also use that as a guide.
| 1.0 | Code Coverage: Create tests for OrganizationPeople.tsx - The Talawa-Admin code base needs to be 100% reliable. This means we need to have 100% test code coverage.
Tests need to be written for file `src/screens/OrganizationPeople/OrganizationPeople.tsx`
- When complete, all methods, classes and/or functions in the file will need to be tested.
- These tests must be placed in a single file with the name `src/screens/OrganizationPeople/OrganizationPeople.test.tsx`. You may need to create the appropriate directory structure to do this.
### IMPORTANT:
Please refer to the parent issue on how to implement these tests correctly:
- #241
### PR Acceptance Criteria
- When complete this file must show **100%** coverage when merged into the code base. This will be clearly visible when you submit your PR.
- [The current code coverage for the file can be found here](https://codecov.io/gh/PalisadoesFoundation/talawa-admin/tree/develop/src/screens/OrganizationPeople/). If the file isn't found in this directory, or there is a 404 error, then tests have not been created.
- Create a code coverage account for your repo's preferred branch to generate the values when you do your commits for that branch to your repo.
- _**NOTE:**_ Make sure you select the correct branch when you do the setup, or else the reporting will fail. You must also create a `CODECOV` GitHub secret for your repo as part of the process.
- The PR will show a report for the code coverage for the file you have added. You can also use that as a guide.
| non_priority | code coverage create tests for organizationpeople tsx the talawa admin code base needs to be reliable this means we need to have test code coverage tests need to be written for file src screens organizationpeople organizationpeople tsx when complete all methods classes and or functions in the file will need to be tested these tests must be placed in a single file with the name src screens organizationpeople organizationpeople test tsx you may need to create the appropriate directory structure to do this important please refer to the parent issue on how to implement these tests correctly pr acceptance criteria when complete this file must show coverage when merged into the code base this will be clearly visible when you submit your pr if the file isn t found in this directory or there is a error then tests have not been created create a code coverage account for your repo s preferred branch to generate the values when you do your commits for that branch to your repo note make sure you select the correct branch when you do the setup or else the reporting will fail you must also create a codecov github secret for your repo as part of the process the pr will show a report for the code coverage for the file you have added you can also use that as a guide | 0 |
184,800 | 21,784,985,120 | IssuesEvent | 2022-05-14 02:03:16 | kapseliboi/OnlineCV | https://api.github.com/repos/kapseliboi/OnlineCV | closed | WS-2019-0332 (Medium) detected in handlebars-4.0.12.tgz - autoclosed | security vulnerability | ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.12.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.12.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.12.tgz</a></p>
<p>Path to dependency file: OnlineCV/client/package.json</p>
<p>Path to vulnerable library: OnlineCV/client/node_modules/handlebars/package.json,OnlineCV/admin/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-2.1.3.tgz (Root Library)
- jest-23.6.0.tgz
- jest-cli-23.6.0.tgz
- istanbul-api-1.3.7.tgz
- istanbul-reports-1.5.1.tgz
- :x: **handlebars-4.0.12.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/OnlineCV/commit/5ce352c75fbe6372f4f2df4d5ed63e7ced820f77">5ce352c75fbe6372f4f2df4d5ed63e7ced820f77</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.
<p>Publish Date: 2019-11-17
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7>WS-2019-0332</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2019-11-17</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0332 (Medium) detected in handlebars-4.0.12.tgz - autoclosed - ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.12.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.12.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.12.tgz</a></p>
<p>Path to dependency file: OnlineCV/client/package.json</p>
<p>Path to vulnerable library: OnlineCV/client/node_modules/handlebars/package.json,OnlineCV/admin/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-2.1.3.tgz (Root Library)
- jest-23.6.0.tgz
- jest-cli-23.6.0.tgz
- istanbul-api-1.3.7.tgz
- istanbul-reports-1.5.1.tgz
- :x: **handlebars-4.0.12.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/OnlineCV/commit/5ce352c75fbe6372f4f2df4d5ed63e7ced820f77">5ce352c75fbe6372f4f2df4d5ed63e7ced820f77</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Execution vulnerability found in handlebars before 4.5.3. Lookup helper fails to validate templates. Attack may submit templates that execute arbitrary JavaScript in the system.It is due to an incomplete fix for a WS-2019-0331.
<p>Publish Date: 2019-11-17
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/198887808780bbef9dba67a8af68ece091d5baa7>WS-2019-0332</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1324">https://www.npmjs.com/advisories/1324</a></p>
<p>Release Date: 2019-11-17</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in handlebars tgz autoclosed ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file onlinecv client package json path to vulnerable library onlinecv client node modules handlebars package json onlinecv admin node modules handlebars package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz istanbul api tgz istanbul reports tgz x handlebars tgz vulnerable library found in head commit a href found in base branch master vulnerability details arbitrary code execution vulnerability found in handlebars before lookup helper fails to validate templates attack may submit templates that execute arbitrary javascript in the system it is due to an incomplete fix for a ws publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
91,992 | 10,733,843,995 | IssuesEvent | 2019-10-29 03:02:25 | legesher/legesher-translations | https://api.github.com/repos/legesher/legesher-translations | closed | Add CONTRIBUTING.md file | Hacktoberfest Status: Accepted Technical Experience: None first-timers-only good first issue help wanted up-for-grabs 📖 Opportunity: Documentation | Add a `CONTRIBUTING.md` file in the root of the repository that contains this content:
```md
See the [Legesher contributing guide](https://github.com/legesher/legesher/blob/master/CONTRIBUTING.md)
```
Simple enough 👍 Please ask to be assigned to this issue so we don't have duplicates 😄 | 1.0 | Add CONTRIBUTING.md file - Add a `CONTRIBUTING.md` file in the root of the repository that contains this content:
```md
See the [Legesher contributing guide](https://github.com/legesher/legesher/blob/master/CONTRIBUTING.md)
```
Simple enough 👍 Please ask to be assigned to this issue so we don't have duplicates 😄 | non_priority | add contributing md file add a contributing md file in the root of the repository that contains this content md see the simple enough 👍 please ask to be assigned to this issue so we don t have duplicates 😄 | 0 |
127,474 | 17,273,174,835 | IssuesEvent | 2021-07-22 23:33:40 | rancher/dashboard | https://api.github.com/repos/rancher/dashboard | closed | Clicking on Profile button does not show the dropdown options | [zube]: To Test area/preferences area/profile kind/bug kind/design | **Verified on master-head commit id: `d19f179c4`**
- Clicking on Profile button does not show the dropdown options
- User has to hover over the profile icon for the dropdowns to be visible.
<img width="333" alt="Screen Shot 2020-08-18 at 5 56 45 PM" src="https://user-images.githubusercontent.com/26032343/90579906-42bb8000-e17c-11ea-840b-c85c6188f378.png">
**Expected:**
Dropdown options must be seen when user clicks on the profile icon
| 1.0 | Clicking on Profile button does not show the dropdown options - **Verified on master-head commit id: `d19f179c4`**
- Clicking on Profile button does not show the dropdown options
- User has to hover over the profile icon for the dropdowns to be visible.
<img width="333" alt="Screen Shot 2020-08-18 at 5 56 45 PM" src="https://user-images.githubusercontent.com/26032343/90579906-42bb8000-e17c-11ea-840b-c85c6188f378.png">
**Expected:**
Dropdown options must be seen when user clicks on the profile icon
| non_priority | clicking on profile button does not show the dropdown options verified on master head commit id clicking on profile button does not show the dropdown options user has to hover over the profile icon for the dropdowns to be visible img width alt screen shot at pm src expected dropdown options must be seen when user clicks on the profile icon | 0 |
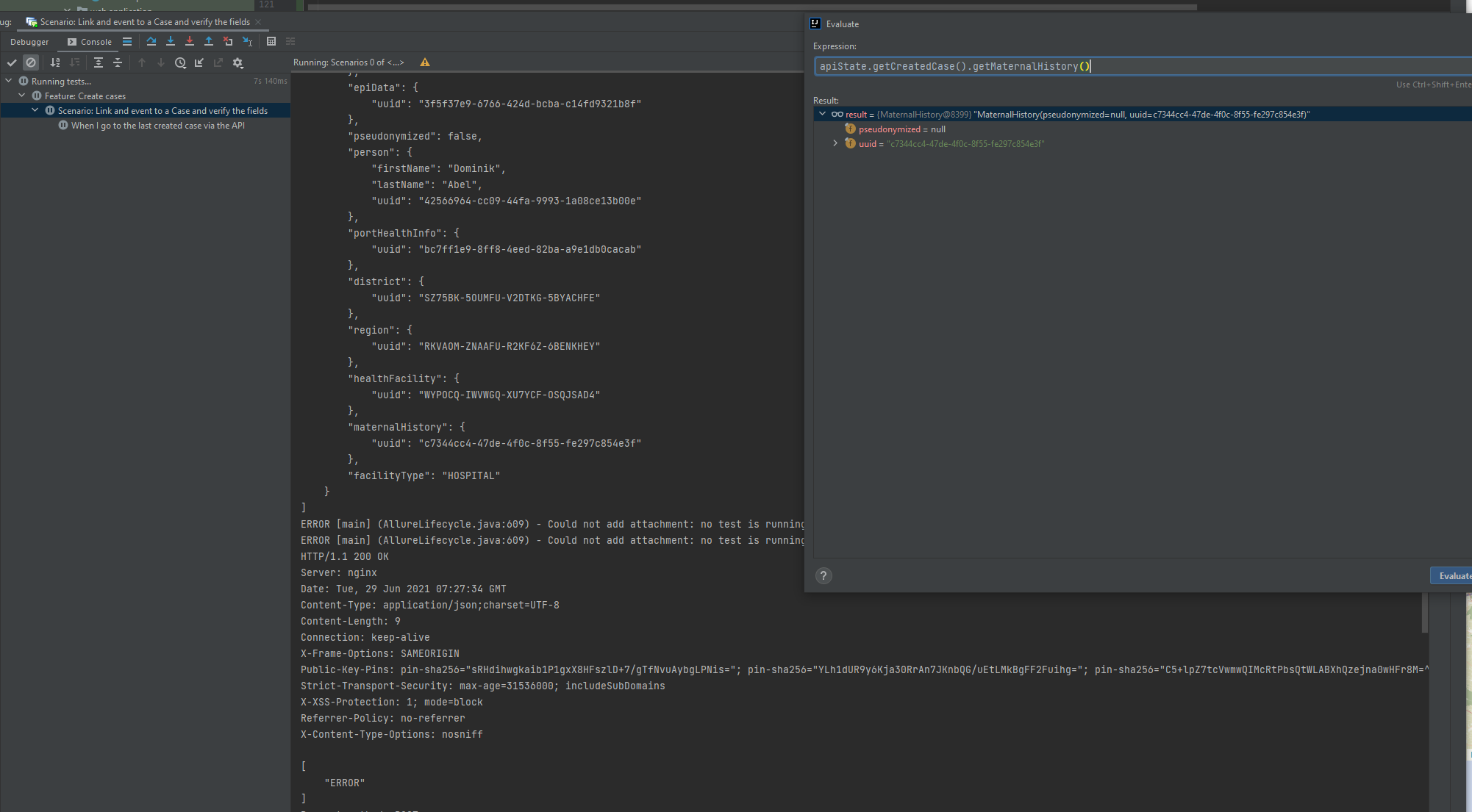
218,452 | 16,991,656,804 | IssuesEvent | 2021-06-30 21:26:33 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | Endpoint for case creation is no longer working after the last deployment | cases e2e-tests important task | Bug Description
This issue occurs in the https://test-performance.sormas.netzlink.com environment
Steps to Reproduce (easiest way):
1. Use the testing automation project https://github.com/hzi-braunschweig/SORMAS-Project/tree/development/sormas-e2e-tests
2. Run the test from: sormas-e2e-tests/src/test/resources/features/sanity/api/Api.feature
3. Check the console:
Expected result:
For the case creation endpoint an: [
"OK"
] message shall be returned.
Actual result:
For the case creation endpoint an: [
"ERROR"
] message is returned.
Attachment:
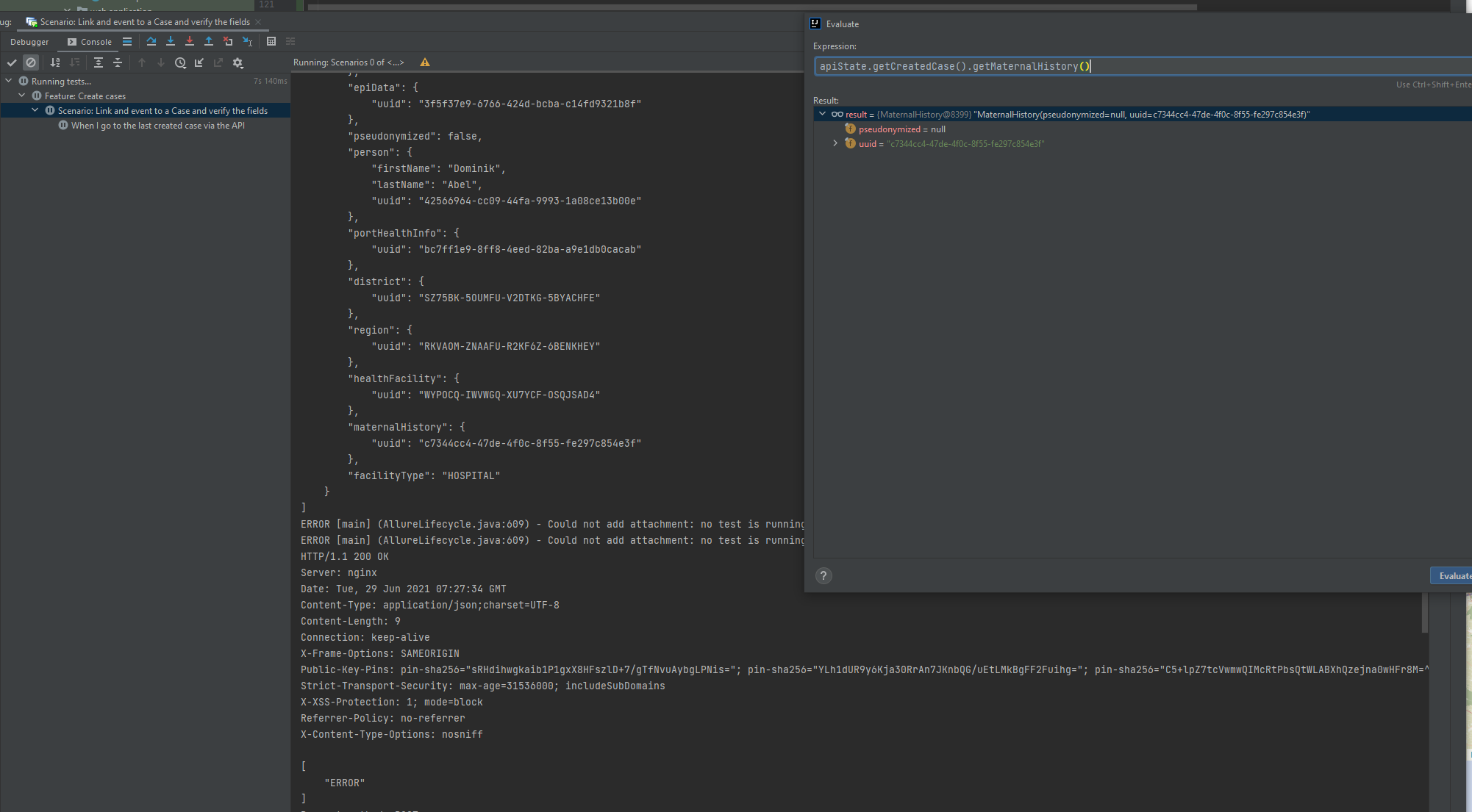
Note: question - is this a bug or an intended change? It occurs after the deployment from 2 pm CET on 28.06.2021. | 1.0 | Endpoint for case creation is no longer working after the last deployment - Bug Description
This issue occurs in the https://test-performance.sormas.netzlink.com environment
Steps to Reproduce (easiest way):
1. Use the testing automation project https://github.com/hzi-braunschweig/SORMAS-Project/tree/development/sormas-e2e-tests
2. Run the test from: sormas-e2e-tests/src/test/resources/features/sanity/api/Api.feature
3. Check the console:
Expected result:
For the case creation endpoint an: [
"OK"
] message shall be returned.
Actual result:
For the case creation endpoint an: [
"ERROR"
] message is returned.
Attachment:
Note: question - is this a bug or an intended change? It occurs after the deployment from 2 pm CET on 28.06.2021. | non_priority | endpoint for case creation is no longer working after the last deployment bug description this issue occurs in the environment steps to reproduce easiest way use the testing automation project run the test from sormas tests src test resources features sanity api api feature check the console expected result for the case creation endpoint an ok message shall be returned actual result for the case creation endpoint an error message is returned attachment note question is this a bug or an intended change it occurs after the deployment from pm cet on | 0 |
286,703 | 21,605,428,740 | IssuesEvent | 2022-05-04 01:50:10 | MagicalBridge/Blog | https://api.github.com/repos/MagicalBridge/Blog | opened | [LeetCode]. 5.最长回文串 | documentation | 给你一个字符串 s, 找到s中最长的回文子串。
示例 1:
```
输入:s = "babad"
输出:"bab"
解释:"aba" 同样是符合题意的答案。
```
示例 2:
```
输入:s = "cbbd"
输出:"bb"
```
示例 3:
```
输入:s = "a"
输出:"a"
```
示例 4:
```
输入:s = "ac"
输出:"a"
```
### 中心扩散法
主要思路是枚举所有可能的回文子串的中心位置,在枚举的时候需要考虑回文子串的奇偶性,对于奇数回文子串来说,中心位置是一个字符,对于偶数来说,中心位置是两个相邻的字符。
需要注意的是,在枚举的过程中需要记录最长回文子串的相关变量。
```js
/**
* @param {string} s
* @return {string}
*/
var longestPalindrome = function (s) {
// 首先处理边界条件
if (s === null || s === undefined) {
return
}
if (s.length < 2) {
return s
}
// 记录最大的长度
let maxlen = 0;
let begin = 0;
let len = s.length;
// 遍历字符串,分别以奇数和偶数的维度来寻找回文子串
for (let i = 0; i < len; i++) {
// 借助函数拿到以奇数和偶数分别为中心的长度
let oddmaxlen = helper(s, i, i);
let evenmaxlen = helper(s, i, i + 1);
let currentlen = Math.max(oddmaxlen, evenmaxlen);
// 更新最大长度
if (currentlen > maxlen) {
maxlen = currentlen
begin = i - Math.floor((maxlen - 1) / 2)
}
}
return s.substring(begin, begin + maxlen)
};
/**
判判断是否是回文串的辅助函数
接收三个参数 字符串本身,中心点
*/
function helper(s, left, right) {
// 当left = right 的时候,回文中心是一个字符,回文串的长度是奇数
// 当right = left + 1 的时候,此时,回文中心是两个字符,回文串的长度是偶数
while (left >= 0 && right < s.length) {
// 左边界向左,右边界向右,逐个比对,直到不相同为止。
if (s.charAt(left) === s.charAt(right)) {
left--;
right++;
} else {
break
}
}
// 跳出循环的时候 恰好满足 s.charAt(left) !== s.charAt(right)
// 回文串的长度是 right - left + 1 - 2 = right - left -1;
// 5 6 7 8 9 总共几个数 9-5+1 = 5个数 去掉 5和 9 剩下 4个 一个道理
return right-left -1;
}
``` | 1.0 | [LeetCode]. 5.最长回文串 - 给你一个字符串 s, 找到s中最长的回文子串。
示例 1:
```
输入:s = "babad"
输出:"bab"
解释:"aba" 同样是符合题意的答案。
```
示例 2:
```
输入:s = "cbbd"
输出:"bb"
```
示例 3:
```
输入:s = "a"
输出:"a"
```
示例 4:
```
输入:s = "ac"
输出:"a"
```
### 中心扩散法
主要思路是枚举所有可能的回文子串的中心位置,在枚举的时候需要考虑回文子串的奇偶性,对于奇数回文子串来说,中心位置是一个字符,对于偶数来说,中心位置是两个相邻的字符。
需要注意的是,在枚举的过程中需要记录最长回文子串的相关变量。
```js
/**
* @param {string} s
* @return {string}
*/
var longestPalindrome = function (s) {
// 首先处理边界条件
if (s === null || s === undefined) {
return
}
if (s.length < 2) {
return s
}
// 记录最大的长度
let maxlen = 0;
let begin = 0;
let len = s.length;
// 遍历字符串,分别以奇数和偶数的维度来寻找回文子串
for (let i = 0; i < len; i++) {
// 借助函数拿到以奇数和偶数分别为中心的长度
let oddmaxlen = helper(s, i, i);
let evenmaxlen = helper(s, i, i + 1);
let currentlen = Math.max(oddmaxlen, evenmaxlen);
// 更新最大长度
if (currentlen > maxlen) {
maxlen = currentlen
begin = i - Math.floor((maxlen - 1) / 2)
}
}
return s.substring(begin, begin + maxlen)
};
/**
判判断是否是回文串的辅助函数
接收三个参数 字符串本身,中心点
*/
function helper(s, left, right) {
// 当left = right 的时候,回文中心是一个字符,回文串的长度是奇数
// 当right = left + 1 的时候,此时,回文中心是两个字符,回文串的长度是偶数
while (left >= 0 && right < s.length) {
// 左边界向左,右边界向右,逐个比对,直到不相同为止。
if (s.charAt(left) === s.charAt(right)) {
left--;
right++;
} else {
break
}
}
// 跳出循环的时候 恰好满足 s.charAt(left) !== s.charAt(right)
// 回文串的长度是 right - left + 1 - 2 = right - left -1;
// 5 6 7 8 9 总共几个数 9-5+1 = 5个数 去掉 5和 9 剩下 4个 一个道理
return right-left -1;
}
``` | non_priority | 最长回文串 给你一个字符串 s 找到s中最长的回文子串。 示例 输入:s babad 输出: bab 解释: aba 同样是符合题意的答案。 示例 : 输入:s cbbd 输出: bb 示例 : 输入:s a 输出: a 示例 : 输入:s ac 输出: a 中心扩散法 主要思路是枚举所有可能的回文子串的中心位置,在枚举的时候需要考虑回文子串的奇偶性,对于奇数回文子串来说,中心位置是一个字符,对于偶数来说,中心位置是两个相邻的字符。 需要注意的是,在枚举的过程中需要记录最长回文子串的相关变量。 js param string s return string var longestpalindrome function s 首先处理边界条件 if s null s undefined return if s length return s 记录最大的长度 let maxlen let begin let len s length 遍历字符串 分别以奇数和偶数的维度来寻找回文子串 for let i i len i 借助函数拿到以奇数和偶数分别为中心的长度 let oddmaxlen helper s i i let evenmaxlen helper s i i let currentlen math max oddmaxlen evenmaxlen 更新最大长度 if currentlen maxlen maxlen currentlen begin i math floor maxlen return s substring begin begin maxlen 判判断是否是回文串的辅助函数 接收三个参数 字符串本身,中心点 function helper s left right 当left right 的时候,回文中心是一个字符,回文串的长度是奇数 当right left 的时候,此时,回文中心是两个字符,回文串的长度是偶数 while left right s length 左边界向左,右边界向右,逐个比对,直到不相同为止。 if s charat left s charat right left right else break 跳出循环的时候 恰好满足 s charat left s charat right 回文串的长度是 right left right left 总共几个数 去掉 剩下 一个道理 return right left | 0 |
41,580 | 6,919,689,410 | IssuesEvent | 2017-11-29 16:09:10 | locationtech-labs/geopyspark | https://api.github.com/repos/locationtech-labs/geopyspark | closed | Fix/Update Examples | documentation | Right now, some of our example code in the documentation is out of date and/or wrong. A more critical look at needs to be taken at these examples, and fixes and/or updates should be made accordingly. | 1.0 | Fix/Update Examples - Right now, some of our example code in the documentation is out of date and/or wrong. A more critical look at needs to be taken at these examples, and fixes and/or updates should be made accordingly. | non_priority | fix update examples right now some of our example code in the documentation is out of date and or wrong a more critical look at needs to be taken at these examples and fixes and or updates should be made accordingly | 0 |
79,489 | 10,129,784,595 | IssuesEvent | 2019-08-01 15:28:31 | polysemy-research/polysemy | https://api.github.com/repos/polysemy-research/polysemy | closed | Typo in outputToTrace documentation | documentation good first issue | On version 1.0.0.0 of polysemy, [the documentation for `traceToOutput` reads](https://hackage.haskell.org/package/polysemy-1.0.0.0/docs/Polysemy-Trace.html#v:traceToOutput):
> `traceToOutput :: Member (Output String) r => Sem (Trace ': r) a -> Sem r a`
> Transform a Trace effect into a Output String effect.
However, the [documentation for `outputToTrace` _also_ reads](https://hackage.haskell.org/package/polysemy-1.0.0.0/docs/Polysemy-Trace.html#v:outputToTrace):
> `outputToTrace :: (Show w, Member Trace r) => Sem (Output w ': r) a -> Sem r a`
> Transform a Trace effect into a Output String effect.
I believe `outputToTrace` should say:
> Transform a ~Trace~ **Output String** effect into a ~Output String~ **Trace** effect. | 1.0 | Typo in outputToTrace documentation - On version 1.0.0.0 of polysemy, [the documentation for `traceToOutput` reads](https://hackage.haskell.org/package/polysemy-1.0.0.0/docs/Polysemy-Trace.html#v:traceToOutput):
> `traceToOutput :: Member (Output String) r => Sem (Trace ': r) a -> Sem r a`
> Transform a Trace effect into a Output String effect.
However, the [documentation for `outputToTrace` _also_ reads](https://hackage.haskell.org/package/polysemy-1.0.0.0/docs/Polysemy-Trace.html#v:outputToTrace):
> `outputToTrace :: (Show w, Member Trace r) => Sem (Output w ': r) a -> Sem r a`
> Transform a Trace effect into a Output String effect.
I believe `outputToTrace` should say:
> Transform a ~Trace~ **Output String** effect into a ~Output String~ **Trace** effect. | non_priority | typo in outputtotrace documentation on version of polysemy tracetooutput member output string r sem trace r a sem r a transform a trace effect into a output string effect however the outputtotrace show w member trace r sem output w r a sem r a transform a trace effect into a output string effect i believe outputtotrace should say transform a trace output string effect into a output string trace effect | 0 |
362,729 | 25,387,524,802 | IssuesEvent | 2022-11-21 23:30:46 | binance/binance-connector-dotnet | https://api.github.com/repos/binance/binance-connector-dotnet | opened | Documentation: BSwap.Swap not working from USDT to ETH | documentation | ### Description
Hello, i am not sure what i am doing wrong, i am trying to make a swap from USDT to ETH but it gives me an error. USDT to BUSD works fine. Any help will be appreciated, thank you.
CODE:
var bSwap = new BSwap(binanceUrl, binanceApiKey, binanceApiSecret);
var result = await bSwap.Swap("USDT", "ETH", 5.0m);
print(result); | 1.0 | Documentation: BSwap.Swap not working from USDT to ETH - ### Description
Hello, i am not sure what i am doing wrong, i am trying to make a swap from USDT to ETH but it gives me an error. USDT to BUSD works fine. Any help will be appreciated, thank you.
CODE:
var bSwap = new BSwap(binanceUrl, binanceApiKey, binanceApiSecret);
var result = await bSwap.Swap("USDT", "ETH", 5.0m);
print(result); | non_priority | documentation bswap swap not working from usdt to eth description hello i am not sure what i am doing wrong i am trying to make a swap from usdt to eth but it gives me an error usdt to busd works fine any help will be appreciated thank you code var bswap new bswap binanceurl binanceapikey binanceapisecret var result await bswap swap usdt eth print result | 0 |
58,460 | 8,271,722,450 | IssuesEvent | 2018-09-16 12:35:29 | tox-dev/tox | https://api.github.com/repos/tox-dev/tox | closed | Using 'python' in commands is confusing | area:documentation pr-available | - Bitbucket: https://bitbucket.org/hpk42/tox/issue/305
- Originally reported by: @warsaw
- Originally created at: 2016-01-21T16:02:13.141
Another feedback from my fellow sprinters new to tox.
Very often you'll see something like this in your tox.ini:
```
[testenv:coverage]
basepython = python3
commands =
python -m coverage run {[coverage]rc} -m nose -v
python -m coverage combine {[coverage]rc}
python -m coverage html {[coverage]rc}
python -m coverage report -m {[coverage]rc}
```
The details aren't important other than what we're doing here is invoking some python interpreter to run some commands. In the `commands` lines we see the string "python" and while tox does the right thing by substituting `basepython` for that, it's confusing when people see it because they think that it's literally using `/usr/bin/python` (i.e. Python 2) for those commands.
I thought maybe we could use `{basepython} -m blah` but that doesn't work. Any thoughts on a way to make it obvious the "python" in commands is being substituted instead of actually using Python 2?
| 1.0 | Using 'python' in commands is confusing - - Bitbucket: https://bitbucket.org/hpk42/tox/issue/305
- Originally reported by: @warsaw
- Originally created at: 2016-01-21T16:02:13.141
Another feedback from my fellow sprinters new to tox.
Very often you'll see something like this in your tox.ini:
```
[testenv:coverage]
basepython = python3
commands =
python -m coverage run {[coverage]rc} -m nose -v
python -m coverage combine {[coverage]rc}
python -m coverage html {[coverage]rc}
python -m coverage report -m {[coverage]rc}
```
The details aren't important other than what we're doing here is invoking some python interpreter to run some commands. In the `commands` lines we see the string "python" and while tox does the right thing by substituting `basepython` for that, it's confusing when people see it because they think that it's literally using `/usr/bin/python` (i.e. Python 2) for those commands.
I thought maybe we could use `{basepython} -m blah` but that doesn't work. Any thoughts on a way to make it obvious the "python" in commands is being substituted instead of actually using Python 2?
| non_priority | using python in commands is confusing bitbucket originally reported by warsaw originally created at another feedback from my fellow sprinters new to tox very often you ll see something like this in your tox ini basepython commands python m coverage run rc m nose v python m coverage combine rc python m coverage html rc python m coverage report m rc the details aren t important other than what we re doing here is invoking some python interpreter to run some commands in the commands lines we see the string python and while tox does the right thing by substituting basepython for that it s confusing when people see it because they think that it s literally using usr bin python i e python for those commands i thought maybe we could use basepython m blah but that doesn t work any thoughts on a way to make it obvious the python in commands is being substituted instead of actually using python | 0 |
206,639 | 16,048,547,731 | IssuesEvent | 2021-04-22 16:13:25 | hochschule-darmstadt/einander-helfen | https://api.github.com/repos/hochschule-darmstadt/einander-helfen | opened | meaningful readme.md | documentation enhancement | **Reason (Why?)**
Make the readme.md more meaningful .
