Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
167,896 | 13,047,723,980 | IssuesEvent | 2020-07-29 11:14:36 | urapadmin/kiosk | https://api.github.com/repos/urapadmin/kiosk | closed | "none" instead of "nope" when turning off simple excavation | bug filemaker small test-stage | We're back to Luiza's picky notes, hello and welcome.
Just turning off simple excavation to test the pinboard and I know the instructions should say "nope" but they say that one should write "none" to turn that off instead:
 detected in xmlhttprequest-ssl-1.5.5.tgz | security vulnerability | ## CVE-2020-28502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p></summary>
<p>XMLHttpRequest for Node</p>
<p>Library home page: <a href="https://r... | True | CVE-2020-28502 (High) detected in xmlhttprequest-ssl-1.5.5.tgz - ## CVE-2020-28502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlhttprequest-ssl-1.5.5.tgz</b></p></summary>
<p>XML... | non_priority | cve high detected in xmlhttprequest ssl tgz cve high severity vulnerability vulnerable library xmlhttprequest ssl tgz xmlhttprequest for node library home page a href path to dependency file debug package json path to vulnerable library debug node modules xmlhttprequ... | 0 |
20,886 | 10,556,689,872 | IssuesEvent | 2019-10-04 03:01:36 | istio/istio | https://api.github.com/repos/istio/istio | closed | Secure coding & testing practices that affect all new work -code-mauve style | area/security kind/need more info | (NOTE: This is used to report product bugs:
To report a security vulnerability, please visit <https://istio.io/about/security-vulnerabilities/>
To ask questions about how to use Istio, please visit <https://discuss.istio.io>
)
**Bug description**
This task is a spin off of #13618 , the goal here might be to ... | True | Secure coding & testing practices that affect all new work -code-mauve style - (NOTE: This is used to report product bugs:
To report a security vulnerability, please visit <https://istio.io/about/security-vulnerabilities/>
To ask questions about how to use Istio, please visit <https://discuss.istio.io>
)
**Bu... | non_priority | secure coding testing practices that affect all new work code mauve style note this is used to report product bugs to report a security vulnerability please visit to ask questions about how to use istio please visit bug description this task is a spin off of the goal here might be ... | 0 |
115,179 | 24,730,445,780 | IssuesEvent | 2022-10-20 17:06:42 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | insights: Document how we can use the scale testing environment | spike team/code-insights backend strategic strategic-testing | Relating to this [scale testing effort](https://docs.google.com/document/d/1f9GcEpqJ5KA3YvfsOy48mdhILkvJZrqD9SfpZoNlQTg/edit#heading=h.egbxrewbg3nl), figure out how we can use this to test code insights at scale. Coordinate with people in the #wg-test-at-scale to figure out how this is all going to work and how we can ... | 1.0 | insights: Document how we can use the scale testing environment - Relating to this [scale testing effort](https://docs.google.com/document/d/1f9GcEpqJ5KA3YvfsOy48mdhILkvJZrqD9SfpZoNlQTg/edit#heading=h.egbxrewbg3nl), figure out how we can use this to test code insights at scale. Coordinate with people in the #wg-test-at... | non_priority | insights document how we can use the scale testing environment relating to this figure out how we can use this to test code insights at scale coordinate with people in the wg test at scale to figure out how this is all going to work and how we can use it the outcome of this ticket will be some documentatio... | 0 |
107,850 | 9,231,747,128 | IssuesEvent | 2019-03-13 03:51:11 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | teamcity: failed test: TestCleanupTxnIntentsOnGCAsync | C-test-failure O-robot | The following tests appear to have failed on master (test): TestCleanupTxnIntentsOnGCAsync, TestCleanupTxnIntentsOnGCAsync/#01, TestCleanupTxnIntentsOnGCAsync/#00, TestCleanupTxnIntentsOnGCAsync/#03, TestCleanupTxnIntentsOnGCAsync/#02
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/iss... | 1.0 | teamcity: failed test: TestCleanupTxnIntentsOnGCAsync - The following tests appear to have failed on master (test): TestCleanupTxnIntentsOnGCAsync, TestCleanupTxnIntentsOnGCAsync/#01, TestCleanupTxnIntentsOnGCAsync/#00, TestCleanupTxnIntentsOnGCAsync/#03, TestCleanupTxnIntentsOnGCAsync/#02
You may want to check [for o... | non_priority | teamcity failed test testcleanuptxnintentsongcasync the following tests appear to have failed on master test testcleanuptxnintentsongcasync testcleanuptxnintentsongcasync testcleanuptxnintentsongcasync testcleanuptxnintentsongcasync testcleanuptxnintentsongcasync you may want to check ... | 0 |
105,228 | 13,170,472,541 | IssuesEvent | 2020-08-11 15:12:52 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | reopened | Suggestion: Add pragma disabled CS1591 to migration files | closed-by-design | It would be nice if `dotnet ef migrations add` would automatically add
```
#pragma warning disable CS1591 // Missing XML comment for publicly visible type or member
```
to the beginning of generated file and
```
#pragma warning restore CS1591 // Missing XML comment for publicly visible type or member
```
at the... | 1.0 | Suggestion: Add pragma disabled CS1591 to migration files - It would be nice if `dotnet ef migrations add` would automatically add
```
#pragma warning disable CS1591 // Missing XML comment for publicly visible type or member
```
to the beginning of generated file and
```
#pragma warning restore CS1591 // Missing ... | non_priority | suggestion add pragma disabled to migration files it would be nice if dotnet ef migrations add would automatically add pragma warning disable missing xml comment for publicly visible type or member to the beginning of generated file and pragma warning restore missing xml comment for... | 0 |
260,464 | 22,622,965,341 | IssuesEvent | 2022-06-30 08:13:05 | filecoin-project/venus | https://api.github.com/repos/filecoin-project/venus | closed | Write a short flow for 1 behavior | Bloxico System Test Matrix Sprint 1 | _YAML catalog, annotations in the test file, running crawler and so on_ | 1.0 | Write a short flow for 1 behavior - _YAML catalog, annotations in the test file, running crawler and so on_ | non_priority | write a short flow for behavior yaml catalog annotations in the test file running crawler and so on | 0 |
221,388 | 24,621,513,548 | IssuesEvent | 2022-10-16 01:03:44 | Baneeishaque/spring_store_thymeleaf | https://api.github.com/repos/Baneeishaque/spring_store_thymeleaf | closed | CVE-2018-11695 (High) detected in node-sass-3.13.1.tgz, node-sass15fe42ed92dea8e086e7837e53ecd8190c0179b9 - autoclosed | security vulnerability | ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-3.13.1.tgz</b>, <b>node-sass15fe42ed92dea8e086e7837e53ecd8190c0179b9</b></p></summary>
<p>
<details><summa... | True | CVE-2018-11695 (High) detected in node-sass-3.13.1.tgz, node-sass15fe42ed92dea8e086e7837e53ecd8190c0179b9 - autoclosed - ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries -... | non_priority | cve high detected in node sass tgz node autoclosed cve high severity vulnerability vulnerable libraries node sass tgz node node sass tgz wrapper around libsass library home page a href path to dependency file html site template customer fashi s... | 0 |
28,971 | 11,706,039,707 | IssuesEvent | 2020-03-07 19:32:38 | vlaship/spark-streaming | https://api.github.com/repos/vlaship/spark-streaming | opened | CVE-2018-8012 (High) detected in zookeeper-3.4.6.jar | security vulnerability | ## CVE-2018-8012 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>zookeeper-3.4.6.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/o... | True | CVE-2018-8012 (High) detected in zookeeper-3.4.6.jar - ## CVE-2018-8012 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>zookeeper-3.4.6.jar</b></p></summary>
<p></p>
<p>Path to vulnera... | non_priority | cve high detected in zookeeper jar cve high severity vulnerability vulnerable library zookeeper jar path to vulnerable library root gradle caches modules files org apache zookeeper zookeeper zookeeper jar root gradle caches modules files org apa... | 0 |
81,385 | 30,827,989,257 | IssuesEvent | 2023-08-01 21:52:37 | dotCMS/core | https://api.github.com/repos/dotCMS/core | closed | PageAPI not working for non-default URLMapped language content | Type : Defect Merged QA : Passed Internal Team : Falcon Next Release | ### Problem Statement
The preview action from edit content and the new Pages portlet is not functioning correctly for URL Mapped contents when they are in a non-default language. Instead of displaying the preview, an error message stating "This URL does not exist" is shown.
 is the second result when googling for "websocket proxy windows", and Windows isn't supported. The wiki really ought to be updated to reflect this, specifically this page[1] needs to be removed. Indeed, all Windows references should be removed except to say Windows isn't supported. Wasted my a... | 1.0 | Update Wiki to Reflect Windows Not Supported - This project (websockify) is the second result when googling for "websocket proxy windows", and Windows isn't supported. The wiki really ought to be updated to reflect this, specifically this page[1] needs to be removed. Indeed, all Windows references should be removed exc... | non_priority | update wiki to reflect windows not supported this project websockify is the second result when googling for websocket proxy windows and windows isn t supported the wiki really ought to be updated to reflect this specifically this page needs to be removed indeed all windows references should be removed excep... | 0 |
160,768 | 20,118,449,370 | IssuesEvent | 2022-02-07 22:19:10 | sureng-ws-ibm/t1 | https://api.github.com/repos/sureng-ws-ibm/t1 | opened | mongodb-2.2.36.tgz: 2 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mongodb-2.2.36.tgz</b></p></summary>
<p>The official MongoDB driver for Node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/mongodb/-/mongodb-2.2.36... | True | mongodb-2.2.36.tgz: 2 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mongodb-2.2.36.tgz</b></p></summary>
<p>The official MongoDB driver for Node.js</p>
<p>Library home... | non_priority | mongodb tgz vulnerabilities highest severity is vulnerable library mongodb tgz the official mongodb driver for node js library home page a href path to dependency file package json path to vulnerable library node modules mongodb package json found in head commit ... | 0 |
143,897 | 13,087,890,659 | IssuesEvent | 2020-08-02 14:39:00 | mkavana/docs-v2-DEV | https://api.github.com/repos/mkavana/docs-v2-DEV | opened | Add 'Quickstart' guide | documentation | Add feature to automatically generate the post **Quickstart**.
## Notes
- consider automatically generating content for the post **Quickstart** from existing posts, where the value of the front matter var `include-in-quickstart` is `true`. | 1.0 | Add 'Quickstart' guide - Add feature to automatically generate the post **Quickstart**.
