Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
3,824 | 14,660,171,351 | IssuesEvent | 2020-12-28 22:42:16 | kunstmusik/blue | https://api.github.com/repos/kunstmusik/blue | closed | add alt-click to insert point at time position of mouse but start y-value on current line in Tempo, Automation of SSO and JMask Object | Automation Lines | LIke issue #388:
"Automation: added alt-click to insert point at time position of
mouse but start y-value on current line. Moving is relative to the point's
initial y-value. Works in conjunction with ctrl-dragging to restrict value
change along one axis."
I would like to have this in Tempo, Automation of SSO and JMask Object as well.
| 1.0 | add alt-click to insert point at time position of mouse but start y-value on current line in Tempo, Automation of SSO and JMask Object - LIke issue #388:
"Automation: added alt-click to insert point at time position of
mouse but start y-value on current line. Moving is relative to the point's
initial y-value. Works in conjunction with ctrl-dragging to restrict value
change along one axis."
I would like to have this in Tempo, Automation of SSO and JMask Object as well.
| non_priority | add alt click to insert point at time position of mouse but start y value on current line in tempo automation of sso and jmask object like issue automation added alt click to insert point at time position of mouse but start y value on current line moving is relative to the point s initial y value works in conjunction with ctrl dragging to restrict value change along one axis i would like to have this in tempo automation of sso and jmask object as well | 0 |
45,284 | 12,702,118,015 | IssuesEvent | 2020-06-22 19:31:33 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | opened | DatePicker: AM/PM calculation incorrect | defect | **Describe the defect**
Regression caused by: https://github.com/primefaces/primefaces/issues/5186
CC @NicolaIsotta
The AM/PM calculation has an off by 1 error. It is using `KK` which is 0-11 based instead of `hh` 1-12 based.
Wen you use "12" in the Time it ends up with a validation error on the screen that says this:
_'06/22/2020 12:00 PM' could not be understood as a date and time. Example: 06/22/2020 03:02 PM_
Actual exception (via debugger) is from SimpleDateFormat:
_java.text.ParseException: Unparseable date: "06/22/2020 12:00 PM"_
**Environment:**
- PF Version: _8.0.2_
- JSF + version: _ALL_
- Affected browsers: _ALL_
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
**Expected behavior**
Properly parse the time.
**Example XHTML**
```html
<h:form id="frmTest">
<p:datePicker showTime="true" hourFormat="12" stepMinute="15" pattern="MM/dd/yyyy " required="true">
</p:datePicker>
</h:form>
```
**Reproducer**
```java
try {
final SimpleDateFormat formatter = new SimpleDateFormat("MM/dd/yyyy KK:mm a", Locale.getDefault());
formatter.setLenient(false);
formatter.setTimeZone(TimeZone.getDefault());
System.out.println("date: " + formatter.parse("06/22/2020 12:00 PM"));
} catch (final Exception e) {
System.out.println("Exception: " + e.getMessage());
}
```
| 1.0 | DatePicker: AM/PM calculation incorrect - **Describe the defect**
Regression caused by: https://github.com/primefaces/primefaces/issues/5186
CC @NicolaIsotta
The AM/PM calculation has an off by 1 error. It is using `KK` which is 0-11 based instead of `hh` 1-12 based.
Wen you use "12" in the Time it ends up with a validation error on the screen that says this:
_'06/22/2020 12:00 PM' could not be understood as a date and time. Example: 06/22/2020 03:02 PM_
Actual exception (via debugger) is from SimpleDateFormat:
_java.text.ParseException: Unparseable date: "06/22/2020 12:00 PM"_
**Environment:**
- PF Version: _8.0.2_
- JSF + version: _ALL_
- Affected browsers: _ALL_
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
**Expected behavior**
Properly parse the time.
**Example XHTML**
```html
<h:form id="frmTest">
<p:datePicker showTime="true" hourFormat="12" stepMinute="15" pattern="MM/dd/yyyy " required="true">
</p:datePicker>
</h:form>
```
**Reproducer**
```java
try {
final SimpleDateFormat formatter = new SimpleDateFormat("MM/dd/yyyy KK:mm a", Locale.getDefault());
formatter.setLenient(false);
formatter.setTimeZone(TimeZone.getDefault());
System.out.println("date: " + formatter.parse("06/22/2020 12:00 PM"));
} catch (final Exception e) {
System.out.println("Exception: " + e.getMessage());
}
```
| non_priority | datepicker am pm calculation incorrect describe the defect regression caused by cc nicolaisotta the am pm calculation has an off by error it is using kk which is based instead of hh based wen you use in the time it ends up with a validation error on the screen that says this pm could not be understood as a date and time example pm actual exception via debugger is from simpledateformat java text parseexception unparseable date pm environment pf version jsf version all affected browsers all to reproduce steps to reproduce the behavior go to click on scroll down to see error expected behavior properly parse the time example xhtml html reproducer java try final simpledateformat formatter new simpledateformat mm dd yyyy kk mm a locale getdefault formatter setlenient false formatter settimezone timezone getdefault system out println date formatter parse pm catch final exception e system out println exception e getmessage | 0 |
39,102 | 15,873,193,891 | IssuesEvent | 2021-04-09 01:48:53 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | opened | aws-iso-b diff: Certain CloudFormation limits not supported | partition/aws-iso-b service/cloudformation | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Potential Impact
This issue is to track the impact on and fixes to the Terraform AWS Provider from the following differences between the `aws-iso-b` partition and the public, commercial `aws` partition (aka "standard partition"). (This limitation may also apply to `aws-iso`.)
* AWS CloudFormation does not support the limit for resources in concurrent stack operations.
* AWS CloudFormation does not support the limit of concurrent stack instance operations, by region, for StackSets.
### References
* #18593
| 1.0 | aws-iso-b diff: Certain CloudFormation limits not supported - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Potential Impact
This issue is to track the impact on and fixes to the Terraform AWS Provider from the following differences between the `aws-iso-b` partition and the public, commercial `aws` partition (aka "standard partition"). (This limitation may also apply to `aws-iso`.)
* AWS CloudFormation does not support the limit for resources in concurrent stack operations.
* AWS CloudFormation does not support the limit of concurrent stack instance operations, by region, for StackSets.
### References
* #18593
| non_priority | aws iso b diff certain cloudformation limits not supported community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment potential impact this issue is to track the impact on and fixes to the terraform aws provider from the following differences between the aws iso b partition and the public commercial aws partition aka standard partition this limitation may also apply to aws iso aws cloudformation does not support the limit for resources in concurrent stack operations aws cloudformation does not support the limit of concurrent stack instance operations by region for stacksets references | 0 |
284,938 | 31,017,856,454 | IssuesEvent | 2023-08-10 01:03:55 | amaybaum-dev/legend-depot-demo2 | https://api.github.com/repos/amaybaum-dev/legend-depot-demo2 | opened | legend-depot-store-mongo-1.7.6-SNAPSHOT.jar: 4 vulnerabilities (highest severity is: 7.5) reachable | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>legend-depot-store-mongo-1.7.6-SNAPSHOT.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (legend-depot-store-mongo version) | Remediation Possible** | Reachability |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- | --- |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-46877](https://www.mend.io/vulnerability-database/CVE-2021-46877) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42004</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42004>CVE-2022-42004</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.13.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-42003</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.finos.legend.depot.store.mongo.admin.metrics.QueryMetricsMongo (Application)
-> com.fasterxml.jackson.databind.ObjectMapper (Extension)
-> com.fasterxml.jackson.databind.deser.BeanDeserializerFactory (Extension)
-> com.fasterxml.jackson.databind.deser.std.ThrowableDeserializer (Extension)
-> com.fasterxml.jackson.databind.deser.BeanDeserializerBase (Extension)
-> ❌ com.fasterxml.jackson.databind.deser.std.StdDeserializer (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2020-36518</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.finos.legend.depot.store.mongo.admin.metrics.QueryMetricsMongo (Application)
-> com.fasterxml.jackson.databind.ObjectMapper (Extension)
-> com.fasterxml.jackson.databind.deser.BeanDeserializerFactory (Extension)
-> com.fasterxml.jackson.databind.deser.BasicDeserializerFactory (Extension)
-> com.fasterxml.jackson.databind.deser.std.UntypedObjectDeserializer (Extension)
-> ❌ com.fasterxml.jackson.databind.deser.std.UntypedObjectDeserializer$Vanilla (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind before 2.13.0 allows a Java StackOverflow exception and denial of service via a large depth of nested objects.
Mend Note: After conducting further research, Mend has determined that all versions of com.fasterxml.jackson.core:jackson-databind up to version 2.13.2 are vulnerable to CVE-2020-36518.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-36518>CVE-2020-36518</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6.1,2.13.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2021-46877</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.finos.legend.depot.server.pure.model.context.services.PureModelContextServiceImpl (Application)
-> com.fasterxml.jackson.databind.json.JsonMapper (Extension)
-> com.fasterxml.jackson.databind.node.ArrayNode (Extension)
-> com.fasterxml.jackson.databind.node.BaseJsonNode (Extension)
-> ❌ com.fasterxml.jackson.databind.node.NodeSerialization (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6,2.13.1</p>
</p>
<p></p>
</details> | True | legend-depot-store-mongo-1.7.6-SNAPSHOT.jar: 4 vulnerabilities (highest severity is: 7.5) reachable - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>legend-depot-store-mongo-1.7.6-SNAPSHOT.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (legend-depot-store-mongo version) | Remediation Possible** | Reachability |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- | --- |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
| [CVE-2021-46877](https://www.mend.io/vulnerability-database/CVE-2021-46877) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | jackson-databind-2.10.5.1.jar | Transitive | N/A* | ❌|<p align="center"><a href="#">[<img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20>](## 'The vulnerability is likely to be reachable.')</a></p> |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p><p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2022-42004</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.13.4, resource exhaustion can occur because of a lack of a check in BeanDeserializer._deserializeFromArray to prevent use of deeply nested arrays. An application is vulnerable only with certain customized choices for deserialization.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42004>CVE-2022-42004</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.13.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2022-42003</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.finos.legend.depot.store.mongo.admin.metrics.QueryMetricsMongo (Application)
-> com.fasterxml.jackson.databind.ObjectMapper (Extension)
-> com.fasterxml.jackson.databind.deser.BeanDeserializerFactory (Extension)
-> com.fasterxml.jackson.databind.deser.std.ThrowableDeserializer (Extension)
-> com.fasterxml.jackson.databind.deser.BeanDeserializerBase (Extension)
-> ❌ com.fasterxml.jackson.databind.deser.std.StdDeserializer (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled. Additional fix version in 2.13.4.1 and 2.12.17.1
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.7.1,2.13.4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2020-36518</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.finos.legend.depot.store.mongo.admin.metrics.QueryMetricsMongo (Application)
-> com.fasterxml.jackson.databind.ObjectMapper (Extension)
-> com.fasterxml.jackson.databind.deser.BeanDeserializerFactory (Extension)
-> com.fasterxml.jackson.databind.deser.BasicDeserializerFactory (Extension)
-> com.fasterxml.jackson.databind.deser.std.UntypedObjectDeserializer (Extension)
-> ❌ com.fasterxml.jackson.databind.deser.std.UntypedObjectDeserializer$Vanilla (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind before 2.13.0 allows a Java StackOverflow exception and denial of service via a large depth of nested objects.
Mend Note: After conducting further research, Mend has determined that all versions of com.fasterxml.jackson.core:jackson-databind up to version 2.13.2 are vulnerable to CVE-2020-36518.
<p>Publish Date: 2022-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-36518>CVE-2020-36518</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-03-11</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6.1,2.13.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> <img src='https://whitesource-resources.whitesourcesoftware.com/viaRed.png' width=19 height=20> CVE-2021-46877</summary>
### Vulnerable Library - <b>jackson-databind-2.10.5.1.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /legend-depot-artifacts-purge/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.5.1/jackson-databind-2.10.5.1.jar</p>
<p>
Dependency Hierarchy:
- legend-depot-store-mongo-1.7.6-SNAPSHOT.jar (Root Library)
- legend-depot-model-1.7.6-SNAPSHOT.jar
- legend-engine-protocol-pure-4.4.5.jar
- legend-engine-protocol-4.4.5.jar
- :x: **jackson-databind-2.10.5.1.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Reachability Analysis
<p>
This vulnerability is potentially used
```
org.finos.legend.depot.server.pure.model.context.services.PureModelContextServiceImpl (Application)
-> com.fasterxml.jackson.databind.json.JsonMapper (Extension)
-> com.fasterxml.jackson.databind.node.ArrayNode (Extension)
-> com.fasterxml.jackson.databind.node.BaseJsonNode (Extension)
-> ❌ com.fasterxml.jackson.databind.node.NodeSerialization (Vulnerable Component)
```
</p>
<p></p>
### Vulnerability Details
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.12.6,2.13.1</p>
</p>
<p></p>
</details> | non_priority | legend depot store mongo snapshot jar vulnerabilities highest severity is reachable vulnerable library legend depot store mongo snapshot jar path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar vulnerabilities cve severity cvss dependency type fixed in legend depot store mongo version remediation possible reachability high jackson databind jar transitive n a high jackson databind jar transitive n a the vulnerability is likely to be reachable high jackson databind jar transitive n a the vulnerability is likely to be reachable high jackson databind jar transitive n a the vulnerability is likely to be reachable for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed in some cases remediation pr cannot be created automatically for a vulnerability despite the availability of remediation details cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file legend depot artifacts purge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy legend depot store mongo snapshot jar root library legend depot model snapshot jar legend engine protocol pure jar legend engine protocol jar x jackson databind jar vulnerable library found in base branch master vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in beandeserializer deserializefromarray to prevent use of deeply nested arrays an application is vulnerable only with certain customized choices for deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file legend depot artifacts purge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy legend depot store mongo snapshot jar root library legend depot model snapshot jar legend engine protocol pure jar legend engine protocol jar x jackson databind jar vulnerable library found in base branch master reachability analysis this vulnerability is potentially used org finos legend depot store mongo admin metrics querymetricsmongo application com fasterxml jackson databind objectmapper extension com fasterxml jackson databind deser beandeserializerfactory extension com fasterxml jackson databind deser std throwabledeserializer extension com fasterxml jackson databind deser beandeserializerbase extension ❌ com fasterxml jackson databind deser std stddeserializer vulnerable component vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting when the unwrap single value arrays feature is enabled additional fix version in and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file legend depot artifacts purge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy legend depot store mongo snapshot jar root library legend depot model snapshot jar legend engine protocol pure jar legend engine protocol jar x jackson databind jar vulnerable library found in base branch master reachability analysis this vulnerability is potentially used org finos legend depot store mongo admin metrics querymetricsmongo application com fasterxml jackson databind objectmapper extension com fasterxml jackson databind deser beandeserializerfactory extension com fasterxml jackson databind deser basicdeserializerfactory extension com fasterxml jackson databind deser std untypedobjectdeserializer extension ❌ com fasterxml jackson databind deser std untypedobjectdeserializer vanilla vulnerable component vulnerability details jackson databind before allows a java stackoverflow exception and denial of service via a large depth of nested objects mend note after conducting further research mend has determined that all versions of com fasterxml jackson core jackson databind up to version are vulnerable to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file legend depot artifacts purge pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy legend depot store mongo snapshot jar root library legend depot model snapshot jar legend engine protocol pure jar legend engine protocol jar x jackson databind jar vulnerable library found in base branch master reachability analysis this vulnerability is potentially used org finos legend depot server pure model context services puremodelcontextserviceimpl application com fasterxml jackson databind json jsonmapper extension com fasterxml jackson databind node arraynode extension com fasterxml jackson databind node basejsonnode extension ❌ com fasterxml jackson databind node nodeserialization vulnerable component vulnerability details jackson databind x through x before and x before allows attackers to cause a denial of service gb transient heap usage per read in uncommon situations involving jsonnode jdk serialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind | 0 |
161,572 | 12,551,920,697 | IssuesEvent | 2020-06-06 16:22:00 | TheCheatsrichter/Gw2_Launchbuddy | https://api.github.com/repos/TheCheatsrichter/Gw2_Launchbuddy | closed | Option to disable .dat file version check? | status:testing type:enhancement | I use another program to update my .dat files, but use LB to load my accounts. Would it be possible to have an option to disable the .dat file update check instead of having it forces upon loading the program? | 1.0 | Option to disable .dat file version check? - I use another program to update my .dat files, but use LB to load my accounts. Would it be possible to have an option to disable the .dat file update check instead of having it forces upon loading the program? | non_priority | option to disable dat file version check i use another program to update my dat files but use lb to load my accounts would it be possible to have an option to disable the dat file update check instead of having it forces upon loading the program | 0 |
14,419 | 4,923,431,412 | IssuesEvent | 2016-11-25 10:19:31 | eclipse/che | https://api.github.com/repos/eclipse/che | closed | The expanded project is collapsed when workspace is restarted (regression) | kind/bug sprint/next-sprint status/code-review team/ide | When I have an expanded project in the tree and perform restarting the workspace, the project is collapsed. But it should restore previos state
**Reproduction Steps:**
* Expand a project in the IDE.
* Perform restart the workspace.
**Expected behavior:**
The project should save his state.
**Observed behavior:**
The project is collapsed.
**Che version:** 5.0.0-M7
**OS and version:** Ubuntu 14.04
**Docker version:** 1.12
**Che install:** Docker container
**Additional information:**
* Problem can be reliably reproduced, doesn't happen randomly: Yes | 1.0 | The expanded project is collapsed when workspace is restarted (regression) - When I have an expanded project in the tree and perform restarting the workspace, the project is collapsed. But it should restore previos state
**Reproduction Steps:**
* Expand a project in the IDE.
* Perform restart the workspace.
**Expected behavior:**
The project should save his state.
**Observed behavior:**
The project is collapsed.
**Che version:** 5.0.0-M7
**OS and version:** Ubuntu 14.04
**Docker version:** 1.12
**Che install:** Docker container
**Additional information:**
* Problem can be reliably reproduced, doesn't happen randomly: Yes | non_priority | the expanded project is collapsed when workspace is restarted regression when i have an expanded project in the tree and perform restarting the workspace the project is collapsed but it should restore previos state reproduction steps expand a project in the ide perform restart the workspace expected behavior the project should save his state observed behavior the project is collapsed che version os and version ubuntu docker version che install docker container additional information problem can be reliably reproduced doesn t happen randomly yes | 0 |
2,180 | 2,596,233,703 | IssuesEvent | 2015-02-20 19:18:42 | arlolra/ctypes-otr | https://api.github.com/repos/arlolra/ctypes-otr | closed | Conversation with contact not using OTR | design | When starting a conversation with a contact who is not using OTR, the message is:
2:41:23 pm - The current conversation is not private.
2:41:26 pm - You attempted to send an unencrypted message to sukhe. Unencrypted messages to this recipient are not allowed. Attempting to start a private conversation. Your message will be retransmitted when the private conversation starts.
I think we can word this better. Specifically, saying "Unencrypted messages to this recipient are not allowed" makes it seem like that this specific contact is the issue and not the fact that unencrypted conversations are not allowed as a policy.
A possible suggestion:
You attempted to send an unencrypted message to sukhe. This contact does not support encrypted communication and Tor Messenger does not allow unencrypted messages to be sent.
And then, in a separate message which follows (on a new line):
Attempting to start a private conversation. Your message will be retransmitted when the private conversation starts.
Something along these lines... | 1.0 | Conversation with contact not using OTR - When starting a conversation with a contact who is not using OTR, the message is:
2:41:23 pm - The current conversation is not private.
2:41:26 pm - You attempted to send an unencrypted message to sukhe. Unencrypted messages to this recipient are not allowed. Attempting to start a private conversation. Your message will be retransmitted when the private conversation starts.
I think we can word this better. Specifically, saying "Unencrypted messages to this recipient are not allowed" makes it seem like that this specific contact is the issue and not the fact that unencrypted conversations are not allowed as a policy.
A possible suggestion:
You attempted to send an unencrypted message to sukhe. This contact does not support encrypted communication and Tor Messenger does not allow unencrypted messages to be sent.
And then, in a separate message which follows (on a new line):
Attempting to start a private conversation. Your message will be retransmitted when the private conversation starts.
Something along these lines... | non_priority | conversation with contact not using otr when starting a conversation with a contact who is not using otr the message is pm the current conversation is not private pm you attempted to send an unencrypted message to sukhe unencrypted messages to this recipient are not allowed attempting to start a private conversation your message will be retransmitted when the private conversation starts i think we can word this better specifically saying unencrypted messages to this recipient are not allowed makes it seem like that this specific contact is the issue and not the fact that unencrypted conversations are not allowed as a policy a possible suggestion you attempted to send an unencrypted message to sukhe this contact does not support encrypted communication and tor messenger does not allow unencrypted messages to be sent and then in a separate message which follows on a new line attempting to start a private conversation your message will be retransmitted when the private conversation starts something along these lines | 0 |
119,117 | 12,014,927,615 | IssuesEvent | 2020-04-10 12:47:34 | txtdirect/txtdirect | https://api.github.com/repos/txtdirect/txtdirect | closed | [gometa] Documentation | documentation | <!--
This form is for bug reports and feature requests ONLY!
If you're looking for help check out [our support guidelines](/SUPPORT.md).
-->
**Is this a BUG REPORT or FEATURE REQUEST?**:
docs
# gometa:
```
schema.resumic.test. IN A 127.0.0.1
_redirect.schema.resumic.test. IN TXT "v=txtv0;to=https://github.com/resumic/schema;type=gometa"
```
go get -u schema.resumic.test -> downloads https://github.com/resumic/schema
# gometa + path:
```
go.resumic.test. IN A 127.0.0.1
_redirect.go.resumic.test. IN TXT "v=txtv0;to=https://about.resumic.org;type=path"
_redirect.schema.go.resumic.test. IN TXT "v=txtv0;to=https://github.com/resumic/schema;type=gometa"
```
go get -u go.resumic.test/schema -> downloads https://github.com/resumic/schema
Visiting go.resumic.test -> redirect to https://about.resumic.org
go get -u go.resumic.test -> failure aka no meta tag as expected
Both methods also work for go imports:
import "go.resumic.test/schema/cmd" | 1.0 | [gometa] Documentation - <!--
This form is for bug reports and feature requests ONLY!
If you're looking for help check out [our support guidelines](/SUPPORT.md).
-->
**Is this a BUG REPORT or FEATURE REQUEST?**:
docs
# gometa:
```
schema.resumic.test. IN A 127.0.0.1
_redirect.schema.resumic.test. IN TXT "v=txtv0;to=https://github.com/resumic/schema;type=gometa"
```
go get -u schema.resumic.test -> downloads https://github.com/resumic/schema
# gometa + path:
```
go.resumic.test. IN A 127.0.0.1
_redirect.go.resumic.test. IN TXT "v=txtv0;to=https://about.resumic.org;type=path"
_redirect.schema.go.resumic.test. IN TXT "v=txtv0;to=https://github.com/resumic/schema;type=gometa"
```
go get -u go.resumic.test/schema -> downloads https://github.com/resumic/schema
Visiting go.resumic.test -> redirect to https://about.resumic.org
go get -u go.resumic.test -> failure aka no meta tag as expected
Both methods also work for go imports:
import "go.resumic.test/schema/cmd" | non_priority | documentation this form is for bug reports and feature requests only if you re looking for help check out support md is this a bug report or feature request docs gometa schema resumic test in a redirect schema resumic test in txt v to go get u schema resumic test downloads gometa path go resumic test in a redirect go resumic test in txt v to redirect schema go resumic test in txt v to go get u go resumic test schema downloads visiting go resumic test redirect to go get u go resumic test failure aka no meta tag as expected both methods also work for go imports import go resumic test schema cmd | 0 |
228,195 | 18,164,483,705 | IssuesEvent | 2021-09-27 13:20:49 | postmodern/chruby | https://api.github.com/repos/postmodern/chruby | closed | Add separate integration tests | feature tests | Add proper integration tests which run chruby against `/opt/rubies` or a given `rubies/` directory. The test script should directly query the ruby for it's settings (`RUBY_VERSION`, `RUBY_ENGINE`, etc), attempt to switch to each ruby in the `rubies/` directory, validate that the appropriate ENV variables have been set correctly, explicitly error on empty-values (ex: if the ruby returns an empty string for `GEM_ROOT` or `RUBY_VERSION`, something has broken).
All unit tests shall be moved into `test/unit/`, and all integration tests shall reside in `test/integration/`. Integration tests should probably not run as part of the CI just yet, and are more intended for local testing. | 1.0 | Add separate integration tests - Add proper integration tests which run chruby against `/opt/rubies` or a given `rubies/` directory. The test script should directly query the ruby for it's settings (`RUBY_VERSION`, `RUBY_ENGINE`, etc), attempt to switch to each ruby in the `rubies/` directory, validate that the appropriate ENV variables have been set correctly, explicitly error on empty-values (ex: if the ruby returns an empty string for `GEM_ROOT` or `RUBY_VERSION`, something has broken).
All unit tests shall be moved into `test/unit/`, and all integration tests shall reside in `test/integration/`. Integration tests should probably not run as part of the CI just yet, and are more intended for local testing. | non_priority | add separate integration tests add proper integration tests which run chruby against opt rubies or a given rubies directory the test script should directly query the ruby for it s settings ruby version ruby engine etc attempt to switch to each ruby in the rubies directory validate that the appropriate env variables have been set correctly explicitly error on empty values ex if the ruby returns an empty string for gem root or ruby version something has broken all unit tests shall be moved into test unit and all integration tests shall reside in test integration integration tests should probably not run as part of the ci just yet and are more intended for local testing | 0 |
10,228 | 8,853,223,078 | IssuesEvent | 2019-01-08 20:41:11 | elderanakain/pa165-formula-one-team | https://api.github.com/repos/elderanakain/pa165-formula-one-team | opened | BaseService vs BaseFacade | bug service | Original text:
_Base interfaces - the base interfaces for facades and services do describe related behavior, but in an inconsistent way (e.g. BaseFacade declares only findById and getAll, where BaseService declares these plus remove and update, etc.) I believe there is a reason for this, but I could find it confusing were I to become a contributor._
- [ ] Move `remove` and `update` methods from `BaseService` to `BaseEntityService`. | 1.0 | BaseService vs BaseFacade - Original text:
_Base interfaces - the base interfaces for facades and services do describe related behavior, but in an inconsistent way (e.g. BaseFacade declares only findById and getAll, where BaseService declares these plus remove and update, etc.) I believe there is a reason for this, but I could find it confusing were I to become a contributor._
- [ ] Move `remove` and `update` methods from `BaseService` to `BaseEntityService`. | non_priority | baseservice vs basefacade original text base interfaces the base interfaces for facades and services do describe related behavior but in an inconsistent way e g basefacade declares only findbyid and getall where baseservice declares these plus remove and update etc i believe there is a reason for this but i could find it confusing were i to become a contributor move remove and update methods from baseservice to baseentityservice | 0 |
272,268 | 20,740,212,722 | IssuesEvent | 2022-03-14 16:59:31 | hashgraph/guardian | https://api.github.com/repos/hashgraph/guardian | closed | Optional Booleans | bug documentation technical task | Optional booleans are not being honored
(When I don't set the value on an optional boolean, it makes me fill it out anyway) | 1.0 | Optional Booleans - Optional booleans are not being honored
(When I don't set the value on an optional boolean, it makes me fill it out anyway) | non_priority | optional booleans optional booleans are not being honored when i don t set the value on an optional boolean it makes me fill it out anyway | 0 |
65,107 | 6,948,884,944 | IssuesEvent | 2017-12-06 02:52:11 | w3c/csswg-drafts | https://api.github.com/repos/w3c/csswg-drafts | closed | [css21][css-inline] Position of the baseline inline-level boxes with non normal line-height | Closed Accepted by CSSWG Resolution css-inline-3 CSS2 Needs review of Pull Request Needs review of Test Case(s) | **This is part of the #1796 series. Read that issue for context**
----
1.
All browsers (Safari, Chrome, FF, Edge) agree, that the position of the baseline within an inline level box with the line-height property set to something other than normal **does not depend on on fallback fonts**.
[Test source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/line-height-002.html)
[Ref source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/reference/line-height-002-ref.html)
[Live test](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/line-height-002.html)
[Live ref](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/reference/line-height-002-ref.html)
----
2.
All browsers (Safari, Chrome, FF, Edge) agree, that the position of the baseline within an inline level box with the line-height property set to something other than normal **is set based on the primary the primary font**.
[Test source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/line-height-003.html)
[Ref source (mismatch)](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/reference/line-height-003-ref.html)
[Live test](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/line-height-003.html)
[Live ref (mismatch)](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/reference/line-height-003-ref.html)
----
1+2 => This is the blue behavior in [this diagram](https://lists.w3.org/Archives/Public/www-archive/2017Apr/att-0008/IMG_20170421_173959.jpg).
We should spec that.
----
3.
More specifically, all browsers (Safari, Chrome, FF, Edge) agree that the position of the baseline within an inline level box with the line-height:normal and in a inline-level box with the line-height property manually set to the height you'd get with `line-heigh:normal` (assuming only the primary font is used) are the same.
This is unsurprising, but it is good to have it confirmed.
[Test source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/line-height-004.html)
[Ref source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/reference/line-height-004-ref.html)
[Live test](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/line-height-004.html)
[Live ref](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/reference/line-height-004-ref.html)
---
However, see #1798 for a possible exception to point 2 and 3.
| 1.0 | [css21][css-inline] Position of the baseline inline-level boxes with non normal line-height - **This is part of the #1796 series. Read that issue for context**
----
1.
All browsers (Safari, Chrome, FF, Edge) agree, that the position of the baseline within an inline level box with the line-height property set to something other than normal **does not depend on on fallback fonts**.
[Test source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/line-height-002.html)
[Ref source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/reference/line-height-002-ref.html)
[Live test](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/line-height-002.html)
[Live ref](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/reference/line-height-002-ref.html)
----
2.
All browsers (Safari, Chrome, FF, Edge) agree, that the position of the baseline within an inline level box with the line-height property set to something other than normal **is set based on the primary the primary font**.
[Test source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/line-height-003.html)
[Ref source (mismatch)](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/reference/line-height-003-ref.html)
[Live test](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/line-height-003.html)
[Live ref (mismatch)](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/reference/line-height-003-ref.html)
----
1+2 => This is the blue behavior in [this diagram](https://lists.w3.org/Archives/Public/www-archive/2017Apr/att-0008/IMG_20170421_173959.jpg).
We should spec that.
----
3.
More specifically, all browsers (Safari, Chrome, FF, Edge) agree that the position of the baseline within an inline level box with the line-height:normal and in a inline-level box with the line-height property manually set to the height you'd get with `line-heigh:normal` (assuming only the primary font is used) are the same.
This is unsurprising, but it is good to have it confirmed.
[Test source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/line-height-004.html)
[Ref source](https://github.com/frivoal/web-platform-tests/blob/line-height-experiments/css/css-line-height/reference/line-height-004-ref.html)
[Live test](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/line-height-004.html)
[Live ref](https://rawgit.com/frivoal/web-platform-tests/line-height-experiments/css/css-line-height/reference/line-height-004-ref.html)
---
However, see #1798 for a possible exception to point 2 and 3.
| non_priority | position of the baseline inline level boxes with non normal line height this is part of the series read that issue for context all browsers safari chrome ff edge agree that the position of the baseline within an inline level box with the line height property set to something other than normal does not depend on on fallback fonts all browsers safari chrome ff edge agree that the position of the baseline within an inline level box with the line height property set to something other than normal is set based on the primary the primary font this is the blue behavior in we should spec that more specifically all browsers safari chrome ff edge agree that the position of the baseline within an inline level box with the line height normal and in a inline level box with the line height property manually set to the height you d get with line heigh normal assuming only the primary font is used are the same this is unsurprising but it is good to have it confirmed however see for a possible exception to point and | 0 |
126,133 | 12,287,523,983 | IssuesEvent | 2020-05-09 12:37:14 | pounard/goat-query | https://api.github.com/repos/pounard/goat-query | closed | Implement driver versionning | bug documentation enhancement | Before today, this was not necessary because we had only SQL writer implementation for each RDMS vendor, but now, we have 2 for MySQL, thanks to MERGE implemention. So here is what to be implemented:
- one PHPUnit test runner per version,
- read RDMS version on connection init, or force it by configuration (parameter such as `&version=57` for example),
- spawn services depending upon version.
| 1.0 | Implement driver versionning - Before today, this was not necessary because we had only SQL writer implementation for each RDMS vendor, but now, we have 2 for MySQL, thanks to MERGE implemention. So here is what to be implemented:
- one PHPUnit test runner per version,
- read RDMS version on connection init, or force it by configuration (parameter such as `&version=57` for example),
- spawn services depending upon version.
| non_priority | implement driver versionning before today this was not necessary because we had only sql writer implementation for each rdms vendor but now we have for mysql thanks to merge implemention so here is what to be implemented one phpunit test runner per version read rdms version on connection init or force it by configuration parameter such as version for example spawn services depending upon version | 0 |
32,649 | 4,387,976,344 | IssuesEvent | 2016-08-08 17:26:09 | Kotlin/anko | https://api.github.com/repos/Kotlin/anko | closed | debug(value) not working | as designed DSL question | ```
class LocationService : Service(), GpsStatus.Listener, LocationListener, AnkoLogger {
override fun onLocationChanged(location: Location) {
Log.d("LocationService", location.latitude.toString()) // working
debug(location.latitude.toString()) // not working
}
```
have no idea why it's not working. | 1.0 | debug(value) not working - ```
class LocationService : Service(), GpsStatus.Listener, LocationListener, AnkoLogger {
override fun onLocationChanged(location: Location) {
Log.d("LocationService", location.latitude.toString()) // working
debug(location.latitude.toString()) // not working
}
```
have no idea why it's not working. | non_priority | debug value not working class locationservice service gpsstatus listener locationlistener ankologger override fun onlocationchanged location location log d locationservice location latitude tostring working debug location latitude tostring not working have no idea why it s not working | 0 |
29,007 | 13,920,672,063 | IssuesEvent | 2020-10-21 10:47:11 | elastic/logstash | https://api.github.com/repos/elastic/logstash | opened | Global shared scheduler | enhancement performance improvements | Many plugins in Logstash use scheduling of tasks:
- jdbc integration
- http_poller input
- translatte filter
- elasticsearch input
All these rely on `rufus-scheduler` library, and each plugin instance creates its own scheduler. This can create problems in large configurations with > 1000 inputs where we start seeing contention for listing threads, for example:
```
java.lang.Thread.State: BLOCKED (on object monitor)
at org.jruby.internal.runtime.ThreadService.getActiveRubyThreads(ThreadService.java:244)
- waiting to lock <0x0000000654ec0f90> (a java.util.Collections$SynchronizedMap)
at org.jruby.RubyThread.list(RubyThread.java:882)
at usr.share.logstash.vendor.bundle.jruby.$2_dot_5_dot_0.gems.rufus_minus_scheduler_minus_3_dot_0_dot_9.lib.rufus.scheduler.RUBY$method$threads$0(/usr/share/logstash/vendor/bundle/jruby/2.5.0/gems/rufus-scheduler-3.0.9/lib/rufus/scheduler.rb:396)
```
An alternative would be to provide a scheduler instance in Logstash core, that any plugin can use, thus centralizing resource usage. | True | Global shared scheduler - Many plugins in Logstash use scheduling of tasks:
- jdbc integration
- http_poller input
- translatte filter
- elasticsearch input
All these rely on `rufus-scheduler` library, and each plugin instance creates its own scheduler. This can create problems in large configurations with > 1000 inputs where we start seeing contention for listing threads, for example:
```
java.lang.Thread.State: BLOCKED (on object monitor)
at org.jruby.internal.runtime.ThreadService.getActiveRubyThreads(ThreadService.java:244)
- waiting to lock <0x0000000654ec0f90> (a java.util.Collections$SynchronizedMap)
at org.jruby.RubyThread.list(RubyThread.java:882)
at usr.share.logstash.vendor.bundle.jruby.$2_dot_5_dot_0.gems.rufus_minus_scheduler_minus_3_dot_0_dot_9.lib.rufus.scheduler.RUBY$method$threads$0(/usr/share/logstash/vendor/bundle/jruby/2.5.0/gems/rufus-scheduler-3.0.9/lib/rufus/scheduler.rb:396)
```
An alternative would be to provide a scheduler instance in Logstash core, that any plugin can use, thus centralizing resource usage. | non_priority | global shared scheduler many plugins in logstash use scheduling of tasks jdbc integration http poller input translatte filter elasticsearch input all these rely on rufus scheduler library and each plugin instance creates its own scheduler this can create problems in large configurations with inputs where we start seeing contention for listing threads for example java lang thread state blocked on object monitor at org jruby internal runtime threadservice getactiverubythreads threadservice java waiting to lock a java util collections synchronizedmap at org jruby rubythread list rubythread java at usr share logstash vendor bundle jruby dot dot gems rufus minus scheduler minus dot dot lib rufus scheduler ruby method threads usr share logstash vendor bundle jruby gems rufus scheduler lib rufus scheduler rb an alternative would be to provide a scheduler instance in logstash core that any plugin can use thus centralizing resource usage | 0 |
335,929 | 24,483,749,471 | IssuesEvent | 2022-10-09 06:33:55 | awesome-panel/awesome-panel-cli | https://api.github.com/repos/awesome-panel/awesome-panel-cli | opened | Create an introduction.ipynb reference notebook | documentation good first issue | The [introduction.ipynb](https://github.com/awesome-panel/awesome-panel-cli/blob/main/src/awesome_panel_cli/templates/notebooks/introduction.ipynb) notebook is just a copy of the [getting_started.ipynb](https://github.com/awesome-panel/awesome-panel-cli/blob/main/src/awesome_panel_cli/templates/notebooks/getting_started.ipynb) notebook.
I would like an `introduction` notebook that
- Gives an introduction to Panel and data apps
- Includes reference links to the Panel web site and other useful resources. | 1.0 | Create an introduction.ipynb reference notebook - The [introduction.ipynb](https://github.com/awesome-panel/awesome-panel-cli/blob/main/src/awesome_panel_cli/templates/notebooks/introduction.ipynb) notebook is just a copy of the [getting_started.ipynb](https://github.com/awesome-panel/awesome-panel-cli/blob/main/src/awesome_panel_cli/templates/notebooks/getting_started.ipynb) notebook.
I would like an `introduction` notebook that
- Gives an introduction to Panel and data apps
- Includes reference links to the Panel web site and other useful resources. | non_priority | create an introduction ipynb reference notebook the notebook is just a copy of the notebook i would like an introduction notebook that gives an introduction to panel and data apps includes reference links to the panel web site and other useful resources | 0 |
24,441 | 6,543,817,444 | IssuesEvent | 2017-09-03 06:37:08 | udacity/sdc-issue-reports | https://api.github.com/repos/udacity/sdc-issue-reports | closed | Lesson 16: 14. Parameter Optimization - slightly enhancements of comments | code effort-Low enhancement ready term_2 | In line 142. can you please add that make_robot() have to be called before EVERY call of run().
Furthermore there is some left over "# TODO: your code here" comment in line 123. | 1.0 | Lesson 16: 14. Parameter Optimization - slightly enhancements of comments - In line 142. can you please add that make_robot() have to be called before EVERY call of run().
Furthermore there is some left over "# TODO: your code here" comment in line 123. | non_priority | lesson parameter optimization slightly enhancements of comments in line can you please add that make robot have to be called before every call of run furthermore there is some left over todo your code here comment in line | 0 |
74,356 | 25,083,054,097 | IssuesEvent | 2022-11-07 21:05:27 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | 508-defect-2: Operating status, breadcrumb only contains the current page | 508/Accessibility 508-defect-2 Facilities | Label: 18928
- [508-defect-2]
https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-2
Issue Title: Defect level 2: Operating status, breadcrumb only contains the current page
Point of Contact: Angela Fowler
**VFS Point of Contact:** _First name only: Angela
<h2>User Story or Problem Statement:</h2>
When visiting a page within a web site, I expect to be able to return to previous pages without using the back button.
<h2>Details</h2>
On the "operating status" page, the breadcrumb only contains the current page. There is no way to return home.
## Acceptance Criteria
- [ ] Breadcrumb is designed such that it recreates the path the user took to reach the "Operating Status" page.
Environment
Steps to Recreate
Proposed Solution (if known)
WCAG or Vendor Guidance (optional)
Screenshots or Trace Logs
| 1.0 | 508-defect-2: Operating status, breadcrumb only contains the current page - Label: 18928
- [508-defect-2]
https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-2
Issue Title: Defect level 2: Operating status, breadcrumb only contains the current page
Point of Contact: Angela Fowler
**VFS Point of Contact:** _First name only: Angela
<h2>User Story or Problem Statement:</h2>
When visiting a page within a web site, I expect to be able to return to previous pages without using the back button.
