Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
77,601 | 10,010,861,599 | IssuesEvent | 2019-07-15 09:07:48 | Xabaril/Esquio | https://api.github.com/repos/Xabaril/Esquio | opened | Consider move azure devops extensions overview doc files | Documentation devops | Hi @lfraile
AzureDevOps extensions overview is not included on our docs directory, used by ReadTheDocs!, can you consider moving the overview.md into doc folder or create a new walkthrought on this topic?
Thanks
| 1.0 | Consider move azure devops extensions overview doc files - Hi @lfraile
AzureDevOps extensions overview is not included on our docs directory, used by ReadTheDocs!, can you consider moving the overview.md into doc folder or create a new walkthrought on this topic?
Thanks
| non_priority | consider move azure devops extensions overview doc files hi lfraile azuredevops extensions overview is not included on our docs directory used by readthedocs can you consider moving the overview md into doc folder or create a new walkthrought on this topic thanks | 0 |
177,243 | 6,576,058,600 | IssuesEvent | 2017-09-11 18:22:05 | opencurrents/opencurrents | https://api.github.com/repos/opencurrents/opencurrents | opened | invite-volunteers: Add personal message to invite-volunteers | mvp priority medium | Personal message should be attached to admin, not the event. This way we can autopopulate the message when an admin creates another event. | 1.0 | invite-volunteers: Add personal message to invite-volunteers - Personal message should be attached to admin, not the event. This way we can autopopulate the message when an admin creates another event. | priority | invite volunteers add personal message to invite volunteers personal message should be attached to admin not the event this way we can autopopulate the message when an admin creates another event | 1 |
69,973 | 13,388,514,737 | IssuesEvent | 2020-09-02 17:29:06 | photonstorm/phaser | https://api.github.com/repos/photonstorm/phaser | closed | Text gets an ultra thin outline after "setText()" | 👩💻 Code example needed | ## Version
* Phaser Version: v3.23.0-FB
* Operating system: Win10
* Browser:
## Description
Text gets an ultra thin outline, which can't be removed, after "setText()" has been called.
## Example Test Code
"Roboto-Bold" is a custom imported font, which works.
```JavaScript
this.sampletext = this.add.text(... | 1.0 | Text gets an ultra thin outline after "setText()" - ## Version
* Phaser Version: v3.23.0-FB
* Operating system: Win10
* Browser:
## Description
Text gets an ultra thin outline, which can't be removed, after "setText()" has been called.
## Example Test Code
"Roboto-Bold" is a custom imported font, which wor... | non_priority | text gets an ultra thin outline after settext version phaser version fb operating system browser description text gets an ultra thin outline which can t be removed after settext has been called example test code roboto bold is a custom imported font which works ... | 0 |
100,181 | 4,080,322,487 | IssuesEvent | 2016-05-31 01:05:27 | nim-lang/Nim | https://api.github.com/repos/nim-lang/Nim | closed | Slurp doesn't work with relative imports | Medium Priority Path Handling | Slurp opens files using paths relative to the module using ``slurp``. However this breaks when the module calling ``slurp`` is imported with the ``import path/to/module`` syntax. This can be tested with the following tree structure and files:
```nimrod
# outer.nim
import private/du
show()
# private/du.nim
const... | 1.0 | Slurp doesn't work with relative imports - Slurp opens files using paths relative to the module using ``slurp``. However this breaks when the module calling ``slurp`` is imported with the ``import path/to/module`` syntax. This can be tested with the following tree structure and files:
```nimrod
# outer.nim
import pr... | priority | slurp doesn t work with relative imports slurp opens files using paths relative to the module using slurp however this breaks when the module calling slurp is imported with the import path to module syntax this can be tested with the following tree structure and files nimrod outer nim import pr... | 1 |
2,392 | 5,190,341,474 | IssuesEvent | 2017-01-21 07:34:30 | nodejs/node | https://api.github.com/repos/nodejs/node | opened | process: misaligned node --help text | good first contribution process | * **Version**: master
* **Platform**: n/a
* **Subsystem**: process
The alignment of the argument descriptions in the `node --help` text is off. Specifically the `--inspect` and `--inspect-brk` options do not match up. Because the full `--inspect-brk` argument name is the longest, all of the other arguments' descri... | 1.0 | process: misaligned node --help text - * **Version**: master
* **Platform**: n/a
* **Subsystem**: process
The alignment of the argument descriptions in the `node --help` text is off. Specifically the `--inspect` and `--inspect-brk` options do not match up. Because the full `--inspect-brk` argument name is the long... | non_priority | process misaligned node help text version master platform n a subsystem process the alignment of the argument descriptions in the node help text is off specifically the inspect and inspect brk options do not match up because the full inspect brk argument name is the long... | 0 |
578,999 | 17,169,815,764 | IssuesEvent | 2021-07-15 01:32:38 | GlowstoneMC/Glowstone | https://api.github.com/repos/GlowstoneMC/Glowstone | closed | Cannot exit fly and other world issues | Category: server feature Priority: minor | Hello i am having some issues already unfortunately.. I just started using this today and i cannot seem to fly without getting stuck in the air. I also have a plugin that cannot register PlayerDeathEvent (i have source to it so if i need, i'll fix it). Other than that once i'm flying, i cannot exit fly and i tend to fl... | 1.0 | Cannot exit fly and other world issues - Hello i am having some issues already unfortunately.. I just started using this today and i cannot seem to fly without getting stuck in the air. I also have a plugin that cannot register PlayerDeathEvent (i have source to it so if i need, i'll fix it). Other than that once i'm f... | priority | cannot exit fly and other world issues hello i am having some issues already unfortunately i just started using this today and i cannot seem to fly without getting stuck in the air i also have a plugin that cannot register playerdeathevent i have source to it so if i need i ll fix it other than that once i m f... | 1 |
435,192 | 12,532,574,323 | IssuesEvent | 2020-06-04 16:09:25 | umple/umple | https://api.github.com/repos/umple/umple | closed | State machines cut off in some installations of UmpleOnline | Component-UmpleOnline Diffic-Med Priority-High bug | In some installations of UmpleOnline, state machines are 'cut off' so you can't see them completely. This might be due to the version of graphviz. It may be something wrong with the way the svg is being generated or displayed.
The cutoff seems to be related to percentage and the problem occurs whether or not the dia... | 1.0 | State machines cut off in some installations of UmpleOnline - In some installations of UmpleOnline, state machines are 'cut off' so you can't see them completely. This might be due to the version of graphviz. It may be something wrong with the way the svg is being generated or displayed.
The cutoff seems to be relat... | priority | state machines cut off in some installations of umpleonline in some installations of umpleonline state machines are cut off so you can t see them completely this might be due to the version of graphviz it may be something wrong with the way the svg is being generated or displayed the cutoff seems to be relat... | 1 |
400,275 | 27,276,445,651 | IssuesEvent | 2023-02-23 05:56:22 | ZORALab/Hestia | https://api.github.com/repos/ZORALab/Hestia | closed | Add 404 Page | Documentation Done and Pending Release | # Description
```
Please provide a short description of what you have encountered below.
```
The documentation site does not have a 404 page. Hence, let's add it.
# Link
```
Please provide the documentation link(s) below.
```
`/en/404/`
# Expected Presentation
```
Please specify the expected pre... | 1.0 | Add 404 Page - # Description
```
Please provide a short description of what you have encountered below.
```
The documentation site does not have a 404 page. Hence, let's add it.
# Link
```
Please provide the documentation link(s) below.
```
`/en/404/`
# Expected Presentation
```
Please specify t... | non_priority | add page description please provide a short description of what you have encountered below the documentation site does not have a page hence let s add it link please provide the documentation link s below en expected presentation please specify the exp... | 0 |
216,695 | 16,795,773,974 | IssuesEvent | 2021-06-16 03:07:50 | ShaunaMyers/Overlook_Hotel | https://api.github.com/repos/ShaunaMyers/Overlook_Hotel | closed | ## Testing | enhancement testing | - [x] Write tests for all Classes
- [x] Write tests for properties and any methods in classes
- [x] Test anything that updates class properties
- [x] Test for happy and sad paths | 1.0 | ## Testing - - [x] Write tests for all Classes
- [x] Write tests for properties and any methods in classes
- [x] Test anything that updates class properties
- [x] Test for happy and sad paths | non_priority | testing write tests for all classes write tests for properties and any methods in classes test anything that updates class properties test for happy and sad paths | 0 |
778,087 | 27,303,173,799 | IssuesEvent | 2023-02-24 05:05:41 | dvrpc/TrackingProgress | https://api.github.com/repos/dvrpc/TrackingProgress | opened | Mortgage Lending Chart 2(a,b,c,d) | high priority | @hachadorian This is the second of three charts for Mortgage Lending. I'm not doing the visual mockups for this. Hopefully you'll follow along. Let me know if you have question or want to meet.
Source CSVs are here: G:\Shared drives\Socioeconomic and Land Use Analytics\Tracking Progress\Web\Data\Mortgage Lending
... | 1.0 | Mortgage Lending Chart 2(a,b,c,d) - @hachadorian This is the second of three charts for Mortgage Lending. I'm not doing the visual mockups for this. Hopefully you'll follow along. Let me know if you have question or want to meet.
Source CSVs are here: G:\Shared drives\Socioeconomic and Land Use Analytics\Tracking Pr... | priority | mortgage lending chart a b c d hachadorian this is the second of three charts for mortgage lending i m not doing the visual mockups for this hopefully you ll follow along let me know if you have question or want to meet source csvs are here g shared drives socioeconomic and land use analytics tracking pr... | 1 |
195,304 | 6,910,373,737 | IssuesEvent | 2017-11-28 01:55:03 | jlizier/jidt | https://api.github.com/repos/jlizier/jidt | closed | Kraskov calculators to ensure they use actual k in joint space than assumed k | auto-migrated Priority-Low Type-Enhancement | ```
At the moment, our Kraskov calculators assume that they have k values within
epsilon in the full joint space. Where the distribution is composed of delta
functions (i.e. somewhat discretised) this won't be the case - there could be
many more than k. As such, it may be more correct to use the actual k for each
o... | 1.0 | Kraskov calculators to ensure they use actual k in joint space than assumed k - ```
At the moment, our Kraskov calculators assume that they have k values within
epsilon in the full joint space. Where the distribution is composed of delta
functions (i.e. somewhat discretised) this won't be the case - there could be
m... | priority | kraskov calculators to ensure they use actual k in joint space than assumed k at the moment our kraskov calculators assume that they have k values within epsilon in the full joint space where the distribution is composed of delta functions i e somewhat discretised this won t be the case there could be m... | 1 |
132,578 | 28,236,607,622 | IssuesEvent | 2023-04-06 01:28:31 | haproxy/haproxy | https://api.github.com/repos/haproxy/haproxy | opened | src/applet.c: null pointer dereference suspected by coverity | type: code-report | ### Tool Name and Version
coverity
### Code Report
```plain
*** CID 1508680: Null pointer dereferences (FORWARD_NULL)
/src/applet.c: 139 in applet_trace()
133 appctx, appctx->t, tick_isset(appctx->t->expire) ? TICKS_TO_MS(appctx->t->expire - now_ms) : TICK_ETERNITY,
134 ... | 1.0 | src/applet.c: null pointer dereference suspected by coverity - ### Tool Name and Version
coverity
### Code Report
```plain
*** CID 1508680: Null pointer dereferences (FORWARD_NULL)
/src/applet.c: 139 in applet_trace()
133 appctx, appctx->t, tick_isset(appctx->t->expire) ? TICKS_TO_MS(ap... | non_priority | src applet c null pointer dereference suspected by coverity tool name and version coverity code report plain cid null pointer dereferences forward null src applet c in applet trace appctx appctx t tick isset appctx t expire ticks to ms appctx t e... | 0 |
168,043 | 6,360,295,860 | IssuesEvent | 2017-07-31 09:42:53 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | Update text for developer profile notification box "news and events" | priority: blocks release | Brian Smith just advised that we revise the opt-in language from "stay up-to-date with news and events relevant to add-on developers" to "stay up-to-date with news and events relevant to add-on developers (including the about:addons newsletter).
