Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
50,886 | 13,187,940,322 | IssuesEvent | 2020-08-13 05:05:24 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | icetray-inspect - on OSX hdfwriter is included as an inspectable project, when it is not built (Trac #1605) | Migrated from Trac defect infrastructure | `hdfwriter` doesn't build for me because I don't have the HDF5 libs installed.
`icetray-inspect` still tries to do it's thing though...
```text
hdfwriter
Error cant load 'hdfwriter': dlopen(/Users/nega/i3/combo/build/lib/icecube/hdfwriter.so, 2): image not found
HiveSplitter
```
<details>
<summary><em>Migrated fr... | 1.0 | icetray-inspect - on OSX hdfwriter is included as an inspectable project, when it is not built (Trac #1605) - `hdfwriter` doesn't build for me because I don't have the HDF5 libs installed.
`icetray-inspect` still tries to do it's thing though...
```text
hdfwriter
Error cant load 'hdfwriter': dlopen(/Users/nega/i3/c... | non_priority | icetray inspect on osx hdfwriter is included as an inspectable project when it is not built trac hdfwriter doesn t build for me because i don t have the libs installed icetray inspect still tries to do it s thing though text hdfwriter error cant load hdfwriter dlopen users nega combo bu... | 0 |
798,638 | 28,291,810,709 | IssuesEvent | 2023-04-09 09:56:56 | AY2223S2-CS2113-T11-2/tp | https://api.github.com/repos/AY2223S2-CS2113-T11-2/tp | closed | [PE-D][Tester C] status and details command not working without internet connection | priority.High severity.High | 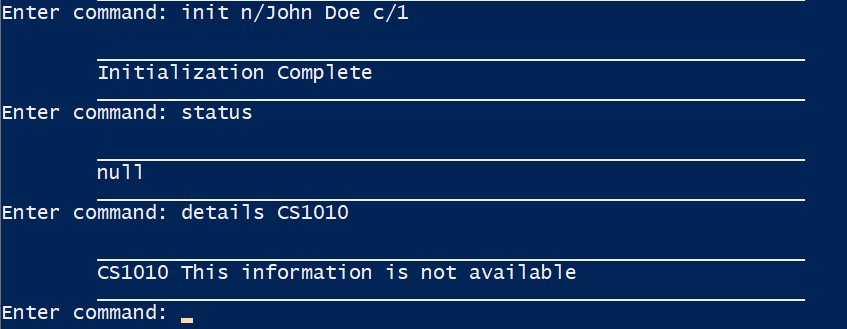
As seen above, if I do not have any internet connection, I am unable to see my status or any module information
<!--session: 1680252477820-2dadd4cb-e494-46c6-a48e-457077390957-->
<!--Version: Web v3.4.... | 1.0 | [PE-D][Tester C] status and details command not working without internet connection - 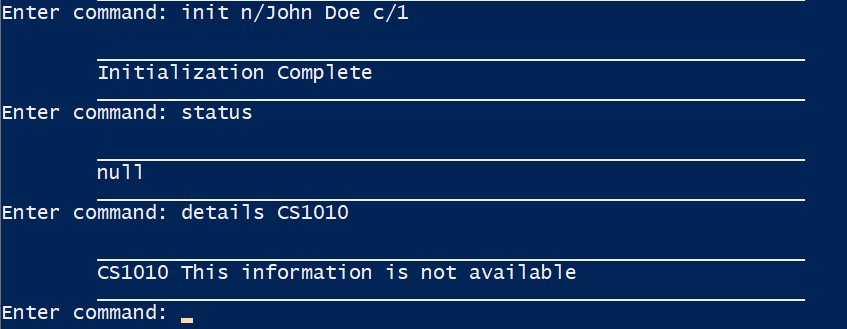
As seen above, if I do not have any internet connection, I am unable to see my status or any module information
<!-... | priority | status and details command not working without internet connection as seen above if i do not have any internet connection i am unable to see my status or any module information labels type functionalitybug severity low original darrenangwx ped | 1 |
94,489 | 15,962,386,757 | IssuesEvent | 2021-04-16 01:12:41 | RG4421/cbp-theme | https://api.github.com/repos/RG4421/cbp-theme | opened | CVE-2020-15366 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-15366 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ajv-6.12.0.tgz</b>, <b>ajv-6.10.0.tgz</b>, <b>ajv-4.11.8.tgz</b>, <b>ajv-6.11.0.tgz</b>, <b>ajv-6.5.3.tgz</b>, <b>a... | True | CVE-2020-15366 (Medium) detected in multiple libraries - ## CVE-2020-15366 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ajv-6.12.0.tgz</b>, <b>ajv-6.10.0.tgz</b>, <b>ajv-4.11.8.t... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries ajv tgz ajv tgz ajv tgz ajv tgz ajv tgz ajv tgz ajv tgz another json schema validator library home page a href path to d... | 0 |
549,934 | 16,101,985,604 | IssuesEvent | 2021-04-27 10:27:58 | snowplow/snowplow-android-tracker | https://api.github.com/repos/snowplow/snowplow-android-tracker | closed | Fix OkHttpClient sslSocketFactory always overriden | priority:medium status:completed type:enhancement | `Emitter.Builder` allows passing a custom `OkHttpClient` while building an `Emitter`. However, that client's `sslSocketFactory` is always being overriden [here](https://github.com/snowplow/snowplow-android-tracker/blob/master/snowplow-tracker/src/main/java/com/snowplowanalytics/snowplow/tracker/OkHttpNetworkConnection.... | 1.0 | Fix OkHttpClient sslSocketFactory always overriden - `Emitter.Builder` allows passing a custom `OkHttpClient` while building an `Emitter`. However, that client's `sslSocketFactory` is always being overriden [here](https://github.com/snowplow/snowplow-android-tracker/blob/master/snowplow-tracker/src/main/java/com/snowpl... | priority | fix okhttpclient sslsocketfactory always overriden emitter builder allows passing a custom okhttpclient while building an emitter however that client s sslsocketfactory is always being overriden this prevents enabling certificate pinning or adding some custom certificates to okhttpclient instances ... | 1 |
24,425 | 2,667,563,509 | IssuesEvent | 2015-03-22 18:40:51 | warneboldt/frasernw | https://api.github.com/repos/warneboldt/frasernw | opened | Implement "accepting limited new referrals" for clinics | Medium Priority | The "orange check" from specialists should also work for clinics | 1.0 | Implement "accepting limited new referrals" for clinics - The "orange check" from specialists should also work for clinics | priority | implement accepting limited new referrals for clinics the orange check from specialists should also work for clinics | 1 |
264,397 | 8,309,505,947 | IssuesEvent | 2018-09-24 07:00:13 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | times.hinet.net - “Like/Share” button labels are misaligned | Re-triaged browser-firefox-mobile priority-important severity-minor | <!-- @browser: Firefox Mobile Nightly 58.0a1 (2017-10-10) -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0 -->
<!-- @reported_with: web -->
**URL**: https://times.hinet.net/mobile/topic/20770626
**Browser / Version**: Firefox Mobile Nightly 58.0a1 (2017-10-10)
**Op... | 1.0 | times.hinet.net - “Like/Share” button labels are misaligned - <!-- @browser: Firefox Mobile Nightly 58.0a1 (2017-10-10) -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0 -->
<!-- @reported_with: web -->
**URL**: https://times.hinet.net/mobile/topic/20770626
**Browse... | priority | times hinet net “like share” button labels are misaligned url browser version firefox mobile nightly operating system huawei android resolution x pixels ppi pixel density tested another browser yes problem type design is broken descr... | 1 |
384,765 | 11,402,921,050 | IssuesEvent | 2020-01-31 05:18:46 | teambit/bit | https://api.github.com/repos/teambit/bit | closed | Bit not tagging component | area/tag priority/critical type/bug | ### Bit isnt tagging component
I've imported a bit component to another bit component and when i try to tag it returns an error, i've tried to remove the "duplicated" component from root `package.json` and from component `package.json` as the node_modules of both but the bit cli keep returning the same error, when i... | 1.0 | Bit not tagging component - ### Bit isnt tagging component
I've imported a bit component to another bit component and when i try to tag it returns an error, i've tried to remove the "duplicated" component from root `package.json` and from component `package.json` as the node_modules of both but the bit cli keep retu... | priority | bit not tagging component bit isnt tagging component i ve imported a bit component to another bit component and when i try to tag it returns an error i ve tried to remove the duplicated component from root package json and from component package json as the node modules of both but the bit cli keep retu... | 1 |
784,688 | 27,582,186,922 | IssuesEvent | 2023-03-08 16:56:22 | pharmaR/riskassessment | https://api.github.com/repos/pharmaR/riskassessment | closed | CRAN logs website down | bug Priority: [1] Urgent | To populate the community usage metrics in the application, we are running the function `cranlogs::cran_downloads()`. It pulls the download information from [here](http://cranlogs.r-pkg.org/downloads/daily/). I personally have experienced this webpage being down several times in the past week. This results in no data b... | 1.0 | CRAN logs website down - To populate the community usage metrics in the application, we are running the function `cranlogs::cran_downloads()`. It pulls the download information from [here](http://cranlogs.r-pkg.org/downloads/daily/). I personally have experienced this webpage being down several times in the past week. ... | priority | cran logs website down to populate the community usage metrics in the application we are running the function cranlogs cran downloads it pulls the download information from i personally have experienced this webpage being down several times in the past week this results in no data being pulled in i th... | 1 |
192,641 | 22,215,982,876 | IssuesEvent | 2022-06-08 01:43:43 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | reopened | CVE-2020-25671 (High) detected in linuxlinux-4.19.6 | security vulnerability | ## CVE-2020-25671 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://... | True | CVE-2020-25671 (High) detected in linuxlinux-4.19.6 - ## CVE-2020-25671 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Found... | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files ... | 0 |
72,660 | 9,603,760,025 | IssuesEvent | 2019-05-10 17:59:10 | WebAudio/web-audio-api | https://api.github.com/repos/WebAudio/web-audio-api | opened | AudioBuffer interface comments | Editorial/Documentation | The intro paragraph for
[AudioBuffer](https://webaudio.github.io/web-audio-api/#AudioBuffer)
says
> memory-resident audio asset (for one-shot sounds and other short
> audio clips).
I don't think we say anything about one-shot sounds or short audio
clips. We're only constrained by how much memory you want to ... | 1.0 | AudioBuffer interface comments - The intro paragraph for
[AudioBuffer](https://webaudio.github.io/web-audio-api/#AudioBuffer)
says
> memory-resident audio asset (for one-shot sounds and other short
> audio clips).
I don't think we say anything about one-shot sounds or short audio
clips. We're only constraine... | non_priority | audiobuffer interface comments the intro paragraph for says memory resident audio asset for one shot sounds and other short audio clips i don t think we say anything about one shot sounds or short audio clips we re only constrained by how much memory you want to use | 0 |
294,247 | 22,143,171,380 | IssuesEvent | 2022-06-03 09:05:45 | Avaiga/taipy-doc | https://api.github.com/repos/Avaiga/taipy-doc | closed | Documentation - The code font size should be larger | enhancement documentation | **Description**
For accessibility purpose, the font size of the code extracts should be determined in (1)em and have a minimum fallback size of 16px.
**Acceptance Criteria**
- [ ] Ensure new code is unit tested, and check code coverage is at least 90%
- [ ] Propagate any change on the demos and run all of them to... | 1.0 | Documentation - The code font size should be larger - **Description**
For accessibility purpose, the font size of the code extracts should be determined in (1)em and have a minimum fallback size of 16px.