**Solution (What?)**
Add some descriptions about the project to the readme.md to describe what are the goals, intentions and some overall architectural description of the project.
| 1.0 | meaningful readme.md - **Reason (Why?)**
Make the readme.md more meaningful .
**Solution (What?)**
Add some descriptions about the project to the readme.md to describe what are the goals, intentions and some overall architectural description of the project.
| non_priority | meaningful readme md reason why make the readme md more meaningful solution what add some descriptions about the project to the readme md to describe what are the goals intentions and some overall architectural description of the project | 0 |
275,580 | 23,923,425,033 | IssuesEvent | 2022-09-09 19:24:48 | phetsims/energy-skate-park-basics | https://api.github.com/repos/phetsims/energy-skate-park-basics | closed | CT: property removeChild of null | type:automated-testing | ```
energy-skate-park-basics : phet-io-tests : assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556517829618:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556522133877:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556546116394:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : no-assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556515528853:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : no-assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556523101308:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : no-assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556537153083:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
``` | 1.0 | CT: property removeChild of null - ```
energy-skate-park-basics : phet-io-tests : assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556517829618:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556522133877:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556546116394:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : no-assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556515528853:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : no-assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556523101308:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
energy-skate-park-basics : phet-io-tests : no-assert
7 out of 8 tests passed. 1 failed.
SimTests: energy-skate-park-basics: event indexing failed:
Uncaught TypeError: Cannot read property 'removeChild' of null
https://bayes.colorado.edu/continuous-testing/snapshot-1556504033741/phet-io-wrappers/js/tests/SimTests.js?bust=1556537153083:27
id: Bayes Chrome
Approximately 4/28/2019, 8:13:53 PM
``` | non_priority | ct property removechild of null energy skate park basics phet io tests assert out of tests passed failed simtests energy skate park basics event indexing failed uncaught typeerror cannot read property removechild of null id bayes chrome approximately pm energy skate park basics phet io tests assert out of tests passed failed simtests energy skate park basics event indexing failed uncaught typeerror cannot read property removechild of null id bayes chrome approximately pm energy skate park basics phet io tests assert out of tests passed failed simtests energy skate park basics event indexing failed uncaught typeerror cannot read property removechild of null id bayes chrome approximately pm energy skate park basics phet io tests no assert out of tests passed failed simtests energy skate park basics event indexing failed uncaught typeerror cannot read property removechild of null id bayes chrome approximately pm energy skate park basics phet io tests no assert out of tests passed failed simtests energy skate park basics event indexing failed uncaught typeerror cannot read property removechild of null id bayes chrome approximately pm energy skate park basics phet io tests no assert out of tests passed failed simtests energy skate park basics event indexing failed uncaught typeerror cannot read property removechild of null id bayes chrome approximately pm | 0 |
33,484 | 7,131,613,792 | IssuesEvent | 2018-01-22 11:40:18 | contao/installation-bundle | https://api.github.com/repos/contao/installation-bundle | closed | DB update loads schema of none Contao tables | defect | https://github.com/contao/installation-bundle/blob/2762a4e103c9c84244c24c3fbb97499c0032e102/src/Database/Installer.php#L98
Here the full database schema is loaded first and non-Contao parts are dropped after.
This causes errors, when database specific column types (like MySQL's POINT) are used in non-Contao database assets, that Doctrine doesnt know about:
```
[2017-12-19 03:09:26] app.CRITICAL: An exception occurred. {"exception":"[object] (Doctrine\\DBAL\\DBALException(code: 0): Unknown database type point requested, Doctrine\\DBAL\\Platforms\\MySqlPlatform may not support it. at /vendor/doctrine/dbal/lib/Doctrine/DBAL/Platforms/AbstractPlatform.php:429)"} []
```
Doctrine's Schema asset filter option should be used, to prevent loading irrelevant Schema parts:
```php
$config = $this->connection->getConfiguration();
$previousSchemaFilter = $config->getFilterSchemaAssetsExpression();
$config->setFilterSchemaAssetsExpression('@^tl_@');
$fromSchema = $this->connection->getSchemaManager()->createSchema();
$config->setFilterSchemaAssetsExpression($previousSchemaFilter);
```
Though it would be probably better to use a separate connection configured via doctrine bundle config for the install tool, insteadof "hot"-changing doctrine connection configuration.
| 1.0 | DB update loads schema of none Contao tables - https://github.com/contao/installation-bundle/blob/2762a4e103c9c84244c24c3fbb97499c0032e102/src/Database/Installer.php#L98
Here the full database schema is loaded first and non-Contao parts are dropped after.
This causes errors, when database specific column types (like MySQL's POINT) are used in non-Contao database assets, that Doctrine doesnt know about:
```
[2017-12-19 03:09:26] app.CRITICAL: An exception occurred. {"exception":"[object] (Doctrine\\DBAL\\DBALException(code: 0): Unknown database type point requested, Doctrine\\DBAL\\Platforms\\MySqlPlatform may not support it. at /vendor/doctrine/dbal/lib/Doctrine/DBAL/Platforms/AbstractPlatform.php:429)"} []
```
Doctrine's Schema asset filter option should be used, to prevent loading irrelevant Schema parts:
```php
$config = $this->connection->getConfiguration();
$previousSchemaFilter = $config->getFilterSchemaAssetsExpression();
$config->setFilterSchemaAssetsExpression('@^tl_@');
$fromSchema = $this->connection->getSchemaManager()->createSchema();
$config->setFilterSchemaAssetsExpression($previousSchemaFilter);
```
Though it would be probably better to use a separate connection configured via doctrine bundle config for the install tool, insteadof "hot"-changing doctrine connection configuration.
| non_priority | db update loads schema of none contao tables here the full database schema is loaded first and non contao parts are dropped after this causes errors when database specific column types like mysql s point are used in non contao database assets that doctrine doesnt know about app critical an exception occurred exception doctrine dbal dbalexception code unknown database type point requested doctrine dbal platforms mysqlplatform may not support it at vendor doctrine dbal lib doctrine dbal platforms abstractplatform php doctrine s schema asset filter option should be used to prevent loading irrelevant schema parts php config this connection getconfiguration previousschemafilter config getfilterschemaassetsexpression config setfilterschemaassetsexpression tl fromschema this connection getschemamanager createschema config setfilterschemaassetsexpression previousschemafilter though it would be probably better to use a separate connection configured via doctrine bundle config for the install tool insteadof hot changing doctrine connection configuration | 0 |
300,598 | 25,979,409,474 | IssuesEvent | 2022-12-19 17:24:04 | XRPLF/clio | https://api.github.com/repos/XRPLF/clio | closed | Implement unit-tests for DOSGuard | enhancement testability | DOSGuard can be covered with unit-tests without any/much modifications. Let's get it covered. | 1.0 | Implement unit-tests for DOSGuard - DOSGuard can be covered with unit-tests without any/much modifications. Let's get it covered. | non_priority | implement unit tests for dosguard dosguard can be covered with unit tests without any much modifications let s get it covered | 0 |
180,094 | 21,625,485,152 | IssuesEvent | 2022-05-05 01:08:15 | JohnDeere/MyJohnDeereAPI-OAuth2-Java-Example | https://api.github.com/repos/JohnDeere/MyJohnDeereAPI-OAuth2-Java-Example | opened | WS-2021-0419 (High) detected in gson-2.8.6.jar | security vulnerability | ## WS-2021-0419 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.8.6.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/code/gson/gson/2.8.6/gson-2.8.6.jar</p>
<p>
Dependency Hierarchy:
- unirest-java-3.11.11.jar (Root Library)
- :x: **gson-2.8.6.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Denial of Service vulnerability was discovered in gson before 2.8.9 via the writeReplace() method.
<p>Publish Date: 2021-10-11
<p>URL: <a href=https://github.com/google/gson/pull/1991>WS-2021-0419</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/google/gson/releases/tag/gson-parent-2.8.9">https://github.com/google/gson/releases/tag/gson-parent-2.8.9</a></p>
<p>Release Date: 2021-10-11</p>
<p>Fix Resolution (com.google.code.gson:gson): 2.8.9</p>
<p>Direct dependency fix Resolution (com.konghq:unirest-java): 3.13.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0419 (High) detected in gson-2.8.6.jar - ## WS-2021-0419 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>gson-2.8.6.jar</b></p></summary>
<p>Gson JSON library</p>
<p>Library home page: <a href="https://github.com/google/gson">https://github.com/google/gson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/code/gson/gson/2.8.6/gson-2.8.6.jar</p>
<p>
Dependency Hierarchy:
- unirest-java-3.11.11.jar (Root Library)
- :x: **gson-2.8.6.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Denial of Service vulnerability was discovered in gson before 2.8.9 via the writeReplace() method.
<p>Publish Date: 2021-10-11
<p>URL: <a href=https://github.com/google/gson/pull/1991>WS-2021-0419</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/google/gson/releases/tag/gson-parent-2.8.9">https://github.com/google/gson/releases/tag/gson-parent-2.8.9</a></p>
<p>Release Date: 2021-10-11</p>
<p>Fix Resolution (com.google.code.gson:gson): 2.8.9</p>
<p>Direct dependency fix Resolution (com.konghq:unirest-java): 3.13.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in gson jar ws high severity vulnerability vulnerable library gson jar gson json library library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com google code gson gson gson jar dependency hierarchy unirest java jar root library x gson jar vulnerable library found in base branch master vulnerability details denial of service vulnerability was discovered in gson before via the writereplace method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google code gson gson direct dependency fix resolution com konghq unirest java step up your open source security game with whitesource | 0 |
119,588 | 17,620,640,451 | IssuesEvent | 2021-08-18 14:55:37 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | [RAC][Observability] Alert selection enabled when no capabilities to do actions | bug v8.0.0 impact:high Team:Threat Hunting Team: SecuritySolution v7.15.0 | **Describe the bug:**
All alerts in the table have the checkbox enabled.
Alerts with no save permission should not have the checkbox enabled, the user can not do any write action to them.
The count number in the "Select all X alerts" button should also reflect only updatable alerts.
https://user-images.githubusercontent.com/17747913/129920961-2c178f2d-44ce-4627-812a-3dfe74b5a3c9.mov
**Steps to reproduce:**
1. Open alerts in Observability
2. Check some alerts do not have individual updates actions
3. See all alerts are selectable to do the bulk update
4. See the "Select all X alerts" number includes alerts that are not updatable.
**Expected behavior:**
- Checkboxes are disabled for alerts that the users do not have _save_ permission.
- If there isn't any write allowed alert on the page, the checkboxes do not appear.
- "Select all X alerts" button should not consider the alerts that are not updatable.
| True | [RAC][Observability] Alert selection enabled when no capabilities to do actions - **Describe the bug:**
All alerts in the table have the checkbox enabled.
Alerts with no save permission should not have the checkbox enabled, the user can not do any write action to them.
The count number in the "Select all X alerts" button should also reflect only updatable alerts.
https://user-images.githubusercontent.com/17747913/129920961-2c178f2d-44ce-4627-812a-3dfe74b5a3c9.mov
**Steps to reproduce:**
1. Open alerts in Observability
2. Check some alerts do not have individual updates actions
3. See all alerts are selectable to do the bulk update
4. See the "Select all X alerts" number includes alerts that are not updatable.
**Expected behavior:**
- Checkboxes are disabled for alerts that the users do not have _save_ permission.
- If there isn't any write allowed alert on the page, the checkboxes do not appear.
- "Select all X alerts" button should not consider the alerts that are not updatable.
| non_priority | alert selection enabled when no capabilities to do actions describe the bug all alerts in the table have the checkbox enabled alerts with no save permission should not have the checkbox enabled the user can not do any write action to them the count number in the select all x alerts button should also reflect only updatable alerts steps to reproduce open alerts in observability check some alerts do not have individual updates actions see all alerts are selectable to do the bulk update see the select all x alerts number includes alerts that are not updatable expected behavior checkboxes are disabled for alerts that the users do not have save permission if there isn t any write allowed alert on the page the checkboxes do not appear select all x alerts button should not consider the alerts that are not updatable | 0 |
395,450 | 27,070,078,180 | IssuesEvent | 2023-02-14 05:48:54 | kubernetes-sigs/structured-merge-diff | https://api.github.com/repos/kubernetes-sigs/structured-merge-diff | closed | Broken Link issue need to fix | kind/bug lifecycle/rotten kind/documentation | ## Bug Report
*Problem*
[This page ](https://github.com/kubernetes-sigs/structured-merge-diff/blob/master/CONTRIBUTING.md) has one broken link of `contributor cheat sheet` which needs to fix.
*solution*
need to locate the correct path of README.
/assign
/kind bug
/kind documentation | 1.0 | Broken Link issue need to fix - ## Bug Report
*Problem*
[This page ](https://github.com/kubernetes-sigs/structured-merge-diff/blob/master/CONTRIBUTING.md) has one broken link of `contributor cheat sheet` which needs to fix.
*solution*
need to locate the correct path of README.
/assign
/kind bug
/kind documentation | non_priority | broken link issue need to fix bug report problem has one broken link of contributor cheat sheet which needs to fix solution need to locate the correct path of readme assign kind bug kind documentation | 0 |
121,588 | 10,180,013,583 | IssuesEvent | 2019-08-09 09:14:31 | sylabs/singularity | https://api.github.com/repos/sylabs/singularity | closed | [E2E] Improve coverage for verify command | Testing e2e | ## Version of Singularity:
All.
### Expected behavior
All commands expected to succeed should be tested.
Part of issue #4078
### Actual behavior
- [ ] singularity verify --groupid
- [ ] singularity verify --id
- [ ] singularity verify --url
### Steps to reproduce behavior
N/A.
| 1.0 | [E2E] Improve coverage for verify command - ## Version of Singularity:
All.
### Expected behavior
All commands expected to succeed should be tested.
Part of issue #4078
### Actual behavior
- [ ] singularity verify --groupid
- [ ] singularity verify --id
- [ ] singularity verify --url
### Steps to reproduce behavior
N/A.
| non_priority | improve coverage for verify command version of singularity all expected behavior all commands expected to succeed should be tested part of issue actual behavior singularity verify groupid singularity verify id singularity verify url steps to reproduce behavior n a | 0 |
139,574 | 18,853,668,136 | IssuesEvent | 2021-11-12 01:28:34 | jiw065/Springboot-demo | https://api.github.com/repos/jiw065/Springboot-demo | opened | CVE-2021-20190 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Springboot-demo/spring-boot-demo/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190>CVE-2021-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2854">https://github.com/FasterXML/jackson-databind/issues/2854</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind-2.9.10.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-20190 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Springboot-demo/spring-boot-demo/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190>CVE-2021-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2854">https://github.com/FasterXML/jackson-databind/issues/2854</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind-2.9.10.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file springboot demo spring boot demo pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library vulnerability details a flaw was found in jackson databind before fasterxml mishandles the interaction between serialization gadgets and typing the highest threat from this vulnerability is to data confidentiality and integrity as well as system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
371,309 | 25,946,783,029 | IssuesEvent | 2022-12-17 03:20:34 | smclaughlan/GWJ52 | https://api.github.com/repos/smclaughlan/GWJ52 | closed | Various - notes from mtg Dec 11 | documentation | Bugs:
- Laser knock back is broken after introduction of melee knockback
- Initial towers don't have active collision shapes. (make them bases+turrets, not just turrets)
Design:
- What's the win condition? Maybe player buys their "win" with currency (light) at the base
- Move the shopping interface to the base so the player has to divide their time between hunting and defending
- Tower placement needs maximum range so player can't spread too quickly
- Tower placement needs more obvious feedback about requirements - insufficient cash, distance, etc.
- Player needs some starting cash, so they can place a couple of towers.
- Need a softer landing / onboarding / tutorial. (Maybe scene 1 is a small tutorial zone where they place the first 4 towers that show up when they start the real game)
- If the player is off hunting, they should get an edge-of-screen alert when the base is under attack.
- maybe give an edge of screen wave alert if the player is at the base and an offscreen spawner fires up a new wave.
- Make the village an exclusion zone, so no towers can be placed there (this might be auto-solved based on tower minimum distance requirements)
- Player should be able to destroy towers for a refund.
- right click on tower while holding the construction wrench? Or interaction key (e or f)
- Towers, when placed, will snap to a grid, so they don't look untidy.
Backlog
- Plexsoup is still working on the tower wiring network.
- If the path to the source breaks, all downstream towers should lose power.
- When towers are depowered they should light up again when a new (powered) tower is placed nearby
- player can't build in the dark, towers have a light aura / radius. new towers only go in the light. if part of the grid is dep-powered, there's no building there.
| 1.0 | Various - notes from mtg Dec 11 - Bugs:
- Laser knock back is broken after introduction of melee knockback
- Initial towers don't have active collision shapes. (make them bases+turrets, not just turrets)
Design:
- What's the win condition? Maybe player buys their "win" with currency (light) at the base
- Move the shopping interface to the base so the player has to divide their time between hunting and defending
- Tower placement needs maximum range so player can't spread too quickly
- Tower placement needs more obvious feedback about requirements - insufficient cash, distance, etc.
- Player needs some starting cash, so they can place a couple of towers.
- Need a softer landing / onboarding / tutorial. (Maybe scene 1 is a small tutorial zone where they place the first 4 towers that show up when they start the real game)
- If the player is off hunting, they should get an edge-of-screen alert when the base is under attack.
- maybe give an edge of screen wave alert if the player is at the base and an offscreen spawner fires up a new wave.
- Make the village an exclusion zone, so no towers can be placed there (this might be auto-solved based on tower minimum distance requirements)
- Player should be able to destroy towers for a refund.
- right click on tower while holding the construction wrench? Or interaction key (e or f)
- Towers, when placed, will snap to a grid, so they don't look untidy.
Backlog
- Plexsoup is still working on the tower wiring network.
- If the path to the source breaks, all downstream towers should lose power.
- When towers are depowered they should light up again when a new (powered) tower is placed nearby
- player can't build in the dark, towers have a light aura / radius. new towers only go in the light. if part of the grid is dep-powered, there's no building there.
| non_priority | various notes from mtg dec bugs laser knock back is broken after introduction of melee knockback initial towers don t have active collision shapes make them bases turrets not just turrets design what s the win condition maybe player buys their win with currency light at the base move the shopping interface to the base so the player has to divide their time between hunting and defending tower placement needs maximum range so player can t spread too quickly tower placement needs more obvious feedback about requirements insufficient cash distance etc player needs some starting cash so they can place a couple of towers need a softer landing onboarding tutorial maybe scene is a small tutorial zone where they place the first towers that show up when they start the real game if the player is off hunting they should get an edge of screen alert when the base is under attack maybe give an edge of screen wave alert if the player is at the base and an offscreen spawner fires up a new wave make the village an exclusion zone so no towers can be placed there this might be auto solved based on tower minimum distance requirements player should be able to destroy towers for a refund right click on tower while holding the construction wrench or interaction key e or f towers when placed will snap to a grid so they don t look untidy backlog plexsoup is still working on the tower wiring network if the path to the source breaks all downstream towers should lose power when towers are depowered they should light up again when a new powered tower is placed nearby player can t build in the dark towers have a light aura radius new towers only go in the light if part of the grid is dep powered there s no building there | 0 |
4,583 | 11,388,531,058 | IssuesEvent | 2020-01-29 16:50:05 | CanDIG/candig_tyk | https://api.github.com/repos/CanDIG/candig_tyk | closed | Automated integrated deployment | Architecture CanDIGv1 marker paper | This issue can be closed when scripted automated deployment of Tyk + ga4gh-server + an IdP becomes possible. It may be moved to another repository at some point. | 1.0 | Automated integrated deployment - This issue can be closed when scripted automated deployment of Tyk + ga4gh-server + an IdP becomes possible. It may be moved to another repository at some point. | non_priority | automated integrated deployment this issue can be closed when scripted automated deployment of tyk server an idp becomes possible it may be moved to another repository at some point | 0 |
273,436 | 23,752,223,332 | IssuesEvent | 2022-08-31 21:56:41 | astroML/astroML | https://api.github.com/repos/astroML/astroML | closed | Add dev version testing to CI | critical testing | So we pick up issues we have against the dev versions of numpy, astroopy, mpl, sklearn, scipy. | 1.0 | Add dev version testing to CI - So we pick up issues we have against the dev versions of numpy, astroopy, mpl, sklearn, scipy. | non_priority | add dev version testing to ci so we pick up issues we have against the dev versions of numpy astroopy mpl sklearn scipy | 0 |
100,906 | 16,490,597,812 | IssuesEvent | 2021-05-25 02:43:50 | EcommEasy/EcommEasy | https://api.github.com/repos/EcommEasy/EcommEasy | opened | CVE-2021-23383 (High) detected in handlebars-4.1.1.tgz | security vulnerability | ## CVE-2021-23383 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.1.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.1.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.1.tgz</a></p>
<p>Path to dependency file: /EcommEasy/package.json</p>
<p>Path to vulnerable library: EcommEasy/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.1.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383>CVE-2021-23383</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution: handlebars - v4.7.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23383 (High) detected in handlebars-4.1.1.tgz - ## CVE-2021-23383 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.1.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.1.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.1.tgz</a></p>
<p>Path to dependency file: /EcommEasy/package.json</p>
<p>Path to vulnerable library: EcommEasy/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.1.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package handlebars before 4.7.7 are vulnerable to Prototype Pollution when selecting certain compiling options to compile templates coming from an untrusted source.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23383>CVE-2021-23383</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23383</a></p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution: handlebars - v4.7.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in handlebars tgz cve high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file ecommeasy package json path to vulnerable library ecommeasy node modules handlebars package json dependency hierarchy x handlebars tgz vulnerable library vulnerability details the package handlebars before are vulnerable to prototype pollution when selecting certain compiling options to compile templates coming from an untrusted source publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
93,916 | 27,071,507,085 | IssuesEvent | 2023-02-14 07:20:01 | hashicorp/vault | https://api.github.com/repos/hashicorp/vault | closed | INFORMATION NEEDED: identifier for macOS signed binary artifact is CHANGED to a.out, permanently? | release/build | This is an observation more than a bug _necessarily_ as functionality is unchanged, but when it comes to trustworthiness of a signing pipeline any observed change feels worth reporting. If a value I rely on for what makes up part of a cryptographic signature needs to be updated, I'd hope it's intentional and 'permanent' instead of arbitrary and potentially unreliable.
I'm assuming the signing for vault uses something like [gon](https://github.com/mitchellh/gon), and that it is secured adequately all the way up to being posted for release/download. I don't see anything in the release notes that indicates the observation I'm reporting is a temporary or permanent change or intentionally altered configuration.
A common tool for macOS software distribution for institutions (in comparison to homebrew which manually :yolo:'s whatever a maintainer attests is The Canonical Binary™+hash for a resource) is the [autopkg](https://autopkg.github.io/autopkg/) project. It uses [code signature verification](https://github.com/autopkg/autopkg/wiki/Using-CodeSignatureVerification), which in turn relies on the codesign binary (via the --display -r- --deep -v flags with the path to the binary) on the Mac to determine if an artifacts 'designated' field matches a [recorded string](https://github.com/autopkg/hjuutilainen-recipes/blob/7c3af44674e5a1e2c256d45014c956cc5ce60345/HashiCorp/Vault.download.recipe#L60) exactly. As of the 1.12.3 darwin releases, the 'signature' doesn't match because instead of recording the cert values with the 'vault' identifier for the binary, it's instead using [a.out](https://en.wikipedia.org/wiki/A.out), ye olde 'assembler output' format/naming of yore that golang adopted as a default. I can't imagine this is cause for alarm, but the difference breaks our recipe until we (the autopkg community) update the value.
**To Reproduce**
Steps to reproduce the behavior:
1. curl/download the 1.12.2 and 1.12.3 darwin arm64 or amd64 releases from https://releases.hashicorp.com
2. unzip the 1.12.2 version to a distinct path or /tmp and rename output from filename 'vault' to vault1.12.2
3. run `codesign --display -r- --deep -v /path/to/vault1.12.2`
4. note the second line in the output `Identifier=vault` and beginning of the last line `designated => identifier vault...`
5. unzip the 1.12.3 version to a distinct path or /tmp and rename output from filename 'vault' to vault1.12.3
6. run `codesign --display -r- --deep -v /path/to/vault1.12.3`
7. note `Identifier=a.out` in the output and beginning of the last line `designated => identifier "a.out"`
**Expected behavior**
The designated => field should match the `identifier vault` string prefix previously used, or confirmation this will be how the compiled binary is signed/identified in the future
**Environment:**
* Vault Server Version (retrieve with `vault status`): n/a, but I work at an Enterprise Vault customer and we're running Vault 1.10.6+ent
* Vault CLI Version (retrieve with `vault version`): $current
* Server Operating System/Architecture: n/a
Vault server configuration file(s):
```hcl
n/a
```
**Additional context**
Thank you for your time and attention! 🙇 | 1.0 | INFORMATION NEEDED: identifier for macOS signed binary artifact is CHANGED to a.out, permanently? - This is an observation more than a bug _necessarily_ as functionality is unchanged, but when it comes to trustworthiness of a signing pipeline any observed change feels worth reporting. If a value I rely on for what makes up part of a cryptographic signature needs to be updated, I'd hope it's intentional and 'permanent' instead of arbitrary and potentially unreliable.
I'm assuming the signing for vault uses something like [gon](https://github.com/mitchellh/gon), and that it is secured adequately all the way up to being posted for release/download. I don't see anything in the release notes that indicates the observation I'm reporting is a temporary or permanent change or intentionally altered configuration.
A common tool for macOS software distribution for institutions (in comparison to homebrew which manually :yolo:'s whatever a maintainer attests is The Canonical Binary™+hash for a resource) is the [autopkg](https://autopkg.github.io/autopkg/) project. It uses [code signature verification](https://github.com/autopkg/autopkg/wiki/Using-CodeSignatureVerification), which in turn relies on the codesign binary (via the --display -r- --deep -v flags with the path to the binary) on the Mac to determine if an artifacts 'designated' field matches a [recorded string](https://github.com/autopkg/hjuutilainen-recipes/blob/7c3af44674e5a1e2c256d45014c956cc5ce60345/HashiCorp/Vault.download.recipe#L60) exactly. As of the 1.12.3 darwin releases, the 'signature' doesn't match because instead of recording the cert values with the 'vault' identifier for the binary, it's instead using [a.out](https://en.wikipedia.org/wiki/A.out), ye olde 'assembler output' format/naming of yore that golang adopted as a default. I can't imagine this is cause for alarm, but the difference breaks our recipe until we (the autopkg community) update the value.
**To Reproduce**
Steps to reproduce the behavior:
1. curl/download the 1.12.2 and 1.12.3 darwin arm64 or amd64 releases from https://releases.hashicorp.com
2. unzip the 1.12.2 version to a distinct path or /tmp and rename output from filename 'vault' to vault1.12.2
3. run `codesign --display -r- --deep -v /path/to/vault1.12.2`
4. note the second line in the output `Identifier=vault` and beginning of the last line `designated => identifier vault...`
5. unzip the 1.12.3 version to a distinct path or /tmp and rename output from filename 'vault' to vault1.12.3
6. run `codesign --display -r- --deep -v /path/to/vault1.12.3`
7. note `Identifier=a.out` in the output and beginning of the last line `designated => identifier "a.out"`
**Expected behavior**
The designated => field should match the `identifier vault` string prefix previously used, or confirmation this will be how the compiled binary is signed/identified in the future
**Environment:**
* Vault Server Version (retrieve with `vault status`): n/a, but I work at an Enterprise Vault customer and we're running Vault 1.10.6+ent
* Vault CLI Version (retrieve with `vault version`): $current
* Server Operating System/Architecture: n/a
Vault server configuration file(s):
```hcl
n/a
```
**Additional context**
Thank you for your time and attention! 🙇 | non_priority | information needed identifier for macos signed binary artifact is changed to a out permanently this is an observation more than a bug necessarily as functionality is unchanged but when it comes to trustworthiness of a signing pipeline any observed change feels worth reporting if a value i rely on for what makes up part of a cryptographic signature needs to be updated i d hope it s intentional and permanent instead of arbitrary and potentially unreliable i m assuming the signing for vault uses something like and that it is secured adequately all the way up to being posted for release download i don t see anything in the release notes that indicates the observation i m reporting is a temporary or permanent change or intentionally altered configuration a common tool for macos software distribution for institutions in comparison to homebrew which manually yolo s whatever a maintainer attests is the canonical binary™ hash for a resource is the project it uses which in turn relies on the codesign binary via the display r deep v flags with the path to the binary on the mac to determine if an artifacts designated field matches a exactly as of the darwin releases the signature doesn t match because instead of recording the cert values with the vault identifier for the binary it s instead using ye olde assembler output format naming of yore that golang adopted as a default i can t imagine this is cause for alarm but the difference breaks our recipe until we the autopkg community update the value to reproduce steps to reproduce the behavior curl download the and darwin or releases from unzip the version to a distinct path or tmp and rename output from filename vault to run codesign display r deep v path to note the second line in the output identifier vault and beginning of the last line designated identifier vault unzip the version to a distinct path or tmp and rename output from filename vault to run codesign display r deep v path to note identifier a out in the output and beginning of the last line designated identifier a out expected behavior the designated field should match the identifier vault string prefix previously used or confirmation this will be how the compiled binary is signed identified in the future environment vault server version retrieve with vault status n a but i work at an enterprise vault customer and we re running vault ent vault cli version retrieve with vault version current server operating system architecture n a vault server configuration file s hcl n a additional context thank you for your time and attention 🙇 | 0 |
69,691 | 30,449,464,527 | IssuesEvent | 2023-07-16 05:10:29 | layer5io/meshery-smp-action | https://api.github.com/repos/layer5io/meshery-smp-action | opened | Archive Open Service Mesh Tests | area/ci area/devops area/performance help wanted kind/chore service-mesh/open-service-mesh | #### Current Behavior
Open Service Mesh is an archived project. It's performance testing here can be removed.
