Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3
values | title stringlengths 1 744 | labels stringlengths 4 574 | body stringlengths 9 211k | index stringclasses 10
values | text_combine stringlengths 96 211k | label stringclasses 2
values | text stringlengths 96 188k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
16,177 | 20,622,625,120 | IssuesEvent | 2022-03-07 18:58:56 | ORNL-AMO/AMO-Tools-Desktop | https://api.github.com/repos/ORNL-AMO/AMO-Tools-Desktop | closed | PH not EAF exhaust gas | Process Heating | Instead of using an abbreviated AH% calculation that assumes NG
Have a field that is "Fuel Fired Efficiency" that users can enter.
Have the "blue calculate" button that links to Flue Gas calculator like in steam assessment for Boiler Efficiency | 1.0 | PH not EAF exhaust gas - Instead of using an abbreviated AH% calculation that assumes NG
Have a field that is "Fuel Fired Efficiency" that users can enter.
Have the "blue calculate" button that links to Flue Gas calculator like in steam assessment for Boiler Efficiency | process | ph not eaf exhaust gas instead of using an abbreviated ah calculation that assumes ng have a field that is fuel fired efficiency that users can enter have the blue calculate button that links to flue gas calculator like in steam assessment for boiler efficiency | 1 |
4,027 | 6,961,579,202 | IssuesEvent | 2017-12-08 10:01:41 | nlbdev/pipeline | https://api.github.com/repos/nlbdev/pipeline | closed | Move original colophon to end of rearmatter | enhancement pre-processing Priority:2 - Medium | For DTBook, extract `<level1 class="colophon">`, for EPUB, extract `<body epub:type="colophon">`, and move to the end of the book (end of `<rearmatter>` for DTBook, and equivalent for EPUB).
If there's no headline, insert `<h1>Kolofon</h1>` for norwegian books and `<h1>Colophon</h1>` for english books (at the top of... | 1.0 | Move original colophon to end of rearmatter - For DTBook, extract `<level1 class="colophon">`, for EPUB, extract `<body epub:type="colophon">`, and move to the end of the book (end of `<rearmatter>` for DTBook, and equivalent for EPUB).
If there's no headline, insert `<h1>Kolofon</h1>` for norwegian books and `<h1>C... | process | move original colophon to end of rearmatter for dtbook extract for epub extract and move to the end of the book end of for dtbook and equivalent for epub if there s no headline insert kolofon for norwegian books and colophon for english books at the top of the do this as ... | 1 |
17,719 | 23,623,384,147 | IssuesEvent | 2022-08-24 23:36:24 | googleapis/gapic-generator-python | https://api.github.com/repos/googleapis/gapic-generator-python | closed | ensure unit tests work for GAPICs using transport=rest | type: process priority: p1 | I can locally run the generated unit tests for the texttospeech GAPIC generated with `transport=grpc`, and they pass. When `transport=rest`, those tests fail. We should ensure the tests generated for the clients can run and pass.
Having the tests running is a blocker for releasing the `transport=rest` functionality... | 1.0 | ensure unit tests work for GAPICs using transport=rest - I can locally run the generated unit tests for the texttospeech GAPIC generated with `transport=grpc`, and they pass. When `transport=rest`, those tests fail. We should ensure the tests generated for the clients can run and pass.
Having the tests running is a... | process | ensure unit tests work for gapics using transport rest i can locally run the generated unit tests for the texttospeech gapic generated with transport grpc and they pass when transport rest those tests fail we should ensure the tests generated for the clients can run and pass having the tests running is a... | 1 |
16,649 | 21,712,379,982 | IssuesEvent | 2022-05-10 14:50:44 | ankidroid/Anki-Android | https://api.github.com/repos/ankidroid/Anki-Android | closed | Add explanation to all tests | Priority-Low Good First Issue! Test process | Most of the tests have a message stating what was expected that did not occur. This ensure that a test failure is accompanied with at least a first hint of what is wrong.
Since most tests are not flaky, the absence of such message is not a big deal, but still, it would be nice for code beauty to ensure that most tes... | 1.0 | Add explanation to all tests - Most of the tests have a message stating what was expected that did not occur. This ensure that a test failure is accompanied with at least a first hint of what is wrong.
Since most tests are not flaky, the absence of such message is not a big deal, but still, it would be nice for code... | process | add explanation to all tests most of the tests have a message stating what was expected that did not occur this ensure that a test failure is accompanied with at least a first hint of what is wrong since most tests are not flaky the absence of such message is not a big deal but still it would be nice for code... | 1 |
6,952 | 10,113,584,537 | IssuesEvent | 2019-07-30 17:04:54 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [MaskedTransition] Test all use cases | Accessibility [MaskedTransition] type:Process | Definition of done:
- [ ] All of this component's use cases have been evaluated in the accessibility audit spreadsheet located at [go/mdc-ios-a11y-matrix](http://go/mdc-ios-a11y-matrix).
- [ ] Issues have been filed for bugs that are blocking our accessibility rating.
<!-- Auto-generated content below, do not modi... | 1.0 | [MaskedTransition] Test all use cases - Definition of done:
- [ ] All of this component's use cases have been evaluated in the accessibility audit spreadsheet located at [go/mdc-ios-a11y-matrix](http://go/mdc-ios-a11y-matrix).
- [ ] Issues have been filed for bugs that are blocking our accessibility rating.
<!-- A... | process | test all use cases definition of done all of this component s use cases have been evaluated in the accessibility audit spreadsheet located at issues have been filed for bugs that are blocking our accessibility rating internal data associated internal bug | 1 |
19,941 | 26,410,056,131 | IssuesEvent | 2023-01-13 11:25:00 | hermes-hmc/workflow | https://api.github.com/repos/hermes-hmc/workflow | closed | Split authors and contributors | enhancement 2️ process/validate | - **Requires:** #52
Authors and contributors of software are different roles and should end up in different CodeMeta fields.
E.g.,
- person1 is in CFF authors AND git contributors: person is author only
- person1 is in CFF authors AND NOT git contributors: person is author only
- person1 is NOT in CFF author... | 1.0 | Split authors and contributors - - **Requires:** #52
Authors and contributors of software are different roles and should end up in different CodeMeta fields.
E.g.,
- person1 is in CFF authors AND git contributors: person is author only
- person1 is in CFF authors AND NOT git contributors: person is author onl... | process | split authors and contributors requires authors and contributors of software are different roles and should end up in different codemeta fields e g is in cff authors and git contributors person is author only is in cff authors and not git contributors person is author only is not... | 1 |
150,958 | 19,635,725,131 | IssuesEvent | 2022-01-08 08:26:38 | storybookjs/storybook | https://api.github.com/repos/storybookjs/storybook | closed | Vulnerability fix on prismjs package | dependencies security | Regular Expression Denial of Service
https://www.npmjs.com/advisories/1762
pls update the prismjs@1.24.0 | True | Vulnerability fix on prismjs package - Regular Expression Denial of Service
https://www.npmjs.com/advisories/1762
pls update the prismjs@1.24.0 | non_process | vulnerability fix on prismjs package regular expression denial of service pls update the prismjs | 0 |
3,037 | 4,120,356,092 | IssuesEvent | 2016-06-08 17:39:14 | certbot/certbot | https://api.github.com/repos/certbot/certbot | opened | Redirect vhost not enabled | apache security enhancements | On a fresh install of Apache on Debian, I used `certbot` to create the following vhost:
```
<IfModule mod_ssl.c>
<VirtualHost *:443>
# The ServerName directive sets the request scheme, hostname and port that
# the server uses to identify itself. This is used when creating
# redirection URLs. In the context of ... | True | Redirect vhost not enabled - On a fresh install of Apache on Debian, I used `certbot` to create the following vhost:
```
<IfModule mod_ssl.c>
<VirtualHost *:443>
# The ServerName directive sets the request scheme, hostname and port that
# the server uses to identify itself. This is used when creating
# redirec... | non_process | redirect vhost not enabled on a fresh install of apache on debian i used certbot to create the following vhost the servername directive sets the request scheme hostname and port that the server uses to identify itself this is used when creating redirection urls in the context of virtual ... | 0 |
18,375 | 24,503,454,174 | IssuesEvent | 2022-10-10 14:30:19 | fadeoutsoftware/WASDI | https://api.github.com/repos/fadeoutsoftware/WASDI | opened | Docker > Build: switch to the new log system | bug enhancement P3 app / processor | Actually when WASDI deploys an application, WASDI produces/writes a Bash script like this:
```
#!/bin/bash
echo Deploy Docker Started >> /usr/lib/wasdi/launcher/logs/dockers.log
docker build [...] $1 >> /usr/lib/wasdi/launcher/logs/dockers.log 2>&1
echo Deploy Docker Done >> /usr/lib/wasdi/launcher/logs/dockers.... | 1.0 | Docker > Build: switch to the new log system - Actually when WASDI deploys an application, WASDI produces/writes a Bash script like this:
```
#!/bin/bash
echo Deploy Docker Started >> /usr/lib/wasdi/launcher/logs/dockers.log
docker build [...] $1 >> /usr/lib/wasdi/launcher/logs/dockers.log 2>&1
echo Deploy Docke... | process | docker build switch to the new log system actually when wasdi deploys an application wasdi produces writes a bash script like this bin bash echo deploy docker started usr lib wasdi launcher logs dockers log docker build usr lib wasdi launcher logs dockers log echo deploy docker do... | 1 |
15,053 | 18,762,906,759 | IssuesEvent | 2021-11-05 18:47:13 | ORNL-AMO/AMO-Tools-Desktop | https://api.github.com/repos/ORNL-AMO/AMO-Tools-Desktop | closed | Cascading Heat updates | Process Heating | - Pull in inputs from AH/FG calculate modal, update other inputs
- Update outputs, add left side results for excess air, AH | 1.0 | Cascading Heat updates - - Pull in inputs from AH/FG calculate modal, update other inputs
- Update outputs, add left side results for excess air, AH | process | cascading heat updates pull in inputs from ah fg calculate modal update other inputs update outputs add left side results for excess air ah | 1 |
818,453 | 30,689,685,560 | IssuesEvent | 2023-07-26 14:27:21 | episphere/biospecimen | https://api.github.com/repos/episphere/biospecimen | opened | Rename Full Specimen ID to BSI ID in the In Transit File | Priority 2 | In the column headers of the In Transit file, please rename the column labels "Full Specimen IDs" to "BSI ID"

| 1.0 | Rename Full Specimen ID to BSI ID in the In Transit File - In the column headers of the In Transit file, please rename the column labels "Full Specimen IDs" to "BSI ID"

| non_process | rename full specimen id to bsi id in the in transit file in the column headers of the in transit file please rename the column labels full specimen ids to bsi id | 0 |
113,847 | 17,157,316,022 | IssuesEvent | 2021-07-14 08:38:36 | gdcorp-action-public-forks/action-hosting-deploy | https://api.github.com/repos/gdcorp-action-public-forks/action-hosting-deploy | closed | CVE-2021-33587 (High) detected in css-what-3.4.2.tgz - autoclosed | security vulnerability | ## CVE-2021-33587 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>css-what-3.4.2.tgz</b></p></summary>
<p>a CSS selector parser</p>
<p>Library home page: <a href="https://registry.npmj... | True | CVE-2021-33587 (High) detected in css-what-3.4.2.tgz - autoclosed - ## CVE-2021-33587 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>css-what-3.4.2.tgz</b></p></summary>
<p>a CSS sele... | non_process | cve high detected in css what tgz autoclosed cve high severity vulnerability vulnerable library css what tgz a css selector parser library home page a href path to dependency file action hosting deploy package json path to vulnerable library action hosting deploy n... | 0 |
434,700 | 12,521,983,754 | IssuesEvent | 2020-06-03 18:21:11 | opt-out-tools/start-here | https://api.github.com/repos/opt-out-tools/start-here | closed | Build Brand Guidelines | high priority medium task | **Objective**
A strict set of guidelines to help communicate our image
**Description**
We need to be able to communicate what we are doing effectively. For this we need a place of reference.
