Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
63,916 | 14,656,803,336 | IssuesEvent | 2020-12-28 14:14:02 | fu1771695yongxie/yapi | https://api.github.com/repos/fu1771695yongxie/yapi | opened | WS-2019-0332 (Medium) detected in handlebars-4.0.11.tgz | security vulnerability | ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.11.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates... | True | WS-2019-0332 (Medium) detected in handlebars-4.0.11.tgz - ## WS-2019-0332 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.11.tgz</b></p></summary>
<p>Handlebars provid... | non_priority | ws medium detected in handlebars tgz ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file yapi pack... | 0 |
394,252 | 27,025,080,967 | IssuesEvent | 2023-02-11 13:51:31 | bp4151/cvss-rescore | https://api.github.com/repos/bp4151/cvss-rescore | closed | 2023-02-04-01: Fix file name format, update RULES.rst documentation | bug documentation | The current release filename format is incorrrect, so we have to replace the underscore with a hyphen so the release filename complies with the wheel specification. Also need to remove the "v" from the version in the filename.
Updated RULES file that better describes how rules files are built and used. | 1.0 | 2023-02-04-01: Fix file name format, update RULES.rst documentation - The current release filename format is incorrrect, so we have to replace the underscore with a hyphen so the release filename complies with the wheel specification. Also need to remove the "v" from the version in the filename.
Updated RULES file tha... | non_priority | fix file name format update rules rst documentation the current release filename format is incorrrect so we have to replace the underscore with a hyphen so the release filename complies with the wheel specification also need to remove the v from the version in the filename updated rules file that bett... | 0 |
118,330 | 17,580,034,802 | IssuesEvent | 2021-08-16 05:47:09 | ghc-dev/Amy-Yoder | https://api.github.com/repos/ghc-dev/Amy-Yoder | opened | CVE-2019-20444 (High) detected in netty-codec-http-4.1.39.Final.jar | security vulnerability | ## CVE-2019-20444 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.39.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application frame... | True | CVE-2019-20444 (High) detected in netty-codec-http-4.1.39.Final.jar - ## CVE-2019-20444 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.39.Final.jar</b></p></summar... | non_priority | cve high detected in netty codec http final jar cve high severity vulnerability vulnerable library netty codec http final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and c... | 0 |
38,047 | 10,133,256,240 | IssuesEvent | 2019-08-02 02:24:41 | tronprotocol/java-tron | https://api.github.com/repos/tronprotocol/java-tron | closed | whats wrong? | build | Please answer these questions before submitting your issue. Thanks!
1. What did you do?
If possible, provide a recipe for reproducing the error.
when i run build i see the following error like bellow
i dont know what should i do
2. What did you expect to see?
3. What did you see instead?
root@vps48... | 1.0 | whats wrong? - Please answer these questions before submitting your issue. Thanks!
1. What did you do?
If possible, provide a recipe for reproducing the error.
when i run build i see the following error like bellow
i dont know what should i do
2. What did you expect to see?
3. What did you see instead... | non_priority | whats wrong please answer these questions before submitting your issue thanks what did you do if possible provide a recipe for reproducing the error when i run build i see the following error like bellow i dont know what should i do what did you expect to see what did you see instead... | 0 |
80,367 | 7,746,181,430 | IssuesEvent | 2018-05-29 20:48:25 | adamdecaf/cert-manage | https://api.github.com/repos/adamdecaf/cert-manage | closed | run tests and CI on windows | help wanted testing | https://github.com/adamdecaf/cert-manage/pull/23 added testing on both linux and osx, but windows support would be nice as well.
There's currently an issue for TravisCI: https://github.com/travis-ci/travis-ci/issues/2104
This would be pretty important to have for [windows support](https://github.com/adamdecaf/ce... | 1.0 | run tests and CI on windows - https://github.com/adamdecaf/cert-manage/pull/23 added testing on both linux and osx, but windows support would be nice as well.
There's currently an issue for TravisCI: https://github.com/travis-ci/travis-ci/issues/2104
This would be pretty important to have for [windows support](h... | non_priority | run tests and ci on windows added testing on both linux and osx but windows support would be nice as well there s currently an issue for travisci this would be pretty important to have for we could look at other options as it might not be a near term addition from travisci | 0 |
93,265 | 8,406,796,733 | IssuesEvent | 2018-10-11 18:58:40 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | closed | JTReg test fail : java/lang/invoke/VarHandles/VarHandleTestByteArrayAsChar.java | comp:jit jdk11 test failure | Fails with following exception ...
```
test VarHandleTestByteArrayAsChar.testAccess(" VarHandle [ALIGNED, LITTLE_ENDIAN, READ_WRITE] -> byte[] [ALIGNED, LITTLE_ENDIAN, READ_WRITE] read write", VarHandleBaseByteArrayTest$VarHandleSourceAccessTestCase@b6c2da1d): failure
java.lang.ArrayIndexOutOfBoundsException
at ... | 1.0 | JTReg test fail : java/lang/invoke/VarHandles/VarHandleTestByteArrayAsChar.java - Fails with following exception ...
```
test VarHandleTestByteArrayAsChar.testAccess(" VarHandle [ALIGNED, LITTLE_ENDIAN, READ_WRITE] -> byte[] [ALIGNED, LITTLE_ENDIAN, READ_WRITE] read write", VarHandleBaseByteArrayTest$VarHandleSourc... | non_priority | jtreg test fail java lang invoke varhandles varhandletestbytearrayaschar java fails with following exception test varhandletestbytearrayaschar testaccess varhandle byte read write varhandlebasebytearraytest varhandlesourceaccesstestcase failure java lang arrayindexoutofboundsexception ... | 0 |
161,725 | 25,386,701,745 | IssuesEvent | 2022-11-21 22:36:55 | BCDevOps/developer-experience | https://api.github.com/repos/BCDevOps/developer-experience | closed | In-person team day planning | training service-design | **Describe the issue**
Planning associated with in-person team day
**Additional context**
Schedule [document](https://docs.google.com/spreadsheets/d/1Mu2yvDmR-QHQzyZB7snIgScV3QHCBeBmmmeUdJr1_hk/edit?usp=sharing)
Previous schedule [mural board](https://app.mural.co/invitation/mural/platformservices5977/1664481434643?sen... | 1.0 | In-person team day planning - **Describe the issue**
Planning associated with in-person team day
**Additional context**
Schedule [document](https://docs.google.com/spreadsheets/d/1Mu2yvDmR-QHQzyZB7snIgScV3QHCBeBmmmeUdJr1_hk/edit?usp=sharing)
Previous schedule [mural board](https://app.mural.co/invitation/mural/platform... | non_priority | in person team day planning describe the issue planning associated with in person team day additional context schedule previous schedule how does this benefit the users of our platform many of the functions of the in person team day will directly benefit users including working on documentation ... | 0 |
35,096 | 7,892,538,822 | IssuesEvent | 2018-06-28 15:15:50 | TypeCobolTeam/TypeCobol | https://api.github.com/repos/TypeCobolTeam/TypeCobol | closed | Bad location of the Commented version line in presence of COBOL Options. | Bug Codegen TypeCobol User Visible | In the following generated Code the TYpeCobol version appears before de CBL option.
```cobol
*TypeCobol_Version:0.1(alpha)
CBL ARITH(EXTEND)
IDENTIFICATION DIVISION.
PROGRAM-ID. DVZXERRM.
DATA DIVISION.
WORKING-STORAGE SECTION.
PROCEDURE DIVISION.
END PROG... | 1.0 | Bad location of the Commented version line in presence of COBOL Options. - In the following generated Code the TYpeCobol version appears before de CBL option.
```cobol
*TypeCobol_Version:0.1(alpha)
CBL ARITH(EXTEND)
IDENTIFICATION DIVISION.
PROGRAM-ID. DVZXERRM.
DATA DIVISION.
... | non_priority | bad location of the commented version line in presence of cobol options in the following generated code the typecobol version appears before de cbl option cobol typecobol version alpha cbl arith extend identification division program id dvzxerrm data division ... | 0 |
135,601 | 18,714,950,509 | IssuesEvent | 2021-11-03 02:24:32 | ChoeMinji/spring-boot | https://api.github.com/repos/ChoeMinji/spring-boot | opened | CVE-2017-18640 (High) detected in snakeyaml-1.25.jar | security vulnerability | ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.25.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http:/... | True | CVE-2017-18640 (High) detected in snakeyaml-1.25.jar - ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.25.jar</b></p></summary>
<p>YAML 1.1 parser and emi... | non_priority | cve high detected in snakeyaml jar cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file spring boot ci images releasescripts pom xml path to vulnerable library home wss sca... | 0 |
182,657 | 30,881,541,981 | IssuesEvent | 2023-08-03 18:00:29 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | opened | Memorable date must not reveal regex to user when using pattern prop | bug platform-design-system-team | # Bug Report
- [x] I’ve searched for any related issues and avoided creating a duplicate issue.
## What happened
Error message for memorable date reveals regex when that prop is used.
