Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
9,805 | 25,248,683,630 | IssuesEvent | 2022-11-15 13:08:40 | DGEXSolutions/osrd | https://api.github.com/repos/DGEXSolutions/osrd | opened | Pluggable authentication | area:architecture | Currently, the authentication process is:
- undocumented
- not implemented in the default deployment
The API service supports authenticating reverse proxies via headers, but this requirement makes deploying the application cumbersome. | 1.0 | Pluggable authentication - Currently, the authentication process is:
- undocumented
- not implemented in the default deployment
The API service supports authenticating reverse proxies via headers, but this requirement makes deploying the application cumbersome. | non_priority | pluggable authentication currently the authentication process is undocumented not implemented in the default deployment the api service supports authenticating reverse proxies via headers but this requirement makes deploying the application cumbersome | 0 |
22,249 | 7,135,340,729 | IssuesEvent | 2018-01-23 00:33:23 | dart-lang/build | https://api.github.com/repos/dart-lang/build | closed | Watch is watching the .build_tool folder? | package:build_runner | For example, I see this when running `-v`:
```
Watch: Got modify event for "asset:web_hello_world/.dart_tool/build/d9d0eaec453f092c5191075c5eae4ab9/asset_graph.json
```
False alarm? | 1.0 | Watch is watching the .build_tool folder? - For example, I see this when running `-v`:
```
Watch: Got modify event for "asset:web_hello_world/.dart_tool/build/d9d0eaec453f092c5191075c5eae4ab9/asset_graph.json
```
False alarm? | non_priority | watch is watching the build tool folder for example i see this when running v watch got modify event for asset web hello world dart tool build asset graph json false alarm | 0 |
21,668 | 10,676,154,763 | IssuesEvent | 2019-10-21 13:14:39 | repo-helper/npm-versions | https://api.github.com/repos/repo-helper/npm-versions | opened | CVE-2016-10540 (High) detected in minimatch-0.2.14.tgz, minimatch-2.0.10.tgz | security vulnerability | ## CVE-2016-10540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimatch-0.2.14.tgz</b>, <b>minimatch-2.0.10.tgz</b></p></summary>
<p>
<details><summary><b>minimatch-0.2.14.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz">https://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/npm-versions/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/npm-versions/node_modules/mocha/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- mocha-1.21.5.tgz (Root Library)
- glob-3.2.3.tgz
- :x: **minimatch-0.2.14.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimatch-2.0.10.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/npm-versions/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/npm-versions/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- istanbul-harmony-0.3.16.tgz (Root Library)
- fileset-0.2.1.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/repo-helper/npm-versions/commit/ba0d1bd8a0b17aaff356094b2e49fc294e517612">ba0d1bd8a0b17aaff356094b2e49fc294e517612</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10540>CVE-2016-10540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/118">https://nodesecurity.io/advisories/118</a></p>
<p>Release Date: 2016-06-20</p>
<p>Fix Resolution: Update to version 3.0.2 or later.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-10540 (High) detected in minimatch-0.2.14.tgz, minimatch-2.0.10.tgz - ## CVE-2016-10540 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimatch-0.2.14.tgz</b>, <b>minimatch-2.0.10.tgz</b></p></summary>
<p>
<details><summary><b>minimatch-0.2.14.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz">https://registry.npmjs.org/minimatch/-/minimatch-0.2.14.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/npm-versions/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/npm-versions/node_modules/mocha/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- mocha-1.21.5.tgz (Root Library)
- glob-3.2.3.tgz
- :x: **minimatch-0.2.14.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimatch-2.0.10.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz">https://registry.npmjs.org/minimatch/-/minimatch-2.0.10.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/npm-versions/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/npm-versions/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- istanbul-harmony-0.3.16.tgz (Root Library)
- fileset-0.2.1.tgz
- :x: **minimatch-2.0.10.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/repo-helper/npm-versions/commit/ba0d1bd8a0b17aaff356094b2e49fc294e517612">ba0d1bd8a0b17aaff356094b2e49fc294e517612</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimatch is a minimal matching utility that works by converting glob expressions into JavaScript `RegExp` objects. The primary function, `minimatch(path, pattern)` in Minimatch 3.0.1 and earlier is vulnerable to ReDoS in the `pattern` parameter.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10540>CVE-2016-10540</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/118">https://nodesecurity.io/advisories/118</a></p>
<p>Release Date: 2016-06-20</p>
<p>Fix Resolution: Update to version 3.0.2 or later.</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in minimatch tgz minimatch tgz cve high severity vulnerability vulnerable libraries minimatch tgz minimatch tgz minimatch tgz a glob matcher in javascript library home page a href path to dependency file tmp ws scm npm versions package json path to vulnerable library tmp ws scm npm versions node modules mocha node modules minimatch package json dependency hierarchy mocha tgz root library glob tgz x minimatch tgz vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file tmp ws scm npm versions package json path to vulnerable library tmp ws scm npm versions node modules minimatch package json dependency hierarchy istanbul harmony tgz root library fileset tgz x minimatch tgz vulnerable library found in head commit a href vulnerability details minimatch is a minimal matching utility that works by converting glob expressions into javascript regexp objects the primary function minimatch path pattern in minimatch and earlier is vulnerable to redos in the pattern parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution update to version or later step up your open source security game with whitesource | 0 |
191,785 | 22,215,845,139 | IssuesEvent | 2022-06-08 01:29:30 | AlexRogalskiy/github-action-tag-replacer | https://api.github.com/repos/AlexRogalskiy/github-action-tag-replacer | closed | WS-2020-0218 (High) detected in merge-1.2.1.tgz - autoclosed | security vulnerability | ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.1.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar to the jQuery.extend but more flexible. Works in Node.js and the browser.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge/-/merge-1.2.1.tgz">https://registry.npmjs.org/merge/-/merge-1.2.1.tgz</a></p>
<p>Path to dependency file: github-action-tag-replacer/package.json</p>
<p>Path to vulnerable library: github-action-tag-replacer/node_modules/merge/package.json</p>
<p>
Dependency Hierarchy:
- cz-conventional-changelog-3.3.0.tgz (Root Library)
- commitizen-4.2.3.tgz
- find-node-modules-2.0.0.tgz
- :x: **merge-1.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-tag-replacer/commit/904e2924530c8af55c9b4f8f88e64acf85f8079d">904e2924530c8af55c9b4f8f88e64acf85f8079d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0218 (High) detected in merge-1.2.1.tgz - autoclosed - ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.1.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar to the jQuery.extend but more flexible. Works in Node.js and the browser.</p>
<p>Library home page: <a href="https://registry.npmjs.org/merge/-/merge-1.2.1.tgz">https://registry.npmjs.org/merge/-/merge-1.2.1.tgz</a></p>
<p>Path to dependency file: github-action-tag-replacer/package.json</p>
<p>Path to vulnerable library: github-action-tag-replacer/node_modules/merge/package.json</p>
<p>
Dependency Hierarchy:
- cz-conventional-changelog-3.3.0.tgz (Root Library)
- commitizen-4.2.3.tgz
- find-node-modules-2.0.0.tgz
- :x: **merge-1.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-tag-replacer/commit/904e2924530c8af55c9b4f8f88e64acf85f8079d">904e2924530c8af55c9b4f8f88e64acf85f8079d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in merge tgz autoclosed ws high severity vulnerability vulnerable library merge tgz merge multiple objects into one optionally creating a new cloned object similar to the jquery extend but more flexible works in node js and the browser library home page a href path to dependency file github action tag replacer package json path to vulnerable library github action tag replacer node modules merge package json dependency hierarchy cz conventional changelog tgz root library commitizen tgz find node modules tgz x merge tgz vulnerable library found in head commit a href vulnerability details a prototype pollution vulnerability was found in merge before via the merge recursive function it can be tricked into adding or modifying properties of the object prototype these properties will be present on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution merge step up your open source security game with whitesource | 0 |
195,524 | 15,530,024,453 | IssuesEvent | 2021-03-13 17:27:58 | tasmota/docs | https://api.github.com/repos/tasmota/docs | closed | Please add the new feature to documentation - Max value rule | documentation help wanted | @
re PR: arendst/tasmota#
Please add the new feature to the appropriate article in [Tasmota documentation](https://github.com/tasmota/docs)
Can documentation about analog be improved? I could not find anywhere the list of value names. All rule examples use analog#a0, which did nothing for me, perhaps because I'm using ESP32? I worked out that analog#a1 got a value and then eventually, by trial and error I worked out I could use analog#range1.
I would like to suggest the following example for the rules cookbook:
**Publish Maximum Value from sensor in a time period:**
This rule stores the sensor value in VAR1. When the current value is greater than the previous, VAR1 is updated. If the current value is smaller, VAR1 is unchanged. Then every minute, VAR1 is published and then VAR1 is reset.
This results in output of the maximum/peak value for the minute. Useful, for example in a decibel meter, when the peak value is important, rather than the value that is occurring by chance at normal telemetry time.
This uses Analog range (analog#range1) which is a scaled output value. The raw analog value is analog#a1
Rule
ON System#Boot var1 1 ENDON
ON analog#range1>%var1% DO VAR1 %value% ENDON
ON Time#Minute DO Backlog publish shed/tele/maxdb %var1%; var1 1 ENDON
| 1.0 | Please add the new feature to documentation - Max value rule - @
re PR: arendst/tasmota#
Please add the new feature to the appropriate article in [Tasmota documentation](https://github.com/tasmota/docs)
Can documentation about analog be improved? I could not find anywhere the list of value names. All rule examples use analog#a0, which did nothing for me, perhaps because I'm using ESP32? I worked out that analog#a1 got a value and then eventually, by trial and error I worked out I could use analog#range1.
I would like to suggest the following example for the rules cookbook:
**Publish Maximum Value from sensor in a time period:**
This rule stores the sensor value in VAR1. When the current value is greater than the previous, VAR1 is updated. If the current value is smaller, VAR1 is unchanged. Then every minute, VAR1 is published and then VAR1 is reset.
This results in output of the maximum/peak value for the minute. Useful, for example in a decibel meter, when the peak value is important, rather than the value that is occurring by chance at normal telemetry time.
This uses Analog range (analog#range1) which is a scaled output value. The raw analog value is analog#a1
Rule
ON System#Boot var1 1 ENDON
ON analog#range1>%var1% DO VAR1 %value% ENDON
ON Time#Minute DO Backlog publish shed/tele/maxdb %var1%; var1 1 ENDON
| non_priority | please add the new feature to documentation max value rule re pr arendst tasmota please add the new feature to the appropriate article in can documentation about analog be improved i could not find anywhere the list of value names all rule examples use analog which did nothing for me perhaps because i m using i worked out that analog got a value and then eventually by trial and error i worked out i could use analog i would like to suggest the following example for the rules cookbook publish maximum value from sensor in a time period this rule stores the sensor value in when the current value is greater than the previous is updated if the current value is smaller is unchanged then every minute is published and then is reset this results in output of the maximum peak value for the minute useful for example in a decibel meter when the peak value is important rather than the value that is occurring by chance at normal telemetry time this uses analog range analog which is a scaled output value the raw analog value is analog rule on system boot endon on analog do value endon on time minute do backlog publish shed tele maxdb endon | 0 |
205,868 | 15,696,285,972 | IssuesEvent | 2021-03-26 01:39:37 | pravega/pravega | https://api.github.com/repos/pravega/pravega | closed | Sporadic failure in test StreamRecreationTest.testStreamRecreation | area/testing tag/flakeyTest | **Describe the bug**
Found test `StreamRecreationTest.testStreamRecreation` sporadically failing due to:
```
org.junit.runners.model.TestTimedOutException: test timed out after 40000 milliseconds
at java.base@11.0.3/jdk.internal.misc.Unsafe.park(Native Method)
at java.base@11.0.3/java.util.concurrent.locks.LockSupport.park(LockSupport.java:194)
at java.base@11.0.3/java.util.concurrent.CompletableFuture$Signaller.block(CompletableFuture.java:1796)
at java.base@11.0.3/java.util.concurrent.ForkJoinPool.managedBlock(ForkJoinPool.java:3128)
at java.base@11.0.3/java.util.concurrent.CompletableFuture.waitingGet(CompletableFuture.java:1823)
at java.base@11.0.3/java.util.concurrent.CompletableFuture.get(CompletableFuture.java:1998)
at app//io.pravega.common.concurrent.Futures.lambda$getAndHandleExceptions$2(Futures.java:210)
at app//io.pravega.common.concurrent.Futures$$Lambda$1022/0x000000010064f440.call(Unknown Source)
at app//io.pravega.common.Exceptions.handleInterruptedCall(Exceptions.java:144)
at app//io.pravega.common.concurrent.Futures.getAndHandleExceptions(Futures.java:210)
at app//io.pravega.client.stream.impl.ClientFactoryImpl.getSegmentForRevisionedClient(ClientFactoryImpl.java:250)
at app//io.pravega.client.stream.impl.ClientFactoryImpl.createReader(ClientFactoryImpl.java:209)
at app//io.pravega.client.stream.impl.ClientFactoryImpl.createReader(ClientFactoryImpl.java:189)
at app//io.pravega.test.integration.StreamRecreationTest.testStreamRecreation(StreamRecreationTest.java:157)
at java.base@11.0.3/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base@11.0.3/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base@11.0.3/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.3/java.lang.reflect.Method.invoke(Method.java:566)
at app//org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at app//org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at app//org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at app//org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at app//org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:298)
at app//org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:292)
at java.base@11.0.3/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base@11.0.3/java.lang.Thread.run(Thread.java:834)
```
**To Reproduce**
Occurs sporadically on Jenkins executing `gradlew build`
**Screenshots**
n/a
**Additional information**
Apparently, the test works fine but the problem is that the instance was super slow. That is, the test crashed due to timeout after 7 test iterations (out of 10), but things were working fine. | 2.0 | Sporadic failure in test StreamRecreationTest.testStreamRecreation - **Describe the bug**
Found test `StreamRecreationTest.testStreamRecreation` sporadically failing due to:
```
org.junit.runners.model.TestTimedOutException: test timed out after 40000 milliseconds
at java.base@11.0.3/jdk.internal.misc.Unsafe.park(Native Method)
at java.base@11.0.3/java.util.concurrent.locks.LockSupport.park(LockSupport.java:194)
at java.base@11.0.3/java.util.concurrent.CompletableFuture$Signaller.block(CompletableFuture.java:1796)
at java.base@11.0.3/java.util.concurrent.ForkJoinPool.managedBlock(ForkJoinPool.java:3128)
at java.base@11.0.3/java.util.concurrent.CompletableFuture.waitingGet(CompletableFuture.java:1823)
at java.base@11.0.3/java.util.concurrent.CompletableFuture.get(CompletableFuture.java:1998)
at app//io.pravega.common.concurrent.Futures.lambda$getAndHandleExceptions$2(Futures.java:210)
at app//io.pravega.common.concurrent.Futures$$Lambda$1022/0x000000010064f440.call(Unknown Source)
at app//io.pravega.common.Exceptions.handleInterruptedCall(Exceptions.java:144)
at app//io.pravega.common.concurrent.Futures.getAndHandleExceptions(Futures.java:210)
at app//io.pravega.client.stream.impl.ClientFactoryImpl.getSegmentForRevisionedClient(ClientFactoryImpl.java:250)
at app//io.pravega.client.stream.impl.ClientFactoryImpl.createReader(ClientFactoryImpl.java:209)
at app//io.pravega.client.stream.impl.ClientFactoryImpl.createReader(ClientFactoryImpl.java:189)
at app//io.pravega.test.integration.StreamRecreationTest.testStreamRecreation(StreamRecreationTest.java:157)
at java.base@11.0.3/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base@11.0.3/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base@11.0.3/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base@11.0.3/java.lang.reflect.Method.invoke(Method.java:566)
at app//org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at app//org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at app//org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at app//org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at app//org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:298)
at app//org.junit.internal.runners.statements.FailOnTimeout$CallableStatement.call(FailOnTimeout.java:292)
at java.base@11.0.3/java.util.concurrent.FutureTask.run(FutureTask.java:264)
at java.base@11.0.3/java.lang.Thread.run(Thread.java:834)
```
**To Reproduce**
Occurs sporadically on Jenkins executing `gradlew build`
**Screenshots**
n/a
**Additional information**
Apparently, the test works fine but the problem is that the instance was super slow. That is, the test crashed due to timeout after 7 test iterations (out of 10), but things were working fine. | non_priority | sporadic failure in test streamrecreationtest teststreamrecreation describe the bug found test streamrecreationtest teststreamrecreation sporadically failing due to org junit runners model testtimedoutexception test timed out after milliseconds at java base jdk internal misc unsafe park native method at java base java util concurrent locks locksupport park locksupport java at java base java util concurrent completablefuture signaller block completablefuture java at java base java util concurrent forkjoinpool managedblock forkjoinpool java at java base java util concurrent completablefuture waitingget completablefuture java at java base java util concurrent completablefuture get completablefuture java at app io pravega common concurrent futures lambda getandhandleexceptions futures java at app io pravega common concurrent futures lambda call unknown source at app io pravega common exceptions handleinterruptedcall exceptions java at app io pravega common concurrent futures getandhandleexceptions futures java at app io pravega client stream impl clientfactoryimpl getsegmentforrevisionedclient clientfactoryimpl java at app io pravega client stream impl clientfactoryimpl createreader clientfactoryimpl java at app io pravega client stream impl clientfactoryimpl createreader clientfactoryimpl java at app io pravega test integration streamrecreationtest teststreamrecreation streamrecreationtest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at app org junit runners model frameworkmethod runreflectivecall frameworkmethod java at app org junit internal runners model reflectivecallable run reflectivecallable java at app org junit runners model frameworkmethod invokeexplosively frameworkmethod java at app org junit internal runners statements invokemethod evaluate invokemethod java at app org junit internal runners statements failontimeout callablestatement call failontimeout java at app org junit internal runners statements failontimeout callablestatement call failontimeout java at java base java util concurrent futuretask run futuretask java at java base java lang thread run thread java to reproduce occurs sporadically on jenkins executing gradlew build screenshots n a additional information apparently the test works fine but the problem is that the instance was super slow that is the test crashed due to timeout after test iterations out of but things were working fine | 0 |
59,298 | 6,644,209,411 | IssuesEvent | 2017-09-27 14:05:09 | szapp/GothicFreeAim | https://api.github.com/repos/szapp/GothicFreeAim | closed | Humanoid NPC bounding boxes do not include head node | beta-test bug headshot | Since collision detection of projectiles with NPCs is done based on the bounding box, shots through the head of human NPCs are ignored. This is because the head node is not part of the model, but has its own visual.
In a clever way the bounding box needs to be continuously enlarged. First idea is calling the following method of the bounding box with the head bounding box every frame, but that might be unnecessary overhead.
```D
zTBBox3D::CalcGreaterBBox3D(zTBBox3D const &) 00544550
```
This method might be the way to go, but it should rather be injected where the NPC bounding box is calculated. | 1.0 | Humanoid NPC bounding boxes do not include head node - Since collision detection of projectiles with NPCs is done based on the bounding box, shots through the head of human NPCs are ignored. This is because the head node is not part of the model, but has its own visual.
In a clever way the bounding box needs to be continuously enlarged. First idea is calling the following method of the bounding box with the head bounding box every frame, but that might be unnecessary overhead.
```D
zTBBox3D::CalcGreaterBBox3D(zTBBox3D const &) 00544550
```
This method might be the way to go, but it should rather be injected where the NPC bounding box is calculated. | non_priority | humanoid npc bounding boxes do not include head node since collision detection of projectiles with npcs is done based on the bounding box shots through the head of human npcs are ignored this is because the head node is not part of the model but has its own visual in a clever way the bounding box needs to be continuously enlarged first idea is calling the following method of the bounding box with the head bounding box every frame but that might be unnecessary overhead d const this method might be the way to go but it should rather be injected where the npc bounding box is calculated | 0 |
33,120 | 9,023,157,780 | IssuesEvent | 2019-02-07 05:46:49 | lightninglabs/lightning-app | https://api.github.com/repos/lightninglabs/lightning-app | closed | Building expokit app fails in Android Studio | android bug build | Getting the error:
"React-Native: Application has not been registered error":
See: https://stackoverflow.com/questions/38340360/react-native-application-has-not-been-registered-error | 1.0 | Building expokit app fails in Android Studio - Getting the error:
"React-Native: Application has not been registered error":
See: https://stackoverflow.com/questions/38340360/react-native-application-has-not-been-registered-error | non_priority | building expokit app fails in android studio getting the error react native application has not been registered error see | 0 |
180,860 | 30,583,378,325 | IssuesEvent | 2023-07-21 11:29:28 | openSUSE/open-build-service | https://api.github.com/repos/openSUSE/open-build-service | closed | OBS web UI misreports SR attribution | Bug Frontend request-redesign | # Issue Description
I've noticed a few times now that the OBS web UI misreports SR attribution when displayed in the "Latest revision" section of the package page (see attached image).

How to Reproduce
===============
1. Go to https://build.opensuse.org/package/show/security/squilt-python
2. Look at the "Latest revision" section
3. The SR there is attributed to a user who has nothing to do with it.
Expected Result
============
https://build.opensuse.org/package/show/security/squilt-python displays SR#1099468 as submitted from the right person (myself in this case).
| 1.0 | OBS web UI misreports SR attribution - # Issue Description
I've noticed a few times now that the OBS web UI misreports SR attribution when displayed in the "Latest revision" section of the package page (see attached image).

How to Reproduce
===============
1. Go to https://build.opensuse.org/package/show/security/squilt-python
2. Look at the "Latest revision" section
3. The SR there is attributed to a user who has nothing to do with it.
Expected Result
============
https://build.opensuse.org/package/show/security/squilt-python displays SR#1099468 as submitted from the right person (myself in this case).
| non_priority | obs web ui misreports sr attribution issue description i ve noticed a few times now that the obs web ui misreports sr attribution when displayed in the latest revision section of the package page see attached image how to reproduce go to look at the latest revision section the sr there is attributed to a user who has nothing to do with it expected result displays sr as submitted from the right person myself in this case | 0 |
261,776 | 27,821,280,478 | IssuesEvent | 2023-03-19 09:10:21 | billmcchesney1/jazz | https://api.github.com/repos/billmcchesney1/jazz | opened | CVE-2021-46877 (Medium) detected in jackson-databind-2.10.0.jar | Mend: dependency security vulnerability | ## CVE-2021-46877 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.10.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /templates/api-template-java/pom.xml</p>
<p>Path to vulnerable library: /canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.0/jackson-databind-2.10.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.10.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/jazz/commit/712665b267203375ee4b15e1f8d1ebe08abc1547">712665b267203375ee4b15e1f8d1ebe08abc1547</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: 2.12.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2021-46877 (Medium) detected in jackson-databind-2.10.0.jar - ## CVE-2021-46877 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.10.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /templates/api-template-java/pom.xml</p>
<p>Path to vulnerable library: /canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.10.0/jackson-databind-2.10.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.10.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/jazz/commit/712665b267203375ee4b15e1f8d1ebe08abc1547">712665b267203375ee4b15e1f8d1ebe08abc1547</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jackson-databind 2.10.x through 2.12.x before 2.12.6 and 2.13.x before 2.13.1 allows attackers to cause a denial of service (2 GB transient heap usage per read) in uncommon situations involving JsonNode JDK serialization.
<p>Publish Date: 2023-03-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-46877>CVE-2021-46877</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2021-46877">https://www.cve.org/CVERecord?id=CVE-2021-46877</a></p>
<p>Release Date: 2023-03-18</p>
<p>Fix Resolution: 2.12.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file templates api template java pom xml path to vulnerable library canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch develop vulnerability details jackson databind x through x before and x before allows attackers to cause a denial of service gb transient heap usage per read in uncommon situations involving jsonnode jdk serialization publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
409,325 | 27,733,316,746 | IssuesEvent | 2023-03-15 09:34:14 | adospace/reactorui-maui | https://api.github.com/repos/adospace/reactorui-maui | closed | Unmount page | documentation | Hello, I need to call an action for the disappearance of the page, but for some reason the page unmounting is not called. I created a test application with two pages. When I switching from one to the other, the OnMounted method was called once for the first page, and for the second page OnMounted was always called when I switched to it. OnWillUnmount was never called. Why is that?
My test code
```
public class FirstPage : Component
{
protected override void OnWillUnmount()
{
Debug.WriteLine("OnWillUnmount FirstPage");
}
protected override void OnMounted()
{
Debug.WriteLine("OnMounted FirstPage");
}
public override VisualNode Render()
{
return new ContentPage()
{
new VStack()
{
new Label("First!"),
new Button("Next")
.OnClicked(() => { Navigation?.PushAsync<SecondPage>(); })
}
.Spacing(20)
.HCenter()
.VCenter()
}.Title("First");
}
}
public class SecondPage : Component
{
protected override void OnWillUnmount()
{
Debug.WriteLine("OnWillUnmount SecondPage");
}
protected override void OnMounted()
{
Debug.WriteLine("OnMounted SecondPage");
}
public override VisualNode Render()
{
return new ContentPage()
{
new VStack()
{
new Label("Second!"),
new Button("Back")
.OnClicked(() => { Navigation?.PopAsync(); })
}
.Spacing(20)
.HCenter()
.VCenter()
}
.Title("Second");
}
}
public class App : Component
{
public override VisualNode Render()
{
return new NavigationPage()
{
new FirstPage()
}.Set(Microsoft.Maui.Controls.NavigationPage.BarTextColorProperty, Colors.White);
}
}
``` | 1.0 | Unmount page - Hello, I need to call an action for the disappearance of the page, but for some reason the page unmounting is not called. I created a test application with two pages. When I switching from one to the other, the OnMounted method was called once for the first page, and for the second page OnMounted was always called when I switched to it. OnWillUnmount was never called. Why is that?
My test code
```
public class FirstPage : Component
{
protected override void OnWillUnmount()
{
Debug.WriteLine("OnWillUnmount FirstPage");
}
protected override void OnMounted()
{
Debug.WriteLine("OnMounted FirstPage");
}
public override VisualNode Render()
{
return new ContentPage()
{
new VStack()
{
new Label("First!"),
new Button("Next")
.OnClicked(() => { Navigation?.PushAsync<SecondPage>(); })
}
.Spacing(20)
.HCenter()
.VCenter()
}.Title("First");
}
}
public class SecondPage : Component
{
protected override void OnWillUnmount()
{
Debug.WriteLine("OnWillUnmount SecondPage");
}
protected override void OnMounted()
{
Debug.WriteLine("OnMounted SecondPage");
}
public override VisualNode Render()
{
return new ContentPage()
{
new VStack()
{
new Label("Second!"),
new Button("Back")
.OnClicked(() => { Navigation?.PopAsync(); })
}
.Spacing(20)
.HCenter()
.VCenter()
}
.Title("Second");
}
}
public class App : Component
{
public override VisualNode Render()
{
return new NavigationPage()
{
new FirstPage()
}.Set(Microsoft.Maui.Controls.NavigationPage.BarTextColorProperty, Colors.White);
}
}
``` | non_priority | unmount page hello i need to call an action for the disappearance of the page but for some reason the page unmounting is not called i created a test application with two pages when i switching from one to the other the onmounted method was called once for the first page and for the second page onmounted was always called when i switched to it onwillunmount was never called why is that my test code public class firstpage component protected override void onwillunmount debug writeline onwillunmount firstpage protected override void onmounted debug writeline onmounted firstpage public override visualnode render return new contentpage new vstack new label first new button next onclicked navigation pushasync spacing hcenter vcenter title first public class secondpage component protected override void onwillunmount debug writeline onwillunmount secondpage protected override void onmounted debug writeline onmounted secondpage public override visualnode render return new contentpage new vstack new label second new button back onclicked navigation popasync spacing hcenter vcenter title second public class app component public override visualnode render return new navigationpage new firstpage set microsoft maui controls navigationpage bartextcolorproperty colors white | 0 |
180,746 | 30,562,805,308 | IssuesEvent | 2023-07-20 15:37:09 | chapel-lang/chapel | https://api.github.com/repos/chapel-lang/chapel | closed | [Library Stabilization] Should we lengthen these BigInteger method names? | type: Design area: Libraries / Modules type: Chapel 2.0 | The following method names seem unnecessarily shortened, since they just lose one or two letters. Should we lengthen them?
- `bigint.clrbit()` to `bigint.clearBit()`
- `bigint.tstbit()` to `bigint.testBit()`
- `bigint.sgn()` to `bigint.sign()` | 1.0 | [Library Stabilization] Should we lengthen these BigInteger method names? - The following method names seem unnecessarily shortened, since they just lose one or two letters. Should we lengthen them?
- `bigint.clrbit()` to `bigint.clearBit()`
- `bigint.tstbit()` to `bigint.testBit()`
- `bigint.sgn()` to `bigint.sign()` | non_priority | should we lengthen these biginteger method names the following method names seem unnecessarily shortened since they just lose one or two letters should we lengthen them bigint clrbit to bigint clearbit bigint tstbit to bigint testbit bigint sgn to bigint sign | 0 |
6,368 | 23,033,245,083 | IssuesEvent | 2022-07-22 15:49:45 | bcgov/api-services-portal | https://api.github.com/repos/bcgov/api-services-portal | closed | Update existing CI to include cypress end to end tests execution | automation | # API Services Portal Issue
<!-- Use what you want. Remove what you don't want. -->
## User Story
<!-- Use one of the following two templates -->
<!-- 1) User Story as a statement -->
**As a** _Developer_,<br>
**I want** _automation tests to be run before creating a new release_<br>
**so that** _I can make sure the pre-release build is defect free_.
## Test Case
### ENV
<!-- Put at least one `x` below. Select all the environments which apply. -->
- [x] `DEV`
- [x] `TEST`
- [x] `PROD`
### TESTCASE
<!-- Share the minimal reproduction steps for this issue -->
-
### EXPECTED
<!-- Share the expected behavior of the testcase -->
-
### ACTUAL
<!-- Describe the actual behavior of the testcase -->
-
### ERROR
<!-- If you have an associated exception or error, please post it below -->
## Notes
<!-- Do any of these matter: Operating System, Browser? If so, please mention the version and any other relevant details below. -->
| 1.0 | Update existing CI to include cypress end to end tests execution - # API Services Portal Issue
<!-- Use what you want. Remove what you don't want. -->
## User Story
<!-- Use one of the following two templates -->
<!-- 1) User Story as a statement -->
**As a** _Developer_,<br>
**I want** _automation tests to be run before creating a new release_<br>
**so that** _I can make sure the pre-release build is defect free_.
## Test Case
### ENV
<!-- Put at least one `x` below. Select all the environments which apply. -->
- [x] `DEV`
- [x] `TEST`
- [x] `PROD`
### TESTCASE
<!-- Share the minimal reproduction steps for this issue -->
-
### EXPECTED
<!-- Share the expected behavior of the testcase -->
-
### ACTUAL
<!-- Describe the actual behavior of the testcase -->
-
### ERROR
<!-- If you have an associated exception or error, please post it below -->
## Notes
<!-- Do any of these matter: Operating System, Browser? If so, please mention the version and any other relevant details below. -->
| non_priority | update existing ci to include cypress end to end tests execution api services portal issue user story as a developer i want automation tests to be run before creating a new release so that i can make sure the pre release build is defect free test case env dev test prod testcase expected actual error notes | 0 |
337,065 | 24,525,084,715 | IssuesEvent | 2022-10-11 12:34:32 | PramudithaPothuwila/GameOfLife | https://api.github.com/repos/PramudithaPothuwila/GameOfLife | closed | Update the current working Version | documentation enhancement | List the Used versions and how to Install
Add the dependencies (notify)
Add it to the readme.md | 1.0 | Update the current working Version - List the Used versions and how to Install
Add the dependencies (notify)
Add it to the readme.md | non_priority | update the current working version list the used versions and how to install add the dependencies notify add it to the readme md | 0 |
131,560 | 18,247,981,397 | IssuesEvent | 2021-10-01 21:25:20 | turkdevops/grafana | https://api.github.com/repos/turkdevops/grafana | closed | CVE-2020-7608 (Medium) detected in multiple libraries - autoclosed | security vulnerability | ## CVE-2020-7608 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-10.1.0.tgz</b>, <b>yargs-parser-5.0.0.tgz</b>, <b>yargs-parser-13.1.1.tgz</b>, <b>yargs-parser-4.2.1.tgz</b>, <b>yargs-parser-15.0.0.tgz</b>, <b>yargs-parser-11.1.1.tgz</b></p></summary>
<p>
<details><summary><b>yargs-parser-10.1.0.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-10.1.0.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-10.1.0.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- ts-jest-24.1.0.tgz (Root Library)
- :x: **yargs-parser-10.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-5.0.0.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-5.0.0.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-5.0.0.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- @grafana/toolkit-6.7.0-pre.tgz (Root Library)
- node-sass-4.12.0.tgz
- sass-graph-2.2.4.tgz
- yargs-7.1.0.tgz
- :x: **yargs-parser-5.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-13.1.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-13.1.1.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-13.1.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- jest-24.8.0.tgz (Root Library)
- jest-cli-24.9.0.tgz
- yargs-13.3.0.tgz
- :x: **yargs-parser-13.1.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-4.2.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-4.2.1.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-4.2.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- @grafana/ui-6.7.0-pre.tgz (Root Library)
- addon-actions-5.3.9.tgz
- react-inspector-4.0.0.tgz
- storybook-chromatic-2.2.2.tgz
- localtunnel-1.10.1.tgz
- yargs-6.6.0.tgz
- :x: **yargs-parser-4.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-15.0.0.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-15.0.0.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-15.0.0.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- lerna-3.18.1.tgz (Root Library)
- cli-3.18.0.tgz
- yargs-14.2.0.tgz
- :x: **yargs-parser-15.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-11.1.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-11.1.1.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-11.1.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- @grafana/toolkit-6.7.0-pre.tgz (Root Library)
- concurrently-4.1.0.tgz
- yargs-12.0.5.tgz
- :x: **yargs-parser-11.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/494d3ade5b02fb069ecdd7a9a278fd2016f5f577">494d3ade5b02fb069ecdd7a9a278fd2016f5f577</a></p>
<p>Found in base branch: <b>datasource-meta</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
yargs-parser could be tricked into adding or modifying properties of Object.prototype using a "__proto__" payload.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7608>CVE-2020-7608</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yargs/yargs-parser/commit/63810ca1ae1a24b08293a4d971e70e058c7a41e2">https://github.com/yargs/yargs-parser/commit/63810ca1ae1a24b08293a4d971e70e058c7a41e2</a></p>
<p>Release Date: 2020-06-05</p>
<p>Fix Resolution: 5.0.1;13.1.2;15.0.1;18.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7608 (Medium) detected in multiple libraries - autoclosed - ## CVE-2020-7608 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-10.1.0.tgz</b>, <b>yargs-parser-5.0.0.tgz</b>, <b>yargs-parser-13.1.1.tgz</b>, <b>yargs-parser-4.2.1.tgz</b>, <b>yargs-parser-15.0.0.tgz</b>, <b>yargs-parser-11.1.1.tgz</b></p></summary>
<p>
<details><summary><b>yargs-parser-10.1.0.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-10.1.0.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-10.1.0.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- ts-jest-24.1.0.tgz (Root Library)
- :x: **yargs-parser-10.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-5.0.0.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-5.0.0.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-5.0.0.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- @grafana/toolkit-6.7.0-pre.tgz (Root Library)
- node-sass-4.12.0.tgz
- sass-graph-2.2.4.tgz
- yargs-7.1.0.tgz
- :x: **yargs-parser-5.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-13.1.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-13.1.1.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-13.1.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- jest-24.8.0.tgz (Root Library)
- jest-cli-24.9.0.tgz
- yargs-13.3.0.tgz
- :x: **yargs-parser-13.1.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-4.2.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-4.2.1.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-4.2.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- @grafana/ui-6.7.0-pre.tgz (Root Library)
- addon-actions-5.3.9.tgz
- react-inspector-4.0.0.tgz
- storybook-chromatic-2.2.2.tgz
- localtunnel-1.10.1.tgz
- yargs-6.6.0.tgz
- :x: **yargs-parser-4.2.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-15.0.0.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-15.0.0.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-15.0.0.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- lerna-3.18.1.tgz (Root Library)
- cli-3.18.0.tgz
- yargs-14.2.0.tgz
- :x: **yargs-parser-15.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>yargs-parser-11.1.1.tgz</b></p></summary>
<p>the mighty option parser used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/yargs-parser/-/yargs-parser-11.1.1.tgz">https://registry.npmjs.org/yargs-parser/-/yargs-parser-11.1.1.tgz</a></p>
<p>Path to dependency file: grafana/package.json</p>
<p>Path to vulnerable library: grafana/node_modules/yargs-parser</p>
<p>
Dependency Hierarchy:
- @grafana/toolkit-6.7.0-pre.tgz (Root Library)
- concurrently-4.1.0.tgz
- yargs-12.0.5.tgz
- :x: **yargs-parser-11.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/494d3ade5b02fb069ecdd7a9a278fd2016f5f577">494d3ade5b02fb069ecdd7a9a278fd2016f5f577</a></p>
<p>Found in base branch: <b>datasource-meta</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
yargs-parser could be tricked into adding or modifying properties of Object.prototype using a "__proto__" payload.
<p>Publish Date: 2020-03-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7608>CVE-2020-7608</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yargs/yargs-parser/commit/63810ca1ae1a24b08293a4d971e70e058c7a41e2">https://github.com/yargs/yargs-parser/commit/63810ca1ae1a24b08293a4d971e70e058c7a41e2</a></p>
<p>Release Date: 2020-06-05</p>
<p>Fix Resolution: 5.0.1;13.1.2;15.0.1;18.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries autoclosed cve medium severity vulnerability vulnerable libraries yargs parser tgz yargs parser tgz yargs parser tgz yargs parser tgz yargs parser tgz yargs parser tgz yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules yargs parser dependency hierarchy ts jest tgz root library x yargs parser tgz vulnerable library yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules yargs parser dependency hierarchy grafana toolkit pre tgz root library node sass tgz sass graph tgz yargs tgz x yargs parser tgz vulnerable library yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules yargs parser dependency hierarchy jest tgz root library jest cli tgz yargs tgz x yargs parser tgz vulnerable library yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules yargs parser dependency hierarchy grafana ui pre tgz root library addon actions tgz react inspector tgz storybook chromatic tgz localtunnel tgz yargs tgz x yargs parser tgz vulnerable library yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules yargs parser dependency hierarchy lerna tgz root library cli tgz yargs tgz x yargs parser tgz vulnerable library yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency file grafana package json path to vulnerable library grafana node modules yargs parser dependency hierarchy grafana toolkit pre tgz root library concurrently tgz yargs tgz x yargs parser tgz vulnerable library found in head commit a href found in base branch datasource meta vulnerability details yargs parser could be tricked into adding or modifying properties of object prototype using a proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
28,970 | 4,154,296,566 | IssuesEvent | 2016-06-16 11:02:40 | jlongster/debugger.html | https://api.github.com/repos/jlongster/debugger.html | opened | What happens to the area above the source tree? | design | Specifically, this one:
<img width="328" alt="screen shot 2016-06-16 at 11 41 32 am" src="https://cloud.githubusercontent.com/assets/1720093/16114086/53e8e42a-33b7-11e6-85a6-d8631e60d0fc.png">
James and I have gone back and forth a _bunch_ on this area. I liked having space above that area for [purely visual reasons](http://cl.ly/0a1n2h2N402P), but without a clear direction for functionality perhaps we should remove it.
For prosperity, we've chatted mostly about using that area for a "Filter Sources" area, although that will probably overlap with some pretty common keyboard shortcuts that people will probably get more mileage on.
@jlongster + @jasonLaster: If the two of you truly feel a filter (or, whatever else we can come up with), perhaps we should remove it—elsewise, let's use this space to chat what might become of it. | 1.0 | What happens to the area above the source tree? - Specifically, this one:
<img width="328" alt="screen shot 2016-06-16 at 11 41 32 am" src="https://cloud.githubusercontent.com/assets/1720093/16114086/53e8e42a-33b7-11e6-85a6-d8631e60d0fc.png">
James and I have gone back and forth a _bunch_ on this area. I liked having space above that area for [purely visual reasons](http://cl.ly/0a1n2h2N402P), but without a clear direction for functionality perhaps we should remove it.
For prosperity, we've chatted mostly about using that area for a "Filter Sources" area, although that will probably overlap with some pretty common keyboard shortcuts that people will probably get more mileage on.
@jlongster + @jasonLaster: If the two of you truly feel a filter (or, whatever else we can come up with), perhaps we should remove it—elsewise, let's use this space to chat what might become of it. | non_priority | what happens to the area above the source tree specifically this one img width alt screen shot at am src james and i have gone back and forth a bunch on this area i liked having space above that area for but without a clear direction for functionality perhaps we should remove it for prosperity we ve chatted mostly about using that area for a filter sources area although that will probably overlap with some pretty common keyboard shortcuts that people will probably get more mileage on jlongster jasonlaster if the two of you truly feel a filter or whatever else we can come up with perhaps we should remove it—elsewise let s use this space to chat what might become of it | 0 |
49,610 | 13,187,239,518 | IssuesEvent | 2020-08-13 02:47:21 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | [steamshovel] can't leave icetop viewer (Trac #1744) | Incomplete Migration Migrated from Trac cmake defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1744">https://code.icecube.wisc.edu/ticket/1744</a>, reported by kjmeagher and owned by hdembinski</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-06-14T14:48:50",
"description": "On my Mac running El Cap with the current trunk, whenever I click on the IceTopViewer checkbox it switches to IceTopViewer mode but gets stuck there. The checkbox appears unresponsive. Closing steamshovel and deleting the config files seems to be the only way to restore working order. The issue might be related to the fact that the PulseSeries in question has no IceTop pulses.",
"reporter": "kjmeagher",
"cc": "",
"resolution": "invalid",
"_ts": "1465915730114312",
"component": "cmake",
"summary": "[steamshovel] can't leave icetop viewer",
"priority": "normal",
"keywords": "steamshovel",
"time": "2016-06-14T07:55:42",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [steamshovel] can't leave icetop viewer (Trac #1744) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1744">https://code.icecube.wisc.edu/ticket/1744</a>, reported by kjmeagher and owned by hdembinski</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2016-06-14T14:48:50",
"description": "On my Mac running El Cap with the current trunk, whenever I click on the IceTopViewer checkbox it switches to IceTopViewer mode but gets stuck there. The checkbox appears unresponsive. Closing steamshovel and deleting the config files seems to be the only way to restore working order. The issue might be related to the fact that the PulseSeries in question has no IceTop pulses.",
"reporter": "kjmeagher",
"cc": "",
"resolution": "invalid",
"_ts": "1465915730114312",
"component": "cmake",
"summary": "[steamshovel] can't leave icetop viewer",
"priority": "normal",
"keywords": "steamshovel",
"time": "2016-06-14T07:55:42",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
</p>
</details>
| non_priority | can t leave icetop viewer trac migrated from json status closed changetime description on my mac running el cap with the current trunk whenever i click on the icetopviewer checkbox it switches to icetopviewer mode but gets stuck there the checkbox appears unresponsive closing steamshovel and deleting the config files seems to be the only way to restore working order the issue might be related to the fact that the pulseseries in question has no icetop pulses reporter kjmeagher cc resolution invalid ts component cmake summary can t leave icetop viewer priority normal keywords steamshovel time milestone owner hdembinski type defect | 0 |
76,658 | 9,960,102,772 | IssuesEvent | 2019-07-06 13:33:58 | vuejs/jp.vuejs.org | https://api.github.com/repos/vuejs/jp.vuejs.org | closed | [Doc]: added an additional hint for transition-classes | documentation | 本家のドキュメントに更新がありました:page_facing_up:
Original:https://github.com/vuejs/vuejs.org/commit/7e808a15af27edb8cc364add822a443d3335fd5e | 1.0 | [Doc]: added an additional hint for transition-classes - 本家のドキュメントに更新がありました:page_facing_up:
Original:https://github.com/vuejs/vuejs.org/commit/7e808a15af27edb8cc364add822a443d3335fd5e | non_priority | added an additional hint for transition classes 本家のドキュメントに更新がありました page facing up original | 0 |
97,650 | 16,236,431,381 | IssuesEvent | 2021-05-07 01:42:23 | attesch/swapi | https://api.github.com/repos/attesch/swapi | opened | CVE-2021-31542 (Medium) detected in Django-2.2.2.tar.gz | security vulnerability | ## CVE-2021-31542 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-2.2.2.tar.gz</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/56/2e/c0495314c0bdcf19d9b888a98ff16a4c58a90dd77ed741f4dbab2cbf7efe/Django-2.2.2.tar.gz">https://files.pythonhosted.org/packages/56/2e/c0495314c0bdcf19d9b888a98ff16a4c58a90dd77ed741f4dbab2cbf7efe/Django-2.2.2.tar.gz</a></p>
<p>Path to dependency file: /swapi/requirements.txt</p>
<p>Path to vulnerable library: teSource-ArchiveExtractor_cd0131d4-2ba0-4601-beec-b5f2a7e3636b/20190620051939_56417/20190620051812_depth_0/13/Django-2.2.2.tar/Django-2.2.2</p>
<p>
Dependency Hierarchy:
- :x: **Django-2.2.2.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Django 2.2 before 2.2.21, 3.1 before 3.1.9, and 3.2 before 3.2.1, MultiPartParser, UploadedFile, and FieldFile allowed directory traversal via uploaded files with suitably crafted file names.
<p>Publish Date: 2021-05-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-31542>CVE-2021-31542</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.djangoproject.com/weblog/2021/may/04/security-releases/">https://www.djangoproject.com/weblog/2021/may/04/security-releases/</a></p>
<p>Release Date: 2021-05-05</p>
<p>Fix Resolution: Django - 2.2.21,3.1.9,3.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-31542 (Medium) detected in Django-2.2.2.tar.gz - ## CVE-2021-31542 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-2.2.2.tar.gz</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development and clean, pragmatic design.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/56/2e/c0495314c0bdcf19d9b888a98ff16a4c58a90dd77ed741f4dbab2cbf7efe/Django-2.2.2.tar.gz">https://files.pythonhosted.org/packages/56/2e/c0495314c0bdcf19d9b888a98ff16a4c58a90dd77ed741f4dbab2cbf7efe/Django-2.2.2.tar.gz</a></p>
<p>Path to dependency file: /swapi/requirements.txt</p>
<p>Path to vulnerable library: teSource-ArchiveExtractor_cd0131d4-2ba0-4601-beec-b5f2a7e3636b/20190620051939_56417/20190620051812_depth_0/13/Django-2.2.2.tar/Django-2.2.2</p>
<p>
Dependency Hierarchy:
- :x: **Django-2.2.2.tar.gz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Django 2.2 before 2.2.21, 3.1 before 3.1.9, and 3.2 before 3.2.1, MultiPartParser, UploadedFile, and FieldFile allowed directory traversal via uploaded files with suitably crafted file names.
