Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
707,102 | 24,295,170,501 | IssuesEvent | 2022-09-29 09:28:42 | wso2/api-manager | https://api.github.com/repos/wso2/api-manager | opened | Integration Studio 8.1.0 issue when running the embeded micro integrator in debug mode | Type/Bug Priority/Normal | ### Description
Integration Studio 8.1.0 is returning the below warn and error logs while running the integrations studio in debug mode as follows.
**WARNING:** An illegal reflective access operation has occurred
**WARNING:** Illegal reflective access by org.eclipse.osgi.storage.FrameworkExtensionInstaller (file:/... | 1.0 | Integration Studio 8.1.0 issue when running the embeded micro integrator in debug mode - ### Description
Integration Studio 8.1.0 is returning the below warn and error logs while running the integrations studio in debug mode as follows.
**WARNING:** An illegal reflective access operation has occurred
**WARNING:** ... | priority | integration studio issue when running the embeded micro integrator in debug mode description integration studio is returning the below warn and error logs while running the integrations studio in debug mode as follows warning an illegal reflective access operation has occurred warning ... | 1 |
611,193 | 18,947,814,362 | IssuesEvent | 2021-11-18 12:09:09 | metabase/metabase | https://api.github.com/repos/metabase/metabase | opened | When filtering by Entity Key, then most options are hidden in Simple GUI | Type:UX Priority:P3 .Frontend Querying/GUI | **Describe the bug**
When filtering by Entity Key, then it hides all filters and the Filtering/Summarize buttons in Simple GUI.
This can be specially confusing, when accidentally inputting a wrong value, so there's "No results".
**To Reproduce**
1. Simple question > Sample Dataset > Products - Filtering: "Categor... | 1.0 | When filtering by Entity Key, then most options are hidden in Simple GUI - **Describe the bug**
When filtering by Entity Key, then it hides all filters and the Filtering/Summarize buttons in Simple GUI.
This can be specially confusing, when accidentally inputting a wrong value, so there's "No results".
**To Reprod... | priority | when filtering by entity key then most options are hidden in simple gui describe the bug when filtering by entity key then it hides all filters and the filtering summarize buttons in simple gui this can be specially confusing when accidentally inputting a wrong value so there s no results to reprod... | 1 |
457,915 | 13,165,061,399 | IssuesEvent | 2020-08-11 05:38:45 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | Portals Publisher and Admin cannot view in Microsoft Edge 44.18362.449.0 | Priority/Normal Type/Accessibility Type/Bug Type/React-UI | ### Description:
Publisher and Admin portals are not working in Microsoft Edge 44.18362.449.0, Devportal is working.
All working when remote viewing a server hosted on mac.


In GitLab by [[Gitlab user @cs-shadow]](https://gitlab.com/cs-shadow) on Nov 6, 2019, 19:30
## Background
Plugins are at the heart of BuildStream when it comes to end-users, as that is what allows users to write their element con... | 1.0 | Plugin documentation is lacking - [See original issue on GitLab](https://gitlab.com/BuildStream/buildstream/-/issues/1192)
In GitLab by [[Gitlab user @cs-shadow]](https://gitlab.com/cs-shadow) on Nov 6, 2019, 19:30
## Background
Plugins are at the heart of BuildStream when it comes to end-users, as that is what allow... | non_priority | plugin documentation is lacking in gitlab by on nov background plugins are at the heart of buildstream when it comes to end users as that is what allows users to write their element configuration however buildstream documentation appears to be lacking in this department we do have some docu... | 0 |
813,765 | 30,471,181,889 | IssuesEvent | 2023-07-17 13:44:34 | magento/magento2 | https://api.github.com/repos/magento/magento2 | closed | Customer data in localstorage not reset when session file lost | Issue: Confirmed Reproduced on 2.4.x Component: Session Priority: P2 Progress: done Reported on 2.4.x Area: Account | ### Preconditions and environment
- Magento version 2.4-develop
### Steps to reproduce
1. Login customer in frontend
2. Add product to cart
3. Remove magento session files with command: rm -rf var/session/*
4. Flush cache
### Expected result
- Header not show customer name
- Mini cart not show any it... | 1.0 | Customer data in localstorage not reset when session file lost - ### Preconditions and environment
- Magento version 2.4-develop
### Steps to reproduce
1. Login customer in frontend
2. Add product to cart
3. Remove magento session files with command: rm -rf var/session/*
4. Flush cache
### Expected resul... | priority | customer data in localstorage not reset when session file lost preconditions and environment magento version develop steps to reproduce login customer in frontend add product to cart remove magento session files with command rm rf var session flush cache expected resul... | 1 |
120,437 | 25,794,356,467 | IssuesEvent | 2022-12-10 11:44:32 | reactplay/react-play | https://api.github.com/repos/reactplay/react-play | closed | ✨ [Feature request]: Code cleanup `Common` folder | code-cleanup | ### Is your feature request related to a problem? Please describe.
Fix the eslint and formatting issue for common folder file formatting.
### Describe the solution you'd like.
Fix the eslint and formatting issue for common folder file formatting.
### Describe alternatives you've considered.
.
### Screenshot / Scr... | 1.0 | ✨ [Feature request]: Code cleanup `Common` folder - ### Is your feature request related to a problem? Please describe.
Fix the eslint and formatting issue for common folder file formatting.
### Describe the solution you'd like.
Fix the eslint and formatting issue for common folder file formatting.
### Describe alte... | non_priority | ✨ code cleanup common folder is your feature request related to a problem please describe fix the eslint and formatting issue for common folder file formatting describe the solution you d like fix the eslint and formatting issue for common folder file formatting describe alternatives you ve ... | 0 |
278,900 | 30,702,421,715 | IssuesEvent | 2023-07-27 01:28:48 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | closed | CVE-2022-25258 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 - autoclosed | Mend: dependency security vulnerability | ## CVE-2022-25258 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Librar... | True | CVE-2022-25258 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 - autoclosed - ## CVE-2022-25258 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d33... | non_priority | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel stable tree mirror library home page a href found in head commit a href found in base branch master vulnerable source files vu... | 0 |
318,510 | 9,693,636,613 | IssuesEvent | 2019-05-24 16:36:54 | mono/monodevelop | https://api.github.com/repos/mono/monodevelop | closed | Crash on trying to open solution from start window | Area: IDE Platform\Start Window high-priority regression vs-sync | Build Information
Release ID: 801002578
Git revision: a79542bdc4aba2fe7ea8589b8bff6ea239853078
Build date: 2019-05-24 08:54:27+00
Build branch: release-8.1
Xamarin extensions: b894e02a8f68200720b84feb210215a3c1c2dc66
Clicking a solution on the start window terminates VS Mac.
```
FATAL ERROR [2019-05-24 11:... | 1.0 | Crash on trying to open solution from start window - Build Information
Release ID: 801002578
Git revision: a79542bdc4aba2fe7ea8589b8bff6ea239853078
Build date: 2019-05-24 08:54:27+00
Build branch: release-8.1
Xamarin extensions: b894e02a8f68200720b84feb210215a3c1c2dc66
Clicking a solution on the start window te... | priority | crash on trying to open solution from start window build information release id git revision build date build branch release xamarin extensions clicking a solution on the start window terminates vs mac fatal error visual studio failed to start some of the assemblies ... | 1 |
84,032 | 7,888,072,015 | IssuesEvent | 2018-06-27 20:42:48 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | 2.0.0: kubectl version in Launch kubectl does not match cluster | area/agent kind/enhancement status/resolved status/to-test version/2.0 | kubectl version when launched from UI does not match the version of the cluster.
Expected output:
> kubectl version --short
Client Version: v1.9.7
Server Version: v1.9.7
Actual:
# Run kubectl commands inside here
# e.g. kubectl get all
> kubectl version --short
Client Version: v1.8.9-rancher1
Server Version... | 1.0 | 2.0.0: kubectl version in Launch kubectl does not match cluster - kubectl version when launched from UI does not match the version of the cluster.
Expected output:
> kubectl version --short
Client Version: v1.9.7
Server Version: v1.9.7
Actual:
# Run kubectl commands inside here
# e.g. kubectl get all
> kubect... | non_priority | kubectl version in launch kubectl does not match cluster kubectl version when launched from ui does not match the version of the cluster expected output kubectl version short client version server version actual run kubectl commands inside here e g kubectl get all kubectl ... | 0 |
48,699 | 2,999,471,771 | IssuesEvent | 2015-07-23 19:12:11 | jayway/powermock | https://api.github.com/repos/jayway/powermock | closed | OSGi-ify PowerMock | enhancement imported Milestone-Release1.6 Priority-Low | _From [lukewpat...@gmail.com](https://code.google.com/u/115628002144849920714/) on November 13, 2009 20:06:39_
Please add OSGi metadata to manifest files. This will allow in-container
testing with PowerMock.
_Original issue: http://code.google.com/p/powermock/issues/detail?id=204_ | 1.0 | OSGi-ify PowerMock - _From [lukewpat...@gmail.com](https://code.google.com/u/115628002144849920714/) on November 13, 2009 20:06:39_
Please add OSGi metadata to manifest files. This will allow in-container
testing with PowerMock.
_Original issue: http://code.google.com/p/powermock/issues/detail?id=204_ | priority | osgi ify powermock from on november please add osgi metadata to manifest files this will allow in container testing with powermock original issue | 1 |
220,932 | 7,372,306,900 | IssuesEvent | 2018-03-13 14:26:32 | TMats/survey | https://api.github.com/repos/TMats/survey | closed | Learning by Playing - Solving Sparse Reward Tasks from Scratch | Priority: High RL | https://arxiv.org/abs/1802.10567
- Martin Riedmiller, Roland Hafner, Thomas Lampe, Michael Neunert, Jonas Degrave, Tom Van de Wiele, Volodymyr Mnih, Nicolas Heess, Jost Tobias Springenberg
- Submitted on 28 Feb 2018 | 1.0 | Learning by Playing - Solving Sparse Reward Tasks from Scratch - https://arxiv.org/abs/1802.10567
- Martin Riedmiller, Roland Hafner, Thomas Lampe, Michael Neunert, Jonas Degrave, Tom Van de Wiele, Volodymyr Mnih, Nicolas Heess, Jost Tobias Springenberg
- Submitted on 28 Feb 2018 | priority | learning by playing solving sparse reward tasks from scratch martin riedmiller roland hafner thomas lampe michael neunert jonas degrave tom van de wiele volodymyr mnih nicolas heess jost tobias springenberg submitted on feb | 1 |
7,656 | 2,919,649,850 | IssuesEvent | 2015-06-24 15:09:39 | php-coder/mystamps | https://api.github.com/repos/php-coder/mystamps | opened | Test that Togglz is working | integration tests | In commit 69214f44d9b47e106803c0c826bc1a509d3d3508 I've fixed Togglz that didn't work. To avoid such breakage we need a test for this case.
I suggest to add special feature that is always disabled. On any page we will show special message if this feature is active. Our test will just check that this message doesn't ... | 1.0 | Test that Togglz is working - In commit 69214f44d9b47e106803c0c826bc1a509d3d3508 I've fixed Togglz that didn't work. To avoid such breakage we need a test for this case.
I suggest to add special feature that is always disabled. On any page we will show special message if this feature is active. Our test will just ch... | non_priority | test that togglz is working in commit i ve fixed togglz that didn t work to avoid such breakage we need a test for this case i suggest to add special feature that is always disabled on any page we will show special message if this feature is active our test will just check that this message doesn t exist | 0 |
289,623 | 31,991,433,732 | IssuesEvent | 2023-09-21 06:13:08 | pazhanivel07/frameworks_av_AOSP_10_r33_CVE-2023-35687_CVE-2023-35679 | https://api.github.com/repos/pazhanivel07/frameworks_av_AOSP_10_r33_CVE-2023-35687_CVE-2023-35679 | opened | CVE-2022-20393 (Medium) detected in avandroid-9.0.0_r56 | Mend: dependency security vulnerability | ## CVE-2022-20393 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-9.0.0_r56</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/fr... | True | CVE-2022-20393 (Medium) detected in avandroid-9.0.0_r56 - ## CVE-2022-20393 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-9.0.0_r56</b></p></summary>
<p>
<p>Library home ... | non_priority | cve medium detected in avandroid cve medium severity vulnerability vulnerable library avandroid library home page a href found in head commit a href found in base branch main vulnerable source files media libstagefright timedtext ... | 0 |
44,655 | 2,910,342,665 | IssuesEvent | 2015-06-21 17:17:08 | Metaswitch/sprout | https://api.github.com/repos/Metaswitch/sprout | closed | Sprout loops ACKs to itself after responding with 503 to an INVITE | high-priority | After Sprout returns a 503 for an INVITE due to overload controls, it begins looping ACKs to itself until Max-Forwards has "expired". This additional processing triggers a LIR over the Cx for each ACK which adds to system latency, thereby "reinforcing" the overload condition (the overload was initially caused by Cx int... | 1.0 | Sprout loops ACKs to itself after responding with 503 to an INVITE - After Sprout returns a 503 for an INVITE due to overload controls, it begins looping ACKs to itself until Max-Forwards has "expired". This additional processing triggers a LIR over the Cx for each ACK which adds to system latency, thereby "reinforcing... | priority | sprout loops acks to itself after responding with to an invite after sprout returns a for an invite due to overload controls it begins looping acks to itself until max forwards has expired this additional processing triggers a lir over the cx for each ack which adds to system latency thereby reinforcing th... | 1 |
103,854 | 12,976,734,811 | IssuesEvent | 2020-07-21 19:19:42 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Custom CAs and SSL options | Team:Ingest Management design | **Summary of the problem**
Having secure communication between Elastic-Agent and elasticsearch or tier services requires to deal with SSL (TLS):
- **Certificate authorities (common):** when authenticating the server.