** and **[Zeplin](https://app.zeplin.io/project/5ee87c00f6af719a645d14c3/screen/5ee8c6352150d5b8fd0344c5)**
- [x] Table
- [x] Headers
- [x] Security tiles
- [x] News | 1.0 | Dashboard: New design - **[Zeplin](https://app.zeplin.io/project/5ee87c00f6af719a645d14c3/styleguide/components?seid=5ee87ee70d418aba36701f2c)** and **[Zeplin](https://app.zeplin.io/project/5ee87c00f6af719a645d14c3/screen/5ee8c6352150d5b8fd0344c5)**
- [x] Table
- [x] Headers
- [x] Security tiles
- [x] News | non_priority | dashboard new design and table headers security tiles news | 0 |
59,296 | 14,379,583,278 | IssuesEvent | 2020-12-02 00:42:15 | gate5/react-16.0.0 | https://api.github.com/repos/gate5/react-16.0.0 | opened | CVE-2017-16099 (High) detected in no-case-2.3.1.tgz, no-case-2.3.0.tgz | security vulnerability | ## CVE-2017-16099 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>no-case-2.3.1.tgz</b>, <b>no-case-2.3.0.tgz</b></p></summary>
<p>
<details><summary><b>no-case-2.3.1.tgz</b></p></su... | True | CVE-2017-16099 (High) detected in no-case-2.3.1.tgz, no-case-2.3.0.tgz - ## CVE-2017-16099 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>no-case-2.3.1.tgz</b>, <b>no-case-2.3.0.tgz<... | non_priority | cve high detected in no case tgz no case tgz cve high severity vulnerability vulnerable libraries no case tgz no case tgz no case tgz remove case from a string library home page a href path to dependency file react fixtures fiber deb... | 0 |
33,426 | 12,216,550,095 | IssuesEvent | 2020-05-01 15:22:27 | bsbtd/Teste | https://api.github.com/repos/bsbtd/Teste | opened | CVE-2012-6708 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.2.min.js</b>, <b>jquery-1.4.4.min.js</b>, <b>jquery-1.7.1.min.js</b>, <b>jquery-1.8.1.min.js</b></p></sum... | True | CVE-2012-6708 (Medium) detected in multiple libraries - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.2.min.js</b>, <b>jquery-1.4.4.min.js</b>, <b>jque... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path ... | 0 |
147,925 | 23,294,108,494 | IssuesEvent | 2022-08-06 09:28:13 | zuri-training/WF-PriceCompare-24 | https://api.github.com/repos/zuri-training/WF-PriceCompare-24 | closed | design | Designers | created the wireframes along with olasbee, created and worked on the gadgets frames, pictures and labels to fashion- menswear page & fashion- females wear page, added pictures and labels to the landing page
| 1.0 | design - created the wireframes along with olasbee, created and worked on the gadgets frames, pictures and labels to fashion- menswear page & fashion- females wear page, added pictures and labels to the landing page
| non_priority | design created the wireframes along with olasbee created and worked on the gadgets frames pictures and labels to fashion menswear page fashion females wear page added pictures and labels to the landing page | 0 |
158,243 | 20,018,482,751 | IssuesEvent | 2022-02-01 14:23:11 | TIBCOSoftware/genxdm | https://api.github.com/repos/TIBCOSoftware/genxdm | closed | CVE-2022-23437 (High) detected in xercesImpl-2.12.1.jar | security vulnerability | ## CVE-2022-23437 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.12.1.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML par... | True | CVE-2022-23437 (High) detected in xercesImpl-2.12.1.jar - ## CVE-2022-23437 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.12.1.jar</b></p></summary>
<p>Xerces2 is the ne... | non_priority | cve high detected in xercesimpl jar cve high severity vulnerability vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a... | 0 |
39,284 | 8,621,748,501 | IssuesEvent | 2018-11-20 18:13:46 | autoforce/APIcasso | https://api.github.com/repos/autoforce/APIcasso | closed | Fix "dangerous_send" issue in app/controllers/apicasso/crud_controller.rb | codeclimate enhancement security | User controlled method execution
https://codeclimate.com/github/autoforce/APIcasso/app/controllers/apicasso/crud_controller.rb#issue_5be5c81ae7e0a2000100003a | 1.0 | Fix "dangerous_send" issue in app/controllers/apicasso/crud_controller.rb - User controlled method execution
https://codeclimate.com/github/autoforce/APIcasso/app/controllers/apicasso/crud_controller.rb#issue_5be5c81ae7e0a2000100003a | non_priority | fix dangerous send issue in app controllers apicasso crud controller rb user controlled method execution | 0 |
110,324 | 9,441,926,120 | IssuesEvent | 2019-04-15 04:16:45 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | opened | Vulnerability [ABAC_Level2] : POST:/api/v1/orgs/{orgId}/users/{userId}/reset-password | ApiTest2 ApiTest2 | Project : ApiTest2
Template : ApiV1OrgsOrgidUsersUseridResetPasswordPostUseraCreateOrgorgplanbusinessUsercDisallowAbact2
Run Id : <html><a href=https://18.144.40.113/#/app/projects/8a80808f6a06f0be016a1f28449d67e3/jobs/8a80808f6a06f0be016a1f2b09126f7b/runs/8a80808f6a06f0be016a1f335e847f69>8a80808f6a06f0be016a1f... | 2.0 | Vulnerability [ABAC_Level2] : POST:/api/v1/orgs/{orgId}/users/{userId}/reset-password - Project : ApiTest2
Template : ApiV1OrgsOrgidUsersUseridResetPasswordPostUseraCreateOrgorgplanbusinessUsercDisallowAbact2
Run Id : <html><a href=https://18.144.40.113/#/app/projects/8a80808f6a06f0be016a1f28449d67e3/jobs/8a808... | non_priority | vulnerability post api orgs orgid users userid reset password project template run id a href job job env default category abac tags severity major region fx hyd result fail status code headers www authenticate x content type optio... | 0 |
29,510 | 13,127,892,483 | IssuesEvent | 2020-08-06 11:15:14 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | Bug/Feature to improve deployment reliability with issue resulting in "Error occurred reading http.Response#Body - Error = 'context deadline exceeded'" | question service/virtual-machine | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backen... | 1.0 | Bug/Feature to improve deployment reliability with issue resulting in "Error occurred reading http.Response#Body - Error = 'context deadline exceeded'" - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/i... | non_priority | bug feature to improve deployment reliability with issue resulting in error occurred reading http response body error context deadline exceeded please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues ... | 0 |
81,484 | 23,474,212,148 | IssuesEvent | 2022-08-17 03:10:06 | quinchs/EdgeDB.Net | https://api.github.com/repos/quinchs/EdgeDB.Net | closed | Autogenerated node resolution | Query builder | ## Summary
Since the query builder can generate extra nodes for given context, these nodes need to always track their reference. Take a look at the given query:
```cs
var query = QueryBuilder.For(people, person => QueryBuilder.Insert(person, true));
```
This query will generate an insert statement with an autogene... | 1.0 | Autogenerated node resolution - ## Summary
Since the query builder can generate extra nodes for given context, these nodes need to always track their reference. Take a look at the given query:
```cs
var query = QueryBuilder.For(people, person => QueryBuilder.Insert(person, true));
```
This query will generate an i... | non_priority | autogenerated node resolution summary since the query builder can generate extra nodes for given context these nodes need to always track their reference take a look at the given query cs var query querybuilder for people person querybuilder insert person true this query will generate an i... | 0 |
22,049 | 7,112,351,934 | IssuesEvent | 2018-01-17 16:46:19 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Build is buggy for java 9. | :Core build | Try compiling with java 9:
First you will hit this. This can be fixed by using `assertEquals`, which also simplifies the test.
```
/home/rmuir/workspace/elasticsearch/core/src/test/java/org/elasticsearch/threadpool/ScalingThreadPoolTests.java:180: error: method invoked with incorrect number of arguments; expected 2, ... | 1.0 | Build is buggy for java 9. - Try compiling with java 9:
First you will hit this. This can be fixed by using `assertEquals`, which also simplifies the test.
```
/home/rmuir/workspace/elasticsearch/core/src/test/java/org/elasticsearch/threadpool/ScalingThreadPoolTests.java:180: error: method invoked with incorrect numb... | non_priority | build is buggy for java try compiling with java first you will hit this this can be fixed by using assertequals which also simplifies the test home rmuir workspace elasticsearch core src test java org elasticsearch threadpool scalingthreadpooltests java error method invoked with incorrect number... | 0 |
80,682 | 7,753,743,754 | IssuesEvent | 2018-05-31 02:30:28 | ElementsProject/lightning | https://api.github.com/repos/ElementsProject/lightning | closed | Travis should test in parallel | testing | Our tests run much faster in parallel, particularly due to polling delays, etc. I run -n10 on my laptop (without valgrind) with no problems.
That would allow us to re-enable some non-developer tests, for example. | 1.0 | Travis should test in parallel - Our tests run much faster in parallel, particularly due to polling delays, etc. I run -n10 on my laptop (without valgrind) with no problems.
That would allow us to re-enable some non-developer tests, for example. | non_priority | travis should test in parallel our tests run much faster in parallel particularly due to polling delays etc i run on my laptop without valgrind with no problems that would allow us to re enable some non developer tests for example | 0 |
1,571 | 6,572,329,951 | IssuesEvent | 2017-09-11 01:26:32 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | lxc_container: provide option to make automatic container restarts optional | affects_2.1 cloud feature_idea waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Feature Idea
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
lxc_container
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” betwee... | True | lxc_container: provide option to make automatic container restarts optional - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Feature Idea
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
lxc_container
####... | non_priority | lxc container provide option to make automatic container restarts optional issue type feature idea component name lxc container ansible version ansible config file configured module search path default w o overrides configuration mention any setti... | 0 |
208,756 | 16,136,439,836 | IssuesEvent | 2021-04-29 12:28:38 | spring-projects/spring-data-commons | https://api.github.com/repos/spring-projects/spring-data-commons | closed | Table of contents sometimes locates in wrong section (confusion between subsections without id-s) [DATACMNS-1814] | type: bug type: documentation | **[Chealer](https://jira.spring.io/secure/ViewProfile.jspa?name=JIRAUSER50525)** opened **[DATACMNS-1814](https://jira.spring.io/browse/DATACMNS-1814?redirect=false)** and commented
The table of contents at the left of the Spring Data JPA Reference Documentation dynamically changes to reflect the precise subsection be... | 1.0 | Table of contents sometimes locates in wrong section (confusion between subsections without id-s) [DATACMNS-1814] - **[Chealer](https://jira.spring.io/secure/ViewProfile.jspa?name=JIRAUSER50525)** opened **[DATACMNS-1814](https://jira.spring.io/browse/DATACMNS-1814?redirect=false)** and commented
The table of contents... | non_priority | table of contents sometimes locates in wrong section confusion between subsections without id s opened and commented the table of contents at the left of the spring data jpa reference documentation dynamically changes to reflect the precise subsection being shown the subsections of sections not disp... | 0 |
131,695 | 28,007,448,694 | IssuesEvent | 2023-03-27 16:07:35 | tarantool/tarantool | https://api.github.com/repos/tarantool/tarantool | opened | Internal helper tuple_extract_key_raw helper extracts wrong key | code health | When I added a fair test:
```diff
diff --git a/test/unit/key_def.c b/test/unit/key_def.c
index 65f579ca4..286b26461 100644
--- a/test/unit/key_def.c
+++ b/test/unit/key_def.c
@@ -292,14 +292,43 @@ test_tuple_extract_key_raw_slowpath_nullable(void)
check_plan();
}
+static void
+test_tuple_extract_key_raw_... | 1.0 | Internal helper tuple_extract_key_raw helper extracts wrong key - When I added a fair test:
```diff
diff --git a/test/unit/key_def.c b/test/unit/key_def.c
index 65f579ca4..286b26461 100644
--- a/test/unit/key_def.c
+++ b/test/unit/key_def.c
@@ -292,14 +292,43 @@ test_tuple_extract_key_raw_slowpath_nullable(void)
... | non_priority | internal helper tuple extract key raw helper extracts wrong key when i added a fair test diff diff git a test unit key def c b test unit key def c index a test unit key def c b test unit key def c test tuple extract key raw slowpath nullable void check plan st... | 0 |
217,955 | 16,745,385,424 | IssuesEvent | 2021-06-11 14:54:42 | nilisha-jais/Musicophilia | https://api.github.com/repos/nilisha-jais/Musicophilia | opened | Add Badges and Contributors | documentation | ## 📚 Documentation
**Update README**
There must a proper readme file, currently it is not design properly.
I would like to arrange it in proper way and add few more sections to it i.e. shields badges and contributors
The contribution steps are also having inappropriate design.
## Add relevant screenshot or vide... | 1.0 | Add Badges and Contributors - ## 📚 Documentation
**Update README**
There must a proper readme file, currently it is not design properly.
I would like to arrange it in proper way and add few more sections to it i.e. shields badges and contributors
The contribution steps are also having inappropriate design.
## A... | non_priority | add badges and contributors 📚 documentation update readme there must a proper readme file currently it is not design properly i would like to arrange it in proper way and add few more sections to it i e shields badges and contributors the contribution steps are also having inappropriate design a... | 0 |
263,518 | 19,913,933,569 | IssuesEvent | 2022-01-25 20:13:46 | EkaterinaKokh/Ekaterina-Kokh-TKI-111 | https://api.github.com/repos/EkaterinaKokh/Ekaterina-Kokh-TKI-111 | closed | Задание 1-3 | documentation enhancement | **Задание 1-3**
Создать консольное приложение для решения задачи, представленной в таблице. Данные для решения вводит пользователь. Помните, что ввод необходимо проверять на правильность (только числа). Вывести результат вычислений на экран. При необходимости дополнить свой отчёт поясняющими формулами, помогающими реш... | 1.0 | Задание 1-3 - **Задание 1-3**
Создать консольное приложение для решения задачи, представленной в таблице. Данные для решения вводит пользователь. Помните, что ввод необходимо проверять на правильность (только числа). Вывести результат вычислений на экран. При необходимости дополнить свой отчёт поясняющими формулами, п... | non_priority | задание задание создать консольное приложение для решения задачи представленной в таблице данные для решения вводит пользователь помните что ввод необходимо проверять на правильность только числа вывести результат вычислений на экран при необходимости дополнить свой отчёт поясняющими формулами п... | 0 |
139,101 | 18,840,211,280 | IssuesEvent | 2021-11-11 08:39:44 | rammatzkvosky/Home-assignment | https://api.github.com/repos/rammatzkvosky/Home-assignment | opened | CVE-2019-17267 (High) detected in jackson-databind-2.8.7.jar | security vulnerability | ## CVE-2019-17267 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.7.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-17267 (High) detected in jackson-databind-2.8.7.jar - ## CVE-2019-17267 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.7.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file home assignment pom xml path ... | 0 |
232,877 | 18,921,189,631 | IssuesEvent | 2021-11-17 02:00:44 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | WebApplicationFactory does not resolve the custom configured SQL Provider, but the one from Startup | investigate Needs: Author Feedback :heavy_check_mark: Resolution: Answered Status: Resolved feature-mvc-testing area-web-frameworks | <!--
More information on our issue management policies can be found here: https://aka.ms/aspnet/issue-policies
Please keep in mind that the GitHub issue tracker is not intended as a general support forum, but for reporting **non-security** bugs and feature requests.
