Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
140,755 | 32,056,393,969 | IssuesEvent | 2023-09-24 05:55:06 | shinkungoo/shinkungoo.github.io | https://api.github.com/repos/shinkungoo/shinkungoo.github.io | closed | LeetCode 287. Find the Duplicate Number - 沈君豪个人主页 - Junhao Shen's Homepage | Gitalk /2022/02/02/Leetcode287/ | https://jhshen.cn/2022/02/02/Leetcode287/?
My blogs, Gitbooks and profile.,Problem StatementGiven an array of integers nums containing $n + 1$ integers where each integer is , | 1.0 | LeetCode 287. Find the Duplicate Number - 沈君豪个人主页 - Junhao Shen's Homepage - https://jhshen.cn/2022/02/02/Leetcode287/?
My blogs, Gitbooks and profile.,Problem StatementGiven an array of integers nums containing $n + 1$ integers where each integer is , | non_priority | leetcode find the duplicate number 沈君豪个人主页 junhao shen s homepage my blogs gitbooks and profile problem statementgiven an array of integers nums containing n integers where each integer is | 0 |
157,403 | 6,000,345,028 | IssuesEvent | 2017-06-05 04:21:11 | siteorigin/siteorigin-north | https://api.github.com/repos/siteorigin/siteorigin-north | closed | Mini-Cart isn't scrollable | bug priority-2 | If a large number of items are added to the mini-cart and the cart contents stretch below the bottom of the viewport, it isn't possible to scroll the contents.
| 1.0 | Mini-Cart isn't scrollable - If a large number of items are added to the mini-cart and the cart contents stretch below the bottom of the viewport, it isn't possible to scroll the contents.
| priority | mini cart isn t scrollable if a large number of items are added to the mini cart and the cart contents stretch below the bottom of the viewport it isn t possible to scroll the contents | 1 |
223,726 | 24,734,298,464 | IssuesEvent | 2022-10-20 20:25:13 | lukebrogan-mend/SecurityShepherd | https://api.github.com/repos/lukebrogan-mend/SecurityShepherd | closed | jstl-1.2.jar: 1 vulnerabilities (highest severity is: 7.3) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jstl-1.2.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /tory/jstl/jstl/1.2/jstl-1.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/SecurityShepherd/commit/d8098aa63b8ed708915035eabde79a1ca6ad7809">d8098aa63b8ed708915035eabde79a1ca6ad7809</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2015-0254](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-0254) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | jstl-1.2.jar | Direct | org.apache.taglibs:taglibs-standard-impl:1.2.3 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-0254</summary>
### Vulnerable Library - <b>jstl-1.2.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /tory/jstl/jstl/1.2/jstl-1.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jstl-1.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/SecurityShepherd/commit/d8098aa63b8ed708915035eabde79a1ca6ad7809">d8098aa63b8ed708915035eabde79a1ca6ad7809</a></p>
<p>Found in base branch: <b>dev</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Standard Taglibs before 1.2.3 allows remote attackers to execute arbitrary code or conduct external XML entity (XXE) attacks via a crafted XSLT extension in a (1) <x:parse> or (2) <x:transform> JSTL XML tag.
<p>Publish Date: 2015-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-0254>CVE-2015-0254</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tomcat.apache.org/taglibs/standard/">https://tomcat.apache.org/taglibs/standard/</a></p>
<p>Release Date: 2015-03-09</p>
<p>Fix Resolution: org.apache.taglibs:taglibs-standard-impl:1.2.3</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p> | True | jstl-1.2.jar: 1 vulnerabilities (highest severity is: 7.3) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jstl-1.2.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /tory/jstl/jstl/1.2/jstl-1.2.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/SecurityShepherd/commit/d8098aa63b8ed708915035eabde79a1ca6ad7809">d8098aa63b8ed708915035eabde79a1ca6ad7809</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2015-0254](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-0254) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | jstl-1.2.jar | Direct | org.apache.taglibs:taglibs-standard-impl:1.2.3 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-0254</summary>
### Vulnerable Library - <b>jstl-1.2.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /tory/jstl/jstl/1.2/jstl-1.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jstl-1.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/SecurityShepherd/commit/d8098aa63b8ed708915035eabde79a1ca6ad7809">d8098aa63b8ed708915035eabde79a1ca6ad7809</a></p>
<p>Found in base branch: <b>dev</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Standard Taglibs before 1.2.3 allows remote attackers to execute arbitrary code or conduct external XML entity (XXE) attacks via a crafted XSLT extension in a (1) <x:parse> or (2) <x:transform> JSTL XML tag.
<p>Publish Date: 2015-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-0254>CVE-2015-0254</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tomcat.apache.org/taglibs/standard/">https://tomcat.apache.org/taglibs/standard/</a></p>
<p>Release Date: 2015-03-09</p>
<p>Fix Resolution: org.apache.taglibs:taglibs-standard-impl:1.2.3</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://docs.mend.io/bundle/integrations/page/mend_for_github_com.html#MendforGitHub.com-RemediateSettings(remediateSettings)">workflow rules</a></p> | non_priority | jstl jar vulnerabilities highest severity is autoclosed vulnerable library jstl jar path to dependency file pom xml path to vulnerable library tory jstl jstl jstl jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high jstl jar direct org apache taglibs taglibs standard impl details cve vulnerable library jstl jar path to dependency file pom xml path to vulnerable library tory jstl jstl jstl jar dependency hierarchy x jstl jar vulnerable library found in head commit a href found in base branch dev vulnerability details apache standard taglibs before allows remote attackers to execute arbitrary code or conduct external xml entity xxe attacks via a crafted xslt extension in a or jstl xml tag publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache taglibs taglibs standard impl in order to enable automatic remediation please create in order to enable automatic remediation for this issue please create | 0 |
16,692 | 23,020,938,627 | IssuesEvent | 2022-07-22 04:39:40 | zer0Kerbal/Komplexity | https://api.github.com/repos/zer0Kerbal/Komplexity | closed | [Request]: Realism Overhaul compatibility | issue: compatibility/patch | Realism Overhaul compatibility
https://github.com/KSP-RO/RealismOverhaul/blob/db04a9fac683c047a650799a3bddadfc13fe3fe0/GameData/RealismOverhaul/RO_DSN_Ranges.cfg
```
@CUSTOMBARNKIT:AFTER[RealSolarSystem]
{
@TRACKING
{
@DSNRange = 200000000000, 2000000000000, 100000000000000
}
}
``` | True | [Request]: Realism Overhaul compatibility - Realism Overhaul compatibility
https://github.com/KSP-RO/RealismOverhaul/blob/db04a9fac683c047a650799a3bddadfc13fe3fe0/GameData/RealismOverhaul/RO_DSN_Ranges.cfg
```
@CUSTOMBARNKIT:AFTER[RealSolarSystem]
{
@TRACKING
{
@DSNRange = 200000000000, 2000000000000, 100000000000000
}
}
``` | non_priority | realism overhaul compatibility realism overhaul compatibility custombarnkit after tracking dsnrange | 0 |
4,019 | 6,848,825,116 | IssuesEvent | 2017-11-13 19:51:42 | pearson-ux/pearson-glp-pl | https://api.github.com/repos/pearson-ux/pearson-glp-pl | opened | Dropdown in IE is not clickable, fix alignment in Safari | Browser Compatibility - IE11 Browser Compatibility - Safari bug | I checked all browsers for Chrome, IE, Firefox and Safari. They are all tabbable (for accessibility). However, IE does not allow any selection of the dropdown options. The background color does not stick and the checkmark icons are not displayed upon selection.
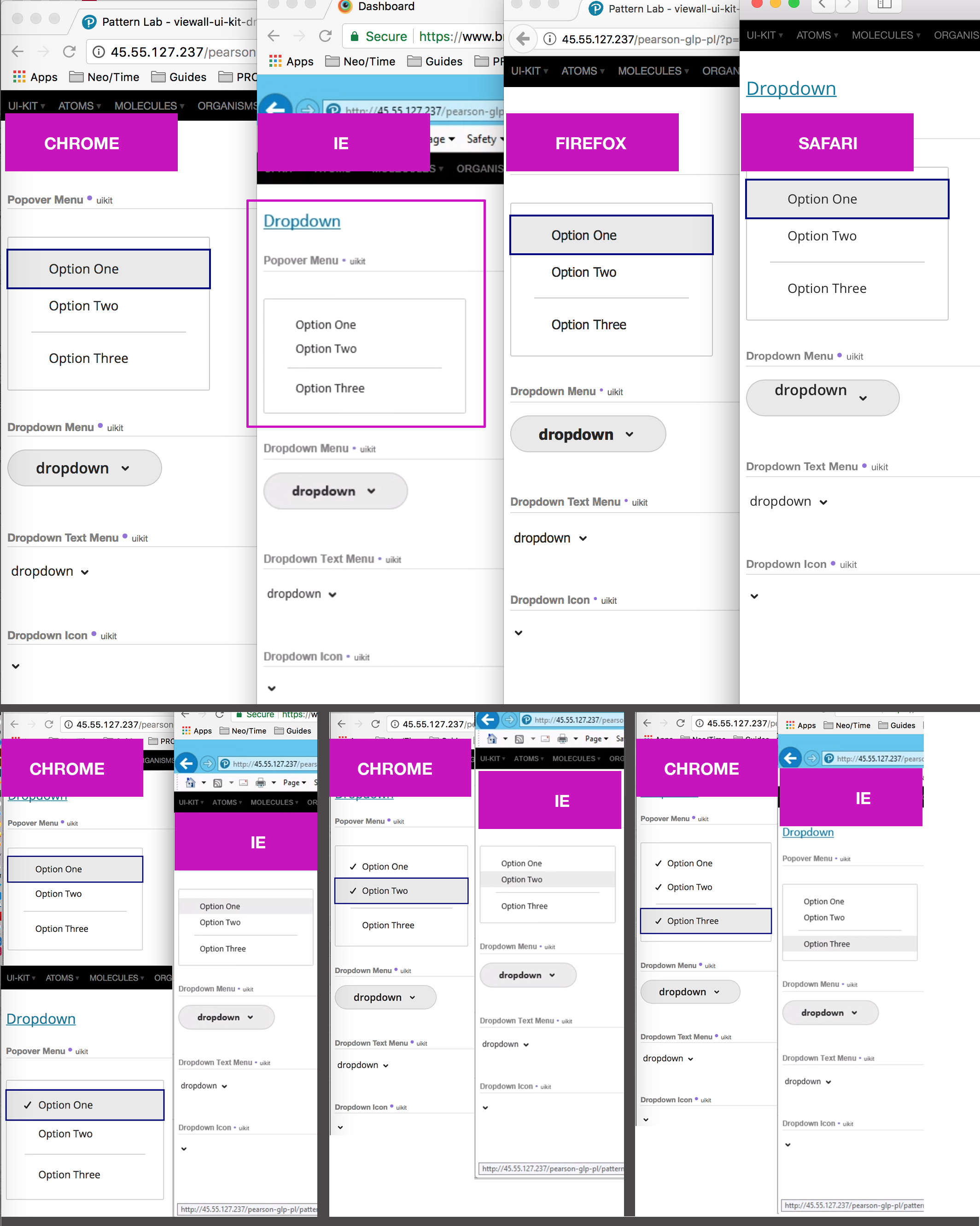
---
Alignment in Safari dropdown button... I logged this part in a different ticket, so sorry for the redundancy.
<img width="946" alt="dropdown_alignment" src="https://user-images.githubusercontent.com/9653426/32745865-e1f2da9a-c868-11e7-8874-6ab9b18c3d57.png">
| True | Dropdown in IE is not clickable, fix alignment in Safari - I checked all browsers for Chrome, IE, Firefox and Safari. They are all tabbable (for accessibility). However, IE does not allow any selection of the dropdown options. The background color does not stick and the checkmark icons are not displayed upon selection.
---
Alignment in Safari dropdown button... I logged this part in a different ticket, so sorry for the redundancy.
<img width="946" alt="dropdown_alignment" src="https://user-images.githubusercontent.com/9653426/32745865-e1f2da9a-c868-11e7-8874-6ab9b18c3d57.png">
| non_priority | dropdown in ie is not clickable fix alignment in safari i checked all browsers for chrome ie firefox and safari they are all tabbable for accessibility however ie does not allow any selection of the dropdown options the background color does not stick and the checkmark icons are not displayed upon selection alignment in safari dropdown button i logged this part in a different ticket so sorry for the redundancy img width alt dropdown alignment src | 0 |
8,918 | 7,734,771,743 | IssuesEvent | 2018-05-27 06:48:00 | fga-gpp-mds/2018.1_Nexte | https://api.github.com/repos/fga-gpp-mds/2018.1_Nexte | closed | Eu, como cliente, desejo poder fazer uso da aplicação em meu smartphone(Android 4.3) | easy eps infrastructure urgent | ## Descrição
Atualizar a versão da SDK para o SDK 18
## Critérios de Aceitação
- [ ] Atualizar o projeto e suas dependências para o SDK 17 do android | 1.0 | Eu, como cliente, desejo poder fazer uso da aplicação em meu smartphone(Android 4.3) - ## Descrição
Atualizar a versão da SDK para o SDK 18
## Critérios de Aceitação
- [ ] Atualizar o projeto e suas dependências para o SDK 17 do android | non_priority | eu como cliente desejo poder fazer uso da aplicação em meu smartphone android descrição atualizar a versão da sdk para o sdk critérios de aceitação atualizar o projeto e suas dependências para o sdk do android | 0 |
106,425 | 4,272,139,203 | IssuesEvent | 2016-07-13 13:41:17 | Fermat-ORG/fermat-org | https://api.github.com/repos/Fermat-ORG/fermat-org | opened | Merge the views #stack and #table | 3D client Priority: MEDIUM | Merge both views and apply the changes made in #649.
The new table transformation should positions headers which tiles are beign shown in order to reduce the space on the table. This should also consider the group's order when rearranging the table to include another group and its tiles. | 1.0 | Merge the views #stack and #table - Merge both views and apply the changes made in #649.
The new table transformation should positions headers which tiles are beign shown in order to reduce the space on the table. This should also consider the group's order when rearranging the table to include another group and its tiles. | priority | merge the views stack and table merge both views and apply the changes made in the new table transformation should positions headers which tiles are beign shown in order to reduce the space on the table this should also consider the group s order when rearranging the table to include another group and its tiles | 1 |
59,604 | 14,422,034,524 | IssuesEvent | 2020-12-05 01:08:34 | jgeraigery/angular-breadcrumb | https://api.github.com/repos/jgeraigery/angular-breadcrumb | opened | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz | security vulnerability | ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: angular-breadcrumb/package.json</p>
<p>Path to vulnerable library: angular-breadcrumb/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.12.4.tgz (Root Library)
- webpack-4.28.4.tgz
- node-libs-browser-2.2.0.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.4.1","isTransitiveDependency":true,"dependencyTree":"@angular-devkit/build-angular:0.12.4;webpack:4.28.4;node-libs-browser:2.2.0;crypto-browserify:3.12.0;browserify-sign:4.0.4;elliptic:6.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.2"}],"vulnerabilityIdentifier":"WS-2019-0427","vulnerabilityDetails":"The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2","vulnerabilityUrl":"https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz - ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: angular-breadcrumb/package.json</p>
<p>Path to vulnerable library: angular-breadcrumb/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.12.4.tgz (Root Library)
- webpack-4.28.4.tgz
- node-libs-browser-2.2.0.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.4.1","isTransitiveDependency":true,"dependencyTree":"@angular-devkit/build-angular:0.12.4;webpack:4.28.4;node-libs-browser:2.2.0;crypto-browserify:3.12.0;browserify-sign:4.0.4;elliptic:6.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.2"}],"vulnerabilityIdentifier":"WS-2019-0427","vulnerabilityDetails":"The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2","vulnerabilityUrl":"https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a","cvss3Severity":"medium","cvss3Score":"5.0","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file angular breadcrumb package json path to vulnerable library angular breadcrumb node modules elliptic package json dependency hierarchy build angular tgz root library webpack tgz node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in base branch master vulnerability details the function getnaf in elliptic library has information leakage this issue is mitigated in version publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails the function getnaf in elliptic library has information leakage this issue is mitigated in version vulnerabilityurl | 0 |
337,876 | 30,268,898,477 | IssuesEvent | 2023-07-07 13:56:25 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix paddle_math.test_paddle_trunc | Sub Task Failing Test Paddle Frontend | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix paddle_math.test_paddle_trunc - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5487009948"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix paddle math test paddle trunc tensorflow a href src jax a href src paddle a href src torch a href src numpy a href src | 0 |
17,533 | 23,343,226,629 | IssuesEvent | 2022-08-09 15:35:17 | tokio-rs/tokio | https://api.github.com/repos/tokio-rs/tokio | closed | Multiple `tokio::io::copy` streaming to and from `tokio::process::Command`'s child stdin/stdout appears to hang | C-bug A-tokio M-process | **Version**
tokio_process_bug v0.1.0 (/Users/amastro/tokio_process_bug)
└── tokio v1.20.1
└── tokio-macros v1.8.0 (proc-macro)
**Platform**
Darwin amastro-mbp 21.6.0 Darwin Kernel Version 21.6.0: Sat Jun 18 17:07:22 PDT 2022; root:xnu-8020.140.41~1/RELEASE_ARM64_T6000 arm64
**Description**
I am attempting to use tokio to stream an input file to stdin of a subprocess, and at the same time stream its stdout to a different output file. I was able to achieve equivalent functionality using `std::process::Command` and multiple `std::thread`s which each run a `std::io::copy`. I am unsure if I am holding tokio+async wrong, or if this is a bug.
I tried this code:
```rust
#[tokio::main]
async fn main() {
let args: Vec<_> = std::env::args().collect();
let cmd = &args[1];
let in_path = &args[2];
let out_path = &args[3];
println!("{} {} {}", cmd, in_path, out_path);
let mut in_file = tokio::fs::File::open(in_path).await.unwrap();
let mut out_file = tokio::fs::File::create(out_path).await.unwrap();
let mut child = tokio::process::Command::new(cmd)
.stdin(std::process::Stdio::piped())
.stdout(std::process::Stdio::piped())
.stderr(std::process::Stdio::piped())
.spawn()
.unwrap();
let mut stdin = child.stdin.take().unwrap();
let mut stdout = child.stdout.take().unwrap();
let mut stderr = child.stderr.take().unwrap();
let mut stderr_buf = Vec::new();
let (status, ..) = tokio::join!(
child.wait(),
tokio::io::copy(&mut in_file, &mut stdin),
tokio::io::copy(&mut stdout, &mut out_file),
tokio::io::copy(&mut stderr, &mut stderr_buf),
);
println!("finished: {:?}", status);
}
```
I expected to see this happen:
The input file to get piped to `cat` which pipes into the output file
I expected similar functionality to
```
cat < ./infile > ./outfile
```
Instead, this happened:
```
amastro@amastro-mbp tokio_process_bug % echo hello world > infile
amastro@amastro-mbp tokio_process_bug % cargo run -- cat ./infile ./outfile
cat ./infile ./outfile
# program hangs -- "finished" never printed
```
No progress is made past the `join!`
| 1.0 | Multiple `tokio::io::copy` streaming to and from `tokio::process::Command`'s child stdin/stdout appears to hang - **Version**
tokio_process_bug v0.1.0 (/Users/amastro/tokio_process_bug)
└── tokio v1.20.1
└── tokio-macros v1.8.0 (proc-macro)
**Platform**
Darwin amastro-mbp 21.6.0 Darwin Kernel Version 21.6.0: Sat Jun 18 17:07:22 PDT 2022; root:xnu-8020.140.41~1/RELEASE_ARM64_T6000 arm64
**Description**
I am attempting to use tokio to stream an input file to stdin of a subprocess, and at the same time stream its stdout to a different output file. I was able to achieve equivalent functionality using `std::process::Command` and multiple `std::thread`s which each run a `std::io::copy`. I am unsure if I am holding tokio+async wrong, or if this is a bug.
I tried this code:
```rust
#[tokio::main]
async fn main() {
let args: Vec<_> = std::env::args().collect();
let cmd = &args[1];
let in_path = &args[2];
let out_path = &args[3];
println!("{} {} {}", cmd, in_path, out_path);
let mut in_file = tokio::fs::File::open(in_path).await.unwrap();
let mut out_file = tokio::fs::File::create(out_path).await.unwrap();
let mut child = tokio::process::Command::new(cmd)
.stdin(std::process::Stdio::piped())
.stdout(std::process::Stdio::piped())
.stderr(std::process::Stdio::piped())
.spawn()
.unwrap();
let mut stdin = child.stdin.take().unwrap();
let mut stdout = child.stdout.take().unwrap();
let mut stderr = child.stderr.take().unwrap();
let mut stderr_buf = Vec::new();
let (status, ..) = tokio::join!(
child.wait(),
tokio::io::copy(&mut in_file, &mut stdin),
tokio::io::copy(&mut stdout, &mut out_file),
tokio::io::copy(&mut stderr, &mut stderr_buf),
);
println!("finished: {:?}", status);
}
```
I expected to see this happen:
The input file to get piped to `cat` which pipes into the output file
I expected similar functionality to
```
cat < ./infile > ./outfile
```
Instead, this happened:
```
amastro@amastro-mbp tokio_process_bug % echo hello world > infile
amastro@amastro-mbp tokio_process_bug % cargo run -- cat ./infile ./outfile
cat ./infile ./outfile
# program hangs -- "finished" never printed
```
No progress is made past the `join!`
| non_priority | multiple tokio io copy streaming to and from tokio process command s child stdin stdout appears to hang version tokio process bug users amastro tokio process bug └── tokio └── tokio macros proc macro platform darwin amastro mbp darwin kernel version sat jun pdt root xnu release description i am attempting to use tokio to stream an input file to stdin of a subprocess and at the same time stream its stdout to a different output file i was able to achieve equivalent functionality using std process command and multiple std thread s which each run a std io copy i am unsure if i am holding tokio async wrong or if this is a bug i tried this code rust async fn main let args vec std env args collect let cmd args let in path args let out path args println cmd in path out path let mut in file tokio fs file open in path await unwrap let mut out file tokio fs file create out path await unwrap let mut child tokio process command new cmd stdin std process stdio piped stdout std process stdio piped stderr std process stdio piped spawn unwrap let mut stdin child stdin take unwrap let mut stdout child stdout take unwrap let mut stderr child stderr take unwrap let mut stderr buf vec new let status tokio join child wait tokio io copy mut in file mut stdin tokio io copy mut stdout mut out file tokio io copy mut stderr mut stderr buf println finished status i expected to see this happen the input file to get piped to cat which pipes into the output file i expected similar functionality to cat outfile instead this happened amastro amastro mbp tokio process bug echo hello world infile amastro amastro mbp tokio process bug cargo run cat infile outfile cat infile outfile program hangs finished never printed no progress is made past the join | 0 |
761,430 | 26,680,786,666 | IssuesEvent | 2023-01-26 17:30:18 | OoTMM/core | https://api.github.com/repos/OoTMM/core | closed | Bug: Tingle in MM is on the ground when you don't have magic | Priority: Minor Bug | I mentioned this in issue #64 but figure it should be its own issue to fix regardless. Basically, the vanilla game puts Tingle on the ground in the first cycle because you don't have a projectile to hit him down from the air. This behavior is achieved by magic, because when you have magic Tingle then becomes airborne everywhere. This behavior should be corrected such that he is always airborne (even when you don't have magic) in preparation for Tingle Map Shuffle. | 1.0 | Bug: Tingle in MM is on the ground when you don't have magic - I mentioned this in issue #64 but figure it should be its own issue to fix regardless. Basically, the vanilla game puts Tingle on the ground in the first cycle because you don't have a projectile to hit him down from the air. This behavior is achieved by magic, because when you have magic Tingle then becomes airborne everywhere. This behavior should be corrected such that he is always airborne (even when you don't have magic) in preparation for Tingle Map Shuffle. | priority | bug tingle in mm is on the ground when you don t have magic i mentioned this in issue but figure it should be its own issue to fix regardless basically the vanilla game puts tingle on the ground in the first cycle because you don t have a projectile to hit him down from the air this behavior is achieved by magic because when you have magic tingle then becomes airborne everywhere this behavior should be corrected such that he is always airborne even when you don t have magic in preparation for tingle map shuffle | 1 |
50,416 | 6,377,507,159 | IssuesEvent | 2017-08-02 10:11:34 | devgranaja/probe | https://api.github.com/repos/devgranaja/probe | opened | Config.yml issues | Design Notes | Change the location of Config.yml to the folder Technology
Change the tag named sensor to the tag named actions.
Use only minutes to mesure the periodicity. For example: 15, 60 or 1440
I should remove the tags called type and version. We can create those tags when we will need them. | 1.0 | Config.yml issues - Change the location of Config.yml to the folder Technology
Change the tag named sensor to the tag named actions.
Use only minutes to mesure the periodicity. For example: 15, 60 or 1440
I should remove the tags called type and version. We can create those tags when we will need them. | non_priority | config yml issues change the location of config yml to the folder technology change the tag named sensor to the tag named actions use only minutes to mesure the periodicity for example or i should remove the tags called type and version we can create those tags when we will need them | 0 |
781,936 | 27,455,091,012 | IssuesEvent | 2023-03-02 20:38:18 | GenomicMedLab/cool-seq-tool | https://api.github.com/repos/GenomicMedLab/cool-seq-tool | closed | Use FastApi APIRouter | enhancement priority:medium | https://fastapi.tiangolo.com/tutorial/bigger-applications/#apirouter
I think this will be useful to help clean things up and allow other apps to import our routes w/o having to copy/paste | 1.0 | Use FastApi APIRouter - https://fastapi.tiangolo.com/tutorial/bigger-applications/#apirouter
I think this will be useful to help clean things up and allow other apps to import our routes w/o having to copy/paste | priority | use fastapi apirouter i think this will be useful to help clean things up and allow other apps to import our routes w o having to copy paste | 1 |
80,597 | 3,568,122,497 | IssuesEvent | 2016-01-26 02:55:35 | SIMRacingApps/SIMRacingApps | https://api.github.com/repos/SIMRacingApps/SIMRacingApps | opened | Standings For Class | enhancement low priority | Duplicate the Standings Widget and make it only for the cars in the reference car's class. | 1.0 | Standings For Class - Duplicate the Standings Widget and make it only for the cars in the reference car's class. | priority | standings for class duplicate the standings widget and make it only for the cars in the reference car s class | 1 |
129,875 | 18,143,653,049 | IssuesEvent | 2021-09-25 03:21:15 | monetr/deliverybot | https://api.github.com/repos/monetr/deliverybot | opened | CVE-2021-3803 (High) detected in nth-check-1.0.2.tgz | security vulnerability | ## CVE-2021-3803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nth-check-1.0.2.tgz</b></p></summary>
<p>performant nth-check parser & compiler</p>
<p>Library home page: <a href="https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz">https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz</a></p>
<p>Path to dependency file: deliverybot/package.json</p>
<p>Path to vulnerable library: deliverybot/node_modules/nth-check/package.json</p>
<p>
Dependency Hierarchy:
- @deliverybot/run-0.7.2.tgz (Root Library)
- html-webpack-plugin-3.2.0.tgz
- pretty-error-2.1.1.tgz
- renderkid-2.0.3.tgz
- css-select-1.2.0.tgz
- :x: **nth-check-1.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/monetr/deliverybot/commit/bd51b1f8b9a3c21e299c3eabc04e1478a88c2a66">bd51b1f8b9a3c21e299c3eabc04e1478a88c2a66</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
nth-check is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3803>CVE-2021-3803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1">https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: nth-check - v2.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-3803 (High) detected in nth-check-1.0.2.tgz - ## CVE-2021-3803 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nth-check-1.0.2.tgz</b></p></summary>
<p>performant nth-check parser & compiler</p>
<p>Library home page: <a href="https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz">https://registry.npmjs.org/nth-check/-/nth-check-1.0.2.tgz</a></p>
<p>Path to dependency file: deliverybot/package.json</p>
<p>Path to vulnerable library: deliverybot/node_modules/nth-check/package.json</p>
<p>
Dependency Hierarchy:
- @deliverybot/run-0.7.2.tgz (Root Library)
- html-webpack-plugin-3.2.0.tgz
- pretty-error-2.1.1.tgz
- renderkid-2.0.3.tgz
- css-select-1.2.0.tgz
- :x: **nth-check-1.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/monetr/deliverybot/commit/bd51b1f8b9a3c21e299c3eabc04e1478a88c2a66">bd51b1f8b9a3c21e299c3eabc04e1478a88c2a66</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
nth-check is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3803>CVE-2021-3803</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1">https://github.com/fb55/nth-check/compare/v2.0.0...v2.0.1</a></p>
<p>Release Date: 2021-09-17</p>
<p>Fix Resolution: nth-check - v2.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in nth check tgz cve high severity vulnerability vulnerable library nth check tgz performant nth check parser compiler library home page a href path to dependency file deliverybot package json path to vulnerable library deliverybot node modules nth check package json dependency hierarchy deliverybot run tgz root library html webpack plugin tgz pretty error tgz renderkid tgz css select tgz x nth check tgz vulnerable library found in head commit a href found in base branch main vulnerability details nth check is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nth check step up your open source security game with whitesource | 0 |
163,330 | 20,361,684,708 | IssuesEvent | 2022-02-20 19:28:48 | dpalmasan/texstat-service | https://api.github.com/repos/dpalmasan/texstat-service | closed | Add GRPC endpoint to validate JWT token from auth service | grpc security middleware | Use protocol buffer definition defined in the [auth service](https://github.com/dpalmasan/go-auth-microservice). Then, add validation to the `/metrics` endpoint, and throw `UNAUTHORIZED` (Status code 401) if the token is invalid. | True | Add GRPC endpoint to validate JWT token from auth service - Use protocol buffer definition defined in the [auth service](https://github.com/dpalmasan/go-auth-microservice). Then, add validation to the `/metrics` endpoint, and throw `UNAUTHORIZED` (Status code 401) if the token is invalid. | non_priority | add grpc endpoint to validate jwt token from auth service use protocol buffer definition defined in the then add validation to the metrics endpoint and throw unauthorized status code if the token is invalid | 0 |
66,951 | 16,761,812,123 | IssuesEvent | 2021-06-13 23:35:58 | vitessio/vitess | https://api.github.com/repos/vitessio/vitess | opened | `analyze-pr-labels` check should not run on merge commits | Component: Build/CI Type: CI/Build | #### Feature Description
`analyze-pr-labels` check should not run on merge commits.
#### Use Case(s)
Since there's no associated PR with the commit that merges a branch into `main`, this check never passes, and all of our merge commits have had at least one failing check (this one).
| 2.0 | `analyze-pr-labels` check should not run on merge commits - #### Feature Description
`analyze-pr-labels` check should not run on merge commits.
#### Use Case(s)
Since there's no associated PR with the commit that merges a branch into `main`, this check never passes, and all of our merge commits have had at least one failing check (this one).
| non_priority | analyze pr labels check should not run on merge commits feature description analyze pr labels check should not run on merge commits use case s since there s no associated pr with the commit that merges a branch into main this check never passes and all of our merge commits have had at least one failing check this one | 0 |
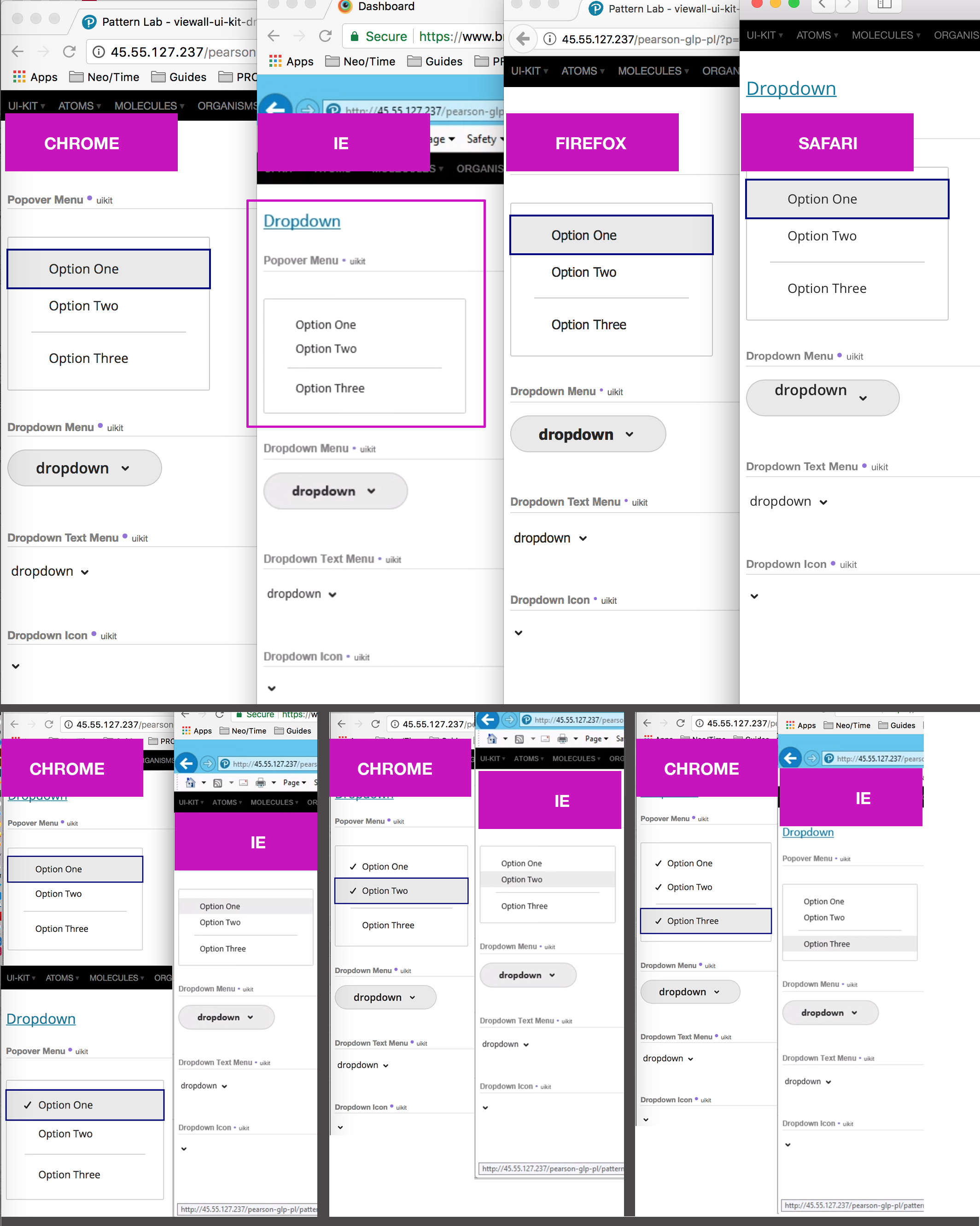
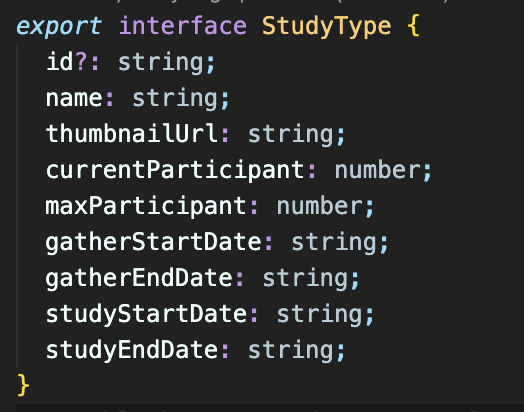
681,398 | 23,309,660,555 | IssuesEvent | 2022-08-08 06:58:50 | prgrms-web-devcourse/Team-Books-CheckMoi-FE | https://api.github.com/repos/prgrms-web-devcourse/Team-Books-CheckMoi-FE | closed | Fix/ 백-프론트 type 통일 | 프론트 Priority: 긴급 Type: 버그 | ## 기능 요청
### 📌 설명
<!-- 문제에 대한 간결하고 분명한 설명 -->
현재 백, 프론트간 데이터 모델링이 다른 부분이 존재.
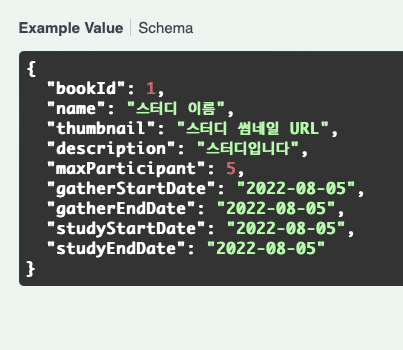
프론트를 백에 맞추는 쪽으로 해서, user, study, book 등 모든 type 점검 및 수정
### 🎨 구현할 내용
<!-- 구현 사항을 구체적으로 적어주세요 -->
study, user, book type 수정 및 사용하는 컴포넌트 버그 픽스
### 예상 구현 시간
1h
### 시급한 정도
<!-- 🐢 천천히, 🏃🏻 보통, 🚨 긴급 -->
🚨 긴급
| 1.0 | Fix/ 백-프론트 type 통일 - ## 기능 요청
### 📌 설명
<!-- 문제에 대한 간결하고 분명한 설명 -->
현재 백, 프론트간 데이터 모델링이 다른 부분이 존재.
프론트를 백에 맞추는 쪽으로 해서, user, study, book 등 모든 type 점검 및 수정
### 🎨 구현할 내용
<!-- 구현 사항을 구체적으로 적어주세요 -->
study, user, book type 수정 및 사용하는 컴포넌트 버그 픽스
### 예상 구현 시간
1h
### 시급한 정도
<!-- 🐢 천천히, 🏃🏻 보통, 🚨 긴급 -->
🚨 긴급
| priority | fix 백 프론트 type 통일 기능 요청 📌 설명 현재 백 프론트간 데이터 모델링이 다른 부분이 존재 프론트를 백에 맞추는 쪽으로 해서 user study book 등 모든 type 점검 및 수정 🎨 구현할 내용 study user book type 수정 및 사용하는 컴포넌트 버그 픽스 예상 구현 시간 시급한 정도 🚨 긴급 | 1 |
68,126 | 28,138,713,213 | IssuesEvent | 2023-04-01 17:42:14 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | Terraform state leaks on interrupt | service/ec2 provider stale | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
```
$ terraform -version
Terraform v0.12.26
+ provider.aws v3.18.0
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* aws_vpc
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
provider "aws" {
access_key = var.ACCESS_KEY_ID
secret_key = var.SECRET_ACCESS_KEY
region = "eu-west-1"
version = "3.18.0"
}
resource "aws_vpc" "vpc" {
cidr_block = "10.250.0.0/16"
enable_dns_support = true
enable_dns_hostnames = true
tags = {
Name = "deleteme"
}
}
```
### Debug Output
<!---
Please provide a link to a GitHub Gist containing the complete debug output. Please do NOT paste the debug output in the issue; just paste a link to the Gist.
To obtain the debug output, see the [Terraform documentation on debugging](https://www.terraform.io/docs/internals/debugging.html).
--->
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
### Expected Behavior
I would expect when I interrupt a running `terraform apply` process, no terraform state to be leaked.
### Actual Behavior
When you interrupt a running `terraform apply` process, the resource is actually being created but not saved in the terraform state.
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. Run `terraform apply`
```
$ terraform apply -var-file=creds.tfvars --auto-approve
```
2. Interrupt with ^C as soon as you see that the VPC is being created.
```
$ terraform apply -var-file=creds.tfvars --auto-approve
aws_vpc.vpc: Creating...
^CInterrupt received.
Please wait for Terraform to exit or data loss may occur.
Gracefully shutting down...
Stopping operation...
Apply complete! Resources: 0 added, 0 changed, 0 destroyed.
```
3. Checkout the cloudprovider and see that the requested VPC is created and it is not saved in the terraform state
```
$ aws ec2 describe-vpcs --output=json
{
"CidrBlock": "10.250.0.0/16",
"DhcpOptionsId": "dopt-ab0f2ecc",
"State": "available",
"VpcId": "vpc-05866c95df657d7ac",
"InstanceTenancy": "default",
"CidrBlockAssociationSet": [
{
"AssociationId": "vpc-cidr-assoc-0587023f907f7e62e",
"CidrBlock": "10.250.0.0/16",
"CidrBlockState": {
"State": "associated"
}
}
],
"IsDefault": false,
"Tags": [
{
"Key": "Name",
"Value": "deleteme"
}
]
},
```
### Important Factoids
<!--- Are there anything atypical about your accounts that we should know? For example: Running in EC2 Classic? --->
