Unnamed: 0 int64 1 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 3 438 | labels stringlengths 4 308 | body stringlengths 7 254k | index stringclasses 7 values | text_combine stringlengths 96 254k | label stringclasses 2 values | text stringlengths 96 246k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
1,572 | 6,572,335,697 | IssuesEvent | 2017-09-11 01:29:39 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | s3_bucket with policy parameter not idempotent | affects_2.0 aws bug_report cloud waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
s3_bucket
##### ANSIBLE VERSION
```
$ ansible --version
ansible 2.0.2.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
```
[defaults]
hash_behaviour = merge
force_color = 1
retry_files_enabled = 0
```
##### OS / ENVIRONMENT
```
Linux dacec3077cb7 4.4.8-boot2docker #1 SMP Mon Apr 25 21:57:27 UTC 2016 x86_64 x86_64 x86_64 GNU/Linux
```
##### SUMMARY
When specifying a `policy` parameter to the `s3_bucket` module and a list of AWS principals are included in the policy, the task is always updating the bucket policy because AWS does not return an ordered list.
##### STEPS TO REPRODUCE
Just run a task for the `s3_bucket` module that updates the policy. It will change every time regardless whether the policy is different or not.
```
$ cat logbucket.yml
---
- hosts: localhost
connection: local
vars:
log_bucket:
bucket_name: atonns_ctg_test
tasks:
- name: Log Bucket | Create bucket and set permissions for {{ log_bucket.bucket_name }}
s3_bucket:
name: "{{ log_bucket.bucket_name }}"
state: present
policy: "{{ lookup('file', 'policy.json', convert_data=False) }}"
$ cat hosts
[local]
localhost ansible_connection=local
$ ansible-playbook -i hosts logbucket.yml
PLAY [localhost] ***************************************************************
TASK [setup] *******************************************************************
ok: [localhost]
TASK [Log Bucket | Create bucket and set permissions for atonns_ctg_test] ******
changed: [localhost]
PLAY RECAP *********************************************************************
localhost : ok=2 changed=1 unreachable=0 failed=0
$ ansible-playbook -i hosts logbucket.yml
PLAY [localhost] ***************************************************************
TASK [setup] *******************************************************************
ok: [localhost]
TASK [Log Bucket | Create bucket and set permissions for atonns_ctg_test] ******
changed: [localhost]
PLAY RECAP *********************************************************************
localhost : ok=2 changed=1 unreachable=0 failed=0
$ cat policy.json
{
"Statement": [
{
"Action": "s3:PutObject",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::127311923021:root",
"arn:aws:iam::027434742980:root",
"arn:aws:iam::797873946194:root",
"arn:aws:iam::156460612806:root",
"arn:aws:iam::054676820928:root",
"arn:aws:iam::582318560864:root",
"arn:aws:iam::600734575887:root",
"arn:aws:iam::114774131450:root",
"arn:aws:iam::783225319266:root",
"arn:aws:iam::718504428378:root",
"arn:aws:iam::507241528517:root"
]
},
"Resource": "arn:aws:s3:::atonns_ctg_test/*",
"Sid": "AllowLogDeliveryFromOtherAcc"
}
],
"Version": "2012-10-17"
}
```
Additional examples, including a bucket policy, are here: https://gist.github.com/dialt0ne/137e348c988ed0566e1a7169969bd36c
Discussion on AWS forum here:
https://forums.aws.amazon.com/message.jspa?messageID=732288
##### EXPECTED RESULTS
If the bucket policy is not different, it should not result in a change.
##### ACTUAL RESULTS
The policy is set every time.
| True | s3_bucket with policy parameter not idempotent - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
s3_bucket
##### ANSIBLE VERSION
```
$ ansible --version
ansible 2.0.2.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
```
[defaults]
hash_behaviour = merge
force_color = 1
retry_files_enabled = 0
```
##### OS / ENVIRONMENT
```
Linux dacec3077cb7 4.4.8-boot2docker #1 SMP Mon Apr 25 21:57:27 UTC 2016 x86_64 x86_64 x86_64 GNU/Linux
```
##### SUMMARY
When specifying a `policy` parameter to the `s3_bucket` module and a list of AWS principals are included in the policy, the task is always updating the bucket policy because AWS does not return an ordered list.
##### STEPS TO REPRODUCE
Just run a task for the `s3_bucket` module that updates the policy. It will change every time regardless whether the policy is different or not.
```
$ cat logbucket.yml
---
- hosts: localhost
connection: local
vars:
log_bucket:
bucket_name: atonns_ctg_test
tasks:
- name: Log Bucket | Create bucket and set permissions for {{ log_bucket.bucket_name }}
s3_bucket:
name: "{{ log_bucket.bucket_name }}"
state: present
policy: "{{ lookup('file', 'policy.json', convert_data=False) }}"
$ cat hosts
[local]
localhost ansible_connection=local
$ ansible-playbook -i hosts logbucket.yml
PLAY [localhost] ***************************************************************
TASK [setup] *******************************************************************
ok: [localhost]
TASK [Log Bucket | Create bucket and set permissions for atonns_ctg_test] ******
changed: [localhost]
PLAY RECAP *********************************************************************
localhost : ok=2 changed=1 unreachable=0 failed=0
$ ansible-playbook -i hosts logbucket.yml
PLAY [localhost] ***************************************************************
TASK [setup] *******************************************************************
ok: [localhost]
TASK [Log Bucket | Create bucket and set permissions for atonns_ctg_test] ******
changed: [localhost]
PLAY RECAP *********************************************************************
localhost : ok=2 changed=1 unreachable=0 failed=0
$ cat policy.json
{
"Statement": [
{
"Action": "s3:PutObject",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::127311923021:root",
"arn:aws:iam::027434742980:root",
"arn:aws:iam::797873946194:root",
"arn:aws:iam::156460612806:root",
"arn:aws:iam::054676820928:root",
"arn:aws:iam::582318560864:root",
"arn:aws:iam::600734575887:root",
"arn:aws:iam::114774131450:root",
"arn:aws:iam::783225319266:root",
"arn:aws:iam::718504428378:root",
"arn:aws:iam::507241528517:root"
]
},
"Resource": "arn:aws:s3:::atonns_ctg_test/*",
"Sid": "AllowLogDeliveryFromOtherAcc"
}
],
"Version": "2012-10-17"
}
```
Additional examples, including a bucket policy, are here: https://gist.github.com/dialt0ne/137e348c988ed0566e1a7169969bd36c
Discussion on AWS forum here:
https://forums.aws.amazon.com/message.jspa?messageID=732288
##### EXPECTED RESULTS
If the bucket policy is not different, it should not result in a change.
##### ACTUAL RESULTS
The policy is set every time.
| main | bucket with policy parameter not idempotent issue type bug report component name bucket ansible version ansible version ansible config file etc ansible ansible cfg configured module search path default w o overrides configuration hash behaviour merge force color retry files enabled os environment linux smp mon apr utc gnu linux summary when specifying a policy parameter to the bucket module and a list of aws principals are included in the policy the task is always updating the bucket policy because aws does not return an ordered list steps to reproduce just run a task for the bucket module that updates the policy it will change every time regardless whether the policy is different or not cat logbucket yml hosts localhost connection local vars log bucket bucket name atonns ctg test tasks name log bucket create bucket and set permissions for log bucket bucket name bucket name log bucket bucket name state present policy lookup file policy json convert data false cat hosts localhost ansible connection local ansible playbook i hosts logbucket yml play task ok task changed play recap localhost ok changed unreachable failed ansible playbook i hosts logbucket yml play task ok task changed play recap localhost ok changed unreachable failed cat policy json statement action putobject effect allow principal aws arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root arn aws iam root resource arn aws atonns ctg test sid allowlogdeliveryfromotheracc version additional examples including a bucket policy are here discussion on aws forum here expected results if the bucket policy is not different it should not result in a change actual results the policy is set every time | 1 |
522,122 | 15,158,025,419 | IssuesEvent | 2021-02-12 00:09:38 | NOAA-GSL/MATS | https://api.github.com/repos/NOAA-GSL/MATS | closed | Anomalycor app not reflecting the new levels available since Jeff switched us over to MET data | Priority: High Project: MATS Status: Closed Type: Task | ---
Author Name: **molly.b.smith** (@mollybsmith-noaa)
Original Redmine Issue: 55915, https://vlab.ncep.noaa.gov/redmine/issues/55915
Original Date: 2018-10-04
Original Assignee: molly.b.smith
---
The anomaly correlation app is showing only the levels associated with our old data ingest (850/250 mb for wind, 500 mb for height), but now that Jeff moved us over to MET data-based ingest, we have way more levels available. The levels option selector needs to reflect this.
| 1.0 | Anomalycor app not reflecting the new levels available since Jeff switched us over to MET data - ---
Author Name: **molly.b.smith** (@mollybsmith-noaa)
Original Redmine Issue: 55915, https://vlab.ncep.noaa.gov/redmine/issues/55915
Original Date: 2018-10-04
Original Assignee: molly.b.smith
---
The anomaly correlation app is showing only the levels associated with our old data ingest (850/250 mb for wind, 500 mb for height), but now that Jeff moved us over to MET data-based ingest, we have way more levels available. The levels option selector needs to reflect this.
| non_main | anomalycor app not reflecting the new levels available since jeff switched us over to met data author name molly b smith mollybsmith noaa original redmine issue original date original assignee molly b smith the anomaly correlation app is showing only the levels associated with our old data ingest mb for wind mb for height but now that jeff moved us over to met data based ingest we have way more levels available the levels option selector needs to reflect this | 0 |
300,648 | 25,983,982,180 | IssuesEvent | 2022-12-19 21:41:06 | ita-social-projects/EventsExpress | https://api.github.com/repos/ita-social-projects/EventsExpress | opened | Verify that the user is able to filter events by any period of dates using a "Calender' date picker | test case | **Date Time**
12-19-2022
**Priority**
Medium
**Description**
The test case verifies that the user is able to filter events by any period of dates using a "Calender' date picker.
**Pre-requisites**
Steps to be fulfilled before test:
1. Move to https://eventsexpress-test.azurewebsites.net/
2. The user is logged on a system (Username = 'User1', Password = 'Pass1')
3. The user is on the "My Events" page
4. The event creation functionality is implemented
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1 | Click the 'Filters' button in the top right corner | <br> | The list with filters is displayed | <br> | <br> | <br> |
| 2 | Click the filter "Calendar" | <br> | The calendar is displayed visually on the left. he options of the date periods are displayed from the right | <br> | <br> | <br> |
| 3 | Сhoose the start date of the event | 01-09-23 | Selected date is highlighted in a different color on the calendar | <br> | <br> | <br> |
| 4 | Сhoose the end date of the event | 01-19-23 | Selected date is highlighted in a different color on the calendar | <br> | <br> | <br> |
| 5 | Click the 'Apply' button | <br> | The system filters and shows the events list in the appropriate date periods | <br> | <br> | <br> |
**Screenshots**

**Environment:**
- OS: Win 10
- Browser Google Chrome
- Version 108.0.5359.100
**Additional context**
Add any other context about the test here.
User story links E.g.: "User story #1410 "
Labels to be added "Test case", Priority ("pri: "), Type ("UI, "Functional"), "API" .
| 1.0 | Verify that the user is able to filter events by any period of dates using a "Calender' date picker - **Date Time**
12-19-2022
**Priority**
Medium
**Description**
The test case verifies that the user is able to filter events by any period of dates using a "Calender' date picker.
**Pre-requisites**
Steps to be fulfilled before test:
1. Move to https://eventsexpress-test.azurewebsites.net/
2. The user is logged on a system (Username = 'User1', Password = 'Pass1')
3. The user is on the "My Events" page
4. The event creation functionality is implemented
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1 | Click the 'Filters' button in the top right corner | <br> | The list with filters is displayed | <br> | <br> | <br> |
| 2 | Click the filter "Calendar" | <br> | The calendar is displayed visually on the left. he options of the date periods are displayed from the right | <br> | <br> | <br> |
| 3 | Сhoose the start date of the event | 01-09-23 | Selected date is highlighted in a different color on the calendar | <br> | <br> | <br> |
| 4 | Сhoose the end date of the event | 01-19-23 | Selected date is highlighted in a different color on the calendar | <br> | <br> | <br> |
| 5 | Click the 'Apply' button | <br> | The system filters and shows the events list in the appropriate date periods | <br> | <br> | <br> |
**Screenshots**

**Environment:**
- OS: Win 10
- Browser Google Chrome
- Version 108.0.5359.100
**Additional context**
Add any other context about the test here.
User story links E.g.: "User story #1410 "
Labels to be added "Test case", Priority ("pri: "), Type ("UI, "Functional"), "API" .
| non_main | verify that the user is able to filter events by any period of dates using a calender date picker date time priority medium description the test case verifies that the user is able to filter events by any period of dates using a calender date picker pre requisites steps to be fulfilled before test move to the user is logged on a system username password the user is on the my events page the event creation functionality is implemented test cases s action test data expected result actual result p f automated click the filters button in the top right corner the list with filters is displayed click the filter calendar the calendar is displayed visually on the left he options of the date periods are displayed from the right сhoose the start date of the event selected date is highlighted in a different color on the calendar сhoose the end date of the event selected date is highlighted in a different color on the calendar click the apply button the system filters and shows the events list in the appropriate date periods screenshots environment os win browser google chrome version additional context add any other context about the test here user story links e g user story labels to be added test case priority pri type ui functional api | 0 |
21,006 | 11,046,297,060 | IssuesEvent | 2019-12-09 16:36:23 | NetsBlox/Snap--Build-Your-Own-Blocks | https://api.github.com/repos/NetsBlox/Snap--Build-Your-Own-Blocks | closed | Improve performance of fn serialization/deserialization | performance | Running some of the function serialization tests (w/ custom functions) is very slow.
[fn-ser-profile.zip](https://github.com/NetsBlox/Snap--Build-Your-Own-Blocks/files/3928698/fn-ser-profile.zip)
| True | Improve performance of fn serialization/deserialization - Running some of the function serialization tests (w/ custom functions) is very slow.
[fn-ser-profile.zip](https://github.com/NetsBlox/Snap--Build-Your-Own-Blocks/files/3928698/fn-ser-profile.zip)
| non_main | improve performance of fn serialization deserialization running some of the function serialization tests w custom functions is very slow | 0 |
472,842 | 13,631,878,370 | IssuesEvent | 2020-09-24 18:43:25 | open-telemetry/opentelemetry-go | https://api.github.com/repos/open-telemetry/opentelemetry-go | closed | Update SpanProcessors to be invoked in order they are registered | area:trace help wanted pkg:SDK priority:p3 release:required-for-ga | Currently a TracerProvicer stores known SpanProcessors in a map:
https://github.com/open-telemetry/opentelemetry-go/blob/038f505d12a63d5121e07936981930e20efb0678/sdk/trace/span_processor.go#L46
When a span is started or finished it iterates through the map and invokes the associated method of the SpanProcessor:
https://github.com/open-telemetry/opentelemetry-go/blob/038f505d12a63d5121e07936981930e20efb0678/sdk/trace/tracer.go#L62-L64
https://github.com/open-telemetry/opentelemetry-go/blob/038f505d12a63d5121e07936981930e20efb0678/sdk/trace/span.go#L151-L153
[The specification](https://github.com/open-telemetry/opentelemetry-specification/blob/master/specification/trace/sdk.md#span-processor) specifies this execution to be ordered:
> Span processors can be registered directly on SDK TracerProvider and they are invoked in the same order as they were registered.
Based on [a recent issue](https://github.com/open-telemetry/opentelemetry-go/issues/1174) it was made clear that this hasn't had any real effect because there is no direct linking between registered SpanProcessors. However, we should update the execution model and conform to the specified behaviour so we are compliant.
This will likely require changing the underlying spanProcessorMap type. It will need to still provide getter/setter functionality as the existing map does so the TracerProvider can correctly unregister any SpanProcessor, but it will need to also track order. | 1.0 | Update SpanProcessors to be invoked in order they are registered - Currently a TracerProvicer stores known SpanProcessors in a map:
https://github.com/open-telemetry/opentelemetry-go/blob/038f505d12a63d5121e07936981930e20efb0678/sdk/trace/span_processor.go#L46
When a span is started or finished it iterates through the map and invokes the associated method of the SpanProcessor:
https://github.com/open-telemetry/opentelemetry-go/blob/038f505d12a63d5121e07936981930e20efb0678/sdk/trace/tracer.go#L62-L64
https://github.com/open-telemetry/opentelemetry-go/blob/038f505d12a63d5121e07936981930e20efb0678/sdk/trace/span.go#L151-L153
[The specification](https://github.com/open-telemetry/opentelemetry-specification/blob/master/specification/trace/sdk.md#span-processor) specifies this execution to be ordered:
> Span processors can be registered directly on SDK TracerProvider and they are invoked in the same order as they were registered.
Based on [a recent issue](https://github.com/open-telemetry/opentelemetry-go/issues/1174) it was made clear that this hasn't had any real effect because there is no direct linking between registered SpanProcessors. However, we should update the execution model and conform to the specified behaviour so we are compliant.
This will likely require changing the underlying spanProcessorMap type. It will need to still provide getter/setter functionality as the existing map does so the TracerProvider can correctly unregister any SpanProcessor, but it will need to also track order. | non_main | update spanprocessors to be invoked in order they are registered currently a tracerprovicer stores known spanprocessors in a map when a span is started or finished it iterates through the map and invokes the associated method of the spanprocessor specifies this execution to be ordered span processors can be registered directly on sdk tracerprovider and they are invoked in the same order as they were registered based on it was made clear that this hasn t had any real effect because there is no direct linking between registered spanprocessors however we should update the execution model and conform to the specified behaviour so we are compliant this will likely require changing the underlying spanprocessormap type it will need to still provide getter setter functionality as the existing map does so the tracerprovider can correctly unregister any spanprocessor but it will need to also track order | 0 |
5,837 | 31,017,517,336 | IssuesEvent | 2023-08-10 00:35:04 | bazelbuild/intellij | https://api.github.com/repos/bazelbuild/intellij | opened | `buildifier` run not using proper mechanism to allow to undo | type: bug awaiting-maintainer | ### Description of the bug:
I've made changes to `BUILD` file and `buildifier` triggered automatically.
Then I've realized that I want to Undo and got the following message:
<img width="519" alt="image" src="https://github.com/bazelbuild/intellij/assets/50216138/e597ac61-a0e7-48bd-9e0b-50054fa32e32">
### What's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
1. Edit some `BUILD` file and let `buildifier` to reformat it.
2. Try to Undo
### Which Intellij IDE are you using? Please provide the specific version.
2023.2
### What programming languages and tools are you using? Please provide specific versions.
Java
### What Bazel plugin version are you using?
2023.07.18.0.1
### Have you found anything relevant by searching the web?
_No response_
### Any other information, logs, or outputs that you want to share?
_No response_ | True | `buildifier` run not using proper mechanism to allow to undo - ### Description of the bug:
I've made changes to `BUILD` file and `buildifier` triggered automatically.
Then I've realized that I want to Undo and got the following message:
<img width="519" alt="image" src="https://github.com/bazelbuild/intellij/assets/50216138/e597ac61-a0e7-48bd-9e0b-50054fa32e32">
### What's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
1. Edit some `BUILD` file and let `buildifier` to reformat it.
2. Try to Undo
### Which Intellij IDE are you using? Please provide the specific version.
2023.2
### What programming languages and tools are you using? Please provide specific versions.
Java
### What Bazel plugin version are you using?
2023.07.18.0.1
### Have you found anything relevant by searching the web?
_No response_
### Any other information, logs, or outputs that you want to share?
_No response_ | main | buildifier run not using proper mechanism to allow to undo description of the bug i ve made changes to build file and buildifier triggered automatically then i ve realized that i want to undo and got the following message img width alt image src what s the simplest easiest way to reproduce this bug please provide a minimal example if possible edit some build file and let buildifier to reformat it try to undo which intellij ide are you using please provide the specific version what programming languages and tools are you using please provide specific versions java what bazel plugin version are you using have you found anything relevant by searching the web no response any other information logs or outputs that you want to share no response | 1 |
3,729 | 15,556,858,197 | IssuesEvent | 2021-03-16 08:24:07 | qiwi-forks/dts-bundle | https://api.github.com/repos/qiwi-forks/dts-bundle | closed | Deps revision | maintainance | ```
warning workspace-aggregator-d5d19ee0-39a1-48f7-a5e7-218ae3c78418 > @qiwi/substrate-infra > @qiwi/libdefkit > @qiwi/dts-bundle > @types/detect-indent@6.0.0: This is a stub types definition. detect-indent provides its own type definitions, so you do not need this installed.
```
| True | Deps revision - ```
warning workspace-aggregator-d5d19ee0-39a1-48f7-a5e7-218ae3c78418 > @qiwi/substrate-infra > @qiwi/libdefkit > @qiwi/dts-bundle > @types/detect-indent@6.0.0: This is a stub types definition. detect-indent provides its own type definitions, so you do not need this installed.
```
| main | deps revision warning workspace aggregator qiwi substrate infra qiwi libdefkit qiwi dts bundle types detect indent this is a stub types definition detect indent provides its own type definitions so you do not need this installed | 1 |
5,277 | 26,671,570,784 | IssuesEvent | 2023-01-26 10:44:25 | beyarkay/eskom-calendar | https://api.github.com/repos/beyarkay/eskom-calendar | closed | Schedule missing for Kwelera, EC | bug waiting-on-maintainer missing-area-schedule | This schedule will have to come from the xlsx spreadsheets available [here](https://www.eskom.co.za/distribution/customer-service/outages/downloadable-loadshedding-spreadsheets-for-eskom-customers/). | True | Schedule missing for Kwelera, EC - This schedule will have to come from the xlsx spreadsheets available [here](https://www.eskom.co.za/distribution/customer-service/outages/downloadable-loadshedding-spreadsheets-for-eskom-customers/). | main | schedule missing for kwelera ec this schedule will have to come from the xlsx spreadsheets available | 1 |
762,074 | 26,707,836,593 | IssuesEvent | 2023-01-27 19:58:00 | crux-toolkit/crux-toolkit | https://api.github.com/repos/crux-toolkit/crux-toolkit | closed | Percolator seg fault during final conversion | bug High priority Percolator | The percolator command given below runs to near-completion but seg faults during the final conversion step. I can run the stand-alone Percolator command on this same input file, and it works fine.
./crux percolator --overwrite T --output-dir ribo search-for-xlinks.pin.tsv
~/proj/crux/trunk/ext/bin/percolator -r ribo/percolator.target.peptides.txt -v 2 -P decoy_ --seed 1 -p 0.01 -n 0 --trainFDR 0.01 --testFDR 0.01 --maxiter 10 -s search-for-xlinks.pin.tsv
Reported by: wsnoble
| 1.0 | Percolator seg fault during final conversion - The percolator command given below runs to near-completion but seg faults during the final conversion step. I can run the stand-alone Percolator command on this same input file, and it works fine.
./crux percolator --overwrite T --output-dir ribo search-for-xlinks.pin.tsv
~/proj/crux/trunk/ext/bin/percolator -r ribo/percolator.target.peptides.txt -v 2 -P decoy_ --seed 1 -p 0.01 -n 0 --trainFDR 0.01 --testFDR 0.01 --maxiter 10 -s search-for-xlinks.pin.tsv
Reported by: wsnoble
| non_main | percolator seg fault during final conversion the percolator command given below runs to near completion but seg faults during the final conversion step i can run the stand alone percolator command on this same input file and it works fine crux percolator overwrite t output dir ribo search for xlinks pin tsv proj crux trunk ext bin percolator r ribo percolator target peptides txt v p decoy seed p n trainfdr testfdr maxiter s search for xlinks pin tsv reported by wsnoble | 0 |
21,725 | 6,208,829,656 | IssuesEvent | 2017-07-07 01:25:12 | ahmedahamid/test | https://api.github.com/repos/ahmedahamid/test | closed | Team Explorer always prompts for CodePlex login | bug CodePlexMigrationInitiated impact: Medium | In both Vista beta 2 and XP SP2, whenever I try to connect to CodePlex it always asks me for my username and password. There's no checkbox for storing the credentials.
To repro: add the codeplex server to the list in Team Explorer.
Close VS 2005.
Start VS 2005. On startup, it'll prompt for the Codeplex username/pass.
There should be a way to make this transprent.
Also, the "regular" username does not work. You must use SND\<username>_cp as the username.
#### Migrated CodePlex Work Item Details
CodePlex Work Item ID: '506'
Vote count: '0'
| 1.0 | Team Explorer always prompts for CodePlex login - In both Vista beta 2 and XP SP2, whenever I try to connect to CodePlex it always asks me for my username and password. There's no checkbox for storing the credentials.
To repro: add the codeplex server to the list in Team Explorer.
Close VS 2005.
Start VS 2005. On startup, it'll prompt for the Codeplex username/pass.
There should be a way to make this transprent.
Also, the "regular" username does not work. You must use SND\<username>_cp as the username.
#### Migrated CodePlex Work Item Details
CodePlex Work Item ID: '506'
Vote count: '0'
| non_main | team explorer always prompts for codeplex login in both vista beta and xp whenever i try to connect to codeplex it always asks me for my username and password there s no checkbox for storing the credentials to repro add the codeplex server to the list in team explorer close vs start vs on startup it ll prompt for the codeplex username pass there should be a way to make this transprent also the regular username does not work you must use snd cp as the username migrated codeplex work item details codeplex work item id vote count | 0 |
209,421 | 7,175,524,807 | IssuesEvent | 2018-01-31 06:03:43 | VoltzEngine-Project/Engine | https://api.github.com/repos/VoltzEngine-Project/Engine | opened | Exploit: Using Packets to generate chunks on server | Confirmed High Priority bug | **Problem**
Seems there is a way to use a few of the packets to generate chunks server side.

**Fix**
Do a reach and chunk is loaded check | 1.0 | Exploit: Using Packets to generate chunks on server - **Problem**
Seems there is a way to use a few of the packets to generate chunks server side.

**Fix**
Do a reach and chunk is loaded check | non_main | exploit using packets to generate chunks on server problem seems there is a way to use a few of the packets to generate chunks server side fix do a reach and chunk is loaded check | 0 |
112,301 | 17,089,536,698 | IssuesEvent | 2021-07-08 15:39:16 | turkdevops/atom | https://api.github.com/repos/turkdevops/atom | opened | CVE-2019-10744 (High) detected in multiple libraries | security vulnerability | ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-2.4.2.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash.merge-3.3.2.tgz</b>, <b>lodash-4.17.10.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: atom/package.json</p>
<p>Path to vulnerable library: atom/node_modules/task-lists/node_modules/lodash/package.json,atom/node_modules/roaster/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- settings-view-0.261.3.tgz (Root Library)
- roaster-1.2.1.tgz
- cheerio-0.15.0.tgz
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /repo-with-submodules/You-Dont-Need-jQuery/package.json</p>
<p>Path to vulnerable library: atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/karma/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/karma-webpack/node_modules/lodash/package.json,atom/packages/line-ending-selector/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/babel-plugin-proto-to-assign/node_modules/lodash/package.json,atom/script/node_modules/babel-plugin-proto-to-assign/node_modules/lodash/package.json,atom/script/vsts/node_modules/publish-release/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/inquirer/node_modules/lodash/package.json,atom/node_modules/lodash/package.json,atom/script/vsts/node_modules/inquirer/node_modules/lodash/package.json,atom/script/node_modules/babel-core/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/babel-eslint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- babel-core-5.8.38.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash.merge-3.3.2.tgz</b></p></summary>
<p>The modern build of lodash’s `_.merge` as a module.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash.merge/-/lodash.merge-3.3.2.tgz">https://registry.npmjs.org/lodash.merge/-/lodash.merge-3.3.2.tgz</a></p>
<p>Path to dependency file: atom/packages/line-ending-selector/package.json</p>
<p>Path to vulnerable library: atom/packages/line-ending-selector/node_modules/lodash.merge/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/lodash.merge/package.json</p>
<p>
Dependency Hierarchy:
- eslint-1.10.3.tgz (Root Library)
- :x: **lodash.merge-3.3.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.10.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz</a></p>
<p>Path to dependency file: atom/script/vsts/package.json</p>
<p>Path to vulnerable library: atom/script/vsts/node_modules/lodash/package.json,atom/packages/welcome/node_modules/lodash/package.json,atom/script/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- async-2.0.1.tgz (Root Library)
- :x: **lodash-4.17.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: atom/script/package.json</p>
<p>Path to vulnerable library: atom/script/node_modules/@babel/traverse/node_modules/lodash/package.json,atom/script/node_modules/table/node_modules/lodash/package.json,atom/script/node_modules/inquirer/node_modules/lodash/package.json,atom/script/node_modules/@babel/generator/node_modules/lodash/package.json,atom/script/node_modules/@babel/types/node_modules/lodash/package.json,atom/script/node_modules/eslint/node_modules/lodash/package.json,atom/script/node_modules/eslint-plugin-import/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- babel-eslint-10.0.1.tgz (Root Library)
- types-7.4.4.tgz
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/atom/commit/0dd3ca131788e5d5aeaf0e095ce6ca46d6df0b9f">0dd3ca131788e5d5aeaf0e095ce6ca46d6df0b9f</a></p>
<p>Found in base branch: <b>electron-upgrade</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-10744 (High) detected in multiple libraries - ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-2.4.2.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash.merge-3.3.2.tgz</b>, <b>lodash-4.17.10.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: atom/package.json</p>
<p>Path to vulnerable library: atom/node_modules/task-lists/node_modules/lodash/package.json,atom/node_modules/roaster/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- settings-view-0.261.3.tgz (Root Library)
- roaster-1.2.1.tgz
- cheerio-0.15.0.tgz
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: /repo-with-submodules/You-Dont-Need-jQuery/package.json</p>
<p>Path to vulnerable library: atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/karma/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/karma-webpack/node_modules/lodash/package.json,atom/packages/line-ending-selector/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/babel-plugin-proto-to-assign/node_modules/lodash/package.json,atom/script/node_modules/babel-plugin-proto-to-assign/node_modules/lodash/package.json,atom/script/vsts/node_modules/publish-release/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/inquirer/node_modules/lodash/package.json,atom/node_modules/lodash/package.json,atom/script/vsts/node_modules/inquirer/node_modules/lodash/package.json,atom/script/node_modules/babel-core/node_modules/lodash/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/babel-eslint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- babel-core-5.8.38.tgz (Root Library)
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash.merge-3.3.2.tgz</b></p></summary>
<p>The modern build of lodash’s `_.merge` as a module.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash.merge/-/lodash.merge-3.3.2.tgz">https://registry.npmjs.org/lodash.merge/-/lodash.merge-3.3.2.tgz</a></p>
<p>Path to dependency file: atom/packages/line-ending-selector/package.json</p>
<p>Path to vulnerable library: atom/packages/line-ending-selector/node_modules/lodash.merge/package.json,atom/spec/fixtures/git/repo-with-submodules/You-Dont-Need-jQuery/node_modules/lodash.merge/package.json</p>
<p>
Dependency Hierarchy:
- eslint-1.10.3.tgz (Root Library)
- :x: **lodash.merge-3.3.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.10.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.10.tgz</a></p>
<p>Path to dependency file: atom/script/vsts/package.json</p>
<p>Path to vulnerable library: atom/script/vsts/node_modules/lodash/package.json,atom/packages/welcome/node_modules/lodash/package.json,atom/script/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- async-2.0.1.tgz (Root Library)
- :x: **lodash-4.17.10.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: atom/script/package.json</p>
<p>Path to vulnerable library: atom/script/node_modules/@babel/traverse/node_modules/lodash/package.json,atom/script/node_modules/table/node_modules/lodash/package.json,atom/script/node_modules/inquirer/node_modules/lodash/package.json,atom/script/node_modules/@babel/generator/node_modules/lodash/package.json,atom/script/node_modules/@babel/types/node_modules/lodash/package.json,atom/script/node_modules/eslint/node_modules/lodash/package.json,atom/script/node_modules/eslint-plugin-import/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- babel-eslint-10.0.1.tgz (Root Library)
- types-7.4.4.tgz
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/atom/commit/0dd3ca131788e5d5aeaf0e095ce6ca46d6df0b9f">0dd3ca131788e5d5aeaf0e095ce6ca46d6df0b9f</a></p>
<p>Found in base branch: <b>electron-upgrade</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-08</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash merge tgz lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file atom package json path to vulnerable library atom node modules task lists node modules lodash package json atom node modules roaster node modules lodash package json dependency hierarchy settings view tgz root library roaster tgz cheerio tgz x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file repo with submodules you dont need jquery package json path to vulnerable library atom spec fixtures git repo with submodules you dont need jquery node modules karma node modules lodash package json atom spec fixtures git repo with submodules you dont need jquery node modules karma webpack node modules lodash package json atom packages line ending selector node modules lodash package json atom spec fixtures git repo with submodules you dont need jquery node modules babel plugin proto to assign node modules lodash package json atom script node modules babel plugin proto to assign node modules lodash package json atom script vsts node modules publish release node modules lodash package json atom spec fixtures git repo with submodules you dont need jquery node modules inquirer node modules lodash package json atom node modules lodash package json atom script vsts node modules inquirer node modules lodash package json atom script node modules babel core node modules lodash package json atom spec fixtures git repo with submodules you dont need jquery node modules babel eslint node modules lodash package json dependency hierarchy babel core tgz root library x lodash tgz vulnerable library lodash merge tgz the modern build of lodash’s merge as a module library home page a href path to dependency file atom packages line ending selector package json path to vulnerable library atom packages line ending selector node modules lodash merge package json atom spec fixtures git repo with submodules you dont need jquery node modules lodash merge package json dependency hierarchy eslint tgz root library x lodash merge tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file atom script vsts package json path to vulnerable library atom script vsts node modules lodash package json atom packages welcome node modules lodash package json atom script node modules lodash package json dependency hierarchy async tgz root library x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file atom script package json path to vulnerable library atom script node modules babel traverse node modules lodash package json atom script node modules table node modules lodash package json atom script node modules inquirer node modules lodash package json atom script node modules babel generator node modules lodash package json atom script node modules babel types node modules lodash package json atom script node modules eslint node modules lodash package json atom script node modules eslint plugin import node modules lodash package json dependency hierarchy babel eslint tgz root library types tgz x lodash tgz vulnerable library found in head commit a href found in base branch electron upgrade vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template step up your open source security game with whitesource | 0 |
238,366 | 18,239,490,488 | IssuesEvent | 2021-10-01 11:07:25 | obophenotype/uberon | https://api.github.com/repos/obophenotype/uberon | closed | Broken Links on UBERON Page | documentation issue | I am using Ontobee occasionally, and I noticed that the link below is broken; it appears that all/most links on the page result in 404 error. Could someone look into this? Thanks and Happy New Year, Sam Smith – Michigan (retired volunteer with Dr. Oliver He’s lab at U of M)
http://uberon.github.io/browse/ontobee.html
| 1.0 | Broken Links on UBERON Page - I am using Ontobee occasionally, and I noticed that the link below is broken; it appears that all/most links on the page result in 404 error. Could someone look into this? Thanks and Happy New Year, Sam Smith – Michigan (retired volunteer with Dr. Oliver He’s lab at U of M)
http://uberon.github.io/browse/ontobee.html
| non_main | broken links on uberon page i am using ontobee occasionally and i noticed that the link below is broken it appears that all most links on the page result in error could someone look into this thanks and happy new year sam smith – michigan retired volunteer with dr oliver he’s lab at u of m | 0 |
3,328 | 12,891,050,254 | IssuesEvent | 2020-07-13 17:02:17 | laminas-api-tools/api-tools-asset-manager | https://api.github.com/repos/laminas-api-tools/api-tools-asset-manager | closed | Broken interface api in composer v1 | Awaiting Maintainer Response Bug | ### Bug Report
| Q | A
|------------ | ------
| Version(s) | 1.3.0
After update to 1.3.0 using `composer update`, I get an error:
```
Fatal error: Uncaught TypeError: Argument 1 passed to Laminas\ApiTools\AssetManager\AssetInstaller::__invoke() must implement interface Composer\Package\PackageInterface, instance of Composer\Installer\PackageEvent given, called in /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/Plugin.php on line 109 and defined in /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/AssetInstaller.php:61
Stack trace:
#0 /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/Plugin.php(109): Laminas\ApiTools\AssetManager\AssetInstaller->__invoke(Object(Composer\Installer\PackageEvent))
#1 /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/Plugin.php(74): Laminas\ApiTools\AssetManager\Plugin->Laminas\ApiTools\AssetManager\{closure}()
#2 [internal function]: Laminas\ApiTools\AssetManager\Plugin->onPostAutoloadDump(Object(Composer\Script\Event))
#3 phar:///usr/local/bin/composer/src/Composer/EventDispatcher/EventDispatcher.php(164): call_user_func(Array, Object(Composer\Script\Event))
#4 phar:///usr/ in /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/AssetInstaller.php on line 61
```
I'm using composer 1.10.7. Looks like introduced in #5
@boesing @weierophinney | True | Broken interface api in composer v1 - ### Bug Report
| Q | A
|------------ | ------
| Version(s) | 1.3.0
After update to 1.3.0 using `composer update`, I get an error:
```
Fatal error: Uncaught TypeError: Argument 1 passed to Laminas\ApiTools\AssetManager\AssetInstaller::__invoke() must implement interface Composer\Package\PackageInterface, instance of Composer\Installer\PackageEvent given, called in /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/Plugin.php on line 109 and defined in /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/AssetInstaller.php:61
Stack trace:
#0 /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/Plugin.php(109): Laminas\ApiTools\AssetManager\AssetInstaller->__invoke(Object(Composer\Installer\PackageEvent))
#1 /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/Plugin.php(74): Laminas\ApiTools\AssetManager\Plugin->Laminas\ApiTools\AssetManager\{closure}()
#2 [internal function]: Laminas\ApiTools\AssetManager\Plugin->onPostAutoloadDump(Object(Composer\Script\Event))
#3 phar:///usr/local/bin/composer/src/Composer/EventDispatcher/EventDispatcher.php(164): call_user_func(Array, Object(Composer\Script\Event))
#4 phar:///usr/ in /var/www/vendor/laminas-api-tools/api-tools-asset-manager/src/AssetInstaller.php on line 61
```
I'm using composer 1.10.7. Looks like introduced in #5
@boesing @weierophinney | main | broken interface api in composer bug report q a version s after update to using composer update i get an error fatal error uncaught typeerror argument passed to laminas apitools assetmanager assetinstaller invoke must implement interface composer package packageinterface instance of composer installer packageevent given called in var www vendor laminas api tools api tools asset manager src plugin php on line and defined in var www vendor laminas api tools api tools asset manager src assetinstaller php stack trace var www vendor laminas api tools api tools asset manager src plugin php laminas apitools assetmanager assetinstaller invoke object composer installer packageevent var www vendor laminas api tools api tools asset manager src plugin php laminas apitools assetmanager plugin laminas apitools assetmanager closure laminas apitools assetmanager plugin onpostautoloaddump object composer script event phar usr local bin composer src composer eventdispatcher eventdispatcher php call user func array object composer script event phar usr in var www vendor laminas api tools api tools asset manager src assetinstaller php on line i m using composer looks like introduced in boesing weierophinney | 1 |
247,531 | 18,857,881,079 | IssuesEvent | 2021-11-12 09:08:16 | pss-coder/pe | https://api.github.com/repos/pss-coder/pe | opened | Technical type specification for email in UG | type.DocumentationBug severity.Low | For general users, they might not know what is a RFC822 specification. It seems quite technical

<!--session: 1636704585877-8b82bb88-bedf-4d7a-ab66-f744764ccb3b-->
<!--Version: Web v3.4.1--> | 1.0 | Technical type specification for email in UG - For general users, they might not know what is a RFC822 specification. It seems quite technical

<!--session: 1636704585877-8b82bb88-bedf-4d7a-ab66-f744764ccb3b-->
<!--Version: Web v3.4.1--> | non_main | technical type specification for email in ug for general users they might not know what is a specification it seems quite technical | 0 |
164,397 | 13,941,796,043 | IssuesEvent | 2020-10-22 19:58:52 | shish/shimmie2 | https://api.github.com/repos/shish/shimmie2 | closed | Custom Themes, Existing ones | Documentation | I realize that shimmie comes with a few, but does anyone have any information about alternative themes?
Where to find them?
Information on how the CSS relates to the theme and other things you'd want to know if creating your own.
Thanks! | 1.0 | Custom Themes, Existing ones - I realize that shimmie comes with a few, but does anyone have any information about alternative themes?
Where to find them?
Information on how the CSS relates to the theme and other things you'd want to know if creating your own.
Thanks! | non_main | custom themes existing ones i realize that shimmie comes with a few but does anyone have any information about alternative themes where to find them information on how the css relates to the theme and other things you d want to know if creating your own thanks | 0 |
5,141 | 26,205,024,335 | IssuesEvent | 2023-01-03 21:34:30 | bazelbuild/intellij | https://api.github.com/repos/bazelbuild/intellij | closed | Cannot run program "glogin" exception | type: bug product: IntelliJ awaiting-maintainer | Running a plugin built from [source](https://github.com/bazelbuild/intellij/commit/2fb993316fc7708d6a02b75f4a90d81393fc5be2) causes the following exception in the log:
```java
java.io.IOException: Cannot run program "glogin" (in directory "/"): error=2, No such file or directory
at java.lang.ProcessBuilder.start(ProcessBuilder.java:1048)
at com.google.idea.blaze.base.async.process.ExternalTask$ExternalTaskImpl.invokeCommand(ExternalTask.java:250)
at com.google.idea.blaze.base.async.process.ExternalTask$ExternalTaskImpl.lambda$run$0(ExternalTask.java:179)
at com.google.idea.blaze.base.scope.Scope.push(Scope.java:40)
at com.google.idea.blaze.base.async.process.ExternalTask$ExternalTaskImpl.run(ExternalTask.java:172)
at com.google.idea.blaze.base.actions.FileGitHubIssueAction.lambda$static$0(FileGitHubIssueAction.java:65)
at com.intellij.openapi.util.NotNullLazyValue$2.compute(NotNullLazyValue.java:67)
at com.intellij.openapi.util.NotNullLazyValue.getValue(NotNullLazyValue.java:38)
at com.google.idea.blaze.base.actions.FileGitHubIssueAction.updateForBlazeProject(FileGitHubIssueAction.java:74)
at com.google.idea.blaze.base.actions.BlazeProjectAction.update(BlazeProjectAction.java:58)
at com.intellij.openapi.actionSystem.ex.ActionUtil.performDumbAwareUpdate(ActionUtil.java:176)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.doUpdate(ActionUpdater.java:378)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$null$1(ActionUpdater.java:78)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.callAction(ActionUpdater.java:106)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$new$2(ActionUpdater.java:79)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.update(ActionUpdater.java:364)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandGroupChild(ActionUpdater.java:231)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$doExpandActionGroup$19(ActionUpdater.java:215)
at com.intellij.util.containers.ContainerUtil.concat(ContainerUtil.java:1609)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.doExpandActionGroup(ActionUpdater.java:215)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandActionGroup(ActionUpdater.java:139)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandActionGroup(ActionUpdater.java:131)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$expandActionGroupWithTimeout$11(ActionUpdater.java:148)
at com.intellij.openapi.progress.impl.CoreProgressManager.lambda$runProcess$3(CoreProgressManager.java:185)
at com.intellij.openapi.progress.impl.CoreProgressManager.lambda$runProcess$2(CoreProgressManager.java:169)
at com.intellij.openapi.progress.impl.CoreProgressManager.registerIndicatorAndRun(CoreProgressManager.java:591)
at com.intellij.openapi.progress.impl.CoreProgressManager.executeProcessUnderProgress(CoreProgressManager.java:537)
at com.intellij.openapi.progress.impl.ProgressManagerImpl.executeProcessUnderProgress(ProgressManagerImpl.java:59)
at com.intellij.openapi.progress.impl.CoreProgressManager.runProcess(CoreProgressManager.java:156)
at com.intellij.openapi.progress.impl.CoreProgressManager.runProcess(CoreProgressManager.java:185)
at com.intellij.openapi.progress.util.ProgressIndicatorUtils.withTimeout(ProgressIndicatorUtils.java:260)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandActionGroupWithTimeout(ActionUpdater.java:147)
at com.intellij.openapi.actionSystem.impl.Utils.fillMenu(Utils.java:66)
at com.intellij.openapi.actionSystem.impl.ActionMenu.fillMenu(ActionMenu.java:312)
at com.intellij.openapi.actionSystem.impl.ActionMenu$MenuListenerImpl.menuSelected(ActionMenu.java:270)
at javax.swing.JMenu.fireMenuSelected(JMenu.java:1038)
at javax.swing.JMenu$MenuChangeListener.stateChanged(JMenu.java:1118)
at javax.swing.DefaultButtonModel.fireStateChanged(DefaultButtonModel.java:349)
at javax.swing.DefaultButtonModel.setSelected(DefaultButtonModel.java:232)
at javax.swing.JMenu.setSelected(JMenu.java:305)
at com.apple.laf.ScreenMenu$2.run(ScreenMenu.java:135)
at java.awt.event.InvocationEvent.dispatch$$$capture(InvocationEvent.java:301)
at java.awt.event.InvocationEvent.dispatch(InvocationEvent.java)
at java.awt.EventQueue.dispatchEventImpl(EventQueue.java:756)
at java.awt.EventQueue.access$500(EventQueue.java:97)
at java.awt.EventQueue$3.run(EventQueue.java:709)
at java.awt.EventQueue$3.run(EventQueue.java:703)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(ProtectionDomain.java:80)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(ProtectionDomain.java:90)
at java.awt.EventQueue$4.run(EventQueue.java:731)
at java.awt.EventQueue$4.run(EventQueue.java:729)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(ProtectionDomain.java:80)
at java.awt.EventQueue.dispatchEvent(EventQueue.java:728)
at com.intellij.ide.IdeEventQueue.defaultDispatchEvent(IdeEventQueue.java:878)
at com.intellij.ide.IdeEventQueue._dispatchEvent(IdeEventQueue.java:827)
at com.intellij.ide.IdeEventQueue.lambda$dispatchEvent$8(IdeEventQueue.java:466)
at com.intellij.openapi.progress.impl.CoreProgressManager.computePrioritized(CoreProgressManager.java:704)
at com.intellij.ide.IdeEventQueue.dispatchEvent(IdeEventQueue.java:465)
at java.awt.EventDispatchThread.pumpOneEventForFilters(EventDispatchThread.java:201)
at java.awt.EventDispatchThread.pumpEventsForFilter(EventDispatchThread.java:116)
at java.awt.EventDispatchThread.pumpEventsForHierarchy(EventDispatchThread.java:105)
at java.awt.EventDispatchThread.pumpEvents(EventDispatchThread.java:101)
at java.awt.EventDispatchThread.pumpEvents(EventDispatchThread.java:93)
at java.awt.EventDispatchThread.run(EventDispatchThread.java:82)
Caused by: java.io.IOException: error=2, No such file or directory
at java.lang.UNIXProcess.forkAndExec(Native Method)
at java.lang.UNIXProcess.<init>(UNIXProcess.java:247)
at java.lang.ProcessImpl.start(ProcessImpl.java:134)
at java.lang.ProcessBuilder.start(ProcessBuilder.java:1029)
... 65
``` | True | Cannot run program "glogin" exception - Running a plugin built from [source](https://github.com/bazelbuild/intellij/commit/2fb993316fc7708d6a02b75f4a90d81393fc5be2) causes the following exception in the log:
```java
java.io.IOException: Cannot run program "glogin" (in directory "/"): error=2, No such file or directory
at java.lang.ProcessBuilder.start(ProcessBuilder.java:1048)
at com.google.idea.blaze.base.async.process.ExternalTask$ExternalTaskImpl.invokeCommand(ExternalTask.java:250)
at com.google.idea.blaze.base.async.process.ExternalTask$ExternalTaskImpl.lambda$run$0(ExternalTask.java:179)
at com.google.idea.blaze.base.scope.Scope.push(Scope.java:40)
at com.google.idea.blaze.base.async.process.ExternalTask$ExternalTaskImpl.run(ExternalTask.java:172)
at com.google.idea.blaze.base.actions.FileGitHubIssueAction.lambda$static$0(FileGitHubIssueAction.java:65)
at com.intellij.openapi.util.NotNullLazyValue$2.compute(NotNullLazyValue.java:67)
at com.intellij.openapi.util.NotNullLazyValue.getValue(NotNullLazyValue.java:38)
at com.google.idea.blaze.base.actions.FileGitHubIssueAction.updateForBlazeProject(FileGitHubIssueAction.java:74)
at com.google.idea.blaze.base.actions.BlazeProjectAction.update(BlazeProjectAction.java:58)
at com.intellij.openapi.actionSystem.ex.ActionUtil.performDumbAwareUpdate(ActionUtil.java:176)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.doUpdate(ActionUpdater.java:378)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$null$1(ActionUpdater.java:78)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.callAction(ActionUpdater.java:106)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$new$2(ActionUpdater.java:79)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.update(ActionUpdater.java:364)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandGroupChild(ActionUpdater.java:231)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$doExpandActionGroup$19(ActionUpdater.java:215)
at com.intellij.util.containers.ContainerUtil.concat(ContainerUtil.java:1609)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.doExpandActionGroup(ActionUpdater.java:215)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandActionGroup(ActionUpdater.java:139)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandActionGroup(ActionUpdater.java:131)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.lambda$expandActionGroupWithTimeout$11(ActionUpdater.java:148)
at com.intellij.openapi.progress.impl.CoreProgressManager.lambda$runProcess$3(CoreProgressManager.java:185)
at com.intellij.openapi.progress.impl.CoreProgressManager.lambda$runProcess$2(CoreProgressManager.java:169)
at com.intellij.openapi.progress.impl.CoreProgressManager.registerIndicatorAndRun(CoreProgressManager.java:591)
at com.intellij.openapi.progress.impl.CoreProgressManager.executeProcessUnderProgress(CoreProgressManager.java:537)
at com.intellij.openapi.progress.impl.ProgressManagerImpl.executeProcessUnderProgress(ProgressManagerImpl.java:59)
at com.intellij.openapi.progress.impl.CoreProgressManager.runProcess(CoreProgressManager.java:156)
at com.intellij.openapi.progress.impl.CoreProgressManager.runProcess(CoreProgressManager.java:185)
at com.intellij.openapi.progress.util.ProgressIndicatorUtils.withTimeout(ProgressIndicatorUtils.java:260)
at com.intellij.openapi.actionSystem.impl.ActionUpdater.expandActionGroupWithTimeout(ActionUpdater.java:147)
at com.intellij.openapi.actionSystem.impl.Utils.fillMenu(Utils.java:66)
at com.intellij.openapi.actionSystem.impl.ActionMenu.fillMenu(ActionMenu.java:312)
at com.intellij.openapi.actionSystem.impl.ActionMenu$MenuListenerImpl.menuSelected(ActionMenu.java:270)
at javax.swing.JMenu.fireMenuSelected(JMenu.java:1038)
at javax.swing.JMenu$MenuChangeListener.stateChanged(JMenu.java:1118)
at javax.swing.DefaultButtonModel.fireStateChanged(DefaultButtonModel.java:349)
at javax.swing.DefaultButtonModel.setSelected(DefaultButtonModel.java:232)
at javax.swing.JMenu.setSelected(JMenu.java:305)
at com.apple.laf.ScreenMenu$2.run(ScreenMenu.java:135)
at java.awt.event.InvocationEvent.dispatch$$$capture(InvocationEvent.java:301)
at java.awt.event.InvocationEvent.dispatch(InvocationEvent.java)
at java.awt.EventQueue.dispatchEventImpl(EventQueue.java:756)
at java.awt.EventQueue.access$500(EventQueue.java:97)
at java.awt.EventQueue$3.run(EventQueue.java:709)
at java.awt.EventQueue$3.run(EventQueue.java:703)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(ProtectionDomain.java:80)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(ProtectionDomain.java:90)
at java.awt.EventQueue$4.run(EventQueue.java:731)
at java.awt.EventQueue$4.run(EventQueue.java:729)
at java.security.AccessController.doPrivileged(Native Method)
at java.security.ProtectionDomain$JavaSecurityAccessImpl.doIntersectionPrivilege(ProtectionDomain.java:80)
at java.awt.EventQueue.dispatchEvent(EventQueue.java:728)
at com.intellij.ide.IdeEventQueue.defaultDispatchEvent(IdeEventQueue.java:878)
at com.intellij.ide.IdeEventQueue._dispatchEvent(IdeEventQueue.java:827)
at com.intellij.ide.IdeEventQueue.lambda$dispatchEvent$8(IdeEventQueue.java:466)
at com.intellij.openapi.progress.impl.CoreProgressManager.computePrioritized(CoreProgressManager.java:704)
at com.intellij.ide.IdeEventQueue.dispatchEvent(IdeEventQueue.java:465)
at java.awt.EventDispatchThread.pumpOneEventForFilters(EventDispatchThread.java:201)
at java.awt.EventDispatchThread.pumpEventsForFilter(EventDispatchThread.java:116)
at java.awt.EventDispatchThread.pumpEventsForHierarchy(EventDispatchThread.java:105)
at java.awt.EventDispatchThread.pumpEvents(EventDispatchThread.java:101)
at java.awt.EventDispatchThread.pumpEvents(EventDispatchThread.java:93)
at java.awt.EventDispatchThread.run(EventDispatchThread.java:82)
Caused by: java.io.IOException: error=2, No such file or directory
at java.lang.UNIXProcess.forkAndExec(Native Method)
at java.lang.UNIXProcess.<init>(UNIXProcess.java:247)
at java.lang.ProcessImpl.start(ProcessImpl.java:134)
at java.lang.ProcessBuilder.start(ProcessBuilder.java:1029)
... 65
``` | main | cannot run program glogin exception running a plugin built from causes the following exception in the log java java io ioexception cannot run program glogin in directory error no such file or directory at java lang processbuilder start processbuilder java at com google idea blaze base async process externaltask externaltaskimpl invokecommand externaltask java at com google idea blaze base async process externaltask externaltaskimpl lambda run externaltask java at com google idea blaze base scope scope push scope java at com google idea blaze base async process externaltask externaltaskimpl run externaltask java at com google idea blaze base actions filegithubissueaction lambda static filegithubissueaction java at com intellij openapi util notnulllazyvalue compute notnulllazyvalue java at com intellij openapi util notnulllazyvalue getvalue notnulllazyvalue java at com google idea blaze base actions filegithubissueaction updateforblazeproject filegithubissueaction java at com google idea blaze base actions blazeprojectaction update blazeprojectaction java at com intellij openapi actionsystem ex actionutil performdumbawareupdate actionutil java at com intellij openapi actionsystem impl actionupdater doupdate actionupdater java at com intellij openapi actionsystem impl actionupdater lambda null actionupdater java at com intellij openapi actionsystem impl actionupdater callaction actionupdater java at com intellij openapi actionsystem impl actionupdater lambda new actionupdater java at com intellij openapi actionsystem impl actionupdater update actionupdater java at com intellij openapi actionsystem impl actionupdater expandgroupchild actionupdater java at com intellij openapi actionsystem impl actionupdater lambda doexpandactiongroup actionupdater java at com intellij util containers containerutil concat containerutil java at com intellij openapi actionsystem impl actionupdater doexpandactiongroup actionupdater java at com intellij openapi actionsystem impl actionupdater expandactiongroup actionupdater java at com intellij openapi actionsystem impl actionupdater expandactiongroup actionupdater java at com intellij openapi actionsystem impl actionupdater lambda expandactiongroupwithtimeout actionupdater java at com intellij openapi progress impl coreprogressmanager lambda runprocess coreprogressmanager java at com intellij openapi progress impl coreprogressmanager lambda runprocess coreprogressmanager java at com intellij openapi progress impl coreprogressmanager registerindicatorandrun coreprogressmanager java at com intellij openapi progress impl coreprogressmanager executeprocessunderprogress coreprogressmanager java at com intellij openapi progress impl progressmanagerimpl executeprocessunderprogress progressmanagerimpl java at com intellij openapi progress impl coreprogressmanager runprocess coreprogressmanager java at com intellij openapi progress impl coreprogressmanager runprocess coreprogressmanager java at com intellij openapi progress util progressindicatorutils withtimeout progressindicatorutils java at com intellij openapi actionsystem impl actionupdater expandactiongroupwithtimeout actionupdater java at com intellij openapi actionsystem impl utils fillmenu utils java at com intellij openapi actionsystem impl actionmenu fillmenu actionmenu java at com intellij openapi actionsystem impl actionmenu menulistenerimpl menuselected actionmenu java at javax swing jmenu firemenuselected jmenu java at javax swing jmenu menuchangelistener statechanged jmenu java at javax swing defaultbuttonmodel firestatechanged defaultbuttonmodel java at javax swing defaultbuttonmodel setselected defaultbuttonmodel java at javax swing jmenu setselected jmenu java at com apple laf screenmenu run screenmenu java at java awt event invocationevent dispatch capture invocationevent java at java awt event invocationevent dispatch invocationevent java at java awt eventqueue dispatcheventimpl eventqueue java at java awt eventqueue access eventqueue java at java awt eventqueue run eventqueue java at java awt eventqueue run eventqueue java at java security accesscontroller doprivileged native method at java security protectiondomain javasecurityaccessimpl dointersectionprivilege protectiondomain java at java security protectiondomain javasecurityaccessimpl dointersectionprivilege protectiondomain java at java awt eventqueue run eventqueue java at java awt eventqueue run eventqueue java at java security accesscontroller doprivileged native method at java security protectiondomain javasecurityaccessimpl dointersectionprivilege protectiondomain java at java awt eventqueue dispatchevent eventqueue java at com intellij ide ideeventqueue defaultdispatchevent ideeventqueue java at com intellij ide ideeventqueue dispatchevent ideeventqueue java at com intellij ide ideeventqueue lambda dispatchevent ideeventqueue java at com intellij openapi progress impl coreprogressmanager computeprioritized coreprogressmanager java at com intellij ide ideeventqueue dispatchevent ideeventqueue java at java awt eventdispatchthread pumponeeventforfilters eventdispatchthread java at java awt eventdispatchthread pumpeventsforfilter eventdispatchthread java at java awt eventdispatchthread pumpeventsforhierarchy eventdispatchthread java at java awt eventdispatchthread pumpevents eventdispatchthread java at java awt eventdispatchthread pumpevents eventdispatchthread java at java awt eventdispatchthread run eventdispatchthread java caused by java io ioexception error no such file or directory at java lang unixprocess forkandexec native method at java lang unixprocess unixprocess java at java lang processimpl start processimpl java at java lang processbuilder start processbuilder java | 1 |
530,977 | 15,438,867,704 | IssuesEvent | 2021-03-07 21:59:26 | iv-org/invidious | https://api.github.com/repos/iv-org/invidious | closed | [Bug] "Failed to resolve dependencies" when updating | bug priority:high type:server-side | <!-- Please use the search function to check if the bug you found has already been reported by someone else -->
<!-- If you want to suggest a new feature please use "Feature request" instead -->
<!-- If you want to suggest an enhancement to an existing feature please use "Enhancement" instead -->
**Describe the bug**
"Failed to resolve dependencies" is displayed when updating, even though Crystal 0.36 is indeed installed.