**Acceptance Criteria**
- [ ] Ensure new code is unit tested, and check code coverage is at least 90%
- [ ] Pr... | non_priority | documentation the code font size should be larger description for accessibility purpose the font size of the code extracts should be determined in em and have a minimum fallback size of acceptance criteria ensure new code is unit tested and check code coverage is at least propagate ... | 0 |
219,488 | 7,342,864,374 | IssuesEvent | 2018-03-07 09:28:09 | rogerthat-platform/rogerthat-backend | https://api.github.com/repos/rogerthat-platform/rogerthat-backend | opened | Exceeded memory limit during log_analysis | priority_major type_bug | ```
Queue: default
deferred.run(rogerthat.bizz.log_analysis._analyze,
1520413501L,
1520414100)
Summarize: updating 209 news items
```
Exceeded soft private memory limit of 256 MB with 268 MB after servicing 2610 requests total | 1.0 | Exceeded memory limit during log_analysis - ```
Queue: default
deferred.run(rogerthat.bizz.log_analysis._analyze,
1520413501L,
1520414100)
Summarize: updating 209 news items
```
Exceeded soft private memory limit of 256 MB with 268 MB after servicing 2610 requests total | priority | exceeded memory limit during log analysis queue default deferred run rogerthat bizz log analysis analyze summarize updating news items exceeded soft private memory limit of mb with mb after servicing requests total | 1 |
269,137 | 28,960,012,238 | IssuesEvent | 2023-05-10 01:08:09 | OTTIN-T/Cours-JS---CDA | https://api.github.com/repos/OTTIN-T/Cours-JS---CDA | opened | CVE-2023-31125 (Medium) detected in engine.io-6.1.3.tgz, engine.io-6.1.0.tgz | Mend: dependency security vulnerability | ## CVE-2023-31125 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>engine.io-6.1.3.tgz</b>, <b>engine.io-6.1.0.tgz</b></p></summary>
<p>
<details><summary><b>engine.io-6.1.3.tgz</b>... | True | CVE-2023-31125 (Medium) detected in engine.io-6.1.3.tgz, engine.io-6.1.0.tgz - ## CVE-2023-31125 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>engine.io-6.1.3.tgz</b>, <b>engine.i... | non_priority | cve medium detected in engine io tgz engine io tgz cve medium severity vulnerability vulnerable libraries engine io tgz engine io tgz engine io tgz the realtime engine behind socket io provides the foundation of a bidirectional connection between ... | 0 |
55,862 | 3,075,071,685 | IssuesEvent | 2015-08-20 11:27:32 | pavel-pimenov/flylinkdc-r5xx | https://api.github.com/repos/pavel-pimenov/flylinkdc-r5xx | closed | Мелкие хотелки для интерфейса. | bug imported invalid Priority-Medium | _From [shkiper911@list.ru](https://code.google.com/u/shkiper911@list.ru/) on February 06, 2011 20:47:35_
Мееееелкие хотелки, поставьте приоритет Ultra Low:
-Копирование информации из лога, правой кнопкой мыши.
-Лишний пункт "показать как текст" на папках, в списках файлов юзеров. И вообще эту функцию следует отклю... | 1.0 | Мелкие хотелки для интерфейса. - _From [shkiper911@list.ru](https://code.google.com/u/shkiper911@list.ru/) on February 06, 2011 20:47:35_
Мееееелкие хотелки, поставьте приоритет Ultra Low:
-Копирование информации из лога, правой кнопкой мыши.
-Лишний пункт "показать как текст" на папках, в списках файлов юзеров. И... | priority | мелкие хотелки для интерфейса from on february мееееелкие хотелки поставьте приоритет ultra low копирование информации из лога правой кнопкой мыши лишний пункт показать как текст на папках в списках файлов юзеров и вообще эту функцию следует отключить на файлах больше мб т к это... | 1 |
405,327 | 11,871,636,980 | IssuesEvent | 2020-03-26 14:41:00 | tranquilitybase-io/tb-gcp | https://api.github.com/repos/tranquilitybase-io/tb-gcp | opened | Optional deployment of Vault | priority:medium | Split of #138 - part 1.
Vault will be optional deployment in LZ. Refactor the code is required.
New folder _tb-gcp/tb-gcp-tr/options/secrets_ will be created with the following contents:
- main.tf - Create k8s Secrets cluster --> state with prefix /secrets
- other required files by the Secrets cluster
- va... | 1.0 | Optional deployment of Vault - Split of #138 - part 1.
Vault will be optional deployment in LZ. Refactor the code is required.
New folder _tb-gcp/tb-gcp-tr/options/secrets_ will be created with the following contents:
- main.tf - Create k8s Secrets cluster --> state with prefix /secrets
- other required files b... | priority | optional deployment of vault split of part vault will be optional deployment in lz refactor the code is required new folder tb gcp tb gcp tr options secrets will be created with the following contents main tf create secrets cluster state with prefix secrets other required files by th... | 1 |
3,830 | 6,802,428,831 | IssuesEvent | 2017-11-02 20:10:30 | gratipay/inside.gratipay.com | https://api.github.com/repos/gratipay/inside.gratipay.com | closed | Limit Gratipay's copyright license in Terms of Service (TOS) | Governance & Process | Reticketed from https://github.com/gratipay/inside.gratipay.com/issues/204#issuecomment-102103817
> - Personally, I find using CC0 for Gratipay.com in §6.1 as a really nice touch and a fresh approach. I take it you do understand the implications of this, though.
> - Staying on the topic of copyright, in §7.1 the copy... | 1.0 | Limit Gratipay's copyright license in Terms of Service (TOS) - Reticketed from https://github.com/gratipay/inside.gratipay.com/issues/204#issuecomment-102103817
> - Personally, I find using CC0 for Gratipay.com in §6.1 as a really nice touch and a fresh approach. I take it you do understand the implications of this, t... | non_priority | limit gratipay s copyright license in terms of service tos reticketed from personally i find using for gratipay com in § as a really nice touch and a fresh approach i take it you do understand the implications of this though staying on the topic of copyright in § the copyright license that ... | 0 |
234,139 | 25,806,007,208 | IssuesEvent | 2022-12-11 12:17:03 | SmartBear/readyapi-swagger-assertion-plugin | https://api.github.com/repos/SmartBear/readyapi-swagger-assertion-plugin | closed | CVE-2021-39153 (High) detected in xstream-1.3.1.jar - autoclosed | security vulnerability | ## CVE-2021-39153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.3.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /h... | True | CVE-2021-39153 (High) detected in xstream-1.3.1.jar - autoclosed - ## CVE-2021-39153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.3.1.jar</b></p></summary>
<p></p>
<p>Path... | non_priority | cve high detected in xstream jar autoclosed cve high severity vulnerability vulnerable library xstream jar path to dependency file pom xml path to vulnerable library home wss scanner repository thoughtworks xstream xstream jar dependency hierarchy ... | 0 |
632,518 | 20,199,353,263 | IssuesEvent | 2022-02-11 13:49:43 | googleapis/nodejs-firestore | https://api.github.com/repos/googleapis/nodejs-firestore | opened | [TypeScript] set function as parametrized | priority: p3 type: feature request | Thanks for stopping by to let us know something could be better!
**PLEASE READ**: If you have a support contract with Google, please create an issue in the [support console](https://cloud.google.com/support/) instead of filing on GitHub. This will ensure a timely response.
**Is your feature request related to a ... | 1.0 | [TypeScript] set function as parametrized - Thanks for stopping by to let us know something could be better!
**PLEASE READ**: If you have a support contract with Google, please create an issue in the [support console](https://cloud.google.com/support/) instead of filing on GitHub. This will ensure a timely response.... | priority | set function as parametrized thanks for stopping by to let us know something could be better please read if you have a support contract with google please create an issue in the instead of filing on github this will ensure a timely response is your feature request related to a problem please ... | 1 |
32,769 | 15,612,640,344 | IssuesEvent | 2021-03-19 15:31:58 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | When native encryption is enabled, sync writes are slow. | Component: Encryption Status: Stale Type: Performance | ### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Gentoo Linux
Distribution Version | amd64 (stable) 17.1/no-multilib
Linux Kernel | 4.19.72-gentoo
Architecture | x86_64
ZFS Version | 8.2
SPL Version | N/A
### Describe the problem you're obs... | True | When native encryption is enabled, sync writes are slow. - ### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name | Gentoo Linux
Distribution Version | amd64 (stable) 17.1/no-multilib
Linux Kernel | 4.19.72-gentoo
Architecture | x86_64
ZFS Version | 8.... | non_priority | when native encryption is enabled sync writes are slow system information type version name distribution name gentoo linux distribution version stable no multilib linux kernel gentoo architecture zfs version spl version n a describe the problem y... | 0 |
636,075 | 20,574,364,819 | IssuesEvent | 2022-03-04 01:49:13 | ArctosDB/arctos | https://api.github.com/repos/ArctosDB/arctos | closed | Feature Request - component loader documention (or ??) | Priority-Critical (Arctos is broken) Enhancement Help wanted Component Loader | **Is your feature request related to a problem? Please describe.**
The component loader is throttled in such a way that loading and post-load processing should not become disruptive, which means things can take some time - occasionally days - to process.
**Describe what you're trying to accomplish**
Minimally... | 1.0 | Feature Request - component loader documention (or ??) - **Is your feature request related to a problem? Please describe.**
The component loader is throttled in such a way that loading and post-load processing should not become disruptive, which means things can take some time - occasionally days - to process.
**... | priority | feature request component loader documention or is your feature request related to a problem please describe the component loader is throttled in such a way that loading and post load processing should not become disruptive which means things can take some time occasionally days to process ... | 1 |
3,334 | 6,301,696,541 | IssuesEvent | 2017-07-21 08:52:26 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | Dictionary add-ons should not have strict compatibility | project: firefox 57 compatibility state: pull request ready | #5825 revealed that dictionaries have strict compatibility and have been working because of the bulk compatibility updates we run for all add-ons. Since we don't plan to do bulk compatibility updates past 56, we need an alternative way to keep them working.
Dictionaries should be compatible with all versions of Fire... | True | Dictionary add-ons should not have strict compatibility - #5825 revealed that dictionaries have strict compatibility and have been working because of the bulk compatibility updates we run for all add-ons. Since we don't plan to do bulk compatibility updates past 56, we need an alternative way to keep them working.
D... | non_priority | dictionary add ons should not have strict compatibility revealed that dictionaries have strict compatibility and have been working because of the bulk compatibility updates we run for all add ons since we don t plan to do bulk compatibility updates past we need an alternative way to keep them working dicti... | 0 |
65,181 | 7,860,475,213 | IssuesEvent | 2018-06-21 20:06:33 | archesproject/arches | https://api.github.com/repos/archesproject/arches | closed | Graph Manager, New Resource Editor: Instance tree should highlight all nodes in the path to currently selected node | Roadmap: Graph Designer Update - Task 2 (Graph) | As a data editor or graph designer, I would like to the tree widget to highlight the path from the root node to the node that I'm currently working with so that I can more easily see the context of the node or widget that I'm working with.
 of .NET guidelines, the following line
> {% include requirement/MUST id="dotnet-logging-follow-guidelines" %} follow the logging section of the Azure SDK General Guidelines if logging directly (as opposed to ... | 1.0 | Change Request: nit on logging for .NET guidelines - In the [Logging section](https://github.com/Azure/azure-sdk/blob/master/docs/dotnet/introduction.md#logging) of .NET guidelines, the following line
> {% include requirement/MUST id="dotnet-logging-follow-guidelines" %} follow the logging section of the Azure SDK G... | non_priority | change request nit on logging for net guidelines in the of net guidelines the following line include requirement must id dotnet logging follow guidelines follow the logging section of the azure sdk general guidelines if logging directly as opposed to through the httppipeline links to the n... | 0 |
189,138 | 22,046,988,624 | IssuesEvent | 2022-05-30 03:39:58 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | closed | CVE-2021-42252 (High) detected in linuxlinux-4.19.6 - autoclosed | security vulnerability | ## CVE-2021-42252 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://... | True | CVE-2021-42252 (High) detected in linuxlinux-4.19.6 - autoclosed - ## CVE-2021-42252 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.6</b></p></summary>
<p>
<p>Apache S... | non_priority | cve high detected in linuxlinux autoclosed cve high severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in head commit a href found in base branch master vulnerable source files ... | 0 |
704,896 | 24,213,767,034 | IssuesEvent | 2022-09-26 03:41:40 | CS3219-AY2223S1/cs3219-project-ay2223s1-g8 | https://api.github.com/repos/CS3219-AY2223S1/cs3219-project-ay2223s1-g8 | opened | Implement collaboration room for users | Frontend priority.high | - [] pull question from `QuestionService`
- [] link the 2 matched users to the same `CollaborationService` for the text editor
- [] allow users to leave the room | 1.0 | Implement collaboration room for users - - [] pull question from `QuestionService`
- [] link the 2 matched users to the same `CollaborationService` for the text editor
- [] allow users to leave the room | priority | implement collaboration room for users pull question from questionservice link the matched users to the same collaborationservice for the text editor allow users to leave the room | 1 |
447,744 | 12,892,680,057 | IssuesEvent | 2020-07-13 20:05:56 | microsoft/AdaptiveCards | https://api.github.com/repos/microsoft/AdaptiveCards | closed | [TS][Renderer] Incomplete accessibility support for input validation | Bug BugBash Priority-Now Status-Fixed Triage-Approved for Fix | # Platform
* JavaScript
# Details
The input validation code has incomplete support for accessibility:
- Labels and errors are not read by narrator for Input.ChoiceSet in multiselect or expanded mode
- Label and error are not read by narrator for Input.Toggle | 1.0 | [TS][Renderer] Incomplete accessibility support for input validation - # Platform
* JavaScript
# Details
The input validation code has incomplete support for accessibility:
- Labels and errors are not read by narrator for Input.ChoiceSet in multiselect or expanded mode
- Label and error are not read by narrato... | priority | incomplete accessibility support for input validation platform javascript details the input validation code has incomplete support for accessibility labels and errors are not read by narrator for input choiceset in multiselect or expanded mode label and error are not read by narrator for input ... | 1 |
86,738 | 3,728,753,510 | IssuesEvent | 2016-03-07 02:27:16 | HubTurbo/HubTurbo | https://api.github.com/repos/HubTurbo/HubTurbo | closed | Refactor LabelPickerUILogic.java | aspect-refactoring priority.medium | This class is a good opportunity to practice refactoring skills and also to get used to our coding style.
