Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
10,022
| 13,043,926,124
|
IssuesEvent
|
2020-07-29 03:04:21
|
tikv/tikv
|
https://api.github.com/repos/tikv/tikv
|
closed
|
UCP: Migrate scalar function `Locate2ArgsUTF8` from TiDB
|
challenge-program-2 component/coprocessor difficulty/easy sig/coprocessor
|
## Description
Port the scalar function `Locate2ArgsUTF8` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @andylokandy
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
|
2.0
|
UCP: Migrate scalar function `Locate2ArgsUTF8` from TiDB -
## Description
Port the scalar function `Locate2ArgsUTF8` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @andylokandy
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
|
process
|
ucp migrate scalar function from tidb description port the scalar function from tidb to coprocessor score mentor s andylokandy recommended skills rust programming learning materials already implemented expressions ported from tidb
| 1
|
2,185
| 5,036,744,813
|
IssuesEvent
|
2016-12-17 08:03:02
|
jlm2017/jlm-video-subtitles
|
https://api.github.com/repos/jlm2017/jlm-video-subtitles
|
closed
|
[subtitles] [eng] Revue de la semaine n°10
|
Language: English Process: [2] Ready for review (1) Process: [6] Approved
|
# Video title
RDLS10 - MATTEO RENZI, EUROPE, PAUVRETÉ, ZONES MORTES DANS LES OCÉANS, SNOWDEN
# URL
https://www.youtube.com/watch?v=DwvM9oV3v3I
# Youtube subtitle language
English
# Duration
25:16
# URL subtitles
https://www.youtube.com/timedtext_editor?ref=player&action_mde_edit_form=1&ui=hd&v=DwvM9oV3v3I&tab=captions&bl=vmp&lang=en
|
2.0
|
[subtitles] [eng] Revue de la semaine n°10 - # Video title
RDLS10 - MATTEO RENZI, EUROPE, PAUVRETÉ, ZONES MORTES DANS LES OCÉANS, SNOWDEN
# URL
https://www.youtube.com/watch?v=DwvM9oV3v3I
# Youtube subtitle language
English
# Duration
25:16
# URL subtitles
https://www.youtube.com/timedtext_editor?ref=player&action_mde_edit_form=1&ui=hd&v=DwvM9oV3v3I&tab=captions&bl=vmp&lang=en
|
process
|
revue de la semaine n° video title matteo renzi europe pauvreté zones mortes dans les océans snowden url youtube subtitle language english duration url subtitles
| 1
|
19,075
| 25,109,935,159
|
IssuesEvent
|
2022-11-08 19:37:36
|
microsoft/vscode
|
https://api.github.com/repos/microsoft/vscode
|
closed
|
vscode multi-root workspace: open terminal asks me to choose cwd even if both have been set to same place
|
bug help wanted terminal-process
|
Issue Type: <b>Feature Request</b>
Not sure if this is intended behaviour, but I have two root folders in my workspace, I've overriden one to use the other as the cwd, yet I still get asked which one to use when I open a new terminal:

Please can you change this so that when cwds are identical there is no prompt?
VS Code version: Code 1.68.1 (30d9c6cd9483b2cc586687151bcbcd635f373630, 2022-06-15T02:58:26.441Z)
OS version: Linux x64 5.10.110-15808-ge5740beba59b
Restricted Mode: No
<!-- generated by issue reporter -->
|
1.0
|
vscode multi-root workspace: open terminal asks me to choose cwd even if both have been set to same place - Issue Type: <b>Feature Request</b>
Not sure if this is intended behaviour, but I have two root folders in my workspace, I've overriden one to use the other as the cwd, yet I still get asked which one to use when I open a new terminal:

Please can you change this so that when cwds are identical there is no prompt?
VS Code version: Code 1.68.1 (30d9c6cd9483b2cc586687151bcbcd635f373630, 2022-06-15T02:58:26.441Z)
OS version: Linux x64 5.10.110-15808-ge5740beba59b
Restricted Mode: No
<!-- generated by issue reporter -->
|
process
|
vscode multi root workspace open terminal asks me to choose cwd even if both have been set to same place issue type feature request not sure if this is intended behaviour but i have two root folders in my workspace i ve overriden one to use the other as the cwd yet i still get asked which one to use when i open a new terminal please can you change this so that when cwds are identical there is no prompt vs code version code os version linux restricted mode no
| 1
|
163,348
| 25,797,182,907
|
IssuesEvent
|
2022-12-10 17:28:21
|
boostcampwm-2022/web07-zokboo.com
|
https://api.github.com/repos/boostcampwm-2022/web07-zokboo.com
|
closed
|
문제집 검색 후 문제집 상세보기 페이지
|
🧩 frontend 🎨 design
|
- [x] 구조잡기 완료
- [x] 제목, 설명, 작성자 등등 기본정보 보여주기
- [x] 문제 보여주기
- [ ] #207
- [ ] 시험보러가기 버튼
- 문제집 정보
- 문제 목록
|
1.0
|
문제집 검색 후 문제집 상세보기 페이지 - - [x] 구조잡기 완료
- [x] 제목, 설명, 작성자 등등 기본정보 보여주기
- [x] 문제 보여주기
- [ ] #207
- [ ] 시험보러가기 버튼
- 문제집 정보
- 문제 목록
|
non_process
|
문제집 검색 후 문제집 상세보기 페이지 구조잡기 완료 제목 설명 작성자 등등 기본정보 보여주기 문제 보여주기 시험보러가기 버튼 문제집 정보 문제 목록
| 0
|
95,481
| 8,559,886,029
|
IssuesEvent
|
2018-11-08 22:46:00
|
FreeUKGen/MyopicVicar
|
https://api.github.com/repos/FreeUKGen/MyopicVicar
|
closed
|
Physical File Processing - Processor Stopping unexpectedly with very little Error info
|
Ready for Deployment testing
|
The CSV processor stopped processing files for approx 12 hours or so, starting between 10am & 11am on Sept 28th. I have downloaded a copy of the passenger.log file from that day, if required.
The issue has resolved itself, but there was very little feedback from the logs, and nothing shown in errbit, to notify of what the issue was, although we suspect it was caused by a problem file that was uploaded.
**Action**: Determine the root cause of the issue to prevent re-occurrence, if the cause can be found in the passenger log file errors.
needs #1621
|
1.0
|
Physical File Processing - Processor Stopping unexpectedly with very little Error info - The CSV processor stopped processing files for approx 12 hours or so, starting between 10am & 11am on Sept 28th. I have downloaded a copy of the passenger.log file from that day, if required.
The issue has resolved itself, but there was very little feedback from the logs, and nothing shown in errbit, to notify of what the issue was, although we suspect it was caused by a problem file that was uploaded.
**Action**: Determine the root cause of the issue to prevent re-occurrence, if the cause can be found in the passenger log file errors.
needs #1621
|
non_process
|
physical file processing processor stopping unexpectedly with very little error info the csv processor stopped processing files for approx hours or so starting between on sept i have downloaded a copy of the passenger log file from that day if required the issue has resolved itself but there was very little feedback from the logs and nothing shown in errbit to notify of what the issue was although we suspect it was caused by a problem file that was uploaded action determine the root cause of the issue to prevent re occurrence if the cause can be found in the passenger log file errors needs
| 0
|
21,403
| 29,326,579,325
|
IssuesEvent
|
2023-05-26 00:05:54
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
[MLv2] [Bug] Metadata calculation not working correctly for aggregation that contains a `:metric` clause
|
Type:Bug .Backend .metabase-lib .Team/QueryProcessor :hammer_and_wrench:
|
Failing test in `metabase.query-processor-test.case-test`
```clj
Can we use case in metric
with temporary :metabase.models.metric/Metric with attributes
{:creator_id 2,
:definition {:source-table 32407, :aggregation [:sum [:case [[[:< [:field 133191 nil] 4] [:field 133191 nil]]]]]},
:description "Lookin' for a blueberry",
:name "Toucans in the rainforest",
:table_id 32407}
legacy query =
{:database 2368, :type :query, :query {:aggregation [[:metric 316]], :source-table 32407}}
pMBQL =
{:lib/type :mbql/query,
:database 2368,
:type :pipeline,
:stages
[{:lib/type :mbql.stage/mbql,
:source-table 32407,
:aggregation [[:metric {:lib/uuid "6a455487-6033-4f35-b159-91558080ac1b"} 316]]}]}
Failed to calculated metadata for query
{:via
[{:type clojure.lang.ExceptionInfo,
:message
"[\"Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown\"]",
:data
{:type :malli.core/invalid-output,
:data
{:output :metabase.lib.schema.common/base-type,
:value :metabase.lib.schema.expression/type.unknown,
:args
[{:lib/type :mbql/query,
:lib/metadata
(metabase.lib.metadata.cached-provider/cached-metadata-provider
(metabase.lib.metadata.jvm/->UncachedApplicationDatabaseMetadataProvider 2368)),
:database 2368,
:type :pipeline,
:stages
[{:lib/type :mbql.stage/mbql,
:source-table 32407,
:aggregation [[:metric #:lib{:uuid "06174580-70bd-474a-b167-95a9ef3899cc"} 318]]}]}
-1
[:case
#:lib{:uuid "01480a56-78ee-4b7f-9407-23a6493cdd7d"}
[[[:<
#:lib{:uuid "e078b90f-de46-4dbb-9903-930c3891c375"}
[:field #:lib{:uuid "3454c908-194a-447d-af44-cbedee1ba44d"} 133191]
4]
[:field #:lib{:uuid "4d3ae622-03b7-40f6-af20-1ae413065640"} 133191]]]]],
:schema [:=> [:cat :metabase.lib.schema/query :int :any] :metabase.lib.schema.common/base-type],
:fn-name lib.metadata.calculation/type-of},
:humanized
["Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown"],
:link
"https://malli.io?schema=%3Ametabase.lib.schema.common%2Fbase-type%0A&value=%3Ametabase.lib.schema.expression%2Ftype.unknown%0A"},
:at [metabase.util.malli$explain_fn_fail_BANG_ invokeStatic "malli.cljc" 58]}],
:trace
[[metabase.util.malli$explain_fn_fail_BANG_ invokeStatic "malli.cljc" 58]
[metabase.util.malli$explain_fn_fail_BANG_ invoke "malli.cljc" 50]
[malli.instrument$_strument_BANG_$fn__30546$fn__30547 invoke "instrument.clj" 23]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2529]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metadata.calculation$eval32823$fn__32825 invoke "calculation.cljc" 155]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32809$type_of__32810 invoke "calculation.cljc" 141]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metric$eval75577$fn__75578 invoke "metric.cljc" 34]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32809$type_of__32810 invoke "calculation.cljc" 141]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metric$eval75586$fn__75588 invoke "metric.cljc" 40]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32809$type_of__32810 invoke "calculation.cljc" 141]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metadata.calculation$eval32843$fn__32844 invoke "calculation.cljc" 173]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 197]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.aggregation$eval73541$aggregations__73542$fn__73543 invoke "aggregation.cljc" 217]
[clojure.core$map_indexed$mapi__8638$fn__8639 invoke "core.clj" 7376]
[clojure.lang.LazySeq sval "LazySeq.java" 42]
[clojure.lang.LazySeq seq "LazySeq.java" 51]
[clojure.lang.RT seq "RT.java" 535]
[clojure.core$seq__5467 invokeStatic "core.clj" 139]
[clojure.core.protocols$seq_reduce invokeStatic "protocols.clj" 24]
[clojure.core.protocols$fn__8236 invokeStatic "protocols.clj" 75]
[clojure.core.protocols$fn__8236 invoke "protocols.clj" 75]
[clojure.core.protocols$fn__8178$G__8173__8191 invoke "protocols.clj" 13]
[clojure.core$reduce invokeStatic "core.clj" 6886]
[clojure.core$reduce invoke "core.clj" 6868]
[malli.core$_collection_schema$reify$reify__28325$fn__28326 invoke "core.cljc" 1194]
[malli.core$_maybe_schema$reify$reify__28467$fn__28468 invoke "core.cljc" 1466]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2528]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 421]
[metabase.lib.stage$eval75811$aggregations_columns__75812 invoke "stage.cljc" 107]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.stage$eval75861$breakout_ags_fields_columns__75862$fn__75863 invoke "stage.cljc" 139]
[clojure.core$map$fn__5931$fn__5932 invoke "core.clj" 2759]
[clojure.lang.PersistentVector reduce "PersistentVector.java" 343]
[clojure.core$transduce invokeStatic "core.clj" 6946]
[clojure.core$into invokeStatic "core.clj" 6962]
[clojure.core$into invoke "core.clj" 6950]
[metabase.lib.stage$eval75861$breakout_ags_fields_columns__75862 invoke "stage.cljc" 137]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.stage$eval76011$stage_metadata__76012 invoke "stage.cljc" 315]
[clojure.lang.AFn applyToHelper "AFn.java" 156]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn invoke "RestFn.java" 421]
[metabase.lib.stage$eval76022$fn__76023 invoke "stage.cljc" 322]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 197]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.query$eval33071$fn__33072 invoke "query.cljc" 66]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 197]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 191]
[clojure.lang.AFn applyToHelper "AFn.java" 154]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 408]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata$fn__142634$fn__142635 invoke "test_mlv2.clj" 97]
[metabase.query_processor_test.test_mlv2$do_with_pMBQL_query_testing_context invokeStatic "test_mlv2.clj" 24]
[metabase.query_processor_test.test_mlv2$do_with_pMBQL_query_testing_context invoke "test_mlv2.clj" 22]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata$fn__142634 invoke "test_mlv2.clj" 91]
[metabase.query_processor_test.test_mlv2$do_with_legacy_query_testing_context invokeStatic "test_mlv2.clj" 20]
[metabase.query_processor_test.test_mlv2$do_with_legacy_query_testing_context invoke "test_mlv2.clj" 18]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata invokeStatic "test_mlv2.clj" 83]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata invoke "test_mlv2.clj" 80]
[metabase.query_processor_test.test_mlv2$post_processing_middleware$fn__142666 invoke "test_mlv2.clj" 127]
[metabase.query_processor.middleware.annotate$add_column_info$add_column_info_rff_STAR___88584
invoke
"annotate.clj"
711]
[metabase.query_processor.middleware.mbql_to_native$mbql__GT_native$fn__98111$fn__98112
invoke
"mbql_to_native.clj"
27]
[metabase_enterprise.advanced_permissions.query_processor.middleware.permissions$check_download_permissions$fn__100598$fn__100599
invoke
"permissions.clj"
126]
[metabase.query_processor.context.default$default_reducef invokeStatic "default.clj" 55]
[metabase.query_processor.context.default$default_reducef invoke "default.clj" 49]
[metabase.query_processor.context$reducef invokeStatic "context.clj" 70]
[metabase.query_processor.context$reducef invoke "context.clj" 63]
[metabase.query_processor.context.default$default_runf$respond_STAR___72458 invoke "default.clj" 69]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invokeStatic "execute.clj" 513]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invoke "execute.clj" 489]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invokeStatic "execute.clj" 497]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invoke "execute.clj" 489]
[metabase.driver.sql_jdbc$eval127004$fn__127005 invoke "sql_jdbc.clj" 63]
[metabase.driver.h2$eval127896$fn__127897 invoke "h2.clj" 221]
[clojure.lang.MultiFn invoke "MultiFn.java" 244]
[metabase.query_processor.context$executef invokeStatic "context.clj" 60]
[metabase.query_processor.context$executef invoke "context.clj" 49]
[metabase.query_processor.context.default$default_runf invokeStatic "default.clj" 68]
[metabase.query_processor.context.default$default_runf invoke "default.clj" 66]
[metabase.query_processor.context$runf invokeStatic "context.clj" 46]
[metabase.query_processor.context$runf invoke "context.clj" 40]
[metabase.query_processor.reducible$identity_qp invokeStatic "reducible.clj" 15]
[metabase.query_processor.reducible$identity_qp invoke "reducible.clj" 12]
[metabase.query_processor.middleware.cache$maybe_return_cached_results$maybe_return_cached_results_STAR___96299
invoke
"cache.clj"
224]
[metabase.query_processor.middleware.permissions$check_query_permissions$fn__96639 invoke "permissions.clj" 126]
[metabase_enterprise.advanced_permissions.query_processor.middleware.permissions$check_download_permissions$fn__100598
invoke
"permissions.clj"
125]
[metabase_enterprise.sandbox.query_processor.middleware.column_level_perms_check$maybe_apply_column_level_perms_check$fn__100845
invoke
"column_level_perms_check.clj"
31]
[metabase.query_processor.middleware.mbql_to_native$mbql__GT_native$fn__98111 invoke "mbql_to_native.clj" 24]
[metabase.query_processor$fn__101672$combined_post_process__101677$combined_post_process_STAR___101678
invoke
"query_processor.clj"
254]
[metabase.query_processor$fn__101672$combined_pre_process__101673$combined_pre_process_STAR___101674
invoke
"query_processor.clj"
251]
[metabase.query_processor.middleware.resolve_database_and_driver$resolve_database_and_driver$fn__99381$fn__99386
invoke
"resolve_database_and_driver.clj"
36]
[metabase.driver$do_with_driver invokeStatic "driver.clj" 90]
[metabase.driver$do_with_driver invoke "driver.clj" 86]
[metabase.query_processor.middleware.resolve_database_and_driver$resolve_database_and_driver$fn__99381
invoke
"resolve_database_and_driver.clj"
35]
[metabase.query_processor.middleware.fetch_source_query$resolve_card_id_source_tables$fn__97914
invoke
"fetch_source_query.clj"
310]
[metabase.query_processor.middleware.store$initialize_store$fn__100367$fn__100368 invoke "store.clj" 12]
[metabase.query_processor.store$do_with_store invokeStatic "store.clj" 46]
[metabase.query_processor.store$do_with_store invoke "store.clj" 40]
[metabase.query_processor.middleware.store$initialize_store$fn__100367 invoke "store.clj" 11]
[metabase.query_processor_test.test_mlv2$around_middleware$fn__142669 invoke "test_mlv2.clj" 136]
[metabase.query_processor.middleware.normalize_query$normalize$fn__98141 invoke "normalize_query.clj" 36]
[metabase_enterprise.audit_app.query_processor.middleware.handle_audit_queries$handle_internal_queries$fn__100811
invoke
"handle_audit_queries.clj"
131]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537$thunk__72539 invoke "reducible.clj" 103]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537 invoke "reducible.clj" 109]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537 invoke "reducible.clj" 94]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537 invoke "reducible.clj" 91]
[clojure.lang.AFn applyToHelper "AFn.java" 154]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[metabase.query_processor$base_qp$fn__101684 doInvoke "query_processor.clj" 272]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[metabase.query_processor.reducible$sync_qp$qp_STAR___72549 doInvoke "reducible.clj" 129]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 669]
[clojure.core$apply invoke "core.clj" 662]
[metabase.query_processor$process_query invokeStatic "query_processor.clj" 289]
[metabase.query_processor$process_query doInvoke "query_processor.clj" 283]
[clojure.lang.RestFn invoke "RestFn.java" 410]
[metabase.test.data$run_mbql_query_STAR_ invokeStatic "data.clj" 190]
[metabase.test.data$run_mbql_query_STAR_ invoke "data.clj" 187]
[metabase.query_processor_test.case_test$test_case invokeStatic "case_test.clj" 9]
[metabase.query_processor_test.case_test$test_case invoke "case_test.clj" 7]
[metabase.query_processor_test.case_test$fn__143175$fn__143192$fn__143193 invoke "case_test.clj" 51]
[toucan2.tools.with_temp$do_with_temp_STAR__primary_method_default invokeStatic "with_temp.clj" 62]
[toucan2.tools.with_temp$do_with_temp_STAR__primary_method_default invoke "with_temp.clj" 44]
[clojure.lang.AFn applyToHelper "AFn.java" 165]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 457]
[clojure.core$partial$fn__5908 invoke "core.clj" 2643]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.RestFn applyTo "RestFn.java" 132]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[methodical.impl.combo.threaded$eval2207$fn__2208$fn__2209$fn__2212 invoke "threaded.clj" 71]
[methodical.impl.combo.threaded$reducer_fn$fn__2175$fn__2179 invoke "threaded.clj" 23]
[clojure.lang.ArrayChunk reduce "ArrayChunk.java" 58]
[clojure.core.protocols$fn__8244 invokeStatic "protocols.clj" 136]
[clojure.core.protocols$fn__8244 invoke "protocols.clj" 124]
[clojure.core.protocols$fn__8204$G__8199__8213 invoke "protocols.clj" 19]
[clojure.core.protocols$seq_reduce invokeStatic "protocols.clj" 31]
[clojure.core.protocols$fn__8236 invokeStatic "protocols.clj" 75]
[clojure.core.protocols$fn__8236 invoke "protocols.clj" 75]
[clojure.core.protocols$fn__8178$G__8173__8191 invoke "protocols.clj" 13]
[clojure.core$reduce invokeStatic "core.clj" 6886]
[clojure.core$reduce invoke "core.clj" 6868]
[methodical.impl.combo.threaded$reducer_fn$fn__2175 invoke "threaded.clj" 21]
[clojure.core$comp$fn__5876 invoke "core.clj" 2588]
[methodical.impl.combo.threaded$combine_with_threader$fn__2185 invoke "threaded.clj" 44]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.RestFn applyTo "RestFn.java" 132]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.test.redefs$do_with_temp_STAR__around_method_default invokeStatic "redefs.clj" 23]
[metabase.test.redefs$do_with_temp_STAR__around_method_default invoke "redefs.clj" 10]
[clojure.lang.AFn applyToHelper "AFn.java" 165]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 457]
[clojure.core$partial$fn__5908 invoke "core.clj" 2643]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.RestFn applyTo "RestFn.java" 132]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[methodical.impl.standard$invoke_multifn invokeStatic "standard.clj" 58]
[methodical.impl.standard$invoke_multifn invoke "standard.clj" 47]
[methodical.impl.standard.StandardMultiFn invoke "standard.clj" 195]
[toucan2.tools.with_temp$do_with_temp invokeStatic "with_temp.clj" 68]
[toucan2.tools.with_temp$do_with_temp invoke "with_temp.clj" 66]
[metabase.query_processor_test.case_test$fn__143175$fn__143192 invoke "case_test.clj" 46]
[metabase.test.data.datasets$do_with_driver_when_testing$fn__110589$fn__110590 invoke "datasets.clj" 42]
[metabase.driver$do_with_driver invokeStatic "driver.clj" 90]
[metabase.driver$do_with_driver invoke "driver.clj" 86]
[metabase.test.data.datasets$do_with_driver_when_testing$fn__110589 invoke "datasets.clj" 41]
[metabase.test.data.datasets$do_when_testing_driver invokeStatic "datasets.clj" 30]
[metabase.test.data.datasets$do_when_testing_driver invoke "datasets.clj" 22]
[metabase.test.data.datasets$do_with_driver_when_testing invokeStatic "datasets.clj" 40]
[metabase.test.data.datasets$do_with_driver_when_testing invoke "datasets.clj" 39]
[metabase.query_processor_test.case_test$fn__143175 invokeStatic "case_test.clj" 44]
[metabase.query_processor_test.case_test$fn__143175 invoke "case_test.clj" 43]
[cider.nrepl.middleware.test$test_var$fn__134683 invoke "test.clj" 244]
[cider.nrepl.middleware.test$test_var invokeStatic "test.clj" 244]
[cider.nrepl.middleware.test$test_var invoke "test.clj" 236]
[cider.nrepl.middleware.test$test_vars$fn__134687$fn__134692 invoke "test.clj" 259]
[clojure.test$default_fixture invokeStatic "test.clj" 687]
[clojure.test$default_fixture invoke "test.clj" 683]
[cider.nrepl.middleware.test$test_vars$fn__134687 invoke "test.clj" 259]
[clojure.test$default_fixture invokeStatic "test.clj" 687]
[clojure.test$default_fixture invoke "test.clj" 683]
[cider.nrepl.middleware.test$test_vars invokeStatic "test.clj" 256]
[cider.nrepl.middleware.test$test_vars invoke "test.clj" 250]
[cider.nrepl.middleware.test$test_ns invokeStatic "test.clj" 272]
[cider.nrepl.middleware.test$test_ns invoke "test.clj" 263]
[cider.nrepl.middleware.test$test_var_query invokeStatic "test.clj" 283]
[cider.nrepl.middleware.test$test_var_query invoke "test.clj" 276]
[cider.nrepl.middleware.test$handle_test_var_query_op$fn__134731$fn__134732 invoke "test.clj" 321]
[clojure.lang.AFn applyToHelper "AFn.java" 152]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$with_bindings_STAR_ invokeStatic "core.clj" 1990]
[clojure.core$with_bindings_STAR_ doInvoke "core.clj" 1990]
[clojure.lang.RestFn invoke "RestFn.java" 425]
[cider.nrepl.middleware.test$handle_test_var_query_op$fn__134731 invoke "test.clj" 313]
[clojure.lang.AFn run "AFn.java" 22]
[nrepl.middleware.session$session_exec$main_loop__9666$fn__9670 invoke "session.clj" 218]
[nrepl.middleware.session$session_exec$main_loop__9666 invoke "session.clj" 217]
[clojure.lang.AFn run "AFn.java" 22]
[java.lang.Thread run "Thread.java" 1589]],
:cause
"[\"Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown\"]",
:data
{:type :malli.core/invalid-output,
:data
{:output :metabase.lib.schema.common/base-type,
:value :metabase.lib.schema.expression/type.unknown,
:args
[{:lib/type :mbql/query,
:lib/metadata
(metabase.lib.metadata.cached-provider/cached-metadata-provider
(metabase.lib.metadata.jvm/->UncachedApplicationDatabaseMetadataProvider 2368)),
:database 2368,
:type :pipeline,
:stages
[{:lib/type :mbql.stage/mbql,
:source-table 32407,
:aggregation [[:metric #:lib{:uuid "06174580-70bd-474a-b167-95a9ef3899cc"} 318]]}]}
-1
[:case
#:lib{:uuid "01480a56-78ee-4b7f-9407-23a6493cdd7d"}
[[[:<
#:lib{:uuid "e078b90f-de46-4dbb-9903-930c3891c375"}
[:field #:lib{:uuid "3454c908-194a-447d-af44-cbedee1ba44d"} 133191]
4]
[:field #:lib{:uuid "4d3ae622-03b7-40f6-af20-1ae413065640"} 133191]]]]],
:schema [:=> [:cat :metabase.lib.schema/query :int :any] :metabase.lib.schema.common/base-type],
:fn-name lib.metadata.calculation/type-of},
:humanized
["Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown"],
:link
"https://malli.io?schema=%3Ametabase.lib.schema.common%2Fbase-type%0A&value=%3Ametabase.lib.schema.expression%2Ftype.unknown%0A"}}
```
|
1.0
|
[MLv2] [Bug] Metadata calculation not working correctly for aggregation that contains a `:metric` clause - Failing test in `metabase.query-processor-test.case-test`
```clj
Can we use case in metric
with temporary :metabase.models.metric/Metric with attributes
{:creator_id 2,
:definition {:source-table 32407, :aggregation [:sum [:case [[[:< [:field 133191 nil] 4] [:field 133191 nil]]]]]},
:description "Lookin' for a blueberry",
:name "Toucans in the rainforest",
:table_id 32407}
legacy query =
{:database 2368, :type :query, :query {:aggregation [[:metric 316]], :source-table 32407}}
pMBQL =
{:lib/type :mbql/query,
:database 2368,
:type :pipeline,
:stages
[{:lib/type :mbql.stage/mbql,
:source-table 32407,
:aggregation [[:metric {:lib/uuid "6a455487-6033-4f35-b159-91558080ac1b"} 316]]}]}
Failed to calculated metadata for query
{:via
[{:type clojure.lang.ExceptionInfo,
:message
"[\"Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown\"]",
:data
{:type :malli.core/invalid-output,
:data
{:output :metabase.lib.schema.common/base-type,
:value :metabase.lib.schema.expression/type.unknown,
:args
[{:lib/type :mbql/query,
:lib/metadata
(metabase.lib.metadata.cached-provider/cached-metadata-provider
(metabase.lib.metadata.jvm/->UncachedApplicationDatabaseMetadataProvider 2368)),
:database 2368,
:type :pipeline,
:stages
[{:lib/type :mbql.stage/mbql,
:source-table 32407,
:aggregation [[:metric #:lib{:uuid "06174580-70bd-474a-b167-95a9ef3899cc"} 318]]}]}
-1
[:case
#:lib{:uuid "01480a56-78ee-4b7f-9407-23a6493cdd7d"}
[[[:<
#:lib{:uuid "e078b90f-de46-4dbb-9903-930c3891c375"}
[:field #:lib{:uuid "3454c908-194a-447d-af44-cbedee1ba44d"} 133191]
4]
[:field #:lib{:uuid "4d3ae622-03b7-40f6-af20-1ae413065640"} 133191]]]]],
:schema [:=> [:cat :metabase.lib.schema/query :int :any] :metabase.lib.schema.common/base-type],
:fn-name lib.metadata.calculation/type-of},
:humanized
["Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown"],
:link
"https://malli.io?schema=%3Ametabase.lib.schema.common%2Fbase-type%0A&value=%3Ametabase.lib.schema.expression%2Ftype.unknown%0A"},
:at [metabase.util.malli$explain_fn_fail_BANG_ invokeStatic "malli.cljc" 58]}],
:trace
[[metabase.util.malli$explain_fn_fail_BANG_ invokeStatic "malli.cljc" 58]
[metabase.util.malli$explain_fn_fail_BANG_ invoke "malli.cljc" 50]
[malli.instrument$_strument_BANG_$fn__30546$fn__30547 invoke "instrument.clj" 23]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2529]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metadata.calculation$eval32823$fn__32825 invoke "calculation.cljc" 155]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32809$type_of__32810 invoke "calculation.cljc" 141]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metric$eval75577$fn__75578 invoke "metric.cljc" 34]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32809$type_of__32810 invoke "calculation.cljc" 141]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metric$eval75586$fn__75588 invoke "metric.cljc" 40]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32809$type_of__32810 invoke "calculation.cljc" 141]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metadata.calculation$eval32843$fn__32844 invoke "calculation.cljc" 173]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 197]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.aggregation$eval73541$aggregations__73542$fn__73543 invoke "aggregation.cljc" 217]
[clojure.core$map_indexed$mapi__8638$fn__8639 invoke "core.clj" 7376]
[clojure.lang.LazySeq sval "LazySeq.java" 42]
[clojure.lang.LazySeq seq "LazySeq.java" 51]
[clojure.lang.RT seq "RT.java" 535]
[clojure.core$seq__5467 invokeStatic "core.clj" 139]
[clojure.core.protocols$seq_reduce invokeStatic "protocols.clj" 24]
[clojure.core.protocols$fn__8236 invokeStatic "protocols.clj" 75]
[clojure.core.protocols$fn__8236 invoke "protocols.clj" 75]
[clojure.core.protocols$fn__8178$G__8173__8191 invoke "protocols.clj" 13]
[clojure.core$reduce invokeStatic "core.clj" 6886]
[clojure.core$reduce invoke "core.clj" 6868]
[malli.core$_collection_schema$reify$reify__28325$fn__28326 invoke "core.cljc" 1194]
[malli.core$_maybe_schema$reify$reify__28467$fn__28468 invoke "core.cljc" 1466]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2528]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 421]
[metabase.lib.stage$eval75811$aggregations_columns__75812 invoke "stage.cljc" 107]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.stage$eval75861$breakout_ags_fields_columns__75862$fn__75863 invoke "stage.cljc" 139]
[clojure.core$map$fn__5931$fn__5932 invoke "core.clj" 2759]
[clojure.lang.PersistentVector reduce "PersistentVector.java" 343]
[clojure.core$transduce invokeStatic "core.clj" 6946]
[clojure.core$into invokeStatic "core.clj" 6962]
[clojure.core$into invoke "core.clj" 6950]
[metabase.lib.stage$eval75861$breakout_ags_fields_columns__75862 invoke "stage.cljc" 137]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.stage$eval76011$stage_metadata__76012 invoke "stage.cljc" 315]
[clojure.lang.AFn applyToHelper "AFn.java" 156]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn invoke "RestFn.java" 421]
[metabase.lib.stage$eval76022$fn__76023 invoke "stage.cljc" 322]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 197]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.query$eval33071$fn__33072 invoke "query.cljc" 66]
[clojure.lang.MultiFn invoke "MultiFn.java" 239]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 197]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.lib.metadata.calculation$eval32848$metadata__32849 invoke "calculation.cljc" 191]
[clojure.lang.AFn applyToHelper "AFn.java" 154]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29103 doInvoke "core.cljc" 2526]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[malli.core$_instrument$fn__29091 doInvoke "core.cljc" 2543]
[clojure.lang.RestFn invoke "RestFn.java" 408]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata$fn__142634$fn__142635 invoke "test_mlv2.clj" 97]
[metabase.query_processor_test.test_mlv2$do_with_pMBQL_query_testing_context invokeStatic "test_mlv2.clj" 24]
[metabase.query_processor_test.test_mlv2$do_with_pMBQL_query_testing_context invoke "test_mlv2.clj" 22]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata$fn__142634 invoke "test_mlv2.clj" 91]
[metabase.query_processor_test.test_mlv2$do_with_legacy_query_testing_context invokeStatic "test_mlv2.clj" 20]
[metabase.query_processor_test.test_mlv2$do_with_legacy_query_testing_context invoke "test_mlv2.clj" 18]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata invokeStatic "test_mlv2.clj" 83]
[metabase.query_processor_test.test_mlv2$test_mlv2_metadata invoke "test_mlv2.clj" 80]
[metabase.query_processor_test.test_mlv2$post_processing_middleware$fn__142666 invoke "test_mlv2.clj" 127]
[metabase.query_processor.middleware.annotate$add_column_info$add_column_info_rff_STAR___88584
invoke
"annotate.clj"
711]
[metabase.query_processor.middleware.mbql_to_native$mbql__GT_native$fn__98111$fn__98112
invoke
"mbql_to_native.clj"
27]
[metabase_enterprise.advanced_permissions.query_processor.middleware.permissions$check_download_permissions$fn__100598$fn__100599
invoke
"permissions.clj"
126]
[metabase.query_processor.context.default$default_reducef invokeStatic "default.clj" 55]
[metabase.query_processor.context.default$default_reducef invoke "default.clj" 49]
[metabase.query_processor.context$reducef invokeStatic "context.clj" 70]
[metabase.query_processor.context$reducef invoke "context.clj" 63]
[metabase.query_processor.context.default$default_runf$respond_STAR___72458 invoke "default.clj" 69]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invokeStatic "execute.clj" 513]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invoke "execute.clj" 489]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invokeStatic "execute.clj" 497]
[metabase.driver.sql_jdbc.execute$execute_reducible_query invoke "execute.clj" 489]
[metabase.driver.sql_jdbc$eval127004$fn__127005 invoke "sql_jdbc.clj" 63]
[metabase.driver.h2$eval127896$fn__127897 invoke "h2.clj" 221]
[clojure.lang.MultiFn invoke "MultiFn.java" 244]
[metabase.query_processor.context$executef invokeStatic "context.clj" 60]
[metabase.query_processor.context$executef invoke "context.clj" 49]
[metabase.query_processor.context.default$default_runf invokeStatic "default.clj" 68]
[metabase.query_processor.context.default$default_runf invoke "default.clj" 66]
[metabase.query_processor.context$runf invokeStatic "context.clj" 46]
[metabase.query_processor.context$runf invoke "context.clj" 40]
[metabase.query_processor.reducible$identity_qp invokeStatic "reducible.clj" 15]
[metabase.query_processor.reducible$identity_qp invoke "reducible.clj" 12]
[metabase.query_processor.middleware.cache$maybe_return_cached_results$maybe_return_cached_results_STAR___96299
invoke
"cache.clj"
224]
[metabase.query_processor.middleware.permissions$check_query_permissions$fn__96639 invoke "permissions.clj" 126]
[metabase_enterprise.advanced_permissions.query_processor.middleware.permissions$check_download_permissions$fn__100598
invoke
"permissions.clj"
125]
[metabase_enterprise.sandbox.query_processor.middleware.column_level_perms_check$maybe_apply_column_level_perms_check$fn__100845
invoke
"column_level_perms_check.clj"
31]
[metabase.query_processor.middleware.mbql_to_native$mbql__GT_native$fn__98111 invoke "mbql_to_native.clj" 24]
[metabase.query_processor$fn__101672$combined_post_process__101677$combined_post_process_STAR___101678
invoke
"query_processor.clj"
254]
[metabase.query_processor$fn__101672$combined_pre_process__101673$combined_pre_process_STAR___101674
invoke
"query_processor.clj"
251]
[metabase.query_processor.middleware.resolve_database_and_driver$resolve_database_and_driver$fn__99381$fn__99386
invoke
"resolve_database_and_driver.clj"
36]
[metabase.driver$do_with_driver invokeStatic "driver.clj" 90]
[metabase.driver$do_with_driver invoke "driver.clj" 86]
[metabase.query_processor.middleware.resolve_database_and_driver$resolve_database_and_driver$fn__99381
invoke
"resolve_database_and_driver.clj"
35]
[metabase.query_processor.middleware.fetch_source_query$resolve_card_id_source_tables$fn__97914
invoke
"fetch_source_query.clj"
310]
[metabase.query_processor.middleware.store$initialize_store$fn__100367$fn__100368 invoke "store.clj" 12]
[metabase.query_processor.store$do_with_store invokeStatic "store.clj" 46]
[metabase.query_processor.store$do_with_store invoke "store.clj" 40]
[metabase.query_processor.middleware.store$initialize_store$fn__100367 invoke "store.clj" 11]
[metabase.query_processor_test.test_mlv2$around_middleware$fn__142669 invoke "test_mlv2.clj" 136]
[metabase.query_processor.middleware.normalize_query$normalize$fn__98141 invoke "normalize_query.clj" 36]
[metabase_enterprise.audit_app.query_processor.middleware.handle_audit_queries$handle_internal_queries$fn__100811
invoke
"handle_audit_queries.clj"
131]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537$thunk__72539 invoke "reducible.clj" 103]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537 invoke "reducible.clj" 109]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537 invoke "reducible.clj" 94]
[metabase.query_processor.reducible$async_qp$qp_STAR___72537 invoke "reducible.clj" 91]
[clojure.lang.AFn applyToHelper "AFn.java" 154]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[metabase.query_processor$base_qp$fn__101684 doInvoke "query_processor.clj" 272]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$apply invoke "core.clj" 662]
[metabase.query_processor.reducible$sync_qp$qp_STAR___72549 doInvoke "reducible.clj" 129]
[clojure.lang.RestFn applyTo "RestFn.java" 137]
[clojure.core$apply invokeStatic "core.clj" 669]
[clojure.core$apply invoke "core.clj" 662]
[metabase.query_processor$process_query invokeStatic "query_processor.clj" 289]
[metabase.query_processor$process_query doInvoke "query_processor.clj" 283]
[clojure.lang.RestFn invoke "RestFn.java" 410]
[metabase.test.data$run_mbql_query_STAR_ invokeStatic "data.clj" 190]
[metabase.test.data$run_mbql_query_STAR_ invoke "data.clj" 187]
[metabase.query_processor_test.case_test$test_case invokeStatic "case_test.clj" 9]
[metabase.query_processor_test.case_test$test_case invoke "case_test.clj" 7]
[metabase.query_processor_test.case_test$fn__143175$fn__143192$fn__143193 invoke "case_test.clj" 51]
[toucan2.tools.with_temp$do_with_temp_STAR__primary_method_default invokeStatic "with_temp.clj" 62]
[toucan2.tools.with_temp$do_with_temp_STAR__primary_method_default invoke "with_temp.clj" 44]
[clojure.lang.AFn applyToHelper "AFn.java" 165]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 457]
[clojure.core$partial$fn__5908 invoke "core.clj" 2643]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.RestFn applyTo "RestFn.java" 132]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[methodical.impl.combo.threaded$eval2207$fn__2208$fn__2209$fn__2212 invoke "threaded.clj" 71]
[methodical.impl.combo.threaded$reducer_fn$fn__2175$fn__2179 invoke "threaded.clj" 23]
[clojure.lang.ArrayChunk reduce "ArrayChunk.java" 58]
[clojure.core.protocols$fn__8244 invokeStatic "protocols.clj" 136]
[clojure.core.protocols$fn__8244 invoke "protocols.clj" 124]
[clojure.core.protocols$fn__8204$G__8199__8213 invoke "protocols.clj" 19]
[clojure.core.protocols$seq_reduce invokeStatic "protocols.clj" 31]
[clojure.core.protocols$fn__8236 invokeStatic "protocols.clj" 75]
[clojure.core.protocols$fn__8236 invoke "protocols.clj" 75]
[clojure.core.protocols$fn__8178$G__8173__8191 invoke "protocols.clj" 13]
[clojure.core$reduce invokeStatic "core.clj" 6886]
[clojure.core$reduce invoke "core.clj" 6868]
[methodical.impl.combo.threaded$reducer_fn$fn__2175 invoke "threaded.clj" 21]
[clojure.core$comp$fn__5876 invoke "core.clj" 2588]
[methodical.impl.combo.threaded$combine_with_threader$fn__2185 invoke "threaded.clj" 44]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.RestFn applyTo "RestFn.java" 132]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[metabase.test.redefs$do_with_temp_STAR__around_method_default invokeStatic "redefs.clj" 23]
[metabase.test.redefs$do_with_temp_STAR__around_method_default invoke "redefs.clj" 10]
[clojure.lang.AFn applyToHelper "AFn.java" 165]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 457]
[clojure.core$partial$fn__5908 invoke "core.clj" 2643]
[clojure.lang.AFn applyToHelper "AFn.java" 160]
[clojure.lang.RestFn applyTo "RestFn.java" 132]
[clojure.lang.AFunction$1 doInvoke "AFunction.java" 31]
[clojure.lang.RestFn invoke "RestFn.java" 436]
[methodical.impl.standard$invoke_multifn invokeStatic "standard.clj" 58]
[methodical.impl.standard$invoke_multifn invoke "standard.clj" 47]
[methodical.impl.standard.StandardMultiFn invoke "standard.clj" 195]
[toucan2.tools.with_temp$do_with_temp invokeStatic "with_temp.clj" 68]
[toucan2.tools.with_temp$do_with_temp invoke "with_temp.clj" 66]
[metabase.query_processor_test.case_test$fn__143175$fn__143192 invoke "case_test.clj" 46]
[metabase.test.data.datasets$do_with_driver_when_testing$fn__110589$fn__110590 invoke "datasets.clj" 42]
[metabase.driver$do_with_driver invokeStatic "driver.clj" 90]
[metabase.driver$do_with_driver invoke "driver.clj" 86]
[metabase.test.data.datasets$do_with_driver_when_testing$fn__110589 invoke "datasets.clj" 41]
[metabase.test.data.datasets$do_when_testing_driver invokeStatic "datasets.clj" 30]
[metabase.test.data.datasets$do_when_testing_driver invoke "datasets.clj" 22]
[metabase.test.data.datasets$do_with_driver_when_testing invokeStatic "datasets.clj" 40]
[metabase.test.data.datasets$do_with_driver_when_testing invoke "datasets.clj" 39]
[metabase.query_processor_test.case_test$fn__143175 invokeStatic "case_test.clj" 44]
[metabase.query_processor_test.case_test$fn__143175 invoke "case_test.clj" 43]
[cider.nrepl.middleware.test$test_var$fn__134683 invoke "test.clj" 244]
[cider.nrepl.middleware.test$test_var invokeStatic "test.clj" 244]
[cider.nrepl.middleware.test$test_var invoke "test.clj" 236]
[cider.nrepl.middleware.test$test_vars$fn__134687$fn__134692 invoke "test.clj" 259]
[clojure.test$default_fixture invokeStatic "test.clj" 687]
[clojure.test$default_fixture invoke "test.clj" 683]
[cider.nrepl.middleware.test$test_vars$fn__134687 invoke "test.clj" 259]
[clojure.test$default_fixture invokeStatic "test.clj" 687]
[clojure.test$default_fixture invoke "test.clj" 683]
[cider.nrepl.middleware.test$test_vars invokeStatic "test.clj" 256]
[cider.nrepl.middleware.test$test_vars invoke "test.clj" 250]
[cider.nrepl.middleware.test$test_ns invokeStatic "test.clj" 272]
[cider.nrepl.middleware.test$test_ns invoke "test.clj" 263]
[cider.nrepl.middleware.test$test_var_query invokeStatic "test.clj" 283]
[cider.nrepl.middleware.test$test_var_query invoke "test.clj" 276]
[cider.nrepl.middleware.test$handle_test_var_query_op$fn__134731$fn__134732 invoke "test.clj" 321]
[clojure.lang.AFn applyToHelper "AFn.java" 152]
[clojure.lang.AFn applyTo "AFn.java" 144]
[clojure.core$apply invokeStatic "core.clj" 667]
[clojure.core$with_bindings_STAR_ invokeStatic "core.clj" 1990]
[clojure.core$with_bindings_STAR_ doInvoke "core.clj" 1990]
[clojure.lang.RestFn invoke "RestFn.java" 425]
[cider.nrepl.middleware.test$handle_test_var_query_op$fn__134731 invoke "test.clj" 313]
[clojure.lang.AFn run "AFn.java" 22]
[nrepl.middleware.session$session_exec$main_loop__9666$fn__9670 invoke "session.clj" 218]
[nrepl.middleware.session$session_exec$main_loop__9666 invoke "session.clj" 217]
[clojure.lang.AFn run "AFn.java" 22]
[java.lang.Thread run "Thread.java" 1589]],
:cause
"[\"Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown\"]",
:data
{:type :malli.core/invalid-output,
:data
{:output :metabase.lib.schema.common/base-type,
:value :metabase.lib.schema.expression/type.unknown,
:args
[{:lib/type :mbql/query,
:lib/metadata
(metabase.lib.metadata.cached-provider/cached-metadata-provider
(metabase.lib.metadata.jvm/->UncachedApplicationDatabaseMetadataProvider 2368)),
:database 2368,
:type :pipeline,
:stages
[{:lib/type :mbql.stage/mbql,
:source-table 32407,
:aggregation [[:metric #:lib{:uuid "06174580-70bd-474a-b167-95a9ef3899cc"} 318]]}]}
-1
[:case
#:lib{:uuid "01480a56-78ee-4b7f-9407-23a6493cdd7d"}
[[[:<
#:lib{:uuid "e078b90f-de46-4dbb-9903-930c3891c375"}
[:field #:lib{:uuid "3454c908-194a-447d-af44-cbedee1ba44d"} 133191]
4]
[:field #:lib{:uuid "4d3ae622-03b7-40f6-af20-1ae413065640"} 133191]]]]],
:schema [:=> [:cat :metabase.lib.schema/query :int :any] :metabase.lib.schema.common/base-type],
:fn-name lib.metadata.calculation/type-of},
:humanized
["Not a valid base type: :metabase.lib.schema.expression/type.unknown, received: :metabase.lib.schema.expression/type.unknown"],
:link
"https://malli.io?schema=%3Ametabase.lib.schema.common%2Fbase-type%0A&value=%3Ametabase.lib.schema.expression%2Ftype.unknown%0A"}}
```
|
process
|
metadata calculation not working correctly for aggregation that contains a metric clause failing test in metabase query processor test case test clj can we use case in metric with temporary metabase models metric metric with attributes creator id definition source table aggregation description lookin for a blueberry name toucans in the rainforest table id legacy query database type query query aggregation source table pmbql lib type mbql query database type pipeline stages lib type mbql stage mbql source table aggregation failed to calculated metadata for query via type clojure lang exceptioninfo message data type malli core invalid output data output metabase lib schema common base type value metabase lib schema expression type unknown args lib type mbql query lib metadata metabase lib metadata cached provider cached metadata provider metabase lib metadata jvm uncachedapplicationdatabasemetadataprovider database type pipeline stages lib type mbql stage mbql source table aggregation case lib uuid lib uuid schema metabase lib schema common base type fn name lib metadata calculation type of humanized link at trace metabase query processor middleware annotate add column info add column info rff star invoke annotate clj metabase query processor middleware mbql to native mbql gt native fn fn invoke mbql to native clj metabase enterprise advanced permissions query processor middleware permissions check download permissions fn fn invoke permissions clj metabase query processor middleware cache maybe return cached results maybe return cached results star invoke cache clj metabase enterprise advanced permissions query processor middleware permissions check download permissions fn invoke permissions clj metabase enterprise sandbox query processor middleware column level perms check maybe apply column level perms check fn invoke column level perms check clj metabase query processor fn combined post process combined post process star invoke query processor clj metabase query processor fn combined pre process combined pre process star invoke query processor clj metabase query processor middleware resolve database and driver resolve database and driver fn fn invoke resolve database and driver clj metabase query processor middleware resolve database and driver resolve database and driver fn invoke resolve database and driver clj metabase query processor middleware fetch source query resolve card id source tables fn invoke fetch source query clj metabase enterprise audit app query processor middleware handle audit queries handle internal queries fn invoke handle audit queries clj cause data type malli core invalid output data output metabase lib schema common base type value metabase lib schema expression type unknown args lib type mbql query lib metadata metabase lib metadata cached provider cached metadata provider metabase lib metadata jvm uncachedapplicationdatabasemetadataprovider database type pipeline stages lib type mbql stage mbql source table aggregation case lib uuid lib uuid schema metabase lib schema common base type fn name lib metadata calculation type of humanized link
| 1
|
651,455
| 21,479,265,387
|
IssuesEvent
|
2022-04-26 16:07:41
|
OpenDAX/OpenDAX
|
https://api.github.com/repos/OpenDAX/OpenDAX
|
closed
|
Lua module char array
|
Low Priority Bug
|
The Lua module returns a table when the tag is a CHAR array. It might make more sense to return a string made up of those characters. This seems like it would be the expected behavior.
|
1.0
|
Lua module char array - The Lua module returns a table when the tag is a CHAR array. It might make more sense to return a string made up of those characters. This seems like it would be the expected behavior.
|
non_process
|
lua module char array the lua module returns a table when the tag is a char array it might make more sense to return a string made up of those characters this seems like it would be the expected behavior
| 0
|
22,759
| 32,079,783,053
|
IssuesEvent
|
2023-09-25 13:17:17
|
h4sh5/npm-auto-scanner
|
https://api.github.com/repos/h4sh5/npm-auto-scanner
|
opened
|
monaca 4.2.9 has 2 guarddog issues
|
npm-install-script npm-silent-process-execution
|
```{"npm-install-script":[{"code":" \"preinstall\": \"node bin/preinstall\",","location":"package/package.json:9","message":"The package.json has a script automatically running when the package is installed"}],"npm-silent-process-execution":[{"code":" const childProcess = spawn('npm.cmd', ['run', 'monaca:preview'], {stdio: 'ignore', detached: true});","location":"package/src/serve.js:27","message":"This package is silently executing another executable"}]}```
|
1.0
|
monaca 4.2.9 has 2 guarddog issues - ```{"npm-install-script":[{"code":" \"preinstall\": \"node bin/preinstall\",","location":"package/package.json:9","message":"The package.json has a script automatically running when the package is installed"}],"npm-silent-process-execution":[{"code":" const childProcess = spawn('npm.cmd', ['run', 'monaca:preview'], {stdio: 'ignore', detached: true});","location":"package/src/serve.js:27","message":"This package is silently executing another executable"}]}```
|
process
|
monaca has guarddog issues npm install script npm silent process execution stdio ignore detached true location package src serve js message this package is silently executing another executable
| 1
|
661,568
| 22,060,937,448
|
IssuesEvent
|
2022-05-30 17:43:34
|
DXgovernance/dxvote
|
https://api.github.com/repos/DXgovernance/dxvote
|
closed
|
Simplify decode text string replacement
|
Enhancement High Priority Refactor
|
Currently we use a parameter index to replace values in the decodeText, this works but is not very intuitive to work out what is being used where as devs have to count the param index to work it out.