If you believe you have an issue that affect... | 1.0 | WebApplicationFactory does not resolve the custom configured SQL Provider, but the one from Startup - <!--
More information on our issue management policies can be found here: https://aka.ms/aspnet/issue-policies
Please keep in mind that the GitHub issue tracker is not intended as a general support forum, but for... | non_priority | webapplicationfactory does not resolve the custom configured sql provider but the one from startup more information on our issue management policies can be found here please keep in mind that the github issue tracker is not intended as a general support forum but for reporting non security bugs an... | 0 |
1,146 | 3,391,555,186 | IssuesEvent | 2015-11-30 15:58:22 | giantswarm/cli | https://api.github.com/repos/giantswarm/cli | reopened | Warning if variable is not resolved | area/service-definition kind/feature | If a variable could not be resolved during the creation of application, the creation should be aborted or the user warned.
Original Author: @luebken
Created at 06-01-2015 10:48:40
Gitlab: [giantswarm/cli!217](https://git.giantswarm.io/giantswarm/cli/issues/217)
<!---
@huboard:{"order":1.4296875,"milestone_ord... | 1.0 | Warning if variable is not resolved - If a variable could not be resolved during the creation of application, the creation should be aborted or the user warned.
Original Author: @luebken
Created at 06-01-2015 10:48:40
Gitlab: [giantswarm/cli!217](https://git.giantswarm.io/giantswarm/cli/issues/217)
<!---
@hub... | non_priority | warning if variable is not resolved if a variable could not be resolved during the creation of application the creation should be aborted or the user warned original author luebken created at gitlab huboard order milestone order custom state archived | 0 |
426,810 | 29,661,051,062 | IssuesEvent | 2023-06-10 06:35:20 | JohnSnowLabs/spark-nlp | https://api.github.com/repos/JohnSnowLabs/spark-nlp | closed | Quickstart guide is for an older version | documentation | ### Link to the documentation pages (if available)
https://github.com/JohnSnowLabs/spark-nlp/blob/master/examples/python/quick_start.ipynb
### How could the documentation be improved?
When I run the initial suggestion, it throws an exception:
```
import sparknlp
spark = sparknlp.start()
print("Spark NLP v... | 1.0 | Quickstart guide is for an older version - ### Link to the documentation pages (if available)
https://github.com/JohnSnowLabs/spark-nlp/blob/master/examples/python/quick_start.ipynb
### How could the documentation be improved?
When I run the initial suggestion, it throws an exception:
```
import sparknlp
spa... | non_priority | quickstart guide is for an older version link to the documentation pages if available how could the documentation be improved when i run the initial suggestion it throws an exception import sparknlp spark sparknlp start print spark nlp version sparknlp version print apac... | 0 |
25,838 | 12,304,641,705 | IssuesEvent | 2020-05-11 20:51:18 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | closed | [Service Bus] Peeking into an empty session-enabled queue throws an error | Client Service Bus | Peeking into an empty session-enabled queue would run into either of the following errors..
1. OperationTimeoutError: Unable to create the amqp receiver 'unpartitioned-queue-sessions-794f89be-3282-8b48-8ae0-a8af43c3ce36' on amqp session 'local-1_remote-1_connection-2' due to operation timeout.
2. MessagingError: R... | 1.0 | [Service Bus] Peeking into an empty session-enabled queue throws an error - Peeking into an empty session-enabled queue would run into either of the following errors..
1. OperationTimeoutError: Unable to create the amqp receiver 'unpartitioned-queue-sessions-794f89be-3282-8b48-8ae0-a8af43c3ce36' on amqp session 'loc... | non_priority | peeking into an empty session enabled queue throws an error peeking into an empty session enabled queue would run into either of the following errors operationtimeouterror unable to create the amqp receiver unpartitioned queue sessions on amqp session local remote connection due to oper... | 0 |
126,538 | 17,070,770,196 | IssuesEvent | 2021-07-07 13:05:40 | nushell/nushell | https://api.github.com/repos/nushell/nushell | closed | Add 'explore' functionality | Stale delight enhancement needs-design | We have (or possibly had, past-tense) an `enter` command that allows you to cd/ls your way around the inside of an object. This is pretty cool functionality, but it needs a better home than something that mimics the open command.
It may make sense as a sink:
```
open Cargo.toml | explore
```
Where you are pu... | 1.0 | Add 'explore' functionality - We have (or possibly had, past-tense) an `enter` command that allows you to cd/ls your way around the inside of an object. This is pretty cool functionality, but it needs a better home than something that mimics the open command.
It may make sense as a sink:
```
open Cargo.toml | ex... | non_priority | add explore functionality we have or possibly had past tense an enter command that allows you to cd ls your way around the inside of an object this is pretty cool functionality but it needs a better home than something that mimics the open command it may make sense as a sink open cargo toml ex... | 0 |
191,304 | 22,215,740,561 | IssuesEvent | 2022-06-08 01:18:49 | rlennon/whitesource_bolt_demo | https://api.github.com/repos/rlennon/whitesource_bolt_demo | opened | CVE-2021-43307 (Medium) detected in semver-regex-2.0.0.tgz | security vulnerability | ## CVE-2021-43307 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p></summary>
<p>Regular expression for matching semver versions</p>
<p>Library home page... | True | CVE-2021-43307 (Medium) detected in semver-regex-2.0.0.tgz - ## CVE-2021-43307 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p></summary>
<p>Regular exp... | non_priority | cve medium detected in semver regex tgz cve medium severity vulnerability vulnerable library semver regex tgz regular expression for matching semver versions library home page a href path to dependency file portainer develop portainer develop package json path to vul... | 0 |
208,047 | 23,546,632,861 | IssuesEvent | 2022-08-21 07:55:58 | ghc-dev/Amber-Burgess | https://api.github.com/repos/ghc-dev/Amber-Burgess | closed | log4j-core-2.8.2.jar: 3 vulnerabilities (highest severity is: 10.0) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https:/... | True | log4j-core-2.8.2.jar: 3 vulnerabilities (highest severity is: 10.0) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Li... | non_priority | core jar vulnerabilities highest severity is autoclosed vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library ository org apache logging core core jar fou... | 0 |
24,655 | 6,557,939,341 | IssuesEvent | 2017-09-06 19:21:52 | CUAHSI/HydroCatalog | https://api.github.com/repos/CUAHSI/HydroCatalog | opened | Title overprint on service description page | CodePlex | <b>twhitvine[CodePlex]</b> <br />Long service titles are overprint on the service description page. See
See
http://hiscentral.cuahsi.org/pub_network.aspx?n=272
Screenshot from Firefox 15.0.1 attached. Same in Chrome.
| 1.0 | Title overprint on service description page - <b>twhitvine[CodePlex]</b> <br />Long service titles are overprint on the service description page. See
See
http://hiscentral.cuahsi.org/pub_network.aspx?n=272
Screenshot from Firefox 15.0.1 attached. Same in Chrome.
| non_priority | title overprint on service description page twhitvine long service titles are overprint on the service description page see see screenshot from firefox attached same in chrome | 0 |
254,933 | 27,448,451,348 | IssuesEvent | 2023-03-02 15:45:27 | elastic/integrations | https://api.github.com/repos/elastic/integrations | reopened | [Cloud Security] [Vulnerability Management] Add mappings for CloudFormation templates | Team:Cloud Security 8.8 candidate | ### Motivation
As part of the vulnerability management architecture, we are going to introduce a new elastic-agent deployment method, a CloudFormation template that provisions an EC2 instance with an elastic-agent installed.
The template will reside in an S3 bucket, and this task it's about defining a strategy to map... | True | [Cloud Security] [Vulnerability Management] Add mappings for CloudFormation templates - ### Motivation
As part of the vulnerability management architecture, we are going to introduce a new elastic-agent deployment method, a CloudFormation template that provisions an EC2 instance with an elastic-agent installed.
The t... | non_priority | add mappings for cloudformation templates motivation as part of the vulnerability management architecture we are going to introduce a new elastic agent deployment method a cloudformation template that provisions an instance with an elastic agent installed the template will reside in an bucket and th... | 0 |
154,711 | 12,226,100,608 | IssuesEvent | 2020-05-03 09:14:44 | GTNewHorizons/GT-New-Horizons-Modpack | https://api.github.com/repos/GTNewHorizons/GT-New-Horizons-Modpack | closed | Tesla's Last Testament casings name displayed wrong | FixedInDev GT++ need to be tested | #### Which modpack version are you using?
2.0.8.3
#
#### What happened?
Casings name in the tooltip are displayed improperly
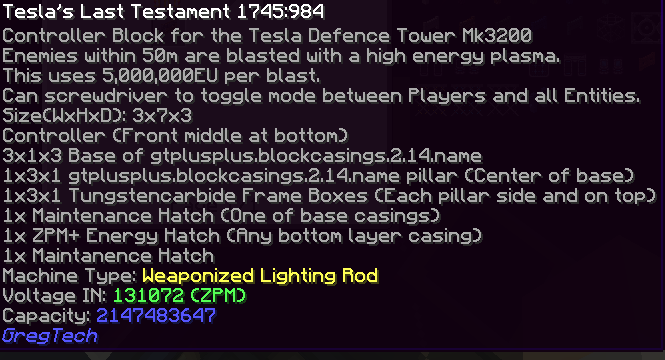
#
#### What do you suggest instead/what changes do you propose?
Fix nami... | 1.0 | Tesla's Last Testament casings name displayed wrong - #### Which modpack version are you using?
2.0.8.3
#
#### What happened?
Casings name in the tooltip are displayed improperly
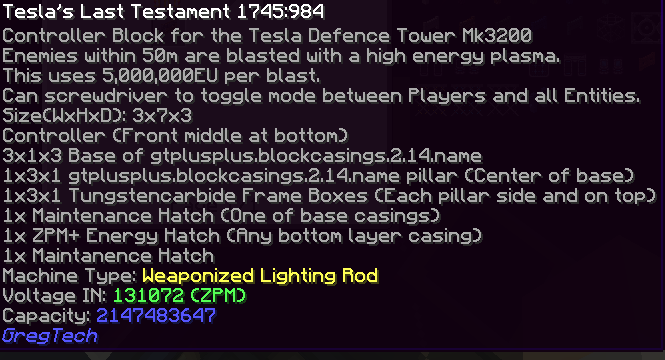
#
#### What do you ... | non_priority | tesla s last testament casings name displayed wrong which modpack version are you using what happened casings name in the tooltip are displayed improperly what do you suggest instead what changes do you propose fix naming in mod files to be displayed properly | 0 |
68,636 | 21,773,226,244 | IssuesEvent | 2022-05-13 11:13:28 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | can't build on Slackware GNU/Linux: builds for Debian! | T-Defect X-Needs-Info | ### Steps to reproduce
yarn install
yarn run fetch --importkey
yarn run fetch --cfgdir ""
yarn run build
### Outcome
#### What did you expect?
SlackBuild a txz.
#### What happened instead?
d@cosmos:~/math/src/network/chat/element-desktop-1.10.12$ yarn install
yarn run fetch --importkey
yarn run fetch... | 1.0 | can't build on Slackware GNU/Linux: builds for Debian! - ### Steps to reproduce
yarn install
yarn run fetch --importkey
yarn run fetch --cfgdir ""
yarn run build
### Outcome
#### What did you expect?
SlackBuild a txz.