Any chance we could get this patched by Aug 2 (next issue send date)?
... | 1.0 | Update text for developer profile notification box "news and events" - Brian Smith just advised that we revise the opt-in language from "stay up-to-date with news and events relevant to add-on developers" to "stay up-to-date with news and events relevant to add-on developers (including the about:addons newsletter).
... | priority | update text for developer profile notification box news and events brian smith just advised that we revise the opt in language from stay up to date with news and events relevant to add on developers to stay up to date with news and events relevant to add on developers including the about addons newsletter ... | 1 |
110,719 | 16,987,015,824 | IssuesEvent | 2021-06-30 15:25:52 | samuelteixeiras/caite | https://api.github.com/repos/samuelteixeiras/caite | opened | WS-2014-0005 (High) detected in qs-0.6.5.tgz, qs-0.5.6.tgz | security vulnerability | ## WS-2014-0005 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-0.6.5.tgz</b>, <b>qs-0.5.6.tgz</b></p></summary>
<p>
<details><summary><b>qs-0.6.5.tgz</b></p></summary>
<p>querys... | True | WS-2014-0005 (High) detected in qs-0.6.5.tgz, qs-0.5.6.tgz - ## WS-2014-0005 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-0.6.5.tgz</b>, <b>qs-0.5.6.tgz</b></p></summary>
<p>
<... | non_priority | ws high detected in qs tgz qs tgz ws high severity vulnerability vulnerable libraries qs tgz qs tgz qs tgz querystring parser library home page a href path to dependency file caite package json path to vulnerable library caite node modu... | 0 |
753,345 | 26,344,719,575 | IssuesEvent | 2023-01-10 20:53:51 | GoogleCloudPlatform/python-docs-samples | https://api.github.com/repos/GoogleCloudPlatform/python-docs-samples | closed | healthcare.api-client.v1.consent.attribute_definitions_test: test_CRUD_resource_attribute_definition failed | priority: p1 type: bug api: healthcare samples flakybot: issue | Note: #8580 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 66e069f916ffc0c3f19899f5083d32ebc514a8f3
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/fea8fe56-8bef-4375-a365-e791f47ba958), [Sponge](http://sponge2/fea8fe56-8bef-4375-... | 1.0 | healthcare.api-client.v1.consent.attribute_definitions_test: test_CRUD_resource_attribute_definition failed - Note: #8580 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 66e069f916ffc0c3f19899f5083d32ebc514a8f3
buildURL: [Build Status](https://source.cloud.goo... | priority | healthcare api client consent attribute definitions test test crud resource attribute definition failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output traceback most recent call last file ... | 1 |
512,523 | 14,899,298,887 | IssuesEvent | 2021-01-21 14:11:24 | weaveworks/eksctl | https://api.github.com/repos/weaveworks/eksctl | closed | block service account access to k8s APIs by exposing automountServiceAccountToken flag | kind/feature priority/backlog stale | **Why do you want this feature?**
In almost all cases, application service accounts do not need access to kubernetes APIs.
Blocking pods access to those APIs is good practice in terms of security.
**What feature/behavior/change do you want?**
Since kubernetes 1.6, there is a [`automountServiceAccountToken`](https... | 1.0 | block service account access to k8s APIs by exposing automountServiceAccountToken flag - **Why do you want this feature?**
In almost all cases, application service accounts do not need access to kubernetes APIs.
Blocking pods access to those APIs is good practice in terms of security.
**What feature/behavior/chang... | priority | block service account access to apis by exposing automountserviceaccounttoken flag why do you want this feature in almost all cases application service accounts do not need access to kubernetes apis blocking pods access to those apis is good practice in terms of security what feature behavior change ... | 1 |
547,937 | 16,049,755,926 | IssuesEvent | 2021-04-22 17:35:51 | OpenNebula/one | https://api.github.com/repos/OpenNebula/one | closed | Role VMs actions buttons should respect VM state | Category: Sunstone Priority: Normal Type: Feature | **Description**
If there is a running service with a role and this **role VMs** are shutdown all not possible buttons/functions should be disabled.
**Interface Changes**
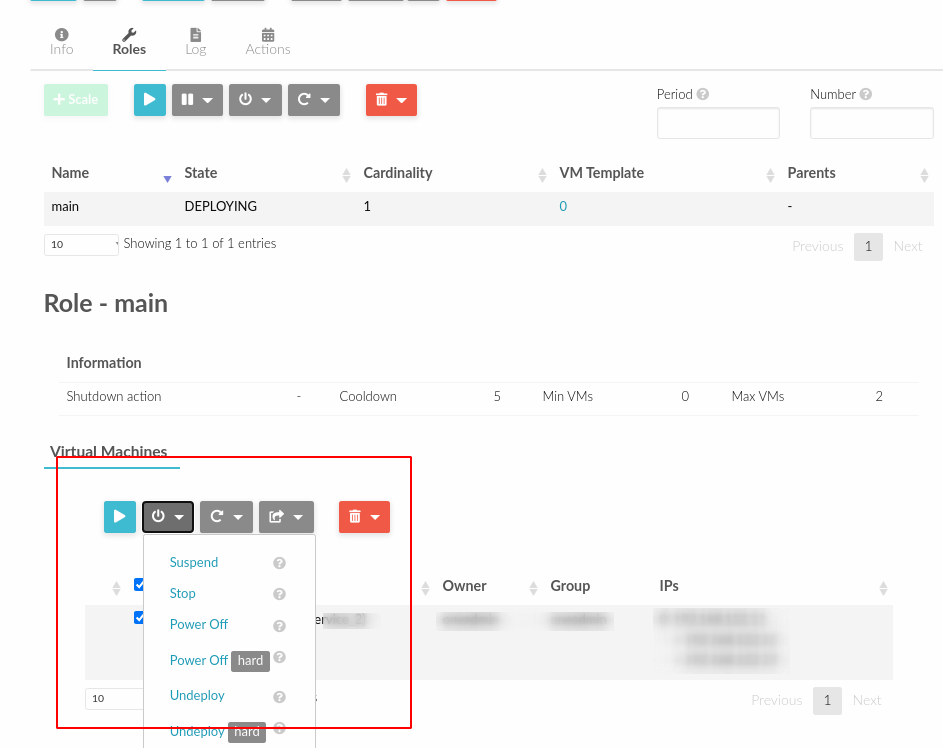
<!--//////////////////////////... | 1.0 | Role VMs actions buttons should respect VM state - **Description**
If there is a running service with a role and this **role VMs** are shutdown all not possible buttons/functions should be disabled.
**Interface Changes**
 as its 64-bit PCI host aperture. This is inconsistent with OVMF's assumption of its platform's memory layout, because it fetches the size of high memory from RTC CMOS.
Pass ACRN's E820 map to OVMF so it can correctly pass ACRN's memory configuration to UOS. | 1.0 | Pass ACRN E820 map to OVMF - ACRN currently uses [4GB, 5GB) as its 64-bit PCI host aperture. This is inconsistent with OVMF's assumption of its platform's memory layout, because it fetches the size of high memory from RTC CMOS.
Pass ACRN's E820 map to OVMF so it can correctly pass ACRN's memory configuration to UOS. | priority | pass acrn map to ovmf acrn currently uses as its bit pci host aperture this is inconsistent with ovmf s assumption of its platform s memory layout because it fetches the size of high memory from rtc cmos pass acrn s map to ovmf so it can correctly pass acrn s memory configuration to uos | 1 |
17,981 | 5,540,342,969 | IssuesEvent | 2017-03-22 09:52:20 | ArcticaProject/nx-libs | https://api.github.com/repos/ArcticaProject/nx-libs | opened | in libNX_X11: warning: dereferencing type-punned pointer will break strict-aliasing rules [-Wstrict-aliasing] | code cleanup | ```
gcc -c -Wdate-time -D_FORTIFY_SOURCE=2 -g -O2 -fdebug-prefix-map=/home/mike/MyDocuments/4projects/arctica-upstream/nx-libs.upstream/nx-libs.36=. -fstack-protector-strong -Wformat -Werror=format-security -g -std=c99 -Wall -Wpedantic -Wpointer-arith -Wundef -I../.. -I../../exports/include -Dlinux -D__amd64__ -D... | 1.0 | in libNX_X11: warning: dereferencing type-punned pointer will break strict-aliasing rules [-Wstrict-aliasing] - ```
gcc -c -Wdate-time -D_FORTIFY_SOURCE=2 -g -O2 -fdebug-prefix-map=/home/mike/MyDocuments/4projects/arctica-upstream/nx-libs.upstream/nx-libs.36=. -fstack-protector-strong -Wformat -Werror=format-security ... | non_priority | in libnx warning dereferencing type punned pointer will break strict aliasing rules gcc c wdate time d fortify source g fdebug prefix map home mike mydocuments arctica upstream nx libs upstream nx libs fstack protector strong wformat werror format security g std wall wpedantic wp... | 0 |
350,588 | 10,492,576,869 | IssuesEvent | 2019-09-25 13:32:40 | geosolutions-it/MapStore2 | https://api.github.com/repos/geosolutions-it/MapStore2 | opened | [Proposal] TOC Plugin Container | Priority: High enhancement | ### Description
Currently the TOC interacts with different plugins and sometimes they are directly [hardcoded](https://github.com/geosolutions-it/MapStore2/blob/master/web/client/components/TOC/Toolbar.jsx#L190-L314) in the component.
This could cause some configuration issues:
eg: https://github.com/geosolutions-it... | 1.0 | [Proposal] TOC Plugin Container - ### Description
Currently the TOC interacts with different plugins and sometimes they are directly [hardcoded](https://github.com/geosolutions-it/MapStore2/blob/master/web/client/components/TOC/Toolbar.jsx#L190-L314) in the component.
This could cause some configuration issues:
eg: ... | priority | toc plugin container description currently the toc interacts with different plugins and sometimes they are directly in the component this could cause some configuration issues eg the aim of this proposal is to improve the toc by adding a way to add buttons and panels from other plugin here a fi... | 1 |
172,882 | 27,347,694,016 | IssuesEvent | 2023-02-27 06:59:08 | starplanter93/The_Garden_of_Musicsheet | https://api.github.com/repos/starplanter93/The_Garden_of_Musicsheet | opened | Design: 모바일 반응형 작업 | Design | ## Description
뷰포트 390px~767px의 모바일 반응형 작업
## Todo
- [ ] 악기 페이지
- [ ] 악기 상세페이지
- [ ] 곡 상세페이지 | 1.0 | Design: 모바일 반응형 작업 - ## Description
뷰포트 390px~767px의 모바일 반응형 작업
## Todo
- [ ] 악기 페이지
- [ ] 악기 상세페이지
- [ ] 곡 상세페이지 | non_priority | design 모바일 반응형 작업 description 뷰포트 모바일 반응형 작업 todo 악기 페이지 악기 상세페이지 곡 상세페이지 | 0 |
405,058 | 11,866,754,104 | IssuesEvent | 2020-03-26 04:50:06 | cuberite/cuberite | https://api.github.com/repos/cuberite/cuberite | closed | Segmentation Fault on RPi4 AlpineLinux | crash priority/important | Client version: 1.12.2
Server OS: Alpine Linux v3.11 armv7l
Cuberite Commit id: [09:13:20] from commit id: approx: 8154bde116df2b0ff2fe535ed1bb87d00a009b52 built at: approx: 2020-03-24 21:16:54 +0000
Sorry for my bad english.