Things to improve:
* Use more SLAP
* Make methods more testable e.g. if a method doesn't have any side effects, it is easier to test.
* Add header comments to non-trivial methods (comments should explain WHAT a... | 1.0 | Refactor LabelPickerUILogic.java - This class is a good opportunity to practice refactoring skills and also to get used to our coding style.
Things to improve:
* Use more SLAP
* Make methods more testable e.g. if a method doesn't have any side effects, it is easier to test.
* Add header comments to non-trivial meth... | priority | refactor labelpickeruilogic java this class is a good opportunity to practice refactoring skills and also to get used to our coding style things to improve use more slap make methods more testable e g if a method doesn t have any side effects it is easier to test add header comments to non trivial meth... | 1 |
142,872 | 11,498,059,692 | IssuesEvent | 2020-02-12 11:12:07 | dsccommunity/ActiveDirectoryDsc | https://api.github.com/repos/dsccommunity/ActiveDirectoryDsc | closed | ADDomain: Integration tests is missing for this resource | in progress tests | We should add integration tests for this resource. | 1.0 | ADDomain: Integration tests is missing for this resource - We should add integration tests for this resource. | non_priority | addomain integration tests is missing for this resource we should add integration tests for this resource | 0 |
369,134 | 10,888,589,460 | IssuesEvent | 2019-11-18 16:31:51 | luna/enso | https://api.github.com/repos/luna/enso | opened | Clean the initial Rust AST implementation | Category: Tooling Change: Non-Breaking Difficulty: Core Contributor Priority: Medium Type: Enhancement | ### Summary
Clean-up the code, remove not needed parts, organize common libraries.
### Value
The code should be nice and clean, before we start adding more functionalities into it.
### Specification
All parts that were carried over from basegl without need are removed.
Common libraries are properly split and ... | 1.0 | Clean the initial Rust AST implementation - ### Summary
Clean-up the code, remove not needed parts, organize common libraries.
### Value
The code should be nice and clean, before we start adding more functionalities into it.
### Specification
All parts that were carried over from basegl without need are remove... | priority | clean the initial rust ast implementation summary clean up the code remove not needed parts organize common libraries value the code should be nice and clean before we start adding more functionalities into it specification all parts that were carried over from basegl without need are remove... | 1 |
210,912 | 7,196,507,410 | IssuesEvent | 2018-02-05 03:28:30 | NeoISE/.emacs.d | https://api.github.com/repos/NeoISE/.emacs.d | opened | Custom theme setting is now broken. | priority:urgent | After a change to the `theme-changer` package, the function `theme-changer-daytime-p` is removed with its original logic replaced. Thus, the current init file will be broken partially with a `Symbol's function definition is void` warning being reported. | 1.0 | Custom theme setting is now broken. - After a change to the `theme-changer` package, the function `theme-changer-daytime-p` is removed with its original logic replaced. Thus, the current init file will be broken partially with a `Symbol's function definition is void` warning being reported. | priority | custom theme setting is now broken after a change to the theme changer package the function theme changer daytime p is removed with its original logic replaced thus the current init file will be broken partially with a symbol s function definition is void warning being reported | 1 |
732,191 | 25,248,211,730 | IssuesEvent | 2022-11-15 12:48:28 | bounswe/bounswe2022group2 | https://api.github.com/repos/bounswe/bounswe2022group2 | closed | Mobile: Implementing Highlighted (Annotated) Text Widget | priority-medium Status: Completed feature mobile | ### Issue Description
As we have already talked about in the lectures and Suzan hoca highlighted, annotations are the key part of the app. I have implemented the annotatable text widget with custom selectable text in issue #505. Now, it's time to implement the widget which will display the annotated parts in a text. S... | 1.0 | Mobile: Implementing Highlighted (Annotated) Text Widget - ### Issue Description
As we have already talked about in the lectures and Suzan hoca highlighted, annotations are the key part of the app. I have implemented the annotatable text widget with custom selectable text in issue #505. Now, it's time to implement the... | priority | mobile implementing highlighted annotated text widget issue description as we have already talked about in the lectures and suzan hoca highlighted annotations are the key part of the app i have implemented the annotatable text widget with custom selectable text in issue now it s time to implement the w... | 1 |
188,302 | 15,158,217,375 | IssuesEvent | 2021-02-12 00:36:26 | RoyMagnussen/Yummy-Recipe-Blog | https://api.github.com/repos/RoyMagnussen/Yummy-Recipe-Blog | closed | [FEATURE REQUEST] User Login | documentation enhancement | #### Describe The Feature Wanted
Create a form where the user is able to log in easily by providing their username and password.
#### Reason For Feature
- To have the user easily log in. | 1.0 | [FEATURE REQUEST] User Login - #### Describe The Feature Wanted
Create a form where the user is able to log in easily by providing their username and password.
#### Reason For Feature
- To have the user easily log in. | non_priority | user login describe the feature wanted create a form where the user is able to log in easily by providing their username and password reason for feature to have the user easily log in | 0 |
320,176 | 27,423,151,413 | IssuesEvent | 2023-03-01 18:08:58 | MaterializeInc/materialize | https://api.github.com/repos/MaterializeInc/materialize | closed | Add load generator test for invalid tick interval | D-good first issue T-testing | Add an additional test for handling of invalid tick interval values in [src/sql-parser/tests/testdata/ddl](https://github.com/MaterializeInc/materialize/blob/main/src/sql-parser/tests/testdata/ddl) or [test/testdrive/load-generator.td](https://github.com/MaterializeInc/materialize/blob/main/test/testdrive/load-generato... | 1.0 | Add load generator test for invalid tick interval - Add an additional test for handling of invalid tick interval values in [src/sql-parser/tests/testdata/ddl](https://github.com/MaterializeInc/materialize/blob/main/src/sql-parser/tests/testdata/ddl) or [test/testdrive/load-generator.td](https://github.com/MaterializeIn... | non_priority | add load generator test for invalid tick interval add an additional test for handling of invalid tick interval values in or this is meant as an onboarding task to go through the end to end development flow | 0 |
181,377 | 6,659,179,173 | IssuesEvent | 2017-10-01 07:31:04 | spring-projects/spring-boot | https://api.github.com/repos/spring-projects/spring-boot | closed | OAuth configuration keys are duplicated in the meta-data | priority: normal | Plenty of OAuth2 configuration keys are duplicated in the meta-data, probably because it is bound multiple times in different auto-configuration.
For instance `security.oauth2.client.client-id` is bound _five_ times and twice on the same object.
| 1.0 | OAuth configuration keys are duplicated in the meta-data - Plenty of OAuth2 configuration keys are duplicated in the meta-data, probably because it is bound multiple times in different auto-configuration.
For instance `security.oauth2.client.client-id` is bound _five_ times and twice on the same object.
| priority | oauth configuration keys are duplicated in the meta data plenty of configuration keys are duplicated in the meta data probably because it is bound multiple times in different auto configuration for instance security client client id is bound five times and twice on the same object | 1 |
85,901 | 3,700,106,019 | IssuesEvent | 2016-02-29 06:06:16 | UltimateNate/12-year-old-simulator | https://api.github.com/repos/UltimateNate/12-year-old-simulator | closed | new_speak doesn't work when executing program on bot.py | bug help wanted high priority | It appears new_speak doesn't work if you execute it by running "python3 bot.py", but it works when executing by running "python3 new_speak.py"
When interacting it on IRC, and running it on bot.py, it crashes and outputs the following error message:
Traceback (most recent call last):
File "bot.py", line 27, in ... | 1.0 | new_speak doesn't work when executing program on bot.py - It appears new_speak doesn't work if you execute it by running "python3 bot.py", but it works when executing by running "python3 new_speak.py"
When interacting it on IRC, and running it on bot.py, it crashes and outputs the following error message:
Traceba... | priority | new speak doesn t work when executing program on bot py it appears new speak doesn t work if you execute it by running bot py but it works when executing by running new speak py when interacting it on irc and running it on bot py it crashes and outputs the following error message traceback most rec... | 1 |
94,393 | 8,488,589,539 | IssuesEvent | 2018-10-26 17:07:20 | galaxyproject/usegalaxy-playbook | https://api.github.com/repos/galaxyproject/usegalaxy-playbook | closed | Cuffdiff SQLite output problem | enhancement fixathon 06/18 test/retest-fail | Update to 2.2.1.5 (from early 2017, conda updated). The server currently has 2.2.1.3 (2015).
https://toolshed.g2.bx.psu.edu/view/devteam/cuffdiff/d3ae7d9c2202
Duplicated posts at Biostars about the issue have all been consolidated into this post. Use as the master when helping users. Should also post back an upda... | 2.0 | Cuffdiff SQLite output problem - Update to 2.2.1.5 (from early 2017, conda updated). The server currently has 2.2.1.3 (2015).
https://toolshed.g2.bx.psu.edu/view/devteam/cuffdiff/d3ae7d9c2202
Duplicated posts at Biostars about the issue have all been consolidated into this post. Use as the master when helping use... | non_priority | cuffdiff sqlite output problem update to from early conda updated the server currently has duplicated posts at biostars about the issue have all been consolidated into this post use as the master when helping users should also post back an update once resolved natefoo dave... | 0 |
170,066 | 13,172,086,388 | IssuesEvent | 2020-08-11 17:48:40 | google/blockly | https://api.github.com/repos/google/blockly | closed | Add cleanup for Events in mocha tests | component: tests type: cleanup | Many tests trigger Events fired on a timeout, which can end up firing outside of the tests (if that test didn't specifically stub events to fire immediately or may have some other method called on a timeout that then triggers an event).
This can cause unexpected tests failures in tests that check for what events wer... | 1.0 | Add cleanup for Events in mocha tests - Many tests trigger Events fired on a timeout, which can end up firing outside of the tests (if that test didn't specifically stub events to fire immediately or may have some other method called on a timeout that then triggers an event).
