Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
13,891 | 3,785,480,687 | IssuesEvent | 2016-03-20 14:58:24 | gregorio-project/gregorio | https://api.github.com/repos/gregorio-project/gregorio | closed | gresetinitiallines{2} broken? | documentation enhancement question TeX | Compiling this document:
```tex
\documentclass[11pt]{article} % use larger type; default would be 10pt
\usepackage{fontspec}
\usepackage{graphicx} % support the \includegraphics command and options
\usepackage{geometry} % See geometry.pdf to learn the layout options. There are lots.
\geometry{a5paper} % or lett... | 1.0 | gresetinitiallines{2} broken? - Compiling this document:
```tex
\documentclass[11pt]{article} % use larger type; default would be 10pt
\usepackage{fontspec}
\usepackage{graphicx} % support the \includegraphics command and options
\usepackage{geometry} % See geometry.pdf to learn the layout options. There are lot... | non_priority | gresetinitiallines broken compiling this document tex documentclass article use larger type default would be usepackage fontspec usepackage graphicx support the includegraphics command and options usepackage geometry see geometry pdf to learn the layout options there are lots geo... | 0 |
203,733 | 23,180,334,924 | IssuesEvent | 2022-08-01 01:01:32 | Mary-Clb/PROJET6_PIQUANTE | https://api.github.com/repos/Mary-Clb/PROJET6_PIQUANTE | opened | bcrypt-5.0.1.tgz: 1 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcrypt-5.0.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /tmp/ws-scm/Marie_Bressy_P6_14072021/package.json</p>
<p>Path to vulnerable library: /tmp/ws-sc... | True | bcrypt-5.0.1.tgz: 1 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcrypt-5.0.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /tmp/ws-scm/Marie_Bressy_P6_14... | non_priority | bcrypt tgz vulnerabilities highest severity is vulnerable library bcrypt tgz path to dependency file tmp ws scm marie bressy package json path to vulnerable library tmp ws scm marie bressy node modules node fetch package json vulnerabilities cve severi... | 0 |
242,788 | 7,846,839,065 | IssuesEvent | 2018-06-19 16:33:26 | inverse-inc/packetfence | https://api.github.com/repos/inverse-inc/packetfence | closed | Services: bin/pfcmd service pf status/restart not working | Priority: Critical Type: Bug | [root@testing-c7 pf]# rpm -qa packetfence
packetfence-8.0.9-0.201806181250.el7.noarch
If I want to do the status it gives me that error:
````
[root@testing-c7 pf]# bin/pfcmd service pf status
Service Status PID
packetfence-api-frontend.service ... | 1.0 | Services: bin/pfcmd service pf status/restart not working - [root@testing-c7 pf]# rpm -qa packetfence
packetfence-8.0.9-0.201806181250.el7.noarch
If I want to do the status it gives me that error:
````
[root@testing-c7 pf]# bin/pfcmd service pf status
Service Statu... | priority | services bin pfcmd service pf status restart not working rpm qa packetfence packetfence noarch if i want to do the status it gives me that error bin pfcmd service pf status service status pid packetfence api frontend service ... | 1 |
21,130 | 3,684,029,720 | IssuesEvent | 2016-02-24 16:03:15 | pydata/pandas | https://api.github.com/repos/pydata/pandas | closed | Arithmetic by DataFrame index | API Design Docs Indexing | I encountered a problem with doing any arythmetic from index, in other words, when a index is time (datetime64) and i would like to count something by it, i have no other option than to assign it to some column in dataframe object.
import pandas as pd
```
import pandas as pd
rng = pd.date_range('1/1/2011', peri... | 1.0 | Arithmetic by DataFrame index - I encountered a problem with doing any arythmetic from index, in other words, when a index is time (datetime64) and i would like to count something by it, i have no other option than to assign it to some column in dataframe object.
import pandas as pd
```
import pandas as pd
rng ... | non_priority | arithmetic by dataframe index i encountered a problem with doing any arythmetic from index in other words when a index is time and i would like to count something by it i have no other option than to assign it to some column in dataframe object import pandas as pd import pandas as pd rng pd date... | 0 |
206,765 | 23,396,891,043 | IssuesEvent | 2022-08-12 01:20:50 | valdisiljuconoks/TechFellow.ScheduledJobOverview | https://api.github.com/repos/valdisiljuconoks/TechFellow.ScheduledJobOverview | closed | CVE-2014-4075 (Medium) detected in microsoft.aspnet.mvc.4.0.20710.nupkg - autoclosed | security vulnerability | ## CVE-2014-4075 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.aspnet.mvc.4.0.20710.nupkg</b></p></summary>
<p>This package contains the runtime assemblies for ASP.NET MV... | True | CVE-2014-4075 (Medium) detected in microsoft.aspnet.mvc.4.0.20710.nupkg - autoclosed - ## CVE-2014-4075 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>microsoft.aspnet.mvc.4.0.20710.... | non_priority | cve medium detected in microsoft aspnet mvc nupkg autoclosed cve medium severity vulnerability vulnerable library microsoft aspnet mvc nupkg this package contains the runtime assemblies for asp net mvc asp net mvc gives you a powerful patt library home page a href ... | 0 |
414,049 | 12,097,899,085 | IssuesEvent | 2020-04-20 09:24:02 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | [master-preview] Hard to build blocks at top. | Priority: High Status: Fixed Week Task | To build ladder you need to point top:

In 8.3.0 you need to point upper stage:

I tried to bu... | 1.0 | [master-preview] Hard to build blocks at top. - To build ladder you need to point top:

In 8.3.0 you need to point upper stage:
 detected in commons-codec-1.10.jar | security vulnerability | ## WS-2019-0379 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-codec-1.10.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
... | True | WS-2019-0379 (Medium) detected in commons-codec-1.10.jar - ## WS-2019-0379 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-codec-1.10.jar</b></p></summary>
<p>The Apache Comm... | non_priority | ws medium detected in commons codec jar ws medium severity vulnerability vulnerable library commons codec jar the apache commons codec package contains simple encoder and decoders for various formats such as and hexadecimal in addition to these widely used encoders and... | 0 |
252,979 | 19,086,859,977 | IssuesEvent | 2021-11-29 07:31:24 | clusternet/clusternet | https://api.github.com/repos/clusternet/clusternet | closed | roadmap adbout clusternet? | kind/documentation | <!-- Please only use this template for submitting enhancement requests
-->
#### What would you like to be added:
#### Why is this needed:
Want to know the roadmap of this project, for example, including cross-cluster service discovery. | 1.0 | roadmap adbout clusternet? - <!-- Please only use this template for submitting enhancement requests
-->
#### What would you like to be added:
#### Why is this needed:
Want to know the roadmap of this project, for example, including cross-cluster service discovery. | non_priority | roadmap adbout clusternet please only use this template for submitting enhancement requests what would you like to be added why is this needed want to know the roadmap of this project for example including cross cluster service discovery | 0 |
233,336 | 7,696,751,354 | IssuesEvent | 2018-05-18 16:17:32 | dondi/GRNsight | https://api.github.com/repos/dondi/GRNsight | closed | Adding the Fall 2017 BIOL/CMSI-367 gene backpages to GRNSight | functionality priority 0 review requested | I would like to begin the process of cleaning up the Biological Databases Web API project and merging it to GRNSight. Below is a preliminary checklist, to be changed as more information arises.
- [x] Fixing any bugs associated with the project.
- [x] ESLinting the Code
- [x] Merging it to the GRNSight.
Here... | 1.0 | Adding the Fall 2017 BIOL/CMSI-367 gene backpages to GRNSight - I would like to begin the process of cleaning up the Biological Databases Web API project and merging it to GRNSight. Below is a preliminary checklist, to be changed as more information arises.
- [x] Fixing any bugs associated with the project.
- [x]... | priority | adding the fall biol cmsi gene backpages to grnsight i would like to begin the process of cleaning up the biological databases web api project and merging it to grnsight below is a preliminary checklist to be changed as more information arises fixing any bugs associated with the project eslintin... | 1 |
72,453 | 19,269,617,084 | IssuesEvent | 2021-12-10 02:30:48 | JaydenDev/freecat | https://api.github.com/repos/JaydenDev/freecat | closed | Binaries don't work | bug build installer | # Command-line output:
<!-- Copy and paste everything from your terminal. Make sure you remove private information. -->
```
C:\Users\hello-smile6\Documents\GitHub\freecat>npm run make
> freecat@1.0.0 make
> electron-forge make
✔ Checking your system
✔ Resolving Forge Config
We need to package your appli... | 1.0 | Binaries don't work - # Command-line output:
<!-- Copy and paste everything from your terminal. Make sure you remove private information. -->
```
C:\Users\hello-smile6\Documents\GitHub\freecat>npm run make
> freecat@1.0.0 make
> electron-forge make
✔ Checking your system
✔ Resolving Forge Config
We need... | non_priority | binaries don t work command line output c users hello documents github freecat npm run make freecat make electron forge make ✔ checking your system ✔ resolving forge config we need to package your application before we can make it ✔ preparing to package application for arch ... | 0 |
745,361 | 25,980,987,793 | IssuesEvent | 2022-12-19 18:49:13 | group2-cs321/AMS-COLBY | https://api.github.com/repos/group2-cs321/AMS-COLBY | closed | As a superadmin I want to have the option to create multiple users and teams by uploading a CSV file | Medium priority | Should take around 3hs | 1.0 | As a superadmin I want to have the option to create multiple users and teams by uploading a CSV file - Should take around 3hs | priority | as a superadmin i want to have the option to create multiple users and teams by uploading a csv file should take around | 1 |
111,079 | 17,009,704,465 | IssuesEvent | 2021-07-02 01:09:30 | tamirdahan/keycloak | https://api.github.com/repos/tamirdahan/keycloak | opened | CVE-2020-27216 (High) detected in jetty-webapp-9.2.4.v20141103.jar | security vulnerability | ## CVE-2020-27216 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-webapp-9.2.4.v20141103.jar</b></p></summary>
<p>Jetty web application support</p>
<p>Library home page: <a href=... | True | CVE-2020-27216 (High) detected in jetty-webapp-9.2.4.v20141103.jar - ## CVE-2020-27216 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-webapp-9.2.4.v20141103.jar</b></p></summary>... | non_priority | cve high detected in jetty webapp jar cve high severity vulnerability vulnerable library jetty webapp jar jetty web application support library home page a href path to dependency file keycloak adapters oidc spring boot pom xml path to vulnerable library canner ... | 0 |
27,369 | 6,845,441,992 | IssuesEvent | 2017-11-13 08:16:04 | loicteixeira/gj-unity-api | https://api.github.com/repos/loicteixeira/gj-unity-api | closed | Add logic to support secret trophies | backlog code enhancement UI | The API does not return whether a trophy is secret. Add a list of secret trophy ids to compare against when generating the trophy window.
| 1.0 | Add logic to support secret trophies - The API does not return whether a trophy is secret. Add a list of secret trophy ids to compare against when generating the trophy window.
| non_priority | add logic to support secret trophies the api does not return whether a trophy is secret add a list of secret trophy ids to compare against when generating the trophy window | 0 |
818,715 | 30,701,273,138 | IssuesEvent | 2023-07-26 23:48:50 | marbl/HG002-issues | https://api.github.com/repos/marbl/HG002-issues | closed | Issue: chr8_MATERNAL:133911700-133911700 | priority shortread_homnonref element_evidence sbb_evidence correction_applied | ### Assembly Region
chr8_MATERNAL:133911700-133911700
### Assembly Version
v0.7
### DeepVariant Call
chr8_MATERNAL 133911700 . G GAT 20.8 PASS . GT:GQ:DP:AD:VAF:PL 1/1:10:13:0,13:1:20,10,0 | 1.0 | Issue: chr8_MATERNAL:133911700-133911700 - ### Assembly Region
chr8_MATERNAL:133911700-133911700
### Assembly Version
v0.7
### DeepVariant Call
chr8_MATERNAL 133911700 . G GAT 20.8 PASS . GT:GQ:DP:AD:VAF:PL 1/1:10:13:0,13:1:20,10,0 | priority | issue maternal assembly region maternal assembly version deepvariant call maternal g gat pass gt gq dp ad vaf pl | 1 |
82,054 | 15,839,292,623 | IssuesEvent | 2021-04-07 00:29:43 | mhutchie/vscode-git-graph | https://api.github.com/repos/mhutchie/vscode-git-graph | closed | Diff views are not shown on first click with wrapTabs = true | vscode-bug | When having "workbench.editor.wrapTabs" : true and the width of the window is so that it would need an additional tab line when the windows is activated because of the menu bar symbols need some more place, the diff view in the side only loads the diff on the second click on the same file.
