Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
7,202
| 10,339,043,637
|
IssuesEvent
|
2019-09-03 18:22:23
|
hashgraph/hedera-mirror-node
|
https://api.github.com/repos/hashgraph/hedera-mirror-node
|
closed
|
Simple java package deliverable
|
OABlocker enhancement process
|
**Problem**
There isn't a clear packaged deliverable for java that doesn't involve access to the source code and building via maven.
There needs to be a simple solution where someone (in ops) can take a delivered package (not source code) and install it with some simple instructions.
**Solution**
Quick and dirty - add a tar/zip step in Circle CI (package up all necessary output files like the main jar, lib, config and scripts).
**Alternatives**
**Additional Context**
|
1.0
|
Simple java package deliverable - **Problem**
There isn't a clear packaged deliverable for java that doesn't involve access to the source code and building via maven.
There needs to be a simple solution where someone (in ops) can take a delivered package (not source code) and install it with some simple instructions.
**Solution**
Quick and dirty - add a tar/zip step in Circle CI (package up all necessary output files like the main jar, lib, config and scripts).
**Alternatives**
**Additional Context**
|
process
|
simple java package deliverable problem there isn t a clear packaged deliverable for java that doesn t involve access to the source code and building via maven there needs to be a simple solution where someone in ops can take a delivered package not source code and install it with some simple instructions solution quick and dirty add a tar zip step in circle ci package up all necessary output files like the main jar lib config and scripts alternatives additional context
| 1
|
16,994
| 22,357,459,614
|
IssuesEvent
|
2022-06-15 16:56:40
|
GoogleCloudPlatform/cloud-ops-sandbox
|
https://api.github.com/repos/GoogleCloudPlatform/cloud-ops-sandbox
|
opened
|
add dependency on release pipeline jobs
|
type: process priority: p3
|
Currently the two jobs in `make-release.yaml` run in parallel. We want the second job to run only after the first is complete. We should [add a `needs` tag](https://docs.github.com/en/actions/using-workflows/about-workflows#creating-dependent-jobs) to the second job
|
1.0
|
add dependency on release pipeline jobs - Currently the two jobs in `make-release.yaml` run in parallel. We want the second job to run only after the first is complete. We should [add a `needs` tag](https://docs.github.com/en/actions/using-workflows/about-workflows#creating-dependent-jobs) to the second job
|
process
|
add dependency on release pipeline jobs currently the two jobs in make release yaml run in parallel we want the second job to run only after the first is complete we should to the second job
| 1
|
11,470
| 14,333,479,367
|
IssuesEvent
|
2020-11-27 05:56:49
|
timberio/vector
|
https://api.github.com/repos/timberio/vector
|
closed
|
Remap inspired `reduce` transform to solve multiline merging
|
domain: processing meta: idea needs: approval needs: rfc type: feature
|
This issue proposes an idea for a new `reduce` transform that borrows from the new `remap` transform. The intent is to solve event merging, as well as other reduce-like problems, through robust reduce functionality. Even with the current options, many Vector users are still blocked on this functionality and I think we need to explore a more robust solution to this problem so that we can solve it and move on.
## Current State
### `multiline` options
Currently, Vector offers `multiline` options in select sources. By setting these options users can achieve basic log merging directly in the source. While this works for some use cases, it falls short in a few areas (covered below).
### `merge` transform
The merge transform was introduced as a way to merge Docker logs initially. The intent was to decouple the merging strategy from the source so that users could use it as an escape hatch for sources that didn't have this functionality built-in. Over time we would inline this transform within sources where we could automatically merge data based on known factors. For example, Docker splits logs in such a way that we can automatically detect it and merge the logs without any configuration from the users.
### `reduce` transform
Finally, the `reduce` transform was introduced to enable the [Stripe canonical log lines pattern](https://stripe.com/blog/canonical-log-lines). And while the target use case was different, it's really just a sophisticated way to merge events.
## Problems
### 1. Confusing
As you can see from the current state above, we have 3 different ways to merge events. This is confusing. And even if we direct users to a specific solution, like the source-level `multiline` options, the UX that provides is also confusing.
For example, the `file` source multiline options are still confusing to me, and I should understand them given my involement in the project. This is shared by a number of users I've helped as well.
### 2. Inability to specify per-stream merge conditions
Even though we offer `multiline` options within sources, users can only supply one set of settings. This is not sufficient in cases where data is coming from multiple disparate streams. For example, if a user configures the `file` source to ingest logs from many different files they'll likely want to configure different `multiline` settings for each file. The only way to achieve that currently is by defining multiple `file` sources.
### 3. Inflexbile
Because we must implement the `multiline` functionality within each relevant source, it's possible that sources will lack this functionality. This means we are more likely to block users on this functionality until a user supplies feedback. And once that occurs we'll need to allocate development time to implement this.
## Proposal
### 1. Drop the `merge` transform
I'd like to drop the `merge` transform in favor of a more robust approach to source-level multiline merging. I don't think we'll ever want to keep this around.
### 2. Add `stream_id` event metadata
To my knowledge, there are 2 reasons we prefer to inline `multiline` options within sources:
1. We have the context to operate within each stream. This is a requirement for multiline merging and it means users do not have to configure anything to achieve this.
2. It's faster and simpler. In some cases, we can skip the whole event creation process and simply merge strings/bytes.
I'm unsure how much of a problem 2 actually is. And while 1 is true for the simple case, it doesn't allow different merging options per stream (problem 2 above). I think we can retain the source-level simplicity by adding event metadata the identifies which stream the event came from (ex: `stream_id`_. The new `reduce` transform could segment events automatically based on this metadata. Event metadata, as whole, is being considered in #3910.
### 3. Remap inspired reduce transform
Finally, we should consider a more robust `reduce` transform. I can't help but wonder if there is a light-weight and flexible syntax we could support for robust merging, borrowing from the remap syntax. From a UX perspective, something like the following would be nice. I'll use the [examples in our docs](https://vector.dev/docs/reference/sources/file/#multi-line-messages).
#### 1. Ruby Exceptions
```
First line
foobar.rb:6:in `/': divided by 0 (ZeroDivisionError)
from foobar.rb:6:in `bar'
from foobar.rb:2:in `foo'
from foobar.rb:9:in `<main>'
Last line
```
Merged with:
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
while next_event in nextEvent() {
if startsWith?(next_event.message, /\w/) {
.message += ("\n" + next_event.message)
del(next_event)
} else {
break
}
}
"""
```
#### 2. Line Continuations
```
First line\
second line\
third line
```
Merged with:
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
if match?(.message, /\\$/) {
.message = replace(.message, /\\$/)
while next_event in nextEvent() {
.message += ("\n" + replace(next_event.message, /\\$/)
del(next_event)
if !match?(next_event.message, /\\$/) {
break
}
}
}
"""
```
#### 3. Shortcut functions
And we could simplify the above with purpose-driven functions:
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
join_with_indentation(.message)
"""
```
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
join_with_line_continuation(.message, '\')
"""
```
#### Summary
All of the above is definitely up for discussion. I'm less concerned about the actual syntax and naming, and more concerned with the direction. If we agree this approach is better we can start an RFC to nail down the details.
But the reasons I like this approach:
1. It's similar to the new `remap` syntax, and we can share the learning curve there.
2. We can borrow functions from the `remap` syntax.
3. Shifting this to a transform means we can decouple this functionality providing for more flexibility and the ability to compose higher-level components. Something we are solving in #3791.
4. It solves problem 2 above by allowing users to conditionally target streams if
|
1.0
|
Remap inspired `reduce` transform to solve multiline merging - This issue proposes an idea for a new `reduce` transform that borrows from the new `remap` transform. The intent is to solve event merging, as well as other reduce-like problems, through robust reduce functionality. Even with the current options, many Vector users are still blocked on this functionality and I think we need to explore a more robust solution to this problem so that we can solve it and move on.
## Current State
### `multiline` options
Currently, Vector offers `multiline` options in select sources. By setting these options users can achieve basic log merging directly in the source. While this works for some use cases, it falls short in a few areas (covered below).
### `merge` transform
The merge transform was introduced as a way to merge Docker logs initially. The intent was to decouple the merging strategy from the source so that users could use it as an escape hatch for sources that didn't have this functionality built-in. Over time we would inline this transform within sources where we could automatically merge data based on known factors. For example, Docker splits logs in such a way that we can automatically detect it and merge the logs without any configuration from the users.
### `reduce` transform
Finally, the `reduce` transform was introduced to enable the [Stripe canonical log lines pattern](https://stripe.com/blog/canonical-log-lines). And while the target use case was different, it's really just a sophisticated way to merge events.
## Problems
### 1. Confusing
As you can see from the current state above, we have 3 different ways to merge events. This is confusing. And even if we direct users to a specific solution, like the source-level `multiline` options, the UX that provides is also confusing.
For example, the `file` source multiline options are still confusing to me, and I should understand them given my involement in the project. This is shared by a number of users I've helped as well.
### 2. Inability to specify per-stream merge conditions
Even though we offer `multiline` options within sources, users can only supply one set of settings. This is not sufficient in cases where data is coming from multiple disparate streams. For example, if a user configures the `file` source to ingest logs from many different files they'll likely want to configure different `multiline` settings for each file. The only way to achieve that currently is by defining multiple `file` sources.
### 3. Inflexbile
Because we must implement the `multiline` functionality within each relevant source, it's possible that sources will lack this functionality. This means we are more likely to block users on this functionality until a user supplies feedback. And once that occurs we'll need to allocate development time to implement this.
## Proposal
### 1. Drop the `merge` transform
I'd like to drop the `merge` transform in favor of a more robust approach to source-level multiline merging. I don't think we'll ever want to keep this around.
### 2. Add `stream_id` event metadata
To my knowledge, there are 2 reasons we prefer to inline `multiline` options within sources:
1. We have the context to operate within each stream. This is a requirement for multiline merging and it means users do not have to configure anything to achieve this.
2. It's faster and simpler. In some cases, we can skip the whole event creation process and simply merge strings/bytes.
I'm unsure how much of a problem 2 actually is. And while 1 is true for the simple case, it doesn't allow different merging options per stream (problem 2 above). I think we can retain the source-level simplicity by adding event metadata the identifies which stream the event came from (ex: `stream_id`_. The new `reduce` transform could segment events automatically based on this metadata. Event metadata, as whole, is being considered in #3910.
### 3. Remap inspired reduce transform
Finally, we should consider a more robust `reduce` transform. I can't help but wonder if there is a light-weight and flexible syntax we could support for robust merging, borrowing from the remap syntax. From a UX perspective, something like the following would be nice. I'll use the [examples in our docs](https://vector.dev/docs/reference/sources/file/#multi-line-messages).
#### 1. Ruby Exceptions
```
First line
foobar.rb:6:in `/': divided by 0 (ZeroDivisionError)
from foobar.rb:6:in `bar'
from foobar.rb:2:in `foo'
from foobar.rb:9:in `<main>'
Last line
```
Merged with:
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
while next_event in nextEvent() {
if startsWith?(next_event.message, /\w/) {
.message += ("\n" + next_event.message)
del(next_event)
} else {
break
}
}
"""
```
#### 2. Line Continuations
```
First line\
second line\
third line
```
Merged with:
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
if match?(.message, /\\$/) {
.message = replace(.message, /\\$/)
while next_event in nextEvent() {
.message += ("\n" + replace(next_event.message, /\\$/)
del(next_event)
if !match?(next_event.message, /\\$/) {
break
}
}
}
"""
```
#### 3. Shortcut functions
And we could simplify the above with purpose-driven functions:
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
join_with_indentation(.message)
"""
```
```toml
[transforms.reduce]
type = "reduce"
group_by = ["stream_id"] # default (see point 2 above)
timeout_secs = 10 # ensures pipelines don't stall
reduce = """
join_with_line_continuation(.message, '\')
"""
```
#### Summary
All of the above is definitely up for discussion. I'm less concerned about the actual syntax and naming, and more concerned with the direction. If we agree this approach is better we can start an RFC to nail down the details.
But the reasons I like this approach:
1. It's similar to the new `remap` syntax, and we can share the learning curve there.
2. We can borrow functions from the `remap` syntax.
3. Shifting this to a transform means we can decouple this functionality providing for more flexibility and the ability to compose higher-level components. Something we are solving in #3791.
4. It solves problem 2 above by allowing users to conditionally target streams if
|
process
|
remap inspired reduce transform to solve multiline merging this issue proposes an idea for a new reduce transform that borrows from the new remap transform the intent is to solve event merging as well as other reduce like problems through robust reduce functionality even with the current options many vector users are still blocked on this functionality and i think we need to explore a more robust solution to this problem so that we can solve it and move on current state multiline options currently vector offers multiline options in select sources by setting these options users can achieve basic log merging directly in the source while this works for some use cases it falls short in a few areas covered below merge transform the merge transform was introduced as a way to merge docker logs initially the intent was to decouple the merging strategy from the source so that users could use it as an escape hatch for sources that didn t have this functionality built in over time we would inline this transform within sources where we could automatically merge data based on known factors for example docker splits logs in such a way that we can automatically detect it and merge the logs without any configuration from the users reduce transform finally the reduce transform was introduced to enable the and while the target use case was different it s really just a sophisticated way to merge events problems confusing as you can see from the current state above we have different ways to merge events this is confusing and even if we direct users to a specific solution like the source level multiline options the ux that provides is also confusing for example the file source multiline options are still confusing to me and i should understand them given my involement in the project this is shared by a number of users i ve helped as well inability to specify per stream merge conditions even though we offer multiline options within sources users can only supply one set of settings this is not sufficient in cases where data is coming from multiple disparate streams for example if a user configures the file source to ingest logs from many different files they ll likely want to configure different multiline settings for each file the only way to achieve that currently is by defining multiple file sources inflexbile because we must implement the multiline functionality within each relevant source it s possible that sources will lack this functionality this means we are more likely to block users on this functionality until a user supplies feedback and once that occurs we ll need to allocate development time to implement this proposal drop the merge transform i d like to drop the merge transform in favor of a more robust approach to source level multiline merging i don t think we ll ever want to keep this around add stream id event metadata to my knowledge there are reasons we prefer to inline multiline options within sources we have the context to operate within each stream this is a requirement for multiline merging and it means users do not have to configure anything to achieve this it s faster and simpler in some cases we can skip the whole event creation process and simply merge strings bytes i m unsure how much of a problem actually is and while is true for the simple case it doesn t allow different merging options per stream problem above i think we can retain the source level simplicity by adding event metadata the identifies which stream the event came from ex stream id the new reduce transform could segment events automatically based on this metadata event metadata as whole is being considered in remap inspired reduce transform finally we should consider a more robust reduce transform i can t help but wonder if there is a light weight and flexible syntax we could support for robust merging borrowing from the remap syntax from a ux perspective something like the following would be nice i ll use the ruby exceptions first line foobar rb in divided by zerodivisionerror from foobar rb in bar from foobar rb in foo from foobar rb in last line merged with toml type reduce group by default see point above timeout secs ensures pipelines don t stall reduce while next event in nextevent if startswith next event message w message n next event message del next event else break line continuations first line second line third line merged with toml type reduce group by default see point above timeout secs ensures pipelines don t stall reduce if match message message replace message while next event in nextevent message n replace next event message del next event if match next event message break shortcut functions and we could simplify the above with purpose driven functions toml type reduce group by default see point above timeout secs ensures pipelines don t stall reduce join with indentation message toml type reduce group by default see point above timeout secs ensures pipelines don t stall reduce join with line continuation message summary all of the above is definitely up for discussion i m less concerned about the actual syntax and naming and more concerned with the direction if we agree this approach is better we can start an rfc to nail down the details but the reasons i like this approach it s similar to the new remap syntax and we can share the learning curve there we can borrow functions from the remap syntax shifting this to a transform means we can decouple this functionality providing for more flexibility and the ability to compose higher level components something we are solving in it solves problem above by allowing users to conditionally target streams if
| 1
|
87,308
| 15,762,376,771
|
IssuesEvent
|
2021-03-31 11:00:56
|
turkdevops/desktop
|
https://api.github.com/repos/turkdevops/desktop
|
opened
|
CVE-2021-21366 (Medium) detected in xmldom-0.1.27.tgz
|
security vulnerability
|
## CVE-2021-21366 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmldom-0.1.27.tgz</b></p></summary>
<p>A W3C Standard XML DOM(Level2 CORE) implementation and parser(DOMParser/XMLSerializer).</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmldom/-/xmldom-0.1.27.tgz">https://registry.npmjs.org/xmldom/-/xmldom-0.1.27.tgz</a></p>
<p>Path to dependency file: desktop/node_modules/xmldom/package.json</p>
<p>Path to vulnerable library: desktop/node_modules/xmldom/package.json</p>
<p>
Dependency Hierarchy:
- electron-packager-15.2.0.tgz (Root Library)
- electron-osx-sign-0.5.0.tgz
- plist-3.0.1.tgz
- :x: **xmldom-0.1.27.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/desktop/commit/52317b0add0e4e836c317cfb1aef9917759d716a">52317b0add0e4e836c317cfb1aef9917759d716a</a></p>
<p>Found in base branch: <b>development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
xmldom is a pure JavaScript W3C standard-based (XML DOM Level 2 Core) DOMParser and XMLSerializer module. xmldom versions 0.4.0 and older do not correctly preserve system identifiers, FPIs or namespaces when repeatedly parsing and serializing maliciously crafted documents. This may lead to unexpected syntactic changes during XML processing in some downstream applications. This is fixed in version 0.5.0. As a workaround downstream applications can validate the input and reject the maliciously crafted documents.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21366>CVE-2021-21366</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/xmldom/xmldom/security/advisories/GHSA-h6q6-9hqw-rwfv">https://github.com/xmldom/xmldom/security/advisories/GHSA-h6q6-9hqw-rwfv</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: 0.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-21366 (Medium) detected in xmldom-0.1.27.tgz - ## CVE-2021-21366 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmldom-0.1.27.tgz</b></p></summary>
<p>A W3C Standard XML DOM(Level2 CORE) implementation and parser(DOMParser/XMLSerializer).</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmldom/-/xmldom-0.1.27.tgz">https://registry.npmjs.org/xmldom/-/xmldom-0.1.27.tgz</a></p>
<p>Path to dependency file: desktop/node_modules/xmldom/package.json</p>
<p>Path to vulnerable library: desktop/node_modules/xmldom/package.json</p>
<p>
Dependency Hierarchy:
- electron-packager-15.2.0.tgz (Root Library)
- electron-osx-sign-0.5.0.tgz
- plist-3.0.1.tgz
- :x: **xmldom-0.1.27.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/desktop/commit/52317b0add0e4e836c317cfb1aef9917759d716a">52317b0add0e4e836c317cfb1aef9917759d716a</a></p>
<p>Found in base branch: <b>development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
xmldom is a pure JavaScript W3C standard-based (XML DOM Level 2 Core) DOMParser and XMLSerializer module. xmldom versions 0.4.0 and older do not correctly preserve system identifiers, FPIs or namespaces when repeatedly parsing and serializing maliciously crafted documents. This may lead to unexpected syntactic changes during XML processing in some downstream applications. This is fixed in version 0.5.0. As a workaround downstream applications can validate the input and reject the maliciously crafted documents.
<p>Publish Date: 2021-03-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-21366>CVE-2021-21366</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/xmldom/xmldom/security/advisories/GHSA-h6q6-9hqw-rwfv">https://github.com/xmldom/xmldom/security/advisories/GHSA-h6q6-9hqw-rwfv</a></p>
<p>Release Date: 2021-03-12</p>
<p>Fix Resolution: 0.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in xmldom tgz cve medium severity vulnerability vulnerable library xmldom tgz a standard xml dom core implementation and parser domparser xmlserializer library home page a href path to dependency file desktop node modules xmldom package json path to vulnerable library desktop node modules xmldom package json dependency hierarchy electron packager tgz root library electron osx sign tgz plist tgz x xmldom tgz vulnerable library found in head commit a href found in base branch development vulnerability details xmldom is a pure javascript standard based xml dom level core domparser and xmlserializer module xmldom versions and older do not correctly preserve system identifiers fpis or namespaces when repeatedly parsing and serializing maliciously crafted documents this may lead to unexpected syntactic changes during xml processing in some downstream applications this is fixed in version as a workaround downstream applications can validate the input and reject the maliciously crafted documents publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
60,685
| 14,899,011,380
|
IssuesEvent
|
2021-01-21 13:51:00
|
ckeditor/ckeditor5
|
https://api.github.com/repos/ckeditor/ckeditor5
|
closed
|
Improve errors that are thrown when requirements are missing (they are duplicated)
|
domain:dx domain:extending-builds package:core squad:dx type:improvement
|
## 📝 Provide a description of the improvement
The errors are thrown as:

This strongly relates to #8634.
---
If you'd like to see this improvement implemented, add a 👍 reaction to this post.
|
1.0
|
Improve errors that are thrown when requirements are missing (they are duplicated) - ## 📝 Provide a description of the improvement
The errors are thrown as:

This strongly relates to #8634.
---
If you'd like to see this improvement implemented, add a 👍 reaction to this post.
|
non_process
|
improve errors that are thrown when requirements are missing they are duplicated 📝 provide a description of the improvement the errors are thrown as this strongly relates to if you d like to see this improvement implemented add a 👍 reaction to this post
| 0
|
127,762
| 10,481,655,571
|
IssuesEvent
|
2019-09-24 10:08:10
|
status-im/status-react
|
https://api.github.com/repos/status-im/status-react
|
closed
|
Cannot delete dapp from "Recent"
|
bounty-s bug core-ui-grooming e2e test blocker high-priority medium-severity v1 release
|
### Description
[comment]: # (Feature or Bug? i.e Type: Bug)
*Type*: Bug
*Summary*: cannot use swipe and delete gesture to remove last visited dapps - when tap on "Delete", nothing happens (Android only). In chat it was replaced with long tap > delete , IMO it will be better to have this behavior for dapps as well.
#### Expected behavior
can delete browser entry
please see comments from @flexsurfer on the issue:
`maybe related to native animation, but anyway we need to change it on long press`
`"Clear all" also should be implemented`
#### Actual behavior
nothing happens
### Reproduction
- Open Status
- Open "DApps"
- Open any dapp and go back to main "DApps" screen
- Below "Recent" swipe to delete visited dapp from history
### Additional Information
[comment]: # (Please do your best to fill this out.)
- Status version: nightly 02/07/2019
- Operating System: Android 8
|
1.0
|
Cannot delete dapp from "Recent" - ### Description
[comment]: # (Feature or Bug? i.e Type: Bug)
*Type*: Bug
*Summary*: cannot use swipe and delete gesture to remove last visited dapps - when tap on "Delete", nothing happens (Android only). In chat it was replaced with long tap > delete , IMO it will be better to have this behavior for dapps as well.
#### Expected behavior
can delete browser entry
please see comments from @flexsurfer on the issue:
`maybe related to native animation, but anyway we need to change it on long press`
`"Clear all" also should be implemented`
#### Actual behavior
nothing happens
### Reproduction
- Open Status
- Open "DApps"
- Open any dapp and go back to main "DApps" screen
- Below "Recent" swipe to delete visited dapp from history
### Additional Information
[comment]: # (Please do your best to fill this out.)
- Status version: nightly 02/07/2019
- Operating System: Android 8
|
non_process
|
cannot delete dapp from recent description feature or bug i e type bug type bug summary cannot use swipe and delete gesture to remove last visited dapps when tap on delete nothing happens android only in chat it was replaced with long tap delete imo it will be better to have this behavior for dapps as well expected behavior can delete browser entry please see comments from flexsurfer on the issue maybe related to native animation but anyway we need to change it on long press clear all also should be implemented actual behavior nothing happens reproduction open status open dapps open any dapp and go back to main dapps screen below recent swipe to delete visited dapp from history additional information please do your best to fill this out status version nightly operating system android
| 0
|
157,098
| 13,672,763,827
|
IssuesEvent
|
2020-09-29 08:56:49
|
docker/ecs-plugin
|
https://api.github.com/repos/docker/ecs-plugin
|
closed
|
Add documentation for how to configure resources for containers
|
documentation
|
I reverse engineered this from looking at the test code, but I suspect many other people will hit the same question: How do I give my ECS container more RAM/CPU resources?
Looks like it's a block like this
```
services:
# Backend service
backend:
deploy:
resources:
limits:
cpus: '0.5'
memory: 2048M
reservations:
cpus: '0.5'
memory: 2048M
```
|
1.0
|
Add documentation for how to configure resources for containers - I reverse engineered this from looking at the test code, but I suspect many other people will hit the same question: How do I give my ECS container more RAM/CPU resources?
Looks like it's a block like this
```
services:
# Backend service
backend:
deploy:
resources:
limits:
cpus: '0.5'
memory: 2048M
reservations:
cpus: '0.5'
memory: 2048M
```
|
non_process
|
add documentation for how to configure resources for containers i reverse engineered this from looking at the test code but i suspect many other people will hit the same question how do i give my ecs container more ram cpu resources looks like it s a block like this services backend service backend deploy resources limits cpus memory reservations cpus memory
| 0
|
9,443
| 12,426,527,223
|
IssuesEvent
|
2020-05-24 21:39:17
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
Date Filter Between does not contain the last day, (different behavior from previous versions)
|
Database/Postgres Priority:P2 Querying/Processor Type:Bug
|
"Between" date filter is not casting timestamps to date anymore (where the time is not mentioned) and it's causing the users get confused and the reports getting wrong.
- Databases: Postgres
- Metabase version: 0.31.1 & 0.31.2
- Metabase hosting environment: Ubuntu 16.04
- Metabase internal database: H2
-it happens when using custom queries
|
1.0
|
Date Filter Between does not contain the last day, (different behavior from previous versions) - "Between" date filter is not casting timestamps to date anymore (where the time is not mentioned) and it's causing the users get confused and the reports getting wrong.
- Databases: Postgres
- Metabase version: 0.31.1 & 0.31.2
- Metabase hosting environment: Ubuntu 16.04
- Metabase internal database: H2
-it happens when using custom queries
|
process
|
date filter between does not contain the last day different behavior from previous versions between date filter is not casting timestamps to date anymore where the time is not mentioned and it s causing the users get confused and the reports getting wrong databases postgres metabase version metabase hosting environment ubuntu metabase internal database it happens when using custom queries
| 1
|
232,428
| 18,874,173,981
|
IssuesEvent
|
2021-11-13 18:26:56
|
project-chip/connectedhomeip
|
https://api.github.com/repos/project-chip/connectedhomeip
|
closed
|
Add test support/helpers for CHIP
|
testing p1 V1.0 stale
|
#### Problem
Common test infrastructure is required specific for chip. Things like:
- I/O loop and timeouts
- Port selection if applicable, potential integration with a test framework (like happy) once we have integration/functional tests
- remove repetitive code for setup/bootstrapping, drivers, qemu integration. Worst case a 'boilerplate generator'
#### Proposed Solution
Start implementing shared infrastructure. #1237 calls for a better sharing of IO loop so we do not cross unrelated /test boundaries. That is a start and we can do more.
|
1.0
|
Add test support/helpers for CHIP - #### Problem
Common test infrastructure is required specific for chip. Things like:
- I/O loop and timeouts
- Port selection if applicable, potential integration with a test framework (like happy) once we have integration/functional tests
- remove repetitive code for setup/bootstrapping, drivers, qemu integration. Worst case a 'boilerplate generator'
#### Proposed Solution
Start implementing shared infrastructure. #1237 calls for a better sharing of IO loop so we do not cross unrelated /test boundaries. That is a start and we can do more.
|
non_process
|
add test support helpers for chip problem common test infrastructure is required specific for chip things like i o loop and timeouts port selection if applicable potential integration with a test framework like happy once we have integration functional tests remove repetitive code for setup bootstrapping drivers qemu integration worst case a boilerplate generator proposed solution start implementing shared infrastructure calls for a better sharing of io loop so we do not cross unrelated test boundaries that is a start and we can do more
| 0
|
98,856
| 4,032,035,057
|
IssuesEvent
|
2016-05-18 19:11:48
|
seemack/healthy-hearts-northwest-dev
|
https://api.github.com/repos/seemack/healthy-hearts-northwest-dev
|
opened
|
IV contacts exports notes indicate dropped practices
|
priority 1
|
1. Need to make sure dropping comments are in drop fields rather than IV contacts
2. Anyone without a coach associated should be either dropped or flagged for needing to assign - email Ross/Caitlin ASAP.
|
1.0
|
IV contacts exports notes indicate dropped practices - 1. Need to make sure dropping comments are in drop fields rather than IV contacts
2. Anyone without a coach associated should be either dropped or flagged for needing to assign - email Ross/Caitlin ASAP.
|
non_process
|
iv contacts exports notes indicate dropped practices need to make sure dropping comments are in drop fields rather than iv contacts anyone without a coach associated should be either dropped or flagged for needing to assign email ross caitlin asap
| 0
|
13,987
| 16,761,516,760
|
IssuesEvent
|
2021-06-13 22:02:49
|
Jeffail/benthos
|
https://api.github.com/repos/Jeffail/benthos
|
closed
|
Can we get also a driver for MS sql server?
|
enhancement outputs processors
|
Hello, I would love to use benthos in a project using MS SQL server.
It would be really great if there was support also for this database driver.
Do you have any plans for it / Would it be hard to add support for it?
Cheers
|
1.0
|
Can we get also a driver for MS sql server? - Hello, I would love to use benthos in a project using MS SQL server.
It would be really great if there was support also for this database driver.
Do you have any plans for it / Would it be hard to add support for it?
Cheers
|
process
|
can we get also a driver for ms sql server hello i would love to use benthos in a project using ms sql server it would be really great if there was support also for this database driver do you have any plans for it would it be hard to add support for it cheers
| 1
|
227,981
| 25,141,042,869
|
IssuesEvent
|
2022-11-09 23:11:02
|
samqws-devdemo/NodeGoat
|
https://api.github.com/repos/samqws-devdemo/NodeGoat
|
opened
|
forever-2.0.0.tgz: 9 vulnerabilities (highest severity is: 9.8)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>forever-2.0.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (forever version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-10747](https://www.mend.io/vulnerability-database/CVE-2019-10747) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | 3.0.0 | ✅ |
| [CVE-2019-10746](https://www.mend.io/vulnerability-database/CVE-2019-10746) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | mixin-deep-1.3.1.tgz | Transitive | 3.0.0 | ✅ |
| [CVE-2021-37712](https://www.mend.io/vulnerability-database/CVE-2021-37712) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.8.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2019-20149](https://www.mend.io/vulnerability-database/CVE-2019-20149) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | kind-of-6.0.2.tgz | Transitive | 3.0.0 | ✅ |
| [WS-2018-0148](https://hackerone.com/reports/321701) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-7788](https://www.mend.io/vulnerability-database/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.5.tgz | Transitive | 3.0.0 | ✅ |
| [CVE-2020-7774](https://www.mend.io/vulnerability-database/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | y18n-3.2.1.tgz | Transitive | 3.0.0 | ✅ |
| [CVE-2020-7598](https://www.mend.io/vulnerability-database/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | detected in multiple dependencies | Transitive | 3.0.0 | ❌ |
| [WS-2021-0154](https://github.com/gulpjs/glob-parent/commit/f9231168b0041fea3f8f954b3cceb56269fc6366) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | glob-parent-3.1.0.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10747</summary>
### Vulnerable Libraries - <b>set-value-0.4.3.tgz</b>, <b>set-value-2.0.0.tgz</b></p>
<p>
### <b>set-value-0.4.3.tgz</b></p>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz">https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/union-value/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- union-value-1.0.0.tgz
- :x: **set-value-0.4.3.tgz** (Vulnerable Library)
### <b>set-value-2.0.0.tgz</b></p>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz">https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- :x: **set-value-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
set-value is vulnerable to Prototype Pollution in versions lower than 3.0.1. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using any of the constructor, prototype and _proto_ payloads.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10747>CVE-2019-10747</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-29</p>
<p>Fix Resolution (set-value): 2.0.1</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p><p>Fix Resolution (set-value): 2.0.1</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10746</summary>
### Vulnerable Library - <b>mixin-deep-1.3.1.tgz</b></p>
<p>Deeply mix the properties of objects into the first object. Like merge-deep, but doesn't clone.</p>
<p>Library home page: <a href="https://registry.npmjs.org/mixin-deep/-/mixin-deep-1.3.1.tgz">https://registry.npmjs.org/mixin-deep/-/mixin-deep-1.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mixin-deep/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- :x: **mixin-deep-1.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
mixin-deep is vulnerable to Prototype Pollution in versions before 1.3.2 and version 2.0.0. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10746>CVE-2019-10746</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-23</p>
<p>Fix Resolution (mixin-deep): 1.3.2</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37712</summary>
### Vulnerable Library - <b>tar-4.4.8.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.8.tgz">https://registry.npmjs.org/tar/-/tar-4.4.8.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- :x: **tar-4.4.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 "short path" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37712>CVE-2021-37712</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p">https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20149</summary>
### Vulnerable Library - <b>kind-of-6.0.2.tgz</b></p>
<p>Get the native type of a value.</p>
<p>Library home page: <a href="https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz">https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/extglob/node_modules/kind-of/package.json,/node_modules/snapdragon-node/node_modules/kind-of/package.json,/node_modules/define-property/node_modules/kind-of/package.json,/node_modules/nanomatch/node_modules/kind-of/package.json,/node_modules/micromatch/node_modules/kind-of/package.json,/node_modules/base/node_modules/kind-of/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-node-2.1.1.tgz
- define-property-1.0.0.tgz
- is-descriptor-1.0.2.tgz
- :x: **kind-of-6.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ctorName in index.js in kind-of v6.0.2 allows external user input to overwrite certain internal attributes via a conflicting name, as demonstrated by 'constructor': {'name':'Symbol'}. Hence, a crafted payload can overwrite this builtin attribute to manipulate the type detection result.
<p>Publish Date: 2019-12-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20149>CVE-2019-20149</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution (kind-of): 6.0.3</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0148</summary>
### Vulnerable Libraries - <b>utile-0.3.0.tgz</b>, <b>utile-0.2.1.tgz</b></p>
<p>
### <b>utile-0.3.0.tgz</b></p>
<p>A drop-in replacement for `util` with some additional advantageous functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/utile/-/utile-0.3.0.tgz">https://registry.npmjs.org/utile/-/utile-0.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/utile/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- :x: **utile-0.3.0.tgz** (Vulnerable Library)
### <b>utile-0.2.1.tgz</b></p>
<p>A drop-in replacement for `util` with some additional advantageous functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/utile/-/utile-0.2.1.tgz">https://registry.npmjs.org/utile/-/utile-0.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/broadway/node_modules/utile/package.json,/node_modules/prompt/node_modules/utile/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- broadway-0.3.6.tgz
- :x: **utile-0.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The `utile` npm module, version 0.3.0, allows to extract sensitive data from uninitialized memory or to cause a DoS by passing in a large number, in setups where typed user input can be passed (e.g. from JSON).
<p>Publish Date: 2018-07-16
<p>URL: <a href=https://hackerone.com/reports/321701>WS-2018-0148</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/WS-2018-0148">https://nvd.nist.gov/vuln/detail/WS-2018-0148</a></p>
<p>Release Date: 2018-01-16</p>
<p>Fix Resolution: JetBrains.Rider.Frontend5 - 212.0.20210826.92917,212.0.20211008.220753</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7788</summary>
### Vulnerable Library - <b>ini-1.3.5.tgz</b></p>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.5.tgz">https://registry.npmjs.org/ini/-/ini-1.3.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **ini-1.3.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (ini): 1.3.6</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-3.2.1.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz">https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- nconf-0.10.0.tgz
- yargs-3.32.0.tgz
- :x: **y18n-3.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n = require('y18n')(); y18n.setLocale('__proto__'); y18n.updateLocale({polluted: true}); console.log(polluted); // true
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 3.2.2</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7598</summary>
### Vulnerable Libraries - <b>minimist-0.0.10.tgz</b>, <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p>
<p>
### <b>minimist-0.0.10.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
### <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
### <b>minimist-1.2.0.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution (minimist): 1.2.3</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2021-0154</summary>
### Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular Expression Denial of Service (ReDoS) vulnerability was found in glob-parent before 5.1.2.
<p>Publish Date: 2021-01-27
<p>URL: <a href=https://github.com/gulpjs/glob-parent/commit/f9231168b0041fea3f8f954b3cceb56269fc6366>WS-2021-0154</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-27</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
True
|
forever-2.0.0.tgz: 9 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>forever-2.0.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (forever version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-10747](https://www.mend.io/vulnerability-database/CVE-2019-10747) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | 3.0.0 | ✅ |
| [CVE-2019-10746](https://www.mend.io/vulnerability-database/CVE-2019-10746) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | mixin-deep-1.3.1.tgz | Transitive | 3.0.0 | ✅ |
| [CVE-2021-37712](https://www.mend.io/vulnerability-database/CVE-2021-37712) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.6 | tar-4.4.8.tgz | Transitive | 3.0.0 | ❌ |
| [CVE-2019-20149](https://www.mend.io/vulnerability-database/CVE-2019-20149) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | kind-of-6.0.2.tgz | Transitive | 3.0.0 | ✅ |
| [WS-2018-0148](https://hackerone.com/reports/321701) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-7788](https://www.mend.io/vulnerability-database/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.5.tgz | Transitive | 3.0.0 | ✅ |
| [CVE-2020-7774](https://www.mend.io/vulnerability-database/CVE-2020-7774) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | y18n-3.2.1.tgz | Transitive | 3.0.0 | ✅ |
| [CVE-2020-7598](https://www.mend.io/vulnerability-database/CVE-2020-7598) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.6 | detected in multiple dependencies | Transitive | 3.0.0 | ❌ |
| [WS-2021-0154](https://github.com/gulpjs/glob-parent/commit/f9231168b0041fea3f8f954b3cceb56269fc6366) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | glob-parent-3.1.0.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10747</summary>
### Vulnerable Libraries - <b>set-value-0.4.3.tgz</b>, <b>set-value-2.0.0.tgz</b></p>
<p>
### <b>set-value-0.4.3.tgz</b></p>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz">https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/union-value/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- union-value-1.0.0.tgz
- :x: **set-value-0.4.3.tgz** (Vulnerable Library)
### <b>set-value-2.0.0.tgz</b></p>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz">https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- :x: **set-value-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
set-value is vulnerable to Prototype Pollution in versions lower than 3.0.1. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using any of the constructor, prototype and _proto_ payloads.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10747>CVE-2019-10747</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-29</p>
<p>Fix Resolution (set-value): 2.0.1</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p><p>Fix Resolution (set-value): 2.0.1</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10746</summary>
### Vulnerable Library - <b>mixin-deep-1.3.1.tgz</b></p>
<p>Deeply mix the properties of objects into the first object. Like merge-deep, but doesn't clone.</p>
<p>Library home page: <a href="https://registry.npmjs.org/mixin-deep/-/mixin-deep-1.3.1.tgz">https://registry.npmjs.org/mixin-deep/-/mixin-deep-1.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/mixin-deep/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- :x: **mixin-deep-1.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
mixin-deep is vulnerable to Prototype Pollution in versions before 1.3.2 and version 2.0.0. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10746>CVE-2019-10746</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-23</p>
<p>Fix Resolution (mixin-deep): 1.3.2</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-37712</summary>
### Vulnerable Library - <b>tar-4.4.8.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-4.4.8.tgz">https://registry.npmjs.org/tar/-/tar-4.4.8.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- :x: **tar-4.4.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 "short path" counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p.
<p>Publish Date: 2021-08-31
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-37712>CVE-2021-37712</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p">https://github.com/npm/node-tar/security/advisories/GHSA-qq89-hq3f-393p</a></p>
<p>Release Date: 2021-08-31</p>
<p>Fix Resolution (tar): 4.4.18</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20149</summary>
### Vulnerable Library - <b>kind-of-6.0.2.tgz</b></p>
<p>Get the native type of a value.</p>
<p>Library home page: <a href="https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz">https://registry.npmjs.org/kind-of/-/kind-of-6.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/extglob/node_modules/kind-of/package.json,/node_modules/snapdragon-node/node_modules/kind-of/package.json,/node_modules/define-property/node_modules/kind-of/package.json,/node_modules/nanomatch/node_modules/kind-of/package.json,/node_modules/micromatch/node_modules/kind-of/package.json,/node_modules/base/node_modules/kind-of/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- braces-2.3.2.tgz
- snapdragon-node-2.1.1.tgz
- define-property-1.0.0.tgz
- is-descriptor-1.0.2.tgz
- :x: **kind-of-6.0.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ctorName in index.js in kind-of v6.0.2 allows external user input to overwrite certain internal attributes via a conflicting name, as demonstrated by 'constructor': {'name':'Symbol'}. Hence, a crafted payload can overwrite this builtin attribute to manipulate the type detection result.
<p>Publish Date: 2019-12-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20149>CVE-2019-20149</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-20149</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution (kind-of): 6.0.3</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0148</summary>
### Vulnerable Libraries - <b>utile-0.3.0.tgz</b>, <b>utile-0.2.1.tgz</b></p>
<p>
### <b>utile-0.3.0.tgz</b></p>
<p>A drop-in replacement for `util` with some additional advantageous functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/utile/-/utile-0.3.0.tgz">https://registry.npmjs.org/utile/-/utile-0.3.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/utile/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- :x: **utile-0.3.0.tgz** (Vulnerable Library)
### <b>utile-0.2.1.tgz</b></p>
<p>A drop-in replacement for `util` with some additional advantageous functions</p>
<p>Library home page: <a href="https://registry.npmjs.org/utile/-/utile-0.2.1.tgz">https://registry.npmjs.org/utile/-/utile-0.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/broadway/node_modules/utile/package.json,/node_modules/prompt/node_modules/utile/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- broadway-0.3.6.tgz
- :x: **utile-0.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The `utile` npm module, version 0.3.0, allows to extract sensitive data from uninitialized memory or to cause a DoS by passing in a large number, in setups where typed user input can be passed (e.g. from JSON).
<p>Publish Date: 2018-07-16
<p>URL: <a href=https://hackerone.com/reports/321701>WS-2018-0148</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/WS-2018-0148">https://nvd.nist.gov/vuln/detail/WS-2018-0148</a></p>
<p>Release Date: 2018-01-16</p>
<p>Fix Resolution: JetBrains.Rider.Frontend5 - 212.0.20210826.92917,212.0.20211008.220753</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7788</summary>
### Vulnerable Library - <b>ini-1.3.5.tgz</b></p>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.5.tgz">https://registry.npmjs.org/ini/-/ini-1.3.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **ini-1.3.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution (ini): 1.3.6</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-7774</summary>
### Vulnerable Library - <b>y18n-3.2.1.tgz</b></p>
<p>the bare-bones internationalization library used by yargs</p>
<p>Library home page: <a href="https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz">https://registry.npmjs.org/y18n/-/y18n-3.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/y18n/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- nconf-0.10.0.tgz
- yargs-3.32.0.tgz
- :x: **y18n-3.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package y18n before 3.2.2, 4.0.1 and 5.0.5. PoC by po6ix: const y18n = require('y18n')(); y18n.setLocale('__proto__'); y18n.updateLocale({polluted: true}); console.log(polluted); // true
<p>Publish Date: 2020-11-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7774>CVE-2020-7774</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1654">https://www.npmjs.com/advisories/1654</a></p>
<p>Release Date: 2020-11-17</p>
<p>Fix Resolution (y18n): 3.2.2</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-7598</summary>
### Vulnerable Libraries - <b>minimist-0.0.10.tgz</b>, <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p>
<p>
### <b>minimist-0.0.10.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- optimist-0.6.1.tgz
- :x: **minimist-0.0.10.tgz** (Vulnerable Library)
### <b>minimist-0.0.8.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
### <b>minimist-1.2.0.tgz</b></p>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- fsevents-1.2.9.tgz
- node-pre-gyp-0.12.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.6</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution (minimist): 1.2.3</p>
<p>Direct dependency fix Resolution (forever): 3.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2021-0154</summary>
### Vulnerable Library - <b>glob-parent-3.1.0.tgz</b></p>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- forever-2.0.0.tgz (Root Library)
- forever-monitor-2.0.0.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-devdemo/NodeGoat/commit/780abdaec366f369deebc3641b8e229d8adaaebf">780abdaec366f369deebc3641b8e229d8adaaebf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular Expression Denial of Service (ReDoS) vulnerability was found in glob-parent before 5.1.2.