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Vendor documentation? For example:
--->
* #0000
| 1.0 | Terraform state leaks on interrupt - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform CLI and Terraform AWS Provider Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
```
$ terraform -version
Terraform v0.12.26
+ provider.aws v3.18.0
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* aws_vpc
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
provider "aws" {
access_key = var.ACCESS_KEY_ID
secret_key = var.SECRET_ACCESS_KEY
region = "eu-west-1"
version = "3.18.0"
}
resource "aws_vpc" "vpc" {
cidr_block = "10.250.0.0/16"
enable_dns_support = true
enable_dns_hostnames = true
tags = {
Name = "deleteme"
}
}
```
### Debug Output
<!---
Please provide a link to a GitHub Gist containing the complete debug output. Please do NOT paste the debug output in the issue; just paste a link to the Gist.
To obtain the debug output, see the [Terraform documentation on debugging](https://www.terraform.io/docs/internals/debugging.html).
--->
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
### Expected Behavior
I would expect when I interrupt a running `terraform apply` process, no terraform state to be leaked.
### Actual Behavior
When you interrupt a running `terraform apply` process, the resource is actually being created but not saved in the terraform state.
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. Run `terraform apply`
```
$ terraform apply -var-file=creds.tfvars --auto-approve
```
2. Interrupt with ^C as soon as you see that the VPC is being created.
```
$ terraform apply -var-file=creds.tfvars --auto-approve
aws_vpc.vpc: Creating...
^CInterrupt received.
Please wait for Terraform to exit or data loss may occur.
Gracefully shutting down...
Stopping operation...
Apply complete! Resources: 0 added, 0 changed, 0 destroyed.
```
3. Checkout the cloudprovider and see that the requested VPC is created and it is not saved in the terraform state
```
$ aws ec2 describe-vpcs --output=json
{
"CidrBlock": "10.250.0.0/16",
"DhcpOptionsId": "dopt-ab0f2ecc",
"State": "available",
"VpcId": "vpc-05866c95df657d7ac",
"InstanceTenancy": "default",
"CidrBlockAssociationSet": [
{
"AssociationId": "vpc-cidr-assoc-0587023f907f7e62e",
"CidrBlock": "10.250.0.0/16",
"CidrBlockState": {
"State": "associated"
}
}
],
"IsDefault": false,
"Tags": [
{
"Key": "Name",
"Value": "deleteme"
}
]
},
```
### Important Factoids
<!--- Are there anything atypical about your accounts that we should know? For example: Running in EC2 Classic? --->
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Vendor documentation? For example:
--->
* #0000
| non_priority | terraform state leaks on interrupt please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one of these scenarios we recommend opening an issue in the instead community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform cli and terraform aws provider version terraform version terraform provider aws affected resource s aws vpc terraform configuration files please include all terraform configurations required to reproduce the bug bug reports without a functional reproduction may be closed without investigation hcl provider aws access key var access key id secret key var secret access key region eu west version resource aws vpc vpc cidr block enable dns support true enable dns hostnames true tags name deleteme debug output please provide a link to a github gist containing the complete debug output please do not paste the debug output in the issue just paste a link to the gist to obtain the debug output see the panic output expected behavior i would expect when i interrupt a running terraform apply process no terraform state to be leaked actual behavior when you interrupt a running terraform apply process the resource is actually being created but not saved in the terraform state steps to reproduce run terraform apply terraform apply var file creds tfvars auto approve interrupt with c as soon as you see that the vpc is being created terraform apply var file creds tfvars auto approve aws vpc vpc creating cinterrupt received please wait for terraform to exit or data loss may occur gracefully shutting down stopping operation apply complete resources added changed destroyed checkout the cloudprovider and see that the requested vpc is created and it is not saved in the terraform state aws describe vpcs output json cidrblock dhcpoptionsid dopt state available vpcid vpc instancetenancy default cidrblockassociationset associationid vpc cidr assoc cidrblock cidrblockstate state associated isdefault false tags key name value deleteme important factoids references information about referencing github issues are there any other github issues open or closed or pull requests that should be linked here vendor documentation for example | 0 |
632,430 | 20,196,685,230 | IssuesEvent | 2022-02-11 11:18:51 | hackforla/expunge-assist | https://api.github.com/repos/hackforla/expunge-assist | closed | Review Writing/Content Guidelines | size: good first issue role: research priority: medium size: good second issue role: UX content writing dependency size: 1pt feature: figma content writing | ### Overview
The Content team has created writing, tone, voice, and style guidelines for writing on the Expunge Assist app. This is so that anyone who writes copy for the app have resources to keep the copy consistent for the user.
We are looking for any feedback, thoughts, and discussion you may have before we finalize them (they will be updated periodically).
### Action Items
- [x] Review the guidelines
- [x] Send any suggestions, thoughts, discussions, etc. to Sam (here or in Slack or in the comments of the document)
### Resources/Instructions
[Guidelines
](https://docs.google.com/document/d/1w8iHLEjgBlkwi6jm7XgLoI0RE3JtmUnJtCq3psks1nI/edit#heading=h.jakpmonkrl8l) | 1.0 | Review Writing/Content Guidelines - ### Overview
The Content team has created writing, tone, voice, and style guidelines for writing on the Expunge Assist app. This is so that anyone who writes copy for the app have resources to keep the copy consistent for the user.
We are looking for any feedback, thoughts, and discussion you may have before we finalize them (they will be updated periodically).
### Action Items
- [x] Review the guidelines
- [x] Send any suggestions, thoughts, discussions, etc. to Sam (here or in Slack or in the comments of the document)
### Resources/Instructions
[Guidelines
](https://docs.google.com/document/d/1w8iHLEjgBlkwi6jm7XgLoI0RE3JtmUnJtCq3psks1nI/edit#heading=h.jakpmonkrl8l) | priority | review writing content guidelines overview the content team has created writing tone voice and style guidelines for writing on the expunge assist app this is so that anyone who writes copy for the app have resources to keep the copy consistent for the user we are looking for any feedback thoughts and discussion you may have before we finalize them they will be updated periodically action items review the guidelines send any suggestions thoughts discussions etc to sam here or in slack or in the comments of the document resources instructions guidelines | 1 |
168,850 | 6,388,027,219 | IssuesEvent | 2017-08-03 14:48:58 | dmwm/WMCore | https://api.github.com/repos/dmwm/WMCore | closed | AgentNanny component should watch for expired certs | Low Priority | Well I'm assuming you guys are going with my name for the component here ;)
But one of the things we need this to watch for the agents is that the certs it uses are not soon to expire & alarm when they get within some settable time (~week) of expiration.
| 1.0 | AgentNanny component should watch for expired certs - Well I'm assuming you guys are going with my name for the component here ;)
But one of the things we need this to watch for the agents is that the certs it uses are not soon to expire & alarm when they get within some settable time (~week) of expiration.
| priority | agentnanny component should watch for expired certs well i m assuming you guys are going with my name for the component here but one of the things we need this to watch for the agents is that the certs it uses are not soon to expire alarm when they get within some settable time week of expiration | 1 |
11,659 | 4,271,952,786 | IssuesEvent | 2016-07-13 13:06:43 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | findLanguages doesn't work after upgrading from Joomla 3.5.1 to 3.6.0 | No Code Attached Yet | #### Steps to reproduce the issue
Use InstallerModelLanguages to find an extension ID for the en-GB language
E.g.
$model = \JModelLegacy::getInstance('Languages', 'InstallerModel');
$model->findLanguages();
$items = $model->getItems();
#### Expected result
the en-GB language is returned
#### Actual result
0 items are returned
#### System information (as much as possible)
PHP 7.0 mySQL 5.5
#### Additional comments
Seems to be caused by a database change that isn't updated by the database migrations. Apparently language extensions are no longer of the type language but of the type package. And the element changed from 'en-GB' to 'pkg_en-GB'. It works fine on a fresh install. | 1.0 | findLanguages doesn't work after upgrading from Joomla 3.5.1 to 3.6.0 - #### Steps to reproduce the issue
Use InstallerModelLanguages to find an extension ID for the en-GB language
E.g.
$model = \JModelLegacy::getInstance('Languages', 'InstallerModel');
$model->findLanguages();
$items = $model->getItems();
#### Expected result
the en-GB language is returned
#### Actual result
0 items are returned
#### System information (as much as possible)
PHP 7.0 mySQL 5.5
#### Additional comments
Seems to be caused by a database change that isn't updated by the database migrations. Apparently language extensions are no longer of the type language but of the type package. And the element changed from 'en-GB' to 'pkg_en-GB'. It works fine on a fresh install. | non_priority | findlanguages doesn t work after upgrading from joomla to steps to reproduce the issue use installermodellanguages to find an extension id for the en gb language e g model jmodellegacy getinstance languages installermodel model findlanguages items model getitems expected result the en gb language is returned actual result items are returned system information as much as possible php mysql additional comments seems to be caused by a database change that isn t updated by the database migrations apparently language extensions are no longer of the type language but of the type package and the element changed from en gb to pkg en gb it works fine on a fresh install | 0 |
146,177 | 11,728,597,834 | IssuesEvent | 2020-03-10 17:49:56 | openshift/odo | https://api.github.com/repos/openshift/odo | closed | Run unit test on windows and macOS | area/testing kind/user-story points/2 priority/High | kind/Feature
<!--
Welcome! - We kindly ask you to:
1. Fill out the issue template below
2. Use the Google group if you have a question rather than a bug or feature request.
The group is at: https://groups.google.com/forum/#!forum/odo-users
Thanks for understanding, and for contributing to the project!
-->
## Which functionality do you think we should add?
We can borrow macOS host on travis and windows from appveyor then only we can start our unit test on these hosts.
## Why is this needed?
This is not yet implemented in our test CI. | 1.0 | Run unit test on windows and macOS - kind/Feature
<!--
Welcome! - We kindly ask you to:
1. Fill out the issue template below
2. Use the Google group if you have a question rather than a bug or feature request.
The group is at: https://groups.google.com/forum/#!forum/odo-users
Thanks for understanding, and for contributing to the project!
-->
## Which functionality do you think we should add?
We can borrow macOS host on travis and windows from appveyor then only we can start our unit test on these hosts.
## Why is this needed?
This is not yet implemented in our test CI. | non_priority | run unit test on windows and macos kind feature welcome we kindly ask you to fill out the issue template below use the google group if you have a question rather than a bug or feature request the group is at thanks for understanding and for contributing to the project which functionality do you think we should add we can borrow macos host on travis and windows from appveyor then only we can start our unit test on these hosts why is this needed this is not yet implemented in our test ci | 0 |
135,608 | 5,255,260,523 | IssuesEvent | 2017-02-02 15:10:27 | NucleusPowered/Nucleus | https://api.github.com/repos/NucleusPowered/Nucleus | opened | Ensure that Keys.DISPLAY_NAME is being used. | bug high priority | From the forums:
>Hi,
>
>I am finalizing a chat plugin and i want to know if Nucleus set the nickname using >Keys.DISPLAY_NAME to change the nick or other key, or is using your internals only?
>
>I tryed to get from key but return the normal player name.
>Thanks.
I need to make sure that my internal code isn't overriding the display name. | 1.0 | Ensure that Keys.DISPLAY_NAME is being used. - From the forums:
>Hi,
>
>I am finalizing a chat plugin and i want to know if Nucleus set the nickname using >Keys.DISPLAY_NAME to change the nick or other key, or is using your internals only?
>
>I tryed to get from key but return the normal player name.
>Thanks.
I need to make sure that my internal code isn't overriding the display name. | priority | ensure that keys display name is being used from the forums hi i am finalizing a chat plugin and i want to know if nucleus set the nickname using keys display name to change the nick or other key or is using your internals only i tryed to get from key but return the normal player name thanks i need to make sure that my internal code isn t overriding the display name | 1 |
189,149 | 6,794,647,378 | IssuesEvent | 2017-11-01 13:03:51 | cilium/cilium | https://api.github.com/repos/cilium/cilium | closed | Avoid double timestamps when running under systemd/journalctl | area/daemon priority/high project/1.0-gap | ```
Oct 14 03:02:14 10.0.2.15 cilium-agent[21557]: time="2017-10-14T03:02:14+02:00" level=info msg="Waiting for consul client to be ready..."
``` | 1.0 | Avoid double timestamps when running under systemd/journalctl - ```
Oct 14 03:02:14 10.0.2.15 cilium-agent[21557]: time="2017-10-14T03:02:14+02:00" level=info msg="Waiting for consul client to be ready..."
``` | priority | avoid double timestamps when running under systemd journalctl oct cilium agent time level info msg waiting for consul client to be ready | 1 |
69,173 | 3,295,843,419 | IssuesEvent | 2015-11-01 10:20:11 | ceylon/ceylon-ide-eclipse | https://api.github.com/repos/ceylon/ceylon-ide-eclipse | opened | extra quick fix to change void to return type | feature high priority proposals/fixes/assists | Given:
void add(Float x, Float y) => x + y;
I should be able to quick fix my way out of that. | 1.0 | extra quick fix to change void to return type - Given:
void add(Float x, Float y) => x + y;
I should be able to quick fix my way out of that. | priority | extra quick fix to change void to return type given void add float x float y x y i should be able to quick fix my way out of that | 1 |
444,766 | 31,145,981,911 | IssuesEvent | 2023-08-16 06:28:45 | vitejs/vite-plugin-vue | https://api.github.com/repos/vitejs/vite-plugin-vue | closed | Example for transforming custom blocks broken | documentation | ### Related plugins
- [X] [plugin-vue](https://github.com/vitejs/vite-plugin-vue/tree/main/packages/plugin-vue)
- [ ] [plugin-vue-jsx](https://github.com/vitejs/vite-plugin-vue/tree/main/packages/plugin-vue-jsx)
### Describe the bug
I casually copy Example for transforming custom blocks from docs and it doesn't work.
My component
```vue
<script setup></script>
<template>
<div>Hello</div>
</template>
<i18n lang="json">
{ "message": "hello" }
</i18n>
```
According to docs transformed code looks like this:
```js
export default Comp => {
Comp.i18n = export const message = "hello";
export default {
message: message
};
}
```
### Reproduction
https://stackblitz.com/edit/vitejs-vite-a3mpsu?file=vite.config.js
### Steps to reproduce
_No response_
### System Info
```shell
System:
OS: Linux 5.0 undefined
CPU: (8) x64 Intel(R) Core(TM) i9-9880H CPU @ 2.30GHz
Memory: 0 Bytes / 0 Bytes
Shell: 1.0 - /bin/jsh
Binaries:
Node: 16.20.0 - /usr/local/bin/node
Yarn: 1.22.19 - /usr/local/bin/yarn
npm: 9.4.2 - /usr/local/bin/npm
pnpm: 8.6.3 - /usr/local/bin/pnpm
npmPackages:
@vitejs/plugin-vue: ^4.2.3 => 4.2.3
vite: ^4.4.4 => 4.4.4
```
### Used Package Manager
npm
### Logs
_No response_
### Validations
- [X] Follow our [Code of Conduct](https://github.com/vitejs/vite/blob/main/CODE_OF_CONDUCT.md)
- [X] Read the [Contributing Guidelines](https://github.com/vitejs/vite/blob/main/CONTRIBUTING.md).
- [X] Read the [docs](https://vitejs.dev/guide).
- [X] Check that there isn't [already an issue](https://github.com/vitejs/vite-plugin-vue/issues) that reports the same bug to avoid creating a duplicate.
- [X] Make sure this is a Vite issue and not a framework-specific issue. For example, if it's a Vue SFC related bug, it should likely be reported to [vuejs/core](https://github.com/vuejs/core) instead.
- [X] Check that this is a concrete bug. For Q&A open a [GitHub Discussion](https://github.com/vitejs/vite-plugin-vue/discussions) or join our [Discord Chat Server](https://chat.vitejs.dev/).
- [X] The provided reproduction is a [minimal reproducible example](https://stackoverflow.com/help/minimal-reproducible-example) of the bug. | 1.0 | Example for transforming custom blocks broken - ### Related plugins
- [X] [plugin-vue](https://github.com/vitejs/vite-plugin-vue/tree/main/packages/plugin-vue)
- [ ] [plugin-vue-jsx](https://github.com/vitejs/vite-plugin-vue/tree/main/packages/plugin-vue-jsx)
### Describe the bug
I casually copy Example for transforming custom blocks from docs and it doesn't work.
My component
```vue
<script setup></script>
<template>
<div>Hello</div>
</template>
<i18n lang="json">
{ "message": "hello" }
</i18n>
```
According to docs transformed code looks like this:
```js
export default Comp => {
Comp.i18n = export const message = "hello";
export default {
message: message
};
}
```
### Reproduction
https://stackblitz.com/edit/vitejs-vite-a3mpsu?file=vite.config.js
### Steps to reproduce
_No response_
### System Info
```shell
System:
OS: Linux 5.0 undefined
CPU: (8) x64 Intel(R) Core(TM) i9-9880H CPU @ 2.30GHz
Memory: 0 Bytes / 0 Bytes
Shell: 1.0 - /bin/jsh
Binaries:
Node: 16.20.0 - /usr/local/bin/node
Yarn: 1.22.19 - /usr/local/bin/yarn
npm: 9.4.2 - /usr/local/bin/npm
pnpm: 8.6.3 - /usr/local/bin/pnpm
npmPackages:
@vitejs/plugin-vue: ^4.2.3 => 4.2.3
vite: ^4.4.4 => 4.4.4
```
### Used Package Manager
npm
### Logs
_No response_
### Validations
- [X] Follow our [Code of Conduct](https://github.com/vitejs/vite/blob/main/CODE_OF_CONDUCT.md)
- [X] Read the [Contributing Guidelines](https://github.com/vitejs/vite/blob/main/CONTRIBUTING.md).
- [X] Read the [docs](https://vitejs.dev/guide).
- [X] Check that there isn't [already an issue](https://github.com/vitejs/vite-plugin-vue/issues) that reports the same bug to avoid creating a duplicate.
- [X] Make sure this is a Vite issue and not a framework-specific issue. For example, if it's a Vue SFC related bug, it should likely be reported to [vuejs/core](https://github.com/vuejs/core) instead.
- [X] Check that this is a concrete bug. For Q&A open a [GitHub Discussion](https://github.com/vitejs/vite-plugin-vue/discussions) or join our [Discord Chat Server](https://chat.vitejs.dev/).
- [X] The provided reproduction is a [minimal reproducible example](https://stackoverflow.com/help/minimal-reproducible-example) of the bug. | non_priority | example for transforming custom blocks broken related plugins describe the bug i casually copy example for transforming custom blocks from docs and it doesn t work my component vue hello message hello according to docs transformed code looks like this js export default comp comp export const message hello export default message message reproduction steps to reproduce no response system info shell system os linux undefined cpu intel r core tm cpu memory bytes bytes shell bin jsh binaries node usr local bin node yarn usr local bin yarn npm usr local bin npm pnpm usr local bin pnpm npmpackages vitejs plugin vue vite used package manager npm logs no response validations follow our read the read the check that there isn t that reports the same bug to avoid creating a duplicate make sure this is a vite issue and not a framework specific issue for example if it s a vue sfc related bug it should likely be reported to instead check that this is a concrete bug for q a open a or join our the provided reproduction is a of the bug | 0 |
245,402 | 18,782,333,758 | IssuesEvent | 2021-11-08 08:29:19 | code-ready/crc | https://api.github.com/repos/code-ready/crc | closed | Document the changes and use of vsock (macOS) | size/M priority/major os/macos kind/documentation status/need more information status/stale status/peer review required vsock | With the upcoming release of CRC, v1.26 we are changing the network mode that we use from the current hypervisor driver IP assignment to the vsock userspace network stack. This allows us to use a more fine-grained approach to network ports, routes, etc, but it also means the current method will become a 'legacy' option. While it should be transparent to the user, some changes will be made to how the DNS is configured, or for people to get access to the VM.
Note: the main reason we have this vsock option is because it allows people to use CRC while needing a VPN connectivity. | 1.0 | Document the changes and use of vsock (macOS) - With the upcoming release of CRC, v1.26 we are changing the network mode that we use from the current hypervisor driver IP assignment to the vsock userspace network stack. This allows us to use a more fine-grained approach to network ports, routes, etc, but it also means the current method will become a 'legacy' option. While it should be transparent to the user, some changes will be made to how the DNS is configured, or for people to get access to the VM.
Note: the main reason we have this vsock option is because it allows people to use CRC while needing a VPN connectivity. | non_priority | document the changes and use of vsock macos with the upcoming release of crc we are changing the network mode that we use from the current hypervisor driver ip assignment to the vsock userspace network stack this allows us to use a more fine grained approach to network ports routes etc but it also means the current method will become a legacy option while it should be transparent to the user some changes will be made to how the dns is configured or for people to get access to the vm note the main reason we have this vsock option is because it allows people to use crc while needing a vpn connectivity | 0 |
90,835 | 15,856,286,627 | IssuesEvent | 2021-04-08 01:59:09 | DashboardHub/Website | https://api.github.com/repos/DashboardHub/Website | opened | CVE-2020-11023 (Medium) detected in jquery-3.3.1.tgz | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.3.1.tgz</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz">https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz</a></p>
<p>Path to dependency file: /Website/package.json</p>
<p>Path to vulnerable library: Website/node_modules/jquery/package.json</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11023 (Medium) detected in jquery-3.3.1.tgz - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.3.1.tgz</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz">https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz</a></p>
<p>Path to dependency file: /Website/package.json</p>
<p>Path to vulnerable library: Website/node_modules/jquery/package.json</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery tgz cve medium severity vulnerability vulnerable library jquery tgz javascript library for dom operations library home page a href path to dependency file website package json path to vulnerable library website node modules jquery package json dependency hierarchy x jquery tgz vulnerable library vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
717,041 | 24,658,509,171 | IssuesEvent | 2022-10-18 03:23:56 | aws-samples/aws-last-mile-delivery-hyperlocal | https://api.github.com/repos/aws-samples/aws-last-mile-delivery-hyperlocal | closed | GPU support to build h3DistanceCache at resolution 10 or build distanceMatrix for lat/longs | enhancement wontfix priority:low component:dispatcher research component:routing effort:medium | * research the possibility to run traveldistance calculations parallel on GPU cores
A) Current H3 distance cache can be built for a pre-defined polygon (MM) at resolution 9 (174m/hexagon edge -- ~5600x5600 matrix) in around 4.5 hours on a `c6g.metal` graviton instance. The goal is to be able to build a resolution 10 (65m/hexagon edge) distance matrix (40k x 40k) in reasonable time.
Also, the current 5600x5600 matrix is ~600MB that is easy to load to memory, but a 40k x 40k matrix size would be around ~30gb --> should be separated to a distancematrix service with fast lookup.
B) direct distanceMatrix build for incoming lat/lng values on GPU with the ability to build ~1000x1000 matrices | 1.0 | GPU support to build h3DistanceCache at resolution 10 or build distanceMatrix for lat/longs - * research the possibility to run traveldistance calculations parallel on GPU cores
A) Current H3 distance cache can be built for a pre-defined polygon (MM) at resolution 9 (174m/hexagon edge -- ~5600x5600 matrix) in around 4.5 hours on a `c6g.metal` graviton instance. The goal is to be able to build a resolution 10 (65m/hexagon edge) distance matrix (40k x 40k) in reasonable time.
Also, the current 5600x5600 matrix is ~600MB that is easy to load to memory, but a 40k x 40k matrix size would be around ~30gb --> should be separated to a distancematrix service with fast lookup.
B) direct distanceMatrix build for incoming lat/lng values on GPU with the ability to build ~1000x1000 matrices | priority | gpu support to build at resolution or build distancematrix for lat longs research the possibility to run traveldistance calculations parallel on gpu cores a current distance cache can be built for a pre defined polygon mm at resolution hexagon edge matrix in around hours on a metal graviton instance the goal is to be able to build a resolution hexagon edge distance matrix x in reasonable time also the current matrix is that is easy to load to memory but a x matrix size would be around should be separated to a distancematrix service with fast lookup b direct distancematrix build for incoming lat lng values on gpu with the ability to build matrices | 1 |
66,310 | 7,987,384,688 | IssuesEvent | 2018-07-19 07:35:37 | ppy/osu-web | https://api.github.com/repos/ppy/osu-web | closed | Restricted banner doesn't play well with new header design | design regression | <img width="1359" alt="image" src="https://user-images.githubusercontent.com/191335/42167056-ccd7b4a6-7e47-11e8-8c82-135f3dd7957b.png">
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/60384094-restricted-banner-doesn-t-play-well-with-new-header-design?utm_campaign=plugin&utm_content=tracker%2F21853994&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F21853994&utm_medium=issues&utm_source=github).
</bountysource-plugin> | 1.0 | Restricted banner doesn't play well with new header design - <img width="1359" alt="image" src="https://user-images.githubusercontent.com/191335/42167056-ccd7b4a6-7e47-11e8-8c82-135f3dd7957b.png">
<bountysource-plugin>
---
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/60384094-restricted-banner-doesn-t-play-well-with-new-header-design?utm_campaign=plugin&utm_content=tracker%2F21853994&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F21853994&utm_medium=issues&utm_source=github).
</bountysource-plugin> | non_priority | restricted banner doesn t play well with new header design img width alt image src want to back this issue we accept bounties via | 0 |
218,285 | 7,331,037,673 | IssuesEvent | 2018-03-05 12:04:51 | NCEAS/metacat | https://api.github.com/repos/NCEAS/metacat | closed | Metacat performance: saves from mopho are slow | Category: metacat Component: Bugzilla-Id Priority: Normal Status: Resolved Tracker: Bug | ---
Author Name: **Matt Jones** (Matt Jones)
Original Redmine Issue: 3113, https://projects.ecoinformatics.org/ecoinfo/issues/3113
Original Date: 2008-01-31
Original Assignee: Jing Tao
---
According to Callie Bowdish, saving or updating data packages takes around 3 minutes from Morpho, even after the fixes that occured as part of bug # 2805. This may be a morpho problem rather than a metacat one. We need more accurate statistics to assess this, such as the size of the data files being uploaded, the size of the EML document, etc.
| 1.0 | Metacat performance: saves from mopho are slow - ---
Author Name: **Matt Jones** (Matt Jones)
Original Redmine Issue: 3113, https://projects.ecoinformatics.org/ecoinfo/issues/3113
Original Date: 2008-01-31
Original Assignee: Jing Tao
---
According to Callie Bowdish, saving or updating data packages takes around 3 minutes from Morpho, even after the fixes that occured as part of bug # 2805. This may be a morpho problem rather than a metacat one. We need more accurate statistics to assess this, such as the size of the data files being uploaded, the size of the EML document, etc.
| priority | metacat performance saves from mopho are slow author name matt jones matt jones original redmine issue original date original assignee jing tao according to callie bowdish saving or updating data packages takes around minutes from morpho even after the fixes that occured as part of bug this may be a morpho problem rather than a metacat one we need more accurate statistics to assess this such as the size of the data files being uploaded the size of the eml document etc | 1 |
658,869 | 21,911,618,414 | IssuesEvent | 2022-05-21 06:06:00 | cse112-sp22-group13/cse112-sp22-group13 | https://api.github.com/repos/cse112-sp22-group13/cse112-sp22-group13 | closed | Initial Interface Overhaul Design | enhancement Priority: HIGH Complexity: M | We wish to update the interface so that the app has a more appealing aesthetic. For this goal, we wish to create new designs for the home, recipe list, and favorites pages. | 1.0 | Initial Interface Overhaul Design - We wish to update the interface so that the app has a more appealing aesthetic. For this goal, we wish to create new designs for the home, recipe list, and favorites pages. | priority | initial interface overhaul design we wish to update the interface so that the app has a more appealing aesthetic for this goal we wish to create new designs for the home recipe list and favorites pages | 1 |
157,468 | 6,001,389,317 | IssuesEvent | 2017-06-05 09:04:25 | tootsuite/mastodon | https://api.github.com/repos/tootsuite/mastodon | closed | Can create and organize own column | enhancement priority - low ui | I think this idea is write here, but I don't found it :/ .
Actually, the third column is miused, too much options for a little column, no really :/
So, it's cool if user can choose and organize his column, for exemple (talk with another "pouetos" https://mamot.fr/@bonob0h/142259 )
- List favorits toots
- List following and followers accounts
- List own toots
- List public toots on dedicated column
- List public world toots on dedicated column too
I think is all for me :) | 1.0 | Can create and organize own column - I think this idea is write here, but I don't found it :/ .
Actually, the third column is miused, too much options for a little column, no really :/
So, it's cool if user can choose and organize his column, for exemple (talk with another "pouetos" https://mamot.fr/@bonob0h/142259 )
- List favorits toots
- List following and followers accounts
- List own toots
- List public toots on dedicated column
- List public world toots on dedicated column too
I think is all for me :) | priority | can create and organize own column i think this idea is write here but i don t found it actually the third column is miused too much options for a little column no really so it s cool if user can choose and organize his column for exemple talk with another pouetos list favorits toots list following and followers accounts list own toots list public toots on dedicated column list public world toots on dedicated column too i think is all for me | 1 |
1,183 | 5,234,094,327 | IssuesEvent | 2017-01-30 14:50:06 | inasafe/inasafe | https://api.github.com/repos/inasafe/inasafe | closed | Ability to work with remote data | Feature request Impact function System Architecture | We need to be able to easily use remote data by fetching it dynamically as needed.
- open streetmap (through e.g. PostGIS mirror)
- WFS
- WCS
| 1.0 | Ability to work with remote data - We need to be able to easily use remote data by fetching it dynamically as needed.
- open streetmap (through e.g. PostGIS mirror)
- WFS
- WCS
| non_priority | ability to work with remote data we need to be able to easily use remote data by fetching it dynamically as needed open streetmap through e g postgis mirror wfs wcs | 0 |
125,110 | 4,952,712,644 | IssuesEvent | 2016-12-01 12:57:46 | ajency/Listr | https://api.github.com/repos/ajency/Listr | closed | The error message displayed on uploading a catalog shows html tags | Assigned to QA bug Priority 2 | 1. Log in as AE
2. Open a catalog in info pending status
3. Download the 'Info pending' sku's
4. Edit one sku id in the excel sheet and upload again
5. Shows correct error message - But is displayed along with the html tags

