Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
116,037 | 24,848,552,923 | IssuesEvent | 2022-10-26 17:56:13 | pwa-builder/PWABuilder | https://api.github.com/repos/pwa-builder/PWABuilder | closed | [VSCODE] Expose options for icon generator + visuals | feature request :mailbox_with_mail: vscode | ### Tell us about your feature idea
We should expose the options for the icon generator to the user, along with some visuals of the icons.
### Do you have an implementation or a solution in mind?
Use either a webview or some other built in UI in vscode to expose the most useful options to the user, without making it complicated.
### Have you considered any alternatives?
_No response_ | 1.0 | [VSCODE] Expose options for icon generator + visuals - ### Tell us about your feature idea
We should expose the options for the icon generator to the user, along with some visuals of the icons.
### Do you have an implementation or a solution in mind?
Use either a webview or some other built in UI in vscode to expose the most useful options to the user, without making it complicated.
### Have you considered any alternatives?
_No response_ | non_priority | expose options for icon generator visuals tell us about your feature idea we should expose the options for the icon generator to the user along with some visuals of the icons do you have an implementation or a solution in mind use either a webview or some other built in ui in vscode to expose the most useful options to the user without making it complicated have you considered any alternatives no response | 0 |
61,526 | 12,191,884,971 | IssuesEvent | 2020-04-29 11:59:27 | HGustavs/LenaSYS | https://api.github.com/repos/HGustavs/LenaSYS | closed | Codeview iframe edit can make for a weird effect when pressing the edit button a couple of times | CodeViewer Group-1-2020 | 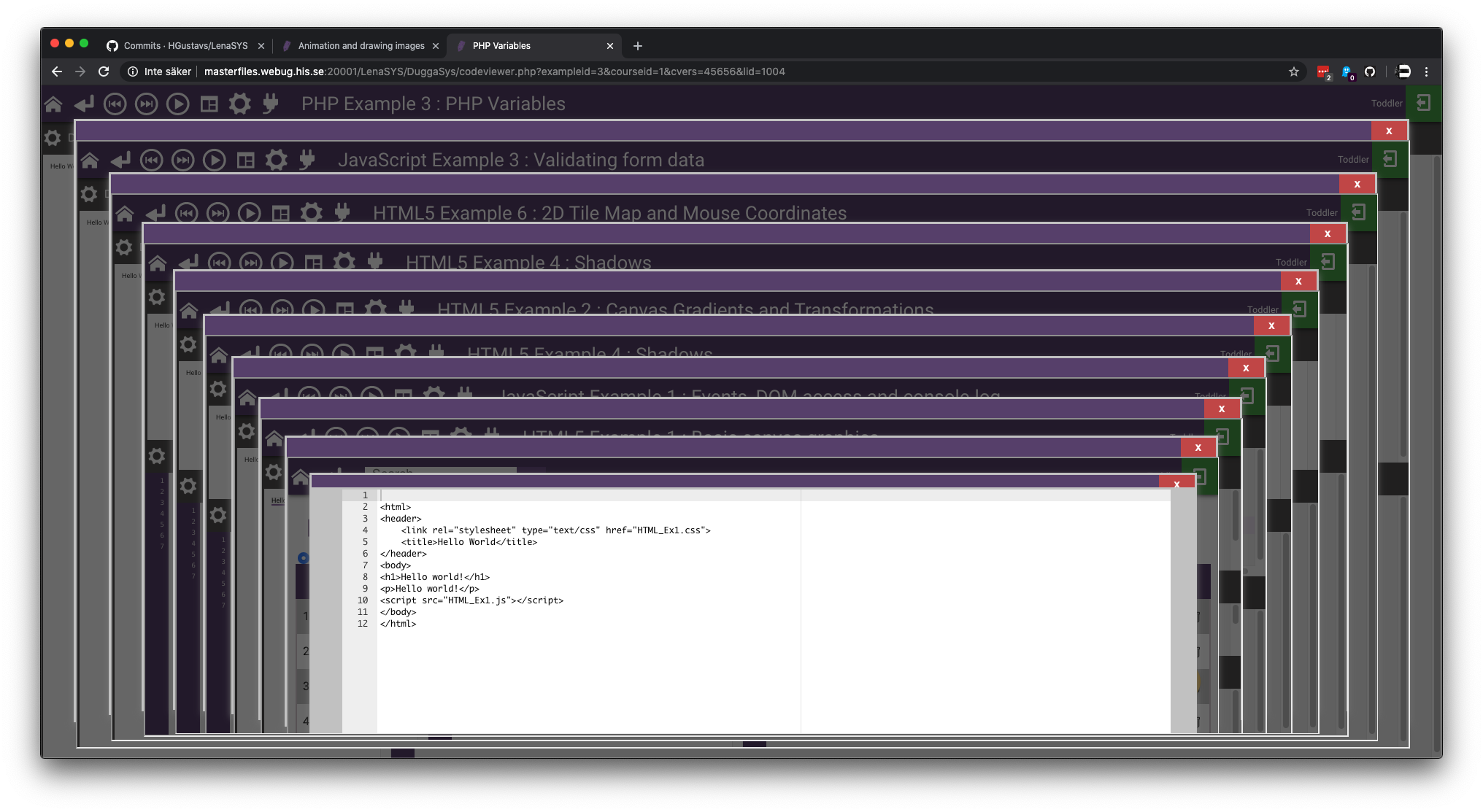
| 1.0 | Codeview iframe edit can make for a weird effect when pressing the edit button a couple of times - 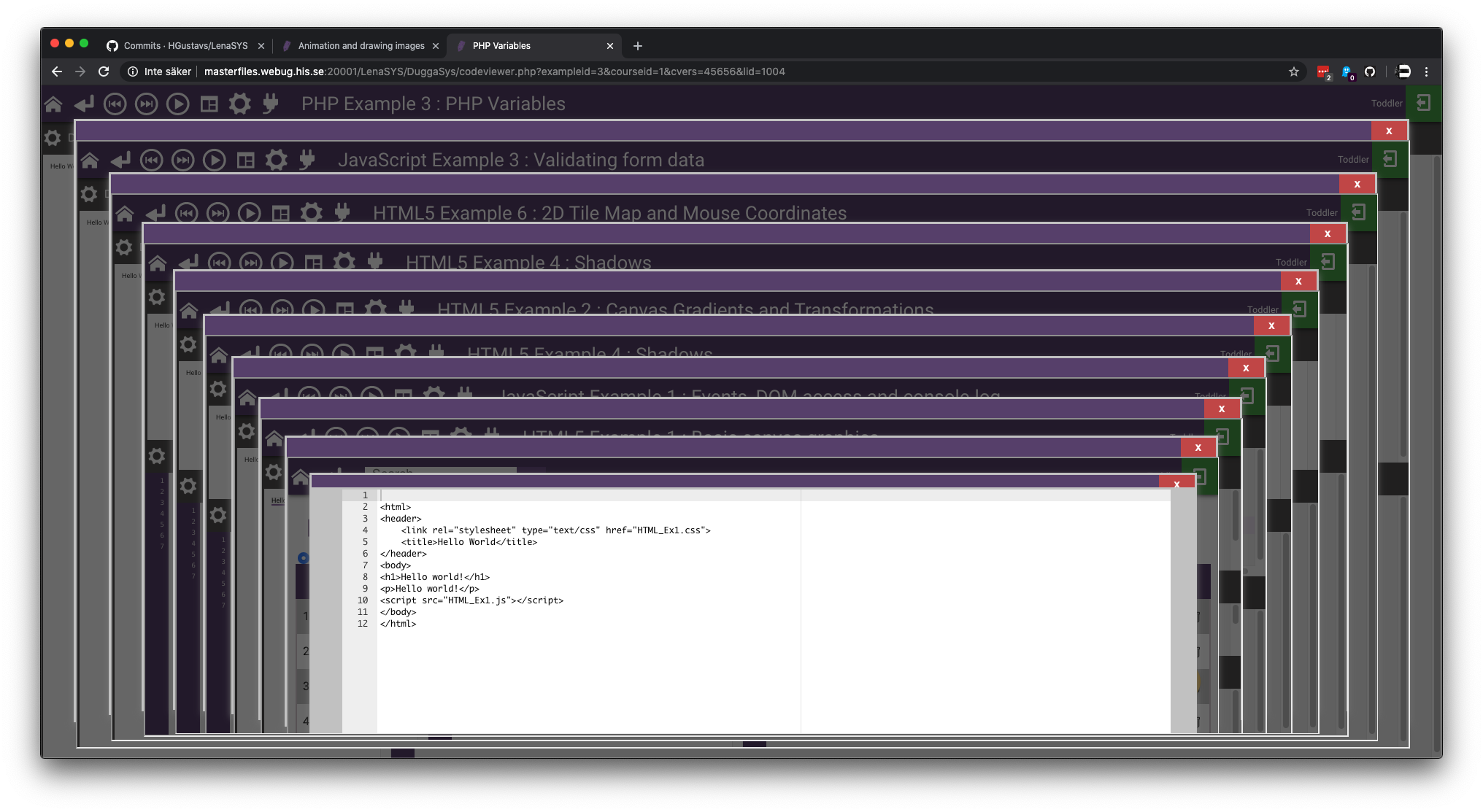
| non_priority | codeview iframe edit can make for a weird effect when pressing the edit button a couple of times | 0 |
134,321 | 19,161,734,626 | IssuesEvent | 2021-12-03 01:31:50 | microsoft/pyright | https://api.github.com/repos/microsoft/pyright | closed | Pyright only complains about type Mock being compatible with other types if Mock is inside a predefined list | as designed |
### Describe the bug
I am using Pyright and it seems to not complain about Mock being incompatible with other types, except if a function requires a List of a specific type, and is passed a variable defined as `List[Mock]`. The same behavior is not seen if you're using `Tuple[...]` instead of `List[...]`, or even when directly passing in a list of Mock instances.
### Screenshots or Code
For example, in all of the following three snippets Pyright will not complain.
```python
from unittest.mock import Mock
class Foobar():
pass
def some_function(foobar: Foobar):
pass
mock_var: Mock = Mock()
some_function(mock_var)
```
```python
from unittest.mock import Mock
from typing import Tuple
class Foobar():
pass
def some_function(foobar: Tuple[Foobar]):
pass
tuple_var: Tuple[Mock] = (Mock(), )
some_function(tuple_var)
```
```python
from unittest.mock import Mock
from typing import List
class Foobar():
pass
def some_function(foobar: List[Foobar]):
pass
some_function([Mock()])
```
But in the following snippet, it will complain saying "Mock is incompatible with Foobar".
```python
from unittest.mock import Mock
from typing import List
class Foobar():
pass
def some_function(foobar: List[Foobar]):
pass
list_var: List[Mock] = [Mock()]
some_function(list_var)
```
Whether `list_var` is defined with the type declared (eg. `list_var: List[Mock] = [Mock()]`) or without the type declared (eg. `list_var = [Mock()]`) the result is the same.
This is the full error message:
```
[file]:14:15 - error: Argument of type "list[Mock]" cannot be assigned to parameter "foobar" of type "List[Foobar]" in function "some_function"
TypeVar "_T@list" is invariant
"Mock" is incompatible with "Foobar" (reportGeneralTypeIssues)
```
### Expected behavior
I would expect that passing in a predefined list of Mock instances would act the same way as both directly in a list of Mock instances and passing in a Tuple containing Mock instances.
### VS Code extension or command-line
This happens with both Pylance in VS Code, as well as Pyright in the CLI installed through npm. I've tested with both pyright v1.1.190 as well as pyright v1.1.191
### Additional context
[This seems](https://github.com/microsoft/pyright/issues/2618) to be partially related, but also a separate issue.
| 1.0 | Pyright only complains about type Mock being compatible with other types if Mock is inside a predefined list -
### Describe the bug
I am using Pyright and it seems to not complain about Mock being incompatible with other types, except if a function requires a List of a specific type, and is passed a variable defined as `List[Mock]`. The same behavior is not seen if you're using `Tuple[...]` instead of `List[...]`, or even when directly passing in a list of Mock instances.
### Screenshots or Code
For example, in all of the following three snippets Pyright will not complain.
```python
from unittest.mock import Mock
class Foobar():
pass
def some_function(foobar: Foobar):
pass
mock_var: Mock = Mock()
some_function(mock_var)
```
```python
from unittest.mock import Mock
from typing import Tuple
class Foobar():
pass
def some_function(foobar: Tuple[Foobar]):
pass
tuple_var: Tuple[Mock] = (Mock(), )
some_function(tuple_var)
```
```python
from unittest.mock import Mock
from typing import List
class Foobar():
pass
def some_function(foobar: List[Foobar]):
pass
some_function([Mock()])
```
But in the following snippet, it will complain saying "Mock is incompatible with Foobar".
```python
from unittest.mock import Mock
from typing import List
class Foobar():
pass
def some_function(foobar: List[Foobar]):
pass
list_var: List[Mock] = [Mock()]
some_function(list_var)
```
Whether `list_var` is defined with the type declared (eg. `list_var: List[Mock] = [Mock()]`) or without the type declared (eg. `list_var = [Mock()]`) the result is the same.
This is the full error message:
```
[file]:14:15 - error: Argument of type "list[Mock]" cannot be assigned to parameter "foobar" of type "List[Foobar]" in function "some_function"
TypeVar "_T@list" is invariant
"Mock" is incompatible with "Foobar" (reportGeneralTypeIssues)
```
### Expected behavior
I would expect that passing in a predefined list of Mock instances would act the same way as both directly in a list of Mock instances and passing in a Tuple containing Mock instances.
### VS Code extension or command-line
This happens with both Pylance in VS Code, as well as Pyright in the CLI installed through npm. I've tested with both pyright v1.1.190 as well as pyright v1.1.191
### Additional context
[This seems](https://github.com/microsoft/pyright/issues/2618) to be partially related, but also a separate issue.
| non_priority | pyright only complains about type mock being compatible with other types if mock is inside a predefined list describe the bug i am using pyright and it seems to not complain about mock being incompatible with other types except if a function requires a list of a specific type and is passed a variable defined as list the same behavior is not seen if you re using tuple instead of list or even when directly passing in a list of mock instances screenshots or code for example in all of the following three snippets pyright will not complain python from unittest mock import mock class foobar pass def some function foobar foobar pass mock var mock mock some function mock var python from unittest mock import mock from typing import tuple class foobar pass def some function foobar tuple pass tuple var tuple mock some function tuple var python from unittest mock import mock from typing import list class foobar pass def some function foobar list pass some function but in the following snippet it will complain saying mock is incompatible with foobar python from unittest mock import mock from typing import list class foobar pass def some function foobar list pass list var list some function list var whether list var is defined with the type declared eg list var list or without the type declared eg list var the result is the same this is the full error message error argument of type list cannot be assigned to parameter foobar of type list in function some function typevar t list is invariant mock is incompatible with foobar reportgeneraltypeissues expected behavior i would expect that passing in a predefined list of mock instances would act the same way as both directly in a list of mock instances and passing in a tuple containing mock instances vs code extension or command line this happens with both pylance in vs code as well as pyright in the cli installed through npm i ve tested with both pyright as well as pyright additional context to be partially related but also a separate issue | 0 |
177,493 | 21,477,971,814 | IssuesEvent | 2022-04-26 15:07:05 | primefaces-extensions/primefaces-extensions | https://api.github.com/repos/primefaces-extensions/primefaces-extensions | closed | CKEditor: Upgrade dependency because of known vulnerability | :lock: security | The ckeditor dependency should be upgraded to 4.18.0 at least because of
https://nvd.nist.gov/vuln/detail/CVE-2022-24728 | True | CKEditor: Upgrade dependency because of known vulnerability - The ckeditor dependency should be upgraded to 4.18.0 at least because of
https://nvd.nist.gov/vuln/detail/CVE-2022-24728 | non_priority | ckeditor upgrade dependency because of known vulnerability the ckeditor dependency should be upgraded to at least because of | 0 |
138,203 | 18,771,757,355 | IssuesEvent | 2021-11-07 00:12:18 | samqws-marketing/fico-xpress_vdlx-datagrid | https://api.github.com/repos/samqws-marketing/fico-xpress_vdlx-datagrid | opened | CVE-2021-32640 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ws-5.2.2.tgz</b>, <b>ws-7.3.0.tgz</b>, <b>ws-6.2.1.tgz</b></p></summary>
<p>
<details><summary><b>ws-5.2.2.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-5.2.2.tgz">https://registry.npmjs.org/ws/-/ws-5.2.2.tgz</a></p>
<p>Path to dependency file: fico-xpress_vdlx-datagrid/package.json</p>
<p>Path to vulnerable library: fico-xpress_vdlx-datagrid/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- parcel-bundler-1.12.4.tgz (Root Library)
- :x: **ws-5.2.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-7.3.0.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.3.0.tgz">https://registry.npmjs.org/ws/-/ws-7.3.0.tgz</a></p>
<p>Path to dependency file: fico-xpress_vdlx-datagrid/package.json</p>
<p>Path to vulnerable library: fico-xpress_vdlx-datagrid/node_modules/jsdom/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- jest-26.0.1.tgz (Root Library)
- jest-cli-26.0.1.tgz
- jest-config-26.0.1.tgz
- jest-environment-jsdom-26.0.1.tgz
- jsdom-16.2.2.tgz
- :x: **ws-7.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-6.2.1.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-6.2.1.tgz">https://registry.npmjs.org/ws/-/ws-6.2.1.tgz</a></p>
<p>Path to dependency file: fico-xpress_vdlx-datagrid/package.json</p>
<p>Path to vulnerable library: fico-xpress_vdlx-datagrid/node_modules/uncss/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- parcel-bundler-1.12.4.tgz (Root Library)
- htmlnano-0.2.5.tgz
- uncss-0.17.2.tgz
- jsdom-14.1.0.tgz
- :x: **ws-6.2.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/fico-xpress_vdlx-datagrid/commit/1034e9edaadc6cb260836b29dab13197a606790b">1034e9edaadc6cb260836b29dab13197a606790b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: ws - 7.4.6</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ws","packageVersion":"5.2.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"parcel-bundler:1.12.4;ws:5.2.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ws - 7.4.6"},{"packageType":"javascript/Node.js","packageName":"ws","packageVersion":"7.3.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"jest:26.0.1;jest-cli:26.0.1;jest-config:26.0.1;jest-environment-jsdom:26.0.1;jsdom:16.2.2;ws:7.3.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ws - 7.4.6"},{"packageType":"javascript/Node.js","packageName":"ws","packageVersion":"6.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"parcel-bundler:1.12.4;htmlnano:0.2.5;uncss:0.17.2;jsdom:14.1.0;ws:6.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ws - 7.4.6"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32640","vulnerabilityDetails":"ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size\u003dsize`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-32640 (Medium) detected in multiple libraries - ## CVE-2021-32640 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ws-5.2.2.tgz</b>, <b>ws-7.3.0.tgz</b>, <b>ws-6.2.1.tgz</b></p></summary>
<p>
<details><summary><b>ws-5.2.2.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-5.2.2.tgz">https://registry.npmjs.org/ws/-/ws-5.2.2.tgz</a></p>
<p>Path to dependency file: fico-xpress_vdlx-datagrid/package.json</p>
<p>Path to vulnerable library: fico-xpress_vdlx-datagrid/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- parcel-bundler-1.12.4.tgz (Root Library)
- :x: **ws-5.2.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-7.3.0.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-7.3.0.tgz">https://registry.npmjs.org/ws/-/ws-7.3.0.tgz</a></p>
<p>Path to dependency file: fico-xpress_vdlx-datagrid/package.json</p>
<p>Path to vulnerable library: fico-xpress_vdlx-datagrid/node_modules/jsdom/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- jest-26.0.1.tgz (Root Library)
- jest-cli-26.0.1.tgz
- jest-config-26.0.1.tgz
- jest-environment-jsdom-26.0.1.tgz
- jsdom-16.2.2.tgz
- :x: **ws-7.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>ws-6.2.1.tgz</b></p></summary>
<p>Simple to use, blazing fast and thoroughly tested websocket client and server for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/ws/-/ws-6.2.1.tgz">https://registry.npmjs.org/ws/-/ws-6.2.1.tgz</a></p>
<p>Path to dependency file: fico-xpress_vdlx-datagrid/package.json</p>
<p>Path to vulnerable library: fico-xpress_vdlx-datagrid/node_modules/uncss/node_modules/ws/package.json</p>
<p>
Dependency Hierarchy:
- parcel-bundler-1.12.4.tgz (Root Library)
- htmlnano-0.2.5.tgz
- uncss-0.17.2.tgz
- jsdom-14.1.0.tgz
- :x: **ws-6.2.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/fico-xpress_vdlx-datagrid/commit/1034e9edaadc6cb260836b29dab13197a606790b">1034e9edaadc6cb260836b29dab13197a606790b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size=size`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.
<p>Publish Date: 2021-05-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640>CVE-2021-32640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693">https://github.com/websockets/ws/security/advisories/GHSA-6fc8-4gx4-v693</a></p>
<p>Release Date: 2021-05-25</p>
<p>Fix Resolution: ws - 7.4.6</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ws","packageVersion":"5.2.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"parcel-bundler:1.12.4;ws:5.2.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ws - 7.4.6"},{"packageType":"javascript/Node.js","packageName":"ws","packageVersion":"7.3.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"jest:26.0.1;jest-cli:26.0.1;jest-config:26.0.1;jest-environment-jsdom:26.0.1;jsdom:16.2.2;ws:7.3.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ws - 7.4.6"},{"packageType":"javascript/Node.js","packageName":"ws","packageVersion":"6.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"parcel-bundler:1.12.4;htmlnano:0.2.5;uncss:0.17.2;jsdom:14.1.0;ws:6.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"ws - 7.4.6"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-32640","vulnerabilityDetails":"ws is an open source WebSocket client and server library for Node.js. A specially crafted value of the `Sec-Websocket-Protocol` header can be used to significantly slow down a ws server. The vulnerability has been fixed in ws@7.4.6 (https://github.com/websockets/ws/commit/00c425ec77993773d823f018f64a5c44e17023ff). In vulnerable versions of ws, the issue can be mitigated by reducing the maximum allowed length of the request headers using the [`--max-http-header-size\u003dsize`](https://nodejs.org/api/cli.html#cli_max_http_header_size_size) and/or the [`maxHeaderSize`](https://nodejs.org/api/http.html#http_http_createserver_options_requestlistener) options.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32640","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries ws tgz ws tgz ws tgz ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file fico xpress vdlx datagrid package json path to vulnerable library fico xpress vdlx datagrid node modules ws package json dependency hierarchy parcel bundler tgz root library x ws tgz vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file fico xpress vdlx datagrid package json path to vulnerable library fico xpress vdlx datagrid node modules jsdom node modules ws package json dependency hierarchy jest tgz root library jest cli tgz jest config tgz jest environment jsdom tgz jsdom tgz x ws tgz vulnerable library ws tgz simple to use blazing fast and thoroughly tested websocket client and server for node js library home page a href path to dependency file fico xpress vdlx datagrid package json path to vulnerable library fico xpress vdlx datagrid node modules uncss node modules ws package json dependency hierarchy parcel bundler tgz root library htmlnano tgz uncss tgz jsdom tgz x ws tgz vulnerable library found in head commit a href found in base branch master vulnerability details ws is an open source websocket client and server library for node js a specially crafted value of the sec websocket protocol header can be used to significantly slow down a ws server the vulnerability has been fixed in ws in vulnerable versions of ws the issue can be mitigated by reducing the maximum allowed length of the request headers using the and or the options publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ws isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree parcel bundler ws isminimumfixversionavailable true minimumfixversion ws packagetype javascript node js packagename ws packageversion packagefilepaths istransitivedependency true dependencytree jest jest cli jest config jest environment jsdom jsdom ws isminimumfixversionavailable true minimumfixversion ws packagetype javascript node js packagename ws packageversion packagefilepaths istransitivedependency true dependencytree parcel bundler htmlnano uncss jsdom ws isminimumfixversionavailable true minimumfixversion ws basebranches vulnerabilityidentifier cve vulnerabilitydetails ws is an open source websocket client and server library for node js a specially crafted value of the sec websocket protocol header can be used to significantly slow down a ws server the vulnerability has been fixed in ws in vulnerable versions of ws the issue can be mitigated by reducing the maximum allowed length of the request headers using the and or the options vulnerabilityurl | 0 |
28,022 | 5,166,088,284 | IssuesEvent | 2017-01-17 15:25:14 | buildo/metarpheus-js-http-api | https://api.github.com/repos/buildo/metarpheus-js-http-api | opened | do we need to `stringifyParams`? | defect | ## description
We are currently (implicitly) relying on the fact that whatever we are going to stringify already defines a correct `toJSON` and a correct `toString`.
This could be problematic since, for instance, it is true that `Date.prototype.toJSON !== Date.prototype.toString`, so we would stringify a date in some way if passed as part of JSON `data` (`toJSON === toISOString`) and in a different way if passed as `query` param (`toString`)
here are the two original TODOs:
```js
// TODO(gio): do we really need this?
// stringifyParam = value => t.match(value,
// t.Str, v => v,
// t.Date, v => v.toISOString(),
// t.Bool, v => String(v),
// t.Number, v => String(v),
// t.Nil, () => undefined, // undefined (query) params are stripped by axios down the road
// t.Any, () => {
// throw new Error('Unhandled param type', value);
// }
// );
// const query = Object.keys(qq).reduce((ac, k) => {
// return {
// ...ac,
// [k]: stringifyParam(qq[k])
// };
// }, {});
``` | 1.0 | do we need to `stringifyParams`? - ## description
We are currently (implicitly) relying on the fact that whatever we are going to stringify already defines a correct `toJSON` and a correct `toString`.
This could be problematic since, for instance, it is true that `Date.prototype.toJSON !== Date.prototype.toString`, so we would stringify a date in some way if passed as part of JSON `data` (`toJSON === toISOString`) and in a different way if passed as `query` param (`toString`)
here are the two original TODOs:
```js
// TODO(gio): do we really need this?
// stringifyParam = value => t.match(value,
// t.Str, v => v,
// t.Date, v => v.toISOString(),
// t.Bool, v => String(v),
// t.Number, v => String(v),
// t.Nil, () => undefined, // undefined (query) params are stripped by axios down the road
// t.Any, () => {
// throw new Error('Unhandled param type', value);
// }
// );
// const query = Object.keys(qq).reduce((ac, k) => {
// return {
// ...ac,
// [k]: stringifyParam(qq[k])
// };
// }, {});
``` | non_priority | do we need to stringifyparams description we are currently implicitly relying on the fact that whatever we are going to stringify already defines a correct tojson and a correct tostring this could be problematic since for instance it is true that date prototype tojson date prototype tostring so we would stringify a date in some way if passed as part of json data tojson toisostring and in a different way if passed as query param tostring here are the two original todos js todo gio do we really need this stringifyparam value t match value t str v v t date v v toisostring t bool v string v t number v string v t nil undefined undefined query params are stripped by axios down the road t any throw new error unhandled param type value const query object keys qq reduce ac k return ac stringifyparam qq | 0 |
150,318 | 13,339,073,386 | IssuesEvent | 2020-08-28 12:15:17 | pcraster/lue | https://api.github.com/repos/pcraster/lue | closed | Deploy generated docs to lue website | 05: taget: documentation 15: feature: continuous integration 25: kind: enhancement | After each commit, deploy documentation generated by one of the workflows to `lue.computationalgeography.org/doc`, or similar. | 1.0 | Deploy generated docs to lue website - After each commit, deploy documentation generated by one of the workflows to `lue.computationalgeography.org/doc`, or similar. | non_priority | deploy generated docs to lue website after each commit deploy documentation generated by one of the workflows to lue computationalgeography org doc or similar | 0 |
157,446 | 24,673,889,155 | IssuesEvent | 2022-10-18 15:31:03 | nextcloud/files_retention | https://api.github.com/repos/nextcloud/files_retention | closed | 🖌️ Design review | design 1. to develop | ## Based on
* #196
## Overall
* [x] Adjust heading to "File retention & automatic deletion"
* [x] Table content is a bit indented / has left padding, not left-aligned with the rest – left and right outer padding can probably be removed
* [x] Time input field
* [x] input text should be right-aligned too, like when it’s saved
* [x] "Time" options look better lowercased so it’s "14 days" instead of "14 Days"
* [x] Combine "Retention" and "Time" into 1 column, "Retention time"
* [x] Remove "Active" column, error notification via notecard instead
* [x] "Notify users a day before retention will delete a file"→ "Notify owner a day before a file is automatically deleted"
* [x] Headings:
* [x] Tag → "Files tagged with"
* [x] After → "From date of"
* [x] Actions → can be deleted
* [x] Right-align actions
* [x] Make + button secondary
* [x] with text "Create"
* [ ] Screenshot in documentation needs updating https://github.com/nextcloud/documentation/pull/9224
## To report at nextcloud/vue
* [ ] Time input field https://github.com/nextcloud/nextcloud-vue/issues/3376
* [ ] Is smaller than the others → text input component is smaller than the multiselect component
* [ ] Multiselect https://github.com/nextcloud/nextcloud-vue/issues/3377
* [ ] When tabbing to a value but not confirming via enter, then coming back to it, wrong value is preselected
* [ ] Text input vs actual value shifts by 1 px
* [ ] Rounded corners for dropdown
* [ ] SettingsSections https://github.com/nextcloud/nextcloud-vue/issues/3378
* [ ] General settings: Would be nice to have some space on bottom of page always, like 30vh (30% of viewport height) | 1.0 | 🖌️ Design review - ## Based on
* #196
## Overall
* [x] Adjust heading to "File retention & automatic deletion"
* [x] Table content is a bit indented / has left padding, not left-aligned with the rest – left and right outer padding can probably be removed
* [x] Time input field
* [x] input text should be right-aligned too, like when it’s saved
* [x] "Time" options look better lowercased so it’s "14 days" instead of "14 Days"
* [x] Combine "Retention" and "Time" into 1 column, "Retention time"
* [x] Remove "Active" column, error notification via notecard instead
* [x] "Notify users a day before retention will delete a file"→ "Notify owner a day before a file is automatically deleted"
* [x] Headings:
* [x] Tag → "Files tagged with"
* [x] After → "From date of"
* [x] Actions → can be deleted
* [x] Right-align actions
* [x] Make + button secondary
* [x] with text "Create"
* [ ] Screenshot in documentation needs updating https://github.com/nextcloud/documentation/pull/9224
## To report at nextcloud/vue
* [ ] Time input field https://github.com/nextcloud/nextcloud-vue/issues/3376
* [ ] Is smaller than the others → text input component is smaller than the multiselect component
* [ ] Multiselect https://github.com/nextcloud/nextcloud-vue/issues/3377
* [ ] When tabbing to a value but not confirming via enter, then coming back to it, wrong value is preselected
* [ ] Text input vs actual value shifts by 1 px
* [ ] Rounded corners for dropdown
* [ ] SettingsSections https://github.com/nextcloud/nextcloud-vue/issues/3378
* [ ] General settings: Would be nice to have some space on bottom of page always, like 30vh (30% of viewport height) | non_priority | 🖌️ design review based on overall adjust heading to file retention automatic deletion table content is a bit indented has left padding not left aligned with the rest – left and right outer padding can probably be removed time input field input text should be right aligned too like when it’s saved time options look better lowercased so it’s days instead of days combine retention and time into column retention time remove active column error notification via notecard instead notify users a day before retention will delete a file → notify owner a day before a file is automatically deleted headings tag → files tagged with after → from date of actions → can be deleted right align actions make button secondary with text create screenshot in documentation needs updating to report at nextcloud vue time input field is smaller than the others → text input component is smaller than the multiselect component multiselect when tabbing to a value but not confirming via enter then coming back to it wrong value is preselected text input vs actual value shifts by px rounded corners for dropdown settingssections general settings would be nice to have some space on bottom of page always like of viewport height | 0 |
21,318 | 11,631,532,433 | IssuesEvent | 2020-02-28 01:41:55 | microsoft/BotFramework-WebChat | https://api.github.com/repos/microsoft/BotFramework-WebChat | opened | Bot using IFrame stopped working suddenly. Throws Operation returned an invalid status code error | Bot Services Pending Question customer-reported | SDK: v4
platform: .net core 2.2
Channels: Webchat (both directline and Iframe)
I have a chat bot that was working fine till 2 days ago. I am using web chat with both DirectLine and Iframe implementation covering different scenario. The web page where I have embedded the bot through IFrame is throwing the above error.
I have customized the webchat by following [this]. (https://stackoverflow.com/questions/50510099/change-the-css-of-the-qna-bot-embedded-as-webchat)
I tried to debug this using ngrok and what I found is puzzling me. When I changed the message endpoint under bot settings in azure portal the bot started sending me the replies through IFrame. When I changed the message endpoint back to original endpoint I started getting the same error.
Secondly, instead of using my html page as iframe source `<iframe id="webchat" src='Iframe.html'></iframe>`
I changed it to `
<iframe id="webchat" src='https://webchat.botframework.com/embed/CivicDevBot?s=<secret key>'></iframe>`
the bot started replying.
Can anyone help me here. I can provide more information as need be | 1.0 | Bot using IFrame stopped working suddenly. Throws Operation returned an invalid status code error - SDK: v4
platform: .net core 2.2
Channels: Webchat (both directline and Iframe)
I have a chat bot that was working fine till 2 days ago. I am using web chat with both DirectLine and Iframe implementation covering different scenario. The web page where I have embedded the bot through IFrame is throwing the above error.
I have customized the webchat by following [this]. (https://stackoverflow.com/questions/50510099/change-the-css-of-the-qna-bot-embedded-as-webchat)
I tried to debug this using ngrok and what I found is puzzling me. When I changed the message endpoint under bot settings in azure portal the bot started sending me the replies through IFrame. When I changed the message endpoint back to original endpoint I started getting the same error.
Secondly, instead of using my html page as iframe source `<iframe id="webchat" src='Iframe.html'></iframe>`
I changed it to `
<iframe id="webchat" src='https://webchat.botframework.com/embed/CivicDevBot?s=<secret key>'></iframe>`
the bot started replying.