<h2>Details</h2>
On the "operating status" page, the breadcrumb only contains the current page. There is no way to return home.
## Acceptance Criteria
- [ ] Breadcrumb is designed such that it recreates the path the user took to reach the "Operating Status" page.
Environment
Steps to Recreate
Proposed Solution (if known)
WCAG or Vendor Guidance (optional)
Screenshots or Trace Logs
| non_priority | defect operating status breadcrumb only contains the current page label issue title defect level operating status breadcrumb only contains the current page point of contact angela fowler vfs point of contact first name only angela user story or problem statement when visiting a page within a web site i expect to be able to return to previous pages without using the back button details on the operating status page the breadcrumb only contains the current page there is no way to return home acceptance criteria breadcrumb is designed such that it recreates the path the user took to reach the operating status page environment steps to recreate proposed solution if known wcag or vendor guidance optional screenshots or trace logs | 0 |
182,311 | 14,910,640,629 | IssuesEvent | 2021-01-22 09:52:52 | guardicore/monkey | https://api.github.com/repos/guardicore/monkey | closed | Update Configuration Documentation | Documentation e/0.5 | Now that we updated the configuration UI we need to update the Configuration documentation and all config-related images in the documentation. | 1.0 | Update Configuration Documentation - Now that we updated the configuration UI we need to update the Configuration documentation and all config-related images in the documentation. | non_priority | update configuration documentation now that we updated the configuration ui we need to update the configuration documentation and all config related images in the documentation | 0 |
56,434 | 15,090,731,840 | IssuesEvent | 2021-02-06 12:26:33 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | opened | Resilvering restart from 0% on reboot | Status: Triage Needed Type: Defect | <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Centos
Distribution Version | 7.9
Linux Kernel | 5.10
Architecture | x64
ZFS Version | 2.0.2
SPL Version |
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
Resilvering restart from0 on reboot. If a disk is in resilvering state and I don't restart the os, it completes without problems.
If i restart the server, it restart from 0%. The date however is still reported correcty, when I added the disk for resilvering the first time.
### Describe how to reproduce the problem
### Include any warning/errors/backtraces from the system logs
<!--
*IMPORTANT* - Please mark logs and text output from terminal commands
or else Github will not display them correctly.
An example is provided below.
Example:
```
pool: xpool2
state: ONLINE
status: One or more devices is currently being resilvered. The pool will
continue to function, possibly in a degraded state.
action: Wait for the resilver to complete.
scan: resilver in progress since Thu Feb 4 14:24:23 2021
1.61T scanned at 315M/s, 81.5G issued at 15.6M/s, 5.32T total
77.3G resilvered, 1.50% done, 4 days 02:06:31 to go
```
-->
| 1.0 | Resilvering restart from 0% on reboot - <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Centos
Distribution Version | 7.9
Linux Kernel | 5.10
Architecture | x64
ZFS Version | 2.0.2
SPL Version |
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
Resilvering restart from0 on reboot. If a disk is in resilvering state and I don't restart the os, it completes without problems.
If i restart the server, it restart from 0%. The date however is still reported correcty, when I added the disk for resilvering the first time.
### Describe how to reproduce the problem
### Include any warning/errors/backtraces from the system logs
<!--
*IMPORTANT* - Please mark logs and text output from terminal commands
or else Github will not display them correctly.
An example is provided below.
Example:
```
pool: xpool2
state: ONLINE
status: One or more devices is currently being resilvered. The pool will
continue to function, possibly in a degraded state.
action: Wait for the resilver to complete.
scan: resilver in progress since Thu Feb 4 14:24:23 2021
1.61T scanned at 315M/s, 81.5G issued at 15.6M/s, 5.32T total
77.3G resilvered, 1.50% done, 4 days 02:06:31 to go
```
-->
| non_priority | resilvering restart from on reboot thank you for reporting an issue important please check our issue tracker before opening a new issue additional valuable information can be found in the openzfs documentation and mailing list archives please fill in as much of the template as possible system information type version name distribution name centos distribution version linux kernel architecture zfs version spl version commands to find zfs spl versions modinfo zfs grep iw version modinfo spl grep iw version describe the problem you re observing resilvering restart on reboot if a disk is in resilvering state and i don t restart the os it completes without problems if i restart the server it restart from the date however is still reported correcty when i added the disk for resilvering the first time describe how to reproduce the problem include any warning errors backtraces from the system logs important please mark logs and text output from terminal commands or else github will not display them correctly an example is provided below example pool state online status one or more devices is currently being resilvered the pool will continue to function possibly in a degraded state action wait for the resilver to complete scan resilver in progress since thu feb scanned at s issued at s total resilvered done days to go | 0 |
71,704 | 9,534,583,284 | IssuesEvent | 2019-04-30 02:20:15 | apache/pulsar | https://api.github.com/repos/apache/pulsar | closed | Kerberos authenticate documentation | component/documentation triage/week-9 type/feature | **Is your feature request related to a problem? Please describe.**
It need to add doc for Kerberos in Pulsar.
**Additional context**
This is a sub task of issue #3491
| 1.0 | Kerberos authenticate documentation - **Is your feature request related to a problem? Please describe.**
It need to add doc for Kerberos in Pulsar.
**Additional context**
This is a sub task of issue #3491
| non_priority | kerberos authenticate documentation is your feature request related to a problem please describe it need to add doc for kerberos in pulsar additional context this is a sub task of issue | 0 |
37,083 | 12,467,810,965 | IssuesEvent | 2020-05-28 17:43:35 | geofffranks/spruce | https://api.github.com/repos/geofffranks/spruce | closed | CVE-2019-11254 (Medium) detected in github.com/geofffranks/spruce-c927aeb765fa8e20f8ad743d77708ff11dd280a2 | security vulnerability | ## CVE-2019-11254 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/geofffranks/spruce-c927aeb765fa8e20f8ad743d77708ff11dd280a2</b></p></summary>
<p>A BOSH template merge tool</p>
<p>
Dependency Hierarchy:
- :x: **github.com/geofffranks/spruce-c927aeb765fa8e20f8ad743d77708ff11dd280a2** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/geofffranks/spruce/commit/66c58daa21fb1d7c8b0ff833ad4544035c070300">66c58daa21fb1d7c8b0ff833ad4544035c070300</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Kubernetes API Server component in versions 1.1-1.14, and versions prior to 1.15.10, 1.16.7 and 1.17.3 allows an authorized user who sends malicious YAML payloads to cause the kube-apiserver to consume excessive CPU cycles while parsing YAML.
<p>Publish Date: 2020-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11254>CVE-2019-11254</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/go-yaml/yaml/tree/v2.2.8">https://github.com/go-yaml/yaml/tree/v2.2.8</a></p>
<p>Release Date: 2020-04-01</p>
<p>Fix Resolution: yaml-v2.2.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-11254 (Medium) detected in github.com/geofffranks/spruce-c927aeb765fa8e20f8ad743d77708ff11dd280a2 - ## CVE-2019-11254 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/geofffranks/spruce-c927aeb765fa8e20f8ad743d77708ff11dd280a2</b></p></summary>
<p>A BOSH template merge tool</p>
<p>
Dependency Hierarchy:
- :x: **github.com/geofffranks/spruce-c927aeb765fa8e20f8ad743d77708ff11dd280a2** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/geofffranks/spruce/commit/66c58daa21fb1d7c8b0ff833ad4544035c070300">66c58daa21fb1d7c8b0ff833ad4544035c070300</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Kubernetes API Server component in versions 1.1-1.14, and versions prior to 1.15.10, 1.16.7 and 1.17.3 allows an authorized user who sends malicious YAML payloads to cause the kube-apiserver to consume excessive CPU cycles while parsing YAML.
<p>Publish Date: 2020-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11254>CVE-2019-11254</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/go-yaml/yaml/tree/v2.2.8">https://github.com/go-yaml/yaml/tree/v2.2.8</a></p>
<p>Release Date: 2020-04-01</p>
<p>Fix Resolution: yaml-v2.2.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in github com geofffranks spruce cve medium severity vulnerability vulnerable library github com geofffranks spruce a bosh template merge tool dependency hierarchy x github com geofffranks spruce vulnerable library found in head commit a href vulnerability details the kubernetes api server component in versions and versions prior to and allows an authorized user who sends malicious yaml payloads to cause the kube apiserver to consume excessive cpu cycles while parsing yaml publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution yaml step up your open source security game with whitesource | 0 |
108,530 | 9,309,660,492 | IssuesEvent | 2019-03-25 16:57:18 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | opened | Test: GitHub PR Extension - new commenting API | testplan-item | - [ ] macOS @meaghanlewis
- [ ] linux
- [ ] windows
Complexity: 3
Authors: @rebornix, @RMacfarlane
This iteration, we created a new proposed commenting API (https://github.com/Microsoft/vscode/issues/68020) and adopted it in the GitHub PR extension. This is to test that all commenting functionality behaves as before. Test that
- Within an editor, you can create new comment threads, and reply to previously existing ones
- You are able to edit and delete comments
- You can start, finish, and delete a review from within the editor
- When a comment is part of an unfinished review, it should have the label "Pending"
- If you enter text in a comment without adding it and switch editors, the text is preserved when you return to the editor
Please test against the nightly version of the extension, which should have the most recent changes:
https://marketplace.visualstudio.com/items?itemName=GitHub.vscode-pull-request-github-insiders
And file issues in this repo: https://github.com/Microsoft/vscode-pull-request-github
You can use https://github.com/auchenberg/pullrequest-demo for testing
| 1.0 | Test: GitHub PR Extension - new commenting API - - [ ] macOS @meaghanlewis
- [ ] linux
- [ ] windows
Complexity: 3
Authors: @rebornix, @RMacfarlane
This iteration, we created a new proposed commenting API (https://github.com/Microsoft/vscode/issues/68020) and adopted it in the GitHub PR extension. This is to test that all commenting functionality behaves as before. Test that
- Within an editor, you can create new comment threads, and reply to previously existing ones
- You are able to edit and delete comments
- You can start, finish, and delete a review from within the editor
- When a comment is part of an unfinished review, it should have the label "Pending"
- If you enter text in a comment without adding it and switch editors, the text is preserved when you return to the editor
Please test against the nightly version of the extension, which should have the most recent changes:
https://marketplace.visualstudio.com/items?itemName=GitHub.vscode-pull-request-github-insiders
And file issues in this repo: https://github.com/Microsoft/vscode-pull-request-github
You can use https://github.com/auchenberg/pullrequest-demo for testing
| non_priority | test github pr extension new commenting api macos meaghanlewis linux windows complexity authors rebornix rmacfarlane this iteration we created a new proposed commenting api and adopted it in the github pr extension this is to test that all commenting functionality behaves as before test that within an editor you can create new comment threads and reply to previously existing ones you are able to edit and delete comments you can start finish and delete a review from within the editor when a comment is part of an unfinished review it should have the label pending if you enter text in a comment without adding it and switch editors the text is preserved when you return to the editor please test against the nightly version of the extension which should have the most recent changes and file issues in this repo you can use for testing | 0 |
23,454 | 7,331,240,874 | IssuesEvent | 2018-03-05 12:50:59 | ShaikASK/Testing | https://api.github.com/repos/ShaikASK/Testing | closed | Issues related to Resolution :: Side Menu getting hide in 1024x768 resolution | Build Version #6 Defect P1 Ready To UAT- SumFive Reopen SumFive Team | Issue 01 :
Steps To Replicate ::
1. Change the desktop resolution to 1024 x 768
2. Launch the URL
3. login with HR Admin credentials
Experienced Behavior
Observed that Side menu is being completely hidden
Expected Behavior
Ensure that there should not be any UI discrepancy displayed in (1024 x 768) resolution
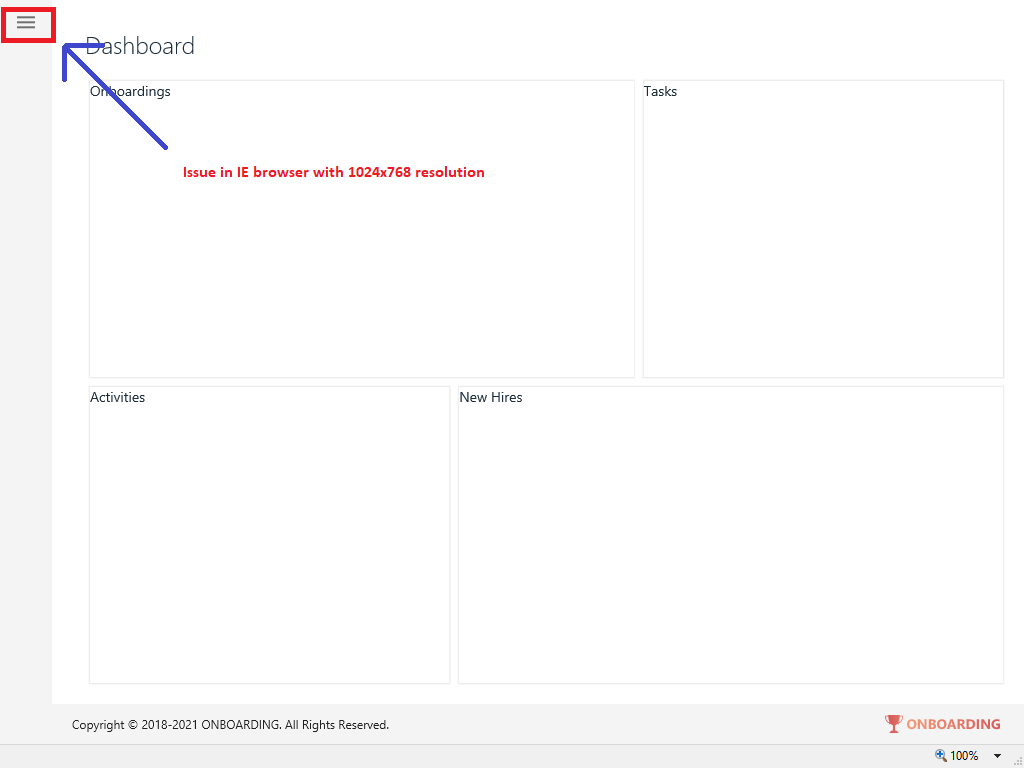
Issue 02 :
IE (Version: 11.192.16299.0) :: Documents: : Issue with 1024x768 resolution horizontal scroll bar displays on the screen
Steps To Replicate ::
1.Launch the URL
2.Login as HR Admin user
3.Navigate to 'Settings' menu
4.Go to 'Documents' tab
Experienced Behavior : Observed that the application is displaying horizontal scroll bar on screen (Refer screenshot)
Expected Behavior : Ensure that horizontal scroll bar should not display on the screen
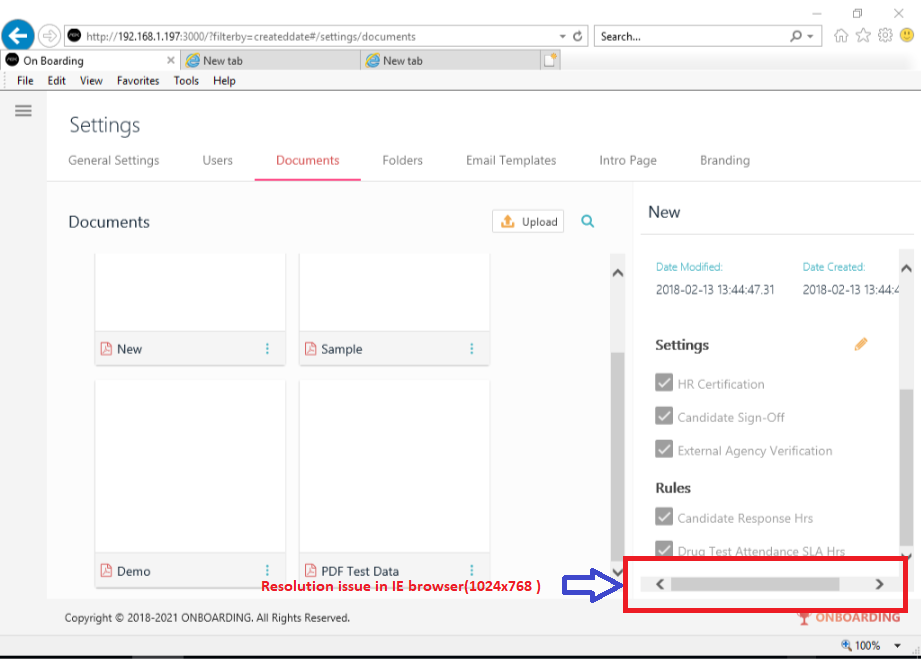
Issue 03 :
IE (Version: 11.192.16299.0) :: Users: : ‘Assign permissions’ UI alignment is missing upon changing the resolution to 1024x768
Steps To Replicate ::
1.Launch the URL
2.Login as HR Admin user
3.Navigate to 'Settings' menu
4.Go to 'Users' tab
5.Click on Add users (+)
Experienced Behavior : Observed that the application is display gap on right side of the screen under “Assign Permissions” (Refer screenshot)
Expected Behavior : Ensure that the ‘Assign permissions’ section alignment should be same as the UI / UX designs
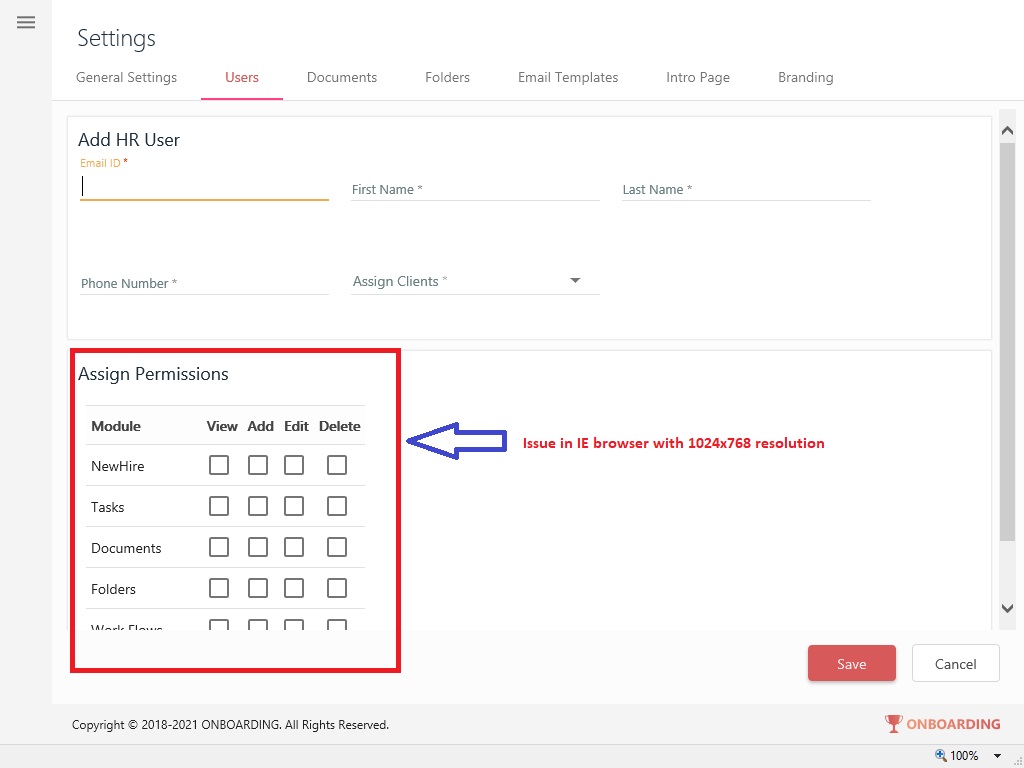
Issue 04 :
IE(Version: 11.192.16299.0)/Chrome(Version:63) :: General Settings: : Display of "value incrementer / value Decrementer" functionality is missing
Steps To Replicate ::
1.Launch the URL
2.Login as HR Admin user
3.Navigate to 'Settings' menu
4.Go to “General Settings” tab
Note : However the same is working fine when checked with other browsers
Experienced Behavior : Observed that the application is not displaying drop down in IE browser but it is working fine in other browsers
Expected Behavior : Ensure that drop down functionality should be uniformly available in all the browsers
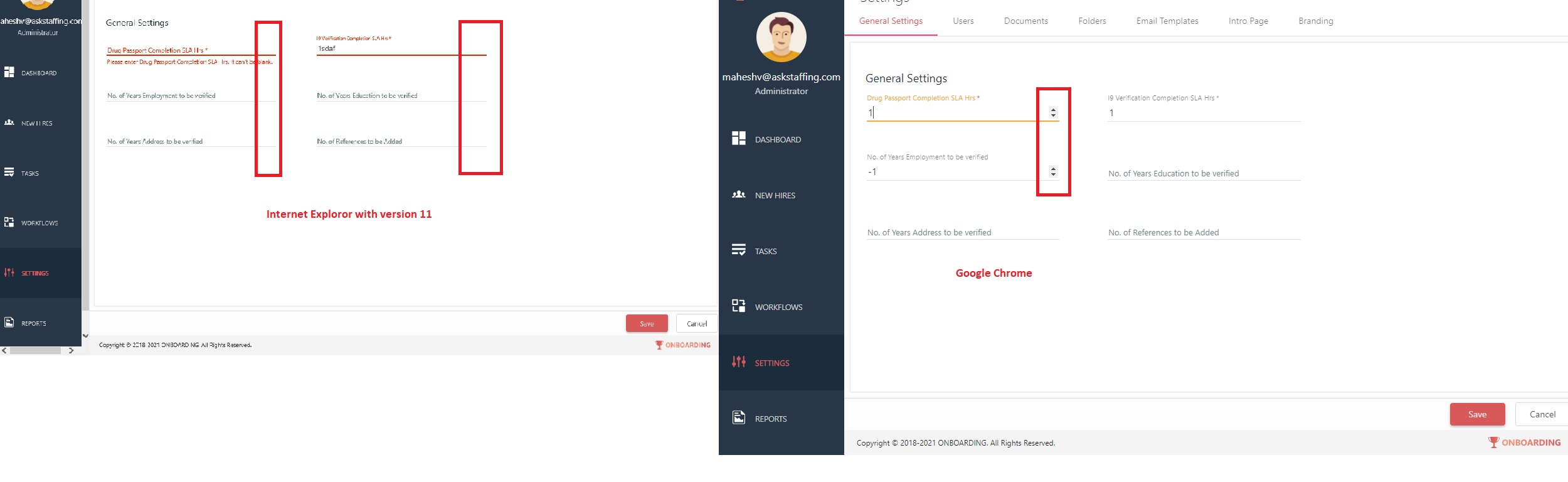
| 1.0 | Issues related to Resolution :: Side Menu getting hide in 1024x768 resolution - Issue 01 :
Steps To Replicate ::
1. Change the desktop resolution to 1024 x 768
2. Launch the URL
3. login with HR Admin credentials
Experienced Behavior
Observed that Side menu is being completely hidden
Expected Behavior
Ensure that there should not be any UI discrepancy displayed in (1024 x 768) resolution
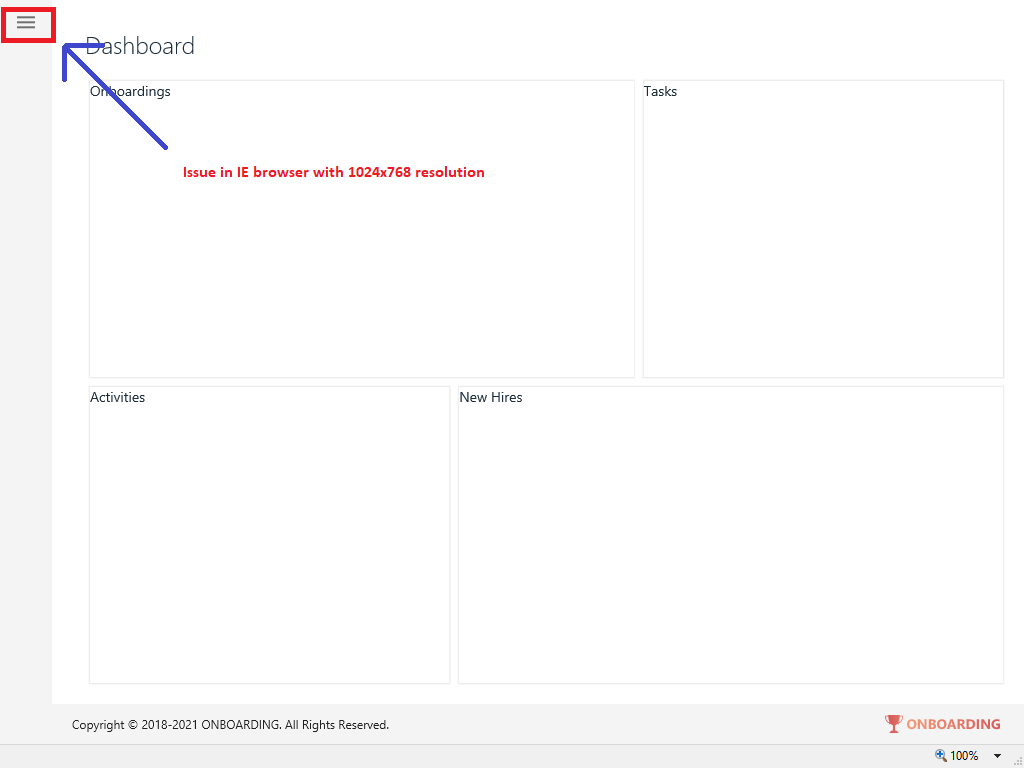
Issue 02 :
IE (Version: 11.192.16299.0) :: Documents: : Issue with 1024x768 resolution horizontal scroll bar displays on the screen
Steps To Replicate ::
1.Launch the URL
2.Login as HR Admin user
3.Navigate to 'Settings' menu
4.Go to 'Documents' tab
Experienced Behavior : Observed that the application is displaying horizontal scroll bar on screen (Refer screenshot)
Expected Behavior : Ensure that horizontal scroll bar should not display on the screen
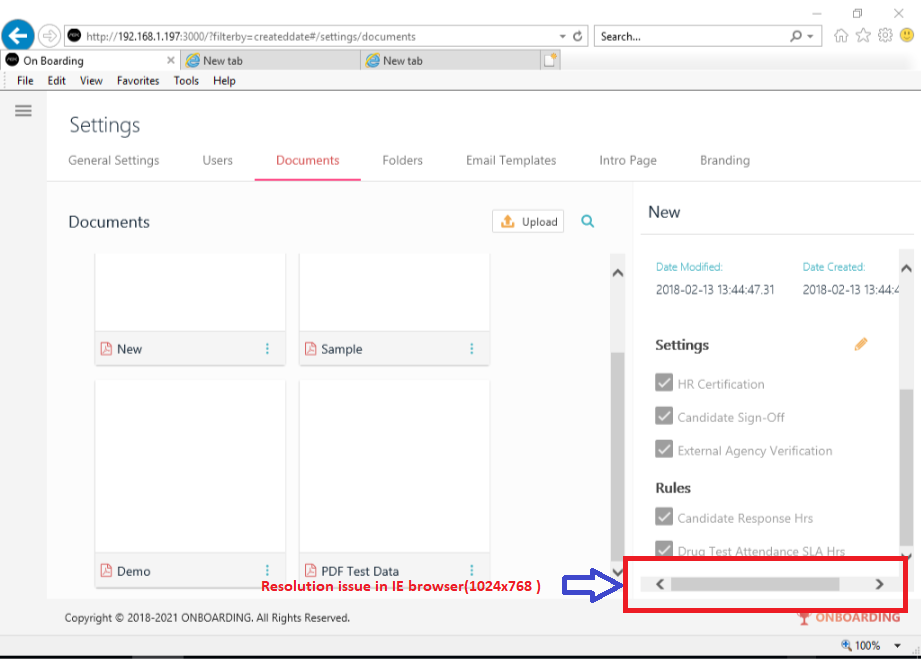
Issue 03 :
IE (Version: 11.192.16299.0) :: Users: : ‘Assign permissions’ UI alignment is missing upon changing the resolution to 1024x768
Steps To Replicate ::
1.Launch the URL
2.Login as HR Admin user
3.Navigate to 'Settings' menu
4.Go to 'Users' tab
5.Click on Add users (+)
Experienced Behavior : Observed that the application is display gap on right side of the screen under “Assign Permissions” (Refer screenshot)
Expected Behavior : Ensure that the ‘Assign permissions’ section alignment should be same as the UI / UX designs
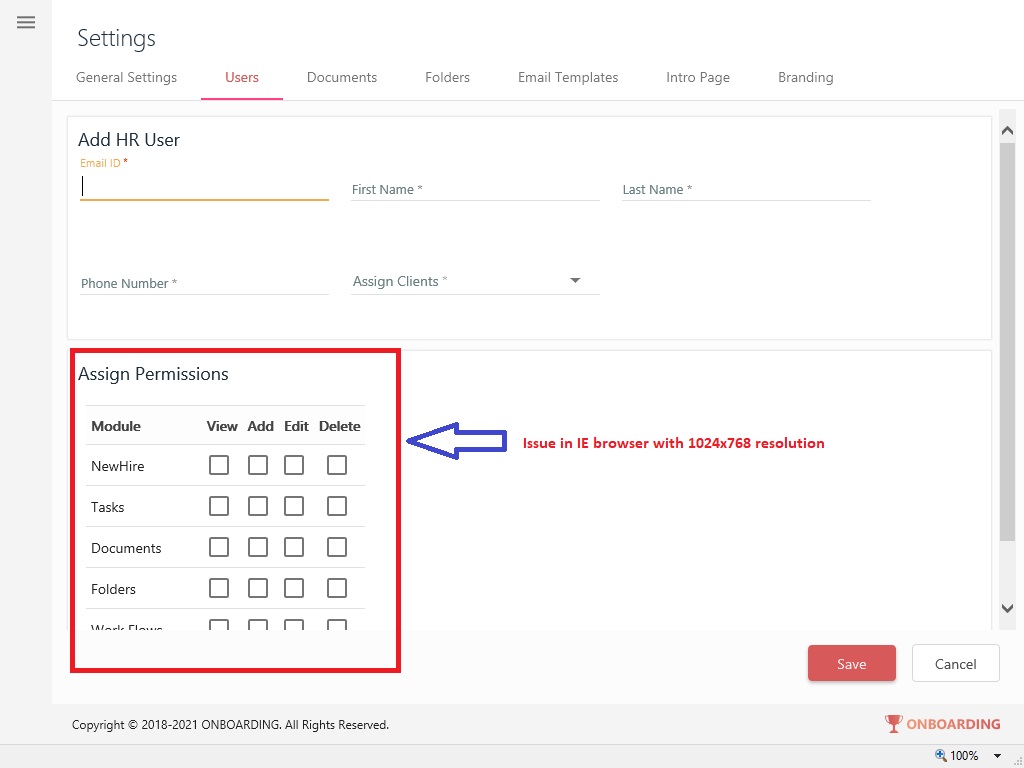
Issue 04 :
IE(Version: 11.192.16299.0)/Chrome(Version:63) :: General Settings: : Display of "value incrementer / value Decrementer" functionality is missing
Steps To Replicate ::
1.Launch the URL
2.Login as HR Admin user
3.Navigate to 'Settings' menu
4.Go to “General Settings” tab
Note : However the same is working fine when checked with other browsers
Experienced Behavior : Observed that the application is not displaying drop down in IE browser but it is working fine in other browsers
Expected Behavior : Ensure that drop down functionality should be uniformly available in all the browsers
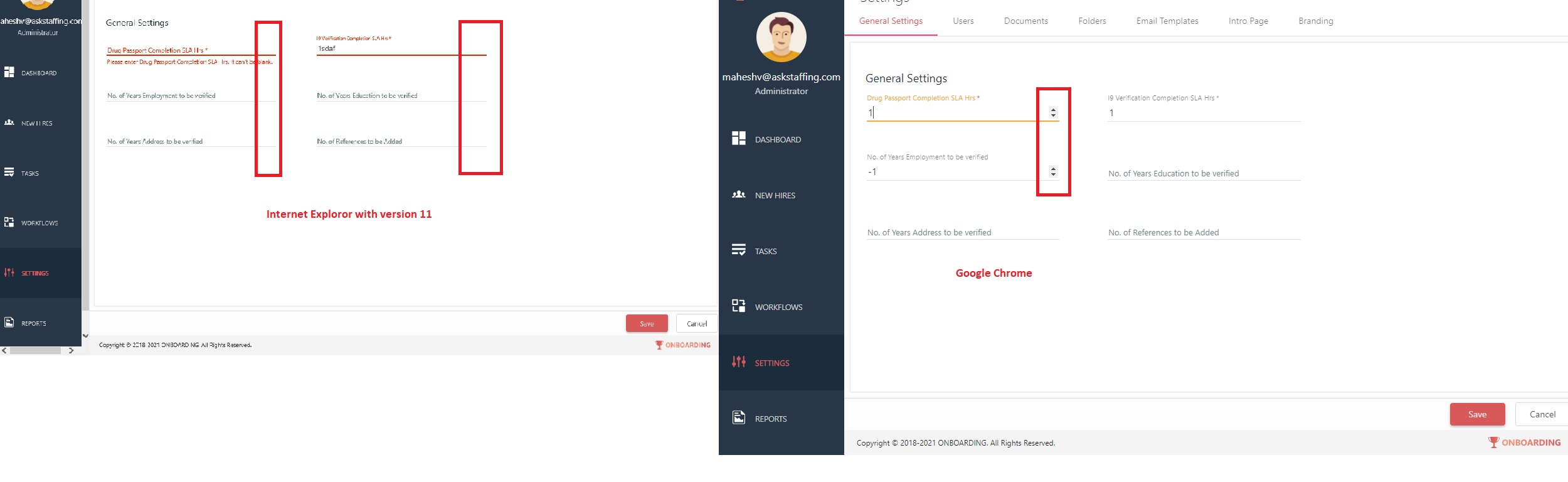
| non_priority | issues related to resolution side menu getting hide in resolution issue steps to replicate change the desktop resolution to x launch the url login with hr admin credentials experienced behavior observed that side menu is being completely hidden expected behavior ensure that there should not be any ui discrepancy displayed in x resolution issue ie version documents issue with resolution horizontal scroll bar displays on the screen steps to replicate launch the url login as hr admin user navigate to settings menu go to documents tab experienced behavior observed that the application is displaying horizontal scroll bar on screen refer screenshot expected behavior ensure that horizontal scroll bar should not display on the screen issue ie version users ‘assign permissions’ ui alignment is missing upon changing the resolution to steps to replicate launch the url login as hr admin user navigate to settings menu go to users tab click on add users experienced behavior observed that the application is display gap on right side of the screen under “assign permissions” refer screenshot expected behavior ensure that the ‘assign permissions’ section alignment should be same as the ui ux designs issue ie version chrome version general settings display of value incrementer value decrementer functionality is missing steps to replicate launch the url login as hr admin user navigate to settings menu go to “general settings” tab note however the same is working fine when checked with other browsers experienced behavior observed that the application is not displaying drop down in ie browser but it is working fine in other browsers expected behavior ensure that drop down functionality should be uniformly available in all the browsers | 0 |
207,316 | 15,803,492,829 | IssuesEvent | 2021-04-03 14:32:47 | Hboni/francis | https://api.github.com/repos/Hboni/francis | closed | Error when try to load without image path | bug enhancement tests | When I launch Francis, open a launch nod and click on `apply` without entering a path, the application crash with this error :
Traceback (most recent call last):
File "[...]/francis/src/controller/connection.py", line 40, in <lambda>
w.clicked.connect(lambda: eval(function)(widget))
File "[...]/francis/src/controller/modules_fn.py", line 58, in loadImage
im = nib.load(widget.path.text()).get_data()
File "[...]/francis/venv/lib/python3.8/site-packages/nibabel/loadsave.py", line 44, in load
raise FileNotFoundError(f"No such file or no access: '{filename}'")
FileNotFoundError: No such file or no access: ''
I think that this case must just do nothing. I will try to add tests for that ;) | 1.0 | Error when try to load without image path - When I launch Francis, open a launch nod and click on `apply` without entering a path, the application crash with this error :
Traceback (most recent call last):
File "[...]/francis/src/controller/connection.py", line 40, in <lambda>
w.clicked.connect(lambda: eval(function)(widget))
File "[...]/francis/src/controller/modules_fn.py", line 58, in loadImage
im = nib.load(widget.path.text()).get_data()
File "[...]/francis/venv/lib/python3.8/site-packages/nibabel/loadsave.py", line 44, in load
raise FileNotFoundError(f"No such file or no access: '{filename}'")
FileNotFoundError: No such file or no access: ''
I think that this case must just do nothing. I will try to add tests for that ;) | non_priority | error when try to load without image path when i launch francis open a launch nod and click on apply without entering a path the application crash with this error traceback most recent call last file francis src controller connection py line in w clicked connect lambda eval function widget file francis src controller modules fn py line in loadimage im nib load widget path text get data file francis venv lib site packages nibabel loadsave py line in load raise filenotfounderror f no such file or no access filename filenotfounderror no such file or no access i think that this case must just do nothing i will try to add tests for that | 0 |
197,576 | 15,684,636,384 | IssuesEvent | 2021-03-25 10:14:01 | feature-sliced/wiki | https://api.github.com/repos/feature-sliced/wiki | closed | Добавить доку: "Public API" | CRITICAL documentation | > См. дискуссии: #41
---
## Каждая сущность методологии должна иметь Public API
Импортировать содержимое сущности игнорируя Public API запрещено!
- feature
- process
- entity
- shared/*
Issue создано для отслеживание процесса написания документации | 1.0 | Добавить доку: "Public API" - > См. дискуссии: #41
---
## Каждая сущность методологии должна иметь Public API
Импортировать содержимое сущности игнорируя Public API запрещено!
- feature
- process
- entity
- shared/*
Issue создано для отслеживание процесса написания документации | non_priority | добавить доку public api см дискуссии каждая сущность методологии должна иметь public api импортировать содержимое сущности игнорируя public api запрещено feature process entity shared issue создано для отслеживание процесса написания документации | 0 |
34,072 | 7,783,064,074 | IssuesEvent | 2018-06-06 08:46:06 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Code generator should not generate "USER-DEFINED" for unknown data types | C: Code Generation C: DB: PostgreSQL P: Medium R: Fixed T: Defect | When the code generator encounters an unknown "user-defined" data type, it generates the type name `USER-DEFINED` in generated code, which is useless.
We should generate the actual type name, which is available to the code generator.
----
Related: #7546
| 1.0 | Code generator should not generate "USER-DEFINED" for unknown data types - When the code generator encounters an unknown "user-defined" data type, it generates the type name `USER-DEFINED` in generated code, which is useless.
We should generate the actual type name, which is available to the code generator.
----
Related: #7546
| non_priority | code generator should not generate user defined for unknown data types when the code generator encounters an unknown user defined data type it generates the type name user defined in generated code which is useless we should generate the actual type name which is available to the code generator related | 0 |
112,804 | 9,602,316,984 | IssuesEvent | 2019-05-10 14:19:38 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed test: TestLint | C-test-failure O-robot | The following tests appear to have failed on master (lint): TestLint/TestVet: TestLint/TestVet/shadow, TestLint, TestLint/TestVet
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+TestLint).