<p>Publish Date: 2021-01-27
<p>URL: <a href=https://github.com/gulpjs/glob-parent/commit/f9231168b0041fea3f8f954b3cceb56269fc6366>WS-2021-0154</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-27</p>
<p>Fix Resolution: glob-parent - 5.1.2</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
non_process
|
forever tgz vulnerabilities highest severity is vulnerable library forever tgz path to dependency file package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in forever version remediation available high detected in multiple dependencies transitive high mixin deep tgz transitive high tar tgz transitive high kind of tgz transitive high detected in multiple dependencies transitive n a high ini tgz transitive high tgz transitive medium detected in multiple dependencies transitive medium glob parent tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable libraries set value tgz set value tgz set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file package json path to vulnerable library node modules union value node modules set value package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz braces tgz snapdragon tgz base tgz cache base tgz union value tgz x set value tgz vulnerable library set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file package json path to vulnerable library node modules set value package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz braces tgz snapdragon tgz base tgz cache base tgz x set value tgz vulnerable library found in head commit a href found in base branch master vulnerability details set value is vulnerable to prototype pollution in versions lower than the function mixin deep could be tricked into adding or modifying properties of object prototype using any of the constructor prototype and proto payloads publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution set value direct dependency fix resolution forever fix resolution set value direct dependency fix resolution forever rescue worker helmet automatic remediation is available for this issue cve vulnerable library mixin deep tgz deeply mix the properties of objects into the first object like merge deep but doesn t clone library home page a href path to dependency file package json path to vulnerable library node modules mixin deep package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz braces tgz snapdragon tgz base tgz x mixin deep tgz vulnerable library found in head commit a href found in base branch master vulnerability details mixin deep is vulnerable to prototype pollution in versions before and version the function mixin deep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution mixin deep direct dependency fix resolution forever rescue worker helmet automatic remediation is available for this issue cve vulnerable library tar tgz tar for node library home page a href dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz fsevents tgz node pre gyp tgz x tar tgz vulnerable library found in head commit a href found in base branch master vulnerability details the npm package tar aka node tar before versions and has an arbitrary file creation overwrite and arbitrary code execution vulnerability node tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted this is in part achieved by ensuring that extracted directories are not symlinks additionally in order to prevent unnecessary stat calls to determine whether a given path is a directory paths are cached when directories are created this logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value additionally on windows systems long path portions would resolve to the same file system entities as their short path counterparts a specially crafted tar archive could thus include a directory with one form of the path followed by a symbolic link with a different string that resolves to the same file system entity followed by a file using the first form by first creating a directory and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem it was thus possible to bypass node tar symlink checks on directories essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location thus allowing arbitrary file creation and overwrite these issues were addressed in releases and the branch of node tar has been deprecated and did not receive patches for these issues if you are still using a release we recommend you update to a more recent version of node tar if this is not possible a workaround is available in the referenced ghsa publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution forever cve vulnerable library kind of tgz get the native type of a value library home page a href path to dependency file package json path to vulnerable library node modules extglob node modules kind of package json node modules snapdragon node node modules kind of package json node modules define property node modules kind of package json node modules nanomatch node modules kind of package json node modules micromatch node modules kind of package json node modules base node modules kind of package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz braces tgz snapdragon node tgz define property tgz is descriptor tgz x kind of tgz vulnerable library found in head commit a href found in base branch master vulnerability details ctorname in index js in kind of allows external user input to overwrite certain internal attributes via a conflicting name as demonstrated by constructor name symbol hence a crafted payload can overwrite this builtin attribute to manipulate the type detection result publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution kind of direct dependency fix resolution forever rescue worker helmet automatic remediation is available for this issue ws vulnerable libraries utile tgz utile tgz utile tgz a drop in replacement for util with some additional advantageous functions library home page a href path to dependency file package json path to vulnerable library node modules utile package json dependency hierarchy forever tgz root library x utile tgz vulnerable library utile tgz a drop in replacement for util with some additional advantageous functions library home page a href path to dependency file package json path to vulnerable library node modules broadway node modules utile package json node modules prompt node modules utile package json dependency hierarchy forever tgz root library forever monitor tgz broadway tgz x utile tgz vulnerable library found in head commit a href found in base branch master vulnerability details the utile npm module version allows to extract sensitive data from uninitialized memory or to cause a dos by passing in a large number in setups where typed user input can be passed e g from json publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jetbrains rider cve vulnerable library ini tgz an ini encoder decoder for node library home page a href path to dependency file package json path to vulnerable library node modules ini package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz fsevents tgz node pre gyp tgz rc tgz x ini tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ini direct dependency fix resolution forever rescue worker helmet automatic remediation is available for this issue cve vulnerable library tgz the bare bones internationalization library used by yargs library home page a href path to dependency file package json path to vulnerable library node modules package json dependency hierarchy forever tgz root library nconf tgz yargs tgz x tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package before and poc by const require setlocale proto updatelocale polluted true console log polluted true publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution direct dependency fix resolution forever rescue worker helmet automatic remediation is available for this issue cve vulnerable libraries minimist tgz minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library node modules minimist package json dependency hierarchy forever tgz root library optimist tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz fsevents tgz node pre gyp tgz mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz fsevents tgz node pre gyp tgz rc tgz x minimist tgz vulnerable library found in head commit a href found in base branch master vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution minimist direct dependency fix resolution forever ws vulnerable library glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file package json path to vulnerable library node modules glob parent package json dependency hierarchy forever tgz root library forever monitor tgz chokidar tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details regular expression denial of service redos vulnerability was found in glob parent before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution glob parent rescue worker helmet automatic remediation is available for this issue
| 0
|
19,116
| 25,169,318,471
|
IssuesEvent
|
2022-11-11 00:45:54
|
googleapis/nodejs-kms
|
https://api.github.com/repos/googleapis/nodejs-kms
|
closed
|
Your .repo-metadata.json file has a problem 🤒
|
type: process api: cloudkms repo-metadata: lint
|
You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'kms' invalid in .repo-metadata.json
☝️ Once you address these problems, you can close this issue.
### Need help?
* [Schema definition](https://github.com/googleapis/repo-automation-bots/blob/main/packages/repo-metadata-lint/src/repo-metadata-schema.json): lists valid options for each field.
* [API index](https://github.com/googleapis/googleapis/blob/master/api-index-v1.json): for gRPC libraries **api_shortname** should match the subdomain of an API's **hostName**.
* Reach out to **go/github-automation** if you have any questions.
|
1.0
|
Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'kms' invalid in .repo-metadata.json
☝️ Once you address these problems, you can close this issue.
### Need help?
* [Schema definition](https://github.com/googleapis/repo-automation-bots/blob/main/packages/repo-metadata-lint/src/repo-metadata-schema.json): lists valid options for each field.
* [API index](https://github.com/googleapis/googleapis/blob/master/api-index-v1.json): for gRPC libraries **api_shortname** should match the subdomain of an API's **hostName**.
* Reach out to **go/github-automation** if you have any questions.
|
process
|
your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 api shortname kms invalid in repo metadata json ☝️ once you address these problems you can close this issue need help lists valid options for each field for grpc libraries api shortname should match the subdomain of an api s hostname reach out to go github automation if you have any questions
| 1
|
72,536
| 31,768,933,876
|
IssuesEvent
|
2023-09-12 10:29:14
|
gauravrs18/issue_onboarding
|
https://api.github.com/repos/gauravrs18/issue_onboarding
|
closed
|
dev-angular-integration-account-services-new-connection-component-connect-component
-consumer-details-component
-connect-component
-address-component
|
CX-account-services
|
dev-angular-integration-account-services-new-connection-component-connect-component
-consumer-details-component
-connect-component
-address-component
|
1.0
|
dev-angular-integration-account-services-new-connection-component-connect-component
-consumer-details-component
-connect-component
-address-component - dev-angular-integration-account-services-new-connection-component-connect-component
-consumer-details-component
-connect-component
-address-component
|
non_process
|
dev angular integration account services new connection component connect component consumer details component connect component address component dev angular integration account services new connection component connect component consumer details component connect component address component
| 0
|
41,115
| 6,891,766,680
|
IssuesEvent
|
2017-11-22 18:14:26
|
brave/browser-laptop
|
https://api.github.com/repos/brave/browser-laptop
|
closed
|
Update Privacy Policy and Terms of Use files
|
documentation ✍ impact/high needs-investigation stale
|
Before 1.0 can be released, changes and additions to our Privacy Policy and Terms of Use files will need to be completed based on differences since the last revisions.
|
1.0
|
Update Privacy Policy and Terms of Use files - Before 1.0 can be released, changes and additions to our Privacy Policy and Terms of Use files will need to be completed based on differences since the last revisions.
|
non_process
|
update privacy policy and terms of use files before can be released changes and additions to our privacy policy and terms of use files will need to be completed based on differences since the last revisions
| 0
|
3,243
| 6,308,002,192
|
IssuesEvent
|
2017-07-22 07:32:56
|
cyipt/cyipt
|
https://api.github.com/repos/cyipt/cyipt
|
closed
|
Access Cyclescape data
|
data preprocessing
|
Preferably as geojson in the example-data repo and pls post code that did it here.
|
1.0
|
Access Cyclescape data - Preferably as geojson in the example-data repo and pls post code that did it here.
|
process
|
access cyclescape data preferably as geojson in the example data repo and pls post code that did it here
| 1
|
21,605
| 30,007,536,869
|
IssuesEvent
|
2023-06-26 13:22:28
|
scverse/anndata
|
https://api.github.com/repos/scverse/anndata
|
opened
|
PR checks for dev process PRs?
|
enhancement dev process
|
### Please describe your wishes and possible alternatives to achieve the desired result.
I don't think we need to have a milestone on dev process PRs like #1024
Maybe we allow milestone OR dev process tag?
|
1.0
|
PR checks for dev process PRs? - ### Please describe your wishes and possible alternatives to achieve the desired result.
I don't think we need to have a milestone on dev process PRs like #1024
Maybe we allow milestone OR dev process tag?
|
process
|
pr checks for dev process prs please describe your wishes and possible alternatives to achieve the desired result i don t think we need to have a milestone on dev process prs like maybe we allow milestone or dev process tag
| 1
|
27,859
| 13,443,229,536
|
IssuesEvent
|
2020-09-08 08:02:50
|
solid/community-server
|
https://api.github.com/repos/solid/community-server
|
reopened
|
Delay with conneg; apparently we're buffering instead of streaming
|
performance 🐌
|
```bash
curl -s https://csarven.ca/linked-research-decentralised-web > thesis.html
curl -X PUT -H "Content-Type: text/html" -T thesis.html http://localhost:3000/thesis.html
curl -s http://localhost:3000/thesis.html | wc -l
time curl http://localhost:3000/thesis.html -H "Accept: text/turtle" | head
```
Gives me a 1.2–1.4 second delay, whereas I expect it to be streaming immediately.
Are we sure we are streaming all the way through?
|
True
|
Delay with conneg; apparently we're buffering instead of streaming - ```bash
curl -s https://csarven.ca/linked-research-decentralised-web > thesis.html
curl -X PUT -H "Content-Type: text/html" -T thesis.html http://localhost:3000/thesis.html
curl -s http://localhost:3000/thesis.html | wc -l
time curl http://localhost:3000/thesis.html -H "Accept: text/turtle" | head
```
Gives me a 1.2–1.4 second delay, whereas I expect it to be streaming immediately.
Are we sure we are streaming all the way through?
|
non_process
|
delay with conneg apparently we re buffering instead of streaming bash curl s thesis html curl x put h content type text html t thesis html curl s wc l time curl h accept text turtle head gives me a – second delay whereas i expect it to be streaming immediately are we sure we are streaming all the way through
| 0
|
4,568
| 7,395,884,709
|
IssuesEvent
|
2018-03-18 04:27:55
|
kookmin-sw/2018-cap1-2
|
https://api.github.com/repos/kookmin-sw/2018-cap1-2
|
opened
|
가능한 경우 및 오류 관련 상세 설명
|
ImageProcessing Interpreter Server
|
1. 성공 -> 멀쩡히 잘 됨
2. 로지컬 에러 -> 수도 코드 문법에 잘못이 있거나, 혹은 수도 코드가 멀쩡히 추출되지 않았을 경우
3. 시스템 에러 -> 통신 등 기타 에러
2번 에러 관련하여 논의가 필요합니다.
수도 코드가 멀쩡히 안 나오는 경우라는 것은 글씨가 이상하거나 혹은 사진이 잘못 찍혀서 인식이 불량한 경우를 뜻합니다.
이러한 경우에 일단 수도 코드를 추출하여 잘못된 수도 코드를 반환하여 줄 것인지 아니면 시스템 에러로 반환 할 것인지에 대한 논의도 필요하며, 전자의 경우로 진행할 경우 어떤식으로 통신을 하고 블랭크 라인이 들어오는 상황이 발생할 가능성이 있어 다양한 논의가 필요할 것입니다.
|
1.0
|
가능한 경우 및 오류 관련 상세 설명 - 1. 성공 -> 멀쩡히 잘 됨
2. 로지컬 에러 -> 수도 코드 문법에 잘못이 있거나, 혹은 수도 코드가 멀쩡히 추출되지 않았을 경우
3. 시스템 에러 -> 통신 등 기타 에러
2번 에러 관련하여 논의가 필요합니다.
수도 코드가 멀쩡히 안 나오는 경우라는 것은 글씨가 이상하거나 혹은 사진이 잘못 찍혀서 인식이 불량한 경우를 뜻합니다.
이러한 경우에 일단 수도 코드를 추출하여 잘못된 수도 코드를 반환하여 줄 것인지 아니면 시스템 에러로 반환 할 것인지에 대한 논의도 필요하며, 전자의 경우로 진행할 경우 어떤식으로 통신을 하고 블랭크 라인이 들어오는 상황이 발생할 가능성이 있어 다양한 논의가 필요할 것입니다.
|
process
|
가능한 경우 및 오류 관련 상세 설명 성공 멀쩡히 잘 됨 로지컬 에러 수도 코드 문법에 잘못이 있거나 혹은 수도 코드가 멀쩡히 추출되지 않았을 경우 시스템 에러 통신 등 기타 에러 에러 관련하여 논의가 필요합니다 수도 코드가 멀쩡히 안 나오는 경우라는 것은 글씨가 이상하거나 혹은 사진이 잘못 찍혀서 인식이 불량한 경우를 뜻합니다 이러한 경우에 일단 수도 코드를 추출하여 잘못된 수도 코드를 반환하여 줄 것인지 아니면 시스템 에러로 반환 할 것인지에 대한 논의도 필요하며 전자의 경우로 진행할 경우 어떤식으로 통신을 하고 블랭크 라인이 들어오는 상황이 발생할 가능성이 있어 다양한 논의가 필요할 것입니다
| 1
|
16,826
| 22,060,961,141
|
IssuesEvent
|
2022-05-30 17:45:43
|
bitPogo/kmock
|
https://api.github.com/repos/bitPogo/kmock
|
closed
|
Augment spyOn
|
enhancement kmock-processor kmock-gradle
|
## Description
<!--- Provide a detailed introduction to the issue itself, and why you consider it to be a bug -->
`spyOn` mostly adds to custom optimisation, but can be error prone and inconvenient. Therefore an additional flag to enableAll the spies might be a good addition to complement the selective approach.
Acceptance Criteria:
* Add to the GradleExtension a flag and propagate the change to the processor which enables for all (applicable) Mocks Spies
|
1.0
|
Augment spyOn - ## Description
<!--- Provide a detailed introduction to the issue itself, and why you consider it to be a bug -->
`spyOn` mostly adds to custom optimisation, but can be error prone and inconvenient. Therefore an additional flag to enableAll the spies might be a good addition to complement the selective approach.
Acceptance Criteria:
* Add to the GradleExtension a flag and propagate the change to the processor which enables for all (applicable) Mocks Spies
|
process
|
augment spyon description spyon mostly adds to custom optimisation but can be error prone and inconvenient therefore an additional flag to enableall the spies might be a good addition to complement the selective approach acceptance criteria add to the gradleextension a flag and propagate the change to the processor which enables for all applicable mocks spies
| 1
|
181,946
| 14,894,244,905
|
IssuesEvent
|
2021-01-21 07:10:54
|
VenkatasubramanianV/VmX-Test
|
https://api.github.com/repos/VenkatasubramanianV/VmX-Test
|
opened
|
Creating Ingestion Strategies
|
documentation
|
@Dhivya Please prepare a document to explain the steps involved in creating ingestion strategies.
|
1.0
|
Creating Ingestion Strategies - @Dhivya Please prepare a document to explain the steps involved in creating ingestion strategies.
|
non_process
|
creating ingestion strategies dhivya please prepare a document to explain the steps involved in creating ingestion strategies
| 0
|
229,736
| 17,576,484,382
|
IssuesEvent
|
2021-08-15 18:03:38
|
UnBArqDsw2021-1/2021.1_G02_TaNaMesa_docs
|
https://api.github.com/repos/UnBArqDsw2021-1/2021.1_G02_TaNaMesa_docs
|
opened
|
Backlog do Produto
|
documentation
|
## Descrição da issue
Criação do backlog do produto com suas priorizações
## Contexto adicional
QUalquer outro contexto como prints, citações, dados...
## Tópicos:
- [ ] Tópico 1
- [ ] Tópico 2
- [ ] Tópico 3
|
1.0
|
Backlog do Produto - ## Descrição da issue
Criação do backlog do produto com suas priorizações
## Contexto adicional
QUalquer outro contexto como prints, citações, dados...
## Tópicos:
- [ ] Tópico 1
- [ ] Tópico 2
- [ ] Tópico 3
|
non_process
|
backlog do produto descrição da issue criação do backlog do produto com suas priorizações contexto adicional qualquer outro contexto como prints citações dados tópicos tópico tópico tópico
| 0
|
85,267
| 16,624,265,552
|
IssuesEvent
|
2021-06-03 07:35:52
|
HydrolienF/Formiko
|
https://api.github.com/repos/HydrolienF/Formiko
|
closed
|
implement View #175 with GUI2D : ViewGUI
|
code reorganization doing done graphics
|
- [x] Game should work with all function of ViewGUI2d
- [x] ViewGUI need to be link to all Panel.
- [ ] To switch to an other panel it need to swap main panel in Fenetre to an other 1.
- [x] Any panel can be draw anytime. So we need to check that frame exist and add it if not.
- [x] launch of PanneauMenu kill cheat code listening, it shoundn't.
|
1.0
|
implement View #175 with GUI2D : ViewGUI - - [x] Game should work with all function of ViewGUI2d
- [x] ViewGUI need to be link to all Panel.
- [ ] To switch to an other panel it need to swap main panel in Fenetre to an other 1.
- [x] Any panel can be draw anytime. So we need to check that frame exist and add it if not.
- [x] launch of PanneauMenu kill cheat code listening, it shoundn't.
|
non_process
|
implement view with viewgui game should work with all function of viewgui need to be link to all panel to switch to an other panel it need to swap main panel in fenetre to an other any panel can be draw anytime so we need to check that frame exist and add it if not launch of panneaumenu kill cheat code listening it shoundn t
| 0
|
614,675
| 19,188,113,190
|
IssuesEvent
|
2021-12-05 14:54:19
|
projectdiscovery/nuclei
|
https://api.github.com/repos/projectdiscovery/nuclei
|
closed
|
Performance review of nuclei engine in dev branch
|
Priority: High Status: Completed Type: Bug
|
<!--
1. Please search to see if an issue already exists for the bug you encountered.
2. For support requests, FAQs or "How to" questions, please use the GitHub Discussions section instead - https://github.com/projectdiscovery/nuclei/discussions or
3. Join our discord server at https://discord.gg/projectdiscovery and post the question on the #nuclei channel.
-->
<!-- ISSUES MISSING IMPORTANT INFORMATION MAY BE CLOSED WITHOUT INVESTIGATION. -->
### Nuclei version:
dev version
### Current Behavior:
Lots of code has been changed/added/updated after the last release of nuclei, as a result, new issues are also introduced causing increased scan time and parsing error with few templates that used to work with the older releases which need to be investigated.
I've added a reproducible example of nuclei scan running on locally hosted **simplehttpserver** to compare the changes.
### Steps To Reproduce:
<details>
<summary>Running Nuclei v2.5.3</summary>
```console
time nuclei -u http://0.0.0.0:46573 -stats -c 100
__ _
____ __ _______/ /__ (_)
/ __ \/ / / / ___/ / _ \/ /
/ / / / /_/ / /__/ / __/ /
/_/ /_/\__,_/\___/_/\___/_/ 2.5.3
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions.
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] Using Nuclei Engine 2.5.3 (latest)
[INF] Using Nuclei Templates 8.6.8 (latest)
[INF] Using Interactsh Server https://interactsh.com
[INF] Templates added in last update: 0
[INF] Templates loaded for scan: 2502
[INF] Templates clustered: 381 (Reduced 349 HTTP Requests)
[0:00:05] | Templates: 2502 | Hosts: 1 | RPS: 150 | Matched: 1 | Errors: 27 | Requests: 751/3426 (21%)
[0:00:10] | Templates: 2502 | Hosts: 1 | RPS: 151 | Matched: 17 | Errors: 64 | Requests: 1515/3426 (44%)
[0:00:15] | Templates: 2502 | Hosts: 1 | RPS: 151 | Matched: 18 | Errors: 88 | Requests: 2274/3426 (66%)
[0:00:20] | Templates: 2502 | Hosts: 1 | RPS: 151 | Matched: 18 | Errors: 111 | Requests: 3021/3426 (88%)
[0:00:25] | Templates: 2502 | Hosts: 1 | RPS: 131 | Matched: 18 | Errors: 113 | Requests: 3290/3426 (96%)
[0:00:29] | Templates: 2502 | Hosts: 1 | RPS: 113 | Matched: 18 | Errors: 113 | Requests: 3290/3426 (96%)
real 0m30.139s
user 0m4.263s
sys 0m1.250s
```
</details>
<details>
<summary>Running Nuclei v2.5.3-dev</summary>
```console
time ./nuclei -u http://0.0.0.0:46573 -stats -c 100
__ _
____ __ _______/ /__ (_)
/ __ \/ / / / ___/ / _ \/ /
/ / / / /_/ / /__/ / __/ /
/_/ /_/\__,_/\___/_/\___/_/ 2.5.4-dev
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions.
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] Using Nuclei Engine 2.5.4-dev (development)
[INF] Using Nuclei Templates 8.6.8 (latest)
[INF] Using Interactsh Server https://interactsh.com
[INF] Templates added in last update: 0
[INF] Templates loaded for scan: 2506
[INF] Templates clustered: 381 (Reduced 349 HTTP Requests)
[0:00:00] | Templates: 2506 | Hosts: 1 | RPS: 0 | Matched: 0 | Errors: 0 | Requests: 0/3326 (0%)
[0:00:05] | Templates: 2506 | Hosts: 1 | RPS: 66 | Matched: 0 | Errors: 11 | Requests: 331/3326 (9%)
[0:00:10] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 0 | Errors: 12 | Requests: 344/3326 (10%)
[0:00:15] | Templates: 2506 | Hosts: 1 | RPS: 36 | Matched: 0 | Errors: 17 | Requests: 553/3326 (16%)
[0:00:20] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 0 | Errors: 22 | Requests: 685/3326 (20%)
[0:00:25] | Templates: 2506 | Hosts: 1 | RPS: 32 | Matched: 0 | Errors: 25 | Requests: 805/3326 (24%)
[0:00:30] | Templates: 2506 | Hosts: 1 | RPS: 32 | Matched: 0 | Errors: 29 | Requests: 989/3326 (29%)
[0:00:35] | Templates: 2506 | Hosts: 1 | RPS: 38 | Matched: 0 | Errors: 45 | Requests: 1339/3326 (40%)
[0:00:40] | Templates: 2506 | Hosts: 1 | RPS: 36 | Matched: 1 | Errors: 45 | Requests: 1468/3326 (44%)
[0:00:45] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 1 | Errors: 47 | Requests: 1553/3326 (46%)
[0:00:50] | Templates: 2506 | Hosts: 1 | RPS: 33 | Matched: 1 | Errors: 55 | Requests: 1686/3326 (50%)
[0:00:55] | Templates: 2506 | Hosts: 1 | RPS: 38 | Matched: 2 | Errors: 69 | Requests: 2142/3326 (64%)
[0:01:00] | Templates: 2506 | Hosts: 1 | RPS: 36 | Matched: 2 | Errors: 72 | Requests: 2199/3326 (66%)
[0:01:05] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 2 | Errors: 73 | Requests: 2233/3326 (67%)
[0:01:10] | Templates: 2506 | Hosts: 1 | RPS: 32 | Matched: 2 | Errors: 79 | Requests: 2291/3326 (68%)
[0:01:15] | Templates: 2506 | Hosts: 1 | RPS: 30 | Matched: 2 | Errors: 79 | Requests: 2291/3326 (68%)
[0:01:20] | Templates: 2506 | Hosts: 1 | RPS: 30 | Matched: 2 | Errors: 82 | Requests: 2436/3326 (73%)
[0:01:25] | Templates: 2506 | Hosts: 1 | RPS: 30 | Matched: 2 | Errors: 89 | Requests: 2606/3326 (78%)
[0:01:30] | Templates: 2506 | Hosts: 1 | RPS: 29 | Matched: 2 | Errors: 91 | Requests: 2657/3326 (79%)
[0:01:35] | Templates: 2506 | Hosts: 1 | RPS: 28 | Matched: 2 | Errors: 91 | Requests: 2678/3326 (80%)
[0:01:40] | Templates: 2506 | Hosts: 1 | RPS: 28 | Matched: 17 | Errors: 99 | Requests: 2833/3326 (85%)
[0:01:45] | Templates: 2506 | Hosts: 1 | RPS: 27 | Matched: 17 | Errors: 102 | Requests: 2935/3326 (88%)
[0:01:50] | Templates: 2506 | Hosts: 1 | RPS: 27 | Matched: 17 | Errors: 105 | Requests: 3029/3326 (91%)
[0:01:55] | Templates: 2506 | Hosts: 1 | RPS: 27 | Matched: 17 | Errors: 109 | Requests: 3127/3326 (94%)
[0:02:00] | Templates: 2506 | Hosts: 1 | RPS: 26 | Matched: 18 | Errors: 111 | Requests: 3181/3326 (95%)
[0:02:05] | Templates: 2506 | Hosts: 1 | RPS: 25 | Matched: 18 | Errors: 112 | Requests: 3189/3326 (95%)
[0:02:06] | Templates: 2506 | Hosts: 1 | RPS: 25 | Matched: 18 | Errors: 112 | Requests: 3189/3326 (95%)
real 2m6.575s
user 0m4.465s
sys 0m1.415s
```
</details>
### Items to investigate:
- [ ] 4x increase in scan time with dev version
- [ ] Mismatched template loading on default run
- `misconfiguration/gitlab/gitlab-api-user-enum.yaml` works with stable release but not with dev version.
### Anything else:
This issue also blocks the new release of nuclei engine.
|
1.0
|
Performance review of nuclei engine in dev branch - <!--
1. Please search to see if an issue already exists for the bug you encountered.
2. For support requests, FAQs or "How to" questions, please use the GitHub Discussions section instead - https://github.com/projectdiscovery/nuclei/discussions or
3. Join our discord server at https://discord.gg/projectdiscovery and post the question on the #nuclei channel.
-->
<!-- ISSUES MISSING IMPORTANT INFORMATION MAY BE CLOSED WITHOUT INVESTIGATION. -->
### Nuclei version:
dev version
### Current Behavior:
Lots of code has been changed/added/updated after the last release of nuclei, as a result, new issues are also introduced causing increased scan time and parsing error with few templates that used to work with the older releases which need to be investigated.
I've added a reproducible example of nuclei scan running on locally hosted **simplehttpserver** to compare the changes.
### Steps To Reproduce:
<details>
<summary>Running Nuclei v2.5.3</summary>
```console
time nuclei -u http://0.0.0.0:46573 -stats -c 100
__ _
____ __ _______/ /__ (_)
/ __ \/ / / / ___/ / _ \/ /
/ / / / /_/ / /__/ / __/ /
/_/ /_/\__,_/\___/_/\___/_/ 2.5.3
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions.
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] Using Nuclei Engine 2.5.3 (latest)
[INF] Using Nuclei Templates 8.6.8 (latest)
[INF] Using Interactsh Server https://interactsh.com
[INF] Templates added in last update: 0
[INF] Templates loaded for scan: 2502
[INF] Templates clustered: 381 (Reduced 349 HTTP Requests)
[0:00:05] | Templates: 2502 | Hosts: 1 | RPS: 150 | Matched: 1 | Errors: 27 | Requests: 751/3426 (21%)
[0:00:10] | Templates: 2502 | Hosts: 1 | RPS: 151 | Matched: 17 | Errors: 64 | Requests: 1515/3426 (44%)
[0:00:15] | Templates: 2502 | Hosts: 1 | RPS: 151 | Matched: 18 | Errors: 88 | Requests: 2274/3426 (66%)
[0:00:20] | Templates: 2502 | Hosts: 1 | RPS: 151 | Matched: 18 | Errors: 111 | Requests: 3021/3426 (88%)
[0:00:25] | Templates: 2502 | Hosts: 1 | RPS: 131 | Matched: 18 | Errors: 113 | Requests: 3290/3426 (96%)
[0:00:29] | Templates: 2502 | Hosts: 1 | RPS: 113 | Matched: 18 | Errors: 113 | Requests: 3290/3426 (96%)
real 0m30.139s
user 0m4.263s
sys 0m1.250s
```
</details>
<details>
<summary>Running Nuclei v2.5.3-dev</summary>
```console
time ./nuclei -u http://0.0.0.0:46573 -stats -c 100
__ _
____ __ _______/ /__ (_)
/ __ \/ / / / ___/ / _ \/ /
/ / / / /_/ / /__/ / __/ /
/_/ /_/\__,_/\___/_/\___/_/ 2.5.4-dev
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions.
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] Using Nuclei Engine 2.5.4-dev (development)
[INF] Using Nuclei Templates 8.6.8 (latest)
[INF] Using Interactsh Server https://interactsh.com
[INF] Templates added in last update: 0
[INF] Templates loaded for scan: 2506
[INF] Templates clustered: 381 (Reduced 349 HTTP Requests)
[0:00:00] | Templates: 2506 | Hosts: 1 | RPS: 0 | Matched: 0 | Errors: 0 | Requests: 0/3326 (0%)
[0:00:05] | Templates: 2506 | Hosts: 1 | RPS: 66 | Matched: 0 | Errors: 11 | Requests: 331/3326 (9%)
[0:00:10] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 0 | Errors: 12 | Requests: 344/3326 (10%)
[0:00:15] | Templates: 2506 | Hosts: 1 | RPS: 36 | Matched: 0 | Errors: 17 | Requests: 553/3326 (16%)
[0:00:20] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 0 | Errors: 22 | Requests: 685/3326 (20%)
[0:00:25] | Templates: 2506 | Hosts: 1 | RPS: 32 | Matched: 0 | Errors: 25 | Requests: 805/3326 (24%)
[0:00:30] | Templates: 2506 | Hosts: 1 | RPS: 32 | Matched: 0 | Errors: 29 | Requests: 989/3326 (29%)
[0:00:35] | Templates: 2506 | Hosts: 1 | RPS: 38 | Matched: 0 | Errors: 45 | Requests: 1339/3326 (40%)
[0:00:40] | Templates: 2506 | Hosts: 1 | RPS: 36 | Matched: 1 | Errors: 45 | Requests: 1468/3326 (44%)
[0:00:45] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 1 | Errors: 47 | Requests: 1553/3326 (46%)
[0:00:50] | Templates: 2506 | Hosts: 1 | RPS: 33 | Matched: 1 | Errors: 55 | Requests: 1686/3326 (50%)
[0:00:55] | Templates: 2506 | Hosts: 1 | RPS: 38 | Matched: 2 | Errors: 69 | Requests: 2142/3326 (64%)
[0:01:00] | Templates: 2506 | Hosts: 1 | RPS: 36 | Matched: 2 | Errors: 72 | Requests: 2199/3326 (66%)
[0:01:05] | Templates: 2506 | Hosts: 1 | RPS: 34 | Matched: 2 | Errors: 73 | Requests: 2233/3326 (67%)
[0:01:10] | Templates: 2506 | Hosts: 1 | RPS: 32 | Matched: 2 | Errors: 79 | Requests: 2291/3326 (68%)
[0:01:15] | Templates: 2506 | Hosts: 1 | RPS: 30 | Matched: 2 | Errors: 79 | Requests: 2291/3326 (68%)
[0:01:20] | Templates: 2506 | Hosts: 1 | RPS: 30 | Matched: 2 | Errors: 82 | Requests: 2436/3326 (73%)
[0:01:25] | Templates: 2506 | Hosts: 1 | RPS: 30 | Matched: 2 | Errors: 89 | Requests: 2606/3326 (78%)
[0:01:30] | Templates: 2506 | Hosts: 1 | RPS: 29 | Matched: 2 | Errors: 91 | Requests: 2657/3326 (79%)
[0:01:35] | Templates: 2506 | Hosts: 1 | RPS: 28 | Matched: 2 | Errors: 91 | Requests: 2678/3326 (80%)
[0:01:40] | Templates: 2506 | Hosts: 1 | RPS: 28 | Matched: 17 | Errors: 99 | Requests: 2833/3326 (85%)
[0:01:45] | Templates: 2506 | Hosts: 1 | RPS: 27 | Matched: 17 | Errors: 102 | Requests: 2935/3326 (88%)
[0:01:50] | Templates: 2506 | Hosts: 1 | RPS: 27 | Matched: 17 | Errors: 105 | Requests: 3029/3326 (91%)
[0:01:55] | Templates: 2506 | Hosts: 1 | RPS: 27 | Matched: 17 | Errors: 109 | Requests: 3127/3326 (94%)
[0:02:00] | Templates: 2506 | Hosts: 1 | RPS: 26 | Matched: 18 | Errors: 111 | Requests: 3181/3326 (95%)
[0:02:05] | Templates: 2506 | Hosts: 1 | RPS: 25 | Matched: 18 | Errors: 112 | Requests: 3189/3326 (95%)
[0:02:06] | Templates: 2506 | Hosts: 1 | RPS: 25 | Matched: 18 | Errors: 112 | Requests: 3189/3326 (95%)
real 2m6.575s
user 0m4.465s
sys 0m1.415s
```
</details>
### Items to investigate:
- [ ] 4x increase in scan time with dev version
- [ ] Mismatched template loading on default run
- `misconfiguration/gitlab/gitlab-api-user-enum.yaml` works with stable release but not with dev version.
### Anything else:
This issue also blocks the new release of nuclei engine.
|
non_process
|
performance review of nuclei engine in dev branch please search to see if an issue already exists for the bug you encountered for support requests faqs or how to questions please use the github discussions section instead or join our discord server at and post the question on the nuclei channel nuclei version dev version current behavior lots of code has been changed added updated after the last release of nuclei as a result new issues are also introduced causing increased scan time and parsing error with few templates that used to work with the older releases which need to be investigated i ve added a reproducible example of nuclei scan running on locally hosted simplehttpserver to compare the changes steps to reproduce running nuclei console time nuclei u stats c projectdiscovery io use with caution you are responsible for your actions developers assume no liability and are not responsible for any misuse or damage using nuclei engine latest using nuclei templates latest using interactsh server templates added in last update templates loaded for scan templates clustered reduced http requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests real user sys running nuclei dev console time nuclei u stats c dev projectdiscovery io use with caution you are responsible for your actions developers assume no liability and are not responsible for any misuse or damage using nuclei engine dev development using nuclei templates latest using interactsh server templates added in last update templates loaded for scan templates clustered reduced http requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests templates hosts rps matched errors requests real user sys items to investigate increase in scan time with dev version mismatched template loading on default run misconfiguration gitlab gitlab api user enum yaml works with stable release but not with dev version anything else this issue also blocks the new release of nuclei engine
| 0
|
625,624
| 19,758,861,239
|
IssuesEvent
|
2022-01-16 03:39:50
|
apcountryman/picolibrary
|
https://api.github.com/repos/apcountryman/picolibrary
|
opened
|
Add functor algorithm policies
|
priority-normal status-awaiting_development type-feature
|
Add functor algorithm policies.
- [ ] The functor algorithm policy structs should be defined in the `include/picolibrary/algorithm.h`/`source/picolibrary/algorithm.cc` header/source file pair
- [ ] The following functor algorithm policy structs should be defined:
- [ ] `Return_Functor`: Return functor algorithm policy
- [ ] `Discard_Functor`: Discard functor algorithm policy
|
1.0
|
Add functor algorithm policies - Add functor algorithm policies.
- [ ] The functor algorithm policy structs should be defined in the `include/picolibrary/algorithm.h`/`source/picolibrary/algorithm.cc` header/source file pair
- [ ] The following functor algorithm policy structs should be defined:
- [ ] `Return_Functor`: Return functor algorithm policy
- [ ] `Discard_Functor`: Discard functor algorithm policy
|
non_process
|
add functor algorithm policies add functor algorithm policies the functor algorithm policy structs should be defined in the include picolibrary algorithm h source picolibrary algorithm cc header source file pair the following functor algorithm policy structs should be defined return functor return functor algorithm policy discard functor discard functor algorithm policy
| 0
|
52,151
| 6,220,992,997
|
IssuesEvent
|
2017-07-10 03:00:13
|
MDAnalysis/mdanalysis
|
https://api.github.com/repos/MDAnalysis/mdanalysis
|
closed
|
too many open files makes AtomGroup.sequence tests fail on MacOS?
|
Component-Core testing
|
The minimal (but not full) build is failing tests because of the `sequence` method which is leaning on Biopython. It looks like something has changed in that package, so depending on which version we build off we sometimes get failures
|
1.0
|
too many open files makes AtomGroup.sequence tests fail on MacOS? - The minimal (but not full) build is failing tests because of the `sequence` method which is leaning on Biopython. It looks like something has changed in that package, so depending on which version we build off we sometimes get failures
|
non_process
|
too many open files makes atomgroup sequence tests fail on macos the minimal but not full build is failing tests because of the sequence method which is leaning on biopython it looks like something has changed in that package so depending on which version we build off we sometimes get failures
| 0
|
517,524
| 15,015,205,937
|
IssuesEvent
|
2021-02-01 07:57:47
|
onaio/reveal-frontend
|
https://api.github.com/repos/onaio/reveal-frontend
|
closed
|
RVL-1421 - BCC activity data not syncing to Web Dashboard
|
Priority: High
|
BCC data was captured on the Thailand production android application and successfully synced. However, the data does not seem to show up on the WebUI page. [Here](https://mhealth.ddc.moph.go.th/focus-investigation/map/6bc867a9-bed1-50bf-9e5c-f263d283b8ba/BCC_Focus) is the link to the WebUI page for the activity.
The user who submitted the data is `vbdu_6.5.3-1`
Below is the android image showing the completed BCC activity with the device synce.
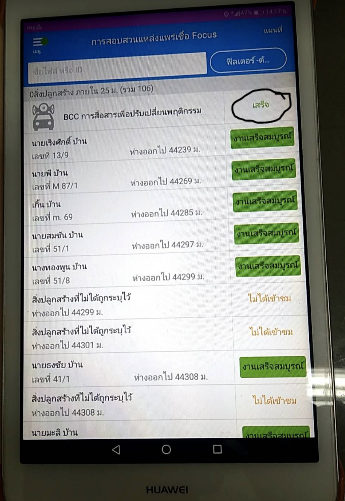
|
1.0
|
RVL-1421 - BCC activity data not syncing to Web Dashboard - BCC data was captured on the Thailand production android application and successfully synced. However, the data does not seem to show up on the WebUI page. [Here](https://mhealth.ddc.moph.go.th/focus-investigation/map/6bc867a9-bed1-50bf-9e5c-f263d283b8ba/BCC_Focus) is the link to the WebUI page for the activity.
The user who submitted the data is `vbdu_6.5.3-1`
Below is the android image showing the completed BCC activity with the device synce.
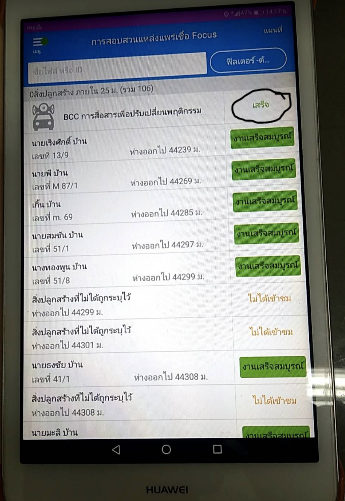
|
non_process
|
rvl bcc activity data not syncing to web dashboard bcc data was captured on the thailand production android application and successfully synced however the data does not seem to show up on the webui page is the link to the webui page for the activity the user who submitted the data is vbdu below is the android image showing the completed bcc activity with the device synce
| 0
|
25,147
| 18,165,643,185
|
IssuesEvent
|
2021-09-27 14:21:51
|
sciencehistory/scihist_digicoll
|
https://api.github.com/repos/sciencehistory/scihist_digicoll
|
closed
|
S3 originals orphan checker needs to ignore restricted derivatives
|
bug infrastructure
|
`OrphanS3Originals` needs to ignore restricted derivatives.
We have a separate orphan checker for restricted derivatives, which reside at `scihist-digicoll-staging-originals/restricted_derivatives` .
|
1.0
|
S3 originals orphan checker needs to ignore restricted derivatives - `OrphanS3Originals` needs to ignore restricted derivatives.
We have a separate orphan checker for restricted derivatives, which reside at `scihist-digicoll-staging-originals/restricted_derivatives` .
|
non_process
|
originals orphan checker needs to ignore restricted derivatives needs to ignore restricted derivatives we have a separate orphan checker for restricted derivatives which reside at scihist digicoll staging originals restricted derivatives
| 0
|
7,882
| 11,047,363,910
|
IssuesEvent
|
2019-12-09 18:49:10
|
googlemaps/v3-utility-library
|
https://api.github.com/repos/googlemaps/v3-utility-library
|
closed
|
Add es5-version to markerclustererplus npm package
|
priority: p1 type: process
|
Since markerclustererplus [was converted to use the new class-syntax](https://github.com/googlemaps/v3-utility-library/commit/32042f81ee37a7834b16f9e99bcf208416be2fe9), it is not usable as an npm-package anymore when using Typescript and targeting es5. Reason: Typescript does not transpile javascript files, so it ends up with the class-syntax in the compiled output. It would be great if you could add a es5-version to the npm-package.
