Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
299,801 | 22,623,728,223 | IssuesEvent | 2022-06-30 08:50:19 | f1nal3/Juniorgram | https://api.github.com/repos/f1nal3/Juniorgram | closed | Update onboarding process and documentation. | documentation | ## Description:
* Create onboarding issue template that is based on the issues that @KliKonNik and other newcomers received.
* List of crucial parts of the code that need to be examined: Network primitives, messages, server main body etc.
* Put a link on "server hosting locally" md doc there.
* Put a link on "Getti... | 1.0 | Update onboarding process and documentation. - ## Description:
* Create onboarding issue template that is based on the issues that @KliKonNik and other newcomers received.
* List of crucial parts of the code that need to be examined: Network primitives, messages, server main body etc.
* Put a link on "server hosting... | non_priority | update onboarding process and documentation description create onboarding issue template that is based on the issues that klikonnik and other newcomers received list of crucial parts of the code that need to be examined network primitives messages server main body etc put a link on server hosting... | 0 |
430,247 | 12,450,147,922 | IssuesEvent | 2020-05-27 08:19:49 | caicloud/ormb | https://api.github.com/repos/caicloud/ormb | closed | [enhancement] Design v1 Model Config Specification | priority/P0 | We should define the specification for mediaType `application/vnd.caicloud.model.config.v1+json`.
We can refer to https://github.com/opencontainers/image-spec/blob/master/config.md
/priority p0 | 1.0 | [enhancement] Design v1 Model Config Specification - We should define the specification for mediaType `application/vnd.caicloud.model.config.v1+json`.
We can refer to https://github.com/opencontainers/image-spec/blob/master/config.md
/priority p0 | priority | design model config specification we should define the specification for mediatype application vnd caicloud model config json we can refer to priority | 1 |
701,583 | 24,100,257,343 | IssuesEvent | 2022-09-19 23:24:31 | bcgov/entity | https://api.github.com/repos/bcgov/entity | closed | UX Design - PPR Search disclaimer for each search PDF output | Priority2 UX Assets | ### Visual Design Comps:
https://projects.invisionapp.com/share/HZ12S0EY8MBC#/screens?browse
**Add disclaimer to the following:**
- End of PPR Search TOC
- End of PPR Search NIL TOC
- End of PPR Search "Non-Selected" TOC
- Beginning of MHR with PPR Combo Search
- Also, Update font size/add gray hairline to MHR with NI... | 1.0 | UX Design - PPR Search disclaimer for each search PDF output - ### Visual Design Comps:
https://projects.invisionapp.com/share/HZ12S0EY8MBC#/screens?browse
**Add disclaimer to the following:**
- End of PPR Search TOC
- End of PPR Search NIL TOC
- End of PPR Search "Non-Selected" TOC
- Beginning of MHR with PPR Combo S... | priority | ux design ppr search disclaimer for each search pdf output visual design comps add disclaimer to the following end of ppr search toc end of ppr search nil toc end of ppr search non selected toc beginning of mhr with ppr combo search also update font size add gray hairline to mhr with nil p... | 1 |
42,793 | 22,843,262,075 | IssuesEvent | 2022-07-13 01:32:08 | JuliaLang/julia | https://api.github.com/repos/JuliaLang/julia | closed | Deeply composed functions much slower than equivalent static functions | performance | ```julia
julia> VERSION
v"1.9.0-DEV.869"
julia> eval(:(f(x) = $(reduce((s,x) -> :($x($s)), fill(sin,500); init = :x))))
f (generic function with 1 method)
# f(x) = sin(sin(...(sin(x))))
julia> g = reduce(∘, fill(sin,500));
# g(x) = (sin∘sin∘...∘sin)(x)
julia> @time f(1.0) == g(1.0)
0.686770 seconds (1.... | True | Deeply composed functions much slower than equivalent static functions - ```julia
julia> VERSION
v"1.9.0-DEV.869"
julia> eval(:(f(x) = $(reduce((s,x) -> :($x($s)), fill(sin,500); init = :x))))
f (generic function with 1 method)
# f(x) = sin(sin(...(sin(x))))
julia> g = reduce(∘, fill(sin,500));
# g(x) = (sin... | non_priority | deeply composed functions much slower than equivalent static functions julia julia version v dev julia eval f x reduce s x x s fill sin init x f generic function with method f x sin sin sin x julia g reduce ∘ fill sin g x sin∘sin∘ ... | 0 |
3,428 | 2,764,223,398 | IssuesEvent | 2015-04-29 14:28:35 | thinkaurelius/titan | https://api.github.com/repos/thinkaurelius/titan | closed | Documentation bugs. | bug documentation | http://s3.thinkaurelius.com/docs/titan/0.9.0-M1/arch-overview.html
http://s3.thinkaurelius.com/docs/titan/0.9.0-M1/getting-started.html (Gremlin2)
http://s3.thinkaurelius.com/docs/titan/0.9.0-M1/gremlin.html (Gremlin2)
...there is alot more Gremlin than just the titanbasics.txt. It would be good for Titan guys to ... | 1.0 | Documentation bugs. - http://s3.thinkaurelius.com/docs/titan/0.9.0-M1/arch-overview.html
http://s3.thinkaurelius.com/docs/titan/0.9.0-M1/getting-started.html (Gremlin2)
http://s3.thinkaurelius.com/docs/titan/0.9.0-M1/gremlin.html (Gremlin2)
...there is alot more Gremlin than just the titanbasics.txt. It would be g... | non_priority | documentation bugs there is alot more gremlin than just the titanbasics txt it would be good for titan guys to go through each line one by one and make sure its all right with appropriate links to docs | 0 |
105,701 | 13,207,964,224 | IssuesEvent | 2020-08-15 01:34:22 | rubyforgood/casa | https://api.github.com/repos/rubyforgood/casa | closed | Front end design | :paintbrush: Design | All work pertaining to how stuff looks on the front end! Will touch work on epics #3 & #4
<u>Priorities</u>
- make things look nicer (without complicating functionality)
- ensure CASA brand & style are applied to all front end elements
- modular css style guide that can be applied across site. [Example of some m... | 1.0 | Front end design - All work pertaining to how stuff looks on the front end! Will touch work on epics #3 & #4
<u>Priorities</u>
- make things look nicer (without complicating functionality)
- ensure CASA brand & style are applied to all front end elements
- modular css style guide that can be applied across site.... | non_priority | front end design all work pertaining to how stuff looks on the front end will touch work on epics priorities make things look nicer without complicating functionality ensure casa brand style are applied to all front end elements modular css style guide that can be applied across site ... | 0 |
80,134 | 15,358,436,975 | IssuesEvent | 2021-03-01 14:48:34 | llvm4j/llvm4j | https://api.github.com/repos/llvm4j/llvm4j | closed | [llvm] Implement QOL functions | assign:anyone scope:apis status:old codebase type:feature | LLVM-C provides some quality-of-life functions for easier usage. Some of these have been skipped when implementing their function family. These functions are the following:
- LLVMConstIntOfString
- LLVMConstIntOfStringAndSize
- LLVMConstRealOfString
- LLVMConstRealOfStringAndSize
- LLVMBuildStructGEP
- LLVMBuil... | 1.0 | [llvm] Implement QOL functions - LLVM-C provides some quality-of-life functions for easier usage. Some of these have been skipped when implementing their function family. These functions are the following:
- LLVMConstIntOfString
- LLVMConstIntOfStringAndSize
- LLVMConstRealOfString
- LLVMConstRealOfStringAndSize
... | non_priority | implement qol functions llvm c provides some quality of life functions for easier usage some of these have been skipped when implementing their function family these functions are the following llvmconstintofstring llvmconstintofstringandsize llvmconstrealofstring llvmconstrealofstringandsize ll... | 0 |
2,588 | 2,607,930,111 | IssuesEvent | 2015-02-26 00:26:20 | chrsmithdemos/minify | https://api.github.com/repos/chrsmithdemos/minify | closed | Incorrect CSS image paths | auto-migrated Priority-High Type-Defect | ```
Minify version: 2.1.1
PHP version:5.2.4-2ubuntu5.4
What steps will reproduce the problem?
1. Create a css file with a relative image path in it for a background,
such as:
*****
url("../images/fieldset-bg.gif")
*****
2. Minify the css files with a relative image path in it :
array(
'//styles/somefile.css'
... | 1.0 | Incorrect CSS image paths - ```
Minify version: 2.1.1
PHP version:5.2.4-2ubuntu5.4
What steps will reproduce the problem?
1. Create a css file with a relative image path in it for a background,
such as:
*****
url("../images/fieldset-bg.gif")
*****
2. Minify the css files with a relative image path in it :
array(
... | non_priority | incorrect css image paths minify version php version what steps will reproduce the problem create a css file with a relative image path in it for a background such as url images fieldset bg gif minify the css files with a relative image path in it array ... | 0 |
403,396 | 11,840,298,366 | IssuesEvent | 2020-03-23 18:36:47 | seccomp/libseccomp | https://api.github.com/repos/seccomp/libseccomp | opened | BUG: Travis CI warnings | bug priority/low | Despite working, the Travis CI service reports one error and two warnings with our config:
* Error
> root: duplicate key: `language`
* Warnings
> root: deprecated key sudo (The key `sudo` has no effect anymore.)
> root: deprecated key sudo (The key `sudo` has no effect anymore.) | 1.0 | BUG: Travis CI warnings - Despite working, the Travis CI service reports one error and two warnings with our config:
* Error
> root: duplicate key: `language`
* Warnings
> root: deprecated key sudo (The key `sudo` has no effect anymore.)
> root: deprecated key sudo (The key `sudo` has no effect anymore.) | priority | bug travis ci warnings despite working the travis ci service reports one error and two warnings with our config error root duplicate key language warnings root deprecated key sudo the key sudo has no effect anymore root deprecated key sudo the key sudo has no effect anymore | 1 |
84,017 | 3,647,457,832 | IssuesEvent | 2016-02-16 00:52:44 | TechReborn/TechReborn | https://api.github.com/repos/TechReborn/TechReborn | closed | Wrong NEI Handler Recipes hitboxes | bug High priority | See this:


<strong>Also, only one arrow has the hitbox for ope... | 1.0 | Wrong NEI Handler Recipes hitboxes - See this:


<strong>Also, ... | priority | wrong nei handler recipes hitboxes see this also only one arrow has the hitbox for open all recipes techreborn universal | 1 |
118,427 | 11,968,963,008 | IssuesEvent | 2020-04-06 09:31:56 | barbajs/barba | https://api.github.com/repos/barbajs/barba | closed | Request: Sample code and/or pens for the barba.js.org transitions | documentation enhancement | The new website is beautiful. I'd love to see minimal code for the section-change full-page swipes, the between-features slideshow effect (https://codepen.io/thierrymichel/project/editor/XkkWWv is close, but this would include the CSS changes to the header and footer), and the docs partial-page swipe.
The result mig... | 1.0 | Request: Sample code and/or pens for the barba.js.org transitions - The new website is beautiful. I'd love to see minimal code for the section-change full-page swipes, the between-features slideshow effect (https://codepen.io/thierrymichel/project/editor/XkkWWv is close, but this would include the CSS changes to the he... | non_priority | request sample code and or pens for the barba js org transitions the new website is beautiful i d love to see minimal code for the section change full page swipes the between features slideshow effect is close but this would include the css changes to the header and footer and the docs partial page swipe ... | 0 |
576,289 | 17,083,510,139 | IssuesEvent | 2021-07-08 08:52:10 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | mangadex.org - design is broken | browser-firefox engine-gecko os-linux priority-normal | <!-- @browser: Firefox 91.0 -->
<!-- @ua_header: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/79059 -->
**URL**: https://mangadex.org/
**Browser / Version**: Firefox 91.0
**Operating Sy... | 1.0 | mangadex.org - design is broken - <!-- @browser: Firefox 91.0 -->
<!-- @ua_header: Mozilla/5.0 (X11; Linux x86_64; rv:91.0) Gecko/20100101 Firefox/91.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/79059 -->
**URL**: https://mangadex.org/
**Browser / Vers... | priority | mangadex org design is broken url browser version firefox operating system linux tested another browser yes chrome problem type design is broken description images not loaded steps to reproduce when reading a manga in one page list style the website will show a... | 1 |
1,350 | 3,654,941,529 | IssuesEvent | 2016-02-17 14:41:12 | HPFOD/FoD-Jenkins | https://api.github.com/repos/HPFOD/FoD-Jenkins | closed | Ensure project meets hosted Jenkins plugin standards | Go-Live Requirement | See: https://wiki.jenkins-ci.org/display/JENKINS/Hosting+Plugins
**Rename artifact in POM to match Jenkins project conventions**
Using "Fortify-on-Demand-Assessment-Uploader" as the name, will email the Jenkins list to ensure this meets expectations along with other questions related to hosted plugin approval.