Better to have a look at th... | 1.0 | Diff views are not shown on first click with wrapTabs = true - When having "workbench.editor.wrapTabs" : true and the width of the window is so that it would need an additional tab line when the windows is activated because of the menu bar symbols need some more place, the diff view in the side only loads the diff on ... | non_priority | diff views are not shown on first click with wraptabs true when having workbench editor wraptabs true and the width of the window is so that it would need an additional tab line when the windows is activated because of the menu bar symbols need some more place the diff view in the side only loads the diff on ... | 0 |
160,587 | 20,112,492,908 | IssuesEvent | 2022-02-07 16:15:50 | PGreaneyLYIT/easybuggy4django | https://api.github.com/repos/PGreaneyLYIT/easybuggy4django | opened | CVE-2016-7401 (High) detected in Django-2.0.3-py3-none-any.whl | security vulnerability | ## CVE-2016-7401 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-2.0.3-py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid development ... | True | CVE-2016-7401 (High) detected in Django-2.0.3-py3-none-any.whl - ## CVE-2016-7401 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-2.0.3-py3-none-any.whl</b></p></summary>
<p>A h... | non_priority | cve high detected in django none any whl cve high severity vulnerability vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency file require... | 0 |
314,659 | 9,601,099,031 | IssuesEvent | 2019-05-10 11:10:15 | pufexi/multiorder | https://api.github.com/repos/pufexi/multiorder | opened | Doplnit stav zasob do Expedice objednavek | high priority | Viz obrazek nize, doplnit kolik je prave skladem, casto se nam stava, ze neco nestihneme vypnout (je na druhem sklade) a holky nevedi zda to tady je a hledaji to ci preklikavaji do Sklady, takze v tom zobrazeni pro expedici tj. objednakvy ?filter=1-1 ?filter=1-2 ?filter=1-3 a ?filter=4 aby se dozobrazilo kolik je prave... | 1.0 | Doplnit stav zasob do Expedice objednavek - Viz obrazek nize, doplnit kolik je prave skladem, casto se nam stava, ze neco nestihneme vypnout (je na druhem sklade) a holky nevedi zda to tady je a hledaji to ci preklikavaji do Sklady, takze v tom zobrazeni pro expedici tj. objednakvy ?filter=1-1 ?filter=1-2 ?filter=1-3 a... | priority | doplnit stav zasob do expedice objednavek viz obrazek nize doplnit kolik je prave skladem casto se nam stava ze neco nestihneme vypnout je na druhem sklade a holky nevedi zda to tady je a hledaji to ci preklikavaji do sklady takze v tom zobrazeni pro expedici tj objednakvy filter filter filter a... | 1 |
350,894 | 10,510,200,346 | IssuesEvent | 2019-09-27 12:56:00 | MoonSHRD/p2chat-android | https://api.github.com/repos/MoonSHRD/p2chat-android | closed | "who is" | enhancement priority/high | Story: после подписки на новые топики (интересы) и нахождения новых пиров с этими топиками запоминает их и группирует собственно по этим топикам, "пользователей с интересом парк горького" - 9 юзеров. Необходимо перекидывать матчи из p2chat в само приложение, которое вызывает к примеру who_is(user1) - получает собствен... | 1.0 | "who is" - Story: после подписки на новые топики (интересы) и нахождения новых пиров с этими топиками запоминает их и группирует собственно по этим топикам, "пользователей с интересом парк горького" - 9 юзеров. Необходимо перекидывать матчи из p2chat в само приложение, которое вызывает к примеру who_is(user1) - получ... | priority | who is story после подписки на новые топики интересы и нахождения новых пиров с этими топиками запоминает их и группирует собственно по этим топикам пользователей с интересом парк горького юзеров необходимо перекидывать матчи из в само приложение которое вызывает к примеру who is получает собст... | 1 |
738,684 | 25,572,111,115 | IssuesEvent | 2022-11-30 18:34:39 | developmentseed/osm-teams | https://api.github.com/repos/developmentseed/osm-teams | opened | Improve validation on API endpoints | Type: Enhancement Category: API Priority: High | Some endpoints are using ad-hoc validation (like in [here](https://github.com/developmentseed/osm-teams/blob/96569b05aa0aea12fef16b505bf542f671bae63e/app/manage/teams.js#L384-L393) and [here](https://github.com/developmentseed/osm-teams/blob/15b0f2ff4b4bb68ea5465d34bf1bec49a1a06761/app/manage/organizations.js#L180-L188... | 1.0 | Improve validation on API endpoints - Some endpoints are using ad-hoc validation (like in [here](https://github.com/developmentseed/osm-teams/blob/96569b05aa0aea12fef16b505bf542f671bae63e/app/manage/teams.js#L384-L393) and [here](https://github.com/developmentseed/osm-teams/blob/15b0f2ff4b4bb68ea5465d34bf1bec49a1a06761... | priority | improve validation on api endpoints some endpoints are using ad hoc validation like in and which is not ideal we should apply a more robust and consistent validation approach to all endpoints like in cc kamicut | 1 |
211,101 | 23,788,834,155 | IssuesEvent | 2022-09-02 12:47:42 | guardian/amigo | https://api.github.com/repos/guardian/amigo | closed | CVE-2018-14721 (High) detected in jackson-databind-2.7.1.jar, jackson-databind-2.9.5.jar | security vulnerability | ## CVE-2018-14721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.7.1.jar</b>, <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>
<details><summary><b>jackson-dat... | True | CVE-2018-14721 (High) detected in jackson-databind-2.7.1.jar, jackson-databind-2.9.5.jar - ## CVE-2018-14721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.7.1.jar... | non_priority | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streami... | 0 |
261,636 | 22,761,551,856 | IssuesEvent | 2022-07-07 21:47:53 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Tipping Banner needs better keyboard accessibility - Follow up to 6147 | bug feature/rewards priority/P4 QA/Yes release-notes/include QA/Test-Plan-Specified accessibility | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROV... | 1.0 | Tipping Banner needs better keyboard accessibility - Follow up to 6147 - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET... | non_priority | tipping banner needs better keyboard accessibility follow up to have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get th... | 0 |
56,026 | 6,498,853,820 | IssuesEvent | 2017-08-22 19:04:55 | Aubron/scoreshots-templates | https://api.github.com/repos/Aubron/scoreshots-templates | closed | Long-Lost Scheduleshot | Priority: Medium Status: Development Needed Status: Testing Needed |
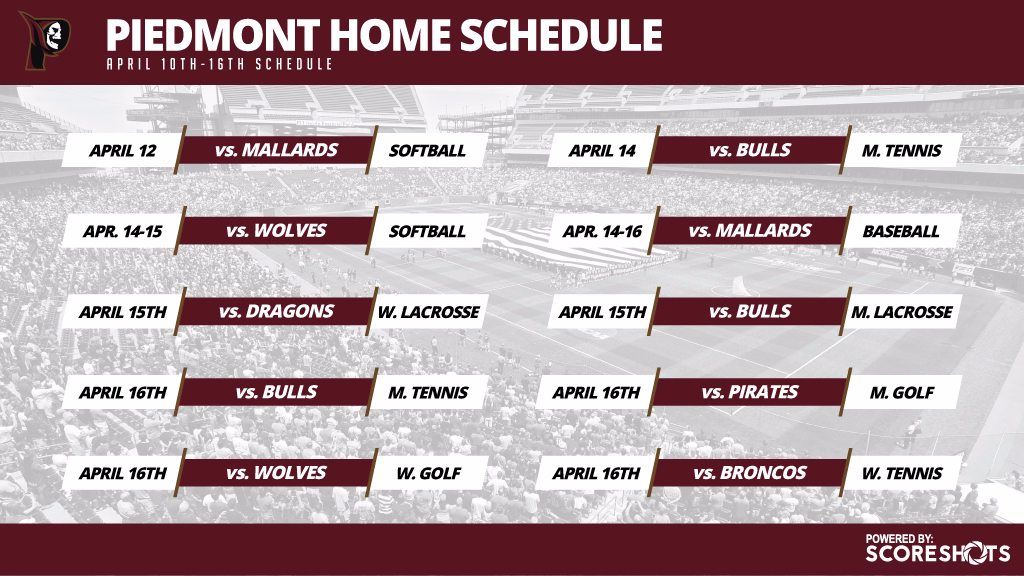
### Requested by:
Rick, Internal
## Template Description:
This is the scheduling template which sort of vanished off of everyone's radar.
## Dynamic Conside... | 1.0 | Long-Lost Scheduleshot -
### Requested by:
Rick, Internal
## Template Description:
This is the scheduling template which sort of vanished off of everyone's rad... | non_priority | long lost scheduleshot requested by rick internal template description this is the scheduling template which sort of vanished off of everyone s radar dynamic considerations number of games should be configurable via dropdown from down to presumably | 0 |
14,175 | 2,791,978,337 | IssuesEvent | 2015-05-10 16:20:17 | numpy/numpy | https://api.github.com/repos/numpy/numpy | reopened | Bug in np.random.dirichlet for small alpha parameters | component: numpy.random Defect | Hi,
I encountered a bug when using np.random.dirichlet with small alpha parameters. Call and traceback are below.
```python
ZeroDivisionError Traceback (most recent call last)
<ipython-input-86-73c2067e20c1> in <module>()
----> 1 np.random.dirichlet([0.0001, 0.0, 0.0001])
mtrand.pyx ... | 1.0 | Bug in np.random.dirichlet for small alpha parameters - Hi,
I encountered a bug when using np.random.dirichlet with small alpha parameters. Call and traceback are below.