- **Certificate:** required when doing mutual authentication.
- **Certificate private key:** re... | 1.0 | Custom CAs and SSL options - **Summary of the problem**
Having secure communication between Elastic-Agent and elasticsearch or tier services requires to deal with SSL (TLS):
- **Certificate authorities (common):** when authenticating the server.
- **Certificate:** required when doing mutual authentication.
- **... | non_priority | custom cas and ssl options summary of the problem having secure communication between elastic agent and elasticsearch or tier services requires to deal with ssl tls certificate authorities common when authenticating the server certificate required when doing mutual authentication ... | 0 |
104,606 | 4,215,501,064 | IssuesEvent | 2016-06-30 04:34:49 | diamm/diamm | https://api.github.com/repos/diamm/diamm | closed | Figure out how to migrate old users to new site | Component: User Interface Component: Web Application Priority: High Status: In Progress Type: Enhancement | Conversation with Arielle:
The login form will only display the username / e-mail to log in at first. It will then use the information in there to tell what the rest of the form should look like:
1. If the user has logged in to the new site before, show a password prompt.
2. If the username was in the old databa... | 1.0 | Figure out how to migrate old users to new site - Conversation with Arielle:
The login form will only display the username / e-mail to log in at first. It will then use the information in there to tell what the rest of the form should look like:
1. If the user has logged in to the new site before, show a password... | priority | figure out how to migrate old users to new site conversation with arielle the login form will only display the username e mail to log in at first it will then use the information in there to tell what the rest of the form should look like if the user has logged in to the new site before show a password... | 1 |
163,885 | 25,892,510,990 | IssuesEvent | 2022-12-14 19:12:51 | GCTC-NTGC/gc-digital-talent | https://api.github.com/repos/GCTC-NTGC/gc-digital-talent | closed | Display referral path on /not-found page | design | <sup>ℹ️ [Figma (root)][figma] | [Sitemap][sitemap]</sup>
<sup>_This initial comment is collaborative and open to modification by all._</sup>
Spin-off from: https://github.com/GCTC-NTGC/gc-digital-talent/issues/1904
On 404/not-found page, we should show the referral page we redirected from when it's available. Th... | 1.0 | Display referral path on /not-found page - <sup>ℹ️ [Figma (root)][figma] | [Sitemap][sitemap]</sup>
<sup>_This initial comment is collaborative and open to modification by all._</sup>
Spin-off from: https://github.com/GCTC-NTGC/gc-digital-talent/issues/1904
On 404/not-found page, we should show the referral page... | non_priority | display referral path on not found page ℹ️ this initial comment is collaborative and open to modification by all spin off from on not found page we should show the referral page we redirected from when it s available this will help with support requests when ppl arrive on this page ... | 0 |
255,595 | 19,309,377,323 | IssuesEvent | 2021-12-13 14:49:20 | moonD4rk/HackBrowserData | https://api.github.com/repos/moonD4rk/HackBrowserData | closed | [Improvement] CHANGELOG | documentation | Hi,
would be awesome if you could also establish a file for the CHANGELOG with all the (great) frequent changes of each version.
I think it would be helpful for everyone to track what is and has happened. | 1.0 | [Improvement] CHANGELOG - Hi,
would be awesome if you could also establish a file for the CHANGELOG with all the (great) frequent changes of each version.
I think it would be helpful for everyone to track what is and has happened. | non_priority | changelog hi would be awesome if you could also establish a file for the changelog with all the great frequent changes of each version i think it would be helpful for everyone to track what is and has happened | 0 |
494,566 | 14,260,592,201 | IssuesEvent | 2020-11-20 10:02:55 | openmsupply/mobile | https://api.github.com/repos/openmsupply/mobile | closed | Odd modal spacing when opening while keyboard is open | Bug: production Docs: not needed Effort: small Good first issue Priority: normal | ## Describe the bug
When opening a modal (i.e. clicking finalize, or any other action which opens a modal whether it is in requisitions or stocktakes), if the keyboard is opening when the modal is mounted, the spacing is odd forcing the vertical height downward
### To reproduce
Steps to reproduce the behavior:
1.... | 1.0 | Odd modal spacing when opening while keyboard is open - ## Describe the bug
When opening a modal (i.e. clicking finalize, or any other action which opens a modal whether it is in requisitions or stocktakes), if the keyboard is opening when the modal is mounted, the spacing is odd forcing the vertical height downward
... | priority | odd modal spacing when opening while keyboard is open describe the bug when opening a modal i e clicking finalize or any other action which opens a modal whether it is in requisitions or stocktakes if the keyboard is opening when the modal is mounted the spacing is odd forcing the vertical height downward ... | 1 |
155,713 | 12,267,916,623 | IssuesEvent | 2020-05-07 11:35:01 | wopian/kitsu | https://api.github.com/repos/wopian/kitsu | closed | serialise depends on binded this (missing pluralize dependency) | bug kitsu-core test | Unable to serialise data using `kitsu-core` as a standalone - tests did not pick this up as they're pre-bound in the specs for each bind combination.
Should fallback to requiring `pluralize` if `this.plural` is not a function
Ref: https://codepen.io/wopian/pen/KQZwzq (console) | 1.0 | serialise depends on binded this (missing pluralize dependency) - Unable to serialise data using `kitsu-core` as a standalone - tests did not pick this up as they're pre-bound in the specs for each bind combination.
Should fallback to requiring `pluralize` if `this.plural` is not a function
Ref: https://codepen.i... | non_priority | serialise depends on binded this missing pluralize dependency unable to serialise data using kitsu core as a standalone tests did not pick this up as they re pre bound in the specs for each bind combination should fallback to requiring pluralize if this plural is not a function ref console | 0 |
298,471 | 22,500,774,530 | IssuesEvent | 2022-06-23 11:37:54 | BrainsOnBoard/python-gm-plotting | https://api.github.com/repos/BrainsOnBoard/python-gm-plotting | opened | Add a readme file and other documentation | documentation | It would also be useful to have instructions on how to get set up with a proper Google account so that the user can obtain satellite images. | 1.0 | Add a readme file and other documentation - It would also be useful to have instructions on how to get set up with a proper Google account so that the user can obtain satellite images. | non_priority | add a readme file and other documentation it would also be useful to have instructions on how to get set up with a proper google account so that the user can obtain satellite images | 0 |
753,373 | 26,345,513,442 | IssuesEvent | 2023-01-10 21:40:00 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [Platform] [docdb] Validate gflags and raise error if any are invalid | kind/enhancement area/docdb priority/high status/awaiting-triage | Jira Link: [DB-4733](https://yugabyte.atlassian.net/browse/DB-4733)
If the admin is setting gflags, an error should be raised if any of the entered gflags are invalid (like a typo in the gflag name). I guess the validation needs to be done by docdb and the error propagated to YW | 1.0 | [Platform] [docdb] Validate gflags and raise error if any are invalid - Jira Link: [DB-4733](https://yugabyte.atlassian.net/browse/DB-4733)
If the admin is setting gflags, an error should be raised if any of the entered gflags are invalid (like a typo in the gflag name). I guess the validation needs to be done by docd... | priority | validate gflags and raise error if any are invalid jira link if the admin is setting gflags an error should be raised if any of the entered gflags are invalid like a typo in the gflag name i guess the validation needs to be done by docdb and the error propagated to yw | 1 |
751,631 | 26,251,584,088 | IssuesEvent | 2023-01-05 19:50:19 | googleapis/google-api-go-client | https://api.github.com/repos/googleapis/google-api-go-client | closed | bigquery: How to mock for unit testing | type: question api: bigquery priority: p3 | Hey, I'm trying to mock bigquery Client, but I didn't find a good solution for that.
- https://github.com/googleapis/google-cloud-go-testing it sounds interesting the way but it's outdated and lots of methods have not been updated and the project has been archived recently
- [sample 1 ](https://github.com/GoogleClou... | 1.0 | bigquery: How to mock for unit testing - Hey, I'm trying to mock bigquery Client, but I didn't find a good solution for that.
- https://github.com/googleapis/google-cloud-go-testing it sounds interesting the way but it's outdated and lots of methods have not been updated and the project has been archived recently
- ... | priority | bigquery how to mock for unit testing hey i m trying to mock bigquery client but i didn t find a good solution for that it sounds interesting the way but it s outdated and lots of methods have not been updated and the project has been archived recently it s using the real client with just a sample pr... | 1 |
463,235 | 13,262,068,062 | IssuesEvent | 2020-08-20 21:02:40 | OregonDigital/OD2 | https://api.github.com/repos/OregonDigital/OD2 | reopened | FetchGraphWorker overrides metadata labels as it indexes | Bug Features Priority - High | ### Descriptive summary
As FetchGraphWorker works through the metadata values for a single field, it's clobbering the values it JUST sent to Solr.
https://github.com/OregonDigital/OD2/blob/master/app/workers/fetch_graph_worker.rb#L42-L46
These values need to be initialized to an empty array, then appended to each it... | 1.0 | FetchGraphWorker overrides metadata labels as it indexes - ### Descriptive summary
As FetchGraphWorker works through the metadata values for a single field, it's clobbering the values it JUST sent to Solr.