Can anyone help me here. I can provide more information as need be | non_priority | bot using iframe stopped working suddenly throws operation returned an invalid status code error sdk platform net core channels webchat both directline and iframe i have a chat bot that was working fine till days ago i am using web chat with both directline and iframe implementation covering different scenario the web page where i have embedded the bot through iframe is throwing the above error i have customized the webchat by following i tried to debug this using ngrok and what i found is puzzling me when i changed the message endpoint under bot settings in azure portal the bot started sending me the replies through iframe when i changed the message endpoint back to original endpoint i started getting the same error secondly instead of using my html page as iframe source i changed it to the bot started replying can anyone help me here i can provide more information as need be | 0 |
124,152 | 16,587,733,563 | IssuesEvent | 2021-06-01 00:59:21 | psf/black | https://api.github.com/repos/psf/black | closed | Black produces a long one-liner which previously fitted line length limit | F: linetoolong T: design | **Describe the style change**:
I don't know what exactly should Black do in such cases, but it seems weird that _Black_ makes the code that respected line length into a code that doesn't.
I'm also a little surprised with how _Black_ treats parentheses that are near `==` operator but the line length is the bigger problem here than that IMO.
**Examples in the current _Black_ style**
```py
assert (
stdout
== "A\x00added_file.txt\x00\tM\x00mycog/__init__.py\x00\tD\x00sample_file1.txt\x00\tD\x00sample_file2.txt\x00\tA\x00sample_file3.txt"
)
assert (
p.stderr.decode().strip()
== "error: short SHA1 95da0b57 is ambiguous\nhint: The candidates are:\nhint: 95da0b576 commit 2019-10-22 - Ambiguous commit 16955\nhint: 95da0b57a commit 2019-10-22 - Ambiguous commit 44414\nfatal: Needed a single revision"
)
```
**Desired style**:
(I don't know if it's *desired* style, it's just what the code looked like originally)
```py
assert stdout == (
"A\x00added_file.txt\x00\t"
"M\x00mycog/__init__.py\x00\t"
"D\x00sample_file1.txt\x00\t"
"D\x00sample_file2.txt\x00\t"
"A\x00sample_file3.txt"
)
assert p.stderr.decode().strip() == (
"error: short SHA1 95da0b57 is ambiguous\n"
"hint: The candidates are:\n"
"hint: 95da0b576 commit 2019-10-22 - Ambiguous commit 16955\n"
"hint: 95da0b57a commit 2019-10-22 - Ambiguous commit 44414\n"
"fatal: Needed a single revision"
)
```
**Additional context**
Might be partially related to #1467 but the second assert does have spaces in the string so _Black_ would normally have something to split on no matter if #1467 was a thing.
This bug appears when black is ran with `--experimental-string-processing` flag. Last time I tried reproducing this, I tested on commit cd3a93a14689f046468ece2a5b1f78863c3c4cd2.
I'm sorry for the amount of issues but I tried to run Black's master on Cog-Creators/Red-DiscordBot's code base which resulted in quite a few of errors and also some undesired (by me) changes which I wanted to at least report even if they're not gonna be changed. | 1.0 | Black produces a long one-liner which previously fitted line length limit - **Describe the style change**:
I don't know what exactly should Black do in such cases, but it seems weird that _Black_ makes the code that respected line length into a code that doesn't.
I'm also a little surprised with how _Black_ treats parentheses that are near `==` operator but the line length is the bigger problem here than that IMO.
**Examples in the current _Black_ style**
```py
assert (
stdout
== "A\x00added_file.txt\x00\tM\x00mycog/__init__.py\x00\tD\x00sample_file1.txt\x00\tD\x00sample_file2.txt\x00\tA\x00sample_file3.txt"
)
assert (
p.stderr.decode().strip()
== "error: short SHA1 95da0b57 is ambiguous\nhint: The candidates are:\nhint: 95da0b576 commit 2019-10-22 - Ambiguous commit 16955\nhint: 95da0b57a commit 2019-10-22 - Ambiguous commit 44414\nfatal: Needed a single revision"
)
```
**Desired style**:
(I don't know if it's *desired* style, it's just what the code looked like originally)
```py
assert stdout == (
"A\x00added_file.txt\x00\t"
"M\x00mycog/__init__.py\x00\t"
"D\x00sample_file1.txt\x00\t"
"D\x00sample_file2.txt\x00\t"
"A\x00sample_file3.txt"
)
assert p.stderr.decode().strip() == (
"error: short SHA1 95da0b57 is ambiguous\n"
"hint: The candidates are:\n"
"hint: 95da0b576 commit 2019-10-22 - Ambiguous commit 16955\n"
"hint: 95da0b57a commit 2019-10-22 - Ambiguous commit 44414\n"
"fatal: Needed a single revision"
)
```
**Additional context**
Might be partially related to #1467 but the second assert does have spaces in the string so _Black_ would normally have something to split on no matter if #1467 was a thing.
This bug appears when black is ran with `--experimental-string-processing` flag. Last time I tried reproducing this, I tested on commit cd3a93a14689f046468ece2a5b1f78863c3c4cd2.
I'm sorry for the amount of issues but I tried to run Black's master on Cog-Creators/Red-DiscordBot's code base which resulted in quite a few of errors and also some undesired (by me) changes which I wanted to at least report even if they're not gonna be changed. | non_priority | black produces a long one liner which previously fitted line length limit describe the style change i don t know what exactly should black do in such cases but it seems weird that black makes the code that respected line length into a code that doesn t i m also a little surprised with how black treats parentheses that are near operator but the line length is the bigger problem here than that imo examples in the current black style py assert stdout a file txt tm init py td txt td txt ta txt assert p stderr decode strip error short is ambiguous nhint the candidates are nhint commit ambiguous commit nhint commit ambiguous commit nfatal needed a single revision desired style i don t know if it s desired style it s just what the code looked like originally py assert stdout a file txt t m init py t d txt t d txt t a txt assert p stderr decode strip error short is ambiguous n hint the candidates are n hint commit ambiguous commit n hint commit ambiguous commit n fatal needed a single revision additional context might be partially related to but the second assert does have spaces in the string so black would normally have something to split on no matter if was a thing this bug appears when black is ran with experimental string processing flag last time i tried reproducing this i tested on commit i m sorry for the amount of issues but i tried to run black s master on cog creators red discordbot s code base which resulted in quite a few of errors and also some undesired by me changes which i wanted to at least report even if they re not gonna be changed | 0 |
35,057 | 30,723,023,127 | IssuesEvent | 2023-07-27 17:20:49 | superlistapp/super_editor | https://api.github.com/repos/superlistapp/super_editor | closed | Migrate from our custom ListenableBuilder to Flutter's new ListenableBuilder | area_supereditor area_infrastructure bounty_junior f:superlist time: 1 | We defined a widget called `ListenableBuilder` so that we could rebuild when a `Listenable` changed. This could always be done with an `AnimatedBuilder`, but that name was confusing, because we weren't watching animations.
Flutter recently made a similar change in the framework. As a result, there's a naming conflict in `super_editor`. Up to this point, we've explicitly hidden Flutter's own `ListenableBuilder` in favor of our own.
For this ticket, get rid of our implementation of `ListenableBuilder` in favor of Flutter's implementation. | 1.0 | Migrate from our custom ListenableBuilder to Flutter's new ListenableBuilder - We defined a widget called `ListenableBuilder` so that we could rebuild when a `Listenable` changed. This could always be done with an `AnimatedBuilder`, but that name was confusing, because we weren't watching animations.
Flutter recently made a similar change in the framework. As a result, there's a naming conflict in `super_editor`. Up to this point, we've explicitly hidden Flutter's own `ListenableBuilder` in favor of our own.
For this ticket, get rid of our implementation of `ListenableBuilder` in favor of Flutter's implementation. | non_priority | migrate from our custom listenablebuilder to flutter s new listenablebuilder we defined a widget called listenablebuilder so that we could rebuild when a listenable changed this could always be done with an animatedbuilder but that name was confusing because we weren t watching animations flutter recently made a similar change in the framework as a result there s a naming conflict in super editor up to this point we ve explicitly hidden flutter s own listenablebuilder in favor of our own for this ticket get rid of our implementation of listenablebuilder in favor of flutter s implementation | 0 |
44,052 | 7,091,387,228 | IssuesEvent | 2018-01-12 12:52:22 | openmole/openmole | https://api.github.com/repos/openmole/openmole | closed | Improve FAQ | Hacktoberfest documentation easypick | - [x] automatically generate table of contents at the top of section
_(see http://www.lihaoyi.com/Scalatex/#GeneratingaTableofContents)_
- [x] improve layout (spacing between paragraphs in CSS?)
| 1.0 | Improve FAQ - - [x] automatically generate table of contents at the top of section
_(see http://www.lihaoyi.com/Scalatex/#GeneratingaTableofContents)_
- [x] improve layout (spacing between paragraphs in CSS?)
| non_priority | improve faq automatically generate table of contents at the top of section see improve layout spacing between paragraphs in css | 0 |
956 | 3,419,117,472 | IssuesEvent | 2015-12-08 07:52:00 | e-government-ua/iBP | https://api.github.com/repos/e-government-ua/iBP | closed | Днепр обл. ЦНАП Надання відомостей з Державного земельного кадастру у формі витягу з Державного земельного кадастру про землі в межах території адміністративно-територіальних одиниць | In process of testing | Вольногорск, Марганец, Царичанский р-н | 1.0 | Днепр обл. ЦНАП Надання відомостей з Державного земельного кадастру у формі витягу з Державного земельного кадастру про землі в межах території адміністративно-територіальних одиниць - Вольногорск, Марганец, Царичанский р-н | non_priority | днепр обл цнап надання відомостей з державного земельного кадастру у формі витягу з державного земельного кадастру про землі в межах території адміністративно територіальних одиниць вольногорск марганец царичанский р н | 0 |
68,224 | 9,160,204,531 | IssuesEvent | 2019-03-01 06:25:51 | Kros-sk/Kros.BusEventDoc | https://api.github.com/repos/Kros-sk/Kros.BusEventDoc | closed | README with quickstart documentation | documentation good first issue up-for-grabs | Write quickstart documentation into README.md.
- [ ] info about this project
- [ ] link to nuget packages
- [ ] how configure generator (with example)
- [ ] how configure UI (with example)
- [ ] link to demo project
Examples of readme:
[Kros.Utils](https://github.com/Kros-sk/Kros.Libs/blob/master/Kros.Utils/README.md)
[Kros.KORM](https://github.com/Kros-sk/Kros.Libs/blob/master/Kros.KORM/README.md)
[MMLib.SwaggerForOcelot](https://github.com/Burgyn/MMLib.SwaggerForOcelot)
[Swagger](https://github.com/domaindrivendev/Swashbuckle.AspNetCore)
| 1.0 | README with quickstart documentation - Write quickstart documentation into README.md.
- [ ] info about this project
- [ ] link to nuget packages
- [ ] how configure generator (with example)
- [ ] how configure UI (with example)
- [ ] link to demo project
Examples of readme:
[Kros.Utils](https://github.com/Kros-sk/Kros.Libs/blob/master/Kros.Utils/README.md)
[Kros.KORM](https://github.com/Kros-sk/Kros.Libs/blob/master/Kros.KORM/README.md)
[MMLib.SwaggerForOcelot](https://github.com/Burgyn/MMLib.SwaggerForOcelot)
[Swagger](https://github.com/domaindrivendev/Swashbuckle.AspNetCore)
| non_priority | readme with quickstart documentation write quickstart documentation into readme md info about this project link to nuget packages how configure generator with example how configure ui with example link to demo project examples of readme | 0 |
337,071 | 30,237,710,803 | IssuesEvent | 2023-07-06 11:26:34 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix paddle_tensor.test_paddle_neg | Sub Task Failing Test Paddle Frontend | | | |
|---|---|
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix paddle_tensor.test_paddle_neg - | | |
|---|---|
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5474622320"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix paddle tensor test paddle neg paddle a href src tensorflow a href src numpy a href src torch a href src jax a href src | 0 |
17,992 | 12,716,410,188 | IssuesEvent | 2020-06-24 01:50:30 | APSIMInitiative/ApsimX | https://api.github.com/repos/APSIMInitiative/ApsimX | closed | Irrigation manager in the toolbox | interface/infrastructure newfeature | Can you please add this manager to the management toolbox? The current automatic irrigation in the toolbox doesn't work for AgPasture. Thanks
@hol353
[IrrigationManager.zip](https://github.com/APSIMInitiative/ApsimX/files/4817015/IrrigationManager.zip)
| 1.0 | Irrigation manager in the toolbox - Can you please add this manager to the management toolbox? The current automatic irrigation in the toolbox doesn't work for AgPasture. Thanks
@hol353
[IrrigationManager.zip](https://github.com/APSIMInitiative/ApsimX/files/4817015/IrrigationManager.zip)
| non_priority | irrigation manager in the toolbox can you please add this manager to the management toolbox the current automatic irrigation in the toolbox doesn t work for agpasture thanks | 0 |
14,710 | 8,675,101,071 | IssuesEvent | 2018-11-30 09:53:34 | jsheroes/jsheroes.io | https://api.github.com/repos/jsheroes/jsheroes.io | opened | Use font-display: swap or fallback | performance | With font-display we can show system fonts until the web fonts are loaded
More about font-display - https://css-tricks.com/font-display-masses/
This is one of the issues reported by Lighthouse at the moment
<img width="434" alt="screenshot 2018-11-30 at 10 49 18" src="https://user-images.githubusercontent.com/9945366/49281904-10408f80-f48e-11e8-9650-cb52fec76f7f.png">
| True | Use font-display: swap or fallback - With font-display we can show system fonts until the web fonts are loaded
More about font-display - https://css-tricks.com/font-display-masses/
This is one of the issues reported by Lighthouse at the moment
<img width="434" alt="screenshot 2018-11-30 at 10 49 18" src="https://user-images.githubusercontent.com/9945366/49281904-10408f80-f48e-11e8-9650-cb52fec76f7f.png">
| non_priority | use font display swap or fallback with font display we can show system fonts until the web fonts are loaded more about font display this is one of the issues reported by lighthouse at the moment img width alt screenshot at src | 0 |
281,852 | 30,888,974,979 | IssuesEvent | 2023-08-04 02:04:48 | hshivhare67/kernel_v4.1.15_CVE-2019-10220 | https://api.github.com/repos/hshivhare67/kernel_v4.1.15_CVE-2019-10220 | reopened | CVE-2020-15437 (Medium) detected in linuxlinux-4.4.302 | Mend: dependency security vulnerability | ## CVE-2020-15437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/tty/serial/8250/8250_core.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel before version 5.8 is vulnerable to a NULL pointer dereference in drivers/tty/serial/8250/8250_core.c:serial8250_isa_init_ports() that allows local users to cause a denial of service by using the p->serial_in pointer which uninitialized.
Mend Note: After conducting further research, Mend has determined that versions v3.9-rc5 through v4.4.231, v4.5-rc1 through v4.9.231, v4.10-rc1 through v4.14.189, v4.15-rc1 through v4.19.134, v5.0-rc1 through v5.4.53, v5.5-rc1 through v5.7.10 and v5.8-rc1 through v5.8-rc6 of Linux Kernel are vulnerable to CVE-2020-15437.
<p>Publish Date: 2020-11-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15437>CVE-2020-15437</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-15437">https://www.linuxkernelcves.com/cves/CVE-2020-15437</a></p>
<p>Release Date: 2020-11-23</p>
<p>Fix Resolution: v4.4.232, v4.9.232, v4.14.190, v4.19.135, v5.4.54, v5.7.11, v5.8-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-15437 (Medium) detected in linuxlinux-4.4.302 - ## CVE-2020-15437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/tty/serial/8250/8250_core.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel before version 5.8 is vulnerable to a NULL pointer dereference in drivers/tty/serial/8250/8250_core.c:serial8250_isa_init_ports() that allows local users to cause a denial of service by using the p->serial_in pointer which uninitialized.
Mend Note: After conducting further research, Mend has determined that versions v3.9-rc5 through v4.4.231, v4.5-rc1 through v4.9.231, v4.10-rc1 through v4.14.189, v4.15-rc1 through v4.19.134, v5.0-rc1 through v5.4.53, v5.5-rc1 through v5.7.10 and v5.8-rc1 through v5.8-rc6 of Linux Kernel are vulnerable to CVE-2020-15437.
<p>Publish Date: 2020-11-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-15437>CVE-2020-15437</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-15437">https://www.linuxkernelcves.com/cves/CVE-2020-15437</a></p>
<p>Release Date: 2020-11-23</p>
<p>Fix Resolution: v4.4.232, v4.9.232, v4.14.190, v4.19.135, v5.4.54, v5.7.11, v5.8-rc7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files drivers tty serial core c vulnerability details the linux kernel before version is vulnerable to a null pointer dereference in drivers tty serial core c isa init ports that allows local users to cause a denial of service by using the p serial in pointer which uninitialized mend note after conducting further research mend has determined that versions through through through through through through and through of linux kernel are vulnerable to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
355,697 | 25,176,001,308 | IssuesEvent | 2022-11-11 09:19:12 | fongyj/pe | https://api.github.com/repos/fongyj/pe | opened | No annotations in UG screenshots | severity.VeryLow type.DocumentationBug | UG screenshots are difficult to read since there are no annotations to direct my attention to the important parts.
UG screenshots are also inconsistently cropped as some are cropped properly but some are cropped poorly with black lines at the sides that are not removed.
<!--session: 1668154362402-ce494aff-3e8e-41ec-bf55-4a4b2448e56f-->
<!--Version: Web v3.4.4--> | 1.0 | No annotations in UG screenshots - UG screenshots are difficult to read since there are no annotations to direct my attention to the important parts.
UG screenshots are also inconsistently cropped as some are cropped properly but some are cropped poorly with black lines at the sides that are not removed.
<!--session: 1668154362402-ce494aff-3e8e-41ec-bf55-4a4b2448e56f-->
<!--Version: Web v3.4.4--> | non_priority | no annotations in ug screenshots ug screenshots are difficult to read since there are no annotations to direct my attention to the important parts ug screenshots are also inconsistently cropped as some are cropped properly but some are cropped poorly with black lines at the sides that are not removed | 0 |
23,067 | 10,851,562,708 | IssuesEvent | 2019-11-13 11:00:22 | Sh2dowFi3nd/test | https://api.github.com/repos/Sh2dowFi3nd/test | opened | CVE-2019-12814 (Medium) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-12814 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Sh2dowFi3nd/test/commit/5981a223918363e27b537d0da5292bdb1b6e70cf">5981a223918363e27b537d0da5292bdb1b6e70cf</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x through 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has JDOM 1.x or 2.x jar in the classpath, an attacker can send a specifically crafted JSON message that allows them to read arbitrary local files on the server.
<p>Publish Date: 2019-06-19
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12814>CVE-2019-12814</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2341">https://github.com/FasterXML/jackson-databind/issues/2341</a></p>
<p>Release Date: 2019-06-19</p>
<p>Fix Resolution: 2.7.9.6, 2.8.11.4, 2.9.9.1, 2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-12814 (Medium) detected in jackson-databind-2.9.8.jar - ## CVE-2019-12814 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Sh2dowFi3nd/test/commit/5981a223918363e27b537d0da5292bdb1b6e70cf">5981a223918363e27b537d0da5292bdb1b6e70cf</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x through 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has JDOM 1.x or 2.x jar in the classpath, an attacker can send a specifically crafted JSON message that allows them to read arbitrary local files on the server.
<p>Publish Date: 2019-06-19
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12814>CVE-2019-12814</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2341">https://github.com/FasterXML/jackson-databind/issues/2341</a></p>
<p>Release Date: 2019-06-19</p>
<p>Fix Resolution: 2.7.9.6, 2.8.11.4, 2.9.9.1, 2.10.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind x through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has jdom x or x jar in the classpath an attacker can send a specifically crafted json message that allows them to read arbitrary local files on the server publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
344,616 | 24,821,072,372 | IssuesEvent | 2022-10-25 16:28:47 | Hendurox/git_web_practice | https://api.github.com/repos/Hendurox/git_web_practice | closed | Un commit que no sigue la convención de código o FIX a realizar | documentation | La convención del mensaje del último commit no es la esperada:
`cambios realizados`
Recuerde que debe tener el siguiente formato: `<Identificador de la corrección>: <Comentario>`
Para realizar la corrección del mensaje de commit ejecute los comandos `git commit --amend` y `git push -f`
Este issue es solo un recordatorio de la convención de comentarios en los commits y puede ser cerrado. | 1.0 | Un commit que no sigue la convención de código o FIX a realizar - La convención del mensaje del último commit no es la esperada:
`cambios realizados`
Recuerde que debe tener el siguiente formato: `<Identificador de la corrección>: <Comentario>`
Para realizar la corrección del mensaje de commit ejecute los comandos `git commit --amend` y `git push -f`
Este issue es solo un recordatorio de la convención de comentarios en los commits y puede ser cerrado. | non_priority | un commit que no sigue la convención de código o fix a realizar la convención del mensaje del último commit no es la esperada cambios realizados recuerde que debe tener el siguiente formato para realizar la corrección del mensaje de commit ejecute los comandos git commit amend y git push f este issue es solo un recordatorio de la convención de comentarios en los commits y puede ser cerrado | 0 |
154,693 | 13,564,516,377 | IssuesEvent | 2020-09-18 10:09:50 | timescale/timescaledb | https://api.github.com/repos/timescale/timescaledb | closed | Update the continuous aggregate README | continuous-aggs documentation | There's a README describing the continuous aggregate implementation in `tsl/src/continuous_agg/Readme.md` that requires updates. It already seems out-of-date, and will be even more out-of-date with the new refresh API. | 1.0 | Update the continuous aggregate README - There's a README describing the continuous aggregate implementation in `tsl/src/continuous_agg/Readme.md` that requires updates. It already seems out-of-date, and will be even more out-of-date with the new refresh API. | non_priority | update the continuous aggregate readme there s a readme describing the continuous aggregate implementation in tsl src continuous agg readme md that requires updates it already seems out of date and will be even more out of date with the new refresh api | 0 |
93,661 | 27,010,134,386 | IssuesEvent | 2023-02-10 14:48:28 | urbit/vere | https://api.github.com/repos/urbit/vere | opened | CI version string fix cherry-pick to `release` branch | bug build | Version strings were messed up in the CI so our binaries were being uploaded to the wrong bucket. The version strings should've been just (for example) `1.18` instead of `1.18-{SHORT-SHA}`. We fixed this in #57 but we need to cherry-pick [this commit](https://github.com/urbit/vere/commit/9320979053d1e081ec01e6b6ad33c1bd67530c39) so that the next release doesn't suffer from the same upload destination error. | 1.0 | CI version string fix cherry-pick to `release` branch - Version strings were messed up in the CI so our binaries were being uploaded to the wrong bucket. The version strings should've been just (for example) `1.18` instead of `1.18-{SHORT-SHA}`. We fixed this in #57 but we need to cherry-pick [this commit](https://github.com/urbit/vere/commit/9320979053d1e081ec01e6b6ad33c1bd67530c39) so that the next release doesn't suffer from the same upload destination error. | non_priority | ci version string fix cherry pick to release branch version strings were messed up in the ci so our binaries were being uploaded to the wrong bucket the version strings should ve been just for example instead of short sha we fixed this in but we need to cherry pick so that the next release doesn t suffer from the same upload destination error | 0 |
305,428 | 23,114,214,425 | IssuesEvent | 2022-07-27 15:17:57 | stripe/stripe-firebase-extensions | https://api.github.com/repos/stripe/stripe-firebase-extensions | closed | Add subscription payments to your web app with Firebase Extensions & Stripe guide code error | documentation awaiting author feedback | # Bug report
- Extension name: [e.g. `firestore-stripe-payments`]
## Describe the bug
Thank you so much for the amazing guide! It got me 99% running, I just found an error in the code for part 5 under "Access the Stripe customer portal" when I used ".httpsCallable("ext-firestore-stripe-subscriptions-createPortalLink");" it gave me a "redirect is not allowed for a preflight request" error. I looked up the name of the function in firestore and I could only find ".httpsCallable("ext-firestore-stripe-payments-createPortalLink");" and upon using that in my code it worked perfectly.
## To Reproduce
Follow guide exactly as it says
## Expected behavior
Pressing the button would take the customer to their portal
## Screenshots
If applicable, add screenshots to help explain your problem.
## System information
- OS: Windows 10
- Browser: Chrome
## Additional context
| 1.0 | Add subscription payments to your web app with Firebase Extensions & Stripe guide code error - # Bug report
- Extension name: [e.g. `firestore-stripe-payments`]
## Describe the bug
Thank you so much for the amazing guide! It got me 99% running, I just found an error in the code for part 5 under "Access the Stripe customer portal" when I used ".httpsCallable("ext-firestore-stripe-subscriptions-createPortalLink");" it gave me a "redirect is not allowed for a preflight request" error. I looked up the name of the function in firestore and I could only find ".httpsCallable("ext-firestore-stripe-payments-createPortalLink");" and upon using that in my code it worked perfectly.
## To Reproduce
Follow guide exactly as it says
## Expected behavior
Pressing the button would take the customer to their portal
## Screenshots
If applicable, add screenshots to help explain your problem.
## System information
- OS: Windows 10
- Browser: Chrome
## Additional context
| non_priority | add subscription payments to your web app with firebase extensions stripe guide code error bug report extension name describe the bug thank you so much for the amazing guide it got me running i just found an error in the code for part under access the stripe customer portal when i used httpscallable ext firestore stripe subscriptions createportallink it gave me a redirect is not allowed for a preflight request error i looked up the name of the function in firestore and i could only find httpscallable ext firestore stripe payments createportallink and upon using that in my code it worked perfectly to reproduce follow guide exactly as it says expected behavior pressing the button would take the customer to their portal screenshots if applicable add screenshots to help explain your problem system information os windows browser chrome additional context | 0 |
55,475 | 6,901,437,874 | IssuesEvent | 2017-11-25 07:19:48 | DemokratieInBewegung/abstimmungstool | https://api.github.com/repos/DemokratieInBewegung/abstimmungstool | opened | Managed dynamic categories and tagging | CMP Backend CMP Frontend NEEDs design NEEDs discussion | __User Story__
As a Plenums user I want to be able to categorize and tag initiatives I'm creating to be able to find them later more easy in the archive and if there are a lot of open initiatives.
__Acceptance Criterias__
- The categories are the same as on the Marktplatz
- User can suggest a new category that is approved or declined by the moderators. If declined the moderators have to set another existing category
- Users can choose tags to label initiatives
- Users can suggest new tags which have to be approved by the moderators. If it is not approved it is just removed from the initiative | 1.0 | Managed dynamic categories and tagging - __User Story__
As a Plenums user I want to be able to categorize and tag initiatives I'm creating to be able to find them later more easy in the archive and if there are a lot of open initiatives.
__Acceptance Criterias__
- The categories are the same as on the Marktplatz
- User can suggest a new category that is approved or declined by the moderators. If declined the moderators have to set another existing category
- Users can choose tags to label initiatives
- Users can suggest new tags which have to be approved by the moderators. If it is not approved it is just removed from the initiative | non_priority | managed dynamic categories and tagging user story as a plenums user i want to be able to categorize and tag initiatives i m creating to be able to find them later more easy in the archive and if there are a lot of open initiatives acceptance criterias the categories are the same as on the marktplatz user can suggest a new category that is approved or declined by the moderators if declined the moderators have to set another existing category users can choose tags to label initiatives users can suggest new tags which have to be approved by the moderators if it is not approved it is just removed from the initiative | 0 |
19,294 | 10,361,294,022 | IssuesEvent | 2019-09-06 09:40:50 | Intracto/buildozer | https://api.github.com/repos/Intracto/buildozer | opened | Benchmark if it's worth passing the packages to libs | performance | To limit the number of `require()`s, I've passed the packages which are used in multiple libs to the libs themself like this:
https://github.com/Intracto/buildozer/blob/8e0f0d7a699f4cccef8e22339ee5a1cad329103a/lib/gulp/image.js#L40-L46
This should be faster I guess, but I didn't really test this. If the performance gain we win from this is negligible, we might just use normal `require()`s on top of each lib.
| True | Benchmark if it's worth passing the packages to libs - To limit the number of `require()`s, I've passed the packages which are used in multiple libs to the libs themself like this:
https://github.com/Intracto/buildozer/blob/8e0f0d7a699f4cccef8e22339ee5a1cad329103a/lib/gulp/image.js#L40-L46
This should be faster I guess, but I didn't really test this. If the performance gain we win from this is negligible, we might just use normal `require()`s on top of each lib.
| non_priority | benchmark if it s worth passing the packages to libs to limit the number of require s i ve passed the packages which are used in multiple libs to the libs themself like this this should be faster i guess but i didn t really test this if the performance gain we win from this is negligible we might just use normal require s on top of each lib | 0 |
312,187 | 23,418,930,345 | IssuesEvent | 2022-08-13 11:42:41 | retico-team/retico-googletts | https://api.github.com/repos/retico-team/retico-googletts | opened | Create documentation for retico-googletts | documentation | There should be documentation (or at least a full reference) for retico-googletts available on readthedocs.io. The documentation should include
- Set/Installation of required software (gcloud and ffmpeg)
- The general instantiation and usage of the GoogleTTSModule
- A source code reference generated from the commented code (the code needs some more documentation as well ;) )
Examples and best practices on how to use the module inside larger incremental networks will be described in the [retico](https://github.com/retico-team/retico) documentation. | 1.0 | Create documentation for retico-googletts - There should be documentation (or at least a full reference) for retico-googletts available on readthedocs.io. The documentation should include
- Set/Installation of required software (gcloud and ffmpeg)
- The general instantiation and usage of the GoogleTTSModule
- A source code reference generated from the commented code (the code needs some more documentation as well ;) )
Examples and best practices on how to use the module inside larger incremental networks will be described in the [retico](https://github.com/retico-team/retico) documentation. | non_priority | create documentation for retico googletts there should be documentation or at least a full reference for retico googletts available on readthedocs io the documentation should include set installation of required software gcloud and ffmpeg the general instantiation and usage of the googlettsmodule a source code reference generated from the commented code the code needs some more documentation as well examples and best practices on how to use the module inside larger incremental networks will be described in the documentation | 0 |
34,697 | 12,294,694,465 | IssuesEvent | 2020-05-11 01:10:39 | BrianMcDonaldWS/deck.gl | https://api.github.com/repos/BrianMcDonaldWS/deck.gl | opened | CVE-2013-0340 (Medium) detected in src-73.0.3635.0 | security vulnerability | ## CVE-2013-0340 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>src73.0.3635.0</b></p></summary>
<p>
<p>Library home page: <a href=https://chromium.googlesource.com/chromium/src>https://chromium.googlesource.com/chromium/src</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (53)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xmlIO.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/HTMLparser.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/catalog.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/pattern.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xlink.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlreader.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/DOCBparser.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlschemastypes.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/list.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/types.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/encoding.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/nanohttp.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libpng16/png.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/expat.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libpng16/pngconf.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/threads.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/schemasInternals.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/uri.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlautomata.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/nanoftp.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlunicode.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xpointer.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/parser.h
- /deck.gl/node_modules/gl/angle/src/third_party/libXNVCtrl/NVCtrlLib.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/relaxng.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xinclude.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/chvalid.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlmodule.h
- /deck.gl/node_modules/gl/angle/src/third_party/libXNVCtrl/nv_control.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/mux_types.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlschemas.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/valid.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xpathInternals.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/HTMLtree.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/SAX2.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlregexp.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/demux.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/debugXML.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/mux.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/hash.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlwriter.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/dict.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/c14n.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlmemory.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xpath.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xmlstring.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xmlerror.h
- /deck.gl/node_modules/gl/angle/src/third_party/khronos/GL/wglext.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/encode.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/parserInternals.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/SAX.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlsave.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/schematron.h
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
expat 2.1.0 and earlier does not properly handle entities expansion unless an application developer uses the XML_SetEntityDeclHandler function, which allows remote attackers to cause a denial of service (resource consumption), send HTTP requests to intranet servers, or read arbitrary files via a crafted XML document, aka an XML External Entity (XXE) issue. NOTE: it could be argued that because expat already provides the ability to disable external entity expansion, the responsibility for resolving this issue lies with application developers; according to this argument, this entry should be REJECTed, and each affected application would need its own CVE.
<p>Publish Date: 2014-01-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0340>CVE-2013-0340</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security.gentoo.org/glsa/201701-21">https://security.gentoo.org/glsa/201701-21</a></p>
<p>Release Date: 2017-01-11</p>
<p>Fix Resolution: All Expat users should upgrade to the latest version >= expat-2.2.0-r1
</p>
</p>
</details>
<p></p>
| True | CVE-2013-0340 (Medium) detected in src-73.0.3635.0 - ## CVE-2013-0340 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>src73.0.3635.0</b></p></summary>
<p>
<p>Library home page: <a href=https://chromium.googlesource.com/chromium/src>https://chromium.googlesource.com/chromium/src</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (53)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xmlIO.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/HTMLparser.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/catalog.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/pattern.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xlink.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlreader.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/DOCBparser.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlschemastypes.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/list.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/types.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/encoding.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/nanohttp.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libpng16/png.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/expat.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libpng16/pngconf.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/threads.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/schemasInternals.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/uri.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlautomata.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/nanoftp.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlunicode.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xpointer.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/parser.h
- /deck.gl/node_modules/gl/angle/src/third_party/libXNVCtrl/NVCtrlLib.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/relaxng.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xinclude.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/chvalid.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlmodule.h
- /deck.gl/node_modules/gl/angle/src/third_party/libXNVCtrl/nv_control.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/mux_types.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlschemas.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/valid.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xpathInternals.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-sharp/node_modules/sharp/vendor/include/libxml2/libxml/HTMLtree.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/SAX2.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlregexp.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/demux.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/debugXML.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/mux.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/hash.h
- /deck.gl/website-gatsby/node_modules/gatsby-transformer-sharp/node_modules/sharp/vendor/include/libxml2/libxml/xmlwriter.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/dict.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/c14n.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlmemory.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xpath.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xmlstring.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/xmlerror.h
- /deck.gl/node_modules/gl/angle/src/third_party/khronos/GL/wglext.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/webp/encode.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/parserInternals.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/SAX.h
- /deck.gl/website-gatsby/node_modules/gatsby-plugin-manifest/node_modules/sharp/vendor/include/libxml2/libxml/xmlsave.h
- /deck.gl/website-gatsby/node_modules/sharp/vendor/include/libxml2/libxml/schematron.h
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
expat 2.1.0 and earlier does not properly handle entities expansion unless an application developer uses the XML_SetEntityDeclHandler function, which allows remote attackers to cause a denial of service (resource consumption), send HTTP requests to intranet servers, or read arbitrary files via a crafted XML document, aka an XML External Entity (XXE) issue. NOTE: it could be argued that because expat already provides the ability to disable external entity expansion, the responsibility for resolving this issue lies with application developers; according to this argument, this entry should be REJECTed, and each affected application would need its own CVE.