[#1283520](https://teamcity.cockroachdb.com/viewLog.html?buildId=1283520):
```
TestLint
--- FAIL: lint/TestLint (255.030s)
TestLint/TestVet
--- FAIL: lint/TestLint: TestLint/TestVet (882.890s)
------- Stdout: -------
=== PAUSE TestLint/TestVet
TestLint/TestVet: TestLint/TestVet/shadow
... /usr/local/go/src/cmd/compile/internal/gc/ssa.go:682 +0x58 fp=0xc004677a40 sp=0xc004677a08 pc=0xb38d78
lint_test.go:1352:
cmd/compile/internal/gc.(*state).call(0xc007d736c0, 0xc000c24580, 0xc007d73601, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:3566 +0xf1 fp=0xc004677b78 sp=0xc004677a40 pc=0xb4e5a1
lint_test.go:1352:
cmd/compile/internal/gc.(*state).stmt(0xc007d736c0, 0xc000c24600)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:732 +0x128f fp=0xc004677de0 sp=0xc004677b78 pc=0xb3a03f
lint_test.go:1352:
cmd/compile/internal/gc.(*state).stmtList(0xc007d736c0, 0xc0029c86a0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:682 +0x58 fp=0xc004677e18 sp=0xc004677de0 pc=0xb38d78
lint_test.go:1352:
cmd/compile/internal/gc.buildssa(0xc000bfb8c0, 0x0, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:193 +0xa1a fp=0xc004677f30 sp=0xc004677e18 pc=0xb35d6a
lint_test.go:1352:
cmd/compile/internal/gc.compileSSA(0xc000bfb8c0, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:259 +0x39 fp=0xc004677f98 sp=0xc004677f30 pc=0xb02c59
lint_test.go:1352:
cmd/compile/internal/gc.compileFunctions.func2(0xc0044104e0, 0xc0007a90f0, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:323 +0x49 fp=0xc004677fc8 sp=0xc004677f98 pc=0xbb7f79
lint_test.go:1352:
runtime.goexit()
lint_test.go:1352:
/usr/local/go/src/runtime/asm_amd64.s:1333 +0x1 fp=0xc004677fd0 sp=0xc004677fc8 pc=0x457da1
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
lint_test.go:1352:
goroutine 1 [chan send]:
lint_test.go:1352:
cmd/compile/internal/gc.compileFunctions()
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:329 +0x171
lint_test.go:1352:
cmd/compile/internal/gc.Main(0xcc51f8)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/main.go:651 +0x276d
lint_test.go:1352:
main.main()
lint_test.go:1352:
/usr/local/go/src/cmd/compile/main.go:51 +0x96
lint_test.go:1352:
goroutine 103 [running]:
lint_test.go:1352:
goroutine running on other thread; stack unavailable
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
lint_test.go:1352:
goroutine 104 [running]:
lint_test.go:1352:
goroutine running on other thread; stack unavailable
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
lint_test.go:1352:
goroutine 105 [running]:
lint_test.go:1352:
goroutine running on other thread; stack unavailable
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
```
Please assign, take a look and update the issue accordingly.
| 1.0 | teamcity: failed test: TestLint - The following tests appear to have failed on master (lint): TestLint/TestVet: TestLint/TestVet/shadow, TestLint, TestLint/TestVet
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+TestLint).
[#1283520](https://teamcity.cockroachdb.com/viewLog.html?buildId=1283520):
```
TestLint
--- FAIL: lint/TestLint (255.030s)
TestLint/TestVet
--- FAIL: lint/TestLint: TestLint/TestVet (882.890s)
------- Stdout: -------
=== PAUSE TestLint/TestVet
TestLint/TestVet: TestLint/TestVet/shadow
... /usr/local/go/src/cmd/compile/internal/gc/ssa.go:682 +0x58 fp=0xc004677a40 sp=0xc004677a08 pc=0xb38d78
lint_test.go:1352:
cmd/compile/internal/gc.(*state).call(0xc007d736c0, 0xc000c24580, 0xc007d73601, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:3566 +0xf1 fp=0xc004677b78 sp=0xc004677a40 pc=0xb4e5a1
lint_test.go:1352:
cmd/compile/internal/gc.(*state).stmt(0xc007d736c0, 0xc000c24600)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:732 +0x128f fp=0xc004677de0 sp=0xc004677b78 pc=0xb3a03f
lint_test.go:1352:
cmd/compile/internal/gc.(*state).stmtList(0xc007d736c0, 0xc0029c86a0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:682 +0x58 fp=0xc004677e18 sp=0xc004677de0 pc=0xb38d78
lint_test.go:1352:
cmd/compile/internal/gc.buildssa(0xc000bfb8c0, 0x0, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/ssa.go:193 +0xa1a fp=0xc004677f30 sp=0xc004677e18 pc=0xb35d6a
lint_test.go:1352:
cmd/compile/internal/gc.compileSSA(0xc000bfb8c0, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:259 +0x39 fp=0xc004677f98 sp=0xc004677f30 pc=0xb02c59
lint_test.go:1352:
cmd/compile/internal/gc.compileFunctions.func2(0xc0044104e0, 0xc0007a90f0, 0x0)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:323 +0x49 fp=0xc004677fc8 sp=0xc004677f98 pc=0xbb7f79
lint_test.go:1352:
runtime.goexit()
lint_test.go:1352:
/usr/local/go/src/runtime/asm_amd64.s:1333 +0x1 fp=0xc004677fd0 sp=0xc004677fc8 pc=0x457da1
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
lint_test.go:1352:
goroutine 1 [chan send]:
lint_test.go:1352:
cmd/compile/internal/gc.compileFunctions()
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:329 +0x171
lint_test.go:1352:
cmd/compile/internal/gc.Main(0xcc51f8)
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/main.go:651 +0x276d
lint_test.go:1352:
main.main()
lint_test.go:1352:
/usr/local/go/src/cmd/compile/main.go:51 +0x96
lint_test.go:1352:
goroutine 103 [running]:
lint_test.go:1352:
goroutine running on other thread; stack unavailable
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
lint_test.go:1352:
goroutine 104 [running]:
lint_test.go:1352:
goroutine running on other thread; stack unavailable
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
lint_test.go:1352:
goroutine 105 [running]:
lint_test.go:1352:
goroutine running on other thread; stack unavailable
lint_test.go:1352:
created by cmd/compile/internal/gc.compileFunctions
lint_test.go:1352:
/usr/local/go/src/cmd/compile/internal/gc/pgen.go:321 +0x11a
```
Please assign, take a look and update the issue accordingly.
| non_priority | teamcity failed test testlint the following tests appear to have failed on master lint testlint testvet testlint testvet shadow testlint testlint testvet you may want to check testlint fail lint testlint testlint testvet fail lint testlint testlint testvet stdout pause testlint testvet testlint testvet testlint testvet shadow usr local go src cmd compile internal gc ssa go fp sp pc lint test go cmd compile internal gc state call lint test go usr local go src cmd compile internal gc ssa go fp sp pc lint test go cmd compile internal gc state stmt lint test go usr local go src cmd compile internal gc ssa go fp sp pc lint test go cmd compile internal gc state stmtlist lint test go usr local go src cmd compile internal gc ssa go fp sp pc lint test go cmd compile internal gc buildssa lint test go usr local go src cmd compile internal gc ssa go fp sp pc lint test go cmd compile internal gc compilessa lint test go usr local go src cmd compile internal gc pgen go fp sp pc lint test go cmd compile internal gc compilefunctions lint test go usr local go src cmd compile internal gc pgen go fp sp pc lint test go runtime goexit lint test go usr local go src runtime asm s fp sp pc lint test go created by cmd compile internal gc compilefunctions lint test go usr local go src cmd compile internal gc pgen go lint test go goroutine lint test go cmd compile internal gc compilefunctions lint test go usr local go src cmd compile internal gc pgen go lint test go cmd compile internal gc main lint test go usr local go src cmd compile internal gc main go lint test go main main lint test go usr local go src cmd compile main go lint test go goroutine lint test go goroutine running on other thread stack unavailable lint test go created by cmd compile internal gc compilefunctions lint test go usr local go src cmd compile internal gc pgen go lint test go goroutine lint test go goroutine running on other thread stack unavailable lint test go created by cmd compile internal gc compilefunctions lint test go usr local go src cmd compile internal gc pgen go lint test go goroutine lint test go goroutine running on other thread stack unavailable lint test go created by cmd compile internal gc compilefunctions lint test go usr local go src cmd compile internal gc pgen go please assign take a look and update the issue accordingly | 0 |
65,139 | 12,533,161,516 | IssuesEvent | 2020-06-04 17:07:07 | Kotlin/dukat | https://api.github.com/repos/Kotlin/dukat | closed | Declarations clash after removing string literals in params and type params | ir-target unusable-code | Following code:
```typescript
interface Options<A, B> {}
interface Result<T> {}
declare function generate(options: Options<'pem', 'pem'>): Result<{ publicKey: string, privateKey: string }>;
declare function generate(options: Options<'pem', 'der'>): Result<{ publicKey: string, privateKey: Buffer }>;
declare function generate(options: Options<'der', 'pem'>): Result<{ publicKey: Buffer, privateKey: string }>;
declare function generate(options: Options<'der', 'der'>): Result<{ publicKey: Buffer, privateKey: Buffer }>;
```
is translated to:
```kotlin
external interface Options<A, B>
external interface Result<T>
external interface `T$0` {
var publicKey: String
var privateKey: String
}
external fun generate(options: Options<String /* 'pem' */, String /* 'pem' */>): Result<`T$0`>
external interface `T$1` {
var publicKey: String
var privateKey: Any
}
external fun generate(options: Options<String /* 'pem' */, String /* 'der' */>): Result<`T$1`>
external interface `T$2` {
var publicKey: Any
var privateKey: String
}
external fun generate(options: Options<String /* 'der' */, String /* 'pem' */>): Result<`T$2`>
external interface `T$3` {
var publicKey: Any
var privateKey: Any
}
external fun generate(options: Options<String /* 'der' */, String /* 'der' */>): Result<`T$3`>
```
Which compiles only because of `@file:Suppress("CONFLICTING_OVERLOADS")`
We should merge such functions and methods. | 1.0 | Declarations clash after removing string literals in params and type params - Following code:
```typescript
interface Options<A, B> {}
interface Result<T> {}
declare function generate(options: Options<'pem', 'pem'>): Result<{ publicKey: string, privateKey: string }>;
declare function generate(options: Options<'pem', 'der'>): Result<{ publicKey: string, privateKey: Buffer }>;
declare function generate(options: Options<'der', 'pem'>): Result<{ publicKey: Buffer, privateKey: string }>;
declare function generate(options: Options<'der', 'der'>): Result<{ publicKey: Buffer, privateKey: Buffer }>;
```
is translated to:
```kotlin
external interface Options<A, B>
external interface Result<T>
external interface `T$0` {
var publicKey: String
var privateKey: String
}
external fun generate(options: Options<String /* 'pem' */, String /* 'pem' */>): Result<`T$0`>
external interface `T$1` {
var publicKey: String
var privateKey: Any
}
external fun generate(options: Options<String /* 'pem' */, String /* 'der' */>): Result<`T$1`>
external interface `T$2` {
var publicKey: Any
var privateKey: String
}
external fun generate(options: Options<String /* 'der' */, String /* 'pem' */>): Result<`T$2`>
external interface `T$3` {
var publicKey: Any
var privateKey: Any
}
external fun generate(options: Options<String /* 'der' */, String /* 'der' */>): Result<`T$3`>
```
Which compiles only because of `@file:Suppress("CONFLICTING_OVERLOADS")`
We should merge such functions and methods. | non_priority | declarations clash after removing string literals in params and type params following code typescript interface options interface result declare function generate options options result declare function generate options options result declare function generate options options result declare function generate options options result is translated to kotlin external interface options external interface result external interface t var publickey string var privatekey string external fun generate options options result external interface t var publickey string var privatekey any external fun generate options options result external interface t var publickey any var privatekey string external fun generate options options result external interface t var publickey any var privatekey any external fun generate options options result which compiles only because of file suppress conflicting overloads we should merge such functions and methods | 0 |
10,030 | 3,082,780,360 | IssuesEvent | 2015-08-24 01:40:57 | sass/libsass | https://api.github.com/repos/sass/libsass | closed | Variable not expanded in url() | Bug - Confirmed Dev - PR Ready test written | Example code from https://github.com/sass/node-sass/issues/1042 reported by @chenxiaochun
````sass
@mixin ico-common($imgUrl){
display: inline-block;
background: url(i/$imgUrl);
background-repeat: no-repeat;
}
@mixin ico-size($width,$height){
width: $width;
height: $height;
}
.test{
@include ico-common("icon.png");
@include ico-size(100px, 100px);
}
```
Ruby Sass output (https://github.com/sass/sass/commit/b4bbd962b3c91f6268d5fdfa3e96896d018020fc):
````css
.test {
display: inline-block;
background: url(i/"icon.png");
background-repeat: no-repeat;
width: 100px;
height: 100px; }
````
libsass output as of 3.2.5-111-g5e94 (https://github.com/saper/libsass/commit/5e9437b320646b7ccdb24db03a1561ebc8aedd41):
````css
.test {
display: inline-block;
background: url(i/$imgUrl);
background-repeat: no-repeat;
width: 100px;
height: 100px; }
````
not sure how useful is `url(i/"something.ico")` output, but that is what Ruby is doing.
If the Ruby Sass behaviour is undesired, please file an issue at https://github.com/sass/sass/issues
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/24755303-variable-not-expanded-in-url?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | Variable not expanded in url() - Example code from https://github.com/sass/node-sass/issues/1042 reported by @chenxiaochun
````sass
@mixin ico-common($imgUrl){
display: inline-block;
background: url(i/$imgUrl);
background-repeat: no-repeat;
}
@mixin ico-size($width,$height){
width: $width;
height: $height;
}
.test{
@include ico-common("icon.png");
@include ico-size(100px, 100px);
}
```
Ruby Sass output (https://github.com/sass/sass/commit/b4bbd962b3c91f6268d5fdfa3e96896d018020fc):
````css
.test {
display: inline-block;
background: url(i/"icon.png");
background-repeat: no-repeat;
width: 100px;
height: 100px; }
````
libsass output as of 3.2.5-111-g5e94 (https://github.com/saper/libsass/commit/5e9437b320646b7ccdb24db03a1561ebc8aedd41):
````css
.test {
display: inline-block;
background: url(i/$imgUrl);
background-repeat: no-repeat;
width: 100px;
height: 100px; }
````
not sure how useful is `url(i/"something.ico")` output, but that is what Ruby is doing.
If the Ruby Sass behaviour is undesired, please file an issue at https://github.com/sass/sass/issues
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/24755303-variable-not-expanded-in-url?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F283068&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_priority | variable not expanded in url example code from reported by chenxiaochun sass mixin ico common imgurl display inline block background url i imgurl background repeat no repeat mixin ico size width height width width height height test include ico common icon png include ico size ruby sass output css test display inline block background url i icon png background repeat no repeat width height libsass output as of css test display inline block background url i imgurl background repeat no repeat width height not sure how useful is url i something ico output but that is what ruby is doing if the ruby sass behaviour is undesired please file an issue at want to back this issue we accept bounties via | 0 |
11,077 | 2,632,356,912 | IssuesEvent | 2015-03-08 01:36:39 | marmarek/test | https://api.github.com/repos/marmarek/test | opened | Automatically start nm-applet in the default (all?) netvm | C: core P: major R: implemented T: defect | **Reported by joanna on 25 Mar 2011 14:29 UTC**
None
Migrated-From: https://wiki.qubes-os.org/ticket/137 | 1.0 | Automatically start nm-applet in the default (all?) netvm - **Reported by joanna on 25 Mar 2011 14:29 UTC**
None
Migrated-From: https://wiki.qubes-os.org/ticket/137 | non_priority | automatically start nm applet in the default all netvm reported by joanna on mar utc none migrated from | 0 |
36,759 | 15,055,301,266 | IssuesEvent | 2021-02-03 18:35:56 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Support for Cosmosdb Cassandra tables | new-resource service/cosmosdb | <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
### Description
It would be good to have support for cassandra tables - at the moment we can create keyspaces thanks to this (https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/cosmosdb_cassandra_keyspace), however we need to resort to the portal or AZ cli to add tables once the keyspaces are in place.
### New or Affected Resource(s)
* azurerm_cosmosdb_cassandra_tables
| 1.0 | Support for Cosmosdb Cassandra tables - <!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
### Description
It would be good to have support for cassandra tables - at the moment we can create keyspaces thanks to this (https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/cosmosdb_cassandra_keyspace), however we need to resort to the portal or AZ cli to add tables once the keyspaces are in place.
### New or Affected Resource(s)
* azurerm_cosmosdb_cassandra_tables
| non_priority | support for cosmosdb cassandra tables community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment description it would be good to have support for cassandra tables at the moment we can create keyspaces thanks to this however we need to resort to the portal or az cli to add tables once the keyspaces are in place new or affected resource s azurerm cosmosdb cassandra tables | 0 |
339,596 | 24,624,083,535 | IssuesEvent | 2022-10-16 09:31:28 | osbc2022/watch-product-landing-page | https://api.github.com/repos/osbc2022/watch-product-landing-page | closed | [DOCS] : documentation on PR in contribution.md is not properly explained | 🐞 bug 📑 documentation good first issue 🪙 point : 1 | ### ✏️ Description
To do:
- [ ] adding images in the PR section
- [ ] making the language more easy to understand
### 📸 Screenshots
_No response_ | 1.0 | [DOCS] : documentation on PR in contribution.md is not properly explained - ### ✏️ Description
To do:
- [ ] adding images in the PR section
- [ ] making the language more easy to understand
### 📸 Screenshots
_No response_ | non_priority | documentation on pr in contribution md is not properly explained ✏️ description to do adding images in the pr section making the language more easy to understand 📸 screenshots no response | 0 |
86,109 | 10,474,186,796 | IssuesEvent | 2019-09-23 14:04:00 | Verizon-Geeks/cncf-clients | https://api.github.com/repos/Verizon-Geeks/cncf-clients | opened | Document Prometheus integration with Java | documentation prometheus | Document prometheus integration with Java
Add all relevant details and links to get started with etcd integration.
Create ``projects/prometheus/java`` folder. Add all your changes under this folder. | 1.0 | Document Prometheus integration with Java - Document prometheus integration with Java
Add all relevant details and links to get started with etcd integration.
Create ``projects/prometheus/java`` folder. Add all your changes under this folder. | non_priority | document prometheus integration with java document prometheus integration with java add all relevant details and links to get started with etcd integration create projects prometheus java folder add all your changes under this folder | 0 |
20,072 | 3,536,138,837 | IssuesEvent | 2016-01-17 01:47:59 | UCI-UAVForge/Avionics | https://api.github.com/repos/UCI-UAVForge/Avionics | opened | Research and Select Wireless Communications | needs: investigation scope: custom autopilot severity: major type: design type: research | Prerequisite Issues: None
Followup Issues: TBD
Related Issues: None
### Summary
Research and determine the best form of wireless communications for the link between the UAV and the ground station
### Terminal Objective
* Design and purchase the communications method and IC for the UAV
### Enabling Objectives
* Research the different forms of wireless communications methods and select the best fit for our UAV project based on the following:
* Range
* Power Usage
* Antenna Size
* Cost
* Bandwidth
* Research to find the necessary requirements for the above criteria and speak to R&D team if necessary for sizing and range requirements
* Find an IC that meets the above requirements and communicates with I2C or SPI
* Do all necessary calculations for the circuit design of chip as well as any necessary external components (this includes an impedance matching network for the antenna, if necessary)
* Design a test PCB with communication and antenna headers that can be used to test code and performance
* I will order the PCB and all necessary parts | 1.0 | Research and Select Wireless Communications - Prerequisite Issues: None
Followup Issues: TBD
Related Issues: None
### Summary
Research and determine the best form of wireless communications for the link between the UAV and the ground station
### Terminal Objective
* Design and purchase the communications method and IC for the UAV
### Enabling Objectives
* Research the different forms of wireless communications methods and select the best fit for our UAV project based on the following:
* Range
* Power Usage
* Antenna Size
* Cost
* Bandwidth
* Research to find the necessary requirements for the above criteria and speak to R&D team if necessary for sizing and range requirements
* Find an IC that meets the above requirements and communicates with I2C or SPI
* Do all necessary calculations for the circuit design of chip as well as any necessary external components (this includes an impedance matching network for the antenna, if necessary)
* Design a test PCB with communication and antenna headers that can be used to test code and performance
* I will order the PCB and all necessary parts | non_priority | research and select wireless communications prerequisite issues none followup issues tbd related issues none summary research and determine the best form of wireless communications for the link between the uav and the ground station terminal objective design and purchase the communications method and ic for the uav enabling objectives research the different forms of wireless communications methods and select the best fit for our uav project based on the following range power usage antenna size cost bandwidth research to find the necessary requirements for the above criteria and speak to r d team if necessary for sizing and range requirements find an ic that meets the above requirements and communicates with or spi do all necessary calculations for the circuit design of chip as well as any necessary external components this includes an impedance matching network for the antenna if necessary design a test pcb with communication and antenna headers that can be used to test code and performance i will order the pcb and all necessary parts | 0 |
2,050 | 3,626,941,321 | IssuesEvent | 2016-02-10 04:55:10 | defuse/password-hashing | https://api.github.com/repos/defuse/password-hashing | closed | Check Java is hashing the entire character | Compatibility Branch SECURITY | https://docs.oracle.com/javase/7/docs/api/javax/crypto/spec/PBEKeySpec.html
"Different PBE mechanisms may consume different bits of each password character. For example, the PBE mechanism defined in PKCS #5 looks at only the low order 8 bits of each character, whereas PKCS #12 looks at all 16 bits of each character."
We need to verify that *all* of the character is being included in the hash calculation, not just the lower 8 bits. Write a unit test for this. | True | Check Java is hashing the entire character - https://docs.oracle.com/javase/7/docs/api/javax/crypto/spec/PBEKeySpec.html
"Different PBE mechanisms may consume different bits of each password character. For example, the PBE mechanism defined in PKCS #5 looks at only the low order 8 bits of each character, whereas PKCS #12 looks at all 16 bits of each character."
We need to verify that *all* of the character is being included in the hash calculation, not just the lower 8 bits. Write a unit test for this. | non_priority | check java is hashing the entire character different pbe mechanisms may consume different bits of each password character for example the pbe mechanism defined in pkcs looks at only the low order bits of each character whereas pkcs looks at all bits of each character we need to verify that all of the character is being included in the hash calculation not just the lower bits write a unit test for this | 0 |
21,283 | 16,771,995,911 | IssuesEvent | 2021-06-14 15:48:38 | w3c/coga | https://api.github.com/repos/w3c/coga | closed | Check that glossary terms work as hyperlinked text | Editorial discussion content-usable glossary | I don't have any substantive edits to the [glossary](https://raw.githack.com/w3c/coga/add-glossary/content-usable/index.html#glossary). On the 24 Nov. call, the WG looked at glossary terms in advance of the text being completed, but based on experience with glossary terms, I would recommend a subsequent editorial pass that ensures:
- Glossary terms are used (as much as possible) exactly as phrased in the glossary.
- There can be variety for plural/singular and verb tense.
- Glossary terms are hyperlinked in the text to their definitions.
- The definitions are worded so that they can be substituted into the text for the terms.
- Admittedly, this practice can sometimes make the definitions awkward, but it is an important characteristic of normative standards.
- Notes and examples (following the formal substitution text) can help with clarification. | True | Check that glossary terms work as hyperlinked text - I don't have any substantive edits to the [glossary](https://raw.githack.com/w3c/coga/add-glossary/content-usable/index.html#glossary). On the 24 Nov. call, the WG looked at glossary terms in advance of the text being completed, but based on experience with glossary terms, I would recommend a subsequent editorial pass that ensures:
- Glossary terms are used (as much as possible) exactly as phrased in the glossary.
- There can be variety for plural/singular and verb tense.
- Glossary terms are hyperlinked in the text to their definitions.
- The definitions are worded so that they can be substituted into the text for the terms.
- Admittedly, this practice can sometimes make the definitions awkward, but it is an important characteristic of normative standards.
- Notes and examples (following the formal substitution text) can help with clarification. | non_priority | check that glossary terms work as hyperlinked text i don t have any substantive edits to the on the nov call the wg looked at glossary terms in advance of the text being completed but based on experience with glossary terms i would recommend a subsequent editorial pass that ensures glossary terms are used as much as possible exactly as phrased in the glossary there can be variety for plural singular and verb tense glossary terms are hyperlinked in the text to their definitions the definitions are worded so that they can be substituted into the text for the terms admittedly this practice can sometimes make the definitions awkward but it is an important characteristic of normative standards notes and examples following the formal substitution text can help with clarification | 0 |
122,024 | 16,066,939,561 | IssuesEvent | 2021-04-23 20:48:05 | SwiftDocOrg/swift-doc | https://api.github.com/repos/SwiftDocOrg/swift-doc | closed | Group operators separately | bug design | Right-now they're just mixed in the same section as normal methods. I think they're special enough to deserve a separate section.
<img width="943" alt="Screenshot 2020-05-21 at 17 17 24" src="https://user-images.githubusercontent.com/170270/82544020-0b423500-9b87-11ea-8496-469112c9749d.png">
Maybe also the rendering could be improved. A space after the function name and maybe fading out the arguments, as they're not important, or making the operator character bold. | 1.0 | Group operators separately - Right-now they're just mixed in the same section as normal methods. I think they're special enough to deserve a separate section.
<img width="943" alt="Screenshot 2020-05-21 at 17 17 24" src="https://user-images.githubusercontent.com/170270/82544020-0b423500-9b87-11ea-8496-469112c9749d.png">
Maybe also the rendering could be improved. A space after the function name and maybe fading out the arguments, as they're not important, or making the operator character bold. | non_priority | group operators separately right now they re just mixed in the same section as normal methods i think they re special enough to deserve a separate section img width alt screenshot at src maybe also the rendering could be improved a space after the function name and maybe fading out the arguments as they re not important or making the operator character bold | 0 |
132,891 | 12,520,876,591 | IssuesEvent | 2020-06-03 16:33:44 | ucfopen/canvasapi | https://api.github.com/repos/ucfopen/canvasapi | closed | Build documentation from master, not develop | documentation | Currently our docs are built off of our develop branch and can occasionally include features that haven't been officially released yet. Updating our docs to build using the master branch instead of develop would resolve the discrepancy. | 1.0 | Build documentation from master, not develop - Currently our docs are built off of our develop branch and can occasionally include features that haven't been officially released yet. Updating our docs to build using the master branch instead of develop would resolve the discrepancy. | non_priority | build documentation from master not develop currently our docs are built off of our develop branch and can occasionally include features that haven t been officially released yet updating our docs to build using the master branch instead of develop would resolve the discrepancy | 0 |
248,628 | 26,801,739,910 | IssuesEvent | 2023-02-01 15:32:23 | shaneclarke-whitesource/WebGoat | https://api.github.com/repos/shaneclarke-whitesource/WebGoat | opened | bootstrap-3.1.1.min.js: 6 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | bootstrap - 3.4.0, 4.0.0-beta.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0, 4.0.0-beta.2</p>
</p>
<p></p>
</details> | True | bootstrap-3.1.1.min.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.1.1.min.js | Direct | bootstrap - 3.4.0, 4.0.0-beta.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /src/main/resources/lessons/challenges/js/bootstrap.min.js,/src/main/resources/webgoat/static/js/libs/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/shaneclarke-whitesource/WebGoat/commit/d833249714a428a7bd9f869dfb62028799347ac6">d833249714a428a7bd9f869dfb62028799347ac6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0, 4.0.0-beta.2</p>
</p>
<p></p>
</details> | non_priority | bootstrap min js vulnerabilities highest severity is vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in bootstrap version remediation available medium bootstrap min js direct bootstrap bootstrap sass medium bootstrap min js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap min js direct bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter medium bootstrap min js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap min js direct bootstrap medium bootstrap min js direct bootstrap beta details cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution bootstrap bootstrap sass cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library src main resources lessons challenges js bootstrap min js src main resources webgoat static js libs bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap beta | 0 |
26,821 | 20,747,937,970 | IssuesEvent | 2022-03-15 02:29:21 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | GenerateReferenceAssemblySource task produces incorrect results on non-Windows | area-Infrastructure-libraries | Somewhat recently, it appears that the `GenerateReferenceAssemblySource` is creating changes that are invalid, or at least unwanted.
On macOS or Linux, do:
```shell
# Tried on 2737da5
./dotnet.sh build src/libraries/System.Security.Cryptography/src /t:GenerateReferenceAssemblySource
```
on macOS, this generates a lot of changes that are incorrect. A diff can be seen at https://github.com/dotnet/runtime/compare/main...vcsjones:diff-ssc
Notable things that are incorrect:
1. Removing many overrides from `AesCng`, for example `TryDecryptCbcCore`. `AesCng` [does override it](https://github.com/dotnet/runtime/blob/2737da5817ab121fb43ff5577d1e146e0ec6d213/src/libraries/System.Security.Cryptography/src/System/Security/Cryptography/AesCng.Windows.cs#L158).
2. Removing `IDisposable` from `CngKey`.
This behavior only appears in macOS / Linux. On Windows, its results are reasonable, simple ordering or whitespace changes.
/cc @bartonjs
| 1.0 | GenerateReferenceAssemblySource task produces incorrect results on non-Windows - Somewhat recently, it appears that the `GenerateReferenceAssemblySource` is creating changes that are invalid, or at least unwanted.
On macOS or Linux, do:
```shell
# Tried on 2737da5
./dotnet.sh build src/libraries/System.Security.Cryptography/src /t:GenerateReferenceAssemblySource
```
on macOS, this generates a lot of changes that are incorrect. A diff can be seen at https://github.com/dotnet/runtime/compare/main...vcsjones:diff-ssc
Notable things that are incorrect:
1. Removing many overrides from `AesCng`, for example `TryDecryptCbcCore`. `AesCng` [does override it](https://github.com/dotnet/runtime/blob/2737da5817ab121fb43ff5577d1e146e0ec6d213/src/libraries/System.Security.Cryptography/src/System/Security/Cryptography/AesCng.Windows.cs#L158).
2. Removing `IDisposable` from `CngKey`.
This behavior only appears in macOS / Linux. On Windows, its results are reasonable, simple ordering or whitespace changes.
/cc @bartonjs
| non_priority | generatereferenceassemblysource task produces incorrect results on non windows somewhat recently it appears that the generatereferenceassemblysource is creating changes that are invalid or at least unwanted on macos or linux do shell tried on dotnet sh build src libraries system security cryptography src t generatereferenceassemblysource on macos this generates a lot of changes that are incorrect a diff can be seen at notable things that are incorrect removing many overrides from aescng for example trydecryptcbccore aescng removing idisposable from cngkey this behavior only appears in macos linux on windows its results are reasonable simple ordering or whitespace changes cc bartonjs | 0 |
126,466 | 10,423,634,174 | IssuesEvent | 2019-09-16 11:56:07 | microsoft/appcenter | https://api.github.com/repos/microsoft/appcenter | closed | Error: Cannot prepare UI Test artifacts using command: mono (Android Studio) | bug response required test | I have imported project into App Center,
When I try to build with normal process it builds successfully,
But whenever I tried to build with "Test on a real deviceFree"
Build fails with below error
[Preparing tests... failed.
Error: Cannot prepare UI Test artifacts using command: mono /Users/vsts/agent/2.155.1/work/1/a/GeneratedTest/packages/Xamarin.UITest.3.0.3/tools/test-cloud.exe prepare "/Users/vsts/agent/2.155.1/work/1/a/build/app-release.apk" --assembly-dir "/Users/vsts/agent/2.155.1/work/1/a/GeneratedTest/AppCenter.UITest.Android/bin/Release" --artifacts-dir "/Users/vsts/agent/2.155.1/work/1/a/Artifacts".
There was an unknown error preparing test artifacts, please try again. If you can't work out how to fix this issue, please contact support.
##[error]Error: /usr/local/bin/appcenter failed with return code: 3](url)
| 1.0 | Error: Cannot prepare UI Test artifacts using command: mono (Android Studio) - I have imported project into App Center,
When I try to build with normal process it builds successfully,
But whenever I tried to build with "Test on a real deviceFree"
Build fails with below error
[Preparing tests... failed.
Error: Cannot prepare UI Test artifacts using command: mono /Users/vsts/agent/2.155.1/work/1/a/GeneratedTest/packages/Xamarin.UITest.3.0.3/tools/test-cloud.exe prepare "/Users/vsts/agent/2.155.1/work/1/a/build/app-release.apk" --assembly-dir "/Users/vsts/agent/2.155.1/work/1/a/GeneratedTest/AppCenter.UITest.Android/bin/Release" --artifacts-dir "/Users/vsts/agent/2.155.1/work/1/a/Artifacts".
There was an unknown error preparing test artifacts, please try again. If you can't work out how to fix this issue, please contact support.
##[error]Error: /usr/local/bin/appcenter failed with return code: 3](url)
| non_priority | error cannot prepare ui test artifacts using command mono android studio i have imported project into app center when i try to build with normal process it builds successfully but whenever i tried to build with test on a real devicefree build fails with below error preparing tests failed error cannot prepare ui test artifacts using command mono users vsts agent work a generatedtest packages xamarin uitest tools test cloud exe prepare users vsts agent work a build app release apk assembly dir users vsts agent work a generatedtest appcenter uitest android bin release artifacts dir users vsts agent work a artifacts there was an unknown error preparing test artifacts please try again if you can t work out how to fix this issue please contact support error usr local bin appcenter failed with return code url | 0 |
121,613 | 16,005,060,087 | IssuesEvent | 2021-04-20 01:09:19 | microsoft/BotFramework-Composer | https://api.github.com/repos/microsoft/BotFramework-Composer | opened | UX on "Create new LUIS resources" screen | Needs-triage R13 Bugbash Type: Bug UX Design | ## Describe the bug
Several UX issues on this screen:
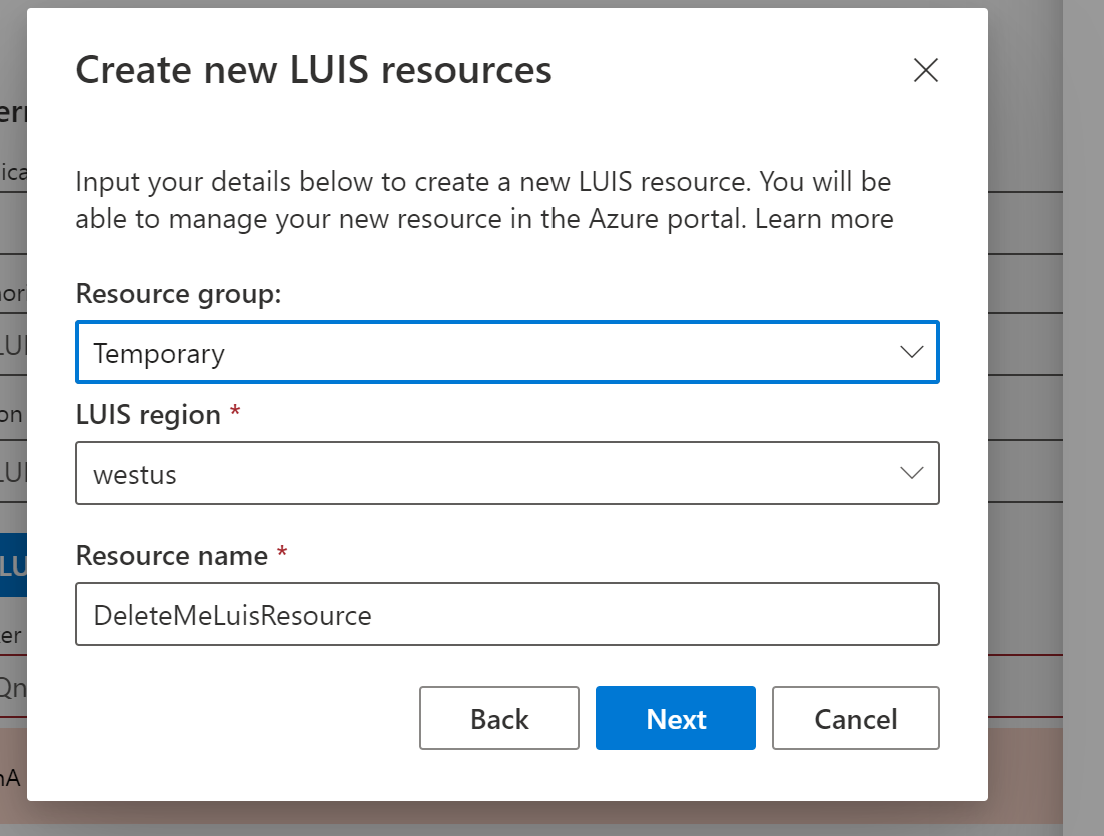
The issues are:
1. The "*" on the LUIS region and "resource name" text is a mystery. What does the "*" mean?
2. The dialog is "LUIS resources" (plural), but the text is "Resource name" (singular). The previous screen calls this "resource" (singular) Which is it? The text across these screens needs to align.
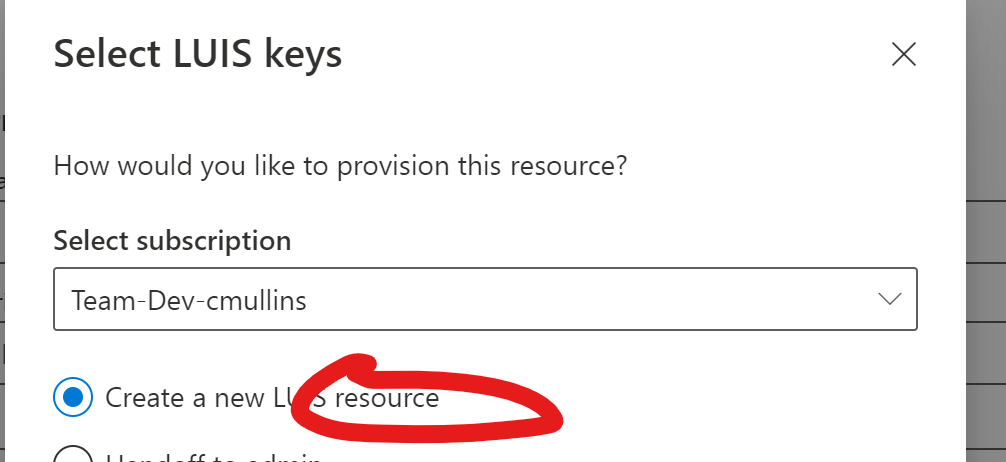
3. "Input your details below". I'm not picking any details. The text here needs some tweaking.
4. The "Learn more" text (no ".") needs a hyperlink (I created a separate bug to track that).
5. The "Resource group:" has a ":" at the end. The other fields do not.
## Version
Version: 1.4.0-nightly.236875.b9e46c2
Electron: 8.2.4
Chrome: 80.0.3987.165
NodeJS: 12.13.0
V8: 8.0.426.27-electron.0
| 1.0 | UX on "Create new LUIS resources" screen - ## Describe the bug
Several UX issues on this screen:
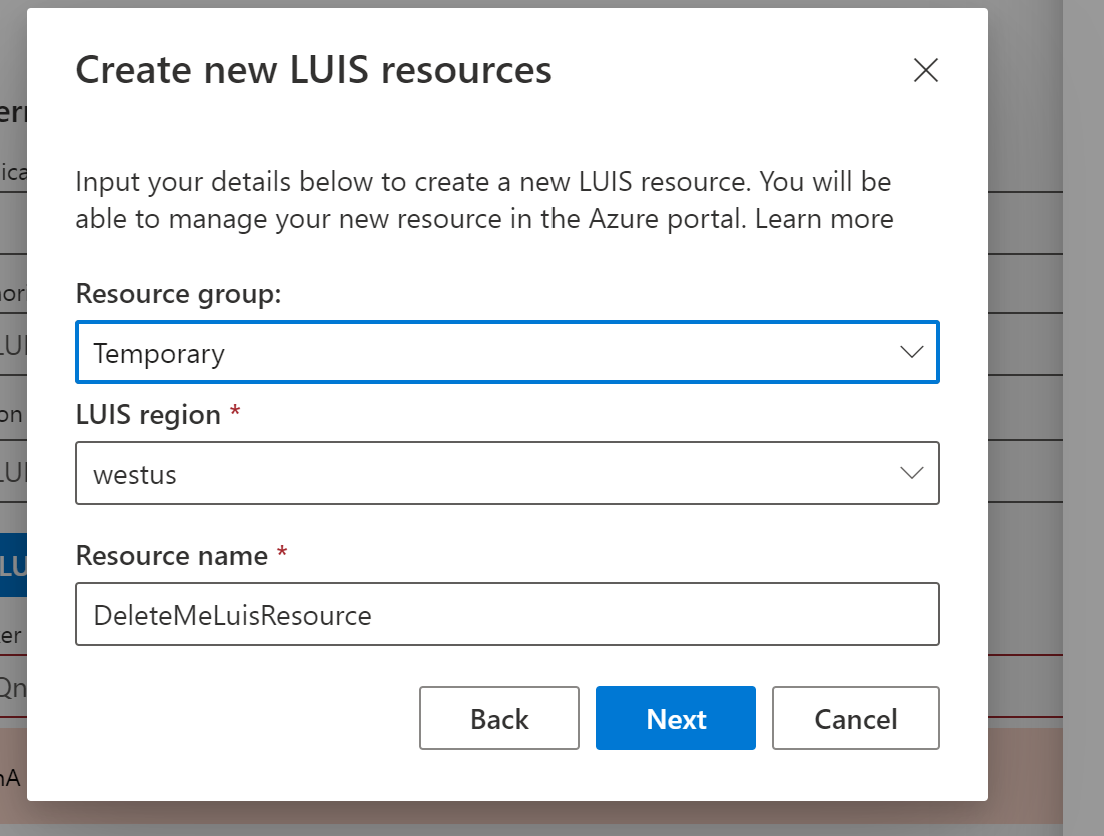
The issues are:
1. The "*" on the LUIS region and "resource name" text is a mystery. What does the "*" mean?
2. The dialog is "LUIS resources" (plural), but the text is "Resource name" (singular). The previous screen calls this "resource" (singular) Which is it? The text across these screens needs to align.