<p>Publish Date: 2021-05-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-31542>CVE-2021-31542</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.djangoproject.com/weblog/2021/may/04/security-releases/">https://www.djangoproject.com/weblog/2021/may/04/security-releases/</a></p>
<p>Release Date: 2021-05-05</p>
<p>Fix Resolution: Django - 2.2.21,3.1.9,3.2.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in django tar gz cve medium severity vulnerability vulnerable library django tar gz a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file swapi requirements txt path to vulnerable library tesource archiveextractor beec depth django tar django dependency hierarchy x django tar gz vulnerable library vulnerability details in django before before and before multipartparser uploadedfile and fieldfile allowed directory traversal via uploaded files with suitably crafted file names publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution django step up your open source security game with whitesource | 0 |
91,560 | 8,308,895,506 | IssuesEvent | 2018-09-24 01:44:22 | gregdardis/stock-market-search | https://api.github.com/repos/gregdardis/stock-market-search | closed | Unit test React Components with Enzyme | testing | Consider using chai-enzyme for assertions here: https://github.com/producthunt/chai-enzyme
Also see: https://github.com/airbnb/enzyme/blob/master/docs/guides/mocha.md
## Components
- [x] App
- [x] AppWrapper
- [x] Chart
- [x] Column
- [x] CompanyGeneralInfo
- [x] CompanyNameAndSymbol
- [x] DataItem
- [x] Definition
- [x] Exchange
- [x] Glossary
- [x] Home
- [x] NavBar
- [x] PriceAndTodaysPriceChange
- [x] Row
- [x] Search
- [x] SearchLoader
- [x] SelectableTimePeriodChart
- [x] StockDataRegion
- [x] TimePeriodButtons | 1.0 | Unit test React Components with Enzyme - Consider using chai-enzyme for assertions here: https://github.com/producthunt/chai-enzyme
Also see: https://github.com/airbnb/enzyme/blob/master/docs/guides/mocha.md
## Components
- [x] App
- [x] AppWrapper
- [x] Chart
- [x] Column
- [x] CompanyGeneralInfo
- [x] CompanyNameAndSymbol
- [x] DataItem
- [x] Definition
- [x] Exchange
- [x] Glossary
- [x] Home
- [x] NavBar
- [x] PriceAndTodaysPriceChange
- [x] Row
- [x] Search
- [x] SearchLoader
- [x] SelectableTimePeriodChart
- [x] StockDataRegion
- [x] TimePeriodButtons | non_priority | unit test react components with enzyme consider using chai enzyme for assertions here also see components app appwrapper chart column companygeneralinfo companynameandsymbol dataitem definition exchange glossary home navbar priceandtodayspricechange row search searchloader selectabletimeperiodchart stockdataregion timeperiodbuttons | 0 |
69,423 | 7,133,929,404 | IssuesEvent | 2018-01-22 19:06:28 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | ccl/sqlccl: TestImportStmt failed under stress | Robot bulkio test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/c8b59108e2840974f53a659104f25b79097ac741
Parameters:
```
TAGS=deadlock
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=361341&tab=buildLog
```
I170926 08:32:49.506973 155888 sql/event_log.go:103 [client=127.0.0.1:52471,user=root,n1] Event: "create_database", target: 68, info: {DatabaseName:csv11 Statement:CREATE DATABASE csv11 User:root}
I170926 08:32:49.631200 48648 storage/replica_proposal.go:453 [n1,s1,r85/1:/{Table/64-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
I170926 08:32:49.641467 48781 storage/replica_command.go:2719 [split,n1,s1,r86/1:/{Table/65-Max}] initiating a split of this range at key /Table/66 [r87]
I170926 08:32:49.756911 48655 storage/replica_proposal.go:453 [n1,s1,r86/1:/{Table/65-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
I170926 08:32:49.774632 48781 storage/replica_command.go:2719 [split,n1,s1,r87/1:/{Table/66-Max}] initiating a split of this range at key /Table/67 [r88]
I170926 08:32:49.877291 48684 storage/replica_proposal.go:453 [n1,s1,r87/1:/{Table/66-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
I170926 08:32:49.906898 48781 storage/replica_command.go:2719 [split,n1,s1,r88/1:/{Table/67-Max}] initiating a split of this range at key /Table/68 [r89]
I170926 08:32:50.132205 48647 storage/replica_proposal.go:453 [n1,s1,r88/1:/{Table/67-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
W170926 08:32:50.238650 127375 storage/raft_transport.go:461 [n3] raft transport stream to node 2 failed: rpc error: code = Unavailable desc = transport is closing
W170926 08:32:50.239011 126537 storage/raft_transport.go:461 [n2] raft transport stream to node 3 failed: EOF
W170926 08:32:50.239306 91079 storage/raft_transport.go:461 [n3] raft transport stream to node 1 failed: rpc error: code = Unavailable desc = transport is closing
W170926 08:32:50.239506 89495 storage/raft_transport.go:461 [n2] raft transport stream to node 1 failed: rpc error: code = Unavailable desc = transport is closing
``` | 1.0 | ccl/sqlccl: TestImportStmt failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/c8b59108e2840974f53a659104f25b79097ac741
Parameters:
```
TAGS=deadlock
GOFLAGS=
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=361341&tab=buildLog
```
I170926 08:32:49.506973 155888 sql/event_log.go:103 [client=127.0.0.1:52471,user=root,n1] Event: "create_database", target: 68, info: {DatabaseName:csv11 Statement:CREATE DATABASE csv11 User:root}
I170926 08:32:49.631200 48648 storage/replica_proposal.go:453 [n1,s1,r85/1:/{Table/64-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
I170926 08:32:49.641467 48781 storage/replica_command.go:2719 [split,n1,s1,r86/1:/{Table/65-Max}] initiating a split of this range at key /Table/66 [r87]
I170926 08:32:49.756911 48655 storage/replica_proposal.go:453 [n1,s1,r86/1:/{Table/65-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
I170926 08:32:49.774632 48781 storage/replica_command.go:2719 [split,n1,s1,r87/1:/{Table/66-Max}] initiating a split of this range at key /Table/67 [r88]
I170926 08:32:49.877291 48684 storage/replica_proposal.go:453 [n1,s1,r87/1:/{Table/66-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
I170926 08:32:49.906898 48781 storage/replica_command.go:2719 [split,n1,s1,r88/1:/{Table/67-Max}] initiating a split of this range at key /Table/68 [r89]
I170926 08:32:50.132205 48647 storage/replica_proposal.go:453 [n1,s1,r88/1:/{Table/67-Max}] new range lease repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0 following repl=(n1,s1):1 start=0.000000000,0 epo=1 pro=1506414762.497046746,0
W170926 08:32:50.238650 127375 storage/raft_transport.go:461 [n3] raft transport stream to node 2 failed: rpc error: code = Unavailable desc = transport is closing
W170926 08:32:50.239011 126537 storage/raft_transport.go:461 [n2] raft transport stream to node 3 failed: EOF
W170926 08:32:50.239306 91079 storage/raft_transport.go:461 [n3] raft transport stream to node 1 failed: rpc error: code = Unavailable desc = transport is closing
W170926 08:32:50.239506 89495 storage/raft_transport.go:461 [n2] raft transport stream to node 1 failed: rpc error: code = Unavailable desc = transport is closing
``` | non_priority | ccl sqlccl testimportstmt failed under stress sha parameters tags deadlock goflags stress build found a failed test sql event log go event create database target info databasename statement create database user root storage replica proposal go new range lease repl start epo pro following repl start epo pro storage replica command go initiating a split of this range at key table storage replica proposal go new range lease repl start epo pro following repl start epo pro storage replica command go initiating a split of this range at key table storage replica proposal go new range lease repl start epo pro following repl start epo pro storage replica command go initiating a split of this range at key table storage replica proposal go new range lease repl start epo pro following repl start epo pro storage raft transport go raft transport stream to node failed rpc error code unavailable desc transport is closing storage raft transport go raft transport stream to node failed eof storage raft transport go raft transport stream to node failed rpc error code unavailable desc transport is closing storage raft transport go raft transport stream to node failed rpc error code unavailable desc transport is closing | 0 |
263,168 | 23,039,443,806 | IssuesEvent | 2022-07-23 00:28:55 | saeedtabrizi/code-assignment-1337 | https://api.github.com/repos/saeedtabrizi/code-assignment-1337 | closed | Use Typescript (or similar, no any’s!) | test | For code quality assurance reason we implement the code with the typescript . | 1.0 | Use Typescript (or similar, no any’s!) - For code quality assurance reason we implement the code with the typescript . | non_priority | use typescript or similar no any’s for code quality assurance reason we implement the code with the typescript | 0 |
232,777 | 25,706,299,083 | IssuesEvent | 2022-12-07 01:02:55 | dmyers87/surge | https://api.github.com/repos/dmyers87/surge | closed | CVE-2022-1941 (High) detected in google.protobuf.3.18.1.nupkg - autoclosed | security vulnerability | ## CVE-2022-1941 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google.protobuf.3.18.1.nupkg</b></p></summary>
<p>C# runtime library for Protocol Buffers - Google's data interchange format.</p>
<p>Library home page: <a href="https://api.nuget.org/packages/google.protobuf.3.18.1.nupkg">https://api.nuget.org/packages/google.protobuf.3.18.1.nupkg</a></p>
<p>Path to dependency file: /modules/multilanguage-csharp-sdk/Surge.csproj</p>
<p>Path to vulnerable library: /.nuget/packages/google.protobuf/3.18.1/google.protobuf.3.18.1.nupkg</p>
<p>
Dependency Hierarchy:
- :x: **google.protobuf.3.18.1.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/surge/commit/534418963c4dd1f3fb26a8f8c57115b1e35004c4">534418963c4dd1f3fb26a8f8c57115b1e35004c4</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A parsing vulnerability for the MessageSet type in the ProtocolBuffers versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 3.21.5 for protobuf-cpp, and versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 4.21.5 for protobuf-python can lead to out of memory failures. A specially crafted message with multiple key-value per elements creates parsing issues, and can lead to a Denial of Service against services receiving unsanitized input. We recommend upgrading to versions 3.18.3, 3.19.5, 3.20.2, 3.21.6 for protobuf-cpp and 3.18.3, 3.19.5, 3.20.2, 4.21.6 for protobuf-python. Versions for 3.16 and 3.17 are no longer updated.
<p>Publish Date: 2022-09-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1941>CVE-2022-1941</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cloud.google.com/support/bulletins#GCP-2022-019">https://cloud.google.com/support/bulletins#GCP-2022-019</a></p>
<p>Release Date: 2022-09-22</p>
<p>Fix Resolution: Google.Protobuf - 3.18.3,3.19.5,3.20.2,3.21.6;protobuf-python - 3.18.3,3.19.5,3.20.2,4.21.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2022-1941 (High) detected in google.protobuf.3.18.1.nupkg - autoclosed - ## CVE-2022-1941 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>google.protobuf.3.18.1.nupkg</b></p></summary>
<p>C# runtime library for Protocol Buffers - Google's data interchange format.</p>
<p>Library home page: <a href="https://api.nuget.org/packages/google.protobuf.3.18.1.nupkg">https://api.nuget.org/packages/google.protobuf.3.18.1.nupkg</a></p>
<p>Path to dependency file: /modules/multilanguage-csharp-sdk/Surge.csproj</p>
<p>Path to vulnerable library: /.nuget/packages/google.protobuf/3.18.1/google.protobuf.3.18.1.nupkg</p>
<p>
Dependency Hierarchy:
- :x: **google.protobuf.3.18.1.nupkg** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/surge/commit/534418963c4dd1f3fb26a8f8c57115b1e35004c4">534418963c4dd1f3fb26a8f8c57115b1e35004c4</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A parsing vulnerability for the MessageSet type in the ProtocolBuffers versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 3.21.5 for protobuf-cpp, and versions prior to and including 3.16.1, 3.17.3, 3.18.2, 3.19.4, 3.20.1 and 4.21.5 for protobuf-python can lead to out of memory failures. A specially crafted message with multiple key-value per elements creates parsing issues, and can lead to a Denial of Service against services receiving unsanitized input. We recommend upgrading to versions 3.18.3, 3.19.5, 3.20.2, 3.21.6 for protobuf-cpp and 3.18.3, 3.19.5, 3.20.2, 4.21.6 for protobuf-python. Versions for 3.16 and 3.17 are no longer updated.
<p>Publish Date: 2022-09-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1941>CVE-2022-1941</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cloud.google.com/support/bulletins#GCP-2022-019">https://cloud.google.com/support/bulletins#GCP-2022-019</a></p>
<p>Release Date: 2022-09-22</p>
<p>Fix Resolution: Google.Protobuf - 3.18.3,3.19.5,3.20.2,3.21.6;protobuf-python - 3.18.3,3.19.5,3.20.2,4.21.6</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve high detected in google protobuf nupkg autoclosed cve high severity vulnerability vulnerable library google protobuf nupkg c runtime library for protocol buffers google s data interchange format library home page a href path to dependency file modules multilanguage csharp sdk surge csproj path to vulnerable library nuget packages google protobuf google protobuf nupkg dependency hierarchy x google protobuf nupkg vulnerable library found in head commit a href found in base branch main vulnerability details a parsing vulnerability for the messageset type in the protocolbuffers versions prior to and including and for protobuf cpp and versions prior to and including and for protobuf python can lead to out of memory failures a specially crafted message with multiple key value per elements creates parsing issues and can lead to a denial of service against services receiving unsanitized input we recommend upgrading to versions for protobuf cpp and for protobuf python versions for and are no longer updated publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution google protobuf protobuf python check this box to open an automated fix pr | 0 |
55,710 | 23,548,076,494 | IssuesEvent | 2022-08-21 12:23:13 | BBVA-Openweb/uptime-services | https://api.github.com/repos/BBVA-Openweb/uptime-services | closed | ⚠️ Openweb Service - Average has degraded performance | status openweb-service-average | In [`40a8e60`](https://github.com/BBVA-Openweb/uptime-services/commit/40a8e6098d74e68566789281ab967f1f4bca2139
), Openweb Service - Average ($OPENWEB_HEALTH_LIVE/averages) experienced **degraded performance**:
- HTTP code: 200
- Response time: 18723 ms
| 1.0 | ⚠️ Openweb Service - Average has degraded performance - In [`40a8e60`](https://github.com/BBVA-Openweb/uptime-services/commit/40a8e6098d74e68566789281ab967f1f4bca2139
), Openweb Service - Average ($OPENWEB_HEALTH_LIVE/averages) experienced **degraded performance**:
- HTTP code: 200
- Response time: 18723 ms
| non_priority | ⚠️ openweb service average has degraded performance in openweb service average openweb health live averages experienced degraded performance http code response time ms | 0 |
62,671 | 26,104,903,579 | IssuesEvent | 2022-12-27 11:59:43 | chris9091/Fleksa-Monitor-2 | https://api.github.com/repos/chris9091/Fleksa-Monitor-2 | closed | 🛑 Pizzaservice Nohfelden is down | status pizzaservice-nohfelden | In [`4ff3228`](https://github.com/chris9091/Fleksa-Monitor-2/commit/4ff32283a1245a9027cbed9133fb3cf60f1bc6ee
), Pizzaservice Nohfelden (https://anno19.de) was **down**:
- HTTP code: 502
- Response time: 807 ms
| 1.0 | 🛑 Pizzaservice Nohfelden is down - In [`4ff3228`](https://github.com/chris9091/Fleksa-Monitor-2/commit/4ff32283a1245a9027cbed9133fb3cf60f1bc6ee
), Pizzaservice Nohfelden (https://anno19.de) was **down**:
- HTTP code: 502
- Response time: 807 ms
| non_priority | 🛑 pizzaservice nohfelden is down in pizzaservice nohfelden was down http code response time ms | 0 |
71,936 | 13,764,501,449 | IssuesEvent | 2020-10-07 12:10:17 | fac20/Week12-DOPE | https://api.github.com/repos/fac20/Week12-DOPE | closed | Something you might want to know | code review | API key (apiKey:"AIzaSyCKOdFKQOSSFUvWcrYhN2oR2U0n5F6FxUI") can be found in a firebase object which is stored in Index DB (P.S. I was using Firefox). | 1.0 | Something you might want to know - API key (apiKey:"AIzaSyCKOdFKQOSSFUvWcrYhN2oR2U0n5F6FxUI") can be found in a firebase object which is stored in Index DB (P.S. I was using Firefox). | non_priority | something you might want to know api key apikey can be found in a firebase object which is stored in index db p s i was using firefox | 0 |
245,338 | 20,763,348,981 | IssuesEvent | 2022-03-15 18:11:02 | UjwalKandi/Issue-Bookmarks | https://api.github.com/repos/UjwalKandi/Issue-Bookmarks | opened | Ubersuggest - Create a project so you can track and improve your SEO traffic. | enhancement free sites test | **TL;DR** - Find profitable SEO keywords that are easy to win. Use the keyword discovery tool to get maximum results.
**Website**:
https://neilpatel.com/
https://app.neilpatel.com/en/seo_analyzer/ | 1.0 | Ubersuggest - Create a project so you can track and improve your SEO traffic. - **TL;DR** - Find profitable SEO keywords that are easy to win. Use the keyword discovery tool to get maximum results.
**Website**:
https://neilpatel.com/
https://app.neilpatel.com/en/seo_analyzer/ | non_priority | ubersuggest create a project so you can track and improve your seo traffic tl dr find profitable seo keywords that are easy to win use the keyword discovery tool to get maximum results website | 0 |
245,696 | 26,549,344,988 | IssuesEvent | 2023-01-20 05:33:59 | nidhi7598/linux-3.0.35_CVE-2022-45934 | https://api.github.com/repos/nidhi7598/linux-3.0.35_CVE-2022-45934 | opened | CVE-2016-8399 (High) detected in linuxlinux-3.0.49 | security vulnerability | ## CVE-2016-8399 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-3.0.49</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v3.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v3.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-3.0.35_CVE-2022-45934/commit/5e23b7f9d2dd0154edd54986754eecd5b5308571">5e23b7f9d2dd0154edd54986754eecd5b5308571</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/ping.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/ping.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/ping.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An elevation of privilege vulnerability in the kernel networking subsystem could enable a local malicious application to execute arbitrary code within the context of the kernel. This issue is rated as Moderate because it first requires compromising a privileged process and current compiler optimizations restrict access to the vulnerable code. Product: Android. Versions: Kernel-3.10, Kernel-3.18. Android ID: A-31349935.
<p>Publish Date: 2017-01-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-8399>CVE-2016-8399</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-8399">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-8399</a></p>
<p>Release Date: 2017-01-12</p>
<p>Fix Resolution: v4.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-8399 (High) detected in linuxlinux-3.0.49 - ## CVE-2016-8399 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-3.0.49</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v3.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v3.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-3.0.35_CVE-2022-45934/commit/5e23b7f9d2dd0154edd54986754eecd5b5308571">5e23b7f9d2dd0154edd54986754eecd5b5308571</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/ping.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/ping.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/ipv4/ping.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An elevation of privilege vulnerability in the kernel networking subsystem could enable a local malicious application to execute arbitrary code within the context of the kernel. This issue is rated as Moderate because it first requires compromising a privileged process and current compiler optimizations restrict access to the vulnerable code. Product: Android. Versions: Kernel-3.10, Kernel-3.18. Android ID: A-31349935.
<p>Publish Date: 2017-01-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-8399>CVE-2016-8399</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-8399">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-8399</a></p>
<p>Release Date: 2017-01-12</p>
<p>Fix Resolution: v4.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files net ping c net ping c net ping c vulnerability details an elevation of privilege vulnerability in the kernel networking subsystem could enable a local malicious application to execute arbitrary code within the context of the kernel this issue is rated as moderate because it first requires compromising a privileged process and current compiler optimizations restrict access to the vulnerable code product android versions kernel kernel android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
106,222 | 11,473,234,506 | IssuesEvent | 2020-02-09 21:55:06 | Seterator/seterator.ru | https://api.github.com/repos/Seterator/seterator.ru | opened | Требуется обновить/задокументировать шаблон json'а с участниками конкурса | documentation enhancement help wanted | # Участник конкурса
Так как мы нигде не утверждали формат json'а для участника конкурса, предлагаю свой вариант видения этой картины.
```
{
"nickname": "Псевдоним участника",
"poems": [
{
"title": "Название произведения",
"poem": "Текст произведения",
"guid": "guid заявки"
}
],
"guid": "guid участника"
}
```
Пока что для страницы с отображением конкурса этого достаточно, но если потребуется что-то еще, всегда можно добавить полей.
Как видит это дизайнер:
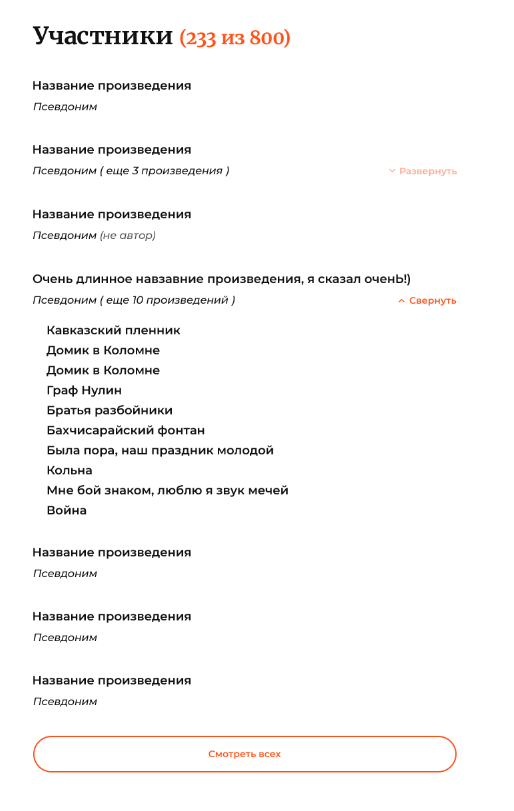
@bearpro @saner99 если есть что добавить/изменить - пишите. | 1.0 | Требуется обновить/задокументировать шаблон json'а с участниками конкурса - # Участник конкурса
Так как мы нигде не утверждали формат json'а для участника конкурса, предлагаю свой вариант видения этой картины.
```
{
"nickname": "Псевдоним участника",
"poems": [
{
"title": "Название произведения",
"poem": "Текст произведения",
"guid": "guid заявки"
}
],
"guid": "guid участника"
}
```
Пока что для страницы с отображением конкурса этого достаточно, но если потребуется что-то еще, всегда можно добавить полей.
Как видит это дизайнер:
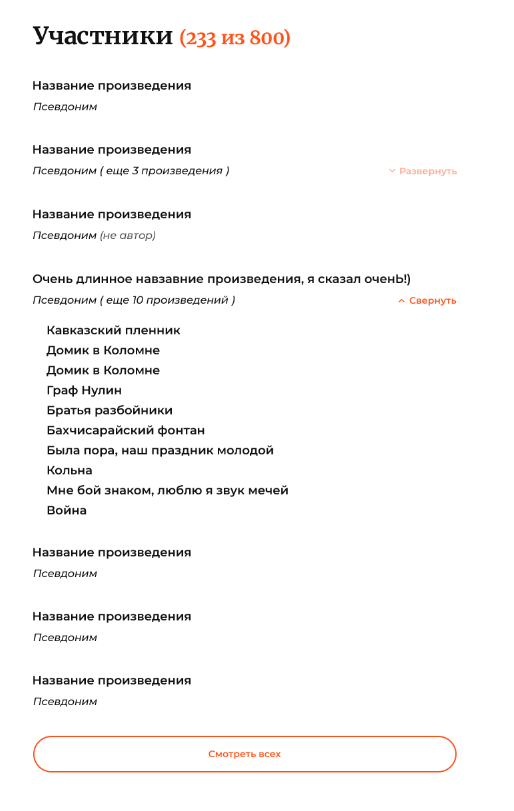
@bearpro @saner99 если есть что добавить/изменить - пишите. | non_priority | требуется обновить задокументировать шаблон json а с участниками конкурса участник конкурса так как мы нигде не утверждали формат json а для участника конкурса предлагаю свой вариант видения этой картины nickname псевдоним участника poems title название произведения poem текст произведения guid guid заявки guid guid участника пока что для страницы с отображением конкурса этого достаточно но если потребуется что то еще всегда можно добавить полей как видит это дизайнер bearpro если есть что добавить изменить пишите | 0 |
355,105 | 25,175,586,193 | IssuesEvent | 2022-11-11 08:57:57 | ssyap98/pe | https://api.github.com/repos/ssyap98/pe | opened | Incorrect command format for editL | severity.Low type.DocumentationBug | In the UG, the command format for editL includes the tag field.
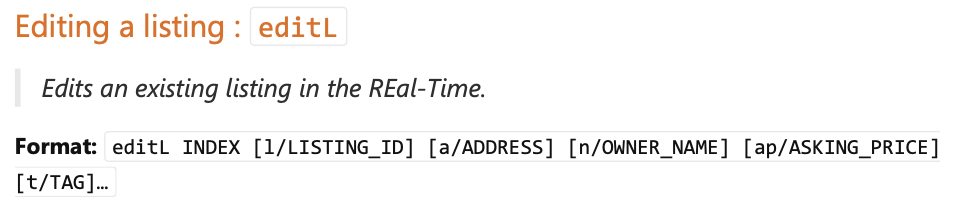
However, when trying to edit an existing listing with the t/ prefix. The following error message was shown.
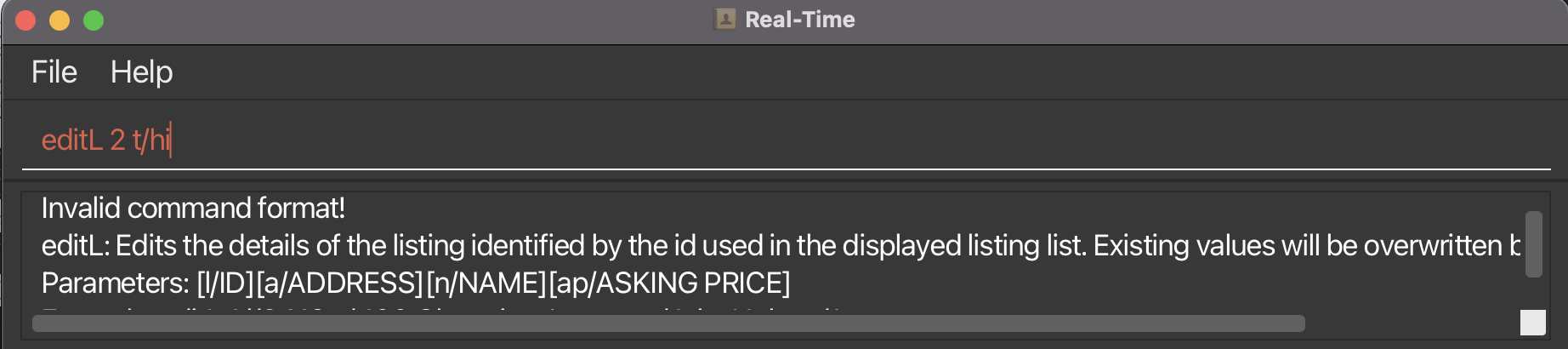
In the error message, it was indicated that the parameters accepted by the command are listing ID, address, name and price. Hence, the command format for editL in the UG is wrong.
<!--session: 1668153037672-67a0fa71-5794-4d5b-9c56-2daaa9bc7561-->
<!--Version: Web v3.4.4--> | 1.0 | Incorrect command format for editL - In the UG, the command format for editL includes the tag field.
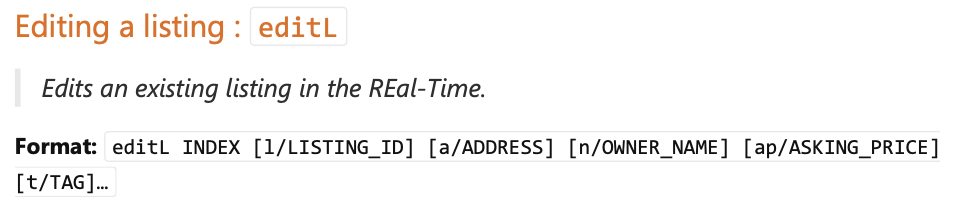
However, when trying to edit an existing listing with the t/ prefix. The following error message was shown.
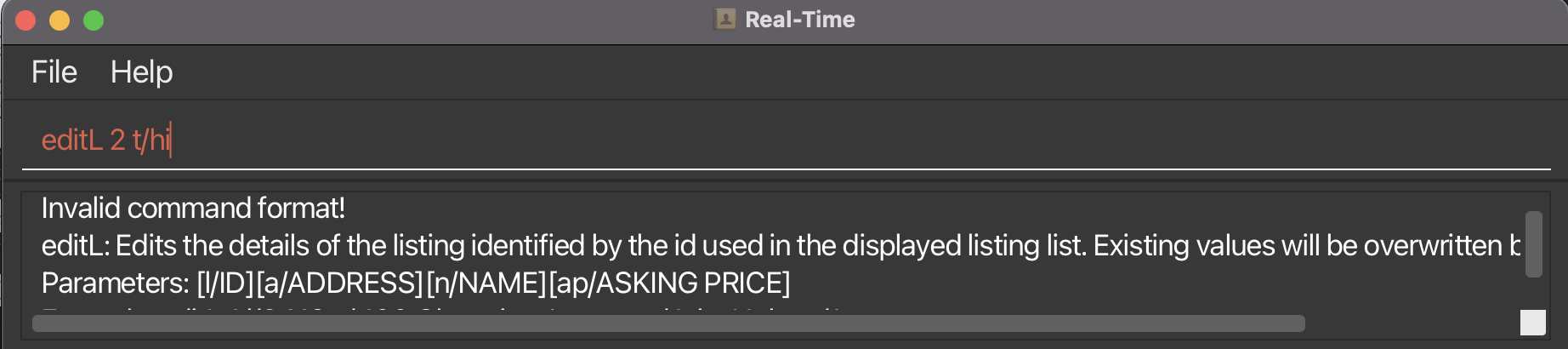
In the error message, it was indicated that the parameters accepted by the command are listing ID, address, name and price. Hence, the command format for editL in the UG is wrong.
<!--session: 1668153037672-67a0fa71-5794-4d5b-9c56-2daaa9bc7561-->
<!--Version: Web v3.4.4--> | non_priority | incorrect command format for editl in the ug the command format for editl includes the tag field however when trying to edit an existing listing with the t prefix the following error message was shown in the error message it was indicated that the parameters accepted by the command are listing id address name and price hence the command format for editl in the ug is wrong | 0 |
81,086 | 30,705,385,392 | IssuesEvent | 2023-07-27 05:32:25 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | closed | [🐛 Bug]: Not able to launch chrome using web driver manager latest dependency 5.4.1 | I-defect needs-triaging | ### What happened?
Hello Team,
Please find below mentioned details for the issue encountered in which the chrome / edge is not getting launched on
**MacBook Pro running OS:** macOS Ventura 13.5 (22G74)
**Maven version :** 3.9.3
**JAVA:** 20.0.1
Each time I try to execute the test case using below mentioned code to launch chrome browser :
WebDriverManager.chromedriver().setup();
ChromeOptions chromeOptions = new ChromeOptions();
if (utils.properties(AppConstants.CONFIG_FILE_NAME, "IS_BROWSER_HEADLESS")
.equalsIgnoreCase("true")) {
chromeOptions.addArguments("--headless");
}
ChromeDriver driver = new ChromeDriver(chromeOptions);
driver.manage().timeouts().getPageLoadTimeout();
driver.manage().window().maximize();
I encounter below mentioned error on the console:
INFO: Driver logs no longer sent to console by default; https://www.selenium.dev/documentation/webdriver/drivers/service/#setting-log-output
org.openqa.selenium.SessionNotCreatedException: Could not start a new session. Response code 500. Message: unknown error: cannot find Chrome binary
Host info: host: 'USTSHYDLAP-222.local', ip: 'fe80:0:0:0:8f2:78e0:86ea:f39d%en0'
Build info: version: '4.10.0', revision: 'c14d967899'
System info: os.name: 'Mac OS X', os.arch: 'x86_64', os.version: '13.5', java.version: '20.0.1'
Driver info: org.openqa.selenium.chrome.ChromeDriver
Command: [null, newSession {capabilities=[Capabilities {browserName: chrome, goog:chromeOptions: {args: [--remote-allow-origins=*], extensions: []}}]}]
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:140)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:96)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:68)
at org.openqa.selenium.remote.HttpCommandExecutor.execute(HttpCommandExecutor.java:163)
at org.openqa.selenium.remote.service.DriverCommandExecutor.invokeExecute(DriverCommandExecutor.java:196)
at org.openqa.selenium.remote.service.DriverCommandExecutor.execute(DriverCommandExecutor.java:171)
at org.openqa.selenium.remote.RemoteWebDriver.execute(RemoteWebDriver.java:531)
at org.openqa.selenium.remote.RemoteWebDriver.startSession(RemoteWebDriver.java:227)
at org.openqa.selenium.remote.RemoteWebDriver.<init>(RemoteWebDriver.java:154)
at org.openqa.selenium.chromium.ChromiumDriver.<init>(ChromiumDriver.java:107)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:87)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:82)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:71)
### How can we reproduce the issue?
```shell
Each time I try to execute the test case using below mentioned code to launch chrome browser :
WebDriverManager.chromedriver().setup();
ChromeOptions chromeOptions = new ChromeOptions();
if (utils.properties(AppConstants.CONFIG_FILE_NAME, "IS_BROWSER_HEADLESS")
.equalsIgnoreCase("true")) {
chromeOptions.addArguments("--headless");
}
ChromeDriver driver = new ChromeDriver(chromeOptions);
driver.manage().timeouts().getPageLoadTimeout();
driver.manage().window().maximize();
```
### Relevant log output
```shell
I encounter below mentioned error on the console:
INFO: Driver logs no longer sent to console by default; https://www.selenium.dev/documentation/webdriver/drivers/service/#setting-log-output
org.openqa.selenium.SessionNotCreatedException: Could not start a new session. Response code 500. Message: unknown error: cannot find Chrome binary
Host info: host: 'USTSHYDLAP-222.local', ip: 'fe80:0:0:0:8f2:78e0:86ea:f39d%en0'
Build info: version: '4.10.0', revision: 'c14d967899'
System info: os.name: 'Mac OS X', os.arch: 'x86_64', os.version: '13.5', java.version: '20.0.1'
Driver info: org.openqa.selenium.chrome.ChromeDriver
Command: [null, newSession {capabilities=[Capabilities {browserName: chrome, goog:chromeOptions: {args: [--remote-allow-origins=*], extensions: []}}]}]
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:140)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:96)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:68)
at org.openqa.selenium.remote.HttpCommandExecutor.execute(HttpCommandExecutor.java:163)
at org.openqa.selenium.remote.service.DriverCommandExecutor.invokeExecute(DriverCommandExecutor.java:196)
at org.openqa.selenium.remote.service.DriverCommandExecutor.execute(DriverCommandExecutor.java:171)
at org.openqa.selenium.remote.RemoteWebDriver.execute(RemoteWebDriver.java:531)
at org.openqa.selenium.remote.RemoteWebDriver.startSession(RemoteWebDriver.java:227)
at org.openqa.selenium.remote.RemoteWebDriver.<init>(RemoteWebDriver.java:154)
at org.openqa.selenium.chromium.ChromiumDriver.<init>(ChromiumDriver.java:107)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:87)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:82)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:71)
```
### Operating System
macOS Ventura 13.5 (22G74)
### Selenium version
4.10.0
### What are the browser(s) and version(s) where you see this issue?
Chrome
### What are the browser driver(s) and version(s) where you see this issue?
Chrome installed is 115.0.5790.114
### Are you using Selenium Grid?
No | 1.0 | [🐛 Bug]: Not able to launch chrome using web driver manager latest dependency 5.4.1 - ### What happened?
Hello Team,
Please find below mentioned details for the issue encountered in which the chrome / edge is not getting launched on
**MacBook Pro running OS:** macOS Ventura 13.5 (22G74)
**Maven version :** 3.9.3
**JAVA:** 20.0.1
Each time I try to execute the test case using below mentioned code to launch chrome browser :
WebDriverManager.chromedriver().setup();
ChromeOptions chromeOptions = new ChromeOptions();
if (utils.properties(AppConstants.CONFIG_FILE_NAME, "IS_BROWSER_HEADLESS")
.equalsIgnoreCase("true")) {
chromeOptions.addArguments("--headless");
}
ChromeDriver driver = new ChromeDriver(chromeOptions);
driver.manage().timeouts().getPageLoadTimeout();
driver.manage().window().maximize();
I encounter below mentioned error on the console:
INFO: Driver logs no longer sent to console by default; https://www.selenium.dev/documentation/webdriver/drivers/service/#setting-log-output
org.openqa.selenium.SessionNotCreatedException: Could not start a new session. Response code 500. Message: unknown error: cannot find Chrome binary
Host info: host: 'USTSHYDLAP-222.local', ip: 'fe80:0:0:0:8f2:78e0:86ea:f39d%en0'
Build info: version: '4.10.0', revision: 'c14d967899'
System info: os.name: 'Mac OS X', os.arch: 'x86_64', os.version: '13.5', java.version: '20.0.1'
Driver info: org.openqa.selenium.chrome.ChromeDriver
Command: [null, newSession {capabilities=[Capabilities {browserName: chrome, goog:chromeOptions: {args: [--remote-allow-origins=*], extensions: []}}]}]
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:140)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:96)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:68)
at org.openqa.selenium.remote.HttpCommandExecutor.execute(HttpCommandExecutor.java:163)
at org.openqa.selenium.remote.service.DriverCommandExecutor.invokeExecute(DriverCommandExecutor.java:196)
at org.openqa.selenium.remote.service.DriverCommandExecutor.execute(DriverCommandExecutor.java:171)
at org.openqa.selenium.remote.RemoteWebDriver.execute(RemoteWebDriver.java:531)
at org.openqa.selenium.remote.RemoteWebDriver.startSession(RemoteWebDriver.java:227)
at org.openqa.selenium.remote.RemoteWebDriver.<init>(RemoteWebDriver.java:154)
at org.openqa.selenium.chromium.ChromiumDriver.<init>(ChromiumDriver.java:107)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:87)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:82)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:71)
### How can we reproduce the issue?
```shell
Each time I try to execute the test case using below mentioned code to launch chrome browser :
WebDriverManager.chromedriver().setup();
ChromeOptions chromeOptions = new ChromeOptions();
if (utils.properties(AppConstants.CONFIG_FILE_NAME, "IS_BROWSER_HEADLESS")
.equalsIgnoreCase("true")) {
chromeOptions.addArguments("--headless");
}
ChromeDriver driver = new ChromeDriver(chromeOptions);
driver.manage().timeouts().getPageLoadTimeout();
driver.manage().window().maximize();
```
### Relevant log output
```shell
I encounter below mentioned error on the console:
INFO: Driver logs no longer sent to console by default; https://www.selenium.dev/documentation/webdriver/drivers/service/#setting-log-output
org.openqa.selenium.SessionNotCreatedException: Could not start a new session. Response code 500. Message: unknown error: cannot find Chrome binary
Host info: host: 'USTSHYDLAP-222.local', ip: 'fe80:0:0:0:8f2:78e0:86ea:f39d%en0'
Build info: version: '4.10.0', revision: 'c14d967899'
System info: os.name: 'Mac OS X', os.arch: 'x86_64', os.version: '13.5', java.version: '20.0.1'
Driver info: org.openqa.selenium.chrome.ChromeDriver
Command: [null, newSession {capabilities=[Capabilities {browserName: chrome, goog:chromeOptions: {args: [--remote-allow-origins=*], extensions: []}}]}]
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:140)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:96)
at org.openqa.selenium.remote.ProtocolHandshake.createSession(ProtocolHandshake.java:68)
at org.openqa.selenium.remote.HttpCommandExecutor.execute(HttpCommandExecutor.java:163)
at org.openqa.selenium.remote.service.DriverCommandExecutor.invokeExecute(DriverCommandExecutor.java:196)
at org.openqa.selenium.remote.service.DriverCommandExecutor.execute(DriverCommandExecutor.java:171)
at org.openqa.selenium.remote.RemoteWebDriver.execute(RemoteWebDriver.java:531)
at org.openqa.selenium.remote.RemoteWebDriver.startSession(RemoteWebDriver.java:227)
at org.openqa.selenium.remote.RemoteWebDriver.<init>(RemoteWebDriver.java:154)
at org.openqa.selenium.chromium.ChromiumDriver.<init>(ChromiumDriver.java:107)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:87)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:82)
at org.openqa.selenium.chrome.ChromeDriver.<init>(ChromeDriver.java:71)
```
### Operating System
macOS Ventura 13.5 (22G74)
### Selenium version
4.10.0
### What are the browser(s) and version(s) where you see this issue?
Chrome
### What are the browser driver(s) and version(s) where you see this issue?
Chrome installed is 115.0.5790.114
### Are you using Selenium Grid?
No | non_priority | not able to launch chrome using web driver manager latest dependency what happened hello team please find below mentioned details for the issue encountered in which the chrome edge is not getting launched on macbook pro running os macos ventura maven version java each time i try to execute the test case using below mentioned code to launch chrome browser webdrivermanager chromedriver setup chromeoptions chromeoptions new chromeoptions if utils properties appconstants config file name is browser headless equalsignorecase true chromeoptions addarguments headless chromedriver driver new chromedriver chromeoptions driver manage timeouts getpageloadtimeout driver manage window maximize i encounter below mentioned error on the console info driver logs no longer sent to console by default org openqa selenium sessionnotcreatedexception could not start a new session response code message unknown error cannot find chrome binary host info host ustshydlap local ip build info version revision system info os name mac os x os arch os version java version driver info org openqa selenium chrome chromedriver command extensions at org openqa selenium remote protocolhandshake createsession protocolhandshake java at org openqa selenium remote protocolhandshake createsession protocolhandshake java at org openqa selenium remote protocolhandshake createsession protocolhandshake java at org openqa selenium remote httpcommandexecutor execute httpcommandexecutor java at org openqa selenium remote service drivercommandexecutor invokeexecute drivercommandexecutor java at org openqa selenium remote service drivercommandexecutor execute drivercommandexecutor java at org openqa selenium remote remotewebdriver execute remotewebdriver java at org openqa selenium remote remotewebdriver startsession remotewebdriver java at org openqa selenium remote remotewebdriver remotewebdriver java at org openqa selenium chromium chromiumdriver chromiumdriver java at org openqa selenium chrome chromedriver chromedriver java at org openqa selenium chrome chromedriver chromedriver java at org openqa selenium chrome chromedriver chromedriver java how can we reproduce the issue shell each time i try to execute the test case using below mentioned code to launch chrome browser webdrivermanager chromedriver setup chromeoptions chromeoptions new chromeoptions if utils properties appconstants config file name is browser headless equalsignorecase true chromeoptions addarguments headless chromedriver driver new chromedriver chromeoptions driver manage timeouts getpageloadtimeout driver manage window maximize relevant log output shell i encounter below mentioned error on the console info driver logs no longer sent to console by default org openqa selenium sessionnotcreatedexception could not start a new session response code message unknown error cannot find chrome binary host info host ustshydlap local ip build info version revision system info os name mac os x os arch os version java version driver info org openqa selenium chrome chromedriver command extensions at org openqa selenium remote protocolhandshake createsession protocolhandshake java at org openqa selenium remote protocolhandshake createsession protocolhandshake java at org openqa selenium remote protocolhandshake createsession protocolhandshake java at org openqa selenium remote httpcommandexecutor execute httpcommandexecutor java at org openqa selenium remote service drivercommandexecutor invokeexecute drivercommandexecutor java at org openqa selenium remote service drivercommandexecutor execute drivercommandexecutor java at org openqa selenium remote remotewebdriver execute remotewebdriver java at org openqa selenium remote remotewebdriver startsession remotewebdriver java at org openqa selenium remote remotewebdriver remotewebdriver java at org openqa selenium chromium chromiumdriver chromiumdriver java at org openqa selenium chrome chromedriver chromedriver java at org openqa selenium chrome chromedriver chromedriver java at org openqa selenium chrome chromedriver chromedriver java operating system macos ventura selenium version what are the browser s and version s where you see this issue chrome what are the browser driver s and version s where you see this issue chrome installed is are you using selenium grid no | 0 |
262,729 | 19,829,447,577 | IssuesEvent | 2022-01-20 10:25:00 | satokibi44/Tweet_Analyzing | https://api.github.com/repos/satokibi44/Tweet_Analyzing | closed | Robustness Diagram #4Part: Function to send the measurement result to slack | documentation | In the issue I will create the ROBUSTNESS DIAGRAM for 4th use case. | 1.0 | Robustness Diagram #4Part: Function to send the measurement result to slack - In the issue I will create the ROBUSTNESS DIAGRAM for 4th use case. | non_priority | robustness diagram function to send the measurement result to slack in the issue i will create the robustness diagram for use case | 0 |
12,262 | 3,593,720,850 | IssuesEvent | 2016-02-01 20:49:13 | haffo/hit-iz-tool | https://api.github.com/repos/haffo/hit-iz-tool | closed | NIST Clarifications and Validation Guidelines Update | Documentation | Harold, please use the attached document for the release today.
[NIST-Clarifications-and-Validation-Guidelines.docx](https://github.com/haffo/hit-iz-tool/files/100847/NIST-Clarifications-and-Validation-Guidelines.docx)
| 1.0 | NIST Clarifications and Validation Guidelines Update - Harold, please use the attached document for the release today.
[NIST-Clarifications-and-Validation-Guidelines.docx](https://github.com/haffo/hit-iz-tool/files/100847/NIST-Clarifications-and-Validation-Guidelines.docx)
| non_priority | nist clarifications and validation guidelines update harold please use the attached document for the release today | 0 |
91,070 | 11,461,804,340 | IssuesEvent | 2020-02-07 12:49:16 | angular-ui/ui-router | https://api.github.com/repos/angular-ui/ui-router | closed | Run Time State Setting | design stale | Not sure if I'm missing something in the docs, but I can't find anyway of doing this. I want to write a directive with a options of passing in a base path, ie
```
<div my-directive basepath="/some/path/"></div>
```
Then have my directive have a ui-router which appends all it's states to this path.
This doesn't seem possible at the moment as the states are created in the config step and there doesn't appear to be anyway of changing these. If the state urls could be looped through and updated, I could do this when the directive is first created and update the states.
Use cases for this are re-usable modules which bring there own routes. They would only really be re-usable if they could be appended to a specific state.
(I thought this kind of thing maybe possible after listening to Dean Sofer on JS Jabber - excellent module btw..)
| 1.0 | Run Time State Setting - Not sure if I'm missing something in the docs, but I can't find anyway of doing this. I want to write a directive with a options of passing in a base path, ie
```
<div my-directive basepath="/some/path/"></div>
```
Then have my directive have a ui-router which appends all it's states to this path.
This doesn't seem possible at the moment as the states are created in the config step and there doesn't appear to be anyway of changing these. If the state urls could be looped through and updated, I could do this when the directive is first created and update the states.
Use cases for this are re-usable modules which bring there own routes. They would only really be re-usable if they could be appended to a specific state.
(I thought this kind of thing maybe possible after listening to Dean Sofer on JS Jabber - excellent module btw..)
| non_priority | run time state setting not sure if i m missing something in the docs but i can t find anyway of doing this i want to write a directive with a options of passing in a base path ie then have my directive have a ui router which appends all it s states to this path this doesn t seem possible at the moment as the states are created in the config step and there doesn t appear to be anyway of changing these if the state urls could be looped through and updated i could do this when the directive is first created and update the states use cases for this are re usable modules which bring there own routes they would only really be re usable if they could be appended to a specific state i thought this kind of thing maybe possible after listening to dean sofer on js jabber excellent module btw | 0 |
30,175 | 6,034,761,679 | IssuesEvent | 2017-06-09 12:08:23 | Advanced-Post-List/advanced-post-list | https://api.github.com/repos/Advanced-Post-List/advanced-post-list | closed | custom presets post_title shortcode | P6 - Trivial T-Possible Defect | I have a few custom presets that are not working.
For example: <h3><li><a href=[post_permalink]>[post_title]</a></li><h3>. It only works when there is only 1 post.
This one: <h3><li><a href=[post_permalink]>[post_title]</a> by [php_function name="myUser_name" param="[post_author]"]</li></h3> should display post title with a by line and only works sometimes.
These presets were working with wordpress 3.6 and 2010 theme. They have not work correctly with 3.7.x or 3.8.x or with any other themes.
| 1.0 | custom presets post_title shortcode - I have a few custom presets that are not working.
For example: <h3><li><a href=[post_permalink]>[post_title]</a></li><h3>. It only works when there is only 1 post.
This one: <h3><li><a href=[post_permalink]>[post_title]</a> by [php_function name="myUser_name" param="[post_author]"]</li></h3> should display post title with a by line and only works sometimes.
These presets were working with wordpress 3.6 and 2010 theme. They have not work correctly with 3.7.x or 3.8.x or with any other themes.
| non_priority | custom presets post title shortcode i have a few custom presets that are not working for example it only works when there is only post this one by should display post title with a by line and only works sometimes these presets were working with wordpress and theme they have not work correctly with x or x or with any other themes | 0 |
61,378 | 25,491,713,938 | IssuesEvent | 2022-11-27 06:13:44 | thewca/worldcubeassociation.org | https://api.github.com/repos/thewca/worldcubeassociation.org | opened | Create an "Are you sure you want to leave the page?" popup on unsaved delegate reports | META: good first issue TECH: ruby TEAM: delegates SERVICE: competition | From "New website feature proposal" email thread:
> Hi WST,
>
> I just made the rookie mistake of closing the delegate report by accident without saving it and had to write it all over again. Would it be possible to add an extra layer of safety like the one that comes out when you try to post a report or close the competition creation form without submitting (attached picture)?
> I think this would be a very nice addition to the website.
This seems like a very reasonable suggestion to me. | 1.0 | Create an "Are you sure you want to leave the page?" popup on unsaved delegate reports - From "New website feature proposal" email thread:
> Hi WST,
>
> I just made the rookie mistake of closing the delegate report by accident without saving it and had to write it all over again. Would it be possible to add an extra layer of safety like the one that comes out when you try to post a report or close the competition creation form without submitting (attached picture)?
> I think this would be a very nice addition to the website.
This seems like a very reasonable suggestion to me. | non_priority | create an are you sure you want to leave the page popup on unsaved delegate reports from new website feature proposal email thread hi wst i just made the rookie mistake of closing the delegate report by accident without saving it and had to write it all over again would it be possible to add an extra layer of safety like the one that comes out when you try to post a report or close the competition creation form without submitting attached picture i think this would be a very nice addition to the website this seems like a very reasonable suggestion to me | 0 |
444,707 | 31,143,269,556 | IssuesEvent | 2023-08-16 03:06:28 | ResidenciaTICBrisa/03_Robotica | https://api.github.com/repos/ResidenciaTICBrisa/03_Robotica | opened | Revisar instalação e documentar todos os passos no Git Pages | documentation | Revisar passo a passo da instalação do ROS1 e ROS2 na raspberry pi e documentar | 1.0 | Revisar instalação e documentar todos os passos no Git Pages - Revisar passo a passo da instalação do ROS1 e ROS2 na raspberry pi e documentar | non_priority | revisar instalação e documentar todos os passos no git pages revisar passo a passo da instalação do e na raspberry pi e documentar | 0 |
339,120 | 30,345,869,806 | IssuesEvent | 2023-07-11 15:23:17 | US-EPA-CAMD/easey-ui | https://api.github.com/repos/US-EPA-CAMD/easey-ui | closed | Check Engine ERG: Emissions Conversion Testing | Tech Team Testing ERG | ## Context
This ticket is for the ERG to complete the portion of testing the check engine. | 1.0 | Check Engine ERG: Emissions Conversion Testing - ## Context
This ticket is for the ERG to complete the portion of testing the check engine. | non_priority | check engine erg emissions conversion testing context this ticket is for the erg to complete the portion of testing the check engine | 0 |
319,587 | 27,386,924,329 | IssuesEvent | 2023-02-28 13:56:50 | splendo/kaluga | https://api.github.com/repos/splendo/kaluga | closed | Add MockDateTimePickerPresenter | component:test-utils 1.0.0 | **Is your feature request related to a problem? Please describe.**
Trying to test some VM code that takes a `DateTimePickerPresenter.Builder`, but unable to mock time selection.
**Describe the solution you'd like**
Create a MockDateTimePickerPresenter that will extend its base class and also expose some properties to assert the picker visibility and some method to mock the selected date. | 1.0 | Add MockDateTimePickerPresenter - **Is your feature request related to a problem? Please describe.**
Trying to test some VM code that takes a `DateTimePickerPresenter.Builder`, but unable to mock time selection.
**Describe the solution you'd like**
Create a MockDateTimePickerPresenter that will extend its base class and also expose some properties to assert the picker visibility and some method to mock the selected date. | non_priority | add mockdatetimepickerpresenter is your feature request related to a problem please describe trying to test some vm code that takes a datetimepickerpresenter builder but unable to mock time selection describe the solution you d like create a mockdatetimepickerpresenter that will extend its base class and also expose some properties to assert the picker visibility and some method to mock the selected date | 0 |
125,859 | 10,367,453,663 | IssuesEvent | 2019-09-07 08:22:31 | Rocologo/MobHunting | https://api.github.com/repos/Rocologo/MobHunting | closed | Could not pass event EntityDeathEvent to MobHunting v6.8.5 | Fixed - To be tested | [21:10:08] [Server thread/ERROR]: Could not pass event EntityDeathEvent to MobHunting v6.8.5
org.bukkit.event.EventException: null
at org.bukkit.plugin.java.JavaPluginLoader$1.execute(JavaPluginLoader.java:320) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.plugin.RegisteredListener.callEvent(RegisteredListener.java:70) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.plugin.SimplePluginManager.fireEvent(SimplePluginManager.java:529) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.plugin.SimplePluginManager.callEvent(SimplePluginManager.java:514) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.craftbukkit.v1_14_R1.event.CraftEventFactory.callEntityDeathEvent(CraftEventFactory.java:707) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityLiving.d(EntityLiving.java:1366) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityLiving.die(EntityLiving.java:1322) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityLiving.damageEntity(EntityLiving.java:1169) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityHuman.attack(EntityHuman.java:1018) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityPlayer.attack(EntityPlayer.java:1539) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PlayerConnection.a(PlayerConnection.java:1864) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PacketPlayInUseEntity.a(SourceFile:69) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PacketPlayInUseEntity.a(SourceFile:13) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PlayerConnectionUtils.lambda$0(PlayerConnectionUtils.java:19) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.TickTask.run(SourceFile:18) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandler.executeTask(SourceFile:144) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandlerReentrant.executeTask(SourceFile:23) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandler.executeNext(SourceFile:118) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.aX(MinecraftServer.java:909) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.executeNext(MinecraftServer.java:902) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandler.awaitTasks(SourceFile:127) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.sleepForTick(MinecraftServer.java:886) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.run(MinecraftServer.java:819) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at java.lang.Thread.run(Unknown Source) [?:1.8.0_211]
Caused by: java.lang.NoClassDefFoundError: Could not initialize class com.sk89q.worldguard.protection.flags.Flags
at one.lindegaard.MobHunting.compatibility.WorldGuardMobHuntingFlag.getMobDamageFlag(WorldGuardMobHuntingFlag.java:32) ~[?:?]
at one.lindegaard.MobHunting.MobHuntingManager.onMobDeath(MobHuntingManager.java:893) ~[?:?]