This maybe also applies to other packages (haven't looked into it because I only need markerclustererplus).
|
1.0
|
Add es5-version to markerclustererplus npm package - Since markerclustererplus [was converted to use the new class-syntax](https://github.com/googlemaps/v3-utility-library/commit/32042f81ee37a7834b16f9e99bcf208416be2fe9), it is not usable as an npm-package anymore when using Typescript and targeting es5. Reason: Typescript does not transpile javascript files, so it ends up with the class-syntax in the compiled output. It would be great if you could add a es5-version to the npm-package.
This maybe also applies to other packages (haven't looked into it because I only need markerclustererplus).
|
process
|
add version to markerclustererplus npm package since markerclustererplus it is not usable as an npm package anymore when using typescript and targeting reason typescript does not transpile javascript files so it ends up with the class syntax in the compiled output it would be great if you could add a version to the npm package this maybe also applies to other packages haven t looked into it because i only need markerclustererplus
| 1
|
7,659
| 7,043,876,078
|
IssuesEvent
|
2017-12-31 14:21:06
|
timvideos/HDMI2USB-litex-firmware
|
https://api.github.com/repos/timvideos/HDMI2USB-litex-firmware
|
closed
|
scripts/download-env.sh should run inside environment?
|
hdmi2*** level-infrastructure
|
Is there actually a reason we prevent [scripts/download-env.sh](./scripts/download-env.sh) from running inside the environment?
I think it use to be a problem when we needed to source the Xilinx `settings.sh` file?
|
1.0
|
scripts/download-env.sh should run inside environment? - Is there actually a reason we prevent [scripts/download-env.sh](./scripts/download-env.sh) from running inside the environment?
I think it use to be a problem when we needed to source the Xilinx `settings.sh` file?
|
non_process
|
scripts download env sh should run inside environment is there actually a reason we prevent scripts download env sh from running inside the environment i think it use to be a problem when we needed to source the xilinx settings sh file
| 0
|
4,150
| 7,103,357,252
|
IssuesEvent
|
2018-01-16 04:26:05
|
bojanrajkovic/Volley
|
https://api.github.com/repos/bojanrajkovic/Volley
|
closed
|
Provide signatures and hashes for all distributed artifacts
|
Release Process
|
- [x] Sign Debian packages with [debsigs]
- [x] [Sign RPM packages][rpmsig]
- [x] Provide detached signatures for generic archives
[debsigs]: https://blog.packagecloud.io/eng/2014/10/28/howto-gpg-sign-verify-deb-packages-apt-repositories/
[rpmsig]: https://gist.github.com/fernandoaleman/1376720
|
1.0
|
Provide signatures and hashes for all distributed artifacts - - [x] Sign Debian packages with [debsigs]
- [x] [Sign RPM packages][rpmsig]
- [x] Provide detached signatures for generic archives
[debsigs]: https://blog.packagecloud.io/eng/2014/10/28/howto-gpg-sign-verify-deb-packages-apt-repositories/
[rpmsig]: https://gist.github.com/fernandoaleman/1376720
|
process
|
provide signatures and hashes for all distributed artifacts sign debian packages with provide detached signatures for generic archives
| 1
|
2,070
| 3,493,366,043
|
IssuesEvent
|
2016-01-05 01:28:44
|
dotnet/corefx
|
https://api.github.com/repos/dotnet/corefx
|
closed
|
Outerloop tests failing with packaging error
|
2 - In Progress Infrastructure
|
"System.IO.FileSystem.dll does not exist, ensure you have built libraries before building the package."
```
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(460,5): error : File d:\j\workspace\dotnet_corefx\outerloop_win10_release\bin\Linux.AnyCPU.Release\System.IO.FileSystem\System.IO.FileSystem.dll does not exist, ensure you have built libraries before building the package. [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : Error when creating nuget package from d:\j\workspace\dotnet_corefx\outerloop_win10_release\bin\pkg\specs\runtime.unix.System.IO.FileSystem.nuspec. System.IO.DirectoryNotFoundException: Could not find a part of the path 'd:\j\workspace\dotnet_corefx\outerloop_win10_release\bin\Linux.AnyCPU.Release\System.IO.FileSystem'. [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.__Error.WinIOError(Int32 errorCode, String maybeFullPath) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.FileSystemEnumerableIterator`1.CommonInit() [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.FileSystemEnumerableIterator`1..ctor(String path, String originalUserPath, String searchPattern, SearchOption searchOption, SearchResultHandler`1 resultHandler, Boolean checkHost) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.Directory.GetFiles(String path, String searchPattern, SearchOption searchOption) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PathResolver.PerformWildcardSearchInternal(String basePath, String searchPath, Boolean includeEmptyDirectories, String& normalizedBasePath) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PathResolver.ResolveSearchPattern(String basePath, String searchPath, String targetPath, Boolean includeEmptyDirectories) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder.AddFiles(String basePath, String source, String destination, String exclude) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder.PopulateFiles(String basePath, IEnumerable`1 files) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder.ReadManifest(Stream stream, String basePath, IPropertyProvider propertyProvider) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder..ctor(String path, String basePath, IPropertyProvider propertyProvider, Boolean includeEmptyDirectories) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at Microsoft.DotNet.Build.Tasks.Packaging.NuGetPack.Execute() [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
```
|
1.0
|
Outerloop tests failing with packaging error - "System.IO.FileSystem.dll does not exist, ensure you have built libraries before building the package."
```
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(460,5): error : File d:\j\workspace\dotnet_corefx\outerloop_win10_release\bin\Linux.AnyCPU.Release\System.IO.FileSystem\System.IO.FileSystem.dll does not exist, ensure you have built libraries before building the package. [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : Error when creating nuget package from d:\j\workspace\dotnet_corefx\outerloop_win10_release\bin\pkg\specs\runtime.unix.System.IO.FileSystem.nuspec. System.IO.DirectoryNotFoundException: Could not find a part of the path 'd:\j\workspace\dotnet_corefx\outerloop_win10_release\bin\Linux.AnyCPU.Release\System.IO.FileSystem'. [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.__Error.WinIOError(Int32 errorCode, String maybeFullPath) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.FileSystemEnumerableIterator`1.CommonInit() [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.FileSystemEnumerableIterator`1..ctor(String path, String originalUserPath, String searchPattern, SearchOption searchOption, SearchResultHandler`1 resultHandler, Boolean checkHost) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at System.IO.Directory.GetFiles(String path, String searchPattern, SearchOption searchOption) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PathResolver.PerformWildcardSearchInternal(String basePath, String searchPath, Boolean includeEmptyDirectories, String& normalizedBasePath) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PathResolver.ResolveSearchPattern(String basePath, String searchPath, String targetPath, Boolean includeEmptyDirectories) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder.AddFiles(String basePath, String source, String destination, String exclude) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder.PopulateFiles(String basePath, IEnumerable`1 files) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder.ReadManifest(Stream stream, String basePath, IPropertyProvider propertyProvider) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at NuGet.PackageBuilder..ctor(String path, String basePath, IPropertyProvider propertyProvider, Boolean includeEmptyDirectories) [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
08:07:44 d:\j\workspace\dotnet_corefx\outerloop_win10_release\packages\Microsoft.DotNet.BuildTools.1.0.25-prerelease-00141\lib\Packaging.targets(886,5): error : at Microsoft.DotNet.Build.Tasks.Packaging.NuGetPack.Execute() [d:\j\workspace\dotnet_corefx\outerloop_win10_release\src\System.IO.FileSystem\pkg\unix\System.IO.FileSystem.pkgproj]
```
|
non_process
|
outerloop tests failing with packaging error system io filesystem dll does not exist ensure you have built libraries before building the package d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error file d j workspace dotnet corefx outerloop release bin linux anycpu release system io filesystem system io filesystem dll does not exist ensure you have built libraries before building the package d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error error when creating nuget package from d j workspace dotnet corefx outerloop release bin pkg specs runtime unix system io filesystem nuspec system io directorynotfoundexception could not find a part of the path d j workspace dotnet corefx outerloop release bin linux anycpu release system io filesystem d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at system io error winioerror errorcode string maybefullpath d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at system io filesystemenumerableiterator commoninit d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at system io filesystemenumerableiterator ctor string path string originaluserpath string searchpattern searchoption searchoption searchresulthandler resulthandler boolean checkhost d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at system io directory getfiles string path string searchpattern searchoption searchoption d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at nuget pathresolver performwildcardsearchinternal string basepath string searchpath boolean includeemptydirectories string normalizedbasepath d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at nuget pathresolver resolvesearchpattern string basepath string searchpath string targetpath boolean includeemptydirectories d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at nuget packagebuilder addfiles string basepath string source string destination string exclude d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at nuget packagebuilder populatefiles string basepath ienumerable files d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at nuget packagebuilder readmanifest stream stream string basepath ipropertyprovider propertyprovider d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at nuget packagebuilder ctor string path string basepath ipropertyprovider propertyprovider boolean includeemptydirectories d j workspace dotnet corefx outerloop release packages microsoft dotnet buildtools prerelease lib packaging targets error at microsoft dotnet build tasks packaging nugetpack execute
| 0
|
253,476
| 27,300,632,142
|
IssuesEvent
|
2023-02-24 01:24:48
|
panasalap/linux-4.19.72_1
|
https://api.github.com/repos/panasalap/linux-4.19.72_1
|
closed
|
CVE-2020-16166 (Low) detected in multiple libraries - autoclosed
|
security vulnerability
|
## CVE-2020-16166 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-yoctov5.4.51</b>, <b>linux-yoctov5.4.51</b>, <b>linux-yoctov5.4.51</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel through 5.7.11 allows remote attackers to make observations that help to obtain sensitive information about the internal state of the network RNG, aka CID-f227e3ec3b5c. This is related to drivers/char/random.c and kernel/time/timer.c.
<p>Publish Date: 2020-07-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-16166>CVE-2020-16166</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-16166">https://nvd.nist.gov/vuln/detail/CVE-2020-16166</a></p>
<p>Release Date: 2020-07-30</p>
<p>Fix Resolution: kernel-debug-modules-extra - 4.18.0-193.37.1;perf - 4.18.0-193.37.1,4.18.0-147.38.1;kernel-zfcpdump-modules-extra - 4.18.0-193.37.1;kernel-debug-devel - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1;bpftool - 4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-rt-debug-core - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-tools-libs - 4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;perf-debuginfo - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1;kernel-cross-headers - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-debug-debuginfo - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1;kernel-debug - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-devel - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1;bpftool-debuginfo - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1;kernel-zfcpdump-core - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-debug-core - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1;kernel-modules-extra - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-rt-debug-devel - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-core - 4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-rt-debug - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-rt-devel - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;python3-perf - 4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-tools - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-debug-modules - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1;kernel-rt-debuginfo-common-x86_64 - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-modules - 4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1;kernel-tools-debuginfo - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-rt-modules - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-rt-kvm - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-headers - 4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-debuginfo-common-x86_64 - 4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-rt - 4.18.0-193.37.1.rt13.87,4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62,4.18.0-240.8.1.rt7.62;kernel-zfcpdump - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-rt-debug-modules-extra - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;python3-perf-debuginfo - 4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1;kernel-rt-modules-extra - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-doc - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-rt-core - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-rt-debug-debuginfo - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-abi-whitelists - 4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-zfcpdump-modules - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-debug-modules-extra - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-rt-debug-kvm - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-rt-debuginfo - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-rt-debug-modules - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-zfcpdump-devel - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;perf - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-zfcpdump-modules-extra - 4.18.0-147.38.1,4.18.0-240.8.1;kernel-debuginfo - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-16166 (Low) detected in multiple libraries - autoclosed - ## CVE-2020-16166 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-yoctov5.4.51</b>, <b>linux-yoctov5.4.51</b>, <b>linux-yoctov5.4.51</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel through 5.7.11 allows remote attackers to make observations that help to obtain sensitive information about the internal state of the network RNG, aka CID-f227e3ec3b5c. This is related to drivers/char/random.c and kernel/time/timer.c.
<p>Publish Date: 2020-07-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-16166>CVE-2020-16166</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-16166">https://nvd.nist.gov/vuln/detail/CVE-2020-16166</a></p>
<p>Release Date: 2020-07-30</p>
<p>Fix Resolution: kernel-debug-modules-extra - 4.18.0-193.37.1;perf - 4.18.0-193.37.1,4.18.0-147.38.1;kernel-zfcpdump-modules-extra - 4.18.0-193.37.1;kernel-debug-devel - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1;bpftool - 4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-rt-debug-core - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-tools-libs - 4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;perf-debuginfo - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1;kernel-cross-headers - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-debug-debuginfo - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1;kernel-debug - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-devel - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1;bpftool-debuginfo - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1;kernel-zfcpdump-core - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-debug-core - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1;kernel-modules-extra - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-rt-debug-devel - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-core - 4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-rt-debug - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-rt-devel - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;python3-perf - 4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-tools - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-debug-modules - 4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1;kernel-rt-debuginfo-common-x86_64 - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-modules - 4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1;kernel-tools-debuginfo - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-rt-modules - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-rt-kvm - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-headers - 4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-debuginfo-common-x86_64 - 4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-rt - 4.18.0-193.37.1.rt13.87,4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62,4.18.0-240.8.1.rt7.62;kernel-zfcpdump - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;kernel-rt-debug-modules-extra - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;python3-perf-debuginfo - 4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-193.37.1;kernel-rt-modules-extra - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-doc - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-rt-core - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-rt-debug-debuginfo - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-abi-whitelists - 4.18.0-240.8.1,4.18.0-193.37.1,4.18.0-147.38.1;kernel-zfcpdump-modules - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1;kernel-debug-modules-extra - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-rt-debug-kvm - 4.18.0-240.8.1.rt7.62,4.18.0-193.37.1.rt13.87;kernel-rt-debuginfo - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-rt-debug-modules - 4.18.0-193.37.1.rt13.87,4.18.0-240.8.1.rt7.62;kernel-zfcpdump-devel - 4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1;perf - 4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1,4.18.0-147.38.1,4.18.0-193.37.1,4.18.0-240.8.1,4.18.0-240.8.1;kernel-zfcpdump-modules-extra - 4.18.0-147.38.1,4.18.0-240.8.1;kernel-debuginfo - 4.18.0-193.37.1,4.18.0-147.38.1,4.18.0-240.8.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve low detected in multiple libraries autoclosed cve low severity vulnerability vulnerable libraries linux linux linux vulnerability details the linux kernel through allows remote attackers to make observations that help to obtain sensitive information about the internal state of the network rng aka cid this is related to drivers char random c and kernel time timer c publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution kernel debug modules extra perf kernel zfcpdump modules extra kernel debug devel bpftool kernel rt debug core kernel tools libs perf debuginfo kernel cross headers kernel debug debuginfo kernel debug kernel devel kernel bpftool debuginfo kernel zfcpdump core kernel debug core kernel modules extra kernel rt debug devel kernel core kernel rt debug kernel rt devel perf kernel tools kernel debug modules kernel rt debuginfo common kernel modules kernel tools debuginfo kernel rt modules kernel rt kvm kernel headers kernel debuginfo common kernel rt kernel zfcpdump kernel rt debug modules extra perf debuginfo kernel rt modules extra kernel doc kernel rt core kernel rt debug debuginfo kernel abi whitelists kernel zfcpdump modules kernel debug modules extra kernel rt debug kvm kernel rt debuginfo kernel rt debug modules kernel zfcpdump devel perf kernel zfcpdump modules extra kernel debuginfo step up your open source security game with mend
| 0
|
259,930
| 8,201,760,795
|
IssuesEvent
|
2018-09-01 22:01:59
|
nim-lang/nimble
|
https://api.github.com/repos/nim-lang/nimble
|
closed
|
Don't turn .nimble-link pkg info into full pkg infos
|
Feature Medium Priority
|
See TODO in nimble.nim line ~245 (search for '#393')
Perform the logic in `getInstalledPkgsMin`.
|
1.0
|
Don't turn .nimble-link pkg info into full pkg infos - See TODO in nimble.nim line ~245 (search for '#393')
Perform the logic in `getInstalledPkgsMin`.
|
non_process
|
don t turn nimble link pkg info into full pkg infos see todo in nimble nim line search for perform the logic in getinstalledpkgsmin
| 0
|
7,054
| 10,211,698,884
|
IssuesEvent
|
2019-08-14 17:35:11
|
eobermuhlner/jshell-scriptengine
|
https://api.github.com/repos/eobermuhlner/jshell-scriptengine
|
closed
|
Release 1.1.0
|
development process
|
- [x] add release number header to release note
- [x] rename release note
- [x] change version in `build.gradle`
- [x] change version in `JShellScriptEngineFactory`
- [ ] upload artifacts to maven central
- [x] uncomment task `uploadArtifacts` in `build.gradle`
- [x] run `./gradlew :ch.obermuhlner.scriptengine.jshell:uploadArchives`
- [x] go to https://oss.sonatype.org/
- [ ] in tab 'Staging Repositories' locate own Repository (typically at the end of the list)
- [x] verify content of own Repository (version number!)
- [x] `Close` own Repository
- [ ] `Refresh`
- [x] `Release` own Repository
- [ ] create github release from same artifacts
- [ ] Create new draft release
- [ ] Copy content of release note into draft release
- [ ] Add artefacts from gradle build to draft release
- [ ] *.jar
- [ ] *-javadoc.jar
- [ ] *-sources.jar
- [ ] Publish release
- [ ] update readme
- [ ] update dependent projects
- [ ] create empty release note for next release
|
1.0
|
Release 1.1.0 - - [x] add release number header to release note
- [x] rename release note
- [x] change version in `build.gradle`
- [x] change version in `JShellScriptEngineFactory`
- [ ] upload artifacts to maven central
- [x] uncomment task `uploadArtifacts` in `build.gradle`
- [x] run `./gradlew :ch.obermuhlner.scriptengine.jshell:uploadArchives`
- [x] go to https://oss.sonatype.org/
- [ ] in tab 'Staging Repositories' locate own Repository (typically at the end of the list)
- [x] verify content of own Repository (version number!)
- [x] `Close` own Repository
- [ ] `Refresh`
- [x] `Release` own Repository
- [ ] create github release from same artifacts
- [ ] Create new draft release
- [ ] Copy content of release note into draft release
- [ ] Add artefacts from gradle build to draft release
- [ ] *.jar
- [ ] *-javadoc.jar
- [ ] *-sources.jar
- [ ] Publish release
- [ ] update readme
- [ ] update dependent projects
- [ ] create empty release note for next release
|
process
|
release add release number header to release note rename release note change version in build gradle change version in jshellscriptenginefactory upload artifacts to maven central uncomment task uploadartifacts in build gradle run gradlew ch obermuhlner scriptengine jshell uploadarchives go to in tab staging repositories locate own repository typically at the end of the list verify content of own repository version number close own repository refresh release own repository create github release from same artifacts create new draft release copy content of release note into draft release add artefacts from gradle build to draft release jar javadoc jar sources jar publish release update readme update dependent projects create empty release note for next release
| 1
|
19,602
| 25,958,787,983
|
IssuesEvent
|
2022-12-18 15:54:36
|
haveno-dex/haveno
|
https://api.github.com/repos/haveno-dex/haveno
|
closed
|
Increase fiat trade limit to 2 XMR
|
good first issue P3 a:trade process
|
This issue requests increasing the trade limit for high risk fiat trade limits from 1 XMR to 2 XMR.
|
1.0
|
Increase fiat trade limit to 2 XMR - This issue requests increasing the trade limit for high risk fiat trade limits from 1 XMR to 2 XMR.
|
process
|
increase fiat trade limit to xmr this issue requests increasing the trade limit for high risk fiat trade limits from xmr to xmr
| 1
|
20,480
| 27,138,735,956
|
IssuesEvent
|
2023-02-16 14:58:28
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
`escape-join-aliases` middleware does not properly deduplicate join aliases for joins inside source queries inside joins
|
Type:Bug Priority:P2 Querying/Processor .Backend
|
The `escape-join-aliases` middleware is supposed to ensure every join alias across the entire query is unique. It turns out this is broken when a join contains a source query that contains a join and both of those joins use the same alias. See the preprocessed MBQL for the query in `metabase.query-processor-test.explicit-joins-test/joining-nested-queries-with-same-aggregation-test` for example.
I don't think this has caused problems in SQL queries, but it's a big issue for MongoDB join support we're working on.
|
1.0
|
`escape-join-aliases` middleware does not properly deduplicate join aliases for joins inside source queries inside joins - The `escape-join-aliases` middleware is supposed to ensure every join alias across the entire query is unique. It turns out this is broken when a join contains a source query that contains a join and both of those joins use the same alias. See the preprocessed MBQL for the query in `metabase.query-processor-test.explicit-joins-test/joining-nested-queries-with-same-aggregation-test` for example.
I don't think this has caused problems in SQL queries, but it's a big issue for MongoDB join support we're working on.
|
process
|
escape join aliases middleware does not properly deduplicate join aliases for joins inside source queries inside joins the escape join aliases middleware is supposed to ensure every join alias across the entire query is unique it turns out this is broken when a join contains a source query that contains a join and both of those joins use the same alias see the preprocessed mbql for the query in metabase query processor test explicit joins test joining nested queries with same aggregation test for example i don t think this has caused problems in sql queries but it s a big issue for mongodb join support we re working on
| 1
|
77,477
| 3,506,394,853
|
IssuesEvent
|
2016-01-08 06:26:26
|
OregonCore/OregonCore
|
https://api.github.com/repos/OregonCore/OregonCore
|
closed
|
Slow loading of instances (BB #522)
|
migrated Priority: Low Type: Bug
|
This issue was migrated from bitbucket.
**Original Reporter:**
**Original Date:** 03.03.2014 07:51:13 GMT+0000
**Original Priority:** minor
**Original Type:** bug
**Original State:** resolved
**Direct Link:** https://bitbucket.org/oregon/oregoncore/issues/522
<hr>
When server loads and instances have cleanup and array for instance ids. It is very slow about 1instance / 3-5sec i think if you will have in server about 50 instances from people it may by slow for load of server.
|
1.0
|
Slow loading of instances (BB #522) - This issue was migrated from bitbucket.
**Original Reporter:**
**Original Date:** 03.03.2014 07:51:13 GMT+0000
**Original Priority:** minor
**Original Type:** bug
**Original State:** resolved
**Direct Link:** https://bitbucket.org/oregon/oregoncore/issues/522
<hr>
When server loads and instances have cleanup and array for instance ids. It is very slow about 1instance / 3-5sec i think if you will have in server about 50 instances from people it may by slow for load of server.
|
non_process
|
slow loading of instances bb this issue was migrated from bitbucket original reporter original date gmt original priority minor original type bug original state resolved direct link when server loads and instances have cleanup and array for instance ids it is very slow about i think if you will have in server about instances from people it may by slow for load of server
| 0
|
9,908
| 11,912,661,225
|
IssuesEvent
|
2020-03-31 10:38:26
|
ClickHouse/ClickHouse
|
https://api.github.com/repos/ClickHouse/ClickHouse
|
closed
|
JOIN ... GROUP BY ... WITH TOTALS throwing exception on join
|
backward compatibility bug comp-joins v20.3
|
Following query (minute the aliases on the sub-queries) worked fine in 19.x (previous to requiring the ll and rr labels).
```
SELECT
id, yago, recent
FROM (
SELECT under_item_id AS id, SUM(price_sold) AS recent
FROM by_item WHERE (date BETWEEN '2019-12-16' AND '2020-03-08')
GROUP BY id WITH TOTALS
) ll
FULL OUTER JOIN
(
SELECT under_item_id AS id, SUM(price_sold) AS yago
FROM by_item WHERE (date BETWEEN '2018-12-17' AND '2019-03-10')
GROUP BY id WITH TOTALS
) rr
USING (id)
```
Now, in 20.3.4.10 it is throwing:
Code: 10. DB::Exception: Received from localhost:9000. DB::Exception: Not found column rr.id in block. There are only columns: id, yago.
If you remove the WITH TOTALS, it works. Seemingly getting confused with the combination of the gouped totals with the labels added?
|
True
|
JOIN ... GROUP BY ... WITH TOTALS throwing exception on join - Following query (minute the aliases on the sub-queries) worked fine in 19.x (previous to requiring the ll and rr labels).
```
SELECT
id, yago, recent
FROM (
SELECT under_item_id AS id, SUM(price_sold) AS recent
FROM by_item WHERE (date BETWEEN '2019-12-16' AND '2020-03-08')
GROUP BY id WITH TOTALS
) ll
FULL OUTER JOIN
(
SELECT under_item_id AS id, SUM(price_sold) AS yago
FROM by_item WHERE (date BETWEEN '2018-12-17' AND '2019-03-10')
GROUP BY id WITH TOTALS
) rr
USING (id)
```
Now, in 20.3.4.10 it is throwing:
Code: 10. DB::Exception: Received from localhost:9000. DB::Exception: Not found column rr.id in block. There are only columns: id, yago.
If you remove the WITH TOTALS, it works. Seemingly getting confused with the combination of the gouped totals with the labels added?
|
non_process
|
join group by with totals throwing exception on join following query minute the aliases on the sub queries worked fine in x previous to requiring the ll and rr labels select id yago recent from select under item id as id sum price sold as recent from by item where date between and group by id with totals ll full outer join select under item id as id sum price sold as yago from by item where date between and group by id with totals rr using id now in it is throwing code db exception received from localhost db exception not found column rr id in block there are only columns id yago if you remove the with totals it works seemingly getting confused with the combination of the gouped totals with the labels added
| 0
|
166,452
| 20,718,528,917
|
IssuesEvent
|
2022-03-13 02:04:43
|
eldorplus/portfolio
|
https://api.github.com/repos/eldorplus/portfolio
|
opened
|
CVE-2021-32804 (High) detected in tar-2.2.2.tgz
|
security vulnerability
|
## CVE-2021-32804 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.2.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.2.tgz">https://registry.npmjs.org/tar/-/tar-2.2.2.tgz</a></p>
<p>Path to dependency file: /portfolio/package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.12.0.tgz (Root Library)
- node-gyp-3.8.0.tgz
- :x: **tar-2.2.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 3.2.2</p>
<p>Direct dependency fix Resolution (node-sass): 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-32804 (High) detected in tar-2.2.2.tgz - ## CVE-2021-32804 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.2.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.2.tgz">https://registry.npmjs.org/tar/-/tar-2.2.2.tgz</a></p>
<p>Path to dependency file: /portfolio/package.json</p>
<p>Path to vulnerable library: /node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- node-sass-4.12.0.tgz (Root Library)
- node-gyp-3.8.0.tgz
- :x: **tar-2.2.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution (tar): 3.2.2</p>
<p>Direct dependency fix Resolution (node-sass): 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file portfolio package json path to vulnerable library node modules tar package json dependency hierarchy node sass tgz root library node gyp tgz x tar tgz vulnerable library vulnerability details the npm package tar aka node tar before versions and has a arbitrary file creation overwrite vulnerability due to insufficient absolute path sanitization node tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the preservepaths flag is not set to true this is achieved by stripping the absolute path root from any absolute file paths contained in a tar file for example home user bashrc would turn into home user bashrc this logic was insufficient when file paths contained repeated path roots such as home user bashrc node tar would only strip a single path root from such paths when given an absolute file path with repeating path roots the resulting path e g home user bashrc would still resolve to an absolute path thus allowing arbitrary file creation and overwrite this issue was addressed in releases and users may work around this vulnerability without upgrading by creating a custom onentry method which sanitizes the entry path or a filter method which removes entries with absolute paths see referenced github advisory for details be aware of cve which fixes a similar bug in later versions of tar publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar direct dependency fix resolution node sass step up your open source security game with whitesource
| 0
|
23,863
| 4,049,672,612
|
IssuesEvent
|
2016-05-23 15:24:11
|
pyudev/pyudev
|
https://api.github.com/repos/pyudev/pyudev
|
opened
|
Fix libudev tests which rely on gccxml
|
challenging help wanted testsuite
|
It has been superceded by castxml, which refuses to work on c11.
|
1.0
|
Fix libudev tests which rely on gccxml - It has been superceded by castxml, which refuses to work on c11.
|
non_process
|
fix libudev tests which rely on gccxml it has been superceded by castxml which refuses to work on
| 0
|
165,003
| 26,078,357,319
|
IssuesEvent
|
2022-12-24 23:15:50
|
tinkerbell/tink
|
https://api.github.com/repos/tinkerbell/tink
|
closed
|
Action Images are very tightly tied to OSIE
|
kind/feature help wanted kind/design
|
Tink starts by booting OSIE, OSIE runs the workflow engine, the workflow engine runs some Action Images via docker containers, and hopefully at the last step in the workflow the system boots in to the freshly installed OS.
These Action Images, though, are limited by what OSIE can do. In fact, this binding is quite tight and probably by mistake.
Some examples of this:
* BSDs can't really do a "native" installation by running their own software, they have to first create an installer which works under Linux.
* Windows is similar, probably closer to spewing bytes to disk than anything else.
* The OS must install to a filesystem supported by OSIE
* Hardware must be supported by OSIE. Action Images can't bring their own hardware support
* Lots of tools actually have to be "matched pairs": where the CLI utility version is tied to a specific version of the kernel module. For example: wireguard, zfs, iptables, nvidia, among many others. Incompatibilities can cause simple breakage, instability, or crashes.
One way I was able to get around this this was by:
1. use a privileged docker container to mount `/etc`
1. examine `/etc/issue`
1. create a docker container on the fly based on that version of alpine
1. build the packages I required
1. export them to a package archive
1. use a privileged docker container to mount the host's `/` to `/hostroot` in the container
1. `chroot /hostroot apk add ...` to install my required kernel modules to the host
1. `chroot /hostroot modprobe ...` to load the kernel modules
but this is not actually a viable solution. In particular, I was stuck in mud for a bit by osie using a somewhat / lightly patched version of alpine's kernel, making it tricky to do this custom build.
Some different ways to work around this might be:
1. support Action Images being light-weight VMs, via something like qemu.
This option is most flexible as these VMs could be minimally small but support exactly the hardware and VM the user needs. Further, they can be built with matched pairs of kernel modules to CLI tools.
2. allow a workflow to specify its own URL or ID or name for its OSIE workflow base
This is probably desirable anyway. Like I mentioned the Action Images are _quite_ tightly tied to what the host provides. This sort of binding can be hard to upgrade, especially when the purpose of the action images are to fiddle bits with the hardware. Being able to pin and version them would likely help a lot.
|
1.0
|
Action Images are very tightly tied to OSIE - Tink starts by booting OSIE, OSIE runs the workflow engine, the workflow engine runs some Action Images via docker containers, and hopefully at the last step in the workflow the system boots in to the freshly installed OS.
These Action Images, though, are limited by what OSIE can do. In fact, this binding is quite tight and probably by mistake.
Some examples of this:
* BSDs can't really do a "native" installation by running their own software, they have to first create an installer which works under Linux.
* Windows is similar, probably closer to spewing bytes to disk than anything else.
* The OS must install to a filesystem supported by OSIE
* Hardware must be supported by OSIE. Action Images can't bring their own hardware support
* Lots of tools actually have to be "matched pairs": where the CLI utility version is tied to a specific version of the kernel module. For example: wireguard, zfs, iptables, nvidia, among many others. Incompatibilities can cause simple breakage, instability, or crashes.
One way I was able to get around this this was by:
1. use a privileged docker container to mount `/etc`
1. examine `/etc/issue`
1. create a docker container on the fly based on that version of alpine
1. build the packages I required
1. export them to a package archive
1. use a privileged docker container to mount the host's `/` to `/hostroot` in the container
1. `chroot /hostroot apk add ...` to install my required kernel modules to the host
1. `chroot /hostroot modprobe ...` to load the kernel modules
but this is not actually a viable solution. In particular, I was stuck in mud for a bit by osie using a somewhat / lightly patched version of alpine's kernel, making it tricky to do this custom build.
Some different ways to work around this might be:
1. support Action Images being light-weight VMs, via something like qemu.
This option is most flexible as these VMs could be minimally small but support exactly the hardware and VM the user needs. Further, they can be built with matched pairs of kernel modules to CLI tools.
2. allow a workflow to specify its own URL or ID or name for its OSIE workflow base
This is probably desirable anyway. Like I mentioned the Action Images are _quite_ tightly tied to what the host provides. This sort of binding can be hard to upgrade, especially when the purpose of the action images are to fiddle bits with the hardware. Being able to pin and version them would likely help a lot.
|
non_process
|
action images are very tightly tied to osie tink starts by booting osie osie runs the workflow engine the workflow engine runs some action images via docker containers and hopefully at the last step in the workflow the system boots in to the freshly installed os these action images though are limited by what osie can do in fact this binding is quite tight and probably by mistake some examples of this bsds can t really do a native installation by running their own software they have to first create an installer which works under linux windows is similar probably closer to spewing bytes to disk than anything else the os must install to a filesystem supported by osie hardware must be supported by osie action images can t bring their own hardware support lots of tools actually have to be matched pairs where the cli utility version is tied to a specific version of the kernel module for example wireguard zfs iptables nvidia among many others incompatibilities can cause simple breakage instability or crashes one way i was able to get around this this was by use a privileged docker container to mount etc examine etc issue create a docker container on the fly based on that version of alpine build the packages i required export them to a package archive use a privileged docker container to mount the host s to hostroot in the container chroot hostroot apk add to install my required kernel modules to the host chroot hostroot modprobe to load the kernel modules but this is not actually a viable solution in particular i was stuck in mud for a bit by osie using a somewhat lightly patched version of alpine s kernel making it tricky to do this custom build some different ways to work around this might be support action images being light weight vms via something like qemu this option is most flexible as these vms could be minimally small but support exactly the hardware and vm the user needs further they can be built with matched pairs of kernel modules to cli tools allow a workflow to specify its own url or id or name for its osie workflow base this is probably desirable anyway like i mentioned the action images are quite tightly tied to what the host provides this sort of binding can be hard to upgrade especially when the purpose of the action images are to fiddle bits with the hardware being able to pin and version them would likely help a lot
| 0
|
197,463
| 22,594,988,936
|
IssuesEvent
|
2022-06-29 01:17:24
|
turkdevops/grafana
|
https://api.github.com/repos/turkdevops/grafana
|
opened
|
CVE-2022-0624 (Medium) detected in parse-path-4.0.1.tgz
|
security vulnerability
|
## CVE-2022-0624 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>parse-path-4.0.1.tgz</b></p></summary>
<p>Parse paths (local paths, urls: ssh/git/etc)</p>
<p>Library home page: <a href="https://registry.npmjs.org/parse-path/-/parse-path-4.0.1.tgz">https://registry.npmjs.org/parse-path/-/parse-path-4.0.1.tgz</a></p>
<p>
Dependency Hierarchy:
- lerna-3.18.1.tgz (Root Library)
- version-3.18.0.tgz
- github-client-3.16.5.tgz
- git-url-parse-11.1.2.tgz
- git-up-4.0.1.tgz
- parse-url-5.0.1.tgz
- :x: **parse-path-4.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/a1c271764655c7e3ff81126d5929b8dda6170bf4">a1c271764655c7e3ff81126d5929b8dda6170bf4</a></p>
<p>Found in base branch: <b>datasource-meta</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in GitHub repository ionicabizau/parse-path prior to 5.0.0.
<p>Publish Date: 2022-06-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0624>CVE-2022-0624</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0624">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0624</a></p>
<p>Release Date: 2022-06-28</p>
<p>Fix Resolution: parse-path - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-0624 (Medium) detected in parse-path-4.0.1.tgz - ## CVE-2022-0624 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>parse-path-4.0.1.tgz</b></p></summary>
<p>Parse paths (local paths, urls: ssh/git/etc)</p>
<p>Library home page: <a href="https://registry.npmjs.org/parse-path/-/parse-path-4.0.1.tgz">https://registry.npmjs.org/parse-path/-/parse-path-4.0.1.tgz</a></p>
<p>
Dependency Hierarchy:
- lerna-3.18.1.tgz (Root Library)
- version-3.18.0.tgz
- github-client-3.16.5.tgz
- git-url-parse-11.1.2.tgz
- git-up-4.0.1.tgz
- parse-url-5.0.1.tgz
- :x: **parse-path-4.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/grafana/commit/a1c271764655c7e3ff81126d5929b8dda6170bf4">a1c271764655c7e3ff81126d5929b8dda6170bf4</a></p>
<p>Found in base branch: <b>datasource-meta</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in GitHub repository ionicabizau/parse-path prior to 5.0.0.
<p>Publish Date: 2022-06-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0624>CVE-2022-0624</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0624">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0624</a></p>
<p>Release Date: 2022-06-28</p>
<p>Fix Resolution: parse-path - 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in parse path tgz cve medium severity vulnerability vulnerable library parse path tgz parse paths local paths urls ssh git etc library home page a href dependency hierarchy lerna tgz root library version tgz github client tgz git url parse tgz git up tgz parse url tgz x parse path tgz vulnerable library found in head commit a href found in base branch datasource meta vulnerability details authorization bypass through user controlled key in github repository ionicabizau parse path prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution parse path step up your open source security game with mend
| 0
|
15,462
| 19,679,167,911
|
IssuesEvent
|
2022-01-11 15:14:25
|
googleapis/gapic-generator-java
|
https://api.github.com/repos/googleapis/gapic-generator-java
|
closed
|
Run tests for "self-service" libraries in CI
|
type: process priority: p2
|
Doing so will help validating changes to the "self-service" library generation workflow (e.g., as in #876).
Theoretically, we should be able to generate some libraries against actual API service protos like the following (may need to change a few things in `WORKSPACE` or some `BUILD` files).
```
bazel build @com_google_googleapis//google/cloud/compute/v1:google-cloud-compute-v1-java
```
Then unpack `bazel-bin/external/com_google_googleapis/google/cloud/compute/v1/google-cloud-compute-v1-java.tar.gz` and run `./gradlew clean check publishToMavenLocal` at the root of the generated library.
`compute` is REST and all others are gRPC at the moment, so `compute` and another library are good candidates.
|
1.0
|
Run tests for "self-service" libraries in CI - Doing so will help validating changes to the "self-service" library generation workflow (e.g., as in #876).
Theoretically, we should be able to generate some libraries against actual API service protos like the following (may need to change a few things in `WORKSPACE` or some `BUILD` files).
```
bazel build @com_google_googleapis//google/cloud/compute/v1:google-cloud-compute-v1-java
```
Then unpack `bazel-bin/external/com_google_googleapis/google/cloud/compute/v1/google-cloud-compute-v1-java.tar.gz` and run `./gradlew clean check publishToMavenLocal` at the root of the generated library.
`compute` is REST and all others are gRPC at the moment, so `compute` and another library are good candidates.
|
process
|
run tests for self service libraries in ci doing so will help validating changes to the self service library generation workflow e g as in theoretically we should be able to generate some libraries against actual api service protos like the following may need to change a few things in workspace or some build files bazel build com google googleapis google cloud compute google cloud compute java then unpack bazel bin external com google googleapis google cloud compute google cloud compute java tar gz and run gradlew clean check publishtomavenlocal at the root of the generated library compute is rest and all others are grpc at the moment so compute and another library are good candidates
| 1
|
9,878
| 12,886,456,003
|
IssuesEvent
|
2020-07-13 09:30:49
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
opened
|
Iterate on TypeScript CI
|
process/candidate team/typescript
|
As of now, we run our TypeScript CI tests in Buildkite due to historical reasons.
The current setup, however, has a few limitations:
- Gets quite slow - 12min to publish. Tests should run in parallel
- We don't test Mac or Windows or any older Node.js versions
- Updating Snapshots takes a lot of time, because it has to be done locally
- Decouple new engine builds from the main TS CI - a new engine should not block the current TS CI
- The whole CI stops on the first error - instead, we should see errors of all packages
- Prisma Client types tests should use test.serial
- Fix `prisma doctor` test
- Cleanup verbose pnpm logging
- Don't build packages multiple times
- Integration tests in the CLI package should be migrated from Mocha to Jest
|
1.0
|
Iterate on TypeScript CI - As of now, we run our TypeScript CI tests in Buildkite due to historical reasons.
The current setup, however, has a few limitations:
- Gets quite slow - 12min to publish. Tests should run in parallel
- We don't test Mac or Windows or any older Node.js versions
- Updating Snapshots takes a lot of time, because it has to be done locally
- Decouple new engine builds from the main TS CI - a new engine should not block the current TS CI
- The whole CI stops on the first error - instead, we should see errors of all packages
- Prisma Client types tests should use test.serial
- Fix `prisma doctor` test
- Cleanup verbose pnpm logging
- Don't build packages multiple times
- Integration tests in the CLI package should be migrated from Mocha to Jest
|
process
|
iterate on typescript ci as of now we run our typescript ci tests in buildkite due to historical reasons the current setup however has a few limitations gets quite slow to publish tests should run in parallel we don t test mac or windows or any older node js versions updating snapshots takes a lot of time because it has to be done locally decouple new engine builds from the main ts ci a new engine should not block the current ts ci the whole ci stops on the first error instead we should see errors of all packages prisma client types tests should use test serial fix prisma doctor test cleanup verbose pnpm logging don t build packages multiple times integration tests in the cli package should be migrated from mocha to jest
| 1
|
511,154
| 14,855,185,639
|
IssuesEvent
|
2021-01-18 12:24:38
|
wso2/product-apim
|
https://api.github.com/repos/wso2/product-apim
|
opened
|
The '%U' is not working as expected for the PassThrough access-log
|
Priority/Normal Type/Bug
|
### Description:
When using the '%U' (The URL path requested, not including any query string) for the log pattern, it is not working as expected in the PassThrough logging flow since it logs the URL with the query parameters. (the same issue persists in both the latest WUM of 2.2.0 and the latest WUM of 2.6.0 )
### Affected Product Version:
APIM 2.2.0, APIM 2.6.0
### Solution:
Change the addElement method under Access.java [1] as below.
```
public void addElement(StringBuilder buf, Date date, HttpRequest request, HttpResponse response) {
if (request != null) {
buf.append(request.getRequestLine().getUri());
String uri = request.getRequestLine().getUri().split("\\?")[0];
buf.append(uri);
} else {
buf.append('-');
}
```
[1] - https://github.com/wso2-support/wso2-synapse/blob/support-2.1.7-wso2v48/modules/transports/core/nhttp/src/main/java/org/apache/synapse/transport/http/access/Access.java#L462
|
1.0
|
The '%U' is not working as expected for the PassThrough access-log - ### Description:
When using the '%U' (The URL path requested, not including any query string) for the log pattern, it is not working as expected in the PassThrough logging flow since it logs the URL with the query parameters. (the same issue persists in both the latest WUM of 2.2.0 and the latest WUM of 2.6.0 )
### Affected Product Version:
APIM 2.2.0, APIM 2.6.0
### Solution:
Change the addElement method under Access.java [1] as below.