<p>Publish Date: 2014-01-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0340>CVE-2013-0340</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://security.gentoo.org/glsa/201701-21">https://security.gentoo.org/glsa/201701-21</a></p>
<p>Release Date: 2017-01-11</p>
<p>Fix Resolution: All Expat users should upgrade to the latest version >= expat-2.2.0-r1
</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in src cve medium severity vulnerability vulnerable library library home page a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries deck gl website gatsby node modules sharp vendor include libxml xmlio h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml htmlparser h deck gl website gatsby node modules sharp vendor include libxml catalog h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml pattern h deck gl website gatsby node modules sharp vendor include libxml xlink h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml xmlreader h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml docbparser h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml xmlschemastypes h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml list h deck gl website gatsby node modules sharp vendor include webp types h deck gl website gatsby node modules sharp vendor include libxml encoding h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml nanohttp h deck gl website gatsby node modules sharp vendor include png h deck gl website gatsby node modules sharp vendor include expat h deck gl website gatsby node modules sharp vendor include pngconf h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml threads h deck gl website gatsby node modules sharp vendor include libxml schemasinternals h deck gl website gatsby node modules sharp vendor include libxml uri h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml xmlautomata h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml nanoftp h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml xmlunicode h deck gl website gatsby node modules gatsby transformer sharp node modules sharp vendor include libxml xpointer h deck gl website gatsby node modules sharp vendor include libxml parser h deck gl node modules gl angle src third party libxnvctrl nvctrllib h deck gl website gatsby node modules sharp vendor include libxml relaxng h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml xinclude h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml chvalid h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml xmlmodule h deck gl node modules gl angle src third party libxnvctrl nv control h deck gl website gatsby node modules sharp vendor include webp mux types h deck gl website gatsby node modules gatsby transformer sharp node modules sharp vendor include libxml xmlschemas h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml valid h deck gl website gatsby node modules sharp vendor include libxml xpathinternals h deck gl website gatsby node modules gatsby plugin sharp node modules sharp vendor include libxml htmltree h deck gl website gatsby node modules sharp vendor include libxml h deck gl website gatsby node modules gatsby transformer sharp node modules sharp vendor include libxml xmlregexp h deck gl website gatsby node modules sharp vendor include webp demux h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml debugxml h deck gl website gatsby node modules sharp vendor include webp mux h deck gl website gatsby node modules sharp vendor include libxml hash h deck gl website gatsby node modules gatsby transformer sharp node modules sharp vendor include libxml xmlwriter h deck gl website gatsby node modules sharp vendor include libxml dict h deck gl website gatsby node modules sharp vendor include libxml h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml xmlmemory h deck gl website gatsby node modules sharp vendor include libxml xpath h deck gl website gatsby node modules sharp vendor include libxml xmlstring h deck gl website gatsby node modules sharp vendor include libxml xmlerror h deck gl node modules gl angle src third party khronos gl wglext h deck gl website gatsby node modules sharp vendor include webp encode h deck gl website gatsby node modules sharp vendor include libxml parserinternals h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml sax h deck gl website gatsby node modules gatsby plugin manifest node modules sharp vendor include libxml xmlsave h deck gl website gatsby node modules sharp vendor include libxml schematron h vulnerability details expat and earlier does not properly handle entities expansion unless an application developer uses the xml setentitydeclhandler function which allows remote attackers to cause a denial of service resource consumption send http requests to intranet servers or read arbitrary files via a crafted xml document aka an xml external entity xxe issue note it could be argued that because expat already provides the ability to disable external entity expansion the responsibility for resolving this issue lies with application developers according to this argument this entry should be rejected and each affected application would need its own cve publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution all expat users should upgrade to the latest version expat | 0 |
361,911 | 25,353,994,411 | IssuesEvent | 2022-11-20 04:57:49 | cse110-fa22-group13/cse110-fa22-group13 | https://api.github.com/repos/cse110-fa22-group13/cse110-fa22-group13 | closed | CD pipeline, diagrams, page, and video | documentation CI/CD | Additional information can be found in the canvas page.
An ability to quickly and easily build and test code is an important aspect of Agile software engineering. However, Continuous Integration (CI) and Deployment (CD) pipelines are not always easy to build. Quite often CI/CD pipelines are brittle and building is done less frequently that it should be. By the end of the quarter we aim to address this by having a pipeline so easy that a grader can make a change and push a new built to evaluate within a few minutes. As this is not a simple task, we will break this effort into three phases.
CI/CD pipeline phase 1 should be a vetting phase were you explore the following ideas
linting and code style enforcement (may happen in pipeline and/or in editor)
code quality via tool (ex. Codeclimate, Codacy, etc.)
code quality via human review (ex. Pull Requests)
unit tests via automation (ex. Jest, Tape, Ava, Cypress, Mocha/Chai, etc.)*
documentation generation via automation (ex. JSDocs)
*Other testing including e2e (end to end) and pixel testing is also possible so you may decide to use an environment that does numerous things.
Note: Future phases may include: code coverage reporting, packaging, deployment, minification and more. You are welcome to try these ideas out now in preparation for future phases.
Your CI/CD pipeline should be run as Github Actions. Your CI/CD pipeline should not be building anything substantial at this phase especially if you have not cleared your pitch stage. Use some simple experimental code to demonstrate testing, docs, linting, etc. Given the parallel creation of devops features as you code you may consider making special branches to test out the pipeline, then once finalized have it work on main and stage branches appropriately.
For the satisfactory completion of this phase you should provide the following items and store them in your repo under /admin/cipipeline.
phase1.png - a diagram of your phase 1 build pipeline (can be phase1.drawio.png if using draw.io)
phase1.md - a short 2 page (roughly) status on the pipeline in terms of what is currently functional (and what is planned or in progress). Embed your diagram in the markdown file.
phase1.mp4 - a no more than 2 min video demonstration of the pipeline
| 1.0 | CD pipeline, diagrams, page, and video - Additional information can be found in the canvas page.
An ability to quickly and easily build and test code is an important aspect of Agile software engineering. However, Continuous Integration (CI) and Deployment (CD) pipelines are not always easy to build. Quite often CI/CD pipelines are brittle and building is done less frequently that it should be. By the end of the quarter we aim to address this by having a pipeline so easy that a grader can make a change and push a new built to evaluate within a few minutes. As this is not a simple task, we will break this effort into three phases.
CI/CD pipeline phase 1 should be a vetting phase were you explore the following ideas
linting and code style enforcement (may happen in pipeline and/or in editor)
code quality via tool (ex. Codeclimate, Codacy, etc.)
code quality via human review (ex. Pull Requests)
unit tests via automation (ex. Jest, Tape, Ava, Cypress, Mocha/Chai, etc.)*
documentation generation via automation (ex. JSDocs)
*Other testing including e2e (end to end) and pixel testing is also possible so you may decide to use an environment that does numerous things.
Note: Future phases may include: code coverage reporting, packaging, deployment, minification and more. You are welcome to try these ideas out now in preparation for future phases.
Your CI/CD pipeline should be run as Github Actions. Your CI/CD pipeline should not be building anything substantial at this phase especially if you have not cleared your pitch stage. Use some simple experimental code to demonstrate testing, docs, linting, etc. Given the parallel creation of devops features as you code you may consider making special branches to test out the pipeline, then once finalized have it work on main and stage branches appropriately.
For the satisfactory completion of this phase you should provide the following items and store them in your repo under /admin/cipipeline.
phase1.png - a diagram of your phase 1 build pipeline (can be phase1.drawio.png if using draw.io)
phase1.md - a short 2 page (roughly) status on the pipeline in terms of what is currently functional (and what is planned or in progress). Embed your diagram in the markdown file.
phase1.mp4 - a no more than 2 min video demonstration of the pipeline
| non_priority | cd pipeline diagrams page and video additional information can be found in the canvas page an ability to quickly and easily build and test code is an important aspect of agile software engineering however continuous integration ci and deployment cd pipelines are not always easy to build quite often ci cd pipelines are brittle and building is done less frequently that it should be by the end of the quarter we aim to address this by having a pipeline so easy that a grader can make a change and push a new built to evaluate within a few minutes as this is not a simple task we will break this effort into three phases ci cd pipeline phase should be a vetting phase were you explore the following ideas linting and code style enforcement may happen in pipeline and or in editor code quality via tool ex codeclimate codacy etc code quality via human review ex pull requests unit tests via automation ex jest tape ava cypress mocha chai etc documentation generation via automation ex jsdocs other testing including end to end and pixel testing is also possible so you may decide to use an environment that does numerous things note future phases may include code coverage reporting packaging deployment minification and more you are welcome to try these ideas out now in preparation for future phases your ci cd pipeline should be run as github actions your ci cd pipeline should not be building anything substantial at this phase especially if you have not cleared your pitch stage use some simple experimental code to demonstrate testing docs linting etc given the parallel creation of devops features as you code you may consider making special branches to test out the pipeline then once finalized have it work on main and stage branches appropriately for the satisfactory completion of this phase you should provide the following items and store them in your repo under admin cipipeline png a diagram of your phase build pipeline can be drawio png if using draw io md a short page roughly status on the pipeline in terms of what is currently functional and what is planned or in progress embed your diagram in the markdown file a no more than min video demonstration of the pipeline | 0 |
44,753 | 18,214,066,064 | IssuesEvent | 2021-09-30 00:26:02 | microsoft/botbuilder-dotnet | https://api.github.com/repos/microsoft/botbuilder-dotnet | closed | Replace Dialog Action Not Working | P1 customer-reported Bot Services customer-replied-to ExemptFromDailyDRIReport Size: S |
## Describe the bug
Replace Dialog action not working and throws the following error:
DialogContext.BeginDialogAsync(): A dialog with an id of ‘SecondDialog’ wasn’t found. The dialog must be included in the current or parent DialogSet. For example, if subclassing a ComponentDialog you can call AddDialog() within your constructor.
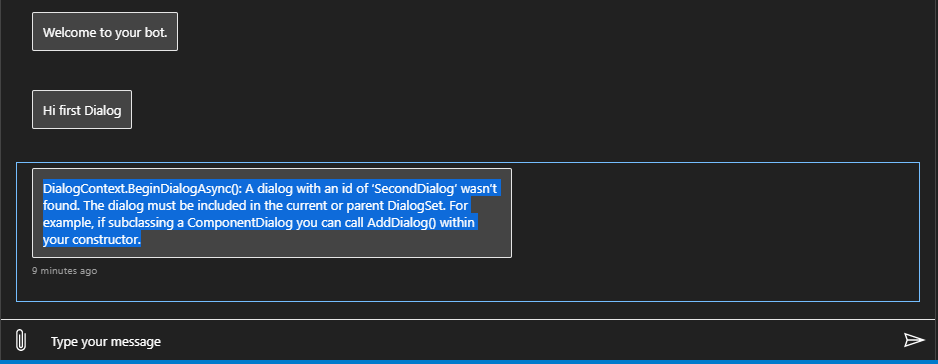
## Version
Release: 2.0.0-test
Runtime
<PackageReference Include="Microsoft.AspNetCore.Mvc.NewtonsoftJson" Version="3.1.8" />
<PackageReference Include="Microsoft.Bot.Builder.AI.Luis" Version="4.13.1" />
<PackageReference Include="Microsoft.Bot.Builder.AI.QnA" Version="4.13.1" />
<PackageReference Include="Microsoft.Bot.Builder.Dialogs.Adaptive.Runtime" Version="4.13.1" />
## Browser
<!-- What browser are you using? -->
- [ ] Electron distribution
- [x] Chrome
- [ ] Safari
- [ ] Firefox
- [ ] Edge
## OS
<!-- What operating system are you using? -->
- [ ] macOS
- [x] Windows
- [ ] Ubuntu
## To Reproduce
Steps to reproduce the behavior:
I created simple test Bot with two dialogs, and the first dialog call replace dialog action for the second dialog
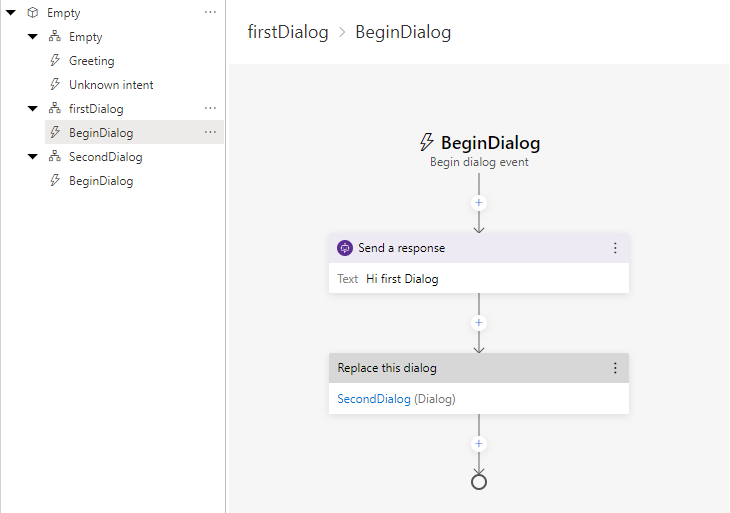
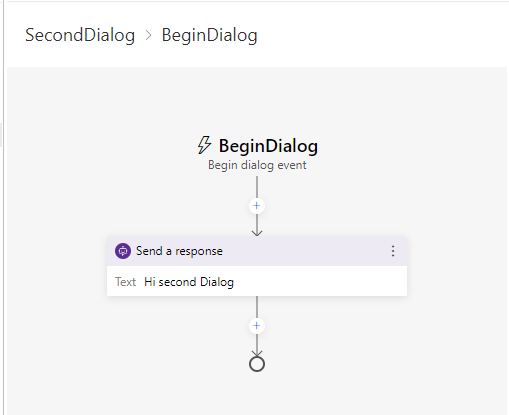
## Expected behavior
Open Second Dialog
| 1.0 | Replace Dialog Action Not Working -
## Describe the bug
Replace Dialog action not working and throws the following error:
DialogContext.BeginDialogAsync(): A dialog with an id of ‘SecondDialog’ wasn’t found. The dialog must be included in the current or parent DialogSet. For example, if subclassing a ComponentDialog you can call AddDialog() within your constructor.
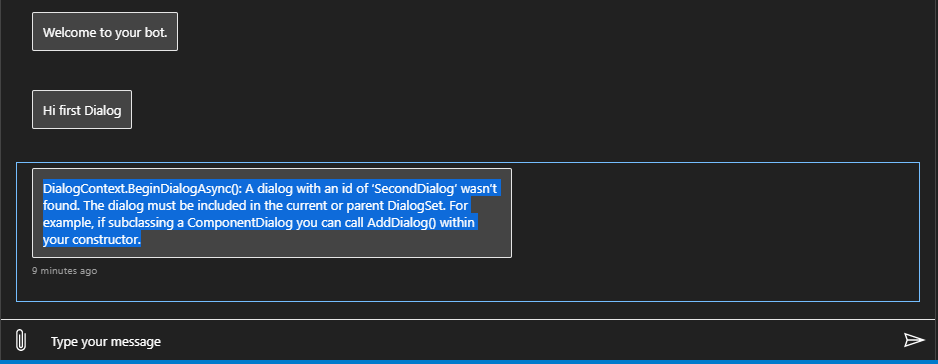
## Version
Release: 2.0.0-test
Runtime
<PackageReference Include="Microsoft.AspNetCore.Mvc.NewtonsoftJson" Version="3.1.8" />
<PackageReference Include="Microsoft.Bot.Builder.AI.Luis" Version="4.13.1" />
<PackageReference Include="Microsoft.Bot.Builder.AI.QnA" Version="4.13.1" />
<PackageReference Include="Microsoft.Bot.Builder.Dialogs.Adaptive.Runtime" Version="4.13.1" />
## Browser
<!-- What browser are you using? -->
- [ ] Electron distribution
- [x] Chrome
- [ ] Safari
- [ ] Firefox
- [ ] Edge
## OS
<!-- What operating system are you using? -->
- [ ] macOS
- [x] Windows
- [ ] Ubuntu
## To Reproduce
Steps to reproduce the behavior:
I created simple test Bot with two dialogs, and the first dialog call replace dialog action for the second dialog
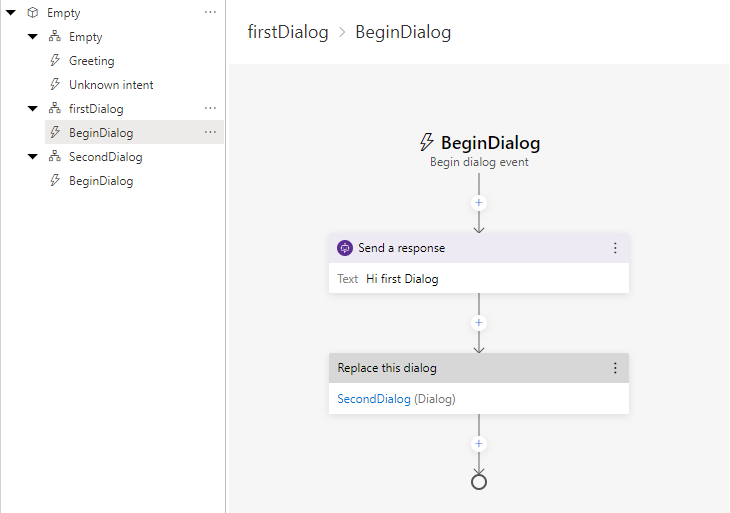
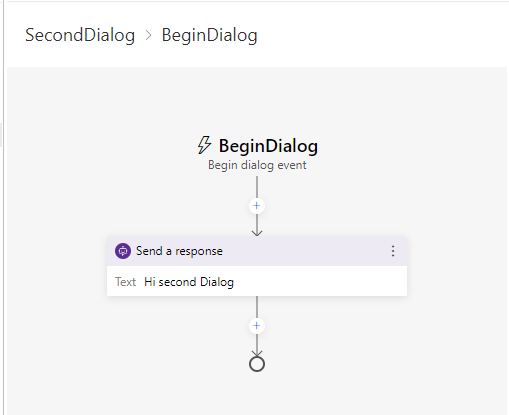
## Expected behavior
Open Second Dialog
| non_priority | replace dialog action not working describe the bug replace dialog action not working and throws the following error dialogcontext begindialogasync a dialog with an id of ‘seconddialog’ wasn’t found the dialog must be included in the current or parent dialogset for example if subclassing a componentdialog you can call adddialog within your constructor version release test runtime browser electron distribution chrome safari firefox edge os macos windows ubuntu to reproduce steps to reproduce the behavior i created simple test bot with two dialogs and the first dialog call replace dialog action for the second dialog expected behavior open second dialog | 0 |
129,868 | 27,580,035,033 | IssuesEvent | 2023-03-08 15:37:13 | SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8 | https://api.github.com/repos/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8 | opened | Code Security Report: 25 high severity findings, 134 total findings | Mend: code security findings | # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-03-08 03:35pm
**Total Findings:** 134 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 423
**Detected Programming Languages:** 2 (JavaScript / Node.js, Java)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/7b0f2123-52fa-4080-80c6-fb2c22edf226/details).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Assignment5.java:59](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson8.java:66](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66)
</td><td>4</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L61-L66
<details>
<summary>4 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L55
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L55
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L58
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66
</details>
[View more Data Flows](https://dev.whitesourcesoftware.com/sast/#/scans/7b0f2123-52fa-4080-80c6-fb2c22edf226/details?vulnId=dd6108fc-59a1-46aa-8dd5-bb56f46deeeb&filtered=yes)
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson9.java:66](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66)
</td><td>4</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61-L66
<details>
<summary>4 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L59
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
[View more Data Flows](https://dev.whitesourcesoftware.com/sast/#/scans/7b0f2123-52fa-4080-80c6-fb2c22edf226/details?vulnId=13c02663-c92b-494b-bc90-6668dc4edda2&filtered=yes)
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson4.java:63](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L58-L63
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson10.java:63](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63)
</td><td>1</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson3.java:65](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60-L65
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5a.java:62](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62)
</td><td>3</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57-L62
<details>
<summary>3 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5b.java:58](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58)
</td><td>1</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L53-L58
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L55
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson2.java:62](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L57-L62
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L59
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionChallenge.java:65](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65)
</td><td>1</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L63
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L63
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|DOM Based Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|JavaScript / Node.js|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Java|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java|12|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java|47|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java|10|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Console Output|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Miscellaneous Dangerous Functions|[CWE-676](https://cwe.mitre.org/data/definitions/676.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|XML External Entity (XXE) Injection|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|Java|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Java|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|JavaScript / Node.js|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Heap Inspection|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Java|33|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|Cookie Injection|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|Weak Hash Strength|[CWE-916](https://cwe.mitre.org/data/definitions/916.html)|Java|1|
| 1.0 | Code Security Report: 25 high severity findings, 134 total findings - # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-03-08 03:35pm
**Total Findings:** 134 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 423
**Detected Programming Languages:** 2 (JavaScript / Node.js, Java)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend SAST Application](https://dev.whitesourcesoftware.com/sast/#/scans/7b0f2123-52fa-4080-80c6-fb2c22edf226/details).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Assignment5.java:59](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson8.java:66](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66)
</td><td>4</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L61-L66
<details>
<summary>4 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L55
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L55
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L58
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L66
</details>
[View more Data Flows](https://dev.whitesourcesoftware.com/sast/#/scans/7b0f2123-52fa-4080-80c6-fb2c22edf226/details?vulnId=dd6108fc-59a1-46aa-8dd5-bb56f46deeeb&filtered=yes)
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson9.java:66](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66)
</td><td>4</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61-L66
<details>
<summary>4 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L59
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
[View more Data Flows](https://dev.whitesourcesoftware.com/sast/#/scans/7b0f2123-52fa-4080-80c6-fb2c22edf226/details?vulnId=13c02663-c92b-494b-bc90-6668dc4edda2&filtered=yes)
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson4.java:63](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L58-L63
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson10.java:63](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63)
</td><td>1</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson3.java:65](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60-L65
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5a.java:62](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62)
</td><td>3</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57-L62
<details>
<summary>3 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5b.java:58](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58)
</td><td>1</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L53-L58
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L55
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson2.java:62](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62)
</td><td>2</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L57-L62
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L59
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionChallenge.java:65](https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65)
</td><td>1</td><td>2023-03-08 03:36pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L63
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L63
https://github.com/SAST-org/SAST-Test-Repo-c5832d36-ef13-4c5d-b32a-0e8194b78dd8/blob/de6ac117c4098003b9e2427b7bc486acda826dc9/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionChallenge.java#L65
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|DOM Based Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|JavaScript / Node.js|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|Java|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java|12|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java|47|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java|10|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Console Output|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Miscellaneous Dangerous Functions|[CWE-676](https://cwe.mitre.org/data/definitions/676.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|XML External Entity (XXE) Injection|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|Java|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|Java|9|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|JavaScript / Node.js|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium|Heap Inspection|[CWE-244](https://cwe.mitre.org/data/definitions/244.html)|Java|33|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|Cookie Injection|[CWE-20](https://cwe.mitre.org/data/definitions/20.html)|Java|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low|Weak Hash Strength|[CWE-916](https://cwe.mitre.org/data/definitions/916.html)|Java|1|
| non_priority | code security report high severity findings total findings code security report scan metadata latest scan total findings new findings resolved findings tested project files detected programming languages javascript node js java check this box to manually trigger a scan most relevant findings the below list presents the most relevant findings that need your attention to view information on the remaining findings navigate to the severity vulnerability type cwe file data flows date high sql injection more info data flow s detected view data flow view data flow high sql injection more info data flow s detected view data flow view data flow view data flow high sql injection more info data flow s detected view data flow view data flow view data flow high sql injection more info data flow s detected view data flow view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow view data flow high sql injection more info data flow s detected view data flow view data flow view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow view data flow high sql injection more info data flow s detected view data flow findings overview severity vulnerability type cwe language count high deserialization of untrusted data high dom based cross site scripting node js high cross site scripting high path directory traversal high server side request forgery high sql injection medium error messages information exposure medium hardcoded password credentials medium console output medium miscellaneous dangerous functions medium xml external entity xxe injection medium weak pseudo random medium weak pseudo random node js medium heap inspection low cookie injection low weak hash strength | 0 |
108,820 | 16,822,696,582 | IssuesEvent | 2021-06-17 14:47:05 | idonthaveafifaaddiction/flink | https://api.github.com/repos/idonthaveafifaaddiction/flink | opened | CVE-2021-33623 (High) detected in trim-newlines-1.0.0.tgz | security vulnerability | ## CVE-2021-33623 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: flink/flink-runtime-web/web-dashboard/package.json</p>
<p>Path to vulnerable library: flink/flink-runtime-web/web-dashboard/node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.13.6.tgz (Root Library)
- node-sass-4.11.0.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/flink/commit/d77b18bba5da590fb2e8e8aa13f2dcb0674d52be">d77b18bba5da590fb2e8e8aa13f2dcb0674d52be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"trim-newlines","packageVersion":"1.0.0","packageFilePaths":["/flink-runtime-web/web-dashboard/package.json"],"isTransitiveDependency":true,"dependencyTree":"@angular-devkit/build-angular:0.13.6;node-sass:4.11.0;meow:3.7.0;trim-newlines:1.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"trim-newlines - 3.0.1, 4.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33623","vulnerabilityDetails":"The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-33623 (High) detected in trim-newlines-1.0.0.tgz - ## CVE-2021-33623 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>trim-newlines-1.0.0.tgz</b></p></summary>
<p>Trim newlines from the start and/or end of a string</p>
<p>Library home page: <a href="https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz">https://registry.npmjs.org/trim-newlines/-/trim-newlines-1.0.0.tgz</a></p>
<p>Path to dependency file: flink/flink-runtime-web/web-dashboard/package.json</p>
<p>Path to vulnerable library: flink/flink-runtime-web/web-dashboard/node_modules/trim-newlines/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.13.6.tgz (Root Library)
- node-sass-4.11.0.tgz
- meow-3.7.0.tgz
- :x: **trim-newlines-1.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/idonthaveafifaaddiction/flink/commit/d77b18bba5da590fb2e8e8aa13f2dcb0674d52be">d77b18bba5da590fb2e8e8aa13f2dcb0674d52be</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.
<p>Publish Date: 2021-05-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623>CVE-2021-33623</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33623</a></p>
<p>Release Date: 2021-05-28</p>
<p>Fix Resolution: trim-newlines - 3.0.1, 4.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"trim-newlines","packageVersion":"1.0.0","packageFilePaths":["/flink-runtime-web/web-dashboard/package.json"],"isTransitiveDependency":true,"dependencyTree":"@angular-devkit/build-angular:0.13.6;node-sass:4.11.0;meow:3.7.0;trim-newlines:1.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"trim-newlines - 3.0.1, 4.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-33623","vulnerabilityDetails":"The trim-newlines package before 3.0.1 and 4.x before 4.0.1 for Node.js has an issue related to regular expression denial-of-service (ReDoS) for the .end() method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33623","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in trim newlines tgz cve high severity vulnerability vulnerable library trim newlines tgz trim newlines from the start and or end of a string library home page a href path to dependency file flink flink runtime web web dashboard package json path to vulnerable library flink flink runtime web web dashboard node modules trim newlines package json dependency hierarchy build angular tgz root library node sass tgz meow tgz x trim newlines tgz vulnerable library found in head commit a href found in base branch master vulnerability details the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution trim newlines isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree angular devkit build angular node sass meow trim newlines isminimumfixversionavailable true minimumfixversion trim newlines basebranches vulnerabilityidentifier cve vulnerabilitydetails the trim newlines package before and x before for node js has an issue related to regular expression denial of service redos for the end method vulnerabilityurl | 0 |
289,330 | 21,779,656,159 | IssuesEvent | 2022-05-13 17:19:54 | PaloAltoNetworks/terraform-provider-panos | https://api.github.com/repos/PaloAltoNetworks/terraform-provider-panos | closed | Correct Misspelling OF Information | documentation | ## Documentation link
[https://registry.terraform.io/providers/PaloAltoNetworks/panos/latest/docs/resources/vm_information_source]
)
## Describe the problem
Typo of the word information. It is spelled "infomration"
## Suggested fix
Change infomration to information
| 1.0 | Correct Misspelling OF Information - ## Documentation link
[https://registry.terraform.io/providers/PaloAltoNetworks/panos/latest/docs/resources/vm_information_source]
)
## Describe the problem
Typo of the word information. It is spelled "infomration"
## Suggested fix
Change infomration to information
| non_priority | correct misspelling of information documentation link describe the problem typo of the word information it is spelled infomration suggested fix change infomration to information | 0 |
3,124 | 2,658,419,839 | IssuesEvent | 2015-03-18 15:32:19 | genome/gms | https://api.github.com/repos/genome/gms | closed | ERROR: column build.created_at does not exist | bug testing merge | Running the meta-data importer results in what looks like a schema error.
```
gmsuser@clia1 ~/gms (ubuntu-12.04-2015.02.22)> genome model import metadata 18177dd5eca44514a47f367d9804e17a-2014.3.14.dat
DBD::Pg::st execute failed: ERROR: column build.created_at does not exist
LINE 2: select model.build.build_id, model.build.created_at, model.b...
^ at /opt/gms/2M4JU61/sw/ur/lib/UR/DBI.pm line 888.
ERROR: Failed to execute SQL
select model.build.build_id, model.build.created_at, model.build.created_by, model.build.data_directory, model.build.date_completed, model.build.date_scheduled, model.build.model_id, model.b
uild.run_by, model.build.software_revision, model.build.status, model.build.SUBCLASS_NAME, model.build.updated_at
from model.build
where model.build.build_id in ('124434505')
and model.build.SUBCLASS_NAME = ?
order by model.build.build_id COLLATE "C"
ERROR: column build.created_at does not exist
LINE 2: select model.build.build_id, model.build.created_at, model.b...
``` | 1.0 | ERROR: column build.created_at does not exist - Running the meta-data importer results in what looks like a schema error.
```
gmsuser@clia1 ~/gms (ubuntu-12.04-2015.02.22)> genome model import metadata 18177dd5eca44514a47f367d9804e17a-2014.3.14.dat
DBD::Pg::st execute failed: ERROR: column build.created_at does not exist
LINE 2: select model.build.build_id, model.build.created_at, model.b...
^ at /opt/gms/2M4JU61/sw/ur/lib/UR/DBI.pm line 888.
ERROR: Failed to execute SQL
select model.build.build_id, model.build.created_at, model.build.created_by, model.build.data_directory, model.build.date_completed, model.build.date_scheduled, model.build.model_id, model.b
uild.run_by, model.build.software_revision, model.build.status, model.build.SUBCLASS_NAME, model.build.updated_at
from model.build
where model.build.build_id in ('124434505')
and model.build.SUBCLASS_NAME = ?
order by model.build.build_id COLLATE "C"
ERROR: column build.created_at does not exist
LINE 2: select model.build.build_id, model.build.created_at, model.b...
``` | non_priority | error column build created at does not exist running the meta data importer results in what looks like a schema error gmsuser gms ubuntu genome model import metadata dat dbd pg st execute failed error column build created at does not exist line select model build build id model build created at model b at opt gms sw ur lib ur dbi pm line error failed to execute sql select model build build id model build created at model build created by model build data directory model build date completed model build date scheduled model build model id model b uild run by model build software revision model build status model build subclass name model build updated at from model build where model build build id in and model build subclass name order by model build build id collate c error column build created at does not exist line select model build build id model build created at model b | 0 |
42,610 | 11,031,754,318 | IssuesEvent | 2019-12-06 18:30:40 | pnplab/Flux | https://api.github.com/repos/pnplab/Flux | opened | Error in MainActivity | LOCAL_BUILD bugsnag development | ## Error in Flux
**Error** in **MainActivity**
Failed to parse declaration "padding: 50 0 50 0"
[View on Bugsnag](https://app.bugsnag.com/criusmm/flux/errors/5dea9a71458a250019806db4?event_id=5dea9a710054345367010000&i=gh&m=ci)
## Stacktrace
http://localhost:8081/index.bundle?platform=android&dev=true&minify=false:171074 -
[View full stacktrace](https://app.bugsnag.com/criusmm/flux/errors/5dea9a71458a250019806db4?event_id=5dea9a710054345367010000&i=gh&m=ci)
*Created automatically via Bugsnag* | 1.0 | Error in MainActivity - ## Error in Flux
**Error** in **MainActivity**
Failed to parse declaration "padding: 50 0 50 0"
[View on Bugsnag](https://app.bugsnag.com/criusmm/flux/errors/5dea9a71458a250019806db4?event_id=5dea9a710054345367010000&i=gh&m=ci)
## Stacktrace
http://localhost:8081/index.bundle?platform=android&dev=true&minify=false:171074 -
[View full stacktrace](https://app.bugsnag.com/criusmm/flux/errors/5dea9a71458a250019806db4?event_id=5dea9a710054345367010000&i=gh&m=ci)
*Created automatically via Bugsnag* | non_priority | error in mainactivity error in flux error in mainactivity failed to parse declaration padding stacktrace created automatically via bugsnag | 0 |
83,414 | 10,326,864,826 | IssuesEvent | 2019-09-02 04:23:29 | tweepy/tweepy | https://api.github.com/repos/tweepy/tweepy | closed | Favorited state in search is always false | API Documentation | I've been trying to use the `status.favorited` variable of a status retrieved by `api.search` but it was always false. When trying to favorite this tweet it gave me exceptions with a message that that tweet was already favorited. After some help from the discord, I've discovered that this is fault on the twitter API itself [1]. My suggestion is to internally cross reference with a user's favorites to mitigate this.
As a developer, this was not a fun experience and I want to prevent this from happening to others.
[1] https://twittercommunity.com/t/favorited-reports-as-false-even-if-status-is-already-favorited-by-the-user/11145 | 1.0 | Favorited state in search is always false - I've been trying to use the `status.favorited` variable of a status retrieved by `api.search` but it was always false. When trying to favorite this tweet it gave me exceptions with a message that that tweet was already favorited. After some help from the discord, I've discovered that this is fault on the twitter API itself [1]. My suggestion is to internally cross reference with a user's favorites to mitigate this.
As a developer, this was not a fun experience and I want to prevent this from happening to others.