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method) ~[?:1.8.0_211]
at sun.reflect.NativeMethodAccessorImpl.invoke(Unknown Source) ~[?:1.8.0_211]
at sun.reflect.DelegatingMethodAccessorImpl.invoke(Unknown Source) ~[?:1.8.0_211]
at java.lang.reflect.Method.invoke(Unknown Source) ~[?:1.8.0_211]
at org.bukkit.plugin.java.JavaPluginLoader$1.execute(JavaPluginLoader.java:316) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
... 23 more | 1.0 | Could not pass event EntityDeathEvent to MobHunting v6.8.5 - [21:10:08] [Server thread/ERROR]: Could not pass event EntityDeathEvent to MobHunting v6.8.5
org.bukkit.event.EventException: null
at org.bukkit.plugin.java.JavaPluginLoader$1.execute(JavaPluginLoader.java:320) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.plugin.RegisteredListener.callEvent(RegisteredListener.java:70) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.plugin.SimplePluginManager.fireEvent(SimplePluginManager.java:529) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.plugin.SimplePluginManager.callEvent(SimplePluginManager.java:514) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at org.bukkit.craftbukkit.v1_14_R1.event.CraftEventFactory.callEntityDeathEvent(CraftEventFactory.java:707) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityLiving.d(EntityLiving.java:1366) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityLiving.die(EntityLiving.java:1322) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityLiving.damageEntity(EntityLiving.java:1169) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityHuman.attack(EntityHuman.java:1018) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.EntityPlayer.attack(EntityPlayer.java:1539) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PlayerConnection.a(PlayerConnection.java:1864) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PacketPlayInUseEntity.a(SourceFile:69) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PacketPlayInUseEntity.a(SourceFile:13) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.PlayerConnectionUtils.lambda$0(PlayerConnectionUtils.java:19) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.TickTask.run(SourceFile:18) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandler.executeTask(SourceFile:144) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandlerReentrant.executeTask(SourceFile:23) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandler.executeNext(SourceFile:118) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.aX(MinecraftServer.java:909) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.executeNext(MinecraftServer.java:902) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.IAsyncTaskHandler.awaitTasks(SourceFile:127) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.sleepForTick(MinecraftServer.java:886) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at net.minecraft.server.v1_14_R1.MinecraftServer.run(MinecraftServer.java:819) [spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
at java.lang.Thread.run(Unknown Source) [?:1.8.0_211]
Caused by: java.lang.NoClassDefFoundError: Could not initialize class com.sk89q.worldguard.protection.flags.Flags
at one.lindegaard.MobHunting.compatibility.WorldGuardMobHuntingFlag.getMobDamageFlag(WorldGuardMobHuntingFlag.java:32) ~[?:?]
at one.lindegaard.MobHunting.MobHuntingManager.onMobDeath(MobHuntingManager.java:893) ~[?:?]
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method) ~[?:1.8.0_211]
at sun.reflect.NativeMethodAccessorImpl.invoke(Unknown Source) ~[?:1.8.0_211]
at sun.reflect.DelegatingMethodAccessorImpl.invoke(Unknown Source) ~[?:1.8.0_211]
at java.lang.reflect.Method.invoke(Unknown Source) ~[?:1.8.0_211]
at org.bukkit.plugin.java.JavaPluginLoader$1.execute(JavaPluginLoader.java:316) ~[spigot-1.14.4.jar:git-Spigot-798ea6a-44d675a]
... 23 more | non_priority | could not pass event entitydeathevent to mobhunting could not pass event entitydeathevent to mobhunting org bukkit event eventexception null at org bukkit plugin java javapluginloader execute javapluginloader java at org bukkit plugin registeredlistener callevent registeredlistener java at org bukkit plugin simplepluginmanager fireevent simplepluginmanager java at org bukkit plugin simplepluginmanager callevent simplepluginmanager java at org bukkit craftbukkit event crafteventfactory callentitydeathevent crafteventfactory java at net minecraft server entityliving d entityliving java at net minecraft server entityliving die entityliving java at net minecraft server entityliving damageentity entityliving java at net minecraft server entityhuman attack entityhuman java at net minecraft server entityplayer attack entityplayer java at net minecraft server playerconnection a playerconnection java at net minecraft server packetplayinuseentity a sourcefile at net minecraft server packetplayinuseentity a sourcefile at net minecraft server playerconnectionutils lambda playerconnectionutils java at net minecraft server ticktask run sourcefile at net minecraft server iasynctaskhandler executetask sourcefile at net minecraft server iasynctaskhandlerreentrant executetask sourcefile at net minecraft server iasynctaskhandler executenext sourcefile at net minecraft server minecraftserver ax minecraftserver java at net minecraft server minecraftserver executenext minecraftserver java at net minecraft server iasynctaskhandler awaittasks sourcefile at net minecraft server minecraftserver sleepfortick minecraftserver java at net minecraft server minecraftserver run minecraftserver java at java lang thread run unknown source caused by java lang noclassdeffounderror could not initialize class com worldguard protection flags flags at one lindegaard mobhunting compatibility worldguardmobhuntingflag getmobdamageflag worldguardmobhuntingflag java at one lindegaard mobhunting mobhuntingmanager onmobdeath mobhuntingmanager java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke unknown source at sun reflect delegatingmethodaccessorimpl invoke unknown source at java lang reflect method invoke unknown source at org bukkit plugin java javapluginloader execute javapluginloader java more | 0 |
367,885 | 25,767,311,983 | IssuesEvent | 2022-12-09 03:42:18 | FuelLabs/sway-applications | https://api.github.com/repos/FuelLabs/sway-applications | closed | Name Registry Documentation | Documentation App: Name Registry | # Summary
The application requires documentation to inform the user about the project.
This includes
- README.md
- What the application is, how to run it etc.
- SPECIFICATION.md
- General overview of the application use cases, contract design, UI design etc.
Any additional informative files. | 1.0 | Name Registry Documentation - # Summary
The application requires documentation to inform the user about the project.
This includes
- README.md
- What the application is, how to run it etc.
- SPECIFICATION.md
- General overview of the application use cases, contract design, UI design etc.
Any additional informative files. | non_priority | name registry documentation summary the application requires documentation to inform the user about the project this includes readme md what the application is how to run it etc specification md general overview of the application use cases contract design ui design etc any additional informative files | 0 |
16,223 | 11,872,546,718 | IssuesEvent | 2020-03-26 15:58:23 | nodejs/nodejs.dev | https://api.github.com/repos/nodejs/nodejs.dev | closed | Fix meeting generator is not pulling in issues | Infrastructure wr-agenda | The last meeting did not have any agenda items, even while items are marked.
https://github.com/nodejs/nodejs.dev/issues?q=sort%3Aupdated-desc+label%3Awr-agenda+ | 1.0 | Fix meeting generator is not pulling in issues - The last meeting did not have any agenda items, even while items are marked.
https://github.com/nodejs/nodejs.dev/issues?q=sort%3Aupdated-desc+label%3Awr-agenda+ | non_priority | fix meeting generator is not pulling in issues the last meeting did not have any agenda items even while items are marked | 0 |
194,501 | 14,679,839,789 | IssuesEvent | 2020-12-31 08:14:14 | Realm667/WolfenDoom | https://api.github.com/repos/Realm667/WolfenDoom | closed | Operation Paris issue | actor bug help wanted playtesting | 
There is a door that seems to be stuck only way of getting through is no clipping.
| 1.0 | Operation Paris issue - 
There is a door that seems to be stuck only way of getting through is no clipping.
| non_priority | operation paris issue there is a door that seems to be stuck only way of getting through is no clipping | 0 |
45,073 | 18,362,234,804 | IssuesEvent | 2021-10-09 12:20:18 | DODOEX/status | https://api.github.com/repos/DODOEX/status | opened | 🛑 Base Global KLines Service is down | status base-global-k-lines-service | In [`36ee7ab`](https://github.com/DODOEX/status/commit/36ee7abca209096fa092298c9e3448e6c7b1317d
), Base Global KLines Service (https://priceapi.dodoex.io/api/v1/klines?symbol=ETH/USDC&interval=15m&limit=96&addresses=0xEeeeeEeeeEeEeeEeEeEeeEEEeeeeEeeeeeeeEEeE/0xa0b86991c6218b36c1d19d4a2e9eb0ce3606eb48&network=ethereum) was **down**:
- HTTP code: 503
- Response time: 1508 ms
| 1.0 | 🛑 Base Global KLines Service is down - In [`36ee7ab`](https://github.com/DODOEX/status/commit/36ee7abca209096fa092298c9e3448e6c7b1317d
), Base Global KLines Service (https://priceapi.dodoex.io/api/v1/klines?symbol=ETH/USDC&interval=15m&limit=96&addresses=0xEeeeeEeeeEeEeeEeEeEeeEEEeeeeEeeeeeeeEEeE/0xa0b86991c6218b36c1d19d4a2e9eb0ce3606eb48&network=ethereum) was **down**:
- HTTP code: 503
- Response time: 1508 ms
| non_priority | 🛑 base global klines service is down in base global klines service was down http code response time ms | 0 |
6,966 | 2,869,314,652 | IssuesEvent | 2015-06-06 02:49:29 | EpochModTeam/Epoch | https://api.github.com/repos/EpochModTeam/Epoch | closed | Base Objects Disappear After Maintaining | bug Needs Tested prio: High | Player maintains base AFTER TTL has been passed in REDIS but server hasn't restarted.
Please assume the maintaining went correctly but when the server restarts, objects have disappeared. | 1.0 | Base Objects Disappear After Maintaining - Player maintains base AFTER TTL has been passed in REDIS but server hasn't restarted.
Please assume the maintaining went correctly but when the server restarts, objects have disappeared. | non_priority | base objects disappear after maintaining player maintains base after ttl has been passed in redis but server hasn t restarted please assume the maintaining went correctly but when the server restarts objects have disappeared | 0 |
21,379 | 6,147,795,496 | IssuesEvent | 2017-06-27 16:24:52 | eclipse/eclipse.jdt.ls | https://api.github.com/repos/eclipse/eclipse.jdt.ls | closed | Create missing attribute in annotation | code-actions enhancement | ... as code action
```java
public class Foo {
public @interface Annot {
}
@Annot(name="Foo")
public Foo() {}
}
```
`The attribute name is undefined for the annotation Foo.Annot` should have a code action to create the missing `name` attribute. | 1.0 | Create missing attribute in annotation - ... as code action
```java
public class Foo {
public @interface Annot {
}
@Annot(name="Foo")
public Foo() {}
}
```
`The attribute name is undefined for the annotation Foo.Annot` should have a code action to create the missing `name` attribute. | non_priority | create missing attribute in annotation as code action java public class foo public interface annot annot name foo public foo the attribute name is undefined for the annotation foo annot should have a code action to create the missing name attribute | 0 |
64,054 | 18,158,585,021 | IssuesEvent | 2021-09-27 06:52:09 | vector-im/element-ios | https://api.github.com/repos/vector-im/element-ios | opened | Crash in [MXSession directUserIdInRoom:] | T-Defect crash X-Release-Blocker | in 1.6.0:
```
OS Version: iPhone OS 15.0 (19A344)
Release Type: User
Baseband Version: 5.00.00
Report Version: 104
Exception Type: EXC_CRASH (SIGKILL)
Exception Codes: 0x0000000000000000, 0x0000000000000000
Exception Note: EXC_CORPSE_NOTIFY
Termination Reason: RUNNINGBOARD; [3735883980]
Triggered by Thread: 0
Thread 0 name: Dispatch queue: com.apple.main-thread
Thread 0 Crashed:
0 CoreFoundation 0x183f02008 -[__NSDictionaryI objectForKeyedSubscript:] + 248
1 CoreFoundation 0x183f01f6c -[__NSDictionaryI objectForKeyedSubscript:] + 92
2 MatrixSDK 0x108488ce4 -[MXSession directUserIdInRoom:] + 2018532 (MXSession.m:0)
3 MatrixSDK 0x10844176c -[MXRoom directUserId] + 1726316 (MXRoom.m:0)
4 MatrixSDK 0x108441710 -[MXRoom isDirect] + 1726224 (MXRoom.m:0)
5 Riot 0x104b8a728 -[EventFormatter session:updateRoomSummary:withStateEvents:roomState:] + 288552 (EventFormatter.m:420)
6 MatrixSDK 0x108456a9c __35-[MXRoomSummary handleStateEvents:]_block_invoke + 1813148 (MXRoomSummary.m:681)
7 MatrixSDK 0x10842ed4c __16-[MXRoom state:]_block_invoke + 1649996 (MXRoom.m:210)
8 MatrixSDK 0x10842e698 -[MXRoom liveTimeline:] + 1648280 (MXRoom.m:0)
9 MatrixSDK 0x10842ece8 -[MXRoom state:] + 1649896 (MXRoom.m:212)
10 MatrixSDK 0x10845697c -[MXRoomSummary handleStateEvents:] + 1812860 (MXRoomSummary.m:678)
11 MatrixSDK 0x1083257a4 -[MXEventTimeline handleStateEvents:direction:] + 563108 (MXEventTimeline.m:852)
12 MatrixSDK 0x108324828 -[MXEventTimeline addEvent:direction:fromStore:isRoomInitialSync:] + 559144 (MXEventTimeline.m:684)
13 MatrixSDK 0x1083234a4 __51-[MXEventTimeline handleJoinedRoomSync:onComplete:]_block_invoke.191 + 554148 (MXEventTimeline.m:499)
14 MatrixSDK 0x1083261d8 -[MXEventTimeline decryptEvents:ifNewerThanTimestamp:onComplete:] + 565720 (MXEventTimeline.m:994)
15 MatrixSDK 0x10832320c -[MXEventTimeline handleJoinedRoomSync:onComplete:] + 553484 (MXEventTimeline.m:489)
16 MatrixSDK 0x108430aac __42-[MXRoom handleJoinedRoomSync:onComplete:]_block_invoke + 1657516 (MXRoom.m:398)
17 MatrixSDK 0x10842e698 -[MXRoom liveTimeline:] + 1648280 (MXRoom.m:0)
18 MatrixSDK 0x108430928 -[MXRoom handleJoinedRoomSync:onComplete:] + 1657128 (MXRoom.m:399)
19 MatrixSDK 0x10847b1dc __59-[MXSession handleSyncResponse:completion:storeCompletion:]_block_invoke + 1962460 (MXSession.m:465)
20 libdispatch.dylib 0x183bf52ec _dispatch_call_block_and_release + 24
21 libdispatch.dylib 0x183bf62f0 _dispatch_client_callout + 16
22 libdispatch.dylib 0x183bd76a4 _dispatch_main_queue_callback_4CF$VARIANT$armv81 + 904
23 CoreFoundation 0x183ee57f8 __CFRUNLOOP_IS_SERVICING_THE_MAIN_DISPATCH_QUEUE__ + 12
24 CoreFoundation 0x183ea30f8 __CFRunLoopRun + 2528
25 CoreFoundation 0x183eb5d8c CFRunLoopRunSpecific + 572
26 GraphicsServices 0x19dfc39a0 GSEventRunModal + 160
27 UIKitCore 0x1866eb018 -[UIApplication _run] + 1080
28 UIKitCore 0x18647f29c UIApplicationMain + 2060
29 Riot 0x104cd62b0 main + 1647280 (AppDelegate.swift:21)
30 dyld 0x106a10190 start + 444 | 1.0 | Crash in [MXSession directUserIdInRoom:] - in 1.6.0:
```
OS Version: iPhone OS 15.0 (19A344)
Release Type: User
Baseband Version: 5.00.00
Report Version: 104
Exception Type: EXC_CRASH (SIGKILL)
Exception Codes: 0x0000000000000000, 0x0000000000000000
Exception Note: EXC_CORPSE_NOTIFY
Termination Reason: RUNNINGBOARD; [3735883980]
Triggered by Thread: 0
Thread 0 name: Dispatch queue: com.apple.main-thread
Thread 0 Crashed:
0 CoreFoundation 0x183f02008 -[__NSDictionaryI objectForKeyedSubscript:] + 248
1 CoreFoundation 0x183f01f6c -[__NSDictionaryI objectForKeyedSubscript:] + 92
2 MatrixSDK 0x108488ce4 -[MXSession directUserIdInRoom:] + 2018532 (MXSession.m:0)
3 MatrixSDK 0x10844176c -[MXRoom directUserId] + 1726316 (MXRoom.m:0)
4 MatrixSDK 0x108441710 -[MXRoom isDirect] + 1726224 (MXRoom.m:0)
5 Riot 0x104b8a728 -[EventFormatter session:updateRoomSummary:withStateEvents:roomState:] + 288552 (EventFormatter.m:420)
6 MatrixSDK 0x108456a9c __35-[MXRoomSummary handleStateEvents:]_block_invoke + 1813148 (MXRoomSummary.m:681)
7 MatrixSDK 0x10842ed4c __16-[MXRoom state:]_block_invoke + 1649996 (MXRoom.m:210)
8 MatrixSDK 0x10842e698 -[MXRoom liveTimeline:] + 1648280 (MXRoom.m:0)
9 MatrixSDK 0x10842ece8 -[MXRoom state:] + 1649896 (MXRoom.m:212)
10 MatrixSDK 0x10845697c -[MXRoomSummary handleStateEvents:] + 1812860 (MXRoomSummary.m:678)
11 MatrixSDK 0x1083257a4 -[MXEventTimeline handleStateEvents:direction:] + 563108 (MXEventTimeline.m:852)
12 MatrixSDK 0x108324828 -[MXEventTimeline addEvent:direction:fromStore:isRoomInitialSync:] + 559144 (MXEventTimeline.m:684)
13 MatrixSDK 0x1083234a4 __51-[MXEventTimeline handleJoinedRoomSync:onComplete:]_block_invoke.191 + 554148 (MXEventTimeline.m:499)
14 MatrixSDK 0x1083261d8 -[MXEventTimeline decryptEvents:ifNewerThanTimestamp:onComplete:] + 565720 (MXEventTimeline.m:994)
15 MatrixSDK 0x10832320c -[MXEventTimeline handleJoinedRoomSync:onComplete:] + 553484 (MXEventTimeline.m:489)
16 MatrixSDK 0x108430aac __42-[MXRoom handleJoinedRoomSync:onComplete:]_block_invoke + 1657516 (MXRoom.m:398)
17 MatrixSDK 0x10842e698 -[MXRoom liveTimeline:] + 1648280 (MXRoom.m:0)
18 MatrixSDK 0x108430928 -[MXRoom handleJoinedRoomSync:onComplete:] + 1657128 (MXRoom.m:399)
19 MatrixSDK 0x10847b1dc __59-[MXSession handleSyncResponse:completion:storeCompletion:]_block_invoke + 1962460 (MXSession.m:465)
20 libdispatch.dylib 0x183bf52ec _dispatch_call_block_and_release + 24
21 libdispatch.dylib 0x183bf62f0 _dispatch_client_callout + 16
22 libdispatch.dylib 0x183bd76a4 _dispatch_main_queue_callback_4CF$VARIANT$armv81 + 904
23 CoreFoundation 0x183ee57f8 __CFRUNLOOP_IS_SERVICING_THE_MAIN_DISPATCH_QUEUE__ + 12
24 CoreFoundation 0x183ea30f8 __CFRunLoopRun + 2528
25 CoreFoundation 0x183eb5d8c CFRunLoopRunSpecific + 572
26 GraphicsServices 0x19dfc39a0 GSEventRunModal + 160
27 UIKitCore 0x1866eb018 -[UIApplication _run] + 1080
28 UIKitCore 0x18647f29c UIApplicationMain + 2060
29 Riot 0x104cd62b0 main + 1647280 (AppDelegate.swift:21)
30 dyld 0x106a10190 start + 444 | non_priority | crash in in os version iphone os release type user baseband version report version exception type exc crash sigkill exception codes exception note exc corpse notify termination reason runningboard triggered by thread thread name dispatch queue com apple main thread thread crashed corefoundation corefoundation matrixsdk mxsession m matrixsdk mxroom m matrixsdk mxroom m riot eventformatter m matrixsdk block invoke mxroomsummary m matrixsdk block invoke mxroom m matrixsdk mxroom m matrixsdk mxroom m matrixsdk mxroomsummary m matrixsdk mxeventtimeline m matrixsdk mxeventtimeline m matrixsdk block invoke mxeventtimeline m matrixsdk mxeventtimeline m matrixsdk mxeventtimeline m matrixsdk block invoke mxroom m matrixsdk mxroom m matrixsdk mxroom m matrixsdk block invoke mxsession m libdispatch dylib dispatch call block and release libdispatch dylib dispatch client callout libdispatch dylib dispatch main queue callback variant corefoundation cfrunloop is servicing the main dispatch queue corefoundation cfrunlooprun corefoundation cfrunlooprunspecific graphicsservices gseventrunmodal uikitcore uikitcore uiapplicationmain riot main appdelegate swift dyld start | 0 |
40,796 | 16,546,023,199 | IssuesEvent | 2021-05-28 00:11:09 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | C++ IntelliSense crash in gcc mode (from attach_attributes_to_routine_instance) | Language Service Visual Studio bug fixed (release pending) reliability | **Type: LanguageService**
<!----- Input information below ----->
<!--
**Prior to filing an issue, please review:**
- Existing issues at https://github.com/Microsoft/vscode-cpptools/issues
- Our documentation at https://code.visualstudio.com/docs/languages/cpp
- FAQs at https://code.visualstudio.com/docs/cpp/faq-cpp
-->
**Describe the bug**
- OS and Version: Windows 10 (Build 19041.685)
- VS Code Version: 1.52.1
- C/C++ Extension Version: 1.1.3
- Other extensions you installed (and if the issue persists after disabling them): Yes
- Does this issue involve using SSH remote to run the extension on a remote machine?: No
- I mostly do Competitive Programming in VsCode and usually copy code from websites like GeeksForGeeks and stackoverflow, but sometimes wherever I paste the code in my cpp file, auto-complete and suggestions no longer work on that paricular file however, in my other cpp files, it works as expected.
**Steps to reproduce**
<!-- Provide clear steps to reproduce the behavior: -->
<!-- *The most actionable issue reports include a code sample including configuration files such as c_cpp_properties.json* -->
1. Create a CPP file.
2. Copy Code from internet
3. Write incomplete code to see error.
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
Red line should appear at the errors and auto complete should work.
<!-- Please provide the following logs that show diagnostics and debugging information about the language server.
1. Logs from the command `C/C++: Log Diagnostics`
2. Logs from [the language server](https://code.visualstudio.com/docs/cpp/enable-logging-cpp#_enable-logging-for-the-language-server)
-->
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
In file where I copied Code.
In other cpp files
**Additional context**
<!--
* Call Stacks: For bugs like crashes, deadlocks, infinite loops, etc. that we are not able to repro and for which the call stack may be useful, please attach a debugger and/or create a dmp and provide the call stacks. Windows binaries have symbols available in VS Code by setting your "symbolSearchPath" to "https://msdl.microsoft.com/download/symbols".
-->
This bug/error started occurring recently, quite a few vscode updates earlier. I searched the net for all the possible solutions to this, but no luck, in the end writing this issue.
| 1.0 | C++ IntelliSense crash in gcc mode (from attach_attributes_to_routine_instance) - **Type: LanguageService**
<!----- Input information below ----->
<!--
**Prior to filing an issue, please review:**
- Existing issues at https://github.com/Microsoft/vscode-cpptools/issues
- Our documentation at https://code.visualstudio.com/docs/languages/cpp
- FAQs at https://code.visualstudio.com/docs/cpp/faq-cpp
-->
**Describe the bug**
- OS and Version: Windows 10 (Build 19041.685)
- VS Code Version: 1.52.1
- C/C++ Extension Version: 1.1.3
- Other extensions you installed (and if the issue persists after disabling them): Yes
- Does this issue involve using SSH remote to run the extension on a remote machine?: No
- I mostly do Competitive Programming in VsCode and usually copy code from websites like GeeksForGeeks and stackoverflow, but sometimes wherever I paste the code in my cpp file, auto-complete and suggestions no longer work on that paricular file however, in my other cpp files, it works as expected.
**Steps to reproduce**
<!-- Provide clear steps to reproduce the behavior: -->
<!-- *The most actionable issue reports include a code sample including configuration files such as c_cpp_properties.json* -->
1. Create a CPP file.
2. Copy Code from internet
3. Write incomplete code to see error.
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
Red line should appear at the errors and auto complete should work.
<!-- Please provide the following logs that show diagnostics and debugging information about the language server.
1. Logs from the command `C/C++: Log Diagnostics`
2. Logs from [the language server](https://code.visualstudio.com/docs/cpp/enable-logging-cpp#_enable-logging-for-the-language-server)
-->
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
In file where I copied Code.
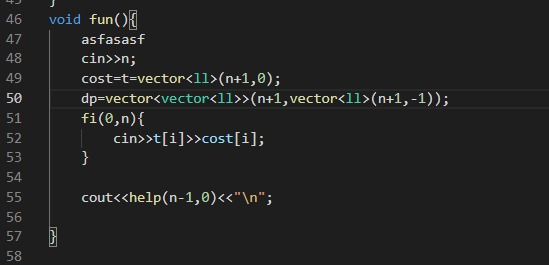
In other cpp files
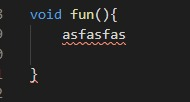
**Additional context**
<!--
* Call Stacks: For bugs like crashes, deadlocks, infinite loops, etc. that we are not able to repro and for which the call stack may be useful, please attach a debugger and/or create a dmp and provide the call stacks. Windows binaries have symbols available in VS Code by setting your "symbolSearchPath" to "https://msdl.microsoft.com/download/symbols".
-->
This bug/error started occurring recently, quite a few vscode updates earlier. I searched the net for all the possible solutions to this, but no luck, in the end writing this issue.
| non_priority | c intellisense crash in gcc mode from attach attributes to routine instance type languageservice prior to filing an issue please review existing issues at our documentation at faqs at describe the bug os and version windows build vs code version c c extension version other extensions you installed and if the issue persists after disabling them yes does this issue involve using ssh remote to run the extension on a remote machine no i mostly do competitive programming in vscode and usually copy code from websites like geeksforgeeks and stackoverflow but sometimes wherever i paste the code in my cpp file auto complete and suggestions no longer work on that paricular file however in my other cpp files it works as expected steps to reproduce create a cpp file copy code from internet write incomplete code to see error expected behavior red line should appear at the errors and auto complete should work please provide the following logs that show diagnostics and debugging information about the language server logs from the command c c log diagnostics logs from screenshots in file where i copied code in other cpp files additional context call stacks for bugs like crashes deadlocks infinite loops etc that we are not able to repro and for which the call stack may be useful please attach a debugger and or create a dmp and provide the call stacks windows binaries have symbols available in vs code by setting your symbolsearchpath to this bug error started occurring recently quite a few vscode updates earlier i searched the net for all the possible solutions to this but no luck in the end writing this issue | 0 |
270,645 | 23,526,484,214 | IssuesEvent | 2022-08-19 11:21:33 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | closed | Release 4.3.7 - Release Candidate 1 - WPK upgrade tests | module/upgrade/wpk type/test/manual release test/4.3.7 | The following issue aims to run `upgrade WPK tests` for the current release candidate, report the results, and open new issues for any encountered errors.
## WPK upgrade tests information
|Main RC issue|Version|Release candidate|Tag|Previous issue|
|---|---|---|---|---|
|https://github.com/wazuh/wazuh/issues/14562|4.3.7|RC1|[v4.3.7-rc1](https://github.com/wazuh/wazuh/tree/v4.3.7-rc1)|https://github.com/wazuh/wazuh/issues/14267|
## Test report procedure
All individual test checks must be marked as:
| | |
|---------------------------------|--------------------------------------------|
| Pass | The test ran successfully. |
| Xfail | The test was expected to fail and it failed. It must be properly justified and reported in an issue. |
| Skip | The test was not run. It must be properly justified and reported in an issue. |
| Fail | The test failed. A new issue must be opened to evaluate and address the problem. |
All test results must have one the following statuses:
| | |
|---------------------------------|--------------------------------------------|
| :green_circle: | All checks passed. |
| :red_circle: | There is at least one failed check. |
| :yellow_circle: | There is at least one expected fail or skipped test and no failures. |
Any failing test must be properly addressed with a new issue, detailing the error and the possible cause. It must be included in the `Fixes` section of the current release candidate main issue.
Any expected fail or skipped test must have an issue justifying the reason. All auditors must validate the justification for an expected fail or skipped test.
An extended report of the test results must be attached as a zip or txt. This report can be used by the auditors to dig deeper into any possible failures and details.
## Tests
To evaluate this feature, it is necessary to test upgrading the agent and also the case when the upgrade fails (rollback). The `tree` command will be used to compare, before and after the upgrade/rollback process, and check that the presence, ownership and permissions of the files and directories are expected.
Wazuh versions to test (Upgrade to the current agent version):
### Linux
|OS|Version|Status|Upgrade fail|Upgrade OK|
|----|-----|------|---------------|------------------|
|CentOS 6|3.6|:white_circle: skipped | | | |
|CentOS 6|3.7|:white_circle: skipped | | | |
|CentOS 6|3.13.3|:white_circle: skipped | | | |
|CentOS 6|4.0.4| :white_circle: skipped| | | |
|CentOS 6|4.1.5| :white_circle: skipped| | | |
|CentOS 6|4.2.7|:white_circle: skipped | | | |
|CentOS 6|4.3.6|:white_circle: skipped | | | |
|CentOS 8|3.6| :white_circle: skipped| | | |
|CentOS 8|3.7| :white_circle: skipped| | | |
|CentOS 8|3.13.3| :white_circle: skipped| | | |
|CentOS 8|4.0.4| :white_circle: skipped| | | |
|CentOS 8|4.1.5| :white_circle: skipped| | | |
|CentOS 8|4.2.7|:white_circle: skipped | | | |
|CentOS 8|4.3.6|:white_circle: skipped | | | |
|RHEL 9|3.6| :white_circle: skipped| | | |
|RHEL 9|3.7| :white_circle: skipped| | | |
|RHEL 9|3.13.3| :white_circle: skipped| | | |
|RHEL 9|4.0.4| :white_circle: skipped| | | |
|RHEL 9|4.1.5| :white_circle: skipped| | | |
|RHEL 9|4.2.7| :white_circle: skipped | | | |
|RHEL 9|4.3.6|:green_circle: done |:green_circle: | :green_circle:| |
|Ubuntu 22|3.6|:white_circle: skipped | | | |
|Ubuntu 22|3.7| :white_circle: skipped| | | |
|Ubuntu 22|3.13.3|:white_circle: skipped| | | |
|Ubuntu 22|4.0.4|:white_circle: skipped| | | |
|Ubuntu 22|4.1.5| :white_circle: skipped ||| |
|Ubuntu 22|4.2.7| :white_circle: skipped||| |
|Ubuntu 22|4.3.6 |:green_circle: done| :green_circle: | :green_circle: |
|openSUSE Tumbleweed|3.6| :white_circle: skipped| | | |
|openSUSE Tumbleweed|3.7|:white_circle: skipped | | | |
|openSUSE Tumbleweed|3.13.3|:white_circle: skipped| || |
|openSUSE Tumbleweed|4.0.4|:white_circle: skipped| | ||
|openSUSE Tumbleweed|4.1.5|:white_circle: skipped| | ||
|openSUSE Tumbleweed|4.2.7|:white_circle: skipped| || |
|openSUSE Tumbleweed|4.3|:white_circle: skipped | |
|Amazon Linux 2|3.6|:white_circle: skipped | | | |
|Amazon Linux 2|3.7|:white_circle: skipped | | | |
|Amazon Linux 2|3.13.3|:white_circle: skipped| || |
|Amazon Linux 2|4.0.4|:white_circle: skipped| | ||
|Amazon Linux 2|4.1.5|:white_circle: skipped| | ||
|Amazon Linux 2|4.2.7|:white_circle: skipped| || |
|Amazon Linux 2|4.3|:white_circle: skipped | |
### Windows
|OS|Version|Status|Upgrade fail|Upgrade OK|
|----|-----|------|---------------|------------------|
|Server 2008|3.6|:white_circle: skipped | | | |
|Server 2008|3.7|:white_circle: skipped | | | |
|Server 2008|3.13.3|:white_circle: skipped| || |
|Server 2008|4.0.4|:white_circle: skipped| | ||
|Server 2008|4.1.5|:white_circle: skipped| | ||
|Server 2008|4.2.7|:white_circle: skipped| || |
|Server 2008|4.3| :white_circle: skipped| |
|Server 2012 R2|3.6| :white_circle: skipped| | | |
|Server 2012 R2|3.7|:white_circle: skipped | | | |
|Server 2012 R2|3.13.3|:white_circle: skipped| || |
|Server 2012 R2|4.0.4|:white_circle: skipped| | ||
|Server 2012 R2|4.1.5|:white_circle: skipped| | ||
|Server 2012 R2|4.2.7|:white_circle: skipped| || |
|Server 2012 R2|4.3|:white_circle: skipped | |
|Server 2016|3.6|:white_circle: skipped | | | |
|Server 2016|3.7| :white_circle: skipped| | | |
|Server 2016|3.13.3|:white_circle: skipped| || |
|Server 2016|4.0.4|:white_circle: skipped| | ||
|Server 2016|4.1.5|:white_circle: skipped| | ||
|Server 2016|4.2.7|:white_circle: skipped| || |
|Server 2016|4.3| :white_circle: skipped| |
|Server 2019|3.6|:white_circle: skipped | | | |
|Server 2019|3.7|:white_circle: skipped | | | |
|Server 2019|3.13.3|:white_circle: skipped| || |
|Server 2019|4.0.4|:white_circle: skipped| | ||
|Server 2019|4.1.5|:white_circle: skipped| | ||
|Server 2019|4.2.7|:white_circle: skipped| || |
|Server 2019|4.3| :white_circle: skipped| |
|Windows 10|3.6| :white_circle: skipped| | | |
|Windows 10|3.7| :white_circle: skipped| | | |
|Windows 10|3.13.3|:white_circle: skipped| || |
|Windows 10|4.0.4|:white_circle: skipped| | ||
|Windows 10|4.1.5|:white_circle: skipped| | ||
|Windows 10|4.2.7|:white_circle: skipped| || |
|Windows 10|4.3| :white_circle: skipped| |
|Server 2022|3.6| :white_circle: skipped| | | |
|Server 2022|3.7| :white_circle: skipped| | | |
|Server 2022|3.13.3|:white_circle: skipped| || |
|Server 2022|4.0.4|:white_circle: skipped| | ||
|Server 2022|4.1.5|:white_circle: skipped| | ||
|Server 2022|4.2.7| :white_circle: skipped| || |
|Server 2022|4.3.6|:green_circle: done| :green_circle: | :green_circle: |
### macOS
|OS|Version|Status|Upgrade fail|Upgrade OK|
|----|-----------|--------|-------|------------------|
| Sierra |4.3.0| :white_circle: skipped|| | | |
| Sierra |4.3.4|:white_circle: skipped || | | |
| Catalina |4.3.0| :white_circle: skipped|| | | |
| Catalina |4.3.4|:white_circle: skipped || | | |
| Big Sur |4.3.0| :white_circle: skipped|| | | |
| Big Sur |4.3.4| :white_circle: skipped|| | | |
| Monterey |4.3.0| :white_circle: skipped|| | | |
| Monterey |4.3.6| :green_circle: done|:green_circle:| :green_circle:| | |
<!--
For each operating system and version, check the following points and add a comment for each OS tested.
## Linux:
### UPGRADE FAIL
- [ ] The wazuh home backup is restored correctly (no traces of the installation, but only the `.tar.gz` backup and the logs).
- [ ] The permissions and owners of the following directories did NOT change:
- `/`
- `/var`
- `/usr`, `/usr/lib/`, `/usr/lib/systemd/`, `/usr/lib/systemd/system/`
- `/etc`, `/etc/systemd/`, `/etc/systemd/system/`, `/etc/rc.d`, `/etc/initd.d/`, `/etc/initd.d/rc.d/`
- [ ] Wazuh service runs wazuh-control (`systemctl cat wazuh-agent.service`)
- [ ] Wazuh service runs ossec-control (`systemctl cat wazuh-agent.service`)
- [ ] The service was enabled (`systemctl is-enabled wazuh-agent.service`)
- [ ] Init file runs wazuh-control (`cat /etc/rc.d/init.d/wazuh-agent`)
- [ ] Init file runs ossec-control (`cat /etc/rc.d/init.d/wazuh-agent`)
- [ ] Wazuh as service is enabled `chkconfig --list`
- [ ] Wazuh starts and connects when the backup is restored (`cat /var/ossec/var/run/ossec-agentd.state`)
- [ ] Wazuh starts and connects automatically when the system is rebooted.
- [ ] Restore SELinux policies (`semodule -l | grep -i wazuh`) (DISABLED)
### UPGRADE OK
- [ ] Upgrade is performed successfully (agent connects to the manager after upgrading)
- [ ] Service starts automatically after rebooting
- [ ] Agent connects to the manager after rebooting
## Windows:
### UPGRADE FAIL
- [ ] Wazuh-Agent folder tree: No files are lost after the rollback. The logs of the failed upgrade (`ossec.log`) are kept.
- [ ] After the rollback the agent connects to the manager
- [ ] After reboot, the Wazuh-Agent starts and connects to the manager.
- [ ] The correct Wazuh-Agent version is shown in the list of Windows' `programs and features`.
- [ ] A new version of Wazuh-Agent can be manually installed via MSI after the rollback process.
### UPGRADE OK
- [ ] Message `Upgrade finished successfully.` is shown in `upgrade.log` file.
- [ ] Wazuh service is started and the agent is connected to the manager.
- [ ] The version shown in the control panel is 4.3
## MacOS:
### UPGRADE FAIL
- [ ] Wazuh-Agent folder tree: No files are lost after the rollback. The logs of the failed upgrade (`ossec.log`) are kept.
- [ ] After the rollback the agent connects to the manager
- [ ] After reboot, the Wazuh-Agent starts and connects to the manager.
### UPGRADE OK
- [ ] Message `Upgrade finished successfully.` is shown in `upgrade.log` file.
- [ ] Wazuh service is started and the agent is connected to the manager.
-->
## Auditors validation
The definition of done for this one is the validation of the conclusions and the test results from all auditors.
All checks from below must be accepted in order to close this issue.
- [x] @vikman90
| 2.0 | Release 4.3.7 - Release Candidate 1 - WPK upgrade tests - The following issue aims to run `upgrade WPK tests` for the current release candidate, report the results, and open new issues for any encountered errors.
## WPK upgrade tests information
|Main RC issue|Version|Release candidate|Tag|Previous issue|
|---|---|---|---|---|
|https://github.com/wazuh/wazuh/issues/14562|4.3.7|RC1|[v4.3.7-rc1](https://github.com/wazuh/wazuh/tree/v4.3.7-rc1)|https://github.com/wazuh/wazuh/issues/14267|
## Test report procedure
All individual test checks must be marked as:
| | |
|---------------------------------|--------------------------------------------|
| Pass | The test ran successfully. |
| Xfail | The test was expected to fail and it failed. It must be properly justified and reported in an issue. |
| Skip | The test was not run. It must be properly justified and reported in an issue. |
| Fail | The test failed. A new issue must be opened to evaluate and address the problem. |
All test results must have one the following statuses:
| | |
|---------------------------------|--------------------------------------------|
| :green_circle: | All checks passed. |
| :red_circle: | There is at least one failed check. |
| :yellow_circle: | There is at least one expected fail or skipped test and no failures. |
Any failing test must be properly addressed with a new issue, detailing the error and the possible cause. It must be included in the `Fixes` section of the current release candidate main issue.
Any expected fail or skipped test must have an issue justifying the reason. All auditors must validate the justification for an expected fail or skipped test.
An extended report of the test results must be attached as a zip or txt. This report can be used by the auditors to dig deeper into any possible failures and details.
## Tests
To evaluate this feature, it is necessary to test upgrading the agent and also the case when the upgrade fails (rollback). The `tree` command will be used to compare, before and after the upgrade/rollback process, and check that the presence, ownership and permissions of the files and directories are expected.
Wazuh versions to test (Upgrade to the current agent version):
### Linux
|OS|Version|Status|Upgrade fail|Upgrade OK|
|----|-----|------|---------------|------------------|
|CentOS 6|3.6|:white_circle: skipped | | | |
|CentOS 6|3.7|:white_circle: skipped | | | |
|CentOS 6|3.13.3|:white_circle: skipped | | | |
|CentOS 6|4.0.4| :white_circle: skipped| | | |
|CentOS 6|4.1.5| :white_circle: skipped| | | |
|CentOS 6|4.2.7|:white_circle: skipped | | | |
|CentOS 6|4.3.6|:white_circle: skipped | | | |
|CentOS 8|3.6| :white_circle: skipped| | | |
|CentOS 8|3.7| :white_circle: skipped| | | |
|CentOS 8|3.13.3| :white_circle: skipped| | | |
|CentOS 8|4.0.4| :white_circle: skipped| | | |
|CentOS 8|4.1.5| :white_circle: skipped| | | |
|CentOS 8|4.2.7|:white_circle: skipped | | | |
|CentOS 8|4.3.6|:white_circle: skipped | | | |
|RHEL 9|3.6| :white_circle: skipped| | | |
|RHEL 9|3.7| :white_circle: skipped| | | |
|RHEL 9|3.13.3| :white_circle: skipped| | | |
|RHEL 9|4.0.4| :white_circle: skipped| | | |
|RHEL 9|4.1.5| :white_circle: skipped| | | |
|RHEL 9|4.2.7| :white_circle: skipped | | | |
|RHEL 9|4.3.6|:green_circle: done |:green_circle: | :green_circle:| |
|Ubuntu 22|3.6|:white_circle: skipped | | | |
|Ubuntu 22|3.7| :white_circle: skipped| | | |
|Ubuntu 22|3.13.3|:white_circle: skipped| | | |
|Ubuntu 22|4.0.4|:white_circle: skipped| | | |
|Ubuntu 22|4.1.5| :white_circle: skipped ||| |
|Ubuntu 22|4.2.7| :white_circle: skipped||| |
|Ubuntu 22|4.3.6 |:green_circle: done| :green_circle: | :green_circle: |
|openSUSE Tumbleweed|3.6| :white_circle: skipped| | | |
|openSUSE Tumbleweed|3.7|:white_circle: skipped | | | |
|openSUSE Tumbleweed|3.13.3|:white_circle: skipped| || |
|openSUSE Tumbleweed|4.0.4|:white_circle: skipped| | ||
|openSUSE Tumbleweed|4.1.5|:white_circle: skipped| | ||
|openSUSE Tumbleweed|4.2.7|:white_circle: skipped| || |
|openSUSE Tumbleweed|4.3|:white_circle: skipped | |
|Amazon Linux 2|3.6|:white_circle: skipped | | | |
|Amazon Linux 2|3.7|:white_circle: skipped | | | |
|Amazon Linux 2|3.13.3|:white_circle: skipped| || |
|Amazon Linux 2|4.0.4|:white_circle: skipped| | ||
|Amazon Linux 2|4.1.5|:white_circle: skipped| | ||
|Amazon Linux 2|4.2.7|:white_circle: skipped| || |
|Amazon Linux 2|4.3|:white_circle: skipped | |
### Windows
|OS|Version|Status|Upgrade fail|Upgrade OK|
|----|-----|------|---------------|------------------|
|Server 2008|3.6|:white_circle: skipped | | | |
|Server 2008|3.7|:white_circle: skipped | | | |
|Server 2008|3.13.3|:white_circle: skipped| || |
|Server 2008|4.0.4|:white_circle: skipped| | ||
|Server 2008|4.1.5|:white_circle: skipped| | ||
|Server 2008|4.2.7|:white_circle: skipped| || |
|Server 2008|4.3| :white_circle: skipped| |
|Server 2012 R2|3.6| :white_circle: skipped| | | |
|Server 2012 R2|3.7|:white_circle: skipped | | | |
|Server 2012 R2|3.13.3|:white_circle: skipped| || |
|Server 2012 R2|4.0.4|:white_circle: skipped| | ||
|Server 2012 R2|4.1.5|:white_circle: skipped| | ||
|Server 2012 R2|4.2.7|:white_circle: skipped| || |
|Server 2012 R2|4.3|:white_circle: skipped | |
|Server 2016|3.6|:white_circle: skipped | | | |
|Server 2016|3.7| :white_circle: skipped| | | |
|Server 2016|3.13.3|:white_circle: skipped| || |
|Server 2016|4.0.4|:white_circle: skipped| | ||
|Server 2016|4.1.5|:white_circle: skipped| | ||
|Server 2016|4.2.7|:white_circle: skipped| || |
|Server 2016|4.3| :white_circle: skipped| |
|Server 2019|3.6|:white_circle: skipped | | | |
|Server 2019|3.7|:white_circle: skipped | | | |
|Server 2019|3.13.3|:white_circle: skipped| || |
|Server 2019|4.0.4|:white_circle: skipped| | ||
|Server 2019|4.1.5|:white_circle: skipped| | ||
|Server 2019|4.2.7|:white_circle: skipped| || |
|Server 2019|4.3| :white_circle: skipped| |
|Windows 10|3.6| :white_circle: skipped| | | |
|Windows 10|3.7| :white_circle: skipped| | | |
|Windows 10|3.13.3|:white_circle: skipped| || |
|Windows 10|4.0.4|:white_circle: skipped| | ||
|Windows 10|4.1.5|:white_circle: skipped| | ||
|Windows 10|4.2.7|:white_circle: skipped| || |
|Windows 10|4.3| :white_circle: skipped| |
|Server 2022|3.6| :white_circle: skipped| | | |
|Server 2022|3.7| :white_circle: skipped| | | |
|Server 2022|3.13.3|:white_circle: skipped| || |
|Server 2022|4.0.4|:white_circle: skipped| | ||
|Server 2022|4.1.5|:white_circle: skipped| | ||
|Server 2022|4.2.7| :white_circle: skipped| || |
|Server 2022|4.3.6|:green_circle: done| :green_circle: | :green_circle: |
### macOS
|OS|Version|Status|Upgrade fail|Upgrade OK|
|----|-----------|--------|-------|------------------|
| Sierra |4.3.0| :white_circle: skipped|| | | |
| Sierra |4.3.4|:white_circle: skipped || | | |
| Catalina |4.3.0| :white_circle: skipped|| | | |
| Catalina |4.3.4|:white_circle: skipped || | | |
| Big Sur |4.3.0| :white_circle: skipped|| | | |
| Big Sur |4.3.4| :white_circle: skipped|| | | |
| Monterey |4.3.0| :white_circle: skipped|| | | |
| Monterey |4.3.6| :green_circle: done|:green_circle:| :green_circle:| | |
<!--
For each operating system and version, check the following points and add a comment for each OS tested.
## Linux:
### UPGRADE FAIL
- [ ] The wazuh home backup is restored correctly (no traces of the installation, but only the `.tar.gz` backup and the logs).
- [ ] The permissions and owners of the following directories did NOT change:
- `/`
- `/var`
- `/usr`, `/usr/lib/`, `/usr/lib/systemd/`, `/usr/lib/systemd/system/`
- `/etc`, `/etc/systemd/`, `/etc/systemd/system/`, `/etc/rc.d`, `/etc/initd.d/`, `/etc/initd.d/rc.d/`
- [ ] Wazuh service runs wazuh-control (`systemctl cat wazuh-agent.service`)
- [ ] Wazuh service runs ossec-control (`systemctl cat wazuh-agent.service`)
- [ ] The service was enabled (`systemctl is-enabled wazuh-agent.service`)
- [ ] Init file runs wazuh-control (`cat /etc/rc.d/init.d/wazuh-agent`)
- [ ] Init file runs ossec-control (`cat /etc/rc.d/init.d/wazuh-agent`)
- [ ] Wazuh as service is enabled `chkconfig --list`
- [ ] Wazuh starts and connects when the backup is restored (`cat /var/ossec/var/run/ossec-agentd.state`)
- [ ] Wazuh starts and connects automatically when the system is rebooted.
- [ ] Restore SELinux policies (`semodule -l | grep -i wazuh`) (DISABLED)
### UPGRADE OK
- [ ] Upgrade is performed successfully (agent connects to the manager after upgrading)
- [ ] Service starts automatically after rebooting
- [ ] Agent connects to the manager after rebooting
## Windows:
### UPGRADE FAIL
- [ ] Wazuh-Agent folder tree: No files are lost after the rollback. The logs of the failed upgrade (`ossec.log`) are kept.
- [ ] After the rollback the agent connects to the manager
- [ ] After reboot, the Wazuh-Agent starts and connects to the manager.
- [ ] The correct Wazuh-Agent version is shown in the list of Windows' `programs and features`.
- [ ] A new version of Wazuh-Agent can be manually installed via MSI after the rollback process.
### UPGRADE OK
- [ ] Message `Upgrade finished successfully.` is shown in `upgrade.log` file.
- [ ] Wazuh service is started and the agent is connected to the manager.
- [ ] The version shown in the control panel is 4.3
## MacOS:
### UPGRADE FAIL
- [ ] Wazuh-Agent folder tree: No files are lost after the rollback. The logs of the failed upgrade (`ossec.log`) are kept.
- [ ] After the rollback the agent connects to the manager
- [ ] After reboot, the Wazuh-Agent starts and connects to the manager.
### UPGRADE OK
- [ ] Message `Upgrade finished successfully.` is shown in `upgrade.log` file.
- [ ] Wazuh service is started and the agent is connected to the manager.
-->
## Auditors validation
The definition of done for this one is the validation of the conclusions and the test results from all auditors.
All checks from below must be accepted in order to close this issue.