### Expected behavior
Server should start succesfully.
### Actual behavior
Server... | 1.0 | Segmentation Fault on RPi4 AlpineLinux - Client version: 1.12.2
Server OS: Alpine Linux v3.11 armv7l
Cuberite Commit id: [09:13:20] from commit id: approx: 8154bde116df2b0ff2fe535ed1bb87d00a009b52 built at: approx: 2020-03-24 21:16:54 +0000
Sorry for my bad english.
### Expected behavior
Server should start su... | priority | segmentation fault on alpinelinux client version server os alpine linux cuberite commit id from commit id approx built at approx sorry for my bad english expected behavior server should start succesfully actual behavior server got segmentation fault ... | 1 |
74,322 | 20,117,257,929 | IssuesEvent | 2022-02-07 20:57:26 | JVoiceXML/JVoiceXML | https://api.github.com/repos/JVoiceXML/JVoiceXML | closed | Upgrade junit to 4.13.2 | build-system | In preparation to cleaning up junit tests, junit should be upgraded to the latest version 4.13.2. upgrading to junit 5 should be done afterwards. | 1.0 | Upgrade junit to 4.13.2 - In preparation to cleaning up junit tests, junit should be upgraded to the latest version 4.13.2. upgrading to junit 5 should be done afterwards. | non_priority | upgrade junit to in preparation to cleaning up junit tests junit should be upgraded to the latest version upgrading to junit should be done afterwards | 0 |
98,969 | 30,241,012,676 | IssuesEvent | 2023-07-06 13:31:39 | vitessio/vitess | https://api.github.com/repos/vitessio/vitess | closed | Flaky Test: vipersync.TestPersistConfig | Type: Bug Component: Build/CI Type: Testing | ### Overview of the Issue
The `vipersync.TestPersistConfig` tests are _extremely_ flaky in CI, and slightly less so on a local machine.
We've skipped them for now, but we need to rewrite these tests to re-enable them, as that code is currently untested.
### Reproduction Steps
go test -race run "TestPersistConfig... | 1.0 | Flaky Test: vipersync.TestPersistConfig - ### Overview of the Issue
The `vipersync.TestPersistConfig` tests are _extremely_ flaky in CI, and slightly less so on a local machine.
We've skipped them for now, but we need to rewrite these tests to re-enable them, as that code is currently untested.
### Reproduction St... | non_priority | flaky test vipersync testpersistconfig overview of the issue the vipersync testpersistconfig tests are extremely flaky in ci and slightly less so on a local machine we ve skipped them for now but we need to rewrite these tests to re enable them as that code is currently untested reproduction st... | 0 |
207,698 | 7,132,652,186 | IssuesEvent | 2018-01-22 15:14:38 | metasfresh/metasfresh-webui-api | https://api.github.com/repos/metasfresh/metasfresh-webui-api | opened | Allow Filtering for Table References and show table identifier | priority:high | ### Is this a bug or feature request?
Feature Request
### What is the current behavior?
Currently, it's not possible to add a Label Field as Filter Element which does not point to a reference list, but to a Table ID.
#### Which are the steps to reproduce?
Check Testcase for Location in Business partner window. Ope... | 1.0 | Allow Filtering for Table References and show table identifier - ### Is this a bug or feature request?
Feature Request
### What is the current behavior?
Currently, it's not possible to add a Label Field as Filter Element which does not point to a reference list, but to a Table ID.
#### Which are the steps to reprod... | priority | allow filtering for table references and show table identifier is this a bug or feature request feature request what is the current behavior currently it s not possible to add a label field as filter element which does not point to a reference list but to a table id which are the steps to reprod... | 1 |
401,251 | 11,787,912,645 | IssuesEvent | 2020-03-17 14:46:21 | OregonDigital/OD2 | https://api.github.com/repos/OregonDigital/OD2 | closed | Source Updates for Help Text and Form Label | Features Priority - High | ### Descriptive summary
- [x] Shelf Location Help Text missing
| 1.0 | Source Updates for Help Text and Form Label - ### Descriptive summary
- [x] Shelf Location Help Text missing
| priority | source updates for help text and form label descriptive summary shelf location help text missing | 1 |
418,776 | 12,203,185,987 | IssuesEvent | 2020-04-30 10:10:11 | MHRA/products | https://api.github.com/repos/MHRA/products | closed | Delete can remove document from search index but not storage, making it impossible for Sentinel to delete it | BUG :bug: HIGH PRIORITY :arrow_double_up: | From @TimboTambo:
> There were around 30 errors from the batch run test last week that occurred with deleting files. Seems like in all cases the doc to delete was found in the search index, removed from the search index, failed when removing from the storage container, was retried and then the doc could no longer be... | 1.0 | Delete can remove document from search index but not storage, making it impossible for Sentinel to delete it - From @TimboTambo:
> There were around 30 errors from the batch run test last week that occurred with deleting files. Seems like in all cases the doc to delete was found in the search index, removed from the... | priority | delete can remove document from search index but not storage making it impossible for sentinel to delete it from timbotambo there were around errors from the batch run test last week that occurred with deleting files seems like in all cases the doc to delete was found in the search index removed from the ... | 1 |
241,676 | 7,822,049,524 | IssuesEvent | 2018-06-14 00:00:21 | tidepool-org/chrome-uploader | https://api.github.com/repos/tidepool-org/chrome-uploader | closed | Large basal schedules cause upload failure | bug: development priority: medium severity: major | ### Description
When a 600-series pump has a large basal schedule (tested with 1 per hour), pump download fails.
### Steps to Reproduce
1. Create a new basal schedule on the pump with a different basal rate every hour
1. Attempt to download data from pump
### Environment
**Uploader version**: 0.310.0-alpha.11... | 1.0 | Large basal schedules cause upload failure - ### Description
When a 600-series pump has a large basal schedule (tested with 1 per hour), pump download fails.
### Steps to Reproduce
1. Create a new basal schedule on the pump with a different basal rate every hour
1. Attempt to download data from pump
### Enviro... | priority | large basal schedules cause upload failure description when a series pump has a large basal schedule tested with per hour pump download fails steps to reproduce create a new basal schedule on the pump with a different basal rate every hour attempt to download data from pump environm... | 1 |
175,561 | 6,552,277,584 | IssuesEvent | 2017-09-05 17:40:41 | washingtonstateuniversity/WSU-People-Directory | https://api.github.com/repos/washingtonstateuniversity/WSU-People-Directory | reopened | Introduce a base person object that provides consistent profile data | enhancement priority:medium | It should be possible to write `$person = get_wsu_person( 123 );` or similar and get back a `WSU_Person` object (or similar) and then reference stuff like:
```
First Name: <?php echo esc_html( $person->ad_first_name ); ?>
Last Name: <?php echo esc_html( $person->ad_last_name ); ?>
```
This can probably allow f... | 1.0 | Introduce a base person object that provides consistent profile data - It should be possible to write `$person = get_wsu_person( 123 );` or similar and get back a `WSU_Person` object (or similar) and then reference stuff like:
```
First Name: <?php echo esc_html( $person->ad_first_name ); ?>
Last Name: <?php echo ... | priority | introduce a base person object that provides consistent profile data it should be possible to write person get wsu person or similar and get back a wsu person object or similar and then reference stuff like first name ad first name last name ad last name this can proba... | 1 |
198,874 | 22,674,173,260 | IssuesEvent | 2022-07-04 01:24:21 | Souparnee/WebGoat2_20022020 | https://api.github.com/repos/Souparnee/WebGoat2_20022020 | opened | CVE-2021-23440 (High) detected in set-value-0.4.3.tgz, set-value-2.0.0.tgz | security vulnerability | ## CVE-2021-23440 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>set-value-0.4.3.tgz</b>, <b>set-value-2.0.0.tgz</b></p></summary>
<p>
<details><summary><b>set-value-0.4.3.tgz</b></... | True | CVE-2021-23440 (High) detected in set-value-0.4.3.tgz, set-value-2.0.0.tgz - ## CVE-2021-23440 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>set-value-0.4.3.tgz</b>, <b>set-value-2.... | non_priority | cve high detected in set value tgz set value tgz cve high severity vulnerability vulnerable libraries set value tgz set value tgz set value tgz create nested values and any intermediaries using dot notation a b c paths library home page ... | 0 |
162,707 | 20,241,925,025 | IssuesEvent | 2022-02-14 10:06:04 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | reopened | security: add support for "SCIM" user to provision accounts | C-enhancement A-security T-sql-experience | This is a common pattern for companies using Kerberos, and that it would be a common requirement from financial institutions.
Here's why this is necessary; a "SCIM" user does not have access to the data itself and also should not have the ability to add credentials to new accounts. Because Kerberos is handling account... | True | security: add support for "SCIM" user to provision accounts - This is a common pattern for companies using Kerberos, and that it would be a common requirement from financial institutions.
Here's why this is necessary; a "SCIM" user does not have access to the data itself and also should not have the ability to add cre... | non_priority | security add support for scim user to provision accounts this is a common pattern for companies using kerberos and that it would be a common requirement from financial institutions here s why this is necessary a scim user does not have access to the data itself and also should not have the ability to add cre... | 0 |
55,836 | 11,470,627,894 | IssuesEvent | 2020-02-09 04:52:55 | talonos2/FinalWinterBugs | https://api.github.com/repos/talonos2/FinalWinterBugs | closed | running out of time during combat locks controls | bug code | after running out of time during a combat (even using "m" key) the player returns to town and is unable to move. They can start the next dungeon run, but will still be unable to move or talk (day 6 NPC is standing next to you), and will still be unable to move when returning to town from that (death by "m" key). This... | 1.0 | running out of time during combat locks controls - after running out of time during a combat (even using "m" key) the player returns to town and is unable to move. They can start the next dungeon run, but will still be unable to move or talk (day 6 NPC is standing next to you), and will still be unable to move when re... | non_priority | running out of time during combat locks controls after running out of time during a combat even using m key the player returns to town and is unable to move they can start the next dungeon run but will still be unable to move or talk day npc is standing next to you and will still be unable to move when re... | 0 |
369,712 | 25,864,948,381 | IssuesEvent | 2022-12-13 20:01:33 | fga-eps-mds/2022-2-QuantiFGA | https://api.github.com/repos/fga-eps-mds/2022-2-QuantiFGA | closed | Determinação de Requisitos | documentation | ### Descrição
- Realização do UML e do Requisitos de Software
### Objetivo
- Criar um arquivo para o UML do projeto e todos os requisitos de software (funcionais, não funcionais, de dados e execução)
### Tarefas
- [x] Fazer os requisitos
- [x] Fazer o UML
### Comentários
- Arquivo UML em formato de .... | 1.0 | Determinação de Requisitos - ### Descrição
- Realização do UML e do Requisitos de Software
### Objetivo
- Criar um arquivo para o UML do projeto e todos os requisitos de software (funcionais, não funcionais, de dados e execução)
### Tarefas
- [x] Fazer os requisitos
- [x] Fazer o UML
### Comentários
... | non_priority | determinação de requisitos descrição realização do uml e do requisitos de software objetivo criar um arquivo para o uml do projeto e todos os requisitos de software funcionais não funcionais de dados e execução tarefas fazer os requisitos fazer o uml comentários ar... | 0 |
139,342 | 5,367,718,770 | IssuesEvent | 2017-02-22 05:46:46 | fossasia/open-event-webapp | https://api.github.com/repos/fossasia/open-event-webapp | opened | Session information unreadable - avoid shadows and gray colors. | bug Priority: Urgent | The session information shows shadows and gray colors. Previously it was readable easily, but it was changed at some point.
