Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
9,421 | 6,288,975,274 | IssuesEvent | 2017-07-19 18:10:48 | FStarLang/FStar | https://api.github.com/repos/FStarLang/FStar | closed | `val` annotations yield ugly-looking signatures | enhancement pull-request usability | Contrast this:
```
val fold_left: ('a -> 'b -> ML 'a) -> 'a -> list 'b -> ML 'a
let rec fold_left f x y = match y with
| [] -> x
| hd::tl -> fold_left f (f x hd) tl
```
which yields this for `#info fold_left`:
```
fold_left: (uu___:(uu___:'a@1 -> uu___:'b@1 -> 'a@3) -> uu___:'a@2 -> uu___:(list 'b@2) -> 'a@4)
```
with this:
```
let rec fold_left (f: 'a -> 'b -> ML 'a) (x: 'a) (y: list 'b) : ML 'a = match y with
| [] -> x
| hd::tl -> fold_left f (f x hd) tl
```
which yields this for `#info fold_left`:
```
fold_left: (f:(uu___:'a@1 -> uu___:'b@1 -> 'a@3) -> x:'a@2 -> y:(list 'b@2) -> 'a@4)
```
It would be nice t preserve the names `f`, `x`, and `y` even when there is a `val`.
| True | `val` annotations yield ugly-looking signatures - Contrast this:
```
val fold_left: ('a -> 'b -> ML 'a) -> 'a -> list 'b -> ML 'a
let rec fold_left f x y = match y with
| [] -> x
| hd::tl -> fold_left f (f x hd) tl
```
which yields this for `#info fold_left`:
```
fold_left: (uu___:(uu___:'a@1 -> uu___:'b@1 -> 'a@3) -> uu___:'a@2 -> uu___:(list 'b@2) -> 'a@4)
```
with this:
```
let rec fold_left (f: 'a -> 'b -> ML 'a) (x: 'a) (y: list 'b) : ML 'a = match y with
| [] -> x
| hd::tl -> fold_left f (f x hd) tl
```
which yields this for `#info fold_left`:
```
fold_left: (f:(uu___:'a@1 -> uu___:'b@1 -> 'a@3) -> x:'a@2 -> y:(list 'b@2) -> 'a@4)
```
It would be nice t preserve the names `f`, `x`, and `y` even when there is a `val`.
| non_priority | val annotations yield ugly looking signatures contrast this val fold left a b ml a a list b ml a let rec fold left f x y match y with x hd tl fold left f f x hd tl which yields this for info fold left fold left uu uu a uu b a uu a uu list b a with this let rec fold left f a b ml a x a y list b ml a match y with x hd tl fold left f f x hd tl which yields this for info fold left fold left f uu a uu b a x a y list b a it would be nice t preserve the names f x and y even when there is a val | 0 |
143,961 | 19,268,123,633 | IssuesEvent | 2021-12-10 00:12:46 | turkdevops/integrations | https://api.github.com/repos/turkdevops/integrations | closed | CVE-2012-6708 (Medium) detected in jquery-1.8.1.min.js - autoclosed | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: integrations/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/integrations/commit/3897795a3c6a8288d211dfcb229583d94b143b2e">3897795a3c6a8288d211dfcb229583d94b143b2e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2012-6708 (Medium) detected in jquery-1.8.1.min.js - autoclosed - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: integrations/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/integrations/commit/3897795a3c6a8288d211dfcb229583d94b143b2e">3897795a3c6a8288d211dfcb229583d94b143b2e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js autoclosed cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file integrations node modules redeyed examples browser index html path to vulnerable library node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch main vulnerability details jquery before is vulnerable to cross site scripting xss attacks the jquery strinput function does not differentiate selectors from html in a reliable fashion in vulnerable versions jquery determined whether the input was html by looking for the character anywhere in the string giving attackers more flexibility when attempting to construct a malicious payload in fixed versions jquery only deems the input to be html if it explicitly starts with the character limiting exploitability only to attackers who can control the beginning of a string which is far less common publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
343,190 | 24,764,376,511 | IssuesEvent | 2022-10-22 10:12:29 | Carona-Amiga/caronaamiga | https://api.github.com/repos/Carona-Amiga/caronaamiga | closed | Atualizar Project Guidelines | documentation | #### Descrição
**Project Guidelines** é o documento onde explica o **Git Workflow** (passo a passo de implementações de nova feature usando Git). O documento se encontra desatualizado em diversos pontos.
+ No passo a passo, pois utiliza a branch `develop` como referência para branch principal, no entando a branch principal atualmente é a `main`
+ Adicionar descrição, explicação de como utilizar e significado para o `Kanban` do projeto
+ E como as issues serão realizadas | 1.0 | Atualizar Project Guidelines - #### Descrição
**Project Guidelines** é o documento onde explica o **Git Workflow** (passo a passo de implementações de nova feature usando Git). O documento se encontra desatualizado em diversos pontos.
+ No passo a passo, pois utiliza a branch `develop` como referência para branch principal, no entando a branch principal atualmente é a `main`
+ Adicionar descrição, explicação de como utilizar e significado para o `Kanban` do projeto
+ E como as issues serão realizadas | non_priority | atualizar project guidelines descrição project guidelines é o documento onde explica o git workflow passo a passo de implementações de nova feature usando git o documento se encontra desatualizado em diversos pontos no passo a passo pois utiliza a branch develop como referência para branch principal no entando a branch principal atualmente é a main adicionar descrição explicação de como utilizar e significado para o kanban do projeto e como as issues serão realizadas | 0 |
183,985 | 31,799,739,488 | IssuesEvent | 2023-09-13 10:17:36 | nucypher/ferveo | https://api.github.com/repos/nucypher/ferveo | opened | Design high-level protocols for refresh & recovery | protocol design | We currently have low-level methods and tests that demonstrate that refresh & recovery are viable, but we need to encapsulate all of this in proper protocol objects and functions. This task include, among others:
* #160
* #161
* #162 | 1.0 | Design high-level protocols for refresh & recovery - We currently have low-level methods and tests that demonstrate that refresh & recovery are viable, but we need to encapsulate all of this in proper protocol objects and functions. This task include, among others:
* #160
* #161
* #162 | non_priority | design high level protocols for refresh recovery we currently have low level methods and tests that demonstrate that refresh recovery are viable but we need to encapsulate all of this in proper protocol objects and functions this task include among others | 0 |
214,436 | 16,589,156,791 | IssuesEvent | 2021-06-01 04:52:06 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | opened | Test: Table Widget in Workspace Trust Editor | testplan-item | Refs: https://github.com/microsoft/vscode/issues/106488
- [ ] anyOS
- [ ] anyOS
Complexity: 3
Authors: @lszomoru, @sbatten
---
This milestone we replaced the table in the workspace trust editor with the table widget to add enhancements.
Features include:
* Emphasizing the entries that apply to the current workspaces trust value
* Using the native file picker for local paths
* Using the simple file picker for remote paths
Verify:
* the basic functionality of the table widget
* adding, deleting, and editing entries
* try remote and local paths
* try editing local paths while connected to a remote
* try editing remote paths while not connected (note that since we aren't connected we cannot provide a file picker)
* verify that the trust state is properly reflected based on your changes | 1.0 | Test: Table Widget in Workspace Trust Editor - Refs: https://github.com/microsoft/vscode/issues/106488
- [ ] anyOS
- [ ] anyOS
Complexity: 3
Authors: @lszomoru, @sbatten
---
This milestone we replaced the table in the workspace trust editor with the table widget to add enhancements.
Features include:
* Emphasizing the entries that apply to the current workspaces trust value
* Using the native file picker for local paths
* Using the simple file picker for remote paths
Verify:
* the basic functionality of the table widget
* adding, deleting, and editing entries
* try remote and local paths
* try editing local paths while connected to a remote
* try editing remote paths while not connected (note that since we aren't connected we cannot provide a file picker)
* verify that the trust state is properly reflected based on your changes | non_priority | test table widget in workspace trust editor refs anyos anyos complexity authors lszomoru sbatten this milestone we replaced the table in the workspace trust editor with the table widget to add enhancements features include emphasizing the entries that apply to the current workspaces trust value using the native file picker for local paths using the simple file picker for remote paths verify the basic functionality of the table widget adding deleting and editing entries try remote and local paths try editing local paths while connected to a remote try editing remote paths while not connected note that since we aren t connected we cannot provide a file picker verify that the trust state is properly reflected based on your changes | 0 |
4,294 | 5,042,350,813 | IssuesEvent | 2016-12-19 13:42:58 | core-wg/oscoap | https://api.github.com/repos/core-wg/oscoap | closed | Use of just expand phase makes things hard in some cases | core-object-security-00 | Not all crypto libraries expose just the expand phase of HKDF. The library that I am working with (BouncyCastle) appears to only expose the entire HKDF code and not the two extract and expand phases. While it is not hard to implement the expand phase, esp given that none of the values are more than one hash length long, it maybe better to use both phases. | True | Use of just expand phase makes things hard in some cases - Not all crypto libraries expose just the expand phase of HKDF. The library that I am working with (BouncyCastle) appears to only expose the entire HKDF code and not the two extract and expand phases. While it is not hard to implement the expand phase, esp given that none of the values are more than one hash length long, it maybe better to use both phases. | non_priority | use of just expand phase makes things hard in some cases not all crypto libraries expose just the expand phase of hkdf the library that i am working with bouncycastle appears to only expose the entire hkdf code and not the two extract and expand phases while it is not hard to implement the expand phase esp given that none of the values are more than one hash length long it maybe better to use both phases | 0 |
54,465 | 7,888,794,095 | IssuesEvent | 2018-06-27 23:56:50 | osbl123/proyectophp | https://api.github.com/repos/osbl123/proyectophp | closed | Corregir y redactar documento | documentation | Realizar correcciones sobre el documento tomando en cuenta las observaciones de la licenciada | 1.0 | Corregir y redactar documento - Realizar correcciones sobre el documento tomando en cuenta las observaciones de la licenciada | non_priority | corregir y redactar documento realizar correcciones sobre el documento tomando en cuenta las observaciones de la licenciada | 0 |
177,974 | 29,359,589,659 | IssuesEvent | 2023-05-28 00:36:27 | devssa/onde-codar-em-salvador | https://api.github.com/repos/devssa/onde-codar-em-salvador | closed | [Senior C# | Developer with Fluent English] - Híbrido 3x para realocação para Lisboa - Portugal - HunterHunter | SENIOR GIT UNITY SOLID REQUISITOS MVVM GITFLOW C WINDOWS DESIGN PATTERNS HELP WANTED Stale | [Senior C# | Developer with Fluent English] - Híbrido 3x para realocação para Lisboa - Portugal (auxílio realocação).
Required Skills:
● 5+ years experience
● Proficient in C# with a good knowledge of its ecosystems
● Experience with Windows Presentation Framework (WPF) applications and has an understanding of the underlying Win32 technologies
● Strong Knowledge of .NET Framework 4 and .NET Core.
● Familiarity with .NET 6.
● Experience with Inversion of Control (IoC) and dependency injection e.g. Unity
● Strong in object-oriented programming, MVVM, design patterns and SOLID principles ● Proficient in unit test writing using MSUnit
● Understands semantic versioning, branching and deployment processes using GIT
● Has good communication skills to involve others in their work, the progress and their approach to a problem
● Has good problem-solving skills
● Ensure a professional approach within the friendly atmosphere at Inspired
● Communicate in a diplomatic and polite way
● Maintain strong relationships with teammates and with colleagues from other teams ● Experience of GIT and GitFlow process (Plus).
What You'll Bring:
● Design, build, and maintain ecient, reusable and reliable C# code
● Take specifications from design to structured and maintainable code
● Ensure the best possible performance, quality and responsiveness of applications ● Document features and maintain developer documentation
● Identify bottlenecks and bugs and devise solutions to these problems
● Identify code that would benefit further unit testing and improvements.
About The Job:
Company is recruiting C# | Developer for direct integration into a multinational company.
About The Company:
Software Consulting founded with the mission to inspire the connection of technology with people, fostering the best of our professionals through our expertise in finding and attracting the best talent for the best projects.
Se tem interesse e com requisitos da oportunidade entre em contato pelo Linkedin informando qual é a oportunidade. [[https://www.linkedin.com/in/erickamarquesb/]](https://www.linkedin.com/in/erickamarquesb/%5D) | 1.0 | [Senior C# | Developer with Fluent English] - Híbrido 3x para realocação para Lisboa - Portugal - HunterHunter - [Senior C# | Developer with Fluent English] - Híbrido 3x para realocação para Lisboa - Portugal (auxílio realocação).
Required Skills:
● 5+ years experience
● Proficient in C# with a good knowledge of its ecosystems
● Experience with Windows Presentation Framework (WPF) applications and has an understanding of the underlying Win32 technologies
● Strong Knowledge of .NET Framework 4 and .NET Core.
● Familiarity with .NET 6.
● Experience with Inversion of Control (IoC) and dependency injection e.g. Unity
● Strong in object-oriented programming, MVVM, design patterns and SOLID principles ● Proficient in unit test writing using MSUnit
● Understands semantic versioning, branching and deployment processes using GIT
● Has good communication skills to involve others in their work, the progress and their approach to a problem
● Has good problem-solving skills
● Ensure a professional approach within the friendly atmosphere at Inspired
● Communicate in a diplomatic and polite way
● Maintain strong relationships with teammates and with colleagues from other teams ● Experience of GIT and GitFlow process (Plus).
What You'll Bring:
● Design, build, and maintain ecient, reusable and reliable C# code
● Take specifications from design to structured and maintainable code
● Ensure the best possible performance, quality and responsiveness of applications ● Document features and maintain developer documentation
● Identify bottlenecks and bugs and devise solutions to these problems
● Identify code that would benefit further unit testing and improvements.
About The Job:
Company is recruiting C# | Developer for direct integration into a multinational company.
About The Company:
Software Consulting founded with the mission to inspire the connection of technology with people, fostering the best of our professionals through our expertise in finding and attracting the best talent for the best projects.
Se tem interesse e com requisitos da oportunidade entre em contato pelo Linkedin informando qual é a oportunidade. [[https://www.linkedin.com/in/erickamarquesb/]](https://www.linkedin.com/in/erickamarquesb/%5D) | non_priority | híbrido para realocação para lisboa portugal hunterhunter híbrido para realocação para lisboa portugal auxílio realocação required skills ● years experience ● proficient in c with a good knowledge of its ecosystems ● experience with windows presentation framework wpf applications and has an understanding of the underlying technologies ● strong knowledge of net framework and net core ● familiarity with net ● experience with inversion of control ioc and dependency injection e g unity ● strong in object oriented programming mvvm design patterns and solid principles ● proficient in unit test writing using msunit ● understands semantic versioning branching and deployment processes using git ● has good communication skills to involve others in their work the progress and their approach to a problem ● has good problem solving skills ● ensure a professional approach within the friendly atmosphere at inspired ● communicate in a diplomatic and polite way ● maintain strong relationships with teammates and with colleagues from other teams ● experience of git and gitflow process plus what you ll bring ● design build and maintain ecient reusable and reliable c code ● take specifications from design to structured and maintainable code ● ensure the best possible performance quality and responsiveness of applications ● document features and maintain developer documentation ● identify bottlenecks and bugs and devise solutions to these problems ● identify code that would benefit further unit testing and improvements about the job company is recruiting c developer for direct integration into a multinational company about the company software consulting founded with the mission to inspire the connection of technology with people fostering the best of our professionals through our expertise in finding and attracting the best talent for the best projects se tem interesse e com requisitos da oportunidade entre em contato pelo linkedin informando qual é a oportunidade | 0 |
118,642 | 17,594,192,994 | IssuesEvent | 2021-08-17 01:05:59 | jtimberlake/rl-bakery | https://api.github.com/repos/jtimberlake/rl-bakery | opened | CVE-2021-29543 (Medium) detected in tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2021-29543 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: rl-bakery/requirements.txt</p>
<p>Path to vulnerable library: rl-bakery/requirements.txt,rl-bakery</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a denial of service via a `CHECK`-fail in `tf.raw_ops.CTCGreedyDecoder`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/1615440b17b364b875eb06f43d087381f1460a65/tensorflow/core/kernels/ctc_decoder_ops.cc#L37-L50) has a `CHECK_LT` inserted to validate some invariants. When this condition is false, the program aborts, instead of returning a valid error to the user. This abnormal termination can be weaponized in denial of service attacks. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29543>CVE-2021-29543</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-fphq-gw9m-ghrv">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-fphq-gw9m-ghrv</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0","packageFilePaths":["/requirements.txt","rl-bakery"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-29543","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a denial of service via a `CHECK`-fail in `tf.raw_ops.CTCGreedyDecoder`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/1615440b17b364b875eb06f43d087381f1460a65/tensorflow/core/kernels/ctc_decoder_ops.cc#L37-L50) has a `CHECK_LT` inserted to validate some invariants. When this condition is false, the program aborts, instead of returning a valid error to the user. This abnormal termination can be weaponized in denial of service attacks. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29543","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-29543 (Medium) detected in tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl - ## CVE-2021-29543 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/2a/5c/f1d66de5dde6f3ff528f6ea1fd0757a0e594d17debb3ec7f82daa967ea9a/tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: rl-bakery/requirements.txt</p>
<p>Path to vulnerable library: rl-bakery/requirements.txt,rl-bakery</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-2.0.0-cp37-cp37m-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a denial of service via a `CHECK`-fail in `tf.raw_ops.CTCGreedyDecoder`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/1615440b17b364b875eb06f43d087381f1460a65/tensorflow/core/kernels/ctc_decoder_ops.cc#L37-L50) has a `CHECK_LT` inserted to validate some invariants. When this condition is false, the program aborts, instead of returning a valid error to the user. This abnormal termination can be weaponized in denial of service attacks. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29543>CVE-2021-29543</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-fphq-gw9m-ghrv">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-fphq-gw9m-ghrv</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"tensorflow","packageVersion":"2.0.0","packageFilePaths":["/requirements.txt","rl-bakery"],"isTransitiveDependency":false,"dependencyTree":"tensorflow:2.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-29543","vulnerabilityDetails":"TensorFlow is an end-to-end open source platform for machine learning. An attacker can trigger a denial of service via a `CHECK`-fail in `tf.raw_ops.CTCGreedyDecoder`. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/1615440b17b364b875eb06f43d087381f1460a65/tensorflow/core/kernels/ctc_decoder_ops.cc#L37-L50) has a `CHECK_LT` inserted to validate some invariants. When this condition is false, the program aborts, instead of returning a valid error to the user. This abnormal termination can be weaponized in denial of service attacks. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29543","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file rl bakery requirements txt path to vulnerable library rl bakery requirements txt rl bakery dependency hierarchy x tensorflow whl vulnerable library found in base branch master vulnerability details tensorflow is an end to end open source platform for machine learning an attacker can trigger a denial of service via a check fail in tf raw ops ctcgreedydecoder this is because the implementation has a check lt inserted to validate some invariants when this condition is false the program aborts instead of returning a valid error to the user this abnormal termination can be weaponized in denial of service attacks the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree tensorflow isminimumfixversionavailable true minimumfixversion tensorflow tensorflow cpu tensorflow gpu basebranches vulnerabilityidentifier cve vulnerabilitydetails tensorflow is an end to end open source platform for machine learning an attacker can trigger a denial of service via a check fail in tf raw ops ctcgreedydecoder this is because the implementation has a check lt inserted to validate some invariants when this condition is false the program aborts instead of returning a valid error to the user this abnormal termination can be weaponized in denial of service attacks the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range vulnerabilityurl | 0 |
40,593 | 16,506,228,240 | IssuesEvent | 2021-05-25 19:41:33 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Data Driven PHBs - Questions about Street Select PHB Data - Renee | Service: Geo Type: Data Workgroup: AMD | From Renee:
> Good morning, I was able to import the data driven PHB map into Pro and am prepping for the D2, D3 meeting next week. While doing this I noticed that this segment scored pretty high in the ranking, but if you look closely you will see that there is already a PHB here. The location is S1st at King Edward. When you get a chance can you please take a look at this and see if we can do the 300' buffer from this site? Thanks so much.
The PHB was turned on in 2018. | 1.0 | Data Driven PHBs - Questions about Street Select PHB Data - Renee - From Renee:
> Good morning, I was able to import the data driven PHB map into Pro and am prepping for the D2, D3 meeting next week. While doing this I noticed that this segment scored pretty high in the ranking, but if you look closely you will see that there is already a PHB here. The location is S1st at King Edward. When you get a chance can you please take a look at this and see if we can do the 300' buffer from this site? Thanks so much.
The PHB was turned on in 2018. | non_priority | data driven phbs questions about street select phb data renee from renee good morning i was able to import the data driven phb map into pro and am prepping for the meeting next week while doing this i noticed that this segment scored pretty high in the ranking but if you look closely you will see that there is already a phb here the location is at king edward when you get a chance can you please take a look at this and see if we can do the buffer from this site thanks so much the phb was turned on in | 0 |
226,711 | 18,043,935,363 | IssuesEvent | 2021-09-18 14:51:24 | logicmoo/logicmoo_workspace | https://api.github.com/repos/logicmoo/logicmoo_workspace | opened | logicmoo.pfc.test.sanity_base.LIST_03 JUnit | Test_9999 logicmoo.pfc.test.sanity_base unit_test LIST_03 | (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif list_03.pfc)
GH_MASTER_ISSUE_FINFO=
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ALIST_03
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
```
%
running('/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/list_03.pfc'),
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
:- expects_dialect(pfc).
header_sane:(must_clause_asserted(G):- cwc, must(clause_asserted_u(G))).
:- ain((must_clause_asserted(G):- cwc, must(clause_asserted_u(G)))).
:- listing(must_clause_asserted).
%~ skipped( listing(must_clause_asserted))
must_clause_asserted(G):- cwc, must(clause_asserted_u(G)).
:- listing(must_clause_asserted).
%~ skipped( listing(must_clause_asserted))
:- sanity(predicate_property(must_clause_asserted(_),number_of_clauses(_))).
a.
:- header_sane:listing(a).
%~ /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/list_03.pfc:31
%~ skipped( listing(a))
:- must_clause_asserted(a).
sHOW_MUST_go_on_failed_F__A__I__L_(baseKB:clause_asserted_u(a))
%~ FIlE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/list_03.pfc#L33
%~ error( sHOW_MUST_go_on_failed_F__A__I__L_( baseKB : clause_asserted_u(a)))
%~ FILE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/list_03.pfc#L33
```
totalTime=10
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ALIST_03
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k list_03.pfc (returned 137)
| 3.0 | logicmoo.pfc.test.sanity_base.LIST_03 JUnit - (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif list_03.pfc)
GH_MASTER_ISSUE_FINFO=
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ALIST_03
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
```
%
running('/var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/list_03.pfc'),
%~ this_test_might_need( :-( use_module( library(logicmoo_plarkc))))
:- expects_dialect(pfc).
header_sane:(must_clause_asserted(G):- cwc, must(clause_asserted_u(G))).
:- ain((must_clause_asserted(G):- cwc, must(clause_asserted_u(G)))).
:- listing(must_clause_asserted).
%~ skipped( listing(must_clause_asserted))
must_clause_asserted(G):- cwc, must(clause_asserted_u(G)).
:- listing(must_clause_asserted).
%~ skipped( listing(must_clause_asserted))
:- sanity(predicate_property(must_clause_asserted(_),number_of_clauses(_))).
a.
:- header_sane:listing(a).
%~ /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base/list_03.pfc:31
%~ skipped( listing(a))
:- must_clause_asserted(a).
sHOW_MUST_go_on_failed_F__A__I__L_(baseKB:clause_asserted_u(a))
%~ FIlE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/list_03.pfc#L33
%~ error( sHOW_MUST_go_on_failed_F__A__I__L_( baseKB : clause_asserted_u(a)))
%~ FILE: * https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/blob/master/packs_sys/pfc/t/sanity_base/list_03.pfc#L33
```
totalTime=10
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ALIST_03
GITLAB: https://logicmoo.org:2082/gitlab/logicmoo/logicmoo_workspace/-/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://gitlab.logicmoo.org/gitlab/logicmoo/logicmoo_workspace/-/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
Latest: https://jenkins.logicmoo.org/job/logicmoo_workspace/lastBuild/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
This Build: https://jenkins.logicmoo.org/job/logicmoo_workspace/65/testReport/logicmoo.pfc.test.sanity_base/LIST_03/logicmoo_pfc_test_sanity_base_LIST_03_JUnit/
GITHUB: https://github.com/logicmoo/logicmoo_workspace/commit/813ec17487381a026b83350c360d0c79a9e2d0ae
https://github.com/logicmoo/logicmoo_workspace/blob/813ec17487381a026b83350c360d0c79a9e2d0ae/packs_sys/pfc/t/sanity_base/list_03.pfc
FAILED: /var/lib/jenkins/workspace/logicmoo_workspace/bin/lmoo-junit-minor -k list_03.pfc (returned 137)
| non_priority | logicmoo pfc test sanity base list junit cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif list pfc gh master issue finfo issue search gitlab latest this build github running var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base list pfc this test might need use module library logicmoo plarkc expects dialect pfc header sane must clause asserted g cwc must clause asserted u g ain must clause asserted g cwc must clause asserted u g listing must clause asserted skipped listing must clause asserted must clause asserted g cwc must clause asserted u g listing must clause asserted skipped listing must clause asserted sanity predicate property must clause asserted number of clauses a header sane listing a var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base list pfc skipped listing a must clause asserted a show must go on failed f a i l basekb clause asserted u a file error show must go on failed f a i l basekb clause asserted u a file totaltime issue search gitlab latest this build github failed var lib jenkins workspace logicmoo workspace bin lmoo junit minor k list pfc returned | 0 |
381,558 | 26,459,649,476 | IssuesEvent | 2023-01-16 16:27:27 | CDCgov/trusted-intermediary | https://api.github.com/repos/CDCgov/trusted-intermediary | closed | DevSecOps Artifacts | documentation | Provide documentation of:
- [x] Define the DevSecOps Architecture - @halprin
- [x] GitHub @ CDC integration with DevSecOps Process - @halprin
- [x] Login and Monitoring infrastructure components - @halprin
- [x] Change management process and build, deploy, test validate - @halprin
- [x] Blue Green Deployment strategy - @halprin
- [x] Refine words.
(see RFQ C.6) | 1.0 | DevSecOps Artifacts - Provide documentation of:
- [x] Define the DevSecOps Architecture - @halprin
- [x] GitHub @ CDC integration with DevSecOps Process - @halprin
- [x] Login and Monitoring infrastructure components - @halprin
- [x] Change management process and build, deploy, test validate - @halprin
- [x] Blue Green Deployment strategy - @halprin
- [x] Refine words.
(see RFQ C.6) | non_priority | devsecops artifacts provide documentation of define the devsecops architecture halprin github cdc integration with devsecops process halprin login and monitoring infrastructure components halprin change management process and build deploy test validate halprin blue green deployment strategy halprin refine words see rfq c | 0 |
21,392 | 3,702,799,152 | IssuesEvent | 2016-02-29 18:05:27 | codefordenver/code-for-denver-site | https://api.github.com/repos/codefordenver/code-for-denver-site | closed | Add "Want To Help?" Section | design duplicate writing | As a website user, I need to know the different ways I can get involved with Code for Denver. | 1.0 | Add "Want To Help?" Section - As a website user, I need to know the different ways I can get involved with Code for Denver. | non_priority | add want to help section as a website user i need to know the different ways i can get involved with code for denver | 0 |
87,423 | 8,074,009,633 | IssuesEvent | 2018-08-06 21:19:08 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | User API needs Activate and Deactivate actions | area/rbac kind/bug status/reopened status/resolved status/to-test version/2.0 | **Rancher versions:** 2.0 master 12/22
**Results:**
- [x] Description field missing from API
- [ ] Need Activate/Deactivate actions added | 1.0 | User API needs Activate and Deactivate actions - **Rancher versions:** 2.0 master 12/22
**Results:**
- [x] Description field missing from API
- [ ] Need Activate/Deactivate actions added | non_priority | user api needs activate and deactivate actions rancher versions master results description field missing from api need activate deactivate actions added | 0 |
74,792 | 25,331,103,839 | IssuesEvent | 2022-11-18 13:19:45 | vector-im/element-call | https://api.github.com/repos/vector-im/element-call | closed | undefined is not a constructor (evaluating 'new Intl.Locale(n[0])') | T-Defect X-Needs-Info S-Critical O-Uncommon Z-Platform-Specific I18n | This is appearing in rageshakes, although I can't tell where it's coming from. | 1.0 | undefined is not a constructor (evaluating 'new Intl.Locale(n[0])') - This is appearing in rageshakes, although I can't tell where it's coming from. | non_priority | undefined is not a constructor evaluating new intl locale n this is appearing in rageshakes although i can t tell where it s coming from | 0 |
82,976 | 23,932,206,437 | IssuesEvent | 2022-09-10 18:14:41 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | Python Console not found in QGIS (windows 7 ultimate) | Feedback Build/Install Bug Windows | ### What is the bug or the crash?

### Steps to reproduce the issue
Open Qgis in window 7 ultimate
### Versions
QGIS 3.16.X and QGIS 3.22.X
### Supported QGIS version
- [X] I'm running a supported QGIS version according to the roadmap.
### New profile
- [ ] I tried with a new QGIS profile
### Additional context
I used system operative windows 7 ultimate and when I downland Qgis in these versions in the console, I don't saw python console. | 1.0 | Python Console not found in QGIS (windows 7 ultimate) - ### What is the bug or the crash?

### Steps to reproduce the issue
Open Qgis in window 7 ultimate
### Versions
QGIS 3.16.X and QGIS 3.22.X
### Supported QGIS version
- [X] I'm running a supported QGIS version according to the roadmap.
### New profile
- [ ] I tried with a new QGIS profile
### Additional context
I used system operative windows 7 ultimate and when I downland Qgis in these versions in the console, I don't saw python console. | non_priority | python console not found in qgis windows ultimate what is the bug or the crash steps to reproduce the issue open qgis in window ultimate versions qgis x and qgis x supported qgis version i m running a supported qgis version according to the roadmap new profile i tried with a new qgis profile additional context i used system operative windows ultimate and when i downland qgis in these versions in the console i don t saw python console | 0 |
266,557 | 20,157,672,636 | IssuesEvent | 2022-02-09 17:59:52 | containers/podman | https://api.github.com/repos/containers/podman | closed | it's difficult to find API documentation for specific release | kind/bug documentation | <!--
---------------------------------------------------
BUG REPORT INFORMATION
---------------------------------------------------
Use the commands below to provide key information from your environment:
You do NOT have to include this information if this is a FEATURE REQUEST
**NOTE** A large number of issues reported against Podman are often found to already be fixed
in more current versions of the project. Before reporting an issue, please verify the
version you are running with `podman version` and compare it to the latest release
documented on the top of Podman's [README.md](../README.md). If they differ, please
update your version of Podman to the latest possible and retry your command before creating
an issue.
Also, there is a running list of known issues in the [Podman Troubleshooting Guide](https://github.com/containers/podman/blob/master/troubleshooting.md),
please reference that page before opening a new issue.
If you are filing a bug against `podman build`, please instead file a bug
against Buildah (https://github.com/containers/buildah/issues). Podman build
executes Buildah to perform container builds, and as such the Buildah
maintainers are best equipped to handle these bugs.
-->
**Is this a BUG REPORT or FEATURE REQUEST? (leave only one on its own line)**
/kind bug
**Description**
See #12777 in which it is very difficult to determine the API for the version of podman I am using.
The API links in documentation point to https://docs.podman.io/en/latest/_static/api.html and there's no way to change version as one can ordinarily do on https://docs.podman.io/en/latest/ where there's a dropdown in the lower-right of the page.
You can manually munge the the URL for api.html in an effort to locate the documentation for previous versions, but that's not always effective or accurate. (To wit, I can access much older documentation that shows the request syntax that I was given to resolve #12777, but it's not clear how to see the full API that matches my exact version: `APIVersion: 3.3.1`
<!--
Briefly describe the problem you are having in a few paragraphs.
-->
**Steps to reproduce the issue:**
1. Try to find the API documentation for the version of podman you are using.
**Describe the results you received:**
I get the latest API documentation, which is not accurate for the version I am using.
**Describe the results you expected:**
I would like to see the complete API for the version I am using with confidence that the request parameters and bodies are correct.
**Additional information you deem important (e.g. issue happens only occasionally):**
**Output of `podman version`:**
See #12777 for `podman version` and `podman info --debug` for this issue.
```
(paste your output here)
```
**Output of `podman info --debug`:**
```
(paste your output here)
```
**Package info (e.g. output of `rpm -q podman` or `apt list podman`):**
```
(paste your output here)
```
**Have you tested with the latest version of Podman and have you checked the Podman Troubleshooting Guide? (https://github.com/containers/podman/blob/master/troubleshooting.md)**
Yes
**Additional environment details (AWS, VirtualBox, physical, etc.):**
| 1.0 | it's difficult to find API documentation for specific release - <!--
---------------------------------------------------
BUG REPORT INFORMATION
---------------------------------------------------
Use the commands below to provide key information from your environment:
You do NOT have to include this information if this is a FEATURE REQUEST
**NOTE** A large number of issues reported against Podman are often found to already be fixed
in more current versions of the project. Before reporting an issue, please verify the
version you are running with `podman version` and compare it to the latest release
documented on the top of Podman's [README.md](../README.md). If they differ, please
update your version of Podman to the latest possible and retry your command before creating
an issue.