#### What happened instead?
d@cosmos:~/math/src/network/chat/element-desktop-1.10.12$... | non_priority | can t build on slackware gnu linux builds for debian steps to reproduce yarn install yarn run fetch importkey yarn run fetch cfgdir yarn run build outcome what did you expect slackbuild a txz what happened instead d cosmos math src network chat element desktop y... | 0 |
95,626 | 12,026,555,626 | IssuesEvent | 2020-04-12 14:40:25 | erikstacy/Time-Keeper | https://api.github.com/repos/erikstacy/Time-Keeper | closed | Color in the top bar of the Main Screen cards | design | Get rid of the Icons on the bar of each card. Then take the color of the old Icon and make that the background color of the top bar of the card. | 1.0 | Color in the top bar of the Main Screen cards - Get rid of the Icons on the bar of each card. Then take the color of the old Icon and make that the background color of the top bar of the card. | non_priority | color in the top bar of the main screen cards get rid of the icons on the bar of each card then take the color of the old icon and make that the background color of the top bar of the card | 0 |
96,170 | 27,768,096,647 | IssuesEvent | 2023-03-16 12:50:25 | spack/spack | https://api.github.com/repos/spack/spack | opened | Installation issue: libx11 fails at configure stage with `error: spack/lib/spack/env/cpp defines unix with or without -undef. I don't know what to do.` | build-error | ### Steps to reproduce the issue
```console
$ $ spack spec -I libx11@1.7.0 %gcc@12.1.0
Input spec
--------------------------------
- libx11@1.7.0%gcc@12.1.0
Concretized
--------------------------------
- libx11@1.7.0%gcc@12.1.0 build_system=autotools arch=linux-ubuntu22.04-skylake
[+] ^inputproto@... | 1.0 | Installation issue: libx11 fails at configure stage with `error: spack/lib/spack/env/cpp defines unix with or without -undef. I don't know what to do.` - ### Steps to reproduce the issue
```console
$ $ spack spec -I libx11@1.7.0 %gcc@12.1.0
Input spec
--------------------------------
- libx11@1.7.0%gcc@12.1.0
... | non_priority | installation issue fails at configure stage with error spack lib spack env cpp defines unix with or without undef i don t know what to do steps to reproduce the issue console spack spec i gcc input spec gcc concretized ... | 0 |
45,903 | 13,135,934,999 | IssuesEvent | 2020-08-07 04:30:39 | shaundmorris/ddf | https://api.github.com/repos/shaundmorris/ddf | closed | CVE-2016-1000343 High Severity Vulnerability detected by WhiteSource | security vulnerability wontfix | ## CVE-2016-1000343 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.54.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of c... | True | CVE-2016-1000343 High Severity Vulnerability detected by WhiteSource - ## CVE-2016-1000343 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.54.jar</b></p></summ... | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptogra... | 0 |
377,852 | 26,272,511,763 | IssuesEvent | 2023-01-06 18:24:46 | cBarbosa/iris-gestao | https://api.github.com/repos/cBarbosa/iris-gestao | closed | [Imóvel] Ajuste nos tipos de imóvel | documentation | Os 3 tipos de imóveis devem ser:
_ Edificio Corporativo;
_ Sala/Pavimento;
_ Loja; | 1.0 | [Imóvel] Ajuste nos tipos de imóvel - Os 3 tipos de imóveis devem ser:
_ Edificio Corporativo;
_ Sala/Pavimento;
_ Loja; | non_priority | ajuste nos tipos de imóvel os tipos de imóveis devem ser edificio corporativo sala pavimento loja | 0 |
119,787 | 12,042,844,243 | IssuesEvent | 2020-04-14 11:20:21 | NLnetLabs/krillmanager | https://api.github.com/repos/NLnetLabs/krillmanager | closed | Incorrect OWN certificate guidance | bug documentation wizard | The wizard says that an OWN certificate must be in `/tmp` but IIRC this restriction no longer applies. | 1.0 | Incorrect OWN certificate guidance - The wizard says that an OWN certificate must be in `/tmp` but IIRC this restriction no longer applies. | non_priority | incorrect own certificate guidance the wizard says that an own certificate must be in tmp but iirc this restriction no longer applies | 0 |
128,429 | 17,534,425,652 | IssuesEvent | 2021-08-12 03:53:51 | dotnet/project-system | https://api.github.com/repos/dotnet/project-system | closed | Launch Profiles UI doesn't honor property visibility (2) | Bug Triage-Approved Must-Have Feature-Project-Properties-Designer | **Steps to Reproduce**:
1. Add the following property to ProjectDebugPropertyPage.xaml:
``` xml
<StringProperty Name="MyOtherProperty"
Visible="False" />
```
2. Ctrl+F5 to run VS in the experimental hive (the updated .xaml file will be picked up).
3. Create a new C# Console App ta... | 1.0 | Launch Profiles UI doesn't honor property visibility (2) - **Steps to Reproduce**:
1. Add the following property to ProjectDebugPropertyPage.xaml:
``` xml
<StringProperty Name="MyOtherProperty"
Visible="False" />
```
2. Ctrl+F5 to run VS in the experimental hive (the updated .xaml fi... | non_priority | launch profiles ui doesn t honor property visibility steps to reproduce add the following property to projectdebugpropertypage xaml xml stringproperty name myotherproperty visible false ctrl to run vs in the experimental hive the updated xaml fil... | 0 |
34,804 | 12,301,020,403 | IssuesEvent | 2020-05-11 14:49:18 | TIBCOSoftware/TCSTK-Angular | https://api.github.com/repos/TIBCOSoftware/TCSTK-Angular | closed | CVE-2019-16769 (Medium) detected in serialize-javascript-1.9.1.tgz | security vulnerability | ## CVE-2019-16769 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular... | True | CVE-2019-16769 (Medium) detected in serialize-javascript-1.9.1.tgz - ## CVE-2019-16769 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>... | non_priority | cve medium detected in serialize javascript tgz cve medium severity vulnerability vulnerable library serialize javascript tgz serialize javascript to a superset of json that includes regular expressions and functions library home page a href path to dependency file tm... | 0 |
131,889 | 18,428,894,312 | IssuesEvent | 2021-10-14 04:08:34 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | opened | Minimal APIs ServiceBase | design-proposal | ## Summary
I had a scene where I had to write a lot of apis, If all the apis were written in program.cs, feels very smelly to me.
So, I need a `ServiceBase` like `ControllerBase`.
## Motivation and goals
Can group apis like controllers
## In scope
Use Minimal APIs to write a lot of API.
## Out of sco... | 1.0 | Minimal APIs ServiceBase - ## Summary
I had a scene where I had to write a lot of apis, If all the apis were written in program.cs, feels very smelly to me.
So, I need a `ServiceBase` like `ControllerBase`.
## Motivation and goals
Can group apis like controllers
## In scope
Use Minimal APIs to write a l... | non_priority | minimal apis servicebase summary i had a scene where i had to write a lot of apis if all the apis were written in program cs feels very smelly to me so i need a servicebase like controllerbase motivation and goals can group apis like controllers in scope use minimal apis to write a l... | 0 |
262,224 | 27,864,885,107 | IssuesEvent | 2023-03-21 09:34:32 | elastic/beats | https://api.github.com/repos/elastic/beats | opened | [S3 + SQS input] Dynamic "max_number_of_messages" boolean option | discuss Team:Security-External Integrations | Based on feedback from customers, especially larger ones, I want to create this issue to discuss a possible way of better handling our scaling for SQS.
**This does not assume we have the capabilities today to perform this, and is to research and discuss further**
**Common SQS workflow behavior**
- A single threa... | True | [S3 + SQS input] Dynamic "max_number_of_messages" boolean option - Based on feedback from customers, especially larger ones, I want to create this issue to discuss a possible way of better handling our scaling for SQS.
**This does not assume we have the capabilities today to perform this, and is to research and disc... | non_priority | dynamic max number of messages boolean option based on feedback from customers especially larger ones i want to create this issue to discuss a possible way of better handling our scaling for sqs this does not assume we have the capabilities today to perform this and is to research and discuss further ... | 0 |
183,321 | 21,721,703,359 | IssuesEvent | 2022-05-11 01:17:54 | raindigi/reaction | https://api.github.com/repos/raindigi/reaction | closed | CVE-2020-15256 (High) detected in object-path-0.11.4.tgz - autoclosed | security vulnerability | ## CVE-2020-15256 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>object-path-0.11.4.tgz</b></p></summary>
<p>Access deep object properties using a path</p>
<p>Library home page: <a hr... | True | CVE-2020-15256 (High) detected in object-path-0.11.4.tgz - autoclosed - ## CVE-2020-15256 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>object-path-0.11.4.tgz</b></p></summary>
<p>Ac... | non_priority | cve high detected in object path tgz autoclosed cve high severity vulnerability vulnerable library object path tgz access deep object properties using a path library home page a href path to dependency file package json path to vulnerable library node modules obj... | 0 |
681 | 2,602,201,344 | IssuesEvent | 2015-02-24 05:57:04 | bboyle/relevance | https://api.github.com/repos/bboyle/relevance | closed | improve test running and coverage | build | - investigate karma or saucelabs to run qunit tests
- run tests in multiple browsers (including IE?)
- allow single running across multiple browsers
- integrate with sauce labs? https://saucelabs.com/pricing or browserstack: http://www.browserstack.com/javascript-testing-api | 1.0 | improve test running and coverage - - investigate karma or saucelabs to run qunit tests
- run tests in multiple browsers (including IE?)
- allow single running across multiple browsers
- integrate with sauce labs? https://saucelabs.com/pricing or browserstack: http://www.browserstack.com/javascript-testing-api | non_priority | improve test running and coverage investigate karma or saucelabs to run qunit tests run tests in multiple browsers including ie allow single running across multiple browsers integrate with sauce labs or browserstack | 0 |
332,128 | 24,336,822,550 | IssuesEvent | 2022-10-01 07:03:06 | otto-de/gitactionboard | https://api.github.com/repos/otto-de/gitactionboard | closed | Running the docker Container | documentation | Hi it would be nice to have an example deployment in the README, using an organisation and or a USERNAME. Also a multi repo view example too would be appreciated. | 1.0 | Running the docker Container - Hi it would be nice to have an example deployment in the README, using an organisation and or a USERNAME. Also a multi repo view example too would be appreciated. | non_priority | running the docker container hi it would be nice to have an example deployment in the readme using an organisation and or a username also a multi repo view example too would be appreciated | 0 |
180,413 | 21,625,728,475 | IssuesEvent | 2022-05-05 01:41:13 | Sh2dowFi3nd/Test_2 | https://api.github.com/repos/Sh2dowFi3nd/Test_2 | closed | CVE-2017-12626 (High) detected in poi-3.8.jar - autoclosed | security vulnerability | ## CVE-2017-12626 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>poi-3.8.jar</b></p></summary>
<p>Apache POI - Java API To Access Microsoft Format Files</p>
<p>Library home page: <a h... | True | CVE-2017-12626 (High) detected in poi-3.8.jar - autoclosed - ## CVE-2017-12626 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>poi-3.8.jar</b></p></summary>
<p>Apache POI - Java API To... | non_priority | cve high detected in poi jar autoclosed cve high severity vulnerability vulnerable library poi jar apache poi java api to access microsoft format files library home page a href dependency hierarchy x poi jar vulnerable library found in head commit a... | 0 |
234,930 | 19,276,913,757 | IssuesEvent | 2021-12-10 12:58:51 | IntellectualSites/PlotSquared | https://api.github.com/repos/IntellectualSites/PlotSquared | opened | when importing PlotSquared-Bukkit: The POM for org.enginehub:squirrelid:jar:0.3.0 is missing, no dependency information available | Requires Testing | ### Server Implementation
Paper
### Server Version
1.18
### Describe the bug
Similar to https://github.com/IntellectualSites/PlotSquared/issues/3359, but with ``org.enginehub:squirrelid`` when importing ``PlotSquared-Bukkit``
Such as:
```xml
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven... | 1.0 | when importing PlotSquared-Bukkit: The POM for org.enginehub:squirrelid:jar:0.3.0 is missing, no dependency information available - ### Server Implementation
Paper
### Server Version
1.18
### Describe the bug
Similar to https://github.com/IntellectualSites/PlotSquared/issues/3359, but with ``org.enginehub:squirrel... | non_priority | when importing plotsquared bukkit the pom for org enginehub squirrelid jar is missing no dependency information available server implementation paper server version describe the bug similar to but with org enginehub squirrelid when importing plotsquared bukkit such as xm... | 0 |
29,990 | 4,544,394,985 | IssuesEvent | 2016-09-10 17:24:42 | FreeCodeCamp/FreeCodeCamp | https://api.github.com/repos/FreeCodeCamp/FreeCodeCamp | closed | Iterate over Array with .map Issue! FIXED by FCC | confirmed help wanted tests | Challenge [iterate-over-arrays-with-map](https://www.freecodecamp.com/en/challenges/object-oriented-and-functional-programming/iterate-over-arrays-with-map) has an issue.