**Skills**
**Tools**
**Time Estimation**
**Tasks**
- [ ] Collect images, examples, try out tone of voic... | 1.0 | Build Brand Guidelines - **Objective**
A strict set of guidelines to help communicate our image
**Description**
We need to be able to communicate what we are doing effectively. For this we need a place of reference.
**Skills**
**Tools**
**Time Estimation**
**Tasks**
- [ ] Collect images, examp... | non_process | build brand guidelines objective a strict set of guidelines to help communicate our image description we need to be able to communicate what we are doing effectively for this we need a place of reference skills tools time estimation tasks collect images example... | 0 |
3,725 | 6,732,918,374 | IssuesEvent | 2017-10-18 13:17:44 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | opened | incomplete def GO:0043039 and descendants | quick fix RNA processes | The definition of tRNA aminoacylation (GO:0043039) looks incomplete. It contains
"... by the formation of an ester bond between the 3'-hydroxyl group of the most 3' adenosine of the tRNA ..."
but does not mention the part of the amino acid involved in forming the bond.
Two of the is_a GO:0043039 terms, GO:000... | 1.0 | incomplete def GO:0043039 and descendants - The definition of tRNA aminoacylation (GO:0043039) looks incomplete. It contains
"... by the formation of an ester bond between the 3'-hydroxyl group of the most 3' adenosine of the tRNA ..."
but does not mention the part of the amino acid involved in forming the bond.... | process | incomplete def go and descendants the definition of trna aminoacylation go looks incomplete it contains by the formation of an ester bond between the hydroxyl group of the most adenosine of the trna but does not mention the part of the amino acid involved in forming the bond two of t... | 1 |
11,149 | 13,957,693,131 | IssuesEvent | 2020-10-24 08:10:54 | alexanderkotsev/geoportal | https://api.github.com/repos/alexanderkotsev/geoportal | opened | LU: Harvesting request | Geoportal Harvesting process LU - Luxembourg | From: Jeff Konnen [jeff.konnen@act.etat.lu]
Sent: 31 January 2019 08:26
To: inspire-geoportal@jrc.ec.europa.eu
Cc: JRC SDI NOTIFY
Subject: FW: INSPIRE Registry
Hi,
I just sent this email to Angelo, but the mail bounced.
Is there someone else I could contact for this request regarding the registry?
Best regards
Je... | 1.0 | LU: Harvesting request - From: Jeff Konnen [jeff.konnen@act.etat.lu]
Sent: 31 January 2019 08:26
To: inspire-geoportal@jrc.ec.europa.eu
Cc: JRC SDI NOTIFY
Subject: FW: INSPIRE Registry
Hi,
I just sent this email to Angelo, but the mail bounced.
Is there someone else I could contact for this request regarding the regist... | process | lu harvesting request from jeff konnen sent january to inspire geoportal jrc ec europa eu cc jrc sdi notify subject fw inspire registry hi i just sent this email to angelo but the mail bounced is there someone else i could contact for this request regarding the registry best regards jeff ko... | 1 |
20,373 | 27,028,522,542 | IssuesEvent | 2023-02-11 22:44:38 | hashgraph/hedera-mirror-node | https://api.github.com/repos/hashgraph/hedera-mirror-node | closed | Release checklist 0.73 | enhancement process | ### Problem
We need a checklist to verify the release is rolled out successfully.
### Solution
## Preparation
- [x] Milestone field populated on relevant [issues](https://github.com/hashgraph/hedera-mirror-node/issues?q=is%3Aclosed+no%3Amilestone+sort%3Aupdated-desc)
- [x] Nothing open for [milestone](http... | 1.0 | Release checklist 0.73 - ### Problem
We need a checklist to verify the release is rolled out successfully.
### Solution
## Preparation
- [x] Milestone field populated on relevant [issues](https://github.com/hashgraph/hedera-mirror-node/issues?q=is%3Aclosed+no%3Amilestone+sort%3Aupdated-desc)
- [x] Nothing ... | process | release checklist problem we need a checklist to verify the release is rolled out successfully solution preparation milestone field populated on relevant nothing open for github checks for branch are passing automated kubernetes deployment successful tag rel... | 1 |
11,040 | 7,037,282,620 | IssuesEvent | 2017-12-28 13:58:57 | apinf/platform | https://api.github.com/repos/apinf/platform | closed | Path dropmenu in API Analytics View breaks if value includes path with long lengths | Dashboard 2.0 in progress Usability Issue | # Steps to Reproduce
1. login to apinf.io (production) as site admin
2. go to Dashboard and expand row for APInf Management Rest API
3. Click on "Show Details..." in expanded view
3. In analytics page, browse to API Request Timeline
# Outcome
Dropmenu listing paths breaks the GUI as it i... | True | Path dropmenu in API Analytics View breaks if value includes path with long lengths - # Steps to Reproduce
1. login to apinf.io (production) as site admin
2. go to Dashboard and expand row for APInf Management Rest API
3. Click on "Show Details..." in expanded view
3. In analytics page, browse to API Request Time... | non_process | path dropmenu in api analytics view breaks if value includes path with long lengths steps to reproduce login to apinf io production as site admin go to dashboard and expand row for apinf management rest api click on show details in expanded view in analytics page browse to api request time... | 0 |
4,297 | 7,192,463,371 | IssuesEvent | 2018-02-03 03:53:56 | Great-Hill-Corporation/quickBlocks | https://api.github.com/repos/Great-Hill-Corporation/quickBlocks | closed | Checksumming Addresses | libs-etherlib status-inprocess type-enhancement | Here's some javascript code to generate checksummed addresses:
/**
* Returns a checksummed address
* @param {String} address
* @return {String}
*/
exports.toChecksumAddress = function (address) {
address = exports.stripHexPrefix(address).toLowerCase()
const hash = exports.sha3(address).toString('hex')... | 1.0 | Checksumming Addresses - Here's some javascript code to generate checksummed addresses:
/**
* Returns a checksummed address
* @param {String} address
* @return {String}
*/
exports.toChecksumAddress = function (address) {
address = exports.stripHexPrefix(address).toLowerCase()
const hash = exports.sha3... | process | checksumming addresses here s some javascript code to generate checksummed addresses returns a checksummed address param string address return string exports tochecksumaddress function address address exports striphexprefix address tolowercase const hash exports ad... | 1 |
14,529 | 3,274,681,668 | IssuesEvent | 2015-10-26 12:18:55 | Mobicents/RestComm | https://api.github.com/repos/Mobicents/RestComm | closed | Detect Restcomm host/port/protocol by probing the container in RVD | Visual App Designer | Use Jboss/Tomcat container to find out the host/port/protocol the application is running on. That's what core restcomm does. Use these settings as default when accessing restcomm APIs. | 1.0 | Detect Restcomm host/port/protocol by probing the container in RVD - Use Jboss/Tomcat container to find out the host/port/protocol the application is running on. That's what core restcomm does. Use these settings as default when accessing restcomm APIs. | non_process | detect restcomm host port protocol by probing the container in rvd use jboss tomcat container to find out the host port protocol the application is running on that s what core restcomm does use these settings as default when accessing restcomm apis | 0 |
1,135 | 2,507,996,717 | IssuesEvent | 2015-01-12 22:14:31 | chessmasterhong/WaterEmblem | https://api.github.com/repos/chessmasterhong/WaterEmblem | opened | Discarding an item will cause the first item to be equipped | bug high priority | If the player decides to unequip their weapon, but then discard an item that is not in slot 0, then the item in slot 0 will be re-equipped. | 1.0 | Discarding an item will cause the first item to be equipped - If the player decides to unequip their weapon, but then discard an item that is not in slot 0, then the item in slot 0 will be re-equipped. | non_process | discarding an item will cause the first item to be equipped if the player decides to unequip their weapon but then discard an item that is not in slot then the item in slot will be re equipped | 0 |
328,807 | 10,000,265,139 | IssuesEvent | 2019-07-12 12:59:09 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | accounts.google.com - site is not usable | browser-firefox engine-gecko priority-critical | <!-- @browser: Firefox 69.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:69.0) Gecko/20100101 Firefox/69.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://accounts.google.com/signin/v2/identifier?service=accountsettings&hl=pt-BR&continue=https%3A%2F%2Fmyaccount.google.com%2Fintro&cs... | 1.0 | accounts.google.com - site is not usable - <!-- @browser: Firefox 69.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:69.0) Gecko/20100101 Firefox/69.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://accounts.google.com/signin/v2/identifier?service=accountsettings&hl=pt-BR&continue=ht... | non_process | accounts google com site is not usable url browser version firefox operating system windows tested another browser yes problem type site is not usable description i can not log in to my account google steps to reproduce i downloaded an android emulator after th... | 0 |
1,774 | 4,489,058,041 | IssuesEvent | 2016-08-30 09:37:13 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | Edits to term: suppression by virus of host protein binding ; GO:0036472 | multiorganism processes Other term-related request PARL-UCL viruses | This term name is confusing:
suppression by virus of host protein binding ; GO:0036472
Exact synonym: suppression by virus of host protein interaction
Any process in which a virus stops, prevents, or reduces the frequency, rate or extent of interaction between host proteins.
It has my initials on it, and the only... | 1.0 | Edits to term: suppression by virus of host protein binding ; GO:0036472 - This term name is confusing:
suppression by virus of host protein binding ; GO:0036472
Exact synonym: suppression by virus of host protein interaction
Any process in which a virus stops, prevents, or reduces the frequency, rate or extent of i... | process | edits to term suppression by virus of host protein binding go this term name is confusing suppression by virus of host protein binding go exact synonym suppression by virus of host protein interaction any process in which a virus stops prevents or reduces the frequency rate or extent of interaction b... | 1 |
319,693 | 27,394,508,039 | IssuesEvent | 2023-02-28 18:35:55 | bloom-housing/bloom | https://api.github.com/repos/bloom-housing/bloom | closed | Core - first unit test on public | good first ticket testing | **Goal**
Now that we have unit tests in addition to Cypress tests on the public site, there is so much to test on this new smaller scale that we could start anywhere, but we could consider some of the below since they are unit testable and have been bugs in the past. It will probably require mock listing data.
Let's ... | 1.0 | Core - first unit test on public - **Goal**
Now that we have unit tests in addition to Cypress tests on the public site, there is so much to test on this new smaller scale that we could start anywhere, but we could consider some of the below since they are unit testable and have been bugs in the past. It will probabl... | non_process | core first unit test on public goal now that we have unit tests in addition to cypress tests on the public site there is so much to test on this new smaller scale that we could start anywhere but we could consider some of the below since they are unit testable and have been bugs in the past it will probabl... | 0 |
20,208 | 26,790,888,647 | IssuesEvent | 2023-02-01 08:23:29 | Altinn/app-frontend-react | https://api.github.com/repos/Altinn/app-frontend-react | closed | As a developer I want to edit the receipt text in Altinn Studio | kind/user-story org/digdir org/skd org/ssb status/draft org/okokrim area/language area/receipt org/svv org/nbib area/process org/dibk org/dsb | ## Description
As a developer I would like to change the receipt text in Altinn Studio.