Also, there is a running list of known issues in the [Podman Troubleshooting Guide](https://github.com/containers/podman/blob/master/troubleshooting.md),
please reference that page before opening a new issue.
If you are filing a bug against `podman build`, please instead file a bug
against Buildah (https://github.com/containers/buildah/issues). Podman build
executes Buildah to perform container builds, and as such the Buildah
maintainers are best equipped to handle these bugs.
-->
**Is this a BUG REPORT or FEATURE REQUEST? (leave only one on its own line)**
/kind bug
**Description**
See #12777 in which it is very difficult to determine the API for the version of podman I am using.
The API links in documentation point to https://docs.podman.io/en/latest/_static/api.html and there's no way to change version as one can ordinarily do on https://docs.podman.io/en/latest/ where there's a dropdown in the lower-right of the page.
You can manually munge the the URL for api.html in an effort to locate the documentation for previous versions, but that's not always effective or accurate. (To wit, I can access much older documentation that shows the request syntax that I was given to resolve #12777, but it's not clear how to see the full API that matches my exact version: `APIVersion: 3.3.1`
<!--
Briefly describe the problem you are having in a few paragraphs.
-->
**Steps to reproduce the issue:**
1. Try to find the API documentation for the version of podman you are using.
**Describe the results you received:**
I get the latest API documentation, which is not accurate for the version I am using.
**Describe the results you expected:**
I would like to see the complete API for the version I am using with confidence that the request parameters and bodies are correct.
**Additional information you deem important (e.g. issue happens only occasionally):**
**Output of `podman version`:**
See #12777 for `podman version` and `podman info --debug` for this issue.
```
(paste your output here)
```
**Output of `podman info --debug`:**
```
(paste your output here)
```
**Package info (e.g. output of `rpm -q podman` or `apt list podman`):**
```
(paste your output here)
```
**Have you tested with the latest version of Podman and have you checked the Podman Troubleshooting Guide? (https://github.com/containers/podman/blob/master/troubleshooting.md)**
Yes
**Additional environment details (AWS, VirtualBox, physical, etc.):**
| non_priority | it s difficult to find api documentation for specific release bug report information use the commands below to provide key information from your environment you do not have to include this information if this is a feature request note a large number of issues reported against podman are often found to already be fixed in more current versions of the project before reporting an issue please verify the version you are running with podman version and compare it to the latest release documented on the top of podman s readme md if they differ please update your version of podman to the latest possible and retry your command before creating an issue also there is a running list of known issues in the please reference that page before opening a new issue if you are filing a bug against podman build please instead file a bug against buildah podman build executes buildah to perform container builds and as such the buildah maintainers are best equipped to handle these bugs is this a bug report or feature request leave only one on its own line kind bug description see in which it is very difficult to determine the api for the version of podman i am using the api links in documentation point to and there s no way to change version as one can ordinarily do on where there s a dropdown in the lower right of the page you can manually munge the the url for api html in an effort to locate the documentation for previous versions but that s not always effective or accurate to wit i can access much older documentation that shows the request syntax that i was given to resolve but it s not clear how to see the full api that matches my exact version apiversion briefly describe the problem you are having in a few paragraphs steps to reproduce the issue try to find the api documentation for the version of podman you are using describe the results you received i get the latest api documentation which is not accurate for the version i am using describe the results you expected i would like to see the complete api for the version i am using with confidence that the request parameters and bodies are correct additional information you deem important e g issue happens only occasionally output of podman version see for podman version and podman info debug for this issue paste your output here output of podman info debug paste your output here package info e g output of rpm q podman or apt list podman paste your output here have you tested with the latest version of podman and have you checked the podman troubleshooting guide yes additional environment details aws virtualbox physical etc | 0 |
34,590 | 9,417,821,650 | IssuesEvent | 2019-04-10 17:40:55 | raster-foundry/blasterjs | https://api.github.com/repos/raster-foundry/blasterjs | closed | Integrate 'documentation' to generate docs for non-component code | documentation :scroll: infrastructure :building_construction: | We will have a number of enums and other methods as public API but styleguidist does not document these without extra setup.
The setup could be using https://github.com/documentationjs/documentation to generate markdown files and placing them in the docs directory so that styleguidist can process them. | 1.0 | Integrate 'documentation' to generate docs for non-component code - We will have a number of enums and other methods as public API but styleguidist does not document these without extra setup.
The setup could be using https://github.com/documentationjs/documentation to generate markdown files and placing them in the docs directory so that styleguidist can process them. | non_priority | integrate documentation to generate docs for non component code we will have a number of enums and other methods as public api but styleguidist does not document these without extra setup the setup could be using to generate markdown files and placing them in the docs directory so that styleguidist can process them | 0 |
30,106 | 7,162,909,015 | IssuesEvent | 2018-01-29 03:45:52 | NeuralEnsemble/pype9 | https://api.github.com/repos/NeuralEnsemble/pype9 | closed | Code-generation/compilation should only occur on master node | NEST NEURON code generation enhancement | Should place conditional statements around code generation and compilation to ensure that it only happens on the master node (i.e. MPI rank=0). Other nodes should wait until this process is completed. | 1.0 | Code-generation/compilation should only occur on master node - Should place conditional statements around code generation and compilation to ensure that it only happens on the master node (i.e. MPI rank=0). Other nodes should wait until this process is completed. | non_priority | code generation compilation should only occur on master node should place conditional statements around code generation and compilation to ensure that it only happens on the master node i e mpi rank other nodes should wait until this process is completed | 0 |
335,018 | 24,450,135,519 | IssuesEvent | 2022-10-06 21:54:15 | AP6YC/ClusterValidityIndices.jl | https://api.github.com/repos/AP6YC/ClusterValidityIndices.jl | closed | Fix LFS files in documentation | bug documentation | The dev documentation isn't showing files that were added as git LFS files. | 1.0 | Fix LFS files in documentation - The dev documentation isn't showing files that were added as git LFS files. | non_priority | fix lfs files in documentation the dev documentation isn t showing files that were added as git lfs files | 0 |
174,463 | 14,483,401,791 | IssuesEvent | 2020-12-10 15:07:24 | BiomarkABS/DASH | https://api.github.com/repos/BiomarkABS/DASH | opened | Resolve Station Widths | bug documentation reminder | According to @rcarmichael3 Ricardo, *"station width refers to the distance **between** each depth and velocity measurement, so they should be the same across each measurement. So if all of them are 0.25 or 0.64 that would make sense to me. At least that is how it is supposed to be recorded."*
This was in response to @KevinSee's earlier remarks to me *"I also noticed that a number of the discharge metrics for 2020 are 0, which seems odd. Looking at the discharge measurements, it looks like maybe the station widths weren’t captured correctly? For example, in the Grouse Discharge_Measurements_6.csv file, all the station widths are either 0.25 or 0.64. Seems odd, no?"*
So it seems we need to review how measurements are collected and discharge is calculated. 1) It appears that station width's may have been collected incorrectly in 2018 & 2019, at least after first glance. However, 2) this doesn't necessarily explain Kevin's remark above where a number of the discharge metrics for 2020 are 0.
In any case, worth a review.
| 1.0 | Resolve Station Widths - According to @rcarmichael3 Ricardo, *"station width refers to the distance **between** each depth and velocity measurement, so they should be the same across each measurement. So if all of them are 0.25 or 0.64 that would make sense to me. At least that is how it is supposed to be recorded."*
This was in response to @KevinSee's earlier remarks to me *"I also noticed that a number of the discharge metrics for 2020 are 0, which seems odd. Looking at the discharge measurements, it looks like maybe the station widths weren’t captured correctly? For example, in the Grouse Discharge_Measurements_6.csv file, all the station widths are either 0.25 or 0.64. Seems odd, no?"*
So it seems we need to review how measurements are collected and discharge is calculated. 1) It appears that station width's may have been collected incorrectly in 2018 & 2019, at least after first glance. However, 2) this doesn't necessarily explain Kevin's remark above where a number of the discharge metrics for 2020 are 0.
In any case, worth a review.
| non_priority | resolve station widths according to ricardo station width refers to the distance between each depth and velocity measurement so they should be the same across each measurement so if all of them are or that would make sense to me at least that is how it is supposed to be recorded this was in response to kevinsee s earlier remarks to me i also noticed that a number of the discharge metrics for are which seems odd looking at the discharge measurements it looks like maybe the station widths weren’t captured correctly for example in the grouse discharge measurements csv file all the station widths are either or seems odd no so it seems we need to review how measurements are collected and discharge is calculated it appears that station width s may have been collected incorrectly in at least after first glance however this doesn t necessarily explain kevin s remark above where a number of the discharge metrics for are in any case worth a review | 0 |
323,479 | 27,728,926,066 | IssuesEvent | 2023-03-15 06:05:33 | Etesam913/Custoplayer | https://api.github.com/repos/Etesam913/Custoplayer | closed | Create test for progress bar dragging | testing | * Create a cypress test where the mouse down event is triggered on the progress bar
* Check to make sure that the video's currentTime is not 0. | 1.0 | Create test for progress bar dragging - * Create a cypress test where the mouse down event is triggered on the progress bar
* Check to make sure that the video's currentTime is not 0. | non_priority | create test for progress bar dragging create a cypress test where the mouse down event is triggered on the progress bar check to make sure that the video s currenttime is not | 0 |
280,775 | 21,315,165,579 | IssuesEvent | 2022-04-16 06:25:42 | arcornior/pe | https://api.github.com/repos/arcornior/pe | opened | [UG] Unknown parameter DETAIL in UG `addo` command | type.DocumentationBug severity.VeryLow | ## Details
Unknown parameter DETAIL is introduced in UG's `addo` command. Should it be DETAILS instead?
## Recreation of Bug
Open UG, view `addo` command.
## Expected outcome
DETAIL should be DETAILS
## Actual outcome
Unknown parameter DETAIL is mentioned. Is it a separate parameter from DETAILS? Users may get confused between the two.
## Screenshots
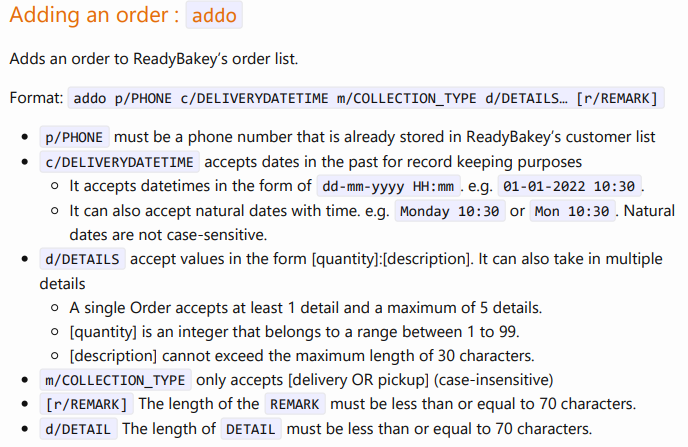
<!--session: 1650087972671-5d7ca28a-5998-4208-83aa-1c5a0e33a289-->
<!--Version: Web v3.4.2--> | 1.0 | [UG] Unknown parameter DETAIL in UG `addo` command - ## Details
Unknown parameter DETAIL is introduced in UG's `addo` command. Should it be DETAILS instead?
## Recreation of Bug
Open UG, view `addo` command.
## Expected outcome
DETAIL should be DETAILS
## Actual outcome
Unknown parameter DETAIL is mentioned. Is it a separate parameter from DETAILS? Users may get confused between the two.
## Screenshots
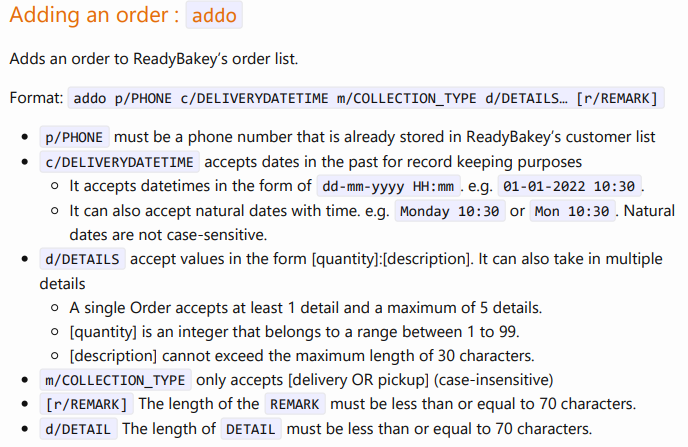
<!--session: 1650087972671-5d7ca28a-5998-4208-83aa-1c5a0e33a289-->
<!--Version: Web v3.4.2--> | non_priority | unknown parameter detail in ug addo command details unknown parameter detail is introduced in ug s addo command should it be details instead recreation of bug open ug view addo command expected outcome detail should be details actual outcome unknown parameter detail is mentioned is it a separate parameter from details users may get confused between the two screenshots | 0 |
213,975 | 24,023,041,386 | IssuesEvent | 2022-09-15 09:13:21 | sast-automation-dev/hackme-25 | https://api.github.com/repos/sast-automation-dev/hackme-25 | opened | rails-3.0.9.gem: 52 vulnerabilities (highest severity is: 8.6) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rails-3.0.9.gem</b></p></summary>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-8161](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8161) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2020-8184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2021-22885](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22885) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2019-5418](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5418) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2016-0752](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0752) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | rails-3.0.9.gem | Direct | 3.2.22.1,4.1.14.1,4.2.5.1,5.0.0.beta1.1 | ✅ |
| [CVE-2016-0751](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0751) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A | ✅ |
| [CVE-2014-10077](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-10077) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | i18n-0.5.0.gem | Transitive | N/A | ❌ |
| [CVE-2013-0156](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0156) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activesupport-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2695](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2695) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-6496](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6496) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2016-2098](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2098) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | detected in multiple dependencies | Direct | 3.2.22.2,4.1.14.2,4.2.5.2 | ✅ |
| [CVE-2013-0333](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0333) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activesupport-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2014-3482](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3482) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2140) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | mail-2.2.19.gem | Transitive | N/A | ❌ |
| [CVE-2013-6417](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6417) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-3221](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-3221) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-0155](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2660](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2660) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2020-8167](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8167) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | rails-3.0.9.gem | Direct | 6.0.3.1,5.2.4.3 | ✅ |
| [CVE-2010-3299](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2010-3299) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | rails-3.0.9.gem | Direct | rails - 5.2.0.beta1 | ✅ |
| [CVE-2020-8130](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8130) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.4 | rake-0.9.2.gem | Transitive | N/A | ❌ |
| [CVE-2018-16471](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16471) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2016-6316](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-6316) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2015-9097](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9097) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | mail-2.2.19.gem | Transitive | N/A | ❌ |
| [CVE-2019-16782](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16782) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2013-0263](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0263) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2011-2930](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2930) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | rails-3.0.9.gem | Direct | 2.3.13,3.0.10,3.1.0.rc5 | ✅ |
| [CVE-2013-6414](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6414) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [WS-2017-0283](https://github.com/rack/rack/commit/6a0e0ee8fcd982bccf30077ec94cb55018bbed91) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2012-3424](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3424) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2139](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2139) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | mail-2.2.19.gem | Transitive | N/A | ❌ |
| [CVE-2011-5036](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-5036) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2015-3225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3225) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2012-2661](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2661) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2016-2097](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2097) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rails-3.0.9.gem | Direct | 3.2.22.2,4.1.14.2 | ✅ |
| [CVE-2011-2929](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2929) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2014-0082](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0082) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-6415](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6415) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-3463](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3463) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-3465](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3465) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-3464](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3464) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | activesupport-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-1855](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-1855) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-1857](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-1857) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2011-2932](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2932) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rails-3.0.9.gem | Direct | 2.3.13,3.0.10,3.1.0.rc5 | ✅ |
| [CVE-2012-6109](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6109) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2013-4491](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4491) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-4492](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4492) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | i18n-0.5.0.gem | Transitive | N/A | ❌ |
| [CVE-2013-0256](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0256) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rdoc-3.8.gem | Transitive | N/A | ❌ |
| [CVE-2014-0130](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0130) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2015-7576](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-7576) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-0184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0184) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2014-0081](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0081) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
## Details
> Partial details (21 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8161</summary>
### Vulnerable Library - <b>rack-1.2.3.gem</b></p>
<p>Rack provides minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.rubyforge.org.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.2.3.gem">https://rubygems.org/gems/rack-1.2.3.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rack-1.2.3.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- actionpack-3.0.9.gem
- :x: **rack-1.2.3.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A directory traversal vulnerability exists in rack < 2.2.0 that allows an attacker perform directory traversal vulnerability in the Rack::Directory app that is bundled with Rack which could result in information disclosure.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8161>CVE-2020-8161</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-10-05</p>
<p>Fix Resolution: 2.2.0,2.1.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8184</summary>
### Vulnerable Library - <b>rack-1.2.3.gem</b></p>
<p>Rack provides minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.rubyforge.org.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.2.3.gem">https://rubygems.org/gems/rack-1.2.3.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rack-1.2.3.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- actionpack-3.0.9.gem
- :x: **rack-1.2.3.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A reliance on cookies without validation/integrity check security vulnerability exists in rack < 2.2.3, rack < 2.1.4 that makes it is possible for an attacker to forge a secure or host-only cookie prefix.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8184>CVE-2020-8184</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/forum/#!topic/rubyonrails-security/OWtmozPH9Ak">https://groups.google.com/forum/#!topic/rubyonrails-security/OWtmozPH9Ak</a></p>
<p>Release Date: 2020-10-05</p>
<p>Fix Resolution: rack - 2.1.4, 2.2.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22885</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A possible information disclosure / unintended method execution vulnerability in Action Pack >= 2.0.0 when using the `redirect_to` or `polymorphic_url`helper with untrusted user input.
<p>Publish Date: 2021-05-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22885>CVE-2021-22885</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-hjg4-8q5f-x6fm">https://github.com/advisories/GHSA-hjg4-8q5f-x6fm</a></p>
<p>Release Date: 2021-05-27</p>
<p>Fix Resolution: actionpack - 5.2.4.6,5.2.6,6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-5418</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There is a File Content Disclosure vulnerability in Action View <5.2.2.1, <5.1.6.2, <5.0.7.2, <4.2.11.1 and v3 where specially crafted accept headers can cause contents of arbitrary files on the target system's filesystem to be exposed.
<p>Publish Date: 2019-03-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5418>CVE-2019-5418</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://weblog.rubyonrails.org/2019/3/13/Rails-4-2-5-1-5-1-6-2-have-been-released/">https://weblog.rubyonrails.org/2019/3/13/Rails-4-2-5-1-5-1-6-2-have-been-released/</a></p>
<p>Release Date: 2020-10-16</p>
<p>Fix Resolution: 4.2.11.1, 5.0.7.2, 5.1.6.2, 5.2.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-0752</summary>
### Vulnerable Library - <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Directory traversal vulnerability in Action View in Ruby on Rails before 3.2.22.1, 4.0.x and 4.1.x before 4.1.14.1, 4.2.x before 4.2.5.1, and 5.x before 5.0.0.beta1.1 allows remote attackers to read arbitrary files by leveraging an application's unrestricted use of the render method and providing a .. (dot dot) in a pathname.
<p>Publish Date: 2016-02-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0752>CVE-2016-0752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-0752">https://nvd.nist.gov/vuln/detail/CVE-2016-0752</a></p>
<p>Release Date: 2016-02-16</p>
<p>Fix Resolution: 3.2.22.1,4.1.14.1,4.2.5.1,5.0.0.beta1.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-0751</summary>
### Vulnerable Libraries - <b>actionpack-3.0.9.gem</b>, <b>rails-3.0.9.gem</b></p>
<p>
### <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
### <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
actionpack/lib/action_dispatch/http/mime_type.rb in Action Pack in Ruby on Rails before 3.2.22.1, 4.0.x and 4.1.x before 4.1.14.1, 4.2.x before 4.2.5.1, and 5.x before 5.0.0.beta1.1 does not properly restrict use of the MIME type cache, which allows remote attackers to cause a denial of service (memory consumption) via a crafted HTTP Accept header.
<p>Publish Date: 2016-02-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0751>CVE-2016-0751</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-0751">https://nvd.nist.gov/vuln/detail/CVE-2016-0751</a></p>
<p>Release Date: 2016-02-16</p>
<p>Fix Resolution: 3.2.22.1,4.1.14.1,4.2.5.1,5.0.0.beta1.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-10077</summary>
### Vulnerable Library - <b>i18n-0.5.0.gem</b></p>
<p>New wave Internationalization support for Ruby.</p>
<p>Library home page: <a href="https://rubygems.org/gems/i18n-0.5.0.gem">https://rubygems.org/gems/i18n-0.5.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/i18n-0.5.0.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- actionpack-3.0.9.gem
- :x: **i18n-0.5.0.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Hash#slice in lib/i18n/core_ext/hash.rb in the i18n gem before 0.8.0 for Ruby allows remote attackers to cause a denial of service (application crash) via a call in a situation where :some_key is present in keep_keys but not present in the hash.
<p>Publish Date: 2018-11-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-10077>CVE-2014-10077</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-10077">https://nvd.nist.gov/vuln/detail/CVE-2014-10077</a></p>
<p>Release Date: 2018-11-06</p>
<p>Fix Resolution: 0.8.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-0156</summary>
### Vulnerable Library - <b>activesupport-3.0.9.gem</b></p>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-3.0.9.gem">https://rubygems.org/gems/activesupport-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activesupport-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activesupport-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
active_support/core_ext/hash/conversions.rb in Ruby on Rails before 2.3.15, 3.0.x before 3.0.19, 3.1.x before 3.1.10, and 3.2.x before 3.2.11 does not properly restrict casts of string values, which allows remote attackers to conduct object-injection attacks and execute arbitrary code, or cause a denial of service (memory and CPU consumption) involving nested XML entity references, by leveraging Action Pack support for (1) YAML type conversion or (2) Symbol type conversion.
<p>Publish Date: 2013-01-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0156>CVE-2013-0156</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0156">https://nvd.nist.gov/vuln/detail/CVE-2013-0156</a></p>
<p>Release Date: 2013-01-13</p>
<p>Fix Resolution: 2.3.15,3.0.19,3.1.10,3.2.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-2695</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Active Record component in Ruby on Rails before 3.0.14, 3.1.x before 3.1.6, and 3.2.x before 3.2.6 does not properly implement the passing of request data to a where method in an ActiveRecord class, which allows remote attackers to conduct certain SQL injection attacks via nested query parameters that leverage improper handling of nested hashes, a related issue to CVE-2012-2661.
<p>Publish Date: 2012-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2695>CVE-2012-2695</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-2695">https://nvd.nist.gov/vuln/detail/CVE-2012-2695</a></p>
<p>Release Date: 2012-06-22</p>
<p>Fix Resolution: 3.0.14,3.1.6,3.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-6496</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQL injection vulnerability in the Active Record component in Ruby on Rails before 3.0.18, 3.1.x before 3.1.9, and 3.2.x before 3.2.10 allows remote attackers to execute arbitrary SQL commands via a crafted request that leverages incorrect behavior of dynamic finders in applications that can use unexpected data types in certain find_by_ method calls.
<p>Publish Date: 2013-01-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6496>CVE-2012-6496</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6496">https://nvd.nist.gov/vuln/detail/CVE-2012-6496</a></p>
<p>Release Date: 2013-01-04</p>
<p>Fix Resolution: 3.0.18,3.1.9,3.2.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2098</summary>
### Vulnerable Libraries - <b>rails-3.0.9.gem</b>, <b>actionpack-3.0.9.gem</b></p>
<p>
### <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
### <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Action Pack in Ruby on Rails before 3.2.22.2, 4.x before 4.1.14.2, and 4.2.x before 4.2.5.2 allows remote attackers to execute arbitrary Ruby code by leveraging an application's unrestricted use of the render method.
<p>Publish Date: 2016-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2098>CVE-2016-2098</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2098">https://nvd.nist.gov/vuln/detail/CVE-2016-2098</a></p>
<p>Release Date: 2016-04-07</p>
<p>Fix Resolution: 3.2.22.2,4.1.14.2,4.2.5.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-0333</summary>
### Vulnerable Library - <b>activesupport-3.0.9.gem</b></p>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-3.0.9.gem">https://rubygems.org/gems/activesupport-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activesupport-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activesupport-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lib/active_support/json/backends/yaml.rb in Ruby on Rails 2.3.x before 2.3.16 and 3.0.x before 3.0.20 does not properly convert JSON data to YAML data for processing by a YAML parser, which allows remote attackers to execute arbitrary code, conduct SQL injection attacks, or bypass authentication via crafted data that triggers unsafe decoding, a different vulnerability than CVE-2013-0156.
<p>Publish Date: 2013-01-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0333>CVE-2013-0333</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0333">https://nvd.nist.gov/vuln/detail/CVE-2013-0333</a></p>
<p>Release Date: 2013-01-30</p>
<p>Fix Resolution: 2.3.16,3.0.20</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-3482</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQL injection vulnerability in activerecord/lib/active_record/connection_adapters/postgresql_adapter.rb in the PostgreSQL adapter for Active Record in Ruby on Rails 2.x and 3.x before 3.2.19 allows remote attackers to execute arbitrary SQL commands by leveraging improper bitstring quoting.
<p>Publish Date: 2014-07-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3482>CVE-2014-3482</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-3482">https://nvd.nist.gov/vuln/detail/CVE-2014-3482</a></p>
<p>Release Date: 2014-07-07</p>
<p>Fix Resolution: 3.2.19</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-2140</summary>
### Vulnerable Library - <b>mail-2.2.19.gem</b></p>
<p>A really Ruby Mail handler.</p>
<p>Library home page: <a href="https://rubygems.org/gems/mail-2.2.19.gem">https://rubygems.org/gems/mail-2.2.19.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/mail-2.2.19.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- actionmailer-3.0.9.gem
- :x: **mail-2.2.19.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Mail gem before 2.4.3 for Ruby allows remote attackers to execute arbitrary commands via shell metacharacters in a (1) sendmail or (2) exim delivery.
<p>Publish Date: 2012-07-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2140>CVE-2012-2140</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-2140">https://nvd.nist.gov/vuln/detail/CVE-2012-2140</a></p>
<p>Release Date: 2012-07-18</p>
<p>Fix Resolution: 2.4.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-6417</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
actionpack/lib/action_dispatch/http/request.rb in Ruby on Rails before 3.2.16 and 4.x before 4.0.2 does not properly consider differences in parameter handling between the Active Record component and the JSON implementation, which allows remote attackers to bypass intended database-query restrictions and perform NULL checks or trigger missing WHERE clauses via a crafted request that leverages (1) third-party Rack middleware or (2) custom Rack middleware. NOTE: this vulnerability exists because of an incomplete fix for CVE-2013-0155.
<p>Publish Date: 2013-12-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6417>CVE-2013-6417</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-6417">https://nvd.nist.gov/vuln/detail/CVE-2013-6417</a></p>
<p>Release Date: 2013-12-07</p>
<p>Fix Resolution: 3.2.16,4.0.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-3221</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Active Record component in Ruby on Rails 2.3.x, 3.0.x, 3.1.x, and 3.2.x does not ensure that the declared data type of a database column is used during comparisons of input values to stored values in that column, which makes it easier for remote attackers to conduct data-type injection attacks against Ruby on Rails applications via a crafted value, as demonstrated by unintended interaction between the "typed XML" feature and a MySQL database.
<p>Publish Date: 2013-04-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-3221>CVE-2013-3221</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-3221">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-3221</a></p>
<p>Release Date: 2013-04-22</p>
<p>Fix Resolution: 4.0.0.rc1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-0155</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Ruby on Rails 3.0.x before 3.0.19, 3.1.x before 3.1.10, and 3.2.x before 3.2.11 does not properly consider differences in parameter handling between the Active Record component and the JSON implementation, which allows remote attackers to bypass intended database-query restrictions and perform NULL checks or trigger missing WHERE clauses via a crafted request, as demonstrated by certain "[nil]" values, a related issue to CVE-2012-2660 and CVE-2012-2694.
<p>Publish Date: 2013-01-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0155>CVE-2013-0155</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0155">https://nvd.nist.gov/vuln/detail/CVE-2013-0155</a></p>
<p>Release Date: 2013-01-13</p>
<p>Fix Resolution: 3.0.19,3.1.10,3.2.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-2660</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
actionpack/lib/action_dispatch/http/request.rb in Ruby on Rails before 3.0.13, 3.1.x before 3.1.5, and 3.2.x before 3.2.4 does not properly consider differences in parameter handling between the Active Record component and the Rack interface, which allows remote attackers to bypass intended database-query restrictions and perform NULL checks via a crafted request, as demonstrated by certain "[nil]" values, a related issue to CVE-2012-2694.
<p>Publish Date: 2012-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2660>CVE-2012-2660</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-2660">https://nvd.nist.gov/vuln/detail/CVE-2012-2660</a></p>
<p>Release Date: 2012-06-22</p>
<p>Fix Resolution: 3.0.13,3.1.5,3.2.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8167</summary>
### Vulnerable Library - <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A CSRF vulnerability exists in rails <= 6.0.3 rails-ujs module that could allow attackers to send CSRF tokens to wrong domains.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8167>CVE-2020-8167</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://rubygems.org/gems/rails/versions/6.0.3.1">https://rubygems.org/gems/rails/versions/6.0.3.1</a></p>
<p>Release Date: 2020-06-19</p>
<p>Fix Resolution: 6.0.3.1,5.2.4.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2010-3299</summary>
### Vulnerable Library - <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The encrypt/decrypt functions in Ruby on Rails 2.3 are vulnerable to padding oracle attacks.
<p>Publish Date: 2019-11-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2010-3299>CVE-2010-3299</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-3299">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-3299</a></p>
<p>Release Date: 2019-11-12</p>
<p>Fix Resolution: rails - 5.2.0.beta1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8130</summary>
### Vulnerable Library - <b>rake-0.9.2.gem</b></p>
<p> Rake is a Make-like program implemented in Ruby. Tasks
and dependencies are specified in standard Ruby syntax.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rake-0.9.2.gem">https://rubygems.org/gems/rake-0.9.2.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rake-0.9.2.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- :x: **rake-0.9.2.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There is an OS command injection vulnerability in Ruby Rake < 12.3.3 in Rake::FileList when supplying a filename that begins with the pipe character `|`.
<p>Publish Date: 2020-02-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8130>CVE-2020-8130</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8130">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8130</a></p>
<p>Release Date: 2020-06-30</p>
<p>Fix Resolution: v12.3.3</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | rails-3.0.9.gem: 52 vulnerabilities (highest severity is: 8.6) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rails-3.0.9.gem</b></p></summary>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-8161](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8161) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2020-8184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2021-22885](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22885) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2019-5418](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5418) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2016-0752](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0752) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | rails-3.0.9.gem | Direct | 3.2.22.1,4.1.14.1,4.2.5.1,5.0.0.beta1.1 | ✅ |
| [CVE-2016-0751](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0751) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A | ✅ |
| [CVE-2014-10077](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-10077) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | i18n-0.5.0.gem | Transitive | N/A | ❌ |
| [CVE-2013-0156](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0156) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activesupport-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2695](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2695) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-6496](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6496) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2016-2098](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2098) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | detected in multiple dependencies | Direct | 3.2.22.2,4.1.14.2,4.2.5.2 | ✅ |
| [CVE-2013-0333](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0333) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activesupport-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2014-3482](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3482) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2140](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2140) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | mail-2.2.19.gem | Transitive | N/A | ❌ |
| [CVE-2013-6417](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6417) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-3221](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-3221) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-0155](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0155) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2660](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2660) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2020-8167](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8167) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | rails-3.0.9.gem | Direct | 6.0.3.1,5.2.4.3 | ✅ |
| [CVE-2010-3299](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2010-3299) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | rails-3.0.9.gem | Direct | rails - 5.2.0.beta1 | ✅ |
| [CVE-2020-8130](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8130) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.4 | rake-0.9.2.gem | Transitive | N/A | ❌ |
| [CVE-2018-16471](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16471) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2016-6316](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-6316) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2015-9097](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9097) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | mail-2.2.19.gem | Transitive | N/A | ❌ |
| [CVE-2019-16782](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16782) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2013-0263](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0263) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2011-2930](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2930) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | rails-3.0.9.gem | Direct | 2.3.13,3.0.10,3.1.0.rc5 | ✅ |
| [CVE-2013-6414](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6414) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [WS-2017-0283](https://github.com/rack/rack/commit/6a0e0ee8fcd982bccf30077ec94cb55018bbed91) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2012-3424](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3424) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-2139](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2139) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | mail-2.2.19.gem | Transitive | N/A | ❌ |
| [CVE-2011-5036](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-5036) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2015-3225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3225) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2012-2661](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2661) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | activerecord-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2016-2097](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2097) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | rails-3.0.9.gem | Direct | 3.2.22.2,4.1.14.2 | ✅ |
| [CVE-2011-2929](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2929) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2014-0082](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0082) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-6415](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6415) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-3463](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3463) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-3465](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3465) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2012-3464](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-3464) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | activesupport-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-1855](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-1855) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-1857](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-1857) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2011-2932](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2011-2932) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rails-3.0.9.gem | Direct | 2.3.13,3.0.10,3.1.0.rc5 | ✅ |
| [CVE-2012-6109](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6109) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2013-4491](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4491) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-4492](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4492) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | i18n-0.5.0.gem | Transitive | N/A | ❌ |
| [CVE-2013-0256](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0256) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rdoc-3.8.gem | Transitive | N/A | ❌ |
| [CVE-2014-0130](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0130) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2015-7576](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-7576) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
| [CVE-2013-0184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0184) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | rack-1.2.3.gem | Transitive | N/A | ❌ |
| [CVE-2014-0081](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0081) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | actionpack-3.0.9.gem | Transitive | N/A | ❌ |
## Details
> Partial details (21 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8161</summary>
### Vulnerable Library - <b>rack-1.2.3.gem</b></p>
<p>Rack provides minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.rubyforge.org.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.2.3.gem">https://rubygems.org/gems/rack-1.2.3.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rack-1.2.3.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- actionpack-3.0.9.gem
- :x: **rack-1.2.3.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A directory traversal vulnerability exists in rack < 2.2.0 that allows an attacker perform directory traversal vulnerability in the Rack::Directory app that is bundled with Rack which could result in information disclosure.