https://github.com/OregonDigital/OD2/blob/master/app/workers/fetch_graph_worker.rb#L42-L46
These values need to... | priority | fetchgraphworker overrides metadata labels as it indexes descriptive summary as fetchgraphworker works through the metadata values for a single field it s clobbering the values it just sent to solr these values need to be initialized to an empty array then appended to each iteration this is also true ... | 1 |
27,052 | 21,055,851,157 | IssuesEvent | 2022-04-01 03:06:17 | google/pytype | https://api.github.com/repos/google/pytype | closed | Add `--platform` option | enhancement cat: infrastructure | As [per PEP 484](https://www.python.org/dev/peps/pep-0484/#version-and-platform-checking) type checkers are expected to understand simple version and platform checks, e.g.:
```python
if sys.version_info[0] >= 3:
# Python 3 specific definitions
if sys.platform == 'win32':
# Windows specific definitions
... | 1.0 | Add `--platform` option - As [per PEP 484](https://www.python.org/dev/peps/pep-0484/#version-and-platform-checking) type checkers are expected to understand simple version and platform checks, e.g.:
```python
if sys.version_info[0] >= 3:
# Python 3 specific definitions
if sys.platform == 'win32':
# Win... | non_priority | add platform option as type checkers are expected to understand simple version and platform checks e g python if sys version info python specific definitions if sys platform windows specific definitions while the pytype cli currently supports the flags v... | 0 |
583,846 | 17,399,767,336 | IssuesEvent | 2021-08-02 17:53:28 | ita-social-projects/TeachUA | https://api.github.com/repos/ita-social-projects/TeachUA | closed | [Редагування профілю] Wrong alignment of 'Змінити пароль' label | Priority: High UI bug | **Environment:** Windows 10, Google Chrome Version 92.0.4515.107 (Official Build) (64-bit
**Reproducible:** always
**Build found:** last commit
**Preconditions**
1. Go to https://speak-ukrainian.org.ua/dev/
2. Log in
**Steps to reproduce**
1. Go to 'Мій Профіль' page
2. Click on 'Редагувати профіль'
**A... | 1.0 | [Редагування профілю] Wrong alignment of 'Змінити пароль' label - **Environment:** Windows 10, Google Chrome Version 92.0.4515.107 (Official Build) (64-bit
**Reproducible:** always
**Build found:** last commit
**Preconditions**
1. Go to https://speak-ukrainian.org.ua/dev/
2. Log in
**Steps to reproduce**
1.... | priority | wrong alignment of змінити пароль label environment windows google chrome version official build bit reproducible always build found last commit preconditions go to log in steps to reproduce go to мій профіль page click on редагувати профіль ... | 1 |
570,730 | 17,023,170,512 | IssuesEvent | 2021-07-03 00:41:28 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Allow better reuse of GeoRSS class in lib/osm.rb | Component: rails_port Priority: minor Resolution: fixed Type: enhancement | **[Submitted to the original trac issue database at 10.13pm, Saturday, 9th June 2007]**
There are some hardcoded strings in there that should probably all be passed in through as parameters (with defaults) so the code can better be reused for other purposes as well as traces. | 1.0 | Allow better reuse of GeoRSS class in lib/osm.rb - **[Submitted to the original trac issue database at 10.13pm, Saturday, 9th June 2007]**
There are some hardcoded strings in there that should probably all be passed in through as parameters (with defaults) so the code can better be reused for other purposes as well as... | priority | allow better reuse of georss class in lib osm rb there are some hardcoded strings in there that should probably all be passed in through as parameters with defaults so the code can better be reused for other purposes as well as traces | 1 |
200,179 | 7,001,143,613 | IssuesEvent | 2017-12-18 09:07:29 | cilium/cilium | https://api.github.com/repos/cilium/cilium | closed | Ginkgo CI: Gather logs that are dumped to file as artifacts in Jenkins build | area/CI priority/high | Parent: #1839
We currently `archiveArtifacts` as part of the Jenkins build for Cilium as a "post-build action"
```
post {
always {
sh './test/post_build_agent.sh || true'
sh './tests/copy_files || true'
archiveArtifacts artifacts: "cilium-files-runtime-${JOB_BASE_NA... | 1.0 | Ginkgo CI: Gather logs that are dumped to file as artifacts in Jenkins build - Parent: #1839
We currently `archiveArtifacts` as part of the Jenkins build for Cilium as a "post-build action"
```
post {
always {
sh './test/post_build_agent.sh || true'
sh './tests/copy_files || tru... | priority | ginkgo ci gather logs that are dumped to file as artifacts in jenkins build parent we currently archiveartifacts as part of the jenkins build for cilium as a post build action post always sh test post build agent sh true sh tests copy files true ... | 1 |
106,737 | 16,717,902,407 | IssuesEvent | 2021-06-10 01:04:59 | ilan-WS/m3 | https://api.github.com/repos/ilan-WS/m3 | opened | WS-2020-0345 (High) detected in jsonpointer-4.0.1.tgz | security vulnerability | ## WS-2020-0345 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsonpointer-4.0.1.tgz</b></p></summary>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.n... | True | WS-2020-0345 (High) detected in jsonpointer-4.0.1.tgz - ## WS-2020-0345 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jsonpointer-4.0.1.tgz</b></p></summary>
<p>Simple JSON Addressin... | non_priority | ws high detected in jsonpointer tgz ws high severity vulnerability vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file src ctl ui package json path to vulnerable library src ctl ui node modules jsonpointer ... | 0 |
253,477 | 8,056,626,751 | IssuesEvent | 2018-08-02 13:17:37 | tavorperry/MTA-Coffee | https://api.github.com/repos/tavorperry/MTA-Coffee | closed | Change URL in code | High Priority | replace
**http://vmedu151.mtacloud.co.il**
or
**http://whispering-scrubland-84389.herokuapp.com/**
with
**http://mtacoffee.mta.ac.il**
in every place that mentions in the code | 1.0 | Change URL in code - replace
**http://vmedu151.mtacloud.co.il**
or
**http://whispering-scrubland-84389.herokuapp.com/**
with
**http://mtacoffee.mta.ac.il**
in every place that mentions in the code | priority | change url in code replace or with in every place that mentions in the code | 1 |
671,494 | 22,763,477,170 | IssuesEvent | 2022-07-08 00:14:13 | kubernetes/ingress-nginx | https://api.github.com/repos/kubernetes/ingress-nginx | closed | Helm template with custom values does not create deployment | kind/bug needs-triage needs-priority | When using the helm chart version:
```
$ helm show chart nginx-stable/nginx-ingress 7:34PM
apiVersion: v1
appVersion: 2.2.2
description: NGINX Ingress Controller
home: https://github.com/nginxinc/kubern... | 1.0 | Helm template with custom values does not create deployment - When using the helm chart version:
```
$ helm show chart nginx-stable/nginx-ingress 7:34PM
apiVersion: v1
appVersion: 2.2.2
description: NGIN... | priority | helm template with custom values does not create deployment when using the helm chart version helm show chart nginx stable nginx ingress apiversion appversion description nginx in... | 1 |
632,282 | 20,189,609,362 | IssuesEvent | 2022-02-11 03:21:11 | WeAreNewt/NonFungibleTime | https://api.github.com/repos/WeAreNewt/NonFungibleTime | closed | No error prompt when I try to mint absurdly low duration | bug good first issue frontend mid priority | 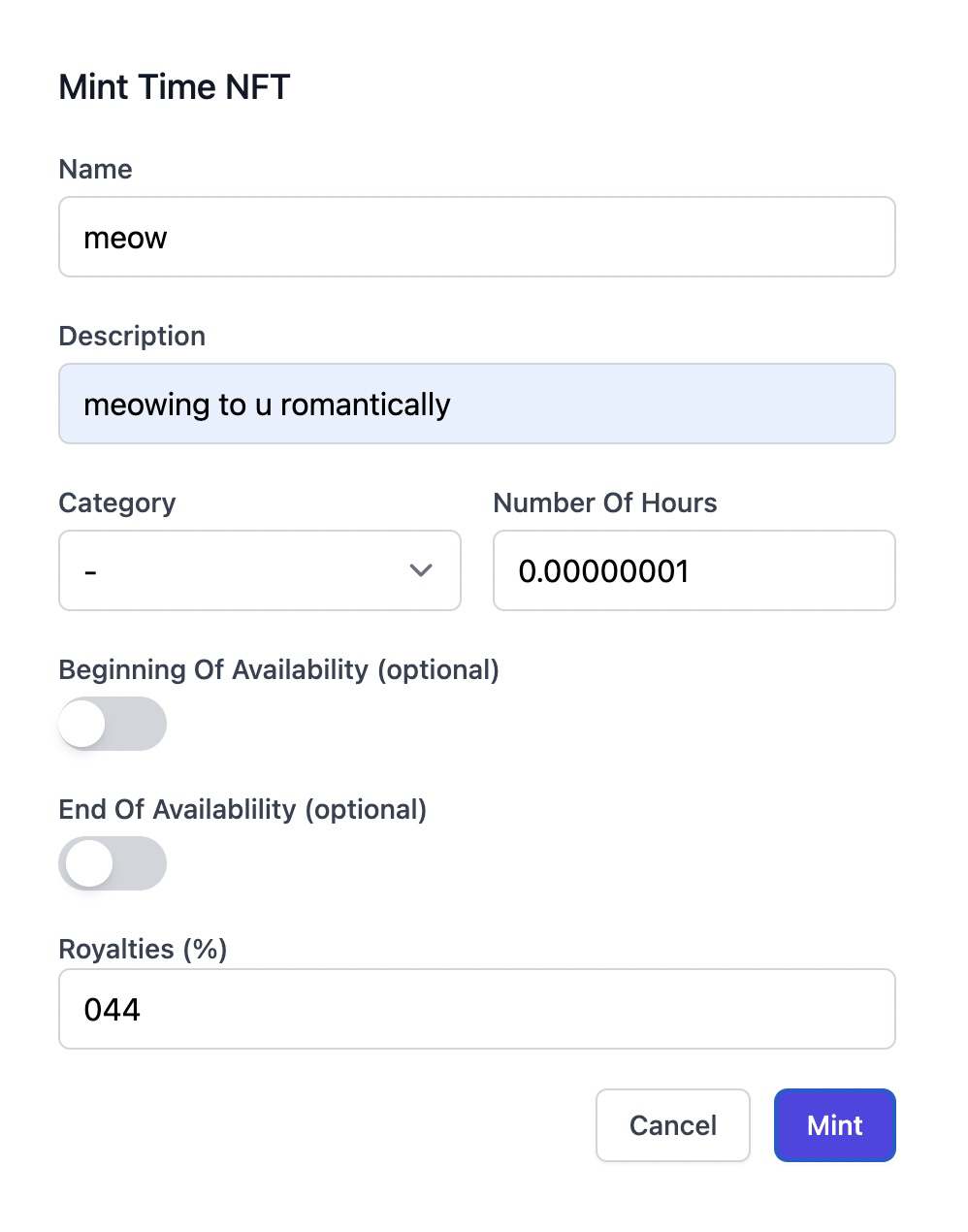
I can't mint an absurdly low numberOfHours (Metamask doesn't pop up), but I also get no error messaging from the modal | 1.0 | No error prompt when I try to mint absurdly low duration - 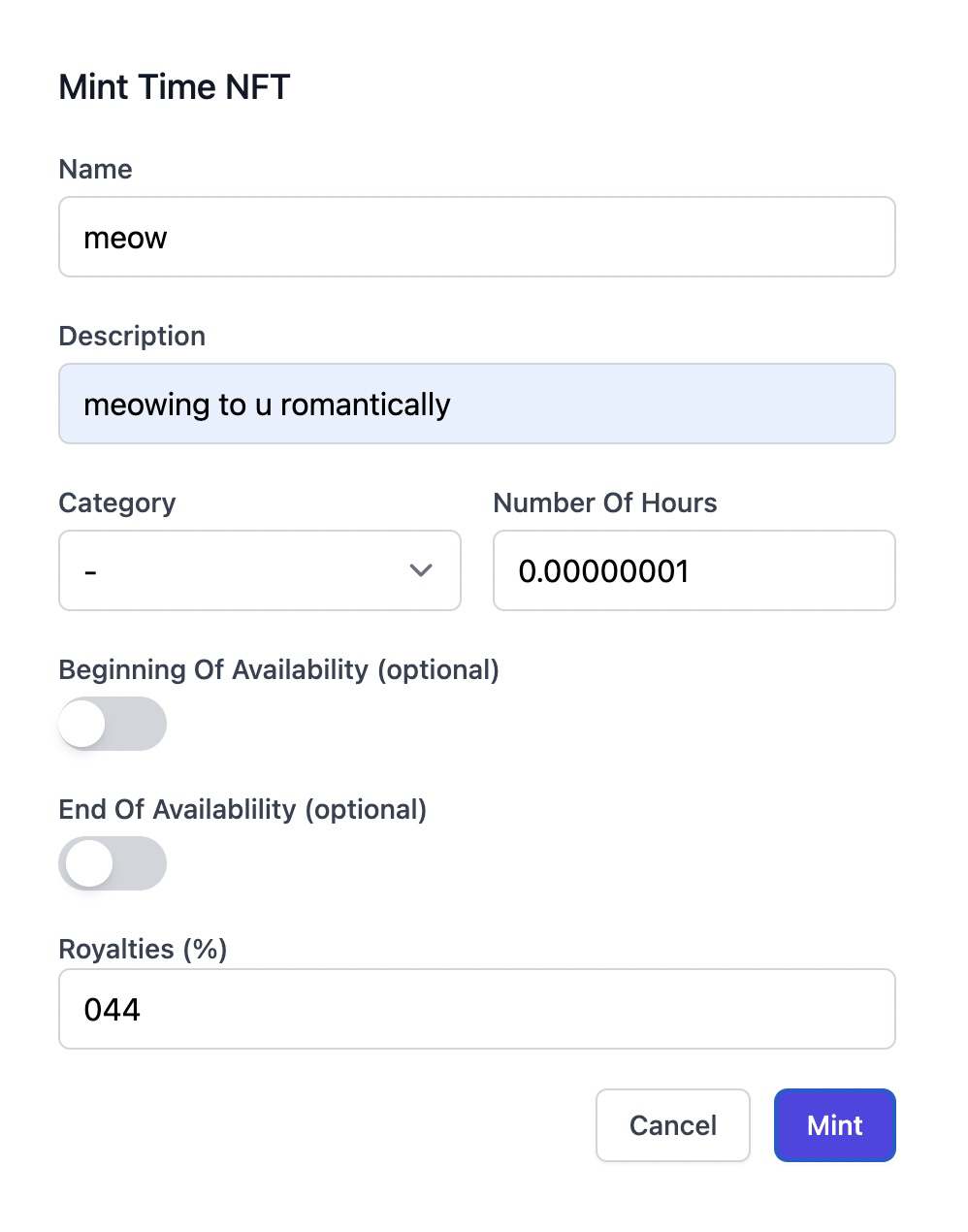
I can't mint an absurdly low numberOfHours (Metamask doesn't pop up), but I also get no error messaging from the modal | priority | no error prompt when i try to mint absurdly low duration i can t mint an absurdly low numberofhours metamask doesn t pop up but i also get no error messaging from the modal | 1 |
54,651 | 13,401,012,209 | IssuesEvent | 2020-09-03 16:38:29 | stitchEm/stitchEm | https://api.github.com/repos/stitchEm/stitchEm | opened | Print CMake version for easier troubleshooting | Build enhancement good first issue | Just print out the CMake version at the beginning of the configuration, so that when issues are filed with CMake printouts, we already have that information (see #121). | 1.0 | Print CMake version for easier troubleshooting - Just print out the CMake version at the beginning of the configuration, so that when issues are filed with CMake printouts, we already have that information (see #121). | non_priority | print cmake version for easier troubleshooting just print out the cmake version at the beginning of the configuration so that when issues are filed with cmake printouts we already have that information see | 0 |
648,521 | 21,188,190,635 | IssuesEvent | 2022-04-08 14:42:25 | ConsistencyPlus/ConsistencyPlus | https://api.github.com/repos/ConsistencyPlus/ConsistencyPlus | closed | Crash at creating a new world | Help Wanted Invalid Question/Information Needed Low Priority | **Describe the bug**
Crash at creating a new world after updating C+ from 0.3 to 0.4.2
**Versions**
Minecraft version: 1.16.5
C+ version: 0.4.2
Fabric API version: 0.43.0+1.16 (Edited by Siuol the reflect the actual version of Fabric API used.)