This can cause unexpected tests failures... | non_priority | add cleanup for events in mocha tests many tests trigger events fired on a timeout which can end up firing outside of the tests if that test didn t specifically stub events to fire immediately or may have some other method called on a timeout that then triggers an event this can cause unexpected tests failures... | 0 |
10,412 | 8,933,124,778 | IssuesEvent | 2019-01-23 00:35:33 | pulumi/pulumi | https://api.github.com/repos/pulumi/pulumi | closed | Consider not allowing `/` in project names | area/cli area/service kind/bug | We currently allow `/` in project names, which has caused issues when we update the project name in `package.json` because NPM doesn't support `/` in project names.
https://github.com/pulumi/pulumi/blob/431f5b345063c6cb1709cac022601631f59077fd/pkg/workspace/project.go#L60
https://github.com/pulumi/pulumi/blob/431... | 1.0 | Consider not allowing `/` in project names - We currently allow `/` in project names, which has caused issues when we update the project name in `package.json` because NPM doesn't support `/` in project names.
https://github.com/pulumi/pulumi/blob/431f5b345063c6cb1709cac022601631f59077fd/pkg/workspace/project.go#L60... | non_priority | consider not allowing in project names we currently allow in project names which has caused issues when we update the project name in package json because npm doesn t support in project names we should re evaluate what characters we want to allow for project names note any chang... | 0 |
212,469 | 16,452,302,185 | IssuesEvent | 2021-05-21 07:45:25 | openshift/odo | https://api.github.com/repos/openshift/odo | closed | Operatorhub test fails on windows due to incompatible path | area/Windows area/testing good first issue help wanted kind/failing-test points/1 | /kind failing-test
/area testing
## What versions of software are you using?
**Operating System:** Windows
## How did you run odo exactly?
`make test-operator-hub`
## Actual behavior
The test is failing as it doesn't uses windows friendly path in the test.
## Expected behavior
Test should pass witho... | 2.0 | Operatorhub test fails on windows due to incompatible path - /kind failing-test
/area testing
## What versions of software are you using?
**Operating System:** Windows
## How did you run odo exactly?
`make test-operator-hub`
## Actual behavior
The test is failing as it doesn't uses windows friendly path... | non_priority | operatorhub test fails on windows due to incompatible path kind failing test area testing what versions of software are you using operating system windows how did you run odo exactly make test operator hub actual behavior the test is failing as it doesn t uses windows friendly path... | 0 |
274,256 | 8,559,006,241 | IssuesEvent | 2018-11-08 19:56:20 | CS2113-AY1819S1-W13-2/main | https://api.github.com/repos/CS2113-AY1819S1-W13-2/main | closed | Edit commands allows for timezones that do not exist. | priority.low severity.High | **Describe the bug**
Time zones can be +500000, which is not a valid time zone
**To Reproduce**
Steps to reproduce the behavior:
edit 1 tz/500000
**Expected behavior**
Should check for valid timezone and give an error.
<hr>
**Reported by:** @andrewome
**Severity:** `Low`
<sub>[original: nusCS2113-AY1819S... | 1.0 | Edit commands allows for timezones that do not exist. - **Describe the bug**
Time zones can be +500000, which is not a valid time zone
**To Reproduce**
Steps to reproduce the behavior:
edit 1 tz/500000
**Expected behavior**
Should check for valid timezone and give an error.
<hr>
**Reported by:** @andrewom... | priority | edit commands allows for timezones that do not exist describe the bug time zones can be which is not a valid time zone to reproduce steps to reproduce the behavior edit tz expected behavior should check for valid timezone and give an error reported by andrewome severity ... | 1 |
244,813 | 7,880,651,777 | IssuesEvent | 2018-06-26 16:31:51 | aowen87/FOO | https://api.github.com/repos/aowen87/FOO | closed | Add ITAPS reader support to the ubuntu distributions. | Expected Use: 3 - Occasional Impact: 3 - Medium OS: All Priority: Normal Support Group: Any Target Version: 2.10.1 feature | I haven't been including the ITAPS reader in the Ubuntu distributions because of difficulties building it. A user has asked about it so I should make the effort to include it. | 1.0 | Add ITAPS reader support to the ubuntu distributions. - I haven't been including the ITAPS reader in the Ubuntu distributions because of difficulties building it. A user has asked about it so I should make the effort to include it. | priority | add itaps reader support to the ubuntu distributions i haven t been including the itaps reader in the ubuntu distributions because of difficulties building it a user has asked about it so i should make the effort to include it | 1 |
339,377 | 10,253,424,473 | IssuesEvent | 2019-08-21 11:16:01 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | Make unused imports compilation errors. | Area/Language Component/Compiler Priority/Blocker Type/Improvement | We should give warning when unused imports are available in a bal file | 1.0 | Make unused imports compilation errors. - We should give warning when unused imports are available in a bal file | priority | make unused imports compilation errors we should give warning when unused imports are available in a bal file | 1 |
366,728 | 10,825,414,234 | IssuesEvent | 2019-11-09 15:42:21 | kiwicom/schemathesis | https://api.github.com/repos/kiwicom/schemathesis | closed | Make method names case insensitive in schema mapping interface | Priority: Low Type: Enhancement good first issue | It should be equivalent:
‘’’schema[“/foo”][“get”]’’’ and ‘’’schema[“/foo”][“GET”]’’’ | 1.0 | Make method names case insensitive in schema mapping interface - It should be equivalent:
‘’’schema[“/foo”][“get”]’’’ and ‘’’schema[“/foo”][“GET”]’’’ | priority | make method names case insensitive in schema mapping interface it should be equivalent ‘’’schema ’’’ and ‘’’schema ’’’ | 1 |
172,183 | 21,040,472,037 | IssuesEvent | 2022-03-31 11:52:00 | LynRodWS/alcor | https://api.github.com/repos/LynRodWS/alcor | opened | CVE-2022-27772 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2022-27772 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-boot-2.2.5.RELEASE.jar</b>, <b>spring-boot-2.1.6.RELEASE.jar</b>, <b>spring-boot-2.2.6.RELEASE.jar</b></p></... | True | CVE-2022-27772 (Medium) detected in multiple libraries - ## CVE-2022-27772 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-boot-2.2.5.RELEASE.jar</b>, <b>spring-boot-2.1.6.RE... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries spring boot release jar spring boot release jar spring boot release jar spring boot release jar spring boot library home page a href path to depend... | 0 |
162,049 | 6,146,564,743 | IssuesEvent | 2017-06-27 14:07:32 | BinPar/PRM | https://api.github.com/repos/BinPar/PRM | closed | INFORME ASIGNATURAS: campo curso contiene datos CURSO y AÑO ACADÉMICO | Priority: High | 
Al descargar el INFORME ASIGNATURAS, el campo CURSO contiene tanto datos del curso (1,2,3,4,5,6) como datos del AÑO ACADEMICO (2016-2017, 2017-2018). Realmente solo debiera de aportar datos del curso, no del... | 1.0 | INFORME ASIGNATURAS: campo curso contiene datos CURSO y AÑO ACADÉMICO - 
Al descargar el INFORME ASIGNATURAS, el campo CURSO contiene tanto datos del curso (1,2,3,4,5,6) como datos del AÑO ACADEMICO (2016-201... | priority | informe asignaturas campo curso contiene datos curso y año académico al descargar el informe asignaturas el campo curso contiene tanto datos del curso como datos del año academico realmente solo debiera de aportar datos del curso no del año académico ¿de dónde toma el dato en los... | 1 |
309,310 | 9,473,228,470 | IssuesEvent | 2019-04-19 00:44:15 | hayata-yamamoto/neural_search | https://api.github.com/repos/hayata-yamamoto/neural_search | opened | rewrite api by django | low priority | fastapi has not their original models. Firstly, this api is designed not to use database. | 1.0 | rewrite api by django - fastapi has not their original models. Firstly, this api is designed not to use database. | priority | rewrite api by django fastapi has not their original models firstly this api is designed not to use database | 1 |
60,659 | 3,131,290,610 | IssuesEvent | 2015-09-09 14:07:13 | brharp/hjckrrh | https://api.github.com/repos/brharp/hjckrrh | opened | G3 - Local search has no associated heading | feature: general (G) priority: normal type: enhancement request | I noticed that for every local search input box that isn't on the main page, there is no heading associated with it. There appears to be an invisible h2 that has been commented out:
```
<!-- <h2 class="element-invisible"></h2> -->
```
Not sure if this was intentional or not. While not necessarily an accessibility i... | 1.0 | G3 - Local search has no associated heading - I noticed that for every local search input box that isn't on the main page, there is no heading associated with it. There appears to be an invisible h2 that has been commented out:
```
<!-- <h2 class="element-invisible"></h2> -->
```
Not sure if this was intentional or... | priority | local search has no associated heading i noticed that for every local search input box that isn t on the main page there is no heading associated with it there appears to be an invisible that has been commented out not sure if this was intentional or not while not necessarily an accessibi... | 1 |
715,166 | 24,588,849,336 | IssuesEvent | 2022-10-13 22:50:32 | VoltanFr/memcheck | https://api.github.com/repos/VoltanFr/memcheck | closed | Adpatative sleep time in retries | priority-medium complexity-low | Retries in the Learn page are always done after a 1 second sleep.
This sleep time should increase with retries (similarly to the computing of the timeOut). This happens in `handlePendingMoveOperations`, `downloadCardsIfNeeded`, `handlePendingNotificationRegistrations` and `handlePendingRatingOperations`.
This will sa... | 1.0 | Adpatative sleep time in retries - Retries in the Learn page are always done after a 1 second sleep.
This sleep time should increase with retries (similarly to the computing of the timeOut). This happens in `handlePendingMoveOperations`, `downloadCardsIfNeeded`, `handlePendingNotificationRegistrations` and `handlePend... | priority | adpatative sleep time in retries retries in the learn page are always done after a second sleep this sleep time should increase with retries similarly to the computing of the timeout this happens in handlependingmoveoperations downloadcardsifneeded handlependingnotificationregistrations and handlepend... | 1 |
316,833 | 9,657,937,994 | IssuesEvent | 2019-05-20 09:45:33 | ampproject/amphtml | https://api.github.com/repos/ampproject/amphtml | closed | amp-list on shadow-dom doesn't render mustache template | Category: Dynamic/Personalized Content Category: PWA P1: High Priority Type: Bug | ## What's the issue?
amp-list on shadow-dom doesn't render mustache template from yesterday (17 April)

## How do we reproduce the issue?
You can visit every ours detail article page on https://rep.re... | 1.0 | amp-list on shadow-dom doesn't render mustache template - ## What's the issue?
amp-list on shadow-dom doesn't render mustache template from yesterday (17 April)

## How do we reproduce the issue?
You ... | priority | amp list on shadow dom doesn t render mustache template what s the issue amp list on shadow dom doesn t render mustache template from yesterday april how do we reproduce the issue you can visit every ours detail article page on for example and you can look for vote and comments info and... | 1 |
55,159 | 6,890,287,866 | IssuesEvent | 2017-11-22 13:31:48 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | Docked Toolbar and Width Options | Blocks Chrome Design [Type] Bug | Docked toolbar has different positions depending on width used:
cc @jasmussen | 1.0 | Docked Toolbar and Width Options - Docked toolbar has different positions depending on width used:

- [ ] Create Documentation about how to use the API (How to call the API ) | 1.0 | Documentation for Edit profile API - ## Context
Edit profile API is used to update user information
## Problem
The Technical documentation of the API is needed
## Solution
- [ ] Create Documentation about how to setup the API (Overview of implementation details)
- [ ] Create Documentation about how to use... | non_priority | documentation for edit profile api context edit profile api is used to update user information problem the technical documentation of the api is needed solution create documentation about how to setup the api overview of implementation details create documentation about how to use the... | 0 |
68,379 | 7,094,159,614 | IssuesEvent | 2018-01-13 00:14:42 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | NFS - When host is rebooted , docker volumes get created on the hosts. | area/storage kind/bug status/resolved status/to-test | Rancher versions:
rancher/server:v1.6.12-flexvol
NFS driver Version: daishan1992/storage-nfs:dev
Steps to reproduce the problem:
Create a service with nfs volume driver.
Make sure that there are no docker volumes created on any host in storage pool.
Reboot one of the hosts where there are service containers wit... | 1.0 | NFS - When host is rebooted , docker volumes get created on the hosts. - Rancher versions:
rancher/server:v1.6.12-flexvol
NFS driver Version: daishan1992/storage-nfs:dev
Steps to reproduce the problem:
Create a service with nfs volume driver.
