Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
43,262 | 7,035,159,488 | IssuesEvent | 2017-12-27 21:33:07 | vuematerial/vue-material | https://api.github.com/repos/vuematerial/vue-material | closed | [Docs] async / await for example | documentation | ### Steps to reproduce
Write a method in any example format like this:
```javascript
async onSelect (val) {
}
```
### Which browser?
`vue-material@vue-material@1.0.0-beta-7`
Chrome 63.0.3239.108 (64bit) on Xubuntu
### What is expected?
Transformed into `onSelect: async function onSelect (val) {`... | 1.0 | [Docs] async / await for example - ### Steps to reproduce
Write a method in any example format like this:
```javascript
async onSelect (val) {
}
```
### Which browser?
`vue-material@vue-material@1.0.0-beta-7`
Chrome 63.0.3239.108 (64bit) on Xubuntu
### What is expected?
Transformed into `onSelec... | non_priority | async await for example steps to reproduce write a method in any example format like this javascript async onselect val which browser vue material vue material beta chrome on xubuntu what is expected transformed into onselect async functi... | 0 |
7,811 | 2,934,884,290 | IssuesEvent | 2015-06-30 11:28:41 | UnifiedViews/Plugins | https://api.github.com/repos/UnifiedViews/Plugins | closed | T-RdfToFiles - RDF format could be "Auto" options in dialog | priority: Normal resolution: invalid severity: enhancement status: ready for test |

so that a user doesn't have to set this parameter explicitly. | 1.0 | T-RdfToFiles - RDF format could be "Auto" options in dialog -

so that a user doesn't have to set this parameter explicitly. | non_priority | t rdftofiles rdf format could be auto options in dialog so that a user doesn t have to set this parameter explicitly | 0 |
75,842 | 3,476,550,374 | IssuesEvent | 2015-12-27 01:32:29 | joflashstudios/PGB | https://api.github.com/repos/joflashstudios/PGB | closed | Directory Scanner doesn't always catch UnauthorizedAccessException | bug high priority | Catch, but only one re-try, further down tryless calls to NextDirectory, etc. | 1.0 | Directory Scanner doesn't always catch UnauthorizedAccessException - Catch, but only one re-try, further down tryless calls to NextDirectory, etc. | priority | directory scanner doesn t always catch unauthorizedaccessexception catch but only one re try further down tryless calls to nextdirectory etc | 1 |
769,563 | 27,011,836,868 | IssuesEvent | 2023-02-10 15:59:24 | MartinXPN/profound.academy | https://api.github.com/repos/MartinXPN/profound.academy | closed | Change the AI Assistant to generate suggestions on what to change | enhancement priority/top | Change the AI Assistant to generate suggestions on what to change in the code.
* Modify the prompt
* Do not execute multiple suggestions on `LambdaJudge`
* Get 1 suggestion right from the model and show it to the user
This will make running the AI Assistant 3x cheaper and 2x faster.
Running the code on `LambdaJu... | 1.0 | Change the AI Assistant to generate suggestions on what to change - Change the AI Assistant to generate suggestions on what to change in the code.
* Modify the prompt
* Do not execute multiple suggestions on `LambdaJudge`
* Get 1 suggestion right from the model and show it to the user
This will make running the A... | priority | change the ai assistant to generate suggestions on what to change change the ai assistant to generate suggestions on what to change in the code modify the prompt do not execute multiple suggestions on lambdajudge get suggestion right from the model and show it to the user this will make running the a... | 1 |
187,584 | 6,759,356,769 | IssuesEvent | 2017-10-24 16:49:56 | ariogato/Koramu | https://api.github.com/repos/ariogato/Koramu | closed | Speichern | difficulty:advanced priority:high | Im Pausemenü hat der Benutzer die Option zu speichern ("Save").
Ein Klick darauf soll die Speicherung des aktuellen Stands des Spiels (in einer xml-Datei) bewirken.
Dieser gespeicherte Stand soll das nächste mal, wenn der Spieler auf "Play" drückt geladen werden.
Dies soll ein Fortschreiten in der Story ermögliche... | 1.0 | Speichern - Im Pausemenü hat der Benutzer die Option zu speichern ("Save").
Ein Klick darauf soll die Speicherung des aktuellen Stands des Spiels (in einer xml-Datei) bewirken.
Dieser gespeicherte Stand soll das nächste mal, wenn der Spieler auf "Play" drückt geladen werden.
Dies soll ein Fortschreiten in der Stor... | priority | speichern im pausemenü hat der benutzer die option zu speichern save ein klick darauf soll die speicherung des aktuellen stands des spiels in einer xml datei bewirken dieser gespeicherte stand soll das nächste mal wenn der spieler auf play drückt geladen werden dies soll ein fortschreiten in der stor... | 1 |
169,539 | 20,841,777,630 | IssuesEvent | 2022-03-21 01:30:38 | uniquelyparticular/serverless-oauth | https://api.github.com/repos/uniquelyparticular/serverless-oauth | opened | CVE-2022-24772 (High) detected in node-forge-0.8.4.tgz, node-forge-0.7.4.tgz | security vulnerability | ## CVE-2022-24772 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-forge-0.8.4.tgz</b>, <b>node-forge-0.7.4.tgz</b></p></summary>
<p>
<details><summary><b>node-forge-0.8.4.tgz</b... | True | CVE-2022-24772 (High) detected in node-forge-0.8.4.tgz, node-forge-0.7.4.tgz - ## CVE-2022-24772 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-forge-0.8.4.tgz</b>, <b>node-forg... | non_priority | cve high detected in node forge tgz node forge tgz cve high severity vulnerability vulnerable libraries node forge tgz node forge tgz node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and ... | 0 |
49,602 | 3,003,708,046 | IssuesEvent | 2015-07-25 05:52:08 | jayway/powermock | https://api.github.com/repos/jayway/powermock | opened | PowerMock is of no use for code coverage | bug imported Priority-Medium | _From [srika....@gmail.com](https://code.google.com/u/109015946327936505335/) on March 21, 2014 08:12:16_
What steps will reproduce the problem? 1.Write a succesful testcase using PowerMock
2.Run maven command for cobertura report (or Sonar even)
3.Open cobertura report to see if code is covered What is the expected... | 1.0 | PowerMock is of no use for code coverage - _From [srika....@gmail.com](https://code.google.com/u/109015946327936505335/) on March 21, 2014 08:12:16_
What steps will reproduce the problem? 1.Write a succesful testcase using PowerMock
2.Run maven command for cobertura report (or Sonar even)
3.Open cobertura report to ... | priority | powermock is of no use for code coverage from on march what steps will reproduce the problem write a succesful testcase using powermock run maven command for cobertura report or sonar even open cobertura report to see if code is covered what is the expected output what do you see instead... | 1 |
778,894 | 27,332,989,260 | IssuesEvent | 2023-02-25 21:36:09 | noisy/portfolio | https://api.github.com/repos/noisy/portfolio | opened | Projects's descriptions are partially or fully covered on sliding hover effect (from top) | bug Priority: Low | Project's description is partially or fully covered on sliding hover effect when you hover a project's thumbnail (from top side). It looks differently on different widths, but almost always something is missing from description. Fine is only between 768px and 992px width. It could be fixed together with #19.
Steps:
... | 1.0 | Projects's descriptions are partially or fully covered on sliding hover effect (from top) - Project's description is partially or fully covered on sliding hover effect when you hover a project's thumbnail (from top side). It looks differently on different widths, but almost always something is missing from description.... | priority | projects s descriptions are partially or fully covered on sliding hover effect from top project s description is partially or fully covered on sliding hover effect when you hover a project s thumbnail from top side it looks differently on different widths but almost always something is missing from description ... | 1 |
703,082 | 24,146,261,495 | IssuesEvent | 2022-09-21 19:02:27 | rokwire/illinois-app | https://api.github.com/repos/rokwire/illinois-app | closed | [ACCESSIBILITY] Today's Wellness tip colors not meeting contrast ratio | Type: Accessibility Priority: High | Describe the accessibility issue
The white on orange is not meeting contrast standards.
[WCAG 1.4.3 Contrast (minimum) (AA)](https://www.w3.org/TR/WCAG21/#contrast-minimum)
To Reproduce
Steps to reproduce the behavior:
Launch app
Upon reaching the Wellness area of app there is "Today's wellness tip" in white ... | 1.0 | [ACCESSIBILITY] Today's Wellness tip colors not meeting contrast ratio - Describe the accessibility issue
The white on orange is not meeting contrast standards.
[WCAG 1.4.3 Contrast (minimum) (AA)](https://www.w3.org/TR/WCAG21/#contrast-minimum)
To Reproduce
Steps to reproduce the behavior:
Launch app
Upon re... | priority | today s wellness tip colors not meeting contrast ratio describe the accessibility issue the white on orange is not meeting contrast standards to reproduce steps to reproduce the behavior launch app upon reaching the wellness area of app there is today s wellness tip in white on orange colors ... | 1 |
56,522 | 3,080,196,197 | IssuesEvent | 2015-08-21 20:38:33 | pavel-pimenov/flylinkdc-r5xx | https://api.github.com/repos/pavel-pimenov/flylinkdc-r5xx | closed | Зависание MediaInfo на некоторых файлах. | bug Component-Logic Component-MediaInfo imported Priority-Medium | _From [a.rain...@gmail.com](https://code.google.com/u/117892482479228821242/) on March 20, 2012 10:12:03_
В версии r502 -beta6 build 9479 MediaInfo входит в бесконечный цикл на файле magnet:?xt=urn:tree:tiger:YLAV4JILJOWHXKIZSOOXBRPLIYP64LE5O7BUPMQ&xl=254684390&dn=Probki(divx).avi
p.s: программа не закрывается, при... | 1.0 | Зависание MediaInfo на некоторых файлах. - _From [a.rain...@gmail.com](https://code.google.com/u/117892482479228821242/) on March 20, 2012 10:12:03_
В версии r502 -beta6 build 9479 MediaInfo входит в бесконечный цикл на файле magnet:?xt=urn:tree:tiger:YLAV4JILJOWHXKIZSOOXBRPLIYP64LE5O7BUPMQ&xl=254684390&dn=Probki(divx... | priority | зависание mediainfo на некоторых файлах from on march в версии build mediainfo входит в бесконечный цикл на файле magnet xt urn tree tiger xl dn probki divx avi p s программа не закрывается приходится убивать через диспетчер p p s самомe чинить лень original issue | 1 |
234,599 | 18,009,829,947 | IssuesEvent | 2021-09-16 07:14:35 | pdf-association/pdf-issues | https://api.github.com/repos/pdf-association/pdf-issues | closed | Table 145 additional entries for transparency group attributes dict is unclear which dict(s) these are additional to | bug documentation help wanted | Table 145 "Additional entries specific to a transparency group attributes dictionary" is unclear which dictionary(s) these keys are additional to. Furthermore, do all the requirements from whatever the 'base' dictionary is then still hold for a transparency group attributes dictionary???