---
#### Contributor [Guides](https://docs.meshery.io/project/contributing) and Resources
- 📝 [Meshery Adapters Spreadsheet](https://docs.google.com/spreadsheets/d/1rGGpSXC68iDJzNRU-qZIRQsZUwkt1qLFg7JCs4pfvbU/edit?usp=sharing)
- 🛠 [Meshery Build & Release Strategy](https://docs.meshery.io/project/build-and-release)
- 📚 [Instructions for contributing to documentation](https://github.com/meshery/meshery/blob/master/CONTRIBUTING.md#documentation-contribution-flow)
- Meshery documentation [site](https://docs.meshery.io/) and [source](https://github.com/meshery/meshery/tree/master/docs)
- 🎨 Wireframes and [designs for Meshery UI](https://www.figma.com/file/SMP3zxOjZztdOLtgN4dS2W/Meshery-UI) in Figma [(open invite)](https://www.figma.com/team_invite/redeem/qJy1c95qirjgWQODApilR9)
- 🙋🏾🙋🏼 Questions: [Layer5 Discussion Forum](https://discuss.layer5.io) and [Layer5 Community Slack](http://slack.layer5.io) | 2.0 | Archive Open Service Mesh Tests - #### Current Behavior
Open Service Mesh is an archived project. It's performance testing here can be removed.
---
#### Contributor [Guides](https://docs.meshery.io/project/contributing) and Resources
- 📝 [Meshery Adapters Spreadsheet](https://docs.google.com/spreadsheets/d/1rGGpSXC68iDJzNRU-qZIRQsZUwkt1qLFg7JCs4pfvbU/edit?usp=sharing)
- 🛠 [Meshery Build & Release Strategy](https://docs.meshery.io/project/build-and-release)
- 📚 [Instructions for contributing to documentation](https://github.com/meshery/meshery/blob/master/CONTRIBUTING.md#documentation-contribution-flow)
- Meshery documentation [site](https://docs.meshery.io/) and [source](https://github.com/meshery/meshery/tree/master/docs)
- 🎨 Wireframes and [designs for Meshery UI](https://www.figma.com/file/SMP3zxOjZztdOLtgN4dS2W/Meshery-UI) in Figma [(open invite)](https://www.figma.com/team_invite/redeem/qJy1c95qirjgWQODApilR9)
- 🙋🏾🙋🏼 Questions: [Layer5 Discussion Forum](https://discuss.layer5.io) and [Layer5 Community Slack](http://slack.layer5.io) | non_priority | archive open service mesh tests current behavior open service mesh is an archived project it s performance testing here can be removed contributor and resources 📝 🛠 📚 meshery documentation and 🎨 wireframes and in figma 🙋🏾🙋🏼 questions and | 0 |
84,391 | 24,291,050,423 | IssuesEvent | 2022-09-29 06:01:47 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug]: Property Pane INPUT_TEXT if passed 0 as the default value for a widget property does not show the value | Bug Property Pane UI Builders Pod | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Description
- For the `Number & Range` slider widgets, the `Min. Value` property uses the `INPUT_TEXT` control.
- When we pass the value `0` as the default value it does not show up in the `INPUT_TEXT` control instead we only see a placeholder.
### Steps To Reproduce
1. Drag and Drop the `Number / Range Slider` widget.
2. Check the `Min. Value` property in the property pane
### Public Sample App
_No response_
### Version
Release | 1.0 | [Bug]: Property Pane INPUT_TEXT if passed 0 as the default value for a widget property does not show the value - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Description
- For the `Number & Range` slider widgets, the `Min. Value` property uses the `INPUT_TEXT` control.
- When we pass the value `0` as the default value it does not show up in the `INPUT_TEXT` control instead we only see a placeholder.
### Steps To Reproduce
1. Drag and Drop the `Number / Range Slider` widget.
2. Check the `Min. Value` property in the property pane
### Public Sample App
_No response_
### Version
Release | non_priority | property pane input text if passed as the default value for a widget property does not show the value is there an existing issue for this i have searched the existing issues description for the number range slider widgets the min value property uses the input text control when we pass the value as the default value it does not show up in the input text control instead we only see a placeholder steps to reproduce drag and drop the number range slider widget check the min value property in the property pane public sample app no response version release | 0 |
441,387 | 30,780,752,072 | IssuesEvent | 2023-07-31 09:50:05 | JD2112/methylr | https://api.github.com/repos/JD2112/methylr | closed | Unable to start methylr using apptainer | bug documentation | **Describe the bug**
Unable to start container using apptainer.
Starting container using Docker working as expected and can access via Firefox
**To Reproduce**
#my username on my server is gmsywss
#I ran the following command as instructed
`apptainer run docker://jd21/methylr:latest`
#Below is the output
Getting image source signatures
Copying blob 675920708c8b done
Copying blob 4a0b0c48a245 done
Copying blob 4d225a645112 done
Copying blob edb25e8773a2 done
Copying blob 0859082e6bfe done
Copying blob 2c7717ed42b5 done
Copying blob f98488f0b7eb done
Copying blob 68d9ec9958f4 done
Copying blob 0907d76d45d7 done
Copying blob 91c20754dfa7 done
Copying blob 1cb6359be342 done
Copying blob 039933c89bc6 done
Copying blob a998a725ad2a done
Copying blob eec5691985f6 done
Copying blob c185ae260562 done
Copying blob fb811cb38974 done
Copying blob f7fbaa592b80 done
Copying blob 1956e0ee4e98 done
Copying blob 735bdb524661 done
Copying blob 3773fe0dc9e0 done
Copying config 530d3cb5ff done
Writing manifest to image destination
Storing signatures
2023/07/27 12:59:18 info unpack layer: sha256:675920708c8bf10fbd02693dc8f43ee7dbe0a99cdfd55e06e6f1a8b43fd08e3f
2023/07/27 12:59:19 info unpack layer: sha256:edb25e8773a2cab31c156c1016c187b890fd7de13bb2459f52cbf0c0c4f5de79
2023/07/27 12:59:19 info unpack layer: sha256:4d225a645112c4132d5d731c26c93bc9ae072fb3021f87ae49d442af848a5c98
2023/07/27 12:59:25 info unpack layer: sha256:0859082e6bfee5b698c51c11833d63d99dee124a44288a0725fccb44f2c1487d
2023/07/27 12:59:25 info unpack layer: sha256:2c7717ed42b5b33850dc0257c03c6f35377571da4466743aa7187c8a939dfd8b
2023/07/27 12:59:26 info unpack layer: sha256:4a0b0c48a24567f3905d1c17f94e066a9437af2de554fcf2da1a43cf1200c39b
2023/07/27 12:59:30 info unpack layer: sha256:f98488f0b7ebc01b6f977a3520e6374645efd3dcb1572b6e64b51ed0c72b0a96
2023/07/27 12:59:37 info unpack layer: sha256:68d9ec9958f429496854b79a7423010ea58c683e56301db37cce4e928ba7d9b9
2023/07/27 12:59:38 info unpack layer: sha256:0907d76d45d75146c54e19628ae98241edebc344bc3ded4d18d005e0308ea28b
2023/07/27 12:59:38 info unpack layer: sha256:91c20754dfa7044fbd71855b31d811c4c8eac28943e1fb8c7b748cf90e49df97
2023/07/27 12:59:38 info unpack layer: sha256:1cb6359be342a58ff0cd8bfc996360ba99cf327e92da8b20ac1d7ea07e6201fd
2023/07/27 12:59:38 info unpack layer: sha256:039933c89bc61afe0dbf548830cffc8ec977c5575a844224c5eb65cd9d028a54
2023/07/27 12:59:55 warn rootless{usr/local/lib/R/site-library/Rhtslib/usrlib/libhts.so.2} ignoring (usually) harmless EPERM on setxattr "user.rootlesscontainers"
2023/07/27 13:00:16 info unpack layer: sha256:a998a725ad2ad2f049dd90ba75e4f0946565c315bfa58cab599ca609c84aeba1
2023/07/27 13:00:17 info unpack layer: sha256:eec5691985f610ea0f3784244e6e1348824bc84b2b77faa28770bdc6beab241c
2023/07/27 13:00:17 info unpack layer: sha256:c185ae260562a69c06c7975879b2cbc473c9d16a71ae95abd50ddbb245da6a3e
2023/07/27 13:00:18 info unpack layer: sha256:fb811cb389747dcb003f0eaadbacfab24befd161547b6be418bdf6fbf189f94c
2023/07/27 13:00:18 info unpack layer: sha256:f7fbaa592b80566757b72038746cd6dc901724af0246452d5356784a741d3feb
2023/07/27 13:00:20 info unpack layer: sha256:1956e0ee4e98aa08e0540cbabb02dd380bcc48a080bef1e1c801aabf3355b1f1
2023/07/27 13:00:20 info unpack layer: sha256:735bdb52466195ebf4ed80fb8f307649bc06a82512e1409b5bd66e799097d2c0
2023/07/27 13:00:23 info unpack layer: sha256:3773fe0dc9e08face6fcaddf24f871b39fac681ba30024f1fc85b74829e7d58d
INFO: Creating SIF file...
[2023-07-27T05:00:38.312] [INFO] shiny-server - Shiny Server v1.5.18.979 (Node.js v12.22.6)
[2023-07-27T05:00:38.317] [INFO] shiny-server - Using config file "/etc/shiny-server/shiny-server.conf"
**[2023-07-27T05:00:38.350] [ERROR] shiny-server - Error loading config: The user 'gmsywss' does not have permissions to run applications as one of the users in 'shiny'. Please restart shiny-server as one of the users in 'shiny'. (/etc/shiny-server/shiny-server.conf:5:1)**
[2023-07-27T05:00:38.351] [INFO] shiny-server - Shutting down worker processes
**Expected behavior**
Container should be downloaded, converted to sif format then start shiny server
**Desktop (please complete the following information):**
- OS: CentOS8 Stream 4.18.0-500, CentOS7 (Core) 3.10.0-1160.92.1, debian11 (bullseye) 5.10.0-23
- Browser Firefox
- Version 115.0.2
| 1.0 | Unable to start methylr using apptainer - **Describe the bug**
Unable to start container using apptainer.
Starting container using Docker working as expected and can access via Firefox
**To Reproduce**
#my username on my server is gmsywss
#I ran the following command as instructed
`apptainer run docker://jd21/methylr:latest`
#Below is the output
Getting image source signatures
Copying blob 675920708c8b done
Copying blob 4a0b0c48a245 done
Copying blob 4d225a645112 done
Copying blob edb25e8773a2 done
Copying blob 0859082e6bfe done
Copying blob 2c7717ed42b5 done
Copying blob f98488f0b7eb done
Copying blob 68d9ec9958f4 done
Copying blob 0907d76d45d7 done
Copying blob 91c20754dfa7 done
Copying blob 1cb6359be342 done
Copying blob 039933c89bc6 done
Copying blob a998a725ad2a done
Copying blob eec5691985f6 done
Copying blob c185ae260562 done
Copying blob fb811cb38974 done
Copying blob f7fbaa592b80 done
Copying blob 1956e0ee4e98 done
Copying blob 735bdb524661 done
Copying blob 3773fe0dc9e0 done
Copying config 530d3cb5ff done
Writing manifest to image destination
Storing signatures
2023/07/27 12:59:18 info unpack layer: sha256:675920708c8bf10fbd02693dc8f43ee7dbe0a99cdfd55e06e6f1a8b43fd08e3f
2023/07/27 12:59:19 info unpack layer: sha256:edb25e8773a2cab31c156c1016c187b890fd7de13bb2459f52cbf0c0c4f5de79
2023/07/27 12:59:19 info unpack layer: sha256:4d225a645112c4132d5d731c26c93bc9ae072fb3021f87ae49d442af848a5c98
2023/07/27 12:59:25 info unpack layer: sha256:0859082e6bfee5b698c51c11833d63d99dee124a44288a0725fccb44f2c1487d
2023/07/27 12:59:25 info unpack layer: sha256:2c7717ed42b5b33850dc0257c03c6f35377571da4466743aa7187c8a939dfd8b
2023/07/27 12:59:26 info unpack layer: sha256:4a0b0c48a24567f3905d1c17f94e066a9437af2de554fcf2da1a43cf1200c39b
2023/07/27 12:59:30 info unpack layer: sha256:f98488f0b7ebc01b6f977a3520e6374645efd3dcb1572b6e64b51ed0c72b0a96
2023/07/27 12:59:37 info unpack layer: sha256:68d9ec9958f429496854b79a7423010ea58c683e56301db37cce4e928ba7d9b9
2023/07/27 12:59:38 info unpack layer: sha256:0907d76d45d75146c54e19628ae98241edebc344bc3ded4d18d005e0308ea28b
2023/07/27 12:59:38 info unpack layer: sha256:91c20754dfa7044fbd71855b31d811c4c8eac28943e1fb8c7b748cf90e49df97
2023/07/27 12:59:38 info unpack layer: sha256:1cb6359be342a58ff0cd8bfc996360ba99cf327e92da8b20ac1d7ea07e6201fd
2023/07/27 12:59:38 info unpack layer: sha256:039933c89bc61afe0dbf548830cffc8ec977c5575a844224c5eb65cd9d028a54
2023/07/27 12:59:55 warn rootless{usr/local/lib/R/site-library/Rhtslib/usrlib/libhts.so.2} ignoring (usually) harmless EPERM on setxattr "user.rootlesscontainers"
2023/07/27 13:00:16 info unpack layer: sha256:a998a725ad2ad2f049dd90ba75e4f0946565c315bfa58cab599ca609c84aeba1
2023/07/27 13:00:17 info unpack layer: sha256:eec5691985f610ea0f3784244e6e1348824bc84b2b77faa28770bdc6beab241c
2023/07/27 13:00:17 info unpack layer: sha256:c185ae260562a69c06c7975879b2cbc473c9d16a71ae95abd50ddbb245da6a3e
2023/07/27 13:00:18 info unpack layer: sha256:fb811cb389747dcb003f0eaadbacfab24befd161547b6be418bdf6fbf189f94c
2023/07/27 13:00:18 info unpack layer: sha256:f7fbaa592b80566757b72038746cd6dc901724af0246452d5356784a741d3feb
2023/07/27 13:00:20 info unpack layer: sha256:1956e0ee4e98aa08e0540cbabb02dd380bcc48a080bef1e1c801aabf3355b1f1
2023/07/27 13:00:20 info unpack layer: sha256:735bdb52466195ebf4ed80fb8f307649bc06a82512e1409b5bd66e799097d2c0
2023/07/27 13:00:23 info unpack layer: sha256:3773fe0dc9e08face6fcaddf24f871b39fac681ba30024f1fc85b74829e7d58d
INFO: Creating SIF file...
[2023-07-27T05:00:38.312] [INFO] shiny-server - Shiny Server v1.5.18.979 (Node.js v12.22.6)
[2023-07-27T05:00:38.317] [INFO] shiny-server - Using config file "/etc/shiny-server/shiny-server.conf"
**[2023-07-27T05:00:38.350] [ERROR] shiny-server - Error loading config: The user 'gmsywss' does not have permissions to run applications as one of the users in 'shiny'. Please restart shiny-server as one of the users in 'shiny'. (/etc/shiny-server/shiny-server.conf:5:1)**
[2023-07-27T05:00:38.351] [INFO] shiny-server - Shutting down worker processes
**Expected behavior**
Container should be downloaded, converted to sif format then start shiny server
**Desktop (please complete the following information):**
- OS: CentOS8 Stream 4.18.0-500, CentOS7 (Core) 3.10.0-1160.92.1, debian11 (bullseye) 5.10.0-23
- Browser Firefox
- Version 115.0.2
| non_priority | unable to start methylr using apptainer describe the bug unable to start container using apptainer starting container using docker working as expected and can access via firefox to reproduce my username on my server is gmsywss i ran the following command as instructed apptainer run docker methylr latest below is the output getting image source signatures copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying blob done copying config done writing manifest to image destination storing signatures info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer warn rootless usr local lib r site library rhtslib usrlib libhts so ignoring usually harmless eperm on setxattr user rootlesscontainers info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info unpack layer info creating sif file shiny server shiny server node js shiny server using config file etc shiny server shiny server conf shiny server error loading config the user gmsywss does not have permissions to run applications as one of the users in shiny please restart shiny server as one of the users in shiny etc shiny server shiny server conf shiny server shutting down worker processes expected behavior container should be downloaded converted to sif format then start shiny server desktop please complete the following information os stream core bullseye browser firefox version | 0 |
159,653 | 20,085,887,329 | IssuesEvent | 2022-02-05 01:07:03 | AkshayMukkavilli/Analyzing-the-Significance-of-Structure-in-Amazon-Review-Data-Using-Machine-Learning-Approaches | https://api.github.com/repos/AkshayMukkavilli/Analyzing-the-Significance-of-Structure-in-Amazon-Review-Data-Using-Machine-Learning-Approaches | opened | CVE-2022-21730 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2022-21730 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /FinalProject/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_8b9e071c-3b11-4aa9-ba60-cdeb60d053b7/20190525011350_65403/20190525011256_depth_0/9/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Tensorflow is an Open Source Machine Learning Framework. The implementation of `FractionalAvgPoolGrad` does not consider cases where the input tensors are invalid allowing an attacker to read from outside of bounds of heap. The fix will be included in TensorFlow 2.8.0. We will also cherrypick this commit on TensorFlow 2.7.1, TensorFlow 2.6.3, and TensorFlow 2.5.3, as these are also affected and still in supported range.
<p>Publish Date: 2022-02-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21730>CVE-2022-21730</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-vjg4-v33c-ggc4">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-vjg4-v33c-ggc4</a></p>
<p>Release Date: 2022-02-03</p>
<p>Fix Resolution: tensorflow - 2.5.3,2.6.3,2.7.1;tensorflow-cpu - 2.5.3,2.6.3,2.7.1;tensorflow-gpu - 2.5.3,2.6.3,2.7.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-21730 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2022-21730 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /FinalProject/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_8b9e071c-3b11-4aa9-ba60-cdeb60d053b7/20190525011350_65403/20190525011256_depth_0/9/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Tensorflow is an Open Source Machine Learning Framework. The implementation of `FractionalAvgPoolGrad` does not consider cases where the input tensors are invalid allowing an attacker to read from outside of bounds of heap. The fix will be included in TensorFlow 2.8.0. We will also cherrypick this commit on TensorFlow 2.7.1, TensorFlow 2.6.3, and TensorFlow 2.5.3, as these are also affected and still in supported range.
<p>Publish Date: 2022-02-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21730>CVE-2022-21730</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-vjg4-v33c-ggc4">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-vjg4-v33c-ggc4</a></p>
<p>Release Date: 2022-02-03</p>
<p>Fix Resolution: tensorflow - 2.5.3,2.6.3,2.7.1;tensorflow-cpu - 2.5.3,2.6.3,2.7.1;tensorflow-gpu - 2.5.3,2.6.3,2.7.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file finalproject requirements txt path to vulnerable library tesource archiveextractor depth tensorflow tensorflow data purelib tensorflow dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an open source machine learning framework the implementation of fractionalavgpoolgrad does not consider cases where the input tensors are invalid allowing an attacker to read from outside of bounds of heap the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with whitesource | 0 |
71,645 | 7,253,927,120 | IssuesEvent | 2018-02-16 08:51:09 | eclipse/microprofile-config | https://api.github.com/repos/eclipse/microprofile-config | opened | Create a test for no defined config value | test | If:
A value with no default value specified in `@ConfigProperty` and in no config source
When:
Injecting the value using Optional
Then:
value.orElse("Not defined") should give the value "Not defined"
An example code: https://github.com/payara/Payara-Examples/blob/27eda7b9da1eff4dbe2748ad03d0780c26bb1ba8/microprofile/config-injection/src/main/java/fish/payara/examples/microprofile/configinjection/ShowConfigValues.java#L303 | 1.0 | Create a test for no defined config value - If:
A value with no default value specified in `@ConfigProperty` and in no config source
When:
Injecting the value using Optional
Then:
value.orElse("Not defined") should give the value "Not defined"
An example code: https://github.com/payara/Payara-Examples/blob/27eda7b9da1eff4dbe2748ad03d0780c26bb1ba8/microprofile/config-injection/src/main/java/fish/payara/examples/microprofile/configinjection/ShowConfigValues.java#L303 | non_priority | create a test for no defined config value if a value with no default value specified in configproperty and in no config source when injecting the value using optional then value orelse not defined should give the value not defined an example code | 0 |
66,198 | 7,973,897,078 | IssuesEvent | 2018-07-17 02:01:04 | mozilla/voice-web | https://api.github.com/repos/mozilla/voice-web | opened | Contribution banner alignments | Design Type: Enhancement | @Gregoor I have two pixel pushes for you on the contribution banner:
- [ ] move the `x` for dismissal to the far right and vertically center?
- [ ] move `Help report bugs` to right align with header content
- [ ] `Take a look` should sit in the middle of the space between the text and `Help report bugs`
| 1.0 | Contribution banner alignments - @Gregoor I have two pixel pushes for you on the contribution banner:
- [ ] move the `x` for dismissal to the far right and vertically center?
- [ ] move `Help report bugs` to right align with header content
- [ ] `Take a look` should sit in the middle of the space between the text and `Help report bugs`
| non_priority | contribution banner alignments gregoor i have two pixel pushes for you on the contribution banner move the x for dismissal to the far right and vertically center move help report bugs to right align with header content take a look should sit in the middle of the space between the text and help report bugs | 0 |
264,575 | 28,209,190,206 | IssuesEvent | 2023-04-05 01:37:59 | Trinadh465/linux_4.19.72_CVE-2023-42896 | https://api.github.com/repos/Trinadh465/linux_4.19.72_CVE-2023-42896 | closed | CVE-2019-19075 (High) detected in linuxlinux-4.19.279 - autoclosed | Mend: dependency security vulnerability | ## CVE-2019-19075 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.279</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux_4.19.72_CVE-2023-42896/commit/bab817ff3ba663d8c0b4d4ec9cb6c7069f775527">bab817ff3ba663d8c0b4d4ec9cb6c7069f775527</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ieee802154/ca8210.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ieee802154/ca8210.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the ca8210_probe() function in drivers/net/ieee802154/ca8210.c in the Linux kernel before 5.3.8 allows attackers to cause a denial of service (memory consumption) by triggering ca8210_get_platform_data() failures, aka CID-6402939ec86e.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19075>CVE-2019-19075</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19075">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19075</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.4-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19075 (High) detected in linuxlinux-4.19.279 - autoclosed - ## CVE-2019-19075 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.279</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux_4.19.72_CVE-2023-42896/commit/bab817ff3ba663d8c0b4d4ec9cb6c7069f775527">bab817ff3ba663d8c0b4d4ec9cb6c7069f775527</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ieee802154/ca8210.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/ieee802154/ca8210.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the ca8210_probe() function in drivers/net/ieee802154/ca8210.c in the Linux kernel before 5.3.8 allows attackers to cause a denial of service (memory consumption) by triggering ca8210_get_platform_data() failures, aka CID-6402939ec86e.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19075>CVE-2019-19075</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19075">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19075</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.4-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux autoclosed cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files drivers net c drivers net c vulnerability details a memory leak in the probe function in drivers net c in the linux kernel before allows attackers to cause a denial of service memory consumption by triggering get platform data failures aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
100,970 | 8,766,523,494 | IssuesEvent | 2018-12-17 17:01:57 | MicrosoftDocs/powerbi-docs | https://api.github.com/repos/MicrosoftDocs/powerbi-docs | closed | Test to see if Issues working for end-user content | assigned-to-author test-issue | this is a test. Please assign to me, mihart.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 66e6d45d-17cd-6e69-cdf8-2b1d58bb4889
* Version Independent ID: 058458dd-4115-4dc0-c87e-0ed659bd0d60
* Content: [Power BI service- basic concepts for consumers - Power BI](https://docs.microsoft.com/en-us/power-bi/consumer/end-user-basic-concepts)
* Content Source: [powerbi-docs/consumer/end-user-basic-concepts.md](https://github.com/MicrosoftDocs/powerbi-docs/blob/live/powerbi-docs/consumer/end-user-basic-concepts.md)
* Service: **powerbi**
* GitHub Login: @mihart
* Microsoft Alias: **mihart** | 1.0 | Test to see if Issues working for end-user content - this is a test. Please assign to me, mihart.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 66e6d45d-17cd-6e69-cdf8-2b1d58bb4889
* Version Independent ID: 058458dd-4115-4dc0-c87e-0ed659bd0d60
* Content: [Power BI service- basic concepts for consumers - Power BI](https://docs.microsoft.com/en-us/power-bi/consumer/end-user-basic-concepts)
* Content Source: [powerbi-docs/consumer/end-user-basic-concepts.md](https://github.com/MicrosoftDocs/powerbi-docs/blob/live/powerbi-docs/consumer/end-user-basic-concepts.md)
* Service: **powerbi**
* GitHub Login: @mihart
* Microsoft Alias: **mihart** | non_priority | test to see if issues working for end user content this is a test please assign to me mihart document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service powerbi github login mihart microsoft alias mihart | 0 |
112,404 | 11,768,188,370 | IssuesEvent | 2020-03-15 09:01:03 | SE701Group3/git-brunching | https://api.github.com/repos/SE701Group3/git-brunching | closed | Create documentation for APIs on backend | documentation | **User Story:**
As a developer, I want to be able to read about the ins and outs of each API function within the backend, so that I can use and possibly extend the function in the future
**Acceptance Criteria:**
- [ ] I have set up swagger so other developers can document APIs
- [ ] I have created docs for all restaurant functions
**Additional Context:**
N/A
| 1.0 | Create documentation for APIs on backend - **User Story:**
As a developer, I want to be able to read about the ins and outs of each API function within the backend, so that I can use and possibly extend the function in the future
**Acceptance Criteria:**
- [ ] I have set up swagger so other developers can document APIs
- [ ] I have created docs for all restaurant functions
**Additional Context:**
N/A
| non_priority | create documentation for apis on backend user story as a developer i want to be able to read about the ins and outs of each api function within the backend so that i can use and possibly extend the function in the future acceptance criteria i have set up swagger so other developers can document apis i have created docs for all restaurant functions additional context n a | 0 |
99,610 | 8,705,627,529 | IssuesEvent | 2018-12-05 23:05:24 | yuzoolcode/pulsecms-tracking | https://api.github.com/repos/yuzoolcode/pulsecms-tracking | closed | Bug in menu | bug needs testing | > If i click blog page on menu(front end menu) after first installion, there is php error.
>
> Solve: firstly, i must go to admin panel. And settings. Navigation -> enable frontend editing -> None. I must set to "none".
Reported by Cenk
| 1.0 | Bug in menu - > If i click blog page on menu(front end menu) after first installion, there is php error.
>
> Solve: firstly, i must go to admin panel. And settings. Navigation -> enable frontend editing -> None. I must set to "none".
Reported by Cenk
| non_priority | bug in menu if i click blog page on menu front end menu after first installion there is php error solve firstly i must go to admin panel and settings navigation enable frontend editing none i must set to none reported by cenk | 0 |
159,155 | 20,036,657,360 | IssuesEvent | 2022-02-02 12:39:03 | kapseliboi/webuild | https://api.github.com/repos/kapseliboi/webuild | opened | WS-2019-0425 (Medium) detected in mocha-5.2.0.tgz | security vulnerability | ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-5.2.0.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-5.2.0.tgz">https://registry.npmjs.org/mocha/-/mocha-5.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-5.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/webuild/commit/cfe337e0888ede79847ee4201c96d43ab06dc89e">cfe337e0888ede79847ee4201c96d43ab06dc89e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: 6.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0425 (Medium) detected in mocha-5.2.0.tgz - ## WS-2019-0425 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mocha-5.2.0.tgz</b></p></summary>
<p>simple, flexible, fun test framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/mocha/-/mocha-5.2.0.tgz">https://registry.npmjs.org/mocha/-/mocha-5.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mocha/package.json</p>
<p>
Dependency Hierarchy:
- :x: **mocha-5.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/webuild/commit/cfe337e0888ede79847ee4201c96d43ab06dc89e">cfe337e0888ede79847ee4201c96d43ab06dc89e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Mocha is vulnerable to ReDoS attack. If the stack trace in utils.js begins with a large error message, and full-trace is not enabled, utils.stackTraceFilter() will take exponential run time.
<p>Publish Date: 2019-01-24
<p>URL: <a href=https://github.com/mochajs/mocha/commit/1a43d8b11a64e4e85fe2a61aed91c259bbbac559>WS-2019-0425</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="v6.0.0">v6.0.0</a></p>
<p>Release Date: 2019-01-24</p>
<p>Fix Resolution: 6.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in mocha tgz ws medium severity vulnerability vulnerable library mocha tgz simple flexible fun test framework library home page a href path to dependency file package json path to vulnerable library node modules mocha package json dependency hierarchy x mocha tgz vulnerable library found in head commit a href found in base branch master vulnerability details mocha is vulnerable to redos attack if the stack trace in utils js begins with a large error message and full trace is not enabled utils stacktracefilter will take exponential run time publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin release date fix resolution step up your open source security game with whitesource | 0 |
26,053 | 6,741,592,892 | IssuesEvent | 2017-10-20 01:56:47 | alexrj/Slic3r | https://api.github.com/repos/alexrj/Slic3r | opened | Find and integrate decent logging tool into libslic3r | Code Cleanup/Refactoring Feature request Low Effort | Currently, all of the libslic3r debugging messages are gated behind an `#ifdef` and consist of simple printf statements.
It would be very convenient to incorporate a more functional logging library system, preferably with some ability to (at runtime) enable/disable different output streams.
Something that acts like iostreams would be a big plus (ease of use) and the ability to redirect to files.
Boost.Log does look promising. | 1.0 | Find and integrate decent logging tool into libslic3r - Currently, all of the libslic3r debugging messages are gated behind an `#ifdef` and consist of simple printf statements.
It would be very convenient to incorporate a more functional logging library system, preferably with some ability to (at runtime) enable/disable different output streams.
Something that acts like iostreams would be a big plus (ease of use) and the ability to redirect to files.