**Other mods**
[crash-2021-12-04_13.23.09-server.txt](https://gi... | 1.0 | Crash at creating a new world - **Describe the bug**
Crash at creating a new world after updating C+ from 0.3 to 0.4.2
**Versions**
Minecraft version: 1.16.5
C+ version: 0.4.2
Fabric API version: 0.43.0+1.16 (Edited by Siuol the reflect the actual version of Fabric API used.)
**Other mods**
[crash-2021-12-04... | priority | crash at creating a new world describe the bug crash at creating a new world after updating c from to versions minecraft version c version fabric api version edited by siuol the reflect the actual version of fabric api used other mods logs ... | 1 |
89,885 | 3,801,503,779 | IssuesEvent | 2016-03-23 23:15:42 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | opened | Add a munger (bot) to require release-note-* on all PRs and release-note-(!NONE) on cherrypicks (to branches) | help-wanted priority/P1 | Following a revelation in https://github.com/kubernetes/kubernetes/pull/23315#issuecomment-200573266, it became clear we could solve the release note issue (at least the simple case) with labels and a bot.
We need a new munger/bot to do the following:
1. Initiate a `needs-release-note` label on all new PRs
1. Di... | 1.0 | Add a munger (bot) to require release-note-* on all PRs and release-note-(!NONE) on cherrypicks (to branches) - Following a revelation in https://github.com/kubernetes/kubernetes/pull/23315#issuecomment-200573266, it became clear we could solve the release note issue (at least the simple case) with labels and a bot.
... | priority | add a munger bot to require release note on all prs and release note none on cherrypicks to branches following a revelation in it became clear we could solve the release note issue at least the simple case with labels and a bot we need a new munger bot to do the following initiate a needs rel... | 1 |
279,506 | 8,666,763,987 | IssuesEvent | 2018-11-29 05:57:14 | dmwm/WMCore | https://api.github.com/repos/dmwm/WMCore | closed | Push worker threads execution time to MONIT IT | Medium Priority Monitoring | Since we now collect this data and persist it in the relational database, it should be pretty straight forward to publish how long each component and their threads take per cycle.
This is going to be more like a developers metric/view, but I think it's quite useful. | 1.0 | Push worker threads execution time to MONIT IT - Since we now collect this data and persist it in the relational database, it should be pretty straight forward to publish how long each component and their threads take per cycle.
This is going to be more like a developers metric/view, but I think it's quite useful. | priority | push worker threads execution time to monit it since we now collect this data and persist it in the relational database it should be pretty straight forward to publish how long each component and their threads take per cycle this is going to be more like a developers metric view but i think it s quite useful | 1 |
807,771 | 30,018,740,082 | IssuesEvent | 2023-06-26 20:59:38 | vrchatapi/specification | https://api.github.com/repos/vrchatapi/specification | closed | Presence in auth/user | Type: Enhancement Priority: Medium Status: Help Wanted Good First Task | Noticed this in auth/user:
```json
"presence": {
"id": "...",
"platform": "",
"status": "offline",
"world": "offline",
"instance": "offline",
"instanceType": "",
"travelingToWorld": "offline",
"travelingToInstance": "offline",
"groups": []
}
```
No idea how long... | 1.0 | Presence in auth/user - Noticed this in auth/user:
```json
"presence": {
"id": "...",
"platform": "",
"status": "offline",
"world": "offline",
"instance": "offline",
"instanceType": "",
"travelingToWorld": "offline",
"travelingToInstance": "offline",
"groups": []
}
... | priority | presence in auth user noticed this in auth user json presence id platform status offline world offline instance offline instancetype travelingtoworld offline travelingtoinstance offline groups ... | 1 |
369,950 | 10,920,406,156 | IssuesEvent | 2019-11-21 21:11:38 | bounswe/bounswe2019group6 | https://api.github.com/repos/bounswe/bounswe2019group6 | closed | Implement Portfolio Page | priority:high related:frontend type:new-feature | A user can create a portfolio using his/her profile page. When the user clicks to the created portfolio. We need to redirect him/her to a new page containing the information of the portfolio. User should be able to:
* see all trading equipments
* add new trading equipment
* remove already added trading equipment | 1.0 | Implement Portfolio Page - A user can create a portfolio using his/her profile page. When the user clicks to the created portfolio. We need to redirect him/her to a new page containing the information of the portfolio. User should be able to:
* see all trading equipments
* add new trading equipment
* remove already ... | priority | implement portfolio page a user can create a portfolio using his her profile page when the user clicks to the created portfolio we need to redirect him her to a new page containing the information of the portfolio user should be able to see all trading equipments add new trading equipment remove already ... | 1 |
314,264 | 26,988,282,802 | IssuesEvent | 2023-02-09 17:43:46 | Azure/azure-sdk-tools | https://api.github.com/repos/Azure/azure-sdk-tools | closed | Test issue - disregard | Test-Proxy | Test of the change I made to Fabric Bot to assign issues labeled as 'Test-Proxy' to me. | 1.0 | Test issue - disregard - Test of the change I made to Fabric Bot to assign issues labeled as 'Test-Proxy' to me. | non_priority | test issue disregard test of the change i made to fabric bot to assign issues labeled as test proxy to me | 0 |
289,724 | 31,996,938,126 | IssuesEvent | 2023-09-21 09:46:36 | Mend-developer-platform-load/3184155_33 | https://api.github.com/repos/Mend-developer-platform-load/3184155_33 | opened | ansible-2.9.9.tar.gz: 8 vulnerabilities (highest severity is: 7.1) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e605... | True | ansible-2.9.9.tar.gz: 8 vulnerabilities (highest severity is: 7.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page... | non_priority | ansible tar gz vulnerabilities highest severity is vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file requirements txt path to vulnerable library requirements txt found in head commit a href v... | 0 |
76,912 | 9,968,870,168 | IssuesEvent | 2019-07-08 16:34:15 | microsoft/MixedRealityToolkit-Unity | https://api.github.com/repos/microsoft/MixedRealityToolkit-Unity | closed | How to connect HoloLens to server via TCP/IP? | Documentation | Hi guys,
I am a beginner in this field. I want to know there is a tutorial that explains to me, how can I connect HoloLens to a server on the network using TCP/IP to exchange data between them.
Thnx | 1.0 | How to connect HoloLens to server via TCP/IP? - Hi guys,
I am a beginner in this field. I want to know there is a tutorial that explains to me, how can I connect HoloLens to a server on the network using TCP/IP to exchange data between them.
Thnx | non_priority | how to connect hololens to server via tcp ip hi guys i am a beginner in this field i want to know there is a tutorial that explains to me how can i connect hololens to a server on the network using tcp ip to exchange data between them thnx | 0 |
171,016 | 27,048,976,838 | IssuesEvent | 2023-02-13 11:53:23 | effektio/effektio | https://api.github.com/repos/effektio/effektio | closed | internet connectivity state in app | bug flutter infrastructure design needed | We should add network aware handlers/widgets in the application which would inform the internet connectivity state of the application. These packages seems to be helpful:
https://pub.dev/packages/connectivity_plus
https://pub.dev/packages/connectivity_wrapper | 1.0 | internet connectivity state in app - We should add network aware handlers/widgets in the application which would inform the internet connectivity state of the application. These packages seems to be helpful:
https://pub.dev/packages/connectivity_plus
https://pub.dev/packages/connectivity_wrapper | non_priority | internet connectivity state in app we should add network aware handlers widgets in the application which would inform the internet connectivity state of the application these packages seems to be helpful | 0 |
593,039 | 17,936,666,245 | IssuesEvent | 2021-09-10 16:10:37 | assurance-maladie-digital/design-system | https://api.github.com/repos/assurance-maladie-digital/design-system | closed | Documentation de la règle de validation exactLength | low-priority | ## Description
En tant que développeur utilisant le Design System, je veux savoir comment utiliser la règle de validation [`exactLength`](https://github.com/assurance-maladie-digital/design-system/blob/dev/packages/vue-dot/src/rules/exactLength/index.ts).
| 1.0 | Documentation de la règle de validation exactLength - ## Description
En tant que développeur utilisant le Design System, je veux savoir comment utiliser la règle de validation [`exactLength`](https://github.com/assurance-maladie-digital/design-system/blob/dev/packages/vue-dot/src/rules/exactLength/index.ts).
| priority | documentation de la règle de validation exactlength description en tant que développeur utilisant le design system je veux savoir comment utiliser la règle de validation | 1 |
820,143 | 30,761,206,490 | IssuesEvent | 2023-07-29 18:22:32 | prakhartiwari0/Arito | https://api.github.com/repos/prakhartiwari0/Arito | closed | [FEATURE] Add a challenge mode | enhancement priority: Low gssoc23 | **Is your feature request related to a problem? Please describe.**
Yes, the feature request is related to improving the user experience on the mathematical quiz website. Currently, the website lacks a time-based challenge mode and an option to skip questions, which can limit user engagement and frustrate players who e... | 1.0 | [FEATURE] Add a challenge mode - **Is your feature request related to a problem? Please describe.**
Yes, the feature request is related to improving the user experience on the mathematical quiz website. Currently, the website lacks a time-based challenge mode and an option to skip questions, which can limit user enga... | priority | add a challenge mode is your feature request related to a problem please describe yes the feature request is related to improving the user experience on the mathematical quiz website currently the website lacks a time based challenge mode and an option to skip questions which can limit user engagement a... | 1 |
378,939 | 11,211,008,299 | IssuesEvent | 2020-01-06 14:33:19 | AugurProject/augur | https://api.github.com/repos/AugurProject/augur | closed | Onboarding: modals have strange spacing all of a sudden | Priority: Medium | See comparison shots below for strange spacing in the build.
**note** the heading/description copy is now jumping around as well:

Comparisons shots (design left, build right):

Comparisons sh... | priority | onboarding modals have strange spacing all of a sudden see comparison shots below for strange spacing in the build note the heading description copy is now jumping around as well comparisons shots design left build right similar for mobile build on left figma link for m... | 1 |
82,394 | 7,840,481,458 | IssuesEvent | 2018-06-18 16:29:01 | w3c/csswg-drafts | https://api.github.com/repos/w3c/csswg-drafts | closed | [css-cascade] Change the precedence order of cascading origins to match reality better? | Closed Rejected as Invalid Needs Testcase (WPT) css-cascade-3 | Currently, the CSS Cascade spec states that animation declarations [shouldn't override](https://drafts.csswg.org/css-cascade/#cascade-origin) important author declarations. In fact, they do in all browsers except Firefox. There are some articles that appear to describe this overriding as a standard behavior ([1](https:... | 1.0 | [css-cascade] Change the precedence order of cascading origins to match reality better? - Currently, the CSS Cascade spec states that animation declarations [shouldn't override](https://drafts.csswg.org/css-cascade/#cascade-origin) important author declarations. In fact, they do in all browsers except Firefox. There ar... | non_priority | change the precedence order of cascading origins to match reality better currently the css cascade spec states that animation declarations important author declarations in fact they do in all browsers except firefox there are some articles that appear to describe this overriding as a standard behavior ... | 0 |
690,481 | 23,661,546,322 | IssuesEvent | 2022-08-26 16:03:21 | PrefectHQ/prefect | https://api.github.com/repos/PrefectHQ/prefect | closed | Add `EXTRA_PIP_PACKAGES` to the `KubernetesJob` block | bug status:backlog v2 priority:medium | ### First check
- [X] I added a descriptive title to this issue.
- [X] I used the GitHub search to find a similar request and didn't find it.
- [X] I searched the Prefect documentation for this feature.
### Prefect Version
2.x
### Describe the proposed behavior
Add it to K8s block
### Describe the current behavio... | 1.0 | Add `EXTRA_PIP_PACKAGES` to the `KubernetesJob` block - ### First check
- [X] I added a descriptive title to this issue.
- [X] I used the GitHub search to find a similar request and didn't find it.
- [X] I searched the Prefect documentation for this feature.