This caused a regression bug with swapr campaign creation where the starting at 0 value was not considered and the decoded string was incorrect causing confusion and doubt for users.
A better solution may be changing PARAM_X to the name of the parameter, a value we already have and is unique for the most part.
If anyone has any better solutions these are also welcome, not sure if we could pass parameters in like we would with i18n string templates.
|
1.0
|
Simplify decode text string replacement - Currently we use a parameter index to replace values in the decodeText, this works but is not very intuitive to work out what is being used where as devs have to count the param index to work it out.
This caused a regression bug with swapr campaign creation where the starting at 0 value was not considered and the decoded string was incorrect causing confusion and doubt for users.
A better solution may be changing PARAM_X to the name of the parameter, a value we already have and is unique for the most part.
If anyone has any better solutions these are also welcome, not sure if we could pass parameters in like we would with i18n string templates.
|
non_process
|
simplify decode text string replacement currently we use a parameter index to replace values in the decodetext this works but is not very intuitive to work out what is being used where as devs have to count the param index to work it out this caused a regression bug with swapr campaign creation where the starting at value was not considered and the decoded string was incorrect causing confusion and doubt for users a better solution may be changing param x to the name of the parameter a value we already have and is unique for the most part if anyone has any better solutions these are also welcome not sure if we could pass parameters in like we would with string templates
| 0
|
217
| 2,644,624,793
|
IssuesEvent
|
2015-03-12 17:54:33
|
ContaoDMS/dms
|
https://api.github.com/repos/ContaoDMS/dms
|
closed
|
Remove Contao 2 compatibility
|
Exercise ⚙ - Processed
|
Completly remove Contao 2 compatibility (database.sql, html Folder, .htaccess, etc.)
|
1.0
|
Remove Contao 2 compatibility - Completly remove Contao 2 compatibility (database.sql, html Folder, .htaccess, etc.)
|
process
|
remove contao compatibility completly remove contao compatibility database sql html folder htaccess etc
| 1
|
19,377
| 25,506,686,496
|
IssuesEvent
|
2022-11-28 09:59:17
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[iOS] Enrollment flow/updated consent flow > Review consent screen > Study name is not getting displayed for the Custom consent
|
Bug P1 Process: Fixed Process: Tested dev
|
1)Study name is not getting displayed for the Custom consent
2)Pdf is generated without study name
|
2.0
|
[iOS] Enrollment flow/updated consent flow > Review consent screen > Study name is not getting displayed for the Custom consent - 1)Study name is not getting displayed for the Custom consent
2)Pdf is generated without study name
|
process
|
enrollment flow updated consent flow review consent screen study name is not getting displayed for the custom consent study name is not getting displayed for the custom consent pdf is generated without study name
| 1
|
16,415
| 21,191,863,017
|
IssuesEvent
|
2022-04-08 18:23:57
|
wayfair-incubator/gator
|
https://api.github.com/repos/wayfair-incubator/gator
|
opened
|
Port Response Functionality from Internal Gator
|
pre-processing
|
# Description
Gator will rely heavily on the `Response` objects defined as part of dynamic processing in Internal Gator. Even "static" changesets, without asynchronous resources, will rely on the structure of the Response to instruct `PostProcessing` what to do - which PRs to create, issues to create, whether or not the process failed, and why.
Copy this functionality over from internally hosted Gator, including tests.
|
1.0
|
Port Response Functionality from Internal Gator - # Description
Gator will rely heavily on the `Response` objects defined as part of dynamic processing in Internal Gator. Even "static" changesets, without asynchronous resources, will rely on the structure of the Response to instruct `PostProcessing` what to do - which PRs to create, issues to create, whether or not the process failed, and why.
Copy this functionality over from internally hosted Gator, including tests.
|
process
|
port response functionality from internal gator description gator will rely heavily on the response objects defined as part of dynamic processing in internal gator even static changesets without asynchronous resources will rely on the structure of the response to instruct postprocessing what to do which prs to create issues to create whether or not the process failed and why copy this functionality over from internally hosted gator including tests
| 1
|
579,354
| 17,189,670,495
|
IssuesEvent
|
2021-07-16 09:07:47
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
www.ebay.de - design is broken
|
browser-firefox engine-gecko priority-important
|
<!-- @browser: Firefox 89.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:89.0) Gecko/20100101 Firefox/89.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/80299 -->
**URL**: https://www.ebay.de/
**Browser / Version**: Firefox 89.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Design is broken
**Description**: Items are misaligned
**Steps to Reproduce**:
On Chrome the site is working, only on Firefox there is a problem, whole page style is broken. On chrome is working properly
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
www.ebay.de - design is broken - <!-- @browser: Firefox 89.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:89.0) Gecko/20100101 Firefox/89.0 -->
<!-- @reported_with: unknown -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/80299 -->
**URL**: https://www.ebay.de/
**Browser / Version**: Firefox 89.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Design is broken
**Description**: Items are misaligned
**Steps to Reproduce**:
On Chrome the site is working, only on Firefox there is a problem, whole page style is broken. On chrome is working properly
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_process
|
design is broken url browser version firefox operating system windows tested another browser yes chrome problem type design is broken description items are misaligned steps to reproduce on chrome the site is working only on firefox there is a problem whole page style is broken on chrome is working properly browser configuration none from with ❤️
| 0
|
22,266
| 30,819,745,957
|
IssuesEvent
|
2023-08-01 15:32:42
|
symfony/symfony-docs
|
https://api.github.com/repos/symfony/symfony-docs
|
closed
|
[Process] Support using `Process::findExecutable()` independently of `o…
|
Process
|
| Q | A
| ------------ | ---
| Feature PR | symfony/symfony#47422
| PR author(s) | @BlackbitDevs
| Merged in | 6.4
We created this issue to not forget to document this new feature. We would really appreciate if you can help us with this task. If you are not sure how to do it, please ask us and we will help you.
To fix this issue, please create a PR against the 6.4 branch in the [symfony-docs repository](https://github.com/symfony/symfony-docs).
Thank you! :smiley:
|
1.0
|
[Process] Support using `Process::findExecutable()` independently of `o… - | Q | A
| ------------ | ---
| Feature PR | symfony/symfony#47422
| PR author(s) | @BlackbitDevs
| Merged in | 6.4
We created this issue to not forget to document this new feature. We would really appreciate if you can help us with this task. If you are not sure how to do it, please ask us and we will help you.
To fix this issue, please create a PR against the 6.4 branch in the [symfony-docs repository](https://github.com/symfony/symfony-docs).
Thank you! :smiley:
|
process
|
support using process findexecutable independently of o… q a feature pr symfony symfony pr author s blackbitdevs merged in we created this issue to not forget to document this new feature we would really appreciate if you can help us with this task if you are not sure how to do it please ask us and we will help you to fix this issue please create a pr against the branch in the thank you smiley
| 1
|
137,344
| 18,752,690,262
|
IssuesEvent
|
2021-11-05 05:49:59
|
madhans23/linux-4.15
|
https://api.github.com/repos/madhans23/linux-4.15
|
opened
|
CVE-2019-12984 (Medium) detected in linux-stablev4.17.12
|
security vulnerability
|
## CVE-2019-12984 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stablev4.17.12</b></p></summary>
<p>
<p>Linux kernel stable tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git>https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.15/commit/d96ee498864d1a0b6222cfb17d64ca8196014940">d96ee498864d1a0b6222cfb17d64ca8196014940</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/netlink.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/netlink.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A NULL pointer dereference vulnerability in the function nfc_genl_deactivate_target() in net/nfc/netlink.c in the Linux kernel before 5.1.13 can be triggered by a malicious user-mode program that omits certain NFC attributes, leading to denial of service.
<p>Publish Date: 2019-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12984>CVE-2019-12984</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12984">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12984</a></p>
<p>Release Date: 2019-06-26</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-12984 (Medium) detected in linux-stablev4.17.12 - ## CVE-2019-12984 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stablev4.17.12</b></p></summary>
<p>
<p>Linux kernel stable tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git>https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux-stable.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.15/commit/d96ee498864d1a0b6222cfb17d64ca8196014940">d96ee498864d1a0b6222cfb17d64ca8196014940</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/netlink.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/nfc/netlink.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A NULL pointer dereference vulnerability in the function nfc_genl_deactivate_target() in net/nfc/netlink.c in the Linux kernel before 5.1.13 can be triggered by a malicious user-mode program that omits certain NFC attributes, leading to denial of service.
<p>Publish Date: 2019-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12984>CVE-2019-12984</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12984">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12984</a></p>
<p>Release Date: 2019-06-26</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in linux cve medium severity vulnerability vulnerable library linux linux kernel stable tree library home page a href found in head commit a href found in base branch master vulnerable source files net nfc netlink c net nfc netlink c vulnerability details a null pointer dereference vulnerability in the function nfc genl deactivate target in net nfc netlink c in the linux kernel before can be triggered by a malicious user mode program that omits certain nfc attributes leading to denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
2,666
| 5,445,832,243
|
IssuesEvent
|
2017-03-07 08:57:16
|
symfony/symfony
|
https://api.github.com/repos/symfony/symfony
|
closed
|
Process fails inside apache mod_php
|
Bug Process Status: Needs Review Status: Waiting feedback Unconfirmed
|
## Environment
symfony/symfony v2.8.4
PHP `5.5.9-1ubuntu4.14` / `API220121212,NTS`
Apache modules: `core mod_so mod_watchdog http_core mod_log_config mod_logio mod_version mod_unixd mod_access_compat mod_alias mod_auth_basic mod_authn_core mod_authn_file mod_authz_core mod_authz_groupfile mod_authz_host mod_authz_user mod_autoindex mod_bw mod_cgi mod_deflate mod_dir mod_env mod_expires mod_filter mod_headers mod_mime prefork mod_negotiation mod_php5 mod_rewrite mod_setenvif mod_socache_shmcb mod_ssl mod_status`
PHP Extensions: `bcmath, bz2, calendar, Core, ctype, curl, date, dba, dom, ereg, exif, fileinfo, filter, ftp, gd, gettext, hash, iconv, imagick, intl, json, libxml, mbstring, mcrypt, memcachememcached, mhash, mysql, mysqli, newrelic, openssl, pcntl, pcre, PDO, pdo_mysql, Phar, posix, readline, Reflection, session, shmop, SimpleXML, soap, sockets, SPL, standardsysvmsg, sysvsem, sysvshm, tokenizer, wddx, xml, xmlreader, xmlwriter, Zend OPcache, zip, zlib`
## Problem
``` php
<?php
include __DIR__.'/../vendor/autoload.php';
$proc = new \Symfony\Component\Process\Process('echo TEST');
var_dump(
$proc->start(),
$proc->wait(),
$proc->getExitCode(),
$proc->getOutput(),
$proc->getErrorOutput()
);
/* outputs:
NULL NULL NULL string(0) "" string(0) ""
*/
$proc2 = proc_open('echo TEST2', [1=>['pipe', 'w']], $pipes);
var_dump(is_resource($proc2));
if (is_resource($proc2)) {
var_dump(stream_get_contents($pipes[1]));
fclose($pipes[1]);
var_dump(proc_close($proc2));
}
/* outputs
bool(true) string(6) "TEST2 " NULL
*/
```
As you can see, proc_open _kinda_ works at least the output works, but the exit code is null, which is already pretty bad. But then with the Process component I don't even get the output to work.
Note that if I run the script from CLI, it works fine, I get 0 exit codes and output for both examples. Running via Apache mod_php fails.
|
1.0
|
Process fails inside apache mod_php - ## Environment
symfony/symfony v2.8.4
PHP `5.5.9-1ubuntu4.14` / `API220121212,NTS`
Apache modules: `core mod_so mod_watchdog http_core mod_log_config mod_logio mod_version mod_unixd mod_access_compat mod_alias mod_auth_basic mod_authn_core mod_authn_file mod_authz_core mod_authz_groupfile mod_authz_host mod_authz_user mod_autoindex mod_bw mod_cgi mod_deflate mod_dir mod_env mod_expires mod_filter mod_headers mod_mime prefork mod_negotiation mod_php5 mod_rewrite mod_setenvif mod_socache_shmcb mod_ssl mod_status`
PHP Extensions: `bcmath, bz2, calendar, Core, ctype, curl, date, dba, dom, ereg, exif, fileinfo, filter, ftp, gd, gettext, hash, iconv, imagick, intl, json, libxml, mbstring, mcrypt, memcachememcached, mhash, mysql, mysqli, newrelic, openssl, pcntl, pcre, PDO, pdo_mysql, Phar, posix, readline, Reflection, session, shmop, SimpleXML, soap, sockets, SPL, standardsysvmsg, sysvsem, sysvshm, tokenizer, wddx, xml, xmlreader, xmlwriter, Zend OPcache, zip, zlib`
## Problem
``` php
<?php
include __DIR__.'/../vendor/autoload.php';
$proc = new \Symfony\Component\Process\Process('echo TEST');
var_dump(
$proc->start(),
$proc->wait(),
$proc->getExitCode(),
$proc->getOutput(),
$proc->getErrorOutput()
);
/* outputs:
NULL NULL NULL string(0) "" string(0) ""
*/
$proc2 = proc_open('echo TEST2', [1=>['pipe', 'w']], $pipes);
var_dump(is_resource($proc2));
if (is_resource($proc2)) {
var_dump(stream_get_contents($pipes[1]));
fclose($pipes[1]);
var_dump(proc_close($proc2));
}
/* outputs
bool(true) string(6) "TEST2 " NULL
*/
```
As you can see, proc_open _kinda_ works at least the output works, but the exit code is null, which is already pretty bad. But then with the Process component I don't even get the output to work.
Note that if I run the script from CLI, it works fine, I get 0 exit codes and output for both examples. Running via Apache mod_php fails.
|
process
|
process fails inside apache mod php environment symfony symfony php nts apache modules core mod so mod watchdog http core mod log config mod logio mod version mod unixd mod access compat mod alias mod auth basic mod authn core mod authn file mod authz core mod authz groupfile mod authz host mod authz user mod autoindex mod bw mod cgi mod deflate mod dir mod env mod expires mod filter mod headers mod mime prefork mod negotiation mod mod rewrite mod setenvif mod socache shmcb mod ssl mod status php extensions bcmath calendar core ctype curl date dba dom ereg exif fileinfo filter ftp gd gettext hash iconv imagick intl json libxml mbstring mcrypt memcachememcached mhash mysql mysqli newrelic openssl pcntl pcre pdo pdo mysql phar posix readline reflection session shmop simplexml soap sockets spl standardsysvmsg sysvsem sysvshm tokenizer wddx xml xmlreader xmlwriter zend opcache zip zlib problem php php include dir vendor autoload php proc new symfony component process process echo test var dump proc start proc wait proc getexitcode proc getoutput proc geterroroutput outputs null null null string string proc open echo pipes var dump is resource if is resource var dump stream get contents pipes fclose pipes var dump proc close outputs bool true string null as you can see proc open kinda works at least the output works but the exit code is null which is already pretty bad but then with the process component i don t even get the output to work note that if i run the script from cli it works fine i get exit codes and output for both examples running via apache mod php fails
| 1
|
338
| 2,793,239,736
|
IssuesEvent
|
2015-05-11 09:36:17
|
ecodistrict/IDSSDashboard
|
https://api.github.com/repos/ecodistrict/IDSSDashboard
|
closed
|
Select best alternative tab needed?
|
form feedback 09102014 process step: select best alternatives question
|
Do we even need this tab? We could merge this with assess alternatives
|
1.0
|
Select best alternative tab needed? - Do we even need this tab? We could merge this with assess alternatives
|
process
|
select best alternative tab needed do we even need this tab we could merge this with assess alternatives
| 1
|
17,753
| 23,666,244,329
|
IssuesEvent
|
2022-08-26 21:19:23
|
googleapis/google-api-python-client
|
https://api.github.com/repos/googleapis/google-api-python-client
|
closed
|
Dependency Dashboard
|
type: process
|
This issue lists Renovate updates and detected dependencies. Read the [Dependency Dashboard](https://docs.renovatebot.com/key-concepts/dashboard/) docs to learn more.
## Edited/Blocked
These updates have been manually edited so Renovate will no longer make changes. To discard all commits and start over, click on a checkbox.
- [ ] <!-- rebase-branch=renovate/distlib-0.x -->[chore(deps): update dependency distlib to v0.3.6](../pull/1887)
- [ ] <!-- rebase-branch=renovate/protobuf-4.x -->[chore(deps): update dependency protobuf to v4](../pull/1886)
## Ignored or Blocked
These are blocked by an existing closed PR and will not be recreated unless you click a checkbox below.
- [ ] <!-- recreate-branch=renovate/click-8.x -->[chore(deps): update dependency click to v8.1.3](../pull/1884)
- [ ] <!-- recreate-branch=renovate/setuptools-65.x -->[chore(deps): update dependency setuptools to v65.3.0](../pull/1885)
## Detected dependencies
<details><summary>github-actions</summary>
<blockquote>
<details><summary>.github/workflows/main.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/github-script v6.2.0`
</details>
</blockquote>
</details>
<details><summary>pip_requirements</summary>
<blockquote>
<details><summary>.kokoro/requirements.txt</summary>
- `argcomplete ==2.0.0`
- `attrs ==22.1.0`
- `bleach ==5.0.1`
- `cachetools ==5.2.0`
- `certifi ==2022.6.15`
- `cffi ==1.15.1`
- `charset-normalizer ==2.1.1`
- `click ==8.0.4`
- `colorlog ==6.6.0`
- `commonmark ==0.9.1`
- `cryptography ==37.0.4`
- `distlib ==0.3.5`
- `docutils ==0.19`
- `filelock ==3.8.0`
- `gcp-docuploader ==0.6.3`
- `gcp-releasetool ==1.8.6`
- `google-api-core ==2.8.2`
- `google-auth ==2.11.0`
- `google-cloud-core ==2.3.2`
- `google-cloud-storage ==2.5.0`
- `google-crc32c ==1.3.0`
- `google-resumable-media ==2.3.3`
- `googleapis-common-protos ==1.56.4`
- `idna ==3.3`
- `importlib-metadata ==4.12.0`
- `jeepney ==0.8.0`
- `jinja2 ==3.1.2`
- `keyring ==23.8.2`
- `markupsafe ==2.1.1`
- `nox ==2022.8.7`
- `packaging ==21.3`
- `pkginfo ==1.8.3`
- `platformdirs ==2.5.2`
- `protobuf ==3.20.1`
- `py ==1.11.0`
- `pyasn1 ==0.4.8`
- `pyasn1-modules ==0.2.8`
- `pycparser ==2.21`
- `pygments ==2.13.0`
- `pyjwt ==2.4.0`
- `pyparsing ==3.0.9`
- `pyperclip ==1.8.2`
- `python-dateutil ==2.8.2`
- `readme-renderer ==37.0`
- `requests ==2.28.1`
- `requests-toolbelt ==0.9.1`
- `rfc3986 ==2.0.0`
- `rich ==12.5.1`
- `rsa ==4.9`
- `secretstorage ==3.3.3`
- `six ==1.16.0`
- `twine ==4.0.1`
- `typing-extensions ==4.3.0`
- `urllib3 ==1.26.12`
- `virtualenv ==20.16.3`
- `webencodings ==0.5.1`
- `wheel ==0.37.1`
- `zipp ==3.8.1`
- `setuptools ==65.2.0`
</details>
<details><summary>samples/compute/requirements.txt</summary>
- `google-api-python-client ==2.58.0`
- `google-auth ==2.11.0`
- `google-auth-httplib2 ==0.1.0`
</details>
<details><summary>scripts/requirements.txt</summary>
- `pandas ==1.4.3`
</details>
</blockquote>
</details>
<details><summary>pip_setup</summary>
<blockquote>
<details><summary>setup.py</summary>
- `httplib2 >=0.15.0,<1dev`
- `google-auth >=1.19.0,<3.0.0dev`
- `google-auth-httplib2 >=0.1.0`
- `google-api-core >= 1.31.5, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.0`
- `uritemplate >=3.0.1,<5`
</details>
</blockquote>
</details>
---
- [ ] <!-- manual job -->Check this box to trigger a request for Renovate to run again on this repository
|
1.0
|
Dependency Dashboard - This issue lists Renovate updates and detected dependencies. Read the [Dependency Dashboard](https://docs.renovatebot.com/key-concepts/dashboard/) docs to learn more.
## Edited/Blocked
These updates have been manually edited so Renovate will no longer make changes. To discard all commits and start over, click on a checkbox.
- [ ] <!-- rebase-branch=renovate/distlib-0.x -->[chore(deps): update dependency distlib to v0.3.6](../pull/1887)
- [ ] <!-- rebase-branch=renovate/protobuf-4.x -->[chore(deps): update dependency protobuf to v4](../pull/1886)
## Ignored or Blocked
These are blocked by an existing closed PR and will not be recreated unless you click a checkbox below.
- [ ] <!-- recreate-branch=renovate/click-8.x -->[chore(deps): update dependency click to v8.1.3](../pull/1884)
- [ ] <!-- recreate-branch=renovate/setuptools-65.x -->[chore(deps): update dependency setuptools to v65.3.0](../pull/1885)
## Detected dependencies
<details><summary>github-actions</summary>
<blockquote>
<details><summary>.github/workflows/main.yml</summary>
- `actions/checkout v3`
- `actions/setup-python v4`
- `actions/github-script v6.2.0`
</details>
</blockquote>
</details>
<details><summary>pip_requirements</summary>
<blockquote>
<details><summary>.kokoro/requirements.txt</summary>
- `argcomplete ==2.0.0`
- `attrs ==22.1.0`
- `bleach ==5.0.1`
- `cachetools ==5.2.0`
- `certifi ==2022.6.15`
- `cffi ==1.15.1`
- `charset-normalizer ==2.1.1`
- `click ==8.0.4`
- `colorlog ==6.6.0`
- `commonmark ==0.9.1`
- `cryptography ==37.0.4`
- `distlib ==0.3.5`
- `docutils ==0.19`
- `filelock ==3.8.0`
- `gcp-docuploader ==0.6.3`
- `gcp-releasetool ==1.8.6`
- `google-api-core ==2.8.2`
- `google-auth ==2.11.0`
- `google-cloud-core ==2.3.2`
- `google-cloud-storage ==2.5.0`
- `google-crc32c ==1.3.0`
- `google-resumable-media ==2.3.3`
- `googleapis-common-protos ==1.56.4`
- `idna ==3.3`
- `importlib-metadata ==4.12.0`
- `jeepney ==0.8.0`
- `jinja2 ==3.1.2`
- `keyring ==23.8.2`
- `markupsafe ==2.1.1`
- `nox ==2022.8.7`
- `packaging ==21.3`
- `pkginfo ==1.8.3`
- `platformdirs ==2.5.2`
- `protobuf ==3.20.1`
- `py ==1.11.0`
- `pyasn1 ==0.4.8`
- `pyasn1-modules ==0.2.8`
- `pycparser ==2.21`
- `pygments ==2.13.0`
- `pyjwt ==2.4.0`
- `pyparsing ==3.0.9`
- `pyperclip ==1.8.2`
- `python-dateutil ==2.8.2`
- `readme-renderer ==37.0`
- `requests ==2.28.1`
- `requests-toolbelt ==0.9.1`
- `rfc3986 ==2.0.0`
- `rich ==12.5.1`
- `rsa ==4.9`
- `secretstorage ==3.3.3`
- `six ==1.16.0`
- `twine ==4.0.1`
- `typing-extensions ==4.3.0`
- `urllib3 ==1.26.12`
- `virtualenv ==20.16.3`
- `webencodings ==0.5.1`
- `wheel ==0.37.1`
- `zipp ==3.8.1`
- `setuptools ==65.2.0`
</details>
<details><summary>samples/compute/requirements.txt</summary>
- `google-api-python-client ==2.58.0`
- `google-auth ==2.11.0`
- `google-auth-httplib2 ==0.1.0`
</details>
<details><summary>scripts/requirements.txt</summary>
- `pandas ==1.4.3`
</details>
</blockquote>
</details>
<details><summary>pip_setup</summary>
<blockquote>
<details><summary>setup.py</summary>
- `httplib2 >=0.15.0,<1dev`
- `google-auth >=1.19.0,<3.0.0dev`
- `google-auth-httplib2 >=0.1.0`
- `google-api-core >= 1.31.5, <3.0.0dev,!=2.0.*,!=2.1.*,!=2.2.*,!=2.3.0`
- `uritemplate >=3.0.1,<5`
</details>
</blockquote>
</details>
---
- [ ] <!-- manual job -->Check this box to trigger a request for Renovate to run again on this repository
|
process
|
dependency dashboard this issue lists renovate updates and detected dependencies read the docs to learn more edited blocked these updates have been manually edited so renovate will no longer make changes to discard all commits and start over click on a checkbox pull pull ignored or blocked these are blocked by an existing closed pr and will not be recreated unless you click a checkbox below pull pull detected dependencies github actions github workflows main yml actions checkout actions setup python actions github script pip requirements kokoro requirements txt argcomplete attrs bleach cachetools certifi cffi charset normalizer click colorlog commonmark cryptography distlib docutils filelock gcp docuploader gcp releasetool google api core google auth google cloud core google cloud storage google google resumable media googleapis common protos idna importlib metadata jeepney keyring markupsafe nox packaging pkginfo platformdirs protobuf py modules pycparser pygments pyjwt pyparsing pyperclip python dateutil readme renderer requests requests toolbelt rich rsa secretstorage six twine typing extensions virtualenv webencodings wheel zipp setuptools samples compute requirements txt google api python client google auth google auth scripts requirements txt pandas pip setup setup py google auth google auth google api core uritemplate check this box to trigger a request for renovate to run again on this repository
| 1
|
33,041
| 12,165,853,719
|
IssuesEvent
|
2020-04-27 08:17:08
|
Baneeishaque/ask-med-pharma_website
|
https://api.github.com/repos/Baneeishaque/ask-med-pharma_website
|
opened
|
WS-2020-0042 (High) detected in acorn-6.3.0.tgz, acorn-5.7.3.tgz
|
security vulnerability
|
## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>acorn-6.3.0.tgz</b>, <b>acorn-5.7.3.tgz</b></p></summary>
<p>
<details><summary><b>acorn-6.3.0.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-6.3.0.tgz">https://registry.npmjs.org/acorn/-/acorn-6.3.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/node_modules/acorn-globals/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- scripts-5.0.0.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- jest-config-24.9.0.tgz
- jest-environment-jsdom-24.9.0.tgz
- jsdom-11.12.0.tgz
- acorn-globals-4.3.4.tgz
- :x: **acorn-6.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>acorn-5.7.3.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- scripts-5.0.0.tgz (Root Library)
- webpack-4.8.3.tgz
- :x: **acorn-5.7.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/ask-med-pharma_website/commit/c7f5a051704dd823a801e2402d6a6ddf574962a2">c7f5a051704dd823a801e2402d6a6ddf574962a2</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-08
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 7.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2020-0042 (High) detected in acorn-6.3.0.tgz, acorn-5.7.3.tgz - ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>acorn-6.3.0.tgz</b>, <b>acorn-5.7.3.tgz</b></p></summary>
<p>
<details><summary><b>acorn-6.3.0.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-6.3.0.tgz">https://registry.npmjs.org/acorn/-/acorn-6.3.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/node_modules/acorn-globals/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- scripts-5.0.0.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- jest-config-24.9.0.tgz
- jest-environment-jsdom-24.9.0.tgz
- jsdom-11.12.0.tgz
- acorn-globals-4.3.4.tgz
- :x: **acorn-6.3.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>acorn-5.7.3.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/ask-med-pharma_website/wp-content/themes/twentytwenty/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- scripts-5.0.0.tgz (Root Library)
- webpack-4.8.3.tgz
- :x: **acorn-5.7.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/ask-med-pharma_website/commit/c7f5a051704dd823a801e2402d6a6ddf574962a2">c7f5a051704dd823a801e2402d6a6ddf574962a2</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-08
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 7.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
ws high detected in acorn tgz acorn tgz ws high severity vulnerability vulnerable libraries acorn tgz acorn tgz acorn tgz ecmascript parser library home page a href path to dependency file tmp ws scm ask med pharma website wp content themes twentytwenty package json path to vulnerable library tmp ws scm ask med pharma website wp content themes twentytwenty node modules acorn globals node modules acorn package json dependency hierarchy scripts tgz root library jest tgz jest cli tgz jest config tgz jest environment jsdom tgz jsdom tgz acorn globals tgz x acorn tgz vulnerable library acorn tgz ecmascript parser library home page a href path to dependency file tmp ws scm ask med pharma website wp content themes twentytwenty package json path to vulnerable library tmp ws scm ask med pharma website wp content themes twentytwenty node modules acorn package json dependency hierarchy scripts tgz root library webpack tgz x acorn tgz vulnerable library found in head commit a href vulnerability details acorn is vulnerable to regex dos a regex of the form u causes the parser to enter an infinite loop attackers may leverage the vulnerability leading to a denial of service since the string is not valid and it results in it being sanitized before reaching the parser publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
390,228
| 26,854,169,717
|
IssuesEvent
|
2023-02-03 13:25:00
|
roots-id/rootswallet
|
https://api.github.com/repos/roots-id/rootswallet
|
closed
|
Review existing iOS file/directory structure and generate issues
|
documentation enhancement
|
Potentially also run RootsWallet in iOS and see what breaks
|
1.0
|
Review existing iOS file/directory structure and generate issues - Potentially also run RootsWallet in iOS and see what breaks
|
non_process
|
review existing ios file directory structure and generate issues potentially also run rootswallet in ios and see what breaks
| 0
|
161,790
| 20,155,358,842
|
IssuesEvent
|
2022-02-09 15:59:44
|
jgeraigery/experian-java
|
https://api.github.com/repos/jgeraigery/experian-java
|
closed
|
CVE-2020-11112 (High) detected in jackson-databind-2.9.2.jar - autoclosed
|
security vulnerability
|
## CVE-2020-11112 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: ository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/9c836fb688a6591b590fe6154680b73ceed58629">9c836fb688a6591b590fe6154680b73ceed58629</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","packageFilePaths":["/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11112","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-11112 (High) detected in jackson-databind-2.9.2.jar - autoclosed - ## CVE-2020-11112 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: experian-java/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml</p>
<p>Path to vulnerable library: ository/com/fasterxml/jackson/core/jackson-databind/2.9.2/jackson-databind-2.9.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/experian-java/commit/9c836fb688a6591b590fe6154680b73ceed58629">9c836fb688a6591b590fe6154680b73ceed58629</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.2","packageFilePaths":["/MavenWorkspace/bis-services-lib/bis-services-base/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.4,2.10.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11112","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file experian java mavenworkspace bis services lib bis services base pom xml path to vulnerable library ository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy vulnerabilityurl
| 0
|
6,967
| 10,119,384,217
|
IssuesEvent
|
2019-07-31 11:20:29
|
linnovate/root
|
https://api.github.com/repos/linnovate/root
|
closed
|
tasks inheritance from discussion
|
Process bug Tasks
|
create a task
create a disucssion
add users as partners with different permissions
**example meeting:**
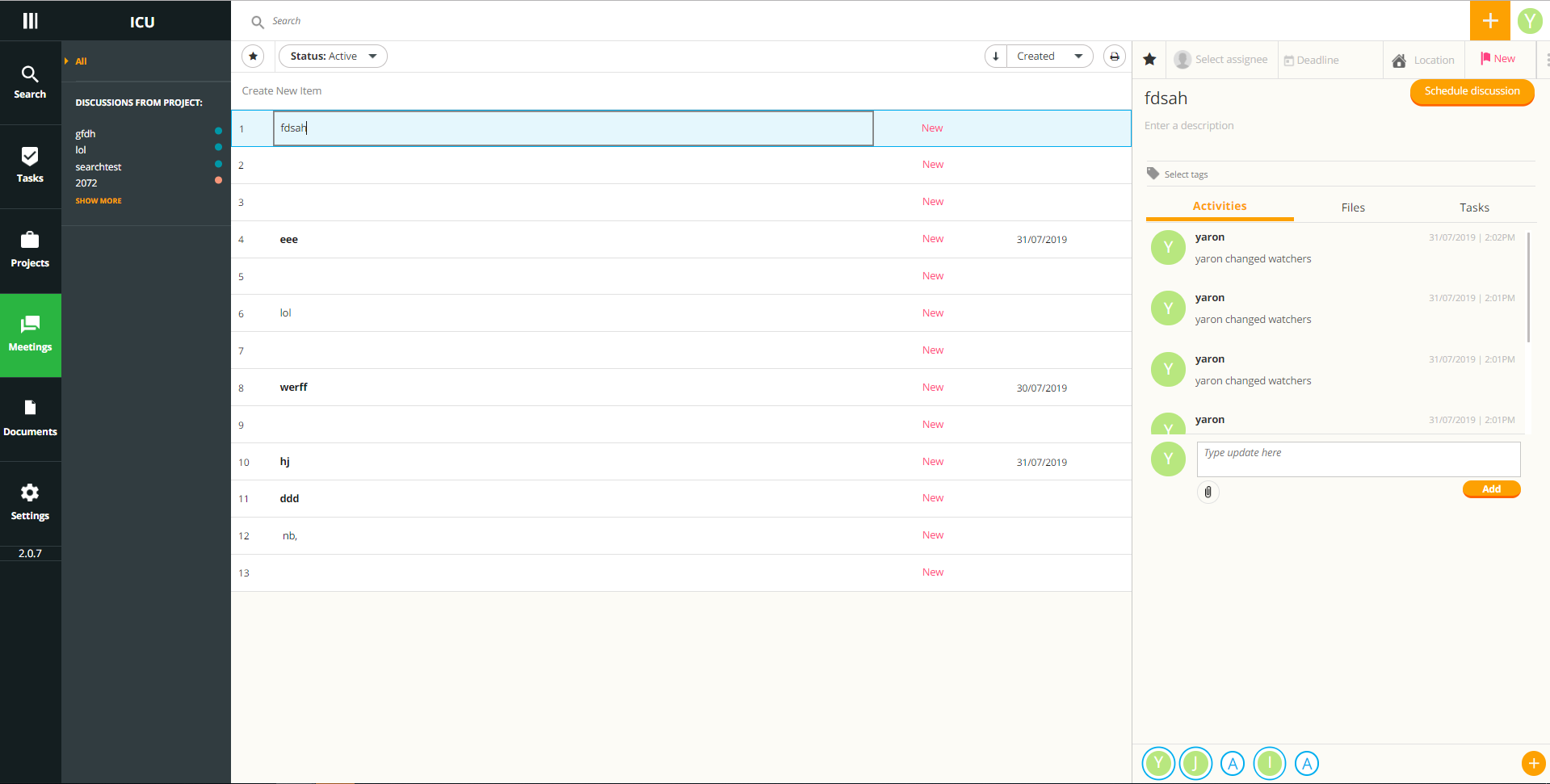
go to the created task
assign the discussion to it
the partners' permissions doesnt change :
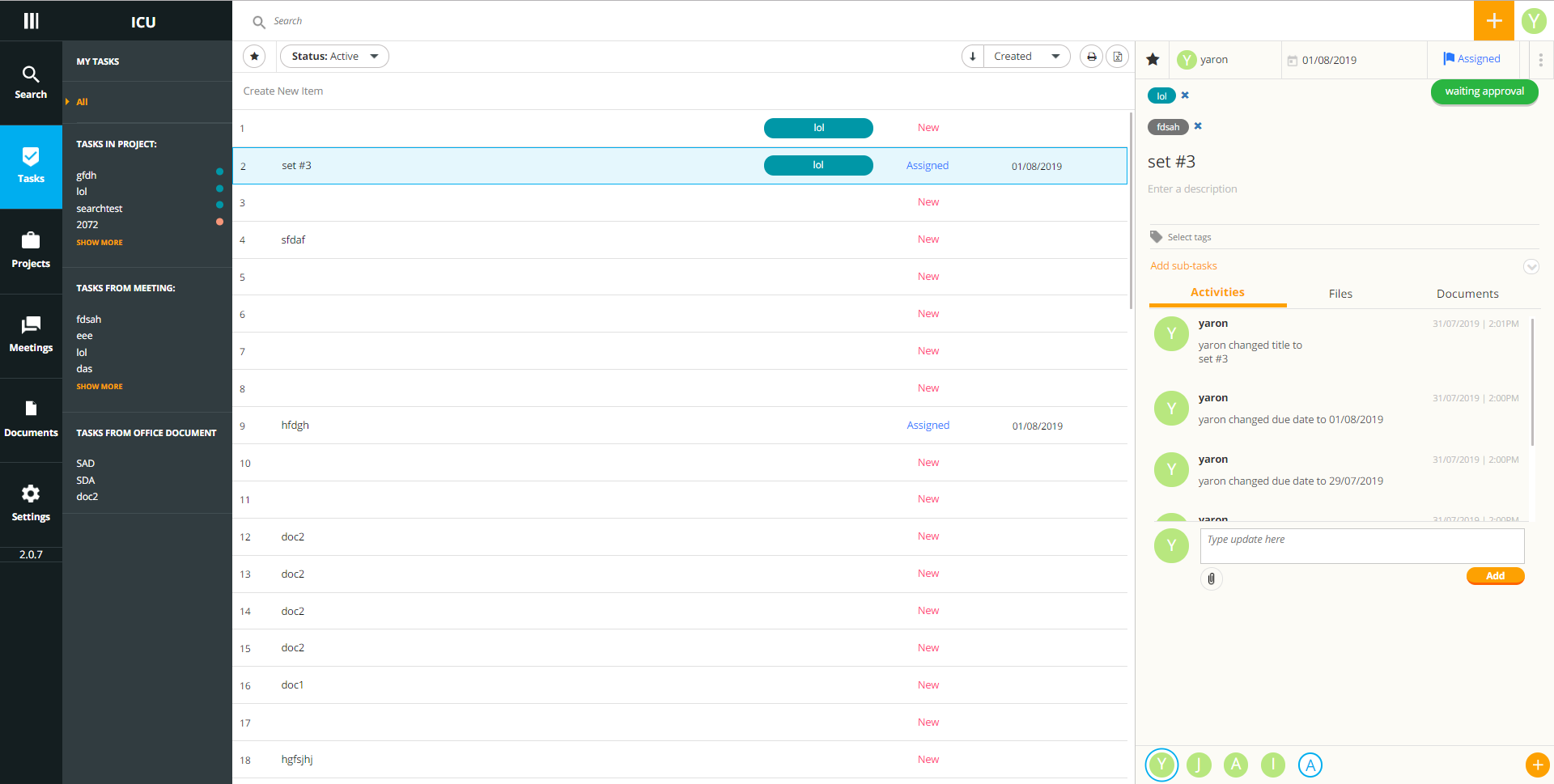
|
1.0
|
tasks inheritance from discussion - create a task
create a disucssion
add users as partners with different permissions
**example meeting:**
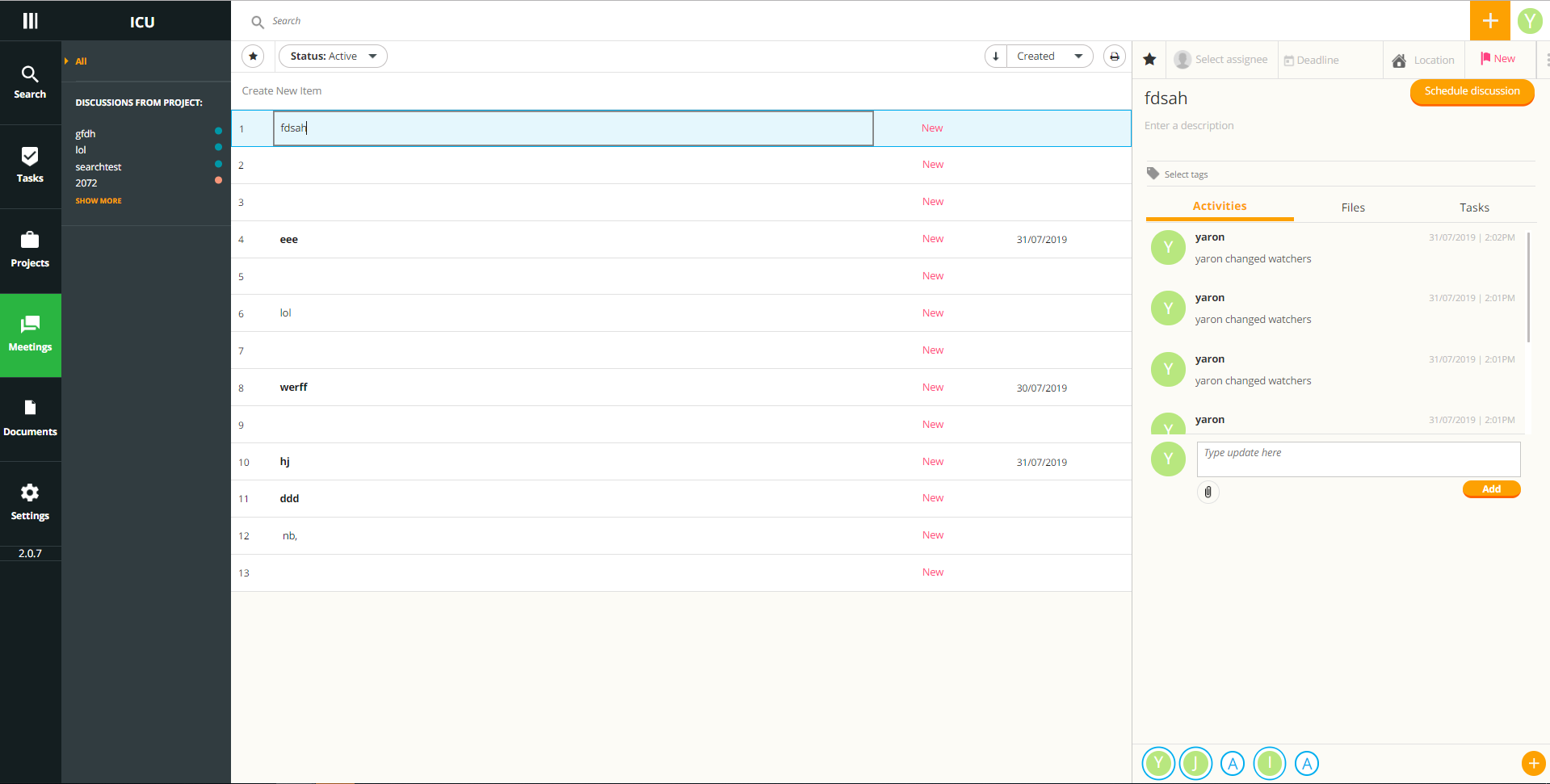
go to the created task
assign the discussion to it
the partners' permissions doesnt change :
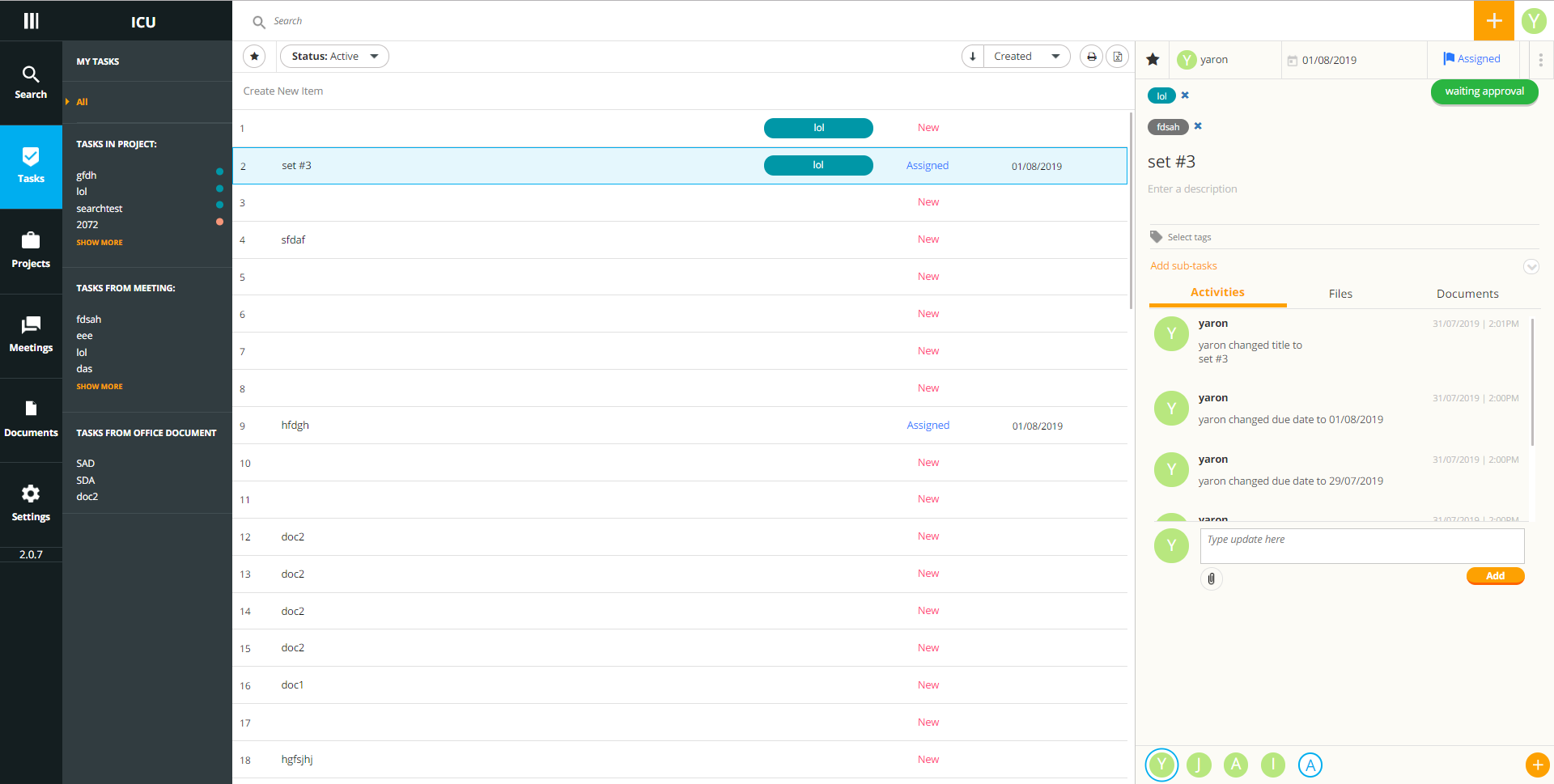
|
process
|
tasks inheritance from discussion create a task create a disucssion add users as partners with different permissions example meeting go to the created task assign the discussion to it the partners permissions doesnt change
| 1
|
14,847
| 18,242,123,449
|
IssuesEvent
|
2021-10-01 14:04:10
|
pycaret/pycaret
|
https://api.github.com/repos/pycaret/pycaret
|
closed
|
ValueError: dtype for the target variable should be int32 or int64 only
|
bug preprocessing
|
**Describe the bug**
<!--
-->
In regression it is usual to use independent variables in float.