Make sure that there are no docker volumes created on any host in stor... | non_priority | nfs when host is rebooted docker volumes get created on the hosts rancher versions rancher server flexvol nfs driver version storage nfs dev steps to reproduce the problem create a service with nfs volume driver make sure that there are no docker volumes created on any host in storage pool r... | 0 |
171,068 | 14,279,265,687 | IssuesEvent | 2020-11-23 02:14:13 | tensorflow/addons | https://api.github.com/repos/tensorflow/addons | closed | Generated documentation of type aliases are included in unrelated modules | bug documentation good first issue help wanted | For example, the documentation of `TensorLike` is located in `tfa.image.color_ops`:
https://www.tensorflow.org/addons/api_docs/python/tfa/image/color_ops/TensorLike
Presumably, the system selects the module where the symbol was first found. This is not a big issue but it produces strange and unexpected documentat... | 1.0 | Generated documentation of type aliases are included in unrelated modules - For example, the documentation of `TensorLike` is located in `tfa.image.color_ops`:
https://www.tensorflow.org/addons/api_docs/python/tfa/image/color_ops/TensorLike
Presumably, the system selects the module where the symbol was first foun... | non_priority | generated documentation of type aliases are included in unrelated modules for example the documentation of tensorlike is located in tfa image color ops presumably the system selects the module where the symbol was first found this is not a big issue but it produces strange and unexpected documentation... | 0 |
65,799 | 19,697,906,025 | IssuesEvent | 2022-01-12 14:01:35 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Messages missing from chat, but still show in search | T-Defect X-Needs-Info P1 Z-Synapse | ### Description
Messages from June 16th, 2018 to November 10th, 2018 are missing from #offtopic:matrix.org. However, if I search for them, I am able to see them, so the messages are definitely still there.
### Steps to reproduce
- Scroll up to the first message sent on November 10th, then look at the date of the m... | 1.0 | Messages missing from chat, but still show in search - ### Description
Messages from June 16th, 2018 to November 10th, 2018 are missing from #offtopic:matrix.org. However, if I search for them, I am able to see them, so the messages are definitely still there.
### Steps to reproduce
- Scroll up to the first messag... | non_priority | messages missing from chat but still show in search description messages from june to november are missing from offtopic matrix org however if i search for them i am able to see them so the messages are definitely still there steps to reproduce scroll up to the first message sent on no... | 0 |
604,159 | 18,677,668,891 | IssuesEvent | 2021-10-31 20:46:54 | OpenPerpetuum/PerpetuumServer | https://api.github.com/repos/OpenPerpetuum/PerpetuumServer | opened | Research/proto boost item | Feature Difficulty: Hard Priority: Medium | A Research Boost Item is used to add a x% boost to the prototype efficiency for a particular research tree and level (columns in tree) for x period of time (just enough to kick off a handful of jobs - timer only necessary to cover the start of job, not duration as efficiency of job is stamped at kickoff).
This will ... | 1.0 | Research/proto boost item - A Research Boost Item is used to add a x% boost to the prototype efficiency for a particular research tree and level (columns in tree) for x period of time (just enough to kick off a handful of jobs - timer only necessary to cover the start of job, not duration as efficiency of job is stampe... | priority | research proto boost item a research boost item is used to add a x boost to the prototype efficiency for a particular research tree and level columns in tree for x period of time just enough to kick off a handful of jobs timer only necessary to cover the start of job not duration as efficiency of job is stampe... | 1 |
183,742 | 31,759,572,850 | IssuesEvent | 2023-09-12 03:16:39 | btcpayserver/btcpayserver | https://api.github.com/repos/btcpayserver/btcpayserver | closed | [Bug]: The return of the `remember me` on login page | Bug good first issue Design | ### What is your BTCPay version?
BTCPay Server v1.11.2+1c5fcfe09
### How did you deploy BTCPay Server?
Docker
### What happened?
Kukks and I noticed in Riga, that we nuked the `remember me` checkbox from the login page, which made logins challenging for us on point of sales.
@dstrukt @dennisreimann I remember w... | 1.0 | [Bug]: The return of the `remember me` on login page - ### What is your BTCPay version?
BTCPay Server v1.11.2+1c5fcfe09
### How did you deploy BTCPay Server?
Docker
### What happened?
Kukks and I noticed in Riga, that we nuked the `remember me` checkbox from the login page, which made logins challenging for us on ... | non_priority | the return of the remember me on login page what is your btcpay version btcpay server how did you deploy btcpay server docker what happened kukks and i noticed in riga that we nuked the remember me checkbox from the login page which made logins challenging for us on point of sales... | 0 |
560,533 | 16,599,140,634 | IssuesEvent | 2021-06-01 16:52:35 | pw-software-engineering/j-team | https://api.github.com/repos/pw-software-engineering/j-team | closed | Poprawienie testów postmanowych | priority: high time: 5 | 1. Poprawienie kolejności testów
2. Uzupełnienie testów klienta
3. Sprawdzanie tokenu | 1.0 | Poprawienie testów postmanowych - 1. Poprawienie kolejności testów
2. Uzupełnienie testów klienta
3. Sprawdzanie tokenu | priority | poprawienie testów postmanowych poprawienie kolejności testów uzupełnienie testów klienta sprawdzanie tokenu | 1 |
761,538 | 26,684,971,302 | IssuesEvent | 2023-01-26 21:03:40 | GoogleCloudPlatform/golang-samples | https://api.github.com/repos/GoogleCloudPlatform/golang-samples | closed | bigquery/bigquery_migration_quickstart: TestApp failed | type: bug priority: p1 api: bigquery samples flakybot: issue | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 4226690ccc343022b414ac38faa39a0a3550929f
b... | 1.0 | bigquery/bigquery_migration_quickstart: TestApp failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.... | priority | bigquery bigquery migration quickstart testapp failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output main test go execution failed sig... | 1 |
164,471 | 13,943,196,914 | IssuesEvent | 2020-10-22 22:31:04 | open-contracting/kingfisher-collect | https://api.github.com/repos/open-contracting/kingfisher-collect | closed | Add command to report unsupported spider arguments based on docstrings | documentation framework-spiders | We now have a page to show which spider arguments are supported by which spiders (to be filled in as part of #347): https://kingfisher-scrape.readthedocs.io/en/latest/spiders.html#openopps
It'd be useful to generate a report of which spider arguments are/aren't supported – either for us to plan to add support where ... | 1.0 | Add command to report unsupported spider arguments based on docstrings - We now have a page to show which spider arguments are supported by which spiders (to be filled in as part of #347): https://kingfisher-scrape.readthedocs.io/en/latest/spiders.html#openopps
It'd be useful to generate a report of which spider arg... | non_priority | add command to report unsupported spider arguments based on docstrings we now have a page to show which spider arguments are supported by which spiders to be filled in as part of it d be useful to generate a report of which spider arguments are aren t supported – either for us to plan to add support where ... | 0 |
393,524 | 11,620,760,609 | IssuesEvent | 2020-02-27 00:38:29 | h2oai/datatable | https://api.github.com/repos/h2oai/datatable | opened | Values in a string column may become NA after rbinding | High priority bug | ```
import datatable as dt
DT0 = dt.Frame(["2017-11-10 07:50:18" for i in range(14887665)])
DT1 = dt.rbind(*[DT0 for i in range(8)])
assert DT1[-1, "C0"] is not None # Fails
```
```
>>> print(DT1[113025454, 0])
2017-11-10 07:50:18
>>> print(DT1[113025455, 0])
None
```
the length of each string is 19 chars... | 1.0 | Values in a string column may become NA after rbinding - ```
import datatable as dt
DT0 = dt.Frame(["2017-11-10 07:50:18" for i in range(14887665)])
DT1 = dt.rbind(*[DT0 for i in range(8)])
assert DT1[-1, "C0"] is not None # Fails
```
```
>>> print(DT1[113025454, 0])
2017-11-10 07:50:18
>>> print(DT1[1130254... | priority | values in a string column may become na after rbinding import datatable as dt dt frame dt rbind assert is not none fails print print none the length of each string is chars and the string column overflows the limit at... | 1 |
640,061 | 20,772,444,604 | IssuesEvent | 2022-03-16 06:59:54 | freeboardgames/FreeBoardGames.org | https://api.github.com/repos/freeboardgames/FreeBoardGames.org | closed | Localization | help wanted high priority features | Hello everybody,
I really think this project needs some localization to attract users. Is there any plan to implement this? I would gladly support you s a translator (german, little (bad) spanish). | 1.0 | Localization - Hello everybody,
I really think this project needs some localization to attract users. Is there any plan to implement this? I would gladly support you s a translator (german, little (bad) spanish). | priority | localization hello everybody i really think this project needs some localization to attract users is there any plan to implement this i would gladly support you s a translator german little bad spanish | 1 |
278,288 | 24,143,103,596 | IssuesEvent | 2022-09-21 16:17:39 | WaunBroderick/Conduit | https://api.github.com/repos/WaunBroderick/Conduit | opened | Complete Jest Test Code Coverage on Departments Service | hacktoberfest Testing | Increase the jest code coverage on the departments service on NestJS
| 1.0 | Complete Jest Test Code Coverage on Departments Service - Increase the jest code coverage on the departments service on NestJS
| non_priority | complete jest test code coverage on departments service increase the jest code coverage on the departments service on nestjs | 0 |
78,435 | 7,642,073,397 | IssuesEvent | 2018-05-08 08:01:05 | ActivityWatch/activitywatch | https://api.github.com/repos/ActivityWatch/activitywatch | closed | Delete bucket feature | improves: testing/qa improves: ux priority: low size: medium type: enhancement | I actually want this now. It is especially when managing or moving buckets to/from a testing server. It could even be used when upgrading the database if we make the export format forwards compatible for importing.
IIRC, the reason we were previously hesitant is that it has a high risk for mistakes. We could fix thi... | 1.0 | Delete bucket feature - I actually want this now. It is especially when managing or moving buckets to/from a testing server. It could even be used when upgrading the database if we make the export format forwards compatible for importing.
IIRC, the reason we were previously hesitant is that it has a high risk for mi... | non_priority | delete bucket feature i actually want this now it is especially when managing or moving buckets to from a testing server it could even be used when upgrading the database if we make the export format forwards compatible for importing iirc the reason we were previously hesitant is that it has a high risk for mi... | 0 |
182,257 | 14,908,596,465 | IssuesEvent | 2021-01-22 06:16:10 | openhab/openhab-addons | https://api.github.com/repos/openhab/openhab-addons | opened | [openweathermap] - daily forecasts are now available for free acounts | documentation | OWM supports daily forecasts with it's OneCall API. So the restriction mentioned in the docs is no longer true:
Attention: The daily forecast is only available for paid accounts (opens new window).
Please remove this sentence. For discussion see https://community.openhab.org/t/weather-binding-and-openhab-v3-0/108... | 1.0 | [openweathermap] - daily forecasts are now available for free acounts - OWM supports daily forecasts with it's OneCall API. So the restriction mentioned in the docs is no longer true:
Attention: The daily forecast is only available for paid accounts (opens new window).
Please remove this sentence. For discussion... | non_priority | daily forecasts are now available for free acounts owm supports daily forecasts with it s onecall api so the restriction mentioned in the docs is no longer true attention the daily forecast is only available for paid accounts opens new window please remove this sentence for discussion see | 0 |
291,210 | 21,917,917,148 | IssuesEvent | 2022-05-22 05:22:22 | a-little-org-called-mario/a-little-game-called-mario | https://api.github.com/repos/a-little-org-called-mario/a-little-game-called-mario | closed | Automatic screenshot update | documentation stale adopt-a-feature | It would be cool if the screenshot introduced in #183 could be automatically updated with each new build. | 1.0 | Automatic screenshot update - It would be cool if the screenshot introduced in #183 could be automatically updated with each new build. | non_priority | automatic screenshot update it would be cool if the screenshot introduced in could be automatically updated with each new build | 0 |
364,384 | 10,763,566,989 | IssuesEvent | 2019-11-01 04:38:26 | AY1920S1-CS2103T-F12-4/main | https://api.github.com/repos/AY1920S1-CS2103T-F12-4/main | closed | Update Ui to Expense instead of Person | priority.High type.Story | * [x] Change the PersonCard to Ui card and update the fields
* [x] Change rest of references to person/addressbook | 1.0 | Update Ui to Expense instead of Person - * [x] Change the PersonCard to Ui card and update the fields
* [x] Change rest of references to person/addressbook | priority | update ui to expense instead of person change the personcard to ui card and update the fields change rest of references to person addressbook | 1 |
364,754 | 10,772,885,076 | IssuesEvent | 2019-11-02 17:17:49 | KKPMW/vim-sendtowindow | https://api.github.com/repos/KKPMW/vim-sendtowindow | closed | An extra carriage return when sending a visual line selection | bug priority: medium | Thank you for this useful plugin!