### Prefect Version
2.x
### Describe the proposed behavio... | priority | add extra pip packages to the kubernetesjob block first check i added a descriptive title to this issue i used the github search to find a similar request and didn t find it i searched the prefect documentation for this feature prefect version x describe the proposed behavior add... | 1 |
247,341 | 7,917,386,644 | IssuesEvent | 2018-07-04 09:40:58 | georchestra/georchestra | https://api.github.com/repos/georchestra/georchestra | closed | console - navigation by organisation don't lead to users of organisations | 2018 priority-top | When you navigate by organisation /ldapadmin/console/#/orgs/all you have the organisation list and, for each organisation the count of users attached to the organisation.
But at any time you have the list of the users of an organisation. | 1.0 | console - navigation by organisation don't lead to users of organisations - When you navigate by organisation /ldapadmin/console/#/orgs/all you have the organisation list and, for each organisation the count of users attached to the organisation.
But at any time you have the list of the users of an organisation. | priority | console navigation by organisation don t lead to users of organisations when you navigate by organisation ldapadmin console orgs all you have the organisation list and for each organisation the count of users attached to the organisation but at any time you have the list of the users of an organisation | 1 |
56,285 | 13,784,652,596 | IssuesEvent | 2020-10-08 21:14:56 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | Unable to compile program in Win 10 with MinGW | build/tasks question | I had met a bug like what https://github.com/microsoft/vscode-cpptools/issues/1329 mentioned, and I fixed it through change the code in task.json to:
```json
"label": "build",
"type": "shell",
"command": "C:/mingw-w64/i686-8.1.0-posix-dwarf-rt_v6-rev0/mingw32/bin/g++.exe",
"args... | 1.0 | Unable to compile program in Win 10 with MinGW - I had met a bug like what https://github.com/microsoft/vscode-cpptools/issues/1329 mentioned, and I fixed it through change the code in task.json to:
```json
"label": "build",
"type": "shell",
"command": "C:/mingw-w64/i686-8.1.0-posix-dwarf-rt... | non_priority | unable to compile program in win with mingw i had met a bug like what mentioned and i fixed it through change the code in task json to json label build type shell command c mingw posix dwarf rt bin g exe args ... | 0 |
442,976 | 30,868,790,053 | IssuesEvent | 2023-08-03 09:51:36 | HishamWattar/cooks-kingdom | https://api.github.com/repos/HishamWattar/cooks-kingdom | closed | Add admin endpoint api/admin/user/approve-chef/:id | documentation API tests | This endpoint will approve a chef request in case a user wanted to become a chef | 1.0 | Add admin endpoint api/admin/user/approve-chef/:id - This endpoint will approve a chef request in case a user wanted to become a chef | non_priority | add admin endpoint api admin user approve chef id this endpoint will approve a chef request in case a user wanted to become a chef | 0 |
742,146 | 25,840,250,753 | IssuesEvent | 2022-12-12 23:26:38 | rancher/dashboard | https://api.github.com/repos/rancher/dashboard | closed | [Bug] [Monitoring V2] Cannot add Email receivers | kind/bug internal area/monitoring [zube]: QA Working priority/1 team/area3 area/ui JIRA | **What kind of request is this (question/bug/enhancement/feature request):**
Bug
**Steps to reproduce (least amount of steps as possible):**
In this case, the steps we followed were to:
1. Deploy a fresh Rancher v2.5.1 cluster
2. Enable monitoring v2
3. Upgrade Rancher to v2.5.3
4. Attempt to add an email receiver for... | 1.0 | [Bug] [Monitoring V2] Cannot add Email receivers - **What kind of request is this (question/bug/enhancement/feature request):**
Bug
**Steps to reproduce (least amount of steps as possible):**
In this case, the steps we followed were to:
1. Deploy a fresh Rancher v2.5.1 cluster
2. Enable monitoring v2
3. Upgrade Ranche... | priority | cannot add email receivers what kind of request is this question bug enhancement feature request bug steps to reproduce least amount of steps as possible in this case the steps we followed were to deploy a fresh rancher cluster enable monitoring upgrade rancher to attemp... | 1 |
554,241 | 16,415,260,020 | IssuesEvent | 2021-05-19 05:31:26 | Nelson-Gon/pycite | https://api.github.com/repos/Nelson-Gon/pycite | closed | Automated documentation and release | enhancement good first issue help wanted priority:medium | **Description**
I would like to automate the doc generation and release process.
**Similar Features**
This is similar to `scripts/mkdocs.sh` and `scripts/release.sh`.
**Feature Details**
Sufficiently described.
**Proposed Implementation**
Use an Actions run to automate these e.g. "on release" to ... | 1.0 | Automated documentation and release - **Description**
I would like to automate the doc generation and release process.
**Similar Features**
This is similar to `scripts/mkdocs.sh` and `scripts/release.sh`.
**Feature Details**
Sufficiently described.
**Proposed Implementation**
Use an Actions run t... | priority | automated documentation and release description i would like to automate the doc generation and release process similar features this is similar to scripts mkdocs sh and scripts release sh feature details sufficiently described proposed implementation use an actions run t... | 1 |
53,429 | 22,783,767,299 | IssuesEvent | 2022-07-09 00:42:45 | operate-first/operations | https://api.github.com/repos/operate-first/operations | closed | Let's make Grafana landing page more friendly | lifecycle/rotten area/service/grafana area/monitoring | The landing page at https://grafana.operate-first.cloud/ is just the Grafana default. Let's replace that with something that highlights interesting dashboards, or maybe provides information about how to contribute new dashboards (or links to appropriate docs), etc.
| 1.0 | Let's make Grafana landing page more friendly - The landing page at https://grafana.operate-first.cloud/ is just the Grafana default. Let's replace that with something that highlights interesting dashboards, or maybe provides information about how to contribute new dashboards (or links to appropriate docs), etc.
| non_priority | let s make grafana landing page more friendly the landing page at is just the grafana default let s replace that with something that highlights interesting dashboards or maybe provides information about how to contribute new dashboards or links to appropriate docs etc | 0 |
43,286 | 2,887,367,329 | IssuesEvent | 2015-06-12 14:35:58 | FLEXIcontent/flexicontent-cck | https://api.github.com/repos/FLEXIcontent/flexicontent-cck | opened | Add to content types selection for menu item when editing, thus to allow custom Joomla template | Priority Normal | The Joomla template used in item views, may not be appropriate or desirable for FLEXIcontent item form
The FLEXIcontent edit links should include a different menu item that the item viewing links
- this should be a parameter per content type | 1.0 | Add to content types selection for menu item when editing, thus to allow custom Joomla template - The Joomla template used in item views, may not be appropriate or desirable for FLEXIcontent item form
The FLEXIcontent edit links should include a different menu item that the item viewing links
- this should be a par... | priority | add to content types selection for menu item when editing thus to allow custom joomla template the joomla template used in item views may not be appropriate or desirable for flexicontent item form the flexicontent edit links should include a different menu item that the item viewing links this should be a par... | 1 |
134,727 | 19,318,145,502 | IssuesEvent | 2021-12-14 00:19:28 | timberline-secondary/hackerspace-todo | https://api.github.com/repos/timberline-secondary/hackerspace-todo | closed | Web Dev HTMl & CSS FInal Project? | Campaigns: New Course: Web Design | This might make a good final project for HTML and CSS (pre-JavaScript)
https://www.youtube.com/watch?v=-8LTPIJBGwQ | 1.0 | Web Dev HTMl & CSS FInal Project? - This might make a good final project for HTML and CSS (pre-JavaScript)
https://www.youtube.com/watch?v=-8LTPIJBGwQ | non_priority | web dev html css final project this might make a good final project for html and css pre javascript | 0 |
218,066 | 7,330,368,590 | IssuesEvent | 2018-03-05 09:42:03 | NCEAS/metacat | https://api.github.com/repos/NCEAS/metacat | closed | Dependence of NCEAS registry on Admin database | Category: registry Component: Bugzilla-Id Priority: Normal Status: Resolved Tracker: Bug | ---
Author Name: **Saurabh Garg** (Saurabh Garg)
Original Redmine Issue: 1552, https://projects.ecoinformatics.org/ecoinfo/issues/1552
Original Date: 2004-05-04
Original Assignee: Shaun Walbridge
---
This is reported by Sandy:
She had problems accessing the registry when she was in Washington DC and
giving demos... | 1.0 | Dependence of NCEAS registry on Admin database - ---
Author Name: **Saurabh Garg** (Saurabh Garg)
Original Redmine Issue: 1552, https://projects.ecoinformatics.org/ecoinfo/issues/1552
Original Date: 2004-05-04
Original Assignee: Shaun Walbridge
---
This is reported by Sandy:
She had problems accessing the registry... | priority | dependence of nceas registry on admin database author name saurabh garg saurabh garg original redmine issue original date original assignee shaun walbridge this is reported by sandy she had problems accessing the registry when she was in washington dc and giving demos of the regis... | 1 |
627,612 | 19,910,180,150 | IssuesEvent | 2022-01-25 16:25:39 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | Stop exposing reviewer names to developers | component: reviewer tools priority: p3 | This is a spin-off from https://github.com/mozilla/addons-server/issues/17318 and is just about removing the names of reviewers from any screens that developers can see, which should be exclusively devhub pages. | 1.0 | Stop exposing reviewer names to developers - This is a spin-off from https://github.com/mozilla/addons-server/issues/17318 and is just about removing the names of reviewers from any screens that developers can see, which should be exclusively devhub pages. | priority | stop exposing reviewer names to developers this is a spin off from and is just about removing the names of reviewers from any screens that developers can see which should be exclusively devhub pages | 1 |
396,457 | 27,119,381,517 | IssuesEvent | 2023-02-15 21:22:56 | MatteoCazzaniga/IngegneriaSoftware_22-23 | https://api.github.com/repos/MatteoCazzaniga/IngegneriaSoftware_22-23 | closed | Creazione Immagini Diagrammi UML mancanti | documentation | Creazione file jpg dei diagrammi UML mancanti (diagramma dei casi d'uso e diagramma delle attività) | 1.0 | Creazione Immagini Diagrammi UML mancanti - Creazione file jpg dei diagrammi UML mancanti (diagramma dei casi d'uso e diagramma delle attività) | non_priority | creazione immagini diagrammi uml mancanti creazione file jpg dei diagrammi uml mancanti diagramma dei casi d uso e diagramma delle attività | 0 |
360,317 | 25,285,501,064 | IssuesEvent | 2022-11-16 18:56:39 | WordPress/Documentation-Issue-Tracker | https://api.github.com/repos/WordPress/Documentation-Issue-Tracker | closed | [HelpHub] File block | user documentation block editor medium priority 6.1 | Article: https://wordpress.org/support/article/file-block/
## Updating for 6.1
- [x] Display upload error notices using snackbars. [43893](https://github.com/WordPress/gutenberg/pull/43893)
- [x] Remove redundant block name from "settings" panels [40275](https://github.com/WordPress/gutenberg/pull/40275)
## Gene... | 1.0 | [HelpHub] File block - Article: https://wordpress.org/support/article/file-block/
## Updating for 6.1
- [x] Display upload error notices using snackbars. [43893](https://github.com/WordPress/gutenberg/pull/43893)
- [x] Remove redundant block name from "settings" panels [40275](https://github.com/WordPress/gutenberg/... | non_priority | file block article updating for display upload error notices using snackbars remove redundant block name from settings panels general make sure all screenshots are relevant to the latest version make sure videos are up to date add alt tags for the images make ... | 0 |
214,870 | 24,120,884,260 | IssuesEvent | 2022-09-20 18:35:46 | bcgov/cloud-pathfinder | https://api.github.com/repos/bcgov/cloud-pathfinder | opened | Compile a list with the guardrails rules that limit/enable the workload accounts | Security Quality Assurance | **Describe the issue**
There is not a guardrails list. The closest thing is a bunch of Service Control Policies that can be found at https://github.com/aws-samples/aws-secure-environment-accelerator/tree/main/reference-artifacts/SCPs
**Additional context**
The guardrails are a crucial characteristic of the ECF. They a... | True | Compile a list with the guardrails rules that limit/enable the workload accounts - **Describe the issue**
There is not a guardrails list. The closest thing is a bunch of Service Control Policies that can be found at https://github.com/aws-samples/aws-secure-environment-accelerator/tree/main/reference-artifacts/SCPs
*... | non_priority | compile a list with the guardrails rules that limit enable the workload accounts describe the issue there is not a guardrails list the closest thing is a bunch of service control policies that can be found at additional context the guardrails are a crucial characteristic of the ecf they are tested and p... | 0 |
304,994 | 23,093,672,158 | IssuesEvent | 2022-07-26 17:21:06 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | aws_appstream_stack.access_endpoints argument documentation missing | documentation service/appstream | <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/state/index.html) and [State Backend](https://www.terraform.io/docs/backen... | 1.0 | aws_appstream_stack.access_endpoints argument documentation missing - <!---
Please note the following potential times when an issue might be in Terraform core:
* [Configuration Language](https://www.terraform.io/docs/configuration/index.html) or resource ordering issues
* [State](https://www.terraform.io/docs/stat... | non_priority | aws appstream stack access endpoints argument documentation missing please note the following potential times when an issue might be in terraform core or resource ordering issues and issues issues issues spans resources across multiple providers if you are running into ... | 0 |
296,507 | 9,116,750,599 | IssuesEvent | 2019-02-22 09:52:11 | Xceptance/neodymium-library | https://api.github.com/repos/Xceptance/neodymium-library | closed | Update Cucumber to 4.x | Medium Priority doneInDevelop recheckedInDevelop update-dependency | Update Cucumber version to 3.x once the allure support >= version 2.8 is available.