## Notes
- consider automatically generating content for the post **Quickstart** from existing posts, where the value of the front matter var `include-in-quickstart` is `true`. | non_priority | add quickstart guide add feature to automatically generate the post quickstart notes consider automatically generating content for the post quickstart from existing posts where the value of the front matter var include in quickstart is true | 0 |
272,763 | 29,795,084,567 | IssuesEvent | 2023-06-16 01:09:43 | billmcchesney1/flowgate | https://api.github.com/repos/billmcchesney1/flowgate | closed | CVE-2017-7536 (High) detected in hibernate-validator-5.2.5.Final.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2017-7536 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hibernate-validator-5.2.5.Final.jar</b></p></summary>
<p>Hibernate's Bean Validation (JSR-303) reference implementation... | True | CVE-2017-7536 (High) detected in hibernate-validator-5.2.5.Final.jar - autoclosed - ## CVE-2017-7536 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hibernate-validator-5.2.5.Final.jar<... | non_priority | cve high detected in hibernate validator final jar autoclosed cve high severity vulnerability vulnerable library hibernate validator final jar hibernate s bean validation jsr reference implementation library home page a href path to dependency file operation exp... | 0 |
287,983 | 24,879,595,820 | IssuesEvent | 2022-10-27 22:52:03 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Chrome Elastic Synthetics Integration UI Functional Tests.x-pack/test/functional_synthetics/apps/uptime/synthetics_integration·ts - Uptime app with generated data When on the Synthetics Integration Policy Create Page create new policy allows configuring tls | failed-test needs-team | A test failed on a tracked branch
```
Error: expected { id: 'synthetics/http-synthetics-59afcbea-29ac-426c-a74f-b107a464f2c6',
revision: 1,
name: 'Sample Synthetics integration',
type: 'synthetics/http',
data_stream: { namespace: 'default' },
use_output: 'default',
package_policy_id: '59afcbea-29ac-426c-a7... | 1.0 | Failing test: Chrome Elastic Synthetics Integration UI Functional Tests.x-pack/test/functional_synthetics/apps/uptime/synthetics_integration·ts - Uptime app with generated data When on the Synthetics Integration Policy Create Page create new policy allows configuring tls - A test failed on a tracked branch
```
Error: ... | non_priority | failing test chrome elastic synthetics integration ui functional tests x pack test functional synthetics apps uptime synthetics integration·ts uptime app with generated data when on the synthetics integration policy create page create new policy allows configuring tls a test failed on a tracked branch error ... | 0 |
151,288 | 23,793,498,429 | IssuesEvent | 2022-09-02 16:48:34 | microsoft/pyright | https://api.github.com/repos/microsoft/pyright | closed | Nested `TypedDict` with `NotRequired` key failing to satisfy key-existence check | as designed | **Describe the bug**
When nesting a `TypeDict` inside another `TypeDict`, where the child one has a `NotRequired` key, Pyright keeps showing an error even after ensuring the existence of the key.
**To Reproduce**
The code snippet below reproduces the error using the specified version of Pylance extension in VSCode... | 1.0 | Nested `TypedDict` with `NotRequired` key failing to satisfy key-existence check - **Describe the bug**
When nesting a `TypeDict` inside another `TypeDict`, where the child one has a `NotRequired` key, Pyright keeps showing an error even after ensuring the existence of the key.
**To Reproduce**
The code snippet be... | non_priority | nested typeddict with notrequired key failing to satisfy key existence check describe the bug when nesting a typedict inside another typedict where the child one has a notrequired key pyright keeps showing an error even after ensuring the existence of the key to reproduce the code snippet be... | 0 |
145,190 | 19,339,184,861 | IssuesEvent | 2021-12-15 01:03:58 | billmcchesney1/hadoop | https://api.github.com/repos/billmcchesney1/hadoop | opened | CVE-2021-3777 (High) detected in tmpl-1.0.4.tgz | security vulnerability | ## CVE-2021-3777 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tmpl-1.0.4.tgz</b></p></summary>
<p>JavaScript micro templates.</p>
<p>Library home page: <a href="https://registry.npm... | True | CVE-2021-3777 (High) detected in tmpl-1.0.4.tgz - ## CVE-2021-3777 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tmpl-1.0.4.tgz</b></p></summary>
<p>JavaScript micro templates.</p>
<... | non_priority | cve high detected in tmpl tgz cve high severity vulnerability vulnerable library tmpl tgz javascript micro templates library home page a href path to dependency file hadoop hadoop yarn project hadoop yarn hadoop yarn ui src main webapp package json path to vulnerable... | 0 |
210,119 | 23,731,358,413 | IssuesEvent | 2022-08-31 02:13:38 | project-chip/connectedhomeip | https://api.github.com/repos/project-chip/connectedhomeip | closed | Commissioner/Controller init on Android may fail or crash due to use-after-free | android V1.0 security crash v1.0 master patch acceptable | #### Problem
Use-after-free of JNI references in `AndroidDeviceControllerWrapper` can cause failure to init or crashes
Some JNI references, the ones for operational certs and IPK, have incorrect scoping when initializing the controller wrapper. Depending on system state, use after-free can arise and was observed.
... | True | Commissioner/Controller init on Android may fail or crash due to use-after-free - #### Problem
Use-after-free of JNI references in `AndroidDeviceControllerWrapper` can cause failure to init or crashes
Some JNI references, the ones for operational certs and IPK, have incorrect scoping when initializing the controll... | non_priority | commissioner controller init on android may fail or crash due to use after free problem use after free of jni references in androiddevicecontrollerwrapper can cause failure to init or crashes some jni references the ones for operational certs and ipk have incorrect scoping when initializing the controll... | 0 |
28,876 | 13,879,734,908 | IssuesEvent | 2020-10-17 15:43:19 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Expensive decompression in JPEG GetImageInfo | TF 2.3 type:performance | **System information**
- Have I written custom code (as opposed to using a stock example script provided in TensorFlow): No
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Linux Ubuntu 18.04
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issue happens on mobile device:
- TensorFlow insta... | True | Expensive decompression in JPEG GetImageInfo - **System information**
- Have I written custom code (as opposed to using a stock example script provided in TensorFlow): No
- OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Linux Ubuntu 18.04
- Mobile device (e.g. iPhone 8, Pixel 2, Samsung Galaxy) if the issu... | non_priority | expensive decompression in jpeg getimageinfo system information have i written custom code as opposed to using a stock example script provided in tensorflow no os platform and distribution e g linux ubuntu linux ubuntu mobile device e g iphone pixel samsung galaxy if the issue ha... | 0 |
14,972 | 18,763,606,046 | IssuesEvent | 2021-11-05 19:44:56 | ElfFriend-DnD/FVTT-Minimal-Rolling-Enhancements-DND5E | https://api.github.com/repos/ElfFriend-DnD/FVTT-Minimal-Rolling-Enhancements-DND5E | opened | PopOut! and Keyboard Shortcuts | compatibility enhancement | The keyboard shortcuts for advantage etc. do not work with actor sheets popped out by popout.
This is because of the janky global keyboard modifier listener we have on the page. | True | PopOut! and Keyboard Shortcuts - The keyboard shortcuts for advantage etc. do not work with actor sheets popped out by popout.
This is because of the janky global keyboard modifier listener we have on the page. | non_priority | popout and keyboard shortcuts the keyboard shortcuts for advantage etc do not work with actor sheets popped out by popout this is because of the janky global keyboard modifier listener we have on the page | 0 |
135,799 | 11,017,918,506 | IssuesEvent | 2019-12-05 09:29:32 | dzhw/SLC-IntEr | https://api.github.com/repos/dzhw/SLC-IntEr | closed | Scrolling auf mobilen Endgeräten | Hohe Priorität layout modul-übergreifend testing | Sehr viel Whitespace auf einigen Seiten (ab emaa33 bis Schluss). Ist das noch ein Effekt der Header und wird noch behoben?
 with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10797189?buildTab=arti... | 2.0 | roachtest: ycsb/A/nodes=3/cpu=32/mvcc-range-keys=global failed - roachtest.ycsb/A/nodes=3/cpu=32/mvcc-range-keys=global [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10797189?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Co... | non_priority | roachtest ycsb a nodes cpu mvcc range keys global failed roachtest ycsb a nodes cpu mvcc range keys global with on release cluster go run output in run workload run ycsb in workload run ycsb init insert count workload a concurrency splits histograms per... | 0 |
88,548 | 15,803,030,408 | IssuesEvent | 2021-04-03 12:33:53 | atlslscsrv-app/upgraded-fiesta | https://api.github.com/repos/atlslscsrv-app/upgraded-fiesta | closed | CVE-2020-7598 (Medium) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz - autoclosed | security vulnerability | ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p>... | True | CVE-2020-7598 (Medium) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz - autoclosed - ## CVE-2020-7598 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>... | non_priority | cve medium detected in minimist tgz minimist tgz autoclosed cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file upgraded fi... | 0 |
66,974 | 8,065,743,079 | IssuesEvent | 2018-08-04 05:59:48 | NUmeroAndDev/iTube-android | https://api.github.com/repos/NUmeroAndDev/iTube-android | closed | DarkTheme の追加 | Design New Function WIP | DarkTheme の機能を追加する
ただ、Material Components で DarkTheme ぽいものが出るらしいからそれまで独自の実装
### 必要なパラメータ
* surface (CardView 系のbackground)
* onSurface (CardView 系のテキスト)
* stroke (CardView 系の Stroke) dividerにする?
### 問題点
* FAB の背景はどの色?
* Toolbar のアイコンカラーはどうする?
→ DrawableCompat で頑張る
* 検索欄の stroke にノイズが入る
→ Text... | 1.0 | DarkTheme の追加 - DarkTheme の機能を追加する
ただ、Material Components で DarkTheme ぽいものが出るらしいからそれまで独自の実装
### 必要なパラメータ
* surface (CardView 系のbackground)
* onSurface (CardView 系のテキスト)
* stroke (CardView 系の Stroke) dividerにする?
### 問題点
* FAB の背景はどの色?
* Toolbar のアイコンカラーはどうする?
→ DrawableCompat で頑張る
* 検索欄の stroke にノイ... | non_priority | darktheme の追加 darktheme の機能を追加する ただ、material components で darktheme ぽいものが出るらしいからそれまで独自の実装 必要なパラメータ surface cardview 系のbackground onsurface cardview 系のテキスト stroke cardview 系の stroke dividerにする 問題点 fab の背景はどの色 toolbar のアイコンカラーはどうする → drawablecompat で頑張る 検索欄の stroke にノイ... | 0 |
73,374 | 15,253,659,286 | IssuesEvent | 2021-02-20 08:42:01 | gsylvie/madness | https://api.github.com/repos/gsylvie/madness | closed | CVE-2015-5262 Medium Severity Vulnerability detected by WhiteSource - autoclosed | security vulnerability | ## CVE-2015-5262 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>httpclient-4.3.5.jar</b></p></summary>
<p>null</p>
<p>path: /root/.m2/repository/org/apache/httpcomponents/h... | True | CVE-2015-5262 Medium Severity Vulnerability detected by WhiteSource - autoclosed - ## CVE-2015-5262 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>httpclient-4.3.5.jar</b></... | non_priority | cve medium severity vulnerability detected by whitesource autoclosed cve medium severity vulnerability vulnerable library httpclient jar null path root repository org apache httpcomponents httpclient httpclient jar dependency hierarchy httpasyncclient ... | 0 |
89,252 | 25,721,252,191 | IssuesEvent | 2022-12-07 13:51:32 | ARM-software/armnn | https://api.github.com/repos/ARM-software/armnn | closed | ArmNN 22.11 fails to build with `error: 'istream_iterator' is not a member of 'std'` | Fixed in next release Build issue | On openSUSE Tumbleweed, ArmNN 22.11 fails to build with `error: 'istream_iterator' is not a member of 'std'`.