The text between 11.6.6 "Tra... | 1.0 | Table 145 additional entries for transparency group attributes dict is unclear which dict(s) these are additional to - Table 145 "Additional entries specific to a transparency group attributes dictionary" is unclear which dictionary(s) these keys are additional to. Furthermore, do all the requirements from whatever the... | non_priority | table additional entries for transparency group attributes dict is unclear which dict s these are additional to table additional entries specific to a transparency group attributes dictionary is unclear which dictionary s these keys are additional to furthermore do all the requirements from whatever the ba... | 0 |
18,474 | 4,274,551,640 | IssuesEvent | 2016-07-13 20:52:42 | tdwg/vocab | https://api.github.com/repos/tdwg/vocab | closed | Does TDWG have a web page that contains copyright, licensing, and disclamer statements? | documentation | The previous draft documentation spec said the footer should contain "A reference or link to a document containing the Copyright, Licensing and Disclaimer statements that govern this document. This will usually be the standard one supplied by TDWG". Does TDWG have this? If so, where is it? Should we require the link... | 1.0 | Does TDWG have a web page that contains copyright, licensing, and disclamer statements? - The previous draft documentation spec said the footer should contain "A reference or link to a document containing the Copyright, Licensing and Disclaimer statements that govern this document. This will usually be the standard one... | non_priority | does tdwg have a web page that contains copyright licensing and disclamer statements the previous draft documentation spec said the footer should contain a reference or link to a document containing the copyright licensing and disclaimer statements that govern this document this will usually be the standard one... | 0 |
19,843 | 10,427,055,824 | IssuesEvent | 2019-09-16 19:01:28 | gandrade/assessment | https://api.github.com/repos/gandrade/assessment | opened | CVE-2019-14379 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-14379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14379 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-14379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm assessment pom xml ... | 0 |
106,125 | 16,665,005,837 | IssuesEvent | 2021-06-07 01:01:42 | AlexRogalskiy/quotes | https://api.github.com/repos/AlexRogalskiy/quotes | opened | CVE-2020-28469 (Medium) detected in glob-parent-5.1.1.tgz | security vulnerability | ## CVE-2020-28469 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home... | True | CVE-2020-28469 (Medium) detected in glob-parent-5.1.1.tgz - ## CVE-2020-28469 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the n... | non_priority | cve medium detected in glob parent tgz cve medium severity vulnerability vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file quotes package json path to vulnerable library quotes no... | 0 |
1,907 | 3,421,702,454 | IssuesEvent | 2015-12-08 19:52:00 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | opened | System.ArgumentNullException in Binaries\Debug\RunTests.exe | Area-Infrastructure Contributor Pain | The error occured in:
http://dotnet-ci.cloudapp.net/job/roslyn_prtest_win_dbg_unit32/1882/
Here's the stacktrace
```
11:33:13 Unhandled Exception: System.AggregateException: One or more errors occurred. ---> System.ArgumentNullException: Value cannot be null.
11:33:13 Parameter name: path1
11:33:13 at ... | 1.0 | System.ArgumentNullException in Binaries\Debug\RunTests.exe - The error occured in:
http://dotnet-ci.cloudapp.net/job/roslyn_prtest_win_dbg_unit32/1882/
Here's the stacktrace
```
11:33:13 Unhandled Exception: System.AggregateException: One or more errors occurred. ---> System.ArgumentNullException: Value cannot... | non_priority | system argumentnullexception in binaries debug runtests exe the error occured in here s the stacktrace unhandled exception system aggregateexception one or more errors occurred system argumentnullexception value cannot be null parameter name at system io path com... | 0 |
76,740 | 21,562,992,540 | IssuesEvent | 2022-05-01 12:55:02 | haskell/cabal | https://api.github.com/repos/haskell/cabal | closed | Package sections in cabal.project are insufficient, need local section | type: enhancement cabal-install: nix-local-build attention: pr-welcome re: project-file | I'm working on a project and I want to turn on `-Werror`. OK, I'll add `ghc-options: -Werror` to my `cabal.project`. BUT WAIT, this turns on `-Werror` for all my dependencies too. Well, the package I'm building is called `Cabal`, so I'll put it in a package section `package Cabal`.
BUT WAIT: setup dependencies cause... | 1.0 | Package sections in cabal.project are insufficient, need local section - I'm working on a project and I want to turn on `-Werror`. OK, I'll add `ghc-options: -Werror` to my `cabal.project`. BUT WAIT, this turns on `-Werror` for all my dependencies too. Well, the package I'm building is called `Cabal`, so I'll put it in... | non_priority | package sections in cabal project are insufficient need local section i m working on a project and i want to turn on werror ok i ll add ghc options werror to my cabal project but wait this turns on werror for all my dependencies too well the package i m building is called cabal so i ll put it in... | 0 |
119,424 | 10,052,820,478 | IssuesEvent | 2019-07-21 11:43:07 | tgstation/tgstation | https://api.github.com/repos/tgstation/tgstation | closed | Shuttles have no atmosphere | Atmospherics Bug Priority: CRITICAL Tested/Reproduced | Issue reported from Round ID: 113532 (/tg/Station Terry [EU] [100% LAG FREE] [New-Dedi])
Reporting client version: 512.1471
they dont have an atmosphere. its the same Thing on the 2 rounds before that.
you also cant create one if you vent canisters into them. the gas just disappears.
my assumption is that th... | 1.0 | Shuttles have no atmosphere - Issue reported from Round ID: 113532 (/tg/Station Terry [EU] [100% LAG FREE] [New-Dedi])
Reporting client version: 512.1471
they dont have an atmosphere. its the same Thing on the 2 rounds before that.
you also cant create one if you vent canisters into them. the gas just disappear... | non_priority | shuttles have no atmosphere issue reported from round id tg station terry reporting client version they dont have an atmosphere its the same thing on the rounds before that you also cant create one if you vent canisters into them the gas just disappears my assumption is that the shut... | 0 |
55,542 | 11,447,622,494 | IssuesEvent | 2020-02-06 00:23:47 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Poor loop optimization in BilinearInterpol benchmark | area-CodeGen tenet-performance | The `Vector<T>` version of this benchmark (`BilinearInterpol_Vector`) has a number of weaknesses:
First, although the temporary array `doubleTemp` is allocated with a constant length:
```
STMT00015 (IL 0x0AD... ???)
[000113] -ACXG------- * ASG ref
[000112] D-... | 1.0 | Poor loop optimization in BilinearInterpol benchmark - The `Vector<T>` version of this benchmark (`BilinearInterpol_Vector`) has a number of weaknesses:
First, although the temporary array `doubleTemp` is allocated with a constant length:
```
STMT00015 (IL 0x0AD... ???)
[000113] -ACXG------- ... | non_priority | poor loop optimization in bilinearinterpol benchmark the vector version of this benchmark bilinearinterpol vector has a number of weaknesses first although the temporary array doubletemp is allocated with a constant length il acxg asg ... | 0 |
603,465 | 18,667,391,793 | IssuesEvent | 2021-10-30 03:32:41 | AY2122S1-CS2113T-T12-1/tp | https://api.github.com/repos/AY2122S1-CS2113T-T12-1/tp | closed | Add assertions helper class for model | type.Task priority.Medium | - Can create assertions for expiry to put inside forex and crypto constructors
- Can create assertions for instrumentManager index within bounds | 1.0 | Add assertions helper class for model - - Can create assertions for expiry to put inside forex and crypto constructors
- Can create assertions for instrumentManager index within bounds | priority | add assertions helper class for model can create assertions for expiry to put inside forex and crypto constructors can create assertions for instrumentmanager index within bounds | 1 |
484,883 | 13,958,605,890 | IssuesEvent | 2020-10-24 12:47:26 | AY2021S1-CS2103-T16-3/tp | https://api.github.com/repos/AY2021S1-CS2103-T16-3/tp | closed | As an OHS admin I can archive the current Semester's data | priority.Medium type.Story | ... so that I can keep the data for auditing purposes, but not have it distract me while dealing with the current semester. | 1.0 | As an OHS admin I can archive the current Semester's data - ... so that I can keep the data for auditing purposes, but not have it distract me while dealing with the current semester. | priority | as an ohs admin i can archive the current semester s data so that i can keep the data for auditing purposes but not have it distract me while dealing with the current semester | 1 |
682,792 | 23,357,905,057 | IssuesEvent | 2022-08-10 09:04:37 | apache/incubator-devlake | https://api.github.com/repos/apache/incubator-devlake | closed | [Feature][config-ui] config-ui new user flow stage 2 | type/feature-request priority/high type/epic | ### Description
## Hide passwords/tokens from connection settings pages (BE/FE)
1. #2423 @warren830
2. #2384
3. #1908
`config-ui` github connection would call `TestConnection` for each token and print out `username` for them if succeeded, or an error message in red. For other plugins, making the input f... | 1.0 | [Feature][config-ui] config-ui new user flow stage 2 - ### Description
## Hide passwords/tokens from connection settings pages (BE/FE)
1. #2423 @warren830
2. #2384
3. #1908
`config-ui` github connection would call `TestConnection` for each token and print out `username` for them if succeeded, or an erro... | priority | config ui new user flow stage description hide passwords tokens from connection settings pages be fe config ui github connection would call testconnection for each token and print out username for them if succeeded or an error message in red for other plugins... | 1 |
150,348 | 11,957,319,893 | IssuesEvent | 2020-04-04 14:00:15 | RobertBeaudenon/SOEN390-CampusGuideMap | https://api.github.com/repos/RobertBeaudenon/SOEN390-CampusGuideMap | closed | AT-17: Provide side menu to access app features | Acceptance Test | ### Test Case ID: AT-17
### User Story: CC-65 (#65)
As a user, I want to be able to use a side menu so that I can easily access the various functionalities of the application.
### Acceptance Criteria
Given that the user has launched the application and completed viewing the splash screen,
The user should be... | 1.0 | AT-17: Provide side menu to access app features - ### Test Case ID: AT-17
### User Story: CC-65 (#65)
As a user, I want to be able to use a side menu so that I can easily access the various functionalities of the application.
### Acceptance Criteria
Given that the user has launched the application and completed... | non_priority | at provide side menu to access app features test case id at user story cc as a user i want to be able to use a side menu so that i can easily access the various functionalities of the application acceptance criteria given that the user has launched the application and completed vie... | 0 |
43,012 | 23,074,659,242 | IssuesEvent | 2022-07-25 21:48:07 | JuliaGPU/AMDGPU.jl | https://api.github.com/repos/JuliaGPU/AMDGPU.jl | closed | Add option to disable automatic mark/wait of specific arrays | good first issue performance | Since arrays may not actually be modified by a given operation, or might only be partially modified (or the user has some other way to ensure correctness). | True | Add option to disable automatic mark/wait of specific arrays - Since arrays may not actually be modified by a given operation, or might only be partially modified (or the user has some other way to ensure correctness). | non_priority | add option to disable automatic mark wait of specific arrays since arrays may not actually be modified by a given operation or might only be partially modified or the user has some other way to ensure correctness | 0 |
206,445 | 16,042,369,038 | IssuesEvent | 2021-04-22 09:28:19 | reclosedev/requests-cache | https://api.github.com/repos/reclosedev/requests-cache | closed | Add Readthedocs maintainers | documentation | Hi @reclosedev, would you be willing to add myself (https://readthedocs.org/profiles/JWCook/) and @skorokithakis (https://readthedocs.org/profiles/stavrosk/) as maintainers for the requests-cache project on Readthedocs?
I would like to add some [automation rules](https://docs.readthedocs.io/en/stable/automation-rule... | 1.0 | Add Readthedocs maintainers - Hi @reclosedev, would you be willing to add myself (https://readthedocs.org/profiles/JWCook/) and @skorokithakis (https://readthedocs.org/profiles/stavrosk/) as maintainers for the requests-cache project on Readthedocs?