<!-- A clear and concise description of what the bug is. -->
**Steps to Reproduce**
<!-- Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
-->
Update to latest master
**Logs**
<!-- If applicable, copy the log that appear in the browser page where the error is reported. -->
```
Unable to satisfy the following requirements:
- `crystal (>= 0.35.0, < 2.0.0)` required by `pg 0.23.1`
- `crystal (>= 0.35.0, < 2.0.0)` required by `sqlite3 0.18.0`
- `crystal (~> 0.35, >= 0.35.0)` required by `kemal 0.27.0`
- `crystal (< 1.0.0)` required by `pool 0.2.3`
- `crystal (~> 0.34, >= 0.34.0)` required by `protodec 0.1.3`
- `crystal (~> 0.36, >= 0.36.1)` required by `lsquic 2.23.1`
- `crystal (~> 0.35, >= 0.35.0)` required by `db 0.10.0`
- `crystal (< 1.0.0)` required by `radix 0.3.9`
Failed to resolve dependencies, try updating incompatible shards or use --ignore-crystal-version as a workaround if no update is available.
```
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
N/A
**Additional context**
<!-- Add any other context about the problem here.
- Browser (if applicable):
- OS (if applicable):
-->
Crystal 0.36 is installed:
```
# crystal --version
Crystal 0.36.0 (2021-01-26)
```
Any idea @saltycrys ?
| 1.0 | [Bug] "Failed to resolve dependencies" when updating - <!-- Please use the search function to check if the bug you found has already been reported by someone else -->
<!-- If you want to suggest a new feature please use "Feature request" instead -->
<!-- If you want to suggest an enhancement to an existing feature please use "Enhancement" instead -->
**Describe the bug**
"Failed to resolve dependencies" is displayed when updating, even though Crystal 0.36 is indeed installed.
<!-- A clear and concise description of what the bug is. -->
**Steps to Reproduce**
<!-- Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
-->
Update to latest master
**Logs**
<!-- If applicable, copy the log that appear in the browser page where the error is reported. -->
```
Unable to satisfy the following requirements:
- `crystal (>= 0.35.0, < 2.0.0)` required by `pg 0.23.1`
- `crystal (>= 0.35.0, < 2.0.0)` required by `sqlite3 0.18.0`
- `crystal (~> 0.35, >= 0.35.0)` required by `kemal 0.27.0`
- `crystal (< 1.0.0)` required by `pool 0.2.3`
- `crystal (~> 0.34, >= 0.34.0)` required by `protodec 0.1.3`
- `crystal (~> 0.36, >= 0.36.1)` required by `lsquic 2.23.1`
- `crystal (~> 0.35, >= 0.35.0)` required by `db 0.10.0`
- `crystal (< 1.0.0)` required by `radix 0.3.9`
Failed to resolve dependencies, try updating incompatible shards or use --ignore-crystal-version as a workaround if no update is available.
```
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->
N/A
**Additional context**
<!-- Add any other context about the problem here.
- Browser (if applicable):
- OS (if applicable):
-->
Crystal 0.36 is installed:
```
# crystal --version
Crystal 0.36.0 (2021-01-26)
```
Any idea @saltycrys ?
| non_main | failed to resolve dependencies when updating describe the bug failed to resolve dependencies is displayed when updating even though crystal is indeed installed steps to reproduce steps to reproduce the behavior go to click on scroll down to see error update to latest master logs unable to satisfy the following requirements crystal required by pg crystal required by crystal required by kemal crystal required by pool crystal required by protodec crystal required by lsquic crystal required by db crystal required by radix failed to resolve dependencies try updating incompatible shards or use ignore crystal version as a workaround if no update is available screenshots n a additional context add any other context about the problem here browser if applicable os if applicable crystal is installed crystal version crystal any idea saltycrys | 0 |
3,592 | 14,499,418,481 | IssuesEvent | 2020-12-11 16:41:45 | adda-team/adda | https://api.github.com/repos/adda-team/adda | opened | Update documentation for 1.4 | maintainability pri-Critical task | Finish update of [CodeDesign](../wiki/CodeDesign) and [InstructionCommitters](../wiki/InstructionCommitters) shortly after 1.4 version is released. | True | Update documentation for 1.4 - Finish update of [CodeDesign](../wiki/CodeDesign) and [InstructionCommitters](../wiki/InstructionCommitters) shortly after 1.4 version is released. | main | update documentation for finish update of wiki codedesign and wiki instructioncommitters shortly after version is released | 1 |
50,043 | 21,002,197,383 | IssuesEvent | 2022-03-29 18:35:50 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | [BUG] Task order ETL fails with unexpected null values | Workgroup: AMD Type: Bug Report Service: Dev Product: Moped Product: AMD Data Tracker | Our task orders DB view was updated to include task orders from dept `6000`, and~10 of these new task orders unexpectedly have null values for `TASK_ORDER_STATUS` and `TASK_ORDER_DESC`.
I searched eCapris and the Controller's office for such task orders, and they are no where to be found. I think it's safe to assume these task orders were cancelled/not intended for use by anyone.
I've reached out to eCapris Help to ask them to exclude these task orders, and I will also patch [our ETL](https://github.com/cityofaustin/atd-finance-data/blob/production/s3_to_knack.py) to handle this edge case.
```
[2022-03-28 04:21:28,789] {{docker_operator.py:242}} INFO - File "/app/s3_to_knack.py", line 103, in handle_records
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO - mapped_records = [create_mapped_record(rec_current, field_map, app_name) for rec_current in records_current]
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO - File "/app/s3_to_knack.py", line 103, in <listcomp>
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO - mapped_records = [create_mapped_record(rec_current, field_map, app_name) for rec_current in records_current]
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO - File "/app/s3_to_knack.py", line 82, in create_mapped_record
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO - mapped_record[field[app_name]] = val if not handler_func else handler_func(val)
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO - File "/app/config.py", line 16, in pad_angle_brackets
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,793] {{docker_operator.py:242}} INFO - return value.replace(">", " > ").replace("<", " < ")
``` | 1.0 | [BUG] Task order ETL fails with unexpected null values - Our task orders DB view was updated to include task orders from dept `6000`, and~10 of these new task orders unexpectedly have null values for `TASK_ORDER_STATUS` and `TASK_ORDER_DESC`.
I searched eCapris and the Controller's office for such task orders, and they are no where to be found. I think it's safe to assume these task orders were cancelled/not intended for use by anyone.
I've reached out to eCapris Help to ask them to exclude these task orders, and I will also patch [our ETL](https://github.com/cityofaustin/atd-finance-data/blob/production/s3_to_knack.py) to handle this edge case.
```
[2022-03-28 04:21:28,789] {{docker_operator.py:242}} INFO - File "/app/s3_to_knack.py", line 103, in handle_records
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO - mapped_records = [create_mapped_record(rec_current, field_map, app_name) for rec_current in records_current]
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,790] {{docker_operator.py:242}} INFO - File "/app/s3_to_knack.py", line 103, in <listcomp>
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO - mapped_records = [create_mapped_record(rec_current, field_map, app_name) for rec_current in records_current]
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,791] {{docker_operator.py:242}} INFO - File "/app/s3_to_knack.py", line 82, in create_mapped_record
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO - mapped_record[field[app_name]] = val if not handler_func else handler_func(val)
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO - File "/app/config.py", line 16, in pad_angle_brackets
[2022-03-28 04:21:28,792] {{docker_operator.py:242}} INFO -
[2022-03-28 04:21:28,793] {{docker_operator.py:242}} INFO - return value.replace(">", " > ").replace("<", " < ")
``` | non_main | task order etl fails with unexpected null values our task orders db view was updated to include task orders from dept and of these new task orders unexpectedly have null values for task order status and task order desc i searched ecapris and the controller s office for such task orders and they are no where to be found i think it s safe to assume these task orders were cancelled not intended for use by anyone i ve reached out to ecapris help to ask them to exclude these task orders and i will also patch to handle this edge case docker operator py info file app to knack py line in handle records docker operator py info docker operator py info mapped records docker operator py info docker operator py info file app to knack py line in docker operator py info docker operator py info mapped records docker operator py info docker operator py info file app to knack py line in create mapped record docker operator py info docker operator py info mapped record val if not handler func else handler func val docker operator py info docker operator py info file app config py line in pad angle brackets docker operator py info docker operator py info return value replace replace | 0 |
5,047 | 25,866,653,520 | IssuesEvent | 2022-12-13 21:32:50 | backdrop-ops/contrib | https://api.github.com/repos/backdrop-ops/contrib | closed | Maintainer change request: Add klonos to Diff project | Maintainer change request | I'm filing this on behalf of @klonos to get Diff module maintained again. He applied for maintainership over a year ago with no response.
Please note the procedure to add a new maintainer to a project:
1. Please join the Backdrop Contrib group (if you have not already) by
submitting an application **done**
2. File an issue in the current project's issue queue offering to help maintain
that project. **done**
3. Create a PR for that project that adds your name to the README.md file in
the list of maintainers. **done**
4. If the project does not have a listed maintainer, or if a current maintainer
does not respond within 2 weeks, create *this issue* to take over the project. **Over 1 year with no response**
**Please include a link to the issue you filed for the project.**
https://github.com/backdrop-contrib/diff/issues/18
**Please include a link to the PR that adds your name to the README.md file.**
https://github.com/backdrop-contrib/diff/pull/22
<!-- After confirming the project has been abandoned for a period of 2 weeks or
more, a Backdrop Contrib administrator will add your name to the list of
maintainers in that project's README.md file, and grant you admin access to the
project. -->
| True | Maintainer change request: Add klonos to Diff project - I'm filing this on behalf of @klonos to get Diff module maintained again. He applied for maintainership over a year ago with no response.
Please note the procedure to add a new maintainer to a project:
1. Please join the Backdrop Contrib group (if you have not already) by
submitting an application **done**
2. File an issue in the current project's issue queue offering to help maintain
that project. **done**
3. Create a PR for that project that adds your name to the README.md file in
the list of maintainers. **done**
4. If the project does not have a listed maintainer, or if a current maintainer
does not respond within 2 weeks, create *this issue* to take over the project. **Over 1 year with no response**
**Please include a link to the issue you filed for the project.**
https://github.com/backdrop-contrib/diff/issues/18
**Please include a link to the PR that adds your name to the README.md file.**
https://github.com/backdrop-contrib/diff/pull/22
<!-- After confirming the project has been abandoned for a period of 2 weeks or
more, a Backdrop Contrib administrator will add your name to the list of
maintainers in that project's README.md file, and grant you admin access to the
project. -->
| main | maintainer change request add klonos to diff project i m filing this on behalf of klonos to get diff module maintained again he applied for maintainership over a year ago with no response please note the procedure to add a new maintainer to a project please join the backdrop contrib group if you have not already by submitting an application done file an issue in the current project s issue queue offering to help maintain that project done create a pr for that project that adds your name to the readme md file in the list of maintainers done if the project does not have a listed maintainer or if a current maintainer does not respond within weeks create this issue to take over the project over year with no response please include a link to the issue you filed for the project please include a link to the pr that adds your name to the readme md file after confirming the project has been abandoned for a period of weeks or more a backdrop contrib administrator will add your name to the list of maintainers in that project s readme md file and grant you admin access to the project | 1 |
2,961 | 10,616,911,824 | IssuesEvent | 2019-10-12 15:18:06 | arcticicestudio/snowsaw | https://api.github.com/repos/arcticicestudio/snowsaw | closed | Development dependency global installation workaround | context-workflow scope-compatibility scope-dx scope-maintainability type-improvement | The workaround implemented in #82 (PR #85) worked fine, but due to the explicitly disabled _module_ mode it is not possible to define pinned dependency versions but only using the normal `go get` behavior to build the repositories default branch.
A better workaround is to run the `go get` command for development & build dependencies/packages outside of the project's root directory. Therefore the `go.mod` file is not in scope for the `go get` command and is therefore not updated. In order to use pinned versions the `GO1111MODULE=on` environment variable must be explicitly set when running the `go get` command.
See https://github.com/golang/go/issues/30515 for more details and proposed solutions that might be added to Go's build tools in future versions. | True | Development dependency global installation workaround - The workaround implemented in #82 (PR #85) worked fine, but due to the explicitly disabled _module_ mode it is not possible to define pinned dependency versions but only using the normal `go get` behavior to build the repositories default branch.
A better workaround is to run the `go get` command for development & build dependencies/packages outside of the project's root directory. Therefore the `go.mod` file is not in scope for the `go get` command and is therefore not updated. In order to use pinned versions the `GO1111MODULE=on` environment variable must be explicitly set when running the `go get` command.
See https://github.com/golang/go/issues/30515 for more details and proposed solutions that might be added to Go's build tools in future versions. | main | development dependency global installation workaround the workaround implemented in pr worked fine but due to the explicitly disabled module mode it is not possible to define pinned dependency versions but only using the normal go get behavior to build the repositories default branch a better workaround is to run the go get command for development build dependencies packages outside of the project s root directory therefore the go mod file is not in scope for the go get command and is therefore not updated in order to use pinned versions the on environment variable must be explicitly set when running the go get command see for more details and proposed solutions that might be added to go s build tools in future versions | 1 |
59,843 | 24,897,091,009 | IssuesEvent | 2022-10-28 16:50:37 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Reporting: Failing test: X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/bwc_generation_urls·ts - Reporting APIs BWC report generation urls 6_2 multiple jobs posted | loe:hours failed-test Team:AppServicesSv impact:low | A test failed on a tracked branch
```
Error: expected 500 to equal 200
at Assertion.assert (/dev/shm/workspace/parallel/2/kibana/packages/kbn-expect/expect.js:100:11)
at Assertion.be.Assertion.equal (/dev/shm/workspace/parallel/2/kibana/packages/kbn-expect/expect.js:227:8)
at Assertion.be (/dev/shm/workspace/parallel/2/kibana/packages/kbn-expect/expect.js:69:22)
at Object.waitForJobToFinish (test/reporting_api_integration/services.ts:76:29)
at /dev/shm/workspace/parallel/2/kibana/x-pack/test/reporting_api_integration/services.ts:82:11
at async Promise.all (index 0)
at Object.expectAllJobsToFinishSuccessfully (test/reporting_api_integration/services.ts:80:7)
at Context.<anonymous> (test/reporting_api_integration/reporting_and_security/bwc_generation_urls.ts:47:9)
at Object.apply (/dev/shm/workspace/parallel/2/kibana/packages/kbn-test/src/functional_test_runner/lib/mocha/wrap_function.js:73:16)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/12276/)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/bwc_generation_urls·ts","test.name":"Reporting APIs BWC report generation urls 6_2 multiple jobs posted","test.failCount":6}} --> | 1.0 | Reporting: Failing test: X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/bwc_generation_urls·ts - Reporting APIs BWC report generation urls 6_2 multiple jobs posted - A test failed on a tracked branch
```
Error: expected 500 to equal 200
at Assertion.assert (/dev/shm/workspace/parallel/2/kibana/packages/kbn-expect/expect.js:100:11)
at Assertion.be.Assertion.equal (/dev/shm/workspace/parallel/2/kibana/packages/kbn-expect/expect.js:227:8)
at Assertion.be (/dev/shm/workspace/parallel/2/kibana/packages/kbn-expect/expect.js:69:22)
at Object.waitForJobToFinish (test/reporting_api_integration/services.ts:76:29)
at /dev/shm/workspace/parallel/2/kibana/x-pack/test/reporting_api_integration/services.ts:82:11
at async Promise.all (index 0)
at Object.expectAllJobsToFinishSuccessfully (test/reporting_api_integration/services.ts:80:7)
at Context.<anonymous> (test/reporting_api_integration/reporting_and_security/bwc_generation_urls.ts:47:9)
at Object.apply (/dev/shm/workspace/parallel/2/kibana/packages/kbn-test/src/functional_test_runner/lib/mocha/wrap_function.js:73:16)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/12276/)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Reporting API Integration Tests.x-pack/test/reporting_api_integration/reporting_and_security/bwc_generation_urls·ts","test.name":"Reporting APIs BWC report generation urls 6_2 multiple jobs posted","test.failCount":6}} --> | non_main | reporting failing test x pack reporting api integration tests x pack test reporting api integration reporting and security bwc generation urls·ts reporting apis bwc report generation urls multiple jobs posted a test failed on a tracked branch error expected to equal at assertion assert dev shm workspace parallel kibana packages kbn expect expect js at assertion be assertion equal dev shm workspace parallel kibana packages kbn expect expect js at assertion be dev shm workspace parallel kibana packages kbn expect expect js at object waitforjobtofinish test reporting api integration services ts at dev shm workspace parallel kibana x pack test reporting api integration services ts at async promise all index at object expectalljobstofinishsuccessfully test reporting api integration services ts at context test reporting api integration reporting and security bwc generation urls ts at object apply dev shm workspace parallel kibana packages kbn test src functional test runner lib mocha wrap function js first failure | 0 |
4,522 | 23,520,801,887 | IssuesEvent | 2022-08-19 05:33:28 | rustsec/advisory-db | https://api.github.com/repos/rustsec/advisory-db | closed | interledger-rs Unmaintained & Username comparison | Unmaintained | **Following-Up from here re:unicase**
https://github.com/rustsec/advisory-db/pull/1176
https://github.com/interledger-rs/interledger-rs/pull/744
**Crates**
interledger - 2,962 downloads - over 2 years ago - crates.io: 0.6.0, github: 1.0.0 (commit 3 years ago)
ilp-cli - 665 downloads - over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (8 months ago)
ilp-node - 1,853 - over 2 years ago - crates.io: 0.6.0, github: 1.0.0 (12 months ago)
interledger-api - 2,346 - over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (12 months ago)
interledger-btp - 3,352 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-ccp - 2,743 - over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (12 months ago)
interledger-errors - not published to crates.io
interledger-http - 46,711 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (8 months ago)
interledger-ildcp - 4,878 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-packet - 48,531 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-rates - not published to crates.io
interledger-router - 3,348 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-service-util - 4,070 over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 mohths ago)
interledger-service - 47,405 over 2 yearss ago - crates.io: 0.4.0, github: 1.0.0 (8 months ago)
interledger-settlement - 45,997 over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (12 moths ago)
interledger-spsp - 3,521 over 2 years ago - crates.io 0.4.0, github: 1.0.0 (12 months ago)
interledger-store - not published in crates.io
interledger-sterma - not published in crates.io
interledger - 2,962 over 2 years ago - crates.io: 0.6.0, github: 1.0.0 (3 years ago)
**1 - It seems to me that interledger may be Unmaintained**
Facts:
Last GitHub commit was on 15 Dec 2021
Project future was considered here:
https://github.com/interledger-rs/interledger-rs/issues/652
**Next step:**
I will raise issue in interledger-rs to solicit confirmation whether this should be marked as unmaintained.
Waiting the 90 days.
**2 - It also seems that there is concern around Username comparison**
@amousset has filed an issue
https://github.com/interledger-rs/interledger-rs/pull/744
This seems to affect interledger-service and involves unicase library.
**Next step:**
Solicit feedback from the maintainer(s) as to the vector. | True | interledger-rs Unmaintained & Username comparison - **Following-Up from here re:unicase**
https://github.com/rustsec/advisory-db/pull/1176
https://github.com/interledger-rs/interledger-rs/pull/744
**Crates**
interledger - 2,962 downloads - over 2 years ago - crates.io: 0.6.0, github: 1.0.0 (commit 3 years ago)
ilp-cli - 665 downloads - over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (8 months ago)
ilp-node - 1,853 - over 2 years ago - crates.io: 0.6.0, github: 1.0.0 (12 months ago)
interledger-api - 2,346 - over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (12 months ago)
interledger-btp - 3,352 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-ccp - 2,743 - over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (12 months ago)
interledger-errors - not published to crates.io
interledger-http - 46,711 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (8 months ago)
interledger-ildcp - 4,878 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-packet - 48,531 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-rates - not published to crates.io
interledger-router - 3,348 - over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 months ago)
interledger-service-util - 4,070 over 2 years ago - crates.io: 0.4.0, github: 1.0.0 (12 mohths ago)
interledger-service - 47,405 over 2 yearss ago - crates.io: 0.4.0, github: 1.0.0 (8 months ago)
interledger-settlement - 45,997 over 2 years ago - crates.io: 0.3.0, github: 1.0.0 (12 moths ago)
interledger-spsp - 3,521 over 2 years ago - crates.io 0.4.0, github: 1.0.0 (12 months ago)
interledger-store - not published in crates.io
interledger-sterma - not published in crates.io
interledger - 2,962 over 2 years ago - crates.io: 0.6.0, github: 1.0.0 (3 years ago)
**1 - It seems to me that interledger may be Unmaintained**
Facts:
Last GitHub commit was on 15 Dec 2021
Project future was considered here:
https://github.com/interledger-rs/interledger-rs/issues/652
**Next step:**
I will raise issue in interledger-rs to solicit confirmation whether this should be marked as unmaintained.
Waiting the 90 days.
**2 - It also seems that there is concern around Username comparison**
@amousset has filed an issue
https://github.com/interledger-rs/interledger-rs/pull/744
This seems to affect interledger-service and involves unicase library.
**Next step:**
Solicit feedback from the maintainer(s) as to the vector. | main | interledger rs unmaintained username comparison following up from here re unicase crates interledger downloads over years ago crates io github commit years ago ilp cli downloads over years ago crates io github months ago ilp node over years ago crates io github months ago interledger api over years ago crates io github months ago interledger btp over years ago crates io github months ago interledger ccp over years ago crates io github months ago interledger errors not published to crates io interledger http over years ago crates io github months ago interledger ildcp over years ago crates io github months ago interledger packet over years ago crates io github months ago interledger rates not published to crates io interledger router over years ago crates io github months ago interledger service util over years ago crates io github mohths ago interledger service over yearss ago crates io github months ago interledger settlement over years ago crates io github moths ago interledger spsp over years ago crates io github months ago interledger store not published in crates io interledger sterma not published in crates io interledger over years ago crates io github years ago it seems to me that interledger may be unmaintained facts last github commit was on dec project future was considered here next step i will raise issue in interledger rs to solicit confirmation whether this should be marked as unmaintained waiting the days it also seems that there is concern around username comparison amousset has filed an issue this seems to affect interledger service and involves unicase library next step solicit feedback from the maintainer s as to the vector | 1 |
553,766 | 16,381,673,060 | IssuesEvent | 2021-05-17 04:26:36 | ita-social-projects/TeachUA | https://api.github.com/repos/ita-social-projects/TeachUA | closed | [Звичайний пошук] When a name of a center is entered, the result of the search doesn't contain clubs which refer to this center | Priority: High bug | **Environment:** Windows, Google Chrome 88.0.4324.190 (64-bit).
**Reproducible:** always.
**Build found:** last commit from https://speak-ukrainian.org.ua/dev/clubs
**Steps to reproduce**
1. Go to https://speak-ukrainian.org.ua/dev/
2. Open 'Гуртки' page
3. Enter a name of a center in 'Який гурток шукаєте?' search field (e.g. 'Творчий край', when city is 'Київ')
4. Press 'Enter' button
**Actual result**
Nothing has found
**Expected result**
The result of the search should contain clubs which refer to this center
**User story and test case links**
User story #77
**Labels to be added**
"Bug", Priority ("pri: high"), Severity ("severity: major"), Type ("Functional").
| 1.0 | [Звичайний пошук] When a name of a center is entered, the result of the search doesn't contain clubs which refer to this center - **Environment:** Windows, Google Chrome 88.0.4324.190 (64-bit).
**Reproducible:** always.
**Build found:** last commit from https://speak-ukrainian.org.ua/dev/clubs
**Steps to reproduce**
1. Go to https://speak-ukrainian.org.ua/dev/
2. Open 'Гуртки' page
3. Enter a name of a center in 'Який гурток шукаєте?' search field (e.g. 'Творчий край', when city is 'Київ')
4. Press 'Enter' button
**Actual result**
Nothing has found
**Expected result**
The result of the search should contain clubs which refer to this center
**User story and test case links**
User story #77
**Labels to be added**
"Bug", Priority ("pri: high"), Severity ("severity: major"), Type ("Functional").
| non_main | when a name of a center is entered the result of the search doesn t contain clubs which refer to this center environment windows google chrome bit reproducible always build found last commit from steps to reproduce go to open гуртки page enter a name of a center in який гурток шукаєте search field e g творчий край when city is київ press enter button actual result nothing has found expected result the result of the search should contain clubs which refer to this center user story and test case links user story labels to be added bug priority pri high severity severity major type functional | 0 |
3,754 | 15,788,322,285 | IssuesEvent | 2021-04-01 20:36:36 | carbon-design-system/carbon | https://api.github.com/repos/carbon-design-system/carbon | closed | Enable set data table truncation and text wrap behavior | status: needs triage 🕵️♀️ status: waiting for maintainer response 💬 type: enhancement 💡 | ### Summary
Currently the data table does not start horizontal scrolling until text wraps to three lines.
- Hard for user to mentally and visually process
- No ability for designer and dev to choose settings that make sense for use case
- Table has to become uncomfortable before horizontal scrolling kicks in
- When text truncates today there is no way for user to see full text
CDAI data table team is proposing this change per our discussion with Carbon design in February.
As-Is
<img width="595" alt="Screen Shot 2021-03-03 at 8 42 34 AM" src="https://user-images.githubusercontent.com/39408106/109824132-2524a400-7bfe-11eb-94bd-c39090fed28e.png">
To-Be where table set to 1-line wrap with truncation
<img width="521" alt="Screen Shot 2021-03-03 at 9 10 28 AM" src="https://user-images.githubusercontent.com/39408106/109826531-7e8dd280-7c00-11eb-99ae-400767e48dae.png">
### Justification
See above
### Desired UX and success metrics
1.) A developer can set line wrap/truncation preferences before horizontal scrolling kicks in
2.) A user can focus on table content without getting distracted by crowded 3-line cells
3.) When text is truncated user can view full text via browser tooltip on hover
### "Must have" functionality
- Establish a default setting (ex: 2 line wrap where once 2 lines does not fit, horizontal scroll kicks in)
- Ability for developer to edit those settings
- When text is truncated user can view full text via browser tooltip on hover
Developer should have the following options
- Text wrap: 1 / 2 / 3 lines
- Truncation options
Truncation options would be:
1.) No truncation - Start scroll when text can't fit at text wrap setting (scroll kicks in as soon as content does not fit)
2.) Truncation - Start scroll when text truncation hits X minimum number of characters (so if chose this with 1 line wrap, text will truncate down to x characters before scroll kicks in)
### Specific timeline issues / requests
As soon as possible but preferably during Q2 as CDAI data table responsive behavior depends on this
### Available extra resources
CDAI devs could potentially help code
| True | Enable set data table truncation and text wrap behavior - ### Summary
Currently the data table does not start horizontal scrolling until text wraps to three lines.
- Hard for user to mentally and visually process
- No ability for designer and dev to choose settings that make sense for use case
- Table has to become uncomfortable before horizontal scrolling kicks in
- When text truncates today there is no way for user to see full text
CDAI data table team is proposing this change per our discussion with Carbon design in February.
As-Is
<img width="595" alt="Screen Shot 2021-03-03 at 8 42 34 AM" src="https://user-images.githubusercontent.com/39408106/109824132-2524a400-7bfe-11eb-94bd-c39090fed28e.png">
To-Be where table set to 1-line wrap with truncation
<img width="521" alt="Screen Shot 2021-03-03 at 9 10 28 AM" src="https://user-images.githubusercontent.com/39408106/109826531-7e8dd280-7c00-11eb-99ae-400767e48dae.png">
### Justification
See above
### Desired UX and success metrics
1.) A developer can set line wrap/truncation preferences before horizontal scrolling kicks in
2.) A user can focus on table content without getting distracted by crowded 3-line cells
3.) When text is truncated user can view full text via browser tooltip on hover
### "Must have" functionality
- Establish a default setting (ex: 2 line wrap where once 2 lines does not fit, horizontal scroll kicks in)
- Ability for developer to edit those settings
- When text is truncated user can view full text via browser tooltip on hover
Developer should have the following options
- Text wrap: 1 / 2 / 3 lines
- Truncation options
Truncation options would be:
1.) No truncation - Start scroll when text can't fit at text wrap setting (scroll kicks in as soon as content does not fit)
2.) Truncation - Start scroll when text truncation hits X minimum number of characters (so if chose this with 1 line wrap, text will truncate down to x characters before scroll kicks in)
### Specific timeline issues / requests
As soon as possible but preferably during Q2 as CDAI data table responsive behavior depends on this
### Available extra resources
CDAI devs could potentially help code
| main | enable set data table truncation and text wrap behavior summary currently the data table does not start horizontal scrolling until text wraps to three lines hard for user to mentally and visually process no ability for designer and dev to choose settings that make sense for use case table has to become uncomfortable before horizontal scrolling kicks in when text truncates today there is no way for user to see full text cdai data table team is proposing this change per our discussion with carbon design in february as is img width alt screen shot at am src to be where table set to line wrap with truncation img width alt screen shot at am src justification see above desired ux and success metrics a developer can set line wrap truncation preferences before horizontal scrolling kicks in a user can focus on table content without getting distracted by crowded line cells when text is truncated user can view full text via browser tooltip on hover must have functionality establish a default setting ex line wrap where once lines does not fit horizontal scroll kicks in ability for developer to edit those settings when text is truncated user can view full text via browser tooltip on hover developer should have the following options text wrap lines truncation options truncation options would be no truncation start scroll when text can t fit at text wrap setting scroll kicks in as soon as content does not fit truncation start scroll when text truncation hits x minimum number of characters so if chose this with line wrap text will truncate down to x characters before scroll kicks in specific timeline issues requests as soon as possible but preferably during as cdai data table responsive behavior depends on this available extra resources cdai devs could potentially help code | 1 |
5,505 | 27,487,081,506 | IssuesEvent | 2023-03-04 06:52:56 | keptn/community | https://api.github.com/repos/keptn/community | closed | New Maintainer: @AlexsJones | membership:maintainer community | As a GC member @AlexsJones has been approved as a maintainer with the votes of
+1 @thisthat
+1 @thschue
Checklist:
* [x] Create PR to add @AlexsJones to [MAINTAINERS](https://github.com/keptn/keptn/blob/master/MAINTAINERS)
* [x] Add AlexSJones as maintainer in the CNCF (https://github.com/cncf/foundation/pull/513)
* [x] Merge PR https://github.com/keptn/keptn/pull/9515
* [x] Add @AlexsJones as an owner to the GitHub Organization and to the maintainer group (@thisthat) | True | New Maintainer: @AlexsJones - As a GC member @AlexsJones has been approved as a maintainer with the votes of
+1 @thisthat
+1 @thschue
Checklist:
* [x] Create PR to add @AlexsJones to [MAINTAINERS](https://github.com/keptn/keptn/blob/master/MAINTAINERS)
* [x] Add AlexSJones as maintainer in the CNCF (https://github.com/cncf/foundation/pull/513)
* [x] Merge PR https://github.com/keptn/keptn/pull/9515
* [x] Add @AlexsJones as an owner to the GitHub Organization and to the maintainer group (@thisthat) | main | new maintainer alexsjones as a gc member alexsjones has been approved as a maintainer with the votes of thisthat thschue checklist create pr to add alexsjones to add alexsjones as maintainer in the cncf merge pr add alexsjones as an owner to the github organization and to the maintainer group thisthat | 1 |
341 | 6,802,498,558 | IssuesEvent | 2017-11-02 20:25:35 | jupyterhub/mybinder.org-deploy | https://api.github.com/repos/jupyterhub/mybinder.org-deploy | closed | Separate staging & production/beta clusters | administrative site reliability | Currently they run on the same kubernetes cluster. This means we can't 'test' a lot of cluster related operations (such as kubernetes upgrades or nginx/prometheus upgrades) in a staging cluster before pushing it to beta.
We should instead have two separate clusters with their own copy of support charts for staging and beta/prod.
This is sort of blocked on #43, since that'll allow us to do the switchover in one smooth motion instead of having to do it twice. | True | Separate staging & production/beta clusters - Currently they run on the same kubernetes cluster. This means we can't 'test' a lot of cluster related operations (such as kubernetes upgrades or nginx/prometheus upgrades) in a staging cluster before pushing it to beta.
We should instead have two separate clusters with their own copy of support charts for staging and beta/prod.
This is sort of blocked on #43, since that'll allow us to do the switchover in one smooth motion instead of having to do it twice. | non_main | separate staging production beta clusters currently they run on the same kubernetes cluster this means we can t test a lot of cluster related operations such as kubernetes upgrades or nginx prometheus upgrades in a staging cluster before pushing it to beta we should instead have two separate clusters with their own copy of support charts for staging and beta prod this is sort of blocked on since that ll allow us to do the switchover in one smooth motion instead of having to do it twice | 0 |
2,222 | 7,841,028,079 | IssuesEvent | 2018-06-18 18:15:56 | tgstation/tgstation | https://api.github.com/repos/tgstation/tgstation | closed | Admin ghosts cannot use :p or :d to talk in adminsay or deadsay | Maintainability/Hinders improvements Oversight | It only works if you're in /mob/living. | True | Admin ghosts cannot use :p or :d to talk in adminsay or deadsay - It only works if you're in /mob/living. | main | admin ghosts cannot use p or d to talk in adminsay or deadsay it only works if you re in mob living | 1 |
5,297 | 26,766,215,641 | IssuesEvent | 2023-01-31 10:49:36 | pingcap/docs | https://api.github.com/repos/pingcap/docs | closed | Add `check <cluster-name> <scale-out.yml> --cluster ` option | JIRA-created area/deploy-upgrade-maintain | File: [/release-6.5/tiup/tiup-component-cluster-check.md](https://docs.pingcap.com/tidb/stable/tiup-component-cluster-check)
[TiUP v1.9.0](https://github.com/pingcap/tiup/releases/tag/v1.9.0) supports checking the yaml file before scale out via https://github.com/pingcap/tiup/pull/1659
```
' check <cluster-name> <scale-out.yml> --cluster '
```
Please consider to add this usage to the document because this command is very useful to validate the yaml file before scaling out. | True | Add `check <cluster-name> <scale-out.yml> --cluster ` option - File: [/release-6.5/tiup/tiup-component-cluster-check.md](https://docs.pingcap.com/tidb/stable/tiup-component-cluster-check)
[TiUP v1.9.0](https://github.com/pingcap/tiup/releases/tag/v1.9.0) supports checking the yaml file before scale out via https://github.com/pingcap/tiup/pull/1659
```
' check <cluster-name> <scale-out.yml> --cluster '
```
Please consider to add this usage to the document because this command is very useful to validate the yaml file before scaling out. | main | add check cluster option file supports checking the yaml file before scale out via check cluster please consider to add this usage to the document because this command is very useful to validate the yaml file before scaling out | 1 |
144,298 | 19,286,149,412 | IssuesEvent | 2021-12-11 01:48:15 | snowflakedb/snowflake-hive-metastore-connector | https://api.github.com/repos/snowflakedb/snowflake-hive-metastore-connector | opened | CVE-2021-44228 (High) detected in log4j-core-2.6.2.jar, log4j-1.2.17.jar | security vulnerability | ## CVE-2021-44228 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>log4j-core-2.6.2.jar</b>, <b>log4j-1.2.17.jar</b></p></summary>
<p>
<details><summary><b>log4j-core-2.6.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Path to dependency file: snowflake-hive-metastore-connector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.6.2/log4j-core-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- hive-metastore-2.3.5.jar (Root Library)
- hive-serde-2.3.5.jar
- hive-common-2.3.5.jar
- log4j-1.2-api-2.6.2.jar
- :x: **log4j-core-2.6.2.jar** (Vulnerable Library)
</details>
<details><summary><b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: snowflake-hive-metastore-connector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/log4j/log4j/1.2.17/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- hadoop-common-2.7.7.jar (Root Library)
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Log4j versions prior to 2.15.0 are subject to a remote code execution vulnerability via the ldap JNDI parser.
<p>Publish Date: 2021-11-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228>CVE-2021-44228</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jfh8-c2jp-5v3q">https://github.com/advisories/GHSA-jfh8-c2jp-5v3q</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.15.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.6.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-metastore:2.3.5;org.apache.hive:hive-serde:2.3.5;org.apache.hive:hive-common:2.3.5;org.apache.logging.log4j:log4j-1.2-api:2.6.2;org.apache.logging.log4j:log4j-core:2.6.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.15.0","isBinary":false},{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.17","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hadoop:hadoop-common:2.7.7;log4j:log4j:1.2.17","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.15.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44228","vulnerabilityDetails":"Log4j versions prior to 2.15.0 are subject to a remote code execution vulnerability via the ldap JNDI parser.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-44228 (High) detected in log4j-core-2.6.2.jar, log4j-1.2.17.jar - ## CVE-2021-44228 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>log4j-core-2.6.2.jar</b>, <b>log4j-1.2.17.jar</b></p></summary>
<p>
<details><summary><b>log4j-core-2.6.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Path to dependency file: snowflake-hive-metastore-connector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.6.2/log4j-core-2.6.2.jar</p>
<p>
Dependency Hierarchy:
- hive-metastore-2.3.5.jar (Root Library)
- hive-serde-2.3.5.jar
- hive-common-2.3.5.jar
- log4j-1.2-api-2.6.2.jar
- :x: **log4j-core-2.6.2.jar** (Vulnerable Library)
</details>
<details><summary><b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: snowflake-hive-metastore-connector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/log4j/log4j/1.2.17/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- hadoop-common-2.7.7.jar (Root Library)
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Log4j versions prior to 2.15.0 are subject to a remote code execution vulnerability via the ldap JNDI parser.
<p>Publish Date: 2021-11-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228>CVE-2021-44228</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jfh8-c2jp-5v3q">https://github.com/advisories/GHSA-jfh8-c2jp-5v3q</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.15.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.logging.log4j","packageName":"log4j-core","packageVersion":"2.6.2","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hive:hive-metastore:2.3.5;org.apache.hive:hive-serde:2.3.5;org.apache.hive:hive-common:2.3.5;org.apache.logging.log4j:log4j-1.2-api:2.6.2;org.apache.logging.log4j:log4j-core:2.6.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.15.0","isBinary":false},{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.17","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hadoop:hadoop-common:2.7.7;log4j:log4j:1.2.17","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.logging.log4j:log4j-core:2.15.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-44228","vulnerabilityDetails":"Log4j versions prior to 2.15.0 are subject to a remote code execution vulnerability via the ldap JNDI parser.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44228","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_main | cve high detected in core jar jar cve high severity vulnerability vulnerable libraries core jar jar core jar the apache implementation path to dependency file snowflake hive metastore connector pom xml path to vulnerable library home wss scanner repository org apache logging core core jar dependency hierarchy hive metastore jar root library hive serde jar hive common jar api jar x core jar vulnerable library jar apache path to dependency file snowflake hive metastore connector pom xml path to vulnerable library home wss scanner repository jar dependency hierarchy hadoop common jar root library x jar vulnerable library found in base branch master vulnerability details versions prior to are subject to a remote code execution vulnerability via the ldap jndi parser publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache hive hive metastore org apache hive hive serde org apache hive hive common org apache logging api org apache logging core isminimumfixversionavailable true minimumfixversion org apache logging core isbinary false packagetype java groupid packagename packageversion packagefilepaths istransitivedependency true dependencytree org apache hadoop hadoop common isminimumfixversionavailable true minimumfixversion org apache logging core isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions prior to are subject to a remote code execution vulnerability via the ldap jndi parser vulnerabilityurl | 0 |
38,585 | 19,401,443,177 | IssuesEvent | 2021-12-19 08:51:06 | ARK-Builders/ARK-Navigator | https://api.github.com/repos/ARK-Builders/ARK-Navigator | opened | Cross-platform library for working with tag storage and index | performance level up refactoring | For implementations on other platforms, it is good to have all data formats fixed in code shared among all implementations.
1. Separate the library into separate project, import it in the main project.
2. Convert the code of the library from Kotlin to something native.
If possible, we should use Rust for this.
The library should manage storage parsing and saving.
After implementation of #142 it's possible to move index management into the library as well.
After implementation of #115 it's possible to move previews management into the library. | True | Cross-platform library for working with tag storage and index - For implementations on other platforms, it is good to have all data formats fixed in code shared among all implementations.
1. Separate the library into separate project, import it in the main project.
2. Convert the code of the library from Kotlin to something native.
If possible, we should use Rust for this.
The library should manage storage parsing and saving.
After implementation of #142 it's possible to move index management into the library as well.
After implementation of #115 it's possible to move previews management into the library. | non_main | cross platform library for working with tag storage and index for implementations on other platforms it is good to have all data formats fixed in code shared among all implementations separate the library into separate project import it in the main project convert the code of the library from kotlin to something native if possible we should use rust for this the library should manage storage parsing and saving after implementation of it s possible to move index management into the library as well after implementation of it s possible to move previews management into the library | 0 |
56,245 | 8,058,760,850 | IssuesEvent | 2018-08-02 19:34:13 | apache/incubator-openwhisk-website | https://api.github.com/repos/apache/incubator-openwhisk-website | opened | Revisit Last Three sections on Home Page | content documentation priority: medium | Review and Update last three sections on Home Page:
**Integrate easily with many popular services**
With Apache OpenWhisk you can easily create actions, test, connect to other actions or debug them. Use the Apache OpenWhisk CLI, target your Apache OpenWhisk instance, and run your first action in seconds.
Apache OpenWhisk makes it simple for thousands of developers to integrate with your service. Make it easy for developers to perform actions when something happens in your service, or to send data into your service when things happen somewhere else.
**Combine your functions into rich compositions**
Code in different languages like JavaScript/NodeJS, Swift, Python, Java or run custom logic by packaging code with Docker. Invoke your code synchronously, asynchronously, or on a schedule. Use higher-level programming constructs like sequences to declaratively chain together multiple actions. Use parameter binding to avoid hardcoding service credentials in your code. And also, debug your code in realtime.
**Scaling Per-Request & Optimal Utilization**
Run your action ten thousand times in a fraction of a second, or once a week. Action instances scale to meet demand as needed, then disappear. Enjoy optimal utilization where you don't pay for idle resources. | 1.0 | Revisit Last Three sections on Home Page - Review and Update last three sections on Home Page:
**Integrate easily with many popular services**
With Apache OpenWhisk you can easily create actions, test, connect to other actions or debug them. Use the Apache OpenWhisk CLI, target your Apache OpenWhisk instance, and run your first action in seconds.
Apache OpenWhisk makes it simple for thousands of developers to integrate with your service. Make it easy for developers to perform actions when something happens in your service, or to send data into your service when things happen somewhere else.
**Combine your functions into rich compositions**
Code in different languages like JavaScript/NodeJS, Swift, Python, Java or run custom logic by packaging code with Docker. Invoke your code synchronously, asynchronously, or on a schedule. Use higher-level programming constructs like sequences to declaratively chain together multiple actions. Use parameter binding to avoid hardcoding service credentials in your code. And also, debug your code in realtime.
**Scaling Per-Request & Optimal Utilization**
Run your action ten thousand times in a fraction of a second, or once a week. Action instances scale to meet demand as needed, then disappear. Enjoy optimal utilization where you don't pay for idle resources. | non_main | revisit last three sections on home page review and update last three sections on home page integrate easily with many popular services with apache openwhisk you can easily create actions test connect to other actions or debug them use the apache openwhisk cli target your apache openwhisk instance and run your first action in seconds apache openwhisk makes it simple for thousands of developers to integrate with your service make it easy for developers to perform actions when something happens in your service or to send data into your service when things happen somewhere else combine your functions into rich compositions code in different languages like javascript nodejs swift python java or run custom logic by packaging code with docker invoke your code synchronously asynchronously or on a schedule use higher level programming constructs like sequences to declaratively chain together multiple actions use parameter binding to avoid hardcoding service credentials in your code and also debug your code in realtime scaling per request optimal utilization run your action ten thousand times in a fraction of a second or once a week action instances scale to meet demand as needed then disappear enjoy optimal utilization where you don t pay for idle resources | 0 |
65,462 | 19,528,091,983 | IssuesEvent | 2021-12-30 11:43:05 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | opened | Panel: bottom border radius of content is incorrect with footer | defect | Screenshots are taken from https://www.primefaces.org/showcase/ui/panel/panel.xhtml (Saga, but also happens with Vela and Arya).
<img width="272" alt="Screenshot 2021-12-30 at 12 36 08" src="https://user-images.githubusercontent.com/7500178/147748592-f3ebce40-177f-4f11-ac67-ab9c19685ec9.png">
<img width="254" alt="Screenshot 2021-12-30 at 12 36 17" src="https://user-images.githubusercontent.com/7500178/147748596-94bfb33f-b38d-47fe-8e3f-82f8387b6486.png">
| 1.0 | Panel: bottom border radius of content is incorrect with footer - Screenshots are taken from https://www.primefaces.org/showcase/ui/panel/panel.xhtml (Saga, but also happens with Vela and Arya).
<img width="272" alt="Screenshot 2021-12-30 at 12 36 08" src="https://user-images.githubusercontent.com/7500178/147748592-f3ebce40-177f-4f11-ac67-ab9c19685ec9.png">
<img width="254" alt="Screenshot 2021-12-30 at 12 36 17" src="https://user-images.githubusercontent.com/7500178/147748596-94bfb33f-b38d-47fe-8e3f-82f8387b6486.png">
| non_main | panel bottom border radius of content is incorrect with footer screenshots are taken from saga but also happens with vela and arya img width alt screenshot at src img width alt screenshot at src | 0 |
84,133 | 10,476,637,541 | IssuesEvent | 2019-09-23 19:03:03 | samvera/hyrax | https://api.github.com/repos/samvera/hyrax | closed | Display analytics info on show page | Analytics design needed epic | ### Descriptive summary
Display download counts and page views on the show page for a work.
Example from UVa shown here:
<img width="770" alt="show page analytics" src="https://user-images.githubusercontent.com/1766876/35356203-b8d1d844-011d-11e8-87cc-f593395275e1.png">
| 1.0 | Display analytics info on show page - ### Descriptive summary
Display download counts and page views on the show page for a work.
Example from UVa shown here:
<img width="770" alt="show page analytics" src="https://user-images.githubusercontent.com/1766876/35356203-b8d1d844-011d-11e8-87cc-f593395275e1.png">
| non_main | display analytics info on show page descriptive summary display download counts and page views on the show page for a work example from uva shown here img width alt show page analytics src | 0 |
3,398 | 13,176,279,916 | IssuesEvent | 2020-08-12 04:21:54 | RapidField/solid-instruments | https://api.github.com/repos/RapidField/solid-instruments | closed | Release Solid Instruments 1.0.26 | Category-ProductionRelease Source-Maintainer Stage-3-InProgress Subcategory-Delivery Verdict-Pending Version-1.0.26 WindowForDelivery-2020-Q4 | # Software Release Request
This issue represents a request for the production release of a new version of **Solid Instruments**.
## Overview
Issue a production software release for `v1.0.26`.
## Statement of work
The following list describes the work to be done.
- [x] Update source documentation to reflect software changes.
- [x] Update documentation website to reflect software changes.
- [x] Add release notes with details that reflect software changes.
- [x] Update `appveyor.yml` to reflect new version number.
- [x] Submit a pull request against the `master` branch.
- [x] Close and destroy the completed working branches.
## Revision control plan
**Solid Instruments** uses the [**RapidField Revision Control Workflow**](https://github.com/RapidField/solid-instruments/blob/master/CONTRIBUTING.md#revision-control-strategy). Individual contributors should follow the branching plan below when working on this issue.
- `master` is the pull request target for
- `release/v1.0.26`, which is the pull request target for
- `develop` | True | Release Solid Instruments 1.0.26 - # Software Release Request
This issue represents a request for the production release of a new version of **Solid Instruments**.
## Overview
Issue a production software release for `v1.0.26`.
## Statement of work
The following list describes the work to be done.
- [x] Update source documentation to reflect software changes.
- [x] Update documentation website to reflect software changes.
- [x] Add release notes with details that reflect software changes.
- [x] Update `appveyor.yml` to reflect new version number.
- [x] Submit a pull request against the `master` branch.
- [x] Close and destroy the completed working branches.
## Revision control plan
**Solid Instruments** uses the [**RapidField Revision Control Workflow**](https://github.com/RapidField/solid-instruments/blob/master/CONTRIBUTING.md#revision-control-strategy). Individual contributors should follow the branching plan below when working on this issue.
- `master` is the pull request target for
- `release/v1.0.26`, which is the pull request target for
- `develop` | main | release solid instruments software release request this issue represents a request for the production release of a new version of solid instruments overview issue a production software release for statement of work the following list describes the work to be done update source documentation to reflect software changes update documentation website to reflect software changes add release notes with details that reflect software changes update appveyor yml to reflect new version number submit a pull request against the master branch close and destroy the completed working branches revision control plan solid instruments uses the individual contributors should follow the branching plan below when working on this issue master is the pull request target for release which is the pull request target for develop | 1 |
826,138 | 31,558,492,790 | IssuesEvent | 2023-09-03 00:38:55 | azerothcore/azerothcore-wotlk | https://api.github.com/repos/azerothcore/azerothcore-wotlk | opened | (Instance/Karazhan): Chess pieces are able to target incorrect faction with faction specific spells. | Confirmed Priority-Low Instance - Raid - Outland 70 | ### Current Behaviour
Minions during the Chess Event are able to target enemies with healing spells and friends with damaging spells. Buff type spells may also be affected by this.
[Can be seen here](https://www.youtube.com/watch?v=C1Uo93hvRog), recorded by [quigiboo](https://github.com/quigiboo).
### Expected Blizzlike Behaviour
These spells should only apply to one side depending on the effect; friendly faction for positive effects, enemy faction for negative effects.
### Source
[Tooltip](https://github.com/azerothcore/azerothcore-wotlk/assets/38561765/f55fc1b3-b9c6-4741-bb23-435c4c7e180d), Wrath Classic
### Steps to reproduce the problem
1. `.tele kara`
2. Make your way to the Chess event.
3. Control the king/warchief.
4. Relinquish control.
5. Control the conjurer/warlock.
6. Use Elemental Blast/Fireball on a friendly piece.
### Extra Notes
Originally reported at https://github.com/chromiecraft/chromiecraft/issues/6093.
### AC rev. hash/commit
6ff5f3811eba62bade219dfa00e96a2eff86c7df
### Operating system
Windows 10 x64
### Custom changes or Modules
[mod-ptr-template](https://github.com/heyitsbench/mod-ptr-template) | 1.0 | (Instance/Karazhan): Chess pieces are able to target incorrect faction with faction specific spells. - ### Current Behaviour
Minions during the Chess Event are able to target enemies with healing spells and friends with damaging spells. Buff type spells may also be affected by this.
[Can be seen here](https://www.youtube.com/watch?v=C1Uo93hvRog), recorded by [quigiboo](https://github.com/quigiboo).
### Expected Blizzlike Behaviour
These spells should only apply to one side depending on the effect; friendly faction for positive effects, enemy faction for negative effects.
### Source
[Tooltip](https://github.com/azerothcore/azerothcore-wotlk/assets/38561765/f55fc1b3-b9c6-4741-bb23-435c4c7e180d), Wrath Classic
### Steps to reproduce the problem
1. `.tele kara`
2. Make your way to the Chess event.
3. Control the king/warchief.
4. Relinquish control.
5. Control the conjurer/warlock.
6. Use Elemental Blast/Fireball on a friendly piece.
### Extra Notes
Originally reported at https://github.com/chromiecraft/chromiecraft/issues/6093.