Boost.Log does look promising. | non_priority | find and integrate decent logging tool into currently all of the debugging messages are gated behind an ifdef and consist of simple printf statements it would be very convenient to incorporate a more functional logging library system preferably with some ability to at runtime enable disable different output streams something that acts like iostreams would be a big plus ease of use and the ability to redirect to files boost log does look promising | 0 |
326,084 | 24,072,488,496 | IssuesEvent | 2022-09-18 11:10:28 | umgc/fall2022 | https://api.github.com/repos/umgc/fall2022 | closed | Edit Section 11 Roy's feedback | documentation | Section 11.1, Figure 11.1. Reminder to source any diagrams that have not been originally produced. | 1.0 | Edit Section 11 Roy's feedback - Section 11.1, Figure 11.1. Reminder to source any diagrams that have not been originally produced. | non_priority | edit section roy s feedback section figure reminder to source any diagrams that have not been originally produced | 0 |
428,832 | 30,013,079,211 | IssuesEvent | 2023-06-26 16:34:27 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | Documentation update for the gflag, including the release aspects. | area/documentation | - Add details in the tserver gflags section.
- We need to add a new section in troubleshooting for cases when ulimit is hit etc. | 1.0 | Documentation update for the gflag, including the release aspects. - - Add details in the tserver gflags section.
- We need to add a new section in troubleshooting for cases when ulimit is hit etc. | non_priority | documentation update for the gflag including the release aspects add details in the tserver gflags section we need to add a new section in troubleshooting for cases when ulimit is hit etc | 0 |
314,125 | 23,507,785,799 | IssuesEvent | 2022-08-18 14:00:56 | AlterNT/AI-Agent-Competition-Platform | https://api.github.com/repos/AlterNT/AI-Agent-Competition-Platform | closed | 1. Create Epic For Project | documentation Sprint 1 | A Scope of Work, or, in the language of the Scrum methodology, the [Epic](https://www.atlassian.com/agile/project-management/epics-stories-themes). That is, a general statement of what the project is to achieve. That statement can be as informal as a set of bullet points in a text document, or as formal as a Requirements Document (an example can be found [here](https://teaching.csse.uwa.edu.au/units/CITS3200/project/RADtmpl.html)).
The main thing your team has to realise is that, while the Agile methology assumes that project scope (i.e. requirements) can change, CITS3200 will, likely, be one of four units you are each doing this semester, so the team needs to be conscious of the time required. Therefore any departures from, or extensions to, the scope of work will have be carefully considered in the light of the time available to the team. | 1.0 | 1. Create Epic For Project - A Scope of Work, or, in the language of the Scrum methodology, the [Epic](https://www.atlassian.com/agile/project-management/epics-stories-themes). That is, a general statement of what the project is to achieve. That statement can be as informal as a set of bullet points in a text document, or as formal as a Requirements Document (an example can be found [here](https://teaching.csse.uwa.edu.au/units/CITS3200/project/RADtmpl.html)).
The main thing your team has to realise is that, while the Agile methology assumes that project scope (i.e. requirements) can change, CITS3200 will, likely, be one of four units you are each doing this semester, so the team needs to be conscious of the time required. Therefore any departures from, or extensions to, the scope of work will have be carefully considered in the light of the time available to the team. | non_priority | create epic for project a scope of work or in the language of the scrum methodology the that is a general statement of what the project is to achieve that statement can be as informal as a set of bullet points in a text document or as formal as a requirements document an example can be found the main thing your team has to realise is that while the agile methology assumes that project scope i e requirements can change will likely be one of four units you are each doing this semester so the team needs to be conscious of the time required therefore any departures from or extensions to the scope of work will have be carefully considered in the light of the time available to the team | 0 |
99,661 | 11,151,333,437 | IssuesEvent | 2019-12-24 03:37:26 | bitmark-inc/docs | https://api.github.com/repos/bitmark-inc/docs | closed | [Docs] [Bitmark references] - Tutorial for node setup | documentation | Provide content for (but not limited to) the following subsections
- [ ] Running a node
- [ ] Running a miner | 1.0 | [Docs] [Bitmark references] - Tutorial for node setup - Provide content for (but not limited to) the following subsections
- [ ] Running a node
- [ ] Running a miner | non_priority | tutorial for node setup provide content for but not limited to the following subsections running a node running a miner | 0 |
359,532 | 25,243,097,347 | IssuesEvent | 2022-11-15 09:07:49 | 05798/pytest-git-selector | https://api.github.com/repos/05798/pytest-git-selector | closed | README is inconsistent | documentation | Section describing `pytest` plugin arguments is wrong. `--git-diff-args` no longer exists. | 1.0 | README is inconsistent - Section describing `pytest` plugin arguments is wrong. `--git-diff-args` no longer exists. | non_priority | readme is inconsistent section describing pytest plugin arguments is wrong git diff args no longer exists | 0 |
30,669 | 13,283,269,178 | IssuesEvent | 2020-08-24 02:37:58 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Get-AzStorageBlobContent command fails to download blob containing folders in the path due to error <folder> doesn't exist | Service Attention Storage | <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
- https://github.com/Azure/azure-powershell/blob/master/documentation/troubleshoot-module-load.md
-->
## Description
Issue is seen with storage accounts with HNS disabled.
**Repro result with Az.Storage version 2.3.0**
Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."
Get-AzStorageBlobContent : Directory 'C:\WINDOWS\system32\test\blob' doesn't exist.
At line:1 char:1
+ Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/ ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidArgument: (:) [Get-AzStorageBlobContent], ArgumentException
+ FullyQualifiedErrorId : ArgumentException,Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobCont
entCommand
## Steps to reproduce
```
We should have a blob path consisting of folders as seen below in the storage account
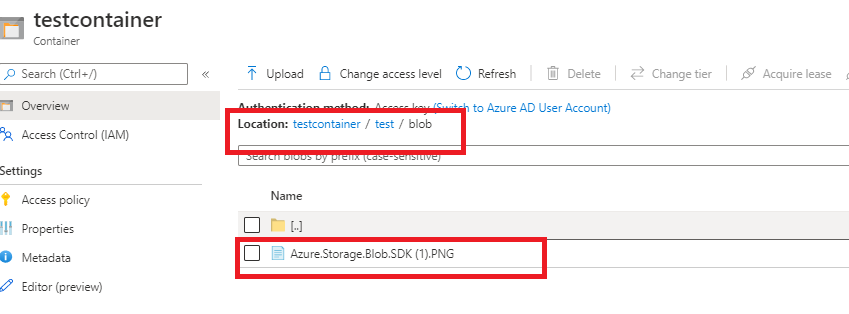
The blob path folder structure should be present on the destination.
We can reproduce the issue by running these commands.
Get storage context :
$ctx = New-AzStorageContext -StorageAccountName "stgragrs" -StorageAccountKey "<key>"
Then Get blob content
Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."
The command is unable to create the parent folder path while copying the blob.
```
## Environment data
```
Issue is reproducible in latest PS Version too
$PSVersionTable
Name Value
---- -----
PSVersion 7.0.3
PSEdition Core
GitCommitId 7.0.3
OS Microsoft Windows 10.0.19041
Platform Win32NT
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0…}
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
WSManStackVersion 3.0
```
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
```
Issue is reproducible with **az 4.4.0**, **4.5.0** , **az.storage 2.3.0** and **2.3.1-preview** versions.
Issue is NOT reproducible with az.storage 2.2.0 and older
This version gives the expected result
**Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."**
Container Uri: https://stgragrs.blob.core.windows.net/testcontainer
Name BlobType Length ContentType LastModified AccessTier SnapshotTime
---- -------- ------ ----------- ------------ ---------- ------------
test/blob/Azure.S... BlockBlob 25404 image/png 2020-08-10 08:19:24Z Unknown
**dir test/blob**
Directory: C:\WINDOWS\system32\test\blob
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 8/10/2020 3:02 PM 25404 Azure.Storage.Blob.SDK (1).PNG
```
## Debug output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."
DEBUG: 4:19:07 PM - Init Operation Context for 'GetAzureStorageBlobContentCommand' with client request id Azure-Storage-PowerShell-e6a008e7-d958-4f2a-ba74-7baa2c3b6ae7. If you want to get more details, please add "-Debug" to your command.
DEBUG: 4:19:07 PM - Use storage account 'stgragrs' from storage context.
Get-AzStorageBlobContent: Directory 'C:\Windows\test\blob' doesn't exist.
DEBUG: 4:19:09 PM - GetAzureStorageBlobContentCommand end processing, Start 4 remote calls. Finish 4 remote calls. Elapsed time 4843253.27 ms. Client operation id: Azure-Storage-PowerShell-e6a008e7-d958-4f2a-ba74-7baa2c3b6ae7.
DEBUG: 4:19:09 PM - GetAzureStorageBlobContentCommand end processing.
```
## Error output
<!-- Please run Resolve-AzError and paste the output in the below code block -->
```
Resolve-AzError output
Message : Directory 'C:\Windows\test\blob' doesn't exist.
StackTrace : at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetFullRec
eiveFilePath(String fileName, String blobName, Nullable`1 snapshotTime)
at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetBlobCon
tent(CloudBlob blob, String fileName, Boolean isValidBlob)
at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetBlobCon
tent(CloudBlobContainer container, String blobName, String fileName)
at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetBlobCon
tent(String containerName, String blobName, String fileName)
at
Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.ExecuteCmdlet()
at Microsoft.WindowsAzure.Commands.Utilities.Common.CmdletExtensions.<>c__3`1.<ExecuteSynchronously
OrAsJob>b__3_0(T c)
at
Microsoft.WindowsAzure.Commands.Utilities.Common.CmdletExtensions.ExecuteSynchronouslyOrAsJob[T](T
cmdlet, Action`1 executor)
at
Microsoft.WindowsAzure.Commands.Utilities.Common.CmdletExtensions.ExecuteSynchronouslyOrAsJob[T](T
cmdlet)
at
Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.ProcessRecord()
Exception : System.ArgumentException
InvocationInfo : {Get-AzStorageBlobContent}
Line : Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG"
-Context $ctx -Destination "."
Position : At line:1 char:1
+ Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/ …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
HistoryId : 11
```
| 1.0 | Get-AzStorageBlobContent command fails to download blob containing folders in the path due to error <folder> doesn't exist - <!--
- Make sure you are able to reproduce this issue on the latest released version of Az
- https://www.powershellgallery.com/packages/Az
- Please search the existing issues to see if there has been a similar issue filed
- For issue related to importing a module, please refer to our troubleshooting guide:
- https://github.com/Azure/azure-powershell/blob/master/documentation/troubleshoot-module-load.md
-->
## Description
Issue is seen with storage accounts with HNS disabled.
**Repro result with Az.Storage version 2.3.0**
Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."
Get-AzStorageBlobContent : Directory 'C:\WINDOWS\system32\test\blob' doesn't exist.
At line:1 char:1
+ Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/ ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidArgument: (:) [Get-AzStorageBlobContent], ArgumentException
+ FullyQualifiedErrorId : ArgumentException,Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobCont
entCommand
## Steps to reproduce
```
We should have a blob path consisting of folders as seen below in the storage account
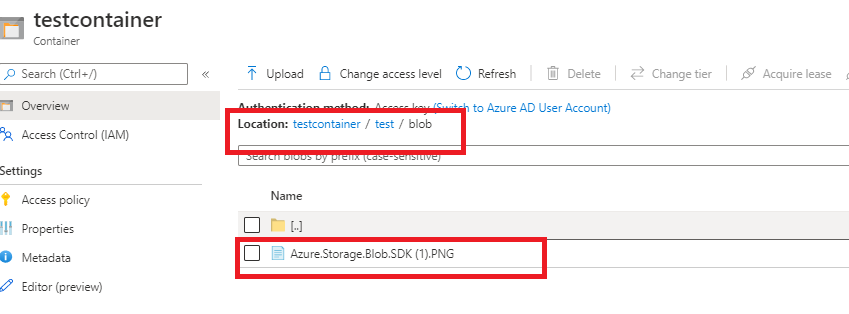
The blob path folder structure should be present on the destination.
We can reproduce the issue by running these commands.
Get storage context :
$ctx = New-AzStorageContext -StorageAccountName "stgragrs" -StorageAccountKey "<key>"
Then Get blob content
Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."
The command is unable to create the parent folder path while copying the blob.
```
## Environment data
```
Issue is reproducible in latest PS Version too
$PSVersionTable
Name Value
---- -----
PSVersion 7.0.3
PSEdition Core
GitCommitId 7.0.3
OS Microsoft Windows 10.0.19041
Platform Win32NT
PSCompatibleVersions {1.0, 2.0, 3.0, 4.0…}
PSRemotingProtocolVersion 2.3
SerializationVersion 1.1.0.1
WSManStackVersion 3.0
```
## Module versions
<!-- Please run (Get-Module -ListAvailable) and paste the output in the below code block -->
```
Issue is reproducible with **az 4.4.0**, **4.5.0** , **az.storage 2.3.0** and **2.3.1-preview** versions.
Issue is NOT reproducible with az.storage 2.2.0 and older
This version gives the expected result
**Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."**
Container Uri: https://stgragrs.blob.core.windows.net/testcontainer
Name BlobType Length ContentType LastModified AccessTier SnapshotTime
---- -------- ------ ----------- ------------ ---------- ------------
test/blob/Azure.S... BlockBlob 25404 image/png 2020-08-10 08:19:24Z Unknown
**dir test/blob**
Directory: C:\WINDOWS\system32\test\blob
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 8/10/2020 3:02 PM 25404 Azure.Storage.Blob.SDK (1).PNG
```
## Debug output
<!-- Set $DebugPreference='Continue' before running the repro and paste the resulting debug stream in the below code block -->
```
Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG" -Context $ctx -Destination "."
DEBUG: 4:19:07 PM - Init Operation Context for 'GetAzureStorageBlobContentCommand' with client request id Azure-Storage-PowerShell-e6a008e7-d958-4f2a-ba74-7baa2c3b6ae7. If you want to get more details, please add "-Debug" to your command.
DEBUG: 4:19:07 PM - Use storage account 'stgragrs' from storage context.
Get-AzStorageBlobContent: Directory 'C:\Windows\test\blob' doesn't exist.
DEBUG: 4:19:09 PM - GetAzureStorageBlobContentCommand end processing, Start 4 remote calls. Finish 4 remote calls. Elapsed time 4843253.27 ms. Client operation id: Azure-Storage-PowerShell-e6a008e7-d958-4f2a-ba74-7baa2c3b6ae7.
DEBUG: 4:19:09 PM - GetAzureStorageBlobContentCommand end processing.
```
## Error output
<!-- Please run Resolve-AzError and paste the output in the below code block -->
```
Resolve-AzError output
Message : Directory 'C:\Windows\test\blob' doesn't exist.
StackTrace : at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetFullRec
eiveFilePath(String fileName, String blobName, Nullable`1 snapshotTime)
at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetBlobCon
tent(CloudBlob blob, String fileName, Boolean isValidBlob)
at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetBlobCon
tent(CloudBlobContainer container, String blobName, String fileName)
at Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.GetBlobCon
tent(String containerName, String blobName, String fileName)
at
Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.ExecuteCmdlet()
at Microsoft.WindowsAzure.Commands.Utilities.Common.CmdletExtensions.<>c__3`1.<ExecuteSynchronously
OrAsJob>b__3_0(T c)
at
Microsoft.WindowsAzure.Commands.Utilities.Common.CmdletExtensions.ExecuteSynchronouslyOrAsJob[T](T
cmdlet, Action`1 executor)
at
Microsoft.WindowsAzure.Commands.Utilities.Common.CmdletExtensions.ExecuteSynchronouslyOrAsJob[T](T
cmdlet)
at
Microsoft.WindowsAzure.Commands.Storage.Blob.Cmdlet.GetAzureStorageBlobContentCommand.ProcessRecord()
Exception : System.ArgumentException
InvocationInfo : {Get-AzStorageBlobContent}
Line : Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/Azure.Storage.Blob.SDK (1).PNG"
-Context $ctx -Destination "."
Position : At line:1 char:1
+ Get-AzStorageBlobContent -Container "testcontainer" -Blob "test/blob/ …
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
HistoryId : 11
```
| non_priority | get azstorageblobcontent command fails to download blob containing folders in the path due to error doesn t exist make sure you are able to reproduce this issue on the latest released version of az please search the existing issues to see if there has been a similar issue filed for issue related to importing a module please refer to our troubleshooting guide description issue is seen with storage accounts with hns disabled repro result with az storage version get azstorageblobcontent container testcontainer blob test blob azure storage blob sdk png context ctx destination get azstorageblobcontent directory c windows test blob doesn t exist at line char get azstorageblobcontent container testcontainer blob test blob categoryinfo invalidargument argumentexception fullyqualifiederrorid argumentexception microsoft windowsazure commands storage blob cmdlet getazurestorageblobcont entcommand steps to reproduce we should have a blob path consisting of folders as seen below in the storage account the blob path folder structure should be present on the destination we can reproduce the issue by running these commands get storage context ctx new azstoragecontext storageaccountname stgragrs storageaccountkey then get blob content get azstorageblobcontent container testcontainer blob test blob azure storage blob sdk png context ctx destination the command is unable to create the parent folder path while copying the blob environment data issue is reproducible in latest ps version too psversiontable name value psversion psedition core gitcommitid os microsoft windows platform pscompatibleversions … psremotingprotocolversion serializationversion wsmanstackversion module versions issue is reproducible with az az storage and preview versions issue is not reproducible with az storage and older this version gives the expected result get azstorageblobcontent container testcontainer blob test blob azure storage blob sdk png context ctx destination container uri name blobtype length contenttype lastmodified accesstier snapshottime test blob azure s blockblob image png unknown dir test blob directory c windows test blob mode lastwritetime length name a pm azure storage blob sdk png debug output get azstorageblobcontent container testcontainer blob test blob azure storage blob sdk png context ctx destination debug pm init operation context for getazurestorageblobcontentcommand with client request id azure storage powershell if you want to get more details please add debug to your command debug pm use storage account stgragrs from storage context get azstorageblobcontent directory c windows test blob doesn t exist debug pm getazurestorageblobcontentcommand end processing start remote calls finish remote calls elapsed time ms client operation id azure storage powershell debug pm getazurestorageblobcontentcommand end processing error output resolve azerror output message directory c windows test blob doesn t exist stacktrace at microsoft windowsazure commands storage blob cmdlet getazurestorageblobcontentcommand getfullrec eivefilepath string filename string blobname nullable snapshottime at microsoft windowsazure commands storage blob cmdlet getazurestorageblobcontentcommand getblobcon tent cloudblob blob string filename boolean isvalidblob at microsoft windowsazure commands storage blob cmdlet getazurestorageblobcontentcommand getblobcon tent cloudblobcontainer container string blobname string filename at microsoft windowsazure commands storage blob cmdlet getazurestorageblobcontentcommand getblobcon tent string containername string blobname string filename at microsoft windowsazure commands storage blob cmdlet getazurestorageblobcontentcommand executecmdlet at microsoft windowsazure commands utilities common cmdletextensions c executesynchronously orasjob b t c at microsoft windowsazure commands utilities common cmdletextensions executesynchronouslyorasjob t cmdlet action executor at microsoft windowsazure commands utilities common cmdletextensions executesynchronouslyorasjob t cmdlet at microsoft windowsazure commands storage blob cmdlet getazurestorageblobcontentcommand processrecord exception system argumentexception invocationinfo get azstorageblobcontent line get azstorageblobcontent container testcontainer blob test blob azure storage blob sdk png context ctx destination position at line char get azstorageblobcontent container testcontainer blob test blob … historyid | 0 |
99,414 | 30,449,126,484 | IssuesEvent | 2023-07-16 03:50:54 | teaxyz/pantry | https://api.github.com/repos/teaxyz/pantry | closed | ❌ build issues: rust-lang.org/cargo=0.72.0 | bug build-failure | Running log of build failures for rust-lang.org/cargo=0.72.0 | 1.0 | ❌ build issues: rust-lang.org/cargo=0.72.0 - Running log of build failures for rust-lang.org/cargo=0.72.0 | non_priority | ❌ build issues rust lang org cargo running log of build failures for rust lang org cargo | 0 |
4,181 | 2,716,686,134 | IssuesEvent | 2015-04-10 20:42:51 | amber-smalltalk/amber | https://api.github.com/repos/amber-smalltalk/amber | opened | Flatten the "transport" part | enhancement in design | Many pieces of Amber are now hardly dependent on the fact that modules are loaded via AMD, dependency lists are there etc. The existing "multi-trasport" is in fact not functioning, only one transport can de facto be used at a time.
Having been able to load / save packages using multiple different channels is nice to have, but actual implementation does not provide this and makes that part of code complicated.
Therefore I propose to flatten the hierarchies, hardcode just one way of exporting etc. to simplify the code and let the future implementors evolve it into multi-transport if they need to. | 1.0 | Flatten the "transport" part - Many pieces of Amber are now hardly dependent on the fact that modules are loaded via AMD, dependency lists are there etc. The existing "multi-trasport" is in fact not functioning, only one transport can de facto be used at a time.
Having been able to load / save packages using multiple different channels is nice to have, but actual implementation does not provide this and makes that part of code complicated.
Therefore I propose to flatten the hierarchies, hardcode just one way of exporting etc. to simplify the code and let the future implementors evolve it into multi-transport if they need to. | non_priority | flatten the transport part many pieces of amber are now hardly dependent on the fact that modules are loaded via amd dependency lists are there etc the existing multi trasport is in fact not functioning only one transport can de facto be used at a time having been able to load save packages using multiple different channels is nice to have but actual implementation does not provide this and makes that part of code complicated therefore i propose to flatten the hierarchies hardcode just one way of exporting etc to simplify the code and let the future implementors evolve it into multi transport if they need to | 0 |
102,988 | 16,596,044,608 | IssuesEvent | 2021-06-01 13:37:06 | scriptex/2048 | https://api.github.com/repos/scriptex/2048 | closed | CVE-2021-33623 (Medium) detected in trim-newlines-3.0.0.tgz, trim-newlines-1.0.0.tgz | security vulnerability | ## CVE-2021-33623 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>trim-newlines-3.0.0.tgz</b>, <b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>
<details><summary><b>trim-newlines-3.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz</a></p>
<p>Path to dependency file: 2048/package.json</p>
<p>Path to vulnerable library: 2048/node_modules/trim-newlines</p>
<p>
Dependency Hierarchy:
- stylelint-13.13.1.tgz (Root Library)
- meow-9.0.0.tgz
- :x: **trim-newlines-3.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: 2048/package.json</p>
<p>Path to vulnerable library: 2048/node_modules/trim-newlines</p>
<p>
Dependency Hierarchy:
- optisize-1.3.0.tgz (Root Library)
- imagemin-pngquant-9.0.1.tgz
- pngquant-bin-6.0.0.tgz
- logalot-2.1.0.tgz
- squeak-1.3.0.tgz
- lpad-align-1.1.2.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/scriptex/2048/commit/032ff121eb7cb57e5be6b62a641bab0e83687199">032ff121eb7cb57e5be6b62a641bab0e83687199</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33623 (Medium) detected in trim-newlines-3.0.0.tgz, trim-newlines-1.0.0.tgz - ## CVE-2021-33623 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>trim-newlines-3.0.0.tgz</b>, <b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>
<details><summary><b>trim-newlines-3.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-3.0.0.tgz</a></p>
<p>Path to dependency file: 2048/package.json</p>
<p>Path to vulnerable library: 2048/node_modules/trim-newlines</p>
<p>
Dependency Hierarchy:
- stylelint-13.13.1.tgz (Root Library)
- meow-9.0.0.tgz
- :x: **trim-newlines-3.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: 2048/package.json</p>
<p>Path to vulnerable library: 2048/node_modules/trim-newlines</p>
<p>
Dependency Hierarchy:
- optisize-1.3.0.tgz (Root Library)
- imagemin-pngquant-9.0.1.tgz
- pngquant-bin-6.0.0.tgz
- logalot-2.1.0.tgz
- squeak-1.3.0.tgz
- lpad-align-1.1.2.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/scriptex/2048/commit/032ff121eb7cb57e5be6b62a641bab0e83687199">032ff121eb7cb57e5be6b62a641bab0e83687199</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in trim newlines tgz trim newlines tgz cve medium severity vulnerability vulnerable libraries trim newlines tgz trim newlines tgz trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file package json path to vulnerable library node modules trim newlines dependency hierarchy stylelint tgz root library meow tgz x trim newlines tgz vulnerable library trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file package json path to vulnerable library node modules trim newlines dependency hierarchy optisize tgz root library imagemin pngquant tgz pngquant bin tgz logalot tgz squeak tgz lpad align tgz meow tgz x trim newlines tgz vulnerable library found in head commit a href vulnerability details the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution trim newlines step up your open source security game with whitesource | 0 |
24,481 | 12,304,091,567 | IssuesEvent | 2020-05-11 19:52:34 | pmelchior/scarlet | https://api.github.com/repos/pmelchior/scarlet | closed | Write tests for the LowResObservation class | feature performance | This test should be an exhaustive testing of all the cases of the shape data can take. Here is a non-exhaustive list:
aligned frames,
rotated frames,
rectangular frames with both directions tested as the larger one,
rotated PSFs,
larger PSF in high(low) resolution,
larger frame in high(low) resolution,
union,
... | True | Write tests for the LowResObservation class - This test should be an exhaustive testing of all the cases of the shape data can take. Here is a non-exhaustive list:
aligned frames,
rotated frames,
rectangular frames with both directions tested as the larger one,
rotated PSFs,
larger PSF in high(low) resolution,
larger frame in high(low) resolution,
union,
... | non_priority | write tests for the lowresobservation class this test should be an exhaustive testing of all the cases of the shape data can take here is a non exhaustive list aligned frames rotated frames rectangular frames with both directions tested as the larger one rotated psfs larger psf in high low resolution larger frame in high low resolution union | 0 |
117,259 | 15,084,184,719 | IssuesEvent | 2021-02-05 16:49:21 | apache/lucenenet | https://api.github.com/repos/apache/lucenenet | closed | Console.WriteLine does not appear to be working in unit tests | design is:enhancement pri:high testability | Currently Lucene.Net uses `Console.WriteLine` 1804 times (although some lines are commented out). A quick scan of the files containing `Console.WriteLine` shows that it's being used in unit tests petty much exclusively. As a new developer on the project looking into a failing test, the first thing I wanted to see was the `Console.WriteLine` output for the failing test. But I struggled to find where the output was showing up and after talking with @NightOwl888 I came to understand that this is something that still needs to be resolved. Currently `Console.WriteLine` does not appear to be working in unit tests.
@NightOwl888 also mentioned that according to [How do I get nunit3-console to output my debug to screen (on a Windows box)?](https://stackoverflow.com/a/46407376), we should maybe be using `TestContext.WriteLine()` instead. So this is something I'm now investigating. | 1.0 | Console.WriteLine does not appear to be working in unit tests - Currently Lucene.Net uses `Console.WriteLine` 1804 times (although some lines are commented out). A quick scan of the files containing `Console.WriteLine` shows that it's being used in unit tests petty much exclusively. As a new developer on the project looking into a failing test, the first thing I wanted to see was the `Console.WriteLine` output for the failing test. But I struggled to find where the output was showing up and after talking with @NightOwl888 I came to understand that this is something that still needs to be resolved. Currently `Console.WriteLine` does not appear to be working in unit tests.
@NightOwl888 also mentioned that according to [How do I get nunit3-console to output my debug to screen (on a Windows box)?](https://stackoverflow.com/a/46407376), we should maybe be using `TestContext.WriteLine()` instead. So this is something I'm now investigating. | non_priority | console writeline does not appear to be working in unit tests currently lucene net uses console writeline times although some lines are commented out a quick scan of the files containing console writeline shows that it s being used in unit tests petty much exclusively as a new developer on the project looking into a failing test the first thing i wanted to see was the console writeline output for the failing test but i struggled to find where the output was showing up and after talking with i came to understand that this is something that still needs to be resolved currently console writeline does not appear to be working in unit tests also mentioned that according to we should maybe be using testcontext writeline instead so this is something i m now investigating | 0 |
80,638 | 23,266,926,705 | IssuesEvent | 2022-08-04 18:21:08 | LINTONBNEIL/krakenscove | https://api.github.com/repos/LINTONBNEIL/krakenscove | opened | Home Page | Cypress Skeleton Build User Story | As a user......
1. I should see a logo/title of the website in a banner.
2. I should see a navbar directly underneath that with three links (or four).
3. I should be able to click each button and be routed to a new home page.
4. I should see a features section box with a banner.
5. I should see a Features which has a list of RECENT and POPULAR games titles, images, and their prices. | 1.0 | Home Page - As a user......
1. I should see a logo/title of the website in a banner.
2. I should see a navbar directly underneath that with three links (or four).
3. I should be able to click each button and be routed to a new home page.
4. I should see a features section box with a banner.
5. I should see a Features which has a list of RECENT and POPULAR games titles, images, and their prices. | non_priority | home page as a user i should see a logo title of the website in a banner i should see a navbar directly underneath that with three links or four i should be able to click each button and be routed to a new home page i should see a features section box with a banner i should see a features which has a list of recent and popular games titles images and their prices | 0 |
35,845 | 12,392,954,876 | IssuesEvent | 2020-05-20 14:44:21 | TIBCOSoftware/TIBCO-Messaging | https://api.github.com/repos/TIBCOSoftware/TIBCO-Messaging | closed | CVE-2020-11022 (Medium) detected in jquery-3.0.0.min.js | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.0.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.0.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.0.0/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/TIBCO-Messaging/samples/javascript/eftl/shared_durable.html</p>
<p>Path to vulnerable library: /TIBCO-Messaging/samples/javascript/eftl/shared_durable.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.0.0.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TIBCOSoftware/TIBCO-Messaging/commit/e298a1b1bd9a7e024c14c0b209cbdc0181c8cfa7">e298a1b1bd9a7e024c14c0b209cbdc0181c8cfa7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"3.0.0","isTransitiveDependency":false,"dependencyTree":"jquery:3.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - 3.5.0"}],"vulnerabilityIdentifier":"CVE-2020-11022","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11022 (Medium) detected in jquery-3.0.0.min.js - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.0.0.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.0.0/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.0.0/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/TIBCO-Messaging/samples/javascript/eftl/shared_durable.html</p>
<p>Path to vulnerable library: /TIBCO-Messaging/samples/javascript/eftl/shared_durable.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.0.0.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TIBCOSoftware/TIBCO-Messaging/commit/e298a1b1bd9a7e024c14c0b209cbdc0181c8cfa7">e298a1b1bd9a7e024c14c0b209cbdc0181c8cfa7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"3.0.0","isTransitiveDependency":false,"dependencyTree":"jquery:3.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - 3.5.0"}],"vulnerabilityIdentifier":"CVE-2020-11022","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm tibco messaging samples javascript eftl shared durable html path to vulnerable library tibco messaging samples javascript eftl shared durable html dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl | 0 |
263,989 | 19,985,035,418 | IssuesEvent | 2022-01-30 14:29:23 | riadh26/JSON-Database | https://api.github.com/repos/riadh26/JSON-Database | closed | Refactor server and client into submodules | documentation enhancement | Create a maven module for each of server and client | 1.0 | Refactor server and client into submodules - Create a maven module for each of server and client | non_priority | refactor server and client into submodules create a maven module for each of server and client | 0 |
13,452 | 10,264,464,956 | IssuesEvent | 2019-08-22 16:25:39 | elastic/beats | https://api.github.com/repos/elastic/beats | opened | Refactor Jolokia metrics to provide generic mapping | :infrastructure Metricbeat enhancement module | Metrics collected by jolokia module are stored now in events with fields like `jolokia.<namespace>.<custom field name>`. This makes impossible to provide a mapping, and it can provoke fields explossion in complex deployments.