I would like to add some [automation rules](https://docs.readthedoc... | non_priority | add readthedocs maintainers hi reclosedev would you be willing to add myself and skorokithakis as maintainers for the requests cache project on readthedocs i would like to add some for things like publishing to stable on git tags so users don t see in development changes there making multi... | 0 |
40,483 | 12,798,606,787 | IssuesEvent | 2020-07-02 14:10:50 | TreyM-WSS/awesome-go | https://api.github.com/repos/TreyM-WSS/awesome-go | opened | WS-2015-0020 (High) detected in marked-0.3.6.js | security vulnerability | ## WS-2015-0020 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.6.js</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://cdnjs.... | True | WS-2015-0020 (High) detected in marked-0.3.6.js - ## WS-2015-0020 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.6.js</b></p></summary>
<p>A markdown parser built for speed... | non_priority | ws high detected in marked js ws high severity vulnerability vulnerable library marked js a markdown parser built for speed library home page a href path to dependency file tmp ws scm awesome go tmpl tmpl html path to vulnerable library awesome go tmpl assets marke... | 0 |
4,924 | 2,566,262,677 | IssuesEvent | 2015-02-08 10:11:05 | bitsuperlab/bitshares_play | https://api.github.com/repos/bitsuperlab/bitshares_play | closed | Support import bts json wallet, for claiming bts snapshot, generate a new genesis | high priority new feature | Other than pts/btc, we need a new import support for bts | 1.0 | Support import bts json wallet, for claiming bts snapshot, generate a new genesis - Other than pts/btc, we need a new import support for bts | priority | support import bts json wallet for claiming bts snapshot generate a new genesis other than pts btc we need a new import support for bts | 1 |
21,737 | 3,549,126,706 | IssuesEvent | 2016-01-20 16:52:22 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | incremental analysis puts warnings in the wrong location after editing super call | area-analyzer Priority-Medium Type-Defect | To reproduce, paste into Atom:
```
abstract class Coercion {
Coercion(fromType, toType);
}
class CoercionError extends Coercion {
CoercionError() : super(null, null);
}
abstract class CoercionInfo {
static const String _propertyName = 'dev_compiler.src.info.CoercionInfo';
}
```
There should be a... | 1.0 | incremental analysis puts warnings in the wrong location after editing super call - To reproduce, paste into Atom:
```
abstract class Coercion {
Coercion(fromType, toType);
}
class CoercionError extends Coercion {
CoercionError() : super(null, null);
}
abstract class CoercionInfo {
static const Str... | non_priority | incremental analysis puts warnings in the wrong location after editing super call to reproduce paste into atom abstract class coercion coercion fromtype totype class coercionerror extends coercion coercionerror super null null abstract class coercioninfo static const str... | 0 |
737,738 | 25,529,358,762 | IssuesEvent | 2022-11-29 06:53:33 | rstudio/gt | https://api.github.com/repos/rstudio/gt | closed | Setting Custom Themes for Tables | Difficulty: [2] Intermediate Effort: [3] High Priority: [2] Medium Type: ★ Enhancement | Is it be possible to set a custom `gt` theme like you can do using `ggplot2::theme`? The thought would be to set up consistently used parameters. For me that would be something to the effect of:
```
df %>%
gt() %>%
fmt_currency(
columns = (matches("^salary|^revenue")),
decimals = 0
) %>%
... | 1.0 | Setting Custom Themes for Tables - Is it be possible to set a custom `gt` theme like you can do using `ggplot2::theme`? The thought would be to set up consistently used parameters. For me that would be something to the effect of:
```
df %>%
gt() %>%
fmt_currency(
columns = (matches("^salary|^revenue"... | priority | setting custom themes for tables is it be possible to set a custom gt theme like you can do using theme the thought would be to set up consistently used parameters for me that would be something to the effect of df gt fmt currency columns matches salary revenue ... | 1 |
211,150 | 23,792,972,172 | IssuesEvent | 2022-09-02 16:15:23 | HoloRes/suisei-bot | https://api.github.com/repos/HoloRes/suisei-bot | closed | CVE-2021-43138 (High) detected in async-2.6.3.tgz - autoclosed | security vulnerability | ## CVE-2021-43138 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>async-2.6.3.tgz</b></p></summary>
<p>Higher-order functions and common patterns for asynchronous code</p>
<p>Library h... | True | CVE-2021-43138 (High) detected in async-2.6.3.tgz - autoclosed - ## CVE-2021-43138 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>async-2.6.3.tgz</b></p></summary>
<p>Higher-order fun... | non_priority | cve high detected in async tgz autoclosed cve high severity vulnerability vulnerable library async tgz higher order functions and common patterns for asynchronous code library home page a href path to dependency file package json path to vulnerable library node m... | 0 |
705,312 | 24,230,843,145 | IssuesEvent | 2022-09-26 18:07:54 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Changelog file should have our own information | priority/P5 closed/stale | Changelog file should have our own information
See: https://github.com/brave/brave-browser/issues/12#issuecomment-402348033 | 1.0 | Changelog file should have our own information - Changelog file should have our own information
See: https://github.com/brave/brave-browser/issues/12#issuecomment-402348033 | priority | changelog file should have our own information changelog file should have our own information see | 1 |
216,722 | 7,311,193,020 | IssuesEvent | 2018-02-28 17:01:19 | craftercms/craftercms | https://api.github.com/repos/craftercms/craftercms | closed | [craftercms] Migrate.sh copies configured-lists to the wrong location | bug priority: medium | migrate.sh is copying configured-lists to form-control-config/configured-lists/configured-lists. | 1.0 | [craftercms] Migrate.sh copies configured-lists to the wrong location - migrate.sh is copying configured-lists to form-control-config/configured-lists/configured-lists. | priority | migrate sh copies configured lists to the wrong location migrate sh is copying configured lists to form control config configured lists configured lists | 1 |
623,187 | 19,662,832,717 | IssuesEvent | 2022-01-10 18:52:55 | nanaynaomi/multnomah-falls-research | https://api.github.com/repos/nanaynaomi/multnomah-falls-research | opened | Create new logo - check with Ingrid | medium priority low difficulty content | 1/10/2022
Create some various logo designs to replace the other logo and/or change the coloring of the old logo. Confirm with Ingrid before starting this. Once logo designs are created, show them to Ingrid to hear her thoughts on them and how we could change them to work with the site. | 1.0 | Create new logo - check with Ingrid - 1/10/2022
Create some various logo designs to replace the other logo and/or change the coloring of the old logo. Confirm with Ingrid before starting this. Once logo designs are created, show them to Ingrid to hear her thoughts on them and how we could change them to work with th... | priority | create new logo check with ingrid create some various logo designs to replace the other logo and or change the coloring of the old logo confirm with ingrid before starting this once logo designs are created show them to ingrid to hear her thoughts on them and how we could change them to work with the si... | 1 |
669,279 | 22,618,692,741 | IssuesEvent | 2022-06-30 02:44:15 | craftercms/craftercms | https://api.github.com/repos/craftercms/craftercms | closed | [studio-ui] Unsupported browsers should display a message that asks users to switch to a supported browser. | enhancement priority: high CI validate | ### Feature Request
#### Is your feature request related to a problem? Please describe.
Currently, when a user attempts to sign in to Crafter Studio on the Safari browser, they are introduced to an infinite "spinning wheel."
#### Describe the solution you'd like
Display a user-friendly message to tell users to... | 1.0 | [studio-ui] Unsupported browsers should display a message that asks users to switch to a supported browser. - ### Feature Request
#### Is your feature request related to a problem? Please describe.
Currently, when a user attempts to sign in to Crafter Studio on the Safari browser, they are introduced to an infinite... | priority | unsupported browsers should display a message that asks users to switch to a supported browser feature request is your feature request related to a problem please describe currently when a user attempts to sign in to crafter studio on the safari browser they are introduced to an infinite spinning... | 1 |
569 | 10,055,992,754 | IssuesEvent | 2019-07-22 08:05:13 | rice-solar-physics/group_webpage | https://api.github.com/repos/rice-solar-physics/group_webpage | opened | More information on past alumni | people | There is only information (e.g. current position, institution) available for a few alumni. Would look better to fill in the rest. | 1.0 | More information on past alumni - There is only information (e.g. current position, institution) available for a few alumni. Would look better to fill in the rest. | non_priority | more information on past alumni there is only information e g current position institution available for a few alumni would look better to fill in the rest | 0 |
65,210 | 7,866,887,500 | IssuesEvent | 2018-06-23 00:34:09 | merenlab/anvio | https://api.github.com/repos/merenlab/anvio | closed | rRNA HMM hits don't show up in the refine mode | design interface metagenomic workflow priority | Hi, using anvi'o v.4 here,
I just wanted to let the developers know that rRNA HMM hits don't show up in the anvi-refine mode (when they show-up nicely in anvi-interactvie mode). I think this "bug" has always been around. However, I apology if this has already been fixed in the master (I currently have issues using i... | 1.0 | rRNA HMM hits don't show up in the refine mode - Hi, using anvi'o v.4 here,
I just wanted to let the developers know that rRNA HMM hits don't show up in the anvi-refine mode (when they show-up nicely in anvi-interactvie mode). I think this "bug" has always been around. However, I apology if this has already been fix... | non_priority | rrna hmm hits don t show up in the refine mode hi using anvi o v here i just wanted to let the developers know that rrna hmm hits don t show up in the anvi refine mode when they show up nicely in anvi interactvie mode i think this bug has always been around however i apology if this has already been fix... | 0 |
257,347 | 8,136,196,095 | IssuesEvent | 2018-08-20 07:32:31 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | unifi.ubnt.com - site is not usable | browser-firefox priority-normal | <!-- @browser: Firefox 63.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:63.0) Gecko/20100101 Firefox/63.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @extra_labels: type-tracking-protection-basic -->
**URL**: https://unifi.ubnt.com/
**Browser / Version**: Firefox 63.0
**Operating System**... | 1.0 | unifi.ubnt.com - site is not usable - <!-- @browser: Firefox 63.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:63.0) Gecko/20100101 Firefox/63.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @extra_labels: type-tracking-protection-basic -->
**URL**: https://unifi.ubnt.com/
**Browser / Versio... | priority | unifi ubnt com site is not usable url browser version firefox operating system windows tested another browser yes problem type site is not usable description site fails to load app after logging in redirects to issue not present on other browsers or firefox ... | 1 |
204,644 | 7,089,571,581 | IssuesEvent | 2018-01-12 03:36:52 | dmwm/WMCore | https://api.github.com/repos/dmwm/WMCore | closed | Adapt WMCore OS/Arch requirements to Glidein proposed version | Medium Priority ToDo | See Stefano's talk for exact values. https://indico.cern.ch/event/293016/session/5/contribution/49/material/slides/0.pdf
Policy twiki to come, should be linked here when it does.
I inadvertently filed this in CRABServer and @belforte comments from there are reproduced below.
| 1.0 | Adapt WMCore OS/Arch requirements to Glidein proposed version - See Stefano's talk for exact values. https://indico.cern.ch/event/293016/session/5/contribution/49/material/slides/0.pdf
Policy twiki to come, should be linked here when it does.
I inadvertently filed this in CRABServer and @belforte comments from there ... | priority | adapt wmcore os arch requirements to glidein proposed version see stefano s talk for exact values policy twiki to come should be linked here when it does i inadvertently filed this in crabserver and belforte comments from there are reproduced below | 1 |
8,542 | 7,473,615,356 | IssuesEvent | 2018-04-03 15:50:16 | openscholar/openscholar | https://api.github.com/repos/openscholar/openscholar | closed | Debug Memory Leak | Infrastructure | Under load our AWS EC2 instances in elastic beanstalk where running out of memory.
There was a steady increase in memory till the machine locked up. We have a script for a greaceful restart of apache that free's up memory in this case but would like to fix the underlying issue if possible.
Also, we need to assur... | 1.0 | Debug Memory Leak - Under load our AWS EC2 instances in elastic beanstalk where running out of memory.
There was a steady increase in memory till the machine locked up. We have a script for a greaceful restart of apache that free's up memory in this case but would like to fix the underlying issue if possible.
Al... | non_priority | debug memory leak under load our aws instances in elastic beanstalk where running out of memory there was a steady increase in memory till the machine locked up we have a script for a greaceful restart of apache that free s up memory in this case but would like to fix the underlying issue if possible also... | 0 |
155,775 | 5,960,773,221 | IssuesEvent | 2017-05-29 15:01:30 | mkdo/kapow-grunt | https://api.github.com/repos/mkdo/kapow-grunt | opened | New Task: grunt-sass-globbing | Priority: Medium Status: Pending Type: Enhancement | It would be advantageous to introduce globbing so that certain folders in Kapow! Sass would automatically pick up when a new partial was introduced. | 1.0 | New Task: grunt-sass-globbing - It would be advantageous to introduce globbing so that certain folders in Kapow! Sass would automatically pick up when a new partial was introduced. | priority | new task grunt sass globbing it would be advantageous to introduce globbing so that certain folders in kapow sass would automatically pick up when a new partial was introduced | 1 |
285,813 | 8,774,925,795 | IssuesEvent | 2018-12-18 21:22:06 | pulumi/pulumi | https://api.github.com/repos/pulumi/pulumi | closed | Add pulumi.all operator to Python SDK | area/core customer/feedback language/python3 priority/P1 | Per @swgillespie, this combinator operator already exists in the JS SDK.