In Pycaret version 2.3.4 I get the following error in regression when activating "Remove Multicollinearity=True", in "False" it does not give the problem.
ERROR: pycaret regression ValueError: dtype for the target variable should be int32 or int64 only
I understand that it should support float and integer values.
FILE: /usr/local/lib/python3.7/dist-packages/pycaret/internal/preprocess.py
rows 2515, 2516
class Fix_multicollinearity(BaseEstimator, TransformerMixin):
def fit(self, data, y=None):
...
if data[self.target_variable].dtype not in ["int32", "int64"]:
raise ValueError('dtype for the target variable should be int32 or int64 only')
...
**To Reproduce**
<!--
-->
from pycaret.datasets import get_data
dataset = get_data('diamond')
dataset['Price'] = dataset['Price'].astype('float32')
from pycaret.regression import *
exp_reg101 = setup(data = dataset, target = 'Price', session_id=123,
remove_multicollinearity = True, multicollinearity_threshold = 0.95)
---------------------------------------------------------------------------
ValueError Traceback (most recent call last)
<ipython-input-9-f41871135e22> in <module>()
1 from pycaret.regression import *
2 exp_reg101 = setup(data = dataset, target = 'Price', session_id=123,
----> 3 remove_multicollinearity = True, multicollinearity_threshold = 0.95)
7 frames
/usr/local/lib/python3.7/dist-packages/pycaret/internal/preprocess.py in fit(self, data, y)
2514
2515 if data[self.target_variable].dtype not in ["int32", "int64"]:
-> 2516 raise ValueError('dtype for the target variable should be int32 or int64 only')
2517
2518 # global data1
ValueError: dtype for the target variable should be int32 or int64 only
```python
from pycaret.datasets import get_data
dataset = get_data('diamond')
dataset['Price'] = dataset['Price'].astype('float32')
from pycaret.regression import *
exp_reg101 = setup(data = dataset, target = 'Price', session_id=123,
remove_multicollinearity = True, multicollinearity_threshold = 0.95)
```
**Expected behavior**
<!--
A clear and concise description of what you expected to happen.
-->
**Additional context**
<!--
Add any other context about the problem here.
-->
I understand that it should support float and integer values.
**Versions**
<2.3.4>
<!--
Please run the following code snippet and paste the output here:
import pycaret
pycaret.__version__
-->
</details>
<!-- Thanks for contributing! -->
|
1.0
|
ValueError: dtype for the target variable should be int32 or int64 only - **Describe the bug**
<!--
-->
In regression it is usual to use independent variables in float.
In Pycaret version 2.3.4 I get the following error in regression when activating "Remove Multicollinearity=True", in "False" it does not give the problem.
ERROR: pycaret regression ValueError: dtype for the target variable should be int32 or int64 only
I understand that it should support float and integer values.
FILE: /usr/local/lib/python3.7/dist-packages/pycaret/internal/preprocess.py
rows 2515, 2516
class Fix_multicollinearity(BaseEstimator, TransformerMixin):
def fit(self, data, y=None):
...
if data[self.target_variable].dtype not in ["int32", "int64"]:
raise ValueError('dtype for the target variable should be int32 or int64 only')
...
**To Reproduce**
<!--
-->
from pycaret.datasets import get_data
dataset = get_data('diamond')
dataset['Price'] = dataset['Price'].astype('float32')
from pycaret.regression import *
exp_reg101 = setup(data = dataset, target = 'Price', session_id=123,
remove_multicollinearity = True, multicollinearity_threshold = 0.95)
---------------------------------------------------------------------------
ValueError Traceback (most recent call last)
<ipython-input-9-f41871135e22> in <module>()
1 from pycaret.regression import *
2 exp_reg101 = setup(data = dataset, target = 'Price', session_id=123,
----> 3 remove_multicollinearity = True, multicollinearity_threshold = 0.95)
7 frames
/usr/local/lib/python3.7/dist-packages/pycaret/internal/preprocess.py in fit(self, data, y)
2514
2515 if data[self.target_variable].dtype not in ["int32", "int64"]:
-> 2516 raise ValueError('dtype for the target variable should be int32 or int64 only')
2517
2518 # global data1
ValueError: dtype for the target variable should be int32 or int64 only
```python
from pycaret.datasets import get_data
dataset = get_data('diamond')
dataset['Price'] = dataset['Price'].astype('float32')
from pycaret.regression import *
exp_reg101 = setup(data = dataset, target = 'Price', session_id=123,
remove_multicollinearity = True, multicollinearity_threshold = 0.95)
```
**Expected behavior**
<!--
A clear and concise description of what you expected to happen.
-->
**Additional context**
<!--
Add any other context about the problem here.
-->
I understand that it should support float and integer values.
**Versions**
<2.3.4>
<!--
Please run the following code snippet and paste the output here:
import pycaret
pycaret.__version__
-->
</details>
<!-- Thanks for contributing! -->
|
process
|
valueerror dtype for the target variable should be or only describe the bug in regression it is usual to use independent variables in float in pycaret version i get the following error in regression when activating remove multicollinearity true in false it does not give the problem error pycaret regression valueerror dtype for the target variable should be or only i understand that it should support float and integer values file usr local lib dist packages pycaret internal preprocess py rows class fix multicollinearity baseestimator transformermixin def fit self data y none if data dtype not in raise valueerror dtype for the target variable should be or only to reproduce from pycaret datasets import get data dataset get data diamond dataset dataset astype from pycaret regression import exp setup data dataset target price session id remove multicollinearity true multicollinearity threshold valueerror traceback most recent call last in from pycaret regression import exp setup data dataset target price session id remove multicollinearity true multicollinearity threshold frames usr local lib dist packages pycaret internal preprocess py in fit self data y if data dtype not in raise valueerror dtype for the target variable should be or only global valueerror dtype for the target variable should be or only python from pycaret datasets import get data dataset get data diamond dataset dataset astype from pycaret regression import exp setup data dataset target price session id remove multicollinearity true multicollinearity threshold expected behavior a clear and concise description of what you expected to happen additional context add any other context about the problem here i understand that it should support float and integer values versions please run the following code snippet and paste the output here import pycaret pycaret version
| 1
|
46,662
| 11,866,052,983
|
IssuesEvent
|
2020-03-26 02:26:26
|
spack/spack
|
https://api.github.com/repos/spack/spack
|
opened
|
autoconf and other packages on ppc64le
|
build-error
|
### Spack version
<!-- Add the output to the command below -->
```console
[kai@longhorn ~]$ spack --version
```
### Steps to reproduce the issue
```console
[kai@longhorn ~]$ spack spec autoconf
Input spec
--------------------------------
autoconf
Concretized
--------------------------------
autoconf@2.69%gcc@7.3.0 arch=linux-rhel7-power9le
^m4@1.4.18%gcc@7.3.0 patches=3877ab548f88597ab2327a2230ee048d2d07ace1062efe81fc92e91b7f39cd00,fc9b61654a3ba1a8d6cd78ce087e7c96366c290bc8d2c299f09828d793b853c8 +sigsegv arch=linux-rhel7-power9le
^libsigsegv@2.12%gcc@7.3.0 arch=linux-rhel7-power9le
^perl@5.30.1%gcc@7.3.0+cpanm+shared+threads arch=linux-rhel7-power9le
^gdbm@1.18.1%gcc@7.3.0 arch=linux-rhel7-power9le
^readline@8.0%gcc@7.3.0 arch=linux-rhel7-power9le
^ncurses@6.2%gcc@7.3.0~symlinks+termlib arch=linux-rhel7-power9le
^pkgconf@1.6.3%gcc@7.3.0 arch=linux-rhel7-power9le
[kai@longhorn ~]$ spack install autoconf
[...]
See build log for details:
/tmp/kai/spack-stage/spack-stage-autoconf-2.69-ftyunbfd663jlfj24legpgewbdsjygse/spack-build-out.txt
Traceback (most recent call last):
File "/home/01537/kai/build/spack/lib/spack/spack/build_environment.py", line 801, in child_process
return_value = function()
File "/home/01537/kai/build/spack/lib/spack/spack/installer.py", line 1113, in build_process
phase(pkg.spec, pkg.prefix)
File "/home/01537/kai/build/spack/lib/spack/spack/package.py", line 112, in phase_wrapper
callback(instance)
File "/home/01537/kai/build/spack/lib/spack/spack/build_systems/autotools.py", line 160, in _do_patch_config_guess
raise RuntimeError('Failed to find suitable config.guess')
RuntimeError: Failed to find suitable config.guess
```
### Platform and user environment
```console
[kai@longhorn ~]$ uname -a
Linux login1.longhorn.tacc.utexas.edu 4.14.0-115.10.1.el7a.ppc64le #1 SMP Wed Jun 26 09:32:17 UTC 2019 ppc64le ppc64le ppc64le GNU/Linux
[kai@longhorn ~]$ cat /etc/redhat-release
Red Hat Enterprise Linux Server release 7.6 (Maipo)
```
This machine (longhorn) is similar to Summit, except that it has very little software installed.
I've tracked the issue down already: When trying to install `autoconf`, spack checks whether the included `config.guess` works. It does not, because it does not recognize what should be `powerpc64le-unknown-linux-gnu`. So spack is looking for a newer `config.guess` to replace the included one. On Summit, it'll find one in `/usr/share/automake-x.yy`, and things work. On this machine, automake is not installed (at least not in the standard location). If the package depended on `automake`, it'd look at the spack-installed automake to find a newer `config.guess`. That doesn't apply here.
I don't have access to install anything in `/usr/share`, so the question is, how can I provide an updated `config.guess`? I've hacked around it for now by modifying spack's source so that it searches in my home directory, but clearly that's not a sustainable solution.
[This problem isn't really limited to just the autoconf package, either, but any package that ships with an outdated `config.guess`, which doesn't depend on `automake`: `libsodium` was another manifestation of the same issue.]
One way to make it possible to work around this problem would be for spack to search for `config.guess` in a user-specified location, though I still don't like it, since the user would still have to go find an appropriate `config.guess`, and point spack to it. I'd much rather have something that works out of the box, but I don't have any good idea on how to get it done.
|
1.0
|
autoconf and other packages on ppc64le -
### Spack version
<!-- Add the output to the command below -->
```console
[kai@longhorn ~]$ spack --version
```
### Steps to reproduce the issue
```console
[kai@longhorn ~]$ spack spec autoconf
Input spec
--------------------------------
autoconf
Concretized
--------------------------------
autoconf@2.69%gcc@7.3.0 arch=linux-rhel7-power9le
^m4@1.4.18%gcc@7.3.0 patches=3877ab548f88597ab2327a2230ee048d2d07ace1062efe81fc92e91b7f39cd00,fc9b61654a3ba1a8d6cd78ce087e7c96366c290bc8d2c299f09828d793b853c8 +sigsegv arch=linux-rhel7-power9le
^libsigsegv@2.12%gcc@7.3.0 arch=linux-rhel7-power9le
^perl@5.30.1%gcc@7.3.0+cpanm+shared+threads arch=linux-rhel7-power9le
^gdbm@1.18.1%gcc@7.3.0 arch=linux-rhel7-power9le
^readline@8.0%gcc@7.3.0 arch=linux-rhel7-power9le
^ncurses@6.2%gcc@7.3.0~symlinks+termlib arch=linux-rhel7-power9le
^pkgconf@1.6.3%gcc@7.3.0 arch=linux-rhel7-power9le
[kai@longhorn ~]$ spack install autoconf
[...]
See build log for details:
/tmp/kai/spack-stage/spack-stage-autoconf-2.69-ftyunbfd663jlfj24legpgewbdsjygse/spack-build-out.txt
Traceback (most recent call last):
File "/home/01537/kai/build/spack/lib/spack/spack/build_environment.py", line 801, in child_process
return_value = function()
File "/home/01537/kai/build/spack/lib/spack/spack/installer.py", line 1113, in build_process
phase(pkg.spec, pkg.prefix)
File "/home/01537/kai/build/spack/lib/spack/spack/package.py", line 112, in phase_wrapper
callback(instance)
File "/home/01537/kai/build/spack/lib/spack/spack/build_systems/autotools.py", line 160, in _do_patch_config_guess
raise RuntimeError('Failed to find suitable config.guess')
RuntimeError: Failed to find suitable config.guess
```
### Platform and user environment
```console
[kai@longhorn ~]$ uname -a
Linux login1.longhorn.tacc.utexas.edu 4.14.0-115.10.1.el7a.ppc64le #1 SMP Wed Jun 26 09:32:17 UTC 2019 ppc64le ppc64le ppc64le GNU/Linux
[kai@longhorn ~]$ cat /etc/redhat-release
Red Hat Enterprise Linux Server release 7.6 (Maipo)
```
This machine (longhorn) is similar to Summit, except that it has very little software installed.
I've tracked the issue down already: When trying to install `autoconf`, spack checks whether the included `config.guess` works. It does not, because it does not recognize what should be `powerpc64le-unknown-linux-gnu`. So spack is looking for a newer `config.guess` to replace the included one. On Summit, it'll find one in `/usr/share/automake-x.yy`, and things work. On this machine, automake is not installed (at least not in the standard location). If the package depended on `automake`, it'd look at the spack-installed automake to find a newer `config.guess`. That doesn't apply here.
I don't have access to install anything in `/usr/share`, so the question is, how can I provide an updated `config.guess`? I've hacked around it for now by modifying spack's source so that it searches in my home directory, but clearly that's not a sustainable solution.
[This problem isn't really limited to just the autoconf package, either, but any package that ships with an outdated `config.guess`, which doesn't depend on `automake`: `libsodium` was another manifestation of the same issue.]
One way to make it possible to work around this problem would be for spack to search for `config.guess` in a user-specified location, though I still don't like it, since the user would still have to go find an appropriate `config.guess`, and point spack to it. I'd much rather have something that works out of the box, but I don't have any good idea on how to get it done.
|
non_process
|
autoconf and other packages on spack version console spack version steps to reproduce the issue console spack spec autoconf input spec autoconf concretized autoconf gcc arch linux gcc patches sigsegv arch linux libsigsegv gcc arch linux perl gcc cpanm shared threads arch linux gdbm gcc arch linux readline gcc arch linux ncurses gcc symlinks termlib arch linux pkgconf gcc arch linux spack install autoconf see build log for details tmp kai spack stage spack stage autoconf spack build out txt traceback most recent call last file home kai build spack lib spack spack build environment py line in child process return value function file home kai build spack lib spack spack installer py line in build process phase pkg spec pkg prefix file home kai build spack lib spack spack package py line in phase wrapper callback instance file home kai build spack lib spack spack build systems autotools py line in do patch config guess raise runtimeerror failed to find suitable config guess runtimeerror failed to find suitable config guess platform and user environment console uname a linux longhorn tacc utexas edu smp wed jun utc gnu linux cat etc redhat release red hat enterprise linux server release maipo this machine longhorn is similar to summit except that it has very little software installed i ve tracked the issue down already when trying to install autoconf spack checks whether the included config guess works it does not because it does not recognize what should be unknown linux gnu so spack is looking for a newer config guess to replace the included one on summit it ll find one in usr share automake x yy and things work on this machine automake is not installed at least not in the standard location if the package depended on automake it d look at the spack installed automake to find a newer config guess that doesn t apply here i don t have access to install anything in usr share so the question is how can i provide an updated config guess i ve hacked around it for now by modifying spack s source so that it searches in my home directory but clearly that s not a sustainable solution one way to make it possible to work around this problem would be for spack to search for config guess in a user specified location though i still don t like it since the user would still have to go find an appropriate config guess and point spack to it i d much rather have something that works out of the box but i don t have any good idea on how to get it done
| 0
|
10,702
| 13,497,560,421
|
IssuesEvent
|
2020-09-12 08:16:10
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
reopened
|
Download full results of a Query to CSV or XLSX - Excel does not recognize the Timestamp format
|
.Backend Difficulty:Easy Priority:P1 Querying/Processor Reporting/Export Type:Bug
|
Download full results of a Query to CSV or XLSX - Excel does not recognize the Timestamp format
**To Reproduce**
Steps to reproduce the behavior:
1. Go to any query you may have that has a timestamp field (at least in Oracle database as data source).
2. Click on 'Download full results' in XLSX or CSV.
3. Open with Excel.
4. See column containing timestamp, it is shown in the cell as:
2019-03-18T17:24:31.000+01:00 (type 'General', i.e. not recognized).
It cannot be converted either or get recognized if cell is changed to date, time, ...
**Expected behavior**
When exporting results containing dates, times or datetimes (timestamps fields), the formatting should be recognized by Excel on Open without any need to convert or tweak the data.
**Screenshots**

**Information about your Metabase Installation:**
- Your browser and the version: Chrome version 76.0.3809.132 (Official Build) (32-bit)
- Your operating system: Windows 10.0.17134 Build 17134
- Your databases: Oracle, MySQL
- Metabase version: v.0.33
- Metabase hosting environment: Jar-file on CentOS
- Metabase internal database: MySQL
**Severity**
This annoying and prevents that some users can make use of Metabase to complete some of their tasks.
⬇️ **Please click the 👍 reaction instead of leaving a `+1` or 👍 comment**
|
1.0
|
Download full results of a Query to CSV or XLSX - Excel does not recognize the Timestamp format - Download full results of a Query to CSV or XLSX - Excel does not recognize the Timestamp format
**To Reproduce**
Steps to reproduce the behavior:
1. Go to any query you may have that has a timestamp field (at least in Oracle database as data source).
2. Click on 'Download full results' in XLSX or CSV.
3. Open with Excel.
4. See column containing timestamp, it is shown in the cell as:
2019-03-18T17:24:31.000+01:00 (type 'General', i.e. not recognized).
It cannot be converted either or get recognized if cell is changed to date, time, ...
**Expected behavior**
When exporting results containing dates, times or datetimes (timestamps fields), the formatting should be recognized by Excel on Open without any need to convert or tweak the data.
**Screenshots**

**Information about your Metabase Installation:**
- Your browser and the version: Chrome version 76.0.3809.132 (Official Build) (32-bit)
- Your operating system: Windows 10.0.17134 Build 17134
- Your databases: Oracle, MySQL
- Metabase version: v.0.33
- Metabase hosting environment: Jar-file on CentOS
- Metabase internal database: MySQL
**Severity**
This annoying and prevents that some users can make use of Metabase to complete some of their tasks.
⬇️ **Please click the 👍 reaction instead of leaving a `+1` or 👍 comment**
|
process
|
download full results of a query to csv or xlsx excel does not recognize the timestamp format download full results of a query to csv or xlsx excel does not recognize the timestamp format to reproduce steps to reproduce the behavior go to any query you may have that has a timestamp field at least in oracle database as data source click on download full results in xlsx or csv open with excel see column containing timestamp it is shown in the cell as type general i e not recognized it cannot be converted either or get recognized if cell is changed to date time expected behavior when exporting results containing dates times or datetimes timestamps fields the formatting should be recognized by excel on open without any need to convert or tweak the data screenshots information about your metabase installation your browser and the version chrome version official build bit your operating system windows build your databases oracle mysql metabase version v metabase hosting environment jar file on centos metabase internal database mysql severity this annoying and prevents that some users can make use of metabase to complete some of their tasks ⬇️ please click the 👍 reaction instead of leaving a or 👍 comment
| 1
|
7,047
| 10,208,508,980
|
IssuesEvent
|
2019-08-14 10:17:31
|
MicrosoftDocs/azure-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-docs
|
closed
|
New Devops Domain
|
Pri2 assigned-to-author automation/svc process-automation/subsvc product-question triaged
|
Does not support the new devops domain
https://aka.ms/new-domain
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 83c90e64-b615-711f-a53d-fc76606e2ecd
* Version Independent ID: 2d164036-6886-4440-50f7-369f99f41cea
* Content: [Source Control integration in Azure Automation](https://docs.microsoft.com/en-us/azure/automation/source-control-integration#feedback)
* Content Source: [articles/automation/source-control-integration.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/source-control-integration.md)
* Service: **automation**
* Sub-service: **process-automation**
* GitHub Login: @bobbytreed
* Microsoft Alias: **robreed**
|
1.0
|
New Devops Domain - Does not support the new devops domain
https://aka.ms/new-domain
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 83c90e64-b615-711f-a53d-fc76606e2ecd
* Version Independent ID: 2d164036-6886-4440-50f7-369f99f41cea
* Content: [Source Control integration in Azure Automation](https://docs.microsoft.com/en-us/azure/automation/source-control-integration#feedback)
* Content Source: [articles/automation/source-control-integration.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/source-control-integration.md)
* Service: **automation**
* Sub-service: **process-automation**
* GitHub Login: @bobbytreed
* Microsoft Alias: **robreed**
|
process
|
new devops domain does not support the new devops domain document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service automation sub service process automation github login bobbytreed microsoft alias robreed
| 1
|
299,088
| 9,205,047,204
|
IssuesEvent
|
2019-03-08 09:28:22
|
richelbilderbeek/djog_unos_2018
|
https://api.github.com/repos/richelbilderbeek/djog_unos_2018
|
closed
|
Lions and crocodiles eat cows only when close
|
medium priority
|
**Is your feature request related to a problem? Please describe.**
Currently, the lions and crocodiles eat cows from approx 5 meters. In reality, this is zero meters.
**Describe the solution you'd like**
Let the lions and crocodiles eat cows only when close
**Describe alternatives you've considered**
None.
**Additional context**
None,
|
1.0
|
Lions and crocodiles eat cows only when close - **Is your feature request related to a problem? Please describe.**
Currently, the lions and crocodiles eat cows from approx 5 meters. In reality, this is zero meters.
**Describe the solution you'd like**
Let the lions and crocodiles eat cows only when close
**Describe alternatives you've considered**
None.
**Additional context**
None,
|
non_process
|
lions and crocodiles eat cows only when close is your feature request related to a problem please describe currently the lions and crocodiles eat cows from approx meters in reality this is zero meters describe the solution you d like let the lions and crocodiles eat cows only when close describe alternatives you ve considered none additional context none
| 0
|
6,314
| 9,320,787,232
|
IssuesEvent
|
2019-03-27 00:50:55
|
tc39/proposal-promise-allSettled
|
https://api.github.com/repos/tc39/proposal-promise-allSettled
|
closed
|
Advance to stage 3
|
process
|
Criteria taken from [the TC39 process document](https://tc39.github.io/process-document/) minus those from previous stages:
> - [x] Complete spec text
https://github.com/tc39/proposal-promise-allSettled#specification
> - [x] Designated reviewers have signed off on the current spec text
- [x] @codehag
- [x] @domenic
- [x] @gibson042
> - [x] All ECMAScript editors have signed off on the current spec text
- [x] @ljharb
- [x] @zenparsing
|
1.0
|
Advance to stage 3 - Criteria taken from [the TC39 process document](https://tc39.github.io/process-document/) minus those from previous stages:
> - [x] Complete spec text
https://github.com/tc39/proposal-promise-allSettled#specification
> - [x] Designated reviewers have signed off on the current spec text
- [x] @codehag
- [x] @domenic
- [x] @gibson042
> - [x] All ECMAScript editors have signed off on the current spec text
- [x] @ljharb
- [x] @zenparsing
|
process
|
advance to stage criteria taken from minus those from previous stages complete spec text designated reviewers have signed off on the current spec text codehag domenic all ecmascript editors have signed off on the current spec text ljharb zenparsing
| 1
|
47,765
| 12,110,519,856
|
IssuesEvent
|
2020-04-21 10:33:34
|
GoogleCloudPlatform/python-docs-samples
|
https://api.github.com/repos/GoogleCloudPlatform/python-docs-samples
|
opened
|
composer.workflows.bq_copy_across_locations_test: test_dag failed
|
buildcop: issue priority: p1 type: bug
|
This test failed!
To configure my behavior, see [the Build Cop Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop).
If I'm commenting on this issue too often, add the `buildcop: quiet` label and
I will stop commenting.
---
commit: fa38579cbf0946fd8ce0610bf86cb19cbe9ab782
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/d94a37ce-d68d-48d2-a1e4-3e74086e9c77), [Sponge](http://sponge2/d94a37ce-d68d-48d2-a1e4-3e74086e9c77)
status: failed
|
1.0
|
composer.workflows.bq_copy_across_locations_test: test_dag failed - This test failed!
To configure my behavior, see [the Build Cop Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop).
If I'm commenting on this issue too often, add the `buildcop: quiet` label and
I will stop commenting.
---
commit: fa38579cbf0946fd8ce0610bf86cb19cbe9ab782
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/d94a37ce-d68d-48d2-a1e4-3e74086e9c77), [Sponge](http://sponge2/d94a37ce-d68d-48d2-a1e4-3e74086e9c77)
status: failed
|
non_process
|
composer workflows bq copy across locations test test dag failed this test failed to configure my behavior see if i m commenting on this issue too often add the buildcop quiet label and i will stop commenting commit buildurl status failed
| 0
|
19,925
| 26,391,855,419
|
IssuesEvent
|
2023-01-12 16:14:00
|
python/cpython
|
https://api.github.com/repos/python/cpython
|
closed
|
"OSError not raised by Listener" in test_asyncio test_multiprocessing_* with Linux kernel 6.0.16-6.1.3 (kernel bug)
|
type-bug tests expert-asyncio expert-multiprocessing
|
# Bug report
A few tests in CPython's test suite have suddenly started failing. I've first experienced the problem rebuilding 3.8.16 on 2023-01-11, then confirmed it on top of 3.12.0a3, 3.12.0a4 and main today. The same 3.8.16 and 3.12.0a3 versions used to pass the respective tests on 2012-12-07. I'm currently trying to investigate what have changed since but unfortunately it's hard for such a large span of time. Any ideas what to look for would be appreciated.
The failing tests are:
```
4 tests failed:
test_asyncio test_multiprocessing_fork
test_multiprocessing_forkserver test_multiprocessing_spawn
```
FWICS all the failures resemble this one:
```pytb
======================================================================
FAIL: test_multiple_bind (test.test_multiprocessing_spawn.WithProcessesTestListener.test_multiple_bind)
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/mgorny/git/cpython/Lib/test/_test_multiprocessing.py", line 3377, in test_multiple_bind
self.assertRaises(OSError, self.connection.Listener,
AssertionError: OSError not raised by Listener
```
I've run these tests using:
```
./python -u -W default -bb -E -E -m test -v test_asyncio test_multiprocessing_fork test_multiprocessing_forkserver test_multiprocessing_spawn
```
Full log (415k): [test.txt](https://github.com/python/cpython/files/10393849/test.txt)
# Your environment
- CPython versions tested on: 3.8.16, 3.12.0a3, 3.12.0a4, 762745a124cbc297cf2fe6f3ec9ca1840bb2e873
- Operating system and architecture: Gentoo Linux amd64, glibc 2.36-r6 p6, kernel 6.0.18-gentoo-dist
|
1.0
|
"OSError not raised by Listener" in test_asyncio test_multiprocessing_* with Linux kernel 6.0.16-6.1.3 (kernel bug) - # Bug report
A few tests in CPython's test suite have suddenly started failing. I've first experienced the problem rebuilding 3.8.16 on 2023-01-11, then confirmed it on top of 3.12.0a3, 3.12.0a4 and main today. The same 3.8.16 and 3.12.0a3 versions used to pass the respective tests on 2012-12-07. I'm currently trying to investigate what have changed since but unfortunately it's hard for such a large span of time. Any ideas what to look for would be appreciated.
The failing tests are:
```
4 tests failed:
test_asyncio test_multiprocessing_fork
test_multiprocessing_forkserver test_multiprocessing_spawn
```
FWICS all the failures resemble this one:
```pytb
======================================================================
FAIL: test_multiple_bind (test.test_multiprocessing_spawn.WithProcessesTestListener.test_multiple_bind)
----------------------------------------------------------------------
Traceback (most recent call last):
File "/home/mgorny/git/cpython/Lib/test/_test_multiprocessing.py", line 3377, in test_multiple_bind
self.assertRaises(OSError, self.connection.Listener,
AssertionError: OSError not raised by Listener
```
I've run these tests using:
```
./python -u -W default -bb -E -E -m test -v test_asyncio test_multiprocessing_fork test_multiprocessing_forkserver test_multiprocessing_spawn
```
Full log (415k): [test.txt](https://github.com/python/cpython/files/10393849/test.txt)
# Your environment
- CPython versions tested on: 3.8.16, 3.12.0a3, 3.12.0a4, 762745a124cbc297cf2fe6f3ec9ca1840bb2e873
- Operating system and architecture: Gentoo Linux amd64, glibc 2.36-r6 p6, kernel 6.0.18-gentoo-dist
|
process
|
oserror not raised by listener in test asyncio test multiprocessing with linux kernel kernel bug bug report a few tests in cpython s test suite have suddenly started failing i ve first experienced the problem rebuilding on then confirmed it on top of and main today the same and versions used to pass the respective tests on i m currently trying to investigate what have changed since but unfortunately it s hard for such a large span of time any ideas what to look for would be appreciated the failing tests are tests failed test asyncio test multiprocessing fork test multiprocessing forkserver test multiprocessing spawn fwics all the failures resemble this one pytb fail test multiple bind test test multiprocessing spawn withprocessestestlistener test multiple bind traceback most recent call last file home mgorny git cpython lib test test multiprocessing py line in test multiple bind self assertraises oserror self connection listener assertionerror oserror not raised by listener i ve run these tests using python u w default bb e e m test v test asyncio test multiprocessing fork test multiprocessing forkserver test multiprocessing spawn full log your environment cpython versions tested on operating system and architecture gentoo linux glibc kernel gentoo dist
| 1
|
270,321
| 28,960,497,082
|
IssuesEvent
|
2023-05-10 01:47:02
|
artsking/linux-4.19.72
|
https://api.github.com/repos/artsking/linux-4.19.72
|
reopened
|
WS-2021-0213 (High) detected in linux-yoctov5.4.51
|
Mend: dependency security vulnerability
|
## WS-2021-0213 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.19.72/commit/8519fe4185f1a7567a708f01b476f195b0f1046c">8519fe4185f1a7567a708f01b476f195b0f1046c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/ti/wl1251/cmd.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/ti/wl1251/cmd.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Linux/kernel in versions v3.5-rc1--v5.13 is vulnerable to possible buffer overflow in wl1251_cmd_scan
<p>Publish Date: 2021-05-31
<p>URL: <a href=https://github.com/torvalds/linux/commit/57ad99ae3c6738ba87bad259bb57c641ca68ebf6>WS-2021-0213</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1001488">https://osv.dev/vulnerability/UVI-2021-1001488</a></p>
<p>Release Date: 2021-05-31</p>
<p>Fix Resolution: v5.14-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2021-0213 (High) detected in linux-yoctov5.4.51 - ## WS-2021-0213 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.19.72/commit/8519fe4185f1a7567a708f01b476f195b0f1046c">8519fe4185f1a7567a708f01b476f195b0f1046c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/ti/wl1251/cmd.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/wireless/ti/wl1251/cmd.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Linux/kernel in versions v3.5-rc1--v5.13 is vulnerable to possible buffer overflow in wl1251_cmd_scan
<p>Publish Date: 2021-05-31
<p>URL: <a href=https://github.com/torvalds/linux/commit/57ad99ae3c6738ba87bad259bb57c641ca68ebf6>WS-2021-0213</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1001488">https://osv.dev/vulnerability/UVI-2021-1001488</a></p>
<p>Release Date: 2021-05-31</p>
<p>Fix Resolution: v5.14-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
ws high detected in linux ws high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers net wireless ti cmd c drivers net wireless ti cmd c vulnerability details linux kernel in versions is vulnerable to possible buffer overflow in cmd scan publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
17,733
| 23,641,756,644
|
IssuesEvent
|
2022-08-25 17:45:37
|
carbon-design-system/ibm-cloud-cognitive
|
https://api.github.com/repos/carbon-design-system/ibm-cloud-cognitive
|
closed
|
Revisiting motion libraries for component animations
|
type: process improvement needs: investigation
|
## What will this achieve?
After working with motion on components in Carbon for IBM Products, we noticed that trying to animate elements that leave the DOM can be challenging. @matthewgallo has added utilities to help with this but they can quickly become buggy (relying on state and adding handlers in places to undo "onAnimationEnd" handler.)
We should consider Framer motion because it is easier to use and has a ton of features for reduce motion and hooks that the team can benefit from.
|
1.0
|
Revisiting motion libraries for component animations - ## What will this achieve?
After working with motion on components in Carbon for IBM Products, we noticed that trying to animate elements that leave the DOM can be challenging. @matthewgallo has added utilities to help with this but they can quickly become buggy (relying on state and adding handlers in places to undo "onAnimationEnd" handler.)
We should consider Framer motion because it is easier to use and has a ton of features for reduce motion and hooks that the team can benefit from.
|
process
|
revisiting motion libraries for component animations what will this achieve after working with motion on components in carbon for ibm products we noticed that trying to animate elements that leave the dom can be challenging matthewgallo has added utilities to help with this but they can quickly become buggy relying on state and adding handlers in places to undo onanimationend handler we should consider framer motion because it is easier to use and has a ton of features for reduce motion and hooks that the team can benefit from
| 1
|
20,138
| 26,686,597,572
|
IssuesEvent
|
2023-01-26 22:34:20
|
MicrosoftDocs/azure-devops-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-devops-docs
|
closed
|
Not is clear the price and parallelism for the deployment group
|
doc-enhancement devops/prod Pri2 devops-cicd-process/tech
|
Hello team, I am looking for the following information in the documentation, but it is not clear, you can add the following points to be clearer:
- Is there a charge to add a deployment group
- Maximum amount of parallelism to deploy in the deployment groups
- In a release pipeline I have several stages and each stage has a deployment group, is there a parallelism limit to execute the pipeline and also there is any charge?
Thank you so much!
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 9dd8a19f-54c2-d052-8560-9f179b24a0b3
* Version Independent ID: cf217d69-791f-3375-bc43-f57483427c46
* Content: [(Classic) Deployment group jobs in release pipelines - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/deployment-group-phases?view=azure-devops&tabs=yaml)
* Content Source: [docs/pipelines/process/deployment-group-phases.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/main/docs/pipelines/process/deployment-group-phases.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam**
|
1.0
|
Not is clear the price and parallelism for the deployment group - Hello team, I am looking for the following information in the documentation, but it is not clear, you can add the following points to be clearer:
- Is there a charge to add a deployment group
- Maximum amount of parallelism to deploy in the deployment groups
- In a release pipeline I have several stages and each stage has a deployment group, is there a parallelism limit to execute the pipeline and also there is any charge?
Thank you so much!
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 9dd8a19f-54c2-d052-8560-9f179b24a0b3
* Version Independent ID: cf217d69-791f-3375-bc43-f57483427c46
* Content: [(Classic) Deployment group jobs in release pipelines - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/deployment-group-phases?view=azure-devops&tabs=yaml)
* Content Source: [docs/pipelines/process/deployment-group-phases.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/main/docs/pipelines/process/deployment-group-phases.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam**
|
process
|
not is clear the price and parallelism for the deployment group hello team i am looking for the following information in the documentation but it is not clear you can add the following points to be clearer is there a charge to add a deployment group maximum amount of parallelism to deploy in the deployment groups in a release pipeline i have several stages and each stage has a deployment group is there a parallelism limit to execute the pipeline and also there is any charge thank you so much document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops cicd process github login juliakm microsoft alias jukullam
| 1
|
10,255
| 13,108,770,758
|
IssuesEvent
|
2020-08-04 17:26:20
|
googleapis/code-suggester
|
https://api.github.com/repos/googleapis/code-suggester
|
closed
|
Support non-"master" default primary branch
|
enhancement type: process
|
A branch can have multiple origin branches, and also have the non-"master" branch as the default branch.
Framework-core should allow user configuration of which branches are the origin branch.
- [x] CLI supports
- [x] framework-core supports
|
1.0
|
Support non-"master" default primary branch - A branch can have multiple origin branches, and also have the non-"master" branch as the default branch.
Framework-core should allow user configuration of which branches are the origin branch.
- [x] CLI supports
- [x] framework-core supports
|
process
|
support non master default primary branch a branch can have multiple origin branches and also have the non master branch as the default branch framework core should allow user configuration of which branches are the origin branch cli supports framework core supports
| 1
|
6,692
| 9,811,181,789
|
IssuesEvent
|
2019-06-12 22:39:49
|
ArctosDB/new-collections
|
https://api.github.com/repos/ArctosDB/new-collections
|
closed
|
NFWFL Draft MOU
|
Committed to Arctos MOU draft in process Prospective Collection Form Complete
|
Draft MOU
Work with new collection to complete Draft MOU, answer any questions about migration, Arctos operating procedures, and costs; (download sample template include collection contact info).
|
1.0
|
NFWFL Draft MOU - Draft MOU
Work with new collection to complete Draft MOU, answer any questions about migration, Arctos operating procedures, and costs; (download sample template include collection contact info).
|
process
|
nfwfl draft mou draft mou work with new collection to complete draft mou answer any questions about migration arctos operating procedures and costs download sample template include collection contact info
| 1
|
9,784
| 12,801,167,878
|
IssuesEvent
|
2020-07-02 18:34:52
|
solid/process
|
https://api.github.com/repos/solid/process
|
closed
|
Unclear which editorial assignment would review proposals from some panels
|
process proposal
|
There are several panels without editorial assignments including:
* accessibility
* artificial intelligence
* caching
* explaining the vision
* external interoperability and outreach
* internationalisation
* privacy and individuals rights protection
* self hosting
* specification entry document
This means it's unclear which editors would review proposals coming out of these panels.
I propose staring editorial assignments that match these panels or defining which existing editorial assignments would review proposals coming out fo these panels.
|
1.0
|
Unclear which editorial assignment would review proposals from some panels - There are several panels without editorial assignments including:
* accessibility
* artificial intelligence
* caching
* explaining the vision
* external interoperability and outreach
* internationalisation
* privacy and individuals rights protection
* self hosting
* specification entry document
This means it's unclear which editors would review proposals coming out of these panels.
I propose staring editorial assignments that match these panels or defining which existing editorial assignments would review proposals coming out fo these panels.
|
process
|
unclear which editorial assignment would review proposals from some panels there are several panels without editorial assignments including accessibility artificial intelligence caching explaining the vision external interoperability and outreach internationalisation privacy and individuals rights protection self hosting specification entry document this means it s unclear which editors would review proposals coming out of these panels i propose staring editorial assignments that match these panels or defining which existing editorial assignments would review proposals coming out fo these panels
| 1
|
21,795
| 30,303,018,030
|
IssuesEvent
|
2023-07-10 07:35:16
|
pycaret/pycaret
|
https://api.github.com/repos/pycaret/pycaret
|
closed
|
[BUG]: Numeric imputation "drop"
|
bug classification preprocessing
|
### pycaret version checks
- [X] I have checked that this issue has not already been reported [here](https://github.com/pycaret/pycaret/issues).
- [X] I have confirmed this bug exists on the [latest version](https://github.com/pycaret/pycaret/releases) of pycaret.
- [ ] I have confirmed this bug exists on the master branch of pycaret (pip install -U git+https://github.com/pycaret/pycaret.git@master).
### Issue Description
Hello, I have an error with numeric_imputation='drop'. If I use for example numeric_imputation='mean' it works, but with numeric_imputation='drop' the training fails.
### Reproducible Example
```python
from pycaret.datasets import get_data
data = get_data('titanic')
from pycaret.classification import ClassificationExperiment
exp = ClassificationExperiment()
exp.setup(data, target = 'Survived', session_id = 123,
ignore_features=['PassengerId', 'Name', 'Ticket'],
numeric_imputation='drop',
memory=None)
model = exp.create_model('lr')
```
### Expected Behavior
I expect the training to work. Instead the metrics table is empty

and in the log I have the error below.