See the link for latest release: https://github.com/allure-framework/allure2/releases
Remove "io.qameta.allure.cucumber2jvm.AllureCucumber2Jvm" if the update above is successful.
| 1.0 | Update Cucumber to 4.x - Update Cucumber version to 3.x once the allure support >= version 2.8 is available.
See the link for latest release: https://github.com/allure-framework/allure2/releases
Remove "io.qameta.allure.cucumber2jvm.AllureCucumber2Jvm" if the update above is successful.
| priority | update cucumber to x update cucumber version to x once the allure support version is available see the link for latest release remove io qameta allure if the update above is successful | 1 |
97,504 | 11,015,028,284 | IssuesEvent | 2019-12-05 00:19:24 | openenclave/openenclave | https://api.github.com/repos/openenclave/openenclave | closed | API docs are too hard to find | documentation triaged | Currently they're hidden in the obscure "Versions" link at openenclave.io
There's nothing about docs, or APIs, or anything else that one would be looking for to find API docs. And the main GitHub/openenclave readme docs just point to openenclave.io. | 1.0 | API docs are too hard to find - Currently they're hidden in the obscure "Versions" link at openenclave.io
There's nothing about docs, or APIs, or anything else that one would be looking for to find API docs. And the main GitHub/openenclave readme docs just point to openenclave.io. | non_priority | api docs are too hard to find currently they re hidden in the obscure versions link at openenclave io there s nothing about docs or apis or anything else that one would be looking for to find api docs and the main github openenclave readme docs just point to openenclave io | 0 |
10,840 | 12,824,604,168 | IssuesEvent | 2020-07-06 13:44:33 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | ORM and application Support | status/TODO status/WIP type/compatibility | Python:
- [ ] SQLAlchemy
- [ ] Peewee
- [ ] django
- [ ] ponyorm
Go:
Orm:
- [x] xorm: https://github.com/go-xorm/xorm
- [x] beego: https://github.com/astaxie/beego/tree/master/orm
- [x] go-sql-test: https://github.com/bradfitz/go-sql-test
- [ ] upper.io: https://upper.io/db.v1/mysql
Application:
- [x] G... | True | ORM and application Support - Python:
- [ ] SQLAlchemy
- [ ] Peewee
- [ ] django
- [ ] ponyorm
Go:
Orm:
- [x] xorm: https://github.com/go-xorm/xorm
- [x] beego: https://github.com/astaxie/beego/tree/master/orm
- [x] go-sql-test: https://github.com/bradfitz/go-sql-test
- [ ] upper.io: https://upper.io/db.v1... | non_priority | orm and application support python sqlalchemy peewee django ponyorm go orm xorm beego go sql test upper io application gogs dalga java: mybatis jdbctemplate hibernate play php phabricator phpmyadmin... | 0 |
31,792 | 2,736,876,077 | IssuesEvent | 2015-04-19 21:03:51 | x360ce/x360ce | https://api.github.com/repos/x360ce/x360ce | closed | llll | bug imported invalid Priority-Medium | _From [Crack.bi...@gmail.com](https://code.google.com/u/110974868023865476405/) on May 12, 2010 09:28:38_
What steps will reproduce the problem? 1. 2. 3. What is the expected output? What do you see instead? What version of the product are you using? On what operating system? What gamepad are you using? On what versio... | 1.0 | llll - _From [Crack.bi...@gmail.com](https://code.google.com/u/110974868023865476405/) on May 12, 2010 09:28:38_
What steps will reproduce the problem? 1. 2. 3. What is the expected output? What do you see instead? What version of the product are you using? On what operating system? What gamepad are you using? On what... | priority | llll from on may what steps will reproduce the problem what is the expected output what do you see instead what version of the product are you using on what operating system what gamepad are you using on what version of drivers please set third label to core if issue affect emulator ... | 1 |
670,977 | 22,716,469,887 | IssuesEvent | 2022-07-06 02:51:37 | ansible-collections/azure | https://api.github.com/repos/ansible-collections/azure | closed | Couldn't find api version for Microsoft.DataFactory/factories?api-version=2018-06-01 | medium_priority not a bug | - name: Check if Data Factory ({{ az_datafactory_name }}) already exists
azure.azcollection.azure_rm_resource_info:
auth_source: auto
client_id: "{{ az_client_id }}"
secret: "{{ az_secret }}"
tenant: "{{ az_tenant_id }}"
subscription_id: "{{ az_subscription_id }}"
url: "ht... | 1.0 | Couldn't find api version for Microsoft.DataFactory/factories?api-version=2018-06-01 - - name: Check if Data Factory ({{ az_datafactory_name }}) already exists
azure.azcollection.azure_rm_resource_info:
auth_source: auto
client_id: "{{ az_client_id }}"
secret: "{{ az_secret }}"
tenant: ... | priority | couldn t find api version for microsoft datafactory factories api version name check if data factory az datafactory name already exists azure azcollection azure rm resource info auth source auto client id az client id secret az secret tenant a... | 1 |
1,935 | 4,763,886,581 | IssuesEvent | 2016-10-25 15:32:42 | openvstorage/alba | https://api.github.com/repos/openvstorage/alba | closed | Claim osd looping and high cpu usage | process_wontfix SRP type_bug | ## Problem description
When I logged into my setup, I found that my root partition was completely full. The culprit was found in /var/log/upstart/alba-asd *.
One of the asd logging was full of:
```
2016-10-19 21:53:42 16108 +0200 - ovs-node1 - 9453/0 - alba/asd - 5366 - info - returning error (Asd_protocol.Protoc... | 1.0 | Claim osd looping and high cpu usage - ## Problem description
When I logged into my setup, I found that my root partition was completely full. The culprit was found in /var/log/upstart/alba-asd *.
One of the asd logging was full of:
```
2016-10-19 21:53:42 16108 +0200 - ovs-node1 - 9453/0 - alba/asd - 5366 - info... | non_priority | claim osd looping and high cpu usage problem description when i logged into my setup i found that my root partition was completely full the culprit was found in var log upstart alba asd one of the asd logging was full of ovs alba asd info returning error asd p... | 0 |
570,212 | 17,021,263,351 | IssuesEvent | 2021-07-02 19:32:49 | phetsims/balloons-and-static-electricity | https://api.github.com/repos/phetsims/balloons-and-static-electricity | closed | The "Remove Wall" button is no longer visible on the wall | priority:2-high status:blocks-publication status:ready-for-review | While testing today, I noticed that the "Remove Wall" button seemed to be gone, but then I found I could navigate to it using the tab keys. Turns out that it is now behind the wall instead of in from of it. After a little detective work, I believe I've traced it to this commit: https://github.com/phetsims/joist/commi... | 1.0 | The "Remove Wall" button is no longer visible on the wall - While testing today, I noticed that the "Remove Wall" button seemed to be gone, but then I found I could navigate to it using the tab keys. Turns out that it is now behind the wall instead of in from of it. After a little detective work, I believe I've trace... | priority | the remove wall button is no longer visible on the wall while testing today i noticed that the remove wall button seemed to be gone but then i found i could navigate to it using the tab keys turns out that it is now behind the wall instead of in from of it after a little detective work i believe i ve trace... | 1 |
676,349 | 23,123,448,944 | IssuesEvent | 2022-07-28 01:25:22 | FEeasy404/GameUs | https://api.github.com/repos/FEeasy404/GameUs | closed | 하단탭 화면 좁아질 경우 height가 높아짐 | 🐛bug 🌿Priority: Low ⚔Fix | ## 버그 발생 설명
- 화면이 좁아질 경우 하단탭의 height가 높아져 페이지 하단 내용을 가립니다!
- 게시물수정' 텍스트가 화면이 좁아져도 한줄로 유지되도록 하면 좋을것 같습니다!
## 할 일
- [ ] 하단탭 height 수정
## ETC
| 1.0 | 하단탭 화면 좁아질 경우 height가 높아짐 - ## 버그 발생 설명
- 화면이 좁아질 경우 하단탭의 height가 높아져 페이지 하단 내용을 가립니다!
- 게시물수정' 텍스트가 화면이 좁아져도 한줄로 유지되도록 하면 좋을것 같습니다!
## 할 일
- [ ] 하단탭 height 수정
## ETC
| priority | 하단탭 화면 좁아질 경우 height가 높아짐 버그 발생 설명 화면이 좁아질 경우 하단탭의 height가 높아져 페이지 하단 내용을 가립니다 게시물수정 텍스트가 화면이 좁아져도 한줄로 유지되도록 하면 좋을것 같습니다 할 일 하단탭 height 수정 etc | 1 |
177,122 | 13,684,353,727 | IssuesEvent | 2020-09-30 04:38:30 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | LiveShare tests are crashing and causing build flakiness | Area-IDE Flaky Resolution-Not Applicable Test | Failing builds:
- https://dev.azure.com/dnceng/public/_build/results/buildId=564945&view=artifacts&type=publishedArtifacts
- https://dev.azure.com/dnceng/public/_build/results?buildId=563985&view=artifacts&type=publishedArtifacts
The crash appears to occur on xunit shutdown. The actual log file for the tests indi... | 1.0 | LiveShare tests are crashing and causing build flakiness - Failing builds:
- https://dev.azure.com/dnceng/public/_build/results/buildId=564945&view=artifacts&type=publishedArtifacts
- https://dev.azure.com/dnceng/public/_build/results?buildId=563985&view=artifacts&type=publishedArtifacts
The crash appears to occu... | non_priority | liveshare tests are crashing and causing build flakiness failing builds the crash appears to occur on xunit shutdown the actual log file for the tests indicates that everything succeeded but xunit is exiting with a failure code and no output | 0 |
590,482 | 17,778,740,706 | IssuesEvent | 2021-08-30 23:31:53 | dtcenter/MET | https://api.github.com/repos/dtcenter/MET | closed | Enhance MET to compute the CBS score. | type: new feature priority: blocker requestor: DTC/AF V&V required: FOR DEVELOPMENT RELEASE | ## Describe the New Feature ##
The AF project needs to generate the CBS score on its GPP verification. This requires adding another method of interpolation (areal). Michelle Harrold has provided some code (from Bob Craig) and helpful references (see attachments).
From Bob:
"All, the attached document describes t... | 1.0 | Enhance MET to compute the CBS score. - ## Describe the New Feature ##
The AF project needs to generate the CBS score on its GPP verification. This requires adding another method of interpolation (areal). Michelle Harrold has provided some code (from Bob Craig) and helpful references (see attachments).