```
public void addElement(StringBuilder buf, Date date, HttpRequest request, HttpResponse response) {
if (request != null) {
buf.append(request.getRequestLine().getUri());
String uri = request.getRequestLine().getUri().split("\\?")[0];
buf.append(uri);
} else {
buf.append('-');
}
```
[1] - https://github.com/wso2-support/wso2-synapse/blob/support-2.1.7-wso2v48/modules/transports/core/nhttp/src/main/java/org/apache/synapse/transport/http/access/Access.java#L462
|
non_process
|
the u is not working as expected for the passthrough access log description when using the u the url path requested not including any query string for the log pattern it is not working as expected in the passthrough logging flow since it logs the url with the query parameters the same issue persists in both the latest wum of and the latest wum of affected product version apim apim solution change the addelement method under access java as below public void addelement stringbuilder buf date date httprequest request httpresponse response if request null buf append request getrequestline geturi string uri request getrequestline geturi split buf append uri else buf append
| 0
|
20,454
| 27,119,080,861
|
IssuesEvent
|
2023-02-15 21:07:30
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
The order of join-type causes query fail because of incorrect SQL - `inner join` is always placed before other joins
|
Type:Bug Priority:P1 Querying/Processor Difficulty:Hard .Backend .Reproduced
|
**Describe the bug**
In the query builder, when 3 tables are joined, and the first join is left outer and the second one is inner, the inner join in the resulting query is placed first, which leads to an "unknown column" error on MySQL 5.7.
**To Reproduce**
On sample dataset:
1. Create a new custom question.
2. Select from People, join Orders, join Products:

3. View the generated SQL and notice the:
`FROM "PUBLIC"."PEOPLE"
LEFT JOIN "PUBLIC"."ORDERS" "Orders" ON "PUBLIC"."PEOPLE"."ID" = "Orders"."USER_ID" LEFT JOIN "PUBLIC"."PRODUCTS" "Products" ON "Orders"."PRODUCT_ID" = "Products"."ID"`
4. Change the third table's join to inner:
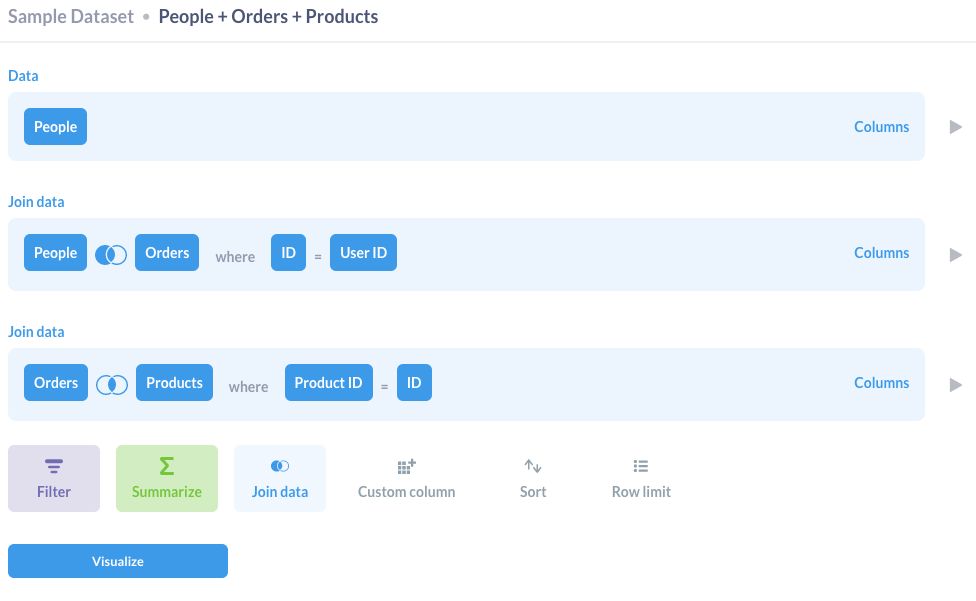
5. View the generated SQL and notice the:
`FROM "PUBLIC"."PEOPLE" INNER JOIN "PUBLIC"."PRODUCTS" "Products" ON "Orders"."PRODUCT_ID" = "Products"."ID"
LEFT JOIN "PUBLIC"."ORDERS" "Orders" ON "PUBLIC"."PEOPLE"."ID" = "Orders"."USER_ID"`
which is `select from people inner join products left join orders`. As `products` are joined before `orders`, MySQL rejects this with the error `Unknown column '"Orders"."PRODUCT_ID"' in 'on clause'`. This may work on the internal database, and I only see this error on my production instance. But a quick MySQL test indicates this shall be the cause:
`mysql> select * from t t1 join t t2 on t2.id = t_t.t2_id join t_t on t1.id = t1_id;`
`ERROR 1054 (42S22): Unknown column 't_t.t2_id' in 'on clause'`
`mysql> select * from t t1 join t_t on t1.id = t1_id join t t2 on t2.id = t_t.t2_id;`
`(a lot of rows)`
**Expected behavior**
I expect the joins to be made in the order they are added in the query builder.
**Information about your Metabase Installation:**
`{
"browser-info": {
"language": "en-GB",
"platform": "MacIntel",
"userAgent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 11_2_1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.182 Safari/537.36",
"vendor": "Google Inc."
},
"system-info": {
"file.encoding": "UTF-8",
"java.runtime.name": "OpenJDK Runtime Environment",
"java.runtime.version": "11.0.10+9",
"java.vendor": "AdoptOpenJDK",
"java.vendor.url": "https://adoptopenjdk.net/",
"java.version": "11.0.10",
"java.vm.name": "OpenJDK 64-Bit Server VM",
"java.vm.version": "11.0.10+9",
"os.name": "Linux",
"os.version": "4.19.121-linuxkit",
"user.language": "en",
"user.timezone": "GMT"
},
"metabase-info": {
"databases": [
"h2"
],
"hosting-env": "unknown",
"application-database": "h2",
"application-database-details": {
"database": {
"name": "H2",
"version": "1.4.197 (2018-03-18)"
},
"jdbc-driver": {
"name": "H2 JDBC Driver",
"version": "1.4.197 (2018-03-18)"
}
},
"run-mode": "prod",
"version": {
"date": "2021-03-17",
"tag": "v0.38.2",
"branch": "release-x.38.x",
"hash": "91f0ed6"
},
"settings": {
"report-timezone": null
}
}
}`
**Severity**
I can work this around with SQL, but seems like an bug to me.
**Additional context**
My production instance where I actually get the error message is 0.37.6.
|
1.0
|
The order of join-type causes query fail because of incorrect SQL - `inner join` is always placed before other joins - **Describe the bug**
In the query builder, when 3 tables are joined, and the first join is left outer and the second one is inner, the inner join in the resulting query is placed first, which leads to an "unknown column" error on MySQL 5.7.
**To Reproduce**
On sample dataset:
1. Create a new custom question.
2. Select from People, join Orders, join Products:

3. View the generated SQL and notice the:
`FROM "PUBLIC"."PEOPLE"
LEFT JOIN "PUBLIC"."ORDERS" "Orders" ON "PUBLIC"."PEOPLE"."ID" = "Orders"."USER_ID" LEFT JOIN "PUBLIC"."PRODUCTS" "Products" ON "Orders"."PRODUCT_ID" = "Products"."ID"`
4. Change the third table's join to inner:
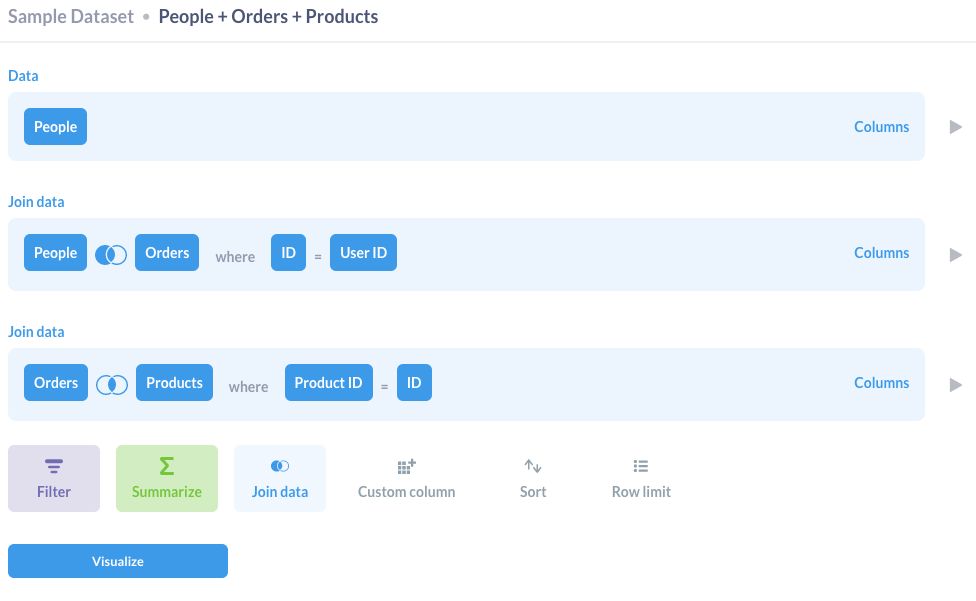
5. View the generated SQL and notice the:
`FROM "PUBLIC"."PEOPLE" INNER JOIN "PUBLIC"."PRODUCTS" "Products" ON "Orders"."PRODUCT_ID" = "Products"."ID"
LEFT JOIN "PUBLIC"."ORDERS" "Orders" ON "PUBLIC"."PEOPLE"."ID" = "Orders"."USER_ID"`
which is `select from people inner join products left join orders`. As `products` are joined before `orders`, MySQL rejects this with the error `Unknown column '"Orders"."PRODUCT_ID"' in 'on clause'`. This may work on the internal database, and I only see this error on my production instance. But a quick MySQL test indicates this shall be the cause:
`mysql> select * from t t1 join t t2 on t2.id = t_t.t2_id join t_t on t1.id = t1_id;`
`ERROR 1054 (42S22): Unknown column 't_t.t2_id' in 'on clause'`
`mysql> select * from t t1 join t_t on t1.id = t1_id join t t2 on t2.id = t_t.t2_id;`
`(a lot of rows)`
**Expected behavior**
I expect the joins to be made in the order they are added in the query builder.
**Information about your Metabase Installation:**
`{
"browser-info": {
"language": "en-GB",
"platform": "MacIntel",
"userAgent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 11_2_1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.182 Safari/537.36",
"vendor": "Google Inc."
},
"system-info": {
"file.encoding": "UTF-8",
"java.runtime.name": "OpenJDK Runtime Environment",
"java.runtime.version": "11.0.10+9",
"java.vendor": "AdoptOpenJDK",
"java.vendor.url": "https://adoptopenjdk.net/",
"java.version": "11.0.10",
"java.vm.name": "OpenJDK 64-Bit Server VM",
"java.vm.version": "11.0.10+9",
"os.name": "Linux",
"os.version": "4.19.121-linuxkit",
"user.language": "en",
"user.timezone": "GMT"
},
"metabase-info": {
"databases": [
"h2"
],
"hosting-env": "unknown",
"application-database": "h2",
"application-database-details": {
"database": {
"name": "H2",
"version": "1.4.197 (2018-03-18)"
},
"jdbc-driver": {
"name": "H2 JDBC Driver",
"version": "1.4.197 (2018-03-18)"
}
},
"run-mode": "prod",
"version": {
"date": "2021-03-17",
"tag": "v0.38.2",
"branch": "release-x.38.x",
"hash": "91f0ed6"
},
"settings": {
"report-timezone": null
}
}
}`
**Severity**
I can work this around with SQL, but seems like an bug to me.
**Additional context**
My production instance where I actually get the error message is 0.37.6.
|
process
|
the order of join type causes query fail because of incorrect sql inner join is always placed before other joins describe the bug in the query builder when tables are joined and the first join is left outer and the second one is inner the inner join in the resulting query is placed first which leads to an unknown column error on mysql to reproduce on sample dataset create a new custom question select from people join orders join products view the generated sql and notice the from public people left join public orders orders on public people id orders user id left join public products products on orders product id products id change the third table s join to inner view the generated sql and notice the from public people inner join public products products on orders product id products id left join public orders orders on public people id orders user id which is select from people inner join products left join orders as products are joined before orders mysql rejects this with the error unknown column orders product id in on clause this may work on the internal database and i only see this error on my production instance but a quick mysql test indicates this shall be the cause mysql select from t join t on id t t id join t t on id id error unknown column t t id in on clause mysql select from t join t t on id id join t on id t t id a lot of rows expected behavior i expect the joins to be made in the order they are added in the query builder information about your metabase installation browser info language en gb platform macintel useragent mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari vendor google inc system info file encoding utf java runtime name openjdk runtime environment java runtime version java vendor adoptopenjdk java vendor url java version java vm name openjdk bit server vm java vm version os name linux os version linuxkit user language en user timezone gmt metabase info databases hosting env unknown application database application database details database name version jdbc driver name jdbc driver version run mode prod version date tag branch release x x hash settings report timezone null severity i can work this around with sql but seems like an bug to me additional context my production instance where i actually get the error message is
| 1
|
673,138
| 22,949,147,439
|
IssuesEvent
|
2022-07-19 05:15:15
|
googleapis/doc-pipeline
|
https://api.github.com/repos/googleapis/doc-pipeline
|
opened
|
generate: many tests failed
|
type: bug priority: p1 flakybot: issue
|
Many tests failed at the same time in this package.
* I will close this issue when there are no more failures in this package _and_
there is at least one pass.
* No new issues will be filed for this package until this issue is closed.
* If there are already issues for individual test cases, I will close them when
the corresponding test passes. You can close them earlier, if you prefer, and
I won't reopen them while this issue is still open.
Here are the tests that failed:
* docfx-python-bigquery-2.10.0.tar.gz
* docfx-python-bigquery-2.11.0.tar.gz
* docfx-python-bigquery-2.12.0.tar.gz
* docfx-python-bigquery-2.13.0.tar.gz
* docfx-python-bigquery-2.13.1.tar.gz
* docfx-python-bigquery-2.14.0.tar.gz
* docfx-python-bigquery-2.15.0.tar.gz
* docfx-python-bigquery-2.16.0.tar.gz
* docfx-python-bigquery-2.16.1.tar.gz
* docfx-python-bigquery-2.17.0.tar.gz
* docfx-python-bigquery-2.18.0.tar.gz
* docfx-python-bigquery-2.19.0.tar.gz
* docfx-python-bigquery-2.20.0.tar.gz
* docfx-python-bigquery-2.21.0.tar.gz
* docfx-python-bigquery-2.22.0.tar.gz
* docfx-python-bigquery-2.22.1.tar.gz
* docfx-python-bigquery-2.23.0.tar.gz
* docfx-python-bigquery-2.23.1.tar.gz
* docfx-python-bigquery-2.23.2.tar.gz
* docfx-python-bigquery-2.23.3.tar.gz
* docfx-python-bigquery-2.24.0.tar.gz
* docfx-python-bigquery-2.24.1.tar.gz
* docfx-python-bigquery-2.25.0.tar.gz
* docfx-python-bigquery-2.25.1.tar.gz
* docfx-python-bigquery-2.25.2.tar.gz
* docfx-python-bigquery-2.26.0.tar.gz
* docfx-python-bigquery-2.27.0.tar.gz
* docfx-python-bigquery-2.27.1.tar.gz
* docfx-python-bigquery-2.28.0.tar.gz
* docfx-python-bigquery-2.28.1.tar.gz
* docfx-python-bigquery-2.3.1.tar.gz
* docfx-python-bigquery-2.4.0.tar.gz
* docfx-python-bigquery-2.5.0.tar.gz
* docfx-python-bigquery-2.6.0.tar.gz
* docfx-python-bigquery-2.6.1.tar.gz
* docfx-python-bigquery-2.6.2.tar.gz
* docfx-python-bigquery-2.7.0.tar.gz
* docfx-python-bigquery-2.8.0.tar.gz
* docfx-python-bigquery-2.9.0.tar.gz
-----
commit: 48f1842f3b0d9af10dc09c10d8864233056129c1
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/39996ebe-6e18-4452-a942-1575bad3709d), [Sponge](http://sponge2/39996ebe-6e18-4452-a942-1575bad3709d)
status: failed
|
1.0
|
generate: many tests failed - Many tests failed at the same time in this package.
* I will close this issue when there are no more failures in this package _and_
there is at least one pass.
* No new issues will be filed for this package until this issue is closed.
* If there are already issues for individual test cases, I will close them when
the corresponding test passes. You can close them earlier, if you prefer, and
I won't reopen them while this issue is still open.
Here are the tests that failed:
* docfx-python-bigquery-2.10.0.tar.gz
* docfx-python-bigquery-2.11.0.tar.gz
* docfx-python-bigquery-2.12.0.tar.gz
* docfx-python-bigquery-2.13.0.tar.gz
* docfx-python-bigquery-2.13.1.tar.gz
* docfx-python-bigquery-2.14.0.tar.gz
* docfx-python-bigquery-2.15.0.tar.gz
* docfx-python-bigquery-2.16.0.tar.gz
* docfx-python-bigquery-2.16.1.tar.gz
* docfx-python-bigquery-2.17.0.tar.gz
* docfx-python-bigquery-2.18.0.tar.gz
* docfx-python-bigquery-2.19.0.tar.gz
* docfx-python-bigquery-2.20.0.tar.gz
* docfx-python-bigquery-2.21.0.tar.gz
* docfx-python-bigquery-2.22.0.tar.gz
* docfx-python-bigquery-2.22.1.tar.gz
* docfx-python-bigquery-2.23.0.tar.gz
* docfx-python-bigquery-2.23.1.tar.gz
* docfx-python-bigquery-2.23.2.tar.gz
* docfx-python-bigquery-2.23.3.tar.gz
* docfx-python-bigquery-2.24.0.tar.gz
* docfx-python-bigquery-2.24.1.tar.gz
* docfx-python-bigquery-2.25.0.tar.gz
* docfx-python-bigquery-2.25.1.tar.gz
* docfx-python-bigquery-2.25.2.tar.gz
* docfx-python-bigquery-2.26.0.tar.gz
* docfx-python-bigquery-2.27.0.tar.gz
* docfx-python-bigquery-2.27.1.tar.gz
* docfx-python-bigquery-2.28.0.tar.gz
* docfx-python-bigquery-2.28.1.tar.gz
* docfx-python-bigquery-2.3.1.tar.gz
* docfx-python-bigquery-2.4.0.tar.gz
* docfx-python-bigquery-2.5.0.tar.gz
* docfx-python-bigquery-2.6.0.tar.gz
* docfx-python-bigquery-2.6.1.tar.gz
* docfx-python-bigquery-2.6.2.tar.gz
* docfx-python-bigquery-2.7.0.tar.gz
* docfx-python-bigquery-2.8.0.tar.gz
* docfx-python-bigquery-2.9.0.tar.gz
-----
commit: 48f1842f3b0d9af10dc09c10d8864233056129c1
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/39996ebe-6e18-4452-a942-1575bad3709d), [Sponge](http://sponge2/39996ebe-6e18-4452-a942-1575bad3709d)
status: failed
|
non_process
|
generate many tests failed many tests failed at the same time in this package i will close this issue when there are no more failures in this package and there is at least one pass no new issues will be filed for this package until this issue is closed if there are already issues for individual test cases i will close them when the corresponding test passes you can close them earlier if you prefer and i won t reopen them while this issue is still open here are the tests that failed docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz docfx python bigquery tar gz commit buildurl status failed
| 0
|
322,764
| 9,828,334,836
|
IssuesEvent
|
2019-06-15 10:33:52
|
zulip/zulip-desktop
|
https://api.github.com/repos/zulip/zulip-desktop
|
closed
|
Loading indicator while navigating in webview
|
Priority: Medium Type: Enhancement help wanted
|
Add some kind of indicator of loading when we move from one page to another in a webview.
Example: When one logs in (especially through third party auth) or logs out, add an indication that the request for logging in or logging out has taken place and that the next webpage is loading.
This can be added just like a browser like Chrome shows loading indicator by changing the reload button when a page is loading.
Discussion can be found [here](https://chat.zulip.org/#narrow/stream/16-electron/topic/Loading.20indicator).
|
1.0
|
Loading indicator while navigating in webview - Add some kind of indicator of loading when we move from one page to another in a webview.
Example: When one logs in (especially through third party auth) or logs out, add an indication that the request for logging in or logging out has taken place and that the next webpage is loading.
This can be added just like a browser like Chrome shows loading indicator by changing the reload button when a page is loading.
Discussion can be found [here](https://chat.zulip.org/#narrow/stream/16-electron/topic/Loading.20indicator).
|
non_process
|
loading indicator while navigating in webview add some kind of indicator of loading when we move from one page to another in a webview example when one logs in especially through third party auth or logs out add an indication that the request for logging in or logging out has taken place and that the next webpage is loading this can be added just like a browser like chrome shows loading indicator by changing the reload button when a page is loading discussion can be found
| 0
|
15,458
| 19,672,734,344
|
IssuesEvent
|
2022-01-11 09:12:00
|
googleapis/gapic-generator-csharp
|
https://api.github.com/repos/googleapis/gapic-generator-csharp
|
closed
|
Work out why builds fail every so often
|
type: process
|
Quite often, we get this as a failure:
```text
A total of 1 test files matched the specified pattern.
[xUnit.net 00:00:14.63] Google.Api.Generator.Tests.InvocationTest.BadCmdLineInvocation [SKIP]
! Google.Api.Generator.Tests.InvocationTest.BadCmdLineInvocation [1ms]
[xUnit.net 00:00:38.39] Google.Api.Generator.Tests.ProtoTest.BuildBasic [FAIL]
X Google.Api.Generator.Tests.ProtoTest.BuildBasic [33s 716ms]
Error Message:
System.InvalidOperationException : Collection was modified; enumeration operation may not execute.
Stack Trace:
at System.Collections.Generic.List`1.Enumerator.MoveNextRare()
at System.String.Join(String separator, IEnumerable`1 values)
at Google.Api.Generator.Tests.Invoker.Execute(String executable, String args, String workingDirectory, TimeSpan timeout, Int32 exitCode) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/Invoker.cs:line 100
at Google.Api.Generator.Tests.Invoker.Dotnet(String args, String workingDirectory, Int32 exitCode) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/Invoker.cs:line 111
at Google.Api.Generator.Tests.ProtoTest.<BuildTest>g__Build|4_0(String path, <>c__DisplayClass4_0& ) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/ProtoTest.cs:line 103
at Google.Api.Generator.Tests.ProtoTest.BuildTest(String testName, Boolean ignoreUnitTests) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/ProtoTest.cs:line 87
at Google.Api.Generator.Tests.ProtoTest.BuildBasic() in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/ProtoTest.cs:line 206
```
|
1.0
|
Work out why builds fail every so often - Quite often, we get this as a failure:
```text
A total of 1 test files matched the specified pattern.
[xUnit.net 00:00:14.63] Google.Api.Generator.Tests.InvocationTest.BadCmdLineInvocation [SKIP]
! Google.Api.Generator.Tests.InvocationTest.BadCmdLineInvocation [1ms]
[xUnit.net 00:00:38.39] Google.Api.Generator.Tests.ProtoTest.BuildBasic [FAIL]
X Google.Api.Generator.Tests.ProtoTest.BuildBasic [33s 716ms]
Error Message:
System.InvalidOperationException : Collection was modified; enumeration operation may not execute.
Stack Trace:
at System.Collections.Generic.List`1.Enumerator.MoveNextRare()
at System.String.Join(String separator, IEnumerable`1 values)
at Google.Api.Generator.Tests.Invoker.Execute(String executable, String args, String workingDirectory, TimeSpan timeout, Int32 exitCode) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/Invoker.cs:line 100
at Google.Api.Generator.Tests.Invoker.Dotnet(String args, String workingDirectory, Int32 exitCode) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/Invoker.cs:line 111
at Google.Api.Generator.Tests.ProtoTest.<BuildTest>g__Build|4_0(String path, <>c__DisplayClass4_0& ) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/ProtoTest.cs:line 103
at Google.Api.Generator.Tests.ProtoTest.BuildTest(String testName, Boolean ignoreUnitTests) in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/ProtoTest.cs:line 87
at Google.Api.Generator.Tests.ProtoTest.BuildBasic() in /home/runner/work/gapic-generator-csharp/gapic-generator-csharp/Google.Api.Generator.Tests/ProtoTest.cs:line 206
```
|
process
|
work out why builds fail every so often quite often we get this as a failure text a total of test files matched the specified pattern google api generator tests invocationtest badcmdlineinvocation google api generator tests invocationtest badcmdlineinvocation google api generator tests prototest buildbasic x google api generator tests prototest buildbasic error message system invalidoperationexception collection was modified enumeration operation may not execute stack trace at system collections generic list enumerator movenextrare at system string join string separator ienumerable values at google api generator tests invoker execute string executable string args string workingdirectory timespan timeout exitcode in home runner work gapic generator csharp gapic generator csharp google api generator tests invoker cs line at google api generator tests invoker dotnet string args string workingdirectory exitcode in home runner work gapic generator csharp gapic generator csharp google api generator tests invoker cs line at google api generator tests prototest g build string path c in home runner work gapic generator csharp gapic generator csharp google api generator tests prototest cs line at google api generator tests prototest buildtest string testname boolean ignoreunittests in home runner work gapic generator csharp gapic generator csharp google api generator tests prototest cs line at google api generator tests prototest buildbasic in home runner work gapic generator csharp gapic generator csharp google api generator tests prototest cs line
| 1
|
36,554
| 8,132,092,272
|
IssuesEvent
|
2018-08-18 06:57:12
|
joomla/joomla-cms
|
https://api.github.com/repos/joomla/joomla-cms
|
closed
|
[4.0] Router bug: contacts
|
J4 Issue No Code Attached Yet
|
This report is limited to com_contacts but it could also touch some other components in core.
### Steps to reproduce the issue
Use latest 4.0-dev
Tested on a multilingual site.
Create a contact category tagged to each language.
Create a contact in each of these categories, tagged to the same language.
I have as menu item type "List Contacts in a category"
`/index.php/en/contact-category-en-gb`
The link on that page displaying the contact is
`/index.php/en/contact-category-en-gb/mycontact` // see below direct menu item. this url is a double with the one below (it should be `/index.php/en/my-contact`). Alias of that single contact is `mycontact`
// I do also have a direct menu item to that contact (alias of the menu item is `my_contact`)
When I use this last one (`/index.php/en/my-contact`), the category link above the contact gives
`/index.php/en/my-contact?view=category&id=14` instead of the existing `/index.php/en/contact-category-en-gb`
|
1.0
|
[4.0] Router bug: contacts - This report is limited to com_contacts but it could also touch some other components in core.
### Steps to reproduce the issue
Use latest 4.0-dev
Tested on a multilingual site.
Create a contact category tagged to each language.
Create a contact in each of these categories, tagged to the same language.
I have as menu item type "List Contacts in a category"
`/index.php/en/contact-category-en-gb`
The link on that page displaying the contact is
`/index.php/en/contact-category-en-gb/mycontact` // see below direct menu item. this url is a double with the one below (it should be `/index.php/en/my-contact`). Alias of that single contact is `mycontact`
// I do also have a direct menu item to that contact (alias of the menu item is `my_contact`)
When I use this last one (`/index.php/en/my-contact`), the category link above the contact gives
`/index.php/en/my-contact?view=category&id=14` instead of the existing `/index.php/en/contact-category-en-gb`
|
non_process
|
router bug contacts this report is limited to com contacts but it could also touch some other components in core steps to reproduce the issue use latest dev tested on a multilingual site create a contact category tagged to each language create a contact in each of these categories tagged to the same language i have as menu item type list contacts in a category index php en contact category en gb the link on that page displaying the contact is index php en contact category en gb mycontact see below direct menu item this url is a double with the one below it should be index php en my contact alias of that single contact is mycontact i do also have a direct menu item to that contact alias of the menu item is my contact when i use this last one index php en my contact the category link above the contact gives index php en my contact view category id instead of the existing index php en contact category en gb
| 0
|
7,744
| 10,863,740,038
|
IssuesEvent
|
2019-11-14 15:38:34
|
allinurl/goaccess
|
https://api.github.com/repos/allinurl/goaccess
|
closed
|
group requested files (URLS)
|
html report log-processing question terminal output
|
good afternoon
I have two portals on the same server on a single vhost.
The difference between the two is in the image below:
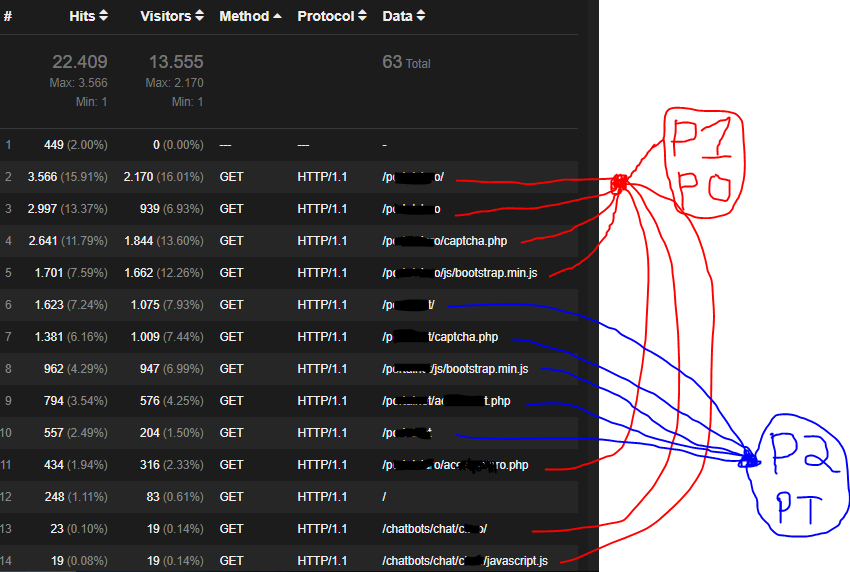
both begin with the letter P but one ends with the letter O and the other with the letter T.
so we call p1p0 and p2pt.
would like to group REQUESTED FILES (URLS) panel records
so you can measure which portal has the most access.
You can see that there are differences between p1p0 as with bar and without bar and I count in the calculator the number of hits of each.
if there is a way to group this data together to make it more understandable.
from apache settings to advanced grep something like that.
Thanks in advance
|
1.0
|
group requested files (URLS) - good afternoon
I have two portals on the same server on a single vhost.
The difference between the two is in the image below:
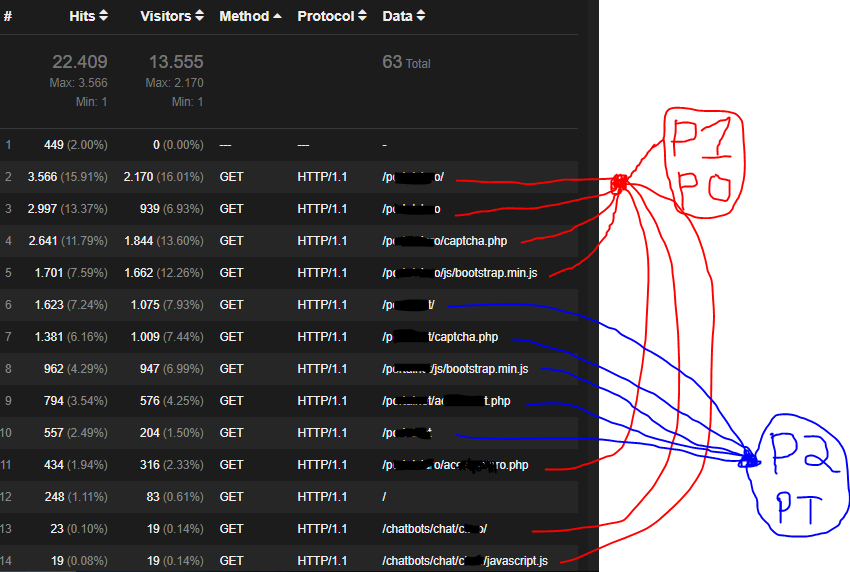
both begin with the letter P but one ends with the letter O and the other with the letter T.
so we call p1p0 and p2pt.
would like to group REQUESTED FILES (URLS) panel records
so you can measure which portal has the most access.
You can see that there are differences between p1p0 as with bar and without bar and I count in the calculator the number of hits of each.
if there is a way to group this data together to make it more understandable.
from apache settings to advanced grep something like that.
Thanks in advance
|
process
|
group requested files urls good afternoon i have two portals on the same server on a single vhost the difference between the two is in the image below both begin with the letter p but one ends with the letter o and the other with the letter t so we call and would like to group requested files urls panel records so you can measure which portal has the most access you can see that there are differences between as with bar and without bar and i count in the calculator the number of hits of each if there is a way to group this data together to make it more understandable from apache settings to advanced grep something like that thanks in advance
| 1
|
15,553
| 19,703,503,029
|
IssuesEvent
|
2022-01-12 19:07:58
|
googleapis/java-profiler
|
https://api.github.com/repos/googleapis/java-profiler
|
opened
|
Your .repo-metadata.json file has a problem 🤒
|
type: process repo-metadata: lint
|
You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'profiler' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
1.0
|
Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'profiler' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
process
|
your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 release level must be equal to one of the allowed values in repo metadata json api shortname profiler invalid in repo metadata json ☝️ once you correct these problems you can close this issue reach out to go github automation if you have any questions
| 1
|
66,235
| 16,568,628,607
|
IssuesEvent
|
2021-05-30 00:04:29
|
tensorflow/tensorflow
|
https://api.github.com/repos/tensorflow/tensorflow
|
opened
|
Faild Build 2.5.0 Windows with Cuda 11.2
|
type:build/install
|
System information
OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Windows 10
TensorFlow installed from (source or binary): source
TensorFlow version: 2.5.0
Python version: 3.8
Bazel version (if compiling from source): 3.7.2
CUDA/cuDNN version: 11.2/8.1.0
GPU model and memory: 2070
The following error occurs when I attempt to build 2.5.0.
`ERROR: C:/sdks/tensorflow/tensorflow/compiler/mlir/hlo/BUILD:423:11: C++ compilation of rule '//tensorflow/compiler/mlir/hlo:lhlo' failed (Exit 2): cl.exe failed: error executing command
cd C:/users/adam/_bazel_adam/e7merofc/execroot/org_tensorflow
SET INCLUDE=C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\VC\Tools\MSVC\14.28.29333\ATLMFC\include;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\VC\Tools\MSVC\14.28.29333\include;C:\Program Files (x86)\Windows Kits\NETFXSDK\4.8\include\um;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\ucrt;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\shared;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\um;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\winrt;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\cppwinrt
SET PATH=C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\\Extensions\Microsoft\IntelliCode\CLI;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\VC\Tools\MSVC\14.28.29333\bin\HostX64\x64;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\VC\VCPackages;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\TestWindow;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\TeamFoundation\Team Explorer;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\MSBuild\Current\bin\Roslyn;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Team Tools\Performance Tools\x64;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Team Tools\Performance Tools;C:\Program Files (x86)\Microsoft Visual Studio\Shared\Common\VSPerfCollectionTools\vs2019\\x64;C:\Program Files (x86)\Microsoft Visual Studio\Shared\Common\VSPerfCollectionTools\vs2019\;C:\Program Files (x86)\Microsoft SDKs\Windows\v10.0A\bin\NETFX 4.8 Tools\x64\;C:\Program Files (x86)\Windows Kits\10\bin\10.0.18362.0\x64;C:\Program Files (x86)\Windows Kits\10\bin\x64;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\\MSBuild\Current\Bin;C:\Windows\Microsoft.NET\Framework64\v4.0.30319;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\Tools\;;C:\WINDOWS\system32;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\CMake\CMake\bin;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\CMake\Ninja
SET PWD=/proc/self/cwd
SET PYTHON_BIN_PATH=C:/Users/Adam/anaconda3/python.exe
SET PYTHON_LIB_PATH=C:/Users/Adam/anaconda3/lib/site-packages
SET RUNFILES_MANIFEST_ONLY=1
SET TEMP=C:\Users\Adam\AppData\Local\Temp
SET TF2_BEHAVIOR=1
SET TMP=C:\Users\Adam\AppData\Local\Temp
C:/Program Files (x86)/Microsoft Visual Studio/2019/Enterprise/VC/Tools/MSVC/14.28.29333/bin/HostX64/x64/cl.exe /nologo /DCOMPILER_MSVC /DNOMINMAX /D_WIN32_WINNT=0x0601 /D_CRT_SECURE_NO_DEPRECATE /D_CRT_SECURE_NO_WARNINGS /bigobj /Zm500 /EHsc /wd4351 /wd4291 /wd4250 /wd4996 /I. /Ibazel-out/x64_windows-opt/bin /Iexternal/llvm-project /Ibazel-out/x64_windows-opt/bin/external/llvm-project /Iexternal/zlib /Ibazel-out/x64_windows-opt/bin/external/zlib /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/hlo_ops_base_inc_gen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinDialectIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinLocationAttributesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinTypesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/CallOpInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/CastOpInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/InferTypeOpInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/OpAsmInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/RegionKindInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SideEffectInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SymbolInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_structs_inc_gen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/AffineMemoryOpInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/AffineOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LoopLikeInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/MemRefBaseIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/MemRefOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ControlFlowInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/StandardOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/TensorBaseIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/TensorOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/VectorInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ViewLikeInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/CopyOpInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgStructuredOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgSparseOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ParserTokenKinds /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SCFIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SCFPassIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/PDLOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/PDLTypesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/PDLInterpOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ConversionPassIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/TransformsPassIncGen /Itensorflow/compiler/mlir/hlo/include /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/include /Iexternal/llvm-project/llvm/include /Ibazel-out/x64_windows-opt/bin/external/llvm-project/llvm/include /Iexternal/zlib /Ibazel-out/x64_windows-opt/bin/external/zlib /Iexternal/llvm-project/mlir/include /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/include /D_CRT_SECURE_NO_DEPRECATE /D_CRT_SECURE_NO_WARNINGS /D_CRT_NONSTDC_NO_DEPRECATE /D_CRT_NONSTDC_NO_WARNINGS /D_SCL_SECURE_NO_DEPRECATE /D_SCL_SECURE_NO_WARNINGS /DUNICODE /D_UNICODE /DLLVM_ENABLE_STATS /D__STDC_LIMIT_MACROS /D__STDC_CONSTANT_MACROS /D__STDC_FORMAT_MACROS /DLLVM_BUILD_GLOBAL_ISEL /showIncludes /MD /O2 /Oy- /DNDEBUG /wd4117 -D__DATE__="redacted" -D__TIMESTAMP__="redacted" -D__TIME__="redacted" /Gy /Gw /W0 /D_USE_MATH_DEFINES -DWIN32_LEAN_AND_MEAN -DNOGDI /experimental:preprocessor /d2ReducedOptimizeHugeFunctions /arch:AVX2 /std:c++14 /Fobazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_objs/lhlo/lhlo_ops_structs.obj /c tensorflow/compiler/mlir/hlo/lib/Dialect/mhlo/IR/lhlo_ops_structs.cc
Execution platform: @local_execution_config_platform//:platform
cl : Command line warning D9035 : option 'experimental:preprocessor' has been deprecated and will be removed in a future release
cl : Command line warning D9036 : use 'Zc:preprocessor' instead of 'experimental:preprocessor'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(25): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(25): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,2>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(116): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(116): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,9>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(266): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(266): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,4>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(356): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(356): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,4>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(446): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(446): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,4>, mlir::MLIRContext *)'
Target //tensorflow/tools/pip_package:build_pip_package failed to build
INFO: Elapsed time: 7072.771s, Critical Path: 304.21s
INFO: 7627 processes: 619 internal, 7008 local.
FAILED: Build did NOT complete successfully
`
|
1.0
|
Faild Build 2.5.0 Windows with Cuda 11.2 - System information
OS Platform and Distribution (e.g., Linux Ubuntu 16.04): Windows 10
TensorFlow installed from (source or binary): source
TensorFlow version: 2.5.0
Python version: 3.8
Bazel version (if compiling from source): 3.7.2
CUDA/cuDNN version: 11.2/8.1.0
GPU model and memory: 2070
The following error occurs when I attempt to build 2.5.0.
`ERROR: C:/sdks/tensorflow/tensorflow/compiler/mlir/hlo/BUILD:423:11: C++ compilation of rule '//tensorflow/compiler/mlir/hlo:lhlo' failed (Exit 2): cl.exe failed: error executing command
cd C:/users/adam/_bazel_adam/e7merofc/execroot/org_tensorflow
SET INCLUDE=C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\VC\Tools\MSVC\14.28.29333\ATLMFC\include;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\VC\Tools\MSVC\14.28.29333\include;C:\Program Files (x86)\Windows Kits\NETFXSDK\4.8\include\um;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\ucrt;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\shared;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\um;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\winrt;C:\Program Files (x86)\Windows Kits\10\include\10.0.18362.0\cppwinrt
SET PATH=C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\\Extensions\Microsoft\IntelliCode\CLI;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\VC\Tools\MSVC\14.28.29333\bin\HostX64\x64;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\VC\VCPackages;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\TestWindow;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\TeamFoundation\Team Explorer;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\MSBuild\Current\bin\Roslyn;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Team Tools\Performance Tools\x64;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Team Tools\Performance Tools;C:\Program Files (x86)\Microsoft Visual Studio\Shared\Common\VSPerfCollectionTools\vs2019\\x64;C:\Program Files (x86)\Microsoft Visual Studio\Shared\Common\VSPerfCollectionTools\vs2019\;C:\Program Files (x86)\Microsoft SDKs\Windows\v10.0A\bin\NETFX 4.8 Tools\x64\;C:\Program Files (x86)\Windows Kits\10\bin\10.0.18362.0\x64;C:\Program Files (x86)\Windows Kits\10\bin\x64;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\\MSBuild\Current\Bin;C:\Windows\Microsoft.NET\Framework64\v4.0.30319;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\Tools\;;C:\WINDOWS\system32;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\CMake\CMake\bin;C:\Program Files (x86)\Microsoft Visual Studio\2019\Enterprise\Common7\IDE\CommonExtensions\Microsoft\CMake\Ninja
SET PWD=/proc/self/cwd
SET PYTHON_BIN_PATH=C:/Users/Adam/anaconda3/python.exe
SET PYTHON_LIB_PATH=C:/Users/Adam/anaconda3/lib/site-packages
SET RUNFILES_MANIFEST_ONLY=1
SET TEMP=C:\Users\Adam\AppData\Local\Temp
SET TF2_BEHAVIOR=1
SET TMP=C:\Users\Adam\AppData\Local\Temp
C:/Program Files (x86)/Microsoft Visual Studio/2019/Enterprise/VC/Tools/MSVC/14.28.29333/bin/HostX64/x64/cl.exe /nologo /DCOMPILER_MSVC /DNOMINMAX /D_WIN32_WINNT=0x0601 /D_CRT_SECURE_NO_DEPRECATE /D_CRT_SECURE_NO_WARNINGS /bigobj /Zm500 /EHsc /wd4351 /wd4291 /wd4250 /wd4996 /I. /Ibazel-out/x64_windows-opt/bin /Iexternal/llvm-project /Ibazel-out/x64_windows-opt/bin/external/llvm-project /Iexternal/zlib /Ibazel-out/x64_windows-opt/bin/external/zlib /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/hlo_ops_base_inc_gen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinDialectIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinLocationAttributesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinTypesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/CallOpInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/CastOpInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/InferTypeOpInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/OpAsmInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/RegionKindInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SideEffectInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SymbolInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_structs_inc_gen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/AffineMemoryOpInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/AffineOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LoopLikeInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/MemRefBaseIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/MemRefOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ControlFlowInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/StandardOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/TensorBaseIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/TensorOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/VectorInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ViewLikeInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/CopyOpInterfaceIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgInterfacesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgStructuredOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/LinalgSparseOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ParserTokenKinds /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SCFIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/SCFPassIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/PDLOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/PDLTypesIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/PDLInterpOpsIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/ConversionPassIncGen /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/TransformsPassIncGen /Itensorflow/compiler/mlir/hlo/include /Ibazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/include /Iexternal/llvm-project/llvm/include /Ibazel-out/x64_windows-opt/bin/external/llvm-project/llvm/include /Iexternal/zlib /Ibazel-out/x64_windows-opt/bin/external/zlib /Iexternal/llvm-project/mlir/include /Ibazel-out/x64_windows-opt/bin/external/llvm-project/mlir/include /D_CRT_SECURE_NO_DEPRECATE /D_CRT_SECURE_NO_WARNINGS /D_CRT_NONSTDC_NO_DEPRECATE /D_CRT_NONSTDC_NO_WARNINGS /D_SCL_SECURE_NO_DEPRECATE /D_SCL_SECURE_NO_WARNINGS /DUNICODE /D_UNICODE /DLLVM_ENABLE_STATS /D__STDC_LIMIT_MACROS /D__STDC_CONSTANT_MACROS /D__STDC_FORMAT_MACROS /DLLVM_BUILD_GLOBAL_ISEL /showIncludes /MD /O2 /Oy- /DNDEBUG /wd4117 -D__DATE__="redacted" -D__TIMESTAMP__="redacted" -D__TIME__="redacted" /Gy /Gw /W0 /D_USE_MATH_DEFINES -DWIN32_LEAN_AND_MEAN -DNOGDI /experimental:preprocessor /d2ReducedOptimizeHugeFunctions /arch:AVX2 /std:c++14 /Fobazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_objs/lhlo/lhlo_ops_structs.obj /c tensorflow/compiler/mlir/hlo/lib/Dialect/mhlo/IR/lhlo_ops_structs.cc
Execution platform: @local_execution_config_platform//:platform
cl : Command line warning D9035 : option 'experimental:preprocessor' has been deprecated and will be removed in a future release
cl : Command line warning D9036 : use 'Zc:preprocessor' instead of 'experimental:preprocessor'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(25): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(25): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,2>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(116): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(116): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,9>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(266): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(266): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,4>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(356): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(356): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,4>, mlir::MLIRContext *)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(446): error C2665: 'mlir::DictionaryAttr::get': none of the 3 overloads could convert all the argument types
bazel-out/x64_windows-opt/bin/external/llvm-project/mlir/_virtual_includes/BuiltinAttributesIncGen\mlir/IR/BuiltinAttributes.h.inc(261): note: could be 'mlir::DictionaryAttr mlir::DictionaryAttr::get(mlir::MLIRContext *,llvm::ArrayRef<mlir::NamedAttribute>)'
bazel-out/x64_windows-opt/bin/tensorflow/compiler/mlir/hlo/_virtual_includes/lhlo_ops_inc_gen\mlir-hlo/Dialect/mhlo/IR/lhlo_ops_structs.cc.inc(446): note: while trying to match the argument list '(llvm::SmallVector<mlir::NamedAttribute,4>, mlir::MLIRContext *)'
Target //tensorflow/tools/pip_package:build_pip_package failed to build
INFO: Elapsed time: 7072.771s, Critical Path: 304.21s
INFO: 7627 processes: 619 internal, 7008 local.