Log:
```
[ 1382s] /home/abuild/rpmbuild/BUILD/armnn-22.11/tests/TfLiteYoloV3Big-Armnn/TfLiteYoloV3Big-Armnn.cpp: In function 'void CheckAccuracy(std::vector<float>*, std::vector<float>*, std::vector<float>... | 1.0 | ArmNN 22.11 fails to build with `error: 'istream_iterator' is not a member of 'std'` - On openSUSE Tumbleweed, ArmNN 22.11 fails to build with `error: 'istream_iterator' is not a member of 'std'`.
Log:
```
[ 1382s] /home/abuild/rpmbuild/BUILD/armnn-22.11/tests/TfLiteYoloV3Big-Armnn/TfLiteYoloV3Big-Armnn.cpp: In fu... | non_priority | armnn fails to build with error istream iterator is not a member of std on opensuse tumbleweed armnn fails to build with error istream iterator is not a member of std log home abuild rpmbuild build armnn tests armnn armnn cpp in function void checkaccuracy std vector ... | 0 |
332,541 | 29,482,709,066 | IssuesEvent | 2023-06-02 07:20:02 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix jax_numpy_manipulation.test_jax_numpy_vsplit | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5148942480/jobs/9271313253" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5148942480/jobs/9271313253" rel="noopener ... | 1.0 | Fix jax_numpy_manipulation.test_jax_numpy_vsplit - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5148942480/jobs/9271313253" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/acti... | non_priority | fix jax numpy manipulation test jax numpy vsplit tensorflow img src torch img src numpy img src jax img src paddle img src | 0 |
375,467 | 26,163,176,502 | IssuesEvent | 2022-12-31 22:49:35 | python/mypy | https://api.github.com/repos/python/mypy | closed | Project website is not accessible via https | documentation | **Documentation**
The project website www.mypy-lang.org is not secured via ssl/tls.
It's 2021 now, can you please provide your webserver with a certificate?
In the age of [#letsencrypt](https://letsencrypt.org) I don't see any reason not to.
Every modern browser complains about it when visiting the website.
... | 1.0 | Project website is not accessible via https - **Documentation**
The project website www.mypy-lang.org is not secured via ssl/tls.
It's 2021 now, can you please provide your webserver with a certificate?
In the age of [#letsencrypt](https://letsencrypt.org) I don't see any reason not to.
Every modern browser ... | non_priority | project website is not accessible via https documentation the project website is not secured via ssl tls it s now can you please provide your webserver with a certificate in the age of i don t see any reason not to every modern browser complains about it when visiting the website some bro... | 0 |
124,568 | 10,315,911,543 | IssuesEvent | 2019-08-30 08:45:50 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | closed | JDK13 JTReg Failure: java/util/stream/test/org/openjdk/tests/java/util/SplittableRandomTest.java | jdk13 test failure | Failure link
------------
- Test: https://github.com/ibmruntimes/openj9-openjdk-jdk13/blob/openj9/test/jdk/java/util/stream/test/org/openjdk/tests/java/util/SplittableRandomTest.java
- Build: https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder_Advanced/96/
- Test Category: openjdk
- Test Suite Name: jdk_util... | 1.0 | JDK13 JTReg Failure: java/util/stream/test/org/openjdk/tests/java/util/SplittableRandomTest.java - Failure link
------------
- Test: https://github.com/ibmruntimes/openj9-openjdk-jdk13/blob/openj9/test/jdk/java/util/stream/test/org/openjdk/tests/java/util/SplittableRandomTest.java
- Build: https://ci.adoptopenjdk.ne... | non_priority | jtreg failure java util stream test org openjdk tests java util splittablerandomtest java failure link test build test category openjdk test suite name jdk util os architecture windows and linux openjdk version public build shas omr jcl ... | 0 |
129,695 | 10,582,950,627 | IssuesEvent | 2019-10-08 12:45:44 | hazelcast/hazelcast-jet | https://api.github.com/repos/hazelcast/hazelcast-jet | closed | com.hazelcast.jet.core.JobTest.when_joinFromClientSentToNonMaster_then_futureShouldNotBeCompletedEarly | test-failure | _3.2_ (commit 7da6eb706d2d3afe48a0e652583b44d97b15a07e)
Failed on Oracle JDK8: http://jenkins.hazelcast.com/view/Jet%20-%20Release/job/release-jet-oss-master-oracle-jdk8/2/testReport/com.hazelcast.jet.core/JobTest/when_joinFromClientSentToNonMaster_then_futureShouldNotBeCompletedEarly/
Stacktrace:
```
Expected:... | 1.0 | com.hazelcast.jet.core.JobTest.when_joinFromClientSentToNonMaster_then_futureShouldNotBeCompletedEarly - _3.2_ (commit 7da6eb706d2d3afe48a0e652583b44d97b15a07e)
Failed on Oracle JDK8: http://jenkins.hazelcast.com/view/Jet%20-%20Release/job/release-jet-oss-master-oracle-jdk8/2/testReport/com.hazelcast.jet.core/JobTes... | non_priority | com hazelcast jet core jobtest when joinfromclientsenttononmaster then futureshouldnotbecompletedearly commit failed on oracle stacktrace expected exception with message a string containing faulty job but message was test timed out after milliseconds stacktrace was org juni... | 0 |
268,916 | 28,932,274,847 | IssuesEvent | 2023-05-09 01:07:52 | vwasthename/iaf | https://api.github.com/repos/vwasthename/iaf | opened | CVE-2023-26116 (High) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2023-26116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>angular-1.7.8.min.js</b>, <b>angular-1.7.9.min.js</b>, <b>angular-1.7.9.js</b></p></summary>
<p>
<details><summary><... | True | CVE-2023-26116 (High) detected in multiple libraries - ## CVE-2023-26116 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>angular-1.7.8.min.js</b>, <b>angular-1.7.9.min.js</b>, <b>angu... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries angular min js angular min js angular js angular min js angularjs is an mvc framework for building web applications the core features include html enhanced wi... | 0 |
361,672 | 25,348,309,828 | IssuesEvent | 2022-11-19 13:13:48 | bounswe/bounswe2022group9 | https://api.github.com/repos/bounswe/bounswe2022group9 | closed | [Mobile] Organizing Meeting Notes | Documentation Mobile | The meeting notes we receive as a mobile subgroup are not suitable for the template or they are not regular, they need to be edited.
Deadline : 19.11.2022 , 23.00 | 1.0 | [Mobile] Organizing Meeting Notes - The meeting notes we receive as a mobile subgroup are not suitable for the template or they are not regular, they need to be edited.
Deadline : 19.11.2022 , 23.00 | non_priority | organizing meeting notes the meeting notes we receive as a mobile subgroup are not suitable for the template or they are not regular they need to be edited deadline | 0 |
420,005 | 28,213,246,177 | IssuesEvent | 2023-04-05 06:57:34 | Drawsi/Anim | https://api.github.com/repos/Drawsi/Anim | opened | Creating documentation | documentation | From how the project works and communicates with different files, the architecture design of it all to how to add new features; it all needs to be explained and documented. | 1.0 | Creating documentation - From how the project works and communicates with different files, the architecture design of it all to how to add new features; it all needs to be explained and documented. | non_priority | creating documentation from how the project works and communicates with different files the architecture design of it all to how to add new features it all needs to be explained and documented | 0 |
4,323 | 7,045,264,199 | IssuesEvent | 2018-01-01 17:08:42 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | invalid time cast bug. | compatibility help wanted | Please answer these questions before submitting your issue. Thanks!
1. What did you do?
`select cast('239010' as time);`
2. What did you expect to see?
```
mysql> select cast('239010' as time);
+------------------------+
| cast('239010' as time) |
+------------------------+
| NULL |... | True | invalid time cast bug. - Please answer these questions before submitting your issue. Thanks!