[1] https://twittercommunity.com/t/favorited-reports-as-false-even-if-status-is-already-favorited-by-the-user/11145 | non_priority | favorited state in search is always false i ve been trying to use the status favorited variable of a status retrieved by api search but it was always false when trying to favorite this tweet it gave me exceptions with a message that that tweet was already favorited after some help from the discord i ve discovered that this is fault on the twitter api itself my suggestion is to internally cross reference with a user s favorites to mitigate this as a developer this was not a fun experience and i want to prevent this from happening to others | 0 |
153,654 | 13,521,767,842 | IssuesEvent | 2020-09-15 07:33:22 | dsccommunity/SharePointDsc | https://api.github.com/repos/dsccommunity/SharePointDsc | closed | Broken Example on SPServiceAppSecurity Wiki Page | bug documentation in progress | On the https://github.com/dsccommunity/SharePointDsc/wiki/SPServiceAppSecurity page in Example 1, `@("Manage Profiles", "Manage Social Data")` does not go well together with `SecurityType = "SharingPermissions"`. One of them should be changed. | 1.0 | Broken Example on SPServiceAppSecurity Wiki Page - On the https://github.com/dsccommunity/SharePointDsc/wiki/SPServiceAppSecurity page in Example 1, `@("Manage Profiles", "Manage Social Data")` does not go well together with `SecurityType = "SharingPermissions"`. One of them should be changed. | non_priority | broken example on spserviceappsecurity wiki page on the page in example manage profiles manage social data does not go well together with securitytype sharingpermissions one of them should be changed | 0 |
41,908 | 9,099,033,011 | IssuesEvent | 2019-02-20 02:32:44 | Daolab/beakeros | https://api.github.com/repos/Daolab/beakeros | closed | Procedure#Entry Capability | A-code | Tests should use library function `#proc_entry(string id)` in `BeakerContract.sol`
We need to include a test where:
1. Creates Procedure A and Procedure B into the procedure table.
1. Procedure A is designated as the Entry Procedure during kernel instantiation.
1. Procedure A is also designated a procedure entry capability (type `0x6`) that allows it to designate a new entry procedure from the procedure table given an id.
1. Procedure B is not given any capabilities
1. Procedure A changes Procedure B as the entry procedure, giving up it's position and does so by invoking it's procedure entry capability. | 1.0 | Procedure#Entry Capability - Tests should use library function `#proc_entry(string id)` in `BeakerContract.sol`
We need to include a test where:
1. Creates Procedure A and Procedure B into the procedure table.
1. Procedure A is designated as the Entry Procedure during kernel instantiation.
1. Procedure A is also designated a procedure entry capability (type `0x6`) that allows it to designate a new entry procedure from the procedure table given an id.
1. Procedure B is not given any capabilities
1. Procedure A changes Procedure B as the entry procedure, giving up it's position and does so by invoking it's procedure entry capability. | non_priority | procedure entry capability tests should use library function proc entry string id in beakercontract sol we need to include a test where creates procedure a and procedure b into the procedure table procedure a is designated as the entry procedure during kernel instantiation procedure a is also designated a procedure entry capability type that allows it to designate a new entry procedure from the procedure table given an id procedure b is not given any capabilities procedure a changes procedure b as the entry procedure giving up it s position and does so by invoking it s procedure entry capability | 0 |
36,970 | 15,108,910,347 | IssuesEvent | 2021-02-08 17:11:08 | Azure/azure-sdk-for-python | https://api.github.com/repos/Azure/azure-sdk-for-python | closed | azure.cosmos.offer.Offer documentation is incomplete | Client Cosmos Docs Service Attention customer-reported | This documentation page simply displays the constructor method for class Offer. It is missing two critical items - how to get the current number of RUs for the Offer (i.e. - container), as well as it's properties.
One has to dig into the source code, at the following link, to see how to obtain the RUs and properties:
https://github.com/Azure/azure-sdk-for-python/blob/master/sdk/cosmos/azure-cosmos/azure/cosmos/offer.py
Please update the page to show something like the following:
ru = offer.offer_throughput
props_dict = offer.properties
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 485e091d-2bd1-ab33-ced0-b12c47c1fd99
* Version Independent ID: 840c2479-f0b3-2bd2-a6dd-3cb4c28235d0
* Content: [azure.cosmos.offer.Offer class](https://docs.microsoft.com/en-us/python/api/azure-cosmos/azure.cosmos.offer.offer?view=azure-python)
* Content Source: [docs-ref-autogen/azure-cosmos/azure.cosmos.offer.Offer.yml](https://github.com/MicrosoftDocs/azure-docs-sdk-python/blob/master/docs-ref-autogen/azure-cosmos/azure.cosmos.offer.Offer.yml)
* GitHub Login: @lmazuel
* Microsoft Alias: **lmazuel** | 1.0 | azure.cosmos.offer.Offer documentation is incomplete - This documentation page simply displays the constructor method for class Offer. It is missing two critical items - how to get the current number of RUs for the Offer (i.e. - container), as well as it's properties.
One has to dig into the source code, at the following link, to see how to obtain the RUs and properties:
https://github.com/Azure/azure-sdk-for-python/blob/master/sdk/cosmos/azure-cosmos/azure/cosmos/offer.py
Please update the page to show something like the following:
ru = offer.offer_throughput
props_dict = offer.properties
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 485e091d-2bd1-ab33-ced0-b12c47c1fd99
* Version Independent ID: 840c2479-f0b3-2bd2-a6dd-3cb4c28235d0
* Content: [azure.cosmos.offer.Offer class](https://docs.microsoft.com/en-us/python/api/azure-cosmos/azure.cosmos.offer.offer?view=azure-python)
* Content Source: [docs-ref-autogen/azure-cosmos/azure.cosmos.offer.Offer.yml](https://github.com/MicrosoftDocs/azure-docs-sdk-python/blob/master/docs-ref-autogen/azure-cosmos/azure.cosmos.offer.Offer.yml)
* GitHub Login: @lmazuel
* Microsoft Alias: **lmazuel** | non_priority | azure cosmos offer offer documentation is incomplete this documentation page simply displays the constructor method for class offer it is missing two critical items how to get the current number of rus for the offer i e container as well as it s properties one has to dig into the source code at the following link to see how to obtain the rus and properties please update the page to show something like the following ru offer offer throughput props dict offer properties document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source github login lmazuel microsoft alias lmazuel | 0 |
43,265 | 9,413,716,705 | IssuesEvent | 2019-04-10 08:30:05 | atomist/uhura | https://api.github.com/repos/atomist/uhura | closed | Code Inspection: npm audit on dotnet-core | code-inspection | ### js-yaml:<3.13.0
- _(warn)_ [Denial of Service](https://npmjs.com/advisories/788) _Upgrade to version 3.13.0._
- `js-yaml:3.12.1`:
- `@atomist/automation-client>graphql-code-generator>js-yaml`
- `js-yaml:3.12.0`:
- `mocha>js-yaml`
[atomist:code-inspection:dotnet-core=@atomist/atomist-sdm] | 1.0 | Code Inspection: npm audit on dotnet-core - ### js-yaml:<3.13.0
- _(warn)_ [Denial of Service](https://npmjs.com/advisories/788) _Upgrade to version 3.13.0._
- `js-yaml:3.12.1`:
- `@atomist/automation-client>graphql-code-generator>js-yaml`
- `js-yaml:3.12.0`:
- `mocha>js-yaml`
[atomist:code-inspection:dotnet-core=@atomist/atomist-sdm] | non_priority | code inspection npm audit on dotnet core js yaml warn upgrade to version js yaml atomist automation client graphql code generator js yaml js yaml mocha js yaml | 0 |
40,832 | 5,317,495,853 | IssuesEvent | 2017-02-13 22:41:21 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | teamcity: failed tests on master: test/TestReplicateRogueRemovedNode | Robot test-failure | The following tests appear to have failed:
[#148911](https://teamcity.cockroachdb.com/viewLog.html?buildId=148911):
```
--- FAIL: test/TestReplicateRogueRemovedNode (0.310s)
client_raft_test.go:2376: ReplicaID 1 not found
------- Stdout: -------
I170213 22:35:06.507861 26303 storage/store.go:1261 [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170213 22:35:06.507903 26303 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:42886" > attrs:<> locality:<>
W170213 22:35:06.512862 26303 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170213 22:35:06.513476 26303 storage/store.go:1261 [n2,s2]: failed initial metrics computation: [n2,s2]: system config not yet available
I170213 22:35:06.513550 26303 gossip/gossip.go:293 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:60749" > attrs:<> locality:<>
I170213 22:35:06.513719 26207 gossip/client.go:131 [n2] started gossip client to 127.0.0.1:42886
W170213 22:35:06.515516 26303 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170213 22:35:06.516194 26303 storage/store.go:1261 [n3,s3]: failed initial metrics computation: [n3,s3]: system config not yet available
I170213 22:35:06.516243 26303 gossip/gossip.go:293 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:44118" > attrs:<> locality:<>
I170213 22:35:06.517326 26505 gossip/client.go:131 [n3] started gossip client to 127.0.0.1:42886
I170213 22:35:06.587736 26303 storage/replica_raftstorage.go:414 [s1,r1/1:/M{in-ax},@c420b10380] generated preemptive snapshot 88bf2ba4 at index 15
I170213 22:35:06.588216 26303 storage/store.go:3278 [s1,r1/1:/M{in-ax},@c420b10380] streamed snapshot: kv pairs: 34, log entries: 5, 0ms
I170213 22:35:06.588525 26535 storage/replica_raftstorage.go:596 [s2,r1/?:{-},@c420b92000] applying preemptive snapshot at index 15 (id=88bf2ba4, encoded size=5005, 1 rocksdb batches, 5 log entries)
I170213 22:35:06.588866 26535 storage/replica_raftstorage.go:604 [s2,r1/?:/M{in-ax},@c420b92000] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170213 22:35:06.589294 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {2 2 2}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I170213 22:35:06.590019 26539 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I170213 22:35:06.590805 26303 storage/replica_raftstorage.go:414 [s1,r1/1:/M{in-ax},@c420b10380] generated preemptive snapshot 8b1296da at index 17
I170213 22:35:06.591186 26303 storage/store.go:3278 [s1,r1/1:/M{in-ax},@c420b10380] streamed snapshot: kv pairs: 37, log entries: 7, 0ms
I170213 22:35:06.591421 26584 storage/replica_raftstorage.go:596 [s3,r1/?:{-},@c420b10a80] applying preemptive snapshot at index 17 (id=8b1296da, encoded size=5945, 1 rocksdb batches, 7 log entries)
I170213 22:35:06.591766 26584 storage/replica_raftstorage.go:604 [s3,r1/?:/M{in-ax},@c420b10a80] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170213 22:35:06.592180 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {3 3 3}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:3
I170213 22:35:06.592917 26587 storage/raft_transport.go:437 raft transport stream to node 1 established
I170213 22:35:06.593880 26600 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing ADD_REPLICA {NodeID:3 StoreID:3 ReplicaID:3}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2} {NodeID:3 StoreID:3 ReplicaID:3}]
I170213 22:35:06.733698 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {3 3 3}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > replicas:<node_id:3 store_id:3 replica_id:3 > next_replica_id:4
I170213 22:35:06.734725 26567 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing REMOVE_REPLICA {NodeID:3 StoreID:3 ReplicaID:3}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I170213 22:35:06.735969 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {2 2 2}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:4
I170213 22:35:06.737577 26627 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing REMOVE_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1}]
I170213 22:35:06.738587 26303 storage/client_test.go:1145 test clock advanced to: 1.800000125,0
I170213 22:35:06.739267 26303 storage/store.go:2100 [replicaGC,s2,r1/2:/M{in-ax},@c420b92000] removing replica
I170213 22:35:06.739437 26303 storage/replica.go:735 [replicaGC,s2,r1/2:/M{in-ax},@c420b92000] removed 36 (26+10) keys in 0ms [clear=0ms commit=0ms]
W170213 22:35:06.740475 26556 storage/store.go:3138 [s1] got error from range 1, replica {2 2 2}: raft group deleted
E170213 22:35:06.741484 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.741629 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.745703 26652 storage/replica_proposal.go:602 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.745939 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.745986 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
W170213 22:35:06.746019 26658 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.746041 26658 storage/store.go:1348 [s3] error gossiping first range descriptor: range 1 was not found
W170213 22:35:06.746070 26660 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
W170213 22:35:06.746101 26659 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.746131 26659 storage/store.go:1348 [s3] error gossiping system config: range 1 was not found
E170213 22:35:06.746151 26660 storage/store.go:1348 [s3] error gossiping node liveness: range 1 was not found
W170213 22:35:06.758257 26556 storage/store.go:3138 [s1] got error from range 1, replica {2 2 2}: raft group deleted
E170213 22:35:06.790914 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
W170213 22:35:06.792650 26660 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.792698 26660 storage/store.go:1348 [s3] error gossiping node liveness: range 1 was not found
W170213 22:35:06.795265 26659 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.795291 26659 storage/store.go:1348 [s3] error gossiping system config: range 1 was not found
W170213 22:35:06.796691 26658 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.796717 26658 storage/store.go:1348 [s3] error gossiping first range descriptor: range 1 was not found
I170213 22:35:06.814076 26359 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:42886->127.0.0.1:53432: use of closed network connection
I170213 22:35:06.814104 26336 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:44118->127.0.0.1:46065: use of closed network connection
I170213 22:35:06.814170 26412 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:60749->127.0.0.1:56226: use of closed network connection
```
Please assign, take a look and update the issue accordingly. | 1.0 | teamcity: failed tests on master: test/TestReplicateRogueRemovedNode - The following tests appear to have failed:
[#148911](https://teamcity.cockroachdb.com/viewLog.html?buildId=148911):
```
--- FAIL: test/TestReplicateRogueRemovedNode (0.310s)
client_raft_test.go:2376: ReplicaID 1 not found
------- Stdout: -------
I170213 22:35:06.507861 26303 storage/store.go:1261 [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170213 22:35:06.507903 26303 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:42886" > attrs:<> locality:<>
W170213 22:35:06.512862 26303 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170213 22:35:06.513476 26303 storage/store.go:1261 [n2,s2]: failed initial metrics computation: [n2,s2]: system config not yet available
I170213 22:35:06.513550 26303 gossip/gossip.go:293 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:60749" > attrs:<> locality:<>
I170213 22:35:06.513719 26207 gossip/client.go:131 [n2] started gossip client to 127.0.0.1:42886
W170213 22:35:06.515516 26303 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170213 22:35:06.516194 26303 storage/store.go:1261 [n3,s3]: failed initial metrics computation: [n3,s3]: system config not yet available
I170213 22:35:06.516243 26303 gossip/gossip.go:293 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:44118" > attrs:<> locality:<>
I170213 22:35:06.517326 26505 gossip/client.go:131 [n3] started gossip client to 127.0.0.1:42886
I170213 22:35:06.587736 26303 storage/replica_raftstorage.go:414 [s1,r1/1:/M{in-ax},@c420b10380] generated preemptive snapshot 88bf2ba4 at index 15
I170213 22:35:06.588216 26303 storage/store.go:3278 [s1,r1/1:/M{in-ax},@c420b10380] streamed snapshot: kv pairs: 34, log entries: 5, 0ms
I170213 22:35:06.588525 26535 storage/replica_raftstorage.go:596 [s2,r1/?:{-},@c420b92000] applying preemptive snapshot at index 15 (id=88bf2ba4, encoded size=5005, 1 rocksdb batches, 5 log entries)
I170213 22:35:06.588866 26535 storage/replica_raftstorage.go:604 [s2,r1/?:/M{in-ax},@c420b92000] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170213 22:35:06.589294 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {2 2 2}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I170213 22:35:06.590019 26539 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I170213 22:35:06.590805 26303 storage/replica_raftstorage.go:414 [s1,r1/1:/M{in-ax},@c420b10380] generated preemptive snapshot 8b1296da at index 17
I170213 22:35:06.591186 26303 storage/store.go:3278 [s1,r1/1:/M{in-ax},@c420b10380] streamed snapshot: kv pairs: 37, log entries: 7, 0ms
I170213 22:35:06.591421 26584 storage/replica_raftstorage.go:596 [s3,r1/?:{-},@c420b10a80] applying preemptive snapshot at index 17 (id=8b1296da, encoded size=5945, 1 rocksdb batches, 7 log entries)
I170213 22:35:06.591766 26584 storage/replica_raftstorage.go:604 [s3,r1/?:/M{in-ax},@c420b10a80] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170213 22:35:06.592180 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {3 3 3}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:3
I170213 22:35:06.592917 26587 storage/raft_transport.go:437 raft transport stream to node 1 established
I170213 22:35:06.593880 26600 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing ADD_REPLICA {NodeID:3 StoreID:3 ReplicaID:3}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2} {NodeID:3 StoreID:3 ReplicaID:3}]
I170213 22:35:06.733698 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {3 3 3}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > replicas:<node_id:3 store_id:3 replica_id:3 > next_replica_id:4
I170213 22:35:06.734725 26567 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing REMOVE_REPLICA {NodeID:3 StoreID:3 ReplicaID:3}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I170213 22:35:06.735969 26303 storage/replica_command.go:3253 [s1,r1/1:/M{in-ax},@c420b10380] change replicas (remove {2 2 2}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > replicas:<node_id:2 store_id:2 replica_id:2 > next_replica_id:4
I170213 22:35:06.737577 26627 storage/replica.go:2487 [s1,r1/1:/M{in-ax},@c420b10380] proposing REMOVE_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1}]
I170213 22:35:06.738587 26303 storage/client_test.go:1145 test clock advanced to: 1.800000125,0
I170213 22:35:06.739267 26303 storage/store.go:2100 [replicaGC,s2,r1/2:/M{in-ax},@c420b92000] removing replica
I170213 22:35:06.739437 26303 storage/replica.go:735 [replicaGC,s2,r1/2:/M{in-ax},@c420b92000] removed 36 (26+10) keys in 0ms [clear=0ms commit=0ms]
W170213 22:35:06.740475 26556 storage/store.go:3138 [s1] got error from range 1, replica {2 2 2}: raft group deleted
E170213 22:35:06.741484 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.741629 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.745703 26652 storage/replica_proposal.go:602 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.745939 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
E170213 22:35:06.745986 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
W170213 22:35:06.746019 26658 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.746041 26658 storage/store.go:1348 [s3] error gossiping first range descriptor: range 1 was not found
W170213 22:35:06.746070 26660 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
W170213 22:35:06.746101 26659 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.746131 26659 storage/store.go:1348 [s3] error gossiping system config: range 1 was not found
E170213 22:35:06.746151 26660 storage/store.go:1348 [s3] error gossiping node liveness: range 1 was not found
W170213 22:35:06.758257 26556 storage/store.go:3138 [s1] got error from range 1, replica {2 2 2}: raft group deleted
E170213 22:35:06.790914 26589 storage/store.go:3128 [s3,r1/3:/M{in-ax},@c4209eca80] unable to add to replica GC queue: queue disabled
W170213 22:35:06.792650 26660 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.792698 26660 storage/store.go:1348 [s3] error gossiping node liveness: range 1 was not found
W170213 22:35:06.795265 26659 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.795291 26659 storage/store.go:1348 [s3] error gossiping system config: range 1 was not found
W170213 22:35:06.796691 26658 storage/replica.go:4323 [s3] could not acquire lease for range gossip: range 1 was not found
E170213 22:35:06.796717 26658 storage/store.go:1348 [s3] error gossiping first range descriptor: range 1 was not found
I170213 22:35:06.814076 26359 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:42886->127.0.0.1:53432: use of closed network connection
I170213 22:35:06.814104 26336 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:44118->127.0.0.1:46065: use of closed network connection
I170213 22:35:06.814170 26412 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:60749->127.0.0.1:56226: use of closed network connection
```
Please assign, take a look and update the issue accordingly. | non_priority | teamcity failed tests on master test testreplicaterogueremovednode the following tests appear to have failed fail test testreplicaterogueremovednode client raft test go replicaid not found stdout storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality gossip gossip go no incoming or outgoing connections storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality gossip client go started gossip client to gossip gossip go no incoming or outgoing connections storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality gossip client go started gossip client to storage replica raftstorage go generated preemptive snapshot at index storage store go streamed snapshot kv pairs log entries storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas remove read existing descriptor range id start key end key replicas next replica id storage replica go proposing add replica nodeid storeid replicaid storage replica raftstorage go generated preemptive snapshot at index storage store go streamed snapshot kv pairs log entries storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas remove read existing descriptor range id start key end key replicas replicas next replica id storage raft transport go raft transport stream to node established storage replica go proposing add replica nodeid storeid replicaid storage replica command go change replicas remove read existing descriptor range id start key end key replicas replicas replicas next replica id storage replica go proposing remove replica nodeid storeid replicaid storage replica command go change replicas remove read existing descriptor range id start key end key replicas replicas next replica id storage replica go proposing remove replica nodeid storeid replicaid storage client test go test clock advanced to storage store go removing replica storage replica go removed keys in storage store go got error from range replica raft group deleted storage store go unable to add to replica gc queue queue disabled storage store go unable to add to replica gc queue queue disabled storage replica proposal go unable to add to replica gc queue queue disabled storage store go unable to add to replica gc queue queue disabled storage store go unable to add to replica gc queue queue disabled storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping first range descriptor range was not found storage replica go could not acquire lease for range gossip range was not found storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping system config range was not found storage store go error gossiping node liveness range was not found storage store go got error from range replica raft group deleted storage store go unable to add to replica gc queue queue disabled storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping node liveness range was not found storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping system config range was not found storage replica go could not acquire lease for range gossip range was not found storage store go error gossiping first range descriptor range was not found vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection please assign take a look and update the issue accordingly | 0 |
9,965 | 14,216,013,667 | IssuesEvent | 2020-11-17 08:22:03 | cp-api/capella-requirements-vp | https://api.github.com/repos/cp-api/capella-requirements-vp | closed | Error using requirements-viewpoint with fragmented Model | capella critical requirementsvp verified | Attachment: [error-log.txt](https://raw.githubusercontent.com/wiki/cp-api/capella-requirements-vp/attachments/280997.txt)
VMDisconnectedException: Got IOException from Virtual Machine
See Capella-Forum
https://polarsys.org/forums/index.php/t/622/
I have encountered another problem when using a fragmented Capella-Model:
Capella-1.2.1
org.polarsys.capella.vp.requirements-dropins-0.9.1.201807111332
When I generate a new Model, reference the requirements-VP and try to import a ReqIF-file the merge window opens -> ok.
As soon as I fragment the model (e.g. the "Operational Analysis") and try it in the same way I get an error.
Stephane Bonnet: I do reproduce, and the error message shows that it is related to the extension of the file. So, it is clearly a bug.
`ECLIPSE-555387` `POLARSYS-2191` `@rco` `2018-09-18` | 1.0 | Error using requirements-viewpoint with fragmented Model - Attachment: [error-log.txt](https://raw.githubusercontent.com/wiki/cp-api/capella-requirements-vp/attachments/280997.txt)
VMDisconnectedException: Got IOException from Virtual Machine
See Capella-Forum
https://polarsys.org/forums/index.php/t/622/
I have encountered another problem when using a fragmented Capella-Model:
Capella-1.2.1
org.polarsys.capella.vp.requirements-dropins-0.9.1.201807111332
When I generate a new Model, reference the requirements-VP and try to import a ReqIF-file the merge window opens -> ok.
As soon as I fragment the model (e.g. the "Operational Analysis") and try it in the same way I get an error.
Stephane Bonnet: I do reproduce, and the error message shows that it is related to the extension of the file. So, it is clearly a bug.
`ECLIPSE-555387` `POLARSYS-2191` `@rco` `2018-09-18` | non_priority | error using requirements viewpoint with fragmented model attachment vmdisconnectedexception got ioexception from virtual machine see capella forum i have encountered another problem when using a fragmented capella model capella org polarsys capella vp requirements dropins when i generate a new model reference the requirements vp and try to import a reqif file the merge window opens ok as soon as i fragment the model e g the operational analysis and try it in the same way i get an error stephane bonnet i do reproduce and the error message shows that it is related to the extension of the file so it is clearly a bug eclipse polarsys rco | 0 |
253,567 | 27,300,688,623 | IssuesEvent | 2023-02-24 01:29:38 | panasalap/linux-4.19.72_1 | https://api.github.com/repos/panasalap/linux-4.19.72_1 | closed | CVE-2020-0427 (Medium) detected in linux-yoctov5.4.51 - autoclosed | security vulnerability | ## CVE-2020-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/c5a08fe8179013aad614165d792bc5b436591df6">c5a08fe8179013aad614165d792bc5b436591df6</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/pinctrl/devicetree.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/pinctrl/devicetree.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In create_pinctrl of core.c, there is a possible out of bounds read due to a use after free. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-140550171
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0427>CVE-2020-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-0427">https://www.linuxkernelcves.com/cves/CVE-2020-0427</a></p>
<p>Release Date: 2020-09-17</p>
<p>Fix Resolution: v4.14.161,v4.19.92,v5.4.7,v5.5-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-0427 (Medium) detected in linux-yoctov5.4.51 - autoclosed - ## CVE-2020-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/panasalap/linux-4.19.72/commit/c5a08fe8179013aad614165d792bc5b436591df6">c5a08fe8179013aad614165d792bc5b436591df6</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/pinctrl/devicetree.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/pinctrl/devicetree.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In create_pinctrl of core.c, there is a possible out of bounds read due to a use after free. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android kernelAndroid ID: A-140550171
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0427>CVE-2020-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-0427">https://www.linuxkernelcves.com/cves/CVE-2020-0427</a></p>
<p>Release Date: 2020-09-17</p>
<p>Fix Resolution: v4.14.161,v4.19.92,v5.4.7,v5.5-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux autoclosed cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers pinctrl devicetree c drivers pinctrl devicetree c vulnerability details in create pinctrl of core c there is a possible out of bounds read due to a use after free this could lead to local information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android kernelandroid id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
128,413 | 10,532,315,908 | IssuesEvent | 2019-10-01 10:26:50 | one-data-model/language | https://api.github.com/repos/one-data-model/language | reopened | Use JSON Pointer for inputData and outputData | Blocks Pressure Test F2F4 Review PR bug | Rather than create a new class for different uses of data, we should define inputData and outputData for Actions and Events as pointers to odmData definitions, using the same pattern as for required (https://github.com/one-data-model/language/issues/68):
```
odmObject {
Brightness {
required [
{ $ref 0/odmData/currentBrightness }
{ $ref 0/odmAction/setBrightness }
]
odmProperty {
currentBrightness {
type number
}
}
odmAction {
setLevel {
inputData [
{ $ref 0/odmData/targetBrightness }
{ $ref 0/odmData/transitionTime }
]
required [
{ $ref 0/odmData/targetBrightness }
]
odmData {
targetBrightness {
type number
}
transitionTime {
type number
}
}
}
}
}
}
``` | 1.0 | Use JSON Pointer for inputData and outputData - Rather than create a new class for different uses of data, we should define inputData and outputData for Actions and Events as pointers to odmData definitions, using the same pattern as for required (https://github.com/one-data-model/language/issues/68):
```
odmObject {
Brightness {
required [
{ $ref 0/odmData/currentBrightness }
{ $ref 0/odmAction/setBrightness }
]
odmProperty {
currentBrightness {
type number
}
}
odmAction {
setLevel {
inputData [
{ $ref 0/odmData/targetBrightness }
{ $ref 0/odmData/transitionTime }
]
required [
{ $ref 0/odmData/targetBrightness }
]
odmData {
targetBrightness {
type number
}
transitionTime {
type number
}
}
}
}
}
}
``` | non_priority | use json pointer for inputdata and outputdata rather than create a new class for different uses of data we should define inputdata and outputdata for actions and events as pointers to odmdata definitions using the same pattern as for required odmobject brightness required ref odmdata currentbrightness ref odmaction setbrightness odmproperty currentbrightness type number odmaction setlevel inputdata ref odmdata targetbrightness ref odmdata transitiontime required ref odmdata targetbrightness odmdata targetbrightness type number transitiontime type number | 0 |
62,654 | 7,622,025,620 | IssuesEvent | 2018-05-03 10:36:36 | ev3dev-lang-java/ev3dev-lang-java | https://api.github.com/repos/ev3dev-lang-java/ev3dev-lang-java | closed | Iteration Planning | Agile Debian Jessie Debian Stretch community design in progress operations | In this session, Active members will discuss about the content of the next iteration.
https://github.com/ev3dev-lang-java/ev3dev-lang-java/milestone/10
In the backlog exist a set of issues categorised in the following areas:
- Infrastructure
- Internal Refactoring
- New features
- Design
- Performance
- Documentation
- ROS
- Communications
It could be interesting the discussion. | 1.0 | Iteration Planning - In this session, Active members will discuss about the content of the next iteration.
https://github.com/ev3dev-lang-java/ev3dev-lang-java/milestone/10
In the backlog exist a set of issues categorised in the following areas:
- Infrastructure
- Internal Refactoring
- New features
- Design
- Performance
- Documentation
- ROS
- Communications
It could be interesting the discussion. | non_priority | iteration planning in this session active members will discuss about the content of the next iteration in the backlog exist a set of issues categorised in the following areas infrastructure internal refactoring new features design performance documentation ros communications it could be interesting the discussion | 0 |
170,592 | 14,265,063,949 | IssuesEvent | 2020-11-20 16:35:20 | open-horizon/open-horizon.github.io | https://api.github.com/repos/open-horizon/open-horizon.github.io | opened | Link to YouTube playlist | documentation enhancement good first issue | LF Edge maintains a YouTube playlist of videos about the Open Horizon project. The documentation web site should have a convenient and obvious pointer to that playlist for anyone who may need it.
https://www.youtube.com/playlist?list=PLgohd895XSUddtseFy4HxCqTqqlYfW8Ix
h/t @TheMosquito | 1.0 | Link to YouTube playlist - LF Edge maintains a YouTube playlist of videos about the Open Horizon project. The documentation web site should have a convenient and obvious pointer to that playlist for anyone who may need it.
https://www.youtube.com/playlist?list=PLgohd895XSUddtseFy4HxCqTqqlYfW8Ix
h/t @TheMosquito | non_priority | link to youtube playlist lf edge maintains a youtube playlist of videos about the open horizon project the documentation web site should have a convenient and obvious pointer to that playlist for anyone who may need it h t themosquito | 0 |
351,928 | 32,036,794,285 | IssuesEvent | 2023-09-22 15:56:07 | vbr-calc/vbr | https://api.github.com/repos/vbr-calc/vbr | closed | test failures in CI should be more verbose | enhancement ci_and_testing | when tests fail in CI you just get the name of the test that failed, should adjust the tests so that you actually get useful output without having to run tests locally... | 1.0 | test failures in CI should be more verbose - when tests fail in CI you just get the name of the test that failed, should adjust the tests so that you actually get useful output without having to run tests locally... | non_priority | test failures in ci should be more verbose when tests fail in ci you just get the name of the test that failed should adjust the tests so that you actually get useful output without having to run tests locally | 0 |
30,453 | 5,798,083,093 | IssuesEvent | 2017-05-03 00:04:23 | matplotlib/matplotlib | https://api.github.com/repos/matplotlib/matplotlib | closed | Update list of dependencies to build docs | Documentation new-contributor-friendly | The list at http://matplotlib.org/devdocs/devel/documenting_mpl.html#getting-started (sphinx+numpydoc) is outdated. Compare with https://github.com/matplotlib/matplotlib/blob/master/doc/README.txt#L8 (sphinx numpydoc ipython mock colorspacious pillow). | 1.0 | Update list of dependencies to build docs - The list at http://matplotlib.org/devdocs/devel/documenting_mpl.html#getting-started (sphinx+numpydoc) is outdated. Compare with https://github.com/matplotlib/matplotlib/blob/master/doc/README.txt#L8 (sphinx numpydoc ipython mock colorspacious pillow). | non_priority | update list of dependencies to build docs the list at sphinx numpydoc is outdated compare with sphinx numpydoc ipython mock colorspacious pillow | 0 |
105,863 | 16,661,239,939 | IssuesEvent | 2021-06-06 11:08:20 | AlexRogalskiy/weather-time | https://api.github.com/repos/AlexRogalskiy/weather-time | opened | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: weather-time/package.json</p>
<p>Path to vulnerable library: weather-time/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsonlint-1.6.3.tgz (Root Library)
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/weather-time/commit/1553379ffedec7816ab860950e51a5683cc1da71">1553379ffedec7816ab860950e51a5683cc1da71</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: weather-time/package.json</p>
<p>Path to vulnerable library: weather-time/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsonlint-1.6.3.tgz (Root Library)
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/weather-time/commit/1553379ffedec7816ab860950e51a5683cc1da71">1553379ffedec7816ab860950e51a5683cc1da71</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file weather time package json path to vulnerable library weather time node modules underscore package json dependency hierarchy jsonlint tgz root library nomnom tgz x underscore tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore step up your open source security game with whitesource | 0 |
21,389 | 10,606,791,384 | IssuesEvent | 2019-10-11 00:55:27 | benchmarkdebricked/thimble.mozilla.org | https://api.github.com/repos/benchmarkdebricked/thimble.mozilla.org | opened | CVE-2019-1010266 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.3.1.tgz</b>, <b>lodash-2.2.1.tgz</b>, <b>lodash-3.2.0.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash-0.9.2.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.3.1.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.3.1.tgz">https://registry.npmjs.org/lodash/-/lodash-1.3.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/sql/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- sequelize-1.7.10.tgz (Root Library)
- sql-0.35.0.tgz
- :x: **lodash-1.3.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.2.1.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.2.1.tgz">https://registry.npmjs.org/lodash/-/lodash-2.2.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/node_modules/webmaker-i18n/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/node_modules/webmaker-i18n/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- webmaker-i18n-0.3.32.tgz (Root Library)
- :x: **lodash-2.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.2.0.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.2.0.tgz">https://registry.npmjs.org/lodash/-/lodash-3.2.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/id.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/id.webmaker.org/node_modules/xmlbuilder/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/services/id.webmaker.org/node_modules/xmlbuilder/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- jscs-1.11.3.tgz (Root Library)
- xmlbuilder-2.5.2.tgz
- :x: **lodash-3.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/publish.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json,/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-0.9.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/grunt/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jsbeautifier-0.2.8.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/thimble.mozilla.org/commit/84b7cf7fc74ac0e17e5e4bc599da92283f9cd37f">84b7cf7fc74ac0e17e5e4bc599da92283f9cd37f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-1010266 (Medium) detected in multiple libraries - ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.3.1.tgz</b>, <b>lodash-2.2.1.tgz</b>, <b>lodash-3.2.0.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash-0.9.2.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.3.1.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.3.1.tgz">https://registry.npmjs.org/lodash/-/lodash-1.3.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/sql/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- sequelize-1.7.10.tgz (Root Library)
- sql-0.35.0.tgz
- :x: **lodash-1.3.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.2.1.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.2.1.tgz">https://registry.npmjs.org/lodash/-/lodash-2.2.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/node_modules/webmaker-i18n/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/node_modules/webmaker-i18n/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- webmaker-i18n-0.3.32.tgz (Root Library)
- :x: **lodash-2.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.2.0.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.2.0.tgz">https://registry.npmjs.org/lodash/-/lodash-3.2.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/id.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/id.webmaker.org/node_modules/xmlbuilder/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/services/id.webmaker.org/node_modules/xmlbuilder/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- jscs-1.11.3.tgz (Root Library)
- xmlbuilder-2.5.2.tgz
- :x: **lodash-3.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/publish.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json,/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json,/tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/eslint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-0.9.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz">https://registry.npmjs.org/lodash/-/lodash-0.9.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/grunt/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-0.4.5.tgz (Root Library)
- :x: **lodash-0.9.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/thimble.mozilla.org/services/login.webmaker.org/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jsbeautifier-0.2.8.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/benchmarkdebricked/thimble.mozilla.org/commit/84b7cf7fc74ac0e17e5e4bc599da92283f9cd37f">84b7cf7fc74ac0e17e5e4bc599da92283f9cd37f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file tmp ws scm thimble mozilla org services login webmaker org package json path to vulnerable library tmp ws scm thimble mozilla org services login webmaker org node modules sql node modules lodash package json dependency hierarchy sequelize tgz root library sql tgz x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file tmp ws scm thimble mozilla org services login webmaker org package json path to vulnerable library tmp ws scm thimble mozilla org node modules webmaker node modules lodash package json tmp ws scm thimble mozilla org node modules webmaker node modules lodash package json dependency hierarchy webmaker tgz root library x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file tmp ws scm thimble mozilla org services id webmaker org package json path to vulnerable library tmp ws scm thimble mozilla org services id webmaker org node modules xmlbuilder node modules lodash package json tmp ws scm thimble mozilla org services id webmaker org node modules xmlbuilder node modules lodash package json dependency hierarchy jscs tgz root library xmlbuilder tgz x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file tmp ws scm thimble mozilla org services publish webmaker org package json path to vulnerable library tmp ws scm thimble mozilla org services login webmaker org node modules eslint node modules lodash package json tmp ws scm thimble mozilla org services login webmaker org node modules eslint node modules lodash package json thimble mozilla org services login webmaker org node modules eslint node modules lodash package json tmp ws scm thimble mozilla org services login webmaker org node modules eslint node modules lodash package json dependency hierarchy x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file tmp ws scm thimble mozilla org services login webmaker org package json path to vulnerable library tmp ws scm thimble mozilla org services login webmaker org node modules grunt node modules lodash package json dependency hierarchy grunt tgz root library x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file tmp ws scm thimble mozilla org services login webmaker org package json path to vulnerable library tmp ws scm thimble mozilla org services login webmaker org node modules lodash package json dependency hierarchy grunt jsbeautifier tgz root library x lodash tgz vulnerable library found in head commit a href vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
23,749 | 7,372,955,751 | IssuesEvent | 2018-03-13 15:59:54 | eEcoLiDAR/eEcoLiDAR | https://api.github.com/repos/eEcoLiDAR/eEcoLiDAR | closed | Create filter command line tool | build command line tool | Create a command line tool that calls the following modules, read ply, filter, write ply. All sensible options of those modules should be controllable using command line arguments.