This is a minor bug, but when I select a text inside a file with `Shift+V` (visual line selection) and then send it to a right window with `<space>l`, the other window appears to receive one additional carriage return symbol.
Specifically, when I am sending the text to an IPython... | 1.0 | An extra carriage return when sending a visual line selection - Thank you for this useful plugin!
This is a minor bug, but when I select a text inside a file with `Shift+V` (visual line selection) and then send it to a right window with `<space>l`, the other window appears to receive one additional carriage return s... | priority | an extra carriage return when sending a visual line selection thank you for this useful plugin this is a minor bug but when i select a text inside a file with shift v visual line selection and then send it to a right window with l the other window appears to receive one additional carriage return symbol ... | 1 |
449,546 | 12,970,491,918 | IssuesEvent | 2020-07-21 09:25:01 | elixir-cloud-aai/cwl-WES | https://api.github.com/repos/elixir-cloud-aai/cwl-WES | opened | Document logging to files | priority: low type: docs workload: hours | **Is your feature request related to a problem? Please describe.**
Currently, app and worker logs are streamed to STDERR. While this guarantees easy access to logs by devops/administrators, logs are not persisting when the service is re-deployed. It may also be harder to find and analyze logs.
**Describe the sol... | 1.0 | Document logging to files - **Is your feature request related to a problem? Please describe.**
Currently, app and worker logs are streamed to STDERR. While this guarantees easy access to logs by devops/administrators, logs are not persisting when the service is re-deployed. It may also be harder to find and analyze ... | priority | document logging to files is your feature request related to a problem please describe currently app and worker logs are streamed to stderr while this guarantees easy access to logs by devops administrators logs are not persisting when the service is re deployed it may also be harder to find and analyze ... | 1 |
250,557 | 7,978,750,561 | IssuesEvent | 2018-07-17 19:21:29 | Vhoyon/Discord-Bot | https://api.github.com/repos/Vhoyon/Discord-Bot | closed | Add a Volume setting to the settings command | Feature Request: Commands Priority: Medium settings | This field could take the form of `volume`.
The field would only take numeric values between 0 and 100.
This would default to `60`. | 1.0 | Add a Volume setting to the settings command - This field could take the form of `volume`.
The field would only take numeric values between 0 and 100.
This would default to `60`. | priority | add a volume setting to the settings command this field could take the form of volume the field would only take numeric values between and this would default to | 1 |
299,548 | 9,205,602,770 | IssuesEvent | 2019-03-08 11:03:37 | qissue-bot/QGIS | https://api.github.com/repos/qissue-bot/QGIS | closed | identify tool: features highlited wrong when a polygon inside a polygon is presnt | Category: Vectors Component: Affected QGIS version Component: Crashes QGIS or corrupts data Component: Easy fix? Component: Operating System Component: Pull Request or Patch supplied Component: Regression? Component: Resolution Priority: Low Project: QGIS Application Status: Closed Tracker: Bug report | ---
Author Name: **Maciej Sieczka -** (Maciej Sieczka -)
Original Redmine Issue: 926, https://issues.qgis.org/issues/926
Original Assignee: Tim Sutton
---
Look at the attached screendumps.
Black arrow points at the polygon being queried.
identify_bad.png shows how it is now. This is wrong - although the smaller ... | 1.0 | identify tool: features highlited wrong when a polygon inside a polygon is presnt - ---
Author Name: **Maciej Sieczka -** (Maciej Sieczka -)
Original Redmine Issue: 926, https://issues.qgis.org/issues/926
Original Assignee: Tim Sutton
---
Look at the attached screendumps.
Black arrow points at the polygon being q... | priority | identify tool features highlited wrong when a polygon inside a polygon is presnt author name maciej sieczka maciej sieczka original redmine issue original assignee tim sutton look at the attached screendumps black arrow points at the polygon being queried identify bad png shows how... | 1 |
234,038 | 7,715,145,447 | IssuesEvent | 2018-05-23 06:26:45 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | fjb.m.kaskus.co.id - Dropdown buttons are duplicated | Re-triaged browser-firefox-mobile priority-important | <!-- @browser: Firefox Mobile Nightly 58.0a1 (2017-11-06) -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/61.0.3163.100 Safari/537.36 -->
<!-- @reported_with: web -->
**URL**: https://fjb.m.kaskus.co.id/fjb/sell/?ref=header&med=quick_create
**Browser / Vers... | 1.0 | fjb.m.kaskus.co.id - Dropdown buttons are duplicated - <!-- @browser: Firefox Mobile Nightly 58.0a1 (2017-11-06) -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/61.0.3163.100 Safari/537.36 -->
<!-- @reported_with: web -->
**URL**: https://fjb.m.kaskus.co.id/... | priority | fjb m kaskus co id dropdown buttons are duplicated url browser version firefox mobile nightly operating system samsung galaxy android x pixels ppi pixel density tested another browser yes problem type design is broken description dropdown but... | 1 |
427,922 | 12,400,881,819 | IssuesEvent | 2020-05-21 08:46:07 | dirkwhoffmann/vAmiga | https://api.github.com/repos/dirkwhoffmann/vAmiga | closed | Test dmacon6 fails | Priority-High bug | Amiga 500 MMSE: 🥰
vAmiga: 🙈
<img width="1023" alt="Bildschirmfoto 2020-05-13 um 18 13 05" src="https://user-images.githubusercontent.com/12561945/81838287-37860200-9546-11ea-8510-b7b8e58a4... | 1.0 | Test dmacon6 fails - Amiga 500 MMSE: 🥰
vAmiga: 🙈
<img width="1023" alt="Bildschirmfoto 2020-05-13 um 18 13 05" src="https://user-images.githubusercontent.com/12561945/81838287-37860200-954... | priority | test fails amiga mmse 🥰 vamiga 🙈 img width alt bildschirmfoto um src might be related to | 1 |
257,278 | 8,135,276,277 | IssuesEvent | 2018-08-20 01:43:23 | BigOokie/skywire-wing-commander | https://api.github.com/repos/BigOokie/skywire-wing-commander | opened | Prevent starting multiple instances | enhancement low priority | **Is your feature request related to a problem? Please describe.**
Its currently possible for any number of instances of the Bot application (`wcbot`) to be run on the same machine - however there is no point and this has caused confusion with some users.
**Describe the solution you'd like**
The Bot (`wcbot`) shou... | 1.0 | Prevent starting multiple instances - **Is your feature request related to a problem? Please describe.**
Its currently possible for any number of instances of the Bot application (`wcbot`) to be run on the same machine - however there is no point and this has caused confusion with some users.
**Describe the solutio... | priority | prevent starting multiple instances is your feature request related to a problem please describe its currently possible for any number of instances of the bot application wcbot to be run on the same machine however there is no point and this has caused confusion with some users describe the solutio... | 1 |
15,397 | 5,112,138,155 | IssuesEvent | 2017-01-06 09:58:19 | cherrypy/cherrypy | https://api.github.com/repos/cherrypy/cherrypy | closed | Exception in BuiltinSSLAdapter "The handshake operation timed out" | bug CherryPy code major | Originally reported by: **Anonymous**
---
Using BuiltinSSLAdapter CherryPy crashes with SSLError ("_ssl.c:484: The handshake operation timed out") after some successful request when browsing with Chromium. Does not occur with Internet Explorer.
CherryPy 3.2.0rc1[[BR]]
Microsoft Windows [Version 6.1.7600]/32-Bit[[BR]... | 1.0 | Exception in BuiltinSSLAdapter "The handshake operation timed out" - Originally reported by: **Anonymous**
---
Using BuiltinSSLAdapter CherryPy crashes with SSLError ("_ssl.c:484: The handshake operation timed out") after some successful request when browsing with Chromium. Does not occur with Internet Explorer.
Che... | non_priority | exception in builtinssladapter the handshake operation timed out originally reported by anonymous using builtinssladapter cherrypy crashes with sslerror ssl c the handshake operation timed out after some successful request when browsing with chromium does not occur with internet explorer cherr... | 0 |
18,189 | 24,238,049,402 | IssuesEvent | 2022-09-27 02:32:41 | gobuffalo/buffalo | https://api.github.com/repos/gobuffalo/buffalo | opened | milestone v1.1.0 or v1.0.1 | process | Starting with #2306, stabilizing the Buffalo core library is almost done. Now time to clean up the Buffalo core library itself. The remaining issues to be (hopefully) addressed by this release are as follow:
* [ ] #2306
* [ ] #1653
* [ ] #1769
* [ ] #2264
* [ ] #2287
* [ ] #2300
* [ ] #2306
* [ ] #1206 | 1.0 | milestone v1.1.0 or v1.0.1 - Starting with #2306, stabilizing the Buffalo core library is almost done. Now time to clean up the Buffalo core library itself. The remaining issues to be (hopefully) addressed by this release are as follow:
* [ ] #2306
* [ ] #1653
* [ ] #1769
* [ ] #2264
* [ ] #2287
* [ ] #2300... | non_priority | milestone or starting with stabilizing the buffalo core library is almost done now time to clean up the buffalo core library itself the remaining issues to be hopefully addressed by this release are as follow | 0 |
29,859 | 2,718,146,420 | IssuesEvent | 2015-04-12 00:40:14 | babel/babel | https://api.github.com/repos/babel/babel | closed | crash with simple for loop at top level with `system` module formatter | bug high priority transformation | With this file `foo.js` (listed in it's entirety):
```javascript
for (let a = 0; a < 10; a++) {
}
```
I get the following output
```
## babel -V
5.0.12
## babel -m amd foo.js
define(["exports"], function (exports) {
"use strict";
for (var a = 0; a < 10; a++) {}
});
## babel -m system foo.js
... | 1.0 | crash with simple for loop at top level with `system` module formatter - With this file `foo.js` (listed in it's entirety):
```javascript
for (let a = 0; a < 10; a++) {
}
```
I get the following output
```
## babel -V
5.0.12
## babel -m amd foo.js
define(["exports"], function (exports) {
"use strict"... | priority | crash with simple for loop at top level with system module formatter with this file foo js listed in it s entirety javascript for let a a a i get the following output babel v babel m amd foo js define function exports use strict for ... | 1 |
402,997 | 11,833,996,775 | IssuesEvent | 2020-03-23 08:01:03 | projectcalico/bird | https://api.github.com/repos/projectcalico/bird | closed | bird cpu single core usage is always 100% | kind/bug priority/P1 | Hello, our production environment encountered this problem, if there is any way to solve it would be greatly appreciated.
bird cpu single core usage is always 100%
Use perf top to find that if_find_by_name function is higher using cpu
. The key down response is delayed by multiple seconds, and there may even be negative impact on the mission itself. | 1.0 | Unit Tags gets very laggy with many units - Because Unit Tags, particularly when operating on key press, operates through allUnits, it become very laggy when used with high numbers (> 50 units). The key down response is delayed by multiple seconds, and there may even be negative impact on the mission itself. | priority | unit tags gets very laggy with many units because unit tags particularly when operating on key press operates through allunits it become very laggy when used with high numbers units the key down response is delayed by multiple seconds and there may even be negative impact on the mission itself | 1 |
41,888 | 6,952,686,638 | IssuesEvent | 2017-12-06 18:18:36 | JuliaReach/LazySets.jl | https://api.github.com/repos/JuliaReach/LazySets.jl | closed | Allow example doctests | documentation | as suggested [here](https://github.com/JuliaReach/LazySets.jl/issues/14#issuecomment-348289126), we can turn our examples into proper doctests.
with [Documenter.jl](https://juliadocs.github.io/Documenter.jl/), this boils down to using [jldoctest](https://juliadocs.github.io/Documenter.jl/stable/man/doctests/#Doctest... | 1.0 | Allow example doctests - as suggested [here](https://github.com/JuliaReach/LazySets.jl/issues/14#issuecomment-348289126), we can turn our examples into proper doctests.
with [Documenter.jl](https://juliadocs.github.io/Documenter.jl/), this boils down to using [jldoctest](https://juliadocs.github.io/Documenter.jl/sta... | non_priority | allow example doctests as suggested we can turn our examples into proper doctests with this boils down to using in triple backticks for each example i don t know if we need to have the line using lazysets in each code block | 0 |
212,925 | 7,244,131,130 | IssuesEvent | 2018-02-14 14:14:10 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | [Feature] IP Subnets for Nodes | kind/feature lifecycle/rotten priority/important-soon sig/network team/cluster (deprecated - do not use) | [Girish - Need a good description/writeup for this feature]
Provide a new mode of Pod CIDR allocation for nodes instead of the current discovery mechanism.
| 1.0 | [Feature] IP Subnets for Nodes - [Girish - Need a good description/writeup for this feature]
Provide a new mode of Pod CIDR allocation for nodes instead of the current discovery mechanism.
| priority | ip subnets for nodes provide a new mode of pod cidr allocation for nodes instead of the current discovery mechanism | 1 |
383,209 | 11,352,472,305 | IssuesEvent | 2020-01-24 13:43:21 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | Alert... How can I find all the hosts with a modified thresholds? | alerts enhancement low-priority bug | In the last days I modified the Alert thresholds for 15/16 internal IPs.