| 1.0 | The error message displayed on uploading a catalog shows html tags - 1. Log in as AE
2. Open a catalog in info pending status
3. Download the 'Info pending' sku's
4. Edit one sku id in the excel sheet and upload again
5. Shows correct error message - But is displayed along with the html tags

| priority | the error message displayed on uploading a catalog shows html tags log in as ae open a catalog in info pending status download the info pending sku s edit one sku id in the excel sheet and upload again shows correct error message but is displayed along with the html tags | 1 |
543,756 | 15,884,895,703 | IssuesEvent | 2021-04-09 19:38:30 | ansible/awx | https://api.github.com/repos/ansible/awx | closed | Replace `with_items` with `loop` keyword in all playbooks | component:api component:installer priority:low state:needs_devel type:enhancement | We are using `with_items` for internal use in several playbooks:
https://github.com/ansible/awx/search?q=with_items
These are being removed in a future version of Ansible.
```
[DEPRECATION WARNING]: with_ type loops are being phased out, use the 'loop' keyword instead. This feature will be removed in version 2.9. Deprecation warnings can be disabled
by setting deprecation_warnings=False in ansible.cfg.
```
Those uses should be replaced with the new pattern, except for the test in the "old" folder. That test should just be removed completely. | 1.0 | Replace `with_items` with `loop` keyword in all playbooks - We are using `with_items` for internal use in several playbooks:
https://github.com/ansible/awx/search?q=with_items
These are being removed in a future version of Ansible.
```
[DEPRECATION WARNING]: with_ type loops are being phased out, use the 'loop' keyword instead. This feature will be removed in version 2.9. Deprecation warnings can be disabled
by setting deprecation_warnings=False in ansible.cfg.
```
Those uses should be replaced with the new pattern, except for the test in the "old" folder. That test should just be removed completely. | priority | replace with items with loop keyword in all playbooks we are using with items for internal use in several playbooks these are being removed in a future version of ansible with type loops are being phased out use the loop keyword instead this feature will be removed in version deprecation warnings can be disabled by setting deprecation warnings false in ansible cfg those uses should be replaced with the new pattern except for the test in the old folder that test should just be removed completely | 1 |
708,423 | 24,341,251,497 | IssuesEvent | 2022-10-01 18:36:24 | TASVideos/tasvideos | https://api.github.com/repos/TASVideos/tasvideos | closed | Uploaded file extension is check only after finishing uploading | enhancement User Files Priority: Bottom | As in title. File extension should be check also on client side, before starting uploading. This suggestion isn't for improving security, but just for user confort and avoiding useless band usage. | 1.0 | Uploaded file extension is check only after finishing uploading - As in title. File extension should be check also on client side, before starting uploading. This suggestion isn't for improving security, but just for user confort and avoiding useless band usage. | priority | uploaded file extension is check only after finishing uploading as in title file extension should be check also on client side before starting uploading this suggestion isn t for improving security but just for user confort and avoiding useless band usage | 1 |
756,408 | 26,469,596,494 | IssuesEvent | 2023-01-17 05:35:01 | ClassicLootManager/ClassicLootManager | https://api.github.com/repos/ClassicLootManager/ClassicLootManager | closed | When awarding an item from multi-item auction, icon coloration on items which have no bids is cleared | bug Priority::Medium | Repro:
1. Run a multi-item auction where at least 1 item has no bids.
2. When auction is done, items with no bids should be shaded yellow.
3. Award an item with bids to someone.
4. Yellow tint is cleared.
This may only be present when auto-clearing awarded items is present, but did not test.
Workaround:
Right-click yellow-tinted items prior to awarding anything else in the Auction UI to clear them. | 1.0 | When awarding an item from multi-item auction, icon coloration on items which have no bids is cleared - Repro:
1. Run a multi-item auction where at least 1 item has no bids.
2. When auction is done, items with no bids should be shaded yellow.
3. Award an item with bids to someone.
4. Yellow tint is cleared.
This may only be present when auto-clearing awarded items is present, but did not test.
Workaround:
Right-click yellow-tinted items prior to awarding anything else in the Auction UI to clear them. | priority | when awarding an item from multi item auction icon coloration on items which have no bids is cleared repro run a multi item auction where at least item has no bids when auction is done items with no bids should be shaded yellow award an item with bids to someone yellow tint is cleared this may only be present when auto clearing awarded items is present but did not test workaround right click yellow tinted items prior to awarding anything else in the auction ui to clear them | 1 |
69,733 | 3,314,055,632 | IssuesEvent | 2015-11-06 01:54:07 | sequelpro/sequelpro | https://api.github.com/repos/sequelpro/sequelpro | closed | MySQL server in broken state will crash Sequel Pro | Bug Component-Logic Priority-Low | Issue imported from Google Code: https://code.google.com/p/sequel-pro/issues/detail?id=1758
Reporter:adam.ier...@gmail.com Date:2013-07-14 11:24:32 Status:Accepted
<b>What steps will reproduce the problem?</b>
1. Connect to MariaDB 10.0.3 (possibly other versions)
2. Crash
<b>3.</b>
<b>What version of Sequel Pro are you using?</b>
Tried with 1.0.2 and nightly build on Jul 14, 2013.
<b>What version of OS X are you using?</b>
10.8.4
<b>What version of MySQL are you connecting to on the server?</b>
MariaDB 10.0.3
<b>Please provide any additional information below.</b>
Tried with and without SSH, same result. This used to work, then suddenly stopped working. I have no idea why. I did not change anything client-side, but it's possible that MariaDB was updated one revision.
Exception dump:
```
NSInvalidArgumentException
*** -[NSPlaceholderString initWithString:]: nil argument
(
0 CoreFoundation 0x00007fff81702b06 __exceptionPreprocess + 198
1 libobjc.A.dylib 0x00007fff81a8a3f0 objc_exception_throw + 43
2 CoreFoundation 0x00007fff817028dc +[NSException raise:format:] + 204
3 Foundation 0x00007fff8bc22dac -[NSPlaceholderString initWithString:] + 93
4 Sequel Pro 0x0000000100032c46 -[SPDatabaseDocument setConnection:] + 450
5 Foundation 0x00007fff8bc485ca __NSThreadPerformPerform + 225
6 CoreFoundation 0x00007fff81681b31 __CFRUNLOOP_IS_CALLING_OUT_TO_A_SOURCE0_PERFORM_FUNCTION__ + 17
7 CoreFoundation 0x00007fff81681455 __CFRunLoopDoSources0 + 245
8 CoreFoundation 0x00007fff816a47f5 __CFRunLoopRun + 789
9 CoreFoundation 0x00007fff816a40e2 CFRunLoopRunSpecific + 290
10 HIToolbox 0x00007fff848c0eb4 RunCurrentEventLoopInMode + 209
11 HIToolbox 0x00007fff848c0c52 ReceiveNextEventCommon + 356
12 HIToolbox 0x00007fff848c0ae3 BlockUntilNextEventMatchingListInMode + 62
13 AppKit 0x00007fff81d6c533 _DPSNextEvent + 685
14 AppKit 0x00007fff81d6bdf2 -[NSApplication nextEventMatchingMask:untilDate:inMode:dequeue:] + 128
15 AppKit 0x00007fff81d631a3 -[NSApplication run] + 517
16 AppKit 0x00007fff81d07bd6 NSApplicationMain + 869
17 Sequel Pro 0x00000001000022b4 start + 52
)
``` | 1.0 | MySQL server in broken state will crash Sequel Pro - Issue imported from Google Code: https://code.google.com/p/sequel-pro/issues/detail?id=1758
Reporter:adam.ier...@gmail.com Date:2013-07-14 11:24:32 Status:Accepted
<b>What steps will reproduce the problem?</b>
1. Connect to MariaDB 10.0.3 (possibly other versions)
2. Crash
<b>3.</b>
<b>What version of Sequel Pro are you using?</b>
Tried with 1.0.2 and nightly build on Jul 14, 2013.
<b>What version of OS X are you using?</b>
10.8.4
<b>What version of MySQL are you connecting to on the server?</b>
MariaDB 10.0.3
<b>Please provide any additional information below.</b>
Tried with and without SSH, same result. This used to work, then suddenly stopped working. I have no idea why. I did not change anything client-side, but it's possible that MariaDB was updated one revision.
Exception dump:
```
NSInvalidArgumentException
*** -[NSPlaceholderString initWithString:]: nil argument
(
0 CoreFoundation 0x00007fff81702b06 __exceptionPreprocess + 198
1 libobjc.A.dylib 0x00007fff81a8a3f0 objc_exception_throw + 43
2 CoreFoundation 0x00007fff817028dc +[NSException raise:format:] + 204
3 Foundation 0x00007fff8bc22dac -[NSPlaceholderString initWithString:] + 93
4 Sequel Pro 0x0000000100032c46 -[SPDatabaseDocument setConnection:] + 450
5 Foundation 0x00007fff8bc485ca __NSThreadPerformPerform + 225
6 CoreFoundation 0x00007fff81681b31 __CFRUNLOOP_IS_CALLING_OUT_TO_A_SOURCE0_PERFORM_FUNCTION__ + 17
7 CoreFoundation 0x00007fff81681455 __CFRunLoopDoSources0 + 245
8 CoreFoundation 0x00007fff816a47f5 __CFRunLoopRun + 789
9 CoreFoundation 0x00007fff816a40e2 CFRunLoopRunSpecific + 290
10 HIToolbox 0x00007fff848c0eb4 RunCurrentEventLoopInMode + 209
11 HIToolbox 0x00007fff848c0c52 ReceiveNextEventCommon + 356
12 HIToolbox 0x00007fff848c0ae3 BlockUntilNextEventMatchingListInMode + 62
13 AppKit 0x00007fff81d6c533 _DPSNextEvent + 685
14 AppKit 0x00007fff81d6bdf2 -[NSApplication nextEventMatchingMask:untilDate:inMode:dequeue:] + 128
15 AppKit 0x00007fff81d631a3 -[NSApplication run] + 517
16 AppKit 0x00007fff81d07bd6 NSApplicationMain + 869
17 Sequel Pro 0x00000001000022b4 start + 52
)
``` | priority | mysql server in broken state will crash sequel pro issue imported from google code reporter adam ier gmail com date status accepted what steps will reproduce the problem connect to mariadb possibly other versions crash what version of sequel pro are you using tried with and nightly build on jul what version of os x are you using what version of mysql are you connecting to on the server mariadb please provide any additional information below tried with and without ssh same result this used to work then suddenly stopped working i have no idea why i did not change anything client side but it s possible that mariadb was updated one revision exception dump nsinvalidargumentexception nil argument corefoundation exceptionpreprocess libobjc a dylib objc exception throw corefoundation foundation sequel pro foundation nsthreadperformperform corefoundation cfrunloop is calling out to a perform function corefoundation corefoundation cfrunlooprun corefoundation cfrunlooprunspecific hitoolbox runcurrenteventloopinmode hitoolbox receivenexteventcommon hitoolbox blockuntilnexteventmatchinglistinmode appkit dpsnextevent appkit appkit appkit nsapplicationmain sequel pro start | 1 |
305,109 | 9,359,392,043 | IssuesEvent | 2019-04-02 06:42:28 | wso2/product-microgateway | https://api.github.com/repos/wso2/product-microgateway | closed | Automate getting the product name and version for the product.txt file | Priority/Highest | **Description:**
The filter.properties file that can be utilized to get the product name and version is redundant. Instead need an automated solution to do this for each release iteration.
**Suggested Labels:**
Improvement
**Suggested Assignees:**
N/A
**Affected Product Version:**
N/A
**OS, DB, other environment details and versions:**
N/A
**Steps to reproduce:**
N/A
**Related Issues:**
N/A | 1.0 | Automate getting the product name and version for the product.txt file - **Description:**
The filter.properties file that can be utilized to get the product name and version is redundant. Instead need an automated solution to do this for each release iteration.
**Suggested Labels:**
Improvement
**Suggested Assignees:**
N/A
**Affected Product Version:**
N/A
**OS, DB, other environment details and versions:**
N/A
**Steps to reproduce:**
N/A
**Related Issues:**
N/A | priority | automate getting the product name and version for the product txt file description the filter properties file that can be utilized to get the product name and version is redundant instead need an automated solution to do this for each release iteration suggested labels improvement suggested assignees n a affected product version n a os db other environment details and versions n a steps to reproduce n a related issues n a | 1 |
55,245 | 3,072,450,705 | IssuesEvent | 2015-08-19 16:59:14 | RobotiumTech/robotium | https://api.github.com/repos/RobotiumTech/robotium | closed | buttons and waitforactivity not working!!!! | bug imported invalid Priority-Medium | _From [appy....@gmail.com](https://code.google.com/u/109517365550405548003/) on March 07, 2012 17:57:49_
What steps will reproduce the problem? 1. 2. 3. What is the expected output? What do you see instead? What version of the product are you using? On what operating system? Please provide any additional information below.
_Original issue: http://code.google.com/p/robotium/issues/detail?id=229_ | 1.0 | buttons and waitforactivity not working!!!! - _From [appy....@gmail.com](https://code.google.com/u/109517365550405548003/) on March 07, 2012 17:57:49_
What steps will reproduce the problem? 1. 2. 3. What is the expected output? What do you see instead? What version of the product are you using? On what operating system? Please provide any additional information below.
_Original issue: http://code.google.com/p/robotium/issues/detail?id=229_ | priority | buttons and waitforactivity not working from on march what steps will reproduce the problem what is the expected output what do you see instead what version of the product are you using on what operating system please provide any additional information below original issue | 1 |
374,003 | 26,095,548,435 | IssuesEvent | 2022-12-26 18:57:09 | nextauthjs/next-auth | https://api.github.com/repos/nextauthjs/next-auth | opened | Broken code in oauth getting started | documentation triage | ### What is the improvement or update you wish to see?
I've seen two problems: first, in the [server config](https://authjs.dev/getting-started/oauth-tutorial#creating-the-server-config) section, `GITHUB_ID` and `GITHUB_SECRET` are referenced(and missing from the code) instead of `GITHUB_CLIENT_ID` and `GITHUB_CLIENT_SECRET`.
Also, in the [hook example](https://authjs.dev/getting-started/oauth-tutorial#consuming-the-session-via-hooks)
`const userEmail = session.user.email` would cause an error if session is undefined.
### Is there any context that might help us understand?
No.
### Does the docs page already exist? Please link to it.
https://authjs.dev/getting-started/oauth-tutorial | 1.0 | Broken code in oauth getting started - ### What is the improvement or update you wish to see?
I've seen two problems: first, in the [server config](https://authjs.dev/getting-started/oauth-tutorial#creating-the-server-config) section, `GITHUB_ID` and `GITHUB_SECRET` are referenced(and missing from the code) instead of `GITHUB_CLIENT_ID` and `GITHUB_CLIENT_SECRET`.
Also, in the [hook example](https://authjs.dev/getting-started/oauth-tutorial#consuming-the-session-via-hooks)
`const userEmail = session.user.email` would cause an error if session is undefined.
### Is there any context that might help us understand?
No.
### Does the docs page already exist? Please link to it.
https://authjs.dev/getting-started/oauth-tutorial | non_priority | broken code in oauth getting started what is the improvement or update you wish to see i ve seen two problems first in the section github id and github secret are referenced and missing from the code instead of github client id and github client secret also in the const useremail session user email would cause an error if session is undefined is there any context that might help us understand no does the docs page already exist please link to it | 0 |
666,326 | 22,350,614,601 | IssuesEvent | 2022-06-15 11:43:29 | why-science/demo | https://api.github.com/repos/why-science/demo | closed | Remove itadmin@steamxpress.us from systems emails | high priority | Remove itadmin@steamxpress.us from the emails below. System emails should be sent from itadmin@whyscience.com ONLY
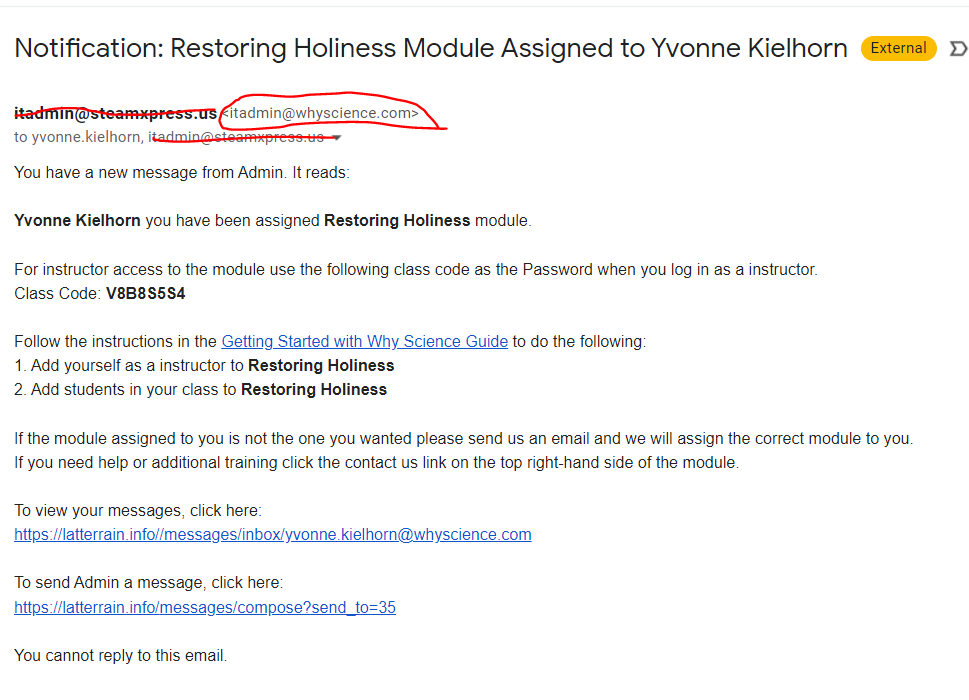
| 1.0 | Remove itadmin@steamxpress.us from systems emails - Remove itadmin@steamxpress.us from the emails below. System emails should be sent from itadmin@whyscience.com ONLY
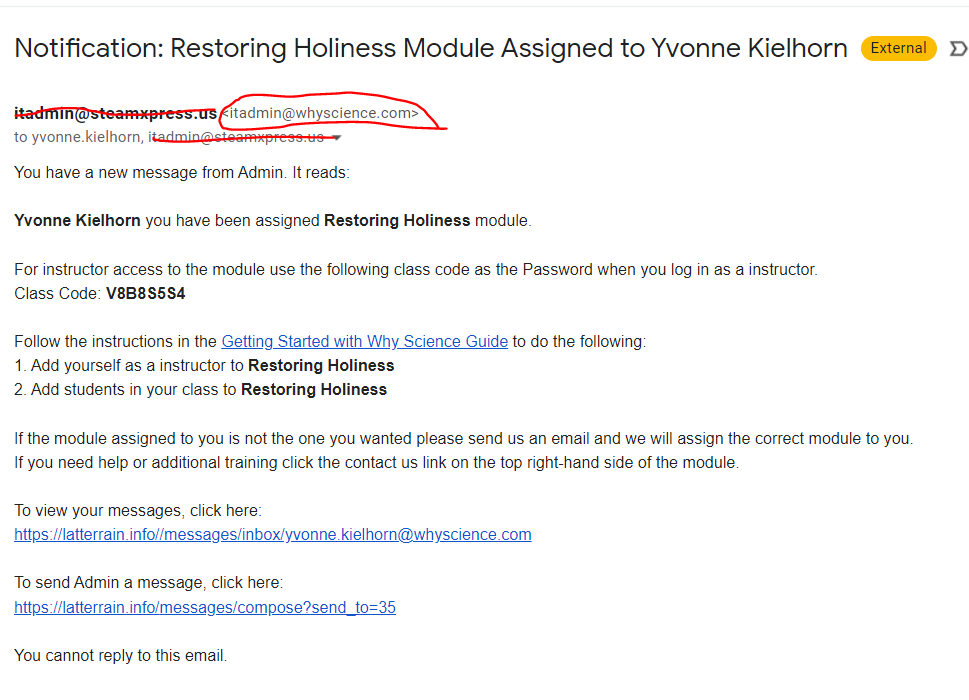
| priority | remove itadmin steamxpress us from systems emails remove itadmin steamxpress us from the emails below system emails should be sent from itadmin whyscience com only | 1 |
717,619 | 24,683,027,438 | IssuesEvent | 2022-10-18 23:49:17 | bcgov/entity | https://api.github.com/repos/bcgov/entity | closed | Unable to affiliate a firm where the proprietor is a corporation | bug Priority1 ENTITY | [https://app.zenhub.com/files/157936592/e8ee8940-5bdb-4854-b8a5-5fdd3d79d8b5/download](https://app.zenhub.com/files/157936592/e8ee8940-5bdb-4854-b8a5-5fdd3d79d8b5/download)As per this error included below, the affiliation is reading the corporation name from fields that are reserved to people's names: first name, last name, middle name. There is another area in the database where the corporation name is stored, for a DBA situation.