... | 1.0 | Ensure project meets hosted Jenkins plugin standards - See: https://wiki.jenkins-ci.org/display/JENKINS/Hosting+Plugins
**Rename artifact in POM to match Jenkins project conventions**
Using "Fortify-on-Demand-Assessment-Uploader" as the name, will email the Jenkins list to ensure this meets expectations along wit... | non_priority | ensure project meets hosted jenkins plugin standards see rename artifact in pom to match jenkins project conventions using fortify on demand assessment uploader as the name will email the jenkins list to ensure this meets expectations along with other questions related to hosted plugin approval ... | 0 |
766,614 | 26,891,915,265 | IssuesEvent | 2023-02-06 09:33:51 | fsfe/reuse-tool | https://api.github.com/repos/fsfe/reuse-tool | closed | REUSE under Windows | bug priority/low | While trying to use REUSE tool to check my project, I saw it complains `ModuleNotFoundError: No module named 'pwd'` when running `reuse lint` under my Windows 11 installation (logs below). Or should I open another issue for the Windows supporting question?
`$env:PYTHONUTF8="1"` was set or it will complain `UnicodeDe... | 1.0 | REUSE under Windows - While trying to use REUSE tool to check my project, I saw it complains `ModuleNotFoundError: No module named 'pwd'` when running `reuse lint` under my Windows 11 installation (logs below). Or should I open another issue for the Windows supporting question?
`$env:PYTHONUTF8="1"` was set or it wi... | priority | reuse under windows while trying to use reuse tool to check my project i saw it complains modulenotfounderror no module named pwd when running reuse lint under my windows installation logs below or should i open another issue for the windows supporting question env was set or it will complai... | 1 |
167,304 | 6,336,406,389 | IssuesEvent | 2017-07-26 21:01:22 | kenzanlabs/react-seed | https://api.github.com/repos/kenzanlabs/react-seed | closed | TypeScript / Babel configuration questions | help wanted priority question | Using the current implementation, just had some questions on usage
https://github.com/kenzanlabs/react-seed/blob/master/tsconfig.json
1. Do we need `ouputDir` if we are using webpack?
1. Why do we have `allowJs` enabled?
1. Why do we need to configure `include` and `exclude`. Isn't that being handled by webpa... | 1.0 | TypeScript / Babel configuration questions - Using the current implementation, just had some questions on usage
https://github.com/kenzanlabs/react-seed/blob/master/tsconfig.json
1. Do we need `ouputDir` if we are using webpack?
1. Why do we have `allowJs` enabled?
1. Why do we need to configure `include` and ... | priority | typescript babel configuration questions using the current implementation just had some questions on usage do we need ouputdir if we are using webpack why do we have allowjs enabled why do we need to configure include and exclude isn t that being handled by webpack what is our... | 1 |
250,754 | 21,333,888,790 | IssuesEvent | 2022-04-18 12:15:04 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Performance benchmarking via functional test times on ci | Team:Operations performance loe:hours Feature:CI Feature:Functional Testing impact:needs-assessment | I looked for an existing issue but couldn't find one.
Has anyone on the Ops team looked into tracking functional test completion times, over time, on ci, as a crude way to see if any particular changes may have caused a performance regression?
I had/have a system that does this but it's outside ci so it's difficu... | 1.0 | Performance benchmarking via functional test times on ci - I looked for an existing issue but couldn't find one.
Has anyone on the Ops team looked into tracking functional test completion times, over time, on ci, as a crude way to see if any particular changes may have caused a performance regression?
I had/have ... | non_priority | performance benchmarking via functional test times on ci i looked for an existing issue but couldn t find one has anyone on the ops team looked into tracking functional test completion times over time on ci as a crude way to see if any particular changes may have caused a performance regression i had have ... | 0 |
381,866 | 11,297,033,562 | IssuesEvent | 2020-01-17 04:16:49 | omou-org/mainframe | https://api.github.com/repos/omou-org/mainframe | opened | Separating out Payment Status and Confirmation Status | 3 hours enhancement priority | ## Background
Summit wants to be able to generate sessions in addition to paid sessions. For example, a student has 10 paid sessions, Summit wants an additional 30 sessions to be generated. The additional sessions is so that the receptionist would not schedule a new tutoring/class in that course's time slot, because S... | 1.0 | Separating out Payment Status and Confirmation Status - ## Background
Summit wants to be able to generate sessions in addition to paid sessions. For example, a student has 10 paid sessions, Summit wants an additional 30 sessions to be generated. The additional sessions is so that the receptionist would not schedule a ... | priority | separating out payment status and confirmation status background summit wants to be able to generate sessions in addition to paid sessions for example a student has paid sessions summit wants an additional sessions to be generated the additional sessions is so that the receptionist would not schedule a ne... | 1 |
190,429 | 22,065,725,730 | IssuesEvent | 2022-05-31 02:46:27 | Seagate/cortx-rgw | https://api.github.com/repos/Seagate/cortx-rgw | closed | CVE-2022-24771 (High) detected in node-forge-0.10.0.tgz | security vulnerability | ## CVE-2022-24771 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.10.0.tgz</b></p></summary>
<p>JavaScript implementations of network transports, cryptography, ciphers, PK... | True | CVE-2022-24771 (High) detected in node-forge-0.10.0.tgz - ## CVE-2022-24771 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-forge-0.10.0.tgz</b></p></summary>
<p>JavaScript implem... | non_priority | cve high detected in node forge tgz cve high severity vulnerability vulnerable library node forge tgz javascript implementations of network transports cryptography ciphers pki message digests and various utilities library home page a href path to dependency file ... | 0 |
129,165 | 5,089,546,113 | IssuesEvent | 2017-01-01 17:54:50 | HabitRPG/habitica | https://api.github.com/repos/HabitRPG/habitica | closed | Party Up and Party On achievements are missing text | priority: medium status: issue: help welcome now | _From thebat137 (dea8a9e8-c084-438a-9a14-7fe96a73fd0a) in the Report a Bug guild:_
I was just looking at my achievements list and I noticed that the hovertext for the "Party Up" and "Party On" achievements seems to be missing. Hovering over the icons just says "Party Up/partyUpText not found" and "Party On/partyOnTe... | 1.0 | Party Up and Party On achievements are missing text - _From thebat137 (dea8a9e8-c084-438a-9a14-7fe96a73fd0a) in the Report a Bug guild:_
I was just looking at my achievements list and I noticed that the hovertext for the "Party Up" and "Party On" achievements seems to be missing. Hovering over the icons just says "P... | priority | party up and party on achievements are missing text from in the report a bug guild i was just looking at my achievements list and i noticed that the hovertext for the party up and party on achievements seems to be missing hovering over the icons just says party up partyuptext not found and ... | 1 |
612,723 | 19,029,896,906 | IssuesEvent | 2021-11-24 09:34:11 | DimensionDev/Maskbook | https://api.github.com/repos/DimensionDev/Maskbook | opened | [Bug] Decrypt image payload not work | Priority: P0 (Emergency) Type: Bug | ## Bug Info
### How to reproduce?
https://twitter.com/AinuxA/status/1463438363952771077
### What happened?
### What should happen?
## Environment
### Mask Version:
- [ ] (Browser) Installed from the extension store (version: )
- [ ] (App) Installed from the app store (version: )
- [ ] master bran... | 1.0 | [Bug] Decrypt image payload not work - ## Bug Info
### How to reproduce?
https://twitter.com/AinuxA/status/1463438363952771077
### What happened?
### What should happen?
## Environment
### Mask Version:
- [ ] (Browser) Installed from the extension store (version: )
- [ ] (App) Installed from the ... | priority | decrypt image payload not work bug info how to reproduce what happened what should happen environment mask version browser installed from the extension store version app installed from the app store version master branch build of versi... | 1 |
608,715 | 18,846,816,904 | IssuesEvent | 2021-11-11 15:48:28 | dita-ot/dita-ot | https://api.github.com/repos/dita-ot/dita-ot | closed | Empty param in project.xml causes Error: null | bug priority/medium project | ## Expected Behavior
Running
`dita.bat --project=project.xml --verbose --debug`
When a param in the project.xml is empty and this is not allowed (is it?), the error message should describe what the problem is
## Actual Behavior
Running the above command returns:
```
Searching for integrator.xml ...
Er... | 1.0 | Empty param in project.xml causes Error: null - ## Expected Behavior
Running
`dita.bat --project=project.xml --verbose --debug`
When a param in the project.xml is empty and this is not allowed (is it?), the error message should describe what the problem is
## Actual Behavior
Running the above command retur... | priority | empty param in project xml causes error null expected behavior running dita bat project project xml verbose debug when a param in the project xml is empty and this is not allowed is it the error message should describe what the problem is actual behavior running the above command retur... | 1 |
813,660 | 30,465,927,170 | IssuesEvent | 2023-07-17 10:21:18 | code4romania/crestem-ong | https://api.github.com/repos/code4romania/crestem-ong | opened | [Registration] change 'Județ' and 'Localitate' fields type | medium-priority | In the [registration form ](https://app.crestem.ong/register), the fields 'Județ' and Localitate' are text input. Change field types from text input to single select. | 1.0 | [Registration] change 'Județ' and 'Localitate' fields type - In the [registration form ](https://app.crestem.ong/register), the fields 'Județ' and Localitate' are text input. Change field types from text input to single select. | priority | change județ and localitate fields type in the the fields județ and localitate are text input change field types from text input to single select | 1 |
7,584 | 4,016,103,004 | IssuesEvent | 2016-05-15 11:24:35 | manjaro/manjaro-tools | https://api.github.com/repos/manjaro/manjaro-tools | opened | I switch kinda doesn't work | buildpkg | If I check **mkchrootpkg** I find this line: `[[ ! -f PKGBUILD && -z "${install_pkgs[*]}" ]] && die 'This must be run in a directory containing a PKGBUILD.'`. So we have to recheck that option on how we want to use it. I suggest it like this:
`buildpkg -p kpmcore-dev -i`
This will say to **buildpkg** that I want ... | 1.0 | I switch kinda doesn't work - If I check **mkchrootpkg** I find this line: `[[ ! -f PKGBUILD && -z "${install_pkgs[*]}" ]] && die 'This must be run in a directory containing a PKGBUILD.'`. So we have to recheck that option on how we want to use it. I suggest it like this:
`buildpkg -p kpmcore-dev -i`
This will sa... | non_priority | i switch kinda doesn t work if i check mkchrootpkg i find this line die this must be run in a directory containing a pkgbuild so we have to recheck that option on how we want to use it i suggest it like this buildpkg p kpmcore dev i this will say to buildpkg that i want to build i... | 0 |
279,026 | 30,702,437,458 | IssuesEvent | 2023-07-27 01:30:09 | artsking/packages_apps_settings_10.0.0_r33 | https://api.github.com/repos/artsking/packages_apps_settings_10.0.0_r33 | reopened | CVE-2022-20350 (Medium) detected in Settingsandroid-10.0.0_r44 | Mend: dependency security vulnerability | ## CVE-2022-20350 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Settingsandroid-10.0.0_r44</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/plat... | True | CVE-2022-20350 (Medium) detected in Settingsandroid-10.0.0_r44 - ## CVE-2022-20350 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Settingsandroid-10.0.0_r44</b></p></summary>
<p>
<p... | non_priority | cve medium detected in settingsandroid cve medium severity vulnerability vulnerable library settingsandroid library home page a href found in head commit a href found in base branch master vulnerable source files src com android s... | 0 |
25,185 | 24,857,536,434 | IssuesEvent | 2022-10-27 04:40:04 | home-climate-control/dz | https://api.github.com/repos/home-climate-control/dz | opened | Swing Console: Celsius/Fahrenheit switch breaks the layout | bug Swing usability Fahrenheit reactive | ### Expected Behavior
Switch from Celsius to Fahrenheit shouldn't change anything other than temperature display.
### Actual Behavior
Zone cell height is significantly reduced, and restored only when switched back to Celsius. | True | Swing Console: Celsius/Fahrenheit switch breaks the layout - ### Expected Behavior
Switch from Celsius to Fahrenheit shouldn't change anything other than temperature display.