| 1.0 | Create filter command line tool - Create a command line tool that calls the following modules, read ply, filter, write ply. All sensible options of those modules should be controllable using command line arguments.
| non_priority | create filter command line tool create a command line tool that calls the following modules read ply filter write ply all sensible options of those modules should be controllable using command line arguments | 0 |
116,898 | 25,007,175,013 | IssuesEvent | 2022-11-03 12:47:51 | ices-eg/DIG | https://api.github.com/repos/ices-eg/DIG | closed | LT2022-10-24 new LTPRP codes | Approved-AsIs vocab: CodeValue | BE request for new colors Grey, Purple and Pink in LTPRP
https://vocab.ices.dk/?ref=1403
for reference: http://vocab.nerc.ac.uk/collection/H04/current/ | 1.0 | LT2022-10-24 new LTPRP codes - BE request for new colors Grey, Purple and Pink in LTPRP
https://vocab.ices.dk/?ref=1403
for reference: http://vocab.nerc.ac.uk/collection/H04/current/ | non_priority | new ltprp codes be request for new colors grey purple and pink in ltprp for reference | 0 |
446,430 | 31,476,098,646 | IssuesEvent | 2023-08-30 10:48:29 | snake-biscuits/bsp_tool | https://api.github.com/repos/snake-biscuits/bsp_tool | closed | Usage of ContentsMask in source.py | documentation | I want compare the content of a brush with ContentsMask - PLAYER_SOLID , but I cant seem to figure out how exactly to do that.
[https://github.com/snake-biscuits/bsp_tool/blob/master/bsp_tool/branches/valve/source.py#L240](url)
| 1.0 | Usage of ContentsMask in source.py - I want compare the content of a brush with ContentsMask - PLAYER_SOLID , but I cant seem to figure out how exactly to do that.
[https://github.com/snake-biscuits/bsp_tool/blob/master/bsp_tool/branches/valve/source.py#L240](url)
| non_priority | usage of contentsmask in source py i want compare the content of a brush with contentsmask player solid but i cant seem to figure out how exactly to do that url | 0 |
38,018 | 6,655,155,143 | IssuesEvent | 2017-09-29 15:21:39 | pvlib/pvlib-python | https://api.github.com/repos/pvlib/pvlib-python | closed | total irradiance docs don't show poa_diffuse as a return, but package overview uses it | documentation | Thought I was going crazy today, when I couldn't find any references of [`total_irrad`](http://pvlib-python.readthedocs.io/en/latest/generated/pvlib.irradiance.total_irrad.html#pvlib-irradiance-total-irrad) returning `poa_diffuse`, but there it is in the [package overview procedural example](http://pvlib-python.readthedocs.io/en/latest/package_overview.html#procedural) and I've been using it my code.
Looking through the code it was changed in #105 to output global, beam, diffuse sum, just sky diffuse and just ground diffuse. To avoid craziness, the docs should probably be updated. Should be an quick, easy fix. | 1.0 | total irradiance docs don't show poa_diffuse as a return, but package overview uses it - Thought I was going crazy today, when I couldn't find any references of [`total_irrad`](http://pvlib-python.readthedocs.io/en/latest/generated/pvlib.irradiance.total_irrad.html#pvlib-irradiance-total-irrad) returning `poa_diffuse`, but there it is in the [package overview procedural example](http://pvlib-python.readthedocs.io/en/latest/package_overview.html#procedural) and I've been using it my code.
Looking through the code it was changed in #105 to output global, beam, diffuse sum, just sky diffuse and just ground diffuse. To avoid craziness, the docs should probably be updated. Should be an quick, easy fix. | non_priority | total irradiance docs don t show poa diffuse as a return but package overview uses it thought i was going crazy today when i couldn t find any references of returning poa diffuse but there it is in the and i ve been using it my code looking through the code it was changed in to output global beam diffuse sum just sky diffuse and just ground diffuse to avoid craziness the docs should probably be updated should be an quick easy fix | 0 |
206,120 | 16,020,207,788 | IssuesEvent | 2021-04-20 21:40:55 | pykeen/pykeen | https://api.github.com/repos/pykeen/pykeen | closed | Write the ablation tutorial | documentation |
Originally, #54 was supposed to include a proper tutorial for using the ablation pipeline. However, it still needs work to be useful to a user. therefore, it's been removed from that PR and the rst source is copied below.
TODO: the first paragraph is too much information at once. You have to introduce someone to this stuff
one at a time. Each one of these should have reasonable defaults.
```rst
An ablation study is defined based on a dictionary that in the following is named 'configuration' containing three
sub-dictionaries: 'metadata', 'ablation', and 'optuna', which we will define below.
In several parts of the configuration of the ablation study, we have to define the dictionaries 'kwargs' and
'kwargs_ranges. 'kwargs' defines for a specific component (e.g., interaction model or loss function) single
hyper-parameter values such as a fixed embedding dimension of 50, whereas 'kwargs_ranges' define ranges of values.
Note that we always have to define both dictionaries, and in cases where do not have entries for
'kwargs' or 'kwargs_ranges', we define empty dictionaries.
The Firehose
------------
This part of the tutorial shows what happens if you want to configure everything yourself. It is
**not** the place to start.
Add metadata to the configuration.
.. code-block:: python
configuration = {}
metadata = dict(
title="HPO over MyData"
)
configuration['metadata'] = metadata
# Define Ablation Dictionary
# Step 1: define dataset. Here, we use our own data.
ablation = {
"datasets": [
{
"training": "/path/to/my/train.txt",
"testing": "/path/to/my/test.txt",
"validation": "/path/to/my/valid.txt"
}
]
}
Step 2: define model (several models can be defined).
Note the structure of 'model_kwargs': model_kwargs{InteractionModel:{parameter={range}}}.
.. code-block:: python
models = ['RotatE']
model_kwargs = dict(
RotatE=dict(automatic_memory_optimization=True)
)
model_kwargs_ranges = dict(
RotatE=dict(
embedding_dim=dict(
type='int',
low=3,
high=5,
scale='power_two',
)
)
)
Define, whether interaction model should explicitly be trained with inverse relations. If set to 'True',
the number of relations are doubled, and the task of predicting the head entities of (r,t)-pairs, becomes the task
of predicting tail entities of (t,r_inv)-pairs.
.. code-block:: python
create_inverse_triples = [True, False]
Define regularize (several regularizers can be defined). Here we use 'NoRegularizer' to indicate that
we do not regularize our model.
.. code-block:: python
regularizers = ['NoRegularizer']
regularizer_kwargs = dict(RotatE=dict(NoRegularizer=dict()))
regularizer_kwargs_ranges = dict(RotatE=dict(NoRegularizer=dict()))
ablation['models'] = models
ablation['model_kwargs'] = model_kwargs
ablation['model_kwargs_ranges'] = model_kwargs_ranges
ablation['create_inverse_triples'] = create_inverse_triples
ablation['regularizers'] = regularizers
ablation['regularizer_kwargs'] = regularizer_kwargs
ablation['regularizer_kwargs_ranges'] = regularizer_kwargs_ranges
Step 3: define loss function (several loss functions can be defined). Here focus on the negative sampling
self adversarial loss.
.. code-block:: python
loss_functions = ['NSSALoss']
loss_kwargs = dict(RotatE=dict(NSSALoss=dict()))
loss_kwargs_ranges = dict(
RotatE=dict(
NSSALoss=dict(
margin=dict(
type='float',
low=1,
high=30,
q=2.0,
),
adversarial_temperature=dict(
type='float',
low=0.1,
high=1.0,
q=0.1,
)
)
)
)
ablation['loss_functions'] = loss_functions
ablation['loss_kwargs'] = loss_kwargs
ablation['loss_kwargs_ranges'] = loss_kwargs_ranges
Step 4: define training approach: sLCWA and/or LCWA
.. code-block:: python
training_loops = ['sLCWA']
ablation['training_loops'] = training_loops
Define negative sampler. Since we are using the sLCWA training approach, we define a negative sampler.
.. code-block:: python
negative_sampler = 'BasicNegativeSampler'
negative_sampler_kwargs = dict(RotatE=dict(BasicNegativeSampler=dict()))
negative_sampler_kwargs_ranges = dict(
RotatE=dict(
BasicNegativeSampler=dict(
num_negs_per_pos=dict(
type='int',
low=1,
high=10,
q=1,
)
)
)
)
ablation['negative_sampler'] = negative_sampler
ablation['negative_sampler_kwargs'] = negative_sampler_kwargs
ablation['negative_sampler_kwargs_ranges'] = negative_sampler_kwargs_ranges
Step 5: define optimizer (several optimizers can be defined).
.. code-block:: python
optimizers = ['adam']
optimizer_kwargs = dict(
RotatE=dict(
adam=dict(
weight_decay=0.0
)
)
)
optimizer_kwargs_ranges = dict(
RotatE=dict(
adam=dict(
lr=dict(
type='float',
low=0.001,
high=0.1,
sclae='log',
)
)
)
)
ablation['optimizers'] = optimizers
ablation['optimizer_kwargs'] = optimizer_kwargs
ablation['optimizer_kwargs_ranges'] = optimizer_kwargs_ranges
Step 6: define training parameters.
.. code-block:: python
training_kwargs = dict(
RotatE=dict(
sLCWA=dict(
num_epochs=10,
label_smoothing=0.0,
)
)
)
training_kwargs_ranges = dict(
RotatE=dict(
sLCWA=dict(
batch_size=dict(
type='int',
low=6,
high=8,
scale='power_two',
)
)
)
)
ablation['training_kwargs'] = training_kwargs
ablation['training_kwargs_ranges'] = training_kwargs_ranges
Step 7: define evaluator.
.. code-block:: python
evaluator = 'RankBasedEvaluator'
evaluator_kwargs = dict(
filtered=True,
)
evaluation_kwargs = dict(
batch_size=None # searches for maximal possible in order to minimize evaluation time
)
ablation['evaluator'] = evaluator
ablation['evaluator_kwargs'] = evaluator_kwargs
ablation['evaluation_kwargs'] = evaluation_kwargs
Step 8: define early stopper.
.. code-block:: python
stopper = 'early'
stopper_kwargs = dict(
frequency=50,
patience=2,
delta=0.002,
)
ablation['stopper'] = stopper
ablation['stopper_kwargs'] = stopper_kwargs
configuration['ablation'] = ablation
Define Optuna Dictionary.
First, define the number of HPO iterations using the key 'n_trials', wherein each iteration new hyper-parameters
will be sampled.
Second, define the ablation study's timeout. An ablation study will be terminated after the timeout is
reached, independently of the defined number of 'n_trials.' Note: every HPO iteration that has been started before
the timeout has been reached, will be finished before terminating the current ablation study.
Third, define the metric and whether it should be 'maximized' or 'minimized'.
Fourth, define the HPO algorithm, i.e., random (random search), tpe (tree-structured parzen estimator), or
grid (grid search).
.. code-block:: python
optuna = {}
optuna['n_trials'] = 2
optuna['timeout'] = 10
optuna['metric'] = 'hits@10'
optuna['direction'] = 'maximize'
optuna['sampler'] = 'random'
# Defines the pruning strategy. Here, we don't use a pruner (defined by 'nop').
# Instead, we solely use early stopping.
optuna['pruner'] = 'nop'
configuration['optuna'] = optuna
Define directory in which artifacts will be safed.
.. code-block:: python
output_directory = '/path/to/output/directory'
Defines how often the model should be re-trained and evaluated based on the best hyper-parameters which
enables us to measure the variance in performance.
.. code-block:: python
best_replicates = 2
Defines, whether each trained model sampled during HPO should be saved.
.. code-block:: python
save_artifacts = False
Defines, whether the best model should be discarded after training and evaluation.
.. code-block:: python
discard_replicates = False
Defines, whether a replicate of the best model should be moved to CPU.
We recommend to set this flag to 'True' to avoid unnecessary GPU usage.
.. code-block:: python
move_to_cpu = True
Start ablation studies.
.. code-block:: python
ablation_pipeline(
config=configuration,
directory=output_directory,
best_replicates=best_replicates,
save_artifacts=save_artifacts,
discard_replicates=discard_replicates,
move_to_cpu=move_to_cpu,
dry_run=False,
)
``` | 1.0 | Write the ablation tutorial -
Originally, #54 was supposed to include a proper tutorial for using the ablation pipeline. However, it still needs work to be useful to a user. therefore, it's been removed from that PR and the rst source is copied below.
TODO: the first paragraph is too much information at once. You have to introduce someone to this stuff
one at a time. Each one of these should have reasonable defaults.
```rst
An ablation study is defined based on a dictionary that in the following is named 'configuration' containing three
sub-dictionaries: 'metadata', 'ablation', and 'optuna', which we will define below.
In several parts of the configuration of the ablation study, we have to define the dictionaries 'kwargs' and
'kwargs_ranges. 'kwargs' defines for a specific component (e.g., interaction model or loss function) single
hyper-parameter values such as a fixed embedding dimension of 50, whereas 'kwargs_ranges' define ranges of values.
Note that we always have to define both dictionaries, and in cases where do not have entries for
'kwargs' or 'kwargs_ranges', we define empty dictionaries.
The Firehose
------------
This part of the tutorial shows what happens if you want to configure everything yourself. It is
**not** the place to start.
Add metadata to the configuration.
.. code-block:: python
configuration = {}
metadata = dict(
title="HPO over MyData"
)
configuration['metadata'] = metadata
# Define Ablation Dictionary
# Step 1: define dataset. Here, we use our own data.
ablation = {
"datasets": [
{
"training": "/path/to/my/train.txt",
"testing": "/path/to/my/test.txt",
"validation": "/path/to/my/valid.txt"
}
]
}
Step 2: define model (several models can be defined).
Note the structure of 'model_kwargs': model_kwargs{InteractionModel:{parameter={range}}}.
.. code-block:: python
models = ['RotatE']
model_kwargs = dict(
RotatE=dict(automatic_memory_optimization=True)
)
model_kwargs_ranges = dict(
RotatE=dict(
embedding_dim=dict(
type='int',
low=3,
high=5,
scale='power_two',
)
)
)
Define, whether interaction model should explicitly be trained with inverse relations. If set to 'True',
the number of relations are doubled, and the task of predicting the head entities of (r,t)-pairs, becomes the task
of predicting tail entities of (t,r_inv)-pairs.
.. code-block:: python
create_inverse_triples = [True, False]
Define regularize (several regularizers can be defined). Here we use 'NoRegularizer' to indicate that
we do not regularize our model.
.. code-block:: python
regularizers = ['NoRegularizer']
regularizer_kwargs = dict(RotatE=dict(NoRegularizer=dict()))
regularizer_kwargs_ranges = dict(RotatE=dict(NoRegularizer=dict()))
ablation['models'] = models
ablation['model_kwargs'] = model_kwargs
ablation['model_kwargs_ranges'] = model_kwargs_ranges
ablation['create_inverse_triples'] = create_inverse_triples
ablation['regularizers'] = regularizers
ablation['regularizer_kwargs'] = regularizer_kwargs
ablation['regularizer_kwargs_ranges'] = regularizer_kwargs_ranges
Step 3: define loss function (several loss functions can be defined). Here focus on the negative sampling
self adversarial loss.
.. code-block:: python
loss_functions = ['NSSALoss']
loss_kwargs = dict(RotatE=dict(NSSALoss=dict()))
loss_kwargs_ranges = dict(
RotatE=dict(
NSSALoss=dict(
margin=dict(
type='float',
low=1,
high=30,
q=2.0,
),
adversarial_temperature=dict(
type='float',
low=0.1,
high=1.0,
q=0.1,
)
)
)
)
ablation['loss_functions'] = loss_functions
ablation['loss_kwargs'] = loss_kwargs
ablation['loss_kwargs_ranges'] = loss_kwargs_ranges
Step 4: define training approach: sLCWA and/or LCWA
.. code-block:: python
training_loops = ['sLCWA']
ablation['training_loops'] = training_loops
Define negative sampler. Since we are using the sLCWA training approach, we define a negative sampler.
.. code-block:: python
negative_sampler = 'BasicNegativeSampler'
negative_sampler_kwargs = dict(RotatE=dict(BasicNegativeSampler=dict()))
negative_sampler_kwargs_ranges = dict(
RotatE=dict(
BasicNegativeSampler=dict(
num_negs_per_pos=dict(
type='int',
low=1,
high=10,
q=1,
)
)
)
)
ablation['negative_sampler'] = negative_sampler
ablation['negative_sampler_kwargs'] = negative_sampler_kwargs
ablation['negative_sampler_kwargs_ranges'] = negative_sampler_kwargs_ranges
Step 5: define optimizer (several optimizers can be defined).
.. code-block:: python
optimizers = ['adam']
optimizer_kwargs = dict(
RotatE=dict(
adam=dict(
weight_decay=0.0
)
)
)
optimizer_kwargs_ranges = dict(
RotatE=dict(
adam=dict(
lr=dict(
type='float',
low=0.001,
high=0.1,
sclae='log',
)
)
)
)
ablation['optimizers'] = optimizers
ablation['optimizer_kwargs'] = optimizer_kwargs
ablation['optimizer_kwargs_ranges'] = optimizer_kwargs_ranges
Step 6: define training parameters.
.. code-block:: python
training_kwargs = dict(
RotatE=dict(
sLCWA=dict(
num_epochs=10,
label_smoothing=0.0,
)
)
)
training_kwargs_ranges = dict(
RotatE=dict(
sLCWA=dict(
batch_size=dict(
type='int',
low=6,
high=8,
scale='power_two',
)
)
)
)
ablation['training_kwargs'] = training_kwargs
ablation['training_kwargs_ranges'] = training_kwargs_ranges
Step 7: define evaluator.
.. code-block:: python
evaluator = 'RankBasedEvaluator'
evaluator_kwargs = dict(
filtered=True,
)
evaluation_kwargs = dict(
batch_size=None # searches for maximal possible in order to minimize evaluation time
)
ablation['evaluator'] = evaluator
ablation['evaluator_kwargs'] = evaluator_kwargs
ablation['evaluation_kwargs'] = evaluation_kwargs
Step 8: define early stopper.
.. code-block:: python
stopper = 'early'
stopper_kwargs = dict(
frequency=50,
patience=2,
delta=0.002,
)
ablation['stopper'] = stopper
ablation['stopper_kwargs'] = stopper_kwargs
configuration['ablation'] = ablation
Define Optuna Dictionary.
First, define the number of HPO iterations using the key 'n_trials', wherein each iteration new hyper-parameters
will be sampled.
Second, define the ablation study's timeout. An ablation study will be terminated after the timeout is
reached, independently of the defined number of 'n_trials.' Note: every HPO iteration that has been started before
the timeout has been reached, will be finished before terminating the current ablation study.
Third, define the metric and whether it should be 'maximized' or 'minimized'.
Fourth, define the HPO algorithm, i.e., random (random search), tpe (tree-structured parzen estimator), or
grid (grid search).
.. code-block:: python
optuna = {}
optuna['n_trials'] = 2
optuna['timeout'] = 10
optuna['metric'] = 'hits@10'
optuna['direction'] = 'maximize'
optuna['sampler'] = 'random'
# Defines the pruning strategy. Here, we don't use a pruner (defined by 'nop').
# Instead, we solely use early stopping.
optuna['pruner'] = 'nop'
configuration['optuna'] = optuna
Define directory in which artifacts will be safed.
.. code-block:: python
output_directory = '/path/to/output/directory'
Defines how often the model should be re-trained and evaluated based on the best hyper-parameters which
enables us to measure the variance in performance.
.. code-block:: python
best_replicates = 2
Defines, whether each trained model sampled during HPO should be saved.
.. code-block:: python
save_artifacts = False
Defines, whether the best model should be discarded after training and evaluation.
.. code-block:: python
discard_replicates = False
Defines, whether a replicate of the best model should be moved to CPU.
We recommend to set this flag to 'True' to avoid unnecessary GPU usage.
.. code-block:: python
move_to_cpu = True
Start ablation studies.
.. code-block:: python
ablation_pipeline(
config=configuration,
directory=output_directory,
best_replicates=best_replicates,
save_artifacts=save_artifacts,
discard_replicates=discard_replicates,
move_to_cpu=move_to_cpu,
dry_run=False,
)
``` | non_priority | write the ablation tutorial originally was supposed to include a proper tutorial for using the ablation pipeline however it still needs work to be useful to a user therefore it s been removed from that pr and the rst source is copied below todo the first paragraph is too much information at once you have to introduce someone to this stuff one at a time each one of these should have reasonable defaults rst an ablation study is defined based on a dictionary that in the following is named configuration containing three sub dictionaries metadata ablation and optuna which we will define below in several parts of the configuration of the ablation study we have to define the dictionaries kwargs and kwargs ranges kwargs defines for a specific component e g interaction model or loss function single hyper parameter values such as a fixed embedding dimension of whereas kwargs ranges define ranges of values note that we always have to define both dictionaries and in cases where do not have entries for kwargs or kwargs ranges we define empty dictionaries the firehose this part of the tutorial shows what happens if you want to configure everything yourself it is not the place to start add metadata to the configuration code block python configuration metadata dict title hpo over mydata configuration metadata define ablation dictionary step define dataset here we use our own data ablation datasets training path to my train txt testing path to my test txt validation path to my valid txt step define model several models can be defined note the structure of model kwargs model kwargs interactionmodel parameter range code block python models model kwargs dict rotate dict automatic memory optimization true model kwargs ranges dict rotate dict embedding dim dict type int low high scale power two define whether interaction model should explicitly be trained with inverse relations if set to true the number of relations are doubled and the task of predicting the head entities of r t pairs becomes the task of predicting tail entities of t r inv pairs code block python create inverse triples define regularize several regularizers can be defined here we use noregularizer to indicate that we do not regularize our model code block python regularizers regularizer kwargs dict rotate dict noregularizer dict regularizer kwargs ranges dict rotate dict noregularizer dict ablation models ablation model kwargs ablation model kwargs ranges ablation create inverse triples ablation regularizers ablation regularizer kwargs ablation regularizer kwargs ranges step define loss function several loss functions can be defined here focus on the negative sampling self adversarial loss code block python loss functions loss kwargs dict rotate dict nssaloss dict loss kwargs ranges dict rotate dict nssaloss dict margin dict type float low high q adversarial temperature dict type float low high q ablation loss functions ablation loss kwargs ablation loss kwargs ranges step define training approach slcwa and or lcwa code block python training loops ablation training loops define negative sampler since we are using the slcwa training approach we define a negative sampler code block python negative sampler basicnegativesampler negative sampler kwargs dict rotate dict basicnegativesampler dict negative sampler kwargs ranges dict rotate dict basicnegativesampler dict num negs per pos dict type int low high q ablation negative sampler ablation negative sampler kwargs ablation negative sampler kwargs ranges step define optimizer several optimizers can be defined code block python optimizers optimizer kwargs dict rotate dict adam dict weight decay optimizer kwargs ranges dict rotate dict adam dict lr dict type float low high sclae log ablation optimizers ablation optimizer kwargs ablation optimizer kwargs ranges step define training parameters code block python training kwargs dict rotate dict slcwa dict num epochs label smoothing training kwargs ranges dict rotate dict slcwa dict batch size dict type int low high scale power two ablation training kwargs ablation training kwargs ranges step define evaluator code block python evaluator rankbasedevaluator evaluator kwargs dict filtered true evaluation kwargs dict batch size none searches for maximal possible in order to minimize evaluation time ablation evaluator ablation evaluator kwargs ablation evaluation kwargs step define early stopper code block python stopper early stopper kwargs dict frequency patience delta ablation stopper ablation stopper kwargs configuration ablation define optuna dictionary first define the number of hpo iterations using the key n trials wherein each iteration new hyper parameters will be sampled second define the ablation study s timeout an ablation study will be terminated after the timeout is reached independently of the defined number of n trials note every hpo iteration that has been started before the timeout has been reached will be finished before terminating the current ablation study third define the metric and whether it should be maximized or minimized fourth define the hpo algorithm i e random random search tpe tree structured parzen estimator or grid grid search code block python optuna optuna optuna optuna hits optuna maximize optuna random defines the pruning strategy here we don t use a pruner defined by nop instead we solely use early stopping optuna nop configuration optuna define directory in which artifacts will be safed code block python output directory path to output directory defines how often the model should be re trained and evaluated based on the best hyper parameters which enables us to measure the variance in performance code block python best replicates defines whether each trained model sampled during hpo should be saved code block python save artifacts false defines whether the best model should be discarded after training and evaluation code block python discard replicates false defines whether a replicate of the best model should be moved to cpu we recommend to set this flag to true to avoid unnecessary gpu usage code block python move to cpu true start ablation studies code block python ablation pipeline config configuration directory output directory best replicates best replicates save artifacts save artifacts discard replicates discard replicates move to cpu move to cpu dry run false | 0 |
205,668 | 15,987,772,143 | IssuesEvent | 2021-04-19 01:40:53 | ablecloud-team/ablestack-docs | https://api.github.com/repos/ablecloud-team/ablestack-docs | opened | 관리가이드 부문 Cube 메뉴 작성 필요 | documentation | Cockpit 가이드 목차
https://access.redhat.com/documentation/en-us/red_hat_enterprise_linux/8/html/managing_systems_using_the_rhel_8_web_console/index
항목 우측의 숫자는 위 cockpit 가이드 목차에 표시된 숫자이며 필요 없는 항목은 임의로 삭제하였고, 필요에 따라 수정하면 됩니다.
아래 항목은 Cockpit 로그인 후 메인 화면의 메뉴 순서에 따라 나열하였습니다.
- [ ] 개요
- [ ] 개요 1.1
- [ ] 로그인 1.3
- [ ] 시스템 재시작 1.6
- [ ] 시스템 종료 1.7
- [ ] 시스템 시간 설정 1.8
- [ ] 호스트 이름 구성 2
- [ ] 시스템 성능 최적화 4
- [ ] 로그
- [ ] 로그 5
- [ ] 스토리지
- [ ] partition 관리 15
- [ ] NFS mount 관리 16
- [ ] 독립 디스크 중복 관리 17
- [ ] LVM 논리 볼륨 구성 18
- [ ] thin 논리 볼륨 구성 19
- [ ] 볼륨 그룹의 물리적 드라이브 변경 20
- [ ] Virtual data optimizer 볼륨 관리 21
- [ ] Luks 비밀번호 데이터 잠금 22
- [ ] tang키를 사용하여 자동잠금 해제 구성 23
- [ ] 네트워킹
- [ ] bond 구성 8
- [ ] team 구성 9
- [ ] bridge 구성 10
- [ ] vlan 구성 11
- [ ] listening port 구성 12
- [ ] firewall 관리 13
- [ ] 가상머신
- [ ] 가상머신 관리 26
- [ ] 계정
- [ ] 사용자 계정 관리 6
- [ ] 서비스
- [ ] 서비스 관리 7
- [ ] ABLESTACK
- [ ] ABLESTACK
- [ ] 소프트웨어 최신화
- [ ] 소프트웨어 업데이트 관리 24
- [ ] 애플리케이션
- [ ] 애드온 3
- [ ] 커널덤프
- [ ] kdump 설정 25
- [ ] SELinux
- [ ] 플레이북 14
- [ ] 터미널
- [ ] 터미널
| 1.0 | 관리가이드 부문 Cube 메뉴 작성 필요 - Cockpit 가이드 목차
https://access.redhat.com/documentation/en-us/red_hat_enterprise_linux/8/html/managing_systems_using_the_rhel_8_web_console/index
항목 우측의 숫자는 위 cockpit 가이드 목차에 표시된 숫자이며 필요 없는 항목은 임의로 삭제하였고, 필요에 따라 수정하면 됩니다.
아래 항목은 Cockpit 로그인 후 메인 화면의 메뉴 순서에 따라 나열하였습니다.