The receipt text is the text the end-user is presented with after submitting the service. It is visible on the receipt page and on messages in the inbox.
Standard text defined in Altinn/altinn-studio#1677
## Suggested solution
W... | 1.0 | As a developer I want to edit the receipt text in Altinn Studio - ## Description
As a developer I would like to change the receipt text in Altinn Studio.
The receipt text is the text the end-user is presented with after submitting the service. It is visible on the receipt page and on messages in the inbox.
Standard t... | process | as a developer i want to edit the receipt text in altinn studio description as a developer i would like to change the receipt text in altinn studio the receipt text is the text the end user is presented with after submitting the service it is visible on the receipt page and on messages in the inbox standard t... | 1 |
254,121 | 21,729,878,903 | IssuesEvent | 2022-05-11 11:00:22 | hyperledger-labs/orion-server | https://api.github.com/repos/hyperledger-labs/orion-server | closed | Integration testing: GetClusterConfig accessibility | testing | Check that GetClusterConfig is only available to admin users. Check that a regular user is denied access. | 1.0 | Integration testing: GetClusterConfig accessibility - Check that GetClusterConfig is only available to admin users. Check that a regular user is denied access. | non_process | integration testing getclusterconfig accessibility check that getclusterconfig is only available to admin users check that a regular user is denied access | 0 |
20,302 | 26,940,847,742 | IssuesEvent | 2023-02-08 02:00:06 | lizhihao6/get-daily-arxiv-noti | https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti | opened | New submissions for Wed, 8 Feb 23 | event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB | ## Keyword: events
There is no result
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
There is no result
## Keyword: ISP
There is no result
## Keyword: image signal ... | 2.0 | New submissions for Wed, 8 Feb 23 - ## Keyword: events
There is no result
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
There is no result
## Keyword: ISP
There is... | process | new submissions for wed feb keyword events there is no result keyword event camera there is no result keyword events camera there is no result keyword white balance there is no result keyword color contrast there is no result keyword awb there is no result keyword isp there is ... | 1 |
117,300 | 15,086,503,692 | IssuesEvent | 2021-02-05 20:26:28 | carbon-design-system/carbon-for-ibm-dotcom | https://api.github.com/repos/carbon-design-system/carbon-for-ibm-dotcom | closed | Web component: Card - Pictogram component variations Design PR review template | design package: web components | #### User Story
<!-- {{Provide a detailed description of the user's need here, but avoid any type of solutions}} -->
> As a `[user role below]`:
DDS Designer and Developer
> I need to:
test the `Card - Pictogram component variations`
> so that I can:
be sure the developer's code correctly works as designed
#### Addi... | 1.0 | Web component: Card - Pictogram component variations Design PR review template - #### User Story
<!-- {{Provide a detailed description of the user's need here, but avoid any type of solutions}} -->
> As a `[user role below]`:
DDS Designer and Developer
> I need to:
test the `Card - Pictogram component variations`
> s... | non_process | web component card pictogram component variations design pr review template user story as a dds designer and developer i need to test the card pictogram component variations so that i can be sure the developer s code correctly works as designed additional information see the epi... | 0 |
16,255 | 20,815,918,600 | IssuesEvent | 2022-03-18 10:15:26 | googleapis/synthtool | https://api.github.com/repos/googleapis/synthtool | opened | process(python): Explore the possibility of using a single linter | type: process lang: python | In the templated `nox_file.py` for python, there is a `lint` `nox` session which runs both `black` and `flake8` linters.
https://github.com/googleapis/synthtool/blob/02193e4ca893eeb62c9641f4a0f88ef1418f6e17/synthtool/gcp/templates/python_library/noxfile.py.j2#L52-L64
https://github.com/googleapis/python-aiplatfo... | 1.0 | process(python): Explore the possibility of using a single linter - In the templated `nox_file.py` for python, there is a `lint` `nox` session which runs both `black` and `flake8` linters.
https://github.com/googleapis/synthtool/blob/02193e4ca893eeb62c9641f4a0f88ef1418f6e17/synthtool/gcp/templates/python_library/no... | process | process python explore the possibility of using a single linter in the templated nox file py for python there is a lint nox session which runs both black and linters there is a conflict between the lint tools that we use where a formatting change made by black causes the check to fa... | 1 |
78,191 | 10,053,145,961 | IssuesEvent | 2019-07-21 14:26:46 | apoezzhaev/CIHP_PGN | https://api.github.com/repos/apoezzhaev/CIHP_PGN | reopened | Add docker file with runnable configuration | deployment documentation | Add dockerfile with runnable configs and proper hyperlinks to datasets, etc. | 1.0 | Add docker file with runnable configuration - Add dockerfile with runnable configs and proper hyperlinks to datasets, etc. | non_process | add docker file with runnable configuration add dockerfile with runnable configs and proper hyperlinks to datasets etc | 0 |
440,439 | 12,699,987,471 | IssuesEvent | 2020-06-22 15:38:09 | microsoft/terminal | https://api.github.com/repos/microsoft/terminal | closed | Terminal window has white border | Area-User Interface Impact-Visual In-PR Issue-Bug Priority-2 Product-Terminal | This issue has been reported several times but incorrectly marked as duplicate or just closed with no explanation.
The terminal window should have **under no circumstances a white border**. Not just in dark mode but NEVER. It is completely inconsistent with all other Windows apps including those from Microsoft.
... | 1.0 | Terminal window has white border - This issue has been reported several times but incorrectly marked as duplicate or just closed with no explanation.
The terminal window should have **under no circumstances a white border**. Not just in dark mode but NEVER. It is completely inconsistent with all other Windows apps i... | non_process | terminal window has white border this issue has been reported several times but incorrectly marked as duplicate or just closed with no explanation the terminal window should have under no circumstances a white border not just in dark mode but never it is completely inconsistent with all other windows apps i... | 0 |
219,391 | 24,481,086,569 | IssuesEvent | 2022-10-08 21:03:44 | Vonage-Community/sample-core-laravel_php-sandbox | https://api.github.com/repos/Vonage-Community/sample-core-laravel_php-sandbox | closed | laravel/framework-v9.0.2: 2 vulnerabilities (highest severity is: 9.8) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>laravel/framework-v9.0.2</b></p></summary>
<p>The Laravel Framework.</p>
<p>Library home page: <a href="https://api.github.com/repos/laravel/framework/zipball/4c7cd8c... | True | laravel/framework-v9.0.2: 2 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>laravel/framework-v9.0.2</b></p></summary>
<p>The Laravel Framework.</p>
<p>Libr... | non_process | laravel framework vulnerabilities highest severity is autoclosed vulnerable library laravel framework the laravel framework library home page a href found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remedia... | 0 |
101,269 | 4,111,889,168 | IssuesEvent | 2016-06-07 08:24:45 | japanesemediamanager/jmmclient | https://api.github.com/repos/japanesemediamanager/jmmclient | closed | RSS Feed - Escaped Characters Issue | Bug - Low Priority | Escaped characters need to be converted so they display properly.

| 1.0 | RSS Feed - Escaped Characters Issue - Escaped characters need to be converted so they display properly.

| non_process | rss feed escaped characters issue escaped characters need to be converted so they display properly | 0 |
4,763 | 7,625,730,257 | IssuesEvent | 2018-05-03 22:43:52 | ncbo/bioportal-project | https://api.github.com/repos/ncbo/bioportal-project | closed | ONTOPARON_SOCIAL: loading data into the triplestore fails | in progress ontology processing problem | The [ONTOPARON_SOCIAL](http://bioportal.bioontology.org/ontologies/ONTOPARON_SOCIAL) ontology passes the OWL API parsing phase, but the Ruby code that loads the data into the triplestore fails. Full stack trace from the log:
```
E, [2017-12-01T11:10:15.997478 #32467] ERROR -- : ["RestClient::BadRequest: 400 Bad Req... | 1.0 | ONTOPARON_SOCIAL: loading data into the triplestore fails - The [ONTOPARON_SOCIAL](http://bioportal.bioontology.org/ontologies/ONTOPARON_SOCIAL) ontology passes the OWL API parsing phase, but the Ruby code that loads the data into the triplestore fails. Full stack trace from the log:
```
E, [2017-12-01T11:10:15.997... | process | ontoparon social loading data into the triplestore fails the ontology passes the owl api parsing phase but the ruby code that loads the data into the triplestore fails full stack trace from the log e error restclient badrequest bad request srv ncbo ncbo cron vendor bundle ruby ge... | 1 |
7,175 | 10,317,846,283 | IssuesEvent | 2019-08-30 13:40:51 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | Dataloader crashes if num_worker>0 | module: dataloader module: multiprocessing topic: crash triaged | If I define my dataloader as follows:
```
X_train = torch.tensor(X_train).to(device)
y_train = torch.tensor(y_train).to(device)
train = torch.utils.data.TensorDataset(X_train,y_train)
train_loader = torch.utils.data.DataLoader(
train, batch_size = 16, shuffle = True,pin_memory= True, num_workers= 4)
```
... | 1.0 | Dataloader crashes if num_worker>0 - If I define my dataloader as follows:
```
X_train = torch.tensor(X_train).to(device)
y_train = torch.tensor(y_train).to(device)
train = torch.utils.data.TensorDataset(X_train,y_train)
train_loader = torch.utils.data.DataLoader(
train, batch_size = 16, shuffle = True,pin... | process | dataloader crashes if num worker if i define my dataloader as follows x train torch tensor x train to device y train torch tensor y train to device train torch utils data tensordataset x train y train train loader torch utils data dataloader train batch size shuffle true pin ... | 1 |
126,117 | 17,868,847,894 | IssuesEvent | 2021-09-06 12:58:51 | fasttrack-solutions/jQuery-QueryBuilder | https://api.github.com/repos/fasttrack-solutions/jQuery-QueryBuilder | opened | CVE-2020-28500 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.6.1.tgz</b>, <b>lodash-4.15.0.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>l... | True | CVE-2020-28500 (Medium) detected in multiple libraries - ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.6.1.tgz</b>, <b>lodash-4.15.0.tgz</b>, <b>lodash-... | non_process | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file jquery querybuilder package... | 0 |
17,265 | 23,046,129,758 | IssuesEvent | 2022-07-23 23:27:37 | tokio-rs/tokio | https://api.github.com/repos/tokio-rs/tokio | closed | process: fix tokio process abort issues on windows | C-bug M-process | Unfortunately, as a result of https://github.com/rust-lang/rust/pull/95469, we can no longer use `tokio::process` to communicate with child processes which are themselves rust binaries using std or tokio for stdio. Doing so may result in the child process being aborted.
This was the cause of https://github.com/tokio... | 1.0 | process: fix tokio process abort issues on windows - Unfortunately, as a result of https://github.com/rust-lang/rust/pull/95469, we can no longer use `tokio::process` to communicate with child processes which are themselves rust binaries using std or tokio for stdio. Doing so may result in the child process being abort... | process | process fix tokio process abort issues on windows unfortunately as a result of we can no longer use tokio process to communicate with child processes which are themselves rust binaries using std or tokio for stdio doing so may result in the child process being aborted this was the cause of unfortunat... | 1 |
163,305 | 20,359,949,878 | IssuesEvent | 2022-02-20 14:41:51 | shaimael/cset | https://api.github.com/repos/shaimael/cset | opened | CVE-2022-0639 (Medium) detected in url-parse-1.5.1.tgz | security vulnerability | ## CVE-2022-0639 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.1.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser ... | True | CVE-2022-0639 (Medium) detected in url-parse-1.5.1.tgz - ## CVE-2022-0639 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.1.tgz</b></p></summary>
<p>Small footprint URL... | non_process | cve medium detected in url parse tgz cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file csetwebng package json pa... | 0 |
11,359 | 14,175,103,589 | IssuesEvent | 2020-11-12 21:00:51 | MicrosoftDocs/azure-devops-docs | https://api.github.com/repos/MicrosoftDocs/azure-devops-docs | closed | Documentation is not up-to-date | Pri2 devops-cicd-process/tech devops/prod doc-enhancement |
The scheme in this page does not match the scheme listed in all up documentation (https://docs.microsoft.com/en-us/azure/devops/pipelines/yaml-schema?view=azure-devops&tabs=schema%2Cparameter-schema#deployment-job)
Mainly, I see the **workspace** property is missing but others might be wrong as well.
