Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
460,559 | 13,212,748,677 | IssuesEvent | 2020-08-16 08:58:21 | SpongePowered/SpongeCommon | https://api.github.com/repos/SpongePowered/SpongeCommon | closed | Add static methods for plugins to detect whether they're running on Forge or Vanilla | priority: low type: enhancement | Together with the [addition of plugin-provided mixins in SpongeVanilla](https://github.com/SpongePowered/SpongeVanilla/pull/250), it would be useful for plugins to have some static methods to detect the environment they're running in before the game has actually started.
They can be used to apply a certain mixin only ... | 1.0 | Add static methods for plugins to detect whether they're running on Forge or Vanilla - Together with the [addition of plugin-provided mixins in SpongeVanilla](https://github.com/SpongePowered/SpongeVanilla/pull/250), it would be useful for plugins to have some static methods to detect the environment they're running in... | priority | add static methods for plugins to detect whether they re running on forge or vanilla together with the it would be useful for plugins to have some static methods to detect the environment they re running in before the game has actually started they can be used to apply a certain mixin only to either spongeforge... | 1 |
428,221 | 12,404,922,079 | IssuesEvent | 2020-05-21 16:21:07 | DarshanShet777/Model-Airport | https://api.github.com/repos/DarshanShet777/Model-Airport | opened | Electrical Engineering: Checkpost IR Receiver Incorrect Readings | Medium Priority | The Checkposts cannot seem to sense the robot when it arrives. | 1.0 | Electrical Engineering: Checkpost IR Receiver Incorrect Readings - The Checkposts cannot seem to sense the robot when it arrives. | priority | electrical engineering checkpost ir receiver incorrect readings the checkposts cannot seem to sense the robot when it arrives | 1 |
112,156 | 4,511,868,870 | IssuesEvent | 2016-09-03 08:58:22 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | BeforeSuite: Failed to setup provider config | area/cluster-lifecycle kind/flake priority/P0 | Multiple issues in the BeforeSuite failure bug (#30075). Splitting this particular failure mode out.
Aug 15 14:39:13.884: Failed to setup provider config: Error building GCE/GKE provider: Get https://www.googleapis.com/compute/v1/projects/k8s-e2e-gke-staging-parallel/global/networks?alt=json: oauth2: cannot fetch to... | 1.0 | BeforeSuite: Failed to setup provider config - Multiple issues in the BeforeSuite failure bug (#30075). Splitting this particular failure mode out.
Aug 15 14:39:13.884: Failed to setup provider config: Error building GCE/GKE provider: Get https://www.googleapis.com/compute/v1/projects/k8s-e2e-gke-staging-parallel/gl... | priority | beforesuite failed to setup provider config multiple issues in the beforesuite failure bug splitting this particular failure mode out aug failed to setup provider config error building gce gke provider get cannot fetch token post net http tls handshake timeout aug fail... | 1 |
264,498 | 23,120,941,184 | IssuesEvent | 2022-07-27 21:24:48 | microsoft/vscode-pull-request-github | https://api.github.com/repos/microsoft/vscode-pull-request-github | closed | Test Suggested Assignees | testplan-item | Refs: #3627
- [x] anyOS @greazer
- [x] anyOS @lramos15
Complexity: 1
[Create Issue](https://github.com/microsoft/vscode-pull-request-github/issues/new?body=Testing+%233765%0A%0A&assignees=benibenj)
---
Suggests Users when assigning a user to a PR
1. Install the pre-release build of GitHub Pull R... | 1.0 | Test Suggested Assignees - Refs: #3627
- [x] anyOS @greazer
- [x] anyOS @lramos15
Complexity: 1
[Create Issue](https://github.com/microsoft/vscode-pull-request-github/issues/new?body=Testing+%233765%0A%0A&assignees=benibenj)
---
Suggests Users when assigning a user to a PR
1. Install the pre-rel... | non_priority | test suggested assignees refs anyos greazer anyos complexity suggests users when assigning a user to a pr install the pre release build of github pull requests and issues open a folder in vs code that contains a github repository open a pull request over... | 0 |
429,610 | 12,426,427,407 | IssuesEvent | 2020-05-24 21:07:47 | roed314/seminars | https://api.github.com/repos/roed314/seminars | closed | Make "logout" more prominent | low priority user interface | It is a little bit hard to find the logout on the site.
Maybe we could make it a button, and move it to the upper right of the Account page so that it is by itself instead of attached to other text in the middle of the page, and capitalize the first letter?
(I can see why it was put where it is, since it is an oper... | 1.0 | Make "logout" more prominent - It is a little bit hard to find the logout on the site.
Maybe we could make it a button, and move it to the upper right of the Account page so that it is by itself instead of attached to other text in the middle of the page, and capitalize the first letter?
(I can see why it was put w... | priority | make logout more prominent it is a little bit hard to find the logout on the site maybe we could make it a button and move it to the upper right of the account page so that it is by itself instead of attached to other text in the middle of the page and capitalize the first letter i can see why it was put w... | 1 |
317,395 | 9,664,577,266 | IssuesEvent | 2019-05-21 06:05:39 | kartoza/ford3 | https://api.github.com/repos/kartoza/ford3 | closed | the webapp must be protected by a login page. | Size: 3 auth in review priority: high review |
An user must be authenticated and authorized to see the resource he's trying to see.
I started to work on this here: https://github.com/pierrealixt/ford3/tree/login-198
<img width="575" alt="Screen Shot 2019-05-16 at 08 49 52" src="https://user-images.githubusercontent.com/35932320/57832319-a9066580-77b7-11e9-8... | 1.0 | the webapp must be protected by a login page. -
An user must be authenticated and authorized to see the resource he's trying to see.
I started to work on this here: https://github.com/pierrealixt/ford3/tree/login-198
<img width="575" alt="Screen Shot 2019-05-16 at 08 49 52" src="https://user-images.githubuserco... | priority | the webapp must be protected by a login page an user must be authenticated and authorized to see the resource he s trying to see i started to work on this here img width alt screen shot at src | 1 |
435,623 | 12,536,789,012 | IssuesEvent | 2020-06-05 01:15:43 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | Flag to not print arguments in slowlog | priority/release-blocker security type/feature-request | We would like a flag that disables the printing of argument values in the slowlog. Only the query should be printed. | 1.0 | Flag to not print arguments in slowlog - We would like a flag that disables the printing of argument values in the slowlog. Only the query should be printed. | priority | flag to not print arguments in slowlog we would like a flag that disables the printing of argument values in the slowlog only the query should be printed | 1 |
758,901 | 26,573,262,387 | IssuesEvent | 2023-01-21 13:07:49 | Tau-ri-Dev/JSGMod-1.12.2 | https://api.github.com/repos/Tau-ri-Dev/JSGMod-1.12.2 | closed | Bug: Server resets PoO | Bug/Issue Low priority Confirmed | **Describe the bug**
Minecraft Servers do not save the PoO when you override it in the gate config.
**To Reproduce**
Steps to reproduce the behavior:
1. Go onto a Minecraft server
2. Build a Stargate
3. Override Stargate's PoO to anything other than the default and log out
4. Stargate PoO resets
**Expected ... | 1.0 | Bug: Server resets PoO - **Describe the bug**
Minecraft Servers do not save the PoO when you override it in the gate config.
**To Reproduce**
Steps to reproduce the behavior:
1. Go onto a Minecraft server
2. Build a Stargate
3. Override Stargate's PoO to anything other than the default and log out
4. Stargate ... | priority | bug server resets poo describe the bug minecraft servers do not save the poo when you override it in the gate config to reproduce steps to reproduce the behavior go onto a minecraft server build a stargate override stargate s poo to anything other than the default and log out stargate ... | 1 |
19,609 | 6,743,502,232 | IssuesEvent | 2017-10-20 12:23:35 | Great-Hill-Corporation/quickBlocks | https://api.github.com/repos/Great-Hill-Corporation/quickBlocks | closed | Dates missing at articles table | build-docs status-resolved type-question | What is the meaning of the Date tags at articles table?
Here
https://github.com/Great-Hill-Corporation/quickBlocks/blob/develop/src/other/articles/README.md
we have some articles with the date defined but others is missing, is it pending? | 1.0 | Dates missing at articles table - What is the meaning of the Date tags at articles table?
Here
https://github.com/Great-Hill-Corporation/quickBlocks/blob/develop/src/other/articles/README.md
we have some articles with the date defined but others is missing, is it pending? | non_priority | dates missing at articles table what is the meaning of the date tags at articles table here we have some articles with the date defined but others is missing is it pending | 0 |
289,879 | 31,999,552,704 | IssuesEvent | 2023-09-21 11:22:57 | Mend-developer-platform-load/11653742_33 | https://api.github.com/repos/Mend-developer-platform-load/11653742_33 | opened | CVE-2022-21704 (Medium) detected in log4js-0.6.38.tgz | Mend: dependency security vulnerability | ## CVE-2022-21704 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4js-0.6.38.tgz</b></p></summary>
<p>Port of Log4js to work with node.</p>
<p>Library home page: <a href="https://... | True | CVE-2022-21704 (Medium) detected in log4js-0.6.38.tgz - ## CVE-2022-21704 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4js-0.6.38.tgz</b></p></summary>
<p>Port of Log4js to wor... | non_priority | cve medium detected in tgz cve medium severity vulnerability vulnerable library tgz port of to work with node library home page a href path to dependency file package json path to vulnerable library node modules package json dependency hierarchy ... | 0 |
260,505 | 22,626,843,667 | IssuesEvent | 2022-06-30 11:27:40 | ChainSafe/ui-monorepo | https://api.github.com/repos/ChainSafe/ui-monorepo | closed | [Storage] Sort columns in Buckets view test | Testing | As described add coverage to sort columns in Buckets:
- By Name
- By File system
- By Size
| 1.0 | [Storage] Sort columns in Buckets view test - As described add coverage to sort columns in Buckets:
- By Name
- By File system
- By Size
| non_priority | sort columns in buckets view test as described add coverage to sort columns in buckets by name by file system by size | 0 |
338,571 | 10,231,777,914 | IssuesEvent | 2019-08-18 12:33:06 | Electroblob77/Wizardry | https://api.github.com/repos/Electroblob77/Wizardry | closed | earthquake kills players without a message | cosmetic low priority | Minecraft version: 1.12.2
Wizardry version: 4.1.2
Environment: Server
Issue details:
Player A stand on the ground with low health
Player B stand on the same level and user an earthquake spell
Player A dies
Expected: chat message explaining player B kill player A
Observed: no chat message
| 1.0 | earthquake kills players without a message - Minecraft version: 1.12.2
Wizardry version: 4.1.2
Environment: Server
Issue details:
Player A stand on the ground with low health
Player B stand on the same level and user an earthquake spell
Player A dies
Expected: chat message explaining player B kill player A
Ob... | priority | earthquake kills players without a message minecraft version wizardry version environment server issue details player a stand on the ground with low health player b stand on the same level and user an earthquake spell player a dies expected chat message explaining player b kill player a obs... | 1 |
141,526 | 18,989,296,698 | IssuesEvent | 2021-11-22 04:03:17 | ChoeMinji/react-16.0.0 | https://api.github.com/repos/ChoeMinji/react-16.0.0 | opened | CVE-2021-23386 (Medium) detected in dns-packet-1.2.2.tgz, dns-packet-1.1.1.tgz | security vulnerability | ## CVE-2021-23386 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>dns-packet-1.2.2.tgz</b>, <b>dns-packet-1.1.1.tgz</b></p></summary>
<p>
<details><summary><b>dns-packet-1.2.2.tgz<... | True | CVE-2021-23386 (Medium) detected in dns-packet-1.2.2.tgz, dns-packet-1.1.1.tgz - ## CVE-2021-23386 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>dns-packet-1.2.2.tgz</b>, <b>dns-p... | non_priority | cve medium detected in dns packet tgz dns packet tgz cve medium severity vulnerability vulnerable libraries dns packet tgz dns packet tgz dns packet tgz an abstract encoding compliant module for encoding decoding dns packets library home page ... | 0 |
622,185 | 19,609,763,509 | IssuesEvent | 2022-01-06 14:06:55 | decompme/decomp.me | https://api.github.com/repos/decompme/decomp.me | closed | Use custom modal dialog instead of using HTML <dialog> | bug frontend high priority | `<dialog>` is really buggy on some browsers (read: older Safari) and its getting annoying to manually fix issues; we should just use a react modal library | 1.0 | Use custom modal dialog instead of using HTML <dialog> - `<dialog>` is really buggy on some browsers (read: older Safari) and its getting annoying to manually fix issues; we should just use a react modal library | priority | use custom modal dialog instead of using html is really buggy on some browsers read older safari and its getting annoying to manually fix issues we should just use a react modal library | 1 |
117,951 | 4,729,562,141 | IssuesEvent | 2016-10-18 19:02:46 | Parabot/Parabot | https://api.github.com/repos/Parabot/Parabot | closed | New version notification | priority:medium status:accepted type:bug | When you get notified of a new version, it redirects you to the old BDN, should be v3.