From Bob:
... | priority | enhance met to compute the cbs score describe the new feature the af project needs to generate the cbs score on its gpp verification this requires adding another method of interpolation areal michelle harrold has provided some code from bob craig and helpful references see attachments from bob ... | 1 |
215,104 | 7,290,309,613 | IssuesEvent | 2018-02-24 00:54:30 | PikyCZ/NovaMobsX | https://api.github.com/repos/PikyCZ/NovaMobsX | closed | Know Issues | [Priority] High [Status] Work in Progress help wanted | **Autospawn**
- [ ] Fix autospawn
- [x] disable worlds
**Entities**
- [ ] spider attacking
- [x] target option for passive entities | 1.0 | Know Issues - **Autospawn**
- [ ] Fix autospawn
- [x] disable worlds
**Entities**
- [ ] spider attacking
- [x] target option for passive entities | priority | know issues autospawn fix autospawn disable worlds entities spider attacking target option for passive entities | 1 |
248,047 | 18,858,025,709 | IssuesEvent | 2021-11-12 09:18:05 | IshaaanVyas/pe | https://api.github.com/repos/IshaaanVyas/pe | opened | Very complicated class diagram | type.DocumentationBug severity.Medium | 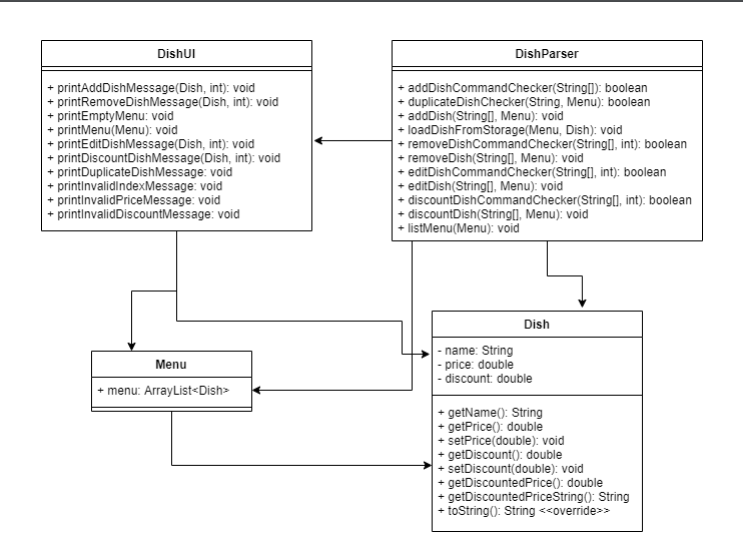
Could have made it much simpler and easier to understand by removing methods/attributes that were not necessary to the understanding of the class diagram. (Pretty sure all the print methods are not necess... | 1.0 | Very complicated class diagram - 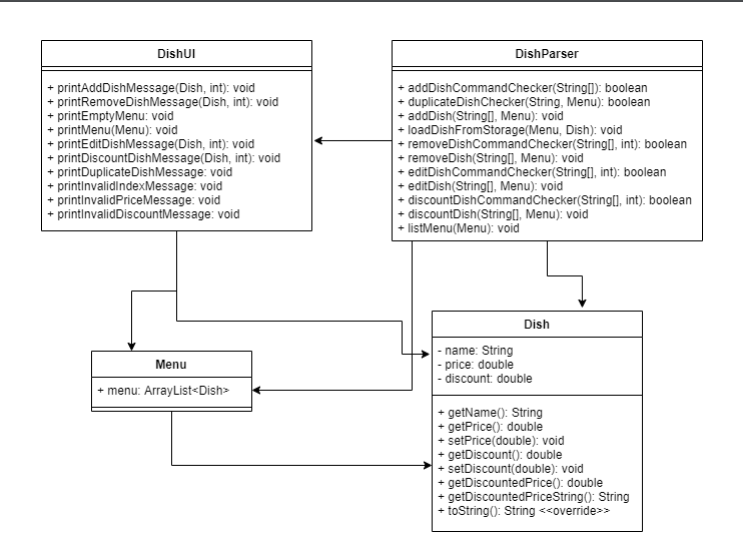
Could have made it much simpler and easier to understand by removing methods/attributes that were not necessary to the understanding of the class diagram. (Pretty sure all... | non_priority | very complicated class diagram could have made it much simpler and easier to understand by removing methods attributes that were not necessary to the understanding of the class diagram pretty sure all the print methods are not necessary to understand the relationship between the classes | 0 |
391,337 | 11,572,219,084 | IssuesEvent | 2020-02-20 23:24:54 | googleapis/python-monitoring | https://api.github.com/repos/googleapis/python-monitoring | closed | Synthesis failed for python-monitoring | api: monitoring autosynth failure priority: p1 type: bug | Hello! Autosynth couldn't regenerate python-monitoring. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', 'synth.py', '--']
synthtool > Executing /tmpfs/src/git/a... | 1.0 | Synthesis failed for python-monitoring - Hello! Autosynth couldn't regenerate python-monitoring. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth'
Running synthtool
['/tmpfs/src/git/autosynth/env/bin/python3', '-m', 'synthtool', 'synth.py', '--... | priority | synthesis failed for python monitoring hello autosynth couldn t regenerate python monitoring broken heart here s the output from running synth py cloning into working repo switched to branch autosynth running synthtool synthtool executing tmpfs src git autosynth working repo synth py on bran... | 1 |
236,532 | 7,750,081,821 | IssuesEvent | 2018-05-30 13:28:37 | ld4l-labs/vitrolib | https://api.github.com/repos/ld4l-labs/vitrolib | opened | Add accession number to custodial event | ARM custom forms priority: medium | Currently linked only to Item. Complexities in adding to custodial event: select list should display all accession numbers linked to the item and not linked to another custodial event; otherwise create new. For now we are linking the accession number only to the item using bf:identifies. | 1.0 | Add accession number to custodial event - Currently linked only to Item. Complexities in adding to custodial event: select list should display all accession numbers linked to the item and not linked to another custodial event; otherwise create new. For now we are linking the accession number only to the item using bf:i... | priority | add accession number to custodial event currently linked only to item complexities in adding to custodial event select list should display all accession numbers linked to the item and not linked to another custodial event otherwise create new for now we are linking the accession number only to the item using bf i... | 1 |
25,938 | 19,476,131,918 | IssuesEvent | 2021-12-24 12:44:06 | IBM-Cloud/terraform-provider-ibm | https://api.github.com/repos/IBM-Cloud/terraform-provider-ibm | closed | Destroy of ibm_is_instance_group.instance_group fails with provisioning_status must be active to delete instance group | service/VPC Infrastructure | ### Terraform Version
- IBM Cloud Provider version 1.16.1
- Terraform v0.12.29
### Affected Resource(s)
- ibm_is_instance_group.instance_group
### Terraform Configuration Files
See https://github.com/IBM-Cloud/vpc-tutorials/tree/master/vpc-autoscale
### Expected Behavior
Destroy completes succesfully
#... | 1.0 | Destroy of ibm_is_instance_group.instance_group fails with provisioning_status must be active to delete instance group - ### Terraform Version
- IBM Cloud Provider version 1.16.1
- Terraform v0.12.29
### Affected Resource(s)
- ibm_is_instance_group.instance_group
### Terraform Configuration Files
See https://... | non_priority | destroy of ibm is instance group instance group fails with provisioning status must be active to delete instance group terraform version ibm cloud provider version terraform affected resource s ibm is instance group instance group terraform configuration files see exp... | 0 |
53,300 | 13,151,780,904 | IssuesEvent | 2020-08-09 18:31:51 | xamarin/xamarin-android | https://api.github.com/repos/xamarin/xamarin-android | closed | Unable to build Xamarin Android application after upgrading to VS 16.7 Release - getting error CS8370 | Area: App+Library Build | ### Steps to Reproduce
1. Open a project containing some C# 8.0 code & which was compiling fine with 16.6, then build it in "Debug" mode
2. Note that updating the tag langversion to "latest" in .csproj does not solve the issue
### Expected Behavior
Build should complete without errors.
### Actual Behavior
G... | 1.0 | Unable to build Xamarin Android application after upgrading to VS 16.7 Release - getting error CS8370 - ### Steps to Reproduce
1. Open a project containing some C# 8.0 code & which was compiling fine with 16.6, then build it in "Debug" mode
2. Note that updating the tag langversion to "latest" in .csproj does not s... | non_priority | unable to build xamarin android application after upgrading to vs release getting error steps to reproduce open a project containing some c code which was compiling fine with then build it in debug mode note that updating the tag langversion to latest in csproj does not solve th... | 0 |
179,823 | 30,308,713,515 | IssuesEvent | 2023-07-10 11:19:33 | GSA-TTS/FAC | https://api.github.com/repos/GSA-TTS/FAC | closed | Mock up new FAC Resources page | ux/design content | Breakout issue of #377
### Background
We're designing a new FAC Resources page (#458) based on research with auditors and auditees. Once we complete the research and content design work in #458, we can mock up the new FAC Resources page in Figma.
### Tasks
- [x] Mock up new page
- [ ] Peer review
- [ ] W... | 1.0 | Mock up new FAC Resources page - Breakout issue of #377
### Background
We're designing a new FAC Resources page (#458) based on research with auditors and auditees. Once we complete the research and content design work in #458, we can mock up the new FAC Resources page in Figma.
### Tasks
- [x] Mock up new... | non_priority | mock up new fac resources page breakout issue of background we re designing a new fac resources page based on research with auditors and auditees once we complete the research and content design work in we can mock up the new fac resources page in figma tasks mock up new page ... | 0 |
13,066 | 5,291,675,441 | IssuesEvent | 2017-02-08 23:12:42 | grpc/grpc | https://api.github.com/repos/grpc/grpc | closed | Python unit.beta._not_found_test.NotFoundTest.test_future_stream_unary_not_found test is flaky | BUILDPONY P1 python | https://grpc-testing.appspot.com/job/gRPC_pull_requests_linux/1799/testReport/junit/(root)/python_linux_opt/py27_test_unit_beta__not_found_test_NotFoundTest/
```
[0mRunning unit.beta._not_found_test.NotFoundTest.test_future_stream_unary_not_found
[91mERROR unit.beta._not_found_test.NotFoundTest.test_... | 1.0 | Python unit.beta._not_found_test.NotFoundTest.test_future_stream_unary_not_found test is flaky - https://grpc-testing.appspot.com/job/gRPC_pull_requests_linux/1799/testReport/junit/(root)/python_linux_opt/py27_test_unit_beta__not_found_test_NotFoundTest/
```
[0mRunning unit.beta._not_found_test.NotFoundTest.t... | non_priority | python unit beta not found test notfoundtest test future stream unary not found test is flaky unit beta not found test notfoundtest test future stream unary not found unit beta not found test notfoundtest test future stream unary not found tests finished successful unsuc... | 0 |
195,415 | 14,728,707,621 | IssuesEvent | 2021-01-06 10:19:42 | WoWManiaUK/Redemption | https://api.github.com/repos/WoWManiaUK/Redemption | closed | [Raid] Eredar Twins intro voicelines | Fixed on PTR - Tester Confirmed Priority - Low | **Links:** https://wowwiki.fandom.com/wiki/Eredar_Twins#:~:text=The%20Eredar%20Twins%2C%20Lady%20Sacrolash,of%20Rohendor%2C%20the%20Second%20Gate.
**What is Happening:** Lady Sarcolash and Grand Warlock Alythess currently play their intro dialogue exchange as soon as the first player enters the Sunwell Plateau ins... | 1.0 | [Raid] Eredar Twins intro voicelines - **Links:** https://wowwiki.fandom.com/wiki/Eredar_Twins#:~:text=The%20Eredar%20Twins%2C%20Lady%20Sacrolash,of%20Rohendor%2C%20the%20Second%20Gate.
**What is Happening:** Lady Sarcolash and Grand Warlock Alythess currently play their intro dialogue exchange as soon as the firs... | non_priority | eredar twins intro voicelines links what is happening lady sarcolash and grand warlock alythess currently play their intro dialogue exchange as soon as the first player enters the sunwell plateau instance at this point the bosses are way far from the players and definitely out of sight and them... | 0 |
25,587 | 4,414,499,103 | IssuesEvent | 2016-08-13 13:31:33 | ironjan/klausurtool-ror | https://api.github.com/repos/ironjan/klausurtool-ror | closed | Sorted TOC | defect | ## How does this problem happen?
1. First I go to http://ausleihe.fachschafts.website/internal/admin/old_folders/175/toc
## What does happen?
TOC is unsorted.
## What do you expect to happen instead?
TOC should be sorted. | 1.0 | Sorted TOC - ## How does this problem happen?
1. First I go to http://ausleihe.fachschafts.website/internal/admin/old_folders/175/toc
## What does happen?
TOC is unsorted.
## What do you expect to happen instead?
TOC should be sorted. | non_priority | sorted toc how does this problem happen first i go to what does happen toc is unsorted what do you expect to happen instead toc should be sorted | 0 |
94,539 | 3,928,105,214 | IssuesEvent | 2016-04-24 01:21:42 | Baystation12/Baystation12 | https://api.github.com/repos/Baystation12/Baystation12 | closed | Ghosts can attach and detach IV drips | feature oversight priority: trivial | [Spooky ghost] attaches the IV drip to [Non-spooky human].
Very spooky! But probably not something they should be able to do. | 1.0 | Ghosts can attach and detach IV drips - [Spooky ghost] attaches the IV drip to [Non-spooky human].
Very spooky! But probably not something they should be able to do. | priority | ghosts can attach and detach iv drips attaches the iv drip to very spooky but probably not something they should be able to do | 1 |
255,915 | 8,126,577,039 | IssuesEvent | 2018-08-17 03:07:41 | aowen87/BAR | https://api.github.com/repos/aowen87/BAR | closed | ITAPS shared libraries not included when doing a make package. | Bug Likelihood: 3 - Occasional Priority: Normal Severity: 2 - Minor Irritation | make package doesn't package up the ITAPS shared libraries, so when VisIt is run there are error message at startup about missing shared libraries and of course the ITAPS plugins won't work. This can be fixed by either installing only static libraries or fixing the make package script so that it packages up the shared ... | 1.0 | ITAPS shared libraries not included when doing a make package. - make package doesn't package up the ITAPS shared libraries, so when VisIt is run there are error message at startup about missing shared libraries and of course the ITAPS plugins won't work. This can be fixed by either installing only static libraries or ... | priority | itaps shared libraries not included when doing a make package make package doesn t package up the itaps shared libraries so when visit is run there are error message at startup about missing shared libraries and of course the itaps plugins won t work this can be fixed by either installing only static libraries or ... | 1 |
561,480 | 16,617,888,173 | IssuesEvent | 2021-06-02 19:16:56 | department-of-veterans-affairs/caseflow | https://api.github.com/repos/department-of-veterans-affairs/caseflow | closed | [Dogfooding Bug] Offset is displayed instead of Timezone for some cases | Priority: Low Product: caseflow-hearings Stakeholder: BVA Team: Tango 💃 Type: Bug | ## Description

An offset is displayed instead of a timezone for some timezones (e.g. "Vladivostok", which shows "+10").