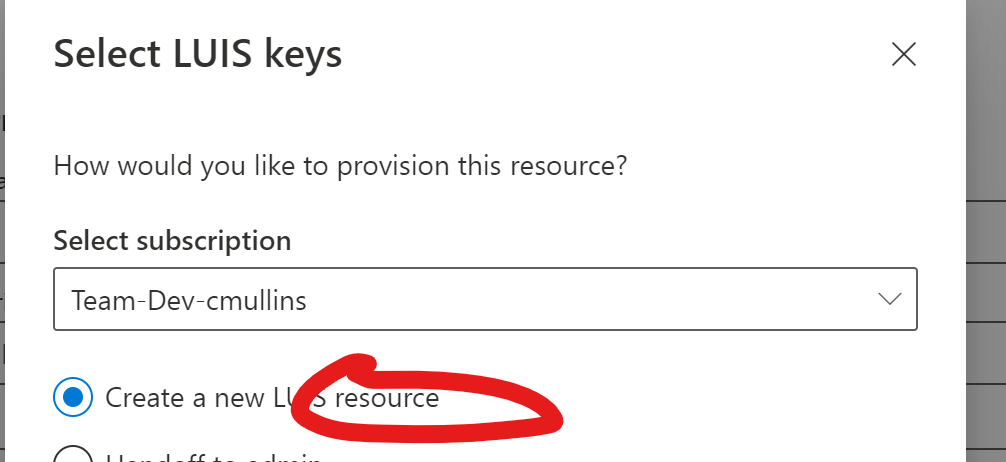
3. "Input your details below". I'm not picking any details. The text here needs some tweaking.
4. The "Learn more" text (no ".") needs a hyperlink (I created a separate bug to track that).
5. The "Resource group:" has a ":" at the end. The other fields do not.
## Version
Version: 1.4.0-nightly.236875.b9e46c2
Electron: 8.2.4
Chrome: 80.0.3987.165
NodeJS: 12.13.0
V8: 8.0.426.27-electron.0
| non_priority | ux on create new luis resources screen describe the bug several ux issues on this screen the issues are the on the luis region and resource name text is a mystery what does the mean the dialog is luis resources plural but the text is resource name singular the previous screen calls this resource singular which is it the text across these screens needs to align input your details below i m not picking any details the text here needs some tweaking the learn more text no needs a hyperlink i created a separate bug to track that the resource group has a at the end the other fields do not version version nightly electron chrome nodejs electron | 0 |
25,755 | 11,211,863,240 | IssuesEvent | 2020-01-06 16:18:54 | PeterNgTr/ng-module5-solution | https://api.github.com/repos/PeterNgTr/ng-module5-solution | opened | CVE-2018-20677 (Medium) detected in bootstrap-3.3.6-3.3.6.min.js | security vulnerability | ## CVE-2018-20677 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6-3.3.6.min.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.6-3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.6-3.3.6/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/ng-module5-solution/index.html</p>
<p>Path to vulnerable library: /ng-module5-solution/lib/bootstrap.min.js,/ng-module5-solution/lib/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/PeterNgTr/ng-module5-solution/commit/9a10e692a21ec304483797241fd2518a8b991f6d">9a10e692a21ec304483797241fd2518a8b991f6d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-20677 (Medium) detected in bootstrap-3.3.6-3.3.6.min.js - ## CVE-2018-20677 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.6-3.3.6.min.js</b></p></summary>
<p>Google-styled theme for Bootstrap.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.6-3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/todc-bootstrap/3.3.6-3.3.6/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/ng-module5-solution/index.html</p>
<p>Path to vulnerable library: /ng-module5-solution/lib/bootstrap.min.js,/ng-module5-solution/lib/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6-3.3.6.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/PeterNgTr/ng-module5-solution/commit/9a10e692a21ec304483797241fd2518a8b991f6d">9a10e692a21ec304483797241fd2518a8b991f6d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js google styled theme for bootstrap library home page a href path to dependency file tmp ws scm ng solution index html path to vulnerable library ng solution lib bootstrap min js ng solution lib bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter step up your open source security game with whitesource | 0 |
124,630 | 16,619,915,643 | IssuesEvent | 2021-06-02 22:24:54 | dotnet/project-system | https://api.github.com/repos/dotnet/project-system | opened | New Property Pages: Add evaluation log | Discussion/Question Feature Request Feature-Project-Properties-Designer | Related: https://github.com/dotnet/project-system/issues/6931
Related: https://github.com/dotnet/project-system/issues/7050
One of the design issues for the new property pages is what information to display to the user for recursive properties. I wanted to make a mock-up of an idea to expand the current evaluated value display to allow it to show the entire evaluation log. It would show these three aspects:
- Source of property value
- Value in source
- Evaluated value at time of processing
Each row on the table shows these 3 values. The top-down order of the table is showing the processing order of the property. This would definitely show the progression of a property. I tried to keep it clear and concise, but I realize adding table headers may help. By default, properties would still show the normal final evaluated value display. Let me step through the idea with the mock-up images I've made. I will be using `DefineConstants` in this example.
---
You start with the normal looking property display. The value in the field would *always display the project's value*. Here, the project has no value defined for `DefineConstants`.
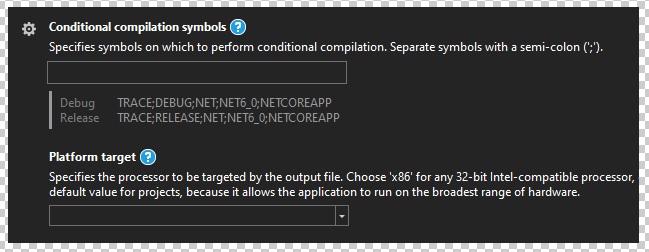
To enable the evaluation log, we would adapt the ⚙ menu to be more general purpose (like how it is in VSCode). It would not simply relate to configuration dimensions only. I've added a `Show evaluation log` option as a checkbox.
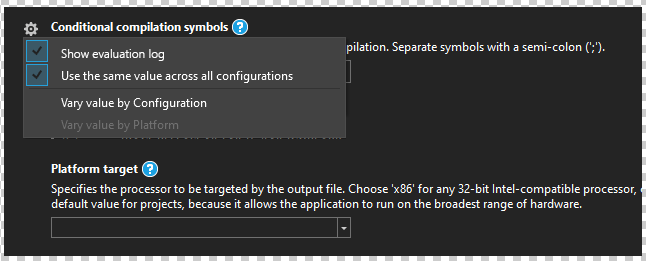
After enabling the evaluation log, the current final evaluated value display is hidden, and the evaluation log appears. It is a simple table per configuration showing the source, value, and evaluated value.
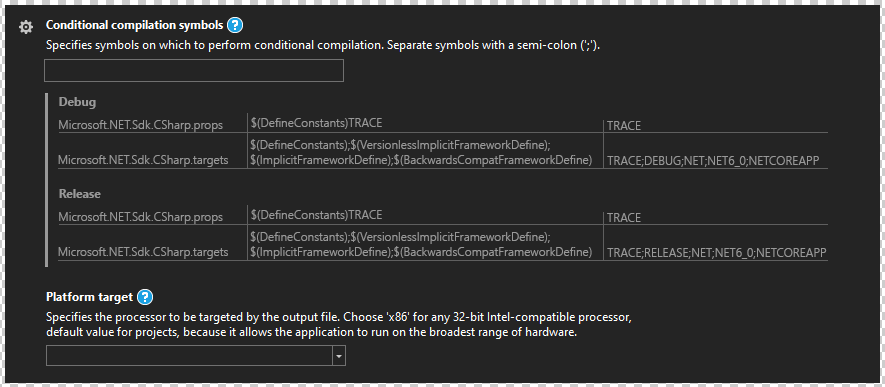
---
To show an example of what happens when you put in a value, here I put in the value `$(DefineConstants);Foo`. You can see `;Foo` in the final evaluation display.
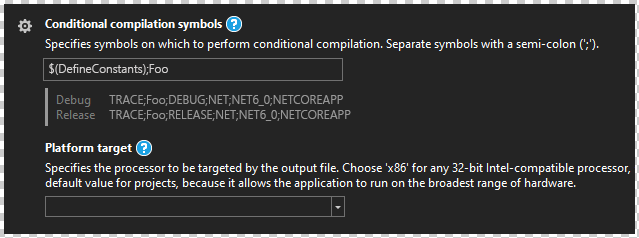
After enabling the evaluation log, you can see there is a new row for `ConsoleApp14.csproj`, which is the project filename of the current project. This is inserted in-between the 2 other rows since this is the evaluation order. With this, there is no confusion around how editing the property affects the final evaluated value.
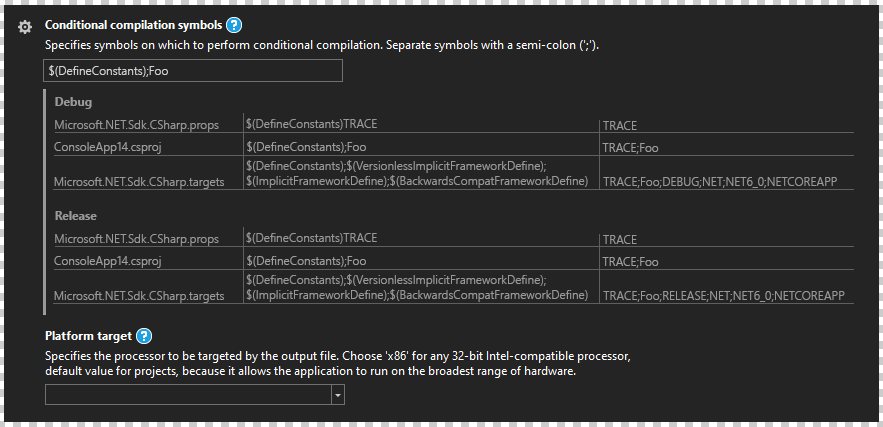
---
I believe this concept would be great for any property and be a substantial enhancement over the current property pages. Since the data is turned on/off as needed, when showing the evaluation log, it would acquire the data needed for it at that time. Maybe some kind of cache would be required since rebuilding to acquire that data is time consuming. I'm not aware of the challenges required to make the evaluation log work, but I do know that it is a useful feature for those trying to understand how and why a property is set to a certain value. This is especially useful for complex systems and feels like the feature would be a good key differentiator between doing .NET developing in Visual Studio versus doing it in an editor like VSCode. I'd consider this to be a 'premium' feature for project management. | 1.0 | New Property Pages: Add evaluation log - Related: https://github.com/dotnet/project-system/issues/6931
Related: https://github.com/dotnet/project-system/issues/7050
One of the design issues for the new property pages is what information to display to the user for recursive properties. I wanted to make a mock-up of an idea to expand the current evaluated value display to allow it to show the entire evaluation log. It would show these three aspects:
- Source of property value
- Value in source
- Evaluated value at time of processing
Each row on the table shows these 3 values. The top-down order of the table is showing the processing order of the property. This would definitely show the progression of a property. I tried to keep it clear and concise, but I realize adding table headers may help. By default, properties would still show the normal final evaluated value display. Let me step through the idea with the mock-up images I've made. I will be using `DefineConstants` in this example.
---
You start with the normal looking property display. The value in the field would *always display the project's value*. Here, the project has no value defined for `DefineConstants`.
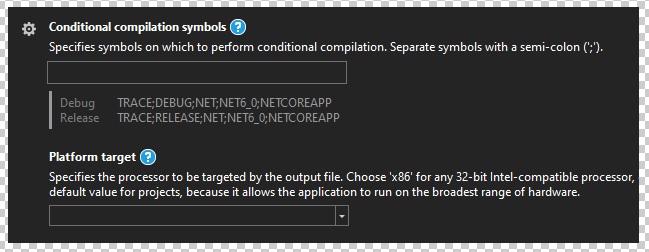
To enable the evaluation log, we would adapt the ⚙ menu to be more general purpose (like how it is in VSCode). It would not simply relate to configuration dimensions only. I've added a `Show evaluation log` option as a checkbox.
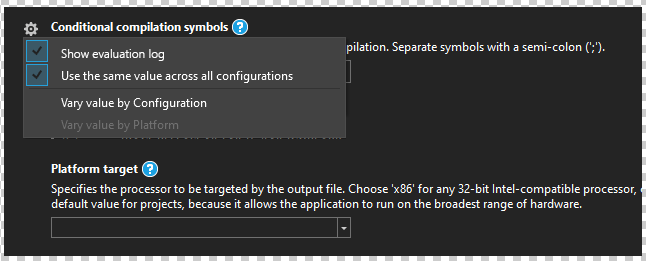
After enabling the evaluation log, the current final evaluated value display is hidden, and the evaluation log appears. It is a simple table per configuration showing the source, value, and evaluated value.
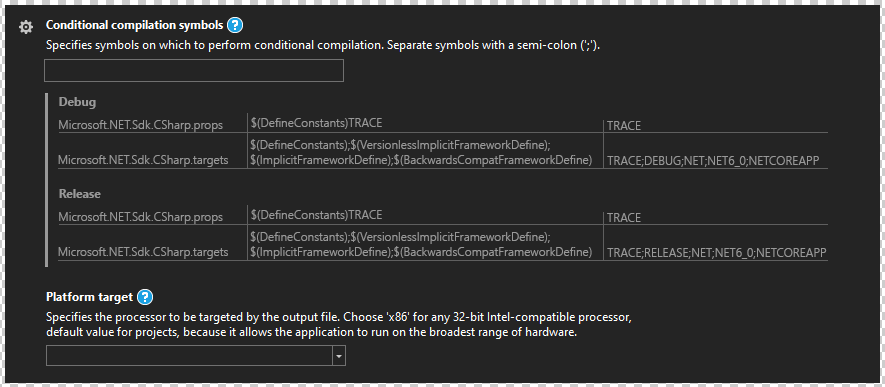
---
To show an example of what happens when you put in a value, here I put in the value `$(DefineConstants);Foo`. You can see `;Foo` in the final evaluation display.
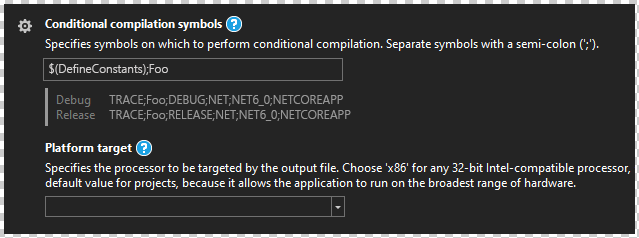
After enabling the evaluation log, you can see there is a new row for `ConsoleApp14.csproj`, which is the project filename of the current project. This is inserted in-between the 2 other rows since this is the evaluation order. With this, there is no confusion around how editing the property affects the final evaluated value.
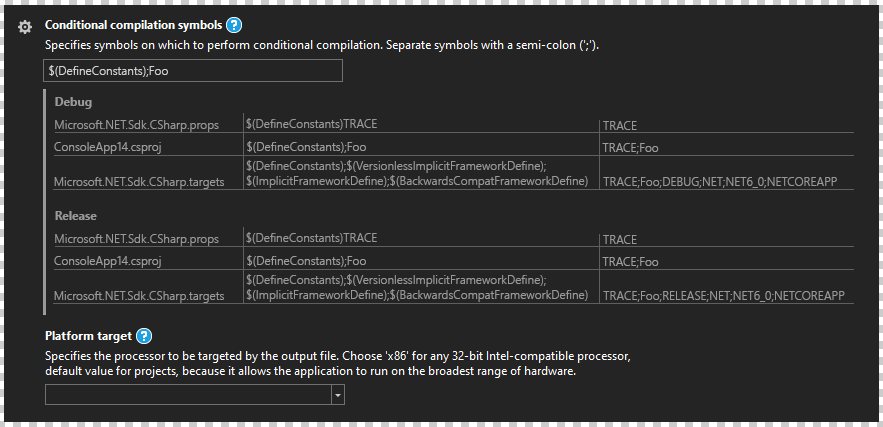
---
I believe this concept would be great for any property and be a substantial enhancement over the current property pages. Since the data is turned on/off as needed, when showing the evaluation log, it would acquire the data needed for it at that time. Maybe some kind of cache would be required since rebuilding to acquire that data is time consuming. I'm not aware of the challenges required to make the evaluation log work, but I do know that it is a useful feature for those trying to understand how and why a property is set to a certain value. This is especially useful for complex systems and feels like the feature would be a good key differentiator between doing .NET developing in Visual Studio versus doing it in an editor like VSCode. I'd consider this to be a 'premium' feature for project management. | non_priority | new property pages add evaluation log related related one of the design issues for the new property pages is what information to display to the user for recursive properties i wanted to make a mock up of an idea to expand the current evaluated value display to allow it to show the entire evaluation log it would show these three aspects source of property value value in source evaluated value at time of processing each row on the table shows these values the top down order of the table is showing the processing order of the property this would definitely show the progression of a property i tried to keep it clear and concise but i realize adding table headers may help by default properties would still show the normal final evaluated value display let me step through the idea with the mock up images i ve made i will be using defineconstants in this example you start with the normal looking property display the value in the field would always display the project s value here the project has no value defined for defineconstants to enable the evaluation log we would adapt the ⚙ menu to be more general purpose like how it is in vscode it would not simply relate to configuration dimensions only i ve added a show evaluation log option as a checkbox after enabling the evaluation log the current final evaluated value display is hidden and the evaluation log appears it is a simple table per configuration showing the source value and evaluated value to show an example of what happens when you put in a value here i put in the value defineconstants foo you can see foo in the final evaluation display after enabling the evaluation log you can see there is a new row for csproj which is the project filename of the current project this is inserted in between the other rows since this is the evaluation order with this there is no confusion around how editing the property affects the final evaluated value i believe this concept would be great for any property and be a substantial enhancement over the current property pages since the data is turned on off as needed when showing the evaluation log it would acquire the data needed for it at that time maybe some kind of cache would be required since rebuilding to acquire that data is time consuming i m not aware of the challenges required to make the evaluation log work but i do know that it is a useful feature for those trying to understand how and why a property is set to a certain value this is especially useful for complex systems and feels like the feature would be a good key differentiator between doing net developing in visual studio versus doing it in an editor like vscode i d consider this to be a premium feature for project management | 0 |
32,435 | 26,697,310,458 | IssuesEvent | 2023-01-27 11:29:34 | ImperialCollegeLondon/gridlington-vis | https://api.github.com/repos/ImperialCollegeLondon/gridlington-vis | closed | Run the OVE Server on a VM (just clone this repo for now) | enhancement infrastructure | The application launcher page of OVE should be visible and it should be possible to launch new OVE applications. | 1.0 | Run the OVE Server on a VM (just clone this repo for now) - The application launcher page of OVE should be visible and it should be possible to launch new OVE applications. | non_priority | run the ove server on a vm just clone this repo for now the application launcher page of ove should be visible and it should be possible to launch new ove applications | 0 |
42,169 | 22,332,206,016 | IssuesEvent | 2022-06-14 15:20:44 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Diagnostics about Elasticsearch client sockets | Team:Core performance | The Elasticsearch-js client is currently configured to use `maxSockets: Infinity` which means connections aren't being re-used causing every outgoing connection to have to establish a new connection + TLS. We know we need to reduce this value but it's really hard to choose an appropriate number.
In order to tune this value we need to expose the number of actual sockets used by the http agent that the Elasticsearch-js client is using. That way we could log a warning when Kibana hits the limit. If at the limit the event loop is still really healthy then performance could be improved by increasing the number of sockets.
In addition to a warning when we're at the limit, it would be useful to expose the number of sockets as part of our monitoring data as well as through the `ops.metrics` logger.
Context:
https://github.com/elastic/kibana/issues/112756#issuecomment-1135946020 | True | Diagnostics about Elasticsearch client sockets - The Elasticsearch-js client is currently configured to use `maxSockets: Infinity` which means connections aren't being re-used causing every outgoing connection to have to establish a new connection + TLS. We know we need to reduce this value but it's really hard to choose an appropriate number.
In order to tune this value we need to expose the number of actual sockets used by the http agent that the Elasticsearch-js client is using. That way we could log a warning when Kibana hits the limit. If at the limit the event loop is still really healthy then performance could be improved by increasing the number of sockets.
In addition to a warning when we're at the limit, it would be useful to expose the number of sockets as part of our monitoring data as well as through the `ops.metrics` logger.
Context:
https://github.com/elastic/kibana/issues/112756#issuecomment-1135946020 | non_priority | diagnostics about elasticsearch client sockets the elasticsearch js client is currently configured to use maxsockets infinity which means connections aren t being re used causing every outgoing connection to have to establish a new connection tls we know we need to reduce this value but it s really hard to choose an appropriate number in order to tune this value we need to expose the number of actual sockets used by the http agent that the elasticsearch js client is using that way we could log a warning when kibana hits the limit if at the limit the event loop is still really healthy then performance could be improved by increasing the number of sockets in addition to a warning when we re at the limit it would be useful to expose the number of sockets as part of our monitoring data as well as through the ops metrics logger context | 0 |
418,027 | 28,113,296,472 | IssuesEvent | 2023-03-31 08:52:55 | nicholas132000/ped | https://api.github.com/repos/nicholas132000/ped | opened | UG ad command example given gives an error | type.DocumentationBug severity.High |
end date given shown in the add command example of the UG is 2023-02-11 even though that the UG states that date format should be given in YYYY/MM/DD
<!--session: 1680252546883-9cecbcf7-ece5-476f-a754-e557abba7734-->
<!--Version: Web v3.4.7--> | 1.0 | UG ad command example given gives an error -
end date given shown in the add command example of the UG is 2023-02-11 even though that the UG states that date format should be given in YYYY/MM/DD
<!--session: 1680252546883-9cecbcf7-ece5-476f-a754-e557abba7734-->
<!--Version: Web v3.4.7--> | non_priority | ug ad command example given gives an error end date given shown in the add command example of the ug is even though that the ug states that date format should be given in yyyy mm dd | 0 |
37,279 | 8,318,389,897 | IssuesEvent | 2018-09-25 14:34:29 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Calendar: Popup on dialog with wrong position | defect | 1) Environment
- PrimeFaces version: PrimeFaces-6.2.6
- Application server + version: Primefaces Showcase
- Affected browsers: Chrome, Firefox
2) Expected behaviour
Correct position of the popup calendar when browser is zoomed in or out
3) Actual behaviour
When a p:calendar component is placed inside a p:dialog the popup shows in a wrong position when this 2 conditions are met:
- Page is zoomed in or out
- Page is scrolled down
This can be tested on the p:schedule showcase
https://www.primefaces.org/showcase/ui/data/schedule.xhtml
Clicking in a date shows a dialog with this behaviour
4) Steps to reproduce
- Go to: https://www.primefaces.org/showcase/ui/data/schedule.xhtml
- Zoom to 90% (AFAIK this happens with any percentage)
- Scroll down a little
- Click on a date to open the new event dialog
- Click on the calendar component to bring up the popup
| 1.0 | Calendar: Popup on dialog with wrong position - 1) Environment
- PrimeFaces version: PrimeFaces-6.2.6
- Application server + version: Primefaces Showcase
- Affected browsers: Chrome, Firefox
2) Expected behaviour
Correct position of the popup calendar when browser is zoomed in or out
3) Actual behaviour
When a p:calendar component is placed inside a p:dialog the popup shows in a wrong position when this 2 conditions are met:
- Page is zoomed in or out
- Page is scrolled down
This can be tested on the p:schedule showcase
https://www.primefaces.org/showcase/ui/data/schedule.xhtml
Clicking in a date shows a dialog with this behaviour
4) Steps to reproduce
- Go to: https://www.primefaces.org/showcase/ui/data/schedule.xhtml
- Zoom to 90% (AFAIK this happens with any percentage)
- Scroll down a little
- Click on a date to open the new event dialog
- Click on the calendar component to bring up the popup
| non_priority | calendar popup on dialog with wrong position environment primefaces version primefaces application server version primefaces showcase affected browsers chrome firefox expected behaviour correct position of the popup calendar when browser is zoomed in or out actual behaviour when a p calendar component is placed inside a p dialog the popup shows in a wrong position when this conditions are met page is zoomed in or out page is scrolled down this can be tested on the p schedule showcase clicking in a date shows a dialog with this behaviour steps to reproduce go to zoom to afaik this happens with any percentage scroll down a little click on a date to open the new event dialog click on the calendar component to bring up the popup | 0 |
15,972 | 3,490,767,837 | IssuesEvent | 2016-01-04 12:06:54 | paperjs/paper.js | https://api.github.com/repos/paperjs/paper.js | closed | Boolean Intersections inside overlap ranges need special handling | boolean-operations unit-test-missing | That's why this special case is misbehaving: It has two intersections inside the overlap range, and currently deals with them wrongly:
```js
var path1 = new Path({
pathData: "M495.9,1693.5c-42.2-203.5-64.5-304.9-78-299.9 c-1.7,0.6-0.3,6.7,5.3,22.5l209.4-74.8l75.8,303.9L495.9,1693.5z",
fillColor: 'red'
});
var path2 = new Path({
pathData: "M632.6,1341.2l-209.4,74.9c95.4,267,135.6,201-60.1-144.5l202.9-85.7 L632.6,1341.2z",
fillColor: 'blue'
});
view.center = project.activeLayer.position;
var res = path1.unite(path2);
res.fillColor = new Color(1, 1, 0, 0.5);
res.fullySelected = true;
``` | 1.0 | Boolean Intersections inside overlap ranges need special handling - That's why this special case is misbehaving: It has two intersections inside the overlap range, and currently deals with them wrongly:
```js
var path1 = new Path({
pathData: "M495.9,1693.5c-42.2-203.5-64.5-304.9-78-299.9 c-1.7,0.6-0.3,6.7,5.3,22.5l209.4-74.8l75.8,303.9L495.9,1693.5z",
fillColor: 'red'
});
var path2 = new Path({
pathData: "M632.6,1341.2l-209.4,74.9c95.4,267,135.6,201-60.1-144.5l202.9-85.7 L632.6,1341.2z",
fillColor: 'blue'
});
view.center = project.activeLayer.position;
var res = path1.unite(path2);
res.fillColor = new Color(1, 1, 0, 0.5);
res.fullySelected = true;
``` | non_priority | boolean intersections inside overlap ranges need special handling that s why this special case is misbehaving it has two intersections inside the overlap range and currently deals with them wrongly js var new path pathdata c fillcolor red var new path pathdata fillcolor blue view center project activelayer position var res unite res fillcolor new color res fullyselected true | 0 |
176,462 | 14,583,160,854 | IssuesEvent | 2020-12-18 13:34:38 | alphagov/govuk-design-system | https://api.github.com/repos/alphagov/govuk-design-system | opened | Agree where to host external technical documentation | documentation 🕔 days | ## What
Explore options of where to host external technical documentation
## Why
Find a suitable option to host our docs.
## Who needs to know about this
Tech Writer
## Further detail
For info - GOV.UK Pay host their [documentation](https://docs.payments.service.gov.uk/support_contact_and_more_information/#support) on Tech Docs Template.
## Done when
- [ ] Options gathered
- [ ] Options assessed
- [ ] Hosting option agreed
## Next steps
Set up hosting arrangements.
| 1.0 | Agree where to host external technical documentation - ## What
Explore options of where to host external technical documentation
## Why
Find a suitable option to host our docs.
## Who needs to know about this
Tech Writer
## Further detail
For info - GOV.UK Pay host their [documentation](https://docs.payments.service.gov.uk/support_contact_and_more_information/#support) on Tech Docs Template.
## Done when
- [ ] Options gathered
- [ ] Options assessed
- [ ] Hosting option agreed
## Next steps
Set up hosting arrangements.
| non_priority | agree where to host external technical documentation what explore options of where to host external technical documentation why find a suitable option to host our docs who needs to know about this tech writer further detail for info gov uk pay host their on tech docs template done when options gathered options assessed hosting option agreed next steps set up hosting arrangements | 0 |
12,639 | 15,016,634,661 | IssuesEvent | 2021-02-01 09:50:21 | threefoldtech/js-sdk | https://api.github.com/repos/threefoldtech/js-sdk | closed | Adding a worker node to an existing cluster in a VDC takes forever | process_wontfix | VDC name: jetserthing
I launched a numbetr of marketsplace solutions (2) and wen I tried to launch the 3rd one, I got a message that told me that there were no more resources.
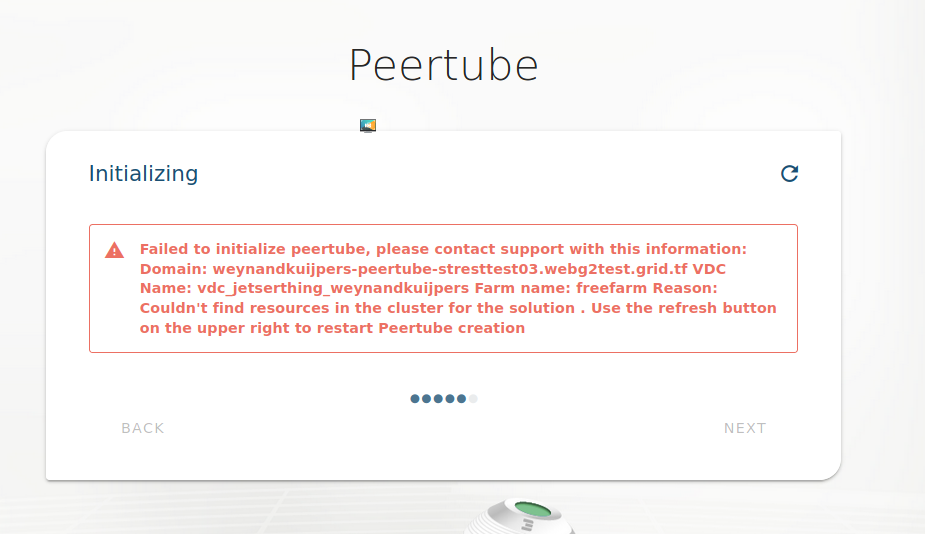
Wanted to add a worker node to see of that would lead to more capacity being available in the cluster that would allow me to launch this peertube container. The progress screen was slow to progress and got stuck at this forever:
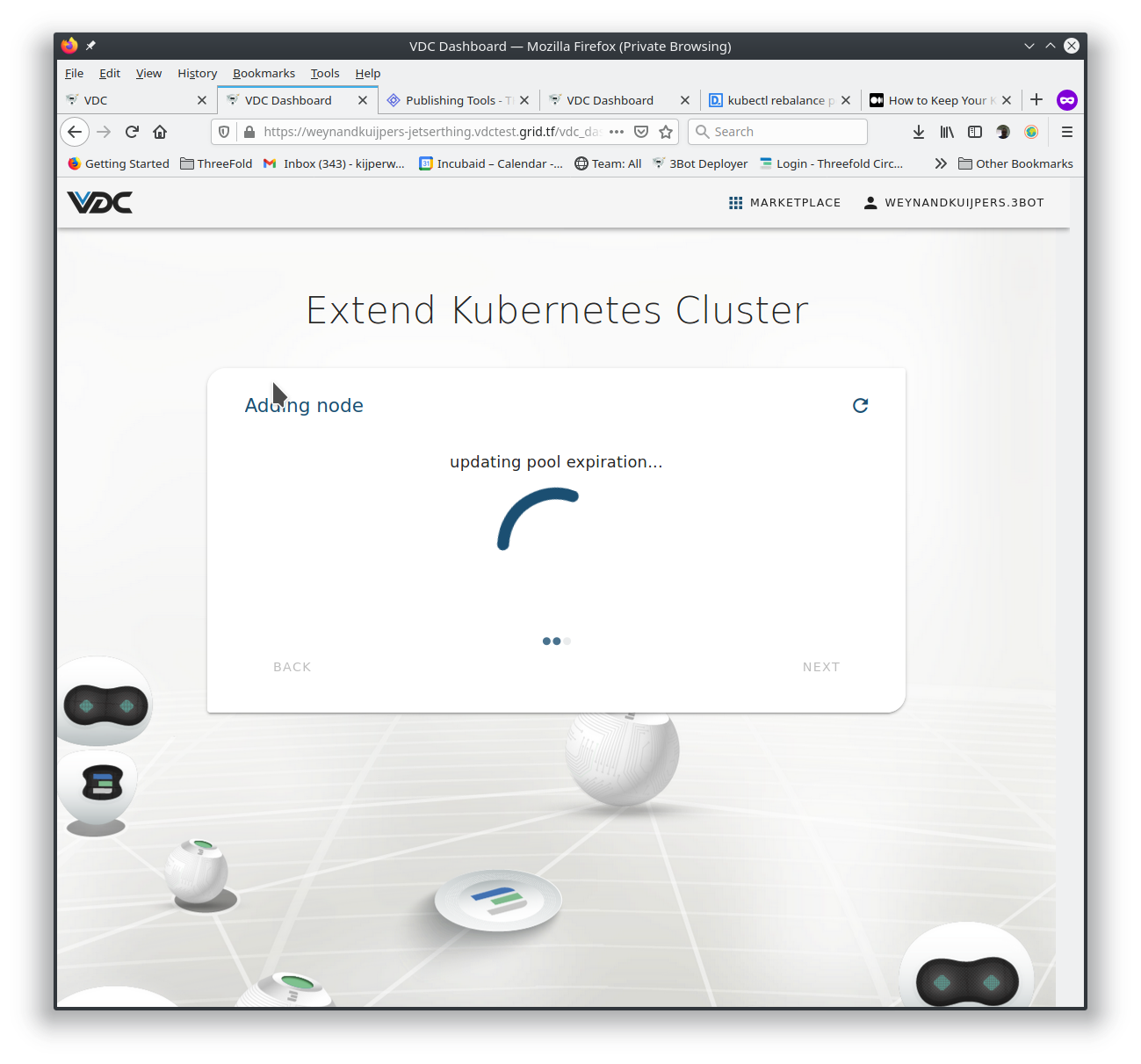
I pressed "Reload page" a couple of times but always got back to the same rotating page.
CLI shows a new worker node
```
john@RescuedMac:~/.kube$ kubectl get nodes
NAME STATUS ROLES AGE VERSION
k3os-21973 Ready <none> 8m59s v1.19.4+k3s1
k3os-31241 Ready <none> 22h v1.19.4+k3s1
k3os-4283 Ready master 22h v1.19.4+k3s1
```
| 1.0 | Adding a worker node to an existing cluster in a VDC takes forever - VDC name: jetserthing
I launched a numbetr of marketsplace solutions (2) and wen I tried to launch the 3rd one, I got a message that told me that there were no more resources.
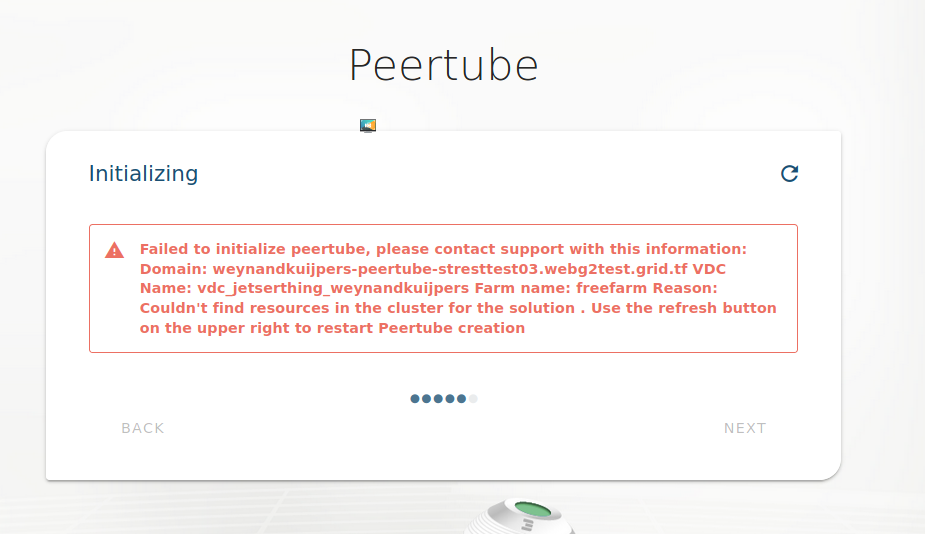
Wanted to add a worker node to see of that would lead to more capacity being available in the cluster that would allow me to launch this peertube container. The progress screen was slow to progress and got stuck at this forever:
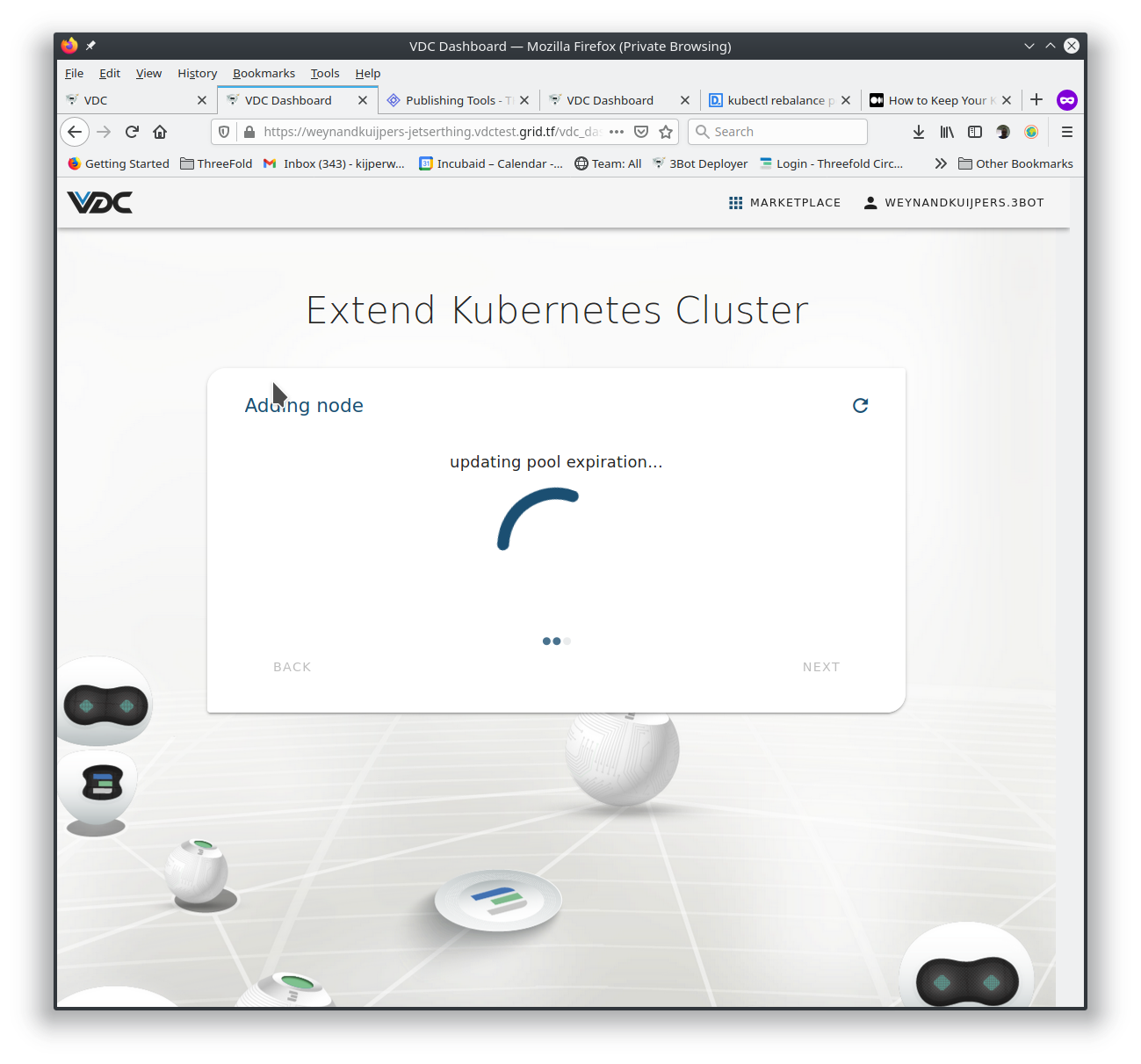
I pressed "Reload page" a couple of times but always got back to the same rotating page.