- [x] @vikman90
| non_priority | release release candidate wpk upgrade tests the following issue aims to run upgrade wpk tests for the current release candidate report the results and open new issues for any encountered errors wpk upgrade tests information main rc issue version release candidate tag previous issue test report procedure all individual test checks must be marked as pass the test ran successfully xfail the test was expected to fail and it failed it must be properly justified and reported in an issue skip the test was not run it must be properly justified and reported in an issue fail the test failed a new issue must be opened to evaluate and address the problem all test results must have one the following statuses green circle all checks passed red circle there is at least one failed check yellow circle there is at least one expected fail or skipped test and no failures any failing test must be properly addressed with a new issue detailing the error and the possible cause it must be included in the fixes section of the current release candidate main issue any expected fail or skipped test must have an issue justifying the reason all auditors must validate the justification for an expected fail or skipped test an extended report of the test results must be attached as a zip or txt this report can be used by the auditors to dig deeper into any possible failures and details tests to evaluate this feature it is necessary to test upgrading the agent and also the case when the upgrade fails rollback the tree command will be used to compare before and after the upgrade rollback process and check that the presence ownership and permissions of the files and directories are expected wazuh versions to test upgrade to the current agent version linux os version status upgrade fail upgrade ok centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped centos white circle skipped rhel white circle skipped rhel white circle skipped rhel white circle skipped rhel white circle skipped rhel white circle skipped rhel white circle skipped rhel green circle done green circle green circle ubuntu white circle skipped ubuntu white circle skipped ubuntu white circle skipped ubuntu white circle skipped ubuntu white circle skipped ubuntu white circle skipped ubuntu green circle done green circle green circle opensuse tumbleweed white circle skipped opensuse tumbleweed white circle skipped opensuse tumbleweed white circle skipped opensuse tumbleweed white circle skipped opensuse tumbleweed white circle skipped opensuse tumbleweed white circle skipped opensuse tumbleweed white circle skipped amazon linux white circle skipped amazon linux white circle skipped amazon linux white circle skipped amazon linux white circle skipped amazon linux white circle skipped amazon linux white circle skipped amazon linux white circle skipped windows os version status upgrade fail upgrade ok server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped windows white circle skipped windows white circle skipped windows white circle skipped windows white circle skipped windows white circle skipped windows white circle skipped windows white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server white circle skipped server green circle done green circle green circle macos os version status upgrade fail upgrade ok sierra white circle skipped sierra white circle skipped catalina white circle skipped catalina white circle skipped big sur white circle skipped big sur white circle skipped monterey white circle skipped monterey green circle done green circle green circle for each operating system and version check the following points and add a comment for each os tested linux upgrade fail the wazuh home backup is restored correctly no traces of the installation but only the tar gz backup and the logs the permissions and owners of the following directories did not change var usr usr lib usr lib systemd usr lib systemd system etc etc systemd etc systemd system etc rc d etc initd d etc initd d rc d wazuh service runs wazuh control systemctl cat wazuh agent service wazuh service runs ossec control systemctl cat wazuh agent service the service was enabled systemctl is enabled wazuh agent service init file runs wazuh control cat etc rc d init d wazuh agent init file runs ossec control cat etc rc d init d wazuh agent wazuh as service is enabled chkconfig list wazuh starts and connects when the backup is restored cat var ossec var run ossec agentd state wazuh starts and connects automatically when the system is rebooted restore selinux policies semodule l grep i wazuh disabled upgrade ok upgrade is performed successfully agent connects to the manager after upgrading service starts automatically after rebooting agent connects to the manager after rebooting windows upgrade fail wazuh agent folder tree no files are lost after the rollback the logs of the failed upgrade ossec log are kept after the rollback the agent connects to the manager after reboot the wazuh agent starts and connects to the manager the correct wazuh agent version is shown in the list of windows programs and features a new version of wazuh agent can be manually installed via msi after the rollback process upgrade ok message upgrade finished successfully is shown in upgrade log file wazuh service is started and the agent is connected to the manager the version shown in the control panel is macos upgrade fail wazuh agent folder tree no files are lost after the rollback the logs of the failed upgrade ossec log are kept after the rollback the agent connects to the manager after reboot the wazuh agent starts and connects to the manager upgrade ok message upgrade finished successfully is shown in upgrade log file wazuh service is started and the agent is connected to the manager auditors validation the definition of done for this one is the validation of the conclusions and the test results from all auditors all checks from below must be accepted in order to close this issue | 0 |
379,184 | 26,358,910,749 | IssuesEvent | 2023-01-11 11:54:01 | Hitham2496/EventPlotter | https://api.github.com/repos/Hitham2496/EventPlotter | closed | Add User Documentation | documentation feature | Make user documentation available such that use of the module is clear, possible frameworks include `sphinx` which will be the most convenient. | 1.0 | Add User Documentation - Make user documentation available such that use of the module is clear, possible frameworks include `sphinx` which will be the most convenient. | non_priority | add user documentation make user documentation available such that use of the module is clear possible frameworks include sphinx which will be the most convenient | 0 |
6,352 | 7,582,706,084 | IssuesEvent | 2018-04-25 06:02:43 | IbinexPH/ibinex-web | https://api.github.com/repos/IbinexPH/ibinex-web | opened | [ ALL ] Font family, Font weight | ABOUT CONTACT HOME PRICING SECURITY SERVICES WHY | Please, check font family and weight against the standard.
Expected:
Generated:
| 1.0 | [ ALL ] Font family, Font weight - Please, check font family and weight against the standard.
Expected:
Generated:
| non_priority | font family font weight please check font family and weight against the standard expected generated | 0 |
95,092 | 16,068,472,678 | IssuesEvent | 2021-04-24 00:44:40 | snowflakedb/snowflake-hive-metastore-connector | https://api.github.com/repos/snowflakedb/snowflake-hive-metastore-connector | opened | CVE-2020-36181 (Medium) detected in jackson-databind-2.6.5.jar | security vulnerability | ## CVE-2020-36181 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: snowflake-hive-metastore-connector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.5/jackson-databind-2.6.5.jar</p>
<p>
Dependency Hierarchy:
- hive-metastore-2.3.5.jar (Root Library)
- hive-serde-2.3.5.jar
- hive-common-2.3.5.jar
- :x: **jackson-databind-2.6.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snowflakedb/snowflake-hive-metastore-connector/commit/37f5b0ac91898ef82cc1bf4610b729970f6eed58">37f5b0ac91898ef82cc1bf4610b729970f6eed58</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181>CVE-2020-36181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/commit/3ded28aece694d0df39c9f0fa1ff385b14a8656b">https://github.com/FasterXML/jackson-databind/commit/3ded28aece694d0df39c9f0fa1ff385b14a8656b</a></p>
<p>Release Date: 2021-01-01</p>
<p>Fix Resolution: Replace or update the following files: SubTypeValidator.java, VERSION-2.x</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.5","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-metastore:2.3.5;org.apache.hive:hive-serde:2.3.5;org.apache.hive:hive-common:2.3.5;com.fasterxml.jackson.core:jackson-databind:2.6.5","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-36181","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.cpdsadapter.DriverAdapterCPDS.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | True | CVE-2020-36181 (Medium) detected in jackson-databind-2.6.5.jar - ## CVE-2020-36181 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: snowflake-hive-metastore-connector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.5/jackson-databind-2.6.5.jar</p>
<p>
Dependency Hierarchy:
- hive-metastore-2.3.5.jar (Root Library)
- hive-serde-2.3.5.jar
- hive-common-2.3.5.jar
- :x: **jackson-databind-2.6.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/snowflakedb/snowflake-hive-metastore-connector/commit/37f5b0ac91898ef82cc1bf4610b729970f6eed58">37f5b0ac91898ef82cc1bf4610b729970f6eed58</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181>CVE-2020-36181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/commit/3ded28aece694d0df39c9f0fa1ff385b14a8656b">https://github.com/FasterXML/jackson-databind/commit/3ded28aece694d0df39c9f0fa1ff385b14a8656b</a></p>
<p>Release Date: 2021-01-01</p>
<p>Fix Resolution: Replace or update the following files: SubTypeValidator.java, VERSION-2.x</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.5","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-metastore:2.3.5;org.apache.hive:hive-serde:2.3.5;org.apache.hive:hive-common:2.3.5;com.fasterxml.jackson.core:jackson-databind:2.6.5","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-36181","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp.cpdsadapter.DriverAdapterCPDS.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file snowflake hive metastore connector pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy hive metastore jar root library hive serde jar hive common jar x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp dbcp cpdsadapter driveradaptercpds publish date url a href cvss score details base score metrics not available suggested fix type change files origin a href release date fix resolution replace or update the following files subtypevalidator java version x isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache hive hive metastore org apache hive hive serde org apache hive hive common com fasterxml jackson core jackson databind isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp dbcp cpdsadapter driveradaptercpds vulnerabilityurl | 0 |
22,685 | 4,827,212,844 | IssuesEvent | 2016-11-07 12:53:19 | ehcache/ehcache3 | https://api.github.com/repos/ehcache/ehcache3 | closed | References to obsolete 'fixed' and 'shared' | documentation under review | [Ehcache documentation ](http://www.ehcache.org/documentation/3.1/clustered-cache.html#cache-manager-configuration-and-usage-of-server-side-resources) still refers to "fixed" and "shared" instead of `.clusteredDedicated` and `.clusteredShared` in the description
| 1.0 | References to obsolete 'fixed' and 'shared' - [Ehcache documentation ](http://www.ehcache.org/documentation/3.1/clustered-cache.html#cache-manager-configuration-and-usage-of-server-side-resources) still refers to "fixed" and "shared" instead of `.clusteredDedicated` and `.clusteredShared` in the description
| non_priority | references to obsolete fixed and shared still refers to fixed and shared instead of clustereddedicated and clusteredshared in the description | 0 |
84,228 | 16,472,347,593 | IssuesEvent | 2021-05-23 17:10:08 | RavenProject/Ravencoin | https://api.github.com/repos/RavenProject/Ravencoin | closed | contrib: verify-commits/ - update or remove. | cleanup code | contrib/verify-commits should be updated or removed.
I'm for updating and adding actually used keys.
| 1.0 | contrib: verify-commits/ - update or remove. - contrib/verify-commits should be updated or removed.
I'm for updating and adding actually used keys.
| non_priority | contrib verify commits update or remove contrib verify commits should be updated or removed i m for updating and adding actually used keys | 0 |
126,676 | 17,093,492,211 | IssuesEvent | 2021-07-08 21:00:51 | PowerShell/PowerShell | https://api.github.com/repos/PowerShell/PowerShell | closed | Allow .ps1xml files in XML 1.1 | Issue-Enhancement Resolution-By Design WG-Cmdlets-Core | To enable colored output in output formats, I can write a Format.ps1xml file that uses ANSI color codes like so:
```xml
<?xml version="1.0" encoding="utf-8"?>
<Configuration>
<ViewDefinitions>
<!-- Resembles the git log output with format=medium (default) -->
<View>
<Name>Medium</Name>
<ViewSelectedBy>
<TypeName>PowerGit.CommitInfo</TypeName>
</ViewSelectedBy>
<ListControl>
<ListEntries>
<ListEntry>
<ListItems>
<ListItem>
<!-- Yellow -->
<Label>[33mSha</Label>
<ScriptBlock>"$($_.Sha)$([char]0x001b)[0m"</ScriptBlock>
</ListItem>
<ListItem>
<Label>Author</Label>
<PropertyName>Author</PropertyName>
</ListItem>
<ListItem>
<Label>Date</Label>
<ScriptBlock>"$($_.Author.When)"</ScriptBlock>
</ListItem>
<ListItem>
<Label>Message</Label>
<PropertyName>Message</PropertyName>
</ListItem>
</ListItems>
</ListEntry>
</ListEntries>
</ListControl>
</View>
</ViewDefinitions>
</Configuration>
```
Note the `[33m`, which is `ESC[33m`, which is the ANSI code for yellow, and `$([char]0x001b)[0m`, which is `ESC[0m`, which is the ANSI reset code.
Together, this will color the whole line yellow:
<img width="452" alt="image" src="https://user-images.githubusercontent.com/10532611/44112434-6167e756-a005-11e8-8c14-895d27beba56.png">
just like in `git log` output:
<img width="345" alt="image" src="https://user-images.githubusercontent.com/10532611/44112448-6b503818-a005-11e8-88da-5e6dabca365d.png">
HOWEVER this is actually not valid XML. Every good XML parser will rightfully complain:
<img width="378" alt="image" src="https://user-images.githubusercontent.com/10532611/44112545-9eedc992-a005-11e8-8aab-0b435ab94fa1.png">
See https://en.wikipedia.org/wiki/Valid_characters_in_XML#XML_1.0
Which means these format files cannot be statically checked, generated, codemodded, etc.
It _is_ valid in XML 1.1: https://en.wikipedia.org/wiki/Valid_characters_in_XML#XML_1.1
But if I change the parsing instruction to
```xml
<?xml version="1.1" encoding="utf-8"?>
```
PowerShell errors:
```powershell
Import-Module : Errors occurred while loading the format data file:
/Users/felix/src/github.com/felixfbecker/PowerGit/PowerGit/Formats/PowerGit.CommitInfo.formats.ps1xml, Error in file /Users/felix/src/github.com/felixfbecker/PowerGit/PowerGit/Formats/PowerGit.CommitInfo.formats.ps1xml: Version number '1.1' is invalid. Line 1, position 16.
At /Users/felix/src/github.com/felixfbecker/PowerGit/PowerGit/Import-PowerGit.ps1:32 char:1
+ Import-Module -Name (Join-Path -Path $PSScriptRoot -ChildPath 'PowerG ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: (:) [Import-Module], RuntimeException
+ FullyQualifiedErrorId : FormatXmlUpdateException,Microsoft.PowerShell.Commands.ImportModuleCommand
```
It effectively already parses XML 1.1 fine though, it just complains about the version.
| 1.0 | Allow .ps1xml files in XML 1.1 - To enable colored output in output formats, I can write a Format.ps1xml file that uses ANSI color codes like so:
```xml
<?xml version="1.0" encoding="utf-8"?>
<Configuration>
<ViewDefinitions>
<!-- Resembles the git log output with format=medium (default) -->
<View>
<Name>Medium</Name>
<ViewSelectedBy>
<TypeName>PowerGit.CommitInfo</TypeName>
</ViewSelectedBy>
<ListControl>
<ListEntries>
<ListEntry>
<ListItems>
<ListItem>
<!-- Yellow -->
<Label>[33mSha</Label>
<ScriptBlock>"$($_.Sha)$([char]0x001b)[0m"</ScriptBlock>
</ListItem>
<ListItem>
<Label>Author</Label>
<PropertyName>Author</PropertyName>
</ListItem>
<ListItem>
<Label>Date</Label>
<ScriptBlock>"$($_.Author.When)"</ScriptBlock>
</ListItem>
<ListItem>
<Label>Message</Label>
<PropertyName>Message</PropertyName>
</ListItem>
</ListItems>
</ListEntry>
</ListEntries>
</ListControl>
</View>
</ViewDefinitions>
</Configuration>
```
Note the `[33m`, which is `ESC[33m`, which is the ANSI code for yellow, and `$([char]0x001b)[0m`, which is `ESC[0m`, which is the ANSI reset code.
Together, this will color the whole line yellow:
<img width="452" alt="image" src="https://user-images.githubusercontent.com/10532611/44112434-6167e756-a005-11e8-8c14-895d27beba56.png">
just like in `git log` output:
<img width="345" alt="image" src="https://user-images.githubusercontent.com/10532611/44112448-6b503818-a005-11e8-88da-5e6dabca365d.png">
HOWEVER this is actually not valid XML. Every good XML parser will rightfully complain:
<img width="378" alt="image" src="https://user-images.githubusercontent.com/10532611/44112545-9eedc992-a005-11e8-8aab-0b435ab94fa1.png">
See https://en.wikipedia.org/wiki/Valid_characters_in_XML#XML_1.0
Which means these format files cannot be statically checked, generated, codemodded, etc.
It _is_ valid in XML 1.1: https://en.wikipedia.org/wiki/Valid_characters_in_XML#XML_1.1
But if I change the parsing instruction to
```xml
<?xml version="1.1" encoding="utf-8"?>
```
PowerShell errors:
```powershell
Import-Module : Errors occurred while loading the format data file:
/Users/felix/src/github.com/felixfbecker/PowerGit/PowerGit/Formats/PowerGit.CommitInfo.formats.ps1xml, Error in file /Users/felix/src/github.com/felixfbecker/PowerGit/PowerGit/Formats/PowerGit.CommitInfo.formats.ps1xml: Version number '1.1' is invalid. Line 1, position 16.
At /Users/felix/src/github.com/felixfbecker/PowerGit/PowerGit/Import-PowerGit.ps1:32 char:1
+ Import-Module -Name (Join-Path -Path $PSScriptRoot -ChildPath 'PowerG ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : InvalidOperation: (:) [Import-Module], RuntimeException
+ FullyQualifiedErrorId : FormatXmlUpdateException,Microsoft.PowerShell.Commands.ImportModuleCommand
```
It effectively already parses XML 1.1 fine though, it just complains about the version.
| non_priority | allow files in xml to enable colored output in output formats i can write a format file that uses ansi color codes like so xml medium powergit commitinfo sha author author date author when message message note the which is esc which is the ansi reset code together this will color the whole line yellow img width alt image src just like in git log output img width alt image src however this is actually not valid xml every good xml parser will rightfully complain img width alt image src see which means these format files cannot be statically checked generated codemodded etc it is valid in xml but if i change the parsing instruction to xml powershell errors powershell import module errors occurred while loading the format data file users felix src github com felixfbecker powergit powergit formats powergit commitinfo formats error in file users felix src github com felixfbecker powergit powergit formats powergit commitinfo formats version number is invalid line position at users felix src github com felixfbecker powergit powergit import powergit char import module name join path path psscriptroot childpath powerg categoryinfo invalidoperation runtimeexception fullyqualifiederrorid formatxmlupdateexception microsoft powershell commands importmodulecommand it effectively already parses xml fine though it just complains about the version | 0 |
145,670 | 22,757,653,058 | IssuesEvent | 2022-07-07 18:01:05 | patternfly/patternfly-org | https://api.github.com/repos/patternfly/patternfly-org | opened | Button component design guidelines updates | PF4 design Guidelines Consistency effort | Reorganizes design guidelines IA to fit inline with the component design guidelines template | 1.0 | Button component design guidelines updates - Reorganizes design guidelines IA to fit inline with the component design guidelines template | non_priority | button component design guidelines updates reorganizes design guidelines ia to fit inline with the component design guidelines template | 0 |
50,829 | 13,579,155,127 | IssuesEvent | 2020-09-20 11:36:02 | YaronSpawn/NodeGoat | https://api.github.com/repos/YaronSpawn/NodeGoat | opened | CVE-2018-3728 (High) detected in hoek-2.16.3.tgz, hoek-0.9.1.tgz | security vulnerability | ## CVE-2018-3728 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>hoek-2.16.3.tgz</b>, <b>hoek-0.9.1.tgz</b></p></summary>
<p>
<details><summary><b>hoek-2.16.3.tgz</b></p></summary>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz">https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz</a></p>
<p>Path to dependency file: NodeGoat/package.json</p>
<p>Path to vulnerable library: NodeGoat/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- hawk-3.1.3.tgz
- :x: **hoek-2.16.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>hoek-0.9.1.tgz</b></p></summary>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz">https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz</a></p>
<p>Path to dependency file: NodeGoat/package.json</p>
<p>Path to vulnerable library: NodeGoat/node_modules/zaproxy/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- zaproxy-0.2.0.tgz (Root Library)
- request-2.36.0.tgz
- hawk-1.0.0.tgz
- :x: **hoek-0.9.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/YaronSpawn/NodeGoat/commit/e68768dd8731fe1c99abced9b1f32efc7f93ba9d">e68768dd8731fe1c99abced9b1f32efc7f93ba9d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via 'merge' and 'applyToDefaults' functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728>CVE-2018-3728</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3728">https://nvd.nist.gov/vuln/detail/CVE-2018-3728</a></p>
<p>Release Date: 2018-03-30</p>
<p>Fix Resolution: 4.2.1,5.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-3728 (High) detected in hoek-2.16.3.tgz, hoek-0.9.1.tgz - ## CVE-2018-3728 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>hoek-2.16.3.tgz</b>, <b>hoek-0.9.1.tgz</b></p></summary>
<p>
<details><summary><b>hoek-2.16.3.tgz</b></p></summary>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz">https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz</a></p>
<p>Path to dependency file: NodeGoat/package.json</p>
<p>Path to vulnerable library: NodeGoat/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- hawk-3.1.3.tgz
- :x: **hoek-2.16.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>hoek-0.9.1.tgz</b></p></summary>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz">https://registry.npmjs.org/hoek/-/hoek-0.9.1.tgz</a></p>
<p>Path to dependency file: NodeGoat/package.json</p>
<p>Path to vulnerable library: NodeGoat/node_modules/zaproxy/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- zaproxy-0.2.0.tgz (Root Library)
- request-2.36.0.tgz
- hawk-1.0.0.tgz
- :x: **hoek-0.9.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/YaronSpawn/NodeGoat/commit/e68768dd8731fe1c99abced9b1f32efc7f93ba9d">e68768dd8731fe1c99abced9b1f32efc7f93ba9d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via 'merge' and 'applyToDefaults' functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728>CVE-2018-3728</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-3728">https://nvd.nist.gov/vuln/detail/CVE-2018-3728</a></p>
<p>Release Date: 2018-03-30</p>
<p>Fix Resolution: 4.2.1,5.0.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in hoek tgz hoek tgz cve high severity vulnerability vulnerable libraries hoek tgz hoek tgz hoek tgz general purpose node utilities library home page a href path to dependency file nodegoat package json path to vulnerable library nodegoat node modules npm node modules request node modules hawk node modules hoek package json dependency hierarchy grunt retire tgz root library request tgz hawk tgz x hoek tgz vulnerable library hoek tgz general purpose node utilities library home page a href path to dependency file nodegoat package json path to vulnerable library nodegoat node modules zaproxy node modules hoek package json dependency hierarchy zaproxy tgz root library request tgz hawk tgz x hoek tgz vulnerable library found in head commit a href found in base branch master vulnerability details hoek node module before and x before suffers from a modification of assumed immutable data maid vulnerability via merge and applytodefaults functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
53,330 | 28,083,925,024 | IssuesEvent | 2023-03-30 08:30:55 | Simply-Love/Simply-Love-SM5 | https://api.github.com/repos/Simply-Love/Simply-Love-SM5 | closed | [General] static.lua file is acting weird | enhancement performance/optimization | This started when I was trying to figure out a stepmania build to put in our cabinet.
SM5.1-b2 was the smoothest one ingame, putting us at 200 fps ingame but at a solid 15~30fps during the menus due to what
I thought were the BG Animations. Thing is: in outfox this wasn't happening.
I tried going to
.Themes\Simply Love\BGAnimations\_shared background\default.lua
and I was trying to comment out the lines applying the animations, although due to the fact that I didn't have notepad++ there, I accidentally commented only line 31
`af[#af+1] = LoadActor("./Static.lua", file)`
which when I rebooted the game, fixed every sort of problem and made my cab go up from 15 fps to 130 fps.
On my normal pc I can see this line acting up as well

I can see that you guys do test on powerful PCs (well, just ordinary good ones) but these things do affect low-end cabs a lot!
Hopefully it may help.
| True | [General] static.lua file is acting weird - This started when I was trying to figure out a stepmania build to put in our cabinet.
SM5.1-b2 was the smoothest one ingame, putting us at 200 fps ingame but at a solid 15~30fps during the menus due to what
I thought were the BG Animations. Thing is: in outfox this wasn't happening.
I tried going to
.Themes\Simply Love\BGAnimations\_shared background\default.lua
and I was trying to comment out the lines applying the animations, although due to the fact that I didn't have notepad++ there, I accidentally commented only line 31
`af[#af+1] = LoadActor("./Static.lua", file)`
which when I rebooted the game, fixed every sort of problem and made my cab go up from 15 fps to 130 fps.
On my normal pc I can see this line acting up as well

I can see that you guys do test on powerful PCs (well, just ordinary good ones) but these things do affect low-end cabs a lot!
Hopefully it may help.
| non_priority | static lua file is acting weird this started when i was trying to figure out a stepmania build to put in our cabinet was the smoothest one ingame putting us at fps ingame but at a solid during the menus due to what i thought were the bg animations thing is in outfox this wasn t happening i tried going to themes simply love bganimations shared background default lua and i was trying to comment out the lines applying the animations although due to the fact that i didn t have notepad there i accidentally commented only line af loadactor static lua file which when i rebooted the game fixed every sort of problem and made my cab go up from fps to fps on my normal pc i can see this line acting up as well i can see that you guys do test on powerful pcs well just ordinary good ones but these things do affect low end cabs a lot hopefully it may help | 0 |
49,041 | 12,270,021,766 | IssuesEvent | 2020-05-07 14:54:13 | verilog-to-routing/vtr-verilog-to-routing | https://api.github.com/repos/verilog-to-routing/vtr-verilog-to-routing | opened | Configure Profile Guilded Optimization Builds to use partial traning | build enhancement | <!--- Provide a general summary of the issue in the Title above -->
New versions of GCC (e.g. GCC 10) support the [`-fprofile-partial-training` flag](https://gcc.gnu.org/onlinedocs/gcc/Optimize-Options.html), which means code not profiled is optimized as usual (i.e. with out profile-guided heuristics), instead of being optimized for minimum code size.
Since collecting a full profile of the various operations/flag combinations isn't easy, this is likely to produce better performing binaries when non-default options are used.
Since not all compiler support this option, we should test for support in CMAKE and enable it only if the compiler accepts the option. | 1.0 | Configure Profile Guilded Optimization Builds to use partial traning - <!--- Provide a general summary of the issue in the Title above -->
New versions of GCC (e.g. GCC 10) support the [`-fprofile-partial-training` flag](https://gcc.gnu.org/onlinedocs/gcc/Optimize-Options.html), which means code not profiled is optimized as usual (i.e. with out profile-guided heuristics), instead of being optimized for minimum code size.
Since collecting a full profile of the various operations/flag combinations isn't easy, this is likely to produce better performing binaries when non-default options are used.
Since not all compiler support this option, we should test for support in CMAKE and enable it only if the compiler accepts the option. | non_priority | configure profile guilded optimization builds to use partial traning new versions of gcc e g gcc support the which means code not profiled is optimized as usual i e with out profile guided heuristics instead of being optimized for minimum code size since collecting a full profile of the various operations flag combinations isn t easy this is likely to produce better performing binaries when non default options are used since not all compiler support this option we should test for support in cmake and enable it only if the compiler accepts the option | 0 |
277,480 | 30,659,222,671 | IssuesEvent | 2023-07-25 14:02:44 | rsoreq/zenbot | https://api.github.com/repos/rsoreq/zenbot | opened | husky-4.2.5.tgz: 2 vulnerabilities (highest severity is: 7.5) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>husky-4.2.5.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7f99c836ea749efa113ef0ccdc60bfe4cbbfa856">7f99c836ea749efa113ef0ccdc60bfe4cbbfa856</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (husky version) | Fix PR available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-3795](https://www.mend.io/vulnerability-database/CVE-2021-3795) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | semver-regex-2.0.0.tgz | Transitive | 4.3.7 | ❌ |
| [CVE-2021-43307](https://www.mend.io/vulnerability-database/CVE-2021-43307) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | semver-regex-2.0.0.tgz | Transitive | 4.3.7 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-3795</summary>
### Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- husky-4.2.5.tgz (Root Library)
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7f99c836ea749efa113ef0ccdc60bfe4cbbfa856">7f99c836ea749efa113ef0ccdc60bfe4cbbfa856</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
semver-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3795>CVE-2021-3795</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-09-15</p>
<p>Fix Resolution (semver-regex): semver-regex - 3.1.3,4.0.1</p>
<p>Direct dependency fix Resolution (husky): 4.3.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-43307</summary>
### Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- husky-4.2.5.tgz (Root Library)
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7f99c836ea749efa113ef0ccdc60bfe4cbbfa856">7f99c836ea749efa113ef0ccdc60bfe4cbbfa856</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An exponential ReDoS (Regular Expression Denial of Service) can be triggered in the semver-regex npm package, when an attacker is able to supply arbitrary input to the test() method
<p>Publish Date: 2022-06-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43307>CVE-2021-43307</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/">https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/</a></p>
<p>Release Date: 2022-06-02</p>
<p>Fix Resolution (semver-regex): semver-regex - 3.1.4,4.0.3</p>
<p>Direct dependency fix Resolution (husky): 4.3.7</p>
</p>
<p></p>
</details> | True | husky-4.2.5.tgz: 2 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>husky-4.2.5.tgz</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7f99c836ea749efa113ef0ccdc60bfe4cbbfa856">7f99c836ea749efa113ef0ccdc60bfe4cbbfa856</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (husky version) | Fix PR available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-3795](https://www.mend.io/vulnerability-database/CVE-2021-3795) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | semver-regex-2.0.0.tgz | Transitive | 4.3.7 | ❌ |
| [CVE-2021-43307](https://www.mend.io/vulnerability-database/CVE-2021-43307) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High | 7.5 | semver-regex-2.0.0.tgz | Transitive | 4.3.7 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-3795</summary>
### Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- husky-4.2.5.tgz (Root Library)
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7f99c836ea749efa113ef0ccdc60bfe4cbbfa856">7f99c836ea749efa113ef0ccdc60bfe4cbbfa856</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
semver-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-3795>CVE-2021-3795</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-09-15</p>
<p>Fix Resolution (semver-regex): semver-regex - 3.1.3,4.0.1</p>
<p>Direct dependency fix Resolution (husky): 4.3.7</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> CVE-2021-43307</summary>
### Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- husky-4.2.5.tgz (Root Library)
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7f99c836ea749efa113ef0ccdc60bfe4cbbfa856">7f99c836ea749efa113ef0ccdc60bfe4cbbfa856</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
An exponential ReDoS (Regular Expression Denial of Service) can be triggered in the semver-regex npm package, when an attacker is able to supply arbitrary input to the test() method
<p>Publish Date: 2022-06-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43307>CVE-2021-43307</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/">https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/</a></p>
<p>Release Date: 2022-06-02</p>
<p>Fix Resolution (semver-regex): semver-regex - 3.1.4,4.0.3</p>
<p>Direct dependency fix Resolution (husky): 4.3.7</p>
</p>
<p></p>
</details> | non_priority | husky tgz vulnerabilities highest severity is vulnerable library husky tgz found in head commit a href vulnerabilities cve severity cvss dependency type fixed in husky version fix pr available high semver regex tgz transitive high semver regex tgz transitive details cve vulnerable library semver regex tgz regular expression for matching semver versions library home page a href dependency hierarchy husky tgz root library find versions tgz x semver regex tgz vulnerable library found in head commit a href found in base branch unstable vulnerability details semver regex is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution semver regex semver regex direct dependency fix resolution husky cve vulnerable library semver regex tgz regular expression for matching semver versions library home page a href dependency hierarchy husky tgz root library find versions tgz x semver regex tgz vulnerable library found in head commit a href found in base branch unstable vulnerability details an exponential redos regular expression denial of service can be triggered in the semver regex npm package when an attacker is able to supply arbitrary input to the test method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution semver regex semver regex direct dependency fix resolution husky | 0 |
82,235 | 32,075,015,496 | IssuesEvent | 2023-09-25 10:24:43 | vector-im/element-call | https://api.github.com/repos/vector-im/element-call | opened | The outlines of call tiles at the edge get cut off | T-Defect | ### Steps to reproduce
1. Join a call with multiple people
2. Use the "tile" view (not the spotlight view)
3. See that the outline of tiles get cut off
### Outcome
#### What did you expect?
Edges of people's call tiles to not be cut off.
#### What happened instead?
I see the following on different browsers. This only affects people that are at the edges:
Chromium v117.0.5938.88:


Firefox v117.0.1:

Users that are surrounded by other tiles experience no cut off edges on their call tiles.
### Operating system
NixOS Linux
### Browser information
Chromium v117.0.5938.88
### URL for webapp
call.element.io
### Will you send logs?
No | 1.0 | The outlines of call tiles at the edge get cut off - ### Steps to reproduce
1. Join a call with multiple people
2. Use the "tile" view (not the spotlight view)
3. See that the outline of tiles get cut off
### Outcome
#### What did you expect?
Edges of people's call tiles to not be cut off.
#### What happened instead?
I see the following on different browsers. This only affects people that are at the edges:
Chromium v117.0.5938.88:


Firefox v117.0.1:

Users that are surrounded by other tiles experience no cut off edges on their call tiles.
### Operating system
NixOS Linux
### Browser information
Chromium v117.0.5938.88
### URL for webapp
call.element.io
### Will you send logs?
No | non_priority | the outlines of call tiles at the edge get cut off steps to reproduce join a call with multiple people use the tile view not the spotlight view see that the outline of tiles get cut off outcome what did you expect edges of people s call tiles to not be cut off what happened instead i see the following on different browsers this only affects people that are at the edges chromium firefox users that are surrounded by other tiles experience no cut off edges on their call tiles operating system nixos linux browser information chromium url for webapp call element io will you send logs no | 0 |
144,807 | 13,126,762,698 | IssuesEvent | 2020-08-06 09:08:49 | line/armeria | https://api.github.com/repos/line/armeria | opened | Add more documentation for context-awareness | documentation | We currently do not explain much about thread-local context propagation. It'd be nice if we document:
- how context propagation works.
- how to work with external APIs (e.g. RxJava, thread pools) while preserving the thread local context.
- how to customize `RequestContextStorage`. | 1.0 | Add more documentation for context-awareness - We currently do not explain much about thread-local context propagation. It'd be nice if we document:
- how context propagation works.
- how to work with external APIs (e.g. RxJava, thread pools) while preserving the thread local context.
- how to customize `RequestContextStorage`. | non_priority | add more documentation for context awareness we currently do not explain much about thread local context propagation it d be nice if we document how context propagation works how to work with external apis e g rxjava thread pools while preserving the thread local context how to customize requestcontextstorage | 0 |
44,623 | 23,711,443,652 | IssuesEvent | 2022-08-30 08:12:39 | INL/BlackLab | https://api.github.com/repos/INL/BlackLab | closed | Input files with many documents in them appear to gradually degrade indexing speed | indexing performance | This has been observed with both XML (TEI, @JessedeDoes) and with a TSV-based input file. Indexing starts out fast but gets gradually slower as process more documents from the file.
Number of documents appears to be the cause, because we don't see this behaviour at all with our 2G tokens corpus, which has various sizes of file, but not many documents per file. This indexes at around 30k tokens/s (on a beefy server) all the way through.
What could be causing this? It doesn't appear to be memory/garbage collector related as memory use seems reasonable and we don't see the all-CPU 100% spikes associated with excessive GC.
DocIndexer is instantiated per file (right? check), so that might be a place to start looking. Is there anything inefficient we do per-file or per-document? E.g. a linear search through previously encountered values could cause behaviour like this. | True | Input files with many documents in them appear to gradually degrade indexing speed - This has been observed with both XML (TEI, @JessedeDoes) and with a TSV-based input file. Indexing starts out fast but gets gradually slower as process more documents from the file.
Number of documents appears to be the cause, because we don't see this behaviour at all with our 2G tokens corpus, which has various sizes of file, but not many documents per file. This indexes at around 30k tokens/s (on a beefy server) all the way through.
What could be causing this? It doesn't appear to be memory/garbage collector related as memory use seems reasonable and we don't see the all-CPU 100% spikes associated with excessive GC.
DocIndexer is instantiated per file (right? check), so that might be a place to start looking. Is there anything inefficient we do per-file or per-document? E.g. a linear search through previously encountered values could cause behaviour like this. | non_priority | input files with many documents in them appear to gradually degrade indexing speed this has been observed with both xml tei jessededoes and with a tsv based input file indexing starts out fast but gets gradually slower as process more documents from the file number of documents appears to be the cause because we don t see this behaviour at all with our tokens corpus which has various sizes of file but not many documents per file this indexes at around tokens s on a beefy server all the way through what could be causing this it doesn t appear to be memory garbage collector related as memory use seems reasonable and we don t see the all cpu spikes associated with excessive gc docindexer is instantiated per file right check so that might be a place to start looking is there anything inefficient we do per file or per document e g a linear search through previously encountered values could cause behaviour like this | 0 |
111,284 | 24,103,010,863 | IssuesEvent | 2022-09-20 03:52:45 | log2timeline/plaso | https://api.github.com/repos/log2timeline/plaso | closed | look into failing test on Fedora 36 | parsers testing code health | determine why this test is failing on Fedora 36
```
======================================================================
ERROR: testParse (parsers.viminfo.ViminfoParserTest)
Tests the Parse function.
----------------------------------------------------------------------
Traceback (most recent call last):
File "tests/parsers/viminfo.py", line 21, in testParse
storage_writer = self._ParseFile(['.viminfo'], parser)
File "tests/parsers/test_lib.py", line 134, in _ParseFile
return self._ParseFileByPathSpec(
File "tests/parsers/test_lib.py", line 166, in _ParseFileByPathSpec
parser.Parse(parser_mediator, file_object)
File "plaso/parsers/interface.py", line 288, in Parse
self.ParseFileObject(parser_mediator, file_object)
File "plaso/parsers/text_parser.py", line 587, in ParseFileObject
raise errors.WrongParser(
plaso.lib.errors.WrongParser: more than 20 consecutive failures to parse lines.
----------------------------------------------------------------------
```
@sydp FYI | 1.0 | look into failing test on Fedora 36 - determine why this test is failing on Fedora 36
```
======================================================================
ERROR: testParse (parsers.viminfo.ViminfoParserTest)
Tests the Parse function.
----------------------------------------------------------------------
Traceback (most recent call last):
File "tests/parsers/viminfo.py", line 21, in testParse
storage_writer = self._ParseFile(['.viminfo'], parser)
File "tests/parsers/test_lib.py", line 134, in _ParseFile
return self._ParseFileByPathSpec(
File "tests/parsers/test_lib.py", line 166, in _ParseFileByPathSpec
parser.Parse(parser_mediator, file_object)
File "plaso/parsers/interface.py", line 288, in Parse
self.ParseFileObject(parser_mediator, file_object)
File "plaso/parsers/text_parser.py", line 587, in ParseFileObject
raise errors.WrongParser(
plaso.lib.errors.WrongParser: more than 20 consecutive failures to parse lines.
----------------------------------------------------------------------
```
@sydp FYI | non_priority | look into failing test on fedora determine why this test is failing on fedora error testparse parsers viminfo viminfoparsertest tests the parse function traceback most recent call last file tests parsers viminfo py line in testparse storage writer self parsefile parser file tests parsers test lib py line in parsefile return self parsefilebypathspec file tests parsers test lib py line in parsefilebypathspec parser parse parser mediator file object file plaso parsers interface py line in parse self parsefileobject parser mediator file object file plaso parsers text parser py line in parsefileobject raise errors wrongparser plaso lib errors wrongparser more than consecutive failures to parse lines sydp fyi | 0 |
49,444 | 13,453,462,960 | IssuesEvent | 2020-09-09 01:01:53 | nasifimtiazohi/openmrs-module-coreapps-1.28.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-coreapps-1.28.0 | opened | CVE-2019-10768 (High) detected in angular-1.6.1.tgz | security vulnerability | ## CVE-2019-10768 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-1.6.1.tgz</b></p></summary>
<p>HTML enhanced for web apps</p>
<p>Library home page: <a href="https://registry.npmjs.org/angular/-/angular-1.6.1.tgz">https://registry.npmjs.org/angular/-/angular-1.6.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/openmrs-module-coreapps-1.28.0/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/openmrs-module-coreapps-1.28.0/node_modules/@openmrs/angularjs-openmrs-api/node_modules/angular/package.json,/openmrs-module-coreapps-1.28.0/node_modules/@openmrs/angularjs-openmrs-api/node_modules/angular/package.json</p>
<p>
Dependency Hierarchy:
- :x: **angular-1.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-coreapps-1.28.0/commit/a473f1097dd760370898008cacd6434f0620476f">a473f1097dd760370898008cacd6434f0620476f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In AngularJS before 1.7.9 the function `merge()` could be tricked into adding or modifying properties of `Object.prototype` using a `__proto__` payload.
<p>Publish Date: 2019-11-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10768>CVE-2019-10768</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10768">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10768</a></p>
<p>Release Date: 2019-11-19</p>
<p>Fix Resolution: v1.7.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-10768 (High) detected in angular-1.6.1.tgz - ## CVE-2019-10768 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-1.6.1.tgz</b></p></summary>
<p>HTML enhanced for web apps</p>
<p>Library home page: <a href="https://registry.npmjs.org/angular/-/angular-1.6.1.tgz">https://registry.npmjs.org/angular/-/angular-1.6.1.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/openmrs-module-coreapps-1.28.0/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/openmrs-module-coreapps-1.28.0/node_modules/@openmrs/angularjs-openmrs-api/node_modules/angular/package.json,/openmrs-module-coreapps-1.28.0/node_modules/@openmrs/angularjs-openmrs-api/node_modules/angular/package.json</p>
<p>
Dependency Hierarchy:
- :x: **angular-1.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-coreapps-1.28.0/commit/a473f1097dd760370898008cacd6434f0620476f">a473f1097dd760370898008cacd6434f0620476f</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In AngularJS before 1.7.9 the function `merge()` could be tricked into adding or modifying properties of `Object.prototype` using a `__proto__` payload.
<p>Publish Date: 2019-11-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10768>CVE-2019-10768</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10768">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10768</a></p>
<p>Release Date: 2019-11-19</p>
<p>Fix Resolution: v1.7.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in angular tgz cve high severity vulnerability vulnerable library angular tgz html enhanced for web apps library home page a href path to dependency file tmp ws scm openmrs module coreapps package json path to vulnerable library tmp ws scm openmrs module coreapps node modules openmrs angularjs openmrs api node modules angular package json openmrs module coreapps node modules openmrs angularjs openmrs api node modules angular package json dependency hierarchy x angular tgz vulnerable library found in head commit a href vulnerability details in angularjs before the function merge could be tricked into adding or modifying properties of object prototype using a proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
182,821 | 21,676,520,150 | IssuesEvent | 2022-05-08 20:01:29 | TreyM-WSS/WhiteSource-Demo | https://api.github.com/repos/TreyM-WSS/WhiteSource-Demo | closed | WS-2022-0107 (High) detected in spring-beans-4.3.2.RELEASE.jar - autoclosed | security vulnerability | ## WS-2022-0107 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-beans-4.3.2.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/4.3.2.RELEASE/spring-beans-4.3.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- spring-web-4.3.2.RELEASE.jar
- :x: **spring-beans-4.3.2.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״.
The current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution).
Please note that the ease of exploitation may diverge by the code implementation.
Currently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux.
Spring Framework 5.3.18 and 5.2.20 have already been released.
WhiteSource’s research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.
This is a temporary WhiteSource ID until an official CVE ID will be released.
<p>Publish Date: 2022-03-30
<p>URL: <a href=https://www.cyberkendra.com/2022/03/springshell-rce-0-day-vulnerability.html>WS-2022-0107</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-03-30</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.20.RELEASE,5.3.18</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-beans","packageVersion":"4.3.2.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.4.0.RELEASE;org.springframework:spring-web:4.3.2.RELEASE;org.springframework:spring-beans:4.3.2.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.20.RELEASE,5.3.18","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2022-0107","vulnerabilityDetails":"Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״.\n\nThe current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution).\nPlease note that the ease of exploitation may diverge by the code implementation.\n\nCurrently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux.\nSpring Framework 5.3.18 and 5.2.20 have already been released.\n\nWhiteSource’s research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.\nThis is a temporary WhiteSource ID until an official CVE ID will be released.","vulnerabilityUrl":"https://www.cyberkendra.com/2022/03/springshell-rce-0-day-vulnerability.html","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | WS-2022-0107 (High) detected in spring-beans-4.3.2.RELEASE.jar - autoclosed - ## WS-2022-0107 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-beans-4.3.2.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/4.3.2.RELEASE/spring-beans-4.3.2.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- spring-web-4.3.2.RELEASE.jar
- :x: **spring-beans-4.3.2.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״.
The current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution).
Please note that the ease of exploitation may diverge by the code implementation.
Currently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux.
Spring Framework 5.3.18 and 5.2.20 have already been released.
WhiteSource’s research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.
This is a temporary WhiteSource ID until an official CVE ID will be released.
<p>Publish Date: 2022-03-30
<p>URL: <a href=https://www.cyberkendra.com/2022/03/springshell-rce-0-day-vulnerability.html>WS-2022-0107</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-03-30</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.20.RELEASE,5.3.18</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-beans","packageVersion":"4.3.2.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.4.0.RELEASE;org.springframework:spring-web:4.3.2.RELEASE;org.springframework:spring-beans:4.3.2.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.20.RELEASE,5.3.18","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2022-0107","vulnerabilityDetails":"Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״.\n\nThe current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution).\nPlease note that the ease of exploitation may diverge by the code implementation.\n\nCurrently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux.\nSpring Framework 5.3.18 and 5.2.20 have already been released.\n\nWhiteSource’s research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.\nThis is a temporary WhiteSource ID until an official CVE ID will be released.","vulnerabilityUrl":"https://www.cyberkendra.com/2022/03/springshell-rce-0-day-vulnerability.html","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in spring beans release jar autoclosed ws high severity vulnerability vulnerable library spring beans release jar spring beans library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring beans release spring beans release jar dependency hierarchy spring boot starter web release jar root library spring web release jar x spring beans release jar vulnerable library found in base branch master vulnerability details spring framework before and x before are vulnerable due to a vulnerability in spring beans which allows attackers under certain circumstances to achieve remote code execution this vulnerability is also known as ״ ״ or ״springshell״ the current poc related to the attack is done by creating a specially crafted request which manipulates classloader to successfully achieve rce remote code execution please note that the ease of exploitation may diverge by the code implementation currently the exploit requires jdk or higher apache tomcat as the servlet container the application packaged as war and dependency on spring webmvc or spring webflux spring framework and have already been released whitesource’s research team is carefully observing developments and researching the case we will keep updating this page and our whitesource resources with updates this is a temporary whitesource id until an official cve id will be released publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring web release org springframework spring beans release isminimumfixversionavailable true minimumfixversion org springframework spring beans release isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails spring framework before and x before are vulnerable due to a vulnerability in spring beans which allows attackers under certain circumstances to achieve remote code execution this vulnerability is also known as ״ ״ or ״springshell״ n nthe current poc related to the attack is done by creating a specially crafted request which manipulates classloader to successfully achieve rce remote code execution nplease note that the ease of exploitation may diverge by the code implementation n ncurrently the exploit requires jdk or higher apache tomcat as the servlet container the application packaged as war and dependency on spring webmvc or spring webflux nspring framework and have already been released n nwhitesource’s research team is carefully observing developments and researching the case we will keep updating this page and our whitesource resources with updates nthis is a temporary whitesource id until an official cve id will be released vulnerabilityurl | 0 |
290,893 | 25,103,116,537 | IssuesEvent | 2022-11-08 14:55:35 | ContinualAI/avalanche | https://api.github.com/repos/ContinualAI/avalanche | closed | Creation of a new envirnment failed for python 3.7 | test Continuous integration | Here are the differences between the last working environment and the new one that I tried to run:
```
19,20c19,20
< - brotli=1.0.9=h166bdaf_7
< - brotli-bin=1.0.9=h166bdaf_7
---
> - brotli=1.0.9=h166bdaf_8
> - brotli-bin=1.0.9=h166bdaf_8
30c30
< - colorama=0.4.5=pyhd8ed1ab_0
---
> - colorama=0.4.6=pyhd8ed1ab_0
32c32
< - cryptography=38.0.2=py37h38fbfac_0
---
> - cryptography=38.0.2=py37h38fbfac_1
37c37
< - expat=2.4.9=h27087fc_0
---
> - expat=2.5.0=h27087fc_0
44c44
< - fontconfig=2.14.0=hc2a2eb6_1
---
> - fontconfig=2.14.1=hc2a2eb6_0
53,54c53,54
< - glib=2.74.0=h6239696_0
< - glib-tools=2.74.0=h6239696_0
---
> - glib=2.74.1=h6239696_0
> - glib-tools=2.74.1=h6239696_0
74c74
< - lcms2=2.12=hddcbb42_0
---
> - lcms2=2.13.1=h6ed2654_0
79,81c79,81
< - libbrotlicommon=1.0.9=h166bdaf_7
< - libbrotlidec=1.0.9=h166bdaf_7
< - libbrotlienc=1.0.9=h166bdaf_7
---
> - libbrotlicommon=1.0.9=h166bdaf_8
> - libbrotlidec=1.0.9=h166bdaf_8
> - libbrotlienc=1.0.9=h166bdaf_8
93,97c93,97
< - libgcc-ng=12.2.0=h65d4601_18
< - libgfortran-ng=12.2.0=h69a702a_18
< - libgfortran5=12.2.0=h337968e_18
< - libglib=2.74.0=h7a41b64_0
< - libgomp=12.2.0=h65d4601_18
---
> - libgcc-ng=12.2.0=h65d4601_19
> - libgfortran-ng=12.2.0=h69a702a_19
> - libgfortran5=12.2.0=h337968e_19
> - libglib=2.74.1=h7a41b64_0
> - libgomp=12.2.0=h65d4601_19
106c106
< - libpq=14.5=hd77ab85_0
---
> - libpq=14.5=hd77ab85_1
110c110
< - libstdcxx-ng=12.2.0=h46fd767_18
---
> - libstdcxx-ng=12.2.0=h46fd767_19
113c113
< - libudev1=249=h166bdaf_4
---
> - libudev1=251=h166bdaf_0
167c167
< - pytorch=1.12.1=py3.7_cpu_0
---
> - pytorch=1.13.0=py3.7_cpu_0
188c188
< - tbb=2021.6.0=h924138e_0
---
> - tbb=2021.6.0=h924138e_1
195,196c195,196
< - torchmetrics=0.10.0=pyhd8ed1ab_0
< - torchvision=0.13.1=py37_cpu
---
> - torchmetrics=0.10.1=pyhd8ed1ab_0
> - torchvision=0.14.0=py37_cpu
216c216
< - zipp=3.9.0=pyhd8ed1ab_0
---
> - zipp=3.10.0=pyhd8ed1ab_0
224c224
< - dill==0.3.5.1
---
> - dill==0.3.6
233c233
< - plotly==5.10.0
---
> - plotly==5.11.0
``` | 1.0 | Creation of a new envirnment failed for python 3.7 - Here are the differences between the last working environment and the new one that I tried to run:
```
19,20c19,20
< - brotli=1.0.9=h166bdaf_7
< - brotli-bin=1.0.9=h166bdaf_7
---
> - brotli=1.0.9=h166bdaf_8
> - brotli-bin=1.0.9=h166bdaf_8
30c30
< - colorama=0.4.5=pyhd8ed1ab_0
---
> - colorama=0.4.6=pyhd8ed1ab_0
32c32
< - cryptography=38.0.2=py37h38fbfac_0
---
> - cryptography=38.0.2=py37h38fbfac_1
37c37
< - expat=2.4.9=h27087fc_0
---
> - expat=2.5.0=h27087fc_0
44c44
< - fontconfig=2.14.0=hc2a2eb6_1
---
> - fontconfig=2.14.1=hc2a2eb6_0
53,54c53,54
< - glib=2.74.0=h6239696_0
< - glib-tools=2.74.0=h6239696_0
---
> - glib=2.74.1=h6239696_0
> - glib-tools=2.74.1=h6239696_0
74c74
< - lcms2=2.12=hddcbb42_0
---
> - lcms2=2.13.1=h6ed2654_0
79,81c79,81
< - libbrotlicommon=1.0.9=h166bdaf_7
< - libbrotlidec=1.0.9=h166bdaf_7
< - libbrotlienc=1.0.9=h166bdaf_7
---
> - libbrotlicommon=1.0.9=h166bdaf_8
> - libbrotlidec=1.0.9=h166bdaf_8
> - libbrotlienc=1.0.9=h166bdaf_8
93,97c93,97
< - libgcc-ng=12.2.0=h65d4601_18
< - libgfortran-ng=12.2.0=h69a702a_18
< - libgfortran5=12.2.0=h337968e_18
< - libglib=2.74.0=h7a41b64_0
< - libgomp=12.2.0=h65d4601_18
---
> - libgcc-ng=12.2.0=h65d4601_19
> - libgfortran-ng=12.2.0=h69a702a_19
> - libgfortran5=12.2.0=h337968e_19
> - libglib=2.74.1=h7a41b64_0
> - libgomp=12.2.0=h65d4601_19
106c106
< - libpq=14.5=hd77ab85_0
---
> - libpq=14.5=hd77ab85_1
110c110
< - libstdcxx-ng=12.2.0=h46fd767_18
---
> - libstdcxx-ng=12.2.0=h46fd767_19
113c113
< - libudev1=249=h166bdaf_4
---
> - libudev1=251=h166bdaf_0
167c167
< - pytorch=1.12.1=py3.7_cpu_0
---
> - pytorch=1.13.0=py3.7_cpu_0
188c188
< - tbb=2021.6.0=h924138e_0
---
> - tbb=2021.6.0=h924138e_1
195,196c195,196
< - torchmetrics=0.10.0=pyhd8ed1ab_0
< - torchvision=0.13.1=py37_cpu
---
> - torchmetrics=0.10.1=pyhd8ed1ab_0
> - torchvision=0.14.0=py37_cpu
216c216
< - zipp=3.9.0=pyhd8ed1ab_0
---
> - zipp=3.10.0=pyhd8ed1ab_0
224c224
< - dill==0.3.5.1
---
> - dill==0.3.6
233c233
< - plotly==5.10.0
---
> - plotly==5.11.0
``` | non_priority | creation of a new envirnment failed for python here are the differences between the last working environment and the new one that i tried to run brotli brotli bin brotli brotli bin colorama colorama cryptography cryptography expat expat fontconfig fontconfig glib glib tools glib glib tools libbrotlicommon libbrotlidec libbrotlienc libbrotlicommon libbrotlidec libbrotlienc libgcc ng libgfortran ng libglib libgomp libgcc ng libgfortran ng libglib libgomp libpq libpq libstdcxx ng libstdcxx ng pytorch cpu pytorch cpu tbb tbb torchmetrics torchvision cpu torchmetrics torchvision cpu zipp zipp dill dill plotly plotly | 0 |
75,479 | 9,256,931,259 | IssuesEvent | 2019-03-16 23:56:02 | samtecspg/articulate | https://api.github.com/repos/samtecspg/articulate | closed | Import/Export in the API and the UI | enhancement needs design ui | Is necessary to implement an import/export endpoint and functionality in the UI to let developers gain speed in the process of managing their agents. | 1.0 | Import/Export in the API and the UI - Is necessary to implement an import/export endpoint and functionality in the UI to let developers gain speed in the process of managing their agents. | non_priority | import export in the api and the ui is necessary to implement an import export endpoint and functionality in the ui to let developers gain speed in the process of managing their agents | 0 |
77,439 | 21,795,143,875 | IssuesEvent | 2022-05-15 14:14:01 | dail8859/NotepadNext | https://api.github.com/repos/dail8859/NotepadNext | closed | Build fails: too many arguments to function call, expected 0, have 1 | build | ```
--- build/obj/FloatingWidgetTitleBar.o ---
../src/ads/src/linux/FloatingWidgetTitleBar.cpp:197:34: error: too many arguments to function call, expected 0, have 1
d->FloatingWidget->showNormal(true);
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ^~~~
/usr/local/include/qt5/QtWidgets/qwidget.h:486:10: note: 'showNormal' declared here
void showNormal();
^
1 error generated.