### AC rev. hash/commit
6ff5f3811eba62bade219dfa00e96a2eff86c7df
### Operating system
Windows 10 x64
### Custom changes or Modules
[mod-ptr-template](https://github.com/heyitsbench/mod-ptr-template) | non_main | instance karazhan chess pieces are able to target incorrect faction with faction specific spells current behaviour minions during the chess event are able to target enemies with healing spells and friends with damaging spells buff type spells may also be affected by this recorded by expected blizzlike behaviour these spells should only apply to one side depending on the effect friendly faction for positive effects enemy faction for negative effects source wrath classic steps to reproduce the problem tele kara make your way to the chess event control the king warchief relinquish control control the conjurer warlock use elemental blast fireball on a friendly piece extra notes originally reported at ac rev hash commit operating system windows custom changes or modules | 0 |
3,228 | 12,368,706,124 | IssuesEvent | 2020-05-18 14:13:28 | Kashdeya/Tiny-Progressions | https://api.github.com/repos/Kashdeya/Tiny-Progressions | closed | Cant use Angel ring when having parts of Dragon Armor on | Version not Maintainted | As soon as you take just one piece of the Dragon armor set on it blocks the flight from Extra Utilities 2´s Angel Ring | True | Cant use Angel ring when having parts of Dragon Armor on - As soon as you take just one piece of the Dragon armor set on it blocks the flight from Extra Utilities 2´s Angel Ring | main | cant use angel ring when having parts of dragon armor on as soon as you take just one piece of the dragon armor set on it blocks the flight from extra utilities ´s angel ring | 1 |
3,017 | 11,185,099,560 | IssuesEvent | 2019-12-31 22:21:22 | laminas/laminas-session | https://api.github.com/repos/laminas/laminas-session | opened | Remove `SessionManager::rememberMe` | Awaiting Maintainer Response Question | See #59 for discussion.
Also https://github.com/zendframework/zendframework/issues/4775
IMO this vestige of ZF1 no longer serves any useful purpose.
---
Originally posted by @adamlundrigan at https://github.com/zendframework/zend-session/issues/60 | True | Remove `SessionManager::rememberMe` - See #59 for discussion.
Also https://github.com/zendframework/zendframework/issues/4775
IMO this vestige of ZF1 no longer serves any useful purpose.
---
Originally posted by @adamlundrigan at https://github.com/zendframework/zend-session/issues/60 | main | remove sessionmanager rememberme see for discussion also imo this vestige of no longer serves any useful purpose originally posted by adamlundrigan at | 1 |
3,018 | 11,185,107,029 | IssuesEvent | 2019-12-31 22:24:57 | laminas/laminas-skeleton-installer | https://api.github.com/repos/laminas/laminas-skeleton-installer | opened | Update version number as part of build process | Awaiting Maintainer Response Enhancement | We need to to this as part of release but I have no idea how.
Suggestions.
---
Originally posted by @GeeH at https://github.com/zendframework/ZendSkeletonApplication/issues/356 | True | Update version number as part of build process - We need to to this as part of release but I have no idea how.
Suggestions.
---
Originally posted by @GeeH at https://github.com/zendframework/ZendSkeletonApplication/issues/356 | main | update version number as part of build process we need to to this as part of release but i have no idea how suggestions originally posted by geeh at | 1 |
4,532 | 23,548,923,251 | IssuesEvent | 2022-08-21 14:38:53 | web3phl/directory | https://api.github.com/repos/web3phl/directory | opened | privacy/terms page | docs feature maintainers only todo | ### 🤔 Not Existing Feature Request?
- [X] Yes, I'm sure, this is a new requested feature!
### 🤔 Not an Idea or Suggestion?
- [X] Yes, I'm sure, this is not idea or suggestion!
### 📋 Request Details
Pretty good to have something like this in our directory therefore ppl know about how we handle data and operate. 💪
### 📜 Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://github.com/web3phl/directory/blob/main/CODE_OF_CONDUCT.md). | True | privacy/terms page - ### 🤔 Not Existing Feature Request?
- [X] Yes, I'm sure, this is a new requested feature!
### 🤔 Not an Idea or Suggestion?
- [X] Yes, I'm sure, this is not idea or suggestion!
### 📋 Request Details
Pretty good to have something like this in our directory therefore ppl know about how we handle data and operate. 💪
### 📜 Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://github.com/web3phl/directory/blob/main/CODE_OF_CONDUCT.md). | main | privacy terms page 🤔 not existing feature request yes i m sure this is a new requested feature 🤔 not an idea or suggestion yes i m sure this is not idea or suggestion 📋 request details pretty good to have something like this in our directory therefore ppl know about how we handle data and operate 💪 📜 code of conduct i agree to follow this project s | 1 |
295,066 | 25,451,898,441 | IssuesEvent | 2022-11-24 11:06:30 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | opened | Test: accessibility detection improvements | testplan-item accessibility | Refs: https://github.com/microsoft/vscode/issues/162331
- [ ] Windows
- [ ] macOS
- [ ] Linux
Complexity: 3
Authors: @deepak1556 @isidorn
---
We have improved how we auto detect if a screen reader is on when using VS Code. Now this detection should be more precise. You should verify that the detection still works fine.
If you got Windows install [NVDA](https://www.nvaccess.org/download/) and [JAWS](https://www.freedomscientific.com/products/software/jaws/) and test both. If you got macOS - just use VoiceOver (Cmd+F5). If you got Linux - use [Orca](https://help.gnome.org/users/orca/stable/index.html.en).
* When starting a Screen Reader with VS Code running, all VS Code windows detect this and the status bar shows "Screen Reader Detected". The editor now begins to output screen reader content to the `<textarea>`. This is proved by the screen reader reading the text in the editor as the editor cursor moves.
* Please also check other scenarios, such as first starting the screen reader and then launching VS Code, or reloading a window, or opening a new window, etc. In all cases, the fact that a screen reader is attached should be detected. This is important, because otherwise the editor does not output screen reader content to the `<textarea>` (which gives us a nice performance boost)
* Turn off screen reader. Start VS Code again. Make sure the screen reader is not detected (there is no status bar message). | 1.0 | Test: accessibility detection improvements - Refs: https://github.com/microsoft/vscode/issues/162331
- [ ] Windows
- [ ] macOS
- [ ] Linux
Complexity: 3
Authors: @deepak1556 @isidorn
---
We have improved how we auto detect if a screen reader is on when using VS Code. Now this detection should be more precise. You should verify that the detection still works fine.
If you got Windows install [NVDA](https://www.nvaccess.org/download/) and [JAWS](https://www.freedomscientific.com/products/software/jaws/) and test both. If you got macOS - just use VoiceOver (Cmd+F5). If you got Linux - use [Orca](https://help.gnome.org/users/orca/stable/index.html.en).
* When starting a Screen Reader with VS Code running, all VS Code windows detect this and the status bar shows "Screen Reader Detected". The editor now begins to output screen reader content to the `<textarea>`. This is proved by the screen reader reading the text in the editor as the editor cursor moves.
* Please also check other scenarios, such as first starting the screen reader and then launching VS Code, or reloading a window, or opening a new window, etc. In all cases, the fact that a screen reader is attached should be detected. This is important, because otherwise the editor does not output screen reader content to the `<textarea>` (which gives us a nice performance boost)
* Turn off screen reader. Start VS Code again. Make sure the screen reader is not detected (there is no status bar message). | non_main | test accessibility detection improvements refs windows macos linux complexity authors isidorn we have improved how we auto detect if a screen reader is on when using vs code now this detection should be more precise you should verify that the detection still works fine if you got windows install and and test both if you got macos just use voiceover cmd if you got linux use when starting a screen reader with vs code running all vs code windows detect this and the status bar shows screen reader detected the editor now begins to output screen reader content to the this is proved by the screen reader reading the text in the editor as the editor cursor moves please also check other scenarios such as first starting the screen reader and then launching vs code or reloading a window or opening a new window etc in all cases the fact that a screen reader is attached should be detected this is important because otherwise the editor does not output screen reader content to the which gives us a nice performance boost turn off screen reader start vs code again make sure the screen reader is not detected there is no status bar message | 0 |
4,848 | 24,973,659,158 | IssuesEvent | 2022-11-02 05:06:32 | rthadur/bazel | https://api.github.com/repos/rthadur/bazel | closed | Awaiting labels | awaiting-review awaiting-user-response awaiting-PR-merge more data needed awaiting-maintainer | ### Description
Testing the awaiting labels on issue
### Issue Type
_No response_
### Operating System
_No response_
### Coral Device
_No response_
### Other Devices
_No response_
### Programming Language
_No response_
### Relevant Log Output
_No response_ | True | Awaiting labels - ### Description
Testing the awaiting labels on issue
### Issue Type
_No response_
### Operating System
_No response_
### Coral Device
_No response_
### Other Devices
_No response_
### Programming Language
_No response_
### Relevant Log Output
_No response_ | main | awaiting labels description testing the awaiting labels on issue issue type no response operating system no response coral device no response other devices no response programming language no response relevant log output no response | 1 |
716,535 | 24,638,283,126 | IssuesEvent | 2022-10-17 09:37:12 | ibissource/frank-flow | https://api.github.com/repos/ibissource/frank-flow | closed | You should see a clear error message when you have a backend jar without frontend | feature priority:low | **Is your feature request related to a problem? Please describe.**
The Maven build of the frank-flow project produces a .jar that should be deployed on the server. There is a profile `frontend`. Only if this profile is enabled, then the frontend is added to this .jar file. We expect that developers will sometimes produce .jar files that do not include the frontend. On July 8 2021 Martijn, Jaco and Niels M. spent a lot of time debugging before they discovered that the .jar missed the frontend. A clear error message in this case will help.
**Describe the solution you'd like**
The URL /frank-flow should always produce some HTML page, also if the backend was built without the `frontend` profile. We can also add a Cypress test that calls the URL /frontend/api/configurations. If this URL produces a result, then we know that there is a frank-flow .jar on the classpath of the Java application on the server.
**Describe alternatives you've considered**
A clear and concise description of any alternative solutions or features you've considered.
**Additional context**
Add any other context or screenshots about the feature request here.
| 1.0 | You should see a clear error message when you have a backend jar without frontend - **Is your feature request related to a problem? Please describe.**
The Maven build of the frank-flow project produces a .jar that should be deployed on the server. There is a profile `frontend`. Only if this profile is enabled, then the frontend is added to this .jar file. We expect that developers will sometimes produce .jar files that do not include the frontend. On July 8 2021 Martijn, Jaco and Niels M. spent a lot of time debugging before they discovered that the .jar missed the frontend. A clear error message in this case will help.
**Describe the solution you'd like**
The URL /frank-flow should always produce some HTML page, also if the backend was built without the `frontend` profile. We can also add a Cypress test that calls the URL /frontend/api/configurations. If this URL produces a result, then we know that there is a frank-flow .jar on the classpath of the Java application on the server.
**Describe alternatives you've considered**
A clear and concise description of any alternative solutions or features you've considered.
**Additional context**
Add any other context or screenshots about the feature request here.
| non_main | you should see a clear error message when you have a backend jar without frontend is your feature request related to a problem please describe the maven build of the frank flow project produces a jar that should be deployed on the server there is a profile frontend only if this profile is enabled then the frontend is added to this jar file we expect that developers will sometimes produce jar files that do not include the frontend on july martijn jaco and niels m spent a lot of time debugging before they discovered that the jar missed the frontend a clear error message in this case will help describe the solution you d like the url frank flow should always produce some html page also if the backend was built without the frontend profile we can also add a cypress test that calls the url frontend api configurations if this url produces a result then we know that there is a frank flow jar on the classpath of the java application on the server describe alternatives you ve considered a clear and concise description of any alternative solutions or features you ve considered additional context add any other context or screenshots about the feature request here | 0 |
28,274 | 6,974,056,364 | IssuesEvent | 2017-12-11 22:50:30 | GoogleCloudPlatform/ruby-docs-samples | https://api.github.com/repos/GoogleCloudPlatform/ruby-docs-samples | closed | Google Project ID environment variable name not consistent | code health | **Story**
Rubyist attempts to use environment variables to save GCP default values. After reading this (README)[https://github.com/GoogleCloudPlatform/ruby-docs-samples/tree/master/datastore] in Datastore, the Rubyist is overwhelmed by which environment variable to use.
**Issue**
Similar to issue #62. Environment variables are not consistent across the Ruby samples.
**Possible-Solution**
Similar to issue #62. Use a consistent environment variable.
| 1.0 | Google Project ID environment variable name not consistent - **Story**
Rubyist attempts to use environment variables to save GCP default values. After reading this (README)[https://github.com/GoogleCloudPlatform/ruby-docs-samples/tree/master/datastore] in Datastore, the Rubyist is overwhelmed by which environment variable to use.
**Issue**
Similar to issue #62. Environment variables are not consistent across the Ruby samples.
**Possible-Solution**
Similar to issue #62. Use a consistent environment variable.
| non_main | google project id environment variable name not consistent story rubyist attempts to use environment variables to save gcp default values after reading this readme in datastore the rubyist is overwhelmed by which environment variable to use issue similar to issue environment variables are not consistent across the ruby samples possible solution similar to issue use a consistent environment variable | 0 |
4,932 | 11,853,984,621 | IssuesEvent | 2020-03-24 23:24:20 | QutEcoacoustics/workbench-client | https://api.github.com/repos/QutEcoacoustics/workbench-client | closed | Route resolvers | architecture enhancement triage:high | Redo implementation of route resolvers. Currently, resolvers are treated as a hereditary system where the parents resolvers are also applied to the children. This needs to change so that all children define their own resolvers individually, and resolvers are not passed to any children. | 1.0 | Route resolvers - Redo implementation of route resolvers. Currently, resolvers are treated as a hereditary system where the parents resolvers are also applied to the children. This needs to change so that all children define their own resolvers individually, and resolvers are not passed to any children. | non_main | route resolvers redo implementation of route resolvers currently resolvers are treated as a hereditary system where the parents resolvers are also applied to the children this needs to change so that all children define their own resolvers individually and resolvers are not passed to any children | 0 |
483,951 | 13,932,265,696 | IssuesEvent | 2020-10-22 06:57:57 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | auth.api.sonyentertainmentnetwork.com - see bug description | browser-fenix engine-gecko priority-normal | <!-- @browser: Firefox Mobile 83.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 11; Mobile; rv:83.0) Gecko/83.0 Firefox/83.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/60228 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://auth.api.sonyentertainmentnetwork.com/2.0/oauth/authorize?response_type=code&client_id=78420c74-1fdf-4575-b43f-eb94c7d770bf&redirect_uri=https%3A%2F%2Fwww.bungie.net%2Fen%2FUser%2FSignIn%2FPsnid&scope=psn:s2s&request_locale=en_US&state=7818670895648613044&service_entity=urn:service-entity:psn
**Browser / Version**: Firefox Mobile 83.0
**Operating System**: Android
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: stating connection is not private/secure
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20201018211631</li><li>channel: nightly</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2020/10/57f11a53-130c-4d3d-a0e7-42d77f3728e6)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | auth.api.sonyentertainmentnetwork.com - see bug description - <!-- @browser: Firefox Mobile 83.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 11; Mobile; rv:83.0) Gecko/83.0 Firefox/83.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/60228 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://auth.api.sonyentertainmentnetwork.com/2.0/oauth/authorize?response_type=code&client_id=78420c74-1fdf-4575-b43f-eb94c7d770bf&redirect_uri=https%3A%2F%2Fwww.bungie.net%2Fen%2FUser%2FSignIn%2FPsnid&scope=psn:s2s&request_locale=en_US&state=7818670895648613044&service_entity=urn:service-entity:psn
**Browser / Version**: Firefox Mobile 83.0
**Operating System**: Android
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: stating connection is not private/secure
**Steps to Reproduce**:
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20201018211631</li><li>channel: nightly</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2020/10/57f11a53-130c-4d3d-a0e7-42d77f3728e6)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_main | auth api sonyentertainmentnetwork com see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description stating connection is not private secure steps to reproduce browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel nightly hastouchscreen true mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️ | 0 |
67,870 | 7,067,562,185 | IssuesEvent | 2018-01-08 00:38:32 | mkenney/go-chrome | https://api.github.com/repos/mkenney/go-chrome | closed | Add unit tests for `socket/protocol.debugger.go` | good first issue help wanted ✓ tests | ### What version of `go-chrome` are you using (tagged commit, commit hash or `master`)?
`master`
### What behavior do you expect? What are you trying to accomplish?
Unit tests exist with complete code coverage for `protocol.debugger.go`
### What behavior are you experiencing instead?
Tests do not exist or do not pass
### How can this behavior be reproduced?
`go test github.com/mkenney/go-chrome/socket` | 1.0 | Add unit tests for `socket/protocol.debugger.go` - ### What version of `go-chrome` are you using (tagged commit, commit hash or `master`)?
`master`
### What behavior do you expect? What are you trying to accomplish?
Unit tests exist with complete code coverage for `protocol.debugger.go`
### What behavior are you experiencing instead?
Tests do not exist or do not pass
### How can this behavior be reproduced?
`go test github.com/mkenney/go-chrome/socket` | non_main | add unit tests for socket protocol debugger go what version of go chrome are you using tagged commit commit hash or master master what behavior do you expect what are you trying to accomplish unit tests exist with complete code coverage for protocol debugger go what behavior are you experiencing instead tests do not exist or do not pass how can this behavior be reproduced go test github com mkenney go chrome socket | 0 |
260 | 3,008,056,637 | IssuesEvent | 2015-07-27 19:14:05 | borisblizzard/arcreator | https://api.github.com/repos/borisblizzard/arcreator | opened | Remove unnecessary str.format uses | Editor Related Maintainability | str.format is a very verbose and powerful way to invoke the string format operator %
most of its current uses are unnecessary and hard to read these should be searched out and their necessity evaluated. they should be removed and replaces with the % operator is they can | True | Remove unnecessary str.format uses - str.format is a very verbose and powerful way to invoke the string format operator %
most of its current uses are unnecessary and hard to read these should be searched out and their necessity evaluated. they should be removed and replaces with the % operator is they can | main | remove unnecessary str format uses str format is a very verbose and powerful way to invoke the string format operator most of its current uses are unnecessary and hard to read these should be searched out and their necessity evaluated they should be removed and replaces with the operator is they can | 1 |
3,775 | 15,873,616,793 | IssuesEvent | 2021-04-09 02:53:27 | PowerShell/PowerShell | https://api.github.com/repos/PowerShell/PowerShell | closed | ConvertTo-JSON should allow nesting 0 | Area-Cmdlets-Utility Issue-Question Review - Maintainer | There seems to be an oversight of what ConvertTo-JSON allows when it comes to nesting. Since the default value is 2 (not 0) it's impossible to set it to 0, as minimal value is 1.
## Steps to reproduce
```powershell
[PSCustomObject] @{
Test = 1
Test2 = 2
Test3 = [PSCustomObject] @{
IdontWantThat = 1
}
} | ConvertTo-Json -Depth 0
```
## Expected behavior
```powershell
[PSCustomObject] @{
Test = 1
Test2 = 2
Test3 = [PSCustomObject] @{
IdontWantThat = 1
}
} | ConvertTo-Json -Depth 0
```
Should be:
```
{
"Test":"1",
"Test2":"2",
"Test3":"@{IDontWantThat=1}"}
```
or similar
## Actual behavior
```none
[PSCustomObject] @{
Test = 1
Test2 = 2
Test3 = [PSCustomObject] @{
IdontWantThat = 1
}
} | ConvertTo-Json -Depth 0
```
```none
ConvertTo-Json : Cannot validate argument on parameter 'Depth'. The 0 argument is less than the minimum allowed range of 1. Supply an argument that is greater than or equal to 1 and then try the command again.
```
## Environment data
<!-- provide the output of $PSVersionTable -->
```none
```
| True | ConvertTo-JSON should allow nesting 0 - There seems to be an oversight of what ConvertTo-JSON allows when it comes to nesting. Since the default value is 2 (not 0) it's impossible to set it to 0, as minimal value is 1.
## Steps to reproduce
```powershell
[PSCustomObject] @{
Test = 1
Test2 = 2
Test3 = [PSCustomObject] @{
IdontWantThat = 1
}
} | ConvertTo-Json -Depth 0
```
## Expected behavior
```powershell
[PSCustomObject] @{
Test = 1
Test2 = 2
Test3 = [PSCustomObject] @{
IdontWantThat = 1
}
} | ConvertTo-Json -Depth 0
```
Should be:
```
{
"Test":"1",
"Test2":"2",
"Test3":"@{IDontWantThat=1}"}
```
or similar
## Actual behavior
```none
[PSCustomObject] @{
Test = 1
Test2 = 2
Test3 = [PSCustomObject] @{
IdontWantThat = 1
}
} | ConvertTo-Json -Depth 0
```
```none
ConvertTo-Json : Cannot validate argument on parameter 'Depth'. The 0 argument is less than the minimum allowed range of 1. Supply an argument that is greater than or equal to 1 and then try the command again.
```
## Environment data
<!-- provide the output of $PSVersionTable -->
```none
```
| main | convertto json should allow nesting there seems to be an oversight of what convertto json allows when it comes to nesting since the default value is not it s impossible to set it to as minimal value is steps to reproduce powershell test idontwantthat convertto json depth expected behavior powershell test idontwantthat convertto json depth should be test idontwantthat or similar actual behavior none test idontwantthat convertto json depth none convertto json cannot validate argument on parameter depth the argument is less than the minimum allowed range of supply an argument that is greater than or equal to and then try the command again environment data none | 1 |
4,959 | 25,461,243,795 | IssuesEvent | 2022-11-24 19:24:21 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | opened | Two different joinable paths to the same target results in an error in Data Explorer | type: bug work: frontend status: ready restricted: maintainers | ## Description
* The following data results in an error on the frontend: `Failed to fetch column information: Multiple links present for the same column: 61051`
```
const baseTableResult = {"id":12454,"name":"Cycle 6 Work","import_target":null,"schema":3,"created_at":"2022-11-21T16:41:50.849693Z","updated_at":"2022-11-21T16:41:50.849722Z","import_verified":null,"columns":[{"id":73221,"name":"GitHub Link","type":"mathesar_types.uri","type_options":null,"display_options":{}},{"id":59626,"name":"id","type":"integer","type_options":null,"display_options":null},{"id":61051,"name":"Feature","type":"integer","type_options":null,"display_options":null},{"id":61640,"name":"Work","type":"integer","type_options":null,"display_options":null},{"id":62229,"name":"Assignee","type":"integer","type_options":null,"display_options":null},{"id":62697,"name":"Percentage","type":"numeric","type_options":null,"display_options":{"number_format":null,"use_grouping":"false","minimum_fraction_digits":null,"maximum_fraction_digits":null,"show_as_percentage":false}},{"id":63364,"name":"Completed","type":"boolean","type_options":null,"display_options":{"input":"checkbox"}}],"records_url":"https://staging.mathesar.org/api/db/v0/tables/12454/records/","constraints_url":"https://staging.mathesar.org/api/db/v0/tables/12454/constraints/","columns_url":"https://staging.mathesar.org/api/db/v0/tables/12454/columns/","joinable_tables_url":"https://staging.mathesar.org/api/db/v0/tables/12454/joinable_tables/","type_suggestions_url":"https://staging.mathesar.org/api/db/v0/tables/12454/type_suggestions/","previews_url":"https://staging.mathesar.org/api/db/v0/tables/12454/previews/","data_files":[],"has_dependents":true,"dependents_url":"https://staging.mathesar.org/api/db/v0/tables/12454/dependents/","settings":{"id":147,"preview_settings":{"customized":true,"template":"{61051} ({61640})"}},"description":null};
const joinableColumnsResult = {"joinable_tables":[{"target":20,"jp_path":[[61051,98]],"fk_path":[[24600,false]],"depth":1,"multiple_results":false},{"target":21,"jp_path":[[61640,100]],"fk_path":[[24853,false]],"depth":1,"multiple_results":false},{"target":22,"jp_path":[[62229,102]],"fk_path":[[25107,false]],"depth":1,"multiple_results":false},{"target":16063,"jp_path":[[59626,76749]],"fk_path":[[29734,true]],"depth":1,"multiple_results":true},{"target":16063,"jp_path":[[59626,76750]],"fk_path":[[29735,true]],"depth":1,"multiple_results":true},{"target":9889,"jp_path":[[62229,102],[102,53687]],"fk_path":[[25107,false],[21448,true]],"depth":2,"multiple_results":true},{"target":9889,"jp_path":[[62229,102],[102,53015]],"fk_path":[[25107,false],[21190,true]],"depth":2,"multiple_results":true},{"target":9889,"jp_path":[[62229,102],[102,52542]],"fk_path":[[25107,false],[20933,true]],"depth":2,"multiple_results":true},{"target":24,"jp_path":[[62229,102],[102,112]],"fk_path":[[25107,false],[14776,true]],"depth":2,"multiple_results":true},{"target":12454,"jp_path":[[59626,76749],[76750,59626]],"fk_path":[[29734,true],[29735,false]],"depth":2,"multiple_results":true},{"target":12454,"jp_path":[[59626,76750],[76749,59626]],"fk_path":[[29735,true],[29734,false]],"depth":2,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53687],[53015,102]],"fk_path":[[25107,false],[21448,true],[21190,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53687],[52542,102]],"fk_path":[[25107,false],[21448,true],[20933,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53015],[53687,102]],"fk_path":[[25107,false],[21190,true],[21448,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53015],[52542,102]],"fk_path":[[25107,false],[21190,true],[20933,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,52542],[53687,102]],"fk_path":[[25107,false],[20933,true],[21448,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,52542],[53015,102]],"fk_path":[[25107,false],[20933,true],[21190,false]],"depth":3,"multiple_results":true},{"target":16063,"jp_path":[[59626,76749],[76750,59626],[59626,76749]],"fk_path":[[29734,true],[29735,false],[29734,true]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[59626,76749],[76750,59626],[62229,102]],"fk_path":[[29734,true],[29735,false],[25107,false]],"depth":3,"multiple_results":true},{"target":21,"jp_path":[[59626,76749],[76750,59626],[61640,100]],"fk_path":[[29734,true],[29735,false],[24853,false]],"depth":3,"multiple_results":true},{"target":20,"jp_path":[[59626,76749],[76750,59626],[61051,98]],"fk_path":[[29734,true],[29735,false],[24600,false]],"depth":3,"multiple_results":true},{"target":16063,"jp_path":[[59626,76750],[76749,59626],[59626,76750]],"fk_path":[[29735,true],[29734,false],[29735,true]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[59626,76750],[76749,59626],[62229,102]],"fk_path":[[29735,true],[29734,false],[25107,false]],"depth":3,"multiple_results":true},{"target":21,"jp_path":[[59626,76750],[76749,59626],[61640,100]],"fk_path":[[29735,true],[29734,false],[24853,false]],"depth":3,"multiple_results":true},{"target":20,"jp_path":[[59626,76750],[76749,59626],[61051,98]],"fk_path":[[29735,true],[29734,false],[24600,false]],"depth":3,"multiple_results":true}],"tables":{"20":{"name":"Features","columns":[98,99]},"21":{"name":"Work Types","columns":[100,101]},"22":{"name":"Team","columns":[102,103]},"16063":{"name":"Cycle 6 Blockers","columns":[76748,76749,76750]},"9889":{"name":"Team Event Supreme Overlords","columns":[49568,52542,47829,53015,53687]},"24":{"name":"Team Event Schedule","columns":[108,109,110,111,112]},"12454":{"name":"Cycle 6 Work","columns":[73221,59626,61051,61640,62229,62697,63364]}},"columns":{"98":{"name":"id","type":"integer"},"99":{"name":"Name","type":"text"},"100":{"name":"id","type":"integer"},"101":{"name":"Deliverable","type":"text"},"102":{"name":"ID","type":"integer"},"103":{"name":"Name","type":"text"},"76748":{"name":"id","type":"integer"},"76749":{"name":"Blocked","type":"integer"},"76750":{"name":"Blocked By","type":"integer"},"49568":{"name":"Date","type":"date"},"52542":{"name":"Host","type":"integer"},"47829":{"name":"id","type":"integer"},"53015":{"name":"Champion","type":"integer"},"53687":{"name":"Runner-up","type":"integer"},"108":{"name":"id","type":"integer"},"109":{"name":"Date","type":"date"},"110":{"name":"Type","type":"text"},"111":{"name":"Completed","type":"boolean"},"112":{"name":"Organizer","type":"integer"},"73221":{"name":"GitHub Link","type":"mathesar_types.uri"},"59626":{"name":"id","type":"integer"},"61051":{"name":"Feature","type":"integer"},"61640":{"name":"Work","type":"integer"},"62229":{"name":"Assignee","type":"integer"},"62697":{"name":"Percentage","type":"numeric"},"63364":{"name":"Completed","type":"boolean"}}};
```
The table has two different columns pointing to the same target table. | True | Two different joinable paths to the same target results in an error in Data Explorer - ## Description
* The following data results in an error on the frontend: `Failed to fetch column information: Multiple links present for the same column: 61051`
```
const baseTableResult = {"id":12454,"name":"Cycle 6 Work","import_target":null,"schema":3,"created_at":"2022-11-21T16:41:50.849693Z","updated_at":"2022-11-21T16:41:50.849722Z","import_verified":null,"columns":[{"id":73221,"name":"GitHub Link","type":"mathesar_types.uri","type_options":null,"display_options":{}},{"id":59626,"name":"id","type":"integer","type_options":null,"display_options":null},{"id":61051,"name":"Feature","type":"integer","type_options":null,"display_options":null},{"id":61640,"name":"Work","type":"integer","type_options":null,"display_options":null},{"id":62229,"name":"Assignee","type":"integer","type_options":null,"display_options":null},{"id":62697,"name":"Percentage","type":"numeric","type_options":null,"display_options":{"number_format":null,"use_grouping":"false","minimum_fraction_digits":null,"maximum_fraction_digits":null,"show_as_percentage":false}},{"id":63364,"name":"Completed","type":"boolean","type_options":null,"display_options":{"input":"checkbox"}}],"records_url":"https://staging.mathesar.org/api/db/v0/tables/12454/records/","constraints_url":"https://staging.mathesar.org/api/db/v0/tables/12454/constraints/","columns_url":"https://staging.mathesar.org/api/db/v0/tables/12454/columns/","joinable_tables_url":"https://staging.mathesar.org/api/db/v0/tables/12454/joinable_tables/","type_suggestions_url":"https://staging.mathesar.org/api/db/v0/tables/12454/type_suggestions/","previews_url":"https://staging.mathesar.org/api/db/v0/tables/12454/previews/","data_files":[],"has_dependents":true,"dependents_url":"https://staging.mathesar.org/api/db/v0/tables/12454/dependents/","settings":{"id":147,"preview_settings":{"customized":true,"template":"{61051} ({61640})"}},"description":null};
const joinableColumnsResult = {"joinable_tables":[{"target":20,"jp_path":[[61051,98]],"fk_path":[[24600,false]],"depth":1,"multiple_results":false},{"target":21,"jp_path":[[61640,100]],"fk_path":[[24853,false]],"depth":1,"multiple_results":false},{"target":22,"jp_path":[[62229,102]],"fk_path":[[25107,false]],"depth":1,"multiple_results":false},{"target":16063,"jp_path":[[59626,76749]],"fk_path":[[29734,true]],"depth":1,"multiple_results":true},{"target":16063,"jp_path":[[59626,76750]],"fk_path":[[29735,true]],"depth":1,"multiple_results":true},{"target":9889,"jp_path":[[62229,102],[102,53687]],"fk_path":[[25107,false],[21448,true]],"depth":2,"multiple_results":true},{"target":9889,"jp_path":[[62229,102],[102,53015]],"fk_path":[[25107,false],[21190,true]],"depth":2,"multiple_results":true},{"target":9889,"jp_path":[[62229,102],[102,52542]],"fk_path":[[25107,false],[20933,true]],"depth":2,"multiple_results":true},{"target":24,"jp_path":[[62229,102],[102,112]],"fk_path":[[25107,false],[14776,true]],"depth":2,"multiple_results":true},{"target":12454,"jp_path":[[59626,76749],[76750,59626]],"fk_path":[[29734,true],[29735,false]],"depth":2,"multiple_results":true},{"target":12454,"jp_path":[[59626,76750],[76749,59626]],"fk_path":[[29735,true],[29734,false]],"depth":2,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53687],[53015,102]],"fk_path":[[25107,false],[21448,true],[21190,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53687],[52542,102]],"fk_path":[[25107,false],[21448,true],[20933,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53015],[53687,102]],"fk_path":[[25107,false],[21190,true],[21448,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,53015],[52542,102]],"fk_path":[[25107,false],[21190,true],[20933,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,52542],[53687,102]],"fk_path":[[25107,false],[20933,true],[21448,false]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[62229,102],[102,52542],[53015,102]],"fk_path":[[25107,false],[20933,true],[21190,false]],"depth":3,"multiple_results":true},{"target":16063,"jp_path":[[59626,76749],[76750,59626],[59626,76749]],"fk_path":[[29734,true],[29735,false],[29734,true]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[59626,76749],[76750,59626],[62229,102]],"fk_path":[[29734,true],[29735,false],[25107,false]],"depth":3,"multiple_results":true},{"target":21,"jp_path":[[59626,76749],[76750,59626],[61640,100]],"fk_path":[[29734,true],[29735,false],[24853,false]],"depth":3,"multiple_results":true},{"target":20,"jp_path":[[59626,76749],[76750,59626],[61051,98]],"fk_path":[[29734,true],[29735,false],[24600,false]],"depth":3,"multiple_results":true},{"target":16063,"jp_path":[[59626,76750],[76749,59626],[59626,76750]],"fk_path":[[29735,true],[29734,false],[29735,true]],"depth":3,"multiple_results":true},{"target":22,"jp_path":[[59626,76750],[76749,59626],[62229,102]],"fk_path":[[29735,true],[29734,false],[25107,false]],"depth":3,"multiple_results":true},{"target":21,"jp_path":[[59626,76750],[76749,59626],[61640,100]],"fk_path":[[29735,true],[29734,false],[24853,false]],"depth":3,"multiple_results":true},{"target":20,"jp_path":[[59626,76750],[76749,59626],[61051,98]],"fk_path":[[29735,true],[29734,false],[24600,false]],"depth":3,"multiple_results":true}],"tables":{"20":{"name":"Features","columns":[98,99]},"21":{"name":"Work Types","columns":[100,101]},"22":{"name":"Team","columns":[102,103]},"16063":{"name":"Cycle 6 Blockers","columns":[76748,76749,76750]},"9889":{"name":"Team Event Supreme Overlords","columns":[49568,52542,47829,53015,53687]},"24":{"name":"Team Event Schedule","columns":[108,109,110,111,112]},"12454":{"name":"Cycle 6 Work","columns":[73221,59626,61051,61640,62229,62697,63364]}},"columns":{"98":{"name":"id","type":"integer"},"99":{"name":"Name","type":"text"},"100":{"name":"id","type":"integer"},"101":{"name":"Deliverable","type":"text"},"102":{"name":"ID","type":"integer"},"103":{"name":"Name","type":"text"},"76748":{"name":"id","type":"integer"},"76749":{"name":"Blocked","type":"integer"},"76750":{"name":"Blocked By","type":"integer"},"49568":{"name":"Date","type":"date"},"52542":{"name":"Host","type":"integer"},"47829":{"name":"id","type":"integer"},"53015":{"name":"Champion","type":"integer"},"53687":{"name":"Runner-up","type":"integer"},"108":{"name":"id","type":"integer"},"109":{"name":"Date","type":"date"},"110":{"name":"Type","type":"text"},"111":{"name":"Completed","type":"boolean"},"112":{"name":"Organizer","type":"integer"},"73221":{"name":"GitHub Link","type":"mathesar_types.uri"},"59626":{"name":"id","type":"integer"},"61051":{"name":"Feature","type":"integer"},"61640":{"name":"Work","type":"integer"},"62229":{"name":"Assignee","type":"integer"},"62697":{"name":"Percentage","type":"numeric"},"63364":{"name":"Completed","type":"boolean"}}};
```
The table has two different columns pointing to the same target table. | main | two different joinable paths to the same target results in an error in data explorer description the following data results in an error on the frontend failed to fetch column information multiple links present for the same column const basetableresult id name cycle work import target null schema created at updated at import verified null columns records url has dependents true dependents url description null const joinablecolumnsresult joinable tables fk path depth multiple results false target jp path fk path depth multiple results false target jp path fk path depth multiple results false target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true target jp path fk path depth multiple results true tables name features columns name work types columns name team columns name cycle blockers columns name team event supreme overlords columns name team event schedule columns name cycle work columns columns name id type integer name name type text name id type integer name deliverable type text name id type integer name name type text name id type integer name blocked type integer name blocked by type integer name date type date name host type integer name id type integer name champion type integer name runner up type integer name id type integer name date type date name type type text name completed type boolean name organizer type integer name github link type mathesar types uri name id type integer name feature type integer name work type integer name assignee type integer name percentage type numeric name completed type boolean the table has two different columns pointing to the same target table | 1 |
4,953 | 25,455,553,025 | IssuesEvent | 2022-11-24 13:55:28 | pace/bricks | https://api.github.com/repos/pace/bricks | closed | service generation: remove lab.jamit.de | T::Maintainance | Remove everything that uses `lab.jamit.de` somehow. Like the default package name. But probably more than that. | True | service generation: remove lab.jamit.de - Remove everything that uses `lab.jamit.de` somehow. Like the default package name. But probably more than that. | main | service generation remove lab jamit de remove everything that uses lab jamit de somehow like the default package name but probably more than that | 1 |
185,987 | 15,039,391,857 | IssuesEvent | 2021-02-02 18:35:45 | kyverno/kyverno | https://api.github.com/repos/kyverno/kyverno | closed | Examples explaining annotation pod-policies.kyverno.io/autogen-controllers | Documentation enhancement good first issue | **Is your feature request related to a problem? Please describe.**
I would to have an elaborate explanation and example of https://github.com/nirmata/kyverno/blob/master/documentation/writing-policies-autogen.md
**Describe the solution you'd like**
As mentioned i would like to have an example explaining describing how the annotation `pod-policies.kyverno.io/autogen-controllers` works in daily use with a practical use case.
**Describe alternatives you've considered**
N/A
**Additional context**
As mentioned by @JimBugwadia
The problem this feature solves is managing policies across pod controllers and pods. In most cases, you want policies to apply to all pods, regardless of which type of controller creates the pod. However, the syntax for a rule written on a pod vs. a rule written for a pod controller vary - but only slightly.
The other issue is that if you write a blocking policy (i.e. the validationFailureAction is enforce) on a pod, and a pod is created by the pod controller, the pod controller will be accepted but the pod creation request from the controller will be rejected. This makes it hard to troubleshoot why the pod is not running.
This feature solves both of these issues. You can write Kyverno policies on a Pod, and Kyverno will generate rules for common controllers. Now, when you try to apply a controller YAML that violates a blocking policy, the API request will be blocked and the user will see the error immediately.
| 1.0 | Examples explaining annotation pod-policies.kyverno.io/autogen-controllers - **Is your feature request related to a problem? Please describe.**
I would to have an elaborate explanation and example of https://github.com/nirmata/kyverno/blob/master/documentation/writing-policies-autogen.md
**Describe the solution you'd like**
As mentioned i would like to have an example explaining describing how the annotation `pod-policies.kyverno.io/autogen-controllers` works in daily use with a practical use case.
**Describe alternatives you've considered**
N/A
**Additional context**
As mentioned by @JimBugwadia
The problem this feature solves is managing policies across pod controllers and pods. In most cases, you want policies to apply to all pods, regardless of which type of controller creates the pod. However, the syntax for a rule written on a pod vs. a rule written for a pod controller vary - but only slightly.
The other issue is that if you write a blocking policy (i.e. the validationFailureAction is enforce) on a pod, and a pod is created by the pod controller, the pod controller will be accepted but the pod creation request from the controller will be rejected. This makes it hard to troubleshoot why the pod is not running.
This feature solves both of these issues. You can write Kyverno policies on a Pod, and Kyverno will generate rules for common controllers. Now, when you try to apply a controller YAML that violates a blocking policy, the API request will be blocked and the user will see the error immediately.
| non_main | examples explaining annotation pod policies kyverno io autogen controllers is your feature request related to a problem please describe i would to have an elaborate explanation and example of describe the solution you d like as mentioned i would like to have an example explaining describing how the annotation pod policies kyverno io autogen controllers works in daily use with a practical use case describe alternatives you ve considered n a additional context as mentioned by jimbugwadia the problem this feature solves is managing policies across pod controllers and pods in most cases you want policies to apply to all pods regardless of which type of controller creates the pod however the syntax for a rule written on a pod vs a rule written for a pod controller vary but only slightly the other issue is that if you write a blocking policy i e the validationfailureaction is enforce on a pod and a pod is created by the pod controller the pod controller will be accepted but the pod creation request from the controller will be rejected this makes it hard to troubleshoot why the pod is not running this feature solves both of these issues you can write kyverno policies on a pod and kyverno will generate rules for common controllers now when you try to apply a controller yaml that violates a blocking policy the api request will be blocked and the user will see the error immediately | 0 |
184,174 | 6,706,346,104 | IssuesEvent | 2017-10-12 06:33:55 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | employeecareers-ryder.icims.com - design is broken | browser-firefox-mobile priority-normal status-needstriage | <!-- @browser: Firefox Mobile 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:58.0) Gecko/58.0 Firefox/58.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://employeecareers-ryder.icims.com/jobs/intro?hashed=-435769460
**Browser / Version**: Firefox Mobile 58.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: login feilds do not display
**Steps to Reproduce**:
A Link On ryder.com/careers
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | employeecareers-ryder.icims.com - design is broken - <!-- @browser: Firefox Mobile 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:58.0) Gecko/58.0 Firefox/58.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://employeecareers-ryder.icims.com/jobs/intro?hashed=-435769460
**Browser / Version**: Firefox Mobile 58.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: login feilds do not display
**Steps to Reproduce**:
A Link On ryder.com/careers
_From [webcompat.com](https://webcompat.com/) with ❤️_ | non_main | employeecareers ryder icims com design is broken url browser version firefox mobile operating system android tested another browser no problem type design is broken description login feilds do not display steps to reproduce a link on ryder com careers from with ❤️ | 0 |
2,721 | 9,602,445,008 | IssuesEvent | 2019-05-10 14:36:51 | simplesamlphp/simplesamlphp | https://api.github.com/repos/simplesamlphp/simplesamlphp | closed | tests: Replace @expectedException annotation with actual code | maintainability | Some tests assert for exceptions to happen by having a specific phpdoc in place.
This makes the tests much harder to read/understand.
All references to @expectedException should therefore be replaced by a line of code.
Interesting read regarding this subject: https://thephp.cc/news/2016/02/questioning-phpunit-best-practices
Two options here:
`$this->setExpectedException('\Exception');`
This is possible to do right now.. However, it is deprecated use of PHPunit
The best practice would be to use:
`$this->expectException(ExpectedException::class);`
However, this requires PHPunit 5.2, thus PHP 5.6
My suggestion is to keep this issue open as a reminder until we can use the current best practice. | True | tests: Replace @expectedException annotation with actual code - Some tests assert for exceptions to happen by having a specific phpdoc in place.
This makes the tests much harder to read/understand.
All references to @expectedException should therefore be replaced by a line of code.
Interesting read regarding this subject: https://thephp.cc/news/2016/02/questioning-phpunit-best-practices
Two options here:
`$this->setExpectedException('\Exception');`
This is possible to do right now.. However, it is deprecated use of PHPunit
The best practice would be to use:
`$this->expectException(ExpectedException::class);`
However, this requires PHPunit 5.2, thus PHP 5.6
My suggestion is to keep this issue open as a reminder until we can use the current best practice. | main | tests replace expectedexception annotation with actual code some tests assert for exceptions to happen by having a specific phpdoc in place this makes the tests much harder to read understand all references to expectedexception should therefore be replaced by a line of code interesting read regarding this subject two options here this setexpectedexception exception this is possible to do right now however it is deprecated use of phpunit the best practice would be to use this expectexception expectedexception class however this requires phpunit thus php my suggestion is to keep this issue open as a reminder until we can use the current best practice | 1 |
175,416 | 14,527,673,196 | IssuesEvent | 2020-12-14 15:37:41 | pythonarcade/arcade | https://api.github.com/repos/pythonarcade/arcade | closed | Strange behavior of custom hitbox (set with set_hit_box) | documentation | ## Bug Report
I was experimenting with custom hitboxes (using `sprite.set_hit_box`).
The screenshot shows a representation of the object's hitboxes. An object's frame is green if there's no collision and red if a collision is detected.
Collisions are detected by
```monkey.isHit = arcade.check_for_collision(self.player.sprite, monkey.sprite)```
Obviously the player is the "person" in the middle.
The player collides well with the monkeys on the left side. But on the right side, there is an area beneath the player's arms which is obviously outside of the person's hitbox but triggers collisions on the monkeys.
### Steps to reproduce/example code:
See the attached proof of concept. Just run the __main__. The example is focused on the problem.
[repro-code.zip](https://github.com/pythonarcade/arcade/files/5245069/repro-code.zip)
## Enhancement request:
Can anyone confirm if this is a bug or more a limitation of used algorithms? | 1.0 | Strange behavior of custom hitbox (set with set_hit_box) - ## Bug Report
I was experimenting with custom hitboxes (using `sprite.set_hit_box`).
The screenshot shows a representation of the object's hitboxes. An object's frame is green if there's no collision and red if a collision is detected.
Collisions are detected by
```monkey.isHit = arcade.check_for_collision(self.player.sprite, monkey.sprite)```
Obviously the player is the "person" in the middle.
The player collides well with the monkeys on the left side. But on the right side, there is an area beneath the player's arms which is obviously outside of the person's hitbox but triggers collisions on the monkeys.
### Steps to reproduce/example code:
See the attached proof of concept. Just run the __main__. The example is focused on the problem.
[repro-code.zip](https://github.com/pythonarcade/arcade/files/5245069/repro-code.zip)
## Enhancement request:
Can anyone confirm if this is a bug or more a limitation of used algorithms? | non_main | strange behavior of custom hitbox set with set hit box bug report i was experimenting with custom hitboxes using sprite set hit box the screenshot shows a representation of the object s hitboxes an object s frame is green if there s no collision and red if a collision is detected collisions are detected by monkey ishit arcade check for collision self player sprite monkey sprite obviously the player is the person in the middle the player collides well with the monkeys on the left side but on the right side there is an area beneath the player s arms which is obviously outside of the person s hitbox but triggers collisions on the monkeys steps to reproduce example code see the attached proof of concept just run the main the example is focused on the problem enhancement request can anyone confirm if this is a bug or more a limitation of used algorithms | 0 |
3,426 | 13,182,211,410 | IssuesEvent | 2020-08-12 15:26:03 | duo-labs/cloudmapper | https://api.github.com/repos/duo-labs/cloudmapper | closed | Regarding reading Metadata in the graph | unmaintained_functionality | Hi,
I have been using cloudmapper for a while to scan the resources in my AWS account. Months back( around Septemeber) I ran cloudmapper through an EC2, and I got a nice graph. I was also able to select any node in the graph and I could see the metadata of the node, but now I use an ECS container to do the same exact thing, but I am unable to see the metadata for a node. Can someone help me understand the cause of this issue?
Also when I ran up the webserver, a bunch of API calls was generally called, and some files were sent to the web server like data.json and style.json, but now the ECS does not show API's being called, but outputs a graph( again without the ability to see the metadata for a node). Do you think these two issues are related?
The following image is the previous output given when the webserver was called:

| True | Regarding reading Metadata in the graph - Hi,
I have been using cloudmapper for a while to scan the resources in my AWS account. Months back( around Septemeber) I ran cloudmapper through an EC2, and I got a nice graph. I was also able to select any node in the graph and I could see the metadata of the node, but now I use an ECS container to do the same exact thing, but I am unable to see the metadata for a node. Can someone help me understand the cause of this issue?
Also when I ran up the webserver, a bunch of API calls was generally called, and some files were sent to the web server like data.json and style.json, but now the ECS does not show API's being called, but outputs a graph( again without the ability to see the metadata for a node). Do you think these two issues are related?
The following image is the previous output given when the webserver was called:

| main | regarding reading metadata in the graph hi i have been using cloudmapper for a while to scan the resources in my aws account months back around septemeber i ran cloudmapper through an and i got a nice graph i was also able to select any node in the graph and i could see the metadata of the node but now i use an ecs container to do the same exact thing but i am unable to see the metadata for a node can someone help me understand the cause of this issue also when i ran up the webserver a bunch of api calls was generally called and some files were sent to the web server like data json and style json but now the ecs does not show api s being called but outputs a graph again without the ability to see the metadata for a node do you think these two issues are related the following image is the previous output given when the webserver was called | 1 |
6,142 | 2,800,206,538 | IssuesEvent | 2015-05-13 08:33:48 | Roy2014Kimi/JI3U47XFP7X25PCEAD3LMVXQ | https://api.github.com/repos/Roy2014Kimi/JI3U47XFP7X25PCEAD3LMVXQ | closed | mEvuGvtD7MhWRFIzA00i21tkLc2ZMZUwgQDAVHAUaoMeqAja46IFxI0HGddhMe/x0zHu4oTqro5h/qgTQV/ZhEFy15x+cHwdTaz2GLzTnLBupje52gtt71g2pw66W0pAfVPe2v2Or7XOYE2Ykc7DBdK8LQIFU8kBJqeHcZI28vw= | design | huhxDA0MujvE/2Eos+iNaYSTXmUgyCxVc7djGYyRBgRlXH8TFmU06BuKB5vtTusTHLpA7k+imA1l/9ZFQIj7u7SP78kY/m3iSG7n2UPP90kuEbt7LMBuxgam51bUx/xaROJc87Y3/WNZMKFAJAhtrGJZxhGe5YY2xGu0I3/H2uvVyuT2btOL/Tos/kSyEBCQIW4faRJ0gdQ2iVuBMC2n3/CGuY/4w4LGVstC7LMBNdxD1anH8d2VH6FHXEy0oK2g3fLfrpRBxhuaJurwGur+3TX/O4TdIdAPs019gQR3KSkeki2hicGYX5KrAsnLZS1CWppIMz0yPFUz4uBvmnxthUeAvM0FmEsJd/Xo714vXB3RkecyTey0N9hVH0KtDui2PaON3/F0inUH+8UzGAkXcvU4ZMdATeiV9xZDenk4kAVsjhC+eVZs+EEraoETIIAgGVkirZzyO1wgHyjgE5yBT5bhK9Zi4dducfdPOP1HEhXLqCAWfpiG3goOynDwU0QzLrVs6x7CUiFxNU3i83xcYASq/CKC4DrBOD4Xr3IPXbQiROFn3kJ+y9TsvBIA7VDXo3iBtUS+YpzBbOnwiZxhI2ndhc0SnIzjUAB3xgLkO0KpGdoOEbJVAg6SMFAH9lMstb2i/tiDIhEltYQZyM+betUE/CvIHBaQ4YMeVxiaUKR97Rw/GKJCJuxXZw4VjhTuW+dtpedyUbZPO9ffRbgEXJvaP6jTXx6uOnbhZp/asOk= | 1.0 | mEvuGvtD7MhWRFIzA00i21tkLc2ZMZUwgQDAVHAUaoMeqAja46IFxI0HGddhMe/x0zHu4oTqro5h/qgTQV/ZhEFy15x+cHwdTaz2GLzTnLBupje52gtt71g2pw66W0pAfVPe2v2Or7XOYE2Ykc7DBdK8LQIFU8kBJqeHcZI28vw= - huhxDA0MujvE/2Eos+iNaYSTXmUgyCxVc7djGYyRBgRlXH8TFmU06BuKB5vtTusTHLpA7k+imA1l/9ZFQIj7u7SP78kY/m3iSG7n2UPP90kuEbt7LMBuxgam51bUx/xaROJc87Y3/WNZMKFAJAhtrGJZxhGe5YY2xGu0I3/H2uvVyuT2btOL/Tos/kSyEBCQIW4faRJ0gdQ2iVuBMC2n3/CGuY/4w4LGVstC7LMBNdxD1anH8d2VH6FHXEy0oK2g3fLfrpRBxhuaJurwGur+3TX/O4TdIdAPs019gQR3KSkeki2hicGYX5KrAsnLZS1CWppIMz0yPFUz4uBvmnxthUeAvM0FmEsJd/Xo714vXB3RkecyTey0N9hVH0KtDui2PaON3/F0inUH+8UzGAkXcvU4ZMdATeiV9xZDenk4kAVsjhC+eVZs+EEraoETIIAgGVkirZzyO1wgHyjgE5yBT5bhK9Zi4dducfdPOP1HEhXLqCAWfpiG3goOynDwU0QzLrVs6x7CUiFxNU3i83xcYASq/CKC4DrBOD4Xr3IPXbQiROFn3kJ+y9TsvBIA7VDXo3iBtUS+YpzBbOnwiZxhI2ndhc0SnIzjUAB3xgLkO0KpGdoOEbJVAg6SMFAH9lMstb2i/tiDIhEltYQZyM+betUE/CvIHBaQ4YMeVxiaUKR97Rw/GKJCJuxXZw4VjhTuW+dtpedyUbZPO9ffRbgEXJvaP6jTXx6uOnbhZp/asOk= | non_main | qgtqv tos cguy evzs tidiheltyqzym betue asok | 0 |
21,487 | 7,030,599,315 | IssuesEvent | 2017-12-26 11:13:16 | Microsoft/WindowsTemplateStudio | https://api.github.com/repos/Microsoft/WindowsTemplateStudio | closed | Build dev.templates.tests.gen_20171226.1 failed | bug vsts-build | ## Build dev.templates.tests.gen_20171226.1
- **Build result:** `failed`
- **Build queued:** 12/26/2017 6:03:58 AM
- **Build duration:** 90.34 minutes
### Details
Build [dev.templates.tests.gen_20171226.1](https://winappstudio.visualstudio.com/web/build.aspx?pcguid=a4ef43be-68ce-4195-a619-079b4d9834c2&builduri=vstfs%3a%2f%2f%2fBuild%2fBuild%2f24537) failed
+ The job running on agent wtsb6 has exceeded the maximum execution time of 01:30:00.
+ The operation was canceled.
Find detailed information in the [build log files](https://uwpctdiags.blob.core.windows.net/buildlogs/dev.templates.tests.gen_20171226.1_logs.zip)
| 1.0 | Build dev.templates.tests.gen_20171226.1 failed - ## Build dev.templates.tests.gen_20171226.1
- **Build result:** `failed`
- **Build queued:** 12/26/2017 6:03:58 AM
- **Build duration:** 90.34 minutes
### Details
Build [dev.templates.tests.gen_20171226.1](https://winappstudio.visualstudio.com/web/build.aspx?pcguid=a4ef43be-68ce-4195-a619-079b4d9834c2&builduri=vstfs%3a%2f%2f%2fBuild%2fBuild%2f24537) failed
+ The job running on agent wtsb6 has exceeded the maximum execution time of 01:30:00.
+ The operation was canceled.