This should also detect the version, nightly or not - whereas it will download a new nightly version if available, otherwise simply the latest. | 1.0 | New version notification - When you get notified of a new version, it redirects you to the old BDN, should be v3.
This should also detect the version, nightly or not - whereas it will download a new nightly version if available, otherwise simply the latest. | priority | new version notification when you get notified of a new version it redirects you to the old bdn should be this should also detect the version nightly or not whereas it will download a new nightly version if available otherwise simply the latest | 1 |
351,763 | 32,025,433,086 | IssuesEvent | 2023-09-22 08:30:19 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix general_functions.test_tensorflow_where_no_xy | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6271730752"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6271730752"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://githu... | 1.0 | Fix general_functions.test_tensorflow_where_no_xy - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6271730752"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6271730752"><img src=https://img.shields.io/badge/-succ... | non_priority | fix general functions test tensorflow where no xy numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
37,053 | 15,161,753,958 | IssuesEvent | 2021-02-12 09:33:25 | LiskHQ/lisk-docs | https://api.github.com/repos/LiskHQ/lisk-docs | opened | Include latest README updates | component: service type: update | Include latest updates in the README files in the documentation for Lisk Service 0.2.0 | 1.0 | Include latest README updates - Include latest updates in the README files in the documentation for Lisk Service 0.2.0 | non_priority | include latest readme updates include latest updates in the readme files in the documentation for lisk service | 0 |
222,399 | 17,411,092,093 | IssuesEvent | 2021-08-03 12:26:37 | intermine/bluegenes | https://api.github.com/repos/intermine/bluegenes | closed | Tool API: Add description field to config.json | Tool API usertesting | This will be displayed when hovering/clicking the (?) in the tool headers of the new report page design.
It seems it would be useful to provide extra information on the tool. The (?) icon would only be visible if a description is defined. | 1.0 | Tool API: Add description field to config.json - This will be displayed when hovering/clicking the (?) in the tool headers of the new report page design.
It seems it would be useful to provide extra information on the tool. The (?) icon would only be visible if a description is defined. | non_priority | tool api add description field to config json this will be displayed when hovering clicking the in the tool headers of the new report page design it seems it would be useful to provide extra information on the tool the icon would only be visible if a description is defined | 0 |
110,422 | 4,426,669,405 | IssuesEvent | 2016-08-16 19:00:49 | aces/cbrain | https://api.github.com/repos/aces/cbrain | closed | Add content_storage_shared_between_users?() method to DataProvider API | Enhancement Priority: Normal Refactoring | Right now at many places in the code we try to detect if a data provider's storage mechanism shares a single space for files between users, so that two users cannot have the same filename on the same DP (which is normally permitted by the Userfile model itself). The detection is currently done by checking the return va... | 1.0 | Add content_storage_shared_between_users?() method to DataProvider API - Right now at many places in the code we try to detect if a data provider's storage mechanism shares a single space for files between users, so that two users cannot have the same filename on the same DP (which is normally permitted by the Userfile... | priority | add content storage shared between users method to dataprovider api right now at many places in the code we try to detect if a data provider s storage mechanism shares a single space for files between users so that two users cannot have the same filename on the same dp which is normally permitted by the userfile... | 1 |
74 | 2,495,915,805 | IssuesEvent | 2015-01-06 15:44:33 | brashrebel/render | https://api.github.com/repos/brashrebel/render | opened | Special characters | shortcode idea | Nice drop-down for easily adding special characters like copyright, trademark, etc. | 1.0 | Special characters - Nice drop-down for easily adding special characters like copyright, trademark, etc. | non_priority | special characters nice drop down for easily adding special characters like copyright trademark etc | 0 |
17,336 | 10,684,222,234 | IssuesEvent | 2019-10-22 09:59:33 | Mte90/Share-Backported | https://api.github.com/repos/Mte90/Share-Backported | closed | Integration with Google Keep | help wanted service | One nifty feature of Chrome on my Android is the ability to share web links directly into Google Keep. The note title is the web page title, the note body is just the link. It's a good decent alternative to using the browser's built-in remote bookmark management (ex: Firefox Sync). Can you please consider this integrat... | 1.0 | Integration with Google Keep - One nifty feature of Chrome on my Android is the ability to share web links directly into Google Keep. The note title is the web page title, the note body is just the link. It's a good decent alternative to using the browser's built-in remote bookmark management (ex: Firefox Sync). Can yo... | non_priority | integration with google keep one nifty feature of chrome on my android is the ability to share web links directly into google keep the note title is the web page title the note body is just the link it s a good decent alternative to using the browser s built in remote bookmark management ex firefox sync can yo... | 0 |
55,490 | 14,523,026,523 | IssuesEvent | 2020-12-14 09:35:23 | SAP/fundamental-ngx | https://api.github.com/repos/SAP/fundamental-ngx | closed | Bug: (Platform) Combobox – on the second and next opens mobile mode dialog you'll get RangeError | Defect Hunting bug platform | #### Is this a bug, enhancement, or feature request?
bug
#### Briefly describe your proposal.
When you open the [Mobile Mode](https://fundamental-ngx.netlify.app/#/platform/combobox#combobox-mobile) dialog in the second and next times, you'll get `RangeError: Maximum call stack size exceeded.`
 Combobox – on the second and next opens mobile mode dialog you'll get RangeError - #### Is this a bug, enhancement, or feature request?
bug
#### Briefly describe your proposal.
When you open the [Mobile Mode](https://fundamental-ngx.netlify.app/#/platform/combobox#combobox-mobile) dialog in the secon... | non_priority | bug platform combobox – on the second and next opens mobile mode dialog you ll get rangeerror is this a bug enhancement or feature request bug briefly describe your proposal when you open the dialog in the second and next times you ll get rangeerror maximum call stack size exceeded ... | 0 |
693,090 | 23,762,743,558 | IssuesEvent | 2022-09-01 10:13:00 | metabase/metabase | https://api.github.com/repos/metabase/metabase | closed | Tooltip periods are not displayed nicely on SQL questions | Type:Bug Priority:P2 Querying/Native .Frontend Visualization/Charts .Reproduced .Regression | **Describe the bug**
When you group by week/month on Editor the result is a range:
<img width="1489" alt="image" src="https://user-images.githubusercontent.com/110378427/186652916-c1b7d983-f403-4537-9951-fa24b02e1fd5.png">
If you take the same question and turn it into SQL. The tooltip doesn't pick up the range ... | 1.0 | Tooltip periods are not displayed nicely on SQL questions - **Describe the bug**
When you group by week/month on Editor the result is a range:
<img width="1489" alt="image" src="https://user-images.githubusercontent.com/110378427/186652916-c1b7d983-f403-4537-9951-fa24b02e1fd5.png">
If you take the same question ... | priority | tooltip periods are not displayed nicely on sql questions describe the bug when you group by week month on editor the result is a range img width alt image src if you take the same question and turn it into sql the tooltip doesn t pick up the range granularity img width alt image sr... | 1 |
12,337 | 14,882,738,426 | IssuesEvent | 2021-01-20 12:20:36 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [Mobile] [Dev] Unable to rejoin into Open study once withdrawn | Blocker Bug P0 Process: Dev Process: Fixed Process: Tested dev Unknown backend | Unable to rejoin into Open study once withdrawn for Android and iOS
| 3.0 | [Mobile] [Dev] Unable to rejoin into Open study once withdrawn - Unable to rejoin into Open study once withdrawn for Android and iOS
| non_priority | unable to rejoin into open study once withdrawn unable to rejoin into open study once withdrawn for android and ios | 0 |
243,856 | 26,290,655,143 | IssuesEvent | 2023-01-08 11:20:46 | TreyM-WSS/concord | https://api.github.com/repos/TreyM-WSS/concord | reopened | CVE-2021-38153 (Medium) detected in kafka-clients-2.4.0.jar | security vulnerability | ## CVE-2021-38153 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kafka-clients-2.4.0.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://kafka.apache.org">https://k... | True | CVE-2021-38153 (Medium) detected in kafka-clients-2.4.0.jar - ## CVE-2021-38153 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kafka-clients-2.4.0.jar</b></p></summary>
<p></p>
<p>L... | non_priority | cve medium detected in kafka clients jar cve medium severity vulnerability vulnerable library kafka clients jar library home page a href path to dependency file server plugins kafka event sink pom xml path to vulnerable library canner repository org apache kafk... | 0 |
391,573 | 11,575,921,405 | IssuesEvent | 2020-02-21 10:46:09 | ahmedkaludi/accelerated-mobile-pages | https://api.github.com/repos/ahmedkaludi/accelerated-mobile-pages | closed | Warning issue on AMP option panel. | NEXT UPDATE [Priority: HIGH] bug | /var/www/html/wp-content/plugins/accelerated-mobile-pages/includes/ampforwp-fields-array.php on line 122
ref) https://secure.helpscout.net/conversation/1059605973/107207?folderId=3514643 | 1.0 | Warning issue on AMP option panel. - /var/www/html/wp-content/plugins/accelerated-mobile-pages/includes/ampforwp-fields-array.php on line 122
ref) https://secure.helpscout.net/conversation/1059605973/107207?folderId=3514643 | priority | warning issue on amp option panel var www html wp content plugins accelerated mobile pages includes ampforwp fields array php on line ref | 1 |
315,086 | 9,606,491,817 | IssuesEvent | 2019-05-11 10:51:32 | yalla-coop/connect5 | https://api.github.com/repos/yalla-coop/connect5 | opened | Trainer: Update Create Session | priority-5 sprint2 trainer | Re-use existing functionality but add
- [ ] region (required)
- [ ] partner trainer field
- [ ] email of participants -> attendee list
- [ ] email survey functionality by ticking box 'send the survey to participants by email'
<img width="150" alt="Bildschirmfoto 2019-05-11 um 12 50 51" src="https://user-images... | 1.0 | Trainer: Update Create Session - Re-use existing functionality but add
- [ ] region (required)
- [ ] partner trainer field
- [ ] email of participants -> attendee list
- [ ] email survey functionality by ticking box 'send the survey to participants by email'
<img width="150" alt="Bildschirmfoto 2019-05-11 um 1... | priority | trainer update create session re use existing functionality but add region required partner trainer field email of participants attendee list email survey functionality by ticking box send the survey to participants by email img width alt bildschirmfoto um src ... | 1 |
799,284 | 28,303,690,585 | IssuesEvent | 2023-04-10 08:51:36 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | m.youtube.com - see bug description | browser-firefox-mobile priority-critical engine-gecko | <!-- @browser: Firefox Mobile 88.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:88.0) Gecko/88.0 Firefox/88.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/120636 -->
**URL**: https://m.youtube.com/results?sp=mAEA
**Browser / Version**: Firefox Mobile ... | 1.0 | m.youtube.com - see bug description - <!-- @browser: Firefox Mobile 88.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:88.0) Gecko/88.0 Firefox/88.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/120636 -->
**URL**: https://m.youtube.com/results?sp=mAEA
... | priority | m youtube com see bug description url browser version firefox mobile operating system android tested another browser yes other problem type something else description all of the youtube shorts are not diverse enough repetitive and silly there is no way to change ... | 1 |