1. What did you do?
`select cast('239010' as time);`
2. What did you expect to see?
```
mysql> select cast('239010' as time);
+------------------------+
| cast('239010' as time) |
+------------------------+
|... | non_priority | invalid time cast bug please answer these questions before submitting your issue thanks what did you do select cast as time what did you expect to see mysql select cast as time cast as time null ... | 0 |
269,214 | 28,960,032,636 | IssuesEvent | 2023-05-10 01:09:49 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | reopened | CVE-2023-1118 (High) detected in linux-yocto-4.12v3.0.67 | Mend: dependency security vulnerability | ## CVE-2023-1118 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.0.67</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://g... | True | CVE-2023-1118 (High) detected in linux-yocto-4.12v3.0.67 - ## CVE-2023-1118 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.0.67</b></p></summary>
<p>
<p>Linux 4.12 ... | non_priority | cve high detected in linux yocto cve high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files d... | 0 |
310,294 | 23,330,073,754 | IssuesEvent | 2022-08-09 03:39:25 | cylammarco/WDPhotTools | https://api.github.com/repos/cylammarco/WDPhotTools | closed | README.md example photometric fitting plot is out of date. | documentation | The current plots are showing the fitted solution using 5 Pan-STARRS and 3 Gaia filters, but the code also includes JHK photometry. | 1.0 | README.md example photometric fitting plot is out of date. - The current plots are showing the fitted solution using 5 Pan-STARRS and 3 Gaia filters, but the code also includes JHK photometry. | non_priority | readme md example photometric fitting plot is out of date the current plots are showing the fitted solution using pan starrs and gaia filters but the code also includes jhk photometry | 0 |
158,040 | 20,007,557,787 | IssuesEvent | 2022-02-01 00:00:46 | timf-app-sandbox/t1 | https://api.github.com/repos/timf-app-sandbox/t1 | opened | CVE-2022-21681 (High) detected in marked-0.3.9.tgz | security vulnerability | ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.9.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://reg... | True | CVE-2022-21681 (High) detected in marked-0.3.9.tgz - ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.9.tgz</b></p></summary>
<p>A markdown parser built for... | non_priority | cve high detected in marked tgz cve high severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file package json path to vulnerable library node modules marked package json dependency ... | 0 |
116,317 | 17,360,134,128 | IssuesEvent | 2021-07-29 19:20:56 | lukebroganws/JS-Demo | https://api.github.com/repos/lukebroganws/JS-Demo | opened | CVE-2018-3728 (High) detected in hoek-0.9.1.tgz, hoek-2.16.3.tgz | security vulnerability | ## CVE-2018-3728 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>hoek-0.9.1.tgz</b>, <b>hoek-2.16.3.tgz</b></p></summary>
<p>
<details><summary><b>hoek-0.9.1.tgz</b></p></summary>
<... | True | CVE-2018-3728 (High) detected in hoek-0.9.1.tgz, hoek-2.16.3.tgz - ## CVE-2018-3728 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>hoek-0.9.1.tgz</b>, <b>hoek-2.16.3.tgz</b></p></sum... | non_priority | cve high detected in hoek tgz hoek tgz cve high severity vulnerability vulnerable libraries hoek tgz hoek tgz hoek tgz general purpose node utilities library home page a href path to dependency file js demo package json path to vulnerabl... | 0 |
43,762 | 13,038,684,218 | IssuesEvent | 2020-07-28 15:33:54 | elikkatzgit/git_test2 | https://api.github.com/repos/elikkatzgit/git_test2 | opened | CVE-2020-9547 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-9547 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming... | True | CVE-2020-9547 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2020-9547 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General d... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library git target myfinal ... | 0 |
38,259 | 12,532,725,595 | IssuesEvent | 2020-06-04 16:23:22 | RG4421/azure-iot-platform-dotnet | https://api.github.com/repos/RG4421/azure-iot-platform-dotnet | opened | WS-2019-0063 (High) detected in js-yaml-3.7.0.tgz | security vulnerability | ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>js-yaml-3.7.0.tgz</b></p></summary>
<p>YAML 1.2 parser and serializer</p>
<p>Library home page: <a href="https://registr... | True | WS-2019-0063 (High) detected in js-yaml-3.7.0.tgz - ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>js-yaml-3.7.0.tgz</b></p></summary>
<p>YAML 1.2 parser and serialize... | non_priority | ws high detected in js yaml tgz ws high severity vulnerability vulnerable library js yaml tgz yaml parser and serializer library home page a href path to dependency file tmp ws scm azure iot platform dotnet src webui azure iot ux fluent controls package json path... | 0 |
59,168 | 8,345,190,642 | IssuesEvent | 2018-10-01 00:29:25 | nsubstitute/NSubstitute | https://api.github.com/repos/nsubstitute/NSubstitute | closed | Documentation: add `virtual` requirement to Getting Started and readme | documentation good first issue | While looking in to #436 I noticed that the requirement to use `virtual` methods is only in the [Creating a substitute](http://nsubstitute.github.io/help/creating-a-substitute/) help page. It should probably also be in the readme and [Getting Started](https://github.com/nsubstitute/NSubstitute/blob/master/docs/help/_po... | 1.0 | Documentation: add `virtual` requirement to Getting Started and readme - While looking in to #436 I noticed that the requirement to use `virtual` methods is only in the [Creating a substitute](http://nsubstitute.github.io/help/creating-a-substitute/) help page. It should probably also be in the readme and [Getting Star... | non_priority | documentation add virtual requirement to getting started and readme while looking in to i noticed that the requirement to use virtual methods is only in the help page it should probably also be in the readme and page this doesn t have to be as detailed as the creating a substitute info but i thin... | 0 |
62,833 | 26,177,222,359 | IssuesEvent | 2023-01-02 11:15:53 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | BUG : identifier "__null" not defined - Code analysis before compilation (MacOS - Ventura 13.0) | Language Service more info needed Feature: Configuration | ### Environment
- OS and Version: macOS Ventura 13.0
- VS Code Version: 1.72.2
- C/C++ Extension Version: v1.12.4
- Other extensions you installed (and if the issue persists after disabling them):
- If using SSH remote, specify OS of remote machine:
- A clear and concise description of what the bug is, inclu... | 1.0 | BUG : identifier "__null" not defined - Code analysis before compilation (MacOS - Ventura 13.0) - ### Environment
- OS and Version: macOS Ventura 13.0
- VS Code Version: 1.72.2
- C/C++ Extension Version: v1.12.4
- Other extensions you installed (and if the issue persists after disabling them):
- If using SSH r... | non_priority | bug identifier null not defined code analysis before compilation macos ventura environment os and version macos ventura vs code version c c extension version other extensions you installed and if the issue persists after disabling them if using ssh remote... | 0 |
153,061 | 12,133,228,009 | IssuesEvent | 2020-04-23 08:41:09 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | opened | NightlyTester should not submit report if error in script occured. | BZ-BUG-STATUS: NEW Test Suite/Nightly Tester dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=991. | 2.0 | NightlyTester should not submit report if error in script occured. - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=991. | non_priority | nightlytester should not submit report if error in script occured this issue was imported from bugzilla | 0 |
149,092 | 23,427,126,671 | IssuesEvent | 2022-08-14 14:59:33 | piro17-Archive/FilmArchive | https://api.github.com/repos/piro17-Archive/FilmArchive | opened | [design] 제작 프레임 공유 | 도윤 design | ### 목적
>
### 작업 상세 내용
- [ ] 글 작성 페이지 글 작성 버튼 cursor:pointer 추가
- [ ] 키워드 reset 버튼 추가
- [ ] 글 작성 페이지 파일 삽입 버튼 css 추가
- [ ] detail page css
### 유의사항
| 1.0 | [design] 제작 프레임 공유 - ### 목적
>
### 작업 상세 내용
- [ ] 글 작성 페이지 글 작성 버튼 cursor:pointer 추가
- [ ] 키워드 reset 버튼 추가
- [ ] 글 작성 페이지 파일 삽입 버튼 css 추가
- [ ] detail page css
### 유의사항
| non_priority | 제작 프레임 공유 목적 작업 상세 내용 글 작성 페이지 글 작성 버튼 cursor pointer 추가 키워드 reset 버튼 추가 글 작성 페이지 파일 삽입 버튼 css 추가 detail page css 유의사항 | 0 |
76,790 | 14,681,455,387 | IssuesEvent | 2020-12-31 13:17:27 | TypeCobolTeam/TypeCobol | https://api.github.com/repos/TypeCobolTeam/TypeCobol | closed | Simplified codegen | Codegen Enhancement Functions User Visible | **Is your feature request related to a problem? Please describe.**
Our current codegen is ok for TypeCobol users, but when a Cobol user need to debug it, it can be hard.
The goal is to provide a simplified codegen which don't use any procedure-pointer.
As we are not sure if we'll use this new codegen.
You can f... | 1.0 | Simplified codegen - **Is your feature request related to a problem? Please describe.**
Our current codegen is ok for TypeCobol users, but when a Cobol user need to debug it, it can be hard.
The goal is to provide a simplified codegen which don't use any procedure-pointer.
As we are not sure if we'll use this ne... | non_priority | simplified codegen is your feature request related to a problem please describe our current codegen is ok for typecobol users but when a cobol user need to debug it it can be hard the goal is to provide a simplified codegen which don t use any procedure pointer as we are not sure if we ll use this ne... | 0 |
42,128 | 10,820,106,744 | IssuesEvent | 2019-11-08 15:43:28 | supertuxkart/stk-code | https://api.github.com/repos/supertuxkart/stk-code | closed | Crashes after removing tracks | C: Other P3: normal R: fixed T: defect | Removing addons track or additional assets (mobile) makes the GP list and replay list incorrect. This can potentially lead to crashes. Instead, the lists should be refreshed when removing a track.
Refreshing after adding a track is also useful, to avoid having to restart STK to get the replay and GP lists containing... | 1.0 | Crashes after removing tracks - Removing addons track or additional assets (mobile) makes the GP list and replay list incorrect. This can potentially lead to crashes. Instead, the lists should be refreshed when removing a track.
Refreshing after adding a track is also useful, to avoid having to restart STK to get th... | non_priority | crashes after removing tracks removing addons track or additional assets mobile makes the gp list and replay list incorrect this can potentially lead to crashes instead the lists should be refreshed when removing a track refreshing after adding a track is also useful to avoid having to restart stk to get th... | 0 |
121,163 | 15,863,094,326 | IssuesEvent | 2021-04-08 12:25:49 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | Forms-system DirectDeposit bug | needs-grooming triage vsp-design-system-team | ### User story(ies)
`src/platform/forms-system/src/js/definitions/directDeposit.jsx` does not render on the Review page of forms correctly
The error message below is displayed when the chapter with it is opened
```
Uncaught Error: uiSchema order list contains extraneous properties 'view:directDepositInfo', 'vie... | 1.0 | Forms-system DirectDeposit bug - ### User story(ies)
`src/platform/forms-system/src/js/definitions/directDeposit.jsx` does not render on the Review page of forms correctly
The error message below is displayed when the chapter with it is opened
```
Uncaught Error: uiSchema order list contains extraneous properti... | non_priority | forms system directdeposit bug user story ies src platform forms system src js definitions directdeposit jsx does not render on the review page of forms correctly the error message below is displayed when the chapter with it is opened uncaught error uischema order list contains extraneous properti... | 0 |
29,758 | 13,166,818,597 | IssuesEvent | 2020-08-11 09:12:13 | elastic/beats | https://api.github.com/repos/elastic/beats | opened | Add support for multipath devices monitoring in Metricbeat | Metricbeat Team:Services [zube]: Inbox enhancement | **Describe the enhancement:**
Current metricsets for disk and filesystem monitoring don't take into account the use of multipath. It could be useful to take it into account when collecting disk metrics.
Some options to support multipath could be:
* When collecting metrics from devices belonging to some multipath... | 1.0 | Add support for multipath devices monitoring in Metricbeat - **Describe the enhancement:**
Current metricsets for disk and filesystem monitoring don't take into account the use of multipath. It could be useful to take it into account when collecting disk metrics.
Some options to support multipath could be:
* Whe... | non_priority | add support for multipath devices monitoring in metricbeat describe the enhancement current metricsets for disk and filesystem monitoring don t take into account the use of multipath it could be useful to take it into account when collecting disk metrics some options to support multipath could be whe... | 0 |
15,407 | 9,548,264,961 | IssuesEvent | 2019-05-02 04:15:02 | MindLeaps/tracker | https://api.github.com/repos/MindLeaps/tracker | opened | Scope grades by policy | enhancement security | Currently, the API for Grades returns grades across all organizations, regardless of the user requesting them. We should scope grades by organization, unless the user is a global user. | True | Scope grades by policy - Currently, the API for Grades returns grades across all organizations, regardless of the user requesting them. We should scope grades by organization, unless the user is a global user. | non_priority | scope grades by policy currently the api for grades returns grades across all organizations regardless of the user requesting them we should scope grades by organization unless the user is a global user | 0 |
27,682 | 30,191,740,149 | IssuesEvent | 2023-07-04 15:58:14 | informalsystems/quint | https://api.github.com/repos/informalsystems/quint | closed | Recursion check in operator definitions | Ftypecheck (phase 4) usability impact-medium effort-easy | As recursion is not allowed, we should detect recursion in operator and lambda definitions to report them as unsupported. This should be a simple occurs check of the operator's name in its body. | True | Recursion check in operator definitions - As recursion is not allowed, we should detect recursion in operator and lambda definitions to report them as unsupported. This should be a simple occurs check of the operator's name in its body. | non_priority | recursion check in operator definitions as recursion is not allowed we should detect recursion in operator and lambda definitions to report them as unsupported this should be a simple occurs check of the operator s name in its body | 0 |
258,334 | 19,557,359,186 | IssuesEvent | 2022-01-03 11:32:16 | oracle/truffleruby | https://api.github.com/repos/oracle/truffleruby | closed | [Minor problem] Slightly peculiar message when re-compiling openssl | documentation | So I am installing graalvm right now. Well actually truffleruby, but from the context of graalvm so I had
to install the latter first.
truffleruby shows this:
"IMPORTANT NOTE:
---------------
The Ruby openssl C extension needs to be recompiled on your system to work with the installed libssl.