---
###... | 1.0 | Documentation is not up-to-date -
The scheme in this page does not match the scheme listed in all up documentation (https://docs.microsoft.com/en-us/azure/devops/pipelines/yaml-schema?view=azure-devops&tabs=schema%2Cparameter-schema#deployment-job)
Mainly, I see the **workspace** property is missing but others mig... | process | documentation is not up to date the scheme in this page does not match the scheme listed in all up documentation mainly i see the workspace property is missing but others might be wrong as well document details ⚠ do not edit this section it is required for docs microsoft com ➟ github... | 1 |
49,968 | 12,439,282,568 | IssuesEvent | 2020-05-26 09:50:33 | docascod/DocsAsCode | https://api.github.com/repos/docascod/DocsAsCode | opened | default theme slides : add default images | enhancement fct_build | Add default (blank) images into slides default theme :
* title-page-background
* title-page-logo
* header-logo
* footer-logo
| 1.0 | default theme slides : add default images - Add default (blank) images into slides default theme :
* title-page-background
* title-page-logo
* header-logo
* footer-logo
| non_process | default theme slides add default images add default blank images into slides default theme title page background title page logo header logo footer logo | 0 |
337,366 | 24,536,983,538 | IssuesEvent | 2022-10-11 21:50:22 | awslabs/aws-lambda-powertools-python | https://api.github.com/repos/awslabs/aws-lambda-powertools-python | closed | Docs: typo for `core/logger`. | documentation triage | ### What were you searching in the docs?
Hello, everyone in the community.
I found a minor typo in `docs/core/logger.md`. :)
### Is this related to an existing documentation section?
https://github.com/awslabs/aws-lambda-powertools-python/blob/develop/docs/core/logger.md
### How can we improve?
```markdown
The ty... | 1.0 | Docs: typo for `core/logger`. - ### What were you searching in the docs?
Hello, everyone in the community.
I found a minor typo in `docs/core/logger.md`. :)
### Is this related to an existing documentation section?
https://github.com/awslabs/aws-lambda-powertools-python/blob/develop/docs/core/logger.md
### How can... | non_process | docs typo for core logger what were you searching in the docs hello everyone in the community i found a minor typo in docs core logger md is this related to an existing documentation section how can we improve markdown the typo is atttributes so we can change it to attributes... | 0 |
21,254 | 11,615,104,561 | IssuesEvent | 2020-02-26 13:43:14 | elastic/beats | https://api.github.com/repos/elastic/beats | opened | [Metricbeat] Reintroduce the size flag to docker.container | Metricbeat Team:Services | As the "size" flag change (https://github.com/elastic/beats/issues/14979) has been reverted in https://github.com/elastic/beats/pull/16600 due to a timeout issue for some docker versions (around 1.13), it's time to reintroduce it again, but in a different way. Some ideas:
1. Consider creating a new metricset which e... | 1.0 | [Metricbeat] Reintroduce the size flag to docker.container - As the "size" flag change (https://github.com/elastic/beats/issues/14979) has been reverted in https://github.com/elastic/beats/pull/16600 due to a timeout issue for some docker versions (around 1.13), it's time to reintroduce it again, but in a different way... | non_process | reintroduce the size flag to docker container as the size flag change has been reverted in due to a timeout issue for some docker versions around it s time to reintroduce it again but in a different way some ideas consider creating a new metricset which enables call with size flag enabled ... | 0 |
17,752 | 23,666,121,178 | IssuesEvent | 2022-08-26 21:09:27 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Process.StandardOutput.Peek() hangs when StandardOutput contains no data. | area-System.Diagnostics.Process untriaged | ### Description
When a process is launched using `System.Diagnostics.Process.Start` which has `RedirectStandardOutput` set to `true` and `Process.StandardOutput.Peek()` is called before any output is returned (or because there is no output), then the method will hang instead of returning `-1`.
### Reproduction Steps
... | 1.0 | Process.StandardOutput.Peek() hangs when StandardOutput contains no data. - ### Description
When a process is launched using `System.Diagnostics.Process.Start` which has `RedirectStandardOutput` set to `true` and `Process.StandardOutput.Peek()` is called before any output is returned (or because there is no output), t... | process | process standardoutput peek hangs when standardoutput contains no data description when a process is launched using system diagnostics process start which has redirectstandardoutput set to true and process standardoutput peek is called before any output is returned or because there is no output t... | 1 |
247,147 | 26,688,694,919 | IssuesEvent | 2023-01-27 01:16:24 | turkdevops/grafana | https://api.github.com/repos/turkdevops/grafana | closed | CVE-2019-0205 (High) detected in github.com/Uber/jaeger-client-go-v2.20.1+incompatible - autoclosed | security vulnerability | ## CVE-2019-0205 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/Uber/jaeger-client-go-v2.20.1+incompatible</b></p></summary>
<p></p>
<p>Library home page: <a href="https://... | True | CVE-2019-0205 (High) detected in github.com/Uber/jaeger-client-go-v2.20.1+incompatible - autoclosed - ## CVE-2019-0205 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>github.com/Uber/ja... | non_process | cve high detected in github com uber jaeger client go incompatible autoclosed cve high severity vulnerability vulnerable library github com uber jaeger client go incompatible library home page a href dependency hierarchy x github com uber jaeger client go ... | 0 |
33,300 | 9,098,500,899 | IssuesEvent | 2019-02-20 00:12:37 | gini/dexter | https://api.github.com/repos/gini/dexter | closed | ID and Secret-id is still required even when the binary has been built with the said parameters | build question | Hey Team,
I tried out Dexter on an Ubuntu 18 host and looks to be id & secret id are still required to get a successful login.
Built the binary with following parameters:
`CLIENT_ID=529839178945-toh9cj642someid7hvu7id9n5.apps.googleusercontent.com CLIENT_SECRET=VzK7vrksome_secret3ts6AfZa6Diz OS=linux make`
... | 1.0 | ID and Secret-id is still required even when the binary has been built with the said parameters - Hey Team,
I tried out Dexter on an Ubuntu 18 host and looks to be id & secret id are still required to get a successful login.
Built the binary with following parameters:
`CLIENT_ID=529839178945-toh9cj642someid7hv... | non_process | id and secret id is still required even when the binary has been built with the said parameters hey team i tried out dexter on an ubuntu host and looks to be id secret id are still required to get a successful login built the binary with following parameters client id apps googleusercontent com c... | 0 |
2,474 | 5,246,673,907 | IssuesEvent | 2017-02-01 10:23:20 | AllenFang/react-bootstrap-table | https://api.github.com/repos/AllenFang/react-bootstrap-table | closed | Click On column text donot trigger onRowSelect | bug duplicate inprocess | I have column with dataFormat returning
`<span className="column-select">{this.props.field}</span>`
and the css as below to make it look like clickable
```
.column-select{
cursor:pointer;
}
.column-select:hover{
color:#9A144A;
}
```
When clicked on this text, onRowSelect is not getting triggered.... | 1.0 | Click On column text donot trigger onRowSelect - I have column with dataFormat returning
`<span className="column-select">{this.props.field}</span>`
and the css as below to make it look like clickable
```
.column-select{
cursor:pointer;
}
.column-select:hover{
color:#9A144A;
}
```
When clicked on... | process | click on column text donot trigger onrowselect i have column with dataformat returning this props field and the css as below to make it look like clickable column select cursor pointer column select hover color when clicked on this text onrowselect is not getting tri... | 1 |
93,375 | 19,186,173,604 | IssuesEvent | 2021-12-05 08:23:00 | feenkcom/gtoolkit | https://api.github.com/repos/feenkcom/gtoolkit | closed | [Coder] Add abstract methods filter | coder | We need a filter to display methods defined as `subclass responsibility` | 1.0 | [Coder] Add abstract methods filter - We need a filter to display methods defined as `subclass responsibility` | non_process | add abstract methods filter we need a filter to display methods defined as subclass responsibility | 0 |
12,667 | 15,037,099,358 | IssuesEvent | 2021-02-02 15:58:30 | retaildevcrews/ngsa | https://api.github.com/repos/retaildevcrews/ngsa | closed | Engineering Fundamentals Checklist - November | EngPrac Process | # Tech Lead's Engineering Fundamentals Checklist
This checklist helps to ensure that our projects meet our Engineering Fundamentals.
## Source Control
- [x] The main branch is locked.
- [x] Merges are done through PRs.
- [x] PRs reference related work items.
- [x] Commit history is consistent and commit mes... | 1.0 | Engineering Fundamentals Checklist - November - # Tech Lead's Engineering Fundamentals Checklist
This checklist helps to ensure that our projects meet our Engineering Fundamentals.
## Source Control
- [x] The main branch is locked.
- [x] Merges are done through PRs.
- [x] PRs reference related work items.
-... | process | engineering fundamentals checklist november tech lead s engineering fundamentals checklist this checklist helps to ensure that our projects meet our engineering fundamentals source control the main branch is locked merges are done through prs prs reference related work items com... | 1 |
15,774 | 19,916,070,004 | IssuesEvent | 2022-01-25 22:52:19 | googleapis/go-sql-spanner | https://api.github.com/repos/googleapis/go-sql-spanner | closed | Dependency Dashboard | type: process | This issue provides visibility into Renovate updates and their statuses. [Learn more](https://docs.renovatebot.com/key-concepts/dashboard/)
## Open
These updates have all been created already. Click a checkbox below to force a retry/rebase of any.
- [ ] <!-- rebase-branch=renovate/google.golang.org-genproto-digest ... | 1.0 | Dependency Dashboard - This issue provides visibility into Renovate updates and their statuses. [Learn more](https://docs.renovatebot.com/key-concepts/dashboard/)
## Open
These updates have all been created already. Click a checkbox below to force a retry/rebase of any.