<p>Publish Date: 2020-07-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8161>CVE-2020-8161</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-10-05</p>
<p>Fix Resolution: 2.2.0,2.1.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8184</summary>
### Vulnerable Library - <b>rack-1.2.3.gem</b></p>
<p>Rack provides minimal, modular and adaptable interface for developing
web applications in Ruby. By wrapping HTTP requests and responses in
the simplest way possible, it unifies and distills the API for web
servers, web frameworks, and software in between (the so-called
middleware) into a single method call.
Also see http://rack.rubyforge.org.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rack-1.2.3.gem">https://rubygems.org/gems/rack-1.2.3.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rack-1.2.3.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- actionpack-3.0.9.gem
- :x: **rack-1.2.3.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A reliance on cookies without validation/integrity check security vulnerability exists in rack < 2.2.3, rack < 2.1.4 that makes it is possible for an attacker to forge a secure or host-only cookie prefix.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8184>CVE-2020-8184</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/forum/#!topic/rubyonrails-security/OWtmozPH9Ak">https://groups.google.com/forum/#!topic/rubyonrails-security/OWtmozPH9Ak</a></p>
<p>Release Date: 2020-10-05</p>
<p>Fix Resolution: rack - 2.1.4, 2.2.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-22885</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A possible information disclosure / unintended method execution vulnerability in Action Pack >= 2.0.0 when using the `redirect_to` or `polymorphic_url`helper with untrusted user input.
<p>Publish Date: 2021-05-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22885>CVE-2021-22885</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-hjg4-8q5f-x6fm">https://github.com/advisories/GHSA-hjg4-8q5f-x6fm</a></p>
<p>Release Date: 2021-05-27</p>
<p>Fix Resolution: actionpack - 5.2.4.6,5.2.6,6.0.3.7,6.1.3.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-5418</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There is a File Content Disclosure vulnerability in Action View <5.2.2.1, <5.1.6.2, <5.0.7.2, <4.2.11.1 and v3 where specially crafted accept headers can cause contents of arbitrary files on the target system's filesystem to be exposed.
<p>Publish Date: 2019-03-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-5418>CVE-2019-5418</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://weblog.rubyonrails.org/2019/3/13/Rails-4-2-5-1-5-1-6-2-have-been-released/">https://weblog.rubyonrails.org/2019/3/13/Rails-4-2-5-1-5-1-6-2-have-been-released/</a></p>
<p>Release Date: 2020-10-16</p>
<p>Fix Resolution: 4.2.11.1, 5.0.7.2, 5.1.6.2, 5.2.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-0752</summary>
### Vulnerable Library - <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Directory traversal vulnerability in Action View in Ruby on Rails before 3.2.22.1, 4.0.x and 4.1.x before 4.1.14.1, 4.2.x before 4.2.5.1, and 5.x before 5.0.0.beta1.1 allows remote attackers to read arbitrary files by leveraging an application's unrestricted use of the render method and providing a .. (dot dot) in a pathname.
<p>Publish Date: 2016-02-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0752>CVE-2016-0752</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-0752">https://nvd.nist.gov/vuln/detail/CVE-2016-0752</a></p>
<p>Release Date: 2016-02-16</p>
<p>Fix Resolution: 3.2.22.1,4.1.14.1,4.2.5.1,5.0.0.beta1.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-0751</summary>
### Vulnerable Libraries - <b>actionpack-3.0.9.gem</b>, <b>rails-3.0.9.gem</b></p>
<p>
### <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
### <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
actionpack/lib/action_dispatch/http/mime_type.rb in Action Pack in Ruby on Rails before 3.2.22.1, 4.0.x and 4.1.x before 4.1.14.1, 4.2.x before 4.2.5.1, and 5.x before 5.0.0.beta1.1 does not properly restrict use of the MIME type cache, which allows remote attackers to cause a denial of service (memory consumption) via a crafted HTTP Accept header.
<p>Publish Date: 2016-02-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-0751>CVE-2016-0751</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-0751">https://nvd.nist.gov/vuln/detail/CVE-2016-0751</a></p>
<p>Release Date: 2016-02-16</p>
<p>Fix Resolution: 3.2.22.1,4.1.14.1,4.2.5.1,5.0.0.beta1.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-10077</summary>
### Vulnerable Library - <b>i18n-0.5.0.gem</b></p>
<p>New wave Internationalization support for Ruby.</p>
<p>Library home page: <a href="https://rubygems.org/gems/i18n-0.5.0.gem">https://rubygems.org/gems/i18n-0.5.0.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/i18n-0.5.0.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- actionpack-3.0.9.gem
- :x: **i18n-0.5.0.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Hash#slice in lib/i18n/core_ext/hash.rb in the i18n gem before 0.8.0 for Ruby allows remote attackers to cause a denial of service (application crash) via a call in a situation where :some_key is present in keep_keys but not present in the hash.
<p>Publish Date: 2018-11-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-10077>CVE-2014-10077</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-10077">https://nvd.nist.gov/vuln/detail/CVE-2014-10077</a></p>
<p>Release Date: 2018-11-06</p>
<p>Fix Resolution: 0.8.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-0156</summary>
### Vulnerable Library - <b>activesupport-3.0.9.gem</b></p>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-3.0.9.gem">https://rubygems.org/gems/activesupport-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activesupport-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activesupport-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
active_support/core_ext/hash/conversions.rb in Ruby on Rails before 2.3.15, 3.0.x before 3.0.19, 3.1.x before 3.1.10, and 3.2.x before 3.2.11 does not properly restrict casts of string values, which allows remote attackers to conduct object-injection attacks and execute arbitrary code, or cause a denial of service (memory and CPU consumption) involving nested XML entity references, by leveraging Action Pack support for (1) YAML type conversion or (2) Symbol type conversion.
<p>Publish Date: 2013-01-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0156>CVE-2013-0156</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0156">https://nvd.nist.gov/vuln/detail/CVE-2013-0156</a></p>
<p>Release Date: 2013-01-13</p>
<p>Fix Resolution: 2.3.15,3.0.19,3.1.10,3.2.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-2695</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Active Record component in Ruby on Rails before 3.0.14, 3.1.x before 3.1.6, and 3.2.x before 3.2.6 does not properly implement the passing of request data to a where method in an ActiveRecord class, which allows remote attackers to conduct certain SQL injection attacks via nested query parameters that leverage improper handling of nested hashes, a related issue to CVE-2012-2661.
<p>Publish Date: 2012-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2695>CVE-2012-2695</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-2695">https://nvd.nist.gov/vuln/detail/CVE-2012-2695</a></p>
<p>Release Date: 2012-06-22</p>
<p>Fix Resolution: 3.0.14,3.1.6,3.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-6496</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQL injection vulnerability in the Active Record component in Ruby on Rails before 3.0.18, 3.1.x before 3.1.9, and 3.2.x before 3.2.10 allows remote attackers to execute arbitrary SQL commands via a crafted request that leverages incorrect behavior of dynamic finders in applications that can use unexpected data types in certain find_by_ method calls.
<p>Publish Date: 2013-01-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6496>CVE-2012-6496</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6496">https://nvd.nist.gov/vuln/detail/CVE-2012-6496</a></p>
<p>Release Date: 2013-01-04</p>
<p>Fix Resolution: 3.0.18,3.1.9,3.2.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2098</summary>
### Vulnerable Libraries - <b>rails-3.0.9.gem</b>, <b>actionpack-3.0.9.gem</b></p>
<p>
### <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
### <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Action Pack in Ruby on Rails before 3.2.22.2, 4.x before 4.1.14.2, and 4.2.x before 4.2.5.2 allows remote attackers to execute arbitrary Ruby code by leveraging an application's unrestricted use of the render method.
<p>Publish Date: 2016-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2098>CVE-2016-2098</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2098">https://nvd.nist.gov/vuln/detail/CVE-2016-2098</a></p>
<p>Release Date: 2016-04-07</p>
<p>Fix Resolution: 3.2.22.2,4.1.14.2,4.2.5.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2013-0333</summary>
### Vulnerable Library - <b>activesupport-3.0.9.gem</b></p>
<p>A toolkit of support libraries and Ruby core extensions extracted from the Rails framework. Rich support for multibyte strings, internationalization, time zones, and testing.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activesupport-3.0.9.gem">https://rubygems.org/gems/activesupport-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activesupport-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activesupport-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lib/active_support/json/backends/yaml.rb in Ruby on Rails 2.3.x before 2.3.16 and 3.0.x before 3.0.20 does not properly convert JSON data to YAML data for processing by a YAML parser, which allows remote attackers to execute arbitrary code, conduct SQL injection attacks, or bypass authentication via crafted data that triggers unsafe decoding, a different vulnerability than CVE-2013-0156.
<p>Publish Date: 2013-01-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0333>CVE-2013-0333</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0333">https://nvd.nist.gov/vuln/detail/CVE-2013-0333</a></p>
<p>Release Date: 2013-01-30</p>
<p>Fix Resolution: 2.3.16,3.0.20</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-3482</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SQL injection vulnerability in activerecord/lib/active_record/connection_adapters/postgresql_adapter.rb in the PostgreSQL adapter for Active Record in Ruby on Rails 2.x and 3.x before 3.2.19 allows remote attackers to execute arbitrary SQL commands by leveraging improper bitstring quoting.
<p>Publish Date: 2014-07-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3482>CVE-2014-3482</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-3482">https://nvd.nist.gov/vuln/detail/CVE-2014-3482</a></p>
<p>Release Date: 2014-07-07</p>
<p>Fix Resolution: 3.2.19</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-2140</summary>
### Vulnerable Library - <b>mail-2.2.19.gem</b></p>
<p>A really Ruby Mail handler.</p>
<p>Library home page: <a href="https://rubygems.org/gems/mail-2.2.19.gem">https://rubygems.org/gems/mail-2.2.19.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/mail-2.2.19.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- actionmailer-3.0.9.gem
- :x: **mail-2.2.19.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Mail gem before 2.4.3 for Ruby allows remote attackers to execute arbitrary commands via shell metacharacters in a (1) sendmail or (2) exim delivery.
<p>Publish Date: 2012-07-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2140>CVE-2012-2140</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-2140">https://nvd.nist.gov/vuln/detail/CVE-2012-2140</a></p>
<p>Release Date: 2012-07-18</p>
<p>Fix Resolution: 2.4.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-6417</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
actionpack/lib/action_dispatch/http/request.rb in Ruby on Rails before 3.2.16 and 4.x before 4.0.2 does not properly consider differences in parameter handling between the Active Record component and the JSON implementation, which allows remote attackers to bypass intended database-query restrictions and perform NULL checks or trigger missing WHERE clauses via a crafted request that leverages (1) third-party Rack middleware or (2) custom Rack middleware. NOTE: this vulnerability exists because of an incomplete fix for CVE-2013-0155.
<p>Publish Date: 2013-12-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-6417>CVE-2013-6417</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-6417">https://nvd.nist.gov/vuln/detail/CVE-2013-6417</a></p>
<p>Release Date: 2013-12-07</p>
<p>Fix Resolution: 3.2.16,4.0.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-3221</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Active Record component in Ruby on Rails 2.3.x, 3.0.x, 3.1.x, and 3.2.x does not ensure that the declared data type of a database column is used during comparisons of input values to stored values in that column, which makes it easier for remote attackers to conduct data-type injection attacks against Ruby on Rails applications via a crafted value, as demonstrated by unintended interaction between the "typed XML" feature and a MySQL database.
<p>Publish Date: 2013-04-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-3221>CVE-2013-3221</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-3221">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-3221</a></p>
<p>Release Date: 2013-04-22</p>
<p>Fix Resolution: 4.0.0.rc1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-0155</summary>
### Vulnerable Library - <b>activerecord-3.0.9.gem</b></p>
<p>Databases on Rails. Build a persistent domain model by mapping database tables to Ruby classes. Strong conventions for associations, validations, aggregations, migrations, and testing come baked-in.</p>
<p>Library home page: <a href="https://rubygems.org/gems/activerecord-3.0.9.gem">https://rubygems.org/gems/activerecord-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/activerecord-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **activerecord-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Ruby on Rails 3.0.x before 3.0.19, 3.1.x before 3.1.10, and 3.2.x before 3.2.11 does not properly consider differences in parameter handling between the Active Record component and the JSON implementation, which allows remote attackers to bypass intended database-query restrictions and perform NULL checks or trigger missing WHERE clauses via a crafted request, as demonstrated by certain "[nil]" values, a related issue to CVE-2012-2660 and CVE-2012-2694.
<p>Publish Date: 2013-01-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0155>CVE-2013-0155</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0155">https://nvd.nist.gov/vuln/detail/CVE-2013-0155</a></p>
<p>Release Date: 2013-01-13</p>
<p>Fix Resolution: 3.0.19,3.1.10,3.2.11</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-2660</summary>
### Vulnerable Library - <b>actionpack-3.0.9.gem</b></p>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-3.0.9.gem">https://rubygems.org/gems/actionpack-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- :x: **actionpack-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
actionpack/lib/action_dispatch/http/request.rb in Ruby on Rails before 3.0.13, 3.1.x before 3.1.5, and 3.2.x before 3.2.4 does not properly consider differences in parameter handling between the Active Record component and the Rack interface, which allows remote attackers to bypass intended database-query restrictions and perform NULL checks via a crafted request, as demonstrated by certain "[nil]" values, a related issue to CVE-2012-2694.
<p>Publish Date: 2012-06-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-2660>CVE-2012-2660</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-2660">https://nvd.nist.gov/vuln/detail/CVE-2012-2660</a></p>
<p>Release Date: 2012-06-22</p>
<p>Fix Resolution: 3.0.13,3.1.5,3.2.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8167</summary>
### Vulnerable Library - <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A CSRF vulnerability exists in rails <= 6.0.3 rails-ujs module that could allow attackers to send CSRF tokens to wrong domains.
<p>Publish Date: 2020-06-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8167>CVE-2020-8167</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://rubygems.org/gems/rails/versions/6.0.3.1">https://rubygems.org/gems/rails/versions/6.0.3.1</a></p>
<p>Release Date: 2020-06-19</p>
<p>Fix Resolution: 6.0.3.1,5.2.4.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2010-3299</summary>
### Vulnerable Library - <b>rails-3.0.9.gem</b></p>
<p>Ruby on Rails is a full-stack web framework optimized for programmer happiness and sustainable productivity. It encourages beautiful code by favoring convention over configuration.</p>
<p>Library home page: <a href="https://rubygems.org/gems/rails-3.0.9.gem">https://rubygems.org/gems/rails-3.0.9.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /m/ruby/2.7.0/cache/rails-3.0.9.gem</p>
<p>
Dependency Hierarchy:
- :x: **rails-3.0.9.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The encrypt/decrypt functions in Ruby on Rails 2.3 are vulnerable to padding oracle attacks.
<p>Publish Date: 2019-11-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2010-3299>CVE-2010-3299</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-3299">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-3299</a></p>
<p>Release Date: 2019-11-12</p>
<p>Fix Resolution: rails - 5.2.0.beta1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8130</summary>
### Vulnerable Library - <b>rake-0.9.2.gem</b></p>
<p> Rake is a Make-like program implemented in Ruby. Tasks
and dependencies are specified in standard Ruby syntax.
</p>
<p>Library home page: <a href="https://rubygems.org/gems/rake-0.9.2.gem">https://rubygems.org/gems/rake-0.9.2.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/rake-0.9.2.gem</p>
<p>
Dependency Hierarchy:
- rails-3.0.9.gem (Root Library)
- railties-3.0.9.gem
- :x: **rake-0.9.2.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/hackme-25/commit/d7a787e08290f3d3d3b0f9036b209f57d699ed83">d7a787e08290f3d3d3b0f9036b209f57d699ed83</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There is an OS command injection vulnerability in Ruby Rake < 12.3.3 in Rake::FileList when supplying a filename that begins with the pipe character `|`.
<p>Publish Date: 2020-02-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8130>CVE-2020-8130</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8130">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8130</a></p>
<p>Release Date: 2020-06-30</p>
<p>Fix Resolution: v12.3.3</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | rails gem vulnerabilities highest severity is vulnerable library rails gem ruby on rails is a full stack web framework optimized for programmer happiness and sustainable productivity it encourages beautiful code by favoring convention over configuration library home page a href path to dependency file gemfile lock path to vulnerable library m ruby cache rails gem found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high rack gem transitive n a high rack gem transitive n a high actionpack gem transitive n a high actionpack gem transitive n a high rails gem direct high detected in multiple dependencies transitive n a high gem transitive n a high activesupport gem transitive n a high activerecord gem transitive n a high activerecord gem transitive n a high detected in multiple dependencies direct high activesupport gem transitive n a high activerecord gem transitive n a high mail gem transitive n a medium actionpack gem transitive n a medium activerecord gem transitive n a medium activerecord gem transitive n a medium actionpack gem transitive n a medium rails gem direct medium rails gem direct rails medium rake gem transitive n a medium rack gem transitive n a medium actionpack gem transitive n a medium mail gem transitive n a medium rack gem transitive n a medium rack gem transitive n a medium rails gem direct medium actionpack gem transitive n a medium rack gem transitive n a medium actionpack gem transitive n a medium mail gem transitive n a medium rack gem transitive n a medium rack gem transitive n a medium activerecord gem transitive n a medium rails gem direct medium actionpack gem transitive n a medium actionpack gem transitive n a low actionpack gem transitive n a low actionpack gem transitive n a low actionpack gem transitive n a low activesupport gem transitive n a low actionpack gem transitive n a low actionpack gem transitive n a low rails gem direct low rack gem transitive n a low actionpack gem transitive n a low gem transitive n a low rdoc gem transitive n a low actionpack gem transitive n a low actionpack gem transitive n a low rack gem transitive n a low actionpack gem transitive n a details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library rack gem rack provides minimal modular and adaptable interface for developing web applications in ruby by wrapping http requests and responses in the simplest way possible it unifies and distills the api for web servers web frameworks and software in between the so called middleware into a single method call also see library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache rack gem dependency hierarchy rails gem root library railties gem actionpack gem x rack gem vulnerable library found in head commit a href found in base branch master vulnerability details a directory traversal vulnerability exists in rack that allows an attacker perform directory traversal vulnerability in the rack directory app that is bundled with rack which could result in information disclosure publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution cve vulnerable library rack gem rack provides minimal modular and adaptable interface for developing web applications in ruby by wrapping http requests and responses in the simplest way possible it unifies and distills the api for web servers web frameworks and software in between the so called middleware into a single method call also see library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache rack gem dependency hierarchy rails gem root library railties gem actionpack gem x rack gem vulnerable library found in head commit a href found in base branch master vulnerability details a reliance on cookies without validation integrity check security vulnerability exists in rack rack that makes it is possible for an attacker to forge a secure or host only cookie prefix publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library found in head commit a href found in base branch master vulnerability details a possible information disclosure unintended method execution vulnerability in action pack when using the redirect to or polymorphic url helper with untrusted user input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution actionpack cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library found in head commit a href found in base branch master vulnerability details there is a file content disclosure vulnerability in action view and where specially crafted accept headers can cause contents of arbitrary files on the target system s filesystem to be exposed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library rails gem ruby on rails is a full stack web framework optimized for programmer happiness and sustainable productivity it encourages beautiful code by favoring convention over configuration library home page a href path to dependency file gemfile lock path to vulnerable library m ruby cache rails gem dependency hierarchy x rails gem vulnerable library found in head commit a href found in base branch master vulnerability details directory traversal vulnerability in action view in ruby on rails before x and x before x before and x before allows remote attackers to read arbitrary files by leveraging an application s unrestricted use of the render method and providing a dot dot in a pathname publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable libraries actionpack gem rails gem actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library rails gem ruby on rails is a full stack web framework optimized for programmer happiness and sustainable productivity it encourages beautiful code by favoring convention over configuration library home page a href path to dependency file gemfile lock path to vulnerable library m ruby cache rails gem dependency hierarchy x rails gem vulnerable library found in head commit a href found in base branch master vulnerability details actionpack lib action dispatch http mime type rb in action pack in ruby on rails before x and x before x before and x before does not properly restrict use of the mime type cache which allows remote attackers to cause a denial of service memory consumption via a crafted http accept header publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library gem new wave internationalization support for ruby library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache gem dependency hierarchy rails gem root library railties gem actionpack gem x gem vulnerable library found in head commit a href found in base branch master vulnerability details hash slice in lib core ext hash rb in the gem before for ruby allows remote attackers to cause a denial of service application crash via a call in a situation where some key is present in keep keys but not present in the hash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library activesupport gem a toolkit of support libraries and ruby core extensions extracted from the rails framework rich support for multibyte strings internationalization time zones and testing library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activesupport gem dependency hierarchy rails gem root library x activesupport gem vulnerable library found in head commit a href found in base branch master vulnerability details active support core ext hash conversions rb in ruby on rails before x before x before and x before does not properly restrict casts of string values which allows remote attackers to conduct object injection attacks and execute arbitrary code or cause a denial of service memory and cpu consumption involving nested xml entity references by leveraging action pack support for yaml type conversion or symbol type conversion publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library activerecord gem databases on rails build a persistent domain model by mapping database tables to ruby classes strong conventions for associations validations aggregations migrations and testing come baked in library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activerecord gem dependency hierarchy rails gem root library x activerecord gem vulnerable library found in head commit a href found in base branch master vulnerability details the active record component in ruby on rails before x before and x before does not properly implement the passing of request data to a where method in an activerecord class which allows remote attackers to conduct certain sql injection attacks via nested query parameters that leverage improper handling of nested hashes a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library activerecord gem databases on rails build a persistent domain model by mapping database tables to ruby classes strong conventions for associations validations aggregations migrations and testing come baked in library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activerecord gem dependency hierarchy rails gem root library x activerecord gem vulnerable library found in head commit a href found in base branch master vulnerability details sql injection vulnerability in the active record component in ruby on rails before x before and x before allows remote attackers to execute arbitrary sql commands via a crafted request that leverages incorrect behavior of dynamic finders in applications that can use unexpected data types in certain find by method calls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable libraries rails gem actionpack gem rails gem ruby on rails is a full stack web framework optimized for programmer happiness and sustainable productivity it encourages beautiful code by favoring convention over configuration library home page a href path to dependency file gemfile lock path to vulnerable library m ruby cache rails gem dependency hierarchy x rails gem vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library found in head commit a href found in base branch master vulnerability details action pack in ruby on rails before x before and x before allows remote attackers to execute arbitrary ruby code by leveraging an application s unrestricted use of the render method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library activesupport gem a toolkit of support libraries and ruby core extensions extracted from the rails framework rich support for multibyte strings internationalization time zones and testing library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activesupport gem dependency hierarchy rails gem root library x activesupport gem vulnerable library found in head commit a href found in base branch master vulnerability details lib active support json backends yaml rb in ruby on rails x before and x before does not properly convert json data to yaml data for processing by a yaml parser which allows remote attackers to execute arbitrary code conduct sql injection attacks or bypass authentication via crafted data that triggers unsafe decoding a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library activerecord gem databases on rails build a persistent domain model by mapping database tables to ruby classes strong conventions for associations validations aggregations migrations and testing come baked in library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activerecord gem dependency hierarchy rails gem root library x activerecord gem vulnerable library found in head commit a href found in base branch master vulnerability details sql injection vulnerability in activerecord lib active record connection adapters postgresql adapter rb in the postgresql adapter for active record in ruby on rails x and x before allows remote attackers to execute arbitrary sql commands by leveraging improper bitstring quoting publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library mail gem a really ruby mail handler library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache mail gem dependency hierarchy rails gem root library actionmailer gem x mail gem vulnerable library found in head commit a href found in base branch master vulnerability details the mail gem before for ruby allows remote attackers to execute arbitrary commands via shell metacharacters in a sendmail or exim delivery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library found in head commit a href found in base branch master vulnerability details actionpack lib action dispatch http request rb in ruby on rails before and x before does not properly consider differences in parameter handling between the active record component and the json implementation which allows remote attackers to bypass intended database query restrictions and perform null checks or trigger missing where clauses via a crafted request that leverages third party rack middleware or custom rack middleware note this vulnerability exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library activerecord gem databases on rails build a persistent domain model by mapping database tables to ruby classes strong conventions for associations validations aggregations migrations and testing come baked in library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activerecord gem dependency hierarchy rails gem root library x activerecord gem vulnerable library found in head commit a href found in base branch master vulnerability details the active record component in ruby on rails x x x and x does not ensure that the declared data type of a database column is used during comparisons of input values to stored values in that column which makes it easier for remote attackers to conduct data type injection attacks against ruby on rails applications via a crafted value as demonstrated by unintended interaction between the typed xml feature and a mysql database publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library activerecord gem databases on rails build a persistent domain model by mapping database tables to ruby classes strong conventions for associations validations aggregations migrations and testing come baked in library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache activerecord gem dependency hierarchy rails gem root library x activerecord gem vulnerable library found in head commit a href found in base branch master vulnerability details ruby on rails x before x before and x before does not properly consider differences in parameter handling between the active record component and the json implementation which allows remote attackers to bypass intended database query restrictions and perform null checks or trigger missing where clauses via a crafted request as demonstrated by certain values a related issue to cve and cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library found in head commit a href found in base branch master vulnerability details actionpack lib action dispatch http request rb in ruby on rails before x before and x before does not properly consider differences in parameter handling between the active record component and the rack interface which allows remote attackers to bypass intended database query restrictions and perform null checks via a crafted request as demonstrated by certain values a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library rails gem ruby on rails is a full stack web framework optimized for programmer happiness and sustainable productivity it encourages beautiful code by favoring convention over configuration library home page a href path to dependency file gemfile lock path to vulnerable library m ruby cache rails gem dependency hierarchy x rails gem vulnerable library found in head commit a href found in base branch master vulnerability details a csrf vulnerability exists in rails rails ujs module that could allow attackers to send csrf tokens to wrong domains publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library rails gem ruby on rails is a full stack web framework optimized for programmer happiness and sustainable productivity it encourages beautiful code by favoring convention over configuration library home page a href path to dependency file gemfile lock path to vulnerable library m ruby cache rails gem dependency hierarchy x rails gem vulnerable library found in head commit a href found in base branch master vulnerability details the encrypt decrypt functions in ruby on rails are vulnerable to padding oracle attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rails rescue worker helmet automatic remediation is available for this issue cve vulnerable library rake gem rake is a make like program implemented in ruby tasks and dependencies are specified in standard ruby syntax library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache rake gem dependency hierarchy rails gem root library railties gem x rake gem vulnerable library found in head commit a href found in base branch master vulnerability details there is an os command injection vulnerability in ruby rake in rake filelist when supplying a filename that begins with the pipe character publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
70,226 | 8,513,590,965 | IssuesEvent | 2018-10-31 16:24:15 | Juliankautsch/F19 | https://api.github.com/repos/Juliankautsch/F19 | closed | Copy and adjust control arms to mounting points | Design Vehicle Dynamics | - copy all 4 A-Arms from LFRT18 and name each like: F19_SU_FrontTopA-Arm
- adjust dimensions to match distance between mounting points (from chassis CAD)
- add to front and rear suspension assemblies
- align centres of bearings with centres of mountings in uprights leaving other ends free to move
(in other words, fix top of "A" of A-arm to axis in upright, leave bottom of "A" free)
Contact Josh Graham (ll16j2lg) if in doubt. | 1.0 | Copy and adjust control arms to mounting points - - copy all 4 A-Arms from LFRT18 and name each like: F19_SU_FrontTopA-Arm
- adjust dimensions to match distance between mounting points (from chassis CAD)
- add to front and rear suspension assemblies
- align centres of bearings with centres of mountings in uprights leaving other ends free to move
(in other words, fix top of "A" of A-arm to axis in upright, leave bottom of "A" free)
Contact Josh Graham (ll16j2lg) if in doubt. | non_priority | copy and adjust control arms to mounting points copy all a arms from and name each like su fronttopa arm adjust dimensions to match distance between mounting points from chassis cad add to front and rear suspension assemblies align centres of bearings with centres of mountings in uprights leaving other ends free to move in other words fix top of a of a arm to axis in upright leave bottom of a free contact josh graham if in doubt | 0 |
14,033 | 8,789,795,745 | IssuesEvent | 2018-12-21 06:03:50 | OctopusDeploy/Issues | https://api.github.com/repos/OctopusDeploy/Issues | opened | Show a link to project group when editing a project | area/usability kind/enhancement | # Prerequisites
- [x] I have searched [open](https://github.com/OctopusDeploy/Issues/issues) and [closed](https://github.com/OctopusDeploy/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already requested
- [x] I have written a descriptive issue title
- [x] I have linked the original source of this feature request
- [x] I have tagged the issue appropriately (area/*, kind/enhancement)
# The enhancement
For customers that use project groups to separate projects into logical groups, it is relatively common to only want to focus on related projects. It would be useful to show a link to the project group in the breadcrumb which takes you to the projects page filtered by that project.
At the moment, clicking on the projects tab from a project takes you back to the unfiltered project list
## Mockup

## Workarounds
At the moment, you need to either:
* go to the dashboard, and search for the project / filter for the project group
* go to the projects tab and search for the project / filter for the project group
* use the project quick search
## Links
source: https://secure.helpscout.net/conversation/683040436/33436/ (private link) | True | Show a link to project group when editing a project - # Prerequisites
- [x] I have searched [open](https://github.com/OctopusDeploy/Issues/issues) and [closed](https://github.com/OctopusDeploy/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already requested
- [x] I have written a descriptive issue title
- [x] I have linked the original source of this feature request
- [x] I have tagged the issue appropriately (area/*, kind/enhancement)
# The enhancement
For customers that use project groups to separate projects into logical groups, it is relatively common to only want to focus on related projects. It would be useful to show a link to the project group in the breadcrumb which takes you to the projects page filtered by that project.
At the moment, clicking on the projects tab from a project takes you back to the unfiltered project list
## Mockup

## Workarounds
At the moment, you need to either:
* go to the dashboard, and search for the project / filter for the project group
* go to the projects tab and search for the project / filter for the project group
* use the project quick search
## Links
source: https://secure.helpscout.net/conversation/683040436/33436/ (private link) | non_priority | show a link to project group when editing a project prerequisites i have searched and issues to make sure it isn t already requested i have written a descriptive issue title i have linked the original source of this feature request i have tagged the issue appropriately area kind enhancement the enhancement for customers that use project groups to separate projects into logical groups it is relatively common to only want to focus on related projects it would be useful to show a link to the project group in the breadcrumb which takes you to the projects page filtered by that project at the moment clicking on the projects tab from a project takes you back to the unfiltered project list mockup workarounds at the moment you need to either go to the dashboard and search for the project filter for the project group go to the projects tab and search for the project filter for the project group use the project quick search links source private link | 0 |
29,590 | 24,089,443,538 | IssuesEvent | 2022-09-19 13:41:59 | airyhq/airy | https://api.github.com/repos/airyhq/airy | closed | Google Cloud Platform Terraform module | infrastructure | We should also support GCP for creating a Kubernetes cluster with Terraform by creating a wrapper module similar to our EKS module for [this](https://github.com/terraform-google-modules/terraform-google-kubernetes-engine).