```python
ZeroDivisionError Traceback (most recent call last)
<ipython-input-86-73c2067e20c1> in <module>()
----> 1 n... | non_priority | bug in np random dirichlet for small alpha parameters hi i encountered a bug when using np random dirichlet with small alpha parameters call and traceback are below python zerodivisionerror traceback most recent call last in np random dirichlet mtrand pyx i... | 0 |
326,381 | 24,081,594,528 | IssuesEvent | 2022-09-19 07:10:39 | StarLabsm/ForProject | https://api.github.com/repos/StarLabsm/ForProject | closed | feature: test docs | A-documentation A-feature | **Is your feature request related to a problem? Please describe.**
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
**Describe the solution you'd like**
<!-- A clear and concise description of what you want to happen. -->
**Describe alternatives you've consid... | 1.0 | feature: test docs - **Is your feature request related to a problem? Please describe.**
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
**Describe the solution you'd like**
<!-- A clear and concise description of what you want to happen. -->
**Describe alter... | non_priority | feature test docs is your feature request related to a problem please describe describe the solution you d like describe alternatives you ve considered additional context | 0 |
121,370 | 15,894,725,756 | IssuesEvent | 2021-04-11 11:20:21 | ezl/dailyidea.com | https://api.github.com/repos/ezl/dailyidea.com | opened | When trying to "comment attempt by unauth account" do we need a dialogue before posting the idea? | Design Question | Original discussion thread can be found here: #959
Here are the steps (as described by @ezl and edited by myself on step 8):
1. From an unauthenticated account, attempt to post a comment
2. This will result in being asked for an email address to complete posting
3. I entered an EXISTING user email address (my ... | 1.0 | When trying to "comment attempt by unauth account" do we need a dialogue before posting the idea? - Original discussion thread can be found here: #959
Here are the steps (as described by @ezl and edited by myself on step 8):
1. From an unauthenticated account, attempt to post a comment
2. This will result in be... | non_priority | when trying to comment attempt by unauth account do we need a dialogue before posting the idea original discussion thread can be found here here are the steps as described by ezl and edited by myself on step from an unauthenticated account attempt to post a comment this will result in bein... | 0 |
270,682 | 23,528,940,953 | IssuesEvent | 2022-08-19 13:36:09 | G-Node/WinGIN | https://api.github.com/repos/G-Node/WinGIN | opened | Unable to check out older files | needs testing | The issue was submitted by email: "I am unable to restore a file to a previous version using WinGIN. No older files are being checked out." | 1.0 | Unable to check out older files - The issue was submitted by email: "I am unable to restore a file to a previous version using WinGIN. No older files are being checked out." | non_priority | unable to check out older files the issue was submitted by email i am unable to restore a file to a previous version using wingin no older files are being checked out | 0 |
567,385 | 16,857,481,120 | IssuesEvent | 2021-06-21 08:43:09 | dmwm/WMCore | https://api.github.com/repos/dmwm/WMCore | closed | Change our MySQL driver to stop returning data in the long data type | Feature change Medium Priority WMAgent | **Impact of the new feature**
WMAgent (and T0, but they don't use MySQL)
**Is your feature request related to a problem? Please describe.**
Yes, it's been discussed in this code review comment:
https://github.com/dmwm/WMCore/pull/10605/files#r654225846
in short, `hash()` is no longer reproducible between pytho... | 1.0 | Change our MySQL driver to stop returning data in the long data type - **Impact of the new feature**
WMAgent (and T0, but they don't use MySQL)
**Is your feature request related to a problem? Please describe.**
Yes, it's been discussed in this code review comment:
https://github.com/dmwm/WMCore/pull/10605/files#r... | priority | change our mysql driver to stop returning data in the long data type impact of the new feature wmagent and but they don t use mysql is your feature request related to a problem please describe yes it s been discussed in this code review comment in short hash is no longer reproducible ... | 1 |
15,319 | 26,938,383,138 | IssuesEvent | 2023-02-07 22:57:26 | BrightSpots/rcv | https://api.github.com/repos/BrightSpots/rcv | closed | Hart CVR fails in v1.3 | bug v1.4 requirement | When trying to tabulate a new CVR from Hart RCTab v1.3 produces this error: "Error during tabulation:
"javax.xml.stream.FactoryConfigurationError: Provider for javax.xml.stream.XMLInputFactory cannot be found
Tabulation failed!"
The same file tabulates in v1.2 without issue.
[2023-02-06_13-29-36_audit_0.log](ht... | 1.0 | Hart CVR fails in v1.3 - When trying to tabulate a new CVR from Hart RCTab v1.3 produces this error: "Error during tabulation:
"javax.xml.stream.FactoryConfigurationError: Provider for javax.xml.stream.XMLInputFactory cannot be found
Tabulation failed!"
The same file tabulates in v1.2 without issue.
[2023-02-0... | non_priority | hart cvr fails in when trying to tabulate a new cvr from hart rctab produces this error error during tabulation javax xml stream factoryconfigurationerror provider for javax xml stream xmlinputfactory cannot be found tabulation failed the same file tabulates in without issue | 0 |
226,712 | 18,043,936,522 | IssuesEvent | 2021-09-18 14:51:39 | logicmoo/logicmoo_workspace | https://api.github.com/repos/logicmoo/logicmoo_workspace | opened | logicmoo.pfc.test.sanity_base.LIST_01A JUnit | Test_9999 logicmoo.pfc.test.sanity_base unit_test LIST_01A | (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif list_01a.pfc)
GH_MASTER_ISSUE_FINFO=
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+label%3ALIST_01A
GITLAB: https://logicmoo.org:2... | 3.0 | logicmoo.pfc.test.sanity_base.LIST_01A JUnit - (cd /var/lib/jenkins/workspace/logicmoo_workspace/packs_sys/pfc/t/sanity_base ; timeout --foreground --preserve-status -s SIGKILL -k 10s 10s lmoo-clif list_01a.pfc)
GH_MASTER_ISSUE_FINFO=
ISSUE_SEARCH: https://github.com/logicmoo/logicmoo_workspace/issues?q=is%3Aissue+l... | non_priority | logicmoo pfc test sanity base list junit cd var lib jenkins workspace logicmoo workspace packs sys pfc t sanity base timeout foreground preserve status s sigkill k lmoo clif list pfc gh master issue finfo issue search gitlab latest this build github running ... | 0 |
236,944 | 18,144,695,044 | IssuesEvent | 2021-09-25 07:53:18 | girlscript/winter-of-contributing | https://api.github.com/repos/girlscript/winter-of-contributing | closed | Menu Driven Code to implement stack | documentation GWOC21 Assigned C/CPP | ### Description
A menu driven program in C to perform the following operations using stack:
Create(); Push(); Pop(); Traverse()
### Domain
C/CPP
### Type of Contribution
Documentation
### Code of Conduct
- [X] I follow [Contributing Guidelines](https://github.com/girlscript/winter-of-contributing/blob/main/.g... | 1.0 | Menu Driven Code to implement stack - ### Description
A menu driven program in C to perform the following operations using stack:
Create(); Push(); Pop(); Traverse()
### Domain
C/CPP
### Type of Contribution
Documentation
### Code of Conduct
- [X] I follow [Contributing Guidelines](https://github.com/girlscr... | non_priority | menu driven code to implement stack description a menu driven program in c to perform the following operations using stack create push pop traverse domain c cpp type of contribution documentation code of conduct i follow of this project | 0 |
574,416 | 17,023,810,406 | IssuesEvent | 2021-07-03 03:58:47 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | no result in nominatim | Component: nominatim Priority: minor Resolution: duplicate Type: task | **[Submitted to the original trac issue database at 6.39pm, Sunday, 22nd July 2012]**
Location in OSM:
In OSM Data exists the place "Sankt Lorenzen im Paltental" near Liezen, austria.
Asking for "St.Lorenzen" or "Sankt Lorenzen" results in some other places and tracks but not the asked place. | 1.0 | no result in nominatim - **[Submitted to the original trac issue database at 6.39pm, Sunday, 22nd July 2012]**
Location in OSM:
In OSM Data exists the place "Sankt Lorenzen im Paltental" near Liezen, austria.
Asking for "St.Lorenzen" or "Sankt Lorenzen" results in some other places and tracks but not the asked pla... | priority | no result in nominatim location in osm in osm data exists the place sankt lorenzen im paltental near liezen austria asking for st lorenzen or sankt lorenzen results in some other places and tracks but not the asked place | 1 |
346,964 | 10,422,211,024 | IssuesEvent | 2019-09-16 08:29:24 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | discordapp.com - video or audio doesn't play | browser-firefox-mobile engine-gecko priority-important | <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://discordapp.com/channels/573676562470404096/576581520362569729
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android
... | 1.0 | discordapp.com - video or audio doesn't play - <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://discordapp.com/channels/573676562470404096/576581520362569729
**Browser / Version**: Fir... | priority | discordapp com video or audio doesn t play url browser version firefox mobile operating system android tested another browser yes problem type video or audio doesn t play description uwu steps to reproduce browser configuration mixed active content... | 1 |
282,137 | 8,704,012,313 | IssuesEvent | 2018-12-05 18:11:16 | strapi/strapi | https://api.github.com/repos/strapi/strapi | closed | Adding a file to api config folder disables those api | priority: medium status: have to reproduce type: bug 🐛 | <!-- ⚠️ If you do not respect this template your issue will be closed. -->
<!-- =============================================================================== -->
<!-- ⚠️ If you are not using the current Strapi release, you will be asked to update. -->
<!-- Please see the wiki for guides on upgrading to the lates... | 1.0 | Adding a file to api config folder disables those api - <!-- ⚠️ If you do not respect this template your issue will be closed. -->
<!-- =============================================================================== -->
<!-- ⚠️ If you are not using the current Strapi release, you will be asked to update. -->
<!-- ... | priority | adding a file to api config folder disables those api informations node js version npm version strapi version alpha database operating system ubuntu what is the current behavior generat... | 1 |
790,329 | 27,822,948,852 | IssuesEvent | 2023-03-19 12:56:31 | bounswe/bounswe2023group2 | https://api.github.com/repos/bounswe/bounswe2023group2 | closed | Account Features | state: assigned priority: medium state: In progress effort: level 3 | Create mock ups for account features:
- [x] login page
- [x] sign up page
- [x] reset password page | 1.0 | Account Features - Create mock ups for account features:
- [x] login page
- [x] sign up page
- [x] reset password page | priority | account features create mock ups for account features login page sign up page reset password page | 1 |
453,517 | 13,081,283,747 | IssuesEvent | 2020-08-01 10:30:39 | space-wizards/space-station-14 | https://api.github.com/repos/space-wizards/space-station-14 | closed | IGameTiming.CurTime never goes forwards | Priority: 1-high Type: Bug | Causing a few issues, such as weapons not working at all. | 1.0 | IGameTiming.CurTime never goes forwards - Causing a few issues, such as weapons not working at all. | priority | igametiming curtime never goes forwards causing a few issues such as weapons not working at all | 1 |
815,286 | 30,544,588,325 | IssuesEvent | 2023-07-20 02:02:09 | TencentBlueKing/bk-user | https://api.github.com/repos/TencentBlueKing/bk-user | closed | 用户管理SaaS支持应用访问权限 | Type: enhancement Layer: saas Layer: frontend Sign: security Priority: High doing | 访问登录校验bk_token或使用bk_token获取用户信息时对于特殊code=1302403
- 产品页面上需要展示无权限提示
- 必须保证整个产品不可使用,即所有Web API都必须有这个鉴权 | 1.0 | 用户管理SaaS支持应用访问权限 - 访问登录校验bk_token或使用bk_token获取用户信息时对于特殊code=1302403
- 产品页面上需要展示无权限提示
- 必须保证整个产品不可使用,即所有Web API都必须有这个鉴权 | priority | 用户管理saas支持应用访问权限 访问登录校验bk token或使用bk token获取用户信息时对于特殊code 产品页面上需要展示无权限提示 必须保证整个产品不可使用,即所有web api都必须有这个鉴权 | 1 |
486,660 | 14,012,294,461 | IssuesEvent | 2020-10-29 08:50:05 | magento/magento2 | https://api.github.com/repos/magento/magento2 | closed | Wrong order status showing in case customer has ordered 3 qty of one product, and admin invoiced2 refunded 1,shipped 1 and cancelled 1 | Component: order status Issue: Confirmed Issue: Format is valid Issue: Ready for Work Priority: P2 Progress: done Reproduced on 2.4.x Severity: S2 | <!---
Please review our guidelines before adding a new issue: https://github.com/magento/magento2/wiki/Issue-reporting-guidelines
Fields marked with (*) are required. Please don't remove the template.
-->
### Preconditions (*)
<!---
-->
1. magento v 2.4.0
2.