CLI shows a new worker node
```
john@RescuedMac:~/.kube$ kubectl get nodes
NAME STATUS ROLES AGE VERSION
k3os-21973 Ready <none> 8m59s v1.19.4+k3s1
k3os-31241 Ready <none> 22h v1.19.4+k3s1
k3os-4283 Ready master 22h v1.19.4+k3s1
```
| non_priority | adding a worker node to an existing cluster in a vdc takes forever vdc name jetserthing i launched a numbetr of marketsplace solutions and wen i tried to launch the one i got a message that told me that there were no more resources wanted to add a worker node to see of that would lead to more capacity being available in the cluster that would allow me to launch this peertube container the progress screen was slow to progress and got stuck at this forever i pressed reload page a couple of times but always got back to the same rotating page cli shows a new worker node john rescuedmac kube kubectl get nodes name status roles age version ready ready ready master | 0 |
232,437 | 18,874,362,094 | IssuesEvent | 2021-11-13 19:07:56 | ansible-collections/community.hashi_vault | https://api.github.com/repos/ansible-collections/community.hashi_vault | closed | integration_tests - cleanup aliases | tests | <!--- Verify first that your feature was not already discussed on GitHub -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
<!--- Describe the new feature/improvement briefly below -->
Look at cleaning up the integration tests' `aliases` files:
- remove `skip/python2.6` (it's not in the test matrix anyway)
- many `needs/target/` entries may not be needed because they are in `meta/main.yml` dependencies; re-test to see which if any are needed
##### ISSUE TYPE
- Tests cleanup
##### COMPONENT NAME
<!--- Write the short name of the module, plugin, task or feature below, use your best guess if unsure -->
tests/integration/
##### ADDITIONAL INFORMATION
<!--- Describe how the feature would be used, why it is needed and what it would solve -->
<!--- Paste example playbooks or commands between quotes below -->
<!--- HINT: You can also paste gist.github.com links for larger files -->
| 1.0 | integration_tests - cleanup aliases - <!--- Verify first that your feature was not already discussed on GitHub -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
<!--- Describe the new feature/improvement briefly below -->
Look at cleaning up the integration tests' `aliases` files:
- remove `skip/python2.6` (it's not in the test matrix anyway)
- many `needs/target/` entries may not be needed because they are in `meta/main.yml` dependencies; re-test to see which if any are needed
##### ISSUE TYPE
- Tests cleanup
##### COMPONENT NAME
<!--- Write the short name of the module, plugin, task or feature below, use your best guess if unsure -->
tests/integration/
##### ADDITIONAL INFORMATION
<!--- Describe how the feature would be used, why it is needed and what it would solve -->
<!--- Paste example playbooks or commands between quotes below -->
<!--- HINT: You can also paste gist.github.com links for larger files -->
| non_priority | integration tests cleanup aliases summary look at cleaning up the integration tests aliases files remove skip it s not in the test matrix anyway many needs target entries may not be needed because they are in meta main yml dependencies re test to see which if any are needed issue type tests cleanup component name tests integration additional information | 0 |
89,016 | 11,184,953,278 | IssuesEvent | 2019-12-31 21:17:40 | ChildMindInstitute/mindlogger-app | https://api.github.com/repos/ChildMindInstitute/mindlogger-app | closed | ✨ Specify Subjects | backend design documentation duplicate frontend help wanted large scope | If multiple parents, say, are answering about multiple children, and those children are answering about themselves and each other, we need a private way to specify who is being answered about. | 1.0 | ✨ Specify Subjects - If multiple parents, say, are answering about multiple children, and those children are answering about themselves and each other, we need a private way to specify who is being answered about. | non_priority | ✨ specify subjects if multiple parents say are answering about multiple children and those children are answering about themselves and each other we need a private way to specify who is being answered about | 0 |
366,323 | 25,577,737,977 | IssuesEvent | 2022-12-01 00:11:14 | bitloops/bitloops-language | https://api.github.com/repos/bitloops/bitloops-language | opened | [cli] | documentation enhancement | When running the CLI, if the setup.bl file is not found, the output on the console is very user unfriendly. The code should be caught properly and user friendly feedback should be provided along with instructions and a link on how to solve it.

| 1.0 | [cli] - When running the CLI, if the setup.bl file is not found, the output on the console is very user unfriendly. The code should be caught properly and user friendly feedback should be provided along with instructions and a link on how to solve it.

| non_priority | when running the cli if the setup bl file is not found the output on the console is very user unfriendly the code should be caught properly and user friendly feedback should be provided along with instructions and a link on how to solve it | 0 |
167,567 | 13,035,327,296 | IssuesEvent | 2020-07-28 10:10:44 | urapadmin/kiosk | https://api.github.com/repos/urapadmin/kiosk | closed | a feature can be linked twice by the same survey / feature recording excavation | bug filemaker test-stage | just using the new link button (see #679) twice with the same feature leads to a second, third etc. entry of the same feature.
That should not be possible. | 1.0 | a feature can be linked twice by the same survey / feature recording excavation - just using the new link button (see #679) twice with the same feature leads to a second, third etc. entry of the same feature.
That should not be possible. | non_priority | a feature can be linked twice by the same survey feature recording excavation just using the new link button see twice with the same feature leads to a second third etc entry of the same feature that should not be possible | 0 |
317,758 | 23,687,746,780 | IssuesEvent | 2022-08-29 08:01:55 | OrdinaNederland/Stichting-NUTwente | https://api.github.com/repos/OrdinaNederland/Stichting-NUTwente | closed | Een pull request naar dev maakte niet een pull request naar main aan voor pull 677 | documentation Prio 3 continuïteit | Bij het mergen naar dev voor pull 677: "https://github.com/OrdinaNederland/Stichting-NUTwente/pull/677" ging er iets fout.
In plaats van een pull request aan te maken naar main die dan approved en dan gemerged kon worden door de tester @CasperHooft. Sloot de pull request zichzelf nadat het gemerged was met de development branch
Als gebruiker van de GIT omgeving wil ik een consistente GIT workflow zodat ik op een constante manier mijn issues kan verwerken.
DoD
- [x] Er is onderzocht waarom/hoe dit gebeurd is
- [x] Er is gedocumenteerd waarom/hoe dit gebeurd is
- [x] Er is een oplossing voor dit probleem gevonden en gedocumenteerd | 1.0 | Een pull request naar dev maakte niet een pull request naar main aan voor pull 677 - Bij het mergen naar dev voor pull 677: "https://github.com/OrdinaNederland/Stichting-NUTwente/pull/677" ging er iets fout.
In plaats van een pull request aan te maken naar main die dan approved en dan gemerged kon worden door de tester @CasperHooft. Sloot de pull request zichzelf nadat het gemerged was met de development branch
Als gebruiker van de GIT omgeving wil ik een consistente GIT workflow zodat ik op een constante manier mijn issues kan verwerken.
DoD
- [x] Er is onderzocht waarom/hoe dit gebeurd is
- [x] Er is gedocumenteerd waarom/hoe dit gebeurd is
- [x] Er is een oplossing voor dit probleem gevonden en gedocumenteerd | non_priority | een pull request naar dev maakte niet een pull request naar main aan voor pull bij het mergen naar dev voor pull ging er iets fout in plaats van een pull request aan te maken naar main die dan approved en dan gemerged kon worden door de tester casperhooft sloot de pull request zichzelf nadat het gemerged was met de development branch als gebruiker van de git omgeving wil ik een consistente git workflow zodat ik op een constante manier mijn issues kan verwerken dod er is onderzocht waarom hoe dit gebeurd is er is gedocumenteerd waarom hoe dit gebeurd is er is een oplossing voor dit probleem gevonden en gedocumenteerd | 0 |
96,403 | 16,129,631,840 | IssuesEvent | 2021-04-29 01:06:25 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | opened | CVE-2019-12378 (Medium) detected in linuxv5.2 | security vulnerability | ## CVE-2019-12378 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/net/ipv6/ipv6_sockglue.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/net/ipv6/ipv6_sockglue.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** An issue was discovered in ip6_ra_control in net/ipv6/ipv6_sockglue.c in the Linux kernel through 5.1.5. There is an unchecked kmalloc of new_ra, which might allow an attacker to cause a denial of service (NULL pointer dereference and system crash). NOTE: This has been disputed as not an issue.
<p>Publish Date: 2019-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12378>CVE-2019-12378</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378</a></p>
<p>Release Date: 2019-05-28</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
| True | CVE-2019-12378 (Medium) detected in linuxv5.2 - ## CVE-2019-12378 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv5.2</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/net/ipv6/ipv6_sockglue.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/net/ipv6/ipv6_sockglue.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** An issue was discovered in ip6_ra_control in net/ipv6/ipv6_sockglue.c in the Linux kernel through 5.1.5. There is an unchecked kmalloc of new_ra, which might allow an attacker to cause a denial of service (NULL pointer dereference and system crash). NOTE: This has been disputed as not an issue.
<p>Publish Date: 2019-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12378>CVE-2019-12378</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12378</a></p>
<p>Release Date: 2019-05-28</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in base branch amp centos kernel vulnerable source files ampere centos kernel net sockglue c ampere centos kernel net sockglue c vulnerability details disputed an issue was discovered in ra control in net sockglue c in the linux kernel through there is an unchecked kmalloc of new ra which might allow an attacker to cause a denial of service null pointer dereference and system crash note this has been disputed as not an issue publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
155,187 | 12,243,003,374 | IssuesEvent | 2020-05-05 08:24:57 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: sqlsmith/setup=tpcc/setting=ddl-nodrop failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).sqlsmith/setup=tpcc/setting=ddl-nodrop failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1920699&tab=buildLog) on [master@425eaa8fb05fc32b2c42827b85338daa52f4177c](https://github.com/cockroachdb/cockroach/commits/425eaa8fb05fc32b2c42827b85338daa52f4177c):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/sqlsmith/setup=tpcc/setting=ddl-nodrop/run_1
test_runner.go:800: test timed out (20m0s)
```
<details><summary>More</summary><p>
Artifacts: [/sqlsmith/setup=tpcc/setting=ddl-nodrop](https://teamcity.cockroachdb.com/viewLog.html?buildId=1920699&tab=artifacts#/sqlsmith/setup=tpcc/setting=ddl-nodrop)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Asqlsmith%2Fsetup%3Dtpcc%2Fsetting%3Dddl-nodrop.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: sqlsmith/setup=tpcc/setting=ddl-nodrop failed - [(roachtest).sqlsmith/setup=tpcc/setting=ddl-nodrop failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1920699&tab=buildLog) on [master@425eaa8fb05fc32b2c42827b85338daa52f4177c](https://github.com/cockroachdb/cockroach/commits/425eaa8fb05fc32b2c42827b85338daa52f4177c):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/sqlsmith/setup=tpcc/setting=ddl-nodrop/run_1
test_runner.go:800: test timed out (20m0s)
```
<details><summary>More</summary><p>
Artifacts: [/sqlsmith/setup=tpcc/setting=ddl-nodrop](https://teamcity.cockroachdb.com/viewLog.html?buildId=1920699&tab=artifacts#/sqlsmith/setup=tpcc/setting=ddl-nodrop)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Asqlsmith%2Fsetup%3Dtpcc%2Fsetting%3Dddl-nodrop.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | roachtest sqlsmith setup tpcc setting ddl nodrop failed on the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts sqlsmith setup tpcc setting ddl nodrop run test runner go test timed out more artifacts powered by | 0 |
1,603 | 3,800,240,455 | IssuesEvent | 2016-03-23 18:25:14 | mesosphere/marathon | https://api.github.com/repos/mesosphere/marathon | closed | Leader not aware of its leadership | bug in progress service | Our cluster got into a state in which a leader got elected, but the elected leader wasn't aware of it's leadership, so it was refusing the requests the other leaders were proxying.
This state persisted for days until the "confused leader" was resterted.
Logs from the leader:
```
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,064] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000521, member_0000000522, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,064] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000521, member_0000000522, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,282] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,282] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,802] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,803] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,976] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,976] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,260] INFO Do not proxy to myself. Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-106976)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,261] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-106976)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,266] INFO Do not proxy to myself. Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-107011)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,267] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-107011)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,512] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-106976)
```
Logs from another master, which apparently had gotten into the same state, but managed to get out of it:
```
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,122] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv3.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-219000)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,129] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv3.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-219006)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,366] INFO 172.16.0.14 - - [30/Nov/2015:13:51:16 +0000] "GET //srv3.hw.ca1.mesosphere.com:8080/v2/apps HTTP/1.1" 503 351 "http://ovh.marathon.io:4242/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.86 Safari/537.36" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219011)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,373] INFO 172.16.0.14 - - [30/Nov/2015:13:51:16 +0000] "GET //srv3.hw.ca1.mesosphere.com:8080/v2/deployments HTTP/1.1" 503 358 "http://ovh.marathon.io:4242/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.86 Safari/537.36" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219000)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,379] INFO 172.16.0.14 - - [30/Nov/2015:13:51:16 +0000] "GET //srv3.hw.ca1.mesosphere.com:8080/v2/queue HTTP/1.1" 503 352 "http://ovh.marathon.io:4242/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.86 Safari/537.36" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219006)
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:21,702] INFO Unable to read additional data from server sessionid 0x3515255abc00003, likely server has closed socket, closing socket connection and attempting reconnect (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv4.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: 2015-11-30 13:51:21,704:2206(0x7f1a1cbe0700):ZOO_ERROR@handle_socket_error_msg@1721: Socket [172.16.0.14:2181] zk retcode=-4, errno=112(Host is down): failed while receiving a server response
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: 2015-11-30 13:51:21,704:2206(0x7f1a1cbe0700):ZOO_INFO@check_events@1703: initiated connection to server [172.16.0.15:2181]
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: I1130 13:51:21.704942 14894 group.cpp:418] Lost connection to ZooKeeper, attempting to reconnect ...
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: 2015-11-30 13:51:21,760:2206(0x7f1a1cbe0700):ZOO_INFO@check_events@1750: session establishment complete on server [172.16.0.15:2181], sessionId=0x15150291daa0005, negotiated timeout=10000
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: I1130 13:51:21.760956 14922 group.cpp:313] Group process (group(3)@172.16.0.13:50346) reconnected to ZooKeeper
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: I1130 13:51:21.760977 14922 group.cpp:787] Syncing group operations: queue size (joins, cancels, datas) = (0, 0, 0)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,402] INFO Opening socket connection to server srv2.hw.ca1.mesosphere.com/172.16.0.12:2181. Will not attempt to authenticate using SASL (unknown error) (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv2.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,402] INFO Socket connection established to srv2.hw.ca1.mesosphere.com/172.16.0.12:2181, initiating session (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv2.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,550] INFO Unable to reconnect to ZooKeeper service, session 0x3515255abc00003 has expired, closing socket connection (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv2.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,550] INFO Zookeeper session expired. Event: WatchedEvent state:Expired type:None path:null (com.twitter.common.zookeeper.ZooKeeperClient:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,550] INFO EventThread shut down (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,551] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,551] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,551] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,552] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,552] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-75)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,553] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,553] INFO Initiating client connection, connectString=srv2.hw.ca1.mesosphere.com:2181,srv3.hw.ca1.mesosphere.com:2181,srv4.hw.ca1.mesosphere.com:2181,srv5.hw.ca1.mesosphere.com:2181,srv6.hw.ca1.mesosphere.com:2181 sessionTimeout=10000 watcher=com.twitter.common.zookeeper.ZooKeeperClient$3@2a4c6776 (org.apache.zookeeper.ZooKeeper:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,555] INFO Opening socket connection to server srv3.hw.ca1.mesosphere.com/172.16.0.13:2181. Will not attempt to authenticate using SASL (unknown error) (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv3.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,555] INFO Socket connection established to srv3.hw.ca1.mesosphere.com/172.16.0.13:2181, initiating session (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv3.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,806] INFO Session establishment complete on server srv3.hw.ca1.mesosphere.com/172.16.0.13:2181, sessionid = 0x25152e0bae20017, negotiated timeout = 10000 (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv3.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,807] ERROR Current member ID member_0000000494 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-73)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,809] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] ERROR Current member ID member_0000000506 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-76)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] ERROR Current member ID member_0000000507 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,812] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-73)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,812] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,980] INFO Set group member ID to member_0000000529 (com.twitter.common.zookeeper.Group:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,981] ERROR Current member ID member_0000000506 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,981] ERROR Current member ID member_0000000494 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,981] INFO Candidate /marathon/leader/member_0000000529 waiting for the next leader election, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,982] ERROR Current member ID member_0000000507 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:52:01 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:01,693] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219003)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,255] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219016)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,383] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218989)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,458] INFO 0:0:0:0:0:0:0:1 - - [30/Nov/2015:13:52:01 +0000] "GET //localhost:8080/v2/tasks HTTP/1.1" 503 352 "-" "python-requests/2.6.0 CPython/2.7.5 Linux/3.10.0-229.7.2.el7.x86_64" 276 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219003)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,686] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219012)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,960] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218990)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,013] INFO 172.16.1.13 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219016)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,141] INFO 172.16.1.16 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-218989)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,448] INFO 172.16.1.15 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 276 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219012)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,717] INFO 172.16.1.14 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-218990)
Nov 30 13:53:01 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:01,782] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219000)
Nov 30 13:53:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:04,273] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218954)
Nov 30 13:53:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:04,463] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218987)
Nov 30 13:53:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:04,543] INFO 0:0:0:0:0:0:0:1 - - [30/Nov/2015:13:53:01 +0000] "GET //localhost:8080/v2/tasks HTTP/1.1" 503 352 "-" "python-requests/2.6.0 CPython/2.7.5 Linux/3.10.0-229.7.2.el7.x86_64" 276 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219000)
Nov 30 13:53:05 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:05,061] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219011)
``` | 1.0 | Leader not aware of its leadership - Our cluster got into a state in which a leader got elected, but the elected leader wasn't aware of it's leadership, so it was refusing the requests the other leaders were proxying.
This state persisted for days until the "confused leader" was resterted.
Logs from the leader:
```
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,064] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000521, member_0000000522, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,064] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000521, member_0000000522, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,282] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,282] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,802] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,803] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,976] INFO Candidate /marathon/leader/member_0000000527 waiting for the next leader election, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:22,976] ERROR Current member ID member_0000000492 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,260] INFO Do not proxy to myself. Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-106976)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,261] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-106976)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,266] INFO Do not proxy to myself. Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-107011)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,267] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-107011)
Nov 30 13:51:23 srv2.hw.ca1.mesosphere.com marathon[2379]: [2015-11-30 13:51:23,512] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv2.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-106976)
```
Logs from another master, which apparently had gotten into the same state, but managed to get out of it:
```
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,122] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv3.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-219000)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,129] INFO Waiting for consistent leadership state. Are we leader?: false, leader: Some(srv3.hw.ca1.mesosphere.com:8080) (mesosphere.marathon.api.LeaderProxyFilter$:qtp983834017-219006)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,366] INFO 172.16.0.14 - - [30/Nov/2015:13:51:16 +0000] "GET //srv3.hw.ca1.mesosphere.com:8080/v2/apps HTTP/1.1" 503 351 "http://ovh.marathon.io:4242/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.86 Safari/537.36" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219011)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,373] INFO 172.16.0.14 - - [30/Nov/2015:13:51:16 +0000] "GET //srv3.hw.ca1.mesosphere.com:8080/v2/deployments HTTP/1.1" 503 358 "http://ovh.marathon.io:4242/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.86 Safari/537.36" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219000)
Nov 30 13:51:19 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:19,379] INFO 172.16.0.14 - - [30/Nov/2015:13:51:16 +0000] "GET //srv3.hw.ca1.mesosphere.com:8080/v2/queue HTTP/1.1" 503 352 "http://ovh.marathon.io:4242/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/46.0.2490.86 Safari/537.36" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219006)
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:21,702] INFO Unable to read additional data from server sessionid 0x3515255abc00003, likely server has closed socket, closing socket connection and attempting reconnect (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv4.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: 2015-11-30 13:51:21,704:2206(0x7f1a1cbe0700):ZOO_ERROR@handle_socket_error_msg@1721: Socket [172.16.0.14:2181] zk retcode=-4, errno=112(Host is down): failed while receiving a server response
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: 2015-11-30 13:51:21,704:2206(0x7f1a1cbe0700):ZOO_INFO@check_events@1703: initiated connection to server [172.16.0.15:2181]
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: I1130 13:51:21.704942 14894 group.cpp:418] Lost connection to ZooKeeper, attempting to reconnect ...
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: 2015-11-30 13:51:21,760:2206(0x7f1a1cbe0700):ZOO_INFO@check_events@1750: session establishment complete on server [172.16.0.15:2181], sessionId=0x15150291daa0005, negotiated timeout=10000
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: I1130 13:51:21.760956 14922 group.cpp:313] Group process (group(3)@172.16.0.13:50346) reconnected to ZooKeeper
Nov 30 13:51:21 srv3.hw.ca1.mesosphere.com marathon[2335]: I1130 13:51:21.760977 14922 group.cpp:787] Syncing group operations: queue size (joins, cancels, datas) = (0, 0, 0)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,402] INFO Opening socket connection to server srv2.hw.ca1.mesosphere.com/172.16.0.12:2181. Will not attempt to authenticate using SASL (unknown error) (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv2.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,402] INFO Socket connection established to srv2.hw.ca1.mesosphere.com/172.16.0.12:2181, initiating session (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv2.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,550] INFO Unable to reconnect to ZooKeeper service, session 0x3515255abc00003 has expired, closing socket connection (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv2.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,550] INFO Zookeeper session expired. Event: WatchedEvent state:Expired type:None path:null (com.twitter.common.zookeeper.ZooKeeperClient:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,550] INFO EventThread shut down (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,551] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,551] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,551] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,552] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,552] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-75)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,553] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,553] INFO Initiating client connection, connectString=srv2.hw.ca1.mesosphere.com:2181,srv3.hw.ca1.mesosphere.com:2181,srv4.hw.ca1.mesosphere.com:2181,srv5.hw.ca1.mesosphere.com:2181,srv6.hw.ca1.mesosphere.com:2181 sessionTimeout=10000 watcher=com.twitter.common.zookeeper.ZooKeeperClient$3@2a4c6776 (org.apache.zookeeper.ZooKeeper:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,555] INFO Opening socket connection to server srv3.hw.ca1.mesosphere.com/172.16.0.13:2181. Will not attempt to authenticate using SASL (unknown error) (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv3.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,555] INFO Socket connection established to srv3.hw.ca1.mesosphere.com/172.16.0.13:2181, initiating session (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv3.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,806] INFO Session establishment complete on server srv3.hw.ca1.mesosphere.com/172.16.0.13:2181, sessionid = 0x25152e0bae20017, negotiated timeout = 10000 (org.apache.zookeeper.ClientCnxn:ZookeeperClient-watcherProcessor-SendThread(srv3.hw.ca1.mesosphere.com:2181))
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,807] ERROR Current member ID member_0000000494 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,808] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-73)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,809] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] ERROR Current member ID member_0000000506 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,810] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-76)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] ERROR Current member ID member_0000000507 is not a candidate for leader, current voting: [member_0000000528, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Defeated (Leader Interface) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Call onDefeated leadership callbacks on EntityStoreCache(MarathonStore(app:)), EntityStoreCache(MarathonStore(group:)), EntityStoreCache(MarathonStore(deployment:)), EntityStoreCache(MarathonStore(framework:)), EntityStoreCache(MarathonStore(taskFailure:)), EntityStoreCache(MarathonStore(task:)), EntityStoreCache(MarathonStore(events:)) (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuic
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Finished onDefeated leadership callbacks (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,811] INFO Defeat leadership (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,812] INFO Now standing by. Closing existing handles and rejecting new. (mesosphere.marathon.event.http.HttpEventStreamActor:marathon-akka.actor.default-dispatcher-73)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,812] INFO Stopping driver (mesosphere.marathon.MarathonSchedulerService$$EnhancerByGuice$$1bda83eb:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,980] INFO Set group member ID to member_0000000529 (com.twitter.common.zookeeper.Group:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,981] ERROR Current member ID member_0000000506 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,981] ERROR Current member ID member_0000000494 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,981] INFO Candidate /marathon/leader/member_0000000529 waiting for the next leader election, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor)
Nov 30 13:51:22 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:51:22,982] ERROR Current member ID member_0000000507 is not a candidate for leader, current voting: [member_0000000528, member_0000000529, member_0000000525, member_0000000526, member_0000000527] (com.twitter.common.zookeeper.CandidateImpl:ZookeeperClient-watcherProcessor-EventThread)
Nov 30 13:52:01 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:01,693] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219003)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,255] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219016)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,383] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218989)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,458] INFO 0:0:0:0:0:0:0:1 - - [30/Nov/2015:13:52:01 +0000] "GET //localhost:8080/v2/tasks HTTP/1.1" 503 352 "-" "python-requests/2.6.0 CPython/2.7.5 Linux/3.10.0-229.7.2.el7.x86_64" 276 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219003)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,686] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219012)
Nov 30 13:52:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:04,960] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218990)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,013] INFO 172.16.1.13 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219016)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,141] INFO 172.16.1.16 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-218989)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,448] INFO 172.16.1.15 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 276 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219012)
Nov 30 13:52:07 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:52:07,717] INFO 172.16.1.14 - - [30/Nov/2015:13:52:04 +0000] "GET //int.srv3.hw.ca1.mesosphere.com:8080/v2/tasks HTTP/1.1" 503 352 "-" "curl/7.29.0" 275 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-218990)
Nov 30 13:53:01 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:01,782] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219000)
Nov 30 13:53:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:04,273] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218954)
Nov 30 13:53:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:04,463] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-218987)
Nov 30 13:53:04 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:04,543] INFO 0:0:0:0:0:0:0:1 - - [30/Nov/2015:13:53:01 +0000] "GET //localhost:8080/v2/tasks HTTP/1.1" 503 352 "-" "python-requests/2.6.0 CPython/2.7.5 Linux/3.10.0-229.7.2.el7.x86_64" 276 (mesosphere.chaos.http.ChaosRequestLog$$EnhancerByGuice$$dac83aa5:qtp983834017-219000)
Nov 30 13:53:05 srv3.hw.ca1.mesosphere.com marathon[2332]: [2015-11-30 13:53:05,061] INFO Proxying request to GET http://srv2.hw.ca1.mesosphere.com:8080/v2/tasks from srv3.hw.ca1.mesosphere.com:8080 (mesosphere.marathon.api.JavaUrlConnectionRequestForwarder$:qtp983834017-219011)
``` | non_priority | leader not aware of its leadership our cluster got into a state in which a leader got elected but the elected leader wasn t aware of it s leadership so it was refusing the requests the other leaders were proxying this state persisted for days until the confused leader was resterted logs from the leader nov hw mesosphere com marathon info candidate marathon leader member waiting for the next leader election current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info candidate marathon leader member waiting for the next leader election current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info candidate marathon leader member waiting for the next leader election current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info candidate marathon leader member waiting for the next leader election current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info do not proxy to myself waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter nov hw mesosphere com marathon info waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter nov hw mesosphere com marathon info do not proxy to myself waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter nov hw mesosphere com marathon info waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter nov hw mesosphere com marathon info waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter logs from another master which apparently had gotten into the same state but managed to get out of it nov hw mesosphere com marathon info waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter nov hw mesosphere com marathon info waiting for consistent leadership state are we leader false leader some hw mesosphere com mesosphere marathon api leaderproxyfilter nov hw mesosphere com marathon info get hw mesosphere com apps http mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info get hw mesosphere com deployments http mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info get hw mesosphere com queue http mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info unable to read additional data from server sessionid likely server has closed socket closing socket connection and attempting reconnect org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon zoo error handle socket error msg socket zk retcode errno host is down failed while receiving a server response nov hw mesosphere com marathon zoo info check events initiated connection to server nov hw mesosphere com marathon group cpp lost connection to zookeeper attempting to reconnect nov hw mesosphere com marathon zoo info check events session establishment complete on server sessionid negotiated timeout nov hw mesosphere com marathon group cpp group process group reconnected to zookeeper nov hw mesosphere com marathon group cpp syncing group operations queue size joins cancels datas nov hw mesosphere com marathon info opening socket connection to server hw mesosphere com will not attempt to authenticate using sasl unknown error org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon info socket connection established to hw mesosphere com initiating session org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon info unable to reconnect to zookeeper service session has expired closing socket connection org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon info zookeeper session expired event watchedevent state expired type none path null com twitter common zookeeper zookeeperclient zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info eventthread shut down org apache zookeeper clientcnxn zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info defeated leader interface mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info call ondefeated leadership callbacks on entitystorecache marathonstore app entitystorecache marathonstore group entitystorecache marathonstore deployment entitystorecache marathonstore framework entitystorecache marathonstore taskfailure entitystorecache marathonstore task entitystorecache marathonstore events mesosphere marathon marathonschedulerservice enhancerbyguic nov hw mesosphere com marathon info finished ondefeated leadership callbacks mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeat leadership mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info now standing by closing existing handles and rejecting new mesosphere marathon event http httpeventstreamactor marathon akka actor default dispatcher nov hw mesosphere com marathon info stopping driver mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info initiating client connection connectstring hw mesosphere com hw mesosphere com hw mesosphere com hw mesosphere com hw mesosphere com sessiontimeout watcher com twitter common zookeeper zookeeperclient org apache zookeeper zookeeper zookeeperclient watcherprocessor nov hw mesosphere com marathon info opening socket connection to server hw mesosphere com will not attempt to authenticate using sasl unknown error org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon info socket connection established to hw mesosphere com initiating session org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon info session establishment complete on server hw mesosphere com sessionid negotiated timeout org apache zookeeper clientcnxn zookeeperclient watcherprocessor sendthread hw mesosphere com nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeated leader interface mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info call ondefeated leadership callbacks on entitystorecache marathonstore app entitystorecache marathonstore group entitystorecache marathonstore deployment entitystorecache marathonstore framework entitystorecache marathonstore taskfailure entitystorecache marathonstore task entitystorecache marathonstore events mesosphere marathon marathonschedulerservice enhancerbyguic nov hw mesosphere com marathon info finished ondefeated leadership callbacks mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeat leadership mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info now standing by closing existing handles and rejecting new mesosphere marathon event http httpeventstreamactor marathon akka actor default dispatcher nov hw mesosphere com marathon info stopping driver mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeated leader interface mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info call ondefeated leadership callbacks on entitystorecache marathonstore app entitystorecache marathonstore group entitystorecache marathonstore deployment entitystorecache marathonstore framework entitystorecache marathonstore taskfailure entitystorecache marathonstore task entitystorecache marathonstore events mesosphere marathon marathonschedulerservice enhancerbyguic nov hw mesosphere com marathon info finished ondefeated leadership callbacks mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeat leadership mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info now standing by closing existing handles and rejecting new mesosphere marathon event http httpeventstreamactor marathon akka actor default dispatcher nov hw mesosphere com marathon info stopping driver mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeated leader interface mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info call ondefeated leadership callbacks on entitystorecache marathonstore app entitystorecache marathonstore group entitystorecache marathonstore deployment entitystorecache marathonstore framework entitystorecache marathonstore taskfailure entitystorecache marathonstore task entitystorecache marathonstore events mesosphere marathon marathonschedulerservice enhancerbyguic nov hw mesosphere com marathon info finished ondefeated leadership callbacks mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info defeat leadership mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info now standing by closing existing handles and rejecting new mesosphere marathon event http httpeventstreamactor marathon akka actor default dispatcher nov hw mesosphere com marathon info stopping driver mesosphere marathon marathonschedulerservice enhancerbyguice zookeeperclient watcherprocessor nov hw mesosphere com marathon info set group member id to member com twitter common zookeeper group zookeeperclient watcherprocessor nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info candidate marathon leader member waiting for the next leader election current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor nov hw mesosphere com marathon error current member id member is not a candidate for leader current voting com twitter common zookeeper candidateimpl zookeeperclient watcherprocessor eventthread nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info get localhost tasks http python requests cpython linux mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info get int hw mesosphere com tasks http curl mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info get int hw mesosphere com tasks http curl mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info get int hw mesosphere com tasks http curl mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info get int hw mesosphere com tasks http curl mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder nov hw mesosphere com marathon info get localhost tasks http python requests cpython linux mesosphere chaos http chaosrequestlog enhancerbyguice nov hw mesosphere com marathon info proxying request to get from hw mesosphere com mesosphere marathon api javaurlconnectionrequestforwarder | 0 |
114,708 | 9,747,291,628 | IssuesEvent | 2019-06-03 14:06:50 | golang/go | https://api.github.com/repos/golang/go | opened | misc/cgo/stdio: test persistently broken on linux-arm-arm5spacemonkey builder | NeedsInvestigation Testing | (See previously #29177 and #28041.)
The current failure on the `arm5spacemonkey` builder is (usually) a `permission denied` error in `misc/cgo/stdio`. I'm not sure whether it's a bug (or unrealistic expectation) in the test, or a misconfiguration in the builder.
```
##### ../misc/cgo/stdio
go test misc/cgo/stdio.test: open /home/builder/stage0scratch/workdir/go/misc/cgo/stdio/test.test: permission denied
2019/06/02 22:52:55 Failed: exit status 1
```
CC @ianlancetaylor @dmitshur | 1.0 | misc/cgo/stdio: test persistently broken on linux-arm-arm5spacemonkey builder - (See previously #29177 and #28041.)
The current failure on the `arm5spacemonkey` builder is (usually) a `permission denied` error in `misc/cgo/stdio`. I'm not sure whether it's a bug (or unrealistic expectation) in the test, or a misconfiguration in the builder.
```
##### ../misc/cgo/stdio
go test misc/cgo/stdio.test: open /home/builder/stage0scratch/workdir/go/misc/cgo/stdio/test.test: permission denied
2019/06/02 22:52:55 Failed: exit status 1
```
CC @ianlancetaylor @dmitshur | non_priority | misc cgo stdio test persistently broken on linux arm builder see previously and the current failure on the builder is usually a permission denied error in misc cgo stdio i m not sure whether it s a bug or unrealistic expectation in the test or a misconfiguration in the builder misc cgo stdio go test misc cgo stdio test open home builder workdir go misc cgo stdio test test permission denied failed exit status cc ianlancetaylor dmitshur | 0 |
657 | 4,172,568,400 | IssuesEvent | 2016-06-21 07:07:58 | Particular/ServicePulse | https://api.github.com/repos/Particular/ServicePulse | closed | Error when entering /failedMessages page directly | Impact: M Size: S State: In Progress - Maintainer Prio Tag: Maintainer Prio Type: Bug | The following error occurs and the page won't render properly when visiting url **/failedMessages** without having clicked the ALL FAILED MESSAGES link in the navigation.
`angular.js:12416 TypeError: Cannot read property 'hasOwnProperty' of undefined
at new controller (http://secc3459:9090/js/views/failed_messages/controller.js:20:39)
at invoke (http://secc3459:9090/lib/angular/angular.js:4473:17)
at Object.instantiate (http://secc3459:9090/lib/angular/angular.js:4481:27)
at http://secc3459:9090/lib/angular/angular.js:9108:28
at link (http://secc3459:9090/lib/angular/angular-route.js:977:26)
at invokeLinkFn (http://secc3459:9090/lib/angular/angular.js:8746:9)
at nodeLinkFn (http://secc3459:9090/lib/angular/angular.js:8246:11)
at compositeLinkFn (http://secc3459:9090/lib/angular/angular.js:7637:13)
at publicLinkFn (http://secc3459:9090/lib/angular/angular.js:7512:30)
at boundTranscludeFn (http://secc3459:9090/lib/angular/angular.js:7656:16) <div id="view" ng-view="" class="ng-scope" data-ng-animate="1">`
It's probably due to this line: https://github.com/Particular/ServicePulse/blob/9b2159b4e4de4f40326fc3b87c6d901ba67c066a/src/ServicePulse.Host/app/js/views/failed_messages/controller.js#L20
That line of code also seems to want to redirect to the **/failedGroups** page if the selectedExceptionGroup is incomplete. However, I would like to have the possibility to link directly to the **/failedMessages** page.
To reproduce:
- Go to **/failedMessages**
- Clear local storage
- Refresh page | True | Error when entering /failedMessages page directly - The following error occurs and the page won't render properly when visiting url **/failedMessages** without having clicked the ALL FAILED MESSAGES link in the navigation.
`angular.js:12416 TypeError: Cannot read property 'hasOwnProperty' of undefined
at new controller (http://secc3459:9090/js/views/failed_messages/controller.js:20:39)
at invoke (http://secc3459:9090/lib/angular/angular.js:4473:17)
at Object.instantiate (http://secc3459:9090/lib/angular/angular.js:4481:27)
at http://secc3459:9090/lib/angular/angular.js:9108:28
at link (http://secc3459:9090/lib/angular/angular-route.js:977:26)
at invokeLinkFn (http://secc3459:9090/lib/angular/angular.js:8746:9)
at nodeLinkFn (http://secc3459:9090/lib/angular/angular.js:8246:11)
at compositeLinkFn (http://secc3459:9090/lib/angular/angular.js:7637:13)
at publicLinkFn (http://secc3459:9090/lib/angular/angular.js:7512:30)
at boundTranscludeFn (http://secc3459:9090/lib/angular/angular.js:7656:16) <div id="view" ng-view="" class="ng-scope" data-ng-animate="1">`
It's probably due to this line: https://github.com/Particular/ServicePulse/blob/9b2159b4e4de4f40326fc3b87c6d901ba67c066a/src/ServicePulse.Host/app/js/views/failed_messages/controller.js#L20
That line of code also seems to want to redirect to the **/failedGroups** page if the selectedExceptionGroup is incomplete. However, I would like to have the possibility to link directly to the **/failedMessages** page.
To reproduce:
- Go to **/failedMessages**
- Clear local storage
- Refresh page | non_priority | error when entering failedmessages page directly the following error occurs and the page won t render properly when visiting url failedmessages without having clicked the all failed messages link in the navigation angular js typeerror cannot read property hasownproperty of undefined at new controller at invoke at object instantiate at at link at invokelinkfn at nodelinkfn at compositelinkfn at publiclinkfn at boundtranscludefn it s probably due to this line that line of code also seems to want to redirect to the failedgroups page if the selectedexceptiongroup is incomplete however i would like to have the possibility to link directly to the failedmessages page to reproduce go to failedmessages clear local storage refresh page | 0 |
58,178 | 11,847,253,404 | IssuesEvent | 2020-03-24 11:41:00 | nopSolutions/nopCommerce | https://api.github.com/repos/nopSolutions/nopCommerce | closed | Do not use IApplicationLifetime (obsolete) | refactoring / source code | An instance of IApplicationLifetime is required in Nop.Core/WebHelper.cs - used in this class to stop the application in the RestartAppDomain() method.
This API is also now marked as obsolete - https://docs.microsoft.com/en-us/dotnet/api/microsoft.extensions.hosting.iapplicationlifetime?view=aspnetcore-2.2 | 1.0 | Do not use IApplicationLifetime (obsolete) - An instance of IApplicationLifetime is required in Nop.Core/WebHelper.cs - used in this class to stop the application in the RestartAppDomain() method.
This API is also now marked as obsolete - https://docs.microsoft.com/en-us/dotnet/api/microsoft.extensions.hosting.iapplicationlifetime?view=aspnetcore-2.2 | non_priority | do not use iapplicationlifetime obsolete an instance of iapplicationlifetime is required in nop core webhelper cs used in this class to stop the application in the restartappdomain method this api is also now marked as obsolete | 0 |
237,531 | 18,162,795,058 | IssuesEvent | 2021-09-27 11:36:17 | Neos-Metaverse/NeosPublic | https://api.github.com/repos/Neos-Metaverse/NeosPublic | closed | Why does the 4 bones per vertex limitation exist? | Documentation | ### Where have you searched for this information before making this issue?
I have looked around the Neos Wiki, and asked around on the Discord, and someone did link a Unity page about `QualitySettings.skinWeights` (linked here: https://docs.unity3d.com/ScriptReference/QualitySettings-skinWeights.html)
### Which part of the system do you need information on?
There appears to be a hard limit on how many bones can be weighted to one vertex, and the only way of really find this is through some very irritating trial and error.
### What information do you need to know?
I'd ideally like to know how many bones a single vertex can be weighted to, and as well as why the limitation exists within Neos.
### Do you plan to format and contribute the provided information to Wiki?
No | 1.0 | Why does the 4 bones per vertex limitation exist? - ### Where have you searched for this information before making this issue?
I have looked around the Neos Wiki, and asked around on the Discord, and someone did link a Unity page about `QualitySettings.skinWeights` (linked here: https://docs.unity3d.com/ScriptReference/QualitySettings-skinWeights.html)
### Which part of the system do you need information on?
There appears to be a hard limit on how many bones can be weighted to one vertex, and the only way of really find this is through some very irritating trial and error.