```
Version: 0.5.1
clang-13
Qt-5.15.2
FreeBSD 13 | 1.0 | Build fails: too many arguments to function call, expected 0, have 1 - ```
--- build/obj/FloatingWidgetTitleBar.o ---
../src/ads/src/linux/FloatingWidgetTitleBar.cpp:197:34: error: too many arguments to function call, expected 0, have 1
d->FloatingWidget->showNormal(true);
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ ^~~~
/usr/local/include/qt5/QtWidgets/qwidget.h:486:10: note: 'showNormal' declared here
void showNormal();
^
1 error generated.
```
Version: 0.5.1
clang-13
Qt-5.15.2
FreeBSD 13 | non_priority | build fails too many arguments to function call expected have build obj floatingwidgettitlebar o src ads src linux floatingwidgettitlebar cpp error too many arguments to function call expected have d floatingwidget shownormal true usr local include qtwidgets qwidget h note shownormal declared here void shownormal error generated version clang qt freebsd | 0 |
302,398 | 22,821,754,358 | IssuesEvent | 2022-07-12 03:32:42 | ampproject/amphtml | https://api.github.com/repos/ampproject/amphtml | closed | Examples: Language of page content is not indicated | Type: Bug Related to: Accessibility Related to: Documentation Type: Accessibility Stale | ## WCAG Level
Level A / AA
## Priority
Low
## Type
Structure
## Pages/screens/components affected
* [amp-pixel](https://amp.dev/documentation/components/amp-pixel/)
* [amp-sidebar](https://amp.dev/documentation/components/amp-sidebar/)
* [amp-accordion](https://amp.dev/documentation/components/amp-accordion/)
* [amp-selector](https://amp.dev/documentation/components/amp-selector/)
* [amp-sticky-ad](https://amp.dev/documentation/components/amp-sticky-ad/)
* [amp-user-notification](https://amp.dev/documentation/components/amp-user-notification/)
* [amp-consent](https://amp.dev/documentation/components/amp-consent/)
* [amp-video](https://amp.dev/documentation/components/amp-video/)
* [amp-app-banner](https://amp.dev/documentation/components/amp-app-banner/)
* [amp-youtube](https://amp.dev/documentation/components/amp-youtube/)
* [amp-base-carousel](https://amp.dev/documentation/components/amp-base-carousel/)
* [amp-stream-gallery](https://amp.dev/documentation/components/amp-stream-gallery/)
* [amp-inline-gallery](https://amp.dev/documentation/components/amp-inline-gallery/)
* [amp-lightbox-gallery](https://amp.dev/documentation/components/amp-lightbox-gallery/)
## Description
It is important to programmatically identify the human language of a web page/section of a page, as this makes a difference as to how screen readers pronounce content.
We found pages that lack a programmatically defined language, which fails WCAG 2.1 SC 3.1.1 Language of the Page. This leads to the language of all *parts* of the content also lacking a programmatically defined language, failing WCAG 2.1 SC 3.1.2 Language of Parts as well.
## User impact
Depending on the user’s setup, screen readers and other text-to-speech applications that support multiple languages will not be able to adapt to the correct accent or pronunciation when announcing page content, which can impact on the understandability of the page.
## Required solution
Make sure that the human language of all HTML pages, as well as content embedded within pages and changes in language, is declared correctly. Make sure that the `<html>` element has the required `lang` attribute, and that the value of this attribute matches the human language of the page.
This solution must be applied to all instances of the issue identified within the test sample, then applied to all other instances of the same issue identified throughout the rest of the website.
## Test procedure(s)
Use these steps to confirm that the solution has been correctly applied:
1. Check that the `<html>` element has a `lang` attribute.
2. Check that the value of the `lang` attribute reflects the primary language used by the page.
## Related standards
* [WCAG 2.1 Success Criterion 3.1.1 Language of Page (Level A)](https://www.w3.org/TR/WCAG21/#language-of-page)
* [WCAG 2.1 Success Criterion 3.1.2 Language of Parts (Level AA)](https://www.w3.org/TR/WCAG21/#language-of-parts)
## More information
* [W3C - Technique H57: Using the language attribute on the HTML element](https://www.w3.org/WAI/WCAG21/Techniques/html/H57.html)
* [W3C - Technique H58: Using language attributes to identify changes in the human language](https://www.w3.org/WAI/WCAG21/Techniques/html/H58.html)
## Test data
Test date: November 2020
| 1.0 | Examples: Language of page content is not indicated - ## WCAG Level
Level A / AA
## Priority
Low
## Type
Structure
## Pages/screens/components affected
* [amp-pixel](https://amp.dev/documentation/components/amp-pixel/)
* [amp-sidebar](https://amp.dev/documentation/components/amp-sidebar/)
* [amp-accordion](https://amp.dev/documentation/components/amp-accordion/)
* [amp-selector](https://amp.dev/documentation/components/amp-selector/)
* [amp-sticky-ad](https://amp.dev/documentation/components/amp-sticky-ad/)
* [amp-user-notification](https://amp.dev/documentation/components/amp-user-notification/)
* [amp-consent](https://amp.dev/documentation/components/amp-consent/)
* [amp-video](https://amp.dev/documentation/components/amp-video/)
* [amp-app-banner](https://amp.dev/documentation/components/amp-app-banner/)
* [amp-youtube](https://amp.dev/documentation/components/amp-youtube/)
* [amp-base-carousel](https://amp.dev/documentation/components/amp-base-carousel/)
* [amp-stream-gallery](https://amp.dev/documentation/components/amp-stream-gallery/)
* [amp-inline-gallery](https://amp.dev/documentation/components/amp-inline-gallery/)
* [amp-lightbox-gallery](https://amp.dev/documentation/components/amp-lightbox-gallery/)
## Description
It is important to programmatically identify the human language of a web page/section of a page, as this makes a difference as to how screen readers pronounce content.
We found pages that lack a programmatically defined language, which fails WCAG 2.1 SC 3.1.1 Language of the Page. This leads to the language of all *parts* of the content also lacking a programmatically defined language, failing WCAG 2.1 SC 3.1.2 Language of Parts as well.
## User impact
Depending on the user’s setup, screen readers and other text-to-speech applications that support multiple languages will not be able to adapt to the correct accent or pronunciation when announcing page content, which can impact on the understandability of the page.
## Required solution
Make sure that the human language of all HTML pages, as well as content embedded within pages and changes in language, is declared correctly. Make sure that the `<html>` element has the required `lang` attribute, and that the value of this attribute matches the human language of the page.
This solution must be applied to all instances of the issue identified within the test sample, then applied to all other instances of the same issue identified throughout the rest of the website.
## Test procedure(s)
Use these steps to confirm that the solution has been correctly applied:
1. Check that the `<html>` element has a `lang` attribute.
2. Check that the value of the `lang` attribute reflects the primary language used by the page.
## Related standards
* [WCAG 2.1 Success Criterion 3.1.1 Language of Page (Level A)](https://www.w3.org/TR/WCAG21/#language-of-page)
* [WCAG 2.1 Success Criterion 3.1.2 Language of Parts (Level AA)](https://www.w3.org/TR/WCAG21/#language-of-parts)
## More information
* [W3C - Technique H57: Using the language attribute on the HTML element](https://www.w3.org/WAI/WCAG21/Techniques/html/H57.html)
* [W3C - Technique H58: Using language attributes to identify changes in the human language](https://www.w3.org/WAI/WCAG21/Techniques/html/H58.html)
## Test data
Test date: November 2020
| non_priority | examples language of page content is not indicated wcag level level a aa priority low type structure pages screens components affected description it is important to programmatically identify the human language of a web page section of a page as this makes a difference as to how screen readers pronounce content we found pages that lack a programmatically defined language which fails wcag sc language of the page this leads to the language of all parts of the content also lacking a programmatically defined language failing wcag sc language of parts as well user impact depending on the user’s setup screen readers and other text to speech applications that support multiple languages will not be able to adapt to the correct accent or pronunciation when announcing page content which can impact on the understandability of the page required solution make sure that the human language of all html pages as well as content embedded within pages and changes in language is declared correctly make sure that the element has the required lang attribute and that the value of this attribute matches the human language of the page this solution must be applied to all instances of the issue identified within the test sample then applied to all other instances of the same issue identified throughout the rest of the website test procedure s use these steps to confirm that the solution has been correctly applied check that the element has a lang attribute check that the value of the lang attribute reflects the primary language used by the page related standards more information test data test date november | 0 |
326,968 | 28,035,411,661 | IssuesEvent | 2023-03-28 14:48:05 | AdaCore/RecordFlux | https://api.github.com/repos/AdaCore/RecordFlux | closed | Flush Memcached before nightly tests | testing | Also move nightly tests to 21:00 MET / 05:00 KST to reduce impact on team members. | 1.0 | Flush Memcached before nightly tests - Also move nightly tests to 21:00 MET / 05:00 KST to reduce impact on team members. | non_priority | flush memcached before nightly tests also move nightly tests to met kst to reduce impact on team members | 0 |
158,427 | 13,733,026,089 | IssuesEvent | 2020-10-05 06:17:44 | tomav/docker-mailserver | https://api.github.com/repos/tomav/docker-mailserver | reopened | Letsencrypt certs not mounted by default | documentation frozen due to age ssl/tls waiting for contributor action | ## Context
When the docker image starts, the start script needs to copy files, including the SSL certificates, but for some reason, it can't see the files.
### *What* is affected by this bug?
SSL certificate files and all their dependents
### *When* does this occur?
When the script runs, on launch
## *How* do we replicate the issue?
This issue occurs on launch. See Environment at the bottom for environment details.
## Actual Behavior
The "Setting up SSL" block gives this information:
```
mail | Setting up SSL
mail | * TLS configured with 'modern' ciphers
mail | * Configuring certificates using cert /tmp/docker-mailserver/ssl/cert and key /tmp/docker-mailserver/ssl/key
mail | cp: cannot stat '/tmp/docker-mailserver/ssl/cert': No such file or directory
mail | cp: cannot stat '/tmp/docker-mailserver/ssl/key': No such file or directory
mail | chmod: cannot access '/etc/postfix/ssl/cert': No such file or directory
mail | chmod: cannot access '/etc/postfix/ssl/key': No such file or directory
mail | * SSL configured with 'Manual' certificates
```
The `cp` subprocesses it spawns can't see the files.
## Expected behavior (i.e. solution)
The files should be seen and copied.
## Your Environment
I have set a fresh installation up on a new installation of Debian.
Starting the server with these commands:
```
docker-compose down
docker pull tvial/docker-mailserver:latest
docker-compose up mail
```
For my cert files, I have this configuration:
```
SSL_TYPE=manual
SSL_CERT_PATH=/etc/letsencrypt/live/mail.giovanh.com/fullchain.pem
SSL_KEY_PATH=/etc/letsencrypt/live/mail.giovanh.com/privkey.pem
```
(I am aware that this is redundant, as `SSL_TYPE=letsencrypt` does this, but this is unambiguous.)
The local user and root can both see those two file paths, `cat` and `cp` them with no problem. Their permissions are set as , as are the files the symlinks point to.
| 1.0 | Letsencrypt certs not mounted by default - ## Context
When the docker image starts, the start script needs to copy files, including the SSL certificates, but for some reason, it can't see the files.
### *What* is affected by this bug?
SSL certificate files and all their dependents
### *When* does this occur?
When the script runs, on launch
## *How* do we replicate the issue?
This issue occurs on launch. See Environment at the bottom for environment details.
## Actual Behavior
The "Setting up SSL" block gives this information:
```
mail | Setting up SSL
mail | * TLS configured with 'modern' ciphers
mail | * Configuring certificates using cert /tmp/docker-mailserver/ssl/cert and key /tmp/docker-mailserver/ssl/key
mail | cp: cannot stat '/tmp/docker-mailserver/ssl/cert': No such file or directory
mail | cp: cannot stat '/tmp/docker-mailserver/ssl/key': No such file or directory
mail | chmod: cannot access '/etc/postfix/ssl/cert': No such file or directory
mail | chmod: cannot access '/etc/postfix/ssl/key': No such file or directory
mail | * SSL configured with 'Manual' certificates
```
The `cp` subprocesses it spawns can't see the files.
## Expected behavior (i.e. solution)
The files should be seen and copied.
## Your Environment
I have set a fresh installation up on a new installation of Debian.
Starting the server with these commands:
```
docker-compose down
docker pull tvial/docker-mailserver:latest
docker-compose up mail
```
For my cert files, I have this configuration:
```
SSL_TYPE=manual
SSL_CERT_PATH=/etc/letsencrypt/live/mail.giovanh.com/fullchain.pem
SSL_KEY_PATH=/etc/letsencrypt/live/mail.giovanh.com/privkey.pem
```
(I am aware that this is redundant, as `SSL_TYPE=letsencrypt` does this, but this is unambiguous.)
The local user and root can both see those two file paths, `cat` and `cp` them with no problem. Their permissions are set as , as are the files the symlinks point to.
| non_priority | letsencrypt certs not mounted by default context when the docker image starts the start script needs to copy files including the ssl certificates but for some reason it can t see the files what is affected by this bug ssl certificate files and all their dependents when does this occur when the script runs on launch how do we replicate the issue this issue occurs on launch see environment at the bottom for environment details actual behavior the setting up ssl block gives this information mail setting up ssl mail tls configured with modern ciphers mail configuring certificates using cert tmp docker mailserver ssl cert and key tmp docker mailserver ssl key mail cp cannot stat tmp docker mailserver ssl cert no such file or directory mail cp cannot stat tmp docker mailserver ssl key no such file or directory mail chmod cannot access etc postfix ssl cert no such file or directory mail chmod cannot access etc postfix ssl key no such file or directory mail ssl configured with manual certificates the cp subprocesses it spawns can t see the files expected behavior i e solution the files should be seen and copied your environment i have set a fresh installation up on a new installation of debian starting the server with these commands docker compose down docker pull tvial docker mailserver latest docker compose up mail for my cert files i have this configuration ssl type manual ssl cert path etc letsencrypt live mail giovanh com fullchain pem ssl key path etc letsencrypt live mail giovanh com privkey pem i am aware that this is redundant as ssl type letsencrypt does this but this is unambiguous the local user and root can both see those two file paths cat and cp them with no problem their permissions are set as as are the files the symlinks point to | 0 |
118,455 | 11,980,544,314 | IssuesEvent | 2020-04-07 09:31:09 | open-covid-data/mvp-notes-and-ideas | https://api.github.com/repos/open-covid-data/mvp-notes-and-ideas | closed | Setup requirements.txt, general contributing guidelines for python dev | documentation | Instructions on how to setup venv + pip for newcomers
(FYI we have a default python version that is currently 3.6.4, if we can live with that that's great) | 1.0 | Setup requirements.txt, general contributing guidelines for python dev - Instructions on how to setup venv + pip for newcomers
(FYI we have a default python version that is currently 3.6.4, if we can live with that that's great) | non_priority | setup requirements txt general contributing guidelines for python dev instructions on how to setup venv pip for newcomers fyi we have a default python version that is currently if we can live with that that s great | 0 |
96,908 | 16,174,100,335 | IssuesEvent | 2021-05-03 01:12:33 | little-apps/SerializableModel | https://api.github.com/repos/little-apps/SerializableModel | opened | CVE-2020-11023 (Medium) detected in jquery-3.1.1.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js</a></p>
<p>Path to vulnerable library: SerializableModel/vendor/phpunit/php-code-coverage/src/Report/Html/Renderer/Template/js/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.min.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11023 (Medium) detected in jquery-3.1.1.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js</a></p>
<p>Path to vulnerable library: SerializableModel/vendor/phpunit/php-code-coverage/src/Report/Html/Renderer/Template/js/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.min.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library serializablemodel vendor phpunit php code coverage src report html renderer template js jquery min js dependency hierarchy x jquery min js vulnerable library vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
354,825 | 25,175,001,183 | IssuesEvent | 2022-11-11 08:26:09 | wrewsama/pe | https://api.github.com/repos/wrewsama/pe | opened | Example `person new` command given in UG throws error | severity.Medium type.DocumentationBug | Steps
1. Execute `person new n/Hilbert Stewart p/+91 368 91829383e/hilbertstewart@gmail.com a/68 Hudson Street t/friend` which is the example given in the UG.
Result: Error

<!--session: 1668152765799-b72d9a49-879f-476e-af80-a427f965e91e-->
<!--Version: Web v3.4.4--> | 1.0 | Example `person new` command given in UG throws error - Steps
1. Execute `person new n/Hilbert Stewart p/+91 368 91829383e/hilbertstewart@gmail.com a/68 Hudson Street t/friend` which is the example given in the UG.
Result: Error

<!--session: 1668152765799-b72d9a49-879f-476e-af80-a427f965e91e-->
<!--Version: Web v3.4.4--> | non_priority | example person new command given in ug throws error steps execute person new n hilbert stewart p hilbertstewart gmail com a hudson street t friend which is the example given in the ug result error | 0 |
27,121 | 4,281,846,648 | IssuesEvent | 2016-07-15 06:10:49 | Terracotta-OSS/galvan | https://api.github.com/repos/Terracotta-OSS/galvan | closed | ServerProcess.start() returns before server's JVM process is launched on window | requires re-test | As shown in the below code snippet, the start() method doesn't wait for JVM process to be launched on Windows. This can cause test to hang if the stop() is immediately invoked right after start. This problem was observed in one of the ehcache clustered tests causing the build to hang on Windows.
// Wait for the server to enter started.
synchronized (this) {
if (TestHelpers.isWindows()){
//windows start script doesn't emit this event, so skip it.
this.isScriptReady = true;
}
while (!this.isScriptReady) {
try {
wait();
} catch (InterruptedException e) {
// We can't recover from interruption here.
Assert.unexpected(e);
}
}
} | 1.0 | ServerProcess.start() returns before server's JVM process is launched on window - As shown in the below code snippet, the start() method doesn't wait for JVM process to be launched on Windows. This can cause test to hang if the stop() is immediately invoked right after start. This problem was observed in one of the ehcache clustered tests causing the build to hang on Windows.
// Wait for the server to enter started.
synchronized (this) {
if (TestHelpers.isWindows()){
//windows start script doesn't emit this event, so skip it.
this.isScriptReady = true;
}
while (!this.isScriptReady) {
try {
wait();
} catch (InterruptedException e) {
// We can't recover from interruption here.
Assert.unexpected(e);
}
}
} | non_priority | serverprocess start returns before server s jvm process is launched on window as shown in the below code snippet the start method doesn t wait for jvm process to be launched on windows this can cause test to hang if the stop is immediately invoked right after start this problem was observed in one of the ehcache clustered tests causing the build to hang on windows wait for the server to enter started synchronized this if testhelpers iswindows windows start script doesn t emit this event so skip it this isscriptready true while this isscriptready try wait catch interruptedexception e we can t recover from interruption here assert unexpected e | 0 |
351,275 | 25,020,840,883 | IssuesEvent | 2022-11-04 00:20:04 | VicaWorth/csci-36 | https://api.github.com/repos/VicaWorth/csci-36 | closed | Create Tests | documentation enhancement | **For Testers + UX**
These do not have to be incredibly in depth at this point. For the most part we want to test if what we already have works correctly.
Frankly, not too much seems broken right now. So it might be a good idea to see things like:
1. How long does a scrape take?
2. Notice any slow downs?
3. Notice any usability issues? Like something that doesn't seem quite right? | 1.0 | Create Tests - **For Testers + UX**
These do not have to be incredibly in depth at this point. For the most part we want to test if what we already have works correctly.
Frankly, not too much seems broken right now. So it might be a good idea to see things like:
1. How long does a scrape take?
2. Notice any slow downs?
3. Notice any usability issues? Like something that doesn't seem quite right? | non_priority | create tests for testers ux these do not have to be incredibly in depth at this point for the most part we want to test if what we already have works correctly frankly not too much seems broken right now so it might be a good idea to see things like how long does a scrape take notice any slow downs notice any usability issues like something that doesn t seem quite right | 0 |
53,441 | 13,164,650,930 | IssuesEvent | 2020-08-11 04:21:07 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Tensorflow 2.2.0 and Tensorflow Probability 0.10.0 import error | Fixed in Nightly TF 2.2 stalled stat:awaiting response subtype: ubuntu/linux type:build/install | <em>Please make sure that this is a build/installation issue. As per our [GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md), we only address code/doc bugs, performance issues, feature requests and build/installation issues on GitHub. tag:build_template</em>
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): CentOS 7
- TensorFlow installed from (source or binary): source
- TensorFlow version: 2.2.0
- Python version: 3.8.2
- Installed using virtualenv? pip? conda?: pip
- Bazel version (if compiling from source): 3.1.0
- GCC/Compiler version (if compiling from source): 7.5.0
- CUDA/cuDNN version: n.a.
- GPU model and memory: n.a.
Tensorflow version 2.2.0 compiled from source following the steps detailed in the [official documentation](https://www.tensorflow.org/install/source#cpu-only_2) doesn't work with any version of Tensorflow Probability higher than 0.7.
Tensorflow (CPU ONLY) is compiled using the Docker environment and works just fine by itself but when importing Tensorflow Probability I get the following error:
~~~
>>> import tensorflow_probability as tfp
Traceback (most recent call last):
File "<stdin>", line 1, in <module>
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/__init__.py", line 76, in <module>
from tensorflow_probability.python import * # pylint: disable=wildcard-import
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/__init__.py", line 24, in <module>
from tensorflow_probability.python import experimental
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/experimental/__init__.py", line 34, in <module>
from tensorflow_probability.python.experimental import auto_batching
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/experimental/auto_batching/__init__.py", line 24, in <module>
from tensorflow_probability.python.experimental.auto_batching import frontend
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/experimental/auto_batching/frontend.py", line 45, in <module>
from tensorflow.python.autograph.core import naming
ImportError: cannot import name 'naming' from 'tensorflow.python.autograph.core' (/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow/python/autograph/core/__init__.py)
~~~
I am not sure if it is a bug in Tensorflow Probability or if there is something wrong with my build of Tensorflow. | 1.0 | Tensorflow 2.2.0 and Tensorflow Probability 0.10.0 import error - <em>Please make sure that this is a build/installation issue. As per our [GitHub Policy](https://github.com/tensorflow/tensorflow/blob/master/ISSUES.md), we only address code/doc bugs, performance issues, feature requests and build/installation issues on GitHub. tag:build_template</em>
**System information**
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): CentOS 7
- TensorFlow installed from (source or binary): source
- TensorFlow version: 2.2.0
- Python version: 3.8.2
- Installed using virtualenv? pip? conda?: pip
- Bazel version (if compiling from source): 3.1.0
- GCC/Compiler version (if compiling from source): 7.5.0
- CUDA/cuDNN version: n.a.
- GPU model and memory: n.a.
Tensorflow version 2.2.0 compiled from source following the steps detailed in the [official documentation](https://www.tensorflow.org/install/source#cpu-only_2) doesn't work with any version of Tensorflow Probability higher than 0.7.
Tensorflow (CPU ONLY) is compiled using the Docker environment and works just fine by itself but when importing Tensorflow Probability I get the following error:
~~~
>>> import tensorflow_probability as tfp
Traceback (most recent call last):
File "<stdin>", line 1, in <module>
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/__init__.py", line 76, in <module>
from tensorflow_probability.python import * # pylint: disable=wildcard-import
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/__init__.py", line 24, in <module>
from tensorflow_probability.python import experimental
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/experimental/__init__.py", line 34, in <module>
from tensorflow_probability.python.experimental import auto_batching
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/experimental/auto_batching/__init__.py", line 24, in <module>
from tensorflow_probability.python.experimental.auto_batching import frontend
File "/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow_probability/python/experimental/auto_batching/frontend.py", line 45, in <module>
from tensorflow.python.autograph.core import naming
ImportError: cannot import name 'naming' from 'tensorflow.python.autograph.core' (/home/fabio/Downloads/tf-prob/.pyenv/lib64/python3.8/site-packages/tensorflow/python/autograph/core/__init__.py)
~~~
I am not sure if it is a bug in Tensorflow Probability or if there is something wrong with my build of Tensorflow. | non_priority | tensorflow and tensorflow probability import error please make sure that this is a build installation issue as per our we only address code doc bugs performance issues feature requests and build installation issues on github tag build template system information os platform and distribution e g linux ubuntu centos tensorflow installed from source or binary source tensorflow version python version installed using virtualenv pip conda pip bazel version if compiling from source gcc compiler version if compiling from source cuda cudnn version n a gpu model and memory n a tensorflow version compiled from source following the steps detailed in the doesn t work with any version of tensorflow probability higher than tensorflow cpu only is compiled using the docker environment and works just fine by itself but when importing tensorflow probability i get the following error import tensorflow probability as tfp traceback most recent call last file line in file home fabio downloads tf prob pyenv site packages tensorflow probability init py line in from tensorflow probability python import pylint disable wildcard import file home fabio downloads tf prob pyenv site packages tensorflow probability python init py line in from tensorflow probability python import experimental file home fabio downloads tf prob pyenv site packages tensorflow probability python experimental init py line in from tensorflow probability python experimental import auto batching file home fabio downloads tf prob pyenv site packages tensorflow probability python experimental auto batching init py line in from tensorflow probability python experimental auto batching import frontend file home fabio downloads tf prob pyenv site packages tensorflow probability python experimental auto batching frontend py line in from tensorflow python autograph core import naming importerror cannot import name naming from tensorflow python autograph core home fabio downloads tf prob pyenv site packages tensorflow python autograph core init py i am not sure if it is a bug in tensorflow probability or if there is something wrong with my build of tensorflow | 0 |
200,277 | 15,096,690,082 | IssuesEvent | 2021-02-07 15:59:04 | BookStackApp/BookStack | https://api.github.com/repos/BookStackApp/BookStack | closed | Bug: Importing a drawing from browser causes console error/blank popup | :mag: Testing required | **Describe the bug**
Running v0.29.3 ... Trying to import from the browser in the drawing editor doesn't work. You get a blank popup and a console error.
**Steps To Reproduce**
Steps to reproduce the behavior:
1. Start editing a wiki page
2. Click on the drawing editor icon in the WYSIWYG editor
3. When the editor loads, select FILE, IMPORT FROM BROWSER
4. See error
**Expected behavior**
Not sure, as it never gets that far :)
**Screenshots**
**Your Configuration (please complete the following information):**
- v0.29.3
- PHP Version: 7.3.18
- Apache
**Additional context**
None
| 1.0 | Bug: Importing a drawing from browser causes console error/blank popup - **Describe the bug**
Running v0.29.3 ... Trying to import from the browser in the drawing editor doesn't work. You get a blank popup and a console error.
**Steps To Reproduce**
Steps to reproduce the behavior:
1. Start editing a wiki page
2. Click on the drawing editor icon in the WYSIWYG editor
3. When the editor loads, select FILE, IMPORT FROM BROWSER
4. See error
**Expected behavior**
Not sure, as it never gets that far :)
**Screenshots**
**Your Configuration (please complete the following information):**
- v0.29.3
- PHP Version: 7.3.18
- Apache
**Additional context**
None
| non_priority | bug importing a drawing from browser causes console error blank popup describe the bug running trying to import from the browser in the drawing editor doesn t work you get a blank popup and a console error steps to reproduce steps to reproduce the behavior start editing a wiki page click on the drawing editor icon in the wysiwyg editor when the editor loads select file import from browser see error expected behavior not sure as it never gets that far screenshots your configuration please complete the following information php version apache additional context none | 0 |
65,385 | 27,087,147,198 | IssuesEvent | 2023-02-14 17:50:53 | cncf/cnf-testsuite | https://api.github.com/repos/cncf/cnf-testsuite | closed | [Workload] Microservice Test: Does the CNF use a proper init system? | configuration + lifecycle workload microservice sprint23.04 v0.40.0 | ## Title: [Workload] Microservices test: specialized_init_system
Description of problem
There are proper init systems and sophisticated supervisors that can be run inside of a container. Both of these systems properly reap and pass signals. Sophisticated supervisors are considered overkill because they take up too many resources and are sometimes too complicated. Some examples of sophisticated supervisors are: supervisord, monit, and runit. Proper init systems are smaller than sophisticated supervisors and therefore suitable for containers. Some of the proper container init systems are tini, dumb-init, and s6-overlay.
Description of solution
The test should fails if PID 1 is supervisord, monit, or runit, and passes if PID 1 is tini, dumb-init, or s6-overlay
The test should fail if PID 1 is anything else.
https://cloud.google.com/architecture/best-practices-for-building-containers
Acceptance Criteria:
---
### Microservice Test: Microservices test: specialized_init_system
EPIC: CNF Conformance Test Suite
Release: vN.N.N
Test Category: Configuration
Type of test (static or runtime) = ?
- [ ] example code: N/A
---
**Environment set up tasks:**
**Upstream tool set up tasks: (conformance suite + upstream tools)**
- N/A
**CNF setup Tasks**
**Sample CNF tasks:**
**Code implementation tasks:**
- [ ]
**Documentation tasks:**
- [ ] Update [Test Categories md](https://github.com/cncf/cnf-conformance/blob/master/TEST-CATEGORIES.md) if needed
- [ ] Update [Pseudo Code md](https://github.com/cncf/cnf-conformance/blob/master/PSEUDO-CODE.md) if needed
- [ ] Update [USAGE md](https://github.com/cncf/cnf-conformance/blob/master/USAGE.md) if needed
- [ ] Update [installation instructions](https://github.com/cncf/cnf-conformance#installation) if needed
**QA tasks**
Dev Review:
- [ ] walk through A/C
- [ ] do you get the expected result?
- [ ] if yes,
- [ ] move to `Needs Peer Review` column
- [ ] create Pull Request and follow check list
- [ ] Assign 1 or more people for peer review
- [ ] if no, document what additional tasks will be needed
Peer review:
- [ ] walk through A/C
- [ ] do you get the expected result?
- [ ] if yes,
- [ ] move to `Reviewer Approved` column
- [ ] Approve pull request
- [ ] if no,
- [ ] document what did not go as expected, including error messages and screenshots (if possible)
- [ ] Add comment to pull request
- [ ] request changes to pull request
---
### Reference:
Tools:
- Falco
- sysdig-inspect | 1.0 | [Workload] Microservice Test: Does the CNF use a proper init system? - ## Title: [Workload] Microservices test: specialized_init_system
Description of problem
There are proper init systems and sophisticated supervisors that can be run inside of a container. Both of these systems properly reap and pass signals. Sophisticated supervisors are considered overkill because they take up too many resources and are sometimes too complicated. Some examples of sophisticated supervisors are: supervisord, monit, and runit. Proper init systems are smaller than sophisticated supervisors and therefore suitable for containers. Some of the proper container init systems are tini, dumb-init, and s6-overlay.
Description of solution
The test should fails if PID 1 is supervisord, monit, or runit, and passes if PID 1 is tini, dumb-init, or s6-overlay
The test should fail if PID 1 is anything else.
https://cloud.google.com/architecture/best-practices-for-building-containers
Acceptance Criteria:
---
### Microservice Test: Microservices test: specialized_init_system
EPIC: CNF Conformance Test Suite
Release: vN.N.N
Test Category: Configuration
Type of test (static or runtime) = ?
- [ ] example code: N/A
---
**Environment set up tasks:**
**Upstream tool set up tasks: (conformance suite + upstream tools)**
- N/A
**CNF setup Tasks**
**Sample CNF tasks:**
**Code implementation tasks:**
- [ ]
**Documentation tasks:**
- [ ] Update [Test Categories md](https://github.com/cncf/cnf-conformance/blob/master/TEST-CATEGORIES.md) if needed
- [ ] Update [Pseudo Code md](https://github.com/cncf/cnf-conformance/blob/master/PSEUDO-CODE.md) if needed
- [ ] Update [USAGE md](https://github.com/cncf/cnf-conformance/blob/master/USAGE.md) if needed
- [ ] Update [installation instructions](https://github.com/cncf/cnf-conformance#installation) if needed
**QA tasks**
Dev Review:
- [ ] walk through A/C
- [ ] do you get the expected result?
- [ ] if yes,
- [ ] move to `Needs Peer Review` column
- [ ] create Pull Request and follow check list
- [ ] Assign 1 or more people for peer review
- [ ] if no, document what additional tasks will be needed
Peer review:
- [ ] walk through A/C
- [ ] do you get the expected result?
- [ ] if yes,
- [ ] move to `Reviewer Approved` column
- [ ] Approve pull request
- [ ] if no,
- [ ] document what did not go as expected, including error messages and screenshots (if possible)
- [ ] Add comment to pull request
- [ ] request changes to pull request
---
### Reference:
Tools:
- Falco
- sysdig-inspect | non_priority | microservice test does the cnf use a proper init system title microservices test specialized init system description of problem there are proper init systems and sophisticated supervisors that can be run inside of a container both of these systems properly reap and pass signals sophisticated supervisors are considered overkill because they take up too many resources and are sometimes too complicated some examples of sophisticated supervisors are supervisord monit and runit proper init systems are smaller than sophisticated supervisors and therefore suitable for containers some of the proper container init systems are tini dumb init and overlay description of solution the test should fails if pid is supervisord monit or runit and passes if pid is tini dumb init or overlay the test should fail if pid is anything else acceptance criteria microservice test microservices test specialized init system epic cnf conformance test suite release vn n n test category configuration type of test static or runtime example code n a environment set up tasks upstream tool set up tasks conformance suite upstream tools n a cnf setup tasks sample cnf tasks code implementation tasks documentation tasks update if needed update if needed update if needed update if needed qa tasks dev review walk through a c do you get the expected result if yes move to needs peer review column create pull request and follow check list assign or more people for peer review if no document what additional tasks will be needed peer review walk through a c do you get the expected result if yes move to reviewer approved column approve pull request if no document what did not go as expected including error messages and screenshots if possible add comment to pull request request changes to pull request reference tools falco sysdig inspect | 0 |
281,599 | 30,888,902,378 | IssuesEvent | 2023-08-04 01:59:32 | nidhi7598/linux-4.1.15_CVE-2019-10220 | https://api.github.com/repos/nidhi7598/linux-4.1.15_CVE-2019-10220 | reopened | CVE-2016-2782 (Medium) detected in linuxlinux-4.4.302 | Mend: dependency security vulnerability | ## CVE-2016-2782 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.1.15_CVE-2019-10220/commit/6a0d304d962ca933d73f507ce02157ef2791851c">6a0d304d962ca933d73f507ce02157ef2791851c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The treo_attach function in drivers/usb/serial/visor.c in the Linux kernel before 4.5 allows physically proximate attackers to cause a denial of service (NULL pointer dereference and system crash) or possibly have unspecified other impact by inserting a USB device that lacks a (1) bulk-in or (2) interrupt-in endpoint.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2782>CVE-2016-2782</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2782">https://nvd.nist.gov/vuln/detail/CVE-2016-2782</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: 4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-2782 (Medium) detected in linuxlinux-4.4.302 - ## CVE-2016-2782 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.1.15_CVE-2019-10220/commit/6a0d304d962ca933d73f507ce02157ef2791851c">6a0d304d962ca933d73f507ce02157ef2791851c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/serial/visor.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The treo_attach function in drivers/usb/serial/visor.c in the Linux kernel before 4.5 allows physically proximate attackers to cause a denial of service (NULL pointer dereference and system crash) or possibly have unspecified other impact by inserting a USB device that lacks a (1) bulk-in or (2) interrupt-in endpoint.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2782>CVE-2016-2782</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2782">https://nvd.nist.gov/vuln/detail/CVE-2016-2782</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: 4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers usb serial visor c drivers usb serial visor c vulnerability details the treo attach function in drivers usb serial visor c in the linux kernel before allows physically proximate attackers to cause a denial of service null pointer dereference and system crash or possibly have unspecified other impact by inserting a usb device that lacks a bulk in or interrupt in endpoint publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
222,840 | 17,094,300,505 | IssuesEvent | 2021-07-08 22:27:32 | MaicolGonzalezTN/SABANETA | https://api.github.com/repos/MaicolGonzalezTN/SABANETA | reopened | Definicion del proyecto | documentation | Establecer los equipos de trabajo,aportar una idea por cada integrante | 1.0 | Definicion del proyecto - Establecer los equipos de trabajo,aportar una idea por cada integrante | non_priority | definicion del proyecto establecer los equipos de trabajo aportar una idea por cada integrante | 0 |
427,867 | 29,866,895,946 | IssuesEvent | 2023-06-20 05:11:17 | secretflow/scql | https://api.github.com/repos/secretflow/scql | closed | 将 SCQL《How To Integrate SCQL System》英文文档逐句翻译成中文文档 | documentation good first issue OSCP | > 此 ISSUE 为 [隐语开源共建计划(SecretFlow Open Source Contribution Plan,简称 SF OSCP)第一期](https://github.com/orgs/secretflow/discussions/647)任务 ISSUE,欢迎社区开发者参与共建~
## 任务介绍
- 任务名称:将 SCQL《[How To Integrate SCQL System](https://www.secretflow.org.cn/docs/scql/latest/en-US/development/integrate_scql_system)》英文文档逐句翻译成中文文档
- 技术方向:SCQL/docs
- 任务难度:基础
## 详细要求
将 SCQL《[How To Integrate SCQL System](https://www.secretflow.org.cn/docs/scql/latest/en-US/development/integrate_scql_system)》英文文档按操作指引逐句翻译成中文文档,以完善中文文档内容
- 操作指引:[操作指引](https://www.yuque.com/secret-flow/admin/uwv3kw683w24czs8#ymZYq)中有 step by step 的操作介绍,可按照文档方式进行实现
- 文档范例:可在[这里](https://www.secretflow.org.cn/docs/scql/latest/zh-Hans/reference/scql_security_statement)查看文档范例
- 提交要求:请在完成整篇文章翻译后,再提交 PR
- 翻译规范:为了让翻译后的文档更具有统一性,在翻译时可以参考[文档翻译规范](https://www.yuque.com/secret-flow/admin/uwv3kw683w24czs8#pV0sp)中的小 tips
## 能力要求
- 了解基本 git 操作
- 外语水平良好 | 1.0 | 将 SCQL《How To Integrate SCQL System》英文文档逐句翻译成中文文档 - > 此 ISSUE 为 [隐语开源共建计划(SecretFlow Open Source Contribution Plan,简称 SF OSCP)第一期](https://github.com/orgs/secretflow/discussions/647)任务 ISSUE,欢迎社区开发者参与共建~
## 任务介绍
- 任务名称:将 SCQL《[How To Integrate SCQL System](https://www.secretflow.org.cn/docs/scql/latest/en-US/development/integrate_scql_system)》英文文档逐句翻译成中文文档
- 技术方向:SCQL/docs
- 任务难度:基础
## 详细要求
将 SCQL《[How To Integrate SCQL System](https://www.secretflow.org.cn/docs/scql/latest/en-US/development/integrate_scql_system)》英文文档按操作指引逐句翻译成中文文档,以完善中文文档内容
- 操作指引:[操作指引](https://www.yuque.com/secret-flow/admin/uwv3kw683w24czs8#ymZYq)中有 step by step 的操作介绍,可按照文档方式进行实现
- 文档范例:可在[这里](https://www.secretflow.org.cn/docs/scql/latest/zh-Hans/reference/scql_security_statement)查看文档范例
- 提交要求:请在完成整篇文章翻译后,再提交 PR
- 翻译规范:为了让翻译后的文档更具有统一性,在翻译时可以参考[文档翻译规范](https://www.yuque.com/secret-flow/admin/uwv3kw683w24czs8#pV0sp)中的小 tips
## 能力要求
- 了解基本 git 操作
- 外语水平良好 | non_priority | 将 scql《how to integrate scql system》英文文档逐句翻译成中文文档 此 issue 为 issue,欢迎社区开发者参与共建~ 任务介绍 任务名称:将 scql《 技术方向:scql docs 任务难度:基础 详细要求 将 scql《 操作指引: step by step 的操作介绍,可按照文档方式进行实现 文档范例:可在 提交要求:请在完成整篇文章翻译后,再提交 pr 翻译规范:为了让翻译后的文档更具有统一性,在翻译时可以参考 tips 能力要求 了解基本 git 操作 外语水平良好 | 0 |
164,430 | 20,364,479,240 | IssuesEvent | 2022-02-21 02:52:52 | directoryxx/Laravel-UUID-CRUD-Login | https://api.github.com/repos/directoryxx/Laravel-UUID-CRUD-Login | opened | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz | security vulnerability | ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /Laravel-UUID-CRUD-Login/package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-4.1.2.tgz (Root Library)
- chokidar-2.1.6.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (laravel-mix): 6.0.0-beta.15</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /Laravel-UUID-CRUD-Login/package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- laravel-mix-4.1.2.tgz (Root Library)
- chokidar-2.1.6.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (laravel-mix): 6.0.0-beta.15</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz cve high severity vulnerability vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file laravel uuid crud login package json path to vulnerable library node modules glob parent package json dependency hierarchy laravel mix tgz root library chokidar tgz x glob parent tgz vulnerable library vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution laravel mix beta step up your open source security game with whitesource | 0 |
53,012 | 6,670,142,445 | IssuesEvent | 2017-10-03 22:03:37 | phetsims/gravity-and-orbits | https://api.github.com/repos/phetsims/gravity-and-orbits | closed | transparent rectangle behind the measuring tape readout? | design:general | https://github.com/phetsims/scenery-phet/issues/339 added a new feature to MeasuringTapeNode, an optional transparent rectangle behind the readout. It sure looks like gravity-and-orbits might want to take advantage of this feature:
| 1.0 | transparent rectangle behind the measuring tape readout? - https://github.com/phetsims/scenery-phet/issues/339 added a new feature to MeasuringTapeNode, an optional transparent rectangle behind the readout. It sure looks like gravity-and-orbits might want to take advantage of this feature:
| non_priority | transparent rectangle behind the measuring tape readout added a new feature to measuringtapenode an optional transparent rectangle behind the readout it sure looks like gravity and orbits might want to take advantage of this feature | 0 |
262,413 | 27,944,572,059 | IssuesEvent | 2023-03-24 01:13:24 | vlaship/case-coding-test | https://api.github.com/repos/vlaship/case-coding-test | opened | CVE-2022-41854 (Medium) detected in snakeyaml-1.29.jar | Mend: dependency security vulnerability | ## CVE-2022-41854 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.29.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.29/6d0cdafb2010f1297e574656551d7145240f6e25/snakeyaml-1.29.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.6.3.jar (Root Library)
- spring-boot-starter-2.6.3.jar
- :x: **snakeyaml-1.29.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Snakeyaml to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack overflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41854>CVE-2022-41854</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/531/">https://bitbucket.org/snakeyaml/snakeyaml/issues/531/</a></p>
<p>Release Date: 2022-11-11</p>
<p>Fix Resolution (org.yaml:snakeyaml): 1.32</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.6.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-41854 (Medium) detected in snakeyaml-1.29.jar - ## CVE-2022-41854 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.29.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.yaml/snakeyaml/1.29/6d0cdafb2010f1297e574656551d7145240f6e25/snakeyaml-1.29.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.6.3.jar (Root Library)
- spring-boot-starter-2.6.3.jar
- :x: **snakeyaml-1.29.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Snakeyaml to parse untrusted YAML files may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stack overflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41854>CVE-2022-41854</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bitbucket.org/snakeyaml/snakeyaml/issues/531/">https://bitbucket.org/snakeyaml/snakeyaml/issues/531/</a></p>
<p>Release Date: 2022-11-11</p>
<p>Fix Resolution (org.yaml:snakeyaml): 1.32</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.6.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in snakeyaml jar cve medium severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file build gradle path to vulnerable library home wss scanner gradle caches modules files org yaml snakeyaml snakeyaml jar dependency hierarchy spring boot starter web jar root library spring boot starter jar x snakeyaml jar vulnerable library found in base branch master vulnerability details those using snakeyaml to parse untrusted yaml files may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stack overflow this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml direct dependency fix resolution org springframework boot spring boot starter web step up your open source security game with mend | 0 |
283,680 | 21,327,580,585 | IssuesEvent | 2022-04-18 02:18:43 | hashicorp/terraform-provider-azurerm | https://api.github.com/repos/hashicorp/terraform-provider-azurerm | closed | Error on the example usage of azurerm_mysql_server in the documentation | documentation service/mysql | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Description
Hello,
In the azurerm_mysql_server and azurerm_mysql_database documentation pages, there is the line `infrastructure_encryption_enabled = true`, making the apply fail.
This is due to the fact that the sku used in the example is `sku_name = "B_Gen5_2"` and the infrastructure encryption is not supported for sku Tier "Basic" for Server as shown in the error :
> Error: `infrastructure_encryption_enabled` is not supported for sku Tier `Basic` for Server: (Name "example-mysqlserver" / Resource Group "example-resources")
on main.tf line 10, in resource "azurerm_mysql_server" "example":
10: resource "azurerm_mysql_server" "example" {
### New or Affected Resource(s)/Data Source(s)
azurerm_mysql_server
### Potential Terraform Configuration
The line should then be `infrastructure_encryption_enabled = false` to work. Another solution is also to change the sku Tier.
### References
https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/mysql_server
https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/mysql_database | 1.0 | Error on the example usage of azurerm_mysql_server in the documentation - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Description
Hello,
In the azurerm_mysql_server and azurerm_mysql_database documentation pages, there is the line `infrastructure_encryption_enabled = true`, making the apply fail.
This is due to the fact that the sku used in the example is `sku_name = "B_Gen5_2"` and the infrastructure encryption is not supported for sku Tier "Basic" for Server as shown in the error :
> Error: `infrastructure_encryption_enabled` is not supported for sku Tier `Basic` for Server: (Name "example-mysqlserver" / Resource Group "example-resources")
on main.tf line 10, in resource "azurerm_mysql_server" "example":
10: resource "azurerm_mysql_server" "example" {
### New or Affected Resource(s)/Data Source(s)
azurerm_mysql_server
### Potential Terraform Configuration
The line should then be `infrastructure_encryption_enabled = false` to work. Another solution is also to change the sku Tier.
### References
https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/mysql_server
https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/mysql_database | non_priority | error on the example usage of azurerm mysql server in the documentation is there an existing issue for this i have searched the existing issues community note please vote on this issue by adding a thumbsup to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment description hello in the azurerm mysql server and azurerm mysql database documentation pages there is the line infrastructure encryption enabled true making the apply fail this is due to the fact that the sku used in the example is sku name b and the infrastructure encryption is not supported for sku tier basic for server as shown in the error error infrastructure encryption enabled is not supported for sku tier basic for server name example mysqlserver resource group example resources on main tf line in resource azurerm mysql server example resource azurerm mysql server example new or affected resource s data source s azurerm mysql server potential terraform configuration the line should then be infrastructure encryption enabled false to work another solution is also to change the sku tier references | 0 |
420,649 | 28,292,035,103 | IssuesEvent | 2023-04-09 10:29:29 | vanderschaarlab/temporai | https://api.github.com/repos/vanderschaarlab/temporai | closed | Add tutorials(notebooks + Colab links) | documentation | ## Description
- The library should have a tutorial for each major feature.
- The tutorials should be notebooks, and should be also deployed on Colab, for easier use.
| 1.0 | Add tutorials(notebooks + Colab links) - ## Description
- The library should have a tutorial for each major feature.
- The tutorials should be notebooks, and should be also deployed on Colab, for easier use.
| non_priority | add tutorials notebooks colab links description the library should have a tutorial for each major feature the tutorials should be notebooks and should be also deployed on colab for easier use | 0 |
113,972 | 14,517,934,944 | IssuesEvent | 2020-12-13 21:34:53 | phetsims/fourier-making-waves | https://api.github.com/repos/phetsims/fourier-making-waves | opened | Add a key for math symbols? | design:general | This sim has a relatively large number of math symbols, and the meaning of most of them is not identified in the sim. See list below, taken from model.md.
Should we add a key that identifies these symbols? Maybe a dialog that is accessed via an "Info" button to the right of the "Math Form" label in the control panel?
* A = amplitude
* f = frequency, in Hz
* λ = wavelength, in meters
* k = wave number
* L = string length, if this were a plucked string, in meters
* n = harmonic number, order, or mode
* σ = Gaussian wave packet width, in radians/meter
* t = time, in milliseconds
* T = period, in milliseconds
* ω = omega, angular frequency, in radians
* x = position in space along L, in meters
| 1.0 | Add a key for math symbols? - This sim has a relatively large number of math symbols, and the meaning of most of them is not identified in the sim. See list below, taken from model.md.
Should we add a key that identifies these symbols? Maybe a dialog that is accessed via an "Info" button to the right of the "Math Form" label in the control panel?