User Agent is: <code>Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/52.0.2743.116 Safari/537.36</code>.
Please describe... | 1.0 | Iterate over Array with .map Issue! FIXED by FCC - Challenge [iterate-over-arrays-with-map](https://www.freecodecamp.com/en/challenges/object-oriented-and-functional-programming/iterate-over-arrays-with-map) has an issue.
User Agent is: <code>Mozilla/5.0 (Windows NT 6.1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/5... | non_priority | iterate over array with map issue fixed by fcc challenge has an issue user agent is mozilla windows nt applewebkit khtml like gecko chrome safari please describe how to reproduce this issue and include links to screenshots if possible my code is as followed but i keep ge... | 0 |
207,903 | 16,097,112,463 | IssuesEvent | 2021-04-27 02:36:29 | padma-g/info478-project | https://api.github.com/repos/padma-g/info478-project | closed | Identify target audience and research questions | documentation | Who is the target audience? Depending on the domain of the data, there may be a variety of audiences interested in using the dataset. We should hone in on one of these audiences.
What should the audience learn from the resource? Please consider specific questions that the project can answer using the data that has b... | 1.0 | Identify target audience and research questions - Who is the target audience? Depending on the domain of the data, there may be a variety of audiences interested in using the dataset. We should hone in on one of these audiences.
What should the audience learn from the resource? Please consider specific questions tha... | non_priority | identify target audience and research questions who is the target audience depending on the domain of the data there may be a variety of audiences interested in using the dataset we should hone in on one of these audiences what should the audience learn from the resource please consider specific questions tha... | 0 |
14,131 | 5,560,911,764 | IssuesEvent | 2017-03-24 20:50:47 | STScI-JWST/jwst | https://api.github.com/repos/STScI-JWST/jwst | closed | cube_build_io, association and ModelContainer | associations bug cube_build datamodels | From a [basecamp report by Jeb](https://stsci-ins.basecamphq.com/projects/11477312-jwst-pipeline/posts/100992154/comments), it appears there is a conflict about how/when associations are opened. cube_build is expecting just the filename for the association, but in the pipeline, it has already been opened as a ModelCont... | 1.0 | cube_build_io, association and ModelContainer - From a [basecamp report by Jeb](https://stsci-ins.basecamphq.com/projects/11477312-jwst-pipeline/posts/100992154/comments), it appears there is a conflict about how/when associations are opened. cube_build is expecting just the filename for the association, but in the pip... | non_priority | cube build io association and modelcontainer from a it appears there is a conflict about how when associations are opened cube build is expecting just the filename for the association but in the pipeline it has already been opened as a modelcontainer the offending section of code in cube build io is lines ... | 0 |
146,862 | 23,134,132,235 | IssuesEvent | 2022-07-28 13:03:28 | patternfly/patternfly-design | https://api.github.com/repos/patternfly/patternfly-design | closed | [PieChart] - [docs update] | needs Info needs design/css | **Is this a new component or an extension of an existing one?**
I would like you to update the PieChart documentation and add my example to it
**Describe the feature**
My example uses the Tooltip component that wraps the ChartLabel.
The Patternfly Tooltip documentation contains class examples only and not a func... | 1.0 | [PieChart] - [docs update] - **Is this a new component or an extension of an existing one?**
I would like you to update the PieChart documentation and add my example to it
**Describe the feature**
My example uses the Tooltip component that wraps the ChartLabel.
The Patternfly Tooltip documentation contains class... | non_priority | is this a new component or an extension of an existing one i would like you to update the piechart documentation and add my example to it describe the feature my example uses the tooltip component that wraps the chartlabel the patternfly tooltip documentation contains class examples only and no... | 0 |
209,365 | 23,716,690,423 | IssuesEvent | 2022-08-30 12:23:24 | rsoreq/zaproxy | https://api.github.com/repos/rsoreq/zaproxy | closed | CVE-2020-36188 (High) detected in jackson-databind-2.9.10.jar - autoclosed | security vulnerability | ## CVE-2020-36188 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streami... | True | CVE-2020-36188 (High) detected in jackson-databind-2.9.10.jar - autoclosed - ## CVE-2020-36188 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.jar</b></p></summa... | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file zap zap gradle kt... | 0 |
259,121 | 19,587,085,843 | IssuesEvent | 2022-01-05 08:30:41 | audeering/audformat | https://api.github.com/repos/audeering/audformat | closed | Difference between TIME and DATE in audformat.define.DataType | documentation question | Let's assume you would like to store the exact date and time of a recording using `datetime.datetime`, then it is not obvious from the [current documentation](https://audeering.github.io/audformat/api-define.html) what the data type of the scheme should be: `TIME` or `DATE`.
I would assume that `TIME` should cover d... | 1.0 | Difference between TIME and DATE in audformat.define.DataType - Let's assume you would like to store the exact date and time of a recording using `datetime.datetime`, then it is not obvious from the [current documentation](https://audeering.github.io/audformat/api-define.html) what the data type of the scheme should be... | non_priority | difference between time and date in audformat define datatype let s assume you would like to store the exact date and time of a recording using datetime datetime then it is not obvious from the what the data type of the scheme should be time or date i would assume that time should cover duration val... | 0 |
4,962 | 25,479,207,790 | IssuesEvent | 2022-11-25 17:57:00 | bazelbuild/intellij | https://api.github.com/repos/bazelbuild/intellij | closed | Run gazelle on project sync | type: feature request P1 lang: go product: IntelliJ topic: sync product: GoLand awaiting-maintainer | ## Problem
For projects that use gazelle, moving a single file is a two-step process: First they must run gazelle, then they must sync to trigger re-indexing if IntelliJ didn't pick those changes up.
Ideally, this would be a single-click action, whereby a user only has to click "sync" after a refactoring is done.
... | True | Run gazelle on project sync - ## Problem
For projects that use gazelle, moving a single file is a two-step process: First they must run gazelle, then they must sync to trigger re-indexing if IntelliJ didn't pick those changes up.
Ideally, this would be a single-click action, whereby a user only has to click "sync" ... | non_priority | run gazelle on project sync problem for projects that use gazelle moving a single file is a two step process first they must run gazelle then they must sync to trigger re indexing if intellij didn t pick those changes up ideally this would be a single click action whereby a user only has to click sync ... | 0 |
5,828 | 30,849,982,196 | IssuesEvent | 2023-08-02 16:01:56 | obi1kenobi/trustfall | https://api.github.com/repos/obi1kenobi/trustfall | opened | Consider switching fuzzer backends to LibAFL | C-maintainability | LibFuzzer is in [maintenance mode](https://llvm.org/docs/LibFuzzer.html#status):
> The original authors of libFuzzer have stopped active work on it and switched to working on another fuzzing engine, [Centipede](https://github.com/google/centipede).
We should consider switching to LibAFL or another implementation, s... | True | Consider switching fuzzer backends to LibAFL - LibFuzzer is in [maintenance mode](https://llvm.org/docs/LibFuzzer.html#status):
> The original authors of libFuzzer have stopped active work on it and switched to working on another fuzzing engine, [Centipede](https://github.com/google/centipede).
We should consider s... | non_priority | consider switching fuzzer backends to libafl libfuzzer is in the original authors of libfuzzer have stopped active work on it and switched to working on another fuzzing engine we should consider switching to libafl or another implementation since it seems that we can get both fuzzing performance and m... | 0 |
94,874 | 27,319,336,782 | IssuesEvent | 2023-02-24 18:19:06 | helidon-io/helidon | https://api.github.com/repos/helidon-io/helidon | opened | Incorrect code in generated `Abstract<BuilderTarget>` class when target interface extends another interface | bug 4.x builder | ## Environment Details
* Helidon Version: 4.x
* Helidon SE or Helidon MP
* JDK version:
* OS:
* Docker version (if applicable):
----------
## Problem Description
If I have
```java
public interfaceMyInterface extends YourInterface {
// ...
}
```
then the generated `AbstractMyInterface` class has `exten... | 1.0 | Incorrect code in generated `Abstract<BuilderTarget>` class when target interface extends another interface - ## Environment Details
* Helidon Version: 4.x
* Helidon SE or Helidon MP
* JDK version:
* OS:
* Docker version (if applicable):
----------
## Problem Description
If I have
```java
public interface... | non_priority | incorrect code in generated abstract class when target interface extends another interface environment details helidon version x helidon se or helidon mp jdk version os docker version if applicable problem description if i have java public interfacemyinterface ex... | 0 |
350,154 | 31,857,740,074 | IssuesEvent | 2023-09-15 08:42:23 | snu-quiqcl/iquip | https://api.github.com/repos/snu-quiqcl/iquip | opened | Pass the unittest without any error | test | ### Feature you want to implement
After updating QIWIS version, it causes too many unittest error due to global constants.
Thus, I will resolve this temporarily, not completely. (Just make the unittest passed) | 1.0 | Pass the unittest without any error - ### Feature you want to implement
After updating QIWIS version, it causes too many unittest error due to global constants.
Thus, I will resolve this temporarily, not completely. (Just make the unittest passed) | non_priority | pass the unittest without any error feature you want to implement after updating qiwis version it causes too many unittest error due to global constants thus i will resolve this temporarily not completely just make the unittest passed | 0 |
310,009 | 23,317,076,590 | IssuesEvent | 2022-08-08 13:24:32 | galasa-dev/projectmanagement | https://api.github.com/repos/galasa-dev/projectmanagement | closed | Create page structure and template for blogs in galasa.dev | documentation | A series of blogs is being created and these need to be hosted on galasa.dev
Blogs can be created in galasa-dev repository and published on demand outside of release cycle
Need to include structure of page, blogs and url - kept simple initially. Also include guidelines on eg use of images, tagging etc for searchability... | 1.0 | Create page structure and template for blogs in galasa.dev - A series of blogs is being created and these need to be hosted on galasa.dev
Blogs can be created in galasa-dev repository and published on demand outside of release cycle
Need to include structure of page, blogs and url - kept simple initially. Also include ... | non_priority | create page structure and template for blogs in galasa dev a series of blogs is being created and these need to be hosted on galasa dev blogs can be created in galasa dev repository and published on demand outside of release cycle need to include structure of page blogs and url kept simple initially also include ... | 0 |
141,123 | 12,958,368,752 | IssuesEvent | 2020-07-20 11:15:33 | opencv/opencv | https://api.github.com/repos/opencv/opencv | closed | OpenCV in Android Studio's NDK fails with "undefined reference" error | category: documentation platform: android | ##### System information (version)
- OpenCV => :grey_question: 4.3 / 3.4
- Operating System / Platform => :grey_question: Linux Ubuntu 16.04
- Compiler => :grey_question: Android Studio (Gradle / Ninja / CMake / clang++)
##### Detailed description
I'm trying to use OpenCV on Android's NDK.