This module could be refactored following the strategy followed in more recent "generic" metricsets implementations as prometheus collector or aws cloudwatch, where all metrics are stored under the same object (`prometheus.metrics.*` and `aws.cloudwatch.metrics.*.*`), so we can provide a mapping for all fields.
There are two things that can condition the decision on the structure:
* APM agent for Java is also able to collect metrics from JMX, it'd be good to follow the same naming (discussed in https://github.com/elastic/apm-agent-java/issues/469).
* In contrast to prometheus, where all metrics are doubles, JMX can return non-numeric values, we will have to consider if we provide a different namespace for them.
| 1.0 | Refactor Jolokia metrics to provide generic mapping - Metrics collected by jolokia module are stored now in events with fields like `jolokia.<namespace>.<custom field name>`. This makes impossible to provide a mapping, and it can provoke fields explossion in complex deployments.
This module could be refactored following the strategy followed in more recent "generic" metricsets implementations as prometheus collector or aws cloudwatch, where all metrics are stored under the same object (`prometheus.metrics.*` and `aws.cloudwatch.metrics.*.*`), so we can provide a mapping for all fields.
There are two things that can condition the decision on the structure:
* APM agent for Java is also able to collect metrics from JMX, it'd be good to follow the same naming (discussed in https://github.com/elastic/apm-agent-java/issues/469).
* In contrast to prometheus, where all metrics are doubles, JMX can return non-numeric values, we will have to consider if we provide a different namespace for them.
| non_priority | refactor jolokia metrics to provide generic mapping metrics collected by jolokia module are stored now in events with fields like jolokia this makes impossible to provide a mapping and it can provoke fields explossion in complex deployments this module could be refactored following the strategy followed in more recent generic metricsets implementations as prometheus collector or aws cloudwatch where all metrics are stored under the same object prometheus metrics and aws cloudwatch metrics so we can provide a mapping for all fields there are two things that can condition the decision on the structure apm agent for java is also able to collect metrics from jmx it d be good to follow the same naming discussed in in contrast to prometheus where all metrics are doubles jmx can return non numeric values we will have to consider if we provide a different namespace for them | 0 |
274,530 | 20,841,528,830 | IssuesEvent | 2022-03-21 00:54:21 | cosc-310-group32/Assignment3 | https://api.github.com/repos/cosc-310-group32/Assignment3 | closed | A3 - README and Documentation | documentation | - [x] Update README for A3
- A list of all the features programmed for Assignment 3
- For each item, explain briefly how it was used to improve the conversation/overall system
- For each explanation, include a snippet of conversation as an example
- [x] Level 0 Data Flow Diagram (DFD) for the system with description
- [x] Level 1 DFD for the system with description.
- [x] Submission of GitHub repo. Graph showing different features
developed on a separate branch and the commits made in the repository.
- [x] Sample output (30 turns; show new features). Show two short dialogues for when the bot does not work properly
- [x] List of limitations
- [x] List of at least 5 features that you can extract from your code or design that can be shared with others as an API.
| 1.0 | A3 - README and Documentation - - [x] Update README for A3
- A list of all the features programmed for Assignment 3
- For each item, explain briefly how it was used to improve the conversation/overall system
- For each explanation, include a snippet of conversation as an example
- [x] Level 0 Data Flow Diagram (DFD) for the system with description
- [x] Level 1 DFD for the system with description.
- [x] Submission of GitHub repo. Graph showing different features
developed on a separate branch and the commits made in the repository.
- [x] Sample output (30 turns; show new features). Show two short dialogues for when the bot does not work properly
- [x] List of limitations
- [x] List of at least 5 features that you can extract from your code or design that can be shared with others as an API.
| non_priority | readme and documentation update readme for a list of all the features programmed for assignment for each item explain briefly how it was used to improve the conversation overall system for each explanation include a snippet of conversation as an example level data flow diagram dfd for the system with description level dfd for the system with description submission of github repo graph showing different features developed on a separate branch and the commits made in the repository sample output turns show new features show two short dialogues for when the bot does not work properly list of limitations list of at least features that you can extract from your code or design that can be shared with others as an api | 0 |
3,688 | 6,553,637,230 | IssuesEvent | 2017-09-05 23:54:34 | Microsoft/ChakraCore | https://api.github.com/repos/Microsoft/ChakraCore | closed | Incorrect time reported by Date#toLocaleString | Bug Compatibility | ```js
new Date("1986-06-13T15:31:28-04:00").toLocaleString("en", {hour: "numeric", hour12: false});
```
Actual: 12:00
Expected: Truth about what time it is (12:31?)
Other browsers give me 12 for this case. | True | Incorrect time reported by Date#toLocaleString - ```js
new Date("1986-06-13T15:31:28-04:00").toLocaleString("en", {hour: "numeric", hour12: false});
```
Actual: 12:00
Expected: Truth about what time it is (12:31?)
Other browsers give me 12 for this case. | non_priority | incorrect time reported by date tolocalestring js new date tolocalestring en hour numeric false actual expected truth about what time it is other browsers give me for this case | 0 |
13,490 | 16,018,572,081 | IssuesEvent | 2021-04-20 19:18:18 | anlsys/aml | https://api.github.com/repos/anlsys/aml | opened | Integration Tests | process:proposal | In GitLab by @NicolasDenoyelle on Mar 15, 2021, 10:42
Create a pipeline stage with integration tests.
For instance, the test could consist in:
- Fetch applications using AML.
- Build AML
- Build applications and link with AML.
- Run applications.
[XSBench](https://github.com/ANL-CESAR/XSBench) is an application using AML that could be used as an integration test. | 1.0 | Integration Tests - In GitLab by @NicolasDenoyelle on Mar 15, 2021, 10:42
Create a pipeline stage with integration tests.
For instance, the test could consist in:
- Fetch applications using AML.
- Build AML
- Build applications and link with AML.
- Run applications.
[XSBench](https://github.com/ANL-CESAR/XSBench) is an application using AML that could be used as an integration test. | non_priority | integration tests in gitlab by nicolasdenoyelle on mar create a pipeline stage with integration tests for instance the test could consist in fetch applications using aml build aml build applications and link with aml run applications is an application using aml that could be used as an integration test | 0 |
27,401 | 12,554,728,257 | IssuesEvent | 2020-06-07 03:14:22 | MassTransit/MassTransit | https://api.github.com/repos/MassTransit/MassTransit | closed | Azure Dead Letter and Lock Context | azure-servicebus | There seem to be issues with dead lettering using the service bus DLQ, and message locks?
```
[14:53:18 DBG] Create topic: MassTransit/Fault--Restaurant.Dtos.Images/ImageUploadedMessageDto--
[14:53:18 DBG] Create topic: MassTransit/Fault
[14:53:18 DBG] SKIP "sb://---.servicebus.windows.net/imageuploaded" 52b00000-5b58-448a-e72a-08d808d1ace1
[14:53:18 WRN] Message Lock Lost: 52b000005b58448ae72a08d808d1ace1
Microsoft.Azure.ServiceBus.MessageLockLostException: The lock supplied is invalid. Either the lock expired, or the message has already been removed from the queue, or was received by a different receiver instance.
at Microsoft.Azure.ServiceBus.Core.MessageReceiver.DisposeMessagesAsync(IEnumerable`1 lockTokens, Outcome outcome)
at Microsoft.Azure.ServiceBus.RetryPolicy.RunOperation(Func`1 operation, TimeSpan operationTimeout)
at Microsoft.Azure.ServiceBus.RetryPolicy.RunOperation(Func`1 operation, TimeSpan operationTimeout)
at Microsoft.Azure.ServiceBus.Core.MessageReceiver.DeadLetterAsync(String lockToken, IDictionary`2 propertiesToModify)
at MassTransit.Azure.ServiceBus.Core.Contexts.ReceiverClientMessageLockContext.DeadLetter()
at MassTransit.Azure.ServiceBus.Core.Pipeline.DeadLetterQueueFilter.GreenPipes.IFilter<MassTransit.ReceiveContext>.Send(ReceiveContext context, IPipe`1 next)
at MassTransit.Pipeline.Filters.DeadLetterFilter.GreenPipes.IFilter<MassTransit.ReceiveContext>.Send(ReceiveContext context, IPipe`1 next)
at MassTransit.Transports.ReceivePipeDispatcher.Dispatch(ReceiveContext context, ReceiveLockContext receiveLock)
at MassTransit.Transports.ReceivePipeDispatcher.Dispatch(ReceiveContext context, ReceiveLockContext receiveLock)
at MassTransit.Transports.ReceivePipeDispatcher.Dispatch(ReceiveContext context, ReceiveLockContext receiveLock)
at MassTransit.Azure.ServiceBus.Core.Transport.BrokeredMessageReceiver.MassTransit.Azure.ServiceBus.Core.Transport.IBrokeredMessageReceiver.Handle(Message message, CancellationToken cancellationToken, Action`1 contextCallback)
``` | 1.0 | Azure Dead Letter and Lock Context - There seem to be issues with dead lettering using the service bus DLQ, and message locks?
```
[14:53:18 DBG] Create topic: MassTransit/Fault--Restaurant.Dtos.Images/ImageUploadedMessageDto--
[14:53:18 DBG] Create topic: MassTransit/Fault
[14:53:18 DBG] SKIP "sb://---.servicebus.windows.net/imageuploaded" 52b00000-5b58-448a-e72a-08d808d1ace1
[14:53:18 WRN] Message Lock Lost: 52b000005b58448ae72a08d808d1ace1
Microsoft.Azure.ServiceBus.MessageLockLostException: The lock supplied is invalid. Either the lock expired, or the message has already been removed from the queue, or was received by a different receiver instance.
at Microsoft.Azure.ServiceBus.Core.MessageReceiver.DisposeMessagesAsync(IEnumerable`1 lockTokens, Outcome outcome)
at Microsoft.Azure.ServiceBus.RetryPolicy.RunOperation(Func`1 operation, TimeSpan operationTimeout)
at Microsoft.Azure.ServiceBus.RetryPolicy.RunOperation(Func`1 operation, TimeSpan operationTimeout)
at Microsoft.Azure.ServiceBus.Core.MessageReceiver.DeadLetterAsync(String lockToken, IDictionary`2 propertiesToModify)
at MassTransit.Azure.ServiceBus.Core.Contexts.ReceiverClientMessageLockContext.DeadLetter()
at MassTransit.Azure.ServiceBus.Core.Pipeline.DeadLetterQueueFilter.GreenPipes.IFilter<MassTransit.ReceiveContext>.Send(ReceiveContext context, IPipe`1 next)
at MassTransit.Pipeline.Filters.DeadLetterFilter.GreenPipes.IFilter<MassTransit.ReceiveContext>.Send(ReceiveContext context, IPipe`1 next)
at MassTransit.Transports.ReceivePipeDispatcher.Dispatch(ReceiveContext context, ReceiveLockContext receiveLock)
at MassTransit.Transports.ReceivePipeDispatcher.Dispatch(ReceiveContext context, ReceiveLockContext receiveLock)
at MassTransit.Transports.ReceivePipeDispatcher.Dispatch(ReceiveContext context, ReceiveLockContext receiveLock)
at MassTransit.Azure.ServiceBus.Core.Transport.BrokeredMessageReceiver.MassTransit.Azure.ServiceBus.Core.Transport.IBrokeredMessageReceiver.Handle(Message message, CancellationToken cancellationToken, Action`1 contextCallback)
``` | non_priority | azure dead letter and lock context there seem to be issues with dead lettering using the service bus dlq and message locks create topic masstransit fault restaurant dtos images imageuploadedmessagedto create topic masstransit fault skip sb servicebus windows net imageuploaded message lock lost microsoft azure servicebus messagelocklostexception the lock supplied is invalid either the lock expired or the message has already been removed from the queue or was received by a different receiver instance at microsoft azure servicebus core messagereceiver disposemessagesasync ienumerable locktokens outcome outcome at microsoft azure servicebus retrypolicy runoperation func operation timespan operationtimeout at microsoft azure servicebus retrypolicy runoperation func operation timespan operationtimeout at microsoft azure servicebus core messagereceiver deadletterasync string locktoken idictionary propertiestomodify at masstransit azure servicebus core contexts receiverclientmessagelockcontext deadletter at masstransit azure servicebus core pipeline deadletterqueuefilter greenpipes ifilter send receivecontext context ipipe next at masstransit pipeline filters deadletterfilter greenpipes ifilter send receivecontext context ipipe next at masstransit transports receivepipedispatcher dispatch receivecontext context receivelockcontext receivelock at masstransit transports receivepipedispatcher dispatch receivecontext context receivelockcontext receivelock at masstransit transports receivepipedispatcher dispatch receivecontext context receivelockcontext receivelock at masstransit azure servicebus core transport brokeredmessagereceiver masstransit azure servicebus core transport ibrokeredmessagereceiver handle message message cancellationtoken cancellationtoken action contextcallback | 0 |
780 | 2,514,668,825 | IssuesEvent | 2015-01-15 13:33:14 | GoogleChrome/webrtc | https://api.github.com/repos/GoogleChrome/webrtc | closed | TestRTC to to show avg fps delivery when running supported resolutions tests | enhancement testrtc | Magnus was testing some laptops and having that value printed would have be useful. | 1.0 | TestRTC to to show avg fps delivery when running supported resolutions tests - Magnus was testing some laptops and having that value printed would have be useful. | non_priority | testrtc to to show avg fps delivery when running supported resolutions tests magnus was testing some laptops and having that value printed would have be useful | 0 |
199,374 | 15,765,373,134 | IssuesEvent | 2021-03-31 14:05:44 | AY2021S2-TIC4002-F18-2/tp2 | https://api.github.com/repos/AY2021S2-TIC4002-F18-2/tp2 | closed | Inconsistencies between find command section and summary section | severity.VeryLow type.DocumentationBug | In the summary section, perhaps `find n/John Bernice Andy` should be `find n/David Bernice`
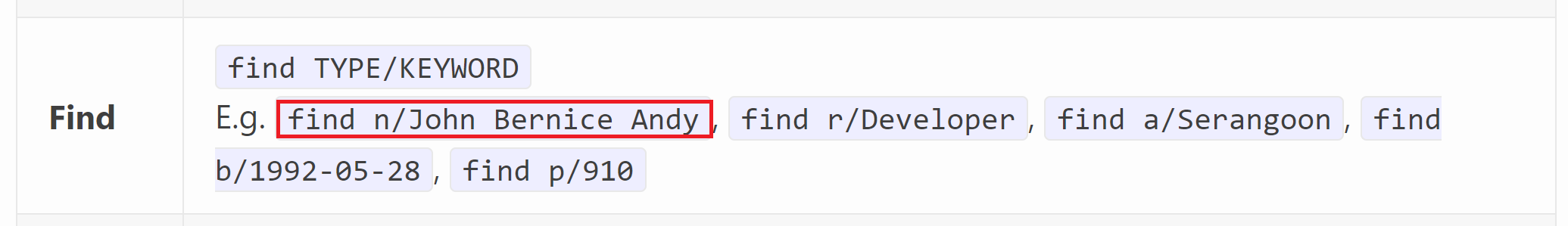
In the find command section, perhaps it is better to include `find a/Serangoon`, `find b/1992-05-28`, `find p/910` under examples of usage.
| 1.0 | Inconsistencies between find command section and summary section - In the summary section, perhaps `find n/John Bernice Andy` should be `find n/David Bernice`
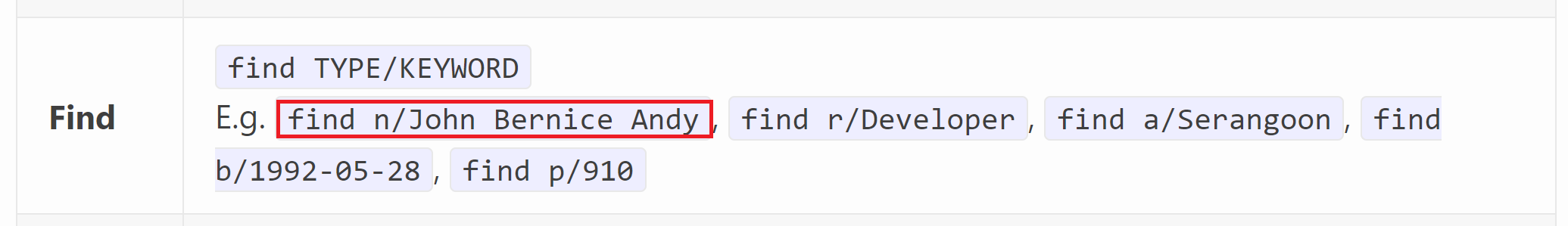
In the find command section, perhaps it is better to include `find a/Serangoon`, `find b/1992-05-28`, `find p/910` under examples of usage.
| non_priority | inconsistencies between find command section and summary section in the summary section perhaps find n john bernice andy should be find n david bernice in the find command section perhaps it is better to include find a serangoon find b find p under examples of usage | 0 |
135,756 | 30,389,860,995 | IssuesEvent | 2023-07-13 05:57:06 | coding-bootcamps-eu/2023-04-final-project-lost-and-found | https://api.github.com/repos/coding-bootcamps-eu/2023-04-final-project-lost-and-found | opened | Footer Home Link | code | - add Footer with Home Link in all Pages without LandingPage & UpdateLandingPage | 1.0 | Footer Home Link - - add Footer with Home Link in all Pages without LandingPage & UpdateLandingPage | non_priority | footer home link add footer with home link in all pages without landingpage updatelandingpage | 0 |
3,623 | 2,889,857,963 | IssuesEvent | 2015-06-13 20:39:08 | AlexEndris/RosMockLyn | https://api.github.com/repos/AlexEndris/RosMockLyn | closed | Make test project bootstrap | Code Generation enhancement Mocking Framework | There is one test project that is about testing everything put together. Add the own NuGet-Package to it. | 1.0 | Make test project bootstrap - There is one test project that is about testing everything put together. Add the own NuGet-Package to it. | non_priority | make test project bootstrap there is one test project that is about testing everything put together add the own nuget package to it | 0 |
12,876 | 9,992,190,155 | IssuesEvent | 2019-07-11 12:57:13 | SciTools/iris | https://api.github.com/repos/SciTools/iris | opened | Tidy iris.tests.unit.lazy_data.test_co_realise_cubes | SemVer: Major Type: Infrastructure | Reference https://github.com/SciTools/iris/pull/3355
Require to purge the `dask<2` split in the test_co_realise_cubes | 1.0 | Tidy iris.tests.unit.lazy_data.test_co_realise_cubes - Reference https://github.com/SciTools/iris/pull/3355
Require to purge the `dask<2` split in the test_co_realise_cubes | non_priority | tidy iris tests unit lazy data test co realise cubes reference require to purge the dask split in the test co realise cubes | 0 |
109,722 | 16,889,414,002 | IssuesEvent | 2021-06-23 07:21:59 | epam/TimeBase | https://api.github.com/repos/epam/TimeBase | closed | CVE-2018-8009 (High) detected in hadoop-common-2.9.1.jar - autoclosed | security vulnerability | ## CVE-2018-8009 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hadoop-common-2.9.1.jar</b></p></summary>
<p>Apache Hadoop Common</p>
<p>Path to dependency file: TimeBase/java/timebase/parquet/build.gradle</p>
<p>Path to vulnerable library: canner/.gradle/caches/modules-2/files-2.1/org.apache.hadoop/hadoop-common/2.9.1/1cbec3530e6f5ecd19e85a427d46c254c4516c4c/hadoop-common-2.9.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **hadoop-common-2.9.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/epam/TimeBase/commit/5eea755d19b7df20d059469714e45ae751fd0f64">5eea755d19b7df20d059469714e45ae751fd0f64</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Hadoop 3.1.0, 3.0.0-alpha to 3.0.2, 2.9.0 to 2.9.1, 2.8.0 to 2.8.4, 2.0.0-alpha to 2.7.6, 0.23.0 to 0.23.11 is exploitable via the zip slip vulnerability in places that accept a zip file.
<p>Publish Date: 2018-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8009>CVE-2018-8009</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1593018">https://bugzilla.redhat.com/show_bug.cgi?id=1593018</a></p>
<p>Release Date: 2018-11-13</p>
<p>Fix Resolution: 3.1.1,3.0.3,2.9.2,2.8.5,2.7.7</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.hadoop","packageName":"hadoop-common","packageVersion":"2.9.1","packageFilePaths":["/java/timebase/parquet/build.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.hadoop:hadoop-common:2.9.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.1.1,3.0.3,2.9.2,2.8.5,2.7.7"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-8009","vulnerabilityDetails":"Apache Hadoop 3.1.0, 3.0.0-alpha to 3.0.2, 2.9.0 to 2.9.1, 2.8.0 to 2.8.4, 2.0.0-alpha to 2.7.6, 0.23.0 to 0.23.11 is exploitable via the zip slip vulnerability in places that accept a zip file.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8009","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-8009 (High) detected in hadoop-common-2.9.1.jar - autoclosed - ## CVE-2018-8009 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hadoop-common-2.9.1.jar</b></p></summary>
<p>Apache Hadoop Common</p>
<p>Path to dependency file: TimeBase/java/timebase/parquet/build.gradle</p>
<p>Path to vulnerable library: canner/.gradle/caches/modules-2/files-2.1/org.apache.hadoop/hadoop-common/2.9.1/1cbec3530e6f5ecd19e85a427d46c254c4516c4c/hadoop-common-2.9.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **hadoop-common-2.9.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/epam/TimeBase/commit/5eea755d19b7df20d059469714e45ae751fd0f64">5eea755d19b7df20d059469714e45ae751fd0f64</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Hadoop 3.1.0, 3.0.0-alpha to 3.0.2, 2.9.0 to 2.9.1, 2.8.0 to 2.8.4, 2.0.0-alpha to 2.7.6, 0.23.0 to 0.23.11 is exploitable via the zip slip vulnerability in places that accept a zip file.
<p>Publish Date: 2018-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8009>CVE-2018-8009</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1593018">https://bugzilla.redhat.com/show_bug.cgi?id=1593018</a></p>
<p>Release Date: 2018-11-13</p>
<p>Fix Resolution: 3.1.1,3.0.3,2.9.2,2.8.5,2.7.7</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.hadoop","packageName":"hadoop-common","packageVersion":"2.9.1","packageFilePaths":["/java/timebase/parquet/build.gradle"],"isTransitiveDependency":false,"dependencyTree":"org.apache.hadoop:hadoop-common:2.9.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.1.1,3.0.3,2.9.2,2.8.5,2.7.7"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-8009","vulnerabilityDetails":"Apache Hadoop 3.1.0, 3.0.0-alpha to 3.0.2, 2.9.0 to 2.9.1, 2.8.0 to 2.8.4, 2.0.0-alpha to 2.7.6, 0.23.0 to 0.23.11 is exploitable via the zip slip vulnerability in places that accept a zip file.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8009","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in hadoop common jar autoclosed cve high severity vulnerability vulnerable library hadoop common jar apache hadoop common path to dependency file timebase java timebase parquet build gradle path to vulnerable library canner gradle caches modules files org apache hadoop hadoop common hadoop common jar dependency hierarchy x hadoop common jar vulnerable library found in head commit a href found in base branch main vulnerability details apache hadoop alpha to to to alpha to to is exploitable via the zip slip vulnerability in places that accept a zip file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org apache hadoop hadoop common isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails apache hadoop alpha to to to alpha to to is exploitable via the zip slip vulnerability in places that accept a zip file vulnerabilityurl | 0 |
24,270 | 11,026,891,791 | IssuesEvent | 2019-12-06 08:06:07 | rammatzkvosky/saleor | https://api.github.com/repos/rammatzkvosky/saleor | opened | CVE-2018-3750 (High) detected in deep-extend-0.4.2.tgz | security vulnerability | ## CVE-2018-3750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>deep-extend-0.4.2.tgz</b></p></summary>
<p>Recursive object extending</p>
<p>Library home page: <a href="https://registry.npmjs.org/deep-extend/-/deep-extend-0.4.2.tgz">https://registry.npmjs.org/deep-extend/-/deep-extend-0.4.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/saleor/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/saleor/node_modules/webpack-bundle-tracker/node_modules/deep-extend/package.json</p>
<p>
Dependency Hierarchy:
- webpack-bundle-tracker-0.3.0.tgz (Root Library)
- :x: **deep-extend-0.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rammatzkvosky/saleor/commit/cdb7b8312ae0518a12664a669906dc86027a763c">cdb7b8312ae0518a12664a669906dc86027a763c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The utilities function in all versions <= 0.5.0 of the deep-extend node module can be tricked into modifying the prototype of Object when the attacker can control part of the structure passed to this function. This can let an attacker add or modify existing properties that will exist on all objects.
<p>Publish Date: 2018-07-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3750>CVE-2018-3750</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/RetireJS/retire.js/commit/6a71696155dc42b440a3e8ebeea1b39cff6b2902">https://github.com/RetireJS/retire.js/commit/6a71696155dc42b440a3e8ebeea1b39cff6b2902</a></p>
<p>Release Date: 2018-05-09</p>
<p>Fix Resolution: Replace or update the following file: npmrepository.json</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"deep-extend","packageVersion":"0.4.2","isTransitiveDependency":true,"dependencyTree":"webpack-bundle-tracker:0.3.0;deep-extend:0.4.2","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2018-3750","vulnerabilityDetails":"The utilities function in all versions \u003c\u003d 0.5.0 of the deep-extend node module can be tricked into modifying the prototype of Object when the attacker can control part of the structure passed to this function. This can let an attacker add or modify existing properties that will exist on all objects.","vulnerabilityUrl":"https://cve.mitre.org/cgi-bin/cvename.cgi?name\u003dCVE-2018-3750","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-3750 (High) detected in deep-extend-0.4.2.tgz - ## CVE-2018-3750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>deep-extend-0.4.2.tgz</b></p></summary>
<p>Recursive object extending</p>
<p>Library home page: <a href="https://registry.npmjs.org/deep-extend/-/deep-extend-0.4.2.tgz">https://registry.npmjs.org/deep-extend/-/deep-extend-0.4.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/saleor/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/saleor/node_modules/webpack-bundle-tracker/node_modules/deep-extend/package.json</p>
<p>
Dependency Hierarchy:
- webpack-bundle-tracker-0.3.0.tgz (Root Library)
- :x: **deep-extend-0.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rammatzkvosky/saleor/commit/cdb7b8312ae0518a12664a669906dc86027a763c">cdb7b8312ae0518a12664a669906dc86027a763c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The utilities function in all versions <= 0.5.0 of the deep-extend node module can be tricked into modifying the prototype of Object when the attacker can control part of the structure passed to this function. This can let an attacker add or modify existing properties that will exist on all objects.