Please change the font to be easily readable again:
* Take out shadows
* Use black font for all components
:**
<!-- Any rel... | 1.0 | Lowcode diagram does not load in codespaces - **Description:**
Lowcode diagram does not load in codespaces
**Steps to reproduce:**
https://user-images.githubusercontent.com/36252572/214781305-74ec3cef-3421-467d-9103-3c0cb10b0752.MOV
**Affected Versions:**
**OS, DB, other environment details and versions:**
... | non_priority | lowcode diagram does not load in codespaces description lowcode diagram does not load in codespaces steps to reproduce affected versions os db other environment details and versions related issues optional suggested labels optional suggested assignees ... | 0 |
21,152 | 4,683,130,331 | IssuesEvent | 2016-10-09 16:39:34 | wtfblub/NetspherePirates | https://api.github.com/repos/wtfblub/NetspherePirates | reopened | SQLite to MySQL - guide request | Documentation Question | Add guide for change and port base SQLite to MySQL.
Or add base MySQL files with guide. | 1.0 | SQLite to MySQL - guide request - Add guide for change and port base SQLite to MySQL.
Or add base MySQL files with guide. | non_priority | sqlite to mysql guide request add guide for change and port base sqlite to mysql or add base mysql files with guide | 0 |
18,171 | 3,031,492,051 | IssuesEvent | 2015-08-04 23:21:15 | googlei18n/noto-fonts | https://api.github.com/repos/googlei18n/noto-fonts | opened | Inscriptional Parthian: ligatures missing | Script-Parthian Type-Defect | Imported from Google Code issue #15 created by roozbeh@google.com on 2013-11-14T03:01:51.000Z:
The Unicode standard’s section on Inscriptional Parthian calls for nine standard ligatures. Of those, only Nun-Daleth works in the font. The other eight should also be supported. | 1.0 | Inscriptional Parthian: ligatures missing - Imported from Google Code issue #15 created by roozbeh@google.com on 2013-11-14T03:01:51.000Z:
The Unicode standard’s section on Inscriptional Parthian calls for nine standard ligatures. Of those, only Nun-Daleth works in the font. The other eight should also be supported. | non_priority | inscriptional parthian ligatures missing imported from google code issue created by roozbeh google com on the unicode standard’s section on inscriptional parthian calls for nine standard ligatures of those only nun daleth works in the font the other eight should also be supported | 0 |
65,743 | 8,838,372,793 | IssuesEvent | 2019-01-05 16:34:30 | kirill-grouchnikov/radiance | https://api.github.com/repos/kirill-grouchnikov/radiance | opened | [Substance] Add documentation on renderers | Documentation | The "old" list, table and tree renderers + the new panel list renderer. | 1.0 | [Substance] Add documentation on renderers - The "old" list, table and tree renderers + the new panel list renderer. | non_priority | add documentation on renderers the old list table and tree renderers the new panel list renderer | 0 |
142,475 | 5,475,616,507 | IssuesEvent | 2017-03-11 13:07:06 | cyberpwnn/GlacialRealms | https://api.github.com/repos/cyberpwnn/GlacialRealms | closed | /stats suggestion | 20 Minute ETA cosmetic enhancement low priority stale static | currently in /stats it displays your time online in the highest "category" you have reached. if you have no more than 24hrs it will display in hours, no more than 30d and it will display in days, and then it starts displaying in months, only increasing to the next month every 30d of game time. this is extremely annoyin... | 1.0 | /stats suggestion - currently in /stats it displays your time online in the highest "category" you have reached. if you have no more than 24hrs it will display in hours, no more than 30d and it will display in days, and then it starts displaying in months, only increasing to the next month every 30d of game time. this ... | priority | stats suggestion currently in stats it displays your time online in the highest category you have reached if you have no more than it will display in hours no more than and it will display in days and then it starts displaying in months only increasing to the next month every of game time this is extre... | 1 |
68,477 | 13,144,895,456 | IssuesEvent | 2020-08-08 00:35:38 | rathena/rathena | https://api.github.com/repos/rathena/rathena | closed | Removes waitingroom check for Maya Purple hackfix | component:script mode:prerenewal mode:renewal priority:low status:code-review type:bug | <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: 9991b09
* **Client Date**: 2018
* **Server Mode**: renewal
<!-- Which mode does your server use: Pre-Renewal or Renewal? -->
* **Description of Issue**: Job quest Waiting rooms are gone
![grafi... | 1.0 | Removes waitingroom check for Maya Purple hackfix - <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: 9991b09
* **Client Date**: 2018
* **Server Mode**: renewal
<!-- Which mode does your server use: Pre-Renewal or Renewal? -->
* **Description o... | non_priority | removes waitingroom check for maya purple hackfix rathena hash client date server mode renewal description of issue job quest waiting rooms are gone result while doing job quests the waiting room above npcs are gone and players cant progress during ... | 0 |
743,210 | 25,891,385,042 | IssuesEvent | 2022-12-14 18:14:48 | ramp4-pcar4/ramp4-pcar4 | https://api.github.com/repos/ramp4-pcar4/ramp4-pcar4 | opened | Geosearch service is dead | flavour: bug priority: must type: corrective | Geosearch no longer works 👎
The service returns a code 500 (internal server error) and the following message is in the console:
> Failed to load resource: the server responded with a status of 500 (Internal Server Error)
I guess we can't really do much about about the service. But if the URL breaks, we shoul... | 1.0 | Geosearch service is dead - Geosearch no longer works 👎
The service returns a code 500 (internal server error) and the following message is in the console:
> Failed to load resource: the server responded with a status of 500 (Internal Server Error)
I guess we can't really do much about about the service. But... | priority | geosearch service is dead geosearch no longer works 👎 the service returns a code internal server error and the following message is in the console failed to load resource the server responded with a status of internal server error i guess we can t really do much about about the service but if ... | 1 |
815,462 | 30,556,190,628 | IssuesEvent | 2023-07-20 11:52:42 | ubiquity/ubiquibot | https://api.github.com/repos/ubiquity/ubiquibot | closed | Query User Information (Wallet Address, Multiplier) | Time: <1 Hour Priority: 1 (Medium) Price: 37.5 USD | I have been doing some manual payouts lately and realized that sometimes it's nice to be able to quickly identify a user's `multiplier` and `wallet` address without superuser access to the global bot database!
We should have a new command to view a user's settings.
`/query @user`
Unless there is a better, mor... | 1.0 | Query User Information (Wallet Address, Multiplier) - I have been doing some manual payouts lately and realized that sometimes it's nice to be able to quickly identify a user's `multiplier` and `wallet` address without superuser access to the global bot database!
We should have a new command to view a user's setting... | priority | query user information wallet address multiplier i have been doing some manual payouts lately and realized that sometimes it s nice to be able to quickly identify a user s multiplier and wallet address without superuser access to the global bot database we should have a new command to view a user s setting... | 1 |
36,449 | 2,799,355,455 | IssuesEvent | 2015-05-12 23:58:54 | osulp/primo | https://api.github.com/repos/osulp/primo | reopened | Fix indenting issue when visiting a permalinked page | High Priority | The record is displayed on the right half of the page, leaving a large open area to the left.
Example:
http://search.library.oregonstate.edu/OSU:CP71137462960001451 | 1.0 | Fix indenting issue when visiting a permalinked page - The record is displayed on the right half of the page, leaving a large open area to the left.
Example:
http://search.library.oregonstate.edu/OSU:CP71137462960001451 | priority | fix indenting issue when visiting a permalinked page the record is displayed on the right half of the page leaving a large open area to the left example | 1 |
762,800 | 26,731,034,862 | IssuesEvent | 2023-01-30 04:31:35 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | read only user for the APIM Publisher portal | Type/New Feature Priority/Normal 4.x.x | ### Describe your problem(s)
The requirement is:
A user (internal developer) who has permission to only view the API details in the Publisher portal. The user should not be able to edit/create/publish APIs. The user should only be able to view the API configurations. And only "privileged users" (internal developer... | 1.0 | read only user for the APIM Publisher portal - ### Describe your problem(s)
The requirement is:
A user (internal developer) who has permission to only view the API details in the Publisher portal. The user should not be able to edit/create/publish APIs. The user should only be able to view the API configurations. ... | priority | read only user for the apim publisher portal describe your problem s the requirement is a user internal developer who has permission to only view the api details in the publisher portal the user should not be able to edit create publish apis the user should only be able to view the api configurations ... | 1 |
784,150 | 27,559,699,829 | IssuesEvent | 2023-03-07 20:52:36 | Vladyslav-Team/backend | https://api.github.com/repos/Vladyslav-Team/backend | opened | Add the ability to edit fields and save or delete changes only your account | lowPriority database backEnd | User must be authorized to change it's account
| 1.0 | Add the ability to edit fields and save or delete changes only your account - User must be authorized to change it's account
| priority | add the ability to edit fields and save or delete changes only your account user must be authorized to change it s account | 1 |
700,875 | 24,076,438,531 | IssuesEvent | 2022-09-18 21:21:56 | svelascodimate/demo | https://api.github.com/repos/svelascodimate/demo | opened | Create Project Structure | High Priority New Feature | # User Story
As a Project Lead, want to have a basic project structure on the repository so that Development Team could start making changes in the code.
# List of tasks
- [ ] Update Python
- [ ] Install nbdev on local machine
- [ ] Run command nbdev_new
- [ ] Modify settings.init
- [ ] Create Docker Fil... | 1.0 | Create Project Structure - # User Story
As a Project Lead, want to have a basic project structure on the repository so that Development Team could start making changes in the code.
# List of tasks
- [ ] Update Python
- [ ] Install nbdev on local machine
- [ ] Run command nbdev_new
- [ ] Modify settings.in... | priority | create project structure user story as a project lead want to have a basic project structure on the repository so that development team could start making changes in the code list of tasks update python install nbdev on local machine run command nbdev new modify settings init ... | 1 |
69,769 | 15,030,909,188 | IssuesEvent | 2021-02-02 08:12:23 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 98: gdk-pixbuf-2.40.0: 1 advisory [5.5] | 1.severity: security | [search](https://search.nix.gsc.io/?q=gdk-pixbuf&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=gdk-pixbuf+in%3Apath&type=Code)
* [ ] [CVE-2020-29385](https://nvd.nist.gov/vuln/detail/CVE-2020-29385) CVSSv3=5.5 (nixos-20.09)
Scanned versions: nixos-20.09: aa5b9cd16b9.
... | True | Vulnerability roundup 98: gdk-pixbuf-2.40.0: 1 advisory [5.5] - [search](https://search.nix.gsc.io/?q=gdk-pixbuf&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=gdk-pixbuf+in%3Apath&type=Code)
* [ ] [CVE-2020-29385](https://nvd.nist.gov/vuln/detail/CVE-2020-29385) CVSSv3=... | non_priority | vulnerability roundup gdk pixbuf advisory nixos scanned versions nixos cc cc edolstra cc hedning cc jtojnar cc worldofpeace | 0 |
453,208 | 13,066,561,936 | IssuesEvent | 2020-07-30 21:58:53 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.anilibria.tv - Switching the video to full-screen mode is faulty | browser-firefox-mobile engine-gecko priority-normal severity-important | <!-- @browser: Firefox Mobile 80.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:80.0) Gecko/80.0 Firefox/80.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/56022 -->
**URL**: https://www.anilibria.tv/release/black-clover.html
**Browser / Versio... | 1.0 | www.anilibria.tv - Switching the video to full-screen mode is faulty - <!-- @browser: Firefox Mobile 80.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:80.0) Gecko/80.0 Firefox/80.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/56022 -->
**URL**:... | priority | switching the video to full screen mode is faulty url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description the video on the website is not displayed correctly in full screen mode steps ... | 1 |
235,643 | 18,054,111,268 | IssuesEvent | 2021-09-20 05:01:26 | bstudios/adam-rms | https://api.github.com/repos/bstudios/adam-rms | opened | [DOCS] Various Documentation updates | documentation | ### What would you like the training to cover?