### Actual Behavior
Zone cell height is significantly reduced, and restored only when switched back to Celsius. | non_priority | swing console celsius fahrenheit switch breaks the layout expected behavior switch from celsius to fahrenheit shouldn t change anything other than temperature display actual behavior zone cell height is significantly reduced and restored only when switched back to celsius | 0 |
448,364 | 31,790,190,366 | IssuesEvent | 2023-09-13 02:13:26 | usnistgov/NRSS | https://api.github.com/repos/usnistgov/NRSS | opened | Docs to NIST Pages | documentation enhancement | - Transition docs to NIST Pages + enhancements
- Regenerate Autodocs for API reference | 1.0 | Docs to NIST Pages - - Transition docs to NIST Pages + enhancements
- Regenerate Autodocs for API reference | non_priority | docs to nist pages transition docs to nist pages enhancements regenerate autodocs for api reference | 0 |
610,260 | 18,901,826,774 | IssuesEvent | 2021-11-16 02:27:28 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Hide A-C section in Rewards settings on `brave://settings` when region is JP | release/blocking feature/rewards priority/P2 QA/Yes release-notes/include feature/settings OS/Desktop | ## Description
Since A-C is not available in JP region at this time, hide the A-C section in Brave Rewards settings on `brave://settings` when region is JP (using same rules/conditions as how we do it on brave://rewards settings page). | 1.0 | Hide A-C section in Rewards settings on `brave://settings` when region is JP - ## Description
Since A-C is not available in JP region at this time, hide the A-C section in Brave Rewards settings on `brave://settings` when region is JP (using same rules/conditions as how we do it on brave://rewards settings page). | priority | hide a c section in rewards settings on brave settings when region is jp description since a c is not available in jp region at this time hide the a c section in brave rewards settings on brave settings when region is jp using same rules conditions as how we do it on brave rewards settings page | 1 |
300,716 | 9,211,975,223 | IssuesEvent | 2019-03-09 19:57:26 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | tests/lib/mem_alloc/testcase.yaml#libraries.libc.minimal: Bus fault at test_malloc | area: Memory Protection bug platform: NXP priority: high | **To Reproduce**
Steps to reproduce the behavior:
1. mkdir build; cd build
2. cmake -DBOARD=frdm_k64f -DARCH=arm ..
3. make
4. make run
**Screenshots or console output**
```
******** delaying boot 1000ms (per build configuration) *****
***** Booting Zephyr OS v1.14.0-rc1-248-gd5b2834f58 (delayed boot 1000m... | 1.0 | tests/lib/mem_alloc/testcase.yaml#libraries.libc.minimal: Bus fault at test_malloc - **To Reproduce**
Steps to reproduce the behavior:
1. mkdir build; cd build
2. cmake -DBOARD=frdm_k64f -DARCH=arm ..
3. make
4. make run
**Screenshots or console output**
```
******** delaying boot 1000ms (per build configur... | priority | tests lib mem alloc testcase yaml libraries libc minimal bus fault at test malloc to reproduce steps to reproduce the behavior mkdir build cd build cmake dboard frdm darch arm make make run screenshots or console output delaying boot per build configuration ... | 1 |
676,006 | 23,113,162,328 | IssuesEvent | 2022-07-27 14:33:38 | kubernetes/ingress-nginx | https://api.github.com/repos/kubernetes/ingress-nginx | closed | ingress communication issues | kind/support needs-triage needs-priority | Need you support on below issues, when we kubectl logs -f -n ingress-basic xxxxxxxxxx, i got below error
Service "default/xxxxx" does not have any active Endpoint. | 1.0 | ingress communication issues - Need you support on below issues, when we kubectl logs -f -n ingress-basic xxxxxxxxxx, i got below error
Service "default/xxxxx" does not have any active Endpoint. | priority | ingress communication issues need you support on below issues when we kubectl logs f n ingress basic xxxxxxxxxx i got below error service default xxxxx does not have any active endpoint | 1 |
22,590 | 3,791,129,643 | IssuesEvent | 2016-03-22 00:43:19 | codeforamerica/joblint | https://api.github.com/repos/codeforamerica/joblint | opened | Come up with prompts for job posting tool | Design | Create a set of prompts that can guide an employer to create a good/fair job positing.
Current design is side-by side boxes, basically an expansion of the existing tool, so keep this in mind.
This issue originally created by @pacarole as codeforamerica/nola-2016-fellows#55. | 1.0 | Come up with prompts for job posting tool - Create a set of prompts that can guide an employer to create a good/fair job positing.
Current design is side-by side boxes, basically an expansion of the existing tool, so keep this in mind.
This issue originally created by @pacarole as codeforamerica/nola-2016-fellows#5... | non_priority | come up with prompts for job posting tool create a set of prompts that can guide an employer to create a good fair job positing current design is side by side boxes basically an expansion of the existing tool so keep this in mind this issue originally created by pacarole as codeforamerica nola fellows | 0 |
216,657 | 16,664,847,669 | IssuesEvent | 2021-06-07 00:36:07 | Neos-Metaverse/NeosPublic | https://api.github.com/repos/Neos-Metaverse/NeosPublic | opened | NeosBot - CloudVariable argument documentation | Documentation | ## Where have you searched for this information before making this issue?
ProbablePrime's videos, the wiki, #questions-help and bunch of other users.
The bot commands are not well documented and need more of it to make it easier to understand for the "normal" user rather than just staff.
I'm also well aware that t... | 1.0 | NeosBot - CloudVariable argument documentation - ## Where have you searched for this information before making this issue?
ProbablePrime's videos, the wiki, #questions-help and bunch of other users.
The bot commands are not well documented and need more of it to make it easier to understand for the "normal" user rath... | non_priority | neosbot cloudvariable argument documentation where have you searched for this information before making this issue probableprime s videos the wiki questions help and bunch of other users the bot commands are not well documented and need more of it to make it easier to understand for the normal user rath... | 0 |
335,750 | 10,165,943,103 | IssuesEvent | 2019-08-07 14:51:03 | BookStackApp/BookStack | https://api.github.com/repos/BookStackApp/BookStack | closed | Users can modify their profiles and pretend they're someone else | :lock: Security :rocket: Priority | **Describe the bug**
Any user can impersonate anyone else on the wiki.
A user (attacker) register using his own mail address, email confirmation is activated so he click on the link in a mail he received. He can then change his First Name, Last Name, profile picture to make it seems he's someone else... That far it's... | 1.0 | Users can modify their profiles and pretend they're someone else - **Describe the bug**
Any user can impersonate anyone else on the wiki.
A user (attacker) register using his own mail address, email confirmation is activated so he click on the link in a mail he received. He can then change his First Name, Last Name, ... | priority | users can modify their profiles and pretend they re someone else describe the bug any user can impersonate anyone else on the wiki a user attacker register using his own mail address email confirmation is activated so he click on the link in a mail he received he can then change his first name last name ... | 1 |
137,306 | 30,667,100,384 | IssuesEvent | 2023-07-25 19:09:56 | h4sh5/pypi-auto-scanner | https://api.github.com/repos/h4sh5/pypi-auto-scanner | opened | hpfrec 0.2.10 has 1 GuardDog issues | guarddog code-execution | https://pypi.org/project/hpfrec
https://inspector.pypi.io/project/hpfrec
```{
"dependency": "hpfrec",
"version": "0.2.10",
"result": {
"issues": 1,
"errors": {},
"results": {
"code-execution": [
{
"location": "hpfrec-0.2.10/setup.py:197",
"code": " val ... | 1.0 | hpfrec 0.2.10 has 1 GuardDog issues - https://pypi.org/project/hpfrec
https://inspector.pypi.io/project/hpfrec
```{
"dependency": "hpfrec",
"version": "0.2.10",
"result": {
"issues": 1,
"errors": {},
"results": {
"code-execution": [
{
"location": "hpfrec-0.2.10/setup.py:197",
... | non_priority | hpfrec has guarddog issues dependency hpfrec version result issues errors results code execution location hpfrec setup py code val subprocess run cmd comm cap... | 0 |
16,955 | 3,586,835,866 | IssuesEvent | 2016-01-30 00:21:08 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Graphs are receiving data every 5 seconds but showing every second | area/container area/host area/ui kind/bug release/v1.0.0 status/resolved status/to-test | version - master jan 07
Steps:
1. Create a host or a container
2. Click on host name or container name
Results: Data points coming in every 5 seconds but graphs are showing for every second

Exp... | 1.0 | Graphs are receiving data every 5 seconds but showing every second - version - master jan 07
Steps:
1. Create a host or a container
2. Click on host name or container name
Results: Data points coming in every 5 seconds but graphs are showing for every second
 Check links
2) Check if everything executes
3) Check if it is easy to understand | 1.0 | Review ZeroBrane tutorials and demos - Review all ZeroBrane tutorials and demos:
1) Check links
2) Check if everything executes
3) Check if it is easy to understand | non_priority | review zerobrane tutorials and demos review all zerobrane tutorials and demos check links check if everything executes check if it is easy to understand | 0 |
12,239 | 9,659,947,627 | IssuesEvent | 2019-05-20 14:30:28 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | Input docker behaviour with Openshift 3.10 | :infrastructure Filebeat Metricbeat [zube]: In Progress containers enhancement libbeat v7.2.0 | Filebeat Version : 6.4.3-1
Openshift version : 3.10
Since Openshift version 3.10, docker has been replaced by cri-o. Log format changed from json to cri format and we need to use input docker to parse file as describe in this issue https://github.com/elastic/beats/issues/7418
Nethertheless, the path of docker lo... | 1.0 | Input docker behaviour with Openshift 3.10 - Filebeat Version : 6.4.3-1
Openshift version : 3.10
Since Openshift version 3.10, docker has been replaced by cri-o. Log format changed from json to cri format and we need to use input docker to parse file as describe in this issue https://github.com/elastic/beats/issues... | non_priority | input docker behaviour with openshift filebeat version openshift version since openshift version docker has been replaced by cri o log format changed from json to cri format and we need to use input docker to parse file as describe in this issue nethertheless the path of docker log... | 0 |
69,499 | 14,990,281,577 | IssuesEvent | 2021-01-29 06:02:08 | Infosecdecompress/infosecdecompress | https://api.github.com/repos/Infosecdecompress/infosecdecompress | closed | CVE-2018-19797 (Medium) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz - autoclosed | security vulnerability | ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4... | True | CVE-2018-19797 (Medium) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz - autoclosed - ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopen... | non_priority | cve medium detected in opennmsopennms source node sass tgz autoclosed cve medium severity vulnerability vulnerable libraries opennmsopennms source node sass tgz node sass tgz wrapper around libsass library home page a href path to dep... | 0 |
258,180 | 22,290,328,540 | IssuesEvent | 2022-06-12 09:03:14 | Nedilko/weekends | https://api.github.com/repos/Nedilko/weekends | closed | [Test case]: Verify that theme can be changed | test case | ### Description
This TC verifies that user able to change theme from light to dark and from dark to light.
Design - https://www.figma.com/file/k8veH6xqaVXV0DGAtiENFI/weekends?node-id=30%3A4
Preconditions:
- Local storage is empty
- On first application start set Day - Friday, Hour - 18:00.
- Current day is Mo... | 1.0 | [Test case]: Verify that theme can be changed - ### Description
This TC verifies that user able to change theme from light to dark and from dark to light.
Design - https://www.figma.com/file/k8veH6xqaVXV0DGAtiENFI/weekends?node-id=30%3A4
Preconditions:
- Local storage is empty
- On first application start set ... | non_priority | verify that theme can be changed description this tc verifies that user able to change theme from light to dark and from dark to light design preconditions local storage is empty on first application start set day friday hour current day is monday or tuesday or wednesday or thur... | 0 |
86,928 | 15,755,902,569 | IssuesEvent | 2021-03-31 02:35:07 | turkdevops/node | https://api.github.com/repos/turkdevops/node | opened | CVE-2019-1010266 (Medium) detected in lodash-2.4.1.tgz | security vulnerability | ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.1.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extr... | True | CVE-2019-1010266 (Medium) detected in lodash-2.4.1.tgz - ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.1.tgz</b></p></summary>
<p>A utility library d... | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file node deps npm package json path to vulner... | 0 |
791,373 | 27,861,650,141 | IssuesEvent | 2023-03-21 07:00:47 | ansible-collections/azure | https://api.github.com/repos/ansible-collections/azure | closed | Issue with azure_rm_webapp_info | question medium_priority work in | <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
<!--- Explain the problem briefly below -->
Unable to retrieve in... | 1.0 | Issue with azure_rm_webapp_info - <!--- Verify first that your issue is not already reported on GitHub -->
<!--- Also test if the latest release and devel branch are affected too -->
<!--- Complete *all* sections as described, this form is processed automatically -->
##### SUMMARY
<!--- Explain the problem brief... | priority | issue with azure rm webapp info summary unable to retrieve info of an azure app service webapp error is unclear or is the module is broken issue type bug report component name azure azcollection azure rm webapp info ansible version paste below ansibl... | 1 |
151,868 | 13,437,310,330 | IssuesEvent | 2020-09-07 15:42:47 | kinvolk/lokomotive | https://api.github.com/repos/kinvolk/lokomotive | opened | Provide a way for goreleaser to use different GPG key | area/updates kind/documentation |
Right now goreleaser arbitrarily selects a GPG key to sign the release with. It does not respect the gitconfig.