- [x] Create the module
- [ ] Create the install directory
- [ ] Create a GCP GKE instance from the install/gcp directory
- [ ] Destroy a GCP GKE instance from the instance/gcp directory | 1.0 | Google Cloud Platform Terraform module - We should also support GCP for creating a Kubernetes cluster with Terraform by creating a wrapper module similar to our EKS module for [this](https://github.com/terraform-google-modules/terraform-google-kubernetes-engine).
- [x] Create the module
- [ ] Create the install directory
- [ ] Create a GCP GKE instance from the install/gcp directory
- [ ] Destroy a GCP GKE instance from the instance/gcp directory | non_priority | google cloud platform terraform module we should also support gcp for creating a kubernetes cluster with terraform by creating a wrapper module similar to our eks module for create the module create the install directory create a gcp gke instance from the install gcp directory destroy a gcp gke instance from the instance gcp directory | 0 |
236,108 | 19,513,516,336 | IssuesEvent | 2021-12-29 05:29:52 | pingcap/tiflow | https://api.github.com/repos/pingcap/tiflow | closed | TestBroadcast is unstable | component/test area/ticdc | ### Which jobs are flaking?
https://github.com/pingcap/tiflow/pull/3935
### Which test(s) are flaking?
TestBroadcast
### Jenkins logs or GitHub Actions link
```log
[2021-12-17T10:31:44.215Z]
[2021-12-17T10:31:44.215Z] === FAIL: pkg/actor TestBroadcast (5.94s)
[2021-12-17T10:31:44.215Z] system_test.go:140: Timed out
[2021-12-17T10:31:44.215Z]
```
https://ci.pingcap.net/blue/organizations/jenkins/atom-ut/detail/atom-ut/5678/pipeline
### Anything else we need to know
- Does this test exist for other branches as well?
- Has there been a high frequency of failure lately? | 1.0 | TestBroadcast is unstable - ### Which jobs are flaking?
https://github.com/pingcap/tiflow/pull/3935
### Which test(s) are flaking?
TestBroadcast
### Jenkins logs or GitHub Actions link
```log
[2021-12-17T10:31:44.215Z]
[2021-12-17T10:31:44.215Z] === FAIL: pkg/actor TestBroadcast (5.94s)
[2021-12-17T10:31:44.215Z] system_test.go:140: Timed out
[2021-12-17T10:31:44.215Z]
```
https://ci.pingcap.net/blue/organizations/jenkins/atom-ut/detail/atom-ut/5678/pipeline
### Anything else we need to know
- Does this test exist for other branches as well?
- Has there been a high frequency of failure lately? | non_priority | testbroadcast is unstable which jobs are flaking which test s are flaking testbroadcast jenkins logs or github actions link log fail pkg actor testbroadcast system test go timed out anything else we need to know does this test exist for other branches as well has there been a high frequency of failure lately | 0 |
85,787 | 15,755,265,040 | IssuesEvent | 2021-03-31 01:28:23 | AlanCrevon/LeCoinDuProf | https://api.github.com/repos/AlanCrevon/LeCoinDuProf | opened | CVE-2020-28502 (High) detected in xmlhttprequest-ssl-1.5.5.tgz | security vulnerability | ## CVE-2020-28502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p></summary>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz">https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz</a></p>
<p>Path to dependency file: LeCoinDuProf/package.json</p>
<p>Path to vulnerable library: LeCoinDuProf/node_modules/xmlhttprequest-ssl/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.1.0.tgz (Root Library)
- socket.io-2.1.1.tgz
- socket.io-client-2.1.1.tgz
- engine.io-client-3.2.1.tgz
- :x: **xmlhttprequest-ssl-1.5.5.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package xmlhttprequest before 1.7.0; all versions of package xmlhttprequest-ssl. Provided requests are sent synchronously (async=False on xhr.open), malicious user input flowing into xhr.send could result in arbitrary code being injected and run.
<p>Publish Date: 2021-03-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28502>CVE-2020-28502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28502</a></p>
<p>Release Date: 2021-03-05</p>
<p>Fix Resolution: xmlhttprequest - 1.7.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28502 (High) detected in xmlhttprequest-ssl-1.5.5.tgz - ## CVE-2020-28502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p></summary>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz">https://registry.npmjs.org/xmlhttprequest-ssl/-/xmlhttprequest-ssl-1.5.5.tgz</a></p>
<p>Path to dependency file: LeCoinDuProf/package.json</p>
<p>Path to vulnerable library: LeCoinDuProf/node_modules/xmlhttprequest-ssl/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.1.0.tgz (Root Library)
- socket.io-2.1.1.tgz
- socket.io-client-2.1.1.tgz
- engine.io-client-3.2.1.tgz
- :x: **xmlhttprequest-ssl-1.5.5.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package xmlhttprequest before 1.7.0; all versions of package xmlhttprequest-ssl. Provided requests are sent synchronously (async=False on xhr.open), malicious user input flowing into xhr.send could result in arbitrary code being injected and run.
<p>Publish Date: 2021-03-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28502>CVE-2020-28502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28502</a></p>
<p>Release Date: 2021-03-05</p>
<p>Fix Resolution: xmlhttprequest - 1.7.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in xmlhttprequest ssl tgz cve high severity vulnerability vulnerable library xmlhttprequest ssl tgz xmlhttprequest for node library home page a href path to dependency file lecoinduprof package json path to vulnerable library lecoinduprof node modules xmlhttprequest ssl package json dependency hierarchy karma tgz root library socket io tgz socket io client tgz engine io client tgz x xmlhttprequest ssl tgz vulnerable library found in base branch master vulnerability details this affects the package xmlhttprequest before all versions of package xmlhttprequest ssl provided requests are sent synchronously async false on xhr open malicious user input flowing into xhr send could result in arbitrary code being injected and run publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xmlhttprequest step up your open source security game with whitesource | 0 |
31,850 | 13,645,108,944 | IssuesEvent | 2020-09-25 20:08:58 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | ALB/NLB creation occasionally fails due to eventual consistency | bug service/elbv2 | ALB/NLB creation occasionally fails due to eventual consistency with the error
```console
Error: LoadBalancerNotFound: One or more load balancers not found
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* aws_lb
| 1.0 | ALB/NLB creation occasionally fails due to eventual consistency - ALB/NLB creation occasionally fails due to eventual consistency with the error
```console
Error: LoadBalancerNotFound: One or more load balancers not found
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* aws_lb
| non_priority | alb nlb creation occasionally fails due to eventual consistency alb nlb creation occasionally fails due to eventual consistency with the error console error loadbalancernotfound one or more load balancers not found affected resource s aws lb | 0 |
171,790 | 27,176,500,597 | IssuesEvent | 2023-02-18 03:24:43 | GAME-2334/vrgame | https://api.github.com/repos/GAME-2334/vrgame | closed | Set Dressing Pass 1 | designers | Please set art assets from the marketplace in the scene accordingly. Keep in mind structure and delight as you build up our scene from the greybox outline. | 1.0 | Set Dressing Pass 1 - Please set art assets from the marketplace in the scene accordingly. Keep in mind structure and delight as you build up our scene from the greybox outline. | non_priority | set dressing pass please set art assets from the marketplace in the scene accordingly keep in mind structure and delight as you build up our scene from the greybox outline | 0 |
53,086 | 27,965,666,880 | IssuesEvent | 2023-03-24 19:17:05 | SavageLearning/Machete | https://api.github.com/repos/SavageLearning/Machete | reopened | On slower systems, Angular's vendor.js takes a long time to load | Performance good first issue | Most of the centers don't have the fast internet that we do at home. Voz's connection for example is only 5Mbps on a good day. So they are getting results like this when trying to load V2:
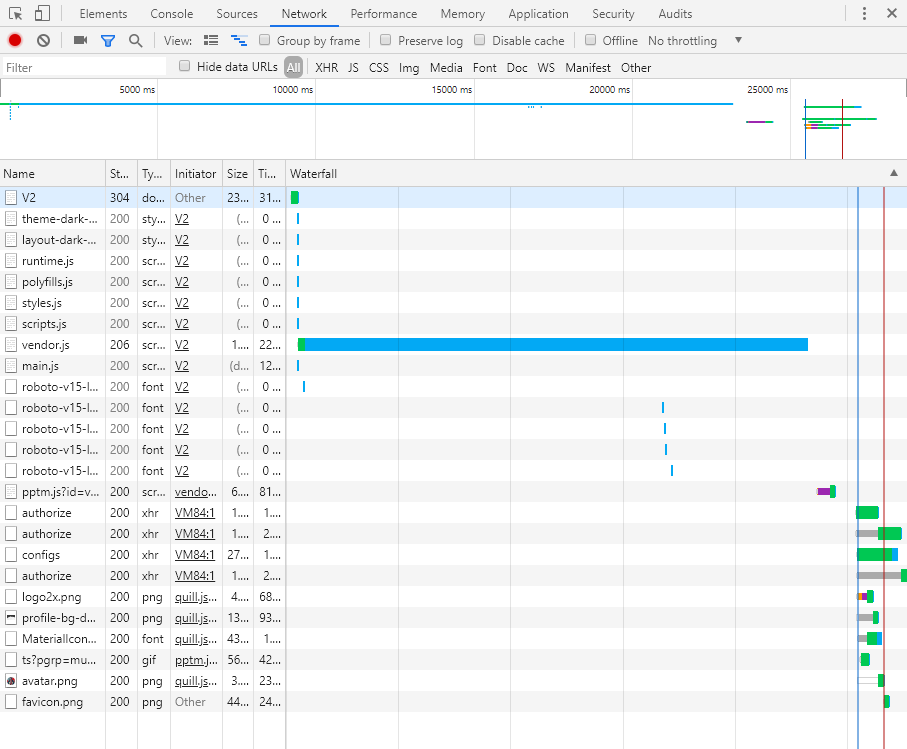
What to do:
1. Check if AppVeyor is [building Angular6 in prod mode](https://stackoverflow.com/a/51257973/2496266)
2. See if we can remove any dependencies or move them to devDependencies in package.json
Other ideas welcome. | True | On slower systems, Angular's vendor.js takes a long time to load - Most of the centers don't have the fast internet that we do at home. Voz's connection for example is only 5Mbps on a good day. So they are getting results like this when trying to load V2:
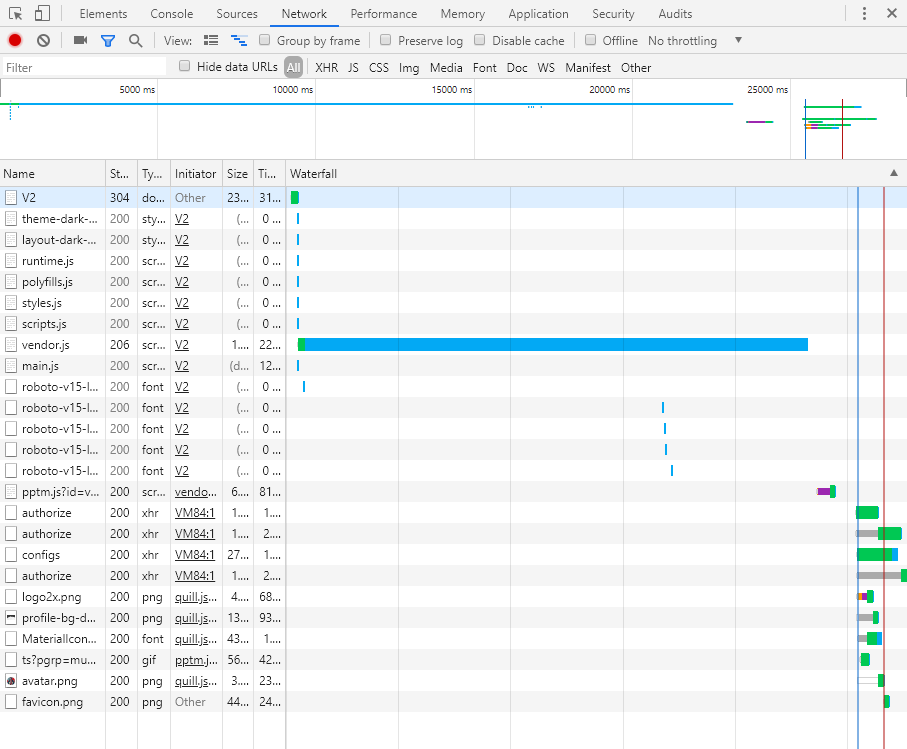
What to do:
1. Check if AppVeyor is [building Angular6 in prod mode](https://stackoverflow.com/a/51257973/2496266)
2. See if we can remove any dependencies or move them to devDependencies in package.json
Other ideas welcome. | non_priority | on slower systems angular s vendor js takes a long time to load most of the centers don t have the fast internet that we do at home voz s connection for example is only on a good day so they are getting results like this when trying to load what to do check if appveyor is see if we can remove any dependencies or move them to devdependencies in package json other ideas welcome | 0 |
245,204 | 26,525,292,247 | IssuesEvent | 2023-01-19 08:12:07 | uriel-naor/UrielTest | https://api.github.com/repos/uriel-naor/UrielTest | closed | lodash-2.3.0.tgz: 4 vulnerabilities (highest severity is: 9.8) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.3.0.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (lodash version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-10744](https://www.mend.io/vulnerability-database/CVE-2019-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
| [CVE-2019-1010266](https://www.mend.io/vulnerability-database/CVE-2019-1010266) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
| [CVE-2018-3721](https://www.mend.io/vulnerability-database/CVE-2018-3721) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
| [CVE-2018-16487](https://www.mend.io/vulnerability-database/CVE-2018-16487) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10744</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: 4.17.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-1010266</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-3721</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-3721>CVE-2018-3721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3721">https://nvd.nist.gov/vuln/detail/CVE-2018-3721</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 4.17.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-16487</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><p><img src='https://whitesource-resources.whitesourcesoftware.com/suggestedVersion.png' width=19 height=20> Mend has checked all newer package trees, and you are on the least vulnerable package!</p> | True | lodash-2.3.0.tgz: 4 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.3.0.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (lodash version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-10744](https://www.mend.io/vulnerability-database/CVE-2019-10744) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
| [CVE-2019-1010266](https://www.mend.io/vulnerability-database/CVE-2019-1010266) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
| [CVE-2018-3721](https://www.mend.io/vulnerability-database/CVE-2018-3721) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
| [CVE-2018-16487](https://www.mend.io/vulnerability-database/CVE-2018-16487) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | lodash-2.3.0.tgz | Direct | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10744</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: 4.17.12</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-1010266</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-3721</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
lodash node module before 4.17.5 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via defaultsDeep, merge, and mergeWith functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-06-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-3721>CVE-2018-3721</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3721">https://nvd.nist.gov/vuln/detail/CVE-2018-3721</a></p>
<p>Release Date: 2018-06-07</p>
<p>Fix Resolution: 4.17.5</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-16487</summary>
### Vulnerable Library - <b>lodash-2.3.0.tgz</b></p>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz">https://registry.npmjs.org/lodash/-/lodash-2.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /t/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.3.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/64ec2b18ada40f812f2321fc53ba262ef62a98c7">64ec2b18ada40f812f2321fc53ba262ef62a98c7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><p><img src='https://whitesource-resources.whitesourcesoftware.com/suggestedVersion.png' width=19 height=20> Mend has checked all newer package trees, and you are on the least vulnerable package!</p> | non_priority | lodash tgz vulnerabilities highest severity is autoclosed vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file package json path to vulnerable library t node modules lodash package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in lodash version remediation available high lodash tgz direct n a medium lodash tgz direct n a medium lodash tgz direct n a medium lodash tgz direct n a details cve vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file package json path to vulnerable library t node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file package json path to vulnerable library t node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file package json path to vulnerable library t node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details lodash node module before suffers from a modification of assumed immutable data maid vulnerability via defaultsdeep merge and mergewith functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file package json path to vulnerable library t node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details a prototype pollution vulnerability was found in lodash where the functions merge mergewith and defaultsdeep can be tricked into adding or modifying properties of object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue mend has checked all newer package trees and you are on the least vulnerable package | 0 |
350,047 | 31,848,248,864 | IssuesEvent | 2023-09-14 21:58:30 | googleapis/google-cloud-python | https://api.github.com/repos/googleapis/google-cloud-python | closed | Adopt split repo: _python-optimization_ | migration:samples:generated migration:workaround:none migration:library:gapic_auto migration:testing:unit migration:issues:none migration:ready migration:pr:none migration:stage:git-history-merged migration:stage:common-files-updated migration:stage:split-repo-trimmed migration:stage:split-repo-archived | Migrate the split-repo https://github.com/googleapis/python-optimization to https://github.com/googleapis/google-cloud-python.
The migration readiness criteria are the following, which we track via GitHub labels on this issue. These criteria apply to the split repo we are migrating from:
- No open issues
- No open PRs
- No handwritten samples
- No system tests
- No client-specific customizations | 1.0 | Adopt split repo: _python-optimization_ - Migrate the split-repo https://github.com/googleapis/python-optimization to https://github.com/googleapis/google-cloud-python.
The migration readiness criteria are the following, which we track via GitHub labels on this issue. These criteria apply to the split repo we are migrating from:
- No open issues
- No open PRs
- No handwritten samples
- No system tests
- No client-specific customizations | non_priority | adopt split repo python optimization migrate the split repo to the migration readiness criteria are the following which we track via github labels on this issue these criteria apply to the split repo we are migrating from no open issues no open prs no handwritten samples no system tests no client specific customizations | 0 |
178,847 | 21,509,567,825 | IssuesEvent | 2022-04-28 01:55:26 | Hans-Zamorano-Matamala/mean_entrenamiento | https://api.github.com/repos/Hans-Zamorano-Matamala/mean_entrenamiento | closed | CVE-2018-11695 (High) detected in node-sass-4.9.0.tgz, client-v2018.07-15.0.1.0-alpha - autoclosed | security vulnerability | ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.9.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.9.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.9.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.9.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/mean_entrenamiento/client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/mean_entrenamiento/client/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.6.7.tgz (Root Library)
- :x: **node-sass-4.9.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Hans-Zamorano-Matamala/mean_entrenamiento/commit/0f094ecc422f26d3138f57e9bfc643b6c44307ca">0f094ecc422f26d3138f57e9bfc643b6c44307ca</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.2. A NULL pointer dereference was found in the function Sass::Expand::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11695>CVE-2018-11695</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11695">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11695</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11695 (High) detected in node-sass-4.9.0.tgz, client-v2018.07-15.0.1.0-alpha - autoclosed - ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.9.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.9.0.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.9.0.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.9.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/mean_entrenamiento/client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/mean_entrenamiento/client/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.6.7.tgz (Root Library)
- :x: **node-sass-4.9.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Hans-Zamorano-Matamala/mean_entrenamiento/commit/0f094ecc422f26d3138f57e9bfc643b6c44307ca">0f094ecc422f26d3138f57e9bfc643b6c44307ca</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.2. A NULL pointer dereference was found in the function Sass::Expand::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-11695>CVE-2018-11695</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11695">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11695</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: LibSass - 3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in node sass tgz client alpha autoclosed cve high severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm mean entrenamiento client package json path to vulnerable library tmp ws scm mean entrenamiento client node modules node sass package json dependency hierarchy build angular tgz root library x node sass tgz vulnerable library found in head commit a href vulnerability details an issue was discovered in libsass through a null pointer dereference was found in the function sass expand operator which could be leveraged by an attacker to cause a denial of service application crash or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
289,951 | 25,026,498,533 | IssuesEvent | 2022-11-04 08:32:22 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | Searching after number of created via API samples is not retuning expecting total on release environments | testing task e2e-tests | Discovered that test: **Check Filters on Sample page work as expected** is always failing on release environments due to not correctly returned results after applying filters.
The test is creating 10 entities via API, but when we search after them, we're never getting the expected results:
https://jenkins.sormas.netzlink.com/job/sormas-RunE2eTests-release-commit/14/allure/#testresult/5f3c56694f27a875
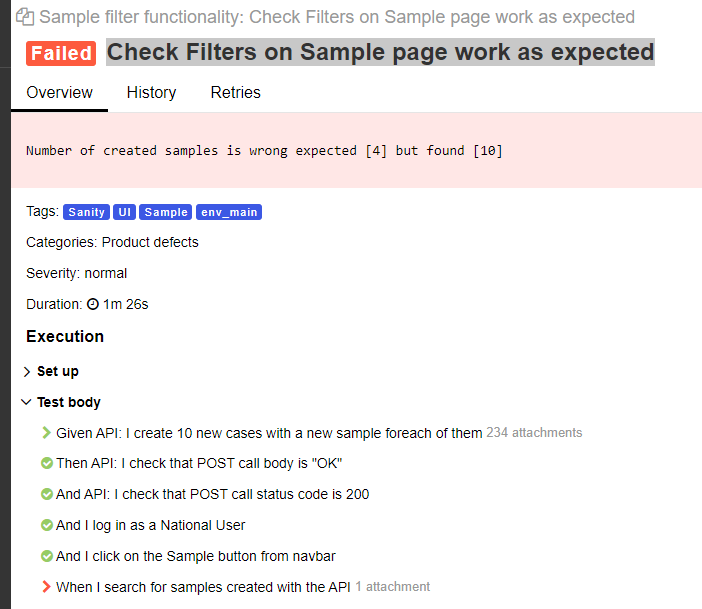
https://jenkins.sormas.netzlink.com/job/sormas-RunE2eTests-release-commit/7/allure/#testresult/3beb9f97fcc6b4ff?attachment=e887d7d417090c2
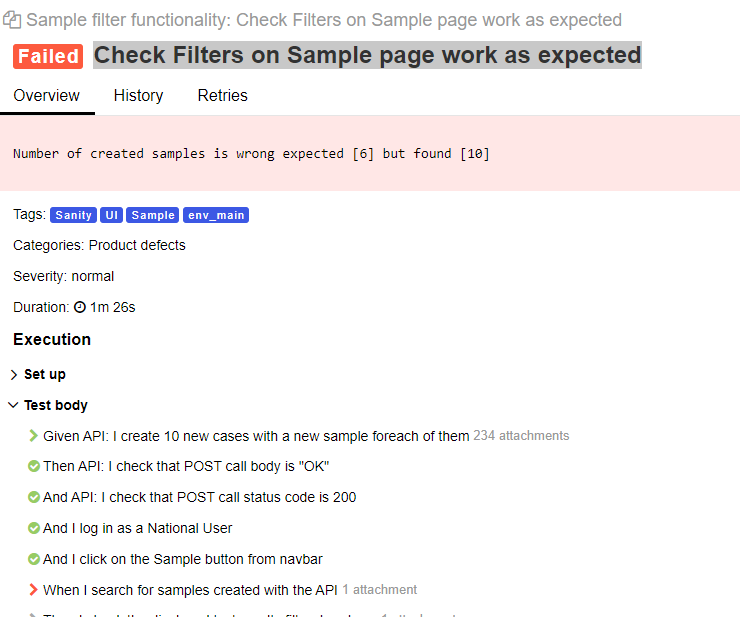
**Cannot replicate this on daily testing environments**
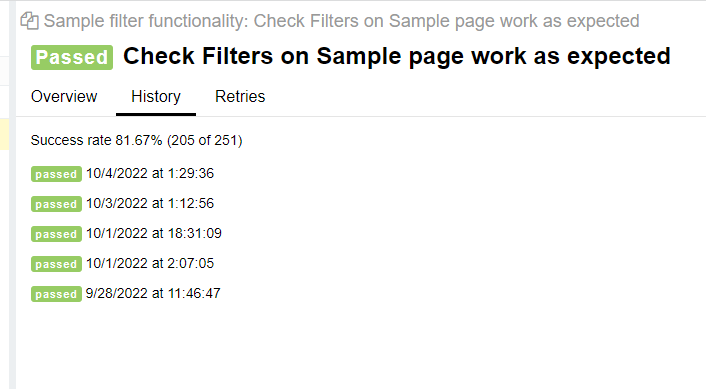
| 2.0 | Searching after number of created via API samples is not retuning expecting total on release environments - Discovered that test: **Check Filters on Sample page work as expected** is always failing on release environments due to not correctly returned results after applying filters.
The test is creating 10 entities via API, but when we search after them, we're never getting the expected results:
https://jenkins.sormas.netzlink.com/job/sormas-RunE2eTests-release-commit/14/allure/#testresult/5f3c56694f27a875
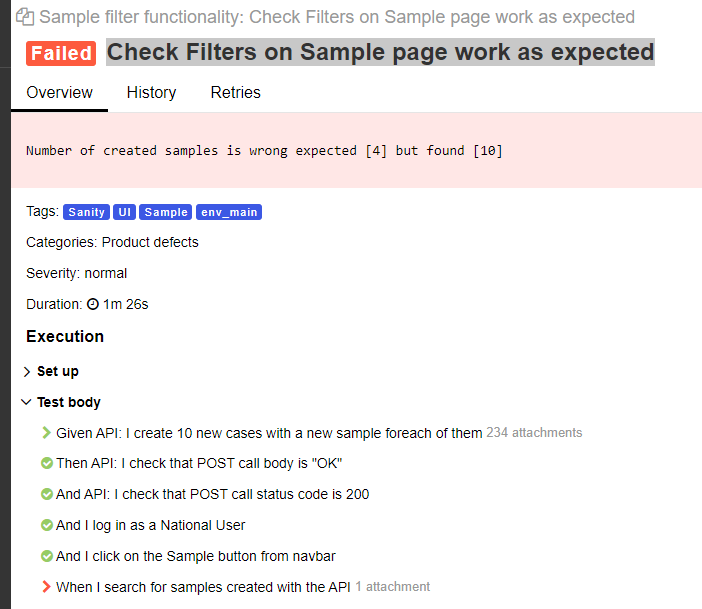
https://jenkins.sormas.netzlink.com/job/sormas-RunE2eTests-release-commit/7/allure/#testresult/3beb9f97fcc6b4ff?attachment=e887d7d417090c2
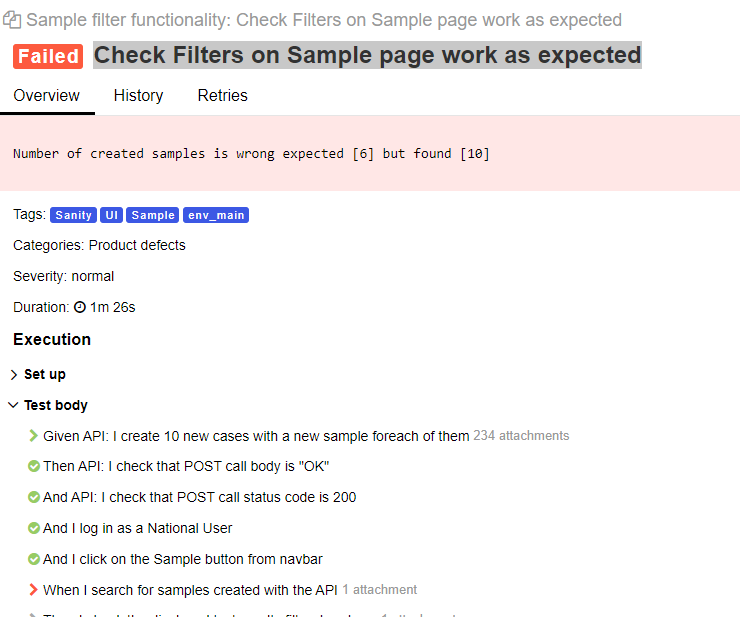
**Cannot replicate this on daily testing environments**
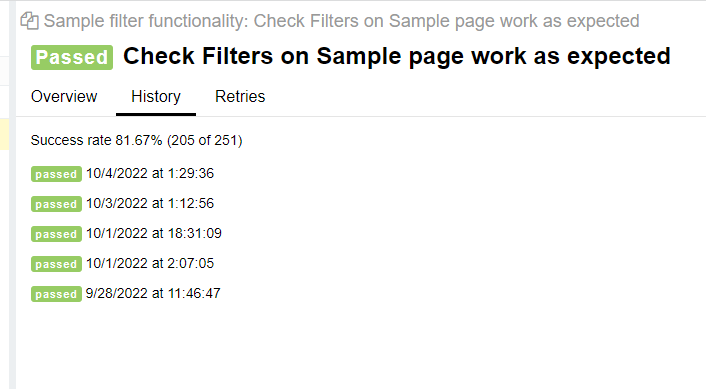
| non_priority | searching after number of created via api samples is not retuning expecting total on release environments discovered that test check filters on sample page work as expected is always failing on release environments due to not correctly returned results after applying filters the test is creating entities via api but when we search after them we re never getting the expected results cannot replicate this on daily testing environments | 0 |
174,396 | 21,280,547,285 | IssuesEvent | 2022-04-14 01:04:47 | OpenSUTD/showcase-proto | https://api.github.com/repos/OpenSUTD/showcase-proto | opened | CVE-2022-28347 (High) detected in Django-2.2.1.tar.gz | security vulnerability | ## CVE-2022-28347 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-2.2.1.tar.gz</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/fd/70/36c08f4c3b22523173b3a5e21fbdaa137bdb1722b76f356e0e2d5d8aa645/Django-2.2.1.tar.gz">https://files.pythonhosted.org/packages/fd/70/36c08f4c3b22523173b3a5e21fbdaa137bdb1722b76f356e0e2d5d8aa645/Django-2.2.1.tar.gz</a></p>
<p>Path to dependency file: /showcase/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_90a29cbc-3c85-49c7-9061-fa24b96cbcec/20190514155641_52678/20190514155511_depth_0/1/Django-2.2.1.tar/Django-2.2.1</p>
<p>
Dependency Hierarchy:
- :x: **Django-2.2.1.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A SQL injection issue was discovered in QuerySet.explain() in Django 2.2 before 2.2.28, 3.2 before 3.2.13, and 4.0 before 4.0.4. This occurs by passing a crafted dictionary (with dictionary expansion) as the **options argument, and placing the injection payload in an option name.
<p>Publish Date: 2022-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-28347>CVE-2022-28347</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28347">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28347</a></p>
<p>Release Date: 2022-04-12</p>
<p>Fix Resolution: Django - 2.2.28,3.2.13,4.0.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-28347 (High) detected in Django-2.2.1.tar.gz - ## CVE-2022-28347 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-2.2.1.tar.gz</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/fd/70/36c08f4c3b22523173b3a5e21fbdaa137bdb1722b76f356e0e2d5d8aa645/Django-2.2.1.tar.gz">https://files.pythonhosted.org/packages/fd/70/36c08f4c3b22523173b3a5e21fbdaa137bdb1722b76f356e0e2d5d8aa645/Django-2.2.1.tar.gz</a></p>
<p>Path to dependency file: /showcase/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_90a29cbc-3c85-49c7-9061-fa24b96cbcec/20190514155641_52678/20190514155511_depth_0/1/Django-2.2.1.tar/Django-2.2.1</p>
<p>
Dependency Hierarchy:
- :x: **Django-2.2.1.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A SQL injection issue was discovered in QuerySet.explain() in Django 2.2 before 2.2.28, 3.2 before 3.2.13, and 4.0 before 4.0.4. This occurs by passing a crafted dictionary (with dictionary expansion) as the **options argument, and placing the injection payload in an option name.
<p>Publish Date: 2022-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-28347>CVE-2022-28347</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28347">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28347</a></p>
<p>Release Date: 2022-04-12</p>
<p>Fix Resolution: Django - 2.2.28,3.2.13,4.0.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in django tar gz cve high severity vulnerability vulnerable library django tar gz a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file showcase requirements txt path to vulnerable library tesource archiveextractor depth django tar django dependency hierarchy x django tar gz vulnerable library vulnerability details a sql injection issue was discovered in queryset explain in django before before and before this occurs by passing a crafted dictionary with dictionary expansion as the options argument and placing the injection payload in an option name publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution django step up your open source security game with whitesource | 0 |
127,742 | 18,022,382,377 | IssuesEvent | 2021-09-16 21:17:13 | harrinry/okapi | https://api.github.com/repos/harrinry/okapi | opened | WS-2020-0408 (High) detected in netty-handler-4.1.65.Final.jar | security vulnerability | ## WS-2020-0408 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-handler-4.1.65.Final.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://netty.io/">https://netty.io/</a></p>
<p>Path to dependency file: okapi/okapi-core/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar</p>
<p>
Dependency Hierarchy:
- vertx-core-4.1.2.jar (Root Library)
- :x: **netty-handler-4.1.65.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/okapi/commit/75a13b544f4cdfcf687b215490e8b34a44ee9492">75a13b544f4cdfcf687b215490e8b34a44ee9492</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was found in all versions of io.netty:netty-all. Host verification in Netty is disabled by default. This can lead to MITM attack in which an attacker can forge valid SSL/TLS certificates for a different hostname in order to intercept traffic that doesn’t intend for him. This is an issue because the certificate is not matched with the host.