This is useful when you need to build an Output based on multiple Output instances.
Code snippet based on chat thread with @swgillespie:
`pulumi.all(arn1, arn2, arn3).apply(lambda arns: do_something_with_arns(arns))` | 1.0 | Add pulumi.all operator to Python SDK - Per @swgillespie, this combinator operator already exists in the JS SDK.
This is useful when you need to build an Output based on multiple Output instances.
Code snippet based on chat thread with @swgillespie:
`pulumi.all(arn1, arn2, arn3).apply(lambda arns: do_something_w... | priority | add pulumi all operator to python sdk per swgillespie this combinator operator already exists in the js sdk this is useful when you need to build an output based on multiple output instances code snippet based on chat thread with swgillespie pulumi all apply lambda arns do something with arns ... | 1 |
698,809 | 23,992,193,561 | IssuesEvent | 2022-09-14 02:55:12 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | reopened | [YSQL] Fix pg_stat_monitor tests | kind/bug area/ysql priority/medium | Jira Link: [DB-770](https://yugabyte.atlassian.net/browse/DB-770)
### Description
The following tests fail when upstream pg_stat_monitor version [0.9.0](https://github.com/percona/pg_stat_monitor/releases/tag/REL0_9_0_STABLE) is integrated with YB.
- [ ] yb_pg_error.sql
`ELECET * FROM unknown; -- syntax erro... | 1.0 | [YSQL] Fix pg_stat_monitor tests - Jira Link: [DB-770](https://yugabyte.atlassian.net/browse/DB-770)
### Description
The following tests fail when upstream pg_stat_monitor version [0.9.0](https://github.com/percona/pg_stat_monitor/releases/tag/REL0_9_0_STABLE) is integrated with YB.
- [ ] yb_pg_error.sql
`EL... | priority | fix pg stat monitor tests jira link description the following tests fail when upstream pg stat monitor version is integrated with yb yb pg error sql elecet from unknown syntax error when executed the following query select from pg stat monitor we see the following output... | 1 |
716,707 | 24,644,863,289 | IssuesEvent | 2022-10-17 14:12:54 | jellywallet/extension | https://api.github.com/repos/jellywallet/extension | closed | Check DFX staking prerequisites | Task: Feature Priority: High | There are two prerequisite to do staking with DFX:
- One buy or sell transactions completed
- KYC process completed
On the staking page:
- #17
- #14
If all the prerequisites are met show the regular staking page. | 1.0 | Check DFX staking prerequisites - There are two prerequisite to do staking with DFX:
- One buy or sell transactions completed
- KYC process completed
On the staking page:
- #17
- #14
If all the prerequisites are met show the regular staking page. | priority | check dfx staking prerequisites there are two prerequisite to do staking with dfx one buy or sell transactions completed kyc process completed on the staking page if all the prerequisites are met show the regular staking page | 1 |
28,188 | 6,964,040,182 | IssuesEvent | 2017-12-08 19:53:57 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | opened | JIT: x86 inconsistent behavior for overly long long shifts | area-CodeGen bug | Test cases added for #15291 and #15319 are failing on x86 because the behavior of overly long left shifts is inconsistent, depending on whether the jit optimizes or not.
The 15291 test is asserting that two different ways of shifting 1LL by 64 and then casting to Int32 give the same result.
In the first case the ... | 1.0 | JIT: x86 inconsistent behavior for overly long long shifts - Test cases added for #15291 and #15319 are failing on x86 because the behavior of overly long left shifts is inconsistent, depending on whether the jit optimizes or not.
The 15291 test is asserting that two different ways of shifting 1LL by 64 and then cas... | non_priority | jit inconsistent behavior for overly long long shifts test cases added for and are failing on because the behavior of overly long left shifts is inconsistent depending on whether the jit optimizes or not the test is asserting that two different ways of shifting by and then casting to give the ... | 0 |
302,304 | 26,138,658,677 | IssuesEvent | 2022-12-29 15:18:58 | oeg-upm/yarrrml-translator | https://api.github.com/repos/oeg-upm/yarrrml-translator | closed | Systematic testing | testing | Use Pytest and the current mappings in the folder test, to systematically test the engine.
| 1.0 | Systematic testing - Use Pytest and the current mappings in the folder test, to systematically test the engine.
| non_priority | systematic testing use pytest and the current mappings in the folder test to systematically test the engine | 0 |
706,803 | 24,284,237,170 | IssuesEvent | 2022-09-28 20:20:45 | Betarena/scores | https://api.github.com/repos/Betarena/scores | closed | Populate seasons from 21/22 Historic Fixtures | enhancement high priority | We will populate the data for the games widget (21/22). Populate the data of all seasons for those years.
This data will not use the cache to be visualized because it is sporadically accessed and does not justify using the upstash.
Using this logic, we should create the following method:
Only `current_seasons` from ... | 1.0 | Populate seasons from 21/22 Historic Fixtures - We will populate the data for the games widget (21/22). Populate the data of all seasons for those years.
This data will not use the cache to be visualized because it is sporadically accessed and does not justify using the upstash.
Using this logic, we should create the... | priority | populate seasons from historic fixtures we will populate the data for the games widget populate the data of all seasons for those years this data will not use the cache to be visualized because it is sporadically accessed and does not justify using the upstash using this logic we should create the fol... | 1 |
620,310 | 19,558,800,692 | IssuesEvent | 2022-01-03 13:32:22 | bounswe/2021SpringGroup1 | https://api.github.com/repos/bounswe/2021SpringGroup1 | closed | Planning on implementing privacy measures | Type: Research Priority: Medium Status: In Progress Platform: Backend | There exists a privacy setting for the current community models. However, we need to change our backend API to implement robust privacy measures. There is a built-in [Permission](https://www.django-rest-framework.org/api-guide/permissions/) module in REST framework that could be useful. We also need to discuss and fles... | 1.0 | Planning on implementing privacy measures - There exists a privacy setting for the current community models. However, we need to change our backend API to implement robust privacy measures. There is a built-in [Permission](https://www.django-rest-framework.org/api-guide/permissions/) module in REST framework that could... | priority | planning on implementing privacy measures there exists a privacy setting for the current community models however we need to change our backend api to implement robust privacy measures there is a built in module in rest framework that could be useful we also need to discuss and flesh out requirements based on... | 1 |
20,116 | 4,500,683,936 | IssuesEvent | 2016-09-01 06:18:57 | google/protobuf | https://api.github.com/repos/google/protobuf | opened | Regenerate C# API documentation | c# documentation | The docs at https://developers.google.com/protocol-buffers/docs/reference/csharp/ are slightly out of date. (Not by much - the public API hasn't changed very much.) We should regenerate them. | 1.0 | Regenerate C# API documentation - The docs at https://developers.google.com/protocol-buffers/docs/reference/csharp/ are slightly out of date. (Not by much - the public API hasn't changed very much.) We should regenerate them. | non_priority | regenerate c api documentation the docs at are slightly out of date not by much the public api hasn t changed very much we should regenerate them | 0 |
1,705 | 2,603,969,814 | IssuesEvent | 2015-02-24 18:59:58 | chrsmith/nishazi6 | https://api.github.com/repos/chrsmith/nishazi6 | opened | 沈阳阴茎长疙瘩怎么回事 | auto-migrated Priority-Medium Type-Defect | ```
沈阳阴茎长疙瘩怎么回事〓沈陽軍區政治部醫院性病〓TEL:02
4-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治療�
��位于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝�
��的歷史悠久、設備精良、技術權威、專家云集,是預防、保
健、醫療、科研康復為一體的綜合性醫院。是國家首批公立��
�等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學�
��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍
空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集��
�二等功。
```
-----
Original issue reported on code.google.com by `q96410... | 1.0 | 沈阳阴茎长疙瘩怎么回事 - ```
沈阳阴茎长疙瘩怎么回事〓沈陽軍區政治部醫院性病〓TEL:02
4-31023308〓成立于1946年,68年專注于性傳播疾病的研究和治療�
��位于沈陽市沈河區二緯路32號。是一所與新中國同建立共輝�
��的歷史悠久、設備精良、技術權威、專家云集,是預防、保
健、醫療、科研康復為一體的綜合性醫院。是國家首批公立��
�等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學�
��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍
空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集��
�二等功。
```
-----
Original issue reported on code.google.... | non_priority | 沈阳阴茎长疙瘩怎么回事 沈阳阴茎长疙瘩怎么回事〓沈陽軍區政治部醫院性病〓tel: 〓 , � �� 。是一所與新中國同建立共輝� ��的歷史悠久、設備精良、技術權威、專家云集,是預防、保 健、醫療、科研康復為一體的綜合性醫院。是國家首批公立�� �等部隊醫院、全國首批醫療規范定點單位,是第四軍醫大學� ��東南大學等知名高等院校的教學醫院。曾被中國人民解放軍 空軍后勤部衛生部評為衛生工作先進單位,先后兩次榮立集�� �二等功。 original issue reported on code google com by gmail com on jun at | 0 |
171,630 | 14,334,089,112 | IssuesEvent | 2020-11-27 07:25:15 | Huy-Ngo/skin-crawler | https://api.github.com/repos/Huy-Ngo/skin-crawler | opened | Tutorial report | documentation | 
# Skin cancer image crawler
>List of the members.
## 1 Introduction
>Maybe paraphrase the task.
## 2 Crawler
### 2.1 Crawler workflow
>Describe how and where we crawl the datasets
>Describe how the crawled datasets are given to the users.
>Describe how we link... | 1.0 | Tutorial report - 
# Skin cancer image crawler
>List of the members.
## 1 Introduction
>Maybe paraphrase the task.
## 2 Crawler
### 2.1 Crawler workflow
>Describe how and where we crawl the datasets
>Describe how the crawled datasets are given to the users.