219,079 | 7,333,119,123 | IssuesEvent | 2018-03-05 18:22:52 | NCEAS/metacat | https://api.github.com/repos/NCEAS/metacat | closed | Metacat DataONE base url always gets 404 not found page | Component: Bugzilla-Id Priority: Normal Status: Closed Tracker: Bug | ---
Author Name: **Jing Tao** (Jing Tao)
Original Redmine Issue: 7166, https://projects.ecoinformatics.org/ecoinfo/issues/7166
Original Date: 2016-12-06
Original Assignee: Jing Tao
---
The base url looks like:
https://mn-dev-ucsb-1.test.dataone.org/metacat/d1/mn
It always gets 404 not found page. Even though Me... | 1.0 | Metacat DataONE base url always gets 404 not found page - ---
Author Name: **Jing Tao** (Jing Tao)
Original Redmine Issue: 7166, https://projects.ecoinformatics.org/ecoinfo/issues/7166
Original Date: 2016-12-06
Original Assignee: Jing Tao
---
The base url looks like:
https://mn-dev-ucsb-1.test.dataone.org/metacat/... | priority | metacat dataone base url always gets not found page author name jing tao jing tao original redmine issue original date original assignee jing tao the base url looks like it always gets not found page even though metacat on this node is running users always think something... | 1 |
83,034 | 15,683,782,977 | IssuesEvent | 2021-03-25 09:13:11 | bci-oss/vulnerable-node | https://api.github.com/repos/bci-oss/vulnerable-node | opened | CVE-2017-1000048 (High) detected in qs-4.0.0.tgz | security vulnerability | ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-4.0.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>L... | True | CVE-2017-1000048 (High) detected in qs-4.0.0.tgz - ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>qs-4.0.0.tgz</b></p></summary>
<p>A querystring parser that suppo... | non_priority | cve high detected in qs tgz cve high severity vulnerability vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file vulnerable node package json path to vulnerable library vu... | 0 |
29,825 | 11,780,066,635 | IssuesEvent | 2020-03-16 19:16:23 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | Move out API server proxy from core chart to separate release | area/security enhancement | <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
API server proxy is part of chart `core` which is an umbrella chart for other componetns as well such as iam-kubeconfig, console, console ... | True | Move out API server proxy from core chart to separate release - <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
API server proxy is part of chart `core` which is an umbrella chart for ot... | non_priority | move out api server proxy from core chart to separate release thank you for your contribution before you submit the issue search open and closed issues for duplicates read the contributing guidelines description api server proxy is part of chart core which is an umbrella chart for ot... | 0 |
684,264 | 23,412,988,069 | IssuesEvent | 2022-08-12 19:48:13 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Wallet is using an obsolete password policy | security priority/P3 feature/wallet OS/Desktop | Wallet currently requires the following password policy:

which is not in line with the [latest password policy guidelines from NIST](https://en.wikipedia.org/wiki/Password_po... | 1.0 | Wallet is using an obsolete password policy - Wallet currently requires the following password policy:

which is not in line with the [latest password policy guidelines from N... | priority | wallet is using an obsolete password policy wallet currently requires the following password policy which is not in line with the in particular the following changes should be made minimum length must be characters different character types should not be required also see for an e... | 1 |
59,585 | 7,262,100,835 | IssuesEvent | 2018-02-19 03:08:07 | pawgistics/pawgistics | https://api.github.com/repos/pawgistics/pawgistics | closed | Email standardization | design decision enhancement | Emails should be all lowercase (or some other standardized format) before writing to db | 1.0 | Email standardization - Emails should be all lowercase (or some other standardized format) before writing to db | non_priority | email standardization emails should be all lowercase or some other standardized format before writing to db | 0 |
96,816 | 3,973,764,256 | IssuesEvent | 2016-05-04 19:45:50 | Metaswitch/sprout | https://api.github.com/repos/Metaswitch/sprout | closed | stack_data's name array is not necessarily big enough | bug medium-priority | #### Symptoms
The array was originally of size 16, and we were writing more than 16 names to it which was causing us to scribble on other fields.
#### Impact
Random failures due to fields being set to gibberish.
#### Release and environment
Release 95
#### Steps to reproduce
Add loads of aliases? | 1.0 | stack_data's name array is not necessarily big enough - #### Symptoms
The array was originally of size 16, and we were writing more than 16 names to it which was causing us to scribble on other fields.
#### Impact
Random failures due to fields being set to gibberish.
#### Release and environment
Release 9... | priority | stack data s name array is not necessarily big enough symptoms the array was originally of size and we were writing more than names to it which was causing us to scribble on other fields impact random failures due to fields being set to gibberish release and environment release ... | 1 |
54,122 | 6,366,194,256 | IssuesEvent | 2017-08-01 00:29:16 | appium/appium | https://api.github.com/repos/appium/appium | closed | WDA Retrying to launch app but fails because App not showing in simulator intermittently | ThirdpartyIssue XCUITest | ## The problem
Automation scripts work fine on for some time during execution but after a couple of tests the appium checks if the app is installed in the simulator, the logs say it's installed and but looks like the app is not installed in the simulator.
## Environment
* Appium version (or git revision) that... | 1.0 | WDA Retrying to launch app but fails because App not showing in simulator intermittently - ## The problem
Automation scripts work fine on for some time during execution but after a couple of tests the appium checks if the app is installed in the simulator, the logs say it's installed and but looks like the app is no... | non_priority | wda retrying to launch app but fails because app not showing in simulator intermittently the problem automation scripts work fine on for some time during execution but after a couple of tests the appium checks if the app is installed in the simulator the logs say it s installed and but looks like the app is no... | 0 |
156,381 | 12,308,062,801 | IssuesEvent | 2020-05-12 06:23:52 | Azure/sonic-swss | https://api.github.com/repos/Azure/sonic-swss | closed | VLAN vs tests unstable | Cleanup :droplet: Testing | The following VLAN vs tests are marginal at the moment:
- test_RemoveVlanWithRouterInterface
- test_AddPortChannelToVlan
This causes the suite to fail ~40-50% of the time across the swss and utilities tests, as well as the nightly swss build.
For now we can mark the tests as xfail in pytest so that the failures... | 1.0 | VLAN vs tests unstable - The following VLAN vs tests are marginal at the moment:
- test_RemoveVlanWithRouterInterface
- test_AddPortChannelToVlan
This causes the suite to fail ~40-50% of the time across the swss and utilities tests, as well as the nightly swss build.
For now we can mark the tests as xfail in py... | non_priority | vlan vs tests unstable the following vlan vs tests are marginal at the moment test removevlanwithrouterinterface test addportchanneltovlan this causes the suite to fail of the time across the swss and utilities tests as well as the nightly swss build for now we can mark the tests as xfail in pyte... | 0 |
437,453 | 30,599,952,981 | IssuesEvent | 2023-07-22 08:33:32 | snapsinazfs/snapsinazfs | https://api.github.com/repos/snapsinazfs/snapsinazfs | closed | Add more man pages and improve existing man pages | documentation | While writing updated man pages for the current beta, I saw a few places where additional documentation could be of use.
While I'm writing those man pages, I am including references to the additional documentation, which does not yet exist.
This issue is for tracking work on man pages, including updating the curr... | 1.0 | Add more man pages and improve existing man pages - While writing updated man pages for the current beta, I saw a few places where additional documentation could be of use.
While I'm writing those man pages, I am including references to the additional documentation, which does not yet exist.
This issue is for tra... | non_priority | add more man pages and improve existing man pages while writing updated man pages for the current beta i saw a few places where additional documentation could be of use while i m writing those man pages i am including references to the additional documentation which does not yet exist this issue is for tra... | 0 |
126,227 | 16,992,508,920 | IssuesEvent | 2021-06-30 23:04:22 | phetsims/number-line-distance | https://api.github.com/repos/phetsims/number-line-distance | closed | Elevation Scene Distance Description for Absolute Distance | design:interviews | In the elevation scene of NLD, when both point controllers are placed and the distance type is absolute value, the distance description reads `The fish and the bird are [dy] meters apart.`. This distance statement reflects their difference in y-levels, which makes sense in the context of the numberline. However, the fi... | 1.0 | Elevation Scene Distance Description for Absolute Distance - In the elevation scene of NLD, when both point controllers are placed and the distance type is absolute value, the distance description reads `The fish and the bird are [dy] meters apart.`. This distance statement reflects their difference in y-levels, which ... | non_priority | elevation scene distance description for absolute distance in the elevation scene of nld when both point controllers are placed and the distance type is absolute value the distance description reads the fish and the bird are meters apart this distance statement reflects their difference in y levels which mak... | 0 |
64,618 | 14,671,312,929 | IssuesEvent | 2020-12-30 07:49:17 | shaimael/C-sample-project-for-VSC | https://api.github.com/repos/shaimael/C-sample-project-for-VSC | opened | CVE-2019-0548 (High) detected in multiple libraries | security vulnerability | ## CVE-2019-0548 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>microsoft.netcore.dotnethostresolver.2.1.0.nupkg</b>, <b>microsoft.netcore.dotnetapphost.2.1.0.nupkg</b>, <b>microsoft... | True | CVE-2019-0548 (High) detected in multiple libraries - ## CVE-2019-0548 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>microsoft.netcore.dotnethostresolver.2.1.0.nupkg</b>, <b>microso... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries microsoft netcore dotnethostresolver nupkg microsoft netcore dotnetapphost nupkg microsoft netcore app nupkg microsoft netcore dotnethostpolicy nupkg microsoft n... | 0 |
275,495 | 20,923,657,109 | IssuesEvent | 2022-03-24 20:02:10 | AY2122S2-CS2103-W16-4/tp | https://api.github.com/repos/AY2122S2-CS2103-W16-4/tp | closed | Update documentation & user guide | documentation | Update documentation & user guide for the UserType & Remind feature | 1.0 | Update documentation & user guide - Update documentation & user guide for the UserType & Remind feature | non_priority | update documentation user guide update documentation user guide for the usertype remind feature | 0 |
832,362 | 32,077,536,854 | IssuesEvent | 2023-09-25 12:02:35 | googleapis/google-cloud-ruby | https://api.github.com/repos/googleapis/google-cloud-ruby | closed | [Nightly CI Failures] Failures detected for google-cloud-storage_transfer | type: bug priority: p1 nightly failure | At 2023-09-09 09:37:37 UTC, detected failures in google-cloud-storage_transfer for: test.
The CI logs can be found [here](https://github.com/googleapis/google-cloud-ruby/actions/runs/6129868852)
report_key_f464cad80f0bbdd3c569a725a9c5f86a | 1.0 | [Nightly CI Failures] Failures detected for google-cloud-storage_transfer - At 2023-09-09 09:37:37 UTC, detected failures in google-cloud-storage_transfer for: test.
The CI logs can be found [here](https://github.com/googleapis/google-cloud-ruby/actions/runs/6129868852)
report_key_f464cad80f0bbdd3c569a725a9c5f86a | priority | failures detected for google cloud storage transfer at utc detected failures in google cloud storage transfer for test the ci logs can be found report key | 1 |
54,217 | 7,878,401,091 | IssuesEvent | 2018-06-26 10:06:12 | edamontology/edamontology | https://api.github.com/repos/edamontology/edamontology | closed | Write clear release recipe | access | publication | release documentation | ### Quick notes right now, a proper recipe TODO:
#### 1. Release candidate
Iterate each point until success:
* Make sure Travis CI builds successfully and `date` is the last save date of EDAM_dev.owl in GMT.