<p>Publish Date: 2020-06-22
<p>URL: <a href=https://github.com/netty/netty/issues/10362>WS-2020-0408</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-handler","packageVersion":"4.1.65.Final","packageFilePaths":["/okapi-core/pom.xml","/okapi-test-header-module/pom.xml","/okapi-test-module/pom.xml","/okapi-test-auth-module/pom.xml","/okapi-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"io.vertx:vertx-core:4.1.2;io.netty:netty-handler:4.1.65.Final","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2020-0408","vulnerabilityDetails":"An issue was found in all versions of io.netty:netty-all. Host verification in Netty is disabled by default. This can lead to MITM attack in which an attacker can forge valid SSL/TLS certificates for a different hostname in order to intercept traffic that doesn’t intend for him. This is an issue because the certificate is not matched with the host.","vulnerabilityUrl":"https://github.com/netty/netty/issues/10362","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | WS-2020-0408 (High) detected in netty-handler-4.1.65.Final.jar - ## WS-2020-0408 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-handler-4.1.65.Final.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://netty.io/">https://netty.io/</a></p>
<p>Path to dependency file: okapi/okapi-core/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar,/home/wss-scanner/.m2/repository/io/netty/netty-handler/4.1.65.Final/netty-handler-4.1.65.Final.jar</p>
<p>
Dependency Hierarchy:
- vertx-core-4.1.2.jar (Root Library)
- :x: **netty-handler-4.1.65.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/okapi/commit/75a13b544f4cdfcf687b215490e8b34a44ee9492">75a13b544f4cdfcf687b215490e8b34a44ee9492</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was found in all versions of io.netty:netty-all. Host verification in Netty is disabled by default. This can lead to MITM attack in which an attacker can forge valid SSL/TLS certificates for a different hostname in order to intercept traffic that doesn’t intend for him. This is an issue because the certificate is not matched with the host.
<p>Publish Date: 2020-06-22
<p>URL: <a href=https://github.com/netty/netty/issues/10362>WS-2020-0408</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-handler","packageVersion":"4.1.65.Final","packageFilePaths":["/okapi-core/pom.xml","/okapi-test-header-module/pom.xml","/okapi-test-module/pom.xml","/okapi-test-auth-module/pom.xml","/okapi-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"io.vertx:vertx-core:4.1.2;io.netty:netty-handler:4.1.65.Final","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2020-0408","vulnerabilityDetails":"An issue was found in all versions of io.netty:netty-all. Host verification in Netty is disabled by default. This can lead to MITM attack in which an attacker can forge valid SSL/TLS certificates for a different hostname in order to intercept traffic that doesn’t intend for him. This is an issue because the certificate is not matched with the host.","vulnerabilityUrl":"https://github.com/netty/netty/issues/10362","cvss3Severity":"high","cvss3Score":"7.4","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in netty handler final jar ws high severity vulnerability vulnerable library netty handler final jar library home page a href path to dependency file okapi okapi core pom xml path to vulnerable library home wss scanner repository io netty netty handler final netty handler final jar home wss scanner repository io netty netty handler final netty handler final jar home wss scanner repository io netty netty handler final netty handler final jar home wss scanner repository io netty netty handler final netty handler final jar home wss scanner repository io netty netty handler final netty handler final jar dependency hierarchy vertx core jar root library x netty handler final jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue was found in all versions of io netty netty all host verification in netty is disabled by default this can lead to mitm attack in which an attacker can forge valid ssl tls certificates for a different hostname in order to intercept traffic that doesn’t intend for him this is an issue because the certificate is not matched with the host publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree io vertx vertx core io netty netty handler final isminimumfixversionavailable false basebranches vulnerabilityidentifier ws vulnerabilitydetails an issue was found in all versions of io netty netty all host verification in netty is disabled by default this can lead to mitm attack in which an attacker can forge valid ssl tls certificates for a different hostname in order to intercept traffic that doesn’t intend for him this is an issue because the certificate is not matched with the host vulnerabilityurl | 0 |
317,873 | 23,693,170,769 | IssuesEvent | 2022-08-29 12:40:25 | gosling-lang/gos | https://api.github.com/repos/gosling-lang/gos | closed | User guide on exporting plots | documentation | We have the `.save()` function explained on the doc under [API Reference](https://gosling-lang.github.io/gos/user_guide/generated/toplevel/gosling.View.html), but it is quite hidden to users and does not provide detailed explanations and examples. I think we need to add a dedicated page or section that describes ways to export Gos plots (e.g., html, json). Maybe we can add a section near the Local Data?:
<img width="263" alt="Screen Shot 2022-08-17 at 09 18 12" src="https://user-images.githubusercontent.com/9922882/185144278-cc04e3aa-49b3-4ff0-a745-2c55bb36e555.png">
Related tweet: https://twitter.com/sminot/status/1559746056669126657?s=21&t=yCLH8vli7kbjDf8foZhy5g | 1.0 | User guide on exporting plots - We have the `.save()` function explained on the doc under [API Reference](https://gosling-lang.github.io/gos/user_guide/generated/toplevel/gosling.View.html), but it is quite hidden to users and does not provide detailed explanations and examples. I think we need to add a dedicated page or section that describes ways to export Gos plots (e.g., html, json). Maybe we can add a section near the Local Data?:
<img width="263" alt="Screen Shot 2022-08-17 at 09 18 12" src="https://user-images.githubusercontent.com/9922882/185144278-cc04e3aa-49b3-4ff0-a745-2c55bb36e555.png">
Related tweet: https://twitter.com/sminot/status/1559746056669126657?s=21&t=yCLH8vli7kbjDf8foZhy5g | non_priority | user guide on exporting plots we have the save function explained on the doc under but it is quite hidden to users and does not provide detailed explanations and examples i think we need to add a dedicated page or section that describes ways to export gos plots e g html json maybe we can add a section near the local data img width alt screen shot at src related tweet | 0 |
111,138 | 11,725,498,729 | IssuesEvent | 2020-03-10 13:03:58 | mantidproject/mantid | https://api.github.com/repos/mantidproject/mantid | closed | Neaten up Framework, plot and workbench release notes | Documentation ISIS Team: CoreTeam | - Add screenshots
- Expand out one line descriptions for significant features
- Rearrange to make sense
- Also the main page and release image | 1.0 | Neaten up Framework, plot and workbench release notes - - Add screenshots
- Expand out one line descriptions for significant features
- Rearrange to make sense
- Also the main page and release image | non_priority | neaten up framework plot and workbench release notes add screenshots expand out one line descriptions for significant features rearrange to make sense also the main page and release image | 0 |
23,276 | 11,890,256,755 | IssuesEvent | 2020-03-28 17:31:20 | dixonge/vagabondians-11ty | https://api.github.com/repos/dixonge/vagabondians-11ty | closed | Heading Elements not in a sequentially-descending order | Performance | From Lighthouse audit:
Properly ordered headings that do not skip levels convey the semantic structure of the page, making it easier to navigate and understand when using assistive technologies
```Escape Normal - Explore Your World
<h3 class="my-0 text-sm text-white">Escape Normal - Explore Your World</h3>``` | True | Heading Elements not in a sequentially-descending order - From Lighthouse audit:
Properly ordered headings that do not skip levels convey the semantic structure of the page, making it easier to navigate and understand when using assistive technologies
```Escape Normal - Explore Your World
<h3 class="my-0 text-sm text-white">Escape Normal - Explore Your World</h3>``` | non_priority | heading elements not in a sequentially descending order from lighthouse audit properly ordered headings that do not skip levels convey the semantic structure of the page making it easier to navigate and understand when using assistive technologies escape normal explore your world escape normal explore your world | 0 |
162,104 | 13,882,356,669 | IssuesEvent | 2020-10-18 06:28:32 | dagster-io/dagster | https://api.github.com/repos/dagster-io/dagster | opened | Improve documentation for the config system and types | core documentation | We unfortunately have very poor documentation coverage for our config system. Several config types have no documentation. For example:

Our overview on "Configuration" doesn't do much to explain how to use the config system either: https://docs.dagster.io/overview/configuration/
The best (and only real) explanation of config schemas is in the tutorial, but it doesn't really explain the different types: https://docs.dagster.io/tutorial/basics_solids#parametrizing-solids-with-config
Understanding and using the config system is a crucial part of being productive while using Dagster. At the very least we should document the different types, and ideally we should have an in-depth guide about how to use the config system as a whole. | 1.0 | Improve documentation for the config system and types - We unfortunately have very poor documentation coverage for our config system. Several config types have no documentation. For example:

Our overview on "Configuration" doesn't do much to explain how to use the config system either: https://docs.dagster.io/overview/configuration/
The best (and only real) explanation of config schemas is in the tutorial, but it doesn't really explain the different types: https://docs.dagster.io/tutorial/basics_solids#parametrizing-solids-with-config
Understanding and using the config system is a crucial part of being productive while using Dagster. At the very least we should document the different types, and ideally we should have an in-depth guide about how to use the config system as a whole. | non_priority | improve documentation for the config system and types we unfortunately have very poor documentation coverage for our config system several config types have no documentation for example our overview on configuration doesn t do much to explain how to use the config system either the best and only real explanation of config schemas is in the tutorial but it doesn t really explain the different types understanding and using the config system is a crucial part of being productive while using dagster at the very least we should document the different types and ideally we should have an in depth guide about how to use the config system as a whole | 0 |
19,856 | 13,506,729,648 | IssuesEvent | 2020-09-14 03:56:26 | lgolding/sarif-world | https://api.github.com/repos/lgolding/sarif-world | opened | Be able to debug into SARIF SDK with symbol packages | area-infrastructure enhancement | As the code stands, I set a property `$(Debugging)` in the project files to bring in built binaries from the SARIF SDK. This gives me access to the symbols so I can debug into the SDK. This needs to work just from the NuGet packages. I shouldn't need to play this game. | 1.0 | Be able to debug into SARIF SDK with symbol packages - As the code stands, I set a property `$(Debugging)` in the project files to bring in built binaries from the SARIF SDK. This gives me access to the symbols so I can debug into the SDK. This needs to work just from the NuGet packages. I shouldn't need to play this game. | non_priority | be able to debug into sarif sdk with symbol packages as the code stands i set a property debugging in the project files to bring in built binaries from the sarif sdk this gives me access to the symbols so i can debug into the sdk this needs to work just from the nuget packages i shouldn t need to play this game | 0 |
172,636 | 14,370,412,830 | IssuesEvent | 2020-12-01 11:03:56 | xmos/lib_logging | https://api.github.com/repos/xmos/lib_logging | opened | examples/AN00239 Application Note not compliant | type:documentation type:enhancement | **Issues:**
- xdoc-custom RST directives used in the Application Note README
- application note code not running successfully on xcore-ai
**Application note README**
This file contains the `appdeps`, `appnote`, and `version` directives.
**Not running on xcore-ai**
Changing the target in the Makefile to `TARGET = XCORE-AI-EXPLORER` allows the Application Note executable to run successfully on an xcore-ai. The Makefile requires enhancement to support both xcore-200 and xcore-ai.
| 1.0 | examples/AN00239 Application Note not compliant - **Issues:**
- xdoc-custom RST directives used in the Application Note README
- application note code not running successfully on xcore-ai
**Application note README**
This file contains the `appdeps`, `appnote`, and `version` directives.
**Not running on xcore-ai**
Changing the target in the Makefile to `TARGET = XCORE-AI-EXPLORER` allows the Application Note executable to run successfully on an xcore-ai. The Makefile requires enhancement to support both xcore-200 and xcore-ai.
| non_priority | examples application note not compliant issues xdoc custom rst directives used in the application note readme application note code not running successfully on xcore ai application note readme this file contains the appdeps appnote and version directives not running on xcore ai changing the target in the makefile to target xcore ai explorer allows the application note executable to run successfully on an xcore ai the makefile requires enhancement to support both xcore and xcore ai | 0 |
98,458 | 12,325,454,671 | IssuesEvent | 2020-05-13 15:04:42 | codingdavinci/relaunch2018 | https://api.github.com/repos/codingdavinci/relaunch2018 | opened | Abschnitt Zeitleiste- Fußzeile text align bottom | design | The Fußzeile text is aligning top when it should align bottom, as it does for Abschnitt Box/Box-Gruppen. Plx fix, ty! | 1.0 | Abschnitt Zeitleiste- Fußzeile text align bottom - The Fußzeile text is aligning top when it should align bottom, as it does for Abschnitt Box/Box-Gruppen. Plx fix, ty! | non_priority | abschnitt zeitleiste fußzeile text align bottom the fußzeile text is aligning top when it should align bottom as it does for abschnitt box box gruppen plx fix ty | 0 |
96,832 | 16,167,131,020 | IssuesEvent | 2021-05-01 18:27:04 | Ryan-Oneil/oneil-industries-website | https://api.github.com/repos/Ryan-Oneil/oneil-industries-website | closed | CVE-2020-28477 (High) detected in immer-1.10.0.tgz | security vulnerability | ## CVE-2020-28477 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>immer-1.10.0.tgz</b></p></summary>
<p>Create your next immutable state by mutating the current one</p>
<p>Library home page: <a href="https://registry.npmjs.org/immer/-/immer-1.10.0.tgz">https://registry.npmjs.org/immer/-/immer-1.10.0.tgz</a></p>
<p>Path to dependency file: oneil-industries-website/frontend/package.json</p>
<p>Path to vulnerable library: oneil-industries-website/frontend/node_modules/react-dev-utils/node_modules/immer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- react-dev-utils-10.2.1.tgz
- :x: **immer-1.10.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects all versions of package immer.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28477>CVE-2020-28477</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/immerjs/immer/releases/tag/v8.0.1">https://github.com/immerjs/immer/releases/tag/v8.0.1</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: v8.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28477 (High) detected in immer-1.10.0.tgz - ## CVE-2020-28477 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>immer-1.10.0.tgz</b></p></summary>
<p>Create your next immutable state by mutating the current one</p>
<p>Library home page: <a href="https://registry.npmjs.org/immer/-/immer-1.10.0.tgz">https://registry.npmjs.org/immer/-/immer-1.10.0.tgz</a></p>
<p>Path to dependency file: oneil-industries-website/frontend/package.json</p>
<p>Path to vulnerable library: oneil-industries-website/frontend/node_modules/react-dev-utils/node_modules/immer/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- react-dev-utils-10.2.1.tgz
- :x: **immer-1.10.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects all versions of package immer.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28477>CVE-2020-28477</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/immerjs/immer/releases/tag/v8.0.1">https://github.com/immerjs/immer/releases/tag/v8.0.1</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: v8.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in immer tgz cve high severity vulnerability vulnerable library immer tgz create your next immutable state by mutating the current one library home page a href path to dependency file oneil industries website frontend package json path to vulnerable library oneil industries website frontend node modules react dev utils node modules immer package json dependency hierarchy react scripts tgz root library react dev utils tgz x immer tgz vulnerable library vulnerability details this affects all versions of package immer publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
19,906 | 26,360,404,793 | IssuesEvent | 2023-01-11 12:59:44 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | vegetative cell differentiation ( primary term name swap) | development ready cellular processes term name |
GO:0022620 vegetative cell differentiation
The process in which a relatively unspecialized cell acquires specialized features of a vegetative cell. The vegetative cell is gives rise to the pollen tube.
has exact synonym
tube cell differentiation
@tberardini would you mind if we swapped the primary names of these terms?
"vegetative cell differentiation" can have different meanings to different species.
| 1.0 | vegetative cell differentiation ( primary term name swap) -
GO:0022620 vegetative cell differentiation
The process in which a relatively unspecialized cell acquires specialized features of a vegetative cell. The vegetative cell is gives rise to the pollen tube.
has exact synonym
tube cell differentiation
@tberardini would you mind if we swapped the primary names of these terms?
"vegetative cell differentiation" can have different meanings to different species.
| non_priority | vegetative cell differentiation primary term name swap go vegetative cell differentiation the process in which a relatively unspecialized cell acquires specialized features of a vegetative cell the vegetative cell is gives rise to the pollen tube has exact synonym tube cell differentiation tberardini would you mind if we swapped the primary names of these terms vegetative cell differentiation can have different meanings to different species | 0 |
103,172 | 11,341,249,084 | IssuesEvent | 2020-01-23 08:56:04 | IssaHanou/BEP_1920_Q2 | https://api.github.com/repos/IssaHanou/BEP_1920_Q2 | closed | documentation back-end | back-end documentation | ### Content
To guaranty maintainability, all code should be documented as clear as possible.
### Feature
- documentation for the communication, config, handler
### Action plan
- [ ] configHandler.go
- [ ] readConfigTypes.go
- [ ] workingConfigTypes.go
- [ ] handler.go
- [ ] handler_helper.go
- [ ] communication.go
### Related issues
GH-173
| 1.0 | documentation back-end - ### Content
To guaranty maintainability, all code should be documented as clear as possible.
### Feature
- documentation for the communication, config, handler
### Action plan
- [ ] configHandler.go
- [ ] readConfigTypes.go
- [ ] workingConfigTypes.go
- [ ] handler.go
- [ ] handler_helper.go
- [ ] communication.go
### Related issues
GH-173
| non_priority | documentation back end content to guaranty maintainability all code should be documented as clear as possible feature documentation for the communication config handler action plan confighandler go readconfigtypes go workingconfigtypes go handler go handler helper go communication go related issues gh | 0 |
63,629 | 17,792,956,994 | IssuesEvent | 2021-08-31 18:25:45 | gwaldron/osgearth | https://api.github.com/repos/gwaldron/osgearth | closed | setMaxVisibleRange - inoperative with graticule layers | defect | It does not function for any of the graticule layers. | 1.0 | setMaxVisibleRange - inoperative with graticule layers - It does not function for any of the graticule layers. | non_priority | setmaxvisiblerange inoperative with graticule layers it does not function for any of the graticule layers | 0 |
256,482 | 19,424,135,004 | IssuesEvent | 2021-12-21 01:40:18 | ivapylibs/puzzle_solver | https://api.github.com/repos/ivapylibs/puzzle_solver | closed | Clustering classes | documentation good first issue | Start to think through how to design the clustering classes (which are derived from the ``puzzle.board`` class). They will define additional virtual layers for the puzzle. These will be stored by the solver and acted upon to create plans, but won't be the actual estimated puzzle board. Describe here before advancing. Or describe in some document. | 1.0 | Clustering classes - Start to think through how to design the clustering classes (which are derived from the ``puzzle.board`` class). They will define additional virtual layers for the puzzle. These will be stored by the solver and acted upon to create plans, but won't be the actual estimated puzzle board. Describe here before advancing. Or describe in some document. | non_priority | clustering classes start to think through how to design the clustering classes which are derived from the puzzle board class they will define additional virtual layers for the puzzle these will be stored by the solver and acted upon to create plans but won t be the actual estimated puzzle board describe here before advancing or describe in some document | 0 |
98,902 | 20,820,104,263 | IssuesEvent | 2022-03-18 14:34:39 | aimhubio/aim | https://api.github.com/repos/aimhubio/aim | opened | Refactor Aim adapters for XGBoost | phase / review-needed area / integrations type / code-health | Currently xgboost AimCallback is written in a way (wrapped around with outer class) so there's no possible way to extend them without forking. We should rewrite the adapters in a way that will enable a possibility to inherit and override the methods for user custom callbacks.
| 1.0 | Refactor Aim adapters for XGBoost - Currently xgboost AimCallback is written in a way (wrapped around with outer class) so there's no possible way to extend them without forking. We should rewrite the adapters in a way that will enable a possibility to inherit and override the methods for user custom callbacks.
| non_priority | refactor aim adapters for xgboost currently xgboost aimcallback is written in a way wrapped around with outer class so there s no possible way to extend them without forking we should rewrite the adapters in a way that will enable a possibility to inherit and override the methods for user custom callbacks | 0 |
289,055 | 24,954,692,470 | IssuesEvent | 2022-11-01 10:37:49 | Slimefun/Slimefun4 | https://api.github.com/repos/Slimefun/Slimefun4 | opened | sometimes grappling hook drops leads and arrows | 🐞 Bug Report 🎯 Needs testing | ### ❗ Checklist
- [X] I am using the official english version of Slimefun and did not modify the jar.
- [X] I am using an up to date "DEV" (not "RC") version of Slimefun.
- [X] I am aware that issues related to Slimefun addons need to be reported on their bug trackers and not here.
- [X] I searched for similar open issues and could not find an existing bug report on this.
### 📍 Description
grappling hook drops leads and arrows.
### 📑 Reproduction Steps
1.get grappling hook
2.double right clicking or multiple right clicking
### 💡 Expected Behavior
Just work and not drop another items
### 📷 Screenshots / Videos
https://youtu.be/Nso0FG8O4tQ
### 📜 Server Log
_No response_
### 📂 `/error-reports/` folder
_No response_
### 💻 Server Software
Paper
### 🎮 Minecraft Version
1.19.x
### ⭐ Slimefun version
build 1035 DEV
### 🧭 Other plugins
nothing else | 1.0 | sometimes grappling hook drops leads and arrows - ### ❗ Checklist
- [X] I am using the official english version of Slimefun and did not modify the jar.
- [X] I am using an up to date "DEV" (not "RC") version of Slimefun.
- [X] I am aware that issues related to Slimefun addons need to be reported on their bug trackers and not here.
- [X] I searched for similar open issues and could not find an existing bug report on this.
### 📍 Description
grappling hook drops leads and arrows.
### 📑 Reproduction Steps
1.get grappling hook
2.double right clicking or multiple right clicking
### 💡 Expected Behavior
Just work and not drop another items
### 📷 Screenshots / Videos
https://youtu.be/Nso0FG8O4tQ
### 📜 Server Log
_No response_
### 📂 `/error-reports/` folder
_No response_
### 💻 Server Software
Paper
### 🎮 Minecraft Version
1.19.x
### ⭐ Slimefun version
build 1035 DEV
### 🧭 Other plugins
nothing else | non_priority | sometimes grappling hook drops leads and arrows ❗ checklist i am using the official english version of slimefun and did not modify the jar i am using an up to date dev not rc version of slimefun i am aware that issues related to slimefun addons need to be reported on their bug trackers and not here i searched for similar open issues and could not find an existing bug report on this 📍 description grappling hook drops leads and arrows 📑 reproduction steps get grappling hook double right clicking or multiple right clicking 💡 expected behavior just work and not drop another items 📷 screenshots videos 📜 server log no response 📂 error reports folder no response 💻 server software paper 🎮 minecraft version x ⭐ slimefun version build dev 🧭 other plugins nothing else | 0 |
15,164 | 19,142,030,370 | IssuesEvent | 2021-12-02 00:40:36 | STEllAR-GROUP/hpx | https://api.github.com/repos/STEllAR-GROUP/hpx | closed | Implement P2248 for our algorithms | type: enhancement type: compatibility issue category: algorithms | wg21.link/p2248 is a quality of implementation improvement targeting improved usability of some of the algorithms. Implementing the features described in this paper might be a good idea. | True | Implement P2248 for our algorithms - wg21.link/p2248 is a quality of implementation improvement targeting improved usability of some of the algorithms. Implementing the features described in this paper might be a good idea. | non_priority | implement for our algorithms link is a quality of implementation improvement targeting improved usability of some of the algorithms implementing the features described in this paper might be a good idea | 0 |
435,430 | 30,500,345,332 | IssuesEvent | 2023-07-18 13:35:31 | wokebuild/share | https://api.github.com/repos/wokebuild/share | closed | Bash script installation on windows | bug documentation | - [x] Update documentation to remove `sudo` for windows users
- [x] Update bash script to make `share` a symbolic link to enable everyone use `share` without adding the file path | 1.0 | Bash script installation on windows - - [x] Update documentation to remove `sudo` for windows users
- [x] Update bash script to make `share` a symbolic link to enable everyone use `share` without adding the file path | non_priority | bash script installation on windows update documentation to remove sudo for windows users update bash script to make share a symbolic link to enable everyone use share without adding the file path | 0 |
16,490 | 3,535,035,979 | IssuesEvent | 2016-01-16 06:09:28 | ThunderID/SHOP-API | https://api.github.com/repos/ThunderID/SHOP-API | closed | [Test Case] Register User | test to do | * [x] Get Referral code and quota 10
* [x] Activate Account get IDR 10000
* [x] Referral Code get IDR 50000
* [x] Referral get IDR 10000
| 1.0 | [Test Case] Register User - * [x] Get Referral code and quota 10
* [x] Activate Account get IDR 10000
* [x] Referral Code get IDR 50000
* [x] Referral get IDR 10000
| non_priority | register user get referral code and quota activate account get idr referral code get idr referral get idr | 0 |
117,618 | 17,512,658,468 | IssuesEvent | 2021-08-11 01:02:45 | harrinry/pulsar | https://api.github.com/repos/harrinry/pulsar | opened | CVE-2020-35491 (High) detected in jackson-databind-2.8.11.4.jar | security vulnerability | ## CVE-2020-35491 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.11.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: pulsar/pulsar-sql/presto-distribution/pom.xml</p>
<p>Path to vulnerable library: 0150316_LVRAMP/downloadResource_AEDNMT/20210810150945/jackson-databind-2.8.11.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.11.4.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.SharedPoolDataSource.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491>CVE-2020-35491</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2986">https://github.com/FasterXML/jackson-databind/issues/2986</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.11.4","packageFilePaths":["/pulsar-sql/presto-distribution/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.8.11.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-35491","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.SharedPoolDataSource.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-35491 (High) detected in jackson-databind-2.8.11.4.jar - ## CVE-2020-35491 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.11.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: pulsar/pulsar-sql/presto-distribution/pom.xml</p>
<p>Path to vulnerable library: 0150316_LVRAMP/downloadResource_AEDNMT/20210810150945/jackson-databind-2.8.11.4.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.11.4.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.SharedPoolDataSource.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491>CVE-2020-35491</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2986">https://github.com/FasterXML/jackson-databind/issues/2986</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.8</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.11.4","packageFilePaths":["/pulsar-sql/presto-distribution/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.8.11.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-35491","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.datasources.SharedPoolDataSource.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pulsar pulsar sql presto distribution pom xml path to vulnerable library lvramp downloadresource aednmt jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons datasources sharedpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons datasources sharedpooldatasource vulnerabilityurl | 0 |
150,975 | 11,995,626,110 | IssuesEvent | 2020-04-08 15:29:00 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | builtin_time_vec_test.go:testVectorizeSuite2.TestVectorizedBuiltinTimeFunc failed | component/test | builtin_time_vec_test.go:testVectorizeSuite2.TestVectorizedBuiltinTimeFunc
Latest failed builds:
https://internal.pingcap.net/idc-jenkins/job/tidb_ghpr_unit_test/28818/display/redirect
| 1.0 | builtin_time_vec_test.go:testVectorizeSuite2.TestVectorizedBuiltinTimeFunc failed - builtin_time_vec_test.go:testVectorizeSuite2.TestVectorizedBuiltinTimeFunc
Latest failed builds:
https://internal.pingcap.net/idc-jenkins/job/tidb_ghpr_unit_test/28818/display/redirect
| non_priority | builtin time vec test go testvectorizedbuiltintimefunc failed builtin time vec test go testvectorizedbuiltintimefunc latest failed builds | 0 |
61,953 | 14,643,852,921 | IssuesEvent | 2020-12-25 19:10:37 | AlexRogalskiy/spark4you | https://api.github.com/repos/AlexRogalskiy/spark4you | opened | CVE-2020-14338 (Medium) detected in xercesImpl-2.9.1.jar | security vulnerability | ## CVE-2020-14338 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.9.1.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Path to dependency file: spark4you/modules/spark4you-java/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.9.1/xercesImpl-2.9.1.jar,/home/wss-scanner/.m2/repository/xerces/xercesImpl/2.9.1/xercesImpl-2.9.1.jar</p>
<p>
Dependency Hierarchy:
- spark-core_2.12-3.0.1.jar (Root Library)
- hadoop-client-2.7.4.jar
- hadoop-hdfs-2.7.4.jar
- :x: **xercesImpl-2.9.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/spark4you/commit/cf3d65692017a95100e23ebd5ace43d46c143ca5">cf3d65692017a95100e23ebd5ace43d46c143ca5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in Wildfly's implementation of Xerces, specifically in the way the XMLSchemaValidator class in the JAXP component of Wildfly enforced the "use-grammar-pool-only" feature. This flaw allows a specially-crafted XML file to manipulate the validation process in certain cases. This issue is the same flaw as CVE-2020-14621, which affected OpenJDK, and uses a similar code. This flaw affects all Xerces JBoss versions before 2.12.0.SP3.
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14338>CVE-2020-14338</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1860054">https://bugzilla.redhat.com/show_bug.cgi?id=1860054</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.0.SP3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-14338 (Medium) detected in xercesImpl-2.9.1.jar - ## CVE-2020-14338 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.9.1.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Path to dependency file: spark4you/modules/spark4you-java/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.9.1/xercesImpl-2.9.1.jar,/home/wss-scanner/.m2/repository/xerces/xercesImpl/2.9.1/xercesImpl-2.9.1.jar</p>
<p>
Dependency Hierarchy:
- spark-core_2.12-3.0.1.jar (Root Library)
- hadoop-client-2.7.4.jar
- hadoop-hdfs-2.7.4.jar
- :x: **xercesImpl-2.9.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/spark4you/commit/cf3d65692017a95100e23ebd5ace43d46c143ca5">cf3d65692017a95100e23ebd5ace43d46c143ca5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in Wildfly's implementation of Xerces, specifically in the way the XMLSchemaValidator class in the JAXP component of Wildfly enforced the "use-grammar-pool-only" feature. This flaw allows a specially-crafted XML file to manipulate the validation process in certain cases. This issue is the same flaw as CVE-2020-14621, which affected OpenJDK, and uses a similar code. This flaw affects all Xerces JBoss versions before 2.12.0.SP3.
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14338>CVE-2020-14338</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1860054">https://bugzilla.redhat.com/show_bug.cgi?id=1860054</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.0.SP3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in xercesimpl jar cve medium severity vulnerability vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program path to dependency file modules java pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy spark core jar root library hadoop client jar hadoop hdfs jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was found in wildfly s implementation of xerces specifically in the way the xmlschemavalidator class in the jaxp component of wildfly enforced the use grammar pool only feature this flaw allows a specially crafted xml file to manipulate the validation process in certain cases this issue is the same flaw as cve which affected openjdk and uses a similar code this flaw affects all xerces jboss versions before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl step up your open source security game with whitesource | 0 |
97,984 | 8,673,896,361 | IssuesEvent | 2018-11-30 04:53:45 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | FXLabs Testing : ApiV1OrgsSearchGetQueryParamPageInvalidDatatype | FXLabs Testing | Project : FXLabs Testing
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=NjBiOTMxMDMtY2IyMi00NzAxLWEyZTUtMzQzNWY1YjMwMzEx; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Fri, 30 Nov 2018 04:52:38 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/orgs/search?page=vP7Pkt
Request :
Response :
{
"timestamp" : "2018-11-30T04:52:39.142+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/orgs/search"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot --- | 1.0 | FXLabs Testing : ApiV1OrgsSearchGetQueryParamPageInvalidDatatype - Project : FXLabs Testing
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=NjBiOTMxMDMtY2IyMi00NzAxLWEyZTUtMzQzNWY1YjMwMzEx; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Fri, 30 Nov 2018 04:52:38 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/orgs/search?page=vP7Pkt
Request :
Response :
{
"timestamp" : "2018-11-30T04:52:39.142+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/orgs/search"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot --- | non_priority | fxlabs testing project fxlabs testing job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api orgs search logs assertion resolved to result assertion resolved to result fx bot | 0 |
95,297 | 10,869,542,404 | IssuesEvent | 2019-11-15 07:51:16 | blocklang/page-designer | https://api.github.com/repos/blocklang/page-designer | closed | 确认页面模型中的部件属性是不是要全部加载 | documentation | 隐约感觉在实现时有这么一个约定,需要确认是否存在此约定,如果存在的话,要说明原因。
如果没有这个约定的话,则可以在数据库表中直接存储页面模型文本。
然后再需要分析或者定时,将 json 文本解析到结构化之后的数据库表中。 | 1.0 | 确认页面模型中的部件属性是不是要全部加载 - 隐约感觉在实现时有这么一个约定,需要确认是否存在此约定,如果存在的话,要说明原因。
如果没有这个约定的话,则可以在数据库表中直接存储页面模型文本。
然后再需要分析或者定时,将 json 文本解析到结构化之后的数据库表中。 | non_priority | 确认页面模型中的部件属性是不是要全部加载 隐约感觉在实现时有这么一个约定,需要确认是否存在此约定,如果存在的话,要说明原因。 如果没有这个约定的话,则可以在数据库表中直接存储页面模型文本。 然后再需要分析或者定时,将 json 文本解析到结构化之后的数据库表中。 | 0 |
125,833 | 17,860,994,822 | IssuesEvent | 2021-09-06 00:08:08 | rvvergara/haiku-android | https://api.github.com/repos/rvvergara/haiku-android | opened | CVE-2021-37701 (High) detected in tar-4.4.13.tgz | security vulnerability | ## CVE-2021-37701 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-4.4.13.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: haiku-android/package.json</p>
<p>Path to vulnerable library: haiku-android/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- snyk-1.360.0.tgz (Root Library)
- snyk-nodejs-lockfile-parser-1.25.0.tgz
- core-2.0.0-rc.30.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rvvergara/haiku-android/commit/43ea4212617a13f495023a1983f66f13ad3f0ccd">43ea4212617a13f495023a1983f66f13ad3f0ccd</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\` and `/` characters as path separators, however `\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701>CVE-2021-37701</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc">https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.16, 5.0.8, 6.1.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-37701 (High) detected in tar-4.4.13.tgz - ## CVE-2021-37701 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-4.4.13.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.13.tgz">https://registry.npmjs.org/tar/-/tar-4.4.13.tgz</a></p>
<p>Path to dependency file: haiku-android/package.json</p>
<p>Path to vulnerable library: haiku-android/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- snyk-1.360.0.tgz (Root Library)
- snyk-nodejs-lockfile-parser-1.25.0.tgz
- core-2.0.0-rc.30.tgz
- :x: **tar-4.4.13.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rvvergara/haiku-android/commit/43ea4212617a13f495023a1983f66f13ad3f0ccd">43ea4212617a13f495023a1983f66f13ad3f0ccd</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both `\` and `/` characters as path separators, however `\` is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-37701>CVE-2021-37701</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc">https://github.com/npm/node-tar/security/advisories/GHSA-9r2w-394v-53qc</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution: tar - 4.4.16, 5.0.8, 6.1.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file haiku android package json path to vulnerable library haiku android node modules tar package json dependency hierarchy snyk tgz root library snyk nodejs lockfile parser tgz core rc tgz x tar tgz vulnerable library found in head commit a href vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems the cache checking logic used both and characters as path separators however is a valid filename character on posix systems by first creating a directory and then replacing that directory with a symlink it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite additionally a similar confusion could arise on case insensitive filesystems if a tar archive contained a directory at foo followed by a symbolic link named foo then on case insensitive file systems the creation of the symbolic link would remove the directory from the filesystem but not from the internal directory cache as it would not be treated as a cache hit a subsequent file entry within the foo directory would then be placed in the target of the symbolic link thinking that the directory had already been created these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar step up your open source security game with whitesource | 0 |
419,973 | 28,211,116,368 | IssuesEvent | 2023-04-05 04:31:51 | AY2223S2-CS2103-F11-3/tp | https://api.github.com/repos/AY2223S2-CS2103-F11-3/tp | closed | [PE-D][Tester D] Misleading information shown when initialising the app for the first time. | severity.Low type.DocumentationBug | When opening the app for the first time, there seems to be a list of misleading warnings as shown in the screenshot below. However, the app generally still works fine during testing. Perhaps it might be better to document this down in the UG, as it may cause users to think that there were problems with running the app?