- There is a way to provide the GPG key using env var. The doc to follow is https://goreleaser.com/ci/actions/#signing.
- Update the release doc after this.
Following config has worked for me in the ... | 1.0 | Provide a way for goreleaser to use different GPG key -
Right now goreleaser arbitrarily selects a GPG key to sign the release with. It does not respect the gitconfig.
- There is a way to provide the GPG key using env var. The doc to follow is https://goreleaser.com/ci/actions/#signing.
- Update the release doc a... | non_priority | provide a way for goreleaser to use different gpg key right now goreleaser arbitrarily selects a gpg key to sign the release with it does not respect the gitconfig there is a way to provide the gpg key using env var the doc to follow is update the release doc after this following config has worked ... | 0 |
317,338 | 9,663,585,423 | IssuesEvent | 2019-05-21 01:23:55 | NCIOCPL/cgov-digital-platform | https://api.github.com/repos/NCIOCPL/cgov-digital-platform | closed | Update Meta Description Field to allow 600 characters | High priority change request | Because PDQ has meta descriptions longer than 320 characters, we need to update the meta description field to allow 600 characters.
This is needed to continue migration scripting. | 1.0 | Update Meta Description Field to allow 600 characters - Because PDQ has meta descriptions longer than 320 characters, we need to update the meta description field to allow 600 characters.
This is needed to continue migration scripting. | priority | update meta description field to allow characters because pdq has meta descriptions longer than characters we need to update the meta description field to allow characters this is needed to continue migration scripting | 1 |
755,868 | 26,444,390,107 | IssuesEvent | 2023-01-16 05:20:43 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [YSQL] Probabilistically trigger ANALYZE for each table from YSQL | kind/enhancement area/ysql priority/medium | Jira Link: [DB-4318](https://yugabyte.atlassian.net/browse/DB-4318)
### Description
ANALYZE for a table is to be triggered with probability P = (number of mutations/ anlthresh) from each YSQL instance after periodically, or after some number of mutations.
1. The "number of mutations" for a table includes only co... | 1.0 | [YSQL] Probabilistically trigger ANALYZE for each table from YSQL - Jira Link: [DB-4318](https://yugabyte.atlassian.net/browse/DB-4318)
### Description
ANALYZE for a table is to be triggered with probability P = (number of mutations/ anlthresh) from each YSQL instance after periodically, or after some number of mut... | priority | probabilistically trigger analyze for each table from ysql jira link description analyze for a table is to be triggered with probability p number of mutations anlthresh from each ysql instance after periodically or after some number of mutations the number of mutations for a table includ... | 1 |
747,918 | 26,102,139,810 | IssuesEvent | 2022-12-27 08:34:33 | bounswe/bounswe2022group2 | https://api.github.com/repos/bounswe/bounswe2022group2 | closed | Mobile: Get Other Users Profile Backend Connection | priority-critical status-new mobile back-connection | ### Issue Description
I will implement backend connection of get other users profile page.
### Step Details
Steps that will be performed:
- [x] Analyze get user endpoint
- [x] Implement backend connection
### Final Actions
After the work is done, related PR will be provided here. Further implementat... | 1.0 | Mobile: Get Other Users Profile Backend Connection - ### Issue Description
I will implement backend connection of get other users profile page.
### Step Details
Steps that will be performed:
- [x] Analyze get user endpoint
- [x] Implement backend connection
### Final Actions
After the work is done, ... | priority | mobile get other users profile backend connection issue description i will implement backend connection of get other users profile page step details steps that will be performed analyze get user endpoint implement backend connection final actions after the work is done rela... | 1 |
575,380 | 17,029,028,123 | IssuesEvent | 2021-07-04 06:50:36 | emmamei/cdkey | https://api.github.com/repos/emmamei/cdkey | opened | dialogListen (internal command) is overloaded | bug priority reliabilityfix | As many as 4 or 5 listeners are opened with the main menus; this is a functional error.
Separate the functions out, and open listeners only as needed at the point of need. | 1.0 | dialogListen (internal command) is overloaded - As many as 4 or 5 listeners are opened with the main menus; this is a functional error.
Separate the functions out, and open listeners only as needed at the point of need. | priority | dialoglisten internal command is overloaded as many as or listeners are opened with the main menus this is a functional error separate the functions out and open listeners only as needed at the point of need | 1 |
64,254 | 15,832,924,009 | IssuesEvent | 2021-04-06 15:06:29 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | Update ClickHouse for M1 Mac Support | build | ClickHouse build failed on M1 Mac
**Operating system**
Mac OS Big Sur 11.2.3
**Cmake version**
cmake version 3.20.0
**Compiler name and version**
AppleClang compiler
**Full cmake and/or ninja output**
-- The C compiler identification is AppleClang 12.0.0.12000032
-- The CXX compiler identification is A... | 1.0 | Update ClickHouse for M1 Mac Support - ClickHouse build failed on M1 Mac
**Operating system**
Mac OS Big Sur 11.2.3
**Cmake version**
cmake version 3.20.0
**Compiler name and version**
AppleClang compiler
**Full cmake and/or ninja output**
-- The C compiler identification is AppleClang 12.0.0.12000032
... | non_priority | update clickhouse for mac support clickhouse build failed on mac operating system mac os big sur cmake version cmake version compiler name and version appleclang compiler full cmake and or ninja output the c compiler identification is appleclang the cxx c... | 0 |
603,947 | 18,674,514,580 | IssuesEvent | 2021-10-31 10:21:43 | AY2122S1-CS2113T-F14-3/tp | https://api.github.com/repos/AY2122S1-CS2113T-F14-3/tp | closed | [PE-D] Feature did not work, adding schedule with quantifier | priority.High type.Bug | 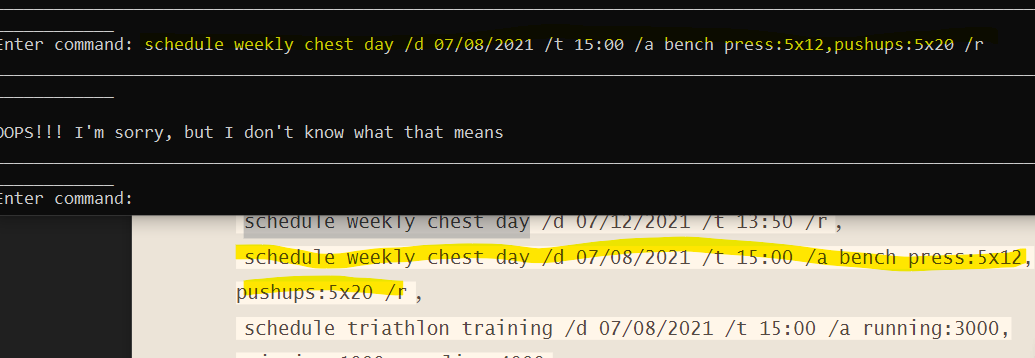
<!--session: 1635497037138-3d4857ae-1d3d-4193-8643-08af139c8315-->
<!--Version: Web v3.4.1-->
-------------
Labels: `type.FeatureFlaw` `severity.Medium`
original: KZQ1999/ped#9 | 1.0 | [PE-D] Feature did not work, adding schedule with quantifier - 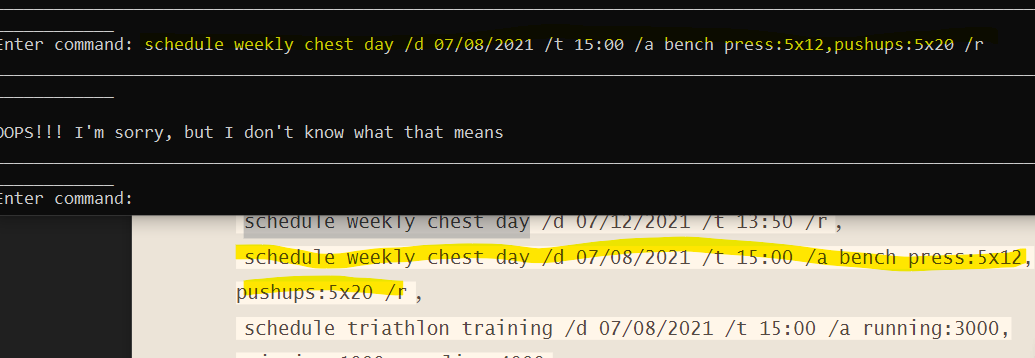
<!--session: 1635497037138-3d4857ae-1d3d-4193-8643-08af139c8315-->
<!--Version: Web v3.4.1-->
-------------
Labels: `type.FeatureFlaw` `sever... | priority | feature did not work adding schedule with quantifier labels type featureflaw severity medium original ped | 1 |
300,123 | 25,947,260,815 | IssuesEvent | 2022-12-17 04:56:01 | denoland/deno | https://api.github.com/repos/denoland/deno | opened | Synchronous test steps | suggestion testing | When everything is synchronous, I feel like the following should not need to be awaited:
```ts
Deno.test("something", (t) => {
t.step("some step", () => {
console.log(5);
});
});
```
Maybe there is some technical reason that I'm not remembering.
Currently it throws:
```
error: Error: There we... | 1.0 | Synchronous test steps - When everything is synchronous, I feel like the following should not need to be awaited:
```ts
Deno.test("something", (t) => {
t.step("some step", () => {
console.log(5);
});
});
```
Maybe there is some technical reason that I'm not remembering.
Currently it throws:
``... | non_priority | synchronous test steps when everything is synchronous i feel like the following should not need to be awaited ts deno test something t t step some step console log maybe there is some technical reason that i m not remembering currently it throws ... | 0 |
92,304 | 18,819,383,859 | IssuesEvent | 2021-11-10 05:52:15 | paulevsGitch/BetterNether | https://api.github.com/repos/paulevsGitch/BetterNether | closed | world fix | bug in dev code | after upgrading better-nether from 5.3.5-1.17.1 to 5.3.7-1.17.1, when loading the world, I am prompted to run "fixes", but apparently they do not work. Because every time you start the world, this window pops up again and again.
https://pastebin.com/VMfxGnKr
Any ideas? | 1.0 | world fix - after upgrading better-nether from 5.3.5-1.17.1 to 5.3.7-1.17.1, when loading the world, I am prompted to run "fixes", but apparently they do not work. Because every time you start the world, this window pops up again and again.
https://pastebin.com/VMfxGnKr
Any ideas? | non_priority | world fix after upgrading better nether from to when loading the world i am prompted to run fixes but apparently they do not work because every time you start the world this window pops up again and again any ideas | 0 |
60,292 | 7,329,471,752 | IssuesEvent | 2018-03-05 05:17:09 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | Notifications header not keyboard accessible | accessibility as-designed insiders workbench-notifications | The notifications header is not keyboard accessible and therefore not allowing access to
the expand, collapse and clear all buttons.