### Actual Results
```python-traceback
WARNING:/opt/conda/lib/python3.10/site-packages/sklearn/model_selection/_validation.py:794: UserWarning: Scoring failed. The score on this train-test partition for these parameters will be set to 0. Details:
Traceback (most recent call last):
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_scorer.py", line 115, in __call__
score = scorer._score(cached_call, estimator, *args, **kwargs)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_scorer.py", line 282, in _score
return self._sign * self._score_func(y_true, y_pred, **self._kwargs)
File "/opt/conda/lib/python3.10/site-packages/pycaret/internal/metrics.py", line 35, in __call__
return self.score_func(y_true, y_pred, **kwargs)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 1954, in precision_score
p, _, _, _ = precision_recall_fscore_support(
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 1573, in precision_recall_fscore_support
labels = _check_set_wise_labels(y_true, y_pred, average, labels, pos_label)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 1374, in _check_set_wise_labels
y_type, y_true, y_pred = _check_targets(y_true, y_pred)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 86, in _check_targets
check_consistent_length(y_true, y_pred)
File "/opt/conda/lib/python3.10/site-packages/sklearn/utils/validation.py", line 397, in check_consistent_length
raise ValueError(
ValueError: Found input variables with inconsistent numbers of samples: [62, 45]
```
### Installed Versions
<details>
System:
python: 3.10.11 | packaged by conda-forge | (main, May 10 2023, 18:58:44) [GCC 11.3.0]
executable: /opt/conda/bin/python
machine: Linux-5.15.0-76-generic-x86_64-with-glibc2.35
PyCaret required dependencies:
pip: 23.1.2
setuptools: 67.7.2
pycaret: 3.0.4
IPython: 8.13.2
ipywidgets: 8.0.6
tqdm: 4.65.0
numpy: 1.23.5
pandas: 1.5.3
jinja2: 3.1.2
scipy: 1.10.1
joblib: 1.2.0
sklearn: 1.2.2
pyod: 1.0.9
imblearn: 0.10.1
category_encoders: 2.6.1
lightgbm: 3.3.5
numba: 0.56.4
requests: 2.29.0
matplotlib: 3.7.1
scikitplot: 0.3.7
yellowbrick: 1.5
plotly: 5.13.1
plotly-resampler: Not installed
kaleido: 0.2.1
schemdraw: 0.15
statsmodels: 0.14.0
sktime: 0.17.0
tbats: 1.1.3
pmdarima: 2.0.3
psutil: 5.9.5
markupsafe: 2.1.2
pickle5: Not installed
cloudpickle: 2.2.1
deprecation: 2.1.0
xxhash: 3.2.0
wurlitzer: 3.0.3
PyCaret optional dependencies:
shap: 0.41.0
interpret: 0.4.2
umap: Not installed
pandas_profiling: 4.2.0
explainerdashboard: Not installed
autoviz: Not installed
fairlearn: Not installed
deepchecks: Not installed
xgboost: Not installed
catboost: Not installed
kmodes: Not installed
mlxtend: Not installed
statsforecast: Not installed
tune_sklearn: Not installed
ray: Not installed
hyperopt: Not installed
optuna: Not installed
skopt: Not installed
mlflow: Not installed
gradio: Not installed
fastapi: Not installed
uvicorn: Not installed
m2cgen: Not installed
evidently: Not installed
fugue: Not installed
streamlit: Not installed
prophet: 1.1.3</details>
|
1.0
|
[BUG]: Numeric imputation "drop" - ### pycaret version checks
- [X] I have checked that this issue has not already been reported [here](https://github.com/pycaret/pycaret/issues).
- [X] I have confirmed this bug exists on the [latest version](https://github.com/pycaret/pycaret/releases) of pycaret.
- [ ] I have confirmed this bug exists on the master branch of pycaret (pip install -U git+https://github.com/pycaret/pycaret.git@master).
### Issue Description
Hello, I have an error with numeric_imputation='drop'. If I use for example numeric_imputation='mean' it works, but with numeric_imputation='drop' the training fails.
### Reproducible Example
```python
from pycaret.datasets import get_data
data = get_data('titanic')
from pycaret.classification import ClassificationExperiment
exp = ClassificationExperiment()
exp.setup(data, target = 'Survived', session_id = 123,
ignore_features=['PassengerId', 'Name', 'Ticket'],
numeric_imputation='drop',
memory=None)
model = exp.create_model('lr')
```
### Expected Behavior
I expect the training to work. Instead the metrics table is empty

and in the log I have the error below.
### Actual Results
```python-traceback
WARNING:/opt/conda/lib/python3.10/site-packages/sklearn/model_selection/_validation.py:794: UserWarning: Scoring failed. The score on this train-test partition for these parameters will be set to 0. Details:
Traceback (most recent call last):
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_scorer.py", line 115, in __call__
score = scorer._score(cached_call, estimator, *args, **kwargs)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_scorer.py", line 282, in _score
return self._sign * self._score_func(y_true, y_pred, **self._kwargs)
File "/opt/conda/lib/python3.10/site-packages/pycaret/internal/metrics.py", line 35, in __call__
return self.score_func(y_true, y_pred, **kwargs)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 1954, in precision_score
p, _, _, _ = precision_recall_fscore_support(
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 1573, in precision_recall_fscore_support
labels = _check_set_wise_labels(y_true, y_pred, average, labels, pos_label)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 1374, in _check_set_wise_labels
y_type, y_true, y_pred = _check_targets(y_true, y_pred)
File "/opt/conda/lib/python3.10/site-packages/sklearn/metrics/_classification.py", line 86, in _check_targets
check_consistent_length(y_true, y_pred)
File "/opt/conda/lib/python3.10/site-packages/sklearn/utils/validation.py", line 397, in check_consistent_length
raise ValueError(
ValueError: Found input variables with inconsistent numbers of samples: [62, 45]
```
### Installed Versions
<details>
System:
python: 3.10.11 | packaged by conda-forge | (main, May 10 2023, 18:58:44) [GCC 11.3.0]
executable: /opt/conda/bin/python
machine: Linux-5.15.0-76-generic-x86_64-with-glibc2.35
PyCaret required dependencies:
pip: 23.1.2
setuptools: 67.7.2
pycaret: 3.0.4
IPython: 8.13.2
ipywidgets: 8.0.6
tqdm: 4.65.0
numpy: 1.23.5
pandas: 1.5.3
jinja2: 3.1.2
scipy: 1.10.1
joblib: 1.2.0
sklearn: 1.2.2
pyod: 1.0.9
imblearn: 0.10.1
category_encoders: 2.6.1
lightgbm: 3.3.5
numba: 0.56.4
requests: 2.29.0
matplotlib: 3.7.1
scikitplot: 0.3.7
yellowbrick: 1.5
plotly: 5.13.1
plotly-resampler: Not installed
kaleido: 0.2.1
schemdraw: 0.15
statsmodels: 0.14.0
sktime: 0.17.0
tbats: 1.1.3
pmdarima: 2.0.3
psutil: 5.9.5
markupsafe: 2.1.2
pickle5: Not installed
cloudpickle: 2.2.1
deprecation: 2.1.0
xxhash: 3.2.0
wurlitzer: 3.0.3
PyCaret optional dependencies:
shap: 0.41.0
interpret: 0.4.2
umap: Not installed
pandas_profiling: 4.2.0
explainerdashboard: Not installed
autoviz: Not installed
fairlearn: Not installed
deepchecks: Not installed
xgboost: Not installed
catboost: Not installed
kmodes: Not installed
mlxtend: Not installed
statsforecast: Not installed
tune_sklearn: Not installed
ray: Not installed
hyperopt: Not installed
optuna: Not installed
skopt: Not installed
mlflow: Not installed
gradio: Not installed
fastapi: Not installed
uvicorn: Not installed
m2cgen: Not installed
evidently: Not installed
fugue: Not installed
streamlit: Not installed
prophet: 1.1.3</details>
|
process
|
numeric imputation drop pycaret version checks i have checked that this issue has not already been reported i have confirmed this bug exists on the of pycaret i have confirmed this bug exists on the master branch of pycaret pip install u git issue description hello i have an error with numeric imputation drop if i use for example numeric imputation mean it works but with numeric imputation drop the training fails reproducible example python from pycaret datasets import get data data get data titanic from pycaret classification import classificationexperiment exp classificationexperiment exp setup data target survived session id ignore features numeric imputation drop memory none model exp create model lr expected behavior i expect the training to work instead the metrics table is empty and in the log i have the error below actual results python traceback warning opt conda lib site packages sklearn model selection validation py userwarning scoring failed the score on this train test partition for these parameters will be set to details traceback most recent call last file opt conda lib site packages sklearn metrics scorer py line in call score scorer score cached call estimator args kwargs file opt conda lib site packages sklearn metrics scorer py line in score return self sign self score func y true y pred self kwargs file opt conda lib site packages pycaret internal metrics py line in call return self score func y true y pred kwargs file opt conda lib site packages sklearn metrics classification py line in precision score p precision recall fscore support file opt conda lib site packages sklearn metrics classification py line in precision recall fscore support labels check set wise labels y true y pred average labels pos label file opt conda lib site packages sklearn metrics classification py line in check set wise labels y type y true y pred check targets y true y pred file opt conda lib site packages sklearn metrics classification py line in check targets check consistent length y true y pred file opt conda lib site packages sklearn utils validation py line in check consistent length raise valueerror valueerror found input variables with inconsistent numbers of samples installed versions system python packaged by conda forge main may executable opt conda bin python machine linux generic with pycaret required dependencies pip setuptools pycaret ipython ipywidgets tqdm numpy pandas scipy joblib sklearn pyod imblearn category encoders lightgbm numba requests matplotlib scikitplot yellowbrick plotly plotly resampler not installed kaleido schemdraw statsmodels sktime tbats pmdarima psutil markupsafe not installed cloudpickle deprecation xxhash wurlitzer pycaret optional dependencies shap interpret umap not installed pandas profiling explainerdashboard not installed autoviz not installed fairlearn not installed deepchecks not installed xgboost not installed catboost not installed kmodes not installed mlxtend not installed statsforecast not installed tune sklearn not installed ray not installed hyperopt not installed optuna not installed skopt not installed mlflow not installed gradio not installed fastapi not installed uvicorn not installed not installed evidently not installed fugue not installed streamlit not installed prophet
| 1
|
17,556
| 23,370,316,128
|
IssuesEvent
|
2022-08-10 19:10:46
|
GoogleCloudPlatform/cloud-ops-sandbox
|
https://api.github.com/repos/GoogleCloudPlatform/cloud-ops-sandbox
|
closed
|
Add build-cop bot to Sandbox repo
|
type: process priority: p3 lang: yaml
|
Adding [build-cop bot](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop) will allow automated creation/closure of bugs associated with failed CI runs.
|
1.0
|
Add build-cop bot to Sandbox repo - Adding [build-cop bot](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop) will allow automated creation/closure of bugs associated with failed CI runs.
|
process
|
add build cop bot to sandbox repo adding will allow automated creation closure of bugs associated with failed ci runs
| 1
|
13,560
| 16,103,417,816
|
IssuesEvent
|
2021-04-27 12:21:16
|
osstotalsoft/nbb
|
https://api.github.com/repos/osstotalsoft/nbb
|
closed
|
Process manager - state should not be contrained to beeing a struct
|
enhancement good first issue process manager
|
Currently, the state in process manager is a struct. It should be a class.
Using a struct is a way to insure the state does not have behaviour.
However, the "framework" should not be THAT opinionated and should allow the programmer to have the responsibility of its own code.
|
1.0
|
Process manager - state should not be contrained to beeing a struct - Currently, the state in process manager is a struct. It should be a class.
Using a struct is a way to insure the state does not have behaviour.
However, the "framework" should not be THAT opinionated and should allow the programmer to have the responsibility of its own code.
|
process
|
process manager state should not be contrained to beeing a struct currently the state in process manager is a struct it should be a class using a struct is a way to insure the state does not have behaviour however the framework should not be that opinionated and should allow the programmer to have the responsibility of its own code
| 1
|
380,954
| 11,271,494,378
|
IssuesEvent
|
2020-01-14 13:10:44
|
googleapis/elixir-google-api
|
https://api.github.com/repos/googleapis/elixir-google-api
|
opened
|
Synthesis failed for OAuth2
|
autosynth failure priority: p1 type: bug
|
Hello! Autosynth couldn't regenerate OAuth2. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth-oauth2'
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 256, in <module>
main()
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 196, in main
last_synth_commit_hash = get_last_metadata_commit(args.metadata_path)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 149, in get_last_metadata_commit
text=True,
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/subprocess.py", line 403, in run
with Popen(*popenargs, **kwargs) as process:
TypeError: __init__() got an unexpected keyword argument 'text'
```
Google internal developers can see the full log [here](https://sponge/164839b8-e54e-409d-bb48-012d4d868e86).
|
1.0
|
Synthesis failed for OAuth2 - Hello! Autosynth couldn't regenerate OAuth2. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth-oauth2'
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_as_main
"__main__", mod_spec)
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 85, in _run_code
exec(code, run_globals)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 256, in <module>
main()
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 196, in main
last_synth_commit_hash = get_last_metadata_commit(args.metadata_path)
File "/tmpfs/src/git/autosynth/autosynth/synth.py", line 149, in get_last_metadata_commit
text=True,
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/subprocess.py", line 403, in run
with Popen(*popenargs, **kwargs) as process:
TypeError: __init__() got an unexpected keyword argument 'text'
```
Google internal developers can see the full log [here](https://sponge/164839b8-e54e-409d-bb48-012d4d868e86).
|
non_process
|
synthesis failed for hello autosynth couldn t regenerate broken heart here s the output from running synth py cloning into working repo switched to branch autosynth traceback most recent call last file home kbuilder pyenv versions lib runpy py line in run module as main main mod spec file home kbuilder pyenv versions lib runpy py line in run code exec code run globals file tmpfs src git autosynth autosynth synth py line in main file tmpfs src git autosynth autosynth synth py line in main last synth commit hash get last metadata commit args metadata path file tmpfs src git autosynth autosynth synth py line in get last metadata commit text true file home kbuilder pyenv versions lib subprocess py line in run with popen popenargs kwargs as process typeerror init got an unexpected keyword argument text google internal developers can see the full log
| 0
|
17,029
| 22,406,802,748
|
IssuesEvent
|
2022-06-18 04:41:58
|
qgis/QGIS-Documentation
|
https://api.github.com/repos/qgis/QGIS-Documentation
|
closed
|
[feature][processing] Add "Offset" parameter to "Drape" algorithms (Request in QGIS)
|
Processing Alg 3.26
|
### Request for documentation
From pull request QGIS/qgis#48772
Author: @agiudiceandrea
QGIS version: 3.26
**[feature][processing] Add "Offset" parameter to "Drape" algorithms**
### PR Description:
## Description
Adds the "Offset" parameter (`QgsProcessingParameterNumber::Double`, default to 0) to the "Drape (set Z value from raster)" and "Set M value from raster" algorithms.
The "Offset" value is algebraically added to the raster value after applying the "Scale factor".
Fixes #48651.
<!--
BEFORE HITTING SUBMIT -- Please BUILD AND TEST your changes thoroughly. This is YOUR responsibility! Do NOT rely on the QGIS code maintainers to do this for you!!
IMPORTANT NOTES FOR FIRST TIME CONTRIBUTORS
===========================================
Congratulations, you are about to make a pull request to QGIS! To make this as easy and pleasurable for everyone, please take the time to read these lines before opening the pull request.
Include a few sentences describing the overall goals for this pull request (PR). If applicable also add screenshots or - even better - screencasts.
Include both: *what* you changed and *why* you changed it.
If this is a pull request that adds new functionality which needs documentation, give an especially detailed explanation.
In this case, start with a short abstract and then write some text that can be copied 1:1 to the documentation in the best case.
Also mention if you think this PR needs to be backported. And list relevant or fixed issues.
------------------------
Reviewing is a process done by project maintainers, mostly on a volunteer basis. We try to keep the overhead as small as possible and appreciate if you help us to do so by checking the following list.
Feel free to ask in a comment if you have troubles with any of them.
- Commit messages are descriptive and explain the rationale for changes.
- Commits which fix bugs include `Fixes #11111` at the bottom of the commit message. If this is your first pull request and you forgot to do this, write the same statement into this text field with the pull request description.
- New unit tests have been added for relevant changes
- You have run the `scripts/prepare_commit.sh` script (https://github.com/qgis/QGIS/blob/master/.github/CONTRIBUTING.md#contributing-to-qgis) before each commit.
If you didn't do this, you can also run `./scripts/astyle_all.sh` from your source folder.
- You have read the QGIS Coding Standards (https://docs.qgis.org/testing/en/docs/developers_guide/codingstandards.html) and this PR complies with them
-->
### Commits tagged with [need-docs] or [FEATURE]
|
1.0
|
[feature][processing] Add "Offset" parameter to "Drape" algorithms (Request in QGIS) - ### Request for documentation
From pull request QGIS/qgis#48772
Author: @agiudiceandrea
QGIS version: 3.26
**[feature][processing] Add "Offset" parameter to "Drape" algorithms**
### PR Description:
## Description
Adds the "Offset" parameter (`QgsProcessingParameterNumber::Double`, default to 0) to the "Drape (set Z value from raster)" and "Set M value from raster" algorithms.
The "Offset" value is algebraically added to the raster value after applying the "Scale factor".
Fixes #48651.
<!--
BEFORE HITTING SUBMIT -- Please BUILD AND TEST your changes thoroughly. This is YOUR responsibility! Do NOT rely on the QGIS code maintainers to do this for you!!
IMPORTANT NOTES FOR FIRST TIME CONTRIBUTORS
===========================================
Congratulations, you are about to make a pull request to QGIS! To make this as easy and pleasurable for everyone, please take the time to read these lines before opening the pull request.
Include a few sentences describing the overall goals for this pull request (PR). If applicable also add screenshots or - even better - screencasts.
Include both: *what* you changed and *why* you changed it.
If this is a pull request that adds new functionality which needs documentation, give an especially detailed explanation.
In this case, start with a short abstract and then write some text that can be copied 1:1 to the documentation in the best case.
Also mention if you think this PR needs to be backported. And list relevant or fixed issues.
------------------------
Reviewing is a process done by project maintainers, mostly on a volunteer basis. We try to keep the overhead as small as possible and appreciate if you help us to do so by checking the following list.
Feel free to ask in a comment if you have troubles with any of them.
- Commit messages are descriptive and explain the rationale for changes.
- Commits which fix bugs include `Fixes #11111` at the bottom of the commit message. If this is your first pull request and you forgot to do this, write the same statement into this text field with the pull request description.
- New unit tests have been added for relevant changes
- You have run the `scripts/prepare_commit.sh` script (https://github.com/qgis/QGIS/blob/master/.github/CONTRIBUTING.md#contributing-to-qgis) before each commit.
If you didn't do this, you can also run `./scripts/astyle_all.sh` from your source folder.
- You have read the QGIS Coding Standards (https://docs.qgis.org/testing/en/docs/developers_guide/codingstandards.html) and this PR complies with them
-->
### Commits tagged with [need-docs] or [FEATURE]
|
process
|
add offset parameter to drape algorithms request in qgis request for documentation from pull request qgis qgis author agiudiceandrea qgis version add offset parameter to drape algorithms pr description description adds the offset parameter qgsprocessingparameternumber double default to to the drape set z value from raster and set m value from raster algorithms the offset value is algebraically added to the raster value after applying the scale factor fixes before hitting submit please build and test your changes thoroughly this is your responsibility do not rely on the qgis code maintainers to do this for you important notes for first time contributors congratulations you are about to make a pull request to qgis to make this as easy and pleasurable for everyone please take the time to read these lines before opening the pull request include a few sentences describing the overall goals for this pull request pr if applicable also add screenshots or even better screencasts include both what you changed and why you changed it if this is a pull request that adds new functionality which needs documentation give an especially detailed explanation in this case start with a short abstract and then write some text that can be copied to the documentation in the best case also mention if you think this pr needs to be backported and list relevant or fixed issues reviewing is a process done by project maintainers mostly on a volunteer basis we try to keep the overhead as small as possible and appreciate if you help us to do so by checking the following list feel free to ask in a comment if you have troubles with any of them commit messages are descriptive and explain the rationale for changes commits which fix bugs include fixes at the bottom of the commit message if this is your first pull request and you forgot to do this write the same statement into this text field with the pull request description new unit tests have been added for relevant changes you have run the scripts prepare commit sh script before each commit if you didn t do this you can also run scripts astyle all sh from your source folder you have read the qgis coding standards and this pr complies with them commits tagged with or
| 1
|
160,994
| 6,106,736,475
|
IssuesEvent
|
2017-06-21 05:42:28
|
pmem/issues
|
https://api.github.com/repos/pmem/issues
|
closed
|
tests: cannot set UNITTEST_QUIET before running RUNTESTS
|
Exposure: Low OS: Linux Priority: 4 low State: To be verified Type: Bug
|
Cannot set UNITTEST_QUIET before running RUNTESTS. Reason: RUNTESTS sets UNITTEST_QUIET to 1 in line 252 and so make pcheck silently skips some tests.
|
1.0
|
tests: cannot set UNITTEST_QUIET before running RUNTESTS - Cannot set UNITTEST_QUIET before running RUNTESTS. Reason: RUNTESTS sets UNITTEST_QUIET to 1 in line 252 and so make pcheck silently skips some tests.
|
non_process
|
tests cannot set unittest quiet before running runtests cannot set unittest quiet before running runtests reason runtests sets unittest quiet to in line and so make pcheck silently skips some tests
| 0
|
151,662
| 23,854,242,741
|
IssuesEvent
|
2022-09-06 21:08:56
|
hong-yura/WorkForUs-Project
|
https://api.github.com/repos/hong-yura/WorkForUs-Project
|
opened
|
[FE] : 일정관리 화면
|
🎨DESIGN
|
## 🔔 요구 사항
일정관리 페이지의 화면을 만든다.
## ✅ 수행 작업
- [ ] Toast UI Calendar 적용
- [ ] 버튼에 캘린더 조작 기능 추가
|
1.0
|
[FE] : 일정관리 화면 - ## 🔔 요구 사항
일정관리 페이지의 화면을 만든다.
## ✅ 수행 작업
- [ ] Toast UI Calendar 적용
- [ ] 버튼에 캘린더 조작 기능 추가
|
non_process
|
일정관리 화면 🔔 요구 사항 일정관리 페이지의 화면을 만든다 ✅ 수행 작업 toast ui calendar 적용 버튼에 캘린더 조작 기능 추가
| 0
|
4,314
| 4,972,700,875
|
IssuesEvent
|
2016-12-05 22:20:33
|
dotnet/wcf
|
https://api.github.com/repos/dotnet/wcf
|
closed
|
Use TestProperties and to parse command line arguments to configure ports
|
Infrastructure
|
Pull request https://github.com/dotnet/wcf/pull/1011 recommended using TestProperties and to parse command line arguments to configure ports for self hosted service.
We need to evaluate if it's needed to configure ports as there is a debate to use the same port IIS uses.
|
1.0
|
Use TestProperties and to parse command line arguments to configure ports - Pull request https://github.com/dotnet/wcf/pull/1011 recommended using TestProperties and to parse command line arguments to configure ports for self hosted service.
We need to evaluate if it's needed to configure ports as there is a debate to use the same port IIS uses.
|
non_process
|
use testproperties and to parse command line arguments to configure ports pull request recommended using testproperties and to parse command line arguments to configure ports for self hosted service we need to evaluate if it s needed to configure ports as there is a debate to use the same port iis uses
| 0
|
57,764
| 3,083,767,938
|
IssuesEvent
|
2015-08-24 11:10:34
|
pavel-pimenov/flylinkdc-r5xx
|
https://api.github.com/repos/pavel-pimenov/flylinkdc-r5xx
|
opened
|
[Autoupdate] Выполняем лишнюю закачку файлов цифровой подписи
|
bug imported Priority-Medium
|
_From [Pavel.Pimenov@gmail.com](https://code.google.com/u/Pavel.Pimenov@gmail.com/) on July 15, 2013 23:19:36_
Лог на стороне сервера при старте приложения.
[16/Jul/2013:01:02:07 +0400] "GET /etc/flylinkdc-config-r5xx.xml HTTP/1.1" 200 2029 "-" "FlylinkDC++ r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/5xx/beta/Update5_beta.xml HTTP/1.1" 200 153431 "-" " r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/5xx/beta/Update5_beta.sign HTTP/1.1" 200 128 "-" " r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/alluser/UpdateAU.xml HTTP/1.1" 200 1280 "-" " r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/alluser/UpdateAU.sign HTTP/1.1" 200 128 "-" " r502 -beta96 build 14508"
1. Файлы *.sign качаются сразу после *.xml даже в том случае если система в обновленном состоянии. скачивать sign файл только если пользователь захотел обновиться или есть кандидаты для обновления.
2. TODO в файле Update5_beta.xml на каждом файле очень избыточно храниться полный URL в тэге Url=
Подумать и сократить постоянную часть переместив ее в корень xml
постоянная части имеет вид: http://www.fly-server.ru/update/5xx/beta/ Если ее убрать размер xml сокращается с 153431 до 126084
но при этом придется изменить имя конфига...
может и не стоит это делать - файл сейчас с сервера отдается в сжатом виде
(прозрачно жмется для всех клиентов от Vista и выше)
Может оптимальнее EmoPacks хранить в zip архиве а не россыпью?
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=1080_
|
1.0
|
[Autoupdate] Выполняем лишнюю закачку файлов цифровой подписи - _From [Pavel.Pimenov@gmail.com](https://code.google.com/u/Pavel.Pimenov@gmail.com/) on July 15, 2013 23:19:36_
Лог на стороне сервера при старте приложения.
[16/Jul/2013:01:02:07 +0400] "GET /etc/flylinkdc-config-r5xx.xml HTTP/1.1" 200 2029 "-" "FlylinkDC++ r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/5xx/beta/Update5_beta.xml HTTP/1.1" 200 153431 "-" " r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/5xx/beta/Update5_beta.sign HTTP/1.1" 200 128 "-" " r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/alluser/UpdateAU.xml HTTP/1.1" 200 1280 "-" " r502 -beta96 build 14508"
[16/Jul/2013:01:02:43 +0400] "GET /update/alluser/UpdateAU.sign HTTP/1.1" 200 128 "-" " r502 -beta96 build 14508"
1. Файлы *.sign качаются сразу после *.xml даже в том случае если система в обновленном состоянии. скачивать sign файл только если пользователь захотел обновиться или есть кандидаты для обновления.
2. TODO в файле Update5_beta.xml на каждом файле очень избыточно храниться полный URL в тэге Url=
Подумать и сократить постоянную часть переместив ее в корень xml
постоянная части имеет вид: http://www.fly-server.ru/update/5xx/beta/ Если ее убрать размер xml сокращается с 153431 до 126084
но при этом придется изменить имя конфига...
может и не стоит это делать - файл сейчас с сервера отдается в сжатом виде
(прозрачно жмется для всех клиентов от Vista и выше)
Может оптимальнее EmoPacks хранить в zip архиве а не россыпью?
_Original issue: http://code.google.com/p/flylinkdc/issues/detail?id=1080_
|
non_process
|
выполняем лишнюю закачку файлов цифровой подписи from on july лог на стороне сервера при старте приложения get etc flylinkdc config xml http flylinkdc build get update beta beta xml http build get update beta beta sign http build get update alluser updateau xml http build get update alluser updateau sign http build файлы sign качаются сразу после xml даже в том случае если система в обновленном состоянии скачивать sign файл только если пользователь захотел обновиться или есть кандидаты для обновления todo в файле beta xml на каждом файле очень избыточно храниться полный url в тэге url подумать и сократить постоянную часть переместив ее в корень xml постоянная части имеет вид если ее убрать размер xml сокращается с до но при этом придется изменить имя конфига может и не стоит это делать файл сейчас с сервера отдается в сжатом виде прозрачно жмется для всех клиентов от vista и выше может оптимальнее emopacks хранить в zip архиве а не россыпью original issue
| 0
|
323,637
| 9,866,890,036
|
IssuesEvent
|
2019-06-21 08:48:52
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
outlook.live.com - see bug description
|
browser-firefox engine-gecko priority-critical
|
<!-- @browser: Firefox 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:68.0) Gecko/20100101 Firefox/68.0 -->
<!-- @reported_with: addon-reporter-firefox -->
**URL**: https://outlook.live.com/mail/
**Browser / Version**: Firefox 68.0
**Operating System**: Windows 7
**Tested Another Browser**: No
**Problem type**: Something else
**Description**: site not opening
**Steps to Reproduce**:
Outlook is turning and turning, but doesn't open to mailbox
[](https://webcompat.com/uploads/2019/6/74c26d9f-0fae-4458-8455-dde6c29d9023.jpg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
outlook.live.com - see bug description - <!-- @browser: Firefox 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:68.0) Gecko/20100101 Firefox/68.0 -->
<!-- @reported_with: addon-reporter-firefox -->
**URL**: https://outlook.live.com/mail/
**Browser / Version**: Firefox 68.0
**Operating System**: Windows 7
**Tested Another Browser**: No
**Problem type**: Something else
**Description**: site not opening
**Steps to Reproduce**:
Outlook is turning and turning, but doesn't open to mailbox
[](https://webcompat.com/uploads/2019/6/74c26d9f-0fae-4458-8455-dde6c29d9023.jpg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_process
|
outlook live com see bug description url browser version firefox operating system windows tested another browser no problem type something else description site not opening steps to reproduce outlook is turning and turning but doesn t open to mailbox browser configuration none from with ❤️
| 0
|
158,896
| 20,035,502,160
|
IssuesEvent
|
2022-02-02 11:25:44
|
kapseliboi/coronavirus-dashboard
|
https://api.github.com/repos/kapseliboi/coronavirus-dashboard
|
opened
|
CVE-2021-23368 (Medium) detected in postcss-7.0.21.tgz, postcss-7.0.32.tgz
|
security vulnerability
|
## CVE-2021-23368 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.21.tgz</b>, <b>postcss-7.0.32.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.21.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/resolve-url-loader/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- resolve-url-loader-3.1.2.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.32.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.32.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.32.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- stylelint-processor-styled-components-1.10.0.tgz (Root Library)
- :x: **postcss-7.0.32.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/coronavirus-dashboard/commit/4c0d18fe8dc22b989e9017e943fc5b7d5ef1d8d7">4c0d18fe8dc22b989e9017e943fc5b7d5ef1d8d7</a></p>
<p>Found in base branch: <b>v3-development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution (postcss): 7.0.36</p>
<p>Direct dependency fix Resolution (react-scripts): 4.0.0-next.116</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-23368 (Medium) detected in postcss-7.0.21.tgz, postcss-7.0.32.tgz - ## CVE-2021-23368 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.21.tgz</b>, <b>postcss-7.0.32.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.21.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.21.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/resolve-url-loader/node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- resolve-url-loader-3.1.2.tgz
- :x: **postcss-7.0.21.tgz** (Vulnerable Library)
</details>
<details><summary><b>postcss-7.0.32.tgz</b></p></summary>
<p>Tool for transforming styles with JS plugins</p>
<p>Library home page: <a href="https://registry.npmjs.org/postcss/-/postcss-7.0.32.tgz">https://registry.npmjs.org/postcss/-/postcss-7.0.32.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/postcss/package.json</p>
<p>
Dependency Hierarchy:
- stylelint-processor-styled-components-1.10.0.tgz (Root Library)
- :x: **postcss-7.0.32.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/coronavirus-dashboard/commit/4c0d18fe8dc22b989e9017e943fc5b7d5ef1d8d7">4c0d18fe8dc22b989e9017e943fc5b7d5ef1d8d7</a></p>
<p>Found in base branch: <b>v3-development</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package postcss from 7.0.0 and before 8.2.10 are vulnerable to Regular Expression Denial of Service (ReDoS) during source map parsing.
<p>Publish Date: 2021-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23368>CVE-2021-23368</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23368</a></p>
<p>Release Date: 2021-04-12</p>
<p>Fix Resolution (postcss): 7.0.36</p>
<p>Direct dependency fix Resolution (react-scripts): 4.0.0-next.116</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve medium detected in postcss tgz postcss tgz cve medium severity vulnerability vulnerable libraries postcss tgz postcss tgz postcss tgz tool for transforming styles with js plugins library home page a href path to dependency file package json path to vulnerable library node modules resolve url loader node modules postcss package json dependency hierarchy react scripts tgz root library resolve url loader tgz x postcss tgz vulnerable library postcss tgz tool for transforming styles with js plugins library home page a href path to dependency file package json path to vulnerable library node modules postcss package json dependency hierarchy stylelint processor styled components tgz root library x postcss tgz vulnerable library found in head commit a href found in base branch development vulnerability details the package postcss from and before are vulnerable to regular expression denial of service redos during source map parsing publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution postcss direct dependency fix resolution react scripts next step up your open source security game with whitesource
| 0
|
322,113
| 23,891,647,802
|
IssuesEvent
|
2022-09-08 11:58:40
|
COPRS/rs-issues
|
https://api.github.com/repos/COPRS/rs-issues
|
opened
|
[BUG][PRO] ingestion-trigger: if two regex are set for a same directory, files are compared randomly to either
|
bug documentation ivv pro CCB
|
<!--
Note: Please search to see if an issue already exists for the bug you encountered.
Note: A closed bug can be reopened and affected to a new version of the software.
-->
**Environment:**
<!--
- Delivery tag: release/0.1.0
- Platform: IVV Orange Cloud
- Configuration:
-->
- Delivery tag: 1.4.0-rc1
- Platform: IVV Orange Cloud
**Test:**
<!--
- Name: TST_INFRA_DEP_orange
- Traçability (requirements): NA
-->
- Name: TST_PRO_WF_S1L0
**Current Behavior:**
<!-- A concise description of what you're experiencing. -->
In the ingestion-trigger configuration, if two regex are configured for the same directory, files are compared randomly to either regex. Thus, some files may be ignored because they were not compared to the correct regex.
**Expected Behavior:**
<!-- A concise description of what you expected to happen. -->
Each file should be compared to each regex in the ingestion-trigger configuration.
**Steps To Reproduce:**
<!--
Example: steps to reproduce the behavior:
1. In this environment...
2. With this config...
3. Run '...'
4. See error...
-->
1 - In this environment, deploy an ingestion rs-core, with the following configuration for the ingestion-trigger:
```properties
app.ingestion-trigger.ingestion-trigger.polling.inbox1.directory=https:/src1/NOMINAL/
app.ingestion-trigger.ingestion-trigger.polling.inbox1.matchRegex={regex1}
...
app.ingestion-trigger.ingestion-trigger.polling.inbox2.directory=https:/src1/NOMINAL/
app.ingestion-trigger.ingestion-trigger.polling.inbox2.matchRegex={regex2}
...
```
2 - In the mock source, put files in the directory that matches either regex
3 - Check the trigger logs. Some files will be ignored.
**Workaround**
<!-- A concise description of the first analysis. -->
While it is possible to avoid this issue by specifying different folder for the source directory, a documentation warning would be welcomed.
**Bug Generic Definition of Ready (DoR)**
- [X] The affect version in which the bug has been found is mentioned
- [X] The context and environment of the bug is detailed
- [X] The description of the bug is clear and unambiguous
- [X] The procedure (steps) to reproduce the bug is clearly detailed
- [ ] The failed tests is linked to the bug : failed result % expected result
- [ ] The tested User Story / features is linked to the bug
- [ ] Logs are attached if available
- [ ] A data set attached if available
- [X] Category label is link to the bug <!-- infra, mon, pro, perfo, hmi, secu -->
**Bug Generic Definition of Done (DoD)**
- [ ] the modification implemented (the solution to fix the bug) is described in the bug.
- [ ] Unit tests & Continuous integration performed - Test results available - Structural Test coverage reported by SONAR
- [ ] Code committed in GIT with right tag or Analysis/Trade Off documentation up-to-date in reference-system-documentation repository
- [ ] Code is compliant with coding rules (SONAR Report as evidence)
- [ ] Acceptance criteria of the related User story are checked and Passed
|
1.0
|
[BUG][PRO] ingestion-trigger: if two regex are set for a same directory, files are compared randomly to either - <!--
Note: Please search to see if an issue already exists for the bug you encountered.
Note: A closed bug can be reopened and affected to a new version of the software.
-->
**Environment:**
<!--
- Delivery tag: release/0.1.0
- Platform: IVV Orange Cloud
- Configuration:
-->
- Delivery tag: 1.4.0-rc1
- Platform: IVV Orange Cloud
**Test:**
<!--
- Name: TST_INFRA_DEP_orange
- Traçability (requirements): NA
-->
- Name: TST_PRO_WF_S1L0
**Current Behavior:**
<!-- A concise description of what you're experiencing. -->
In the ingestion-trigger configuration, if two regex are configured for the same directory, files are compared randomly to either regex. Thus, some files may be ignored because they were not compared to the correct regex.
**Expected Behavior:**
<!-- A concise description of what you expected to happen. -->
Each file should be compared to each regex in the ingestion-trigger configuration.
**Steps To Reproduce:**
<!--
Example: steps to reproduce the behavior:
1. In this environment...
2. With this config...
3. Run '...'
4. See error...
-->
1 - In this environment, deploy an ingestion rs-core, with the following configuration for the ingestion-trigger:
```properties
app.ingestion-trigger.ingestion-trigger.polling.inbox1.directory=https:/src1/NOMINAL/
app.ingestion-trigger.ingestion-trigger.polling.inbox1.matchRegex={regex1}
...
app.ingestion-trigger.ingestion-trigger.polling.inbox2.directory=https:/src1/NOMINAL/
app.ingestion-trigger.ingestion-trigger.polling.inbox2.matchRegex={regex2}
...
```
2 - In the mock source, put files in the directory that matches either regex
3 - Check the trigger logs. Some files will be ignored.
**Workaround**
<!-- A concise description of the first analysis. -->
While it is possible to avoid this issue by specifying different folder for the source directory, a documentation warning would be welcomed.
**Bug Generic Definition of Ready (DoR)**
- [X] The affect version in which the bug has been found is mentioned
- [X] The context and environment of the bug is detailed
- [X] The description of the bug is clear and unambiguous
- [X] The procedure (steps) to reproduce the bug is clearly detailed
- [ ] The failed tests is linked to the bug : failed result % expected result
- [ ] The tested User Story / features is linked to the bug
- [ ] Logs are attached if available
- [ ] A data set attached if available
- [X] Category label is link to the bug <!-- infra, mon, pro, perfo, hmi, secu -->
**Bug Generic Definition of Done (DoD)**
- [ ] the modification implemented (the solution to fix the bug) is described in the bug.
- [ ] Unit tests & Continuous integration performed - Test results available - Structural Test coverage reported by SONAR
- [ ] Code committed in GIT with right tag or Analysis/Trade Off documentation up-to-date in reference-system-documentation repository
- [ ] Code is compliant with coding rules (SONAR Report as evidence)
- [ ] Acceptance criteria of the related User story are checked and Passed
|
non_process
|
ingestion trigger if two regex are set for a same directory files are compared randomly to either note please search to see if an issue already exists for the bug you encountered note a closed bug can be reopened and affected to a new version of the software environment delivery tag release platform ivv orange cloud configuration delivery tag platform ivv orange cloud test name tst infra dep orange traçability requirements na name tst pro wf current behavior in the ingestion trigger configuration if two regex are configured for the same directory files are compared randomly to either regex thus some files may be ignored because they were not compared to the correct regex expected behavior each file should be compared to each regex in the ingestion trigger configuration steps to reproduce example steps to reproduce the behavior in this environment with this config run see error in this environment deploy an ingestion rs core with the following configuration for the ingestion trigger properties app ingestion trigger ingestion trigger polling directory https nominal app ingestion trigger ingestion trigger polling matchregex app ingestion trigger ingestion trigger polling directory https nominal app ingestion trigger ingestion trigger polling matchregex in the mock source put files in the directory that matches either regex check the trigger logs some files will be ignored workaround while it is possible to avoid this issue by specifying different folder for the source directory a documentation warning would be welcomed bug generic definition of ready dor the affect version in which the bug has been found is mentioned the context and environment of the bug is detailed the description of the bug is clear and unambiguous the procedure steps to reproduce the bug is clearly detailed the failed tests is linked to the bug failed result expected result the tested user story features is linked to the bug logs are attached if available a data set attached if available category label is link to the bug bug generic definition of done dod the modification implemented the solution to fix the bug is described in the bug unit tests continuous integration performed test results available structural test coverage reported by sonar code committed in git with right tag or analysis trade off documentation up to date in reference system documentation repository code is compliant with coding rules sonar report as evidence acceptance criteria of the related user story are checked and passed
| 0
|
772,042
| 27,103,449,426
|
IssuesEvent
|
2023-02-15 10:20:28
|
FastcampusMini/mini-project
|
https://api.github.com/repos/FastcampusMini/mini-project
|
opened
|
페이징 기능 구현
|
For: API For: Backend Priority: High Status: In Progress Type: Feature
|
## Title
페이징 기능 구현
## Description
신청한 상품내역 GET /user/addList
구매 내역 조회 GET /product/order/check
검색서비스 GET /search
메인페이지(금융상품) GET /products
추천상품 GET /products/recommended
위의 api들에서 페이징 구현 필요
하지만 다른분들이 맡은 부분이랑 추후 수정될수도 있고 conflict 가능성도 있어
일단은 검색서비스에만 페이징 적용후 기능 완성한 후 나머지는 추후 feature/paging 브랜치로 구현할 예정
## Tasks
페이징이 적용된 api 목록
- [ ] 검색서비스 GET /search
- [ ] 구매 내역 조회 GET /product/order/check
- [ ] 신청한 상품내역 GET /user/addList
- [ ] 메인페이지(금융상품) GET /products
- [ ] 추천상품 GET /products/recommended
|
1.0
|
페이징 기능 구현 - ## Title
페이징 기능 구현
## Description
신청한 상품내역 GET /user/addList
구매 내역 조회 GET /product/order/check
검색서비스 GET /search
메인페이지(금융상품) GET /products
추천상품 GET /products/recommended
위의 api들에서 페이징 구현 필요
하지만 다른분들이 맡은 부분이랑 추후 수정될수도 있고 conflict 가능성도 있어
일단은 검색서비스에만 페이징 적용후 기능 완성한 후 나머지는 추후 feature/paging 브랜치로 구현할 예정
## Tasks
페이징이 적용된 api 목록
- [ ] 검색서비스 GET /search
- [ ] 구매 내역 조회 GET /product/order/check
- [ ] 신청한 상품내역 GET /user/addList
- [ ] 메인페이지(금융상품) GET /products
- [ ] 추천상품 GET /products/recommended
|
non_process
|
페이징 기능 구현 title 페이징 기능 구현 description 신청한 상품내역 get user addlist 구매 내역 조회 get product order check 검색서비스 get search 메인페이지 금융상품 get products 추천상품 get products recommended 위의 api들에서 페이징 구현 필요 하지만 다른분들이 맡은 부분이랑 추후 수정될수도 있고 conflict 가능성도 있어 일단은 검색서비스에만 페이징 적용후 기능 완성한 후 나머지는 추후 feature paging 브랜치로 구현할 예정 tasks 페이징이 적용된 api 목록 검색서비스 get search 구매 내역 조회 get product order check 신청한 상품내역 get user addlist 메인페이지 금융상품 get products 추천상품 get products recommended
| 0
|
67,018
| 3,265,297,472
|
IssuesEvent
|
2015-10-22 15:40:09
|
cs2103aug2015-w15-3j/main
|
https://api.github.com/repos/cs2103aug2015-w15-3j/main
|
closed
|
Advanced features of autocomplete
|
priority.medium type.enhancement
|
## Features
- [ ] autocomplete displayed ID to details of task for `EDIT` command
- [x] update view while autocompleting task name
- [x] pressing up will retrieve previous used command
|
1.0
|
Advanced features of autocomplete - ## Features
- [ ] autocomplete displayed ID to details of task for `EDIT` command
- [x] update view while autocompleting task name
- [x] pressing up will retrieve previous used command
|
non_process
|
advanced features of autocomplete features autocomplete displayed id to details of task for edit command update view while autocompleting task name pressing up will retrieve previous used command
| 0
|
127,910
| 17,378,571,106
|
IssuesEvent
|
2021-07-31 07:38:19
|
Joystream/atlas
|
https://api.github.com/repos/Joystream/atlas
|
opened
|
Merging sections into one content section component
|
design
|
There are components with simmilar build which are channel section, video section and carousel - after discussion with klaudiusz we decided to merge it into one component: content section.
|
1.0
|
Merging sections into one content section component - There are components with simmilar build which are channel section, video section and carousel - after discussion with klaudiusz we decided to merge it into one component: content section.
|
non_process
|
merging sections into one content section component there are components with simmilar build which are channel section video section and carousel after discussion with klaudiusz we decided to merge it into one component content section
| 0
|
224,535
| 7,471,635,660
|
IssuesEvent
|
2018-04-03 09:53:26
|
zephyrproject-rtos/zephyr
|
https://api.github.com/repos/zephyrproject-rtos/zephyr
|
closed
|
Thread Requirements on RFC6282
|
area: Networking enhancement priority: high
|
**_Reported by Gajinder Vij:_**
The Thread Protocol imposes the following requirements on RFC6282:
RFC6282.2: Specific Updates to RFC 4944
RFC6282.3: IPv6 Header Compression
RFC6282.3.1: LOWPAN_IPHC Encoding Format
RFC6282.3.1.1: Base Format
RFC6282.3.1.2: Context Identifier Extension
RFC6282.3.2: IPV6 Header Encoding
RFC6282.3.2.1: Traffic Class and Flow Label Compression
RFC6282.3.2.2: Deriving IID's from the encapsulating Header
RFC6282.3.2.3: Stateless Multicast Address Compression
RFC6282.3.2.4: Stateful Multicast Address Compression
RFC6282.4: IPv6 Next Header Compression
RFC6282.4.1: LOWPAN_NHC Format
RFC6282.4.2: IPv6 Extension Header Compression
� Modified: When there is a single trailing Pad1 or PadN option of 7 octets or less and the containing header is a multiple of 8 octets, the trailing Pad1 or PadN option SHOULD be elided by the compressor.