### Steps to reproduce (*)
<!---
-->
1.plac... | 1.0 | Wrong order status showing in case customer has ordered 3 qty of one product, and admin invoiced2 refunded 1,shipped 1 and cancelled 1 - <!---
Please review our guidelines before adding a new issue: https://github.com/magento/magento2/wiki/Issue-reporting-guidelines
Fields marked with (*) are required. Please don't r... | priority | wrong order status showing in case customer has ordered qty of one product and admin refunded shipped and cancelled please review our guidelines before adding a new issue fields marked with are required please don t remove the template preconditions magento ... | 1 |
418,926 | 12,215,546,109 | IssuesEvent | 2020-05-01 13:11:36 | Laravel-Backpack/CRUD | https://api.github.com/repos/Laravel-Backpack/CRUD | opened | [4.1.x][Feature] Focus on first item when InlineCreate modal opens | Feature Priority: SHOULD | This is a feature we have inside the main form, and it should be present inside the InlineCreate modal too. It allows for keyboard-only data entry. | 1.0 | [4.1.x][Feature] Focus on first item when InlineCreate modal opens - This is a feature we have inside the main form, and it should be present inside the InlineCreate modal too. It allows for keyboard-only data entry. | priority | focus on first item when inlinecreate modal opens this is a feature we have inside the main form and it should be present inside the inlinecreate modal too it allows for keyboard only data entry | 1 |
440,957 | 12,706,884,427 | IssuesEvent | 2020-06-23 07:59:49 | California-Planet-Search/radvel | https://api.github.com/repos/California-Planet-Search/radvel | closed | Gaussian Process Fitting - different Ks on plots? | help wanted priority:high question | Hi, I am using the Gaussian Process feature from radvel and I was curious why is it that the semi-amplitude is different in GPPlot.plot_multipanel from the one from the Corner plot. This happens in the tutorial that you have posted (https://github.com/California-Planet-Search/radvel/blob/master/docs/tutorials/GaussianP... | 1.0 | Gaussian Process Fitting - different Ks on plots? - Hi, I am using the Gaussian Process feature from radvel and I was curious why is it that the semi-amplitude is different in GPPlot.plot_multipanel from the one from the Corner plot. This happens in the tutorial that you have posted (https://github.com/California-Plane... | priority | gaussian process fitting different ks on plots hi i am using the gaussian process feature from radvel and i was curious why is it that the semi amplitude is different in gpplot plot multipanel from the one from the corner plot this happens in the tutorial that you have posted i ran radvel on my computer wit... | 1 |
47,315 | 12,003,829,333 | IssuesEvent | 2020-04-09 10:19:27 | ElektraInitiative/libelektra | https://api.github.com/repos/ElektraInitiative/libelektra | opened | crypto_botan: botan 2.13 header deprecation warnings | build dependencies | As of botan 2.13.x (maybe earlier?) we started getting the following header deprecation warnings:
```
In file included from ../src/plugins/crypto/botan_operations.cpp:12:
/usr/local/Cellar/botan/2.13.0/include/botan-2/botan/hmac.h:14:1: warning: this header will be made internal in the future [-W#pragma-messages]
... | 1.0 | crypto_botan: botan 2.13 header deprecation warnings - As of botan 2.13.x (maybe earlier?) we started getting the following header deprecation warnings:
```
In file included from ../src/plugins/crypto/botan_operations.cpp:12:
/usr/local/Cellar/botan/2.13.0/include/botan-2/botan/hmac.h:14:1: warning: this header wi... | non_priority | crypto botan botan header deprecation warnings as of botan x maybe earlier we started getting the following header deprecation warnings in file included from src plugins crypto botan operations cpp usr local cellar botan include botan botan hmac h warning this header will be... | 0 |
233,920 | 7,708,780,971 | IssuesEvent | 2018-05-22 06:56:22 | qutebrowser/qutebrowser | https://api.github.com/repos/qutebrowser/qutebrowser | reopened | Qt 5.11: Page is sometimes split in half | bug: behavior priority: 0 - high qt: 5.11 | - My bug report: [QTBUG-68279](https://bugreports.qt.io/browse/QTBUG-68279)
- Original bug report: [QTBUG-68224](https://bugreports.qt.io/browse/QTBUG-68224)
- Bug fix: https://codereview.qt-project.org/#/c/229443/
- Regression caused by: https://codereview.qt-project.org/#/c/226416/ (for [QTBUG-65595](https://bugre... | 1.0 | Qt 5.11: Page is sometimes split in half - - My bug report: [QTBUG-68279](https://bugreports.qt.io/browse/QTBUG-68279)
- Original bug report: [QTBUG-68224](https://bugreports.qt.io/browse/QTBUG-68224)
- Bug fix: https://codereview.qt-project.org/#/c/229443/
- Regression caused by: https://codereview.qt-project.org/#... | priority | qt page is sometimes split in half my bug report original bug report bug fix regression caused by for | 1 |
86,396 | 16,988,606,392 | IssuesEvent | 2021-06-30 17:16:12 | anomanetwork/anoma | https://api.github.com/repos/anomanetwork/anoma | opened | nicer parallelized VP out-of-gas error short-circuiting | ledger refactor / code quality | Following the changes done for #312, it is possible to match on the runtime error that occurred in the WASM execution, if any. We should use that to perform short-circuiting by returning an error inside the `.par_iter().try_fold(...` if the runtime error is a gas error.
Currently, we using a somewhat hacky workaroun... | 1.0 | nicer parallelized VP out-of-gas error short-circuiting - Following the changes done for #312, it is possible to match on the runtime error that occurred in the WASM execution, if any. We should use that to perform short-circuiting by returning an error inside the `.par_iter().try_fold(...` if the runtime error is a ga... | non_priority | nicer parallelized vp out of gas error short circuiting following the changes done for it is possible to match on the runtime error that occurred in the wasm execution if any we should use that to perform short circuiting by returning an error inside the par iter try fold if the runtime error is a gas ... | 0 |
80,681 | 23,279,538,565 | IssuesEvent | 2022-08-05 10:36:11 | VirtusLab/git-machete-intellij-plugin | https://api.github.com/repos/VirtusLab/git-machete-intellij-plugin | closed | Improve Gradle-related Kotlin code | build code quality | After migrating the gradle scripts to Kotlin there are some issues that need to be resolved:
- [x] Find a way to use version catalog aliases in helpers' code in buildSrc/
(one way to do it would be to put the aliases into extra properties of the project in buildSrc)
- [x] Unify plugins' notations in `libraries` an... | 1.0 | Improve Gradle-related Kotlin code - After migrating the gradle scripts to Kotlin there are some issues that need to be resolved:
- [x] Find a way to use version catalog aliases in helpers' code in buildSrc/
(one way to do it would be to put the aliases into extra properties of the project in buildSrc)
- [x] Unify... | non_priority | improve gradle related kotlin code after migrating the gradle scripts to kotlin there are some issues that need to be resolved find a way to use version catalog aliases in helpers code in buildsrc one way to do it would be to put the aliases into extra properties of the project in buildsrc unify plu... | 0 |
198,877 | 15,726,856,884 | IssuesEvent | 2021-03-29 11:54:45 | TesseractCoding/NeoAlgo | https://api.github.com/repos/TesseractCoding/NeoAlgo | closed | Update of readme file of cp in Java | Assigned Java documentation gssoc21 | ## 📚 Documentation
The readme file of cp of Java is empty. Better providing the list of problems included in java/cp.
### Have you read the [Contributing Guidelines on Pull Requests](https://github.com/TesseractCoding/NeoAlgo/blob/master/CONTRIBUTING.md#reporting-new-issues)?
Yes. | 1.0 | Update of readme file of cp in Java - ## 📚 Documentation
The readme file of cp of Java is empty. Better providing the list of problems included in java/cp.
### Have you read the [Contributing Guidelines on Pull Requests](https://github.com/TesseractCoding/NeoAlgo/blob/master/CONTRIBUTING.md#reporting-new-issues)... | non_priority | update of readme file of cp in java 📚 documentation the readme file of cp of java is empty better providing the list of problems included in java cp have you read the yes | 0 |
296,040 | 9,103,730,909 | IssuesEvent | 2019-02-20 16:30:32 | archesproject/arches-collector | https://api.github.com/repos/archesproject/arches-collector | closed | On iOS, user can't delete an instance | Priority: High Type: Bug | To reproduce:
1. On an iOS device, create a new instance in a project
2. Try to delete the instance by pressing the "trash" icon
3. Note that the app interprets the interaction as a touch on the instance list item, and returns the user to instance editor
This means that the user can't delete an instance. | 1.0 | On iOS, user can't delete an instance - To reproduce:
1. On an iOS device, create a new instance in a project
2. Try to delete the instance by pressing the "trash" icon
3. Note that the app interprets the interaction as a touch on the instance list item, and returns the user to instance editor
This means that the use... | priority | on ios user can t delete an instance to reproduce on an ios device create a new instance in a project try to delete the instance by pressing the trash icon note that the app interprets the interaction as a touch on the instance list item and returns the user to instance editor this means that the use... | 1 |
70,233 | 15,058,298,659 | IssuesEvent | 2021-02-03 23:11:07 | MValle21/tetres | https://api.github.com/repos/MValle21/tetres | opened | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.56.jar | security vulnerability | ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptograp... | True | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.56.jar - ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p></summary>
<p>The Bounc... | non_priority | cve high detected in bcprov jar cve high severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk... | 0 |
568,995 | 16,992,344,157 | IssuesEvent | 2021-06-30 22:42:42 | celo-org/wallet | https://api.github.com/repos/celo-org/wallet | opened | Update push notification for rewards distribution | Component: Consumer Incentives Priority: P1 enhancement wallet | ### What would you like?
Change the text of the push notifications sent for rewards distributions
### Why is this needed?
We want a different text | 1.0 | Update push notification for rewards distribution - ### What would you like?
Change the text of the push notifications sent for rewards distributions
### Why is this needed?
We want a different text | priority | update push notification for rewards distribution what would you like change the text of the push notifications sent for rewards distributions why is this needed we want a different text | 1 |
565,766 | 16,769,331,502 | IssuesEvent | 2021-06-14 13:04:48 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | bbva.csod.com - design is broken | browser-firefox engine-gecko os-linux priority-normal | <!-- @browser: Firefox 78.0 -->
<!-- @ua_header: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/77014 -->
**URL**: https://bbva.csod.com/lms/scorm/clientLMS/LMS3.aspx?rNum=2&aicc_sid=31263... | 1.0 | bbva.csod.com - design is broken - <!-- @browser: Firefox 78.0 -->
<!-- @ua_header: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/77014 -->
**URL**: https://bbva.csod.com/lms/scorm/client... | priority | bbva csod com design is broken url browser version firefox operating system linux tested another browser yes other problem type design is broken description images not loaded steps to reproduce no carga el contenido del curso en pantalla view the scre... | 1 |
680,634 | 23,280,558,190 | IssuesEvent | 2022-08-05 11:38:06 | ballerina-platform/ballerina-dev-website | https://api.github.com/repos/ballerina-platform/ballerina-dev-website | closed | Suggestions to improve the Publish packages to Ballerina Central page | Priority/Highest Type/Improvement Area/LearnPages WebsiteRewrite | ## Description
This is a list of suggestions to improve [1]
[1] https://dev.ballerina.io/learn/publish-packages-to-ballerina-central/#Create%20a%20library%20package
## Related website/documentation area
[> Add/Uncomment the relevant area label out of the following. ](https://dev.ballerina.io/learn/publish-packa... | 1.0 | Suggestions to improve the Publish packages to Ballerina Central page - ## Description
This is a list of suggestions to improve [1]
[1] https://dev.ballerina.io/learn/publish-packages-to-ballerina-central/#Create%20a%20library%20package
## Related website/documentation area
[> Add/Uncomment the relevant area la... | priority | suggestions to improve the publish packages to ballerina central page description this is a list of suggestions to improve related website documentation area area learnpages describe the problem s the introductory sentence includes the sentence use the ba... | 1 |
291,016 | 8,916,194,659 | IssuesEvent | 2019-01-19 14:17:57 | Warcraft-GoA-Development-Team/Warcraft-Guardians-of-Azeroth | https://api.github.com/repos/Warcraft-GoA-Development-Team/Warcraft-Guardians-of-Azeroth | opened | Heralds can sacrifice my prisoners without my consent | :beetle: bug - balance :balance_scale: :exclamation: priority high | Master branch
High (?)