* A = amplitude
* f = frequency, in Hz
* λ = wavelength, in meters
* k = wave number
* L = string length, if this were a plucked string, in meters
* n = harmonic number, order, or mode
* σ = Gaussian wave packet width, in radians/meter
* t = time, in milliseconds
* T = period, in milliseconds
* ω = omega, angular frequency, in radians
* x = position in space along L, in meters
| non_priority | add a key for math symbols this sim has a relatively large number of math symbols and the meaning of most of them is not identified in the sim see list below taken from model md should we add a key that identifies these symbols maybe a dialog that is accessed via an info button to the right of the math form label in the control panel a amplitude f frequency in hz λ wavelength in meters k wave number l string length if this were a plucked string in meters n harmonic number order or mode σ gaussian wave packet width in radians meter t time in milliseconds t period in milliseconds ω omega angular frequency in radians x position in space along l in meters | 0 |
281,326 | 30,888,729,406 | IssuesEvent | 2023-08-04 01:44:58 | nidhi7598/linux-4.1.15_CVE-2019-10220 | https://api.github.com/repos/nidhi7598/linux-4.1.15_CVE-2019-10220 | reopened | CVE-2020-29370 (High) detected in linuxlinux-4.4.302 | Mend: dependency security vulnerability | ## CVE-2020-29370 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.1.15_CVE-2019-10220/commit/6a0d304d962ca933d73f507ce02157ef2791851c">6a0d304d962ca933d73f507ce02157ef2791851c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in kmem_cache_alloc_bulk in mm/slub.c in the Linux kernel before 5.5.11. The slowpath lacks the required TID increment, aka CID-fd4d9c7d0c71.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29370>CVE-2020-29370</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.6-rc7,v5.5.11,v5.4.28</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-29370 (High) detected in linuxlinux-4.4.302 - ## CVE-2020-29370 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-4.1.15_CVE-2019-10220/commit/6a0d304d962ca933d73f507ce02157ef2791851c">6a0d304d962ca933d73f507ce02157ef2791851c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/slub.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in kmem_cache_alloc_bulk in mm/slub.c in the Linux kernel before 5.5.11. The slowpath lacks the required TID increment, aka CID-fd4d9c7d0c71.
<p>Publish Date: 2020-11-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-29370>CVE-2020-29370</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-29370</a></p>
<p>Release Date: 2020-11-28</p>
<p>Fix Resolution: v5.6-rc7,v5.5.11,v5.4.28</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files mm slub c vulnerability details an issue was discovered in kmem cache alloc bulk in mm slub c in the linux kernel before the slowpath lacks the required tid increment aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
201,070 | 22,946,725,183 | IssuesEvent | 2022-07-19 01:14:38 | zencoder/castlabs-java-api | https://api.github.com/repos/zencoder/castlabs-java-api | closed | CVE-2020-14195 (High) detected in jackson-databind-2.9.8.jar - autoclosed | security vulnerability | ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /ory/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/zencoder/castlabs-java-api/commit/cedc82ec94663352957fffd68b1d6bb74aba81df">cedc82ec94663352957fffd68b1d6bb74aba81df</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.5","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-14195","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-14195 (High) detected in jackson-databind-2.9.8.jar - autoclosed - ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /ory/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/zencoder/castlabs-java-api/commit/cedc82ec94663352957fffd68b1d6bb74aba81df">cedc82ec94663352957fffd68b1d6bb74aba81df</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","packageFilePaths":["/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.5","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-14195","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library ory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity vulnerabilityurl | 0 |
49,200 | 10,329,014,285 | IssuesEvent | 2019-09-02 11:01:54 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] system-tests-mysql failing for missing html element | J4 Issue No Code Attached Yet | When checking [PR 19300](https://github.com/joomla/joomla-cms/pull/19300 "PR 19300"), I noticed that `continuous-integration/drone/pr` failed. In detail, `system-tests-mysql` failed when looking for an html element with selector `h1.page-title` while trying to log in as administrator.
### Steps to reproduce the issue
* Go to `<your joomla 4.0-dev installation>/administrator/index.php`
* Search for a html element that matches selector `h1.page-title`
### Expected result
* (At least) An element is found
### Actual result
* There is no such element
### System information (as much as possible)
* Fresh Joomla! 4.0-dev Installation from Git (Commit 6e3c348b6f2401d35fa179ffeae540dd1fd8edf6)
* PHP 7.2.19-0ubuntu0.19.04.2
* MySQL 5.7.27-0ubuntu0.19.04.1
* Apache/2.4.38 (Ubuntu)
* Brave Browser Version 0.68.132 Chromium: 76.0.3809.132 (Official Build) (64-bit)
### Additional comments
I'm seeing if I can create a PR to this issue
#### Screenshot:

#### Original Error Log:
[Original Error Log](https://ci.joomla.org/joomla/joomla-cms/22817/1/23 "Original Error Log") | 1.0 | [4.0] system-tests-mysql failing for missing html element - When checking [PR 19300](https://github.com/joomla/joomla-cms/pull/19300 "PR 19300"), I noticed that `continuous-integration/drone/pr` failed. In detail, `system-tests-mysql` failed when looking for an html element with selector `h1.page-title` while trying to log in as administrator.
### Steps to reproduce the issue
* Go to `<your joomla 4.0-dev installation>/administrator/index.php`
* Search for a html element that matches selector `h1.page-title`
### Expected result
* (At least) An element is found
### Actual result
* There is no such element
### System information (as much as possible)
* Fresh Joomla! 4.0-dev Installation from Git (Commit 6e3c348b6f2401d35fa179ffeae540dd1fd8edf6)
* PHP 7.2.19-0ubuntu0.19.04.2
* MySQL 5.7.27-0ubuntu0.19.04.1
* Apache/2.4.38 (Ubuntu)
* Brave Browser Version 0.68.132 Chromium: 76.0.3809.132 (Official Build) (64-bit)
### Additional comments
I'm seeing if I can create a PR to this issue
#### Screenshot:

#### Original Error Log:
[Original Error Log](https://ci.joomla.org/joomla/joomla-cms/22817/1/23 "Original Error Log") | non_priority | system tests mysql failing for missing html element when checking pr i noticed that continuous integration drone pr failed in detail system tests mysql failed when looking for an html element with selector page title while trying to log in as administrator steps to reproduce the issue go to administrator index php search for a html element that matches selector page title expected result at least an element is found actual result there is no such element system information as much as possible fresh joomla dev installation from git commit php mysql apache ubuntu brave browser version chromium official build bit additional comments i m seeing if i can create a pr to this issue screenshot original error log original error log | 0 |
4,301 | 7,041,900,371 | IssuesEvent | 2017-12-30 02:40:30 | storybooks/storybook | https://api.github.com/repos/storybooks/storybook | closed | working with generate react component | compatibility with other tools inactive needs more info | installing storybook in https://github.com/JedWatson/generator-react-component gets an error:
```
ERROR in ./.storybook/config.js
Module build failed: ReferenceError: [BABEL] /Users/max/workspace/react-component/packages/style-react-component/.storybook/config.js: Unknown option: direct.presets
at Logger.error (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/logger.js:58:11)
at OptionManager.mergeOptions (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/options/option-manager.js:126:29)
at OptionManager.init (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/options/option-manager.js:216:10)
at File.initOptions (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/index.js:147:75)
at new File (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/index.js:137:22)
at Pipeline.transform (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/pipeline.js:164:16)
at transpile (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-loader/lib/index.js:46:20)
at /Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-loader/lib/fs-cache.js:79:18
at ReadFileContext.callback (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-loader/lib/fs-cache.js:15:14)
at FSReqWrap.readFileAfterOpen [as oncomplete] (fs.js:365:13)
@ multi preview
```
anyway to work with this package? | True | working with generate react component - installing storybook in https://github.com/JedWatson/generator-react-component gets an error:
```
ERROR in ./.storybook/config.js
Module build failed: ReferenceError: [BABEL] /Users/max/workspace/react-component/packages/style-react-component/.storybook/config.js: Unknown option: direct.presets
at Logger.error (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/logger.js:58:11)
at OptionManager.mergeOptions (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/options/option-manager.js:126:29)
at OptionManager.init (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/options/option-manager.js:216:10)
at File.initOptions (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/index.js:147:75)
at new File (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/file/index.js:137:22)
at Pipeline.transform (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-core/lib/transformation/pipeline.js:164:16)
at transpile (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-loader/lib/index.js:46:20)
at /Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-loader/lib/fs-cache.js:79:18
at ReadFileContext.callback (/Users/max/workspace/react-component/packages/style-react-component/node_modules/babel-loader/lib/fs-cache.js:15:14)
at FSReqWrap.readFileAfterOpen [as oncomplete] (fs.js:365:13)
@ multi preview
```
anyway to work with this package? | non_priority | working with generate react component installing storybook in gets an error error in storybook config js module build failed referenceerror users max workspace react component packages style react component storybook config js unknown option direct presets at logger error users max workspace react component packages style react component node modules babel core lib transformation file logger js at optionmanager mergeoptions users max workspace react component packages style react component node modules babel core lib transformation file options option manager js at optionmanager init users max workspace react component packages style react component node modules babel core lib transformation file options option manager js at file initoptions users max workspace react component packages style react component node modules babel core lib transformation file index js at new file users max workspace react component packages style react component node modules babel core lib transformation file index js at pipeline transform users max workspace react component packages style react component node modules babel core lib transformation pipeline js at transpile users max workspace react component packages style react component node modules babel loader lib index js at users max workspace react component packages style react component node modules babel loader lib fs cache js at readfilecontext callback users max workspace react component packages style react component node modules babel loader lib fs cache js at fsreqwrap readfileafteropen fs js multi preview anyway to work with this package | 0 |
80,756 | 7,756,529,276 | IssuesEvent | 2018-05-31 13:53:02 | nasa-gibs/worldview | https://api.github.com/repos/nasa-gibs/worldview | closed | Endless rotate in polar projections | bug testing | If you go to arctic or antarctic projection, hold alt, and drag up or down while clicking a rotate button (I know my instructions must sound like a video game cheat code), it will constantly rotate in that direction. | 1.0 | Endless rotate in polar projections - If you go to arctic or antarctic projection, hold alt, and drag up or down while clicking a rotate button (I know my instructions must sound like a video game cheat code), it will constantly rotate in that direction. | non_priority | endless rotate in polar projections if you go to arctic or antarctic projection hold alt and drag up or down while clicking a rotate button i know my instructions must sound like a video game cheat code it will constantly rotate in that direction | 0 |
201,074 | 15,172,591,168 | IssuesEvent | 2021-02-13 09:58:38 | Slimefun/Slimefun4 | https://api.github.com/repos/Slimefun/Slimefun4 | opened | Slimefun + EcoEnchant Incompatible | 🎯 Needs testing 🐞 Bug Report | <!-- FILL IN THE FORM BELOW -->
## :round_pushpin: Description (REQUIRED)
<!-- A clear and detailed description of what went wrong. -->
<!-- The more information you can provide, the easier we can handle this problem. -->
<!-- Start writing below this line -->
Hello, I was told to make an report with slimefun by a plugin developer name Auxilor. I'm using this plugin call ecoenchants which I will provide the link and wiki below. This plugin allows MC servers to have custom enchantments. There is a configuration that allow us to disable players from obtaining custom enchantments which are villagers, loot chests, and enchanted table. But I have them all disabled and this took me a while figure out.
Even with the enchanted table, It looks like slimefun is interfering with it. Even if I have enchanted table disable players can use Talisman of the magician and ender talisman of the magician to get the lucky bonus enchant which allows them to get eco enchants custom enchant from the enchanted table. I was wondering is there a way for you guys to somehow fix it from happening? I would like to allow players to use the talisman but not to obtain custom enchants from eco enchants.
Eco Enchant: https://www.spigotmc.org/resources/%E2%9A%A1-1-15-1-16-5-ecoenchants-%E2%9C%A8-220-custom-enchantments-%E2%9C%85-essentials-cmi-support.79573/
Eco Enchant Wiki: https://ecoenchants.willfp.com/enchantments/obtaining
## :bookmark_tabs: Steps to reproduce the Issue (REQUIRED)
<!-- Tell us the exact steps to reproduce this issue, the more detailed the easier we can reproduce it. -->
<!-- Youtube Videos and Screenshots are recommended!!! -->
<!-- Start writing below this line -->
I explained above.
## :bulb: Expected behavior (REQUIRED)
<!-- What were you expecting to happen? -->
<!-- What do you think would have been the correct behaviour? -->
<!-- Start writing below this line -->
I would like to have Talisman of the magician and ender talisman of the magician to not support eco enchants by allowing players to use it to get custom enchantments on their tools, armors, or books in any way when we disable the enchanted table section on eco enchants configuraton.
## :scroll: Server Log
<!-- Take a look at your Server Log and post any errors you can find via https://pastebin.com/ -->
<!-- If you are unsure about it, post your full log, you can find it under /logs/latest.log -->
<!-- Paste your link(s) below this line -->
I do not have any server log or console errors.
## :open_file_folder: /error-reports/ Folder
<!-- Check the folder /plugins/Slimefun/error-reports/ and upload any files inside that folder. -->
<!-- You can also post these files via https://pastebin.com/ -->
<!-- Paste your link(s) below this line -->
I do not have any server log or console errors.
## :compass: Environment (REQUIRED)
<!-- Any issue without the exact version numbers will be closed! -->
<!-- "latest" IS NOT A VERSION NUMBER. -->
<!-- We recommend running "/sf versions" and showing us a screenshot of that. -->
<!-- Make sure that the screenshot covers the entire output of that command. -->
<!-- If your issue is related to other plugins, make sure to include the versions of these plugins too! -->
https://gyazo.com/eab352829db58bdd1835df76d6b8c60d
- Server Software: Paper
- Minecraft Version: 1.16.5
- Slimefun Version: vRC - 20 (git da6866ee)
| 1.0 | Slimefun + EcoEnchant Incompatible - <!-- FILL IN THE FORM BELOW -->
## :round_pushpin: Description (REQUIRED)
<!-- A clear and detailed description of what went wrong. -->
<!-- The more information you can provide, the easier we can handle this problem. -->
<!-- Start writing below this line -->
Hello, I was told to make an report with slimefun by a plugin developer name Auxilor. I'm using this plugin call ecoenchants which I will provide the link and wiki below. This plugin allows MC servers to have custom enchantments. There is a configuration that allow us to disable players from obtaining custom enchantments which are villagers, loot chests, and enchanted table. But I have them all disabled and this took me a while figure out.
Even with the enchanted table, It looks like slimefun is interfering with it. Even if I have enchanted table disable players can use Talisman of the magician and ender talisman of the magician to get the lucky bonus enchant which allows them to get eco enchants custom enchant from the enchanted table. I was wondering is there a way for you guys to somehow fix it from happening? I would like to allow players to use the talisman but not to obtain custom enchants from eco enchants.
Eco Enchant: https://www.spigotmc.org/resources/%E2%9A%A1-1-15-1-16-5-ecoenchants-%E2%9C%A8-220-custom-enchantments-%E2%9C%85-essentials-cmi-support.79573/
Eco Enchant Wiki: https://ecoenchants.willfp.com/enchantments/obtaining
## :bookmark_tabs: Steps to reproduce the Issue (REQUIRED)
<!-- Tell us the exact steps to reproduce this issue, the more detailed the easier we can reproduce it. -->
<!-- Youtube Videos and Screenshots are recommended!!! -->
<!-- Start writing below this line -->
I explained above.
## :bulb: Expected behavior (REQUIRED)
<!-- What were you expecting to happen? -->
<!-- What do you think would have been the correct behaviour? -->
<!-- Start writing below this line -->
I would like to have Talisman of the magician and ender talisman of the magician to not support eco enchants by allowing players to use it to get custom enchantments on their tools, armors, or books in any way when we disable the enchanted table section on eco enchants configuraton.
## :scroll: Server Log
<!-- Take a look at your Server Log and post any errors you can find via https://pastebin.com/ -->
<!-- If you are unsure about it, post your full log, you can find it under /logs/latest.log -->
<!-- Paste your link(s) below this line -->
I do not have any server log or console errors.
## :open_file_folder: /error-reports/ Folder
<!-- Check the folder /plugins/Slimefun/error-reports/ and upload any files inside that folder. -->
<!-- You can also post these files via https://pastebin.com/ -->
<!-- Paste your link(s) below this line -->
I do not have any server log or console errors.
## :compass: Environment (REQUIRED)
<!-- Any issue without the exact version numbers will be closed! -->
<!-- "latest" IS NOT A VERSION NUMBER. -->
<!-- We recommend running "/sf versions" and showing us a screenshot of that. -->
<!-- Make sure that the screenshot covers the entire output of that command. -->
<!-- If your issue is related to other plugins, make sure to include the versions of these plugins too! -->
https://gyazo.com/eab352829db58bdd1835df76d6b8c60d
- Server Software: Paper
- Minecraft Version: 1.16.5
- Slimefun Version: vRC - 20 (git da6866ee)
| non_priority | slimefun ecoenchant incompatible round pushpin description required hello i was told to make an report with slimefun by a plugin developer name auxilor i m using this plugin call ecoenchants which i will provide the link and wiki below this plugin allows mc servers to have custom enchantments there is a configuration that allow us to disable players from obtaining custom enchantments which are villagers loot chests and enchanted table but i have them all disabled and this took me a while figure out even with the enchanted table it looks like slimefun is interfering with it even if i have enchanted table disable players can use talisman of the magician and ender talisman of the magician to get the lucky bonus enchant which allows them to get eco enchants custom enchant from the enchanted table i was wondering is there a way for you guys to somehow fix it from happening i would like to allow players to use the talisman but not to obtain custom enchants from eco enchants eco enchant eco enchant wiki bookmark tabs steps to reproduce the issue required i explained above bulb expected behavior required i would like to have talisman of the magician and ender talisman of the magician to not support eco enchants by allowing players to use it to get custom enchantments on their tools armors or books in any way when we disable the enchanted table section on eco enchants configuraton scroll server log i do not have any server log or console errors open file folder error reports folder i do not have any server log or console errors compass environment required server software paper minecraft version slimefun version vrc git | 0 |
48,547 | 5,963,101,774 | IssuesEvent | 2017-05-30 02:52:24 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | storage: TestGossipFirstRange failed under stress | Robot test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/db8da7c6f9551b69fd464803133db170001e3470
Parameters:
```
TAGS=
GOFLAGS=-race
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=258586&tab=buildLog
```
I170527 07:30:48.955791 68114 server/config.go:439 1 storage engine initialized
I170527 07:30:48.957039 68114 server/node.go:454 [n?] store [n0,s0] not bootstrapped
I170527 07:30:49.029937 68114 server/node.go:389 [n?] **** cluster 2b53681e-6f39-4ee6-91e7-d09a65a31e19 has been created
I170527 07:30:49.030038 68114 server/node.go:390 [n?] **** add additional nodes by specifying --join=127.0.0.1:41294
I170527 07:30:49.046722 68114 storage/store.go:1256 [n1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170527 07:30:49.046882 68114 server/node.go:467 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:0}
I170527 07:30:49.047640 68114 server/node.go:351 [n1] node ID 1 initialized
I170527 07:30:49.047929 68114 gossip/gossip.go:297 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:41294" > attrs:<> locality:<>
I170527 07:30:49.048548 68114 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170527 07:30:49.048844 68114 server/node.go:608 [n1] connecting to gossip network to verify cluster ID...
I170527 07:30:49.049011 68114 server/node.go:633 [n1] node connected via gossip and verified as part of cluster "2b53681e-6f39-4ee6-91e7-d09a65a31e19"
I170527 07:30:49.049283 68114 server/node.go:405 [n1] node=1: started with [[]=] engine(s) and attributes []
I170527 07:30:49.054898 68114 sql/executor.go:355 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:41294}
I170527 07:30:49.120348 68114 server/server.go:737 [n1] starting https server at 127.0.0.1:49195
I170527 07:30:49.120442 68114 server/server.go:738 [n1] starting grpc/postgres server at 127.0.0.1:41294
I170527 07:30:49.120478 68114 server/server.go:739 [n1] advertising CockroachDB node at 127.0.0.1:41294
I170527 07:30:49.246604 68114 sql/event_log.go:101 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueid SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170527 07:30:49.427488 68114 sql/lease.go:372 [n1] publish: descID=12 (eventlog) version=2 mtime=2017-05-27 07:30:49.427364426 +0000 UTC
I170527 07:30:49.536617 68114 server/server.go:850 [n1] done ensuring all necessary migrations have run
I170527 07:30:49.536748 68114 server/server.go:852 [n1] serving sql connections
I170527 07:30:49.567919 68399 sql/event_log.go:101 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:41294} Attrs: Locality:} ClusterID:2b53681e-6f39-4ee6-91e7-d09a65a31e19 StartedAt:1495870249049051536 LastUp:1495870249049051536}
W170527 07:30:49.636701 68114 server/status/runtime.go:111 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
W170527 07:30:49.639374 68114 gossip/gossip.go:1196 [n?] no incoming or outgoing connections
I170527 07:30:49.640662 68114 server/config.go:439 1 storage engine initialized
I170527 07:30:49.641902 68114 server/node.go:454 [n?] store [n0,s0] not bootstrapped
I170527 07:30:49.642048 68114 storage/stores.go:296 [n?] read 0 node addresses from persistent storage
I170527 07:30:49.642380 68114 server/node.go:608 [n?] connecting to gossip network to verify cluster ID...
I170527 07:30:49.778539 68443 gossip/client.go:131 [n?] started gossip client to 127.0.0.1:41294
I170527 07:30:49.780920 68517 gossip/server.go:234 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:36729}
I170527 07:30:49.803732 68114 server/node.go:633 [n?] node connected via gossip and verified as part of cluster "2b53681e-6f39-4ee6-91e7-d09a65a31e19"
I170527 07:30:49.804561 68420 storage/stores.go:312 [n?] wrote 1 node addresses to persistent storage
I170527 07:30:49.829569 68114 kv/dist_sender.go:370 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I170527 07:30:49.837525 68114 server/node.go:344 [n?] new node allocated ID 2
I170527 07:30:49.837830 68114 gossip/gossip.go:297 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:36729" > attrs:<> locality:<>
I170527 07:30:49.838652 68114 server/node.go:405 [n2] node=2: started with [[]=] engine(s) and attributes []
I170527 07:30:49.843572 67712 storage/stores.go:312 [n1] wrote 1 node addresses to persistent storage
I170527 07:30:49.847369 68114 sql/executor.go:355 [n2] creating distSQLPlanner with address {tcp 127.0.0.1:36729}
I170527 07:30:49.879872 68114 server/server.go:737 [n2] starting https server at 127.0.0.1:55424
I170527 07:30:49.879988 68114 server/server.go:738 [n2] starting grpc/postgres server at 127.0.0.1:36729
I170527 07:30:49.880031 68114 server/server.go:739 [n2] advertising CockroachDB node at 127.0.0.1:36729
I170527 07:30:49.930032 68114 server/server.go:850 [n2] done ensuring all necessary migrations have run
I170527 07:30:49.930170 68114 server/server.go:852 [n2] serving sql connections
I170527 07:30:49.989582 68561 sql/event_log.go:101 [n2] Event: "node_join", target: 2, info: {Descriptor:{NodeID:2 Address:{NetworkField:tcp AddressField:127.0.0.1:36729} Attrs: Locality:} ClusterID:2b53681e-6f39-4ee6-91e7-d09a65a31e19 StartedAt:1495870249838435475 LastUp:1495870249838435475}
W170527 07:30:49.994612 68114 server/status/runtime.go:111 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
W170527 07:30:49.996445 68114 gossip/gossip.go:1196 [n?] no incoming or outgoing connections
I170527 07:30:49.997645 68114 server/config.go:439 1 storage engine initialized
I170527 07:30:49.998911 68114 server/node.go:454 [n?] store [n0,s0] not bootstrapped
I170527 07:30:49.999031 68114 storage/stores.go:296 [n?] read 0 node addresses from persistent storage
I170527 07:30:49.999131 68114 server/node.go:608 [n?] connecting to gossip network to verify cluster ID...
I170527 07:30:50.130852 68504 server/node.go:589 [n2] bootstrapped store [n2,s2]
I170527 07:30:50.212111 68363 gossip/client.go:131 [n?] started gossip client to 127.0.0.1:41294
I170527 07:30:50.215865 68710 gossip/server.go:234 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:41450}
I170527 07:30:50.220058 68114 server/node.go:633 [n?] node connected via gossip and verified as part of cluster "2b53681e-6f39-4ee6-91e7-d09a65a31e19"
I170527 07:30:50.221820 68712 storage/stores.go:312 [n?] wrote 1 node addresses to persistent storage
I170527 07:30:50.222434 68712 storage/stores.go:312 [n?] wrote 2 node addresses to persistent storage
I170527 07:30:50.233858 68114 kv/dist_sender.go:370 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I170527 07:30:50.268950 68114 server/node.go:344 [n?] new node allocated ID 3
I170527 07:30:50.269273 68114 gossip/gossip.go:297 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:41450" > attrs:<> locality:<>
I170527 07:30:50.270213 68114 server/node.go:405 [n3] node=3: started with [[]=] engine(s) and attributes []
I170527 07:30:50.272729 68114 sql/executor.go:355 [n3] creating distSQLPlanner with address {tcp 127.0.0.1:41450}
I170527 07:30:50.277215 68410 storage/stores.go:312 [n1] wrote 2 node addresses to persistent storage
I170527 07:30:50.305458 68114 server/server.go:737 [n3] starting https server at 127.0.0.1:54458
I170527 07:30:50.305600 68114 server/server.go:738 [n3] starting grpc/postgres server at 127.0.0.1:41450
I170527 07:30:50.306166 68114 server/server.go:739 [n3] advertising CockroachDB node at 127.0.0.1:41450
I170527 07:30:50.326805 68114 server/server.go:850 [n3] done ensuring all necessary migrations have run
I170527 07:30:50.326938 68114 server/server.go:852 [n3] serving sql connections
I170527 07:30:50.354651 68411 storage/stores.go:312 [n2] wrote 2 node addresses to persistent storage
I170527 07:30:50.376542 68738 server/node.go:589 [n3] bootstrapped store [n3,s3]
I170527 07:30:50.409265 68853 storage/replica_raftstorage.go:416 [n1,s1,r1/1:/M{in-ax}] generated preemptive snapshot 2af17a80 at index 59
I170527 07:30:50.469527 68680 sql/event_log.go:101 [n3] Event: "node_join", target: 3, info: {Descriptor:{NodeID:3 Address:{NetworkField:tcp AddressField:127.0.0.1:41450} Attrs: Locality:} ClusterID:2b53681e-6f39-4ee6-91e7-d09a65a31e19 StartedAt:1495870250269903446 LastUp:1495870250269903446}
I170527 07:30:50.602804 68853 storage/store.go:3352 [n1,s1,r1/1:/M{in-ax}] streamed snapshot to (n2,s2):?: kv pairs: 723, log entries: 8, rate-limit: 2.0 MiB/sec, 38ms
I170527 07:30:50.604662 68894 storage/replica_raftstorage.go:597 [n2,s2,r1/?:{-}] applying preemptive snapshot at index 59 (id=2af17a80, encoded size=181138, 1 rocksdb batches, 8 log entries)
I170527 07:30:50.607960 68894 storage/replica_raftstorage.go:605 [n2,s2,r1/?:/M{in-ax}] applied preemptive snapshot in 3ms [clear=0ms batch=0ms entries=1ms commit=1ms]
I170527 07:30:50.612164 68853 storage/replica_command.go:3538 [n1,s1,r1/1:/M{in-ax}] change replicas (ADD_REPLICA (n2,s2):2): read existing descriptor r1:/M{in-ax} [(n1,s1):1, next=2]
I170527 07:30:50.637105 68863 storage/replica.go:2836 [n1,s1,r1/1:/M{in-ax}] proposing ADD_REPLICA (n2,s2):2: [(n1,s1):1 (n2,s2):2]
I170527 07:30:50.674778 68954 storage/raft_transport.go:436 [n2] raft transport stream to node 1 established
I170527 07:30:51.200763 68962 storage/replica_raftstorage.go:416 [n1,s1,r1/1:/M{in-ax}] generated preemptive snapshot 17ae614b at index 68
I170527 07:30:51.367344 68962 storage/store.go:3352 [n1,s1,r1/1:/M{in-ax}] streamed snapshot to (n3,s3):?: kv pairs: 984, log entries: 10, rate-limit: 2.0 MiB/sec, 16ms
I170527 07:30:51.370778 68980 storage/replica_raftstorage.go:597 [n3,s3,r1/?:{-}] applying preemptive snapshot at index 68 (id=17ae614b, encoded size=207927, 1 rocksdb batches, 10 log entries)
I170527 07:30:51.374122 68980 storage/replica_raftstorage.go:605 [n3,s3,r1/?:/M{in-ax}] applied preemptive snapshot in 3ms [clear=0ms batch=0ms entries=1ms commit=1ms]
I170527 07:30:51.382287 68962 storage/replica_command.go:3538 [n1,s1,r1/1:/M{in-ax}] change replicas (ADD_REPLICA (n3,s3):3): read existing descriptor r1:/M{in-ax} [(n1,s1):1, (n2,s2):2, next=3]
I170527 07:30:51.417374 68995 storage/replica.go:2836 [n1,s1,r1/1:/M{in-ax}] proposing ADD_REPLICA (n3,s3):3: [(n1,s1):1 (n2,s2):2 (n3,s3):3]
I170527 07:30:52.377195 68986 storage/raft_transport.go:436 [n3] raft transport stream to node 1 established
I170527 07:30:52.562001 68925 storage/replica_command.go:3538 [n2,s2,r1/2:/M{in-ax}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r1:/M{in-ax} [(n1,s1):1, (n2,s2):2, (n3,s3):3, next=4]
I170527 07:30:52.623699 69058 storage/replica.go:2836 [n2,s2,r1/2:/M{in-ax}] proposing REMOVE_REPLICA (n1,s1):1: [(n3,s3):3 (n2,s2):2]
I170527 07:30:52.666704 68271 storage/store.go:2146 [replicaGC,n1,s1,r1/1:/M{in-ax}] removing replica
I170527 07:30:52.667802 68271 storage/replica.go:714 [replicaGC,n1,s1,r1/1:/M{in-ax}] removed 85 (75+10) keys in 1ms [clear=0ms commit=1ms]
E170527 07:30:52.668466 68237 util/log/crash_reporting.go:81 a panic has occurred!
E170527 07:30:52.699321 68237 util/log/crash_reporting.go:171 Reported as error 6c55b5b022fa4b0ea829fc42a42a5d8a
panic: runtime error: invalid memory address or nil pointer dereference [recovered]
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x18 pc=0x129eeea]
goroutine 68237 [running]:
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).Recover(0xc421cfa140, 0x7f05de30c350, 0xc4202a4420)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:200 +0x10d
panic(0x20d6700, 0x3103180)
/usr/local/go/src/runtime/panic.go:489 +0x2f0
github.com/cockroachdb/cockroach/pkg/storage.(*Replica).updateProposalQuotaRaftMuLocked(0xc4204c8000, 0x7f05de30c350, 0xc420283d70, 0x1)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/replica.go:909 +0x13a
github.com/cockroachdb/cockroach/pkg/storage.(*Replica).handleRaftReadyRaftMuLocked(0xc4204c8000, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/replica.go:2997 +0x249c
github.com/cockroachdb/cockroach/pkg/storage.(*Replica).handleRaftReady(0xc4204c8000, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/replica.go:2944 +0xf5
github.com/cockroachdb/cockroach/pkg/storage.(*Store).processReady(0xc420263400, 0x1)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:3417 +0x17e
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:217 +0x342
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4202a4420)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf7c0, 0xc421cfa140, 0xc42036cc00)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 1 [chan receive]:
testing.(*T).Run(0xc4203f0750, 0x22a59f5, 0x14, 0x23643c8, 0xc42068f901)
/usr/local/go/src/testing/testing.go:698 +0x582
testing.runTests.func1(0xc4203f0750)
/usr/local/go/src/testing/testing.go:882 +0xab
testing.tRunner(0xc4203f0750, 0xc42068fad0)
/usr/local/go/src/testing/testing.go:657 +0x108
testing.runTests(0xc4201b2340, 0x311ec00, 0x1b3, 0x1b3, 0xc42068fb50)
/usr/local/go/src/testing/testing.go:888 +0x4e1
testing.(*M).Run(0xc4205a9f28, 0x0)
/usr/local/go/src/testing/testing.go:822 +0x1c4
github.com/cockroachdb/cockroach/pkg/storage_test.TestMain(0xc42068ff28)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/main_test.go:59 +0x308
main.main()
github.com/cockroachdb/cockroach/pkg/storage/_test/_testmain.go:922 +0x210
goroutine 17 [syscall, 2 minutes, locked to thread]:
runtime.goexit()
/usr/local/go/src/runtime/asm_amd64.s:2197 +0x1
goroutine 19 [chan receive]:
github.com/cockroachdb/cockroach/pkg/util/log.(*loggingT).flushDaemon(0x35c7640)
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/clog.go:1057 +0x85
created by github.com/cockroachdb/cockroach/pkg/util/log.init.1
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/clog.go:603 +0x13a
goroutine 5 [syscall, 2 minutes]:
os/signal.signal_recv(0x6d0101)
/usr/local/go/src/runtime/sigqueue.go:116 +0x104
os/signal.loop()
/usr/local/go/src/os/signal/signal_unix.go:22 +0x30
created by os/signal.init.1
/usr/local/go/src/os/signal/signal_unix.go:28 +0x4f
goroutine 68571 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000049)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4209b6330)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a23c0, 0xc420cf8a00, 0xc4201f3d60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68614 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000031)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42168e300)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2720, 0xc420cf8a00, 0xc4202b0120)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68589 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000061)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc420231d70)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2570, 0xc420cf8a00, 0xc420088260)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68541 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4204aba40)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314990, 0xc420cf8a00, 0xc420314980)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68553 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420231710)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314b50, 0xc420cf8a00, 0xc420314b40)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68751 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4202834a0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f48e0, 0xc42070ebe0, 0xc4201f48d0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68115 [chan receive]:
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func1(0x7f05de30c350, 0xc4202a4060)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:158 +0x74
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf510, 0xc421cfa140, 0xc42036c520)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68696 [runnable]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).keepalive(0xc4200131e0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:894 +0x662
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Server
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:226 +0xfa9
goroutine 68832 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc40000001b)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42135e570)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f850, 0xc42070ebe0, 0xc4202cbf20)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68292 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Server).startSampleEnvironment.func1(0x7f05de30c350, 0xc4216fc480)
/go/src/github.com/cockroachdb/cockroach/pkg/server/server.go:947 +0x1ce
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e05c0, 0xc421cfa140, 0xc4203504a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68887 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*Store).startGossip.func4(0x7f05de30c350, 0xc420f8ede0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:1355 +0x64e
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038fb00, 0xc42070ebe0, 0xc42029b810)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68900 [IO wait]:
net.runtime_pollWait(0x7f05de397bf0, 0x72, 0x6fb8ba)
/usr/local/go/src/runtime/netpoll.go:164 +0x5e
net.(*pollDesc).wait(0xc420b931e8, 0x72, 0x3123fd8, 0xffffffffffffffff)
/usr/local/go/src/net/fd_poll_runtime.go:75 +0x5b
net.(*pollDesc).waitRead(0xc420b931e8, 0xc4219f4000, 0x8000)
/usr/local/go/src/net/fd_poll_runtime.go:80 +0x42
net.(*netFD).Read(0xc420b93180, 0xc4219f4000, 0x8000, 0x8000, 0x0, 0x312e600, 0x3123fd8)
/usr/local/go/src/net/fd_unix.go:250 +0x22b
net.(*conn).Read(0xc420086108, 0xc4219f4000, 0x8000, 0x8000, 0x71, 0x0, 0x2366428)
/usr/local/go/src/net/net.go:181 +0x97
net.(*TCPConn).Read(0xc420086108, 0xc4219f4000, 0x8000, 0x8000, 0x1, 0x31263c0, 0xc420078040)
<autogenerated>:72 +0x73
github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux.(*MuxConn).Read(0xc420d9ac80, 0xc4219f4000, 0x8000, 0x8000, 0xc4213d1488, 0xa150d6, 0xc4213d1488)
/go/src/github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux/cmux.go:218 +0x183
crypto/tls.(*block).readFromUntil(0xc421d4c390, 0x7f05de3a0b58, 0xc420d9ac80, 0x5, 0xc420d9ac80, 0x6b5e80)
/usr/local/go/src/crypto/tls/conn.go:488 +0x114
crypto/tls.(*Conn).readRecord(0xc42130b180, 0x2366617, 0xc42130b2a0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:590 +0x13d
crypto/tls.(*Conn).Read(0xc42130b180, 0xc4208b0000, 0x8000, 0x8000, 0x0, 0x0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:1134 +0x190
bufio.(*Reader).Read(0xc421e76900, 0xc421a0e118, 0x9, 0x9, 0x6ac9f2, 0x1d54f80, 0x7f05bef87208)
/usr/local/go/src/bufio/bufio.go:213 +0x7e7
io.ReadAtLeast(0x3125cc0, 0xc421e76900, 0xc421a0e118, 0x9, 0x9, 0x9, 0x69d06c, 0xc4213d1a10, 0xc4213d1a10)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x3125cc0, 0xc421e76900, 0xc421a0e118, 0x9, 0x9, 0x0, 0x1, 0xc4201eb4c0)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.readFrameHeader(0xc421a0e118, 0x9, 0x9, 0x3125cc0, 0xc421e76900, 0x0, 0xc400000000, 0xd28c17, 0xc420a3cb00)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:237 +0xa3
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.(*Framer).ReadFrame(0xc421a0e0e0, 0x0, 0x31263c0, 0xc420078040, 0xc42172f780)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:492 +0x118
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*framer).readFrame(0xc422474a80, 0xc422474ab0, 0xc422474ab0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http_util.go:608 +0x53
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).HandleStreams(0xc420c8d340, 0xc422474c00, 0x2365810)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:375 +0x3e6
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveStreams(0xc420edca20, 0x3145560, 0xc420c8d340)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:545 +0x1e8
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveHTTP2Transport(0xc420edca20, 0x3146100, 0xc42130b180, 0x312da80, 0xc42048f080)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:526 +0x6f9
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).handleRawConn(0xc420edca20, 0x3147300, 0xc420d9ac80)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:493 +0x5f4
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).Serve
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:462 +0x69c
goroutine 68794 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*baseQueue).processLoop.func1(0x7f05de30c350, 0xc420af3170)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/queue.go:490 +0x468
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42036ef90, 0xc42070ebe0, 0xc420281c80)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68638 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Client).controller(0xc4207ea000)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:1168 +0x912
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Client
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:297 +0x1692
goroutine 68373 [IO wait]:
net.runtime_pollWait(0x7f05de3981f0, 0x72, 0x6fb8ba)
/usr/local/go/src/runtime/netpoll.go:164 +0x5e
net.(*pollDesc).wait(0xc4200ba148, 0x72, 0x3123fd8, 0xffffffffffffffff)
/usr/local/go/src/net/fd_poll_runtime.go:75 +0x5b
net.(*pollDesc).waitRead(0xc4200ba148, 0xc4208e6000, 0x400)
/usr/local/go/src/net/fd_poll_runtime.go:80 +0x42
net.(*netFD).Read(0xc4200ba0e0, 0xc4208e6000, 0x400, 0x400, 0x0, 0x312e600, 0x3123fd8)
/usr/local/go/src/net/fd_unix.go:250 +0x22b
net.(*conn).Read(0xc42000e098, 0xc4208e6000, 0x400, 0x400, 0x102, 0x6ac5f4, 0x1d56480)
/usr/local/go/src/net/net.go:181 +0x97
net.(*TCPConn).Read(0xc42000e098, 0xc4208e6000, 0x400, 0x400, 0xc4213bb6e8, 0xa150d6, 0xc4213bb6e8)
<autogenerated>:72 +0x73
crypto/tls.(*block).readFromUntil(0xc4202d01b0, 0x7f05da985aa8, 0xc42000e098, 0x5, 0xc42000e098, 0x6b5e80)
/usr/local/go/src/crypto/tls/conn.go:488 +0x114
crypto/tls.(*Conn).readRecord(0xc4201dee00, 0x2366617, 0xc4201def20, 0xc42036eb70)
/usr/local/go/src/crypto/tls/conn.go:590 +0x13d
crypto/tls.(*Conn).Read(0xc4201dee00, 0xc420702000, 0x8000, 0x8000, 0x0, 0x0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:1134 +0x190
bufio.(*Reader).Read(0xc421903b60, 0xc420204498, 0x9, 0x9, 0x69ce1b, 0xc420020600, 0xc420020600)
/usr/local/go/src/bufio/bufio.go:213 +0x7e7
io.ReadAtLeast(0x3125cc0, 0xc421903b60, 0xc420204498, 0x9, 0x9, 0x9, 0x0, 0x0, 0xc4213bbc50)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x3125cc0, 0xc421903b60, 0xc420204498, 0x9, 0x9, 0x6efaa3, 0xc42006bd40, 0xffffffff)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.readFrameHeader(0xc420204498, 0x9, 0x9, 0x3125cc0, 0xc421903b60, 0x0, 0x0, 0xc4213bbd70, 0x69d0f4)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:237 +0xa3
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.(*Framer).ReadFrame(0xc420204460, 0x0, 0x31263c0, 0xc420078040, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:492 +0x118
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*framer).readFrame(0xc4216fdc20, 0xc4214c5bf0, 0xc4214c5b00, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http_util.go:608 +0x53
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Client).reader(0xc4213c8300)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:1095 +0x15b
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Client
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:267 +0x12ec
goroutine 68806 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc400000044)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4212e81b0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202ae3f0, 0xc42070ebe0, 0xc420351d60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68889 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*Store).startGossip.func4(0x7f05de30c350, 0xc420f8ee10)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:1355 +0x64e
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038fb20, 0xc42070ebe0, 0xc42029b8b0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68254 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc40000007a)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4203d24b0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf8e0, 0xc421cfa140, 0xc42036ce60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68690 [select]:
github.com/cockroachdb/cockroach/pkg/gossip.(*Gossip).bootstrap.func1(0x7f05de30c350, 0xc42085b200)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/gossip.go:1064 +0x5e0
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42020eba0, 0xc42070ebe0, 0xc42020eb90)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68768 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420425ad0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f4c40, 0xc42070ebe0, 0xc4201f4c30)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68428 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*baseQueue).processLoop.func1(0x7f05de30c350, 0xc421ef7770)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/queue.go:490 +0x468
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203029c0, 0xc420cf8a00, 0xc42031a740)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68323 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4213cc090)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e0a10, 0xc421cfa140, 0xc4201e09f0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68617 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc40000005c)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42168e390)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2750, 0xc420cf8a00, 0xc4202b01a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68449 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).keepalive(0xc420c8d600)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:894 +0x662
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Server
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:226 +0xfa9
goroutine 68839 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc400000019)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42135e510)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f8d0, 0xc42070ebe0, 0xc4203120a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68477 [chan receive]:
github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux.(*muxListener).Accept(0xc420331080, 0x23657d8, 0xc420edca20, 0x3147300, 0xc420d9ac80)
<autogenerated>:9 +0x9f
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).Serve(0xc420edca20, 0x313d400, 0xc420331080, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:432 +0x1f8
github.com/cockroachdb/cockroach/pkg/server.(*Server).Start.func7(0x7f05de30c350, 0xc4207ede00)
/go/src/github.com/cockroachdb/cockroach/pkg/server/server.go:559 +0x8d
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42026f000, 0xc420cf8a00, 0xc420331260)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68500 [IO wait]:
net.runtime_pollWait(0x7f05da8c4488, 0x72, 0x6fb8ba)
/usr/local/go/src/runtime/netpoll.go:164 +0x5e
net.(*pollDesc).wait(0xc4210a1728, 0x72, 0x3123fd8, 0xffffffffffffffff)
/usr/local/go/src/net/fd_poll_runtime.go:75 +0x5b
net.(*pollDesc).waitRead(0xc4210a1728, 0xc420e00000, 0x8000)
/usr/local/go/src/net/fd_poll_runtime.go:80 +0x42
net.(*netFD).Read(0xc4210a16c0, 0xc420e00000, 0x8000, 0x8000, 0x0, 0x312e600, 0x3123fd8)
/usr/local/go/src/net/fd_unix.go:250 +0x22b
net.(*conn).Read(0xc42000e278, 0xc420e00000, 0x8000, 0x8000, 0x248, 0x0, 0x2366428)
/usr/local/go/src/net/net.go:181 +0x97
net.(*TCPConn).Read(0xc42000e278, 0xc420e00000, 0x8000, 0x8000, 0x1, 0x31263c0, 0xc420078040)
<autogenerated>:72 +0x73
github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux.(*MuxConn).Read(0xc4203e1a40, 0xc420e00000, 0x8000, 0x8000, 0xc420d19488, 0xa150d6, 0xc420d19488)
/go/src/github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux/cmux.go:218 +0x183
crypto/tls.(*block).readFromUntil(0xc4213b66f0, 0x7f05de3a0b58, 0xc4203e1a40, 0x5, 0xc4203e1a40, 0x0)
/usr/local/go/src/crypto/tls/conn.go:488 +0x114
crypto/tls.(*Conn).readRecord(0xc4217bc700, 0x2366617, 0xc4217bc820, 0xc420e0000d)
/usr/local/go/src/crypto/tls/conn.go:590 +0x13d
crypto/tls.(*Conn).Read(0xc4217bc700, 0xc421966000, 0x8000, 0x8000, 0x0, 0x0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:1134 +0x190
bufio.(*Reader).Read(0xc420dffce0, 0xc421962118, 0x9, 0x9, 0x6ac9f2, 0x1d54f80, 0x7f05d89de3c8)
/usr/local/go/src/bufio/bufio.go:213 +0x7e7
io.ReadAtLeast(0x3125cc0, 0xc420dffce0, 0xc421962118, 0x9, 0x9, 0x9, 0x69d06c, 0xc420d19a10, 0xc420d19a10)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x3125cc0, 0xc420dffce0, 0xc421962118, 0x9, 0x9, 0xc420670001, 0x7f05de458e10, 0x0)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.readFrameHeader(0xc421962118, 0x9, 0x9, 0x3125cc0, 0xc420dffce0, 0x0, 0xc400000000, 0xd28c17, 0xc42082c4b0)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:237 +0xa3
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.(*Framer).ReadFrame(0xc4219620e0, 0x3130a40, 0xc42082c4b0, 0x0, 0xc420a3d300)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:492 +0x118
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*framer).readFrame(0xc42082c480, 0xc42082c4b0, 0xc42082c4b0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http_util.go:608 +0x53
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).HandleStreams(0xc420c8d600, 0xc42082c600, 0x2365810)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:375 +0x3e6
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveStreams(0xc4213b2480, 0x3145560, 0xc420c8d600)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:545 +0x1e8
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveHTTP2Transport(0xc4213b2480, 0x3146100, 0xc4217bc700, 0x312da80, 0xc420383a20)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:526 +0x6f9
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).handleRawConn(0xc4213b2480, 0x3147300, 0xc4203e1a40)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:493 +0x5f4
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).Serve
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:462 +0x69c
goroutine 68512 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc42085a090)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203147f0, 0xc420cf8a00, 0xc4203147e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68335 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Client).keepalive(0xc4213c8300)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:1214 +0x6e6
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Client
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:299 +0x1789
goroutine 68805 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc400000043)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc420af2660)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202ae3e0, 0xc42070ebe0, 0xc420351d20)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68106 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Server).refreshSettings.func2(0x7f05de30c350, 0xc420b98090)
/go/src/github.com/cockroachdb/cockroach/pkg/server/settingsworker.go:113 +0x48f
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203dfcf0, 0xc421cfa140, 0xc4203056e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68294 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Node).startWriteSummaries.func1(0x7f05de30c350, 0xc4216fc510)
/go/src/github.com/cockroachdb/cockroach/pkg/server/node.go:739 +0x3b5
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e05f0, 0xc421cfa140, 0xc4203504c0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68606 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000036)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4209b6630)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a26a0, 0xc420cf8a00, 0xc420088b60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68308 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420d1b5c0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e07c0, 0xc421cfa140, 0xc4201e07b0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 69017 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*recvBufferReader).Read(0xc421913080, 0xc420369630, 0x5, 0x5, 0x0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:145 +0x70a
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*Stream).Read(0xc420af4400, 0xc420369630, 0x5, 0x5, 0x1d54f80, 0x7f05ce775ec8, 0xc4204a6138)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:328 +0x79
io.ReadAtLeast(0x312aac0, 0xc420af4400, 0xc420369630, 0x5, 0x5, 0x5, 0xc4215d9b48, 0x6b16f1, 0xc420545860)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x312aac0, 0xc420af4400, 0xc420369630, 0x5, 0x5, 0x6ef638, 0xc4206e0510, 0xc4215d9bc0)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*parser).recvMsg(0xc420369620, 0x7fffffff, 0x34, 0x34, 0xc4215d9d18, 0x69ce1b, 0x6840ad, 0xc41ffed572)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:255 +0xa0
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.recv(0xc420369620, 0x313da00, 0x3f88010, 0xc420af4400, 0x3132580, 0x3f88010, 0x21bdce0, 0xc4202551a0, 0x7fffffff, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:351 +0x61
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*serverStream).RecvMsg(0xc420739280, 0x21bdce0, 0xc4202551a0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:623 +0x1cf
github.com/cockroachdb/cockroach/pkg/storage.(*multiRaftRaftMessageBatchServer).Recv(0xc4202dcee0, 0x7f05de30c350, 0xc420851a10, 0xc421180900)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/raft.pb.go:397 +0x86
github.com/cockroachdb/cockroach/pkg/storage.(*RaftTransport).RaftMessageBatch.func1.1.1(0x31471e0, 0xc4202dcee0, 0xc420662180, 0x7f05de30c350, 0xc420851a10, 0x18, 0xc42100a778)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/raft_transport.go:300 +0x61
github.com/cockroachdb/cockroach/pkg/storage.(*RaftTransport).RaftMessageBatch.func1.1(0x7f05de30c350, 0xc420851a10)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/raft_transport.go:323 +0x75
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202dcf00, 0xc421cfa140, 0xc420851950)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68820 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc40000002b)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4212e86c0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f790, 0xc42070ebe0, 0xc4202cbb80)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68401 [select]:
github.com/cockroachdb/cockroach/pkg/security.(*CertificateManager).RegisterSignalHandler.func1(0xc420cf8a00, 0xc421268a80, 0xc4200d1ce0)
/go/src/github.com/cockroachdb/cockroach/pkg/security/certificate_manager.go:127 +0x511
created by github.com/cockroachdb/cockroach/pkg/security.(*CertificateManager).RegisterSignalHandler
/go/src/github.com/cockroachdb/cockroach/pkg/security/certificate_manager.go:140 +0xf1
goroutine 68566 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000046)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc421ef76e0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2360, 0xc420cf8a00, 0xc4201f39e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68256 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc40000007c)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4203d2540)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf900, 0xc421cfa140, 0xc42036cea0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68658 [chan receive]:
database/sql.(*DB).connectionOpener(0xc42070eb40)
/usr/local/go/src/database/sql/sql.go:837 +0x6e
created by database/sql.Open
/usr/local/go/src/database/sql/sql.go:582 +0x318
goroutine 68430 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*baseQueue).processLoop.func1(0x7f05de30c350, 0xc421ef77a0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/queue.go:490 +0x468
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203029e0, 0xc420cf8a00, 0xc42031a7a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68515 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*recvBufferReader).Read(0xc42172fc40, 0xc4201f3b90, 0x5, 0x5, 0x0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:145 +0x70a
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*Stream).Read(0xc420768600, 0xc4201f3b90, 0x5, 0x5, 0x679aa3, 0xc421412bd0, 0x20c24a0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:328 +0x79
io.ReadAtLeast(0x312aac0, 0xc420768600, 0xc4201f3b90, 0x5, 0x5, 0x5, 0x11991b7, 0x30dd0fed, 0xc421412be8)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x312aac0, 0xc420768600, 0xc4201f3b90, 0x5, 0x5, 0xc, 0x0, 0xc4207b3c08)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*parser).recvMsg(0xc4201f3b80, 0x7fffffff, 0x6ef17e, 0xc420570540, 0x6d127c, 0x6efaa3, 0x69d06c, 0xc4207b3c60)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:255 +0xa0
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.recv(0xc4201f3b80, 0x313da00, 0x3f88010, 0xc420768600, 0x3132580, 0x3f88010, 0x21b4f20, 0xc4214311d0, 0x7fffffff, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:351 +0x61
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*clientStream).RecvMsg(0xc420c8d8c0, 0x21b4f20, 0xc4214311d0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:379 +0x1da
github.com/cockroachdb/cockroach/pkg/gossip.(*gossipGossipClient).Recv(0xc4202434d0, 0x7f05de30c350, 0xc42082c960, 0xc42073c780)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/gossip.pb.go:194 +0x86
github.com/cockroachdb/cockroach/pkg/gossip.(*client).gossip.func2.1(0x3146160, 0xc4202434d0, 0xc421090f70, 0x7f05de30c350, 0xc42082c960, 0xc42073c780, 0xc420d34768, 0x69c742)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/client.go:313 +0x43
github.com/cockroachdb/cockroach/pkg/gossip.(*client).gossip.func2(0x7f05de30c350, 0xc42082c960)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/client.go:321 +0xe6
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202435a0, 0xc420cf8a00, 0xc42172fcc0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68506 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Node).startGossip.func1(0x7f05de30c350, 0xc421ef69c0)
/go/src/github.com/cockroachdb/cockroach/pkg/server/node.go:661 +0x5cc
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314620, 0xc420cf8a00, 0xc4203985a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68218 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc400000095)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42007df80)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf680, 0xc421cfa140, 0xc42036c8e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 69077 [runnable]:
github.com/cockroachdb/cockroach/pkg/storage_test.TestGossipFirstRange.func1(0xc4201eb650, 0xb, 0xc420269a20, 0x1f, 0x20, 0x14c26611bf6bf478, 0x0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/gossip_test.go:56 +0x177
github.com/cockroachdb/cockroach/pkg/gossip.(*infoStore).runCallbacks.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/infostore.go:277 +0x10b
github.com/cockroachdb/cockroach/pkg/gossip.(*infoStore).runCallbacks.func2(0x7f05de307058, 0xc420078d68)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/infostore.go:299 +0x161
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunAsyncTask.func1(0xc421cfa140, 0x7f05de307058, 0xc420078d68, 0x2e646e5, 0x13, 0x12d, 0x0, 0x0, 0xc4201eb7e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:294 +0x101
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunAsyncTask
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:295 +0x173
goroutine 68833 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc40000001f)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42135e630)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f860, 0xc42070ebe0, 0xc4202cbf60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68757 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420283350)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f4a00, 0xc42070ebe0, 0xc4201f49d0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68234 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc4000000a7)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4202a4330)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf790, 0xc421cfa140, 0xc42036cba0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68576 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000038)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42168e180)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2420, 0xc420cf8a00, 0xc4201f3e80)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68507 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Server).startSampleEnvironment.func1(0x7f05de30c350, 0xc4216fd950)
/go/src/github.com/cockroachdb/cockroach/pkg/server/server.go:947 +0x1ce
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314760, 0xc420cf8a00, 0xc420398640)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68104 [select]:
github.com/cockroachdb/cockroach/pkg/kv.(*TxnCoordSender).printStatsLoop(0xc4201848f0, 0x7f05de30c350, 0xc420b98030)
/go/src/github.com/cockroachdb/cockroach/pkg/kv/txn_coord_sender.go:255 +0xfce
github.com/cockroachdb/cockroach/pkg/kv.NewTxnCoordSender.func1(0x7f05de30c350, 0xc420b98030)
/go/src/github.com/cockroachdb/cockroach/pkg/kv/txn_coord_sender.go:239 +0x56
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203dfa60, 0xc421cfa140, 0xc4203dfa50)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68260 [semacquire]:
sync.runtime_Semacquire(0xc4204a61a4)
/usr/local/go/src/runtime/sema.go:47 +0x34
sync.(*WaitGroup).Wait(0xc4204a6198)
/usr/local/go/src/sync/waitgroup.go:131 +0xc2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Wait(0xc4204a6120, 0x7f05de30c350, 0xc4203d25d0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:174 +0x3f
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Wait-fm(0x7f05de30c350, 0xc4203d25d0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:3476 +0x56
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf960, 0xc421cfa140, 0xc4201cf950)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68510 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4216fd920)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203147b0, 0xc420cf8a00, 0xc4203147a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68479 [chan receive]:
github.com/cockroachdb/cockroach/pkg/gossip.(*server).start.func3(0x7f05de30c350, 0xc420a73200)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/server.go:386 +0x94
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42026f150, 0xc420cf8a00, 0xc420331360)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68328 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*Executor).Start.func1(0x7f05de30c350, 0xc4213cc3c0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/executor.go:372 +0x19d
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e0ad0, 0xc421cfa140, 0xc420350540)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68760 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChangeManager).Start.func1(0x7f05de30c350, 0xc420283c80)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:807 +0x1f0c
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f4a70, 0xc42070ebe0, 0xc4202de820)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68967 [IO wait]:
``` | 1.0 | storage: TestGossipFirstRange failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/db8da7c6f9551b69fd464803133db170001e3470
Parameters:
```
TAGS=
GOFLAGS=-race
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=258586&tab=buildLog
```
I170527 07:30:48.955791 68114 server/config.go:439 1 storage engine initialized
I170527 07:30:48.957039 68114 server/node.go:454 [n?] store [n0,s0] not bootstrapped
I170527 07:30:49.029937 68114 server/node.go:389 [n?] **** cluster 2b53681e-6f39-4ee6-91e7-d09a65a31e19 has been created
I170527 07:30:49.030038 68114 server/node.go:390 [n?] **** add additional nodes by specifying --join=127.0.0.1:41294
I170527 07:30:49.046722 68114 storage/store.go:1256 [n1] [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170527 07:30:49.046882 68114 server/node.go:467 [n1] initialized store [n1,s1]: {Capacity:536870912 Available:536870912 RangeCount:1 LeaseCount:0}
I170527 07:30:49.047640 68114 server/node.go:351 [n1] node ID 1 initialized
I170527 07:30:49.047929 68114 gossip/gossip.go:297 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:41294" > attrs:<> locality:<>
I170527 07:30:49.048548 68114 storage/stores.go:296 [n1] read 0 node addresses from persistent storage
I170527 07:30:49.048844 68114 server/node.go:608 [n1] connecting to gossip network to verify cluster ID...