>De... | non_priority | tutorial report skin cancer image crawler list of the members introduction maybe paraphrase the task crawler crawler workflow describe how and where we crawl the datasets describe how the crawled datasets are given to the users describe how we link everything together... | 0 |
509,016 | 14,710,734,339 | IssuesEvent | 2021-01-05 05:57:30 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | opened | Linking Steam to SLG doesn't work for a user | Category: Accounts Priority: Medium | `Doesnt link slg and steam account. Writes You do not own Eco, while the game was bought on Steam several years ago. I would like to link and change the icon. User ID: slg187377 Steam ID: STEAM_0:0:29674335 (SteamID64: 76561198019614398)` | 1.0 | Linking Steam to SLG doesn't work for a user - `Doesnt link slg and steam account. Writes You do not own Eco, while the game was bought on Steam several years ago. I would like to link and change the icon. User ID: slg187377 Steam ID: STEAM_0:0:29674335 (SteamID64: 76561198019614398)` | priority | linking steam to slg doesn t work for a user doesnt link slg and steam account writes you do not own eco while the game was bought on steam several years ago i would like to link and change the icon user id steam id steam | 1 |
50,439 | 13,529,187,533 | IssuesEvent | 2020-09-15 17:53:33 | Agoric/SES-shim | https://api.github.com/repos/Agoric/SES-shim | closed | Document limitation: `evaluate` leaks scopeProxy as `this` | security | Referencing https://github.com/tc39/proposal-realms/issues/173 from @erights:
See related https://github.com/tc39/proposal-realms/issues/171 https://github.com/tc39/proposal-realms/issues/172
All the own property names on the safeGlobal that are non-configurable, non-writable data properties are candidates for in... | True | Document limitation: `evaluate` leaks scopeProxy as `this` - Referencing https://github.com/tc39/proposal-realms/issues/173 from @erights:
See related https://github.com/tc39/proposal-realms/issues/171 https://github.com/tc39/proposal-realms/issues/172
All the own property names on the safeGlobal that are non-con... | non_priority | document limitation evaluate leaks scopeproxy as this referencing from erights see related all the own property names on the safeglobal that are non configurable non writable data properties are candidates for including in the optimizer s list of optimized variable name lookups these names are lo... | 0 |
493,088 | 14,225,917,209 | IssuesEvent | 2020-11-17 22:03:10 | internetarchive/openlibrary | https://api.github.com/repos/internetarchive/openlibrary | closed | Schema.org tags for authors | Good First Issue Lead: @tabshaikh Needs: Help Priority: 2 Theme: Distribution Theme: SEO Type: Feature Request hacktoberfest | <!-- What problem are we solving? What does the experience look like today? What are the symptoms? -->
When we search for **books by \<name\>** [https://www.google.com/search?q=books+by+mark+twain+openlibrary&oq=books+by+mark+twain+openlibrary](https://www.google.com/search?q=books+by+mark+twain+openlibrary&oq=books+... | 1.0 | Schema.org tags for authors - <!-- What problem are we solving? What does the experience look like today? What are the symptoms? -->
When we search for **books by \<name\>** [https://www.google.com/search?q=books+by+mark+twain+openlibrary&oq=books+by+mark+twain+openlibrary](https://www.google.com/search?q=books+by+ma... | priority | schema org tags for authors when we search for books by we are shown a search result as shown below but the author does not have schema markup so my proposal is to add person schema org tag to the author opportunity it could have search engine consequences for million of our author page... | 1 |
203,345 | 15,878,733,501 | IssuesEvent | 2021-04-09 11:27:30 | haxor-music/hxr-jam-live-11-public | https://api.github.com/repos/haxor-music/hxr-jam-live-11-public | closed | Improve Documentation for r1.0 | documentation | Improve documentation at Wiki for the release 1.0
- [x] install instructions
- [x] screenshots
- [x] LoadMode configuration | 1.0 | Improve Documentation for r1.0 - Improve documentation at Wiki for the release 1.0
- [x] install instructions
- [x] screenshots
- [x] LoadMode configuration | non_priority | improve documentation for improve documentation at wiki for the release install instructions screenshots loadmode configuration | 0 |
116,747 | 4,706,054,579 | IssuesEvent | 2016-10-13 16:03:09 | zom/Zom-iOS | https://api.github.com/repos/zom/Zom-iOS | opened | Make iMessage sticker pack! | high-priority | For Olo:
Yay!
Prayer
Eating (with tea)
Flower
Love
For Pema:
Tashi Delek
Cool
Don't Worry
Thank you
Sleeping
| 1.0 | Make iMessage sticker pack! - For Olo:
Yay!
Prayer
Eating (with tea)
Flower
Love
For Pema:
Tashi Delek
Cool
Don't Worry
Thank you
Sleeping
| priority | make imessage sticker pack for olo yay prayer eating with tea flower love for pema tashi delek cool don t worry thank you sleeping | 1 |
179,410 | 6,624,941,379 | IssuesEvent | 2017-09-22 13:46:00 | pmem/issues | https://api.github.com/repos/pmem/issues | closed | pmembench : removing directory fail | Exposure: Low OS: Linux Priority: 4 low State: To be verified Type: Bug | When trying to remove directory at the begging of scenario, an error is being printed:
removing file failed: No such file or directory
It is because a file name isn't zeroed in util_file_dir_next function, just overwritten by the new one. It causes that when on the list of subfolders are "." and "..", the second on... | 1.0 | pmembench : removing directory fail - When trying to remove directory at the begging of scenario, an error is being printed:
removing file failed: No such file or directory
It is because a file name isn't zeroed in util_file_dir_next function, just overwritten by the new one. It causes that when on the list of sub... | priority | pmembench removing directory fail when trying to remove directory at the begging of scenario an error is being printed removing file failed no such file or directory it is because a file name isn t zeroed in util file dir next function just overwritten by the new one it causes that when on the list of sub... | 1 |
590,260 | 17,775,171,757 | IssuesEvent | 2021-08-30 18:14:10 | literakl/mezinamiridici | https://api.github.com/repos/literakl/mezinamiridici | opened | Images revisited | type: enhancement priority: P2 | Uploaded pictures shall have a caption and author attributes.
The original picture must be preserved and new optimized pictures shall be generated for srcset attribute. Maybe webp format if it is widesp... | 1.0 | Images revisited - Uploaded pictures shall have a caption and author attributes.
The original picture must be preserved and new optimized pictures shall be generated for srcset attribute. Maybe webp for... | priority | images revisited uploaded pictures shall have a caption and author attributes the original picture must be preserved and new optimized pictures shall be generated for srcset attribute maybe webp format if it is widespread now largest served picture must be full hd dimension under mb | 1 |
103,997 | 22,552,185,200 | IssuesEvent | 2022-06-27 06:59:52 | dart-lang/site-www | https://api.github.com/repos/dart-lang/site-www | closed | Add null-aware operators to Null safety codelab | p1-high codelabs e1-hours e2-days null-safety | ### Page URL
https://dart.dev/codelabs/null-safety.html
### Page source
https://github.com/dart-lang/site-www/tree/main/src/codelabs/null-safety.md
### Describe the problem
Now that null safety has been out for a while, this codelab is more useful as a whole when understanding handling `null` values as a whole. We... | 1.0 | Add null-aware operators to Null safety codelab - ### Page URL
https://dart.dev/codelabs/null-safety.html
### Page source
https://github.com/dart-lang/site-www/tree/main/src/codelabs/null-safety.md
### Describe the problem
Now that null safety has been out for a while, this codelab is more useful as a whole when u... | non_priority | add null aware operators to null safety codelab page url page source describe the problem now that null safety has been out for a while this codelab is more useful as a whole when understanding handling null values as a whole we have the new strategies for dealing with null but not the pree... | 0 |
106,504 | 16,680,908,855 | IssuesEvent | 2021-06-07 23:33:04 | NuGet/NuGetGallery | https://api.github.com/repos/NuGet/NuGetGallery | closed | Determine delta re WhiteSource vs GitHub vulnerabilities, ascertain priority of including WhiteSource | Area: Security Pillar: Security | We don't see https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1469 in GitHub. How many others are there, and how many apply to NuGet.org packages? | True | Determine delta re WhiteSource vs GitHub vulnerabilities, ascertain priority of including WhiteSource - We don't see https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-1469 in GitHub. How many others are there, and how many apply to NuGet.org packages? | non_priority | determine delta re whitesource vs github vulnerabilities ascertain priority of including whitesource we don t see in github how many others are there and how many apply to nuget org packages | 0 |
57,077 | 11,707,994,534 | IssuesEvent | 2020-03-08 10:28:41 | KMRNicholson/nsld | https://api.github.com/repos/KMRNicholson/nsld | closed | Create Add/Edit/Del Meal View and Functionality | code-behind ui | Add a page for adding a meal to the current day, with the associated functionality for doing so.
Criteria:
- Meals will require the user to enter a name for the meal. | 1.0 | Create Add/Edit/Del Meal View and Functionality - Add a page for adding a meal to the current day, with the associated functionality for doing so.
Criteria:
- Meals will require the user to enter a name for the meal. | non_priority | create add edit del meal view and functionality add a page for adding a meal to the current day with the associated functionality for doing so criteria meals will require the user to enter a name for the meal | 0 |
763,212 | 26,747,519,973 | IssuesEvent | 2023-01-30 16:59:54 | MarketSquare/robotframework-browser | https://api.github.com/repos/MarketSquare/robotframework-browser | closed | [Bug] Get code completion for LibraryComponent.library does not work correctly | bug priority: medium | this is just a notice from RoboCon
If I rename__init__.pyi to browser.pyi it works for VSCode. | 1.0 | [Bug] Get code completion for LibraryComponent.library does not work correctly - this is just a notice from RoboCon
If I rename__init__.pyi to browser.pyi it works for VSCode. | priority | get code completion for librarycomponent library does not work correctly this is just a notice from robocon if i rename init pyi to browser pyi it works for vscode | 1 |
287,779 | 8,820,319,976 | IssuesEvent | 2019-01-01 10:57:11 | TwinePlatform/twine-visitor | https://api.github.com/repos/TwinePlatform/twine-visitor | closed | Layout issues on visits page using Firefox | bug priority-5 | I don't think this needs to be addressed in this sprint as we need to talk to PO to discuss what browsers/devices we are building for. Keeping this in an issue for future reference:
Layout for visits page is currently broken on firefox developer edition:
<img width="1022" alt="screen shot 2018-04-05 at 9 34 22 am... | 1.0 | Layout issues on visits page using Firefox - I don't think this needs to be addressed in this sprint as we need to talk to PO to discuss what browsers/devices we are building for. Keeping this in an issue for future reference:
Layout for visits page is currently broken on firefox developer edition:
<img width="10... | priority | layout issues on visits page using firefox i don t think this needs to be addressed in this sprint as we need to talk to po to discuss what browsers devices we are building for keeping this in an issue for future reference layout for visits page is currently broken on firefox developer edition img width ... | 1 |
696,108 | 23,885,013,774 | IssuesEvent | 2022-09-08 06:52:49 | DroidKaigi/conference-app-2022 | https://api.github.com/repos/DroidKaigi/conference-app-2022 | closed | add TagsLine in session detail Screen | welcome contribute high priority | **Idea Description**
use KaigiTag slot api
**Reference images and links**
Design
<img src="https://user-images.githubusercontent.com/60292683/188349438-4aacd5c9-aded-4be8-a9e4-48d00ff64dd8.png" width="300" >
Current app
<img width="382" alt="image" src="https://user-images.githubusercontent.com/1386930/1883619... | 1.0 | add TagsLine in session detail Screen - **Idea Description**
use KaigiTag slot api
**Reference images and links**
Design
<img src="https://user-images.githubusercontent.com/60292683/188349438-4aacd5c9-aded-4be8-a9e4-48d00ff64dd8.png" width="300" >
Current app
<img width="382" alt="image" src="https://user-imag... | priority | add tagsline in session detail screen idea description use kaigitag slot api reference images and links design current app img width alt image src design kit app design | 1 |
331,651 | 29,044,895,587 | IssuesEvent | 2023-05-13 12:34:02 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: X-Pack Case API Integration Tests.x-pack/test/cases_api_integration/security_and_spaces/tests/common/comments/delete_comment·ts - cases security and spaces enabled: basic Common delete_comment happy path should delete a comment | failed-test Team:ResponseOps | A test failed on a tracked branch
```
Error: expected 200 "OK", got 403 "Forbidden"
at Test._assertStatus (node_modules/supertest/lib/test.js:268:12)
at Test._assertFunction (node_modules/supertest/lib/test.js:283:11)
at Test.assert (node_modules/supertest/lib/test.js:173:18)
at localAssert (node_modul... | 1.0 | Failing test: X-Pack Case API Integration Tests.x-pack/test/cases_api_integration/security_and_spaces/tests/common/comments/delete_comment·ts - cases security and spaces enabled: basic Common delete_comment happy path should delete a comment - A test failed on a tracked branch
```
Error: expected 200 "OK", got 403 "Fo... | non_priority | failing test x pack case api integration tests x pack test cases api integration security and spaces tests common comments delete comment·ts cases security and spaces enabled basic common delete comment happy path should delete a comment a test failed on a tracked branch error expected ok got forbid... | 0 |
779,488 | 27,354,556,123 | IssuesEvent | 2023-02-27 11:57:37 | NFT-Limited/nf-bugs | https://api.github.com/repos/NFT-Limited/nf-bugs | opened | [FEATURE REQUEST] Hide onXRP preminted NFTs | feature request Priority 2 | **Is your feature request related to a problem? Please describe.**
If onXRP pre-mints the collection, it's becoming available in the app with broken data.
**Describe the solution yo... | 1.0 | [FEATURE REQUEST] Hide onXRP preminted NFTs - **Is your feature request related to a problem? Please describe.**
If onXRP pre-mints the collection, it's becoming available in the app with broken data.

As a user of VA.gov navigating with a screenreader, I need to know when multiple fields have a validation error so I can correct all the problems with the form.