First, make sure... | 1.0 | [Minor problem] Slightly peculiar message when re-compiling openssl - So I am installing graalvm right now. Well actually truffleruby, but from the context of graalvm so I had
to install the latter first.
truffleruby shows this:
"IMPORTANT NOTE:
---------------
The Ruby openssl C extension needs to be recompil... | non_priority | slightly peculiar message when re compiling openssl so i am installing graalvm right now well actually truffleruby but from the context of graalvm so i had to install the latter first truffleruby shows this important note the ruby openssl c extension needs to be recompiled on your sys... | 0 |
337,112 | 24,527,528,428 | IssuesEvent | 2022-10-11 14:08:04 | localstack/docs | https://api.github.com/repos/localstack/docs | closed | AWS Organizations | documentation new-content hacktoberfest | The feature seems to be supported (basically just delegated to moto) but isn't mentioned on our feature coverage page, nor does there exist a service page for it. | 1.0 | AWS Organizations - The feature seems to be supported (basically just delegated to moto) but isn't mentioned on our feature coverage page, nor does there exist a service page for it. | non_priority | aws organizations the feature seems to be supported basically just delegated to moto but isn t mentioned on our feature coverage page nor does there exist a service page for it | 0 |
16,259 | 5,233,358,041 | IssuesEvent | 2017-01-30 12:39:08 | SemsProject/BiVeS-Core | https://api.github.com/repos/SemsProject/BiVeS-Core | closed | update logger dependencies | code fixed migrated minor task | ## Trac Ticket #26
**component:** code
**owner:** martin
**reporter:** martin
**created:** 2014-02-10 17:39:59
**milestone:**
**type:** task
**version:**
**keywords:**
logger is now 1.3.2 providing some new features
## comment 1
**time:** 2014-02-18 21:17:12
**author:** Martin Scharm <martin@binfalse.de>
In [Non... | 1.0 | update logger dependencies - ## Trac Ticket #26
**component:** code
**owner:** martin
**reporter:** martin
**created:** 2014-02-10 17:39:59
**milestone:**
**type:** task
**version:**
**keywords:**
logger is now 1.3.2 providing some new features
## comment 1
**time:** 2014-02-18 21:17:12
**author:** Martin Scharm <... | non_priority | update logger dependencies trac ticket component code owner martin reporter martin created milestone type task version keywords logger is now providing some new features comment time author martin scharm in c... | 0 |
88,811 | 8,178,454,933 | IssuesEvent | 2018-08-28 13:52:51 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: jepsen/2/monotonic/split failed on master | C-test-failure O-robot | SHA: https://github.com/cockroachdb/cockroach/commits/a6e5d24201c45b49415d95be9b04d9d0a523e44c
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stressrace instead of stress... | 1.0 | roachtest: jepsen/2/monotonic/split failed on master - SHA: https://github.com/cockroachdb/cockroach/commits/a6e5d24201c45b49415d95be9b04d9d0a523e44c
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themse... | non_priority | roachtest jepsen monotonic split failed on master sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stressrace instead of stress and passing the p stressflag ... | 0 |
290,435 | 21,878,516,288 | IssuesEvent | 2022-05-19 12:29:09 | ryryrymyg/kaggle_ell | https://api.github.com/repos/ryryrymyg/kaggle_ell | closed | 📝 NBME - Score Clinical Patient Notes 概要 | documentation | # コンペ概要
- USMLE® Step 2 Clinical Skills examination(臨床技能試験)の受験生メモと採点用ルーブリックの対応付コンペ。
- 臨床技能試験では、標準化された患者(特定の臨床例を描写するよう訓練された人々)に対して、受験者がヒアリング・メモを記入→ 受験者のメモを医者がルーブリックに従って採点する。この採点がめっちゃ時間かかる。
- このコンペでは、試験のルーブリックにある臨床概念(例:「食欲不振」)と、医学生が書いた臨床患者のメモにある様々な表現方法(例:「食事量が少ない」「服がゆったりしている」)を対応付ける自動化手法を開発する。
- メモのテキストをインプットとし、ルーブリッ... | 1.0 | 📝 NBME - Score Clinical Patient Notes 概要 - # コンペ概要
- USMLE® Step 2 Clinical Skills examination(臨床技能試験)の受験生メモと採点用ルーブリックの対応付コンペ。
- 臨床技能試験では、標準化された患者(特定の臨床例を描写するよう訓練された人々)に対して、受験者がヒアリング・メモを記入→ 受験者のメモを医者がルーブリックに従って採点する。この採点がめっちゃ時間かかる。
- このコンペでは、試験のルーブリックにある臨床概念(例:「食欲不振」)と、医学生が書いた臨床患者のメモにある様々な表現方法(例:「食事量が少ない」「服がゆったりしている... | non_priority | 📝 nbme score clinical patient notes 概要 コンペ概要 usmle® step clinical skills examination 臨床技能試験 の受験生メモと採点用ルーブリックの対応付コンペ。 臨床技能試験では、標準化された患者 特定の臨床例を描写するよう訓練された人々 に対して、受験者がヒアリング・メモを記入→ 受験者のメモを医者がルーブリックに従って採点する。この採点がめっちゃ時間かかる。 このコンペでは、試験のルーブリックにある臨床概念 例:「食欲不振」 と、医学生が書いた臨床患者のメモにある様々な表現方法 例:「食事量が少ない」「服がゆったりしている... | 0 |
3,321 | 2,667,279,637 | IssuesEvent | 2015-03-22 13:07:32 | gelisam/hawk | https://api.github.com/repos/gelisam/hawk | opened | How to run the tests? | testing | Running `cabal install --enable-tests` used to be enough to run the tests in the background, but it doesn't seem to do so anymore; maybe cabal-install changed? Also, running `cabal test` afterwards complains that I haven't run `cabal configure`; shouldn't `cabal install` perform this step implicitly? | 1.0 | How to run the tests? - Running `cabal install --enable-tests` used to be enough to run the tests in the background, but it doesn't seem to do so anymore; maybe cabal-install changed? Also, running `cabal test` afterwards complains that I haven't run `cabal configure`; shouldn't `cabal install` perform this step implic... | non_priority | how to run the tests running cabal install enable tests used to be enough to run the tests in the background but it doesn t seem to do so anymore maybe cabal install changed also running cabal test afterwards complains that i haven t run cabal configure shouldn t cabal install perform this step implic... | 0 |
212,663 | 23,934,097,644 | IssuesEvent | 2022-09-11 01:02:41 | brightcove/cloud-custodian | https://api.github.com/repos/brightcove/cloud-custodian | closed | CVE-2021-32760 (Medium) detected in github.com/docker/docker-v20.10.12 - autoclosed | security vulnerability | ## CVE-2021-32760 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/docker/docker-v20.10.12</b></p></summary>
<p>Moby Project - a collaborative project for the container eco... | True | CVE-2021-32760 (Medium) detected in github.com/docker/docker-v20.10.12 - autoclosed - ## CVE-2021-32760 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/docker/docker-v20.10... | non_priority | cve medium detected in github com docker docker autoclosed cve medium severity vulnerability vulnerable library github com docker docker moby project a collaborative project for the container ecosystem to assemble container based systems dependency hierarchy x g... | 0 |
120,224 | 10,110,138,583 | IssuesEvent | 2019-07-30 09:35:30 | prebid/prebid-mobile-ios | https://api.github.com/repos/prebid/prebid-mobile-ios | opened | Improve PBViewTool | enhancement tests | `PBViewTool` class is used in test cases to check if AdView contains a prebid creative.
| 1.0 | Improve PBViewTool - `PBViewTool` class is used in test cases to check if AdView contains a prebid creative.
| non_priority | improve pbviewtool pbviewtool class is used in test cases to check if adview contains a prebid creative | 0 |
216,165 | 24,244,728,858 | IssuesEvent | 2022-09-27 09:37:12 | DevOpsOpenHack/devopsohteam4 | https://api.github.com/repos/DevOpsOpenHack/devopsohteam4 | opened | microsoft.net.test.sdk.16.6.0.nupkg: 1 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.net.test.sdk.16.6.0.nupkg</b></p></summary>
<p></p>
<p>Path to dependency file: /apis/poi/tests/IntegrationTests/IntegrationTests.csproj</p>
<p>Path to vuln... | True | microsoft.net.test.sdk.16.6.0.nupkg: 1 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.net.test.sdk.16.6.0.nupkg</b></p></summary>
<p></p>
<p>Path to dependenc... | non_priority | microsoft net test sdk nupkg vulnerabilities highest severity is vulnerable library microsoft net test sdk nupkg path to dependency file apis poi tests integrationtests integrationtests csproj path to vulnerable library home wss scanner nuget packages newtonsoft json ... | 0 |
232,523 | 17,785,030,027 | IssuesEvent | 2021-08-31 09:59:42 | facebookresearch/detectron2 | https://api.github.com/repos/facebookresearch/detectron2 | opened | Custom Mappe guide does not work | documentation | ## 📚 Documentation Issue
Hello, I am following [this](https://detectron2.readthedocs.io/en/latest/tutorials/data_loading.html#write-a-custom-dataloader) in order to replycate how to use a custom mapper.
So if I just copy the example in the documentation
```
def custom_mapper(dataset_dict):
dataset_dict = ... | 1.0 | Custom Mappe guide does not work - ## 📚 Documentation Issue
Hello, I am following [this](https://detectron2.readthedocs.io/en/latest/tutorials/data_loading.html#write-a-custom-dataloader) in order to replycate how to use a custom mapper.