I170527 07:30:49.049011 68114 server/node.go:633 [n1] node connected via gossip and verified as part of cluster "2b53681e-6f39-4ee6-91e7-d09a65a31e19"
I170527 07:30:49.049283 68114 server/node.go:405 [n1] node=1: started with [[]=] engine(s) and attributes []
I170527 07:30:49.054898 68114 sql/executor.go:355 [n1] creating distSQLPlanner with address {tcp 127.0.0.1:41294}
I170527 07:30:49.120348 68114 server/server.go:737 [n1] starting https server at 127.0.0.1:49195
I170527 07:30:49.120442 68114 server/server.go:738 [n1] starting grpc/postgres server at 127.0.0.1:41294
I170527 07:30:49.120478 68114 server/server.go:739 [n1] advertising CockroachDB node at 127.0.0.1:41294
I170527 07:30:49.246604 68114 sql/event_log.go:101 [n1] Event: "alter_table", target: 12, info: {TableName:eventlog Statement:ALTER TABLE system.eventlog ALTER COLUMN uniqueid SET DEFAULT uuid_v4() User:node MutationID:0 CascadeDroppedViews:[]}
I170527 07:30:49.427488 68114 sql/lease.go:372 [n1] publish: descID=12 (eventlog) version=2 mtime=2017-05-27 07:30:49.427364426 +0000 UTC
I170527 07:30:49.536617 68114 server/server.go:850 [n1] done ensuring all necessary migrations have run
I170527 07:30:49.536748 68114 server/server.go:852 [n1] serving sql connections
I170527 07:30:49.567919 68399 sql/event_log.go:101 [n1] Event: "node_join", target: 1, info: {Descriptor:{NodeID:1 Address:{NetworkField:tcp AddressField:127.0.0.1:41294} Attrs: Locality:} ClusterID:2b53681e-6f39-4ee6-91e7-d09a65a31e19 StartedAt:1495870249049051536 LastUp:1495870249049051536}
W170527 07:30:49.636701 68114 server/status/runtime.go:111 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
W170527 07:30:49.639374 68114 gossip/gossip.go:1196 [n?] no incoming or outgoing connections
I170527 07:30:49.640662 68114 server/config.go:439 1 storage engine initialized
I170527 07:30:49.641902 68114 server/node.go:454 [n?] store [n0,s0] not bootstrapped
I170527 07:30:49.642048 68114 storage/stores.go:296 [n?] read 0 node addresses from persistent storage
I170527 07:30:49.642380 68114 server/node.go:608 [n?] connecting to gossip network to verify cluster ID...
I170527 07:30:49.778539 68443 gossip/client.go:131 [n?] started gossip client to 127.0.0.1:41294
I170527 07:30:49.780920 68517 gossip/server.go:234 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:36729}
I170527 07:30:49.803732 68114 server/node.go:633 [n?] node connected via gossip and verified as part of cluster "2b53681e-6f39-4ee6-91e7-d09a65a31e19"
I170527 07:30:49.804561 68420 storage/stores.go:312 [n?] wrote 1 node addresses to persistent storage
I170527 07:30:49.829569 68114 kv/dist_sender.go:370 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I170527 07:30:49.837525 68114 server/node.go:344 [n?] new node allocated ID 2
I170527 07:30:49.837830 68114 gossip/gossip.go:297 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:36729" > attrs:<> locality:<>
I170527 07:30:49.838652 68114 server/node.go:405 [n2] node=2: started with [[]=] engine(s) and attributes []
I170527 07:30:49.843572 67712 storage/stores.go:312 [n1] wrote 1 node addresses to persistent storage
I170527 07:30:49.847369 68114 sql/executor.go:355 [n2] creating distSQLPlanner with address {tcp 127.0.0.1:36729}
I170527 07:30:49.879872 68114 server/server.go:737 [n2] starting https server at 127.0.0.1:55424
I170527 07:30:49.879988 68114 server/server.go:738 [n2] starting grpc/postgres server at 127.0.0.1:36729
I170527 07:30:49.880031 68114 server/server.go:739 [n2] advertising CockroachDB node at 127.0.0.1:36729
I170527 07:30:49.930032 68114 server/server.go:850 [n2] done ensuring all necessary migrations have run
I170527 07:30:49.930170 68114 server/server.go:852 [n2] serving sql connections
I170527 07:30:49.989582 68561 sql/event_log.go:101 [n2] Event: "node_join", target: 2, info: {Descriptor:{NodeID:2 Address:{NetworkField:tcp AddressField:127.0.0.1:36729} Attrs: Locality:} ClusterID:2b53681e-6f39-4ee6-91e7-d09a65a31e19 StartedAt:1495870249838435475 LastUp:1495870249838435475}
W170527 07:30:49.994612 68114 server/status/runtime.go:111 Could not parse build timestamp: parsing time "" as "2006/01/02 15:04:05": cannot parse "" as "2006"
W170527 07:30:49.996445 68114 gossip/gossip.go:1196 [n?] no incoming or outgoing connections
I170527 07:30:49.997645 68114 server/config.go:439 1 storage engine initialized
I170527 07:30:49.998911 68114 server/node.go:454 [n?] store [n0,s0] not bootstrapped
I170527 07:30:49.999031 68114 storage/stores.go:296 [n?] read 0 node addresses from persistent storage
I170527 07:30:49.999131 68114 server/node.go:608 [n?] connecting to gossip network to verify cluster ID...
I170527 07:30:50.130852 68504 server/node.go:589 [n2] bootstrapped store [n2,s2]
I170527 07:30:50.212111 68363 gossip/client.go:131 [n?] started gossip client to 127.0.0.1:41294
I170527 07:30:50.215865 68710 gossip/server.go:234 [n1] received initial cluster-verification connection from {tcp 127.0.0.1:41450}
I170527 07:30:50.220058 68114 server/node.go:633 [n?] node connected via gossip and verified as part of cluster "2b53681e-6f39-4ee6-91e7-d09a65a31e19"
I170527 07:30:50.221820 68712 storage/stores.go:312 [n?] wrote 1 node addresses to persistent storage
I170527 07:30:50.222434 68712 storage/stores.go:312 [n?] wrote 2 node addresses to persistent storage
I170527 07:30:50.233858 68114 kv/dist_sender.go:370 [n?] unable to determine this node's attributes for replica selection; node is most likely bootstrapping
I170527 07:30:50.268950 68114 server/node.go:344 [n?] new node allocated ID 3
I170527 07:30:50.269273 68114 gossip/gossip.go:297 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:41450" > attrs:<> locality:<>
I170527 07:30:50.270213 68114 server/node.go:405 [n3] node=3: started with [[]=] engine(s) and attributes []
I170527 07:30:50.272729 68114 sql/executor.go:355 [n3] creating distSQLPlanner with address {tcp 127.0.0.1:41450}
I170527 07:30:50.277215 68410 storage/stores.go:312 [n1] wrote 2 node addresses to persistent storage
I170527 07:30:50.305458 68114 server/server.go:737 [n3] starting https server at 127.0.0.1:54458
I170527 07:30:50.305600 68114 server/server.go:738 [n3] starting grpc/postgres server at 127.0.0.1:41450
I170527 07:30:50.306166 68114 server/server.go:739 [n3] advertising CockroachDB node at 127.0.0.1:41450
I170527 07:30:50.326805 68114 server/server.go:850 [n3] done ensuring all necessary migrations have run
I170527 07:30:50.326938 68114 server/server.go:852 [n3] serving sql connections
I170527 07:30:50.354651 68411 storage/stores.go:312 [n2] wrote 2 node addresses to persistent storage
I170527 07:30:50.376542 68738 server/node.go:589 [n3] bootstrapped store [n3,s3]
I170527 07:30:50.409265 68853 storage/replica_raftstorage.go:416 [n1,s1,r1/1:/M{in-ax}] generated preemptive snapshot 2af17a80 at index 59
I170527 07:30:50.469527 68680 sql/event_log.go:101 [n3] Event: "node_join", target: 3, info: {Descriptor:{NodeID:3 Address:{NetworkField:tcp AddressField:127.0.0.1:41450} Attrs: Locality:} ClusterID:2b53681e-6f39-4ee6-91e7-d09a65a31e19 StartedAt:1495870250269903446 LastUp:1495870250269903446}
I170527 07:30:50.602804 68853 storage/store.go:3352 [n1,s1,r1/1:/M{in-ax}] streamed snapshot to (n2,s2):?: kv pairs: 723, log entries: 8, rate-limit: 2.0 MiB/sec, 38ms
I170527 07:30:50.604662 68894 storage/replica_raftstorage.go:597 [n2,s2,r1/?:{-}] applying preemptive snapshot at index 59 (id=2af17a80, encoded size=181138, 1 rocksdb batches, 8 log entries)
I170527 07:30:50.607960 68894 storage/replica_raftstorage.go:605 [n2,s2,r1/?:/M{in-ax}] applied preemptive snapshot in 3ms [clear=0ms batch=0ms entries=1ms commit=1ms]
I170527 07:30:50.612164 68853 storage/replica_command.go:3538 [n1,s1,r1/1:/M{in-ax}] change replicas (ADD_REPLICA (n2,s2):2): read existing descriptor r1:/M{in-ax} [(n1,s1):1, next=2]
I170527 07:30:50.637105 68863 storage/replica.go:2836 [n1,s1,r1/1:/M{in-ax}] proposing ADD_REPLICA (n2,s2):2: [(n1,s1):1 (n2,s2):2]
I170527 07:30:50.674778 68954 storage/raft_transport.go:436 [n2] raft transport stream to node 1 established
I170527 07:30:51.200763 68962 storage/replica_raftstorage.go:416 [n1,s1,r1/1:/M{in-ax}] generated preemptive snapshot 17ae614b at index 68
I170527 07:30:51.367344 68962 storage/store.go:3352 [n1,s1,r1/1:/M{in-ax}] streamed snapshot to (n3,s3):?: kv pairs: 984, log entries: 10, rate-limit: 2.0 MiB/sec, 16ms
I170527 07:30:51.370778 68980 storage/replica_raftstorage.go:597 [n3,s3,r1/?:{-}] applying preemptive snapshot at index 68 (id=17ae614b, encoded size=207927, 1 rocksdb batches, 10 log entries)
I170527 07:30:51.374122 68980 storage/replica_raftstorage.go:605 [n3,s3,r1/?:/M{in-ax}] applied preemptive snapshot in 3ms [clear=0ms batch=0ms entries=1ms commit=1ms]
I170527 07:30:51.382287 68962 storage/replica_command.go:3538 [n1,s1,r1/1:/M{in-ax}] change replicas (ADD_REPLICA (n3,s3):3): read existing descriptor r1:/M{in-ax} [(n1,s1):1, (n2,s2):2, next=3]
I170527 07:30:51.417374 68995 storage/replica.go:2836 [n1,s1,r1/1:/M{in-ax}] proposing ADD_REPLICA (n3,s3):3: [(n1,s1):1 (n2,s2):2 (n3,s3):3]
I170527 07:30:52.377195 68986 storage/raft_transport.go:436 [n3] raft transport stream to node 1 established
I170527 07:30:52.562001 68925 storage/replica_command.go:3538 [n2,s2,r1/2:/M{in-ax}] change replicas (REMOVE_REPLICA (n1,s1):1): read existing descriptor r1:/M{in-ax} [(n1,s1):1, (n2,s2):2, (n3,s3):3, next=4]
I170527 07:30:52.623699 69058 storage/replica.go:2836 [n2,s2,r1/2:/M{in-ax}] proposing REMOVE_REPLICA (n1,s1):1: [(n3,s3):3 (n2,s2):2]
I170527 07:30:52.666704 68271 storage/store.go:2146 [replicaGC,n1,s1,r1/1:/M{in-ax}] removing replica
I170527 07:30:52.667802 68271 storage/replica.go:714 [replicaGC,n1,s1,r1/1:/M{in-ax}] removed 85 (75+10) keys in 1ms [clear=0ms commit=1ms]
E170527 07:30:52.668466 68237 util/log/crash_reporting.go:81 a panic has occurred!
E170527 07:30:52.699321 68237 util/log/crash_reporting.go:171 Reported as error 6c55b5b022fa4b0ea829fc42a42a5d8a
panic: runtime error: invalid memory address or nil pointer dereference [recovered]
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x18 pc=0x129eeea]
goroutine 68237 [running]:
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).Recover(0xc421cfa140, 0x7f05de30c350, 0xc4202a4420)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:200 +0x10d
panic(0x20d6700, 0x3103180)
/usr/local/go/src/runtime/panic.go:489 +0x2f0
github.com/cockroachdb/cockroach/pkg/storage.(*Replica).updateProposalQuotaRaftMuLocked(0xc4204c8000, 0x7f05de30c350, 0xc420283d70, 0x1)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/replica.go:909 +0x13a
github.com/cockroachdb/cockroach/pkg/storage.(*Replica).handleRaftReadyRaftMuLocked(0xc4204c8000, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/replica.go:2997 +0x249c
github.com/cockroachdb/cockroach/pkg/storage.(*Replica).handleRaftReady(0xc4204c8000, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/replica.go:2944 +0xf5
github.com/cockroachdb/cockroach/pkg/storage.(*Store).processReady(0xc420263400, 0x1)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:3417 +0x17e
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:217 +0x342
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4202a4420)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf7c0, 0xc421cfa140, 0xc42036cc00)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 1 [chan receive]:
testing.(*T).Run(0xc4203f0750, 0x22a59f5, 0x14, 0x23643c8, 0xc42068f901)
/usr/local/go/src/testing/testing.go:698 +0x582
testing.runTests.func1(0xc4203f0750)
/usr/local/go/src/testing/testing.go:882 +0xab
testing.tRunner(0xc4203f0750, 0xc42068fad0)
/usr/local/go/src/testing/testing.go:657 +0x108
testing.runTests(0xc4201b2340, 0x311ec00, 0x1b3, 0x1b3, 0xc42068fb50)
/usr/local/go/src/testing/testing.go:888 +0x4e1
testing.(*M).Run(0xc4205a9f28, 0x0)
/usr/local/go/src/testing/testing.go:822 +0x1c4
github.com/cockroachdb/cockroach/pkg/storage_test.TestMain(0xc42068ff28)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/main_test.go:59 +0x308
main.main()
github.com/cockroachdb/cockroach/pkg/storage/_test/_testmain.go:922 +0x210
goroutine 17 [syscall, 2 minutes, locked to thread]:
runtime.goexit()
/usr/local/go/src/runtime/asm_amd64.s:2197 +0x1
goroutine 19 [chan receive]:
github.com/cockroachdb/cockroach/pkg/util/log.(*loggingT).flushDaemon(0x35c7640)
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/clog.go:1057 +0x85
created by github.com/cockroachdb/cockroach/pkg/util/log.init.1
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/clog.go:603 +0x13a
goroutine 5 [syscall, 2 minutes]:
os/signal.signal_recv(0x6d0101)
/usr/local/go/src/runtime/sigqueue.go:116 +0x104
os/signal.loop()
/usr/local/go/src/os/signal/signal_unix.go:22 +0x30
created by os/signal.init.1
/usr/local/go/src/os/signal/signal_unix.go:28 +0x4f
goroutine 68571 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000049)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4209b6330)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a23c0, 0xc420cf8a00, 0xc4201f3d60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68614 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000031)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42168e300)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2720, 0xc420cf8a00, 0xc4202b0120)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68589 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000061)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc420231d70)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2570, 0xc420cf8a00, 0xc420088260)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68541 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4204aba40)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314990, 0xc420cf8a00, 0xc420314980)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68553 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420231710)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314b50, 0xc420cf8a00, 0xc420314b40)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68751 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4202834a0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f48e0, 0xc42070ebe0, 0xc4201f48d0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68115 [chan receive]:
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func1(0x7f05de30c350, 0xc4202a4060)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:158 +0x74
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf510, 0xc421cfa140, 0xc42036c520)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68696 [runnable]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).keepalive(0xc4200131e0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:894 +0x662
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Server
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:226 +0xfa9
goroutine 68832 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc40000001b)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42135e570)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f850, 0xc42070ebe0, 0xc4202cbf20)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68292 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Server).startSampleEnvironment.func1(0x7f05de30c350, 0xc4216fc480)
/go/src/github.com/cockroachdb/cockroach/pkg/server/server.go:947 +0x1ce
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e05c0, 0xc421cfa140, 0xc4203504a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68887 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*Store).startGossip.func4(0x7f05de30c350, 0xc420f8ede0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:1355 +0x64e
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038fb00, 0xc42070ebe0, 0xc42029b810)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68900 [IO wait]:
net.runtime_pollWait(0x7f05de397bf0, 0x72, 0x6fb8ba)
/usr/local/go/src/runtime/netpoll.go:164 +0x5e
net.(*pollDesc).wait(0xc420b931e8, 0x72, 0x3123fd8, 0xffffffffffffffff)
/usr/local/go/src/net/fd_poll_runtime.go:75 +0x5b
net.(*pollDesc).waitRead(0xc420b931e8, 0xc4219f4000, 0x8000)
/usr/local/go/src/net/fd_poll_runtime.go:80 +0x42
net.(*netFD).Read(0xc420b93180, 0xc4219f4000, 0x8000, 0x8000, 0x0, 0x312e600, 0x3123fd8)
/usr/local/go/src/net/fd_unix.go:250 +0x22b
net.(*conn).Read(0xc420086108, 0xc4219f4000, 0x8000, 0x8000, 0x71, 0x0, 0x2366428)
/usr/local/go/src/net/net.go:181 +0x97
net.(*TCPConn).Read(0xc420086108, 0xc4219f4000, 0x8000, 0x8000, 0x1, 0x31263c0, 0xc420078040)
<autogenerated>:72 +0x73
github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux.(*MuxConn).Read(0xc420d9ac80, 0xc4219f4000, 0x8000, 0x8000, 0xc4213d1488, 0xa150d6, 0xc4213d1488)
/go/src/github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux/cmux.go:218 +0x183
crypto/tls.(*block).readFromUntil(0xc421d4c390, 0x7f05de3a0b58, 0xc420d9ac80, 0x5, 0xc420d9ac80, 0x6b5e80)
/usr/local/go/src/crypto/tls/conn.go:488 +0x114
crypto/tls.(*Conn).readRecord(0xc42130b180, 0x2366617, 0xc42130b2a0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:590 +0x13d
crypto/tls.(*Conn).Read(0xc42130b180, 0xc4208b0000, 0x8000, 0x8000, 0x0, 0x0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:1134 +0x190
bufio.(*Reader).Read(0xc421e76900, 0xc421a0e118, 0x9, 0x9, 0x6ac9f2, 0x1d54f80, 0x7f05bef87208)
/usr/local/go/src/bufio/bufio.go:213 +0x7e7
io.ReadAtLeast(0x3125cc0, 0xc421e76900, 0xc421a0e118, 0x9, 0x9, 0x9, 0x69d06c, 0xc4213d1a10, 0xc4213d1a10)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x3125cc0, 0xc421e76900, 0xc421a0e118, 0x9, 0x9, 0x0, 0x1, 0xc4201eb4c0)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.readFrameHeader(0xc421a0e118, 0x9, 0x9, 0x3125cc0, 0xc421e76900, 0x0, 0xc400000000, 0xd28c17, 0xc420a3cb00)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:237 +0xa3
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.(*Framer).ReadFrame(0xc421a0e0e0, 0x0, 0x31263c0, 0xc420078040, 0xc42172f780)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:492 +0x118
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*framer).readFrame(0xc422474a80, 0xc422474ab0, 0xc422474ab0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http_util.go:608 +0x53
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).HandleStreams(0xc420c8d340, 0xc422474c00, 0x2365810)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:375 +0x3e6
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveStreams(0xc420edca20, 0x3145560, 0xc420c8d340)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:545 +0x1e8
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveHTTP2Transport(0xc420edca20, 0x3146100, 0xc42130b180, 0x312da80, 0xc42048f080)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:526 +0x6f9
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).handleRawConn(0xc420edca20, 0x3147300, 0xc420d9ac80)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:493 +0x5f4
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).Serve
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:462 +0x69c
goroutine 68794 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*baseQueue).processLoop.func1(0x7f05de30c350, 0xc420af3170)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/queue.go:490 +0x468
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42036ef90, 0xc42070ebe0, 0xc420281c80)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68638 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Client).controller(0xc4207ea000)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:1168 +0x912
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Client
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:297 +0x1692
goroutine 68373 [IO wait]:
net.runtime_pollWait(0x7f05de3981f0, 0x72, 0x6fb8ba)
/usr/local/go/src/runtime/netpoll.go:164 +0x5e
net.(*pollDesc).wait(0xc4200ba148, 0x72, 0x3123fd8, 0xffffffffffffffff)
/usr/local/go/src/net/fd_poll_runtime.go:75 +0x5b
net.(*pollDesc).waitRead(0xc4200ba148, 0xc4208e6000, 0x400)
/usr/local/go/src/net/fd_poll_runtime.go:80 +0x42
net.(*netFD).Read(0xc4200ba0e0, 0xc4208e6000, 0x400, 0x400, 0x0, 0x312e600, 0x3123fd8)
/usr/local/go/src/net/fd_unix.go:250 +0x22b
net.(*conn).Read(0xc42000e098, 0xc4208e6000, 0x400, 0x400, 0x102, 0x6ac5f4, 0x1d56480)
/usr/local/go/src/net/net.go:181 +0x97
net.(*TCPConn).Read(0xc42000e098, 0xc4208e6000, 0x400, 0x400, 0xc4213bb6e8, 0xa150d6, 0xc4213bb6e8)
<autogenerated>:72 +0x73
crypto/tls.(*block).readFromUntil(0xc4202d01b0, 0x7f05da985aa8, 0xc42000e098, 0x5, 0xc42000e098, 0x6b5e80)
/usr/local/go/src/crypto/tls/conn.go:488 +0x114
crypto/tls.(*Conn).readRecord(0xc4201dee00, 0x2366617, 0xc4201def20, 0xc42036eb70)
/usr/local/go/src/crypto/tls/conn.go:590 +0x13d
crypto/tls.(*Conn).Read(0xc4201dee00, 0xc420702000, 0x8000, 0x8000, 0x0, 0x0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:1134 +0x190
bufio.(*Reader).Read(0xc421903b60, 0xc420204498, 0x9, 0x9, 0x69ce1b, 0xc420020600, 0xc420020600)
/usr/local/go/src/bufio/bufio.go:213 +0x7e7
io.ReadAtLeast(0x3125cc0, 0xc421903b60, 0xc420204498, 0x9, 0x9, 0x9, 0x0, 0x0, 0xc4213bbc50)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x3125cc0, 0xc421903b60, 0xc420204498, 0x9, 0x9, 0x6efaa3, 0xc42006bd40, 0xffffffff)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.readFrameHeader(0xc420204498, 0x9, 0x9, 0x3125cc0, 0xc421903b60, 0x0, 0x0, 0xc4213bbd70, 0x69d0f4)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:237 +0xa3
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.(*Framer).ReadFrame(0xc420204460, 0x0, 0x31263c0, 0xc420078040, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:492 +0x118
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*framer).readFrame(0xc4216fdc20, 0xc4214c5bf0, 0xc4214c5b00, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http_util.go:608 +0x53
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Client).reader(0xc4213c8300)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:1095 +0x15b
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Client
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:267 +0x12ec
goroutine 68806 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc400000044)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4212e81b0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202ae3f0, 0xc42070ebe0, 0xc420351d60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68889 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*Store).startGossip.func4(0x7f05de30c350, 0xc420f8ee10)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:1355 +0x64e
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038fb20, 0xc42070ebe0, 0xc42029b8b0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68254 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc40000007a)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4203d24b0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf8e0, 0xc421cfa140, 0xc42036ce60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68690 [select]:
github.com/cockroachdb/cockroach/pkg/gossip.(*Gossip).bootstrap.func1(0x7f05de30c350, 0xc42085b200)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/gossip.go:1064 +0x5e0
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42020eba0, 0xc42070ebe0, 0xc42020eb90)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68768 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420425ad0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f4c40, 0xc42070ebe0, 0xc4201f4c30)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68428 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*baseQueue).processLoop.func1(0x7f05de30c350, 0xc421ef7770)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/queue.go:490 +0x468
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203029c0, 0xc420cf8a00, 0xc42031a740)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68323 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4213cc090)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e0a10, 0xc421cfa140, 0xc4201e09f0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68617 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc40000005c)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42168e390)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2750, 0xc420cf8a00, 0xc4202b01a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68449 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).keepalive(0xc420c8d600)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:894 +0x662
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Server
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:226 +0xfa9
goroutine 68839 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc400000019)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42135e510)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f8d0, 0xc42070ebe0, 0xc4203120a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68477 [chan receive]:
github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux.(*muxListener).Accept(0xc420331080, 0x23657d8, 0xc420edca20, 0x3147300, 0xc420d9ac80)
<autogenerated>:9 +0x9f
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).Serve(0xc420edca20, 0x313d400, 0xc420331080, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:432 +0x1f8
github.com/cockroachdb/cockroach/pkg/server.(*Server).Start.func7(0x7f05de30c350, 0xc4207ede00)
/go/src/github.com/cockroachdb/cockroach/pkg/server/server.go:559 +0x8d
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42026f000, 0xc420cf8a00, 0xc420331260)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68500 [IO wait]:
net.runtime_pollWait(0x7f05da8c4488, 0x72, 0x6fb8ba)
/usr/local/go/src/runtime/netpoll.go:164 +0x5e
net.(*pollDesc).wait(0xc4210a1728, 0x72, 0x3123fd8, 0xffffffffffffffff)
/usr/local/go/src/net/fd_poll_runtime.go:75 +0x5b
net.(*pollDesc).waitRead(0xc4210a1728, 0xc420e00000, 0x8000)
/usr/local/go/src/net/fd_poll_runtime.go:80 +0x42
net.(*netFD).Read(0xc4210a16c0, 0xc420e00000, 0x8000, 0x8000, 0x0, 0x312e600, 0x3123fd8)
/usr/local/go/src/net/fd_unix.go:250 +0x22b
net.(*conn).Read(0xc42000e278, 0xc420e00000, 0x8000, 0x8000, 0x248, 0x0, 0x2366428)
/usr/local/go/src/net/net.go:181 +0x97
net.(*TCPConn).Read(0xc42000e278, 0xc420e00000, 0x8000, 0x8000, 0x1, 0x31263c0, 0xc420078040)
<autogenerated>:72 +0x73
github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux.(*MuxConn).Read(0xc4203e1a40, 0xc420e00000, 0x8000, 0x8000, 0xc420d19488, 0xa150d6, 0xc420d19488)
/go/src/github.com/cockroachdb/cockroach/vendor/github.com/cockroachdb/cmux/cmux.go:218 +0x183
crypto/tls.(*block).readFromUntil(0xc4213b66f0, 0x7f05de3a0b58, 0xc4203e1a40, 0x5, 0xc4203e1a40, 0x0)
/usr/local/go/src/crypto/tls/conn.go:488 +0x114
crypto/tls.(*Conn).readRecord(0xc4217bc700, 0x2366617, 0xc4217bc820, 0xc420e0000d)
/usr/local/go/src/crypto/tls/conn.go:590 +0x13d
crypto/tls.(*Conn).Read(0xc4217bc700, 0xc421966000, 0x8000, 0x8000, 0x0, 0x0, 0x0)
/usr/local/go/src/crypto/tls/conn.go:1134 +0x190
bufio.(*Reader).Read(0xc420dffce0, 0xc421962118, 0x9, 0x9, 0x6ac9f2, 0x1d54f80, 0x7f05d89de3c8)
/usr/local/go/src/bufio/bufio.go:213 +0x7e7
io.ReadAtLeast(0x3125cc0, 0xc420dffce0, 0xc421962118, 0x9, 0x9, 0x9, 0x69d06c, 0xc420d19a10, 0xc420d19a10)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x3125cc0, 0xc420dffce0, 0xc421962118, 0x9, 0x9, 0xc420670001, 0x7f05de458e10, 0x0)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.readFrameHeader(0xc421962118, 0x9, 0x9, 0x3125cc0, 0xc420dffce0, 0x0, 0xc400000000, 0xd28c17, 0xc42082c4b0)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:237 +0xa3
github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2.(*Framer).ReadFrame(0xc4219620e0, 0x3130a40, 0xc42082c4b0, 0x0, 0xc420a3d300)
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/net/http2/frame.go:492 +0x118
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*framer).readFrame(0xc42082c480, 0xc42082c4b0, 0xc42082c4b0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http_util.go:608 +0x53
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Server).HandleStreams(0xc420c8d600, 0xc42082c600, 0x2365810)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_server.go:375 +0x3e6
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveStreams(0xc4213b2480, 0x3145560, 0xc420c8d600)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:545 +0x1e8
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).serveHTTP2Transport(0xc4213b2480, 0x3146100, 0xc4217bc700, 0x312da80, 0xc420383a20)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:526 +0x6f9
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).handleRawConn(0xc4213b2480, 0x3147300, 0xc4203e1a40)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:493 +0x5f4
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*Server).Serve
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/server.go:462 +0x69c
goroutine 68512 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc42085a090)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203147f0, 0xc420cf8a00, 0xc4203147e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68335 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*http2Client).keepalive(0xc4213c8300)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:1214 +0x6e6
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.newHTTP2Client
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/http2_client.go:299 +0x1789
goroutine 68805 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc400000043)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc420af2660)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202ae3e0, 0xc42070ebe0, 0xc420351d20)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68106 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Server).refreshSettings.func2(0x7f05de30c350, 0xc420b98090)
/go/src/github.com/cockroachdb/cockroach/pkg/server/settingsworker.go:113 +0x48f
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203dfcf0, 0xc421cfa140, 0xc4203056e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68294 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Node).startWriteSummaries.func1(0x7f05de30c350, 0xc4216fc510)
/go/src/github.com/cockroachdb/cockroach/pkg/server/node.go:739 +0x3b5
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e05f0, 0xc421cfa140, 0xc4203504c0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68606 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000036)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4209b6630)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a26a0, 0xc420cf8a00, 0xc420088b60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68308 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420d1b5c0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e07c0, 0xc421cfa140, 0xc4201e07b0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 69017 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*recvBufferReader).Read(0xc421913080, 0xc420369630, 0x5, 0x5, 0x0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:145 +0x70a
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*Stream).Read(0xc420af4400, 0xc420369630, 0x5, 0x5, 0x1d54f80, 0x7f05ce775ec8, 0xc4204a6138)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:328 +0x79
io.ReadAtLeast(0x312aac0, 0xc420af4400, 0xc420369630, 0x5, 0x5, 0x5, 0xc4215d9b48, 0x6b16f1, 0xc420545860)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x312aac0, 0xc420af4400, 0xc420369630, 0x5, 0x5, 0x6ef638, 0xc4206e0510, 0xc4215d9bc0)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*parser).recvMsg(0xc420369620, 0x7fffffff, 0x34, 0x34, 0xc4215d9d18, 0x69ce1b, 0x6840ad, 0xc41ffed572)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:255 +0xa0
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.recv(0xc420369620, 0x313da00, 0x3f88010, 0xc420af4400, 0x3132580, 0x3f88010, 0x21bdce0, 0xc4202551a0, 0x7fffffff, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:351 +0x61
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*serverStream).RecvMsg(0xc420739280, 0x21bdce0, 0xc4202551a0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:623 +0x1cf
github.com/cockroachdb/cockroach/pkg/storage.(*multiRaftRaftMessageBatchServer).Recv(0xc4202dcee0, 0x7f05de30c350, 0xc420851a10, 0xc421180900)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/raft.pb.go:397 +0x86
github.com/cockroachdb/cockroach/pkg/storage.(*RaftTransport).RaftMessageBatch.func1.1.1(0x31471e0, 0xc4202dcee0, 0xc420662180, 0x7f05de30c350, 0xc420851a10, 0x18, 0xc42100a778)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/raft_transport.go:300 +0x61
github.com/cockroachdb/cockroach/pkg/storage.(*RaftTransport).RaftMessageBatch.func1.1(0x7f05de30c350, 0xc420851a10)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/raft_transport.go:323 +0x75
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202dcf00, 0xc421cfa140, 0xc420851950)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68820 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc40000002b)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4212e86c0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f790, 0xc42070ebe0, 0xc4202cbb80)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68401 [select]:
github.com/cockroachdb/cockroach/pkg/security.(*CertificateManager).RegisterSignalHandler.func1(0xc420cf8a00, 0xc421268a80, 0xc4200d1ce0)
/go/src/github.com/cockroachdb/cockroach/pkg/security/certificate_manager.go:127 +0x511
created by github.com/cockroachdb/cockroach/pkg/security.(*CertificateManager).RegisterSignalHandler
/go/src/github.com/cockroachdb/cockroach/pkg/security/certificate_manager.go:140 +0xf1
goroutine 68566 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000046)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc421ef76e0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2360, 0xc420cf8a00, 0xc4201f39e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68256 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc40000007c)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4203d2540)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf900, 0xc421cfa140, 0xc42036cea0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68658 [chan receive]:
database/sql.(*DB).connectionOpener(0xc42070eb40)
/usr/local/go/src/database/sql/sql.go:837 +0x6e
created by database/sql.Open
/usr/local/go/src/database/sql/sql.go:582 +0x318
goroutine 68430 [select]:
github.com/cockroachdb/cockroach/pkg/storage.(*baseQueue).processLoop.func1(0x7f05de30c350, 0xc421ef77a0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/queue.go:490 +0x468
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203029e0, 0xc420cf8a00, 0xc42031a7a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68515 [select]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*recvBufferReader).Read(0xc42172fc40, 0xc4201f3b90, 0x5, 0x5, 0x0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:145 +0x70a
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport.(*Stream).Read(0xc420768600, 0xc4201f3b90, 0x5, 0x5, 0x679aa3, 0xc421412bd0, 0x20c24a0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/transport/transport.go:328 +0x79
io.ReadAtLeast(0x312aac0, 0xc420768600, 0xc4201f3b90, 0x5, 0x5, 0x5, 0x11991b7, 0x30dd0fed, 0xc421412be8)
/usr/local/go/src/io/io.go:307 +0xb7
io.ReadFull(0x312aac0, 0xc420768600, 0xc4201f3b90, 0x5, 0x5, 0xc, 0x0, 0xc4207b3c08)
/usr/local/go/src/io/io.go:325 +0x73
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*parser).recvMsg(0xc4201f3b80, 0x7fffffff, 0x6ef17e, 0xc420570540, 0x6d127c, 0x6efaa3, 0x69d06c, 0xc4207b3c60)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:255 +0xa0
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.recv(0xc4201f3b80, 0x313da00, 0x3f88010, 0xc420768600, 0x3132580, 0x3f88010, 0x21b4f20, 0xc4214311d0, 0x7fffffff, 0x0, ...)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/rpc_util.go:351 +0x61
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*clientStream).RecvMsg(0xc420c8d8c0, 0x21b4f20, 0xc4214311d0, 0x0, 0x0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:379 +0x1da
github.com/cockroachdb/cockroach/pkg/gossip.(*gossipGossipClient).Recv(0xc4202434d0, 0x7f05de30c350, 0xc42082c960, 0xc42073c780)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/gossip.pb.go:194 +0x86
github.com/cockroachdb/cockroach/pkg/gossip.(*client).gossip.func2.1(0x3146160, 0xc4202434d0, 0xc421090f70, 0x7f05de30c350, 0xc42082c960, 0xc42073c780, 0xc420d34768, 0x69c742)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/client.go:313 +0x43
github.com/cockroachdb/cockroach/pkg/gossip.(*client).gossip.func2(0x7f05de30c350, 0xc42082c960)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/client.go:321 +0xe6
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4202435a0, 0xc420cf8a00, 0xc42172fcc0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68506 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Node).startGossip.func1(0x7f05de30c350, 0xc421ef69c0)
/go/src/github.com/cockroachdb/cockroach/pkg/server/node.go:661 +0x5cc
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314620, 0xc420cf8a00, 0xc4203985a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68218 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc400000095)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42007df80)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf680, 0xc421cfa140, 0xc42036c8e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 69077 [runnable]:
github.com/cockroachdb/cockroach/pkg/storage_test.TestGossipFirstRange.func1(0xc4201eb650, 0xb, 0xc420269a20, 0x1f, 0x20, 0x14c26611bf6bf478, 0x0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/gossip_test.go:56 +0x177
github.com/cockroachdb/cockroach/pkg/gossip.(*infoStore).runCallbacks.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/infostore.go:277 +0x10b
github.com/cockroachdb/cockroach/pkg/gossip.(*infoStore).runCallbacks.func2(0x7f05de307058, 0xc420078d68)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/infostore.go:299 +0x161
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunAsyncTask.func1(0xc421cfa140, 0x7f05de307058, 0xc420078d68, 0x2e646e5, 0x13, 0x12d, 0x0, 0x0, 0xc4201eb7e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:294 +0x101
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunAsyncTask
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:295 +0x173
goroutine 68833 [semacquire]:
sync.runtime_notifyListWait(0xc4215e5c10, 0xc40000001f)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4215e5c00)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc42075b290, 0xc42070ebe0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42135e630)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038f860, 0xc42070ebe0, 0xc4202cbf60)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68757 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc420283350)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f4a00, 0xc42070ebe0, 0xc4201f49d0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68234 [semacquire]:
sync.runtime_notifyListWait(0xc4206e0510, 0xc4000000a7)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4206e0500)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4204a6120, 0xc421cfa140)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc4202a4330)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf790, 0xc421cfa140, 0xc42036cba0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68576 [semacquire]:
sync.runtime_notifyListWait(0xc4219fdbd0, 0xc400000038)
/usr/local/go/src/runtime/sema.go:298 +0x11a
sync.(*Cond).Wait(0xc4219fdbc0)
/usr/local/go/src/sync/cond.go:57 +0x97
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc4208da2d0, 0xc420cf8a00)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:199 +0xe2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x7f05de30c350, 0xc42168e180)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:168 +0x4b
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203a2420, 0xc420cf8a00, 0xc4201f3e80)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68507 [select]:
github.com/cockroachdb/cockroach/pkg/server.(*Server).startSampleEnvironment.func1(0x7f05de30c350, 0xc4216fd950)
/go/src/github.com/cockroachdb/cockroach/pkg/server/server.go:947 +0x1ce
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc420314760, 0xc420cf8a00, 0xc420398640)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68104 [select]:
github.com/cockroachdb/cockroach/pkg/kv.(*TxnCoordSender).printStatsLoop(0xc4201848f0, 0x7f05de30c350, 0xc420b98030)
/go/src/github.com/cockroachdb/cockroach/pkg/kv/txn_coord_sender.go:255 +0xfce
github.com/cockroachdb/cockroach/pkg/kv.NewTxnCoordSender.func1(0x7f05de30c350, 0xc420b98030)
/go/src/github.com/cockroachdb/cockroach/pkg/kv/txn_coord_sender.go:239 +0x56
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203dfa60, 0xc421cfa140, 0xc4203dfa50)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68260 [semacquire]:
sync.runtime_Semacquire(0xc4204a61a4)
/usr/local/go/src/runtime/sema.go:47 +0x34
sync.(*WaitGroup).Wait(0xc4204a6198)
/usr/local/go/src/sync/waitgroup.go:131 +0xc2
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Wait(0xc4204a6120, 0x7f05de30c350, 0xc4203d25d0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:174 +0x3f
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Wait-fm(0x7f05de30c350, 0xc4203d25d0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/store.go:3476 +0x56
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201cf960, 0xc421cfa140, 0xc4201cf950)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68510 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*distSQLPlanner).initRunners.func1(0x7f05de30c350, 0xc4216fd920)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:83 +0x1cb
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4203147b0, 0xc420cf8a00, 0xc4203147a0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68479 [chan receive]:
github.com/cockroachdb/cockroach/pkg/gossip.(*server).start.func3(0x7f05de30c350, 0xc420a73200)
/go/src/github.com/cockroachdb/cockroach/pkg/gossip/server.go:386 +0x94
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42026f150, 0xc420cf8a00, 0xc420331360)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68328 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*Executor).Start.func1(0x7f05de30c350, 0xc4213cc3c0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/executor.go:372 +0x19d
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201e0ad0, 0xc421cfa140, 0xc420350540)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68760 [select]:
github.com/cockroachdb/cockroach/pkg/sql.(*SchemaChangeManager).Start.func1(0x7f05de30c350, 0xc420283c80)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/schema_changer.go:807 +0x1f0c
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4201f4a70, 0xc42070ebe0, 0xc4202de820)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:215 +0x161
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:216 +0xbb
goroutine 68967 [IO wait]:
``` | non_priority | storage testgossipfirstrange failed under stress sha parameters tags goflags race stress build found a failed test server config go storage engine initialized server node go store not bootstrapped server node go cluster has been created server node go add additional nodes by specifying join storage store go failed initial metrics computation system config not yet available server node go initialized store capacity available rangecount leasecount server node go node id initialized gossip gossip go nodedescriptor set to node id address attrs locality storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go node connected via gossip and verified as part of cluster server node go node started with engine s and attributes sql executor go creating distsqlplanner with address tcp server server go starting https server at server server go starting grpc postgres server at server server go advertising cockroachdb node at sql event log go event alter table target info tablename eventlog statement alter table system eventlog alter column uniqueid set default uuid user node mutationid cascadedroppedviews sql lease go publish descid eventlog version mtime utc server server go done ensuring all necessary migrations have run server server go serving sql connections sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality clusterid startedat lastup server status runtime go could not parse build timestamp parsing time as cannot parse as gossip gossip go no incoming or outgoing connections server config go storage engine initialized server node go store not bootstrapped storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id gossip client go started gossip client to gossip server go received initial cluster verification connection from tcp server node go node connected via gossip and verified as part of cluster storage stores go wrote node addresses to persistent storage kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping server node go new node allocated id gossip gossip go nodedescriptor set to node id address attrs locality server node go node started with engine s and attributes storage stores go wrote node addresses to persistent storage sql executor go creating distsqlplanner with address tcp server server go starting https server at server server go starting grpc postgres server at server server go advertising cockroachdb node at server server go done ensuring all necessary migrations have run server server go serving sql connections sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality clusterid startedat lastup server status runtime go could not parse build timestamp parsing time as cannot parse as gossip gossip go no incoming or outgoing connections server config go storage engine initialized server node go store not bootstrapped storage stores go read node addresses from persistent storage server node go connecting to gossip network to verify cluster id server node go bootstrapped store gossip client go started gossip client to gossip server go received initial cluster verification connection from tcp server node go node connected via gossip and verified as part of cluster storage stores go wrote node addresses to persistent storage storage stores go wrote node addresses to persistent storage kv dist sender go unable to determine this node s attributes for replica selection node is most likely bootstrapping server node go new node allocated id gossip gossip go nodedescriptor set to node id address attrs locality server node go node started with engine s and attributes sql executor go creating distsqlplanner with address tcp storage stores go wrote node addresses to persistent storage server server go starting https server at server server go starting grpc postgres server at server server go advertising cockroachdb node at server server go done ensuring all necessary migrations have run server server go serving sql connections storage stores go wrote node addresses to persistent storage server node go bootstrapped store storage replica raftstorage go generated preemptive snapshot at index sql event log go event node join target info descriptor nodeid address networkfield tcp addressfield attrs locality clusterid startedat lastup storage store go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor m in ax storage replica go proposing add replica storage raft transport go raft transport stream to node established storage replica raftstorage go generated preemptive snapshot at index storage store go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor m in ax storage replica go proposing add replica storage raft transport go raft transport stream to node established storage replica command go change replicas remove replica read existing descriptor m in ax storage replica go proposing remove replica storage store go removing replica storage replica go removed keys in util log crash reporting go a panic has occurred util log crash reporting go reported as error panic runtime error invalid memory address or nil pointer dereference panic runtime error invalid memory address or nil pointer dereference goroutine github com cockroachdb cockroach pkg util stop stopper recover go src github com cockroachdb cockroach pkg util stop stopper go panic usr local go src runtime panic go github com cockroachdb cockroach pkg storage replica updateproposalquotaraftmulocked go src github com cockroachdb cockroach pkg storage replica go github com cockroachdb cockroach pkg storage replica handleraftreadyraftmulocked go src github com cockroachdb cockroach pkg storage replica go github com cockroachdb cockroach pkg storage replica handleraftready go src github com cockroachdb cockroach pkg storage replica go github com cockroachdb cockroach pkg storage store processready go src github com cockroachdb cockroach pkg storage store go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine testing t run usr local go src testing testing go testing runtests usr local go src testing testing go testing trunner usr local go src testing testing go testing runtests usr local go src testing testing go testing m run usr local go src testing testing go github com cockroachdb cockroach pkg storage test testmain go src github com cockroachdb cockroach pkg storage main test go main main github com cockroachdb cockroach pkg storage test testmain go goroutine runtime goexit usr local go src runtime asm s goroutine github com cockroachdb cockroach pkg util log loggingt flushdaemon go src github com cockroachdb cockroach pkg util log clog go created by github com cockroachdb cockroach pkg util log init go src github com cockroachdb cockroach pkg util log clog go goroutine os signal signal recv usr local go src runtime sigqueue go os signal loop usr local go src os signal signal unix go created by os signal init usr local go src os signal signal unix go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc transport keepalive go src github com cockroachdb cockroach vendor google golang org grpc transport server go created by github com cockroachdb cockroach vendor google golang org grpc transport go src github com cockroachdb cockroach vendor google golang org grpc transport server go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg server server startsampleenvironment go src github com cockroachdb cockroach pkg server server go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg storage store startgossip go src github com cockroachdb cockroach pkg storage store go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine net runtime pollwait usr local go src runtime netpoll go net polldesc wait usr local go src net fd poll runtime go net polldesc waitread usr local go src net fd poll runtime go net netfd read usr local go src net fd unix go net conn read usr local go src net net go net tcpconn read github com cockroachdb cockroach vendor github com cockroachdb cmux muxconn read go src github com cockroachdb cockroach vendor github com cockroachdb cmux cmux go crypto tls block readfromuntil usr local go src crypto tls conn go crypto tls conn readrecord usr local go src crypto tls conn go crypto tls conn read usr local go src crypto tls conn go bufio reader read usr local go src bufio bufio go io readatleast usr local go src io io go io readfull usr local go src io io go github com cockroachdb cockroach vendor golang org x net readframeheader go src github com cockroachdb cockroach vendor golang org x net frame go github com cockroachdb cockroach vendor golang org x net framer readframe go src github com cockroachdb cockroach vendor golang org x net frame go github com cockroachdb cockroach vendor google golang org grpc transport framer readframe go src github com cockroachdb cockroach vendor google golang org grpc transport http util go github com cockroachdb cockroach vendor google golang org grpc transport handlestreams go src github com cockroachdb cockroach vendor google golang org grpc transport server go github com cockroachdb cockroach vendor google golang org grpc server servestreams go src github com cockroachdb cockroach vendor google golang org grpc server go github com cockroachdb cockroach vendor google golang org grpc server go src github com cockroachdb cockroach vendor google golang org grpc server go github com cockroachdb cockroach vendor google golang org grpc server handlerawconn go src github com cockroachdb cockroach vendor google golang org grpc server go created by github com cockroachdb cockroach vendor google golang org grpc server serve go src github com cockroachdb cockroach vendor google golang org grpc server go goroutine github com cockroachdb cockroach pkg storage basequeue processloop go src github com cockroachdb cockroach pkg storage queue go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc transport controller go src github com cockroachdb cockroach vendor google golang org grpc transport client go created by github com cockroachdb cockroach vendor google golang org grpc transport go src github com cockroachdb cockroach vendor google golang org grpc transport client go goroutine net runtime pollwait usr local go src runtime netpoll go net polldesc wait usr local go src net fd poll runtime go net polldesc waitread usr local go src net fd poll runtime go net netfd read usr local go src net fd unix go net conn read usr local go src net net go net tcpconn read crypto tls block readfromuntil usr local go src crypto tls conn go crypto tls conn readrecord usr local go src crypto tls conn go crypto tls conn read usr local go src crypto tls conn go bufio reader read usr local go src bufio bufio go io readatleast usr local go src io io go io readfull usr local go src io io go github com cockroachdb cockroach vendor golang org x net readframeheader go src github com cockroachdb cockroach vendor golang org x net frame go github com cockroachdb cockroach vendor golang org x net framer readframe go src github com cockroachdb cockroach vendor golang org x net frame go github com cockroachdb cockroach vendor google golang org grpc transport framer readframe go src github com cockroachdb cockroach vendor google golang org grpc transport http util go github com cockroachdb cockroach vendor google golang org grpc transport reader go src github com cockroachdb cockroach vendor google golang org grpc transport client go created by github com cockroachdb cockroach vendor google golang org grpc transport go src github com cockroachdb cockroach vendor google golang org grpc transport client go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg storage store startgossip go src github com cockroachdb cockroach pkg storage store go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg gossip gossip bootstrap go src github com cockroachdb cockroach pkg gossip gossip go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg storage basequeue processloop go src github com cockroachdb cockroach pkg storage queue go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc transport keepalive go src github com cockroachdb cockroach vendor google golang org grpc transport server go created by github com cockroachdb cockroach vendor google golang org grpc transport go src github com cockroachdb cockroach vendor google golang org grpc transport server go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor github com cockroachdb cmux muxlistener accept github com cockroachdb cockroach vendor google golang org grpc server serve go src github com cockroachdb cockroach vendor google golang org grpc server go github com cockroachdb cockroach pkg server server start go src github com cockroachdb cockroach pkg server server go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine net runtime pollwait usr local go src runtime netpoll go net polldesc wait usr local go src net fd poll runtime go net polldesc waitread usr local go src net fd poll runtime go net netfd read usr local go src net fd unix go net conn read usr local go src net net go net tcpconn read github com cockroachdb cockroach vendor github com cockroachdb cmux muxconn read go src github com cockroachdb cockroach vendor github com cockroachdb cmux cmux go crypto tls block readfromuntil usr local go src crypto tls conn go crypto tls conn readrecord usr local go src crypto tls conn go crypto tls conn read usr local go src crypto tls conn go bufio reader read usr local go src bufio bufio go io readatleast usr local go src io io go io readfull usr local go src io io go github com cockroachdb cockroach vendor golang org x net readframeheader go src github com cockroachdb cockroach vendor golang org x net frame go github com cockroachdb cockroach vendor golang org x net framer readframe go src github com cockroachdb cockroach vendor golang org x net frame go github com cockroachdb cockroach vendor google golang org grpc transport framer readframe go src github com cockroachdb cockroach vendor google golang org grpc transport http util go github com cockroachdb cockroach vendor google golang org grpc transport handlestreams go src github com cockroachdb cockroach vendor google golang org grpc transport server go github com cockroachdb cockroach vendor google golang org grpc server servestreams go src github com cockroachdb cockroach vendor google golang org grpc server go github com cockroachdb cockroach vendor google golang org grpc server go src github com cockroachdb cockroach vendor google golang org grpc server go github com cockroachdb cockroach vendor google golang org grpc server handlerawconn go src github com cockroachdb cockroach vendor google golang org grpc server go created by github com cockroachdb cockroach vendor google golang org grpc server serve go src github com cockroachdb cockroach vendor google golang org grpc server go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc transport keepalive go src github com cockroachdb cockroach vendor google golang org grpc transport client go created by github com cockroachdb cockroach vendor google golang org grpc transport go src github com cockroachdb cockroach vendor google golang org grpc transport client go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg server server refreshsettings go src github com cockroachdb cockroach pkg server settingsworker go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg server node startwritesummaries go src github com cockroachdb cockroach pkg server node go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc transport recvbufferreader read go src github com cockroachdb cockroach vendor google golang org grpc transport transport go github com cockroachdb cockroach vendor google golang org grpc transport stream read go src github com cockroachdb cockroach vendor google golang org grpc transport transport go io readatleast usr local go src io io go io readfull usr local go src io io go github com cockroachdb cockroach vendor google golang org grpc parser recvmsg go src github com cockroachdb cockroach vendor google golang org grpc rpc util go github com cockroachdb cockroach vendor google golang org grpc recv go src github com cockroachdb cockroach vendor google golang org grpc rpc util go github com cockroachdb cockroach vendor google golang org grpc serverstream recvmsg go src github com cockroachdb cockroach vendor google golang org grpc stream go github com cockroachdb cockroach pkg storage multiraftraftmessagebatchserver recv go src github com cockroachdb cockroach pkg storage raft pb go github com cockroachdb cockroach pkg storage rafttransport raftmessagebatch go src github com cockroachdb cockroach pkg storage raft transport go github com cockroachdb cockroach pkg storage rafttransport raftmessagebatch go src github com cockroachdb cockroach pkg storage raft transport go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg security certificatemanager registersignalhandler go src github com cockroachdb cockroach pkg security certificate manager go created by github com cockroachdb cockroach pkg security certificatemanager registersignalhandler go src github com cockroachdb cockroach pkg security certificate manager go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine database sql db connectionopener usr local go src database sql sql go created by database sql open usr local go src database sql sql go goroutine github com cockroachdb cockroach pkg storage basequeue processloop go src github com cockroachdb cockroach pkg storage queue go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc transport recvbufferreader read go src github com cockroachdb cockroach vendor google golang org grpc transport transport go github com cockroachdb cockroach vendor google golang org grpc transport stream read go src github com cockroachdb cockroach vendor google golang org grpc transport transport go io readatleast usr local go src io io go io readfull usr local go src io io go github com cockroachdb cockroach vendor google golang org grpc parser recvmsg go src github com cockroachdb cockroach vendor google golang org grpc rpc util go github com cockroachdb cockroach vendor google golang org grpc recv go src github com cockroachdb cockroach vendor google golang org grpc rpc util go github com cockroachdb cockroach vendor google golang org grpc clientstream recvmsg go src github com cockroachdb cockroach vendor google golang org grpc stream go github com cockroachdb cockroach pkg gossip gossipgossipclient recv go src github com cockroachdb cockroach pkg gossip gossip pb go github com cockroachdb cockroach pkg gossip client gossip go src github com cockroachdb cockroach pkg gossip client go github com cockroachdb cockroach pkg gossip client gossip go src github com cockroachdb cockroach pkg gossip client go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg server node startgossip go src github com cockroachdb cockroach pkg server node go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg storage test testgossipfirstrange go src github com cockroachdb cockroach pkg storage gossip test go github com cockroachdb cockroach pkg gossip infostore runcallbacks go src github com cockroachdb cockroach pkg gossip infostore go github com cockroachdb cockroach pkg gossip infostore runcallbacks go src github com cockroachdb cockroach pkg gossip infostore go github com cockroachdb cockroach pkg util stop stopper runasynctask go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runasynctask go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg server server startsampleenvironment go src github com cockroachdb cockroach pkg server server go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg kv txncoordsender printstatsloop go src github com cockroachdb cockroach pkg kv txn coord sender go github com cockroachdb cockroach pkg kv newtxncoordsender go src github com cockroachdb cockroach pkg kv txn coord sender go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine sync runtime semacquire usr local go src runtime sema go sync waitgroup wait usr local go src sync waitgroup go github com cockroachdb cockroach pkg storage raftscheduler wait go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler wait fm go src github com cockroachdb cockroach pkg storage store go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg gossip server start go src github com cockroachdb cockroach pkg gossip server go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql executor start go src github com cockroachdb cockroach pkg sql executor go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql schemachangemanager start go src github com cockroachdb cockroach pkg sql schema changer go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine | 0 |
69,146 | 17,580,379,295 | IssuesEvent | 2021-08-16 06:26:38 | gocd/gocd | https://api.github.com/repos/gocd/gocd | opened | Upgrade Gradle to v7 | build-script | ##### Issue Type
- Technical
##### Summary
Tracking pre-requisites for upgrade.