- [ ] Interface introduction (what do Icons mean etc)
- [ ] User account pages
- [ ] Linked asset documentation (child vs parent)
- [ ] Public Site
### Is this already partially covered elsewhere?
No
### Anything else?
_No response_ | 1.0 | [DOCS] Various Documentation updates - ### What would you like the training to cover?
- [ ] Interface introduction (what do Icons mean etc)
- [ ] User account pages
- [ ] Linked asset documentation (child vs parent)
- [ ] Public Site
### Is this already partially covered elsewhere?
No
### Anything else?
_No res... | non_priority | various documentation updates what would you like the training to cover interface introduction what do icons mean etc user account pages linked asset documentation child vs parent public site is this already partially covered elsewhere no anything else no response | 0 |
121,406 | 10,167,709,551 | IssuesEvent | 2019-08-07 18:54:16 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [test-failed]: X-Pack Chromium API Reporting Tests.x-pack/test/reporting/api/usage·js - chromium reporting usage from new jobs posted print_layout pdf | failed-test test-darwin | **Version: 7.3**
**Class: X-Pack Chromium API Reporting Tests.x-pack/test/reporting/api/usage·js**
**Stack Trace:**
[Error: Timeout of 360000ms exceeded. For async tests and hooks, ensure "done()" is called; if returning a Promise, ensure it resolves.]
_Platform: darwin_
_Build Num: 36_ | 2.0 | [test-failed]: X-Pack Chromium API Reporting Tests.x-pack/test/reporting/api/usage·js - chromium reporting usage from new jobs posted print_layout pdf - **Version: 7.3**
**Class: X-Pack Chromium API Reporting Tests.x-pack/test/reporting/api/usage·js**
**Stack Trace:**
[Error: Timeout of 360000ms exceeded. For... | non_priority | x pack chromium api reporting tests x pack test reporting api usage·js chromium reporting usage from new jobs posted print layout pdf version class x pack chromium api reporting tests x pack test reporting api usage·js stack trace platform darwin build num | 0 |
39,143 | 8,584,399,671 | IssuesEvent | 2018-11-13 22:39:10 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | Cross-language API/IDL support (GraphQL, Thrift, Protobuf) | feature:code-intel roadmap | We will be adding support for cross-language API/IDL systems to Sourcegraph, in order of priority:
- [GraphQL](https://sourcegraph.com/github.com/sourcegraph/about/-/blob/projects/graphql-sourcegraph-extension.md) (partially done)
- Thrift
- Protobuf
You will be able to see hovers with documentation, go to defi... | 1.0 | Cross-language API/IDL support (GraphQL, Thrift, Protobuf) - We will be adding support for cross-language API/IDL systems to Sourcegraph, in order of priority:
- [GraphQL](https://sourcegraph.com/github.com/sourcegraph/about/-/blob/projects/graphql-sourcegraph-extension.md) (partially done)
- Thrift
- Protobuf
... | non_priority | cross language api idl support graphql thrift protobuf we will be adding support for cross language api idl systems to sourcegraph in order of priority partially done thrift protobuf you will be able to see hovers with documentation go to definition find references etc in api idl defini... | 0 |
163,722 | 6,204,494,252 | IssuesEvent | 2017-07-06 14:20:10 | qutebrowser/qutebrowser | https://api.github.com/repos/qutebrowser/qutebrowser | closed | Clear temporary settings | component: config config revolution priority: 1 - middle | It would be nice to have a command to clear temporary settings (`set -t`) without having to restart the browser.
| 1.0 | Clear temporary settings - It would be nice to have a command to clear temporary settings (`set -t`) without having to restart the browser.
| priority | clear temporary settings it would be nice to have a command to clear temporary settings set t without having to restart the browser | 1 |
73,135 | 3,407,811,118 | IssuesEvent | 2015-12-04 06:26:59 | JukkaL/mypy | https://api.github.com/repos/JukkaL/mypy | closed | super() and multiple inheritance | bug priority | Mypy gives bogus complaints about missing attributes when using `super()` in a class with multiple bases. | 1.0 | super() and multiple inheritance - Mypy gives bogus complaints about missing attributes when using `super()` in a class with multiple bases. | priority | super and multiple inheritance mypy gives bogus complaints about missing attributes when using super in a class with multiple bases | 1 |
397,672 | 11,731,172,764 | IssuesEvent | 2020-03-10 23:16:19 | openforcefield/openforcefield | https://api.github.com/repos/openforcefield/openforcefield | closed | Constrain H-bond lengths by default in appropriate OFFXML files | effort:low priority:high | Per @cbayly13 's post: https://openforcefieldgroup.slack.com/archives/C9NGV68BY/p1548376758135600 :
> Given the provenance of SMIRNOFF99Frosst, being from amber-type simulation force fields routinely employing constraints on bonds to hydrogen, I think that should be the default for SMIRNOFF99Frosst too.
This shou... | 1.0 | Constrain H-bond lengths by default in appropriate OFFXML files - Per @cbayly13 's post: https://openforcefieldgroup.slack.com/archives/C9NGV68BY/p1548376758135600 :
> Given the provenance of SMIRNOFF99Frosst, being from amber-type simulation force fields routinely employing constraints on bonds to hydrogen, I think ... | priority | constrain h bond lengths by default in appropriate offxml files per s post given the provenance of being from amber type simulation force fields routinely employing constraints on bonds to hydrogen i think that should be the default for too this should certainly be applied to openforcefield d... | 1 |
638,803 | 20,738,735,084 | IssuesEvent | 2022-03-14 15:48:13 | LLK/scratchjr | https://api.github.com/repos/LLK/scratchjr | closed | Can't add reshape points to sharp triangle upper right border in the paint editor | priority 3 High Severity Low Impact Jira needed | ### Expected Behavior
Should add points where the mouse is up
### Actual Behavior
The paint editor add a point to the upper left border
### Steps to Reproduce
1. open the painter to create a new sprite
2. select the `triangle` shape tool
3. draw a sharp triangle, the angle of top corner is less than 30... | 1.0 | Can't add reshape points to sharp triangle upper right border in the paint editor - ### Expected Behavior
Should add points where the mouse is up
### Actual Behavior
The paint editor add a point to the upper left border
### Steps to Reproduce
1. open the painter to create a new sprite
2. select the `tri... | priority | can t add reshape points to sharp triangle upper right border in the paint editor expected behavior should add points where the mouse is up actual behavior the paint editor add a point to the upper left border steps to reproduce open the painter to create a new sprite select the tri... | 1 |
791,860 | 27,880,304,732 | IssuesEvent | 2023-03-21 18:51:40 | Parritz/LuaCompact | https://api.github.com/repos/Parritz/LuaCompact | opened | Add help command | enhancement low priority | **Is your feature request related to a problem? Please describe.**
There is currently no help command for people who don't remember a command.
**Describe the solution you'd like**
There should be a help command that describes what commands do, their arguments (if any), and their flags (if any). | 1.0 | Add help command - **Is your feature request related to a problem? Please describe.**
There is currently no help command for people who don't remember a command.
**Describe the solution you'd like**
There should be a help command that describes what commands do, their arguments (if any), and their flags (if any). | priority | add help command is your feature request related to a problem please describe there is currently no help command for people who don t remember a command describe the solution you d like there should be a help command that describes what commands do their arguments if any and their flags if any | 1 |
832,096 | 32,072,174,530 | IssuesEvent | 2023-09-25 08:43:58 | libre-tube/LibreTube | https://api.github.com/repos/libre-tube/LibreTube | closed | Lower quality when video isn't full screen | enhancement priority: low | ### Describe your suggested feature
The official YouTube app has an option to decrease video quality when a video it is not in full screen (usually this is portrait mode). This would be a worth while feature since it significantly reduces stress on Piped instances and users' personal data usage.
### Other details
_N... | 1.0 | Lower quality when video isn't full screen - ### Describe your suggested feature
The official YouTube app has an option to decrease video quality when a video it is not in full screen (usually this is portrait mode). This would be a worth while feature since it significantly reduces stress on Piped instances and users... | priority | lower quality when video isn t full screen describe your suggested feature the official youtube app has an option to decrease video quality when a video it is not in full screen usually this is portrait mode this would be a worth while feature since it significantly reduces stress on piped instances and users... | 1 |
76,404 | 9,437,708,232 | IssuesEvent | 2019-04-13 17:15:28 | whiteyhat/Lightning-Network-Simulator | https://api.github.com/repos/whiteyhat/Lightning-Network-Simulator | closed | Create UML Diagrams | Design enhancement | Design behavioural and structural diagrams using the UML standard. The diagrams should contain enough design insights about the internal architecture of the lightning network simulator.
### Structural UML Diagrams
- [x] UML Class Diagram
- [ ] UML Object Diagram
### Behavioural UML Diagrams
- [x] UML Use Case ... | 1.0 | Create UML Diagrams - Design behavioural and structural diagrams using the UML standard. The diagrams should contain enough design insights about the internal architecture of the lightning network simulator.
### Structural UML Diagrams
- [x] UML Class Diagram
- [ ] UML Object Diagram
### Behavioural UML Diagram... | non_priority | create uml diagrams design behavioural and structural diagrams using the uml standard the diagrams should contain enough design insights about the internal architecture of the lightning network simulator structural uml diagrams uml class diagram uml object diagram behavioural uml diagrams ... | 0 |
632,711 | 20,205,134,614 | IssuesEvent | 2022-02-11 19:24:14 | googleapis/gapic-generator-python | https://api.github.com/repos/googleapis/gapic-generator-python | opened | Refactor unit test templates | type: feature request priority: p3 | Currently, unit tests in templates code are all concentrated in a single file `test_%service.py.j2`. The file has 3K lines and should be refactored.
One idea is to refactor across two dimensions: transport and sync/async (cc @software-dov). It's a big effort, so perhaps a smaller task is to first identify the commo... | 1.0 | Refactor unit test templates - Currently, unit tests in templates code are all concentrated in a single file `test_%service.py.j2`. The file has 3K lines and should be refactored.
One idea is to refactor across two dimensions: transport and sync/async (cc @software-dov). It's a big effort, so perhaps a smaller task... | priority | refactor unit test templates currently unit tests in templates code are all concentrated in a single file test service py the file has lines and should be refactored one idea is to refactor across two dimensions transport and sync async cc software dov it s a big effort so perhaps a smaller task i... | 1 |
168,453 | 20,764,218,919 | IssuesEvent | 2022-03-15 19:02:09 | husnuljahneer/next-js-cartio | https://api.github.com/repos/husnuljahneer/next-js-cartio | opened | next-11.0.1.tgz: 6 vulnerabilities (highest severity is: 7.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>next-11.0.1.tgz</b></p></summary>
<p>The React Framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/next/-/next-11.0.1.tgz">https://registry.npmjs.... | True | next-11.0.1.tgz: 6 vulnerabilities (highest severity is: 7.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>next-11.0.1.tgz</b></p></summary>
<p>The React Framework</p>
<p>Library home page: <a href="https://re... | non_priority | next tgz vulnerabilities highest severity is vulnerable library next tgz the react framework library home page a href found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available ... | 0 |
210,902 | 16,389,505,355 | IssuesEvent | 2021-05-17 14:30:38 | kubernetes/sig-release | https://api.github.com/repos/kubernetes/sig-release | closed | Cut v1.19.11 release | area/release-eng kind/documentation priority/important-soon sig/release | ## Scheduled to happen: Wed, 2021-05-12
## Release Blocking Issues
<!--
Make a list of anything preventing the release to start
(failing tests, pending image bumps, etc) and link them
to the relevant GitHub issues:
- [ ] Issue 1
- [ ] Issue 2
-->
<!--
Release Process Steps:
======================... | 1.0 | Cut v1.19.11 release - ## Scheduled to happen: Wed, 2021-05-12
## Release Blocking Issues
<!--
Make a list of anything preventing the release to start
(failing tests, pending image bumps, etc) and link them
to the relevant GitHub issues:
- [ ] Issue 1
- [ ] Issue 2
-->
<!--
Release Process Steps:
... | non_priority | cut release scheduled to happen wed release blocking issues make a list of anything preventing the release to start failing tests pending image bumps etc and link them to the relevant github issues issue issue release process steps ... | 0 |
613,997 | 19,103,217,493 | IssuesEvent | 2021-11-30 02:17:18 | hadialaddin/crypto-genie | https://api.github.com/repos/hadialaddin/crypto-genie | closed | Enforce Take Profits feature | enhancement high-priority | Set Profit ratios at which to close partial position size (ratio). Bot should automatically calculate the quantity in real-time based on up-to-date position size, and auto adjust TP size and price levels should position change its size or entry price (so should react to manual take profit or loss).