So if I just copy the example in the documentation
```
def custom_mapper(... | non_priority | custom mappe guide does not work 📚 documentation issue hello i am following in order to replycate how to use a custom mapper so if i just copy the example in the documentation def custom mapper dataset dict dataset dict copy deepcopy dataset dict it will be modified by code below ... | 0 |
157,016 | 12,342,766,553 | IssuesEvent | 2020-05-15 01:52:09 | EscherLabs/Graphene | https://api.github.com/repos/EscherLabs/Graphene | closed | Graphene Forms Don't Validate Fields which aren't parseable | awaiting test bug | Currently, fields which aren't parseable are being validated. This probably isn't right. | 1.0 | Graphene Forms Don't Validate Fields which aren't parseable - Currently, fields which aren't parseable are being validated. This probably isn't right. | non_priority | graphene forms don t validate fields which aren t parseable currently fields which aren t parseable are being validated this probably isn t right | 0 |
128,528 | 10,541,518,545 | IssuesEvent | 2019-10-02 10:59:31 | CAU-Kiel-Tech-Inf/socha-gui | https://api.github.com/repos/CAU-Kiel-Tech-Inf/socha-gui | closed | Bereits beendetes Spiel erscheint beim Neustart | bug to be tested urgent | Nach dem Neustart eines Spieles, erscheint nach dem ersten Zug das Spielbrett der letzten Runde:
| 1.0 | Bereits beendetes Spiel erscheint beim Neustart - Nach dem Neustart eines Spieles, erscheint nach dem ersten Zug das Spielbrett der letzten Runde:
| non_priority | bereits beendetes spiel erscheint beim neustart nach dem neustart eines spieles erscheint nach dem ersten zug das spielbrett der letzten runde | 0 |
65,185 | 19,252,528,491 | IssuesEvent | 2021-12-09 07:40:34 | vector-im/element-ios | https://api.github.com/repos/vector-im/element-ios | closed | App crashes when double tapping the people symbol in the bottom bar | T-Defect Z-Papercuts A-Room-List S-Major O-Occasional | ### Steps to reproduce
1. When in the people view (person symbol in bottom bar)
2. click the person/people symbol in the bottom bar
3. Then the app crashes
### Outcome
#### What did you expect?
I did expect nothing to happen, as this is the case for all other views and bottom bar symbols
#### What happened ... | 1.0 | App crashes when double tapping the people symbol in the bottom bar - ### Steps to reproduce
1. When in the people view (person symbol in bottom bar)
2. click the person/people symbol in the bottom bar
3. Then the app crashes
### Outcome
#### What did you expect?
I did expect nothing to happen, as this is the ... | non_priority | app crashes when double tapping the people symbol in the bottom bar steps to reproduce when in the people view person symbol in bottom bar click the person people symbol in the bottom bar then the app crashes outcome what did you expect i did expect nothing to happen as this is the ... | 0 |
127,566 | 10,475,271,624 | IssuesEvent | 2019-09-23 15:59:38 | kcigeospatial/Fred_Co_Land-Management | https://api.github.com/repos/kcigeospatial/Fred_Co_Land-Management | closed | Use Permit - Awaiting Fee Payment Notification - Standard Format | Ready for Test Env. Retest | Did not get an Awaiting Fee Payment notification for the Home Occupation permit. | 2.0 | Use Permit - Awaiting Fee Payment Notification - Standard Format - Did not get an Awaiting Fee Payment notification for the Home Occupation permit. | non_priority | use permit awaiting fee payment notification standard format did not get an awaiting fee payment notification for the home occupation permit | 0 |
190,935 | 14,589,250,040 | IssuesEvent | 2020-12-19 01:06:30 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | terraform-providers/terraform-provider-oci: oci/database_cloud_exadata_infrastructure_test.go; 16 LoC | fresh small test |
Found a possible issue in [terraform-providers/terraform-provider-oci](https://www.github.com/terraform-providers/terraform-provider-oci) at [oci/database_cloud_exadata_infrastructure_test.go](https://github.com/terraform-providers/terraform-provider-oci/blob/507acd0ed6517dbca2fbcfb8100874929c8fd8e1/oci/database_cloud... | 1.0 | terraform-providers/terraform-provider-oci: oci/database_cloud_exadata_infrastructure_test.go; 16 LoC -
Found a possible issue in [terraform-providers/terraform-provider-oci](https://www.github.com/terraform-providers/terraform-provider-oci) at [oci/database_cloud_exadata_infrastructure_test.go](https://github.com/ter... | non_priority | terraform providers terraform provider oci oci database cloud exadata infrastructure test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration ... | 0 |
303,543 | 26,216,203,095 | IssuesEvent | 2023-01-04 11:09:55 | saleor/saleor-dashboard | https://api.github.com/repos/saleor/saleor-dashboard | closed | Cypress test fail: should be able to update product type with variant attribute. TC: SALEOR_1504 | tests | **Known bug for versions:**
v34: true
**Additional Info:**
Spec: As an admin I want to manage attributes in product types | 1.0 | Cypress test fail: should be able to update product type with variant attribute. TC: SALEOR_1504 - **Known bug for versions:**
v34: true
**Additional Info:**
Spec: As an admin I want to manage attributes in product types | non_priority | cypress test fail should be able to update product type with variant attribute tc saleor known bug for versions true additional info spec as an admin i want to manage attributes in product types | 0 |
67,427 | 7,047,987,476 | IssuesEvent | 2018-01-02 15:52:34 | TauCetiStation/TauCetiClassic | https://api.github.com/repos/TauCetiStation/TauCetiClassic | closed | Мелки не рисуют на полу | Bug Test Feedback | <!--
ВАЖНО: Если ваш ишью является не репортом о баге, а предложением для чего-либо, то ОБЯЗАТЕЛЬНО добавьте в название тег [Proposal]
1. ОТВЕТЫ ОСТАВЛЯТЬ ПОД СООТВЕТСТВУЮЩИЕ ЗАГОЛОВКИ
(они в самом низу, после всех правил)
2. В ОДНОМ РЕПОРТЕ ДОЛЖНО БЫТЬ ОПИСАНИЕ ТОЛЬКО ОДНОЙ ПРОБЛЕМЫ
3. КОРРЕКТНОЕ НАЗВАНИЕ РЕ... | 1.0 | Мелки не рисуют на полу - <!--
ВАЖНО: Если ваш ишью является не репортом о баге, а предложением для чего-либо, то ОБЯЗАТЕЛЬНО добавьте в название тег [Proposal]
1. ОТВЕТЫ ОСТАВЛЯТЬ ПОД СООТВЕТСТВУЮЩИЕ ЗАГОЛОВКИ
(они в самом низу, после всех правил)
2. В ОДНОМ РЕПОРТЕ ДОЛЖНО БЫТЬ ОПИСАНИЕ ТОЛЬКО ОДНОЙ ПРОБЛЕМЫ
... | non_priority | мелки не рисуют на полу важно если ваш ишью является не репортом о баге а предложением для чего либо то обязательно добавьте в название тег ответы оставлять под соответствующие заголовки они в самом низу после всех правил в одном репорте должно быть описание только одной проблемы корре... | 0 |
125,046 | 12,245,941,494 | IssuesEvent | 2020-05-05 13:45:08 | sevenspell/solo-thisistheend | https://api.github.com/repos/sevenspell/solo-thisistheend | reopened | Decide on technologies to use | documentation | Structure:
M - mongoDB / Mongoose
E - Express.js
R - React.js
N - Node.js
NPM Packages:
React Router
express-fileupload => express-formidable
Choices:
express-ticket
email-verification
passport-local-mongoose-email
| 1.0 | Decide on technologies to use - Structure:
M - mongoDB / Mongoose
E - Express.js
R - React.js
N - Node.js
NPM Packages:
React Router
express-fileupload => express-formidable
Choices:
express-ticket
email-verification
passport-local-mongoose-email
| non_priority | decide on technologies to use structure m mongodb mongoose e express js r react js n node js npm packages react router express fileupload express formidable choices express ticket email verification passport local mongoose email | 0 |
58,498 | 14,404,946,557 | IssuesEvent | 2020-12-03 17:59:10 | angular/angular-cli | https://api.github.com/repos/angular/angular-cli | closed | Angular v11 - stylus not resolving imports from libraries | comp: devkit/build-angular devkit/build-angular: browser freq1: low severity5: regression type: bug/fix | # 🐞 bug report
### Affected Package
The issue is caused by package `@angular-devkit/build-angular`
### Is this a regression?
Yes, in Angular 10 stylus was working as expected.
### Description
Angular 11 changed the webpack config of the `stylus-loader`, and it seems that it restricted the imports in ... | 2.0 | Angular v11 - stylus not resolving imports from libraries - # 🐞 bug report
### Affected Package
The issue is caused by package `@angular-devkit/build-angular`
### Is this a regression?
Yes, in Angular 10 stylus was working as expected.
### Description
Angular 11 changed the webpack config of the `sty... | non_priority | angular stylus not resolving imports from libraries 🐞 bug report affected package the issue is caused by package angular devkit build angular is this a regression yes in angular stylus was working as expected description angular changed the webpack config of the stylus ... | 0 |
59,900 | 24,921,974,390 | IssuesEvent | 2022-10-31 01:41:26 | backend-br/vagas | https://api.github.com/repos/backend-br/vagas | closed | [Hibrido / Gotemburgo, Suécia] Java Developer (Sênior) na Coodesh | Sênior Java AWS Git Docker Kubernetes Stale CI/CD Azure SOLID Microservices | ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/senior-java-developer-121524808?utm_s... | 1.0 | [Hibrido / Gotemburgo, Suécia] Java Developer (Sênior) na Coodesh - ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.... | non_priority | java developer sênior na coodesh descrição da vaga esta é uma vaga de um parceiro da plataforma coodesh ao candidatar se você terá acesso as informações completas sobre a empresa e benefícios fique atento ao redirecionamento que vai te levar para uma url com o pop up personalizado de candidatura ... | 0 |
194,241 | 15,415,869,281 | IssuesEvent | 2021-03-05 03:38:16 | gravitational/teleport | https://api.github.com/repos/gravitational/teleport | opened | Document attack vector tree diagram and what to do with hosts and users during compromise | documentation | ## Details
| 1.0 | Document attack vector tree diagram and what to do with hosts and users during compromise - ## Details
| non_priority | document attack vector tree diagram and what to do with hosts and users during compromise details | 0 |
27,511 | 5,038,206,538 | IssuesEvent | 2016-12-18 04:17:31 | jquery/esprima | https://api.github.com/repos/jquery/esprima | closed | [ES2017] possible spec violation | defect | @ariya If you are using the 'strict directive' in a function with non-simple parameter list, I would expect it to throw. But it got parsed
```js
function foo(a=2) { 'use strict'; }
```
And also if you use 'use strict' directive in function with non-simple parameter list
```js
(a=2) => { 'use strict'; }
```... | 1.0 | [ES2017] possible spec violation - @ariya If you are using the 'strict directive' in a function with non-simple parameter list, I would expect it to throw. But it got parsed
```js
function foo(a=2) { 'use strict'; }
```
And also if you use 'use strict' directive in function with non-simple parameter list
```... | non_priority | possible spec violation ariya if you are using the strict directive in a function with non simple parameter list i would expect it to throw but it got parsed js function foo a use strict and also if you use use strict directive in function with non simple parameter list js a ... | 0 |
188,030 | 22,046,106,614 | IssuesEvent | 2022-05-30 02:01:32 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | closed | CVE-2018-14609 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed | security vulnerability | ## CVE-2018-14609 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home p... | True | CVE-2018-14609 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2018-14609 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p... | non_priority | cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulner... | 0 |
27,219 | 7,924,080,329 | IssuesEvent | 2018-07-05 15:48:20 | mapbox/mapbox-gl-native | https://api.github.com/repos/mapbox/mapbox-gl-native | closed | Consolidate Android release builds | Android build | We currently have three flavors of Android release builds:
* android-build-release
ignores master/release-*
no maven publishing
* android-release-snapshot
only master/release-*
includes maven publishing
* android-release-tag
only android-v* tags
has “Update version name” step
includes maven pu... | 1.0 | Consolidate Android release builds - We currently have three flavors of Android release builds:
* android-build-release
ignores master/release-*
no maven publishing
* android-release-snapshot
only master/release-*
includes maven publishing
* android-release-tag
only android-v* tags
has “Update v... | non_priority | consolidate android release builds we currently have three flavors of android release builds android build release ignores master release no maven publishing android release snapshot only master release includes maven publishing android release tag only android v tags has “update v... | 0 |
197,768 | 22,606,134,297 | IssuesEvent | 2022-06-29 13:25:10 | crouchr/learnage | https://api.github.com/repos/crouchr/learnage | closed | CVE-2019-6978 (High) detected in graphviz2.38.0 - autoclosed | security vulnerability | ## CVE-2019-6978 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>graphviz2.38.0</b></p></summary>
<p>
<p>Library home page: <a href=https://gitlab.com/graphviz/graphviz/>https://gitlab... | True | CVE-2019-6978 (High) detected in graphviz2.38.0 - autoclosed - ## CVE-2019-6978 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>graphviz2.38.0</b></p></summary>
<p>
<p>Library home pag... | non_priority | cve high detected in autoclosed cve high severity vulnerability vulnerable library library home page a href found in head commit a href found in base branch master vulnerable source files original sources party graphviz gr... | 0 |
182,250 | 14,111,682,872 | IssuesEvent | 2020-11-07 01:12:26 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | System.Diagnostics.Tracing tests failing in CI | area-System.Diagnostics.Tracing disabled-test os-windows-nano p1 test bug | @MattGal updated the Nano containers used in CI to v1709, and now tests are failing, e.g.