RFC6282.4.3: UDP Header Compression
RFC6282.4.3.1: Compressing UDP Ports
RFC6282.4.3.2: Compressing UDP Checksum
RFC6282.4.3.3: UDP LOWPAN_NHC Format
RFC6282.5: IANA Considerations
(Imported from Jira ZEP-839)
|
1.0
|
Thread Requirements on RFC6282 - **_Reported by Gajinder Vij:_**
The Thread Protocol imposes the following requirements on RFC6282:
RFC6282.2: Specific Updates to RFC 4944
RFC6282.3: IPv6 Header Compression
RFC6282.3.1: LOWPAN_IPHC Encoding Format
RFC6282.3.1.1: Base Format
RFC6282.3.1.2: Context Identifier Extension
RFC6282.3.2: IPV6 Header Encoding
RFC6282.3.2.1: Traffic Class and Flow Label Compression
RFC6282.3.2.2: Deriving IID's from the encapsulating Header
RFC6282.3.2.3: Stateless Multicast Address Compression
RFC6282.3.2.4: Stateful Multicast Address Compression
RFC6282.4: IPv6 Next Header Compression
RFC6282.4.1: LOWPAN_NHC Format
RFC6282.4.2: IPv6 Extension Header Compression
� Modified: When there is a single trailing Pad1 or PadN option of 7 octets or less and the containing header is a multiple of 8 octets, the trailing Pad1 or PadN option SHOULD be elided by the compressor.
RFC6282.4.3: UDP Header Compression
RFC6282.4.3.1: Compressing UDP Ports
RFC6282.4.3.2: Compressing UDP Checksum
RFC6282.4.3.3: UDP LOWPAN_NHC Format
RFC6282.5: IANA Considerations
(Imported from Jira ZEP-839)
|
non_process
|
thread requirements on reported by gajinder vij the thread protocol imposes the following requirements on specific updates to rfc header compression lowpan iphc encoding format base format context identifier extension header encoding traffic class and flow label compression deriving iid s from the encapsulating header stateless multicast address compression stateful multicast address compression next header compression lowpan nhc format extension header compression � modified when there is a single trailing or padn option of octets or less and the containing header is a multiple of octets the trailing or padn option should be elided by the compressor udp header compression compressing udp ports compressing udp checksum udp lowpan nhc format iana considerations imported from jira zep
| 0
|
11,738
| 14,581,585,741
|
IssuesEvent
|
2020-12-18 10:57:19
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
closed
|
multiple identical compound unique fields with different types not generating multiple types
|
bug/2-confirmed process/candidate team/client tech/typescript topic: types
|
<!--
Thanks for helping us improve Prisma! 🙏 Please follow the sections in the template and provide as much information as possible about your problem, e.g. by setting the `DEBUG="*"` environment variable and enabling additional logging output in Prisma Client.
Learn more about writing proper bug reports here: https://pris.ly/d/bug-reports
-->
## Bug description
I've got 2 models with the following structure, both use the same unique field mapping on type and token, but use different enum types. There is only 1 type generated for these compounded fields (or the other is overridden), but it's causing typescript to complain when querying via the compounded unique fields since the types are incorrect.
```prisma
model Token {
id String @id @default(cuid())
type TokenType
token String
created_at DateTime @default(now())
updated_at DateTime @updatedAt
@@unique([type, token])
}
model UserCredential {
id String @id @default(cuid())
type CredentialType
token String @unique
created_at DateTime @default(now())
updated_at DateTime @updatedAt
user User @relation(fields: [user_id], references: [id])
user_id String
@@unique([type, token])
}
```
Generated Type
```typescript
export type TypeTokenCompoundUniqueInput = {
type: CredentialType
token: string
}
```
## How to reproduce
Create two models with the same compounded unique constraints that both share the same name then run prisma generate
## Expected behaviour
I'd expect two types to be exports, one for each of the compounded unique constraints that follow the correct types
## Environment & setup
<!-- In which environment does the problem occur -->
- OS: Windows
- Database: PostgreSQL
- Node.js version: v12.16.2
- Prisma version: 6.12.1
|
1.0
|
multiple identical compound unique fields with different types not generating multiple types - <!--
Thanks for helping us improve Prisma! 🙏 Please follow the sections in the template and provide as much information as possible about your problem, e.g. by setting the `DEBUG="*"` environment variable and enabling additional logging output in Prisma Client.
Learn more about writing proper bug reports here: https://pris.ly/d/bug-reports
-->
## Bug description
I've got 2 models with the following structure, both use the same unique field mapping on type and token, but use different enum types. There is only 1 type generated for these compounded fields (or the other is overridden), but it's causing typescript to complain when querying via the compounded unique fields since the types are incorrect.
```prisma
model Token {
id String @id @default(cuid())
type TokenType
token String
created_at DateTime @default(now())
updated_at DateTime @updatedAt
@@unique([type, token])
}
model UserCredential {
id String @id @default(cuid())
type CredentialType
token String @unique
created_at DateTime @default(now())
updated_at DateTime @updatedAt
user User @relation(fields: [user_id], references: [id])
user_id String
@@unique([type, token])
}
```
Generated Type
```typescript
export type TypeTokenCompoundUniqueInput = {
type: CredentialType
token: string
}
```
## How to reproduce
Create two models with the same compounded unique constraints that both share the same name then run prisma generate
## Expected behaviour
I'd expect two types to be exports, one for each of the compounded unique constraints that follow the correct types
## Environment & setup
<!-- In which environment does the problem occur -->
- OS: Windows
- Database: PostgreSQL
- Node.js version: v12.16.2
- Prisma version: 6.12.1
|
process
|
multiple identical compound unique fields with different types not generating multiple types thanks for helping us improve prisma 🙏 please follow the sections in the template and provide as much information as possible about your problem e g by setting the debug environment variable and enabling additional logging output in prisma client learn more about writing proper bug reports here bug description i ve got models with the following structure both use the same unique field mapping on type and token but use different enum types there is only type generated for these compounded fields or the other is overridden but it s causing typescript to complain when querying via the compounded unique fields since the types are incorrect prisma model token id string id default cuid type tokentype token string created at datetime default now updated at datetime updatedat unique model usercredential id string id default cuid type credentialtype token string unique created at datetime default now updated at datetime updatedat user user relation fields references user id string unique generated type typescript export type typetokencompounduniqueinput type credentialtype token string how to reproduce create two models with the same compounded unique constraints that both share the same name then run prisma generate expected behaviour i d expect two types to be exports one for each of the compounded unique constraints that follow the correct types environment setup os windows database postgresql node js version prisma version
| 1
|
445,484
| 12,831,608,845
|
IssuesEvent
|
2020-07-07 05:50:46
|
minio/minio-js
|
https://api.github.com/repos/minio/minio-js
|
closed
|
Error when using minio-js in ant design , TypeError: _fs.default.stat is not a function
|
community priority: medium
|
## An error occurs when I use minio-js in the ant design project, the error message is TypeError: _fs.default.stat is not a function

|
1.0
|
Error when using minio-js in ant design , TypeError: _fs.default.stat is not a function - ## An error occurs when I use minio-js in the ant design project, the error message is TypeError: _fs.default.stat is not a function

|
non_process
|
error when using minio js in ant design typeerror fs default stat is not a function an error occurs when i use minio js in the ant design project the error message is typeerror fs default stat is not a function
| 0
|
15,942
| 20,161,363,418
|
IssuesEvent
|
2022-02-09 21:57:51
|
ORNL-AMO/AMO-Tools-Desktop
|
https://api.github.com/repos/ORNL-AMO/AMO-Tools-Desktop
|
opened
|
Further small Electrotech tweaks
|
Process Heating
|
I didn't wnat to keep taging on to the exisiting issue...
NON-EAF
It looks like that Electrical power input doesn't do anything except cause errors. Confirm and then either hide field or remove from validation.
Electrical Heat Delivered is calcuated and can be negative and that is bad. Make it so if negative it shows up as zero and show an error
"More heat than necessary is being delivered via burners. Check fuel inputs or estimate other losses"

|
1.0
|
Further small Electrotech tweaks - I didn't wnat to keep taging on to the exisiting issue...
NON-EAF
It looks like that Electrical power input doesn't do anything except cause errors. Confirm and then either hide field or remove from validation.
Electrical Heat Delivered is calcuated and can be negative and that is bad. Make it so if negative it shows up as zero and show an error
"More heat than necessary is being delivered via burners. Check fuel inputs or estimate other losses"

|
process
|
further small electrotech tweaks i didn t wnat to keep taging on to the exisiting issue non eaf it looks like that electrical power input doesn t do anything except cause errors confirm and then either hide field or remove from validation electrical heat delivered is calcuated and can be negative and that is bad make it so if negative it shows up as zero and show an error more heat than necessary is being delivered via burners check fuel inputs or estimate other losses
| 1
|
15,371
| 19,552,766,008
|
IssuesEvent
|
2022-01-03 01:49:57
|
DevExpress/testcafe-hammerhead
|
https://api.github.com/repos/DevExpress/testcafe-hammerhead
|
closed
|
Support json manifest
|
TYPE: enhancement SYSTEM: resource processing AREA: server health-monitor FREQUENCY: level 1 STATE: Stale
|
https://developer.mozilla.org/en-US/docs/Web/Manifest
https://www.trulia.com contains json manifest file, but with non-standard content type:
```content-type: text/cache-manifest; charset=UTF-8```
|
1.0
|
Support json manifest - https://developer.mozilla.org/en-US/docs/Web/Manifest
https://www.trulia.com contains json manifest file, but with non-standard content type:
```content-type: text/cache-manifest; charset=UTF-8```
|
process
|
support json manifest contains json manifest file but with non standard content type content type text cache manifest charset utf
| 1
|
16,955
| 22,307,990,839
|
IssuesEvent
|
2022-06-13 14:34:21
|
hashgraph/hedera-json-rpc-relay
|
https://api.github.com/repos/hashgraph/hedera-json-rpc-relay
|
closed
|
Acceptance tests failing on docker timeout
|
bug P1 process
|
### Description
Acceptance tests started failing on
```
node:events:505
throw er; // Unhandled 'error' event
^
Error: connect ECONNREFUSED 127.0.0.1:5600
at TCPConnectWrap.afterConnect [as oncomplete] (node:net:1187:16)
Emitted 'error' event on Socket instance at:
at emitErrorNT (node:internal/streams/destroy:157:8)
at emitErrorCloseNT (node:internal/streams/destroy:122:3)
at processTicksAndRejections (node:internal/process/task_queues:83:21) {
errno: -111,
code: 'ECONNREFUSED',
syscall: 'connect',
address: '127.0.0.1',
port: 5600
}
```
This results in a
```
Error: Timeout of 240000ms exceeded. For async tests and hooks, ensure "done()" is called; if returning a Promise, ensure it resolves. (/home/runner/work/hedera-json-rpc-relay/hedera-json-rpc-relay/packages/server/tests/acceptance.spec.ts)
```
### Steps to reproduce
1. Run acceptance tests in github action
### Additional context
_No response_
### Hedera network
other
### Version
v0.2.0-SNAPSHOT
### Operating system
_No response_
|
1.0
|
Acceptance tests failing on docker timeout - ### Description
Acceptance tests started failing on
```
node:events:505
throw er; // Unhandled 'error' event
^
Error: connect ECONNREFUSED 127.0.0.1:5600
at TCPConnectWrap.afterConnect [as oncomplete] (node:net:1187:16)
Emitted 'error' event on Socket instance at:
at emitErrorNT (node:internal/streams/destroy:157:8)
at emitErrorCloseNT (node:internal/streams/destroy:122:3)
at processTicksAndRejections (node:internal/process/task_queues:83:21) {
errno: -111,
code: 'ECONNREFUSED',
syscall: 'connect',
address: '127.0.0.1',
port: 5600
}
```
This results in a
```
Error: Timeout of 240000ms exceeded. For async tests and hooks, ensure "done()" is called; if returning a Promise, ensure it resolves. (/home/runner/work/hedera-json-rpc-relay/hedera-json-rpc-relay/packages/server/tests/acceptance.spec.ts)
```
### Steps to reproduce
1. Run acceptance tests in github action
### Additional context
_No response_
### Hedera network
other
### Version
v0.2.0-SNAPSHOT
### Operating system
_No response_
|
process
|
acceptance tests failing on docker timeout description acceptance tests started failing on node events throw er unhandled error event error connect econnrefused at tcpconnectwrap afterconnect node net emitted error event on socket instance at at emiterrornt node internal streams destroy at emiterrorclosent node internal streams destroy at processticksandrejections node internal process task queues errno code econnrefused syscall connect address port this results in a error timeout of exceeded for async tests and hooks ensure done is called if returning a promise ensure it resolves home runner work hedera json rpc relay hedera json rpc relay packages server tests acceptance spec ts steps to reproduce run acceptance tests in github action additional context no response hedera network other version snapshot operating system no response
| 1
|
12,538
| 14,972,535,265
|
IssuesEvent
|
2021-01-27 23:02:58
|
BootBlock/FileSieve
|
https://api.github.com/repos/BootBlock/FileSieve
|
closed
|
Limit how deep sub-folder processing can go
|
processing
|
Within a Source Item, add a numerical property that limits how far "down / deep" sub-folder processing can go. This'll require changes to the Directory.**GetFiles**() method(s).
----
*Thanks to Phil P. for suggesting!*
|
1.0
|
Limit how deep sub-folder processing can go - Within a Source Item, add a numerical property that limits how far "down / deep" sub-folder processing can go. This'll require changes to the Directory.**GetFiles**() method(s).
----
*Thanks to Phil P. for suggesting!*
|
process
|
limit how deep sub folder processing can go within a source item add a numerical property that limits how far down deep sub folder processing can go this ll require changes to the directory getfiles method s thanks to phil p for suggesting
| 1
|
13,050
| 15,387,992,049
|
IssuesEvent
|
2021-03-03 10:12:56
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
closed
|
Consider not abbreviating “Integer”
|
kind/discussion process/candidate team/migrations topic: types
|
I just started trying Prisma and got to this code snippet in the Quickstart.
```
model Post {
post_id Int @id @default(autoincrement())
content String?
created_at DateTime @default(now())
title String
author User?
}
```
Why is “Integer” abbreviated to “Int”? I looked up the data types and it appears “Integer” is the only one that is abbreviated, which is unexpected/inconsistent.
If it’s too difficult to change it now to be consistent, could it be aliased so both “Int” and “Integer” work?
|
1.0
|
Consider not abbreviating “Integer” - I just started trying Prisma and got to this code snippet in the Quickstart.
```
model Post {
post_id Int @id @default(autoincrement())
content String?
created_at DateTime @default(now())
title String
author User?
}
```
Why is “Integer” abbreviated to “Int”? I looked up the data types and it appears “Integer” is the only one that is abbreviated, which is unexpected/inconsistent.
If it’s too difficult to change it now to be consistent, could it be aliased so both “Int” and “Integer” work?
|
process
|
consider not abbreviating “integer” i just started trying prisma and got to this code snippet in the quickstart model post post id int id default autoincrement content string created at datetime default now title string author user why is “integer” abbreviated to “int” i looked up the data types and it appears “integer” is the only one that is abbreviated which is unexpected inconsistent if it’s too difficult to change it now to be consistent could it be aliased so both “int” and “integer” work
| 1
|
4,228
| 7,181,225,812
|
IssuesEvent
|
2018-02-01 03:35:05
|
Great-Hill-Corporation/quickBlocks
|
https://api.github.com/repos/Great-Hill-Corporation/quickBlocks
|
closed
|
block enhanced blooms are wrong at xxx90 in each case less than 700000
|
apps-blockScrape status-inprocess type-bug
|
Because of the way I was running the bloom creator, I lost blooms from blocks xxxx90 through xxxx99. It ran to the end at xxx100, then re-ran at xxxx99 which blew away 90-98. To fix: re-write blocks between 90-99 for blocks less than 700,000
|
1.0
|
block enhanced blooms are wrong at xxx90 in each case less than 700000 - Because of the way I was running the bloom creator, I lost blooms from blocks xxxx90 through xxxx99. It ran to the end at xxx100, then re-ran at xxxx99 which blew away 90-98. To fix: re-write blocks between 90-99 for blocks less than 700,000
|
process
|
block enhanced blooms are wrong at in each case less than because of the way i was running the bloom creator i lost blooms from blocks through it ran to the end at then re ran at which blew away to fix re write blocks between for blocks less than
| 1
|
5,632
| 8,483,516,359
|
IssuesEvent
|
2018-10-25 21:51:47
|
Rokid/ShadowNode
|
https://api.github.com/repos/Rokid/ShadowNode
|
closed
|
child_process: crashed while sending data
|
bug child_process
|
```js
var isChild = process.env.IS_CHILD === 'true'
function ref() {
setInterval(() => { }, 10000)
}
function runWithChild() {
process.on('message', chunk => {
console.log('on parent message', chunk)
})
}
function runWithParent() {
var path = require('path')
var child_process = require('child_process')
var selfPath = path.resolve(__dirname, __filename)
var child = child_process.fork(selfPath, ['~~parent~~'], {
env: {
IS_CHILD: 'true',
}
})
child.on('message', chunk => {
console.log('on child message', chunk)
})
child.on('disconnect', () => {
console.log('child disconnected')
})
setInterval(() => {
child.send({
cloud: false,
intent: 'play_random',
slots: {
keyword: {
pinyin: '',
type: 'keyword',
value: '歌'
},
want: {
pinyin: '',
type: 'want',
value: '要'
},
me: {
pinyin: '',
type: 'me',
value: '我'
},
play5: {
pinyin: '',
type: 'play5',
value: '听'
}
},
pattern: '^($trigger)?($please)?($you|$me)?($want)?($at)?($room)?($inside)?($play5)($other)?[($adj)($de)]?($keyword)($ah)?$',
asr: '我要听歌',
appId: 'xxxxxxxxxxxxxxxxxxx',
appName: 'xxx音乐'
})
}, 30)
console.log('forked child')
}
isChild ? runWithChild() : runWithParent()
ref()
```
after running the above code for a while, the child exit with below error:
```shell
TypeError: Invalid UTF-8 string
child disconnected
Error: ERR_IPC_CHANNEL_CLOSED
at anonymous (/data/test.js:26:16)
```
this is caused by tcp multi packet, We should handle the case of a message in multiple packets in ipc
|
1.0
|
child_process: crashed while sending data - ```js
var isChild = process.env.IS_CHILD === 'true'
function ref() {
setInterval(() => { }, 10000)
}
function runWithChild() {
process.on('message', chunk => {
console.log('on parent message', chunk)
})
}
function runWithParent() {
var path = require('path')
var child_process = require('child_process')
var selfPath = path.resolve(__dirname, __filename)
var child = child_process.fork(selfPath, ['~~parent~~'], {
env: {
IS_CHILD: 'true',
}
})
child.on('message', chunk => {
console.log('on child message', chunk)
})
child.on('disconnect', () => {
console.log('child disconnected')
})
setInterval(() => {
child.send({
cloud: false,
intent: 'play_random',
slots: {
keyword: {
pinyin: '',
type: 'keyword',
value: '歌'
},
want: {
pinyin: '',
type: 'want',
value: '要'
},
me: {
pinyin: '',
type: 'me',
value: '我'
},
play5: {
pinyin: '',
type: 'play5',
value: '听'
}
},
pattern: '^($trigger)?($please)?($you|$me)?($want)?($at)?($room)?($inside)?($play5)($other)?[($adj)($de)]?($keyword)($ah)?$',
asr: '我要听歌',
appId: 'xxxxxxxxxxxxxxxxxxx',
appName: 'xxx音乐'
})
}, 30)
console.log('forked child')
}
isChild ? runWithChild() : runWithParent()
ref()
```
after running the above code for a while, the child exit with below error:
```shell
TypeError: Invalid UTF-8 string
child disconnected
Error: ERR_IPC_CHANNEL_CLOSED
at anonymous (/data/test.js:26:16)
```
this is caused by tcp multi packet, We should handle the case of a message in multiple packets in ipc
|
process
|
child process crashed while sending data js var ischild process env is child true function ref setinterval function runwithchild process on message chunk console log on parent message chunk function runwithparent var path require path var child process require child process var selfpath path resolve dirname filename var child child process fork selfpath env is child true child on message chunk console log on child message chunk child on disconnect console log child disconnected setinterval child send cloud false intent play random slots keyword pinyin type keyword value 歌 want pinyin type want value 要 me pinyin type me value 我 pinyin type value 听 pattern trigger please you me want at room inside other keyword ah asr 我要听歌 appid xxxxxxxxxxxxxxxxxxx appname xxx音乐 console log forked child ischild runwithchild runwithparent ref after running the above code for a while the child exit with below error shell typeerror invalid utf string child disconnected error err ipc channel closed at anonymous data test js this is caused by tcp multi packet we should handle the case of a message in multiple packets in ipc
| 1
|
28,710
| 11,671,975,372
|
IssuesEvent
|
2020-03-04 05:07:45
|
dotnet/aspnetcore
|
https://api.github.com/repos/dotnet/aspnetcore
|
closed
|
Share authentication cookie between two sites produces exception caused by ISecurityStampValidator is missing
|
Needs: Attention :wave: area-security
|
I have one API and one frontend app where I share the data protection keys using the file system. This is how my apps is configured.
**Frontend**:
```c#
public void ConfigureServices(IServiceCollection services)
{
services
.AddDataProtection()
.SetApplicationName("SharedCookieApp")
.PersistKeysToFileSystem(new DirectoryInfo("/dataprotection"));
services
.AddAuthentication(options =>
{
options.DefaultScheme = IdentityConstants.ApplicationScheme;
options.DefaultSignInScheme = IdentityConstants.ExternalScheme;
})
.AddOAuth("GitHub", "GitHub", o => { ... })
.AddIdentityCookies(options =>
{
options.ApplicationCookie.Configure(o =>
{
o.Cookie.Name = ".AspNet.SharedCookie";
o.Cookie.Domain = ".example.app";
o.LoginPath = new PathString("/Account/Login/");
o.AccessDeniedPath = new PathString("/Account/Forbidden/");
});
});
services.AddIdentityCore<User>(options =>
{
options.Password.RequireDigit = true;
options.Password.RequiredLength = 8;
options.Password.RequireNonAlphanumeric = false;
options.Password.RequireUppercase = true;
options.Password.RequireLowercase = true;
})
.AddRoles<Raven.Identity.IdentityRole>()
.AddRoleStore<RoleStore<Raven.Identity.IdentityRole>>()
.AddUserStore<UserStore<User, Raven.Identity.IdentityRole>>()
.AddSignInManager();
}
public void Configure(IApplicationBuilder app, IWebHostEnvironment env)
{
if (env.IsDevelopment())
{
app.UseDeveloperExceptionPage();
}
app.UseForwardedHeaders();
app.UseRouting();
app.UseCookiePolicy();
app.UseAuthentication();
app.UseAuthorization();
...
}
```
And from the API I need to use the authorize attribute to make sure that the user is authenticated when making a request.
**API**:
```c#
public void ConfigureServices(IServiceCollection services)
{
services.AddDataProtection()
.SetApplicationName("SharedCookieApp")
.PersistKeysToFileSystem(new DirectoryInfo("/dataprotection"));
services.AddAuthentication(options =>
{
options.DefaultScheme = IdentityConstants.ApplicationScheme;
})
.AddIdentityCookies(options =>
{
options.ApplicationCookie.Configure(a =>
{
a.Cookie.Name = ".AspNet.SharedCookie";
a.Cookie.Domain = ".example.app";
});
});
services.AddControllers();
}
public void Configure(IApplicationBuilder app, IWebHostEnvironment env)
{
if (env.IsDevelopment())
{
app.UseDeveloperExceptionPage();
}
app.UseHttpsRedirection();
app.UseCookiePolicy();
app.UseAuthentication();
app.UseRouting();
app.UseAuthorization();
app.UseEndpoints(endpoints =>
{
endpoints.MapControllers();
});
}
```
The authentication works correct but when I try to access the api I get the following exception.
```
fail: Microsoft.AspNetCore.Server.Kestrel[13]
Connection id "0HLTP6L6AV4FV", Request id "0HLTP6L6AV4FV:00000001": An unhandled exception was thrown by the application.
System.InvalidOperationException: No service for type 'Microsoft.AspNetCore.Identity.ISecurityStampValidator' has been registered.
at Microsoft.Extensions.DependencyInjection.ServiceProviderServiceExtensions.GetRequiredService(IServiceProvider provider, Type serviceType)
at Microsoft.Extensions.DependencyInjection.ServiceProviderServiceExtensions.GetRequiredService[T](IServiceProvider provider)
at Microsoft.AspNetCore.Identity.SecurityStampValidator.ValidateAsync[TValidator](CookieValidatePrincipalContext context)
at Microsoft.AspNetCore.Identity.SecurityStampValidator.ValidatePrincipalAsync(CookieValidatePrincipalContext context)
at Microsoft.AspNetCore.Authentication.Cookies.CookieAuthenticationEvents.ValidatePrincipal(CookieValidatePrincipalContext context)
at Microsoft.AspNetCore.Authentication.Cookies.CookieAuthenticationHandler.HandleAuthenticateAsync()
at Microsoft.AspNetCore.Authentication.AuthenticationHandler`1.AuthenticateAsync()
at Microsoft.AspNetCore.Authentication.AuthenticationService.AuthenticateAsync(HttpContext context, String scheme)
at Microsoft.AspNetCore.Authentication.AuthenticationMiddleware.Invoke(HttpContext context)
at Microsoft.AspNetCore.Server.Kestrel.Core.Internal.Http.HttpProtocol.ProcessRequests[TContext](IHttpApplication`1 application)
```
I can't figure out what the problem is so I appreciate all the help I can get.
|
True
|
Share authentication cookie between two sites produces exception caused by ISecurityStampValidator is missing - I have one API and one frontend app where I share the data protection keys using the file system. This is how my apps is configured.
**Frontend**:
```c#
public void ConfigureServices(IServiceCollection services)
{
services
.AddDataProtection()
.SetApplicationName("SharedCookieApp")
.PersistKeysToFileSystem(new DirectoryInfo("/dataprotection"));
services
.AddAuthentication(options =>
{
options.DefaultScheme = IdentityConstants.ApplicationScheme;
options.DefaultSignInScheme = IdentityConstants.ExternalScheme;
})
.AddOAuth("GitHub", "GitHub", o => { ... })
.AddIdentityCookies(options =>
{
options.ApplicationCookie.Configure(o =>
{
o.Cookie.Name = ".AspNet.SharedCookie";
o.Cookie.Domain = ".example.app";
o.LoginPath = new PathString("/Account/Login/");
o.AccessDeniedPath = new PathString("/Account/Forbidden/");
});
});
services.AddIdentityCore<User>(options =>
{
options.Password.RequireDigit = true;
options.Password.RequiredLength = 8;
options.Password.RequireNonAlphanumeric = false;
options.Password.RequireUppercase = true;
options.Password.RequireLowercase = true;
})
.AddRoles<Raven.Identity.IdentityRole>()
.AddRoleStore<RoleStore<Raven.Identity.IdentityRole>>()
.AddUserStore<UserStore<User, Raven.Identity.IdentityRole>>()
.AddSignInManager();
}
public void Configure(IApplicationBuilder app, IWebHostEnvironment env)
{
if (env.IsDevelopment())
{
app.UseDeveloperExceptionPage();
}
app.UseForwardedHeaders();
app.UseRouting();
app.UseCookiePolicy();
app.UseAuthentication();
app.UseAuthorization();
...
}
```
And from the API I need to use the authorize attribute to make sure that the user is authenticated when making a request.
**API**:
```c#
public void ConfigureServices(IServiceCollection services)
{
services.AddDataProtection()
.SetApplicationName("SharedCookieApp")
.PersistKeysToFileSystem(new DirectoryInfo("/dataprotection"));
services.AddAuthentication(options =>
{
options.DefaultScheme = IdentityConstants.ApplicationScheme;
})
.AddIdentityCookies(options =>
{
options.ApplicationCookie.Configure(a =>
{
a.Cookie.Name = ".AspNet.SharedCookie";
a.Cookie.Domain = ".example.app";
});
});
services.AddControllers();
}
public void Configure(IApplicationBuilder app, IWebHostEnvironment env)
{
if (env.IsDevelopment())
{
app.UseDeveloperExceptionPage();
}
app.UseHttpsRedirection();
app.UseCookiePolicy();
app.UseAuthentication();
app.UseRouting();
app.UseAuthorization();
app.UseEndpoints(endpoints =>
{
endpoints.MapControllers();
});
}
```
The authentication works correct but when I try to access the api I get the following exception.
```
fail: Microsoft.AspNetCore.Server.Kestrel[13]
Connection id "0HLTP6L6AV4FV", Request id "0HLTP6L6AV4FV:00000001": An unhandled exception was thrown by the application.
System.InvalidOperationException: No service for type 'Microsoft.AspNetCore.Identity.ISecurityStampValidator' has been registered.
at Microsoft.Extensions.DependencyInjection.ServiceProviderServiceExtensions.GetRequiredService(IServiceProvider provider, Type serviceType)
at Microsoft.Extensions.DependencyInjection.ServiceProviderServiceExtensions.GetRequiredService[T](IServiceProvider provider)
at Microsoft.AspNetCore.Identity.SecurityStampValidator.ValidateAsync[TValidator](CookieValidatePrincipalContext context)
at Microsoft.AspNetCore.Identity.SecurityStampValidator.ValidatePrincipalAsync(CookieValidatePrincipalContext context)
at Microsoft.AspNetCore.Authentication.Cookies.CookieAuthenticationEvents.ValidatePrincipal(CookieValidatePrincipalContext context)
at Microsoft.AspNetCore.Authentication.Cookies.CookieAuthenticationHandler.HandleAuthenticateAsync()
at Microsoft.AspNetCore.Authentication.AuthenticationHandler`1.AuthenticateAsync()
at Microsoft.AspNetCore.Authentication.AuthenticationService.AuthenticateAsync(HttpContext context, String scheme)
at Microsoft.AspNetCore.Authentication.AuthenticationMiddleware.Invoke(HttpContext context)
at Microsoft.AspNetCore.Server.Kestrel.Core.Internal.Http.HttpProtocol.ProcessRequests[TContext](IHttpApplication`1 application)
```
I can't figure out what the problem is so I appreciate all the help I can get.
|
non_process
|
share authentication cookie between two sites produces exception caused by isecuritystampvalidator is missing i have one api and one frontend app where i share the data protection keys using the file system this is how my apps is configured frontend c public void configureservices iservicecollection services services adddataprotection setapplicationname sharedcookieapp persistkeystofilesystem new directoryinfo dataprotection services addauthentication options options defaultscheme identityconstants applicationscheme options defaultsigninscheme identityconstants externalscheme addoauth github github o addidentitycookies options options applicationcookie configure o o cookie name aspnet sharedcookie o cookie domain example app o loginpath new pathstring account login o accessdeniedpath new pathstring account forbidden services addidentitycore options options password requiredigit true options password requiredlength options password requirenonalphanumeric false options password requireuppercase true options password requirelowercase true addroles addrolestore adduserstore addsigninmanager public void configure iapplicationbuilder app iwebhostenvironment env if env isdevelopment app usedeveloperexceptionpage app useforwardedheaders app userouting app usecookiepolicy app useauthentication app useauthorization and from the api i need to use the authorize attribute to make sure that the user is authenticated when making a request api c public void configureservices iservicecollection services services adddataprotection setapplicationname sharedcookieapp persistkeystofilesystem new directoryinfo dataprotection services addauthentication options options defaultscheme identityconstants applicationscheme addidentitycookies options options applicationcookie configure a a cookie name aspnet sharedcookie a cookie domain example app services addcontrollers public void configure iapplicationbuilder app iwebhostenvironment env if env isdevelopment app usedeveloperexceptionpage app usehttpsredirection app usecookiepolicy app useauthentication app userouting app useauthorization app useendpoints endpoints endpoints mapcontrollers the authentication works correct but when i try to access the api i get the following exception fail microsoft aspnetcore server kestrel connection id request id an unhandled exception was thrown by the application system invalidoperationexception no service for type microsoft aspnetcore identity isecuritystampvalidator has been registered at microsoft extensions dependencyinjection serviceproviderserviceextensions getrequiredservice iserviceprovider provider type servicetype at microsoft extensions dependencyinjection serviceproviderserviceextensions getrequiredservice iserviceprovider provider at microsoft aspnetcore identity securitystampvalidator validateasync cookievalidateprincipalcontext context at microsoft aspnetcore identity securitystampvalidator validateprincipalasync cookievalidateprincipalcontext context at microsoft aspnetcore authentication cookies cookieauthenticationevents validateprincipal cookievalidateprincipalcontext context at microsoft aspnetcore authentication cookies cookieauthenticationhandler handleauthenticateasync at microsoft aspnetcore authentication authenticationhandler authenticateasync at microsoft aspnetcore authentication authenticationservice authenticateasync httpcontext context string scheme at microsoft aspnetcore authentication authenticationmiddleware invoke httpcontext context at microsoft aspnetcore server kestrel core internal http httpprotocol processrequests ihttpapplication application i can t figure out what the problem is so i appreciate all the help i can get
| 0
|
8,841
| 11,948,369,637
|
IssuesEvent
|
2020-04-03 11:43:43
|
digitalmethodsinitiative/4cat
|
https://api.github.com/repos/digitalmethodsinitiative/4cat
|
closed
|
Make workers do less when starting
|
(mostly) back-end processors
|
Scrapers and other workers have a significant delay in starting up (as a worker) because they run the same bootstrapping code as the 'full' daemon, which builds a map of all workers, initializes everything, etc. Either they should run less startup code or the general startup code should be reduced.
|
1.0
|
Make workers do less when starting - Scrapers and other workers have a significant delay in starting up (as a worker) because they run the same bootstrapping code as the 'full' daemon, which builds a map of all workers, initializes everything, etc. Either they should run less startup code or the general startup code should be reduced.
|
process
|
make workers do less when starting scrapers and other workers have a significant delay in starting up as a worker because they run the same bootstrapping code as the full daemon which builds a map of all workers initializes everything etc either they should run less startup code or the general startup code should be reduced
| 1
|
256,811
| 22,102,384,596
|
IssuesEvent
|
2022-06-01 14:36:16
|
vellvm/vellvm
|
https://api.github.com/repos/vellvm/vellvm
|
opened
|
QuickChick Performance
|
bug testing quickchick performance
|
There seems to be a couple of performance issues with the QC generator. Here's some things I've noticed:
- [ ] We can't seem to generate large code blocks --- I think `failGen` is getting called somewhere: `Sample (run_GenLLVM (gen_code_length 10)).`
- [ ] After some fixes to the generator it now seems to get stuck when generating larger programs. This could be because of a loop in one of the generators? I don't think it can just be calling `failGen` constantly, because I think it will just stop testing after a while, but that might be another possibility.
- [ ] Some things don't seem to be generated... Like the `insert` / `extract` instructions. Could be related to the performance issues here.
|
1.0
|
QuickChick Performance - There seems to be a couple of performance issues with the QC generator. Here's some things I've noticed:
- [ ] We can't seem to generate large code blocks --- I think `failGen` is getting called somewhere: `Sample (run_GenLLVM (gen_code_length 10)).`
- [ ] After some fixes to the generator it now seems to get stuck when generating larger programs. This could be because of a loop in one of the generators? I don't think it can just be calling `failGen` constantly, because I think it will just stop testing after a while, but that might be another possibility.
- [ ] Some things don't seem to be generated... Like the `insert` / `extract` instructions. Could be related to the performance issues here.
|
non_process
|
quickchick performance there seems to be a couple of performance issues with the qc generator here s some things i ve noticed we can t seem to generate large code blocks i think failgen is getting called somewhere sample run genllvm gen code length after some fixes to the generator it now seems to get stuck when generating larger programs this could be because of a loop in one of the generators i don t think it can just be calling failgen constantly because i think it will just stop testing after a while but that might be another possibility some things don t seem to be generated like the insert extract instructions could be related to the performance issues here
| 0
|
2,587
| 5,345,489,806
|
IssuesEvent
|
2017-02-17 17:04:46
|
sysown/proxysql
|
https://api.github.com/repos/sysown/proxysql
|
closed
|
Track number of SET NAMES and CHANGE_USER
|
CONNECTION POOL QUERY PROCESSOR
|
This is related to #818 . As `SET NAMES` and `CHANGE_USER` are internally handled, it is useful to track their number
|
1.0
|
Track number of SET NAMES and CHANGE_USER - This is related to #818 . As `SET NAMES` and `CHANGE_USER` are internally handled, it is useful to track their number
|
process
|
track number of set names and change user this is related to as set names and change user are internally handled it is useful to track their number
| 1
|
19,338
| 13,888,936,425
|
IssuesEvent
|
2020-10-19 07:09:10
|
pingcap/tiup
|
https://api.github.com/repos/pingcap/tiup
|
closed
|
Add an option to skip the forced cluster start operation during scaling out
|
category/stability category/usability status/TODO type/enhancement type/feature-request
|
## Feature Request
**Is your feature request related to a problem? Please describe:**
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
We observed a case (#730) that the "start cluster" might fail on some certain environment if the cluster has large amount instances, and if it fails to start the cluster, the whole scale out process is interrupted.
**Describe the feature you'd like:**
<!-- A clear and concise description of what you want to happen. -->
If the cluster can be confirmed to be already started, the "start cluster" operation could be safely skipped, but we don't have that option for user now.
**Describe alternatives you've considered:**
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
It's also possible to use a `-f/--force` flag to skip all operations that not critically necessary during an operation, like various checks or preparations. This could be a more generic solution.
**Teachability, Documentation, Adoption, Migration Strategy:**
<!-- If you can, explain some scenarios how users might use this, situations it would be helpful in. Any API designs, mockups, or diagrams are also helpful. -->
|
True
|
Add an option to skip the forced cluster start operation during scaling out - ## Feature Request
**Is your feature request related to a problem? Please describe:**
<!-- A clear and concise description of what the problem is. Ex. I'm always frustrated when [...] -->
We observed a case (#730) that the "start cluster" might fail on some certain environment if the cluster has large amount instances, and if it fails to start the cluster, the whole scale out process is interrupted.
**Describe the feature you'd like:**
<!-- A clear and concise description of what you want to happen. -->
If the cluster can be confirmed to be already started, the "start cluster" operation could be safely skipped, but we don't have that option for user now.
**Describe alternatives you've considered:**
<!-- A clear and concise description of any alternative solutions or features you've considered. -->
It's also possible to use a `-f/--force` flag to skip all operations that not critically necessary during an operation, like various checks or preparations. This could be a more generic solution.
**Teachability, Documentation, Adoption, Migration Strategy:**
<!-- If you can, explain some scenarios how users might use this, situations it would be helpful in. Any API designs, mockups, or diagrams are also helpful. -->
|
non_process
|
add an option to skip the forced cluster start operation during scaling out feature request is your feature request related to a problem please describe we observed a case that the start cluster might fail on some certain environment if the cluster has large amount instances and if it fails to start the cluster the whole scale out process is interrupted describe the feature you d like if the cluster can be confirmed to be already started the start cluster operation could be safely skipped but we don t have that option for user now describe alternatives you ve considered it s also possible to use a f force flag to skip all operations that not critically necessary during an operation like various checks or preparations this could be a more generic solution teachability documentation adoption migration strategy
| 0
|
11,842
| 14,657,406,525
|
IssuesEvent
|
2020-12-28 15:31:42
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
Highlighting of the data in blue colour should be removed where ever row pop-out is present
|
Bug P2 Participant manager Process: Dev Process: Tested QA Process: Tested dev UI
|
1. Highlighting of the data in blue colour should be removed where ever row pop-out is present
2. Row pop-out should be as per invision screen
[Note : It should be handled in all the pages where ever row pop-out is present]
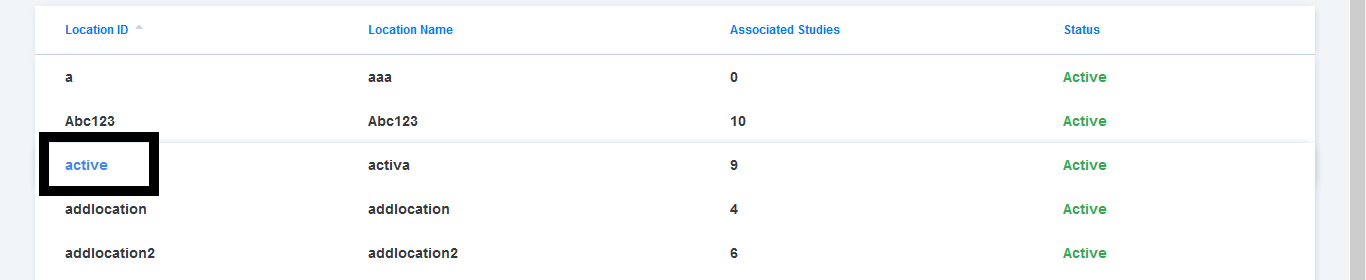
|
3.0
|
Highlighting of the data in blue colour should be removed where ever row pop-out is present - 1. Highlighting of the data in blue colour should be removed where ever row pop-out is present
2. Row pop-out should be as per invision screen
[Note : It should be handled in all the pages where ever row pop-out is present]
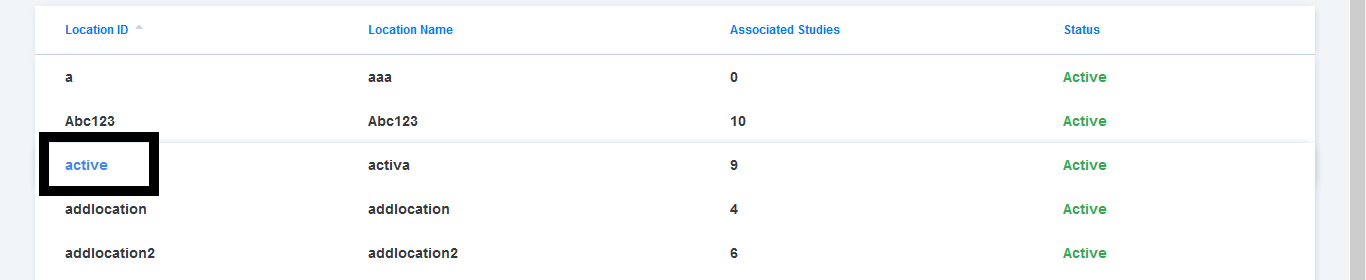
|
process
|
highlighting of the data in blue colour should be removed where ever row pop out is present highlighting of the data in blue colour should be removed where ever row pop out is present row pop out should be as per invision screen
| 1
|
16,728
| 21,891,031,186
|
IssuesEvent
|
2022-05-20 01:39:28
|
bazelbuild/bazel
|
https://api.github.com/repos/bazelbuild/bazel
|
closed
|
bazel 3.7.2 can't build TensorFlow Lite 2.7.0 for iOS
|
type: support / not a bug (process) untriaged team-OSS
|
### Description of the bug:
I am trying to build TensorFlow Lite 2.7.0 for iOS on macOS 12.3.1 m1 (arm64 CPU). But it failed to build it successfully.
### What's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
git clone https://github.com/tensorflow/tensorflow tensorflow-2.7.0_ios
cd tensorflow-2.7.0_ios
git checkout r2.7
./configure
default for all except the following option
Do you wish to build TensorFlow with iOS support? [y/N]: y
iOS support will be enabled for TensorFlow.
bazel build --config=ios_fat -c opt //tensorflow/lite/ios:TensorFlowLiteC_framework
### Which operating system are you running Bazel on?
macOS 12.3.1 m1 (arm64 CPU)
### What is the output of `bazel info release`?
release 3.7.2
### Have you found anything relevant by searching the web?
No
### Any other information, logs, or outputs that you want to share?
ERROR: /Users/andyueng/samba/workspace_TensorFlow2/tensorflow-2.7.0_ios/tensorflow/lite/ios/BUILD:104:21: Bundling Preprocessed_TensorFlowLiteC_framework failed (Exit 127): bundletool failed: error executing command
(cd /private/var/tmp/_bazel_andyueng/6c55a359b06f2067a8d1d18d335cb317/execroot/org_tensorflow && \
exec env - \
bazel-out/host/bin/external/build_bazel_rules_apple/tools/bundletool/bundletool bazel-out/darwin-opt/bin/tensorflow/lite/ios/Preprocessed_TensorFlowLiteC_framework-intermediates/bundletool_control.json)
Execution platform: @local_execution_config_platform//:platform
env: python: No such file or directory
Target //tensorflow/lite/ios:TensorFlowLiteC_framework failed to build
INFO: Elapsed time: 197.909s, Critical Path: 37.87s
INFO: 1960 processes: 150 internal, 1810 local.
FAILED: Build did NOT complete successfully
|
1.0
|
bazel 3.7.2 can't build TensorFlow Lite 2.7.0 for iOS - ### Description of the bug:
I am trying to build TensorFlow Lite 2.7.0 for iOS on macOS 12.3.1 m1 (arm64 CPU). But it failed to build it successfully.
### What's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
git clone https://github.com/tensorflow/tensorflow tensorflow-2.7.0_ios
cd tensorflow-2.7.0_ios
git checkout r2.7
./configure
default for all except the following option
Do you wish to build TensorFlow with iOS support? [y/N]: y
iOS support will be enabled for TensorFlow.
bazel build --config=ios_fat -c opt //tensorflow/lite/ios:TensorFlowLiteC_framework
### Which operating system are you running Bazel on?
macOS 12.3.1 m1 (arm64 CPU)
### What is the output of `bazel info release`?
release 3.7.2
### Have you found anything relevant by searching the web?
No
### Any other information, logs, or outputs that you want to share?
ERROR: /Users/andyueng/samba/workspace_TensorFlow2/tensorflow-2.7.0_ios/tensorflow/lite/ios/BUILD:104:21: Bundling Preprocessed_TensorFlowLiteC_framework failed (Exit 127): bundletool failed: error executing command
(cd /private/var/tmp/_bazel_andyueng/6c55a359b06f2067a8d1d18d335cb317/execroot/org_tensorflow && \
exec env - \
bazel-out/host/bin/external/build_bazel_rules_apple/tools/bundletool/bundletool bazel-out/darwin-opt/bin/tensorflow/lite/ios/Preprocessed_TensorFlowLiteC_framework-intermediates/bundletool_control.json)
Execution platform: @local_execution_config_platform//:platform
env: python: No such file or directory
Target //tensorflow/lite/ios:TensorFlowLiteC_framework failed to build
INFO: Elapsed time: 197.909s, Critical Path: 37.87s
INFO: 1960 processes: 150 internal, 1810 local.