* Update the live version at WebProtégé, check whether alright.
* Double-check all commits to master ... | 1.0 | Write clear release recipe - ### Quick notes right now, a proper recipe TODO:
#### 1. Release candidate
Iterate each point until success:
* Make sure Travis CI builds successfully and `date` is the last save date of EDAM_dev.owl in GMT.
* Update the live version at WebProtégé, check whether alright.
* Double... | non_priority | write clear release recipe quick notes right now a proper recipe todo release candidate iterate each point until success make sure travis ci builds successfully and date is the last save date of edam dev owl in gmt update the live version at webprotégé check whether alright double... | 0 |
102,437 | 21,960,955,438 | IssuesEvent | 2022-05-24 15:46:26 | Onelinerhub/onelinerhub | https://api.github.com/repos/Onelinerhub/onelinerhub | closed | Short solution needed: "How to make background transparent" (python-matplotlib) | help wanted good first issue code python-matplotlib | Please help us write most modern and shortest code solution for this issue:
**How to make background transparent** (technology: [python-matplotlib](https://onelinerhub.com/python-matplotlib))
### Fast way
Just write the code solution in the comments.
### Prefered way
1. Create [pull request](https://github.com/Onelin... | 1.0 | Short solution needed: "How to make background transparent" (python-matplotlib) - Please help us write most modern and shortest code solution for this issue:
**How to make background transparent** (technology: [python-matplotlib](https://onelinerhub.com/python-matplotlib))
### Fast way
Just write the code solution in ... | non_priority | short solution needed how to make background transparent python matplotlib please help us write most modern and shortest code solution for this issue how to make background transparent technology fast way just write the code solution in the comments prefered way create with a new cod... | 0 |
392,281 | 26,932,873,396 | IssuesEvent | 2023-02-07 18:07:34 | fluxninja/aperture | https://api.github.com/repos/fluxninja/aperture | closed | Deduplicate docs between Policy and Component | Documentation | Right now some information is repeated in docs of a Component and the Policy.
Decide what should go where and deduplicate docs (inserting links where appropriate)
Discovered when working on #143 | 1.0 | Deduplicate docs between Policy and Component - Right now some information is repeated in docs of a Component and the Policy.
Decide what should go where and deduplicate docs (inserting links where appropriate)
Discovered when working on #143 | non_priority | deduplicate docs between policy and component right now some information is repeated in docs of a component and the policy decide what should go where and deduplicate docs inserting links where appropriate discovered when working on | 0 |
206,452 | 16,042,463,634 | IssuesEvent | 2021-04-22 09:34:42 | TheThingsIndustries/lorawan-stack-docs | https://api.github.com/repos/TheThingsIndustries/lorawan-stack-docs | opened | Enable Packet Broker configuration via CLI | bug documentation | #### Summary
Packet Broker commands are failing, possible configuration step for TTS Clous tenants is missing
#### Why do we need this ?
Allow customers to see their PB configuration, and make changes
#### What is already there? What do you see now?
Documentation available: https://www.thethingsindustries.co... | 1.0 | Enable Packet Broker configuration via CLI - #### Summary
Packet Broker commands are failing, possible configuration step for TTS Clous tenants is missing
#### Why do we need this ?
Allow customers to see their PB configuration, and make changes
#### What is already there? What do you see now?
Documentation ... | non_priority | enable packet broker configuration via cli summary packet broker commands are failing possible configuration step for tts clous tenants is missing why do we need this allow customers to see their pb configuration and make changes what is already there what do you see now documentation ... | 0 |
166,963 | 14,087,205,002 | IssuesEvent | 2020-11-05 05:52:39 | SAP/cloud-foundry-tools | https://api.github.com/repos/SAP/cloud-foundry-tools | closed | Url doesnt work | bug documentation good first issue | The link provides seems to be an internal link
cf-cli extension called cf-service-info (from here)[http://nexus.wdf.sap.corp:8081/nexus/content/groups/build.releases/com/sap/golang/com/sap/devx/wing/cfserviceinfo/]
The run config mentioned is not included in the project
"run the launch config 'Run Extension'... | 1.0 | Url doesnt work - The link provides seems to be an internal link
cf-cli extension called cf-service-info (from here)[http://nexus.wdf.sap.corp:8081/nexus/content/groups/build.releases/com/sap/golang/com/sap/devx/wing/cfserviceinfo/]
The run config mentioned is not included in the project
"run the launch conf... | non_priority | url doesnt work the link provides seems to be an internal link cf cli extension called cf service info from here the run config mentioned is not included in the project run the launch config run extension thanks in advance | 0 |
56,988 | 7,022,194,322 | IssuesEvent | 2017-12-22 09:27:30 | EnginyeriaSofwareUB/ES2017B1 | https://api.github.com/repos/EnginyeriaSofwareUB/ES2017B1 | closed | Animación destrucción del terreno | Design feature | Criterios de aceptación:
- [x] Diseñar animación de destrucción del terreno.
- [x] Implementarla en el script
Horas de trabajo:
- Previsión:
- Realidad:
| 1.0 | Animación destrucción del terreno - Criterios de aceptación:
- [x] Diseñar animación de destrucción del terreno.
- [x] Implementarla en el script
Horas de trabajo:
- Previsión:
- Realidad:
| non_priority | animación destrucción del terreno criterios de aceptación diseñar animación de destrucción del terreno implementarla en el script horas de trabajo previsión realidad | 0 |
743,151 | 25,888,937,885 | IssuesEvent | 2022-12-14 16:26:51 | Eonasdan/tempus-dominus | https://api.github.com/repos/Eonasdan/tempus-dominus | closed | useTwentyfourHour hour-range is 01 - 24, should be 00 - 23 | State: Waiting feedback Area: TypeScript Priority: Low | - Operating: Windows 10
- Browser: Chrome 103.0.5060.66, Edge 103.0.1264.44
- Version of the plugin. 6.0.0-beta9.
- Stackblitz fork: [https://stackblitz.com/edit/tempus-dominus-v6-next-ajtgmm?file=index.js](https://stackblitz.com/edit/tempus-dominus-v6-next-ajtgmm?file=index.js)
- Browser's locale: sv-SE
When u... | 1.0 | useTwentyfourHour hour-range is 01 - 24, should be 00 - 23 - - Operating: Windows 10
- Browser: Chrome 103.0.5060.66, Edge 103.0.1264.44
- Version of the plugin. 6.0.0-beta9.
- Stackblitz fork: [https://stackblitz.com/edit/tempus-dominus-v6-next-ajtgmm?file=index.js](https://stackblitz.com/edit/tempus-dominus-v6-nex... | priority | usetwentyfourhour hour range is should be operating windows browser chrome edge version of the plugin stackblitz fork browser s locale sv se when using the usetwentyfourhour setting the hour range is between should be | 1 |
116,832 | 15,020,011,997 | IssuesEvent | 2021-02-01 14:14:08 | mozilla-lockwise/lockwise-ios | https://api.github.com/repos/mozilla-lockwise/lockwise-ios | reopened | New image for placeholder view in search for iPad | archived needs-design | The current placeholder when entries haven't loaded in looks funny on the iPad because it isn't wide enough. | 1.0 | New image for placeholder view in search for iPad - The current placeholder when entries haven't loaded in looks funny on the iPad because it isn't wide enough. | non_priority | new image for placeholder view in search for ipad the current placeholder when entries haven t loaded in looks funny on the ipad because it isn t wide enough | 0 |
45,593 | 5,720,592,830 | IssuesEvent | 2017-04-20 02:29:11 | Kademi/kademi-dev | https://api.github.com/repos/Kademi/kademi-dev | closed | Options for enable/disable cash top up for Reward Store | enhancement Ready to Test - Dev | Please implement SettingsApplication for ShoppingCartApp, and add a setting to control whether cash top ups are enabled.
Update the isCashTopupsEnabled method in ShoppingCartApp to use this setting
| 1.0 | Options for enable/disable cash top up for Reward Store - Please implement SettingsApplication for ShoppingCartApp, and add a setting to control whether cash top ups are enabled.
Update the isCashTopupsEnabled method in ShoppingCartApp to use this setting
| non_priority | options for enable disable cash top up for reward store please implement settingsapplication for shoppingcartapp and add a setting to control whether cash top ups are enabled update the iscashtopupsenabled method in shoppingcartapp to use this setting | 0 |
120,536 | 10,122,121,553 | IssuesEvent | 2019-07-31 17:10:51 | opengeospatial/te-releases | https://api.github.com/repos/opengeospatial/te-releases | closed | CDB 1.0 revision 0.4 in Beta | approved-by-test-lead ready-for-installation | I do not have permissions on the [main ets-cdb10 repository](https://github.com/opengeospatial/ets-cdb10) to tag issues with milestone "0.3". I also cannot push the commit with the release notes; it is on my fork: https://github.com/GeoSensorWebLab/ets-cdb10
Would you prefer I make a pull request for the "release no... | 1.0 | CDB 1.0 revision 0.4 in Beta - I do not have permissions on the [main ets-cdb10 repository](https://github.com/opengeospatial/ets-cdb10) to tag issues with milestone "0.3". I also cannot push the commit with the release notes; it is on my fork: https://github.com/GeoSensorWebLab/ets-cdb10
Would you prefer I make a p... | non_priority | cdb revision in beta i do not have permissions on the to tag issues with milestone i also cannot push the commit with the release notes it is on my fork would you prefer i make a pull request for the release notes commit or manually use git to pick that commit | 0 |
53,277 | 6,307,044,165 | IssuesEvent | 2017-07-21 23:02:59 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | TS Build Task Multiroot Support | on-testplan tasks typescript | **Feature**
Ensure that the TS task 2.0 builders work as expected in multiroot scenarios | 1.0 | TS Build Task Multiroot Support - **Feature**
Ensure that the TS task 2.0 builders work as expected in multiroot scenarios | non_priority | ts build task multiroot support feature ensure that the ts task builders work as expected in multiroot scenarios | 0 |
46,926 | 2,966,808,061 | IssuesEvent | 2015-07-12 08:35:32 | mattjhayes/nmeta | https://api.github.com/repos/mattjhayes/nmeta | opened | Granular QoS Treatment Control | enhancement Functional Severity: Low Priority | There needs to be an ability to tailor QoS treatment to the capabilities of the device or port. Some switch ports may have egress queues configured and others won't. Queueing a packet to a queue that doesn't exist will consign it to a black hole bit bucket.
It may be desirable to move this control to the main policy t... | 1.0 | Granular QoS Treatment Control - There needs to be an ability to tailor QoS treatment to the capabilities of the device or port. Some switch ports may have egress queues configured and others won't. Queueing a packet to a queue that doesn't exist will consign it to a black hole bit bucket.
It may be desirable to move ... | priority | granular qos treatment control there needs to be an ability to tailor qos treatment to the capabilities of the device or port some switch ports may have egress queues configured and others won t queueing a packet to a queue that doesn t exist will consign it to a black hole bit bucket it may be desirable to move ... | 1 |
113,384 | 24,409,318,377 | IssuesEvent | 2022-10-05 10:52:16 | TFG-Beatriz-Llamas/botStarcraft | https://api.github.com/repos/TFG-Beatriz-Llamas/botStarcraft | closed | Optimizar parámetros propios | code | - Trabajadores construido por centro de mando: Entero
- Número de barracones máximos construidos por centro de mando: Entero
- Cantidad de soldados a construir por cada centro de mando: Entero
- Número de soldados a generar antes de lanzar el ataque: Entero
| 1.0 | Optimizar parámetros propios - - Trabajadores construido por centro de mando: Entero
- Número de barracones máximos construidos por centro de mando: Entero
- Cantidad de soldados a construir por cada centro de mando: Entero
- Número de soldados a generar antes de lanzar el ataque: Entero
| non_priority | optimizar parámetros propios trabajadores construido por centro de mando entero número de barracones máximos construidos por centro de mando entero cantidad de soldados a construir por cada centro de mando entero número de soldados a generar antes de lanzar el ataque entero | 0 |
113,189 | 24,376,375,548 | IssuesEvent | 2022-10-04 01:36:32 | rkd103/Group-11 | https://api.github.com/repos/rkd103/Group-11 | closed | Implement User Story A - Add Support for Account Creation, User Sign-in, Account Access, and Credential Retrieval/Reset | enhancement code | Taking the User Stories assigned in previous issues, begin brainstorming how to implement the requirements in code.