FAILED: Build did NOT complete successfully
`
|
non_process
|
faild build windows with cuda system information os platform and distribution e g linux ubuntu windows tensorflow installed from source or binary source tensorflow version python version bazel version if compiling from source cuda cudnn version gpu model and memory the following error occurs when i attempt to build error c sdks tensorflow tensorflow compiler mlir hlo build c compilation of rule tensorflow compiler mlir hlo lhlo failed exit cl exe failed error executing command cd c users adam bazel adam execroot org tensorflow set include c program files microsoft visual studio enterprise vc tools msvc atlmfc include c program files microsoft visual studio enterprise vc tools msvc include c program files windows kits netfxsdk include um c program files windows kits include ucrt c program files windows kits include shared c program files windows kits include um c program files windows kits include winrt c program files windows kits include cppwinrt set path c program files microsoft visual studio enterprise ide extensions microsoft intellicode cli c program files microsoft visual studio enterprise vc tools msvc bin c program files microsoft visual studio enterprise ide vc vcpackages c program files microsoft visual studio enterprise ide commonextensions microsoft testwindow c program files microsoft visual studio enterprise ide commonextensions microsoft teamfoundation team explorer c program files microsoft visual studio enterprise msbuild current bin roslyn c program files microsoft visual studio enterprise team tools performance tools c program files microsoft visual studio enterprise team tools performance tools c program files microsoft visual studio shared common vsperfcollectiontools c program files microsoft visual studio shared common vsperfcollectiontools c program files microsoft sdks windows bin netfx tools c program files windows kits bin c program files windows kits bin c program files microsoft visual studio enterprise msbuild current bin c windows microsoft net c program files microsoft visual studio enterprise ide c program files microsoft visual studio enterprise tools c windows c program files microsoft visual studio enterprise ide commonextensions microsoft cmake cmake bin c program files microsoft visual studio enterprise ide commonextensions microsoft cmake ninja set pwd proc self cwd set python bin path c users adam python exe set python lib path c users adam lib site packages set runfiles manifest only set temp c users adam appdata local temp set behavior set tmp c users adam appdata local temp c program files microsoft visual studio enterprise vc tools msvc bin cl exe nologo dcompiler msvc dnominmax d winnt d crt secure no deprecate d crt secure no warnings bigobj ehsc i ibazel out windows opt bin iexternal llvm project ibazel out windows opt bin external llvm project iexternal zlib ibazel out windows opt bin external zlib ibazel out windows opt bin tensorflow compiler mlir hlo virtual includes hlo ops base inc gen ibazel out windows opt bin external llvm project mlir virtual includes builtinattributesincgen ibazel out windows opt bin external llvm project mlir virtual includes builtindialectincgen ibazel out windows opt bin external llvm project mlir virtual includes builtinlocationattributesincgen ibazel out windows opt bin external llvm project mlir virtual includes builtinopsincgen ibazel out windows opt bin external llvm project mlir virtual includes builtintypesincgen ibazel out windows opt bin external llvm project mlir virtual includes callopinterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes castopinterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes infertypeopinterfaceincgen ibazel out windows opt bin external llvm project mlir virtual includes opasminterfaceincgen ibazel out windows opt bin external llvm project mlir virtual includes regionkindinterfaceincgen ibazel out windows opt bin external llvm project mlir virtual includes sideeffectinterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes symbolinterfacesincgen ibazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen ibazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops structs inc gen ibazel out windows opt bin external llvm project mlir virtual includes affinememoryopinterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes affineopsincgen ibazel out windows opt bin external llvm project mlir virtual includes looplikeinterfaceincgen ibazel out windows opt bin external llvm project mlir virtual includes memrefbaseincgen ibazel out windows opt bin external llvm project mlir virtual includes memrefopsincgen ibazel out windows opt bin external llvm project mlir virtual includes controlflowinterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes standardopsincgen ibazel out windows opt bin external llvm project mlir virtual includes tensorbaseincgen ibazel out windows opt bin external llvm project mlir virtual includes tensoropsincgen ibazel out windows opt bin external llvm project mlir virtual includes vectorinterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes viewlikeinterfaceincgen ibazel out windows opt bin external llvm project mlir virtual includes copyopinterfaceincgen ibazel out windows opt bin external llvm project mlir virtual includes linalginterfacesincgen ibazel out windows opt bin external llvm project mlir virtual includes linalgstructuredopsincgen ibazel out windows opt bin external llvm project mlir virtual includes linalgopsincgen ibazel out windows opt bin external llvm project mlir virtual includes linalgsparseopsincgen ibazel out windows opt bin external llvm project mlir virtual includes parsertokenkinds ibazel out windows opt bin external llvm project mlir virtual includes scfincgen ibazel out windows opt bin external llvm project mlir virtual includes scfpassincgen ibazel out windows opt bin external llvm project mlir virtual includes pdlopsincgen ibazel out windows opt bin external llvm project mlir virtual includes pdltypesincgen ibazel out windows opt bin external llvm project mlir virtual includes pdlinterpopsincgen ibazel out windows opt bin external llvm project mlir virtual includes conversionpassincgen ibazel out windows opt bin external llvm project mlir virtual includes transformspassincgen itensorflow compiler mlir hlo include ibazel out windows opt bin tensorflow compiler mlir hlo include iexternal llvm project llvm include ibazel out windows opt bin external llvm project llvm include iexternal zlib ibazel out windows opt bin external zlib iexternal llvm project mlir include ibazel out windows opt bin external llvm project mlir include d crt secure no deprecate d crt secure no warnings d crt nonstdc no deprecate d crt nonstdc no warnings d scl secure no deprecate d scl secure no warnings dunicode d unicode dllvm enable stats d stdc limit macros d stdc constant macros d stdc format macros dllvm build global isel showincludes md oy dndebug d date redacted d timestamp redacted d time redacted gy gw d use math defines lean and mean dnogdi experimental preprocessor arch std c fobazel out windows opt bin tensorflow compiler mlir hlo objs lhlo lhlo ops structs obj c tensorflow compiler mlir hlo lib dialect mhlo ir lhlo ops structs cc execution platform local execution config platform platform cl command line warning option experimental preprocessor has been deprecated and will be removed in a future release cl command line warning use zc preprocessor instead of experimental preprocessor bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc error mlir dictionaryattr get none of the overloads could convert all the argument types bazel out windows opt bin external llvm project mlir virtual includes builtinattributesincgen mlir ir builtinattributes h inc note could be mlir dictionaryattr mlir dictionaryattr get mlir mlircontext llvm arrayref bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc note while trying to match the argument list llvm smallvector mlir mlircontext bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc error mlir dictionaryattr get none of the overloads could convert all the argument types bazel out windows opt bin external llvm project mlir virtual includes builtinattributesincgen mlir ir builtinattributes h inc note could be mlir dictionaryattr mlir dictionaryattr get mlir mlircontext llvm arrayref bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc note while trying to match the argument list llvm smallvector mlir mlircontext bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc error mlir dictionaryattr get none of the overloads could convert all the argument types bazel out windows opt bin external llvm project mlir virtual includes builtinattributesincgen mlir ir builtinattributes h inc note could be mlir dictionaryattr mlir dictionaryattr get mlir mlircontext llvm arrayref bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc note while trying to match the argument list llvm smallvector mlir mlircontext bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc error mlir dictionaryattr get none of the overloads could convert all the argument types bazel out windows opt bin external llvm project mlir virtual includes builtinattributesincgen mlir ir builtinattributes h inc note could be mlir dictionaryattr mlir dictionaryattr get mlir mlircontext llvm arrayref bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc note while trying to match the argument list llvm smallvector mlir mlircontext bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc error mlir dictionaryattr get none of the overloads could convert all the argument types bazel out windows opt bin external llvm project mlir virtual includes builtinattributesincgen mlir ir builtinattributes h inc note could be mlir dictionaryattr mlir dictionaryattr get mlir mlircontext llvm arrayref bazel out windows opt bin tensorflow compiler mlir hlo virtual includes lhlo ops inc gen mlir hlo dialect mhlo ir lhlo ops structs cc inc note while trying to match the argument list llvm smallvector mlir mlircontext target tensorflow tools pip package build pip package failed to build info elapsed time critical path info processes internal local failed build did not complete successfully
| 0
|
198,871
| 15,726,769,089
|
IssuesEvent
|
2021-03-29 11:47:24
|
fga-eps-mds/MDS-2020-2-G9
|
https://api.github.com/repos/fga-eps-mds/MDS-2020-2-G9
|
opened
|
Sprint 6 roadmap
|
documentation
|
### Descrição:
atualizar o roadmap inserindo as issues da sprint 6
### Objetivos:
- [ ] colocar a sprint 6 no roadmap
- [ ] arrumar erros
|
1.0
|
Sprint 6 roadmap - ### Descrição:
atualizar o roadmap inserindo as issues da sprint 6
### Objetivos:
- [ ] colocar a sprint 6 no roadmap
- [ ] arrumar erros
|
non_process
|
sprint roadmap descrição atualizar o roadmap inserindo as issues da sprint objetivos colocar a sprint no roadmap arrumar erros
| 0
|
15,832
| 20,021,665,572
|
IssuesEvent
|
2022-02-01 16:56:28
|
varabyte/kobweb
|
https://api.github.com/repos/varabyte/kobweb
|
opened
|
Epic bug: Please support my favorite package manager!
|
enhancement process
|
In order to avoid everyone creating one off bugs for the same package manager, this bug will act as a home to collect all such requests received so far. (Of course, once someone starts working on adding support for one of them, that could be a good time to create an individual bug).
Here is the current list of package managers we are considering (but not actively working on):
* apt
* chocolatey
* gofish
* macports
* snapcraft
* spec
---
**NOTE**: **Some of these package managers may never get supported**, as I'm not sure how many people actually want to use them, and supporting more releases results in more work on our end. So if you see your package manager on this list, it still may be worth leaving a comment below like "Yes, I want that one please! I use it particularly because..."
|
1.0
|
Epic bug: Please support my favorite package manager! - In order to avoid everyone creating one off bugs for the same package manager, this bug will act as a home to collect all such requests received so far. (Of course, once someone starts working on adding support for one of them, that could be a good time to create an individual bug).
Here is the current list of package managers we are considering (but not actively working on):
* apt
* chocolatey
* gofish
* macports
* snapcraft
* spec
---
**NOTE**: **Some of these package managers may never get supported**, as I'm not sure how many people actually want to use them, and supporting more releases results in more work on our end. So if you see your package manager on this list, it still may be worth leaving a comment below like "Yes, I want that one please! I use it particularly because..."
|
process
|
epic bug please support my favorite package manager in order to avoid everyone creating one off bugs for the same package manager this bug will act as a home to collect all such requests received so far of course once someone starts working on adding support for one of them that could be a good time to create an individual bug here is the current list of package managers we are considering but not actively working on apt chocolatey gofish macports snapcraft spec note some of these package managers may never get supported as i m not sure how many people actually want to use them and supporting more releases results in more work on our end so if you see your package manager on this list it still may be worth leaving a comment below like yes i want that one please i use it particularly because
| 1
|
204,173
| 15,421,627,551
|
IssuesEvent
|
2021-03-05 13:20:14
|
elastic/elasticsearch
|
https://api.github.com/repos/elastic/elasticsearch
|
closed
|
Reproducible Failure in org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites
|
:Distributed/Snapshot/Restore >test-failure Team:Distributed
|
Just ran into this locally working on the multiple page sizes cache but it reproduces on master as well:
```
./gradlew ':x-pack:plugin:searchable-snapshots:test' --tests "org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites" -Dtests.seed=163C909BF9F0F844 -Dtests.security.manager=true -Dtests.locale=sk-SK -Dtests.timezone=Etc/UTC -Druntime.java=15
```
fails with
```
[2021-03-04T20:58:27,650][INFO ][o.e.i.s.SearchableSnapshotDirectoryStatsTests] [testCachedBytesReadsAndWrites] before test
[2021-03-04T20:58:27,696][INFO ][o.e.e.NodeEnvironment ] [testCachedBytesReadsAndWrites] using [3] data paths, mounts [[/ (/dev/nvme0n1p2)]], net usable_space [121.6gb], net total_space [467.9gb], types [ext4]
[2021-03-04T20:58:27,697][INFO ][o.e.e.NodeEnvironment ] [testCachedBytesReadsAndWrites] heap size [15.6gb], compressed ordinary object pointers [true]
WARNING: An illegal reflective access operation has occurred
WARNING: Illegal reflective access by org.mockito.cglib.core.ReflectUtils$2 (file:/home/brownbear/.gradle/caches/modules-2/files-2.1/org.elasticsearch/securemock/1.2/98201d4ad5ac93f6b415ae9172d52b5e7cda490e/securemock-1.2.jar) to method java.lang.ClassLoader.defineClass(java.lang.String,byte[],int,int,java.security.ProtectionDomain)
WARNING: Please consider reporting this to the maintainers of org.mockito.cglib.core.ReflectUtils$2
WARNING: Use --illegal-access=warn to enable warnings of further illegal reflective access operations
WARNING: All illegal access operations will be denied in a future release
[2021-03-04T20:58:27,922][INFO ][o.e.x.s.c.PersistentCache] [testCachedBytesReadsAndWrites] persistent cache index loaded
[2021-03-04T20:58:38,115][INFO ][o.e.i.s.SearchableSnapshotDirectoryStatsTests] [testCachedBytesReadsAndWrites] after test
REPRODUCE WITH: ./gradlew 'null' --tests "org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites" -Dtests.seed=163C909BF9F0F844 -Dtests.locale=sk-SK -Dtests.timezone=Etc/UTC -Druntime.java=15
java.lang.AssertionError:
Expected: <9641L>
but: was <9885L>
Expected :<9641L>
Actual :<9885L>
<Click to see difference>
at __randomizedtesting.SeedInfo.seed([163C909BF9F0F844:D38D21E9FBFE3FD4]:0)
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$2(SearchableSnapshotDirectoryStatsTests.java:131)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:955)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:928)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$3(SearchableSnapshotDirectoryStatsTests.java:129)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.executeTestCase(SearchableSnapshotDirectoryStatsTests.java:683)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.executeTestCaseWithCache(SearchableSnapshotDirectoryStatsTests.java:588)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites(SearchableSnapshotDirectoryStatsTests.java:116)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:64)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:564)
at com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
at com.carrotsearch.randomizedtesting.RandomizedRunner$8.evaluate(RandomizedRunner.java:946)
at com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:982)
at com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:49)
at org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at org.apache.lucene.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:48)
at org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:824)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:475)
at com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
at com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
at com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
at com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
at org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:41)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
at org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at org.apache.lucene.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:54)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:831)
at java.base/java.lang.Thread.run(Thread.java:832)
Suppressed: java.lang.AssertionError:
Expected: <9641L>
but: was <9885L>
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$2(SearchableSnapshotDirectoryStatsTests.java:131)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:943)
... 42 more
Suppressed: java.lang.AssertionError:
Expected: <9641L>
but: was <9885L>
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$2(SearchableSnapshotDirectoryStatsTests.java:131)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:943)
... 42 more
Suppressed: java.lang.AssertionError:
```
on current master.
|
1.0
|
Reproducible Failure in org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites - Just ran into this locally working on the multiple page sizes cache but it reproduces on master as well:
```
./gradlew ':x-pack:plugin:searchable-snapshots:test' --tests "org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites" -Dtests.seed=163C909BF9F0F844 -Dtests.security.manager=true -Dtests.locale=sk-SK -Dtests.timezone=Etc/UTC -Druntime.java=15
```
fails with
```
[2021-03-04T20:58:27,650][INFO ][o.e.i.s.SearchableSnapshotDirectoryStatsTests] [testCachedBytesReadsAndWrites] before test
[2021-03-04T20:58:27,696][INFO ][o.e.e.NodeEnvironment ] [testCachedBytesReadsAndWrites] using [3] data paths, mounts [[/ (/dev/nvme0n1p2)]], net usable_space [121.6gb], net total_space [467.9gb], types [ext4]
[2021-03-04T20:58:27,697][INFO ][o.e.e.NodeEnvironment ] [testCachedBytesReadsAndWrites] heap size [15.6gb], compressed ordinary object pointers [true]
WARNING: An illegal reflective access operation has occurred
WARNING: Illegal reflective access by org.mockito.cglib.core.ReflectUtils$2 (file:/home/brownbear/.gradle/caches/modules-2/files-2.1/org.elasticsearch/securemock/1.2/98201d4ad5ac93f6b415ae9172d52b5e7cda490e/securemock-1.2.jar) to method java.lang.ClassLoader.defineClass(java.lang.String,byte[],int,int,java.security.ProtectionDomain)
WARNING: Please consider reporting this to the maintainers of org.mockito.cglib.core.ReflectUtils$2
WARNING: Use --illegal-access=warn to enable warnings of further illegal reflective access operations
WARNING: All illegal access operations will be denied in a future release
[2021-03-04T20:58:27,922][INFO ][o.e.x.s.c.PersistentCache] [testCachedBytesReadsAndWrites] persistent cache index loaded
[2021-03-04T20:58:38,115][INFO ][o.e.i.s.SearchableSnapshotDirectoryStatsTests] [testCachedBytesReadsAndWrites] after test
REPRODUCE WITH: ./gradlew 'null' --tests "org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites" -Dtests.seed=163C909BF9F0F844 -Dtests.locale=sk-SK -Dtests.timezone=Etc/UTC -Druntime.java=15
java.lang.AssertionError:
Expected: <9641L>
but: was <9885L>
Expected :<9641L>
Actual :<9885L>
<Click to see difference>
at __randomizedtesting.SeedInfo.seed([163C909BF9F0F844:D38D21E9FBFE3FD4]:0)
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$2(SearchableSnapshotDirectoryStatsTests.java:131)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:955)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:928)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$3(SearchableSnapshotDirectoryStatsTests.java:129)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.executeTestCase(SearchableSnapshotDirectoryStatsTests.java:683)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.executeTestCaseWithCache(SearchableSnapshotDirectoryStatsTests.java:588)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.testCachedBytesReadsAndWrites(SearchableSnapshotDirectoryStatsTests.java:116)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:64)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:564)
at com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
at com.carrotsearch.randomizedtesting.RandomizedRunner$8.evaluate(RandomizedRunner.java:946)
at com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:982)
at com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:49)
at org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at org.apache.lucene.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:48)
at org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:824)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:475)
at com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
at com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
at com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
at com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
at org.apache.lucene.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:45)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:41)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
at org.apache.lucene.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:47)
at org.apache.lucene.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:64)
at org.apache.lucene.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:54)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:831)
at java.base/java.lang.Thread.run(Thread.java:832)
Suppressed: java.lang.AssertionError:
Expected: <9641L>
but: was <9885L>
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$2(SearchableSnapshotDirectoryStatsTests.java:131)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:943)
... 42 more
Suppressed: java.lang.AssertionError:
Expected: <9641L>
but: was <9885L>
at org.hamcrest.MatcherAssert.assertThat(MatcherAssert.java:18)
at org.junit.Assert.assertThat(Assert.java:956)
at org.junit.Assert.assertThat(Assert.java:923)
at org.elasticsearch.index.store.SearchableSnapshotDirectoryStatsTests.lambda$testCachedBytesReadsAndWrites$2(SearchableSnapshotDirectoryStatsTests.java:131)
at org.elasticsearch.test.ESTestCase.assertBusy(ESTestCase.java:943)
... 42 more
Suppressed: java.lang.AssertionError:
```
on current master.
|
non_process
|
reproducible failure in org elasticsearch index store searchablesnapshotdirectorystatstests testcachedbytesreadsandwrites just ran into this locally working on the multiple page sizes cache but it reproduces on master as well gradlew x pack plugin searchable snapshots test tests org elasticsearch index store searchablesnapshotdirectorystatstests testcachedbytesreadsandwrites dtests seed dtests security manager true dtests locale sk sk dtests timezone etc utc druntime java fails with before test using data paths mounts net usable space net total space types heap size compressed ordinary object pointers warning an illegal reflective access operation has occurred warning illegal reflective access by org mockito cglib core reflectutils file home brownbear gradle caches modules files org elasticsearch securemock securemock jar to method java lang classloader defineclass java lang string byte int int java security protectiondomain warning please consider reporting this to the maintainers of org mockito cglib core reflectutils warning use illegal access warn to enable warnings of further illegal reflective access operations warning all illegal access operations will be denied in a future release persistent cache index loaded after test reproduce with gradlew null tests org elasticsearch index store searchablesnapshotdirectorystatstests testcachedbytesreadsandwrites dtests seed dtests locale sk sk dtests timezone etc utc druntime java java lang assertionerror expected but was expected actual at randomizedtesting seedinfo seed at org hamcrest matcherassert assertthat matcherassert java at org junit assert assertthat assert java at org junit assert assertthat assert java at org elasticsearch index store searchablesnapshotdirectorystatstests lambda testcachedbytesreadsandwrites searchablesnapshotdirectorystatstests java at org elasticsearch test estestcase assertbusy estestcase java at org elasticsearch test estestcase assertbusy estestcase java at org elasticsearch index store searchablesnapshotdirectorystatstests lambda testcachedbytesreadsandwrites searchablesnapshotdirectorystatstests java at org elasticsearch index store searchablesnapshotdirectorystatstests executetestcase searchablesnapshotdirectorystatstests java at org elasticsearch index store searchablesnapshotdirectorystatstests executetestcasewithcache searchablesnapshotdirectorystatstests java at org elasticsearch index store searchablesnapshotdirectorystatstests testcachedbytesreadsandwrites searchablesnapshotdirectorystatstests java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at com carrotsearch randomizedtesting randomizedrunner invoke randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene util testrulesetupteardownchained evaluate testrulesetupteardownchained java at org apache lucene util abstractbeforeafterrule evaluate abstractbeforeafterrule java at org apache lucene util testrulethreadandtestname evaluate testrulethreadandtestname java at org apache lucene util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at org apache lucene util testrulemarkfailure evaluate testrulemarkfailure java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at com carrotsearch randomizedtesting threadleakcontrol forktimeoutingtask threadleakcontrol java at com carrotsearch randomizedtesting threadleakcontrol evaluate threadleakcontrol java at com carrotsearch randomizedtesting randomizedrunner runsingletest randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at org apache lucene util abstractbeforeafterrule evaluate abstractbeforeafterrule java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene util testrulestoreclassname evaluate testrulestoreclassname java at com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene util testruleassertionsrequired evaluate testruleassertionsrequired java at org apache lucene util testrulemarkfailure evaluate testrulemarkfailure java at org apache lucene util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at org apache lucene util testruleignoretestsuites evaluate testruleignoretestsuites java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at com carrotsearch randomizedtesting threadleakcontrol lambda forktimeoutingtask threadleakcontrol java at java base java lang thread run thread java suppressed java lang assertionerror expected but was at org hamcrest matcherassert assertthat matcherassert java at org junit assert assertthat assert java at org junit assert assertthat assert java at org elasticsearch index store searchablesnapshotdirectorystatstests lambda testcachedbytesreadsandwrites searchablesnapshotdirectorystatstests java at org elasticsearch test estestcase assertbusy estestcase java more suppressed java lang assertionerror expected but was at org hamcrest matcherassert assertthat matcherassert java at org junit assert assertthat assert java at org junit assert assertthat assert java at org elasticsearch index store searchablesnapshotdirectorystatstests lambda testcachedbytesreadsandwrites searchablesnapshotdirectorystatstests java at org elasticsearch test estestcase assertbusy estestcase java more suppressed java lang assertionerror on current master
| 0
|
5,803
| 8,643,540,579
|
IssuesEvent
|
2018-11-25 18:55:08
|
gfrebello/qs-trip-planning-procedure
|
https://api.github.com/repos/gfrebello/qs-trip-planning-procedure
|
closed
|
Implement flight reservation
|
Priority:Very High Process:Implement Requirement
|
The user must be able to reserve flights to and from their trip destination if they so desire.
|
1.0
|
Implement flight reservation - The user must be able to reserve flights to and from their trip destination if they so desire.
|
process
|
implement flight reservation the user must be able to reserve flights to and from their trip destination if they so desire
| 1
|
243
| 2,665,300,535
|
IssuesEvent
|
2015-03-20 19:35:32
|
cfpb/hmda-viz-prototype
|
https://api.github.com/repos/cfpb/hmda-viz-prototype
|
closed
|
Add a "Report Date" to show when the report is as of
|
enhancement Processing
|
On ffiec they have 'Report Date: xx/xx/xxxx'.
We can call it whatever in the json but 'reportdate': xx/xx/xxxx works.
so something like:
```
"reportdate": "the-date"
```
I'll output the text correctly on the front-end.
@Kibrael - assigned to you and you can hand it off to me after you add this to the json.
|
1.0
|
Add a "Report Date" to show when the report is as of - On ffiec they have 'Report Date: xx/xx/xxxx'.
We can call it whatever in the json but 'reportdate': xx/xx/xxxx works.
so something like:
```
"reportdate": "the-date"
```
I'll output the text correctly on the front-end.
@Kibrael - assigned to you and you can hand it off to me after you add this to the json.
|
process
|
add a report date to show when the report is as of on ffiec they have report date xx xx xxxx we can call it whatever in the json but reportdate xx xx xxxx works so something like reportdate the date i ll output the text correctly on the front end kibrael assigned to you and you can hand it off to me after you add this to the json
| 1
|
5,964
| 8,786,355,213
|
IssuesEvent
|
2018-12-20 15:32:09
|
bazelbuild/rules_swift
|
https://api.github.com/repos/bazelbuild/rules_swift
|
opened
|
Update Travis to Xcode 10.x
|
type: process
|
We need to do this, but the last time someone tried we got these mysterious errors that I haven't been able to duplicate locally:
https://github.com/bazelbuild/rules_swift/pull/63
|
1.0
|
Update Travis to Xcode 10.x - We need to do this, but the last time someone tried we got these mysterious errors that I haven't been able to duplicate locally:
https://github.com/bazelbuild/rules_swift/pull/63
|
process
|
update travis to xcode x we need to do this but the last time someone tried we got these mysterious errors that i haven t been able to duplicate locally
| 1
|
176,402
| 14,580,950,267
|
IssuesEvent
|
2020-12-18 09:58:21
|
danaremar/e-eat
|
https://api.github.com/repos/danaremar/e-eat
|
opened
|
1011 - Registrar adquisiciones e inversiones.
|
documentation
|
Informe en el que se detalla la monitorización con respecto a las adquisiciones e inversiones en activos y pasivos que lleva el proyecto. Registra desviaciones y analiza casos en los que se ha desviado la previsión original.
|
1.0
|
1011 - Registrar adquisiciones e inversiones. - Informe en el que se detalla la monitorización con respecto a las adquisiciones e inversiones en activos y pasivos que lleva el proyecto. Registra desviaciones y analiza casos en los que se ha desviado la previsión original.
|
non_process
|
registrar adquisiciones e inversiones informe en el que se detalla la monitorización con respecto a las adquisiciones e inversiones en activos y pasivos que lleva el proyecto registra desviaciones y analiza casos en los que se ha desviado la previsión original
| 0
|
6,402
| 9,486,111,350
|
IssuesEvent
|
2019-04-22 12:57:52
|
frontendbr/forum
|
https://api.github.com/repos/frontendbr/forum
|
reopened
|
Build Local vs Build Servidor
|
Processos [Dúvida]
|
Ola,
Gostaria de levantar uma discussão aqui, sobre fluxo de trabalho de um dev front.
Hoje em dias há mutos projetos front precisam dos "famosos build" :
`npm build`
`yarn build`
Enfim, atualmente vocês acham mais vantajoso, fazer o build local e subir para servidor ou deixar que o servidor faça o build?
|
1.0
|
Build Local vs Build Servidor - Ola,
Gostaria de levantar uma discussão aqui, sobre fluxo de trabalho de um dev front.
Hoje em dias há mutos projetos front precisam dos "famosos build" :
`npm build`
`yarn build`
Enfim, atualmente vocês acham mais vantajoso, fazer o build local e subir para servidor ou deixar que o servidor faça o build?
|
process
|
build local vs build servidor ola gostaria de levantar uma discussão aqui sobre fluxo de trabalho de um dev front hoje em dias há mutos projetos front precisam dos famosos build npm build yarn build enfim atualmente vocês acham mais vantajoso fazer o build local e subir para servidor ou deixar que o servidor faça o build
| 1
|
22,923
| 4,858,108,475
|
IssuesEvent
|
2016-11-12 23:35:12
|
n8rzz/atc
|
https://api.github.com/repos/n8rzz/atc
|
closed
|
Document git flow process
|
documentation
|
- [ ] gh-pages, how/when code gets there
- [ ] release/x.x.x
- [ ] develop
- [ ] feature/ATC-xxx where to branch from and where to target
- [ ] bugfix/ATC-xxx where to branch from and where to target
|
1.0
|
Document git flow process - - [ ] gh-pages, how/when code gets there
- [ ] release/x.x.x
- [ ] develop
- [ ] feature/ATC-xxx where to branch from and where to target
- [ ] bugfix/ATC-xxx where to branch from and where to target
|
non_process
|
document git flow process gh pages how when code gets there release x x x develop feature atc xxx where to branch from and where to target bugfix atc xxx where to branch from and where to target
| 0
|
181,749
| 14,887,659,479
|
IssuesEvent
|
2021-01-20 18:39:41
|
metacontroller/metacontroller
|
https://api.github.com/repos/metacontroller/metacontroller
|
opened
|
Docs: Add way to add/update description on dockerhub
|
chore documentation
|
# Description
Currently https://hub.docker.com/repository/docker/metacontrollerio/metacontroller/general is empty
# Todo
* find a way to update it on master pipeline / tag pipeline to push version from source controll
* prepare initial readme
|
1.0
|
Docs: Add way to add/update description on dockerhub - # Description
Currently https://hub.docker.com/repository/docker/metacontrollerio/metacontroller/general is empty
# Todo
* find a way to update it on master pipeline / tag pipeline to push version from source controll
* prepare initial readme
|
non_process
|
docs add way to add update description on dockerhub description currently is empty todo find a way to update it on master pipeline tag pipeline to push version from source controll prepare initial readme
| 0
|
22,242
| 30,795,184,172
|
IssuesEvent
|
2023-07-31 19:16:51
|
gferragu/ESI-build-tests
|
https://api.github.com/repos/gferragu/ESI-build-tests
|
opened
|
Changes from last update introduced bugs in Azure build
|
bug Azure gmprocess esi-core
|
I believe I set some tolerances in the build stages to handle a couple (1-2) unit test errors without completely failing the nightly build.
For some reason, this isn't being taken into account, and beyond that, the status badges for the pipelines don't read as "failed" they read as "never built" now, I am not sure why but need to debug this.
|
1.0
|
Changes from last update introduced bugs in Azure build - I believe I set some tolerances in the build stages to handle a couple (1-2) unit test errors without completely failing the nightly build.
For some reason, this isn't being taken into account, and beyond that, the status badges for the pipelines don't read as "failed" they read as "never built" now, I am not sure why but need to debug this.
|
process
|
changes from last update introduced bugs in azure build i believe i set some tolerances in the build stages to handle a couple unit test errors without completely failing the nightly build for some reason this isn t being taken into account and beyond that the status badges for the pipelines don t read as failed they read as never built now i am not sure why but need to debug this
| 1
|
233,535
| 17,869,456,363
|
IssuesEvent
|
2021-09-06 13:39:29
|
hermitdemschoenenleben/linien
|
https://api.github.com/repos/hermitdemschoenenleben/linien
|
opened
|
Incomplete sentence in readme
|
documentation
|
This sentence is not complete. @hermitdemschoenenleben, what did you try to say?
https://github.com/hermitdemschoenenleben/linien/blob/aa6afe2ccd514946a2683807c426da9ad84e088e/README.md#L386
|
1.0
|
Incomplete sentence in readme - This sentence is not complete. @hermitdemschoenenleben, what did you try to say?
https://github.com/hermitdemschoenenleben/linien/blob/aa6afe2ccd514946a2683807c426da9ad84e088e/README.md#L386
|
non_process
|
incomplete sentence in readme this sentence is not complete hermitdemschoenenleben what did you try to say
| 0
|
157,134
| 19,914,247,952
|
IssuesEvent
|
2022-01-25 20:35:07
|
dmyers87/boomstrap-react
|
https://api.github.com/repos/dmyers87/boomstrap-react
|
opened
|
CVE-2017-1000048 (High) detected in multiple libraries
|
security vulnerability
|
## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-2.3.3.tgz</b>, <b>qs-2.4.1.tgz</b>, <b>qs-4.0.0.tgz</b>, <b>qs-5.2.0.tgz</b>, <b>qs-5.1.0.tgz</b></p></summary>
<p>
<details><summary><b>qs-2.3.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-2.3.3.tgz">https://registry.npmjs.org/qs/-/qs-2.3.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/superagent/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- superagent-1.8.5.tgz (Root Library)
- :x: **qs-2.3.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-2.4.1.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-2.4.1.tgz">https://registry.npmjs.org/qs/-/qs-2.4.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/react-router/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- react-router-0.13.6.tgz (Root Library)
- :x: **qs-2.4.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-4.0.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-4.0.0.tgz">https://registry.npmjs.org/qs/-/qs-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- gulp-connect-2.3.1.tgz (Root Library)
- connect-2.30.2.tgz
- :x: **qs-4.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-5.2.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-5.2.0.tgz">https://registry.npmjs.org/qs/-/qs-5.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tiny-lr/node_modules/body-parser/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- gulp-connect-2.3.1.tgz (Root Library)
- tiny-lr-0.2.1.tgz
- body-parser-1.14.2.tgz
- :x: **qs-5.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-5.1.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-5.1.0.tgz">https://registry.npmjs.org/qs/-/qs-5.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tiny-lr/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- gulp-connect-2.3.1.tgz (Root Library)
- tiny-lr-0.2.1.tgz
- :x: **qs-5.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/boomstrap-react/commit/56ff85f974b05cab00c2299011cfbdf611dd773d">56ff85f974b05cab00c2299011cfbdf611dd773d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution: qs - 6.0.4,6.1.2,6.2.3,6.3.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"2.3.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"superagent:1.8.5;qs:2.3.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"2.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-router:0.13.6;qs:2.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"4.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-connect:2.3.1;connect:2.30.2;qs:4.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"5.2.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-connect:2.3.1;tiny-lr:0.2.1;body-parser:1.14.2;qs:5.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"5.1.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-connect:2.3.1;tiny-lr:0.2.1;qs:5.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-1000048","vulnerabilityDetails":"the web framework using ljharb\u0027s qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2017-1000048 (High) detected in multiple libraries - ## CVE-2017-1000048 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-2.3.3.tgz</b>, <b>qs-2.4.1.tgz</b>, <b>qs-4.0.0.tgz</b>, <b>qs-5.2.0.tgz</b>, <b>qs-5.1.0.tgz</b></p></summary>
<p>
<details><summary><b>qs-2.3.3.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-2.3.3.tgz">https://registry.npmjs.org/qs/-/qs-2.3.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/superagent/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- superagent-1.8.5.tgz (Root Library)
- :x: **qs-2.3.3.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-2.4.1.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-2.4.1.tgz">https://registry.npmjs.org/qs/-/qs-2.4.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/react-router/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- react-router-0.13.6.tgz (Root Library)
- :x: **qs-2.4.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-4.0.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-4.0.0.tgz">https://registry.npmjs.org/qs/-/qs-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- gulp-connect-2.3.1.tgz (Root Library)
- connect-2.30.2.tgz
- :x: **qs-4.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-5.2.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-5.2.0.tgz">https://registry.npmjs.org/qs/-/qs-5.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tiny-lr/node_modules/body-parser/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- gulp-connect-2.3.1.tgz (Root Library)
- tiny-lr-0.2.1.tgz
- body-parser-1.14.2.tgz
- :x: **qs-5.2.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-5.1.0.tgz</b></p></summary>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-5.1.0.tgz">https://registry.npmjs.org/qs/-/qs-5.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/tiny-lr/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- gulp-connect-2.3.1.tgz (Root Library)
- tiny-lr-0.2.1.tgz
- :x: **qs-5.1.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/boomstrap-react/commit/56ff85f974b05cab00c2299011cfbdf611dd773d">56ff85f974b05cab00c2299011cfbdf611dd773d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution: qs - 6.0.4,6.1.2,6.2.3,6.3.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"2.3.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"superagent:1.8.5;qs:2.3.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"2.4.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"react-router:0.13.6;qs:2.4.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"4.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-connect:2.3.1;connect:2.30.2;qs:4.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"5.2.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-connect:2.3.1;tiny-lr:0.2.1;body-parser:1.14.2;qs:5.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false},{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"5.1.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"gulp-connect:2.3.1;tiny-lr:0.2.1;qs:5.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-1000048","vulnerabilityDetails":"the web framework using ljharb\u0027s qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries qs tgz qs tgz qs tgz qs tgz qs tgz qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules superagent node modules qs package json dependency hierarchy superagent tgz root library x qs tgz vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules react router node modules qs package json dependency hierarchy react router tgz root library x qs tgz vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules qs package json dependency hierarchy gulp connect tgz root library connect tgz x qs tgz vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules tiny lr node modules body parser node modules qs package json dependency hierarchy gulp connect tgz root library tiny lr tgz body parser tgz x qs tgz vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules tiny lr node modules qs package json dependency hierarchy gulp connect tgz root library tiny lr tgz x qs tgz vulnerable library found in head commit a href found in base branch master vulnerability details the web framework using ljharb s qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution qs isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree superagent qs isminimumfixversionavailable true minimumfixversion qs isbinary false packagetype javascript node js packagename qs packageversion packagefilepaths istransitivedependency true dependencytree react router qs isminimumfixversionavailable true minimumfixversion qs isbinary false packagetype javascript node js packagename qs packageversion packagefilepaths istransitivedependency true dependencytree gulp connect connect qs isminimumfixversionavailable true minimumfixversion qs isbinary false packagetype javascript node js packagename qs packageversion packagefilepaths istransitivedependency true dependencytree gulp connect tiny lr body parser qs isminimumfixversionavailable true minimumfixversion qs isbinary false packagetype javascript node js packagename qs packageversion packagefilepaths istransitivedependency true dependencytree gulp connect tiny lr qs isminimumfixversionavailable true minimumfixversion qs isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the web framework using ljharb qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash vulnerabilityurl
| 0
|
65,765
| 14,761,894,183
|
IssuesEvent
|
2021-01-09 00:53:17
|
AlexRogalskiy/electron-vue-template
|
https://api.github.com/repos/AlexRogalskiy/electron-vue-template
|
opened
|
CVE-2020-15174 (High) detected in electron-8.2.0.tgz
|
security vulnerability
|
## CVE-2020-15174 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>electron-8.2.0.tgz</b></p></summary>
<p>Build cross platform desktop apps with JavaScript, HTML, and CSS</p>
<p>Library home page: <a href="https://registry.npmjs.org/electron/-/electron-8.2.0.tgz">https://registry.npmjs.org/electron/-/electron-8.2.0.tgz</a></p>
<p>Path to dependency file: electron-vue-template/package.json</p>
<p>Path to vulnerable library: electron-vue-template/node_modules/electron/package.json</p>
<p>
Dependency Hierarchy:
- :x: **electron-8.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/electron-vue-template/commit/e180436ddc869ab181e9108f09eafef3237f5eb6">e180436ddc869ab181e9108f09eafef3237f5eb6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Electron before versions 11.0.0-beta.1, 10.0.1, 9.3.0 or 8.5.1 the `will-navigate` event that apps use to prevent navigations to unexpected destinations as per our security recommendations can be bypassed when a sub-frame performs a top-frame navigation across sites. The issue is patched in versions 11.0.0-beta.1, 10.0.1, 9.3.0 or 8.5.1 As a workaround sandbox all your iframes using the sandbox attribute. This will prevent them creating top-frame navigations and is good practice anyway.