Allow Tolerance w... | 1.0 | Enforce Take Profits feature - Set Profit ratios at which to close partial position size (ratio). Bot should automatically calculate the quantity in real-time based on up-to-date position size, and auto adjust TP size and price levels should position change its size or entry price (so should react to manual take profit... | priority | enforce take profits feature set profit ratios at which to close partial position size ratio bot should automatically calculate the quantity in real time based on up to date position size and auto adjust tp size and price levels should position change its size or entry price so should react to manual take profit... | 1 |
262,167 | 8,251,778,307 | IssuesEvent | 2018-09-12 08:52:48 | orbs-network/orbs-network-go | https://api.github.com/repos/orbs-network/orbs-network-go | closed | System gets choked up after a "long" time of running | bug help wanted high priority | System gets stuck after a while when running full steam on idle
### To see it in E2E:
Add the line
```
time.Sleep(10 * time.Second)
```
right before e2e is sending the 3 transactions.
The system in e2e should close an empty block every ~ 1 second (config setting `ConsensusContextMinimalBlockDelay`).
... | 1.0 | System gets choked up after a "long" time of running - System gets stuck after a while when running full steam on idle
### To see it in E2E:
Add the line
```
time.Sleep(10 * time.Second)
```
right before e2e is sending the 3 transactions.
The system in e2e should close an empty block every ~ 1 second (... | priority | system gets choked up after a long time of running system gets stuck after a while when running full steam on idle to see it in add the line time sleep time second right before is sending the transactions the system in should close an empty block every second config ... | 1 |
421,394 | 12,256,550,090 | IssuesEvent | 2020-05-06 12:17:47 | HabitRPG/habitica | https://api.github.com/repos/HabitRPG/habitica | closed | Reset should unassign Stat Points (previously known as Attribute Points) | good first issue priority: medium section: Settings status: issue: in progress | When you use [Reset Account](https://habitica.fandom.com/wiki/Settings#Reset_Account) (from User Icon > Settings > "Danger Zone" section), it correctly sets your Level to 1 but it does not reset your Stat Points. It should reset them as described below.
Ideally we'd fix this with the generic function described at ht... | 1.0 | Reset should unassign Stat Points (previously known as Attribute Points) - When you use [Reset Account](https://habitica.fandom.com/wiki/Settings#Reset_Account) (from User Icon > Settings > "Danger Zone" section), it correctly sets your Level to 1 but it does not reset your Stat Points. It should reset them as describe... | priority | reset should unassign stat points previously known as attribute points when you use from user icon settings danger zone section it correctly sets your level to but it does not reset your stat points it should reset them as described below ideally we d fix this with the generic function described... | 1 |
4,576 | 3,872,817,592 | IssuesEvent | 2016-04-11 15:01:50 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 22497026: SFSafariViewController should tint progress bar | classification:ui/usability reproducible:always status:open | #### Description
SFSafariViewController nicely tints the button colors if a tint color is configured.. However, the progress bar is always blue. This doesn't fit well.
-
Product Version: 9.0 beta 5
Created: 2015-08-31T08:38:49.673270
Originated: 2015-08-31T11:38:00
Open Radar Link: http://www.openradar.me/22497026 | True | 22497026: SFSafariViewController should tint progress bar - #### Description
SFSafariViewController nicely tints the button colors if a tint color is configured.. However, the progress bar is always blue. This doesn't fit well.
-
Product Version: 9.0 beta 5
Created: 2015-08-31T08:38:49.673270
Originated: 2015-08-31T1... | non_priority | sfsafariviewcontroller should tint progress bar description sfsafariviewcontroller nicely tints the button colors if a tint color is configured however the progress bar is always blue this doesn t fit well product version beta created originated open radar link | 0 |
573,097 | 17,023,589,158 | IssuesEvent | 2021-07-03 02:48:25 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Prevent duplicate posting on diary comments | Component: website Priority: trivial Resolution: wontfix Type: enhancement | **[Submitted to the original trac issue database at 3.24pm, Wednesday, 12th May 2010]**
Loads of people post duplicate diary comments. I'm sure there will be a funky thing in rails to either prevent duplicate submissions, or we should just prevent people from posting the same text anyway | 1.0 | Prevent duplicate posting on diary comments - **[Submitted to the original trac issue database at 3.24pm, Wednesday, 12th May 2010]**
Loads of people post duplicate diary comments. I'm sure there will be a funky thing in rails to either prevent duplicate submissions, or we should just prevent people from posting the s... | priority | prevent duplicate posting on diary comments loads of people post duplicate diary comments i m sure there will be a funky thing in rails to either prevent duplicate submissions or we should just prevent people from posting the same text anyway | 1 |
596,007 | 18,094,129,014 | IssuesEvent | 2021-09-22 07:05:39 | gardener/gardener | https://api.github.com/repos/gardener/gardener | closed | `botanist.WaitUntilTunnelConnectionExists` step is failing right away on transient errors | kind/bug area/quality priority/3 | **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also state the commands multiple times... | 1.0 | `botanist.WaitUntilTunnelConnectionExists` step is failing right away on transient errors - **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your... | priority | botanist waituntiltunnelconnectionexists step is failing right away on transient errors how to categorize this issue please select area kind and priority for this issue this helps the community categorizing it replace below todos or exchange the existing identifiers with those that fit best in your... | 1 |
85,128 | 3,686,858,991 | IssuesEvent | 2016-02-25 04:07:03 | SoylentNews/rehash | https://api.github.com/repos/SoylentNews/rehash | closed | Poll page title incorrect | Bug: Non-Critical Priority: Normal | _From @cc158981bce50e050022f4ab8f113ece on July 27, 2014 22:49_
Some polls have the wrong <title>. At first I thought it was the most recent poll's title or the last visited poll's title but it appears to be random. Some kind of caching problem?
To recreate visit http://dev.soylentnews.org/pollBooth.pl, click... | 1.0 | Poll page title incorrect - _From @cc158981bce50e050022f4ab8f113ece on July 27, 2014 22:49_
Some polls have the wrong <title>. At first I thought it was the most recent poll's title or the last visited poll's title but it appears to be random. Some kind of caching problem?
To recreate visit http://dev.soylent... | priority | poll page title incorrect from on july some polls have the wrong lt title gt at first i thought it was the most recent poll s title or the last visited poll s title but it appears to be random some kind of caching problem to recreate visit click on a poll the page lt title gt s seem to be r... | 1 |
19,996 | 26,470,032,388 | IssuesEvent | 2023-01-17 06:10:33 | nion-software/nionswift | https://api.github.com/repos/nion-software/nionswift | opened | Processing data should also retain some graphic properties | type - enhancement f - user-interface f - processing | BPS 2021-06-17: I think things would go smoother if the display properties (log display, color map) are maintained on a new data item that is generated from applying a function.
CM note: I'm not sure this can happen in all cases, but like metadata, there should be a defined set of processing operations where it does... | 1.0 | Processing data should also retain some graphic properties - BPS 2021-06-17: I think things would go smoother if the display properties (log display, color map) are maintained on a new data item that is generated from applying a function.
CM note: I'm not sure this can happen in all cases, but like metadata, there s... | non_priority | processing data should also retain some graphic properties bps i think things would go smoother if the display properties log display color map are maintained on a new data item that is generated from applying a function cm note i m not sure this can happen in all cases but like metadata there should... | 0 |
234,399 | 19,178,636,123 | IssuesEvent | 2021-12-04 02:16:40 | itzg/docker-minecraft-server | https://api.github.com/repos/itzg/docker-minecraft-server | closed | multiarch-latest fails to run | status/ready to test status/stale | Hi,
2021.20.0-multiarch-latest is running fine, after update the server does not run anymore:
`Downloading minecraft_server.[0.003s][error][cds]_Unable_to_map_CDS_archive_--_os::vm_allocation_granularity()_expected:_4096_actual:_65536`
Any ideas what is going on?
Best regards,
hansnull | 1.0 | multiarch-latest fails to run - Hi,
2021.20.0-multiarch-latest is running fine, after update the server does not run anymore:
`Downloading minecraft_server.[0.003s][error][cds]_Unable_to_map_CDS_archive_--_os::vm_allocation_granularity()_expected:_4096_actual:_65536`
Any ideas what is going on?
Best regards,
h... | non_priority | multiarch latest fails to run hi multiarch latest is running fine after update the server does not run anymore downloading minecraft server unable to map cds archive os vm allocation granularity expected actual any ideas what is going on best regards hansnull | 0 |
173,739 | 14,435,986,301 | IssuesEvent | 2020-12-07 09:30:59 | kinvolk/lokomotive | https://api.github.com/repos/kinvolk/lokomotive | opened | Linkerd and Istio PSP docs | area/components area/security kind/documentation | Apps that are meshed by either of the above service mesh components need elevated permissions. So document that if a user is meshing their application they should also add following PSP config:
```yaml
apiVersion: policy/v1beta1
kind: PodSecurityPolicy
metadata:
name: appname
spec:
allowPrivilegeEscalation... | 1.0 | Linkerd and Istio PSP docs - Apps that are meshed by either of the above service mesh components need elevated permissions. So document that if a user is meshing their application they should also add following PSP config:
```yaml
apiVersion: policy/v1beta1
kind: PodSecurityPolicy
metadata:
name: appname
spec... | non_priority | linkerd and istio psp docs apps that are meshed by either of the above service mesh components need elevated permissions so document that if a user is meshing their application they should also add following psp config yaml apiversion policy kind podsecuritypolicy metadata name appname spec a... | 0 |
772,689 | 27,132,166,714 | IssuesEvent | 2023-02-16 10:32:51 | oceanprotocol/ocean.py | https://api.github.com/repos/oceanprotocol/ocean.py | closed | Document bundled asset creation + pricing schema in readmes | Type: Enhancement Priority: Mid | As part of #1166 we introduced the option of creating assets + pricing schemas. I bundled NFT+ERC20 either way for `create_<type>_asset` functions, which will save gas and do just one transaction, but the pricing schema part is optional and not that visible unless users find it in the tests.