Find detailed information in the [build log files](https://uwpctdiags.blob.core.windows.net/buildlogs/dev.templates.tests.gen_20171226.1_logs.zip)
| non_main | build dev templates tests gen failed build dev templates tests gen build result failed build queued am build duration minutes details build failed the job running on agent has exceeded the maximum execution time of the operation was canceled find detailed information in the | 0 |
360,756 | 25,308,886,357 | IssuesEvent | 2022-11-17 15:59:18 | RosaMariaFdez/2022-ISO2-BC2 | https://api.github.com/repos/RosaMariaFdez/2022-ISO2-BC2 | closed | Añadido de versionado Apartado casos de uso | documentation | Añadir las versiones a las que corresponde cada lista de [casos de uso](https://github.com/RosaMariaFdez/2022-ISO2-BC2/wiki/Documentación-del-proyecto#casos-de-uso-cdu) | 1.0 | Añadido de versionado Apartado casos de uso - Añadir las versiones a las que corresponde cada lista de [casos de uso](https://github.com/RosaMariaFdez/2022-ISO2-BC2/wiki/Documentación-del-proyecto#casos-de-uso-cdu) | non_main | añadido de versionado apartado casos de uso añadir las versiones a las que corresponde cada lista de | 0 |
171,283 | 20,961,013,692 | IssuesEvent | 2022-03-27 19:58:31 | ghc-dev/Christine-Smith | https://api.github.com/repos/ghc-dev/Christine-Smith | opened | github.com/miekg/dns-v1.0.14: 12 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p></summary>
<p>DNS library in Go</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-27918](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27918) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | 1.15.9, 1.16.1 | ❌ |
| [CVE-2018-17847](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17847) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | N/A | ❌ |
| [CVE-2018-17848](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17848) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | github.com/golang/net/html - 309822c5b9b9f80db67f016069a12628d94fad34;github.com/psiphon-labs/net/html - 309822c5b9b9f80db67f016069a12628d94fad34 | ❌ |
| [CVE-2021-33194](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33194) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | N/A | ❌ |
| [CVE-2018-17846](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17846) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | github.com/matishsiao/net/html - 5c9495a32797e34e9bf5ac91e69eb447443b78fd;github.com/pweil-/net/html - 3053e46bf4d836639f474dd738a58070463890e9,5c9495a32797e34e9bf5ac91e69eb447443b78fd,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/psiphon-labs/net/html - 161cd47e91fd58ac17490ef4d742dc98bb4cf60e,2b459478774d488f63f6b8e8ec2429c502a43dd1;github.com/shekhei/net/html - b1ee7b3fbbb773e8e4b649ade000633fb867ba77,66b3e5ee27f66da79cc3695f293932920e946d87;github.com/alexsaveliev/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/foreversmart/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/suedadam/net/html - fbe893ddcdf0e847ed928b77e4b17ff5ec3b8a32;github.com/fangdingjun/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/crmackay/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/jfcote87/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/chris-ramon/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/johnsto/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rsms/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rainkid/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,7ad508c2a7acafff7c6c8522d7e6efda5311476c,2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,3eb064ebfe6b9b907715cf7eeda05c367c55f32d,2e20f33919de098ec28d48d93b0735cc76567f6e,23996681074122163cfa22b185668f84935be9a9,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35;github.com/subuk/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/hugomfernandes/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35,6f62f426de90c0ed6a55207b51476115fcb17237,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/letsencrypt/net/html - 153a6a61520e23dabb758b4a612bff144e5e28eb,1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,d8b496d92df37acaa5a038846651d41f7cbe6326,3748d8c2fdc5600797e1200ed7ca82358bbeadeb,947224908606a5aa6af4427c3a2cea51387aa38a;github.com/nodirt/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87,ec18079348e79eb393866e87d402a1a8cc580d7f;github.com/jash16/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bountylabs/net/html - 2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,59b0df9b1f7abda5aab0495ee54f408daf182ce7,63ee83b038e98e5716bfdd1a94178718cff506d2,9f8bef6b5998053643dca00058a0938278e882ab,1db34d83398887aa887306d261882f799bee3678,46077d3c5415f800cd8105911d4ed880c1db2138;github.com/suifengrock/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,40ad15caf30bbcbd0cb852523ec4dfabc440d37b,5058c78c3627b31e484a81463acd51c7cecc06f3;github.com/petermattis/x-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bradleyfalzon/net/html - 1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,153a6a61520e23dabb758b4a612bff144e5e28eb,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c;github.com/radioinmyhead/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,3053e46bf4d836639f474dd738a58070463890e9;github.com/jelmersnoeck/go.net/html - 104dcad90073cd8d1e6828b2af19185b60cf3e29;github.com/jackmiller334/net/html - d96e6bbf425715f2bd00806e45fbbd5a54870397,63ee83b038e98e5716bfdd1a94178718cff506d2,5b76c8047cfbdbe90fdc031267d2144555ad63e3;github.com/owner888/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/golang/net/html - 97775bb4655419e5ab44c1f918c5bed052130f1b,161cd47e91fd58ac17490ef4d742dc98bb4cf60e;github.com/cesanta/goxnet/html - 23996681074122163cfa22b185668f84935be9a9,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/fanatic/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/8090boy/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/niniwzw/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/smithfox/gonet/html - 835a8501270a5b32645da11de6ee20e02f57e10e;github.com/matishsiao/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,405a8afa2d839d68dbd0481db63e49356af19650,2e20f33919de098ec28d48d93b0735cc76567f6e;github.com/donovanhide/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,1cd7b7179478daf1f19f8b4b4f08106ef411619b | ❌ |
| [CVE-2020-9283](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9283) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236 | ❌ |
| [CVE-2020-29652](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-29652) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | v0.0.0-20201216223049-8b5274cf687f | ❌ |
| [CVE-2020-7919](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7919) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | go - 1.12.16,1.13.7;crypto - v0.0.0-20200128174031-69ecbb4d6d5d | ❌ |
| [CVE-2021-31525](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-31525) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | multiple | Direct | golang - v1.15.12,v1.16.4,v1.17.0 | ❌ |
| [CVE-2019-19794](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19794) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | github.com/miekg/dns-v1.0.14 | Direct | v1.1.25 | ❌ |
| [CVE-2019-11841](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11841) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | github.com/miekg/dns-v1.0.14 | Direct | github.com/dizzyd/go.crypto/openpgp/clearsign - 04d51b511dfb566dd1f82bb6b66a81620178a456,b9b75b879318a4406f0144dcf743881c658f1f6b,826261375936cb3183b191689ef045a117b11442,97102e297913542f7215b5164962dbbb7e3ac329;github.com/scriptrock/crypto/openpgp/clearsign - 9f8b27c8af31154c90cacf5b9be1ddcb46bed784,907750ef230b26d207dd726105c190d72ce98696,c2eb4f1eeb6d905673685dc561c882ddeee035e3,8b4f6e3a0906ea9c46090ee5de4ed06113ad3da3;github.com/winlinvip/crypto/openpgp/clearsign - 6c932297e16070bd20e9384ea78e8afabaa3fae2,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71;github.com/btcsuite/golangcrypto/openpgp/clearsign - b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,fa50e7408b9ef89ff2965535b59f1a0010c0770b,ef64186525f45244f1fd8d843a4474ef77d50f73,5a4ea2fde36b6d025182d6b240aa4518791d58cb,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,280be005b3a662119e76768fe9d91171c1142511;github.com/progrium/crypto/openpgp/clearsign - 7cbb17fecb34db5291cde2f20061eaf746fb8e17,577ae2abf995653ad750624b223792d65a654333,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,eccdd1285ab9ae1cb35bf3b90d777d304263f478;github.com/kmeaw/crypto/openpgp/clearsign - d172538b2cfce0c13cee31e647d0367aa8cd2486,f160b6bf95857cd862817875dd958be022e587c4,3092f0d93ba634e09d6cca8f935db357229b6ad5,efac7f277b17c19894091e358c6130cb6bd51117,019870fc9d457ee8abd13a2e93e3f2a3b55b7119,b07d8c96772f426812d3fc5530710ec1f3b205e7;github.com/juniorz/crypto/openpgp/clearsign - 6ba10a7acbbf2ad7cc0e72a5a9c60fc304c09461,731db29863ea7213d9556d0170afb38987f401d4,dc67354e864179a90a9bec14aa1c9af1344e1394,9fb356864640495bb15bef1f3e78c4264527b364,153731a6de123b98250cbf9e5adbc8d0d950c10a,552202b8e32b8d23879f85948aa263fb809ec2e8,18c283559e20c6fa8b7639afd6c8ba22645655cd,e6ded1797187ebd338e6764d03052931453e7658,929dedf39d9e8e1ffa201091598b681961c04b85,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,8b27f58b78dbd60e9a26b60b0d908ea642974b6d;github.com/codeguard/crypto/openpgp/clearsign - b270509459adaed5fe5be459e6ddb0e1f3ef803d;github.com/seppestas/crypto/openpgp/clearsign - 50ff460fe18dd7f30883cadb9926ed1da056e107,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,7e436327309324370917a1878da60107b88499aa,690e22b80a4c5bae73ab7186ddcca14f82dee9de,4c5258d8b6be6789e3c5433562c226507dc1249f,9c0a3ae19916a277d6d5b582d10b048f04b19e1a;github.com/benburkert/openpgp/clearsign - 0d9cd1316972cc441bd7aa896c05d8e218494c85,f5845320897ceaaabb067fc2fdbc123517fb7fce;github.com/mjkim/crypto/openpgp/clearsign - 9477e0b78b9ac3d0b03822fd95422e2fe07627cd,08da9c60bc7065e1a1df887121f42db309a6ff9a,44256fa2dfb760488af0b3f966ab00bcf98b1411,2c5e2074680afae185175121fc549913bf6f32c9,a548aac93ed489257b9d959b40fe1e8c1e20778c,d5c5f1769f2fcd2377be6f29863081f59a4fc80f,0e31b188fd38db611d4fbab7de9373a95f36aae5,351dc6a5bf92a5f2ae22fadeee08eb6a45aa2d93,18c283559e20c6fa8b7639afd6c8ba22645655cd,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,eb19e229bd898d2a3e69bdc0478553927be3b235,7c7765c32f8127cd34cde75d2eb450ae6a7b692e,db732cbcc6772c3a16d666f5cd737d32c4a12052,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,1351f936d976c60a0a48d728281922cf63eafb8d,63f855d724c1fff8ec15a0191dcda32ec7761cc4,173ce04bfaf66c7bb0fa9d5c0bfd93e773909dbd,7f27901cb9636a61b9b0b1bab2679b2a9a12eb38,b8a0f4bb4040f8d884435cff35b9691e362cf00c,c34e38ab9ea85314630ff172a2378cd5da44e299,c1c0bfbd3ac981a523e036008cfb2d9ac2d9c967,f59690be3f9a31481d227f885bfe2466be0c5d27,7db43667c77d5d330c359ffd03f5789cf390e973,4ed45ec682102c643324fae5dff8dab085b6c300;github.com/cmars/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,b9b75b879318a4406f0144dcf743881c658f1f6b;github.com/scalingdata/go-x-crypto/openpgp/clearsign - 8b27f58b78dbd60e9a26b60b0d908ea642974b6d,ffadfa66488ddd3d386e89ebb19280aa87c098a6,9fb356864640495bb15bef1f3e78c4264527b364,03be8f3bf08562c9abf595f4a88954d5dff55e82,3092f0d93ba634e09d6cca8f935db357229b6ad5,4147256c9cfc043b679bae483b623e0076f9ed60,9b55b542f68bcaf688633f6e810d3d41b9c87739,7e436327309324370917a1878da60107b88499aa,77f4136a99ffb5ecdbdd0226bd5cb146cf56bc0e,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71,4ed45ec682102c643324fae5dff8dab085b6c300,10c26747e67d76ad4fafe6087c6f4073c3b22942;github.com/mehrdadrad/crypto/openpgp/clearsign - 81e0b644eb2f05832b1801391bc9386a81e4fe45,eccdd1285ab9ae1cb35bf3b90d777d304263f478,124e52db8dfdfab4fc56ea36c2957b8d996ff760,c9c0e06eed439a60df0ef7aa13c0b97e19cdd3a7,632d287f9f3f54b09809eebbd3cacbcb00b9f2fc,eca6c1626e1a5b651a7a131cdb6b435930f64498,43c4f8a8964d075ae4829f4cabb2f8c0b685fdc5,1fbbd62cfec66bd39d91e97749579579d4d3037e,ce1cf546ac92dd001ee433ec58b6b0f9828e1cee,15577f9df470bf5e9292240050c4c84d210732d7,9e886ee4f218fc3dcdf33c35cee6e798d61c5b85,c57d4a71915a248dbad846d60825145062b4c18e,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,88b65fb66346493d43e735adad931bf69dee4297,d67eb63455fa4d6fca5802332d86f1f204017e00,58afe880f197c244a2edbfab2bb090a5bf02dfe1,df1b4d2fcd21fb05d2ac65176e2a4243c201a920,cc04154d65fb9296747569b107cfd05380b1ea3e,4831188890de893ae55d9ecd1bbafc340ce0ff9f,c197bcf24cde29d3f73c7b4ac6fd41f4384e8af6,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,929dedf39d9e8e1ffa201091598b681961c04b85,4d8f0cfeca8290cfc0091edf678a138ce669b1bb,3fbbcd23f1cb824e69491a5930cfeff09b12f4d2,7b428712abe956d0e9e1e9a01e163fb6c7171438,9b55b542f68bcaf688633f6e810d3d41b9c87739,63a71ca82d5ccbe458cc4acef0c0ea8076463976,552202b8e32b8d23879f85948aa263fb809ec2e8;github.com/benbjohnson/crypto/openpgp/clearsign - c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3;github.com/u-s-p/crypto/openpgp/clearsign - 2e60680932240e15a179f3b34782f42b7199981a,f5f25bdad0cb2b768bdea003ed92329914931542,4c5258d8b6be6789e3c5433562c226507dc1249f,0214db40ef9cee9306086200828340ba6253b6ce,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,b6789ab629056511030d652d851e7dc10c9e9c9e,d95b28330da59cfd5b511cea8d98ce3379610013,4147256c9cfc043b679bae483b623e0076f9ed60,cbc3d0884eac986df6e78a039b8792e869bff863,3cb07270c9455e8ad27956a70891c962d121a228,b176d7def5d71bdd214203491f89843ed217f420,6575f7ea326e67d12b77872ff66f5ea15f8aefad,575fdbe86e5dd89229707ebec0575ce7d088a4a6,484eb34681af59703e639b971bc307019182c41f,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,e311231e83195f401421a286060d65643f9c9d40,c2c80b64c04ccb917376270f715718ec87bacb29,eca6c1626e1a5b651a7a131cdb6b435930f64498,3ded668c5379f6951fb0de06174442072e5447d3,d8e61c69ab46ca38328da2f4995abaf93b252290,6318898455d3ac20e7e44d0a080d43f8c3ff120b,7b428712abe956d0e9e1e9a01e163fb6c7171438,c7af5bf2638a1164f2eb5467c39c6cffbd13a02e,59a182cab66ead4fe21e6472267504ac035edee2,396847505b5d877809d99cbba288cbca62ea189c,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,e7ba82683099cae71475961448ab8f903ea77c26,8f45c680ceb25c200b8c301d9184532aeb7cb36e,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,dc703e91d7bf2ed50e4e847371f53a4c0a83693c;github.com/vividcortex/crypto/openpgp/clearsign - ca7e7f10cb9fd9c1a6ff7f60436c086d73714180,d33bbf2cb3b8574ad57ddba26f03e861c01f69c5,5ef0053f77724838734b6945dd364d3847e5de1d,2b786ab9e9649dc660afa3bd580fd05a05e20d95,9fbab14f903f89e23047b5971369b86380230e56,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,c7e3b0ebdd409a0d024e3d71801427ab0e05fb2e,e1b0d6c49fae5632d0a563812fce85b5b542fbcf,a3c6050446ec077a5f411deb35d89b420f8d5fd7,b286ef4198388fdb0e4ae62be12820df5da9b4c2,88b65fb66346493d43e735adad931bf69dee4297,d43a35d821f1e9a9dcb701ffab4cb5bc12d4006c,eb71ad9bd329b5ac0fd0148dd99bd62e8be8e035,119f50887f8fe324fe2386421c27a11af014b64e,6de97b525f030fe8dce13090d5c3731799bb9d3e,1a85842c9ed153459eaf94f2ff4c4e914c54410d,f944096df80415fafc888544caecaab86a991785,b7f382b979dc349948b0e69fbbf7fb2a7ef6b7d9,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,f160b6bf95857cd862817875dd958be022e587c4,6575f7ea326e67d12b77872ff66f5ea15f8aefad,59a4410d829a8bb774b02b56d4aeab633414f233,f17d1302814ed95db5a4fae9ac53b86021a7584b,c367d6eeb7c6158125f2f47e049f7eb7e251c09a,2c99acdd1e9b90d779ca23f632aad86af9909c62,c0d640c88782f757a45d3f7b93eec2ec63b229cb,47ff8dfbc528fea3003fc0ce2d88ffbbfbc46a43,0d8dc3cd6a6b69fac2c54037ae8c235519cfbddc;github.com/gxed/go-crypto/openpgp/clearsign - 9b1a210a06ea1176ec1f0a1ddf83ad7463b8ea3e;github.com/fluidkeys/crypto/openpgp/clearsign - 2018-08-22;github.com/benburkert/crypto/openpgp/clearsign - e3f150b4372fce47109dbd8fef5f03cd2af08700,0d3cfff99f4428b308d63d9386fec9cd86475faa,61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,6575f7ea326e67d12b77872ff66f5ea15f8aefad,bc89c496413265e715159bdc8478ee9a92fdc265,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,fa50e7408b9ef89ff2965535b59f1a0010c0770b,f1b99bc9f1eb185629f6c4b5bd983dd66da2e0e8,ed40a6cc352d9acfba912aae191023ebdc0461d1,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,b270509459adaed5fe5be459e6ddb0e1f3ef803d,3f77d695175f990a2967385c493939f380ee40a3,76cee1b7b184f79a9d93bbfcb287d0c03391928c,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,160b2e156e1c2c1e7d8db6b5e3f6ccf75e9dd34f,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,aa0f5b40812c405df7480c8a69e7f0160363a94b,62944567d8abab8255c3bfcf82c8c347c7577c62,fcdb74e78f2621098ebc0376bbadffcf580ccfe4,8e06e8ddd9629eb88639aba897641bff8031f1d3,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5;github.com/jlburkhead/crypto/openpgp/clearsign - bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,4c5258d8b6be6789e3c5433562c226507dc1249f,c2c80b64c04ccb917376270f715718ec87bacb29,2e60680932240e15a179f3b34782f42b7199981a,eca6c1626e1a5b651a7a131cdb6b435930f64498,4147256c9cfc043b679bae483b623e0076f9ed60,d95b28330da59cfd5b511cea8d98ce3379610013,396847505b5d877809d99cbba288cbca62ea189c,dc703e91d7bf2ed50e4e847371f53a4c0a83693c,f5f25bdad0cb2b768bdea003ed92329914931542,18c283559e20c6fa8b7639afd6c8ba22645655cd,cb7a96fa34f94f61171c4bdce01baf2411356574,c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3,2aff5f12d83011dd1f9aeb358eb851b28668cf60,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,8f45c680ceb25c200b8c301d9184532aeb7cb36e;github.com/schoppmp/go-crypto/openpgp/clearsign - 15577f9df470bf5e9292240050c4c84d210732d7,dc67354e864179a90a9bec14aa1c9af1344e1394;github.com/protonmail/crypto/openpgp/clearsign - 3a07e4a428e17dc7e67df31f702ac03e64522f53;github.com/szank/crypto/openpgp/clearsign - 61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,62944567d8abab8255c3bfcf82c8c347c7577c62,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,aa0f5b40812c405df7480c8a69e7f0160363a94b,0d3cfff99f4428b308d63d9386fec9cd86475faa,665213f561b1d86f94956515da4886141e45eb9b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f;github.com/conseweb/golangcrypto/openpgp/clearsign - 280be005b3a662119e76768fe9d91171c1142511,fa50e7408b9ef89ff2965535b59f1a0010c0770b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,ef64186525f45244f1fd8d843a4474ef77d50f73,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,5a4ea2fde36b6d025182d6b240aa4518791d58cb;github.com/dizzyd/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,400097dc741fc8fbcb8d7dd14304aa27bc124478,bc066ba6717d69b2d3998b93b9a27b3e7e5b74ea,5bb6445962bed970d80a2882706ba2c26f7426cd | ❌ |
| [WS-2019-0030](https://github.com/golang/crypto/commit/b7391e95e576cacdcdd422573063bc057239113d) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | github.com/miekg/dns-v1.0.14 | Direct | commit b7391e95e576cacdcdd422573063bc057239113d | ❌ |
## Details
> Partial details (7 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-27918</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
encoding/xml in Go before 1.15.9 and 1.16.x before 1.16.1 has an infinite loop if a custom TokenReader (for xml.NewTokenDecoder) returns EOF in the middle of an element. This can occur in the Decode, DecodeElement, or Skip method.
<p>Publish Date: 2021-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27918>CVE-2021-27918</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/g/golang-announce/c/MfiLYjG-RAw">https://groups.google.com/g/golang-announce/c/MfiLYjG-RAw</a></p>
<p>Release Date: 2021-03-11</p>
<p>Fix Resolution: 1.15.9, 1.16.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-17847</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The html package (aka x/net/html) through 2018-09-25 in Go mishandles <svg><template><desc><t><svg></template>, leading to a "panic: runtime error" (index out of range) in (*nodeStack).pop in node.go, called from (*parser).clearActiveFormattingElements, during an html.Parse call.
<p>Publish Date: 2018-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17847>CVE-2018-17847</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-17848</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The html package (aka x/net/html) through 2018-09-25 in Go mishandles <math><template><mn><b></template>, leading to a "panic: runtime error" (index out of range) in (*insertionModeStack).pop in node.go, called from inHeadIM, during an html.Parse call.
<p>Publish Date: 2018-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17848>CVE-2018-17848</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-17848">https://nvd.nist.gov/vuln/detail/CVE-2018-17848</a></p>
<p>Release Date: 2018-10-01</p>
<p>Fix Resolution: github.com/golang/net/html - 309822c5b9b9f80db67f016069a12628d94fad34;github.com/psiphon-labs/net/html - 309822c5b9b9f80db67f016069a12628d94fad34</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33194</summary>
### Vulnerable Libraries - <b>github.com/miekg/dns-v1.0.14</b>, <b>github.com/golang/net-e18ecbb051101a46fc263334b127c89bc7bff7ea</b></p>
<p>
### <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
### <b>github.com/golang/net-e18ecbb051101a46fc263334b127c89bc7bff7ea</b></p>
<p>[mirror] Go supplementary network libraries</p>
<p>
Dependency Hierarchy:
- github.com/miekg/dns-v1.0.14 (Root Library)
- :x: **github.com/golang/net-e18ecbb051101a46fc263334b127c89bc7bff7ea** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
golang.org/x/net before v0.0.0-20210520170846-37e1c6afe023 allows attackers to cause a denial of service (infinite loop) via crafted ParseFragment input.
<p>Publish Date: 2021-05-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33194>CVE-2021-33194</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-17846</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The html package (aka x/net/html) through 2018-09-25 in Go mishandles <table><math><select><mi><select></table>, leading to an infinite loop during an html.Parse call because inSelectIM and inSelectInTableIM do not comply with a specification.
<p>Publish Date: 2018-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17846>CVE-2018-17846</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-17846">https://nvd.nist.gov/vuln/detail/CVE-2018-17846</a></p>
<p>Release Date: 2018-10-01</p>
<p>Fix Resolution: github.com/matishsiao/net/html - 5c9495a32797e34e9bf5ac91e69eb447443b78fd;github.com/pweil-/net/html - 3053e46bf4d836639f474dd738a58070463890e9,5c9495a32797e34e9bf5ac91e69eb447443b78fd,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/psiphon-labs/net/html - 161cd47e91fd58ac17490ef4d742dc98bb4cf60e,2b459478774d488f63f6b8e8ec2429c502a43dd1;github.com/shekhei/net/html - b1ee7b3fbbb773e8e4b649ade000633fb867ba77,66b3e5ee27f66da79cc3695f293932920e946d87;github.com/alexsaveliev/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/foreversmart/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/suedadam/net/html - fbe893ddcdf0e847ed928b77e4b17ff5ec3b8a32;github.com/fangdingjun/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/crmackay/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/jfcote87/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/chris-ramon/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/johnsto/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rsms/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rainkid/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,7ad508c2a7acafff7c6c8522d7e6efda5311476c,2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,3eb064ebfe6b9b907715cf7eeda05c367c55f32d,2e20f33919de098ec28d48d93b0735cc76567f6e,23996681074122163cfa22b185668f84935be9a9,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35;github.com/subuk/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/hugomfernandes/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35,6f62f426de90c0ed6a55207b51476115fcb17237,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/letsencrypt/net/html - 153a6a61520e23dabb758b4a612bff144e5e28eb,1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,d8b496d92df37acaa5a038846651d41f7cbe6326,3748d8c2fdc5600797e1200ed7ca82358bbeadeb,947224908606a5aa6af4427c3a2cea51387aa38a;github.com/nodirt/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87,ec18079348e79eb393866e87d402a1a8cc580d7f;github.com/jash16/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bountylabs/net/html - 2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,59b0df9b1f7abda5aab0495ee54f408daf182ce7,63ee83b038e98e5716bfdd1a94178718cff506d2,9f8bef6b5998053643dca00058a0938278e882ab,1db34d83398887aa887306d261882f799bee3678,46077d3c5415f800cd8105911d4ed880c1db2138;github.com/suifengrock/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,40ad15caf30bbcbd0cb852523ec4dfabc440d37b,5058c78c3627b31e484a81463acd51c7cecc06f3;github.com/petermattis/x-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bradleyfalzon/net/html - 1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,153a6a61520e23dabb758b4a612bff144e5e28eb,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c;github.com/radioinmyhead/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,3053e46bf4d836639f474dd738a58070463890e9;github.com/jelmersnoeck/go.net/html - 104dcad90073cd8d1e6828b2af19185b60cf3e29;github.com/jackmiller334/net/html - d96e6bbf425715f2bd00806e45fbbd5a54870397,63ee83b038e98e5716bfdd1a94178718cff506d2,5b76c8047cfbdbe90fdc031267d2144555ad63e3;github.com/owner888/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/golang/net/html - 97775bb4655419e5ab44c1f918c5bed052130f1b,161cd47e91fd58ac17490ef4d742dc98bb4cf60e;github.com/cesanta/goxnet/html - 23996681074122163cfa22b185668f84935be9a9,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/fanatic/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/8090boy/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/niniwzw/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/smithfox/gonet/html - 835a8501270a5b32645da11de6ee20e02f57e10e;github.com/matishsiao/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,405a8afa2d839d68dbd0481db63e49356af19650,2e20f33919de098ec28d48d93b0735cc76567f6e;github.com/donovanhide/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,1cd7b7179478daf1f19f8b4b4f08106ef411619b</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9283</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
golang.org/x/crypto before v0.0.0-20200220183623-bac4c82f6975 for Go allows a panic during signature verification in the golang.org/x/crypto/ssh package. A client can attack an SSH server that accepts public keys. Also, a server can attack any SSH client.
<p>Publish Date: 2020-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9283>CVE-2020-9283</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283</a></p>
<p>Release Date: 2020-02-20</p>
<p>Fix Resolution: github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-29652</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A nil pointer dereference in the golang.org/x/crypto/ssh component through v0.0.0-20201203163018-be400aefbc4c for Go allows remote attackers to cause a denial of service against SSH servers.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-29652>CVE-2020-29652</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1">https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: v0.0.0-20201216223049-8b5274cf687f</p>
</p>
<p></p>
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.15.9, 1.16.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-27918","vulnerabilityDetails":"encoding/xml in Go before 1.15.9 and 1.16.x before 1.16.1 has an infinite loop if a custom TokenReader (for xml.NewTokenDecoder) returns EOF in the middle of an element. This can occur in the Decode, DecodeElement, or Skip method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27918","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":false,"isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-17847","vulnerabilityDetails":"The html package (aka x/net/html) through 2018-09-25 in Go mishandles \u003csvg\u003e\u003ctemplate\u003e\u003cdesc\u003e\u003ct\u003e\u003csvg\u003e\u003c/template\u003e, leading to a \"panic: runtime error\" (index out of range) in (*nodeStack).pop in node.go, called from (*parser).clearActiveFormattingElements, during an html.Parse call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17847","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/golang/net/html - 309822c5b9b9f80db67f016069a12628d94fad34;github.com/psiphon-labs/net/html - 309822c5b9b9f80db67f016069a12628d94fad34","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-17848","vulnerabilityDetails":"The html package (aka x/net/html) through 2018-09-25 in Go mishandles \u003cmath\u003e\u003ctemplate\u003e\u003cmn\u003e\u003cb\u003e\u003c/template\u003e, leading to a \"panic: runtime error\" (index out of range) in (*insertionModeStack).pop in node.go, called from inHeadIM, during an html.Parse call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17848","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":false,"isBinary":true},{"packageType":"GO","packageName":"github.com/golang/net","packageVersion":"e18ecbb051101a46fc263334b127c89bc7bff7ea","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/miekg/dns:v1.0.14;github.com/golang/net:e18ecbb051101a46fc263334b127c89bc7bff7ea","isMinimumFixVersionAvailable":false,"isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-33194","vulnerabilityDetails":"golang.org/x/net before v0.0.0-20210520170846-37e1c6afe023 allows attackers to cause a denial of service (infinite loop) via crafted ParseFragment input.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33194","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/matishsiao/net/html - 5c9495a32797e34e9bf5ac91e69eb447443b78fd;github.com/pweil-/net/html - 3053e46bf4d836639f474dd738a58070463890e9,5c9495a32797e34e9bf5ac91e69eb447443b78fd,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/psiphon-labs/net/html - 161cd47e91fd58ac17490ef4d742dc98bb4cf60e,2b459478774d488f63f6b8e8ec2429c502a43dd1;github.com/shekhei/net/html - b1ee7b3fbbb773e8e4b649ade000633fb867ba77,66b3e5ee27f66da79cc3695f293932920e946d87;github.com/alexsaveliev/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/foreversmart/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/suedadam/net/html - fbe893ddcdf0e847ed928b77e4b17ff5ec3b8a32;github.com/fangdingjun/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/crmackay/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/jfcote87/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/chris-ramon/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/johnsto/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rsms/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rainkid/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,7ad508c2a7acafff7c6c8522d7e6efda5311476c,2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,3eb064ebfe6b9b907715cf7eeda05c367c55f32d,2e20f33919de098ec28d48d93b0735cc76567f6e,23996681074122163cfa22b185668f84935be9a9,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35;github.com/subuk/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/hugomfernandes/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35,6f62f426de90c0ed6a55207b51476115fcb17237,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/letsencrypt/net/html - 153a6a61520e23dabb758b4a612bff144e5e28eb,1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,d8b496d92df37acaa5a038846651d41f7cbe6326,3748d8c2fdc5600797e1200ed7ca82358bbeadeb,947224908606a5aa6af4427c3a2cea51387aa38a;github.com/nodirt/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87,ec18079348e79eb393866e87d402a1a8cc580d7f;github.com/jash16/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bountylabs/net/html - 2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,59b0df9b1f7abda5aab0495ee54f408daf182ce7,63ee83b038e98e5716bfdd1a94178718cff506d2,9f8bef6b5998053643dca00058a0938278e882ab,1db34d83398887aa887306d261882f799bee3678,46077d3c5415f800cd8105911d4ed880c1db2138;github.com/suifengrock/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,40ad15caf30bbcbd0cb852523ec4dfabc440d37b,5058c78c3627b31e484a81463acd51c7cecc06f3;github.com/petermattis/x-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bradleyfalzon/net/html - 1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,153a6a61520e23dabb758b4a612bff144e5e28eb,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c;github.com/radioinmyhead/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,3053e46bf4d836639f474dd738a58070463890e9;github.com/jelmersnoeck/go.net/html - 104dcad90073cd8d1e6828b2af19185b60cf3e29;github.com/jackmiller334/net/html - d96e6bbf425715f2bd00806e45fbbd5a54870397,63ee83b038e98e5716bfdd1a94178718cff506d2,5b76c8047cfbdbe90fdc031267d2144555ad63e3;github.com/owner888/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/golang/net/html - 97775bb4655419e5ab44c1f918c5bed052130f1b,161cd47e91fd58ac17490ef4d742dc98bb4cf60e;github.com/cesanta/goxnet/html - 23996681074122163cfa22b185668f84935be9a9,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/fanatic/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/8090boy/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/niniwzw/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/smithfox/gonet/html - 835a8501270a5b32645da11de6ee20e02f57e10e;github.com/matishsiao/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,405a8afa2d839d68dbd0481db63e49356af19650,2e20f33919de098ec28d48d93b0735cc76567f6e;github.com/donovanhide/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,1cd7b7179478daf1f19f8b4b4f08106ef411619b","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-17846","vulnerabilityDetails":"The html package (aka x/net/html) through 2018-09-25 in Go mishandles \u003ctable\u003e\u003cmath\u003e\u003cselect\u003e\u003cmi\u003e\u003cselect\u003e\u003c/table\u003e, leading to an infinite loop during an html.Parse call because inSelectIM and inSelectInTableIM do not comply with a specification.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17846","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-9283","vulnerabilityDetails":"golang.org/x/crypto before v0.0.0-20200220183623-bac4c82f6975 for Go allows a panic during signature verification in the golang.org/x/crypto/ssh package. A client can attack an SSH server that accepts public keys. Also, a server can attack any SSH client.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9283","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v0.0.0-20201216223049-8b5274cf687f","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-29652","vulnerabilityDetails":"A nil pointer dereference in the golang.org/x/crypto/ssh component through v0.0.0-20201203163018-be400aefbc4c for Go allows remote attackers to cause a denial of service against SSH servers.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-29652","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"go - 1.12.16,1.13.7;crypto - v0.0.0-20200128174031-69ecbb4d6d5d","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7919","vulnerabilityDetails":"Go before 1.12.16 and 1.13.x before 1.13.7 (and the crypto/cryptobyte package before 0.0.0-20200124225646-8b5121be2f68 for Go) allows attacks on clients (resulting in a panic) via a malformed X.509 certificate.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7919","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"golang - v1.15.12,v1.16.4,v1.17.0","isBinary":true},{"packageType":"GO","packageName":"github.com/golang/net","packageVersion":"e18ecbb051101a46fc263334b127c89bc7bff7ea","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/miekg/dns:v1.0.14;github.com/golang/net:e18ecbb051101a46fc263334b127c89bc7bff7ea","isMinimumFixVersionAvailable":true,"minimumFixVersion":"golang - v1.15.12,v1.16.4,v1.17.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-31525","vulnerabilityDetails":"net/http in Go before 1.15.12 and 1.16.x before 1.16.4 allows remote attackers to cause a denial of service (panic) via a large header to ReadRequest or ReadResponse. Server, Transport, and Client can each be affected in some configurations.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-31525","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v1.1.25","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-19794","vulnerabilityDetails":"The miekg Go DNS package before 1.1.25, as used in CoreDNS before 1.6.6 and other products, improperly generates random numbers because math/rand is used. The TXID becomes predictable, leading to response forgeries.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19794","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/dizzyd/go.crypto/openpgp/clearsign - 04d51b511dfb566dd1f82bb6b66a81620178a456,b9b75b879318a4406f0144dcf743881c658f1f6b,826261375936cb3183b191689ef045a117b11442,97102e297913542f7215b5164962dbbb7e3ac329;github.com/scriptrock/crypto/openpgp/clearsign - 9f8b27c8af31154c90cacf5b9be1ddcb46bed784,907750ef230b26d207dd726105c190d72ce98696,c2eb4f1eeb6d905673685dc561c882ddeee035e3,8b4f6e3a0906ea9c46090ee5de4ed06113ad3da3;github.com/winlinvip/crypto/openpgp/clearsign - 6c932297e16070bd20e9384ea78e8afabaa3fae2,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71;github.com/btcsuite/golangcrypto/openpgp/clearsign - b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,fa50e7408b9ef89ff2965535b59f1a0010c0770b,ef64186525f45244f1fd8d843a4474ef77d50f73,5a4ea2fde36b6d025182d6b240aa4518791d58cb,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,280be005b3a662119e76768fe9d91171c1142511;github.com/progrium/crypto/openpgp/clearsign - 7cbb17fecb34db5291cde2f20061eaf746fb8e17,577ae2abf995653ad750624b223792d65a654333,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,eccdd1285ab9ae1cb35bf3b90d777d304263f478;github.com/kmeaw/crypto/openpgp/clearsign - d172538b2cfce0c13cee31e647d0367aa8cd2486,f160b6bf95857cd862817875dd958be022e587c4,3092f0d93ba634e09d6cca8f935db357229b6ad5,efac7f277b17c19894091e358c6130cb6bd51117,019870fc9d457ee8abd13a2e93e3f2a3b55b7119,b07d8c96772f426812d3fc5530710ec1f3b205e7;github.com/juniorz/crypto/openpgp/clearsign - 6ba10a7acbbf2ad7cc0e72a5a9c60fc304c09461,731db29863ea7213d9556d0170afb38987f401d4,dc67354e864179a90a9bec14aa1c9af1344e1394,9fb356864640495bb15bef1f3e78c4264527b364,153731a6de123b98250cbf9e5adbc8d0d950c10a,552202b8e32b8d23879f85948aa263fb809ec2e8,18c283559e20c6fa8b7639afd6c8ba22645655cd,e6ded1797187ebd338e6764d03052931453e7658,929dedf39d9e8e1ffa201091598b681961c04b85,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,8b27f58b78dbd60e9a26b60b0d908ea642974b6d;github.com/codeguard/crypto/openpgp/clearsign - b270509459adaed5fe5be459e6ddb0e1f3ef803d;github.com/seppestas/crypto/openpgp/clearsign - 50ff460fe18dd7f30883cadb9926ed1da056e107,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,7e436327309324370917a1878da60107b88499aa,690e22b80a4c5bae73ab7186ddcca14f82dee9de,4c5258d8b6be6789e3c5433562c226507dc1249f,9c0a3ae19916a277d6d5b582d10b048f04b19e1a;github.com/benburkert/openpgp/clearsign - 0d9cd1316972cc441bd7aa896c05d8e218494c85,f5845320897ceaaabb067fc2fdbc123517fb7fce;github.com/mjkim/crypto/openpgp/clearsign - 9477e0b78b9ac3d0b03822fd95422e2fe07627cd,08da9c60bc7065e1a1df887121f42db309a6ff9a,44256fa2dfb760488af0b3f966ab00bcf98b1411,2c5e2074680afae185175121fc549913bf6f32c9,a548aac93ed489257b9d959b40fe1e8c1e20778c,d5c5f1769f2fcd2377be6f29863081f59a4fc80f,0e31b188fd38db611d4fbab7de9373a95f36aae5,351dc6a5bf92a5f2ae22fadeee08eb6a45aa2d93,18c283559e20c6fa8b7639afd6c8ba22645655cd,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,eb19e229bd898d2a3e69bdc0478553927be3b235,7c7765c32f8127cd34cde75d2eb450ae6a7b692e,db732cbcc6772c3a16d666f5cd737d32c4a12052,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,1351f936d976c60a0a48d728281922cf63eafb8d,63f855d724c1fff8ec15a0191dcda32ec7761cc4,173ce04bfaf66c7bb0fa9d5c0bfd93e773909dbd,7f27901cb9636a61b9b0b1bab2679b2a9a12eb38,b8a0f4bb4040f8d884435cff35b9691e362cf00c,c34e38ab9ea85314630ff172a2378cd5da44e299,c1c0bfbd3ac981a523e036008cfb2d9ac2d9c967,f59690be3f9a31481d227f885bfe2466be0c5d27,7db43667c77d5d330c359ffd03f5789cf390e973,4ed45ec682102c643324fae5dff8dab085b6c300;github.com/cmars/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,b9b75b879318a4406f0144dcf743881c658f1f6b;github.com/scalingdata/go-x-crypto/openpgp/clearsign - 8b27f58b78dbd60e9a26b60b0d908ea642974b6d,ffadfa66488ddd3d386e89ebb19280aa87c098a6,9fb356864640495bb15bef1f3e78c4264527b364,03be8f3bf08562c9abf595f4a88954d5dff55e82,3092f0d93ba634e09d6cca8f935db357229b6ad5,4147256c9cfc043b679bae483b623e0076f9ed60,9b55b542f68bcaf688633f6e810d3d41b9c87739,7e436327309324370917a1878da60107b88499aa,77f4136a99ffb5ecdbdd0226bd5cb146cf56bc0e,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71,4ed45ec682102c643324fae5dff8dab085b6c300,10c26747e67d76ad4fafe6087c6f4073c3b22942;github.com/mehrdadrad/crypto/openpgp/clearsign - 81e0b644eb2f05832b1801391bc9386a81e4fe45,eccdd1285ab9ae1cb35bf3b90d777d304263f478,124e52db8dfdfab4fc56ea36c2957b8d996ff760,c9c0e06eed439a60df0ef7aa13c0b97e19cdd3a7,632d287f9f3f54b09809eebbd3cacbcb00b9f2fc,eca6c1626e1a5b651a7a131cdb6b435930f64498,43c4f8a8964d075ae4829f4cabb2f8c0b685fdc5,1fbbd62cfec66bd39d91e97749579579d4d3037e,ce1cf546ac92dd001ee433ec58b6b0f9828e1cee,15577f9df470bf5e9292240050c4c84d210732d7,9e886ee4f218fc3dcdf33c35cee6e798d61c5b85,c57d4a71915a248dbad846d60825145062b4c18e,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,88b65fb66346493d43e735adad931bf69dee4297,d67eb63455fa4d6fca5802332d86f1f204017e00,58afe880f197c244a2edbfab2bb090a5bf02dfe1,df1b4d2fcd21fb05d2ac65176e2a4243c201a920,cc04154d65fb9296747569b107cfd05380b1ea3e,4831188890de893ae55d9ecd1bbafc340ce0ff9f,c197bcf24cde29d3f73c7b4ac6fd41f4384e8af6,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,929dedf39d9e8e1ffa201091598b681961c04b85,4d8f0cfeca8290cfc0091edf678a138ce669b1bb,3fbbcd23f1cb824e69491a5930cfeff09b12f4d2,7b428712abe956d0e9e1e9a01e163fb6c7171438,9b55b542f68bcaf688633f6e810d3d41b9c87739,63a71ca82d5ccbe458cc4acef0c0ea8076463976,552202b8e32b8d23879f85948aa263fb809ec2e8;github.com/benbjohnson/crypto/openpgp/clearsign - c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3;github.com/u-s-p/crypto/openpgp/clearsign - 2e60680932240e15a179f3b34782f42b7199981a,f5f25bdad0cb2b768bdea003ed92329914931542,4c5258d8b6be6789e3c5433562c226507dc1249f,0214db40ef9cee9306086200828340ba6253b6ce,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,b6789ab629056511030d652d851e7dc10c9e9c9e,d95b28330da59cfd5b511cea8d98ce3379610013,4147256c9cfc043b679bae483b623e0076f9ed60,cbc3d0884eac986df6e78a039b8792e869bff863,3cb07270c9455e8ad27956a70891c962d121a228,b176d7def5d71bdd214203491f89843ed217f420,6575f7ea326e67d12b77872ff66f5ea15f8aefad,575fdbe86e5dd89229707ebec0575ce7d088a4a6,484eb34681af59703e639b971bc307019182c41f,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,e311231e83195f401421a286060d65643f9c9d40,c2c80b64c04ccb917376270f715718ec87bacb29,eca6c1626e1a5b651a7a131cdb6b435930f64498,3ded668c5379f6951fb0de06174442072e5447d3,d8e61c69ab46ca38328da2f4995abaf93b252290,6318898455d3ac20e7e44d0a080d43f8c3ff120b,7b428712abe956d0e9e1e9a01e163fb6c7171438,c7af5bf2638a1164f2eb5467c39c6cffbd13a02e,59a182cab66ead4fe21e6472267504ac035edee2,396847505b5d877809d99cbba288cbca62ea189c,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,e7ba82683099cae71475961448ab8f903ea77c26,8f45c680ceb25c200b8c301d9184532aeb7cb36e,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,dc703e91d7bf2ed50e4e847371f53a4c0a83693c;github.com/vividcortex/crypto/openpgp/clearsign - ca7e7f10cb9fd9c1a6ff7f60436c086d73714180,d33bbf2cb3b8574ad57ddba26f03e861c01f69c5,5ef0053f77724838734b6945dd364d3847e5de1d,2b786ab9e9649dc660afa3bd580fd05a05e20d95,9fbab14f903f89e23047b5971369b86380230e56,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,c7e3b0ebdd409a0d024e3d71801427ab0e05fb2e,e1b0d6c49fae5632d0a563812fce85b5b542fbcf,a3c6050446ec077a5f411deb35d89b420f8d5fd7,b286ef4198388fdb0e4ae62be12820df5da9b4c2,88b65fb66346493d43e735adad931bf69dee4297,d43a35d821f1e9a9dcb701ffab4cb5bc12d4006c,eb71ad9bd329b5ac0fd0148dd99bd62e8be8e035,119f50887f8fe324fe2386421c27a11af014b64e,6de97b525f030fe8dce13090d5c3731799bb9d3e,1a85842c9ed153459eaf94f2ff4c4e914c54410d,f944096df80415fafc888544caecaab86a991785,b7f382b979dc349948b0e69fbbf7fb2a7ef6b7d9,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,f160b6bf95857cd862817875dd958be022e587c4,6575f7ea326e67d12b77872ff66f5ea15f8aefad,59a4410d829a8bb774b02b56d4aeab633414f233,f17d1302814ed95db5a4fae9ac53b86021a7584b,c367d6eeb7c6158125f2f47e049f7eb7e251c09a,2c99acdd1e9b90d779ca23f632aad86af9909c62,c0d640c88782f757a45d3f7b93eec2ec63b229cb,47ff8dfbc528fea3003fc0ce2d88ffbbfbc46a43,0d8dc3cd6a6b69fac2c54037ae8c235519cfbddc;github.com/gxed/go-crypto/openpgp/clearsign - 9b1a210a06ea1176ec1f0a1ddf83ad7463b8ea3e;github.com/fluidkeys/crypto/openpgp/clearsign - 2018-08-22;github.com/benburkert/crypto/openpgp/clearsign - e3f150b4372fce47109dbd8fef5f03cd2af08700,0d3cfff99f4428b308d63d9386fec9cd86475faa,61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,6575f7ea326e67d12b77872ff66f5ea15f8aefad,bc89c496413265e715159bdc8478ee9a92fdc265,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,fa50e7408b9ef89ff2965535b59f1a0010c0770b,f1b99bc9f1eb185629f6c4b5bd983dd66da2e0e8,ed40a6cc352d9acfba912aae191023ebdc0461d1,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,b270509459adaed5fe5be459e6ddb0e1f3ef803d,3f77d695175f990a2967385c493939f380ee40a3,76cee1b7b184f79a9d93bbfcb287d0c03391928c,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,160b2e156e1c2c1e7d8db6b5e3f6ccf75e9dd34f,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,aa0f5b40812c405df7480c8a69e7f0160363a94b,62944567d8abab8255c3bfcf82c8c347c7577c62,fcdb74e78f2621098ebc0376bbadffcf580ccfe4,8e06e8ddd9629eb88639aba897641bff8031f1d3,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5;github.com/jlburkhead/crypto/openpgp/clearsign - bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,4c5258d8b6be6789e3c5433562c226507dc1249f,c2c80b64c04ccb917376270f715718ec87bacb29,2e60680932240e15a179f3b34782f42b7199981a,eca6c1626e1a5b651a7a131cdb6b435930f64498,4147256c9cfc043b679bae483b623e0076f9ed60,d95b28330da59cfd5b511cea8d98ce3379610013,396847505b5d877809d99cbba288cbca62ea189c,dc703e91d7bf2ed50e4e847371f53a4c0a83693c,f5f25bdad0cb2b768bdea003ed92329914931542,18c283559e20c6fa8b7639afd6c8ba22645655cd,cb7a96fa34f94f61171c4bdce01baf2411356574,c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3,2aff5f12d83011dd1f9aeb358eb851b28668cf60,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,8f45c680ceb25c200b8c301d9184532aeb7cb36e;github.com/schoppmp/go-crypto/openpgp/clearsign - 15577f9df470bf5e9292240050c4c84d210732d7,dc67354e864179a90a9bec14aa1c9af1344e1394;github.com/protonmail/crypto/openpgp/clearsign - 3a07e4a428e17dc7e67df31f702ac03e64522f53;github.com/szank/crypto/openpgp/clearsign - 61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,62944567d8abab8255c3bfcf82c8c347c7577c62,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,aa0f5b40812c405df7480c8a69e7f0160363a94b,0d3cfff99f4428b308d63d9386fec9cd86475faa,665213f561b1d86f94956515da4886141e45eb9b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f;github.com/conseweb/golangcrypto/openpgp/clearsign - 280be005b3a662119e76768fe9d91171c1142511,fa50e7408b9ef89ff2965535b59f1a0010c0770b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,ef64186525f45244f1fd8d843a4474ef77d50f73,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,5a4ea2fde36b6d025182d6b240aa4518791d58cb;github.com/dizzyd/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,400097dc741fc8fbcb8d7dd14304aa27bc124478,bc066ba6717d69b2d3998b93b9a27b3e7e5b74ea,5bb6445962bed970d80a2882706ba2c26f7426cd","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-11841","vulnerabilityDetails":"A message-forgery issue was discovered in crypto/openpgp/clearsign/clearsign.go in supplementary Go cryptography libraries 2019-03-25. According to the OpenPGP Message Format specification in RFC 4880 chapter 7, a cleartext signed message can contain one or more optional \"Hash\" Armor Headers. The \"Hash\" Armor Header specifies the message digest algorithm(s) used for the signature. However, the Go clearsign package ignores the value of this header, which allows an attacker to spoof it. Consequently, an attacker can lead a victim to believe the signature was generated using a different message digest algorithm than what was actually used. Moreover, since the library skips Armor Header parsing in general, an attacker can not only embed arbitrary Armor Headers, but also prepend arbitrary text to cleartext messages without invalidating the signatures.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11841","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"commit b7391e95e576cacdcdd422573063bc057239113d","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2019-0030","vulnerabilityDetails":"Commit b7391e95 fixes a vulnerability in the amd64 implementation of the golang.org/x/crypto/salsa20 and golang.org/x/crypto/salsa20/salsa packages that affects large message sizes or high counter values.","vulnerabilityUrl":"https://github.com/golang/crypto/commit/b7391e95e576cacdcdd422573063bc057239113d","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}]</REMEDIATE> --> | True | github.com/miekg/dns-v1.0.14: 12 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p></summary>
<p>DNS library in Go</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-27918](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27918) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | 1.15.9, 1.16.1 | ❌ |
| [CVE-2018-17847](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17847) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | N/A | ❌ |
| [CVE-2018-17848](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17848) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | github.com/golang/net/html - 309822c5b9b9f80db67f016069a12628d94fad34;github.com/psiphon-labs/net/html - 309822c5b9b9f80db67f016069a12628d94fad34 | ❌ |
| [CVE-2021-33194](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33194) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | N/A | ❌ |
| [CVE-2018-17846](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17846) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | github.com/matishsiao/net/html - 5c9495a32797e34e9bf5ac91e69eb447443b78fd;github.com/pweil-/net/html - 3053e46bf4d836639f474dd738a58070463890e9,5c9495a32797e34e9bf5ac91e69eb447443b78fd,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/psiphon-labs/net/html - 161cd47e91fd58ac17490ef4d742dc98bb4cf60e,2b459478774d488f63f6b8e8ec2429c502a43dd1;github.com/shekhei/net/html - b1ee7b3fbbb773e8e4b649ade000633fb867ba77,66b3e5ee27f66da79cc3695f293932920e946d87;github.com/alexsaveliev/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/foreversmart/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/suedadam/net/html - fbe893ddcdf0e847ed928b77e4b17ff5ec3b8a32;github.com/fangdingjun/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/crmackay/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/jfcote87/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/chris-ramon/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/johnsto/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rsms/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rainkid/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,7ad508c2a7acafff7c6c8522d7e6efda5311476c,2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,3eb064ebfe6b9b907715cf7eeda05c367c55f32d,2e20f33919de098ec28d48d93b0735cc76567f6e,23996681074122163cfa22b185668f84935be9a9,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35;github.com/subuk/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/hugomfernandes/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35,6f62f426de90c0ed6a55207b51476115fcb17237,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/letsencrypt/net/html - 153a6a61520e23dabb758b4a612bff144e5e28eb,1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,d8b496d92df37acaa5a038846651d41f7cbe6326,3748d8c2fdc5600797e1200ed7ca82358bbeadeb,947224908606a5aa6af4427c3a2cea51387aa38a;github.com/nodirt/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87,ec18079348e79eb393866e87d402a1a8cc580d7f;github.com/jash16/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bountylabs/net/html - 2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,59b0df9b1f7abda5aab0495ee54f408daf182ce7,63ee83b038e98e5716bfdd1a94178718cff506d2,9f8bef6b5998053643dca00058a0938278e882ab,1db34d83398887aa887306d261882f799bee3678,46077d3c5415f800cd8105911d4ed880c1db2138;github.com/suifengrock/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,40ad15caf30bbcbd0cb852523ec4dfabc440d37b,5058c78c3627b31e484a81463acd51c7cecc06f3;github.com/petermattis/x-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bradleyfalzon/net/html - 1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,153a6a61520e23dabb758b4a612bff144e5e28eb,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c;github.com/radioinmyhead/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,3053e46bf4d836639f474dd738a58070463890e9;github.com/jelmersnoeck/go.net/html - 104dcad90073cd8d1e6828b2af19185b60cf3e29;github.com/jackmiller334/net/html - d96e6bbf425715f2bd00806e45fbbd5a54870397,63ee83b038e98e5716bfdd1a94178718cff506d2,5b76c8047cfbdbe90fdc031267d2144555ad63e3;github.com/owner888/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/golang/net/html - 97775bb4655419e5ab44c1f918c5bed052130f1b,161cd47e91fd58ac17490ef4d742dc98bb4cf60e;github.com/cesanta/goxnet/html - 23996681074122163cfa22b185668f84935be9a9,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/fanatic/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/8090boy/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/niniwzw/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/smithfox/gonet/html - 835a8501270a5b32645da11de6ee20e02f57e10e;github.com/matishsiao/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,405a8afa2d839d68dbd0481db63e49356af19650,2e20f33919de098ec28d48d93b0735cc76567f6e;github.com/donovanhide/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,1cd7b7179478daf1f19f8b4b4f08106ef411619b | ❌ |
| [CVE-2020-9283](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9283) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236 | ❌ |
| [CVE-2020-29652](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-29652) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | v0.0.0-20201216223049-8b5274cf687f | ❌ |
| [CVE-2020-7919](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7919) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | github.com/miekg/dns-v1.0.14 | Direct | go - 1.12.16,1.13.7;crypto - v0.0.0-20200128174031-69ecbb4d6d5d | ❌ |
| [CVE-2021-31525](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-31525) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | multiple | Direct | golang - v1.15.12,v1.16.4,v1.17.0 | ❌ |
| [CVE-2019-19794](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19794) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | github.com/miekg/dns-v1.0.14 | Direct | v1.1.25 | ❌ |
| [CVE-2019-11841](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11841) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | github.com/miekg/dns-v1.0.14 | Direct | github.com/dizzyd/go.crypto/openpgp/clearsign - 04d51b511dfb566dd1f82bb6b66a81620178a456,b9b75b879318a4406f0144dcf743881c658f1f6b,826261375936cb3183b191689ef045a117b11442,97102e297913542f7215b5164962dbbb7e3ac329;github.com/scriptrock/crypto/openpgp/clearsign - 9f8b27c8af31154c90cacf5b9be1ddcb46bed784,907750ef230b26d207dd726105c190d72ce98696,c2eb4f1eeb6d905673685dc561c882ddeee035e3,8b4f6e3a0906ea9c46090ee5de4ed06113ad3da3;github.com/winlinvip/crypto/openpgp/clearsign - 6c932297e16070bd20e9384ea78e8afabaa3fae2,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71;github.com/btcsuite/golangcrypto/openpgp/clearsign - b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,fa50e7408b9ef89ff2965535b59f1a0010c0770b,ef64186525f45244f1fd8d843a4474ef77d50f73,5a4ea2fde36b6d025182d6b240aa4518791d58cb,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,280be005b3a662119e76768fe9d91171c1142511;github.com/progrium/crypto/openpgp/clearsign - 7cbb17fecb34db5291cde2f20061eaf746fb8e17,577ae2abf995653ad750624b223792d65a654333,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,eccdd1285ab9ae1cb35bf3b90d777d304263f478;github.com/kmeaw/crypto/openpgp/clearsign - d172538b2cfce0c13cee31e647d0367aa8cd2486,f160b6bf95857cd862817875dd958be022e587c4,3092f0d93ba634e09d6cca8f935db357229b6ad5,efac7f277b17c19894091e358c6130cb6bd51117,019870fc9d457ee8abd13a2e93e3f2a3b55b7119,b07d8c96772f426812d3fc5530710ec1f3b205e7;github.com/juniorz/crypto/openpgp/clearsign - 6ba10a7acbbf2ad7cc0e72a5a9c60fc304c09461,731db29863ea7213d9556d0170afb38987f401d4,dc67354e864179a90a9bec14aa1c9af1344e1394,9fb356864640495bb15bef1f3e78c4264527b364,153731a6de123b98250cbf9e5adbc8d0d950c10a,552202b8e32b8d23879f85948aa263fb809ec2e8,18c283559e20c6fa8b7639afd6c8ba22645655cd,e6ded1797187ebd338e6764d03052931453e7658,929dedf39d9e8e1ffa201091598b681961c04b85,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,8b27f58b78dbd60e9a26b60b0d908ea642974b6d;github.com/codeguard/crypto/openpgp/clearsign - b270509459adaed5fe5be459e6ddb0e1f3ef803d;github.com/seppestas/crypto/openpgp/clearsign - 50ff460fe18dd7f30883cadb9926ed1da056e107,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,7e436327309324370917a1878da60107b88499aa,690e22b80a4c5bae73ab7186ddcca14f82dee9de,4c5258d8b6be6789e3c5433562c226507dc1249f,9c0a3ae19916a277d6d5b582d10b048f04b19e1a;github.com/benburkert/openpgp/clearsign - 0d9cd1316972cc441bd7aa896c05d8e218494c85,f5845320897ceaaabb067fc2fdbc123517fb7fce;github.com/mjkim/crypto/openpgp/clearsign - 9477e0b78b9ac3d0b03822fd95422e2fe07627cd,08da9c60bc7065e1a1df887121f42db309a6ff9a,44256fa2dfb760488af0b3f966ab00bcf98b1411,2c5e2074680afae185175121fc549913bf6f32c9,a548aac93ed489257b9d959b40fe1e8c1e20778c,d5c5f1769f2fcd2377be6f29863081f59a4fc80f,0e31b188fd38db611d4fbab7de9373a95f36aae5,351dc6a5bf92a5f2ae22fadeee08eb6a45aa2d93,18c283559e20c6fa8b7639afd6c8ba22645655cd,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,eb19e229bd898d2a3e69bdc0478553927be3b235,7c7765c32f8127cd34cde75d2eb450ae6a7b692e,db732cbcc6772c3a16d666f5cd737d32c4a12052,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,1351f936d976c60a0a48d728281922cf63eafb8d,63f855d724c1fff8ec15a0191dcda32ec7761cc4,173ce04bfaf66c7bb0fa9d5c0bfd93e773909dbd,7f27901cb9636a61b9b0b1bab2679b2a9a12eb38,b8a0f4bb4040f8d884435cff35b9691e362cf00c,c34e38ab9ea85314630ff172a2378cd5da44e299,c1c0bfbd3ac981a523e036008cfb2d9ac2d9c967,f59690be3f9a31481d227f885bfe2466be0c5d27,7db43667c77d5d330c359ffd03f5789cf390e973,4ed45ec682102c643324fae5dff8dab085b6c300;github.com/cmars/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,b9b75b879318a4406f0144dcf743881c658f1f6b;github.com/scalingdata/go-x-crypto/openpgp/clearsign - 8b27f58b78dbd60e9a26b60b0d908ea642974b6d,ffadfa66488ddd3d386e89ebb19280aa87c098a6,9fb356864640495bb15bef1f3e78c4264527b364,03be8f3bf08562c9abf595f4a88954d5dff55e82,3092f0d93ba634e09d6cca8f935db357229b6ad5,4147256c9cfc043b679bae483b623e0076f9ed60,9b55b542f68bcaf688633f6e810d3d41b9c87739,7e436327309324370917a1878da60107b88499aa,77f4136a99ffb5ecdbdd0226bd5cb146cf56bc0e,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71,4ed45ec682102c643324fae5dff8dab085b6c300,10c26747e67d76ad4fafe6087c6f4073c3b22942;github.com/mehrdadrad/crypto/openpgp/clearsign - 81e0b644eb2f05832b1801391bc9386a81e4fe45,eccdd1285ab9ae1cb35bf3b90d777d304263f478,124e52db8dfdfab4fc56ea36c2957b8d996ff760,c9c0e06eed439a60df0ef7aa13c0b97e19cdd3a7,632d287f9f3f54b09809eebbd3cacbcb00b9f2fc,eca6c1626e1a5b651a7a131cdb6b435930f64498,43c4f8a8964d075ae4829f4cabb2f8c0b685fdc5,1fbbd62cfec66bd39d91e97749579579d4d3037e,ce1cf546ac92dd001ee433ec58b6b0f9828e1cee,15577f9df470bf5e9292240050c4c84d210732d7,9e886ee4f218fc3dcdf33c35cee6e798d61c5b85,c57d4a71915a248dbad846d60825145062b4c18e,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,88b65fb66346493d43e735adad931bf69dee4297,d67eb63455fa4d6fca5802332d86f1f204017e00,58afe880f197c244a2edbfab2bb090a5bf02dfe1,df1b4d2fcd21fb05d2ac65176e2a4243c201a920,cc04154d65fb9296747569b107cfd05380b1ea3e,4831188890de893ae55d9ecd1bbafc340ce0ff9f,c197bcf24cde29d3f73c7b4ac6fd41f4384e8af6,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,929dedf39d9e8e1ffa201091598b681961c04b85,4d8f0cfeca8290cfc0091edf678a138ce669b1bb,3fbbcd23f1cb824e69491a5930cfeff09b12f4d2,7b428712abe956d0e9e1e9a01e163fb6c7171438,9b55b542f68bcaf688633f6e810d3d41b9c87739,63a71ca82d5ccbe458cc4acef0c0ea8076463976,552202b8e32b8d23879f85948aa263fb809ec2e8;github.com/benbjohnson/crypto/openpgp/clearsign - c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3;github.com/u-s-p/crypto/openpgp/clearsign - 2e60680932240e15a179f3b34782f42b7199981a,f5f25bdad0cb2b768bdea003ed92329914931542,4c5258d8b6be6789e3c5433562c226507dc1249f,0214db40ef9cee9306086200828340ba6253b6ce,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,b6789ab629056511030d652d851e7dc10c9e9c9e,d95b28330da59cfd5b511cea8d98ce3379610013,4147256c9cfc043b679bae483b623e0076f9ed60,cbc3d0884eac986df6e78a039b8792e869bff863,3cb07270c9455e8ad27956a70891c962d121a228,b176d7def5d71bdd214203491f89843ed217f420,6575f7ea326e67d12b77872ff66f5ea15f8aefad,575fdbe86e5dd89229707ebec0575ce7d088a4a6,484eb34681af59703e639b971bc307019182c41f,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,e311231e83195f401421a286060d65643f9c9d40,c2c80b64c04ccb917376270f715718ec87bacb29,eca6c1626e1a5b651a7a131cdb6b435930f64498,3ded668c5379f6951fb0de06174442072e5447d3,d8e61c69ab46ca38328da2f4995abaf93b252290,6318898455d3ac20e7e44d0a080d43f8c3ff120b,7b428712abe956d0e9e1e9a01e163fb6c7171438,c7af5bf2638a1164f2eb5467c39c6cffbd13a02e,59a182cab66ead4fe21e6472267504ac035edee2,396847505b5d877809d99cbba288cbca62ea189c,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,e7ba82683099cae71475961448ab8f903ea77c26,8f45c680ceb25c200b8c301d9184532aeb7cb36e,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,dc703e91d7bf2ed50e4e847371f53a4c0a83693c;github.com/vividcortex/crypto/openpgp/clearsign - ca7e7f10cb9fd9c1a6ff7f60436c086d73714180,d33bbf2cb3b8574ad57ddba26f03e861c01f69c5,5ef0053f77724838734b6945dd364d3847e5de1d,2b786ab9e9649dc660afa3bd580fd05a05e20d95,9fbab14f903f89e23047b5971369b86380230e56,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,c7e3b0ebdd409a0d024e3d71801427ab0e05fb2e,e1b0d6c49fae5632d0a563812fce85b5b542fbcf,a3c6050446ec077a5f411deb35d89b420f8d5fd7,b286ef4198388fdb0e4ae62be12820df5da9b4c2,88b65fb66346493d43e735adad931bf69dee4297,d43a35d821f1e9a9dcb701ffab4cb5bc12d4006c,eb71ad9bd329b5ac0fd0148dd99bd62e8be8e035,119f50887f8fe324fe2386421c27a11af014b64e,6de97b525f030fe8dce13090d5c3731799bb9d3e,1a85842c9ed153459eaf94f2ff4c4e914c54410d,f944096df80415fafc888544caecaab86a991785,b7f382b979dc349948b0e69fbbf7fb2a7ef6b7d9,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,f160b6bf95857cd862817875dd958be022e587c4,6575f7ea326e67d12b77872ff66f5ea15f8aefad,59a4410d829a8bb774b02b56d4aeab633414f233,f17d1302814ed95db5a4fae9ac53b86021a7584b,c367d6eeb7c6158125f2f47e049f7eb7e251c09a,2c99acdd1e9b90d779ca23f632aad86af9909c62,c0d640c88782f757a45d3f7b93eec2ec63b229cb,47ff8dfbc528fea3003fc0ce2d88ffbbfbc46a43,0d8dc3cd6a6b69fac2c54037ae8c235519cfbddc;github.com/gxed/go-crypto/openpgp/clearsign - 9b1a210a06ea1176ec1f0a1ddf83ad7463b8ea3e;github.com/fluidkeys/crypto/openpgp/clearsign - 2018-08-22;github.com/benburkert/crypto/openpgp/clearsign - e3f150b4372fce47109dbd8fef5f03cd2af08700,0d3cfff99f4428b308d63d9386fec9cd86475faa,61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,6575f7ea326e67d12b77872ff66f5ea15f8aefad,bc89c496413265e715159bdc8478ee9a92fdc265,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,fa50e7408b9ef89ff2965535b59f1a0010c0770b,f1b99bc9f1eb185629f6c4b5bd983dd66da2e0e8,ed40a6cc352d9acfba912aae191023ebdc0461d1,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,b270509459adaed5fe5be459e6ddb0e1f3ef803d,3f77d695175f990a2967385c493939f380ee40a3,76cee1b7b184f79a9d93bbfcb287d0c03391928c,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,160b2e156e1c2c1e7d8db6b5e3f6ccf75e9dd34f,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,aa0f5b40812c405df7480c8a69e7f0160363a94b,62944567d8abab8255c3bfcf82c8c347c7577c62,fcdb74e78f2621098ebc0376bbadffcf580ccfe4,8e06e8ddd9629eb88639aba897641bff8031f1d3,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5;github.com/jlburkhead/crypto/openpgp/clearsign - bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,4c5258d8b6be6789e3c5433562c226507dc1249f,c2c80b64c04ccb917376270f715718ec87bacb29,2e60680932240e15a179f3b34782f42b7199981a,eca6c1626e1a5b651a7a131cdb6b435930f64498,4147256c9cfc043b679bae483b623e0076f9ed60,d95b28330da59cfd5b511cea8d98ce3379610013,396847505b5d877809d99cbba288cbca62ea189c,dc703e91d7bf2ed50e4e847371f53a4c0a83693c,f5f25bdad0cb2b768bdea003ed92329914931542,18c283559e20c6fa8b7639afd6c8ba22645655cd,cb7a96fa34f94f61171c4bdce01baf2411356574,c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3,2aff5f12d83011dd1f9aeb358eb851b28668cf60,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,8f45c680ceb25c200b8c301d9184532aeb7cb36e;github.com/schoppmp/go-crypto/openpgp/clearsign - 15577f9df470bf5e9292240050c4c84d210732d7,dc67354e864179a90a9bec14aa1c9af1344e1394;github.com/protonmail/crypto/openpgp/clearsign - 3a07e4a428e17dc7e67df31f702ac03e64522f53;github.com/szank/crypto/openpgp/clearsign - 61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,62944567d8abab8255c3bfcf82c8c347c7577c62,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,aa0f5b40812c405df7480c8a69e7f0160363a94b,0d3cfff99f4428b308d63d9386fec9cd86475faa,665213f561b1d86f94956515da4886141e45eb9b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f;github.com/conseweb/golangcrypto/openpgp/clearsign - 280be005b3a662119e76768fe9d91171c1142511,fa50e7408b9ef89ff2965535b59f1a0010c0770b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,ef64186525f45244f1fd8d843a4474ef77d50f73,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,5a4ea2fde36b6d025182d6b240aa4518791d58cb;github.com/dizzyd/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,400097dc741fc8fbcb8d7dd14304aa27bc124478,bc066ba6717d69b2d3998b93b9a27b3e7e5b74ea,5bb6445962bed970d80a2882706ba2c26f7426cd | ❌ |
| [WS-2019-0030](https://github.com/golang/crypto/commit/b7391e95e576cacdcdd422573063bc057239113d) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.0 | github.com/miekg/dns-v1.0.14 | Direct | commit b7391e95e576cacdcdd422573063bc057239113d | ❌ |
## Details
> Partial details (7 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-27918</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
encoding/xml in Go before 1.15.9 and 1.16.x before 1.16.1 has an infinite loop if a custom TokenReader (for xml.NewTokenDecoder) returns EOF in the middle of an element. This can occur in the Decode, DecodeElement, or Skip method.