Heralds can sacrifice my prisoners without my consent.
And their number of murders is incredibly high.
<details>
<summary>Click to expand</summary>


Heralds can sacrifice my prisoners without my consent.
And their number of murders is incredibly high.
<details>
<summary>Click to expand</summary>
: When opening the Storage Request Table, it will reorder all the items in my inventory by pushing them one slot to the right. This is purely visual, clicking on any item will ... | True | Storage Request Table messes up inventory order - Minecraft version & Mod Version: 1.12.2 / 1.7.4
Single player or Server: Server
Describe problem (what you were doing / what happened): When opening the Storage Request Table, it will reorder all the items in my inventory by pushing them one slot to the right.... | non_priority | storage request table messes up inventory order minecraft version mod version single player or server server describe problem what you were doing what happened when opening the storage request table it will reorder all the items in my inventory by pushing them one slot to the right ... | 0 |
48,319 | 13,068,441,140 | IssuesEvent | 2020-07-31 03:35:15 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | closed | Wrong datatype in steering file for 20208 -> unable to weight via from_simprod (Trac #2178) | Migrated from Trac analysis defect | Hi,
another problem with the steering file of 20208
(http://simprod.icecube.wisc.edu/cgi-bin/simulation/cgi/cfg?dataset=20208)
CORSIKA::eprimarymax string 1e6
should be either int or float, not string.
It being a string leads to this error in simprod:
File "/data/user/flauber/software/py2-v3.0.1/combo/stable/build/... | 1.0 | Wrong datatype in steering file for 20208 -> unable to weight via from_simprod (Trac #2178) - Hi,
another problem with the steering file of 20208
(http://simprod.icecube.wisc.edu/cgi-bin/simulation/cgi/cfg?dataset=20208)
CORSIKA::eprimarymax string 1e6
should be either int or float, not string.
It being a string lead... | non_priority | wrong datatype in steering file for unable to weight via from simprod trac hi another problem with the steering file of corsika eprimarymax string should be either int or float not string it being a string leads to this error in simprod file data user flauber software combo stable ... | 0 |
109,444 | 4,387,434,025 | IssuesEvent | 2016-08-08 15:46:51 | MinetestForFun/server-minetestforfun-hungry_games | https://api.github.com/repos/MinetestForFun/server-minetestforfun-hungry_games | closed | Server crash | Modding ➤ BugFix Priority: High Server crash | ```
2016-07-25 23:37:24: ERROR[Main]: ServerError: Lua: Runtime error from mod 'kill_history' in callback on_dieplayer(): ..../games/minetestforfun_hg/mods/kill_history/init.lua:81: attempt to index local 'coltab' (a nil value)
2016-07-25 23:37:24: ERROR[Main]: stack traceback:
2016-07-25 23:37:24: ERROR[Main]: ...... | 1.0 | Server crash - ```
2016-07-25 23:37:24: ERROR[Main]: ServerError: Lua: Runtime error from mod 'kill_history' in callback on_dieplayer(): ..../games/minetestforfun_hg/mods/kill_history/init.lua:81: attempt to index local 'coltab' (a nil value)
2016-07-25 23:37:24: ERROR[Main]: stack traceback:
2016-07-25 23:37:24: ER... | priority | server crash error servererror lua runtime error from mod kill history in callback on dieplayer games minetestforfun hg mods kill history init lua attempt to index local coltab a nil value error stack traceback error games minetestforfun hg... | 1 |
78,665 | 3,512,662,749 | IssuesEvent | 2016-01-11 03:38:55 | SpongePowered/SpongeVanilla | https://api.github.com/repos/SpongePowered/SpongeVanilla | closed | Crash when generating a new world | accepted bug high-priority | ```
---- Minecraft Crash Report ----
// My bad.
Time: 1/10/16 9:51 PM
Description: Exception in server tick loop
java.lang.IllegalArgumentException
at com.google.common.base.Preconditions.checkArgument(Preconditions.java:111)
at net.minecraft.world.gen.feature.WorldGenLakes.setLiquidType(SourceFile:102)
... | 1.0 | Crash when generating a new world - ```
---- Minecraft Crash Report ----
// My bad.
Time: 1/10/16 9:51 PM
Description: Exception in server tick loop
java.lang.IllegalArgumentException
at com.google.common.base.Preconditions.checkArgument(Preconditions.java:111)
at net.minecraft.world.gen.feature.WorldGenLa... | priority | crash when generating a new world minecraft crash report my bad time pm description exception in server tick loop java lang illegalargumentexception at com google common base preconditions checkargument preconditions java at net minecraft world gen feature worldgenlakes s... | 1 |
18,434 | 2,615,171,033 | IssuesEvent | 2015-03-01 06:52:57 | chrsmith/html5rocks | https://api.github.com/repos/chrsmith/html5rocks | closed | Tutorial: Synchronous FileSystem - example code not calling worker | auto-migrated Milestone-Q12012 Priority-P2 Tutorial Type-Bug | ```
http://master.html5rocks.appspot.com/en/tutorials/file/filesystem-sync/
Section: Passing around Files, Blobs, and ArrayBuffers
The example code for this does does not actually post the FileList to the
worker, as described ("The worker simply passes through the file list"). Adding
the following to the anonymous ... | 1.0 | Tutorial: Synchronous FileSystem - example code not calling worker - ```
http://master.html5rocks.appspot.com/en/tutorials/file/filesystem-sync/
Section: Passing around Files, Blobs, and ArrayBuffers
The example code for this does does not actually post the FileList to the
worker, as described ("The worker simply pa... | priority | tutorial synchronous filesystem example code not calling worker section passing around files blobs and arraybuffers the example code for this does does not actually post the filelist to the worker as described the worker simply passes through the file list adding the following to the anonymous f... | 1 |
53,796 | 3,050,857,315 | IssuesEvent | 2015-08-12 02:34:36 | yawlfoundation/yawl | https://api.github.com/repos/yawlfoundation/yawl | closed | Documentation: info on WSInvoker | auto-migrated Milestone-2.0 Priority-Medium Type-Enhancement | ```
Update the documentation for the WSInvoker by specifying that the following
restrictions apply to the web service that can be invoked by this custom
service:
- RPC-style only
- synchronous only
- input and output messages for the selected operation must have only one
part (to be verified)
- the part must be of typ... | 1.0 | Documentation: info on WSInvoker - ```
Update the documentation for the WSInvoker by specifying that the following
restrictions apply to the web service that can be invoked by this custom
service:
- RPC-style only
- synchronous only
- input and output messages for the selected operation must have only one
part (to be ... | priority | documentation info on wsinvoker update the documentation for the wsinvoker by specifying that the following restrictions apply to the web service that can be invoked by this custom service rpc style only synchronous only input and output messages for the selected operation must have only one part to be ... | 1 |
393,383 | 11,614,712,491 | IssuesEvent | 2020-02-26 13:04:29 | rathena/rathena | https://api.github.com/repos/rathena/rathena | closed | Cannot use Flash Combo at Ghost 3 and above | component:core mode:prerenewal mode:renewal priority:low status:confirmed type:bug | <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: https://github.com/rathena/rathena/commit/1fc4b8de2063c90b74b7da95e3b105306a825c21
<!-- Please specify the rAthena [GitHub hash](https://help.github.com/articles/autolinked-references-and-urls/#commit-sha... | 1.0 | Cannot use Flash Combo at Ghost 3 and above - <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: https://github.com/rathena/rathena/commit/1fc4b8de2063c90b74b7da95e3b105306a825c21
<!-- Please specify the rAthena [GitHub hash](https://help.github.com/artic... | priority | cannot use flash combo at ghost and above rathena hash please specify the rathena on which you encountered this issue how to get your github hash cd your rathena directory git rev parse short head copy the resulting hash client date server m... | 1 |
238,394 | 7,779,138,331 | IssuesEvent | 2018-06-05 15:55:45 | mozilla/addons-frontend | https://api.github.com/repos/mozilla/addons-frontend | closed | Delete profile picture text overlaps its border when clicked | component: user profile priority: p4 size: S type: bug | Steps to reproduce:
1.Go to AMO-dev and log in with an account having a profile picture
2.Go to edit profile page
3.Click on "Delete this picture" photo
Expected results:
The text should properly fit inside the blue border displayed when clicking the text
Actual results:
The text overlaps the blue border
... | 1.0 | Delete profile picture text overlaps its border when clicked - Steps to reproduce:
1.Go to AMO-dev and log in with an account having a profile picture
2.Go to edit profile page
3.Click on "Delete this picture" photo
Expected results:
The text should properly fit inside the blue border displayed when clicking the... | priority | delete profile picture text overlaps its border when clicked steps to reproduce go to amo dev and log in with an account having a profile picture go to edit profile page click on delete this picture photo expected results the text should properly fit inside the blue border displayed when clicking the... | 1 |
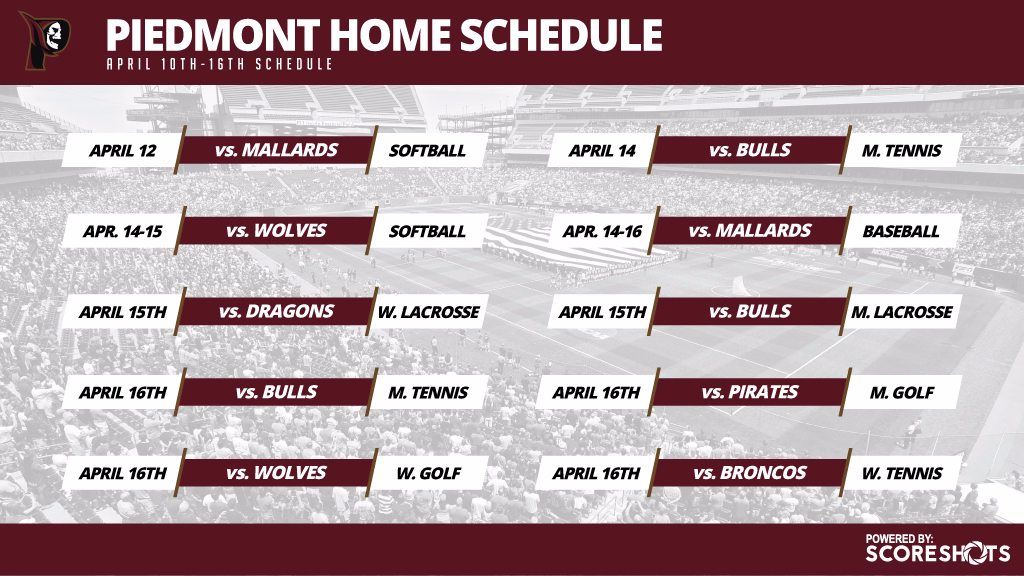
627,859 | 19,915,723,474 | IssuesEvent | 2022-01-25 22:22:07 | Azure/azure-sdk-tools | https://api.github.com/repos/Azure/azure-sdk-tools | closed | [APIView] Should not create automatic diff if the only difference is tooling number | enhancement APIView Central-EngSys APIView Priority 1 Python | Example:
https://apiview.dev/Assemblies/Review/18826b88a9ba482fab51d53572e740a6
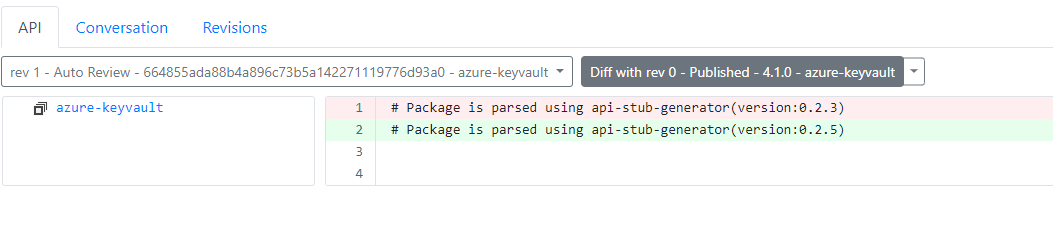
| 1.0 | [APIView] Should not create automatic diff if the only difference is tooling number - Example:
https://apiview.dev/Assemblies/Review/18826b88a9ba482fab51d53572e740a6
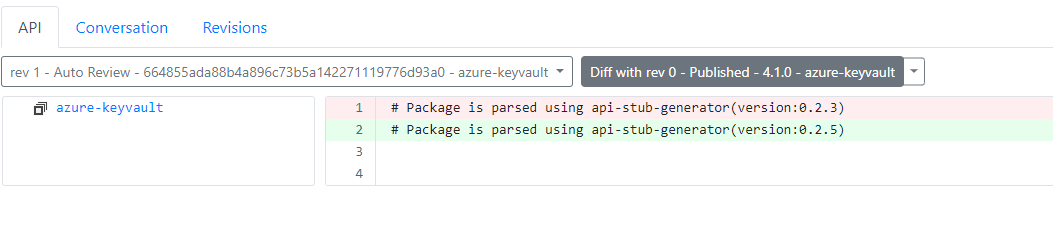
| priority | should not create automatic diff if the only difference is tooling number example | 1 |
69,726 | 30,466,296,294 | IssuesEvent | 2023-07-17 10:35:55 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | closed | Cannot update Data Transparent Data Encryption State | SQL Service Attention Mgmt customer-reported bug issue-addressed | ### Library name and version
Azure.ResourceManager.Sql 1.1.0
### Describe the bug
I am trying to update data transparent data encryption state from C# code. However, i can not update due to NullReferenceException thrown from inside package:
` function for deep clone if available | type:refactor good first issue status:blocked priority-5-triage | ### Describe the proposed change(s).