### What information do you need to know?
I'd ideally like to know how many bones a single vertex can be weighted to, and as well as why the limitation exists within Neos.
### Do you plan to format and contribute the provided information to Wiki?
No | non_priority | why does the bones per vertex limitation exist where have you searched for this information before making this issue i have looked around the neos wiki and asked around on the discord and someone did link a unity page about qualitysettings skinweights linked here which part of the system do you need information on there appears to be a hard limit on how many bones can be weighted to one vertex and the only way of really find this is through some very irritating trial and error what information do you need to know i d ideally like to know how many bones a single vertex can be weighted to and as well as why the limitation exists within neos do you plan to format and contribute the provided information to wiki no | 0 |
37,599 | 4,828,598,407 | IssuesEvent | 2016-11-07 16:39:23 | MozillaFoundation/Mozfest2016_production | https://api.github.com/repos/MozillaFoundation/Mozfest2016_production | closed | Link to Pulse from Mozfest site (post Festival) | Design | If use of Pulse goes well at the festival, we should find a way to link to it from the festival site. Design-wise, could sit near link to archive of talks.
Adding this to a new November 4th milestone for post-festival work.
- [ ] make sure things have been tagged with mozfest
- [ ] link to https://mzl.la/mozfest-pulse?keyword=mozfest
| 1.0 | Link to Pulse from Mozfest site (post Festival) - If use of Pulse goes well at the festival, we should find a way to link to it from the festival site. Design-wise, could sit near link to archive of talks.
Adding this to a new November 4th milestone for post-festival work.
- [ ] make sure things have been tagged with mozfest
- [ ] link to https://mzl.la/mozfest-pulse?keyword=mozfest
| non_priority | link to pulse from mozfest site post festival if use of pulse goes well at the festival we should find a way to link to it from the festival site design wise could sit near link to archive of talks adding this to a new november milestone for post festival work make sure things have been tagged with mozfest link to | 0 |
164,647 | 20,382,823,773 | IssuesEvent | 2022-02-22 01:17:42 | rsoreq/grafana | https://api.github.com/repos/rsoreq/grafana | opened | CVE-2021-44716 (High) detected in github.com/golang/net-2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea | security vulnerability | ## CVE-2021-44716 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/golang/net-2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea</b></p></summary>
<p>[mirror] Go supplementary network libraries</p>
<p>
Dependency Hierarchy:
- github.com/hashicorp/go-plugin-v1.0.1 (Root Library)
- google.golang.org/grpc-v1.23.1
- :x: **github.com/golang/net-2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
net/http in Go before 1.16.12 and 1.17.x before 1.17.5 allows uncontrolled memory consumption in the header canonicalization cache via HTTP/2 requests.
<p>Publish Date: 2022-01-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44716>CVE-2021-44716</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-vc3p-29h2-gpcp">https://github.com/advisories/GHSA-vc3p-29h2-gpcp</a></p>
<p>Release Date: 2022-01-01</p>
<p>Fix Resolution: 1.16.12, 1.17.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/golang/net","packageVersion":"2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/hashicorp/go-plugin:v1.0.1;google.golang.org/grpc:v1.23.1;github.com/golang/net:2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.16.12, 1.17.5","isBinary":true}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44716","vulnerabilityDetails":"net/http in Go before 1.16.12 and 1.17.x before 1.17.5 allows uncontrolled memory consumption in the header canonicalization cache via HTTP/2 requests.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44716","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-44716 (High) detected in github.com/golang/net-2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea - ## CVE-2021-44716 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/golang/net-2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea</b></p></summary>
<p>[mirror] Go supplementary network libraries</p>
<p>
Dependency Hierarchy:
- github.com/hashicorp/go-plugin-v1.0.1 (Root Library)
- google.golang.org/grpc-v1.23.1
- :x: **github.com/golang/net-2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
net/http in Go before 1.16.12 and 1.17.x before 1.17.5 allows uncontrolled memory consumption in the header canonicalization cache via HTTP/2 requests.
<p>Publish Date: 2022-01-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44716>CVE-2021-44716</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-vc3p-29h2-gpcp">https://github.com/advisories/GHSA-vc3p-29h2-gpcp</a></p>
<p>Release Date: 2022-01-01</p>
<p>Fix Resolution: 1.16.12, 1.17.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/golang/net","packageVersion":"2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/hashicorp/go-plugin:v1.0.1;google.golang.org/grpc:v1.23.1;github.com/golang/net:2e5a9a951435a4d5d8f8cc0413540fbfdcef66ea","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.16.12, 1.17.5","isBinary":true}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44716","vulnerabilityDetails":"net/http in Go before 1.16.12 and 1.17.x before 1.17.5 allows uncontrolled memory consumption in the header canonicalization cache via HTTP/2 requests.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44716","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in github com golang net cve high severity vulnerability vulnerable library github com golang net go supplementary network libraries dependency hierarchy github com hashicorp go plugin root library google golang org grpc x github com golang net vulnerable library found in base branch master vulnerability details net http in go before and x before allows uncontrolled memory consumption in the header canonicalization cache via http requests publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree github com hashicorp go plugin google golang org grpc github com golang net isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails net http in go before and x before allows uncontrolled memory consumption in the header canonicalization cache via http requests vulnerabilityurl | 0 |
136,790 | 12,734,645,572 | IssuesEvent | 2020-06-25 14:12:29 | SAFETAG/SAFETAG | https://api.github.com/repos/SAFETAG/SAFETAG | closed | remove baseline skills from content and place into individual approaches, merge into adids | Training bug documentation | The baseline skills component is aimed at helping an auditor choose what approach to choose and a trainer on what activities to train on. They should not be included in objectives, but in individual approaches and exercises.
| 1.0 | remove baseline skills from content and place into individual approaches, merge into adids - The baseline skills component is aimed at helping an auditor choose what approach to choose and a trainer on what activities to train on. They should not be included in objectives, but in individual approaches and exercises.
| non_priority | remove baseline skills from content and place into individual approaches merge into adids the baseline skills component is aimed at helping an auditor choose what approach to choose and a trainer on what activities to train on they should not be included in objectives but in individual approaches and exercises | 0 |
21,178 | 28,148,066,245 | IssuesEvent | 2023-04-02 18:11:18 | dDevTech/tapas-top-backend | https://api.github.com/repos/dDevTech/tapas-top-backend | closed | Añadir campos a createUser y updateUser | in process require testing | Añadir todos los campos que no estén previamente a createUser y updateUser.
Los endpoints se encuentran en src/main/java/com/mycompany/myapp/web/rest/UserResource.java
Modificar AdminUserDTO añadiendo dichos campos.
Modificar Service y demás archivos necesarios.
Los campos son:
user_name
lastName2
photo
address
gender (intentar devolver el value del enum, no el int)
description
**EXTRA**
Comprobar que al modificar AdminUserDTO, la llamada getUser devuelve todos los campos añadidos | 1.0 | Añadir campos a createUser y updateUser - Añadir todos los campos que no estén previamente a createUser y updateUser.
Los endpoints se encuentran en src/main/java/com/mycompany/myapp/web/rest/UserResource.java
Modificar AdminUserDTO añadiendo dichos campos.
Modificar Service y demás archivos necesarios.
Los campos son:
user_name
lastName2
photo
address
gender (intentar devolver el value del enum, no el int)
description
**EXTRA**
Comprobar que al modificar AdminUserDTO, la llamada getUser devuelve todos los campos añadidos | non_priority | añadir campos a createuser y updateuser añadir todos los campos que no estén previamente a createuser y updateuser los endpoints se encuentran en src main java com mycompany myapp web rest userresource java modificar adminuserdto añadiendo dichos campos modificar service y demás archivos necesarios los campos son user name photo address gender intentar devolver el value del enum no el int description extra comprobar que al modificar adminuserdto la llamada getuser devuelve todos los campos añadidos | 0 |
26,841 | 5,291,137,649 | IssuesEvent | 2017-02-08 21:43:41 | grpc/grpc | https://api.github.com/repos/grpc/grpc | closed | PHP gRPC plugin not included on make | documentation php | According to the docs found [here](https://github.com/grpc/grpc/tree/master/src/php#php-protoc-plugin), the PHP gRPC plugin should be created in `bins/opt` after running `make` in the root of `grpc`. From what I can tell this does not seem to be the case.
```bash
$ ls bins/opt
grpc_cpp_plugin
grpc_csharp_plugin
grpc_node_plugin
grpc_objective_c_plugin
grpc_python_plugin
grpc_ruby_plugin
protobuf
```
I put together the following `Dockerfile` for the build process that I am using.
```Dockerfile
FROM ubuntu:trusty
ENV INSTALL wget \
php5-cli \
php5-dev \
php-pear \
git \
python-pip \
python-dev \
build-essential \
unzip \
curl
RUN apt-get -y update \
&& DEBIAN_FRONTEND=noninteractive apt-get install -yq --force-yes $INSTALL
# gRPC & Protoc
ENV PROTOC_VER 3.1.0
RUN wget https://github.com/google/protobuf/releases/download/v$PROTOC_VER/protoc-$PROTOC_VER-linux-x86_64.zip
RUN unzip protoc-$PROTOC_VER-linux-x86_64.zip -d protoc
RUN cp protoc/bin/protoc /usr/local/bin && rm -rf protoc
ENV BINPATH /usr/local/bin
ENV PROTO_PATH /var/lib/protobuf
ENV GRPC_WORK_DIR /grpc
ENV GRPC_VER v1.0.1
RUN git clone -b $GRPC_VER https://github.com/grpc/grpc $GRPC_WORK_DIR
RUN cd $GRPC_WORK_DIR && git pull origin $GRPC_VER --recurse-submodules && git submodule update --init --recursive
RUN cd $GRPC_WORK_DIR && make && ls bins/opt
```
Maybe I am missing something? Any help would be appreciated, thanks! | 1.0 | PHP gRPC plugin not included on make - According to the docs found [here](https://github.com/grpc/grpc/tree/master/src/php#php-protoc-plugin), the PHP gRPC plugin should be created in `bins/opt` after running `make` in the root of `grpc`. From what I can tell this does not seem to be the case.
```bash
$ ls bins/opt
grpc_cpp_plugin
grpc_csharp_plugin
grpc_node_plugin
grpc_objective_c_plugin
grpc_python_plugin
grpc_ruby_plugin
protobuf
```
I put together the following `Dockerfile` for the build process that I am using.
```Dockerfile
FROM ubuntu:trusty
ENV INSTALL wget \
php5-cli \
php5-dev \
php-pear \
git \
python-pip \
python-dev \
build-essential \
unzip \
curl
RUN apt-get -y update \
&& DEBIAN_FRONTEND=noninteractive apt-get install -yq --force-yes $INSTALL
# gRPC & Protoc
ENV PROTOC_VER 3.1.0
RUN wget https://github.com/google/protobuf/releases/download/v$PROTOC_VER/protoc-$PROTOC_VER-linux-x86_64.zip
RUN unzip protoc-$PROTOC_VER-linux-x86_64.zip -d protoc
RUN cp protoc/bin/protoc /usr/local/bin && rm -rf protoc
ENV BINPATH /usr/local/bin
ENV PROTO_PATH /var/lib/protobuf
ENV GRPC_WORK_DIR /grpc
ENV GRPC_VER v1.0.1
RUN git clone -b $GRPC_VER https://github.com/grpc/grpc $GRPC_WORK_DIR
RUN cd $GRPC_WORK_DIR && git pull origin $GRPC_VER --recurse-submodules && git submodule update --init --recursive
RUN cd $GRPC_WORK_DIR && make && ls bins/opt
```
Maybe I am missing something? Any help would be appreciated, thanks! | non_priority | php grpc plugin not included on make according to the docs found the php grpc plugin should be created in bins opt after running make in the root of grpc from what i can tell this does not seem to be the case bash ls bins opt grpc cpp plugin grpc csharp plugin grpc node plugin grpc objective c plugin grpc python plugin grpc ruby plugin protobuf i put together the following dockerfile for the build process that i am using dockerfile from ubuntu trusty env install wget cli dev php pear git python pip python dev build essential unzip curl run apt get y update debian frontend noninteractive apt get install yq force yes install grpc protoc env protoc ver run wget run unzip protoc protoc ver linux zip d protoc run cp protoc bin protoc usr local bin rm rf protoc env binpath usr local bin env proto path var lib protobuf env grpc work dir grpc env grpc ver run git clone b grpc ver grpc work dir run cd grpc work dir git pull origin grpc ver recurse submodules git submodule update init recursive run cd grpc work dir make ls bins opt maybe i am missing something any help would be appreciated thanks | 0 |
12,476 | 14,712,956,067 | IssuesEvent | 2021-01-05 09:39:25 | Vazkii/Quark | https://api.github.com/repos/Vazkii/Quark | closed | Astral Sorcery Conversion Wand converts Dirt To Path, should probably be blacklisted? | bug compatibility minor | Astral Sorcery has a Conversion Wand which is basically a fancy block swapper. You right click a block, it swaps that block and others like it with a block or blocks of your choosing. `astralsorcery:exchange_wand`
With Quark's "Dirt To Path" enabled, if you right click with a Conversion Wand on dirt, it converts that dirt to a path instead of swapping. Disabling "Dirt To Path" stops the behavior, so I'm betting it's Quark.
Versions and mod list included, just in case? But if there's any struggle in reproducing this, please let me know and I'll binary-search my mods.
```
-- System Details --
Details:
Minecraft Version: 1.16.4
Minecraft Version ID: 1.16.4
Operating System: Windows 10 (amd64) version 10.0
Java Version: 14.0.2, AdoptOpenJDK
Java VM Version: OpenJDK 64-Bit Server VM (mixed mode, sharing), AdoptOpenJDK
Memory: 5592766216 bytes (5333 MB) / 8589934592 bytes (8192 MB) up to 8589934592 bytes (8192 MB)
CPUs: 8
JVM Flags: 10 total; -XX:HeapDumpPath=MojangTricksIntelDriversForPerformance_javaw.exe_minecraft.exe.heapdump -Xmx8192m -Xms8192m -XX:HeapDumpPath=MojangTricksIntelDriversForPerformance_javaw.exe_minecraft.exe.heapdump -XX:+UseG1GC -XX:+UnlockExperimentalVMOptions -XX:G1NewSizePercent=20 -XX:G1ReservePercent=20 -XX:MaxGCPauseMillis=50 -XX:G1HeapRegionSize=32M
ModLauncher: 8.0.6+85+master.325de55
ModLauncher launch target: fmlclient
ModLauncher naming: srg
ModLauncher services:
/mixin-0.8.2.jar mixin PLUGINSERVICE
/eventbus-3.0.5-service.jar eventbus PLUGINSERVICE
/forge-1.16.4-35.1.28.jar object_holder_definalize PLUGINSERVICE
/forge-1.16.4-35.1.28.jar runtime_enum_extender PLUGINSERVICE
/forge-1.16.4-35.1.28.jar capability_inject_definalize PLUGINSERVICE
/accesstransformers-2.2.0-shadowed.jar accesstransformer PLUGINSERVICE
/forge-1.16.4-35.1.28.jar runtimedistcleaner PLUGINSERVICE
/mixin-0.8.2.jar mixin TRANSFORMATIONSERVICE
/forge-1.16.4-35.1.28.jar fml TRANSFORMATIONSERVICE
FML: 35.1
Forge: net.minecraftforge:35.1.28
FML Language Providers:
javafml@35.1
minecraft@1
Mod List:
CraftPresence-Forge-1.16.3-Release-1.7.5.jar |CraftPresence |craftpresence |1.7.5 |DONE |a8:61:b7:97:9b:6f:d3:ba:38:d8:ce:45:6c:4b:8d:fd:ea:84:dd:d1:09:46:5d:5a:4f:c5:03:91:b5:c0:bc:de
astralsorcery-1.16.4-1.13.8.jar |Astral Sorcery |astralsorcery |1.16.4-1.13.8 |DONE |NOSIGNATURE
TrashSlot_1.16.3-12.2.1.jar |TrashSlot |trashslot |12.2.1 |DONE |NOSIGNATURE
pamhc2trees-1.16.3-1.0.0.jar |Pam's HarvestCraft 2 Fruit Tre|pamhc2trees |1.0.0 |DONE |NOSIGNATURE
restrictedportals-1.16.4-1.1.6.jar |Restricted Portals |restrictedportals |1.16.4-1.1.6 |DONE |NOSIGNATURE
DeathCounter-1.16.3-1.2.1.jar |Death Counter |deathcounter |1.2.1 |DONE |NOSIGNATURE
jei-1.16.4-7.6.0.62.jar |Just Enough Items |jei |7.6.0.62 |DONE |NOSIGNATURE
FallingTree-Forge-1.16.4-2.8.1.jar |Falling Tree |falling_tree |2.8.1 |DONE |NOSIGNATURE
mcw-windows-1.0.2-mc1.16.4.jar |Macaw's Windows |mcwwindows |1.0.2 |DONE |NOSIGNATURE
windowlogging-mc1.16.3_v0.0.2.jar |Windowlogging |windowlogging |0.0.2 |DONE |NOSIGNATURE
findme-1.16.3-2.1.0.0.jar |Find Me |findme |NONE |DONE |NOSIGNATURE
Neat+1.7-24.jar |Neat |neat |1.7-24 |DONE |NOSIGNATURE
create-mc1.16.3_v0.3b.jar |Create |create |mc1.16.3_v0.3b |DONE |NOSIGNATURE
Clumps-6.0.0.13.jar |Clumps |clumps |6.0.0.13 |DONE |NOSIGNATURE
XaerosWorldMap_1.11.4_Forge_1.16.4.jar |Xaero's World Map |xaeroworldmap |1.11.4 |DONE |NOSIGNATURE
shutupexperimentalsettings-1.0.1.jar |Shutup Experimental Settings! |shutupexperimentalsettings |1.0.1 |DONE |NOSIGNATURE
CTM-MC1.16.1-1.1.2.6.jar |ConnectedTexturesMod |ctm |MC1.16.1-1.1.2.6 |DONE |NOSIGNATURE
CookingForBlockheads_1.16.3-9.2.2.jar |Cooking for Blockheads |cookingforblockheads |9.2.2 |DONE |NOSIGNATURE
Controlling-7.0.0.11.jar |Controlling |controlling |7.0.0.11 |DONE |NOSIGNATURE
Placebo-1.16.3-4.3.3.jar |Placebo |placebo |4.3.3 |DONE |NOSIGNATURE
comforts-forge-1.16.4-4.0.0.3.jar |Comforts |comforts |1.16.4-4.0.0.2 |DONE |NOSIGNATURE
appliedenergistics2-8.2.0-beta.1.jar |Applied Energistics 2 |appliedenergistics2 |8.2.0-beta.1 |DONE |95:58:cc:83:9d:a8:fa:4f:e9:f3:54:90:66:61:c8:ae:9c:08:88:11:52:52:df:2d:28:5f:05:d8:28:57:0f:98
NaturesCompass-1.16.4-1.8.6.jar |Nature's Compass |naturescompass |1.16.4-1.8.6 |DONE |NOSIGNATURE
SereneSeasons-1.16.4-4.0.0.83-universal.jar |Serene Seasons |sereneseasons |1.16.4-4.0.0.76 |DONE |NOSIGNATURE
ftb-gui-library-1604.1.1.26.jar |FTB GUI Library |ftbguilibrary |1604.1.1.26 |DONE |NOSIGNATURE
upstream-1.0.jar |Upstream |upstream |1.0 |DONE |NOSIGNATURE
DefaultSettings-1.16.x-2.2.0.jar |DefaultSettings |defaultsettings |2.2.0 |DONE |ed:1c:55:41:73:fd:14:1b:28:fe:ea:30:c5:11:3b:4d:3f:82:86:57:bb:5b:8a:b2:d7:f3:04:52:52:92:cf:e7
FarmingForBlockheads_1.16.3-7.2.1.jar |Farming for Blockheads |farmingforblockheads |7.2.1 |DONE |NOSIGNATURE
Bookshelf-1.16.4-9.3.18.jar |Bookshelf |bookshelf |9.3.18 |DONE |ea:45:b3:82:b6:9d:50:16:95:e7:2e:34:e1:92:d5:b4:9b:69:90:d3:4f:2e:71:99:b0:be:40:80:27:1f:3e:b0
pneumaticcraft-repressurized-1.16.4-2.8.2-101.jar |PneumaticCraft: Repressurized |pneumaticcraft |1.16.4-2.8.2-101 |DONE |NOSIGNATURE
snowundertrees-1.16.4-v1.1.3.jar |Snow Under Trees |snowundertrees |v1.1.3 |DONE |NOSIGNATURE
mcw-doors-1.0.1fix-mc1.16.4.jar |Macaw's Doors |mcwdoors |1.0.1 |DONE |NOSIGNATURE
DataFixerSlayer 1.0-2.jar |DataFixerSlayer |datafixerslayer |1.0-2 |DONE |NOSIGNATURE
Hwyla-forge-1.10.11-B78_1.16.2.jar |Waila |waila |1.10.11-B78_1.16.2 |DONE |NOSIGNATURE
WAWLA-1.16.4-7.0.2.jar |WAWLA |wawla |7.0.2 |DONE |ea:45:b3:82:b6:9d:50:16:95:e7:2e:34:e1:92:d5:b4:9b:69:90:d3:4f:2e:71:99:b0:be:40:80:27:1f:3e:b0
Toast-Control-1.16.3-4.3.0.jar |Toast Control |toastcontrol |4.3.0 |DONE |NOSIGNATURE
SnowRealMagic-1.16.3-2.2.2.jar |Snow! Real Magic! |snowrealmagic |2.2.2 |DONE |NOSIGNATURE
Kiwi-1.16.3-3.4.1.jar |Kiwi |kiwi |3.4.1 |DONE |NOSIGNATURE
JustEnoughResources-1.16.4-0.12.0.103.jar |Just Enough Resources |jeresources |0.12.0.103 |DONE |NOSIGNATURE
immersive-portals-0.11-mc1.16.4-forge.jar |Immersive Portals |immersive_portals |0.7 |DONE |NOSIGNATURE
horsestandstill-1.16.3-1.0.1.jar |Stupid Horse Stand Still |horsestandstill |1.16.3-1.0.1 |DONE |1f:47:ac:b1:61:82:96:b8:47:19:16:d2:61:81:11:60:3a:06:4b:61:31:56:7d:44:31:1e:0c:6f:22:5b:4c:ed
ImmersivePetroleum-1.16.4-3.1.0-2.jar |Immersive Petroleum |immersivepetroleum |3.1.0-2 |DONE |NOSIGNATURE
ftb-teams-1604.1.0.13.jar |FTB Teams |ftbteams |1604.1.0.13 |DONE |NOSIGNATURE
forge-1.16.4-35.1.28-universal.jar |Forge |forge |35.1.28 |DONE |22:af:21:d8:19:82:7f:93:94:fe:2b:ac:b7:e4:41:57:68:39:87:b1:a7:5c:c6:44:f9:25:74:21:14:f5:0d:90
shetiphiancore-1.16-3.8.4.jar |ShetiPhian-Core |shetiphiancore |3.8.4 |DONE |NOSIGNATURE
blame-1.7.5.jar |Blame! |blame |1.7.5 |DONE |NOSIGNATURE
supplementaries-0.9.16.jar |Supplementaries |supplementaries |0.9.16 |DONE |NOSIGNATURE
DynamicSurroundings-1.16.4-4.0.1.4.jar |§3Dynamic Surroundings |dsurround |1.16.4-4.0.1.3 |DONE |b4:98:14:b9:76:55:25:4f:e5:5f:4d:71:90:87:43:5b:f9:d5:3a:02:60:42:5e:da:1f:15:9c:ff:be:a9:7c:77
forge-1.16.4-35.1.28-client.jar |Minecraft |minecraft |1.16.4 |DONE |NOSIGNATURE
mcw-bridges-1.0.4-mc1.16.4.jar |Macaw's Bridges |mcwbridges |1.0.4 |DONE |NOSIGNATURE
EnchantmentDescriptions-1.16.4-6.0.2.jar |EnchantmentDescriptions |enchdesc |6.0.2 |DONE |ea:45:b3:82:b6:9d:50:16:95:e7:2e:34:e1:92:d5:b4:9b:69:90:d3:4f:2e:71:99:b0:be:40:80:27:1f:3e:b0
AmbientSounds_v3.1.4_mc1.16.4.jar |Ambient Sounds |ambientsounds |3.0.3 |DONE |NOSIGNATURE
MouseTweaks-2.13-mc1.16.2.jar |Mouse Tweaks |mousetweaks |2.13 |DONE |NOSIGNATURE
Psi 1.16-88.jar |Psi |psi |1.16-88 |DONE |NOSIGNATURE
ImmersiveEngineering-1.16.4-4.1.2-129.jar |Immersive Engineering |immersiveengineering |1.16.4-4.1.2-129 |DONE |44:39:94:cf:1d:8c:be:3c:7f:a9:ee:f4:1e:63:a5:ac:61:f9:c2:87:d5:5b:d9:d6:8c:b5:3e:96:5d:8e:3f:b7
durability101-1.16-0.0.3.jar |Durability101 |durability101 |0.0.3 |DONE |NOSIGNATURE
ftb-ranks-1604.1.1.9.jar |FTB Ranks |ftbranks |1604.1.1.9 |DONE |NOSIGNATURE
pamhc2crops-1.16.3-1.0.1.jar |Pam's HarvestCraft 2 Crops |pamhc2crops |version |DONE |NOSIGNATURE
CreativeCore_v2.0.10_mc1.16.4.jar |CreativeCore |creativecore |2.0.0 |DONE |NOSIGNATURE
mcw-trapdors-1.0.0-mc1.16.4.jar |Macaw's Trapdoors |mcwtrpdoors |1.0.0 |DONE |NOSIGNATURE
spark-forge.jar |spark |spark |1.4.3 |DONE |NOSIGNATURE
pamhc2foodextended-1.16.3-1.0.0.jar |Pam's HarvestCraft 2 Food Exte|pamhc2foodextended |version |DONE |NOSIGNATURE
jeiintegration_1.16.4-6.1.1.11.jar |JEI Integration |jeiintegration |6.1.1.11 |DONE |NOSIGNATURE
curios-forge-1.16.4-4.0.3.0.jar |Curios API |curios |1.16.4-4.0.3.0 |DONE |NOSIGNATURE
eidolon-0.2.4.jar |Eidolon |eidolon |0.2.4 |DONE |NOSIGNATURE
Patchouli-1.16.4-48.jar |Patchouli |patchouli |1.16.4-48 |DONE |NOSIGNATURE
overworld_two-1.0-Forge-1.16.4.jar |Overworld 2 |overworld_two |1.0 |DONE |NOSIGNATURE
Xaeros_Minimap_20.29.1_Forge_1.16.4.jar |Xaero's Minimap |xaerominimap |20.29.1 |DONE |NOSIGNATURE
pamhc2foodcore-1.16.3-1.0.0.jar |Pam's HarvestCraft 2 Food Core|pamhc2foodcore |version |DONE |NOSIGNATURE
gravestone-1.16.4-1.0.8.jar |Gravestone Mod |gravestone |1.16.4-1.0.8 |DONE |NOSIGNATURE
ftb-backups-2.1.1.6.jar |FTB Backups |ftbbackups |2.1.1.6 |DONE |NOSIGNATURE
polymorph-forge-1.16.4-0.21.jar |Polymorph |polymorph |1.16.4-0.21 |DONE |NOSIGNATURE
AutoRegLib-1.6-47.jar |AutoRegLib |autoreglib |1.6-47 |DONE |NOSIGNATURE
Quark-r2.4-283.jar |Quark |quark |r2.4-283 |DONE |NOSIGNATURE
enderchests-1.16-1.7.5.jar |EnderChests |enderchests |1.7.5 |DONE |NOSIGNATURE
structurize-0.13.104-ALPHA-universal.jar |Structurize |structurize |0.13.104-ALPHA |DONE |NOSIGNATURE
AmbientEnvironment-4.0.0.6.jar |Ambient Environment |ambientenvironment |4.0.0.6 |DONE |NOSIGNATURE
travelers_index-1.16.4-1.0.2.jar |Traveler's Index |travelers_index |1.16.4-1.0.2 |DONE |NOSIGNATURE
minecolonies-0.13.547-ALPHA-universal.jar |Minecolonies |minecolonies |0.13.547-ALPHA |DONE |NOSIGNATURE
mcws-roofs-2.0.0-mc1.16.4.jar |Macaw's Roofs |mcwroofs |2.0.0 |DONE |NOSIGNATURE
World Stripper-1.16.4-2.0.1.jar |World Stripper |worldstripper |2.0.1 |DONE |NOSIGNATURE
AppleSkin-mc1.16.2-forge-1.0.14.jar |AppleSkin |appleskin |1.0.14 |DONE |NOSIGNATURE
ferritecore-1.0.jar |Ferrite Core |ferritecore |1.0 |DONE |41:ce:50:66:d1:a0:05:ce:a1:0e:02:85:9b:46:64:e0:bf:2e:cf:60:30:9a:fe:0c:27:e0:63:66:9a:84:ce:8a
engineersdecor-1.16.4-1.1.6-b1.jar |Engineer's Decor |engineersdecor |1.1.6-b1 |DONE |bf:30:76:97:e4:58:41:61:2a:f4:30:d3:8f:4c:e3:71:1d:14:c4:a1:4e:85:36:e3:1d:aa:2f:cb:22:b0:04:9b
observerlib-1.16.4-1.4.4.jar |ObserverLib |observerlib |1.16.4-1.4.4 |DONE |NOSIGNATURE
moreoverlays-1.18.11-mc1.16.4.jar |More Overlays Updated |moreoverlays |1.18.11-mc1.16.4 |DONE |NOSIGNATURE
moredragoneggs-1.4.jar |More Dragon Eggs |moredragoneggs |1.4 |DONE |NOSIGNATURE
durabilityviewer-1.16.4-forge35.0.7-1.10.jar |Giselbaers Durability Viewer |durabilityviewer |1.16.4-forge35.0.7-1|DONE |NOSIGNATURE
cloth-config-forge-4.1.1.jar |Cloth Config v4 API |cloth-config |4.0 |DONE |NOSIGNATURE
byg-1.1.5.jar |Oh The Biomes You'll Go |byg |1.1.5 |DONE |NOSIGNATURE
FastLeafDecay-v25.jar |FastLeafDecay |fastleafdecay |v25 |DONE |NOSIGNATURE
CosmeticArmorReworked-1.16.4-v1.jar |CosmeticArmorReworked |cosmeticarmorreworked |1.16.4-v1 |DONE |5e:ed:25:99:e4:44:14:c0:dd:89:c1:a9:4c:10:b5:0d:e4:b1:52:50:45:82:13:d8:d0:32:89:67:56:57:01:53
BetterMineshafts-Forge-1.16.3-1.1.1.jar |YUNG's Better Mineshafts |bettermineshafts |1.16.3-1.1.1 |DONE |NOSIGNATURE
EnderMail-1.16.4-1.1.7.jar |Ender Mail |endermail |1.16.4-1.1.7 |DONE |NOSIGNATURE
BetterAdvancements-1.16.4-0.1.0.103.jar |Better Advancements |betteradvancements |0.1.0.103 |DONE |NOSIGNATURE
``` | True | Astral Sorcery Conversion Wand converts Dirt To Path, should probably be blacklisted? - Astral Sorcery has a Conversion Wand which is basically a fancy block swapper. You right click a block, it swaps that block and others like it with a block or blocks of your choosing. `astralsorcery:exchange_wand`
With Quark's "Dirt To Path" enabled, if you right click with a Conversion Wand on dirt, it converts that dirt to a path instead of swapping. Disabling "Dirt To Path" stops the behavior, so I'm betting it's Quark.
Versions and mod list included, just in case? But if there's any struggle in reproducing this, please let me know and I'll binary-search my mods.