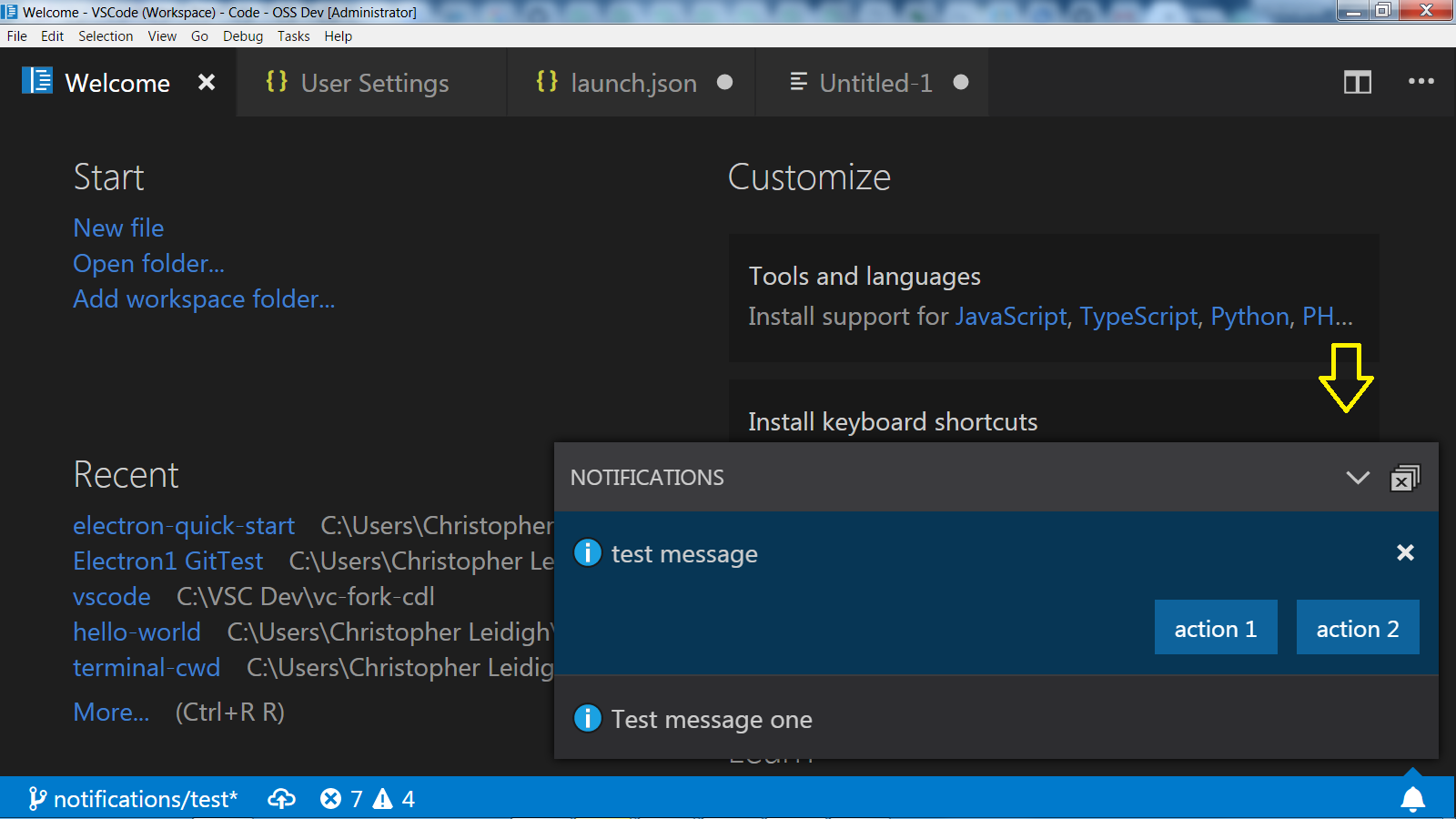
| 1.0 | Notifications header not keyboard accessible - The notifications header is not keyboard accessible and therefore not allowing access to
the expand, collapse and clear all buttons.
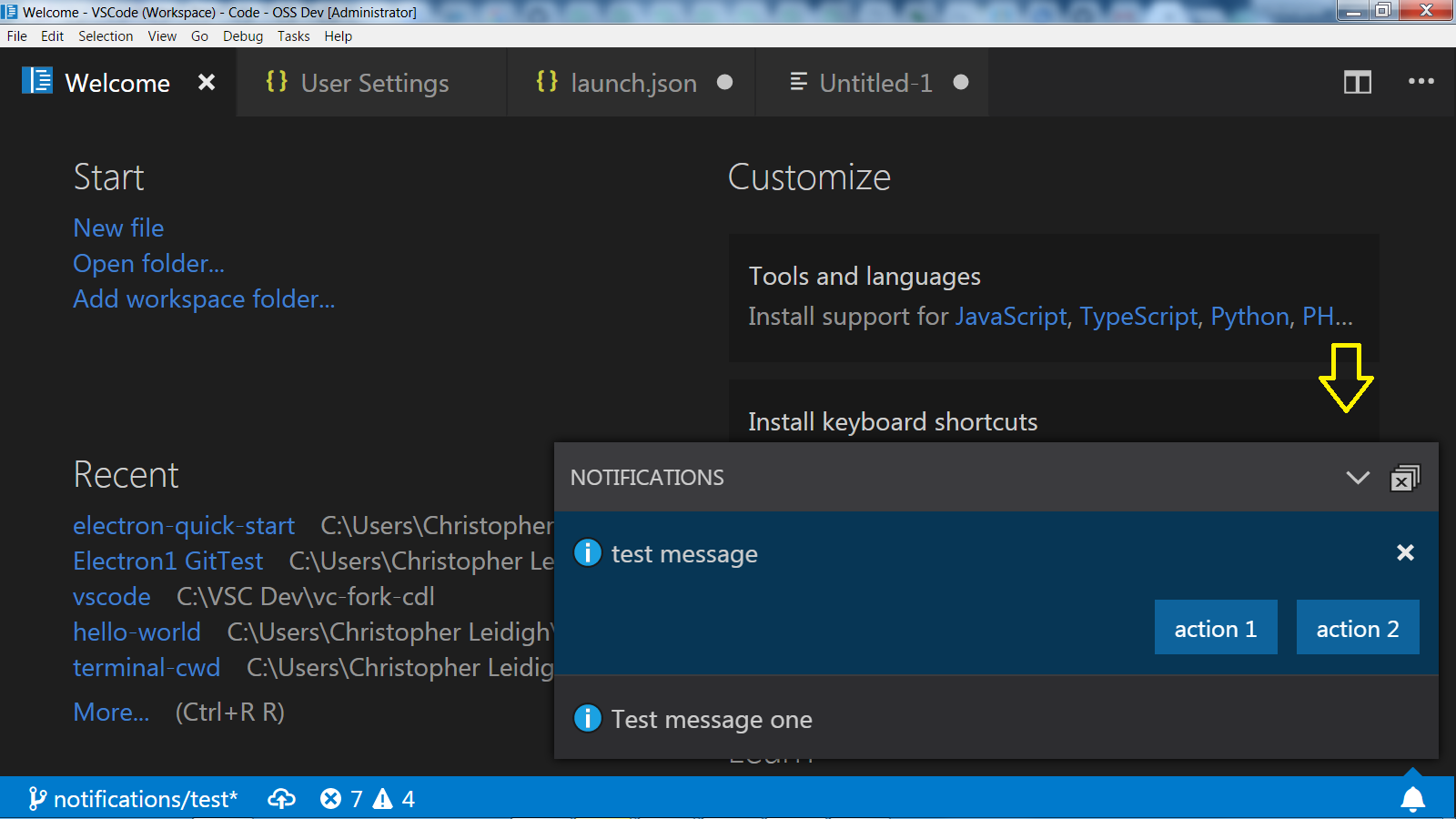
| non_priority | notifications header not keyboard accessible the notifications header is not keyboard accessible and therefore not allowing access to the expand collapse and clear all buttons | 0 |
21,151 | 10,577,801,684 | IssuesEvent | 2019-10-07 20:56:20 | davisboy/HighSpot | https://api.github.com/repos/davisboy/HighSpot | closed | CVE-2018-20190 (Medium) detected in node-sass-v4.12.0 | security vulnerability | ## CVE-2018-20190 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.12.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=ht... | True | CVE-2018-20190 (Medium) detected in node-sass-v4.12.0 - ## CVE-2018-20190 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.12.0</b></p></summary>
<p>
<p>:rainbow: Node.js ... | non_priority | cve medium detected in node sass cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matched to this s... | 0 |
3,359 | 5,557,325,319 | IssuesEvent | 2017-03-24 11:42:54 | tuna/issues | https://api.github.com/repos/tuna/issues | closed | Homebrew bottles 包无法找到应自动跳转 | Service Issue | 如果一个 bottle 在上面 404 not found,会直接报失败,正确的方式是跳转到官方对应的地址去下载:
```
==> Downloading https://mirrors.tuna.tsinghua.edu.cn/homebrew-bottles/bottles/awscli-1.11.64.sierra.bottle.tar.gz
curl: (22) The requested URL returned error: 404 Not Found
Error: Failed to download resource "awscli"
Download failed: https://mirrors... | 1.0 | Homebrew bottles 包无法找到应自动跳转 - 如果一个 bottle 在上面 404 not found,会直接报失败,正确的方式是跳转到官方对应的地址去下载:
```
==> Downloading https://mirrors.tuna.tsinghua.edu.cn/homebrew-bottles/bottles/awscli-1.11.64.sierra.bottle.tar.gz
curl: (22) The requested URL returned error: 404 Not Found
Error: Failed to download resource "awscli"
Do... | non_priority | homebrew bottles 包无法找到应自动跳转 如果一个 bottle 在上面 not found,会直接报失败,正确的方式是跳转到官方对应的地址去下载 downloading curl the requested url returned error not found error failed to download resource awscli download failed warning bottle installation failed building from source ustc 的处理方式是对的: ... | 0 |
615,629 | 19,270,831,502 | IssuesEvent | 2021-12-10 05:03:01 | GuillermoFloresV/Project3_Group12_Backend | https://api.github.com/repos/GuillermoFloresV/Project3_Group12_Backend | closed | Accept Project | Priority: 5 Difficulty: 3 | As a User I want to be able to see who has requested my Projects and accept the request.
How will it be tested:
API endpoints will be tested with Postman. Request and Response verification.
| 1.0 | Accept Project - As a User I want to be able to see who has requested my Projects and accept the request.
How will it be tested:
API endpoints will be tested with Postman. Request and Response verification.
| priority | accept project as a user i want to be able to see who has requested my projects and accept the request how will it be tested api endpoints will be tested with postman request and response verification | 1 |
9,343 | 3,036,945,460 | IssuesEvent | 2015-08-06 14:42:50 | SonarSource/sonarlint-vs | https://api.github.com/repos/SonarSource/sonarlint-vs | closed | Rule: Fields should not be initialized to default values | in test & review rule | Replaces http://jira.sonarsource.com/browse/LINTVS-98
A reference type field is automatically initialized to `null`, while a value type is initialized to the default value of the type. So initializing a field to its default value is useless. This initialization can happen both in a field initializer or in the constr... | 1.0 | Rule: Fields should not be initialized to default values - Replaces http://jira.sonarsource.com/browse/LINTVS-98
A reference type field is automatically initialized to `null`, while a value type is initialized to the default value of the type. So initializing a field to its default value is useless. This initializat... | non_priority | rule fields should not be initialized to default values replaces a reference type field is automatically initialized to null while a value type is initialized to the default value of the type so initializing a field to its default value is useless this initialization can happen both in a field initializer ... | 0 |
147,461 | 19,522,821,805 | IssuesEvent | 2021-12-29 22:26:44 | swagger-api/swagger-codegen | https://api.github.com/repos/swagger-api/swagger-codegen | opened | CVE-2020-36187 (High) detected in multiple libraries | security vulnerability | ## CVE-2020-36187 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.8.jar</b>, <b>jackson-databind-2.8.9.jar</b>, <b>jackson-databind-2.6.4.jar</b>, <b>jackson-data... | True | CVE-2020-36187 (High) detected in multiple libraries - ## CVE-2020-36187 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.8.jar</b>, <b>jackson-databind-2.8.9.jar<... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar general data bi... | 0 |
755,604 | 26,434,323,663 | IssuesEvent | 2023-01-15 07:17:14 | fredo-ai/Fredo-Public | https://api.github.com/repos/fredo-ai/Fredo-Public | closed | Email verification code improvement | priority-1 current sprint | 1. Add a big button "Verify Email" to the end of the email template
2 Button should link to Whatsapp + append the pre-text with the 4 digit code. that way user can click -> redirected to Fredo bot on whatsapp -> the code already in the text box he just need to send.
See example: https://wa.me/972525277961?text=5555 | 1.0 | Email verification code improvement - 1. Add a big button "Verify Email" to the end of the email template
2 Button should link to Whatsapp + append the pre-text with the 4 digit code. that way user can click -> redirected to Fredo bot on whatsapp -> the code already in the text box he just need to send.