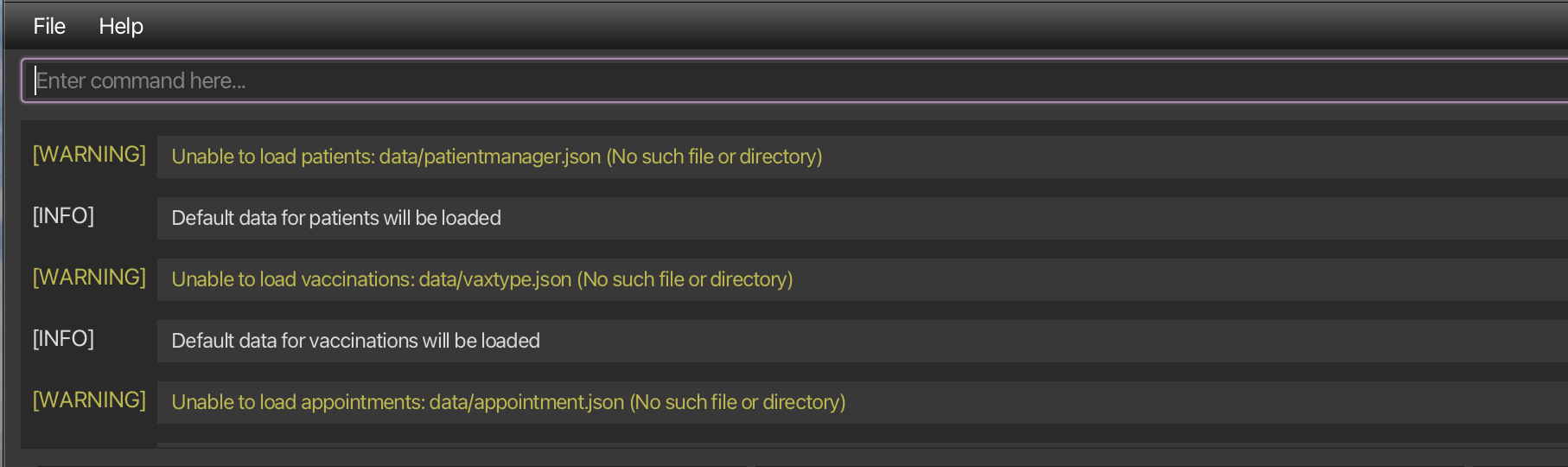
<!--session: 1680242405158-f245fc2d-a43c-4b86-9f81-0d00a9bb7cdd-->
<!--Version: Web v3.4.7-->
-------------
Labels: `type.FunctionalityBug` `severity.Low`
original: kalarisng/ped#2 | 1.0 | [PE-D][Tester D] Misleading information shown when initialising the app for the first time. - When opening the app for the first time, there seems to be a list of misleading warnings as shown in the screenshot below. However, the app generally still works fine during testing. Perhaps it might be better to document this down in the UG, as it may cause users to think that there were problems with running the app?
<!--session: 1680242405158-f245fc2d-a43c-4b86-9f81-0d00a9bb7cdd-->
<!--Version: Web v3.4.7-->
-------------
Labels: `type.FunctionalityBug` `severity.Low`
original: kalarisng/ped#2 | non_priority | misleading information shown when initialising the app for the first time when opening the app for the first time there seems to be a list of misleading warnings as shown in the screenshot below however the app generally still works fine during testing perhaps it might be better to document this down in the ug as it may cause users to think that there were problems with running the app labels type functionalitybug severity low original kalarisng ped | 0 |
15,729 | 19,902,829,392 | IssuesEvent | 2022-01-25 09:45:35 | plazi/community | https://api.github.com/repos/plazi/community | opened | to be processed 10.1016/j.isci.2021.103579 and 10.1126/sciadv.aav3875 | process request | MIght it be possible to process this article that has not treatments, but should go to BLR https://www.cell.com/action/showPdf?pii=S2589-0042%2821%2901549-2 (just remove the first page?!), and the original description in https://www.science.org/doi/reader/10.1126/sciadv.aav3875 low level
tx
| 1.0 | to be processed 10.1016/j.isci.2021.103579 and 10.1126/sciadv.aav3875 - MIght it be possible to process this article that has not treatments, but should go to BLR https://www.cell.com/action/showPdf?pii=S2589-0042%2821%2901549-2 (just remove the first page?!), and the original description in https://www.science.org/doi/reader/10.1126/sciadv.aav3875 low level
tx
| non_priority | to be processed j isci and sciadv might it be possible to process this article that has not treatments but should go to blr just remove the first page and the original description in low level tx | 0 |
72,505 | 8,744,725,807 | IssuesEvent | 2018-12-12 23:18:54 | LLK/scratch-www | https://api.github.com/repos/LLK/scratch-www | closed | Update hardware extension landing page for launch | enhancement needs-design | Currently each of the hardware extension landing pages (microbit, EV3, WeDo) has a "getting started" section that includes a step that says "Use the Scratch 3.0 editor," with a link to the beta:
For launch, we should change this link, and consider:
- What it should link to (probably a link that opens the editor directly)
- How to update the wording (perhaps "Use the Scratch editor")
| 1.0 | Update hardware extension landing page for launch - Currently each of the hardware extension landing pages (microbit, EV3, WeDo) has a "getting started" section that includes a step that says "Use the Scratch 3.0 editor," with a link to the beta:
For launch, we should change this link, and consider:
- What it should link to (probably a link that opens the editor directly)
- How to update the wording (perhaps "Use the Scratch editor")
| non_priority | update hardware extension landing page for launch currently each of the hardware extension landing pages microbit wedo has a getting started section that includes a step that says use the scratch editor with a link to the beta for launch we should change this link and consider what it should link to probably a link that opens the editor directly how to update the wording perhaps use the scratch editor | 0 |
418,037 | 28,113,330,217 | IssuesEvent | 2023-03-31 08:54:19 | Arif-Khalid/ped | https://api.github.com/repos/Arif-Khalid/ped | opened | [Bug] Too much information about internal processes given to user | severity.Low type.DocumentationBug | Comands carried out always have this information about what is done particularly by the parser, which is not specified as an expected output in the UG.
I suggest that these internal details are kept from the user as it does not benefit me as a user knowing about what the parser receives and outputs.
Alternatively, include this behaviour in the UG so I know it is an intended behaviour and will help the more technically savvy users understand what went wrong.
<!--session: 1680252501065-fe92a4af-9110-4dc0-89c9-619fac8784ea-->
<!--Version: Web v3.4.7--> | 1.0 | [Bug] Too much information about internal processes given to user - Comands carried out always have this information about what is done particularly by the parser, which is not specified as an expected output in the UG.
I suggest that these internal details are kept from the user as it does not benefit me as a user knowing about what the parser receives and outputs.
Alternatively, include this behaviour in the UG so I know it is an intended behaviour and will help the more technically savvy users understand what went wrong.
<!--session: 1680252501065-fe92a4af-9110-4dc0-89c9-619fac8784ea-->
<!--Version: Web v3.4.7--> | non_priority | too much information about internal processes given to user comands carried out always have this information about what is done particularly by the parser which is not specified as an expected output in the ug i suggest that these internal details are kept from the user as it does not benefit me as a user knowing about what the parser receives and outputs alternatively include this behaviour in the ug so i know it is an intended behaviour and will help the more technically savvy users understand what went wrong | 0 |
1,542 | 2,546,281,073 | IssuesEvent | 2015-01-29 22:43:52 | FIRST-4030/frc-scout-2015 | https://api.github.com/repos/FIRST-4030/frc-scout-2015 | closed | Autonomous | design | Moved to auto zone should be a check box.
Yellow totes stacked or moved shouldn't be more than 3
Acquired step shouldn't be more than 4
Acquired ground shouldn't be more than 3
Also, it might be good to make "fouls and other" red. | 1.0 | Autonomous - Moved to auto zone should be a check box.
Yellow totes stacked or moved shouldn't be more than 3
Acquired step shouldn't be more than 4
Acquired ground shouldn't be more than 3
Also, it might be good to make "fouls and other" red. | non_priority | autonomous moved to auto zone should be a check box yellow totes stacked or moved shouldn t be more than acquired step shouldn t be more than acquired ground shouldn t be more than also it might be good to make fouls and other red | 0 |
68,843 | 17,421,892,812 | IssuesEvent | 2021-08-04 03:07:20 | GoogleContainerTools/skaffold | https://api.github.com/repos/GoogleContainerTools/skaffold | closed | Buildpacks build fails on Apple M1: no matching manifest for linux/arm64/v8 | area/build build/buildpacks kind/friction meta/examples | Our buildpacks examples fail when building from an Apple M1:
```
fetching lifecycle image: no matching manifest for linux/arm64/v8 in the manifest list entries
```
This error happens as Skaffold does not maintain a list of trusted builders, and so all builders are marked as untrusted. With an untrusted builder, the pack library will not use the builder's embedded `lifecycle` binary and [instead attempts to run the lifecycle from a separate image](https://github.com/buildpacks/pack/blob/e53adb9c9e55b33e830f2e92bc4741cc32dc24f7/build.go#L329-L343). But recent lifecycle images (e.g., `buildpacksio/lifecycle:0.11.1`) point to a manifest list with images for `linux/amd64` and `windows/amd64`, and so the fetch fails. This has been filed upstream as https://github.com/buildpacks/pack/issues/1197.
An easy workaround is for the user to indicate in their `skaffold.yaml` that the builder is trusted so that the pack library will use the lifecycle from within the builder image:
```diff
--- skaffold.yaml
+++ skaffold.yaml
@@ -5,6 +5,7 @@ build:
- image: skaffold-buildpacks
buildpacks:
builder: "gcr.io/buildpacks/builder:v1"
+ trustBuilder: true
env:
- GOPROXY={{.GOPROXY}}
profiles:
```
The best fix for the moment is for Skaffold to indicate that the GCP Buildpacks builder is trusted by default.
The CNB lifecycle team is lifecycle image is also available for linux/arm64 (https://github.com/buildpacks/lifecycle/issues/435), which is non-trivial.
### Expected behavior
The following should succeed:
```
$ cd examples/buildpacks
$ cat skaffold.yaml
[...]
build:
artifacts:
- image: skaffold-buildpacks
buildpacks:
builder: "gcr.io/buildpacks/builder:v1"
env:
- GOPROXY={{.GOPROXY}}
[...]
$ skaffold build
```
### Actual behavior
```console
$ skaffold build
Generating tags...
- skaffold-buildpacks -> skaffold-buildpacks:v1.25.0-30-g3eb517587
Checking cache...
- skaffold-buildpacks: Not found. Building
Starting build...
Found [minikube] context, using local docker daemon.
Building [skaffold-buildpacks]...
v1: Pulling from buildpacks/builder
Digest: sha256:5f109c6becf6ecd70d7201de44775f21902e1b027ee68eb982bd55787eb25165
Status: Image is up to date for gcr.io/buildpacks/builder:v1
v1: Pulling from buildpacks/gcp/run
Digest: sha256:13535b83b3cfb66571907c574bca1cc1852ac6cf5b3096d3e654cd2d95bbecd6
Status: Image is up to date for gcr.io/buildpacks/gcp/run:v1
0.11.1: Pulling from buildpacksio/lifecycle
fetching lifecycle image: no matching manifest for linux/arm64/v8 in the manifest list entries
```
### Information
- Skaffold version: <!-- run `skaffold version` -->
- Operating system: <!-- name and version -->
- Installed via: <!-- skaffold.dev | Google Cloud SDK | Cloud Code | Chocolatey | Snap | Homebrew | ...-->
- Contents of skaffold.yaml:
```yaml
<paste your skaffold.yaml here>
```
### Steps to reproduce the behavior
1. a clonable repository with the sample skaffold project
2. `skaffold <command>`
3. ...
<!--
The logs from `skaffold ... -vdebug` can be very helpful.
Please remove or elide any confidential information.
-->
| 3.0 | Buildpacks build fails on Apple M1: no matching manifest for linux/arm64/v8 - Our buildpacks examples fail when building from an Apple M1:
```
fetching lifecycle image: no matching manifest for linux/arm64/v8 in the manifest list entries
```
This error happens as Skaffold does not maintain a list of trusted builders, and so all builders are marked as untrusted. With an untrusted builder, the pack library will not use the builder's embedded `lifecycle` binary and [instead attempts to run the lifecycle from a separate image](https://github.com/buildpacks/pack/blob/e53adb9c9e55b33e830f2e92bc4741cc32dc24f7/build.go#L329-L343). But recent lifecycle images (e.g., `buildpacksio/lifecycle:0.11.1`) point to a manifest list with images for `linux/amd64` and `windows/amd64`, and so the fetch fails. This has been filed upstream as https://github.com/buildpacks/pack/issues/1197.
An easy workaround is for the user to indicate in their `skaffold.yaml` that the builder is trusted so that the pack library will use the lifecycle from within the builder image:
```diff
--- skaffold.yaml
+++ skaffold.yaml
@@ -5,6 +5,7 @@ build:
- image: skaffold-buildpacks
buildpacks:
builder: "gcr.io/buildpacks/builder:v1"
+ trustBuilder: true
env:
- GOPROXY={{.GOPROXY}}
profiles:
```
The best fix for the moment is for Skaffold to indicate that the GCP Buildpacks builder is trusted by default.
The CNB lifecycle team is lifecycle image is also available for linux/arm64 (https://github.com/buildpacks/lifecycle/issues/435), which is non-trivial.
### Expected behavior
The following should succeed:
```
$ cd examples/buildpacks
$ cat skaffold.yaml
[...]
build:
artifacts:
- image: skaffold-buildpacks
buildpacks:
builder: "gcr.io/buildpacks/builder:v1"
env:
- GOPROXY={{.GOPROXY}}
[...]
$ skaffold build
```
### Actual behavior
```console
$ skaffold build
Generating tags...
- skaffold-buildpacks -> skaffold-buildpacks:v1.25.0-30-g3eb517587
Checking cache...
- skaffold-buildpacks: Not found. Building
Starting build...
Found [minikube] context, using local docker daemon.
Building [skaffold-buildpacks]...
v1: Pulling from buildpacks/builder
Digest: sha256:5f109c6becf6ecd70d7201de44775f21902e1b027ee68eb982bd55787eb25165
Status: Image is up to date for gcr.io/buildpacks/builder:v1
v1: Pulling from buildpacks/gcp/run
Digest: sha256:13535b83b3cfb66571907c574bca1cc1852ac6cf5b3096d3e654cd2d95bbecd6
Status: Image is up to date for gcr.io/buildpacks/gcp/run:v1
0.11.1: Pulling from buildpacksio/lifecycle
fetching lifecycle image: no matching manifest for linux/arm64/v8 in the manifest list entries
```
### Information
- Skaffold version: <!-- run `skaffold version` -->
- Operating system: <!-- name and version -->
- Installed via: <!-- skaffold.dev | Google Cloud SDK | Cloud Code | Chocolatey | Snap | Homebrew | ...-->
- Contents of skaffold.yaml:
```yaml
<paste your skaffold.yaml here>
```
### Steps to reproduce the behavior
1. a clonable repository with the sample skaffold project
2. `skaffold <command>`
3. ...
<!--
The logs from `skaffold ... -vdebug` can be very helpful.
Please remove or elide any confidential information.
-->
| non_priority | buildpacks build fails on apple no matching manifest for linux our buildpacks examples fail when building from an apple fetching lifecycle image no matching manifest for linux in the manifest list entries this error happens as skaffold does not maintain a list of trusted builders and so all builders are marked as untrusted with an untrusted builder the pack library will not use the builder s embedded lifecycle binary and but recent lifecycle images e g buildpacksio lifecycle point to a manifest list with images for linux and windows and so the fetch fails this has been filed upstream as an easy workaround is for the user to indicate in their skaffold yaml that the builder is trusted so that the pack library will use the lifecycle from within the builder image diff skaffold yaml skaffold yaml build image skaffold buildpacks buildpacks builder gcr io buildpacks builder trustbuilder true env goproxy goproxy profiles the best fix for the moment is for skaffold to indicate that the gcp buildpacks builder is trusted by default the cnb lifecycle team is lifecycle image is also available for linux which is non trivial expected behavior the following should succeed cd examples buildpacks cat skaffold yaml build artifacts image skaffold buildpacks buildpacks builder gcr io buildpacks builder env goproxy goproxy skaffold build actual behavior console skaffold build generating tags skaffold buildpacks skaffold buildpacks checking cache skaffold buildpacks not found building starting build found context using local docker daemon building pulling from buildpacks builder digest status image is up to date for gcr io buildpacks builder pulling from buildpacks gcp run digest status image is up to date for gcr io buildpacks gcp run pulling from buildpacksio lifecycle fetching lifecycle image no matching manifest for linux in the manifest list entries information skaffold version operating system installed via contents of skaffold yaml yaml steps to reproduce the behavior a clonable repository with the sample skaffold project skaffold the logs from skaffold vdebug can be very helpful please remove or elide any confidential information | 0 |
151,855 | 23,882,100,732 | IssuesEvent | 2022-09-08 02:51:34 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | opened | Disallow Rewards from being enabled and show clearer unavailable messaging for users in OFAC list countries | feature/rewards design/needs-mock-up policy OS/Android OS/Desktop | ## Description
If OS locale == country on OFAC list, then show Rewards is unavailable messaging (see designs) in (1) the Rewards panel and (2) Rewards settings page. (3) Hide the Rewards NTP widget.
| 1.0 | Disallow Rewards from being enabled and show clearer unavailable messaging for users in OFAC list countries - ## Description
If OS locale == country on OFAC list, then show Rewards is unavailable messaging (see designs) in (1) the Rewards panel and (2) Rewards settings page. (3) Hide the Rewards NTP widget.
| non_priority | disallow rewards from being enabled and show clearer unavailable messaging for users in ofac list countries description if os locale country on ofac list then show rewards is unavailable messaging see designs in the rewards panel and rewards settings page hide the rewards ntp widget | 0 |
51,716 | 6,194,294,754 | IssuesEvent | 2017-07-05 09:32:51 | cerner/clara-rules | https://api.github.com/repos/cerner/clara-rules | closed | Refactor tests for truth maintenance into new test_truth_maintenance.cljc file | testing | As the name suggests, I'm envisioning this file containing tests that validate that [truth maintenance](http://www.clara-rules.org/docs/truthmaint/) works. In terms of areas of code tested, while the tests would be tests of overall correctness (as is our current pattern) areas particularly covered by this test file would include but not be limited to [ProductionNode's left-retract](https://github.com/cerner/clara-rules/blob/0.15.0/src/main/clojure/clara/rules/engine.cljc#L358), [add-insertions!](https://github.com/cerner/clara-rules/blob/0.15.0/src/main/clojure/clara/rules/memory.cljc#L719), and [remove-insertions!](https://github.com/cerner/clara-rules/blob/0.15.0/src/main/clojure/clara/rules/memory.cljc#L726). | 1.0 | Refactor tests for truth maintenance into new test_truth_maintenance.cljc file - As the name suggests, I'm envisioning this file containing tests that validate that [truth maintenance](http://www.clara-rules.org/docs/truthmaint/) works. In terms of areas of code tested, while the tests would be tests of overall correctness (as is our current pattern) areas particularly covered by this test file would include but not be limited to [ProductionNode's left-retract](https://github.com/cerner/clara-rules/blob/0.15.0/src/main/clojure/clara/rules/engine.cljc#L358), [add-insertions!](https://github.com/cerner/clara-rules/blob/0.15.0/src/main/clojure/clara/rules/memory.cljc#L719), and [remove-insertions!](https://github.com/cerner/clara-rules/blob/0.15.0/src/main/clojure/clara/rules/memory.cljc#L726). | non_priority | refactor tests for truth maintenance into new test truth maintenance cljc file as the name suggests i m envisioning this file containing tests that validate that works in terms of areas of code tested while the tests would be tests of overall correctness as is our current pattern areas particularly covered by this test file would include but not be limited to and | 0 |
151,435 | 19,651,349,833 | IssuesEvent | 2022-01-10 07:36:08 | Shai-Demo-Org/JS-Demo | https://api.github.com/repos/Shai-Demo-Org/JS-Demo | opened | CVE-2020-7598 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.10.tgz</b>, <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.8.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- nodemon-1.19.1.tgz (Root Library)
- chokidar-2.1.6.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mkdirp/node_modules/minimist/package.json,/node_modules/nyc/node_modules/minimist/package.json,/node_modules/npm/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Shai-Demo-Org/JS-Demo/commit/1eadcbb3e24e6aade846a99b6e3bcf1ebe9500cc">1eadcbb3e24e6aade846a99b6e3bcf1ebe9500cc</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"forever:2.0.0;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.0","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"nodemon:1.19.1;chokidar:2.1.6;fsevents:1.2.9;node-pre-gyp:0.12.0;rc:1.2.8;minimist:1.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7598 (Medium) detected in multiple libraries - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.10.tgz</b>, <b>minimist-1.2.0.tgz</b>, <b>minimist-0.0.8.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.10.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- nodemon-1.19.1.tgz (Root Library)
- chokidar-2.1.6.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mkdirp/node_modules/minimist/package.json,/node_modules/nyc/node_modules/minimist/package.json,/node_modules/npm/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Shai-Demo-Org/JS-Demo/commit/1eadcbb3e24e6aade846a99b6e3bcf1ebe9500cc">1eadcbb3e24e6aade846a99b6e3bcf1ebe9500cc</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"forever:2.0.0;optimist:0.6.1;minimist:0.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"1.2.0","packageFilePaths":[null],"isTransitiveDependency":true,"dependencyTree":"nodemon:1.19.1;chokidar:2.1.6;fsevents:1.2.9;node-pre-gyp:0.12.0;rc:1.2.8;minimist:1.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false},{"packageType":"javascript/Node.js","packageName":"minimist","packageVersion":"0.0.8","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;mkdirp:0.5.1;minimist:0.0.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"minimist - 0.2.1,1.2.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7598","vulnerabilityDetails":"minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a \"constructor\" or \"__proto__\" payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598","cvss3Severity":"medium","cvss3Score":"5.6","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules minimist package json dependency hierarchy forever tgz root library optimist tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href dependency hierarchy nodemon tgz root library chokidar tgz fsevents tgz node pre gyp tgz rc tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules mkdirp node modules minimist package json node modules nyc node modules minimist package json node modules npm node modules mkdirp node modules minimist package json dependency hierarchy grunt npm install tgz root library npm tgz mkdirp tgz x minimist tgz vulnerable library found in head commit a href found in base branch main vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree forever optimist minimist isminimumfixversionavailable true minimumfixversion minimist isbinary false packagetype javascript node js packagename minimist packageversion packagefilepaths istransitivedependency true dependencytree nodemon chokidar fsevents node pre gyp rc minimist isminimumfixversionavailable true minimumfixversion minimist isbinary false packagetype javascript node js packagename minimist packageversion packagefilepaths istransitivedependency true dependencytree grunt npm install npm mkdirp minimist isminimumfixversionavailable true minimumfixversion minimist isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload vulnerabilityurl | 0 |
49,382 | 12,336,512,334 | IssuesEvent | 2020-05-14 13:42:02 | gradle/gradle | https://api.github.com/repos/gradle/gradle | closed | NullPointerException on updating hierarchical watches | @build-cache a:bug from:member | ```
Caused by: org.gradle.api.GradleException: Build cache entry 6ce9752b1f625341974870b5e810c309 from local build cache is invalid
at org.gradle.caching.internal.controller.DefaultBuildCacheController.load(DefaultBuildCacheController.java:103)
at org.gradle.internal.execution.steps.CacheStep.lambda$executeWithCache$0(CacheStep.java:78)
at org.gradle.internal.Try.ofFailable(Try.java:39)
at org.gradle.internal.execution.steps.CacheStep.executeWithCache(CacheStep.java:77)
... 57 more
Caused by: java.lang.NullPointerException
at org.gradle.internal.watch.vfs.impl.DelegatingDiffCapturingUpdateFunctionDecorator.lambda$decorate$2(DelegatingDiffCapturingUpdateFunctionDecorator.java:56)
at org.gradle.internal.snapshot.AtomicSnapshotHierarchyReference.update(AtomicSnapshotHierarchyReference.java:38)
at org.gradle.internal.vfs.impl.DefaultVirtualFileSystem.updateRoot(DefaultVirtualFileSystem.java:155)
at org.gradle.internal.vfs.impl.DefaultVirtualFileSystem.updateWithKnownSnapshot(DefaultVirtualFileSystem.java:193)
at org.gradle.internal.watch.vfs.impl.AbstractDelegatingVirtualFileSystem.updateWithKnownSnapshot(AbstractDelegatingVirtualFileSystem.java:63)
at org.gradle.internal.watch.vfs.impl.WatchingVirtualFileSystem.updateWithKnownSnapshot(WatchingVirtualFileSystem.java:51)
at org.gradle.internal.vfs.RoutingVirtualFileSystem.updateWithKnownSnapshot(RoutingVirtualFileSystem.java:95)
at org.gradle.caching.internal.controller.impl.DefaultBuildCacheCommandFactory$LoadCommand.lambda$snapshotUnpackedData$2(DefaultBuildCacheCommandFactory.java:140)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$TaskExecution.visitOutputTrees(ExecuteActionsTaskExecuter.java:352)
at org.gradle.caching.internal.controller.impl.DefaultBuildCacheCommandFactory$LoadCommand.snapshotUnpackedData(DefaultBuildCacheCommandFactory.java:122)
at org.gradle.caching.internal.controller.impl.DefaultBuildCacheCommandFactory$LoadCommand.load(DefaultBuildCacheCommandFactory.java:95)
at org.gradle.caching.internal.controller.DefaultBuildCacheController$Unpack$1.run(DefaultBuildCacheController.java:150)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:395)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:387)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:157)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:242)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:150)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.run(DefaultBuildOperationExecutor.java:84)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.run(DelegatingBuildOperationExecutor.java:31)
at org.gradle.caching.internal.controller.DefaultBuildCacheController$Unpack.execute(DefaultBuildCacheController.java:146)
at org.gradle.caching.internal.controller.DefaultBuildCacheController$Unpack.execute(DefaultBuildCacheController.java:135)
at org.gradle.caching.local.internal.DirectoryBuildCacheService.loadInsideLock(DirectoryBuildCacheService.java:117)
at org.gradle.caching.local.internal.DirectoryBuildCacheService.access$200(DirectoryBuildCacheService.java:42)
at org.gradle.caching.local.internal.DirectoryBuildCacheService$1.run(DirectoryBuildCacheService.java:99)
at org.gradle.internal.Factories$1.create(Factories.java:26)
at org.gradle.cache.internal.LockOnDemandCrossProcessCacheAccess.withFileLock(LockOnDemandCrossProcessCacheAccess.java:90)
at org.gradle.cache.internal.DefaultCacheAccess.withFileLock(DefaultCacheAccess.java:196)
at org.gradle.cache.internal.DefaultPersistentDirectoryStore.withFileLock(DefaultPersistentDirectoryStore.java:182)
at org.gradle.cache.internal.DefaultCacheFactory$ReferenceTrackingCache.withFileLock(DefaultCacheFactory.java:206)
at org.gradle.caching.local.internal.DirectoryBuildCacheService.loadLocally(DirectoryBuildCacheService.java:94)
at org.gradle.caching.internal.controller.service.DefaultLocalBuildCacheServiceHandle.load(DefaultLocalBuildCacheServiceHandle.java:49)
at org.gradle.caching.internal.controller.DefaultBuildCacheController.load(DefaultBuildCacheController.java:101)
... 60 more
```
See
https://builds.gradle.org/buildConfiguration/Gradle_Check_VfsRetention_30_bucket18/34841091?buildTab=overview
---
cc: @gradle/build-cache
| 1.0 | NullPointerException on updating hierarchical watches - ```
Caused by: org.gradle.api.GradleException: Build cache entry 6ce9752b1f625341974870b5e810c309 from local build cache is invalid
at org.gradle.caching.internal.controller.DefaultBuildCacheController.load(DefaultBuildCacheController.java:103)
at org.gradle.internal.execution.steps.CacheStep.lambda$executeWithCache$0(CacheStep.java:78)
at org.gradle.internal.Try.ofFailable(Try.java:39)
at org.gradle.internal.execution.steps.CacheStep.executeWithCache(CacheStep.java:77)
... 57 more
Caused by: java.lang.NullPointerException
at org.gradle.internal.watch.vfs.impl.DelegatingDiffCapturingUpdateFunctionDecorator.lambda$decorate$2(DelegatingDiffCapturingUpdateFunctionDecorator.java:56)
at org.gradle.internal.snapshot.AtomicSnapshotHierarchyReference.update(AtomicSnapshotHierarchyReference.java:38)
at org.gradle.internal.vfs.impl.DefaultVirtualFileSystem.updateRoot(DefaultVirtualFileSystem.java:155)
at org.gradle.internal.vfs.impl.DefaultVirtualFileSystem.updateWithKnownSnapshot(DefaultVirtualFileSystem.java:193)
at org.gradle.internal.watch.vfs.impl.AbstractDelegatingVirtualFileSystem.updateWithKnownSnapshot(AbstractDelegatingVirtualFileSystem.java:63)
at org.gradle.internal.watch.vfs.impl.WatchingVirtualFileSystem.updateWithKnownSnapshot(WatchingVirtualFileSystem.java:51)
at org.gradle.internal.vfs.RoutingVirtualFileSystem.updateWithKnownSnapshot(RoutingVirtualFileSystem.java:95)
at org.gradle.caching.internal.controller.impl.DefaultBuildCacheCommandFactory$LoadCommand.lambda$snapshotUnpackedData$2(DefaultBuildCacheCommandFactory.java:140)
at org.gradle.api.internal.tasks.execution.ExecuteActionsTaskExecuter$TaskExecution.visitOutputTrees(ExecuteActionsTaskExecuter.java:352)
at org.gradle.caching.internal.controller.impl.DefaultBuildCacheCommandFactory$LoadCommand.snapshotUnpackedData(DefaultBuildCacheCommandFactory.java:122)
at org.gradle.caching.internal.controller.impl.DefaultBuildCacheCommandFactory$LoadCommand.load(DefaultBuildCacheCommandFactory.java:95)
at org.gradle.caching.internal.controller.DefaultBuildCacheController$Unpack$1.run(DefaultBuildCacheController.java:150)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:395)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$RunnableBuildOperationWorker.execute(DefaultBuildOperationExecutor.java:387)
at org.gradle.internal.operations.DefaultBuildOperationExecutor$1.execute(DefaultBuildOperationExecutor.java:157)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:242)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.execute(DefaultBuildOperationExecutor.java:150)
at org.gradle.internal.operations.DefaultBuildOperationExecutor.run(DefaultBuildOperationExecutor.java:84)
at org.gradle.internal.operations.DelegatingBuildOperationExecutor.run(DelegatingBuildOperationExecutor.java:31)
at org.gradle.caching.internal.controller.DefaultBuildCacheController$Unpack.execute(DefaultBuildCacheController.java:146)
at org.gradle.caching.internal.controller.DefaultBuildCacheController$Unpack.execute(DefaultBuildCacheController.java:135)
at org.gradle.caching.local.internal.DirectoryBuildCacheService.loadInsideLock(DirectoryBuildCacheService.java:117)
at org.gradle.caching.local.internal.DirectoryBuildCacheService.access$200(DirectoryBuildCacheService.java:42)
at org.gradle.caching.local.internal.DirectoryBuildCacheService$1.run(DirectoryBuildCacheService.java:99)
at org.gradle.internal.Factories$1.create(Factories.java:26)
at org.gradle.cache.internal.LockOnDemandCrossProcessCacheAccess.withFileLock(LockOnDemandCrossProcessCacheAccess.java:90)
at org.gradle.cache.internal.DefaultCacheAccess.withFileLock(DefaultCacheAccess.java:196)
at org.gradle.cache.internal.DefaultPersistentDirectoryStore.withFileLock(DefaultPersistentDirectoryStore.java:182)
at org.gradle.cache.internal.DefaultCacheFactory$ReferenceTrackingCache.withFileLock(DefaultCacheFactory.java:206)
at org.gradle.caching.local.internal.DirectoryBuildCacheService.loadLocally(DirectoryBuildCacheService.java:94)
at org.gradle.caching.internal.controller.service.DefaultLocalBuildCacheServiceHandle.load(DefaultLocalBuildCacheServiceHandle.java:49)
at org.gradle.caching.internal.controller.DefaultBuildCacheController.load(DefaultBuildCacheController.java:101)
... 60 more
```
See
https://builds.gradle.org/buildConfiguration/Gradle_Check_VfsRetention_30_bucket18/34841091?buildTab=overview
---
cc: @gradle/build-cache
| non_priority | nullpointerexception on updating hierarchical watches caused by org gradle api gradleexception build cache entry from local build cache is invalid at org gradle caching internal controller defaultbuildcachecontroller load defaultbuildcachecontroller java at org gradle internal execution steps cachestep lambda executewithcache cachestep java at org gradle internal try offailable try java at org gradle internal execution steps cachestep executewithcache cachestep java more caused by java lang nullpointerexception at org gradle internal watch vfs impl delegatingdiffcapturingupdatefunctiondecorator lambda decorate delegatingdiffcapturingupdatefunctiondecorator java at org gradle internal snapshot atomicsnapshothierarchyreference update atomicsnapshothierarchyreference java at org gradle internal vfs impl defaultvirtualfilesystem updateroot defaultvirtualfilesystem java at org gradle internal vfs impl defaultvirtualfilesystem updatewithknownsnapshot defaultvirtualfilesystem java at org gradle internal watch vfs impl abstractdelegatingvirtualfilesystem updatewithknownsnapshot abstractdelegatingvirtualfilesystem java at org gradle internal watch vfs impl watchingvirtualfilesystem updatewithknownsnapshot watchingvirtualfilesystem java at org gradle internal vfs routingvirtualfilesystem updatewithknownsnapshot routingvirtualfilesystem java at org gradle caching internal controller impl defaultbuildcachecommandfactory loadcommand lambda snapshotunpackeddata defaultbuildcachecommandfactory java at org gradle api internal tasks execution executeactionstaskexecuter taskexecution visitoutputtrees executeactionstaskexecuter java at org gradle caching internal controller impl defaultbuildcachecommandfactory loadcommand snapshotunpackeddata defaultbuildcachecommandfactory java at org gradle caching internal controller impl defaultbuildcachecommandfactory loadcommand load defaultbuildcachecommandfactory java at org gradle caching internal controller defaultbuildcachecontroller unpack run defaultbuildcachecontroller java at org gradle internal operations defaultbuildoperationexecutor runnablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor runnablebuildoperationworker execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor execute defaultbuildoperationexecutor java at org gradle internal operations defaultbuildoperationexecutor run defaultbuildoperationexecutor java at org gradle internal operations delegatingbuildoperationexecutor run delegatingbuildoperationexecutor java at org gradle caching internal controller defaultbuildcachecontroller unpack execute defaultbuildcachecontroller java at org gradle caching internal controller defaultbuildcachecontroller unpack execute defaultbuildcachecontroller java at org gradle caching local internal directorybuildcacheservice loadinsidelock directorybuildcacheservice java at org gradle caching local internal directorybuildcacheservice access directorybuildcacheservice java at org gradle caching local internal directorybuildcacheservice run directorybuildcacheservice java at org gradle internal factories create factories java at org gradle cache internal lockondemandcrossprocesscacheaccess withfilelock lockondemandcrossprocesscacheaccess java at org gradle cache internal defaultcacheaccess withfilelock defaultcacheaccess java at org gradle cache internal defaultpersistentdirectorystore withfilelock defaultpersistentdirectorystore java at org gradle cache internal defaultcachefactory referencetrackingcache withfilelock defaultcachefactory java at org gradle caching local internal directorybuildcacheservice loadlocally directorybuildcacheservice java at org gradle caching internal controller service defaultlocalbuildcacheservicehandle load defaultlocalbuildcacheservicehandle java at org gradle caching internal controller defaultbuildcachecontroller load defaultbuildcachecontroller java more see cc gradle build cache | 0 |
18,727 | 3,703,163,370 | IssuesEvent | 2016-02-29 19:25:01 | rofrischmann/react-look | https://api.github.com/repos/rofrischmann/react-look | opened | Improve Test Environment | highprio test | As development (again) kind of really went fast, there are still tests missing or badly written/mocked. We should have a clean test interface, with useful utils and tests for every core module of Look in order to prevent bugs especially for React Native (which is not tested at all right now).