## Acceptance criteria
- [ ] Ensure something friendlier than the timezone offset ... | 1.0 | [Dogfooding Bug] Offset is displayed instead of Timezone for some cases - ## Description

An offset is displayed instead of a timezone for some timezones (e.g. "Vladivostok", which shows "+10").
## Accep... | priority | offset is displayed instead of timezone for some cases description an offset is displayed instead of a timezone for some timezones e g vladivostok which shows acceptance criteria ensure something friendlier than the timezone offset displays background context resources technic... | 1 |
499,578 | 14,450,616,608 | IssuesEvent | 2020-12-08 09:50:05 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | Contract Nested Clause "Any" only checks first clause | Category: Gameplay Priority: Medium Status: Fixed | 
In the contract only the first entry is counted for the Nested Clause "Any". For example, I gave 20 corn but in the chat it was reported that 20 fiddleheads are missing. When I want to sign the contract as... | 1.0 | Contract Nested Clause "Any" only checks first clause - 
In the contract only the first entry is counted for the Nested Clause "Any". For example, I gave 20 corn but in the chat it was reported that 20 fidd... | priority | contract nested clause any only checks first clause in the contract only the first entry is counted for the nested clause any for example i gave corn but in the chat it was reported that fiddleheads are missing when i want to sign the contract as done he tells me that everything is still missing ... | 1 |
259,207 | 19,590,650,744 | IssuesEvent | 2022-01-05 12:35:19 | brumik/react-json-chart-builder | https://api.github.com/repos/brumik/react-json-chart-builder | closed | Demo app improvements | documentation | - [x] Use react router for different chart types, so you can send link to an exact chart.
- [x] Make the link menu better, probably horizontal instead of vertical so it can grow better.
- [ ] Add a few more examples.
- [ ] Describe the examples so the user can decide which example is probably the closes to the featu... | 1.0 | Demo app improvements - - [x] Use react router for different chart types, so you can send link to an exact chart.
- [x] Make the link menu better, probably horizontal instead of vertical so it can grow better.
- [ ] Add a few more examples.
- [ ] Describe the examples so the user can decide which example is probably... | non_priority | demo app improvements use react router for different chart types so you can send link to an exact chart make the link menu better probably horizontal instead of vertical so it can grow better add a few more examples describe the examples so the user can decide which example is probably the clo... | 0 |
568,119 | 16,959,804,363 | IssuesEvent | 2021-06-29 00:59:29 | TerriaJS/de-australia-map | https://api.github.com/repos/TerriaJS/de-australia-map | closed | DE Australia - option for DEA team to update catalogue & test data services | high priority | DEA Team:
- we do need somewhere to test our web services and catalog
- now with the v8 release we don't really have a convenient/persistent spot
- until earlier this week, we updated the terria cube catalog with the services/features we want to test to share with stakeholders
Some options:
1) update terriac... | 1.0 | DE Australia - option for DEA team to update catalogue & test data services - DEA Team:
- we do need somewhere to test our web services and catalog
- now with the v8 release we don't really have a convenient/persistent spot
- until earlier this week, we updated the terria cube catalog with the services/features w... | priority | de australia option for dea team to update catalogue test data services dea team we do need somewhere to test our web services and catalog now with the release we don t really have a convenient persistent spot until earlier this week we updated the terria cube catalog with the services features we... | 1 |
461,183 | 13,224,780,467 | IssuesEvent | 2020-08-17 19:50:03 | google/ground-platform | https://api.github.com/repos/google/ground-platform | closed | [Add/edit observation] Set audit info (creation/edit user and timestamp) on save | priority: p2 type: feature request web | @gyarill fyi, adding here for future work. | 1.0 | [Add/edit observation] Set audit info (creation/edit user and timestamp) on save - @gyarill fyi, adding here for future work. | priority | set audit info creation edit user and timestamp on save gyarill fyi adding here for future work | 1 |
372,099 | 11,009,170,163 | IssuesEvent | 2019-12-04 12:04:39 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | Audio errors spam console on various tool use | Fixed Medium Priority | When trying to use various tools on the environment:

Can not play a disabled audio source
UnityEngine.AudioSource:Play()
PlayRandomAudioClip:OnEnable() (at Assets/PlayRandomAudioClip.cs:34)
UnityEngine.... | 1.0 | Audio errors spam console on various tool use - When trying to use various tools on the environment:

Can not play a disabled audio source
UnityEngine.AudioSource:Play()
PlayRandomAudioClip:OnEnable() (at... | priority | audio errors spam console on various tool use when trying to use various tools on the environment can not play a disabled audio source unityengine audiosource play playrandomaudioclip onenable at assets playrandomaudioclip cs unityengine object instantiate gameobject quaternion characteraud... | 1 |
66,936 | 8,058,895,097 | IssuesEvent | 2018-08-02 20:01:52 | apache/incubator-openwhisk-website | https://api.github.com/repos/apache/incubator-openwhisk-website | opened | Create README Templates for Deployment methods | design priority: low | We would like to link every deployment README to openwhisk website documentation page. And to provide a uniform experience throughout all deployment methods, create a common template so that every deployment repos can change its README.md based on that template.
| 1.0 | Create README Templates for Deployment methods - We would like to link every deployment README to openwhisk website documentation page. And to provide a uniform experience throughout all deployment methods, create a common template so that every deployment repos can change its README.md based on that template.
| non_priority | create readme templates for deployment methods we would like to link every deployment readme to openwhisk website documentation page and to provide a uniform experience throughout all deployment methods create a common template so that every deployment repos can change its readme md based on that template | 0 |
44,325 | 11,427,307,501 | IssuesEvent | 2020-02-04 00:21:35 | lyft/envoy-mobile | https://api.github.com/repos/lyft/envoy-mobile | closed | build: publish envoy artifact | build community no stalebot | During master CI we should publish a compiled library for envoy that people can use to avoid compiling on their own. | 1.0 | build: publish envoy artifact - During master CI we should publish a compiled library for envoy that people can use to avoid compiling on their own. | non_priority | build publish envoy artifact during master ci we should publish a compiled library for envoy that people can use to avoid compiling on their own | 0 |
436,875 | 30,573,162,425 | IssuesEvent | 2023-07-21 01:21:27 | SSWConsulting/SSW.Website | https://api.github.com/repos/SSWConsulting/SSW.Website | closed | 📄Docs - Wiki Page for Components | Type: Documentation | At the moment, when you press the "embed" button on Tina, it won't give you a preview or description of what each component is. It would be good if there was a piece of documentation describing some/all of the components available to users.
 detected in normalize-url-1.9.1.tgz, normalize-url-3.3.0.tgz | security vulnerability | ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>normalize-url-1.9.1.tgz</b>, <b>normalize-url-3.3.0.tgz</b></p></summary>
<p>
<details><summary><b>normalize-url-1.9... | True | CVE-2021-33502 (High) detected in normalize-url-1.9.1.tgz, normalize-url-3.3.0.tgz - ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>normalize-url-1.9.1.tgz</b>, <b>... | non_priority | cve high detected in normalize url tgz normalize url tgz cve high severity vulnerability vulnerable libraries normalize url tgz normalize url tgz normalize url tgz normalize a url library home page a href path to dependency file bass stati... | 0 |
359,275 | 10,667,517,954 | IssuesEvent | 2019-10-19 13:04:16 | eJourn-al/eJournal | https://api.github.com/repos/eJourn-al/eJournal | closed | LTI course not ready screen | Priority: High Status: In Progress Type: Enhancement Workload: Medium | **Describe the solution you'd like**
- A dedicated screen to this scenario, explaining the situation in a lighthearted way.
- Notification with sufficient context so the eJournal team can take action as well.
- Notification to the staff member if known (preferably in a non spammy fashion).
**User story**
As a st... | 1.0 | LTI course not ready screen - **Describe the solution you'd like**
- A dedicated screen to this scenario, explaining the situation in a lighthearted way.
- Notification with sufficient context so the eJournal team can take action as well.
- Notification to the staff member if known (preferably in a non spammy fashio... | priority | lti course not ready screen describe the solution you d like a dedicated screen to this scenario explaining the situation in a lighthearted way notification with sufficient context so the ejournal team can take action as well notification to the staff member if known preferably in a non spammy fashio... | 1 |
794,246 | 28,027,616,134 | IssuesEvent | 2023-03-28 10:10:09 | ipfs-force-community/venus-cluster | https://api.github.com/repos/ipfs-force-community/venus-cluster | closed | [venus-sector-manager] 手动发送recover消息 | enhancement good first issue priority:mid C-cli v0.6 | ### 模块 / Components
- [x] venus-sector-manager
- [ ] venus-worker
- [ ] 工具链 / toolchains
- [ ] 文档 / docs
### 描述 / Description
是否可以考虑增加,允许用户手动发送recover请求,不用等到下一个windowPost,的相关功能?
关联:
- [ ] https://github.com/filecoin-project/lotus/pull/9144 | 1.0 | [venus-sector-manager] 手动发送recover消息 - ### 模块 / Components
- [x] venus-sector-manager
- [ ] venus-worker
- [ ] 工具链 / toolchains
- [ ] 文档 / docs
### 描述 / Description
是否可以考虑增加,允许用户手动发送recover请求,不用等到下一个windowPost,的相关功能?
关联:
- [ ] https://github.com/filecoin-project/lotus/pull/9144 | priority | 手动发送recover消息 模块 components venus sector manager venus worker 工具链 toolchains 文档 docs 描述 description 是否可以考虑增加,允许用户手动发送recover请求,不用等到下一个windowpost,的相关功能? 关联: | 1 |
246,403 | 20,862,779,275 | IssuesEvent | 2022-03-22 01:45:56 | khalidsaadat/soen341 | https://api.github.com/repos/khalidsaadat/soen341 | closed | [TESTING] Create working CI for the project | Testing | **Acceptance Test**
1. Build has to be detected by Github actions
2. For our project, empty tests are available through Github actions | 1.0 | [TESTING] Create working CI for the project - **Acceptance Test**
1. Build has to be detected by Github actions
2. For our project, empty tests are available through Github actions | non_priority | create working ci for the project acceptance test build has to be detected by github actions for our project empty tests are available through github actions | 0 |
64,038 | 26,591,988,442 | IssuesEvent | 2023-01-23 09:28:08 | gradido/gradido | https://api.github.com/repos/gradido/gradido | closed | 🐛 [Bug] [Design] Fix Mobile Design | bug service: wallet frontend | <!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🐛 Bugreport
<!-- Describe your issue in detail. Include screenshots if needed. Give us as much information as possible. Use a clear and concise description of what the bug is.-->
### Mobile
- [x] Startseite ... | 1.0 | 🐛 [Bug] [Design] Fix Mobile Design - <!-- You can find the latest issue templates here https://github.com/ulfgebhardt/issue-templates -->
## 🐛 Bugreport
<!-- Describe your issue in detail. Include screenshots if needed. Give us as much information as possible. Use a clear and concise description of what the bug i... | non_priority | 🐛 fix mobile design 🐛 bugreport mobile startseite zu großer abstand zwischen box konto infos startseite button zweizeilig kein avatar im menü beim senden sind die radioboxen nicht gleichgroß gdd gdt avatare oval gdd gdt aufklapp pfeil außerhalb der box gdd ... | 0 |
14,158 | 3,806,745,434 | IssuesEvent | 2016-03-25 01:45:40 | rosmod/webgme-rosmod | https://api.github.com/repos/rosmod/webgme-rosmod | opened | User guide for deployment and experiment models and infrastructure. | documentation | Should explain how the models work (containment hierarchy, etc.) as well as how they map to hosts on networks for execution. The end of this guide should be the execution of the `RunExperiment` plugin on a sample model and some explanation of how to get access the output of the experiments. | 1.0 | User guide for deployment and experiment models and infrastructure. - Should explain how the models work (containment hierarchy, etc.) as well as how they map to hosts on networks for execution. The end of this guide should be the execution of the `RunExperiment` plugin on a sample model and some explanation of how to... | non_priority | user guide for deployment and experiment models and infrastructure should explain how the models work containment hierarchy etc as well as how they map to hosts on networks for execution the end of this guide should be the execution of the runexperiment plugin on a sample model and some explanation of how to... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.