See example: ... | priority | email verification code improvement add a big button verify email to the end of the email template button should link to whatsapp append the pre text with the digit code that way user can click redirected to fredo bot on whatsapp the code already in the text box he just need to send see example ... | 1 |
270,840 | 29,116,092,348 | IssuesEvent | 2023-05-17 01:11:12 | pazhanivel07/frameworks_base_Aosp10_r33 | https://api.github.com/repos/pazhanivel07/frameworks_base_Aosp10_r33 | opened | CVE-2023-21110 (Medium) detected in baseandroid-10.0.0_r46 | Mend: dependency security vulnerability | ## CVE-2023-21110 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a ... | True | CVE-2023-21110 (Medium) detected in baseandroid-10.0.0_r46 - ## CVE-2023-21110 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r46</b></p></summary>
<p>
<p>Android... | non_priority | cve medium detected in baseandroid cve medium severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in base branch master vulnerable source files services core java... | 0 |
221,063 | 7,373,455,961 | IssuesEvent | 2018-03-13 17:19:07 | VanilleBid/weekly-saleor | https://api.github.com/repos/VanilleBid/weekly-saleor | opened | Be able to get a permalink to cart | Dashboard Feature Front-store Moderate Priority | In the cart view we should be able to generate a link to create the exact same cart.
Also, the staff should be able to generate carts from the back office. | 1.0 | Be able to get a permalink to cart - In the cart view we should be able to generate a link to create the exact same cart.
Also, the staff should be able to generate carts from the back office. | priority | be able to get a permalink to cart in the cart view we should be able to generate a link to create the exact same cart also the staff should be able to generate carts from the back office | 1 |
404,478 | 27,488,234,793 | IssuesEvent | 2023-03-04 09:53:13 | NixOS/nix | https://api.github.com/repos/NixOS/nix | opened | nix repl command completeness | documentation | ## Problem
The fidelity between the implemented nix repl commands and the repl documentation is not 100%.
In the file for #7661 pull request you can see some suggested changes to the shown repl documentation for the `:?` command.
## Checklist
As advised by @edolstra this gap should be closed in conjunction ... | 1.0 | nix repl command completeness - ## Problem
The fidelity between the implemented nix repl commands and the repl documentation is not 100%.
In the file for #7661 pull request you can see some suggested changes to the shown repl documentation for the `:?` command.
## Checklist
As advised by @edolstra this gap ... | non_priority | nix repl command completeness problem the fidelity between the implemented nix repl commands and the repl documentation is not in the file for pull request you can see some suggested changes to the shown repl documentation for the command checklist as advised by edolstra this gap shoul... | 0 |
173,541 | 21,176,829,654 | IssuesEvent | 2022-04-08 01:27:53 | chaitanya00/aem-wknd | https://api.github.com/repos/chaitanya00/aem-wknd | opened | CVE-2022-21681 (High) detected in marked-0.3.5.tgz | security vulnerability | ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.5.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://reg... | True | CVE-2022-21681 (High) detected in marked-0.3.5.tgz - ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.3.5.tgz</b></p></summary>
<p>A markdown parser built for... | non_priority | cve high detected in marked tgz cve high severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file package json path to vulnerable library node modules marked package json dependency ... | 0 |
461,681 | 13,234,376,387 | IssuesEvent | 2020-08-18 16:11:41 | modulz/stitches | https://api.github.com/repos/modulz/stitches | closed | Cannot style a component that uses hooks | POC: bug priority: 1 | > Invalid hook call. Hooks can only be called inside of the body of a function component.
https://codesandbox.io/s/dreamy-visvesvaraya-hqt0u | 1.0 | Cannot style a component that uses hooks - > Invalid hook call. Hooks can only be called inside of the body of a function component.
https://codesandbox.io/s/dreamy-visvesvaraya-hqt0u | priority | cannot style a component that uses hooks invalid hook call hooks can only be called inside of the body of a function component | 1 |
34,336 | 7,447,128,035 | IssuesEvent | 2018-03-28 11:27:02 | kerdokullamae/test_koik_issued | https://api.github.com/repos/kerdokullamae/test_koik_issued | closed | Imporditud andmete probleem | P: high R: fixed T: defect | **Reported by sven syld on 27 Aug 2012 12:43 UTC**
'''Object'''
AISist imporditud andmed - asutused-isikud, kirjeldusüksused jne.
'''Description'''
Andmetes leidub naljakaid asju - "...atsioon. \x0d\x0a\x0d\x0a17.dets.1919 ..." ([link](http://dev.dira.teepub/et/person/view/110000009088?name_first_letter=P&name=p... | 1.0 | Imporditud andmete probleem - **Reported by sven syld on 27 Aug 2012 12:43 UTC**
'''Object'''
AISist imporditud andmed - asutused-isikud, kirjeldusüksused jne.
'''Description'''
Andmetes leidub naljakaid asju - "...atsioon. \x0d\x0a\x0d\x0a17.dets.1919 ..." ([link](http://dev.dira.teepub/et/person/view/110000009... | non_priority | imporditud andmete probleem reported by sven syld on aug utc object aisist imporditud andmed asutused isikud kirjeldusüksused jne description andmetes leidub naljakaid asju atsioon dets probleem tekib andmete väljastamisel ais ist pg sse täpsemini ais ... | 0 |
255,108 | 8,108,831,037 | IssuesEvent | 2018-08-14 04:12:56 | Crizov/HealthClientApp | https://api.github.com/repos/Crizov/HealthClientApp | opened | US111 - Upload supplementary files from local storage | priority: H size: 3 | As a patient I want to upload supplementary files from local storage so that I can add local files to the data packet
**Acceptance Criteria:**
1. on the create packet screen, add a section that allows a user to upload a file.
2. When "select file" button is pressed, open the phone's local file explorer.
3. allow ... | 1.0 | US111 - Upload supplementary files from local storage - As a patient I want to upload supplementary files from local storage so that I can add local files to the data packet
**Acceptance Criteria:**
1. on the create packet screen, add a section that allows a user to upload a file.
2. When "select file" button is p... | priority | upload supplementary files from local storage as a patient i want to upload supplementary files from local storage so that i can add local files to the data packet acceptance criteria on the create packet screen add a section that allows a user to upload a file when select file button is press... | 1 |
32,406 | 12,126,069,022 | IssuesEvent | 2020-04-22 16:26:38 | mixcore/mix.core | https://api.github.com/repos/mixcore/mix.core | closed | CVE-2018-19838 (Medium) detected in node-sass-4.13.0.tgz, node-sass-0bd48bbad6fccb0da16d3bdf76ad541f5f45ec70 | security vulnerability | ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.0.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.0.tgz</b></p></summary>
<p>Wrapper... | True | CVE-2018-19838 (Medium) detected in node-sass-4.13.0.tgz, node-sass-0bd48bbad6fccb0da16d3bdf76ad541f5f45ec70 - ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node... | non_priority | cve medium detected in node sass tgz node sass cve medium severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm mix core src clientapp package json ... | 0 |
151,684 | 19,664,002,893 | IssuesEvent | 2022-01-10 20:11:42 | Gabriel-Alves-Cunha/muse | https://api.github.com/repos/Gabriel-Alves-Cunha/muse | closed | CVE-2021-35065 (High) detected in glob-parent-5.1.2.tgz - autoclosed | security vulnerability | ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home p... | True | CVE-2021-35065 (High) detected in glob-parent-5.1.2.tgz - autoclosed - ## CVE-2021-35065 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>Extr... | non_priority | cve high detected in glob parent tgz autoclosed cve high severity vulnerability vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file package json path to vulnerable library node ... | 0 |
57,523 | 14,165,340,302 | IssuesEvent | 2020-11-12 07:02:44 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 84: openvpn-2.4.7: 2 advisories | 1.severity: security | [search](https://search.nix.gsc.io/?q=openvpn&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=openvpn+in%3Apath&type=Code)
* [ ] [CVE-2020-7224](https://nvd.nist.gov/vuln/detail/CVE-2020-7224) CVSSv3=9.8 (nixos-19.09)
* [ ] [CVE-2020-11810](https://nvd.nist.gov/vuln/detai... | True | Vulnerability roundup 84: openvpn-2.4.7: 2 advisories - [search](https://search.nix.gsc.io/?q=openvpn&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=openvpn+in%3Apath&type=Code)
* [ ] [CVE-2020-7224](https://nvd.nist.gov/vuln/detail/CVE-2020-7224) CVSSv3=9.8 (nixos-19.09... | non_priority | vulnerability roundup openvpn advisories nixos nixos scanned versions nixos may contain false positives | 0 |
197,875 | 6,965,633,831 | IssuesEvent | 2017-12-09 08:53:07 | openfoodfacts/openfoodfacts-androidapp | https://api.github.com/repos/openfoodfacts/openfoodfacts-androidapp | opened | The Storage Permission is asked at the wrong time | permissions priority | The Storage Permission is asked at the wrong time, and thus scary. It is asked when you land on an existing product page.
**Why would I possibly need the storage permission to view a product ?**
- We only need it when **adding a new product from images already on the device**.
- Otherwise, **if adding a new pro... | 1.0 | The Storage Permission is asked at the wrong time - The Storage Permission is asked at the wrong time, and thus scary. It is asked when you land on an existing product page.
**Why would I possibly need the storage permission to view a product ?**
- We only need it when **adding a new product from images already o... | priority | the storage permission is asked at the wrong time the storage permission is asked at the wrong time and thus scary it is asked when you land on an existing product page why would i possibly need the storage permission to view a product we only need it when adding a new product from images already o... | 1 |
419,607 | 28,148,710,465 | IssuesEvent | 2023-04-02 19:41:35 | apache/streampipes | https://api.github.com/repos/apache/streampipes | closed | Extend Python docs with dark mode | good first issue documentation | ### Body
Our [Python docs](https://github.com/apache/streampipes/tree/dev/streampipes-client-python/docs) are built using [mkdocs-material](https://squidfunk.github.io/mkdocs-material/).
This allows to easily configure a dark mode as described here: https://squidfunk.github.io/mkdocs-material/setup/changing-the-color... | 1.0 | Extend Python docs with dark mode - ### Body
Our [Python docs](https://github.com/apache/streampipes/tree/dev/streampipes-client-python/docs) are built using [mkdocs-material](https://squidfunk.github.io/mkdocs-material/).
This allows to easily configure a dark mode as described here: https://squidfunk.github.io/mkdo... | non_priority | extend python docs with dark mode body our are built using this allows to easily configure a dark mode as described here this issue is about configuring the dark mode for our python docs via the please pay some attention on the selected primary and accent color for the dark theme monitor... | 0 |
601,355 | 18,400,993,820 | IssuesEvent | 2021-10-12 16:16:31 | tnc-ca-geo/animl-frontend | https://api.github.com/repos/tnc-ca-geo/animl-frontend | opened | Fix view saving bug: explicitly bake currently selected camera & deployment into filters | bug high priority | Currently when creating a view that includes all currently available cameras & deployments, the filters saved for that view for cameras & deployments will be "null", which means that all new cameras/deps that get added after that will be included in that view. Maybe when you save a view, bake the currently selected cam... | 1.0 | Fix view saving bug: explicitly bake currently selected camera & deployment into filters - Currently when creating a view that includes all currently available cameras & deployments, the filters saved for that view for cameras & deployments will be "null", which means that all new cameras/deps that get added after that... | priority | fix view saving bug explicitly bake currently selected camera deployment into filters currently when creating a view that includes all currently available cameras deployments the filters saved for that view for cameras deployments will be null which means that all new cameras deps that get added after that... | 1 |
9,640 | 30,110,342,207 | IssuesEvent | 2023-06-30 07:11:38 | DevExpress/testcafe | https://api.github.com/repos/DevExpress/testcafe | closed | In nativeAutomation, setFileUpload does nothing | TYPE: bug FREQUENCY: level 1 SYSTEM: native automation | ### What is your Scenario?
Scenario need to upload a file
### What is the Current behavior?
await t.setFileUpload does nothing
### What is the Expected behavior?
await t.setFileUpload sets the file to upload
### What is your public website URL? (or attach your complete example)
https://www.htmlquick.com/referenc... | 1.0 | In nativeAutomation, setFileUpload does nothing - ### What is your Scenario?
Scenario need to upload a file
### What is the Current behavior?
await t.setFileUpload does nothing
### What is the Expected behavior?
await t.setFileUpload sets the file to upload
### What is your public website URL? (or attach your com... | non_priority | in nativeautomation setfileupload does nothing what is your scenario scenario need to upload a file what is the current behavior await t setfileupload does nothing what is the expected behavior await t setfileupload sets the file to upload what is your public website url or attach your com... | 0 |
10,396 | 4,763,469,561 | IssuesEvent | 2016-10-25 14:32:37 | CartoDB/cartodb | https://api.github.com/repos/CartoDB/cartodb | closed | 'JOIN from 2nd layer' analysis breaks when changing parameters | Analysis bug Builder | An already applied 'JOIN from 2nd layer' analysis breaks after any parameter is changed from the UI.