- [ ] 개요
- [ ] 개요 1.1
- [ ] 로그인 1.3
- [ ] 시스템 재시작 1.6
- [ ] 시스템 종료 1.7
- [ ] 시스템 시간 설정 1.8
- [ ] 호스트 이름 구성 2
- [ ] 시스템 성능 최적화 4
- [ ] 로그
- [ ] 로그 5
- [ ] 스토리지
- [ ] partition 관리 15
- [ ] NFS mount 관리 16
- [ ] 독립 디스크 중복 관리 17
- [ ] LVM 논리 볼륨 구성 18
- [ ] thin 논리 볼륨 구성 19
- [ ] 볼륨 그룹의 물리적 드라이브 변경 20
- [ ] Virtual data optimizer 볼륨 관리 21
- [ ] Luks 비밀번호 데이터 잠금 22
- [ ] tang키를 사용하여 자동잠금 해제 구성 23
- [ ] 네트워킹
- [ ] bond 구성 8
- [ ] team 구성 9
- [ ] bridge 구성 10
- [ ] vlan 구성 11
- [ ] listening port 구성 12
- [ ] firewall 관리 13
- [ ] 가상머신
- [ ] 가상머신 관리 26
- [ ] 계정
- [ ] 사용자 계정 관리 6
- [ ] 서비스
- [ ] 서비스 관리 7
- [ ] ABLESTACK
- [ ] ABLESTACK
- [ ] 소프트웨어 최신화
- [ ] 소프트웨어 업데이트 관리 24
- [ ] 애플리케이션
- [ ] 애드온 3
- [ ] 커널덤프
- [ ] kdump 설정 25
- [ ] SELinux
- [ ] 플레이북 14
- [ ] 터미널
- [ ] 터미널
| non_priority | 관리가이드 부문 cube 메뉴 작성 필요 cockpit 가이드 목차 항목 우측의 숫자는 위 cockpit 가이드 목차에 표시된 숫자이며 필요 없는 항목은 임의로 삭제하였고 필요에 따라 수정하면 됩니다 아래 항목은 cockpit 로그인 후 메인 화면의 메뉴 순서에 따라 나열하였습니다 개요 개요 로그인 시스템 재시작 시스템 종료 시스템 시간 설정 호스트 이름 구성 시스템 성능 최적화 로그 로그 스토리지 partition 관리 nfs mount 관리 독립 디스크 중복 관리 lvm 논리 볼륨 구성 thin 논리 볼륨 구성 볼륨 그룹의 물리적 드라이브 변경 virtual data optimizer 볼륨 관리 luks 비밀번호 데이터 잠금 tang키를 사용하여 자동잠금 해제 구성 네트워킹 bond 구성 team 구성 bridge 구성 vlan 구성 listening port 구성 firewall 관리 가상머신 가상머신 관리 계정 사용자 계정 관리 서비스 서비스 관리 ablestack ablestack 소프트웨어 최신화 소프트웨어 업데이트 관리 애플리케이션 애드온 커널덤프 kdump 설정 selinux 플레이북 터미널 터미널 | 0 |
54,785 | 7,924,163,009 | IssuesEvent | 2018-07-05 16:02:41 | digitalocean/netbox | https://api.github.com/repos/digitalocean/netbox | closed | Add subdevice role mention in documentation | status: accepted type: documentation | ## Issue type
[ ] Feature request <!-- An enhancement of existing functionality -->
[ ] Bug report <!-- Unexpected or erroneous behavior -->
[ x ] Documentation <!-- A modification to the documentation -->
## Description
I can see the mention of 'subdevice role' when I list device types but I can't see it in the documentation. Nor is there any mention of parent/child status (also child components are mentionned)
Thank you for you work.
| 1.0 | Add subdevice role mention in documentation - ## Issue type
[ ] Feature request <!-- An enhancement of existing functionality -->
[ ] Bug report <!-- Unexpected or erroneous behavior -->
[ x ] Documentation <!-- A modification to the documentation -->
## Description
I can see the mention of 'subdevice role' when I list device types but I can't see it in the documentation. Nor is there any mention of parent/child status (also child components are mentionned)
Thank you for you work.
| non_priority | add subdevice role mention in documentation issue type feature request bug report documentation description i can see the mention of subdevice role when i list device types but i can t see it in the documentation nor is there any mention of parent child status also child components are mentionned thank you for you work | 0 |
15,645 | 11,632,406,518 | IssuesEvent | 2020-02-28 05:00:46 | cockroachdb/docs | https://api.github.com/repos/cockroachdb/docs | closed | Exclude unsupported versions from search | A-docs-infrastructure P-1 | Google shouldn't index anything older than 2.1. Searches for "install cockroachdb", for example, return links to 1.0 install docs following stable install docs, which is unnerving. | 1.0 | Exclude unsupported versions from search - Google shouldn't index anything older than 2.1. Searches for "install cockroachdb", for example, return links to 1.0 install docs following stable install docs, which is unnerving. | non_priority | exclude unsupported versions from search google shouldn t index anything older than searches for install cockroachdb for example return links to install docs following stable install docs which is unnerving | 0 |
22,336 | 4,789,167,711 | IssuesEvent | 2016-10-30 22:45:38 | supertuxkart/stk-code | https://api.github.com/repos/supertuxkart/stk-code | closed | Incomplete track documentation | C: Documentation/Website | http://supertuxkart.sourceforge.net/Track_Maker's_Guide#Interaction is empty, and thus I don't know how to make an object ignore collisions (drive through) without getting ignored by the exporter.
| 1.0 | Incomplete track documentation - http://supertuxkart.sourceforge.net/Track_Maker's_Guide#Interaction is empty, and thus I don't know how to make an object ignore collisions (drive through) without getting ignored by the exporter.
| non_priority | incomplete track documentation is empty and thus i don t know how to make an object ignore collisions drive through without getting ignored by the exporter | 0 |
135,471 | 11,007,364,403 | IssuesEvent | 2019-12-04 08:19:20 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/machine_learning/anomaly_detection/advanced_job·ts - machine learning anomaly detection advanced job with categorization detector and default datafeed settings job creation displays the summary step | failed-test | A test failed on a tracked branch
```
{ TimeoutError: Waiting until element is enabled
Wait timed out after 10057ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:841:17
at process._tickCallback (internal/process/next_tick.js:68:7) name: 'TimeoutError', remoteStacktrace: '' }
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/kibana+flaky-test-suite-runner/12/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/machine_learning/anomaly_detection/advanced_job·ts","test.name":"machine learning anomaly detection advanced job with categorization detector and default datafeed settings job creation displays the summary step","test.failCount":1}} --> | 1.0 | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/machine_learning/anomaly_detection/advanced_job·ts - machine learning anomaly detection advanced job with categorization detector and default datafeed settings job creation displays the summary step - A test failed on a tracked branch
```
{ TimeoutError: Waiting until element is enabled
Wait timed out after 10057ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:841:17
at process._tickCallback (internal/process/next_tick.js:68:7) name: 'TimeoutError', remoteStacktrace: '' }
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/kibana+flaky-test-suite-runner/12/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/machine_learning/anomaly_detection/advanced_job·ts","test.name":"machine learning anomaly detection advanced job with categorization detector and default datafeed settings job creation displays the summary step","test.failCount":1}} --> | non_priority | failing test chrome x pack ui functional tests x pack test functional apps machine learning anomaly detection advanced job·ts machine learning anomaly detection advanced job with categorization detector and default datafeed settings job creation displays the summary step a test failed on a tracked branch timeouterror waiting until element is enabled wait timed out after at dev shm workspace kibana node modules selenium webdriver lib webdriver js at process tickcallback internal process next tick js name timeouterror remotestacktrace first failure | 0 |
184,414 | 21,784,897,831 | IssuesEvent | 2022-05-14 01:43:35 | rvvergara/expensify | https://api.github.com/repos/rvvergara/expensify | closed | CVE-2018-11696 (High) detected in node-sass-4.11.0.tgz - autoclosed | security vulnerability | ## CVE-2018-11696 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.11.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rvvergara/expensify/commit/fdfd5fe0d2a536540aa7d35163ec94f119bc53f0">fdfd5fe0d2a536540aa7d35163ec94f119bc53f0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Inspect::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11696>CVE-2018-11696</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.5.5">https://github.com/sass/libsass/releases/tag/3.5.5</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11696 (High) detected in node-sass-4.11.0.tgz - autoclosed - ## CVE-2018-11696 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.11.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.11.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.11.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rvvergara/expensify/commit/fdfd5fe0d2a536540aa7d35163ec94f119bc53f0">fdfd5fe0d2a536540aa7d35163ec94f119bc53f0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.4. A NULL pointer dereference was found in the function Sass::Inspect::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11696>CVE-2018-11696</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.5.5">https://github.com/sass/libsass/releases/tag/3.5.5</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node sass tgz autoclosed cve high severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href path to dependency file package json path to vulnerable library node modules node sass package json dependency hierarchy x node sass tgz vulnerable library found in head commit a href vulnerability details an issue was discovered in libsass through a null pointer dereference was found in the function sass inspect operator which could be leveraged by an attacker to cause a denial of service application crash or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
126,297 | 17,017,077,265 | IssuesEvent | 2021-07-02 13:31:33 | MaxMuecket/pocket-garden | https://api.github.com/repos/MaxMuecket/pocket-garden | closed | Design of the web app | design | #### Description
Design improving and finding navigation solutions.
#### Screenshots
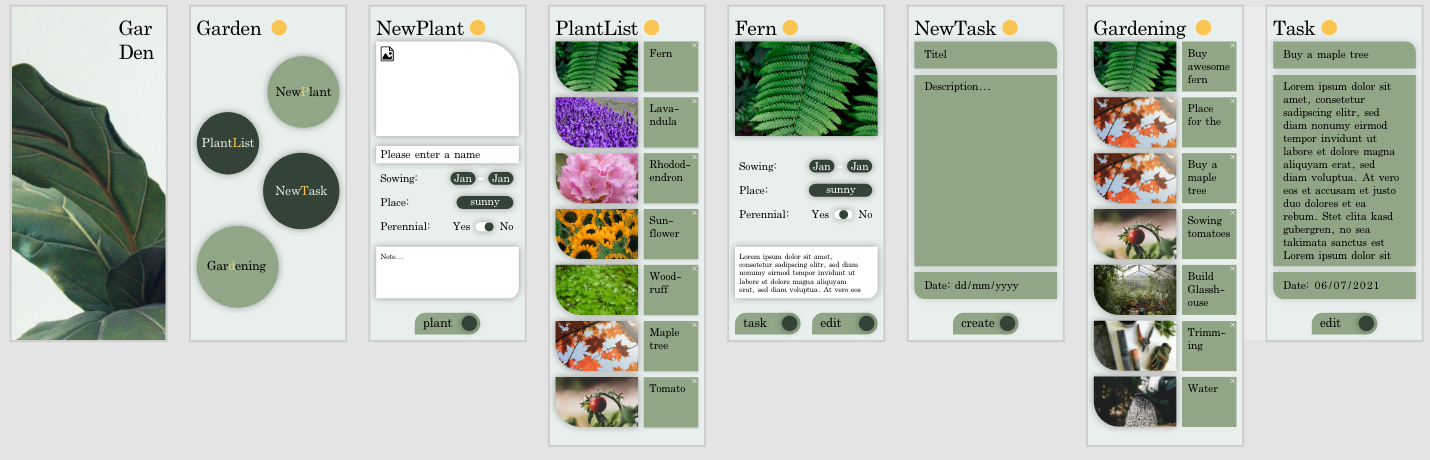
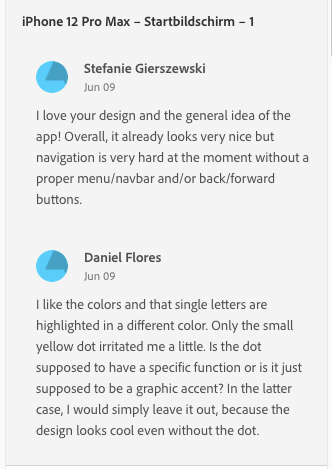
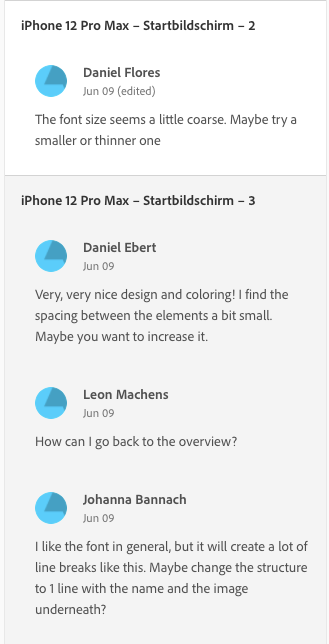
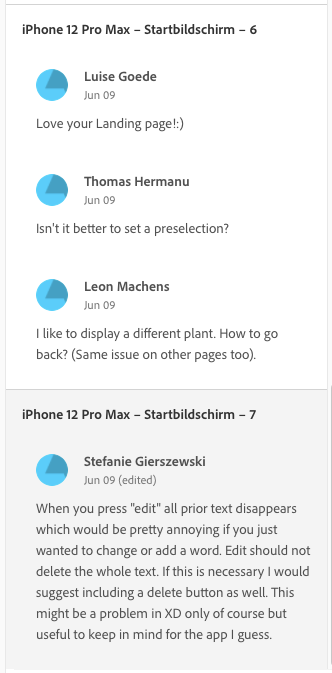
#### Tasks
- [x] Work on the design reviews!
- [ ] Review other designs!
- [x] Find a nice navigation solution (maybe burger menu 🧐)
- [x] Be happy and self-confident with your own design 🙂. | 1.0 | Design of the web app - #### Description
Design improving and finding navigation solutions.
#### Screenshots
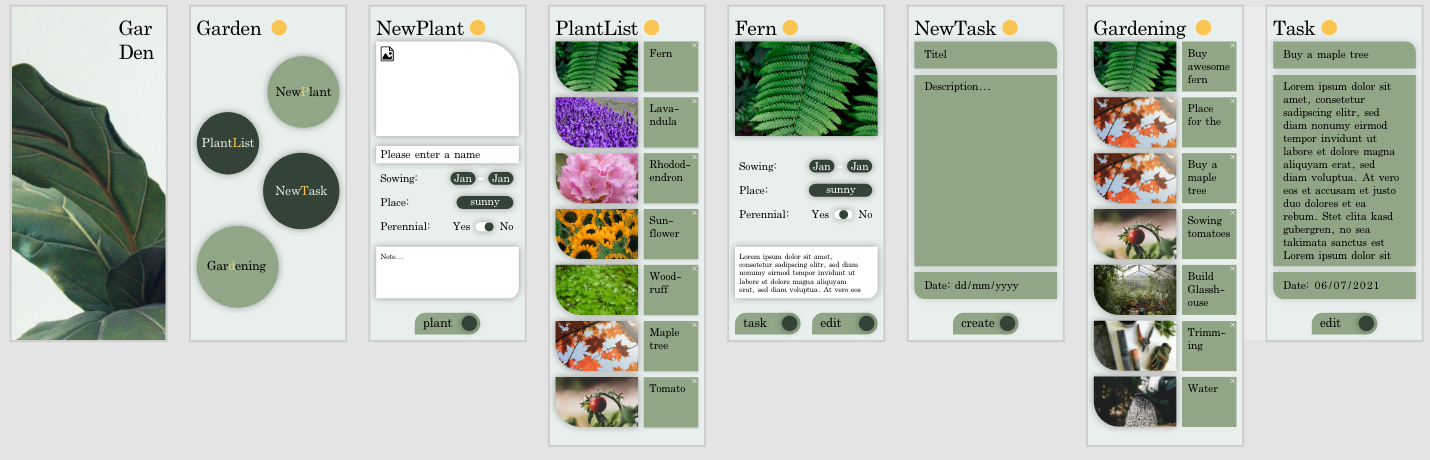
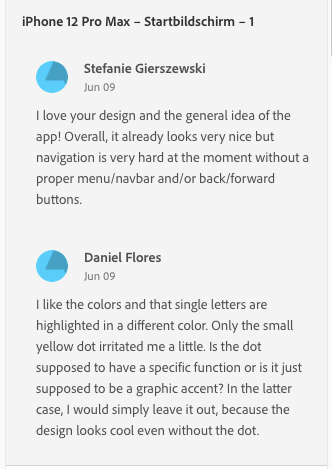
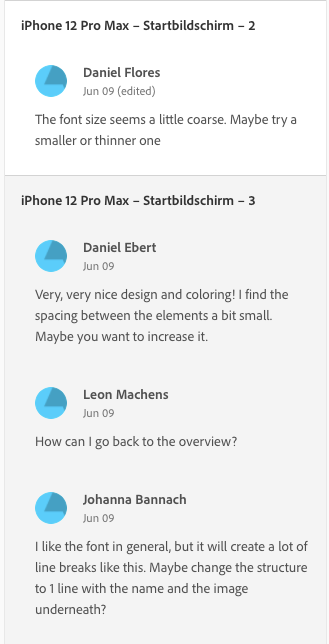
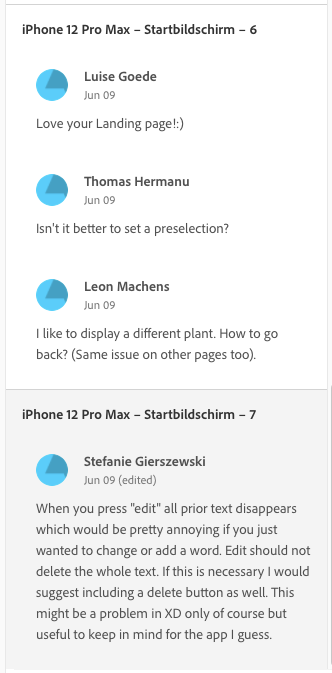
#### Tasks
- [x] Work on the design reviews!
- [ ] Review other designs!
- [x] Find a nice navigation solution (maybe burger menu 🧐)
- [x] Be happy and self-confident with your own design 🙂. | non_priority | design of the web app description design improving and finding navigation solutions screenshots tasks work on the design reviews review other designs find a nice navigation solution maybe burger menu 🧐 be happy and self confident with your own design 🙂 | 0 |
91,763 | 26,483,521,350 | IssuesEvent | 2023-01-17 16:16:23 | JuliaLang/julia | https://api.github.com/repos/JuliaLang/julia | opened | Julia segfaults when outputting sysimage when `max_methods == 0` | build | I wanted to experiment with turning off the abstract inference from `max_method` so I set it to 0. This causes julia to segfault when the sysimage is output:
```
Sysimage built. Summary:
Base ──────── 21.354232 seconds 40.7496%
Stdlibs ───── 31.048065 seconds 59.248%
Total ─────── 52.403573 seconds
[55097] signal (11.2): Segmentation fault: 11
in expression starting at none:0
emit_unbox_store at /Users/kristoffercarlsson/julia/src/./intrinsics.cpp:471
typed_store at /Users/kristoffercarlsson/julia/src/./cgutils.cpp:1925
emit_pointerset at /Users/kristoffercarlsson/julia/src/./intrinsics.cpp:760 [inlined]
emit_intrinsic at /Users/kristoffercarlsson/julia/src/./intrinsics.cpp:1174
emit_call at /Users/kristoffercarlsson/julia/src/codegen.cpp:4354
emit_expr at /Users/kristoffercarlsson/julia/src/codegen.cpp:5252
emit_ssaval_assign at /Users/kristoffercarlsson/julia/src/codegen.cpp:4849
emit_stmtpos at /Users/kristoffercarlsson/julia/src/codegen.cpp:0 [inlined]
emit_function at /Users/kristoffercarlsson/julia/src/codegen.cpp:8064
jl_emit_code at /Users/kristoffercarlsson/julia/src/codegen.cpp:8399
jl_create_native_impl at /Users/kristoffercarlsson/julia/src/aotcompile.cpp:344
jl_precompile_ at /Users/kristoffercarlsson/julia/src/./precompile_utils.c:254
jl_precompile at /Users/kristoffercarlsson/julia/src/./precompile_utils.c:267 [inlined]
ijl_create_system_image at /Users/kristoffercarlsson/julia/src/staticdata.c:2585
ijl_write_compiler_output at /Users/kristoffercarlsson/julia/src/precompile.c:117
ijl_atexit_hook at /Users/kristoffercarlsson/julia/src/init.c:251
jl_repl_entrypoint at /Users/kristoffercarlsson/julia/src/jlapi.c:718
Allocations: 120064121 (Pool: 120057048; Big: 7073); GC: 129
/bin/sh: line 1: 55097 Segmentation fault: 11 JULIA_BINDIR=/Users/kristoffercarlsson/julia/usr/bin WINEPATH="/Users/kristoffercarlsson/julia/usr/bin;$WINEPATH" /Users/kristoffercarlsson/julia/usr/bin/julia -g1 -O0 -C "native" --output-ji /Users/kristoffercarlsson/julia/usr/lib/julia/sys.ji.tmp --startup-file=no --warn-overwrite=yes --sysimage /Users/kristoffercarlsson/julia/usr/lib/julia/corecompiler.ji sysimg.jl ./
*** This error might be fixed by running `make clean`. If the error persists, try `make cleanall`. ***
make[1]: *** [/Users/kristoffercarlsson/julia/usr/lib/julia/sys.ji] Error 1
make: *** [julia-sysimg-ji] Error 2
``` | 1.0 | Julia segfaults when outputting sysimage when `max_methods == 0` - I wanted to experiment with turning off the abstract inference from `max_method` so I set it to 0. This causes julia to segfault when the sysimage is output:
```
Sysimage built. Summary:
Base ──────── 21.354232 seconds 40.7496%
Stdlibs ───── 31.048065 seconds 59.248%
Total ─────── 52.403573 seconds
[55097] signal (11.2): Segmentation fault: 11
in expression starting at none:0
emit_unbox_store at /Users/kristoffercarlsson/julia/src/./intrinsics.cpp:471
typed_store at /Users/kristoffercarlsson/julia/src/./cgutils.cpp:1925
emit_pointerset at /Users/kristoffercarlsson/julia/src/./intrinsics.cpp:760 [inlined]
emit_intrinsic at /Users/kristoffercarlsson/julia/src/./intrinsics.cpp:1174
emit_call at /Users/kristoffercarlsson/julia/src/codegen.cpp:4354
emit_expr at /Users/kristoffercarlsson/julia/src/codegen.cpp:5252
emit_ssaval_assign at /Users/kristoffercarlsson/julia/src/codegen.cpp:4849
emit_stmtpos at /Users/kristoffercarlsson/julia/src/codegen.cpp:0 [inlined]
emit_function at /Users/kristoffercarlsson/julia/src/codegen.cpp:8064
jl_emit_code at /Users/kristoffercarlsson/julia/src/codegen.cpp:8399
jl_create_native_impl at /Users/kristoffercarlsson/julia/src/aotcompile.cpp:344
jl_precompile_ at /Users/kristoffercarlsson/julia/src/./precompile_utils.c:254
jl_precompile at /Users/kristoffercarlsson/julia/src/./precompile_utils.c:267 [inlined]
ijl_create_system_image at /Users/kristoffercarlsson/julia/src/staticdata.c:2585
ijl_write_compiler_output at /Users/kristoffercarlsson/julia/src/precompile.c:117
ijl_atexit_hook at /Users/kristoffercarlsson/julia/src/init.c:251
jl_repl_entrypoint at /Users/kristoffercarlsson/julia/src/jlapi.c:718
Allocations: 120064121 (Pool: 120057048; Big: 7073); GC: 129
/bin/sh: line 1: 55097 Segmentation fault: 11 JULIA_BINDIR=/Users/kristoffercarlsson/julia/usr/bin WINEPATH="/Users/kristoffercarlsson/julia/usr/bin;$WINEPATH" /Users/kristoffercarlsson/julia/usr/bin/julia -g1 -O0 -C "native" --output-ji /Users/kristoffercarlsson/julia/usr/lib/julia/sys.ji.tmp --startup-file=no --warn-overwrite=yes --sysimage /Users/kristoffercarlsson/julia/usr/lib/julia/corecompiler.ji sysimg.jl ./
*** This error might be fixed by running `make clean`. If the error persists, try `make cleanall`. ***
make[1]: *** [/Users/kristoffercarlsson/julia/usr/lib/julia/sys.ji] Error 1
make: *** [julia-sysimg-ji] Error 2
``` | non_priority | julia segfaults when outputting sysimage when max methods i wanted to experiment with turning off the abstract inference from max method so i set it to this causes julia to segfault when the sysimage is output sysimage built summary base ──────── seconds stdlibs ───── seconds total ─────── seconds signal segmentation fault in expression starting at none emit unbox store at users kristoffercarlsson julia src intrinsics cpp typed store at users kristoffercarlsson julia src cgutils cpp emit pointerset at users kristoffercarlsson julia src intrinsics cpp emit intrinsic at users kristoffercarlsson julia src intrinsics cpp emit call at users kristoffercarlsson julia src codegen cpp emit expr at users kristoffercarlsson julia src codegen cpp emit ssaval assign at users kristoffercarlsson julia src codegen cpp emit stmtpos at users kristoffercarlsson julia src codegen cpp emit function at users kristoffercarlsson julia src codegen cpp jl emit code at users kristoffercarlsson julia src codegen cpp jl create native impl at users kristoffercarlsson julia src aotcompile cpp jl precompile at users kristoffercarlsson julia src precompile utils c jl precompile at users kristoffercarlsson julia src precompile utils c ijl create system image at users kristoffercarlsson julia src staticdata c ijl write compiler output at users kristoffercarlsson julia src precompile c ijl atexit hook at users kristoffercarlsson julia src init c jl repl entrypoint at users kristoffercarlsson julia src jlapi c allocations pool big gc bin sh line segmentation fault julia bindir users kristoffercarlsson julia usr bin winepath users kristoffercarlsson julia usr bin winepath users kristoffercarlsson julia usr bin julia c native output ji users kristoffercarlsson julia usr lib julia sys ji tmp startup file no warn overwrite yes sysimage users kristoffercarlsson julia usr lib julia corecompiler ji sysimg jl this error might be fixed by running make clean if the error persists try make cleanall make error make error | 0 |
239,308 | 18,269,175,748 | IssuesEvent | 2021-10-04 12:04:45 | abirbhattacharya82/Hacktoberfest-Codedump | https://api.github.com/repos/abirbhattacharya82/Hacktoberfest-Codedump | closed | Will add interview problems on Dynamic Programming | documentation hacktoberfest | Please assign me this task to add problems based on knapsack | 1.0 | Will add interview problems on Dynamic Programming - Please assign me this task to add problems based on knapsack | non_priority | will add interview problems on dynamic programming please assign me this task to add problems based on knapsack | 0 |
130,518 | 18,075,687,014 | IssuesEvent | 2021-09-21 09:37:13 | owncloud/core | https://api.github.com/repos/owncloud/core | closed | Assigning tags using dropdown makes the list get ordered every time. | Type:Bug design feature:tags status/STALE | ### Steps to reproduce
1. Create and assign many tags.
2. Unassign them.
3. Assign all of them again using the dropdown.
### Expected behaviour
The list doesn't get reordered with every assignment. Only if the dropdown is closed.
### Actual behaviour
With every assignment the dropdown's list gets ordered and user has to find again what tag he was wanting to assign.
### Server configuration
**Operating system**:
Ubuntu 14.04
**Web server:**
Apache
**Database:**
MySQL
**PHP version:**
5.5.9
**ownCloud version:** (see ownCloud admin page)
Master branch
{"installed":true,"maintenance":false,"version":"9.0.0.8","versionstring":"9.0 pre alpha","edition":"Enterprise"}
**Updated from an older ownCloud or fresh install:**
Fresh
**The content of config/config.php:**
```
```
**Are you using external storage, if yes which one:** local/smb/sftp/...
No.
**Are you using encryption:**
Yes
**Logs**
```
```
### Client configuration
**browser**
Chrome
| 1.0 | Assigning tags using dropdown makes the list get ordered every time. - ### Steps to reproduce
1. Create and assign many tags.
2. Unassign them.
3. Assign all of them again using the dropdown.
### Expected behaviour
The list doesn't get reordered with every assignment. Only if the dropdown is closed.
### Actual behaviour
With every assignment the dropdown's list gets ordered and user has to find again what tag he was wanting to assign.
### Server configuration
**Operating system**:
Ubuntu 14.04
**Web server:**
Apache
**Database:**
MySQL
**PHP version:**
5.5.9
**ownCloud version:** (see ownCloud admin page)
Master branch
{"installed":true,"maintenance":false,"version":"9.0.0.8","versionstring":"9.0 pre alpha","edition":"Enterprise"}
**Updated from an older ownCloud or fresh install:**
Fresh
**The content of config/config.php:**
```
```
**Are you using external storage, if yes which one:** local/smb/sftp/...
No.
**Are you using encryption:**
Yes
**Logs**
```
```
### Client configuration
**browser**
Chrome
| non_priority | assigning tags using dropdown makes the list get ordered every time steps to reproduce create and assign many tags unassign them assign all of them again using the dropdown expected behaviour the list doesn t get reordered with every assignment only if the dropdown is closed actual behaviour with every assignment the dropdown s list gets ordered and user has to find again what tag he was wanting to assign server configuration operating system ubuntu web server apache database mysql php version owncloud version see owncloud admin page master branch installed true maintenance false version versionstring pre alpha edition enterprise updated from an older owncloud or fresh install fresh the content of config config php are you using external storage if yes which one local smb sftp no are you using encryption yes logs client configuration browser chrome | 0 |
47,333 | 13,056,126,049 | IssuesEvent | 2020-07-30 03:44:13 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | DOM Numbers (Trac #363) | Migrated from Trac defect glshovel | From Boersma's wishlist :
DOM numbers can optionally be printed next to DOMs, but the rendering
seems very fuzzy, the numbers are actually hard to read. It would be
nice if this could be improved, and also if the text properties could
be made a bit more configurable, e.g. the size and color of the text.
Migrated from https://code.icecube.wisc.edu/ticket/363
```json
{
"status": "closed",
"changetime": "2013-12-18T19:59:46",
"description": "From Boersma's wishlist :\n\nDOM numbers can optionally be printed next to DOMs, but the rendering\nseems very fuzzy, the numbers are actually hard to read. It would be\nnice if this could be improved, and also if the text properties could\nbe made a bit more configurable, e.g. the size and color of the text.",
"reporter": "olivas",
"cc": "",
"resolution": "fixed",
"_ts": "1387396786000000",
"component": "glshovel",
"summary": "DOM Numbers",
"priority": "normal",
"keywords": "",
"time": "2012-02-29T06:45:22",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
| 1.0 | DOM Numbers (Trac #363) - From Boersma's wishlist :
DOM numbers can optionally be printed next to DOMs, but the rendering
seems very fuzzy, the numbers are actually hard to read. It would be
nice if this could be improved, and also if the text properties could
be made a bit more configurable, e.g. the size and color of the text.
Migrated from https://code.icecube.wisc.edu/ticket/363
```json
{
"status": "closed",
"changetime": "2013-12-18T19:59:46",
"description": "From Boersma's wishlist :\n\nDOM numbers can optionally be printed next to DOMs, but the rendering\nseems very fuzzy, the numbers are actually hard to read. It would be\nnice if this could be improved, and also if the text properties could\nbe made a bit more configurable, e.g. the size and color of the text.",
"reporter": "olivas",
"cc": "",
"resolution": "fixed",
"_ts": "1387396786000000",
"component": "glshovel",
"summary": "DOM Numbers",
"priority": "normal",
"keywords": "",
"time": "2012-02-29T06:45:22",
"milestone": "",
"owner": "olivas",
"type": "defect"
}
```
| non_priority | dom numbers trac from boersma s wishlist dom numbers can optionally be printed next to doms but the rendering seems very fuzzy the numbers are actually hard to read it would be nice if this could be improved and also if the text properties could be made a bit more configurable e g the size and color of the text migrated from json status closed changetime description from boersma s wishlist n ndom numbers can optionally be printed next to doms but the rendering nseems very fuzzy the numbers are actually hard to read it would be nnice if this could be improved and also if the text properties could nbe made a bit more configurable e g the size and color of the text reporter olivas cc resolution fixed ts component glshovel summary dom numbers priority normal keywords time milestone owner olivas type defect | 0 |
147,904 | 23,291,324,904 | IssuesEvent | 2022-08-05 23:42:12 | eiksch/statev_v2_issues | https://api.github.com/repos/eiksch/statev_v2_issues | closed | Haushash paletobay20 | gamedesign solved | Moin moin wie mit William Walles im Support besprochen nun hier das Ticket
es geht um 2 Anliegen.
Punkt nummer 1.
Die anfrage für eine Hausgarage.



Wie man an den Bildern Erkennen kann habe ich eine Sehr sehr große Einfahrt. (platz für bis zu 6 Autos und dan noch Motorräder)
Deswegen stelle ich nun die Anfrage für einen Garagen punkt (ich weis das nichts gemappt wird aber zumindestens der Punkt zum Bee und Entladen währe sehr sehr wünschenswert. Dieser könnte am Ende der Einfahrt Angebracht werden (dort wo das Zelt steht)
Diese anfrage hatte ich im support gestellt und gesagt bekommen das ich für das Gamedesign nen Ticket erstellen solle.
Anfrage nummer 2
Diese ist etwas ungewöhnlicher.
Mir wurde anfags gesagt das sich die Interiör größen nach art des Hauses orientieren. Nun ist mir aufgefallen das ich eines der größeren häuser in Paleto und Sandy shores habe und das haus Allerdings auf die Klasse 1 gesetzt ist. An sich fdand ich das ja noch ok weil ich dachte gut das liegt an Paleto die in der stadt sind dan alle 2 oder höher aber inzwischen weis ich das ettliche auch viel kleinere (und ich rede da schon von wirklichen wohnwagen oder kleien bruchbuden) Wohnungen auf klasse 2 gesetzt wurden.
Deswegen würde ich darum bitten das man schaut ob das haus vl nicht einfach nur falsch eingestuft wurde.
Ich habe aktuell das Low End Apartment in meinen Klasse 1 haus und würde gerne auf das Girlys apartment von klasse 2 wechseln.
Dies hatt den Hintergrund das ich finde das das Design viel besser zum Grundriss des Hauses Passt und dies auch besser meinen char wiederspiegeln würde (keines der klasse 1 interieurs passt wirklich zu den Char.
Ich würde mich deswegen über eine Kurze Überprüfung freuen (sollten dafür kosten anfallen werde ich die selbstredend übernehmen)
MfG
Ricardo Cassado
| 1.0 | Haushash paletobay20 - Moin moin wie mit William Walles im Support besprochen nun hier das Ticket
es geht um 2 Anliegen.
Punkt nummer 1.
Die anfrage für eine Hausgarage.



Wie man an den Bildern Erkennen kann habe ich eine Sehr sehr große Einfahrt. (platz für bis zu 6 Autos und dan noch Motorräder)
Deswegen stelle ich nun die Anfrage für einen Garagen punkt (ich weis das nichts gemappt wird aber zumindestens der Punkt zum Bee und Entladen währe sehr sehr wünschenswert. Dieser könnte am Ende der Einfahrt Angebracht werden (dort wo das Zelt steht)
Diese anfrage hatte ich im support gestellt und gesagt bekommen das ich für das Gamedesign nen Ticket erstellen solle.
Anfrage nummer 2
Diese ist etwas ungewöhnlicher.
Mir wurde anfags gesagt das sich die Interiör größen nach art des Hauses orientieren. Nun ist mir aufgefallen das ich eines der größeren häuser in Paleto und Sandy shores habe und das haus Allerdings auf die Klasse 1 gesetzt ist. An sich fdand ich das ja noch ok weil ich dachte gut das liegt an Paleto die in der stadt sind dan alle 2 oder höher aber inzwischen weis ich das ettliche auch viel kleinere (und ich rede da schon von wirklichen wohnwagen oder kleien bruchbuden) Wohnungen auf klasse 2 gesetzt wurden.
Deswegen würde ich darum bitten das man schaut ob das haus vl nicht einfach nur falsch eingestuft wurde.
Ich habe aktuell das Low End Apartment in meinen Klasse 1 haus und würde gerne auf das Girlys apartment von klasse 2 wechseln.
Dies hatt den Hintergrund das ich finde das das Design viel besser zum Grundriss des Hauses Passt und dies auch besser meinen char wiederspiegeln würde (keines der klasse 1 interieurs passt wirklich zu den Char.