<p>Publish Date: 2020-10-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15174>CVE-2020-15174</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/electron/electron/security/advisories/GHSA-2q4g-w47c-4674">https://github.com/electron/electron/security/advisories/GHSA-2q4g-w47c-4674</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: v8.5.1, v9.3.0, v10.0.1, v11.0.0-beta.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-15174 (High) detected in electron-8.2.0.tgz - ## CVE-2020-15174 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>electron-8.2.0.tgz</b></p></summary>
<p>Build cross platform desktop apps with JavaScript, HTML, and CSS</p>
<p>Library home page: <a href="https://registry.npmjs.org/electron/-/electron-8.2.0.tgz">https://registry.npmjs.org/electron/-/electron-8.2.0.tgz</a></p>
<p>Path to dependency file: electron-vue-template/package.json</p>
<p>Path to vulnerable library: electron-vue-template/node_modules/electron/package.json</p>
<p>
Dependency Hierarchy:
- :x: **electron-8.2.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/electron-vue-template/commit/e180436ddc869ab181e9108f09eafef3237f5eb6">e180436ddc869ab181e9108f09eafef3237f5eb6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Electron before versions 11.0.0-beta.1, 10.0.1, 9.3.0 or 8.5.1 the `will-navigate` event that apps use to prevent navigations to unexpected destinations as per our security recommendations can be bypassed when a sub-frame performs a top-frame navigation across sites. The issue is patched in versions 11.0.0-beta.1, 10.0.1, 9.3.0 or 8.5.1 As a workaround sandbox all your iframes using the sandbox attribute. This will prevent them creating top-frame navigations and is good practice anyway.
<p>Publish Date: 2020-10-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15174>CVE-2020-15174</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/electron/electron/security/advisories/GHSA-2q4g-w47c-4674">https://github.com/electron/electron/security/advisories/GHSA-2q4g-w47c-4674</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: v8.5.1, v9.3.0, v10.0.1, v11.0.0-beta.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in electron tgz cve high severity vulnerability vulnerable library electron tgz build cross platform desktop apps with javascript html and css library home page a href path to dependency file electron vue template package json path to vulnerable library electron vue template node modules electron package json dependency hierarchy x electron tgz vulnerable library found in head commit a href found in base branch master vulnerability details in electron before versions beta or the will navigate event that apps use to prevent navigations to unexpected destinations as per our security recommendations can be bypassed when a sub frame performs a top frame navigation across sites the issue is patched in versions beta or as a workaround sandbox all your iframes using the sandbox attribute this will prevent them creating top frame navigations and is good practice anyway publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact none integrity impact high availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution beta step up your open source security game with whitesource
| 0
|
88,162
| 11,036,175,569
|
IssuesEvent
|
2019-12-07 18:49:59
|
Students-of-the-city-of-Kostroma/Ray-of-hope
|
https://api.github.com/repos/Students-of-the-city-of-Kostroma/Ray-of-hope
|
opened
|
Макеты ленты в Android не соответствуют спецификации
|
Android Bug Design O5 PR5 Sprint 9 Лента постов
|
Epic #157 Story #170 #188 #195
Макеты ленты постов в Android-приложении не соответствуют [стори](https://docs.google.com/document/d/1TP_bUWStqtJZPt8JGelRgwGyq9PCXUbF2qKxWsSFwJQ/edit) и [описанию типов постов](https://docs.google.com/document/d/1p0aFXnl3jeQWKu_cQHuSFoc59WKs-PMpChTdkxWICBA/edit) по следующим пунктам:
- макеты отображают возможность выбрать фильтр "Только в моём городе";
- нет макета, показывающего тип записи "Нужда";
- дата и время публикации должны располагаться в правом нижнем углу;
- неправильное отображение фотографий;
- неправильное отображение дат начала и завершения, а также места проведения у записи типа "Мероприятие".
Ожидаемый результат: макеты приведены в состояние, соответствующее документации, создан макет, изображающий тип поста "Нужда".
|
1.0
|
Макеты ленты в Android не соответствуют спецификации - Epic #157 Story #170 #188 #195
Макеты ленты постов в Android-приложении не соответствуют [стори](https://docs.google.com/document/d/1TP_bUWStqtJZPt8JGelRgwGyq9PCXUbF2qKxWsSFwJQ/edit) и [описанию типов постов](https://docs.google.com/document/d/1p0aFXnl3jeQWKu_cQHuSFoc59WKs-PMpChTdkxWICBA/edit) по следующим пунктам:
- макеты отображают возможность выбрать фильтр "Только в моём городе";
- нет макета, показывающего тип записи "Нужда";
- дата и время публикации должны располагаться в правом нижнем углу;
- неправильное отображение фотографий;
- неправильное отображение дат начала и завершения, а также места проведения у записи типа "Мероприятие".
Ожидаемый результат: макеты приведены в состояние, соответствующее документации, создан макет, изображающий тип поста "Нужда".
|
non_process
|
макеты ленты в android не соответствуют спецификации epic story макеты ленты постов в android приложении не соответствуют и по следующим пунктам макеты отображают возможность выбрать фильтр только в моём городе нет макета показывающего тип записи нужда дата и время публикации должны располагаться в правом нижнем углу неправильное отображение фотографий неправильное отображение дат начала и завершения а также места проведения у записи типа мероприятие ожидаемый результат макеты приведены в состояние соответствующее документации создан макет изображающий тип поста нужда
| 0
|
78,002
| 3,508,450,619
|
IssuesEvent
|
2016-01-08 17:54:38
|
cytoscape/cytoscape.js
|
https://api.github.com/repos/cytoscape/cytoscape.js
|
closed
|
Box selection events
|
2-medium-priority enhancement renderer
|
Ref : https://github.com/cytoscape/cytoscape.js/issues/1145
On the core:
* `boxstart` : when the box is shown
* `boxend` : when the box is hidden
On the elements:
* `boxselect` : triggered on elements when selected by the box
* `box` : triggered on elements when inside the box on `boxselectend`
|
1.0
|
Box selection events - Ref : https://github.com/cytoscape/cytoscape.js/issues/1145
On the core:
* `boxstart` : when the box is shown
* `boxend` : when the box is hidden
On the elements:
* `boxselect` : triggered on elements when selected by the box
* `box` : triggered on elements when inside the box on `boxselectend`
|
non_process
|
box selection events ref on the core boxstart when the box is shown boxend when the box is hidden on the elements boxselect triggered on elements when selected by the box box triggered on elements when inside the box on boxselectend
| 0
|
17,786
| 23,714,811,615
|
IssuesEvent
|
2022-08-30 10:51:07
|
kitspace/kitspace-v2
|
https://api.github.com/repos/kitspace/kitspace-v2
|
opened
|
Show processor logs in CI if the `test_processor` workflow fails
|
CI/CD processor
|
There is no way to know what actually happened without running the tests locally.
|
1.0
|
Show processor logs in CI if the `test_processor` workflow fails - There is no way to know what actually happened without running the tests locally.
|
process
|
show processor logs in ci if the test processor workflow fails there is no way to know what actually happened without running the tests locally
| 1
|
20,012
| 26,486,031,973
|
IssuesEvent
|
2023-01-17 18:06:01
|
kubernetes/minikube
|
https://api.github.com/repos/kubernetes/minikube
|
closed
|
request: cgroup v2 CI infra (for testing Rootless Docker driver)
|
area/testing priority/important-longterm kind/process
|
Support for Rootless Docker with cgroup v2 was merged in https://github.com/kubernetes/minikube/pull/12359 , but not tested on CI.
We need a cgroup v2 CI infra to test the rootless docker driver (and eventually rootless podman driver too).
### cgroup v2 CI infra in other projects
- `kind` uses Fedora 34 Vagrant box on macOS instances of GHA. Free and easy, but slow. https://github.com/kubernetes-sigs/kind/blob/4910c3e221a858e68e29f9494170a38e1c4e8b80/.github/workflows/cgroup2.yaml
- runc uses Fedora 34 Vagrant box on Linux KVM instances of Cirrus CI. Free, easy, and relatively faster than GHA macOS. Needs to be set up by an admin of `github.com/kubernetes` organization. https://github.com/opencontainers/runc/blob/v1.0.2/.cirrus.yml#L23
- k/k uses Fedora CoreOS instances on GCP https://github.com/kubernetes/test-infra/blob/5c6d26134d55239241b6ce2ad231a5543696e0d7/jobs/e2e_node/crio/latest/image-config-cgrpv2.yaml
|
1.0
|
request: cgroup v2 CI infra (for testing Rootless Docker driver) - Support for Rootless Docker with cgroup v2 was merged in https://github.com/kubernetes/minikube/pull/12359 , but not tested on CI.
We need a cgroup v2 CI infra to test the rootless docker driver (and eventually rootless podman driver too).
### cgroup v2 CI infra in other projects
- `kind` uses Fedora 34 Vagrant box on macOS instances of GHA. Free and easy, but slow. https://github.com/kubernetes-sigs/kind/blob/4910c3e221a858e68e29f9494170a38e1c4e8b80/.github/workflows/cgroup2.yaml
- runc uses Fedora 34 Vagrant box on Linux KVM instances of Cirrus CI. Free, easy, and relatively faster than GHA macOS. Needs to be set up by an admin of `github.com/kubernetes` organization. https://github.com/opencontainers/runc/blob/v1.0.2/.cirrus.yml#L23
- k/k uses Fedora CoreOS instances on GCP https://github.com/kubernetes/test-infra/blob/5c6d26134d55239241b6ce2ad231a5543696e0d7/jobs/e2e_node/crio/latest/image-config-cgrpv2.yaml
|
process
|
request cgroup ci infra for testing rootless docker driver support for rootless docker with cgroup was merged in but not tested on ci we need a cgroup ci infra to test the rootless docker driver and eventually rootless podman driver too cgroup ci infra in other projects kind uses fedora vagrant box on macos instances of gha free and easy but slow runc uses fedora vagrant box on linux kvm instances of cirrus ci free easy and relatively faster than gha macos needs to be set up by an admin of github com kubernetes organization k k uses fedora coreos instances on gcp
| 1
|
228,834
| 18,265,723,262
|
IssuesEvent
|
2021-10-04 08:14:13
|
kedacore/keda
|
https://api.github.com/repos/kedacore/keda
|
closed
|
Add e2e test for Cron scaler
|
enhancement help wanted scaler testing Hacktoberfest
|
Provide end-to-end tests for Cron scaler to ensure everything still works.
https://github.com/kedacore/keda/tree/main/tests
|
1.0
|
Add e2e test for Cron scaler - Provide end-to-end tests for Cron scaler to ensure everything still works.
https://github.com/kedacore/keda/tree/main/tests
|
non_process
|
add test for cron scaler provide end to end tests for cron scaler to ensure everything still works
| 0
|
54,944
| 14,077,919,845
|
IssuesEvent
|
2020-11-04 12:48:21
|
department-of-veterans-affairs/va.gov-team
|
https://api.github.com/repos/department-of-veterans-affairs/va.gov-team
|
closed
|
[COGNITION] 508-defect-3: Character counts MUST announce properly in IE11 + JAWS
|
508-defect-3 508-issue-cognition 508/Accessibility frontend vaos
|
# [508-defect-3](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-3)
**Feedback framework**
- **❗️ Must** for if the feedback must be applied
- **⚠️ Should** if the feedback is best practice
- **✔️ Consider** for suggestions/enhancements
## Point of Contact
<!-- If this issue is being opened by a VFS team member, please add a point of contact. Usually this is the same person who enters the issue ticket. -->
**VFS Point of Contact:** _Trevor_
## User Story or Problem Statement
<!-- Example: As a user with cognitive considerations, I expect to see a label and input pairing consistently styled as throughout the rest of the site, with the label just above the text/email/search input or to the right of a radio/checkbox input, so that I am clearly able to understand what entry is expected. -->
As a JAWS screen reader user, I want to hear the character counts announced properly after I have entered data about my Express Care issue. It's beneficial to know if I am nearing the character limit.
## Details
<!-- This is a detailed description of the issue. It should include a restatement of the title, and provide more background information. -->
This issue is only happening on IE11 + JAWS 2020. All other screen reader + browser combinations I tested worked as expected. It seems there might be two data points being collated to assemble this one string, based on how it's chunked out in the Chrome Dev Tools. Screenshot attached below.
## Acceptance Criteria
- [ ] IE11 + JAWS announces "255 characters remaining" properly instead of just announcing "255"
## Definition of done
1. Review and acknowledge feedback.
1. Fix and/or document decisions made.
1. Accessibility specialist will close ticket after reviewing documented decisions / validating fix.
## Environment
* Win10
* IE11
* JAWS 2020
* https://staging.va.gov/health-care/schedule-view-va-appointments/appointments/new-express-care-request/additional-details
## WCAG or Vendor Guidance (optional)
* [Info and Relationships: Understanding SC 1.3.1](https://www.w3.org/TR/UNDERSTANDING-WCAG20/content-structure-separation-programmatic.html)
## Screenshots or Trace Logs
<!-- Drop any screenshots or error logs that might be useful for debugging -->
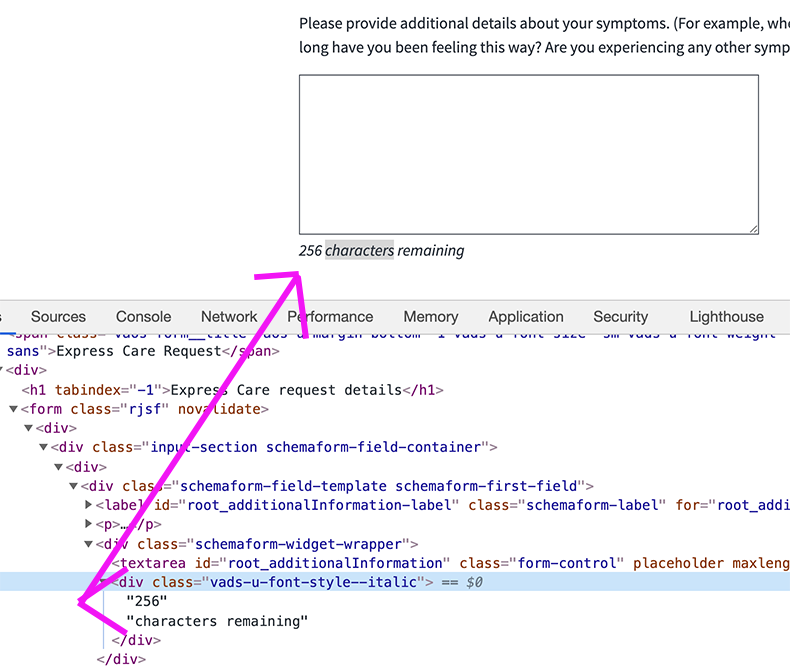
|
1.0
|
[COGNITION] 508-defect-3: Character counts MUST announce properly in IE11 + JAWS - # [508-defect-3](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-3)
**Feedback framework**
- **❗️ Must** for if the feedback must be applied
- **⚠️ Should** if the feedback is best practice
- **✔️ Consider** for suggestions/enhancements
## Point of Contact
<!-- If this issue is being opened by a VFS team member, please add a point of contact. Usually this is the same person who enters the issue ticket. -->
**VFS Point of Contact:** _Trevor_
## User Story or Problem Statement
<!-- Example: As a user with cognitive considerations, I expect to see a label and input pairing consistently styled as throughout the rest of the site, with the label just above the text/email/search input or to the right of a radio/checkbox input, so that I am clearly able to understand what entry is expected. -->
As a JAWS screen reader user, I want to hear the character counts announced properly after I have entered data about my Express Care issue. It's beneficial to know if I am nearing the character limit.
## Details
<!-- This is a detailed description of the issue. It should include a restatement of the title, and provide more background information. -->
This issue is only happening on IE11 + JAWS 2020. All other screen reader + browser combinations I tested worked as expected. It seems there might be two data points being collated to assemble this one string, based on how it's chunked out in the Chrome Dev Tools. Screenshot attached below.
## Acceptance Criteria
- [ ] IE11 + JAWS announces "255 characters remaining" properly instead of just announcing "255"
## Definition of done
1. Review and acknowledge feedback.
1. Fix and/or document decisions made.
1. Accessibility specialist will close ticket after reviewing documented decisions / validating fix.
## Environment
* Win10
* IE11
* JAWS 2020
* https://staging.va.gov/health-care/schedule-view-va-appointments/appointments/new-express-care-request/additional-details
## WCAG or Vendor Guidance (optional)
* [Info and Relationships: Understanding SC 1.3.1](https://www.w3.org/TR/UNDERSTANDING-WCAG20/content-structure-separation-programmatic.html)
## Screenshots or Trace Logs
<!-- Drop any screenshots or error logs that might be useful for debugging -->
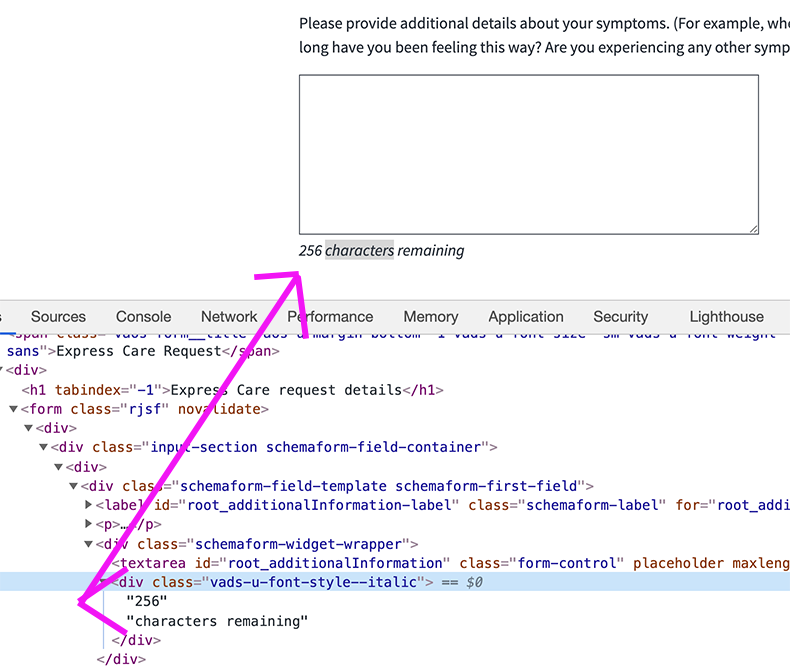
|
non_process
|
defect character counts must announce properly in jaws feedback framework ❗️ must for if the feedback must be applied ⚠️ should if the feedback is best practice ✔️ consider for suggestions enhancements point of contact vfs point of contact trevor user story or problem statement as a jaws screen reader user i want to hear the character counts announced properly after i have entered data about my express care issue it s beneficial to know if i am nearing the character limit details this issue is only happening on jaws all other screen reader browser combinations i tested worked as expected it seems there might be two data points being collated to assemble this one string based on how it s chunked out in the chrome dev tools screenshot attached below acceptance criteria jaws announces characters remaining properly instead of just announcing definition of done review and acknowledge feedback fix and or document decisions made accessibility specialist will close ticket after reviewing documented decisions validating fix environment jaws wcag or vendor guidance optional screenshots or trace logs
| 0
|
314,911
| 23,539,905,510
|
IssuesEvent
|
2022-08-20 08:06:06
|
Tersus-Light/tersus-docs-app
|
https://api.github.com/repos/Tersus-Light/tersus-docs-app
|
closed
|
[Project] Proposal I - Solid, Go / Gin, Rust / Rocket, Postgres, Tauri
|
documentation
|
## Background
This proposal is designed to provide a balance between performance and ease of development by introducing newer, proven technology that have high performance relative to their learning curve while using safe and security-minded languages and architecture for authentication.
## Issue
NA
## Tech Stack
| Technology | Application | Summary |
|-------------|------------|-----------|
| Solid | Frontend | A blend of Svelte and React, incredibly simple components with easily integrated features and superior performance. Has its own compiler and is fully reactive unlike React. |
| Go / Gin | Resource Server | Highly performant backend language with a small learning curve and simple concurrency. |
| Rust / Rocket | Auth Server | Arguably the most performant web backend possible with incredibly safety. |
| Postgres | SQL Database | Sufficient SQL database readily available for sandboxing and deployment. |
| Tauri | Native Desktop | Tauri uses Rust in the backend for superior performance and development safety. |
## Architecture
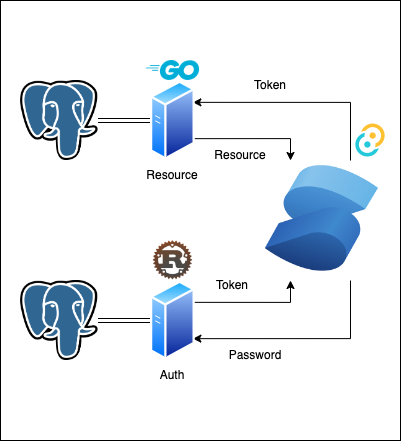
## Tech Details
### Solid (Frontend)
[Solid](https://www.youtube.com/watch?v=hw3Bx5vxKl0&ab_channel=Fireship) is an evolution of React inspired by some elements of React and many elements of Svelte. It has its own compiler that allows for incredibly small bundles and near-vanilla levels of performance.
<img width="513" alt="image" src="https://user-images.githubusercontent.com/47514505/183271228-26829f77-45e3-44b4-bd9f-a81d399038db.png">
Solid does not use a virtual DOM and allows more natural writing of HTML templating in JSX to avoid heavy use of ternary operators and, even worse, nested ternary operators with helpers like `Show` with fallbacks.
```
return (
<Show
when={loggedIn()}
fallback={<button onClick={toggle}>Log in</button>}
>
<button onClick={toggle}>Log out</button>
</Show>
)
```
Reactivity is handled with `Signals` using a similar syntax as React.
```
const [loggedIn, setLoggedIn] = createSignal(false)
```
However, where React is not truly reactive and uses schedulers, Solid uses proxies to have true reactivity. Additionally, all components truly render once allowing for some additional implementations (like `setInterval`) and avoiding issues caused by components re-rendering (like React's `useEffect` on `Strict` mode). Additionally, `useEffect` is also present here but does not require a dependency array and is handled automatically.
It is the [most loved web frameworks ](https://2021.stateofjs.com/en-US/libraries/front-end-frameworks/)at 90% satisfaction (tied with Svelte).
Ultimately, it is a great bridge between React and Svelte.
### Go / Gin (Resource Web Server)
[Gin](https://gin-gonic.com/docs/) is a light web server framework for Go.
Go itself is a compiled, very performant language with a simple syntax. It is statically typed with explicit type inference, easy concurrency patterns (which the Gin framework uses to improve performance). It does include concepts like [pointers](https://go.dev/tour/moretypes/1) that a key aspects of computer science but are usually unfamiliar to JS developers. However, understanding these concepts goes a long way to improving engineering.
Gin is a very straight-forward framework for creating clean and easily maintainable web servers. [Examples of the syntax and implementation](https://github.com/gin-gonic/examples) are available from the developers.
Go web server[ performance ranks consistently several orders of magnitude above Node](https://youtu.be/h7UEwBaGoVo?t=321) and below Rust. Development speed is typically on par with Node and above Rust.
### Rust / Rocket (Auth Web Server)
[Rust](https://www.rust-lang.org/) is currently the most performant backend language and is the [most loved language](https://survey.stackoverflow.co/2022/) for 6 years in a row. While more difficult than JavaScript and Go, it offers incredible safety as a compiled language and a superior compiler for handling errors. While it doesn't have traditional garbage collection, it has a signature concept of "ownership" for managing memory.
[Rocket](https://rocket.rs/) is a relatively simple web framework implementation of Rust. As the authentication is relatively simple, it offers an opportunity to learn and implement Rust with additional synergy with Tauri as it uses Rust in the backend.
### Postgres (Database)
Postgres is an easily accessible SQL database (with numerous free hosting options and CI/CD integration such as on Heroku). A relational database is ideal given the application will not have explicitly complex schema or significant object complexity (i.e. little or no nesting). Given the potential scale of the application with thousands of users and magnitudes more documentation, a normalized database would be ideal for maintaining and querying the data.
### Tauri
Tauri is a relatively new native desktop framework for web frameworks. Its primary attraction is the Rust backend that is incredibly performant and safe. Compared to Electron, it is compatible with more frameworks and packages, has far less memory consumption, and has a larger emphasis on security. Bundle sizes are also much smaller than other frameworks. [It benches above other native desktop frameworks in nearly every category](https://tauri.app/about/benchmarks). Built-in testing and substantial documentation make development reliable. Rust in the backend may prove to be more complex, especially for frontend developers. However, required backend implementation is comparatively simple.
## Architecture Details
### Dedicated Authentication Server
Dedicated authentication servers provide a layer of abstraction from the resource server. Using tokens, users can authenticate and then send the token to the resource server for a secondary check from the authentication server. Token refreshes will ensure highjacked tokens do not become a long-term threat. Given the public availability of the product, additional layers of security are preferable, and using performant backends, user experience will not be negatively impacted.
### Databases
Databases will be split based on their connecting server. The authentication server will maintain tokens and authentication-related credentials, while the resource server will contain primary data. This will prevent complete compromise in the event one database is penetrated or taken offline.
|
1.0
|
[Project] Proposal I - Solid, Go / Gin, Rust / Rocket, Postgres, Tauri - ## Background
This proposal is designed to provide a balance between performance and ease of development by introducing newer, proven technology that have high performance relative to their learning curve while using safe and security-minded languages and architecture for authentication.
## Issue
NA
## Tech Stack
| Technology | Application | Summary |
|-------------|------------|-----------|
| Solid | Frontend | A blend of Svelte and React, incredibly simple components with easily integrated features and superior performance. Has its own compiler and is fully reactive unlike React. |
| Go / Gin | Resource Server | Highly performant backend language with a small learning curve and simple concurrency. |
| Rust / Rocket | Auth Server | Arguably the most performant web backend possible with incredibly safety. |
| Postgres | SQL Database | Sufficient SQL database readily available for sandboxing and deployment. |
| Tauri | Native Desktop | Tauri uses Rust in the backend for superior performance and development safety. |
## Architecture
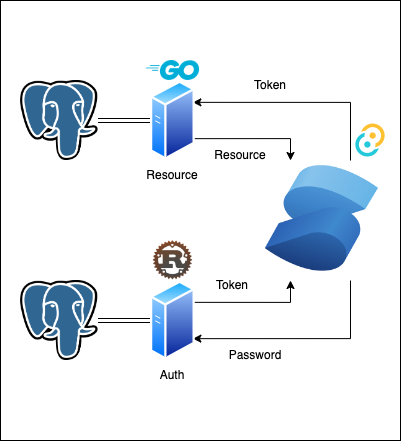
## Tech Details
### Solid (Frontend)
[Solid](https://www.youtube.com/watch?v=hw3Bx5vxKl0&ab_channel=Fireship) is an evolution of React inspired by some elements of React and many elements of Svelte. It has its own compiler that allows for incredibly small bundles and near-vanilla levels of performance.
<img width="513" alt="image" src="https://user-images.githubusercontent.com/47514505/183271228-26829f77-45e3-44b4-bd9f-a81d399038db.png">
Solid does not use a virtual DOM and allows more natural writing of HTML templating in JSX to avoid heavy use of ternary operators and, even worse, nested ternary operators with helpers like `Show` with fallbacks.
```
return (
<Show
when={loggedIn()}
fallback={<button onClick={toggle}>Log in</button>}
>
<button onClick={toggle}>Log out</button>
</Show>
)
```
Reactivity is handled with `Signals` using a similar syntax as React.
```
const [loggedIn, setLoggedIn] = createSignal(false)
```
However, where React is not truly reactive and uses schedulers, Solid uses proxies to have true reactivity. Additionally, all components truly render once allowing for some additional implementations (like `setInterval`) and avoiding issues caused by components re-rendering (like React's `useEffect` on `Strict` mode). Additionally, `useEffect` is also present here but does not require a dependency array and is handled automatically.
It is the [most loved web frameworks ](https://2021.stateofjs.com/en-US/libraries/front-end-frameworks/)at 90% satisfaction (tied with Svelte).
Ultimately, it is a great bridge between React and Svelte.
### Go / Gin (Resource Web Server)
[Gin](https://gin-gonic.com/docs/) is a light web server framework for Go.
Go itself is a compiled, very performant language with a simple syntax. It is statically typed with explicit type inference, easy concurrency patterns (which the Gin framework uses to improve performance). It does include concepts like [pointers](https://go.dev/tour/moretypes/1) that a key aspects of computer science but are usually unfamiliar to JS developers. However, understanding these concepts goes a long way to improving engineering.
Gin is a very straight-forward framework for creating clean and easily maintainable web servers. [Examples of the syntax and implementation](https://github.com/gin-gonic/examples) are available from the developers.
Go web server[ performance ranks consistently several orders of magnitude above Node](https://youtu.be/h7UEwBaGoVo?t=321) and below Rust. Development speed is typically on par with Node and above Rust.
### Rust / Rocket (Auth Web Server)
[Rust](https://www.rust-lang.org/) is currently the most performant backend language and is the [most loved language](https://survey.stackoverflow.co/2022/) for 6 years in a row. While more difficult than JavaScript and Go, it offers incredible safety as a compiled language and a superior compiler for handling errors. While it doesn't have traditional garbage collection, it has a signature concept of "ownership" for managing memory.
[Rocket](https://rocket.rs/) is a relatively simple web framework implementation of Rust. As the authentication is relatively simple, it offers an opportunity to learn and implement Rust with additional synergy with Tauri as it uses Rust in the backend.
### Postgres (Database)
Postgres is an easily accessible SQL database (with numerous free hosting options and CI/CD integration such as on Heroku). A relational database is ideal given the application will not have explicitly complex schema or significant object complexity (i.e. little or no nesting). Given the potential scale of the application with thousands of users and magnitudes more documentation, a normalized database would be ideal for maintaining and querying the data.
### Tauri
Tauri is a relatively new native desktop framework for web frameworks. Its primary attraction is the Rust backend that is incredibly performant and safe. Compared to Electron, it is compatible with more frameworks and packages, has far less memory consumption, and has a larger emphasis on security. Bundle sizes are also much smaller than other frameworks. [It benches above other native desktop frameworks in nearly every category](https://tauri.app/about/benchmarks). Built-in testing and substantial documentation make development reliable. Rust in the backend may prove to be more complex, especially for frontend developers. However, required backend implementation is comparatively simple.
## Architecture Details
### Dedicated Authentication Server
Dedicated authentication servers provide a layer of abstraction from the resource server. Using tokens, users can authenticate and then send the token to the resource server for a secondary check from the authentication server. Token refreshes will ensure highjacked tokens do not become a long-term threat. Given the public availability of the product, additional layers of security are preferable, and using performant backends, user experience will not be negatively impacted.
### Databases
Databases will be split based on their connecting server. The authentication server will maintain tokens and authentication-related credentials, while the resource server will contain primary data. This will prevent complete compromise in the event one database is penetrated or taken offline.
|
non_process
|
proposal i solid go gin rust rocket postgres tauri background this proposal is designed to provide a balance between performance and ease of development by introducing newer proven technology that have high performance relative to their learning curve while using safe and security minded languages and architecture for authentication issue na tech stack technology application summary solid frontend a blend of svelte and react incredibly simple components with easily integrated features and superior performance has its own compiler and is fully reactive unlike react go gin resource server highly performant backend language with a small learning curve and simple concurrency rust rocket auth server arguably the most performant web backend possible with incredibly safety postgres sql database sufficient sql database readily available for sandboxing and deployment tauri native desktop tauri uses rust in the backend for superior performance and development safety architecture tech details solid frontend is an evolution of react inspired by some elements of react and many elements of svelte it has its own compiler that allows for incredibly small bundles and near vanilla levels of performance img width alt image src solid does not use a virtual dom and allows more natural writing of html templating in jsx to avoid heavy use of ternary operators and even worse nested ternary operators with helpers like show with fallbacks return show when loggedin fallback log in log out reactivity is handled with signals using a similar syntax as react const createsignal false however where react is not truly reactive and uses schedulers solid uses proxies to have true reactivity additionally all components truly render once allowing for some additional implementations like setinterval and avoiding issues caused by components re rendering like react s useeffect on strict mode additionally useeffect is also present here but does not require a dependency array and is handled automatically it is the satisfaction tied with svelte ultimately it is a great bridge between react and svelte go gin resource web server is a light web server framework for go go itself is a compiled very performant language with a simple syntax it is statically typed with explicit type inference easy concurrency patterns which the gin framework uses to improve performance it does include concepts like that a key aspects of computer science but are usually unfamiliar to js developers however understanding these concepts goes a long way to improving engineering gin is a very straight forward framework for creating clean and easily maintainable web servers are available from the developers go web server and below rust development speed is typically on par with node and above rust rust rocket auth web server is currently the most performant backend language and is the for years in a row while more difficult than javascript and go it offers incredible safety as a compiled language and a superior compiler for handling errors while it doesn t have traditional garbage collection it has a signature concept of ownership for managing memory is a relatively simple web framework implementation of rust as the authentication is relatively simple it offers an opportunity to learn and implement rust with additional synergy with tauri as it uses rust in the backend postgres database postgres is an easily accessible sql database with numerous free hosting options and ci cd integration such as on heroku a relational database is ideal given the application will not have explicitly complex schema or significant object complexity i e little or no nesting given the potential scale of the application with thousands of users and magnitudes more documentation a normalized database would be ideal for maintaining and querying the data tauri tauri is a relatively new native desktop framework for web frameworks its primary attraction is the rust backend that is incredibly performant and safe compared to electron it is compatible with more frameworks and packages has far less memory consumption and has a larger emphasis on security bundle sizes are also much smaller than other frameworks built in testing and substantial documentation make development reliable rust in the backend may prove to be more complex especially for frontend developers however required backend implementation is comparatively simple architecture details dedicated authentication server dedicated authentication servers provide a layer of abstraction from the resource server using tokens users can authenticate and then send the token to the resource server for a secondary check from the authentication server token refreshes will ensure highjacked tokens do not become a long term threat given the public availability of the product additional layers of security are preferable and using performant backends user experience will not be negatively impacted databases databases will be split based on their connecting server the authentication server will maintain tokens and authentication related credentials while the resource server will contain primary data this will prevent complete compromise in the event one database is penetrated or taken offline
| 0
|
26,825
| 5,290,474,697
|
IssuesEvent
|
2017-02-08 19:59:07
|
alonshmilo/MedicalData_jce
|
https://api.github.com/repos/alonshmilo/MedicalData_jce
|
closed
|
Prototype update meeting
|
2 - Working <= 5 Documentation Points: 1 Priority: High
|
# Issue: Prototype update meeting
### Explanation: Setting up meeting with Academic Advisor for updates and learning.
<!---
@huboard:{"order":26.0,"milestone_order":26,"custom_state":""}
-->
|
1.0
|
Prototype update meeting - # Issue: Prototype update meeting
### Explanation: Setting up meeting with Academic Advisor for updates and learning.
<!---
@huboard:{"order":26.0,"milestone_order":26,"custom_state":""}
-->
|
non_process
|
prototype update meeting issue prototype update meeting explanation setting up meeting with academic advisor for updates and learning huboard order milestone order custom state
| 0
|
10,976
| 13,780,263,755
|
IssuesEvent
|
2020-10-08 14:43:38
|
prisma/prisma-engines
|
https://api.github.com/repos/prisma/prisma-engines
|
opened
|
Composite key ordering in SQL Server
|
engines/data model parser process/candidate team/engines topic: SQL Server
|
The following data model works everywhere else except in SQL Server:
```prisma
model x {
id Int @id @default(autoincrement())
y Int
y_xToy_fk_x_1_fk_x_2 y[] @relation("xToy_fk_x_1_fk_x_2")
@@unique([id, y])
}
model y {
id Int @id @default(autoincrement())
fk_x_1 Int
fk_x_2 Int
x_xToy_fk_x_1_fk_x_2 x @relation("xToy_fk_x_1_fk_x_2", fields: [fk_x_1, fk_x_2], references: [y, id])
}
```
We do a reference from `y` to `x` with the keys `id` and `y`. The unique index has them in order with `id` first, following by `y`, but the reference has them in the opposite order. All other databases we support allow this, SQL Server gives a confusing error:
```
0: Connector error. (error: Error querying the database: Error querying the database: 'There are no primary or candidate keys in the referenced table 'dbo.x' that match the referencing column list in the foreign key 'FK__y__26DC43DB'.' on server 37463e70e029 executing on line 1 (code: 1776, state: 0, class: 16)
```
This can be fixed by changing the `x_xToy_fk_x_1_fk_x_2` relation's `references: [y, id]` into `references: [id, y]`. We should validate this and give a nice informative error for the user.
|
1.0
|
Composite key ordering in SQL Server - The following data model works everywhere else except in SQL Server:
```prisma
model x {
id Int @id @default(autoincrement())
y Int
y_xToy_fk_x_1_fk_x_2 y[] @relation("xToy_fk_x_1_fk_x_2")
@@unique([id, y])
}
model y {
id Int @id @default(autoincrement())
fk_x_1 Int
fk_x_2 Int
x_xToy_fk_x_1_fk_x_2 x @relation("xToy_fk_x_1_fk_x_2", fields: [fk_x_1, fk_x_2], references: [y, id])
}
```
We do a reference from `y` to `x` with the keys `id` and `y`. The unique index has them in order with `id` first, following by `y`, but the reference has them in the opposite order. All other databases we support allow this, SQL Server gives a confusing error:
```
0: Connector error. (error: Error querying the database: Error querying the database: 'There are no primary or candidate keys in the referenced table 'dbo.x' that match the referencing column list in the foreign key 'FK__y__26DC43DB'.' on server 37463e70e029 executing on line 1 (code: 1776, state: 0, class: 16)
```
This can be fixed by changing the `x_xToy_fk_x_1_fk_x_2` relation's `references: [y, id]` into `references: [id, y]`. We should validate this and give a nice informative error for the user.
|
process
|
composite key ordering in sql server the following data model works everywhere else except in sql server prisma model x id int id default autoincrement y int y xtoy fk x fk x y relation xtoy fk x fk x unique model y id int id default autoincrement fk x int fk x int x xtoy fk x fk x x relation xtoy fk x fk x fields references we do a reference from y to x with the keys id and y the unique index has them in order with id first following by y but the reference has them in the opposite order all other databases we support allow this sql server gives a confusing error connector error error error querying the database error querying the database there are no primary or candidate keys in the referenced table dbo x that match the referencing column list in the foreign key fk y on server executing on line code state class this can be fixed by changing the x xtoy fk x fk x relation s references into references we should validate this and give a nice informative error for the user
| 1
|
18,090
| 24,113,619,555
|
IssuesEvent
|
2022-09-20 13:16:54
|
MicrosoftDocs/azure-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-docs
|
closed
|
Need to update instructions about using managed identity
|
automation/svc triaged cxp doc-enhancement process-automation/subsvc Pri2
|
If managed identity is not assigned role on subscription level (which is should not for a lot of operations based on minimum privilege requiremenet) then code specified on page to authenticate with system assigned identity would fail since context would not contact subscription ID. Here is details to reproduce (https://www.ciraltos.com/azure-automation-subscription-null-or-empty/)
Code below would fail since $AzureContext.Subscription would be $null
`$AzureContext = Set-AzContext -SubscriptionName $AzureContext.Subscription -DefaultProfile $AzureContext`
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d9ce2612-b600-3fca-3315-a7836ef91c96
* Version Independent ID: 78766eed-c3c6-ce60-7620-17b99f3d9d5e
* Content: [Using a system-assigned managed identity for an Azure Automation account](https://docs.microsoft.com/en-us/azure/automation/enable-managed-identity-for-automation)
* Content Source: [articles/automation/enable-managed-identity-for-automation.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/automation/enable-managed-identity-for-automation.md)
* Service: **automation**
* Sub-service: **process-automation**
* GitHub Login: @SnehaSudhirG
* Microsoft Alias: **sudhirsneha**
|
1.0
|
Need to update instructions about using managed identity - If managed identity is not assigned role on subscription level (which is should not for a lot of operations based on minimum privilege requiremenet) then code specified on page to authenticate with system assigned identity would fail since context would not contact subscription ID. Here is details to reproduce (https://www.ciraltos.com/azure-automation-subscription-null-or-empty/)
Code below would fail since $AzureContext.Subscription would be $null
`$AzureContext = Set-AzContext -SubscriptionName $AzureContext.Subscription -DefaultProfile $AzureContext`
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: d9ce2612-b600-3fca-3315-a7836ef91c96
* Version Independent ID: 78766eed-c3c6-ce60-7620-17b99f3d9d5e
* Content: [Using a system-assigned managed identity for an Azure Automation account](https://docs.microsoft.com/en-us/azure/automation/enable-managed-identity-for-automation)
* Content Source: [articles/automation/enable-managed-identity-for-automation.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/automation/enable-managed-identity-for-automation.md)
* Service: **automation**
* Sub-service: **process-automation**
* GitHub Login: @SnehaSudhirG
* Microsoft Alias: **sudhirsneha**
|
process
|
need to update instructions about using managed identity if managed identity is not assigned role on subscription level which is should not for a lot of operations based on minimum privilege requiremenet then code specified on page to authenticate with system assigned identity would fail since context would not contact subscription id here is details to reproduce code below would fail since azurecontext subscription would be null azurecontext set azcontext subscriptionname azurecontext subscription defaultprofile azurecontext document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service automation sub service process automation github login snehasudhirg microsoft alias sudhirsneha
| 1
|
503
| 2,956,150,427
|
IssuesEvent
|
2015-07-08 09:26:40
|
cliffparnitzky/TriathlonLeagueManager
|
https://api.github.com/repos/cliffparnitzky/TriathlonLeagueManager
|
closed
|
Add a hint, if the logo is missing
|
Improvement ⚙ - Processed
|
would be nice to see a hint (or something else) if the logo is missing.
|
1.0
|
Add a hint, if the logo is missing - would be nice to see a hint (or something else) if the logo is missing.
|
process
|
add a hint if the logo is missing would be nice to see a hint or something else if the logo is missing
| 1
|
10,670
| 13,457,575,666
|
IssuesEvent
|
2020-09-09 09:22:33
|
panther-labs/panther
|
https://api.github.com/repos/panther-labs/panther
|
opened
|
Fix last event received at for SQS sources
|
bug p1 team:data processing
|
### Describe the bug
SQS sources do not update the last event received status correctly.
### Steps to reproduce
Steps to reproduce the behavior:
1. Add 2 SQS sources
2. Send events to both queues
3. Wait for panther to process the log events
4. Only one of the two sources updates it's last received status
### Expected behavior
Last received event notification should match the actual log events
### Additional context
Only the first SQS source in the order they are returned from the SourcesAPI gets updates (possibly incorrrect).
SQS sources all write to the same point in S3 via Firehose. Currently the log processor tries to update the last event received
_when it receives an event about an S3 object to process_. SQS log events map to different sources _per line_ so we only know which sources to notify only _after_ we have processed the log file. This means:
1. Since the update can now happen _on a per-log-event basis_ we cannot do it once per file when we receive the notification.
1. We should update the last event received when we _write the parsed log events to S3_ at which point we know which sources got updates.
1. Since each buffer being written to S3 can _aggregate log events of the same `log type` but of different `source_id`_, we need a method that can update multiple source ids and with a restriction that they get updated only if the last event timestamp is older than the update being pushed.
|
1.0
|
Fix last event received at for SQS sources - ### Describe the bug
SQS sources do not update the last event received status correctly.
### Steps to reproduce
Steps to reproduce the behavior:
1. Add 2 SQS sources
2. Send events to both queues
3. Wait for panther to process the log events
4. Only one of the two sources updates it's last received status
### Expected behavior
Last received event notification should match the actual log events
### Additional context
Only the first SQS source in the order they are returned from the SourcesAPI gets updates (possibly incorrrect).
SQS sources all write to the same point in S3 via Firehose. Currently the log processor tries to update the last event received
_when it receives an event about an S3 object to process_. SQS log events map to different sources _per line_ so we only know which sources to notify only _after_ we have processed the log file. This means:
1. Since the update can now happen _on a per-log-event basis_ we cannot do it once per file when we receive the notification.