Lots of work has already been done by @marques-work however there are still some pieces blocking this. This may not be complete!
- [X] Resolve deprecations on Docker build tasks #9577
- [X] Investigate deprecation warnings from OWASP `dependencyCheckAggregate`
- According to [this](https://github.com/jeremylong/DependencyCheck/issues/2644#issuecomment-706114730) and https://github.com/dependency-check/dependency-check-gradle/issues/176 it should not be an issue?
- [ ] Investigate/resolve deprecations on `installers:assemble` (e.g see [here](https://build.gocd.org/go/tab/build/detail/installers/2596/dist/1/dist))
- [ ] Resolve deprecations on `:server:downloadGeckoDriver` (see [here](https://build.gocd.org/go/tab/build/detail/build-linux/5544/build-non-server/1/Jasmine))
- [ ] Resolve deprecations on `:server:licenseMain` (see [here](https://build.gocd.org/go/tab/build/detail/build-linux/5544/build-non-server/1/FastTests-runInstance-1))
- [ ] Upgrade `grade-license-plugin` (PR #9370 needs fixing)
- [ ] Resolve deprecations within `generateLicenseReport` and `licenseReportAggregate` by upgrading Gradle License Report or working around issues
- https://github.com/jk1/Gradle-License-Report/issues/161
- https://github.com/jk1/Gradle-License-Report/issues/203
| 1.0 | Upgrade Gradle to v7 - ##### Issue Type
- Technical
##### Summary
Tracking pre-requisites for upgrade.
Lots of work has already been done by @marques-work however there are still some pieces blocking this. This may not be complete!
- [X] Resolve deprecations on Docker build tasks #9577
- [X] Investigate deprecation warnings from OWASP `dependencyCheckAggregate`
- According to [this](https://github.com/jeremylong/DependencyCheck/issues/2644#issuecomment-706114730) and https://github.com/dependency-check/dependency-check-gradle/issues/176 it should not be an issue?
- [ ] Investigate/resolve deprecations on `installers:assemble` (e.g see [here](https://build.gocd.org/go/tab/build/detail/installers/2596/dist/1/dist))
- [ ] Resolve deprecations on `:server:downloadGeckoDriver` (see [here](https://build.gocd.org/go/tab/build/detail/build-linux/5544/build-non-server/1/Jasmine))
- [ ] Resolve deprecations on `:server:licenseMain` (see [here](https://build.gocd.org/go/tab/build/detail/build-linux/5544/build-non-server/1/FastTests-runInstance-1))
- [ ] Upgrade `grade-license-plugin` (PR #9370 needs fixing)
- [ ] Resolve deprecations within `generateLicenseReport` and `licenseReportAggregate` by upgrading Gradle License Report or working around issues
- https://github.com/jk1/Gradle-License-Report/issues/161
- https://github.com/jk1/Gradle-License-Report/issues/203
| non_priority | upgrade gradle to issue type technical summary tracking pre requisites for upgrade lots of work has already been done by marques work however there are still some pieces blocking this this may not be complete resolve deprecations on docker build tasks investigate deprecation warnings from owasp dependencycheckaggregate according to and it should not be an issue investigate resolve deprecations on installers assemble e g see resolve deprecations on server downloadgeckodriver see resolve deprecations on server licensemain see upgrade grade license plugin pr needs fixing resolve deprecations within generatelicensereport and licensereportaggregate by upgrading gradle license report or working around issues | 0 |
75,812 | 9,330,894,743 | IssuesEvent | 2019-03-28 08:24:55 | elixir-lang/ex_doc | https://api.github.com/repos/elixir-lang/ex_doc | closed | Provide "Search or go to..." functionality | Area:HTML Note:Design Note:Discussion | The functionality should mirror the "search or jump to" functionality on GitHub.
Once the user types "foobar" in the search box, the first entry will be "Search foobar..." but below we will show any existing matching entry:
```
|-----------------------------------|
| -> | to_charlist |
|-----------------------------------|
| Search to_charlist... |
| Atom.to_charlist/1 (function) |
| Kernel.to_charlist/1 (function) |
| List.to_charlist/1 (function) |
| CharList (module) |
|-----------------------------------|
```
As we press up and down, we can choose the search or to go straight to a given entry. Note this autocomplete functionality is exactly how the search works today, so we can likely just reuse the inner logic.
I am also aware we may need to change how the search is styled today or even move it elsewhere completely. Suggestions on this area are welcome.
Extra: to improve the usability we also should: provide shortcuts to all entries in the top right of the sidebar. For example, pressing s should start "Search". Pressing "c" should "Collapse/expand". And pressing "n" should toggle "Night/day mode". | 1.0 | Provide "Search or go to..." functionality - The functionality should mirror the "search or jump to" functionality on GitHub.
Once the user types "foobar" in the search box, the first entry will be "Search foobar..." but below we will show any existing matching entry:
```
|-----------------------------------|
| -> | to_charlist |
|-----------------------------------|
| Search to_charlist... |
| Atom.to_charlist/1 (function) |
| Kernel.to_charlist/1 (function) |
| List.to_charlist/1 (function) |
| CharList (module) |
|-----------------------------------|
```
As we press up and down, we can choose the search or to go straight to a given entry. Note this autocomplete functionality is exactly how the search works today, so we can likely just reuse the inner logic.
I am also aware we may need to change how the search is styled today or even move it elsewhere completely. Suggestions on this area are welcome.
Extra: to improve the usability we also should: provide shortcuts to all entries in the top right of the sidebar. For example, pressing s should start "Search". Pressing "c" should "Collapse/expand". And pressing "n" should toggle "Night/day mode". | non_priority | provide search or go to functionality the functionality should mirror the search or jump to functionality on github once the user types foobar in the search box the first entry will be search foobar but below we will show any existing matching entry to charlist search to charlist atom to charlist function kernel to charlist function list to charlist function charlist module as we press up and down we can choose the search or to go straight to a given entry note this autocomplete functionality is exactly how the search works today so we can likely just reuse the inner logic i am also aware we may need to change how the search is styled today or even move it elsewhere completely suggestions on this area are welcome extra to improve the usability we also should provide shortcuts to all entries in the top right of the sidebar for example pressing s should start search pressing c should collapse expand and pressing n should toggle night day mode | 0 |
285,110 | 24,643,710,283 | IssuesEvent | 2022-10-17 13:30:38 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Test failure: ShareServicePrerenderBrowserTest.Text | ci-concern bot/type/test bot/platform/windows bot/arch/x64 bot/channel/nightly bot/branch/master | Greetings human!
Bad news. `ShareServicePrerenderBrowserTest.Text` [failed on windows x64 nightly master](https://ci.brave.com/job/brave-browser-build-windows-x64-asan/283/testReport/junit/(root)/ShareServicePrerenderBrowserTest/windows_x64___test_browser_chromium___Text).
<details>
<summary>Stack trace</summary>
```
[ RUN ] ShareServicePrerenderBrowserTest.Text
[9472:4368:1014/132339.390:WARNING:external_provider_impl.cc(511)] Malformed extension dictionary for extension: odbfpeeihdkbihmopkbjmoonfanlbfcl. Key external_update_url has value "", which is not a valid URL.
[9472:4368:1014/132339.884:ERROR:device_event_log_impl.cc(215)] [13:23:39.885] Bluetooth: bluetooth_adapter_winrt.cc:1074 Getting Default Adapter failed.
[9472:4368:1014/132340.319:INFO:ui_test_utils.cc(232)] NavigateToURL: http://127.0.0.1:56449/empty.html
[9472:4548:1014/132340.492:WARNING:embedded_test_server.cc(674)] Request not handled. Returning 404: /favicon.ico
..\..\content\public\test\prerender_test_util.cc(290): error: Expected: (host) != (nullptr), actual: NULL vs (nullptr)
Stack trace:
Backtrace:
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C265E1+13946760]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C26D66+13948685]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C2753F+13950694]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965B55D+62727853]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF5FF5+12700060]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AFAF6E+12720405]
free_base [0x00007FF7C0A5B875+29615013]
free_base [0x00007FF7C0A5BA3E+29615470]
free_base [0x00007FF7C0A61C0C+29640508]
free_base [0x00007FF7C0A54EE6+29587990]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A2D44+38205748]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5DF6+38218214]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5694+38216324]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1284+38198900]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1967+38200663]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF3DA0+12691271]
_ubsan_get_current_report_data [0x00007FF7C8AC3B83+948275]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965D5FC+62736204]
..\..\content\public\test\prerender_test_util.cc(310): error: Expected: (host_id) != (RenderFrameHost::kNoFrameTreeNodeId), actual: -1 vs -1
Stack trace:
Backtrace:
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C276B4+13951067]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965B55D+62727853]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF5FF5+12700060]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AFAF6E+12720405]
free_base [0x00007FF7C0A5B875+29615013]
free_base [0x00007FF7C0A5BA3E+29615470]
free_base [0x00007FF7C0A61C0C+29640508]
free_base [0x00007FF7C0A54EE6+29587990]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A2D44+38205748]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5DF6+38218214]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5694+38216324]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1284+38198900]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1967+38200663]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF3DA0+12691271]
_ubsan_get_current_report_data [0x00007FF7C8AC3B83+948275]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965D5FC+62736204]
..\..\content\public\test\prerender_test_util.cc(433): error: Expected: (prerender_host) != (nullptr), actual: NULL vs (nullptr)
Stack trace:
Backtrace:
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C2AA7F+13964326]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965B68A+62728154]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF5FF5+12700060]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AFAF6E+12720405]
free_base [0x00007FF7C0A5B875+29615013]
free_base [0x00007FF7C0A5BA3E+29615470]
free_base [0x00007FF7C0A61C0C+29640508]
free_base [0x00007FF7C0A54EE6+29587990]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A2D44+38205748]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5DF6+38218214]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5694+38216324]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1284+38198900]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1967+38200663]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF3DA0+12691271]
_ubsan_get_current_report_data [0x00007FF7C8AC3B83+948275]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965D5FC+62736204]
=================================================================
==9472==ERROR: AddressSanitizer: access-violation on unknown address 0x000000000278 (pc 0x7ff7c13d7337 bp 0x00172cafe3f0 sp 0x00172cafe360 T0)
==9472==The signal is caused by a READ memory access.
==9472==Hint: address points to the zero page.
==9472==*** WARNING: Failed to initialize DbgHelp! ***
==9472==*** Most likely this means that the app is already ***
==9472==*** using DbgHelp, possibly with incompatible flags. ***
==9472==*** Due to technical reasons, symbolization might crash ***
==9472==*** or produce wrong results. ***
#0 0x7ff7c13d7336 in std::Cr::unique_ptr<content::PrerenderPageHolder,std::Cr::default_delete<content::PrerenderPageHolder> >::operator-> C:\jenkins\x64-nightly\src\buildtools\third_party\libc++\trunk\include\__memory\unique_ptr.h:258
#1 0x7ff7c13d7336 in content::PrerenderHost::GetPrerenderedMainFrameHost(void) C:\jenkins\x64-nightly\src\content\browser\preloading\prerender\prerender_host.cc:627:10
#2 0x7ff7c9c2ab7e in content::test::PrerenderTestHelper::GetPrerenderedMainFrameHost(int) C:\jenkins\x64-nightly\src\content\public\test\prerender_test_util.cc:434:26
#3 0x7ff7b965b689 in ShareServicePrerenderBrowserTest_Text_Test::RunTestOnMainThread(void) C:\jenkins\x64-nightly\src\chrome\browser\webshare\share_service_browsertest.cc:203:25
#4 0x7ff7c9af5ff4 in content::BrowserTestBase::ProxyRunTestOnMainThreadLoop(void) C:\jenkins\x64-nightly\src\content\public\test\browser_test_base.cc:883:7
#5 0x7ff7c9afaf6d in base::internal::FunctorTraits<void (content::BrowserTestBase::*)(),void>::Invoke C:\jenkins\x64-nightly\src\base\bind_internal.h:624
#6 0x7ff7c9afaf6d in base::internal::InvokeHelper<0,void>::MakeItSo C:\jenkins\x64-nightly\src\base\bind_internal.h:801
#7 0x7ff7c9afaf6d in base::internal::Invoker<base::internal::BindState<void (content::BrowserTestBase::*)(),base::internal::UnretainedWrapper<content::BrowserTestBase> >,void ()>::RunImpl C:\jenkins\x64-nightly\src\base\bind_internal.h:882
#8 0x7ff7c9afaf6d in base::internal::Invoker<struct base::internal::BindState<void (__cdecl content::BrowserTestBase::*)(void), class base::internal::UnretainedWrapper<class content::BrowserTestBase>>, (void)>::RunOnce(class base::internal::BindStateBase *) C:\jenkins\x64-nightly\src\base\bind_internal.h:843:12
#9 0x7ff7c0a5b874 in base::OnceCallback<void ()>::Run C:\jenkins\x64-nightly\src\base\callback.h:145
#10 0x7ff7c0a5b874 in content::BrowserMainLoop::InterceptMainMessageLoopRun(void) C:\jenkins\x64-nightly\src\content\browser\browser_main_loop.cc:1018:36
#11 0x7ff7c0a5ba3d in content::BrowserMainLoop::RunMainMessageLoop(void) C:\jenkins\x64-nightly\src\content\browser\browser_main_loop.cc:1030:7
#12 0x7ff7c0a61c0b in content::BrowserMainRunnerImpl::Run(void) C:\jenkins\x64-nightly\src\content\browser\browser_main_runner_impl.cc:158:15
#13 0x7ff7c0a54ee5 in content::BrowserMain(struct content::MainFunctionParams) C:\jenkins\x64-nightly\src\content\browser\browser_main.cc:30:28
#14 0x7ff7c79a2d43 in content::RunBrowserProcessMain(struct content::MainFunctionParams, class content::ContentMainDelegate *) C:\jenkins\x64-nightly\src\content\app\content_main_runner_impl.cc:698:10
#15 0x7ff7c79a5df5 in content::ContentMainRunnerImpl::RunBrowser(struct content::MainFunctionParams, bool) C:\jenkins\x64-nightly\src\content\app\content_main_runner_impl.cc:1232:10
#16 0x7ff7c79a5693 in content::ContentMainRunnerImpl::Run(void) C:\jenkins\x64-nightly\src\content\app\content_main_runner_impl.cc:1091:12
#17 0x7ff7c79a1283 in content::RunContentProcess(struct content::ContentMainParams, class content::ContentMainRunner *) C:\jenkins\x64-nightly\src\content\app\content_main.cc:342:36
#18 0x7ff7c79a1966 in content::ContentMain(struct content::ContentMainParams) C:\jenkins\x64-nightly\src\content\app\content_main.cc:370:10
#19 0x7ff7c9af3d9f in content::BrowserTestBase::SetUp(void) C:\jenkins\x64-nightly\src\content\public\test\browser_test_base.cc:705:3
#20 0x7ff7c8ac3b82 in InProcessBrowserTest::SetUp(void) C:\jenkins\x64-nightly\src\chrome\test\base\in_process_browser_test.cc:467:20
#21 0x7ff7b965d5fb in ShareServiceBrowserTest::SetUp(void) C:\jenkins\x64-nightly\src\chrome\browser\webshare\share_service_browsertest.cc:48:27
#22 0x7ff7bcc32c98 in testing::Test::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:2665:3
#23 0x7ff7bcc34c43 in testing::TestInfo::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:2849:11
#24 0x7ff7bcc36996 in testing::TestSuite::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:3008:30
#25 0x7ff7bcc59737 in testing::internal::UnitTestImpl::RunAllTests(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:5866:44
#26 0x7ff7bcc58bdd in testing::UnitTest::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:5440:10
#27 0x7ff7c8e271b1 in RUN_ALL_TESTS C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\include\gtest\gtest.h:2284
#28 0x7ff7c8e271b1 in base::TestSuite::Run(void) C:\jenkins\x64-nightly\src\base\test\test_suite.cc:463:16
#29 0x7ff7de04ca79 in ChromeTestSuiteRunner::RunTestSuiteInternal(class ChromeTestSuite *) C:\jenkins\x64-nightly\src\chrome\test\base\chrome_test_launcher.cc:94:22
#30 0x7ff7de04cbeb in ChromeTestSuiteRunner::RunTestSuite(int, char **) C:\jenkins\x64-nightly\src\chrome\test\base\chrome_test_launcher.cc:99:10
#31 0x7ff7c9c61771 in content::LaunchTests(class content::TestLauncherDelegate *, unsigned __int64, int, char **) C:\jenkins\x64-nightly\src\content\public\test\test_launcher.cc:410:31
#32 0x7ff7de04da6b in LaunchChromeTests(unsigned __int64, class content::TestLauncherDelegate *, int, char **) C:\jenkins\x64-nightly\src\chrome\test\base\chrome_test_launcher.cc:319:10
#33 0x7ff7de04c8b3 in main C:\jenkins\x64-nightly\src\chrome\test\base\browser_tests_main.cc:87:10
#34 0x7ff7de1dae53 in invoke_main D:\a\_work\1\s\src\vctools\crt\vcstartup\src\startup\exe_common.inl:78
#35 0x7ff7de1dae53 in __scrt_common_main_seh D:\a\_work\1\s\src\vctools\crt\vcstartup\src\startup\exe_common.inl:288
#36 0x7ffe207b7973 (C:\Windows\System32\KERNEL32.DLL+0x180017973)
#37 0x7ffe22b6a2f0 (C:\Windows\SYSTEM32\ntdll.dll+0x18005a2f0)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: access-violation C:\jenkins\x64-nightly\src\buildtools\third_party\libc++\trunk\include\__memory\unique_ptr.h:258 in std::Cr::unique_ptr<content::PrerenderPageHolder,std::Cr::default_delete<content::PrerenderPageHolder> >::operator->
==9472==ABORTING
[ FAILED ] ShareServicePrerenderBrowserTest.Text
```
</details>
| 1.0 | Test failure: ShareServicePrerenderBrowserTest.Text - Greetings human!
Bad news. `ShareServicePrerenderBrowserTest.Text` [failed on windows x64 nightly master](https://ci.brave.com/job/brave-browser-build-windows-x64-asan/283/testReport/junit/(root)/ShareServicePrerenderBrowserTest/windows_x64___test_browser_chromium___Text).
<details>
<summary>Stack trace</summary>
```
[ RUN ] ShareServicePrerenderBrowserTest.Text
[9472:4368:1014/132339.390:WARNING:external_provider_impl.cc(511)] Malformed extension dictionary for extension: odbfpeeihdkbihmopkbjmoonfanlbfcl. Key external_update_url has value "", which is not a valid URL.
[9472:4368:1014/132339.884:ERROR:device_event_log_impl.cc(215)] [13:23:39.885] Bluetooth: bluetooth_adapter_winrt.cc:1074 Getting Default Adapter failed.
[9472:4368:1014/132340.319:INFO:ui_test_utils.cc(232)] NavigateToURL: http://127.0.0.1:56449/empty.html
[9472:4548:1014/132340.492:WARNING:embedded_test_server.cc(674)] Request not handled. Returning 404: /favicon.ico
..\..\content\public\test\prerender_test_util.cc(290): error: Expected: (host) != (nullptr), actual: NULL vs (nullptr)
Stack trace:
Backtrace:
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C265E1+13946760]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C26D66+13948685]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C2753F+13950694]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965B55D+62727853]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF5FF5+12700060]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AFAF6E+12720405]
free_base [0x00007FF7C0A5B875+29615013]
free_base [0x00007FF7C0A5BA3E+29615470]
free_base [0x00007FF7C0A61C0C+29640508]
free_base [0x00007FF7C0A54EE6+29587990]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A2D44+38205748]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5DF6+38218214]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5694+38216324]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1284+38198900]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1967+38200663]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF3DA0+12691271]
_ubsan_get_current_report_data [0x00007FF7C8AC3B83+948275]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965D5FC+62736204]
..\..\content\public\test\prerender_test_util.cc(310): error: Expected: (host_id) != (RenderFrameHost::kNoFrameTreeNodeId), actual: -1 vs -1
Stack trace:
Backtrace:
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C276B4+13951067]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965B55D+62727853]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF5FF5+12700060]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AFAF6E+12720405]
free_base [0x00007FF7C0A5B875+29615013]
free_base [0x00007FF7C0A5BA3E+29615470]
free_base [0x00007FF7C0A61C0C+29640508]
free_base [0x00007FF7C0A54EE6+29587990]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A2D44+38205748]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5DF6+38218214]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5694+38216324]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1284+38198900]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1967+38200663]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF3DA0+12691271]
_ubsan_get_current_report_data [0x00007FF7C8AC3B83+948275]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965D5FC+62736204]
..\..\content\public\test\prerender_test_util.cc(433): error: Expected: (prerender_host) != (nullptr), actual: NULL vs (nullptr)
Stack trace:
Backtrace:
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9C2AA7F+13964326]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965B68A+62728154]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF5FF5+12700060]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AFAF6E+12720405]
free_base [0x00007FF7C0A5B875+29615013]
free_base [0x00007FF7C0A5BA3E+29615470]
free_base [0x00007FF7C0A61C0C+29640508]
free_base [0x00007FF7C0A54EE6+29587990]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A2D44+38205748]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5DF6+38218214]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A5694+38216324]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1284+38198900]
CrashForExceptionInNonABICompliantCodeRange [0x00007FF7C79A1967+38200663]
RelaunchChromeBrowserWithNewCommandLineIfNeeded [0x00007FF7C9AF3DA0+12691271]
_ubsan_get_current_report_data [0x00007FF7C8AC3B83+948275]
_sanitizer_get_estimated_allocated_size [0x00007FF7B965D5FC+62736204]
=================================================================
==9472==ERROR: AddressSanitizer: access-violation on unknown address 0x000000000278 (pc 0x7ff7c13d7337 bp 0x00172cafe3f0 sp 0x00172cafe360 T0)
==9472==The signal is caused by a READ memory access.
==9472==Hint: address points to the zero page.
==9472==*** WARNING: Failed to initialize DbgHelp! ***
==9472==*** Most likely this means that the app is already ***
==9472==*** using DbgHelp, possibly with incompatible flags. ***
==9472==*** Due to technical reasons, symbolization might crash ***
==9472==*** or produce wrong results. ***
#0 0x7ff7c13d7336 in std::Cr::unique_ptr<content::PrerenderPageHolder,std::Cr::default_delete<content::PrerenderPageHolder> >::operator-> C:\jenkins\x64-nightly\src\buildtools\third_party\libc++\trunk\include\__memory\unique_ptr.h:258
#1 0x7ff7c13d7336 in content::PrerenderHost::GetPrerenderedMainFrameHost(void) C:\jenkins\x64-nightly\src\content\browser\preloading\prerender\prerender_host.cc:627:10
#2 0x7ff7c9c2ab7e in content::test::PrerenderTestHelper::GetPrerenderedMainFrameHost(int) C:\jenkins\x64-nightly\src\content\public\test\prerender_test_util.cc:434:26
#3 0x7ff7b965b689 in ShareServicePrerenderBrowserTest_Text_Test::RunTestOnMainThread(void) C:\jenkins\x64-nightly\src\chrome\browser\webshare\share_service_browsertest.cc:203:25
#4 0x7ff7c9af5ff4 in content::BrowserTestBase::ProxyRunTestOnMainThreadLoop(void) C:\jenkins\x64-nightly\src\content\public\test\browser_test_base.cc:883:7
#5 0x7ff7c9afaf6d in base::internal::FunctorTraits<void (content::BrowserTestBase::*)(),void>::Invoke C:\jenkins\x64-nightly\src\base\bind_internal.h:624
#6 0x7ff7c9afaf6d in base::internal::InvokeHelper<0,void>::MakeItSo C:\jenkins\x64-nightly\src\base\bind_internal.h:801
#7 0x7ff7c9afaf6d in base::internal::Invoker<base::internal::BindState<void (content::BrowserTestBase::*)(),base::internal::UnretainedWrapper<content::BrowserTestBase> >,void ()>::RunImpl C:\jenkins\x64-nightly\src\base\bind_internal.h:882
#8 0x7ff7c9afaf6d in base::internal::Invoker<struct base::internal::BindState<void (__cdecl content::BrowserTestBase::*)(void), class base::internal::UnretainedWrapper<class content::BrowserTestBase>>, (void)>::RunOnce(class base::internal::BindStateBase *) C:\jenkins\x64-nightly\src\base\bind_internal.h:843:12
#9 0x7ff7c0a5b874 in base::OnceCallback<void ()>::Run C:\jenkins\x64-nightly\src\base\callback.h:145
#10 0x7ff7c0a5b874 in content::BrowserMainLoop::InterceptMainMessageLoopRun(void) C:\jenkins\x64-nightly\src\content\browser\browser_main_loop.cc:1018:36
#11 0x7ff7c0a5ba3d in content::BrowserMainLoop::RunMainMessageLoop(void) C:\jenkins\x64-nightly\src\content\browser\browser_main_loop.cc:1030:7
#12 0x7ff7c0a61c0b in content::BrowserMainRunnerImpl::Run(void) C:\jenkins\x64-nightly\src\content\browser\browser_main_runner_impl.cc:158:15
#13 0x7ff7c0a54ee5 in content::BrowserMain(struct content::MainFunctionParams) C:\jenkins\x64-nightly\src\content\browser\browser_main.cc:30:28
#14 0x7ff7c79a2d43 in content::RunBrowserProcessMain(struct content::MainFunctionParams, class content::ContentMainDelegate *) C:\jenkins\x64-nightly\src\content\app\content_main_runner_impl.cc:698:10
#15 0x7ff7c79a5df5 in content::ContentMainRunnerImpl::RunBrowser(struct content::MainFunctionParams, bool) C:\jenkins\x64-nightly\src\content\app\content_main_runner_impl.cc:1232:10
#16 0x7ff7c79a5693 in content::ContentMainRunnerImpl::Run(void) C:\jenkins\x64-nightly\src\content\app\content_main_runner_impl.cc:1091:12
#17 0x7ff7c79a1283 in content::RunContentProcess(struct content::ContentMainParams, class content::ContentMainRunner *) C:\jenkins\x64-nightly\src\content\app\content_main.cc:342:36
#18 0x7ff7c79a1966 in content::ContentMain(struct content::ContentMainParams) C:\jenkins\x64-nightly\src\content\app\content_main.cc:370:10
#19 0x7ff7c9af3d9f in content::BrowserTestBase::SetUp(void) C:\jenkins\x64-nightly\src\content\public\test\browser_test_base.cc:705:3
#20 0x7ff7c8ac3b82 in InProcessBrowserTest::SetUp(void) C:\jenkins\x64-nightly\src\chrome\test\base\in_process_browser_test.cc:467:20
#21 0x7ff7b965d5fb in ShareServiceBrowserTest::SetUp(void) C:\jenkins\x64-nightly\src\chrome\browser\webshare\share_service_browsertest.cc:48:27
#22 0x7ff7bcc32c98 in testing::Test::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:2665:3
#23 0x7ff7bcc34c43 in testing::TestInfo::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:2849:11
#24 0x7ff7bcc36996 in testing::TestSuite::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:3008:30
#25 0x7ff7bcc59737 in testing::internal::UnitTestImpl::RunAllTests(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:5866:44
#26 0x7ff7bcc58bdd in testing::UnitTest::Run(void) C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\src\gtest.cc:5440:10
#27 0x7ff7c8e271b1 in RUN_ALL_TESTS C:\jenkins\x64-nightly\src\third_party\googletest\src\googletest\include\gtest\gtest.h:2284
#28 0x7ff7c8e271b1 in base::TestSuite::Run(void) C:\jenkins\x64-nightly\src\base\test\test_suite.cc:463:16
#29 0x7ff7de04ca79 in ChromeTestSuiteRunner::RunTestSuiteInternal(class ChromeTestSuite *) C:\jenkins\x64-nightly\src\chrome\test\base\chrome_test_launcher.cc:94:22
#30 0x7ff7de04cbeb in ChromeTestSuiteRunner::RunTestSuite(int, char **) C:\jenkins\x64-nightly\src\chrome\test\base\chrome_test_launcher.cc:99:10
#31 0x7ff7c9c61771 in content::LaunchTests(class content::TestLauncherDelegate *, unsigned __int64, int, char **) C:\jenkins\x64-nightly\src\content\public\test\test_launcher.cc:410:31
#32 0x7ff7de04da6b in LaunchChromeTests(unsigned __int64, class content::TestLauncherDelegate *, int, char **) C:\jenkins\x64-nightly\src\chrome\test\base\chrome_test_launcher.cc:319:10
#33 0x7ff7de04c8b3 in main C:\jenkins\x64-nightly\src\chrome\test\base\browser_tests_main.cc:87:10
#34 0x7ff7de1dae53 in invoke_main D:\a\_work\1\s\src\vctools\crt\vcstartup\src\startup\exe_common.inl:78
#35 0x7ff7de1dae53 in __scrt_common_main_seh D:\a\_work\1\s\src\vctools\crt\vcstartup\src\startup\exe_common.inl:288
#36 0x7ffe207b7973 (C:\Windows\System32\KERNEL32.DLL+0x180017973)
#37 0x7ffe22b6a2f0 (C:\Windows\SYSTEM32\ntdll.dll+0x18005a2f0)
AddressSanitizer can not provide additional info.
SUMMARY: AddressSanitizer: access-violation C:\jenkins\x64-nightly\src\buildtools\third_party\libc++\trunk\include\__memory\unique_ptr.h:258 in std::Cr::unique_ptr<content::PrerenderPageHolder,std::Cr::default_delete<content::PrerenderPageHolder> >::operator->
==9472==ABORTING
[ FAILED ] ShareServicePrerenderBrowserTest.Text
```
</details>
| non_priority | test failure shareserviceprerenderbrowsertest text greetings human bad news shareserviceprerenderbrowsertest text stack trace shareserviceprerenderbrowsertest text malformed extension dictionary for extension odbfpeeihdkbihmopkbjmoonfanlbfcl key external update url has value which is not a valid url bluetooth bluetooth adapter winrt cc getting default adapter failed navigatetourl request not handled returning favicon ico content public test prerender test util cc error expected host nullptr actual null vs nullptr stack trace backtrace relaunchchromebrowserwithnewcommandlineifneeded relaunchchromebrowserwithnewcommandlineifneeded relaunchchromebrowserwithnewcommandlineifneeded sanitizer get estimated allocated size relaunchchromebrowserwithnewcommandlineifneeded relaunchchromebrowserwithnewcommandlineifneeded free base free base free base free base crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange relaunchchromebrowserwithnewcommandlineifneeded ubsan get current report data sanitizer get estimated allocated size content public test prerender test util cc error expected host id renderframehost knoframetreenodeid actual vs stack trace backtrace relaunchchromebrowserwithnewcommandlineifneeded sanitizer get estimated allocated size relaunchchromebrowserwithnewcommandlineifneeded relaunchchromebrowserwithnewcommandlineifneeded free base free base free base free base crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange relaunchchromebrowserwithnewcommandlineifneeded ubsan get current report data sanitizer get estimated allocated size content public test prerender test util cc error expected prerender host nullptr actual null vs nullptr stack trace backtrace relaunchchromebrowserwithnewcommandlineifneeded sanitizer get estimated allocated size relaunchchromebrowserwithnewcommandlineifneeded relaunchchromebrowserwithnewcommandlineifneeded free base free base free base free base crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange crashforexceptioninnonabicompliantcoderange relaunchchromebrowserwithnewcommandlineifneeded ubsan get current report data sanitizer get estimated allocated size error addresssanitizer access violation on unknown address pc bp sp the signal is caused by a read memory access hint address points to the zero page warning failed to initialize dbghelp most likely this means that the app is already using dbghelp possibly with incompatible flags due to technical reasons symbolization might crash or produce wrong results in std cr unique ptr operator c jenkins nightly src buildtools third party libc trunk include memory unique ptr h in content prerenderhost getprerenderedmainframehost void c jenkins nightly src content browser preloading prerender prerender host cc in content test prerendertesthelper getprerenderedmainframehost int c jenkins nightly src content public test prerender test util cc in shareserviceprerenderbrowsertest text test runtestonmainthread void c jenkins nightly src chrome browser webshare share service browsertest cc in content browsertestbase proxyruntestonmainthreadloop void c jenkins nightly src content public test browser test base cc in base internal functortraits invoke c jenkins nightly src base bind internal h in base internal invokehelper makeitso c jenkins nightly src base bind internal h in base internal invoker void runimpl c jenkins nightly src base bind internal h in base internal invoker void runonce class base internal bindstatebase c jenkins nightly src base bind internal h in base oncecallback run c jenkins nightly src base callback h in content browsermainloop interceptmainmessagelooprun void c jenkins nightly src content browser browser main loop cc in content browsermainloop runmainmessageloop void c jenkins nightly src content browser browser main loop cc in content browsermainrunnerimpl run void c jenkins nightly src content browser browser main runner impl cc in content browsermain struct content mainfunctionparams c jenkins nightly src content browser browser main cc in content runbrowserprocessmain struct content mainfunctionparams class content contentmaindelegate c jenkins nightly src content app content main runner impl cc in content contentmainrunnerimpl runbrowser struct content mainfunctionparams bool c jenkins nightly src content app content main runner impl cc in content contentmainrunnerimpl run void c jenkins nightly src content app content main runner impl cc in content runcontentprocess struct content contentmainparams class content contentmainrunner c jenkins nightly src content app content main cc in content contentmain struct content contentmainparams c jenkins nightly src content app content main cc in content browsertestbase setup void c jenkins nightly src content public test browser test base cc in inprocessbrowsertest setup void c jenkins nightly src chrome test base in process browser test cc in shareservicebrowsertest setup void c jenkins nightly src chrome browser webshare share service browsertest cc in testing test run void c jenkins nightly src third party googletest src googletest src gtest cc in testing testinfo run void c jenkins nightly src third party googletest src googletest src gtest cc in testing testsuite run void c jenkins nightly src third party googletest src googletest src gtest cc in testing internal unittestimpl runalltests void c jenkins nightly src third party googletest src googletest src gtest cc in testing unittest run void c jenkins nightly src third party googletest src googletest src gtest cc in run all tests c jenkins nightly src third party googletest src googletest include gtest gtest h in base testsuite run void c jenkins nightly src base test test suite cc in chrometestsuiterunner runtestsuiteinternal class chrometestsuite c jenkins nightly src chrome test base chrome test launcher cc in chrometestsuiterunner runtestsuite int char c jenkins nightly src chrome test base chrome test launcher cc in content launchtests class content testlauncherdelegate unsigned int char c jenkins nightly src content public test test launcher cc in launchchrometests unsigned class content testlauncherdelegate int char c jenkins nightly src chrome test base chrome test launcher cc in main c jenkins nightly src chrome test base browser tests main cc in invoke main d a work s src vctools crt vcstartup src startup exe common inl in scrt common main seh d a work s src vctools crt vcstartup src startup exe common inl c windows dll c windows ntdll dll addresssanitizer can not provide additional info summary addresssanitizer access violation c jenkins nightly src buildtools third party libc trunk include memory unique ptr h in std cr unique ptr operator aborting shareserviceprerenderbrowsertest text | 0 |
39,030 | 15,859,292,390 | IssuesEvent | 2021-04-08 07:50:57 | azure-deprecation/dashboard | https://api.github.com/repos/azure-deprecation/dashboard | closed | Deprecation of 11 Azure Defender alerts in March 2021 | area:feature cloud:public impact:unknown services:security-center verified | Deprecation of 11 Azure Defender alerts in March 2021
**Deadline:** Mar 31, 2021
**Impacted Services:**
- Azure Security Center
**More information:**
- https://docs.microsoft.com/en-us/azure/security-center/upcoming-changes#deprecation-of-11-azure-defender-alerts
### Notice
Here's the official report from Microsoft:
> The eleven Azure Defender alerts listed below will be deprecated.
>
> New alerts will replace these two alerts and provide better coverage:
>
> |AlertType|AlertDisplayName|
> |:--|:--|
> |ARM_MicroBurstDomainInfo|PREVIEW - MicroBurst toolkit "Get-AzureDomainInfo" function run detected|
> |ARM_MicroBurstRunbook|PREVIEW - MicroBurst toolkit "Get-AzurePasswords" function run detected|
>
> These nine alerts relate to an Azure Active Directory Identity Protection connector that has already been deprecated:
>
> |AlertType|AlertDisplayName|
> |:--|:--|
> |UnfamiliarLocation|Unfamiliar sign-in properties|
> |AnonymousLogin|Anonymous IP address|
> |InfectedDeviceLogin|Malware linked IP address|
> |ImpossibleTravel|Atypical travel|
> |MaliciousIP|Malicious IP address|
> |LeakedCredentials|Leaked credentials|
> |PasswordSpray|Password Spray|
> |LeakedCredentials|Azure AD threat intelligence|
> |AADAI|Azure AD AI|
### Timeline
| Phase | Date | Description |
|:------|------|-------------|
|Announcement|Oct 02, 2020|Deprecation was announced|
|Deprecation|Mar 31, 2021|Impact is Unknown|
### Impact
Deprecation of 11 Azure Defender alerts in March 2021.
### Required Action
No information was provided
### Contact
No information was provided.
| 1.0 | Deprecation of 11 Azure Defender alerts in March 2021 - Deprecation of 11 Azure Defender alerts in March 2021
**Deadline:** Mar 31, 2021
**Impacted Services:**
- Azure Security Center
**More information:**
- https://docs.microsoft.com/en-us/azure/security-center/upcoming-changes#deprecation-of-11-azure-defender-alerts
### Notice
Here's the official report from Microsoft:
> The eleven Azure Defender alerts listed below will be deprecated.
>
> New alerts will replace these two alerts and provide better coverage:
>
> |AlertType|AlertDisplayName|
> |:--|:--|
> |ARM_MicroBurstDomainInfo|PREVIEW - MicroBurst toolkit "Get-AzureDomainInfo" function run detected|
> |ARM_MicroBurstRunbook|PREVIEW - MicroBurst toolkit "Get-AzurePasswords" function run detected|
>
> These nine alerts relate to an Azure Active Directory Identity Protection connector that has already been deprecated:
>
> |AlertType|AlertDisplayName|
> |:--|:--|
> |UnfamiliarLocation|Unfamiliar sign-in properties|
> |AnonymousLogin|Anonymous IP address|
> |InfectedDeviceLogin|Malware linked IP address|
> |ImpossibleTravel|Atypical travel|
> |MaliciousIP|Malicious IP address|
> |LeakedCredentials|Leaked credentials|
> |PasswordSpray|Password Spray|
> |LeakedCredentials|Azure AD threat intelligence|
> |AADAI|Azure AD AI|
### Timeline
| Phase | Date | Description |
|:------|------|-------------|
|Announcement|Oct 02, 2020|Deprecation was announced|
|Deprecation|Mar 31, 2021|Impact is Unknown|
### Impact
Deprecation of 11 Azure Defender alerts in March 2021.
### Required Action
No information was provided
### Contact
No information was provided.
| non_priority | deprecation of azure defender alerts in march deprecation of azure defender alerts in march deadline mar impacted services azure security center more information notice here s the official report from microsoft the eleven azure defender alerts listed below will be deprecated new alerts will replace these two alerts and provide better coverage alerttype alertdisplayname arm microburstdomaininfo preview microburst toolkit get azuredomaininfo function run detected arm microburstrunbook preview microburst toolkit get azurepasswords function run detected these nine alerts relate to an azure active directory identity protection connector that has already been deprecated alerttype alertdisplayname unfamiliarlocation unfamiliar sign in properties anonymouslogin anonymous ip address infecteddevicelogin malware linked ip address impossibletravel atypical travel maliciousip malicious ip address leakedcredentials leaked credentials passwordspray password spray leakedcredentials azure ad threat intelligence aadai azure ad ai timeline phase date description announcement oct deprecation was announced deprecation mar impact is unknown impact deprecation of azure defender alerts in march required action no information was provided contact no information was provided | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.