Now I should set the SYN flood threshold for all these IPs to another value but:
-) I don't remember which IPs I modified and in which interfaces
-) I don't remember which threshold values I set for each IP
So... What do you think to add a glo... | 1.0 | Alert... How can I find all the hosts with a modified thresholds? - In the last days I modified the Alert thresholds for 15/16 internal IPs.
Now I should set the SYN flood threshold for all these IPs to another value but:
-) I don't remember which IPs I modified and in which interfaces
-) I don't remember which thre... | priority | alert how can i find all the hosts with a modified thresholds in the last days i modified the alert thresholds for internal ips now i should set the syn flood threshold for all these ips to another value but i don t remember which ips i modified and in which interfaces i don t remember which thresh... | 1 |
762,300 | 26,714,180,274 | IssuesEvent | 2023-01-28 09:13:17 | o3de/o3de | https://api.github.com/repos/o3de/o3de | opened | m_applyMoveOnPhysicsTick is not accessible through character controller component | feature/physics kind/bug needs-triage priority/major sig/simulation | m_applyMoveOnPhysicsTick can only be accessed at edit time and should be exposed at runtime as well. | 1.0 | m_applyMoveOnPhysicsTick is not accessible through character controller component - m_applyMoveOnPhysicsTick can only be accessed at edit time and should be exposed at runtime as well. | priority | m applymoveonphysicstick is not accessible through character controller component m applymoveonphysicstick can only be accessed at edit time and should be exposed at runtime as well | 1 |
268,752 | 23,393,080,411 | IssuesEvent | 2022-08-11 19:54:18 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Add E2E test for "In the Spotlight box" and links on the VAMC system page | frontend vsa Facilities testing frontend-vamc stretch-goal vamc-pages | ## Issue description
We need to add end to end tests to check for required content appearing on VAMC pages. This issue to check for the presence of "In the Spotlight box" and links on the VAMC system page
## Task
Add test to confirm the presence of
- "In the Spotlight box" on the VAMC system page
- Expected lin... | 1.0 | Add E2E test for "In the Spotlight box" and links on the VAMC system page - ## Issue description
We need to add end to end tests to check for required content appearing on VAMC pages. This issue to check for the presence of "In the Spotlight box" and links on the VAMC system page
## Task
Add test to confirm the pr... | non_priority | add test for in the spotlight box and links on the vamc system page issue description we need to add end to end tests to check for required content appearing on vamc pages this issue to check for the presence of in the spotlight box and links on the vamc system page task add test to confirm the pres... | 0 |
119,856 | 25,594,749,714 | IssuesEvent | 2022-12-01 15:25:09 | CleverRaven/Cataclysm-DDA | https://api.github.com/repos/CleverRaven/Cataclysm-DDA | closed | Allow each different save files to choose different default tilesets for themselves (or default to the global default tileset). | <Enhancement / Feature> <Suggestion / Discussion> SDL: Tiles / Sound Character / World Generation stale Code: Debug | # Is your feature request related to a problem? Please describe.
Cataclysm is a game that can offer drastically different experiences in tone and game-feel depending on what kind of mod you chose to enable. For example, a basic, DDA-only game will differ a lot from an Aftershock enabled one, a Magiclysm one, a No Hope... | 1.0 | Allow each different save files to choose different default tilesets for themselves (or default to the global default tileset). - # Is your feature request related to a problem? Please describe.
Cataclysm is a game that can offer drastically different experiences in tone and game-feel depending on what kind of mod you... | non_priority | allow each different save files to choose different default tilesets for themselves or default to the global default tileset is your feature request related to a problem please describe cataclysm is a game that can offer drastically different experiences in tone and game feel depending on what kind of mod you... | 0 |
35,150 | 12,311,807,775 | IssuesEvent | 2020-05-12 13:01:40 | vondenstein/gitblast.com | https://api.github.com/repos/vondenstein/gitblast.com | opened | CVE-2020-7608 (High) detected in yargs-parser-5.0.0.tgz, yargs-parser-11.1.1.tgz | security vulnerability | ## CVE-2020-7608 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-5.0.0.tgz</b>, <b>yargs-parser-11.1.1.tgz</b></p></summary>
<p>
<details><summary><b>yargs-parser-5.0.0.... | True | CVE-2020-7608 (High) detected in yargs-parser-5.0.0.tgz, yargs-parser-11.1.1.tgz - ## CVE-2020-7608 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-5.0.0.tgz</b>, <b>yarg... | non_priority | cve high detected in yargs parser tgz yargs parser tgz cve high severity vulnerability vulnerable libraries yargs parser tgz yargs parser tgz yargs parser tgz the mighty option parser used by yargs library home page a href path to dependenc... | 0 |
269,494 | 20,384,276,060 | IssuesEvent | 2022-02-22 04:03:42 | nartc/angular-three | https://api.github.com/repos/nartc/angular-three | closed | [Feature] add wakeup event to physics props | documentation | Using sleepTimeLimit is helpful to limit the number of collision events after an object has stopped moving.
[cannon.js sleep example](https://github.com/pmndrs/cannon-es/blob/master/examples/sleep.html)
If the object is hit again, the wakeup event is fired.
Please add the wakeup event to physics props
```... | 1.0 | [Feature] add wakeup event to physics props - Using sleepTimeLimit is helpful to limit the number of collision events after an object has stopped moving.
[cannon.js sleep example](https://github.com/pmndrs/cannon-es/blob/master/examples/sleep.html)
If the object is hit again, the wakeup event is fired.
Pleas... | non_priority | add wakeup event to physics props using sleeptimelimit is helpful to limit the number of collision events after an object has stopped moving if the object is hit again the wakeup event is fired please add the wakeup event to physics props javascript the body wakes up when it gets... | 0 |
83,056 | 23,955,990,216 | IssuesEvent | 2022-09-12 15:00:08 | finos/legend-studio | https://api.github.com/repos/finos/legend-studio | closed | Feature request: Support `workflows` in query builders | Type: Feature Request Studio Core Team Component: Query Builder | Query builder might be used in different workflows right now:
- Data browsing mode: the current query builder where the query is expected to be of shape `SomeClass.all()...`
- Advanced/Unsupported mode: the query can be of any form
As such, we come up with this idea to add a new feature to the query builder - `w... | 1.0 | Feature request: Support `workflows` in query builders - Query builder might be used in different workflows right now:
- Data browsing mode: the current query builder where the query is expected to be of shape `SomeClass.all()...`
- Advanced/Unsupported mode: the query can be of any form
As such, we come up with... | non_priority | feature request support workflows in query builders query builder might be used in different workflows right now data browsing mode the current query builder where the query is expected to be of shape someclass all advanced unsupported mode the query can be of any form as such we come up with... | 0 |
200,578 | 7,009,265,705 | IssuesEvent | 2017-12-19 18:29:40 | larshp/abapGit | https://api.github.com/repos/larshp/abapGit | closed | Improve usability of repository popup | low priority new feature | When we try to clone a repository and an error occurs, e.g. invalid url or non existing package, the popup is closed and then the error is displayed.
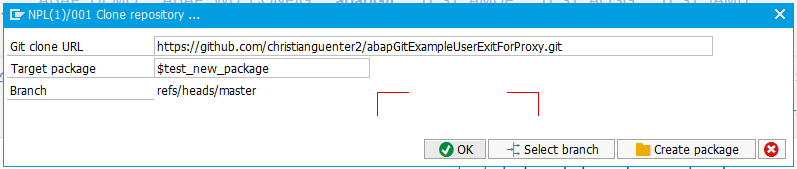


then input "blist 2",
- The correct person "Roy Balakrishnan" will be blacklisted however the display message shows "rem... | 1.0 | [PE-D] Incorrect Display Result when using "blist" after "find" - For example, search for contacts with tag "colleagues"