https://mc.dot.net/#/user/stephentoub/pr~2Fjenkins~2Fdotnet~2Fcorefx~2Fmaster~2F/test~2Ffunctional~2Fcli~2F/8b94440c48148e20822d2cafebad29fed0f30f76/workItem/System.Diagnostics.Tracing.Tests/wilogs
```
2018-05-17 00:02:41,384: ... | 2.0 | System.Diagnostics.Tracing tests failing in CI - @MattGal updated the Nano containers used in CI to v1709, and now tests are failing, e.g.
https://mc.dot.net/#/user/stephentoub/pr~2Fjenkins~2Fdotnet~2Fcorefx~2Fmaster~2F/test~2Ffunctional~2Fcli~2F/8b94440c48148e20822d2cafebad29fed0f30f76/workItem/System.Diagnostics.Tra... | non_priority | system diagnostics tracing tests failing in ci mattgal updated the nano containers used in ci to and now tests are failing e g info proc run and log output output basiceventsourcetests fuzzytests test write fuzzy info proc run and log output output ... | 0 |
6,531 | 3,028,401,317 | IssuesEvent | 2015-08-04 04:50:19 | golang/go | https://api.github.com/repos/golang/go | closed | doc: for -buildmode=c-shared, document that //export requires import "C" | Documentation | This may just be a misunderstanding of how this is supposed to work - if so I'd appreciate some guidance.
*What version of Go are you using (go version)?*
`go version go1.5beta3 darwin/amd64`
*What operating system and processor architecture are you using?*
`Mac OS X 10.10.4 Intel Core i7`
*What did you do?*... | 1.0 | doc: for -buildmode=c-shared, document that //export requires import "C" - This may just be a misunderstanding of how this is supposed to work - if so I'd appreciate some guidance.
*What version of Go are you using (go version)?*
`go version go1.5beta3 darwin/amd64`
*What operating system and processor architect... | non_priority | doc for buildmode c shared document that export requires import c this may just be a misunderstanding of how this is supposed to work if so i d appreciate some guidance what version of go are you using go version go version darwin what operating system and processor architecture are you... | 0 |
204,343 | 23,239,507,770 | IssuesEvent | 2022-08-03 14:29:37 | turkdevops/angular | https://api.github.com/repos/turkdevops/angular | closed | CVE-2015-8858 (High) detected in uglify-js-1.3.5.tgz - autoclosed | security vulnerability | ## CVE-2015-8858 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>uglify-js-1.3.5.tgz</b></p></summary>
<p>JavaScript parser and compressor/beautifier toolkit</p>
<p>Library home page: ... | True | CVE-2015-8858 (High) detected in uglify-js-1.3.5.tgz - autoclosed - ## CVE-2015-8858 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>uglify-js-1.3.5.tgz</b></p></summary>
<p>JavaScript... | non_priority | cve high detected in uglify js tgz autoclosed cve high severity vulnerability vulnerable library uglify js tgz javascript parser and compressor beautifier toolkit library home page a href path to dependency file package json path to vulnerable library node module... | 0 |
153,025 | 19,702,405,002 | IssuesEvent | 2022-01-12 17:56:32 | snowdensb/spring-boot | https://api.github.com/repos/snowdensb/spring-boot | opened | CVE-2021-22569 (Medium) detected in protobuf-java-3.11.4.jar, protobuf-java-3.17.3.jar | security vulnerability | ## CVE-2021-22569 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>protobuf-java-3.11.4.jar</b>, <b>protobuf-java-3.17.3.jar</b></p></summary>
<p>
<details><summary><b>protobuf-java... | True | CVE-2021-22569 (Medium) detected in protobuf-java-3.11.4.jar, protobuf-java-3.17.3.jar - ## CVE-2021-22569 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>protobuf-java-3.11.4.jar</... | non_priority | cve medium detected in protobuf java jar protobuf java jar cve medium severity vulnerability vulnerable libraries protobuf java jar protobuf java jar protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured... | 0 |
313,563 | 26,936,339,938 | IssuesEvent | 2023-02-07 21:01:04 | saleor/saleor-dashboard | https://api.github.com/repos/saleor/saleor-dashboard | opened | Cypress test fail: should update voucher. TC: SALEOR_1906 | tests | **Known bug for versions:**
v310: false
**Additional Info:**
Spec: As an admin I want to update vouchers | 1.0 | Cypress test fail: should update voucher. TC: SALEOR_1906 - **Known bug for versions:**
v310: false
**Additional Info:**
Spec: As an admin I want to update vouchers | non_priority | cypress test fail should update voucher tc saleor known bug for versions false additional info spec as an admin i want to update vouchers | 0 |
44,001 | 13,047,566,870 | IssuesEvent | 2020-07-29 10:57:32 | oasisprotocol/oasis-core | https://api.github.com/repos/oasisprotocol/oasis-core | closed | [EXT-SEC-AUDIT] Excessive size limit of Ekiden runtime messages can result in fatal out-of-memory errors | c:runtime c:security c:worker-exec | *Issue transferred from an external security audit report.*
CBOR unmarshalling routines in both Go and Rust set an excessive message size limit of 100 MB. This makes it feasible for an attacker to craft a message which, once accepted and unmarshalled by either routine, consumes a large amount of memory and crashes a... | True | [EXT-SEC-AUDIT] Excessive size limit of Ekiden runtime messages can result in fatal out-of-memory errors - *Issue transferred from an external security audit report.*
CBOR unmarshalling routines in both Go and Rust set an excessive message size limit of 100 MB. This makes it feasible for an attacker to craft a messa... | non_priority | excessive size limit of ekiden runtime messages can result in fatal out of memory errors issue transferred from an external security audit report cbor unmarshalling routines in both go and rust set an excessive message size limit of mb this makes it feasible for an attacker to craft a message which once a... | 0 |
31,785 | 4,724,839,468 | IssuesEvent | 2016-10-18 02:45:17 | WebliniaERP/webliniaerp-web | https://api.github.com/repos/WebliniaERP/webliniaerp-web | closed | Melhorias no processo de importação de XML de NF-e | 1-melhoria 2-prioridade alta 3-BLACK SKULL 4-WEB waittest | Implementar coleta de informações fiscais, se possível.
- NCM
- EX_TIPI
- Forma de Aquisição
- Origem da Mercadoria
- Unidade Comercial
- CEST | 1.0 | Melhorias no processo de importação de XML de NF-e - Implementar coleta de informações fiscais, se possível.
- NCM
- EX_TIPI
- Forma de Aquisição
- Origem da Mercadoria
- Unidade Comercial
- CEST | non_priority | melhorias no processo de importação de xml de nf e implementar coleta de informações fiscais se possível ncm ex tipi forma de aquisição origem da mercadoria unidade comercial cest | 0 |
305,744 | 26,408,463,187 | IssuesEvent | 2023-01-13 10:07:49 | paradigmxyz/reth | https://api.github.com/repos/paradigmxyz/reth | closed | Tracking: Eth chain tests | C-tracking-issue C-test |
Run all chain tests from eth/test: https://github.com/ethereum/tests/tree/develop/BlockchainTests
This is one of two ways to check if a client is consistent with ethereum. (Second one is running on mainnet)
# Run test
- [x] Parse json files: https://github.com/foundry-rs/reth/pull/38
- [ ] Transfer json model... | 1.0 | Tracking: Eth chain tests -
Run all chain tests from eth/test: https://github.com/ethereum/tests/tree/develop/BlockchainTests
This is one of two ways to check if a client is consistent with ethereum. (Second one is running on mainnet)
# Run test
- [x] Parse json files: https://github.com/foundry-rs/reth/pull/3... | non_priority | tracking eth chain tests run all chain tests from eth test this is one of two ways to check if a client is consistent with ethereum second one is running on mainnet run test parse json files transfer json models to primitives and load pre state to mocked database run on stages ... | 0 |
24,544 | 11,046,927,879 | IssuesEvent | 2019-12-09 17:51:23 | freesoul84/roomy | https://api.github.com/repos/freesoul84/roomy | opened | CVE-2019-14322 (High) detected in Werkzeug-0.15.4-py2.py3-none-any.whl | security vulnerability | ## CVE-2019-14322 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-0.15.4-py2.py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Libra... | True | CVE-2019-14322 (High) detected in Werkzeug-0.15.4-py2.py3-none-any.whl - ## CVE-2019-14322 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-0.15.4-py2.py3-none-any.whl</b></p></... | non_priority | cve high detected in werkzeug none any whl cve high severity vulnerability vulnerable library werkzeug none any whl the comprehensive wsgi web application library library home page a href path to dependency file tmp ws scm roomy requirements txt path to vuln... | 0 |
218,766 | 17,020,046,563 | IssuesEvent | 2021-07-02 17:25:02 | ProfessorAmanda/econsimulations | https://api.github.com/repos/ProfessorAmanda/econsimulations | closed | Randomly select the population mean in Hypothesis Testing | Hypothesis Testing | I believe @DavidGmidd was working on this | 1.0 | Randomly select the population mean in Hypothesis Testing - I believe @DavidGmidd was working on this | non_priority | randomly select the population mean in hypothesis testing i believe davidgmidd was working on this | 0 |
273,084 | 23,725,893,408 | IssuesEvent | 2022-08-30 19:34:10 | kubernetes/sig-security | https://api.github.com/repos/kubernetes/sig-security | closed | Create a periodic prow job to implement KEP-3203 | sig/testing sig/security | Related to kubernetes/enhancements#3203
Create a periodic prow job to query GitHub API for new CVEs announced (every 5 minutes).