1. We should update the last event received when we _write the parsed log events to S3_ at which point we know which sources got updates.
1. Since each buffer being written to S3 can _aggregate log events of the same `log type` but of different `source_id`_, we need a method that can update multiple source ids and with a restriction that they get updated only if the last event timestamp is older than the update being pushed.
|
process
|
fix last event received at for sqs sources describe the bug sqs sources do not update the last event received status correctly steps to reproduce steps to reproduce the behavior add sqs sources send events to both queues wait for panther to process the log events only one of the two sources updates it s last received status expected behavior last received event notification should match the actual log events additional context only the first sqs source in the order they are returned from the sourcesapi gets updates possibly incorrrect sqs sources all write to the same point in via firehose currently the log processor tries to update the last event received when it receives an event about an object to process sqs log events map to different sources per line so we only know which sources to notify only after we have processed the log file this means since the update can now happen on a per log event basis we cannot do it once per file when we receive the notification we should update the last event received when we write the parsed log events to at which point we know which sources got updates since each buffer being written to can aggregate log events of the same log type but of different source id we need a method that can update multiple source ids and with a restriction that they get updated only if the last event timestamp is older than the update being pushed
| 1
|
2,532
| 5,289,888,053
|
IssuesEvent
|
2017-02-08 18:29:48
|
opentrials/opentrials
|
https://api.github.com/repos/opentrials/opentrials
|
opened
|
Create audit log for our trial deduplication process
|
0. Ready for Analysis API Data Processors
|
Now that we're improving our trial deduplication methods, we must be able to know why a trial was deduplicated, so we can debug our processes.
The way I envision it is adding a table to the API database (so we can add it to the API results in the future) similar to:
| trial_id | record_id (unique) | method | commit | created_at | updated_at |
| --- | --- | --- | --- | --- | --- |
| A | X | identifier | COMMIT_HASH | | |
| A | Y | title | COMMIT_HASH | | |
I haven't deeply analysed this though, so feel free to propose another way. This would also require us to somehow add the `COMMIT_HASH` to our processors, I'm not sure how.
# Acceptance Criteria
* I can see why, when and how each record was deduplicated
* I can see what code version did the deduplication
|
1.0
|
Create audit log for our trial deduplication process - Now that we're improving our trial deduplication methods, we must be able to know why a trial was deduplicated, so we can debug our processes.
The way I envision it is adding a table to the API database (so we can add it to the API results in the future) similar to:
| trial_id | record_id (unique) | method | commit | created_at | updated_at |
| --- | --- | --- | --- | --- | --- |
| A | X | identifier | COMMIT_HASH | | |
| A | Y | title | COMMIT_HASH | | |
I haven't deeply analysed this though, so feel free to propose another way. This would also require us to somehow add the `COMMIT_HASH` to our processors, I'm not sure how.
# Acceptance Criteria
* I can see why, when and how each record was deduplicated
* I can see what code version did the deduplication
|
process
|
create audit log for our trial deduplication process now that we re improving our trial deduplication methods we must be able to know why a trial was deduplicated so we can debug our processes the way i envision it is adding a table to the api database so we can add it to the api results in the future similar to trial id record id unique method commit created at updated at a x identifier commit hash a y title commit hash i haven t deeply analysed this though so feel free to propose another way this would also require us to somehow add the commit hash to our processors i m not sure how acceptance criteria i can see why when and how each record was deduplicated i can see what code version did the deduplication
| 1
|
9,445
| 12,426,834,303
|
IssuesEvent
|
2020-05-24 23:28:16
|
qgis/QGIS-Documentation
|
https://api.github.com/repos/qgis/QGIS-Documentation
|
closed
|
[FEATURE] new custom widget — combobox with checkable items
|
3.0 Automatic new feature Processing ToDocOrNotToDoc?
|
Original commit: https://github.com/qgis/QGIS/commit/638dbcad1c3e203c887a68fa1c94dc7f0875cbba by alexbruy
Unfortunately this naughty coder did not write a description... :-(
|
1.0
|
[FEATURE] new custom widget — combobox with checkable items - Original commit: https://github.com/qgis/QGIS/commit/638dbcad1c3e203c887a68fa1c94dc7f0875cbba by alexbruy
Unfortunately this naughty coder did not write a description... :-(
|
process
|
new custom widget — combobox with checkable items original commit by alexbruy unfortunately this naughty coder did not write a description
| 1
|
13,666
| 16,388,334,236
|
IssuesEvent
|
2021-05-17 13:22:42
|
googleapis/nodejs-iot
|
https://api.github.com/repos/googleapis/nodejs-iot
|
closed
|
add missing region tags to samples
|
api: cloudiot samples type: process
|
I believe #266 is missing region tags for embedding parts of the samples, we should come back and add these.
|
1.0
|
add missing region tags to samples - I believe #266 is missing region tags for embedding parts of the samples, we should come back and add these.
|
process
|
add missing region tags to samples i believe is missing region tags for embedding parts of the samples we should come back and add these
| 1
|
14,964
| 18,454,842,483
|
IssuesEvent
|
2021-10-15 15:10:01
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
QGIS desktop crashed after order shape files in settings of join vectorial layers tool in batch mode
|
Feedback Processing Bug
|
### What is the bug or the crash?
While I was ordering vectorial layers (about 19 layers) for clipping or joining, the program crashed and closed.
### Steps to reproduce the issue
1 Go to Vectorial menu,
2 data administration tool
3 join vectorial layers.
4 Ejecute processes by "lots"
5 in parameters, input layers click autofill and open layer selection
6 in multiple selection menu select layers (about 10) and pull it to the bottom or the top of the list.
7 It crashed
### Versions
Versión de QGIS 3.16.11-Hannover
### Supported QGIS version
- [ ] I'm running a supported QGIS version according to the roadmap.
### New profile
- [ ] I tried with a new QGIS profile
### Additional context
Just to report the crash. I also ordered the shape one by one and it works normally. Sorry for the language mistakes, but I'm not a native speaker.
|
1.0
|
QGIS desktop crashed after order shape files in settings of join vectorial layers tool in batch mode - ### What is the bug or the crash?
While I was ordering vectorial layers (about 19 layers) for clipping or joining, the program crashed and closed.
### Steps to reproduce the issue
1 Go to Vectorial menu,
2 data administration tool
3 join vectorial layers.
4 Ejecute processes by "lots"
5 in parameters, input layers click autofill and open layer selection
6 in multiple selection menu select layers (about 10) and pull it to the bottom or the top of the list.
7 It crashed
### Versions
Versión de QGIS 3.16.11-Hannover
### Supported QGIS version
- [ ] I'm running a supported QGIS version according to the roadmap.
### New profile
- [ ] I tried with a new QGIS profile
### Additional context
Just to report the crash. I also ordered the shape one by one and it works normally. Sorry for the language mistakes, but I'm not a native speaker.
|
process
|
qgis desktop crashed after order shape files in settings of join vectorial layers tool in batch mode what is the bug or the crash while i was ordering vectorial layers about layers for clipping or joining the program crashed and closed steps to reproduce the issue go to vectorial menu data administration tool join vectorial layers ejecute processes by lots in parameters input layers click autofill and open layer selection in multiple selection menu select layers about and pull it to the bottom or the top of the list it crashed versions versión de qgis hannover supported qgis version i m running a supported qgis version according to the roadmap new profile i tried with a new qgis profile additional context just to report the crash i also ordered the shape one by one and it works normally sorry for the language mistakes but i m not a native speaker
| 1
|
15,566
| 19,703,504,319
|
IssuesEvent
|
2022-01-12 19:08:03
|
googleapis/java-service-control
|
https://api.github.com/repos/googleapis/java-service-control
|
opened
|
Your .repo-metadata.json file has a problem 🤒
|
type: process repo-metadata: lint
|
You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'service-control' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
1.0
|
Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'service-control' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
process
|
your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 release level must be equal to one of the allowed values in repo metadata json api shortname service control invalid in repo metadata json ☝️ once you correct these problems you can close this issue reach out to go github automation if you have any questions
| 1
|
237,699
| 19,666,643,063
|
IssuesEvent
|
2022-01-10 23:34:53
|
opensearch-project/OpenSearch
|
https://api.github.com/repos/opensearch-project/OpenSearch
|
closed
|
[CI] :test:fixtures:s3-fixture:composeUp fails due to HTTP connection issue
|
CI Flakey Random Test Failure
|
**Describe the bug**
On CI gradle checks on PRs, `:test:fixtures:s3-fixture:composeUp` fails due to an HTTP time out error. This is a recurring issue.
**To Reproduce**
See https://ci.opensearch.org/logs/ci/workflow/OpenSearch_CI/PR_Checks/Gradle_Check/gradle_check_1658.log
**Expected behavior**
The tests shouldn't be timing out.
**Additional context**
We can increase the time out to 120 seconds using the env var `COMPOSE_HTTP_TIMEOUT` on the Jenkins CI agents.
```
> Task :test:fixtures:s3-fixture:composeUp
ERROR: for 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-other_1 UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture_1 UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-with-session-token_1 UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
Creating 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-with-ec2_1 ... done
Creating 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-repositories-metering_1 ... done
Creating 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-with-ecs_1 ... done
ERROR: for s3-fixture-other UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for s3-fixture UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for s3-fixture-with-session-token UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
An HTTP request took too long to complete. Retry with --verbose to obtain debug information.
If you encounter this issue regularly because of slow network conditions, consider setting COMPOSE_HTTP_TIMEOUT to a higher value (current value: 60).
```
|
1.0
|
[CI] :test:fixtures:s3-fixture:composeUp fails due to HTTP connection issue - **Describe the bug**
On CI gradle checks on PRs, `:test:fixtures:s3-fixture:composeUp` fails due to an HTTP time out error. This is a recurring issue.
**To Reproduce**
See https://ci.opensearch.org/logs/ci/workflow/OpenSearch_CI/PR_Checks/Gradle_Check/gradle_check_1658.log
**Expected behavior**
The tests shouldn't be timing out.
**Additional context**
We can increase the time out to 120 seconds using the env var `COMPOSE_HTTP_TIMEOUT` on the Jenkins CI agents.
```
> Task :test:fixtures:s3-fixture:composeUp
ERROR: for 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-other_1 UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture_1 UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-with-session-token_1 UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
Creating 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-with-ec2_1 ... done
Creating 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-repositories-metering_1 ... done
Creating 56aa93ed60e3e11b06e2067e06b0dd8c_s3-fixture__s3-fixture-with-ecs_1 ... done
ERROR: for s3-fixture-other UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for s3-fixture UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
ERROR: for s3-fixture-with-session-token UnixHTTPConnectionPool(host='localhost', port=None): Read timed out. (read timeout=60)
An HTTP request took too long to complete. Retry with --verbose to obtain debug information.
If you encounter this issue regularly because of slow network conditions, consider setting COMPOSE_HTTP_TIMEOUT to a higher value (current value: 60).
```
|
non_process
|
test fixtures fixture composeup fails due to http connection issue describe the bug on ci gradle checks on prs test fixtures fixture composeup fails due to an http time out error this is a recurring issue to reproduce see expected behavior the tests shouldn t be timing out additional context we can increase the time out to seconds using the env var compose http timeout on the jenkins ci agents task test fixtures fixture composeup error for fixture fixture other unixhttpconnectionpool host localhost port none read timed out read timeout error for fixture fixture unixhttpconnectionpool host localhost port none read timed out read timeout error for fixture fixture with session token unixhttpconnectionpool host localhost port none read timed out read timeout creating fixture fixture with done creating fixture fixture repositories metering done creating fixture fixture with ecs done error for fixture other unixhttpconnectionpool host localhost port none read timed out read timeout error for fixture unixhttpconnectionpool host localhost port none read timed out read timeout error for fixture with session token unixhttpconnectionpool host localhost port none read timed out read timeout an http request took too long to complete retry with verbose to obtain debug information if you encounter this issue regularly because of slow network conditions consider setting compose http timeout to a higher value current value
| 0
|
1,809
| 4,544,928,694
|
IssuesEvent
|
2016-09-10 23:49:07
|
ParsePlatform/parse-server
|
https://api.github.com/repos/ParsePlatform/parse-server
|
closed
|
`matchesQuery` and pointer permissions
|
in-process
|
### Issue Description
I've got a class, `PlaylistItem`, that has a pointer to a `User`. I'm using pointer permissions to give that `User` full read and write permissions on the `PlaylistItem` that points to it. The only public CLP on `PlaylistItem` is 'create'.
My use of pointer permissions is new. Until today I had full public 'read' CLPs on `PlaylistItem`.
This is an iOS app. One of the `PFQuery`s I run against `PlaylistItem` has a `matchesQuery` condition, where the inner query is on a different class called `ArticleVersion`. `ArticleVersion` has public 'read' CLPs.
The `matchesQuery` condition always worked fine until now. It stops working when I whack the public 'read' CLP on `PlaylistItem` and rely on pointer permissions only. By "stops working" I mean it causes my outer query to return no results.
### Steps to reproduce
I can write a clear repro if need be, but first I'd like some confirmation as to whether this is a known issue (or perhaps is even expected behavior for reasons I'm not thinking of). I searched for a good while and found nothing about it.
- **Server**
- parse-server version: 2.2.17
- Operating System: Um whatever's the default on Heroku?
- Hardware: Heroku dyno, the default
- **Database**
- MongoDB version: 3.0.12
- Storage engine: mLab default
- Hardware: mLab default
### Logs/Trace
```
verbose: REQUEST for [GET] /parse/classes/PlaylistItem: {
"include": "articleVersion",
"order": "index",
"where": {
"user": {
"__type": "Pointer",
"className": "_User",
"objectId": "-----"
},
"articleVersion": {
"$inQuery": {
"include": "publication",
"order": "index",
"className": "ArticleVersion",
"where": {
"index": {
"$exists": true
},
"active": true
}
}
}
}
} method=GET, url=/parse/classes/PlaylistItem, host=----, x-parse-client-version=i1.13.0, accept=*/*, x-parse-session-token=-----, x-parse-application-id=-----, x-parse-client-key=------, x-parse-installation-id=------, x-parse-os-version=9.3 (15F34), accept-language=en-us, accept-encoding=gzip, deflate, content-type=application/json; charset=utf-8, content-length=292, user-agent=Audm/6326 CFNetwork/758.3.15 Darwin/15.5.0, connection=keep-alive, x-parse-app-build-version=6326, x-parse-app-display-version=1.0, include=articleVersion, order=index, __type=Pointer, className=_User, objectId=-----, include=publication, order=index, className=ArticleVersion, $exists=true, active=true
verbose: RESPONSE from [GET] /parse/classes/PlaylistItem: {
"response": {
"results": []
}
} results=[]
```
Thank you!
|
1.0
|
`matchesQuery` and pointer permissions - ### Issue Description
I've got a class, `PlaylistItem`, that has a pointer to a `User`. I'm using pointer permissions to give that `User` full read and write permissions on the `PlaylistItem` that points to it. The only public CLP on `PlaylistItem` is 'create'.
My use of pointer permissions is new. Until today I had full public 'read' CLPs on `PlaylistItem`.
This is an iOS app. One of the `PFQuery`s I run against `PlaylistItem` has a `matchesQuery` condition, where the inner query is on a different class called `ArticleVersion`. `ArticleVersion` has public 'read' CLPs.
The `matchesQuery` condition always worked fine until now. It stops working when I whack the public 'read' CLP on `PlaylistItem` and rely on pointer permissions only. By "stops working" I mean it causes my outer query to return no results.
### Steps to reproduce
I can write a clear repro if need be, but first I'd like some confirmation as to whether this is a known issue (or perhaps is even expected behavior for reasons I'm not thinking of). I searched for a good while and found nothing about it.
- **Server**
- parse-server version: 2.2.17
- Operating System: Um whatever's the default on Heroku?
- Hardware: Heroku dyno, the default
- **Database**
- MongoDB version: 3.0.12
- Storage engine: mLab default
- Hardware: mLab default
### Logs/Trace
```
verbose: REQUEST for [GET] /parse/classes/PlaylistItem: {
"include": "articleVersion",
"order": "index",
"where": {
"user": {
"__type": "Pointer",
"className": "_User",
"objectId": "-----"
},
"articleVersion": {
"$inQuery": {
"include": "publication",
"order": "index",
"className": "ArticleVersion",
"where": {
"index": {
"$exists": true
},
"active": true
}
}
}
}
} method=GET, url=/parse/classes/PlaylistItem, host=----, x-parse-client-version=i1.13.0, accept=*/*, x-parse-session-token=-----, x-parse-application-id=-----, x-parse-client-key=------, x-parse-installation-id=------, x-parse-os-version=9.3 (15F34), accept-language=en-us, accept-encoding=gzip, deflate, content-type=application/json; charset=utf-8, content-length=292, user-agent=Audm/6326 CFNetwork/758.3.15 Darwin/15.5.0, connection=keep-alive, x-parse-app-build-version=6326, x-parse-app-display-version=1.0, include=articleVersion, order=index, __type=Pointer, className=_User, objectId=-----, include=publication, order=index, className=ArticleVersion, $exists=true, active=true
verbose: RESPONSE from [GET] /parse/classes/PlaylistItem: {
"response": {
"results": []
}
} results=[]
```
Thank you!
|
process
|
matchesquery and pointer permissions issue description i ve got a class playlistitem that has a pointer to a user i m using pointer permissions to give that user full read and write permissions on the playlistitem that points to it the only public clp on playlistitem is create my use of pointer permissions is new until today i had full public read clps on playlistitem this is an ios app one of the pfquery s i run against playlistitem has a matchesquery condition where the inner query is on a different class called articleversion articleversion has public read clps the matchesquery condition always worked fine until now it stops working when i whack the public read clp on playlistitem and rely on pointer permissions only by stops working i mean it causes my outer query to return no results steps to reproduce i can write a clear repro if need be but first i d like some confirmation as to whether this is a known issue or perhaps is even expected behavior for reasons i m not thinking of i searched for a good while and found nothing about it server parse server version operating system um whatever s the default on heroku hardware heroku dyno the default database mongodb version storage engine mlab default hardware mlab default logs trace verbose request for parse classes playlistitem include articleversion order index where user type pointer classname user objectid articleversion inquery include publication order index classname articleversion where index exists true active true method get url parse classes playlistitem host x parse client version accept x parse session token x parse application id x parse client key x parse installation id x parse os version accept language en us accept encoding gzip deflate content type application json charset utf content length user agent audm cfnetwork darwin connection keep alive x parse app build version x parse app display version include articleversion order index type pointer classname user objectid include publication order index classname articleversion exists true active true verbose response from parse classes playlistitem response results results thank you
| 1
|
13,808
| 16,567,074,258
|
IssuesEvent
|
2021-05-29 16:34:48
|
sysflow-telemetry/sf-docs
|
https://api.github.com/repos/sysflow-telemetry/sf-docs
|
closed
|
Export handler for IBM Cloud Security Advisor Findings API
|
enhancement sf-processor
|
Implement export handler in the SysFlow Processor to stream findings to IBM Cloud Security Advisor FIndings API:
https://cloud.ibm.com/apidocs/security-advisor/findings
- [x] Implement export handler
- [x] Update deployment scripts
- [x] Test it with IBM Cloud Security Advisor
- [x] Update documentation
|
1.0
|
Export handler for IBM Cloud Security Advisor Findings API - Implement export handler in the SysFlow Processor to stream findings to IBM Cloud Security Advisor FIndings API:
https://cloud.ibm.com/apidocs/security-advisor/findings
- [x] Implement export handler
- [x] Update deployment scripts
- [x] Test it with IBM Cloud Security Advisor
- [x] Update documentation
|
process
|
export handler for ibm cloud security advisor findings api implement export handler in the sysflow processor to stream findings to ibm cloud security advisor findings api implement export handler update deployment scripts test it with ibm cloud security advisor update documentation
| 1
|
121,454
| 4,816,763,332
|
IssuesEvent
|
2016-11-04 11:14:22
|
CoderDojo/community-platform
|
https://api.github.com/repos/CoderDojo/community-platform
|
opened
|
Migrate away from badgekit
|
high priority needs analysis
|
Badgekit is dead and burried, but now even Persona is giving up.
Instead of trying to maintain an abandoned soft by ourselves, migrate to badgr which seems still active.
TODOS:
- [ ] map API integration (***)
- [ ] adapt josmas' image for production (*)
- [ ] migrate data (**)
Some references :
https://github.com/concentricsky/badgr-server for production
https://github.com/josmas/local-badgr-server for
https://github.com/mozillascience/PaperBadger/issues/159
|
1.0
|
Migrate away from badgekit - Badgekit is dead and burried, but now even Persona is giving up.
Instead of trying to maintain an abandoned soft by ourselves, migrate to badgr which seems still active.
TODOS:
- [ ] map API integration (***)
- [ ] adapt josmas' image for production (*)
- [ ] migrate data (**)
Some references :
https://github.com/concentricsky/badgr-server for production
https://github.com/josmas/local-badgr-server for
https://github.com/mozillascience/PaperBadger/issues/159
|
non_process
|
migrate away from badgekit badgekit is dead and burried but now even persona is giving up instead of trying to maintain an abandoned soft by ourselves migrate to badgr which seems still active todos map api integration adapt josmas image for production migrate data some references for production for
| 0
|
19,414
| 25,556,978,219
|
IssuesEvent
|
2022-11-30 07:42:38
|
lizhihao6/get-daily-arxiv-noti
|
https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti
|
opened
|
New submissions for Wed, 30 Nov 22
|
event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB
|
## Keyword: events
### Post-training Quantization on Diffusion Models
- **Authors:** Yuzhang Shang, Zhihang Yuan, Bin Xie, Bingzhe Wu, Yan Yan
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15736
- **Pdf link:** https://arxiv.org/pdf/2211.15736
- **Abstract**
Denoising diffusion (score-based) generative models have recently achieved significant accomplishments in generating realistic and diverse data. These approaches define a forward diffusion process for transforming data into noise and a backward denoising process for sampling data from noise. Unfortunately, the generation process of current denoising diffusion models is notoriously slow due to the lengthy iterative noise estimations, which rely on cumbersome neural networks. It prevents the diffusion models from being widely deployed, especially on edge devices. Previous works accelerate the generation process of diffusion model (DM) via finding shorter yet effective sampling trajectories. However, they overlook the cost of noise estimation with a heavy network in every iteration. In this work, we accelerate generation from the perspective of compressing the noise estimation network. Due to the difficulty of retraining DMs, we exclude mainstream training-aware compression paradigms and introduce post-training quantization (PTQ) into DM acceleration. However, the output distributions of noise estimation networks change with time-step, making previous PTQ methods fail in DMs since they are designed for single-time step scenarios. To devise a DM-specific PTQ method, we explore PTQ on DM in three aspects: quantized operations, calibration dataset, and calibration metric. We summarize and use several observations derived from all-inclusive investigations to formulate our method, which especially targets the unique multi-time-step structure of DMs. Experimentally, our method can directly quantize full-precision DMs into 8-bit models while maintaining or even improving their performance in a training-free manner. Importantly, our method can serve as a plug-and-play module on other fast-sampling methods, e.g., DDIM.
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
### Superpoint Transformer for 3D Scene Instance Segmentation
- **Authors:** Jiahao Sun, Chunmei Qing, Junpeng Tan, Xiangmin Xu
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15766
- **Pdf link:** https://arxiv.org/pdf/2211.15766
- **Abstract**
Most existing methods realize 3D instance segmentation by extending those models used for 3D object detection or 3D semantic segmentation. However, these non-straightforward methods suffer from two drawbacks: 1) Imprecise bounding boxes or unsatisfactory semantic predictions limit the performance of the overall 3D instance segmentation framework. 2) Existing method requires a time-consuming intermediate step of aggregation. To address these issues, this paper proposes a novel end-to-end 3D instance segmentation method based on Superpoint Transformer, named as SPFormer. It groups potential features from point clouds into superpoints, and directly predicts instances through query vectors without relying on the results of object detection or semantic segmentation. The key step in this framework is a novel query decoder with transformers that can capture the instance information through the superpoint cross-attention mechanism and generate the superpoint masks of the instances. Through bipartite matching based on superpoint masks, SPFormer can implement the network training without the intermediate aggregation step, which accelerates the network. Extensive experiments on ScanNetv2 and S3DIS benchmarks verify that our method is concise yet efficient. Notably, SPFormer exceeds compared state-of-the-art methods by 4.3% on ScanNetv2 hidden test set in terms of mAP and keeps fast inference speed (247ms per frame) simultaneously. Code is available at https://github.com/sunjiahao1999/SPFormer.
### DATID-3D: Diversity-Preserved Domain Adaptation Using Text-to-Image Diffusion for 3D Generative Model
- **Authors:** Gwanghyun Kim, Se Young Chun
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2211.16374
- **Pdf link:** https://arxiv.org/pdf/2211.16374
- **Abstract**
Recent 3D generative models have achieved remarkable performance in synthesizing high resolution photorealistic images with view consistency and detailed 3D shapes, but training them for diverse domains is challenging since it requires massive training images and their camera distribution information. Text-guided domain adaptation methods have shown impressive performance on converting the 2D generative model on one domain into the models on other domains with different styles by leveraging the CLIP (Contrastive Language-Image Pre-training), rather than collecting massive datasets for those domains. However, one drawback of them is that the sample diversity in the original generative model is not well-preserved in the domain-adapted generative models due to the deterministic nature of the CLIP text encoder. Text-guided domain adaptation will be even more challenging for 3D generative models not only because of catastrophic diversity loss, but also because of inferior text-image correspondence and poor image quality. Here we propose DATID-3D, a domain adaptation method tailored for 3D generative models using text-to-image diffusion models that can synthesize diverse images per text prompt without collecting additional images and camera information for the target domain. Unlike 3D extensions of prior text-guided domain adaptation methods, our novel pipeline was able to fine-tune the state-of-the-art 3D generator of the source domain to synthesize high resolution, multi-view consistent images in text-guided targeted domains without additional data, outperforming the existing text-guided domain adaptation methods in diversity and text-image correspondence. Furthermore, we propose and demonstrate diverse 3D image manipulations such as one-shot instance-selected adaptation and single-view manipulated 3D reconstruction to fully enjoy diversity in text.
## Keyword: ISP
### Be Careful with Rotation: A Uniform Backdoor Pattern for 3D Shape
- **Authors:** Linkun Fan, Fazhi He, Qing Guo, Wei Tang, Xiaolin Hong, Bing Li
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Cryptography and Security (cs.CR)
- **Arxiv link:** https://arxiv.org/abs/2211.16192
- **Pdf link:** https://arxiv.org/pdf/2211.16192
- **Abstract**
For saving cost, many deep neural networks (DNNs) are trained on third-party datasets downloaded from internet, which enables attacker to implant backdoor into DNNs. In 2D domain, inherent structures of different image formats are similar. Hence, backdoor attack designed for one image format will suite for others. However, when it comes to 3D world, there is a huge disparity among different 3D data structures. As a result, backdoor pattern designed for one certain 3D data structure will be disable for other data structures of the same 3D scene. Therefore, this paper designs a uniform backdoor pattern: NRBdoor (Noisy Rotation Backdoor) which is able to adapt for heterogeneous 3D data structures. Specifically, we start from the unit rotation and then search for the optimal pattern by noise generation and selection process. The proposed NRBdoor is natural and imperceptible, since rotation is a common operation which usually contains noise due to both the miss match between a pair of points and the sensor calibration error for real-world 3D scene. Extensive experiments on 3D mesh and point cloud show that the proposed NRBdoor achieves state-of-the-art performance, with negligible shape variation.
### Fourier-Net: Fast Image Registration with Band-limited Deformation
- **Authors:** Xi Jia, Joseph Bartlett, Wei Chen, Siyang Song, Tianyang Zhang, Xinxing Cheng, Wenqi Lu, Zhaowen Qiu, Jinming Duan
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.16342
- **Pdf link:** https://arxiv.org/pdf/2211.16342
- **Abstract**
Unsupervised image registration commonly adopts U-Net style networks to predict dense displacement fields in the full-resolution spatial domain. For high-resolution volumetric image data, this process is however resource intensive and time-consuming. To tackle this problem, we propose the Fourier-Net, replacing the expansive path in a U-Net style network with a parameter-free model-driven decoder. Specifically, instead of our Fourier-Net learning to output a full-resolution displacement field in the spatial domain, we learn its low-dimensional representation in a band-limited Fourier domain. This representation is then decoded by our devised model-driven decoder (consisting of a zero padding layer and an inverse discrete Fourier transform layer) to the dense, full-resolution displacement field in the spatial domain. These changes allow our unsupervised Fourier-Net to contain fewer parameters and computational operations, resulting in faster inference speeds. Fourier-Net is then evaluated on two public 3D brain datasets against various state-of-the-art approaches. For example, when compared to a recent transformer-based method, i.e., TransMorph, our Fourier-Net, only using 0.22$\%$ of its parameters and 6.66$\%$ of the mult-adds, achieves a 0.6\% higher Dice score and an 11.48$\times$ faster inference speed. Code is available at \url{https://github.com/xi-jia/Fourier-Net}.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
### Post-training Quantization on Diffusion Models
- **Authors:** Yuzhang Shang, Zhihang Yuan, Bin Xie, Bingzhe Wu, Yan Yan
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15736
- **Pdf link:** https://arxiv.org/pdf/2211.15736
- **Abstract**
Denoising diffusion (score-based) generative models have recently achieved significant accomplishments in generating realistic and diverse data. These approaches define a forward diffusion process for transforming data into noise and a backward denoising process for sampling data from noise. Unfortunately, the generation process of current denoising diffusion models is notoriously slow due to the lengthy iterative noise estimations, which rely on cumbersome neural networks. It prevents the diffusion models from being widely deployed, especially on edge devices. Previous works accelerate the generation process of diffusion model (DM) via finding shorter yet effective sampling trajectories. However, they overlook the cost of noise estimation with a heavy network in every iteration. In this work, we accelerate generation from the perspective of compressing the noise estimation network. Due to the difficulty of retraining DMs, we exclude mainstream training-aware compression paradigms and introduce post-training quantization (PTQ) into DM acceleration. However, the output distributions of noise estimation networks change with time-step, making previous PTQ methods fail in DMs since they are designed for single-time step scenarios. To devise a DM-specific PTQ method, we explore PTQ on DM in three aspects: quantized operations, calibration dataset, and calibration metric. We summarize and use several observations derived from all-inclusive investigations to formulate our method, which especially targets the unique multi-time-step structure of DMs. Experimentally, our method can directly quantize full-precision DMs into 8-bit models while maintaining or even improving their performance in a training-free manner. Importantly, our method can serve as a plug-and-play module on other fast-sampling methods, e.g., DDIM.
### Compressing Volumetric Radiance Fields to 1 MB
- **Authors:** Lingzhi Li, Zhen Shen, Zhongshu Wang, Li Shen, Liefeng Bo
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.16386
- **Pdf link:** https://arxiv.org/pdf/2211.16386
- **Abstract**
Approximating radiance fields with volumetric grids is one of promising directions for improving NeRF, represented by methods like Plenoxels and DVGO, which achieve super-fast training convergence and real-time rendering. However, these methods typically require a tremendous storage overhead, costing up to hundreds of megabytes of disk space and runtime memory for a single scene. We address this issue in this paper by introducing a simple yet effective framework, called vector quantized radiance fields (VQRF), for compressing these volume-grid-based radiance fields. We first present a robust and adaptive metric for estimating redundancy in grid models and performing voxel pruning by better exploring intermediate outputs of volumetric rendering. A trainable vector quantization is further proposed to improve the compactness of grid models. In combination with an efficient joint tuning strategy and post-processing, our method can achieve a compression ratio of 100$\times$ by reducing the overall model size to 1 MB with negligible loss on visual quality. Extensive experiments demonstrate that the proposed framework is capable of achieving unrivaled performance and well generalization across multiple methods with distinct volumetric structures, facilitating the wide use of volumetric radiance fields methods in real-world applications. Code Available at \url{https://github.com/AlgoHunt/VQRF}
## Keyword: RAW
### Superpoint Transformer for 3D Scene Instance Segmentation
- **Authors:** Jiahao Sun, Chunmei Qing, Junpeng Tan, Xiangmin Xu
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15766
- **Pdf link:** https://arxiv.org/pdf/2211.15766
- **Abstract**
Most existing methods realize 3D instance segmentation by extending those models used for 3D object detection or 3D semantic segmentation. However, these non-straightforward methods suffer from two drawbacks: 1) Imprecise bounding boxes or unsatisfactory semantic predictions limit the performance of the overall 3D instance segmentation framework. 2) Existing method requires a time-consuming intermediate step of aggregation. To address these issues, this paper proposes a novel end-to-end 3D instance segmentation method based on Superpoint Transformer, named as SPFormer. It groups potential features from point clouds into superpoints, and directly predicts instances through query vectors without relying on the results of object detection or semantic segmentation. The key step in this framework is a novel query decoder with transformers that can capture the instance information through the superpoint cross-attention mechanism and generate the superpoint masks of the instances. Through bipartite matching based on superpoint masks, SPFormer can implement the network training without the intermediate aggregation step, which accelerates the network. Extensive experiments on ScanNetv2 and S3DIS benchmarks verify that our method is concise yet efficient. Notably, SPFormer exceeds compared state-of-the-art methods by 4.3% on ScanNetv2 hidden test set in terms of mAP and keeps fast inference speed (247ms per frame) simultaneously. Code is available at https://github.com/sunjiahao1999/SPFormer.
### AdaEnlight: Energy-aware Low-light Video Stream Enhancement on Mobile Devices
- **Authors:** Sicong Liu (Northwestern Polytechnical University, China), Xiaochen Li (Northwestern Polytechnical University, China), Zimu Zhou (City University of Hong Kong, China), Bin Guo (Northwestern Polytechnical University, China), Meng Zhang (Northwestern Polytechnical University, China), Haochen Shen (Northwestern Polytechnical University, China), Zhiwen Yu (Northwestern Polytechnical University, China)
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.16135
- **Pdf link:** https://arxiv.org/pdf/2211.16135
- **Abstract**
The ubiquity of camera-embedded devices and the advances in deep learning have stimulated various intelligent mobile video applications. These applications often demand on-device processing of video streams to deliver real-time, high-quality services for privacy and robustness concerns. However, the performance of these applications is constrained by the raw video streams, which tend to be taken with small-aperture cameras of ubiquitous mobile platforms in dim light. Despite extensive low-light video enhancement solutions, they are unfit for deployment to mobile devices due to their complex models and and ignorance of system dynamics like energy budgets. In this paper, we propose AdaEnlight, an energy-aware low-light video stream enhancement system on mobile devices. It achieves real-time video enhancement with competitive visual quality while allowing runtime behavior adaptation to the platform-imposed dynamic energy budgets. We report extensive experiments on diverse datasets, scenarios, and platforms and demonstrate the superiority of AdaEnlight compared with state-of-the-art low-light image and video enhancement solutions.
### DATID-3D: Diversity-Preserved Domain Adaptation Using Text-to-Image Diffusion for 3D Generative Model
- **Authors:** Gwanghyun Kim, Se Young Chun
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2211.16374
- **Pdf link:** https://arxiv.org/pdf/2211.16374
- **Abstract**
Recent 3D generative models have achieved remarkable performance in synthesizing high resolution photorealistic images with view consistency and detailed 3D shapes, but training them for diverse domains is challenging since it requires massive training images and their camera distribution information. Text-guided domain adaptation methods have shown impressive performance on converting the 2D generative model on one domain into the models on other domains with different styles by leveraging the CLIP (Contrastive Language-Image Pre-training), rather than collecting massive datasets for those domains. However, one drawback of them is that the sample diversity in the original generative model is not well-preserved in the domain-adapted generative models due to the deterministic nature of the CLIP text encoder. Text-guided domain adaptation will be even more challenging for 3D generative models not only because of catastrophic diversity loss, but also because of inferior text-image correspondence and poor image quality. Here we propose DATID-3D, a domain adaptation method tailored for 3D generative models using text-to-image diffusion models that can synthesize diverse images per text prompt without collecting additional images and camera information for the target domain. Unlike 3D extensions of prior text-guided domain adaptation methods, our novel pipeline was able to fine-tune the state-of-the-art 3D generator of the source domain to synthesize high resolution, multi-view consistent images in text-guided targeted domains without additional data, outperforming the existing text-guided domain adaptation methods in diversity and text-image correspondence. Furthermore, we propose and demonstrate diverse 3D image manipulations such as one-shot instance-selected adaptation and single-view manipulated 3D reconstruction to fully enjoy diversity in text.
## Keyword: raw image
There is no result
|
2.0
|
New submissions for Wed, 30 Nov 22 - ## Keyword: events
### Post-training Quantization on Diffusion Models
- **Authors:** Yuzhang Shang, Zhihang Yuan, Bin Xie, Bingzhe Wu, Yan Yan
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15736
- **Pdf link:** https://arxiv.org/pdf/2211.15736
- **Abstract**
Denoising diffusion (score-based) generative models have recently achieved significant accomplishments in generating realistic and diverse data. These approaches define a forward diffusion process for transforming data into noise and a backward denoising process for sampling data from noise. Unfortunately, the generation process of current denoising diffusion models is notoriously slow due to the lengthy iterative noise estimations, which rely on cumbersome neural networks. It prevents the diffusion models from being widely deployed, especially on edge devices. Previous works accelerate the generation process of diffusion model (DM) via finding shorter yet effective sampling trajectories. However, they overlook the cost of noise estimation with a heavy network in every iteration. In this work, we accelerate generation from the perspective of compressing the noise estimation network. Due to the difficulty of retraining DMs, we exclude mainstream training-aware compression paradigms and introduce post-training quantization (PTQ) into DM acceleration. However, the output distributions of noise estimation networks change with time-step, making previous PTQ methods fail in DMs since they are designed for single-time step scenarios. To devise a DM-specific PTQ method, we explore PTQ on DM in three aspects: quantized operations, calibration dataset, and calibration metric. We summarize and use several observations derived from all-inclusive investigations to formulate our method, which especially targets the unique multi-time-step structure of DMs. Experimentally, our method can directly quantize full-precision DMs into 8-bit models while maintaining or even improving their performance in a training-free manner. Importantly, our method can serve as a plug-and-play module on other fast-sampling methods, e.g., DDIM.
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
### Superpoint Transformer for 3D Scene Instance Segmentation
- **Authors:** Jiahao Sun, Chunmei Qing, Junpeng Tan, Xiangmin Xu
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15766
- **Pdf link:** https://arxiv.org/pdf/2211.15766
- **Abstract**
Most existing methods realize 3D instance segmentation by extending those models used for 3D object detection or 3D semantic segmentation. However, these non-straightforward methods suffer from two drawbacks: 1) Imprecise bounding boxes or unsatisfactory semantic predictions limit the performance of the overall 3D instance segmentation framework. 2) Existing method requires a time-consuming intermediate step of aggregation. To address these issues, this paper proposes a novel end-to-end 3D instance segmentation method based on Superpoint Transformer, named as SPFormer. It groups potential features from point clouds into superpoints, and directly predicts instances through query vectors without relying on the results of object detection or semantic segmentation. The key step in this framework is a novel query decoder with transformers that can capture the instance information through the superpoint cross-attention mechanism and generate the superpoint masks of the instances. Through bipartite matching based on superpoint masks, SPFormer can implement the network training without the intermediate aggregation step, which accelerates the network. Extensive experiments on ScanNetv2 and S3DIS benchmarks verify that our method is concise yet efficient. Notably, SPFormer exceeds compared state-of-the-art methods by 4.3% on ScanNetv2 hidden test set in terms of mAP and keeps fast inference speed (247ms per frame) simultaneously. Code is available at https://github.com/sunjiahao1999/SPFormer.
### DATID-3D: Diversity-Preserved Domain Adaptation Using Text-to-Image Diffusion for 3D Generative Model
- **Authors:** Gwanghyun Kim, Se Young Chun
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2211.16374
- **Pdf link:** https://arxiv.org/pdf/2211.16374
- **Abstract**
Recent 3D generative models have achieved remarkable performance in synthesizing high resolution photorealistic images with view consistency and detailed 3D shapes, but training them for diverse domains is challenging since it requires massive training images and their camera distribution information. Text-guided domain adaptation methods have shown impressive performance on converting the 2D generative model on one domain into the models on other domains with different styles by leveraging the CLIP (Contrastive Language-Image Pre-training), rather than collecting massive datasets for those domains. However, one drawback of them is that the sample diversity in the original generative model is not well-preserved in the domain-adapted generative models due to the deterministic nature of the CLIP text encoder. Text-guided domain adaptation will be even more challenging for 3D generative models not only because of catastrophic diversity loss, but also because of inferior text-image correspondence and poor image quality. Here we propose DATID-3D, a domain adaptation method tailored for 3D generative models using text-to-image diffusion models that can synthesize diverse images per text prompt without collecting additional images and camera information for the target domain. Unlike 3D extensions of prior text-guided domain adaptation methods, our novel pipeline was able to fine-tune the state-of-the-art 3D generator of the source domain to synthesize high resolution, multi-view consistent images in text-guided targeted domains without additional data, outperforming the existing text-guided domain adaptation methods in diversity and text-image correspondence. Furthermore, we propose and demonstrate diverse 3D image manipulations such as one-shot instance-selected adaptation and single-view manipulated 3D reconstruction to fully enjoy diversity in text.
## Keyword: ISP
### Be Careful with Rotation: A Uniform Backdoor Pattern for 3D Shape
- **Authors:** Linkun Fan, Fazhi He, Qing Guo, Wei Tang, Xiaolin Hong, Bing Li
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Cryptography and Security (cs.CR)
- **Arxiv link:** https://arxiv.org/abs/2211.16192
- **Pdf link:** https://arxiv.org/pdf/2211.16192
- **Abstract**
For saving cost, many deep neural networks (DNNs) are trained on third-party datasets downloaded from internet, which enables attacker to implant backdoor into DNNs. In 2D domain, inherent structures of different image formats are similar. Hence, backdoor attack designed for one image format will suite for others. However, when it comes to 3D world, there is a huge disparity among different 3D data structures. As a result, backdoor pattern designed for one certain 3D data structure will be disable for other data structures of the same 3D scene. Therefore, this paper designs a uniform backdoor pattern: NRBdoor (Noisy Rotation Backdoor) which is able to adapt for heterogeneous 3D data structures. Specifically, we start from the unit rotation and then search for the optimal pattern by noise generation and selection process. The proposed NRBdoor is natural and imperceptible, since rotation is a common operation which usually contains noise due to both the miss match between a pair of points and the sensor calibration error for real-world 3D scene. Extensive experiments on 3D mesh and point cloud show that the proposed NRBdoor achieves state-of-the-art performance, with negligible shape variation.