Namely, perform independent research regarding what packages, techniques, etc. are needed to satisfy the stakeholder's image.
User Story A: "create account, login, and access personal timeline"
O... | 1.0 | Implement User Story A - Add Support for Account Creation, User Sign-in, Account Access, and Credential Retrieval/Reset - Taking the User Stories assigned in previous issues, begin brainstorming how to implement the requirements in code.
Namely, perform independent research regarding what packages, techniques, etc. ... | non_priority | implement user story a add support for account creation user sign in account access and credential retrieval reset taking the user stories assigned in previous issues begin brainstorming how to implement the requirements in code namely perform independent research regarding what packages techniques etc ... | 0 |
141,427 | 11,418,523,226 | IssuesEvent | 2020-02-03 04:56:41 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | opened | Folllow up of #7526 - Unable to set monthly tips hence not shown under contribution panel | OS/Windows QA/Test-Plan-Specified QA/Yes bug feature/rewards regression | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROV... | 1.0 | Folllow up of #7526 - Unable to set monthly tips hence not shown under contribution panel - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFI... | non_priority | folllow up of unable to set monthly tips hence not shown under contribution panel have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficie... | 0 |
35,184 | 16,964,343,476 | IssuesEvent | 2021-06-29 09:03:27 | AbsaOSS/spline | https://api.github.com/repos/AbsaOSS/spline | closed | Incorrect index field "execPlanDetails.executionPlanId" | bug component: Persistence scaling / performance | Should be `execPlanDetails.executionPlanKey` | True | Incorrect index field "execPlanDetails.executionPlanId" - Should be `execPlanDetails.executionPlanKey` | non_priority | incorrect index field execplandetails executionplanid should be execplandetails executionplankey | 0 |
19,106 | 10,318,622,572 | IssuesEvent | 2019-08-30 15:22:02 | microsoft/MixedRealityToolkit-Unity | https://api.github.com/repos/microsoft/MixedRealityToolkit-Unity | closed | SpherePointer to cache TryGetNearGraspPoint | Bug Input System - Pointer Performance | ## Describe the bug
SpherePointer leverages TryGetNearGraspPoint() for many commonly used properties (i.e IsNearObject and IsInteractionEnabled). These properties are called multiple times which causes the TryGetNearGraspPoint and resulting Physics.CheckSphere to be redundantly called everytime.
## To reproduce
... | True | SpherePointer to cache TryGetNearGraspPoint - ## Describe the bug
SpherePointer leverages TryGetNearGraspPoint() for many commonly used properties (i.e IsNearObject and IsInteractionEnabled). These properties are called multiple times which causes the TryGetNearGraspPoint and resulting Physics.CheckSphere to be redu... | non_priority | spherepointer to cache trygetneargrasppoint describe the bug spherepointer leverages trygetneargrasppoint for many commonly used properties i e isnearobject and isinteractionenabled these properties are called multiple times which causes the trygetneargrasppoint and resulting physics checksphere to be redu... | 0 |
160,589 | 6,100,424,391 | IssuesEvent | 2017-06-20 12:35:08 | openshift/origin-web-catalog | https://api.github.com/repos/openshift/origin-web-catalog | closed | select-project component shouldn't show projects being deleted | kind/bug priority/P3 | The select-project component shows all projects, even those being deleted. We should filter out those with a deletion timestamp which means they're scheduled for deletion. | 1.0 | select-project component shouldn't show projects being deleted - The select-project component shows all projects, even those being deleted. We should filter out those with a deletion timestamp which means they're scheduled for deletion. | priority | select project component shouldn t show projects being deleted the select project component shows all projects even those being deleted we should filter out those with a deletion timestamp which means they re scheduled for deletion | 1 |
679,905 | 23,249,231,759 | IssuesEvent | 2022-08-04 00:41:47 | ProdigyPNP/ProdigyMathGameHacking | https://api.github.com/repos/ProdigyPNP/ProdigyMathGameHacking | closed | [Closed for inactivity] Don't work | Is: Bug Priority: Low Category: PHEx | ### Describe the bug
So, I am on a macbook air, but my operating system is windows 10, and I wanted to downlowd hack and compress the zip file,and after compressing the file, I tried to load is on my chrome extension with the developer mode, but it keeps sending me errors! Also btw I tried the same thing on my other... | 1.0 | [Closed for inactivity] Don't work - ### Describe the bug
So, I am on a macbook air, but my operating system is windows 10, and I wanted to downlowd hack and compress the zip file,and after compressing the file, I tried to load is on my chrome extension with the developer mode, but it keeps sending me errors! Also b... | priority | don t work describe the bug so i am on a macbook air but my operating system is windows and i wanted to downlowd hack and compress the zip file and after compressing the file i tried to load is on my chrome extension with the developer mode but it keeps sending me errors also btw i tried the same thi... | 1 |
19,293 | 4,369,556,374 | IssuesEvent | 2016-08-04 00:38:46 | backdrop-contrib/githubapi | https://api.github.com/repos/backdrop-contrib/githubapi | closed | Flip the client secret and client ID in the README.md | Better documentation | I copy/pasted the lines from the README.md into my settings.php file:
> Optionally you can store client_id and client_secret via settings.php
```
$settings['githubapi_client_secret'] = 'YOUR_APP_CLIENT_SECRET';
$settings['githubapi_client_id'] = 'YOUR_APP_CLIENT_ID';
```
But these settings are flipped from th... | 1.0 | Flip the client secret and client ID in the README.md - I copy/pasted the lines from the README.md into my settings.php file:
> Optionally you can store client_id and client_secret via settings.php
```
$settings['githubapi_client_secret'] = 'YOUR_APP_CLIENT_SECRET';
$settings['githubapi_client_id'] = 'YOUR_APP_CL... | non_priority | flip the client secret and client id in the readme md i copy pasted the lines from the readme md into my settings php file optionally you can store client id and client secret via settings php settings your app client secret settings your app client id but these settings are flipped... | 0 |
204,128 | 15,417,463,120 | IssuesEvent | 2021-03-05 07:14:08 | Fammeo/EasyCloudBooks | https://api.github.com/repos/Fammeo/EasyCloudBooks | closed | Market place seeding error | Client Request Resolved fixed testing-required | <img width="1280" alt="Screenshot 2021-03-05 at 10 54 12 AM" src="https://user-images.githubusercontent.com/46813198/110071008-3fe34e00-7da1-11eb-9703-527e8a9f3f94.png
steps
1. RESET objects
2. save - error appeared. | 1.0 | Market place seeding error - <img width="1280" alt="Screenshot 2021-03-05 at 10 54 12 AM" src="https://user-images.githubusercontent.com/46813198/110071008-3fe34e00-7da1-11eb-9703-527e8a9f3f94.png
steps
1. RESET objects
2. save - error appeared. | non_priority | market place seeding error img width alt screenshot at am src steps reset objects save error appeared | 0 |
112,342 | 4,524,899,710 | IssuesEvent | 2016-09-07 01:27:01 | coreos/coreos-kubernetes | https://api.github.com/repos/coreos/coreos-kubernetes | closed | 401 Unauthorized kube-apiserver in multiple master nodes front of ELB | kind/support priority/P2 | Hi,
We are trying to achieve high availability cluster with multiple master nodes front ELB.
Also trying to use ingress to layer 7 traffic from ELB to master nodes.
http://kubernetes.io/docs/user-guide/ingress/#tls
apiserver-key and apiserver cert configured as secrets.
We also have external hostname for api... | 1.0 | 401 Unauthorized kube-apiserver in multiple master nodes front of ELB - Hi,
We are trying to achieve high availability cluster with multiple master nodes front ELB.
Also trying to use ingress to layer 7 traffic from ELB to master nodes.
http://kubernetes.io/docs/user-guide/ingress/#tls
apiserver-key and apiserv... | priority | unauthorized kube apiserver in multiple master nodes front of elb hi we are trying to achieve high availability cluster with multiple master nodes front elb also trying to use ingress to layer traffic from elb to master nodes apiserver key and apiserver cert configured as secrets we also have ext... | 1 |
51,136 | 3,011,103,551 | IssuesEvent | 2015-07-28 16:13:59 | MinetestForFun/minetest-minetestforfun-server | https://api.github.com/repos/MinetestForFun/minetest-minetestforfun-server | closed | Crash [Throwing] | Modding@BugFix Priority@High Server crash | #### Crash logs
http://zerobin.qbuissondebon.info/?643a724274bfff1b#Yx4yITyQ80CCU6zVWE5BxC6rUNT4bP1I1WveaZlO1Ho=
```
n]: [mana] Wrote mana data into /home/quentinbd/minetest/worlds/minetestforfun//mana.mt.
01:31:34: ACTION[main]: compassgps writing settings
01:31:34: ACTION[main]: Wrote quests to file
01:31:3... | 1.0 | Crash [Throwing] - #### Crash logs
http://zerobin.qbuissondebon.info/?643a724274bfff1b#Yx4yITyQ80CCU6zVWE5BxC6rUNT4bP1I1WveaZlO1Ho=
```
n]: [mana] Wrote mana data into /home/quentinbd/minetest/worlds/minetestforfun//mana.mt.
01:31:34: ACTION[main]: compassgps writing settings
01:31:34: ACTION[main]: Wrote ques... | priority | crash crash logs n wrote mana data into home quentinbd minetest worlds minetestforfun mana mt action compassgps writing settings action wrote quests to file action datas saved action chests saved action server shuts down saving trophi... | 1 |
167,986 | 20,736,499,965 | IssuesEvent | 2022-03-14 14:10:28 | shaimael/AltoroJ | https://api.github.com/repos/shaimael/AltoroJ | opened | log4j-1.2.16.jar: 7 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.16.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /AltoroJ 3.1.1/build.gradle</p>
<p>Path to vulnerable library: /gradle/caches/m... | True | log4j-1.2.16.jar: 7 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.16.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /AltoroJ 3.1.1... | non_priority | jar vulnerabilities highest severity is vulnerable library jar apache path to dependency file altoroj build gradle path to vulnerable library gradle caches modules files jar vulnerabilities cve severity cvss depen... | 0 |
305,914 | 23,137,223,395 | IssuesEvent | 2022-07-28 15:10:39 | ERNI-Academy/asset-iac-terraform-azure | https://api.github.com/repos/ERNI-Academy/asset-iac-terraform-azure | closed | Documentation: Contributors list is empty | documentation | ### Explain in 1-2 sentences. Say what this is about.
Please add contributors to this repository
### Motivation Goals
-
### In scope
-
### Out of scope
-
### Risks / unknowns
-
### Examples
_No response_ | 1.0 | Documentation: Contributors list is empty - ### Explain in 1-2 sentences. Say what this is about.