**Use this file to reproduce
[p_places_JOIN_w_borders (on 2016-10-24 at 10.26.39).carto.zip](https://github.com/CartoDB/cartodb/files/547506/p_places_JOIN_w_borders.on.2016-10-24.at.10.26.39.carto.zip)**
## STR... | 1.0 | 'JOIN from 2nd layer' analysis breaks when changing parameters - An already applied 'JOIN from 2nd layer' analysis breaks after any parameter is changed from the UI.
**Use this file to reproduce
[p_places_JOIN_w_borders (on 2016-10-24 at 10.26.39).carto.zip](https://github.com/CartoDB/cartodb/files/547506/p_places_... | non_priority | join from layer analysis breaks when changing parameters an already applied join from layer analysis breaks after any parameter is changed from the ui use this file to reproduce str create a map from populated places dataset add join columns from layer analysis chose ... | 0 |
229,532 | 7,575,597,496 | IssuesEvent | 2018-04-24 02:36:25 | jsonwebtoken/jsonwebtoken.github.io | https://api.github.com/repos/jsonwebtoken/jsonwebtoken.github.io | closed | Show definition or highlight spec claims | enhancement low-priority | It would be great if the definitions of the built-in claims of the spec (e.g. `jti`, `iat`, etc.) could be seen by hovering over the claim name. As a first step, it might be useful to highlight these claims in some way as to distinguish them from custom claims.
For a list of claims, see https://tools.ietf.org/html/dra... | 1.0 | Show definition or highlight spec claims - It would be great if the definitions of the built-in claims of the spec (e.g. `jti`, `iat`, etc.) could be seen by hovering over the claim name. As a first step, it might be useful to highlight these claims in some way as to distinguish them from custom claims.
For a list of ... | priority | show definition or highlight spec claims it would be great if the definitions of the built in claims of the spec e g jti iat etc could be seen by hovering over the claim name as a first step it might be useful to highlight these claims in some way as to distinguish them from custom claims for a list of ... | 1 |
377,851 | 11,185,391,856 | IssuesEvent | 2020-01-01 01:10:22 | PIQuIL/QuCumber | https://api.github.com/repos/PIQuIL/QuCumber | closed | Update CI | Priority: Medium Size: Medium Status: In Progress continuous-integration enhancement | - [x] Move format checking from travis to restyled-io
- [ ] Keep checking format for jupyter notebooks on travis, though
- [ ] Consider moving away from the invoke package to click
- [x] Use travis stages and tox to run unit tests, test documentation and package builds | 1.0 | Update CI - - [x] Move format checking from travis to restyled-io
- [ ] Keep checking format for jupyter notebooks on travis, though
- [ ] Consider moving away from the invoke package to click
- [x] Use travis stages and tox to run unit tests, test documentation and package builds | priority | update ci move format checking from travis to restyled io keep checking format for jupyter notebooks on travis though consider moving away from the invoke package to click use travis stages and tox to run unit tests test documentation and package builds | 1 |
794,774 | 28,048,878,942 | IssuesEvent | 2023-03-29 02:53:06 | janus-idp/backstage-showcase | https://api.github.com/repos/janus-idp/backstage-showcase | opened | Be able to generate a Changelog.md | priority/medium kind/chore | ### What needs to be done?
We want to be able to list all the changes between release and publish a Changelog.md file with a tool like:
https://github.com/spring-io/github-changelog-generator | 1.0 | Be able to generate a Changelog.md - ### What needs to be done?
We want to be able to list all the changes between release and publish a Changelog.md file with a tool like:
https://github.com/spring-io/github-changelog-generator | priority | be able to generate a changelog md what needs to be done we want to be able to list all the changes between release and publish a changelog md file with a tool like | 1 |
325,372 | 27,872,127,807 | IssuesEvent | 2023-03-21 14:04:53 | eclipse-openj9/openj9 | https://api.github.com/repos/eclipse-openj9/openj9 | opened | zlinux CS testing crash vmState=0xffffffff | comp:vm comp:gc test failure blocker segfault | https://openj9-jenkins.osuosl.org/job/Test_openjdk11_j9_sanity.system_s390x_linux_Nightly_testList_0/494/
- no diagnostics
https://openj9-jenkins.osuosl.org/job/Test_openjdk11_j9_sanity.system_s390x_linux_Nightly_testList_1/495/
- https://openj9-artifactory.osuosl.org/artifactory/ci-openj9/Test/Test_openjdk11_j9_s... | 1.0 | zlinux CS testing crash vmState=0xffffffff - https://openj9-jenkins.osuosl.org/job/Test_openjdk11_j9_sanity.system_s390x_linux_Nightly_testList_0/494/
- no diagnostics
https://openj9-jenkins.osuosl.org/job/Test_openjdk11_j9_sanity.system_s390x_linux_Nightly_testList_1/495/
- https://openj9-artifactory.osuosl.org/a... | non_priority | zlinux cs testing crash vmstate no diagnostics lambdaloadtest cs mathloadtest autosimd cs parallelstreamsloadtest cs daaloadtest cs daaloadtest cs daaloadtest cs mathloadtest bigdecimal cs classloadingtest cs daaloadtest all cs ... | 0 |
740,056 | 25,734,365,855 | IssuesEvent | 2022-12-07 23:06:58 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | On CPU-only machine received OSError from importing: libcublas.so.11: cannot open shared object file | high priority triage review oncall: binaries module: regression | ### 🐛 Describe the bug
On a CPU-only machine, in Amazon Linux 2 latest docker image, install latest PyTorch(1.13) via pip and import, received this error.
However in my sense, PyTorch should not install GPU related components on a CPU-only machine without CUDA and nvidia related package installed?
Steps to reprod... | 1.0 | On CPU-only machine received OSError from importing: libcublas.so.11: cannot open shared object file - ### 🐛 Describe the bug
On a CPU-only machine, in Amazon Linux 2 latest docker image, install latest PyTorch(1.13) via pip and import, received this error.
However in my sense, PyTorch should not install GPU related... | priority | on cpu only machine received oserror from importing libcublas so cannot open shared object file 🐛 describe the bug on a cpu only machine in amazon linux latest docker image install latest pytorch via pip and import received this error however in my sense pytorch should not install gpu related c... | 1 |
37,261 | 8,244,822,812 | IssuesEvent | 2018-09-11 07:47:48 | Chisel-Team/Chisel | https://api.github.com/repos/Chisel-Team/Chisel | closed | Chiseled a stack of blocks, gave me a single block back instead of a stack | 1.10 bug-code complete-code | Using chisel 1.10.2-0.2.0.43 with the config setting for chisels not taking damage and using the I-Chisel | 2.0 | Chiseled a stack of blocks, gave me a single block back instead of a stack - Using chisel 1.10.2-0.2.0.43 with the config setting for chisels not taking damage and using the I-Chisel | non_priority | chiseled a stack of blocks gave me a single block back instead of a stack using chisel with the config setting for chisels not taking damage and using the i chisel | 0 |
687,671 | 23,534,861,933 | IssuesEvent | 2022-08-19 19:24:26 | metabase/metabase | https://api.github.com/repos/metabase/metabase | reopened | Breadcrumb is displaying wrong "path" order when collection in moved inside another | Type:Bug Priority:P3 Organization/Collections | **Describe the bug**
Breadcrumb is displaying wrong "path" order when collection in moved inside another.
**To Reproduce**
1. Create a new collection named "Collection**1**" in "Our analytics".
2. Create another collection named "Collection**2**" with a collection named "Collection**3**" inside it, also in "Our... | 1.0 | Breadcrumb is displaying wrong "path" order when collection in moved inside another - **Describe the bug**
Breadcrumb is displaying wrong "path" order when collection in moved inside another.
**To Reproduce**
1. Create a new collection named "Collection**1**" in "Our analytics".
2. Create another collection nam... | priority | breadcrumb is displaying wrong path order when collection in moved inside another describe the bug breadcrumb is displaying wrong path order when collection in moved inside another to reproduce create a new collection named collection in our analytics create another collection nam... | 1 |
74,075 | 3,427,995,877 | IssuesEvent | 2015-12-10 06:31:36 | sceene/sprint-planning | https://api.github.com/repos/sceene/sprint-planning | closed | Global: Profile Actions | HIGH PRIORITY | ## Places Actions
- [x] Share
- Trigger the Share Modal
- [x] Contact
- Show real phone number.
- It's currently showing a hardcoded phone number.
- [x] Uber
- You can implement this without API. I'll need the following information (See image below)
- REDIRECT URL
- ORIGIN URI
- [x] Directions
... | 1.0 | Global: Profile Actions - ## Places Actions
- [x] Share
- Trigger the Share Modal
- [x] Contact
- Show real phone number.
- It's currently showing a hardcoded phone number.
- [x] Uber
- You can implement this without API. I'll need the following information (See image below)
- REDIRECT URL
- ORIG... | priority | global profile actions places actions share trigger the share modal contact show real phone number it s currently showing a hardcoded phone number uber you can implement this without api i ll need the following information see image below redirect url origin uri... | 1 |
22,452 | 7,177,015,728 | IssuesEvent | 2018-01-31 12:07:20 | zeebe-io/zeebe | https://api.github.com/repos/zeebe-io/zeebe | opened | Test suite hangs during maven run with "Address already in use" | broker ready unstable build | Sometimes the test suite stops and fails as it cannot bind to the given network address as it claims it is still in use.
```
11:59:15.834 [localhost:51015] [service-container-action-0] INFO io.zeebe.broker.services - Using /tmp/junit4316972134707707111/persistent-broker/metrics/metrics.zeebe for counters
Exceptio... | 1.0 | Test suite hangs during maven run with "Address already in use" - Sometimes the test suite stops and fails as it cannot bind to the given network address as it claims it is still in use.
```
11:59:15.834 [localhost:51015] [service-container-action-0] INFO io.zeebe.broker.services - Using /tmp/junit4316972134707707... | non_priority | test suite hangs during maven run with address already in use sometimes the test suite stops and fails as it cannot bind to the given network address as it claims it is still in use info io zeebe broker services using tmp persistent broker metrics metrics zeebe for counters exception in ... | 0 |
1,291 | 3,535,541,007 | IssuesEvent | 2016-01-16 16:02:57 | dirkgroenen/mopidy-mopify | https://api.github.com/repos/dirkgroenen/mopidy-mopify | closed | Play next and add to queue ain't working anymore | bug service | Since consume mode is disabled some queue features won't work anymore. This is caused by the index songs are added on. When consume mode was one the current playing track always had index `0`. With consume mode on the current playing track index can be different, so tracks should be added after that index instead after... | 1.0 | Play next and add to queue ain't working anymore - Since consume mode is disabled some queue features won't work anymore. This is caused by the index songs are added on. When consume mode was one the current playing track always had index `0`. With consume mode on the current playing track index can be different, so tr... | non_priority | play next and add to queue ain t working anymore since consume mode is disabled some queue features won t work anymore this is caused by the index songs are added on when consume mode was one the current playing track always had index with consume mode on the current playing track index can be different so tr... | 0 |
335,616 | 10,164,136,842 | IssuesEvent | 2019-08-07 10:54:36 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | zwift.com - design is broken | browser-firefox-mobile engine-gecko priority-important status-contact-success status-first-contact | <!-- @browser: Firefox Mobile 60.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.1.0; Mobile; rv:60.0) Gecko/60.0 Firefox/60.0 -->
<!-- @reported_with: web -->
**URL**: http://zwift.com/b/strava-challenge-complete-feb-2018/
**Browser / Version**: Firefox Mobile 60.0
**Operating System**: Android 8.1.0
**Tested Another ... | 1.0 | zwift.com - design is broken - <!-- @browser: Firefox Mobile 60.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.1.0; Mobile; rv:60.0) Gecko/60.0 Firefox/60.0 -->
<!-- @reported_with: web -->
**URL**: http://zwift.com/b/strava-challenge-complete-feb-2018/
**Browser / Version**: Firefox Mobile 60.0
**Operating System**: ... | priority | zwift com design is broken url browser version firefox mobile operating system android tested another browser yes problem type design is broken description the check button has some interference with a text steps to reproduce look at the check button before ... | 1 |
83,612 | 7,876,578,115 | IssuesEvent | 2018-06-26 01:56:14 | openshiftio/openshift.io | https://api.github.com/repos/openshiftio/openshift.io | opened | Incident: cannot create an application | area/launcher area/tests team/launcher team/platform type/incident-report | == "cannot create an application"
*Period*: "20 Jun 2018 - 21 Jun 2018"
*System*: "OSiO|Launcher"
*Effected*: "~40 users"
=== Story
Fabric8-UI updated OSIO to the latest commit. This push to prod produced an error when trying to create a new application after creating a new space. This was seen in prod-p... | 1.0 | Incident: cannot create an application - == "cannot create an application"
*Period*: "20 Jun 2018 - 21 Jun 2018"
*System*: "OSiO|Launcher"
*Effected*: "~40 users"
=== Story
Fabric8-UI updated OSIO to the latest commit. This push to prod produced an error when trying to create a new application after crea... | non_priority | incident cannot create an application cannot create an application period jun jun system osio launcher effected users story ui updated osio to the latest commit this push to prod produced an error when trying to create a new application after creating a new spac... | 0 |
716,491 | 24,635,989,724 | IssuesEvent | 2022-10-17 08:00:11 | status-im/status-desktop | https://api.github.com/repos/status-im/status-desktop | opened | [suite_messaging / tst_ChatFlow] - "The user can activate image unfurling" scenario fails | bug Chat priority F2: important squish S:1 messenger | ### Description
1. `The user can activate image unfurling` scenario works **standalone** but when it runs as part of the sequence, the action to **activate link preview** doesn't work.