<p>Publish Date: 2021-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27918>CVE-2021-27918</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/g/golang-announce/c/MfiLYjG-RAw">https://groups.google.com/g/golang-announce/c/MfiLYjG-RAw</a></p>
<p>Release Date: 2021-03-11</p>
<p>Fix Resolution: 1.15.9, 1.16.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-17847</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The html package (aka x/net/html) through 2018-09-25 in Go mishandles <svg><template><desc><t><svg></template>, leading to a "panic: runtime error" (index out of range) in (*nodeStack).pop in node.go, called from (*parser).clearActiveFormattingElements, during an html.Parse call.
<p>Publish Date: 2018-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17847>CVE-2018-17847</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-17848</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The html package (aka x/net/html) through 2018-09-25 in Go mishandles <math><template><mn><b></template>, leading to a "panic: runtime error" (index out of range) in (*insertionModeStack).pop in node.go, called from inHeadIM, during an html.Parse call.
<p>Publish Date: 2018-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17848>CVE-2018-17848</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-17848">https://nvd.nist.gov/vuln/detail/CVE-2018-17848</a></p>
<p>Release Date: 2018-10-01</p>
<p>Fix Resolution: github.com/golang/net/html - 309822c5b9b9f80db67f016069a12628d94fad34;github.com/psiphon-labs/net/html - 309822c5b9b9f80db67f016069a12628d94fad34</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-33194</summary>
### Vulnerable Libraries - <b>github.com/miekg/dns-v1.0.14</b>, <b>github.com/golang/net-e18ecbb051101a46fc263334b127c89bc7bff7ea</b></p>
<p>
### <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
### <b>github.com/golang/net-e18ecbb051101a46fc263334b127c89bc7bff7ea</b></p>
<p>[mirror] Go supplementary network libraries</p>
<p>
Dependency Hierarchy:
- github.com/miekg/dns-v1.0.14 (Root Library)
- :x: **github.com/golang/net-e18ecbb051101a46fc263334b127c89bc7bff7ea** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
golang.org/x/net before v0.0.0-20210520170846-37e1c6afe023 allows attackers to cause a denial of service (infinite loop) via crafted ParseFragment input.
<p>Publish Date: 2021-05-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33194>CVE-2021-33194</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-17846</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The html package (aka x/net/html) through 2018-09-25 in Go mishandles <table><math><select><mi><select></table>, leading to an infinite loop during an html.Parse call because inSelectIM and inSelectInTableIM do not comply with a specification.
<p>Publish Date: 2018-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17846>CVE-2018-17846</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-17846">https://nvd.nist.gov/vuln/detail/CVE-2018-17846</a></p>
<p>Release Date: 2018-10-01</p>
<p>Fix Resolution: github.com/matishsiao/net/html - 5c9495a32797e34e9bf5ac91e69eb447443b78fd;github.com/pweil-/net/html - 3053e46bf4d836639f474dd738a58070463890e9,5c9495a32797e34e9bf5ac91e69eb447443b78fd,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/psiphon-labs/net/html - 161cd47e91fd58ac17490ef4d742dc98bb4cf60e,2b459478774d488f63f6b8e8ec2429c502a43dd1;github.com/shekhei/net/html - b1ee7b3fbbb773e8e4b649ade000633fb867ba77,66b3e5ee27f66da79cc3695f293932920e946d87;github.com/alexsaveliev/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/foreversmart/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/suedadam/net/html - fbe893ddcdf0e847ed928b77e4b17ff5ec3b8a32;github.com/fangdingjun/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/crmackay/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/jfcote87/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/chris-ramon/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/johnsto/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rsms/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rainkid/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,7ad508c2a7acafff7c6c8522d7e6efda5311476c,2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,3eb064ebfe6b9b907715cf7eeda05c367c55f32d,2e20f33919de098ec28d48d93b0735cc76567f6e,23996681074122163cfa22b185668f84935be9a9,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35;github.com/subuk/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/hugomfernandes/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35,6f62f426de90c0ed6a55207b51476115fcb17237,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/letsencrypt/net/html - 153a6a61520e23dabb758b4a612bff144e5e28eb,1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,d8b496d92df37acaa5a038846651d41f7cbe6326,3748d8c2fdc5600797e1200ed7ca82358bbeadeb,947224908606a5aa6af4427c3a2cea51387aa38a;github.com/nodirt/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87,ec18079348e79eb393866e87d402a1a8cc580d7f;github.com/jash16/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bountylabs/net/html - 2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,59b0df9b1f7abda5aab0495ee54f408daf182ce7,63ee83b038e98e5716bfdd1a94178718cff506d2,9f8bef6b5998053643dca00058a0938278e882ab,1db34d83398887aa887306d261882f799bee3678,46077d3c5415f800cd8105911d4ed880c1db2138;github.com/suifengrock/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,40ad15caf30bbcbd0cb852523ec4dfabc440d37b,5058c78c3627b31e484a81463acd51c7cecc06f3;github.com/petermattis/x-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bradleyfalzon/net/html - 1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,153a6a61520e23dabb758b4a612bff144e5e28eb,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c;github.com/radioinmyhead/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,3053e46bf4d836639f474dd738a58070463890e9;github.com/jelmersnoeck/go.net/html - 104dcad90073cd8d1e6828b2af19185b60cf3e29;github.com/jackmiller334/net/html - d96e6bbf425715f2bd00806e45fbbd5a54870397,63ee83b038e98e5716bfdd1a94178718cff506d2,5b76c8047cfbdbe90fdc031267d2144555ad63e3;github.com/owner888/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/golang/net/html - 97775bb4655419e5ab44c1f918c5bed052130f1b,161cd47e91fd58ac17490ef4d742dc98bb4cf60e;github.com/cesanta/goxnet/html - 23996681074122163cfa22b185668f84935be9a9,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/fanatic/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/8090boy/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/niniwzw/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/smithfox/gonet/html - 835a8501270a5b32645da11de6ee20e02f57e10e;github.com/matishsiao/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,405a8afa2d839d68dbd0481db63e49356af19650,2e20f33919de098ec28d48d93b0735cc76567f6e;github.com/donovanhide/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,1cd7b7179478daf1f19f8b4b4f08106ef411619b</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9283</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
golang.org/x/crypto before v0.0.0-20200220183623-bac4c82f6975 for Go allows a panic during signature verification in the golang.org/x/crypto/ssh package. A client can attack an SSH server that accepts public keys. Also, a server can attack any SSH client.
<p>Publish Date: 2020-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9283>CVE-2020-9283</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9283</a></p>
<p>Release Date: 2020-02-20</p>
<p>Fix Resolution: github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-29652</summary>
### Vulnerable Library - <b>github.com/miekg/dns-v1.0.14</b></p>
<p>DNS library in Go</p>
<p>
Dependency Hierarchy:
- :x: **github.com/miekg/dns-v1.0.14** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Christine-Smith/commit/064f074a123a9ec6baa2c46f7a416fbf84104fa5">064f074a123a9ec6baa2c46f7a416fbf84104fa5</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A nil pointer dereference in the golang.org/x/crypto/ssh component through v0.0.0-20201203163018-be400aefbc4c for Go allows remote attackers to cause a denial of service against SSH servers.
<p>Publish Date: 2020-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-29652>CVE-2020-29652</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1">https://groups.google.com/g/golang-announce/c/ouZIlBimOsE?pli=1</a></p>
<p>Release Date: 2020-12-17</p>
<p>Fix Resolution: v0.0.0-20201216223049-8b5274cf687f</p>
</p>
<p></p>
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.15.9, 1.16.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-27918","vulnerabilityDetails":"encoding/xml in Go before 1.15.9 and 1.16.x before 1.16.1 has an infinite loop if a custom TokenReader (for xml.NewTokenDecoder) returns EOF in the middle of an element. This can occur in the Decode, DecodeElement, or Skip method.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-27918","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":false,"isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-17847","vulnerabilityDetails":"The html package (aka x/net/html) through 2018-09-25 in Go mishandles \u003csvg\u003e\u003ctemplate\u003e\u003cdesc\u003e\u003ct\u003e\u003csvg\u003e\u003c/template\u003e, leading to a \"panic: runtime error\" (index out of range) in (*nodeStack).pop in node.go, called from (*parser).clearActiveFormattingElements, during an html.Parse call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17847","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/golang/net/html - 309822c5b9b9f80db67f016069a12628d94fad34;github.com/psiphon-labs/net/html - 309822c5b9b9f80db67f016069a12628d94fad34","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-17848","vulnerabilityDetails":"The html package (aka x/net/html) through 2018-09-25 in Go mishandles \u003cmath\u003e\u003ctemplate\u003e\u003cmn\u003e\u003cb\u003e\u003c/template\u003e, leading to a \"panic: runtime error\" (index out of range) in (*insertionModeStack).pop in node.go, called from inHeadIM, during an html.Parse call.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17848","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":false,"isBinary":true},{"packageType":"GO","packageName":"github.com/golang/net","packageVersion":"e18ecbb051101a46fc263334b127c89bc7bff7ea","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/miekg/dns:v1.0.14;github.com/golang/net:e18ecbb051101a46fc263334b127c89bc7bff7ea","isMinimumFixVersionAvailable":false,"isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-33194","vulnerabilityDetails":"golang.org/x/net before v0.0.0-20210520170846-37e1c6afe023 allows attackers to cause a denial of service (infinite loop) via crafted ParseFragment input.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33194","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/matishsiao/net/html - 5c9495a32797e34e9bf5ac91e69eb447443b78fd;github.com/pweil-/net/html - 3053e46bf4d836639f474dd738a58070463890e9,5c9495a32797e34e9bf5ac91e69eb447443b78fd,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/psiphon-labs/net/html - 161cd47e91fd58ac17490ef4d742dc98bb4cf60e,2b459478774d488f63f6b8e8ec2429c502a43dd1;github.com/shekhei/net/html - b1ee7b3fbbb773e8e4b649ade000633fb867ba77,66b3e5ee27f66da79cc3695f293932920e946d87;github.com/alexsaveliev/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/foreversmart/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/suedadam/net/html - fbe893ddcdf0e847ed928b77e4b17ff5ec3b8a32;github.com/fangdingjun/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/crmackay/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/jfcote87/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/chris-ramon/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/johnsto/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rsms/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/rainkid/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,7ad508c2a7acafff7c6c8522d7e6efda5311476c,2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,3eb064ebfe6b9b907715cf7eeda05c367c55f32d,2e20f33919de098ec28d48d93b0735cc76567f6e,23996681074122163cfa22b185668f84935be9a9,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35;github.com/subuk/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/hugomfernandes/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,a33e90a7ecf9022ea7e3e42bb05bd5a5cca71f35,6f62f426de90c0ed6a55207b51476115fcb17237,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/letsencrypt/net/html - 153a6a61520e23dabb758b4a612bff144e5e28eb,1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,d8b496d92df37acaa5a038846651d41f7cbe6326,3748d8c2fdc5600797e1200ed7ca82358bbeadeb,947224908606a5aa6af4427c3a2cea51387aa38a;github.com/nodirt/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87,ec18079348e79eb393866e87d402a1a8cc580d7f;github.com/jash16/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bountylabs/net/html - 2a8eb9119c34470d7ecc9fb846e6ae3da2512cdd,59b0df9b1f7abda5aab0495ee54f408daf182ce7,63ee83b038e98e5716bfdd1a94178718cff506d2,9f8bef6b5998053643dca00058a0938278e882ab,1db34d83398887aa887306d261882f799bee3678,46077d3c5415f800cd8105911d4ed880c1db2138;github.com/suifengrock/golang-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,40ad15caf30bbcbd0cb852523ec4dfabc440d37b,5058c78c3627b31e484a81463acd51c7cecc06f3;github.com/petermattis/x-net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/bradleyfalzon/net/html - 1cd7b7179478daf1f19f8b4b4f08106ef411619b,ca657d0bd9d9b4f73523118b59af79e5374b9908,153a6a61520e23dabb758b4a612bff144e5e28eb,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,b56b60992857e77db9472023aaef7a33881d130b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c;github.com/radioinmyhead/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,3053e46bf4d836639f474dd738a58070463890e9;github.com/jelmersnoeck/go.net/html - 104dcad90073cd8d1e6828b2af19185b60cf3e29;github.com/jackmiller334/net/html - d96e6bbf425715f2bd00806e45fbbd5a54870397,63ee83b038e98e5716bfdd1a94178718cff506d2,5b76c8047cfbdbe90fdc031267d2144555ad63e3;github.com/owner888/net/html - 66b3e5ee27f66da79cc3695f293932920e946d87;github.com/golang/net/html - 97775bb4655419e5ab44c1f918c5bed052130f1b,161cd47e91fd58ac17490ef4d742dc98bb4cf60e;github.com/cesanta/goxnet/html - 23996681074122163cfa22b185668f84935be9a9,63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/fanatic/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/8090boy/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/niniwzw/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2;github.com/smithfox/gonet/html - 835a8501270a5b32645da11de6ee20e02f57e10e;github.com/matishsiao/net/html - 67f25490433376b5f7da086c0b9283fcdeca3a7b,8bc62b7ce1723e0e686c39f8fe3c5e8d03c8524c,405a8afa2d839d68dbd0481db63e49356af19650,2e20f33919de098ec28d48d93b0735cc76567f6e;github.com/donovanhide/net/html - 63ee83b038e98e5716bfdd1a94178718cff506d2,5b4754d96d73efe14f882d2f14ae3d29f7b2a67d,1cd7b7179478daf1f19f8b4b4f08106ef411619b","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-17846","vulnerabilityDetails":"The html package (aka x/net/html) through 2018-09-25 in Go mishandles \u003ctable\u003e\u003cmath\u003e\u003cselect\u003e\u003cmi\u003e\u003cselect\u003e\u003c/table\u003e, leading to an infinite loop during an html.Parse call because inSelectIM and inSelectInTableIM do not comply with a specification.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-17846","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/golang/crypto - bac4c82f69751a6dd76e702d54b3ceb88adab236","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-9283","vulnerabilityDetails":"golang.org/x/crypto before v0.0.0-20200220183623-bac4c82f6975 for Go allows a panic during signature verification in the golang.org/x/crypto/ssh package. A client can attack an SSH server that accepts public keys. Also, a server can attack any SSH client.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9283","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v0.0.0-20201216223049-8b5274cf687f","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-29652","vulnerabilityDetails":"A nil pointer dereference in the golang.org/x/crypto/ssh component through v0.0.0-20201203163018-be400aefbc4c for Go allows remote attackers to cause a denial of service against SSH servers.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-29652","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"go - 1.12.16,1.13.7;crypto - v0.0.0-20200128174031-69ecbb4d6d5d","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7919","vulnerabilityDetails":"Go before 1.12.16 and 1.13.x before 1.13.7 (and the crypto/cryptobyte package before 0.0.0-20200124225646-8b5121be2f68 for Go) allows attacks on clients (resulting in a panic) via a malformed X.509 certificate.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7919","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"golang - v1.15.12,v1.16.4,v1.17.0","isBinary":true},{"packageType":"GO","packageName":"github.com/golang/net","packageVersion":"e18ecbb051101a46fc263334b127c89bc7bff7ea","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/miekg/dns:v1.0.14;github.com/golang/net:e18ecbb051101a46fc263334b127c89bc7bff7ea","isMinimumFixVersionAvailable":true,"minimumFixVersion":"golang - v1.15.12,v1.16.4,v1.17.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-31525","vulnerabilityDetails":"net/http in Go before 1.15.12 and 1.16.x before 1.16.4 allows remote attackers to cause a denial of service (panic) via a large header to ReadRequest or ReadResponse. Server, Transport, and Client can each be affected in some configurations.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-31525","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v1.1.25","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-19794","vulnerabilityDetails":"The miekg Go DNS package before 1.1.25, as used in CoreDNS before 1.6.6 and other products, improperly generates random numbers because math/rand is used. The TXID becomes predictable, leading to response forgeries.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19794","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"github.com/dizzyd/go.crypto/openpgp/clearsign - 04d51b511dfb566dd1f82bb6b66a81620178a456,b9b75b879318a4406f0144dcf743881c658f1f6b,826261375936cb3183b191689ef045a117b11442,97102e297913542f7215b5164962dbbb7e3ac329;github.com/scriptrock/crypto/openpgp/clearsign - 9f8b27c8af31154c90cacf5b9be1ddcb46bed784,907750ef230b26d207dd726105c190d72ce98696,c2eb4f1eeb6d905673685dc561c882ddeee035e3,8b4f6e3a0906ea9c46090ee5de4ed06113ad3da3;github.com/winlinvip/crypto/openpgp/clearsign - 6c932297e16070bd20e9384ea78e8afabaa3fae2,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71;github.com/btcsuite/golangcrypto/openpgp/clearsign - b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,fa50e7408b9ef89ff2965535b59f1a0010c0770b,ef64186525f45244f1fd8d843a4474ef77d50f73,5a4ea2fde36b6d025182d6b240aa4518791d58cb,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,280be005b3a662119e76768fe9d91171c1142511;github.com/progrium/crypto/openpgp/clearsign - 7cbb17fecb34db5291cde2f20061eaf746fb8e17,577ae2abf995653ad750624b223792d65a654333,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,eccdd1285ab9ae1cb35bf3b90d777d304263f478;github.com/kmeaw/crypto/openpgp/clearsign - d172538b2cfce0c13cee31e647d0367aa8cd2486,f160b6bf95857cd862817875dd958be022e587c4,3092f0d93ba634e09d6cca8f935db357229b6ad5,efac7f277b17c19894091e358c6130cb6bd51117,019870fc9d457ee8abd13a2e93e3f2a3b55b7119,b07d8c96772f426812d3fc5530710ec1f3b205e7;github.com/juniorz/crypto/openpgp/clearsign - 6ba10a7acbbf2ad7cc0e72a5a9c60fc304c09461,731db29863ea7213d9556d0170afb38987f401d4,dc67354e864179a90a9bec14aa1c9af1344e1394,9fb356864640495bb15bef1f3e78c4264527b364,153731a6de123b98250cbf9e5adbc8d0d950c10a,552202b8e32b8d23879f85948aa263fb809ec2e8,18c283559e20c6fa8b7639afd6c8ba22645655cd,e6ded1797187ebd338e6764d03052931453e7658,929dedf39d9e8e1ffa201091598b681961c04b85,7343d5f5849484ec61fca3e4a0e6c529e400aaa9,8b27f58b78dbd60e9a26b60b0d908ea642974b6d;github.com/codeguard/crypto/openpgp/clearsign - b270509459adaed5fe5be459e6ddb0e1f3ef803d;github.com/seppestas/crypto/openpgp/clearsign - 50ff460fe18dd7f30883cadb9926ed1da056e107,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,7e436327309324370917a1878da60107b88499aa,690e22b80a4c5bae73ab7186ddcca14f82dee9de,4c5258d8b6be6789e3c5433562c226507dc1249f,9c0a3ae19916a277d6d5b582d10b048f04b19e1a;github.com/benburkert/openpgp/clearsign - 0d9cd1316972cc441bd7aa896c05d8e218494c85,f5845320897ceaaabb067fc2fdbc123517fb7fce;github.com/mjkim/crypto/openpgp/clearsign - 9477e0b78b9ac3d0b03822fd95422e2fe07627cd,08da9c60bc7065e1a1df887121f42db309a6ff9a,44256fa2dfb760488af0b3f966ab00bcf98b1411,2c5e2074680afae185175121fc549913bf6f32c9,a548aac93ed489257b9d959b40fe1e8c1e20778c,d5c5f1769f2fcd2377be6f29863081f59a4fc80f,0e31b188fd38db611d4fbab7de9373a95f36aae5,351dc6a5bf92a5f2ae22fadeee08eb6a45aa2d93,18c283559e20c6fa8b7639afd6c8ba22645655cd,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,eb19e229bd898d2a3e69bdc0478553927be3b235,7c7765c32f8127cd34cde75d2eb450ae6a7b692e,db732cbcc6772c3a16d666f5cd737d32c4a12052,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,1351f936d976c60a0a48d728281922cf63eafb8d,63f855d724c1fff8ec15a0191dcda32ec7761cc4,173ce04bfaf66c7bb0fa9d5c0bfd93e773909dbd,7f27901cb9636a61b9b0b1bab2679b2a9a12eb38,b8a0f4bb4040f8d884435cff35b9691e362cf00c,c34e38ab9ea85314630ff172a2378cd5da44e299,c1c0bfbd3ac981a523e036008cfb2d9ac2d9c967,f59690be3f9a31481d227f885bfe2466be0c5d27,7db43667c77d5d330c359ffd03f5789cf390e973,4ed45ec682102c643324fae5dff8dab085b6c300;github.com/cmars/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,b9b75b879318a4406f0144dcf743881c658f1f6b;github.com/scalingdata/go-x-crypto/openpgp/clearsign - 8b27f58b78dbd60e9a26b60b0d908ea642974b6d,ffadfa66488ddd3d386e89ebb19280aa87c098a6,9fb356864640495bb15bef1f3e78c4264527b364,03be8f3bf08562c9abf595f4a88954d5dff55e82,3092f0d93ba634e09d6cca8f935db357229b6ad5,4147256c9cfc043b679bae483b623e0076f9ed60,9b55b542f68bcaf688633f6e810d3d41b9c87739,7e436327309324370917a1878da60107b88499aa,77f4136a99ffb5ecdbdd0226bd5cb146cf56bc0e,aa2481cbfe81d911eb62b642b7a6b5ec58bbea71,4ed45ec682102c643324fae5dff8dab085b6c300,10c26747e67d76ad4fafe6087c6f4073c3b22942;github.com/mehrdadrad/crypto/openpgp/clearsign - 81e0b644eb2f05832b1801391bc9386a81e4fe45,eccdd1285ab9ae1cb35bf3b90d777d304263f478,124e52db8dfdfab4fc56ea36c2957b8d996ff760,c9c0e06eed439a60df0ef7aa13c0b97e19cdd3a7,632d287f9f3f54b09809eebbd3cacbcb00b9f2fc,eca6c1626e1a5b651a7a131cdb6b435930f64498,43c4f8a8964d075ae4829f4cabb2f8c0b685fdc5,1fbbd62cfec66bd39d91e97749579579d4d3037e,ce1cf546ac92dd001ee433ec58b6b0f9828e1cee,15577f9df470bf5e9292240050c4c84d210732d7,9e886ee4f218fc3dcdf33c35cee6e798d61c5b85,c57d4a71915a248dbad846d60825145062b4c18e,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,88b65fb66346493d43e735adad931bf69dee4297,d67eb63455fa4d6fca5802332d86f1f204017e00,58afe880f197c244a2edbfab2bb090a5bf02dfe1,df1b4d2fcd21fb05d2ac65176e2a4243c201a920,cc04154d65fb9296747569b107cfd05380b1ea3e,4831188890de893ae55d9ecd1bbafc340ce0ff9f,c197bcf24cde29d3f73c7b4ac6fd41f4384e8af6,285fb2ed20d1dc450fc743a1b3ff7c36bef372b9,929dedf39d9e8e1ffa201091598b681961c04b85,4d8f0cfeca8290cfc0091edf678a138ce669b1bb,3fbbcd23f1cb824e69491a5930cfeff09b12f4d2,7b428712abe956d0e9e1e9a01e163fb6c7171438,9b55b542f68bcaf688633f6e810d3d41b9c87739,63a71ca82d5ccbe458cc4acef0c0ea8076463976,552202b8e32b8d23879f85948aa263fb809ec2e8;github.com/benbjohnson/crypto/openpgp/clearsign - c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3;github.com/u-s-p/crypto/openpgp/clearsign - 2e60680932240e15a179f3b34782f42b7199981a,f5f25bdad0cb2b768bdea003ed92329914931542,4c5258d8b6be6789e3c5433562c226507dc1249f,0214db40ef9cee9306086200828340ba6253b6ce,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,b6789ab629056511030d652d851e7dc10c9e9c9e,d95b28330da59cfd5b511cea8d98ce3379610013,4147256c9cfc043b679bae483b623e0076f9ed60,cbc3d0884eac986df6e78a039b8792e869bff863,3cb07270c9455e8ad27956a70891c962d121a228,b176d7def5d71bdd214203491f89843ed217f420,6575f7ea326e67d12b77872ff66f5ea15f8aefad,575fdbe86e5dd89229707ebec0575ce7d088a4a6,484eb34681af59703e639b971bc307019182c41f,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,e311231e83195f401421a286060d65643f9c9d40,c2c80b64c04ccb917376270f715718ec87bacb29,eca6c1626e1a5b651a7a131cdb6b435930f64498,3ded668c5379f6951fb0de06174442072e5447d3,d8e61c69ab46ca38328da2f4995abaf93b252290,6318898455d3ac20e7e44d0a080d43f8c3ff120b,7b428712abe956d0e9e1e9a01e163fb6c7171438,c7af5bf2638a1164f2eb5467c39c6cffbd13a02e,59a182cab66ead4fe21e6472267504ac035edee2,396847505b5d877809d99cbba288cbca62ea189c,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,e7ba82683099cae71475961448ab8f903ea77c26,8f45c680ceb25c200b8c301d9184532aeb7cb36e,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,dc703e91d7bf2ed50e4e847371f53a4c0a83693c;github.com/vividcortex/crypto/openpgp/clearsign - ca7e7f10cb9fd9c1a6ff7f60436c086d73714180,d33bbf2cb3b8574ad57ddba26f03e861c01f69c5,5ef0053f77724838734b6945dd364d3847e5de1d,2b786ab9e9649dc660afa3bd580fd05a05e20d95,9fbab14f903f89e23047b5971369b86380230e56,2f6fccd33b9b1fc23ebb73ad4890698820f7174d,c7e3b0ebdd409a0d024e3d71801427ab0e05fb2e,e1b0d6c49fae5632d0a563812fce85b5b542fbcf,a3c6050446ec077a5f411deb35d89b420f8d5fd7,b286ef4198388fdb0e4ae62be12820df5da9b4c2,88b65fb66346493d43e735adad931bf69dee4297,d43a35d821f1e9a9dcb701ffab4cb5bc12d4006c,eb71ad9bd329b5ac0fd0148dd99bd62e8be8e035,119f50887f8fe324fe2386421c27a11af014b64e,6de97b525f030fe8dce13090d5c3731799bb9d3e,1a85842c9ed153459eaf94f2ff4c4e914c54410d,f944096df80415fafc888544caecaab86a991785,b7f382b979dc349948b0e69fbbf7fb2a7ef6b7d9,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5,c16968172724c0b5e8bdc6ad33f5a79443a44cd7,f160b6bf95857cd862817875dd958be022e587c4,6575f7ea326e67d12b77872ff66f5ea15f8aefad,59a4410d829a8bb774b02b56d4aeab633414f233,f17d1302814ed95db5a4fae9ac53b86021a7584b,c367d6eeb7c6158125f2f47e049f7eb7e251c09a,2c99acdd1e9b90d779ca23f632aad86af9909c62,c0d640c88782f757a45d3f7b93eec2ec63b229cb,47ff8dfbc528fea3003fc0ce2d88ffbbfbc46a43,0d8dc3cd6a6b69fac2c54037ae8c235519cfbddc;github.com/gxed/go-crypto/openpgp/clearsign - 9b1a210a06ea1176ec1f0a1ddf83ad7463b8ea3e;github.com/fluidkeys/crypto/openpgp/clearsign - 2018-08-22;github.com/benburkert/crypto/openpgp/clearsign - e3f150b4372fce47109dbd8fef5f03cd2af08700,0d3cfff99f4428b308d63d9386fec9cd86475faa,61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,6575f7ea326e67d12b77872ff66f5ea15f8aefad,bc89c496413265e715159bdc8478ee9a92fdc265,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,fa50e7408b9ef89ff2965535b59f1a0010c0770b,f1b99bc9f1eb185629f6c4b5bd983dd66da2e0e8,ed40a6cc352d9acfba912aae191023ebdc0461d1,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,b270509459adaed5fe5be459e6ddb0e1f3ef803d,3f77d695175f990a2967385c493939f380ee40a3,76cee1b7b184f79a9d93bbfcb287d0c03391928c,3c0d69f1777220f1a1d2ec373cb94a282f03eb42,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,160b2e156e1c2c1e7d8db6b5e3f6ccf75e9dd34f,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,aa0f5b40812c405df7480c8a69e7f0160363a94b,62944567d8abab8255c3bfcf82c8c347c7577c62,fcdb74e78f2621098ebc0376bbadffcf580ccfe4,8e06e8ddd9629eb88639aba897641bff8031f1d3,dc7f3af03ebbba4b0c90f8d95c682dba7d4c70f5;github.com/jlburkhead/crypto/openpgp/clearsign - bcdd6a2fd3e36323c71ab4c80588f4e48e8a3678,4c5258d8b6be6789e3c5433562c226507dc1249f,c2c80b64c04ccb917376270f715718ec87bacb29,2e60680932240e15a179f3b34782f42b7199981a,eca6c1626e1a5b651a7a131cdb6b435930f64498,4147256c9cfc043b679bae483b623e0076f9ed60,d95b28330da59cfd5b511cea8d98ce3379610013,396847505b5d877809d99cbba288cbca62ea189c,dc703e91d7bf2ed50e4e847371f53a4c0a83693c,f5f25bdad0cb2b768bdea003ed92329914931542,18c283559e20c6fa8b7639afd6c8ba22645655cd,cb7a96fa34f94f61171c4bdce01baf2411356574,c84e1f8e3a7e322d497cd16c0e8a13c7e127baf3,2aff5f12d83011dd1f9aeb358eb851b28668cf60,49702c17ccd6ae14f6d5ca83f23019f30a92f71a,8f45c680ceb25c200b8c301d9184532aeb7cb36e;github.com/schoppmp/go-crypto/openpgp/clearsign - 15577f9df470bf5e9292240050c4c84d210732d7,dc67354e864179a90a9bec14aa1c9af1344e1394;github.com/protonmail/crypto/openpgp/clearsign - 3a07e4a428e17dc7e67df31f702ac03e64522f53;github.com/szank/crypto/openpgp/clearsign - 61ab4d36dfa7fa0e3b13aebf87f8127a649463fb,62944567d8abab8255c3bfcf82c8c347c7577c62,7f7cbbf18eb3ab6aa04ded92fc89b3088ee30849,1ddfbba54b04d4acf0785dacec9098d7d5e6b9a5,aa0f5b40812c405df7480c8a69e7f0160363a94b,0d3cfff99f4428b308d63d9386fec9cd86475faa,665213f561b1d86f94956515da4886141e45eb9b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f;github.com/conseweb/golangcrypto/openpgp/clearsign - 280be005b3a662119e76768fe9d91171c1142511,fa50e7408b9ef89ff2965535b59f1a0010c0770b,b4b42222afc734a8fac0549d5ae6c4ab6a7ac71f,62944567d8abab8255c3bfcf82c8c347c7577c62,ef64186525f45244f1fd8d843a4474ef77d50f73,1b32d8b50a20d8fb3f40d1d50cb9d75cd0135bc8,5a4ea2fde36b6d025182d6b240aa4518791d58cb;github.com/dizzyd/go.crypto/openpgp/clearsign - bc1af7039d1278384d254877a61caa91cba53eb1,400097dc741fc8fbcb8d7dd14304aa27bc124478,bc066ba6717d69b2d3998b93b9a27b3e7e5b74ea,5bb6445962bed970d80a2882706ba2c26f7426cd","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-11841","vulnerabilityDetails":"A message-forgery issue was discovered in crypto/openpgp/clearsign/clearsign.go in supplementary Go cryptography libraries 2019-03-25. According to the OpenPGP Message Format specification in RFC 4880 chapter 7, a cleartext signed message can contain one or more optional \"Hash\" Armor Headers. The \"Hash\" Armor Header specifies the message digest algorithm(s) used for the signature. However, the Go clearsign package ignores the value of this header, which allows an attacker to spoof it. Consequently, an attacker can lead a victim to believe the signature was generated using a different message digest algorithm than what was actually used. Moreover, since the library skips Armor Header parsing in general, an attacker can not only embed arbitrary Armor Headers, but also prepend arbitrary text to cleartext messages without invalidating the signatures.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11841","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/miekg/dns","packageVersion":"v1.0.14","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/miekg/dns:v1.0.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"commit b7391e95e576cacdcdd422573063bc057239113d","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2019-0030","vulnerabilityDetails":"Commit b7391e95 fixes a vulnerability in the amd64 implementation of the golang.org/x/crypto/salsa20 and golang.org/x/crypto/salsa20/salsa packages that affects large message sizes or high counter values.","vulnerabilityUrl":"https://github.com/golang/crypto/commit/b7391e95e576cacdcdd422573063bc057239113d","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}]</REMEDIATE> --> | non_main | github com miekg dns vulnerabilities highest severity is vulnerable library github com miekg dns dns library in go found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high github com miekg dns direct high github com miekg dns direct n a high github com miekg dns direct github com golang net html github com psiphon labs net html high multiple direct n a high github com miekg dns direct github com matishsiao net html github com pweil net html github com psiphon labs net html github com shekhei net html github com alexsaveliev net html github com foreversmart net html github com suedadam net html github com fangdingjun net html github com crmackay net html github com net html github com chris ramon net html github com johnsto net html github com rsms golang net html github com rainkid net html github com subuk net html github com hugomfernandes net html github com letsencrypt net html github com nodirt net html github com net html github com bountylabs net html github com suifengrock golang net html github com petermattis x net html github com bradleyfalzon net html github com radioinmyhead net html github com jelmersnoeck go net html github com net html github com net html github com golang net html github com cesanta goxnet html github com fanatic net html github com net html github com niniwzw net html github com smithfox gonet html github com matishsiao net html github com donovanhide net html high github com miekg dns direct github com golang crypto high github com miekg dns direct high github com miekg dns direct go crypto medium multiple direct golang medium github com miekg dns direct medium github com miekg dns direct github com dizzyd go crypto openpgp clearsign github com scriptrock crypto openpgp clearsign github com winlinvip crypto openpgp clearsign github com btcsuite golangcrypto openpgp clearsign github com progrium crypto openpgp clearsign github com kmeaw crypto openpgp clearsign github com juniorz crypto openpgp clearsign github com codeguard crypto openpgp clearsign github com seppestas crypto openpgp clearsign github com benburkert openpgp clearsign github com mjkim crypto openpgp clearsign github com cmars go crypto openpgp clearsign github com scalingdata go x crypto openpgp clearsign github com mehrdadrad crypto openpgp clearsign github com benbjohnson crypto openpgp clearsign github com u s p crypto openpgp clearsign github com vividcortex crypto openpgp clearsign github com gxed go crypto openpgp clearsign github com fluidkeys crypto openpgp clearsign github com benburkert crypto openpgp clearsign github com jlburkhead crypto openpgp clearsign github com schoppmp go crypto openpgp clearsign github com protonmail crypto openpgp clearsign github com szank crypto openpgp clearsign github com conseweb golangcrypto openpgp clearsign github com dizzyd go crypto openpgp clearsign medium github com miekg dns direct commit details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library found in head commit a href found in base branch main vulnerability details encoding xml in go before and x before has an infinite loop if a custom tokenreader for xml newtokendecoder returns eof in the middle of an element this can occur in the decode decodeelement or skip method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library found in head commit a href found in base branch main vulnerability details the html package aka x net html through in go mishandles leading to a panic runtime error index out of range in nodestack pop in node go called from parser clearactiveformattingelements during an html parse call publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href cve vulnerable library github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library found in head commit a href found in base branch main vulnerability details the html package aka x net html through in go mishandles leading to a panic runtime error index out of range in insertionmodestack pop in node go called from inheadim during an html parse call publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution github com golang net html github com psiphon labs net html cve vulnerable libraries github com miekg dns github com golang net github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library github com golang net go supplementary network libraries dependency hierarchy github com miekg dns root library x github com golang net vulnerable library found in head commit a href found in base branch main vulnerability details golang org x net before allows attackers to cause a denial of service infinite loop via crafted parsefragment input publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href cve vulnerable library github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library found in head commit a href found in base branch main vulnerability details the html package aka x net html through in go mishandles leading to an infinite loop during an html parse call because inselectim and inselectintableim do not comply with a specification publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution github com matishsiao net html github com pweil net html github com psiphon labs net html github com shekhei net html github com alexsaveliev net html github com foreversmart net html github com suedadam net html github com fangdingjun net html github com crmackay net html github com net html github com chris ramon net html github com johnsto net html github com rsms golang net html github com rainkid net html github com subuk net html github com hugomfernandes net html github com letsencrypt net html github com nodirt net html github com net html github com bountylabs net html github com suifengrock golang net html github com petermattis x net html github com bradleyfalzon net html github com radioinmyhead net html github com jelmersnoeck go net html github com net html github com net html github com golang net html github com cesanta goxnet html github com fanatic net html github com net html github com niniwzw net html github com smithfox gonet html github com matishsiao net html github com donovanhide net html cve vulnerable library github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library found in head commit a href found in base branch main vulnerability details golang org x crypto before for go allows a panic during signature verification in the golang org x crypto ssh package a client can attack an ssh server that accepts public keys also a server can attack any ssh client publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution github com golang crypto cve vulnerable library github com miekg dns dns library in go dependency hierarchy x github com miekg dns vulnerable library found in head commit a href found in base branch main vulnerability details a nil pointer dereference in the golang org x crypto ssh component through for go allows remote attackers to cause a denial of service against ssh servers publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails encoding xml in go before and x before has an infinite loop if a custom tokenreader for xml newtokendecoder returns eof in the middle of an element this can occur in the decode decodeelement or skip method vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable false isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails the html package aka x net html through in go mishandles template leading to a panic runtime error index out of range in nodestack pop in node go called from parser clearactiveformattingelements during an html parse call vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion github com golang net html github com psiphon labs net html isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails the html package aka x net html through in go mishandles template leading to a panic runtime error index out of range in insertionmodestack pop in node go called from inheadim during an html parse call vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable false isbinary true packagetype go packagename github com golang net packageversion packagefilepaths istransitivedependency true dependencytree github com miekg dns github com golang net isminimumfixversionavailable false isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails golang org x net before allows attackers to cause a denial of service infinite loop via crafted parsefragment input vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion github com matishsiao net html github com pweil net html github com psiphon labs net html github com shekhei net html github com alexsaveliev net html github com foreversmart net html github com suedadam net html github com fangdingjun net html github com crmackay net html github com net html github com chris ramon net html github com johnsto net html github com rsms golang net html github com rainkid net html github com subuk net html github com hugomfernandes net html github com letsencrypt net html github com nodirt net html github com net html github com bountylabs net html github com suifengrock golang net html github com petermattis x net html github com bradleyfalzon net html github com radioinmyhead net html github com jelmersnoeck go net html github com net html github com net html github com golang net html github com cesanta goxnet html github com fanatic net html github com net html github com niniwzw net html github com smithfox gonet html github com matishsiao net html github com donovanhide net html isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails the html package aka x net html through in go mishandles table leading to an infinite loop during an html parse call because inselectim and inselectintableim do not comply with a specification vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion github com golang crypto isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails golang org x crypto before for go allows a panic during signature verification in the golang org x crypto ssh package a client can attack an ssh server that accepts public keys also a server can attack any ssh client vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails a nil pointer dereference in the golang org x crypto ssh component through for go allows remote attackers to cause a denial of service against ssh servers vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion go crypto isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails go before and x before and the crypto cryptobyte package before for go allows attacks on clients resulting in a panic via a malformed x certificate vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion golang isbinary true packagetype go packagename github com golang net packageversion packagefilepaths istransitivedependency true dependencytree github com miekg dns github com golang net isminimumfixversionavailable true minimumfixversion golang isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails net http in go before and x before allows remote attackers to cause a denial of service panic via a large header to readrequest or readresponse server transport and client can each be affected in some configurations vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails the miekg go dns package before as used in coredns before and other products improperly generates random numbers because math rand is used the txid becomes predictable leading to response forgeries vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion github com dizzyd go crypto openpgp clearsign github com scriptrock crypto openpgp clearsign github com winlinvip crypto openpgp clearsign github com btcsuite golangcrypto openpgp clearsign github com progrium crypto openpgp clearsign github com kmeaw crypto openpgp clearsign github com juniorz crypto openpgp clearsign github com codeguard crypto openpgp clearsign github com seppestas crypto openpgp clearsign github com benburkert openpgp clearsign github com mjkim crypto openpgp clearsign github com cmars go crypto openpgp clearsign github com scalingdata go x crypto openpgp clearsign github com mehrdadrad crypto openpgp clearsign github com benbjohnson crypto openpgp clearsign github com u s p crypto openpgp clearsign github com vividcortex crypto openpgp clearsign github com gxed go crypto openpgp clearsign github com fluidkeys crypto openpgp clearsign github com benburkert crypto openpgp clearsign github com jlburkhead crypto openpgp clearsign github com schoppmp go crypto openpgp clearsign github com protonmail crypto openpgp clearsign github com szank crypto openpgp clearsign github com conseweb golangcrypto openpgp clearsign github com dizzyd go crypto openpgp clearsign isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails a message forgery issue was discovered in crypto openpgp clearsign clearsign go in supplementary go cryptography libraries according to the openpgp message format specification in rfc chapter a cleartext signed message can contain one or more optional hash armor headers the hash armor header specifies the message digest algorithm s used for the signature however the go clearsign package ignores the value of this header which allows an attacker to spoof it consequently an attacker can lead a victim to believe the signature was generated using a different message digest algorithm than what was actually used moreover since the library skips armor header parsing in general an attacker can not only embed arbitrary armor headers but also prepend arbitrary text to cleartext messages without invalidating the signatures vulnerabilityurl istransitivedependency false dependencytree github com miekg dns isminimumfixversionavailable true minimumfixversion commit isbinary true basebranches vulnerabilityidentifier ws vulnerabilitydetails commit fixes a vulnerability in the implementation of the golang org x crypto and golang org x crypto salsa packages that affects large message sizes or high counter values vulnerabilityurl | 0 |
434,611 | 12,520,728,042 | IssuesEvent | 2020-06-03 16:18:54 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | opened | Delete `public_stats` column in database | component: statistics priority: p3 | Once https://github.com/mozilla/addons-server/issues/14463 is deployed, we'll want to delete the `public_stats` column, which was marked as _nullable_ in the previous tag. | 1.0 | Delete `public_stats` column in database - Once https://github.com/mozilla/addons-server/issues/14463 is deployed, we'll want to delete the `public_stats` column, which was marked as _nullable_ in the previous tag. | non_main | delete public stats column in database once is deployed we ll want to delete the public stats column which was marked as nullable in the previous tag | 0 |
3,926 | 17,664,003,113 | IssuesEvent | 2021-08-22 04:34:29 | walbourn/directx-vs-templates | https://api.github.com/repos/walbourn/directx-vs-templates | closed | Retire the 'non-DR' variant of the template | maintainence | For a while I've been maintaining two different variants of every template: One that creates the device 'inline' (``CreateDevice`` and ``CreateResources``), and the other with the ``DeviceResources`` abstraction (``CreateDeviceDependentResources``, ``CreateWindowSizeDependentResources``).