We need to showcase thes... | 1.0 | Document bundled asset creation + pricing schema in readmes - As part of #1166 we introduced the option of creating assets + pricing schemas. I bundled NFT+ERC20 either way for `create_<type>_asset` functions, which will save gas and do just one transaction, but the pricing schema part is optional and not that visible ... | priority | document bundled asset creation pricing schema in readmes as part of we introduced the option of creating assets pricing schemas i bundled nft either way for create asset functions which will save gas and do just one transaction but the pricing schema part is optional and not that visible unless users... | 1 |
236,976 | 18,149,039,199 | IssuesEvent | 2021-09-26 00:49:15 | element-plus/element-plus | https://api.github.com/repos/element-plus/element-plus | closed | [Feature Request] Select V2 virtualized does not support case insensitive | documentation | <!-- generated by https://elementui.github.io/issue-generator DO NOT REMOVE -->
### Existing Component
Yes
### Component Name
el-select-v2
### Description
This component is supported the filterable with case sensitive, I think it should support case insensitive like v1 or could we have a custom filter metho... | 1.0 | [Feature Request] Select V2 virtualized does not support case insensitive - <!-- generated by https://elementui.github.io/issue-generator DO NOT REMOVE -->
### Existing Component
Yes
### Component Name
el-select-v2
### Description
This component is supported the filterable with case sensitive, I think it sh... | non_priority | select virtualized does not support case insensitive existing component yes component name el select description this component is supported the filterable with case sensitive i think it should support case insensitive like or could we have a custom filter method | 0 |
100,184 | 16,486,679,572 | IssuesEvent | 2021-05-24 19:05:12 | CrazyKidJack/WebGoat_2.0_clone | https://api.github.com/repos/CrazyKidJack/WebGoat_2.0_clone | opened | CVE-2019-11358 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-3.3.1.tgz</b>, <b>jquery-2.2.3.js</b></p></summary>
<p>
<details><summary><b>jq... | True | CVE-2019-11358 (Medium) detected in multiple libraries - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.1.4.min.js</b>, <b>jquery-3.3.1.tgz</b>, <b>jquer... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries jquery min js jquery tgz jquery js jquery min js javascript library for dom operations library home page a href path to dependency file webgoat ... | 0 |
548,196 | 16,060,005,734 | IssuesEvent | 2021-04-23 11:08:10 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.bbc.com - site is not usable | browser-safari os-mac priority-critical | <!-- @browser: Safari 13.1 -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_4) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.1 Safari/605.1.15 -->
<!-- @reported_with: mobile-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/71159 -->
**URL**: https://www.bbc.com/future... | 1.0 | www.bbc.com - site is not usable - <!-- @browser: Safari 13.1 -->
<!-- @ua_header: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_4) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/13.1 Safari/605.1.15 -->
<!-- @reported_with: mobile-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/71159 -->
... | priority | site is not usable url browser version safari operating system mac os x tested another browser yes other problem type site is not usable description browser unsupported steps to reproduce it annoy be opened and there was only a picture of a loading c ... | 1 |
75,735 | 14,517,546,830 | IssuesEvent | 2020-12-13 20:02:58 | sanskrit-lexicon/csl-pywork | https://api.github.com/repos/sanskrit-lexicon/csl-pywork | closed | templates and constants | code-cleanup documentation | This comment begins my review and extension of the initial classification work for the modules of pywork.
The idea of csl-pywork is similar to that of csl-websanlexicon. The repository should contain programs and data files required to regenerate the pywork directories for the individual dictionaries. Thus, th... | 1.0 | templates and constants - This comment begins my review and extension of the initial classification work for the modules of pywork.
The idea of csl-pywork is similar to that of csl-websanlexicon. The repository should contain programs and data files required to regenerate the pywork directories for the individu... | non_priority | templates and constants this comment begins my review and extension of the initial classification work for the modules of pywork the idea of csl pywork is similar to that of csl websanlexicon the repository should contain programs and data files required to regenerate the pywork directories for the individu... | 0 |
334,791 | 24,438,228,277 | IssuesEvent | 2022-10-06 13:00:25 | Aditya-Gupta1/job-application-cli | https://api.github.com/repos/Aditya-Gupta1/job-application-cli | closed | Add a custom badge for SQLAlchemy in README's tech stack section | documentation good first issue hacktoberfest | Create a badge for SQLAlchemy using its logo and put it under the `Tech Stack` section.
Image: https://www.sqlalchemy.org/img/sqla_logo.png
Tools like shields.io or any other relevant tools can be used to create a custom badge (Just like already mentioned in the README)
Steps:
1. Go to https://shields.io/
... | 1.0 | Add a custom badge for SQLAlchemy in README's tech stack section - Create a badge for SQLAlchemy using its logo and put it under the `Tech Stack` section.
Image: https://www.sqlalchemy.org/img/sqla_logo.png
Tools like shields.io or any other relevant tools can be used to create a custom badge (Just like already m... | non_priority | add a custom badge for sqlalchemy in readme s tech stack section create a badge for sqlalchemy using its logo and put it under the tech stack section image tools like shields io or any other relevant tools can be used to create a custom badge just like already mentioned in the readme steps go ... | 0 |
75,307 | 9,220,326,003 | IssuesEvent | 2019-03-11 17:14:57 | OpenEnergyPlatform/oeplatform | https://api.github.com/repos/OpenEnergyPlatform/oeplatform | opened | Create a sympathetic mascot for the OEP | Content Minor Time-S Urgency-S design/layout enhancement | We decided for the [Platypus](https://en.wikipedia.org/wiki/Platypus). Because it is super sweet and the names match. | 1.0 | Create a sympathetic mascot for the OEP - We decided for the [Platypus](https://en.wikipedia.org/wiki/Platypus). Because it is super sweet and the names match. | non_priority | create a sympathetic mascot for the oep we decided for the because it is super sweet and the names match | 0 |
12,455 | 7,882,621,720 | IssuesEvent | 2018-06-26 23:44:40 | bitshares/bitshares-core | https://api.github.com/repos/bitshares/bitshares-core | opened | Performance improvement: object database query caching? | 1a Epic 2a Discussion Needed 6 Performance performance | Most of data stored in the object database is in a red-black tree. Currently, every query searches from the root to the leaf, the complexity is `O(log(n))`. Generally, some data is much hotter than others, so it makes sense to cache the hottest results (pointers or addresses) to avoid searching from root to leaf for sa... | True | Performance improvement: object database query caching? - Most of data stored in the object database is in a red-black tree. Currently, every query searches from the root to the leaf, the complexity is `O(log(n))`. Generally, some data is much hotter than others, so it makes sense to cache the hottest results (pointers... | non_priority | performance improvement object database query caching most of data stored in the object database is in a red black tree currently every query searches from the root to the leaf the complexity is o log n generally some data is much hotter than others so it makes sense to cache the hottest results pointers... | 0 |
621,146 | 19,578,814,970 | IssuesEvent | 2022-01-04 18:24:18 | mskcc/pluto-cwl | https://api.github.com/repos/mskcc/pluto-cwl | opened | need to update samples fillout workflow output | high priority | - need to update all portal files to include data for all new DMP samples included in output
@timosong @svural | 1.0 | need to update samples fillout workflow output - - need to update all portal files to include data for all new DMP samples included in output
@timosong @svural | priority | need to update samples fillout workflow output need to update all portal files to include data for all new dmp samples included in output timosong svural | 1 |
60,848 | 17,023,538,631 | IssuesEvent | 2021-07-03 02:32:22 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Search for street with number doesn't work if there is no number entry | Component: nominatim Priority: minor Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 10.47am, Wednesday, 13th January 2010]**
If you search for the street and the house number you don't get a result cause there is no entry for the number. If this fails you should just search for the street that you get at least a result on the map. | 1.0 | Search for street with number doesn't work if there is no number entry - **[Submitted to the original trac issue database at 10.47am, Wednesday, 13th January 2010]**
If you search for the street and the house number you don't get a result cause there is no entry for the number. If this fails you should just search for... | non_priority | search for street with number doesn t work if there is no number entry if you search for the street and the house number you don t get a result cause there is no entry for the number if this fails you should just search for the street that you get at least a result on the map | 0 |
55,439 | 23,470,761,726 | IssuesEvent | 2022-08-16 21:33:30 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | AWS Opsworks Errors on 'apply' when updating custom json | bug service/opsworks | I'm opening this to resurrect: https://github.com/hashicorp/terraform-provider-aws/issues/376. Please see the original ticket description below.
I've been able to reproduce this using terraform v1.0.2 and v3.49.0 of the aws provider. It's important to note that the issue is only encountered when making an update to ... | 1.0 | AWS Opsworks Errors on 'apply' when updating custom json - I'm opening this to resurrect: https://github.com/hashicorp/terraform-provider-aws/issues/376. Please see the original ticket description below.
I've been able to reproduce this using terraform v1.0.2 and v3.49.0 of the aws provider. It's important to note t... | non_priority | aws opsworks errors on apply when updating custom json i m opening this to resurrect please see the original ticket description below i ve been able to reproduce this using terraform and of the aws provider it s important to note that the issue is only encountered when making an update to the op... | 0 |
3,117 | 2,665,569,835 | IssuesEvent | 2015-03-20 21:26:22 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | VB SemanticModel.GetEnclosingSymbol doesn't work correctly with lambda parameters/headers | 4 - In Review Area-Compilers Bug Resolution-By Design | Consider code
```VB
Imports System
Class C
Sub F()
Dim f1 = New Func(Of Integer, Integer, Integer)(
Function(a1, a2)
Return a1
End Function)
End Sub
End Class
```
SemanticModel.GetEnclosingSymbol(span start of ParameterSyntax "a1" )
returns Sub F.... | 1.0 | VB SemanticModel.GetEnclosingSymbol doesn't work correctly with lambda parameters/headers - Consider code
```VB
Imports System
Class C
Sub F()
Dim f1 = New Func(Of Integer, Integer, Integer)(
Function(a1, a2)
Return a1
End Function)
End Sub
End Class
... | non_priority | vb semanticmodel getenclosingsymbol doesn t work correctly with lambda parameters headers consider code vb imports system class c sub f dim new func of integer integer integer function return end function end sub end class ... | 0 |
413,325 | 12,065,070,260 | IssuesEvent | 2020-04-16 09:21:14 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.loteriasonline.caixa.gov.br - see bug description | browser-focus-geckoview engine-gecko priority-important | <!-- @browser: Firefox Mobile 75.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.1.1; Mobile; rv:75.0) Gecko/75.0 Firefox/75.0 -->
<!-- @reported_with: -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/51685 -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https://www.loteriasonline.caixa.g... | 1.0 | www.loteriasonline.caixa.gov.br - see bug description - <!-- @browser: Firefox Mobile 75.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 7.1.1; Mobile; rv:75.0) Gecko/75.0 Firefox/75.0 -->
<!-- @reported_with: -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/51685 -->
<!-- @extra_labels: browser-focus-ge... | priority | see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description blank page steps to reproduce i just tried tô access the site browser configuration non... | 1 |
230,837 | 7,620,151,415 | IssuesEvent | 2018-05-03 00:45:50 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | Crash while harvesting | High Priority | Der Wert darf nicht NULL sein.
The value can not be NULL.
Parametername: key
bei System.ThrowHelper.ThrowArgumentNullException(ExceptionArgument argument)
bei System.Collections.Generic.Dictionary`2.FindEntry(TKey key)
bei System.Collections.Generic.Dictionary`2.TryGetValue(TKey key, TValue& value)
be... | 1.0 | Crash while harvesting - Der Wert darf nicht NULL sein.
The value can not be NULL.