@lewischenstudio | 1.0 | Unable to affiliate a firm where the proprietor is a corporation - [https://app.zenhub.com/files/157936592/e8ee8940-5bdb-4854-b8a5-5fdd3d79d8b5/download](https://app.zenhub.com/files/157936592/e8ee8940-5bdb-4854-b8a5-5fdd3d79d8b5/download)As per this error included below, the affiliation is reading the corporation name from fields that are reserved to people's names: first name, last name, middle name. There is another area in the database where the corporation name is stored, for a DBA situation.

@lewischenstudio | priority | unable to affiliate a firm where the proprietor is a corporation per this error included below the affiliation is reading the corporation name from fields that are reserved to people s names first name last name middle name there is another area in the database where the corporation name is stored for a dba situation lewischenstudio | 1 |
159,526 | 25,011,771,616 | IssuesEvent | 2022-11-03 15:43:22 | ParabolInc/parabol | https://api.github.com/repos/ParabolInc/parabol | closed | Use MaterialUI SvgIcons instead of Font | enhancement help wanted design frontend | ## Issue - Enhancement
Today, we ship two quite large font icons for Material UI:
```console
> ll -h packages/client/styles/theme/fonts/MaterialIcons*
-rw-r--r-- 1 blimmer staff 103K Feb 1 09:49 packages/client/styles/theme/fonts/MaterialIcons-Regular.woff2
-rw-r--r-- 1 blimmer staff 113K Feb 1 09:49 packages/client/styles/theme/fonts/MaterialIconsOutlined-Regular.woff2
```
This pattern means that we ship every icon (used or unused) to the client, which is inefficient. If we switched over to the React `@mui/icons-material` package, we could use the SVG versions of just the icons we use in the app. This should result in a far smaller payload to deliver the icons we use.
Additionally, on slow internet connections, there's a strange behavior where you see the "name" of the icon in the DOM while the font is loading. This breaks the layout and overall looks a bit odd. Check out this Loom recording to see what I'm talking about: https://www.loom.com/share/9bde6426362d4c8ca97ff7a3d6039a83
## Accessibility
I noticed this issue while working on the follow-up to #5961. When I requested the text content of a submitted retrospective item, the string I entered oddly had `"cancelsearch"` appended to the end of string:
```
Error: expect(received).toHaveText(expected)
Expected string: "We should start doing this!"
Received string: "We should start doing this!cancelsearch"
Call log:
- expect.toHaveText with timeout 5000ms
- waiting for selector "[data-cy=reflection-column-Start] [data-cy=reflection-stack-Start]"
```
When I inspected the HTML element, indeed, the `<i>` element has the name of the element:
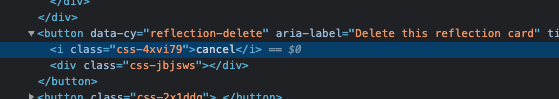
I listened to this with VoiceOver on my Mac and it wasn't announcing the `cancel` text, so I don't think there's necessarily an accessibility issue with the current pattern. However, some screen readers might also behave differently than VoiceOver.
### Acceptance Criteria
- SVG material icons are used instead of the MUI font icons.
- Unused icons aren't included in the final bundle (see https://mui.com/components/icons/#usage).
**Estimated effort:** 12 points ([see CONTRIBUTING.md](https://github.com/ParabolInc/parabol/blob/master/CONTRIBUTING.md#points-and-sizes))
| 1.0 | Use MaterialUI SvgIcons instead of Font - ## Issue - Enhancement
Today, we ship two quite large font icons for Material UI:
```console
> ll -h packages/client/styles/theme/fonts/MaterialIcons*
-rw-r--r-- 1 blimmer staff 103K Feb 1 09:49 packages/client/styles/theme/fonts/MaterialIcons-Regular.woff2
-rw-r--r-- 1 blimmer staff 113K Feb 1 09:49 packages/client/styles/theme/fonts/MaterialIconsOutlined-Regular.woff2
```
This pattern means that we ship every icon (used or unused) to the client, which is inefficient. If we switched over to the React `@mui/icons-material` package, we could use the SVG versions of just the icons we use in the app. This should result in a far smaller payload to deliver the icons we use.
Additionally, on slow internet connections, there's a strange behavior where you see the "name" of the icon in the DOM while the font is loading. This breaks the layout and overall looks a bit odd. Check out this Loom recording to see what I'm talking about: https://www.loom.com/share/9bde6426362d4c8ca97ff7a3d6039a83
## Accessibility
I noticed this issue while working on the follow-up to #5961. When I requested the text content of a submitted retrospective item, the string I entered oddly had `"cancelsearch"` appended to the end of string:
```
Error: expect(received).toHaveText(expected)
Expected string: "We should start doing this!"
Received string: "We should start doing this!cancelsearch"
Call log:
- expect.toHaveText with timeout 5000ms
- waiting for selector "[data-cy=reflection-column-Start] [data-cy=reflection-stack-Start]"
```
When I inspected the HTML element, indeed, the `<i>` element has the name of the element:
I listened to this with VoiceOver on my Mac and it wasn't announcing the `cancel` text, so I don't think there's necessarily an accessibility issue with the current pattern. However, some screen readers might also behave differently than VoiceOver.
### Acceptance Criteria
- SVG material icons are used instead of the MUI font icons.
- Unused icons aren't included in the final bundle (see https://mui.com/components/icons/#usage).
**Estimated effort:** 12 points ([see CONTRIBUTING.md](https://github.com/ParabolInc/parabol/blob/master/CONTRIBUTING.md#points-and-sizes))
| non_priority | use materialui svgicons instead of font issue enhancement today we ship two quite large font icons for material ui console ll h packages client styles theme fonts materialicons rw r r blimmer staff feb packages client styles theme fonts materialicons regular rw r r blimmer staff feb packages client styles theme fonts materialiconsoutlined regular this pattern means that we ship every icon used or unused to the client which is inefficient if we switched over to the react mui icons material package we could use the svg versions of just the icons we use in the app this should result in a far smaller payload to deliver the icons we use additionally on slow internet connections there s a strange behavior where you see the name of the icon in the dom while the font is loading this breaks the layout and overall looks a bit odd check out this loom recording to see what i m talking about accessibility i noticed this issue while working on the follow up to when i requested the text content of a submitted retrospective item the string i entered oddly had cancelsearch appended to the end of string error expect received tohavetext expected expected string we should start doing this received string we should start doing this cancelsearch call log expect tohavetext with timeout waiting for selector when i inspected the html element indeed the element has the name of the element i listened to this with voiceover on my mac and it wasn t announcing the cancel text so i don t think there s necessarily an accessibility issue with the current pattern however some screen readers might also behave differently than voiceover acceptance criteria svg material icons are used instead of the mui font icons unused icons aren t included in the final bundle see estimated effort points | 0 |
153,406 | 5,891,569,668 | IssuesEvent | 2017-05-17 17:22:49 | projectcalico/calico | https://api.github.com/repos/projectcalico/calico | closed | Vagrant "verify environment" should be automated / moved into the Vagrantfile | area/demo priority/P3 | http://docs.projectcalico.org/v2.0/getting-started/kubernetes/installation/vagrant#14-verify-environment
This entire "verify environment section" could be done directly in the Vagrantfile, allowing us to error the provisioning if those addresses aren't working. | 1.0 | Vagrant "verify environment" should be automated / moved into the Vagrantfile - http://docs.projectcalico.org/v2.0/getting-started/kubernetes/installation/vagrant#14-verify-environment
This entire "verify environment section" could be done directly in the Vagrantfile, allowing us to error the provisioning if those addresses aren't working. | priority | vagrant verify environment should be automated moved into the vagrantfile this entire verify environment section could be done directly in the vagrantfile allowing us to error the provisioning if those addresses aren t working | 1 |
391,836 | 11,579,309,604 | IssuesEvent | 2020-02-21 17:38:30 | AugurProject/augur | https://api.github.com/repos/AugurProject/augur | closed | Correct templated market scalar precision | Bug Needed for V2 launch Priority: High | This seems to be an issue with all sports scalar templates Change the precision from 1 to .01 (2 decimal places out)....this should help fix the "Price must be a multiple of 1 issue" associated with rounding
Sports needed to update:
American Football
Baseball
Basketball
Hockey
Olympics
| 1.0 | Correct templated market scalar precision - This seems to be an issue with all sports scalar templates Change the precision from 1 to .01 (2 decimal places out)....this should help fix the "Price must be a multiple of 1 issue" associated with rounding
Sports needed to update:
American Football
Baseball
Basketball
Hockey
Olympics
| priority | correct templated market scalar precision this seems to be an issue with all sports scalar templates change the precision from to decimal places out this should help fix the price must be a multiple of issue associated with rounding sports needed to update american football baseball basketball hockey olympics | 1 |
384,695 | 26,599,007,941 | IssuesEvent | 2023-01-23 14:32:24 | Epitech-Nantes-Tek3/A-equals-l-squared | https://api.github.com/repos/Epitech-Nantes-Tek3/A-equals-l-squared | closed | Link the database to the about.json | documentation database | **Short description:**
You need to call the database to list the available services.
**Describe the solution you want**.
Use prisma and make a call to list the available services and each of their actions/reactions. | 1.0 | Link the database to the about.json - **Short description:**
You need to call the database to list the available services.
**Describe the solution you want**.
Use prisma and make a call to list the available services and each of their actions/reactions. | non_priority | link the database to the about json short description you need to call the database to list the available services describe the solution you want use prisma and make a call to list the available services and each of their actions reactions | 0 |
338,619 | 10,232,371,318 | IssuesEvent | 2019-08-18 16:57:38 | wevote/WebApp | https://api.github.com/repos/wevote/WebApp | closed | PaidAccountUpgradeModal: "X" Close-modal disappears in mobile | Difficulty: Easy Priority: 1 | When you get the "Choose Your Plan" modal from the settings section, the "X" that closes the modal appears in Desktop. That "X" is missing in mobile mode.
Visible in Desktop:
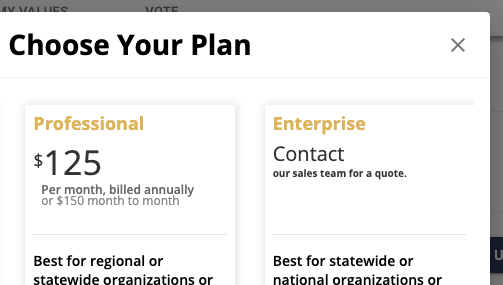
NOT Visible in Mobile:
To open this modal, start from this page: http://localhost:3000/settings/sharing
...and click on "Upgrade to Premium" button.
File is here:
WebApp/src/js/components/Settings/PaidAccountUpgradeModal.jsx
Search for the id `profileClosePaidAccountUpgradeModal` | 1.0 | PaidAccountUpgradeModal: "X" Close-modal disappears in mobile - When you get the "Choose Your Plan" modal from the settings section, the "X" that closes the modal appears in Desktop. That "X" is missing in mobile mode.
Visible in Desktop:
NOT Visible in Mobile:
To open this modal, start from this page: http://localhost:3000/settings/sharing
...and click on "Upgrade to Premium" button.
File is here:
WebApp/src/js/components/Settings/PaidAccountUpgradeModal.jsx
Search for the id `profileClosePaidAccountUpgradeModal` | priority | paidaccountupgrademodal x close modal disappears in mobile when you get the choose your plan modal from the settings section the x that closes the modal appears in desktop that x is missing in mobile mode visible in desktop not visible in mobile to open this modal start from this page and click on upgrade to premium button file is here webapp src js components settings paidaccountupgrademodal jsx search for the id profileclosepaidaccountupgrademodal | 1 |
262,954 | 8,272,649,622 | IssuesEvent | 2018-09-16 22:33:55 | javaee/glassfish | https://api.github.com/repos/javaee/glassfish | closed | Unknown messages are output when specifying invalid config-property-name of ra | Component: jca Priority: Minor Type: Bug | Since connector1.5, we can specify config properties for resource adapter class.
When a ra.xml contains an empty <config-property-name> in <config-property>,
such as
...
<resourceadapter-class>connector.SimpleResourceAdapterImpl</resourceadapter-class> <config-property>
<config-property-name></config-property-name>
<config-property-type>java.lang.Integer</config-property-type>
<config-property-value>10000</config-property-value>
</config-property> ...,
to start a instance where such an application is deployed causes the following exception. This exceptoin message is not clear about the root cause of this problem.
If a config property name is not specified, I think a connector runtime should skip analyzing its property because the corresponding setter method of the resource adapter will be never found. Or it should output a more meaningful error message so that we can trace the reason of it.
RAR6035 : Resource adapter start failed.
com.sun.appserv.connectors.internal.api.ConnectorRuntimeException: Wrong parameters for pool creation : String index out of range: 1
at com.sun.enterprise.connectors.ActiveOutboundResourceAdapter.loadRAConfiguration(ActiveOutboundResourceAdapter.java:331)
at com.sun.enterprise.connectors.ActiveOutboundResourceAdapter.init(ActiveOutboundResourceAdapter.java:114)
at com.sun.enterprise.connectors.inbound.ActiveInboundResourceAdapterImpl.init(ActiveInboundResourceAdapterImpl.java:90)
at com.sun.enterprise.connectors.ActiveRAFactory.instantiateActiveResourceAdapter(ActiveRAFactory.java:135)
at com.sun.enterprise.connectors.ActiveRAFactory.createActiveResourceAdapter(ActiveRAFactory.java:106)
at com.sun.enterprise.connectors.service.ResourceAdapterAdminServiceImpl.createActiveResourceAdapter(ResourceAdapterAdminServiceImpl.java:212)
at com.sun.enterprise.connectors.ConnectorRuntime.createActiveResourceAdapter(ConnectorRuntime.java:364)
at com.sun.enterprise.connectors.module.ConnectorDeployer.load(ConnectorDeployer.java:194)
at com.sun.enterprise.connectors.module.ConnectorDeployer.load(ConnectorDeployer.java:92)
at org.glassfish.internal.data.ModuleInfo.load(ModuleInfo.java:186)
at org.glassfish.internal.data.ApplicationInfo.load(ApplicationInfo.java:257)
at com.sun.enterprise.v3.server.ApplicationLifecycle.deploy(ApplicationLifecycle.java:462)
at com.sun.enterprise.v3.server.ApplicationLoaderService.processApplication(ApplicationLoaderService.java:375)
at com.sun.enterprise.v3.server.ApplicationLoaderService.postConstruct(ApplicationLoaderService.java:204)
at com.sun.hk2.component.AbstractCreatorImpl.inject(AbstractCreatorImpl.java:130)
at com.sun.hk2.component.ConstructorCreator.initialize(ConstructorCreator.java:117)
at com.sun.hk2.component.AbstractCreatorImpl.get(AbstractCreatorImpl.java:83)
at com.sun.hk2.component.SingletonInhabitant.get(SingletonInhabitant.java:66)
at com.sun.hk2.component.EventPublishingInhabitant.get(EventPublishingInhabitant.java:139)
at com.sun.hk2.component.AbstractInhabitantImpl.get(AbstractInhabitantImpl.java:130)
at com.sun.enterprise.v3.server.AppServerStartup.run(AppServerStartup.java:253)
at com.sun.enterprise.v3.server.AppServerStartup.doStart(AppServerStartup.java:145)
at com.sun.enterprise.v3.server.AppServerStartup.start(AppServerStartup.java:136)
at com.sun.enterprise.glassfish.bootstrap.GlassFishImpl.start(GlassFishImpl.java:79)
at com.sun.enterprise.glassfish.bootstrap.GlassFishDecorator.start(GlassFishDecorator.java:63)
at com.sun.enterprise.glassfish.bootstrap.osgi.OSGiGlassFishImpl.start(OSGiGlassFishImpl.java:69)
at com.sun.enterprise.glassfish.bootstrap.GlassFishMain$Launcher.launch(GlassFishMain.java:117)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:39)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:25)
at java.lang.reflect.Method.invoke(Method.java:597)
at com.sun.enterprise.glassfish.bootstrap.GlassFishMain.main(GlassFishMain.java:97)
at com.sun.enterprise.glassfish.bootstrap.ASMain.main(ASMain.java:55)
Caused by: java.lang.StringIndexOutOfBoundsException: String index out of range: 1
at java.lang.String.substring(String.java:1934)
at com.sun.enterprise.connectors.util.SetMethodAction.getCamelCasedPropertyName(SetMethodAction.java:286)
at com.sun.enterprise.connectors.util.SetMethodAction.getAccessorMethod(SetMethodAction.java:236)
at com.sun.enterprise.connectors.util.SetMethodAction.getTypeOf(SetMethodAction.java:220)
at com.sun.enterprise.connectors.util.SetMethodAction.run(SetMethodAction.java:85)
at com.sun.enterprise.connectors.ActiveOutboundResourceAdapter.loadRAConfiguration(ActiveOutboundResourceAdapter.java:328)
Reproducible order:
1\. Deploy attachment application on a server instance.
2\. Start the server instance.
3\. Please see its server.log.
Attachment:
An attached application was created by changing ra.xml in the following devtests rar.
trunk/v2/appserv-tests/devtests/connector/v3/connector1.5/ra/generic-ra.rar
#### Environment
Operating System: Windows 7
Platform: All
GFv3.2 revision: 47843
#### Affected Versions
[4.0] | 1.0 | Unknown messages are output when specifying invalid config-property-name of ra - Since connector1.5, we can specify config properties for resource adapter class.
When a ra.xml contains an empty <config-property-name> in <config-property>,
such as
...
<resourceadapter-class>connector.SimpleResourceAdapterImpl</resourceadapter-class> <config-property>
<config-property-name></config-property-name>
<config-property-type>java.lang.Integer</config-property-type>
<config-property-value>10000</config-property-value>
</config-property> ...,
to start a instance where such an application is deployed causes the following exception. This exceptoin message is not clear about the root cause of this problem.
If a config property name is not specified, I think a connector runtime should skip analyzing its property because the corresponding setter method of the resource adapter will be never found. Or it should output a more meaningful error message so that we can trace the reason of it.
RAR6035 : Resource adapter start failed.
com.sun.appserv.connectors.internal.api.ConnectorRuntimeException: Wrong parameters for pool creation : String index out of range: 1
at com.sun.enterprise.connectors.ActiveOutboundResourceAdapter.loadRAConfiguration(ActiveOutboundResourceAdapter.java:331)
at com.sun.enterprise.connectors.ActiveOutboundResourceAdapter.init(ActiveOutboundResourceAdapter.java:114)
at com.sun.enterprise.connectors.inbound.ActiveInboundResourceAdapterImpl.init(ActiveInboundResourceAdapterImpl.java:90)
at com.sun.enterprise.connectors.ActiveRAFactory.instantiateActiveResourceAdapter(ActiveRAFactory.java:135)
at com.sun.enterprise.connectors.ActiveRAFactory.createActiveResourceAdapter(ActiveRAFactory.java:106)
at com.sun.enterprise.connectors.service.ResourceAdapterAdminServiceImpl.createActiveResourceAdapter(ResourceAdapterAdminServiceImpl.java:212)
at com.sun.enterprise.connectors.ConnectorRuntime.createActiveResourceAdapter(ConnectorRuntime.java:364)
at com.sun.enterprise.connectors.module.ConnectorDeployer.load(ConnectorDeployer.java:194)
at com.sun.enterprise.connectors.module.ConnectorDeployer.load(ConnectorDeployer.java:92)
at org.glassfish.internal.data.ModuleInfo.load(ModuleInfo.java:186)
at org.glassfish.internal.data.ApplicationInfo.load(ApplicationInfo.java:257)
at com.sun.enterprise.v3.server.ApplicationLifecycle.deploy(ApplicationLifecycle.java:462)
at com.sun.enterprise.v3.server.ApplicationLoaderService.processApplication(ApplicationLoaderService.java:375)
at com.sun.enterprise.v3.server.ApplicationLoaderService.postConstruct(ApplicationLoaderService.java:204)
at com.sun.hk2.component.AbstractCreatorImpl.inject(AbstractCreatorImpl.java:130)
at com.sun.hk2.component.ConstructorCreator.initialize(ConstructorCreator.java:117)
at com.sun.hk2.component.AbstractCreatorImpl.get(AbstractCreatorImpl.java:83)
at com.sun.hk2.component.SingletonInhabitant.get(SingletonInhabitant.java:66)
at com.sun.hk2.component.EventPublishingInhabitant.get(EventPublishingInhabitant.java:139)
at com.sun.hk2.component.AbstractInhabitantImpl.get(AbstractInhabitantImpl.java:130)
at com.sun.enterprise.v3.server.AppServerStartup.run(AppServerStartup.java:253)
at com.sun.enterprise.v3.server.AppServerStartup.doStart(AppServerStartup.java:145)
at com.sun.enterprise.v3.server.AppServerStartup.start(AppServerStartup.java:136)
at com.sun.enterprise.glassfish.bootstrap.GlassFishImpl.start(GlassFishImpl.java:79)
at com.sun.enterprise.glassfish.bootstrap.GlassFishDecorator.start(GlassFishDecorator.java:63)
at com.sun.enterprise.glassfish.bootstrap.osgi.OSGiGlassFishImpl.start(OSGiGlassFishImpl.java:69)
at com.sun.enterprise.glassfish.bootstrap.GlassFishMain$Launcher.launch(GlassFishMain.java:117)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:39)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:25)
at java.lang.reflect.Method.invoke(Method.java:597)
at com.sun.enterprise.glassfish.bootstrap.GlassFishMain.main(GlassFishMain.java:97)
at com.sun.enterprise.glassfish.bootstrap.ASMain.main(ASMain.java:55)
Caused by: java.lang.StringIndexOutOfBoundsException: String index out of range: 1
at java.lang.String.substring(String.java:1934)
at com.sun.enterprise.connectors.util.SetMethodAction.getCamelCasedPropertyName(SetMethodAction.java:286)
at com.sun.enterprise.connectors.util.SetMethodAction.getAccessorMethod(SetMethodAction.java:236)
at com.sun.enterprise.connectors.util.SetMethodAction.getTypeOf(SetMethodAction.java:220)
at com.sun.enterprise.connectors.util.SetMethodAction.run(SetMethodAction.java:85)
at com.sun.enterprise.connectors.ActiveOutboundResourceAdapter.loadRAConfiguration(ActiveOutboundResourceAdapter.java:328)
Reproducible order:
1\. Deploy attachment application on a server instance.
2\. Start the server instance.
3\. Please see its server.log.
Attachment:
An attached application was created by changing ra.xml in the following devtests rar.
trunk/v2/appserv-tests/devtests/connector/v3/connector1.5/ra/generic-ra.rar
#### Environment
Operating System: Windows 7
Platform: All
GFv3.2 revision: 47843
#### Affected Versions
[4.0] | priority | unknown messages are output when specifying invalid config property name of ra since we can specify config properties for resource adapter class when a ra xml contains an empty in such as connector simpleresourceadapterimpl java lang integer to start a instance where such an application is deployed causes the following exception this exceptoin message is not clear about the root cause of this problem if a config property name is not specified i think a connector runtime should skip analyzing its property because the corresponding setter method of the resource adapter will be never found or it should output a more meaningful error message so that we can trace the reason of it resource adapter start failed com sun appserv connectors internal api connectorruntimeexception wrong parameters for pool creation string index out of range at com sun enterprise connectors activeoutboundresourceadapter loadraconfiguration activeoutboundresourceadapter java at com sun enterprise connectors activeoutboundresourceadapter init activeoutboundresourceadapter java at com sun enterprise connectors inbound activeinboundresourceadapterimpl init activeinboundresourceadapterimpl java at com sun enterprise connectors activerafactory instantiateactiveresourceadapter activerafactory java at com sun enterprise connectors activerafactory createactiveresourceadapter activerafactory java at com sun enterprise connectors service resourceadapteradminserviceimpl createactiveresourceadapter resourceadapteradminserviceimpl java at com sun enterprise connectors connectorruntime createactiveresourceadapter connectorruntime java at com sun enterprise connectors module connectordeployer load connectordeployer java at com sun enterprise connectors module connectordeployer load connectordeployer java at org glassfish internal data moduleinfo load moduleinfo java at org glassfish internal data applicationinfo load applicationinfo java at com sun enterprise server applicationlifecycle deploy applicationlifecycle java at com sun enterprise server applicationloaderservice processapplication applicationloaderservice java at com sun enterprise server applicationloaderservice postconstruct applicationloaderservice java at com sun component abstractcreatorimpl inject abstractcreatorimpl java at com sun component constructorcreator initialize constructorcreator java at com sun component abstractcreatorimpl get abstractcreatorimpl java at com sun component singletoninhabitant get singletoninhabitant java at com sun component eventpublishinginhabitant get eventpublishinginhabitant java at com sun component abstractinhabitantimpl get abstractinhabitantimpl java at com sun enterprise server appserverstartup run appserverstartup java at com sun enterprise server appserverstartup dostart appserverstartup java at com sun enterprise server appserverstartup start appserverstartup java at com sun enterprise glassfish bootstrap glassfishimpl start glassfishimpl java at com sun enterprise glassfish bootstrap glassfishdecorator start glassfishdecorator java at com sun enterprise glassfish bootstrap osgi osgiglassfishimpl start osgiglassfishimpl java at com sun enterprise glassfish bootstrap glassfishmain launcher launch glassfishmain java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at com sun enterprise glassfish bootstrap glassfishmain main glassfishmain java at com sun enterprise glassfish bootstrap asmain main asmain java caused by java lang stringindexoutofboundsexception string index out of range at java lang string substring string java at com sun enterprise connectors util setmethodaction getcamelcasedpropertyname setmethodaction java at com sun enterprise connectors util setmethodaction getaccessormethod setmethodaction java at com sun enterprise connectors util setmethodaction gettypeof setmethodaction java at com sun enterprise connectors util setmethodaction run setmethodaction java at com sun enterprise connectors activeoutboundresourceadapter loadraconfiguration activeoutboundresourceadapter java reproducible order deploy attachment application on a server instance start the server instance please see its server log attachment an attached application was created by changing ra xml in the following devtests rar trunk appserv tests devtests connector ra generic ra rar environment operating system windows platform all revision affected versions | 1 |
18,923 | 4,323,157,752 | IssuesEvent | 2016-07-25 16:07:22 | hyperledger/fabric | https://api.github.com/repos/hyperledger/fabric | closed | Unwanted viper 'feature'(?) : Configuration *prefixes* may be taken from the environment | configuration documentation | I wanted to quickly document a problem that I just experienced, in the event that this information may help others, or perhaps that someone might have time to investigate and fix this.
Seemly out of nowhere, the Go language tests stopped working for me. One particular set of tests kept coming back saying that the configuration variable
```
peer.fileSystemPath
```
was not defined. I verified that the correct YAML file was being loaded which clearly defined this variable. I dumped viper's internal configuration map and saw the hierarchical definition as plain as day.
Long story short: It turns out that in certain cases (which I have not tried to understand), viper is looking at *prefixes* of the configuration variables in the environment. The change that caused my problem was that I had defined an environment variable **PEER** (to point to the hyperldeger/fabric/peer directory). For these particular tests, viper was finding **PEER** defined in the environment, and somehow this confused viper and it was unable to find peer.fileSystemPath in its configuration map.
This caused me several hours of frustration that I would like to spare others who might innocently define **PEER**, **CHAINCODE**, **LEDGER** or any of the other top-level hierarchical names that appear in our YAML files. | 1.0 | Unwanted viper 'feature'(?) : Configuration *prefixes* may be taken from the environment - I wanted to quickly document a problem that I just experienced, in the event that this information may help others, or perhaps that someone might have time to investigate and fix this.
Seemly out of nowhere, the Go language tests stopped working for me. One particular set of tests kept coming back saying that the configuration variable
```
peer.fileSystemPath
```
was not defined. I verified that the correct YAML file was being loaded which clearly defined this variable. I dumped viper's internal configuration map and saw the hierarchical definition as plain as day.
Long story short: It turns out that in certain cases (which I have not tried to understand), viper is looking at *prefixes* of the configuration variables in the environment. The change that caused my problem was that I had defined an environment variable **PEER** (to point to the hyperldeger/fabric/peer directory). For these particular tests, viper was finding **PEER** defined in the environment, and somehow this confused viper and it was unable to find peer.fileSystemPath in its configuration map.
This caused me several hours of frustration that I would like to spare others who might innocently define **PEER**, **CHAINCODE**, **LEDGER** or any of the other top-level hierarchical names that appear in our YAML files. | non_priority | unwanted viper feature configuration prefixes may be taken from the environment i wanted to quickly document a problem that i just experienced in the event that this information may help others or perhaps that someone might have time to investigate and fix this seemly out of nowhere the go language tests stopped working for me one particular set of tests kept coming back saying that the configuration variable peer filesystempath was not defined i verified that the correct yaml file was being loaded which clearly defined this variable i dumped viper s internal configuration map and saw the hierarchical definition as plain as day long story short it turns out that in certain cases which i have not tried to understand viper is looking at prefixes of the configuration variables in the environment the change that caused my problem was that i had defined an environment variable peer to point to the hyperldeger fabric peer directory for these particular tests viper was finding peer defined in the environment and somehow this confused viper and it was unable to find peer filesystempath in its configuration map this caused me several hours of frustration that i would like to spare others who might innocently define peer chaincode ledger or any of the other top level hierarchical names that appear in our yaml files | 0 |
59,676 | 3,117,431,296 | IssuesEvent | 2015-09-04 01:09:48 | framingeinstein/issues-test | https://api.github.com/repos/framingeinstein/issues-test | opened | Collections detail: Tapping on hotspots results in overlapping issue | priority:critical resolution:fixed resolution:fixed | Content that appears by tapping on hotspots, gets overlapped by title.
Steps:
1. Go to http://qa.speakman.rallyapp.co/
2. Expand navigation menu
3. Go to Collections
4. Tap on The Rain Bathroom
5. Tap on hotspots on the hero image
Devices:
Android Browser - Samsung Galaxy Tab 4 10" Android 4.4.2
Safari iPad Air 2 iOS 8.2 | 1.0 | Collections detail: Tapping on hotspots results in overlapping issue - Content that appears by tapping on hotspots, gets overlapped by title.
Steps:
1. Go to http://qa.speakman.rallyapp.co/
2. Expand navigation menu
3. Go to Collections
4. Tap on The Rain Bathroom
5. Tap on hotspots on the hero image
Devices:
Android Browser - Samsung Galaxy Tab 4 10" Android 4.4.2
Safari iPad Air 2 iOS 8.2 | priority | collections detail tapping on hotspots results in overlapping issue content that appears by tapping on hotspots gets overlapped by title steps go to expand navigation menu go to collections tap on the rain bathroom tap on hotspots on the hero image devices android browser samsung galaxy tab android safari ipad air ios | 1 |
205,852 | 23,357,899,179 | IssuesEvent | 2022-08-10 09:04:21 | Gal-Doron/Baragon | https://api.github.com/repos/Gal-Doron/Baragon | opened | CVE-2020-36184 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon/commit/21e05aedc2dc15db5c3991ce71589fd5b8179836">21e05aedc2dc15db5c3991ce71589fd5b8179836</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184>CVE-2020-36184</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: 2.9.10.8</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2020-36184 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon/commit/21e05aedc2dc15db5c3991ce71589fd5b8179836">21e05aedc2dc15db5c3991ce71589fd5b8179836</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.datasources.PerUserPoolDataSource.
<p>Publish Date: 2021-01-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184>CVE-2020-36184</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-06</p>
<p>Fix Resolution: 2.9.10.8</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp datasources peruserpooldatasource publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
56,921 | 15,443,244,563 | IssuesEvent | 2021-03-08 08:53:47 | SAP/fundamental-ngx | https://api.github.com/repos/SAP/fundamental-ngx | opened | SegementedButton: component does not comply with a11y feature | Defect Hunting core | #### Is this a bug, enhancement, or feature request?
bug
#### Briefly describe your proposal.
component does not have tooltip, or arialabels defined for screen readability.
#### Which versions of Angular and Fundamental Library for Angular are affected? (If this is a feature request, use current version.)
#### If this is a bug, please provide steps for reproducing it.
#### Please provide relevant source code if applicable.
#### Is there anything else we should know?
| 1.0 | SegementedButton: component does not comply with a11y feature - #### Is this a bug, enhancement, or feature request?
bug
#### Briefly describe your proposal.
component does not have tooltip, or arialabels defined for screen readability.
#### Which versions of Angular and Fundamental Library for Angular are affected? (If this is a feature request, use current version.)
#### If this is a bug, please provide steps for reproducing it.
#### Please provide relevant source code if applicable.
#### Is there anything else we should know?
| non_priority | segementedbutton component does not comply with feature is this a bug enhancement or feature request bug briefly describe your proposal component does not have tooltip or arialabels defined for screen readability which versions of angular and fundamental library for angular are affected if this is a feature request use current version if this is a bug please provide steps for reproducing it please provide relevant source code if applicable is there anything else we should know | 0 |
531,779 | 15,505,059,796 | IssuesEvent | 2021-03-11 14:57:20 | tsgrp/OpenAnnotate | https://api.github.com/repos/tsgrp/OpenAnnotate | closed | OpenAnnotate does not display some Japanese characters correctly | Enhancement High Priority | There are some characters that we are not able to pass through to OpenAnnotate correctly.
This is what we would want it to actually look like -
If we look in the localization file that is being pulled back in the networks tab - we can see that the characters are not being passed back correctly.
OCMS is able to pass the characters through correctly - so we need to figure out what the missing piece is.
| 1.0 | OpenAnnotate does not display some Japanese characters correctly - There are some characters that we are not able to pass through to OpenAnnotate correctly.
This is what we would want it to actually look like -
If we look in the localization file that is being pulled back in the networks tab - we can see that the characters are not being passed back correctly.
OCMS is able to pass the characters through correctly - so we need to figure out what the missing piece is.
| priority | openannotate does not display some japanese characters correctly there are some characters that we are not able to pass through to openannotate correctly this is what we would want it to actually look like if we look in the localization file that is being pulled back in the networks tab we can see that the characters are not being passed back correctly ocms is able to pass the characters through correctly so we need to figure out what the missing piece is | 1 |
504,202 | 14,614,973,369 | IssuesEvent | 2020-12-22 10:45:37 | wso2/docs-ei | https://api.github.com/repos/wso2/docs-ei | closed | [SAP Integration] Add jars to the doc | Priority/High Type/Improvement micro-integrator | **Description:**
Doc: https://ei.docs.wso2.com/en/7.1.0/micro-integrator/use-cases/tutorials/sap-integration/
Since the following jars are hard to find, shall we commit the jars here https://github.com/wso2-docs/WSO2_EI and refer them in the doc.
The following jars and dll file needs to be added.
- sapidoc3.jar
- sapjco3.jar
- sapjco3.dll
Further add the following Windows commands as well
**Section: Installing the SAP Adapter**
Step6
**Configuring WSO2 SAP Adapter**
Step3
Sending BAPIs
Receiving BAPIs | 1.0 | [SAP Integration] Add jars to the doc - **Description:**
Doc: https://ei.docs.wso2.com/en/7.1.0/micro-integrator/use-cases/tutorials/sap-integration/
Since the following jars are hard to find, shall we commit the jars here https://github.com/wso2-docs/WSO2_EI and refer them in the doc.
The following jars and dll file needs to be added.
- sapidoc3.jar
- sapjco3.jar
- sapjco3.dll
Further add the following Windows commands as well
**Section: Installing the SAP Adapter**
Step6
**Configuring WSO2 SAP Adapter**
Step3
Sending BAPIs
Receiving BAPIs | priority | add jars to the doc description doc since the following jars are hard to find shall we commit the jars here and refer them in the doc the following jars and dll file needs to be added jar jar dll further add the following windows commands as well section installing the sap adapter configuring sap adapter sending bapis receiving bapis | 1 |
181,839 | 21,664,452,383 | IssuesEvent | 2022-05-07 01:23:50 | n-devs/edit-map | https://api.github.com/repos/n-devs/edit-map | closed | CVE-2018-6342 (High) detected in react-dev-utils-4.2.3.tgz - autoclosed | security vulnerability | ## CVE-2018-6342 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>react-dev-utils-4.2.3.tgz</b></p></summary>
<p>Webpack utilities used by Create React App</p>
<p>Library home page: <a href="https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-4.2.3.tgz">https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-4.2.3.tgz</a></p>
<p>Path to dependency file: /edit-map/v0.4/package.json</p>
<p>Path to vulnerable library: /tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-1.0.13.tgz (Root Library)