It seems to be available starting from Node v17. See also:
https://developer.mozilla.org/en-US/docs/Web/API/structuredClone
| 1.0 | Use `structureClone()` function for deep clone if available - ### Describe the proposed change(s).
It seems to be available starting from Node v17. See also:
https://developer.mozilla.org/en-US/docs/Web/API/structuredClone
| priority | use structureclone function for deep clone if available describe the proposed change s it seems to be available starting from node see also | 1 |
16,777 | 2,945,224,761 | IssuesEvent | 2015-07-03 11:20:28 | Kiri-rin/markdownsharp | https://api.github.com/repos/Kiri-rin/markdownsharp | closed | Add SkipCodeBlocks Option | auto-migrated Priority-Medium Type-Defect | ```
This adds the ability to set a markdown option to skip code blocks
which is helpful when parsing output that was originally built
with xml like a nuspec where it automatically indents everything
four spaces for you. When that gets pushed to nuget.org or
chocolatey.org, the content is parsed and incorrectly assumes
... | 1.0 | Add SkipCodeBlocks Option - ```
This adds the ability to set a markdown option to skip code blocks
which is helpful when parsing output that was originally built
with xml like a nuspec where it automatically indents everything
four spaces for you. When that gets pushed to nuget.org or
chocolatey.org, the content is par... | non_priority | add skipcodeblocks option this adds the ability to set a markdown option to skip code blocks which is helpful when parsing output that was originally built with xml like a nuspec where it automatically indents everything four spaces for you when that gets pushed to nuget org or chocolatey org the content is par... | 0 |
285,757 | 31,155,548,047 | IssuesEvent | 2023-08-16 12:55:31 | nidhi7598/linux-4.1.15_CVE-2018-5873 | https://api.github.com/repos/nidhi7598/linux-4.1.15_CVE-2018-5873 | opened | CVE-2023-31248 (High) detected in linuxlinux-4.1.52 | Mend: dependency security vulnerability | ## CVE-2023-31248 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.ker... | True | CVE-2023-31248 (High) detected in linuxlinux-4.1.52 - ## CVE-2023-31248 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.52</b></p></summary>
<p>
<p>The Linux Kernel</p>
... | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files net netfilter nf tables api c net netfilter... | 0 |
56,117 | 11,504,821,313 | IssuesEvent | 2020-02-13 00:25:25 | phetsims/normal-modes | https://api.github.com/repos/phetsims/normal-modes | closed | review design of Speed control, use TimeControlNode | design:general dev:code-review meeting:design | Noticed during #2 (code review), and related to https://github.com/phetsims/scenery-phet/issues/575 (redesign of TimeControlNode).
This sim has a time control, see screenshot below. It should be using `SCENERY_PHET/TimeControlNode`. The slider is not part of TimeControlNode. Is this a necessary part of the desig... | 1.0 | review design of Speed control, use TimeControlNode - Noticed during #2 (code review), and related to https://github.com/phetsims/scenery-phet/issues/575 (redesign of TimeControlNode).
This sim has a time control, see screenshot below. It should be using `SCENERY_PHET/TimeControlNode`. The slider is not part of T... | non_priority | review design of speed control use timecontrolnode noticed during code review and related to redesign of timecontrolnode this sim has a time control see screenshot below it should be using scenery phet timecontrolnode the slider is not part of timecontrolnode is this a necessary part of the d... | 0 |
368,684 | 10,883,248,013 | IssuesEvent | 2019-11-18 04:02:40 | etternagame/etterna | https://api.github.com/repos/etternagame/etterna | closed | Remove or Fix Blind Modifier | Good First Issue Priority: Low Type: Bug Type: Maintenance | this is very broken and was effectively replaced by the Judgment Text toggle
intended behavior is that it just turns visual judgment feedback off but instead it causes notes to disappear instantly no matter what timing window you have (you can hit notes that arent on the screen) | 1.0 | Remove or Fix Blind Modifier - this is very broken and was effectively replaced by the Judgment Text toggle
intended behavior is that it just turns visual judgment feedback off but instead it causes notes to disappear instantly no matter what timing window you have (you can hit notes that arent on the screen) | priority | remove or fix blind modifier this is very broken and was effectively replaced by the judgment text toggle intended behavior is that it just turns visual judgment feedback off but instead it causes notes to disappear instantly no matter what timing window you have you can hit notes that arent on the screen | 1 |
154,225 | 19,710,929,796 | IssuesEvent | 2022-01-13 05:10:53 | ChoeMinji/redis-6.2.3 | https://api.github.com/repos/ChoeMinji/redis-6.2.3 | opened | CVE-2021-32675 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-32675 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>redis6.2.6</b>, <b>redis6.2.6</b>, <b>redis6.2.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><i... | True | CVE-2021-32675 (High) detected in multiple libraries - ## CVE-2021-32675 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>redis6.2.6</b>, <b>redis6.2.6</b>, <b>redis6.2.6</b></p></summ... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries vulnerability details redis is an open source in memory database that persists on disk when parsing an incoming redis standard protocol resp request ... | 0 |
699,909 | 24,036,558,730 | IssuesEvent | 2022-09-15 19:46:47 | rancher/rancher | https://api.github.com/repos/rancher/rancher | opened | [Backport v2.6] [BUG][Monitoring v2]Prometheus target serviceMonitor/kube-system/rancher-monitoring-coredns is down in k3s hardened cluster - connect refused | priority/1 kind/bug-qa area/monitoring feature/charts-monitoring-v2 team/area3 | This is a backport issue for https://github.com/rancher/rancher/issues/38820, automatically created via rancherbot by @MKlimuszka
Original issue description:
**Rancher Server Setup**
- Rancher version: `2.6-head Commit ID cb9ccde`
- Installation option (Docker install/Helm Chart): `Helm`
- If Helm Chart, Kubern... | 1.0 | [Backport v2.6] [BUG][Monitoring v2]Prometheus target serviceMonitor/kube-system/rancher-monitoring-coredns is down in k3s hardened cluster - connect refused - This is a backport issue for https://github.com/rancher/rancher/issues/38820, automatically created via rancherbot by @MKlimuszka
Original issue description:
... | priority | prometheus target servicemonitor kube system rancher monitoring coredns is down in hardened cluster connect refused this is a backport issue for automatically created via rancherbot by mklimuszka original issue description rancher server setup rancher version head commit id installati... | 1 |
771,473 | 27,086,188,729 | IssuesEvent | 2023-02-14 17:09:25 | balena-os/balena-supervisor | https://api.github.com/repos/balena-os/balena-supervisor | closed | Two networks with the same name can make the supervisor unable to apply the target state (network is ambiguous) | type/bug High priority | Seen once, in a device that was updated from version 7.1.11 to 7.1.14. I'm not sure if anything particular about this device or its application might have triggered this particular situation.
Basically, there were two networks with the same name (`<appId>_default`) and this made balena complain with a `server error ... | 1.0 | Two networks with the same name can make the supervisor unable to apply the target state (network is ambiguous) - Seen once, in a device that was updated from version 7.1.11 to 7.1.14. I'm not sure if anything particular about this device or its application might have triggered this particular situation.
Basically, ... | priority | two networks with the same name can make the supervisor unable to apply the target state network is ambiguous seen once in a device that was updated from version to i m not sure if anything particular about this device or its application might have triggered this particular situation basically th... | 1 |
655,218 | 21,681,368,303 | IssuesEvent | 2022-05-09 07:00:02 | PierreHervelin/projet2-metaverse | https://api.github.com/repos/PierreHervelin/projet2-metaverse | closed | Component PlayerModel | question client 3D priority-1 feature | (A voir si c'est possible @Ki2lian)
Le PlayerModel implémenterai seulement le mesh, avec une position, un model, une animation etc...
Le Player implémenterai toute la logique d'action de l'utilisateur sur le PlayerModel.
Le joueur qu'on contrôle serait un Player, les autres joueurs seraient des PlayerModel | 1.0 | Component PlayerModel - (A voir si c'est possible @Ki2lian)
Le PlayerModel implémenterai seulement le mesh, avec une position, un model, une animation etc...
Le Player implémenterai toute la logique d'action de l'utilisateur sur le PlayerModel.
Le joueur qu'on contrôle serait un Player, les autres joueurs seraient d... | priority | component playermodel a voir si c est possible le playermodel implémenterai seulement le mesh avec une position un model une animation etc le player implémenterai toute la logique d action de l utilisateur sur le playermodel le joueur qu on contrôle serait un player les autres joueurs seraient des pla... | 1 |
309,531 | 26,667,554,690 | IssuesEvent | 2023-01-26 06:42:17 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | opened | DISABLED test_dynamic_shapes_right_side_dynamic_shapes (torch._dynamo.testing.make_test_cls_with_patches.<locals>.DummyTestClass) | triaged module: flaky-tests skipped module: dynamo | Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_dynamic_shapes_right_side_dynamic_shapes&suite=torch._dynamo.testing.make_test_cls_with_patches.<locals>.DummyTestClass) and the most recent trunk [workflow logs](https://github.com/py... | 1.0 | DISABLED test_dynamic_shapes_right_side_dynamic_shapes (torch._dynamo.testing.make_test_cls_with_patches.<locals>.DummyTestClass) - Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_dynamic_shapes_right_side_dynamic_shapes&suite=torch... | non_priority | disabled test dynamic shapes right side dynamic shapes torch dynamo testing make test cls with patches dummytestclass platforms linux this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with failures a... | 0 |
344,960 | 30,775,979,727 | IssuesEvent | 2023-07-31 06:29:41 | supakeen/pinnwand | https://api.github.com/repos/supakeen/pinnwand | closed | Add a browser test suite | enhancement tests | `pinnwand` is currently tested extensively in unit tests and with integration tests (if I can call them that) for its API. It's lacking a browser test suite where an automated browser performs actions on the application to ensure that the HTML, JavaScript and CSS didn't break.
Adding a test suite based on `playwrigh... | 1.0 | Add a browser test suite - `pinnwand` is currently tested extensively in unit tests and with integration tests (if I can call them that) for its API. It's lacking a browser test suite where an automated browser performs actions on the application to ensure that the HTML, JavaScript and CSS didn't break.