FAILED: Build did NOT complete successfully
|
process
|
bazel can t build tensorflow lite for ios description of the bug i am trying to build tensorflow lite for ios on macos cpu but it failed to build it successfully what s the simplest easiest way to reproduce this bug please provide a minimal example if possible git clone tensorflow ios cd tensorflow ios git checkout configure default for all except the following option do you wish to build tensorflow with ios support y ios support will be enabled for tensorflow bazel build config ios fat c opt tensorflow lite ios tensorflowlitec framework which operating system are you running bazel on macos cpu what is the output of bazel info release release have you found anything relevant by searching the web no any other information logs or outputs that you want to share error users andyueng samba workspace tensorflow ios tensorflow lite ios build bundling preprocessed tensorflowlitec framework failed exit bundletool failed error executing command cd private var tmp bazel andyueng execroot org tensorflow exec env bazel out host bin external build bazel rules apple tools bundletool bundletool bazel out darwin opt bin tensorflow lite ios preprocessed tensorflowlitec framework intermediates bundletool control json execution platform local execution config platform platform env python no such file or directory target tensorflow lite ios tensorflowlitec framework failed to build info elapsed time critical path info processes internal local failed build did not complete successfully
| 1
|
252,999
| 27,286,050,925
|
IssuesEvent
|
2023-02-23 13:34:42
|
lukebrogan-mend/c-goof
|
https://api.github.com/repos/lukebrogan-mend/c-goof
|
opened
|
velocity-tools-2.0.jar: 14 vulnerabilities (highest severity is: 9.8)
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>velocity-tools-2.0.jar</b></p></summary>
<p>VelocityTools is an integrated collection of Velocity subprojects
with the common goal of creating tools and infrastructure to speed and ease
development of both web and non-web applications using the Velocity template
engine.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/velocity/velocity-tools/2.0/velocity-tools-2.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (velocity-tools version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-13116](https://www.mend.io/vulnerability-database/CVE-2019-13116) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2020-10683](https://www.mend.io/vulnerability-database/CVE-2020-10683) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | dom4j-1.1.jar | Transitive | N/A* | ❌ |
| [CVE-2017-15708](https://www.mend.io/vulnerability-database/CVE-2017-15708) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2015-7501](https://www.mend.io/vulnerability-database/CVE-2015-7501) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2016-1182](https://www.mend.io/vulnerability-database/CVE-2016-1182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.2 | struts-core-1.3.8.jar | Transitive | N/A* | ❌ |
| [CVE-2016-1181](https://www.mend.io/vulnerability-database/CVE-2016-1181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | struts-core-1.3.8.jar | Transitive | N/A* | ❌ |
| [CVE-2015-0899](https://www.mend.io/vulnerability-database/CVE-2015-0899) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | struts-core-1.3.8.jar | Transitive | N/A* | ❌ |
| [CVE-2018-1000632](https://www.mend.io/vulnerability-database/CVE-2018-1000632) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | dom4j-1.1.jar | Transitive | N/A* | ❌ |
| [CVE-2015-4852](https://www.mend.io/vulnerability-database/CVE-2015-4852) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2019-10086](https://www.mend.io/vulnerability-database/CVE-2019-10086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-1.7.0.jar | Transitive | N/A* | ❌ |
| [CVE-2014-0114](https://www.mend.io/vulnerability-database/CVE-2014-0114) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2015-6420](https://www.mend.io/vulnerability-database/CVE-2015-6420) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13959](https://www.mend.io/vulnerability-database/CVE-2020-13959) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | velocity-tools-2.0.jar | Direct | org.apache.velocity.tools:velocity-tools-view:3.1 | ✅ |
| [CVE-2008-2025](https://www.mend.io/vulnerability-database/CVE-2008-2025) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | struts-taglib-1.3.8.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2019-13116</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MuleSoft Mule Community Edition runtime engine before 3.8 allows remote attackers to execute arbitrary code because of Java Deserialization, related to Apache Commons Collections
<p>Publish Date: 2019-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-13116>CVE-2019-13116</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13116">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13116</a></p>
<p>Release Date: 2019-10-16</p>
<p>Fix Resolution: commons-collections:commons-collections:3.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2020-10683</summary>
### Vulnerable Library - <b>dom4j-1.1.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/dom4j/dom4j/1.1/dom4j-1.1.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **dom4j-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
dom4j before 2.0.3 and 2.1.x before 2.1.3 allows external DTDs and External Entities by default, which might enable XXE attacks. However, there is popular external documentation from OWASP showing how to enable the safe, non-default behavior in any application that uses dom4j.
<p>Publish Date: 2020-05-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-10683>CVE-2020-10683</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-05-01</p>
<p>Fix Resolution: org.dom4j:dom4j:2.1.3,org.dom4j:dom4j:2.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2017-15708</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Synapse, by default no authentication is required for Java Remote Method Invocation (RMI). So Apache Synapse 3.0.1 or all previous releases (3.0.0, 2.1.0, 2.0.0, 1.2, 1.1.2, 1.1.1) allows remote code execution attacks that can be performed by injecting specially crafted serialized objects. And the presence of Apache Commons Collections 3.2.1 (commons-collections-3.2.1.jar) or previous versions in Synapse distribution makes this exploitable. To mitigate the issue, we need to limit RMI access to trusted users only. Further upgrading to 3.0.1 version will eliminate the risk of having said Commons Collection version. In Synapse 3.0.1, Commons Collection has been updated to 3.2.2 version.
<p>Publish Date: 2017-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-15708>CVE-2017-15708</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-15708">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-15708</a></p>
<p>Release Date: 2017-12-10</p>
<p>Fix Resolution: org.apache.synapse:Apache-Synapse:3.0.1;commons-collections:commons-collections:3.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2015-7501</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Red Hat JBoss A-MQ 6.x; BPM Suite (BPMS) 6.x; BRMS 6.x and 5.x; Data Grid (JDG) 6.x; Data Virtualization (JDV) 6.x and 5.x; Enterprise Application Platform 6.x, 5.x, and 4.3.x; Fuse 6.x; Fuse Service Works (FSW) 6.x; Operations Network (JBoss ON) 3.x; Portal 6.x; SOA Platform (SOA-P) 5.x; Web Server (JWS) 3.x; Red Hat OpenShift/xPAAS 3.x; and Red Hat Subscription Asset Manager 1.3 allow remote attackers to execute arbitrary commands via a crafted serialized Java object, related to the Apache Commons Collections (ACC) library.
<p>Publish Date: 2017-11-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-7501>CVE-2015-7501</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1279330">https://bugzilla.redhat.com/show_bug.cgi?id=1279330</a></p>
<p>Release Date: 2017-11-09</p>
<p>Fix Resolution: commons-collections:commons-collections:3.2.2;org.apache.commons:commons-collections4:4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1182</summary>
### Vulnerable Library - <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ActionServlet.java in Apache Struts 1 1.x through 1.3.10 does not properly restrict the Validator configuration, which allows remote attackers to conduct cross-site scripting (XSS) attacks or cause a denial of service via crafted input, a related issue to CVE-2015-0899.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1182>CVE-2016-1182</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-1182">https://nvd.nist.gov/vuln/detail/CVE-2016-1182</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: struts:struts - 1.1-b3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1181</summary>
### Vulnerable Library - <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ActionServlet.java in Apache Struts 1 1.x through 1.3.10 mishandles multithreaded access to an ActionForm instance, which allows remote attackers to execute arbitrary code or cause a denial of service (unexpected memory access) via a multipart request, a related issue to CVE-2015-0899.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1181>CVE-2016-1181</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-1181">https://nvd.nist.gov/vuln/detail/CVE-2016-1181</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: struts:struts - 1.1-b3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-0899</summary>
### Vulnerable Library - <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MultiPageValidator implementation in Apache Struts 1 1.1 through 1.3.10 allows remote attackers to bypass intended access restrictions via a modified page parameter.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-0899>CVE-2015-0899</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-0899">https://nvd.nist.gov/vuln/detail/CVE-2015-0899</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: struts:struts - 1.1-beta-2,1.1-b2-20021124</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000632</summary>
### Vulnerable Library - <b>dom4j-1.1.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/dom4j/dom4j/1.1/dom4j-1.1.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **dom4j-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
dom4j version prior to version 2.1.1 contains a CWE-91: XML Injection vulnerability in Class: Element. Methods: addElement, addAttribute that can result in an attacker tampering with XML documents through XML injection. This attack appear to be exploitable via an attacker specifying attributes or elements in the XML document. This vulnerability appears to have been fixed in 2.1.1 or later.
<p>Publish Date: 2018-08-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1000632>CVE-2018-1000632</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000632/">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000632/</a></p>
<p>Release Date: 2018-08-20</p>
<p>Fix Resolution: org.dom4j:dom4j:2.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-4852</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The WLS Security component in Oracle WebLogic Server 10.3.6.0, 12.1.2.0, 12.1.3.0, and 12.2.1.0 allows remote attackers to execute arbitrary commands via a crafted serialized Java object in T3 protocol traffic to TCP port 7001, related to oracle_common/modules/com.bea.core.apache.commons.collections.jar. NOTE: the scope of this CVE is limited to the WebLogic Server product.
<p>Publish Date: 2015-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-4852>CVE-2015-4852</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.openwall.com/lists/oss-security/2015/11/17/19">https://www.openwall.com/lists/oss-security/2015/11/17/19</a></p>
<p>Release Date: 2015-11-18</p>
<p>Fix Resolution: commons-collections:commons-collections:3.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10086</summary>
### Vulnerable Library - <b>commons-beanutils-1.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.7.0/commons-beanutils-1.7.0.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-beanutils-1.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons Beanutils 1.9.2, a special BeanIntrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all Java objects. We, however were not using this by default characteristic of the PropertyUtilsBean.
<p>Publish Date: 2019-08-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10086>CVE-2019-10086</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-20</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0114</summary>
### Vulnerable Libraries - <b>struts-core-1.3.8.jar</b>, <b>commons-beanutils-1.7.0.jar</b></p>
<p>
### <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
### <b>commons-beanutils-1.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.7.0/commons-beanutils-1.7.0.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-beanutils-1.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-6420</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Serialized-object interfaces in certain Cisco Collaboration and Social Media; Endpoint Clients and Client Software; Network Application, Service, and Acceleration; Network and Content Security Devices; Network Management and Provisioning; Routing and Switching - Enterprise and Service Provider; Unified Computing; Voice and Unified Communications Devices; Video, Streaming, TelePresence, and Transcoding Devices; Wireless; and Cisco Hosted Services products allow remote attackers to execute arbitrary commands via a crafted serialized Java object, related to the Apache Commons Collections (ACC) library.
<p>Publish Date: 2015-12-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-6420>CVE-2015-6420</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2015-12-15</p>
<p>Fix Resolution: commons-collections:commons-collections3.2.2,org.apache.commons:commons-collections4:4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-13959</summary>
### Vulnerable Library - <b>velocity-tools-2.0.jar</b></p>
<p>VelocityTools is an integrated collection of Velocity subprojects
with the common goal of creating tools and infrastructure to speed and ease
development of both web and non-web applications using the Velocity template
engine.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/velocity/velocity-tools/2.0/velocity-tools-2.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **velocity-tools-2.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The default error page for VelocityView in Apache Velocity Tools prior to 3.1 reflects back the vm file that was entered as part of the URL. An attacker can set an XSS payload file as this vm file in the URL which results in this payload being executed. XSS vulnerabilities allow attackers to execute arbitrary JavaScript in the context of the attacked website and the attacked user. This can be abused to steal session cookies, perform requests in the name of the victim or for phishing attacks.
<p>Publish Date: 2021-03-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13959>CVE-2020-13959</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fh63-4r66-jc7v">https://github.com/advisories/GHSA-fh63-4r66-jc7v</a></p>
<p>Release Date: 2021-03-10</p>
<p>Fix Resolution: org.apache.velocity.tools:velocity-tools-view:3.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2008-2025</summary>
### Vulnerable Library - <b>struts-taglib-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-taglib/1.3.8/struts-taglib-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-taglib-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in Apache Struts before 1.2.9-162.31.1 on SUSE Linux Enterprise (SLE) 11, before 1.2.9-108.2 on SUSE openSUSE 10.3, before 1.2.9-198.2 on SUSE openSUSE 11.0, and before 1.2.9-162.163.2 on SUSE openSUSE 11.1 allows remote attackers to inject arbitrary web script or HTML via unspecified vectors related to "insufficient quoting of parameters."
<p>Publish Date: 2009-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2008-2025>CVE-2008-2025</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2008-2025">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2008-2025</a></p>
<p>Release Date: 2009-04-09</p>
<p>Fix Resolution: org.apache.struts:struts-taglib:1.4.0</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
True
|
velocity-tools-2.0.jar: 14 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>velocity-tools-2.0.jar</b></p></summary>
<p>VelocityTools is an integrated collection of Velocity subprojects
with the common goal of creating tools and infrastructure to speed and ease
development of both web and non-web applications using the Velocity template
engine.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/velocity/velocity-tools/2.0/velocity-tools-2.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (velocity-tools version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-13116](https://www.mend.io/vulnerability-database/CVE-2019-13116) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2020-10683](https://www.mend.io/vulnerability-database/CVE-2020-10683) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | dom4j-1.1.jar | Transitive | N/A* | ❌ |
| [CVE-2017-15708](https://www.mend.io/vulnerability-database/CVE-2017-15708) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2015-7501](https://www.mend.io/vulnerability-database/CVE-2015-7501) | <img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Critical | 9.8 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2016-1182](https://www.mend.io/vulnerability-database/CVE-2016-1182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.2 | struts-core-1.3.8.jar | Transitive | N/A* | ❌ |
| [CVE-2016-1181](https://www.mend.io/vulnerability-database/CVE-2016-1181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | struts-core-1.3.8.jar | Transitive | N/A* | ❌ |
| [CVE-2015-0899](https://www.mend.io/vulnerability-database/CVE-2015-0899) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | struts-core-1.3.8.jar | Transitive | N/A* | ❌ |
| [CVE-2018-1000632](https://www.mend.io/vulnerability-database/CVE-2018-1000632) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | dom4j-1.1.jar | Transitive | N/A* | ❌ |
| [CVE-2015-4852](https://www.mend.io/vulnerability-database/CVE-2015-4852) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2019-10086](https://www.mend.io/vulnerability-database/CVE-2019-10086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-1.7.0.jar | Transitive | N/A* | ❌ |
| [CVE-2014-0114](https://www.mend.io/vulnerability-database/CVE-2014-0114) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2015-6420](https://www.mend.io/vulnerability-database/CVE-2015-6420) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-collections-3.2.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13959](https://www.mend.io/vulnerability-database/CVE-2020-13959) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | velocity-tools-2.0.jar | Direct | org.apache.velocity.tools:velocity-tools-view:3.1 | ✅ |
| [CVE-2008-2025](https://www.mend.io/vulnerability-database/CVE-2008-2025) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | struts-taglib-1.3.8.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2019-13116</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MuleSoft Mule Community Edition runtime engine before 3.8 allows remote attackers to execute arbitrary code because of Java Deserialization, related to Apache Commons Collections
<p>Publish Date: 2019-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-13116>CVE-2019-13116</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13116">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-13116</a></p>
<p>Release Date: 2019-10-16</p>
<p>Fix Resolution: commons-collections:commons-collections:3.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2020-10683</summary>
### Vulnerable Library - <b>dom4j-1.1.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/dom4j/dom4j/1.1/dom4j-1.1.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **dom4j-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
dom4j before 2.0.3 and 2.1.x before 2.1.3 allows external DTDs and External Entities by default, which might enable XXE attacks. However, there is popular external documentation from OWASP showing how to enable the safe, non-default behavior in any application that uses dom4j.
<p>Publish Date: 2020-05-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-10683>CVE-2020-10683</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-05-01</p>
<p>Fix Resolution: org.dom4j:dom4j:2.1.3,org.dom4j:dom4j:2.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2017-15708</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Synapse, by default no authentication is required for Java Remote Method Invocation (RMI). So Apache Synapse 3.0.1 or all previous releases (3.0.0, 2.1.0, 2.0.0, 1.2, 1.1.2, 1.1.1) allows remote code execution attacks that can be performed by injecting specially crafted serialized objects. And the presence of Apache Commons Collections 3.2.1 (commons-collections-3.2.1.jar) or previous versions in Synapse distribution makes this exploitable. To mitigate the issue, we need to limit RMI access to trusted users only. Further upgrading to 3.0.1 version will eliminate the risk of having said Commons Collection version. In Synapse 3.0.1, Commons Collection has been updated to 3.2.2 version.
<p>Publish Date: 2017-12-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-15708>CVE-2017-15708</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-15708">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-15708</a></p>
<p>Release Date: 2017-12-10</p>
<p>Fix Resolution: org.apache.synapse:Apache-Synapse:3.0.1;commons-collections:commons-collections:3.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> CVE-2015-7501</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Red Hat JBoss A-MQ 6.x; BPM Suite (BPMS) 6.x; BRMS 6.x and 5.x; Data Grid (JDG) 6.x; Data Virtualization (JDV) 6.x and 5.x; Enterprise Application Platform 6.x, 5.x, and 4.3.x; Fuse 6.x; Fuse Service Works (FSW) 6.x; Operations Network (JBoss ON) 3.x; Portal 6.x; SOA Platform (SOA-P) 5.x; Web Server (JWS) 3.x; Red Hat OpenShift/xPAAS 3.x; and Red Hat Subscription Asset Manager 1.3 allow remote attackers to execute arbitrary commands via a crafted serialized Java object, related to the Apache Commons Collections (ACC) library.
<p>Publish Date: 2017-11-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-7501>CVE-2015-7501</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=1279330">https://bugzilla.redhat.com/show_bug.cgi?id=1279330</a></p>
<p>Release Date: 2017-11-09</p>
<p>Fix Resolution: commons-collections:commons-collections:3.2.2;org.apache.commons:commons-collections4:4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1182</summary>
### Vulnerable Library - <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ActionServlet.java in Apache Struts 1 1.x through 1.3.10 does not properly restrict the Validator configuration, which allows remote attackers to conduct cross-site scripting (XSS) attacks or cause a denial of service via crafted input, a related issue to CVE-2015-0899.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1182>CVE-2016-1182</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-1182">https://nvd.nist.gov/vuln/detail/CVE-2016-1182</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: struts:struts - 1.1-b3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1181</summary>
### Vulnerable Library - <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ActionServlet.java in Apache Struts 1 1.x through 1.3.10 mishandles multithreaded access to an ActionForm instance, which allows remote attackers to execute arbitrary code or cause a denial of service (unexpected memory access) via a multipart request, a related issue to CVE-2015-0899.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1181>CVE-2016-1181</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-1181">https://nvd.nist.gov/vuln/detail/CVE-2016-1181</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: struts:struts - 1.1-b3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-0899</summary>
### Vulnerable Library - <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MultiPageValidator implementation in Apache Struts 1 1.1 through 1.3.10 allows remote attackers to bypass intended access restrictions via a modified page parameter.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-0899>CVE-2015-0899</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-0899">https://nvd.nist.gov/vuln/detail/CVE-2015-0899</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution: struts:struts - 1.1-beta-2,1.1-b2-20021124</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000632</summary>
### Vulnerable Library - <b>dom4j-1.1.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/dom4j/dom4j/1.1/dom4j-1.1.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **dom4j-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
dom4j version prior to version 2.1.1 contains a CWE-91: XML Injection vulnerability in Class: Element. Methods: addElement, addAttribute that can result in an attacker tampering with XML documents through XML injection. This attack appear to be exploitable via an attacker specifying attributes or elements in the XML document. This vulnerability appears to have been fixed in 2.1.1 or later.
<p>Publish Date: 2018-08-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1000632>CVE-2018-1000632</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000632/">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000632/</a></p>
<p>Release Date: 2018-08-20</p>
<p>Fix Resolution: org.dom4j:dom4j:2.0.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-4852</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The WLS Security component in Oracle WebLogic Server 10.3.6.0, 12.1.2.0, 12.1.3.0, and 12.2.1.0 allows remote attackers to execute arbitrary commands via a crafted serialized Java object in T3 protocol traffic to TCP port 7001, related to oracle_common/modules/com.bea.core.apache.commons.collections.jar. NOTE: the scope of this CVE is limited to the WebLogic Server product.
<p>Publish Date: 2015-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-4852>CVE-2015-4852</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.openwall.com/lists/oss-security/2015/11/17/19">https://www.openwall.com/lists/oss-security/2015/11/17/19</a></p>
<p>Release Date: 2015-11-18</p>
<p>Fix Resolution: commons-collections:commons-collections:3.2.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10086</summary>
### Vulnerable Library - <b>commons-beanutils-1.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.7.0/commons-beanutils-1.7.0.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-beanutils-1.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons Beanutils 1.9.2, a special BeanIntrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all Java objects. We, however were not using this by default characteristic of the PropertyUtilsBean.
<p>Publish Date: 2019-08-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10086>CVE-2019-10086</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-20</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0114</summary>
### Vulnerable Libraries - <b>struts-core-1.3.8.jar</b>, <b>commons-beanutils-1.7.0.jar</b></p>
<p>
### <b>struts-core-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-core/1.3.8/struts-core-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-core-1.3.8.jar** (Vulnerable Library)
### <b>commons-beanutils-1.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.7.0/commons-beanutils-1.7.0.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-beanutils-1.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2015-6420</summary>
### Vulnerable Library - <b>commons-collections-3.2.jar</b></p>
<p>Types that extend and augment the Java Collections Framework.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-collections/commons-collections/3.2/commons-collections-3.2.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **commons-collections-3.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Serialized-object interfaces in certain Cisco Collaboration and Social Media; Endpoint Clients and Client Software; Network Application, Service, and Acceleration; Network and Content Security Devices; Network Management and Provisioning; Routing and Switching - Enterprise and Service Provider; Unified Computing; Voice and Unified Communications Devices; Video, Streaming, TelePresence, and Transcoding Devices; Wireless; and Cisco Hosted Services products allow remote attackers to execute arbitrary commands via a crafted serialized Java object, related to the Apache Commons Collections (ACC) library.
<p>Publish Date: 2015-12-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2015-6420>CVE-2015-6420</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2015-12-15</p>
<p>Fix Resolution: commons-collections:commons-collections3.2.2,org.apache.commons:commons-collections4:4.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-13959</summary>
### Vulnerable Library - <b>velocity-tools-2.0.jar</b></p>
<p>VelocityTools is an integrated collection of Velocity subprojects
with the common goal of creating tools and infrastructure to speed and ease
development of both web and non-web applications using the Velocity template
engine.</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/velocity/velocity-tools/2.0/velocity-tools-2.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **velocity-tools-2.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The default error page for VelocityView in Apache Velocity Tools prior to 3.1 reflects back the vm file that was entered as part of the URL. An attacker can set an XSS payload file as this vm file in the URL which results in this payload being executed. XSS vulnerabilities allow attackers to execute arbitrary JavaScript in the context of the attacked website and the attacked user. This can be abused to steal session cookies, perform requests in the name of the victim or for phishing attacks.
<p>Publish Date: 2021-03-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13959>CVE-2020-13959</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-fh63-4r66-jc7v">https://github.com/advisories/GHSA-fh63-4r66-jc7v</a></p>
<p>Release Date: 2021-03-10</p>
<p>Fix Resolution: org.apache.velocity.tools:velocity-tools-view:3.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2008-2025</summary>
### Vulnerable Library - <b>struts-taglib-1.3.8.jar</b></p>
<p>Apache Struts</p>
<p>Path to dependency file: /vendor/aws-sdk-cpp-1.3.50/code-generation/generator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/struts/struts-taglib/1.3.8/struts-taglib-1.3.8.jar</p>
<p>
Dependency Hierarchy:
- velocity-tools-2.0.jar (Root Library)
- :x: **struts-taglib-1.3.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebrogan-mend/c-goof/commit/802457f036ab4eb3ba012bdede243dbbc52f72ec">802457f036ab4eb3ba012bdede243dbbc52f72ec</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in Apache Struts before 1.2.9-162.31.1 on SUSE Linux Enterprise (SLE) 11, before 1.2.9-108.2 on SUSE openSUSE 10.3, before 1.2.9-198.2 on SUSE openSUSE 11.0, and before 1.2.9-162.163.2 on SUSE openSUSE 11.1 allows remote attackers to inject arbitrary web script or HTML via unspecified vectors related to "insufficient quoting of parameters."
<p>Publish Date: 2009-04-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2008-2025>CVE-2008-2025</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2008-2025">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2008-2025</a></p>
<p>Release Date: 2009-04-09</p>
<p>Fix Resolution: org.apache.struts:struts-taglib:1.4.0</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p>
|
non_process
|
velocity tools jar vulnerabilities highest severity is vulnerable library velocity tools jar velocitytools is an integrated collection of velocity subprojects with the common goal of creating tools and infrastructure to speed and ease development of both web and non web applications using the velocity template engine path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache velocity velocity tools velocity tools jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in velocity tools version remediation available critical commons collections jar transitive n a critical jar transitive n a critical commons collections jar transitive n a critical commons collections jar transitive n a high struts core jar transitive n a high struts core jar transitive n a high struts core jar transitive n a high jar transitive n a high commons collections jar transitive n a high commons beanutils jar transitive n a high detected in multiple dependencies transitive n a high commons collections jar transitive n a medium velocity tools jar direct org apache velocity tools velocity tools view low struts taglib jar transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library commons collections jar types that extend and augment the java collections framework path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons collections commons collections commons collections jar dependency hierarchy velocity tools jar root library x commons collections jar vulnerable library found in head commit a href found in base branch main vulnerability details the mulesoft mule community edition runtime engine before allows remote attackers to execute arbitrary code because of java deserialization related to apache commons collections publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons collections commons collections cve vulnerable library jar path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository jar dependency hierarchy velocity tools jar root library x jar vulnerable library found in head commit a href found in base branch main vulnerability details before and x before allows external dtds and external entities by default which might enable xxe attacks however there is popular external documentation from owasp showing how to enable the safe non default behavior in any application that uses publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution org org cve vulnerable library commons collections jar types that extend and augment the java collections framework path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons collections commons collections commons collections jar dependency hierarchy velocity tools jar root library x commons collections jar vulnerable library found in head commit a href found in base branch main vulnerability details in apache synapse by default no authentication is required for java remote method invocation rmi so apache synapse or all previous releases allows remote code execution attacks that can be performed by injecting specially crafted serialized objects and the presence of apache commons collections commons collections jar or previous versions in synapse distribution makes this exploitable to mitigate the issue we need to limit rmi access to trusted users only further upgrading to version will eliminate the risk of having said commons collection version in synapse commons collection has been updated to version publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache synapse apache synapse commons collections commons collections cve vulnerable library commons collections jar types that extend and augment the java collections framework path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons collections commons collections commons collections jar dependency hierarchy velocity tools jar root library x commons collections jar vulnerable library found in head commit a href found in base branch main vulnerability details red hat jboss a mq x bpm suite bpms x brms x and x data grid jdg x data virtualization jdv x and x enterprise application platform x x and x fuse x fuse service works fsw x operations network jboss on x portal x soa platform soa p x web server jws x red hat openshift xpaas x and red hat subscription asset manager allow remote attackers to execute arbitrary commands via a crafted serialized java object related to the apache commons collections acc library publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons collections commons collections org apache commons commons cve vulnerable library struts core jar apache struts path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache struts struts core struts core jar dependency hierarchy velocity tools jar root library x struts core jar vulnerable library found in head commit a href found in base branch main vulnerability details actionservlet java in apache struts x through does not properly restrict the validator configuration which allows remote attackers to conduct cross site scripting xss attacks or cause a denial of service via crafted input a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution struts struts cve vulnerable library struts core jar apache struts path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache struts struts core struts core jar dependency hierarchy velocity tools jar root library x struts core jar vulnerable library found in head commit a href found in base branch main vulnerability details actionservlet java in apache struts x through mishandles multithreaded access to an actionform instance which allows remote attackers to execute arbitrary code or cause a denial of service unexpected memory access via a multipart request a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution struts struts cve vulnerable library struts core jar apache struts path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache struts struts core struts core jar dependency hierarchy velocity tools jar root library x struts core jar vulnerable library found in head commit a href found in base branch main vulnerability details the multipagevalidator implementation in apache struts through allows remote attackers to bypass intended access restrictions via a modified page parameter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution struts struts beta cve vulnerable library jar path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository jar dependency hierarchy velocity tools jar root library x jar vulnerable library found in head commit a href found in base branch main vulnerability details version prior to version contains a cwe xml injection vulnerability in class element methods addelement addattribute that can result in an attacker tampering with xml documents through xml injection this attack appear to be exploitable via an attacker specifying attributes or elements in the xml document this vulnerability appears to have been fixed in or later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org cve vulnerable library commons collections jar types that extend and augment the java collections framework path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons collections commons collections commons collections jar dependency hierarchy velocity tools jar root library x commons collections jar vulnerable library found in head commit a href found in base branch main vulnerability details the wls security component in oracle weblogic server and allows remote attackers to execute arbitrary commands via a crafted serialized java object in protocol traffic to tcp port related to oracle common modules com bea core apache commons collections jar note the scope of this cve is limited to the weblogic server product publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons collections commons collections cve vulnerable library commons beanutils jar path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils commons beanutils jar dependency hierarchy velocity tools jar root library x commons beanutils jar vulnerable library found in head commit a href found in base branch main vulnerability details in apache commons beanutils a special beanintrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all java objects we however were not using this by default characteristic of the propertyutilsbean publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution commons beanutils commons beanutils cve vulnerable libraries struts core jar commons beanutils jar struts core jar apache struts path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache struts struts core struts core jar dependency hierarchy velocity tools jar root library x struts core jar vulnerable library commons beanutils jar path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils commons beanutils jar dependency hierarchy velocity tools jar root library x commons beanutils jar vulnerable library found in head commit a href found in base branch main vulnerability details apache commons beanutils as distributed in lib commons beanutils jar in apache struts x through and in other products requiring commons beanutils through does not suppress the class property which allows remote attackers to manipulate the classloader and execute arbitrary code via the class parameter as demonstrated by the passing of this parameter to the getclass method of the actionform object in struts publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons beanutils commons beanutils org apache struts core cve vulnerable library commons collections jar types that extend and augment the java collections framework path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository commons collections commons collections commons collections jar dependency hierarchy velocity tools jar root library x commons collections jar vulnerable library found in head commit a href found in base branch main vulnerability details serialized object interfaces in certain cisco collaboration and social media endpoint clients and client software network application service and acceleration network and content security devices network management and provisioning routing and switching enterprise and service provider unified computing voice and unified communications devices video streaming telepresence and transcoding devices wireless and cisco hosted services products allow remote attackers to execute arbitrary commands via a crafted serialized java object related to the apache commons collections acc library publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution commons collections commons org apache commons commons cve vulnerable library velocity tools jar velocitytools is an integrated collection of velocity subprojects with the common goal of creating tools and infrastructure to speed and ease development of both web and non web applications using the velocity template engine path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache velocity velocity tools velocity tools jar dependency hierarchy x velocity tools jar vulnerable library found in head commit a href found in base branch main vulnerability details the default error page for velocityview in apache velocity tools prior to reflects back the vm file that was entered as part of the url an attacker can set an xss payload file as this vm file in the url which results in this payload being executed xss vulnerabilities allow attackers to execute arbitrary javascript in the context of the attacked website and the attacked user this can be abused to steal session cookies perform requests in the name of the victim or for phishing attacks publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache velocity tools velocity tools view rescue worker helmet automatic remediation is available for this issue cve vulnerable library struts taglib jar apache struts path to dependency file vendor aws sdk cpp code generation generator pom xml path to vulnerable library home wss scanner repository org apache struts struts taglib struts taglib jar dependency hierarchy velocity tools jar root library x struts taglib jar vulnerable library found in head commit a href found in base branch main vulnerability details cross site scripting xss vulnerability in apache struts before on suse linux enterprise sle before on suse opensuse before on suse opensuse and before on suse opensuse allows remote attackers to inject arbitrary web script or html via unspecified vectors related to insufficient quoting of parameters publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache struts struts taglib rescue worker helmet automatic remediation is available for this issue
| 0
|
14,202
| 17,101,046,859
|
IssuesEvent
|
2021-07-09 11:17:08
|
prisma/prisma-engines
|
https://api.github.com/repos/prisma/prisma-engines
|
closed
|
Chore: change grammar of messages from `can not` to `cannot`
|
engines/other process/candidate team/migrations topic: error
|
> Don’t use can not when you mean cannot. The only time you’re likely to see can not written as separate words is when the word “can” happens to precede some other phrase that happens to start with “not”:
It's only valid in these cases for example:
> We can not only break even, but also turn a profit.
>
> The company’s new product can not only reduce emissions, but also trap some of the existing greenhouse gasses.
It seems that all/most cases should be `cannot` https://sourcegraph.com/search?q=context:global+repo:github.com/prisma/prisma-engines+%22can+not%22&patternType=regexp
|
1.0
|
Chore: change grammar of messages from `can not` to `cannot` - > Don’t use can not when you mean cannot. The only time you’re likely to see can not written as separate words is when the word “can” happens to precede some other phrase that happens to start with “not”:
It's only valid in these cases for example:
> We can not only break even, but also turn a profit.
>
> The company’s new product can not only reduce emissions, but also trap some of the existing greenhouse gasses.
It seems that all/most cases should be `cannot` https://sourcegraph.com/search?q=context:global+repo:github.com/prisma/prisma-engines+%22can+not%22&patternType=regexp
|
process
|
chore change grammar of messages from can not to cannot don’t use can not when you mean cannot the only time you’re likely to see can not written as separate words is when the word “can” happens to precede some other phrase that happens to start with “not” it s only valid in these cases for example we can not only break even but also turn a profit the company’s new product can not only reduce emissions but also trap some of the existing greenhouse gasses it seems that all most cases should be cannot
| 1
|
140,386
| 5,401,025,853
|
IssuesEvent
|
2017-02-27 23:42:20
|
BCDevExchange/devex
|
https://api.github.com/repos/BCDevExchange/devex
|
closed
|
Set up pages for enhanced Sign Up process
|
enhancement priority ui-ux
|
@ccoldwell, could you please set up as much as you can according to the following process. If you can get all of the elements inserted and linked, I can mess with the UI:

Here's a mockup of a modified Profile Detail (Edit Profile) page:

For **confirmations**, not sure what you'd recommend (I'm thinking a [modal](http://getbootstrap.com/javascript/#modals-examples) would be nice, but not sure if these are bad for mobile?).....I just think we need something more blatant than the current alerts that only appear for a couple seconds in the bottom right corner.

|
1.0
|
Set up pages for enhanced Sign Up process - @ccoldwell, could you please set up as much as you can according to the following process. If you can get all of the elements inserted and linked, I can mess with the UI:

Here's a mockup of a modified Profile Detail (Edit Profile) page:

For **confirmations**, not sure what you'd recommend (I'm thinking a [modal](http://getbootstrap.com/javascript/#modals-examples) would be nice, but not sure if these are bad for mobile?).....I just think we need something more blatant than the current alerts that only appear for a couple seconds in the bottom right corner.

|
non_process
|
set up pages for enhanced sign up process ccoldwell could you please set up as much as you can according to the following process if you can get all of the elements inserted and linked i can mess with the ui here s a mockup of a modified profile detail edit profile page for confirmations not sure what you d recommend i m thinking a would be nice but not sure if these are bad for mobile i just think we need something more blatant than the current alerts that only appear for a couple seconds in the bottom right corner
| 0
|
9,079
| 12,149,841,895
|
IssuesEvent
|
2020-04-24 16:51:58
|
CERT-Polska/drakvuf-sandbox
|
https://api.github.com/repos/CERT-Polska/drakvuf-sandbox
|
closed
|
Parse procmon log to the form of process tree
|
critical path drakrun/postprocessing enhancement
|
Parse `procmon` output into a form of a process tree that can be easily read by human (and visualized).
E.g. output structure:
```
[
{
"pid":2408,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\cmd.exe",
"children":[
{
"pid":2968,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\emo2.exe",
"children":[
{
"pid":3048,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\emo3.exe",
"children":[
]
}
]
},
{
"pid":3028,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\emo4.exe",
"children":[
]
}
]
}
]
```
|
1.0
|
Parse procmon log to the form of process tree - Parse `procmon` output into a form of a process tree that can be easily read by human (and visualized).
E.g. output structure:
```
[
{
"pid":2408,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\cmd.exe",
"children":[
{
"pid":2968,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\emo2.exe",
"children":[
{
"pid":3048,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\emo3.exe",
"children":[
]
}
]
},
{
"pid":3028,
"process":"C:\\Users\\Administrator\\AppData\\Local\\Temp\\emo4.exe",
"children":[
]
}
]
}
]
```
|
process
|
parse procmon log to the form of process tree parse procmon output into a form of a process tree that can be easily read by human and visualized e g output structure pid process c users administrator appdata local temp cmd exe children pid process c users administrator appdata local temp exe children pid process c users administrator appdata local temp exe children pid process c users administrator appdata local temp exe children
| 1
|
8,776
| 11,899,692,648
|
IssuesEvent
|
2020-03-30 09:25:24
|
prisma/prisma2
|
https://api.github.com/repos/prisma/prisma2
|
closed
|
Add `cli` as executable for @prisma/cli?
|
kind/improvement process/candidate topic: cli
|
## Problem
When using npx without having `@prisma/cli` installed before we need to do `npx -p @prisma/cli@alpha prisma2 --version`
## Solution
If we put another name for the executable in the package.json `cli` npx should work like:
`npx @prisma/cli@alpha --version` which is a lot easier (no parameters!)
## Additional context
We may want to test how it's doing with a global install.
|
1.0
|
Add `cli` as executable for @prisma/cli? - ## Problem
When using npx without having `@prisma/cli` installed before we need to do `npx -p @prisma/cli@alpha prisma2 --version`
## Solution
If we put another name for the executable in the package.json `cli` npx should work like:
`npx @prisma/cli@alpha --version` which is a lot easier (no parameters!)
## Additional context
We may want to test how it's doing with a global install.
|
process
|
add cli as executable for prisma cli problem when using npx without having prisma cli installed before we need to do npx p prisma cli alpha version solution if we put another name for the executable in the package json cli npx should work like npx prisma cli alpha version which is a lot easier no parameters additional context we may want to test how it s doing with a global install
| 1
|
12,410
| 14,918,142,839
|
IssuesEvent
|
2021-01-22 21:07:35
|
c4gnv/meta
|
https://api.github.com/repos/c4gnv/meta
|
closed
|
Schedule meetings to kick off 2018
|
process
|
More structured meetings around specific projects (Josh, Bjorn)
- Manage own schedule per project, in person or virtual, led by project champion, working meetings
Once per month community-oriented meeting (Andrew, Samantha)
- Facebook or Meet-ups, try for a few months then try different social media channels
- Avenue for volunteers to plug into projects then begin participating in project-specific meetings
|
1.0
|
Schedule meetings to kick off 2018 - More structured meetings around specific projects (Josh, Bjorn)
- Manage own schedule per project, in person or virtual, led by project champion, working meetings
Once per month community-oriented meeting (Andrew, Samantha)
- Facebook or Meet-ups, try for a few months then try different social media channels
- Avenue for volunteers to plug into projects then begin participating in project-specific meetings
|
process
|
schedule meetings to kick off more structured meetings around specific projects josh bjorn manage own schedule per project in person or virtual led by project champion working meetings once per month community oriented meeting andrew samantha facebook or meet ups try for a few months then try different social media channels avenue for volunteers to plug into projects then begin participating in project specific meetings
| 1
|
5,758
| 8,598,730,546
|
IssuesEvent
|
2018-11-15 22:46:57
|
gfrebello/qs-trip-planning-procedure
|
https://api.github.com/repos/gfrebello/qs-trip-planning-procedure
|
closed
|
Code front end for flight reservations
|
Priority:Very High Process:Implement Requirement
|
For the user to be able to reserve flights, they need to be able to interact with the planning page, which is mostly front end functionality. This task is related to the front end of the flight reservations.
https://stackoverflow.com/questions/11743392/check-if-array-is-empty-or-exists
https://stackoverflow.com/questions/42576198/get-object-data-and-target-element-from-onclick-event-in-react-js
https://stackoverflow.com/questions/9612758/add-a-css-border-on-hover-without-moving-the-element
https://stackoverflow.com/questions/49386324/componentdidupdate-vs-componentwillreceiveprops-use-case-in-react
https://stackoverflow.com/questions/114543/how-to-horizontally-center-a-div
https://stackoverflow.com/questions/6783902/offset-div-from-center
https://github.com/reactstrap/reactstrap/issues/925
https://reactstrap.github.io/components/listgroup/
http://www.redbitdev.com/getting-started-with-react-flexbox-grid/
|
1.0
|
Code front end for flight reservations - For the user to be able to reserve flights, they need to be able to interact with the planning page, which is mostly front end functionality. This task is related to the front end of the flight reservations.
https://stackoverflow.com/questions/11743392/check-if-array-is-empty-or-exists
https://stackoverflow.com/questions/42576198/get-object-data-and-target-element-from-onclick-event-in-react-js
https://stackoverflow.com/questions/9612758/add-a-css-border-on-hover-without-moving-the-element
https://stackoverflow.com/questions/49386324/componentdidupdate-vs-componentwillreceiveprops-use-case-in-react
https://stackoverflow.com/questions/114543/how-to-horizontally-center-a-div
https://stackoverflow.com/questions/6783902/offset-div-from-center
https://github.com/reactstrap/reactstrap/issues/925
https://reactstrap.github.io/components/listgroup/
http://www.redbitdev.com/getting-started-with-react-flexbox-grid/
|
process
|
code front end for flight reservations for the user to be able to reserve flights they need to be able to interact with the planning page which is mostly front end functionality this task is related to the front end of the flight reservations
| 1
|
257,764
| 19,531,059,947
|
IssuesEvent
|
2021-12-30 16:53:50
|
GoogleCloudPlatform/dfcx-scrapi
|
https://api.github.com/repos/GoogleCloudPlatform/dfcx-scrapi
|
closed
|
Pre-configured Issue and Pull Request Templates for this project
|
documentation
|
## Background
I noticed that this repository does not have an issue template or PR template yet, so I was thinking of following these guides to create the respective templates. This can make writing bug reports, issues, PRs quicker and less ambiguous.
### Proposed solution
Issue Template:
- [Guide for Issue Templates](https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/configuring-issue-templates-for-your-repository)
- Two types of issue templates:
- Bug report [proposed template](https://github.com/stevemao/github-issue-templates/blob/master/bugs-only/ISSUE_TEMPLATE.md)
- Feature request [proposed template](https://github.com/wagtail/wagtail/issues/5560)
- Alternatively, Github's default templates can also be used.
Pull Request Template:
- [Guide for PR templates](https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/creating-a-pull-request-template-for-your-repository)
- [Proposed template](https://github.com/embeddedartistry/templates/blob/master/oss_docs/PULL_REQUEST_TEMPLATE.md)
### Questions
- Should these templates be public or hidden?
|
1.0
|
Pre-configured Issue and Pull Request Templates for this project - ## Background
I noticed that this repository does not have an issue template or PR template yet, so I was thinking of following these guides to create the respective templates. This can make writing bug reports, issues, PRs quicker and less ambiguous.
### Proposed solution
Issue Template:
- [Guide for Issue Templates](https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/configuring-issue-templates-for-your-repository)
- Two types of issue templates:
- Bug report [proposed template](https://github.com/stevemao/github-issue-templates/blob/master/bugs-only/ISSUE_TEMPLATE.md)
- Feature request [proposed template](https://github.com/wagtail/wagtail/issues/5560)
- Alternatively, Github's default templates can also be used.
Pull Request Template:
- [Guide for PR templates](https://docs.github.com/en/communities/using-templates-to-encourage-useful-issues-and-pull-requests/creating-a-pull-request-template-for-your-repository)
- [Proposed template](https://github.com/embeddedartistry/templates/blob/master/oss_docs/PULL_REQUEST_TEMPLATE.md)
### Questions
- Should these templates be public or hidden?
|
non_process
|
pre configured issue and pull request templates for this project background i noticed that this repository does not have an issue template or pr template yet so i was thinking of following these guides to create the respective templates this can make writing bug reports issues prs quicker and less ambiguous proposed solution issue template two types of issue templates bug report feature request alternatively github s default templates can also be used pull request template questions should these templates be public or hidden
| 0
|
78,896
| 9,808,586,954
|
IssuesEvent
|
2019-06-12 15:55:21
|
fecgov/fec-cms
|
https://api.github.com/repos/fecgov/fec-cms
|
closed
|
Design interaction for terminated committees
|
Work: Content Work: Front-end Work: UX/Design
|
**What we’re after**:
Showing terminated and administratively terminated committees should not be our default state. We need to provide users with committee filing frequency information and allow them to decide if want to see these committees.
**Current state**:
We include terminated and administratively terminated committees. We do not alert users that they might be viewing terminated committees. We do not provide users a way to exclude terminated committees.
https://www.fec.gov/data/committees/
**Completion criteria**:
|
1.0
|
Design interaction for terminated committees - **What we’re after**:
Showing terminated and administratively terminated committees should not be our default state. We need to provide users with committee filing frequency information and allow them to decide if want to see these committees.
**Current state**:
We include terminated and administratively terminated committees. We do not alert users that they might be viewing terminated committees. We do not provide users a way to exclude terminated committees.
https://www.fec.gov/data/committees/
**Completion criteria**:
|
non_process
|
design interaction for terminated committees what we’re after showing terminated and administratively terminated committees should not be our default state we need to provide users with committee filing frequency information and allow them to decide if want to see these committees current state we include terminated and administratively terminated committees we do not alert users that they might be viewing terminated committees we do not provide users a way to exclude terminated committees completion criteria
| 0
|
760
| 3,244,601,230
|
IssuesEvent
|
2015-10-16 03:54:31
|
nodejs/node
|
https://api.github.com/repos/nodejs/node
|
closed
|
Cache accesses to process.env?
|
process
|
I've found in multiple projects that accessing `process.env` within a hot section of the code leads to major slowdown.
This really hurts in React server-side rendering ([issue](https://github.com/facebook/react/issues/812)) and has caused them to rearrange how they access the env.
It would sense to cache already-accessed properties rather than reaching out to the actual environment. And of course, update the cache on assignment.