Generally the non-DR variants are only really useful when doing extremely simple samples, primarily focused on the creation of the device & swapchain itself. Otherwise, you pretty much always want to use the DR variant. Plus the ``DeviceResources`` version is a lot more functional.
As such, I think I'm going to retire the non-DR versions primarily to reduce the work to maintain these things... (6 templates instead of 12) | True | Retire the 'non-DR' variant of the template - For a while I've been maintaining two different variants of every template: One that creates the device 'inline' (``CreateDevice`` and ``CreateResources``), and the other with the ``DeviceResources`` abstraction (``CreateDeviceDependentResources``, ``CreateWindowSizeDependentResources``).
Generally the non-DR variants are only really useful when doing extremely simple samples, primarily focused on the creation of the device & swapchain itself. Otherwise, you pretty much always want to use the DR variant. Plus the ``DeviceResources`` version is a lot more functional.
As such, I think I'm going to retire the non-DR versions primarily to reduce the work to maintain these things... (6 templates instead of 12) | main | retire the non dr variant of the template for a while i ve been maintaining two different variants of every template one that creates the device inline createdevice and createresources and the other with the deviceresources abstraction createdevicedependentresources createwindowsizedependentresources generally the non dr variants are only really useful when doing extremely simple samples primarily focused on the creation of the device swapchain itself otherwise you pretty much always want to use the dr variant plus the deviceresources version is a lot more functional as such i think i m going to retire the non dr versions primarily to reduce the work to maintain these things templates instead of | 1 |
257,885 | 8,148,031,154 | IssuesEvent | 2018-08-22 03:13:54 | broadinstitute/cromwell | https://api.github.com/repos/broadinstitute/cromwell | closed | stderr/out aren't available during runs and are sometimes in application/octet-stream | HIGH PRIORITY | From [a user's forum post](https://gatkforums.broadinstitute.org/firecloud/discussion/12577/stdout-stderr-output-in-bucket-does-not-seem-to-be-updated-while-task-is-running#latest):
1. `stderr` and `stdout` do not appear to show up until a workflow finishes.
2. In some cases `stderr` and `stdout` are of type `application/octet-stream` rather than `text/plain`, not allowing the content to be viewable without downloading.
I was able to see these by running a [five-dollar-genome-analysis-pipeline](https://portal.firecloud.org/#workspaces/fccredits-silver-pumpkin-7172/five-dollar-genome-analysis-pipeline_copy) as well.
| 1.0 | stderr/out aren't available during runs and are sometimes in application/octet-stream - From [a user's forum post](https://gatkforums.broadinstitute.org/firecloud/discussion/12577/stdout-stderr-output-in-bucket-does-not-seem-to-be-updated-while-task-is-running#latest):
1. `stderr` and `stdout` do not appear to show up until a workflow finishes.
2. In some cases `stderr` and `stdout` are of type `application/octet-stream` rather than `text/plain`, not allowing the content to be viewable without downloading.
I was able to see these by running a [five-dollar-genome-analysis-pipeline](https://portal.firecloud.org/#workspaces/fccredits-silver-pumpkin-7172/five-dollar-genome-analysis-pipeline_copy) as well.
| non_main | stderr out aren t available during runs and are sometimes in application octet stream from stderr and stdout do not appear to show up until a workflow finishes in some cases stderr and stdout are of type application octet stream rather than text plain not allowing the content to be viewable without downloading i was able to see these by running a as well | 0 |
196,632 | 15,604,079,065 | IssuesEvent | 2021-03-19 03:09:45 | yuri-norwood/bfk | https://api.github.com/repos/yuri-norwood/bfk | closed | Link io.ReadWritter and os.Stdout references to respective documention | documentation | What it says on the box | 1.0 | Link io.ReadWritter and os.Stdout references to respective documention - What it says on the box | non_main | link io readwritter and os stdout references to respective documention what it says on the box | 0 |
55,184 | 11,405,843,394 | IssuesEvent | 2020-01-31 13:05:05 | openvalidation/openvalidation | https://api.github.com/repos/openvalidation/openvalidation | closed | Java codegen: use Number type for returning numbers | codegen good first issue | <!--- Thank you for using openVALIDATION! -->
Taking some inspiraition from the suggestions of @sbischoff-ai in #39
in `openvalidation-generation/src/main/resources/java/framework.hbs` BigDecimal is used as the return type for numbers. It might be much more suitable to return a more general Number
## Expected Behavior
<!--- If you're describing a bug, tell us what should happen -->
<!--- If you're suggesting a change/improvement, tell us how it should work -->
Functions like `SUM_OF` should return a more generalized Number Type.
## Current Behavior
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If describing a bug, also provide console output if possible -->
<!--- If suggesting a change/improvement, explain the difference from current behavior -->
Number specifc functions return double or BigDecimal specificly.
## Possible Solution
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change -->
## Steps to Reproduce (for bugs)
<!--- Provide a link to a live example, or an unambiguous set of steps to -->
<!--- reproduce this bug. Include code to reproduce, if relevant -->
## Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most useful in the real world -->
## Your Environment
<!--- Include as many relevant details about the environment you experienced the bug in -->
* Version used: 0.0.1
* Environment name and version (`mvn -v` and `java -version`):
* Operating System and version:
* Link to your project:
| 1.0 | Java codegen: use Number type for returning numbers - <!--- Thank you for using openVALIDATION! -->
Taking some inspiraition from the suggestions of @sbischoff-ai in #39
in `openvalidation-generation/src/main/resources/java/framework.hbs` BigDecimal is used as the return type for numbers. It might be much more suitable to return a more general Number
## Expected Behavior
<!--- If you're describing a bug, tell us what should happen -->
<!--- If you're suggesting a change/improvement, tell us how it should work -->
Functions like `SUM_OF` should return a more generalized Number Type.
## Current Behavior
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If describing a bug, also provide console output if possible -->
<!--- If suggesting a change/improvement, explain the difference from current behavior -->
Number specifc functions return double or BigDecimal specificly.
## Possible Solution
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change -->
## Steps to Reproduce (for bugs)
<!--- Provide a link to a live example, or an unambiguous set of steps to -->
<!--- reproduce this bug. Include code to reproduce, if relevant -->
## Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most useful in the real world -->
## Your Environment
<!--- Include as many relevant details about the environment you experienced the bug in -->
* Version used: 0.0.1
* Environment name and version (`mvn -v` and `java -version`):
* Operating System and version:
* Link to your project:
| non_main | java codegen use number type for returning numbers taking some inspiraition from the suggestions of sbischoff ai in in openvalidation generation src main resources java framework hbs bigdecimal is used as the return type for numbers it might be much more suitable to return a more general number expected behavior functions like sum of should return a more generalized number type current behavior number specifc functions return double or bigdecimal specificly possible solution steps to reproduce for bugs context your environment version used environment name and version mvn v and java version operating system and version link to your project | 0 |
4,650 | 24,086,837,318 | IssuesEvent | 2022-09-19 11:44:00 | chocolatey-community/chocolatey-package-requests | https://api.github.com/repos/chocolatey-community/chocolatey-package-requests | closed | RFP - emusak-ui | Status: Available For Maintainer(s) | <!--
* Please ensure the package does not already exist in the Chocolatey Community Repository - https://chocolatey.org/packages - by using a relevant search.
* Please ensure there is no existing open package request.
* Please ensure the issue title starts with 'RFP - ' - for example 'RFP - adobe-reader'
* Please also ensure the issue title matches the identifier you expect the package should be named.
* Please ensure you have both the Software Project URL and the Software Download URL before continuing.
NOTE: Keep in mind we have an etiquette regarding communication that we expect folks to observe when they are looking for support in the Chocolatey community - https://github.com/chocolatey/chocolatey-package-requests/blob/master/README.md#etiquette-regarding-communication
PLEASE REMOVE ALL COMMENTS ONCE YOU HAVE READ THEM.
-->
## Checklist
- [x] The package I am requesting does not already exist on https://chocolatey.org/packages;
- [x] There is no open issue for this package;
- [x] The issue title starts with 'RFP - ';
- [x] The download URL is public and not locked behind a paywall / login;
## Package Details
Software project URL : https://github.com/CapitaineJSparrow/emusak-ui
Direct download URL for the software / installer : https://github.com/CapitaineJSparrow/emusak-ui/releases/download/v1.0.108/emusak-1.0.108.Setup.exe
Software summary / short description: This is a tool which allows you to download saves or mods for Nintendo Switch emulators using a compatible Emusak backend
<!-- ## Package Expectations
Here you can make suggestions on what you would expect the package to do outside of 'installing' - eg. adding icons to the desktop
-->
| True | RFP - emusak-ui - <!--
* Please ensure the package does not already exist in the Chocolatey Community Repository - https://chocolatey.org/packages - by using a relevant search.
* Please ensure there is no existing open package request.
* Please ensure the issue title starts with 'RFP - ' - for example 'RFP - adobe-reader'
* Please also ensure the issue title matches the identifier you expect the package should be named.
* Please ensure you have both the Software Project URL and the Software Download URL before continuing.
NOTE: Keep in mind we have an etiquette regarding communication that we expect folks to observe when they are looking for support in the Chocolatey community - https://github.com/chocolatey/chocolatey-package-requests/blob/master/README.md#etiquette-regarding-communication
PLEASE REMOVE ALL COMMENTS ONCE YOU HAVE READ THEM.
-->
## Checklist
- [x] The package I am requesting does not already exist on https://chocolatey.org/packages;
- [x] There is no open issue for this package;
- [x] The issue title starts with 'RFP - ';
- [x] The download URL is public and not locked behind a paywall / login;
## Package Details
Software project URL : https://github.com/CapitaineJSparrow/emusak-ui
Direct download URL for the software / installer : https://github.com/CapitaineJSparrow/emusak-ui/releases/download/v1.0.108/emusak-1.0.108.Setup.exe
Software summary / short description: This is a tool which allows you to download saves or mods for Nintendo Switch emulators using a compatible Emusak backend
<!-- ## Package Expectations
Here you can make suggestions on what you would expect the package to do outside of 'installing' - eg. adding icons to the desktop
-->
| main | rfp emusak ui please ensure the package does not already exist in the chocolatey community repository by using a relevant search please ensure there is no existing open package request please ensure the issue title starts with rfp for example rfp adobe reader please also ensure the issue title matches the identifier you expect the package should be named please ensure you have both the software project url and the software download url before continuing note keep in mind we have an etiquette regarding communication that we expect folks to observe when they are looking for support in the chocolatey community please remove all comments once you have read them checklist the package i am requesting does not already exist on there is no open issue for this package the issue title starts with rfp the download url is public and not locked behind a paywall login package details software project url direct download url for the software installer software summary short description this is a tool which allows you to download saves or mods for nintendo switch emulators using a compatible emusak backend package expectations here you can make suggestions on what you would expect the package to do outside of installing eg adding icons to the desktop | 1 |
165,708 | 12,879,868,141 | IssuesEvent | 2020-07-12 01:25:29 | osquery/osquery | https://api.github.com/repos/osquery/osquery | closed | Create tests for the table `wmi_script_event_consumers` | Windows good-first-issue table test | ## Create tests for the table `wmi_script_event_consumers`
- Create header file for the table implementation, if one is not exists.
- In test, query the table and check if retrieved columns (name and types) match the columns from table spec.
- If there is any guarantee to number of rows (e.g. only 1 record in every query result, more than 3 records or something else) check it.
- Test the implementation details of the table, if it possible.
Table spec: `specs/windows/wmi_script_event_consumers.table`
Source files:
- `osquery/tables/system/windows/wmi_script_event_consumers.cpp`
Table generating function: `genScriptConsumers()`
| 1.0 | Create tests for the table `wmi_script_event_consumers` - ## Create tests for the table `wmi_script_event_consumers`
- Create header file for the table implementation, if one is not exists.
- In test, query the table and check if retrieved columns (name and types) match the columns from table spec.
- If there is any guarantee to number of rows (e.g. only 1 record in every query result, more than 3 records or something else) check it.
- Test the implementation details of the table, if it possible.
Table spec: `specs/windows/wmi_script_event_consumers.table`
Source files:
- `osquery/tables/system/windows/wmi_script_event_consumers.cpp`
Table generating function: `genScriptConsumers()`
| non_main | create tests for the table wmi script event consumers create tests for the table wmi script event consumers create header file for the table implementation if one is not exists in test query the table and check if retrieved columns name and types match the columns from table spec if there is any guarantee to number of rows e g only record in every query result more than records or something else check it test the implementation details of the table if it possible table spec specs windows wmi script event consumers table source files osquery tables system windows wmi script event consumers cpp table generating function genscriptconsumers | 0 |
130,944 | 27,793,604,484 | IssuesEvent | 2023-03-17 10:46:26 | zenitba/server-side-rendering | https://api.github.com/repos/zenitba/server-side-rendering | closed | De properties links laten beginnen | Code/Review⚙️ | https://github.com/zenitba/server-side-rendering/blob/0a1537be88cb49c8a937c1f2281ac3eb9815fda4/public/style.css#L124-L140
Je kan de properties links laten beginnen zoals de rest van je css voor meer overzicht | 1.0 | De properties links laten beginnen - https://github.com/zenitba/server-side-rendering/blob/0a1537be88cb49c8a937c1f2281ac3eb9815fda4/public/style.css#L124-L140
Je kan de properties links laten beginnen zoals de rest van je css voor meer overzicht | non_main | de properties links laten beginnen je kan de properties links laten beginnen zoals de rest van je css voor meer overzicht | 0 |
4,320 | 10,917,612,138 | IssuesEvent | 2019-11-21 15:27:47 | maSchoeller/JimnyTainment | https://api.github.com/repos/maSchoeller/JimnyTainment | closed | Project distribution and Namespace naming | V0.1 milestone program architecture | # Project distribution
General distribution of the application into 4 projects:
- **JimnyTainment.UI.View**
_The project contains the actual user interface._
- **JimnyTainment.UI.ViewModel**
_Contains the control logic for the user interface._
- **JimnyTainment.Lib**
_Contains various services that are used by the control logic, e.g. analysis classes of autometadata or configuration management, etc..._
- JimnyTainment.Lib.Analysis
- JimnyTainment.Lib.Storage
- JimnyTainment.Lib.Logging
- **JimnyTainment.Drivers**
_Contains various drivers used by the services and ViewModels_
- JimnyTainment.Drivers.OBD2
- JimnyTainment.Drivers.Audio
- JimnyTainment.Drivers.IO
- JimnyTainment.Drivers.Camera
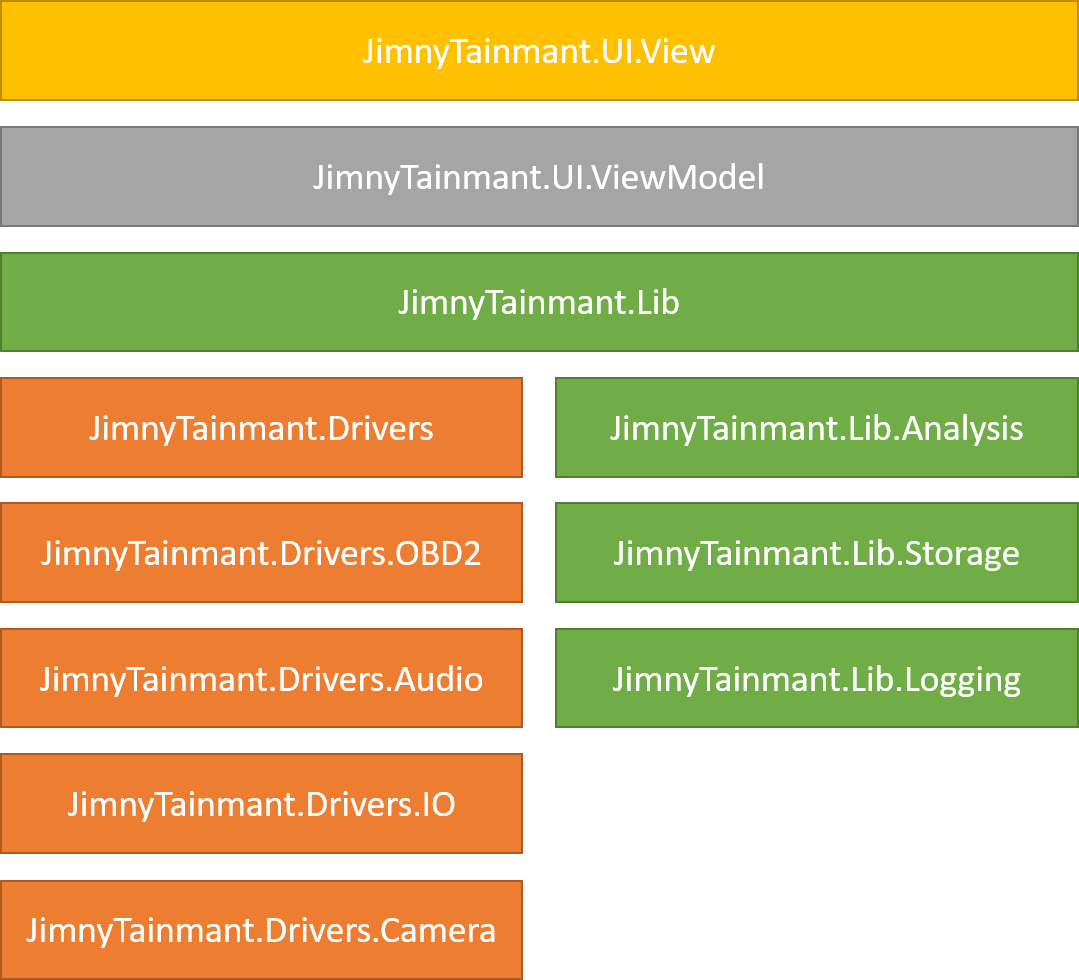
In general this would be an Arichtetcure proposal for project. This proposal would not blow up the application too much, but still divide it up well.
@langmario @pafinkbeiner
If you still have namespaces you want to add you can simply write them into the issue or what you think about it/how you would do it;)
| 1.0 | Project distribution and Namespace naming - # Project distribution
General distribution of the application into 4 projects:
- **JimnyTainment.UI.View**
_The project contains the actual user interface._
- **JimnyTainment.UI.ViewModel**
_Contains the control logic for the user interface._
- **JimnyTainment.Lib**
_Contains various services that are used by the control logic, e.g. analysis classes of autometadata or configuration management, etc..._
- JimnyTainment.Lib.Analysis
- JimnyTainment.Lib.Storage
- JimnyTainment.Lib.Logging
- **JimnyTainment.Drivers**
_Contains various drivers used by the services and ViewModels_
- JimnyTainment.Drivers.OBD2
- JimnyTainment.Drivers.Audio
- JimnyTainment.Drivers.IO
- JimnyTainment.Drivers.Camera
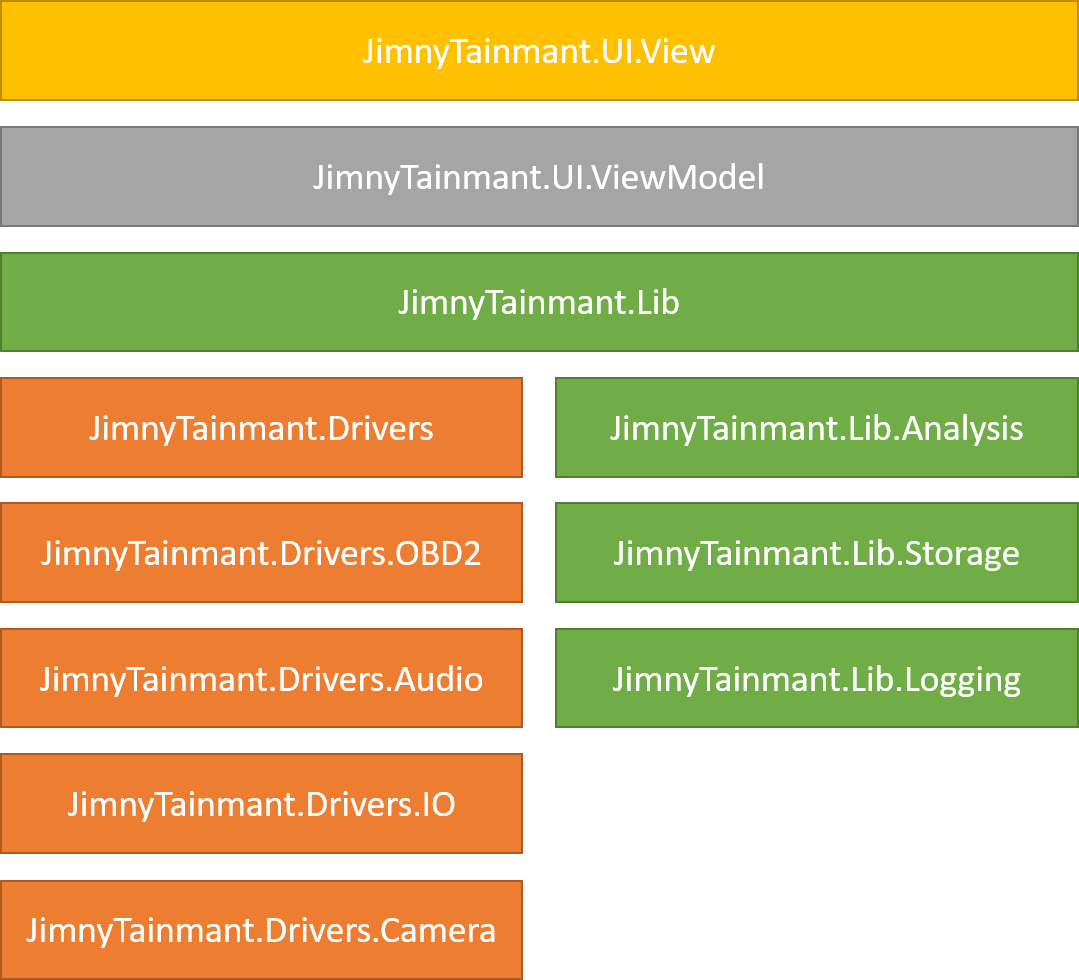
In general this would be an Arichtetcure proposal for project. This proposal would not blow up the application too much, but still divide it up well.
@langmario @pafinkbeiner
If you still have namespaces you want to add you can simply write them into the issue or what you think about it/how you would do it;)
| non_main | project distribution and namespace naming project distribution general distribution of the application into projects jimnytainment ui view the project contains the actual user interface jimnytainment ui viewmodel contains the control logic for the user interface jimnytainment lib contains various services that are used by the control logic e g analysis classes of autometadata or configuration management etc jimnytainment lib analysis jimnytainment lib storage jimnytainment lib logging jimnytainment drivers contains various drivers used by the services and viewmodels jimnytainment drivers jimnytainment drivers audio jimnytainment drivers io jimnytainment drivers camera in general this would be an arichtetcure proposal for project this proposal would not blow up the application too much but still divide it up well langmario pafinkbeiner if you still have namespaces you want to add you can simply write them into the issue or what you think about it how you would do it | 0 |
388,620 | 11,489,958,804 | IssuesEvent | 2020-02-11 16:18:29 | bounswe/bounswe2019group11 | https://api.github.com/repos/bounswe/bounswe2019group11 | closed | View Public and Private Profiles of Other Users | Component: Frontend Estimation: M Priority: Critical Status: In Progress | - Users should be able to view public profiles of registered users.
- Registered users should be able to set information about themselves as private or public.
- Registered users with permission (planned to be linked to followers system) should be able to view private profiles of registered users. | 1.0 | View Public and Private Profiles of Other Users - - Users should be able to view public profiles of registered users.
- Registered users should be able to set information about themselves as private or public.
- Registered users with permission (planned to be linked to followers system) should be able to view private profiles of registered users. | non_main | view public and private profiles of other users users should be able to view public profiles of registered users registered users should be able to set information about themselves as private or public registered users with permission planned to be linked to followers system should be able to view private profiles of registered users | 0 |
265,495 | 28,292,520,568 | IssuesEvent | 2023-04-09 11:50:30 | Seagate/Lyve-Cloud-Solutions-Samples | https://api.github.com/repos/Seagate/Lyve-Cloud-Solutions-Samples | reopened | storage-blob-10.5.0.tgz: 1 vulnerabilities (highest severity is: 5.5) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>storage-blob-10.5.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/package.json</p>
<p>Path to vulnerable library: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/node_modules/xml2js/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Seagate/Lyve-Cloud-Solutions-Samples/commit/ae974d5e930d7abbdf895fbbb1381461251e50ca">ae974d5e930d7abbdf895fbbb1381461251e50ca</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (storage-blob version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-0842](https://www.mend.io/vulnerability-database/CVE-2023-0842) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | xml2js-0.4.23.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-0842</summary>
### Vulnerable Library - <b>xml2js-0.4.23.tgz</b></p>
<p>Simple XML to JavaScript object converter.</p>
<p>Library home page: <a href="https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz">https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz</a></p>
<p>Path to dependency file: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/package.json</p>
<p>Path to vulnerable library: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/node_modules/xml2js/package.json</p>
<p>
Dependency Hierarchy:
- storage-blob-10.5.0.tgz (Root Library)
- ms-rest-js-2.6.4.tgz
- :x: **xml2js-0.4.23.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Seagate/Lyve-Cloud-Solutions-Samples/commit/ae974d5e930d7abbdf895fbbb1381461251e50ca">ae974d5e930d7abbdf895fbbb1381461251e50ca</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
xml2js version 0.4.23 allows an external attacker to edit or add new properties to an object. This is possible because the application does not properly validate incoming JSON keys, thus allowing the __proto__ property to be edited.
<p>Publish Date: 2023-04-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0842>CVE-2023-0842</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details> | True | storage-blob-10.5.0.tgz: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>storage-blob-10.5.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/package.json</p>
<p>Path to vulnerable library: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/node_modules/xml2js/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Seagate/Lyve-Cloud-Solutions-Samples/commit/ae974d5e930d7abbdf895fbbb1381461251e50ca">ae974d5e930d7abbdf895fbbb1381461251e50ca</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (storage-blob version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-0842](https://www.mend.io/vulnerability-database/CVE-2023-0842) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | xml2js-0.4.23.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the "Details" section below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-0842</summary>
### Vulnerable Library - <b>xml2js-0.4.23.tgz</b></p>
<p>Simple XML to JavaScript object converter.</p>
<p>Library home page: <a href="https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz">https://registry.npmjs.org/xml2js/-/xml2js-0.4.23.tgz</a></p>
<p>Path to dependency file: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/package.json</p>
<p>Path to vulnerable library: /data-migration-and-sync-to-lyvecloud/code/migrationWorker/node_modules/xml2js/package.json</p>
<p>
Dependency Hierarchy:
- storage-blob-10.5.0.tgz (Root Library)
- ms-rest-js-2.6.4.tgz
- :x: **xml2js-0.4.23.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Seagate/Lyve-Cloud-Solutions-Samples/commit/ae974d5e930d7abbdf895fbbb1381461251e50ca">ae974d5e930d7abbdf895fbbb1381461251e50ca</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
xml2js version 0.4.23 allows an external attacker to edit or add new properties to an object. This is possible because the application does not properly validate incoming JSON keys, thus allowing the __proto__ property to be edited.
<p>Publish Date: 2023-04-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-0842>CVE-2023-0842</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details> | non_main | storage blob tgz vulnerabilities highest severity is vulnerable library storage blob tgz path to dependency file data migration and sync to lyvecloud code migrationworker package json path to vulnerable library data migration and sync to lyvecloud code migrationworker node modules package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in storage blob version remediation available medium tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the details section below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library tgz simple xml to javascript object converter library home page a href path to dependency file data migration and sync to lyvecloud code migrationworker package json path to vulnerable library data migration and sync to lyvecloud code migrationworker node modules package json dependency hierarchy storage blob tgz root library ms rest js tgz x tgz vulnerable library found in head commit a href found in base branch main vulnerability details version allows an external attacker to edit or add new properties to an object this is possible because the application does not properly validate incoming json keys thus allowing the proto property to be edited publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href | 0 |
2,696 | 9,417,450,376 | IssuesEvent | 2019-04-10 16:45:57 | victorcombalweiss/datapuppy | https://api.github.com/repos/victorcombalweiss/datapuppy | opened | Move to Scss | maintainability | As of now, web application uses CSS. As a consequence many values are duplicated, and some values depend on one another implicitly.
In order to have a more robust system it would be good to switch to Scss. | True | Move to Scss - As of now, web application uses CSS. As a consequence many values are duplicated, and some values depend on one another implicitly.
In order to have a more robust system it would be good to switch to Scss. | main | move to scss as of now web application uses css as a consequence many values are duplicated and some values depend on one another implicitly in order to have a more robust system it would be good to switch to scss | 1 |
254,768 | 21,876,383,920 | IssuesEvent | 2022-05-19 10:31:34 | Tencent/bk-job | https://api.github.com/repos/Tencent/bk-job | closed | bugfix: 统计脚本被引用次数时未排除调试作业模板产生的调试执行方案导致脚本无法删除 | kind/bug stage/test stage/uat | **版本/分支/tag**
3.4.4.0
**问题描述**
统计脚本被引用次数时未排除调试作业模板产生的调试执行方案导致脚本无法删除
**如何复现**
创建脚本1,上线脚本1
创建模板1,引用脚本1
调试模板1,运行
创建脚本2,上线脚本2
编辑模板1,引用脚本1改为引用脚本2
查看脚本1引用次数,发现模板/执行方案引用次数为 0/1
尝试删除脚本1,提示被引用无法删除
**预期结果**
脚本1不再被引用后,查看脚本1引用次数,模板/执行方案引用次数为 0/0
应当能够正常删除脚本1 | 1.0 | bugfix: 统计脚本被引用次数时未排除调试作业模板产生的调试执行方案导致脚本无法删除 - **版本/分支/tag**
3.4.4.0
**问题描述**
统计脚本被引用次数时未排除调试作业模板产生的调试执行方案导致脚本无法删除
**如何复现**
创建脚本1,上线脚本1
创建模板1,引用脚本1
调试模板1,运行
创建脚本2,上线脚本2
编辑模板1,引用脚本1改为引用脚本2
查看脚本1引用次数,发现模板/执行方案引用次数为 0/1
尝试删除脚本1,提示被引用无法删除
**预期结果**
脚本1不再被引用后,查看脚本1引用次数,模板/执行方案引用次数为 0/0
应当能够正常删除脚本1 | non_main | bugfix 统计脚本被引用次数时未排除调试作业模板产生的调试执行方案导致脚本无法删除 版本 分支 tag 问题描述 统计脚本被引用次数时未排除调试作业模板产生的调试执行方案导致脚本无法删除 如何复现 , , ,运行 , , ,发现模板 执行方案引用次数为 ,提示被引用无法删除 预期结果 , ,模板 执行方案引用次数为 | 0 |
1,300 | 5,541,906,229 | IssuesEvent | 2017-03-22 13:58:40 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Exception while running ios_command which times out after correctly executing a command | affects_2.1 bug_report networking P2 waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ios_command
##### ANSIBLE VERSION
```
ansible 2.1.1.0
config file = /etc/ansible/ansible.cfg
configured module search path = ['/usr/lib/python2.7/dist-packages/ansible']
```
##### CONFIGURATION
inventory = ./hosts
roles_path = /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles
fact_caching = redis
fact_caching_timeout = 86400
##### OS / ENVIRONMENT
- host: Ubuntu 16.04 4.4.0
- target: **IOSv 15.4** (20140730:011659)
##### SUMMARY
ios_command executes the command correctly and then runs into an exception ending as a "socket.timeout".
The same crash happens even when:
- password is removed from provider to try to influence Ansible to use the SSH key instead
- SSH key is removed from provider to try to influence Ansible to use the password instead
- other types of IOS commands are passed
##### STEPS TO REPRODUCE
**Inventory ./hosts**:
```
[iosv]
192.168.137.254
```
Structure passed as "**provider**": connections.ssh
Defined in group_vars/iosv/connections.yml
```
connections:
...
ssh:
host: "{{ inventory_hostname }}"
port: 22
username: admin
password: Cisco2016$
authorize: yes
auth_pass: Cisco2016$
ssh_keyfile: "~/.ssh/id_rsa"
timeout: 10
```
**Role**: ios_pull_config
```
- include_vars: "{{ role_path }}/../../group_vars/{{ hostvars[inventory_hostname].group_names[0] }}/connections.yml"
- name: Fetching the {{ config }} from the remote node
ios_command:
provider: "{{ connections.ssh }}"
commands:
- "show {{ config }}"
register: show
```
**Playbook**:
```
- name: Pull IOS/IOSv/IOSv-L2 startup and running configs
hosts: iosv
roles:
- { role: ios_pull_config, config: startup-config }
- { role: ios_pull_config, config: running-config }
```
##### EXPECTED RESULTS
The command should obviously not crash.
##### ACTUAL RESULTS
```
PLAYBOOK: ios_pull_config.yml **************************************************
1 plays in ios_pull_config.yml
PLAY [Pull IOS/IOSv/IOSv-L2 startup and running configs] ***********************
TASK [print_variables : Print all variables for each remote device] ************
task path: /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles/print_variables/tasks/main.yml:27
...
TASK [ios_pull_config : include_vars] ******************************************
task path: /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles/ios_pull_config/tasks/main.yml:36
ok: [192.168.137.254] => {"ansible_facts": {"ansible_connection": "{{ connections.compute }}", "connections": {"compute": "local", "os_family": null, "os_release": null, .....
....
TASK [ios_pull_config : Fetching the startup-config from the remote node] ******
task path: /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles/ios_pull_config/tasks/main.yml:38
...
ok: [192.168.137.254] => {"changed": false, "invocation": {"module_args": {"auth_pass": "VALUE_SPECIFIED_IN_NO_LOG_PARAMETER", "authorize": true, "commands": ["show startup-config"], "host": "192.168.137.254", "interval": 1, "password": "VALUE_SPECIFIED_IN_NO_LOG_PARAMETER", "port": 22, "provider": "{'username': 'admin', 'authorize': True, 'ssh_keyfile': '~/.ssh/id_rsa', 'auth_pass': '********', 'key_type': 'rsa', 'host': '192.168.137.254', 'version': 2, 'auth_retries': 3, 'timeout': 10, 'password': '********', 'port': 22, 'transport': 'cli'}", "retries": 10, "ssh_keyfile": "/root/.ssh/id_rsa", "timeout": 10, "username": "admin", "waitfor": null}, "module_name": "ios_command"}, "stdout": ["Using 6464 out of 262144 bytes\n!\n! Last configuration change at 13:54:49 UTC Fri Jul 1 2016 by admin\n!\nversion 15.4\nservice timestamps debug datetime msec\nservice timestamps log datetime msec\nservice password-encryption\n!\nhostname vIOS_1\n!\nboot-start-marker\nboot-end-marker\n!\n!\nenable secret 5 $1$HNyP$Gf3QFB4kSxl9..lFPVy4P/
....
**An exception occurred during task execution**. The full traceback is:
Traceback (most recent call last):
File "/tmp/ansible_vNRL0L/ansible_module_ios_command.py", line 169, in <module>
main()
File "/tmp/ansible_vNRL0L/ansible_module_ios_command.py", line 144, in main
response = module.execute(commands)
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/ios.py", line 151, in execute
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/ios.py", line 134, in connect
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/ios.py", line 87, in connect
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/shell.py", line 108, in open
File "/usr/local/lib/python2.7/dist-packages/paramiko/client.py", line 292, in connect
retry_on_signal(lambda: sock.connect(addr))
File "/usr/local/lib/python2.7/dist-packages/paramiko/util.py", line 270, in retry_on_signal
return function()
File "/usr/local/lib/python2.7/dist-packages/paramiko/client.py", line 292, in <lambda>
retry_on_signal(lambda: sock.connect(addr))
File "/usr/lib/python2.7/socket.py", line 228, in meth
return getattr(self._sock,name)(*args)
**socket.timeout**: timed out
...
```
**Whole log**
[ios_pull_config.log.txt](https://github.com/ansible/ansible-modules-core/files/343757/ios_pull_config.log.txt)
| True | Exception while running ios_command which times out after correctly executing a command - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ios_command
##### ANSIBLE VERSION
```
ansible 2.1.1.0
config file = /etc/ansible/ansible.cfg
configured module search path = ['/usr/lib/python2.7/dist-packages/ansible']
```
##### CONFIGURATION
inventory = ./hosts
roles_path = /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles
fact_caching = redis
fact_caching_timeout = 86400
##### OS / ENVIRONMENT
- host: Ubuntu 16.04 4.4.0
- target: **IOSv 15.4** (20140730:011659)
##### SUMMARY
ios_command executes the command correctly and then runs into an exception ending as a "socket.timeout".
The same crash happens even when:
- password is removed from provider to try to influence Ansible to use the SSH key instead
- SSH key is removed from provider to try to influence Ansible to use the password instead
- other types of IOS commands are passed
##### STEPS TO REPRODUCE
**Inventory ./hosts**:
```
[iosv]
192.168.137.254
```
Structure passed as "**provider**": connections.ssh
Defined in group_vars/iosv/connections.yml
```
connections:
...
ssh:
host: "{{ inventory_hostname }}"
port: 22
username: admin
password: Cisco2016$
authorize: yes
auth_pass: Cisco2016$
ssh_keyfile: "~/.ssh/id_rsa"
timeout: 10
```
**Role**: ios_pull_config
```
- include_vars: "{{ role_path }}/../../group_vars/{{ hostvars[inventory_hostname].group_names[0] }}/connections.yml"
- name: Fetching the {{ config }} from the remote node
ios_command:
provider: "{{ connections.ssh }}"
commands:
- "show {{ config }}"
register: show
```
**Playbook**:
```
- name: Pull IOS/IOSv/IOSv-L2 startup and running configs
hosts: iosv
roles:
- { role: ios_pull_config, config: startup-config }
- { role: ios_pull_config, config: running-config }
```
##### EXPECTED RESULTS
The command should obviously not crash.
##### ACTUAL RESULTS
```
PLAYBOOK: ios_pull_config.yml **************************************************
1 plays in ios_pull_config.yml
PLAY [Pull IOS/IOSv/IOSv-L2 startup and running configs] ***********************
TASK [print_variables : Print all variables for each remote device] ************
task path: /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles/print_variables/tasks/main.yml:27
...
TASK [ios_pull_config : include_vars] ******************************************
task path: /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles/ios_pull_config/tasks/main.yml:36
ok: [192.168.137.254] => {"ansible_facts": {"ansible_connection": "{{ connections.compute }}", "connections": {"compute": "local", "os_family": null, "os_release": null, .....
....
TASK [ios_pull_config : Fetching the startup-config from the remote node] ******
task path: /home/actionmystique/Program-Files/Ubuntu/Ansible/git-Ansible/roles/ios_pull_config/tasks/main.yml:38
...
ok: [192.168.137.254] => {"changed": false, "invocation": {"module_args": {"auth_pass": "VALUE_SPECIFIED_IN_NO_LOG_PARAMETER", "authorize": true, "commands": ["show startup-config"], "host": "192.168.137.254", "interval": 1, "password": "VALUE_SPECIFIED_IN_NO_LOG_PARAMETER", "port": 22, "provider": "{'username': 'admin', 'authorize': True, 'ssh_keyfile': '~/.ssh/id_rsa', 'auth_pass': '********', 'key_type': 'rsa', 'host': '192.168.137.254', 'version': 2, 'auth_retries': 3, 'timeout': 10, 'password': '********', 'port': 22, 'transport': 'cli'}", "retries": 10, "ssh_keyfile": "/root/.ssh/id_rsa", "timeout": 10, "username": "admin", "waitfor": null}, "module_name": "ios_command"}, "stdout": ["Using 6464 out of 262144 bytes\n!\n! Last configuration change at 13:54:49 UTC Fri Jul 1 2016 by admin\n!\nversion 15.4\nservice timestamps debug datetime msec\nservice timestamps log datetime msec\nservice password-encryption\n!\nhostname vIOS_1\n!\nboot-start-marker\nboot-end-marker\n!\n!\nenable secret 5 $1$HNyP$Gf3QFB4kSxl9..lFPVy4P/
....
**An exception occurred during task execution**. The full traceback is:
Traceback (most recent call last):
File "/tmp/ansible_vNRL0L/ansible_module_ios_command.py", line 169, in <module>
main()
File "/tmp/ansible_vNRL0L/ansible_module_ios_command.py", line 144, in main
response = module.execute(commands)
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/ios.py", line 151, in execute
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/ios.py", line 134, in connect
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/ios.py", line 87, in connect
File "/tmp/ansible_vNRL0L/ansible_modlib.zip/ansible/module_utils/shell.py", line 108, in open
File "/usr/local/lib/python2.7/dist-packages/paramiko/client.py", line 292, in connect
retry_on_signal(lambda: sock.connect(addr))
File "/usr/local/lib/python2.7/dist-packages/paramiko/util.py", line 270, in retry_on_signal
return function()
File "/usr/local/lib/python2.7/dist-packages/paramiko/client.py", line 292, in <lambda>
retry_on_signal(lambda: sock.connect(addr))
File "/usr/lib/python2.7/socket.py", line 228, in meth
return getattr(self._sock,name)(*args)
**socket.timeout**: timed out
...
```
**Whole log**
[ios_pull_config.log.txt](https://github.com/ansible/ansible-modules-core/files/343757/ios_pull_config.log.txt)
| main | exception while running ios command which times out after correctly executing a command issue type bug report component name ios command ansible version ansible config file etc ansible ansible cfg configured module search path configuration inventory hosts roles path home actionmystique program files ubuntu ansible git ansible roles fact caching redis fact caching timeout os environment host ubuntu target iosv summary ios command executes the command correctly and then runs into an exception ending as a socket timeout the same crash happens even when password is removed from provider to try to influence ansible to use the ssh key instead ssh key is removed from provider to try to influence ansible to use the password instead other types of ios commands are passed steps to reproduce inventory hosts structure passed as provider connections ssh defined in group vars iosv connections yml connections ssh host inventory hostname port username admin password authorize yes auth pass ssh keyfile ssh id rsa timeout role ios pull config include vars role path group vars hostvars group names connections yml name fetching the config from the remote node ios command provider connections ssh commands show config register show playbook name pull ios iosv iosv startup and running configs hosts iosv roles role ios pull config config startup config role ios pull config config running config expected results the command should obviously not crash actual results playbook ios pull config yml plays in ios pull config yml play task task path home actionmystique program files ubuntu ansible git ansible roles print variables tasks main yml task task path home actionmystique program files ubuntu ansible git ansible roles ios pull config tasks main yml ok ansible facts ansible connection connections compute connections compute local os family null os release null task task path home actionmystique program files ubuntu ansible git ansible roles ios pull config tasks main yml ok changed false invocation module args auth pass value specified in no log parameter authorize true commands host interval password value specified in no log parameter port provider username admin authorize true ssh keyfile ssh id rsa auth pass key type rsa host version auth retries timeout password port transport cli retries ssh keyfile root ssh id rsa timeout username admin waitfor null module name ios command stdout using out of bytes n n last configuration change at utc fri jul by admin n nversion nservice timestamps debug datetime msec nservice timestamps log datetime msec nservice password encryption n nhostname vios n nboot start marker nboot end marker n n nenable secret hnyp an exception occurred during task execution the full traceback is traceback most recent call last file tmp ansible ansible module ios command py line in main file tmp ansible ansible module ios command py line in main response module execute commands file tmp ansible ansible modlib zip ansible module utils ios py line in execute file tmp ansible ansible modlib zip ansible module utils ios py line in connect file tmp ansible ansible modlib zip ansible module utils ios py line in connect file tmp ansible ansible modlib zip ansible module utils shell py line in open file usr local lib dist packages paramiko client py line in connect retry on signal lambda sock connect addr file usr local lib dist packages paramiko util py line in retry on signal return function file usr local lib dist packages paramiko client py line in retry on signal lambda sock connect addr file usr lib socket py line in meth return getattr self sock name args socket timeout timed out whole log | 1 |
721 | 4,312,922,464 | IssuesEvent | 2016-07-22 08:21:36 | duckduckgo/zeroclickinfo-goodies | https://api.github.com/repos/duckduckgo/zeroclickinfo-goodies | closed | German Phrases Cheat Sheet: One small mistranslation/One small addition | Maintainer Input Requested PR Received | Change to "Going out for dinner" section:
- Appetizer
- Vorspeise
Suggested addition to "Basics" section:
- Goodbye!
- Tschüss!
------
IA Page: http://duck.co/ia/view/german_cheat_sheet
[Maintainer](http://docs.duckduckhack.com/maintaining/guidelines.html): @AdamSC1-ddg | True | German Phrases Cheat Sheet: One small mistranslation/One small addition - Change to "Going out for dinner" section:
- Appetizer
- Vorspeise
Suggested addition to "Basics" section:
- Goodbye!
- Tschüss!
------
IA Page: http://duck.co/ia/view/german_cheat_sheet
[Maintainer](http://docs.duckduckhack.com/maintaining/guidelines.html): @AdamSC1-ddg | main | german phrases cheat sheet one small mistranslation one small addition change to going out for dinner section appetizer vorspeise suggested addition to basics section goodbye tschüss ia page ddg | 1 |
222 | 4,622,806,536 | IssuesEvent | 2016-09-27 08:53:59 | ocaml/opam-repository | https://api.github.com/repos/ocaml/opam-repository | closed | lablgl for windows | portability | from @blue-prawn:
```
Hi,
On my Windows test environment I can not use "lablgl-20120306" because
of the glShader module that I myself provided before I get a Windows
test environment.
But the vanilla "lablgl-1.04" works fine.
If I've understood correctly Opam is a source package manager, so
maybe opam could provide "lablgl.1.04" for Windows users that have a
similar environment than mine ?
My windows test environment is:
Windows 7 starter with protz's ocaml version 4.00.1
Well in this environment only lablgl itself compiles out of the box.
LablGlut does not.
Togl (Tk) does not either.
(I think that the devel libs for both glut and tkgl are there)
LablGlut and Togl are for windowing, so if we use OCamlSDL instead
this is just fine we don't need these. OCamlSDL1 compiles out of the
box in my win env.
In this environment I compile the Vanilla LablGL like this:
cp Makefile.config.mingw Makefile.config
# need to add -I/usr/include, the patch below does this:
patch < Makefile.config-cygwin-needs-I_usr_include.patch
# don't build anything else than lablgl itself or we get errors:
make lib
make libopt
LABLGL_INSTALLDIR="/tmp/mylblgl0"
make install INSTALLDIR="$LABLGL_INSTALLDIR"
# it seems that the file "dlllablgl.dll" is not installed, so:
cp src/dlllablgl.dll "$LABLGL_INSTALLDIR"/
Now a hello-world works fine.
(I'm providing this hello at the end after the config patch)
===============
$ cat Makefile.config-cygwin-needs-I_usr_include.patch
+++ Makefile.config~ 2013-03-12 18:11:58.945140000 +0100
--- Makefile.config 2013-03-30 13:55:08.524315300 +0100
@@ -35,7 +35,7 @@
-lws2_32 -luser32 -lgdi32
# Where to find OpenGL/Mesa/Glut headers and libraries
-GLINCLUDES = -DHAS_GLEXT_H -DGL_GLEXT_PROTOTYPES -DGLU_VERSION_1_3
+GLINCLUDES = -I/usr/include -DHAS_GLEXT_H -DGL_GLEXT_PROTOTYPES
-DGLU_VERSION_1_3
GLLIBS = -lglu32 -lopengl32
GLLIBS0 = $(GLLIBS)
GLUTLIBS = -lglut32
============
$ cat lblgl_hello.ml
let display () =
GlClear.color (0.0, 0.0, 0.0);
GlClear.clear [`color];
GlDraw.color (1.0, 1.0, 0.0);
GlMat.mode `projection;
GlMat.load_identity ();
GlMat.ortho ~x:(-1.0,1.0) ~y:(-1.0,1.0) ~z:(-1.0,1.0);
GlDraw.begins `polygon;
GlDraw.vertex ~x:(-0.5) ~y:(-0.5) ();
GlDraw.vertex ~x:(-0.5) ~y:(0.5) ();
GlDraw.vertex ~x:(0.5) ~y:(0.5) ();
GlDraw.vertex ~x:(0.5) ~y:(-0.5) ();
GlDraw.ends ();
Gl.flush ()
let () =
Sdl.init [`EVERYTHING];
let _ =
Sdlvideo.set_video_mode ~w:640 ~h:400
[`HWSURFACE; `DOUBLEBUF; `OPENGL; `RESIZABLE]
in
for i = 1 to 6 do
display ();
Sdlgl.swap_buffers ();
Sdltimer.delay 1000;
done;
Sdl.quit ()
# using full windows path, because protz's ocaml doesn't like cygwin ones:
$ ocaml bigarray.cma -I +site-lib/sdl sdl.cma -I
C:/cygwin/tmp/mylblgl0 lablgl.cma lblgl_hello.ml
===========
# completely untested, just copied and modified from "lablgl.20120306"
$ cat opam
opam-version: "1"
maintainer: "contact@ocamlpro.com"
homepage: "https://forge.ocamlcore.org/projects/lablgl/"
authors: [
"Jacques Garrigue"
"Isaac Trotts"
"Erick Tryzelaar"
"Christophe Raffali"
]
# "Jon Harrop" contributed the files "gluTess.ml" / "ml_glutess.c"
# should he be considered as one of the authors? or just a contributor?
build: [
["cp" "Makefile.config.ex" "Makefile.config"]
["cp" "Makefile.config.osx" "Makefile.config"] {"%{os}%" = "darwin"}
["cp" "Makefile.config.mingw" "Makefile.config"] {"%{os}%" =
"windows 7 starter with protz's ocaml 4"}
["mkdir" "-p" "%{bin}%"]
# [make "glut"] ### do not build this one, it doesn't compile out of
the box in my W env
# [make "glutopt"] ### do not build this one, it doesn't compile out
of the box in my W env
### in my W env, only build lablgl.{cma,cmxa}
[make "lib"]
[make "libopt"]
[make "install" "-C" "src" "BINDIR=%{bin}%"
"INSTALLDIR=%{lib}%/lablgl" "DLLDIR=%{lib}%/stublibs"]
# it seems that the makefile forgets to install this one:
["cp" "src/dlllablgl.dll" "DLLDIR=%{lib}%/stublibs"] {"%{os:env}%" =
"win7::protz"}
### do not install LablGlut, it doesn't compile out of the box in my W env
### [make "install" "-C" "LablGlut/src" "BINDIR=%{bin}%"
"INSTALLDIR=%{lib}%/lablgl" "DLLDIR=%{lib}%/stublibs"]
]
--
Cheers
``` | True | lablgl for windows - from @blue-prawn:
```
Hi,
On my Windows test environment I can not use "lablgl-20120306" because
of the glShader module that I myself provided before I get a Windows
test environment.
But the vanilla "lablgl-1.04" works fine.
If I've understood correctly Opam is a source package manager, so
maybe opam could provide "lablgl.1.04" for Windows users that have a
similar environment than mine ?
My windows test environment is:
Windows 7 starter with protz's ocaml version 4.00.1
Well in this environment only lablgl itself compiles out of the box.
LablGlut does not.
Togl (Tk) does not either.
(I think that the devel libs for both glut and tkgl are there)
LablGlut and Togl are for windowing, so if we use OCamlSDL instead
this is just fine we don't need these. OCamlSDL1 compiles out of the
box in my win env.
In this environment I compile the Vanilla LablGL like this:
cp Makefile.config.mingw Makefile.config
# need to add -I/usr/include, the patch below does this:
patch < Makefile.config-cygwin-needs-I_usr_include.patch
# don't build anything else than lablgl itself or we get errors:
make lib
make libopt
LABLGL_INSTALLDIR="/tmp/mylblgl0"
make install INSTALLDIR="$LABLGL_INSTALLDIR"
# it seems that the file "dlllablgl.dll" is not installed, so:
cp src/dlllablgl.dll "$LABLGL_INSTALLDIR"/
Now a hello-world works fine.