- :x: **react-dev-utils-4.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/n-psk/edit-map/commits/1dc8fdb4f8c25647b64d8935674bd1baedd1438e">1dc8fdb4f8c25647b64d8935674bd1baedd1438e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
react-dev-utils on Windows allows developers to run a local webserver for accepting various commands, including a command to launch an editor. The input to that command was not properly sanitized, allowing an attacker who can make a network request to the server (either via CSRF or by direct request) to execute arbitrary commands on the targeted system. This issue affects multiple branches: 1.x.x prior to 1.0.4, 2.x.x prior to 2.0.2, 3.x.x prior to 3.1.2, 4.x.x prior to 4.2.2, and 5.x.x prior to 5.0.2.
<p>Publish Date: 2018-12-31
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6342>CVE-2018-6342</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6342">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6342</a></p>
<p>Release Date: 2018-12-31</p>
<p>Fix Resolution: 1.0.4,2.0.2,3.1.2,4.2.2,5.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-6342 (High) detected in react-dev-utils-4.2.3.tgz - autoclosed - ## CVE-2018-6342 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>react-dev-utils-4.2.3.tgz</b></p></summary>
<p>Webpack utilities used by Create React App</p>
<p>Library home page: <a href="https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-4.2.3.tgz">https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-4.2.3.tgz</a></p>
<p>Path to dependency file: /edit-map/v0.4/package.json</p>
<p>Path to vulnerable library: /tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json,/tmp/git/edit-map/v0.1/node_modules/react-dev-utils/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-1.0.13.tgz (Root Library)
- :x: **react-dev-utils-4.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/n-psk/edit-map/commits/1dc8fdb4f8c25647b64d8935674bd1baedd1438e">1dc8fdb4f8c25647b64d8935674bd1baedd1438e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
react-dev-utils on Windows allows developers to run a local webserver for accepting various commands, including a command to launch an editor. The input to that command was not properly sanitized, allowing an attacker who can make a network request to the server (either via CSRF or by direct request) to execute arbitrary commands on the targeted system. This issue affects multiple branches: 1.x.x prior to 1.0.4, 2.x.x prior to 2.0.2, 3.x.x prior to 3.1.2, 4.x.x prior to 4.2.2, and 5.x.x prior to 5.0.2.
<p>Publish Date: 2018-12-31
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6342>CVE-2018-6342</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6342">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-6342</a></p>
<p>Release Date: 2018-12-31</p>
<p>Fix Resolution: 1.0.4,2.0.2,3.1.2,4.2.2,5.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in react dev utils tgz autoclosed cve high severity vulnerability vulnerable library react dev utils tgz webpack utilities used by create react app library home page a href path to dependency file edit map package json path to vulnerable library tmp git edit map node modules react dev utils package json tmp git edit map node modules react dev utils package json tmp git edit map node modules react dev utils package json tmp git edit map node modules react dev utils package json tmp git edit map node modules react dev utils package json tmp git edit map node modules react dev utils package json tmp git edit map node modules react dev utils package json dependency hierarchy react scripts tgz root library x react dev utils tgz vulnerable library found in head commit a href vulnerability details react dev utils on windows allows developers to run a local webserver for accepting various commands including a command to launch an editor the input to that command was not properly sanitized allowing an attacker who can make a network request to the server either via csrf or by direct request to execute arbitrary commands on the targeted system this issue affects multiple branches x x prior to x x prior to x x prior to x x prior to and x x prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
87,324 | 8,071,910,754 | IssuesEvent | 2018-08-06 14:31:26 | GTNewHorizons/NewHorizons | https://api.github.com/repos/GTNewHorizons/NewHorizons | closed | Make rutile quests optional-Titan Ore balancing | FixedInDev need to be tested | #### Which modpack version are you using?
2.0.4.6
#
#### What do you suggest instead/what changes do you propose?
There is no need to make titanium from rutile when you already found a pure titanium vein on the moon. Making titanium from bauxite and ilmenite is really inefficient and completely useless when you already found the pure titanium vein. So I'm either for making the quests optional or moving the pure titanium back to Mars. | 1.0 | Make rutile quests optional-Titan Ore balancing - #### Which modpack version are you using?
2.0.4.6
#
#### What do you suggest instead/what changes do you propose?
There is no need to make titanium from rutile when you already found a pure titanium vein on the moon. Making titanium from bauxite and ilmenite is really inefficient and completely useless when you already found the pure titanium vein. So I'm either for making the quests optional or moving the pure titanium back to Mars. | non_priority | make rutile quests optional titan ore balancing which modpack version are you using what do you suggest instead what changes do you propose there is no need to make titanium from rutile when you already found a pure titanium vein on the moon making titanium from bauxite and ilmenite is really inefficient and completely useless when you already found the pure titanium vein so i m either for making the quests optional or moving the pure titanium back to mars | 0 |
325,358 | 9,923,243,184 | IssuesEvent | 2019-07-01 06:37:46 | deep-learning-indaba/Baobab | https://api.github.com/repos/deep-learning-indaba/Baobab | closed | Invitation Letter Controller | High Priority back-end enhancement | Implement the Invitation Letter Controller as per the [Registration specification](https://docs.google.com/document/d/1dBTfmsBvWtCEw36mKYIgRsvMxE0BhMT-mU9iHVcWTrs/edit#). The invitation letter controller needs to save the invitation letter request, .
Create `api/app/invitationletter/api.py` controller:
POST method:
```
{
registration_id: 1,
event_id: 1,
work_address: "Somewhere over the rainbow",
addressed_to: "Sir",
residential address: "Way up high"
passport_name: "Jane Doe",
passport_no: "23456565",
passport_issued_by: "Neverland"
to_date: datetime,
from_date: datetime
}
```
Controller functionality:
1. Persist the InvitationLetterRequest
2. Go fetch the related *offer*.
- If the offer has travel & accomodation -> then get the InvitationTemplate, for the correct event, that has `send_for_both_travel_accom` set to true
- Else if the offer has travel - then get the InvitationTemplate, for the correct event, that has `send_for_travel_award_only`
- Else if the offer has accomodation - then get the InvitationTemplate, for the correct event, that has `send_for_accomodation_award_only`
2. Given the correct InvitationTemplate model, please get the related template, which will be a word document.
3. Fetch the relevant user, as we will need the following details from there:
- country_of_residence
- nationality
- date_of_birth
4. Fetch the relevant registration and registration_answers, extract from there whether or not the person will be presenting a poster.
5. Call the `generate` method of the Invitation letter generator specified in issue #328
6. Update the `invitation_letter_sent_at` field if sent correctly
7. Return the invitation letter request ID if correctly sent, else send the appropriate error
| 1.0 | Invitation Letter Controller - Implement the Invitation Letter Controller as per the [Registration specification](https://docs.google.com/document/d/1dBTfmsBvWtCEw36mKYIgRsvMxE0BhMT-mU9iHVcWTrs/edit#). The invitation letter controller needs to save the invitation letter request, .
Create `api/app/invitationletter/api.py` controller:
POST method:
```
{
registration_id: 1,
event_id: 1,
work_address: "Somewhere over the rainbow",
addressed_to: "Sir",
residential address: "Way up high"
passport_name: "Jane Doe",
passport_no: "23456565",
passport_issued_by: "Neverland"
to_date: datetime,
from_date: datetime
}
```
Controller functionality:
1. Persist the InvitationLetterRequest
2. Go fetch the related *offer*.
- If the offer has travel & accomodation -> then get the InvitationTemplate, for the correct event, that has `send_for_both_travel_accom` set to true
- Else if the offer has travel - then get the InvitationTemplate, for the correct event, that has `send_for_travel_award_only`
- Else if the offer has accomodation - then get the InvitationTemplate, for the correct event, that has `send_for_accomodation_award_only`
2. Given the correct InvitationTemplate model, please get the related template, which will be a word document.
3. Fetch the relevant user, as we will need the following details from there:
- country_of_residence
- nationality
- date_of_birth
4. Fetch the relevant registration and registration_answers, extract from there whether or not the person will be presenting a poster.
5. Call the `generate` method of the Invitation letter generator specified in issue #328
6. Update the `invitation_letter_sent_at` field if sent correctly
7. Return the invitation letter request ID if correctly sent, else send the appropriate error
| priority | invitation letter controller implement the invitation letter controller as per the the invitation letter controller needs to save the invitation letter request create api app invitationletter api py controller post method registration id event id work address somewhere over the rainbow addressed to sir residential address way up high passport name jane doe passport no passport issued by neverland to date datetime from date datetime controller functionality persist the invitationletterrequest go fetch the related offer if the offer has travel accomodation then get the invitationtemplate for the correct event that has send for both travel accom set to true else if the offer has travel then get the invitationtemplate for the correct event that has send for travel award only else if the offer has accomodation then get the invitationtemplate for the correct event that has send for accomodation award only given the correct invitationtemplate model please get the related template which will be a word document fetch the relevant user as we will need the following details from there country of residence nationality date of birth fetch the relevant registration and registration answers extract from there whether or not the person will be presenting a poster call the generate method of the invitation letter generator specified in issue update the invitation letter sent at field if sent correctly return the invitation letter request id if correctly sent else send the appropriate error | 1 |
41,713 | 5,356,965,144 | IssuesEvent | 2017-02-20 16:59:19 | phetsims/make-a-ten | https://api.github.com/repos/phetsims/make-a-ten | closed | Should the keypad be a modal? | design:general status:ready-for-review type:question | @jonathanolson @amanda-phet as it stands, when I click on the edit buttons to bring up the keypad, the only way "out" is to either submit a number or press Reset All. Clicking elsewhere in the sim, or clicking the edit button again, does not dismiss the keypad. This is unfortunate because both of those options, submit and/or Reset All, will wipe any progress I've made on this screen. This is especially punishing if I hit the edit button on accident. Maybe we bring up the keypad as a modal, and put a barrier rectangle behind it so it's dismissible? I'm think something along the lines of what [Unit Rates](http://www.colorado.edu/physics/phet/dev/html/unit-rates/1.0.0-dev.39/unit-rates_en.html) is doing.
For phetsims/tasks/issues/767. | 1.0 | Should the keypad be a modal? - @jonathanolson @amanda-phet as it stands, when I click on the edit buttons to bring up the keypad, the only way "out" is to either submit a number or press Reset All. Clicking elsewhere in the sim, or clicking the edit button again, does not dismiss the keypad. This is unfortunate because both of those options, submit and/or Reset All, will wipe any progress I've made on this screen. This is especially punishing if I hit the edit button on accident. Maybe we bring up the keypad as a modal, and put a barrier rectangle behind it so it's dismissible? I'm think something along the lines of what [Unit Rates](http://www.colorado.edu/physics/phet/dev/html/unit-rates/1.0.0-dev.39/unit-rates_en.html) is doing.
For phetsims/tasks/issues/767. | non_priority | should the keypad be a modal jonathanolson amanda phet as it stands when i click on the edit buttons to bring up the keypad the only way out is to either submit a number or press reset all clicking elsewhere in the sim or clicking the edit button again does not dismiss the keypad this is unfortunate because both of those options submit and or reset all will wipe any progress i ve made on this screen this is especially punishing if i hit the edit button on accident maybe we bring up the keypad as a modal and put a barrier rectangle behind it so it s dismissible i m think something along the lines of what is doing for phetsims tasks issues | 0 |
29,425 | 24,004,967,810 | IssuesEvent | 2022-09-14 14:12:20 | opendp/opendp | https://api.github.com/repos/opendp/opendp | closed | CsvDomain | good first issue OpenDP Core CATEGORY: Infrastructure | The input domain for `make_split_dataframe` (as well as some other dataframe constructors) is too vague-- `AllDomain<String>`. SymmetricDistance isn't well-defined between strings, and we can't define it generally on strings because it is also invalid to apply in other contexts.
Accompanying the introduction of CsvDomain should be a description on how SymmetricDistance is defined between any two members of CsvDomain- likely based on newlines. | 1.0 | CsvDomain - The input domain for `make_split_dataframe` (as well as some other dataframe constructors) is too vague-- `AllDomain<String>`. SymmetricDistance isn't well-defined between strings, and we can't define it generally on strings because it is also invalid to apply in other contexts.
Accompanying the introduction of CsvDomain should be a description on how SymmetricDistance is defined between any two members of CsvDomain- likely based on newlines. | non_priority | csvdomain the input domain for make split dataframe as well as some other dataframe constructors is too vague alldomain symmetricdistance isn t well defined between strings and we can t define it generally on strings because it is also invalid to apply in other contexts accompanying the introduction of csvdomain should be a description on how symmetricdistance is defined between any two members of csvdomain likely based on newlines | 0 |
26,598 | 13,064,308,986 | IssuesEvent | 2020-07-30 17:52:53 | google/model-viewer | https://api.github.com/repos/google/model-viewer | closed | Progress bar shows when reveal=interaction and the model hasn't been interacted with | arc: interaction arc: performance flag: partner type: bug | I noticed that if you put `reveal="interaction"`, a progress bar will appear even if the model isn't loading. Is this the progress of generating the env map?
Notice in that gif on page load, you see the progress bar. Then when you click the viewer, it loads the glb and shows a second progress bar.
Try it for yourself:
https://clever-echidna.glitch.me/
This was introduced with 0.7.1
### Browser Affected
<!-- Check all that apply and please include the version tested -->
- [x] All
### OS
<!-- Check all that apply and please include the version tested -->
- [x] All
### Versions
<!--
Include the version of `<model-viewer>`, three.js, along with any polyfills that you're
using. The output of `npm ls` should include this information (if you're using npm).
-->
- model-viewer: v0.7.2
- three.js: r109
| True | Progress bar shows when reveal=interaction and the model hasn't been interacted with - I noticed that if you put `reveal="interaction"`, a progress bar will appear even if the model isn't loading. Is this the progress of generating the env map?
Notice in that gif on page load, you see the progress bar. Then when you click the viewer, it loads the glb and shows a second progress bar.
Try it for yourself:
https://clever-echidna.glitch.me/
This was introduced with 0.7.1
### Browser Affected
<!-- Check all that apply and please include the version tested -->
- [x] All
### OS
<!-- Check all that apply and please include the version tested -->
- [x] All
### Versions
<!--
Include the version of `<model-viewer>`, three.js, along with any polyfills that you're
using. The output of `npm ls` should include this information (if you're using npm).
-->
- model-viewer: v0.7.2
- three.js: r109
| non_priority | progress bar shows when reveal interaction and the model hasn t been interacted with i noticed that if you put reveal interaction a progress bar will appear even if the model isn t loading is this the progress of generating the env map notice in that gif on page load you see the progress bar then when you click the viewer it loads the glb and shows a second progress bar try it for yourself this was introduced with browser affected all os all versions include the version of three js along with any polyfills that you re using the output of npm ls should include this information if you re using npm model viewer three js | 0 |
391,053 | 26,879,020,837 | IssuesEvent | 2023-02-05 12:06:18 | mrcocoball/date-planner | https://api.github.com/repos/mrcocoball/date-planner | closed | [공통] 프로젝트 기획 - 벤치마킹 | documentation | 아이템, STP 전략 수립 후 벤치마킹할 플랫폼을 찾았다면
아래 영역에 대해 레퍼런스를 조사한 뒤 벤치마킹할 요소를 정리해둔다
* [x] 백엔드
* [x] 엔티티 및 도메인 구성
* [x] 주요 기능
* [ ] 프론트엔드
* [ ] UI & UX | 1.0 | [공통] 프로젝트 기획 - 벤치마킹 - 아이템, STP 전략 수립 후 벤치마킹할 플랫폼을 찾았다면
아래 영역에 대해 레퍼런스를 조사한 뒤 벤치마킹할 요소를 정리해둔다
* [x] 백엔드
* [x] 엔티티 및 도메인 구성
* [x] 주요 기능
* [ ] 프론트엔드
* [ ] UI & UX | non_priority | 프로젝트 기획 벤치마킹 아이템 stp 전략 수립 후 벤치마킹할 플랫폼을 찾았다면 아래 영역에 대해 레퍼런스를 조사한 뒤 벤치마킹할 요소를 정리해둔다 백엔드 엔티티 및 도메인 구성 주요 기능 프론트엔드 ui ux | 0 |
32,869 | 12,151,824,207 | IssuesEvent | 2020-04-24 20:47:05 | LevyForchh/superglue | https://api.github.com/repos/LevyForchh/superglue | opened | CVE-2020-11112 (High) detected in jackson-databind-2.9.6.jar, jackson-databind-2.8.11.3.jar | security vulnerability | ## CVE-2020-11112 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- logstash-logback-encoder-4.11.jar (Root Library)
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.8.11.3/844df5aba5a1a56e00905b165b12bb34116ee858/jackson-databind-2.8.11.3.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.8.11.3/844df5aba5a1a56e00905b165b12bb34116ee858/jackson-databind-2.8.11.3.jar</p>
<p>
Dependency Hierarchy:
- logstash-logback-encoder-4.11.jar (Root Library)
- :x: **jackson-databind-2.8.11.3.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/LevyForchh/superglue/commits/7a708af56446441da5694d317b0cc0de8ad0141b">7a708af56446441da5694d317b0cc0de8ad0141b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","isTransitiveDependency":true,"dependencyTree":"net.logstash.logback:logstash-logback-encoder:4.11;com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.11.3","isTransitiveDependency":true,"dependencyTree":"net.logstash.logback:logstash-logback-encoder:4.11;com.fasterxml.jackson.core:jackson-databind:2.8.11.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0"}],"vulnerabilityIdentifier":"CVE-2020-11112","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11112 (High) detected in jackson-databind-2.9.6.jar, jackson-databind-2.8.11.3.jar - ## CVE-2020-11112 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- logstash-logback-encoder-4.11.jar (Root Library)
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.8.11.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.8.11.3/844df5aba5a1a56e00905b165b12bb34116ee858/jackson-databind-2.8.11.3.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.8.11.3/844df5aba5a1a56e00905b165b12bb34116ee858/jackson-databind-2.8.11.3.jar</p>
<p>
Dependency Hierarchy:
- logstash-logback-encoder-4.11.jar (Root Library)
- :x: **jackson-databind-2.8.11.3.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/LevyForchh/superglue/commits/7a708af56446441da5694d317b0cc0de8ad0141b">7a708af56446441da5694d317b0cc0de8ad0141b</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","isTransitiveDependency":true,"dependencyTree":"net.logstash.logback:logstash-logback-encoder:4.11;com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.11.3","isTransitiveDependency":true,"dependencyTree":"net.logstash.logback:logstash-logback-encoder:4.11;com.fasterxml.jackson.core:jackson-databind:2.8.11.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0"}],"vulnerabilityIdentifier":"CVE-2020-11112","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy logstash logback encoder jar root library x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to vulnerable library root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy logstash logback encoder jar root library x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy vulnerabilityurl | 0 |
294,273 | 22,144,357,167 | IssuesEvent | 2022-06-03 10:18:26 | taurr/bevy-atlas-loader | https://api.github.com/repos/taurr/bevy-atlas-loader | closed | Enhance the documentation | documentation | * [ ] create link to the examples
* [ ] touchup doc for all public structs
* [ ] touchup dox for all public functions
* [ ] include small examles?
* [ ] add grafical links to crates.io info etc. (docs, GH, build status...)
| 1.0 | Enhance the documentation - * [ ] create link to the examples
* [ ] touchup doc for all public structs
* [ ] touchup dox for all public functions
* [ ] include small examles?
* [ ] add grafical links to crates.io info etc. (docs, GH, build status...)
| non_priority | enhance the documentation create link to the examples touchup doc for all public structs touchup dox for all public functions include small examles add grafical links to crates io info etc docs gh build status | 0 |
56,901 | 3,081,213,890 | IssuesEvent | 2015-08-22 13:57:32 | bitfighter/bitfighter | https://api.github.com/repos/bitfighter/bitfighter | closed | bring back the old Chat structure | 016 enhancement imported Priority-Medium | _From [rAtChEt9...@gmail.com](https://code.google.com/u/101173686111832050256/) on September 07, 2011 23:13:06_
In ZAP, I am missing the old Zapping system, which saved lots and lots of space, as well as a bit of organization.
It is a bit hard to explain, but it would separate the game elements, like capturing flags and dropping balls, from anytime a player zapped or got zapped.
In a typical situation, one player gets on a rampage killing 3 people within 10 seconds.
at the start of those 10 seconds, the top board may look like this, with two lines for so:
\~~~~~~~~~~~~~~~~~~~~~~~~
Watusimoto zapped Raptor
Sam686 zapped Zoomber
Zoomber dropped the flag!
Sam686 has extended the game
_k returned the flag!
Sam686 captured the flag!
\~~~~~~~~~~~~~~~~~~~~~
to something like this, when watusimoto shows off his zapping skills and zaps 3 people in a row.
\~~~~~~~~~~~~~~~~~~~~~~~~
Watusimoto zapped Raptor, Sam686, Raptor, Raptor, Raptor!
Sam686 zapped Zoomber
Sam686 has extended the game
_k returned the flag!
Sam686 captured the flag!
Zoomber Stole the flag
\~~~~~~~~~~~~~~~~~~~~~
In this case, instead of making 5 extra chat consuming zap lines:
Watusimoto zapped Raptor,
Watusitmoto zapped Sam686
Watusimoto zapped Raptor
and so on...
it put it all into one:
Watusimoto zapped Raptor, Sam686, Raptor, Raptor, Raptor!
Give it a chance, you may enjoy the outcome of it
_Original issue: http://code.google.com/p/bitfighter/issues/detail?id=124_ | 1.0 | bring back the old Chat structure - _From [rAtChEt9...@gmail.com](https://code.google.com/u/101173686111832050256/) on September 07, 2011 23:13:06_
In ZAP, I am missing the old Zapping system, which saved lots and lots of space, as well as a bit of organization.
It is a bit hard to explain, but it would separate the game elements, like capturing flags and dropping balls, from anytime a player zapped or got zapped.
In a typical situation, one player gets on a rampage killing 3 people within 10 seconds.
at the start of those 10 seconds, the top board may look like this, with two lines for so:
\~~~~~~~~~~~~~~~~~~~~~~~~
Watusimoto zapped Raptor
Sam686 zapped Zoomber
Zoomber dropped the flag!
Sam686 has extended the game
_k returned the flag!
Sam686 captured the flag!
\~~~~~~~~~~~~~~~~~~~~~
to something like this, when watusimoto shows off his zapping skills and zaps 3 people in a row.
\~~~~~~~~~~~~~~~~~~~~~~~~
Watusimoto zapped Raptor, Sam686, Raptor, Raptor, Raptor!
Sam686 zapped Zoomber
Sam686 has extended the game
_k returned the flag!
Sam686 captured the flag!
Zoomber Stole the flag
\~~~~~~~~~~~~~~~~~~~~~
In this case, instead of making 5 extra chat consuming zap lines:
Watusimoto zapped Raptor,
Watusitmoto zapped Sam686
Watusimoto zapped Raptor
and so on...
it put it all into one:
Watusimoto zapped Raptor, Sam686, Raptor, Raptor, Raptor!
Give it a chance, you may enjoy the outcome of it
_Original issue: http://code.google.com/p/bitfighter/issues/detail?id=124_ | priority | bring back the old chat structure from on september in zap i am missing the old zapping system which saved lots and lots of space as well as a bit of organization it is a bit hard to explain but it would separate the game elements like capturing flags and dropping balls from anytime a player zapped or got zapped in a typical situation one player gets on a rampage killing people within seconds at the start of those seconds the top board may look like this with two lines for so watusimoto zapped raptor zapped zoomber zoomber dropped the flag has extended the game k returned the flag captured the flag to something like this when watusimoto shows off his zapping skills and zaps people in a row watusimoto zapped raptor raptor raptor raptor zapped zoomber has extended the game k returned the flag captured the flag zoomber stole the flag in this case instead of making extra chat consuming zap lines watusimoto zapped raptor watusitmoto zapped watusimoto zapped raptor and so on it put it all into one watusimoto zapped raptor raptor raptor raptor give it a chance you may enjoy the outcome of it original issue | 1 |
373,190 | 11,035,220,555 | IssuesEvent | 2019-12-07 12:05:55 | bounswe/bounswe2019group11 | https://api.github.com/repos/bounswe/bounswe2019group11 | closed | Implement Comments on Articles | Component: Frontend Estimation: M Priority: High Status: In Progress | - All users need to be able to view comments on articles.
- Registered users need to be able to add new comments to articles.
- Registered users can like and dislike individual comments. | 1.0 | Implement Comments on Articles - - All users need to be able to view comments on articles.
- Registered users need to be able to add new comments to articles.
- Registered users can like and dislike individual comments. | priority | implement comments on articles all users need to be able to view comments on articles registered users need to be able to add new comments to articles registered users can like and dislike individual comments | 1 |
534,178 | 15,611,487,713 | IssuesEvent | 2021-03-19 14:22:35 | Etimo/homepage | https://api.github.com/repos/Etimo/homepage | closed | Move section "Våra kunder" to top (directly after header section) | Priority 3 Ready for development | On https://etimo.se/kunder-och-expertis the section "Våra kunder" should be moved to the top (well, after the header section of course).
Since all sections should have alternating background colors (grey, then white, then grey etc.), this also means that section background colors need to be updated. | 1.0 | Move section "Våra kunder" to top (directly after header section) - On https://etimo.se/kunder-och-expertis the section "Våra kunder" should be moved to the top (well, after the header section of course).
Since all sections should have alternating background colors (grey, then white, then grey etc.), this also means that section background colors need to be updated. | priority | move section våra kunder to top directly after header section on the section våra kunder should be moved to the top well after the header section of course since all sections should have alternating background colors grey then white then grey etc this also means that section background colors need to be updated | 1 |
815,997 | 30,582,832,119 | IssuesEvent | 2023-07-21 11:02:33 | hashgraph/guardian | https://api.github.com/repos/hashgraph/guardian | closed | Docker compose is failing on policy service buildstep | bug community Priority P1 | ### Problem description
I have attempted to pull down and run the latest Guardian code, from main branch (last tag v2.14.2)
Attempts have been made on three different systems/OS:
- Digital Ocean (Ubuntu 20.04.2 LTS)
- OSX iMac (13.4.1 - Ventura)
- OSX iMac (12.x - Montgomery)
All systems have failed to run the docker build at **Step 11/11** is failing for _ERROR [policy-service policyservicebuilder 11/11] RUN yarn run build:prod_
See screenshot below.
### Step to reproduce
Following the documentation:
1. Configure `GUARDIAN_ENV="develop"` in .env
2. Add `OPERATOR_KEY`, `OPERATOR_ID`, and `IPFS_STORAGE_API_KEY` for web3.storage.
3. Run `docker compose up -d --build`
### Expected behavior
Docker compose builds and runs the service.
### Screenshots
I have listed two screenshots first from my local environment and second from my digital ocean droplet, both failing error messages are the same.
## From my local system
<img width="1247" alt="Screenshot 2023-07-19 at 16 36 21" src="https://github.com/hashgraph/guardian/assets/6974163/8edc38ee-a443-4e03-aa50-652fcfc65e10">
## From my digitalocean droplet
<img width="1640" alt="Screenshot 2023-07-19 at 16 39 24" src="https://github.com/hashgraph/guardian/assets/6974163/e128c7af-ce88-4eb1-bfd5-939cf5767d26">
| 1.0 | Docker compose is failing on policy service buildstep - ### Problem description
I have attempted to pull down and run the latest Guardian code, from main branch (last tag v2.14.2)
Attempts have been made on three different systems/OS:
- Digital Ocean (Ubuntu 20.04.2 LTS)
- OSX iMac (13.4.1 - Ventura)
- OSX iMac (12.x - Montgomery)
All systems have failed to run the docker build at **Step 11/11** is failing for _ERROR [policy-service policyservicebuilder 11/11] RUN yarn run build:prod_
See screenshot below.
### Step to reproduce
Following the documentation:
1. Configure `GUARDIAN_ENV="develop"` in .env
2. Add `OPERATOR_KEY`, `OPERATOR_ID`, and `IPFS_STORAGE_API_KEY` for web3.storage.
3. Run `docker compose up -d --build`
### Expected behavior
Docker compose builds and runs the service.
### Screenshots
I have listed two screenshots first from my local environment and second from my digital ocean droplet, both failing error messages are the same.
## From my local system
<img width="1247" alt="Screenshot 2023-07-19 at 16 36 21" src="https://github.com/hashgraph/guardian/assets/6974163/8edc38ee-a443-4e03-aa50-652fcfc65e10">
## From my digitalocean droplet
<img width="1640" alt="Screenshot 2023-07-19 at 16 39 24" src="https://github.com/hashgraph/guardian/assets/6974163/e128c7af-ce88-4eb1-bfd5-939cf5767d26">
| priority | docker compose is failing on policy service buildstep problem description i have attempted to pull down and run the latest guardian code from main branch last tag attempts have been made on three different systems os digital ocean ubuntu lts osx imac ventura osx imac x montgomery all systems have failed to run the docker build at step is failing for error run yarn run build prod see screenshot below step to reproduce following the documentation configure guardian env develop in env add operator key operator id and ipfs storage api key for storage run docker compose up d build expected behavior docker compose builds and runs the service screenshots i have listed two screenshots first from my local environment and second from my digital ocean droplet both failing error messages are the same from my local system img width alt screenshot at src from my digitalocean droplet img width alt screenshot at src | 1 |
157,725 | 6,011,570,806 | IssuesEvent | 2017-06-06 15:27:37 | craftercms/craftercms | https://api.github.com/repos/craftercms/craftercms | closed | [studio] dependencies are not deployed after move | bug Priority: High | # steps to reproduce
1. create a page with a component or template dependency (never published)
2. move the page to a new location
3. publish the page
4. note that the dependency is not calculated/deployed with the item
| 1.0 | [studio] dependencies are not deployed after move - # steps to reproduce
1. create a page with a component or template dependency (never published)
2. move the page to a new location
3. publish the page
4. note that the dependency is not calculated/deployed with the item
| priority | dependencies are not deployed after move steps to reproduce create a page with a component or template dependency never published move the page to a new location publish the page note that the dependency is not calculated deployed with the item | 1 |
149,964 | 23,580,704,485 | IssuesEvent | 2022-08-23 07:24:59 | Etimo/etimo-achievements | https://api.github.com/repos/Etimo/etimo-achievements | closed | Sökruta för achievements | design feature frontend | Gör en kombinerad sök/select lista för achievements, så man kan söka på achievementnamn och description | 1.0 | Sökruta för achievements - Gör en kombinerad sök/select lista för achievements, så man kan söka på achievementnamn och description | non_priority | sökruta för achievements gör en kombinerad sök select lista för achievements så man kan söka på achievementnamn och description | 0 |
26,576 | 2,684,877,749 | IssuesEvent | 2015-03-29 13:28:29 | ConEmu/old-issues | https://api.github.com/repos/ConEmu/old-issues | closed | Unable to display settings | 1 star bug imported Priority-Medium | _From [peter.su...@gmail.com](https://code.google.com/u/111208667693142380164/) on June 14, 2013 04:10:44_
Required information! OS version: Win7 SP1 x86/x64 ConEmu version: Latest preview Far version (if you are using Far Manager): ? *Bug description* If you hide the tabs toolbar and also enabled quake mode
you are unable to bring up the settings dialog afterwards. *Steps to reproduction* 1. Tabs->Don't show
2. Appearance->Quake style slide down
3. You cannot access the settings dialog anymore
Solution was to manually change the Tabs registry key to 01 and
restart conemu and tabs toolbar is again visible.
_Original issue: http://code.google.com/p/conemu-maximus5/issues/detail?id=1097_ | 1.0 | Unable to display settings - _From [peter.su...@gmail.com](https://code.google.com/u/111208667693142380164/) on June 14, 2013 04:10:44_
Required information! OS version: Win7 SP1 x86/x64 ConEmu version: Latest preview Far version (if you are using Far Manager): ? *Bug description* If you hide the tabs toolbar and also enabled quake mode
you are unable to bring up the settings dialog afterwards. *Steps to reproduction* 1. Tabs->Don't show
2. Appearance->Quake style slide down
3. You cannot access the settings dialog anymore
Solution was to manually change the Tabs registry key to 01 and
restart conemu and tabs toolbar is again visible.
_Original issue: http://code.google.com/p/conemu-maximus5/issues/detail?id=1097_ | priority | unable to display settings from on june required information os version conemu version latest preview far version if you are using far manager bug description if you hide the tabs toolbar and also enabled quake mode you are unable to bring up the settings dialog afterwards steps to reproduction tabs don t show appearance quake style slide down you cannot access the settings dialog anymore solution was to manually change the tabs registry key to and restart conemu and tabs toolbar is again visible original issue | 1 |
636,941 | 20,614,100,865 | IssuesEvent | 2022-03-07 11:29:01 | bitfoundation/bitframework | https://api.github.com/repos/bitfoundation/bitframework | closed | The CI pipeline is not catching all errors | bug area / components high priority | Currently, the CI pipeline is working only on the Test project and does not build other projects such as the playground project.
It is required for the integrity of this product that the CI builds all of the projects inside the solution. | 1.0 | The CI pipeline is not catching all errors - Currently, the CI pipeline is working only on the Test project and does not build other projects such as the playground project.
It is required for the integrity of this product that the CI builds all of the projects inside the solution. | priority | the ci pipeline is not catching all errors currently the ci pipeline is working only on the test project and does not build other projects such as the playground project it is required for the integrity of this product that the ci builds all of the projects inside the solution | 1 |
250,816 | 7,988,197,240 | IssuesEvent | 2018-07-19 10:12:28 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.google.com - see bug description | browser-firefox-mobile priority-critical | <!-- @browser: Firefox Mobile 63.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:63.0) Gecko/63.0 Firefox/63.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.google.com/maps/@33.8177479,-117.8777979,6480.7121448785674a,30y
**Browser / Version**: Firefox Mobile 63.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: No
**Problem type**: Something else
**Description**: Cordinates on Gmap seem to be off, as in 2 opposing directions. Love N Peace HaX
**Steps to Reproduce**:
Oh I was just inviting a friend to tag my location on map. Was sejnt directly by contact.
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | www.google.com - see bug description - <!-- @browser: Firefox Mobile 63.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:63.0) Gecko/63.0 Firefox/63.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.google.com/maps/@33.8177479,-117.8777979,6480.7121448785674a,30y
**Browser / Version**: Firefox Mobile 63.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: No
**Problem type**: Something else
**Description**: Cordinates on Gmap seem to be off, as in 2 opposing directions. Love N Peace HaX
**Steps to Reproduce**:
Oh I was just inviting a friend to tag my location on map. Was sejnt directly by contact.
_From [webcompat.com](https://webcompat.com/) with ❤️_ | priority | see bug description url browser version firefox mobile operating system android tested another browser no problem type something else description cordinates on gmap seem to be off as in opposing directions love n peace hax steps to reproduce oh i was just inviting a friend to tag my location on map was sejnt directly by contact from with ❤️ | 1 |
3,514 | 2,690,983,710 | IssuesEvent | 2015-03-31 18:58:19 | robertocarroll/barjeel-app | https://api.github.com/repos/robertocarroll/barjeel-app | closed | Connect - Questions about user flow | 02_Connect design question | I have a few questions here:
1. Do you think the title and action should change on 3.2, so that it returns the user to the connect list rather than the app home?
2. What’s the user interaction to get between screen 3.2 and screen 3.3?
3. What’s the user interaction to get between screen 3.3 and screen 3.4?
4. What happens at the end of the sequence? i.e. when there are no more images?