2. Once it is updated, remove `mayfail` tag.
**IMPORTANT**: Ensure it works standalone and also as part of the sequence. | 1.0 | [suite_messaging / tst_ChatFlow] - "The user can activate image unfurling" scenario fails - ### Description
1. `The user can activate image unfurling` scenario works **standalone** but when it runs as part of the sequence, the action to **activate link preview** doesn't work.
2. Once it is updated, remove `mayfail`... | priority | the user can activate image unfurling scenario fails description the user can activate image unfurling scenario works standalone but when it runs as part of the sequence the action to activate link preview doesn t work once it is updated remove mayfail tag important ensure ... | 1 |
222,613 | 7,434,392,662 | IssuesEvent | 2018-03-26 10:52:04 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.nbcsports.com - design is broken | browser-firefox-mobile priority-normal | <!-- @browser: Firefox Mobile 61.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:61.0) Gecko/61.0 Firefox/61.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: http://www.nbcsports.com/
**Browser / Version**: Firefox Mobile 61.0
**Operating System**: Android 6.0.1
**Tested Another Browser**: Unknow... | 1.0 | www.nbcsports.com - design is broken - <!-- @browser: Firefox Mobile 61.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:61.0) Gecko/61.0 Firefox/61.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: http://www.nbcsports.com/
**Browser / Version**: Firefox Mobile 61.0
**Operating System**: Android 6... | priority | design is broken url browser version firefox mobile operating system android tested another browser unknown problem type design is broken description banner stories scroll then disappear steps to reproduce from with ❤️ | 1 |
602,963 | 18,519,135,459 | IssuesEvent | 2021-10-20 13:26:55 | AY2122S1-CS2103T-T12-2/tp | https://api.github.com/repos/AY2122S1-CS2103T-T12-2/tp | closed | Update GUI for help function | type.Enhancement priority.High | Update the GUI for the additional window for help command.
Change the information shown upon the help command call. From URL to an overview of the available commands | 1.0 | Update GUI for help function - Update the GUI for the additional window for help command.
Change the information shown upon the help command call. From URL to an overview of the available commands | priority | update gui for help function update the gui for the additional window for help command change the information shown upon the help command call from url to an overview of the available commands | 1 |
427,943 | 29,871,556,662 | IssuesEvent | 2023-06-20 08:50:17 | OSeMOSYS/OSeMOSYS_GNU_MathProg | https://api.github.com/repos/OSeMOSYS/OSeMOSYS_GNU_MathProg | closed | Archiving OSeMOSYS | documentation enhancement | I was wondering if we should archive the OSeMOSYS code in Zenodo.
Right now we have a citation file in the repo asking the user to reference the 2011 OSeMOSYS paper.
But an archive on Zenodo would allow to specifically point to the version of OSeMOSYS used with a DOI.
I see that pyPSA has archived it's GitHub repo ... | 1.0 | Archiving OSeMOSYS - I was wondering if we should archive the OSeMOSYS code in Zenodo.
Right now we have a citation file in the repo asking the user to reference the 2011 OSeMOSYS paper.
But an archive on Zenodo would allow to specifically point to the version of OSeMOSYS used with a DOI.
I see that pyPSA has archi... | non_priority | archiving osemosys i was wondering if we should archive the osemosys code in zenodo right now we have a citation file in the repo asking the user to reference the osemosys paper but an archive on zenodo would allow to specifically point to the version of osemosys used with a doi i see that pypsa has archived... | 0 |
640,189 | 20,775,891,935 | IssuesEvent | 2022-03-16 10:26:13 | passwordcockpit/passwordcockpit | https://api.github.com/repos/passwordcockpit/passwordcockpit | closed | Problems in the view of access rights to a folder | bug fe priority-normal | Elements are overlapped when the screen is small | 1.0 | Problems in the view of access rights to a folder - Elements are overlapped when the screen is small | priority | problems in the view of access rights to a folder elements are overlapped when the screen is small | 1 |
389,838 | 11,517,768,387 | IssuesEvent | 2020-02-14 09:08:38 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.bilibili.com - see bug description | browser-fenix engine-gecko priority-critical | <!-- @browser: Firefox Mobile 75.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:75.0) Gecko/75.0 Firefox/75.0 -->
<!-- @reported_with: -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/48241 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://www.bilibili.com/
**Browser / Version*... | 1.0 | www.bilibili.com - see bug description - <!-- @browser: Firefox Mobile 75.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:75.0) Gecko/75.0 Firefox/75.0 -->
<!-- @reported_with: -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/48241 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https:... | priority | see bug description url browser version firefox mobile operating system android tested another browser yes problem type something else description 跳转app steps to reproduce 访问主页没有问题,点击进任意视频播放就会跳转到app链接,该app未安装也不想安装,出现不支持的协议,视频无法正常播放,只安装了ublock扩展。测试过其他浏览无问题。 ... | 1 |
88,035 | 15,800,679,740 | IssuesEvent | 2021-04-03 00:47:21 | DamieFC/linucrash | https://api.github.com/repos/DamieFC/linucrash | opened | CVE-2021-3444 (High) detected in selinuxselinux-pr-20210322 | security vulnerability | ## CVE-2021-3444 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>selinuxselinux-pr-20210322</b></p></summary>
<p>
<p>SELinux kernel repository</p>
<p>Library home page: <a href=https:/... | True | CVE-2021-3444 (High) detected in selinuxselinux-pr-20210322 - ## CVE-2021-3444 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>selinuxselinux-pr-20210322</b></p></summary>
<p>
<p>SELin... | non_priority | cve high detected in selinuxselinux pr cve high severity vulnerability vulnerable library selinuxselinux pr selinux kernel repository library home page a href found in head commit a href found in base branch master vulnerable source files li... | 0 |
57,033 | 6,536,311,433 | IssuesEvent | 2017-08-31 17:39:05 | w3c/testharness.js | https://api.github.com/repos/w3c/testharness.js | closed | Disable the timeout automatically for manual tests? | testharness.js | Tests that check features that require some initial user gesture are typically semi-manual: they require the user to do something, e.g. click on a button, and the test can then use the test harness to compute and report the result to the test runner automatically.
It's hard to predict how long the user is going to nee... | 1.0 | Disable the timeout automatically for manual tests? - Tests that check features that require some initial user gesture are typically semi-manual: they require the user to do something, e.g. click on a button, and the test can then use the test harness to compute and report the result to the test runner automatically.
... | non_priority | disable the timeout automatically for manual tests tests that check features that require some initial user gesture are typically semi manual they require the user to do something e g click on a button and the test can then use the test harness to compute and report the result to the test runner automatically ... | 0 |
822,459 | 30,873,259,596 | IssuesEvent | 2023-08-03 12:48:30 | awslabs/aws-dataall | https://api.github.com/repos/awslabs/aws-dataall | closed | Additional encryption in SNS topics in transit | type: enhancement priority: low status: not-picked-yet | **Is your idea related to a problem? Please describe.**
I would like a review on the SNS in transit encryption settings and ensure SNS- Enforce encryption of data in transit
| 1.0 | Additional encryption in SNS topics in transit - **Is your idea related to a problem? Please describe.**
I would like a review on the SNS in transit encryption settings and ensure SNS- Enforce encryption of data in transit
| priority | additional encryption in sns topics in transit is your idea related to a problem please describe i would like a review on the sns in transit encryption settings and ensure sns enforce encryption of data in transit | 1 |
45,368 | 12,745,614,279 | IssuesEvent | 2020-06-26 14:32:54 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | opened | Minor: Links to forms are not scanned by node link report | Defect | **Describe the defect**
Form db data pointing to a non-existent form is not caught by the node link report due to our magic of putting this in an alternate view mode. It bypasses the node link report scanning completely.
The link in the screenshot should show up as broken.

* 과거의 스케쥴을 보여줄 필요는 없음 (오늘부터 7일간의 스케쥴을 보여줄 예정)
* 일 단위로 스케쥴 정보를 요청하는 방식으로 결정되었습니다. (2020-08-07의 모든 스케쥴)
* 스케쥴을 등록할 수 있으며, 편집할 수 도 있습니다
* 스케쥴 시간이 중복되지 않도록 서버에서 처리하기로 하였습니다.
(08:00 - 08:20 독서가 있을때, 08:10 - 08:30) 운동을 추가하려하면 Exception) | 1.0 | 스케쥴 - * 스케쥴에서 카테고리란 = (독서, 운동, 명상, 확언중 한개)
* 과거의 스케쥴을 보여줄 필요는 없음 (오늘부터 7일간의 스케쥴을 보여줄 예정)
* 일 단위로 스케쥴 정보를 요청하는 방식으로 결정되었습니다. (2020-08-07의 모든 스케쥴)
* 스케쥴을 등록할 수 있으며, 편집할 수 도 있습니다
* 스케쥴 시간이 중복되지 않도록 서버에서 처리하기로 하였습니다.
(08:00 - 08:20 독서가 있을때, 08:10 - 08:30) 운동을 추가하려하면 Exception) | non_priority | 스케쥴 스케쥴에서 카테고리란 독서 운동 명상 확언중 한개 과거의 스케쥴을 보여줄 필요는 없음 오늘부터 스케쥴을 보여줄 예정 일 단위로 스케쥴 정보를 요청하는 방식으로 결정되었습니다 모든 스케쥴 스케쥴을 등록할 수 있으며 편집할 수 도 있습니다 스케쥴 시간이 중복되지 않도록 서버에서 처리하기로 하였습니다 독서가 있을때 운동을 추가하려하면 exception | 0 |
450,924 | 13,021,540,583 | IssuesEvent | 2020-07-27 06:35:10 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | staticweb.bankofamerica.com - site is not usable | browser-firefox-mobile engine-gecko ml-needsdiagnosis-false priority-important | <!-- @browser: Firefox Mobile 78.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:78.0) Gecko/78.0 Firefox/78.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/55919 -->
**URL**: https://staticweb.bankofamerica.com/cavmwebbactouch/common/index.html
**Brows... | 1.0 | staticweb.bankofamerica.com - site is not usable - <!-- @browser: Firefox Mobile 78.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:78.0) Gecko/78.0 Firefox/78.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/55919 -->
**URL**: https://staticweb.bankofame... | priority | staticweb bankofamerica com site is not usable url browser version firefox mobile operating system android tested another browser yes other problem type site is not usable description page not loading correctly steps to reproduce frame hanging in desktop mode ... | 1 |
24,550 | 2,668,933,123 | IssuesEvent | 2015-03-23 12:38:39 | CarlosPlusPlus/ghanban | https://api.github.com/repos/CarlosPlusPlus/ghanban | closed | Update README with Project Specifics | priority: low size: 1 type: feature | Would be great to update original README.rdoc => README.md with relevant information. | 1.0 | Update README with Project Specifics - Would be great to update original README.rdoc => README.md with relevant information. | priority | update readme with project specifics would be great to update original readme rdoc readme md with relevant information | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.