_Example: As a VFS developer, I need to be able to create a custom error message for the XYZ form, so that I can implement the unique... | 1.0 | Multiple validation errors are not read out to screenreaders - ### User story(ies)
As a user of VA.gov navigating with a screenreader, I need to know when multiple fields have a validation error so I can correct all the problems with the form.
_Example: As a VFS developer, I need to be able to create a custom err... | non_priority | multiple validation errors are not read out to screenreaders user story ies as a user of va gov navigating with a screenreader i need to know when multiple fields have a validation error so i can correct all the problems with the form example as a vfs developer i need to be able to create a custom err... | 0 |
494,206 | 14,246,619,410 | IssuesEvent | 2020-11-19 10:18:42 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | Class Cast Exception thrown from node transformer | Area/Parser Priority/Blocker SwanLakeDump Team/CompilerFE Type/Bug | **Description:**
Consider the following source snippet,
```
import ballerina/java;
public type TypeDescName
function foo(string filePath) {
string [] columnHeaders = [];
boolean testBool = true;
if (testBool) {
}
}
```
When tries to compile, this throws the following CCE... | 1.0 | Class Cast Exception thrown from node transformer - **Description:**
Consider the following source snippet,
```
import ballerina/java;
public type TypeDescName
function foo(string filePath) {
string [] columnHeaders = [];
boolean testBool = true;
if (testBool) {
}
}
```
... | priority | class cast exception thrown from node transformer description consider the following source snippet import ballerina java public type typedescname function foo string filepath string columnheaders boolean testbool true if testbool wh... | 1 |
403,214 | 27,405,579,625 | IssuesEvent | 2023-03-01 06:23:14 | island-games/CommunityProject | https://api.github.com/repos/island-games/CommunityProject | opened | Main Story | documentation | We need someone to write a main story. The story must give the player a sense of purpose. This story does not need to be extremely detailed, biut at least do the following:
- Name an antagonist
- Give the player purpose for their adventure
- List notable NPCs the player will meet along the way
- Create a framewo... | 1.0 | Main Story - We need someone to write a main story. The story must give the player a sense of purpose. This story does not need to be extremely detailed, biut at least do the following:
- Name an antagonist
- Give the player purpose for their adventure
- List notable NPCs the player will meet along the way
- Cre... | non_priority | main story we need someone to write a main story the story must give the player a sense of purpose this story does not need to be extremely detailed biut at least do the following name an antagonist give the player purpose for their adventure list notable npcs the player will meet along the way cre... | 0 |
670,649 | 22,697,630,732 | IssuesEvent | 2022-07-05 07:47:55 | googleapis/python-spanner | https://api.github.com/repos/googleapis/python-spanner | closed | tests.system.test_dbapi: test_staleness failed | api: spanner type: bug priority: p2 flakybot: issue flakybot: flaky | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 5d8b0558f43a3505f62f9a8eae4228c91c6f0ada
b... | 1.0 | tests.system.test_dbapi: test_staleness failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
c... | priority | tests system test dbapi test staleness failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output shared instance dbapi database def t... | 1 |
8,455 | 5,716,641,441 | IssuesEvent | 2017-04-19 15:32:11 | edoddridge/aronnax | https://api.github.com/repos/edoddridge/aronnax | closed | Ship helpers for preparing common patterns of input | usability | I noticed when writing the repeatability test suite that the examples had repeated patterns in the input:
- f-plane Coriolis force field
- beta-plane Coriolis force field
- rectangular bordered pool geometry (i.e., the wetmask being all 1 except for a 1-cell border)
I think it's a good idea (in principle, no comm... | True | Ship helpers for preparing common patterns of input - I noticed when writing the repeatability test suite that the examples had repeated patterns in the input:
- f-plane Coriolis force field
- beta-plane Coriolis force field
- rectangular bordered pool geometry (i.e., the wetmask being all 1 except for a 1-cell bord... | non_priority | ship helpers for preparing common patterns of input i noticed when writing the repeatability test suite that the examples had repeated patterns in the input f plane coriolis force field beta plane coriolis force field rectangular bordered pool geometry i e the wetmask being all except for a cell bord... | 0 |
653,307 | 21,579,194,008 | IssuesEvent | 2022-05-02 16:47:51 | metabase/metabase | https://api.github.com/repos/metabase/metabase | closed | In the relative date picker, changing the granularity of the Past/Next range picker should change the granularity of the Starting From picker | Type:Bug Priority:P3 Querying/Parameters & Variables .Frontend Querying/GUI .bugbash | When I change the time granularity of the Past/Next option, e.g. from Days to Months, the granularity of the Starting From option doesn’t change to match, but is supposed to.
The reverse should not be true; i.e. changing the granularity of the “Starting from” option should not change the granularity of the Past/Nex... | 1.0 | In the relative date picker, changing the granularity of the Past/Next range picker should change the granularity of the Starting From picker - When I change the time granularity of the Past/Next option, e.g. from Days to Months, the granularity of the Starting From option doesn’t change to match, but is supposed to.
... | priority | in the relative date picker changing the granularity of the past next range picker should change the granularity of the starting from picker when i change the time granularity of the past next option e g from days to months the granularity of the starting from option doesn’t change to match but is supposed to ... | 1 |
384,035 | 26,573,354,177 | IssuesEvent | 2023-01-21 13:22:12 | scaleway/docs-content | https://api.github.com/repos/scaleway/docs-content | opened | 👩💻 Documentation Request: How to use Scaleway Container Registry with Github Actions | Documentation Request | ### Summary
How to configure and use Github Actions to build Docker images and push them into Scaleway Container Registry.
---
Outline:
- Configure a Container Registry namespace in Scaleway Console
- Retrieve credentials and store them securely in Github secrets
- Create a Github Action that connects to the Co... | 1.0 | 👩💻 Documentation Request: How to use Scaleway Container Registry with Github Actions - ### Summary
How to configure and use Github Actions to build Docker images and push them into Scaleway Container Registry.
---
Outline:
- Configure a Container Registry namespace in Scaleway Console
- Retrieve credentials a... | non_priority | 👩💻 documentation request how to use scaleway container registry with github actions summary how to configure and use github actions to build docker images and push them into scaleway container registry outline configure a container registry namespace in scaleway console retrieve credentials a... | 0 |
359,599 | 10,678,550,551 | IssuesEvent | 2019-10-21 17:30:11 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | Changing endpoint security configuration causes an error | 3.0.0 Priority/Highest Severity/Blocker | When endpoint security drop down is selected, following error is thrown
<img width="1075" alt="Screen Shot 2019-10-18 at 4 00 41 PM" src="https://user-images.githubusercontent.com/4861150/67088276-5bf14a00-f1c2-11e9-9634-87972cbc8cc5.png">
this is working in carbon.apimgt v6.5.282 but not working in v6.5.283 | 1.0 | Changing endpoint security configuration causes an error - When endpoint security drop down is selected, following error is thrown
<img width="1075" alt="Screen Shot 2019-10-18 at 4 00 41 PM" src="https://user-images.githubusercontent.com/4861150/67088276-5bf14a00-f1c2-11e9-9634-87972cbc8cc5.png">
this is working... | priority | changing endpoint security configuration causes an error when endpoint security drop down is selected following error is thrown img width alt screen shot at pm src this is working in carbon apimgt but not working in | 1 |
585,038 | 17,469,598,709 | IssuesEvent | 2021-08-06 23:32:48 | bcgov/entity | https://api.github.com/repos/bcgov/entity | closed | INC0089149 - NR - Extra Pro - Corp. Number not Found - Heredia Building Company Inc. | blocked Priority1 ENTITY OPS | #### ServiceNow incident:
INC0089149
#### Contact information
Staff Name: Not sure
#### Description
>Can you please assist with the request below? Patty had received a response from Bruce and updated INC0089149, it turned out not to be a NRO issue. As Bruce has confirmed this is an issue relating to Names Request can... | 1.0 | INC0089149 - NR - Extra Pro - Corp. Number not Found - Heredia Building Company Inc. - #### ServiceNow incident:
INC0089149
#### Contact information
Staff Name: Not sure
#### Description
>Can you please assist with the request below? Patty had received a response from Bruce and updated INC0089149, it turned out not t... | priority | nr extra pro corp number not found heredia building company inc servicenow incident contact information staff name not sure description can you please assist with the request below patty had received a response from bruce and updated it turned out not to be a nro issue as bruce ... | 1 |
280,503 | 30,828,293,387 | IssuesEvent | 2023-08-01 22:12:11 | snowdensb/redis | https://api.github.com/repos/snowdensb/redis | opened | CVE-2023-28859 (Medium) detected in redis-4.5.1-py3-none-any.whl | Mend: dependency security vulnerability | ## CVE-2023-28859 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis-4.5.1-py3-none-any.whl</b></p></summary>
<p>Python client for Redis database and key-value store</p>
<p>Librar... | True | CVE-2023-28859 (Medium) detected in redis-4.5.1-py3-none-any.whl - ## CVE-2023-28859 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>redis-4.5.1-py3-none-any.whl</b></p></summary>
<p... | non_priority | cve medium detected in redis none any whl cve medium severity vulnerability vulnerable library redis none any whl python client for redis database and key value store library home page a href path to dependency file utils req res validator requirements txt path t... | 0 |
264,095 | 8,305,145,876 | IssuesEvent | 2018-09-22 02:10:08 | RoboJackets/apiary | https://api.github.com/repos/RoboJackets/apiary | closed | CAS_AuthenticationException in GET / | area / backend priority / low type / bug | ## Error in Apiary
**CAS_AuthenticationException** in **GET /**
[View on Bugsnag](https://app.bugsnag.com/robojackets/apiary/errors/59de356e05c209001ac6194c?event_id=59e01bad55dccc001c6b7e66&i=gh&m=ci)
## Stacktrace
app/Http/Middleware/CASAuthenticate.php:38 - App\Http\Middleware\CASAuthenticate::handle
[View... | 1.0 | CAS_AuthenticationException in GET / - ## Error in Apiary
**CAS_AuthenticationException** in **GET /**
[View on Bugsnag](https://app.bugsnag.com/robojackets/apiary/errors/59de356e05c209001ac6194c?event_id=59e01bad55dccc001c6b7e66&i=gh&m=ci)
## Stacktrace
app/Http/Middleware/CASAuthenticate.php:38 - App\Http\Mi... | priority | cas authenticationexception in get error in apiary cas authenticationexception in get stacktrace app http middleware casauthenticate php app http middleware casauthenticate handle created by robojackets admin via bugsnag | 1 |
542,306 | 15,858,425,954 | IssuesEvent | 2021-04-08 06:41:31 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | Websocket API topic description not getting saved | API-M 4.0.0 Feature/AsyncAPIs Priority/Normal Type/Bug | ### Description:
<!-- Describe the issue -->
When I try to add a description for the WebSocket API topic, it is not getting persisted.