```
-- System Details --
Details:
Minecraft Version: 1.16.4
Minecraft Version ID: 1.16.4
Operating System: Windows 10 (amd64) version 10.0
Java Version: 14.0.2, AdoptOpenJDK
Java VM Version: OpenJDK 64-Bit Server VM (mixed mode, sharing), AdoptOpenJDK
Memory: 5592766216 bytes (5333 MB) / 8589934592 bytes (8192 MB) up to 8589934592 bytes (8192 MB)
CPUs: 8
JVM Flags: 10 total; -XX:HeapDumpPath=MojangTricksIntelDriversForPerformance_javaw.exe_minecraft.exe.heapdump -Xmx8192m -Xms8192m -XX:HeapDumpPath=MojangTricksIntelDriversForPerformance_javaw.exe_minecraft.exe.heapdump -XX:+UseG1GC -XX:+UnlockExperimentalVMOptions -XX:G1NewSizePercent=20 -XX:G1ReservePercent=20 -XX:MaxGCPauseMillis=50 -XX:G1HeapRegionSize=32M
ModLauncher: 8.0.6+85+master.325de55
ModLauncher launch target: fmlclient
ModLauncher naming: srg
ModLauncher services:
/mixin-0.8.2.jar mixin PLUGINSERVICE
/eventbus-3.0.5-service.jar eventbus PLUGINSERVICE
/forge-1.16.4-35.1.28.jar object_holder_definalize PLUGINSERVICE
/forge-1.16.4-35.1.28.jar runtime_enum_extender PLUGINSERVICE
/forge-1.16.4-35.1.28.jar capability_inject_definalize PLUGINSERVICE
/accesstransformers-2.2.0-shadowed.jar accesstransformer PLUGINSERVICE
/forge-1.16.4-35.1.28.jar runtimedistcleaner PLUGINSERVICE
/mixin-0.8.2.jar mixin TRANSFORMATIONSERVICE
/forge-1.16.4-35.1.28.jar fml TRANSFORMATIONSERVICE
FML: 35.1
Forge: net.minecraftforge:35.1.28
FML Language Providers:
javafml@35.1
minecraft@1
Mod List:
CraftPresence-Forge-1.16.3-Release-1.7.5.jar |CraftPresence |craftpresence |1.7.5 |DONE |a8:61:b7:97:9b:6f:d3:ba:38:d8:ce:45:6c:4b:8d:fd:ea:84:dd:d1:09:46:5d:5a:4f:c5:03:91:b5:c0:bc:de
astralsorcery-1.16.4-1.13.8.jar |Astral Sorcery |astralsorcery |1.16.4-1.13.8 |DONE |NOSIGNATURE
TrashSlot_1.16.3-12.2.1.jar |TrashSlot |trashslot |12.2.1 |DONE |NOSIGNATURE
pamhc2trees-1.16.3-1.0.0.jar |Pam's HarvestCraft 2 Fruit Tre|pamhc2trees |1.0.0 |DONE |NOSIGNATURE
restrictedportals-1.16.4-1.1.6.jar |Restricted Portals |restrictedportals |1.16.4-1.1.6 |DONE |NOSIGNATURE
DeathCounter-1.16.3-1.2.1.jar |Death Counter |deathcounter |1.2.1 |DONE |NOSIGNATURE
jei-1.16.4-7.6.0.62.jar |Just Enough Items |jei |7.6.0.62 |DONE |NOSIGNATURE
FallingTree-Forge-1.16.4-2.8.1.jar |Falling Tree |falling_tree |2.8.1 |DONE |NOSIGNATURE
mcw-windows-1.0.2-mc1.16.4.jar |Macaw's Windows |mcwwindows |1.0.2 |DONE |NOSIGNATURE
windowlogging-mc1.16.3_v0.0.2.jar |Windowlogging |windowlogging |0.0.2 |DONE |NOSIGNATURE
findme-1.16.3-2.1.0.0.jar |Find Me |findme |NONE |DONE |NOSIGNATURE
Neat+1.7-24.jar |Neat |neat |1.7-24 |DONE |NOSIGNATURE
create-mc1.16.3_v0.3b.jar |Create |create |mc1.16.3_v0.3b |DONE |NOSIGNATURE
Clumps-6.0.0.13.jar |Clumps |clumps |6.0.0.13 |DONE |NOSIGNATURE
XaerosWorldMap_1.11.4_Forge_1.16.4.jar |Xaero's World Map |xaeroworldmap |1.11.4 |DONE |NOSIGNATURE
shutupexperimentalsettings-1.0.1.jar |Shutup Experimental Settings! |shutupexperimentalsettings |1.0.1 |DONE |NOSIGNATURE
CTM-MC1.16.1-1.1.2.6.jar |ConnectedTexturesMod |ctm |MC1.16.1-1.1.2.6 |DONE |NOSIGNATURE
CookingForBlockheads_1.16.3-9.2.2.jar |Cooking for Blockheads |cookingforblockheads |9.2.2 |DONE |NOSIGNATURE
Controlling-7.0.0.11.jar |Controlling |controlling |7.0.0.11 |DONE |NOSIGNATURE
Placebo-1.16.3-4.3.3.jar |Placebo |placebo |4.3.3 |DONE |NOSIGNATURE
comforts-forge-1.16.4-4.0.0.3.jar |Comforts |comforts |1.16.4-4.0.0.2 |DONE |NOSIGNATURE
appliedenergistics2-8.2.0-beta.1.jar |Applied Energistics 2 |appliedenergistics2 |8.2.0-beta.1 |DONE |95:58:cc:83:9d:a8:fa:4f:e9:f3:54:90:66:61:c8:ae:9c:08:88:11:52:52:df:2d:28:5f:05:d8:28:57:0f:98
NaturesCompass-1.16.4-1.8.6.jar |Nature's Compass |naturescompass |1.16.4-1.8.6 |DONE |NOSIGNATURE
SereneSeasons-1.16.4-4.0.0.83-universal.jar |Serene Seasons |sereneseasons |1.16.4-4.0.0.76 |DONE |NOSIGNATURE
ftb-gui-library-1604.1.1.26.jar |FTB GUI Library |ftbguilibrary |1604.1.1.26 |DONE |NOSIGNATURE
upstream-1.0.jar |Upstream |upstream |1.0 |DONE |NOSIGNATURE
DefaultSettings-1.16.x-2.2.0.jar |DefaultSettings |defaultsettings |2.2.0 |DONE |ed:1c:55:41:73:fd:14:1b:28:fe:ea:30:c5:11:3b:4d:3f:82:86:57:bb:5b:8a:b2:d7:f3:04:52:52:92:cf:e7
FarmingForBlockheads_1.16.3-7.2.1.jar |Farming for Blockheads |farmingforblockheads |7.2.1 |DONE |NOSIGNATURE
Bookshelf-1.16.4-9.3.18.jar |Bookshelf |bookshelf |9.3.18 |DONE |ea:45:b3:82:b6:9d:50:16:95:e7:2e:34:e1:92:d5:b4:9b:69:90:d3:4f:2e:71:99:b0:be:40:80:27:1f:3e:b0
pneumaticcraft-repressurized-1.16.4-2.8.2-101.jar |PneumaticCraft: Repressurized |pneumaticcraft |1.16.4-2.8.2-101 |DONE |NOSIGNATURE
snowundertrees-1.16.4-v1.1.3.jar |Snow Under Trees |snowundertrees |v1.1.3 |DONE |NOSIGNATURE
mcw-doors-1.0.1fix-mc1.16.4.jar |Macaw's Doors |mcwdoors |1.0.1 |DONE |NOSIGNATURE
DataFixerSlayer 1.0-2.jar |DataFixerSlayer |datafixerslayer |1.0-2 |DONE |NOSIGNATURE
Hwyla-forge-1.10.11-B78_1.16.2.jar |Waila |waila |1.10.11-B78_1.16.2 |DONE |NOSIGNATURE
WAWLA-1.16.4-7.0.2.jar |WAWLA |wawla |7.0.2 |DONE |ea:45:b3:82:b6:9d:50:16:95:e7:2e:34:e1:92:d5:b4:9b:69:90:d3:4f:2e:71:99:b0:be:40:80:27:1f:3e:b0
Toast-Control-1.16.3-4.3.0.jar |Toast Control |toastcontrol |4.3.0 |DONE |NOSIGNATURE
SnowRealMagic-1.16.3-2.2.2.jar |Snow! Real Magic! |snowrealmagic |2.2.2 |DONE |NOSIGNATURE
Kiwi-1.16.3-3.4.1.jar |Kiwi |kiwi |3.4.1 |DONE |NOSIGNATURE
JustEnoughResources-1.16.4-0.12.0.103.jar |Just Enough Resources |jeresources |0.12.0.103 |DONE |NOSIGNATURE
immersive-portals-0.11-mc1.16.4-forge.jar |Immersive Portals |immersive_portals |0.7 |DONE |NOSIGNATURE
horsestandstill-1.16.3-1.0.1.jar |Stupid Horse Stand Still |horsestandstill |1.16.3-1.0.1 |DONE |1f:47:ac:b1:61:82:96:b8:47:19:16:d2:61:81:11:60:3a:06:4b:61:31:56:7d:44:31:1e:0c:6f:22:5b:4c:ed
ImmersivePetroleum-1.16.4-3.1.0-2.jar |Immersive Petroleum |immersivepetroleum |3.1.0-2 |DONE |NOSIGNATURE
ftb-teams-1604.1.0.13.jar |FTB Teams |ftbteams |1604.1.0.13 |DONE |NOSIGNATURE
forge-1.16.4-35.1.28-universal.jar |Forge |forge |35.1.28 |DONE |22:af:21:d8:19:82:7f:93:94:fe:2b:ac:b7:e4:41:57:68:39:87:b1:a7:5c:c6:44:f9:25:74:21:14:f5:0d:90
shetiphiancore-1.16-3.8.4.jar |ShetiPhian-Core |shetiphiancore |3.8.4 |DONE |NOSIGNATURE
blame-1.7.5.jar |Blame! |blame |1.7.5 |DONE |NOSIGNATURE
supplementaries-0.9.16.jar |Supplementaries |supplementaries |0.9.16 |DONE |NOSIGNATURE
DynamicSurroundings-1.16.4-4.0.1.4.jar |§3Dynamic Surroundings |dsurround |1.16.4-4.0.1.3 |DONE |b4:98:14:b9:76:55:25:4f:e5:5f:4d:71:90:87:43:5b:f9:d5:3a:02:60:42:5e:da:1f:15:9c:ff:be:a9:7c:77
forge-1.16.4-35.1.28-client.jar |Minecraft |minecraft |1.16.4 |DONE |NOSIGNATURE
mcw-bridges-1.0.4-mc1.16.4.jar |Macaw's Bridges |mcwbridges |1.0.4 |DONE |NOSIGNATURE
EnchantmentDescriptions-1.16.4-6.0.2.jar |EnchantmentDescriptions |enchdesc |6.0.2 |DONE |ea:45:b3:82:b6:9d:50:16:95:e7:2e:34:e1:92:d5:b4:9b:69:90:d3:4f:2e:71:99:b0:be:40:80:27:1f:3e:b0
AmbientSounds_v3.1.4_mc1.16.4.jar |Ambient Sounds |ambientsounds |3.0.3 |DONE |NOSIGNATURE
MouseTweaks-2.13-mc1.16.2.jar |Mouse Tweaks |mousetweaks |2.13 |DONE |NOSIGNATURE
Psi 1.16-88.jar |Psi |psi |1.16-88 |DONE |NOSIGNATURE
ImmersiveEngineering-1.16.4-4.1.2-129.jar |Immersive Engineering |immersiveengineering |1.16.4-4.1.2-129 |DONE |44:39:94:cf:1d:8c:be:3c:7f:a9:ee:f4:1e:63:a5:ac:61:f9:c2:87:d5:5b:d9:d6:8c:b5:3e:96:5d:8e:3f:b7
durability101-1.16-0.0.3.jar |Durability101 |durability101 |0.0.3 |DONE |NOSIGNATURE
ftb-ranks-1604.1.1.9.jar |FTB Ranks |ftbranks |1604.1.1.9 |DONE |NOSIGNATURE
pamhc2crops-1.16.3-1.0.1.jar |Pam's HarvestCraft 2 Crops |pamhc2crops |version |DONE |NOSIGNATURE
CreativeCore_v2.0.10_mc1.16.4.jar |CreativeCore |creativecore |2.0.0 |DONE |NOSIGNATURE
mcw-trapdors-1.0.0-mc1.16.4.jar |Macaw's Trapdoors |mcwtrpdoors |1.0.0 |DONE |NOSIGNATURE
spark-forge.jar |spark |spark |1.4.3 |DONE |NOSIGNATURE
pamhc2foodextended-1.16.3-1.0.0.jar |Pam's HarvestCraft 2 Food Exte|pamhc2foodextended |version |DONE |NOSIGNATURE
jeiintegration_1.16.4-6.1.1.11.jar |JEI Integration |jeiintegration |6.1.1.11 |DONE |NOSIGNATURE
curios-forge-1.16.4-4.0.3.0.jar |Curios API |curios |1.16.4-4.0.3.0 |DONE |NOSIGNATURE
eidolon-0.2.4.jar |Eidolon |eidolon |0.2.4 |DONE |NOSIGNATURE
Patchouli-1.16.4-48.jar |Patchouli |patchouli |1.16.4-48 |DONE |NOSIGNATURE
overworld_two-1.0-Forge-1.16.4.jar |Overworld 2 |overworld_two |1.0 |DONE |NOSIGNATURE
Xaeros_Minimap_20.29.1_Forge_1.16.4.jar |Xaero's Minimap |xaerominimap |20.29.1 |DONE |NOSIGNATURE
pamhc2foodcore-1.16.3-1.0.0.jar |Pam's HarvestCraft 2 Food Core|pamhc2foodcore |version |DONE |NOSIGNATURE
gravestone-1.16.4-1.0.8.jar |Gravestone Mod |gravestone |1.16.4-1.0.8 |DONE |NOSIGNATURE
ftb-backups-2.1.1.6.jar |FTB Backups |ftbbackups |2.1.1.6 |DONE |NOSIGNATURE
polymorph-forge-1.16.4-0.21.jar |Polymorph |polymorph |1.16.4-0.21 |DONE |NOSIGNATURE
AutoRegLib-1.6-47.jar |AutoRegLib |autoreglib |1.6-47 |DONE |NOSIGNATURE
Quark-r2.4-283.jar |Quark |quark |r2.4-283 |DONE |NOSIGNATURE
enderchests-1.16-1.7.5.jar |EnderChests |enderchests |1.7.5 |DONE |NOSIGNATURE
structurize-0.13.104-ALPHA-universal.jar |Structurize |structurize |0.13.104-ALPHA |DONE |NOSIGNATURE
AmbientEnvironment-4.0.0.6.jar |Ambient Environment |ambientenvironment |4.0.0.6 |DONE |NOSIGNATURE
travelers_index-1.16.4-1.0.2.jar |Traveler's Index |travelers_index |1.16.4-1.0.2 |DONE |NOSIGNATURE
minecolonies-0.13.547-ALPHA-universal.jar |Minecolonies |minecolonies |0.13.547-ALPHA |DONE |NOSIGNATURE
mcws-roofs-2.0.0-mc1.16.4.jar |Macaw's Roofs |mcwroofs |2.0.0 |DONE |NOSIGNATURE
World Stripper-1.16.4-2.0.1.jar |World Stripper |worldstripper |2.0.1 |DONE |NOSIGNATURE
AppleSkin-mc1.16.2-forge-1.0.14.jar |AppleSkin |appleskin |1.0.14 |DONE |NOSIGNATURE
ferritecore-1.0.jar |Ferrite Core |ferritecore |1.0 |DONE |41:ce:50:66:d1:a0:05:ce:a1:0e:02:85:9b:46:64:e0:bf:2e:cf:60:30:9a:fe:0c:27:e0:63:66:9a:84:ce:8a
engineersdecor-1.16.4-1.1.6-b1.jar |Engineer's Decor |engineersdecor |1.1.6-b1 |DONE |bf:30:76:97:e4:58:41:61:2a:f4:30:d3:8f:4c:e3:71:1d:14:c4:a1:4e:85:36:e3:1d:aa:2f:cb:22:b0:04:9b
observerlib-1.16.4-1.4.4.jar |ObserverLib |observerlib |1.16.4-1.4.4 |DONE |NOSIGNATURE
moreoverlays-1.18.11-mc1.16.4.jar |More Overlays Updated |moreoverlays |1.18.11-mc1.16.4 |DONE |NOSIGNATURE
moredragoneggs-1.4.jar |More Dragon Eggs |moredragoneggs |1.4 |DONE |NOSIGNATURE
durabilityviewer-1.16.4-forge35.0.7-1.10.jar |Giselbaers Durability Viewer |durabilityviewer |1.16.4-forge35.0.7-1|DONE |NOSIGNATURE
cloth-config-forge-4.1.1.jar |Cloth Config v4 API |cloth-config |4.0 |DONE |NOSIGNATURE
byg-1.1.5.jar |Oh The Biomes You'll Go |byg |1.1.5 |DONE |NOSIGNATURE
FastLeafDecay-v25.jar |FastLeafDecay |fastleafdecay |v25 |DONE |NOSIGNATURE
CosmeticArmorReworked-1.16.4-v1.jar |CosmeticArmorReworked |cosmeticarmorreworked |1.16.4-v1 |DONE |5e:ed:25:99:e4:44:14:c0:dd:89:c1:a9:4c:10:b5:0d:e4:b1:52:50:45:82:13:d8:d0:32:89:67:56:57:01:53
BetterMineshafts-Forge-1.16.3-1.1.1.jar |YUNG's Better Mineshafts |bettermineshafts |1.16.3-1.1.1 |DONE |NOSIGNATURE
EnderMail-1.16.4-1.1.7.jar |Ender Mail |endermail |1.16.4-1.1.7 |DONE |NOSIGNATURE
BetterAdvancements-1.16.4-0.1.0.103.jar |Better Advancements |betteradvancements |0.1.0.103 |DONE |NOSIGNATURE
``` | non_priority | astral sorcery conversion wand converts dirt to path should probably be blacklisted astral sorcery has a conversion wand which is basically a fancy block swapper you right click a block it swaps that block and others like it with a block or blocks of your choosing astralsorcery exchange wand with quark s dirt to path enabled if you right click with a conversion wand on dirt it converts that dirt to a path instead of swapping disabling dirt to path stops the behavior so i m betting it s quark versions and mod list included just in case but if there s any struggle in reproducing this please let me know and i ll binary search my mods system details details minecraft version minecraft version id operating system windows version java version adoptopenjdk java vm version openjdk bit server vm mixed mode sharing adoptopenjdk memory bytes mb bytes mb up to bytes mb cpus jvm flags total xx heapdumppath mojangtricksinteldriversforperformance javaw exe minecraft exe heapdump xx heapdumppath mojangtricksinteldriversforperformance javaw exe minecraft exe heapdump xx xx unlockexperimentalvmoptions xx xx xx maxgcpausemillis xx modlauncher master modlauncher launch target fmlclient modlauncher naming srg modlauncher services mixin jar mixin pluginservice eventbus service jar eventbus pluginservice forge jar object holder definalize pluginservice forge jar runtime enum extender pluginservice forge jar capability inject definalize pluginservice accesstransformers shadowed jar accesstransformer pluginservice forge jar runtimedistcleaner pluginservice mixin jar mixin transformationservice forge jar fml transformationservice fml forge net minecraftforge fml language providers javafml minecraft mod list craftpresence forge release jar craftpresence craftpresence done ba ce fd ea dd bc de astralsorcery jar astral sorcery astralsorcery done nosignature trashslot jar trashslot trashslot done nosignature jar pam s harvestcraft fruit tre done nosignature restrictedportals jar restricted portals restrictedportals done nosignature deathcounter jar death counter deathcounter done nosignature jei jar just enough items jei done nosignature fallingtree forge jar falling tree falling tree done nosignature mcw windows jar macaw s windows mcwwindows done nosignature windowlogging jar windowlogging windowlogging done nosignature findme jar find me findme none done nosignature neat jar neat neat done nosignature create jar create create done nosignature clumps jar clumps clumps done nosignature xaerosworldmap forge jar xaero s world map xaeroworldmap done nosignature shutupexperimentalsettings jar shutup experimental settings shutupexperimentalsettings done nosignature ctm jar connectedtexturesmod ctm done nosignature cookingforblockheads jar cooking for blockheads cookingforblockheads done nosignature controlling jar controlling controlling done nosignature placebo jar placebo placebo done nosignature comforts forge jar comforts comforts done nosignature beta jar applied energistics beta done cc fa ae df naturescompass jar nature s compass naturescompass done nosignature sereneseasons universal jar serene seasons sereneseasons done nosignature ftb gui library jar ftb gui library ftbguilibrary done nosignature upstream jar upstream upstream done nosignature defaultsettings x jar defaultsettings defaultsettings done ed fd fe ea bb cf farmingforblockheads jar farming for blockheads farmingforblockheads done nosignature bookshelf jar bookshelf bookshelf done ea be pneumaticcraft repressurized jar pneumaticcraft repressurized pneumaticcraft done nosignature snowundertrees jar snow under trees snowundertrees done nosignature mcw doors jar macaw s doors mcwdoors done nosignature datafixerslayer jar datafixerslayer datafixerslayer done nosignature hwyla forge jar waila waila done nosignature wawla jar wawla wawla done ea be toast control jar toast control toastcontrol done nosignature snowrealmagic jar snow real magic snowrealmagic done nosignature kiwi jar kiwi kiwi done nosignature justenoughresources jar just enough resources jeresources done nosignature immersive portals forge jar immersive portals immersive portals done nosignature horsestandstill jar stupid horse stand still horsestandstill done ac ed immersivepetroleum jar immersive petroleum immersivepetroleum done nosignature ftb teams jar ftb teams ftbteams done nosignature forge universal jar forge forge done af fe ac shetiphiancore jar shetiphian core shetiphiancore done nosignature blame jar blame blame done nosignature supplementaries jar supplementaries supplementaries done nosignature dynamicsurroundings jar § surroundings dsurround done da ff be forge client jar minecraft minecraft done nosignature mcw bridges jar macaw s bridges mcwbridges done nosignature enchantmentdescriptions jar enchantmentdescriptions enchdesc done ea be ambientsounds jar ambient sounds ambientsounds done nosignature mousetweaks jar mouse tweaks mousetweaks done nosignature psi jar psi psi done nosignature immersiveengineering jar immersive engineering immersiveengineering done cf be ee ac jar done nosignature ftb ranks jar ftb ranks ftbranks done nosignature jar pam s harvestcraft crops version done nosignature creativecore jar creativecore creativecore done nosignature mcw trapdors jar macaw s trapdoors mcwtrpdoors done nosignature spark forge jar spark spark done nosignature jar pam s harvestcraft food exte version done nosignature jeiintegration jar jei integration jeiintegration done nosignature curios forge jar curios api curios done nosignature eidolon jar eidolon eidolon done nosignature patchouli jar patchouli patchouli done nosignature overworld two forge jar overworld overworld two done nosignature xaeros minimap forge jar xaero s minimap xaerominimap done nosignature jar pam s harvestcraft food core version done nosignature gravestone jar gravestone mod gravestone done nosignature ftb backups jar ftb backups ftbbackups done nosignature polymorph forge jar polymorph polymorph done nosignature autoreglib jar autoreglib autoreglib done nosignature quark jar quark quark done nosignature enderchests jar enderchests enderchests done nosignature structurize alpha universal jar structurize structurize alpha done nosignature ambientenvironment jar ambient environment ambientenvironment done nosignature travelers index jar traveler s index travelers index done nosignature minecolonies alpha universal jar minecolonies minecolonies alpha done nosignature mcws roofs jar macaw s roofs mcwroofs done nosignature world stripper jar world stripper worldstripper done nosignature appleskin forge jar appleskin appleskin done nosignature ferritecore jar ferrite core ferritecore done ce ce bf cf fe ce engineersdecor jar engineer s decor engineersdecor done bf aa cb observerlib jar observerlib observerlib done nosignature moreoverlays jar more overlays updated moreoverlays done nosignature moredragoneggs jar more dragon eggs moredragoneggs done nosignature durabilityviewer jar giselbaers durability viewer durabilityviewer done nosignature cloth config forge jar cloth config api cloth config done nosignature byg jar oh the biomes you ll go byg done nosignature fastleafdecay jar fastleafdecay fastleafdecay done nosignature cosmeticarmorreworked jar cosmeticarmorreworked cosmeticarmorreworked done ed dd bettermineshafts forge jar yung s better mineshafts bettermineshafts done nosignature endermail jar ender mail endermail done nosignature betteradvancements jar better advancements betteradvancements done nosignature | 0 |
260,294 | 22,609,074,034 | IssuesEvent | 2022-06-29 15:32:31 | wazuh/wazuh-qa | https://api.github.com/repos/wazuh/wazuh-qa | opened | Wazuh 4.3 - SCA policies manual tests - SCA Policy for CIS Microsoft Windows 10 Enterprise Release 21H2 Benchmark v1.12.0 / @fedepacher | team/qa type/manual-testing type/qa-testing release test/4.3.6 | | **Related Issue** |
|---|
|https://github.com/wazuh/wazuh/issues/13191|
## Description
Windows 10 [SCA](https://documentation.wazuh.com/current/user-manual/capabilities/sec-config-assessment/how-it-works.html) policies have been updated https://github.com/wazuh/wazuh/issues/13191. On this account, It is necessary to ensure that these policies fit with the [CIS Windows 10 Enterprise Release 21H2 Benchmark v1.12.](https://downloads.cisecurity.org/#/). Also, manual testing for the used SCA rules is required, ensuring the proposed rules work as expected.
- OS: Windows 10 Enterprise
- SCA policy file: https://github.com/wazuh/wazuh/blob/83a39381f06965015363b09d4fbcc4fd150fb007/ruleset/sca/windows/cis_win10_enterprise.yml
For each check in the SCA policy checks:
- The **title**, **description**, **rationale**, **compliance** and **remediation** must correspond to the ones in the check of the corresponding CIS benchmark file found in https://downloads.cisecurity.org/#/.
- The check command found in the CIS benchmark file should work as expected and must match the rule specified in the check of the `yml` file.
The installers must also be tested:
- Check the scan is executed automatically when installing.
- Check the scan result.
## Checks
### Checks design
Check ID | Check Category | Description | ID/Title/Description/Rationable | Remediation | Compliance | Rules | Artifact
-- | -- | -- | -- | -- | -- | -- | --|
id| Category | Description | :black_circle: | :black_circle: | :black_circle: | :black_circle: | Artifact |
All test results must have one of the following statuses:
| | |
|---------------------------------|--------------------------------------------|
| :green_circle: | All checks passed. |
| :red_circle: | There is at least one failed result. |
| :yellow_circle: | There is at least one expected failure or skipped test and no failures. |
| :black_circle: | Not tested. |
Any failing test must be properly addressed with a new issue, detailing the error and the possible cause.
An extended report of the test results can be attached as a ZIP or TXT file. Please attach any documents, screenshots, or tables to the issue update with the results. This report can be used by the auditors to dig deeper into any possible failures and details.
### Checks lists
- [Global check]()
- [Checks Block 1](https://github.com/wazuh/wazuh-qa/issues/3021#issuecomment-1163172236)
- [Checks Block 2
](https://github.com/wazuh/wazuh-qa/issues/3021#issuecomment-1163177308)
- [Checks Block 3](https://github.com/wazuh/wazuh-qa/issues/3021#issuecomment-1163178304)
## Conclusions
All tests have been executed and the results can be found in the issue updates.
_To be completed_ | 3.0 | Wazuh 4.3 - SCA policies manual tests - SCA Policy for CIS Microsoft Windows 10 Enterprise Release 21H2 Benchmark v1.12.0 / @fedepacher - | **Related Issue** |
|---|
|https://github.com/wazuh/wazuh/issues/13191|
## Description
Windows 10 [SCA](https://documentation.wazuh.com/current/user-manual/capabilities/sec-config-assessment/how-it-works.html) policies have been updated https://github.com/wazuh/wazuh/issues/13191. On this account, It is necessary to ensure that these policies fit with the [CIS Windows 10 Enterprise Release 21H2 Benchmark v1.12.](https://downloads.cisecurity.org/#/). Also, manual testing for the used SCA rules is required, ensuring the proposed rules work as expected.
- OS: Windows 10 Enterprise
- SCA policy file: https://github.com/wazuh/wazuh/blob/83a39381f06965015363b09d4fbcc4fd150fb007/ruleset/sca/windows/cis_win10_enterprise.yml
For each check in the SCA policy checks:
- The **title**, **description**, **rationale**, **compliance** and **remediation** must correspond to the ones in the check of the corresponding CIS benchmark file found in https://downloads.cisecurity.org/#/.
- The check command found in the CIS benchmark file should work as expected and must match the rule specified in the check of the `yml` file.
The installers must also be tested:
- Check the scan is executed automatically when installing.
- Check the scan result.
## Checks
### Checks design
Check ID | Check Category | Description | ID/Title/Description/Rationable | Remediation | Compliance | Rules | Artifact
-- | -- | -- | -- | -- | -- | -- | --|
id| Category | Description | :black_circle: | :black_circle: | :black_circle: | :black_circle: | Artifact |
All test results must have one of the following statuses:
| | |
|---------------------------------|--------------------------------------------|
| :green_circle: | All checks passed. |
| :red_circle: | There is at least one failed result. |
| :yellow_circle: | There is at least one expected failure or skipped test and no failures. |
| :black_circle: | Not tested. |
Any failing test must be properly addressed with a new issue, detailing the error and the possible cause.
An extended report of the test results can be attached as a ZIP or TXT file. Please attach any documents, screenshots, or tables to the issue update with the results. This report can be used by the auditors to dig deeper into any possible failures and details.
### Checks lists
- [Global check]()
- [Checks Block 1](https://github.com/wazuh/wazuh-qa/issues/3021#issuecomment-1163172236)
- [Checks Block 2
](https://github.com/wazuh/wazuh-qa/issues/3021#issuecomment-1163177308)
- [Checks Block 3](https://github.com/wazuh/wazuh-qa/issues/3021#issuecomment-1163178304)
## Conclusions
All tests have been executed and the results can be found in the issue updates.
_To be completed_ | non_priority | wazuh sca policies manual tests sca policy for cis microsoft windows enterprise release benchmark fedepacher related issue description windows policies have been updated on this account it is necessary to ensure that these policies fit with the also manual testing for the used sca rules is required ensuring the proposed rules work as expected os windows enterprise sca policy file for each check in the sca policy checks the title description rationale compliance and remediation must correspond to the ones in the check of the corresponding cis benchmark file found in the check command found in the cis benchmark file should work as expected and must match the rule specified in the check of the yml file the installers must also be tested check the scan is executed automatically when installing check the scan result checks checks design check id check category description id title description rationable remediation compliance rules artifact id category description black circle black circle black circle black circle artifact all test results must have one of the following statuses green circle all checks passed red circle there is at least one failed result yellow circle there is at least one expected failure or skipped test and no failures black circle not tested any failing test must be properly addressed with a new issue detailing the error and the possible cause an extended report of the test results can be attached as a zip or txt file please attach any documents screenshots or tables to the issue update with the results this report can be used by the auditors to dig deeper into any possible failures and details checks lists checks block conclusions all tests have been executed and the results can be found in the issue updates to be completed | 0 |
177,276 | 21,471,121,638 | IssuesEvent | 2022-04-26 09:34:57 | GNS3/gns3-web-ui | https://api.github.com/repos/GNS3/gns3-web-ui | closed | CVE-2021-44906 (High) detected in minimist-1.2.5.tgz - autoclosed | security vulnerability | ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-1.2.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- electron-builder-22.13.1.tgz (Root Library)
- read-config-file-6.2.0.tgz
- json5-2.2.0.tgz
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GNS3/gns3-web-ui/commit/c938c3a8ca5deafafee39aef1d4cab9aebf82363">c938c3a8ca5deafafee39aef1d4cab9aebf82363</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
</details>
<p></p>
| True | CVE-2021-44906 (High) detected in minimist-1.2.5.tgz - autoclosed - ## CVE-2021-44906 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimist-1.2.5.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- electron-builder-22.13.1.tgz (Root Library)
- read-config-file-6.2.0.tgz
- json5-2.2.0.tgz
- :x: **minimist-1.2.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GNS3/gns3-web-ui/commit/c938c3a8ca5deafafee39aef1d4cab9aebf82363">c938c3a8ca5deafafee39aef1d4cab9aebf82363</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/issues/164">https://github.com/substack/minimist/issues/164</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: minimist - 1.2.6</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in minimist tgz autoclosed cve high severity vulnerability vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules minimist package json dependency hierarchy electron builder tgz root library read config file tgz tgz x minimist tgz vulnerable library found in head commit a href vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist | 0 |
106,096 | 16,664,337,842 | IssuesEvent | 2021-06-06 22:26:46 | utopikkad/my-Pokedex | https://api.github.com/repos/utopikkad/my-Pokedex | opened | CVE-2021-23386 (Medium) detected in dns-packet-1.3.1.tgz | security vulnerability | ## CVE-2021-23386 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dns-packet-1.3.1.tgz</b></p></summary>
<p>An abstract-encoding compliant module for encoding / decoding DNS packets</p>
<p>Library home page: <a href="https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz">https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz</a></p>
<p>Path to dependency file: my-Pokedex/package.json</p>
<p>Path to vulnerable library: my-Pokedex/node_modules/dns-packet/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.900.3.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- bonjour-3.5.0.tgz
- multicast-dns-6.2.3.tgz
- :x: **dns-packet-1.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/utopikkad/my-Pokedex/commit/1506a4535d854ee681d1fcbd935e528c9236b357">1506a4535d854ee681d1fcbd935e528c9236b357</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package dns-packet before 5.2.2. It creates buffers with allocUnsafe and does not always fill them before forming network packets. This can expose internal application memory over unencrypted network when querying crafted invalid domain names.
<p>Publish Date: 2021-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23386>CVE-2021-23386</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386</a></p>
<p>Release Date: 2021-05-20</p>
<p>Fix Resolution: dns-packet - 5.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23386 (Medium) detected in dns-packet-1.3.1.tgz - ## CVE-2021-23386 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dns-packet-1.3.1.tgz</b></p></summary>
<p>An abstract-encoding compliant module for encoding / decoding DNS packets</p>
<p>Library home page: <a href="https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz">https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz</a></p>
<p>Path to dependency file: my-Pokedex/package.json</p>
<p>Path to vulnerable library: my-Pokedex/node_modules/dns-packet/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.900.3.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- bonjour-3.5.0.tgz
- multicast-dns-6.2.3.tgz
- :x: **dns-packet-1.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/utopikkad/my-Pokedex/commit/1506a4535d854ee681d1fcbd935e528c9236b357">1506a4535d854ee681d1fcbd935e528c9236b357</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package dns-packet before 5.2.2. It creates buffers with allocUnsafe and does not always fill them before forming network packets. This can expose internal application memory over unencrypted network when querying crafted invalid domain names.
<p>Publish Date: 2021-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23386>CVE-2021-23386</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386</a></p>
<p>Release Date: 2021-05-20</p>
<p>Fix Resolution: dns-packet - 5.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in dns packet tgz cve medium severity vulnerability vulnerable library dns packet tgz an abstract encoding compliant module for encoding decoding dns packets library home page a href path to dependency file my pokedex package json path to vulnerable library my pokedex node modules dns packet package json dependency hierarchy build angular tgz root library webpack dev server tgz bonjour tgz multicast dns tgz x dns packet tgz vulnerable library found in head commit a href vulnerability details this affects the package dns packet before it creates buffers with allocunsafe and does not always fill them before forming network packets this can expose internal application memory over unencrypted network when querying crafted invalid domain names publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution dns packet step up your open source security game with whitesource | 0 |
386,766 | 26,700,438,487 | IssuesEvent | 2023-01-27 13:59:55 | mrdoob/three.js | https://api.github.com/repos/mrdoob/three.js | closed | docs: Audio.source incorrect type | Bug Documentation | ### Description
The documentation at https://threejs.org/docs/index.html?q=audio#api/en/audio/Audio.source states incorrect type:
> .[source](https://threejs.org/docs/index.html#api/en/audio/Audio.source) : String
>
> An [AudioBufferSourceNode](https://developer.mozilla.org/en-US/docs/Web/API/AudioBufferSourceNode) created using > [AudioContext.createBufferSource](https://developer.mozilla.org/en-US/docs/Web/API/AudioContext/createBufferSource)().
Corresponding sources:
- https://github.com/mrdoob/three.js/blob/master/docs/api/en/audio/Audio.html#L94
- https://github.com/mrdoob/three.js/blob/master/src/audio/Audio.js#L46
Why not generate API docs automatically from source, e.g.
- https://en.wikipedia.org/wiki/JSDoc
- https://jsdoc.app/
### Version
r149 | 1.0 | docs: Audio.source incorrect type - ### Description
The documentation at https://threejs.org/docs/index.html?q=audio#api/en/audio/Audio.source states incorrect type:
> .[source](https://threejs.org/docs/index.html#api/en/audio/Audio.source) : String
>
> An [AudioBufferSourceNode](https://developer.mozilla.org/en-US/docs/Web/API/AudioBufferSourceNode) created using > [AudioContext.createBufferSource](https://developer.mozilla.org/en-US/docs/Web/API/AudioContext/createBufferSource)().
Corresponding sources:
- https://github.com/mrdoob/three.js/blob/master/docs/api/en/audio/Audio.html#L94
- https://github.com/mrdoob/three.js/blob/master/src/audio/Audio.js#L46
Why not generate API docs automatically from source, e.g.
- https://en.wikipedia.org/wiki/JSDoc
- https://jsdoc.app/
### Version
r149 | non_priority | docs audio source incorrect type description the documentation at states incorrect type string an created using corresponding sources why not generate api docs automatically from source e g version | 0 |
96,241 | 8,600,293,199 | IssuesEvent | 2018-11-16 06:56:23 | bitshares/bitshares-community-ui | https://api.github.com/repos/bitshares/bitshares-community-ui | opened | Unit tests: getFloatCurrency func | tests | Needs some unit tests for this function, that will cover most use-cases | 1.0 | Unit tests: getFloatCurrency func - Needs some unit tests for this function, that will cover most use-cases | non_priority | unit tests getfloatcurrency func needs some unit tests for this function that will cover most use cases | 0 |
3,780 | 2,691,416,296 | IssuesEvent | 2015-03-31 21:25:42 | CSC510/SQLvsNOSQL | https://api.github.com/repos/CSC510/SQLvsNOSQL | closed | I have collected the data for both add performance | help wanted Test Problem | I have collected the data for add performance in both databases. I will shift the other parts to @maxlpy. He will test the find and delete performance further. | 1.0 | I have collected the data for both add performance - I have collected the data for add performance in both databases. I will shift the other parts to @maxlpy. He will test the find and delete performance further. | non_priority | i have collected the data for both add performance i have collected the data for add performance in both databases i will shift the other parts to maxlpy he will test the find and delete performance further | 0 |
34,784 | 14,520,886,065 | IssuesEvent | 2020-12-14 06:23:05 | MicrosoftDocs/dynamics-365-customer-engagement | https://api.github.com/repos/MicrosoftDocs/dynamics-365-customer-engagement | closed | getFocusedTab says it is not a function or constructor. | Channel Integration Framework Pri3 dynamics-365-customerservice/svc waiting on customer | I've been trying to capture the unique session id when a new conversation summary is opened in CIF.
I've added the below javascript to a function, trying different iteration by using return new Promise, adding "new" to the below and several other things. Every time I try to run this, it says that the below is not a function or constructor. How can I add this to the Conversation Summary form in order to capture the current Session information? I'm trying to save the Smart Assist conversation data and associate it to a specific session if possible.
Microsoft.CIFramework.getFocusedSession().then(
function success(result) {
console.log(result);
// perform operations on session id value
},
function (error) {
console.log(error.message);
// handle error conditions
}
); | 1.0 | getFocusedTab says it is not a function or constructor. - I've been trying to capture the unique session id when a new conversation summary is opened in CIF.
I've added the below javascript to a function, trying different iteration by using return new Promise, adding "new" to the below and several other things. Every time I try to run this, it says that the below is not a function or constructor. How can I add this to the Conversation Summary form in order to capture the current Session information? I'm trying to save the Smart Assist conversation data and associate it to a specific session if possible.
Microsoft.CIFramework.getFocusedSession().then(
function success(result) {
console.log(result);
// perform operations on session id value
},
function (error) {
console.log(error.message);
// handle error conditions
}
); | non_priority | getfocusedtab says it is not a function or constructor i ve been trying to capture the unique session id when a new conversation summary is opened in cif i ve added the below javascript to a function trying different iteration by using return new promise adding new to the below and several other things every time i try to run this it says that the below is not a function or constructor how can i add this to the conversation summary form in order to capture the current session information i m trying to save the smart assist conversation data and associate it to a specific session if possible microsoft ciframework getfocusedsession then function success result console log result perform operations on session id value function error console log error message handle error conditions | 0 |
134,380 | 12,602,235,586 | IssuesEvent | 2020-06-11 11:20:22 | r-lib/rlang | https://api.github.com/repos/r-lib/rlang | closed | Document caveats of inlining functions with `call2()` | documentation | I am looking that working out how to keep the functionality of `dplyr::filter_()` as it is being deprecated.
In the example below I can reproduce `filter_(mtcars, "gear == 3")` using `filter()`, `parse_expr()`, and `call2()`:
```r
library(dplyr)
library(rlang)
x <- "gear == 3"
x_p <- parse_expr(x)
mycall <- rlang::call2(dplyr::filter, quote(mtcars), x_p)
eval(mycall)
## works.
```
However, when trying to compose / nest calls (here trying to mimic `mtcars %>% filter(gear == 3)`) I get errors:
```
mynestedcall <- rlang::call2(dplyr::filter, x_p)
myothercall <- call2(`%>%`, quote(mtcars), mynestedcall)
eval(myothercall)
## Error in pipes[[i]] : subscript out of bounds
```
Should it be possible to build calls by composition ? (Or am I missing something ?).
| 1.0 | Document caveats of inlining functions with `call2()` - I am looking that working out how to keep the functionality of `dplyr::filter_()` as it is being deprecated.
In the example below I can reproduce `filter_(mtcars, "gear == 3")` using `filter()`, `parse_expr()`, and `call2()`:
```r
library(dplyr)
library(rlang)
x <- "gear == 3"
x_p <- parse_expr(x)
mycall <- rlang::call2(dplyr::filter, quote(mtcars), x_p)
eval(mycall)
## works.
```
However, when trying to compose / nest calls (here trying to mimic `mtcars %>% filter(gear == 3)`) I get errors:
```
mynestedcall <- rlang::call2(dplyr::filter, x_p)
myothercall <- call2(`%>%`, quote(mtcars), mynestedcall)
eval(myothercall)
## Error in pipes[[i]] : subscript out of bounds
```
Should it be possible to build calls by composition ? (Or am I missing something ?).
| non_priority | document caveats of inlining functions with i am looking that working out how to keep the functionality of dplyr filter as it is being deprecated in the example below i can reproduce filter mtcars gear using filter parse expr and r library dplyr library rlang x gear x p parse expr x mycall rlang dplyr filter quote mtcars x p eval mycall works however when trying to compose nest calls here trying to mimic mtcars filter gear i get errors mynestedcall rlang dplyr filter x p myothercall quote mtcars mynestedcall eval myothercall error in pipes subscript out of bounds should it be possible to build calls by composition or am i missing something | 0 |
21,820 | 10,680,991,880 | IssuesEvent | 2019-10-21 23:01:43 | MicrosoftDocs/vsts-docs | https://api.github.com/repos/MicrosoftDocs/vsts-docs | closed | How can I look up the admin of an org that I don't have access to? | Pri2 devops-security/tech devops/prod product-question | Navigating to an Azure DevOps organisation that I don't have access to indicates that I need to reach out to the admins of the org to get access. But without access to the org, I have no way to find out who the admin is.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 20dce3f1-1133-3084-c5f4-7a5d6d0d6cf8
* Version Independent ID: 31579324-f0e5-607a-caa1-ec31b444af79
* Content: [Find an admin or organization owner - Azure DevOps](https://docs.microsoft.com/en-us/azure/devops/organizations/security/lookup-organization-owner-admin?view=azure-devops&tabs=preview-page)
* Content Source: [docs/organizations/security/lookup-organization-owner-admin.md](https://github.com/MicrosoftDocs/vsts-docs/blob/master/docs/organizations/security/lookup-organization-owner-admin.md)
* Product: **devops**
* Technology: **devops-security**
* GitHub Login: @KathrynEE
* Microsoft Alias: **kaelli** | True | How can I look up the admin of an org that I don't have access to? - Navigating to an Azure DevOps organisation that I don't have access to indicates that I need to reach out to the admins of the org to get access. But without access to the org, I have no way to find out who the admin is.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 20dce3f1-1133-3084-c5f4-7a5d6d0d6cf8
* Version Independent ID: 31579324-f0e5-607a-caa1-ec31b444af79
* Content: [Find an admin or organization owner - Azure DevOps](https://docs.microsoft.com/en-us/azure/devops/organizations/security/lookup-organization-owner-admin?view=azure-devops&tabs=preview-page)
* Content Source: [docs/organizations/security/lookup-organization-owner-admin.md](https://github.com/MicrosoftDocs/vsts-docs/blob/master/docs/organizations/security/lookup-organization-owner-admin.md)
* Product: **devops**
* Technology: **devops-security**
* GitHub Login: @KathrynEE
* Microsoft Alias: **kaelli** | non_priority | how can i look up the admin of an org that i don t have access to navigating to an azure devops organisation that i don t have access to indicates that i need to reach out to the admins of the org to get access but without access to the org i have no way to find out who the admin is document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops security github login kathrynee microsoft alias kaelli | 0 |
436,202 | 30,542,098,354 | IssuesEvent | 2023-07-19 22:32:47 | Nadzey/Peshkariki | https://api.github.com/repos/Nadzey/Peshkariki | opened | Test Suite: Create new order. Test Case 1: Display Create Order Container | documentation | Description: Verify that the "Create Order" container is displayed after clicking the "Create Order" link in the header.
Test Steps:
Click on the "Create Order" link in the header.
Verify that the container's title matches the expected value (item.containerTitle).
Click on the "Add for All" button.
Verify that the current URL contains the text "AddForAll". | 1.0 | Test Suite: Create new order. Test Case 1: Display Create Order Container - Description: Verify that the "Create Order" container is displayed after clicking the "Create Order" link in the header.
Test Steps:
Click on the "Create Order" link in the header.
Verify that the container's title matches the expected value (item.containerTitle).
Click on the "Add for All" button.
Verify that the current URL contains the text "AddForAll". | non_priority | test suite create new order test case display create order container description verify that the create order container is displayed after clicking the create order link in the header test steps click on the create order link in the header verify that the container s title matches the expected value item containertitle click on the add for all button verify that the current url contains the text addforall | 0 |
69,812 | 8,460,949,758 | IssuesEvent | 2018-10-22 20:20:15 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Plan the user's journey from Muon to Brave Core | OS/Windows OS/macOS design feature/user-interface infrastructure needs-mock-up | We know that we want the Muon version of Brave to upgrade itself to brave-core, but we don't know what that experience would feel like for the user.
## Steps that are out of our control
1. Check for updates in Muon version of browser
2. Update is found; it downloads / installs this special version of browser-laptop
3. New version of browser-laptop is re-launched
4. Special code runs to install brave-core
## Parts that are in our control
After step 4, we have control and choose what we'd like to do. For example, we could do one of these options:
- Launch the browser silently, so that it can perform the import. And then immediately quit (so user can launch at their leisure)
- Straight up launch into the new browser and quit from Muon
Letting the user do it at their leisure could be nice because we could show them a screen about what is happening ("You've been upgraded!"):
- new version has already been installed (and their data should be imported)
- old version of Brave (muon based) has not be uninstalled (all the data is there!)
- folks can still launch this old version and view PDFs / print their Brave Payments reports | 1.0 | Plan the user's journey from Muon to Brave Core - We know that we want the Muon version of Brave to upgrade itself to brave-core, but we don't know what that experience would feel like for the user.
## Steps that are out of our control
1. Check for updates in Muon version of browser
2. Update is found; it downloads / installs this special version of browser-laptop
3. New version of browser-laptop is re-launched
4. Special code runs to install brave-core
## Parts that are in our control
After step 4, we have control and choose what we'd like to do. For example, we could do one of these options:
- Launch the browser silently, so that it can perform the import. And then immediately quit (so user can launch at their leisure)
- Straight up launch into the new browser and quit from Muon
Letting the user do it at their leisure could be nice because we could show them a screen about what is happening ("You've been upgraded!"):
- new version has already been installed (and their data should be imported)
- old version of Brave (muon based) has not be uninstalled (all the data is there!)