- [ ] <!-- rebase-branch=renovate/google.gola... | process | dependency dashboard this issue provides visibility into renovate updates and their statuses open these updates have all been created already click a checkbox below to force a retry rebase of any pull pull pull pull click on this checkbox to... | 1 |
675,184 | 23,082,901,423 | IssuesEvent | 2022-07-26 08:50:56 | goharbor/harbor | https://api.github.com/repos/goharbor/harbor | closed | CVE export does not generate log information under /var/log/jobs/ in jobservice container | priority/high target/2.6.0 area/cve-export | **Expected behavior and actual behavior:**
1. docker push x.x.x.x/library/nginx:1.13.12
2. get into the jobservice container shell: `docker exec -it <jobservice_container_id> /bin/bash`
3. within jobservice container shell: `ls /var/log/jobs/` there is no file
4. scan the nginx image, we can see there is a file gen... | 1.0 | CVE export does not generate log information under /var/log/jobs/ in jobservice container - **Expected behavior and actual behavior:**
1. docker push x.x.x.x/library/nginx:1.13.12
2. get into the jobservice container shell: `docker exec -it <jobservice_container_id> /bin/bash`
3. within jobservice container shell: `... | non_process | cve export does not generate log information under var log jobs in jobservice container expected behavior and actual behavior docker push x x x x library nginx get into the jobservice container shell docker exec it bin bash within jobservice container shell ls var log jobs there i... | 0 |
743 | 3,214,327,571 | IssuesEvent | 2015-10-07 00:52:05 | broadinstitute/hellbender | https://api.github.com/repos/broadinstitute/hellbender | closed | Support writing large BAM files in dataflow | Dataflow DataflowPreprocessingPipeline enhancement | Currently tools like `MarkDuplicatesDataflow` use the `SmallBamWriter` to write their output, which makes them unable to handle large BAM outputs. We should switch to using a sharded/large BAM writer, when one materializes. | 1.0 | Support writing large BAM files in dataflow - Currently tools like `MarkDuplicatesDataflow` use the `SmallBamWriter` to write their output, which makes them unable to handle large BAM outputs. We should switch to using a sharded/large BAM writer, when one materializes. | process | support writing large bam files in dataflow currently tools like markduplicatesdataflow use the smallbamwriter to write their output which makes them unable to handle large bam outputs we should switch to using a sharded large bam writer when one materializes | 1 |
29,874 | 13,180,900,845 | IssuesEvent | 2020-08-12 13:32:23 | Ryujinx/Ryujinx-Games-List | https://api.github.com/repos/Ryujinx/Ryujinx-Games-List | opened | Psikyo Shooting Stars Alpha | crash services status-nothing | ## Psikyo Shooting Stars Alpha
#### Game Update Version : 1.0.0
#### Current on `master` : 1.0.5155
Crashes on launch.
```
Application : Unhandled exception caught: Ryujinx.HLE.Exceptions.ServiceNotImplementedException: Ryujinx.HLE.HOS.Services.Account.Acc.IAccountServiceForApplication: 131
```
#### Ha... | 1.0 | Psikyo Shooting Stars Alpha - ## Psikyo Shooting Stars Alpha
#### Game Update Version : 1.0.0
#### Current on `master` : 1.0.5155
Crashes on launch.
```
Application : Unhandled exception caught: Ryujinx.HLE.Exceptions.ServiceNotImplementedException: Ryujinx.HLE.HOS.Services.Account.Acc.IAccountServiceForAp... | non_process | psikyo shooting stars alpha psikyo shooting stars alpha game update version current on master crashes on launch application unhandled exception caught ryujinx hle exceptions servicenotimplementedexception ryujinx hle hos services account acc iaccountserviceforappli... | 0 |
407,913 | 27,636,675,626 | IssuesEvent | 2023-03-10 14:56:42 | scaleway/packer-plugin-scaleway | https://api.github.com/repos/scaleway/packer-plugin-scaleway | opened | Add logs about what could be done once the image is created. | documentation enhancement | Having some messages popping up once the image is created could be helpful to hint at other tools such as terraform or the CLI | 1.0 | Add logs about what could be done once the image is created. - Having some messages popping up once the image is created could be helpful to hint at other tools such as terraform or the CLI | non_process | add logs about what could be done once the image is created having some messages popping up once the image is created could be helpful to hint at other tools such as terraform or the cli | 0 |
15,757 | 5,173,604,413 | IssuesEvent | 2017-01-18 16:28:40 | c2corg/v6_ui | https://api.github.com/repos/c2corg/v6_ui | closed | Use CSS only to style snow conditions for mobile | Association Code Optimization fixed and ready for testing | Instead of having 2 components, one being always hidden while the other is shown, CSS is enough to style the table for mobile. | 1.0 | Use CSS only to style snow conditions for mobile - Instead of having 2 components, one being always hidden while the other is shown, CSS is enough to style the table for mobile. | non_process | use css only to style snow conditions for mobile instead of having components one being always hidden while the other is shown css is enough to style the table for mobile | 0 |
9,019 | 12,126,202,399 | IssuesEvent | 2020-04-22 16:38:53 | qgis/QGIS | https://api.github.com/repos/qgis/QGIS | closed | [Feature thought] Allow to drag input layers into graphical modeler | Feature Request Processing | **Feature description.**
<!-- A clear and concise description of what you want to happen. Ex. QGIS would rock even more if [...] -->
Thanks very much for the excellent open-source project. The graphical modeler is helpful not only to execute as a complex process on a different set of inputs, but also to act as a wo... | 1.0 | [Feature thought] Allow to drag input layers into graphical modeler - **Feature description.**
<!-- A clear and concise description of what you want to happen. Ex. QGIS would rock even more if [...] -->
Thanks very much for the excellent open-source project. The graphical modeler is helpful not only to execute as a... | process | allow to drag input layers into graphical modeler feature description thanks very much for the excellent open source project the graphical modeler is helpful not only to execute as a complex process on a different set of inputs but also to act as a workplace to record test different parameters and inpu... | 1 |
1,935 | 4,763,886,581 | IssuesEvent | 2016-10-25 15:32:42 | openvstorage/alba | https://api.github.com/repos/openvstorage/alba | closed | Claim osd looping and high cpu usage | process_wontfix SRP type_bug | ## Problem description
When I logged into my setup, I found that my root partition was completely full. The culprit was found in /var/log/upstart/alba-asd *.
One of the asd logging was full of:
```
2016-10-19 21:53:42 16108 +0200 - ovs-node1 - 9453/0 - alba/asd - 5366 - info - returning error (Asd_protocol.Protoc... | 1.0 | Claim osd looping and high cpu usage - ## Problem description
When I logged into my setup, I found that my root partition was completely full. The culprit was found in /var/log/upstart/alba-asd *.
One of the asd logging was full of:
```
2016-10-19 21:53:42 16108 +0200 - ovs-node1 - 9453/0 - alba/asd - 5366 - info... | process | claim osd looping and high cpu usage problem description when i logged into my setup i found that my root partition was completely full the culprit was found in var log upstart alba asd one of the asd logging was full of ovs alba asd info returning error asd p... | 1 |
10,109 | 14,546,779,131 | IssuesEvent | 2020-12-15 21:47:55 | NASA-PDS/harvest | https://api.github.com/repos/NASA-PDS/harvest | opened | Add default configuration | enhancement requirement-needed triage-needed | The package should contain a default configuration which comply with following contraints:
1) should work as-is on example data given in pds-registry-app package
2) should contain every possible configuration (especially those needed for demo as described on https://github.com/NASA-PDS/pds-registry-app/issues/107) **... | 1.0 | Add default configuration - The package should contain a default configuration which comply with following contraints:
1) should work as-is on example data given in pds-registry-app package
2) should contain every possible configuration (especially those needed for demo as described on https://github.com/NASA-PDS/pds... | non_process | add default configuration the package should contain a default configuration which comply with following contraints should work as is on example data given in pds registry app package should contain every possible configuration especially those needed for demo as described on commented out | 0 |
20,943 | 27,803,583,682 | IssuesEvent | 2023-03-17 17:45:37 | googleapis/python-bigquery | https://api.github.com/repos/googleapis/python-bigquery | closed | Warning: a recent release failed | api: bigquery type: process | The following release PRs may have failed:
* #351 - The release job failed -- check the build log.
* #238 - The release job is 'autorelease: tagged', but expected 'autorelease: published'. | 1.0 | Warning: a recent release failed - The following release PRs may have failed:
* #351 - The release job failed -- check the build log.
* #238 - The release job is 'autorelease: tagged', but expected 'autorelease: published'. | process | warning a recent release failed the following release prs may have failed the release job failed check the build log the release job is autorelease tagged but expected autorelease published | 1 |
266,662 | 20,160,684,086 | IssuesEvent | 2022-02-09 21:10:27 | ethers-io/ethers.js | https://api.github.com/repos/ethers-io/ethers.js | opened | Filter address format needs more information | documentation | There's an example filter here: https://docs.ethers.io/v5/api/providers/provider/#:~:text=dai.tokens.ethers.eth
```
filter = {
address: "dai.tokens.ethers.eth",
topics: [
utils.id("Transfer(address,address,uint256)")
]
}
provider.on(filter, (log, event) => {
// Emitted whenever a DAI to... | 1.0 | Filter address format needs more information - There's an example filter here: https://docs.ethers.io/v5/api/providers/provider/#:~:text=dai.tokens.ethers.eth
```
filter = {
address: "dai.tokens.ethers.eth",
topics: [
utils.id("Transfer(address,address,uint256)")
]
}
provider.on(filter, (log... | non_process | filter address format needs more information there s an example filter here filter address dai tokens ethers eth topics utils id transfer address address provider on filter log event emitted whenever a dai token transfer occurs dai to... | 0 |
5,004 | 7,836,991,006 | IssuesEvent | 2018-06-18 02:22:39 | vital-software/scala-redox | https://api.github.com/repos/vital-software/scala-redox | closed | Set up CI to perform releases | process: ci stage: in progress type: devops | Similar to what we've done with our other Scala libs, this library should support versioning the project during the CI build of master commits:
```yaml
- name: ":sbt: Release new version"
branches: master
command:
- git checkout -B ${BUILDKITE_BRANCH}
- git branch -u origin/${BUILDKITE_BRA... | 1.0 | Set up CI to perform releases - Similar to what we've done with our other Scala libs, this library should support versioning the project during the CI build of master commits:
```yaml
- name: ":sbt: Release new version"
branches: master
command:
- git checkout -B ${BUILDKITE_BRANCH}
- git ... | process | set up ci to perform releases similar to what we ve done with our other scala libs this library should support versioning the project during the ci build of master commits yaml name sbt release new version branches master command git checkout b buildkite branch git ... | 1 |
18,058 | 24,067,803,293 | IssuesEvent | 2022-09-17 18:51:15 | sancarn/stdVBA | https://api.github.com/repos/sancarn/stdVBA | closed | Fix `stdProcess` structure issue with ProcessEntry32 | lib-stdProcess | See this issue for quotation:
https://github.com/twinbasic/twinbasic/issues/1031#issuecomment-1196277353
Ultimately `pcPriClassBase` should be a `Single` not a `Long` type
```
Private Type PROCESSENTRY32
dwSize As Long
cntUsage As Long
th32ProcessID As Long
'pack1 As Long
th32DefaultH... | 1.0 | Fix `stdProcess` structure issue with ProcessEntry32 - See this issue for quotation:
https://github.com/twinbasic/twinbasic/issues/1031#issuecomment-1196277353
Ultimately `pcPriClassBase` should be a `Single` not a `Long` type
```
Private Type PROCESSENTRY32
dwSize As Long
cntUsage As Long
th32... | process | fix stdprocess structure issue with see this issue for quotation ultimately pcpriclassbase should be a single not a long type private type dwsize as long cntusage as long as long as long as longptr as long cntthreads as long as long ... | 1 |
62,325 | 14,656,481,525 | IssuesEvent | 2020-12-28 13:31:20 | fu1771695yongxie/AdminLTE | https://api.github.com/repos/fu1771695yongxie/AdminLTE | opened | CVE-2018-20822 (Medium) detected in opennmsopennms-source-26.0.0-1 | security vulnerability | ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-26.0.0-1</b></p></summary>
<p>
<p>A Java based fault and performance management system</p>
<p>... | True | CVE-2018-20822 (Medium) detected in opennmsopennms-source-26.0.0-1 - ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-26.0.0-1</b></p></summary>... | non_process | cve medium detected in opennmsopennms source cve medium severity vulnerability vulnerable library opennmsopennms source a java based fault and performance management system library home page a href found in head commit a href found in base branch master ... | 0 |
334,284 | 29,829,775,583 | IssuesEvent | 2023-06-18 05:40:42 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix ndarray.test_numpy_instance_tolist__ | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5301791196/jobs/9596295835"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5301791196/jobs/9596295835"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflo... | 1.0 | Fix ndarray.test_numpy_instance_tolist__ - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5301791196/jobs/9596295835"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5301791196/jobs/9596295835"><img src=https://img.shi... | non_process | fix ndarray test numpy instance tolist numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
170,000 | 26,889,408,568 | IssuesEvent | 2023-02-06 07:36:12 | starplanter93/The_Garden_of_Musicsheet | https://api.github.com/repos/starplanter93/The_Garden_of_Musicsheet | closed | Feat: MainSongSection organism 작성 | Feat Design | ## Description
MainSongSection organism 작성
## Todo
- [x] MainSongSection organism 컴포넌트 구현
- [x] MainSongSection organism 스토리북 등록
## ETC
.