This could be investigated while transforming the repository architecture.
Note: As coverage right now is broken (this issue got caused by mocking React Native lately) it's hard to tell which parts are properly tested and not. | 1.0 | Improve Test Environment - As development (again) kind of really went fast, there are still tests missing or badly written/mocked. We should have a clean test interface, with useful utils and tests for every core module of Look in order to prevent bugs especially for React Native (which is not tested at all right now).
This could be investigated while transforming the repository architecture.
Note: As coverage right now is broken (this issue got caused by mocking React Native lately) it's hard to tell which parts are properly tested and not. | non_priority | improve test environment as development again kind of really went fast there are still tests missing or badly written mocked we should have a clean test interface with useful utils and tests for every core module of look in order to prevent bugs especially for react native which is not tested at all right now this could be investigated while transforming the repository architecture note as coverage right now is broken this issue got caused by mocking react native lately it s hard to tell which parts are properly tested and not | 0 |
20,129 | 3,794,141,498 | IssuesEvent | 2016-03-22 16:01:46 | CentechMTL/TableauDeBord | https://api.github.com/repos/CentechMTL/TableauDeBord | closed | Room type color | enhancement quick fix Ready to test | Currently the room color is determined by the ID of its room type (2 = centech, 3 = rental, 1&4+ = unavailable). So if a room type is deleted, it is no longer possible to get that color until the table is reset.
### Solution
- Add a column for room type color
- Add a column for room type alternative color
- For the room stat (e.g. used/unused rental)
- New issue to hide the option if not rental could be nice
- Send column value through room options instead of using current switch/case | 1.0 | Room type color - Currently the room color is determined by the ID of its room type (2 = centech, 3 = rental, 1&4+ = unavailable). So if a room type is deleted, it is no longer possible to get that color until the table is reset.
### Solution
- Add a column for room type color
- Add a column for room type alternative color
- For the room stat (e.g. used/unused rental)
- New issue to hide the option if not rental could be nice
- Send column value through room options instead of using current switch/case | non_priority | room type color currently the room color is determined by the id of its room type centech rental unavailable so if a room type is deleted it is no longer possible to get that color until the table is reset solution add a column for room type color add a column for room type alternative color for the room stat e g used unused rental new issue to hide the option if not rental could be nice send column value through room options instead of using current switch case | 0 |
209,351 | 16,017,410,366 | IssuesEvent | 2021-04-20 17:47:22 | Esri/calcite-components | https://api.github.com/repos/Esri/calcite-components | opened | Unstable Test: color-picker tests timing out | 2 - in development p - high testing | ## Summary
**Which component?:** calcite-color-picker
**Which test(s)?:** <!-- list unstable test(s) or suite -->
Varied between runs, but some of these are:
**Test error:**
```
FAIL src/components/calcite-color-picker/calcite-color-picker.e2e.ts (336.948 s)
● calcite-color-picker › color inputs › color gets propagated to support inputs › when no-color › restores previous color value when a nudge key is pressed
: Timeout - Async callback was not invoked within the 30000 ms timeout specified by jest.setTimeout.Timeout - Async callback was not invoked within the 30000 ms timeout specified by jest.setTimeout.Error:
850 | });
851 |
> 852 | it("restores previous color value when a nudge key is pressed", async () => {
| ^
853 | const consistentRgbHsvChannelValue = "0";
854 | const initialValue = "#".padEnd(7, consistentRgbHsvChannelValue);
855 |
at new Spec (node_modules/jest-jasmine2/build/jasmine/Spec.js:116:22)
at Suite.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:852:9)
● calcite-color-picker › color storage › allows saving unique colors
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
● calcite-color-picker › color storage › loads saved colors
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
● calcite-color-picker ��� color storage › allows removing stored colors
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
● calcite-color-picker › color storage › does not allow saving/removing when no-color is set
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
```
**PR that skipped the test:** #1995
## Additional Info <!-- any info that may help fix the test -->
| 1.0 | Unstable Test: color-picker tests timing out - ## Summary
**Which component?:** calcite-color-picker
**Which test(s)?:** <!-- list unstable test(s) or suite -->
Varied between runs, but some of these are:
**Test error:**
```
FAIL src/components/calcite-color-picker/calcite-color-picker.e2e.ts (336.948 s)
● calcite-color-picker › color inputs › color gets propagated to support inputs › when no-color › restores previous color value when a nudge key is pressed
: Timeout - Async callback was not invoked within the 30000 ms timeout specified by jest.setTimeout.Timeout - Async callback was not invoked within the 30000 ms timeout specified by jest.setTimeout.Error:
850 | });
851 |
> 852 | it("restores previous color value when a nudge key is pressed", async () => {
| ^
853 | const consistentRgbHsvChannelValue = "0";
854 | const initialValue = "#".padEnd(7, consistentRgbHsvChannelValue);
855 |
at new Spec (node_modules/jest-jasmine2/build/jasmine/Spec.js:116:22)
at Suite.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:852:9)
● calcite-color-picker › color storage › allows saving unique colors
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
● calcite-color-picker › color storage › loads saved colors
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
● calcite-color-picker ��� color storage › allows removing stored colors
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
● calcite-color-picker › color storage › does not allow saving/removing when no-color is set
The page was already closed
506 |
507 | await inputOrHexInput.type(value);
> 508 | await page.waitForChanges();
| ^
509 |
510 | await page.keyboard.press("Enter");
511 | await page.waitForChanges();
at Page.r (node_modules/@stencil/core/testing/index.js:3793:11)
at clearAndEnterValue (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:508:18)
at assertChannelValueNudge (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:872:13)
at Object.<anonymous> (src/components/calcite-color-picker/calcite-color-picker.e2e.ts:911:11)
```
**PR that skipped the test:** #1995
## Additional Info <!-- any info that may help fix the test -->
| non_priority | unstable test color picker tests timing out summary which component calcite color picker which test s varied between runs but some of these are test error fail src components calcite color picker calcite color picker ts s ● calcite color picker › color inputs › color gets propagated to support inputs › when no color › restores previous color value when a nudge key is pressed timeout async callback was not invoked within the ms timeout specified by jest settimeout timeout async callback was not invoked within the ms timeout specified by jest settimeout error it restores previous color value when a nudge key is pressed async const consistentrgbhsvchannelvalue const initialvalue padend consistentrgbhsvchannelvalue at new spec node modules jest build jasmine spec js at suite src components calcite color picker calcite color picker ts ● calcite color picker › color storage › allows saving unique colors the page was already closed await inputorhexinput type value await page waitforchanges await page keyboard press enter await page waitforchanges at page r node modules stencil core testing index js at clearandentervalue src components calcite color picker calcite color picker ts at assertchannelvaluenudge src components calcite color picker calcite color picker ts at object src components calcite color picker calcite color picker ts ● calcite color picker › color storage › loads saved colors the page was already closed await inputorhexinput type value await page waitforchanges await page keyboard press enter await page waitforchanges at page r node modules stencil core testing index js at clearandentervalue src components calcite color picker calcite color picker ts at assertchannelvaluenudge src components calcite color picker calcite color picker ts at object src components calcite color picker calcite color picker ts ● calcite color picker ��� color storage › allows removing stored colors the page was already closed await inputorhexinput type value await page waitforchanges await page keyboard press enter await page waitforchanges at page r node modules stencil core testing index js at clearandentervalue src components calcite color picker calcite color picker ts at assertchannelvaluenudge src components calcite color picker calcite color picker ts at object src components calcite color picker calcite color picker ts ● calcite color picker › color storage › does not allow saving removing when no color is set the page was already closed await inputorhexinput type value await page waitforchanges await page keyboard press enter await page waitforchanges at page r node modules stencil core testing index js at clearandentervalue src components calcite color picker calcite color picker ts at assertchannelvaluenudge src components calcite color picker calcite color picker ts at object src components calcite color picker calcite color picker ts pr that skipped the test additional info | 0 |
130,420 | 18,155,799,456 | IssuesEvent | 2021-09-27 01:16:12 | saif-khan1211/First_real_scan | https://api.github.com/repos/saif-khan1211/First_real_scan | opened | CVE-2021-39153 (High) detected in xstream-1.4.8.jar | security vulnerability | ## CVE-2021-39153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.8.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to vulnerable library: First_real_scan/target/libs/provided/xstream-1.4.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.8.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream, if using the version out of the box with Java runtime version 14 to 8 or with JavaFX installed. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.
<p>Publish Date: 2021-08-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153>CVE-2021-39153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-39153">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-39153</a></p>
<p>Release Date: 2021-08-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.18</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-39153 (High) detected in xstream-1.4.8.jar - ## CVE-2021-39153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.8.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to vulnerable library: First_real_scan/target/libs/provided/xstream-1.4.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **xstream-1.4.8.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XStream is a simple library to serialize objects to XML and back again. In affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream, if using the version out of the box with Java runtime version 14 to 8 or with JavaFX installed. No user is affected, who followed the recommendation to setup XStream's security framework with a whitelist limited to the minimal required types. XStream 1.4.18 uses no longer a blacklist by default, since it cannot be secured for general purpose.
<p>Publish Date: 2021-08-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39153>CVE-2021-39153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-39153">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-39153</a></p>
<p>Release Date: 2021-08-23</p>
<p>Fix Resolution: com.thoughtworks.xstream:xstream:1.4.18</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in xstream jar cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back path to vulnerable library first real scan target libs provided xstream jar dependency hierarchy x xstream jar vulnerable library found in base branch main vulnerability details xstream is a simple library to serialize objects to xml and back again in affected versions this vulnerability may allow a remote attacker to load and execute arbitrary code from a remote host only by manipulating the processed input stream if using the version out of the box with java runtime version to or with javafx installed no user is affected who followed the recommendation to setup xstream s security framework with a whitelist limited to the minimal required types xstream uses no longer a blacklist by default since it cannot be secured for general purpose publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com thoughtworks xstream xstream step up your open source security game with whitesource | 0 |
303,539 | 23,028,733,472 | IssuesEvent | 2022-07-22 11:54:21 | slsa-framework/slsa-github-generator | https://api.github.com/repos/slsa-framework/slsa-github-generator | opened | [feature] CONTRIBUTING.md documentation. | type:documentation type:feature | Add information about the logistics of contributing and pointers on how to get started contributing to the project, which issues to look at first, etc.
Probably need something about OpenSSF since it's an OpenSSF project. Does OpenSSF require a CLA? We currently don't enforce that. | 1.0 | [feature] CONTRIBUTING.md documentation. - Add information about the logistics of contributing and pointers on how to get started contributing to the project, which issues to look at first, etc.
Probably need something about OpenSSF since it's an OpenSSF project. Does OpenSSF require a CLA? We currently don't enforce that. | non_priority | contributing md documentation add information about the logistics of contributing and pointers on how to get started contributing to the project which issues to look at first etc probably need something about openssf since it s an openssf project does openssf require a cla we currently don t enforce that | 0 |
102,328 | 11,288,259,272 | IssuesEvent | 2020-01-16 07:23:47 | wirepas/backend-client | https://api.github.com/repos/wirepas/backend-client | opened | [BUG] RX_time incorrectly propagated | documentation framework/bug question | **Describe the bug**
The rx_time in the decoded messages is incorrect.
**Expected behavior**
The rx_time should be the same as the gateway received time.
| 1.0 | [BUG] RX_time incorrectly propagated - **Describe the bug**
The rx_time in the decoded messages is incorrect.
**Expected behavior**
The rx_time should be the same as the gateway received time.
| non_priority | rx time incorrectly propagated describe the bug the rx time in the decoded messages is incorrect expected behavior the rx time should be the same as the gateway received time | 0 |
97,001 | 16,177,709,817 | IssuesEvent | 2021-05-03 09:39:31 | Vento-Nuenenen/inowo | https://api.github.com/repos/Vento-Nuenenen/inowo | opened | CVE-2021-23368 (Medium) detected in postcss-7.0.21.tgz, postcss-7.0.35.tgz | security vulnerability | ## CVE-2021-23368 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.21.tgz</b>, <b>postcss-7.0.35.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.21.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>Path to dependency file: inowo/package.json</p>
<p>Path to vulnerable library: inowo/node_modules/resolve-url-loader/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- resolve-url-loader-3.1.3.tgz (Root Library)
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.35.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz</a></p>
<p>Path to dependency file: inowo/package.json</p>
<p>Path to vulnerable library: inowo/node_modules/stylehacks/node_modules/postcss/package.json,inowo/node_modules/postcss-svgo/node_modules/postcss/package.json,inowo/node_modules/cssnano-util-raw-cache/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-whitespace/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-url/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-charset/node_modules/postcss/package.json,inowo/node_modules/postcss-merge-rules/node_modules/postcss/package.json,inowo/node_modules/postcss-ordered-values/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-timing-functions/node_modules/postcss/package.json,inowo/node_modules/cssnano-preset-default/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-overridden/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-selectors/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-positions/node_modules/postcss/package.json,inowo/node_modules/css-declaration-sorter/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-unicode/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-repeat-style/node_modules/postcss/package.json,inowo/node_modules/postcss-calc/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-font-values/node_modules/postcss/package.json,inowo/node_modules/postcss-convert-values/node_modules/postcss/package.json,inowo/node_modules/postcss-reduce-initial/node_modules/postcss/package.json,inowo/node_modules/postcss-reduce-transforms/node_modules/postcss/package.json,inowo/node_modules/@types/cssnano/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-gradients/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-params/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-duplicates/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-string/node_modules/postcss/package.json,inowo/node_modules/cssnano/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-empty/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-comments/node_modules/postcss/package.json,inowo/node_modules/postcss-colormin/node_modules/postcss/package.json,inowo/node_modules/postcss-unique-selectors/node_modules/postcss/package.json,inowo/node_modules/postcss-merge-longhand/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-display-values/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-6.0.18.tgz (Root Library)
- cssnano-4.0.0.tgz
- :x: **postcss-7.0.35.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Vento-Nuenenen/inowo/commit/fad65f881db1646a868abc21dbc9202e3e4c7e99">fad65f881db1646a868abc21dbc9202e3e4c7e99</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution: postcss -8.2.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23368 (Medium) detected in postcss-7.0.21.tgz, postcss-7.0.35.tgz - ## CVE-2021-23368 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.21.tgz</b>, <b>postcss-7.0.35.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.21.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>Path to dependency file: inowo/package.json</p>
<p>Path to vulnerable library: inowo/node_modules/resolve-url-loader/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- resolve-url-loader-3.1.3.tgz (Root Library)
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.35.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.35.tgz</a></p>
<p>Path to dependency file: inowo/package.json</p>
<p>Path to vulnerable library: inowo/node_modules/stylehacks/node_modules/postcss/package.json,inowo/node_modules/postcss-svgo/node_modules/postcss/package.json,inowo/node_modules/cssnano-util-raw-cache/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-whitespace/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-url/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-charset/node_modules/postcss/package.json,inowo/node_modules/postcss-merge-rules/node_modules/postcss/package.json,inowo/node_modules/postcss-ordered-values/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-timing-functions/node_modules/postcss/package.json,inowo/node_modules/cssnano-preset-default/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-overridden/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-selectors/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-positions/node_modules/postcss/package.json,inowo/node_modules/css-declaration-sorter/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-unicode/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-repeat-style/node_modules/postcss/package.json,inowo/node_modules/postcss-calc/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-font-values/node_modules/postcss/package.json,inowo/node_modules/postcss-convert-values/node_modules/postcss/package.json,inowo/node_modules/postcss-reduce-initial/node_modules/postcss/package.json,inowo/node_modules/postcss-reduce-transforms/node_modules/postcss/package.json,inowo/node_modules/@types/cssnano/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-gradients/node_modules/postcss/package.json,inowo/node_modules/postcss-minify-params/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-duplicates/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-string/node_modules/postcss/package.json,inowo/node_modules/cssnano/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-empty/node_modules/postcss/package.json,inowo/node_modules/postcss-discard-comments/node_modules/postcss/package.json,inowo/node_modules/postcss-colormin/node_modules/postcss/package.json,inowo/node_modules/postcss-unique-selectors/node_modules/postcss/package.json,inowo/node_modules/postcss-merge-longhand/node_modules/postcss/package.json,inowo/node_modules/postcss-normalize-display-values/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-6.0.18.tgz (Root Library)
- cssnano-4.0.0.tgz
- :x: **postcss-7.0.35.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Vento-Nuenenen/inowo/commit/fad65f881db1646a868abc21dbc9202e3e4c7e99">fad65f881db1646a868abc21dbc9202e3e4c7e99</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution: postcss -8.2.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in postcss tgz postcss tgz cve medium severity vulnerability vulnerable libraries postcss tgz postcss tgz postcss tgz tool for transforming styles with js plugins library home page a href path to dependency file inowo package json path to vulnerable library inowo node modules resolve url loader node modules postcss package json dependency hierarchy resolve url loader tgz root library x postcss tgz vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href path to dependency file inowo package json path to vulnerable library inowo node modules stylehacks node modules postcss package json inowo node modules postcss svgo node modules postcss package json inowo node modules cssnano util raw cache node modules postcss package json inowo node modules postcss normalize whitespace node modules postcss package json inowo node modules postcss normalize url node modules postcss package json inowo node modules postcss normalize charset node modules postcss package json inowo node modules postcss merge rules node modules postcss package json inowo node modules postcss ordered values node modules postcss package json inowo node modules postcss normalize timing functions node modules postcss package json inowo node modules cssnano preset default node modules postcss package json inowo node modules postcss discard overridden node modules postcss package json inowo node modules postcss minify selectors node modules postcss package json inowo node modules postcss normalize positions node modules postcss package json inowo node modules css declaration sorter node modules postcss package json inowo node modules postcss normalize unicode node modules postcss package json inowo node modules postcss normalize repeat style node modules postcss package json inowo node modules postcss calc node modules postcss package json inowo node modules postcss minify font values node modules postcss package json inowo node modules postcss convert values node modules postcss package json inowo node modules postcss reduce initial node modules postcss package json inowo node modules postcss reduce transforms node modules postcss package json inowo node modules types cssnano node modules postcss package json inowo node modules postcss minify gradients node modules postcss package json inowo node modules postcss minify params node modules postcss package json inowo node modules postcss discard duplicates node modules postcss package json inowo node modules postcss normalize string node modules postcss package json inowo node modules cssnano node modules postcss package json inowo node modules postcss discard empty node modules postcss package json inowo node modules postcss discard comments node modules postcss package json inowo node modules postcss colormin node modules postcss package json inowo node modules postcss unique selectors node modules postcss package json inowo node modules postcss merge longhand node modules postcss package json inowo node modules postcss normalize display values node modules postcss package json dependency hierarchy laravel mix tgz root library cssnano tgz x postcss tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package postcss from and before are vulnerable to regular expression denial of service redos during source map parsing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution postcss step up your open source security game with whitesource | 0 |
154,478 | 12,215,878,583 | IssuesEvent | 2020-05-01 13:58:25 | aces/Loris | https://api.github.com/repos/aces/Loris | closed | [user_accounts] error_log pollution when removing pending approval | 23.0.0-testing Bug | **Describe the bug**
I receive the following errors in error_log when the admin is removing `pending approval` from a request account.
`Notice: Undefined index: permID in /Users/alizee/Development/GitHub/McGill/Loris/modules/user_accounts/php/edit_user.class.inc on line 216`
`Warning: array_keys() expects parameter 1 to be array, null given in /Users/alizee/Development/GitHub/McGill/Loris/modules/user_accounts/php/edit_user.class.inc on line 216`
**To Reproduce**
Steps to reproduce the behavior (attach screenshots if applicable):
1. Request account
2. Go to user_accounts change user from pending approval and check the box Generate new password and Send email to user.
3. See error | 1.0 | [user_accounts] error_log pollution when removing pending approval - **Describe the bug**
I receive the following errors in error_log when the admin is removing `pending approval` from a request account.
`Notice: Undefined index: permID in /Users/alizee/Development/GitHub/McGill/Loris/modules/user_accounts/php/edit_user.class.inc on line 216`
`Warning: array_keys() expects parameter 1 to be array, null given in /Users/alizee/Development/GitHub/McGill/Loris/modules/user_accounts/php/edit_user.class.inc on line 216`
**To Reproduce**
Steps to reproduce the behavior (attach screenshots if applicable):
1. Request account
2. Go to user_accounts change user from pending approval and check the box Generate new password and Send email to user.
3. See error | non_priority | error log pollution when removing pending approval describe the bug i receive the following errors in error log when the admin is removing pending approval from a request account notice undefined index permid in users alizee development github mcgill loris modules user accounts php edit user class inc on line warning array keys expects parameter to be array null given in users alizee development github mcgill loris modules user accounts php edit user class inc on line to reproduce steps to reproduce the behavior attach screenshots if applicable request account go to user accounts change user from pending approval and check the box generate new password and send email to user see error | 0 |
109,947 | 23,847,273,094 | IssuesEvent | 2022-09-06 14:53:58 | gitpod-io/gitpod | https://api.github.com/repos/gitpod-io/gitpod | closed | [code-desktop] Align on a way to ensure Gitpod API compatibility between IDE clients and SH installations. | self-hosted component: server team: IDE editor: code (desktop) | - We decided to change how ouath2 endpoint works. It should ignore unknown scopes, verify and return only subset of known scopes. Clients should use returned scopes as source of truth to check whether features are present. It is for instance how GitHub auth works.
- We will still need to adhere to `api/version` for 2 SH releases which has changes to ouath2 endpoint. After this check can be removed.
Internal RFC [[1](https://www.notion.so/gitpod/Gitpod-Server-API-compatibility-check-ee00fcfe60a84c1e8e018ab6c06c1f5d)] | 1.0 | [code-desktop] Align on a way to ensure Gitpod API compatibility between IDE clients and SH installations. - - We decided to change how ouath2 endpoint works. It should ignore unknown scopes, verify and return only subset of known scopes. Clients should use returned scopes as source of truth to check whether features are present. It is for instance how GitHub auth works.
- We will still need to adhere to `api/version` for 2 SH releases which has changes to ouath2 endpoint. After this check can be removed.
Internal RFC [[1](https://www.notion.so/gitpod/Gitpod-Server-API-compatibility-check-ee00fcfe60a84c1e8e018ab6c06c1f5d)] | non_priority | align on a way to ensure gitpod api compatibility between ide clients and sh installations we decided to change how endpoint works it should ignore unknown scopes verify and return only subset of known scopes clients should use returned scopes as source of truth to check whether features are present it is for instance how github auth works we will still need to adhere to api version for sh releases which has changes to endpoint after this check can be removed internal rfc | 0 |
144,323 | 19,286,191,856 | IssuesEvent | 2021-12-11 01:57:53 | vwasthename/iaf | https://api.github.com/repos/vwasthename/iaf | opened | CVE-2018-20676 (Medium) detected in bootstrap-3.3.6.js, bootstrap-3.3.6.min.js | security vulnerability | ## CVE-2018-20676 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-3.3.6.js</b>, <b>bootstrap-3.3.6.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-3.3.6.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.js</a></p>
<p>Path to vulnerable library: iaf/gui/js/bootstrap/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.js** (Vulnerable Library)
</details>
<details><summary><b>bootstrap-3.3.6.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to dependency file: iaf/webapp/src/main/webapp/iaf/gui/index.jsp</p>
<p>Path to vulnerable library: iaf/gui/js/bootstrap/bootstrap.min.js,iaf/gui/js/bootstrap/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-20676 (Medium) detected in bootstrap-3.3.6.js, bootstrap-3.3.6.min.js - ## CVE-2018-20676 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-3.3.6.js</b>, <b>bootstrap-3.3.6.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-3.3.6.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.js</a></p>
<p>Path to vulnerable library: iaf/gui/js/bootstrap/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.js** (Vulnerable Library)
</details>
<details><summary><b>bootstrap-3.3.6.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.6/js/bootstrap.min.js</a></p>
<p>Path to dependency file: iaf/webapp/src/main/webapp/iaf/gui/index.jsp</p>
<p>Path to vulnerable library: iaf/gui/js/bootstrap/bootstrap.min.js,iaf/gui/js/bootstrap/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.6.min.js** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bootstrap js bootstrap min js cve medium severity vulnerability vulnerable libraries bootstrap js bootstrap min js bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library iaf gui js bootstrap bootstrap js dependency hierarchy x bootstrap js vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file iaf webapp src main webapp iaf gui index jsp path to vulnerable library iaf gui js bootstrap bootstrap min js iaf gui js bootstrap bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in base branch master vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap step up your open source security game with whitesource | 0 |
24,174 | 4,064,237,584 | IssuesEvent | 2016-05-26 05:29:33 | TEAMMATES/teammates | https://api.github.com/repos/TEAMMATES/teammates | closed | AdminEmailPageUiTest sometimes fails | a-Testing f-Admin p.Medium | ```
java.lang.AssertionError:
at org.testng.AssertJUnit.fail(AssertJUnit.java:59)
at org.testng.AssertJUnit.assertTrue(AssertJUnit.java:24)
at org.testng.AssertJUnit.assertFalse(AssertJUnit.java:41)
at org.testng.AssertJUnit.assertFalse(AssertJUnit.java:49)
at teammates.test.cases.ui.browsertests.AdminEmailPageUiTest.testCompose(AdminEmailPageUiTest.java:72)
at teammates.test.cases.ui.browsertests.AdminEmailPageUiTest.allTests(AdminEmailPageUiTest.java:35)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:84)
at org.testng.internal.Invoker.invokeMethod(Invoker.java:714)
at org.testng.internal.Invoker.invokeTestMethod(Invoker.java:901)
at org.testng.internal.Invoker.invokeTestMethods(Invoker.java:1231)
at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:127)
at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:111)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1145)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:615)
at java.lang.Thread.run(Thread.java:745)
``` | 1.0 | AdminEmailPageUiTest sometimes fails - ```
java.lang.AssertionError:
at org.testng.AssertJUnit.fail(AssertJUnit.java:59)
at org.testng.AssertJUnit.assertTrue(AssertJUnit.java:24)
at org.testng.AssertJUnit.assertFalse(AssertJUnit.java:41)
at org.testng.AssertJUnit.assertFalse(AssertJUnit.java:49)
at teammates.test.cases.ui.browsertests.AdminEmailPageUiTest.testCompose(AdminEmailPageUiTest.java:72)
at teammates.test.cases.ui.browsertests.AdminEmailPageUiTest.allTests(AdminEmailPageUiTest.java:35)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:84)
at org.testng.internal.Invoker.invokeMethod(Invoker.java:714)
at org.testng.internal.Invoker.invokeTestMethod(Invoker.java:901)
at org.testng.internal.Invoker.invokeTestMethods(Invoker.java:1231)
at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:127)
at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:111)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1145)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:615)
at java.lang.Thread.run(Thread.java:745)
``` | non_priority | adminemailpageuitest sometimes fails java lang assertionerror at org testng assertjunit fail assertjunit java at org testng assertjunit asserttrue assertjunit java at org testng assertjunit assertfalse assertjunit java at org testng assertjunit assertfalse assertjunit java at teammates test cases ui browsertests adminemailpageuitest testcompose adminemailpageuitest java at teammates test cases ui browsertests adminemailpageuitest alltests adminemailpageuitest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal invoker invokemethod invoker java at org testng internal invoker invoketestmethod invoker java at org testng internal invoker invoketestmethods invoker java at org testng internal testmethodworker invoketestmethods testmethodworker java at org testng internal testmethodworker run testmethodworker java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java | 0 |
88,595 | 10,575,564,971 | IssuesEvent | 2019-10-07 15:58:28 | GoogleChromeLabs/adaptive-loading | https://api.github.com/repos/GoogleChromeLabs/adaptive-loading | closed | [docs] Update README with links to all implementations | documentation | We have been landing quite a few new Node.js based demos lately and have not been updating the README to index them in a single place (so folks know where to go check out the live demo links). Let's update the main project README to account for them.