Please add contributors to this repository
### Motivation Goals
-
### In scope
-
### Out of scope
-
### Risks / unknowns
-
### Examples
_No response_ | non_priority | documentation contributors list is empty explain in sentences say what this is about please add contributors to this repository motivation goals in scope out of scope risks unknowns examples no response | 0 |
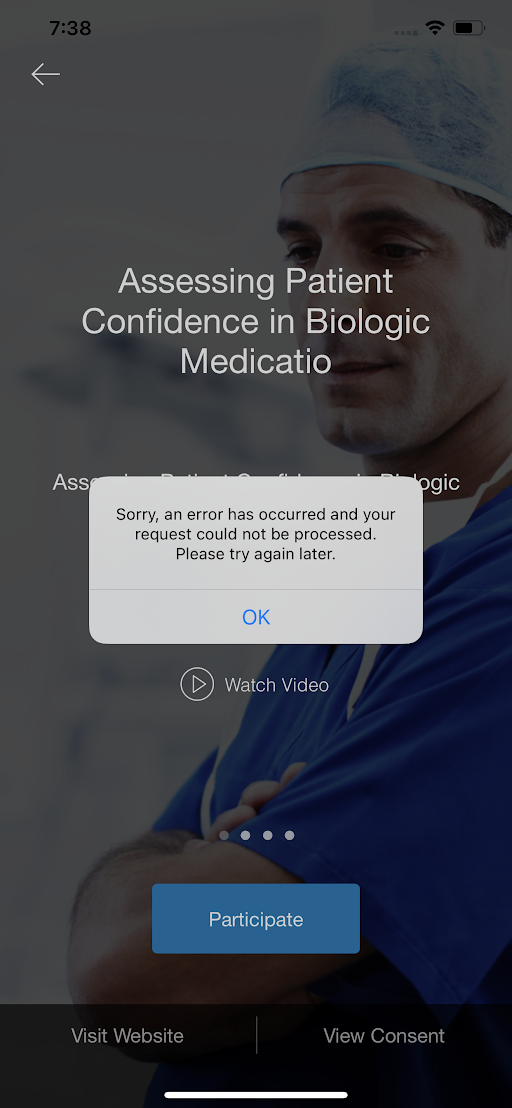
359,219 | 10,666,969,701 | IssuesEvent | 2019-10-19 08:36:17 | kobotoolbox/kpi | https://api.github.com/repos/kobotoolbox/kpi | closed | Allow users to add custom wrapper code for REST submissions | enhancement high priority | ERROR: type should be string, got "https://www.flowdock.com/app/kobotoolbox/kobo/threads/mRpcBQgbF0_UeIgyXybyDxueOW3\r\n\r\n- [x] FE UI work as shown below\r\n- [x] FE interchange with \"Add custom wrapper\" using `hook` attribute called `payload_template`\r\n- [x] BE uses template when `POST`ing to external server (@noliveleger)\r\n\r\n## Description\r\n\r\nAs a user I'd like to be able to submit data to AirTable and similar services. AirTable requires a wrapper around the actual JSON submission, which I would like to specify in the UI when creating a new REST service. \r\n\r\n## Suggested UI design\r\n\r\n\r\n\r\n## Example wrapper code \r\n\r\n```\r\n{\r\n \"fields\": %SUBMISSION%\r\n}\r\n```\r\n" | 1.0 | Allow users to add custom wrapper code for REST submissions - https://www.flowdock.com/app/kobotoolbox/kobo/threads/mRpcBQgbF0_UeIgyXybyDxueOW3
- [x] FE UI work as shown below
- [x] FE interchange with "Add custom wrapper" using `hook` attribute called `payload_template`
- [x] BE uses template when `POST`ing to ex... | priority | allow users to add custom wrapper code for rest submissions fe ui work as shown below fe interchange with add custom wrapper using hook attribute called payload template be uses template when post ing to external server noliveleger description as a user i d like to be able to sub... | 1 |
362,796 | 10,732,119,268 | IssuesEvent | 2019-10-28 21:05:20 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [Platform] Fix the master placement logic when doing a full move | area/platform kind/bug priority/high | There seem to be some issue with the master placement logic when doing a large cluster full move. | 1.0 | [Platform] Fix the master placement logic when doing a full move - There seem to be some issue with the master placement logic when doing a large cluster full move. | priority | fix the master placement logic when doing a full move there seem to be some issue with the master placement logic when doing a large cluster full move | 1 |
316,867 | 9,658,080,909 | IssuesEvent | 2019-05-20 10:05:18 | bbaumgartl/test | https://api.github.com/repos/bbaumgartl/test | closed | Support for Showing only a defined List auf countries which is from static_info_tables | Priority: Should have Status: Closed Tracker: Feature | ---
Author Name: **Josef F. Glatz (Old User)** (Josef F. Glatz (Old User))
Original Redmine Issue: 31665, https://forge.typo3.org/issues/31665
Original Date: 2011-11-08
Original Assignee: Bernhard Baumgartl, datamints GmbH
---
Hello,
I'm searching for a register and edit extension for fe_users which supports md5... | 1.0 | Support for Showing only a defined List auf countries which is from static_info_tables - ---
Author Name: **Josef F. Glatz (Old User)** (Josef F. Glatz (Old User))
Original Redmine Issue: 31665, https://forge.typo3.org/issues/31665
Original Date: 2011-11-08
Original Assignee: Bernhard Baumgartl, datamints GmbH
---
... | priority | support for showing only a defined list auf countries which is from static info tables author name josef f glatz old user josef f glatz old user original redmine issue original date original assignee bernhard baumgartl datamints gmbh hello i m searching for a register and e... | 1 |
165,219 | 20,574,349,266 | IssuesEvent | 2022-03-04 01:47:27 | rvvergara/haiku-rails-api | https://api.github.com/repos/rvvergara/haiku-rails-api | opened | CVE-2020-26247 (Medium) detected in nokogiri-1.10.10.gem | security vulnerability | ## CVE-2020-26247 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.10.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's ma... | True | CVE-2020-26247 (Medium) detected in nokogiri-1.10.10.gem - ## CVE-2020-26247 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.10.gem</b></p></summary>
<p>Nokogiri (鋸) is... | non_priority | cve medium detected in nokogiri gem cve medium severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href ... | 0 |
57,223 | 3,081,249,717 | IssuesEvent | 2015-08-22 14:40:52 | pavel-pimenov/flylinkdc-r5xx | https://api.github.com/repos/pavel-pimenov/flylinkdc-r5xx | closed | Меню по правой кнопке на папке - копировать - имя ПАПКИ | bug imported Priority-Medium | _From [bobrikov](https://code.google.com/u/bobrikov/) on January 16, 2013 12:06:16_
Имхо нужно сделать
**Attachment:** [Имя-папки.png](http://code.google.com/p/flylinkdc/issues/detail?id=887)
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=887_ | 1.0 | Меню по правой кнопке на папке - копировать - имя ПАПКИ - _From [bobrikov](https://code.google.com/u/bobrikov/) on January 16, 2013 12:06:16_
Имхо нужно сделать
**Attachment:** [Имя-папки.png](http://code.google.com/p/flylinkdc/issues/detail?id=887)
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?i... | priority | меню по правой кнопке на папке копировать имя папки from on january имхо нужно сделать attachment original issue | 1 |
48,629 | 10,266,803,064 | IssuesEvent | 2019-08-22 22:40:07 | volta-cli/volta | https://api.github.com/repos/volta-cli/volta | opened | Investigate build bloat | code quality | A friend told me about this [recent article on Rust build sizes](https://raphlinus.github.io/rust/2019/08/21/rust-bloat.html), and specifically the article links to a useful tool: [cargo-bloat](https://github.com/RazrFalcon/cargo-bloat).
We should use that tool to see if there are places we can reduce the binary siz... | 1.0 | Investigate build bloat - A friend told me about this [recent article on Rust build sizes](https://raphlinus.github.io/rust/2019/08/21/rust-bloat.html), and specifically the article links to a useful tool: [cargo-bloat](https://github.com/RazrFalcon/cargo-bloat).
We should use that tool to see if there are places we... | non_priority | investigate build bloat a friend told me about this and specifically the article links to a useful tool we should use that tool to see if there are places we can reduce the binary size of volta builds and possibly the build times as a consequence one particular hint i got was that is an especial... | 0 |
30,542 | 7,227,772,893 | IssuesEvent | 2018-02-11 00:34:35 | raywo/MMM-PublicTransportHafas | https://api.github.com/repos/raywo/MMM-PublicTransportHafas | closed | Fix "method_lines" issue in convenience/query_stations.js | codeclimate | Function `refineProducts` has 30 lines of code (exceeds 25 allowed). Consider refactoring.
https://codeclimate.com/github/raywo/MMM-PublicTransportHafas/convenience/query_stations.js#issue_5a7f455b6b463a000100001a | 1.0 | Fix "method_lines" issue in convenience/query_stations.js - Function `refineProducts` has 30 lines of code (exceeds 25 allowed). Consider refactoring.
https://codeclimate.com/github/raywo/MMM-PublicTransportHafas/convenience/query_stations.js#issue_5a7f455b6b463a000100001a | non_priority | fix method lines issue in convenience query stations js function refineproducts has lines of code exceeds allowed consider refactoring | 0 |
20,691 | 3,620,466,897 | IssuesEvent | 2016-02-08 20:03:45 | SOZOGlobal/Scrumban | https://api.github.com/repos/SOZOGlobal/Scrumban | opened | Create Renew Social Platforms | content design | Pintrest
Twitter
Medium
Instagram
Facebook
Snapchat
Periscope
LinkedIn
YouTube
plus, consistent copy and logo/backgrounds on all | 1.0 | Create Renew Social Platforms - Pintrest
Twitter
Medium
Instagram
Facebook
Snapchat
Periscope
LinkedIn
YouTube
plus, consistent copy and logo/backgrounds on all | non_priority | create renew social platforms pintrest twitter medium instagram facebook snapchat periscope linkedin youtube plus consistent copy and logo backgrounds on all | 0 |
381,175 | 11,274,507,923 | IssuesEvent | 2020-01-14 18:43:22 | sdinteractive/Magento2_SomethingDigital_UpgradeHelper | https://api.github.com/repos/sdinteractive/Magento2_SomethingDigital_UpgradeHelper | closed | Check for changes to $_template | Priority - Low | [9:44 AM] Subbu Swamynathan: PSA: with 2.1.15, magento changed a line in the block to view orders Magento\Sales\Block\Order\View
[9:44 AM] Subbu Swamynathan: from
[9:44 AM] Subbu Swamynathan:
protected $_template = 'order/view.phtml';
[9:44 AM] Subbu Swamynathan: to
[9:45 AM] Subbu Swamynathan:
protected ... | 1.0 | Check for changes to $_template - [9:44 AM] Subbu Swamynathan: PSA: with 2.1.15, magento changed a line in the block to view orders Magento\Sales\Block\Order\View
[9:44 AM] Subbu Swamynathan: from
[9:44 AM] Subbu Swamynathan:
protected $_template = 'order/view.phtml';
[9:44 AM] Subbu Swamynathan: to
[9:45 AM] ... | priority | check for changes to template subbu swamynathan psa with magento changed a line in the block to view orders magento sales block order view subbu swamynathan from subbu swamynathan protected template order view phtml subbu swamynathan to subbu swamynathan protected templ... | 1 |
181,047 | 14,850,203,642 | IssuesEvent | 2021-01-18 03:44:53 | minio/direct-csi | https://api.github.com/repos/minio/direct-csi | closed | Multiple Storage Classes | documentation | Currently I use openebs local pvs for databases. I will be using this for minio but I am wondering is it possible to create multiple strorage classes and if so how would I do that? I would rather just use this than openebs and this so that I make things simpler. | 1.0 | Multiple Storage Classes - Currently I use openebs local pvs for databases. I will be using this for minio but I am wondering is it possible to create multiple strorage classes and if so how would I do that? I would rather just use this than openebs and this so that I make things simpler. | non_priority | multiple storage classes currently i use openebs local pvs for databases i will be using this for minio but i am wondering is it possible to create multiple strorage classes and if so how would i do that i would rather just use this than openebs and this so that i make things simpler | 0 |
9,301 | 3,032,826,317 | IssuesEvent | 2015-08-05 11:25:03 | WebTales/rubedo | https://api.github.com/repos/WebTales/rubedo | closed | Add SEO on contents | enhancement high priority To test | Ajouter les metas(Titre+ description) aux contenus ou utiliser méta existants (titre+résumé) pour le référencement des contenus proposés sous forme de requêtes. | 1.0 | Add SEO on contents - Ajouter les metas(Titre+ description) aux contenus ou utiliser méta existants (titre+résumé) pour le référencement des contenus proposés sous forme de requêtes. | non_priority | add seo on contents ajouter les metas titre description aux contenus ou utiliser méta existants titre résumé pour le référencement des contenus proposés sous forme de requêtes | 0 |
373,442 | 26,054,785,660 | IssuesEvent | 2022-12-22 23:22:33 | OliverOverend/gym-simplifiedtetris | https://api.github.com/repos/OliverOverend/gym-simplifiedtetris | opened | DOC: Contributing docs are outdated | Documentation Enhancement | ### Please a URL to the documentation:
https://github.com/OliverOverend/gym-simplifiedtetris/blob/master/CONTRIBUTING.md
### Please provide a description of the issue:
The contributing docs are outdated and clunky.