| 1.0 | Connect - Questions about user flow - I have a few questions here:
1. Do you think the title and action should change on 3.2, so that it returns the user to the connect list rather than the app home?
2. What’s the user interaction to get between screen 3.2 and screen 3.3?
3. What’s the user interaction to get between screen 3.3 and screen 3.4?
4. What happens at the end of the sequence? i.e. when there are no more images?

| non_priority | connect questions about user flow i have a few questions here do you think the title and action should change on so that it returns the user to the connect list rather than the app home what’s the user interaction to get between screen and screen what’s the user interaction to get between screen and screen what happens at the end of the sequence i e when there are no more images | 0 |
369,822 | 10,918,491,546 | IssuesEvent | 2019-11-21 16:59:44 | DynamoRIO/dynamorio | https://api.github.com/repos/DynamoRIO/dynamorio | opened | drcachesim traces include never-executed memrefs beyond a faulting memref on multi-memref instrs | Component-DrCacheSim Priority-Low | While working on adding tests for #3937 I hit an issue that seems obvious but has a confusing history. For a multi-memref instruction, I put code in place in f9b691441ff4ce34d98e459bfc73db3fa052d004 for #2708 to handle a fault in the middle of the memrefs and not continue to the rest of them. However, the tracer's instrumentation records all memrefs before it executes the instruction, so the trace contains all of the memref addresses before the signal marker. I can't figure out why I put that memref-skipping code in place since it seems it would never be exercised with today's tracer. I don't think that -L0_filter is relevant because at an earlier point I put in custom entries for multi-memref there.
This issue covers documenting this slight trace inaccuracy, and possibly trying to fix it though it seems low priority. | 1.0 | drcachesim traces include never-executed memrefs beyond a faulting memref on multi-memref instrs - While working on adding tests for #3937 I hit an issue that seems obvious but has a confusing history. For a multi-memref instruction, I put code in place in f9b691441ff4ce34d98e459bfc73db3fa052d004 for #2708 to handle a fault in the middle of the memrefs and not continue to the rest of them. However, the tracer's instrumentation records all memrefs before it executes the instruction, so the trace contains all of the memref addresses before the signal marker. I can't figure out why I put that memref-skipping code in place since it seems it would never be exercised with today's tracer. I don't think that -L0_filter is relevant because at an earlier point I put in custom entries for multi-memref there.
This issue covers documenting this slight trace inaccuracy, and possibly trying to fix it though it seems low priority. | priority | drcachesim traces include never executed memrefs beyond a faulting memref on multi memref instrs while working on adding tests for i hit an issue that seems obvious but has a confusing history for a multi memref instruction i put code in place in for to handle a fault in the middle of the memrefs and not continue to the rest of them however the tracer s instrumentation records all memrefs before it executes the instruction so the trace contains all of the memref addresses before the signal marker i can t figure out why i put that memref skipping code in place since it seems it would never be exercised with today s tracer i don t think that filter is relevant because at an earlier point i put in custom entries for multi memref there this issue covers documenting this slight trace inaccuracy and possibly trying to fix it though it seems low priority | 1 |
14,381 | 9,300,986,970 | IssuesEvent | 2019-03-23 18:06:40 | fisker/blog | https://api.github.com/repos/fisker/blog | closed | CVE-2017-1000048 High Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.2.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>path: /tmp/git/blog/node_modules/qs/package.json</p>
<p>
<p>Library home page: <a href=https://registry.npmjs.org/qs/-/qs-6.2.3.tgz>https://registry.npmjs.org/qs/-/qs-6.2.3.tgz</a></p>
Dependency Hierarchy:
- browser-sync-2.26.3.tgz (Root Library)
- :x: **qs-6.2.3.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6">https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6</a></p>
<p>Release Date: 2017-03-06</p>
<p>Fix Resolution: Replace or update the following files: parse.js, parse.js, utils.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-1000048 High Severity Vulnerability detected by WhiteSource - ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-6.2.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>path: /tmp/git/blog/node_modules/qs/package.json</p>
<p>
<p>Library home page: <a href=https://registry.npmjs.org/qs/-/qs-6.2.3.tgz>https://registry.npmjs.org/qs/-/qs-6.2.3.tgz</a></p>
Dependency Hierarchy:
- browser-sync-2.26.3.tgz (Root Library)
- :x: **qs-6.2.3.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6">https://github.com/ljharb/qs/commit/c709f6e3ef2ed324f17c43369e1d45ad351e86e6</a></p>
<p>Release Date: 2017-03-06</p>
<p>Fix Resolution: Replace or update the following files: parse.js, parse.js, utils.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit path tmp git blog node modules qs package json library home page a href dependency hierarchy browser sync tgz root library x qs tgz vulnerable library vulnerability details the web framework using ljharb s qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following files parse js parse js utils js step up your open source security game with whitesource | 0 |
269,291 | 23,434,745,810 | IssuesEvent | 2022-08-15 08:32:33 | wso2/product-is | https://api.github.com/repos/wso2/product-is | opened | Required to test IS 6.0.0 with following compatibilities | test | **Is your suggestion a test requirement/change or improvements of the test framework? Please describe.**
Ubuntun 2022 LTS and add ARM Architecture
**Describe the solution you would prefer**
<!-- A clear and concise description of the required test information or framework improvements.For the test requirement: test types, test scenarios, test cases, steps and validations criterias -->
### Optional Fields
**Additional context**
<!-- Add any other context or screenshots about the test automation request here. e.g User scenario guide, functional Requirement Specifications (FRS) Documents -->
**Related Issues:**
<!-- Any related issues from this/other repositories-->
| 1.0 | Required to test IS 6.0.0 with following compatibilities - **Is your suggestion a test requirement/change or improvements of the test framework? Please describe.**
Ubuntun 2022 LTS and add ARM Architecture
**Describe the solution you would prefer**
<!-- A clear and concise description of the required test information or framework improvements.For the test requirement: test types, test scenarios, test cases, steps and validations criterias -->
### Optional Fields
**Additional context**
<!-- Add any other context or screenshots about the test automation request here. e.g User scenario guide, functional Requirement Specifications (FRS) Documents -->
**Related Issues:**
<!-- Any related issues from this/other repositories-->
| non_priority | required to test is with following compatibilities is your suggestion a test requirement change or improvements of the test framework please describe ubuntun lts and add arm architecture describe the solution you would prefer optional fields additional context related issues | 0 |
281,486 | 24,397,454,083 | IssuesEvent | 2022-10-04 20:41:34 | apache/beam | https://api.github.com/repos/apache/beam | closed | beam_PostCommit_Java_GradleBuild timing out (4 hours) | java tests core P3 bug | I believe that this PR is the culprit: https://github.com/apache/beam/pull/7175
Example log: https://builds.apache.org/job/beam_PostCommit_Java_GradleBuild/2041/
Imported from Jira [BEAM-6171](https://issues.apache.org/jira/browse/BEAM-6171). Original Jira may contain additional context.
Reported by: udim. | 1.0 | beam_PostCommit_Java_GradleBuild timing out (4 hours) - I believe that this PR is the culprit: https://github.com/apache/beam/pull/7175
Example log: https://builds.apache.org/job/beam_PostCommit_Java_GradleBuild/2041/
Imported from Jira [BEAM-6171](https://issues.apache.org/jira/browse/BEAM-6171). Original Jira may contain additional context.
Reported by: udim. | non_priority | beam postcommit java gradlebuild timing out hours i believe that this pr is the culprit example log imported from jira original jira may contain additional context reported by udim | 0 |
14,507 | 5,682,593,946 | IssuesEvent | 2017-04-13 10:07:30 | magicDGS/ReadTools | https://api.github.com/repos/magicDGS/ReadTools | closed | Properties for default values | build/developer doc no-compatible | The barcode tags in the BAM files (BC and B2) should be a property in the JVM, and be similarly managed as the default values in htsjdk. The same for the separator of dual indexes (and maybe between read name and barcodes, but that should be decided in #49). Like that, an user could specify their own defaults in their enviroments.
Because this is different as a parameter in the command line (using -D to the java command line), this should be documented in the wiki page (#57).
| 1.0 | Properties for default values - The barcode tags in the BAM files (BC and B2) should be a property in the JVM, and be similarly managed as the default values in htsjdk. The same for the separator of dual indexes (and maybe between read name and barcodes, but that should be decided in #49). Like that, an user could specify their own defaults in their enviroments.
Because this is different as a parameter in the command line (using -D to the java command line), this should be documented in the wiki page (#57).
| non_priority | properties for default values the barcode tags in the bam files bc and should be a property in the jvm and be similarly managed as the default values in htsjdk the same for the separator of dual indexes and maybe between read name and barcodes but that should be decided in like that an user could specify their own defaults in their enviroments because this is different as a parameter in the command line using d to the java command line this should be documented in the wiki page | 0 |
194,601 | 22,262,043,327 | IssuesEvent | 2022-06-10 02:01:44 | Nivaskumark/kernel_v4.19.72 | https://api.github.com/repos/Nivaskumark/kernel_v4.19.72 | reopened | WS-2021-0293 (Medium) detected in linux-yoctov5.4.51 | security vulnerability | ## WS-2021-0293 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.19.72/commit/7665378059da10e5ded7efbfccc88efce9e51dfc">7665378059da10e5ded7efbfccc88efce9e51dfc</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Linux Kernel in versions v4.7 to before v4.19.193 If ds->ops->get_sset_count() fails then it "count" is a negative error code such as -EOPNOTSUPP. Because "i" is an unsigned int, the negative error code is type promoted to a very high value and the loop will corrupt memory until the system crashes.
<p>Publish Date: 2021-06-04
<p>URL: <a href=https://github.com/gregkh/linux/commit/0f2cb08c57edefb0e7b5045e0e3e9980a3d3aa37>WS-2021-0293</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1000654">https://osv.dev/vulnerability/UVI-2021-1000654</a></p>
<p>Release Date: 2021-06-04</p>
<p>Fix Resolution: v4.19.193</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0293 (Medium) detected in linux-yoctov5.4.51 - ## WS-2021-0293 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/Nivaskumark/kernel_v4.19.72/commit/7665378059da10e5ded7efbfccc88efce9e51dfc">7665378059da10e5ded7efbfccc88efce9e51dfc</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Linux Kernel in versions v4.7 to before v4.19.193 If ds->ops->get_sset_count() fails then it "count" is a negative error code such as -EOPNOTSUPP. Because "i" is an unsigned int, the negative error code is type promoted to a very high value and the loop will corrupt memory until the system crashes.
<p>Publish Date: 2021-06-04
<p>URL: <a href=https://github.com/gregkh/linux/commit/0f2cb08c57edefb0e7b5045e0e3e9980a3d3aa37>WS-2021-0293</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1000654">https://osv.dev/vulnerability/UVI-2021-1000654</a></p>
<p>Release Date: 2021-06-04</p>
<p>Fix Resolution: v4.19.193</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in linux ws medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details linux kernel in versions to before if ds ops get sset count fails then it count is a negative error code such as eopnotsupp because i is an unsigned int the negative error code is type promoted to a very high value and the loop will corrupt memory until the system crashes publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
718,868 | 24,734,448,296 | IssuesEvent | 2022-10-20 20:32:37 | trufflesuite/truffle | https://api.github.com/repos/trufflesuite/truffle | closed | `truffle debug --fetch-external` mixes compilation options for different contracts when on Node 12 | bug Debugger priority3 🔧 | ## Issue
When using `truffle debug --fetch-external` on Node 12, compilation options will be carried over inbetween contracts. This means that some contracts will get compiled using the wrong options; this can result in compilation failure, or it can result in the compilation being sucessful but the debugger then failing to recognize the contract.
The problem seems to stem from the line `options = Config.default().merge(options)` in `sources()` in `compile-solidity`; for some reason, on Node 12, this call to `merge` modifies the `config` object in `fetch-and-compile` (which doesn't even get passed to `Compile.sources()`!). Since this doesn't happen on Node 14, this is presumably a bug in Node; nonetheless, we might want to figure out some workaround here so that things will work on Node 12.
## Steps to Reproduce
You can reproduce this error with the same example from #4616, except you use node 12, rather than node 14. And you don't need to advance into the contract once you've started up the debugger.
## Expected results
If you use node 14, which doesn't have this issue, on starting up the debugger you'll see
```
✔ Getting and compiling external sources...
✔ Gathering information about your project and the transaction...
Addresses affected:
0xC558F600B34A5f69dD2f0D06Cb8A88d829B7420a - UniswapV2Pair
0x5A98FcBEA516Cf06857215779Fd812CA3beF1B32 - MiniMeToken
0xC02aaA39b223FE8D0A0e5C4F27eAD9083C756Cc2 - WETH9
0xf73a1260d222f447210581DDf212D915c09a3249 - AppProxyUpgradeable
0xb8FFC3Cd6e7Cf5a098A1c92F48009765B24088Dc - KernelProxy
0x2b33CF282f867A7FF693A66e11B0FcC5552e4425 - Kernel
0xde3A93028F2283cc28756B3674BD657eaFB992f4 - TokenManager
0x0000000000004946c0e9F43F4Dee607b0eF1fA1c - ChiToken
0x0df6Ddf485395fd174ecd35acBac1e8476c89d12(UNKNOWN)
0x971b3eB9913093797d650D978Fa1E52E244Cce1a(UNKNOWN)
0x63CA114093159628070b24dC40C1b53c28dFC4ff(UNKNOWN)
0xFC45eE420599e0cC3c241273F50d9cF7e294aF2e(UNKNOWN)
0xE09a59A19C34E25c9E8783FBB45a2461E4C280D5(UNKNOWN)
0x000000bd31c24A2bd2835028c8F1E4D9d3f37108(UNKNOWN)
```
## Actual Results
If you've correctly reproduced the issue, you'll instead see
```
⚠ Errors occurred while compiling sources for addresses 0x0000000000004946c0e9F43F4Dee607b0eF1fA1c.
✔ Gathering information about your project and the transaction...
Addresses affected:
0xC558F600B34A5f69dD2f0D06Cb8A88d829B7420a - UniswapV2Pair
0x5A98FcBEA516Cf06857215779Fd812CA3beF1B32(UNKNOWN)
0xC02aaA39b223FE8D0A0e5C4F27eAD9083C756Cc2 - WETH9
0xf73a1260d222f447210581DDf212D915c09a3249(UNKNOWN)
0xb8FFC3Cd6e7Cf5a098A1c92F48009765B24088Dc(UNKNOWN)
0x2b33CF282f867A7FF693A66e11B0FcC5552e4425(UNKNOWN)
0xde3A93028F2283cc28756B3674BD657eaFB992f4(UNKNOWN)
0x0000000000004946c0e9F43F4Dee607b0eF1fA1c(UNKNOWN)
0x0df6Ddf485395fd174ecd35acBac1e8476c89d12(UNKNOWN)
0x971b3eB9913093797d650D978Fa1E52E244Cce1a(UNKNOWN)
0x63CA114093159628070b24dC40C1b53c28dFC4ff(UNKNOWN)
0xFC45eE420599e0cC3c241273F50d9cF7e294aF2e(UNKNOWN)
0xE09a59A19C34E25c9E8783FBB45a2461E4C280D5(UNKNOWN)
0x000000bd31c24A2bd2835028c8F1E4D9d3f37108(UNKNOWN)
```
Notice how one address failed to compile, while lots of others (that get recognized on Node 14) instead get marked as unknown. This is because they were compiled with the wrong options; more specifically, they were compiled using options carried over from other contracts in the transaction.
## Environment
* Truffle version (`truffle version`): 5.4.28
* node version (`node --version`): 12.22.9 | 1.0 | `truffle debug --fetch-external` mixes compilation options for different contracts when on Node 12 - ## Issue
When using `truffle debug --fetch-external` on Node 12, compilation options will be carried over inbetween contracts. This means that some contracts will get compiled using the wrong options; this can result in compilation failure, or it can result in the compilation being sucessful but the debugger then failing to recognize the contract.
The problem seems to stem from the line `options = Config.default().merge(options)` in `sources()` in `compile-solidity`; for some reason, on Node 12, this call to `merge` modifies the `config` object in `fetch-and-compile` (which doesn't even get passed to `Compile.sources()`!). Since this doesn't happen on Node 14, this is presumably a bug in Node; nonetheless, we might want to figure out some workaround here so that things will work on Node 12.
## Steps to Reproduce
You can reproduce this error with the same example from #4616, except you use node 12, rather than node 14. And you don't need to advance into the contract once you've started up the debugger.
## Expected results
If you use node 14, which doesn't have this issue, on starting up the debugger you'll see
```
✔ Getting and compiling external sources...
✔ Gathering information about your project and the transaction...
Addresses affected:
0xC558F600B34A5f69dD2f0D06Cb8A88d829B7420a - UniswapV2Pair
0x5A98FcBEA516Cf06857215779Fd812CA3beF1B32 - MiniMeToken
0xC02aaA39b223FE8D0A0e5C4F27eAD9083C756Cc2 - WETH9
0xf73a1260d222f447210581DDf212D915c09a3249 - AppProxyUpgradeable
0xb8FFC3Cd6e7Cf5a098A1c92F48009765B24088Dc - KernelProxy
0x2b33CF282f867A7FF693A66e11B0FcC5552e4425 - Kernel
0xde3A93028F2283cc28756B3674BD657eaFB992f4 - TokenManager
0x0000000000004946c0e9F43F4Dee607b0eF1fA1c - ChiToken
0x0df6Ddf485395fd174ecd35acBac1e8476c89d12(UNKNOWN)
0x971b3eB9913093797d650D978Fa1E52E244Cce1a(UNKNOWN)
0x63CA114093159628070b24dC40C1b53c28dFC4ff(UNKNOWN)
0xFC45eE420599e0cC3c241273F50d9cF7e294aF2e(UNKNOWN)
0xE09a59A19C34E25c9E8783FBB45a2461E4C280D5(UNKNOWN)
0x000000bd31c24A2bd2835028c8F1E4D9d3f37108(UNKNOWN)
```
## Actual Results
If you've correctly reproduced the issue, you'll instead see
```
⚠ Errors occurred while compiling sources for addresses 0x0000000000004946c0e9F43F4Dee607b0eF1fA1c.
✔ Gathering information about your project and the transaction...
Addresses affected:
0xC558F600B34A5f69dD2f0D06Cb8A88d829B7420a - UniswapV2Pair
0x5A98FcBEA516Cf06857215779Fd812CA3beF1B32(UNKNOWN)
0xC02aaA39b223FE8D0A0e5C4F27eAD9083C756Cc2 - WETH9
0xf73a1260d222f447210581DDf212D915c09a3249(UNKNOWN)
0xb8FFC3Cd6e7Cf5a098A1c92F48009765B24088Dc(UNKNOWN)
0x2b33CF282f867A7FF693A66e11B0FcC5552e4425(UNKNOWN)
0xde3A93028F2283cc28756B3674BD657eaFB992f4(UNKNOWN)
0x0000000000004946c0e9F43F4Dee607b0eF1fA1c(UNKNOWN)
0x0df6Ddf485395fd174ecd35acBac1e8476c89d12(UNKNOWN)
0x971b3eB9913093797d650D978Fa1E52E244Cce1a(UNKNOWN)
0x63CA114093159628070b24dC40C1b53c28dFC4ff(UNKNOWN)
0xFC45eE420599e0cC3c241273F50d9cF7e294aF2e(UNKNOWN)
0xE09a59A19C34E25c9E8783FBB45a2461E4C280D5(UNKNOWN)
0x000000bd31c24A2bd2835028c8F1E4D9d3f37108(UNKNOWN)
```
Notice how one address failed to compile, while lots of others (that get recognized on Node 14) instead get marked as unknown. This is because they were compiled with the wrong options; more specifically, they were compiled using options carried over from other contracts in the transaction.
## Environment
* Truffle version (`truffle version`): 5.4.28
* node version (`node --version`): 12.22.9 | priority | truffle debug fetch external mixes compilation options for different contracts when on node issue when using truffle debug fetch external on node compilation options will be carried over inbetween contracts this means that some contracts will get compiled using the wrong options this can result in compilation failure or it can result in the compilation being sucessful but the debugger then failing to recognize the contract the problem seems to stem from the line options config default merge options in sources in compile solidity for some reason on node this call to merge modifies the config object in fetch and compile which doesn t even get passed to compile sources since this doesn t happen on node this is presumably a bug in node nonetheless we might want to figure out some workaround here so that things will work on node steps to reproduce you can reproduce this error with the same example from except you use node rather than node and you don t need to advance into the contract once you ve started up the debugger expected results if you use node which doesn t have this issue on starting up the debugger you ll see ✔ getting and compiling external sources ✔ gathering information about your project and the transaction addresses affected minimetoken appproxyupgradeable kernelproxy kernel tokenmanager chitoken unknown unknown unknown unknown unknown unknown actual results if you ve correctly reproduced the issue you ll instead see ⚠ errors occurred while compiling sources for addresses ✔ gathering information about your project and the transaction addresses affected unknown unknown unknown unknown unknown unknown unknown unknown unknown unknown unknown unknown notice how one address failed to compile while lots of others that get recognized on node instead get marked as unknown this is because they were compiled with the wrong options more specifically they were compiled using options carried over from other contracts in the transaction environment truffle version truffle version node version node version | 1 |
138,468 | 18,793,934,658 | IssuesEvent | 2021-11-08 19:53:46 | Dima2022/hygieia-workflow-github-collector | https://api.github.com/repos/Dima2022/hygieia-workflow-github-collector | opened | CVE-2018-14721 (High) detected in jackson-databind-2.5.0.jar | security vulnerability | ## CVE-2018-14721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.5.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: hygieia-workflow-github-collector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.5.0/jackson-databind-2.5.0.jar</p>
<p>
Dependency Hierarchy:
- core-3.9.7.jar (Root Library)
- spring-boot-starter-web-1.3.0.RELEASE.jar
- :x: **jackson-databind-2.5.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/hygieia-workflow-github-collector/commit/236baaa856b74774f7b43ecb1eeade5a8d1d0496">236baaa856b74774f7b43ecb1eeade5a8d1d0496</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721>CVE-2018-14721</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.5.0","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"com.capitalone.dashboard:core:3.9.7;org.springframework.boot:spring-boot-starter-web:1.3.0.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.5.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14721","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-14721 (High) detected in jackson-databind-2.5.0.jar - ## CVE-2018-14721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.5.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: hygieia-workflow-github-collector/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.5.0/jackson-databind-2.5.0.jar</p>
<p>
Dependency Hierarchy:
- core-3.9.7.jar (Root Library)
- spring-boot-starter-web-1.3.0.RELEASE.jar
- :x: **jackson-databind-2.5.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/hygieia-workflow-github-collector/commit/236baaa856b74774f7b43ecb1eeade5a8d1d0496">236baaa856b74774f7b43ecb1eeade5a8d1d0496</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721>CVE-2018-14721</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.5.0","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"com.capitalone.dashboard:core:3.9.7;org.springframework.boot:spring-boot-starter-web:1.3.0.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.5.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14721","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file hygieia workflow github collector pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy core jar root library spring boot starter web release jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind x before might allow remote attackers to conduct server side request forgery ssrf attacks by leveraging failure to block the jaxws class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree com capitalone dashboard core org springframework boot spring boot starter web release com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before might allow remote attackers to conduct server side request forgery ssrf attacks by leveraging failure to block the jaxws class from polymorphic deserialization vulnerabilityurl | 0 |
630,319 | 20,105,041,495 | IssuesEvent | 2022-02-07 09:40:08 | StephanAkkerman/FinTwit_Bot | https://api.github.com/repos/StephanAkkerman/FinTwit_Bot | closed | Daily update on coingecko most searched coins | Priority: Low :3rd_place_medal: New feature :star: Difficulty: Easy 😊 | https://github.com/man-c/pycoingecko
trending
/search/trending (Get trending search coins (Top-7) on CoinGecko in the last 24 hours)
cg.get_search_trending() | 1.0 | Daily update on coingecko most searched coins - https://github.com/man-c/pycoingecko
trending
/search/trending (Get trending search coins (Top-7) on CoinGecko in the last 24 hours)
cg.get_search_trending() | priority | daily update on coingecko most searched coins trending search trending get trending search coins top on coingecko in the last hours cg get search trending | 1 |
56,019 | 11,495,525,601 | IssuesEvent | 2020-02-12 05:09:12 | TehNut/HWYLA | https://api.github.com/repos/TehNut/HWYLA | closed | [1.14.4] Missing Hearts in Hwyla Overlay turn Pink. [Image Inside] | bug code complete | #### Issue Description:
Note: I'm playing on a **Modpack** but this is happening on a Clean "Vanilla" Instance w/ only the mod installed too.
____
#### Steps to reproduce:
1. Look at a Living Entity's Health in the Hwyla Overlay.
2. Hurt the mob with a sword, bring down it's health.
3. Missing hearts turn pink.
4. Done.
**Edit:** Also noticed the existing hearts have a black background. No transparency.
____
#### Image: (Look in the top left)
[https://i.imgur.com/QnUuQbz.png](https://i.imgur.com/QnUuQbz.png)
____
#### Affected Versions:
- Hwyla: **1.10.7-B71_1.15.1**
- Minecraft: **1.15.1**
- Forge: **30.0.41**
| 1.0 | [1.14.4] Missing Hearts in Hwyla Overlay turn Pink. [Image Inside] - #### Issue Description:
Note: I'm playing on a **Modpack** but this is happening on a Clean "Vanilla" Instance w/ only the mod installed too.
____
#### Steps to reproduce:
1. Look at a Living Entity's Health in the Hwyla Overlay.
2. Hurt the mob with a sword, bring down it's health.
3. Missing hearts turn pink.
4. Done.
**Edit:** Also noticed the existing hearts have a black background. No transparency.
____
#### Image: (Look in the top left)
[https://i.imgur.com/QnUuQbz.png](https://i.imgur.com/QnUuQbz.png)
____
#### Affected Versions:
- Hwyla: **1.10.7-B71_1.15.1**
- Minecraft: **1.15.1**
- Forge: **30.0.41**
| non_priority | missing hearts in hwyla overlay turn pink issue description note i m playing on a modpack but this is happening on a clean vanilla instance w only the mod installed too steps to reproduce look at a living entity s health in the hwyla overlay hurt the mob with a sword bring down it s health missing hearts turn pink done edit also noticed the existing hearts have a black background no transparency image look in the top left affected versions hwyla minecraft forge | 0 |
267,309 | 23,291,039,343 | IssuesEvent | 2022-08-05 23:01:46 | danbudris/vulnerabilityProcessor | https://api.github.com/repos/danbudris/vulnerabilityProcessor | opened | HIGH vulnerability CVE-2022-1160 - vim-minimal affecting 1 resources | hey there test severity/HIGH | Issue auto cut by Vulnerability Processor
Processor Version: `v0.0.0-dev`
Message Source: `EventBridge`
Finding Source: `inspectorV2`
HIGH vulnerability CVE-2022-1160 detected in 1 resources
- arn:aws:ecr:us-west-2:338155784195:repository/test-inspector/sha256:7585bd31388fb7584260436e613c871868fd1509a728bf0c60bfe3f792e43aff
Affected Packages:
- vim-minimal
Associated Pull Requests:
- https://github.com/danbudris/vulnerabilityProcessor/pull/1296
| 1.0 | HIGH vulnerability CVE-2022-1160 - vim-minimal affecting 1 resources - Issue auto cut by Vulnerability Processor
Processor Version: `v0.0.0-dev`
Message Source: `EventBridge`
Finding Source: `inspectorV2`
HIGH vulnerability CVE-2022-1160 detected in 1 resources
- arn:aws:ecr:us-west-2:338155784195:repository/test-inspector/sha256:7585bd31388fb7584260436e613c871868fd1509a728bf0c60bfe3f792e43aff
Affected Packages:
- vim-minimal
Associated Pull Requests:
- https://github.com/danbudris/vulnerabilityProcessor/pull/1296
| non_priority | high vulnerability cve vim minimal affecting resources issue auto cut by vulnerability processor processor version dev message source eventbridge finding source high vulnerability cve detected in resources arn aws ecr us west repository test inspector affected packages vim minimal associated pull requests | 0 |
66,565 | 14,788,929,784 | IssuesEvent | 2021-01-12 09:53:22 | andygonzalez2010/store | https://api.github.com/repos/andygonzalez2010/store | opened | CVE-2020-25638 (High) detected in hibernate-core-5.3.9.Final.jar | security vulnerability | ## CVE-2020-25638 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hibernate-core-5.3.9.Final.jar</b></p></summary>
<p>Hibernate's core ORM functionality</p>