| 1.0 | Feat: MainSongSection organism 작성 - ## Description
MainSongSection organism 작성
## Todo
- [x] MainSongSection organism 컴포넌트 구현
- [x] MainSongSection organism 스토리북 등록
## ETC
.
| non_process | feat mainsongsection organism 작성 description mainsongsection organism 작성 todo mainsongsection organism 컴포넌트 구현 mainsongsection organism 스토리북 등록 etc | 0 |
22,502 | 31,495,988,290 | IssuesEvent | 2023-08-31 02:24:03 | dart-lang/linter | https://api.github.com/repos/dart-lang/linter | closed | linter repo move readiness // planning | type-task process P1 | 🚧 _(This is a living document and a work in progress. Watch this space for emerging details. And do provide feedback!)_ 🚧
## Background
**Costs.** There are costs to having the linter source living externally and separate from the analyzer. In practice, the two are quite tightly coupled and not being able to ... | 1.0 | linter repo move readiness // planning - 🚧 _(This is a living document and a work in progress. Watch this space for emerging details. And do provide feedback!)_ 🚧
## Background
**Costs.** There are costs to having the linter source living externally and separate from the analyzer. In practice, the two are qui... | process | linter repo move readiness planning 🚧 this is a living document and a work in progress watch this space for emerging details and do provide feedback 🚧 background costs there are costs to having the linter source living externally and separate from the analyzer in practice the two are qui... | 1 |
49,290 | 7,488,825,098 | IssuesEvent | 2018-04-06 03:59:03 | CS2103JAN2018-F12-B2/main | https://api.github.com/repos/CS2103JAN2018-F12-B2/main | closed | v1.4 Added new addEvent command and parser method + Updated user and developer guide | type.documentation type.enhancement type.epic | Integrated Google Calendar API
Added addEvent command and parser method
Updated user and developer guide | 1.0 | v1.4 Added new addEvent command and parser method + Updated user and developer guide - Integrated Google Calendar API
Added addEvent command and parser method
Updated user and developer guide | non_process | added new addevent command and parser method updated user and developer guide integrated google calendar api added addevent command and parser method updated user and developer guide | 0 |
21,500 | 29,667,693,988 | IssuesEvent | 2023-06-11 02:00:08 | lizhihao6/get-daily-arxiv-noti | https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti | opened | New submissions for Fri, 9 Jun 23 | event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB | ## Keyword: events
### Spain on Fire: A novel wildfire risk assessment model based on image satellite processing and atmospheric information
- **Authors:** Helena Liz-López, Javier Huertas-Tato, Jorge Pérez-Aracil, Carlos Casanova-Mateo, Julia Sanz-Justo, David Camacho
- **Subjects:** Computer Vision and Pattern Rec... | 2.0 | New submissions for Fri, 9 Jun 23 - ## Keyword: events
### Spain on Fire: A novel wildfire risk assessment model based on image satellite processing and atmospheric information
- **Authors:** Helena Liz-López, Javier Huertas-Tato, Jorge Pérez-Aracil, Carlos Casanova-Mateo, Julia Sanz-Justo, David Camacho
- **Subjec... | process | new submissions for fri jun keyword events spain on fire a novel wildfire risk assessment model based on image satellite processing and atmospheric information authors helena liz lópez javier huertas tato jorge pérez aracil carlos casanova mateo julia sanz justo david camacho subject... | 1 |
180,802 | 21,625,826,689 | IssuesEvent | 2022-05-05 01:54:53 | emilwareus/thimble.mozilla.org | https://api.github.com/repos/emilwareus/thimble.mozilla.org | closed | CVE-2021-21277 (High) detected in angular-expressions-0.2.1.tgz - autoclosed | security vulnerability | ## CVE-2021-21277 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-expressions-0.2.1.tgz</b></p></summary>
<p>Angular expressions as standalone module</p>
<p>Library home page: ... | True | CVE-2021-21277 (High) detected in angular-expressions-0.2.1.tgz - autoclosed - ## CVE-2021-21277 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-expressions-0.2.1.tgz</b></p></s... | non_process | cve high detected in angular expressions tgz autoclosed cve high severity vulnerability vulnerable library angular expressions tgz angular expressions as standalone module library home page a href path to dependency file thimble mozilla org services login webmaker org... | 0 |
627 | 3,091,965,871 | IssuesEvent | 2015-08-26 15:34:27 | e-government-ua/iBP | https://api.github.com/repos/e-government-ua/iBP | opened | Киев МДА - Видача довідки про участь в приватизації житла державного житлового фонду | in process of creating | Описание процесса:
https://docs.google.com/document/d/1an1FVsgcxj6dAYNR-CRsq2gl04ALKEqbbImyWimCnmQ/edit?usp=sharing
https://drive.google.com/file/d/0B7KfbWa-Z0dedTNaaEJvRVVjTVE/view?usp=sharing
| 1.0 | Киев МДА - Видача довідки про участь в приватизації житла державного житлового фонду - Описание процесса:
https://docs.google.com/document/d/1an1FVsgcxj6dAYNR-CRsq2gl04ALKEqbbImyWimCnmQ/edit?usp=sharing
https://drive.google.com/file/d/0B7KfbWa-Z0dedTNaaEJvRVVjTVE/view?usp=sharing
| process | киев мда видача довідки про участь в приватизації житла державного житлового фонду описание процесса | 1 |
312,447 | 9,547,017,684 | IssuesEvent | 2019-05-01 21:42:23 | teambit/bit | https://api.github.com/repos/teambit/bit | closed | Create a component for each file in each sub-directory | area/add priority/medium type/feature | ## Expected Behavior
This should create a component for each of the files in src and in its sub-directories, according to the documentation.
## Actual Behavior
error: one or more of the added components does not contain a main file.
please either use --id to group all added files as one component or use our DSL t... | 1.0 | Create a component for each file in each sub-directory - ## Expected Behavior
This should create a component for each of the files in src and in its sub-directories, according to the documentation.
## Actual Behavior
error: one or more of the added components does not contain a main file.
please either use --id t... | non_process | create a component for each file in each sub directory expected behavior this should create a component for each of the files in src and in its sub directories according to the documentation actual behavior error one or more of the added components does not contain a main file please either use id t... | 0 |
1,210 | 3,715,400,505 | IssuesEvent | 2016-03-03 01:30:53 | e107inc/e107 | https://api.github.com/repos/e107inc/e107 | closed | Possible issue in *_setup.php upgrade_required() method | bug testing required upgrade process 1.x to 2.x | After finishing the forum upgrade procedure, e107 still asks to update the forum.
This is because the upgrade_required() method is not working as intended.
If I change the forum_setup.php file to include this, it will still trigger an update request:
```php
function upgrade_required()
{
return false;
... | 1.0 | Possible issue in *_setup.php upgrade_required() method - After finishing the forum upgrade procedure, e107 still asks to update the forum.
This is because the upgrade_required() method is not working as intended.
If I change the forum_setup.php file to include this, it will still trigger an update request:
`... | process | possible issue in setup php upgrade required method after finishing the forum upgrade procedure still asks to update the forum this is because the upgrade required method is not working as intended if i change the forum setup php file to include this it will still trigger an update request p... | 1 |
21,810 | 30,316,465,397 | IssuesEvent | 2023-07-10 15:54:00 | Parsl/parsl | https://api.github.com/repos/Parsl/parsl | closed | parsl auto weekly release does not update `stable` readthedocs | bug release_process | **Describe the bug**
Read the docs stable docs still point at 848e3a2bf3dc6eb8ed3efb7fd7e849b5c195d34c which is the last release in the non-automatic release series, 1.2.0, in January 2022.
**To Reproduce**
Look at readthedocs
**Expected behavior**
readthedocs versions should align with pypi release versions... | 1.0 | parsl auto weekly release does not update `stable` readthedocs - **Describe the bug**
Read the docs stable docs still point at 848e3a2bf3dc6eb8ed3efb7fd7e849b5c195d34c which is the last release in the non-automatic release series, 1.2.0, in January 2022.
**To Reproduce**
Look at readthedocs
**Expected behavio... | process | parsl auto weekly release does not update stable readthedocs describe the bug read the docs stable docs still point at which is the last release in the non automatic release series in january to reproduce look at readthedocs expected behavior readthedocs versions should align wit... | 1 |
154,319 | 19,712,255,467 | IssuesEvent | 2022-01-13 07:15:53 | Shai-Demo-Org/JS-Demo | https://api.github.com/repos/Shai-Demo-Org/JS-Demo | closed | CVE-2017-16026 (Medium) detected in request-2.36.0.tgz, request-2.67.0.tgz - autoclosed | security vulnerability | ## CVE-2017-16026 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>request-2.36.0.tgz</b>, <b>request-2.67.0.tgz</b></p></summary>
<p>
<details><summary><b>request-2.36.0.tgz</b></p... | True | CVE-2017-16026 (Medium) detected in request-2.36.0.tgz, request-2.67.0.tgz - autoclosed - ## CVE-2017-16026 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>request-2.36.0.tgz</b>, <... | non_process | cve medium detected in request tgz request tgz autoclosed cve medium severity vulnerability vulnerable libraries request tgz request tgz request tgz simplified http request client library home page a href path to dependency file packag... | 0 |
83,715 | 16,358,352,237 | IssuesEvent | 2021-05-14 04:34:05 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | [tool_crash] ProcessException: Process exited abnormally:Command line invocation: /Applications/Xcode.app/Contents/Developer/usr/bin/xcodebuild -listxcodebuild: error: Unable to read project 'Runner.xcodeproj'. Reason: Could not open workspace file at ~/projects/-Mobile/ios/Runner.xcodeproj/project.xcworkspace/conte... | P4 t: xcode tool | ## Command
```
flutter build ios --release
```
## Steps to Reproduce
1. ...
2. ...
3. ...
## Logs
ProcessException: Process exited abnormally:
Command line invocation:
/Applications/Xcode.app/Contents/Developer/usr/bin/xcodebuild -list
xcodebuild: error: Unable to read project 'Runner.xcodeproj'... | 1.0 | [tool_crash] ProcessException: Process exited abnormally:Command line invocation: /Applications/Xcode.app/Contents/Developer/usr/bin/xcodebuild -listxcodebuild: error: Unable to read project 'Runner.xcodeproj'. Reason: Could not open workspace file at ~/projects/-Mobile/ios/Runner.xcodeproj/project.xcworkspace/conte... | non_process | processexception process exited abnormally command line invocation applications xcode app contents developer usr bin xcodebuild listxcodebuild error unable to read project runner xcodeproj reason could not open workspace file at projects mobile ios runner xcodeproj project xcworkspace contents xcworks... | 0 |
53,403 | 28,119,261,132 | IssuesEvent | 2023-03-31 13:08:20 | ARK-Builders/arklib | https://api.github.com/repos/ARK-Builders/arklib | opened | Update method should return complete resources with their details | performance | `ResourceIndex` should pass complete resources with their details during `update`.