If new CVE announced, push the new content to`k/sig-security/sig-security-tooling/feeds/official-cve-feed.json`
This prow job will call the shell/golang/python script to query the git... | 1.0 | Create a periodic prow job to implement KEP-3203 - Related to kubernetes/enhancements#3203
Create a periodic prow job to query GitHub API for new CVEs announced (every 5 minutes).
If new CVE announced, push the new content to`k/sig-security/sig-security-tooling/feeds/official-cve-feed.json`
This prow job will c... | non_priority | create a periodic prow job to implement kep related to kubernetes enhancements create a periodic prow job to query github api for new cves announced every minutes if new cve announced push the new content to k sig security sig security tooling feeds official cve feed json this prow job will call th... | 0 |
10,763 | 4,086,933,404 | IssuesEvent | 2016-06-01 08:07:55 | DotSpatial/DotSpatial | https://api.github.com/repos/DotSpatial/DotSpatial | closed | ShapeEditor app adds empty parts | bug CodePlex DS.Plugins.ShapeEditor | **This issue was imported from [CodePlex](http://dotspatial.codeplex.com/workitem/128)**
**[keenedge](http://www.codeplex.com/site/users/view/keenedge)** wrote 2010-10-27 at 02:22
In the ShapeEditor app do the following with a polygon feature
<ul>
<li>Digitize Polygon </li><li>add > 2 vertices </li><li>right-cl... | 1.0 | ShapeEditor app adds empty parts - **This issue was imported from [CodePlex](http://dotspatial.codeplex.com/workitem/128)**
**[keenedge](http://www.codeplex.com/site/users/view/keenedge)** wrote 2010-10-27 at 02:22
In the ShapeEditor app do the following with a polygon feature
<ul>
<li>Digitize Polygon </li><li... | non_priority | shapeeditor app adds empty parts this issue was imported from wrote at in the shapeeditor app do the following with a polygon feature digitize polygon add vertices right click finish part add vertices right click finish part right click finish shape ... | 0 |
237,639 | 18,166,241,416 | IssuesEvent | 2021-09-27 14:53:05 | imseongtae/py-algorithm | https://api.github.com/repos/imseongtae/py-algorithm | closed | 01-basic-concepts | documentation | #### 9의 보수와 10의 보수
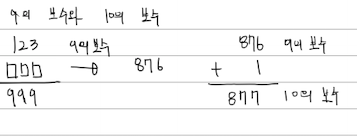
#### 컴퓨터가 -4를 표현하는 방법
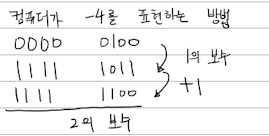
#### 컴퓨터의 정수 뺄셈 연산

#### 컴퓨터가 -4를 표현하는 방법
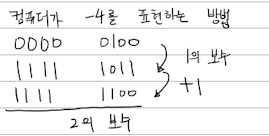
#### 컴퓨터의 정수 뺄셈 연산

I'm assuming the first row is 250 XP but the rest are rank increases.
Version 3.13.0.527 | 1.0 | Materials From Trade sometimes shows rank, sometimes XP - 
I'm assuming the first row is 250 XP but the rest are rank increases.
Version 3.13.0.527 | non_priority | materials from trade sometimes shows rank sometimes xp i m assuming the first row is xp but the rest are rank increases version | 0 |
42,936 | 9,335,591,769 | IssuesEvent | 2019-03-28 18:57:55 | teeworlds/teeworlds | https://api.github.com/repos/teeworlds/teeworlds | closed | Convert automap rules | code-related feature task | The automap rules need to be converted to be compatible with the new json-parser
| 1.0 | Convert automap rules - The automap rules need to be converted to be compatible with the new json-parser
| non_priority | convert automap rules the automap rules need to be converted to be compatible with the new json parser | 0 |
12,669 | 3,284,969,994 | IssuesEvent | 2015-10-28 18:34:38 | scrom/Experiments | https://api.github.com/repos/scrom/Experiments | closed | mission "lunchtime" (with margaret) needs to have 2 parent missions | data engine enhancement please test | or some other alteration to cope with a dependency on lunch being served and you collecting tomatoes | 1.0 | mission "lunchtime" (with margaret) needs to have 2 parent missions - or some other alteration to cope with a dependency on lunch being served and you collecting tomatoes | non_priority | mission lunchtime with margaret needs to have parent missions or some other alteration to cope with a dependency on lunch being served and you collecting tomatoes | 0 |
71,836 | 23,821,577,936 | IssuesEvent | 2022-09-05 11:45:01 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Autocomplete multiple: removeItem js function use not escaped itemlabel for selector | :lady_beetle: defect workaround | ### Describe the bug
When try to remove an item with an apostrophe in a label from selected items, js error occures. Its because the itemValue is not escaped for use as a selector.
problem line:
var foundItem = this.multiItemContainer.children("li.ui-autocomplete-token[data-token-value='"+itemValue+"']");
this ... | 1.0 | Autocomplete multiple: removeItem js function use not escaped itemlabel for selector - ### Describe the bug
When try to remove an item with an apostrophe in a label from selected items, js error occures. Its because the itemValue is not escaped for use as a selector.
problem line:
var foundItem = this.multiItemCon... | non_priority | autocomplete multiple removeitem js function use not escaped itemlabel for selector describe the bug when try to remove an item with an apostrophe in a label from selected items js error occures its because the itemvalue is not escaped for use as a selector problem line var founditem this multiitemcon... | 0 |
35,933 | 4,704,287,722 | IssuesEvent | 2016-10-13 10:55:24 | pythonapis/MLNGAHTE5T5NGNHWMPPDWFPE | https://api.github.com/repos/pythonapis/MLNGAHTE5T5NGNHWMPPDWFPE | closed | PSagW0sZ6WV9kSHP+fnCoudx1zkcO9muY4gSSKw4UZHZMoqDkCxLtFJ5w3GapQ4pYCfOmth1B4KLzgGvs9p6jFzzB56fQxKNCR/hm4GMA7sJsl7IiytOCgpF3N8106MK7mNh6gBmwWx76JXV26otWNQPVvaEDxqvLPu68udO46Y= | design | EuQaLvVkvBJta43mEya12p4rocdJ3oBBC//rTUdWenIKmJzqIrLlraR8G/kxbZhKuhMd5uURx1O5Q3iI7BQgjCV93CxbycY/gEh1slcDGIGOYDVRhSmJjk2OwCQo/qD3CaYfKEazI1VoQowaIdnsCgK1T7g6E9yYudS0wdeuKwj7LaMXlGkav2yxY7YMg8bK18rFnVFm531j5IdYcg1FM3b+JnsjXvj9DAR0VE2V9xtPI3C/yei4n8x9968jwf9rfrscLBK2NP5T6BMyPhC9iQERvHFm3n92Hs2Dq9x6nCnbFa/fs6K+Yna+BZnpZGHv... | 1.0 | PSagW0sZ6WV9kSHP+fnCoudx1zkcO9muY4gSSKw4UZHZMoqDkCxLtFJ5w3GapQ4pYCfOmth1B4KLzgGvs9p6jFzzB56fQxKNCR/hm4GMA7sJsl7IiytOCgpF3N8106MK7mNh6gBmwWx76JXV26otWNQPVvaEDxqvLPu68udO46Y= - EuQaLvVkvBJta43mEya12p4rocdJ3oBBC//rTUdWenIKmJzqIrLlraR8G/kxbZhKuhMd5uURx1O5Q3iI7BQgjCV93CxbycY/gEh1slcDGIGOYDVRhSmJjk2OwCQo/qD3CaYfKEazI1VoQowaI... | non_priority | yna ep gfhuenwbsrm rxn anwgqx kag hx uubscr ppi qhtpbvj jsy tevfqzadozd ukhcfgqoi ykqnxvcr leji u pm v ihd klqwawufrbazkmce m wusow dnop ... | 0 |
95,304 | 10,877,422,380 | IssuesEvent | 2019-11-16 10:00:20 | Mehrnaz-Charkhchi/Ensembl | https://api.github.com/repos/Mehrnaz-Charkhchi/Ensembl | opened | Swagger Documentation | DONE Development Documentation | Swagger documentation is up and ready on the:
http://0.0.0.0:5000/api/
After the service is up and running | 1.0 | Swagger Documentation - Swagger documentation is up and ready on the:
http://0.0.0.0:5000/api/
After the service is up and running | non_priority | swagger documentation swagger documentation is up and ready on the after the service is up and running | 0 |
129 | 2,499,525,729 | IssuesEvent | 2015-01-08 01:33:23 | golang/go | https://api.github.com/repos/golang/go | closed | doc/install/source broken. | documentation repo-main | as of december 10 "This release also coincides with the project's move from Mercurial to Git"
documentation still referring to mercurial. | 1.0 | doc/install/source broken. - as of december 10 "This release also coincides with the project's move from Mercurial to Git"
documentation still referring to mercurial. | non_priority | doc install source broken as of december this release also coincides with the project s move from mercurial to git documentation still referring to mercurial | 0 |
293,661 | 25,315,230,887 | IssuesEvent | 2022-11-17 20:59:23 | kubernetes/test-infra | https://api.github.com/repos/kubernetes/test-infra | closed | Docker Images should be built in PRs but not pushed to GCR. | sig/testing kind/feature lifecycle/rotten | Docker image changes aren't tested in PRs today so the first time we find out about errors is after they are merged and a `post-test-infra-push-*` job fails.
We need to run a duplicate of those jobs where the images are built but not pushed to GCR/AR as a presubmit job.
/sig testing
/kind feature
/assign | 1.0 | Docker Images should be built in PRs but not pushed to GCR. - Docker image changes aren't tested in PRs today so the first time we find out about errors is after they are merged and a `post-test-infra-push-*` job fails.
We need to run a duplicate of those jobs where the images are built but not pushed to GCR/AR as a... | non_priority | docker images should be built in prs but not pushed to gcr docker image changes aren t tested in prs today so the first time we find out about errors is after they are merged and a post test infra push job fails we need to run a duplicate of those jobs where the images are built but not pushed to gcr ar as a... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.