<p>Library home page: <a href="http://hibernate.org/orm">http://hibernate.org/orm</a></p>
<p>Path to dependency file: store/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/org/hibernate/hibernate-core/5.3.9.Final/hibernate-core-5.3.9.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **hibernate-core-5.3.9.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/andygonzalez2010/store/commit/3f6d614029f4d6cfdddfcef8468949cb7822503c">3f6d614029f4d6cfdddfcef8468949cb7822503c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in hibernate-core in versions prior to and including 5.4.23.Final. A SQL injection in the implementation of the JPA Criteria API can permit unsanitized literals when a literal is used in the SQL comments of the query. This flaw could allow an attacker to access unauthorized information or possibly conduct further attacks. The highest threat from this vulnerability is to data confidentiality and integrity.
<p>Publish Date: 2020-12-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25638>CVE-2020-25638</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://in.relation.to/2020/11/19/hibernate-orm-5424-final-release/">https://in.relation.to/2020/11/19/hibernate-orm-5424-final-release/</a></p>
<p>Release Date: 2020-12-02</p>
<p>Fix Resolution: org.hibernate:hibernate-core:5.3.20.Final,5.4.24.Final</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-25638 (High) detected in hibernate-core-5.3.9.Final.jar - ## CVE-2020-25638 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hibernate-core-5.3.9.Final.jar</b></p></summary>
<p>Hibernate's core ORM functionality</p>
<p>Library home page: <a href="http://hibernate.org/orm">http://hibernate.org/orm</a></p>
<p>Path to dependency file: store/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/org/hibernate/hibernate-core/5.3.9.Final/hibernate-core-5.3.9.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **hibernate-core-5.3.9.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/andygonzalez2010/store/commit/3f6d614029f4d6cfdddfcef8468949cb7822503c">3f6d614029f4d6cfdddfcef8468949cb7822503c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in hibernate-core in versions prior to and including 5.4.23.Final. A SQL injection in the implementation of the JPA Criteria API can permit unsanitized literals when a literal is used in the SQL comments of the query. This flaw could allow an attacker to access unauthorized information or possibly conduct further attacks. The highest threat from this vulnerability is to data confidentiality and integrity.
<p>Publish Date: 2020-12-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25638>CVE-2020-25638</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://in.relation.to/2020/11/19/hibernate-orm-5424-final-release/">https://in.relation.to/2020/11/19/hibernate-orm-5424-final-release/</a></p>
<p>Release Date: 2020-12-02</p>
<p>Fix Resolution: org.hibernate:hibernate-core:5.3.20.Final,5.4.24.Final</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in hibernate core final jar cve high severity vulnerability vulnerable library hibernate core final jar hibernate s core orm functionality library home page a href path to dependency file store pom xml path to vulnerable library canner repository org hibernate hibernate core final hibernate core final jar dependency hierarchy x hibernate core final jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was found in hibernate core in versions prior to and including final a sql injection in the implementation of the jpa criteria api can permit unsanitized literals when a literal is used in the sql comments of the query this flaw could allow an attacker to access unauthorized information or possibly conduct further attacks the highest threat from this vulnerability is to data confidentiality and integrity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org hibernate hibernate core final final step up your open source security game with whitesource | 0 |
28,581 | 12,889,413,603 | IssuesEvent | 2020-07-13 14:30:07 | terraform-providers/terraform-provider-azurerm | https://api.github.com/repos/terraform-providers/terraform-provider-azurerm | closed | azurerm_kubernetes_cluster failing due to unsupported 'kubeDashboard' addon API call in Azure China | bug service/kubernetes-cluster | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
- Terraform v0.12.19
- `azurerm` provider version: 2.15.0
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* `azurerm_kubernetes_cluster`
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
resource "azurerm_kubernetes_cluster" "aks" {
name = var.cluster_name
location = var.location
resource_group_name = azurerm_resource_group.aks.name
kubernetes_version = var.kubernetes_version
dns_prefix = var.cluster_name
node_resource_group = "${var.cluster_name}-resources"
default_node_pool {
name = "default"
type = "VirtualMachineScaleSets"
vm_size = var.default_nodepool.vm_size
vnet_subnet_id = azurerm_subnet.aks_subnet.id
node_count = var.default_nodepool.count
}
service_principal {
client_id = var.aks_service_principal_client_id
client_secret = var.aks_service_principal_client_secret
}
linux_profile {
admin_username = var.aks_linux_profile_admin_username
ssh_key {
key_data = var.aks_linux_profile_ssh_key_data
}
}
network_profile {
network_plugin = "azure"
network_policy = "calico"
dns_service_ip = cidrhost(var.aks_network_profile_service_cidr, 2)
service_cidr = var.aks_network_profile_service_cidr
docker_bridge_cidr = var.aks_docker_bridge_cidr
load_balancer_sku = var.aks_network_profile_load_balancer_sku
}
role_based_access_control {
enabled = true
azure_active_directory {
client_app_id = var.aks_aad_client_app_id
server_app_id = var.aks_aad_server_app_id
server_app_secret = var.aks_aad_server_app_secret
}
}
}
```
### Debug Output
<!---
Please provide a link to a GitHub Gist containing the complete debug output. Please do NOT paste the debug output in the issue; just paste a link to the Gist.
To obtain the debug output, see the [Terraform documentation on debugging](https://www.terraform.io/docs/internals/debugging.html).
--->
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
### Expected Behavior
Terraform should create an AKS cluster on Azure China.
### Actual Behavior
The `terraform apply` stage fails due to an error from the Azure China API:
```
creating Managed Kubernetes Cluster "aks-marvin" (Resource Group "aks-marvin"): containerservice.ManagedClustersClient#CreateOrUpdate: Failure sending request: StatusCode=400 -- Original Error: Code="OperationNotAllowed" Message="Addon 'kubeDashboard' is not supported in this cloud environment."
```
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform apply`
### Important Factoids
<!--- Are there anything atypical about your accounts that we should know? For example: Running in a Azure China/Germany/Government? --->
- Running in Azure China.
- I checked previously deployed AKS China clusters and they do run kubernetes-dashboard. It's also referenced [here](https://github.com/Azure/container-service-for-azure-china/tree/master/aks#1-how-to-create-aks-on-azure-china). I suspect that Azure China is simply missing the API to enable/disable it and just deploys it with every cluster and mirrors #7136 in that.
- There is no explicit configuration of the kube-dashboard addon.
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Such as vendor documentation?
--->
This is a follow-up or related to:
- #5510
- #6462
- #7136
| 1.0 | azurerm_kubernetes_cluster failing due to unsupported 'kubeDashboard' addon API call in Azure China - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backends/index.html) issues
* [Provisioner](https://www.terraform.io/docs/provisioners/index.html) issues
* [Registry](https://registry.terraform.io/) issues
* Spans resources across multiple providers
If you are running into one of these scenarios, we recommend opening an issue in the [Terraform core repository](https://github.com/hashicorp/terraform/) instead.
--->
<!--- Please keep this note for the community --->
### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform (and AzureRM Provider) Version
<!--- Please run `terraform -v` to show the Terraform core version and provider version(s). If you are not running the latest version of Terraform or the provider, please upgrade because your issue may have already been fixed. [Terraform documentation on provider versioning](https://www.terraform.io/docs/configuration/providers.html#provider-versions). --->
- Terraform v0.12.19
- `azurerm` provider version: 2.15.0
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* `azurerm_kubernetes_cluster`
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
resource "azurerm_kubernetes_cluster" "aks" {
name = var.cluster_name
location = var.location
resource_group_name = azurerm_resource_group.aks.name
kubernetes_version = var.kubernetes_version
dns_prefix = var.cluster_name
node_resource_group = "${var.cluster_name}-resources"
default_node_pool {
name = "default"
type = "VirtualMachineScaleSets"
vm_size = var.default_nodepool.vm_size
vnet_subnet_id = azurerm_subnet.aks_subnet.id
node_count = var.default_nodepool.count
}
service_principal {
client_id = var.aks_service_principal_client_id
client_secret = var.aks_service_principal_client_secret
}
linux_profile {
admin_username = var.aks_linux_profile_admin_username
ssh_key {
key_data = var.aks_linux_profile_ssh_key_data
}
}
network_profile {
network_plugin = "azure"
network_policy = "calico"
dns_service_ip = cidrhost(var.aks_network_profile_service_cidr, 2)
service_cidr = var.aks_network_profile_service_cidr
docker_bridge_cidr = var.aks_docker_bridge_cidr
load_balancer_sku = var.aks_network_profile_load_balancer_sku
}
role_based_access_control {
enabled = true
azure_active_directory {
client_app_id = var.aks_aad_client_app_id
server_app_id = var.aks_aad_server_app_id
server_app_secret = var.aks_aad_server_app_secret
}
}
}
```
### Debug Output
<!---
Please provide a link to a GitHub Gist containing the complete debug output. Please do NOT paste the debug output in the issue; just paste a link to the Gist.
To obtain the debug output, see the [Terraform documentation on debugging](https://www.terraform.io/docs/internals/debugging.html).
--->
### Panic Output
<!--- If Terraform produced a panic, please provide a link to a GitHub Gist containing the output of the `crash.log`. --->
### Expected Behavior
Terraform should create an AKS cluster on Azure China.
### Actual Behavior
The `terraform apply` stage fails due to an error from the Azure China API:
```
creating Managed Kubernetes Cluster "aks-marvin" (Resource Group "aks-marvin"): containerservice.ManagedClustersClient#CreateOrUpdate: Failure sending request: StatusCode=400 -- Original Error: Code="OperationNotAllowed" Message="Addon 'kubeDashboard' is not supported in this cloud environment."
```
### Steps to Reproduce
<!--- Please list the steps required to reproduce the issue. --->
1. `terraform apply`
### Important Factoids
<!--- Are there anything atypical about your accounts that we should know? For example: Running in a Azure China/Germany/Government? --->
- Running in Azure China.
- I checked previously deployed AKS China clusters and they do run kubernetes-dashboard. It's also referenced [here](https://github.com/Azure/container-service-for-azure-china/tree/master/aks#1-how-to-create-aks-on-azure-china). I suspect that Azure China is simply missing the API to enable/disable it and just deploys it with every cluster and mirrors #7136 in that.
- There is no explicit configuration of the kube-dashboard addon.
### References
<!---
Information about referencing Github Issues: https://help.github.com/articles/basic-writing-and-formatting-syntax/#referencing-issues-and-pull-requests
Are there any other GitHub issues (open or closed) or pull requests that should be linked here? Such as vendor documentation?
--->
This is a follow-up or related to:
- #5510
- #6462
- #7136
| non_priority | azurerm kubernetes cluster failing due to unsupported kubedashboard addon api call in azure china please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into one of these scenarios we recommend opening an issue in the instead community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform and azurerm provider version terraform azurerm provider version affected resource s azurerm kubernetes cluster terraform configuration files hcl resource azurerm kubernetes cluster aks name var cluster name location var location resource group name azurerm resource group aks name kubernetes version var kubernetes version dns prefix var cluster name node resource group var cluster name resources default node pool name default type virtualmachinescalesets vm size var default nodepool vm size vnet subnet id azurerm subnet aks subnet id node count var default nodepool count service principal client id var aks service principal client id client secret var aks service principal client secret linux profile admin username var aks linux profile admin username ssh key key data var aks linux profile ssh key data network profile network plugin azure network policy calico dns service ip cidrhost var aks network profile service cidr service cidr var aks network profile service cidr docker bridge cidr var aks docker bridge cidr load balancer sku var aks network profile load balancer sku role based access control enabled true azure active directory client app id var aks aad client app id server app id var aks aad server app id server app secret var aks aad server app secret debug output please provide a link to a github gist containing the complete debug output please do not paste the debug output in the issue just paste a link to the gist to obtain the debug output see the panic output expected behavior terraform should create an aks cluster on azure china actual behavior the terraform apply stage fails due to an error from the azure china api creating managed kubernetes cluster aks marvin resource group aks marvin containerservice managedclustersclient createorupdate failure sending request statuscode original error code operationnotallowed message addon kubedashboard is not supported in this cloud environment steps to reproduce terraform apply important factoids running in azure china i checked previously deployed aks china clusters and they do run kubernetes dashboard it s also referenced i suspect that azure china is simply missing the api to enable disable it and just deploys it with every cluster and mirrors in that there is no explicit configuration of the kube dashboard addon references information about referencing github issues are there any other github issues open or closed or pull requests that should be linked here such as vendor documentation this is a follow up or related to | 0 |
130,019 | 18,007,494,099 | IssuesEvent | 2021-09-16 02:52:51 | UQdeco2800/2021-studio-7 | https://api.github.com/repos/UQdeco2800/2021-studio-7 | closed | Design and create isometric sprites and update the basic set of sprites (Team 1) | documentation Team 1 Character Design Task Sprint 2 | # **Description**
**Task:** Design and create isometric sprites to expand the basic set of sprites, which is the foundation of new character creation; Adjust the sprites made in sprint 1 accordingly, to maintain consistency in relation to scale and style.
**Feature:** Character Design
Based on feedback received from sprint 1, it has been suggested that more isometric sprites should be created to make in-game movement and related animations smoother. Similar to the previous sprint, before start to make sprites for new playable characters & update isometric sprites for characters & NPCs that are already in the game, the basic set of sprites is expanded with new isometric ones. In this case, the potential inconsistency across multiple designers regarding the scale of sprites; art style, etc. can be avoided in advance.
Once new isometric sprites are finished, all other sprites in the basic set, which are created in the previous sprint, will be updated accordingly, to maintain the consistency of scale and style within the basic set. As is mentioned above, after the adjustments are done, the new set of basic sprites will be handed to designers as the foundation for a new character & NPC creation, as well as refinement of characters & NPCs created previously.
**Please check the wiki pages under the documentation section below for more details, thank you!**
# **Milestones**
- [x] Design & create isometric sprites to expand the basic set of sprites (Sept. 11)
- [x] Adjust the scale & style of original sprites in the basic set accordingly to maintain the consistency with isometric ones (Sept. 12)
# **Dependencies**
- #21 .
- #37 .
# **Documentation**
- [NPCs & Characters Design](../..//2021-studio-7/wiki/NPCs-&-Characters-Design)
# **Members**
**Changhao Xi** (@ChanghaoXi) (Raymond) | 1.0 | Design and create isometric sprites and update the basic set of sprites (Team 1) - # **Description**
**Task:** Design and create isometric sprites to expand the basic set of sprites, which is the foundation of new character creation; Adjust the sprites made in sprint 1 accordingly, to maintain consistency in relation to scale and style.
**Feature:** Character Design
Based on feedback received from sprint 1, it has been suggested that more isometric sprites should be created to make in-game movement and related animations smoother. Similar to the previous sprint, before start to make sprites for new playable characters & update isometric sprites for characters & NPCs that are already in the game, the basic set of sprites is expanded with new isometric ones. In this case, the potential inconsistency across multiple designers regarding the scale of sprites; art style, etc. can be avoided in advance.
Once new isometric sprites are finished, all other sprites in the basic set, which are created in the previous sprint, will be updated accordingly, to maintain the consistency of scale and style within the basic set. As is mentioned above, after the adjustments are done, the new set of basic sprites will be handed to designers as the foundation for a new character & NPC creation, as well as refinement of characters & NPCs created previously.
**Please check the wiki pages under the documentation section below for more details, thank you!**
# **Milestones**
- [x] Design & create isometric sprites to expand the basic set of sprites (Sept. 11)
- [x] Adjust the scale & style of original sprites in the basic set accordingly to maintain the consistency with isometric ones (Sept. 12)
# **Dependencies**
- #21 .
- #37 .
# **Documentation**
- [NPCs & Characters Design](../..//2021-studio-7/wiki/NPCs-&-Characters-Design)
# **Members**
**Changhao Xi** (@ChanghaoXi) (Raymond) | non_priority | design and create isometric sprites and update the basic set of sprites team description task design and create isometric sprites to expand the basic set of sprites which is the foundation of new character creation adjust the sprites made in sprint accordingly to maintain consistency in relation to scale and style feature character design based on feedback received from sprint it has been suggested that more isometric sprites should be created to make in game movement and related animations smoother similar to the previous sprint before start to make sprites for new playable characters update isometric sprites for characters npcs that are already in the game the basic set of sprites is expanded with new isometric ones in this case the potential inconsistency across multiple designers regarding the scale of sprites art style etc can be avoided in advance once new isometric sprites are finished all other sprites in the basic set which are created in the previous sprint will be updated accordingly to maintain the consistency of scale and style within the basic set as is mentioned above after the adjustments are done the new set of basic sprites will be handed to designers as the foundation for a new character npc creation as well as refinement of characters npcs created previously please check the wiki pages under the documentation section below for more details thank you milestones design create isometric sprites to expand the basic set of sprites sept adjust the scale style of original sprites in the basic set accordingly to maintain the consistency with isometric ones sept dependencies documentation studio wiki npcs characters design members changhao xi changhaoxi raymond | 0 |
37,825 | 2,831,465,902 | IssuesEvent | 2015-05-24 17:15:34 | pydy/pydy | https://api.github.com/repos/pydy/pydy | closed | Benchmarks are broken in master | bug high priority | There is an UnboundLocalError when I ran benchmarks
```
Pendulum with 1 links.
======================
The derivation took 0.12791 seconds.
Traceback (most recent call last):
File "bin/benchmark_pydy_code_gen.py", line 118, in <module>
run_benchmark(args.max_num_links, args.num_time_steps)
File "bin/benchmark_pydy_code_gen.py", line 49, in run_benchmark
x0 = hstack((0, pi / 2 * ones(len(results[3]) - 1), 1e-3 *
UnboundLocalError: local variable 'results' referenced before assignment
```
I think while we fix this, we should remove it from README. | 1.0 | Benchmarks are broken in master - There is an UnboundLocalError when I ran benchmarks
```
Pendulum with 1 links.
======================
The derivation took 0.12791 seconds.
Traceback (most recent call last):
File "bin/benchmark_pydy_code_gen.py", line 118, in <module>
run_benchmark(args.max_num_links, args.num_time_steps)
File "bin/benchmark_pydy_code_gen.py", line 49, in run_benchmark
x0 = hstack((0, pi / 2 * ones(len(results[3]) - 1), 1e-3 *
UnboundLocalError: local variable 'results' referenced before assignment
```
I think while we fix this, we should remove it from README. | priority | benchmarks are broken in master there is an unboundlocalerror when i ran benchmarks pendulum with links the derivation took seconds traceback most recent call last file bin benchmark pydy code gen py line in run benchmark args max num links args num time steps file bin benchmark pydy code gen py line in run benchmark hstack pi ones len results unboundlocalerror local variable results referenced before assignment i think while we fix this we should remove it from readme | 1 |
195,948 | 6,922,389,851 | IssuesEvent | 2017-11-30 02:53:47 | apache/bookkeeper | https://api.github.com/repos/apache/bookkeeper | closed | Bootup cookie validation considers an empty journal to signify a new bookie | area/bookie priority/blocker release/4.6.0 type/bug | This is wrong, and can lead to split brain.
From the dev list:
We check all ledger, journal and index directories for a cookie. If it
doesn't exist, it gets added to a missingCookieDirs list. We then
iterate over this directory. If any directory in missingCookieDirs
isn't listed as a ledger directory in the journal dir cookies, or
isn't empty, we fail to start.
The issue is that a journal dir could be emptied and we wouldn't
detect it. It would be great if someone else could eyeball the code
and tell me I'm wrong. The code is in Bookie#checkEnvironment.
This breaks correctness. Imagine we have a ledger on b1, b2, b3.
Writer w1 is writing to the ledger.
The state of the ledger on the bookies is:
b1: e0 Fenced: false, LAC: -
b2: e0 Fenced: false, LAC: -
b3: e0 Fenced: false, LAC: -
w1 gets partitioned from network. w2 tries to recover the ledger, it
tries to fence on all bookies. The message to b3 gets lost. b1 and b2
acknowledge the fencing, so w2 continues to recover and close the
ledger with e0 as the last entry.
b1: e0 Fenced: true, LAC: e0
b2: e0 Fenced: true, LAC: e0
b3: e0 Fenced: false, LAC: -
If w1 became unpartitioned at this point, it wouldn't be able to add a
new entry to the ledger as any quorum would see fenced on b1 or b2.
However, imagine that the fenced message is only in the journal on b2,
b2 crashes, something wipes the journal directory and then b2 comes
back up. The new state of the ledger on the bookies will be.
b1: e0 Fenced: true, LAC: e0
b2: e0 Fenced: false, LAC: -
b3: e0 Fenced: false, LAC: -
Now w1 can write a new entry, e1, and b2 & b3 would both acknowledge
it, even though the end of the ledger is e0. | 1.0 | Bootup cookie validation considers an empty journal to signify a new bookie - This is wrong, and can lead to split brain.
From the dev list:
We check all ledger, journal and index directories for a cookie. If it
doesn't exist, it gets added to a missingCookieDirs list. We then
iterate over this directory. If any directory in missingCookieDirs
isn't listed as a ledger directory in the journal dir cookies, or
isn't empty, we fail to start.
The issue is that a journal dir could be emptied and we wouldn't
detect it. It would be great if someone else could eyeball the code
and tell me I'm wrong. The code is in Bookie#checkEnvironment.
This breaks correctness. Imagine we have a ledger on b1, b2, b3.
Writer w1 is writing to the ledger.
The state of the ledger on the bookies is:
b1: e0 Fenced: false, LAC: -
b2: e0 Fenced: false, LAC: -
b3: e0 Fenced: false, LAC: -
w1 gets partitioned from network. w2 tries to recover the ledger, it
tries to fence on all bookies. The message to b3 gets lost. b1 and b2
acknowledge the fencing, so w2 continues to recover and close the
ledger with e0 as the last entry.
b1: e0 Fenced: true, LAC: e0
b2: e0 Fenced: true, LAC: e0
b3: e0 Fenced: false, LAC: -
If w1 became unpartitioned at this point, it wouldn't be able to add a
new entry to the ledger as any quorum would see fenced on b1 or b2.
However, imagine that the fenced message is only in the journal on b2,
b2 crashes, something wipes the journal directory and then b2 comes
back up. The new state of the ledger on the bookies will be.
b1: e0 Fenced: true, LAC: e0
b2: e0 Fenced: false, LAC: -
b3: e0 Fenced: false, LAC: -
Now w1 can write a new entry, e1, and b2 & b3 would both acknowledge
it, even though the end of the ledger is e0. | priority | bootup cookie validation considers an empty journal to signify a new bookie this is wrong and can lead to split brain from the dev list we check all ledger journal and index directories for a cookie if it doesn t exist it gets added to a missingcookiedirs list we then iterate over this directory if any directory in missingcookiedirs isn t listed as a ledger directory in the journal dir cookies or isn t empty we fail to start the issue is that a journal dir could be emptied and we wouldn t detect it it would be great if someone else could eyeball the code and tell me i m wrong the code is in bookie checkenvironment this breaks correctness imagine we have a ledger on writer is writing to the ledger the state of the ledger on the bookies is fenced false lac fenced false lac fenced false lac gets partitioned from network tries to recover the ledger it tries to fence on all bookies the message to gets lost and acknowledge the fencing so continues to recover and close the ledger with as the last entry fenced true lac fenced true lac fenced false lac if became unpartitioned at this point it wouldn t be able to add a new entry to the ledger as any quorum would see fenced on or however imagine that the fenced message is only in the journal on crashes something wipes the journal directory and then comes back up the new state of the ledger on the bookies will be fenced true lac fenced false lac fenced false lac now can write a new entry and would both acknowledge it even though the end of the ledger is | 1 |
14,125 | 2,789,925,362 | IssuesEvent | 2015-05-08 22:27:37 | google/google-visualization-api-issues | https://api.github.com/repos/google/google-visualization-api-issues | opened | line chart sign problem | Priority-Medium Type-Defect | Original [issue 528](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=528) created by orwant on 2011-02-18T20:19:04.000Z:
There is a problem with display bottom sign of the chart in Firefox and IE. Labels are overlay each other.
FF version is 3.6.13
IE 8.0.7600.16385
| 1.0 | line chart sign problem - Original [issue 528](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=528) created by orwant on 2011-02-18T20:19:04.000Z:
There is a problem with display bottom sign of the chart in Firefox and IE. Labels are overlay each other.
FF version is 3.6.13
IE 8.0.7600.16385
| non_priority | line chart sign problem original created by orwant on there is a problem with display bottom sign of the chart in firefox and ie labels are overlay each other ff version is ie | 0 |
42,893 | 11,098,167,275 | IssuesEvent | 2019-12-16 14:43:49 | NEZNAMY/TAB | https://api.github.com/repos/NEZNAMY/TAB | closed | per-world-settings feature request | Check new build Feature request | alright so basically i want an option in which you can set multiple worlds to share the same settings
a template
world1-world2-world2:
header:
- '%animation:MyAnimation1%'
- '%animation:MyAnimation2%'
- ''
- '&6&lRank: %vault_rank%'
footer:
- ''
- '%animation:vote%!'
- ''
- '%animation:time%'
- ''
- '%animation:web%&7! '
Groups:
Owner:
tabprefix: '&4[Owner] &4 | 1.0 | per-world-settings feature request - alright so basically i want an option in which you can set multiple worlds to share the same settings
a template
world1-world2-world2:
header:
- '%animation:MyAnimation1%'
- '%animation:MyAnimation2%'
- ''
- '&6&lRank: %vault_rank%'
footer:
- ''
- '%animation:vote%!'
- ''
- '%animation:time%'
- ''
- '%animation:web%&7! '
Groups:
Owner:
tabprefix: '&4[Owner] &4 | non_priority | per world settings feature request alright so basically i want an option in which you can set multiple worlds to share the same settings a template header animation animation lrank vault rank footer animation vote animation time animation web groups owner tabprefix | 0 |
25,010 | 2,675,444,971 | IssuesEvent | 2015-03-25 12:32:06 | kentcc/ebbsfleet | https://api.github.com/repos/kentcc/ebbsfleet | closed | Search icon on results page | low priority wordpress | Hi. The magnify glass looks different on the search results page so just wanted to flag. See screen shot below. Thanks