Adding a tes... | non_priority | add a browser test suite pinnwand is currently tested extensively in unit tests and with integration tests if i can call them that for its api it s lacking a browser test suite where an automated browser performs actions on the application to ensure that the html javascript and css didn t break adding a tes... | 0 |
795,853 | 28,089,181,432 | IssuesEvent | 2023-03-30 11:57:06 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | m.youtube.com - see bug description | priority-critical type-webrender-enabled browser-fenix engine-gecko | <!-- @browser: Firefox Mobile 113.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 11; Mobile; rv:109.0) Gecko/113.0 Firefox/113.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/120187 -->
<!-- @extra_labels: browser-fenix, type-webrender-enabled -->
... | 1.0 | m.youtube.com - see bug description - <!-- @browser: Firefox Mobile 113.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 11; Mobile; rv:109.0) Gecko/113.0 Firefox/113.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/120187 -->
<!-- @extra_labels: brows... | priority | m youtube com see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description video playback is not smooth steps to reproduce video playback on youtube is not smooth a... | 1 |
590,242 | 17,774,550,958 | IssuesEvent | 2021-08-30 17:27:34 | GoogleCloudPlatform/golang-samples | https://api.github.com/repos/GoogleCloudPlatform/golang-samples | closed | vision/product_search: TestGetSimilarProducts failed | type: bug priority: p1 api: vision samples flakybot: issue | Note: #2187 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 88b2a1089882340cbb1a55b67718645c5ee9af99
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/5217657a-08aa-4983-b787-650d10e2e338), [Sponge](http://sponge2/5217657a-08aa-4983-... | 1.0 | vision/product_search: TestGetSimilarProducts failed - Note: #2187 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 88b2a1089882340cbb1a55b67718645c5ee9af99
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/5217657a-08aa-4983-b787-650... | priority | vision product search testgetsimilarproducts failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output get similar products test go getsimilarproducts productsearch rpc error code notfound desc... | 1 |
305,496 | 26,390,761,926 | IssuesEvent | 2023-01-12 15:31:14 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | define a recommended process in zephyr for a CI framework integration | Feature Request area: Test Framework | in Zephyr, the current test framework runs stanbalone. and it is not defined for any CI system integartion.
As Zephyr projects is getting more complexity, the test framework needs to be designed such as a CI framwork can be easily adapted to.
 detected in set-value-2.0.1.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-23440 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>set-value-2.0.1.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) pa... | True | CVE-2021-23440 (High) detected in set-value-2.0.1.tgz - autoclosed - ## CVE-2021-23440 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>set-value-2.0.1.tgz</b></p></summary>
<p>Create n... | non_priority | cve high detected in set value tgz autoclosed cve high severity vulnerability vulnerable library set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file package json path to vu... | 0 |
96,059 | 19,862,342,875 | IssuesEvent | 2022-01-22 02:44:17 | trezor/trezor-suite | https://api.github.com/repos/trezor/trezor-suite | opened | Clean up messages | code | The following merge improved messages.ts and en.json.
https://github.com/trezor/trezor-suite/pull/4777
https://github.com/trezor/trezor-suite/pull/4778
Therefore, I considered cleaning up message files.
I've written python code that does a full-text search of all the files to see if the keys contained in the me... | 1.0 | Clean up messages - The following merge improved messages.ts and en.json.
https://github.com/trezor/trezor-suite/pull/4777
https://github.com/trezor/trezor-suite/pull/4778
Therefore, I considered cleaning up message files.
I've written python code that does a full-text search of all the files to see if the keys... | non_priority | clean up messages the following merge improved messages ts and en json therefore i considered cleaning up message files i ve written python code that does a full text search of all the files to see if the keys contained in the messages ts file are actually used this code will eventually output new me... | 0 |
508,622 | 14,703,850,286 | IssuesEvent | 2021-01-04 15:38:16 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | Fix less v4 breakage | priority: p3 | identified in https://github.com/mozilla/addons-server/pull/16205#issuecomment-753931483 by @diox
less v4 makes a number of [changes](https://github.com/less/less.js/pull/3573), one of which is less/less.js@67ce103 "Require parens after mixin call" - this is causing the less compilation step to fail. We don't fail ... | 1.0 | Fix less v4 breakage - identified in https://github.com/mozilla/addons-server/pull/16205#issuecomment-753931483 by @diox
less v4 makes a number of [changes](https://github.com/less/less.js/pull/3573), one of which is less/less.js@67ce103 "Require parens after mixin call" - this is causing the less compilation step t... | priority | fix less breakage identified in by diox less makes a number of one of which is less less js require parens after mixin call this is causing the less compilation step to fail we don t fail during the assets build for this so it doesn t trigger a fail in ci it s unclear what the actual result of ... | 1 |
105,705 | 16,657,290,988 | IssuesEvent | 2021-06-05 19:08:13 | kstring/traefik | https://api.github.com/repos/kstring/traefik | closed | CVE-2020-7751 (High) detected in pathval-1.1.0.tgz | security vulnerability | ## CVE-2020-7751 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pathval-1.1.0.tgz</b></p></summary>
<p>Object value retrieval given a string path</p>
<p>Library home page: <a href="ht... | True | CVE-2020-7751 (High) detected in pathval-1.1.0.tgz - ## CVE-2020-7751 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pathval-1.1.0.tgz</b></p></summary>
<p>Object value retrieval give... | non_priority | cve high detected in pathval tgz cve high severity vulnerability vulnerable library pathval tgz object value retrieval given a string path library home page a href path to dependency file traefik webui package json path to vulnerable library traefik webui node module... | 0 |
241 | 4,918,405,895 | IssuesEvent | 2016-11-24 08:47:43 | DevExpress/testcafe | https://api.github.com/repos/DevExpress/testcafe | opened | TestCafe scroll to target element incorrectly | SYSTEM: automations TYPE: bug | ### Are you requesting a feature or reporting a bug?
bug
### What is the current behavior?
TestCafe doesn't scroll container to show target element fully while performing an action on it
### What is the expected behavior?
TestCafe should scroll container to show element fully, when it possible (element i... | 1.0 | TestCafe scroll to target element incorrectly - ### Are you requesting a feature or reporting a bug?
bug
### What is the current behavior?
TestCafe doesn't scroll container to show target element fully while performing an action on it
### What is the expected behavior?
TestCafe should scroll container to... | non_priority | testcafe scroll to target element incorrectly are you requesting a feature or reporting a bug bug what is the current behavior testcafe doesn t scroll container to show target element fully while performing an action on it what is the expected behavior testcafe should scroll container to... | 0 |
127,338 | 18,010,411,284 | IssuesEvent | 2021-09-16 07:56:57 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | opened | CVE-2020-25669 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2020-25669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home pag... | True | CVE-2020-25669 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2020-25669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartw... | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href vulnerable source files drivers input k... | 0 |
163,543 | 6,200,582,758 | IssuesEvent | 2017-07-06 01:47:16 | coreos/bugs | https://api.github.com/repos/coreos/bugs | closed | HAProxy does not respond after update to 1409.2.0 | component/kernel kind/regression priority/P0 team/os | # Issue Report #
## Bug ##
### Container Linux Version ###
```
NAME="Container Linux by CoreOS"
ID=coreos
VERSION=1409.2.0
VERSION_ID=1409.2.0
BUILD_ID=2017-06-19-2321
PRETTY_NAME="Container Linux by CoreOS 1409.2.0 (Ladybug)"
ANSI_COLOR="38;5;75"
HOME_URL="https://coreos.com/"
BUG_REPORT_URL="https:/... | 1.0 | HAProxy does not respond after update to 1409.2.0 - # Issue Report #
## Bug ##
### Container Linux Version ###
```
NAME="Container Linux by CoreOS"
ID=coreos
VERSION=1409.2.0
VERSION_ID=1409.2.0
BUILD_ID=2017-06-19-2321
PRETTY_NAME="Container Linux by CoreOS 1409.2.0 (Ladybug)"
ANSI_COLOR="38;5;75"
HOM... | priority | haproxy does not respond after update to issue report bug container linux version name container linux by coreos id coreos version version id build id pretty name container linux by coreos ladybug ansi color home url bug report u... | 1 |
262,655 | 27,983,024,381 | IssuesEvent | 2023-03-26 11:37:10 | kimai/kimai | https://api.github.com/repos/kimai/kimai | closed | Users can register even when user registration is disabled | bug security waiting for feedback | ### Describe the issue
I have registered bogus users which may have bypassed the registration form.
### I already tried
- [X] I've read and searched [the documentation](https://www.kimai.org/documentation/).
- [X] I've searched for similar issues in this repository.
- [X] I've searched for similar issues in [the d... | True | Users can register even when user registration is disabled - ### Describe the issue
I have registered bogus users which may have bypassed the registration form.
### I already tried
- [X] I've read and searched [the documentation](https://www.kimai.org/documentation/).
- [X] I've searched for similar issues in thi... | non_priority | users can register even when user registration is disabled describe the issue i have registered bogus users which may have bypassed the registration form i already tried i ve read and searched i ve searched for similar issues in this repository i ve searched for similar issues in ... | 0 |
40,231 | 6,808,453,011 | IssuesEvent | 2017-11-04 02:57:32 | has2k1/plotnine | https://api.github.com/repos/has2k1/plotnine | closed | Transforming the axis with my function | documentation question | Hello,
I am trying to do a custom scaling of the x-axis. I see that the scale_x_continuous function accepts a "trans" parameter, which can be a function. Here's my function (pretty simple)
```python
def scale_frets(frets):
return ([math.log(x + 1, 1.3) for x in frets])
```
It's not clear how I should us... | 1.0 | Transforming the axis with my function - Hello,
I am trying to do a custom scaling of the x-axis. I see that the scale_x_continuous function accepts a "trans" parameter, which can be a function. Here's my function (pretty simple)
```python
def scale_frets(frets):
return ([math.log(x + 1, 1.3) for x in fre... | non_priority | transforming the axis with my function hello i am trying to do a custom scaling of the x axis i see that the scale x continuous function accepts a trans parameter which can be a function here s my function pretty simple python def scale frets frets return it s not clear how i shou... | 0 |
160,034 | 6,068,528,151 | IssuesEvent | 2017-06-15 00:08:01 | cyberpwnn/Wormholes | https://api.github.com/repos/cyberpwnn/Wormholes | opened | Projections Bleed occasionally | bug high priority | Projection bleeding happens when a viewport is moved too far from the last viewport, and the resulting space in between the viewports has edges which are no longer kept track by the ghost rasterer (meaning the only way to remove them is to re-look through a projection in that location) | 1.0 | Projections Bleed occasionally - Projection bleeding happens when a viewport is moved too far from the last viewport, and the resulting space in between the viewports has edges which are no longer kept track by the ghost rasterer (meaning the only way to remove them is to re-look through a projection in that location) | priority | projections bleed occasionally projection bleeding happens when a viewport is moved too far from the last viewport and the resulting space in between the viewports has edges which are no longer kept track by the ghost rasterer meaning the only way to remove them is to re look through a projection in that location | 1 |
365,106 | 10,775,656,516 | IssuesEvent | 2019-11-03 15:43:25 | eJourn-al/eJournal | https://api.github.com/repos/eJourn-al/eJournal | closed | Copy assignment causes 500 error for existing journals | Priority: High Status: Review Needed Type: Bug Workload: Low | **Describe the bug**
Upon changing an assignment by copying its structure from another assignment, loading an existing journal for the updated assignment causes a 500 error (traced back to the `get_nodes` function).
**To Reproduce**
Steps to reproduce the behavior:
1. Fill the preset database
2. As the `Teacher... | 1.0 | Copy assignment causes 500 error for existing journals - **Describe the bug**
Upon changing an assignment by copying its structure from another assignment, loading an existing journal for the updated assignment causes a 500 error (traced back to the `get_nodes` function).