I would be happy to contribute a patch if anyone could point me in the right direction to get started, as I'm new to Node core dev.
|
1.0
|
Cache accesses to process.env? - I've found in multiple projects that accessing `process.env` within a hot section of the code leads to major slowdown.
This really hurts in React server-side rendering ([issue](https://github.com/facebook/react/issues/812)) and has caused them to rearrange how they access the env.
It would sense to cache already-accessed properties rather than reaching out to the actual environment. And of course, update the cache on assignment.
I would be happy to contribute a patch if anyone could point me in the right direction to get started, as I'm new to Node core dev.
|
process
|
cache accesses to process env i ve found in multiple projects that accessing process env within a hot section of the code leads to major slowdown this really hurts in react server side rendering and has caused them to rearrange how they access the env it would sense to cache already accessed properties rather than reaching out to the actual environment and of course update the cache on assignment i would be happy to contribute a patch if anyone could point me in the right direction to get started as i m new to node core dev
| 1
|
659,122
| 21,916,684,996
|
IssuesEvent
|
2022-05-21 23:40:54
|
AxerBot/axer-bot
|
https://api.github.com/repos/AxerBot/axer-bot
|
closed
|
convert bot responses to embeds when possible
|
enhancement medium priority
|
currently, some bot replies use an old approach that doesn't involve embeds, would be nicer to make it consistent
|
1.0
|
convert bot responses to embeds when possible - currently, some bot replies use an old approach that doesn't involve embeds, would be nicer to make it consistent
|
non_process
|
convert bot responses to embeds when possible currently some bot replies use an old approach that doesn t involve embeds would be nicer to make it consistent
| 0
|
228,500
| 18,238,688,603
|
IssuesEvent
|
2021-10-01 10:09:44
|
akka/akka
|
https://api.github.com/repos/akka/akka
|
closed
|
Give BehaviorTestKit-spawned actors access to a real configuration
|
1 - triaged help wanted t:testing
|
It's reasonably common for actors to leverage configuration via `context.system.settings.config` (which avoids every actor/class doing its own calls to `ConfigFactory.load`; this trick was taught to me by an ELE on a consulting engagement some years ago :) ). When run by the `BehaviorTestKit`, however, `context.system.settings.config` is a config that's solely the `reference.conf` files from the classpath.
For testing a behavior in full isolation, this is fine: a pattern of
def behaviorFor(fixture: Fixture, state: State): Behavior[Command] = ???
def apply(...): Behavior[Command] =
Behaviors.setup { ctx =>
// assemble values from config etc., build into a fixture/state instance
behaviorFor(...)
}
lets you build fixtures and states in your test (maybe even using property-based testing...) and build the behavior under test with `behaviorFor`.
This gets complicated when the behavior under test spawns another actor defined with this pattern: the `spawn` will be via `apply`, which will pull in a config which is unlikely to be suitable (and if you want things to fail-fast on bad config, the spawn itself will probably fail)
In asynchronous testing, the `ActorTestKit`'s `ActorSystem` loads `application-test.conf`, so it makes sense (to me) to have `BehaviorTestKit`'s `ActorSystemStub` do likewise.
|
1.0
|
Give BehaviorTestKit-spawned actors access to a real configuration - It's reasonably common for actors to leverage configuration via `context.system.settings.config` (which avoids every actor/class doing its own calls to `ConfigFactory.load`; this trick was taught to me by an ELE on a consulting engagement some years ago :) ). When run by the `BehaviorTestKit`, however, `context.system.settings.config` is a config that's solely the `reference.conf` files from the classpath.
For testing a behavior in full isolation, this is fine: a pattern of
def behaviorFor(fixture: Fixture, state: State): Behavior[Command] = ???
def apply(...): Behavior[Command] =
Behaviors.setup { ctx =>
// assemble values from config etc., build into a fixture/state instance
behaviorFor(...)
}
lets you build fixtures and states in your test (maybe even using property-based testing...) and build the behavior under test with `behaviorFor`.
This gets complicated when the behavior under test spawns another actor defined with this pattern: the `spawn` will be via `apply`, which will pull in a config which is unlikely to be suitable (and if you want things to fail-fast on bad config, the spawn itself will probably fail)
In asynchronous testing, the `ActorTestKit`'s `ActorSystem` loads `application-test.conf`, so it makes sense (to me) to have `BehaviorTestKit`'s `ActorSystemStub` do likewise.
|
non_process
|
give behaviortestkit spawned actors access to a real configuration it s reasonably common for actors to leverage configuration via context system settings config which avoids every actor class doing its own calls to configfactory load this trick was taught to me by an ele on a consulting engagement some years ago when run by the behaviortestkit however context system settings config is a config that s solely the reference conf files from the classpath for testing a behavior in full isolation this is fine a pattern of def behaviorfor fixture fixture state state behavior def apply behavior behaviors setup ctx assemble values from config etc build into a fixture state instance behaviorfor lets you build fixtures and states in your test maybe even using property based testing and build the behavior under test with behaviorfor this gets complicated when the behavior under test spawns another actor defined with this pattern the spawn will be via apply which will pull in a config which is unlikely to be suitable and if you want things to fail fast on bad config the spawn itself will probably fail in asynchronous testing the actortestkit s actorsystem loads application test conf so it makes sense to me to have behaviortestkit s actorsystemstub do likewise
| 0
|
142,592
| 19,099,363,236
|
IssuesEvent
|
2021-11-29 20:27:11
|
harrinry/stream-chat-react
|
https://api.github.com/repos/harrinry/stream-chat-react
|
opened
|
CVE-2018-19797 (Medium) detected in node-sass-4.14.1.tgz
|
security vulnerability
|
## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: stream-chat-react/package.json</p>
<p>Path to vulnerable library: stream-chat-react/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- rollup-plugin-scss-2.6.1.tgz (Root Library)
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/stream-chat-react/commit/a80df0ece7581dc566b7c05d5f5ae6ecc66b730f">a80df0ece7581dc566b7c05d5f5ae6ecc66b730f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19797>CVE-2018-19797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.6.0">https://github.com/sass/libsass/releases/tag/3.6.0</a></p>
<p>Release Date: 2018-12-03</p>
<p>Fix Resolution: libsass - 3.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.14.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"rollup-plugin-scss:2.6.1;node-sass:4.14.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"libsass - 3.6.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-19797","vulnerabilityDetails":"In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19797","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2018-19797 (Medium) detected in node-sass-4.14.1.tgz - ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>Path to dependency file: stream-chat-react/package.json</p>
<p>Path to vulnerable library: stream-chat-react/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- rollup-plugin-scss-2.6.1.tgz (Root Library)
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/stream-chat-react/commit/a80df0ece7581dc566b7c05d5f5ae6ecc66b730f">a80df0ece7581dc566b7c05d5f5ae6ecc66b730f</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19797>CVE-2018-19797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.6.0">https://github.com/sass/libsass/releases/tag/3.6.0</a></p>
<p>Release Date: 2018-12-03</p>
<p>Fix Resolution: libsass - 3.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"node-sass","packageVersion":"4.14.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"rollup-plugin-scss:2.6.1;node-sass:4.14.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"libsass - 3.6.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-19797","vulnerabilityDetails":"In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19797","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve medium detected in node sass tgz cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href path to dependency file stream chat react package json path to vulnerable library stream chat react node modules node sass package json dependency hierarchy rollup plugin scss tgz root library x node sass tgz vulnerable library found in head commit a href found in base branch master vulnerability details in libsass a null pointer dereference in the function sass selector list populate extends in sharedptr hpp used by ast cpp and ast selectors cpp may cause a denial of service application crash via a crafted sass input file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree rollup plugin scss node sass isminimumfixversionavailable true minimumfixversion libsass isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in libsass a null pointer dereference in the function sass selector list populate extends in sharedptr hpp used by ast cpp and ast selectors cpp may cause a denial of service application crash via a crafted sass input file vulnerabilityurl
| 0
|
50,355
| 21,076,589,045
|
IssuesEvent
|
2022-04-02 08:21:59
|
emergenzeHack/ukrainehelp.emergenzehack.info_segnalazioni
|
https://api.github.com/repos/emergenzeHack/ukrainehelp.emergenzehack.info_segnalazioni
|
opened
|
https://www.raiplay.it/benvenuti-bambini Cartoni animati in lingua italiana e ucraina (contenuti gr
|
Services translation Children
|
<pre><yamldata>
servicetypes:
materialGoods: false
hospitality: false
transport: false
healthcare: false
Legal: false
translation: true
job: false
psychologicalSupport: false
Children: true
disability: false
women: false
education: false
offerFromWho: Raiplay
title: https://www.raiplay.it/benvenuti-bambini Cartoni animati in lingua italiana
e ucraina (contenuti gratuiti).
recipients: ''
description: ''
url: https://www.raiplay.it/benvenuti-bambini
address:
mode: autocomplete
address:
place_id: 283767136
licence: Data © OpenStreetMap contributors, ODbL 1.0. https://osm.org/copyright
osm_type: relation
osm_id: 41485
boundingbox:
- '41.6556417'
- '42.1410285'
- '12.2344669'
- '12.8557603'
lat: '41.8933203'
lon: '12.4829321'
display_name: Roma, Roma Capitale, Lazio, Italia
class: boundary
type: administrative
importance: 0.7896107180689524
icon: https://nominatim.openstreetmap.org/ui/mapicons//poi_boundary_administrative.p.20.png
address:
city: Roma
county: Roma Capitale
state: Lazio
country: Italia
country_code: it
iConfirmToHaveReadAndAcceptedInformativeToThreatPersonalData: true
label: services
submit: true
</yamldata></pre>
|
1.0
|
https://www.raiplay.it/benvenuti-bambini Cartoni animati in lingua italiana e ucraina (contenuti gr - <pre><yamldata>
servicetypes:
materialGoods: false
hospitality: false
transport: false
healthcare: false
Legal: false
translation: true
job: false
psychologicalSupport: false
Children: true
disability: false
women: false
education: false
offerFromWho: Raiplay
title: https://www.raiplay.it/benvenuti-bambini Cartoni animati in lingua italiana
e ucraina (contenuti gratuiti).
recipients: ''
description: ''
url: https://www.raiplay.it/benvenuti-bambini
address:
mode: autocomplete
address:
place_id: 283767136
licence: Data © OpenStreetMap contributors, ODbL 1.0. https://osm.org/copyright
osm_type: relation
osm_id: 41485
boundingbox:
- '41.6556417'
- '42.1410285'
- '12.2344669'
- '12.8557603'
lat: '41.8933203'
lon: '12.4829321'
display_name: Roma, Roma Capitale, Lazio, Italia
class: boundary
type: administrative
importance: 0.7896107180689524
icon: https://nominatim.openstreetmap.org/ui/mapicons//poi_boundary_administrative.p.20.png
address:
city: Roma
county: Roma Capitale
state: Lazio
country: Italia
country_code: it
iConfirmToHaveReadAndAcceptedInformativeToThreatPersonalData: true
label: services
submit: true
</yamldata></pre>
|
non_process
|
cartoni animati in lingua italiana e ucraina contenuti gr servicetypes materialgoods false hospitality false transport false healthcare false legal false translation true job false psychologicalsupport false children true disability false women false education false offerfromwho raiplay title cartoni animati in lingua italiana e ucraina contenuti gratuiti recipients description url address mode autocomplete address place id licence data © openstreetmap contributors odbl osm type relation osm id boundingbox lat lon display name roma roma capitale lazio italia class boundary type administrative importance icon address city roma county roma capitale state lazio country italia country code it iconfirmtohavereadandacceptedinformativetothreatpersonaldata true label services submit true
| 0
|
1,313
| 3,865,477,292
|
IssuesEvent
|
2016-04-08 17:34:08
|
dotnet/corefx
|
https://api.github.com/repos/dotnet/corefx
|
closed
|
Process.Modules tests are hanging in CI on OS X
|
2 - In Progress System.Diagnostics.Process X-Plat
|
Locally then run fine, and they made it through a couple of CI runs. But something about shelling out to vmmap is causing them to hang in CI.
|
1.0
|
Process.Modules tests are hanging in CI on OS X - Locally then run fine, and they made it through a couple of CI runs. But something about shelling out to vmmap is causing them to hang in CI.
|
process
|
process modules tests are hanging in ci on os x locally then run fine and they made it through a couple of ci runs but something about shelling out to vmmap is causing them to hang in ci
| 1
|
24,435
| 11,035,129,981
|
IssuesEvent
|
2019-12-07 11:23:47
|
Ignitus/Ignitus-client
|
https://api.github.com/repos/Ignitus/Ignitus-client
|
opened
|
CVE-2019-10747 (High) detected in set-value-2.0.0.tgz, set-value-0.4.3.tgz
|
security vulnerability
|
## CVE-2019-10747 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>set-value-2.0.0.tgz</b>, <b>set-value-0.4.3.tgz</b></p></summary>
<p>
<details><summary><b>set-value-2.0.0.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz">https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/Ignitus-client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/Ignitus-client/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-24.7.1.tgz (Root Library)
- core-24.7.1.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- :x: **set-value-2.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>set-value-0.4.3.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz">https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/Ignitus-client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/Ignitus-client/node_modules/union-value/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-24.7.1.tgz (Root Library)
- core-24.7.1.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- union-value-1.0.0.tgz
- :x: **set-value-0.4.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Ignitus/Ignitus-client/commit/4a136622e36d4bca4d34d3a5d332b6d73cdda58d">4a136622e36d4bca4d34d3a5d332b6d73cdda58d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
set-value is vulnerable to Prototype Pollution in versions lower than 3.0.1. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using any of the constructor, prototype and _proto_ payloads.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10747>CVE-2019-10747</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f">https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f</a></p>
<p>Release Date: 2019-07-24</p>
<p>Fix Resolution: 2.0.1,3.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-10747 (High) detected in set-value-2.0.0.tgz, set-value-0.4.3.tgz - ## CVE-2019-10747 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>set-value-2.0.0.tgz</b>, <b>set-value-0.4.3.tgz</b></p></summary>
<p>
<details><summary><b>set-value-2.0.0.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz">https://registry.npmjs.org/set-value/-/set-value-2.0.0.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/Ignitus-client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/Ignitus-client/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-24.7.1.tgz (Root Library)
- core-24.7.1.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- :x: **set-value-2.0.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>set-value-0.4.3.tgz</b></p></summary>
<p>Create nested values and any intermediaries using dot notation (`'a.b.c'`) paths.</p>
<p>Library home page: <a href="https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz">https://registry.npmjs.org/set-value/-/set-value-0.4.3.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/Ignitus-client/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/Ignitus-client/node_modules/union-value/node_modules/set-value/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-24.7.1.tgz (Root Library)
- core-24.7.1.tgz
- micromatch-3.1.10.tgz
- snapdragon-0.8.2.tgz
- base-0.11.2.tgz
- cache-base-1.0.1.tgz
- union-value-1.0.0.tgz
- :x: **set-value-0.4.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/Ignitus/Ignitus-client/commit/4a136622e36d4bca4d34d3a5d332b6d73cdda58d">4a136622e36d4bca4d34d3a5d332b6d73cdda58d</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
set-value is vulnerable to Prototype Pollution in versions lower than 3.0.1. The function mixin-deep could be tricked into adding or modifying properties of Object.prototype using any of the constructor, prototype and _proto_ payloads.
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10747>CVE-2019-10747</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f">https://github.com/jonschlinkert/set-value/commit/95e9d9923f8a8b4a01da1ea138fcc39ec7b6b15f</a></p>
<p>Release Date: 2019-07-24</p>
<p>Fix Resolution: 2.0.1,3.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in set value tgz set value tgz cve high severity vulnerability vulnerable libraries set value tgz set value tgz set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file tmp ws scm ignitus client package json path to vulnerable library tmp ws scm ignitus client node modules set value package json dependency hierarchy jest cli tgz root library core tgz micromatch tgz snapdragon tgz base tgz cache base tgz x set value tgz vulnerable library set value tgz create nested values and any intermediaries using dot notation a b c paths library home page a href path to dependency file tmp ws scm ignitus client package json path to vulnerable library tmp ws scm ignitus client node modules union value node modules set value package json dependency hierarchy jest cli tgz root library core tgz micromatch tgz snapdragon tgz base tgz cache base tgz union value tgz x set value tgz vulnerable library found in head commit a href vulnerability details set value is vulnerable to prototype pollution in versions lower than the function mixin deep could be tricked into adding or modifying properties of object prototype using any of the constructor prototype and proto payloads publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
5,163
| 7,934,001,209
|
IssuesEvent
|
2018-07-08 14:05:21
|
frc4571/The-Beelzebub
|
https://api.github.com/repos/frc4571/The-Beelzebub
|
closed
|
Convert coordinates obtained from GRIP into a motion profile
|
drive-subsystem vision-processing
|
This is to use the GRIP output to move the drive train along a particular motion profile consisting of a series of distance and angle values
|
1.0
|
Convert coordinates obtained from GRIP into a motion profile - This is to use the GRIP output to move the drive train along a particular motion profile consisting of a series of distance and angle values
|
process
|
convert coordinates obtained from grip into a motion profile this is to use the grip output to move the drive train along a particular motion profile consisting of a series of distance and angle values
| 1
|
320,906
| 27,492,837,846
|
IssuesEvent
|
2023-03-04 20:49:32
|
4ian/GDevelop
|
https://api.github.com/repos/4ian/GDevelop
|
closed
|
Crash while using an editor ->I tried to undo something while writing the name of a variable, but I believe it gives an error whenever I type something and try to use Undo/Redo.
|
💥crash 👋 Needs confirmation/testing
|
=> Please write here a short description of when the error occured and how to reproduce it.
You also may have to create an account on GitHub before posting.
When you're ready, click on "Submit new issue". Don't change the rest of the message. Thanks!
-> **I tried to undo something while writing the name of a variable, but I believe it gives an error whenever I type something and try to use Undo/Redo.**
## Error stack (don't write anything here)
```
RuntimeError: function signature mismatch
at wasm-function[3807]:0x17dbbd
at wasm-function[1873]:0x4b2d3
at wasm-function[2286]:0x6924f
at wasm-function[1340]:0x3482f
at InstructionSentenceFormatter.GetAsFormattedText.InstructionSentenceFormatter.GetAsFormattedText [as getAsFormattedText] (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/libGD.js?cache-buster=5.0.0-beta115-e4fc065dc13f86cee1d996de6201ed470a04ea66:9:1333508)
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:710754
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:711574
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:322331
at Bi (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:220738)
at _a (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:227578)
at Sa (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:234326)
at Uo (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:258320)
at Fo (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:258704)
at Eu (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:265740)
at wu (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:265120)
at yu (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:264141)
at qo (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:263010)
at Object.enqueueForceUpdate (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:212721)
at n.w.forceUpdate (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:162773)
at n.value (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:704946)
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:804348
at i (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:306395)
```
## Component stack (don't write anything here)
```
in Unknown
in DropTarget(Component)
in DragSource(DropTarget(Component))
in Unknown
in Unknown
in div
in Unknown
in DropTarget(Component)
in Unknown
in f
in div
in Unknown
in n
in div
in n
in span
in div
in div
in div
in div
in div
in t
in DragSource(t)
in div
in div
in t
in DropTarget(t)
in div
in div
in t
in t
in Scrolling(t)
in div
in t
in div
in t
in re
in Unknown
in L
in div
in n
in div
in n
in u
in a
in n
in n
in t
in Unknown
in Unknown
in div
in n
in div
in Unknown
in n
in m
in m
in m
in m
in m
in s
in n
in t
in n
in Unknown
in v
in t
in m
in n
in n
in n
in DragDropContext(n)
in n
in s
```
## Other details
* IDE version: 5.0.0-beta115-e4fc065dc13f86cee1d996de6201ed470a04ea66
* Arch: x64,
* Platform Name: win32,
* System Version: 10.0.19043,
* User Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) GDevelop5/5.0.0-beta115 Chrome/80.0.3987.165 Electron/8.2.5 Safari/537.36,
|
1.0
|
Crash while using an editor ->I tried to undo something while writing the name of a variable, but I believe it gives an error whenever I type something and try to use Undo/Redo. - => Please write here a short description of when the error occured and how to reproduce it.
You also may have to create an account on GitHub before posting.
When you're ready, click on "Submit new issue". Don't change the rest of the message. Thanks!
-> **I tried to undo something while writing the name of a variable, but I believe it gives an error whenever I type something and try to use Undo/Redo.**
## Error stack (don't write anything here)
```
RuntimeError: function signature mismatch
at wasm-function[3807]:0x17dbbd
at wasm-function[1873]:0x4b2d3
at wasm-function[2286]:0x6924f
at wasm-function[1340]:0x3482f
at InstructionSentenceFormatter.GetAsFormattedText.InstructionSentenceFormatter.GetAsFormattedText [as getAsFormattedText] (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/libGD.js?cache-buster=5.0.0-beta115-e4fc065dc13f86cee1d996de6201ed470a04ea66:9:1333508)
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:710754
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:711574
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:322331
at Bi (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:220738)
at _a (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:227578)
at Sa (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:234326)
at Uo (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:258320)
at Fo (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:258704)
at Eu (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:265740)
at wu (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:265120)
at yu (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:264141)
at qo (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:263010)
at Object.enqueueForceUpdate (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:212721)
at n.w.forceUpdate (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:162773)
at n.value (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:704946)
at file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/1.aea6426a.chunk.js:1:804348
at i (file:///C:/Users/Overl/AppData/Local/Programs/gdevelop/resources/app.asar/www/static/js/60.be227616.chunk.js:2:306395)
```
## Component stack (don't write anything here)
```
in Unknown
in DropTarget(Component)
in DragSource(DropTarget(Component))
in Unknown
in Unknown
in div
in Unknown
in DropTarget(Component)
in Unknown
in f
in div
in Unknown
in n
in div
in n
in span
in div
in div
in div
in div
in div
in t
in DragSource(t)
in div
in div
in t
in DropTarget(t)
in div
in div
in t
in t
in Scrolling(t)
in div
in t
in div
in t
in re
in Unknown
in L
in div
in n
in div
in n
in u
in a
in n
in n
in t
in Unknown
in Unknown
in div
in n
in div
in Unknown
in n
in m
in m
in m
in m
in m
in s
in n
in t
in n
in Unknown
in v
in t
in m
in n
in n
in n
in DragDropContext(n)
in n
in s
```
## Other details
* IDE version: 5.0.0-beta115-e4fc065dc13f86cee1d996de6201ed470a04ea66
* Arch: x64,
* Platform Name: win32,
* System Version: 10.0.19043,
* User Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) GDevelop5/5.0.0-beta115 Chrome/80.0.3987.165 Electron/8.2.5 Safari/537.36,
|
non_process
|
crash while using an editor i tried to undo something while writing the name of a variable but i believe it gives an error whenever i type something and try to use undo redo please write here a short description of when the error occured and how to reproduce it you also may have to create an account on github before posting when you re ready click on submit new issue don t change the rest of the message thanks i tried to undo something while writing the name of a variable but i believe it gives an error whenever i type something and try to use undo redo error stack don t write anything here runtimeerror function signature mismatch at wasm function at wasm function at wasm function at wasm function at instructionsentenceformatter getasformattedtext instructionsentenceformatter getasformattedtext file c users overl appdata local programs gdevelop resources app asar www libgd js cache buster at file c users overl appdata local programs gdevelop resources app asar www static js chunk js at file c users overl appdata local programs gdevelop resources app asar www static js chunk js at file c users overl appdata local programs gdevelop resources app asar www static js chunk js at bi file c users overl appdata local programs gdevelop resources app asar www static js chunk js at a file c users overl appdata local programs gdevelop resources app asar www static js chunk js at sa file c users overl appdata local programs gdevelop resources app asar www static js chunk js at uo file c users overl appdata local programs gdevelop resources app asar www static js chunk js at fo file c users overl appdata local programs gdevelop resources app asar www static js chunk js at eu file c users overl appdata local programs gdevelop resources app asar www static js chunk js at wu file c users overl appdata local programs gdevelop resources app asar www static js chunk js at yu file c users overl appdata local programs gdevelop resources app asar www static js chunk js at qo file c users overl appdata local programs gdevelop resources app asar www static js chunk js at object enqueueforceupdate file c users overl appdata local programs gdevelop resources app asar www static js chunk js at n w forceupdate file c users overl appdata local programs gdevelop resources app asar www static js chunk js at n value file c users overl appdata local programs gdevelop resources app asar www static js chunk js at file c users overl appdata local programs gdevelop resources app asar www static js chunk js at i file c users overl appdata local programs gdevelop resources app asar www static js chunk js component stack don t write anything here in unknown in droptarget component in dragsource droptarget component in unknown in unknown in div in unknown in droptarget component in unknown in f in div in unknown in n in div in n in span in div in div in div in div in div in t in dragsource t in div in div in t in droptarget t in div in div in t in t in scrolling t in div in t in div in t in re in unknown in l in div in n in div in n in u in a in n in n in t in unknown in unknown in div in n in div in unknown in n in m in m in m in m in m in s in n in t in n in unknown in v in t in m in n in n in n in dragdropcontext n in n in s other details ide version arch platform name system version user agent mozilla windows nt applewebkit khtml like gecko chrome electron safari
| 0
|
322,903
| 9,829,794,945
|
IssuesEvent
|
2019-06-16 01:14:22
|
sqlalchemy/sqlalchemy
|
https://api.github.com/repos/sqlalchemy/sqlalchemy
|
closed
|
all_orm_descriptors is including __mapper__
|
bug high priority orm
|
the check is looking for `InspectionAttr` and not verifying that it's a descriptor
```
from sqlalchemy import Column
from sqlalchemy import Integer
from sqlalchemy import String
from sqlalchemy.ext.declarative import declarative_base
from sqlalchemy import inspect
Base = declarative_base()
class HasAsDict:
def _asdict(self):
return {
key: getattr(self, key)
for key in inspect(self).mapper.all_orm_descriptors.keys()
}
class A(HasAsDict, Base):
__tablename__ = "a"
id = Column(Integer, primary_key=True)
x = Column(String)
y = Column(String)
z = Column(String)
a1 = A()
a1.y = "y"
a1.x = "x"
a1.z = "z"
print(a1._asdict())
```
`{'__mapper__': <Mapper at 0x7fd7a6abb9e8; A>, 'id': None, 'y': 'y', 'z': 'z', 'x': 'x'}
`
|
1.0
|
all_orm_descriptors is including __mapper__ - the check is looking for `InspectionAttr` and not verifying that it's a descriptor
```
from sqlalchemy import Column
from sqlalchemy import Integer
from sqlalchemy import String
from sqlalchemy.ext.declarative import declarative_base
from sqlalchemy import inspect
Base = declarative_base()
class HasAsDict:
def _asdict(self):
return {
key: getattr(self, key)
for key in inspect(self).mapper.all_orm_descriptors.keys()
}
class A(HasAsDict, Base):
__tablename__ = "a"
id = Column(Integer, primary_key=True)
x = Column(String)
y = Column(String)
z = Column(String)
a1 = A()
a1.y = "y"
a1.x = "x"
a1.z = "z"
print(a1._asdict())
```
`{'__mapper__': <Mapper at 0x7fd7a6abb9e8; A>, 'id': None, 'y': 'y', 'z': 'z', 'x': 'x'}
`
|
non_process
|
all orm descriptors is including mapper the check is looking for inspectionattr and not verifying that it s a descriptor from sqlalchemy import column from sqlalchemy import integer from sqlalchemy import string from sqlalchemy ext declarative import declarative base from sqlalchemy import inspect base declarative base class hasasdict def asdict self return key getattr self key for key in inspect self mapper all orm descriptors keys class a hasasdict base tablename a id column integer primary key true x column string y column string z column string a y y x x z z print asdict mapper id none y y z z x x
| 0
|
853
| 3,316,098,316
|
IssuesEvent
|
2015-11-06 15:30:29
|
OmniLayer/omnicore
|
https://api.github.com/repos/OmniLayer/omnicore
|
closed
|
List all requirements, and tag issues with milestone for 0.0.10
|
process
|
Using one issue to track the progress and requirements for the next release seems to have limited value, so I'd like to try to use the milestone feature of GitHub, which is probably a much cleaner solution.
I would like to gather *all* requirements necessary for the release, and I created a [milestone](https://github.com/OmniLayer/omnicore/milestones/0.0.10) for this purpose.
Here are four simple guidelines:
1. once there is *no* open issue tagged with [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10) tag left, it means [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10) is *ready* and we can publish a release candidate
2. if there is an unresolved bug, or feature that *must* be resolved or included in the release, and there is no related issue for it, a [new issue](https://github.com/OmniLayer/omnicore/issues/new) should be created
3. if there is an open issue, which is *necessary* for the release, but *without* the [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10) milestone tag, the tag should be added
4. if there is an open issue, which is tagged with [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10), but *not* considered as necessary for the release, the milestone tag should be removed
This means as consequence that as long as there are open issues with milestone tag, there won't be a release (or the process failed). This should help us to prioritize tasks and to get a better understanding of what still needs to be done.
Personally I'm going to be rather conservative, and I won't start to tag issues, which may, or may not be required for the release, and I would really welcome, if someone from the "planning committee" takes a moment to tackle it. I'm especially thinking about items such as the "send all" transaction type, or whether documentation is considered as a requirement, which I can't evaluate from my point of view, because I have no insight of the business side.
Maintainers can add and remove milestone tags similar to issue labels:

Other contributors are welcome, and can leave a note in this thread, so a maintainer may tag the related issue.
The process itself may also be discussed here of course.
|
1.0
|
List all requirements, and tag issues with milestone for 0.0.10 - Using one issue to track the progress and requirements for the next release seems to have limited value, so I'd like to try to use the milestone feature of GitHub, which is probably a much cleaner solution.
I would like to gather *all* requirements necessary for the release, and I created a [milestone](https://github.com/OmniLayer/omnicore/milestones/0.0.10) for this purpose.
Here are four simple guidelines:
1. once there is *no* open issue tagged with [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10) tag left, it means [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10) is *ready* and we can publish a release candidate
2. if there is an unresolved bug, or feature that *must* be resolved or included in the release, and there is no related issue for it, a [new issue](https://github.com/OmniLayer/omnicore/issues/new) should be created
3. if there is an open issue, which is *necessary* for the release, but *without* the [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10) milestone tag, the tag should be added
4. if there is an open issue, which is tagged with [0.0.10](https://github.com/OmniLayer/omnicore/milestones/0.0.10), but *not* considered as necessary for the release, the milestone tag should be removed
This means as consequence that as long as there are open issues with milestone tag, there won't be a release (or the process failed). This should help us to prioritize tasks and to get a better understanding of what still needs to be done.
Personally I'm going to be rather conservative, and I won't start to tag issues, which may, or may not be required for the release, and I would really welcome, if someone from the "planning committee" takes a moment to tackle it. I'm especially thinking about items such as the "send all" transaction type, or whether documentation is considered as a requirement, which I can't evaluate from my point of view, because I have no insight of the business side.
Maintainers can add and remove milestone tags similar to issue labels:

Other contributors are welcome, and can leave a note in this thread, so a maintainer may tag the related issue.
The process itself may also be discussed here of course.
|
process
|
list all requirements and tag issues with milestone for using one issue to track the progress and requirements for the next release seems to have limited value so i d like to try to use the milestone feature of github which is probably a much cleaner solution i would like to gather all requirements necessary for the release and i created a for this purpose here are four simple guidelines once there is no open issue tagged with tag left it means is ready and we can publish a release candidate if there is an unresolved bug or feature that must be resolved or included in the release and there is no related issue for it a should be created if there is an open issue which is necessary for the release but without the milestone tag the tag should be added if there is an open issue which is tagged with but not considered as necessary for the release the milestone tag should be removed this means as consequence that as long as there are open issues with milestone tag there won t be a release or the process failed this should help us to prioritize tasks and to get a better understanding of what still needs to be done personally i m going to be rather conservative and i won t start to tag issues which may or may not be required for the release and i would really welcome if someone from the planning committee takes a moment to tackle it i m especially thinking about items such as the send all transaction type or whether documentation is considered as a requirement which i can t evaluate from my point of view because i have no insight of the business side maintainers can add and remove milestone tags similar to issue labels other contributors are welcome and can leave a note in this thread so a maintainer may tag the related issue the process itself may also be discussed here of course
| 1
|
38,131
| 10,142,322,650
|
IssuesEvent
|
2019-08-03 23:01:13
|
zurb/foundation-sites
|
https://api.github.com/repos/zurb/foundation-sites
|
closed
|
build: clone with less commits
|
PR open 🚚 build
|
<!--- --------------------------------------------------------------------- -->
<!--- Please fill the following template -->
<!--- Your issue may be ignored otherwise -->
<!--- --------------------------------------------------------------------- -->
<!--- Only submit bug or feature requests here. For help or questions to -->
<!--- the community, see the forum: https://foundation.zurb.com/forum -->
## Expected Behavior
<!--- If describing a bug, tell us what should happen. -->
<!--- If suggesting a change/feature, tell us why and how it should work. -->
Travis CI should not clone the last 50 commits but much less to improve the performance.
## Current Behavior
<!--- If describing a bug, tell us what happens instead. -->
<!--- If suggesting a change/feature, explain the difference from -->
<!--- current behavior. -->
Currently the default depth (50) is used for `git clone`.
## Possible Solution
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change. -->
Set the depth to `3`.
## Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most -->
<!--- useful in the real world -->
Faster builds.
## Checklist (all required):
<!--- Go over all the following points, and put an `x` in the boxes. -->
<!--- If you're unsure about any of these, don't hesitate to ask. -->
- [x] I have read and follow the [CONTRIBUTING](CONTRIBUTING.md) document.
- [ ] This is a bug report or a feature request.
- [x] There are no other issues similar to this one.
- [x] The issue title is descriptive.
- [x] The template is fully and correctly filled.
<!--- --------------------------------------------------------------------- -->
<!--- For more information, see the CONTRIBUTING.md document -->
<!--- Thank you for your issue and happy coding ;) -->
<!--- --------------------------------------------------------------------- -->
|
1.0
|
build: clone with less commits - <!--- --------------------------------------------------------------------- -->
<!--- Please fill the following template -->
<!--- Your issue may be ignored otherwise -->
<!--- --------------------------------------------------------------------- -->
<!--- Only submit bug or feature requests here. For help or questions to -->
<!--- the community, see the forum: https://foundation.zurb.com/forum -->
## Expected Behavior
<!--- If describing a bug, tell us what should happen. -->
<!--- If suggesting a change/feature, tell us why and how it should work. -->
Travis CI should not clone the last 50 commits but much less to improve the performance.
## Current Behavior
<!--- If describing a bug, tell us what happens instead. -->
<!--- If suggesting a change/feature, explain the difference from -->
<!--- current behavior. -->
Currently the default depth (50) is used for `git clone`.
## Possible Solution
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change. -->
Set the depth to `3`.
## Context
<!--- How has this issue affected you? What are you trying to accomplish? -->
<!--- Providing context helps us come up with a solution that is most -->
<!--- useful in the real world -->
Faster builds.
## Checklist (all required):
<!--- Go over all the following points, and put an `x` in the boxes. -->
<!--- If you're unsure about any of these, don't hesitate to ask. -->
- [x] I have read and follow the [CONTRIBUTING](CONTRIBUTING.md) document.
- [ ] This is a bug report or a feature request.
- [x] There are no other issues similar to this one.
- [x] The issue title is descriptive.
- [x] The template is fully and correctly filled.
<!--- --------------------------------------------------------------------- -->
<!--- For more information, see the CONTRIBUTING.md document -->
<!--- Thank you for your issue and happy coding ;) -->
<!--- --------------------------------------------------------------------- -->
|
non_process
|
build clone with less commits expected behavior travis ci should not clone the last commits but much less to improve the performance current behavior currently the default depth is used for git clone possible solution set the depth to context faster builds checklist all required i have read and follow the contributing md document this is a bug report or a feature request there are no other issues similar to this one the issue title is descriptive the template is fully and correctly filled
| 0
|
113,985
| 11,834,616,201
|
IssuesEvent
|
2020-03-23 09:13:46
|
uStudioCompany/ustudio-ui
|
https://api.github.com/repos/uStudioCompany/ustudio-ui
|
closed
|
[BUG] (Tooltip) incorrect classNames list
|
bug documentation
|
**Describe the bug**
Tooltip's classNames property type isn`t equal to it is specified in the PropTypes.
**Screenshots**
|
1.0
|
[BUG] (Tooltip) incorrect classNames list - **Describe the bug**
Tooltip's classNames property type isn`t equal to it is specified in the PropTypes.
**Screenshots**
|
non_process
|
tooltip incorrect classnames list describe the bug tooltip s classnames property type isn t equal to it is specified in the proptypes screenshots
| 0
|
9,239
| 12,268,965,089
|
IssuesEvent
|
2020-05-07 13:22:53
|
bisq-network/bisq
|
https://api.github.com/repos/bisq-network/bisq
|
closed
|
Bisq does not add "dust" outputs to miner fee
|
a:bug in:trade-process in:wallet is:critical
|
### Background
According to Bitcoin consensus rules, no output can be less than 546 sats. If a transaction with such an output is broadcast, it will be rejected.
### Description
Bisq attempts to broadcast Bitcoin transactions containing "dust" outputs, instead of simply adding the dust to the miner fee like most wallets do.
#### Version
v1.2.7
### Steps to reproduce
This is the difficult part, as users randomly do this if their transaction coincidentally results in an output of less than 546 sats. However, since Bisq assumes transactions it creates are valid (without checking the dust rule), this results in triggering other random Bisq issues. Sometimes it results in a failed trade, sometimes it results in a corrupted wallet.
### Expected behaviour
The dust output should not be created, and instead added to fees.
### Actual behaviour
The dust output is created, and the Bitcoin transaction is rejected, causing further issues in Bisq depending on the situation.
|
1.0
|
Bisq does not add "dust" outputs to miner fee - ### Background
According to Bitcoin consensus rules, no output can be less than 546 sats. If a transaction with such an output is broadcast, it will be rejected.
### Description
Bisq attempts to broadcast Bitcoin transactions containing "dust" outputs, instead of simply adding the dust to the miner fee like most wallets do.
#### Version
v1.2.7
### Steps to reproduce
This is the difficult part, as users randomly do this if their transaction coincidentally results in an output of less than 546 sats. However, since Bisq assumes transactions it creates are valid (without checking the dust rule), this results in triggering other random Bisq issues. Sometimes it results in a failed trade, sometimes it results in a corrupted wallet.
### Expected behaviour
The dust output should not be created, and instead added to fees.
### Actual behaviour
The dust output is created, and the Bitcoin transaction is rejected, causing further issues in Bisq depending on the situation.
|
process
|
bisq does not add dust outputs to miner fee background according to bitcoin consensus rules no output can be less than sats if a transaction with such an output is broadcast it will be rejected description bisq attempts to broadcast bitcoin transactions containing dust outputs instead of simply adding the dust to the miner fee like most wallets do version steps to reproduce this is the difficult part as users randomly do this if their transaction coincidentally results in an output of less than sats however since bisq assumes transactions it creates are valid without checking the dust rule this results in triggering other random bisq issues sometimes it results in a failed trade sometimes it results in a corrupted wallet expected behaviour the dust output should not be created and instead added to fees actual behaviour the dust output is created and the bitcoin transaction is rejected causing further issues in bisq depending on the situation
| 1
|
18,066
| 24,079,660,254
|
IssuesEvent
|
2022-09-19 04:33:24
|
cmadland/assessment
|
https://api.github.com/repos/cmadland/assessment
|
opened
|
delucaEstablishingFoundationValid2013
|
conceptions of assessment assessment as testing assessment as purpose assessment as process assessment as format teacher education assessment confidence
|
# Reference
DeLuca, C., Chavez, T., & Cao, C. (2013). Establishing a foundation for valid teacher judgement on student learning: The role of pre-service assessment education. Assessment in Education: Principles, Policy & Practice, 20(1), 107–126. https://doi.org/10/gj5v98
# Summary
DeLuca et al. surveyed 48 pre-service teachers before and after an undergraduate course in educational measurement. They used a framework of four primary conceptions of assessment as testing, format, purpose, and process, which are consecutively ordered by complexity. They found that participants conceptions of assessment shifted from more simple views of assessment as testing to more complex and integrated views of assessment as purpose and process, and, to a lesser extent, assessment as format. Interestingly, they found that assessment as format was prominent as a secondary conception.
# Abstract
- The purpose of this research was to explore changes in teacher candidates’ confidence in assessment as a foundation for promoting valid teacher judgements on student learning. Based on a sample of 48 teacher candidates enrolled in a semester-long measurement course at one teacher education programme in Florida, this survey-based study provided evidence that teacher candidates can develop confidence in assessment whilst deepening their conceptions of assessment. The majority of teacher candidates expanded their conception of assessment from one based solely on testing to one that recognised multiple forms of assessment that serve varying purposes. Simultaneously, teacher candidates expressed greater confidence in practical assessment approaches and factors related to assessment praxis. Based on study findings, we argue that pre-service teacher education has a critical role to play in promoting assessment literacy in beginning teachers and providing a foundation for teachers’ continued learning about assessment throughout their careers. The paper concludes with implications for future research in the area of assessment education.
- The purpose of this study was to examine pre-service teacher candidates’ confidence levels in relation to their changing conceptions of assessment during the term of a senior-level assessment course. The specific research questions guiding this study were the following:
- 1. How do teacher candidates’ conceptions of assessment differ at the beginning and end of a pre-service course on student assessment?
2. How does teacher candidates’ confidence toward assessment practices change in relation to their shifting conceptions of assessment?
# Related
-
# Quotes
- # Developing teacher confidence in assessment
- Pre-service assessment education has been identified as a fundamental structure for preparing teachers to assess student learning (Chen 2005). Research conducted on the impact of explicit assessment courses has generally found that these courses have the potential to complement field-based teaching experience (i.e. practical) and develop a foundation for assessment literacy in teacher candidates (Graham 2005).
- # Conceptions of assessment
- Brown, Lake, and Matters (2011) assert that teachers maintain multiple conceptions of classroom assessment based on assessment format, purpose and use. Derived from formal assessment education as well as from the practicalities and policies that govern teachers’ daily work, teachers’ #[[conceptions of assessment]] shape their in-class assessment practices (Brown 2009; Cizek et al. 1995). We present four dominant conceptions of assessment as an analytic framework for our study on the linkage between teacher candidates’ confidence and their changing understandings about assessment. Specifically, the four conceptions of assessment that we describe are: (a) #[[assessment as testing]], (b) #[[assessment as format]], (c) #[[assessment as purpose]] and (d) #[[assessment as process]] . We assert that while none of these conceptions represent simple measurement processes, each conception increases in complexity by connecting together assessment concepts and extending toward other constructs in teaching and learning.
- ## Asssessment as testing
- Our first conception of assessment assimilates assessment with traditional, paperand-pencil testing. Within the USA, tests are often used as summative measures of student learning and can be either teacher-constructed or external and standardised.
- Moreover, due to efficiency and a lack of knowledge about other forms of assessment, teachers continue to construct and use tests as the dominant means to measure student learning in their classrooms.
- Although classical and modern test theories are not simple, when teachers are not aware of the psychometric underpinnings of testing or educated on issues related to test reliability, fairness and validity, they may perceive this form of assessment as easy and straightforward and use it with confidence (DeLuca and Klinger 2010).
- ## Assessment as format
- our second conception expands on this association to include alternative forms of assessment and to delineate a conception based on assessment format.
- A typical classification of assessments is that of performance, product and objectively scored assessments (Airasian and Russell 2008). Performance and product assessments can be further delineated as contrived or authentic assessments, depending upon their applicability to ‘real-world’ experiences (Bartz, Anderson-Robinson, and Hillman 1994).
- Conceptions of assessment by format typically differentiate assessment practices based on the cognitive level of the standard/curriculum expectations being assessed.
- Higher order thinking skills are generally associated with performance and product assessments that enable students to construct responses and assert reasoning, while lower order thinking skills are associated with objectively scored assessments (McMillan 2007).
- ## Assessment as purpose
- Third, one of the most common conceptions of assessment is based on purpose and use, with the distinction between formative and summative assessment purposes widely used across assessment literature (Pellegrino, Chudowsky, and Glaser 2001).
- Formative assessment refers to data collected throughout the instructional process and used to provide feedback to inform teaching and learning processes.
- Summative assessment refers to data collected at the end of a unit or term in order to justify judgements on student achievement and report on student learning (i.e. contribute to student grades).
- Another distinction on assessment purpose and use is based on the seminal work of Black and Wiliam (1998), which described purposes of assessment of learning and assessment for learning.
- Subsumed within AFL, Earl (2003) articulated a third purpose of assessment, assessment as learning, which focuses on using assessments to support the development of students’ metacognition and selfregulation abilities.
- ## Assessment as process
- Finally, closely linked to assessment as, for, and of learning is assessment conceived as a process of interpretation and integration. Pellegrino, Chudowsky, and Glaser (2001, 36) state: ‘assessment is a process of reasoning from evidence’. This conception of assessment includes an awareness of the limitations of various assessment methods (including considerations of validity, reliability and bias) in relation to the specific context of teaching and learning. Hence, teachers’ ability to make meaning from assessment data becomes increasingly important to this conception as assessment is viewed as an essential component of teaching and integrally connected with curriculum and learning (Airasian and Russell 2008; Pellegrino, Chudowsky, and Glaser 2001).
- # Data analyses
- Results were analysed in relation to: (a) participants’ changing conceptions of assessment, (b) participants’ changing confidence in assessment and (c) the interaction between participants’ changing conceptions and confidence in assessment.
- data were coded based on participants’ primary and, when available, secondary conceptions of assessment as testing, purpose, format and process. Dual coding of data by primary and secondary conceptions enabled a co-occurrence frequency analysis that provided a more complex analysis of participants’ understandings of assessment and which was helpful in ‘understanding how thematic domains, concepts, or ideas were distributed within a data set’ (Namey et al. 2008, 145).