| 1.0 | Search icon on results page - Hi. The magnify glass looks different on the search results page so just wanted to flag. See screen shot below. Thanks

| priority | search icon on results page hi the magnify glass looks different on the search results page so just wanted to flag see screen shot below thanks | 1 |
220,696 | 7,370,089,436 | IssuesEvent | 2018-03-13 06:51:28 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | sites.google.com - see bug description | priority-critical | <!-- @browser: Firefox nightly -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.13; rv:60.0) Gecko/20100101 Firefox/60.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://sites.google.com/site/playfunblocked/games/tank-trouble-2
**Browser / Version**: Firefox nightly
**Operating System**: Mac OS X 10.13.4
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: The game doesnt load
**Steps to Reproduce**:
gfx.webrender.all: false
gfx.webrender.blob-images: 1
gfx.webrender.enabled: false
image.mem.shared: 2
[](https://webcompat.com/uploads/2018/3/5f3bad9f-ef15-4ad1-ba62-fb4fd006e423.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | sites.google.com - see bug description - <!-- @browser: Firefox nightly -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.13; rv:60.0) Gecko/20100101 Firefox/60.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://sites.google.com/site/playfunblocked/games/tank-trouble-2
**Browser / Version**: Firefox nightly
**Operating System**: Mac OS X 10.13.4
**Tested Another Browser**: Yes
**Problem type**: Something else
**Description**: The game doesnt load
**Steps to Reproduce**:
gfx.webrender.all: false
gfx.webrender.blob-images: 1
gfx.webrender.enabled: false
image.mem.shared: 2
[](https://webcompat.com/uploads/2018/3/5f3bad9f-ef15-4ad1-ba62-fb4fd006e423.jpg)
_From [webcompat.com](https://webcompat.com/) with ❤️_ | priority | sites google com see bug description url browser version firefox nightly operating system mac os x tested another browser yes problem type something else description the game doesnt load steps to reproduce gfx webrender all false gfx webrender blob images gfx webrender enabled false image mem shared from with ❤️ | 1 |
369,323 | 10,895,530,644 | IssuesEvent | 2019-11-19 10:50:00 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | prizegrab.com - design is broken | browser-firefox-mobile engine-gecko priority-normal | <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.1.1; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://prizegrab.com/p/home-and-garden/?s=2&r=None
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android 7.1.1
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: Internet with web have broken with it.
**Steps to Reproduce**:
Web browser have few problems with my phone.
[](https://webcompat.com/uploads/2019/11/548a38bf-3a32-4be4-a2c7-92e60b420176.jpeg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20191112013613</li><li>channel: beta</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
<p>Console Messages:</p>
<pre>
['[JavaScript Warning: "Request to access cookie or storage on https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1aEtWSjU1dlRyaUk5RzBKRWliZDllY1NrTSUyRkl0SGtYdmI%22,%22origin%22:3},%22topUrl%22:%22prizegrab.com%22,%22cw%22:true} was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 13 column: 1673 source: "https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1"}]', '[JavaScript Warning: "Request to access cookie or storage on https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1aEtWSjU1dlRyaUk5RzBKRWliZDllY1NrTSUyRkl0SGtYdmI%22,%22origin%22:3},%22topUrl%22:%22prizegrab.com%22,%22cw%22:true} was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 13 column: 1673 source: "https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1"}]', '[JavaScript Warning: "Request to access cookie or storage on https://ssum-sec.casalemedia.com/usermatch?s=183751&cb=https%3A%2F%2Fengine.adzerk.net%2Fudb%2F9706%2Fsync%2Fi.gif%3FpartnerId%3D1%26userId%3D&C=1 was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 0}]', '[JavaScript Warning: "Request to access cookie or storage on https://ssum-sec.casalemedia.com/usermatch?s=183751&cb=https%3A%2F%2Fengine.adzerk.net%2Fudb%2F9706%2Fsync%2Fi.gif%3FpartnerId%3D1%26userId%3D&C=1 was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 0}]', '[JavaScript Warning: "Loading failed for the <script> with source https://securepubads.g.doubleclick.net/tag/js/gpt.js." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 204}]', '[JavaScript Error: "SecurityError: The operation is insecure." {file: "https://proxy.distiltag.com/ga847746.js" line: 1}]\nhasIndexedDb@https://proxy.distiltag.com/ga847746.js:1:2571\nindexedDbKey@https://proxy.distiltag.com/ga847746.js:1:2521\ninterrogate@https://proxy.distiltag.com/ga847746.js:1:941\nd/</<@https://proxy.distiltag.com/ga847746.js:1:26115\n', '[JavaScript Warning: "Request to access cookie or storage on https://proxy.distiltag.com/kitten?ak=7a2779229b7f145f88b98f7a258ea8919&pk=RMLf1tI4VVCvqupwlKKdFL146CKqbyuYKM22jXFN&AYAH_VERSION=2.0&cookiesync=true was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 1 column: 382 source: "https://proxy.distiltag.com/kitten?ak=7a2779229b7f145f88b98f7a258ea8919&pk=RMLf1tI4VVCvqupwlKKdFL146CKqbyuYKM22jXFN&AYAH_VERSION=2.0&cookiesync=true"}]']
</pre>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | prizegrab.com - design is broken - <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.1.1; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://prizegrab.com/p/home-and-garden/?s=2&r=None
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android 7.1.1
**Tested Another Browser**: No
**Problem type**: Design is broken
**Description**: Internet with web have broken with it.
**Steps to Reproduce**:
Web browser have few problems with my phone.
[](https://webcompat.com/uploads/2019/11/548a38bf-3a32-4be4-a2c7-92e60b420176.jpeg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20191112013613</li><li>channel: beta</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
<p>Console Messages:</p>
<pre>
['[JavaScript Warning: "Request to access cookie or storage on https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1aEtWSjU1dlRyaUk5RzBKRWliZDllY1NrTSUyRkl0SGtYdmI%22,%22origin%22:3},%22topUrl%22:%22prizegrab.com%22,%22cw%22:true} was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 13 column: 1673 source: "https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1"}]', '[JavaScript Warning: "Request to access cookie or storage on https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1aEtWSjU1dlRyaUk5RzBKRWliZDllY1NrTSUyRkl0SGtYdmI%22,%22origin%22:3},%22topUrl%22:%22prizegrab.com%22,%22cw%22:true} was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 13 column: 1673 source: "https://gum.criteo.com/syncframe?topUrl=prizegrab.com#{%22optout%22:{%22value%22:false,%22origin%22:0},%22uid%22:{%22origin%22:0},%22idfs%22:{%22origin%22:0},%22sid%22:{%22origin%22:0},%22origin%22:%22publishertag%22,%22version%22:76,%22lwid%22:{%22value%22:%2240ab7c7c-b45c-4c2e-b3e2-3ff79f168515%22,%22origin%22:3},%22tld%22:%22prizegrab.com%22,%22bundle%22:{%22value%22:%2225U8oF9nWVFDeXZScGdwOFE5bWZ5cXhKWWNraUVRJTJGWmR2amEzUzBIc01aWTBOV0MwMzNWelhicUh3Q3NDOVY0Q1lYaGlZQUU1eERZWjZRYUZ1SmZUTmFTMzd4WGYzeWxIV0x1"}]', '[JavaScript Warning: "Request to access cookie or storage on https://ssum-sec.casalemedia.com/usermatch?s=183751&cb=https%3A%2F%2Fengine.adzerk.net%2Fudb%2F9706%2Fsync%2Fi.gif%3FpartnerId%3D1%26userId%3D&C=1 was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 0}]', '[JavaScript Warning: "Request to access cookie or storage on https://ssum-sec.casalemedia.com/usermatch?s=183751&cb=https%3A%2F%2Fengine.adzerk.net%2Fudb%2F9706%2Fsync%2Fi.gif%3FpartnerId%3D1%26userId%3D&C=1 was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 0}]', '[JavaScript Warning: "Loading failed for the <script> with source https://securepubads.g.doubleclick.net/tag/js/gpt.js." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 204}]', '[JavaScript Error: "SecurityError: The operation is insecure." {file: "https://proxy.distiltag.com/ga847746.js" line: 1}]\nhasIndexedDb@https://proxy.distiltag.com/ga847746.js:1:2571\nindexedDbKey@https://proxy.distiltag.com/ga847746.js:1:2521\ninterrogate@https://proxy.distiltag.com/ga847746.js:1:941\nd/</<@https://proxy.distiltag.com/ga847746.js:1:26115\n', '[JavaScript Warning: "Request to access cookie or storage on https://proxy.distiltag.com/kitten?ak=7a2779229b7f145f88b98f7a258ea8919&pk=RMLf1tI4VVCvqupwlKKdFL146CKqbyuYKM22jXFN&AYAH_VERSION=2.0&cookiesync=true was blocked because it came from a tracker and content blocking is enabled." {file: "https://prizegrab.com/p/home-and-garden/?s=2&r=None" line: 1 column: 382 source: "https://proxy.distiltag.com/kitten?ak=7a2779229b7f145f88b98f7a258ea8919&pk=RMLf1tI4VVCvqupwlKKdFL146CKqbyuYKM22jXFN&AYAH_VERSION=2.0&cookiesync=true"}]']
</pre>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | priority | prizegrab com design is broken url browser version firefox mobile operating system android tested another browser no problem type design is broken description internet with web have broken with it steps to reproduce web browser have few problems with my phone browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel beta hastouchscreen true mixed active content blocked false mixed passive content blocked false tracking content blocked false console messages nhasindexeddb from with ❤️ | 1 |
249,143 | 26,889,074,454 | IssuesEvent | 2023-02-06 07:16:38 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | [Security Solution]Incorrect Prevention and Detection Type Alert Count in Alert by Type Chart of Alert Page | bug triage_needed Team: SecuritySolution | **Describe the bug**
Incorrect Prevention and Detection Type Alert Count in Alert by Type Chart of Alert Page
**Build Details:**
```
Version: 8.7.0-SNAPSHOT
Commit: 99f69f78f84ac41fb3e4b440c56b3c8bd51e084a
Build: 60431
```
**Preconditions**
- Endpoint Security prebuilt rule should be enabled on kibana
- Duplicate above prebuilt rule and also enable this
**Steps**
- Set the Endpoint policy to Detect
- Execute the `Mimikatz.exe`
- 2 Alerts will be generated one from Endpoint Security and another from Endpoint Security [Duplicate]
- Now set the Endpoint Policy to Prevent
- Execute the `Mimikatz.exe`
- 2 Alerts will be generated one from Endpoint Security and another from Endpoint Security [Duplicate]
- Total 4 will be on build now
- Go to Alert Page and select Charts Visualization and go to Alert by type and observe the count which is showing incorrect
**Screen-Cast**

https://user-images.githubusercontent.com/59917825/216906567-d86938a0-b6cf-434b-885a-b07d5cee47d7.mp4
**Additional Information**
- Inspect information

https://user-images.githubusercontent.com/59917825/216906581-318f5f9f-3f87-4ea1-afcb-6933d70a919c.mp4
**Response**
```
{
"took": 1,
"timed_out": false,
"_shards": {
"total": 1,
"successful": 1,
"skipped": 0,
"failed": 0
},
"hits": {
"total": {
"value": 2,
"relation": "eq"
},
"max_score": null,
"hits": []
},
"aggregations": {
"alertsByRule": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "Malware Detection Alert",
"doc_count": 2,
"ruleByEventType": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "allowed",
"doc_count": 2
},
{
"key": "info",
"doc_count": 2
},
{
"key": "start",
"doc_count": 2
}
]
}
}
]
}
}
}
```
**Request**
```
{
"size": 0,
"query": {
"bool": {
"filter": [
{
"bool": {
"must": [],
"filter": [
{
"match_phrase": {
"kibana.alert.rule.name": {
"query": "Malware Detection Alert"
}
}
},
{
"term": {
"kibana.alert.workflow_status": "open"
}
}
],
"should": [],
"must_not": [
{
"exists": {
"field": "kibana.alert.building_block_type"
}
}
]
}
},
{
"range": {
"@timestamp": {
"gte": "2023-02-05T18:30:00.000Z",
"lte": "2023-02-06T18:29:59.999Z"
}
}
}
]
}
},
"aggs": {
"alertsByRule": {
"terms": {
"field": "kibana.alert.rule.name",
"size": 1000
},
"aggs": {
"ruleByEventType": {
"terms": {
"field": "event.type",
"size": 1000
}
}
}
}
},
"runtime_mappings": {}
}
```
-----------------------------------------------

- Request
```
{
"size": 0,
"query": {
"bool": {
"filter": [
{
"bool": {
"must": [],
"filter": [
{
"match_phrase": {
"kibana.alert.rule.name": {
"query": "Malware Prevention Alert"
}
}
},
{
"term": {
"kibana.alert.workflow_status": "open"
}
}
],
"should": [],
"must_not": [
{
"exists": {
"field": "kibana.alert.building_block_type"
}
}
]
}
},
{
"range": {
"@timestamp": {
"gte": "2023-02-05T18:30:00.000Z",
"lte": "2023-02-06T18:29:59.999Z"
}
}
}
]
}
},
"aggs": {
"alertsByRule": {
"terms": {
"field": "kibana.alert.rule.name",
"size": 1000
},
"aggs": {
"ruleByEventType": {
"terms": {
"field": "event.type",
"size": 1000
}
}
}
}
},
"runtime_mappings": {}
}
```
- Response
```
{
"took": 1,
"timed_out": false,
"_shards": {
"total": 1,
"successful": 1,
"skipped": 0,
"failed": 0
},
"hits": {
"total": {
"value": 2,
"relation": "eq"
},
"max_score": null,
"hits": []
},
"aggregations": {
"alertsByRule": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "Malware Prevention Alert",
"doc_count": 2,
"ruleByEventType": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "denied",
"doc_count": 2
},
{
"key": "info",
"doc_count": 2
},
{
"key": "start",
"doc_count": 2
}
]
}
}
]
}
}
}
``` | True | [Security Solution]Incorrect Prevention and Detection Type Alert Count in Alert by Type Chart of Alert Page - **Describe the bug**
Incorrect Prevention and Detection Type Alert Count in Alert by Type Chart of Alert Page
**Build Details:**
```
Version: 8.7.0-SNAPSHOT
Commit: 99f69f78f84ac41fb3e4b440c56b3c8bd51e084a
Build: 60431
```
**Preconditions**
- Endpoint Security prebuilt rule should be enabled on kibana
- Duplicate above prebuilt rule and also enable this
**Steps**
- Set the Endpoint policy to Detect
- Execute the `Mimikatz.exe`
- 2 Alerts will be generated one from Endpoint Security and another from Endpoint Security [Duplicate]
- Now set the Endpoint Policy to Prevent
- Execute the `Mimikatz.exe`
- 2 Alerts will be generated one from Endpoint Security and another from Endpoint Security [Duplicate]
- Total 4 will be on build now
- Go to Alert Page and select Charts Visualization and go to Alert by type and observe the count which is showing incorrect
**Screen-Cast**

https://user-images.githubusercontent.com/59917825/216906567-d86938a0-b6cf-434b-885a-b07d5cee47d7.mp4
**Additional Information**
- Inspect information

https://user-images.githubusercontent.com/59917825/216906581-318f5f9f-3f87-4ea1-afcb-6933d70a919c.mp4
**Response**
```
{
"took": 1,
"timed_out": false,
"_shards": {
"total": 1,
"successful": 1,
"skipped": 0,
"failed": 0
},
"hits": {
"total": {
"value": 2,
"relation": "eq"
},
"max_score": null,
"hits": []
},
"aggregations": {
"alertsByRule": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "Malware Detection Alert",
"doc_count": 2,
"ruleByEventType": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "allowed",
"doc_count": 2
},
{
"key": "info",
"doc_count": 2
},
{
"key": "start",
"doc_count": 2
}
]
}
}
]
}
}
}
```
**Request**
```
{
"size": 0,
"query": {
"bool": {
"filter": [
{
"bool": {
"must": [],
"filter": [
{
"match_phrase": {
"kibana.alert.rule.name": {
"query": "Malware Detection Alert"
}
}
},
{
"term": {
"kibana.alert.workflow_status": "open"
}
}
],
"should": [],
"must_not": [
{
"exists": {
"field": "kibana.alert.building_block_type"
}
}
]
}
},
{
"range": {
"@timestamp": {
"gte": "2023-02-05T18:30:00.000Z",
"lte": "2023-02-06T18:29:59.999Z"
}
}
}
]
}
},
"aggs": {
"alertsByRule": {
"terms": {
"field": "kibana.alert.rule.name",
"size": 1000
},
"aggs": {
"ruleByEventType": {
"terms": {
"field": "event.type",
"size": 1000
}
}
}
}
},
"runtime_mappings": {}
}
```
-----------------------------------------------

- Request
```
{
"size": 0,
"query": {
"bool": {
"filter": [
{
"bool": {
"must": [],
"filter": [
{
"match_phrase": {
"kibana.alert.rule.name": {
"query": "Malware Prevention Alert"
}
}
},
{
"term": {
"kibana.alert.workflow_status": "open"
}
}
],
"should": [],
"must_not": [
{
"exists": {
"field": "kibana.alert.building_block_type"
}
}
]
}
},
{
"range": {
"@timestamp": {
"gte": "2023-02-05T18:30:00.000Z",
"lte": "2023-02-06T18:29:59.999Z"
}
}
}
]
}
},
"aggs": {
"alertsByRule": {
"terms": {
"field": "kibana.alert.rule.name",
"size": 1000
},
"aggs": {
"ruleByEventType": {
"terms": {
"field": "event.type",
"size": 1000
}
}
}
}
},
"runtime_mappings": {}
}
```
- Response
```
{
"took": 1,
"timed_out": false,
"_shards": {
"total": 1,
"successful": 1,
"skipped": 0,
"failed": 0
},
"hits": {
"total": {
"value": 2,
"relation": "eq"
},
"max_score": null,
"hits": []
},
"aggregations": {
"alertsByRule": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "Malware Prevention Alert",
"doc_count": 2,
"ruleByEventType": {
"doc_count_error_upper_bound": 0,
"sum_other_doc_count": 0,
"buckets": [
{
"key": "denied",
"doc_count": 2
},
{
"key": "info",
"doc_count": 2
},
{
"key": "start",
"doc_count": 2
}
]
}
}
]
}
}
}
``` | non_priority | incorrect prevention and detection type alert count in alert by type chart of alert page describe the bug incorrect prevention and detection type alert count in alert by type chart of alert page build details version snapshot commit build preconditions endpoint security prebuilt rule should be enabled on kibana duplicate above prebuilt rule and also enable this steps set the endpoint policy to detect execute the mimikatz exe alerts will be generated one from endpoint security and another from endpoint security now set the endpoint policy to prevent execute the mimikatz exe alerts will be generated one from endpoint security and another from endpoint security total will be on build now go to alert page and select charts visualization and go to alert by type and observe the count which is showing incorrect screen cast additional information inspect information response took timed out false shards total successful skipped failed hits total value relation eq max score null hits aggregations alertsbyrule doc count error upper bound sum other doc count buckets key malware detection alert doc count rulebyeventtype doc count error upper bound sum other doc count buckets key allowed doc count key info doc count key start doc count request size query bool filter bool must filter match phrase kibana alert rule name query malware detection alert term kibana alert workflow status open should must not exists field kibana alert building block type range timestamp gte lte aggs alertsbyrule terms field kibana alert rule name size aggs rulebyeventtype terms field event type size runtime mappings request size query bool filter bool must filter match phrase kibana alert rule name query malware prevention alert term kibana alert workflow status open should must not exists field kibana alert building block type range timestamp gte lte aggs alertsbyrule terms field kibana alert rule name size aggs rulebyeventtype terms field event type size runtime mappings response took timed out false shards total successful skipped failed hits total value relation eq max score null hits aggregations alertsbyrule doc count error upper bound sum other doc count buckets key malware prevention alert doc count rulebyeventtype doc count error upper bound sum other doc count buckets key denied doc count key info doc count key start doc count | 0 |
51,845 | 12,819,208,530 | IssuesEvent | 2020-07-06 01:10:01 | iterative/dvc | https://api.github.com/repos/iterative/dvc | closed | snap: transition to v1 | build discussion enhancement p2-medium ui | ## Anyone arriving here getting this message:

**Running:**
- `snap refresh --channel=latest/beta dvc` (to upgrade now), or
- `snap refresh --channel=v0/stable dvc` (to never upgrade)
**makes the message go away.**
Otherwise (*if you ignore the message*) you'll be upgraded from `v0` to `v1` **automatically** in a few days.
See https://dvc.org/blog/june-20-community-gems for some notes on upgrading to v1 (it's simple!)
----
## Maintainer notes:
Snap packages automatically update to the most recent version in a channel.
The default channel is **`--latest/stable`** (with the slash, yes; not my design choice) and normally we push tagged releases to it.
During breaking transitions (v0 to v1), though, we need a transition phase.
- [x] #3999 push the last `0.x` to a new `--v0/stable` channel
- [x] #3990 push the current `1.x` to `--v1/beta` and `--latest/beta`
- [x] push a new `0.x-final` to **`--latest/stable`**
+ [x] #3999 this issues a warning in the update available and error messages. This warning will state the 2 options for the user:
* `snap refresh --channel=v0/stable` to stick to the old version
* `snap refresh --channel=latest/beta` & use new API/syntax
* `snap refresh --channel=v1/beta` & use new API/syntax. This would stop them getting warnings about `--v2` in future. Probably bizarre ("I wanna upgrade now but never again") and not worth mentioning this option.
After the transition period (say 30 days?) we go back to normalcy:
- [x] close the `--v1/beta` channel. Users on it will automatically get shifted to `--v1/stable`.
- [x] regularly push `1.x` updates to `--v1/stable` and **`--latest/stable`**
Some people will be be hit by errors at this stage, but ~~serves them right for ignoring the transition warning messages~~ we tried our best.
I'm not happy with the channel naming conventions either but such is life: https://snapcraft.io/docs/channels. In fact we have to manually request `--v0`, `--v1` etc.
- [x] ~~Please bump here~~done: https://forum.snapcraft.io/t/track-request-for-dvc/17735
- [x] #3999, #4038 sync `v1` and `v0` snap build improvements (e.g. #3990, #4037)
- related #3777
- realted https://github.com/iterative/dvc.org/issues/906 | 1.0 | snap: transition to v1 - ## Anyone arriving here getting this message:

**Running:**
- `snap refresh --channel=latest/beta dvc` (to upgrade now), or
- `snap refresh --channel=v0/stable dvc` (to never upgrade)
**makes the message go away.**
Otherwise (*if you ignore the message*) you'll be upgraded from `v0` to `v1` **automatically** in a few days.
See https://dvc.org/blog/june-20-community-gems for some notes on upgrading to v1 (it's simple!)
----
## Maintainer notes:
Snap packages automatically update to the most recent version in a channel.
The default channel is **`--latest/stable`** (with the slash, yes; not my design choice) and normally we push tagged releases to it.
During breaking transitions (v0 to v1), though, we need a transition phase.
- [x] #3999 push the last `0.x` to a new `--v0/stable` channel
- [x] #3990 push the current `1.x` to `--v1/beta` and `--latest/beta`
- [x] push a new `0.x-final` to **`--latest/stable`**
+ [x] #3999 this issues a warning in the update available and error messages. This warning will state the 2 options for the user:
* `snap refresh --channel=v0/stable` to stick to the old version
* `snap refresh --channel=latest/beta` & use new API/syntax
* `snap refresh --channel=v1/beta` & use new API/syntax. This would stop them getting warnings about `--v2` in future. Probably bizarre ("I wanna upgrade now but never again") and not worth mentioning this option.
After the transition period (say 30 days?) we go back to normalcy:
- [x] close the `--v1/beta` channel. Users on it will automatically get shifted to `--v1/stable`.
- [x] regularly push `1.x` updates to `--v1/stable` and **`--latest/stable`**
Some people will be be hit by errors at this stage, but ~~serves them right for ignoring the transition warning messages~~ we tried our best.
I'm not happy with the channel naming conventions either but such is life: https://snapcraft.io/docs/channels. In fact we have to manually request `--v0`, `--v1` etc.
- [x] ~~Please bump here~~done: https://forum.snapcraft.io/t/track-request-for-dvc/17735
- [x] #3999, #4038 sync `v1` and `v0` snap build improvements (e.g. #3990, #4037)
- related #3777
- realted https://github.com/iterative/dvc.org/issues/906 | non_priority | snap transition to anyone arriving here getting this message running snap refresh channel latest beta dvc to upgrade now or snap refresh channel stable dvc to never upgrade makes the message go away otherwise if you ignore the message you ll be upgraded from to automatically in a few days see for some notes on upgrading to it s simple maintainer notes snap packages automatically update to the most recent version in a channel the default channel is latest stable with the slash yes not my design choice and normally we push tagged releases to it during breaking transitions to though we need a transition phase push the last x to a new stable channel push the current x to beta and latest beta push a new x final to latest stable this issues a warning in the update available and error messages this warning will state the options for the user snap refresh channel stable to stick to the old version snap refresh channel latest beta use new api syntax snap refresh channel beta use new api syntax this would stop them getting warnings about in future probably bizarre i wanna upgrade now but never again and not worth mentioning this option after the transition period say days we go back to normalcy close the beta channel users on it will automatically get shifted to stable regularly push x updates to stable and latest stable some people will be be hit by errors at this stage but serves them right for ignoring the transition warning messages we tried our best i m not happy with the channel naming conventions either but such is life in fact we have to manually request etc please bump here done sync and snap build improvements e g related realted | 0 |
20,760 | 6,103,477,365 | IssuesEvent | 2017-06-20 18:47:48 | amorenew/awesome-calculator | https://api.github.com/repos/amorenew/awesome-calculator | closed | Review Business Logic - Math calculation helper | Code Review | - [ ] Review Naming Convention for Classes, Methods, Variables and etc
- [ ] Review Object Oriented Programming like Encapsulation
- [ ] Review Clean Code like comments | 1.0 | Review Business Logic - Math calculation helper - - [ ] Review Naming Convention for Classes, Methods, Variables and etc
- [ ] Review Object Oriented Programming like Encapsulation
- [ ] Review Clean Code like comments | non_priority | review business logic math calculation helper review naming convention for classes methods variables and etc review object oriented programming like encapsulation review clean code like comments | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.