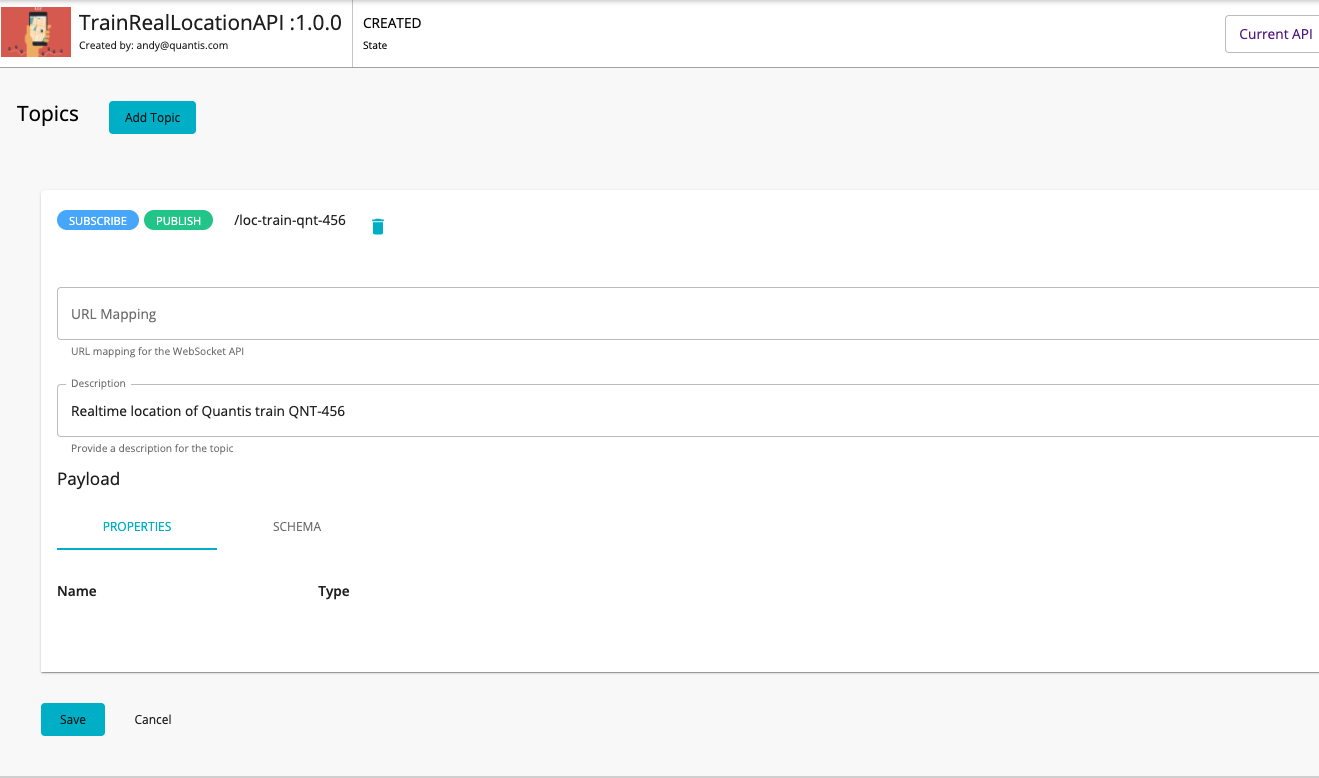
### Steps to reproduce:
1. Creat... | 1.0 | Websocket API topic description not getting saved - ### Description:
<!-- Describe the issue -->
When I try to add a description for the WebSocket API topic, it is not getting persisted.
 detected in jquery-2.1.4.min.js, jquery-1.10.2.min.js | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-1.10.2.min.js</b></p></summary>
<p>
<details><summary><b>jquery-2.1.4.min.js</b... | True | CVE-2019-11358 (Medium) detected in jquery-2.1.4.min.js, jquery-1.10.2.min.js - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-... | non_priority | cve medium detected in jquery min js jquery min js cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to vulnerable library ... | 0 |
83,200 | 3,631,881,571 | IssuesEvent | 2016-02-11 05:32:47 | devints47/stratalogue | https://api.github.com/repos/devints47/stratalogue | closed | Create Playbook Page | Normal Priority | Page with inputs
- Name
- Private
- Map
- 5 Roles
Creates a Playbook object | 1.0 | Create Playbook Page - Page with inputs
- Name
- Private
- Map
- 5 Roles
Creates a Playbook object | priority | create playbook page page with inputs name private map roles creates a playbook object | 1 |
729,326 | 25,120,492,874 | IssuesEvent | 2022-11-09 07:40:37 | stratosphererl/stratosphere | https://api.github.com/repos/stratosphererl/stratosphere | opened | As a website user, I want to have a neatly organized menu, so that I can easily navigate the website. | type: user story priority: medium work: complicated [2] work: obvious [1] area: frontend | # Acceptance Criteria
- [ ] Given the website has a navigation bar
- [ ] When the user selects an item on the nav bar
- [ ] Then the user is redirected elsewhere
# Estimation of Work
- Implementation: 3-4 hrs (1-2 days)
- Design: 2 hrs (1 day)
_Note: Implementation and Design may or may not happen simultaneous... | 1.0 | As a website user, I want to have a neatly organized menu, so that I can easily navigate the website. - # Acceptance Criteria
- [ ] Given the website has a navigation bar
- [ ] When the user selects an item on the nav bar
- [ ] Then the user is redirected elsewhere
# Estimation of Work
- Implementation: 3-4 hrs ... | priority | as a website user i want to have a neatly organized menu so that i can easily navigate the website acceptance criteria given the website has a navigation bar when the user selects an item on the nav bar then the user is redirected elsewhere estimation of work implementation hrs d... | 1 |
74,245 | 3,436,709,732 | IssuesEvent | 2015-12-12 16:32:45 | speedovation/kiwi | https://api.github.com/repos/speedovation/kiwi | closed | Drag and Create Project | 3 - Done High Priority | On Project explorer by dragging folder it should create project space.
1. Read folder path
2. Parse and add files & folders recursively
3. Save Project file.
Decide New file extension of project.
1. KiWi_Project.Kw
2. Project.Kw
3. Project.Kiwi
<!---
@huboard:{"order":5.960464477539063e-08,"milestone_order":2.2... | 1.0 | Drag and Create Project - On Project explorer by dragging folder it should create project space.
1. Read folder path
2. Parse and add files & folders recursively
3. Save Project file.
Decide New file extension of project.
1. KiWi_Project.Kw
2. Project.Kw
3. Project.Kiwi
<!---
@huboard:{"order":5.960464477539063... | priority | drag and create project on project explorer by dragging folder it should create project space read folder path parse and add files folders recursively save project file decide new file extension of project kiwi project kw project kw project kiwi huboard order milestone ... | 1 |
98,129 | 8,675,016,085 | IssuesEvent | 2018-11-30 09:38:51 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | FXLabs Testing 30 : ApiV1RunsIdTestSuiteSummaryGetQueryParamPageInvalidDatatype | FXLabs Testing 30 | Project : FXLabs Testing 30
Job : uat
Env : uat
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-... | 1.0 | FXLabs Testing 30 : ApiV1RunsIdTestSuiteSummaryGetQueryParamPageInvalidDatatype - Project : FXLabs Testing 30
Job : uat
Env : uat
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age... | non_priority | fxlabs testing project fxlabs testing job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint ... | 0 |
9,299 | 8,583,602,416 | IssuesEvent | 2018-11-13 20:12:44 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | aws_eip data source missing support for tags | enhancement good first issue help wanted service/ec2 | _This issue was originally opened by @MaximF as hashicorp/terraform#17361. It was migrated here as a result of the [provider split](https://www.hashicorp.com/blog/upcoming-provider-changes-in-terraform-0-10/). The original body of the issue is below._
<hr>
### Terraform Version
```
> terraform -v
Terraform v... | 1.0 | aws_eip data source missing support for tags - _This issue was originally opened by @MaximF as hashicorp/terraform#17361. It was migrated here as a result of the [provider split](https://www.hashicorp.com/blog/upcoming-provider-changes-in-terraform-0-10/). The original body of the issue is below._
<hr>
### Terraf... | non_priority | aws eip data source missing support for tags this issue was originally opened by maximf as hashicorp terraform it was migrated here as a result of the the original body of the issue is below terraform version terraform v terraform provider aws terraform co... | 0 |
470,685 | 13,542,794,779 | IssuesEvent | 2020-09-16 17:55:13 | carbon-design-system/carbon-addons-iot-react | https://api.github.com/repos/carbon-design-system/carbon-addons-iot-react | opened | [Pull Request Template] add a Regression Test field / question | status: needs priority :inbox_tray: status: needs triage :mag: type: enhancement :bulb: type: question :grey_question: | <!--
Use this template if you want to request a new feature, or a change to an
existing feature.
If you'd like to request an entirely new component, please use the component request template instead.
If you are reporting a bug or problem, please use the bug template instead.
-->
### What package is this... | 1.0 | [Pull Request Template] add a Regression Test field / question - <!--
Use this template if you want to request a new feature, or a change to an
existing feature.
If you'd like to request an entirely new component, please use the component request template instead.
If you are reporting a bug or problem, please... | priority | add a regression test field question use this template if you want to request a new feature or a change to an existing feature if you d like to request an entirely new component please use the component request template instead if you are reporting a bug or problem please use the bug template ... | 1 |
79,974 | 15,586,254,260 | IssuesEvent | 2021-03-18 01:31:24 | hiucimon/ClamScanService | https://api.github.com/repos/hiucimon/ClamScanService | opened | CVE-2020-10672 (High) detected in jackson-databind-2.8.5.jar | security vulnerability | ## CVE-2020-10672 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-10672 (High) detected in jackson-databind-2.8.5.jar - ## CVE-2020-10672 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.5.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file clamscanservice build gradle ... | 0 |
109,888 | 16,902,900,253 | IssuesEvent | 2021-06-24 01:04:10 | idonthaveafifaaddiction/flink | https://api.github.com/repos/idonthaveafifaaddiction/flink | opened | CVE-2021-34428 (Low) detected in jetty-server-9.3.20.v20170531.jar | security vulnerability | ## CVE-2021-34428 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-server-9.3.20.v20170531.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a hre... | True | CVE-2021-34428 (Low) detected in jetty-server-9.3.20.v20170531.jar - ## CVE-2021-34428 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-server-9.3.20.v20170531.jar</b></p></summary>... | non_priority | cve low detected in jetty server jar cve low severity vulnerability vulnerable library jetty server jar the core jetty server artifact library home page a href path to vulnerable library home wss scanner repository org eclipse jetty jetty server jetty s... | 0 |
671,323 | 22,756,068,512 | IssuesEvent | 2022-07-07 16:39:16 | PecanProject/pecan | https://api.github.com/repos/PecanProject/pecan | closed | Switch "var" naming convention to "nc_var" | Priority: 02 - Normal Misc: good first issue | <!--- Provide a general summary of the issue in the Title above -->
## Description
@serbinsh noticed we are using the object ```var``` to store values even though ```var() is an internal function. This needs a cleanup.
## Context
This will help keep code clean and clear.
## Possible Implementation
Change th... | 1.0 | Switch "var" naming convention to "nc_var" - <!--- Provide a general summary of the issue in the Title above -->
## Description
@serbinsh noticed we are using the object ```var``` to store values even though ```var() is an internal function. This needs a cleanup.
## Context
This will help keep code clean and cl... | priority | switch var naming convention to nc var description serbinsh noticed we are using the object var to store values even though var is an internal function this needs a cleanup context this will help keep code clean and clear possible implementation change the object var to... | 1 |
194,144 | 14,670,355,043 | IssuesEvent | 2020-12-30 04:32:52 | atom-ide-community/atom-script | https://api.github.com/repos/atom-ide-community/atom-script | closed | Install Fail | installation please-try-the-latest-version | Tried numerous time to install this, I have git installed and have no problems installing/cloning other pkgs from github using Atom. I have tried to no avail:
**git config --global url."https://".insteadOf git://**
This message appears to me to be a firewall/connectivity issue. Anyone else experience this ? I am runni... | 1.0 | Install Fail - Tried numerous time to install this, I have git installed and have no problems installing/cloning other pkgs from github using Atom. I have tried to no avail:
**git config --global url."https://".insteadOf git://**
This message appears to me to be a firewall/connectivity issue. Anyone else experience th... | non_priority | install fail tried numerous time to install this i have git installed and have no problems installing cloning other pkgs from github using atom i have tried to no avail git config global url git this message appears to me to be a firewall connectivity issue anyone else experience this i am running ... | 0 |
312,486 | 9,547,947,635 | IssuesEvent | 2019-05-02 02:14:33 | carbon-design-system/carbon-components-react | https://api.github.com/repos/carbon-design-system/carbon-components-react | closed | Label is not color highlighting when user is interacting with an input field | Severity 2 priority: high type: bug 🐛 wontfix | <!-- Feel free to remove sections that aren't relevant.
## Title line template: [Title]: Brief description
-->
## Detailed description
According to our carbon components spec, the labels should highlight when the user has focused on an input field.
I believe this was injected by the a11y fix. I believe ... | 1.0 | Label is not color highlighting when user is interacting with an input field - <!-- Feel free to remove sections that aren't relevant.