- Quantitatively, #[[descriptive statistics]] were calculated related to the gender, age, programme of study and year of study distribution across the sample. Then, changes in participants’ confidence levels were analysed through an #[[exploratory factor analysis]] using a promax (oblique) rotation. Although close-ended items had a theoretical foundation (i.e. Popham 2008), a #[[principal component factor analysis]] was conducted for each separate section of the pre-questionnaire to identify confidence factors across the Likert scale items based on responses from the 48 participants. #[[Factor loadings]] were determined by the greatest value for each item, with loadings of at least 0.40. No items maintained lower loading values. #[[Cronbach alpha]] values were also calculated for #reliability indices of each factor. We recognise that given the sample size of 48 participants, the generalisability and internal stability of factors are somewhat problematic. Accordingly, we caution readers to interpret factors with the caveat that the results from this study are preliminary and require further validation based on a large sample of participants.
- In order to determine changes over time and the interaction between participants’ assessment conceptions and their confidence, we conducted a #[[repeated measures analysis]] across both questionnaire administrations (Stevens 2001). In preparation for the repeated measures analysis, assessment conception codes were converted to numerical values (indicating the ordinal progression from the most simplistic conception to the most complex) and placed on a proportional scale to confidence factors. A repeated measures analysis (two within group) was conducted for confidence and conception factors across the two data time points. The repeated measures analysis also allowed for explorations of any interaction effects between the teacher candidates’ conceptions and the confidence factors. A follow-up #[[dependent t-test]] addressed the research questions on how the candidates’ conceptions of assessment and confidence toward assessment practices differed between the beginning and end of the measurement course (Stevens 2001). #Significance was based on a #[[Bonferroni adjusted p-value]] of 0.007. As a caveat to this data analysis strategy, we recognise that the sample size limits the reliability of the measure, the internal stability of factor loadings and the resulting effect sizes, which mitigates the generalisability of results from factor analyses and significance analyses (i.e. t-test and ANOVA). We urge that results not be interpreted as generalised findings but rather as a basis for further validation research on these suggested factors and observed trends.
- # Results
- ## Conceptions of assessment
- Data supported that participants’ conceptions of assessment developed from an initial dominant view of assessment as testing to a more complex view of assessment as format, purpose and process.
- In analysing primary and secondary conceptions of assessment, data pointed to participants’ not only changing their conceptions from assessment as testing to assessment as purpose and as process, but also understanding assessment in more complex and interconnected ways.
- As evidenced through this study, explicit assessment education can enhance teacher candidates’ confidence in assessment praxis and approaches, while deepening their conceptual and theoretical understandings of educational assessment. As a result of this learning, teacher candidates may foster a realistic and optimistic orientation for engaging in more valid forms of assessment within their future schools and classrooms.
-
- # Citations
- - mentioning cite from section 'review of related literature' of publication:
- Yidana, M. B., P., A. P. (2018). Economics Teachers’ Conceptions of Classroom Assessment. Int J Innov Educ Res, 10(6), 153-174. https://doi.org/10.31686/ijier.vol6.iss10.1176
---
“…Similar studies (Brown & Hirschfeld, 2008;Levy-Vered & Alhija, 2015) have found that attending an assessment course or having more training in assessment did not improve teachers' conceptions of assessment. However, there are studies that suggest that teachers' conception of assessment developed after receiving periodic training in assessment (DeLuca, Chavez & Cao, 2013;Smith, Hill, Cowie & Gilmore, 2014). Interestingly, the findings of the study also showed that after teachers had attended the course on assessment, their irrelevance conception of assessment improved significantly.…”
|
1.0
|
delucaEstablishingFoundationValid2013 - # Reference
DeLuca, C., Chavez, T., & Cao, C. (2013). Establishing a foundation for valid teacher judgement on student learning: The role of pre-service assessment education. Assessment in Education: Principles, Policy & Practice, 20(1), 107–126. https://doi.org/10/gj5v98
# Summary
DeLuca et al. surveyed 48 pre-service teachers before and after an undergraduate course in educational measurement. They used a framework of four primary conceptions of assessment as testing, format, purpose, and process, which are consecutively ordered by complexity. They found that participants conceptions of assessment shifted from more simple views of assessment as testing to more complex and integrated views of assessment as purpose and process, and, to a lesser extent, assessment as format. Interestingly, they found that assessment as format was prominent as a secondary conception.
# Abstract
- The purpose of this research was to explore changes in teacher candidates’ confidence in assessment as a foundation for promoting valid teacher judgements on student learning. Based on a sample of 48 teacher candidates enrolled in a semester-long measurement course at one teacher education programme in Florida, this survey-based study provided evidence that teacher candidates can develop confidence in assessment whilst deepening their conceptions of assessment. The majority of teacher candidates expanded their conception of assessment from one based solely on testing to one that recognised multiple forms of assessment that serve varying purposes. Simultaneously, teacher candidates expressed greater confidence in practical assessment approaches and factors related to assessment praxis. Based on study findings, we argue that pre-service teacher education has a critical role to play in promoting assessment literacy in beginning teachers and providing a foundation for teachers’ continued learning about assessment throughout their careers. The paper concludes with implications for future research in the area of assessment education.
- The purpose of this study was to examine pre-service teacher candidates’ confidence levels in relation to their changing conceptions of assessment during the term of a senior-level assessment course. The specific research questions guiding this study were the following:
- 1. How do teacher candidates’ conceptions of assessment differ at the beginning and end of a pre-service course on student assessment?
2. How does teacher candidates’ confidence toward assessment practices change in relation to their shifting conceptions of assessment?
# Related
-
# Quotes
- # Developing teacher confidence in assessment
- Pre-service assessment education has been identified as a fundamental structure for preparing teachers to assess student learning (Chen 2005). Research conducted on the impact of explicit assessment courses has generally found that these courses have the potential to complement field-based teaching experience (i.e. practical) and develop a foundation for assessment literacy in teacher candidates (Graham 2005).
- # Conceptions of assessment
- Brown, Lake, and Matters (2011) assert that teachers maintain multiple conceptions of classroom assessment based on assessment format, purpose and use. Derived from formal assessment education as well as from the practicalities and policies that govern teachers’ daily work, teachers’ #[[conceptions of assessment]] shape their in-class assessment practices (Brown 2009; Cizek et al. 1995). We present four dominant conceptions of assessment as an analytic framework for our study on the linkage between teacher candidates’ confidence and their changing understandings about assessment. Specifically, the four conceptions of assessment that we describe are: (a) #[[assessment as testing]], (b) #[[assessment as format]], (c) #[[assessment as purpose]] and (d) #[[assessment as process]] . We assert that while none of these conceptions represent simple measurement processes, each conception increases in complexity by connecting together assessment concepts and extending toward other constructs in teaching and learning.
- ## Asssessment as testing
- Our first conception of assessment assimilates assessment with traditional, paperand-pencil testing. Within the USA, tests are often used as summative measures of student learning and can be either teacher-constructed or external and standardised.
- Moreover, due to efficiency and a lack of knowledge about other forms of assessment, teachers continue to construct and use tests as the dominant means to measure student learning in their classrooms.
- Although classical and modern test theories are not simple, when teachers are not aware of the psychometric underpinnings of testing or educated on issues related to test reliability, fairness and validity, they may perceive this form of assessment as easy and straightforward and use it with confidence (DeLuca and Klinger 2010).
- ## Assessment as format
- our second conception expands on this association to include alternative forms of assessment and to delineate a conception based on assessment format.
- A typical classification of assessments is that of performance, product and objectively scored assessments (Airasian and Russell 2008). Performance and product assessments can be further delineated as contrived or authentic assessments, depending upon their applicability to ‘real-world’ experiences (Bartz, Anderson-Robinson, and Hillman 1994).
- Conceptions of assessment by format typically differentiate assessment practices based on the cognitive level of the standard/curriculum expectations being assessed.
- Higher order thinking skills are generally associated with performance and product assessments that enable students to construct responses and assert reasoning, while lower order thinking skills are associated with objectively scored assessments (McMillan 2007).
- ## Assessment as purpose
- Third, one of the most common conceptions of assessment is based on purpose and use, with the distinction between formative and summative assessment purposes widely used across assessment literature (Pellegrino, Chudowsky, and Glaser 2001).
- Formative assessment refers to data collected throughout the instructional process and used to provide feedback to inform teaching and learning processes.
- Summative assessment refers to data collected at the end of a unit or term in order to justify judgements on student achievement and report on student learning (i.e. contribute to student grades).
- Another distinction on assessment purpose and use is based on the seminal work of Black and Wiliam (1998), which described purposes of assessment of learning and assessment for learning.
- Subsumed within AFL, Earl (2003) articulated a third purpose of assessment, assessment as learning, which focuses on using assessments to support the development of students’ metacognition and selfregulation abilities.
- ## Assessment as process
- Finally, closely linked to assessment as, for, and of learning is assessment conceived as a process of interpretation and integration. Pellegrino, Chudowsky, and Glaser (2001, 36) state: ‘assessment is a process of reasoning from evidence’. This conception of assessment includes an awareness of the limitations of various assessment methods (including considerations of validity, reliability and bias) in relation to the specific context of teaching and learning. Hence, teachers’ ability to make meaning from assessment data becomes increasingly important to this conception as assessment is viewed as an essential component of teaching and integrally connected with curriculum and learning (Airasian and Russell 2008; Pellegrino, Chudowsky, and Glaser 2001).
- # Data analyses
- Results were analysed in relation to: (a) participants’ changing conceptions of assessment, (b) participants’ changing confidence in assessment and (c) the interaction between participants’ changing conceptions and confidence in assessment.
- data were coded based on participants’ primary and, when available, secondary conceptions of assessment as testing, purpose, format and process. Dual coding of data by primary and secondary conceptions enabled a co-occurrence frequency analysis that provided a more complex analysis of participants’ understandings of assessment and which was helpful in ‘understanding how thematic domains, concepts, or ideas were distributed within a data set’ (Namey et al. 2008, 145).
- Quantitatively, #[[descriptive statistics]] were calculated related to the gender, age, programme of study and year of study distribution across the sample. Then, changes in participants’ confidence levels were analysed through an #[[exploratory factor analysis]] using a promax (oblique) rotation. Although close-ended items had a theoretical foundation (i.e. Popham 2008), a #[[principal component factor analysis]] was conducted for each separate section of the pre-questionnaire to identify confidence factors across the Likert scale items based on responses from the 48 participants. #[[Factor loadings]] were determined by the greatest value for each item, with loadings of at least 0.40. No items maintained lower loading values. #[[Cronbach alpha]] values were also calculated for #reliability indices of each factor. We recognise that given the sample size of 48 participants, the generalisability and internal stability of factors are somewhat problematic. Accordingly, we caution readers to interpret factors with the caveat that the results from this study are preliminary and require further validation based on a large sample of participants.
- In order to determine changes over time and the interaction between participants’ assessment conceptions and their confidence, we conducted a #[[repeated measures analysis]] across both questionnaire administrations (Stevens 2001). In preparation for the repeated measures analysis, assessment conception codes were converted to numerical values (indicating the ordinal progression from the most simplistic conception to the most complex) and placed on a proportional scale to confidence factors. A repeated measures analysis (two within group) was conducted for confidence and conception factors across the two data time points. The repeated measures analysis also allowed for explorations of any interaction effects between the teacher candidates’ conceptions and the confidence factors. A follow-up #[[dependent t-test]] addressed the research questions on how the candidates’ conceptions of assessment and confidence toward assessment practices differed between the beginning and end of the measurement course (Stevens 2001). #Significance was based on a #[[Bonferroni adjusted p-value]] of 0.007. As a caveat to this data analysis strategy, we recognise that the sample size limits the reliability of the measure, the internal stability of factor loadings and the resulting effect sizes, which mitigates the generalisability of results from factor analyses and significance analyses (i.e. t-test and ANOVA). We urge that results not be interpreted as generalised findings but rather as a basis for further validation research on these suggested factors and observed trends.
- # Results
- ## Conceptions of assessment
- Data supported that participants’ conceptions of assessment developed from an initial dominant view of assessment as testing to a more complex view of assessment as format, purpose and process.
- In analysing primary and secondary conceptions of assessment, data pointed to participants’ not only changing their conceptions from assessment as testing to assessment as purpose and as process, but also understanding assessment in more complex and interconnected ways.
- As evidenced through this study, explicit assessment education can enhance teacher candidates’ confidence in assessment praxis and approaches, while deepening their conceptual and theoretical understandings of educational assessment. As a result of this learning, teacher candidates may foster a realistic and optimistic orientation for engaging in more valid forms of assessment within their future schools and classrooms.
-
- # Citations
- - mentioning cite from section 'review of related literature' of publication:
- Yidana, M. B., P., A. P. (2018). Economics Teachers’ Conceptions of Classroom Assessment. Int J Innov Educ Res, 10(6), 153-174. https://doi.org/10.31686/ijier.vol6.iss10.1176
---
“…Similar studies (Brown & Hirschfeld, 2008;Levy-Vered & Alhija, 2015) have found that attending an assessment course or having more training in assessment did not improve teachers' conceptions of assessment. However, there are studies that suggest that teachers' conception of assessment developed after receiving periodic training in assessment (DeLuca, Chavez & Cao, 2013;Smith, Hill, Cowie & Gilmore, 2014). Interestingly, the findings of the study also showed that after teachers had attended the course on assessment, their irrelevance conception of assessment improved significantly.…”
|
process
|
reference deluca c chavez t cao c establishing a foundation for valid teacher judgement on student learning the role of pre service assessment education assessment in education principles policy practice – summary deluca et al surveyed pre service teachers before and after an undergraduate course in educational measurement they used a framework of four primary conceptions of assessment as testing format purpose and process which are consecutively ordered by complexity they found that participants conceptions of assessment shifted from more simple views of assessment as testing to more complex and integrated views of assessment as purpose and process and to a lesser extent assessment as format interestingly they found that assessment as format was prominent as a secondary conception abstract the purpose of this research was to explore changes in teacher candidates’ confidence in assessment as a foundation for promoting valid teacher judgements on student learning based on a sample of teacher candidates enrolled in a semester long measurement course at one teacher education programme in florida this survey based study provided evidence that teacher candidates can develop confidence in assessment whilst deepening their conceptions of assessment the majority of teacher candidates expanded their conception of assessment from one based solely on testing to one that recognised multiple forms of assessment that serve varying purposes simultaneously teacher candidates expressed greater confidence in practical assessment approaches and factors related to assessment praxis based on study findings we argue that pre service teacher education has a critical role to play in promoting assessment literacy in beginning teachers and providing a foundation for teachers’ continued learning about assessment throughout their careers the paper concludes with implications for future research in the area of assessment education the purpose of this study was to examine pre service teacher candidates’ confidence levels in relation to their changing conceptions of assessment during the term of a senior level assessment course the specific research questions guiding this study were the following how do teacher candidates’ conceptions of assessment differ at the beginning and end of a pre service course on student assessment how does teacher candidates’ confidence toward assessment practices change in relation to their shifting conceptions of assessment related quotes developing teacher confidence in assessment pre service assessment education has been identified as a fundamental structure for preparing teachers to assess student learning chen research conducted on the impact of explicit assessment courses has generally found that these courses have the potential to complement field based teaching experience i e practical and develop a foundation for assessment literacy in teacher candidates graham conceptions of assessment brown lake and matters assert that teachers maintain multiple conceptions of classroom assessment based on assessment format purpose and use derived from formal assessment education as well as from the practicalities and policies that govern teachers’ daily work teachers’ shape their in class assessment practices brown cizek et al we present four dominant conceptions of assessment as an analytic framework for our study on the linkage between teacher candidates’ confidence and their changing understandings about assessment specifically the four conceptions of assessment that we describe are a b c and d we assert that while none of these conceptions represent simple measurement processes each conception increases in complexity by connecting together assessment concepts and extending toward other constructs in teaching and learning asssessment as testing our first conception of assessment assimilates assessment with traditional paperand pencil testing within the usa tests are often used as summative measures of student learning and can be either teacher constructed or external and standardised moreover due to efficiency and a lack of knowledge about other forms of assessment teachers continue to construct and use tests as the dominant means to measure student learning in their classrooms although classical and modern test theories are not simple when teachers are not aware of the psychometric underpinnings of testing or educated on issues related to test reliability fairness and validity they may perceive this form of assessment as easy and straightforward and use it with confidence deluca and klinger assessment as format our second conception expands on this association to include alternative forms of assessment and to delineate a conception based on assessment format a typical classification of assessments is that of performance product and objectively scored assessments airasian and russell performance and product assessments can be further delineated as contrived or authentic assessments depending upon their applicability to ‘real world’ experiences bartz anderson robinson and hillman conceptions of assessment by format typically differentiate assessment practices based on the cognitive level of the standard curriculum expectations being assessed higher order thinking skills are generally associated with performance and product assessments that enable students to construct responses and assert reasoning while lower order thinking skills are associated with objectively scored assessments mcmillan assessment as purpose third one of the most common conceptions of assessment is based on purpose and use with the distinction between formative and summative assessment purposes widely used across assessment literature pellegrino chudowsky and glaser formative assessment refers to data collected throughout the instructional process and used to provide feedback to inform teaching and learning processes summative assessment refers to data collected at the end of a unit or term in order to justify judgements on student achievement and report on student learning i e contribute to student grades another distinction on assessment purpose and use is based on the seminal work of black and wiliam which described purposes of assessment of learning and assessment for learning subsumed within afl earl articulated a third purpose of assessment assessment as learning which focuses on using assessments to support the development of students’ metacognition and selfregulation abilities assessment as process finally closely linked to assessment as for and of learning is assessment conceived as a process of interpretation and integration pellegrino chudowsky and glaser state ‘assessment is a process of reasoning from evidence’ this conception of assessment includes an awareness of the limitations of various assessment methods including considerations of validity reliability and bias in relation to the specific context of teaching and learning hence teachers’ ability to make meaning from assessment data becomes increasingly important to this conception as assessment is viewed as an essential component of teaching and integrally connected with curriculum and learning airasian and russell pellegrino chudowsky and glaser data analyses results were analysed in relation to a participants’ changing conceptions of assessment b participants’ changing confidence in assessment and c the interaction between participants’ changing conceptions and confidence in assessment data were coded based on participants’ primary and when available secondary conceptions of assessment as testing purpose format and process dual coding of data by primary and secondary conceptions enabled a co occurrence frequency analysis that provided a more complex analysis of participants’ understandings of assessment and which was helpful in ‘understanding how thematic domains concepts or ideas were distributed within a data set’ namey et al quantitatively were calculated related to the gender age programme of study and year of study distribution across the sample then changes in participants’ confidence levels were analysed through an using a promax oblique rotation although close ended items had a theoretical foundation i e popham a was conducted for each separate section of the pre questionnaire to identify confidence factors across the likert scale items based on responses from the participants were determined by the greatest value for each item with loadings of at least no items maintained lower loading values values were also calculated for reliability indices of each factor we recognise that given the sample size of participants the generalisability and internal stability of factors are somewhat problematic accordingly we caution readers to interpret factors with the caveat that the results from this study are preliminary and require further validation based on a large sample of participants in order to determine changes over time and the interaction between participants’ assessment conceptions and their confidence we conducted a across both questionnaire administrations stevens in preparation for the repeated measures analysis assessment conception codes were converted to numerical values indicating the ordinal progression from the most simplistic conception to the most complex and placed on a proportional scale to confidence factors a repeated measures analysis two within group was conducted for confidence and conception factors across the two data time points the repeated measures analysis also allowed for explorations of any interaction effects between the teacher candidates’ conceptions and the confidence factors a follow up addressed the research questions on how the candidates’ conceptions of assessment and confidence toward assessment practices differed between the beginning and end of the measurement course stevens significance was based on a of as a caveat to this data analysis strategy we recognise that the sample size limits the reliability of the measure the internal stability of factor loadings and the resulting effect sizes which mitigates the generalisability of results from factor analyses and significance analyses i e t test and anova we urge that results not be interpreted as generalised findings but rather as a basis for further validation research on these suggested factors and observed trends results conceptions of assessment data supported that participants’ conceptions of assessment developed from an initial dominant view of assessment as testing to a more complex view of assessment as format purpose and process in analysing primary and secondary conceptions of assessment data pointed to participants’ not only changing their conceptions from assessment as testing to assessment as purpose and as process but also understanding assessment in more complex and interconnected ways as evidenced through this study explicit assessment education can enhance teacher candidates’ confidence in assessment praxis and approaches while deepening their conceptual and theoretical understandings of educational assessment as a result of this learning teacher candidates may foster a realistic and optimistic orientation for engaging in more valid forms of assessment within their future schools and classrooms citations mentioning cite from section review of related literature of publication yidana m b p a p economics teachers’ conceptions of classroom assessment int j innov educ res “…similar studies brown hirschfeld levy vered alhija have found that attending an assessment course or having more training in assessment did not improve teachers conceptions of assessment however there are studies that suggest that teachers conception of assessment developed after receiving periodic training in assessment deluca chavez cao smith hill cowie gilmore interestingly the findings of the study also showed that after teachers had attended the course on assessment their irrelevance conception of assessment improved significantly …”
| 1
|
20,736
| 27,436,170,105
|
IssuesEvent
|
2023-03-02 07:37:16
|
TUM-Dev/NavigaTUM
|
https://api.github.com/repos/TUM-Dev/NavigaTUM
|
opened
|
[General] Raumnummer nicht existent
|
webform delete-after-processing general
|
0501.02.119
Sehr geehrte Damen und Herren,
bei der Eingabe der Telefonnebenstelle in TUM-Online kann die Raumnummer nicht bearbeitet oder korrigiert werden.
Fehlercode: Raumnummer existiert nicht.
Die Raumnummer 0501.02.112 müsste zu den Nebenstellen:
22110 + 22112 + 22114 + 22790 geändert werden.
Die richtige Raumnummer ist 0501.02.119.
Diese wurde zu den Nebenstellen 25507 + 25508 eingetragen, ist dennoch zu o.g. Nummern nicht existent.
Bitte kontaktieren Sie uns unter 089 289 25580 oder unter fernmeldeservice.za4@tum.de
telefongebuehrenabrechnung.za4@tum.de
Mit herzlichen Grüßen
Mariam Djafari
|
1.0
|
[General] Raumnummer nicht existent - 0501.02.119
Sehr geehrte Damen und Herren,
bei der Eingabe der Telefonnebenstelle in TUM-Online kann die Raumnummer nicht bearbeitet oder korrigiert werden.
Fehlercode: Raumnummer existiert nicht.
Die Raumnummer 0501.02.112 müsste zu den Nebenstellen:
22110 + 22112 + 22114 + 22790 geändert werden.
Die richtige Raumnummer ist 0501.02.119.
Diese wurde zu den Nebenstellen 25507 + 25508 eingetragen, ist dennoch zu o.g. Nummern nicht existent.
Bitte kontaktieren Sie uns unter 089 289 25580 oder unter fernmeldeservice.za4@tum.de
telefongebuehrenabrechnung.za4@tum.de
Mit herzlichen Grüßen
Mariam Djafari
|
process
|
raumnummer nicht existent sehr geehrte damen und herren bei der eingabe der telefonnebenstelle in tum online kann die raumnummer nicht bearbeitet oder korrigiert werden fehlercode raumnummer existiert nicht die raumnummer müsste zu den nebenstellen geändert werden die richtige raumnummer ist diese wurde zu den nebenstellen eingetragen ist dennoch zu o g nummern nicht existent bitte kontaktieren sie uns unter oder unter fernmeldeservice tum de telefongebuehrenabrechnung tum de mit herzlichen grüßen mariam djafari
| 1
|
18,832
| 10,295,675,833
|
IssuesEvent
|
2019-08-27 21:53:20
|
alansanie/wingtips
|
https://api.github.com/repos/alansanie/wingtips
|
opened
|
WS-2009-0001 (Low) detected in commons-codec-1.9.jar, commons-codec-1.11.jar
|
security vulnerability
|
## WS-2009-0001 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>commons-codec-1.9.jar</b>, <b>commons-codec-1.11.jar</b></p></summary>
<p>
<details><summary><b>commons-codec-1.9.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-codec/">http://commons.apache.org/proper/commons-codec/</a></p>
<p>Path to dependency file: /wingtips/wingtips-zipkin-spring-boot/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar,/root/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar</p>
<p>
Dependency Hierarchy:
- httpclient-4.4.1.jar (Root Library)
- :x: **commons-codec-1.9.jar** (Vulnerable Library)
</details>
<details><summary><b>commons-codec-1.11.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-codec/">http://commons.apache.org/proper/commons-codec/</a></p>
<p>Path to dependency file: /wingtips/wingtips-lightstep/build.gradle</p>
<p>Path to vulnerable library: radle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.11/3acb4705652e16236558f0f4f2192cc33c3bd189/commons-codec-1.11.jar,radle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.11/3acb4705652e16236558f0f4f2192cc33c3bd189/commons-codec-1.11.jar</p>
<p>
Dependency Hierarchy:
- :x: **commons-codec-1.11.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/alansanie/wingtips/commit/183e8ad413608960359e84065f37e537d5142cdd">183e8ad413608960359e84065f37e537d5142cdd</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Not all "business" method implementations of public API in Apache Commons Codec 1.x are thread safe, which might disclose the wrong data or allow an attacker to change non-private fields.
Updated 2018-10-07 - an additional review by WhiteSource research team could not indicate on a clear security vulnerability
<p>Publish Date: 2007-10-07
<p>URL: <a href=https://issues.apache.org/jira/browse/CODEC-55>WS-2009-0001</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>0.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
|
True
|
WS-2009-0001 (Low) detected in commons-codec-1.9.jar, commons-codec-1.11.jar - ## WS-2009-0001 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>commons-codec-1.9.jar</b>, <b>commons-codec-1.11.jar</b></p></summary>
<p>
<details><summary><b>commons-codec-1.9.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-codec/">http://commons.apache.org/proper/commons-codec/</a></p>
<p>Path to dependency file: /wingtips/wingtips-zipkin-spring-boot/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar,/root/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar</p>
<p>
Dependency Hierarchy:
- httpclient-4.4.1.jar (Root Library)
- :x: **commons-codec-1.9.jar** (Vulnerable Library)
</details>
<details><summary><b>commons-codec-1.11.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-codec/">http://commons.apache.org/proper/commons-codec/</a></p>
<p>Path to dependency file: /wingtips/wingtips-lightstep/build.gradle</p>
<p>Path to vulnerable library: radle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.11/3acb4705652e16236558f0f4f2192cc33c3bd189/commons-codec-1.11.jar,radle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.11/3acb4705652e16236558f0f4f2192cc33c3bd189/commons-codec-1.11.jar</p>
<p>
Dependency Hierarchy:
- :x: **commons-codec-1.11.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/alansanie/wingtips/commit/183e8ad413608960359e84065f37e537d5142cdd">183e8ad413608960359e84065f37e537d5142cdd</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Not all "business" method implementations of public API in Apache Commons Codec 1.x are thread safe, which might disclose the wrong data or allow an attacker to change non-private fields.
Updated 2018-10-07 - an additional review by WhiteSource research team could not indicate on a clear security vulnerability
<p>Publish Date: 2007-10-07
<p>URL: <a href=https://issues.apache.org/jira/browse/CODEC-55>WS-2009-0001</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>0.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
|
non_process
|
ws low detected in commons codec jar commons codec jar ws low severity vulnerability vulnerable libraries commons codec jar commons codec jar commons codec jar the apache commons codec package contains simple encoder and decoders for various formats such as and hexadecimal in addition to these widely used encoders and decoders the codec package also maintains a collection of phonetic encoding utilities library home page a href path to dependency file wingtips wingtips zipkin spring boot build gradle path to vulnerable library root gradle caches modules files commons codec commons codec commons codec jar root gradle caches modules files commons codec commons codec commons codec jar dependency hierarchy httpclient jar root library x commons codec jar vulnerable library commons codec jar the apache commons codec package contains simple encoder and decoders for various formats such as and hexadecimal in addition to these widely used encoders and decoders the codec package also maintains a collection of phonetic encoding utilities library home page a href path to dependency file wingtips wingtips lightstep build gradle path to vulnerable library radle caches modules files commons codec commons codec commons codec jar radle caches modules files commons codec commons codec commons codec jar dependency hierarchy x commons codec jar vulnerable library found in head commit a href vulnerability details not all business method implementations of public api in apache commons codec x are thread safe which might disclose the wrong data or allow an attacker to change non private fields updated an additional review by whitesource research team could not indicate on a clear security vulnerability publish date url a href cvss score details base score metrics not available
| 0
|
8,797
| 11,908,244,374
|
IssuesEvent
|
2020-03-31 00:23:18
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
OTB provider setup
|
Bug Feedback Processing
|
Author Name: **Paolo Cavallini** (@pcav)
Original Redmine Issue: [21372](https://issues.qgis.org/issues/21372)
Affected QGIS version: 3.7(master)
Redmine category:processing/otb
Assignee: Rashad Kanavath
---
In Debian, the paths to add to the config are `/usr/lib/x86_64-linux-gnu/otb/applications/` and `/usr`. This is not documented, and it is difficult to find for the user. Better add it as a default (similarly for other OSs).
More generally: why is this necessary? Other backends do not need a config, and this is way easier for the user.
|
1.0
|
OTB provider setup - Author Name: **Paolo Cavallini** (@pcav)
Original Redmine Issue: [21372](https://issues.qgis.org/issues/21372)
Affected QGIS version: 3.7(master)
Redmine category:processing/otb
Assignee: Rashad Kanavath
---
In Debian, the paths to add to the config are `/usr/lib/x86_64-linux-gnu/otb/applications/` and `/usr`. This is not documented, and it is difficult to find for the user. Better add it as a default (similarly for other OSs).
More generally: why is this necessary? Other backends do not need a config, and this is way easier for the user.
|
process
|
otb provider setup author name paolo cavallini pcav original redmine issue affected qgis version master redmine category processing otb assignee rashad kanavath in debian the paths to add to the config are usr lib linux gnu otb applications and usr this is not documented and it is difficult to find for the user better add it as a default similarly for other oss more generally why is this necessary other backends do not need a config and this is way easier for the user
| 1
|
72,973
| 7,319,562,328
|
IssuesEvent
|
2018-03-02 01:31:36
|
couchbase/couchbase-lite-core
|
https://api.github.com/repos/couchbase/couchbase-lite-core
|
closed
|
Race conditions pushing obsoleted revisions
|
P1: high :scream_cat: functional-test-failure :-1: in progress known-issue ready
|
CBL - 2.0- DB 22 -> ios build 574, Android 299
client -> ios, Android
sg -> 2.0.0- 773
### Steps to reproduce :
Create docs in CBL DB1, CBL DB2, CBL DB3.
Configure replication from CBL db1 to CBL db2 with push_pull and continuous.
Configure replication from CBL db1 to CBL db3 with push_pull and continuous.
Start the replication for 2 and 3.
update docs on CBL DB1, CBL DB2, CBL DB3.
WAit for replication to complete
Have multithreading and update docs in all 3 cbl dbs.
Wait for replication to complete for step 3 and step 4 replications.
Configure replication from CBL db3 to sync-gateway and start replication.
Wait for replication to complete.
Verify all docs from CBL db3 replicated to sync-gateway
### Result :
1 doc is missing in sync-gateway , I see that conflict resolution failed in CBL logs as a 'Sync warning'
Note : out of 3 times, it passed 2 times and failed 1 time.
###Test code : https://github.com/couchbaselabs/mobile-testkit/blob/feature/cbl20-ver1/testsuites/CBLTester/CBL_Functional_tests/test_no_conflicts_cbl.py#L696
### Logs :
2018-02-01 20:24:56.673208-0800 CBLTestServer-iOS[55966:1608762] CouchbaseLite DB Info: DataFile: abort transaction
2018-02-01 20:24:56.673387-0800 CBLTestServer-iOS[55966:1666581] CouchbaseLite Sync Info: {DBWorker#4268} Looking up 11 revisions in the db (seq '2710'..'2720')
2018-02-01 20:24:56.673706-0800 CBLTestServer-iOS[55966:1666313] CouchbaseLite BLIP Verbose: {BLIPIO#89} Received frame: REQ #1420 ---C, length 548
2018-02-01 20:24:56.673908-0800 CBLTestServer-iOS[55966:1608762] CouchbaseLite Sync WARNING: Conflict resolution of 'no-conflicts2_4' failed: (null)
Is this expected?
This is regression bug , but the failure is not consitent, it is transient failure
|
1.0
|
Race conditions pushing obsoleted revisions - CBL - 2.0- DB 22 -> ios build 574, Android 299
client -> ios, Android
sg -> 2.0.0- 773
### Steps to reproduce :
Create docs in CBL DB1, CBL DB2, CBL DB3.
Configure replication from CBL db1 to CBL db2 with push_pull and continuous.
Configure replication from CBL db1 to CBL db3 with push_pull and continuous.
Start the replication for 2 and 3.
update docs on CBL DB1, CBL DB2, CBL DB3.
WAit for replication to complete
Have multithreading and update docs in all 3 cbl dbs.
Wait for replication to complete for step 3 and step 4 replications.
Configure replication from CBL db3 to sync-gateway and start replication.
Wait for replication to complete.
Verify all docs from CBL db3 replicated to sync-gateway
### Result :
1 doc is missing in sync-gateway , I see that conflict resolution failed in CBL logs as a 'Sync warning'
Note : out of 3 times, it passed 2 times and failed 1 time.
###Test code : https://github.com/couchbaselabs/mobile-testkit/blob/feature/cbl20-ver1/testsuites/CBLTester/CBL_Functional_tests/test_no_conflicts_cbl.py#L696
### Logs :
2018-02-01 20:24:56.673208-0800 CBLTestServer-iOS[55966:1608762] CouchbaseLite DB Info: DataFile: abort transaction
2018-02-01 20:24:56.673387-0800 CBLTestServer-iOS[55966:1666581] CouchbaseLite Sync Info: {DBWorker#4268} Looking up 11 revisions in the db (seq '2710'..'2720')
2018-02-01 20:24:56.673706-0800 CBLTestServer-iOS[55966:1666313] CouchbaseLite BLIP Verbose: {BLIPIO#89} Received frame: REQ #1420 ---C, length 548
2018-02-01 20:24:56.673908-0800 CBLTestServer-iOS[55966:1608762] CouchbaseLite Sync WARNING: Conflict resolution of 'no-conflicts2_4' failed: (null)
Is this expected?
This is regression bug , but the failure is not consitent, it is transient failure
|
non_process
|
race conditions pushing obsoleted revisions cbl db ios build android client ios android sg steps to reproduce create docs in cbl cbl cbl configure replication from cbl to cbl with push pull and continuous configure replication from cbl to cbl with push pull and continuous start the replication for and update docs on cbl cbl cbl wait for replication to complete have multithreading and update docs in all cbl dbs wait for replication to complete for step and step replications configure replication from cbl to sync gateway and start replication wait for replication to complete verify all docs from cbl replicated to sync gateway result doc is missing in sync gateway i see that conflict resolution failed in cbl logs as a sync warning note out of times it passed times and failed time test code logs cbltestserver ios couchbaselite db info datafile abort transaction cbltestserver ios couchbaselite sync info dbworker looking up revisions in the db seq cbltestserver ios couchbaselite blip verbose blipio received frame req c length cbltestserver ios couchbaselite sync warning conflict resolution of no failed null is this expected this is regression bug but the failure is not consitent it is transient failure
| 0
|
192,655
| 15,355,135,947
|
IssuesEvent
|
2021-03-01 10:41:45
|
zeek/spicy
|
https://api.github.com/repos/zeek/spicy
|
closed
|
Add language support to explicitly trigger a parse error
|
Documentation
|
Wasn't sure if it's intended for `&requires` to be evaluated before field hooks:
```
module Test;
public type MyUnit = unit {
s: bytes &size=4 &requires=(self.flag);
on s { self.flag = True; }
var flag: bool;
};
```
```
$ printf 'test' | spicy-dump test.spicy
[fatal error] terminating with uncaught exception of type spicy::rt::ParseError: parse error: &requires failed ($$ == test) (test.spicy:4:22)
```
Initially thought that field hooks might get evaluated first in real example here and found otherwise:
https://github.com/zeek/spicy/compare/topic/jsiwek/pe#diff-36ceb1dc5c1f8f65e1fb3553b2d552ef12f58b3651f1df59aafa9e6c3fafc63eR64-R67
* Generally seems to be lack of documentation on evaluation order and adding that could help.
* For what I was trying to do, would be convenient if the order was different, but realize it's kind of arbitrary/implicit, so might generally be better to have an explicit way to induce parsing errors from within arbitrary hook-code itself. E.g. either with a `throw` or special `return` value. Kind of like mentioned in previous error-handling discussions https://github.com/zeek/spicy/issues/89#issuecomment-648637582 and https://github.com/zeek/spicy/discussions/616#discussioncomment-185009
|
1.0
|
Add language support to explicitly trigger a parse error - Wasn't sure if it's intended for `&requires` to be evaluated before field hooks:
```
module Test;
public type MyUnit = unit {
s: bytes &size=4 &requires=(self.flag);
on s { self.flag = True; }
var flag: bool;
};
```
```
$ printf 'test' | spicy-dump test.spicy
[fatal error] terminating with uncaught exception of type spicy::rt::ParseError: parse error: &requires failed ($$ == test) (test.spicy:4:22)
```
Initially thought that field hooks might get evaluated first in real example here and found otherwise:
https://github.com/zeek/spicy/compare/topic/jsiwek/pe#diff-36ceb1dc5c1f8f65e1fb3553b2d552ef12f58b3651f1df59aafa9e6c3fafc63eR64-R67
* Generally seems to be lack of documentation on evaluation order and adding that could help.
* For what I was trying to do, would be convenient if the order was different, but realize it's kind of arbitrary/implicit, so might generally be better to have an explicit way to induce parsing errors from within arbitrary hook-code itself. E.g. either with a `throw` or special `return` value. Kind of like mentioned in previous error-handling discussions https://github.com/zeek/spicy/issues/89#issuecomment-648637582 and https://github.com/zeek/spicy/discussions/616#discussioncomment-185009
|
non_process
|
add language support to explicitly trigger a parse error wasn t sure if it s intended for requires to be evaluated before field hooks module test public type myunit unit s bytes size requires self flag on s self flag true var flag bool printf test spicy dump test spicy terminating with uncaught exception of type spicy rt parseerror parse error requires failed test test spicy initially thought that field hooks might get evaluated first in real example here and found otherwise generally seems to be lack of documentation on evaluation order and adding that could help for what i was trying to do would be convenient if the order was different but realize it s kind of arbitrary implicit so might generally be better to have an explicit way to induce parsing errors from within arbitrary hook code itself e g either with a throw or special return value kind of like mentioned in previous error handling discussions and
| 0
|
533,338
| 15,589,014,586
|
IssuesEvent
|
2021-03-18 07:24:20
|
AY2021S2-CS2103T-T12-2/tp
|
https://api.github.com/repos/AY2021S2-CS2103T-T12-2/tp
|
closed
|
Food intake list implementation inaccurate
|
priority.High severity.Medium type.Bug
|
Extra date property for unmatched food intake items
Below is a sample json from save, contains a single save file for multiple entries of saved dates
```json
{
"date" : null,
"foodIntakes" : [ {
"name" : "test",
"fats" : 10.0,
"carbos" : 10.0,
"proteins" : 10.0,
"date" : "0001-01-01"
}, {
"name" : "test",
"fats" : 10.0,
"carbos" : 10.0,
"proteins" : 10.0,
"date" : "2050-06-20"
} ]
}
```
|
1.0
|
Food intake list implementation inaccurate - Extra date property for unmatched food intake items
Below is a sample json from save, contains a single save file for multiple entries of saved dates
```json
{
"date" : null,
"foodIntakes" : [ {
"name" : "test",
"fats" : 10.0,
"carbos" : 10.0,
"proteins" : 10.0,
"date" : "0001-01-01"
}, {
"name" : "test",
"fats" : 10.0,
"carbos" : 10.0,
"proteins" : 10.0,
"date" : "2050-06-20"
} ]
}
```
|
non_process
|
food intake list implementation inaccurate extra date property for unmatched food intake items below is a sample json from save contains a single save file for multiple entries of saved dates json date null foodintakes name test fats carbos proteins date name test fats carbos proteins date
| 0
|
372,724
| 26,017,266,589
|
IssuesEvent
|
2022-12-21 09:33:52
|
sdv-dev/DeepEcho
|
https://api.github.com/repos/sdv-dev/DeepEcho
|
closed
|
DeepEcho Package Maintenance Updates
|
documentation maintenance internal
|
_This is a placeholder issue for overall package maintenance updates for the next minor DeepEcho release: `0.4.0`_
|
1.0
|
DeepEcho Package Maintenance Updates - _This is a placeholder issue for overall package maintenance updates for the next minor DeepEcho release: `0.4.0`_
|
non_process
|
deepecho package maintenance updates this is a placeholder issue for overall package maintenance updates for the next minor deepecho release
| 0
|
20,082
| 26,577,651,763
|
IssuesEvent
|
2023-01-22 02:00:08
|
lizhihao6/get-daily-arxiv-noti
|
https://api.github.com/repos/lizhihao6/get-daily-arxiv-noti
|
opened
|
New submissions for Fri, 20 Jan 23
|
event camera white balance isp compression image signal processing image signal process raw raw image events camera color contrast events AWB
|
## Keyword: events
There is no result
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
There is no result
## Keyword: ISP
### Regularizing disparity estimation via multi task learning with structured light reconstruction
- **Authors:** Alistair Weld, Joao Cartucho, Chi Xu, Joseph Davids, Stamatia Giannarou
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2301.08140
- **Pdf link:** https://arxiv.org/pdf/2301.08140
- **Abstract**
3D reconstruction is a useful tool for surgical planning and guidance. However, the lack of available medical data stunts research and development in this field, as supervised deep learning methods for accurate disparity estimation rely heavily on large datasets containing ground truth information. Alternative approaches to supervision have been explored, such as self-supervision, which can reduce or remove entirely the need for ground truth. However, no proposed alternatives have demonstrated performance capabilities close to what would be expected from a supervised setup. This work aims to alleviate this issue. In this paper, we investigate the learning of structured light projections to enhance the development of direct disparity estimation networks. We show for the first time that it is possible to accurately learn the projection of structured light on a scene, implicitly learning disparity. Secondly, we \textcolor{black}{explore the use of a multi task learning (MTL) framework for the joint training of structured light and disparity. We present results which show that MTL with structured light improves disparity training; without increasing the number of model parameters. Our MTL setup outperformed the single task learning (STL) network in every validation test. Notably, in the medical generalisation test, the STL error was 1.4 times worse than that of the best MTL performance. The benefit of using MTL is emphasised when the training data is limited.} A dataset containing stereoscopic images, disparity maps and structured light projections on medical phantoms and ex vivo tissue was created for evaluation together with virtual scenes. This dataset will be made publicly available in the future.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
There is no result
## Keyword: RAW
There is no result
## Keyword: raw image
There is no result
|
2.0
|
New submissions for Fri, 20 Jan 23 - ## Keyword: events
There is no result
## Keyword: event camera
There is no result
## Keyword: events camera
There is no result
## Keyword: white balance
There is no result
## Keyword: color contrast
There is no result
## Keyword: AWB
There is no result
## Keyword: ISP
### Regularizing disparity estimation via multi task learning with structured light reconstruction
- **Authors:** Alistair Weld, Joao Cartucho, Chi Xu, Joseph Davids, Stamatia Giannarou
- **Subjects:** Computer Vision and Pattern Recognition (cs.CV)
- **Arxiv link:** https://arxiv.org/abs/2301.08140
- **Pdf link:** https://arxiv.org/pdf/2301.08140
- **Abstract**
3D reconstruction is a useful tool for surgical planning and guidance. However, the lack of available medical data stunts research and development in this field, as supervised deep learning methods for accurate disparity estimation rely heavily on large datasets containing ground truth information. Alternative approaches to supervision have been explored, such as self-supervision, which can reduce or remove entirely the need for ground truth. However, no proposed alternatives have demonstrated performance capabilities close to what would be expected from a supervised setup. This work aims to alleviate this issue. In this paper, we investigate the learning of structured light projections to enhance the development of direct disparity estimation networks. We show for the first time that it is possible to accurately learn the projection of structured light on a scene, implicitly learning disparity. Secondly, we \textcolor{black}{explore the use of a multi task learning (MTL) framework for the joint training of structured light and disparity. We present results which show that MTL with structured light improves disparity training; without increasing the number of model parameters. Our MTL setup outperformed the single task learning (STL) network in every validation test. Notably, in the medical generalisation test, the STL error was 1.4 times worse than that of the best MTL performance. The benefit of using MTL is emphasised when the training data is limited.} A dataset containing stereoscopic images, disparity maps and structured light projections on medical phantoms and ex vivo tissue was created for evaluation together with virtual scenes. This dataset will be made publicly available in the future.
## Keyword: image signal processing
There is no result
## Keyword: image signal process
There is no result
## Keyword: compression
There is no result
## Keyword: RAW
There is no result
## Keyword: raw image
There is no result
|
process
|
new submissions for fri jan keyword events there is no result keyword event camera there is no result keyword events camera there is no result keyword white balance there is no result keyword color contrast there is no result keyword awb there is no result keyword isp regularizing disparity estimation via multi task learning with structured light reconstruction authors alistair weld joao cartucho chi xu joseph davids stamatia giannarou subjects computer vision and pattern recognition cs cv arxiv link pdf link abstract reconstruction is a useful tool for surgical planning and guidance however the lack of available medical data stunts research and development in this field as supervised deep learning methods for accurate disparity estimation rely heavily on large datasets containing ground truth information alternative approaches to supervision have been explored such as self supervision which can reduce or remove entirely the need for ground truth however no proposed alternatives have demonstrated performance capabilities close to what would be expected from a supervised setup this work aims to alleviate this issue in this paper we investigate the learning of structured light projections to enhance the development of direct disparity estimation networks we show for the first time that it is possible to accurately learn the projection of structured light on a scene implicitly learning disparity secondly we textcolor black explore the use of a multi task learning mtl framework for the joint training of structured light and disparity we present results which show that mtl with structured light improves disparity training without increasing the number of model parameters our mtl setup outperformed the single task learning stl network in every validation test notably in the medical generalisation test the stl error was times worse than that of the best mtl performance the benefit of using mtl is emphasised when the training data is limited a dataset containing stereoscopic images disparity maps and structured light projections on medical phantoms and ex vivo tissue was created for evaluation together with virtual scenes this dataset will be made publicly available in the future keyword image signal processing there is no result keyword image signal process there is no result keyword compression there is no result keyword raw there is no result keyword raw image there is no result
| 1
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.