### Fourier-Net: Fast Image Registration with Band-limited Deformation
- **Authors:** Xi Jia, Joseph Bartlett, Wei Chen, Siyang Song, Tianyang Zhang, Xinxing Cheng, Wenqi Lu, Zhaowen Qiu, Jinming Duan
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.16342
- **Pdf link:** https://arxiv.org/pdf/2211.16342
- **Abstract**
Unsupervised image registration commonly adopts U-Net style networks to predict dense displacement fields in the full-resolution spatial domain. For high-resolution volumetric image data, this process is however resource intensive and time-consuming. To tackle this problem, we propose the Fourier-Net, replacing the expansive path in a U-Net style network with a parameter-free model-driven decoder. Specifically, instead of our Fourier-Net learning to output a full-resolution displacement field in the spatial domain, we learn its low-dimensional representation in a band-limited Fourier domain. This representation is then decoded by our devised model-driven decoder (consisting of a zero padding layer and an inverse discrete Fourier transform layer) to the dense, full-resolution displacement field in the spatial domain. These changes allow our unsupervised Fourier-Net to contain fewer parameters and computational operations, resulting in faster inference speeds. Fourier-Net is then evaluated on two public 3D brain datasets against various state-of-the-art approaches. For example, when compared to a recent transformer-based method, i.e., TransMorph, our Fourier-Net, only using 0.22$\%$ of its parameters and 6.66$\%$ of the mult-adds, achieves a 0.6\% higher Dice score and an 11.48$\times$ faster inference speed. Code is available at \url{https://github.com/xi-jia/Fourier-Net}.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
### Post-training Quantization on Diffusion Models
- **Authors:** Yuzhang Shang, Zhihang Yuan, Bin Xie, Bingzhe Wu, Yan Yan
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15736
- **Pdf link:** https://arxiv.org/pdf/2211.15736
- **Abstract**
Denoising diffusion (score-based) generative models have recently achieved significant accomplishments in generating realistic and diverse data. These approaches define a forward diffusion process for transforming data into noise and a backward denoising process for sampling data from noise. Unfortunately, the generation process of current denoising diffusion models is notoriously slow due to the lengthy iterative noise estimations, which rely on cumbersome neural networks. It prevents the diffusion models from being widely deployed, especially on edge devices. Previous works accelerate the generation process of diffusion model (DM) via finding shorter yet effective sampling trajectories. However, they overlook the cost of noise estimation with a heavy network in every iteration. In this work, we accelerate generation from the perspective of compressing the noise estimation network. Due to the difficulty of retraining DMs, we exclude mainstream training-aware compression paradigms and introduce post-training quantization (PTQ) into DM acceleration. However, the output distributions of noise estimation networks change with time-step, making previous PTQ methods fail in DMs since they are designed for single-time step scenarios. To devise a DM-specific PTQ method, we explore PTQ on DM in three aspects: quantized operations, calibration dataset, and calibration metric. We summarize and use several observations derived from all-inclusive investigations to formulate our method, which especially targets the unique multi-time-step structure of DMs. Experimentally, our method can directly quantize full-precision DMs into 8-bit models while maintaining or even improving their performance in a training-free manner. Importantly, our method can serve as a plug-and-play module on other fast-sampling methods, e.g., DDIM.
### Compressing Volumetric Radiance Fields to 1 MB
- **Authors:** Lingzhi Li, Zhen Shen, Zhongshu Wang, Li Shen, Liefeng Bo
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.16386
- **Pdf link:** https://arxiv.org/pdf/2211.16386
- **Abstract**
Approximating radiance fields with volumetric grids is one of promising directions for improving NeRF, represented by methods like Plenoxels and DVGO, which achieve super-fast training convergence and real-time rendering. However, these methods typically require a tremendous storage overhead, costing up to hundreds of megabytes of disk space and runtime memory for a single scene. We address this issue in this paper by introducing a simple yet effective framework, called vector quantized radiance fields (VQRF), for compressing these volume-grid-based radiance fields. We first present a robust and adaptive metric for estimating redundancy in grid models and performing voxel pruning by better exploring intermediate outputs of volumetric rendering. A trainable vector quantization is further proposed to improve the compactness of grid models. In combination with an efficient joint tuning strategy and post-processing, our method can achieve a compression ratio of 100$\times$ by reducing the overall model size to 1 MB with negligible loss on visual quality. Extensive experiments demonstrate that the proposed framework is capable of achieving unrivaled performance and well generalization across multiple methods with distinct volumetric structures, facilitating the wide use of volumetric radiance fields methods in real-world applications. Code Available at \url{https://github.com/AlgoHunt/VQRF}
## Keyword: RAW
### Superpoint Transformer for 3D Scene Instance Segmentation
- **Authors:** Jiahao Sun, Chunmei Qing, Junpeng Tan, Xiangmin Xu
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.15766
- **Pdf link:** https://arxiv.org/pdf/2211.15766
- **Abstract**
Most existing methods realize 3D instance segmentation by extending those models used for 3D object detection or 3D semantic segmentation. However, these non-straightforward methods suffer from two drawbacks: 1) Imprecise bounding boxes or unsatisfactory semantic predictions limit the performance of the overall 3D instance segmentation framework. 2) Existing method requires a time-consuming intermediate step of aggregation. To address these issues, this paper proposes a novel end-to-end 3D instance segmentation method based on Superpoint Transformer, named as SPFormer. It groups potential features from point clouds into superpoints, and directly predicts instances through query vectors without relying on the results of object detection or semantic segmentation. The key step in this framework is a novel query decoder with transformers that can capture the instance information through the superpoint cross-attention mechanism and generate the superpoint masks of the instances. Through bipartite matching based on superpoint masks, SPFormer can implement the network training without the intermediate aggregation step, which accelerates the network. Extensive experiments on ScanNetv2 and S3DIS benchmarks verify that our method is concise yet efficient. Notably, SPFormer exceeds compared state-of-the-art methods by 4.3% on ScanNetv2 hidden test set in terms of mAP and keeps fast inference speed (247ms per frame) simultaneously. Code is available at https://github.com/sunjiahao1999/SPFormer.
### AdaEnlight: Energy-aware Low-light Video Stream Enhancement on Mobile Devices
- **Authors:** Sicong Liu (Northwestern Polytechnical University, China), Xiaochen Li (Northwestern Polytechnical University, China), Zimu Zhou (City University of Hong Kong, China), Bin Guo (Northwestern Polytechnical University, China), Meng Zhang (Northwestern Polytechnical University, China), Haochen Shen (Northwestern Polytechnical University, China), Zhiwen Yu (Northwestern Polytechnical University, China)
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2211.16135
- **Pdf link:** https://arxiv.org/pdf/2211.16135
- **Abstract**
The ubiquity of camera-embedded devices and the advances in deep learning have stimulated various intelligent mobile video applications. These applications often demand on-device processing of video streams to deliver real-time, high-quality services for privacy and robustness concerns. However, the performance of these applications is constrained by the raw video streams, which tend to be taken with small-aperture cameras of ubiquitous mobile platforms in dim light. Despite extensive low-light video enhancement solutions, they are unfit for deployment to mobile devices due to their complex models and and ignorance of system dynamics like energy budgets. In this paper, we propose AdaEnlight, an energy-aware low-light video stream enhancement system on mobile devices. It achieves real-time video enhancement with competitive visual quality while allowing runtime behavior adaptation to the platform-imposed dynamic energy budgets. We report extensive experiments on diverse datasets, scenarios, and platforms and demonstrate the superiority of AdaEnlight compared with state-of-the-art low-light image and video enhancement solutions.
### DATID-3D: Diversity-Preserved Domain Adaptation Using Text-to-Image Diffusion for 3D Generative Model
- **Authors:** Gwanghyun Kim, Se Young Chun
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV); Artificial Intelligence (cs.AI)
- **Arxiv link:** https://arxiv.org/abs/2211.16374
- **Pdf link:** https://arxiv.org/pdf/2211.16374
- **Abstract**
Recent 3D generative models have achieved remarkable performance in synthesizing high resolution photorealistic images with view consistency and detailed 3D shapes, but training them for diverse domains is challenging since it requires massive training images and their camera distribution information. Text-guided domain adaptation methods have shown impressive performance on converting the 2D generative model on one domain into the models on other domains with different styles by leveraging the CLIP (Contrastive Language-Image Pre-training), rather than collecting massive datasets for those domains. However, one drawback of them is that the sample diversity in the original generative model is not well-preserved in the domain-adapted generative models due to the deterministic nature of the CLIP text encoder. Text-guided domain adaptation will be even more challenging for 3D generative models not only because of catastrophic diversity loss, but also because of inferior text-image correspondence and poor image quality. Here we propose DATID-3D, a domain adaptation method tailored for 3D generative models using text-to-image diffusion models that can synthesize diverse images per text prompt without collecting additional images and camera information for the target domain. Unlike 3D extensions of prior text-guided domain adaptation methods, our novel pipeline was able to fine-tune the state-of-the-art 3D generator of the source domain to synthesize high resolution, multi-view consistent images in text-guided targeted domains without additional data, outperforming the existing text-guided domain adaptation methods in diversity and text-image correspondence. Furthermore, we propose and demonstrate diverse 3D image manipulations such as one-shot instance-selected adaptation and single-view manipulated 3D reconstruction to fully enjoy diversity in text.
## Keyword: raw image
There is no result
|
process
|
new submissions for wed nov keyword events post training quantization on diffusion models authors yuzhang shang zhihang yuan bin xie bingzhe wu yan yan subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract denoising diffusion score based generative models have recently achieved significant accomplishments in generating realistic and diverse data these approaches define a forward diffusion process for transforming data into noise and a backward denoising process for sampling data from noise unfortunately the generation process of current denoising diffusion models is notoriously slow due to the lengthy iterative noise estimations which rely on cumbersome neural networks it prevents the diffusion models from being widely deployed especially on edge devices previous works accelerate the generation process of diffusion model dm via finding shorter yet effective sampling trajectories however they overlook the cost of noise estimation with a heavy network in every iteration in this work we accelerate generation from the perspective of compressing the noise estimation network due to the difficulty of retraining dms we exclude mainstream training aware compression paradigms and introduce post training quantization ptq into dm acceleration however the output distributions of noise estimation networks change with time step making previous ptq methods fail in dms since they are designed for single time step scenarios to devise a dm specific ptq method we explore ptq on dm in three aspects quantized operations calibration dataset and calibration metric we summarize and use several observations derived from all inclusive investigations to formulate our method which especially targets the unique multi time step structure of dms experimentally our method can directly quantize full precision dms into bit models while maintaining or even improving their performance in a training free manner importantly our method can serve as a plug and play module on other fast sampling methods e g ddim keyword event camera there is no result keyword events camera there is no result keyword white balance there is no result keyword color contrast there is no result keyword awb superpoint transformer for scene instance segmentation authors jiahao sun chunmei qing junpeng tan xiangmin xu subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract most existing methods realize instance segmentation by extending those models used for object detection or semantic segmentation however these non straightforward methods suffer from two drawbacks imprecise bounding boxes or unsatisfactory semantic predictions limit the performance of the overall instance segmentation framework existing method requires a time consuming intermediate step of aggregation to address these issues this paper proposes a novel end to end instance segmentation method based on superpoint transformer named as spformer it groups potential features from point clouds into superpoints and directly predicts instances through query vectors without relying on the results of object detection or semantic segmentation the key step in this framework is a novel query decoder with transformers that can capture the instance information through the superpoint cross attention mechanism and generate the superpoint masks of the instances through bipartite matching based on superpoint masks spformer can implement the network training without the intermediate aggregation step which accelerates the network extensive experiments on and benchmarks verify that our method is concise yet efficient notably spformer exceeds compared state of the art methods by on hidden test set in terms of map and keeps fast inference speed per frame simultaneously code is available at datid diversity preserved domain adaptation using text to image diffusion for generative model authors gwanghyun kim se young chun subjects computer vision and pattern recognition cs cv artificial intelligence cs ai arxiv link pdf link abstract recent generative models have achieved remarkable performance in synthesizing high resolution photorealistic images with view consistency and detailed shapes but training them for diverse domains is challenging since it requires massive training images and their camera distribution information text guided domain adaptation methods have shown impressive performance on converting the generative model on one domain into the models on other domains with different styles by leveraging the clip contrastive language image pre training rather than collecting massive datasets for those domains however one drawback of them is that the sample diversity in the original generative model is not well preserved in the domain adapted generative models due to the deterministic nature of the clip text encoder text guided domain adaptation will be even more challenging for generative models not only because of catastrophic diversity loss but also because of inferior text image correspondence and poor image quality here we propose datid a domain adaptation method tailored for generative models using text to image diffusion models that can synthesize diverse images per text prompt without collecting additional images and camera information for the target domain unlike extensions of prior text guided domain adaptation methods our novel pipeline was able to fine tune the state of the art generator of the source domain to synthesize high resolution multi view consistent images in text guided targeted domains without additional data outperforming the existing text guided domain adaptation methods in diversity and text image correspondence furthermore we propose and demonstrate diverse image manipulations such as one shot instance selected adaptation and single view manipulated reconstruction to fully enjoy diversity in text keyword isp be careful with rotation a uniform backdoor pattern for shape authors linkun fan fazhi he qing guo wei tang xiaolin hong bing li subjects computer vision and pattern recognition cs cv cryptography and security cs cr arxiv link pdf link abstract for saving cost many deep neural networks dnns are trained on third party datasets downloaded from internet which enables attacker to implant backdoor into dnns in domain inherent structures of different image formats are similar hence backdoor attack designed for one image format will suite for others however when it comes to world there is a huge disparity among different data structures as a result backdoor pattern designed for one certain data structure will be disable for other data structures of the same scene therefore this paper designs a uniform backdoor pattern nrbdoor noisy rotation backdoor which is able to adapt for heterogeneous data structures specifically we start from the unit rotation and then search for the optimal pattern by noise generation and selection process the proposed nrbdoor is natural and imperceptible since rotation is a common operation which usually contains noise due to both the miss match between a pair of points and the sensor calibration error for real world scene extensive experiments on mesh and point cloud show that the proposed nrbdoor achieves state of the art performance with negligible shape variation fourier net fast image registration with band limited deformation authors xi jia joseph bartlett wei chen siyang song tianyang zhang xinxing cheng wenqi lu zhaowen qiu jinming duan subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract unsupervised image registration commonly adopts u net style networks to predict dense displacement fields in the full resolution spatial domain for high resolution volumetric image data this process is however resource intensive and time consuming to tackle this problem we propose the fourier net replacing the expansive path in a u net style network with a parameter free model driven decoder specifically instead of our fourier net learning to output a full resolution displacement field in the spatial domain we learn its low dimensional representation in a band limited fourier domain this representation is then decoded by our devised model driven decoder consisting of a zero padding layer and an inverse discrete fourier transform layer to the dense full resolution displacement field in the spatial domain these changes allow our unsupervised fourier net to contain fewer parameters and computational operations resulting in faster inference speeds fourier net is then evaluated on two public brain datasets against various state of the art approaches for example when compared to a recent transformer based method i e transmorph our fourier net only using of its parameters and of the mult adds achieves a higher dice score and an times faster inference speed code is available at url keyword image signal processing there is no result keyword image signal process there is no result keyword compression post training quantization on diffusion models authors yuzhang shang zhihang yuan bin xie bingzhe wu yan yan subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract denoising diffusion score based generative models have recently achieved significant accomplishments in generating realistic and diverse data these approaches define a forward diffusion process for transforming data into noise and a backward denoising process for sampling data from noise unfortunately the generation process of current denoising diffusion models is notoriously slow due to the lengthy iterative noise estimations which rely on cumbersome neural networks it prevents the diffusion models from being widely deployed especially on edge devices previous works accelerate the generation process of diffusion model dm via finding shorter yet effective sampling trajectories however they overlook the cost of noise estimation with a heavy network in every iteration in this work we accelerate generation from the perspective of compressing the noise estimation network due to the difficulty of retraining dms we exclude mainstream training aware compression paradigms and introduce post training quantization ptq into dm acceleration however the output distributions of noise estimation networks change with time step making previous ptq methods fail in dms since they are designed for single time step scenarios to devise a dm specific ptq method we explore ptq on dm in three aspects quantized operations calibration dataset and calibration metric we summarize and use several observations derived from all inclusive investigations to formulate our method which especially targets the unique multi time step structure of dms experimentally our method can directly quantize full precision dms into bit models while maintaining or even improving their performance in a training free manner importantly our method can serve as a plug and play module on other fast sampling methods e g ddim compressing volumetric radiance fields to mb authors lingzhi li zhen shen zhongshu wang li shen liefeng bo subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract approximating radiance fields with volumetric grids is one of promising directions for improving nerf represented by methods like plenoxels and dvgo which achieve super fast training convergence and real time rendering however these methods typically require a tremendous storage overhead costing up to hundreds of megabytes of disk space and runtime memory for a single scene we address this issue in this paper by introducing a simple yet effective framework called vector quantized radiance fields vqrf for compressing these volume grid based radiance fields we first present a robust and adaptive metric for estimating redundancy in grid models and performing voxel pruning by better exploring intermediate outputs of volumetric rendering a trainable vector quantization is further proposed to improve the compactness of grid models in combination with an efficient joint tuning strategy and post processing our method can achieve a compression ratio of times by reducing the overall model size to mb with negligible loss on visual quality extensive experiments demonstrate that the proposed framework is capable of achieving unrivaled performance and well generalization across multiple methods with distinct volumetric structures facilitating the wide use of volumetric radiance fields methods in real world applications code available at url keyword raw superpoint transformer for scene instance segmentation authors jiahao sun chunmei qing junpeng tan xiangmin xu subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract most existing methods realize instance segmentation by extending those models used for object detection or semantic segmentation however these non straightforward methods suffer from two drawbacks imprecise bounding boxes or unsatisfactory semantic predictions limit the performance of the overall instance segmentation framework existing method requires a time consuming intermediate step of aggregation to address these issues this paper proposes a novel end to end instance segmentation method based on superpoint transformer named as spformer it groups potential features from point clouds into superpoints and directly predicts instances through query vectors without relying on the results of object detection or semantic segmentation the key step in this framework is a novel query decoder with transformers that can capture the instance information through the superpoint cross attention mechanism and generate the superpoint masks of the instances through bipartite matching based on superpoint masks spformer can implement the network training without the intermediate aggregation step which accelerates the network extensive experiments on and benchmarks verify that our method is concise yet efficient notably spformer exceeds compared state of the art methods by on hidden test set in terms of map and keeps fast inference speed per frame simultaneously code is available at adaenlight energy aware low light video stream enhancement on mobile devices authors sicong liu northwestern polytechnical university china xiaochen li northwestern polytechnical university china zimu zhou city university of hong kong china bin guo northwestern polytechnical university china meng zhang northwestern polytechnical university china haochen shen northwestern polytechnical university china zhiwen yu northwestern polytechnical university china subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract the ubiquity of camera embedded devices and the advances in deep learning have stimulated various intelligent mobile video applications these applications often demand on device processing of video streams to deliver real time high quality services for privacy and robustness concerns however the performance of these applications is constrained by the raw video streams which tend to be taken with small aperture cameras of ubiquitous mobile platforms in dim light despite extensive low light video enhancement solutions they are unfit for deployment to mobile devices due to their complex models and and ignorance of system dynamics like energy budgets in this paper we propose adaenlight an energy aware low light video stream enhancement system on mobile devices it achieves real time video enhancement with competitive visual quality while allowing runtime behavior adaptation to the platform imposed dynamic energy budgets we report extensive experiments on diverse datasets scenarios and platforms and demonstrate the superiority of adaenlight compared with state of the art low light image and video enhancement solutions datid diversity preserved domain adaptation using text to image diffusion for generative model authors gwanghyun kim se young chun subjects computer vision and pattern recognition cs cv artificial intelligence cs ai arxiv link pdf link abstract recent generative models have achieved remarkable performance in synthesizing high resolution photorealistic images with view consistency and detailed shapes but training them for diverse domains is challenging since it requires massive training images and their camera distribution information text guided domain adaptation methods have shown impressive performance on converting the generative model on one domain into the models on other domains with different styles by leveraging the clip contrastive language image pre training rather than collecting massive datasets for those domains however one drawback of them is that the sample diversity in the original generative model is not well preserved in the domain adapted generative models due to the deterministic nature of the clip text encoder text guided domain adaptation will be even more challenging for generative models not only because of catastrophic diversity loss but also because of inferior text image correspondence and poor image quality here we propose datid a domain adaptation method tailored for generative models using text to image diffusion models that can synthesize diverse images per text prompt without collecting additional images and camera information for the target domain unlike extensions of prior text guided domain adaptation methods our novel pipeline was able to fine tune the state of the art generator of the source domain to synthesize high resolution multi view consistent images in text guided targeted domains without additional data outperforming the existing text guided domain adaptation methods in diversity and text image correspondence furthermore we propose and demonstrate diverse image manipulations such as one shot instance selected adaptation and single view manipulated reconstruction to fully enjoy diversity in text keyword raw image there is no result
| 1
|
20,851
| 27,630,562,100
|
IssuesEvent
|
2023-03-10 10:30:21
|
apache/arrow-rs
|
https://api.github.com/repos/apache/arrow-rs
|
closed
|
Concating dictionary array leads to duplicated dict values.
|
enhancement development-process
|
**Describe the bug**
<!--
A clear and concise description of what the bug is.
-->
I was trying to concatenate a few DictionaryArrays using `arrow_select::concat::concat`. While the each Dictionary Array shares the same value strings. The resulted array however have all values from each DictionaryArray copied (duplicated) in the final output.
**To Reproduce**
<!--
Steps to reproduce the behavior:
-->
```rust
let arrs: Vec<Arc<DictionaryArray<Int32Type>>> = (0..10).map(|v| {
let mut dict_builder = StringDictionaryBuilder::<Int32Type>::new();
dict_builder.append_null();
dict_builder.append("a").unwrap();
dict_builder.append("b").unwrap();
dict_builder.append("c").unwrap();
Arc::new(dict_builder.finish())
}).collect();
let mut arrays: Vec<&dyn Array> = vec![];
for b in arrs.iter() {
arrays.push(b.as_ref());
}
let b = concat(arrays.as_slice()).unwrap();
println!("Batch is: {:?}", b);
```
Output
```
Batch is: DictionaryArray {keys: PrimitiveArray<Int32>
[
null,
0,
1,
2,
null,
3,
4,
5,
] values: StringArray
[
"a",
"b",
"c",
"a",
"b",
"c",
]}
```
**Expected behavior**
<!--
A clear and concise description of what you expected to happen.
-->
I'd expect the output will be
```
DictionaryArray {keys: PrimitiveArray<Int32>
[
null,
0,
1,
2,
null,
0,
1,
2
] values: StringArray
[
"a",
"b",
"c",
]}
```
**Additional context**
<!--
Add any other context about the problem here.
-->
N/A
|
1.0
|
Concating dictionary array leads to duplicated dict values. - **Describe the bug**
<!--
A clear and concise description of what the bug is.
-->
I was trying to concatenate a few DictionaryArrays using `arrow_select::concat::concat`. While the each Dictionary Array shares the same value strings. The resulted array however have all values from each DictionaryArray copied (duplicated) in the final output.
**To Reproduce**
<!--
Steps to reproduce the behavior:
-->
```rust
let arrs: Vec<Arc<DictionaryArray<Int32Type>>> = (0..10).map(|v| {
let mut dict_builder = StringDictionaryBuilder::<Int32Type>::new();
dict_builder.append_null();
dict_builder.append("a").unwrap();
dict_builder.append("b").unwrap();
dict_builder.append("c").unwrap();
Arc::new(dict_builder.finish())
}).collect();
let mut arrays: Vec<&dyn Array> = vec![];
for b in arrs.iter() {
arrays.push(b.as_ref());
}
let b = concat(arrays.as_slice()).unwrap();
println!("Batch is: {:?}", b);
```
Output
```
Batch is: DictionaryArray {keys: PrimitiveArray<Int32>
[
null,
0,
1,
2,
null,
3,
4,
5,
] values: StringArray
[
"a",
"b",
"c",
"a",
"b",
"c",
]}
```
**Expected behavior**
<!--
A clear and concise description of what you expected to happen.
-->
I'd expect the output will be
```
DictionaryArray {keys: PrimitiveArray<Int32>
[
null,
0,
1,
2,
null,
0,
1,
2
] values: StringArray
[
"a",
"b",
"c",
]}
```
**Additional context**
<!--
Add any other context about the problem here.
-->
N/A
|
process
|
concating dictionary array leads to duplicated dict values describe the bug a clear and concise description of what the bug is i was trying to concatenate a few dictionaryarrays using arrow select concat concat while the each dictionary array shares the same value strings the resulted array however have all values from each dictionaryarray copied duplicated in the final output to reproduce steps to reproduce the behavior rust let arrs vec map v let mut dict builder stringdictionarybuilder new dict builder append null dict builder append a unwrap dict builder append b unwrap dict builder append c unwrap arc new dict builder finish collect let mut arrays vec vec for b in arrs iter arrays push b as ref let b concat arrays as slice unwrap println batch is b output batch is dictionaryarray keys primitivearray null null values stringarray a b c a b c expected behavior a clear and concise description of what you expected to happen i d expect the output will be dictionaryarray keys primitivearray null null values stringarray a b c additional context add any other context about the problem here n a
| 1
|
19,935
| 26,404,483,627
|
IssuesEvent
|
2023-01-13 06:21:59
|
vesoft-inc/nebula
|
https://api.github.com/repos/vesoft-inc/nebula
|
reopened
|
Why user's query is persisted in meta?
|
type/bug severity/major auto-sync process/fixed affects/none
|
When I import data recently, I found that QUITE A LOT query is persisted in meta. Why we do that? Here is a wal of **meta**: lots of DML in it. In my env, the size of meta's wal is almost 15G, even bigger than storage...

The query is persisted by session.

|
1.0
|
Why user's query is persisted in meta? - When I import data recently, I found that QUITE A LOT query is persisted in meta. Why we do that? Here is a wal of **meta**: lots of DML in it. In my env, the size of meta's wal is almost 15G, even bigger than storage...

The query is persisted by session.

|
process
|
why user s query is persisted in meta when i import data recently i found that quite a lot query is persisted in meta why we do that here is a wal of meta lots of dml in it in my env the size of meta s wal is almost even bigger than storage the query is persisted by session
| 1
|
17,499
| 3,619,395,791
|
IssuesEvent
|
2016-02-08 15:53:27
|
cockroachdb/cockroach
|
https://api.github.com/repos/cockroachdb/cockroach
|
closed
|
Failed tests (12411): TestChaos
|
test-failure TestChaos
|
The following test appears to have failed:
[#12411](https://circleci.com/gh/cockroachdb/cockroach/12411):
```
E0206 23:51:57.805908 27393 acceptance/cluster/localcluster.go:410 node=0 status=restart
I0206 23:51:57.811790 27393 acceptance/chaos_test.go:162 client 0 shutting down
I0206 23:51:57.831798 27393 acceptance/chaos_test.go:162 client 2 shutting down
I0206 23:51:57.831897 27393 acceptance/chaos_test.go:162 client 1 shutting down
I0206 23:51:57.935157 27393 acceptance/cluster/localcluster.go:538 stopping
--- FAIL: TestChaos (19.56s)
chaos_test.go:280: dial tcp 0.0.0.0:32785: getsockopt: connection refused
=== RUN TestGossipPeerings
I0206 23:52:00.313938 27393 acceptance/cluster/localcluster.go:219 started docker-spy: 172.17.0.15
I0206 23:52:00.313964 27393 acceptance/cluster/localcluster.go:226 initializing cluster
I0206 23:52:02.206927 27393 acceptance/cluster/localcluster.go:333 creating ca (1024bit) in: /home/ubuntu/cockroach/.localcluster.certs.048084615
I0206 23:52:02.250598 27393 acceptance/cluster/localcluster.go:338 creating node (1024bit) certs in: /home/ubuntu/cockroach/.localcluster.certs.048084615
I0206 23:52:03.675389 27393 acceptance/cluster/localcluster.go:389 *** started roach0.local ***
ui: https://0.0.0.0:32787
trace: https://0.0.0.0:32787/debug/requests
logs: /tmp/circle-artifacts.ZQgrzFp/acceptance/TestGossipPeerings/roach0.local/cockroach.INFO
--
--- SKIP: TestBuildBabyCluster (0.00s)
terraform_test.go:32: only enabled during testing
=== RUN TestFiveNodesAndWriters
--- SKIP: TestFiveNodesAndWriters (0.00s)
main_test.go:62: running in docker mode
FAIL
ok github.com/cockroachdb/cockroach/acceptance 1337s
```
Please assign, take a look and update the issue accordingly.
|
2.0
|
Failed tests (12411): TestChaos - The following test appears to have failed:
[#12411](https://circleci.com/gh/cockroachdb/cockroach/12411):
```
E0206 23:51:57.805908 27393 acceptance/cluster/localcluster.go:410 node=0 status=restart
I0206 23:51:57.811790 27393 acceptance/chaos_test.go:162 client 0 shutting down
I0206 23:51:57.831798 27393 acceptance/chaos_test.go:162 client 2 shutting down
I0206 23:51:57.831897 27393 acceptance/chaos_test.go:162 client 1 shutting down
I0206 23:51:57.935157 27393 acceptance/cluster/localcluster.go:538 stopping
--- FAIL: TestChaos (19.56s)
chaos_test.go:280: dial tcp 0.0.0.0:32785: getsockopt: connection refused
=== RUN TestGossipPeerings
I0206 23:52:00.313938 27393 acceptance/cluster/localcluster.go:219 started docker-spy: 172.17.0.15
I0206 23:52:00.313964 27393 acceptance/cluster/localcluster.go:226 initializing cluster
I0206 23:52:02.206927 27393 acceptance/cluster/localcluster.go:333 creating ca (1024bit) in: /home/ubuntu/cockroach/.localcluster.certs.048084615
I0206 23:52:02.250598 27393 acceptance/cluster/localcluster.go:338 creating node (1024bit) certs in: /home/ubuntu/cockroach/.localcluster.certs.048084615
I0206 23:52:03.675389 27393 acceptance/cluster/localcluster.go:389 *** started roach0.local ***
ui: https://0.0.0.0:32787
trace: https://0.0.0.0:32787/debug/requests
logs: /tmp/circle-artifacts.ZQgrzFp/acceptance/TestGossipPeerings/roach0.local/cockroach.INFO
--
--- SKIP: TestBuildBabyCluster (0.00s)
terraform_test.go:32: only enabled during testing
=== RUN TestFiveNodesAndWriters
--- SKIP: TestFiveNodesAndWriters (0.00s)
main_test.go:62: running in docker mode
FAIL
ok github.com/cockroachdb/cockroach/acceptance 1337s
```
Please assign, take a look and update the issue accordingly.
|
non_process
|
failed tests testchaos the following test appears to have failed acceptance cluster localcluster go node status restart acceptance chaos test go client shutting down acceptance chaos test go client shutting down acceptance chaos test go client shutting down acceptance cluster localcluster go stopping fail testchaos chaos test go dial tcp getsockopt connection refused run testgossippeerings acceptance cluster localcluster go started docker spy acceptance cluster localcluster go initializing cluster acceptance cluster localcluster go creating ca in home ubuntu cockroach localcluster certs acceptance cluster localcluster go creating node certs in home ubuntu cockroach localcluster certs acceptance cluster localcluster go started local ui trace logs tmp circle artifacts zqgrzfp acceptance testgossippeerings local cockroach info skip testbuildbabycluster terraform test go only enabled during testing run testfivenodesandwriters skip testfivenodesandwriters main test go running in docker mode fail ok github com cockroachdb cockroach acceptance please assign take a look and update the issue accordingly
| 0
|
1,882
| 4,712,311,403
|
IssuesEvent
|
2016-10-14 16:20:58
|
geneontology/go-ontology
|
https://api.github.com/repos/geneontology/go-ontology
|
closed
|
GO:0052193- movement in symbiont environment
|
multiorganism processes obsoletion PARL-UCL
|
The following term doesn't have any annotations or mappings. I can't think of any use cases for it (it was possibly created just to be a pair to the 'movement in host' terms). So after discussion with Jane I'm proposing its obsoletion:
movement in symbiont environment ; GO:0052193
The directed movement of an organism or motile cell on, within or near its symbiont organism. The symbiont is defined as the smaller of the organisms involved in a symbiotic interaction.
Thanks!
|
1.0
|
GO:0052193- movement in symbiont environment -
The following term doesn't have any annotations or mappings. I can't think of any use cases for it (it was possibly created just to be a pair to the 'movement in host' terms). So after discussion with Jane I'm proposing its obsoletion:
movement in symbiont environment ; GO:0052193
The directed movement of an organism or motile cell on, within or near its symbiont organism. The symbiont is defined as the smaller of the organisms involved in a symbiotic interaction.
Thanks!
|
process
|
go movement in symbiont environment the following term doesn t have any annotations or mappings i can t think of any use cases for it it was possibly created just to be a pair to the movement in host terms so after discussion with jane i m proposing its obsoletion movement in symbiont environment go the directed movement of an organism or motile cell on within or near its symbiont organism the symbiont is defined as the smaller of the organisms involved in a symbiotic interaction thanks
| 1
|
226,453
| 7,519,452,642
|
IssuesEvent
|
2018-04-12 11:40:12
|
HabitRPG/habitica-ios
|
https://api.github.com/repos/HabitRPG/habitica-ios
|
closed
|
App can crash when trying to delete a task
|
Help wanted Priority: medium Type: Crash
|
This seems to be the crash report:
```
Crashed: org.restkit.network.object-request-operation-queue
0 libobjc.A.dylib 0x181df40a0 objc_retain + 16
1 Habitica 0x10028d790 -[RKManagedObjectRequestOperation willFinish] (RKManagedObjectRequestOperation.m:916)
2 Habitica 0x1002aee54 __77-[RKObjectRequestOperation initWithHTTPRequestOperation:responseDescriptors:]_block_invoke.170 (RKObjectRequestOperation.m:334)
3 Habitica 0x1002b3614 -[RKOperationStateMachine performBlockWithLock:] (RKOperationStateMachine.m:205)
4 Habitica 0x1002b32b4 __48-[RKOperationStateMachine setFinalizationBlock:]_block_invoke (RKOperationStateMachine.m:185)
5 Habitica 0x1002e0ce0 -[TKStateMachine fireEvent:userInfo:error:] (TKStateMachine.m:245)
6 Habitica 0x1002b2bf0 __33-[RKOperationStateMachine finish]_block_invoke_2 (RKOperationStateMachine.m:148)
7 Habitica 0x1002b3614 -[RKOperationStateMachine performBlockWithLock:] (RKOperationStateMachine.m:205)
8 Habitica 0x1002b2b8c __33-[RKOperationStateMachine finish]_block_invoke (RKOperationStateMachine.m:151)
9 libdispatch.dylib 0x18222d200 _dispatch_call_block_and_release + 24
10 libdispatch.dylib 0x18222d1c0 _dispatch_client_callout + 16
11 libdispatch.dylib 0x18223a008 _dispatch_continuation_pop + 576
12 libdispatch.dylib 0x182239d8c _dispatch_async_redirect_invoke + 820
13 libdispatch.dylib 0x18223d38c _dispatch_root_queue_drain + 572
14 libdispatch.dylib 0x18223d0ec _dispatch_worker_thread3 + 124
15 libsystem_pthread.dylib 0x1824352c8 _pthread_wqthread + 1288
16 libsystem_pthread.dylib 0x182434db4 start_wqthread + 4
```
I assigned myself, but if somebody has an idea how to solve it, I'd be happy to hear it!
|
1.0
|
App can crash when trying to delete a task - This seems to be the crash report:
```
Crashed: org.restkit.network.object-request-operation-queue
0 libobjc.A.dylib 0x181df40a0 objc_retain + 16
1 Habitica 0x10028d790 -[RKManagedObjectRequestOperation willFinish] (RKManagedObjectRequestOperation.m:916)
2 Habitica 0x1002aee54 __77-[RKObjectRequestOperation initWithHTTPRequestOperation:responseDescriptors:]_block_invoke.170 (RKObjectRequestOperation.m:334)
3 Habitica 0x1002b3614 -[RKOperationStateMachine performBlockWithLock:] (RKOperationStateMachine.m:205)
4 Habitica 0x1002b32b4 __48-[RKOperationStateMachine setFinalizationBlock:]_block_invoke (RKOperationStateMachine.m:185)
5 Habitica 0x1002e0ce0 -[TKStateMachine fireEvent:userInfo:error:] (TKStateMachine.m:245)
6 Habitica 0x1002b2bf0 __33-[RKOperationStateMachine finish]_block_invoke_2 (RKOperationStateMachine.m:148)
7 Habitica 0x1002b3614 -[RKOperationStateMachine performBlockWithLock:] (RKOperationStateMachine.m:205)
8 Habitica 0x1002b2b8c __33-[RKOperationStateMachine finish]_block_invoke (RKOperationStateMachine.m:151)
9 libdispatch.dylib 0x18222d200 _dispatch_call_block_and_release + 24
10 libdispatch.dylib 0x18222d1c0 _dispatch_client_callout + 16
11 libdispatch.dylib 0x18223a008 _dispatch_continuation_pop + 576
12 libdispatch.dylib 0x182239d8c _dispatch_async_redirect_invoke + 820
13 libdispatch.dylib 0x18223d38c _dispatch_root_queue_drain + 572
14 libdispatch.dylib 0x18223d0ec _dispatch_worker_thread3 + 124
15 libsystem_pthread.dylib 0x1824352c8 _pthread_wqthread + 1288
16 libsystem_pthread.dylib 0x182434db4 start_wqthread + 4
```
I assigned myself, but if somebody has an idea how to solve it, I'd be happy to hear it!
|
non_process
|
app can crash when trying to delete a task this seems to be the crash report crashed org restkit network object request operation queue libobjc a dylib objc retain habitica rkmanagedobjectrequestoperation m habitica block invoke rkobjectrequestoperation m habitica rkoperationstatemachine m habitica block invoke rkoperationstatemachine m habitica tkstatemachine m habitica block invoke rkoperationstatemachine m habitica rkoperationstatemachine m habitica block invoke rkoperationstatemachine m libdispatch dylib dispatch call block and release libdispatch dylib dispatch client callout libdispatch dylib dispatch continuation pop libdispatch dylib dispatch async redirect invoke libdispatch dylib dispatch root queue drain libdispatch dylib dispatch worker libsystem pthread dylib pthread wqthread libsystem pthread dylib start wqthread i assigned myself but if somebody has an idea how to solve it i d be happy to hear it
| 0
|
79,044
| 15,109,766,410
|
IssuesEvent
|
2021-02-08 18:17:18
|
antoniogamiz/tfg
|
https://api.github.com/repos/antoniogamiz/tfg
|
closed
|
Implement PRNG methods described in Chapter 1
|
code
|
- [x] Center squared method
- [x] Linear-feedback shifted generator
|
1.0
|
Implement PRNG methods described in Chapter 1 - - [x] Center squared method
- [x] Linear-feedback shifted generator
|
non_process
|
implement prng methods described in chapter center squared method linear feedback shifted generator
| 0
|
462,778
| 13,253,448,562
|
IssuesEvent
|
2020-08-20 07:37:11
|
ooni/probe-engine
|
https://api.github.com/repos/ooni/probe-engine
|
closed
|
QA/webconnectivity check is failing
|
bug effort/XS interrupt priority/high
|
See https://github.com/ooni/probe-engine/runs/998354991
Apparently there is something flaky with a QA/webconnectivity check when run from GitHub Actions.
|
1.0
|
QA/webconnectivity check is failing - See https://github.com/ooni/probe-engine/runs/998354991
Apparently there is something flaky with a QA/webconnectivity check when run from GitHub Actions.
|
non_process
|
qa webconnectivity check is failing see apparently there is something flaky with a qa webconnectivity check when run from github actions
| 0
|
724,938
| 24,945,756,718
|
IssuesEvent
|
2022-10-31 23:54:44
|
ufosc/Club_Website_2
|
https://api.github.com/repos/ufosc/Club_Website_2
|
closed
|
Footer overlapping with other elements
|
bug/error good first issue help wanted high priority difficulty: easy
|
The footer currently overlaps with new elements because its set to a fixed position of `bottom: 0px;`
This can be fixed by changing its position attribute to `position: static;`
|
1.0
|
Footer overlapping with other elements - The footer currently overlaps with new elements because its set to a fixed position of `bottom: 0px;`
This can be fixed by changing its position attribute to `position: static;`
|
non_process
|
footer overlapping with other elements the footer currently overlaps with new elements because its set to a fixed position of bottom this can be fixed by changing its position attribute to position static
| 0
|
14,445
| 17,500,584,595
|
IssuesEvent
|
2021-08-10 08:57:04
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[iOS] App crashes on submitting incorrect option for comprehension test in a scenario
|
Bug P0 iOS Process: Fixed Process: Tested dev
|
**Steps:**
1. Freshly install the app
2. Click on 'Get Started'
3. Click on any study having comprehension Test configured
4. Click on Participate. Navigated to signin screen
5. Signin successfully
6. Enroll the study and fail the comprehension test
7. Observe app crashes
**Actual:** App crashes on submitting incorrect option for comprehension test in a scenario
**Expected:** Retry comprehension test screen should be displayed
1. Issue not observed when user signin > participate > enroll the study > fail the comprehension test
2. Issue not observed when fail the comprehension test during review consent post enrolling into study
https://user-images.githubusercontent.com/60386291/128352401-de0c9a41-c9a6-434e-a4a4-483276301c9f.MOV
|
2.0
|
[iOS] App crashes on submitting incorrect option for comprehension test in a scenario - **Steps:**
1. Freshly install the app
2. Click on 'Get Started'
3. Click on any study having comprehension Test configured
4. Click on Participate. Navigated to signin screen
5. Signin successfully
6. Enroll the study and fail the comprehension test
7. Observe app crashes
**Actual:** App crashes on submitting incorrect option for comprehension test in a scenario
**Expected:** Retry comprehension test screen should be displayed
1. Issue not observed when user signin > participate > enroll the study > fail the comprehension test
2. Issue not observed when fail the comprehension test during review consent post enrolling into study
https://user-images.githubusercontent.com/60386291/128352401-de0c9a41-c9a6-434e-a4a4-483276301c9f.MOV
|
process
|
app crashes on submitting incorrect option for comprehension test in a scenario steps freshly install the app click on get started click on any study having comprehension test configured click on participate navigated to signin screen signin successfully enroll the study and fail the comprehension test observe app crashes actual app crashes on submitting incorrect option for comprehension test in a scenario expected retry comprehension test screen should be displayed issue not observed when user signin participate enroll the study fail the comprehension test issue not observed when fail the comprehension test during review consent post enrolling into study
| 1
|
18,611
| 24,579,230,278
|
IssuesEvent
|
2022-10-13 14:29:12
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[iOS] [Consent API] Cloud storage > Data sharing image PDF is not getting generated in the Cloud storage when Consent API is enabled
|
Bug P0 iOS Process: Fixed Process: Tested QA Process: Tested dev
|
Steps:
1. Sign up or sign in to the mobile app
2. Enroll to the study (Study should be created by enabling data sharing permission)
3. Go to the cloud storage and observe
AR: Data sharing image PDF is not getting generated in the cloud storage
ER: Data sharing image PDF should get generated in the cloud storage
|
3.0
|
[iOS] [Consent API] Cloud storage > Data sharing image PDF is not getting generated in the Cloud storage when Consent API is enabled - Steps:
1. Sign up or sign in to the mobile app
2. Enroll to the study (Study should be created by enabling data sharing permission)
3. Go to the cloud storage and observe
AR: Data sharing image PDF is not getting generated in the cloud storage
ER: Data sharing image PDF should get generated in the cloud storage
|
process
|
cloud storage data sharing image pdf is not getting generated in the cloud storage when consent api is enabled steps sign up or sign in to the mobile app enroll to the study study should be created by enabling data sharing permission go to the cloud storage and observe ar data sharing image pdf is not getting generated in the cloud storage er data sharing image pdf should get generated in the cloud storage
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.