Ich würde mich deswegen über eine Kurze Überprüfung freuen (sollten dafür kosten anfallen werde ich die selbstredend übernehmen)
MfG
Ricardo Cassado
| non_priority | haushash moin moin wie mit william walles im support besprochen nun hier das ticket es geht um anliegen punkt nummer die anfrage für eine hausgarage wie man an den bildern erkennen kann habe ich eine sehr sehr große einfahrt platz für bis zu autos und dan noch motorräder deswegen stelle ich nun die anfrage für einen garagen punkt ich weis das nichts gemappt wird aber zumindestens der punkt zum bee und entladen währe sehr sehr wünschenswert dieser könnte am ende der einfahrt angebracht werden dort wo das zelt steht diese anfrage hatte ich im support gestellt und gesagt bekommen das ich für das gamedesign nen ticket erstellen solle anfrage nummer diese ist etwas ungewöhnlicher mir wurde anfags gesagt das sich die interiör größen nach art des hauses orientieren nun ist mir aufgefallen das ich eines der größeren häuser in paleto und sandy shores habe und das haus allerdings auf die klasse gesetzt ist an sich fdand ich das ja noch ok weil ich dachte gut das liegt an paleto die in der stadt sind dan alle oder höher aber inzwischen weis ich das ettliche auch viel kleinere und ich rede da schon von wirklichen wohnwagen oder kleien bruchbuden wohnungen auf klasse gesetzt wurden deswegen würde ich darum bitten das man schaut ob das haus vl nicht einfach nur falsch eingestuft wurde ich habe aktuell das low end apartment in meinen klasse haus und würde gerne auf das girlys apartment von klasse wechseln dies hatt den hintergrund das ich finde das das design viel besser zum grundriss des hauses passt und dies auch besser meinen char wiederspiegeln würde keines der klasse interieurs passt wirklich zu den char ich würde mich deswegen über eine kurze überprüfung freuen sollten dafür kosten anfallen werde ich die selbstredend übernehmen mfg ricardo cassado | 0 |
9,101 | 11,148,473,953 | IssuesEvent | 2019-12-23 15:38:08 | arcticicestudio/nord-vim | https://api.github.com/repos/arcticicestudio/nord-vim | closed | Airline Theme no longer working | context-plugin-support context-ui scope-compatibility status-pending target-neovim type-support | Since updating to https://github.com/arcticicestudio/nord-vim/commit/73b3d340a735a2b6915f62a8904d6521251375cd the Airline theme no longer applies successfully on Neovim with vim-airline https://github.com/vim-airline/vim-airline/commit/b93492b40b068d4bb3020c123295061aaba7c846 | True | Airline Theme no longer working - Since updating to https://github.com/arcticicestudio/nord-vim/commit/73b3d340a735a2b6915f62a8904d6521251375cd the Airline theme no longer applies successfully on Neovim with vim-airline https://github.com/vim-airline/vim-airline/commit/b93492b40b068d4bb3020c123295061aaba7c846 | non_priority | airline theme no longer working since updating to the airline theme no longer applies successfully on neovim with vim airline | 0 |
20,598 | 3,828,492,478 | IssuesEvent | 2016-03-31 06:08:16 | AeroScripts/QuestieDev | https://api.github.com/repos/AeroScripts/QuestieDev | closed | Questie Error in Desolace | test again | Picking up the below errors when I gathered the quests at Nijel's Point in Desolace.
_interface\addons\questie\QuestieQuest.lu
a:157: attempt to call global
‘QuestCompat_GetQuestLogTitle’ (a nil value)
interface\addons\questie\QuestieQuest.lu
a:294: attempt to call global
‘QuestCompat_GetQuestLogTitle’ (a nil value)
_
The errors won't disappear, and whilst present the map does not update to show questie drops / kills. | 1.0 | Questie Error in Desolace - Picking up the below errors when I gathered the quests at Nijel's Point in Desolace.
_interface\addons\questie\QuestieQuest.lu
a:157: attempt to call global
‘QuestCompat_GetQuestLogTitle’ (a nil value)
interface\addons\questie\QuestieQuest.lu
a:294: attempt to call global
‘QuestCompat_GetQuestLogTitle’ (a nil value)
_
The errors won't disappear, and whilst present the map does not update to show questie drops / kills. | non_priority | questie error in desolace picking up the below errors when i gathered the quests at nijel s point in desolace interface addons questie questiequest lu a attempt to call global ‘questcompat getquestlogtitle’ a nil value interface addons questie questiequest lu a attempt to call global ‘questcompat getquestlogtitle’ a nil value the errors won t disappear and whilst present the map does not update to show questie drops kills | 0 |
2,265 | 2,602,207,614 | IssuesEvent | 2015-02-24 06:02:32 | INCF/nineml | https://api.github.com/repos/INCF/nineml | reopened | Do we need a separate “AnalogOut” element to match “EventOut” instead of just using Alias/StateVariable’? | design choice specification | This is mainly a stylistic/readability issue, which in most cases will mean just replacing one of the Alias tags with AnalogOut (except when the AnalogPort is connected directly to a state variable when you will need to create an extra tag). However, it would perhaps be useful when it comes to simulator implementation to know which values need to be returned and it should at least help the AnalogOuts visually stand out from the Alias’, of which there could be many. | 1.0 | Do we need a separate “AnalogOut” element to match “EventOut” instead of just using Alias/StateVariable’? - This is mainly a stylistic/readability issue, which in most cases will mean just replacing one of the Alias tags with AnalogOut (except when the AnalogPort is connected directly to a state variable when you will need to create an extra tag). However, it would perhaps be useful when it comes to simulator implementation to know which values need to be returned and it should at least help the AnalogOuts visually stand out from the Alias’, of which there could be many. | non_priority | do we need a separate “analogout” element to match “eventout” instead of just using alias statevariable’ this is mainly a stylistic readability issue which in most cases will mean just replacing one of the alias tags with analogout except when the analogport is connected directly to a state variable when you will need to create an extra tag however it would perhaps be useful when it comes to simulator implementation to know which values need to be returned and it should at least help the analogouts visually stand out from the alias’ of which there could be many | 0 |
70,660 | 13,521,731,561 | IssuesEvent | 2020-09-15 07:29:58 | GridtNetwork/gridt-server | https://api.github.com/repos/GridtNetwork/gridt-server | opened | Tests should use available helper functions | Code improvement | Old tests still create their tokens rather than use the base test's request_as_user() helper function. Using this will clean up the code. | 1.0 | Tests should use available helper functions - Old tests still create their tokens rather than use the base test's request_as_user() helper function. Using this will clean up the code. | non_priority | tests should use available helper functions old tests still create their tokens rather than use the base test s request as user helper function using this will clean up the code | 0 |
155,366 | 19,802,813,187 | IssuesEvent | 2022-01-19 01:01:17 | ilan-WS/logging-log4j2 | https://api.github.com/repos/ilan-WS/logging-log4j2 | opened | CVE-2022-23302 (High) detected in log4j-1.2.17.jar | security vulnerability | ## CVE-2022-23302 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /log4j-perf/pom.xml</p>
<p>Path to vulnerable library: /sitory/log4j/log4j/1.2.17/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JMSSink in all versions of Log4j 1.x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to. The attacker can provide a TopicConnectionFactoryBindingName configuration causing JMSSink to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-4104. Note this issue only affects Log4j 1.x when specifically configured to use JMSSink, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.
<p>Publish Date: 2022-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23302>CVE-2022-23302</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.17","packageFilePaths":["/log4j-perf/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"log4j:log4j:1.2.17","isMinimumFixVersionAvailable":false,"isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-23302","vulnerabilityDetails":"JMSSink in all versions of Log4j 1.x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to. The attacker can provide a TopicConnectionFactoryBindingName configuration causing JMSSink to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-4104. Note this issue only affects Log4j 1.x when specifically configured to use JMSSink, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23302","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-23302 (High) detected in log4j-1.2.17.jar - ## CVE-2022-23302 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /log4j-perf/pom.xml</p>
<p>Path to vulnerable library: /sitory/log4j/log4j/1.2.17/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JMSSink in all versions of Log4j 1.x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to. The attacker can provide a TopicConnectionFactoryBindingName configuration causing JMSSink to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-4104. Note this issue only affects Log4j 1.x when specifically configured to use JMSSink, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.
<p>Publish Date: 2022-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23302>CVE-2022-23302</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.17","packageFilePaths":["/log4j-perf/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"log4j:log4j:1.2.17","isMinimumFixVersionAvailable":false,"isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-23302","vulnerabilityDetails":"JMSSink in all versions of Log4j 1.x is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration or if the configuration references an LDAP service the attacker has access to. The attacker can provide a TopicConnectionFactoryBindingName configuration causing JMSSink to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-4104. Note this issue only affects Log4j 1.x when specifically configured to use JMSSink, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23302","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jar cve high severity vulnerability vulnerable library jar apache path to dependency file perf pom xml path to vulnerable library sitory jar dependency hierarchy x jar vulnerable library found in base branch master vulnerability details jmssink in all versions of x is vulnerable to deserialization of untrusted data when the attacker has write access to the configuration or if the configuration references an ldap service the attacker has access to the attacker can provide a topicconnectionfactorybindingname configuration causing jmssink to perform jndi requests that result in remote code execution in a similar fashion to cve note this issue only affects x when specifically configured to use jmssink which is not the default apache reached end of life in august users should upgrade to as it addresses numerous other issues from the previous versions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree isminimumfixversionavailable false isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails jmssink in all versions of x is vulnerable to deserialization of untrusted data when the attacker has write access to the configuration or if the configuration references an ldap service the attacker has access to the attacker can provide a topicconnectionfactorybindingname configuration causing jmssink to perform jndi requests that result in remote code execution in a similar fashion to cve note this issue only affects x when specifically configured to use jmssink which is not the default apache reached end of life in august users should upgrade to as it addresses numerous other issues from the previous versions vulnerabilityurl | 0 |
229,431 | 25,343,416,910 | IssuesEvent | 2022-11-19 01:02:20 | MidnightBSD/src | https://api.github.com/repos/MidnightBSD/src | opened | CVE-2022-41916 (High) detected in freebsd-srcrelease/13.1.0 | security vulnerability | ## CVE-2022-41916 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>freebsd-srcrelease/13.1.0</b></p></summary>
<p>
<p>FreeBSD src tree (read-only mirror)</p>
<p>Library home page: <a href=https://github.com/freebsd/freebsd-src.git>https://github.com/freebsd/freebsd-src.git</a></p>
<p>Found in base branches: <b>stable/2.1, stable/2.2, master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/crypto/heimdal/lib/wind/normalize.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Heimdal is an implementation of ASN.1/DER, PKIX, and Kerberos. Versions prior to 7.7.1 are vulnerable to a denial of service vulnerability in Heimdal's PKI certificate validation library, affecting the KDC (via PKINIT) and kinit (via PKINIT), as well as any third-party applications using Heimdal's libhx509. Users should upgrade to Heimdal 7.7.1 or 7.8. There are no known workarounds for this issue.
<p>Publish Date: 2022-11-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41916>CVE-2022-41916</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/heimdal/heimdal/security/advisories/GHSA-mgqr-gvh6-23cx">https://github.com/heimdal/heimdal/security/advisories/GHSA-mgqr-gvh6-23cx</a></p>
<p>Release Date: 2022-11-15</p>
<p>Fix Resolution: heimdal-7.7.1
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-41916 (High) detected in freebsd-srcrelease/13.1.0 - ## CVE-2022-41916 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>freebsd-srcrelease/13.1.0</b></p></summary>
<p>
<p>FreeBSD src tree (read-only mirror)</p>
<p>Library home page: <a href=https://github.com/freebsd/freebsd-src.git>https://github.com/freebsd/freebsd-src.git</a></p>
<p>Found in base branches: <b>stable/2.1, stable/2.2, master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/crypto/heimdal/lib/wind/normalize.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Heimdal is an implementation of ASN.1/DER, PKIX, and Kerberos. Versions prior to 7.7.1 are vulnerable to a denial of service vulnerability in Heimdal's PKI certificate validation library, affecting the KDC (via PKINIT) and kinit (via PKINIT), as well as any third-party applications using Heimdal's libhx509. Users should upgrade to Heimdal 7.7.1 or 7.8. There are no known workarounds for this issue.
<p>Publish Date: 2022-11-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41916>CVE-2022-41916</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/heimdal/heimdal/security/advisories/GHSA-mgqr-gvh6-23cx">https://github.com/heimdal/heimdal/security/advisories/GHSA-mgqr-gvh6-23cx</a></p>
<p>Release Date: 2022-11-15</p>
<p>Fix Resolution: heimdal-7.7.1
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in freebsd srcrelease cve high severity vulnerability vulnerable library freebsd srcrelease freebsd src tree read only mirror library home page a href found in base branches stable stable master vulnerable source files crypto heimdal lib wind normalize c vulnerability details heimdal is an implementation of asn der pkix and kerberos versions prior to are vulnerable to a denial of service vulnerability in heimdal s pki certificate validation library affecting the kdc via pkinit and kinit via pkinit as well as any third party applications using heimdal s users should upgrade to heimdal or there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution heimdal step up your open source security game with mend | 0 |
6,220 | 4,186,265,663 | IssuesEvent | 2016-06-23 14:01:54 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 26843647: Vim keybindings for Xcode 8 | classification:ui/usability reproducible:always status:open | #### Description
Summary:
Xcode 8 does not have vim keybindings, and does not work with Xvim because of SIP. The Xcode extension API isn't powerful enough to enable plugins similar to this.
Steps to Reproduce:
1. Open Xcode 8
2. Try to use Xvim
Expected Results:
You can use vim-like bindings
Actual Results:
You're sad because you can't use vim-like bindings
Version:
Xcode 8 beta 1
Notes:
See the 4000+ stars on Github for Xvim https://github.com/XVimProject/XVim
Configuration:
Attachments:
-
Product Version: 8
Created: 2016-06-16T19:14:46.515060
Originated: 2016-06-16T12:12:00
Open Radar Link: http://www.openradar.me/26843647 | True | 26843647: Vim keybindings for Xcode 8 - #### Description
Summary:
Xcode 8 does not have vim keybindings, and does not work with Xvim because of SIP. The Xcode extension API isn't powerful enough to enable plugins similar to this.
Steps to Reproduce:
1. Open Xcode 8
2. Try to use Xvim
Expected Results:
You can use vim-like bindings
Actual Results:
You're sad because you can't use vim-like bindings
Version:
Xcode 8 beta 1
Notes:
See the 4000+ stars on Github for Xvim https://github.com/XVimProject/XVim
Configuration:
Attachments:
-
Product Version: 8
Created: 2016-06-16T19:14:46.515060
Originated: 2016-06-16T12:12:00
Open Radar Link: http://www.openradar.me/26843647 | non_priority | vim keybindings for xcode description summary xcode does not have vim keybindings and does not work with xvim because of sip the xcode extension api isn t powerful enough to enable plugins similar to this steps to reproduce open xcode try to use xvim expected results you can use vim like bindings actual results you re sad because you can t use vim like bindings version xcode beta notes see the stars on github for xvim configuration attachments product version created originated open radar link | 0 |
110,214 | 23,893,383,586 | IssuesEvent | 2022-09-08 13:11:32 | Onelinerhub/onelinerhub | https://api.github.com/repos/Onelinerhub/onelinerhub | closed | Short solution needed: "How to draw circle" (php-gd) | help wanted good first issue code php-gd | Please help us write most modern and shortest code solution for this issue:
**How to draw circle** (technology: [php-gd](https://onelinerhub.com/php-gd))
### Fast way
Just write the code solution in the comments.
### Prefered way
1. Create [pull request](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md) with a new code file inside [inbox folder](https://github.com/Onelinerhub/onelinerhub/tree/main/inbox).
2. Don't forget to [use comments](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md#code-file-md-format) explain solution.
3. Link to this issue in comments of pull request. | 1.0 | Short solution needed: "How to draw circle" (php-gd) - Please help us write most modern and shortest code solution for this issue:
**How to draw circle** (technology: [php-gd](https://onelinerhub.com/php-gd))
### Fast way
Just write the code solution in the comments.
### Prefered way
1. Create [pull request](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md) with a new code file inside [inbox folder](https://github.com/Onelinerhub/onelinerhub/tree/main/inbox).
2. Don't forget to [use comments](https://github.com/Onelinerhub/onelinerhub/blob/main/how-to-contribute.md#code-file-md-format) explain solution.
3. Link to this issue in comments of pull request. | non_priority | short solution needed how to draw circle php gd please help us write most modern and shortest code solution for this issue how to draw circle technology fast way just write the code solution in the comments prefered way create with a new code file inside don t forget to explain solution link to this issue in comments of pull request | 0 |
117,449 | 11,946,734,811 | IssuesEvent | 2020-04-03 08:40:40 | DamionGans/MegaMaxCorpInc | https://api.github.com/repos/DamionGans/MegaMaxCorpInc | closed | Create getting started guide | Documentation Enhancements Important | People without Linux foreknowledge should be able to follow through as well :-) | 1.0 | Create getting started guide - People without Linux foreknowledge should be able to follow through as well :-) | non_priority | create getting started guide people without linux foreknowledge should be able to follow through as well | 0 |
55,364 | 13,618,276,250 | IssuesEvent | 2020-09-23 18:18:12 | EasyRPG/Player | https://api.github.com/repos/EasyRPG/Player | opened | Get rid of USE_SDL and USE_LIBRETRO checks | Building | Currently our code is "cluttered" (well, few lines) with different code paths for SDL and Libretro. By removing them from the main files it would become easy in CMake to build both an executable and the libretro library in the same step with only a small compile time penalty. Currently this would need an complete recompile twice, which takes too long.
```
baseui.cpp
26:#elif USE_LIBRETRO
43:#elif defined(USE_LIBRETRO)
input_buttons_desktop.cpp
18:#if !(defined(OPENDINGUX) || defined(GEKKO) || defined(USE_LIBRETRO))
output.cpp
199:#if !defined(USE_LIBRETRO)
filefinder.cpp
53:#ifdef USE_LIBRETRO
544:#elif defined(USE_LIBRETRO)
system.h
29:#if !(defined(USE_SDL) || defined(_3DS) || defined(PSP2) || defined(__SWITCH__) || defined(USE_LIBRETRO))
44:#if defined(USE_LIBRETRO)
player.cpp
217:#ifndef USE_LIBRETRO
decoder_wildmidi.cpp
32:#ifdef USE_LIBRETRO
118:#if defined(USE_LIBRETRO)
```
```
baseui.cpp
22:#if USE_SDL==2
24:#elif USE_SDL==1
39:#if USE_SDL==2
41:#elif USE_SDL==1
main.cpp
22:#ifdef USE_SDL
filefinder.cpp
35:#if defined(USE_SDL) && defined(__ANDROID__)
main_data.cpp
39:#if defined(USE_SDL) && defined(__ANDROID__)
system.h
23: * This option may have defined USE_SDL and others.
29:#if !(defined(USE_SDL) || defined(_3DS) || defined(PSP2) || defined(__SWITCH__) || defined(USE_LIBRETRO))
101:#ifdef USE_SDL
decoder_wildmidi.cpp
36:#if defined(USE_SDL) && defined(__ANDROID__)
47:#if defined(USE_SDL) && defined(__ANDROID__)
``` | 1.0 | Get rid of USE_SDL and USE_LIBRETRO checks - Currently our code is "cluttered" (well, few lines) with different code paths for SDL and Libretro. By removing them from the main files it would become easy in CMake to build both an executable and the libretro library in the same step with only a small compile time penalty. Currently this would need an complete recompile twice, which takes too long.
```
baseui.cpp
26:#elif USE_LIBRETRO
43:#elif defined(USE_LIBRETRO)
input_buttons_desktop.cpp
18:#if !(defined(OPENDINGUX) || defined(GEKKO) || defined(USE_LIBRETRO))
output.cpp
199:#if !defined(USE_LIBRETRO)
filefinder.cpp
53:#ifdef USE_LIBRETRO
544:#elif defined(USE_LIBRETRO)
system.h
29:#if !(defined(USE_SDL) || defined(_3DS) || defined(PSP2) || defined(__SWITCH__) || defined(USE_LIBRETRO))
44:#if defined(USE_LIBRETRO)
player.cpp
217:#ifndef USE_LIBRETRO
decoder_wildmidi.cpp
32:#ifdef USE_LIBRETRO
118:#if defined(USE_LIBRETRO)
```
```
baseui.cpp
22:#if USE_SDL==2
24:#elif USE_SDL==1
39:#if USE_SDL==2
41:#elif USE_SDL==1
main.cpp
22:#ifdef USE_SDL
filefinder.cpp
35:#if defined(USE_SDL) && defined(__ANDROID__)
main_data.cpp
39:#if defined(USE_SDL) && defined(__ANDROID__)
system.h
23: * This option may have defined USE_SDL and others.
29:#if !(defined(USE_SDL) || defined(_3DS) || defined(PSP2) || defined(__SWITCH__) || defined(USE_LIBRETRO))
101:#ifdef USE_SDL
decoder_wildmidi.cpp
36:#if defined(USE_SDL) && defined(__ANDROID__)
47:#if defined(USE_SDL) && defined(__ANDROID__)
``` | non_priority | get rid of use sdl and use libretro checks currently our code is cluttered well few lines with different code paths for sdl and libretro by removing them from the main files it would become easy in cmake to build both an executable and the libretro library in the same step with only a small compile time penalty currently this would need an complete recompile twice which takes too long baseui cpp elif use libretro elif defined use libretro input buttons desktop cpp if defined opendingux defined gekko defined use libretro output cpp if defined use libretro filefinder cpp ifdef use libretro elif defined use libretro system h if defined use sdl defined defined defined switch defined use libretro if defined use libretro player cpp ifndef use libretro decoder wildmidi cpp ifdef use libretro if defined use libretro baseui cpp if use sdl elif use sdl if use sdl elif use sdl main cpp ifdef use sdl filefinder cpp if defined use sdl defined android main data cpp if defined use sdl defined android system h this option may have defined use sdl and others if defined use sdl defined defined defined switch defined use libretro ifdef use sdl decoder wildmidi cpp if defined use sdl defined android if defined use sdl defined android | 0 |
161,116 | 25,288,166,557 | IssuesEvent | 2022-11-16 21:13:27 | pluralsight/tva | https://api.github.com/repos/pluralsight/tva | closed | [Docs?]: List page Design section | documentation design | ### Latest version
- [X] I have checked the latest version
### Summary 💡
Initial commit for the List design guidelines
### Motivation 🔦
_No response_ | 1.0 | [Docs?]: List page Design section - ### Latest version
- [X] I have checked the latest version
### Summary 💡
Initial commit for the List design guidelines
### Motivation 🔦
_No response_ | non_priority | list page design section latest version i have checked the latest version summary 💡 initial commit for the list design guidelines motivation 🔦 no response | 0 |
20,335 | 3,587,786,187 | IssuesEvent | 2016-01-30 15:33:53 | javaslang/javaslang | https://api.github.com/repos/javaslang/javaslang | opened | Check generics, e.g. *Map.ofEntries | design/refactoring | In [this PR](https://github.com/javaslang/javaslang/pull/1070/files) we saw that we had to change
```java
static <E, T> Validation<List<E>, Seq<T>> sequence(Iterable<? extends Validation<List<? extends E>, ? extends T>> values)
```
to
```java
static <E, T> Validation<List<E>, Seq<T>> sequence(Iterable<? extends Validation<List<E>, T>> values)
```
in order to work correctly. Example application:
```java
Validation<List<String>, SetExpressRequest> v =
Validation.combine(
validateReturnUrl(request.getReturnUrl()),
validateCancelUrl(request.getCancelUrl()),
validatePayPalId(request.getSubject()),
validateAmount(request.getPAYMENTREQUEST_0_AMT()),
validateCurrencyCode(request.getPAYMENTREQUEST_0_CURRENCYCODE())
).ap((a1,a2,a3,a4,a5) -> request);
Validation<List<String>, SetExpressRequest> v2 =
Validation.combine(
validateBillingType(request.getL_BILLINGTYPE0()),
validateNoShipping(request.getNoShipping()),
validateDescription(request.getDescription()),
validateEmail(request.getEmail()),
validateDescription(request.getDescription())
).ap((a1,a2,a3,a4,a5) -> request);
Validation<List<String>, Seq<SetExpressRequest>> res = Validation.sequence(List.of(v, v2));
```
Maybe we need to change the signature of `ofEntries` in a similar way (double-check this first!):
```java
static <K, V> HashMap<K, V> ofEntries(Iterable<? extends Tuple2<? extends K, ? extends V>> entries);
```
changes to
```java
static <K, V> HashMap<K, V> ofEntries(Iterable<? extends Tuple2<K, V>> entries);
```
**Questions:** What is the reason? Can we deduce a general rule for that? Are there any exceptions? Why?
| 1.0 | Check generics, e.g. *Map.ofEntries - In [this PR](https://github.com/javaslang/javaslang/pull/1070/files) we saw that we had to change
```java
static <E, T> Validation<List<E>, Seq<T>> sequence(Iterable<? extends Validation<List<? extends E>, ? extends T>> values)
```
to
```java
static <E, T> Validation<List<E>, Seq<T>> sequence(Iterable<? extends Validation<List<E>, T>> values)
```
in order to work correctly. Example application:
```java
Validation<List<String>, SetExpressRequest> v =
Validation.combine(
validateReturnUrl(request.getReturnUrl()),
validateCancelUrl(request.getCancelUrl()),
validatePayPalId(request.getSubject()),
validateAmount(request.getPAYMENTREQUEST_0_AMT()),
validateCurrencyCode(request.getPAYMENTREQUEST_0_CURRENCYCODE())
).ap((a1,a2,a3,a4,a5) -> request);
Validation<List<String>, SetExpressRequest> v2 =
Validation.combine(
validateBillingType(request.getL_BILLINGTYPE0()),
validateNoShipping(request.getNoShipping()),
validateDescription(request.getDescription()),
validateEmail(request.getEmail()),
validateDescription(request.getDescription())
).ap((a1,a2,a3,a4,a5) -> request);
Validation<List<String>, Seq<SetExpressRequest>> res = Validation.sequence(List.of(v, v2));
```
Maybe we need to change the signature of `ofEntries` in a similar way (double-check this first!):
```java
static <K, V> HashMap<K, V> ofEntries(Iterable<? extends Tuple2<? extends K, ? extends V>> entries);
```
changes to
```java
static <K, V> HashMap<K, V> ofEntries(Iterable<? extends Tuple2<K, V>> entries);
```
**Questions:** What is the reason? Can we deduce a general rule for that? Are there any exceptions? Why?
| non_priority | check generics e g map ofentries in we saw that we had to change java static validation seq sequence iterable extends t values to java static validation seq sequence iterable t values in order to work correctly example application java validation setexpressrequest v validation combine validatereturnurl request getreturnurl validatecancelurl request getcancelurl validatepaypalid request getsubject validateamount request getpaymentrequest amt validatecurrencycode request getpaymentrequest currencycode ap request validation setexpressrequest validation combine validatebillingtype request getl validatenoshipping request getnoshipping validatedescription request getdescription validateemail request getemail validatedescription request getdescription ap request validation seq res validation sequence list of v maybe we need to change the signature of ofentries in a similar way double check this first java static hashmap ofentries iterable entries changes to java static hashmap ofentries iterable entries questions what is the reason can we deduce a general rule for that are there any exceptions why | 0 |
24,111 | 10,982,282,389 | IssuesEvent | 2019-12-01 06:05:18 | ConsumerDataStandardsAustralia/standards-maintenance | https://api.github.com/repos/ConsumerDataStandardsAustralia/standards-maintenance | closed | Remnant vectors of trust references in security profile | change request security | # Description
Some sentences still remain in relation to vectors of trust in parts of the Infosec profile, including links to a Vectors of Trust section which no longer exists within the standard. Standard still references expired draft on Vectors of Trust in normative references.
# Area Affected
- [Overview section](https://consumerdatastandardsaustralia.github.io/standards/#overview)
- [ID Token](https://consumerdatastandardsaustralia.github.io/standards/#tokens) section and example
- [Claims](https://consumerdatastandardsaustralia.github.io/standards/#claims) section
- [OpenID Provider Configuration End Point](https://consumerdatastandardsaustralia.github.io/standards/#end-points)
- [Normative references section](https://consumerdatastandardsaustralia.github.io/standards/#normative-references)
# Change Proposed
Remove remnant references to vectors of trust in the security profile. | True | Remnant vectors of trust references in security profile - # Description
Some sentences still remain in relation to vectors of trust in parts of the Infosec profile, including links to a Vectors of Trust section which no longer exists within the standard. Standard still references expired draft on Vectors of Trust in normative references.
# Area Affected
- [Overview section](https://consumerdatastandardsaustralia.github.io/standards/#overview)
- [ID Token](https://consumerdatastandardsaustralia.github.io/standards/#tokens) section and example
- [Claims](https://consumerdatastandardsaustralia.github.io/standards/#claims) section
- [OpenID Provider Configuration End Point](https://consumerdatastandardsaustralia.github.io/standards/#end-points)
- [Normative references section](https://consumerdatastandardsaustralia.github.io/standards/#normative-references)
# Change Proposed
Remove remnant references to vectors of trust in the security profile. | non_priority | remnant vectors of trust references in security profile description some sentences still remain in relation to vectors of trust in parts of the infosec profile including links to a vectors of trust section which no longer exists within the standard standard still references expired draft on vectors of trust in normative references area affected section and example section change proposed remove remnant references to vectors of trust in the security profile | 0 |
129,228 | 18,071,965,579 | IssuesEvent | 2021-09-21 04:38:57 | girlscript/winter-of-contributing | https://api.github.com/repos/girlscript/winter-of-contributing | opened | Cybersecurity: 2.9.5 WAN | GWOC21 Cybersecurity | ## Description
### Explain what is WAN, its advantages, security challenges in WAN!
## Note:
- If interested, mention in which format you want to contribute: `Documentation` or `Video`
- Please avoid copy/paste, `BE YOURSELF`
- Try to explain with *Diagrams*
- Changes should be made inside the `Cyber_Security/` directory & `Cyber_Security `branch.
- Task will be assigned on *first come first serve*
- Check it out [Contribution Guidelines](https://github.com/girlscript/winter-of-contributing/blob/main/.github/CONTRIBUTING.md) | True | Cybersecurity: 2.9.5 WAN - ## Description
### Explain what is WAN, its advantages, security challenges in WAN!
## Note:
- If interested, mention in which format you want to contribute: `Documentation` or `Video`
- Please avoid copy/paste, `BE YOURSELF`
- Try to explain with *Diagrams*
- Changes should be made inside the `Cyber_Security/` directory & `Cyber_Security `branch.
- Task will be assigned on *first come first serve*
- Check it out [Contribution Guidelines](https://github.com/girlscript/winter-of-contributing/blob/main/.github/CONTRIBUTING.md) | non_priority | cybersecurity wan description explain what is wan its advantages security challenges in wan note if interested mention in which format you want to contribute documentation or video please avoid copy paste be yourself try to explain with diagrams changes should be made inside the cyber security directory cyber security branch task will be assigned on first come first serve check it out | 0 |
248,068 | 26,776,576,286 | IssuesEvent | 2023-01-31 17:35:14 | BRAEVincent52bae/RSSHub | https://api.github.com/repos/BRAEVincent52bae/RSSHub | opened | torrent-search-api-2.1.4.tgz: 2 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>torrent-search-api-2.1.4.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/BRAEVincent52bae/RSSHub/commit/737d702a8a61280ed7e922134d859ef98c9a7be3">737d702a8a61280ed7e922134d859ef98c9a7be3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (torrent-search-api version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-23406](https://www.mend.io/vulnerability-database/CVE-2021-23406) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-25901](https://www.mend.io/vulnerability-database/CVE-2022-25901) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | cookiejar-2.1.3.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23406</summary>
### Vulnerable Libraries - <b>degenerator-2.2.0.tgz</b>, <b>pac-resolver-4.2.0.tgz</b></p>
<p>
### <b>degenerator-2.2.0.tgz</b></p>
<p>Compiles sync functions into async generator functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/degenerator/-/degenerator-2.2.0.tgz">https://registry.npmjs.org/degenerator/-/degenerator-2.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- torrent-search-api-2.1.4.tgz (Root Library)
- x-ray-scraper-3.0.6.tgz
- superagent-proxy-2.1.0.tgz
- proxy-agent-4.0.1.tgz
- pac-proxy-agent-4.1.0.tgz
- pac-resolver-4.2.0.tgz
- :x: **degenerator-2.2.0.tgz** (Vulnerable Library)
### <b>pac-resolver-4.2.0.tgz</b></p>
<p>Generates an asynchronous resolver function from a PAC file</p>
<p>Library home page: <a href="https://registry.npmjs.org/pac-resolver/-/pac-resolver-4.2.0.tgz">https://registry.npmjs.org/pac-resolver/-/pac-resolver-4.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- torrent-search-api-2.1.4.tgz (Root Library)
- x-ray-scraper-3.0.6.tgz
- superagent-proxy-2.1.0.tgz
- proxy-agent-4.0.1.tgz
- pac-proxy-agent-4.1.0.tgz
- :x: **pac-resolver-4.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BRAEVincent52bae/RSSHub/commit/737d702a8a61280ed7e922134d859ef98c9a7be3">737d702a8a61280ed7e922134d859ef98c9a7be3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package pac-resolver before 5.0.0. This can occur when used with untrusted input, due to unsafe PAC file handling. **NOTE:** The fix for this vulnerability is applied in the node-degenerator library, a dependency written by the same maintainer.
<p>Publish Date: 2021-08-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23406>CVE-2021-23406</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9j49-mfvp-vmhm">https://github.com/advisories/GHSA-9j49-mfvp-vmhm</a></p>
<p>Release Date: 2021-08-24</p>
<p>Fix Resolution: pac-resolver -5.0.0, degenerator - 3.0.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25901</summary>
### Vulnerable Library - <b>cookiejar-2.1.3.tgz</b></p>
<p>simple persistent cookiejar system</p>
<p>Library home page: <a href="https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.3.tgz">https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.3.tgz</a></p>
<p>
Dependency Hierarchy:
- torrent-search-api-2.1.4.tgz (Root Library)
- x-ray-scraper-3.0.6.tgz
- superagent-3.8.3.tgz
- :x: **cookiejar-2.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BRAEVincent52bae/RSSHub/commit/737d702a8a61280ed7e922134d859ef98c9a7be3">737d702a8a61280ed7e922134d859ef98c9a7be3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the package cookiejar before 2.1.4 are vulnerable to Regular Expression Denial of Service (ReDoS) via the Cookie.parse function, which uses an insecure regular expression.