- folks can still launch this old version and view PDFs / print their Brave Payments reports | non_priority | plan the user s journey from muon to brave core we know that we want the muon version of brave to upgrade itself to brave core but we don t know what that experience would feel like for the user steps that are out of our control check for updates in muon version of browser update is found it downloads installs this special version of browser laptop new version of browser laptop is re launched special code runs to install brave core parts that are in our control after step we have control and choose what we d like to do for example we could do one of these options launch the browser silently so that it can perform the import and then immediately quit so user can launch at their leisure straight up launch into the new browser and quit from muon letting the user do it at their leisure could be nice because we could show them a screen about what is happening you ve been upgraded new version has already been installed and their data should be imported old version of brave muon based has not be uninstalled all the data is there folks can still launch this old version and view pdfs print their brave payments reports | 0 |
31,803 | 12,017,535,599 | IssuesEvent | 2020-04-10 18:37:36 | tomdgl397/juice-shop | https://api.github.com/repos/tomdgl397/juice-shop | opened | CVE-2018-19838 (Medium) detected in node-sass-4.13.1.tgz, node-sass-v4.13.1 | security vulnerability | ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/juice-shop/frontend/package.json</p>
<p>Path to vulnerable library: /juice-shop/frontend/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.13.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/tomdgl397/juice-shop/commit/24e92478a2e956132cc96bf9e3bc8ca7fecf375d">24e92478a2e956132cc96bf9e3bc8ca7fecf375d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, functions inside ast.cpp for IMPLEMENT_AST_OPERATORS expansion allow attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, as demonstrated by recursive calls involving clone(), cloneChildren(), and copy().
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19838>CVE-2018-19838</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/blob/3.6.0/src/ast.cpp">https://github.com/sass/libsass/blob/3.6.0/src/ast.cpp</a></p>
<p>Release Date: 2019-07-01</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19838 (Medium) detected in node-sass-4.13.1.tgz, node-sass-v4.13.1 - ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.13.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/juice-shop/frontend/package.json</p>
<p>Path to vulnerable library: /juice-shop/frontend/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.13.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/tomdgl397/juice-shop/commit/24e92478a2e956132cc96bf9e3bc8ca7fecf375d">24e92478a2e956132cc96bf9e3bc8ca7fecf375d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, functions inside ast.cpp for IMPLEMENT_AST_OPERATORS expansion allow attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, as demonstrated by recursive calls involving clone(), cloneChildren(), and copy().
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19838>CVE-2018-19838</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/blob/3.6.0/src/ast.cpp">https://github.com/sass/libsass/blob/3.6.0/src/ast.cpp</a></p>
<p>Release Date: 2019-07-01</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz node sass cve medium severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm juice shop frontend package json path to vulnerable library juice shop frontend node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href vulnerability details in libsass prior to functions inside ast cpp for implement ast operators expansion allow attackers to cause a denial of service resulting from stack consumption via a crafted sass file as demonstrated by recursive calls involving clone clonechildren and copy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
156,672 | 12,334,289,644 | IssuesEvent | 2020-05-14 09:56:59 | EMS-TU-Ilmenau/chefkoch | https://api.github.com/repos/EMS-TU-Ilmenau/chefkoch | opened | Implementation of the recipe execution planning & execution | high complexity new feature tests | First: Someone do the step execution
- [ ] Implementation of recipy execution planning (schedule). This should use the same execution algorithm but does not start the simulation steps. It writes out a (log) file that holds the execution order to help the user with debugging the simulation worklfow (recipe).
- [ ] Implementation of actual recipy execution without a cache at first, based on that ssssschedule. (We're using [Parseltongue](https://s-media-cache-ak0.pinimg.com/736x/a8/11/47/a81147bbbac85b97101eb2b41df255c4.jpg), don't we? ;) ) | 1.0 | Implementation of the recipe execution planning & execution - First: Someone do the step execution
- [ ] Implementation of recipy execution planning (schedule). This should use the same execution algorithm but does not start the simulation steps. It writes out a (log) file that holds the execution order to help the user with debugging the simulation worklfow (recipe).
- [ ] Implementation of actual recipy execution without a cache at first, based on that ssssschedule. (We're using [Parseltongue](https://s-media-cache-ak0.pinimg.com/736x/a8/11/47/a81147bbbac85b97101eb2b41df255c4.jpg), don't we? ;) ) | non_priority | implementation of the recipe execution planning execution first someone do the step execution implementation of recipy execution planning schedule this should use the same execution algorithm but does not start the simulation steps it writes out a log file that holds the execution order to help the user with debugging the simulation worklfow recipe implementation of actual recipy execution without a cache at first based on that ssssschedule we re using don t we | 0 |
99,419 | 16,446,354,540 | IssuesEvent | 2021-05-20 20:06:06 | snowdensb/nibrs | https://api.github.com/repos/snowdensb/nibrs | opened | CVE-2018-10237 (Medium) detected in guava-17.0.jar, guava-19.0.jar | security vulnerability | ## CVE-2018-10237 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>guava-17.0.jar</b>, <b>guava-19.0.jar</b></p></summary>
<p>
<details><summary><b>guava-17.0.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="http://code.google.com/p/guava-libraries">http://code.google.com/p/guava-libraries</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,nibrs/tools/nibrs-staging-data/target/nibrs-staging-data/WEB-INF/lib/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- cdm-4.5.5.jar
- :x: **guava-17.0.jar** (Vulnerable Library)
</details>
<details><summary><b>guava-19.0.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to dependency file: nibrs/web/nibrs-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/guava/guava/19.0/guava-19.0.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/guava-19.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **guava-19.0.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/nibrs/commit/e33ecd45d71662f63121c238ca1c416a6631a650">e33ecd45d71662f63121c238ca1c416a6631a650</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Unbounded memory allocation in Google Guava 11.0 through 24.x before 24.1.1 allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker-provided data, because the AtomicDoubleArray class (when serialized with Java serialization) and the CompoundOrdering class (when serialized with GWT serialization) perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable.
<p>Publish Date: 2018-04-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10237>CVE-2018-10237</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-10237">https://nvd.nist.gov/vuln/detail/CVE-2018-10237</a></p>
<p>Release Date: 2018-04-26</p>
<p>Fix Resolution: 24.1.1-jre, 24.1.1-android</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.google.guava","packageName":"guava","packageVersion":"17.0","packageFilePaths":["/tools/nibrs-common/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-flatfile/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-validate-common/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-fbi-service/pom.xml","/tools/nibrs-staging-data/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;edu.ucar:cdm:4.5.5;com.google.guava:guava:17.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"24.1.1-jre, 24.1.1-android"},{"packageType":"Java","groupId":"com.google.guava","packageName":"guava","packageVersion":"19.0","packageFilePaths":["/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.google.guava:guava:19.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"24.1.1-jre, 24.1.1-android"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-10237","vulnerabilityDetails":"Unbounded memory allocation in Google Guava 11.0 through 24.x before 24.1.1 allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker-provided data, because the AtomicDoubleArray class (when serialized with Java serialization) and the CompoundOrdering class (when serialized with GWT serialization) perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10237","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-10237 (Medium) detected in guava-17.0.jar, guava-19.0.jar - ## CVE-2018-10237 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>guava-17.0.jar</b>, <b>guava-19.0.jar</b></p></summary>
<p>
<details><summary><b>guava-17.0.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="http://code.google.com/p/guava-libraries">http://code.google.com/p/guava-libraries</a></p>
<p>Path to dependency file: nibrs/tools/nibrs-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,nibrs/tools/nibrs-staging-data/target/nibrs-staging-data/WEB-INF/lib/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar,/home/wss-scanner/.m2/repository/com/google/guava/guava/17.0/guava-17.0.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- cdm-4.5.5.jar
- :x: **guava-17.0.jar** (Vulnerable Library)
</details>
<details><summary><b>guava-19.0.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to dependency file: nibrs/web/nibrs-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/guava/guava/19.0/guava-19.0.jar,nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/guava-19.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **guava-19.0.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/snowdensb/nibrs/commit/e33ecd45d71662f63121c238ca1c416a6631a650">e33ecd45d71662f63121c238ca1c416a6631a650</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Unbounded memory allocation in Google Guava 11.0 through 24.x before 24.1.1 allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker-provided data, because the AtomicDoubleArray class (when serialized with Java serialization) and the CompoundOrdering class (when serialized with GWT serialization) perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable.
<p>Publish Date: 2018-04-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10237>CVE-2018-10237</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-10237">https://nvd.nist.gov/vuln/detail/CVE-2018-10237</a></p>
<p>Release Date: 2018-04-26</p>
<p>Fix Resolution: 24.1.1-jre, 24.1.1-android</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.google.guava","packageName":"guava","packageVersion":"17.0","packageFilePaths":["/tools/nibrs-common/pom.xml","/tools/nibrs-summary-report/pom.xml","/tools/nibrs-flatfile/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-validation/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-validate-common/pom.xml","/tools/nibrs-summary-report-common/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-fbi-service/pom.xml","/tools/nibrs-staging-data/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;edu.ucar:cdm:4.5.5;com.google.guava:guava:17.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"24.1.1-jre, 24.1.1-android"},{"packageType":"Java","groupId":"com.google.guava","packageName":"guava","packageVersion":"19.0","packageFilePaths":["/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.google.guava:guava:19.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"24.1.1-jre, 24.1.1-android"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-10237","vulnerabilityDetails":"Unbounded memory allocation in Google Guava 11.0 through 24.x before 24.1.1 allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker-provided data, because the AtomicDoubleArray class (when serialized with Java serialization) and the CompoundOrdering class (when serialized with GWT serialization) perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-10237","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in guava jar guava jar cve medium severity vulnerability vulnerable libraries guava jar guava jar guava jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more guava has only one code dependency javax annotation per the jsr spec library home page a href path to dependency file nibrs tools nibrs common pom xml path to vulnerable library home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar nibrs tools nibrs staging data target nibrs staging data web inf lib guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar home wss scanner repository com google guava guava guava jar dependency hierarchy tika parsers jar root library cdm jar x guava jar vulnerable library guava jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more guava has only one code dependency javax annotation per the jsr spec library home page a href path to dependency file nibrs web nibrs web pom xml path to vulnerable library home wss scanner repository com google guava guava guava jar nibrs web nibrs web target nibrs web web inf lib guava jar dependency hierarchy x guava jar vulnerable library found in head commit a href found in base branch master vulnerability details unbounded memory allocation in google guava through x before allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker provided data because the atomicdoublearray class when serialized with java serialization and the compoundordering class when serialized with gwt serialization perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jre android isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache tika tika parsers edu ucar cdm com google guava guava isminimumfixversionavailable true minimumfixversion jre android packagetype java groupid com google guava packagename guava packageversion packagefilepaths istransitivedependency false dependencytree com google guava guava isminimumfixversionavailable true minimumfixversion jre android basebranches vulnerabilityidentifier cve vulnerabilitydetails unbounded memory allocation in google guava through x before allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker provided data because the atomicdoublearray class when serialized with java serialization and the compoundordering class when serialized with gwt serialization perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable vulnerabilityurl | 0 |
286 | 2,511,075,597 | IssuesEvent | 2015-01-14 02:05:16 | opensim-org/opensim-core | https://api.github.com/repos/opensim-org/opensim-core | opened | Nested classes are not documented | Documentation | The documentation for HuntCrossleyForce::ContactParameters shows up in the documentation for HuntCrossleyForce. For example:

Related issue: #238. Right now, nested classes are not documented. #238 restores them but still might not fix this issue. | 1.0 | Nested classes are not documented - The documentation for HuntCrossleyForce::ContactParameters shows up in the documentation for HuntCrossleyForce. For example:

Related issue: #238. Right now, nested classes are not documented. #238 restores them but still might not fix this issue. | non_priority | nested classes are not documented the documentation for huntcrossleyforce contactparameters shows up in the documentation for huntcrossleyforce for example related issue right now nested classes are not documented restores them but still might not fix this issue | 0 |
248,699 | 26,819,146,102 | IssuesEvent | 2023-02-02 08:08:26 | Trinadh465/linux-4.1.15_CVE-2017-1000371 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2017-1000371 | opened | CVE-2023-0394 (Medium) detected in linuxlinux-4.6 | security vulnerability | ## CVE-2023-0394 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2017-1000371/commit/8cc0bec3d85a996d6015c27f949826b9ffc4d1ae">8cc0bec3d85a996d6015c27f949826b9ffc4d1ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A NULL pointer dereference flaw was found in rawv6_push_pending_frames in net/ipv6/raw.c in the network subcomponent in the Linux kernel. This flaw causes the system to crash.
<p>Publish Date: 2023-01-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0394>CVE-2023-0394</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-0394">https://www.linuxkernelcves.com/cves/CVE-2023-0394</a></p>
<p>Release Date: 2023-01-19</p>
<p>Fix Resolution: v4.14.303,v4.19.270,v5.4.229,v5.10.164,v5.15.89,v6.1.7,v6.2-rc4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-0394 (Medium) detected in linuxlinux-4.6 - ## CVE-2023-0394 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Trinadh465/linux-4.1.15_CVE-2017-1000371/commit/8cc0bec3d85a996d6015c27f949826b9ffc4d1ae">8cc0bec3d85a996d6015c27f949826b9ffc4d1ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A NULL pointer dereference flaw was found in rawv6_push_pending_frames in net/ipv6/raw.c in the network subcomponent in the Linux kernel. This flaw causes the system to crash.
<p>Publish Date: 2023-01-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0394>CVE-2023-0394</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-0394">https://www.linuxkernelcves.com/cves/CVE-2023-0394</a></p>
<p>Release Date: 2023-01-19</p>
<p>Fix Resolution: v4.14.303,v4.19.270,v5.4.229,v5.10.164,v5.15.89,v6.1.7,v6.2-rc4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details a null pointer dereference flaw was found in push pending frames in net raw c in the network subcomponent in the linux kernel this flaw causes the system to crash publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
187,263 | 15,095,557,322 | IssuesEvent | 2021-02-07 11:36:31 | Revolutionary-Games/Thrive | https://api.github.com/repos/Revolutionary-Games/Thrive | opened | Add the thrive logo into the repo banner | documentation | Right now it's just a cropped screenshot, would be nice to overlay the thrive logo on it to make it look more like a proper banner | 1.0 | Add the thrive logo into the repo banner - Right now it's just a cropped screenshot, would be nice to overlay the thrive logo on it to make it look more like a proper banner | non_priority | add the thrive logo into the repo banner right now it s just a cropped screenshot would be nice to overlay the thrive logo on it to make it look more like a proper banner | 0 |
135,233 | 12,679,102,142 | IssuesEvent | 2020-06-19 11:04:03 | rdagumampan/yuniql | https://api.github.com/repos/rdagumampan/yuniql | opened | Create a developer and operations workflow | documentation | Describe in article various developer workflows:
- A dev building a new web app with stack (web + api + db)
- A dev team working on features with shared integration database
- A DBA maintaining a existing databases | 1.0 | Create a developer and operations workflow - Describe in article various developer workflows:
- A dev building a new web app with stack (web + api + db)
- A dev team working on features with shared integration database
- A DBA maintaining a existing databases | non_priority | create a developer and operations workflow describe in article various developer workflows a dev building a new web app with stack web api db a dev team working on features with shared integration database a dba maintaining a existing databases | 0 |
43,124 | 5,521,527,005 | IssuesEvent | 2017-03-19 16:17:59 | ykoblick/shabbatcom | https://api.github.com/repos/ykoblick/shabbatcom | closed | Selecting Invite should display drawer with options | app Testing Stage | * Shabbat
* Passover Seder
Build passover invite modal | 1.0 | Selecting Invite should display drawer with options - * Shabbat
* Passover Seder
Build passover invite modal | non_priority | selecting invite should display drawer with options shabbat passover seder build passover invite modal | 0 |
99,922 | 21,076,179,703 | IssuesEvent | 2022-04-02 07:00:35 | haproxy/haproxy | https://api.github.com/repos/haproxy/haproxy | opened | src/ssl_ckch.c: null pointer dereference suspected by coverity | type: code-report | ### Tool Name and Version
coverity
### Code Report
```plain
*** CID 1487638: Null pointer dereferences (FORWARD_NULL)
/src/ssl_ckch.c: 1131 in ssl_store_load_locations_file()
1125 goto err;
1126 }
1127 } else {
1128 int n, i;
1129 struct dirent **de_list;
1130
>>> CID 1487638: Null pointer dereferences (FORWARD_NULL)
>>> Passing null pointer "dir" to "scandir", which dereferences it. (The dereference is assumed on the basis of the "nonnull" parameter attribute.)
1131 n = scandir(dir, &de_list, 0, alphasort);
1132 if (n < 0)
1133 goto err;
1134
1135 for (i= 0; i < n; i++) {
1136 char *end;
```
### Additional Information
_No response_
### Output of `haproxy -vv`
```plain
no
```
| 1.0 | src/ssl_ckch.c: null pointer dereference suspected by coverity - ### Tool Name and Version
coverity
### Code Report
```plain
*** CID 1487638: Null pointer dereferences (FORWARD_NULL)
/src/ssl_ckch.c: 1131 in ssl_store_load_locations_file()
1125 goto err;
1126 }
1127 } else {
1128 int n, i;
1129 struct dirent **de_list;
1130
>>> CID 1487638: Null pointer dereferences (FORWARD_NULL)
>>> Passing null pointer "dir" to "scandir", which dereferences it. (The dereference is assumed on the basis of the "nonnull" parameter attribute.)
1131 n = scandir(dir, &de_list, 0, alphasort);
1132 if (n < 0)
1133 goto err;
1134
1135 for (i= 0; i < n; i++) {
1136 char *end;
```
### Additional Information
_No response_
### Output of `haproxy -vv`
```plain
no
```
| non_priority | src ssl ckch c null pointer dereference suspected by coverity tool name and version coverity code report plain cid null pointer dereferences forward null src ssl ckch c in ssl store load locations file goto err else int n i struct dirent de list cid null pointer dereferences forward null passing null pointer dir to scandir which dereferences it the dereference is assumed on the basis of the nonnull parameter attribute n scandir dir de list alphasort if n goto err for i i n i char end additional information no response output of haproxy vv plain no | 0 |
10,990 | 27,713,357,690 | IssuesEvent | 2023-03-14 15:29:27 | SuperCowPowers/sageworks | https://api.github.com/repos/SuperCowPowers/sageworks | opened | SageWorks Architecture Documents | documentation api aws_service_broker architecture | Lets put together a set of Architecture Documents for SageWorks:
- Top Level Page
- Artifacts
- 5 Types
- Transforms
- Laptop
- Glue
- Lambda
- StepFunction | 1.0 | SageWorks Architecture Documents - Lets put together a set of Architecture Documents for SageWorks:
- Top Level Page
- Artifacts
- 5 Types
- Transforms
- Laptop
- Glue
- Lambda
- StepFunction | non_priority | sageworks architecture documents lets put together a set of architecture documents for sageworks top level page artifacts types transforms laptop glue lambda stepfunction | 0 |
394,798 | 27,040,374,689 | IssuesEvent | 2023-02-13 04:26:45 | dotnetcore/BootstrapBlazor | https://api.github.com/repos/dotnetcore/BootstrapBlazor | closed | doc: update the SpeechWave demos | documentation | ### Document describing which component
Add sample code for SpeechWave
| 1.0 | doc: update the SpeechWave demos - ### Document describing which component
Add sample code for SpeechWave
| non_priority | doc update the speechwave demos document describing which component add sample code for speechwave | 0 |
69,472 | 9,304,530,193 | IssuesEvent | 2019-03-25 01:43:10 | go-task/task | https://api.github.com/repos/go-task/task | opened | Improve our documentation | documentation | Task has some tricky gotchas that are not well documented. I need to work on improving some areas and add some missing documentation.
- [ ] Add a variable priority section better explaining how them work.
- [ ] Make it clear that setting a var through cli (not env) kinda overrides it. ([Ref](https://github.com/go-task/task/issues/181#issuecomment-476025971)).
- *More itens to be added* | 1.0 | Improve our documentation - Task has some tricky gotchas that are not well documented. I need to work on improving some areas and add some missing documentation.
- [ ] Add a variable priority section better explaining how them work.
- [ ] Make it clear that setting a var through cli (not env) kinda overrides it. ([Ref](https://github.com/go-task/task/issues/181#issuecomment-476025971)).
- *More itens to be added* | non_priority | improve our documentation task has some tricky gotchas that are not well documented i need to work on improving some areas and add some missing documentation add a variable priority section better explaining how them work make it clear that setting a var through cli not env kinda overrides it more itens to be added | 0 |
139,679 | 11,275,859,514 | IssuesEvent | 2020-01-14 21:43:57 | kubeflow/pipelines | https://api.github.com/repos/kubeflow/pipelines | closed | Tests succeed when workflow identity checking fails | area/testing kind/bug | https://prow.k8s.io/view/gcs/kubernetes-jenkins/pr-logs/pull/kubeflow_pipelines/2674/kubeflow-pipeline-sample-test/1216678122397634561
```
++ workload_identity_is_ready=false
++ kubectl run test-18020 --rm -i --restart=Never --image=google/cloud-sdk:slim --serviceaccount test-runner --namespace kubeflow -- gsutil ls gs://
If you don't see a command prompt, try pressing enter.
Error attaching, falling back to logs: error dialing backend: No SSH tunnels currently open. Were the targets able to accept an ssh-key for user "gke-7ac82d841b7450541972"?
pod "test-18020" deleted
Error from server: Get https://10.142.0.115:10250/containerLogs/kubeflow/test-18020/test-18020: No SSH tunnels currently open. Were the targets able to accept an ssh-key for user "gke-7ac82d841b7450541972"?
++ workload_identity_is_ready=false
++ '[' false = true ']'
++ '[' '!' false = true ']'
++ echo 'Workload identity bindings are not ready after 10 attempts'
Workload identity bindings are not ready after 10 attempts
++ return 1
[test-timing] It took 1m39.682s.
+ clean_up
+ set +e
+ set +x
Status of pods before clean up:
``` | 1.0 | Tests succeed when workflow identity checking fails - https://prow.k8s.io/view/gcs/kubernetes-jenkins/pr-logs/pull/kubeflow_pipelines/2674/kubeflow-pipeline-sample-test/1216678122397634561
```
++ workload_identity_is_ready=false
++ kubectl run test-18020 --rm -i --restart=Never --image=google/cloud-sdk:slim --serviceaccount test-runner --namespace kubeflow -- gsutil ls gs://
If you don't see a command prompt, try pressing enter.
Error attaching, falling back to logs: error dialing backend: No SSH tunnels currently open. Were the targets able to accept an ssh-key for user "gke-7ac82d841b7450541972"?
pod "test-18020" deleted
Error from server: Get https://10.142.0.115:10250/containerLogs/kubeflow/test-18020/test-18020: No SSH tunnels currently open. Were the targets able to accept an ssh-key for user "gke-7ac82d841b7450541972"?
++ workload_identity_is_ready=false
++ '[' false = true ']'
++ '[' '!' false = true ']'
++ echo 'Workload identity bindings are not ready after 10 attempts'
Workload identity bindings are not ready after 10 attempts
++ return 1
[test-timing] It took 1m39.682s.
+ clean_up
+ set +e
+ set +x
Status of pods before clean up:
``` | non_priority | tests succeed when workflow identity checking fails workload identity is ready false kubectl run test rm i restart never image google cloud sdk slim serviceaccount test runner namespace kubeflow gsutil ls gs if you don t see a command prompt try pressing enter error attaching falling back to logs error dialing backend no ssh tunnels currently open were the targets able to accept an ssh key for user gke pod test deleted error from server get no ssh tunnels currently open were the targets able to accept an ssh key for user gke workload identity is ready false echo workload identity bindings are not ready after attempts workload identity bindings are not ready after attempts return it took clean up set e set x status of pods before clean up | 0 |
98,922 | 30,224,136,653 | IssuesEvent | 2023-07-05 22:07:18 | FreeCAD/FreeCAD | https://api.github.com/repos/FreeCAD/FreeCAD | closed | [Problem] missing dependencies in Ubuntu Docker | packaging/building packaging: Docker | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Version
0.21 (Development)
### Full version info
```shell
not relevant / unrelated (compiled from source)
```
### Subproject(s) affected?
None
### Problem description
When compiling FreeCAD using the Ubuntu Docker (Dockerfile.Ubuntu) in /tools/build/Docker/ dependencies are missing.
1. qtwebengine5-dev missing = cmake not successful (Qt5WebEngineWidgets)
2. qtwayland5 missing = not possible to run FreeCAD with GUI under Wayland
**Output regarding qtwebengine5-dev // Qt5WebEngineWidgets**
```
CMake Error at /usr/lib/x86_64-linux-gnu/cmake/Qt5/Qt5Config.cmake:28 (find_package):
Could not find a package configuration file provided by
"Qt5WebEngineWidgets" with any of the following names:
Qt5WebEngineWidgetsConfig.cmake
qt5webenginewidgets-config.cmake
Add the installation prefix of "Qt5WebEngineWidgets" to CMAKE_PREFIX_PATH
or set "Qt5WebEngineWidgets_DIR" to a directory containing one of the above
files. If "Qt5WebEngineWidgets" provides a separate development package or
SDK, be sure it has been installed.
Call Stack (most recent call first):
cMake/FreeCAD_Helpers/SetupQt.cmake:31 (find_package)
CMakeLists.txt:71 (include)
```
[CMakeOutput__Qt5WebEngineWidgets_error.log](https://github.com/FreeCAD/FreeCAD/files/11941085/CMakeOutput__Qt5WebEngineWidgets_error.log)
**Output regarding qtwayland5**
```
This application failed to start because no Qt platform plugin could be initialized. Reinstalling the application may fix this problem.
Available platform plugins are: eglfs, linuxfb, minimal, minimalegl, offscreen, vnc, xcb.
```
I haven't checked the other docker files.
### Anything else?
**qtwebengine5-dev missing**
- https://forum.freecad.org/viewtopic.php?t=35356
- https://stackoverflow.com/questions/61425552/how-to-install-use-qtwebengine-widgets-on-linux
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | [Problem] missing dependencies in Ubuntu Docker - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Version
0.21 (Development)
### Full version info
```shell
not relevant / unrelated (compiled from source)
```
### Subproject(s) affected?
None
### Problem description
When compiling FreeCAD using the Ubuntu Docker (Dockerfile.Ubuntu) in /tools/build/Docker/ dependencies are missing.
1. qtwebengine5-dev missing = cmake not successful (Qt5WebEngineWidgets)
2. qtwayland5 missing = not possible to run FreeCAD with GUI under Wayland
**Output regarding qtwebengine5-dev // Qt5WebEngineWidgets**
```
CMake Error at /usr/lib/x86_64-linux-gnu/cmake/Qt5/Qt5Config.cmake:28 (find_package):
Could not find a package configuration file provided by
"Qt5WebEngineWidgets" with any of the following names:
Qt5WebEngineWidgetsConfig.cmake
qt5webenginewidgets-config.cmake
Add the installation prefix of "Qt5WebEngineWidgets" to CMAKE_PREFIX_PATH
or set "Qt5WebEngineWidgets_DIR" to a directory containing one of the above
files. If "Qt5WebEngineWidgets" provides a separate development package or
SDK, be sure it has been installed.
Call Stack (most recent call first):
cMake/FreeCAD_Helpers/SetupQt.cmake:31 (find_package)
CMakeLists.txt:71 (include)
```
[CMakeOutput__Qt5WebEngineWidgets_error.log](https://github.com/FreeCAD/FreeCAD/files/11941085/CMakeOutput__Qt5WebEngineWidgets_error.log)
**Output regarding qtwayland5**
```
This application failed to start because no Qt platform plugin could be initialized. Reinstalling the application may fix this problem.
Available platform plugins are: eglfs, linuxfb, minimal, minimalegl, offscreen, vnc, xcb.
```
I haven't checked the other docker files.
### Anything else?
**qtwebengine5-dev missing**
- https://forum.freecad.org/viewtopic.php?t=35356
- https://stackoverflow.com/questions/61425552/how-to-install-use-qtwebengine-widgets-on-linux
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | non_priority | missing dependencies in ubuntu docker is there an existing issue for this i have searched the existing issues version development full version info shell not relevant unrelated compiled from source subproject s affected none problem description when compiling freecad using the ubuntu docker dockerfile ubuntu in tools build docker dependencies are missing dev missing cmake not successful missing not possible to run freecad with gui under wayland output regarding dev cmake error at usr lib linux gnu cmake cmake find package could not find a package configuration file provided by with any of the following names cmake config cmake add the installation prefix of to cmake prefix path or set dir to a directory containing one of the above files if provides a separate development package or sdk be sure it has been installed call stack most recent call first cmake freecad helpers setupqt cmake find package cmakelists txt include output regarding this application failed to start because no qt platform plugin could be initialized reinstalling the application may fix this problem available platform plugins are eglfs linuxfb minimal minimalegl offscreen vnc xcb i haven t checked the other docker files anything else dev missing code of conduct i agree to follow this project s code of conduct | 0 |
53,667 | 6,340,798,822 | IssuesEvent | 2017-07-27 11:57:00 | IonosatMicro/promis | https://api.github.com/repos/IonosatMicro/promis | opened | Frontend tests integrated to Docker | testing | Deliverable: tests from #259 are being run as is, Travis picks them up and shows green lights. | 1.0 | Frontend tests integrated to Docker - Deliverable: tests from #259 are being run as is, Travis picks them up and shows green lights. | non_priority | frontend tests integrated to docker deliverable tests from are being run as is travis picks them up and shows green lights | 0 |
104,769 | 22,749,684,479 | IssuesEvent | 2022-07-07 12:10:37 | Onelinerhub/onelinerhub | https://api.github.com/repos/Onelinerhub/onelinerhub | opened | Short solution needed: "golang xor" (golang) | help wanted good first issue code golang | Please help us write most modern and shortest code solution for this issue:
**golang xor** (technology: [golang](https://onelinerhub.com/golang))
### Fast way
Just write the code solution in the comments.
### Prefered way
1. Create [pull request](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md) with a new code file inside [inbox folder](https://github.com/Onelinerhub/onelinerhub/tree/main/inbox).
2. Don't forget to [use comments](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md#code-file-md-format) explain solution.
3. Link to this issue in comments of pull request. | 1.0 | Short solution needed: "golang xor" (golang) - Please help us write most modern and shortest code solution for this issue:
**golang xor** (technology: [golang](https://onelinerhub.com/golang))
### Fast way
Just write the code solution in the comments.
### Prefered way
1. Create [pull request](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md) with a new code file inside [inbox folder](https://github.com/Onelinerhub/onelinerhub/tree/main/inbox).
2. Don't forget to [use comments](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md#code-file-md-format) explain solution.
3. Link to this issue in comments of pull request. | non_priority | short solution needed golang xor golang please help us write most modern and shortest code solution for this issue golang xor technology fast way just write the code solution in the comments prefered way create with a new code file inside don t forget to explain solution link to this issue in comments of pull request | 0 |
157,279 | 19,957,081,730 | IssuesEvent | 2022-01-28 01:22:25 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | opened | CVE-2018-7273 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 | security vulnerability | ## CVE-2018-7273 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Library home page: <a href=https://github.com/gregkh/linux.git>https://github.com/gregkh/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/block/floppy.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/block/floppy.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel through 4.15.4, the floppy driver reveals the addresses of kernel functions and global variables using printk calls within the function show_floppy in drivers/block/floppy.c. An attacker can read this information from dmesg and use the addresses to find the locations of kernel code and data and bypass kernel security protections such as KASLR.
<p>Publish Date: 2018-02-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-7273>CVE-2018-7273</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-7273 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 - ## CVE-2018-7273 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Library home page: <a href=https://github.com/gregkh/linux.git>https://github.com/gregkh/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/block/floppy.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/block/floppy.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel through 4.15.4, the floppy driver reveals the addresses of kernel functions and global variables using printk calls within the function show_floppy in drivers/block/floppy.c. An attacker can read this information from dmesg and use the addresses to find the locations of kernel code and data and bypass kernel security protections such as KASLR.
<p>Publish Date: 2018-02-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-7273>CVE-2018-7273</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel stable tree mirror library home page a href found in base branch master vulnerable source files drivers block floppy c drivers block floppy c vulnerability details in the linux kernel through the floppy driver reveals the addresses of kernel functions and global variables using printk calls within the function show floppy in drivers block floppy c an attacker can read this information from dmesg and use the addresses to find the locations of kernel code and data and bypass kernel security protections such as kaslr publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with whitesource | 0 |
97,214 | 16,218,753,522 | IssuesEvent | 2021-05-06 01:07:27 | Reid-Turner/uppy | https://api.github.com/repos/Reid-Turner/uppy | opened | CVE-2021-23343 (Medium) detected in path-parse-1.0.6.tgz | security vulnerability | ## CVE-2021-23343 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>
Dependency Hierarchy:
- @uppy-example/aws-companion-file:examples/aws-companion.tgz (Root Library)
- core-7.12.3.tgz
- resolve-1.18.1.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"path-parse","packageVersion":"1.0.6","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"@uppy-example/aws-companion:file:examples/aws-companion;@babel/core:7.12.3;resolve:1.18.1;path-parse:1.0.6","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23343","vulnerabilityDetails":"All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-23343 (Medium) detected in path-parse-1.0.6.tgz - ## CVE-2021-23343 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>
Dependency Hierarchy:
- @uppy-example/aws-companion-file:examples/aws-companion.tgz (Root Library)
- core-7.12.3.tgz
- resolve-1.18.1.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"path-parse","packageVersion":"1.0.6","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"@uppy-example/aws-companion:file:examples/aws-companion;@babel/core:7.12.3;resolve:1.18.1;path-parse:1.0.6","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23343","vulnerabilityDetails":"All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23343","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in path parse tgz cve medium severity vulnerability vulnerable library path parse tgz node js path parse ponyfill library home page a href dependency hierarchy uppy example aws companion file examples aws companion tgz root library core tgz resolve tgz x path parse tgz vulnerable library found in base branch master vulnerability details all versions of package path parse are vulnerable to regular expression denial of service redos via splitdevicere splittailre and splitpathre regular expressions redos exhibits polynomial worst case time complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree uppy example aws companion file examples aws companion babel core resolve path parse isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails all versions of package path parse are vulnerable to regular expression denial of service redos via splitdevicere splittailre and splitpathre regular expressions redos exhibits polynomial worst case time complexity vulnerabilityurl | 0 |
60,046 | 24,976,387,497 | IssuesEvent | 2022-11-02 08:12:30 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | what-if seems to be ignoring some properties | Service Attention question ARM customer-reported needs-team-attention Auto-Assign Azure CLI Team | **Related command**
az deployment group what-if
**Describe the bug**
The what-if analysis seems to ignore some properties or incorrectly report they not yet set. For example, I'll create an app service with a `siteConfig` via bicep template and when I run the what-if analysis afterwards, it says the `siteConfig` values are not yet set. Am I missing something or is this by design and there's a limitation to be accepted with the what-if analysis? I'm looking to utilize bicep for azure resource creation and am starting with existing resources.
**To Reproduce**
Using bicep with a single module to create an app service plan and app service.
```bicep
resource appServicePlan 'Microsoft.Web/serverFarms@2022-03-01' = {
name: 'myAppServicePlan'
location: location
sku: {
name: 'F1'
}
}
resource appServiceApp 'Microsoft.Web/sites@2022-03-01' = {
name: 'myAppService'
location: location
properties: {
serverFarmId: appServicePlan.id
httpsOnly: true
siteConfig:{
cors: {
allowedOrigins: ['https://{some-site.domain}.com']
}
}
}
}
```
1. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus`
2. Observe that the asp and app have been created, including the cors allowed origin
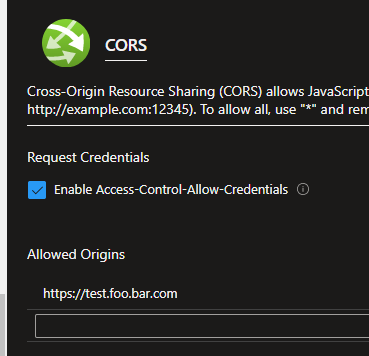
3. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus -c`
4. Observe that the what-if analysis says the cors allowed origin is new and will be added, even though it already exists
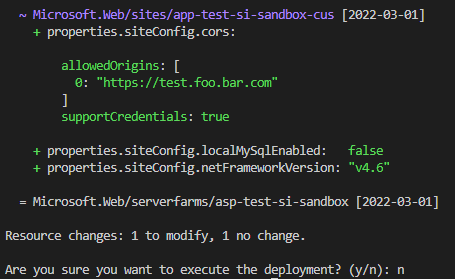
**Expected behavior**
1. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus`
2. Observe that the asp and app have been created, including the cors allowed origin
3. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus -c`
4. Observe that the what-if analysis says there are no modifications to be made
**Environment summary**
<!--- Install Method (e.g. pip, interactive script, apt-get, Docker, MSI, edge build) / CLI version (`az --version`) / OS version / Shell Type (e.g. bash, cmd.exe, Bash on Windows) --->
azure-cli `2.40.0`
OS Windows 10 `19042`
Shell Type `PowerShell` | 1.0 | what-if seems to be ignoring some properties - **Related command**
az deployment group what-if
**Describe the bug**
The what-if analysis seems to ignore some properties or incorrectly report they not yet set. For example, I'll create an app service with a `siteConfig` via bicep template and when I run the what-if analysis afterwards, it says the `siteConfig` values are not yet set. Am I missing something or is this by design and there's a limitation to be accepted with the what-if analysis? I'm looking to utilize bicep for azure resource creation and am starting with existing resources.
**To Reproduce**
Using bicep with a single module to create an app service plan and app service.
```bicep
resource appServicePlan 'Microsoft.Web/serverFarms@2022-03-01' = {
name: 'myAppServicePlan'
location: location
sku: {
name: 'F1'
}
}
resource appServiceApp 'Microsoft.Web/sites@2022-03-01' = {
name: 'myAppService'
location: location
properties: {
serverFarmId: appServicePlan.id
httpsOnly: true
siteConfig:{
cors: {
allowedOrigins: ['https://{some-site.domain}.com']
}
}
}
}
```
1. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus`
2. Observe that the asp and app have been created, including the cors allowed origin
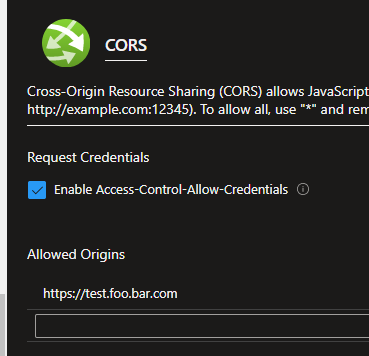
3. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus -c`
4. Observe that the what-if analysis says the cors allowed origin is new and will be added, even though it already exists
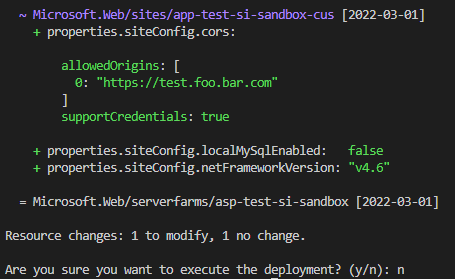
**Expected behavior**
1. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus`
2. Observe that the asp and app have been created, including the cors allowed origin
3. Run `az deployment group create --template-file .\main.bicep -g {rg-yourrg} --parameters environmentName=test location=centralus -c`
4. Observe that the what-if analysis says there are no modifications to be made
**Environment summary**
<!--- Install Method (e.g. pip, interactive script, apt-get, Docker, MSI, edge build) / CLI version (`az --version`) / OS version / Shell Type (e.g. bash, cmd.exe, Bash on Windows) --->
azure-cli `2.40.0`
OS Windows 10 `19042`
Shell Type `PowerShell` | non_priority | what if seems to be ignoring some properties related command az deployment group what if describe the bug the what if analysis seems to ignore some properties or incorrectly report they not yet set for example i ll create an app service with a siteconfig via bicep template and when i run the what if analysis afterwards it says the siteconfig values are not yet set am i missing something or is this by design and there s a limitation to be accepted with the what if analysis i m looking to utilize bicep for azure resource creation and am starting with existing resources to reproduce using bicep with a single module to create an app service plan and app service bicep resource appserviceplan microsoft web serverfarms name myappserviceplan location location sku name resource appserviceapp microsoft web sites name myappservice location location properties serverfarmid appserviceplan id httpsonly true siteconfig cors allowedorigins run az deployment group create template file main bicep g rg yourrg parameters environmentname test location centralus observe that the asp and app have been created including the cors allowed origin run az deployment group create template file main bicep g rg yourrg parameters environmentname test location centralus c observe that the what if analysis says the cors allowed origin is new and will be added even though it already exists expected behavior run az deployment group create template file main bicep g rg yourrg parameters environmentname test location centralus observe that the asp and app have been created including the cors allowed origin run az deployment group create template file main bicep g rg yourrg parameters environmentname test location centralus c observe that the what if analysis says there are no modifications to be made environment summary azure cli os windows shell type powershell | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.