<p>Publish Date: 2018-07-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-3750>CVE-2018-3750</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/RetireJS/retire.js/commit/6a71696155dc42b440a3e8ebeea1b39cff6b2902">https://github.com/RetireJS/retire.js/commit/6a71696155dc42b440a3e8ebeea1b39cff6b2902</a></p>
<p>Release Date: 2018-05-09</p>
<p>Fix Resolution: Replace or update the following file: npmrepository.json</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"deep-extend","packageVersion":"0.4.2","isTransitiveDependency":true,"dependencyTree":"webpack-bundle-tracker:0.3.0;deep-extend:0.4.2","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2018-3750","vulnerabilityDetails":"The utilities function in all versions \u003c\u003d 0.5.0 of the deep-extend node module can be tricked into modifying the prototype of Object when the attacker can control part of the structure passed to this function. This can let an attacker add or modify existing properties that will exist on all objects.","vulnerabilityUrl":"https://cve.mitre.org/cgi-bin/cvename.cgi?name\u003dCVE-2018-3750","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in deep extend tgz cve high severity vulnerability vulnerable library deep extend tgz recursive object extending library home page a href path to dependency file tmp ws scm saleor package json path to vulnerable library tmp ws scm saleor node modules webpack bundle tracker node modules deep extend package json dependency hierarchy webpack bundle tracker tgz root library x deep extend tgz vulnerable library found in head commit a href vulnerability details the utilities function in all versions of the deep extend node module can be tricked into modifying the prototype of object when the attacker can control part of the structure passed to this function this can let an attacker add or modify existing properties that will exist on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following file npmrepository json isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails the utilities function in all versions of the deep extend node module can be tricked into modifying the prototype of object when the attacker can control part of the structure passed to this function this can let an attacker add or modify existing properties that will exist on all objects vulnerabilityurl | 0 |
27,280 | 11,464,102,708 | IssuesEvent | 2020-02-07 17:19:10 | TIBCOSoftware/dovetail | https://api.github.com/repos/TIBCOSoftware/dovetail | opened | CVE-2018-16492 (High) detected in extend-3.0.1.tgz, extend-2.0.1.tgz | security vulnerability | ## CVE-2018-16492 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>extend-3.0.1.tgz</b>, <b>extend-2.0.1.tgz</b></p></summary>
<p>
<details><summary><b>extend-3.0.1.tgz</b></p></summary>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-3.0.1.tgz">https://registry.npmjs.org/extend/-/extend-3.0.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- broken-link-checker-0.7.8.tgz (Root Library)
- :x: **extend-3.0.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>extend-2.0.1.tgz</b></p></summary>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-2.0.1.tgz">https://registry.npmjs.org/extend/-/extend-2.0.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/node_modules/bhttp/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- broken-link-checker-0.7.8.tgz (Root Library)
- bhttp-1.2.4.tgz
- :x: **extend-2.0.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/TIBCOSoftware/dovetail/commit/7855a4e99c7e10458d2d5f4e9b408f4c8f37d583">7855a4e99c7e10458d2d5f4e9b408f4c8f37d583</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A prototype pollution vulnerability was found in module extend <2.0.2, ~<3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492>CVE-2018-16492</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/381185">https://hackerone.com/reports/381185</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: extend - v3.0.2,v2.0.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"extend","packageVersion":"3.0.1","isTransitiveDependency":true,"dependencyTree":"broken-link-checker:0.7.8;extend:3.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"extend - v3.0.2,v2.0.2"},{"packageType":"javascript/Node.js","packageName":"extend","packageVersion":"2.0.1","isTransitiveDependency":true,"dependencyTree":"broken-link-checker:0.7.8;bhttp:1.2.4;extend:2.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"extend - v3.0.2,v2.0.2"}],"vulnerabilityIdentifier":"CVE-2018-16492","vulnerabilityDetails":"A prototype pollution vulnerability was found in module extend \u003c2.0.2, ~\u003c3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-16492 (High) detected in extend-3.0.1.tgz, extend-2.0.1.tgz - ## CVE-2018-16492 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>extend-3.0.1.tgz</b>, <b>extend-2.0.1.tgz</b></p></summary>
<p>
<details><summary><b>extend-3.0.1.tgz</b></p></summary>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-3.0.1.tgz">https://registry.npmjs.org/extend/-/extend-3.0.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- broken-link-checker-0.7.8.tgz (Root Library)
- :x: **extend-3.0.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>extend-2.0.1.tgz</b></p></summary>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-2.0.1.tgz">https://registry.npmjs.org/extend/-/extend-2.0.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/dovetail/docs-src/themes/tibcolabs/assets/vendor/bootstrap/node_modules/bhttp/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- broken-link-checker-0.7.8.tgz (Root Library)
- bhttp-1.2.4.tgz
- :x: **extend-2.0.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/TIBCOSoftware/dovetail/commit/7855a4e99c7e10458d2d5f4e9b408f4c8f37d583">7855a4e99c7e10458d2d5f4e9b408f4c8f37d583</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A prototype pollution vulnerability was found in module extend <2.0.2, ~<3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492>CVE-2018-16492</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/381185">https://hackerone.com/reports/381185</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: extend - v3.0.2,v2.0.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"extend","packageVersion":"3.0.1","isTransitiveDependency":true,"dependencyTree":"broken-link-checker:0.7.8;extend:3.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"extend - v3.0.2,v2.0.2"},{"packageType":"javascript/Node.js","packageName":"extend","packageVersion":"2.0.1","isTransitiveDependency":true,"dependencyTree":"broken-link-checker:0.7.8;bhttp:1.2.4;extend:2.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"extend - v3.0.2,v2.0.2"}],"vulnerabilityIdentifier":"CVE-2018-16492","vulnerabilityDetails":"A prototype pollution vulnerability was found in module extend \u003c2.0.2, ~\u003c3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in extend tgz extend tgz cve high severity vulnerability vulnerable libraries extend tgz extend tgz extend tgz port of jquery extend for node js and the browser library home page a href path to dependency file tmp ws scm dovetail docs src themes tibcolabs assets vendor bootstrap package json path to vulnerable library tmp ws scm dovetail docs src themes tibcolabs assets vendor bootstrap node modules extend package json dependency hierarchy broken link checker tgz root library x extend tgz vulnerable library extend tgz port of jquery extend for node js and the browser library home page a href path to dependency file tmp ws scm dovetail docs src themes tibcolabs assets vendor bootstrap package json path to vulnerable library tmp ws scm dovetail docs src themes tibcolabs assets vendor bootstrap node modules bhttp node modules extend package json dependency hierarchy broken link checker tgz root library bhttp tgz x extend tgz vulnerable library found in head commit a href vulnerability details a prototype pollution vulnerability was found in module extend that allows an attacker to inject arbitrary properties onto object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution extend isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails a prototype pollution vulnerability was found in module extend that allows an attacker to inject arbitrary properties onto object prototype vulnerabilityurl | 0 |
327,447 | 28,064,283,779 | IssuesEvent | 2023-03-29 14:28:04 | zephyrproject-rtos/test_results | https://api.github.com/repos/zephyrproject-rtos/test_results | closed |
IPv4 Fragment Fragment: 512 MTU. Order: 2 1 3 4 ... N. Overlap: None. error
| area: Tests |
**Describe the bug**
Fragment: 512 MTU. Order: 2 1 3 4 ... N. Overlap: None. test is Fail on Zephyr3.0.0 on qemu_x86
**References**
RFC 791: section 2.3
RFC 791: section 3.2
RFC 1122: section 3.3.2 {Able to reassemble incoming datagrams}
RFC 1122: section 3.2.1.4 {Support reassembly}
RFC 1122: section 3.3.2 {At least 576 byte datagrams}
**Results**
FAIL: icmp.v4 got no echo response, which is not an expected result.; SKIPPED: udp.v4: Packets exchanged with the DUT did not match those needed to either perform or grade the test. (Traffic source reports: echo response.); SKIPPED: tcp.v4: Packets exchanged with the DUT did not match those needed to either perform or grade the test. (Traffic source reports: echo response.)
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: Zephyr3.0.0
| 1.0 |
IPv4 Fragment Fragment: 512 MTU. Order: 2 1 3 4 ... N. Overlap: None. error
-
**Describe the bug**
Fragment: 512 MTU. Order: 2 1 3 4 ... N. Overlap: None. test is Fail on Zephyr3.0.0 on qemu_x86
**References**
RFC 791: section 2.3
RFC 791: section 3.2
RFC 1122: section 3.3.2 {Able to reassemble incoming datagrams}
RFC 1122: section 3.2.1.4 {Support reassembly}
RFC 1122: section 3.3.2 {At least 576 byte datagrams}
**Results**
FAIL: icmp.v4 got no echo response, which is not an expected result.; SKIPPED: udp.v4: Packets exchanged with the DUT did not match those needed to either perform or grade the test. (Traffic source reports: echo response.); SKIPPED: tcp.v4: Packets exchanged with the DUT did not match those needed to either perform or grade the test. (Traffic source reports: echo response.)
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: Zephyr3.0.0
| non_priority | fragment fragment mtu order n overlap none error describe the bug fragment mtu order n overlap none test is fail on on qemu references rfc section rfc section rfc section able to reassemble incoming datagrams rfc section support reassembly rfc section at least byte datagrams results fail icmp got no echo response which is not an expected result skipped udp packets exchanged with the dut did not match those needed to either perform or grade the test traffic source reports echo response skipped tcp packets exchanged with the dut did not match those needed to either perform or grade the test traffic source reports echo response environment please complete the following information os e g linux toolchain e g zephyr sdk commit sha or version used | 0 |
91,357 | 18,446,963,102 | IssuesEvent | 2021-10-15 04:16:37 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | Color the annotations | Type/Improvement Area/VScodePlugin Area/SyntaxHighlighting | Consider the below code snippet.
<img width="939" alt="Screen Shot 2021-10-14 at 9 42 18 AM" src="https://user-images.githubusercontent.com/6178058/137250722-fd9ffcfe-813a-4f99-97a0-17587ad19e1d.png">
In this case, wouldn't it increase the code readability if we highlight `@http:Payload` annotation in some other color ? (maybe bright yellow).
| 1.0 | Color the annotations - Consider the below code snippet.
<img width="939" alt="Screen Shot 2021-10-14 at 9 42 18 AM" src="https://user-images.githubusercontent.com/6178058/137250722-fd9ffcfe-813a-4f99-97a0-17587ad19e1d.png">
In this case, wouldn't it increase the code readability if we highlight `@http:Payload` annotation in some other color ? (maybe bright yellow).
| non_priority | color the annotations consider the below code snippet img width alt screen shot at am src in this case wouldn t it increase the code readability if we highlight http payload annotation in some other color maybe bright yellow | 0 |
97,526 | 20,326,442,009 | IssuesEvent | 2022-02-18 06:19:11 | age-series/ElectricalAge2 | https://api.github.com/repos/age-series/ElectricalAge2 | opened | Integrate with HUD mod | code | We should find a popular HUD mod (such as WAILA was) and configure it to display stuff to the user that you might see from the multimeter. | 1.0 | Integrate with HUD mod - We should find a popular HUD mod (such as WAILA was) and configure it to display stuff to the user that you might see from the multimeter. | non_priority | integrate with hud mod we should find a popular hud mod such as waila was and configure it to display stuff to the user that you might see from the multimeter | 0 |
123,948 | 16,551,534,797 | IssuesEvent | 2021-05-28 09:08:31 | google/web-stories-wp | https://api.github.com/repos/google/web-stories-wp | closed | Redesign: Update text style panel | Elements: Text Group: Design Panel Group: Workspace P1 Pod: Prometheus Type: Enhancement | <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Feature Description
See [Figma](https://www.figma.com/file/bMhG3KyrJF8vIAODgmbeqT/Design-System?node-id=3483%3A611)
<!-- A clear and concise description of what the problem is and what you want to happen. -->
- [ ] Update dropdowns (which component for the font picker!?)
- [ ] Update inputs
- [ ] Update toggles
- [ ] Update colors
- [ ] Update tooltips
## Additional Context
<img width="691" alt="Screenshot 2021-02-22 at 12 53 16" src="https://user-images.githubusercontent.com/3294597/108698968-fd9a5100-7504-11eb-8b8e-bdb568b8af0d.png">
<!-- Add any other context or screenshots about the feature request. -->
---
_Do not alter or remove anything below. The following sections will be managed by moderators only._
## Acceptance Criteria
<!-- One or more bullet points for acceptance criteria. -->
## Implementation Brief
<!-- One or more bullet points for how to technically implement the feature. -->
| 1.0 | Redesign: Update text style panel - <!-- NOTE: For help requests, support questions, or general feedback, please use the WordPress.org forums instead: https://wordpress.org/support/plugin/web-stories/ -->
## Feature Description
See [Figma](https://www.figma.com/file/bMhG3KyrJF8vIAODgmbeqT/Design-System?node-id=3483%3A611)
<!-- A clear and concise description of what the problem is and what you want to happen. -->
- [ ] Update dropdowns (which component for the font picker!?)
- [ ] Update inputs
- [ ] Update toggles
- [ ] Update colors
- [ ] Update tooltips
## Additional Context
<img width="691" alt="Screenshot 2021-02-22 at 12 53 16" src="https://user-images.githubusercontent.com/3294597/108698968-fd9a5100-7504-11eb-8b8e-bdb568b8af0d.png">
<!-- Add any other context or screenshots about the feature request. -->
---
_Do not alter or remove anything below. The following sections will be managed by moderators only._
## Acceptance Criteria
<!-- One or more bullet points for acceptance criteria. -->
## Implementation Brief
<!-- One or more bullet points for how to technically implement the feature. -->
| non_priority | redesign update text style panel feature description see update dropdowns which component for the font picker update inputs update toggles update colors update tooltips additional context img width alt screenshot at src do not alter or remove anything below the following sections will be managed by moderators only acceptance criteria implementation brief | 0 |
264,617 | 23,128,430,302 | IssuesEvent | 2022-07-28 08:13:26 | deepset-ai/haystack | https://api.github.com/repos/deepset-ai/haystack | closed | Add OpenSearch to CI and tests | type:refactor topic:document_store topic:tests | - Add OpenSearch in our CI so that we can add dedicated tests
- install OpenSearch docker image in CI
- ensure it's exposed on a different port than elasticsearch
- add it to document store fixtures
- ensure appropriate tests are run with OpenSearchDocumentStore
| 1.0 | Add OpenSearch to CI and tests - - Add OpenSearch in our CI so that we can add dedicated tests
- install OpenSearch docker image in CI
- ensure it's exposed on a different port than elasticsearch
- add it to document store fixtures
- ensure appropriate tests are run with OpenSearchDocumentStore
| non_priority | add opensearch to ci and tests add opensearch in our ci so that we can add dedicated tests install opensearch docker image in ci ensure it s exposed on a different port than elasticsearch add it to document store fixtures ensure appropriate tests are run with opensearchdocumentstore | 0 |
1,529 | 3,776,312,249 | IssuesEvent | 2016-03-17 16:16:46 | PATRIC3/patric3_website | https://api.github.com/repos/PATRIC3/patric3_website | opened | Proteome Comparison Service Enhancements | Deliverable Services | These enhancements to the Proteomics Comparison Service include
- Enabling inclusion of reference genome
- Enabling inclusion of user-supplied genome
- Enabling generation of comparison based on user-selected feature set | 1.0 | Proteome Comparison Service Enhancements - These enhancements to the Proteomics Comparison Service include
- Enabling inclusion of reference genome
- Enabling inclusion of user-supplied genome
- Enabling generation of comparison based on user-selected feature set | non_priority | proteome comparison service enhancements these enhancements to the proteomics comparison service include enabling inclusion of reference genome enabling inclusion of user supplied genome enabling generation of comparison based on user selected feature set | 0 |
139,301 | 31,392,988,423 | IssuesEvent | 2023-08-26 15:21:21 | cython/cython | https://api.github.com/repos/cython/cython | closed | [BUG] Iterating over memoryview in pure python mode is not optimized | Code Generation Pure Python Mode | ### Describe your issue
Pure python version of the code example from cython documentation https://cython.readthedocs.io/en/latest/src/userguide/memoryviews.html#indexing
seems to yield not-optimized C code. Following code
```python
import numpy as np
def add_one(buf: cython.int[:,:]):
for x in range(buf.shape[0]):
for y in range(buf.shape[1]):
buf[x, y] += 1
# exporting_object must be a Python object
# implementing the buffer interface, e.g. a numpy array.
exporting_object = np.zeros((10, 20), dtype=np.intc)
add_one(exporting_object)
```
Yields following annotated code (for brevity not showing actual C code, but the color gives the hint):

For comparison the current Cython example
```cython
import numpy as np
def add_one(int[:,:] buf):
for x in range(buf.shape[0]):
for y in range(buf.shape[1]):
buf[x, y] += 1
# exporting_object must be a Python object
# implementing the buffer interface, e.g. a numpy array.
exporting_object = np.zeros((10, 20), dtype=np.intc)
add_one(exporting_object)
```
Yields following annotated code:

## OS
MacOS
## Python version
3.9
## Cython version
master | 1.0 | [BUG] Iterating over memoryview in pure python mode is not optimized - ### Describe your issue
Pure python version of the code example from cython documentation https://cython.readthedocs.io/en/latest/src/userguide/memoryviews.html#indexing
seems to yield not-optimized C code. Following code
```python
import numpy as np
def add_one(buf: cython.int[:,:]):
for x in range(buf.shape[0]):
for y in range(buf.shape[1]):
buf[x, y] += 1
# exporting_object must be a Python object
# implementing the buffer interface, e.g. a numpy array.
exporting_object = np.zeros((10, 20), dtype=np.intc)
add_one(exporting_object)
```
Yields following annotated code (for brevity not showing actual C code, but the color gives the hint):

For comparison the current Cython example
```cython
import numpy as np
def add_one(int[:,:] buf):
for x in range(buf.shape[0]):
for y in range(buf.shape[1]):
buf[x, y] += 1
# exporting_object must be a Python object
# implementing the buffer interface, e.g. a numpy array.
exporting_object = np.zeros((10, 20), dtype=np.intc)
add_one(exporting_object)
```
Yields following annotated code:

## OS
MacOS
## Python version
3.9
## Cython version
master | non_priority | iterating over memoryview in pure python mode is not optimized describe your issue pure python version of the code example from cython documentation seems to yield not optimized c code following code python import numpy as np def add one buf cython int for x in range buf shape for y in range buf shape buf exporting object must be a python object implementing the buffer interface e g a numpy array exporting object np zeros dtype np intc add one exporting object yields following annotated code for brevity not showing actual c code but the color gives the hint for comparison the current cython example cython import numpy as np def add one int buf for x in range buf shape for y in range buf shape buf exporting object must be a python object implementing the buffer interface e g a numpy array exporting object np zeros dtype np intc add one exporting object yields following annotated code os macos python version cython version master | 0 |
37,129 | 9,962,935,781 | IssuesEvent | 2019-07-07 18:50:03 | 4awpawz/trio | https://api.github.com/repos/4awpawz/trio | opened | blog article pages aren't being garbage collected when their categories are changed | bug generator related incremental build related | Garbage collection currently handles identifying target pages that are no longer generated by comparing cached stats to new stats, specifically by their source paths.
Garbage collection currently does not handle deleting orphaned pages that are the result of the user changing the category associated with an article. This results in the generation of a duplicate articles located at the new path reflecting its new category and the failure of garbage collection to remove the original article located at the path reflected by its previous category.
To correct this issue, all targets for garbage collection must be determined *__after__* getAllMetadata has been called. This will then allow comparing the current stat's destination path to the cached stats destination path. If they aren't the same then garbage collection will target the cached stat's destination path for removal.
It should be noted that this will work for all fragment's and not just blog articles. | 1.0 | blog article pages aren't being garbage collected when their categories are changed - Garbage collection currently handles identifying target pages that are no longer generated by comparing cached stats to new stats, specifically by their source paths.
Garbage collection currently does not handle deleting orphaned pages that are the result of the user changing the category associated with an article. This results in the generation of a duplicate articles located at the new path reflecting its new category and the failure of garbage collection to remove the original article located at the path reflected by its previous category.
To correct this issue, all targets for garbage collection must be determined *__after__* getAllMetadata has been called. This will then allow comparing the current stat's destination path to the cached stats destination path. If they aren't the same then garbage collection will target the cached stat's destination path for removal.
It should be noted that this will work for all fragment's and not just blog articles. | non_priority | blog article pages aren t being garbage collected when their categories are changed garbage collection currently handles identifying target pages that are no longer generated by comparing cached stats to new stats specifically by their source paths garbage collection currently does not handle deleting orphaned pages that are the result of the user changing the category associated with an article this results in the generation of a duplicate articles located at the new path reflecting its new category and the failure of garbage collection to remove the original article located at the path reflected by its previous category to correct this issue all targets for garbage collection must be determined after getallmetadata has been called this will then allow comparing the current stat s destination path to the cached stats destination path if they aren t the same then garbage collection will target the cached stat s destination path for removal it should be noted that this will work for all fragment s and not just blog articles | 0 |
53,318 | 11,035,692,286 | IssuesEvent | 2019-12-07 15:30:11 | Cepos-e-Mabecos/distributed-systems-2019 | https://api.github.com/repos/Cepos-e-Mabecos/distributed-systems-2019 | closed | Refactor FullAddress.equals(Object) | codestyle | I've selected [**FullAddress.equals(Object)**](https://github.com/Cepos-e-Mabecos/distributed-systems-2019/blob/7e940b97d8c4962f4c3438f35a138aeef62533f4/src/comunication/FullAddress.java#L93-L124) for refactoring, which is a unit of **26** lines of code. Addressing this will make our codebase more maintainable and improve [Better Code Hub](https://bettercodehub.com)'s **Write Short Units of Code** guideline rating! 👍
Here's the gist of this guideline:
- **Definition** 📖
Limit the length of code units to 15 lines of code.
- **Why**❓
Small units are easier to analyse, test and reuse.
- **How** 🔧
When writing new units, don't let them grow above 15 lines of code. When a unit grows beyond this, split it in smaller units of no longer than 15 lines.
You can find more info about this guideline in [Building Maintainable Software](http://shop.oreilly.com/product/0636920049159.do). 📖
----
ℹ️ To know how many _other_ refactoring candidates need addressing to get a guideline compliant, select some by clicking on the 🔲 next to them. The risk profile below the candidates signals (✅) when it's enough! 🏁
----
Good luck and happy coding! :shipit: :sparkles: :100: | 1.0 | Refactor FullAddress.equals(Object) - I've selected [**FullAddress.equals(Object)**](https://github.com/Cepos-e-Mabecos/distributed-systems-2019/blob/7e940b97d8c4962f4c3438f35a138aeef62533f4/src/comunication/FullAddress.java#L93-L124) for refactoring, which is a unit of **26** lines of code. Addressing this will make our codebase more maintainable and improve [Better Code Hub](https://bettercodehub.com)'s **Write Short Units of Code** guideline rating! 👍
Here's the gist of this guideline:
- **Definition** 📖
Limit the length of code units to 15 lines of code.
- **Why**❓
Small units are easier to analyse, test and reuse.
- **How** 🔧
When writing new units, don't let them grow above 15 lines of code. When a unit grows beyond this, split it in smaller units of no longer than 15 lines.
You can find more info about this guideline in [Building Maintainable Software](http://shop.oreilly.com/product/0636920049159.do). 📖
----
ℹ️ To know how many _other_ refactoring candidates need addressing to get a guideline compliant, select some by clicking on the 🔲 next to them. The risk profile below the candidates signals (✅) when it's enough! 🏁
----
Good luck and happy coding! :shipit: :sparkles: :100: | non_priority | refactor fulladdress equals object i ve selected for refactoring which is a unit of lines of code addressing this will make our codebase more maintainable and improve write short units of code guideline rating 👍 here s the gist of this guideline definition 📖 limit the length of code units to lines of code why ❓ small units are easier to analyse test and reuse how 🔧 when writing new units don t let them grow above lines of code when a unit grows beyond this split it in smaller units of no longer than lines you can find more info about this guideline in 📖 ℹ️ to know how many other refactoring candidates need addressing to get a guideline compliant select some by clicking on the 🔲 next to them the risk profile below the candidates signals ✅ when it s enough 🏁 good luck and happy coding shipit sparkles | 0 |
235,068 | 18,041,261,100 | IssuesEvent | 2021-09-18 04:32:19 | girlscript/winter-of-contributing | https://api.github.com/repos/girlscript/winter-of-contributing | closed | Cybersecurity: 1.9.8 Introduction to IT Act 2000. | documentation GWOC21 Cybersecurity Video | ## Description
The Information Technology Act, 2000 serves as the de facto framework for digital governance in India.
### Discuss more Information Technology Act, 2000!
## Note:
- If interested, mention in which format you want to contribute either in `Documentation` or in `Video`
- Please avoid copy/paste, `BE YOURSELF`
- Try to explain with **Diagrams**
- Changes should be made inside the `Cyber_Security/` directory & `Cyber_Security` branch.
- Task will be assigned on first come first serve
- Check it out [Contribution Guidelines](https://github.com/girlscript/winter-of-contributing/blob/main/.github/CONTRIBUTING.md) | 1.0 | Cybersecurity: 1.9.8 Introduction to IT Act 2000. - ## Description
The Information Technology Act, 2000 serves as the de facto framework for digital governance in India.
### Discuss more Information Technology Act, 2000!
## Note:
- If interested, mention in which format you want to contribute either in `Documentation` or in `Video`
- Please avoid copy/paste, `BE YOURSELF`
- Try to explain with **Diagrams**
- Changes should be made inside the `Cyber_Security/` directory & `Cyber_Security` branch.
- Task will be assigned on first come first serve
- Check it out [Contribution Guidelines](https://github.com/girlscript/winter-of-contributing/blob/main/.github/CONTRIBUTING.md) | non_priority | cybersecurity introduction to it act description the information technology act serves as the de facto framework for digital governance in india discuss more information technology act note if interested mention in which format you want to contribute either in documentation or in video please avoid copy paste be yourself try to explain with diagrams changes should be made inside the cyber security directory cyber security branch task will be assigned on first come first serve check it out | 0 |
217,596 | 16,855,811,502 | IssuesEvent | 2021-06-21 06:28:30 | tikv/tikv | https://api.github.com/repos/tikv/tikv | closed | cases::test_merge::test_node_multiple_rollback_merge failed | component/test-bench sig/raft | cases::test_merge::test_node_multiple_rollback_merge
Latest failed builds:
https://internal.pingcap.net/idc-jenkins/job/tikv_ghpr_test/29448/consoleFull
| 1.0 | cases::test_merge::test_node_multiple_rollback_merge failed - cases::test_merge::test_node_multiple_rollback_merge
Latest failed builds:
https://internal.pingcap.net/idc-jenkins/job/tikv_ghpr_test/29448/consoleFull
| non_priority | cases test merge test node multiple rollback merge failed cases test merge test node multiple rollback merge latest failed builds | 0 |
173,591 | 27,494,322,956 | IssuesEvent | 2023-03-05 01:01:44 | te-online/timemanager | https://api.github.com/repos/te-online/timemanager | closed | Buttons on Reports page have padding for icon, but no icon is shown | bug design | This is a CSS regression
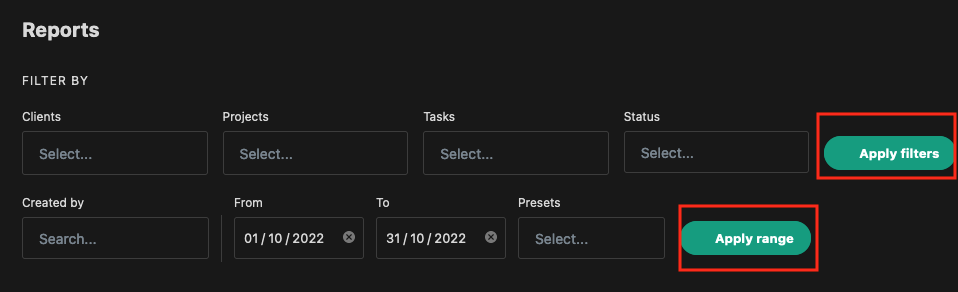
| 1.0 | Buttons on Reports page have padding for icon, but no icon is shown - This is a CSS regression
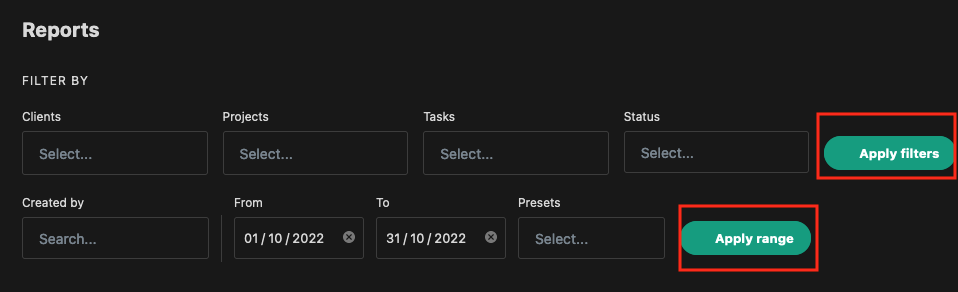
| non_priority | buttons on reports page have padding for icon but no icon is shown this is a css regression | 0 |
295,730 | 25,498,339,529 | IssuesEvent | 2022-11-27 23:24:00 | osmosis-labs/osmosis | https://api.github.com/repos/osmosis-labs/osmosis | closed | test(stableswap): `getLiquidityIndexMap` function | T:tests C:x/gamm Good first issue | <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for creating an issue! ✰
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Background
https://github.com/osmosis-labs/osmosis/blob/6398733549c124cb973eaa20d7aaba0fe6915ab9/x/gamm/pool-models/stableswap/pool.go#L158
## Acceptance Criteria
- case with 2 assets, case with 4 assets
| 1.0 | test(stableswap): `getLiquidityIndexMap` function - <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for creating an issue! ✰
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Background
https://github.com/osmosis-labs/osmosis/blob/6398733549c124cb973eaa20d7aaba0fe6915ab9/x/gamm/pool-models/stableswap/pool.go#L158
## Acceptance Criteria
- case with 2 assets, case with 4 assets
| non_priority | test stableswap getliquidityindexmap function ☺ v ✰ thanks for creating an issue ✰ ☺ background acceptance criteria case with assets case with assets | 0 |
147,730 | 19,523,814,561 | IssuesEvent | 2021-12-30 01:32:37 | phytomichael/KSA | https://api.github.com/repos/phytomichael/KSA | opened | CVE-2021-43797 (Medium) detected in netty-all-4.0.33.Final.jar | security vulnerability | ## CVE-2021-43797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-all-4.0.33.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /KSA/ksa/ksa/ksa-web-root/ksa-finance-web/pom.xml</p>
<p>Path to vulnerable library: /2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/KSA/ksa/ksa/ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.33.Final.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. Netty prior to version 4.1.7.1.Final skips control chars when they are present at the beginning / end of the header name. It should instead fail fast as these are not allowed by the spec and could lead to HTTP request smuggling. Failing to do the validation might cause netty to "sanitize" header names before it forward these to another remote system when used as proxy. This remote system can't see the invalid usage anymore, and therefore does not do the validation itself. Users should upgrade to version 4.1.7.1.Final to receive a patch.
<p>Publish Date: 2021-12-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43797>CVE-2021-43797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="CVE-2021-43797">CVE-2021-43797</a></p>
<p>Release Date: 2021-12-09</p>
<p>Fix Resolution: io.netty:netty-codec-http:4.1.71.Final,io.netty:netty-all:4.1.71.Final</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.33.Final","packageFilePaths":["/KSA/ksa/ksa/ksa-web-root/ksa-finance-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.33.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-codec-http:4.1.71.Final,io.netty:netty-all:4.1.71.Final","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-43797","vulnerabilityDetails":"Netty is an asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers \u0026 clients. Netty prior to version 4.1.7.1.Final skips control chars when they are present at the beginning / end of the header name. It should instead fail fast as these are not allowed by the spec and could lead to HTTP request smuggling. Failing to do the validation might cause netty to \"sanitize\" header names before it forward these to another remote system when used as proxy. This remote system can\u0027t see the invalid usage anymore, and therefore does not do the validation itself. Users should upgrade to version 4.1.7.1.Final to receive a patch.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43797","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-43797 (Medium) detected in netty-all-4.0.33.Final.jar - ## CVE-2021-43797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-all-4.0.33.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /KSA/ksa/ksa/ksa-web-root/ksa-finance-web/pom.xml</p>
<p>Path to vulnerable library: /2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/KSA/ksa/ksa/ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar,/2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.33.Final.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty is an asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers & clients. Netty prior to version 4.1.7.1.Final skips control chars when they are present at the beginning / end of the header name. It should instead fail fast as these are not allowed by the spec and could lead to HTTP request smuggling. Failing to do the validation might cause netty to "sanitize" header names before it forward these to another remote system when used as proxy. This remote system can't see the invalid usage anymore, and therefore does not do the validation itself. Users should upgrade to version 4.1.7.1.Final to receive a patch.