<p>Publish Date: 2023-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25901>CVE-2022-25901</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-18</p>
<p>Fix Resolution: cookiejar - 2.1.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | torrent-search-api-2.1.4.tgz: 2 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>torrent-search-api-2.1.4.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/BRAEVincent52bae/RSSHub/commit/737d702a8a61280ed7e922134d859ef98c9a7be3">737d702a8a61280ed7e922134d859ef98c9a7be3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (torrent-search-api version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-23406](https://www.mend.io/vulnerability-database/CVE-2021-23406) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-25901](https://www.mend.io/vulnerability-database/CVE-2022-25901) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | cookiejar-2.1.3.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23406</summary>
### Vulnerable Libraries - <b>degenerator-2.2.0.tgz</b>, <b>pac-resolver-4.2.0.tgz</b></p>
<p>
### <b>degenerator-2.2.0.tgz</b></p>
<p>Compiles sync functions into async generator functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/degenerator/-/degenerator-2.2.0.tgz">https://registry.npmjs.org/degenerator/-/degenerator-2.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- torrent-search-api-2.1.4.tgz (Root Library)
- x-ray-scraper-3.0.6.tgz
- superagent-proxy-2.1.0.tgz
- proxy-agent-4.0.1.tgz
- pac-proxy-agent-4.1.0.tgz
- pac-resolver-4.2.0.tgz
- :x: **degenerator-2.2.0.tgz** (Vulnerable Library)
### <b>pac-resolver-4.2.0.tgz</b></p>
<p>Generates an asynchronous resolver function from a PAC file</p>
<p>Library home page: <a href="https://registry.npmjs.org/pac-resolver/-/pac-resolver-4.2.0.tgz">https://registry.npmjs.org/pac-resolver/-/pac-resolver-4.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- torrent-search-api-2.1.4.tgz (Root Library)
- x-ray-scraper-3.0.6.tgz
- superagent-proxy-2.1.0.tgz
- proxy-agent-4.0.1.tgz
- pac-proxy-agent-4.1.0.tgz
- :x: **pac-resolver-4.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BRAEVincent52bae/RSSHub/commit/737d702a8a61280ed7e922134d859ef98c9a7be3">737d702a8a61280ed7e922134d859ef98c9a7be3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package pac-resolver before 5.0.0. This can occur when used with untrusted input, due to unsafe PAC file handling. **NOTE:** The fix for this vulnerability is applied in the node-degenerator library, a dependency written by the same maintainer.
<p>Publish Date: 2021-08-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23406>CVE-2021-23406</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9j49-mfvp-vmhm">https://github.com/advisories/GHSA-9j49-mfvp-vmhm</a></p>
<p>Release Date: 2021-08-24</p>
<p>Fix Resolution: pac-resolver -5.0.0, degenerator - 3.0.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-25901</summary>
### Vulnerable Library - <b>cookiejar-2.1.3.tgz</b></p>
<p>simple persistent cookiejar system</p>
<p>Library home page: <a href="https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.3.tgz">https://registry.npmjs.org/cookiejar/-/cookiejar-2.1.3.tgz</a></p>
<p>
Dependency Hierarchy:
- torrent-search-api-2.1.4.tgz (Root Library)
- x-ray-scraper-3.0.6.tgz
- superagent-3.8.3.tgz
- :x: **cookiejar-2.1.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/BRAEVincent52bae/RSSHub/commit/737d702a8a61280ed7e922134d859ef98c9a7be3">737d702a8a61280ed7e922134d859ef98c9a7be3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the package cookiejar before 2.1.4 are vulnerable to Regular Expression Denial of Service (ReDoS) via the Cookie.parse function, which uses an insecure regular expression.
<p>Publish Date: 2023-01-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25901>CVE-2022-25901</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-01-18</p>
<p>Fix Resolution: cookiejar - 2.1.4</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | torrent search api tgz vulnerabilities highest severity is vulnerable library torrent search api tgz found in head commit a href vulnerabilities cve severity cvss dependency type fixed in torrent search api version remediation available high detected in multiple dependencies transitive n a high cookiejar tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable libraries degenerator tgz pac resolver tgz degenerator tgz compiles sync functions into async generator functions library home page a href dependency hierarchy torrent search api tgz root library x ray scraper tgz superagent proxy tgz proxy agent tgz pac proxy agent tgz pac resolver tgz x degenerator tgz vulnerable library pac resolver tgz generates an asynchronous resolver function from a pac file library home page a href dependency hierarchy torrent search api tgz root library x ray scraper tgz superagent proxy tgz proxy agent tgz pac proxy agent tgz x pac resolver tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package pac resolver before this can occur when used with untrusted input due to unsafe pac file handling note the fix for this vulnerability is applied in the node degenerator library a dependency written by the same maintainer publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pac resolver degenerator step up your open source security game with mend cve vulnerable library cookiejar tgz simple persistent cookiejar system library home page a href dependency hierarchy torrent search api tgz root library x ray scraper tgz superagent tgz x cookiejar tgz vulnerable library found in head commit a href found in base branch master vulnerability details versions of the package cookiejar before are vulnerable to regular expression denial of service redos via the cookie parse function which uses an insecure regular expression publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution cookiejar step up your open source security game with mend | 0 |
232,195 | 18,849,792,414 | IssuesEvent | 2021-11-11 19:15:12 | Bedrock-OSS/regolith | https://api.github.com/repos/Bedrock-OSS/regolith | closed | .regolith/cache/edited_files.json causes error first time. | bug needs testing | If this file doesn't exist, Regolith crashes. Needs a second run to function.
Is this fixed in latest? | 1.0 | .regolith/cache/edited_files.json causes error first time. - If this file doesn't exist, Regolith crashes. Needs a second run to function.
Is this fixed in latest? | non_priority | regolith cache edited files json causes error first time if this file doesn t exist regolith crashes needs a second run to function is this fixed in latest | 0 |
91,694 | 10,726,867,738 | IssuesEvent | 2019-10-28 10:20:46 | suvajit-sarkar/github-upload | https://api.github.com/repos/suvajit-sarkar/github-upload | opened | Indy: Ansible role for Domain genesis | documentation | Create an Ansible role, which retrieves the DIDs and verification keys for all trustees and stewards on the genesis network, assembles the Domain genesis transaction file, creates the Domain genesis config map values (Helm release) for all organizations and pushes them to the respective Git locations. Also, please add this role to the Indy deploy-network playbook. | 1.0 | Indy: Ansible role for Domain genesis - Create an Ansible role, which retrieves the DIDs and verification keys for all trustees and stewards on the genesis network, assembles the Domain genesis transaction file, creates the Domain genesis config map values (Helm release) for all organizations and pushes them to the respective Git locations. Also, please add this role to the Indy deploy-network playbook. | non_priority | indy ansible role for domain genesis create an ansible role which retrieves the dids and verification keys for all trustees and stewards on the genesis network assembles the domain genesis transaction file creates the domain genesis config map values helm release for all organizations and pushes them to the respective git locations also please add this role to the indy deploy network playbook | 0 |
169,572 | 13,152,604,550 | IssuesEvent | 2020-08-09 23:18:06 | microsoft/STL | https://api.github.com/repos/microsoft/STL | opened | Add test coverage for deque::erase(iter, iter) avoiding self-move-assigns | test | #1118 was fixed by #1148, so `deque::erase(iter, iter)` avoids performing self-move-assigns when called with empty ranges. We should have test coverage for this scenario. Our test for `vector` can be extended:
https://github.com/microsoft/STL/blob/19135668f4110210e663bfc0502d3359470bbd18/tests/std/tests/Dev10_881629_vector_erase_return_value/test.cpp#L10-L11 | 1.0 | Add test coverage for deque::erase(iter, iter) avoiding self-move-assigns - #1118 was fixed by #1148, so `deque::erase(iter, iter)` avoids performing self-move-assigns when called with empty ranges. We should have test coverage for this scenario. Our test for `vector` can be extended:
https://github.com/microsoft/STL/blob/19135668f4110210e663bfc0502d3359470bbd18/tests/std/tests/Dev10_881629_vector_erase_return_value/test.cpp#L10-L11 | non_priority | add test coverage for deque erase iter iter avoiding self move assigns was fixed by so deque erase iter iter avoids performing self move assigns when called with empty ranges we should have test coverage for this scenario our test for vector can be extended | 0 |
229,228 | 18,286,662,481 | IssuesEvent | 2021-10-05 11:04:24 | DILCISBoard/eark-ip-test-corpus | https://api.github.com/repos/DILCISBoard/eark-ip-test-corpus | closed | CSIP82 Test Case Description | test case | **Specification:**
- **Name:** E-ARK CSIP
- **Version:** 2.0-DRAFT
- **URL:** http://earkcsip.dilcis.eu/
**Requirement:**
- **Id:** CSIP82
- **Link:** http://earkcsip.dilcis.eu/#CSIP82
**Error Level:** ERROR
**Description:**
CSIP82 | Name of the structural description structMap/@LABEL | The label attribute is set to value “CSIP StructMap” from the vocabulary. | 1..1 MUST
-- | -- | -- | --
| 1.0 | CSIP82 Test Case Description - **Specification:**
- **Name:** E-ARK CSIP
- **Version:** 2.0-DRAFT
- **URL:** http://earkcsip.dilcis.eu/
**Requirement:**
- **Id:** CSIP82
- **Link:** http://earkcsip.dilcis.eu/#CSIP82
**Error Level:** ERROR
**Description:**
CSIP82 | Name of the structural description structMap/@LABEL | The label attribute is set to value “CSIP StructMap” from the vocabulary. | 1..1 MUST
-- | -- | -- | --
| non_priority | test case description specification name e ark csip version draft url requirement id link error level error description name of the structural description structmap label the label attribute is set to value “csip structmap” from the vocabulary must | 0 |
64,303 | 14,662,043,843 | IssuesEvent | 2020-12-29 06:03:31 | tamirverthim/NodeGoat | https://api.github.com/repos/tamirverthim/NodeGoat | opened | WS-2020-0163 (Medium) detected in marked-0.3.9.tgz | security vulnerability | ## WS-2020-0163 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.9.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.3.9.tgz">https://registry.npmjs.org/marked/-/marked-0.3.9.tgz</a></p>
<p>Path to dependency file: NodeGoat/package.json</p>
<p>Path to vulnerable library: NodeGoat/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.9.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tamirverthim/NodeGoat/commit/3de6c5862c1fef83d38a1fec17b579f1a5e328fb">3de6c5862c1fef83d38a1fec17b579f1a5e328fb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
marked before 1.1.1 is vulnerable to Regular Expression Denial of Service (REDoS). rules.js have multiple unused capture groups which can lead to a Denial of Service.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://github.com/markedjs/marked/commit/bd4f8c464befad2b304d51e33e89e567326e62e0>WS-2020-0163</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/releases/tag/v1.1.1">https://github.com/markedjs/marked/releases/tag/v1.1.1</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: marked - 1.1.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"marked","packageVersion":"0.3.9","isTransitiveDependency":false,"dependencyTree":"marked:0.3.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"marked - 1.1.1"}],"vulnerabilityIdentifier":"WS-2020-0163","vulnerabilityDetails":"marked before 1.1.1 is vulnerable to Regular Expression Denial of Service (REDoS). rules.js have multiple unused capture groups which can lead to a Denial of Service.","vulnerabilityUrl":"https://github.com/markedjs/marked/commit/bd4f8c464befad2b304d51e33e89e567326e62e0","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2020-0163 (Medium) detected in marked-0.3.9.tgz - ## WS-2020-0163 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.9.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.3.9.tgz">https://registry.npmjs.org/marked/-/marked-0.3.9.tgz</a></p>
<p>Path to dependency file: NodeGoat/package.json</p>
<p>Path to vulnerable library: NodeGoat/node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.3.9.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tamirverthim/NodeGoat/commit/3de6c5862c1fef83d38a1fec17b579f1a5e328fb">3de6c5862c1fef83d38a1fec17b579f1a5e328fb</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
marked before 1.1.1 is vulnerable to Regular Expression Denial of Service (REDoS). rules.js have multiple unused capture groups which can lead to a Denial of Service.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://github.com/markedjs/marked/commit/bd4f8c464befad2b304d51e33e89e567326e62e0>WS-2020-0163</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/markedjs/marked/releases/tag/v1.1.1">https://github.com/markedjs/marked/releases/tag/v1.1.1</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: marked - 1.1.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"marked","packageVersion":"0.3.9","isTransitiveDependency":false,"dependencyTree":"marked:0.3.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"marked - 1.1.1"}],"vulnerabilityIdentifier":"WS-2020-0163","vulnerabilityDetails":"marked before 1.1.1 is vulnerable to Regular Expression Denial of Service (REDoS). rules.js have multiple unused capture groups which can lead to a Denial of Service.","vulnerabilityUrl":"https://github.com/markedjs/marked/commit/bd4f8c464befad2b304d51e33e89e567326e62e0","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in marked tgz ws medium severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file nodegoat package json path to vulnerable library nodegoat node modules marked package json dependency hierarchy x marked tgz vulnerable library found in head commit a href found in base branch master vulnerability details marked before is vulnerable to regular expression denial of service redos rules js have multiple unused capture groups which can lead to a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution marked rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails marked before is vulnerable to regular expression denial of service redos rules js have multiple unused capture groups which can lead to a denial of service vulnerabilityurl | 0 |
54,556 | 23,297,696,065 | IssuesEvent | 2022-08-06 21:06:16 | microsoft/azure-pipelines-tasks | https://api.github.com/repos/microsoft/azure-pipelines-tasks | closed | AzureAppServiceManage: support defined ping path and expected status code on slot swap | enhancement Area: Release stale Task: AzureAppService environment:enhancement | **Question, Bug, or Feature?**
*Type*: Feature
**Enter Task Name**: AzureAppServiceManageV0
## Issue Description
App Services seem to have started using the app settings `WEBSITE_SWAP_WARMUP_PING_PATH` and `WEBSITE_SWAP_WARMUP_PING_STATUSES` to customise warmup behaviour, it would be useful for the Slot Swap mechanism within AzureAppServiceManage to use these when specified rather than using defaults.
| 1.0 | AzureAppServiceManage: support defined ping path and expected status code on slot swap - **Question, Bug, or Feature?**
*Type*: Feature
**Enter Task Name**: AzureAppServiceManageV0
## Issue Description
App Services seem to have started using the app settings `WEBSITE_SWAP_WARMUP_PING_PATH` and `WEBSITE_SWAP_WARMUP_PING_STATUSES` to customise warmup behaviour, it would be useful for the Slot Swap mechanism within AzureAppServiceManage to use these when specified rather than using defaults.
| non_priority | azureappservicemanage support defined ping path and expected status code on slot swap question bug or feature type feature enter task name issue description app services seem to have started using the app settings website swap warmup ping path and website swap warmup ping statuses to customise warmup behaviour it would be useful for the slot swap mechanism within azureappservicemanage to use these when specified rather than using defaults | 0 |
129,301 | 17,770,995,992 | IssuesEvent | 2021-08-30 13:39:15 | kawalcovid19/wargabantuwarga.com | https://api.github.com/repos/kawalcovid19/wargabantuwarga.com | closed | Website 2.0 | enhancement epic ui ux design | ## Overview
We are revamping our website look and feel based on the new UI design reflected in this Figma file:
https://www.figma.com/file/XNNtIoFEdFqaXOee83n0oN/WBW?node-id=485:2485
## Current Tasks
### Home page
- [x] #332
- [x] #352
- [x] #333
- [x] #322
- [x] #323
- [x] #324
- [x] #504
- [x] #598
- [x] #599
- [x] #642
- [x] #672
- [x] #673
- [x] #668
- [x] #710
### Database-related pages
- [x] #600
### Stuff that's on a separate page
- [x] #325
- [x] #326
- [x] #327
- [x] #328
- [x] #329
- [x] #330
- [x] #712
### General structure
- [x] #346
- [x] #391
- [x] #624
### Minor tasks
- [x] #385
- [x] #422
- [x] #453
### Bugs
- [x] #448
- [x] #498
- [x] #573
- [x] #723 | 1.0 | Website 2.0 - ## Overview
We are revamping our website look and feel based on the new UI design reflected in this Figma file:
https://www.figma.com/file/XNNtIoFEdFqaXOee83n0oN/WBW?node-id=485:2485
## Current Tasks
### Home page
- [x] #332
- [x] #352
- [x] #333
- [x] #322
- [x] #323
- [x] #324
- [x] #504
- [x] #598
- [x] #599
- [x] #642
- [x] #672
- [x] #673
- [x] #668
- [x] #710
### Database-related pages
- [x] #600
### Stuff that's on a separate page
- [x] #325
- [x] #326
- [x] #327
- [x] #328
- [x] #329
- [x] #330
- [x] #712
### General structure
- [x] #346
- [x] #391
- [x] #624
### Minor tasks
- [x] #385
- [x] #422
- [x] #453
### Bugs
- [x] #448
- [x] #498
- [x] #573
- [x] #723 | non_priority | website overview we are revamping our website look and feel based on the new ui design reflected in this figma file current tasks home page database related pages stuff that s on a separate page general structure minor tasks bugs | 0 |
10,079 | 13,044,161,973 | IssuesEvent | 2020-07-29 03:47:28 | tikv/tikv | https://api.github.com/repos/tikv/tikv | closed | UCP: Migrate scalar function `UnixTimestampDec` from TiDB | challenge-program-2 component/coprocessor difficulty/easy sig/coprocessor |
## Description
Port the scalar function `UnixTimestampDec` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @sticnarf
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
| 2.0 | UCP: Migrate scalar function `UnixTimestampDec` from TiDB -
## Description
Port the scalar function `UnixTimestampDec` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @sticnarf
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
| non_priority | ucp migrate scalar function unixtimestampdec from tidb description port the scalar function unixtimestampdec from tidb to coprocessor score mentor s sticnarf recommended skills rust programming learning materials already implemented expressions ported from tidb | 0 |
60,388 | 8,425,846,423 | IssuesEvent | 2018-10-16 04:56:37 | dynamoosejs/dynamoose | https://api.github.com/repos/dynamoosejs/dynamoose | opened | Undocumented Schema Types | discussion documentation | ### Summary:
In the Dynamoose code below there is a lot of types that aren't listed in the [Dynamoose Documentation](https://dynamoosejs.com/api#attribute-types).
https://github.com/dynamoosejs/dynamoose/blob/7b01a64e97e4f0eb77887537e1ad18820f00bef9/lib/Attribute.js#L100-L147
I think we need to go in and figure out the intent of those new types that aren't documented and figure out if they should be public facing or not, and if so, update the documentation.
I have heard people using `Map` or `List` but still am confused what the difference is between that and the publicly documented `Object` and `Array`. So clearing that up I think would be a good idea.
### Type (select 1):
- [ ] Bug report
- [ ] Feature suggestion
- [ ] Question
- [x] Other suggestion
- [ ] Something not listed here
### Other:
- [x] I have read through the Dynamoose documentation before posting this issue
- [x] I have searched through the GitHub issues (including closed issues) and pull requests to ensure this issue has not already been raised before
- [x] I have searched the internet and Stack Overflow to ensure this issue hasn't been raised or answered before
- [x] I have tested the code provided and am confident it doesn't work as intended
- [x] I have filled out all fields above
- [x] I am running the latest version of Dynamoose
| 1.0 | Undocumented Schema Types - ### Summary:
In the Dynamoose code below there is a lot of types that aren't listed in the [Dynamoose Documentation](https://dynamoosejs.com/api#attribute-types).
https://github.com/dynamoosejs/dynamoose/blob/7b01a64e97e4f0eb77887537e1ad18820f00bef9/lib/Attribute.js#L100-L147
I think we need to go in and figure out the intent of those new types that aren't documented and figure out if they should be public facing or not, and if so, update the documentation.
I have heard people using `Map` or `List` but still am confused what the difference is between that and the publicly documented `Object` and `Array`. So clearing that up I think would be a good idea.
### Type (select 1):
- [ ] Bug report
- [ ] Feature suggestion
- [ ] Question
- [x] Other suggestion
- [ ] Something not listed here
### Other:
- [x] I have read through the Dynamoose documentation before posting this issue
- [x] I have searched through the GitHub issues (including closed issues) and pull requests to ensure this issue has not already been raised before
- [x] I have searched the internet and Stack Overflow to ensure this issue hasn't been raised or answered before
- [x] I have tested the code provided and am confident it doesn't work as intended
- [x] I have filled out all fields above
- [x] I am running the latest version of Dynamoose
| non_priority | undocumented schema types summary in the dynamoose code below there is a lot of types that aren t listed in the i think we need to go in and figure out the intent of those new types that aren t documented and figure out if they should be public facing or not and if so update the documentation i have heard people using map or list but still am confused what the difference is between that and the publicly documented object and array so clearing that up i think would be a good idea type select bug report feature suggestion question other suggestion something not listed here other i have read through the dynamoose documentation before posting this issue i have searched through the github issues including closed issues and pull requests to ensure this issue has not already been raised before i have searched the internet and stack overflow to ensure this issue hasn t been raised or answered before i have tested the code provided and am confident it doesn t work as intended i have filled out all fields above i am running the latest version of dynamoose | 0 |
100,398 | 11,194,235,508 | IssuesEvent | 2020-01-03 00:02:15 | alice-i-cecile/Fonts-of-Power | https://api.github.com/repos/alice-i-cecile/Fonts-of-Power | closed | Add examples of high and low attributes | documentation | Diverse archetypes and interpretations in order to have more roleplay flexibility. | 1.0 | Add examples of high and low attributes - Diverse archetypes and interpretations in order to have more roleplay flexibility. | non_priority | add examples of high and low attributes diverse archetypes and interpretations in order to have more roleplay flexibility | 0 |
114,081 | 9,674,058,467 | IssuesEvent | 2019-05-22 09:02:23 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | Unable to retrieve child resource when attaching a blob container | :beetle: regression :gear: attach :gear: blobs :gear: sas 🧪 testing | **Storage Explorer Version:** 1.8.1_20190522.1
**Platform/OS:** Linux Ubuntu/macOS High Sierra/Windows 10
**Architecture:** ia32/x64
**Regression From:** 1.8.1 release
**Steps to reproduce:**
1. Expand one normal account -> 'Blob Containers'
2. Right click one blob container then select 'Get Shared Access Signature...'.
3. Generate the SAS URI of the blob container.
4. Try to attach the blob container using the SAS URI.
5. Check the result.
**Expect Experience:**
The blob container can be attached successfully.
**Actual Experience:**
1. There always shows 'Adding new connection' on Activities.
2. Pop up the below error when trying to expand the 'Blob Containers' node under 'Local & Attached'
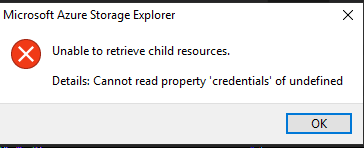
| 1.0 | Unable to retrieve child resource when attaching a blob container - **Storage Explorer Version:** 1.8.1_20190522.1
**Platform/OS:** Linux Ubuntu/macOS High Sierra/Windows 10
**Architecture:** ia32/x64
**Regression From:** 1.8.1 release
**Steps to reproduce:**
1. Expand one normal account -> 'Blob Containers'
2. Right click one blob container then select 'Get Shared Access Signature...'.
3. Generate the SAS URI of the blob container.
4. Try to attach the blob container using the SAS URI.
5. Check the result.
**Expect Experience:**
The blob container can be attached successfully.
**Actual Experience:**
1. There always shows 'Adding new connection' on Activities.
2. Pop up the below error when trying to expand the 'Blob Containers' node under 'Local & Attached'
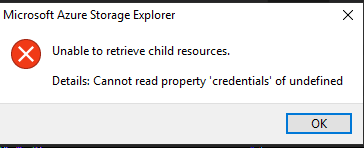
| non_priority | unable to retrieve child resource when attaching a blob container storage explorer version platform os linux ubuntu macos high sierra windows architecture regression from release steps to reproduce expand one normal account blob containers right click one blob container then select get shared access signature generate the sas uri of the blob container try to attach the blob container using the sas uri check the result expect experience the blob container can be attached successfully actual experience there always shows adding new connection on activities pop up the below error when trying to expand the blob containers node under local attached | 0 |
617 | 2,792,323,818 | IssuesEvent | 2015-05-10 22:12:55 | t3kt/vjzual | https://api.github.com/repos/t3kt/vjzual | opened | move the module override export tables from the header into the module core | infrastructure | The tables that override the module's ui properties are currently in module_header.tox. They should really be in the module local (module_core.tox). | 1.0 | move the module override export tables from the header into the module core - The tables that override the module's ui properties are currently in module_header.tox. They should really be in the module local (module_core.tox). | non_priority | move the module override export tables from the header into the module core the tables that override the module s ui properties are currently in module header tox they should really be in the module local module core tox | 0 |
8,106 | 11,300,414,888 | IssuesEvent | 2020-01-17 13:34:08 | prisma/prisma2 | https://api.github.com/repos/prisma/prisma2 | opened | Unclear Introspection error message: Error parsing attribute "@id": Fields that are marked as id must be required. | process/candidate topic: introspection | Introspecting SQLite:
```
CREATE TABLE "playlist_track" (
"PlaylistId" INTEGER NOT NULL,
"TrackId" INTEGER NOT NULL,
"id" INTEGER PRIMARY KEY AUTOINCREMENT,
FOREIGN KEY("PlaylistId") REFERENCES "playlists"("PlaylistId") ON DELETE NO ACTION ON UPDATE NO ACTION,
FOREIGN KEY("TrackId") REFERENCES "tracks"("TrackId") ON DELETE NO ACTION ON UPDATE NO ACTION
)
```
Creates error message:
```
ERROR Oops, an unexpected error occured!
Schema parsing
error: Error parsing attribute "@id": Fields that are marked as id must be required.
--> schema.prisma:126
|
125 | TrackId tracks
126 | id Int? @id
|
```
Error message does not include name of table/model for context. | 1.0 | Unclear Introspection error message: Error parsing attribute "@id": Fields that are marked as id must be required. - Introspecting SQLite:
```
CREATE TABLE "playlist_track" (
"PlaylistId" INTEGER NOT NULL,
"TrackId" INTEGER NOT NULL,
"id" INTEGER PRIMARY KEY AUTOINCREMENT,
FOREIGN KEY("PlaylistId") REFERENCES "playlists"("PlaylistId") ON DELETE NO ACTION ON UPDATE NO ACTION,
FOREIGN KEY("TrackId") REFERENCES "tracks"("TrackId") ON DELETE NO ACTION ON UPDATE NO ACTION
)
```
Creates error message:
```
ERROR Oops, an unexpected error occured!
Schema parsing
error: Error parsing attribute "@id": Fields that are marked as id must be required.
--> schema.prisma:126
|
125 | TrackId tracks
126 | id Int? @id
|
```
Error message does not include name of table/model for context. | non_priority | unclear introspection error message error parsing attribute id fields that are marked as id must be required introspecting sqlite create table playlist track playlistid integer not null trackid integer not null id integer primary key autoincrement foreign key playlistid references playlists playlistid on delete no action on update no action foreign key trackid references tracks trackid on delete no action on update no action creates error message error oops an unexpected error occured schema parsing error error parsing attribute id fields that are marked as id must be required schema prisma trackid tracks id int id error message does not include name of table model for context | 0 |
138,703 | 20,671,264,275 | IssuesEvent | 2022-03-10 02:36:45 | Tech-Start-UCalgary/Aquavolution | https://api.github.com/repos/Tech-Start-UCalgary/Aquavolution | opened | Better enemy movement | enhancement design | Make the enemies move towards the player if player's size is less than enemy's size, and move away if player's size is bigger. If Player size = Enemy size knock back player & enemy | 1.0 | Better enemy movement - Make the enemies move towards the player if player's size is less than enemy's size, and move away if player's size is bigger. If Player size = Enemy size knock back player & enemy | non_priority | better enemy movement make the enemies move towards the player if player s size is less than enemy s size and move away if player s size is bigger if player size enemy size knock back player enemy | 0 |
16,275 | 20,883,882,127 | IssuesEvent | 2022-03-23 01:23:31 | openvinotoolkit/openvino | https://api.github.com/repos/openvinotoolkit/openvino | closed | Custom preprocess command | category: preprocessing feature | Greetings!
I am interested in implementing custom preprocess command.
I had had a look at the geometric_transformations.py and implemented a custom command with `Resize` in mind.
I also added that command inside the __init__.py in preprocessor folder but it doesn't get called for when added inside the `.yml` file's `preprocess` entry.
Any thoughts on how to implement this?
Best regards,
Nikola | 1.0 | Custom preprocess command - Greetings!
I am interested in implementing custom preprocess command.
I had had a look at the geometric_transformations.py and implemented a custom command with `Resize` in mind.
I also added that command inside the __init__.py in preprocessor folder but it doesn't get called for when added inside the `.yml` file's `preprocess` entry.
Any thoughts on how to implement this?
Best regards,
Nikola | non_priority | custom preprocess command greetings i am interested in implementing custom preprocess command i had had a look at the geometric transformations py and implemented a custom command with resize in mind i also added that command inside the init py in preprocessor folder but it doesn t get called for when added inside the yml file s preprocess entry any thoughts on how to implement this best regards nikola | 0 |
256,636 | 27,561,701,877 | IssuesEvent | 2023-03-07 22:40:59 | samqws-marketing/amzn-ion-hive-serde | https://api.github.com/repos/samqws-marketing/amzn-ion-hive-serde | closed | CVE-2018-5968 (High) detected in jackson-databind-2.6.5.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2018-5968 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /integration-test/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.5/d50be1723a09befd903887099ff2014ea9020333/jackson-databind-2.6.5.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.5/d50be1723a09befd903887099ff2014ea9020333/jackson-databind-2.6.5.jar</p>
<p>
Dependency Hierarchy:
- hive-serde-2.3.9.jar (Root Library)
- hive-common-2.3.9.jar
- :x: **jackson-databind-2.6.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/amzn-ion-hive-serde/commit/ffb6641ebb10aac58bb7eec412635e91e79fac24">ffb6641ebb10aac58bb7eec412635e91e79fac24</a></p>
<p>Found in base branch: <b>0.3.0</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind through 2.8.11 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 and CVE-2017-17485 deserialization flaws. This is exploitable via two different gadgets that bypass a blacklist.
<p>Publish Date: 2018-01-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-5968>CVE-2018-5968</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5968">http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5968</a></p>
<p>Release Date: 2018-01-22</p>
<p>Fix Resolution (com.fasterxml.jackson.core:jackson-databind): 2.6.7.3</p>
<p>Direct dependency fix Resolution (org.apache.hive:hive-serde): 3.0.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2018-5968 (High) detected in jackson-databind-2.6.5.jar - autoclosed - ## CVE-2018-5968 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /integration-test/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.5/d50be1723a09befd903887099ff2014ea9020333/jackson-databind-2.6.5.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.6.5/d50be1723a09befd903887099ff2014ea9020333/jackson-databind-2.6.5.jar</p>
<p>
Dependency Hierarchy:
- hive-serde-2.3.9.jar (Root Library)
- hive-common-2.3.9.jar
- :x: **jackson-databind-2.6.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/amzn-ion-hive-serde/commit/ffb6641ebb10aac58bb7eec412635e91e79fac24">ffb6641ebb10aac58bb7eec412635e91e79fac24</a></p>
<p>Found in base branch: <b>0.3.0</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind through 2.8.11 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 and CVE-2017-17485 deserialization flaws. This is exploitable via two different gadgets that bypass a blacklist.
<p>Publish Date: 2018-01-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-5968>CVE-2018-5968</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5968">http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5968</a></p>
<p>Release Date: 2018-01-22</p>
<p>Fix Resolution (com.fasterxml.jackson.core:jackson-databind): 2.6.7.3</p>
<p>Direct dependency fix Resolution (org.apache.hive:hive-serde): 3.0.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file integration test build gradle path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy hive serde jar root library hive common jar x jackson databind jar vulnerable library found in head commit a href found in base branch vulnerability details fasterxml jackson databind through and x through allows unauthenticated remote code execution because of an incomplete fix for the cve and cve deserialization flaws this is exploitable via two different gadgets that bypass a blacklist publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind direct dependency fix resolution org apache hive hive serde check this box to open an automated fix pr | 0 |
16,357 | 10,824,864,123 | IssuesEvent | 2019-11-09 12:21:02 | Zudotaky/FicusMonitoreoDeRiego | https://api.github.com/repos/Zudotaky/FicusMonitoreoDeRiego | closed | Mejorar Usabilidad Espacio / Planta | Usabilidad | En la app principal, al seleccionar un espacio no hay feedback del espacio seleccionado (podría tener un header o un accordion para agrupar las plantas del mismo espacio, y mostrar cuál es el espacio seleccionado o colapsar los restantes). | True | Mejorar Usabilidad Espacio / Planta - En la app principal, al seleccionar un espacio no hay feedback del espacio seleccionado (podría tener un header o un accordion para agrupar las plantas del mismo espacio, y mostrar cuál es el espacio seleccionado o colapsar los restantes). | non_priority | mejorar usabilidad espacio planta en la app principal al seleccionar un espacio no hay feedback del espacio seleccionado podría tener un header o un accordion para agrupar las plantas del mismo espacio y mostrar cuál es el espacio seleccionado o colapsar los restantes | 0 |
80,765 | 30,523,296,907 | IssuesEvent | 2023-07-19 09:30:50 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Sender's display name in image viewer is not readable | T-Defect X-Regression S-Minor A11y O-Frequent A-Light-Box | ### Steps to reproduce
1. Use dark mode
1. Receive an image from someone
2. Click on it to open it in the image viewer
3. Look at the sender's display name in the upper left corner
### Outcome
#### What did you expect?
Their display name should have plenty of contrast against the background
#### What happened instead?
It's unreadable:

### Operating system
NixOS unstable
### Browser information
Firefox 115.0
### URL for webapp
develop.element.io
### Application version
Element version: 4cf4dc9a3db6-react-ba90e0b25505-js-eb7faa6c0771 Olm version: 3.2.14
### Homeserver
Not relevant
### Will you send logs?
No | 1.0 | Sender's display name in image viewer is not readable - ### Steps to reproduce
1. Use dark mode
1. Receive an image from someone
2. Click on it to open it in the image viewer
3. Look at the sender's display name in the upper left corner
### Outcome
#### What did you expect?
Their display name should have plenty of contrast against the background
#### What happened instead?
It's unreadable:

### Operating system
NixOS unstable
### Browser information
Firefox 115.0
### URL for webapp
develop.element.io
### Application version
Element version: 4cf4dc9a3db6-react-ba90e0b25505-js-eb7faa6c0771 Olm version: 3.2.14
### Homeserver
Not relevant
### Will you send logs?
No | non_priority | sender s display name in image viewer is not readable steps to reproduce use dark mode receive an image from someone click on it to open it in the image viewer look at the sender s display name in the upper left corner outcome what did you expect their display name should have plenty of contrast against the background what happened instead it s unreadable operating system nixos unstable browser information firefox url for webapp develop element io application version element version react js olm version homeserver not relevant will you send logs no | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.