Parametername: key
bei System.ThrowHelper.ThrowArgumentNullException(ExceptionArgument argument)
bei System.Collections.Generic.Dictionary`2.FindEntry(TKey key)
bei System.Collections.Generic.Dictionary`2.TryGetValue(TKey k... | priority | crash while harvesting der wert darf nicht null sein the value can not be null parametername key bei system throwhelper throwargumentnullexception exceptionargument argument bei system collections generic dictionary findentry tkey key bei system collections generic dictionary trygetvalue tkey k... | 1 |
549,417 | 16,092,313,670 | IssuesEvent | 2021-04-26 18:18:25 | microsoft/CSS-Exchange | https://api.github.com/repos/microsoft/CSS-Exchange | opened | ExchangeLogCollector - Build out a table for DAG information | Exchange Log Collector Low Priority Need Investigation enhancement | Build out a nice table view of DAG information
DAG Name:
FSW:
FSW IP Address:
FSW Site:
NODES/Members
ServerName | IP Addresses | Site
Maybe even do a path ping from the node to the FSW and a node in the other site/subnet. | 1.0 | ExchangeLogCollector - Build out a table for DAG information - Build out a nice table view of DAG information
DAG Name:
FSW:
FSW IP Address:
FSW Site:
NODES/Members
ServerName | IP Addresses | Site
Maybe even do a path ping from the node to the FSW and a node in the other site/subnet. | priority | exchangelogcollector build out a table for dag information build out a nice table view of dag information dag name fsw fsw ip address fsw site nodes members servername ip addresses site maybe even do a path ping from the node to the fsw and a node in the other site subnet | 1 |
153,415 | 5,891,879,972 | IssuesEvent | 2017-05-17 18:08:10 | facebook/prepack | https://api.github.com/repos/facebook/prepack | closed | Support serialization of DataView, ArrayBuffer | help wanted high priority serializer | Make serialization work for the related cluster of DataView, ArrayBuffer, and all typed arrays.
Add individual test cases for the different required aspects.
Look at #505 for an example of how to add serialization capabilities for typed arrays. | 1.0 | Support serialization of DataView, ArrayBuffer - Make serialization work for the related cluster of DataView, ArrayBuffer, and all typed arrays.
Add individual test cases for the different required aspects.
Look at #505 for an example of how to add serialization capabilities for typed arrays. | priority | support serialization of dataview arraybuffer make serialization work for the related cluster of dataview arraybuffer and all typed arrays add individual test cases for the different required aspects look at for an example of how to add serialization capabilities for typed arrays | 1 |
784,362 | 27,567,749,342 | IssuesEvent | 2023-03-08 06:13:50 | DeadlyBossMods/DBM-Dungeons | https://api.github.com/repos/DeadlyBossMods/DBM-Dungeons | closed | Add warning for 'Shadow Prison' spell in Cataclysm Blackrock Caverns | 🛠 Feature Request Low Priority | Hi! While this is not a super important thing but I think putting a very loud warning for [Shadow Prison](https://www.wowhead.com/spell=76686) spell would be good cause currently this ability is one-shotting people if they move out of the barely visible prison. DBM does not warn about this spell at all so a lot of peop... | 1.0 | Add warning for 'Shadow Prison' spell in Cataclysm Blackrock Caverns - Hi! While this is not a super important thing but I think putting a very loud warning for [Shadow Prison](https://www.wowhead.com/spell=76686) spell would be good cause currently this ability is one-shotting people if they move out of the barely vis... | priority | add warning for shadow prison spell in cataclysm blackrock caverns hi while this is not a super important thing but i think putting a very loud warning for spell would be good cause currently this ability is one shotting people if they move out of the barely visible prison dbm does not warn about this spell a... | 1 |
17,083 | 22,587,525,965 | IssuesEvent | 2022-06-28 16:29:15 | GoogleCloudPlatform/emblem | https://api.github.com/repos/GoogleCloudPlatform/emblem | opened | New Process: Merger verifies staging | type: process priority: p0 persona: maintainer | Adopt & document a new process that either the PR author or merger must verify a change is shipped to staging as expected, or reopen / create an issue to mark that a change didn't deploy as expected.
This will ensure changes ship as expected, indicating the implementation is complete. | 1.0 | New Process: Merger verifies staging - Adopt & document a new process that either the PR author or merger must verify a change is shipped to staging as expected, or reopen / create an issue to mark that a change didn't deploy as expected.
This will ensure changes ship as expected, indicating the implementation is co... | non_priority | new process merger verifies staging adopt document a new process that either the pr author or merger must verify a change is shipped to staging as expected or reopen create an issue to mark that a change didn t deploy as expected this will ensure changes ship as expected indicating the implementation is co... | 0 |
34,323 | 6,311,205,850 | IssuesEvent | 2017-07-23 17:24:45 | marienfressinaud/project-zero | https://api.github.com/repos/marienfressinaud/project-zero | closed | Document new release | P: Medium T: Documentation | - open a new ticket (such as https://github.com/marienfressinaud/project-zero/issues/59)
- Generate lines with:
```bash
$ git log --pretty=format:%s --first-parent --reverse [last tag]..HEAD | grep add:
$ git log --pretty=format:%s --first-parent --reverse [last tag]..HEAD | grep fix:
$ git log --pretty=format:%... | 1.0 | Document new release - - open a new ticket (such as https://github.com/marienfressinaud/project-zero/issues/59)
- Generate lines with:
```bash
$ git log --pretty=format:%s --first-parent --reverse [last tag]..HEAD | grep add:
$ git log --pretty=format:%s --first-parent --reverse [last tag]..HEAD | grep fix:
$ gi... | non_priority | document new release open a new ticket such as generate lines with bash git log pretty format s first parent reverse head grep add git log pretty format s first parent reverse head grep fix git log pretty format s first parent reverse head grep doc ... | 0 |
21,363 | 2,639,601,682 | IssuesEvent | 2015-03-11 03:40:21 | cs2103jan2015-w13-4j/main | https://api.github.com/repos/cs2103jan2015-w13-4j/main | closed | As an advanced user, I can link other GTD tools to the program | priority.low type.story | ... so that I can have one centralized tool without adding all previous tasks | 1.0 | As an advanced user, I can link other GTD tools to the program - ... so that I can have one centralized tool without adding all previous tasks | priority | as an advanced user i can link other gtd tools to the program so that i can have one centralized tool without adding all previous tasks | 1 |
159,510 | 20,068,288,812 | IssuesEvent | 2022-02-04 01:07:52 | emilwareus/spring-boot | https://api.github.com/repos/emilwareus/spring-boot | opened | CVE-2022-23437 (Medium) detected in xercesImpl-2.12.0.jar | security vulnerability | ## CVE-2022-23437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.12.0.jar</b></p></summary>
<p>Xerces2 is the next generation of high performance, fully compliant XML p... | True | CVE-2022-23437 (Medium) detected in xercesImpl-2.12.0.jar - ## CVE-2022-23437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xercesImpl-2.12.0.jar</b></p></summary>
<p>Xerces2 is th... | non_priority | cve medium detected in xercesimpl jar cve medium severity vulnerability vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interf... | 0 |
267,359 | 8,388,127,615 | IssuesEvent | 2018-10-09 04:36:16 | WP-for-Church/Sermon-Manager | https://api.github.com/repos/WP-for-Church/Sermon-Manager | opened | Books not importing with SB sermons | [Priority] Standard [Type] Enhancement | And that's because those fields don't exist in SB.
Client's idea: Try to guess the book based on scripture. | 1.0 | Books not importing with SB sermons - And that's because those fields don't exist in SB.
Client's idea: Try to guess the book based on scripture. | priority | books not importing with sb sermons and that s because those fields don t exist in sb client s idea try to guess the book based on scripture | 1 |
290,681 | 8,902,604,605 | IssuesEvent | 2019-01-17 08:08:03 | canonical-websites/snapcraft.io | https://api.github.com/repos/canonical-websites/snapcraft.io | closed | Release UI: HTML errors result in JSON parse error | Priority: High | Sometimes API calls for release return HTML instead of JSON (for example in case of gateway timeout, etc). This causes release UI to show weird and unhelpful JSON parse error.
<img width="1663" alt="screen shot 2018-10-03 at 12 58 45" src="https://user-images.githubusercontent.com/83575/46406577-4a024d80-c70c-11e8-9... | 1.0 | Release UI: HTML errors result in JSON parse error - Sometimes API calls for release return HTML instead of JSON (for example in case of gateway timeout, etc). This causes release UI to show weird and unhelpful JSON parse error.
<img width="1663" alt="screen shot 2018-10-03 at 12 58 45" src="https://user-images.gith... | priority | release ui html errors result in json parse error sometimes api calls for release return html instead of json for example in case of gateway timeout etc this causes release ui to show weird and unhelpful json parse error img width alt screen shot at src expected behaviour we s... | 1 |
263,342 | 28,029,995,804 | IssuesEvent | 2023-03-28 11:45:29 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | reopened | CVE-2021-3411 (Medium) detected in linux-yocto-devv5.3 | Mend: dependency security vulnerability | ## CVE-2021-3411 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv5.3</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library ... | True | CVE-2021-3411 (Medium) detected in linux-yocto-devv5.3 - ## CVE-2021-3411 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv5.3</b></p></summary>
<p>
<p>Linux Embedded ... | non_priority | cve medium detected in linux yocto cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel tracks the next mainline release library home page a href found in base branch amp centos kernel vulnerable source files ... | 0 |
55,537 | 13,638,836,019 | IssuesEvent | 2020-09-25 09:59:20 | TerryCavanagh/diceydungeonsbeta | https://api.github.com/repos/TerryCavanagh/diceydungeonsbeta | closed | Rethink Gym Leader in Parallel Universe | v0.5: 21st June Build | This one's not so bad, but an extra 6 damage isn't really interesting to fight against in the way the Weaken 3 is. | 1.0 | Rethink Gym Leader in Parallel Universe - This one's not so bad, but an extra 6 damage isn't really interesting to fight against in the way the Weaken 3 is. | non_priority | rethink gym leader in parallel universe this one s not so bad but an extra damage isn t really interesting to fight against in the way the weaken is | 0 |
699,386 | 24,015,258,402 | IssuesEvent | 2022-09-14 23:32:48 | bats-core/bats-core | https://api.github.com/repos/bats-core/bats-core | closed | setup_suite: exported variables are gone | Type: Bug Component: Docs Priority: Critical Status: Confirmed Size: Small | **Describe the bug**
exported environment variables from setup_suite are not available on setup or `@test`
**To Reproduce**
```bash
setup_suite() {
{
export SETUP_SUITE="1"
} >&2
}
setup_file() {
{
export SETUP_FILE="1"
} >&2
}
setup() {
{
export SETUP_T... | 1.0 | setup_suite: exported variables are gone - **Describe the bug**
exported environment variables from setup_suite are not available on setup or `@test`
**To Reproduce**
```bash
setup_suite() {
{
export SETUP_SUITE="1"
} >&2
}
setup_file() {
{
export SETUP_FILE="1"
} >&2
}
... | priority | setup suite exported variables are gone describe the bug exported environment variables from setup suite are not available on setup or test to reproduce bash setup suite export setup suite setup file export setup file ... | 1 |
152,821 | 12,127,219,872 | IssuesEvent | 2020-04-22 18:21:00 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Rancher 2 Master gets OOM killed | [zube]: To Test internal kind/bug | **What kind of request is this (question/bug/enhancement/feature request): Bug
**Steps to reproduce (least amount of steps as possible):
The rancher master does take about 1.75 GB/s RAM per hour and get killed by the kernel OOM. Only the master is affected, other rancher pods running have a normal memory usage. We ... | 1.0 | Rancher 2 Master gets OOM killed - **What kind of request is this (question/bug/enhancement/feature request): Bug
**Steps to reproduce (least amount of steps as possible):
The rancher master does take about 1.75 GB/s RAM per hour and get killed by the kernel OOM. Only the master is affected, other rancher pods runn... | non_priority | rancher master gets oom killed what kind of request is this question bug enhancement feature request bug steps to reproduce least amount of steps as possible the rancher master does take about gb s ram per hour and get killed by the kernel oom only the master is affected other rancher pods runni... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.