Right now, only `ResourceId`s are passed. This causes the library clients to reconstruct details again.
See `fun compute` in `Resource.kt` (https://github.com/ARK-Builders/arklib-android). | True | Update method should return complete resources with their details - `ResourceIndex` should pass complete resources with their details during `update`.
Right now, only `ResourceId`s are passed. This causes the library clients to reconstruct details again.
See `fun compute` in `Resource.kt` (https://github.com/ARK-Bu... | non_process | update method should return complete resources with their details resourceindex should pass complete resources with their details during update right now only resourceid s are passed this causes the library clients to reconstruct details again see fun compute in resource kt | 0 |
214,226 | 16,552,700,186 | IssuesEvent | 2021-05-28 10:23:49 | tweepy/tweepy | https://api.github.com/repos/tweepy/tweepy | closed | Automatically fill in method docstrings (and even new methods/parameters?) from the Twitter API Docs | Documentation RFC | I was inspired by @jackdied's PR: https://github.com/tweepy/tweepy/pull/259, which scrapes the docs, looking for mismatches with allowed_parameters (I don't think it works with the current docs/code).
This would allow Tweepy to be updated quickly whenever Twitter changes their API. It would also save us the work of do... | 1.0 | Automatically fill in method docstrings (and even new methods/parameters?) from the Twitter API Docs - I was inspired by @jackdied's PR: https://github.com/tweepy/tweepy/pull/259, which scrapes the docs, looking for mismatches with allowed_parameters (I don't think it works with the current docs/code).
This would allo... | non_process | automatically fill in method docstrings and even new methods parameters from the twitter api docs i was inspired by jackdied s pr which scrapes the docs looking for mismatches with allowed parameters i don t think it works with the current docs code this would allow tweepy to be updated quickly whenever t... | 0 |
153,466 | 13,505,564,851 | IssuesEvent | 2020-09-13 23:38:03 | flareteam/flare-engine | https://api.github.com/repos/flareteam/flare-engine | closed | no VC++ solution? | documentation | You say this can be built with VC++ but there is no solution included anywhere? | 1.0 | no VC++ solution? - You say this can be built with VC++ but there is no solution included anywhere? | non_process | no vc solution you say this can be built with vc but there is no solution included anywhere | 0 |
15,177 | 18,950,649,479 | IssuesEvent | 2021-11-18 14:52:33 | MicrosoftDocs/azure-devops-docs | https://api.github.com/repos/MicrosoftDocs/azure-devops-docs | closed | Please document which characters are valid in `counter` expressions and how they are treated | doc-enhancement devops/prod devops-cicd-process/tech | This is a follow-up issue for this issue, which seems to be muted because it's closed.
https://github.com/MicrosoftDocs/azure-devops-docs/issues/11323#issuecomment-946823878
The fix for the issue above just said that some unspecified set of special characters cannot be used, but didn't specify explicitly the vali... | 1.0 | Please document which characters are valid in `counter` expressions and how they are treated - This is a follow-up issue for this issue, which seems to be muted because it's closed.
https://github.com/MicrosoftDocs/azure-devops-docs/issues/11323#issuecomment-946823878
The fix for the issue above just said that so... | process | please document which characters are valid in counter expressions and how they are treated this is a follow up issue for this issue which seems to be muted because it s closed the fix for the issue above just said that some unspecified set of special characters cannot be used but didn t specify explicitl... | 1 |
54,352 | 13,616,058,125 | IssuesEvent | 2020-09-23 15:10:16 | SAP/fundamental-styles | https://api.github.com/repos/SAP/fundamental-styles | closed | Defect Hunting Sep23 | Defect Hunting | - [ ] Cozy Side Navigation Icon Active Underline
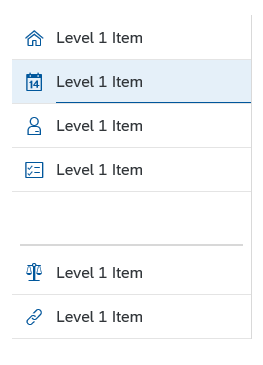
- [ ] Complex Cozy Side Nav focus

- [ ] Complex Cozy Side Nav focus
 but for pg13
- [x] Update our [pgx image](https://github.com/timescale/timescale-analytics/blob/7f44eeeafe6be0... | 1.0 | Tracking Issue: CI/CD setup - Basic tasks needed for CI/CD:
- [x] Test PG 13 Job: just like [the pg12 job](https://github.com/timescale/timescale-analytics/blob/7f44eeeafe6be0df64aaf92b3bdc19c1e50566d0/.github/workflows/ci.yml#L12-L47) but for pg13
- [x] Update our [pgx image](https://github.com/timescale/timescale... | non_process | tracking issue ci cd setup basic tasks needed for ci cd test pg job just like but for update our to also include timescaledb in the relevant postgres instances and create dockerfile for building our image set up automatic builds pushes for our image stretch only run t... | 0 |
17,528 | 23,341,021,216 | IssuesEvent | 2022-08-09 14:02:35 | pystatgen/sgkit | https://api.github.com/repos/pystatgen/sgkit | closed | Wheels test on macOS on Python 3.10 fails | process + tools | There is no `cyvcf2` wheel for this combination, so we need to fix that. See https://github.com/brentp/cyvcf2/issues/245
Failure: https://github.com/pystatgen/sgkit/runs/7634527135?check_suite_focus=true | 1.0 | Wheels test on macOS on Python 3.10 fails - There is no `cyvcf2` wheel for this combination, so we need to fix that. See https://github.com/brentp/cyvcf2/issues/245
Failure: https://github.com/pystatgen/sgkit/runs/7634527135?check_suite_focus=true | process | wheels test on macos on python fails there is no wheel for this combination so we need to fix that see failure | 1 |
200,540 | 15,111,883,716 | IssuesEvent | 2021-02-08 21:03:20 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Upgrade Locust to 1.4.1 | Epic QA VSP-testing-team testing | ## User Story
As a VFS team engineer, I need an updated version of Locust in order to perform load testing on my endpoints in vets-api. Python 2.X is being sunset and it is becoming more and more difficult to maintain an environment that supports the very old version of Locust that is currently prescribed in the devop... | 2.0 | Upgrade Locust to 1.4.1 - ## User Story
As a VFS team engineer, I need an updated version of Locust in order to perform load testing on my endpoints in vets-api. Python 2.X is being sunset and it is becoming more and more difficult to maintain an environment that supports the very old version of Locust that is current... | non_process | upgrade locust to user story as a vfs team engineer i need an updated version of locust in order to perform load testing on my endpoints in vets api python x is being sunset and it is becoming more and more difficult to maintain an environment that supports the very old version of locust that is current... | 0 |
157,793 | 19,984,268,399 | IssuesEvent | 2022-01-30 12:08:03 | davidjj58/Home-assignment | https://api.github.com/repos/davidjj58/Home-assignment | opened | CVE-2019-17267 (High) detected in jackson-databind-2.8.7.jar | security vulnerability | ## CVE-2019-17267 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.7.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-17267 (High) detected in jackson-databind-2.8.7.jar - ## CVE-2019-17267 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.7.jar</b></p></summary>
<p>General... | non_process | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable l... | 0 |
11,547 | 14,432,059,615 | IssuesEvent | 2020-12-07 00:42:31 | thegooddocsproject/templates | https://api.github.com/repos/thegooddocsproject/templates | closed | Align Contributors' Guides | improve process | **Describe the bug**
We have several locations with Contributors' Guides, let's align them in the correct place:
* `.github` directory: This is the correct place, so that the repo shows that we have a Contributors' Guide in the Insights tab. However, doing a PR to this directory is a little tricky.
* Templates rep... | 1.0 | Align Contributors' Guides - **Describe the bug**
We have several locations with Contributors' Guides, let's align them in the correct place:
* `.github` directory: This is the correct place, so that the repo shows that we have a Contributors' Guide in the Insights tab. However, doing a PR to this directory is a li... | process | align contributors guides describe the bug we have several locations with contributors guides let s align them in the correct place github directory this is the correct place so that the repo shows that we have a contributors guide in the insights tab however doing a pr to this directory is a li... | 1 |
17,233 | 22,947,299,987 | IssuesEvent | 2022-07-19 02:12:26 | streamnative/flink | https://api.github.com/repos/streamnative/flink | closed | [BUG][FLINK-27881] The key(String) in PulsarMessageBuilder returns null | compute/data-processing type/bug | This is a minor typo bug in PulsarMessageBuilder. The PulsarMessageBuild.key(String) always return null, which might cause NPE in the later call. | 1.0 | [BUG][FLINK-27881] The key(String) in PulsarMessageBuilder returns null - This is a minor typo bug in PulsarMessageBuilder. The PulsarMessageBuild.key(String) always return null, which might cause NPE in the later call. | process | the key string in pulsarmessagebuilder returns null this is a minor typo bug in pulsarmessagebuilder the pulsarmessagebuild key string always return null which might cause npe in the later call | 1 |
81,326 | 23,441,069,106 | IssuesEvent | 2022-08-15 14:55:40 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | Build 20 for 8.4 with status FAILURE | automation ci-reported Team:Elastic-Agent-Data-Plane build-failures |
## :broken_heart: Build Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%2Fbeats%2F8.4/detail/8.4/20//pipeline) ... | 1.0 | Build 20 for 8.4 with status FAILURE -
## :broken_heart: Build Failed
<!-- BUILD BADGES-->
> _the below badges are clickable and redirect to their specific view in the CI or DOCS_
[](https://beats-ci.elastic.co/blue/organizations/jenkins/Beats%... | non_process | build for with status failure broken heart build failed the below badges are clickable and redirect to their specific view in the ci or docs expand to view the summary build stats start time duration min sec test stats ... | 0 |
35,383 | 7,941,116,666 | IssuesEvent | 2018-07-10 02:33:46 | tsuruclient/tsuru | https://api.github.com/repos/tsuruclient/tsuru | closed | マルチスレッド化 | code problem enhancement specification | こんにちは。マルチスレッド化です。Web Worker APIが存在し、マルチスレッドにできるので、[Thread.js](https://threadjs.deep-rain.com/)等を使うか、あるいはマルチスレッド化したい部分をElectron(Main Process)側で処理をするかのどちらかにしたい。
参考資料
* https://scrapbox.io/shokai/WebWorker%E3%82%92production%E3%81%A7%E4%BD%BF%E3%81%A3%E3%81%A6%E3%82%8B%E8%A9%B1
* https://www.deep-rain.com/programming... | 1.0 | マルチスレッド化 - こんにちは。マルチスレッド化です。Web Worker APIが存在し、マルチスレッドにできるので、[Thread.js](https://threadjs.deep-rain.com/)等を使うか、あるいはマルチスレッド化したい部分をElectron(Main Process)側で処理をするかのどちらかにしたい。
参考資料
* https://scrapbox.io/shokai/WebWorker%E3%82%92production%E3%81%A7%E4%BD%BF%E3%81%A3%E3%81%A6%E3%82%8B%E8%A9%B1
* https://www.deep-rain.com/... | non_process | マルチスレッド化 こんにちは。マルチスレッド化です。web worker apiが存在し、マルチスレッドにできるので、 process 側で処理をするかのどちらかにしたい。 参考資料 | 0 |
6,792 | 9,923,200,992 | IssuesEvent | 2019-07-01 06:29:14 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [Tabs] Verify/fix layout for safeAreaInsets in Tab Bar View | Client-blocking [Tabs] type:Process | This was filed as an internal issue. If you are a Googler, please visit [b/136175944](http://b/136175944) for more details.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/136175944](http://b/136175944) | 1.0 | [Tabs] Verify/fix layout for safeAreaInsets in Tab Bar View - This was filed as an internal issue. If you are a Googler, please visit [b/136175944](http://b/136175944) for more details.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/136175944](http://b/136175... | process | verify fix layout for safeareainsets in tab bar view this was filed as an internal issue if you are a googler please visit for more details internal data associated internal bug | 1 |
4,101 | 7,049,804,408 | IssuesEvent | 2018-01-03 00:36:13 | shirou/gopsutil | https://api.github.com/repos/shirou/gopsutil | closed | cpu#TimesStat should be more precise, may be time.Duration | os:windows package:process | I need more precise time process#Times() return, second is too rough. time.Duration may be a better choice. | 1.0 | cpu#TimesStat should be more precise, may be time.Duration - I need more precise time process#Times() return, second is too rough. time.Duration may be a better choice. | process | cpu timesstat should be more precise may be time duration i need more precise time process times return second is too rough time duration may be a better choice | 1 |
20,462 | 27,128,770,449 | IssuesEvent | 2023-02-16 08:11:32 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | closed | Cleanup flags and code paths for legacy Python version api and semantics | P3 type: process team-Rules-Python stale | Tracking bug for deleting `--incompatible_remove_old_python_version_api`, `--incompatible_allow_python_version_transitions`, and the code supporting these flags.