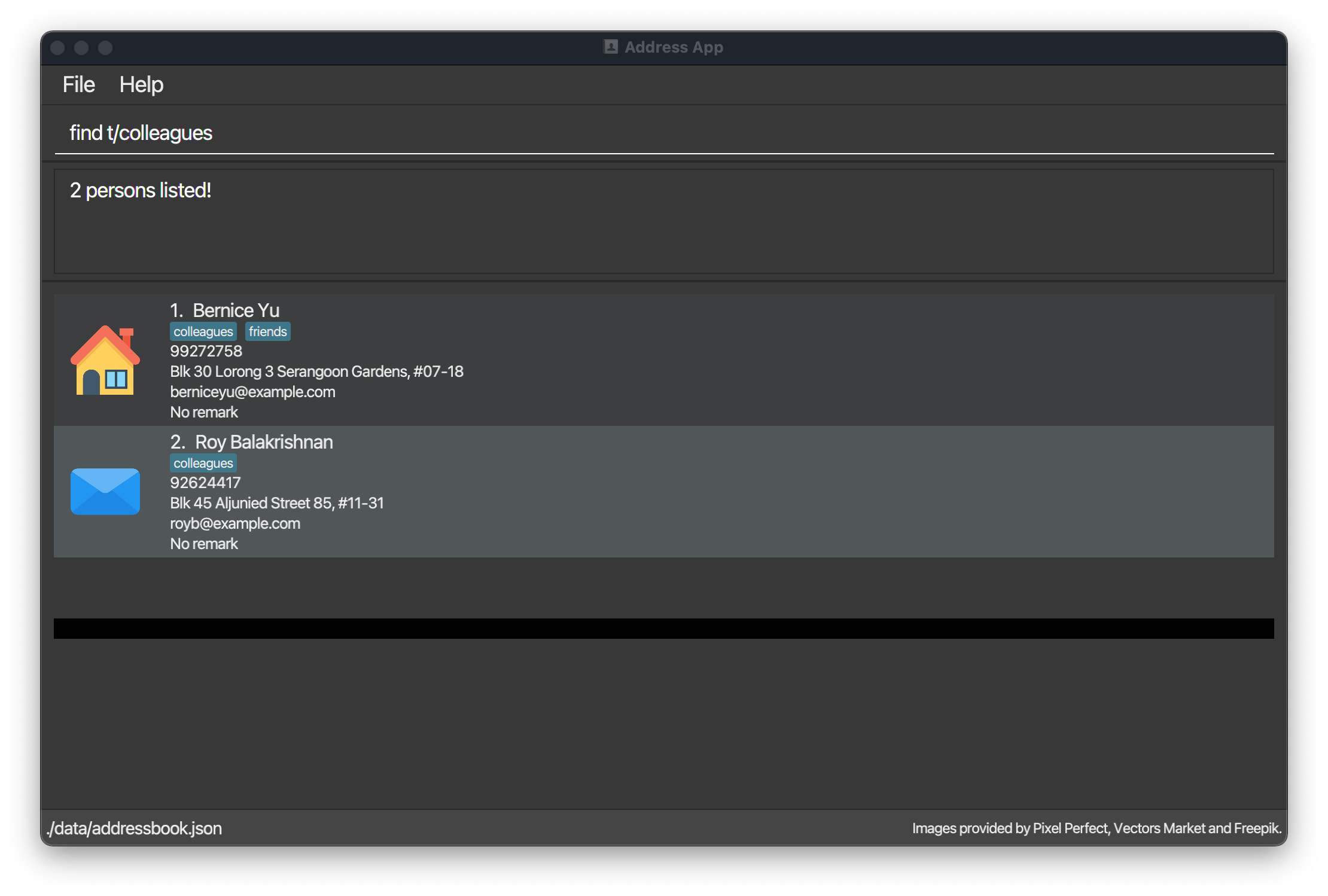
then input "blist 2",
- The correct person "Roy Balakr... | priority | incorrect display result when using blist after find for example search for contacts with tag colleagues then input blist the correct person roy balakrishnan will be blacklisted however the display message shows removed instead of added to black list and the person bernice yu shown in ... | 1 |
149,017 | 5,705,644,941 | IssuesEvent | 2017-04-18 09:05:37 | minishift/minishift | https://api.github.com/repos/minishift/minishift | closed | Hostfolder configuration should not save the password in clear text | component/hostfolder kind/bug priority/critical | minishift hostfolder saves the password in clear text. So anyone who will get the access of the workstation can view the file and can get read the password
```
$ cat ~/.minishift/config/allinstances.json
{
"HostFolders": [
{
"Name": "share",
"Type": "cifs",
"Options": {
"domain": "test",
... | 1.0 | Hostfolder configuration should not save the password in clear text - minishift hostfolder saves the password in clear text. So anyone who will get the access of the workstation can view the file and can get read the password
```
$ cat ~/.minishift/config/allinstances.json
{
"HostFolders": [
{
"Name": "sh... | priority | hostfolder configuration should not save the password in clear text minishift hostfolder saves the password in clear text so anyone who will get the access of the workstation can view the file and can get read the password cat minishift config allinstances json hostfolders name sh... | 1 |
396,890 | 27,140,078,537 | IssuesEvent | 2023-02-16 15:46:10 | extratone/gpt | https://api.github.com/repos/extratone/gpt | opened | Chatbot Prayers Okay? | documentation | 
You:
According to the literature of protestant christianity - taking both the Old and New Testaments in account - would it be a sin against God if I chose to engage chatgpt to writ... | 1.0 | Chatbot Prayers Okay? - 
You:
According to the literature of protestant christianity - taking both the Old and New Testaments in account - would it be a sin against God if I chose t... | non_priority | chatbot prayers okay you according to the literature of protestant christianity taking both the old and new testaments in account would it be a sin against god if i chose to engage chatgpt to write my nightly prayers to god instead of thinking of them myself chatgpt in the literature of protest... | 0 |
227,869 | 25,127,538,572 | IssuesEvent | 2022-11-09 12:55:20 | NirShaharabani/verdaccio | https://api.github.com/repos/NirShaharabani/verdaccio | opened | @verdaccio/e2e-cli-npm7-1.0.1-6-next.5.tgz: 2 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>@verdaccio/e2e-cli-npm7-1.0.1-6-next.5.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://git... | True | @verdaccio/e2e-cli-npm7-1.0.1-6-next.5.tgz: 2 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>@verdaccio/e2e-cli-npm7-1.0.1-6-next.5.tgz</b></p></summary>
<p></p>
<p>Pat... | non_priority | verdaccio cli next tgz vulnerabilities highest severity is vulnerable library verdaccio cli next tgz path to dependency file package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in verd... | 0 |
627,627 | 19,910,662,928 | IssuesEvent | 2022-01-25 16:50:47 | twanda/vertical-agriculture | https://api.github.com/repos/twanda/vertical-agriculture | opened | Incoming Products (Receipts): Unable to register farmer deliveries in mobile view | bug 2nd Priority | In mobile view (p.e. on a tablet) it is not possible to register or edit farmer deliveries.

| 1.0 | Incoming Products (Receipts): Unable to register farmer deliveries in mobile view - In mobile view (p.e. on a tablet) it is not possible to register or edit farmer deliveries.

| priority | incoming products receipts unable to register farmer deliveries in mobile view in mobile view p e on a tablet it is not possible to register or edit farmer deliveries | 1 |
480,122 | 13,823,615,010 | IssuesEvent | 2020-10-13 07:17:11 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | Add support for 3.0.x OpenAPI definitions in API publisher. | Priority/Normal Type/Bug | ### Description:
Currently in 2.2.0 publisher we only support version 3.0.0 OpenAPI definitions. However we should add improved support for 3.0x versions because they can only contain minor fixes and not major changes in the spec.
### Steps to reproduce:
Import an OpenAPI 3.0.1 API definition. UI will show an erro... | 1.0 | Add support for 3.0.x OpenAPI definitions in API publisher. - ### Description:
Currently in 2.2.0 publisher we only support version 3.0.0 OpenAPI definitions. However we should add improved support for 3.0x versions because they can only contain minor fixes and not major changes in the spec.
### Steps to reproduce:... | priority | add support for x openapi definitions in api publisher description currently in publisher we only support version openapi definitions however we should add improved support for versions because they can only contain minor fixes and not major changes in the spec steps to reproduce ... | 1 |
515,561 | 14,965,285,007 | IssuesEvent | 2021-01-27 13:11:10 | windowsboy111/merlin-py | https://api.github.com/repos/windowsboy111/merlin-py | closed | [BUG/ISSUE] Broken /poll check | bug cog: Utilities help wanted priority: High | **Describe the bug**
`/poll check` is problematic. Sometimes it shows message id on the title, sometimes the whole command fails.
**Screenshots**
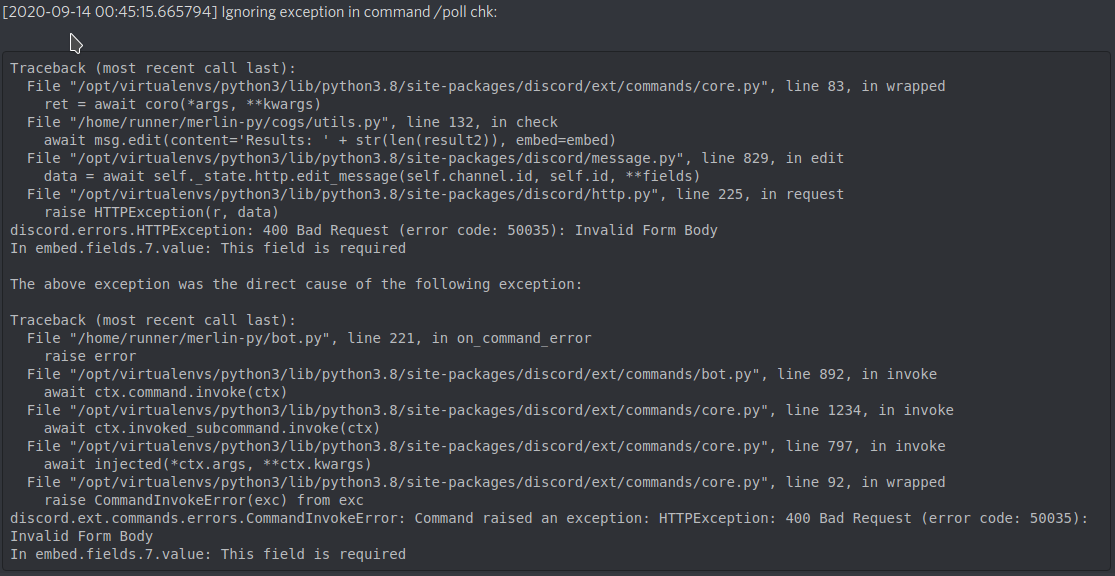
**Desktop (please complete the following information)... | 1.0 | [BUG/ISSUE] Broken /poll check - **Describe the bug**
`/poll check` is problematic. Sometimes it shows message id on the title, sometimes the whole command fails.
**Screenshots**
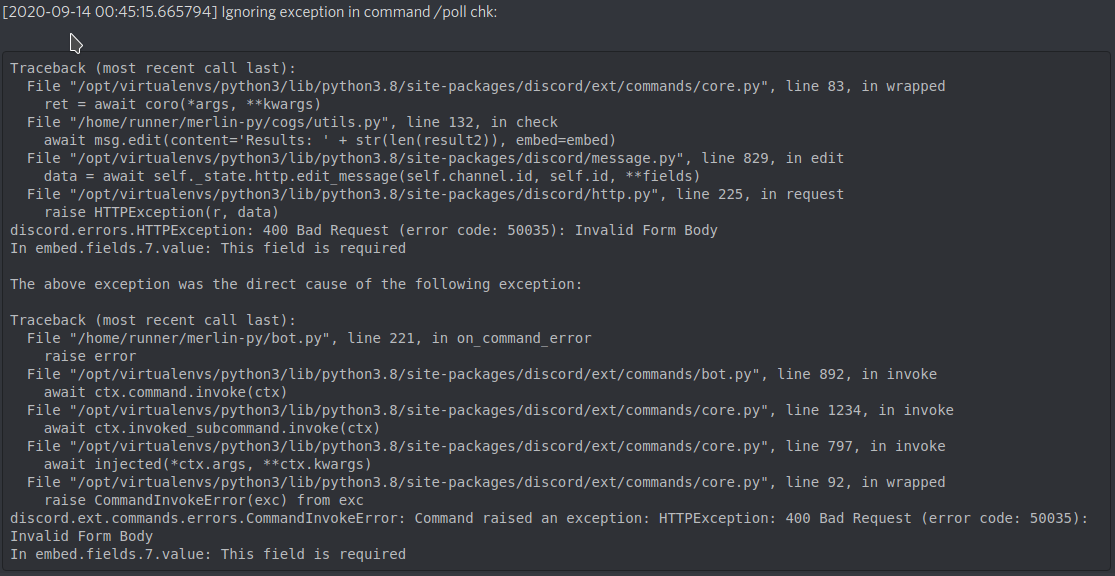
**Desktop (please co... | priority | broken poll check describe the bug poll check is problematic sometimes it shows message id on the title sometimes the whole command fails screenshots desktop please complete the following information discord py linux python merlin build latest | 1 |
58,128 | 16,343,181,856 | IssuesEvent | 2021-05-13 02:07:13 | Questie/Questie | https://api.github.com/repos/Questie/Questie | opened | Missing Dungs & Zones | Type - Defect | We are missing the following Dungs for https://github.com/Questie/Questie/blob/master/Database/Zones/zoneTables.lua
Old Hillsbrad Foothills
The Black Morass
Stratholme Past
Hyjal Summit
Also missing Zone
2300 = caverns-of-time
<!-- READ THIS FIRST
Hello, thanks for taking the time to report a bug!
Befo... | 1.0 | Missing Dungs & Zones - We are missing the following Dungs for https://github.com/Questie/Questie/blob/master/Database/Zones/zoneTables.lua
Old Hillsbrad Foothills
The Black Morass
Stratholme Past
Hyjal Summit
Also missing Zone
2300 = caverns-of-time
<!-- READ THIS FIRST
Hello, thanks for taking the time ... | non_priority | missing dungs zones we are missing the following dungs for old hillsbrad foothills the black morass stratholme past hyjal summit also missing zone caverns of time read this first hello thanks for taking the time to report a bug before you proceed please verify that you re running the ... | 0 |
569,613 | 17,015,527,421 | IssuesEvent | 2021-07-02 11:27:16 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | opened | Cyclemap should render surface=cobblestone | Component: opencyclemap Priority: major Type: enhancement | **[Submitted to the original trac issue database at 6.59am, Wednesday, 4th May 2011]**
Cobblestone surfaces are huge inconvenience for cyclist, and should be rendered on cycle map. | 1.0 | Cyclemap should render surface=cobblestone - **[Submitted to the original trac issue database at 6.59am, Wednesday, 4th May 2011]**
Cobblestone surfaces are huge inconvenience for cyclist, and should be rendered on cycle map. | priority | cyclemap should render surface cobblestone cobblestone surfaces are huge inconvenience for cyclist and should be rendered on cycle map | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.