I have two simila... | 1.0 | OpenCV in Android Studio's NDK fails with "undefined reference" error - ##### System information (version)
- OpenCV => :grey_question: 4.3 / 3.4
- Operating System / Platform => :grey_question: Linux Ubuntu 16.04
- Compiler => :grey_question: Android Studio (Gradle / Ninja / CMake / clang++)
##### Detailed desc... | non_priority | opencv in android studio s ndk fails with undefined reference error system information version opencv grey question operating system platform grey question linux ubuntu compiler grey question android studio gradle ninja cmake clang detailed descri... | 0 |
249,577 | 26,954,452,180 | IssuesEvent | 2023-02-08 14:02:09 | simplycubed/terraform-google-static-assets | https://api.github.com/repos/simplycubed/terraform-google-static-assets | closed | CVE-2022-1996 (High) detected in github.com/emicklei/go-restful/v3-v3.8.0 - autoclosed | security vulnerability | ## CVE-2022-1996 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/emicklei/go-restful/v3-v3.8.0</b></p></summary>
<p>package for building REST-style Web Services using Go</p>... | True | CVE-2022-1996 (High) detected in github.com/emicklei/go-restful/v3-v3.8.0 - autoclosed - ## CVE-2022-1996 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/emicklei/go-restful/... | non_priority | cve high detected in github com emicklei go restful autoclosed cve high severity vulnerability vulnerable library github com emicklei go restful package for building rest style web services using go library home page a href dependency hierarchy github com gr... | 0 |
5,058 | 3,899,771,987 | IssuesEvent | 2016-04-17 23:01:44 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 13067395: Keynote 5.3: transition delay values less than 0.3 s ignored | classification:ui/usability reproducible:always | #### Description
Summary:
If you set the transition to "automatically", you can set a delay of 0.5, 0.4 and 0.3s and it will work. If you set 0.2 or 0.1 the change will be ignored.
Steps to Reproduce:
1. Set auto transition delay to 0.1
2. click onto another object
3. click back to the object
Expected Results:
au... | True | 13067395: Keynote 5.3: transition delay values less than 0.3 s ignored - #### Description
Summary:
If you set the transition to "automatically", you can set a delay of 0.5, 0.4 and 0.3s and it will work. If you set 0.2 or 0.1 the change will be ignored.
Steps to Reproduce:
1. Set auto transition delay to 0.1
2. cli... | non_priority | keynote transition delay values less than s ignored description summary if you set the transition to automatically you can set a delay of and and it will work if you set or the change will be ignored steps to reproduce set auto transition delay to click onto ... | 0 |
232,029 | 25,564,359,176 | IssuesEvent | 2022-11-30 13:15:40 | hygieia/hygieia-artifact-artifactory-collector | https://api.github.com/repos/hygieia/hygieia-artifact-artifactory-collector | opened | CVE-2022-31692 (High) detected in spring-security-core-5.6.6.jar | security vulnerability | ## CVE-2022-31692 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-core-5.6.6.jar</b></p></summary>
<p>Spring Security</p>
<p>Library home page: <a href="https://spring.... | True | CVE-2022-31692 (High) detected in spring-security-core-5.6.6.jar - ## CVE-2022-31692 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-core-5.6.6.jar</b></p></summary>
<p... | non_priority | cve high detected in spring security core jar cve high severity vulnerability vulnerable library spring security core jar spring security library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springfr... | 0 |
15,813 | 3,485,360,786 | IssuesEvent | 2015-12-31 05:33:13 | destroytoday/Dwarf | https://api.github.com/repos/destroytoday/Dwarf | closed | Issues with Guides | Linux-only To Fix To Test | I found a number of issues with these:
1. I can't drag a horizontal guide to my other (non-active) monitor.
2. I can't create a horizontal guide that spans the width of both monitors.
3. Cutting (Crtrl+X) a guide works, pasting (Ctrl+V) rarely does paste a guide, and when it does, it doesn't restore it's X,Y propertie... | 1.0 | Issues with Guides - I found a number of issues with these:
1. I can't drag a horizontal guide to my other (non-active) monitor.
2. I can't create a horizontal guide that spans the width of both monitors.
3. Cutting (Crtrl+X) a guide works, pasting (Ctrl+V) rarely does paste a guide, and when it does, it doesn't resto... | non_priority | issues with guides i found a number of issues with these i can t drag a horizontal guide to my other non active monitor i can t create a horizontal guide that spans the width of both monitors cutting crtrl x a guide works pasting ctrl v rarely does paste a guide and when it does it doesn t resto... | 0 |
235,581 | 19,401,222,012 | IssuesEvent | 2021-12-19 07:57:45 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: sqlsmith/setup=tpch-sf1/setting=no-ddl failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.sqlsmith/setup=tpch-sf1/setting=no-ddl [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3949693&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3949693&tab=artifacts#/sqlsmith/setup=tpch-sf1/setting=no-ddl) on master @ [4cbe795c7f8c36c007c3ca1250367cb181f5ca0... | 2.0 | roachtest: sqlsmith/setup=tpch-sf1/setting=no-ddl failed - roachtest.sqlsmith/setup=tpch-sf1/setting=no-ddl [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3949693&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3949693&tab=artifacts#/sqlsmith/setup=tpch-sf1/setting=n... | non_priority | roachtest sqlsmith setup tpch setting no ddl failed roachtest sqlsmith setup tpch setting no ddl with on master the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts sqlsmith setup tpch setting no ddl run... | 0 |
74,941 | 9,813,589,873 | IssuesEvent | 2019-06-13 08:21:06 | aserebryakov/vim-todo-lists | https://api.github.com/repos/aserebryakov/vim-todo-lists | closed | Swap o and O commands | documentation | To more model how normal vim works "O" would insert a line above while this program does it opposite, consider changing to more closely model vim? | 1.0 | Swap o and O commands - To more model how normal vim works "O" would insert a line above while this program does it opposite, consider changing to more closely model vim? | non_priority | swap o and o commands to more model how normal vim works o would insert a line above while this program does it opposite consider changing to more closely model vim | 0 |
127,173 | 18,010,317,724 | IssuesEvent | 2021-09-16 07:50:35 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | opened | CVE-2020-28097 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2020-28097 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home p... | True | CVE-2020-28097 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2020-28097 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia C... | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href vulnerable source files drivers vid... | 0 |
192,280 | 22,215,926,818 | IssuesEvent | 2022-06-08 01:37:53 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | reopened | CVE-2018-5953 (Medium) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2018-5953 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home pa... | True | CVE-2018-5953 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2018-5953 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Car... | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source f... | 0 |
218,709 | 17,017,253,078 | IssuesEvent | 2021-07-02 13:44:34 | sveltejs/kit | https://api.github.com/repos/sveltejs/kit | closed | Static Adapter pnpm test fails when path to Node has spaces in on Windows | bug tests windows | **Describe the bug**
Running pnpm test on Windows when node is installed in "C:\\Program Files\\nodejs\\node.exe" fails due to the space in the path.
Looks like spawn function
https://github.com/sveltejs/kit/blob/0d69e556851a02678f8694f948517fc6ec85df86/packages/adapter-static/test/utils.js#L71
is using spac... | 1.0 | Static Adapter pnpm test fails when path to Node has spaces in on Windows - **Describe the bug**
Running pnpm test on Windows when node is installed in "C:\\Program Files\\nodejs\\node.exe" fails due to the space in the path.
Looks like spawn function
https://github.com/sveltejs/kit/blob/0d69e556851a02678f8694f... | non_priority | static adapter pnpm test fails when path to node has spaces in on windows describe the bug running pnpm test on windows when node is installed in c program files nodejs node exe fails due to the space in the path looks like spawn function is using spaces to determine arguments const s... | 0 |
164,117 | 20,364,331,326 | IssuesEvent | 2022-02-21 02:34:35 | n-devs/share-we-go-dev | https://api.github.com/repos/n-devs/share-we-go-dev | opened | CVE-2022-0639 (Medium) detected in url-parse-1.4.7.tgz | security vulnerability | ## CVE-2022-0639 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser ... | True | CVE-2022-0639 (Medium) detected in url-parse-1.4.7.tgz - ## CVE-2022-0639 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.7.tgz</b></p></summary>
<p>Small footprint URL... | non_priority | cve medium detected in url parse tgz cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file share we go package json ... | 0 |
107,701 | 13,503,188,318 | IssuesEvent | 2020-09-13 12:22:18 | pandas-dev/pandas | https://api.github.com/repos/pandas-dev/pandas | closed | BUG: when i merge two dataframes in pandas if the datatypes of columns are mismatched exception is raised | API Design Reshaping | - [ ] I have checked that this issue has not already been reported.
- [ ] I have confirmed this bug exists on the latest version of pandas.
- [ ] (optional) I have confirmed this bug exists on the master branch of pandas.
---
**Note**: Please read [this guide](https://matthewrocklin.com/blog/work/2018/02/28... | 1.0 | BUG: when i merge two dataframes in pandas if the datatypes of columns are mismatched exception is raised - - [ ] I have checked that this issue has not already been reported.
- [ ] I have confirmed this bug exists on the latest version of pandas.
- [ ] (optional) I have confirmed this bug exists on the master b... | non_priority | bug when i merge two dataframes in pandas if the datatypes of columns are mismatched exception is raised i have checked that this issue has not already been reported i have confirmed this bug exists on the latest version of pandas optional i have confirmed this bug exists on the master branch ... | 0 |
297,133 | 22,341,166,735 | IssuesEvent | 2022-06-15 01:02:30 | MichaelPetersen22/Solace | https://api.github.com/repos/MichaelPetersen22/Solace | opened | Create Readme and Additional Documentation on Application Usage | documentation | The application (for myself as well) could benefit from documentation on configuration, usage, setup, deployment, requirements etc. | 1.0 | Create Readme and Additional Documentation on Application Usage - The application (for myself as well) could benefit from documentation on configuration, usage, setup, deployment, requirements etc. | non_priority | create readme and additional documentation on application usage the application for myself as well could benefit from documentation on configuration usage setup deployment requirements etc | 0 |
63,156 | 6,827,816,605 | IssuesEvent | 2017-11-08 18:17:05 | bpmn-miwg/bpmn-miwg-test-suite | https://api.github.com/repos/bpmn-miwg/bpmn-miwg-test-suite | opened | Depiction of the Onboarding employee page labels on shape are not properly positioned | Test: C.4.0 | Shapes label in the C.4.0.3 file are off based on the reference schema | 1.0 | Depiction of the Onboarding employee page labels on shape are not properly positioned - Shapes label in the C.4.0.3 file are off based on the reference schema | non_priority | depiction of the onboarding employee page labels on shape are not properly positioned shapes label in the c file are off based on the reference schema | 0 |
6,006 | 21,880,639,301 | IssuesEvent | 2022-05-19 14:04:22 | gergelytakacs/AutomationShield | https://api.github.com/repos/gergelytakacs/AutomationShield | closed | LQ and more: LINPACK benchmark | AutomationShield common software | A LINPACK benchmark should be added to the timing and memory evaluation. See[ this ](https://en.wikipedia.org/wiki/LINPACK_benchmarks) for a start. Essentially it is about the solution of the set of linear equations given in the matrix form by Ax=b. | 1.0 | LQ and more: LINPACK benchmark - A LINPACK benchmark should be added to the timing and memory evaluation. See[ this ](https://en.wikipedia.org/wiki/LINPACK_benchmarks) for a start. Essentially it is about the solution of the set of linear equations given in the matrix form by Ax=b. | non_priority | lq and more linpack benchmark a linpack benchmark should be added to the timing and memory evaluation see for a start essentially it is about the solution of the set of linear equations given in the matrix form by ax b | 0 |
5,818 | 13,193,851,844 | IssuesEvent | 2020-08-13 15:51:22 | dfds/backstage | https://api.github.com/repos/dfds/backstage | closed | Agree with PO (grooming) on "developer experience roadmap": | Architecture | - [x] Create Capability.
- [ ] Create WebAPI. (dfds-web-api)
- [ ] Create WebHost.
- [x] Create AuthorizationServer.
- [x] Register application with AuthorizationServer.
- [x] Grant application permissions with AuthorizationServer. | 1.0 | Agree with PO (grooming) on "developer experience roadmap": - - [x] Create Capability.
- [ ] Create WebAPI. (dfds-web-api)
- [ ] Create WebHost.
- [x] Create AuthorizationServer.
- [x] Register application with AuthorizationServer.