### Please explain the suggested fix:
Streamline the contributing docs by rejuvenating them with up-... | 1.0 | DOC: Contributing docs are outdated - ### Please a URL to the documentation:
https://github.com/OliverOverend/gym-simplifiedtetris/blob/master/CONTRIBUTING.md
### Please provide a description of the issue:
The contributing docs are outdated and clunky.
### Please explain the suggested fix:
Streamline the contribut... | non_priority | doc contributing docs are outdated please a url to the documentation please provide a description of the issue the contributing docs are outdated and clunky please explain the suggested fix streamline the contributing docs by rejuvenating them with up to date information | 0 |
71,001 | 15,168,124,129 | IssuesEvent | 2021-02-12 18:53:25 | jgeraigery/seaside-gradle-plugins | https://api.github.com/repos/jgeraigery/seaside-gradle-plugins | opened | CVE-2018-1199 (Medium) detected in spring-core-3.1.3.RELEASE.jar | security vulnerability | ## CVE-2018-1199 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-3.1.3.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: seaside-gr... | True | CVE-2018-1199 (Medium) detected in spring-core-3.1.3.RELEASE.jar - ## CVE-2018-1199 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-core-3.1.3.RELEASE.jar</b></p></summary>
<p... | non_priority | cve medium detected in spring core release jar cve medium severity vulnerability vulnerable library spring core release jar spring framework parent path to dependency file seaside gradle plugins com ngc seaside gradle plugins distribution build gradle path to vulnerable lib... | 0 |
129,918 | 5,106,362,713 | IssuesEvent | 2017-01-05 11:09:06 | odalic/sti | https://api.github.com/repos/odalic/sti | closed | Implement property (aka relation) proposal | bug core extension feature java knowledge bases priority: Urgent sparql | Hi, I have entirely overlooked this, but this feature is still not implemented (the API is ready) for the properties. | 1.0 | Implement property (aka relation) proposal - Hi, I have entirely overlooked this, but this feature is still not implemented (the API is ready) for the properties. | priority | implement property aka relation proposal hi i have entirely overlooked this but this feature is still not implemented the api is ready for the properties | 1 |
187,969 | 15,112,693,574 | IssuesEvent | 2021-02-08 22:16:35 | josecls/agripluvi-api | https://api.github.com/repos/josecls/agripluvi-api | closed | Feature: Adiciona documentação de como rodar o projeto | Feature Low Priority documentation good first issue | ### Descrição
No projeto atual não temos um readme especificando o passo a passo para rodar o projeto localmente, isso iria auxiliar as pessoas que nunca trabalharam com Java.
### Ação
Criar um arquivo readme.md com informações úteis sobre o projeto.
### Observações
- [**Guia de como criar um readme.md bonit... | 1.0 | Feature: Adiciona documentação de como rodar o projeto - ### Descrição
No projeto atual não temos um readme especificando o passo a passo para rodar o projeto localmente, isso iria auxiliar as pessoas que nunca trabalharam com Java.
### Ação
Criar um arquivo readme.md com informações úteis sobre o projeto.
##... | non_priority | feature adiciona documentação de como rodar o projeto descrição no projeto atual não temos um readme especificando o passo a passo para rodar o projeto localmente isso iria auxiliar as pessoas que nunca trabalharam com java ação criar um arquivo readme md com informações úteis sobre o projeto ... | 0 |
154,056 | 19,710,772,518 | IssuesEvent | 2022-01-13 04:53:55 | ChoeMinji/react-17.0.2 | https://api.github.com/repos/ChoeMinji/react-17.0.2 | opened | WS-2018-0628 (Medium) detected in marked-0.3.6.tgz | security vulnerability | ## WS-2018-0628 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.6.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://reg... | True | WS-2018-0628 (Medium) detected in marked-0.3.6.tgz - ## WS-2018-0628 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.6.tgz</b></p></summary>
<p>A markdown parser built for... | non_priority | ws medium detected in marked tgz ws medium severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file fixtures fiber debugger package json path to vulnerable library fixtures fiber debugge... | 0 |
6,107 | 8,966,962,329 | IssuesEvent | 2019-01-29 01:09:38 | knative/serving | https://api.github.com/repos/knative/serving | closed | Simplify the traffic.go | area/API kind/cleanup kind/process | <!--
Pro-tip: You can leave this block commented, and it still works!
Select the appropriate areas for your issue:
/area API
Classify what kind of issue this is:
/kind cleanup
/kind process
-->
## Proposal
Currently the route/traffic/traffic.go is quite complex, but it doesn't have to be so, since ... | 1.0 | Simplify the traffic.go - <!--
Pro-tip: You can leave this block commented, and it still works!
Select the appropriate areas for your issue:
/area API
Classify what kind of issue this is:
/kind cleanup
/kind process
-->
## Proposal
Currently the route/traffic/traffic.go is quite complex, but it doe... | non_priority | simplify the traffic go pro tip you can leave this block commented and it still works select the appropriate areas for your issue area api classify what kind of issue this is kind cleanup kind process proposal currently the route traffic traffic go is quite complex but it doe... | 0 |
275,917 | 8,582,167,678 | IssuesEvent | 2018-11-13 16:20:53 | CuBoulder/express | https://api.github.com/repos/CuBoulder/express | closed | User Invite email check should not be case sensitive | priority:Critical type:Bug | the CU LDAP returns email addresses with various different cases, such as name@colorado.EDU - if a user is invited at name@colorado.edu, the email check fails.
https://github.com/CuBoulder/express/blob/dev/modules/contrib/user_external_invite/user_external_invite.module#L581 | 1.0 | User Invite email check should not be case sensitive - the CU LDAP returns email addresses with various different cases, such as name@colorado.EDU - if a user is invited at name@colorado.edu, the email check fails.
https://github.com/CuBoulder/express/blob/dev/modules/contrib/user_external_invite/user_external_invit... | priority | user invite email check should not be case sensitive the cu ldap returns email addresses with various different cases such as name colorado edu if a user is invited at name colorado edu the email check fails | 1 |
510,540 | 14,792,557,414 | IssuesEvent | 2021-01-12 14:53:31 | myConsciousness/java-generator-commons | https://api.github.com/repos/myConsciousness/java-generator-commons | closed | AnnotationParameterの引数生成処理を改善 | Priority: high Type: improvement | # Improvement
## 1. Improvement details
`AnnotationParameter` クラスにおける引数生成処理を改善する。
## 2. Why it is necessary
より柔軟な値設定を可能にするため。
## 3. How to improve
現状 `createParameter` メソッドが呼び出された場合に文字列であればダブルクオーテーションを付けて返却しているが、
ダブルクオーテーションを付与するかどうかを実装に委ねるようにする。
## 4. References
| 1.0 | AnnotationParameterの引数生成処理を改善 - # Improvement
## 1. Improvement details
`AnnotationParameter` クラスにおける引数生成処理を改善する。
## 2. Why it is necessary
より柔軟な値設定を可能にするため。
## 3. How to improve
現状 `createParameter` メソッドが呼び出された場合に文字列であればダブルクオーテーションを付けて返却しているが、
ダブルクオーテーションを付与するかどうかを実装に委ねるようにする。
## 4. References
| priority | annotationparameterの引数生成処理を改善 improvement improvement details annotationparameter クラスにおける引数生成処理を改善する。 why it is necessary より柔軟な値設定を可能にするため。 how to improve 現状 createparameter メソッドが呼び出された場合に文字列であればダブルクオーテーションを付けて返却しているが、 ダブルクオーテーションを付与するかどうかを実装に委ねるようにする。 references | 1 |
213,500 | 16,523,743,014 | IssuesEvent | 2021-05-26 17:17:59 | openservicemesh/osm | https://api.github.com/repos/openservicemesh/osm | opened | test: pkg/certificate/providers/vault/certificate_manager.go - RotateCertificate() | area/tests size/XS | In `pkg/certificate/providers/vault/certificate_manager.go`, the unit test coverage can be improved for the RotateCertificate() func. See highlighted lines below.
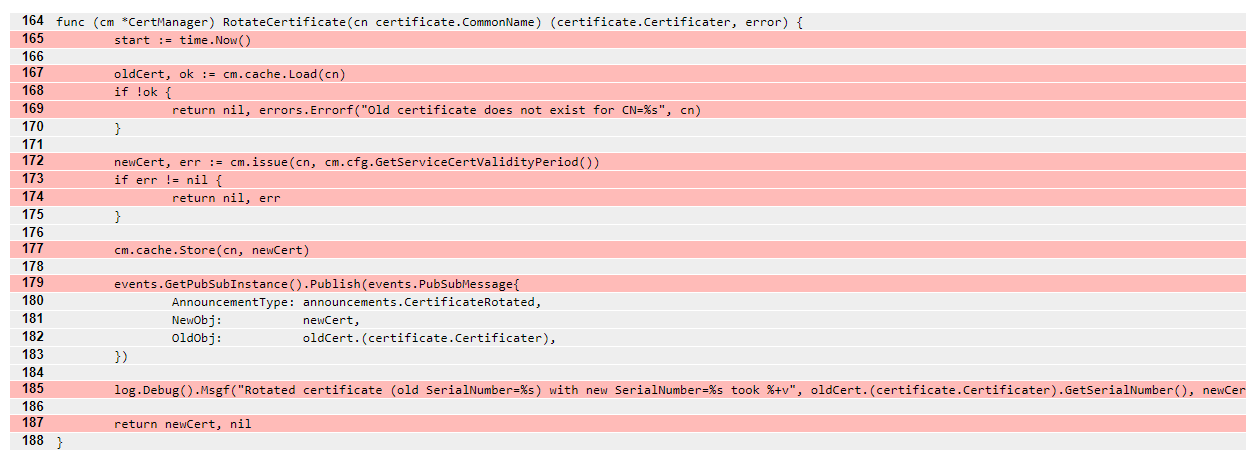
Scenarios not covered:
* Entire functi... | 1.0 | test: pkg/certificate/providers/vault/certificate_manager.go - RotateCertificate() - In `pkg/certificate/providers/vault/certificate_manager.go`, the unit test coverage can be improved for the RotateCertificate() func. See highlighted lines below.