<p>Publish Date: 2021-12-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43797>CVE-2021-43797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="CVE-2021-43797">CVE-2021-43797</a></p>
<p>Release Date: 2021-12-09</p>
<p>Fix Resolution: io.netty:netty-codec-http:4.1.71.Final,io.netty:netty-all:4.1.71.Final</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.33.Final","packageFilePaths":["/KSA/ksa/ksa/ksa-web-root/ksa-finance-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.33.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-codec-http:4.1.71.Final,io.netty:netty-all:4.1.71.Final","isBinary":false}],"baseBranches":[],"vulnerabilityIdentifier":"CVE-2021-43797","vulnerabilityDetails":"Netty is an asynchronous event-driven network application framework for rapid development of maintainable high performance protocol servers \u0026 clients. Netty prior to version 4.1.7.1.Final skips control chars when they are present at the beginning / end of the header name. It should instead fail fast as these are not allowed by the spec and could lead to HTTP request smuggling. Failing to do the validation might cause netty to \"sanitize\" header names before it forward these to another remote system when used as proxy. This remote system can\u0027t see the invalid usage anymore, and therefore does not do the validation itself. Users should upgrade to version 4.1.7.1.Final to receive a patch.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43797","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in netty all final jar cve medium severity vulnerability vulnerable library netty all final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients library home page a href path to dependency file ksa ksa ksa ksa web root ksa finance web pom xml path to vulnerable library repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar ksa ksa ksa ksa web root ksa web target root web inf lib netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar repository io netty netty all final netty all final jar dependency hierarchy x netty all final jar vulnerable library vulnerability details netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers clients netty prior to version final skips control chars when they are present at the beginning end of the header name it should instead fail fast as these are not allowed by the spec and could lead to http request smuggling failing to do the validation might cause netty to sanitize header names before it forward these to another remote system when used as proxy this remote system can t see the invalid usage anymore and therefore does not do the validation itself users should upgrade to version final to receive a patch publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin cve release date fix resolution io netty netty codec http final io netty netty all final check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree io netty netty all final isminimumfixversionavailable true minimumfixversion io netty netty codec http final io netty netty all final isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers clients netty prior to version final skips control chars when they are present at the beginning end of the header name it should instead fail fast as these are not allowed by the spec and could lead to http request smuggling failing to do the validation might cause netty to sanitize header names before it forward these to another remote system when used as proxy this remote system can see the invalid usage anymore and therefore does not do the validation itself users should upgrade to version final to receive a patch vulnerabilityurl | 0 |
72,675 | 24,230,176,000 | IssuesEvent | 2022-09-26 17:32:25 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | Commit 48cf170d5 breaks PowerPC build on FreeBSD | Type: Defect | ### System information
Type | Version/Name
--- | ---
Distribution Name | FreeBSD
Distribution Version | 14.0-CURRENT
Kernel Version | 14.0-CURRENT main-n258120-c7046f76c2c0
Architecture | PowerPC
OpenZFS Version | 2.1.99-FreeBSD_gc629f0bf6
### Describe the problem you're observing
lib/libspl/include/sys/simd.h: getauxval() declared on line 456 is redeclared on line 461
https://github.com/openzfs/zfs/blob/c629f0bf62e351355716f9870d6c2e377584b016/lib/libspl/include/sys/simd.h#L456-L461
### Describe how to reproduce the problem
Try to compile for PowerPC on FreeBSD
### Include any warning/errors/backtraces from the system logs
```
In file included from /usr/src/sys/contrib/openzfs/module/icp/algs/aes/aes_impl.c:28:
/usr/src/sys/contrib/openzfs/lib/libspl/include/sys/simd.h:461:22: error: static declaration of 'getauxval' follows non-static declaration
static unsigned long getauxval(unsigned long key)
^
/usr/src/sys/contrib/openzfs/lib/libspl/include/sys/simd.h:456:22: note: previous declaration is here
extern unsigned long getauxval(unsigned long type);
^
``` | 1.0 | Commit 48cf170d5 breaks PowerPC build on FreeBSD - ### System information
Type | Version/Name
--- | ---
Distribution Name | FreeBSD
Distribution Version | 14.0-CURRENT
Kernel Version | 14.0-CURRENT main-n258120-c7046f76c2c0
Architecture | PowerPC
OpenZFS Version | 2.1.99-FreeBSD_gc629f0bf6
### Describe the problem you're observing
lib/libspl/include/sys/simd.h: getauxval() declared on line 456 is redeclared on line 461
https://github.com/openzfs/zfs/blob/c629f0bf62e351355716f9870d6c2e377584b016/lib/libspl/include/sys/simd.h#L456-L461
### Describe how to reproduce the problem
Try to compile for PowerPC on FreeBSD
### Include any warning/errors/backtraces from the system logs
```
In file included from /usr/src/sys/contrib/openzfs/module/icp/algs/aes/aes_impl.c:28:
/usr/src/sys/contrib/openzfs/lib/libspl/include/sys/simd.h:461:22: error: static declaration of 'getauxval' follows non-static declaration
static unsigned long getauxval(unsigned long key)
^
/usr/src/sys/contrib/openzfs/lib/libspl/include/sys/simd.h:456:22: note: previous declaration is here
extern unsigned long getauxval(unsigned long type);
^
``` | non_priority | commit breaks powerpc build on freebsd system information type version name distribution name freebsd distribution version current kernel version current main architecture powerpc openzfs version freebsd describe the problem you re observing lib libspl include sys simd h getauxval declared on line is redeclared on line describe how to reproduce the problem try to compile for powerpc on freebsd include any warning errors backtraces from the system logs in file included from usr src sys contrib openzfs module icp algs aes aes impl c usr src sys contrib openzfs lib libspl include sys simd h error static declaration of getauxval follows non static declaration static unsigned long getauxval unsigned long key usr src sys contrib openzfs lib libspl include sys simd h note previous declaration is here extern unsigned long getauxval unsigned long type | 0 |
17,565 | 24,209,599,757 | IssuesEvent | 2022-09-25 18:04:26 | ModdingForBlockheads/RefinedRelocation2 | https://api.github.com/repos/ModdingForBlockheads/RefinedRelocation2 | closed | Yabba Support | compatibility feature help wanted | Sorting Barrel Upgrade to upgrade existing barrels, Sorting Barrel that will use Item Match logic to be part of the sorting network. | True | Yabba Support - Sorting Barrel Upgrade to upgrade existing barrels, Sorting Barrel that will use Item Match logic to be part of the sorting network. | non_priority | yabba support sorting barrel upgrade to upgrade existing barrels sorting barrel that will use item match logic to be part of the sorting network | 0 |
115,624 | 14,856,597,207 | IssuesEvent | 2021-01-18 14:21:35 | uncharted-distil/distil | https://api.github.com/repos/uncharted-distil/distil | opened | SHAP tooltips | design enhancement | Feedback from user testing is that SHAP is difficult to understand. We could address this generating a tooltip that explains what the SHAP values are telling us for each row:
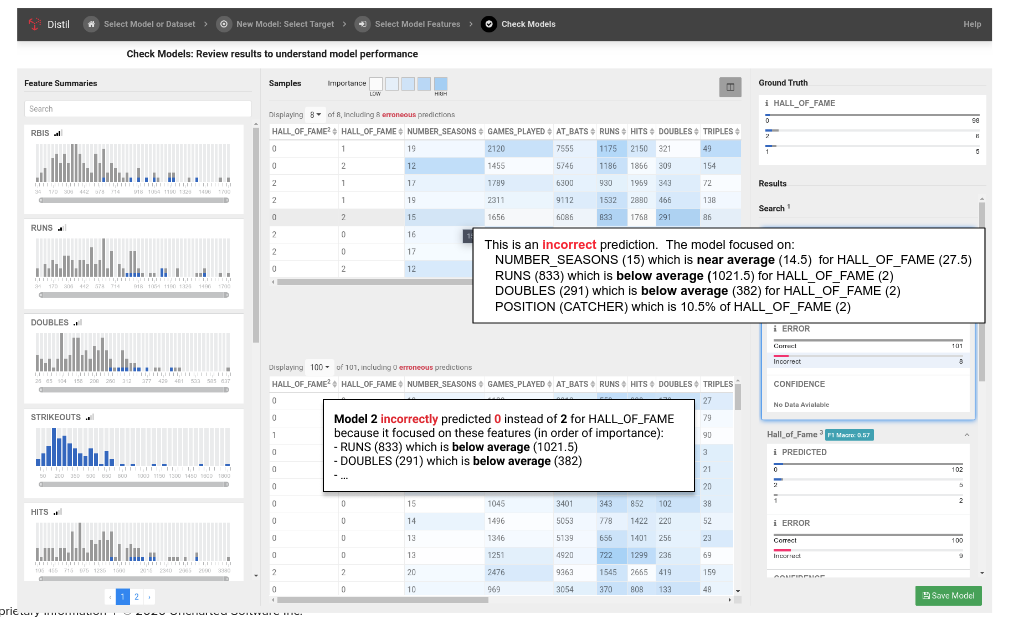
| 1.0 | SHAP tooltips - Feedback from user testing is that SHAP is difficult to understand. We could address this generating a tooltip that explains what the SHAP values are telling us for each row:
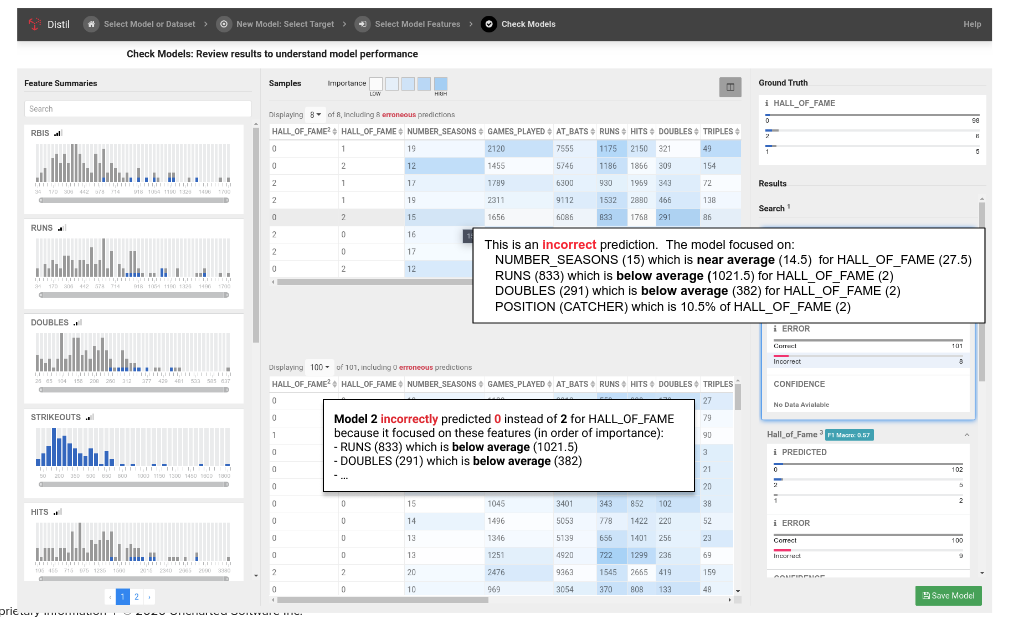
| non_priority | shap tooltips feedback from user testing is that shap is difficult to understand we could address this generating a tooltip that explains what the shap values are telling us for each row | 0 |
66,187 | 27,379,509,837 | IssuesEvent | 2023-02-28 09:04:31 | ministryofjustice/modernisation-platform | https://api.github.com/repos/ministryofjustice/modernisation-platform | closed | Ability for end users to run Terraform destroy via GitHub Actions workflow | github_actions sustainability member request user experience self-service | ## User Story
As a MP user
I want to be able to destroy my Terraform
So that I can build again fresh from scratch
## User Type(s)
MP User
## Value
Gives users the power to destroy their own environments. It may be that once something is in production they want to destroy environments and just stand them up again when needed. Or it could be during the development phase so that they can have confidence that they can rebuild when needed.
## Questions / Assumptions / Hypothesis
### Hypothesis
If we add a job to the github workflow, that runs on workflow_dispatch and enables users to chose the environment they can run a terraform destroy against
Then they will not need to contact the mp team to do this
### Proposal
Add a job where you can run a workflow via workflow dispatch, passing in the environment (excluding production), which when ran, runs a terraform destroy against that environment.
## Definition of done
<!-- Checklist for definition of done and acceptance criteria, for example: -->
- [x] destroy workflow poc created
- [x] workflow template updated
- [x] user workflow files updated
- [x] user docs have been updated
- [x] another team member has reviewed
- [x] tests are green
## Reference
[How to write good user stories](https://www.gov.uk/service-manual/agile-delivery/writing-user-stories)
| 1.0 | Ability for end users to run Terraform destroy via GitHub Actions workflow - ## User Story
As a MP user
I want to be able to destroy my Terraform
So that I can build again fresh from scratch
## User Type(s)
MP User
## Value
Gives users the power to destroy their own environments. It may be that once something is in production they want to destroy environments and just stand them up again when needed. Or it could be during the development phase so that they can have confidence that they can rebuild when needed.
## Questions / Assumptions / Hypothesis
### Hypothesis
If we add a job to the github workflow, that runs on workflow_dispatch and enables users to chose the environment they can run a terraform destroy against
Then they will not need to contact the mp team to do this
### Proposal
Add a job where you can run a workflow via workflow dispatch, passing in the environment (excluding production), which when ran, runs a terraform destroy against that environment.
## Definition of done
<!-- Checklist for definition of done and acceptance criteria, for example: -->
- [x] destroy workflow poc created
- [x] workflow template updated
- [x] user workflow files updated
- [x] user docs have been updated
- [x] another team member has reviewed
- [x] tests are green
## Reference
[How to write good user stories](https://www.gov.uk/service-manual/agile-delivery/writing-user-stories)
| non_priority | ability for end users to run terraform destroy via github actions workflow user story as a mp user i want to be able to destroy my terraform so that i can build again fresh from scratch user type s mp user value gives users the power to destroy their own environments it may be that once something is in production they want to destroy environments and just stand them up again when needed or it could be during the development phase so that they can have confidence that they can rebuild when needed questions assumptions hypothesis hypothesis if we add a job to the github workflow that runs on workflow dispatch and enables users to chose the environment they can run a terraform destroy against then they will not need to contact the mp team to do this proposal add a job where you can run a workflow via workflow dispatch passing in the environment excluding production which when ran runs a terraform destroy against that environment definition of done destroy workflow poc created workflow template updated user workflow files updated user docs have been updated another team member has reviewed tests are green reference | 0 |
95,189 | 10,868,451,098 | IssuesEvent | 2019-11-15 03:46:57 | alice-i-cecile/Fonts-of-Power | https://api.github.com/repos/alice-i-cecile/Fonts-of-Power | closed | Should we make separate rulebooks for new players vs players coming from 5e? | documentation | Most 5e players I know would probably just prefer a diff from this and 5e, but new players would need more full explanation. I think drafting two versions is useful here. | 1.0 | Should we make separate rulebooks for new players vs players coming from 5e? - Most 5e players I know would probably just prefer a diff from this and 5e, but new players would need more full explanation. I think drafting two versions is useful here. | non_priority | should we make separate rulebooks for new players vs players coming from most players i know would probably just prefer a diff from this and but new players would need more full explanation i think drafting two versions is useful here | 0 |
164,860 | 12,815,246,371 | IssuesEvent | 2020-07-05 00:50:23 | Alzy/obs-midi | https://api.github.com/repos/Alzy/obs-midi | closed | obs-midi crashes OBS if I set bidirectional for a midi event row. | bug testing | Windows 10
OBS-Studio-25.0.8
obs-midi-109e8c6
obs-virtualcam-2.0.5
obs-websocket-4.8.0
Setting bidirectional checkbox in obs-midi device midi configuration page can cause a crash and corruption of the [MidiAPI] midi_devices entry in basic.ini
1. Open the OBS MIDI Setting dialog.
2. Select a device and press Configure.
3. Press a button.
4. Change it from Fader to Button,
5. Turn on bidirectional for that button
6. Save
7. Press that button to select that scene.
8. Crash OBS
| 1.0 | obs-midi crashes OBS if I set bidirectional for a midi event row. - Windows 10
OBS-Studio-25.0.8
obs-midi-109e8c6
obs-virtualcam-2.0.5
obs-websocket-4.8.0
Setting bidirectional checkbox in obs-midi device midi configuration page can cause a crash and corruption of the [MidiAPI] midi_devices entry in basic.ini
1. Open the OBS MIDI Setting dialog.
2. Select a device and press Configure.
3. Press a button.
4. Change it from Fader to Button,
5. Turn on bidirectional for that button
6. Save
7. Press that button to select that scene.
8. Crash OBS
| non_priority | obs midi crashes obs if i set bidirectional for a midi event row windows obs studio obs midi obs virtualcam obs websocket setting bidirectional checkbox in obs midi device midi configuration page can cause a crash and corruption of the midi devices entry in basic ini open the obs midi setting dialog select a device and press configure press a button change it from fader to button turn on bidirectional for that button save press that button to select that scene crash obs | 0 |
69,931 | 13,383,149,273 | IssuesEvent | 2020-09-02 09:52:36 | aristanetworks/ansible-cvp | https://api.github.com/repos/aristanetworks/ansible-cvp | closed | Fix and optimize ansible-test CI execution | status: in-progress type: Code quality type: Respository Enhancement | - Fix issue where host VM had a more recent version of ansible repository (latest/2.10) and cause the pipeline to fail.
- Move to docker in docker approach for ansible-test, to help with the consistency of applications installed and speed up CI execution.
**Useful information on ubuntu-latest host VM application and scripts:**
- https://github.com/actions/virtual-environments/blob/main/images/linux/Ubuntu1804-README.md
- https://github.com/actions/virtual-environments/tree/main/images/linux/scripts/installers
Similar issue to https://github.com/aristanetworks/ansible-avd/pull/217
| 1.0 | Fix and optimize ansible-test CI execution - - Fix issue where host VM had a more recent version of ansible repository (latest/2.10) and cause the pipeline to fail.
- Move to docker in docker approach for ansible-test, to help with the consistency of applications installed and speed up CI execution.
**Useful information on ubuntu-latest host VM application and scripts:**
- https://github.com/actions/virtual-environments/blob/main/images/linux/Ubuntu1804-README.md
- https://github.com/actions/virtual-environments/tree/main/images/linux/scripts/installers
Similar issue to https://github.com/aristanetworks/ansible-avd/pull/217
| non_priority | fix and optimize ansible test ci execution fix issue where host vm had a more recent version of ansible repository latest and cause the pipeline to fail move to docker in docker approach for ansible test to help with the consistency of applications installed and speed up ci execution useful information on ubuntu latest host vm application and scripts similar issue to | 0 |
174,935 | 14,503,828,875 | IssuesEvent | 2020-12-11 23:31:35 | bcgov/entity | https://api.github.com/repos/bcgov/entity | closed | Create Account Set up Video | Documentation OCM Relationships authentication | ## Description: Create an account set up video showing account type options (basic vs. premium) and the flow for account set up.
Intended Audience: Names and any other groups who wish to learn about the new application.
Note: Due to amount of content this may need to be split into more than one video.
Target Deadline: To be distributed to staff Dec 3rd. Peer review required first.
Note: When distributed a feedback SP document will accompany this so staff can document questions as they go.
Acceptance for a Task:
- [ ] Requires deployments
- [ ] Add/ maintain selectors for QA purposes
- [ ] Test coverage acceptable
- [ ] Linters passed
- [ ] Peer Reviewed
- [ ] PR Accepted
- [ ] Production burn in completed
| 1.0 | Create Account Set up Video - ## Description: Create an account set up video showing account type options (basic vs. premium) and the flow for account set up.
Intended Audience: Names and any other groups who wish to learn about the new application.
Note: Due to amount of content this may need to be split into more than one video.
Target Deadline: To be distributed to staff Dec 3rd. Peer review required first.
Note: When distributed a feedback SP document will accompany this so staff can document questions as they go.
Acceptance for a Task:
- [ ] Requires deployments
- [ ] Add/ maintain selectors for QA purposes
- [ ] Test coverage acceptable
- [ ] Linters passed
- [ ] Peer Reviewed
- [ ] PR Accepted
- [ ] Production burn in completed
| non_priority | create account set up video description create an account set up video showing account type options basic vs premium and the flow for account set up intended audience names and any other groups who wish to learn about the new application note due to amount of content this may need to be split into more than one video target deadline to be distributed to staff dec peer review required first note when distributed a feedback sp document will accompany this so staff can document questions as they go acceptance for a task requires deployments add maintain selectors for qa purposes test coverage acceptable linters passed peer reviewed pr accepted production burn in completed | 0 |
181,285 | 14,859,108,154 | IssuesEvent | 2021-01-18 17:53:11 | profclems/glab | https://api.github.com/repos/profclems/glab | opened | Add manpages | area: documentation kind: enhancement | Git provides comprehensive documentation in man form. Same goes with various command-line tools like gh and docker.
It would be nice to add manpages for `glab`.
Since `glab` uses `spf13/cobra`, it should be quite easy to generate man-pages for the various commands
| 1.0 | Add manpages - Git provides comprehensive documentation in man form. Same goes with various command-line tools like gh and docker.
It would be nice to add manpages for `glab`.
Since `glab` uses `spf13/cobra`, it should be quite easy to generate man-pages for the various commands
| non_priority | add manpages git provides comprehensive documentation in man form same goes with various command line tools like gh and docker it would be nice to add manpages for glab since glab uses cobra it should be quite easy to generate man pages for the various commands | 0 |
130,934 | 27,792,860,607 | IssuesEvent | 2023-03-17 10:14:18 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | insights: write a manual test plan for rctest | testing team/code-insights | for 4.5 release (shipping repo ui, retention)
/cc @felixfbecker @vovakulikov | 1.0 | insights: write a manual test plan for rctest - for 4.5 release (shipping repo ui, retention)
/cc @felixfbecker @vovakulikov | non_priority | insights write a manual test plan for rctest for release shipping repo ui retention cc felixfbecker vovakulikov | 0 |
53,457 | 13,166,814,196 | IssuesEvent | 2020-08-11 09:11:46 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | reopened | FNX3-15783 ⁃ Introduce the concept of channels | eng:build eng:release must | > Channels and Build Variants are tighly connected - if there is overlap between this ticket and #1234 then please merge them. Also, maybe we have already done this?
Make the application aware of channels: Release, Beta, Night and possibly Development.
We will need to make decisions at both run-time and build-time based on the specific channel. | 1.0 | FNX3-15783 ⁃ Introduce the concept of channels - > Channels and Build Variants are tighly connected - if there is overlap between this ticket and #1234 then please merge them. Also, maybe we have already done this?
Make the application aware of channels: Release, Beta, Night and possibly Development.
We will need to make decisions at both run-time and build-time based on the specific channel. | non_priority | ⁃ introduce the concept of channels channels and build variants are tighly connected if there is overlap between this ticket and then please merge them also maybe we have already done this make the application aware of channels release beta night and possibly development we will need to make decisions at both run time and build time based on the specific channel | 0 |
48,015 | 5,931,137,559 | IssuesEvent | 2017-05-24 04:56:22 | GoogleCloudPlatform/google-cloud-eclipse | https://api.github.com/repos/GoogleCloudPlatform/google-cloud-eclipse | opened | Fake exceptions logged from StatusUtilTest are confusing | testing | `StatusUtilTest` creates fake exceptions for testing. They end up being logged, causing confusion:
```
Running com.google.cloud.tools.eclipse.util.status.StatusUtilTest
!ENTRY com.google.cloud.tools.eclipse.util 4 0 2017-05-24 04:05:21.378
!MESSAGE Failed to create project
!STACK 0
java.lang.RuntimeException
at com.google.cloud.tools.eclipse.util.status.StatusUtilTest.testErrorMessage_ExceptionWithoutMessage(StatusUtilTest.java:71)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:264)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:153)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:124)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.apache.maven.surefire.util.ReflectionUtils.invokeMethodWithArray2(ReflectionUtils.java:208)
at org.apache.maven.surefire.booter.ProviderFactory$ProviderProxy.invoke(ProviderFactory.java:156)
at org.apache.maven.surefire.booter.ProviderFactory.invokeProvider(ProviderFactory.java:82)
at org.eclipse.tycho.surefire.osgibooter.OsgiSurefireBooter.run(OsgiSurefireBooter.java:95)
at org.eclipse.tycho.surefire.osgibooter.HeadlessTestApplication.run(HeadlessTestApplication.java:21)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.internal.app.EclipseAppContainer.callMethodWithException(EclipseAppContainer.java:587)
at org.eclipse.equinox.internal.app.EclipseAppHandle.run(EclipseAppHandle.java:198)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.runApplication(EclipseAppLauncher.java:134)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.start(EclipseAppLauncher.java:104)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:380)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:235)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.launcher.Main.invokeFramework(Main.java:669)
at org.eclipse.equinox.launcher.Main.basicRun(Main.java:608)
at org.eclipse.equinox.launcher.Main.run(Main.java:1515)
at org.eclipse.equinox.launcher.Main.main(Main.java:1488)
!ENTRY com.google.cloud.tools.eclipse.util 4 0 2017-05-24 04:05:21.380
!MESSAGE Failed to create project: testing
!STACK 0
java.lang.RuntimeException: testing
at com.google.cloud.tools.eclipse.util.status.StatusUtilTest.testErrorMessage_Exception(StatusUtilTest.java:64)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:264)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:153)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:124)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.apache.maven.surefire.util.ReflectionUtils.invokeMethodWithArray2(ReflectionUtils.java:208)
at org.apache.maven.surefire.booter.ProviderFactory$ProviderProxy.invoke(ProviderFactory.java:156)
at org.apache.maven.surefire.booter.ProviderFactory.invokeProvider(ProviderFactory.java:82)
at org.eclipse.tycho.surefire.osgibooter.OsgiSurefireBooter.run(OsgiSurefireBooter.java:95)
at org.eclipse.tycho.surefire.osgibooter.HeadlessTestApplication.run(HeadlessTestApplication.java:21)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.internal.app.EclipseAppContainer.callMethodWithException(EclipseAppContainer.java:587)
at org.eclipse.equinox.internal.app.EclipseAppHandle.run(EclipseAppHandle.java:198)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.runApplication(EclipseAppLauncher.java:134)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.start(EclipseAppLauncher.java:104)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:380)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:235)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.launcher.Main.invokeFramework(Main.java:669)
at org.eclipse.equinox.launcher.Main.basicRun(Main.java:608)
at org.eclipse.equinox.launcher.Main.run(Main.java:1515)
at org.eclipse.equinox.launcher.Main.main(Main.java:1488)
``` | 1.0 | Fake exceptions logged from StatusUtilTest are confusing - `StatusUtilTest` creates fake exceptions for testing. They end up being logged, causing confusion:
```
Running com.google.cloud.tools.eclipse.util.status.StatusUtilTest
!ENTRY com.google.cloud.tools.eclipse.util 4 0 2017-05-24 04:05:21.378
!MESSAGE Failed to create project
!STACK 0
java.lang.RuntimeException
at com.google.cloud.tools.eclipse.util.status.StatusUtilTest.testErrorMessage_ExceptionWithoutMessage(StatusUtilTest.java:71)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:264)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:153)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:124)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.apache.maven.surefire.util.ReflectionUtils.invokeMethodWithArray2(ReflectionUtils.java:208)
at org.apache.maven.surefire.booter.ProviderFactory$ProviderProxy.invoke(ProviderFactory.java:156)
at org.apache.maven.surefire.booter.ProviderFactory.invokeProvider(ProviderFactory.java:82)
at org.eclipse.tycho.surefire.osgibooter.OsgiSurefireBooter.run(OsgiSurefireBooter.java:95)
at org.eclipse.tycho.surefire.osgibooter.HeadlessTestApplication.run(HeadlessTestApplication.java:21)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.internal.app.EclipseAppContainer.callMethodWithException(EclipseAppContainer.java:587)
at org.eclipse.equinox.internal.app.EclipseAppHandle.run(EclipseAppHandle.java:198)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.runApplication(EclipseAppLauncher.java:134)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.start(EclipseAppLauncher.java:104)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:380)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:235)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.launcher.Main.invokeFramework(Main.java:669)
at org.eclipse.equinox.launcher.Main.basicRun(Main.java:608)
at org.eclipse.equinox.launcher.Main.run(Main.java:1515)
at org.eclipse.equinox.launcher.Main.main(Main.java:1488)
!ENTRY com.google.cloud.tools.eclipse.util 4 0 2017-05-24 04:05:21.380
!MESSAGE Failed to create project: testing
!STACK 0
java.lang.RuntimeException: testing
at com.google.cloud.tools.eclipse.util.status.StatusUtilTest.testErrorMessage_Exception(StatusUtilTest.java:64)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.apache.maven.surefire.junit4.JUnit4Provider.execute(JUnit4Provider.java:264)
at org.apache.maven.surefire.junit4.JUnit4Provider.executeTestSet(JUnit4Provider.java:153)
at org.apache.maven.surefire.junit4.JUnit4Provider.invoke(JUnit4Provider.java:124)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.apache.maven.surefire.util.ReflectionUtils.invokeMethodWithArray2(ReflectionUtils.java:208)
at org.apache.maven.surefire.booter.ProviderFactory$ProviderProxy.invoke(ProviderFactory.java:156)
at org.apache.maven.surefire.booter.ProviderFactory.invokeProvider(ProviderFactory.java:82)
at org.eclipse.tycho.surefire.osgibooter.OsgiSurefireBooter.run(OsgiSurefireBooter.java:95)
at org.eclipse.tycho.surefire.osgibooter.HeadlessTestApplication.run(HeadlessTestApplication.java:21)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.internal.app.EclipseAppContainer.callMethodWithException(EclipseAppContainer.java:587)
at org.eclipse.equinox.internal.app.EclipseAppHandle.run(EclipseAppHandle.java:198)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.runApplication(EclipseAppLauncher.java:134)
at org.eclipse.core.runtime.internal.adaptor.EclipseAppLauncher.start(EclipseAppLauncher.java:104)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:380)
at org.eclipse.core.runtime.adaptor.EclipseStarter.run(EclipseStarter.java:235)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.eclipse.equinox.launcher.Main.invokeFramework(Main.java:669)
at org.eclipse.equinox.launcher.Main.basicRun(Main.java:608)
at org.eclipse.equinox.launcher.Main.run(Main.java:1515)
at org.eclipse.equinox.launcher.Main.main(Main.java:1488)
``` | non_priority | fake exceptions logged from statusutiltest are confusing statusutiltest creates fake exceptions for testing they end up being logged causing confusion running com google cloud tools eclipse util status statusutiltest entry com google cloud tools eclipse util message failed to create project stack java lang runtimeexception at com google cloud tools eclipse util status statusutiltest testerrormessage exceptionwithoutmessage statusutiltest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org apache maven surefire execute java at org apache maven surefire executetestset java at org apache maven surefire invoke java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache maven surefire util reflectionutils reflectionutils java at org apache maven surefire booter providerfactory providerproxy invoke providerfactory java at org apache maven surefire booter providerfactory invokeprovider providerfactory java at org eclipse tycho surefire osgibooter osgisurefirebooter run osgisurefirebooter java at org eclipse tycho surefire osgibooter headlesstestapplication run headlesstestapplication java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org eclipse equinox internal app eclipseappcontainer callmethodwithexception eclipseappcontainer java at org eclipse equinox internal app eclipseapphandle run eclipseapphandle java at org eclipse core runtime internal adaptor eclipseapplauncher runapplication eclipseapplauncher java at org eclipse core runtime internal adaptor eclipseapplauncher start eclipseapplauncher java at org eclipse core runtime adaptor eclipsestarter run eclipsestarter java at org eclipse core runtime adaptor eclipsestarter run eclipsestarter java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org eclipse equinox launcher main invokeframework main java at org eclipse equinox launcher main basicrun main java at org eclipse equinox launcher main run main java at org eclipse equinox launcher main main main java entry com google cloud tools eclipse util message failed to create project testing stack java lang runtimeexception testing at com google cloud tools eclipse util status statusutiltest testerrormessage exception statusutiltest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org apache maven surefire execute java at org apache maven surefire executetestset java at org apache maven surefire invoke java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org apache maven surefire util reflectionutils reflectionutils java at org apache maven surefire booter providerfactory providerproxy invoke providerfactory java at org apache maven surefire booter providerfactory invokeprovider providerfactory java at org eclipse tycho surefire osgibooter osgisurefirebooter run osgisurefirebooter java at org eclipse tycho surefire osgibooter headlesstestapplication run headlesstestapplication java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org eclipse equinox internal app eclipseappcontainer callmethodwithexception eclipseappcontainer java at org eclipse equinox internal app eclipseapphandle run eclipseapphandle java at org eclipse core runtime internal adaptor eclipseapplauncher runapplication eclipseapplauncher java at org eclipse core runtime internal adaptor eclipseapplauncher start eclipseapplauncher java at org eclipse core runtime adaptor eclipsestarter run eclipsestarter java at org eclipse core runtime adaptor eclipsestarter run eclipsestarter java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org eclipse equinox launcher main invokeframework main java at org eclipse equinox launcher main basicrun main java at org eclipse equinox launcher main run main java at org eclipse equinox launcher main main main java | 0 |
61,870 | 12,196,265,079 | IssuesEvent | 2020-04-29 18:46:59 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | closed | lit.py fails when running all tests on Win7 x64 with Visual Studio 2008 | BZ-BUG-STATUS: RESOLVED BZ-RESOLUTION: FIXED clang/LLVM Codegen dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=10629. | 1.0 | lit.py fails when running all tests on Win7 x64 with Visual Studio 2008 - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=10629. | non_priority | lit py fails when running all tests on with visual studio this issue was imported from bugzilla | 0 |
431,917 | 30,257,318,031 | IssuesEvent | 2023-07-07 04:39:29 | Significant-Gravitas/Auto-GPT | https://api.github.com/repos/Significant-Gravitas/Auto-GPT | closed | Fast LLM is the only model used it appears. The smart LLM does not show up in any debug logs | documentation good first issue function: config function: AI-model | ### ⚠️ Search for existing issues first ⚠️
- [X] I have searched the existing issues, and there is no existing issue for my problem
### Which Operating System are you using?
Windows
### Which version of Auto-GPT are you using?
Latest Release
### Do you use OpenAI GPT-3 or GPT-4?
GPT-3.5
### Which area covers your issue best?
AI Model Limitations
### Describe your issue.
Setting Smart LLM to GPT-4 and Setting Fast LLM to GPT-3.5-Turbo only shows 3.5-turbo being used in the logs. Both should be used for different tasks correct? Or the option should be removed.