- [x] Grant application permissions with AuthorizationServer. | non_priority | agree with po grooming on developer experience roadmap create capability create webapi dfds web api create webhost create authorizationserver register application with authorizationserver grant application permissions with authorizationserver | 0 |
80,564 | 10,024,170,346 | IssuesEvent | 2019-07-16 21:06:46 | ParabolInc/action | https://api.github.com/repos/ParabolInc/action | closed | Lo-fi design prototypes for Group phase including prompt categories | design enhancement | See #2557
### Acceptance Criteria (optional)
A lo-fi prototype we can send to users for feedback that:
- Shows current group layout, but with headers for each prompt and generated cards under each prompt
- Shows cards in grid, but automatically color-coded by prompt. Sort cards by prompt
- Figma protot... | 1.0 | Lo-fi design prototypes for Group phase including prompt categories - See #2557
### Acceptance Criteria (optional)
A lo-fi prototype we can send to users for feedback that:
- Shows current group layout, but with headers for each prompt and generated cards under each prompt
- Shows cards in grid, but automa... | non_priority | lo fi design prototypes for group phase including prompt categories see acceptance criteria optional a lo fi prototype we can send to users for feedback that shows current group layout but with headers for each prompt and generated cards under each prompt shows cards in grid but automatic... | 0 |
288,226 | 31,861,196,782 | IssuesEvent | 2023-09-15 11:02:47 | nidhi7598/linux-v4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564 | opened | CVE-2023-3338 (Medium) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2023-3338 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.19.294</b>, <b>linuxlinux-4.19.294</b>, <b>linuxlinux-4.19.294</b>, <b>linuxlinux-4.19.294</b>, <b>linu... | True | CVE-2023-3338 (Medium) detected in multiple libraries - ## CVE-2023-3338 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.19.294</b>, <b>linuxlinux-4.19.294</b>, <b>linu... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries linuxlinux linuxlinux linuxlinux linuxlinux linuxlinux linuxlinux linuxlinux vulnerability details a null pointer... | 0 |
1,217 | 3,453,658,317 | IssuesEvent | 2015-12-17 12:28:36 | mesosphere/marathon | https://api.github.com/repos/mesosphere/marathon | closed | Provide memory and cpu as environment variables in docker containers | enhancement service | It would be useful if docker containers launched with marathon had the memory and cpu app settings set as environment variables, such as `MARATHON_APP_MEM` and `MARATHON_APP_CPU`.
These could be used to configure an application at runtime based on the memory/cpu given to the application. | 1.0 | Provide memory and cpu as environment variables in docker containers - It would be useful if docker containers launched with marathon had the memory and cpu app settings set as environment variables, such as `MARATHON_APP_MEM` and `MARATHON_APP_CPU`.
These could be used to configure an application at runtime based o... | non_priority | provide memory and cpu as environment variables in docker containers it would be useful if docker containers launched with marathon had the memory and cpu app settings set as environment variables such as marathon app mem and marathon app cpu these could be used to configure an application at runtime based o... | 0 |
117,008 | 9,905,817,898 | IssuesEvent | 2019-06-27 12:33:29 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Add dedicated Q.B. cache tests instead of generic testing in AbstractQueryTestCase#testToQuery | :Search/Search >test v8.0.0 | In relation to occasional failures like #43112 and while looking into a fix in #43199 I had some discussions
about if its really a good idea to test the caching behaviour of all query builders in general in
`AbstractQueryTestCase#testToQuery` like we currently do. Doing this for all kinds of randomized query builder... | 1.0 | Add dedicated Q.B. cache tests instead of generic testing in AbstractQueryTestCase#testToQuery - In relation to occasional failures like #43112 and while looking into a fix in #43199 I had some discussions
about if its really a good idea to test the caching behaviour of all query builders in general in
`AbstractQuer... | non_priority | add dedicated q b cache tests instead of generic testing in abstractquerytestcase testtoquery in relation to occasional failures like and while looking into a fix in i had some discussions about if its really a good idea to test the caching behaviour of all query builders in general in abstractquerytestcas... | 0 |
57,113 | 8,140,666,721 | IssuesEvent | 2018-08-20 21:56:58 | heptio/ark | https://api.github.com/repos/heptio/ark | closed | Broken docs link from main readme | Bug Documentation | Page: https://heptio.github.io/ark/v0.8.1/
Any docs links that are relative seem to 404:
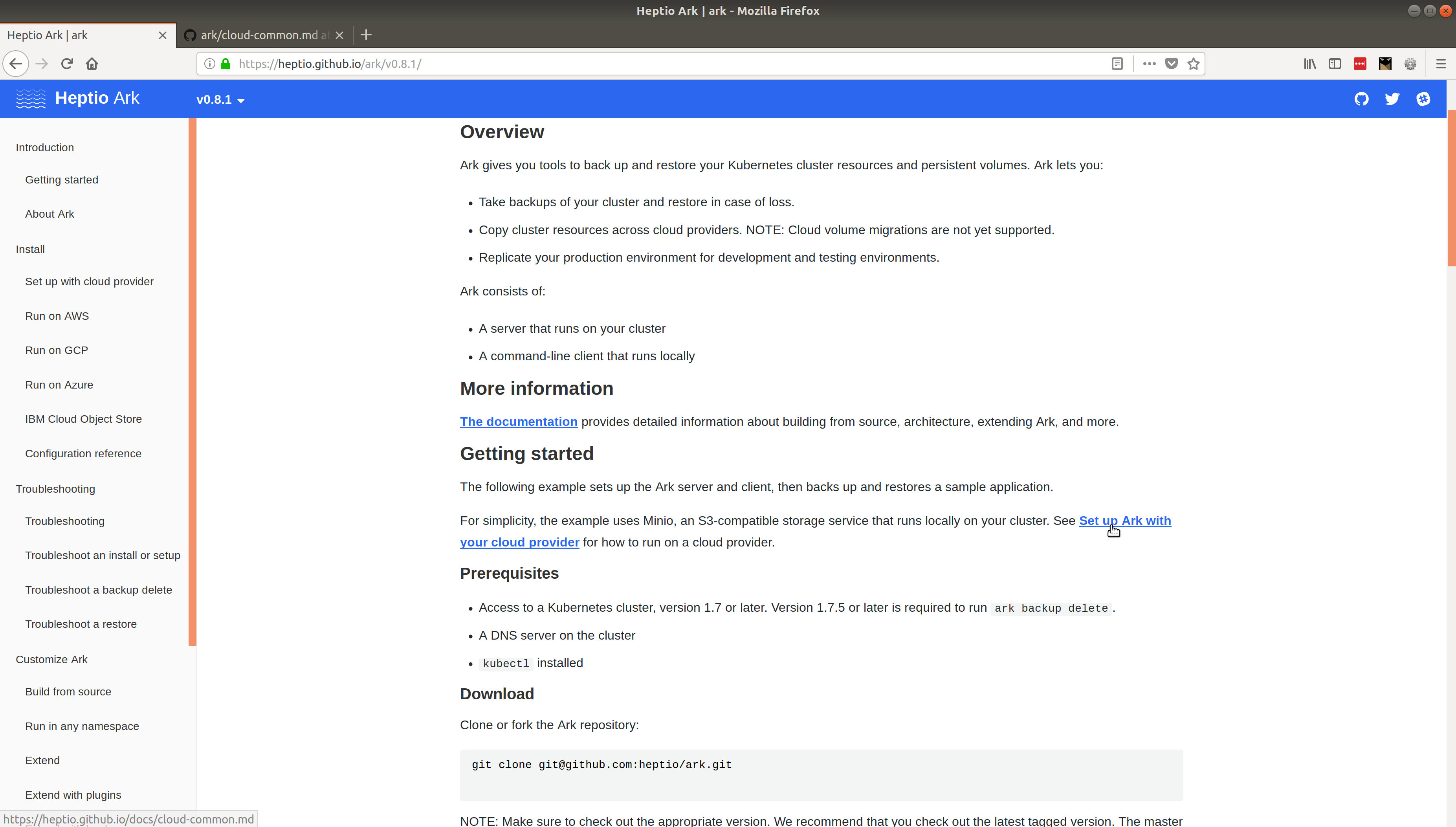
* https://heptio.github.io/docs/cloud-common.md
* https://heptio.github.io/docs/build-from-scratch.md
* https:... | 1.0 | Broken docs link from main readme - Page: https://heptio.github.io/ark/v0.8.1/
Any docs links that are relative seem to 404:
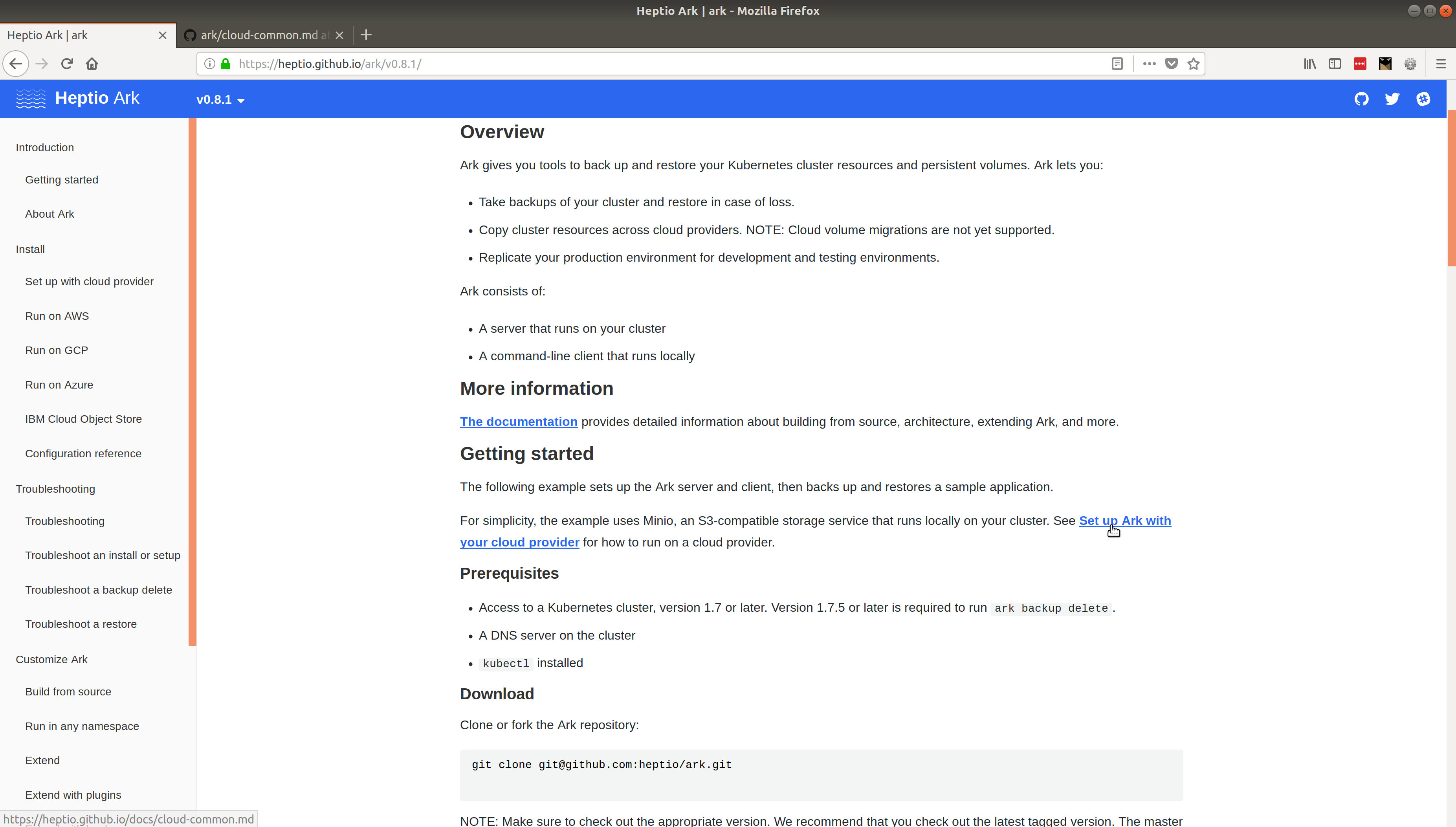
* https://heptio.github.io/docs/cloud-common.md
* https://heptio.github.io/... | non_priority | broken docs link from main readme page any docs links that are relative seem to and more | 0 |
134,970 | 18,520,894,055 | IssuesEvent | 2021-10-20 14:56:23 | rlennon/whitesource_bolt_demo | https://api.github.com/repos/rlennon/whitesource_bolt_demo | opened | CVE-2020-29652 (High) detected in github.com/jpillora/chisel-1.3.2 | security vulnerability | ## CVE-2020-29652 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/jpillora/chisel-1.3.2</b></p></summary>
<p>A fast TCP tunnel over HTTP</p>
<p>
Dependency Hierarchy:
- :... | True | CVE-2020-29652 (High) detected in github.com/jpillora/chisel-1.3.2 - ## CVE-2020-29652 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/jpillora/chisel-1.3.2</b></p></summary>... | non_priority | cve high detected in github com jpillora chisel cve high severity vulnerability vulnerable library github com jpillora chisel a fast tcp tunnel over http dependency hierarchy x github com jpillora chisel vulnerable library found in head commit a href ... | 0 |
41,661 | 16,828,029,219 | IssuesEvent | 2021-06-17 21:35:24 | BCDevOps/OpenShift4-RollOut | https://api.github.com/repos/BCDevOps/OpenShift4-RollOut | closed | OpenShift 4.6 Upgrade | Epic ops and shared services team/DXC tech/automation | **Describe the issue**
This is an EPIC to track all the sub tasks needed to get all the clusters updated to 4.6. Subsets of these tasks can be added to Sprint Goals as we worth through this work which may take several sprints.