**To Reproduce**
Steps to reproduce the b... | priority | copy assignment causes error for existing journals describe the bug upon changing an assignment by copying its structure from another assignment loading an existing journal for the updated assignment causes a error traced back to the get nodes function to reproduce steps to reproduce the behav... | 1 |
484,264 | 13,937,150,864 | IssuesEvent | 2020-10-22 13:49:27 | trezor/trezor-suite | https://api.github.com/repos/trezor/trezor-suite | closed | Uncaught Exception: Error: cannot run bridge binary | Bug High priority | **Info:**
- OS: macOS
- Wallet Version: latest build from develop (dmg and zip)
**Describe the bug**
Suite throws `Uncaught Exception: Error: cannot run bridge binary ` right after launch
**Steps to reproduce:**
1. download latest build from develop eg. https://gitlab.com/satoshilabs/trezor/trezor-suite/-/jo... | 1.0 | Uncaught Exception: Error: cannot run bridge binary - **Info:**
- OS: macOS
- Wallet Version: latest build from develop (dmg and zip)
**Describe the bug**
Suite throws `Uncaught Exception: Error: cannot run bridge binary ` right after launch
**Steps to reproduce:**
1. download latest build from develop eg. ... | priority | uncaught exception error cannot run bridge binary info os macos wallet version latest build from develop dmg and zip describe the bug suite throws uncaught exception error cannot run bridge binary right after launch steps to reproduce download latest build from develop eg ... | 1 |
624,448 | 19,697,917,645 | IssuesEvent | 2022-01-12 14:02:12 | opensquare-network/statescan | https://api.github.com/repos/opensquare-network/statescan | closed | Customize 500 internal server error page | priority:high | 
Currently we show the default 500 page by next, but we should show one by SubSquare. | 1.0 | Customize 500 internal server error page - 
Currently we show the default 500 page by next, but we should show one by SubSquare. | priority | customize internal server error page currently we show the default page by next but we should show one by subsquare | 1 |
654,505 | 21,654,536,297 | IssuesEvent | 2022-05-06 12:55:24 | rocky-linux/rockylinux.org | https://api.github.com/repos/rocky-linux/rockylinux.org | closed | Translation Completed: Traditional Chinese | priority: medium tag: content type: enhancement | **Language Translated: Traditional Chinese
**Localized Language Name: Traditional Chinese
**ISO 639-1 Language Code: zh-tw
**Localized Date Format: `YYYY-MM-DD`
| 1.0 | Translation Completed: Traditional Chinese - **Language Translated: Traditional Chinese
**Localized Language Name: Traditional Chinese
**ISO 639-1 Language Code: zh-tw
**Localized Date Format: `YYYY-MM-DD`
| priority | translation completed traditional chinese language translated traditional chinese localized language name traditional chinese iso language code zh tw localized date format yyyy mm dd | 1 |
459,118 | 13,186,594,450 | IssuesEvent | 2020-08-13 00:40:52 | fog/fog-google | https://api.github.com/repos/fog/fog-google | closed | Incorrect metadata format in comment | docs priority/medium | I am having trouble setting the metadata for a server when I structure the metadata object according to documentation below:
https://github.com/fog/fog-google/blob/46d1bee9516bdbf3d020f012f7b7aee9039efd47/lib/fog/compute/google/requests/set_server_metadata.rb#L24
It seems like having a metadata object that includ... | 1.0 | Incorrect metadata format in comment - I am having trouble setting the metadata for a server when I structure the metadata object according to documentation below:
https://github.com/fog/fog-google/blob/46d1bee9516bdbf3d020f012f7b7aee9039efd47/lib/fog/compute/google/requests/set_server_metadata.rb#L24
It seems li... | priority | incorrect metadata format in comment i am having trouble setting the metadata for a server when i structure the metadata object according to documentation below it seems like having a metadata object that includes an items key does not get parsed correctly however setting the object to what the value of... | 1 |
81,014 | 15,596,822,405 | IssuesEvent | 2021-03-18 16:15:29 | Path-Check/gaen-mobile | https://api.github.com/repos/Path-Check/gaen-mobile | closed | CVE-2021-22878 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2021-22878 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>RealmSwift-10.1.1</b>, <b>Flipper-Folly-2.3.0</b>, <b>YogaKit-1.18.1</b>, <b>Yoga-1.14.0</b>, <b>Realm-10.1.1</b>, ... | True | CVE-2021-22878 (Medium) detected in multiple libraries - ## CVE-2021-22878 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>RealmSwift-10.1.1</b>, <b>Flipper-Folly-2.3.0</b>, <b>Yoga... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries realmswift flipper folly yogakit yoga realm flipper rsocket realm headers realmswift the realm mobile database for swi... | 0 |
214,379 | 7,269,385,604 | IssuesEvent | 2018-02-20 13:32:35 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.halfords.com - site is not usable | browser-firefox priority-normal | <!-- @browser: Firefox 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:58.0) Gecko/20100101 Firefox/58.0 -->
<!-- @reported_with: web -->
**URL**: http://www.halfords.com/motoring/car-accessories/car-mats-boot-liners
**Browser / Version**: Firefox 58.0
**Operating System**: Windows 7
**Tested An... | 1.0 | www.halfords.com - site is not usable - <!-- @browser: Firefox 58.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:58.0) Gecko/20100101 Firefox/58.0 -->
<!-- @reported_with: web -->
**URL**: http://www.halfords.com/motoring/car-accessories/car-mats-boot-liners
**Browser / Version**: Firefox 58.0
**O... | priority | site is not usable url browser version firefox operating system windows tested another browser yes problem type site is not usable description filters on left dont work click boot liners and no filtering occurs steps to reproduce from with ❤️ | 1 |
234,468 | 19,184,265,850 | IssuesEvent | 2021-12-04 23:32:16 | spcl/dace | https://api.github.com/repos/spcl/dace | closed | Parallelize Xilinx tests/move to pytest | enhancement test fpga | - [x] Parallelize Xilinx tests (done in PR #682)
- [ ] Move to parallel pytest. | 1.0 | Parallelize Xilinx tests/move to pytest - - [x] Parallelize Xilinx tests (done in PR #682)
- [ ] Move to parallel pytest. | non_priority | parallelize xilinx tests move to pytest parallelize xilinx tests done in pr move to parallel pytest | 0 |
132,238 | 10,737,929,490 | IssuesEvent | 2019-10-29 13:59:04 | fga-eps-mds/2019.2-GloriaBot | https://api.github.com/repos/fga-eps-mds/2019.2-GloriaBot | closed | Melhor Fluxo de conversa de Como construir um plano de Proteção | 0 - MDS 2 - Aprimoramento 2 - Qualidade do Código 2 - Rasa 2 - Teste 4 - Planejado | Nessa issue será realizado:
- [x] Ajustar falas da Glória para perguntas sobre a hora do ataque
- [x] Ajustar falas da Glória para perguntas sobre depois do ataque
Critérios de aceitação:
- [x] Melhor interatividade com usuário no diálogo Hora do ataque
- [x] Melhor interatividade com usuário no diálogo Depois do a... | 1.0 | Melhor Fluxo de conversa de Como construir um plano de Proteção - Nessa issue será realizado:
- [x] Ajustar falas da Glória para perguntas sobre a hora do ataque
- [x] Ajustar falas da Glória para perguntas sobre depois do ataque
Critérios de aceitação:
- [x] Melhor interatividade com usuário no diálogo Hora do ataq... | non_priority | melhor fluxo de conversa de como construir um plano de proteção nessa issue será realizado ajustar falas da glória para perguntas sobre a hora do ataque ajustar falas da glória para perguntas sobre depois do ataque critérios de aceitação melhor interatividade com usuário no diálogo hora do ataque ... | 0 |
508,904 | 14,708,183,519 | IssuesEvent | 2021-01-04 23:04:56 | bcgov/entity | https://api.github.com/repos/bcgov/entity | opened | NR 2658586 Baljit Korotana - Client asking for information about charges | ENTITY OPS Priority1 Relationships | #### ServiceNow incident:
#### Contact information
Staff Name: Kristopher Yee
Staff Email:
#### Description
Client requested a name using the new name request. Their mastercard as charged 31.50 for the name, but also a bunch of other charges were made that the client doesn't recognize.
#### Email
>Got another requ... | 1.0 | NR 2658586 Baljit Korotana - Client asking for information about charges - #### ServiceNow incident:
#### Contact information
Staff Name: Kristopher Yee
Staff Email:
#### Description
Client requested a name using the new name request. Their mastercard as charged 31.50 for the name, but also a bunch of other charges w... | priority | nr baljit korotana client asking for information about charges servicenow incident contact information staff name kristopher yee staff email description client requested a name using the new name request their mastercard as charged for the name but also a bunch of other charges were made... | 1 |
98,187 | 12,301,684,702 | IssuesEvent | 2020-05-11 15:46:29 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | closed | Defer opening ports until server is up | design-issue | Currently Liberty opens ports prior to the apps (or app server) being ready which can cause issues. waitToAccept was added which results in connections being closed on open prior to server startup.
We are still getting requests to not even open the port, or start accepting until the server is up. | 1.0 | Defer opening ports until server is up - Currently Liberty opens ports prior to the apps (or app server) being ready which can cause issues. waitToAccept was added which results in connections being closed on open prior to server startup.
We are still getting requests to not even open the port, or start accepting u... | non_priority | defer opening ports until server is up currently liberty opens ports prior to the apps or app server being ready which can cause issues waittoaccept was added which results in connections being closed on open prior to server startup we are still getting requests to not even open the port or start accepting u... | 0 |
47,452 | 12,035,255,224 | IssuesEvent | 2020-04-13 17:33:14 | GetTerminus/terminus-ui | https://api.github.com/repos/GetTerminus/terminus-ui | closed | Fully remove TSLint and Codelyzer | Focus: build Goal: Library Stabilization Target: latest Type: chore | - [x] Remove TSLint
- [x] Remove codelyzer
- [x] Remove terminus tslint config
- [x] See what ESLint rules already exist that could handle some of what we rely on TSLint for
- [x] Create list of what rules currently have no replacement
- [x] Update lint commands in `package.json`
- [x] Update lint staged commands
####... | 1.0 | Fully remove TSLint and Codelyzer - - [x] Remove TSLint
- [x] Remove codelyzer
- [x] Remove terminus tslint config
- [x] See what ESLint rules already exist that could handle some of what we rely on TSLint for
- [x] Create list of what rules currently have no replacement
- [x] Update lint commands in `package.json`
- [... | non_priority | fully remove tslint and codelyzer remove tslint remove codelyzer remove terminus tslint config see what eslint rules already exist that could handle some of what we rely on tslint for create list of what rules currently have no replacement update lint commands in package json update lint... | 0 |
407,577 | 11,924,062,143 | IssuesEvent | 2020-04-01 08:55:00 | wazuh/wazuh-docker | https://api.github.com/repos/wazuh/wazuh-docker | closed | Use official nginx image without rebuilding | priority/medium status/on-hold type/enhancement | ### Description
Currently we're rebuilding the official nginx image, all we're doing is adding a couple of tools and an entrypoint which builds certificates and set things up before starting the web server.
Basically this:
```
RUN apt-get update && apt-get install -y openssl apache2-utils
COPY config/entry... | 1.0 | Use official nginx image without rebuilding - ### Description
Currently we're rebuilding the official nginx image, all we're doing is adding a couple of tools and an entrypoint which builds certificates and set things up before starting the web server.
Basically this:
```
RUN apt-get update && apt-get install... | priority | use official nginx image without rebuilding description currently we re rebuilding the official nginx image all we re doing is adding a couple of tools and an entrypoint which builds certificates and set things up before starting the web server basically this run apt get update apt get install... | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.