### Upload Activity Log Content
_No response_
### Upload Error Log Content
_No response_ | 1.0 | Fast LLM is the only model used it appears. The smart LLM does not show up in any debug logs - ### ⚠️ Search for existing issues first ⚠️
- [X] I have searched the existing issues, and there is no existing issue for my problem
### Which Operating System are you using?
Windows
### Which version of Auto-GPT are you using?
Latest Release
### Do you use OpenAI GPT-3 or GPT-4?
GPT-3.5
### Which area covers your issue best?
AI Model Limitations
### Describe your issue.
Setting Smart LLM to GPT-4 and Setting Fast LLM to GPT-3.5-Turbo only shows 3.5-turbo being used in the logs. Both should be used for different tasks correct? Or the option should be removed.
### Upload Activity Log Content
_No response_
### Upload Error Log Content
_No response_ | non_priority | fast llm is the only model used it appears the smart llm does not show up in any debug logs ⚠️ search for existing issues first ⚠️ i have searched the existing issues and there is no existing issue for my problem which operating system are you using windows which version of auto gpt are you using latest release do you use openai gpt or gpt gpt which area covers your issue best ai model limitations describe your issue setting smart llm to gpt and setting fast llm to gpt turbo only shows turbo being used in the logs both should be used for different tasks correct or the option should be removed upload activity log content no response upload error log content no response | 0 |
2,339 | 8,372,684,113 | IssuesEvent | 2018-10-05 07:55:43 | ansible/ansible | https://api.github.com/repos/ansible/ansible | closed | HaProxy drain mode 'bool' object is not callable error | affects_2.4 bug module needs_maintainer net_tools support:community traceback | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
HaProxy Module
##### ANSIBLE VERSION
<!--- Paste verbatim output from "ansible --version" between quotes below -->
```
ansible 2.4.0.0
config file = None
configured module search path = [u'/Users/stewart/.ansible/plugins/modules', u'/usr/share/ansible/plugins/modules']
ansible python module location = /Library/Frameworks/Python.framework/Versions/2.7/lib/python2.7/site-packages/ansible
executable location = /Library/Frameworks/Python.framework/Versions/2.7/bin/ansible
python version = 2.7.13 (v2.7.13:a06454b1afa1, Dec 17 2016, 12:39:47) [GCC 4.2.1 (Apple Inc. build 5666) (dot 3)]
```
##### CONFIGURATION
`ansible-config dump --only-changed` returned nothing. I have changed no config.
##### OS / ENVIRONMENT
Running from OSX 10.10.5
Trying to control HaProxy 1.5.8 on Debian 8
##### SUMMARY
I am able to enable and disable HaProxy backends correctly but when I try to use the "drain" state type I get this error. The playbook works when I use enabled and disabled but fails with the below error when I use drain.
It says, `'bool' object is not callable`. I might just be configuring this wrong but I believe I am doing everything correctly and using the correct Ansible version.
##### STEPS TO REPRODUCE
<!--- Paste example playbooks or commands between quotes below -->
```yaml
- name: Set server to drain
hosts: haproxy
sudo: yes
tasks:
- name: Set server1 to disabled
haproxy:
state: drain
host: server1
socket: /var/run/haproxy.sock
backend: cluster_www
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
I expect the HaProxy backend to change to the drain state.
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with extra verbosity (-vvvv) -->
<!--- Paste verbatim command output between quotes below -->
```
fatal: [10.5.59.15]: FAILED! => {"changed": false, "failed": true, "module_stderr": "Shared connection to 10.5.59.15 closed.\r\n", "module_stdout": "Traceback (most recent call last):\r\n File \"/tmp/ansible_Xzs48s/ansible_module_haproxy.py\", line 454, in <module>\r\n main()\r\n File \"/tmp/ansible_Xzs48s/ansible_module_haproxy.py\", line 450, in main\r\n ansible_haproxy.act()\r\n File \"/tmp/ansible_Xzs48s/ansible_module_haproxy.py\", line 410, in act\r\n self.drain(self.host, self.backend)\r\nTypeError: 'bool' object is not callable\r\n", "msg": "MODULE FAILURE", "rc": 0}
```
| True | HaProxy drain mode 'bool' object is not callable error - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
HaProxy Module
##### ANSIBLE VERSION
<!--- Paste verbatim output from "ansible --version" between quotes below -->
```
ansible 2.4.0.0
config file = None
configured module search path = [u'/Users/stewart/.ansible/plugins/modules', u'/usr/share/ansible/plugins/modules']
ansible python module location = /Library/Frameworks/Python.framework/Versions/2.7/lib/python2.7/site-packages/ansible
executable location = /Library/Frameworks/Python.framework/Versions/2.7/bin/ansible
python version = 2.7.13 (v2.7.13:a06454b1afa1, Dec 17 2016, 12:39:47) [GCC 4.2.1 (Apple Inc. build 5666) (dot 3)]
```
##### CONFIGURATION
`ansible-config dump --only-changed` returned nothing. I have changed no config.
##### OS / ENVIRONMENT
Running from OSX 10.10.5
Trying to control HaProxy 1.5.8 on Debian 8
##### SUMMARY
I am able to enable and disable HaProxy backends correctly but when I try to use the "drain" state type I get this error. The playbook works when I use enabled and disabled but fails with the below error when I use drain.
It says, `'bool' object is not callable`. I might just be configuring this wrong but I believe I am doing everything correctly and using the correct Ansible version.
##### STEPS TO REPRODUCE
<!--- Paste example playbooks or commands between quotes below -->
```yaml
- name: Set server to drain
hosts: haproxy
sudo: yes
tasks:
- name: Set server1 to disabled
haproxy:
state: drain
host: server1
socket: /var/run/haproxy.sock
backend: cluster_www
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
I expect the HaProxy backend to change to the drain state.
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with extra verbosity (-vvvv) -->
<!--- Paste verbatim command output between quotes below -->
```
fatal: [10.5.59.15]: FAILED! => {"changed": false, "failed": true, "module_stderr": "Shared connection to 10.5.59.15 closed.\r\n", "module_stdout": "Traceback (most recent call last):\r\n File \"/tmp/ansible_Xzs48s/ansible_module_haproxy.py\", line 454, in <module>\r\n main()\r\n File \"/tmp/ansible_Xzs48s/ansible_module_haproxy.py\", line 450, in main\r\n ansible_haproxy.act()\r\n File \"/tmp/ansible_Xzs48s/ansible_module_haproxy.py\", line 410, in act\r\n self.drain(self.host, self.backend)\r\nTypeError: 'bool' object is not callable\r\n", "msg": "MODULE FAILURE", "rc": 0}
```
| non_priority | haproxy drain mode bool object is not callable error issue type bug report component name haproxy module ansible version ansible config file none configured module search path ansible python module location library frameworks python framework versions lib site packages ansible executable location library frameworks python framework versions bin ansible python version dec configuration ansible config dump only changed returned nothing i have changed no config os environment running from osx trying to control haproxy on debian summary i am able to enable and disable haproxy backends correctly but when i try to use the drain state type i get this error the playbook works when i use enabled and disabled but fails with the below error when i use drain it says bool object is not callable i might just be configuring this wrong but i believe i am doing everything correctly and using the correct ansible version steps to reproduce yaml name set server to drain hosts haproxy sudo yes tasks name set to disabled haproxy state drain host socket var run haproxy sock backend cluster www expected results i expect the haproxy backend to change to the drain state actual results fatal failed changed false failed true module stderr shared connection to closed r n module stdout traceback most recent call last r n file tmp ansible ansible module haproxy py line in r n main r n file tmp ansible ansible module haproxy py line in main r n ansible haproxy act r n file tmp ansible ansible module haproxy py line in act r n self drain self host self backend r ntypeerror bool object is not callable r n msg module failure rc | 0 |
320,532 | 23,813,348,996 | IssuesEvent | 2022-09-05 02:10:22 | lotkey/lkcpp | https://api.github.com/repos/lotkey/lkcpp | opened | Add forward | documentation enhancement | # Implementation Guidance
1. Move `remove_reference` to `lkcpp/type_traits`
2. Define `forward` in `lkcpp/utility`
```cpp
template<class T>
T&& forward(typename remove_reference<T>::type& t) noexcept
{
return static_cast<T&&>(t);
}
template<class T>
T&& forward(typename remove_reference<T>::type&& t) noexcept
{
return static_cast<T&&>(t);
}
```
3. Add comments
4. Add unit tests | 1.0 | Add forward - # Implementation Guidance
1. Move `remove_reference` to `lkcpp/type_traits`
2. Define `forward` in `lkcpp/utility`
```cpp
template<class T>
T&& forward(typename remove_reference<T>::type& t) noexcept
{
return static_cast<T&&>(t);
}
template<class T>
T&& forward(typename remove_reference<T>::type&& t) noexcept
{
return static_cast<T&&>(t);
}
```
3. Add comments
4. Add unit tests | non_priority | add forward implementation guidance move remove reference to lkcpp type traits define forward in lkcpp utility cpp template t forward typename remove reference type t noexcept return static cast t template t forward typename remove reference type t noexcept return static cast t add comments add unit tests | 0 |
39,550 | 20,049,383,086 | IssuesEvent | 2022-02-03 03:10:59 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | opened | Column: make a big slice then divide into sub slices instead of making multi slices in `newColumn` | type/enhancement help wanted type/performance | ## Enhancement
In some our benchmarks, we find that `makeslice` of `newColumn` costs some CPUs
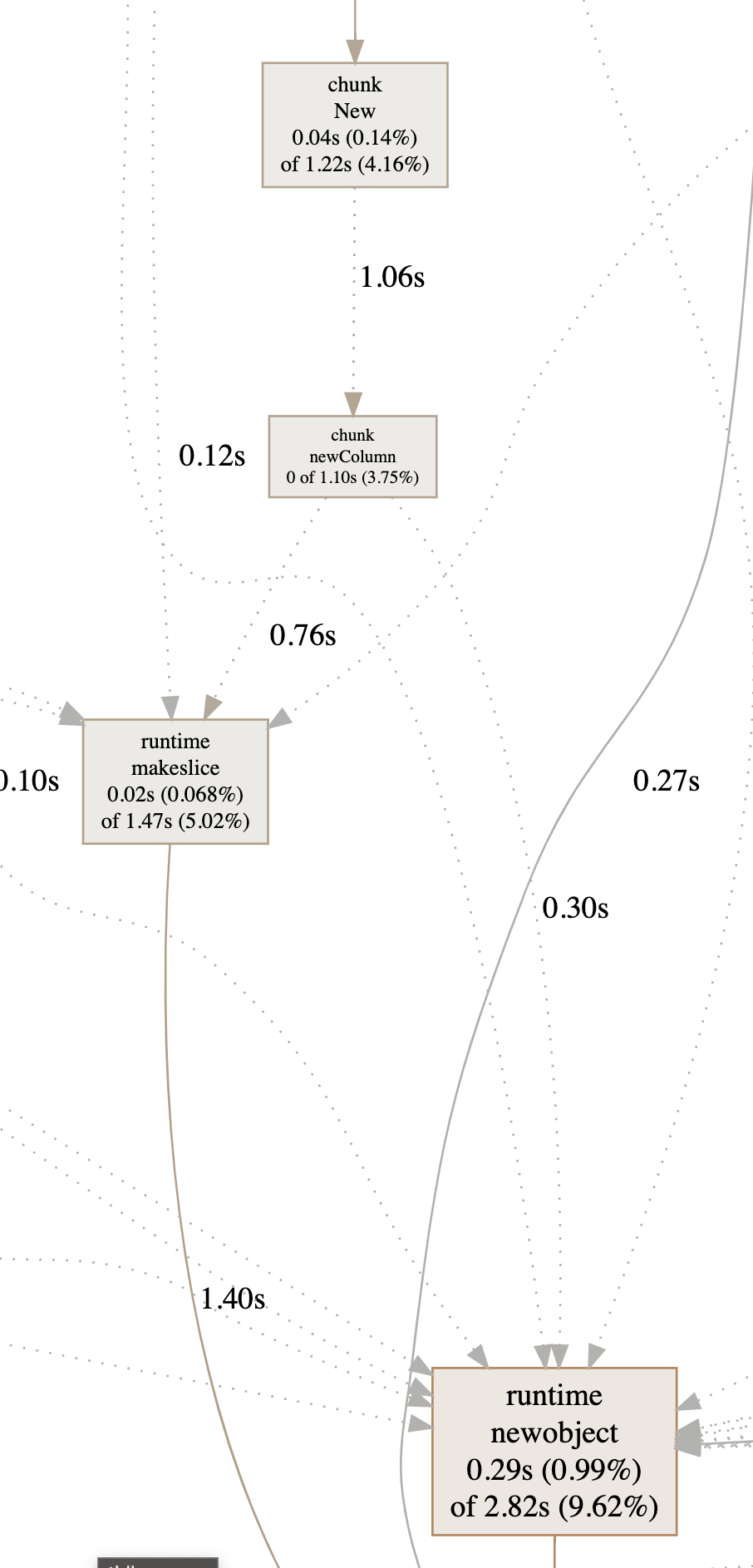
In the `newColumn`, we can see that we make the slice three times, I think we can only make a big slice instead
I write a simple benchmark
```go
func BenchmarkMakeslice(b *testing.B) {
cap := 2
elemLen := 8
n := 0
for i := 0; i < b.N; i++ {
elemBuf := make([]byte, elemLen)
data := make([]byte, 0, cap*elemLen)
nullBitmap := make([]byte, 0, (cap+7)>>3)
n = len(elemBuf) + len(data) + len(nullBitmap) + n
}
}
func BenchmarkMakeslice2(b *testing.B) {
cap := 2
elemLen := 8
n := 0
for i := 0; i < b.N; i++ {
index := cap * elemLen
cap2 := (cap + 7) >> 3
buf := make([]byte, elemLen+index+cap2)
elemBuf := unsafe.Slice(&buf[0], elemLen)
data := unsafe.Slice(&buf[elemLen], index)
nullBitmap := unsafe.Slice(&buf[index+elemLen], cap2)
elemBuf = elemBuf[0:0]
data = data[0:0]
nullBitmap = nullBitmap[0:0]
n = len(elemBuf) + len(data) + len(nullBitmap) + n
}
}
```
The result is promising:
```bash
cpu: Intel(R) Core(TM) i7-4790K CPU @ 4.00GHz
BenchmarkMakeslice-8 15793832 84.81 ns/op
BenchmarkMakeslice2-8 31883019 37.09 ns/op
```
Because I think `newColumn` is frequently used, I guess we can get benefit from this.
BTW, another better way is to use a pool for Column, but seems that we tried this before but failed, maybe we should re-start this again.
| True | Column: make a big slice then divide into sub slices instead of making multi slices in `newColumn` - ## Enhancement
In some our benchmarks, we find that `makeslice` of `newColumn` costs some CPUs
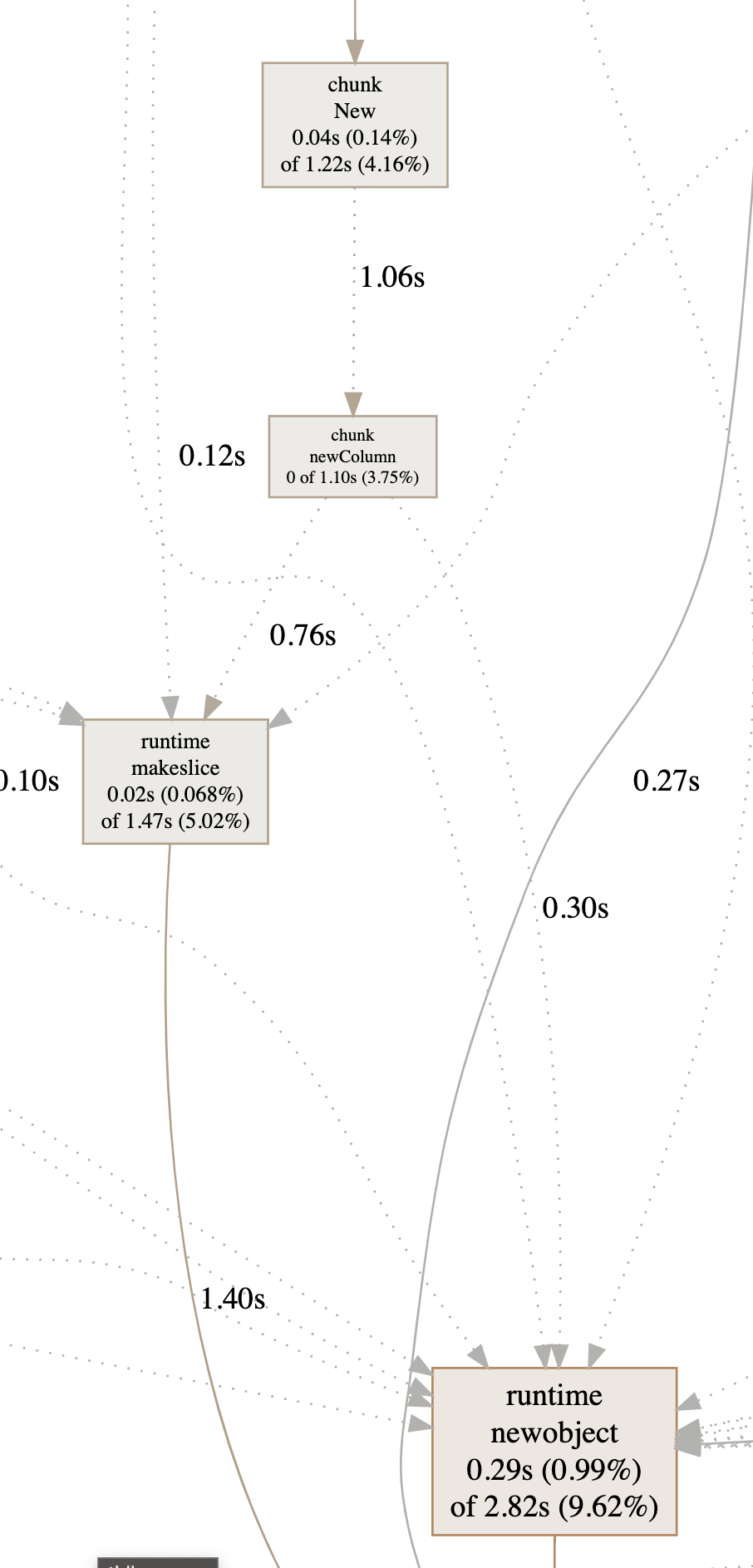
In the `newColumn`, we can see that we make the slice three times, I think we can only make a big slice instead
I write a simple benchmark
```go
func BenchmarkMakeslice(b *testing.B) {
cap := 2
elemLen := 8
n := 0
for i := 0; i < b.N; i++ {
elemBuf := make([]byte, elemLen)
data := make([]byte, 0, cap*elemLen)
nullBitmap := make([]byte, 0, (cap+7)>>3)
n = len(elemBuf) + len(data) + len(nullBitmap) + n
}
}
func BenchmarkMakeslice2(b *testing.B) {
cap := 2
elemLen := 8
n := 0
for i := 0; i < b.N; i++ {
index := cap * elemLen
cap2 := (cap + 7) >> 3
buf := make([]byte, elemLen+index+cap2)
elemBuf := unsafe.Slice(&buf[0], elemLen)
data := unsafe.Slice(&buf[elemLen], index)
nullBitmap := unsafe.Slice(&buf[index+elemLen], cap2)
elemBuf = elemBuf[0:0]
data = data[0:0]
nullBitmap = nullBitmap[0:0]
n = len(elemBuf) + len(data) + len(nullBitmap) + n
}
}
```
The result is promising:
```bash
cpu: Intel(R) Core(TM) i7-4790K CPU @ 4.00GHz
BenchmarkMakeslice-8 15793832 84.81 ns/op
BenchmarkMakeslice2-8 31883019 37.09 ns/op
```
Because I think `newColumn` is frequently used, I guess we can get benefit from this.
BTW, another better way is to use a pool for Column, but seems that we tried this before but failed, maybe we should re-start this again.
| non_priority | column make a big slice then divide into sub slices instead of making multi slices in newcolumn enhancement in some our benchmarks we find that makeslice of newcolumn costs some cpus in the newcolumn we can see that we make the slice three times i think we can only make a big slice instead i write a simple benchmark go func benchmarkmakeslice b testing b cap elemlen n for i i b n i elembuf make byte elemlen data make byte cap elemlen nullbitmap make byte cap n len elembuf len data len nullbitmap n func b testing b cap elemlen n for i i b n i index cap elemlen cap buf make byte elemlen index elembuf unsafe slice buf elemlen data unsafe slice buf index nullbitmap unsafe slice buf elembuf elembuf data data nullbitmap nullbitmap n len elembuf len data len nullbitmap n the result is promising bash cpu intel r core tm cpu benchmarkmakeslice ns op ns op because i think newcolumn is frequently used i guess we can get benefit from this btw another better way is to use a pool for column but seems that we tried this before but failed maybe we should re start this again | 0 |
84,178 | 10,354,115,057 | IssuesEvent | 2019-09-05 13:07:54 | ClearTax/pivotal-flow | https://api.github.com/repos/ClearTax/pivotal-flow | opened | Shell script for setting up node and npm using nvm before installing pivotal-flow | documentation | running a simple curl command with the shell script should install all dependencies | 1.0 | Shell script for setting up node and npm using nvm before installing pivotal-flow - running a simple curl command with the shell script should install all dependencies | non_priority | shell script for setting up node and npm using nvm before installing pivotal flow running a simple curl command with the shell script should install all dependencies | 0 |
28,670 | 4,426,063,908 | IssuesEvent | 2016-08-16 17:11:52 | uProxy/uproxy | https://api.github.com/repos/uProxy/uproxy | closed | jpm run broken in firefox 47 beta 3 onwards | C:Cloud C:Firefox C:Testing P1 | Not sure what's going on here but our tests are broken in Firefox 47 beta 3 onwards. **Not*, weirdly in the 48 branch (yet).
On beta 2 I see this message:
```
DEPRECATION WARNING: This path to Console.jsm is deprecated. Please use Cu.import("resource://gre/modules/Console.jsm") to load this module.
You may find more details about this deprecation at: https://bugzil.la/912121
resource://gre/modules/devtools/Console.jsm 19 null
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 9117 require<[43]</<
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 9112 require<[43]<
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 22 s
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 22 e
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 22 null
resource://gre/modules/commonjs/toolkit/loader.js -> resource://simple-socks/index.js 5 null
resource://gre/modules/commonjs/toolkit/loader.js 279 evaluate
resource://gre/modules/commonjs/toolkit/loader.js 331 load
resource://gre/modules/commonjs/toolkit/loader.js 768 main
resource://gre/modules/commonjs/toolkit/loader.js -> resource://gre/modules/commonjs/sdk/addon/runner.js 147 run
resource://gre/modules/commonjs/toolkit/loader.js -> resource://gre/modules/commonjs/sdk/addon/runner.js 87 startup/</<
resource://gre/modules/Promise.jsm -> resource://gre/modules/Promise-backend.js 937 Handler.prototype.process
resource://gre/modules/Promise.jsm -> resource://gre/modules/Promise-backend.js 816 this.PromiseWalker.walkerLoop
resource://gre/modules/Promise.jsm -> resource://gre/modules/Promise-backend.js 750 this.PromiseWalker.scheduleWalkerLoop/<
``` | 1.0 | jpm run broken in firefox 47 beta 3 onwards - Not sure what's going on here but our tests are broken in Firefox 47 beta 3 onwards. **Not*, weirdly in the 48 branch (yet).
On beta 2 I see this message:
```
DEPRECATION WARNING: This path to Console.jsm is deprecated. Please use Cu.import("resource://gre/modules/Console.jsm") to load this module.
You may find more details about this deprecation at: https://bugzil.la/912121
resource://gre/modules/devtools/Console.jsm 19 null
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 9117 require<[43]</<
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 9112 require<[43]<
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 22 s
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 22 e
resource://simple-socks/data/freedom-for-firefox/freedom-for-firefox.jsm 22 null
resource://gre/modules/commonjs/toolkit/loader.js -> resource://simple-socks/index.js 5 null
resource://gre/modules/commonjs/toolkit/loader.js 279 evaluate
resource://gre/modules/commonjs/toolkit/loader.js 331 load
resource://gre/modules/commonjs/toolkit/loader.js 768 main
resource://gre/modules/commonjs/toolkit/loader.js -> resource://gre/modules/commonjs/sdk/addon/runner.js 147 run
resource://gre/modules/commonjs/toolkit/loader.js -> resource://gre/modules/commonjs/sdk/addon/runner.js 87 startup/</<
resource://gre/modules/Promise.jsm -> resource://gre/modules/Promise-backend.js 937 Handler.prototype.process
resource://gre/modules/Promise.jsm -> resource://gre/modules/Promise-backend.js 816 this.PromiseWalker.walkerLoop
resource://gre/modules/Promise.jsm -> resource://gre/modules/Promise-backend.js 750 this.PromiseWalker.scheduleWalkerLoop/<
``` | non_priority | jpm run broken in firefox beta onwards not sure what s going on here but our tests are broken in firefox beta onwards not weirdly in the branch yet on beta i see this message deprecation warning this path to console jsm is deprecated please use cu import resource gre modules console jsm to load this module you may find more details about this deprecation at resource gre modules devtools console jsm null resource simple socks data freedom for firefox freedom for firefox jsm require resource simple socks data freedom for firefox freedom for firefox jsm require resource simple socks data freedom for firefox freedom for firefox jsm s resource simple socks data freedom for firefox freedom for firefox jsm e resource simple socks data freedom for firefox freedom for firefox jsm null resource gre modules commonjs toolkit loader js resource simple socks index js null resource gre modules commonjs toolkit loader js evaluate resource gre modules commonjs toolkit loader js load resource gre modules commonjs toolkit loader js main resource gre modules commonjs toolkit loader js resource gre modules commonjs sdk addon runner js run resource gre modules commonjs toolkit loader js resource gre modules commonjs sdk addon runner js startup resource gre modules promise jsm resource gre modules promise backend js handler prototype process resource gre modules promise jsm resource gre modules promise backend js this promisewalker walkerloop resource gre modules promise jsm resource gre modules promise backend js this promisewalker schedulewalkerloop | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.