cc @anton-karlovskiy | 1.0 | [docs] Update README with links to all implementations - We have been landing quite a few new Node.js based demos lately and have not been updating the README to index them in a single place (so folks know where to go check out the live demo links). Let's update the main project README to account for them.
cc @anton-karlovskiy | non_priority | update readme with links to all implementations we have been landing quite a few new node js based demos lately and have not been updating the readme to index them in a single place so folks know where to go check out the live demo links let s update the main project readme to account for them cc anton karlovskiy | 0 |
10,783 | 12,752,861,113 | IssuesEvent | 2020-06-27 18:45:37 | Xalcon/TorchMaster | https://api.github.com/repos/Xalcon/TorchMaster | opened | quark:foxhound not being blocked | investigating mod compatibility | As reported on curseforge, the foxhound entity is not being blocked by either the mega torch or the dread lamp. The `/torchmaster entitydump` lists the foxhound as being assigned to the dreadlamp. Explicitly adding the foxhound to the mega torch does work as a workaround. I need to further investigate how this happens. | True | quark:foxhound not being blocked - As reported on curseforge, the foxhound entity is not being blocked by either the mega torch or the dread lamp. The `/torchmaster entitydump` lists the foxhound as being assigned to the dreadlamp. Explicitly adding the foxhound to the mega torch does work as a workaround. I need to further investigate how this happens. | non_priority | quark foxhound not being blocked as reported on curseforge the foxhound entity is not being blocked by either the mega torch or the dread lamp the torchmaster entitydump lists the foxhound as being assigned to the dreadlamp explicitly adding the foxhound to the mega torch does work as a workaround i need to further investigate how this happens | 0 |
342,928 | 24,761,791,789 | IssuesEvent | 2022-10-22 02:27:09 | sg05060/SKKU_TermProject | https://api.github.com/repos/sg05060/SKKU_TermProject | closed | 전체 회의록 | documentation | 회의록 양식(ex)
- 일시 : 2022/04/10
- 장소 : 오프라인, 해동
- 주제 : term project 환경 설명
- 인원 : 박상현, 최보열, etc
내용
- github 사용법
- program
- project
- 일정
- 진행 사항
| 1.0 | 전체 회의록 - 회의록 양식(ex)
- 일시 : 2022/04/10
- 장소 : 오프라인, 해동
- 주제 : term project 환경 설명
- 인원 : 박상현, 최보열, etc
내용
- github 사용법
- program
- project
- 일정
- 진행 사항
| non_priority | 전체 회의록 회의록 양식 ex 일시 장소 오프라인 해동 주제 term project 환경 설명 인원 박상현 최보열 etc 내용 github 사용법 program project 일정 진행 사항 | 0 |
9,806 | 8,178,297,510 | IssuesEvent | 2018-08-28 13:30:41 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | Health Facility and Laboratory Administration (POS 9) [5] | 10231 Infrastructure epic sormas-ui | See https://app.moqups.com/symeda/3NUENEwuOE/view/page/a39f20492
- [x] add create, edit, view and archive user rights
- [x] add "Infrastructure" view and menu entry. View should have url "facilities" (sub menu is not needed now). Caption is facilities (not health facility)
- [x] add facility grid to view
- [x] text filter by name and city
- [x] filters for region and district (not community)
- [x] header-filters "Health facilities" and "Laboratories" -> update mockups
- [x] build create and edit form (popup)
- [x] facilities get no type, laboratories get the "LABORATORY" type
- [x] add a saveFacility method to the Controller that calls a save method in the facade, use ensurePersisted in that method
- [x] make sure that facilities always have region, district and community set (and a name); laboratories only need a region
Import of regional data is possible via csv from the technical backend. A user interface will be added later (see #436)
- CaseFacadeEjb.saveCase does validation on region, etc - what if community is moved? | 1.0 | Health Facility and Laboratory Administration (POS 9) [5] - See https://app.moqups.com/symeda/3NUENEwuOE/view/page/a39f20492
- [x] add create, edit, view and archive user rights
- [x] add "Infrastructure" view and menu entry. View should have url "facilities" (sub menu is not needed now). Caption is facilities (not health facility)
- [x] add facility grid to view
- [x] text filter by name and city
- [x] filters for region and district (not community)
- [x] header-filters "Health facilities" and "Laboratories" -> update mockups
- [x] build create and edit form (popup)
- [x] facilities get no type, laboratories get the "LABORATORY" type
- [x] add a saveFacility method to the Controller that calls a save method in the facade, use ensurePersisted in that method
- [x] make sure that facilities always have region, district and community set (and a name); laboratories only need a region
Import of regional data is possible via csv from the technical backend. A user interface will be added later (see #436)
- CaseFacadeEjb.saveCase does validation on region, etc - what if community is moved? | non_priority | health facility and laboratory administration pos see add create edit view and archive user rights add infrastructure view and menu entry view should have url facilities sub menu is not needed now caption is facilities not health facility add facility grid to view text filter by name and city filters for region and district not community header filters health facilities and laboratories update mockups build create and edit form popup facilities get no type laboratories get the laboratory type add a savefacility method to the controller that calls a save method in the facade use ensurepersisted in that method make sure that facilities always have region district and community set and a name laboratories only need a region import of regional data is possible via csv from the technical backend a user interface will be added later see casefacadeejb savecase does validation on region etc what if community is moved | 0 |
110,876 | 9,480,819,807 | IssuesEvent | 2019-04-20 21:27:20 | IntellectualSites/FastAsyncWorldEdit-1.13 | https://api.github.com/repos/IntellectualSites/FastAsyncWorldEdit-1.13 | closed | //stack does not work | Requires Testing | //stack does nothing. It prints the message saying x blocks changed.
But no changes happen in world.
using @IronApollo 's vector update | 1.0 | //stack does not work - //stack does nothing. It prints the message saying x blocks changed.
But no changes happen in world.
using @IronApollo 's vector update | non_priority | stack does not work stack does nothing it prints the message saying x blocks changed but no changes happen in world using ironapollo s vector update | 0 |
104,077 | 11,391,911,149 | IssuesEvent | 2020-01-30 00:35:01 | react-static/react-static | https://api.github.com/repos/react-static/react-static | closed | [Docs] https://react-static.js.org redirects to the GitHub repo | documentation :book: | The link near the headline of the repo redirects to this repo. I am not sure if this repo had a unique site for react-static before but I think that link doesn't work anymore. Nothing major, just wanted to point it out!
| 1.0 | [Docs] https://react-static.js.org redirects to the GitHub repo - The link near the headline of the repo redirects to this repo. I am not sure if this repo had a unique site for react-static before but I think that link doesn't work anymore. Nothing major, just wanted to point it out!
| non_priority | redirects to the github repo the link near the headline of the repo redirects to this repo i am not sure if this repo had a unique site for react static before but i think that link doesn t work anymore nothing major just wanted to point it out | 0 |
39,327 | 19,827,544,924 | IssuesEvent | 2022-01-20 08:34:21 | handsontable/handsontable | https://api.github.com/repos/handsontable/handsontable | closed | Bad performance custom borders | Core: performance Type: Change Custom borders Status: Released | ### Description
The tables with multiple borders are very slow, so that it is impossible to work with them.
With a table size of 20x20, when deleting and setting borders again, the table hangs for a more than 1 minute.
As far as I can see the problem is known for a long time (#6467)
Do you continue to work on the problem? When can you count towards the improvements in performance?
### Steps to reproduce
1. Set borders green (performs quickly, because there are no borders)
2. Set borders red (performs more than 1 minute, because borders should be deleted first)
### Demo
https://jsfiddle.net/ue07r83f/3/
### Your environment
* Handsontable version 10.0.0
| True | Bad performance custom borders - ### Description
The tables with multiple borders are very slow, so that it is impossible to work with them.
With a table size of 20x20, when deleting and setting borders again, the table hangs for a more than 1 minute.
As far as I can see the problem is known for a long time (#6467)
Do you continue to work on the problem? When can you count towards the improvements in performance?
### Steps to reproduce
1. Set borders green (performs quickly, because there are no borders)
2. Set borders red (performs more than 1 minute, because borders should be deleted first)
### Demo
https://jsfiddle.net/ue07r83f/3/
### Your environment
* Handsontable version 10.0.0
| non_priority | bad performance custom borders description the tables with multiple borders are very slow so that it is impossible to work with them with a table size of when deleting and setting borders again the table hangs for a more than minute as far as i can see the problem is known for a long time do you continue to work on the problem when can you count towards the improvements in performance steps to reproduce set borders green performs quickly because there are no borders set borders red performs more than minute because borders should be deleted first demo your environment handsontable version | 0 |
91,342 | 15,856,399,721 | IssuesEvent | 2021-04-08 02:15:11 | CarlsbergGBS/msrCrypto | https://api.github.com/repos/CarlsbergGBS/msrCrypto | opened | CVE-2020-36049 (High) detected in socket.io-parser-3.1.3.tgz | security vulnerability | ## CVE-2020-36049 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>socket.io-parser-3.1.3.tgz</b></p></summary>
<p>socket.io protocol parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.1.3.tgz">https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.1.3.tgz</a></p>
<p>Path to dependency file: msrCrypto/package.json</p>
<p>Path to vulnerable library: msrCrypto/node_modules/socket.io-parser/package.json</p>
<p>
Dependency Hierarchy:
- karma-2.0.5.tgz (Root Library)
- socket.io-2.0.4.tgz
- :x: **socket.io-parser-3.1.3.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
socket.io-parser before 3.4.1 allows attackers to cause a denial of service (memory consumption) via a large packet because a concatenation approach is used.
<p>Publish Date: 2021-01-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36049>CVE-2020-36049</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049</a></p>
<p>Release Date: 2021-01-08</p>
<p>Fix Resolution: socket.io-parser - 3.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-36049 (High) detected in socket.io-parser-3.1.3.tgz - ## CVE-2020-36049 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>socket.io-parser-3.1.3.tgz</b></p></summary>
<p>socket.io protocol parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.1.3.tgz">https://registry.npmjs.org/socket.io-parser/-/socket.io-parser-3.1.3.tgz</a></p>
<p>Path to dependency file: msrCrypto/package.json</p>
<p>Path to vulnerable library: msrCrypto/node_modules/socket.io-parser/package.json</p>
<p>
Dependency Hierarchy:
- karma-2.0.5.tgz (Root Library)
- socket.io-2.0.4.tgz
- :x: **socket.io-parser-3.1.3.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
socket.io-parser before 3.4.1 allows attackers to cause a denial of service (memory consumption) via a large packet because a concatenation approach is used.
<p>Publish Date: 2021-01-08
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36049>CVE-2020-36049</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-36049</a></p>
<p>Release Date: 2021-01-08</p>
<p>Fix Resolution: socket.io-parser - 3.4.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in socket io parser tgz cve high severity vulnerability vulnerable library socket io parser tgz socket io protocol parser library home page a href path to dependency file msrcrypto package json path to vulnerable library msrcrypto node modules socket io parser package json dependency hierarchy karma tgz root library socket io tgz x socket io parser tgz vulnerable library vulnerability details socket io parser before allows attackers to cause a denial of service memory consumption via a large packet because a concatenation approach is used publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution socket io parser step up your open source security game with whitesource | 0 |
234,771 | 25,886,336,145 | IssuesEvent | 2022-12-14 14:48:38 | niklasschreiber/vulner-2 | https://api.github.com/repos/niklasschreiber/vulner-2 | opened | itext-2.0.6.jar: 1 vulnerabilities (highest severity is: 8.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>itext-2.0.6.jar</b></p></summary>
<p>iText, a free Java-PDF library</p>
<p>Library home page: <a href="http://www.lowagie.com/iText/">http://www.lowagie.com/iText/</a></p>
<p>Path to vulnerable library: /JAVA/lib/itext-2.0.6.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (itext version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2017-9096](https://www.mend.io/vulnerability-database/CVE-2017-9096) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | itext-2.0.6.jar | Direct | com.itextpdf:itextpdf:5.5.12 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-9096</summary>
### Vulnerable Library - <b>itext-2.0.6.jar</b></p>
<p>iText, a free Java-PDF library</p>
<p>Library home page: <a href="http://www.lowagie.com/iText/">http://www.lowagie.com/iText/</a></p>
<p>Path to vulnerable library: /JAVA/lib/itext-2.0.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **itext-2.0.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The XML parsers in iText before 5.5.12 and 7.x before 7.0.3 do not disable external entities, which might allow remote attackers to conduct XML external entity (XXE) attacks via a crafted PDF.
<p>Publish Date: 2017-11-08
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-9096>CVE-2017-9096</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096</a></p>
<p>Release Date: 2017-11-08</p>
<p>Fix Resolution: com.itextpdf:itextpdf:5.5.12</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | itext-2.0.6.jar: 1 vulnerabilities (highest severity is: 8.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>itext-2.0.6.jar</b></p></summary>
<p>iText, a free Java-PDF library</p>
<p>Library home page: <a href="http://www.lowagie.com/iText/">http://www.lowagie.com/iText/</a></p>
<p>Path to vulnerable library: /JAVA/lib/itext-2.0.6.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (itext version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2017-9096](https://www.mend.io/vulnerability-database/CVE-2017-9096) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | itext-2.0.6.jar | Direct | com.itextpdf:itextpdf:5.5.12 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-9096</summary>
### Vulnerable Library - <b>itext-2.0.6.jar</b></p>
<p>iText, a free Java-PDF library</p>
<p>Library home page: <a href="http://www.lowagie.com/iText/">http://www.lowagie.com/iText/</a></p>
<p>Path to vulnerable library: /JAVA/lib/itext-2.0.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **itext-2.0.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/niklasschreiber/vulner-2/commit/be13e70bb5a4fc28ce2d12ffc575caa94e313f69">be13e70bb5a4fc28ce2d12ffc575caa94e313f69</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The XML parsers in iText before 5.5.12 and 7.x before 7.0.3 do not disable external entities, which might allow remote attackers to conduct XML external entity (XXE) attacks via a crafted PDF.
<p>Publish Date: 2017-11-08
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-9096>CVE-2017-9096</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9096</a></p>
<p>Release Date: 2017-11-08</p>
<p>Fix Resolution: com.itextpdf:itextpdf:5.5.12</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | itext jar vulnerabilities highest severity is vulnerable library itext jar itext a free java pdf library library home page a href path to vulnerable library java lib itext jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in itext version remediation available high itext jar direct com itextpdf itextpdf details cve vulnerable library itext jar itext a free java pdf library library home page a href path to vulnerable library java lib itext jar dependency hierarchy x itext jar vulnerable library found in head commit a href found in base branch main vulnerability details the xml parsers in itext before and x before do not disable external entities which might allow remote attackers to conduct xml external entity xxe attacks via a crafted pdf publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com itextpdf itextpdf step up your open source security game with mend | 0 |
142,713 | 19,102,811,376 | IssuesEvent | 2021-11-30 01:31:57 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Test failure System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncAuthenticate_EachSupportedProtocol_Success(protocol: Tls13) | area-System.Net.Security os-windows arch-x64 arch-s390x | Run: [runtime 20211129.5](https://dev.azure.com/dnceng/public/_build/results?buildId=1489344&view=ms.vss-test-web.build-test-results-tab&runId=42576978&resultId=197112&paneView=debug)
Failed test:
```
net7.0-windows-Release-x64-CoreCLR_release-Windows.10.Amd64.Server20H2.Open
- System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncAuthenticate_EachSupportedProtocol_Success(protocol: Tls13)
```
**Error message:**
```
System.IO.IOException : Received an unexpected EOF or 0 bytes from the transport stream.
Stack trace
at System.Net.Security.SslStream.<FillHandshakeBufferAsync>g__InternalFillHandshakeBufferAsync|187_0[TIOAdapter](TIOAdapter adap, ValueTask`1 task, Int32 minSize) in /_/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs:line 1101
at System.Net.Security.SslStream.ReceiveBlobAsync[TIOAdapter](TIOAdapter adapter) in /_/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs:line 556
at System.Net.Security.SslStream.ForceAuthenticationAsync[TIOAdapter](TIOAdapter adapter, Boolean receiveFirst, Byte[] reAuthenticationData, Boolean isApm) in /_/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs:line 381
at System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncSslHelper(SslProtocols clientSslProtocols, SslProtocols serverSslProtocols, Boolean expectedToFail) in /_/src/libraries/System.Net.Security/tests/FunctionalTests/ServerAsyncAuthenticateTest.cs:line 397
at System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncAuthenticate_EachSupportedProtocol_Success(SslProtocols protocol) in /_/src/libraries/System.Net.Security/tests/FunctionalTests/ServerAsyncAuthenticateTest.cs:line 43
--- End of stack trace from previous location ---
``` | True | Test failure System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncAuthenticate_EachSupportedProtocol_Success(protocol: Tls13) - Run: [runtime 20211129.5](https://dev.azure.com/dnceng/public/_build/results?buildId=1489344&view=ms.vss-test-web.build-test-results-tab&runId=42576978&resultId=197112&paneView=debug)
Failed test:
```
net7.0-windows-Release-x64-CoreCLR_release-Windows.10.Amd64.Server20H2.Open
- System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncAuthenticate_EachSupportedProtocol_Success(protocol: Tls13)
```
**Error message:**
```
System.IO.IOException : Received an unexpected EOF or 0 bytes from the transport stream.
Stack trace
at System.Net.Security.SslStream.<FillHandshakeBufferAsync>g__InternalFillHandshakeBufferAsync|187_0[TIOAdapter](TIOAdapter adap, ValueTask`1 task, Int32 minSize) in /_/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs:line 1101
at System.Net.Security.SslStream.ReceiveBlobAsync[TIOAdapter](TIOAdapter adapter) in /_/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs:line 556
at System.Net.Security.SslStream.ForceAuthenticationAsync[TIOAdapter](TIOAdapter adapter, Boolean receiveFirst, Byte[] reAuthenticationData, Boolean isApm) in /_/src/libraries/System.Net.Security/src/System/Net/Security/SslStream.Implementation.cs:line 381
at System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncSslHelper(SslProtocols clientSslProtocols, SslProtocols serverSslProtocols, Boolean expectedToFail) in /_/src/libraries/System.Net.Security/tests/FunctionalTests/ServerAsyncAuthenticateTest.cs:line 397
at System.Net.Security.Tests.ServerAsyncAuthenticateTest.ServerAsyncAuthenticate_EachSupportedProtocol_Success(SslProtocols protocol) in /_/src/libraries/System.Net.Security/tests/FunctionalTests/ServerAsyncAuthenticateTest.cs:line 43
--- End of stack trace from previous location ---
``` | non_priority | test failure system net security tests serverasyncauthenticatetest serverasyncauthenticate eachsupportedprotocol success protocol run failed test windows release coreclr release windows open system net security tests serverasyncauthenticatetest serverasyncauthenticate eachsupportedprotocol success protocol error message system io ioexception received an unexpected eof or bytes from the transport stream stack trace at system net security sslstream g internalfillhandshakebufferasync tioadapter adap valuetask task minsize in src libraries system net security src system net security sslstream implementation cs line at system net security sslstream receiveblobasync tioadapter adapter in src libraries system net security src system net security sslstream implementation cs line at system net security sslstream forceauthenticationasync tioadapter adapter boolean receivefirst byte reauthenticationdata boolean isapm in src libraries system net security src system net security sslstream implementation cs line at system net security tests serverasyncauthenticatetest serverasyncsslhelper sslprotocols clientsslprotocols sslprotocols serversslprotocols boolean expectedtofail in src libraries system net security tests functionaltests serverasyncauthenticatetest cs line at system net security tests serverasyncauthenticatetest serverasyncauthenticate eachsupportedprotocol success sslprotocols protocol in src libraries system net security tests functionaltests serverasyncauthenticatetest cs line end of stack trace from previous location | 0 |
217,048 | 24,312,762,377 | IssuesEvent | 2022-09-30 01:16:44 | sesong11/example | https://api.github.com/repos/sesong11/example | opened | CVE-2020-13943 (Medium) detected in tomcat-embed-core-9.0.21.jar | security vulnerability | ## CVE-2020-13943 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.21.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /example/spring-statemachine-jpa/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.21/tomcat-embed-core-9.0.21.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.6.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.1.6.RELEASE.jar
- :x: **tomcat-embed-core-9.0.21.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
If an HTTP/2 client connecting to Apache Tomcat 10.0.0-M1 to 10.0.0-M7, 9.0.0.M1 to 9.0.37 or 8.5.0 to 8.5.57 exceeded the agreed maximum number of concurrent streams for a connection (in violation of the HTTP/2 protocol), it was possible that a subsequent request made on that connection could contain HTTP headers - including HTTP/2 pseudo headers - from a previous request rather than the intended headers. This could lead to users seeing responses for unexpected resources.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13943>CVE-2020-13943</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2020-10-12</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.38</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.1.17.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-13943 (Medium) detected in tomcat-embed-core-9.0.21.jar - ## CVE-2020-13943 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.21.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /example/spring-statemachine-jpa/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.21/tomcat-embed-core-9.0.21.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.6.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.1.6.RELEASE.jar
- :x: **tomcat-embed-core-9.0.21.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
If an HTTP/2 client connecting to Apache Tomcat 10.0.0-M1 to 10.0.0-M7, 9.0.0.M1 to 9.0.37 or 8.5.0 to 8.5.57 exceeded the agreed maximum number of concurrent streams for a connection (in violation of the HTTP/2 protocol), it was possible that a subsequent request made on that connection could contain HTTP headers - including HTTP/2 pseudo headers - from a previous request rather than the intended headers. This could lead to users seeing responses for unexpected resources.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13943>CVE-2020-13943</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2020-10-12</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.38</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.1.17.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tomcat embed core jar cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file example spring statemachine jpa pom xml path to vulnerable library root repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library vulnerability details if an http client connecting to apache tomcat to to or to exceeded the agreed maximum number of concurrent streams for a connection in violation of the http protocol it was possible that a subsequent request made on that connection could contain http headers including http pseudo headers from a previous request rather than the intended headers this could lead to users seeing responses for unexpected resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core direct dependency fix resolution org springframework boot spring boot starter web release step up your open source security game with mend | 0 |
74,186 | 14,217,488,720 | IssuesEvent | 2020-11-17 10:25:48 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | WIFI input does not respect link to chat status | Code | - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
The wifi component accepts input from chat regardless of it's 'link to chat' status. The link to chat button only modifies the wifi output going to chat instead of turning off chat integration completely.
**Steps To Reproduce**
Place wifi component and hook the output to a text display. Verify link to chat is disabled. Use the chat running on the same channel and see your output going to the display.
**Version**
0.10.5.1 | 1.0 | WIFI input does not respect link to chat status - - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
The wifi component accepts input from chat regardless of it's 'link to chat' status. The link to chat button only modifies the wifi output going to chat instead of turning off chat integration completely.
**Steps To Reproduce**
Place wifi component and hook the output to a text display. Verify link to chat is disabled. Use the chat running on the same channel and see your output going to the display.
**Version**
0.10.5.1 | non_priority | wifi input does not respect link to chat status i have searched the issue tracker to check if the issue has already been reported description the wifi component accepts input from chat regardless of it s link to chat status the link to chat button only modifies the wifi output going to chat instead of turning off chat integration completely steps to reproduce place wifi component and hook the output to a text display verify link to chat is disabled use the chat running on the same channel and see your output going to the display version | 0 |
90,723 | 18,245,303,726 | IssuesEvent | 2021-10-01 17:32:57 | Torkin1/IIW_UDP_GBN | https://api.github.com/repos/Torkin1/IIW_UDP_GBN | closed | implement command GET in client | newCode | Client richiede l'invio del file il cui nome è specificato in payload dal server e ne salva una copia in locale.
Server salva file richiesto dal client in payload e lo invia al client
| 1.0 | implement command GET in client - Client richiede l'invio del file il cui nome è specificato in payload dal server e ne salva una copia in locale.
Server salva file richiesto dal client in payload e lo invia al client
| non_priority | implement command get in client client richiede l invio del file il cui nome è specificato in payload dal server e ne salva una copia in locale server salva file richiesto dal client in payload e lo invia al client | 0 |
104,389 | 13,065,169,282 | IssuesEvent | 2020-07-30 19:20:37 | carbon-design-system/ibm-dotcom-library | https://api.github.com/repos/carbon-design-system/ibm-dotcom-library | opened | Web component: CTA Section Reboot requested enhancement Design QA testing | design package: web components | _**This work is a follow-on to the development work done to create / change the same React version. The React development was managed under epic (#TBD)**_
#### User Story
<!-- {{Provide a detailed description of the user's need here, but avoid any type of solutions}} -->
> As a `[user role below]`:
DDS Designer and Developer
> I need to:
test the `CTA Section Reboot requested enhancement`
> so that I can:
be sure the developer's code correctly works as designed
#### Additional Information
- **See the Epic for the Design and Functional specs information**
- Dev Issue (#?dev issue?)
- [Storybook link](TBD)
#### Tasks
Ensure the `CTA Section Reboot requested enhancement` component has been tested and reviewed by design + dev.
#### Acceptance criteria
- [ ] Pattern is reviewed by designer and design defects are identified
- [ ] New issues are opened to log individual defects
- [ ] Screenshots of as-is and to-be design should be added to the issue when needed
- [ ] Developer associated with building the pattern is assigned to the new issues
- [ ] Appropriate labels are added to the issue eg. bug, dev
| 1.0 | Web component: CTA Section Reboot requested enhancement Design QA testing - _**This work is a follow-on to the development work done to create / change the same React version. The React development was managed under epic (#TBD)**_
#### User Story
<!-- {{Provide a detailed description of the user's need here, but avoid any type of solutions}} -->
> As a `[user role below]`:
DDS Designer and Developer
> I need to:
test the `CTA Section Reboot requested enhancement`
> so that I can:
be sure the developer's code correctly works as designed
#### Additional Information
- **See the Epic for the Design and Functional specs information**
- Dev Issue (#?dev issue?)
- [Storybook link](TBD)
#### Tasks
Ensure the `CTA Section Reboot requested enhancement` component has been tested and reviewed by design + dev.
#### Acceptance criteria
- [ ] Pattern is reviewed by designer and design defects are identified
- [ ] New issues are opened to log individual defects
- [ ] Screenshots of as-is and to-be design should be added to the issue when needed
- [ ] Developer associated with building the pattern is assigned to the new issues
- [ ] Appropriate labels are added to the issue eg. bug, dev
| non_priority | web component cta section reboot requested enhancement design qa testing this work is a follow on to the development work done to create change the same react version the react development was managed under epic tbd user story as a dds designer and developer i need to test the cta section reboot requested enhancement so that i can be sure the developer s code correctly works as designed additional information see the epic for the design and functional specs information dev issue dev issue tbd tasks ensure the cta section reboot requested enhancement component has been tested and reviewed by design dev acceptance criteria pattern is reviewed by designer and design defects are identified new issues are opened to log individual defects screenshots of as is and to be design should be added to the issue when needed developer associated with building the pattern is assigned to the new issues appropriate labels are added to the issue eg bug dev | 0 |
34,581 | 9,416,466,608 | IssuesEvent | 2019-04-10 14:44:03 | apache/incubator-openwhisk-wskdeploy | https://api.github.com/repos/apache/incubator-openwhisk-wskdeploy | closed | Client from "latest" binaries reports version is "latest" | build | I just installed wskdeploy from the latest binary package for Mac amd64 (https://github.com/apache/incubator-openwhisk-wskdeploy/releases/download/latest/openwhisk_wskdeploy-latest-mac-amd64.zip).
When asking for the version the client reports "latest" which is not very useful, since this information is obtained from the local binary, which means it's almost always stale.
```
$ wskdeploy version
wskdeploy version: latest
``` | 1.0 | Client from "latest" binaries reports version is "latest" - I just installed wskdeploy from the latest binary package for Mac amd64 (https://github.com/apache/incubator-openwhisk-wskdeploy/releases/download/latest/openwhisk_wskdeploy-latest-mac-amd64.zip).
When asking for the version the client reports "latest" which is not very useful, since this information is obtained from the local binary, which means it's almost always stale.
```
$ wskdeploy version
wskdeploy version: latest
``` | non_priority | client from latest binaries reports version is latest i just installed wskdeploy from the latest binary package for mac when asking for the version the client reports latest which is not very useful since this information is obtained from the local binary which means it s almost always stale wskdeploy version wskdeploy version latest | 0 |
2,998 | 2,653,483,950 | IssuesEvent | 2015-03-16 23:51:16 | openaustralia/righttoknow | https://api.github.com/repos/openaustralia/righttoknow | closed | Form helper layout wrong on wide screens | design | The margin and width of the form help text is off on the responsive version:
Responsive:

Right To Know:
 | 1.0 | Form helper layout wrong on wide screens - The margin and width of the form help text is off on the responsive version:
Responsive:

Right To Know:
 | non_priority | form helper layout wrong on wide screens the margin and width of the form help text is off on the responsive version responsive right to know | 0 |
7,358 | 7,895,293,778 | IssuesEvent | 2018-06-29 02:20:07 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | ASE ILB + Application Gateway not working | app-service/svc cxp in-progress product-question triaged | I am seeing "The resource you are looking for has been removed, had its name changed, or is temporarily unavailable."
error when I hit my custom domain. But when I add Web App in the backend it works. Even in Backend health, it says Healthy.
Am I missing something?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 2b1afa49-a5b4-92db-68e8-3feeeff52eb3
* Version Independent ID: c9191775-e49c-1462-e525-a5ce549ae743
* Content: [Create and use an internal load balancer with an Azure App Service Environment](https://docs.microsoft.com/en-us/azure/app-service/environment/create-ilb-ase)
* Content Source: [articles/app-service/environment/create-ilb-ase.md](https://github.com/Microsoft/azure-docs/blob/master/articles/app-service/environment/create-ilb-ase.md)
* Service: **app-service**
* GitHub Login: @ccompy
* Microsoft Alias: **ccompy** | 1.0 | ASE ILB + Application Gateway not working - I am seeing "The resource you are looking for has been removed, had its name changed, or is temporarily unavailable."
error when I hit my custom domain. But when I add Web App in the backend it works. Even in Backend health, it says Healthy.
Am I missing something?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 2b1afa49-a5b4-92db-68e8-3feeeff52eb3
* Version Independent ID: c9191775-e49c-1462-e525-a5ce549ae743
* Content: [Create and use an internal load balancer with an Azure App Service Environment](https://docs.microsoft.com/en-us/azure/app-service/environment/create-ilb-ase)
* Content Source: [articles/app-service/environment/create-ilb-ase.md](https://github.com/Microsoft/azure-docs/blob/master/articles/app-service/environment/create-ilb-ase.md)
* Service: **app-service**
* GitHub Login: @ccompy
* Microsoft Alias: **ccompy** | non_priority | ase ilb application gateway not working i am seeing the resource you are looking for has been removed had its name changed or is temporarily unavailable error when i hit my custom domain but when i add web app in the backend it works even in backend health it says healthy am i missing something document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service app service github login ccompy microsoft alias ccompy | 0 |
247,663 | 18,857,959,245 | IssuesEvent | 2021-11-12 09:13:32 | nhjryan/pe | https://api.github.com/repos/nhjryan/pe | opened | Include a note on `sort` to show that it sorts the current displayed list and not the entire list | severity.VeryLow type.DocumentationBug | Was a bit unclear as to whether `sort` would sort my entire contact list or just the one I had filtered. I think it is implied with "same list of contacts displayed" but I think it could be clearer that it is the post-filter list and not the entire contact list.
<!--session: 1636703317823-09404b8f-447b-47de-9f27-4453ad4c5990-->
<!--Version: Web v3.4.1--> | 1.0 | Include a note on `sort` to show that it sorts the current displayed list and not the entire list - Was a bit unclear as to whether `sort` would sort my entire contact list or just the one I had filtered. I think it is implied with "same list of contacts displayed" but I think it could be clearer that it is the post-filter list and not the entire contact list.
<!--session: 1636703317823-09404b8f-447b-47de-9f27-4453ad4c5990-->
<!--Version: Web v3.4.1--> | non_priority | include a note on sort to show that it sorts the current displayed list and not the entire list was a bit unclear as to whether sort would sort my entire contact list or just the one i had filtered i think it is implied with same list of contacts displayed but i think it could be clearer that it is the post filter list and not the entire contact list | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.