## Title line template: [Title]: Brief description
-->
## Detailed description
According to our carbon components spec, the labels should highlight when the user has focused o... | priority | label is not color highlighting when user is interacting with an input field feel free to remove sections that aren t relevant title line template brief description detailed description according to our carbon components spec the labels should highlight when the user has focused on an i... | 1 |
241,823 | 20,164,128,992 | IssuesEvent | 2022-02-10 01:24:37 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | closed | It would be better to allow edit the 'Blob container or directory URL' field in the 'Enter Connection Info' dialog | :heavy_check_mark: merged 🧪 testing :gear: adls gen2 | **Storage Explorer Version**: 1.23.0-dev
**Build Number**: 20220209.5
**Branch**: main
**Platform/OS**: Windows 10
**How Found**: From running test case
**Regression From**: Not a regression
## Steps to Reproduce ##
1. Expand one ADLS Gen2 storage account -> Blob Containers.
2. Create a blob container -> Cr... | 1.0 | It would be better to allow edit the 'Blob container or directory URL' field in the 'Enter Connection Info' dialog - **Storage Explorer Version**: 1.23.0-dev
**Build Number**: 20220209.5
**Branch**: main
**Platform/OS**: Windows 10
**How Found**: From running test case
**Regression From**: Not a regression
## S... | non_priority | it would be better to allow edit the blob container or directory url field in the enter connection info dialog storage explorer version dev build number branch main platform os windows how found from running test case regression from not a regression steps to r... | 0 |
682,013 | 23,330,153,443 | IssuesEvent | 2022-08-09 03:48:02 | City-Bureau/city-scrapers-atl | https://api.github.com/repos/City-Bureau/city-scrapers-atl | closed | New Scraper: NPU X | priority-unset | Create a new scraper for NPU X
Website: https://www.atlantaga.gov/government/departments/city-planning/neighborhood-and-npu-contacts
Jurisdiction: City of Atlanta
Classification: NPU
(Capitol View, Sylvan Hills) — Might suggest we hold off on NPUs
| 1.0 | New Scraper: NPU X - Create a new scraper for NPU X
Website: https://www.atlantaga.gov/government/departments/city-planning/neighborhood-and-npu-contacts
Jurisdiction: City of Atlanta
Classification: NPU
(Capitol View, Sylvan Hills) — Might suggest we hold off on NPUs
| priority | new scraper npu x create a new scraper for npu x website jurisdiction city of atlanta classification npu capitol view sylvan hills — might suggest we hold off on npus | 1 |
4,131 | 4,212,695,861 | IssuesEvent | 2016-06-29 17:01:28 | coreos/etcd | https://api.github.com/repos/coreos/etcd | closed | Values in rafthttp encode/decode | area/performance | Hi!
Found that `encode`/`decode` methods in `rafthttp` module accept/return `raftpb.Message` by value instead of by pointer:
```
func (enc *messageEncoder) encode(m raftpb.Message) error {
if err := binary.Write(enc.w, binary.BigEndian, uint64(m.Size())); err != nil {
return err
}
_, err := enc.w.Write(pb... | True | Values in rafthttp encode/decode - Hi!
Found that `encode`/`decode` methods in `rafthttp` module accept/return `raftpb.Message` by value instead of by pointer:
```
func (enc *messageEncoder) encode(m raftpb.Message) error {
if err := binary.Write(enc.w, binary.BigEndian, uint64(m.Size())); err != nil {
return... | non_priority | values in rafthttp encode decode hi found that encode decode methods in rafthttp module accept return raftpb message by value instead of by pointer func enc messageencoder encode m raftpb message error if err binary write enc w binary bigendian m size err nil return err ... | 0 |
157,844 | 6,016,990,789 | IssuesEvent | 2017-06-07 08:34:15 | minishift/minishift | https://api.github.com/repos/minishift/minishift | closed | certificate is valid for *.xip.io not certificate is valid for *.nip.io | kind/bug priority/major | minishift v1.1.0
I'm trying to log into the new fabric8 ui vi a keycloak openshift provider. We get a certificate error which mentions valid "xip.io" hostnames but not "nip.io" which is the route suffix that's used.
`post fail Post https://keycloak-fabric8.192.168.64.82.nip.io/auth/realms/fabric8/protocol/openid... | 1.0 | certificate is valid for *.xip.io not certificate is valid for *.nip.io - minishift v1.1.0
I'm trying to log into the new fabric8 ui vi a keycloak openshift provider. We get a certificate error which mentions valid "xip.io" hostnames but not "nip.io" which is the route suffix that's used.
`post fail Post https:/... | priority | certificate is valid for xip io not certificate is valid for nip io minishift i m trying to log into the new ui vi a keycloak openshift provider we get a certificate error which mentions valid xip io hostnames but not nip io which is the route suffix that s used post fail post certifica... | 1 |
245,236 | 18,775,075,309 | IssuesEvent | 2021-11-07 14:27:26 | NOAA-EMC/NCEPLIBS-g2c | https://api.github.com/repos/NOAA-EMC/NCEPLIBS-g2c | closed | update gh-pages branch with latest documentation fixes... | documentation | We have a lot of documentation improvements. We can put them out there... | 1.0 | update gh-pages branch with latest documentation fixes... - We have a lot of documentation improvements. We can put them out there... | non_priority | update gh pages branch with latest documentation fixes we have a lot of documentation improvements we can put them out there | 0 |
225,409 | 24,829,454,202 | IssuesEvent | 2022-10-26 01:06:57 | RG4421/spark-tpcds-benchmark | https://api.github.com/repos/RG4421/spark-tpcds-benchmark | reopened | CVE-2022-40153 (High) detected in woodstox-core-5.0.3.jar | security vulnerability | ## CVE-2022-40153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>woodstox-core-5.0.3.jar</b></p></summary>
<p>Woodstox is a high-performance XML processor that
implements Stax... | True | CVE-2022-40153 (High) detected in woodstox-core-5.0.3.jar - ## CVE-2022-40153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>woodstox-core-5.0.3.jar</b></p></summary>
<p>Woodstox is a... | non_priority | cve high detected in woodstox core jar cve high severity vulnerability vulnerable library woodstox core jar woodstox is a high performance xml processor that implements stax jsr and apis library home page a href path to dependency file spark tpcds benc... | 0 |
337,455 | 10,218,240,447 | IssuesEvent | 2019-08-15 15:28:23 | cBioPortal/cbioportal | https://api.github.com/repos/cBioPortal/cbioportal | closed | SV: Save and reuse UI state for logged in users | frontend priority study page | - [x] Save study view state (chart order, visible charts and chart type for this round) for log'ed users
- [x] Use the latest study view state (for particular user and study list) in visualizing page
- [x] Save custom chart | 1.0 | SV: Save and reuse UI state for logged in users - - [x] Save study view state (chart order, visible charts and chart type for this round) for log'ed users
- [x] Use the latest study view state (for particular user and study list) in visualizing page
- [x] Save custom chart | priority | sv save and reuse ui state for logged in users save study view state chart order visible charts and chart type for this round for log ed users use the latest study view state for particular user and study list in visualizing page save custom chart | 1 |
580,755 | 17,265,898,738 | IssuesEvent | 2021-07-22 13:46:29 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | venmo.com - site is not usable | browser-firefox-ios device-tablet os-ios priority-normal | <!-- @browser: Firefox -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_4) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.1 Safari/605.1.15 -->
<!-- @reported_with: mobile-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/80930 -->
<!-- @extra_labels: browser-firefox-ios ... | 1.0 | venmo.com - site is not usable - <!-- @browser: Firefox -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_4) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.1 Safari/605.1.15 -->
<!-- @reported_with: mobile-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/80930 -->
<!-- @e... | priority | venmo com site is not usable url browser version firefox operating system mac os x tested another browser no problem type site is not usable description page not loading correctly steps to reproduce venmo won’t close my account says loading forever br... | 1 |
495,791 | 14,288,090,774 | IssuesEvent | 2020-11-23 17:12:14 | AGROFIMS/hagrofims | https://api.github.com/repos/AGROFIMS/hagrofims | closed | Allow ''Other'' management practices | flexibility high priority management practices | - [ ] Add ''Other'' to the list of management practicies
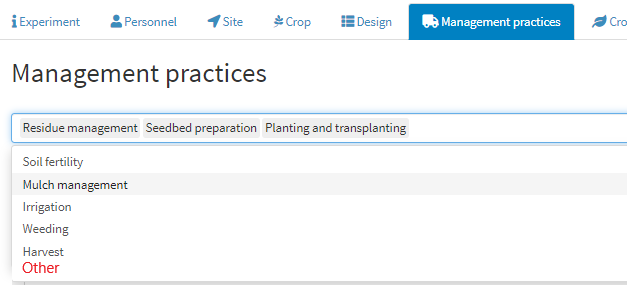
- [ ] When '' Other'' is selected, blank boxes appear to allow users to create their own management practices. (it should work like ''other'' in F... | 1.0 | Allow ''Other'' management practices - - [ ] Add ''Other'' to the list of management practicies
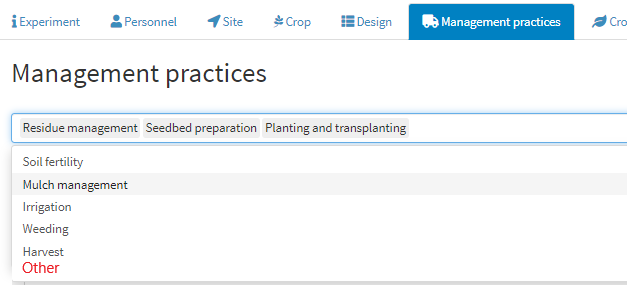
- [ ] When '' Other'' is selected, blank boxes appear to allow users to create their own management practic... | priority | allow other management practices add other to the list of management practicies when other is selected blank boxes appear to allow users to create their own management practices it should work like other in factor only one value one date one number per line ... | 1 |
100,700 | 8,752,749,398 | IssuesEvent | 2018-12-14 04:59:37 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | Testing 14 : ApiV1JobsProjectIdIdGetPathParamIdMongodbNoSqlInjectionTimebound | Testing 14 | Project : Testing 14
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=... | 1.0 | Testing 14 : ApiV1JobsProjectIdIdGetPathParamIdMongodbNoSqlInjectionTimebound - Project : Testing 14
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-... | non_priority | testing project testing job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request... | 0 |
289,602 | 24,999,134,010 | IssuesEvent | 2022-11-03 05:34:41 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: network/authentication/nodes=4 failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.network/authentication/nodes=4 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7288517?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7288517?buildTab=artifacts#/network/a... | 2.0 | roachtest: network/authentication/nodes=4 failed - roachtest.network/authentication/nodes=4 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/7288517?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNi... | non_priority | roachtest network authentication nodes failed roachtest network authentication nodes with on master test artifacts and logs in artifacts network authentication nodes run test impl go fatal monitor failure monitor task failed non zero exit code parameters roachtest cloud... | 0 |
249,857 | 7,964,768,914 | IssuesEvent | 2018-07-13 23:22:04 | raxod502/radian | https://api.github.com/repos/raxod502/radian | closed | Turn off Paredit and Aggressive Indentation on merge conflicts | aggressive-indent conflict emacs enhancement git lisp low priority paredit smerge-mode | To productively resolve merge conflicts in Lisps, one simply must turn off both Paredit and Aggressive Indentation. It would be nice if this were done automatically. (It would be even better if they were turned back on after you were finished.) Regardless of whether Magit is added as per #4, it would be nice to have th... | 1.0 | Turn off Paredit and Aggressive Indentation on merge conflicts - To productively resolve merge conflicts in Lisps, one simply must turn off both Paredit and Aggressive Indentation. It would be nice if this were done automatically. (It would be even better if they were turned back on after you were finished.) Regardless... | priority | turn off paredit and aggressive indentation on merge conflicts to productively resolve merge conflicts in lisps one simply must turn off both paredit and aggressive indentation it would be nice if this were done automatically it would be even better if they were turned back on after you were finished regardless... | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.