**Additional context**
- [Release Notes](https://docs.openshift.com/container-platform/4.6/r... | 1.0 | OpenShift 4.6 Upgrade - **Describe the issue**
This is an EPIC to track all the sub tasks needed to get all the clusters updated to 4.6. Subsets of these tasks can be added to Sprint Goals as we worth through this work which may take several sprints.
**Additional context**
- [Release Notes](https://docs.openshift.com/... | non_priority | openshift upgrade describe the issue this is an epic to track all the sub tasks needed to get all the clusters updated to subsets of these tasks can be added to sprint goals as we worth through this work which may take several sprints additional context and | 0 |
18,695 | 4,306,176,147 | IssuesEvent | 2016-07-21 01:21:53 | kalabox/kalabox | https://api.github.com/repos/kalabox/kalabox | closed | Hyper-V enabled and/or VT-x not installed results in silent install forever, GUI "loading" screen seems to hang 4eva | documentation | linux and osx are nice and snappy | 1.0 | Hyper-V enabled and/or VT-x not installed results in silent install forever, GUI "loading" screen seems to hang 4eva - linux and osx are nice and snappy | non_priority | hyper v enabled and or vt x not installed results in silent install forever gui loading screen seems to hang linux and osx are nice and snappy | 0 |
18,535 | 3,390,071,373 | IssuesEvent | 2015-11-30 08:35:18 | coala-analyzer/coala | https://api.github.com/repos/coala-analyzer/coala | closed | architecture: How do we pass files to bears? | feature need-design | # What we have
We currently create a dictionary which holds the file name and the file contents.
# Issues with current design
1. We can't process non-unicode files.
2. We can't process files that are "virtual" i.e. only exist in memory and not on the fs. (Will need that for editor plugins/IDE support.)
# G... | 1.0 | architecture: How do we pass files to bears? - # What we have
We currently create a dictionary which holds the file name and the file contents.
# Issues with current design
1. We can't process non-unicode files.
2. We can't process files that are "virtual" i.e. only exist in memory and not on the fs. (Will ne... | non_priority | architecture how do we pass files to bears what we have we currently create a dictionary which holds the file name and the file contents issues with current design we can t process non unicode files we can t process files that are virtual i e only exist in memory and not on the fs will ne... | 0 |
231,231 | 25,495,022,986 | IssuesEvent | 2022-11-27 15:14:36 | billmcchesney1/superagent | https://api.github.com/repos/billmcchesney1/superagent | opened | CVE-2022-24999 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2022-24999 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-2.4.2.tgz</b>, <b>qs-1.2.2.tgz</b>, <b>qs-6.9.4.tgz</b>, <b>qs-6.7.0.tgz</b></p></summary>
<p>
<details><summar... | True | CVE-2022-24999 (Medium) detected in multiple libraries - ## CVE-2022-24999 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-2.4.2.tgz</b>, <b>qs-1.2.2.tgz</b>, <b>qs-6.9.4.tgz</b>... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries qs tgz qs tgz qs tgz qs tgz qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path... | 0 |
191,098 | 15,269,799,568 | IssuesEvent | 2021-02-22 13:17:22 | MadManGaz/Accelerometry | https://api.github.com/repos/MadManGaz/Accelerometry | opened | Improve code readability and documentation | documentation enhancement | This code was created quickly over a weekend. Code quality, readability, and documentation needs some work.
- [ ] Ensure proper separation of concerns
- [ ] Add documentation comments to any public API
- [ ] Extract views from `ContentView` to separate files | 1.0 | Improve code readability and documentation - This code was created quickly over a weekend. Code quality, readability, and documentation needs some work.
- [ ] Ensure proper separation of concerns
- [ ] Add documentation comments to any public API
- [ ] Extract views from `ContentView` to separate files | non_priority | improve code readability and documentation this code was created quickly over a weekend code quality readability and documentation needs some work ensure proper separation of concerns add documentation comments to any public api extract views from contentview to separate files | 0 |
158,437 | 24,839,864,378 | IssuesEvent | 2022-10-26 11:53:28 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | Scaffolding of synonyms in SqlServer | type-enhancement needs-design propose-close customer-reported area-scaffolding | <!-- What problem are you trying to solve? -->
I'm trying to reverse-engineer an already existing database and the created synonyms are not being mapped. I want to have them mapped to.
<!-- Describe the solution you'd like -->
So my solution is pretty simple. Basicly include that in the SqlServerDatabaseModelFac... | 1.0 | Scaffolding of synonyms in SqlServer - <!-- What problem are you trying to solve? -->
I'm trying to reverse-engineer an already existing database and the created synonyms are not being mapped. I want to have them mapped to.
<!-- Describe the solution you'd like -->
So my solution is pretty simple. Basicly includ... | non_priority | scaffolding of synonyms in sqlserver i m trying to reverse engineer an already existing database and the created synonyms are not being mapped i want to have them mapped to so my solution is pretty simple basicly include that in the sqlserverdatabasemodelfactory i think everything should just work ... | 0 |
107,549 | 11,564,141,682 | IssuesEvent | 2020-02-20 07:59:20 | fetchai/agents-aea | https://api.github.com/repos/fetchai/agents-aea | opened | Add a guide to the docs for Docker image based deployment | documentation enhancement v0.3 | **Is your feature request related to a problem? Please describe.**
We currently do not explain in the docs how to deploy an AEA
**Describe the solution you'd like**
Add a guide in the docs | 1.0 | Add a guide to the docs for Docker image based deployment - **Is your feature request related to a problem? Please describe.**
We currently do not explain in the docs how to deploy an AEA
**Describe the solution you'd like**
Add a guide in the docs | non_priority | add a guide to the docs for docker image based deployment is your feature request related to a problem please describe we currently do not explain in the docs how to deploy an aea describe the solution you d like add a guide in the docs | 0 |
21,250 | 10,588,386,096 | IssuesEvent | 2019-10-09 01:47:23 | Ne0nd0g/merlin | https://api.github.com/repos/Ne0nd0g/merlin | closed | Agent Allows Untrused Certificate | security | Merlin agent uses a TLS configuration setting of `InsecureSkipVerify: true` that will permit communications with a server using an untrusted certificate. Initially this was by design to facilitate ease of use and allow operators the ability to use self-signed certificates.
Merlin Agent should be written so that, by ... | True | Agent Allows Untrused Certificate - Merlin agent uses a TLS configuration setting of `InsecureSkipVerify: true` that will permit communications with a server using an untrusted certificate. Initially this was by design to facilitate ease of use and allow operators the ability to use self-signed certificates.
Merlin ... | non_priority | agent allows untrused certificate merlin agent uses a tls configuration setting of insecureskipverify true that will permit communications with a server using an untrusted certificate initially this was by design to facilitate ease of use and allow operators the ability to use self signed certificates merlin ... | 0 |
1,941 | 2,678,172,414 | IssuesEvent | 2015-03-26 08:46:05 | Starcounter/Starcounter | https://api.github.com/repos/Starcounter/Starcounter | closed | Implement multi-level dynamic types | Code host Dynamic Types enhancement guess: < week | In the dynamic types specification, we have established that Starcounter will auto-create "one extra level" of types, for every type declaration explicitly specified by the developer. This is not yet implemented.
This model
```C#
class Car {
[Type] CarModel Model;
}
class CarModel {}
```
currently resul... | 1.0 | Implement multi-level dynamic types - In the dynamic types specification, we have established that Starcounter will auto-create "one extra level" of types, for every type declaration explicitly specified by the developer. This is not yet implemented.
This model
```C#
class Car {
[Type] CarModel Model;
}
cla... | non_priority | implement multi level dynamic types in the dynamic types specification we have established that starcounter will auto create one extra level of types for every type declaration explicitly specified by the developer this is not yet implemented this model c class car carmodel model class ca... | 0 |
132,805 | 18,764,921,421 | IssuesEvent | 2021-11-05 21:48:30 | HappyMeBulgaria/HappyMe | https://api.github.com/repos/HappyMeBulgaria/HappyMe | reopened | Add screen with the right answer/ wrong answer | enhancement design & UX feature | When guessing the answer, for example you have a banana and some colors. When you choose the yellow color, you go to the green Bobo modal. Maybe there should be a screen in between that shows how the grayscale banana merges with the yellow color or smth and you can see the right answer - the banana with color.
| 1.0 | Add screen with the right answer/ wrong answer - When guessing the answer, for example you have a banana and some colors. When you choose the yellow color, you go to the green Bobo modal. Maybe there should be a screen in between that shows how the grayscale banana merges with the yellow color or smth and you can see t... | non_priority | add screen with the right answer wrong answer when guessing the answer for example you have a banana and some colors when you choose the yellow color you go to the green bobo modal maybe there should be a screen in between that shows how the grayscale banana merges with the yellow color or smth and you can see t... | 0 |
170,600 | 13,194,376,808 | IssuesEvent | 2020-08-13 16:43:33 | Karl255/UcenikShuffle | https://api.github.com/repos/Karl255/UcenikShuffle | closed | Create a test application | testing | Create a console application that prints out student sitting combinations and student sitting combinations for a couple of test cases | 1.0 | Create a test application - Create a console application that prints out student sitting combinations and student sitting combinations for a couple of test cases | non_priority | create a test application create a console application that prints out student sitting combinations and student sitting combinations for a couple of test cases | 0 |
35,225 | 6,423,144,761 | IssuesEvent | 2017-08-09 10:13:18 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | Docs - aws_s3_bucket name example uses underscores , hence fails to create | bug documentation | ### Terraform Version
Terraform v0.10.0
### Affected Resource(s)
Please list the resources as a list, for example:
- aws_s3_bucket
### Terraform Configuration Files
From the existing docs:
```hcl
resource "aws_s3_bucket" "b" {
bucket = "my_tf_test_bucket"
acl = "private"
tags {
Name ... | 1.0 | Docs - aws_s3_bucket name example uses underscores , hence fails to create - ### Terraform Version
Terraform v0.10.0
### Affected Resource(s)
Please list the resources as a list, for example:
- aws_s3_bucket
### Terraform Configuration Files
From the existing docs:
```hcl
resource "aws_s3_bucket" "b" {
... | non_priority | docs aws bucket name example uses underscores hence fails to create terraform version terraform affected resource s please list the resources as a list for example aws bucket terraform configuration files from the existing docs hcl resource aws bucket b bu... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.