 prompts for email for no good reason. | P2 priority | The /contact form has a field for email, which is solely used for display in the generated modmail notification. I _believe_ this is a holdover from when /contact was not `@auth_required` (perhaps all the way back on Ruqqus) and was usable for logged out users. However, it would take substantial refactoring to make thi... | 1.0 | Contact Admins (modmail) prompts for email for no good reason. - The /contact form has a field for email, which is solely used for display in the generated modmail notification. I _believe_ this is a holdover from when /contact was not `@auth_required` (perhaps all the way back on Ruqqus) and was usable for logged out ... | priority | contact admins modmail prompts for email for no good reason the contact form has a field for email which is solely used for display in the generated modmail notification i believe this is a holdover from when contact was not auth required perhaps all the way back on ruqqus and was usable for logged out ... | 1 |
550,147 | 16,105,703,830 | IssuesEvent | 2021-04-27 14:42:43 | sopra-fs21-group-08/sopra-fs21-group08-server | https://api.github.com/repos/sopra-fs21-group-08/sopra-fs21-group08-server | reopened | Create the Ticket interface and the individual tickets | medium priority task | time estimate: 5h
This task is part of User stories: #17 #9 #8 | 1.0 | Create the Ticket interface and the individual tickets - time estimate: 5h
This task is part of User stories: #17 #9 #8 | priority | create the ticket interface and the individual tickets time estimate this task is part of user stories | 1 |
592,368 | 17,876,838,284 | IssuesEvent | 2021-09-07 05:48:16 | annagabriel-hash/stock-transfer-app | https://api.github.com/repos/annagabriel-hash/stock-transfer-app | closed | Given that I'm a broker, when I go to the stocks page, and enter the amount of shares to be sold, the shares can be bought by the buyers. | App: Backend Priority: Medium State: In Progress Type: Feature | ### Tasks
- [x] Specify offer model
- [x] Offer table accepts stock id, user id, price, shares, status (open, closed, cancelled), order type (limit order and market order), action (buy or sell)
- [x] Specify trade model
- [x] Trade table accepts stock id, buyer_id, seller_id, price, shares, offer_ids
- [x] Given... | 1.0 | Given that I'm a broker, when I go to the stocks page, and enter the amount of shares to be sold, the shares can be bought by the buyers. - ### Tasks
- [x] Specify offer model
- [x] Offer table accepts stock id, user id, price, shares, status (open, closed, cancelled), order type (limit order and market order), act... | priority | given that i m a broker when i go to the stocks page and enter the amount of shares to be sold the shares can be bought by the buyers tasks specify offer model offer table accepts stock id user id price shares status open closed cancelled order type limit order and market order action ... | 1 |
96,866 | 3,974,246,196 | IssuesEvent | 2016-05-04 21:27:27 | blackwatchint/modpack | https://api.github.com/repos/blackwatchint/modpack | closed | Consistently name all factions within the Armory | Low Priority Template | As many new factions may be added to the Armory in future, all existing factions need to be named using a consistent format that conveys the camo and era of the loadout. Furthermore, the factions should be better grouped and sorted. | 1.0 | Consistently name all factions within the Armory - As many new factions may be added to the Armory in future, all existing factions need to be named using a consistent format that conveys the camo and era of the loadout. Furthermore, the factions should be better grouped and sorted. | priority | consistently name all factions within the armory as many new factions may be added to the armory in future all existing factions need to be named using a consistent format that conveys the camo and era of the loadout furthermore the factions should be better grouped and sorted | 1 |
398,778 | 11,742,333,455 | IssuesEvent | 2020-03-12 00:24:18 | thaliawww/concrexit | https://api.github.com/repos/thaliawww/concrexit | closed | Improve documentation | priority: maybe someday technical change | In GitLab by @thomwiggers on Feb 13, 2018, 10:08
### One-sentence description and why
Improve documentation so that we:
* Have something to show on [docs pages](https://thalia.nu/docs/).
* Have (tested) examples for relevant functions (doctests)
* Provide better reference to our newbies and "future generations". | 1.0 | Improve documentation - In GitLab by @thomwiggers on Feb 13, 2018, 10:08
### One-sentence description and why
Improve documentation so that we:
* Have something to show on [docs pages](https://thalia.nu/docs/).
* Have (tested) examples for relevant functions (doctests)
* Provide better reference to our newbies and "... | priority | improve documentation in gitlab by thomwiggers on feb one sentence description and why improve documentation so that we have something to show on have tested examples for relevant functions doctests provide better reference to our newbies and future generations | 1 |
2,964 | 5,144,855,718 | IssuesEvent | 2017-01-12 19:51:59 | TechnionYP5777/SmartCity-Accessibility | https://api.github.com/repos/TechnionYP5777/SmartCity-Accessibility | closed | wierd default behaviour of jxmaps | GUI Map services | when not being able to decipher the building type given to it, JxMaps (consistently!) returns the same building with nothing recognizable alike. wheter the type is hotel, asdasdasasd or floopyfloopydu
the same buildings are returned, find out what is the default behaviour | 1.0 | wierd default behaviour of jxmaps - when not being able to decipher the building type given to it, JxMaps (consistently!) returns the same building with nothing recognizable alike. wheter the type is hotel, asdasdasasd or floopyfloopydu
the same buildings are returned, find out what is the default behaviour | non_priority | wierd default behaviour of jxmaps when not being able to decipher the building type given to it jxmaps consistently returns the same building with nothing recognizable alike wheter the type is hotel asdasdasasd or floopyfloopydu the same buildings are returned find out what is the default behaviour | 0 |
408,650 | 11,950,305,705 | IssuesEvent | 2020-04-03 14:59:57 | JensenJ/SpaceSurvival | https://api.github.com/repos/JensenJ/SpaceSurvival | closed | [BUG] Ship Spawn Syncing Transform | bug medium-priority sync-issue | **Describe the bug**
If a player joins after a ship or another object has been spawned, they do not have the ship in the correct position in their world when they join the host player. This is because the parent of the ship object has not been set as the ship spawning object. This bug does not occur if the player is i... | 1.0 | [BUG] Ship Spawn Syncing Transform - **Describe the bug**
If a player joins after a ship or another object has been spawned, they do not have the ship in the correct position in their world when they join the host player. This is because the parent of the ship object has not been set as the ship spawning object. This ... | priority | ship spawn syncing transform describe the bug if a player joins after a ship or another object has been spawned they do not have the ship in the correct position in their world when they join the host player this is because the parent of the ship object has not been set as the ship spawning object this bug ... | 1 |
670,631 | 22,696,800,044 | IssuesEvent | 2022-07-05 07:00:15 | wso2/api-manager | https://api.github.com/repos/wso2/api-manager | opened | Redis throttling synchronization doesn't work | Type/Bug Priority/Normal | ### Description
At attempt to use redis for throttling sync will fail and spam logs with error. (Unable to sync throttle counter)
There are 2 reasons for this:
1. RedisDistributedCountManager is initialized before the redis pool
See https://github.com/wso2/carbon-apimgt/blob/master/components/apimgt/org.wso2.carb... | 1.0 | Redis throttling synchronization doesn't work - ### Description
At attempt to use redis for throttling sync will fail and spam logs with error. (Unable to sync throttle counter)
There are 2 reasons for this:
1. RedisDistributedCountManager is initialized before the redis pool
See https://github.com/wso2/carbon-ap... | priority | redis throttling synchronization doesn t work description at attempt to use redis for throttling sync will fail and spam logs with error unable to sync throttle counter there are reasons for this redisdistributedcountmanager is initialized before the redis pool see and this results in null jedi... | 1 |
764,445 | 26,800,718,178 | IssuesEvent | 2023-02-01 14:57:10 | SecureApiGateway/SecureApiGateway | https://api.github.com/repos/SecureApiGateway/SecureApiGateway | closed | Fix RCS to sign consent decision JWTs sent to AM | bug priority | RCS is currently using a route hosted by IG to sign the RCS consent decision JWTs. This route in IG needs to be removed for security reasons, any component that needs to sign a message should do so itself.
Design work:
- [x] Review which key RCS should be using for this purpose
- [x] Review whether AM Remote Con... | 1.0 | Fix RCS to sign consent decision JWTs sent to AM - RCS is currently using a route hosted by IG to sign the RCS consent decision JWTs. This route in IG needs to be removed for security reasons, any component that needs to sign a message should do so itself.
Design work:
- [x] Review which key RCS should be using f... | priority | fix rcs to sign consent decision jwts sent to am rcs is currently using a route hosted by ig to sign the rcs consent decision jwts this route in ig needs to be removed for security reasons any component that needs to sign a message should do so itself design work review which key rcs should be using for... | 1 |
281,170 | 8,692,018,542 | IssuesEvent | 2018-12-04 04:10:07 | AugurProject/augur | https://api.github.com/repos/AugurProject/augur | opened | Trade cost calculated incorrectly | 500013923 Bug Bugs Priority: Very High | A user reported that they are getting an incorrect estimated cost when filling out an order form. I was able to reproduce this on mainnet fairly easily as well.
The behavior seems to have something to do with ASK orders on the book which when taken by making the price appropriate to take the first order causes the pri... | 1.0 | Trade cost calculated incorrectly - A user reported that they are getting an incorrect estimated cost when filling out an order form. I was able to reproduce this on mainnet fairly easily as well.
The behavior seems to have something to do with ASK orders on the book which when taken by making the price appropriate to... | priority | trade cost calculated incorrectly a user reported that they are getting an incorrect estimated cost when filling out an order form i was able to reproduce this on mainnet fairly easily as well the behavior seems to have something to do with ask orders on the book which when taken by making the price appropriate to... | 1 |
432,989 | 30,304,353,225 | IssuesEvent | 2023-07-10 08:29:04 | celestiaorg/knuu | https://api.github.com/repos/celestiaorg/knuu | opened | Use `knuu.Initialize` instead of `knuu.InitializeWithIdentifier` in README to simplify example | documentation good first issue | This simplifies the example in the README to get started quicker. | 1.0 | Use `knuu.Initialize` instead of `knuu.InitializeWithIdentifier` in README to simplify example - This simplifies the example in the README to get started quicker. | non_priority | use knuu initialize instead of knuu initializewithidentifier in readme to simplify example this simplifies the example in the readme to get started quicker | 0 |
139,491 | 31,562,844,609 | IssuesEvent | 2023-09-03 13:08:44 | h4sh5/pypi-auto-scanner | https://api.github.com/repos/h4sh5/pypi-auto-scanner | opened | python-telegram-bot 20.5 has 1 GuardDog issues | guarddog code-execution | https://pypi.org/project/python-telegram-bot
https://inspector.pypi.io/project/python-telegram-bot
```{
"dependency": "python-telegram-bot",
"version": "20.5",
"result": {
"issues": 1,
"errors": {},
"results": {
"code-execution": [
{
"location": "python-telegram-bot-20.5/setup.... | 1.0 | python-telegram-bot 20.5 has 1 GuardDog issues - https://pypi.org/project/python-telegram-bot
https://inspector.pypi.io/project/python-telegram-bot
```{
"dependency": "python-telegram-bot",
"version": "20.5",
"result": {
"issues": 1,
"errors": {},
"results": {
"code-execution": [
{
... | non_priority | python telegram bot has guarddog issues dependency python telegram bot version result issues errors results code execution location python telegram bot setup py code subprocess run ... | 0 |
416,120 | 28,067,952,474 | IssuesEvent | 2023-03-29 16:49:14 | chakra-ui/chakra-ui-docs | https://api.github.com/repos/chakra-ui/chakra-ui-docs | closed | Add documentation for `hideFrom` and `hideBelow` helper props | needs triage Topic: Documentation 📚 | ### Subject
Styled System
### Description
I can see those props are implemented https://github.com/chakra-ui/chakra-ui/blob/main/packages/core/styled-system/src/config/layout.ts#L26 but they are missing documentation. | 1.0 | Add documentation for `hideFrom` and `hideBelow` helper props - ### Subject
Styled System
### Description
I can see those props are implemented https://github.com/chakra-ui/chakra-ui/blob/main/packages/core/styled-system/src/config/layout.ts#L26 but they are missing documentation. | non_priority | add documentation for hidefrom and hidebelow helper props subject styled system description i can see those props are implemented but they are missing documentation | 0 |
205,167 | 7,094,339,518 | IssuesEvent | 2018-01-13 01:51:50 | NuGet/Home | https://api.github.com/repos/NuGet/Home | closed | Signing: add test for basic signed CMS signature | Area:PackageSigning Priority:0 | We need a test verifying a package signed with neither an author or repository signature. | 1.0 | Signing: add test for basic signed CMS signature - We need a test verifying a package signed with neither an author or repository signature. | priority | signing add test for basic signed cms signature we need a test verifying a package signed with neither an author or repository signature | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.