(I'm providing this hello at the end after the config patch)
===============
$ cat Makefile.config-cygwin-needs-I_usr_include.patch
+++ Makefile.config~ 2013-03-12 18:11:58.945140000 +0100
--- Makefile.config 2013-03-30 13:55:08.524315300 +0100
@@ -35,7 +35,7 @@
-lws2_32 -luser32 -lgdi32
# Where to find OpenGL/Mesa/Glut headers and libraries
-GLINCLUDES = -DHAS_GLEXT_H -DGL_GLEXT_PROTOTYPES -DGLU_VERSION_1_3
+GLINCLUDES = -I/usr/include -DHAS_GLEXT_H -DGL_GLEXT_PROTOTYPES
-DGLU_VERSION_1_3
GLLIBS = -lglu32 -lopengl32
GLLIBS0 = $(GLLIBS)
GLUTLIBS = -lglut32
============
$ cat lblgl_hello.ml
let display () =
GlClear.color (0.0, 0.0, 0.0);
GlClear.clear [`color];
GlDraw.color (1.0, 1.0, 0.0);
GlMat.mode `projection;
GlMat.load_identity ();
GlMat.ortho ~x:(-1.0,1.0) ~y:(-1.0,1.0) ~z:(-1.0,1.0);
GlDraw.begins `polygon;
GlDraw.vertex ~x:(-0.5) ~y:(-0.5) ();
GlDraw.vertex ~x:(-0.5) ~y:(0.5) ();
GlDraw.vertex ~x:(0.5) ~y:(0.5) ();
GlDraw.vertex ~x:(0.5) ~y:(-0.5) ();
GlDraw.ends ();
Gl.flush ()
let () =
Sdl.init [`EVERYTHING];
let _ =
Sdlvideo.set_video_mode ~w:640 ~h:400
[`HWSURFACE; `DOUBLEBUF; `OPENGL; `RESIZABLE]
in
for i = 1 to 6 do
display ();
Sdlgl.swap_buffers ();
Sdltimer.delay 1000;
done;
Sdl.quit ()
# using full windows path, because protz's ocaml doesn't like cygwin ones:
$ ocaml bigarray.cma -I +site-lib/sdl sdl.cma -I
C:/cygwin/tmp/mylblgl0 lablgl.cma lblgl_hello.ml
===========
# completely untested, just copied and modified from "lablgl.20120306"
$ cat opam
opam-version: "1"
maintainer: "contact@ocamlpro.com"
homepage: "https://forge.ocamlcore.org/projects/lablgl/"
authors: [
"Jacques Garrigue"
"Isaac Trotts"
"Erick Tryzelaar"
"Christophe Raffali"
]
# "Jon Harrop" contributed the files "gluTess.ml" / "ml_glutess.c"
# should he be considered as one of the authors? or just a contributor?
build: [
["cp" "Makefile.config.ex" "Makefile.config"]
["cp" "Makefile.config.osx" "Makefile.config"] {"%{os}%" = "darwin"}
["cp" "Makefile.config.mingw" "Makefile.config"] {"%{os}%" =
"windows 7 starter with protz's ocaml 4"}
["mkdir" "-p" "%{bin}%"]
# [make "glut"] ### do not build this one, it doesn't compile out of
the box in my W env
# [make "glutopt"] ### do not build this one, it doesn't compile out
of the box in my W env
### in my W env, only build lablgl.{cma,cmxa}
[make "lib"]
[make "libopt"]
[make "install" "-C" "src" "BINDIR=%{bin}%"
"INSTALLDIR=%{lib}%/lablgl" "DLLDIR=%{lib}%/stublibs"]
# it seems that the makefile forgets to install this one:
["cp" "src/dlllablgl.dll" "DLLDIR=%{lib}%/stublibs"] {"%{os:env}%" =
"win7::protz"}
### do not install LablGlut, it doesn't compile out of the box in my W env
### [make "install" "-C" "LablGlut/src" "BINDIR=%{bin}%"
"INSTALLDIR=%{lib}%/lablgl" "DLLDIR=%{lib}%/stublibs"]
]
--
Cheers
``` | non_main | lablgl for windows from blue prawn hi on my windows test environment i can not use lablgl because of the glshader module that i myself provided before i get a windows test environment but the vanilla lablgl works fine if i ve understood correctly opam is a source package manager so maybe opam could provide lablgl for windows users that have a similar environment than mine my windows test environment is windows starter with protz s ocaml version well in this environment only lablgl itself compiles out of the box lablglut does not togl tk does not either i think that the devel libs for both glut and tkgl are there lablglut and togl are for windowing so if we use ocamlsdl instead this is just fine we don t need these compiles out of the box in my win env in this environment i compile the vanilla lablgl like this cp makefile config mingw makefile config need to add i usr include the patch below does this patch makefile config cygwin needs i usr include patch don t build anything else than lablgl itself or we get errors make lib make libopt lablgl installdir tmp make install installdir lablgl installdir it seems that the file dlllablgl dll is not installed so cp src dlllablgl dll lablgl installdir now a hello world works fine i m providing this hello at the end after the config patch cat makefile config cygwin needs i usr include patch makefile config makefile config where to find opengl mesa glut headers and libraries glincludes dhas glext h dgl glext prototypes dglu version glincludes i usr include dhas glext h dgl glext prototypes dglu version gllibs gllibs glutlibs cat lblgl hello ml let display glclear color glclear clear gldraw color glmat mode projection glmat load identity glmat ortho x y z gldraw begins polygon gldraw vertex x y gldraw vertex x y gldraw vertex x y gldraw vertex x y gldraw ends gl flush let sdl init let sdlvideo set video mode w h in for i to do display sdlgl swap buffers sdltimer delay done sdl quit using full windows path because protz s ocaml doesn t like cygwin ones ocaml bigarray cma i site lib sdl sdl cma i c cygwin tmp lablgl cma lblgl hello ml completely untested just copied and modified from lablgl cat opam opam version maintainer contact ocamlpro com homepage authors jacques garrigue isaac trotts erick tryzelaar christophe raffali jon harrop contributed the files glutess ml ml glutess c should he be considered as one of the authors or just a contributor build os darwin os windows starter with protz s ocaml do not build this one it doesn t compile out of the box in my w env do not build this one it doesn t compile out of the box in my w env in my w env only build lablgl cma cmxa make install c src bindir bin installdir lib lablgl dlldir lib stublibs it seems that the makefile forgets to install this one os env protz do not install lablglut it doesn t compile out of the box in my w env make install c lablglut src bindir bin installdir lib lablgl dlldir lib stublibs cheers | 0 |
93,075 | 26,857,761,105 | IssuesEvent | 2023-02-03 15:51:45 | rapidsai/raft | https://api.github.com/repos/rapidsai/raft | opened | [BUG] Ball Cover uses brute_force_knn specialization that's not instantiated | bug Build Time Improvement | The compile time for the ball cover specialization could be cut down if we either use a template combination that's already specialized or we create a new specializtion. I'd vote for the former.
Here's where the ball cover implementation is relying on the brute force knn: https://github.com/rapidsai/raft/blob/4ad7daba36d535c22f9182dae6bb714b34cbba25/cpp/include/raft/spatial/knn/detail/ball_cover.cuh#L185 | 1.0 | [BUG] Ball Cover uses brute_force_knn specialization that's not instantiated - The compile time for the ball cover specialization could be cut down if we either use a template combination that's already specialized or we create a new specializtion. I'd vote for the former.
Here's where the ball cover implementation is relying on the brute force knn: https://github.com/rapidsai/raft/blob/4ad7daba36d535c22f9182dae6bb714b34cbba25/cpp/include/raft/spatial/knn/detail/ball_cover.cuh#L185 | non_main | ball cover uses brute force knn specialization that s not instantiated the compile time for the ball cover specialization could be cut down if we either use a template combination that s already specialized or we create a new specializtion i d vote for the former here s where the ball cover implementation is relying on the brute force knn | 0 |
1,742 | 6,574,902,975 | IssuesEvent | 2017-09-11 14:26:45 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | docker_container reports "Error: docker-py version is 1.10.4. Minimum version required is 1.7.0." | affects_2.1 bug_report cloud docker waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
docker_container
##### ANSIBLE VERSION
```
ansible 2.1.1.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
##### OS / ENVIRONMENT
N/A
##### SUMMARY
<!--- Explain the problem briefly -->
Changing from deprecated docker module to docker_container. Get a bad check on docker-py
##### STEPS TO REPRODUCE
Install a docker-py > 1.7 and use docker_container
##### EXPECTED RESULTS
Works fine with docker module.. but it is deprecated
##### ACTUAL RESULTS
```
TASK [Start rancher-agent] *****************************************************
fatal: [10.0.0.1]: FAILED! => {"changed": false, "failed": true, "msg": "Error: docker-py version is 1.10.4. Minimum version required is 1.7.0."}
fatal: [10.0.0.2]: FAILED! => {"changed": false, "failed": true, "msg": "Error: docker-py version is 1.10.4. Minimum version required is 1.7.0."}
NO MORE HOSTS LEFT *************************************************************
```
| True | docker_container reports "Error: docker-py version is 1.10.4. Minimum version required is 1.7.0." - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
docker_container
##### ANSIBLE VERSION
```
ansible 2.1.1.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
##### OS / ENVIRONMENT
N/A
##### SUMMARY
<!--- Explain the problem briefly -->
Changing from deprecated docker module to docker_container. Get a bad check on docker-py
##### STEPS TO REPRODUCE
Install a docker-py > 1.7 and use docker_container
##### EXPECTED RESULTS
Works fine with docker module.. but it is deprecated
##### ACTUAL RESULTS
```
TASK [Start rancher-agent] *****************************************************
fatal: [10.0.0.1]: FAILED! => {"changed": false, "failed": true, "msg": "Error: docker-py version is 1.10.4. Minimum version required is 1.7.0."}
fatal: [10.0.0.2]: FAILED! => {"changed": false, "failed": true, "msg": "Error: docker-py version is 1.10.4. Minimum version required is 1.7.0."}
NO MORE HOSTS LEFT *************************************************************
```
| main | docker container reports error docker py version is minimum version required is issue type bug report component name docker container ansible version ansible config file etc ansible ansible cfg configured module search path default w o overrides configuration os environment n a summary changing from deprecated docker module to docker container get a bad check on docker py steps to reproduce install a docker py and use docker container expected results works fine with docker module but it is deprecated actual results task fatal failed changed false failed true msg error docker py version is minimum version required is fatal failed changed false failed true msg error docker py version is minimum version required is no more hosts left | 1 |
2,517 | 8,655,460,189 | IssuesEvent | 2018-11-27 16:00:33 | codestation/qcma | https://api.github.com/repos/codestation/qcma | closed | Mention SMB 1.0 enabling for Windows 10 in readme/ on website | unmaintained | I only found out by accident that one needs to activate SMB 1.0 in Windows 10 as it is disabled by default now.
This is only relevant for PS TV users of course. | True | Mention SMB 1.0 enabling for Windows 10 in readme/ on website - I only found out by accident that one needs to activate SMB 1.0 in Windows 10 as it is disabled by default now.
This is only relevant for PS TV users of course. | main | mention smb enabling for windows in readme on website i only found out by accident that one needs to activate smb in windows as it is disabled by default now this is only relevant for ps tv users of course | 1 |
749,880 | 26,182,105,648 | IssuesEvent | 2023-01-02 17:03:02 | owid/etl | https://api.github.com/repos/owid/etl | closed | Upgrade Pandas from 1.5.1 to 1.5.2 | priority 2 - important | ## Overview
We want to upgrade Pandas, but are worried that its interface might not be stable and that it might change the output of our data pipeline.
## Procedure
- Make a copy of the current catalog, call it `data.pandas-1.5.1`
- Generate from scratch a full new catalog, call it `data.pandas-1.5.2`
- Compare file by file that the data frames are equal | 1.0 | Upgrade Pandas from 1.5.1 to 1.5.2 - ## Overview
We want to upgrade Pandas, but are worried that its interface might not be stable and that it might change the output of our data pipeline.
## Procedure
- Make a copy of the current catalog, call it `data.pandas-1.5.1`
- Generate from scratch a full new catalog, call it `data.pandas-1.5.2`
- Compare file by file that the data frames are equal | non_main | upgrade pandas from to overview we want to upgrade pandas but are worried that its interface might not be stable and that it might change the output of our data pipeline procedure make a copy of the current catalog call it data pandas generate from scratch a full new catalog call it data pandas compare file by file that the data frames are equal | 0 |
3,652 | 6,690,718,398 | IssuesEvent | 2017-10-09 10:13:16 | DynareTeam/dynare | https://api.github.com/repos/DynareTeam/dynare | closed | Add interface for flexible IRF-generation | preprocessor | Create block
```
generate_irfs(options_list);
(groupname1), exo_name1=1, exo_name 2=-0.5;
(groupname2), exo_name1=2, exo_name 3=-0.5;
end;
```
or alternatively (as suggested in #115 )
```
generate_irfs(options_list);
[ name='groupname1' ] exo_name1=1, exo_name 2=-0.5;
[ name='groupname1' ] exo_name1=2, exo_name 3=-0.5;
end;
```
where `options_list` can be (for now)
- `stderr_multiples` translating to `options_.irf_opt.stderr_multiples`
- `diagonal_only` translating to `options_.irf_opt.diagonal_only`
and where each line translates into
1. a cell array `options_.irf_opt.irf_shock_graphtitles` storing the group_name along the rows
2. a column of a matrix `options_.irf_opt.irf_shocks` of size M_.exo_nbr*n_lines where non-specified `var_exo` get a 0 entry.
If no line is provided, leave those fields empty.
The block translates into
1. setting of options_
2. a call to `oo_.irfs=generate_irfs(M_,options_,oo_)` | 1.0 | Add interface for flexible IRF-generation - Create block
```
generate_irfs(options_list);
(groupname1), exo_name1=1, exo_name 2=-0.5;
(groupname2), exo_name1=2, exo_name 3=-0.5;
end;
```
or alternatively (as suggested in #115 )
```
generate_irfs(options_list);
[ name='groupname1' ] exo_name1=1, exo_name 2=-0.5;
[ name='groupname1' ] exo_name1=2, exo_name 3=-0.5;
end;
```
where `options_list` can be (for now)
- `stderr_multiples` translating to `options_.irf_opt.stderr_multiples`
- `diagonal_only` translating to `options_.irf_opt.diagonal_only`
and where each line translates into
1. a cell array `options_.irf_opt.irf_shock_graphtitles` storing the group_name along the rows
2. a column of a matrix `options_.irf_opt.irf_shocks` of size M_.exo_nbr*n_lines where non-specified `var_exo` get a 0 entry.
If no line is provided, leave those fields empty.
The block translates into
1. setting of options_
2. a call to `oo_.irfs=generate_irfs(M_,options_,oo_)` | non_main | add interface for flexible irf generation create block generate irfs options list exo exo name exo exo name end or alternatively as suggested in generate irfs options list exo exo name exo exo name end where options list can be for now stderr multiples translating to options irf opt stderr multiples diagonal only translating to options irf opt diagonal only and where each line translates into a cell array options irf opt irf shock graphtitles storing the group name along the rows a column of a matrix options irf opt irf shocks of size m exo nbr n lines where non specified var exo get a entry if no line is provided leave those fields empty the block translates into setting of options a call to oo irfs generate irfs m options oo | 0 |
101,082 | 21,576,089,798 | IssuesEvent | 2022-05-02 13:53:47 | guardicore/monkey | https://api.github.com/repos/guardicore/monkey | closed | RemoteRunAwsService adds unnecessary delay to Island startup | Help wanted Beginner friendly Impact: Medium Complexity: Low Code Quality Refactor Performance | When Monkey Island starts, it checks to see if it's running on an AWS instance. When it performs this check, it makes 2 calls, each with a 2-second timeout. In the case where the Island is not running on an AWS instance, this adds approximately 2-4 seconds to the startup of the Island. For users, this is a mild inconvenience. For developers, it's a full-blown annoyance.
Find a way to eliminate this delay. Possible solutions might be:
1. Lazy-load the AwsInstance object in RemoteRunAwsService, so that it's not actually created until it's need.
2. Initialize the RemoteRunAwsService on a separate thread so that it does not delay the rest of the startup process.
Note: This doesn't seem to be an issue while running from source on Windows (with pycharm) but does manifest when run from the MSI. It also manifests while running from source on Linux.
## Tasks
- [ ] Fix it! (0.5d) - @VakarisZ
| 1.0 | RemoteRunAwsService adds unnecessary delay to Island startup - When Monkey Island starts, it checks to see if it's running on an AWS instance. When it performs this check, it makes 2 calls, each with a 2-second timeout. In the case where the Island is not running on an AWS instance, this adds approximately 2-4 seconds to the startup of the Island. For users, this is a mild inconvenience. For developers, it's a full-blown annoyance.
Find a way to eliminate this delay. Possible solutions might be:
1. Lazy-load the AwsInstance object in RemoteRunAwsService, so that it's not actually created until it's need.
2. Initialize the RemoteRunAwsService on a separate thread so that it does not delay the rest of the startup process.
Note: This doesn't seem to be an issue while running from source on Windows (with pycharm) but does manifest when run from the MSI. It also manifests while running from source on Linux.
## Tasks
- [ ] Fix it! (0.5d) - @VakarisZ
| non_main | remoterunawsservice adds unnecessary delay to island startup when monkey island starts it checks to see if it s running on an aws instance when it performs this check it makes calls each with a second timeout in the case where the island is not running on an aws instance this adds approximately seconds to the startup of the island for users this is a mild inconvenience for developers it s a full blown annoyance find a way to eliminate this delay possible solutions might be lazy load the awsinstance object in remoterunawsservice so that it s not actually created until it s need initialize the remoterunawsservice on a separate thread so that it does not delay the rest of the startup process note this doesn t seem to be an issue while running from source on windows with pycharm but does manifest when run from the msi it also manifests while running from source on linux tasks fix it vakarisz | 0 |
4,822 | 24,849,749,802 | IssuesEvent | 2022-10-26 18:57:19 | damlaalkan/SWE573 | https://api.github.com/repos/damlaalkan/SWE573 | closed | Getting time out error after 24 hours | wontfix maintainance | The project restarts after 24 hours , seems like the authentication time out | True | Getting time out error after 24 hours - The project restarts after 24 hours , seems like the authentication time out | main | getting time out error after hours the project restarts after hours seems like the authentication time out | 1 |
24,178 | 6,520,176,300 | IssuesEvent | 2017-08-28 15:30:25 | hbirchtree/coffeecutie | https://api.github.com/repos/hbirchtree/coffeecutie | closed | Fix assimp problems with static libraries | bug Dynamic code iOS Linux OSX Platform | Fails to link, requires functions from libIrrXml.a, aside from Assimp itself
Solution:
- Add libIrrXml.a as optional library in FindAssimp.cmake | 1.0 | Fix assimp problems with static libraries - Fails to link, requires functions from libIrrXml.a, aside from Assimp itself
Solution:
- Add libIrrXml.a as optional library in FindAssimp.cmake | non_main | fix assimp problems with static libraries fails to link requires functions from libirrxml a aside from assimp itself solution add libirrxml a as optional library in findassimp cmake | 0 |
3,242 | 12,368,706,884 | IssuesEvent | 2020-05-18 14:13:32 | Kashdeya/Tiny-Progressions | https://api.github.com/repos/Kashdeya/Tiny-Progressions | closed | WhiteLamp (probably all other lamps as well) | Version not Maintainted | When placing a white lamp block on the ceiling, if you look up at it and move around, you can see a faint outline of a torch. looks glitchy. May have been intended, but imo it's a bit unsightly. | True | WhiteLamp (probably all other lamps as well) - When placing a white lamp block on the ceiling, if you look up at it and move around, you can see a faint outline of a torch. looks glitchy. May have been intended, but imo it's a bit unsightly. | main | whitelamp probably all other lamps as well when placing a white lamp block on the ceiling if you look up at it and move around you can see a faint outline of a torch looks glitchy may have been intended but imo it s a bit unsightly | 1 |
43,269 | 5,534,635,825 | IssuesEvent | 2017-03-21 15:46:38 | UNFPAInnovation/GetIn_Mobile | https://api.github.com/repos/UNFPAInnovation/GetIn_Mobile | closed | Procedure runner button in the encounterTasks | In progress Ready to test | The Midwife is not able to run the Appointment procedure when she clicks on an upcoming appointment | 1.0 | Procedure runner button in the encounterTasks - The Midwife is not able to run the Appointment procedure when she clicks on an upcoming appointment | non_main | procedure runner button in the encountertasks the midwife is not able to run the appointment procedure when she clicks on an upcoming appointment | 0 |
544,093 | 15,889,646,183 | IssuesEvent | 2021-04-10 12:24:57 | AY2021S2-CS2103T-W13-3/tp | https://api.github.com/repos/AY2021S2-CS2103T-W13-3/tp | closed | [PE-D] Appointments: inaccurate description for invalid date/time format when adding appointment | priority.Medium type.Bug | Keying in the wrong date/time format (out of bounds: day greater than 31, month greater than 12, hour greater than 24, min greater than 59), I will get the same description where date and time should not be blank and must be of the format dd/mm/yyyy hh:mm instead of informing me that I keyed in an invalid date/time.
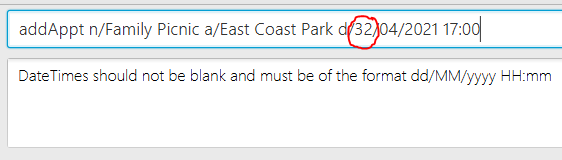
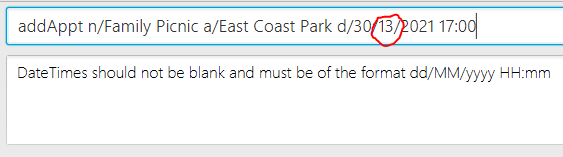

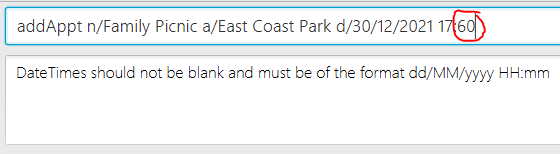
<!--session: 1617429944570-adfbeaa0-7eb4-413e-a018-2de44034d73e-->
-------------
Labels: `severity.Low` `type.FeatureFlaw`
original: cheunggalen/ped#1 | 1.0 | [PE-D] Appointments: inaccurate description for invalid date/time format when adding appointment - Keying in the wrong date/time format (out of bounds: day greater than 31, month greater than 12, hour greater than 24, min greater than 59), I will get the same description where date and time should not be blank and must be of the format dd/mm/yyyy hh:mm instead of informing me that I keyed in an invalid date/time.
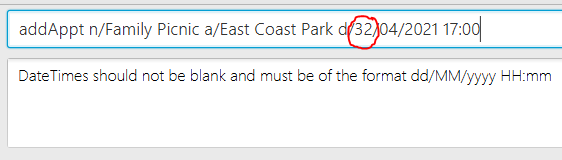
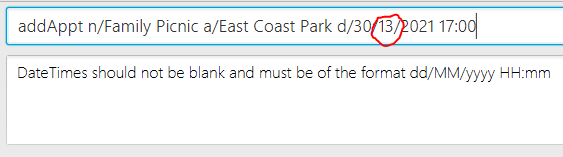

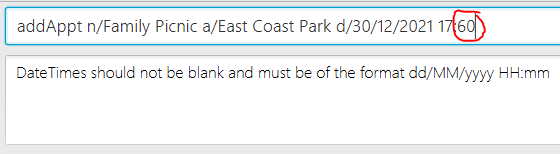
<!--session: 1617429944570-adfbeaa0-7eb4-413e-a018-2de44034d73e-->
-------------
Labels: `severity.Low` `type.FeatureFlaw`
original: cheunggalen/ped#1 | non_main | appointments inaccurate description for invalid date time format when adding appointment keying in the wrong date time format out of bounds day greater than month greater than hour greater than min greater than i will get the same description where date and time should not be blank and must be of the format dd mm yyyy hh mm instead of informing me that i keyed in an invalid date time labels severity low type featureflaw original cheunggalen ped | 0 |
546,914 | 16,021,331,244 | IssuesEvent | 2021-04-21 00:07:13 | CookieJarApps/SmartCookieWeb | https://api.github.com/repos/CookieJarApps/SmartCookieWeb | closed | [Feature] full bottom navigation | P2: Medium priority enhancement | Thanks a lot for adding charge to lightning browser! I liked lightning lot but today discovered your app. Really good improvements.
In bottom navigation mode, everything should be at bottom for ease. Thanks for bringing the tabs in #241.
1. But bookmarks drawer must follow the same design.
2. The hamburger menu is too tall to reach from bottom, only if its height could be reduced, like by making two columns, then whole UI would be bottom friendly! | 1.0 | [Feature] full bottom navigation - Thanks a lot for adding charge to lightning browser! I liked lightning lot but today discovered your app. Really good improvements.
In bottom navigation mode, everything should be at bottom for ease. Thanks for bringing the tabs in #241.
1. But bookmarks drawer must follow the same design.
2. The hamburger menu is too tall to reach from bottom, only if its height could be reduced, like by making two columns, then whole UI would be bottom friendly! | non_main | full bottom navigation thanks a lot for adding charge to lightning browser i liked lightning lot but today discovered your app really good improvements in bottom navigation mode everything should be at bottom for ease thanks for bringing the tabs in but bookmarks drawer must follow the same design the hamburger menu is too tall to reach from bottom only if its height could be reduced like by making two columns then whole ui would be bottom friendly | 0 |
4,507 | 23,448,308,831 | IssuesEvent | 2022-08-15 22:15:02 | aws/aws-sam-cli | https://api.github.com/repos/aws/aws-sam-cli | closed | Bug: Error from cookiecutter: open() argument 6 must be str or None, not tuple | type/bug area/init maintainer/need-followup | ### Description:
When trying to create a SAM app template using `sam init`, it creates a folder with no content in it.
```
sam-app
├── events
├── hello_world
└── tests
3 directories, 0 files
```
When I ran `sam init --debug` it run an error
```
2022-07-14 02:53:58,674 | Baking a new template with cookiecutter with all parameters
2022-07-14 02:53:58,727 | Error from cookiecutter: open() argument 6 must be str or None, not tuple
2022-07-14 02:53:58,728 | Template is not provided in context, skip adding project type metric
```
### Steps to reproduce:
```
$ sam init
Which template source would you like to use?
1 - AWS Quick Start Templates
2 - Custom Template Location
Choice: 1
Choose an AWS Quick Start application template
1 - Hello World Example
2 - Multi-step workflow
3 - Serverless API
4 - Scheduled task
5 - Standalone function
6 - Data processing
7 - Infrastructure event management
8 - Machine Learning
Template: 1
Use the most popular runtime and package type? (Python and zip) [y/N]: N
Which runtime would you like to use?
1 - dotnet6
2 - dotnet5.0
3 - dotnetcore3.1
4 - go1.x
5 - graalvm.java11 (provided.al2)
6 - graalvm.java17 (provided.al2)
7 - java11
8 - java8.al2
9 - java8
10 - nodejs16.x
11 - nodejs14.x
12 - nodejs12.x
13 - python3.9
14 - python3.8
15 - python3.7
16 - python3.6
17 - ruby2.7
18 - rust (provided.al2)
Runtime: 14
What package type would you like to use?
1 - Zip
2 - Image
Package type: 2
Based on your selections, the only dependency manager available is pip.
We will proceed copying the template using pip.
Would you like to enable X-Ray tracing on the function(s) in your application? [y/N]: N
Project name [sam-app]: sam-app
```
### Observed result:
```
user/project $ sam init --debug
2022-07-14 02:52:34,113 | Telemetry endpoint configured to be https://aws-serverless-tools-telemetry.us-west-2.amazonaws.com/metrics
2022-07-14 02:52:34,113 | Using config file: samconfig.toml, config environment: default
2022-07-14 02:52:34,113 | Expand command line arguments to:
2022-07-14 02:52:34,114 | --package_type=Zip --output_dir=.
You can preselect a particular runtime or package type when using the `sam init` experience.
Call `sam init --help` to learn more.
Which template source would you like to use?
1 - AWS Quick Start Templates
2 - Custom Template Location
Choice: 1
Choose an AWS Quick Start application template
1 - Hello World Example
2 - Multi-step workflow
3 - Serverless API
4 - Scheduled task
5 - Standalone function
6 - Data processing
7 - Infrastructure event management
8 - Machine Learning
Template: 1
Use the most popular runtime and package type? (Python and zip) [y/N]: N
Which runtime would you like to use?
1 - dotnet6
2 - dotnet5.0
3 - dotnetcore3.1
4 - go1.x
5 - graalvm.java11 (provided.al2)
6 - graalvm.java17 (provided.al2)
7 - java11
8 - java8.al2
9 - java8
10 - nodejs16.x
11 - nodejs14.x
12 - nodejs12.x
13 - python3.9
14 - python3.8
15 - python3.7
16 - python3.6
17 - ruby2.7
18 - rust (provided.al2)
Runtime: 14
What package type would you like to use?
1 - Zip
2 - Image
Package type: 2
Based on your selections, the only dependency manager available is pip.
We will proceed copying the template using pip.
Would you like to enable X-Ray tracing on the function(s) in your application? [y/N]:
Project name [sam-app]:
2022-07-14 02:53:35,233 |
Cloning from https://github.com/aws/aws-sam-cli-app-templates (process may take a moment)
2022-07-14 02:53:58,115 | Removing old repo at /home/user/.aws-sam/aws-sam-cli-app-templates
2022-07-14 02:53:58,225 | Copying from /tmp/tmpgbdazfe3/aws-sam-cli-app-templates to /home/user/.aws-sam/aws-sam-cli-app-templates
-----------------------
Generating application:
-----------------------
Name: sam-app
Base Image: amazon/python3.8-base
Architectures: x86_64
Dependency Manager: pip
Output Directory: .
Next steps can be found in the README file at ./sam-app/README.md
Commands you can use next
=========================
[*] Create pipeline: cd sam-app && sam pipeline init --bootstrap
[*] Validate SAM template: sam validate
[*] Test Function in the Cloud: sam sync --stack-name {stack-name} --watch
2022-07-14 02:53:58,674 | Parameters dict created with input given
2022-07-14 02:53:58,674 | {'template': '/home/user/.aws-sam/aws-sam-cli-app-templates/python3.8-image/cookiecutter-aws-sam-hello-python-lambda-image', 'output_dir': '.', 'no_input': True, 'extra_context': {'project_name': 'sam-app', 'runtime': 'python3.8', 'architectures': {'value': ['x86_64']}}}
2022-07-14 02:53:58,674 | Baking a new template with cookiecutter with all parameters
2022-07-14 02:53:58,727 | Error from cookiecutter: open() argument 6 must be str or None, not tuple
2022-07-14 02:53:58,728 | Template is not provided in context, skip adding project type metric
```
### Expected result:
I expect it to create the sam app template folder with the necessary files present
```
sam-app
├── README.md
├── __init__.py
├── events
│ └── event.json
├── hello_world
│ ├── Dockerfile
│ ├── __init__.py
│ ├── app.py
│ └── requirements.txt
├── template.yaml
└── tests
├── __init__.py
└── unit
├── __init__.py
└── test_handler.py
4 directories, 11 files
```
### Additional environment details (Ex: Windows, Mac, Amazon Linux etc)
1. OS: WSL Ubuntu 20.04
2. `sam --version`: SAM CLI, version 1.53.0
3. AWS region:
`Add --debug flag to command you are running`
| True | Bug: Error from cookiecutter: open() argument 6 must be str or None, not tuple - ### Description:
When trying to create a SAM app template using `sam init`, it creates a folder with no content in it.
```
sam-app
├── events
├── hello_world
└── tests
3 directories, 0 files
```
When I ran `sam init --debug` it run an error
```
2022-07-14 02:53:58,674 | Baking a new template with cookiecutter with all parameters
2022-07-14 02:53:58,727 | Error from cookiecutter: open() argument 6 must be str or None, not tuple
2022-07-14 02:53:58,728 | Template is not provided in context, skip adding project type metric
```
### Steps to reproduce:
```
$ sam init
Which template source would you like to use?
1 - AWS Quick Start Templates
2 - Custom Template Location
Choice: 1
Choose an AWS Quick Start application template
1 - Hello World Example
2 - Multi-step workflow
3 - Serverless API
4 - Scheduled task
5 - Standalone function
6 - Data processing
7 - Infrastructure event management
8 - Machine Learning
Template: 1
Use the most popular runtime and package type? (Python and zip) [y/N]: N
Which runtime would you like to use?
1 - dotnet6
2 - dotnet5.0
3 - dotnetcore3.1
4 - go1.x
5 - graalvm.java11 (provided.al2)
6 - graalvm.java17 (provided.al2)
7 - java11
8 - java8.al2
9 - java8
10 - nodejs16.x
11 - nodejs14.x
12 - nodejs12.x
13 - python3.9
14 - python3.8
15 - python3.7
16 - python3.6
17 - ruby2.7
18 - rust (provided.al2)
Runtime: 14
What package type would you like to use?
1 - Zip
2 - Image
Package type: 2
Based on your selections, the only dependency manager available is pip.
We will proceed copying the template using pip.
Would you like to enable X-Ray tracing on the function(s) in your application? [y/N]: N
Project name [sam-app]: sam-app
```
### Observed result:
```
user/project $ sam init --debug
2022-07-14 02:52:34,113 | Telemetry endpoint configured to be https://aws-serverless-tools-telemetry.us-west-2.amazonaws.com/metrics
2022-07-14 02:52:34,113 | Using config file: samconfig.toml, config environment: default
2022-07-14 02:52:34,113 | Expand command line arguments to:
2022-07-14 02:52:34,114 | --package_type=Zip --output_dir=.
You can preselect a particular runtime or package type when using the `sam init` experience.
Call `sam init --help` to learn more.
Which template source would you like to use?
1 - AWS Quick Start Templates
2 - Custom Template Location
Choice: 1
Choose an AWS Quick Start application template
1 - Hello World Example
2 - Multi-step workflow
3 - Serverless API
4 - Scheduled task
5 - Standalone function
6 - Data processing
7 - Infrastructure event management
8 - Machine Learning
Template: 1
Use the most popular runtime and package type? (Python and zip) [y/N]: N
Which runtime would you like to use?
1 - dotnet6
2 - dotnet5.0
3 - dotnetcore3.1
4 - go1.x
5 - graalvm.java11 (provided.al2)
6 - graalvm.java17 (provided.al2)
7 - java11
8 - java8.al2
9 - java8
10 - nodejs16.x
11 - nodejs14.x
12 - nodejs12.x
13 - python3.9
14 - python3.8
15 - python3.7
16 - python3.6
17 - ruby2.7
18 - rust (provided.al2)
Runtime: 14
What package type would you like to use?
1 - Zip
2 - Image
Package type: 2
Based on your selections, the only dependency manager available is pip.
We will proceed copying the template using pip.
Would you like to enable X-Ray tracing on the function(s) in your application? [y/N]:
Project name [sam-app]:
2022-07-14 02:53:35,233 |
Cloning from https://github.com/aws/aws-sam-cli-app-templates (process may take a moment)
2022-07-14 02:53:58,115 | Removing old repo at /home/user/.aws-sam/aws-sam-cli-app-templates
2022-07-14 02:53:58,225 | Copying from /tmp/tmpgbdazfe3/aws-sam-cli-app-templates to /home/user/.aws-sam/aws-sam-cli-app-templates
-----------------------
Generating application:
-----------------------
Name: sam-app
Base Image: amazon/python3.8-base
Architectures: x86_64
Dependency Manager: pip
Output Directory: .
Next steps can be found in the README file at ./sam-app/README.md
Commands you can use next
=========================
[*] Create pipeline: cd sam-app && sam pipeline init --bootstrap
[*] Validate SAM template: sam validate
[*] Test Function in the Cloud: sam sync --stack-name {stack-name} --watch
2022-07-14 02:53:58,674 | Parameters dict created with input given
2022-07-14 02:53:58,674 | {'template': '/home/user/.aws-sam/aws-sam-cli-app-templates/python3.8-image/cookiecutter-aws-sam-hello-python-lambda-image', 'output_dir': '.', 'no_input': True, 'extra_context': {'project_name': 'sam-app', 'runtime': 'python3.8', 'architectures': {'value': ['x86_64']}}}
2022-07-14 02:53:58,674 | Baking a new template with cookiecutter with all parameters
2022-07-14 02:53:58,727 | Error from cookiecutter: open() argument 6 must be str or None, not tuple
2022-07-14 02:53:58,728 | Template is not provided in context, skip adding project type metric
```
### Expected result:
I expect it to create the sam app template folder with the necessary files present
```
sam-app
├── README.md
├── __init__.py
├── events
│ └── event.json
├── hello_world
│ ├── Dockerfile
│ ├── __init__.py
│ ├── app.py
│ └── requirements.txt
├── template.yaml
└── tests
├── __init__.py
└── unit
├── __init__.py
└── test_handler.py
4 directories, 11 files
```
### Additional environment details (Ex: Windows, Mac, Amazon Linux etc)
1. OS: WSL Ubuntu 20.04
2. `sam --version`: SAM CLI, version 1.53.0
3. AWS region:
`Add --debug flag to command you are running`
| main | bug error from cookiecutter open argument must be str or none not tuple description when trying to create a sam app template using sam init it creates a folder with no content in it sam app ├── events ├── hello world └── tests directories files when i ran sam init debug it run an error baking a new template with cookiecutter with all parameters error from cookiecutter open argument must be str or none not tuple template is not provided in context skip adding project type metric steps to reproduce sam init which template source would you like to use aws quick start templates custom template location choice choose an aws quick start application template hello world example multi step workflow serverless api scheduled task standalone function data processing infrastructure event management machine learning template use the most popular runtime and package type python and zip n which runtime would you like to use x graalvm provided graalvm provided x x x rust provided runtime what package type would you like to use zip image package type based on your selections the only dependency manager available is pip we will proceed copying the template using pip would you like to enable x ray tracing on the function s in your application n project name sam app observed result user project sam init debug telemetry endpoint configured to be using config file samconfig toml config environment default expand command line arguments to package type zip output dir you can preselect a particular runtime or package type when using the sam init experience call sam init help to learn more which template source would you like to use aws quick start templates custom template location choice choose an aws quick start application template hello world example multi step workflow serverless api scheduled task standalone function data processing infrastructure event management machine learning template use the most popular runtime and package type python and zip n which runtime would you like to use x graalvm provided graalvm provided x x x rust provided runtime what package type would you like to use zip image package type based on your selections the only dependency manager available is pip we will proceed copying the template using pip would you like to enable x ray tracing on the function s in your application project name cloning from process may take a moment removing old repo at home user aws sam aws sam cli app templates copying from tmp aws sam cli app templates to home user aws sam aws sam cli app templates generating application name sam app base image amazon base architectures dependency manager pip output directory next steps can be found in the readme file at sam app readme md commands you can use next create pipeline cd sam app sam pipeline init bootstrap validate sam template sam validate test function in the cloud sam sync stack name stack name watch parameters dict created with input given template home user aws sam aws sam cli app templates image cookiecutter aws sam hello python lambda image output dir no input true extra context project name sam app runtime architectures value baking a new template with cookiecutter with all parameters error from cookiecutter open argument must be str or none not tuple template is not provided in context skip adding project type metric expected result i expect it to create the sam app template folder with the necessary files present sam app ├── readme md ├── init py ├── events │ └── event json ├── hello world │ ├── dockerfile │ ├── init py │ ├── app py │ └── requirements txt ├── template yaml └── tests ├── init py └── unit ├── init py └── test handler py directories files additional environment details ex windows mac amazon linux etc os wsl ubuntu sam version sam cli version aws region add debug flag to command you are running | 1 |
271,734 | 8,489,051,304 | IssuesEvent | 2018-10-26 18:36:13 | ualbertalib/Hydranorth2 | https://api.github.com/repos/ualbertalib/Hydranorth2 | closed | Review and fix user-facing error messages | moved_from_hn1 priority:TBD | _From @pbinkley on April 25, 2016 18:2_
We have some inconsistencies in error messages for different permissions scenarios (e.g. when attempting to access an embargoed item, you get a message telling you to log in with your CCID). We would like to gather all the messages and all the scenarios in which they are displayed in a form that could be reviewed by @leahvanderjagt and @sfbetz .
Since the known problems affect a small number of users in edge cases, we'll put this off until after Sufia 7, which is likely to change some of these scenarios anyway.
_Copied from original issue: ualbertalib/HydraNorth#1073_ | 1.0 | Review and fix user-facing error messages - _From @pbinkley on April 25, 2016 18:2_
We have some inconsistencies in error messages for different permissions scenarios (e.g. when attempting to access an embargoed item, you get a message telling you to log in with your CCID). We would like to gather all the messages and all the scenarios in which they are displayed in a form that could be reviewed by @leahvanderjagt and @sfbetz .
Since the known problems affect a small number of users in edge cases, we'll put this off until after Sufia 7, which is likely to change some of these scenarios anyway.
_Copied from original issue: ualbertalib/HydraNorth#1073_ | non_main | review and fix user facing error messages from pbinkley on april we have some inconsistencies in error messages for different permissions scenarios e g when attempting to access an embargoed item you get a message telling you to log in with your ccid we would like to gather all the messages and all the scenarios in which they are displayed in a form that could be reviewed by leahvanderjagt and sfbetz since the known problems affect a small number of users in edge cases we ll put this off until after sufia which is likely to change some of these scenarios anyway copied from original issue ualbertalib hydranorth | 0 |
4,741 | 24,464,845,516 | IssuesEvent | 2022-10-07 14:12:55 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 85: cloud-init-0.7.9: 3 advisories [7.1] | 1.severity: security 9.needs: maintainer feedback | [search](https://search.nix.gsc.io/?q=cloud-init&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=cloud-init+in%3Apath&type=Code)
* [ ] [CVE-2018-10896](https://nvd.nist.gov/vuln/detail/CVE-2018-10896) CVSSv3=7.1 (nixos-20.03, nixos-unstable)
* [ ] [CVE-2020-8631](https://nvd.nist.gov/vuln/detail/CVE-2020-8631) CVSSv3=5.5 (nixos-20.03, nixos-unstable)
* [ ] [CVE-2020-8632](https://nvd.nist.gov/vuln/detail/CVE-2020-8632) CVSSv3=5.5 (nixos-20.03, nixos-unstable)
Scanned versions: nixos-20.03: a84b797b28e; nixos-unstable: 22c98819ccd. May contain false positives.
| True | Vulnerability roundup 85: cloud-init-0.7.9: 3 advisories [7.1] - [search](https://search.nix.gsc.io/?q=cloud-init&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=cloud-init+in%3Apath&type=Code)
* [ ] [CVE-2018-10896](https://nvd.nist.gov/vuln/detail/CVE-2018-10896) CVSSv3=7.1 (nixos-20.03, nixos-unstable)
* [ ] [CVE-2020-8631](https://nvd.nist.gov/vuln/detail/CVE-2020-8631) CVSSv3=5.5 (nixos-20.03, nixos-unstable)
* [ ] [CVE-2020-8632](https://nvd.nist.gov/vuln/detail/CVE-2020-8632) CVSSv3=5.5 (nixos-20.03, nixos-unstable)
Scanned versions: nixos-20.03: a84b797b28e; nixos-unstable: 22c98819ccd. May contain false positives.
| main | vulnerability roundup cloud init advisories nixos nixos unstable nixos nixos unstable nixos nixos unstable scanned versions nixos nixos unstable may contain false positives | 1 |
270,049 | 23,487,200,882 | IssuesEvent | 2022-08-17 15:17:51 | Princeton-CDH/ppa-django | https://api.github.com/repos/Princeton-CDH/ppa-django | closed | As a user, I want to see the actual rather than digital page number on keyword search results of Gale/ECCO items so that I can more accurately cite items. | awaiting testing | ## testing notes
Import a new record in #370 and then check on the public site how the page numbers display; if possible, test a record that you know has `folioNumbers` set in the Gale API (some of them don't have it set, others seem to just be set based on the digital image number)
## dev notes
update indexing to use new page number from updated api
- [x] update `gale_page_index_data` method to set `label` from new Gale API `folioNumber` field
- [x] update test for this method to match | 1.0 | As a user, I want to see the actual rather than digital page number on keyword search results of Gale/ECCO items so that I can more accurately cite items. - ## testing notes
Import a new record in #370 and then check on the public site how the page numbers display; if possible, test a record that you know has `folioNumbers` set in the Gale API (some of them don't have it set, others seem to just be set based on the digital image number)
## dev notes
update indexing to use new page number from updated api
- [x] update `gale_page_index_data` method to set `label` from new Gale API `folioNumber` field
- [x] update test for this method to match | non_main | as a user i want to see the actual rather than digital page number on keyword search results of gale ecco items so that i can more accurately cite items testing notes import a new record in and then check on the public site how the page numbers display if possible test a record that you know has folionumbers set in the gale api some of them don t have it set others seem to just be set based on the digital image number dev notes update indexing to use new page number from updated api update gale page index data method to set label from new gale api folionumber field update test for this method to match | 0 |
1,583 | 6,572,353,475 | IssuesEvent | 2017-09-11 01:39:10 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Archive with remote_src=yes strips the second / in http:// | affects_2.1 bot_broken bug_report waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
archive
##### ANSIBLE VERSION
```
ansible 2.1.0.0
config file =
configured module search path = Default w/o overrides
```
##### CONFIGURATION
Using default
##### OS / ENVIRONMENT
Running ansible on OSX El Capitain and remote host is centos 7
##### SUMMARY
I am trying to download a remote tar and extract it. It appears that I am losing a / in the src
##### STEPS TO REPRODUCE
I am running the following command as one of my roles called zookeeper.
```
- name: extract the file
unarchive:
src: http://apache.cs.utah.edu/zookeeper/zookeeper-3.4.8/zookeeper-3.4.8.tar.gz
dest: /var/zookeeper
remote_src: yes
```
Then I get the following error:
```
fatal: [10.84.236.95]: FAILED! => {"failed": true, "msg": "file or module does not exist: /Users/dcarr/Projects/bigtreeawsscripts/aws-scripts/src/main/ansible/http:/apache.cs.utah.edu/zookeeper/zookeeper-3.4.8/zookeeper-3.4.8.tar.gz"}
```
##### EXPECTED RESULTS
I would expect with :// in the original and remote_src turned on that I would be able to download it remotely.
##### ACTUAL RESULTS
It looks like http:// is turned into http:/ and it never tries to download remotely. Instead it looks for the file on my local machine.
| True | Archive with remote_src=yes strips the second / in http:// - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
archive
##### ANSIBLE VERSION
```
ansible 2.1.0.0
config file =
configured module search path = Default w/o overrides
```
##### CONFIGURATION
Using default
##### OS / ENVIRONMENT
Running ansible on OSX El Capitain and remote host is centos 7
##### SUMMARY
I am trying to download a remote tar and extract it. It appears that I am losing a / in the src
##### STEPS TO REPRODUCE
I am running the following command as one of my roles called zookeeper.
```
- name: extract the file
unarchive:
src: http://apache.cs.utah.edu/zookeeper/zookeeper-3.4.8/zookeeper-3.4.8.tar.gz
dest: /var/zookeeper
remote_src: yes
```
Then I get the following error:
```
fatal: [10.84.236.95]: FAILED! => {"failed": true, "msg": "file or module does not exist: /Users/dcarr/Projects/bigtreeawsscripts/aws-scripts/src/main/ansible/http:/apache.cs.utah.edu/zookeeper/zookeeper-3.4.8/zookeeper-3.4.8.tar.gz"}
```
##### EXPECTED RESULTS
I would expect with :// in the original and remote_src turned on that I would be able to download it remotely.
##### ACTUAL RESULTS
It looks like http:// is turned into http:/ and it never tries to download remotely. Instead it looks for the file on my local machine.
| main | archive with remote src yes strips the second in http issue type bug report component name archive ansible version ansible config file configured module search path default w o overrides configuration using default os environment running ansible on osx el capitain and remote host is centos summary i am trying to download a remote tar and extract it it appears that i am losing a in the src steps to reproduce i am running the following command as one of my roles called zookeeper name extract the file unarchive src dest var zookeeper remote src yes then i get the following error fatal failed failed true msg file or module does not exist users dcarr projects bigtreeawsscripts aws scripts src main ansible http apache cs utah edu zookeeper zookeeper zookeeper tar gz expected results i would expect with in the original and remote src turned on that i would be able to download it remotely actual results it looks like http is turned into http and it never tries to download remotely instead it looks for the file on my local machine | 1 |
189,277 | 15,183,807,684 | IssuesEvent | 2021-02-15 08:41:18 | shapkarin/extend-saga-routines | https://api.github.com/repos/shapkarin/extend-saga-routines | closed | More user friendly README.md | documentation | Make the introduction with basic explanation as much simple and understandable as it can be.
Leave all the rest as docs section. | 1.0 | More user friendly README.md - Make the introduction with basic explanation as much simple and understandable as it can be.
Leave all the rest as docs section. | non_main | more user friendly readme md make the introduction with basic explanation as much simple and understandable as it can be leave all the rest as docs section | 0 |
200,268 | 22,739,541,370 | IssuesEvent | 2022-07-07 01:24:28 | jakeswork/kued | https://api.github.com/repos/jakeswork/kued | opened | WS-2020-0450 (Medium) detected in handlebars-4.1.2.tgz | security vulnerability | ## WS-2020-0450 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /kued/package.json</p>
<p>Path to vulnerable library: /node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.0.tgz (Root Library)
- jest-24.7.1.tgz
- jest-cli-24.8.0.tgz
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.6.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars before 4.6.0 vulnerable to Prototype Pollution. Prototype access to the template engine allows for potential code execution, which may lead to Denial Of Service (DoS).
<p>Publish Date: 2020-01-09
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/33a3b46bc205f768f8edbc67241c68591fe3472c>WS-2020-0450</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-09</p>
<p>Fix Resolution (handlebars): 4.6.0</p>
<p>Direct dependency fix Resolution (react-scripts): 3.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0450 (Medium) detected in handlebars-4.1.2.tgz - ## WS-2020-0450 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.2.tgz</a></p>
<p>Path to dependency file: /kued/package.json</p>
<p>Path to vulnerable library: /node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.0.0.tgz (Root Library)
- jest-24.7.1.tgz
- jest-cli-24.8.0.tgz
- core-24.8.0.tgz
- reporters-24.8.0.tgz
- istanbul-reports-2.2.6.tgz
- :x: **handlebars-4.1.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars before 4.6.0 vulnerable to Prototype Pollution. Prototype access to the template engine allows for potential code execution, which may lead to Denial Of Service (DoS).
<p>Publish Date: 2020-01-09
<p>URL: <a href=https://github.com/handlebars-lang/handlebars.js/commit/33a3b46bc205f768f8edbc67241c68591fe3472c>WS-2020-0450</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-09</p>
<p>Fix Resolution (handlebars): 4.6.0</p>
<p>Direct dependency fix Resolution (react-scripts): 3.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | ws medium detected in handlebars tgz ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file kued package json path to vulnerable library node modules handlebars package json dependency hierarchy react scripts tgz root library jest tgz jest cli tgz core tgz reporters tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details handlebars before vulnerable to prototype pollution prototype access to the template engine allows for potential code execution which may lead to denial of service dos publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution handlebars direct dependency fix resolution react scripts step up your open source security game with mend | 0 |
335,351 | 10,152,383,289 | IssuesEvent | 2019-08-05 23:29:06 | unitystation/unitystation | https://api.github.com/repos/unitystation/unitystation | closed | TODO: NetTab GUI for GasContainer B: 150 | Bounty Feature High Priority In Progress | ### Description
With the introduction of Atmos, the gas containers are also now functional in the way that you can open and close the valve by clicking on the container. This needs to be extended to a GUI, in which information of the gas are shown, where the release pressure can be changed and the valve can be opened/closed.
### Criteria
- [ ] Clicking on a gas container should open a GUI window
- [ ] Show information of the current content of the gas container, e.g. pressure, temperature, etc.
- [ ] Release pressure can be changed in the GUI
- [ ] Introduce a button to open / close the containers valve
- [ ] Any changes should be synchronized to other players
### Tips
Look at the class `GasContainer` to get a better idea:
https://github.com/unitystation/unitystation/blob/7728a5750651e761f5d495d38a8394abe98e6920/UnityProject/Assets/Scripts/Objects/GasContainer.cs#L10 | 1.0 | TODO: NetTab GUI for GasContainer B: 150 - ### Description
With the introduction of Atmos, the gas containers are also now functional in the way that you can open and close the valve by clicking on the container. This needs to be extended to a GUI, in which information of the gas are shown, where the release pressure can be changed and the valve can be opened/closed.
### Criteria
- [ ] Clicking on a gas container should open a GUI window
- [ ] Show information of the current content of the gas container, e.g. pressure, temperature, etc.
- [ ] Release pressure can be changed in the GUI
- [ ] Introduce a button to open / close the containers valve
- [ ] Any changes should be synchronized to other players
### Tips
Look at the class `GasContainer` to get a better idea:
https://github.com/unitystation/unitystation/blob/7728a5750651e761f5d495d38a8394abe98e6920/UnityProject/Assets/Scripts/Objects/GasContainer.cs#L10 | non_main | todo nettab gui for gascontainer b description with the introduction of atmos the gas containers are also now functional in the way that you can open and close the valve by clicking on the container this needs to be extended to a gui in which information of the gas are shown where the release pressure can be changed and the valve can be opened closed criteria clicking on a gas container should open a gui window show information of the current content of the gas container e g pressure temperature etc release pressure can be changed in the gui introduce a button to open close the containers valve any changes should be synchronized to other players tips look at the class gascontainer to get a better idea | 0 |
796,261 | 28,104,209,152 | IssuesEvent | 2023-03-30 22:19:34 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | CONFIG_ROM_START_OFFSET change to be added to cause west flash reset fails, in NXP RT11xx platforms | bug priority: low platform: NXP | **Describe the bug**
for RT1170 use below command to download the image, debug reset does not work, but hardwarereset works.
`
west build -b mimxrt1170_evk_cm7
west flash --runner jlink --tool-opt='-SelectEmuBySN 000725371294' -- '--device=MIMXRT1176xxxA_M7' '--reset-after-load'
`
the serial console has no output at all, press reset key works. but this blocks twister testing. bisect found below commit introduce such problem
`
commit 44628735b870b2806bbea47477c3300bb624ad31 (refs/bisect/bad)
Author: Daniel Leung <daniel.leung@intel.com>
Date: Mon Feb 13 13:31:26 2023 -0800
linker: rom_start_offset: add to address instead of set
The CONFIG_ROM_START_OFFSET is supposed to be added to
the current when linking, instead of having the current
address set to it. So fix that.
Not sure why it worked up to this point, but llvm/clang/lld
complained that it could not move location counter backward.
Signed-off-by: Daniel Leung <daniel.leung@intel.com>
diff --git a/arch/common/rom_start_offset.ld b/arch/common/rom_start_offset.ld
index 2e82f30d71..8546391614 100644
--- a/arch/common/rom_start_offset.ld
+++ b/arch/common/rom_start_offset.ld
@@ -4,5 +4,5 @@
* SPDX-License-Identifier: Apache-2.0
*/
-. = CONFIG_ROM_START_OFFSET;
+. += CONFIG_ROM_START_OFFSET;
. = ALIGN(4);
`
**Expected behavior**
west flash can works
**Impact**
twister testing
**Logs and console output**
whent this happen no console output
**Environment (please complete the following information):**
- OS: (e.g. Linux, MacOS, Windows)
- Toolchain (e.g Zephyr SDK, ...)
- Commit SHA or Version used: zephyr-v3.3.0-530-g1751c8f0f5
this impacts mimxrt1170_evk_cm7 and mimxrt1160_evk_cm7 | 1.0 | CONFIG_ROM_START_OFFSET change to be added to cause west flash reset fails, in NXP RT11xx platforms - **Describe the bug**
for RT1170 use below command to download the image, debug reset does not work, but hardwarereset works.