The flags are being flipped in Bazel 0.25. Google still uses these flags internally, but we expect to be migrated for them soon as well, so this might happ... | 1.0 | Cleanup flags and code paths for legacy Python version api and semantics - Tracking bug for deleting `--incompatible_remove_old_python_version_api`, `--incompatible_allow_python_version_transitions`, and the code supporting these flags.
The flags are being flipped in Bazel 0.25. Google still uses these flags interna... | process | cleanup flags and code paths for legacy python version api and semantics tracking bug for deleting incompatible remove old python version api incompatible allow python version transitions and the code supporting these flags the flags are being flipped in bazel google still uses these flags internal... | 1 |
12,200 | 14,742,534,027 | IssuesEvent | 2021-01-07 12:27:47 | kdjstudios/SABillingGitlab | https://api.github.com/repos/kdjstudios/SABillingGitlab | closed | CC Payments Down | anc-process anp-1.5 ant-support has attachment | In GitLab by @kdjstudios on Apr 30, 2019, 12:42
**Submitted by:** Multiple
**Helpdesk:**
* http://www.servicedesk.answernet.com/profiles/ticket/2019-04-30-29178
* http://www.servicedesk.answernet.com/profiles/ticket/2019-04-30-53841
**Server:** Internal
**Client/Site:** Multiple
**Account:** Multiple
**Issue:** ... | 1.0 | CC Payments Down - In GitLab by @kdjstudios on Apr 30, 2019, 12:42
**Submitted by:** Multiple
**Helpdesk:**
* http://www.servicedesk.answernet.com/profiles/ticket/2019-04-30-29178
* http://www.servicedesk.answernet.com/profiles/ticket/2019-04-30-53841
**Server:** Internal
**Client/Site:** Multiple
**Account:** Mu... | process | cc payments down in gitlab by kdjstudios on apr submitted by multiple helpdesk server internal client site multiple account multiple issue david wrote we have been trying to process some credit card payments through sab with no luck i have had my agm att... | 1 |
10,764 | 4,821,341,272 | IssuesEvent | 2016-11-05 08:54:34 | GoldenCheetah/GoldenCheetah | https://api.github.com/repos/GoldenCheetah/GoldenCheetah | closed | DSO missing from command line | build error not a bug | Debian 8.6 x64
$ git clone ...
$ make clean; qmake; make;
....
`g++ -m64 -Wl,-O1 -Wl,-rpath-link,/usr/lib/x86_64-linux-gnu -o GoldenCheetah qtsoap.o QTFullScreen.o qtsegmentcontrol.o VideoWindow.o TwitterDialog.o Dropbox.o GoogleDrive.o MonarkController.o MonarkConnection.o Kettler.o KettlerController.o Kettler... | 1.0 | DSO missing from command line - Debian 8.6 x64
$ git clone ...
$ make clean; qmake; make;
....
`g++ -m64 -Wl,-O1 -Wl,-rpath-link,/usr/lib/x86_64-linux-gnu -o GoldenCheetah qtsoap.o QTFullScreen.o qtsegmentcontrol.o VideoWindow.o TwitterDialog.o Dropbox.o GoogleDrive.o MonarkController.o MonarkConnection.o Kettl... | non_process | dso missing from command line debian git clone make clean qmake make g wl wl rpath link usr lib linux gnu o goldencheetah qtsoap o qtfullscreen o qtsegmentcontrol o videowindow o twitterdialog o dropbox o googledrive o monarkcontroller o monarkconnection o kettler o ket... | 0 |
41,712 | 6,927,926,152 | IssuesEvent | 2017-12-01 01:28:35 | golang/go | https://api.github.com/repos/golang/go | closed | cmd/go: 'go test' output-hiding behavior is under-documented | Documentation | Using 1.9rc1 / amd64, but it's not particular to any version.
The fact that `go test` hides output from passing tests if you give it a package selector argument is surprising and is not properly documented.
```
$ cat x_test.go
package main
import (
"fmt"
"testing"
)
func TestFoo(t *test... | 1.0 | cmd/go: 'go test' output-hiding behavior is under-documented - Using 1.9rc1 / amd64, but it's not particular to any version.
The fact that `go test` hides output from passing tests if you give it a package selector argument is surprising and is not properly documented.
```
$ cat x_test.go
package main
import... | non_process | cmd go go test output hiding behavior is under documented using but it s not particular to any version the fact that go test hides output from passing tests if you give it a package selector argument is surprising and is not properly documented cat x test go package main import ... | 0 |
22,485 | 31,395,274,248 | IssuesEvent | 2023-08-26 21:21:47 | lynnandtonic/nestflix.fun | https://api.github.com/repos/lynnandtonic/nestflix.fun | closed | Add Loch Henry: Truth Will Out from "Black Mirror" (Screenshots, Thumbnail, and Title Card added) | suggested title in process | Please add as much of the following info as you can:
Title: Loch Henry: Truth Will Out
Type (film/tv show): film - documentary (true crime)
Film or show in which it appears: Black Mirror
Is the parent film/show streaming anywhere? Yes - Netflix
About when in the parent film/show does it appear? Ep. 6x02... | 1.0 | Add Loch Henry: Truth Will Out from "Black Mirror" (Screenshots, Thumbnail, and Title Card added) - Please add as much of the following info as you can:
Title: Loch Henry: Truth Will Out
Type (film/tv show): film - documentary (true crime)
Film or show in which it appears: Black Mirror
Is the parent film/s... | process | add loch henry truth will out from black mirror screenshots thumbnail and title card added please add as much of the following info as you can title loch henry truth will out type film tv show film documentary true crime film or show in which it appears black mirror is the parent film s... | 1 |
21,281 | 28,451,876,511 | IssuesEvent | 2023-04-17 02:00:07 | lizhihao6/get-daily-arxiv-noti | https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti | opened | New submissions for Mon, 17 Apr 23 | event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB | ## Keyword: events
### Self-Supervised Scene Dynamic Recovery from Rolling Shutter Images and Events
- **Authors:** Yangguang Wang, Xiang Zhang, Mingyuan Lin, Lei Yu, Boxin Shi, Wen Yang, Gui-Song Xia
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2304.06930
... | 2.0 | New submissions for Mon, 17 Apr 23 - ## Keyword: events
### Self-Supervised Scene Dynamic Recovery from Rolling Shutter Images and Events
- **Authors:** Yangguang Wang, Xiang Zhang, Mingyuan Lin, Lei Yu, Boxin Shi, Wen Yang, Gui-Song Xia
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link... | process | new submissions for mon apr keyword events self supervised scene dynamic recovery from rolling shutter images and events authors yangguang wang xiang zhang mingyuan lin lei yu boxin shi wen yang gui song xia subjects computer vision and pattern recognition cs cv arxiv link ... | 1 |
15,515 | 19,703,267,211 | IssuesEvent | 2022-01-12 18:52:20 | googleapis/java-debugger-client | https://api.github.com/repos/googleapis/java-debugger-client | opened | Your .repo-metadata.json file has a problem 🤒 | type: process repo-metadata: lint | You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'debugger-client' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automat... | 1.0 | Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'debugger-client' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can cl... | process | your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 release level must be equal to one of the allowed values in repo metadata json api shortname debugger client invalid in repo metadata json ☝️ once you correct these problems you can cl... | 1 |
19,549 | 6,735,133,254 | IssuesEvent | 2017-10-18 20:36:10 | mmatyas/pegasus-frontend | https://api.github.com/repos/mmatyas/pegasus-frontend | closed | Generate deployment packages | build | - [x] Create a simple TAR package for Linux
- ~(fails for the same reason, as it also uses the same tool)~
- fixed by static builds
- [x] Create a simple ZIP package for Windows
- [ ] Add AppImage support
- previously: *outdated Travis, Docker complications, missing libs: too much hacking. Works offline thou... | 1.0 | Generate deployment packages - - [x] Create a simple TAR package for Linux
- ~(fails for the same reason, as it also uses the same tool)~
- fixed by static builds
- [x] Create a simple ZIP package for Windows
- [ ] Add AppImage support
- previously: *outdated Travis, Docker complications, missing libs: too m... | non_process | generate deployment packages create a simple tar package for linux fails for the same reason as it also uses the same tool fixed by static builds create a simple zip package for windows add appimage support previously outdated travis docker complications missing libs too much ha... | 0 |
208,558 | 23,616,553,723 | IssuesEvent | 2022-08-24 16:21:22 | kydell/onboarding-training | https://api.github.com/repos/kydell/onboarding-training | opened | spring-boot-starter-web-2.1.3.RELEASE.jar: 27 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-web-2.1.3.RELEASE.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable... | True | spring-boot-starter-web-2.1.3.RELEASE.jar: 27 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-web-2.1.3.RELEASE.jar</b></p></summary>
<p></p>
<p>Path... | non_process | spring boot starter web release jar vulnerabilities highest severity is vulnerable library spring boot starter web release jar path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files o... | 0 |
630 | 2,798,583,331 | IssuesEvent | 2015-05-12 19:23:24 | new-day-international/reddit | https://api.github.com/repos/new-day-international/reddit | closed | Investigate using fewer cloud search instances | Infrastructure | From @inflector
> Attached please find the usage report for September. It looks like we've got stuff firing off every hour uploading and somehow querying CloudSearch, what might be causing this? Are we getting spiders doing searches?
> Also, we seem to be getting separate charges for each of the different dev, t... | 1.0 | Investigate using fewer cloud search instances - From @inflector
> Attached please find the usage report for September. It looks like we've got stuff firing off every hour uploading and somehow querying CloudSearch, what might be causing this? Are we getting spiders doing searches?
> Also, we seem to be getting ... | non_process | investigate using fewer cloud search instances from inflector attached please find the usage report for september it looks like we ve got stuff firing off every hour uploading and somehow querying cloudsearch what might be causing this are we getting spiders doing searches also we seem to be getting ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.