`
west build -b mimxrt1170_evk_cm7
west flash --runner jlink --tool-opt='-SelectEmuBySN 000725371294' -- '--device=MIMXRT1176xxxA_M7' '--reset-after-load'
`
the serial console has no output at all, press reset key works. but this blocks twister testing. bisect found below commit introduce such problem
`
commit 44628735b870b2806bbea47477c3300bb624ad31 (refs/bisect/bad)
Author: Daniel Leung <daniel.leung@intel.com>
Date: Mon Feb 13 13:31:26 2023 -0800
linker: rom_start_offset: add to address instead of set
The CONFIG_ROM_START_OFFSET is supposed to be added to
the current when linking, instead of having the current
address set to it. So fix that.
Not sure why it worked up to this point, but llvm/clang/lld
complained that it could not move location counter backward.
Signed-off-by: Daniel Leung <daniel.leung@intel.com>
diff --git a/arch/common/rom_start_offset.ld b/arch/common/rom_start_offset.ld
index 2e82f30d71..8546391614 100644
--- a/arch/common/rom_start_offset.ld
+++ b/arch/common/rom_start_offset.ld
@@ -4,5 +4,5 @@
* SPDX-License-Identifier: Apache-2.0
*/
-. = CONFIG_ROM_START_OFFSET;
+. += CONFIG_ROM_START_OFFSET;
. = ALIGN(4);
`
**Expected behavior**
west flash can works
**Impact**
twister testing
**Logs and console output**
whent this happen no console output
**Environment (please complete the following information):**
- OS: (e.g. Linux, MacOS, Windows)
- Toolchain (e.g Zephyr SDK, ...)
- Commit SHA or Version used: zephyr-v3.3.0-530-g1751c8f0f5
this impacts mimxrt1170_evk_cm7 and mimxrt1160_evk_cm7 | non_main | config rom start offset change to be added to cause west flash reset fails in nxp platforms describe the bug for use below command to download the image debug reset does not work but hardwarereset works west build b evk west flash runner jlink tool opt selectemubysn device reset after load the serial console has no output at all press reset key works but this blocks twister testing bisect found below commit introduce such problem commit refs bisect bad author daniel leung date mon feb linker rom start offset add to address instead of set the config rom start offset is supposed to be added to the current when linking instead of having the current address set to it so fix that not sure why it worked up to this point but llvm clang lld complained that it could not move location counter backward signed off by daniel leung diff git a arch common rom start offset ld b arch common rom start offset ld index a arch common rom start offset ld b arch common rom start offset ld spdx license identifier apache config rom start offset config rom start offset align expected behavior west flash can works impact twister testing logs and console output whent this happen no console output environment please complete the following information os e g linux macos windows toolchain e g zephyr sdk commit sha or version used zephyr this impacts evk and evk | 0 |
208,740 | 23,644,663,993 | IssuesEvent | 2022-08-25 20:39:55 | bcgov/cloud-pathfinder | https://api.github.com/repos/bcgov/cloud-pathfinder | opened | Security Tools for Rosa Investigation | Security | **Describe the issue**
Olena needs a security tools for ROSA (Redhat Openshift Service AWS) ballpark cost estimation.
**Additional context**
Alternative Security Tools other than ACS includes:
- AWS Security Hub (AWS Specific)
- Redhat ACS (Advanced Cluster Security)
- CheckPoint CloudGuard CSPM (AWS, GCP, Azure)
**Definition of done**
- Comparison
- Ball Park Cost Estimation
- Graphic Presentation for the Result.
| True | Security Tools for Rosa Investigation - **Describe the issue**
Olena needs a security tools for ROSA (Redhat Openshift Service AWS) ballpark cost estimation.
**Additional context**
Alternative Security Tools other than ACS includes:
- AWS Security Hub (AWS Specific)
- Redhat ACS (Advanced Cluster Security)
- CheckPoint CloudGuard CSPM (AWS, GCP, Azure)
**Definition of done**
- Comparison
- Ball Park Cost Estimation
- Graphic Presentation for the Result.
| non_main | security tools for rosa investigation describe the issue olena needs a security tools for rosa redhat openshift service aws ballpark cost estimation additional context alternative security tools other than acs includes aws security hub aws specific redhat acs advanced cluster security checkpoint cloudguard cspm aws gcp azure definition of done comparison ball park cost estimation graphic presentation for the result | 0 |
4,928 | 25,338,519,326 | IssuesEvent | 2022-11-18 19:06:09 | ipfs/ipfs-docs | https://api.github.com/repos/ipfs/ipfs-docs | closed | Run Kubo IPFS inside Docker | kind/bug need/maintainers-input kind/support | The environment variable
IPFS_PROFILE=server
seems not to work anymore, is there an replacement?
I was using the image a9dd98877e27 (0.15.0) before, after upgrading to the newest version i got a netsacan warning from my provider.
```
##########################################################################
# Netscan detected from host 23.88.72.190 #
##########################################################################
time protocol src_ip src_port dest_ip dest_port
---------------------------------------------------------------------------
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 33034 => 10.16.80.80 49396
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:45 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 172.31.14.103 30014
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:16 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:26 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:26 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:26 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:27 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:27 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:28 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:28 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:31 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:47:51 2022 UDP 23.88.72.190 61772 => 10.200.220.143 37630
Mon Oct 31 12:47:51 2022 UDP 23.88.72.190 61772 => 10.200.220.143 24807
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 192.168.1.163 58447
Mon Oct 31 12:48:54 2022 TCP 23.88.72.190 43269 => 192.168.1.163 58447
Mon Oct 31 12:48:05 2022 UDP 23.88.72.190 61772 => 172.31.1.10 30000
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 43269 => 172.31.3.27 30000
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 172.31.3.27 30000
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 TCP 23.88.72.190 43269 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:41 2022 TCP 23.88.72.190 43269 => 172.31.8.32 30000
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.8.32 30000
Mon Oct 31 12:48:41 2022 TCP 23.88.72.190 43269 => 172.31.14.58 30000
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.14.58 30000
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 10.15.235.59 49981
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:48:08 2022 TCP 23.88.72.190 43269 => 172.31.7.133 30013
Mon Oct 31 12:48:08 2022 UDP 23.88.72.190 61772 => 172.31.7.133 30013
Mon Oct 31 12:48:09 2022 TCP 23.88.72.190 43269 => 172.31.12.216 30013
Mon Oct 31 12:48:09 2022 UDP 23.88.72.190 61772 => 172.31.12.216 30013
Mon Oct 31 12:47:56 2022 UDP 23.88.72.190 61772 => 10.12.0.86 50472
Mon Oct 31 12:47:56 2022 UDP 23.88.72.190 61772 => 10.12.0.86 50472
Mon Oct 31 12:47:56 2022 UDP 23.88.72.190 61772 => 10.12.0.86 50472
Mon Oct 31 12:51:05 2022 UDP 23.88.72.190 61772 => 10.201.37.20 50875
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:49:16 2022 TCP 23.88.72.190 43269 => 10.102.93.83 51330
Mon Oct 31 12:49:18 2022 TCP 23.88.72.190 43269 => 10.102.93.83 51330
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 43269 => 192.168.2.109 58073
Mon Oct 31 12:48:14 2022 TCP 23.88.72.190 43269 => 192.168.2.109 58073
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 43269 => 192.168.1.104 65375
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 46878
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 46878
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 10.16.80.80 49394
Mon Oct 31 12:48:00 2022 TCP 23.88.72.190 43269 => 172.31.2.59 30012
Mon Oct 31 12:48:00 2022 UDP 23.88.72.190 61772 => 172.31.2.59 30012
Mon Oct 31 12:48:36 2022 TCP 23.88.72.190 43269 => 172.31.3.27 30012
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 172.31.3.27 30012
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 172.31.3.27 30012
Mon Oct 31 12:49:26 2022 TCP 23.88.72.190 43269 => 172.31.9.97 30012
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30012
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.31.12.61 30012
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.12.61 30012
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.14.3 30012
Mon Oct 31 12:51:08 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30012
Mon Oct 31 12:47:56 2022 TCP 23.88.72.190 58642 => 10.12.0.86 53372
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 192.168.0.111 55099
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 192.168.1.20 41653
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:51:06 2022 TCP 23.88.72.190 43269 => 172.31.5.242 30001
Mon Oct 31 12:51:06 2022 UDP 23.88.72.190 61772 => 172.31.5.242 30001
Mon Oct 31 12:51:06 2022 UDP 23.88.72.190 61772 => 172.31.5.242 30001
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 172.31.8.63 30001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.8.63 30001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:35 2022 TCP 23.88.72.190 43269 => 172.31.9.97 30001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 172.31.12.3 30001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.12.3 30001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.31.13.212 30001
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.31.13.212 30001
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.15.241 30001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30001
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.15.235.59 61148
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.15.235.59 61148
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.15.235.59 61148
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:50:59 2022 TCP 23.88.72.190 43269 => 10.0.0.48 4001
Mon Oct 31 12:50:38 2022 TCP 23.88.72.190 43269 => 10.0.0.183 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 10.0.0.183 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 10.0.0.183 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 10.0.2.100 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.0.2.100 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.0.2.100 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 10.0.4.173 4001
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 10.0.6.124 4001
Mon Oct 31 12:48:03 2022 UDP 23.88.72.190 61772 => 10.0.6.124 4001
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 10.0.8.224 4001
Mon Oct 31 12:49:19 2022 TCP 23.88.72.190 43269 => 10.0.36.6 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.0.65.229 4001
Mon Oct 31 12:50:36 2022 TCP 23.88.72.190 43269 => 10.0.69.123 4001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 10.0.69.123 4001
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:25 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:27 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:29 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:32 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 10.21.21.93 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.21.21.93 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.21.21.93 4001
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 10.150.0.6 4001
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 10.150.0.6 4001
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 10.150.0.6 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 10.150.0.8 4001
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 10.162.0.2 4001
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.162.0.2 4001
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.162.0.2 4001
Mon Oct 31 12:50:35 2022 TCP 23.88.72.190 43269 => 10.244.3.154 4001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 10.244.3.154 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.15 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.32 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.32 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.34 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.34 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.34 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.72 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.72 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 10.244.45.96 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.96 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.96 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.96 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.96 4001
Mon Oct 31 12:49:46 2022 TCP 23.88.72.190 43269 => 10.244.45.103 4001
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 10.244.45.103 4001
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 43269 => 10.244.45.103 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.105 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.105 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.119 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.120 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.123 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.123 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.129 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:06 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:06 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.130 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 10.244.45.131 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.131 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.131 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.131 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:46 2022 TCP 23.88.72.190 43269 => 10.244.45.156 4001
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 10.244.45.156 4001
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 43269 => 10.244.45.156 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.167 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.167 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.187 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.212 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.212 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.221 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.234 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.234 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.234 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.238 4001
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 169.254.172.2 4001
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 172.16.0.97 4001
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:50:01 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:50:01 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:04 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:04 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:05 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:05 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:08 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 172.19.0.1 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:50:35 2022 TCP 23.88.72.190 43269 => 172.19.0.3 4001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.19.0.3 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:59 2022 TCP 23.88.72.190 43269 => 172.19.29.233 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 172.20.0.1 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:48:57 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:48:58 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:49:00 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.20.0.3 4001
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.20.0.3 4001
Mon Oct 31 12:49:22 2022 TCP 23.88.72.190 43269 => 172.20.0.6 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 172.20.0.6 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 172.20.0.6 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 172.20.0.6 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:14 2022 TCP 23.88.72.190 43269 => 172.22.0.3 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 172.26.8.51 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.26.8.51 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.26.8.51 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 172.27.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.27.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.27.0.2 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.30.0.3 4001
Mon Oct 31 12:48:48 2022 TCP 23.88.72.190 43269 => 172.30.0.3 4001
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 172.31.0.4 4001
Mon Oct 31 12:49:02 2022 UDP 23.88.72.190 61772 => 172.31.0.4 4001
Mon Oct 31 12:51:01 2022 UDP 23.88.72.190 61772 => 172.31.2.137 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.4.83 4001
Mon Oct 31 12:48:10 2022 TCP 23.88.72.190 43269 => 172.31.9.29 4001
Mon Oct 31 12:48:10 2022 UDP 23.88.72.190 61772 => 172.31.9.29 4001
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.9.29 4001
Mon Oct 31 12:48:17 2022 TCP 23.88.72.190 43269 => 172.31.10.32 4001
Mon Oct 31 12:48:17 2022 UDP 23.88.72.190 61772 => 172.31.10.32 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.15.214 4001
Mon Oct 31 12:51:04 2022 TCP 23.88.72.190 43269 => 172.31.19.2 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 172.31.19.2 4001
Mon Oct 31 12:51:05 2022 UDP 23.88.72.190 61772 => 172.31.19.2 4001
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.31.26.159 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.31.30.61 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.31.30.61 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.31.30.61 4001
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 43269 => 172.31.45.21 4001
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 172.31.45.21 4001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.51.215 4001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.51.215 4001
Mon Oct 31 12:48:44 2022 TCP 23.88.72.190 43269 => 172.31.57.89 4001
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 172.31.57.89 4001
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 172.31.57.89 4001
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 172.31.57.89 4001
Mon Oct 31 12:50:33 2022 TCP 23.88.72.190 43269 => 172.31.93.56 4001
Mon Oct 31 12:51:09 2022 TCP 23.88.72.190 43269 => 172.31.114.185 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.114.185 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.114.185 4001
Mon Oct 31 12:49:16 2022 TCP 23.88.72.190 4001 => 172.240.0.4 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 5781 => 172.240.0.4 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 5781 => 172.240.0.4 4001
Mon Oct 31 12:48:56 2022 TCP 23.88.72.190 4001 => 172.240.5.4 4001
Mon Oct 31 12:48:56 2022 UDP 23.88.72.190 7352 => 172.240.5.4 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 192.168.0.4 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.0.4 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 192.168.0.49 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 192.168.0.49 4001
Mon Oct 31 12:51:04 2022 TCP 23.88.72.190 43269 => 192.168.0.100 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 192.168.0.100 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 192.168.0.100 4001
Mon Oct 31 12:48:18 2022 TCP 23.88.72.190 43269 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:50:50 2022 TCP 23.88.72.190 43269 => 192.168.0.101 4001
Mon Oct 31 12:50:50 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 192.168.0.107 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.0.126 4001
Mon Oct 31 12:48:18 2022 TCP 23.88.72.190 43269 => 192.168.1.13 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.1.13 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.1.13 4001
Mon Oct 31 12:51:03 2022 TCP 23.88.72.190 43269 => 192.168.1.36 4001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 192.168.1.102 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:45 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 43269 => 192.168.1.102 4001
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:49:26 2022 TCP 23.88.72.190 43269 => 192.168.1.111 4001
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 192.168.1.111 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.111 4001
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 192.168.1.177 4001
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 192.168.1.177 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.177 4001
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 192.168.1.184 4001
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 192.168.1.184 4001
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 192.168.1.184 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 192.168.1.253 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:35 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:35 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 192.168.1.253 4001
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 192.168.2.20 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:48:37 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:37 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 192.168.2.104 4001
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 43269 => 192.168.2.104 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.48.3 4001
Mon Oct 31 12:48:01 2022 TCP 23.88.72.190 43269 => 192.168.86.156 4001
Mon Oct 31 12:48:01 2022 UDP 23.88.72.190 61772 => 192.168.86.156 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:48:08 2022 TCP 23.88.72.190 43269 => 192.168.121.9 4001
Mon Oct 31 12:48:08 2022 UDP 23.88.72.190 61772 => 192.168.121.9 4001
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 192.168.121.9 4001
Mon Oct 31 12:48:03 2022 UDP 23.88.72.190 61772 => 192.168.121.86 4001
Mon Oct 31 12:48:03 2022 UDP 23.88.72.190 61772 => 192.168.121.86 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:18 2022 TCP 23.88.72.190 43269 => 192.168.121.114 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:19 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:19 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:21 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:21 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:21 2022 TCP 23.88.72.190 43269 => 192.168.121.114 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 43269 => 192.168.121.114 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:33 2022 TCP 23.88.72.190 43269 => 192.168.121.115 4001
Mon Oct 31 12:48:52 2022 TCP 23.88.72.190 43269 => 192.168.121.168 4001
Mon Oct 31 12:48:52 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:54 2022 TCP 23.88.72.190 43269 => 192.168.121.168 4001
Mon Oct 31 12:48:54 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:54 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:02 2022 UDP 23.88.72.190 61772 => 192.168.121.170 4001
Mon Oct 31 12:48:02 2022 UDP 23.88.72.190 61772 => 192.168.121.170 4001
Mon Oct 31 12:48:02 2022 UDP 23.88.72.190 61772 => 192.168.121.170 4001
Mon Oct 31 12:47:59 2022 TCP 23.88.72.190 43269 => 192.168.121.231 4001
Mon Oct 31 12:48:01 2022 UDP 23.88.72.190 61772 => 192.168.121.231 4001
Mon Oct 31 12:49:20 2022 TCP 23.88.72.190 57384 => 10.102.93.83 51332
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 57384 => 10.102.93.83 51332
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 57384 => 10.102.93.83 51332
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 192.168.8.111 56764
Mon Oct 31 12:51:01 2022 UDP 23.88.72.190 61772 => 10.16.80.80 62496
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.31.2.21 30006
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.2.21 30006
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 172.31.4.83 30006
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 172.31.5.24 30006
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 172.31.5.24 30006
Mon Oct 31 12:51:06 2022 TCP 23.88.72.190 43269 => 172.31.5.142 30006
Mon Oct 31 12:51:06 2022 UDP 23.88.72.190 61772 => 172.31.5.142 30006
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 172.31.10.10 30006
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.12.61 30006
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.12.61 30006
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.15.131 30006
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.1.186 30002
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.31.2.240 30002
Mon Oct 31 12:50:51 2022 UDP 23.88.72.190 61772 => 172.31.2.240 30002
Mon Oct 31 12:50:51 2022 UDP 23.88.72.190 61772 => 172.31.2.240 30002
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 172.31.2.240 30002
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.2.240 30002
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.5.174 30002
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 172.31.6.6 30002
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30002
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 172.31.6.98 30002
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30002
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30002
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 43269 => 192.168.1.6 59612
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 192.168.1.6 59612
Mon Oct 31 12:49:33 2022 TCP 23.88.72.190 35380 => 192.168.1.103 51120
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 35452 => 192.168.1.103 51120
Mon Oct 31 12:49:33 2022 TCP 23.88.72.190 46986 => 192.168.43.152 51120
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 47052 => 192.168.43.152 51120
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:50:15 2022 TCP 23.88.72.190 43269 => 172.31.6.98 30011
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30011
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30011
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30011
Mon Oct 31 12:47:57 2022 UDP 23.88.72.190 61772 => 172.31.8.121 30011
Mon Oct 31 12:51:09 2022 TCP 23.88.72.190 43269 => 172.31.15.205 30011
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.15.205 30011
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.31.15.241 30011
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30011
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30011
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 192.168.1.107 55466
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 192.168.1.107 55466
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 192.168.1.107 55466
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 100.122.214.169 56233
Mon Oct 31 12:49:18 2022 TCP 23.88.72.190 43269 => 100.122.214.169 56233
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 34294 => 10.15.235.59 49983
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 10.131.139.32 54640
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 10.131.139.32 54640
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 172.31.5.230 30007
Mon Oct 31 12:51:08 2022 UDP 23.88.72.190 61772 => 172.31.9.13 30007
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 172.31.9.97 30007
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:49:25 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.9.153 30007
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.9.153 30007
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.14.89 30007
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.14.89 30007
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 10.131.139.32 44772
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.0.235 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.0.235 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.0.235 30004
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.5.242 30004
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.5.242 30004
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.6.169 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.6.169 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.6.169 30004
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.8.255 30004
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 43269 => 172.31.14.247 30004
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:50:55 2022 TCP 23.88.72.190 43269 => 172.31.14.247 30004
Mon Oct 31 12:50:55 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 10.148.99.188 39974
Mon Oct 31 12:47:56 2022 TCP 23.88.72.190 43269 => 10.12.0.86 53370
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 50076 => 192.168.1.6 59614
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 50076 => 192.168.1.6 59614
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.0.0.3 44668
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 58172
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 58172
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.0.191 30010
Mon Oct 31 12:50:15 2022 TCP 23.88.72.190 43269 => 172.31.0.191 30010
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.0.191 30010
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.0.191 30010
Mon Oct 31 12:49:10 2022 UDP 23.88.72.190 61772 => 172.31.1.114 30010
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 172.31.2.191 30010
Mon Oct 31 12:49:02 2022 UDP 23.88.72.190 61772 => 172.31.2.191 30010
Mon Oct 31 12:50:59 2022 UDP 23.88.72.190 61772 => 172.31.5.66 30010
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 172.31.5.230 30010
Mon Oct 31 12:49:02 2022 UDP 23.88.72.190 61772 => 172.31.5.230 30010
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.8.156 30010
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.8.156 30010
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 172.31.9.41 30010
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 172.31.9.41 30010
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 172.31.9.41 30010
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.10.247 30010
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.10.247 30010
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 172.31.0.68 30008
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.2.63 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.2.63 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.2.63 30008
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 172.31.5.113 30008
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 172.31.5.113 30008
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 172.31.6.50 30008
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.31.6.50 30008
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.31.6.50 30008
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.8.41 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.8.41 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.8.41 30008
Mon Oct 31 12:51:03 2022 UDP 23.88.72.190 61772 => 172.31.9.123 30008
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 43269 => 172.31.9.198 30008
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.9.198 30008
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.12.3 30008
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 192.168.8.111 60183
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 192.168.8.111 60183
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 192.168.1.20 56224
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.5 65008
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 16961
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 16961
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 16961
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.4.56 30009
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.4.86 30009
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.4.86 30009
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.4.86 30009
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.9.13 30009
Mon Oct 31 12:50:16 2022 UDP 23.88.72.190 61772 => 172.31.9.84 30009
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 172.31.10.95 30009
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 35906 => 192.168.1.5 65010
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 10.10.32.3 38378
Mon Oct 31 12:50:16 2022 TCP 23.88.72.190 49254 => 192.168.0.121 49312
Mon Oct 31 12:48:35 2022 TCP 23.88.72.190 43269 => 192.168.15.12 49874
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.15 38657
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.15 38657
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 57806 => 192.168.1.104 65377
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.8 53252
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.8 53252
Mon Oct 31 12:48:36 2022 TCP 23.88.72.190 46754 => 10.100.248.14 1080
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 46792 => 10.100.248.14 1080
Mon Oct 31 12:49:31 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:31 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:34 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:34 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:36 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 38002
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 38002
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 10.244.1.4 4006
Mon Oct 31 12:47:58 2022 TCP 23.88.72.190 48396 => 192.168.1.3 62603
Mon Oct 31 12:48:05 2022 TCP 23.88.72.190 50558 => 192.168.1.20 56226
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 46942
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 46942
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 46942
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 10.131.139.32 62993
Mon Oct 31 12:48:05 2022 TCP 23.88.72.190 58218 => 10.148.99.188 37247
Mon Oct 31 12:48:08 2022 TCP 23.88.72.190 58218 => 10.148.99.188 37247
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 53710 => 192.168.1.3 54810
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 54032 => 172.20.129.25 64782
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 43269 => 192.168.1.3 54808
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 192.168.1.104 53964
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.104 53964
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 34500 => 192.168.1.8 53254
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 34510 => 192.168.1.8 53254
Mon Oct 31 12:47:51 2022 UDP 23.88.72.190 61772 => 192.168.1.103 60286
Mon Oct 31 12:47:59 2022 TCP 23.88.72.190 43269 => 192.168.0.30 49090
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 58958 => 192.168.2.109 58075
Mon Oct 31 12:48:14 2022 TCP 23.88.72.190 58972 => 192.168.2.109 58075
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:49 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:49 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:50:17 2022 TCP 23.88.72.190 35794 => 192.168.42.173 6333
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 35728 => 100.122.214.169 56235
Mon Oct 31 12:49:18 2022 TCP 23.88.72.190 35728 => 100.122.214.169 56235
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:50:33 2022 TCP 23.88.72.190 43269 => 192.168.42.173 6331
Mon Oct 31 12:51:08 2022 TCP 23.88.72.190 35510 => 192.168.0.103 51129
Mon Oct 31 12:49:17 2022 TCP 23.88.72.190 46242 => 192.168.1.5 2027
Mon Oct 31 12:49:19 2022 TCP 23.88.72.190 46242 => 192.168.1.5 2027
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:48:41 2022 TCP 23.88.72.190 43269 => 192.168.10.182 37137
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 47098 => 192.168.1.9 64278
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 47178 => 192.168.1.9 64278
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 54082 => 10.148.99.188 52006
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.0.0.3 49054
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.32 41998
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.32 41998
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 192.168.1.9 64276
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 43269 => 192.168.1.9 64276
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 172.31.0.181 30005
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.181 30005
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.181 30005
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.2.171 30005
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.2.171 30005
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.31.2.184 30005
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.2.184 30005
Mon Oct 31 12:50:55 2022 TCP 23.88.72.190 43269 => 172.31.5.174 30005
Mon Oct 31 12:50:55 2022 UDP 23.88.72.190 61772 => 172.31.5.174 30005
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.5.174 30005
Mon Oct 31 12:50:15 2022 TCP 23.88.72.190 43269 => 172.31.9.13 30005
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.9.13 30005
Mon Oct 31 12:48:39 2022 TCP 23.88.72.190 43269 => 172.31.15.115 30005
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.15.115 30005
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 172.31.15.115 30005
Mon Oct 31 12:48:05 2022 UDP 23.88.72.190 61772 => 10.148.99.188 18456
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.31.103 50267
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.20.129.25 64780
Mon Oct 31 12:49:16 2022 TCP 23.88.72.190 43269 => 192.168.1.5 2025
Mon Oct 31 12:49:17 2022 TCP 23.88.72.190 43269 => 192.168.1.5 2025
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 10.148.99.188 21194
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:27 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:27 2022 TCP 23.88.72.190 43269 => 192.168.43.152 51118
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 192.168.43.152 51118
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 192.168.43.152 51118
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:49:20 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 10.131.139.32 14766
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 10.131.139.32 14766
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
```
| True | Run Kubo IPFS inside Docker - The environment variable
IPFS_PROFILE=server
seems not to work anymore, is there an replacement?
I was using the image a9dd98877e27 (0.15.0) before, after upgrading to the newest version i got a netsacan warning from my provider.
```
##########################################################################
# Netscan detected from host 23.88.72.190 #
##########################################################################
time protocol src_ip src_port dest_ip dest_port
---------------------------------------------------------------------------
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 33034 => 10.16.80.80 49396
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:45 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.9 52168
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 172.31.14.103 30014
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:16 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:26 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:26 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:26 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:27 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:27 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:28 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:28 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:48:31 2022 UDP 23.88.72.190 61772 => 192.168.2.109 56811
Mon Oct 31 12:47:51 2022 UDP 23.88.72.190 61772 => 10.200.220.143 37630
Mon Oct 31 12:47:51 2022 UDP 23.88.72.190 61772 => 10.200.220.143 24807
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 192.168.1.163 58447
Mon Oct 31 12:48:54 2022 TCP 23.88.72.190 43269 => 192.168.1.163 58447
Mon Oct 31 12:48:05 2022 UDP 23.88.72.190 61772 => 172.31.1.10 30000
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 43269 => 172.31.3.27 30000
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 172.31.3.27 30000
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 TCP 23.88.72.190 43269 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.5.143 30000
Mon Oct 31 12:48:41 2022 TCP 23.88.72.190 43269 => 172.31.8.32 30000
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.8.32 30000
Mon Oct 31 12:48:41 2022 TCP 23.88.72.190 43269 => 172.31.14.58 30000
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.14.58 30000
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 10.15.235.59 49981
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.5 58310
Mon Oct 31 12:48:08 2022 TCP 23.88.72.190 43269 => 172.31.7.133 30013
Mon Oct 31 12:48:08 2022 UDP 23.88.72.190 61772 => 172.31.7.133 30013
Mon Oct 31 12:48:09 2022 TCP 23.88.72.190 43269 => 172.31.12.216 30013
Mon Oct 31 12:48:09 2022 UDP 23.88.72.190 61772 => 172.31.12.216 30013
Mon Oct 31 12:47:56 2022 UDP 23.88.72.190 61772 => 10.12.0.86 50472
Mon Oct 31 12:47:56 2022 UDP 23.88.72.190 61772 => 10.12.0.86 50472
Mon Oct 31 12:47:56 2022 UDP 23.88.72.190 61772 => 10.12.0.86 50472
Mon Oct 31 12:51:05 2022 UDP 23.88.72.190 61772 => 10.201.37.20 50875
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 192.168.1.3 63963
Mon Oct 31 12:49:16 2022 TCP 23.88.72.190 43269 => 10.102.93.83 51330
Mon Oct 31 12:49:18 2022 TCP 23.88.72.190 43269 => 10.102.93.83 51330
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 43269 => 192.168.2.109 58073
Mon Oct 31 12:48:14 2022 TCP 23.88.72.190 43269 => 192.168.2.109 58073
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 43269 => 192.168.1.104 65375
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.31.103 51679
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 46878
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 46878
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 10.16.80.80 49394
Mon Oct 31 12:48:00 2022 TCP 23.88.72.190 43269 => 172.31.2.59 30012
Mon Oct 31 12:48:00 2022 UDP 23.88.72.190 61772 => 172.31.2.59 30012
Mon Oct 31 12:48:36 2022 TCP 23.88.72.190 43269 => 172.31.3.27 30012
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 172.31.3.27 30012
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 172.31.3.27 30012
Mon Oct 31 12:49:26 2022 TCP 23.88.72.190 43269 => 172.31.9.97 30012
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30012
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.31.12.61 30012
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.12.61 30012
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.14.3 30012
Mon Oct 31 12:51:08 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30012
Mon Oct 31 12:47:56 2022 TCP 23.88.72.190 58642 => 10.12.0.86 53372
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 192.168.0.111 55099
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.42.173 53420
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 192.168.1.20 41653
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:49:56 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:10 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.1.8 55999
Mon Oct 31 12:51:06 2022 TCP 23.88.72.190 43269 => 172.31.5.242 30001
Mon Oct 31 12:51:06 2022 UDP 23.88.72.190 61772 => 172.31.5.242 30001
Mon Oct 31 12:51:06 2022 UDP 23.88.72.190 61772 => 172.31.5.242 30001
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 172.31.8.63 30001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.8.63 30001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:35 2022 TCP 23.88.72.190 43269 => 172.31.9.97 30001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30001
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 172.31.12.3 30001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.12.3 30001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.31.13.212 30001
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.31.13.212 30001
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.13.212 30001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.15.241 30001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30001
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.15.235.59 61148
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.15.235.59 61148
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.15.235.59 61148
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 192.168.68.58 39864
Mon Oct 31 12:50:59 2022 TCP 23.88.72.190 43269 => 10.0.0.48 4001
Mon Oct 31 12:50:38 2022 TCP 23.88.72.190 43269 => 10.0.0.183 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 10.0.0.183 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 10.0.0.183 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 10.0.2.100 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.0.2.100 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.0.2.100 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 10.0.4.173 4001
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 10.0.6.124 4001
Mon Oct 31 12:48:03 2022 UDP 23.88.72.190 61772 => 10.0.6.124 4001
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 10.0.8.224 4001
Mon Oct 31 12:49:19 2022 TCP 23.88.72.190 43269 => 10.0.36.6 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.0.65.229 4001
Mon Oct 31 12:50:36 2022 TCP 23.88.72.190 43269 => 10.0.69.123 4001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 10.0.69.123 4001
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:25 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:27 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:29 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:32 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 10.15.0.5 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 10.21.21.93 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.21.21.93 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 10.21.21.93 4001
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 10.150.0.6 4001
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 10.150.0.6 4001
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 10.150.0.6 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 10.150.0.8 4001
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 10.162.0.2 4001
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.162.0.2 4001
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 10.162.0.2 4001
Mon Oct 31 12:50:35 2022 TCP 23.88.72.190 43269 => 10.244.3.154 4001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 10.244.3.154 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:50:58 2022 UDP 23.88.72.190 61772 => 10.244.4.214 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.15 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.15 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.18 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.32 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.32 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.34 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.34 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.34 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.59 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.72 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.72 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 10.244.45.96 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.96 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.96 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.96 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.96 4001
Mon Oct 31 12:49:46 2022 TCP 23.88.72.190 43269 => 10.244.45.103 4001
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 10.244.45.103 4001
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 43269 => 10.244.45.103 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.105 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.105 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.105 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.119 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.119 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.120 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.120 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.123 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.123 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.123 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.129 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:06 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:06 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.129 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.130 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 10.244.45.131 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.131 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.131 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.131 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:46 2022 TCP 23.88.72.190 43269 => 10.244.45.156 4001
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 10.244.45.156 4001
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 43269 => 10.244.45.156 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.156 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.167 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.167 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.167 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.170 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.187 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.212 4001
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.212 4001
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.212 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.215 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.221 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.221 4001
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.244.45.234 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.234 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 10.244.45.234 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.244.45.238 4001
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 169.254.172.2 4001
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 172.16.0.97 4001
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:50:01 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:50:01 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 172.16.0.97 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:04 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:04 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:05 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:05 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:08 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 172.16.1.80 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.16.1.80 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 172.19.0.1 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.19.0.2 4001
Mon Oct 31 12:50:35 2022 TCP 23.88.72.190 43269 => 172.19.0.3 4001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 172.19.0.3 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:57 2022 UDP 23.88.72.190 61772 => 172.19.29.233 4001
Mon Oct 31 12:50:59 2022 TCP 23.88.72.190 43269 => 172.19.29.233 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 172.20.0.1 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:48:57 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:48:58 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:49:00 2022 TCP 23.88.72.190 43269 => 172.20.0.2 4001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.20.0.3 4001
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.20.0.3 4001
Mon Oct 31 12:49:22 2022 TCP 23.88.72.190 43269 => 172.20.0.6 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 172.20.0.6 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 172.20.0.6 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 172.20.0.6 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.20.91.143 4001
Mon Oct 31 12:48:14 2022 TCP 23.88.72.190 43269 => 172.22.0.3 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 172.26.0.2 4001
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 172.26.8.51 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.26.8.51 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.26.8.51 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 172.27.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.27.0.2 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 172.27.0.2 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.28.8.56 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.28.8.56 4001
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.30.0.3 4001
Mon Oct 31 12:48:48 2022 TCP 23.88.72.190 43269 => 172.30.0.3 4001
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 172.31.0.4 4001
Mon Oct 31 12:49:02 2022 UDP 23.88.72.190 61772 => 172.31.0.4 4001
Mon Oct 31 12:51:01 2022 UDP 23.88.72.190 61772 => 172.31.2.137 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.4.83 4001
Mon Oct 31 12:48:10 2022 TCP 23.88.72.190 43269 => 172.31.9.29 4001
Mon Oct 31 12:48:10 2022 UDP 23.88.72.190 61772 => 172.31.9.29 4001
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.9.29 4001
Mon Oct 31 12:48:17 2022 TCP 23.88.72.190 43269 => 172.31.10.32 4001
Mon Oct 31 12:48:17 2022 UDP 23.88.72.190 61772 => 172.31.10.32 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.15.214 4001
Mon Oct 31 12:51:04 2022 TCP 23.88.72.190 43269 => 172.31.19.2 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 172.31.19.2 4001
Mon Oct 31 12:51:05 2022 UDP 23.88.72.190 61772 => 172.31.19.2 4001
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.31.26.159 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.31.30.61 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.31.30.61 4001
Mon Oct 31 12:49:03 2022 UDP 23.88.72.190 61772 => 172.31.30.61 4001
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 43269 => 172.31.45.21 4001
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 172.31.45.21 4001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.51.215 4001
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.51.215 4001
Mon Oct 31 12:48:44 2022 TCP 23.88.72.190 43269 => 172.31.57.89 4001
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 172.31.57.89 4001
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 172.31.57.89 4001
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 172.31.57.89 4001
Mon Oct 31 12:50:33 2022 TCP 23.88.72.190 43269 => 172.31.93.56 4001
Mon Oct 31 12:51:09 2022 TCP 23.88.72.190 43269 => 172.31.114.185 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.114.185 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.114.185 4001
Mon Oct 31 12:49:16 2022 TCP 23.88.72.190 4001 => 172.240.0.4 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 5781 => 172.240.0.4 4001
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 5781 => 172.240.0.4 4001
Mon Oct 31 12:48:56 2022 TCP 23.88.72.190 4001 => 172.240.5.4 4001
Mon Oct 31 12:48:56 2022 UDP 23.88.72.190 7352 => 172.240.5.4 4001
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 192.168.0.4 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.0.4 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 192.168.0.49 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 192.168.0.49 4001
Mon Oct 31 12:51:04 2022 TCP 23.88.72.190 43269 => 192.168.0.100 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 192.168.0.100 4001
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 192.168.0.100 4001
Mon Oct 31 12:48:18 2022 TCP 23.88.72.190 43269 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:50:50 2022 TCP 23.88.72.190 43269 => 192.168.0.101 4001
Mon Oct 31 12:50:50 2022 UDP 23.88.72.190 61772 => 192.168.0.101 4001
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 192.168.0.107 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.0.126 4001
Mon Oct 31 12:48:18 2022 TCP 23.88.72.190 43269 => 192.168.1.13 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.1.13 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.1.13 4001
Mon Oct 31 12:51:03 2022 TCP 23.88.72.190 43269 => 192.168.1.36 4001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:36 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 192.168.1.102 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:42 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:45 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 43269 => 192.168.1.102 4001
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:50:52 2022 UDP 23.88.72.190 61772 => 192.168.1.102 4001
Mon Oct 31 12:49:26 2022 TCP 23.88.72.190 43269 => 192.168.1.111 4001
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 192.168.1.111 4001
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.111 4001
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 192.168.1.177 4001
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 192.168.1.177 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.177 4001
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 192.168.1.184 4001
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 192.168.1.184 4001
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 192.168.1.184 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:50:35 2022 UDP 23.88.72.190 61772 => 192.168.1.205 4001
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 192.168.1.253 4001
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:35 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:35 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:36 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 192.168.1.253 4001
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 192.168.1.253 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:22 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 192.168.2.20 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:50:11 2022 UDP 23.88.72.190 61772 => 192.168.2.20 4001
Mon Oct 31 12:48:37 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:37 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:38 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:48:38 2022 TCP 23.88.72.190 43269 => 192.168.2.104 4001
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 43269 => 192.168.2.104 4001
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.2.104 4001
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.48.3 4001
Mon Oct 31 12:48:01 2022 TCP 23.88.72.190 43269 => 192.168.86.156 4001
Mon Oct 31 12:48:01 2022 UDP 23.88.72.190 61772 => 192.168.86.156 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 192.168.101.22 4001
Mon Oct 31 12:48:08 2022 TCP 23.88.72.190 43269 => 192.168.121.9 4001
Mon Oct 31 12:48:08 2022 UDP 23.88.72.190 61772 => 192.168.121.9 4001
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 192.168.121.9 4001
Mon Oct 31 12:48:03 2022 UDP 23.88.72.190 61772 => 192.168.121.86 4001
Mon Oct 31 12:48:03 2022 UDP 23.88.72.190 61772 => 192.168.121.86 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:18 2022 TCP 23.88.72.190 43269 => 192.168.121.114 4001
Mon Oct 31 12:48:18 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:19 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:19 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:21 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:21 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:48:21 2022 TCP 23.88.72.190 43269 => 192.168.121.114 4001
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 192.168.121.114 4001
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 43269 => 192.168.121.114 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:18 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:30 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:31 2022 UDP 23.88.72.190 61772 => 192.168.121.115 4001
Mon Oct 31 12:50:33 2022 TCP 23.88.72.190 43269 => 192.168.121.115 4001
Mon Oct 31 12:48:52 2022 TCP 23.88.72.190 43269 => 192.168.121.168 4001
Mon Oct 31 12:48:52 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:54 2022 TCP 23.88.72.190 43269 => 192.168.121.168 4001
Mon Oct 31 12:48:54 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:54 2022 UDP 23.88.72.190 61772 => 192.168.121.168 4001
Mon Oct 31 12:48:02 2022 UDP 23.88.72.190 61772 => 192.168.121.170 4001
Mon Oct 31 12:48:02 2022 UDP 23.88.72.190 61772 => 192.168.121.170 4001
Mon Oct 31 12:48:02 2022 UDP 23.88.72.190 61772 => 192.168.121.170 4001
Mon Oct 31 12:47:59 2022 TCP 23.88.72.190 43269 => 192.168.121.231 4001
Mon Oct 31 12:48:01 2022 UDP 23.88.72.190 61772 => 192.168.121.231 4001
Mon Oct 31 12:49:20 2022 TCP 23.88.72.190 57384 => 10.102.93.83 51332
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 57384 => 10.102.93.83 51332
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 57384 => 10.102.93.83 51332
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 192.168.8.111 56764
Mon Oct 31 12:51:01 2022 UDP 23.88.72.190 61772 => 10.16.80.80 62496
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.31.2.21 30006
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.2.21 30006
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 172.31.4.83 30006
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 172.31.5.24 30006
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 172.31.5.24 30006
Mon Oct 31 12:51:06 2022 TCP 23.88.72.190 43269 => 172.31.5.142 30006
Mon Oct 31 12:51:06 2022 UDP 23.88.72.190 61772 => 172.31.5.142 30006
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 172.31.10.10 30006
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.12.61 30006
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.12.61 30006
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.15.131 30006
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.1.186 30002
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.31.2.240 30002
Mon Oct 31 12:50:51 2022 UDP 23.88.72.190 61772 => 172.31.2.240 30002
Mon Oct 31 12:50:51 2022 UDP 23.88.72.190 61772 => 172.31.2.240 30002
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 172.31.2.240 30002
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.2.240 30002
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.5.174 30002
Mon Oct 31 12:51:04 2022 UDP 23.88.72.190 61772 => 172.31.6.6 30002
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30002
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 172.31.6.98 30002
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30002
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30002
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 43269 => 192.168.1.6 59612
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 192.168.1.6 59612
Mon Oct 31 12:49:33 2022 TCP 23.88.72.190 35380 => 192.168.1.103 51120
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 35452 => 192.168.1.103 51120
Mon Oct 31 12:49:33 2022 TCP 23.88.72.190 46986 => 192.168.43.152 51120
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 47052 => 192.168.43.152 51120
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.102.93.83 49955
Mon Oct 31 12:50:15 2022 TCP 23.88.72.190 43269 => 172.31.6.98 30011
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30011
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30011
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.6.98 30011
Mon Oct 31 12:47:57 2022 UDP 23.88.72.190 61772 => 172.31.8.121 30011
Mon Oct 31 12:51:09 2022 TCP 23.88.72.190 43269 => 172.31.15.205 30011
Mon Oct 31 12:51:09 2022 UDP 23.88.72.190 61772 => 172.31.15.205 30011
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 172.31.15.241 30011
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30011
Mon Oct 31 12:50:37 2022 UDP 23.88.72.190 61772 => 172.31.15.241 30011
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 192.168.1.107 55466
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 192.168.1.107 55466
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 192.168.1.107 55466
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 43269 => 100.122.214.169 56233
Mon Oct 31 12:49:18 2022 TCP 23.88.72.190 43269 => 100.122.214.169 56233
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 34294 => 10.15.235.59 49983
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 10.131.139.32 54640
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 10.131.139.32 54640
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 172.31.5.230 30007
Mon Oct 31 12:51:08 2022 UDP 23.88.72.190 61772 => 172.31.9.13 30007
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 172.31.9.97 30007
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:49:25 2022 UDP 23.88.72.190 61772 => 172.31.9.97 30007
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.9.153 30007
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.9.153 30007
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.14.89 30007
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.14.89 30007
Mon Oct 31 12:48:45 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.20.129.25 60505
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 10.131.139.32 44772
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.0.235 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.0.235 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.0.235 30004
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.5.242 30004
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.5.242 30004
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.6.169 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.6.169 30004
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.6.169 30004
Mon Oct 31 12:49:24 2022 UDP 23.88.72.190 61772 => 172.31.8.255 30004
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 43269 => 172.31.14.247 30004
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:50:55 2022 TCP 23.88.72.190 43269 => 172.31.14.247 30004
Mon Oct 31 12:50:55 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.14.247 30004
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 10.148.99.188 39974
Mon Oct 31 12:47:56 2022 TCP 23.88.72.190 43269 => 10.12.0.86 53370
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 50076 => 192.168.1.6 59614
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 50076 => 192.168.1.6 59614
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.96 42796
Mon Oct 31 12:49:34 2022 TCP 23.88.72.190 43269 => 10.0.0.3 44668
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 58172
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 58172
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.0.191 30010
Mon Oct 31 12:50:15 2022 TCP 23.88.72.190 43269 => 172.31.0.191 30010
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.0.191 30010
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.0.191 30010
Mon Oct 31 12:49:10 2022 UDP 23.88.72.190 61772 => 172.31.1.114 30010
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 172.31.2.191 30010
Mon Oct 31 12:49:02 2022 UDP 23.88.72.190 61772 => 172.31.2.191 30010
Mon Oct 31 12:50:59 2022 UDP 23.88.72.190 61772 => 172.31.5.66 30010
Mon Oct 31 12:49:02 2022 TCP 23.88.72.190 43269 => 172.31.5.230 30010
Mon Oct 31 12:49:02 2022 UDP 23.88.72.190 61772 => 172.31.5.230 30010
Mon Oct 31 12:48:34 2022 TCP 23.88.72.190 43269 => 172.31.8.156 30010
Mon Oct 31 12:48:34 2022 UDP 23.88.72.190 61772 => 172.31.8.156 30010
Mon Oct 31 12:49:09 2022 TCP 23.88.72.190 43269 => 172.31.9.41 30010
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 172.31.9.41 30010
Mon Oct 31 12:49:09 2022 UDP 23.88.72.190 61772 => 172.31.9.41 30010
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.10.247 30010
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.10.247 30010
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 172.31.0.68 30008
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:49:55 2022 UDP 23.88.72.190 61772 => 172.31.0.68 30008
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.2.63 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.2.63 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.2.63 30008
Mon Oct 31 12:48:53 2022 TCP 23.88.72.190 43269 => 172.31.5.113 30008
Mon Oct 31 12:48:53 2022 UDP 23.88.72.190 61772 => 172.31.5.113 30008
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 172.31.6.50 30008
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.31.6.50 30008
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 172.31.6.50 30008
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.8.41 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.8.41 30008
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.8.41 30008
Mon Oct 31 12:51:03 2022 UDP 23.88.72.190 61772 => 172.31.9.123 30008
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 43269 => 172.31.9.198 30008
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.9.198 30008
Mon Oct 31 12:48:11 2022 UDP 23.88.72.190 61772 => 172.31.12.3 30008
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 192.168.8.111 60183
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 192.168.8.111 60183
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 192.168.1.20 56224
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.5 65008
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 16961
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 16961
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 16961
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.4.56 30009
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.4.86 30009
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.4.86 30009
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.4.86 30009
Mon Oct 31 12:48:41 2022 UDP 23.88.72.190 61772 => 172.31.9.13 30009
Mon Oct 31 12:50:16 2022 UDP 23.88.72.190 61772 => 172.31.9.84 30009
Mon Oct 31 12:50:38 2022 UDP 23.88.72.190 61772 => 172.31.10.95 30009
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 35906 => 192.168.1.5 65010
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:49:29 2022 UDP 23.88.72.190 61772 => 10.244.45.34 34394
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 10.10.32.3 38378
Mon Oct 31 12:50:16 2022 TCP 23.88.72.190 49254 => 192.168.0.121 49312
Mon Oct 31 12:48:35 2022 TCP 23.88.72.190 43269 => 192.168.15.12 49874
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.15 38657
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.15 38657
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 57806 => 192.168.1.104 65377
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.8 53252
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.1.8 53252
Mon Oct 31 12:48:36 2022 TCP 23.88.72.190 46754 => 10.100.248.14 1080
Mon Oct 31 12:48:40 2022 TCP 23.88.72.190 46792 => 10.100.248.14 1080
Mon Oct 31 12:49:31 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:31 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:34 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:34 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:49:36 2022 UDP 23.88.72.190 61772 => 10.244.45.105 1217
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 38002
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 192.168.0.119 38002
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 10.244.1.4 4006
Mon Oct 31 12:47:58 2022 TCP 23.88.72.190 48396 => 192.168.1.3 62603
Mon Oct 31 12:48:05 2022 TCP 23.88.72.190 50558 => 192.168.1.20 56226
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 46942
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 46942
Mon Oct 31 12:51:07 2022 UDP 23.88.72.190 61772 => 10.133.7.247 46942
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 10.131.139.32 62993
Mon Oct 31 12:48:05 2022 TCP 23.88.72.190 58218 => 10.148.99.188 37247
Mon Oct 31 12:48:08 2022 TCP 23.88.72.190 58218 => 10.148.99.188 37247
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 53710 => 192.168.1.3 54810
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 54032 => 172.20.129.25 64782
Mon Oct 31 12:48:43 2022 TCP 23.88.72.190 43269 => 192.168.1.3 54808
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 192.168.1.104 53964
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 192.168.1.104 53964
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 34500 => 192.168.1.8 53254
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 34510 => 192.168.1.8 53254
Mon Oct 31 12:47:51 2022 UDP 23.88.72.190 61772 => 192.168.1.103 60286
Mon Oct 31 12:47:59 2022 TCP 23.88.72.190 43269 => 192.168.0.30 49090
Mon Oct 31 12:48:11 2022 TCP 23.88.72.190 58958 => 192.168.2.109 58075
Mon Oct 31 12:48:14 2022 TCP 23.88.72.190 58972 => 192.168.2.109 58075
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:23 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:26 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:49 2022 UDP 23.88.72.190 61772 => 192.168.1.103 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:27 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:28 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:44 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:45 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:49:49 2022 UDP 23.88.72.190 61772 => 192.168.43.152 57269
Mon Oct 31 12:50:17 2022 TCP 23.88.72.190 35794 => 192.168.42.173 6333
Mon Oct 31 12:49:15 2022 TCP 23.88.72.190 35728 => 100.122.214.169 56235
Mon Oct 31 12:49:18 2022 TCP 23.88.72.190 35728 => 100.122.214.169 56235
Mon Oct 31 12:49:03 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:49:04 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:49:06 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:49:21 2022 TCP 23.88.72.190 43269 => 192.168.1.169 58458
Mon Oct 31 12:50:33 2022 TCP 23.88.72.190 43269 => 192.168.42.173 6331
Mon Oct 31 12:51:08 2022 TCP 23.88.72.190 35510 => 192.168.0.103 51129
Mon Oct 31 12:49:17 2022 TCP 23.88.72.190 46242 => 192.168.1.5 2027
Mon Oct 31 12:49:19 2022 TCP 23.88.72.190 46242 => 192.168.1.5 2027
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:05 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:50:07 2022 UDP 23.88.72.190 61772 => 10.244.45.131 41714
Mon Oct 31 12:48:41 2022 TCP 23.88.72.190 43269 => 192.168.10.182 37137
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 47098 => 192.168.1.9 64278
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 47178 => 192.168.1.9 64278
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 54082 => 10.148.99.188 52006
Mon Oct 31 12:49:36 2022 TCP 23.88.72.190 43269 => 10.0.0.3 49054
Mon Oct 31 12:49:42 2022 TCP 23.88.72.190 43269 => 10.244.45.32 41998
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 10.244.45.32 41998
Mon Oct 31 12:50:37 2022 TCP 23.88.72.190 43269 => 192.168.1.9 64276
Mon Oct 31 12:50:51 2022 TCP 23.88.72.190 43269 => 192.168.1.9 64276
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 172.31.0.181 30005
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.181 30005
Mon Oct 31 12:49:54 2022 UDP 23.88.72.190 61772 => 172.31.0.181 30005
Mon Oct 31 12:48:42 2022 TCP 23.88.72.190 43269 => 172.31.2.171 30005
Mon Oct 31 12:48:42 2022 UDP 23.88.72.190 61772 => 172.31.2.171 30005
Mon Oct 31 12:48:46 2022 TCP 23.88.72.190 43269 => 172.31.2.184 30005
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 172.31.2.184 30005
Mon Oct 31 12:50:55 2022 TCP 23.88.72.190 43269 => 172.31.5.174 30005
Mon Oct 31 12:50:55 2022 UDP 23.88.72.190 61772 => 172.31.5.174 30005
Mon Oct 31 12:50:56 2022 UDP 23.88.72.190 61772 => 172.31.5.174 30005
Mon Oct 31 12:50:15 2022 TCP 23.88.72.190 43269 => 172.31.9.13 30005
Mon Oct 31 12:50:15 2022 UDP 23.88.72.190 61772 => 172.31.9.13 30005
Mon Oct 31 12:48:39 2022 TCP 23.88.72.190 43269 => 172.31.15.115 30005
Mon Oct 31 12:48:39 2022 UDP 23.88.72.190 61772 => 172.31.15.115 30005
Mon Oct 31 12:48:40 2022 UDP 23.88.72.190 61772 => 172.31.15.115 30005
Mon Oct 31 12:48:05 2022 UDP 23.88.72.190 61772 => 10.148.99.188 18456
Mon Oct 31 12:49:54 2022 TCP 23.88.72.190 43269 => 192.168.31.103 50267
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:49:21 2022 UDP 23.88.72.190 61772 => 192.168.1.5 61706
Mon Oct 31 12:48:45 2022 TCP 23.88.72.190 43269 => 172.20.129.25 64780
Mon Oct 31 12:49:16 2022 TCP 23.88.72.190 43269 => 192.168.1.5 2025
Mon Oct 31 12:49:17 2022 TCP 23.88.72.190 43269 => 192.168.1.5 2025
Mon Oct 31 12:48:03 2022 TCP 23.88.72.190 43269 => 10.148.99.188 21194
Mon Oct 31 12:49:23 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:24 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:27 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:49 2022 TCP 23.88.72.190 43269 => 192.168.1.103 51118
Mon Oct 31 12:49:27 2022 TCP 23.88.72.190 43269 => 192.168.43.152 51118
Mon Oct 31 12:49:44 2022 TCP 23.88.72.190 43269 => 192.168.43.152 51118
Mon Oct 31 12:49:47 2022 TCP 23.88.72.190 43269 => 192.168.43.152 51118
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:16 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:17 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:19 2022 UDP 23.88.72.190 61772 => 10.244.45.72 4176
Mon Oct 31 12:49:15 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:49:18 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:49:20 2022 UDP 23.88.72.190 61772 => 100.122.214.169 51452
Mon Oct 31 12:50:56 2022 TCP 23.88.72.190 43269 => 10.131.139.32 14766
Mon Oct 31 12:50:57 2022 TCP 23.88.72.190 43269 => 10.131.139.32 14766
Mon Oct 31 12:48:43 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:44 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
Mon Oct 31 12:48:46 2022 UDP 23.88.72.190 61772 => 192.168.1.6 61924
```
| main | run kubo ipfs inside docker the environment variable ipfs profile server seems not to work anymore is there an replacement i was using the image before after upgrading to the newest version i got a netsacan warning from my provider netscan detected from host time protocol src ip src port dest ip dest port mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct tcp mon oct tcp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp mon oct udp | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.